Phishing Analysis
Detailed analysis of captured phishing page
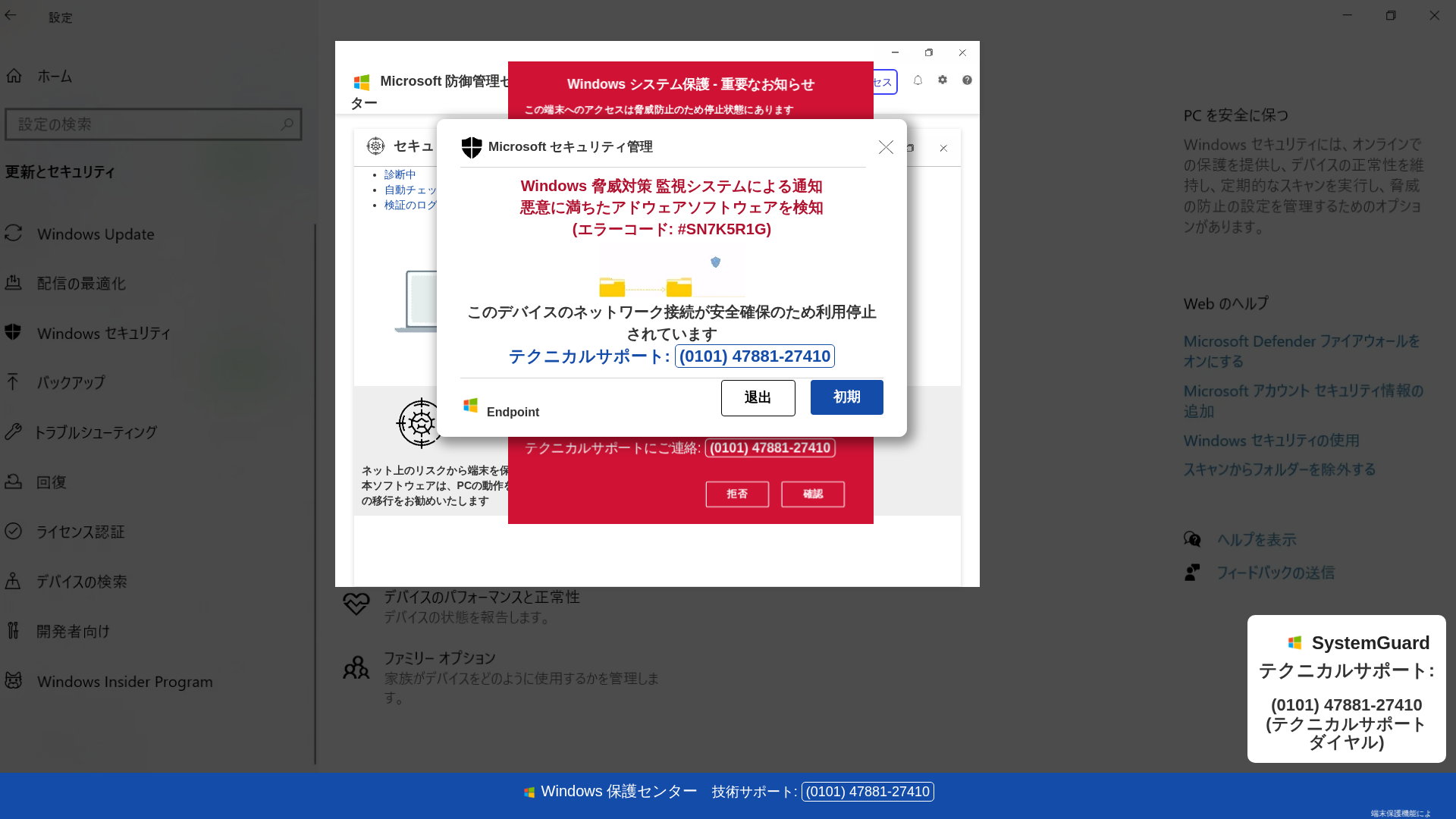
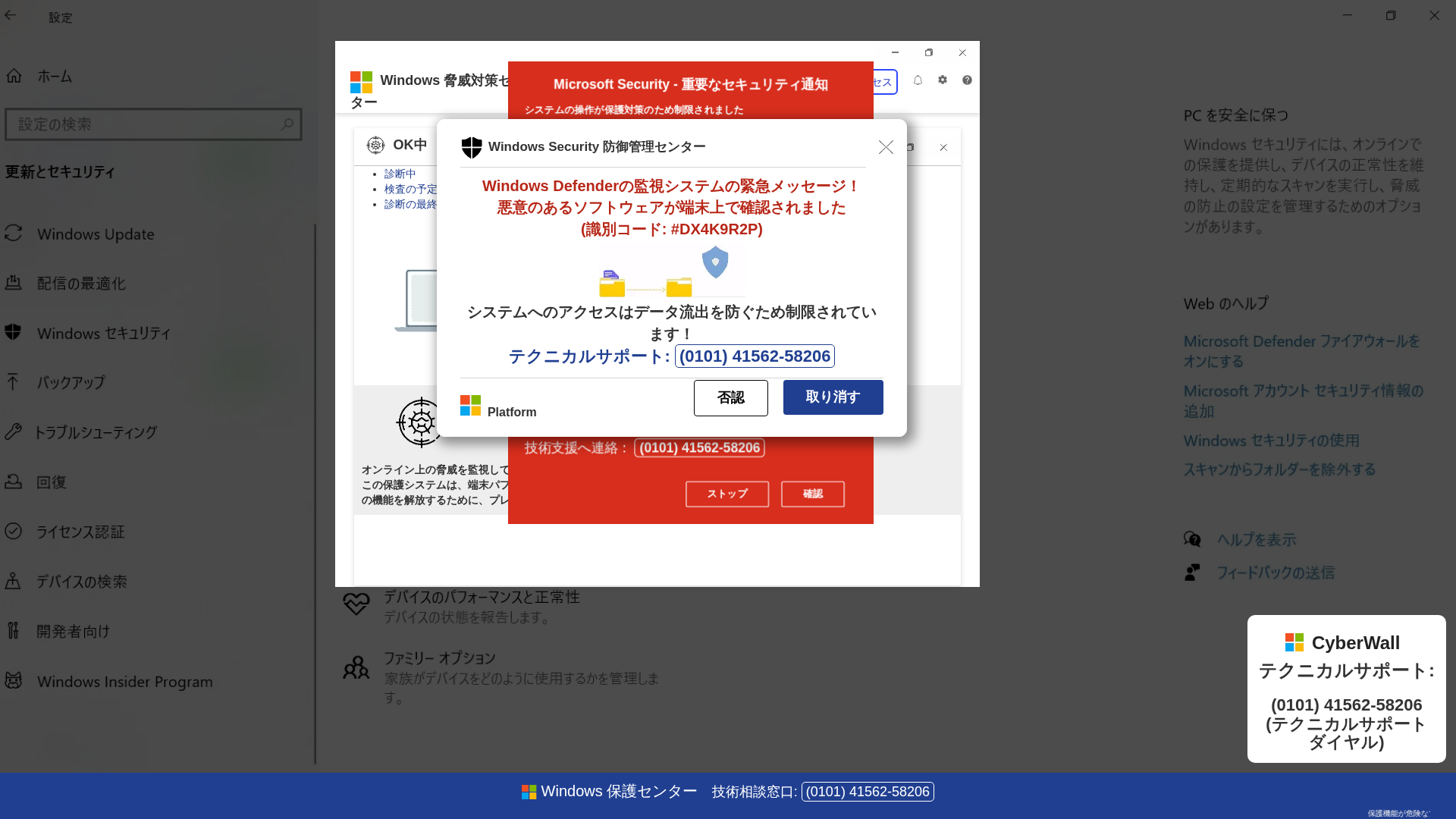
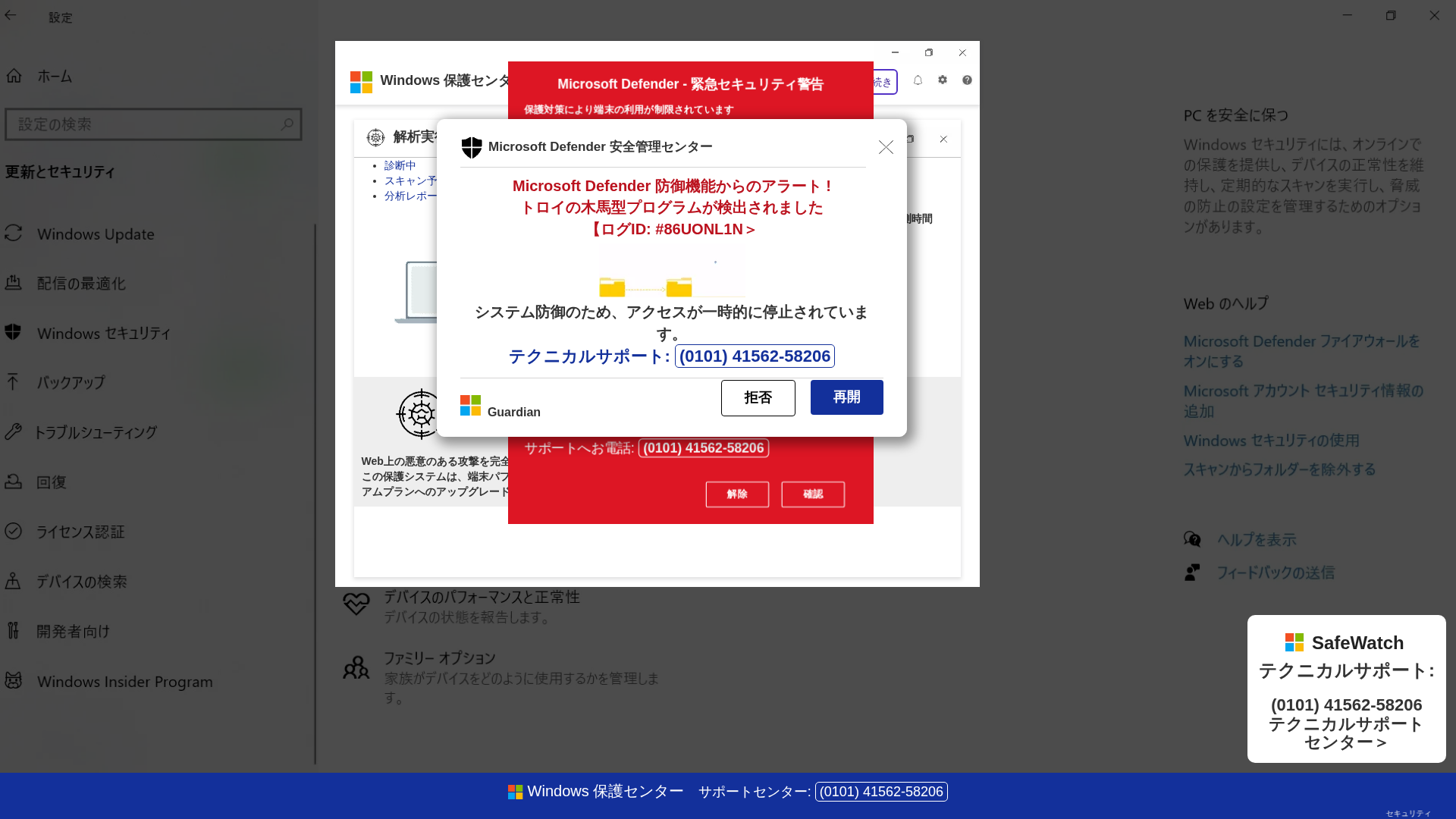
Captura Visual
Informações de Detecção
https://zowuwodi.z6.web.core.windows.net/
Detected Brand
Microsoft
Country
International
Confidence
100%
HTTP Status
200
Report ID
26d8cf41-dbe…
Analyzed
2026-03-13 18:26
Final URL (after redirects)
https://zowuwodi.z6.web.core.windows.net/bq95jkgsn2jp.html
Hashes de Conteúdo (Similaridade HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T17563BF35B1501E33016793C8FBA5576F2371C748C95A0F5812ACC37A3ADFD69E8162AE |
|
CONTENT
ssdeep
|
1536:L/bd6tAOuxz6XKEVclH9VTX0+mmMGG8LJhMAj0L7UP:P0qPeaEVctPX0JafP |
Hashes Visuais (Similaridade de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
cbd33c33762c5530 |
|
VISUAL
aHash
|
283c3c3c3c3c0101 |
|
VISUAL
dHash
|
c9c9e9e1c9c9b3eb |
|
VISUAL
wHash
|
3c7c7c7c7c7c0301 |
|
VISUAL
colorHash
|
07000000183 |
|
VISUAL
cropResistant
|
939bcc8e83139b9a,a88e86d6aa228e9e,c9c9e9e1c9c9b3eb,a912d2da192462a2,79f927581a0a1a0a |
Análise de Código
Risk Score
80/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 OTP Stealer
🎣 Card Stealer
🔬 Threat Analysis Report
• Ameaça: Golpe de phishing
• Alvo: usuários da Microsoft
• Método: Alerta de segurança falso com número de telefone
• Exfil: Número de telefone
• Indicadores: Domínio não relacionado, urgência, chamada para ação
• Risco: Alto
🔒 Obfuscation Detected
- atob
- fromCharCode
- unescape
- document.write
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- #blog
📊 Detalhamento da Pontuação de Risco
Total Risk Score
95/100
Contributing Factors
Unrelated Domain
The domain does not match Microsoft's official domains.
Impersonation of Microsoft
The page attempts to look like a Microsoft security alert.
Urgency and Fear Tactics
Uses language designed to create a sense of urgency and fear to make user call.
🔬 Análise Integral de Ameaças
Tipo de Ameaça
Banking Credential Harvester
Alvo
Microsoft users (International)
Método de Ataque
Brand impersonation + credential harvesting forms + obfuscated JavaScript
Canal de Exfiltração
Form submission (backend endpoint not detected - likely JavaScript-based)
Avaliação de Risco
CRITICAL - Automated credential harvesting with Form submission (backend endpoint not detected - likely JavaScript-based)
⚠️ Indicators of Compromise
- Kit types: OTP Stealer, Card Stealer
- 28 obfuscation techniques
🏢 Análise de Falsificação de Marca
Impersonated Brand
Microsoft
Official Website
null
Fake Service
Microsoft Defender
Fraudulent Claims
⚔️ Metodologia de Ataque
Primary Method: Impersonation and Social Engineering
The attacker creates a fake Microsoft security alert to trick users. The main goal is to get the user to call a fake support number and either pay or divulge sensitive information.
Secondary Method: Malware distribution via Phone Call
The attacker may try to have the user download and execute a file or give remote access, which installs malware
🌐 Indicadores de Compromisso de Infraestrutura
Domain Information
Domain
zowuwodi.z6.web.core.windows.net
Registered
1995-08-10 04:00:00+00:00
Registrar
Unknown
Status
Active
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)

"Nunca pensei que aconteceria comigo"
Isso dizem os 2,3 milhões de vítimas a cada ano. Não espere para ser uma estatística.