
Phishing Analysis
Detailed analysis of captured phishing page
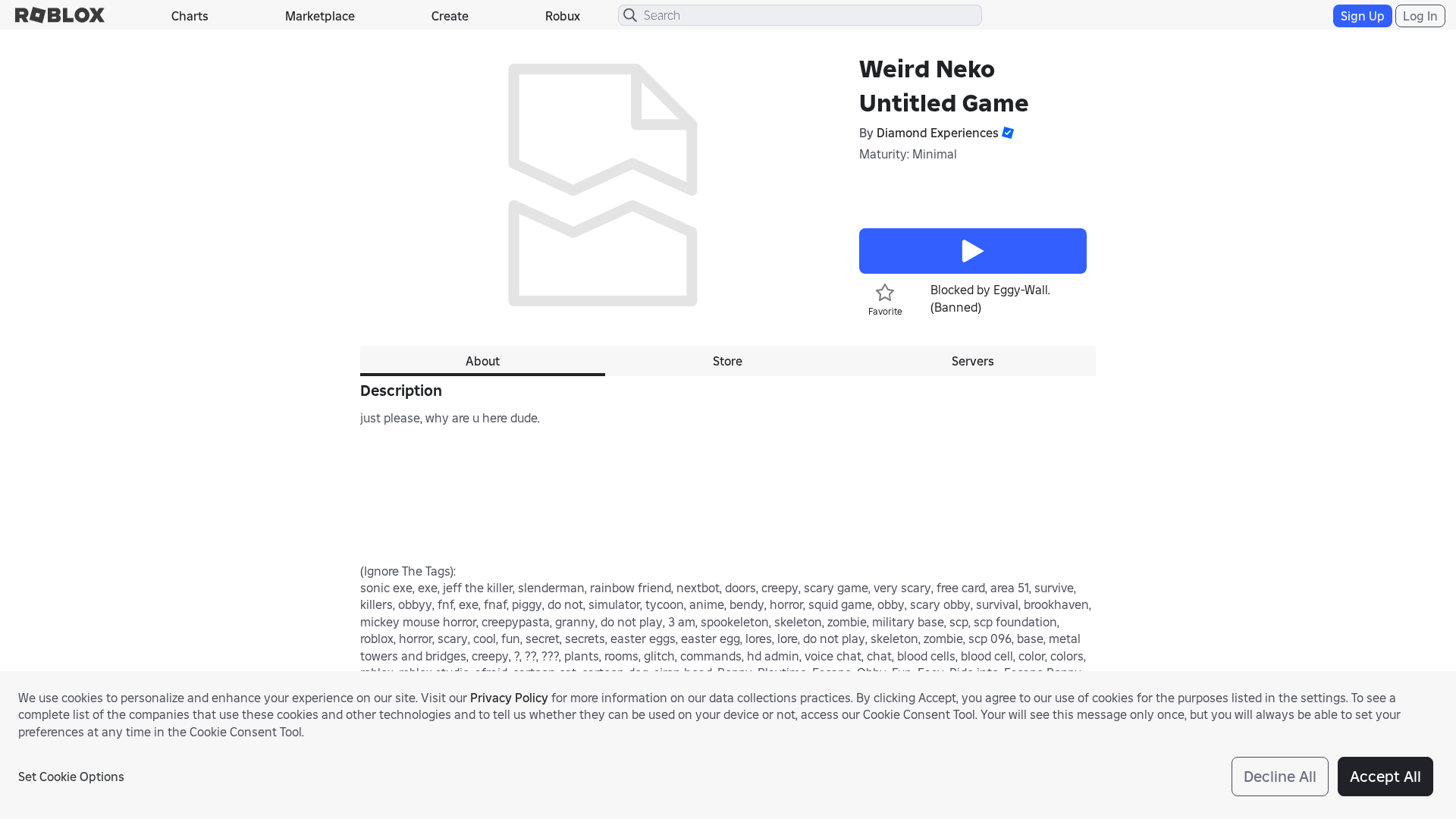
Captura Visual
Informações de Detecção
https://robiox.com.af/games/76106209840076/Weird-Neko-Untitled-Game?privateServerLinkCode=20571888870702570683313096754436
Detected Brand
Roblox
Country
Unknown
Confidence
100%
HTTP Status
200
Report ID
2d2322b5-658…
Analyzed
2026-03-20 07:39
Hashes de Conteúdo (Similaridade HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T12D33C932A1201833A1BFA3D9F555F71592D3E74EC68297E2A1F8A3760ED9C21FD1341A |
|
CONTENT
ssdeep
|
768:Ck/kC6kkXB1DyfQk+uFbyskbiVTrvrvED3D06qvBR7n8A7F9NpBxJ8m8:jcXB1Dy4kTFvjMzcXP9NTxJ8m8 |
Hashes Visuais (Similaridade de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
eded55b296284549 |
|
VISUAL
aHash
|
72f3f3dfffd70100 |
|
VISUAL
dHash
|
96161236200617e0 |
|
VISUAL
wHash
|
22f3e3dfffc30000 |
|
VISUAL
colorHash
|
070000001c0 |
|
VISUAL
cropResistant
|
96161236200617e0 |
Análise de Código
Risk Score
100/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🎣 Card Stealer
🎣 Banking
🎣 Personal Info
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- hex_escape
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- /login?returnUrl=3287289277861444
- https://robiox.com.af/info/blog?locale=en_us
- https://robiox.com.af/catalog?CatalogContext=1&Keyword=
- /catalog
- https://robiox.com.af/badges/486519516383569/ADMINHAMMERBADGE-kick
📡 API Calls Detected
- POST
- GET
- https://ro.blox.com/Ebh5?pid=experiencestart_mobileweb&is_retargeting=false&af_dp=
- get
- https://apis.
- https://en.help.roblox.com/hc/articles/7997207259156
📤 Form Action Targets
- /search
📊 Detalhamento da Pontuação de Risco
Total Risk Score
100/100
Contributing Factors
Active Phishing Kit
Detected kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
Credential Harvesting
Credential harvesting detected with 1 form(s) capturing sensitive data
Code Obfuscation
JavaScript code obfuscated using 175 technique(s) to evade detection
🔬 Análise Integral de Ameaças
Tipo de Ameaça
Banking Credential Harvester
Alvo
Roblox users
Método de Ataque
credential harvesting forms + obfuscated JavaScript
Canal de Exfiltração
HTTP POST to backend
Avaliação de Risco
CRITICAL - Automated credential harvesting with HTTP POST to backend
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 175 obfuscation techniques
🏢 Análise de Falsificação de Marca
Impersonated Brand
Roblox
Official Website
https://www.roblox.com
Fake Service
Banking/payment service
⚔️ Metodologia de Ataque
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 175 techniques to evade detection by security scanners and make reverse engineering more difficult.
🌐 Indicadores de Compromisso de Infraestrutura
Domain Information
Domain
robiox.com.af
Registered
2025-12-25 15:04:19+00:00
Registrar
PAMIR ALPHA TECHNOLOGIES
Status
Active (82 days old)
Hosting Information
Provider
PAMIR ALPHA TECHNOLOGIES
ASN
🤖 AI-Extracted Threat Intelligence
Scan History for robiox.com.af
Found 10 other scans for this domain
-
https://robiox.com.af/games/18552244424/Kuriko-Tes...
https://robiox.com.af/games/102168567330694/Charac...
https://robiox.com.af/games/126884695634066/Grow-a...
https://robiox.com.af/games/124473577469410/Be-a-L...
https://robiox.com.af/users/2586908335/profile
https://robiox.com.af/users/1097451436/profile
https://robiox.com.af/games/79798983053805/Untitle...
https://robiox.com.af/games/85966125008822/Untitle...
https://robiox.com.af/users/3501451974/profile
https://robiox.com.af/games/891852901/Greenville?p...

"Nunca pensei que aconteceria comigo"
Isso dizem os 2,3 milhões de vítimas a cada ano. Não espere para ser uma estatística.