
Phishing Analysis
Detailed analysis of captured phishing page
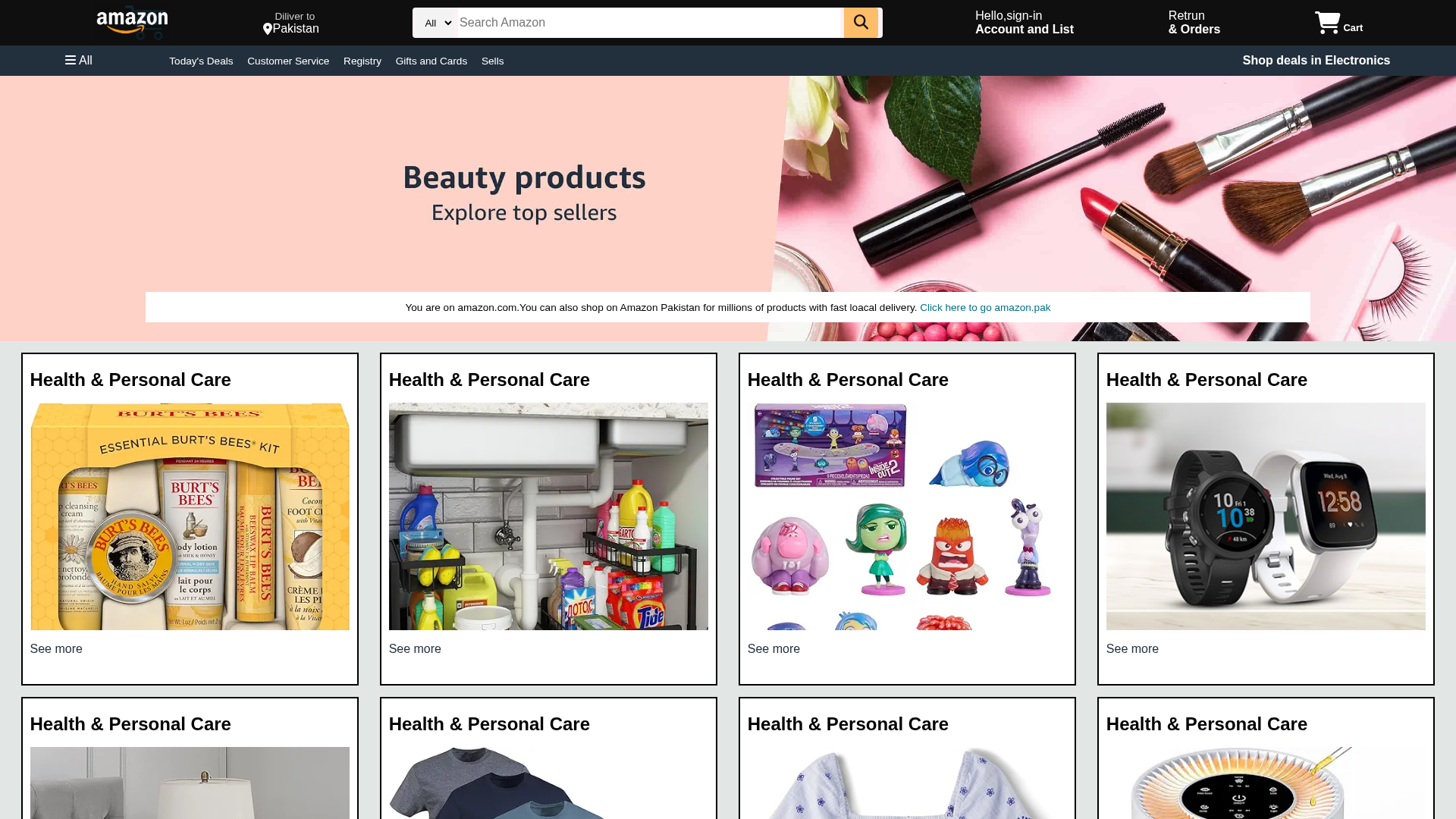
Captura Visual
Informações de Detecção
Hashes de Conteúdo (Similaridade HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1B69158709481BA3301D7C791DF34AB6B73D88A95EA83570953F9D3588EDAE8FCE21850 |
|
CONTENT
ssdeep
|
96:T7vhJJoqmwPMTuJ2P+HN16evcIzENx67vSSxa/B/B/B/zeyKr:3vjJoqvQ/B/B/B/ayKr |
Hashes Visuais (Similaridade de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
ca4d4d171e871a4f |
|
VISUAL
aHash
|
00f0f9ff840cffdf |
|
VISUAL
dHash
|
629695a51d198bb5 |
|
VISUAL
wHash
|
00f0f1ff040cff1d |
|
VISUAL
colorHash
|
06202048000 |
|
VISUAL
cropResistant
|
8080e26a6aa28080,969595ad1d19aab5,72e3967683959545,236edc634b87e763,c0d0656cecf8f9f1,8e8bcde5830b4f46,3d6d6d6465372e3c,3a7a393ccaca5ad6 |
Análise de Código
📊 Detalhamento da Pontuação de Risco
🔬 Análise Integral de Ameaças
🏢 Análise de Falsificação de Marca
⚔️ Metodologia de Ataque
Primary Method: Search Engine Manipulation
Fake Amazon site positioned to capture victims through SEO tactics, typosquatting, or paid advertising. Serves as entry point for multi-stage attacks including credential theft and malware distribution.
Secondary Method: Standard Phishing Techniques
Uses typical phishing tactics including brand impersonation, urgency tactics, and social engineering to trick victims into providing sensitive information.
🌐 Indicadores de Compromisso de Infraestrutura
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
Scan History for www.amazon-clone-psi-eight.vercel.app
Found 1 other scan for this domain
