
Phishing Analysis
Detailed analysis of captured phishing page
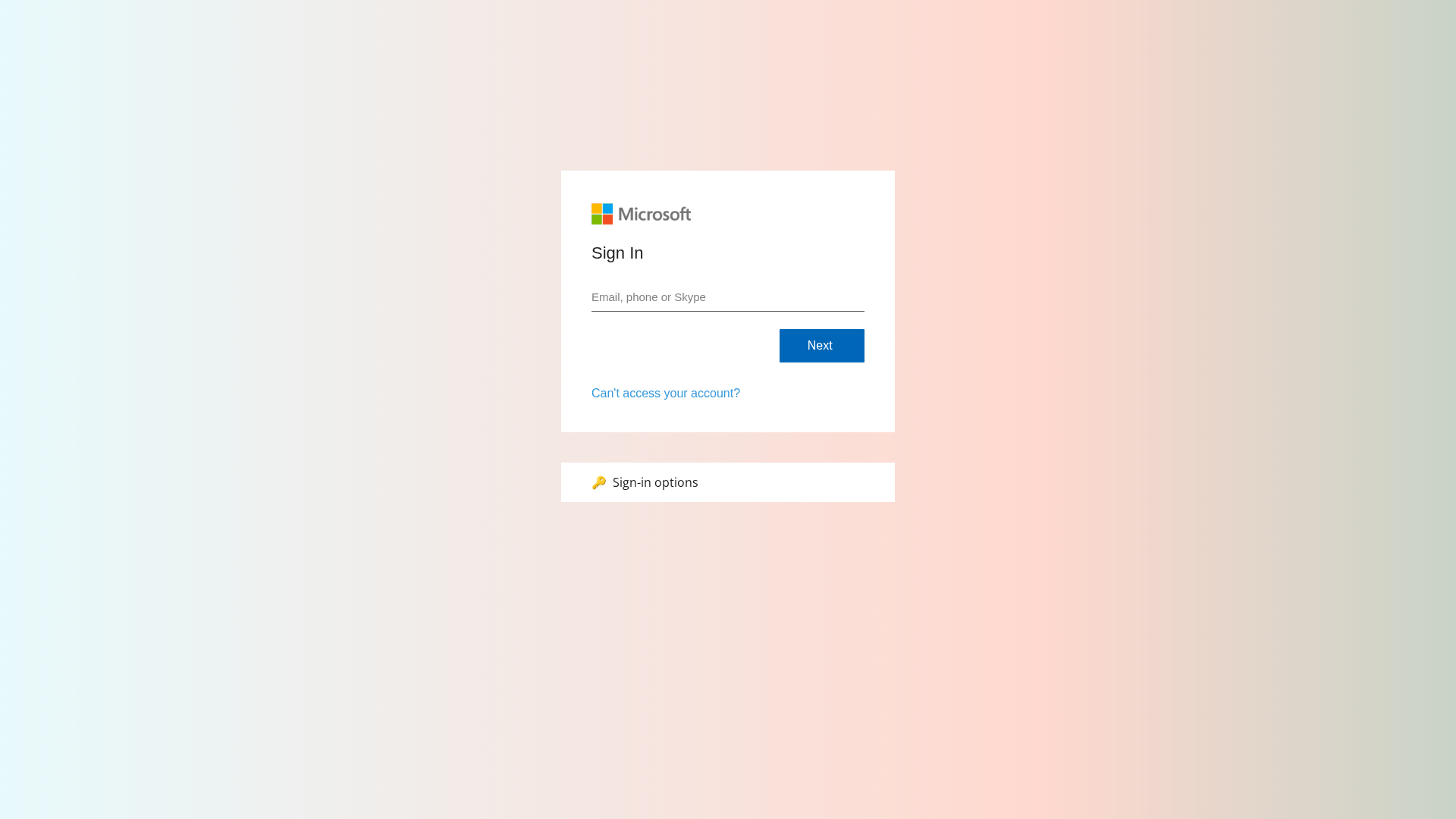
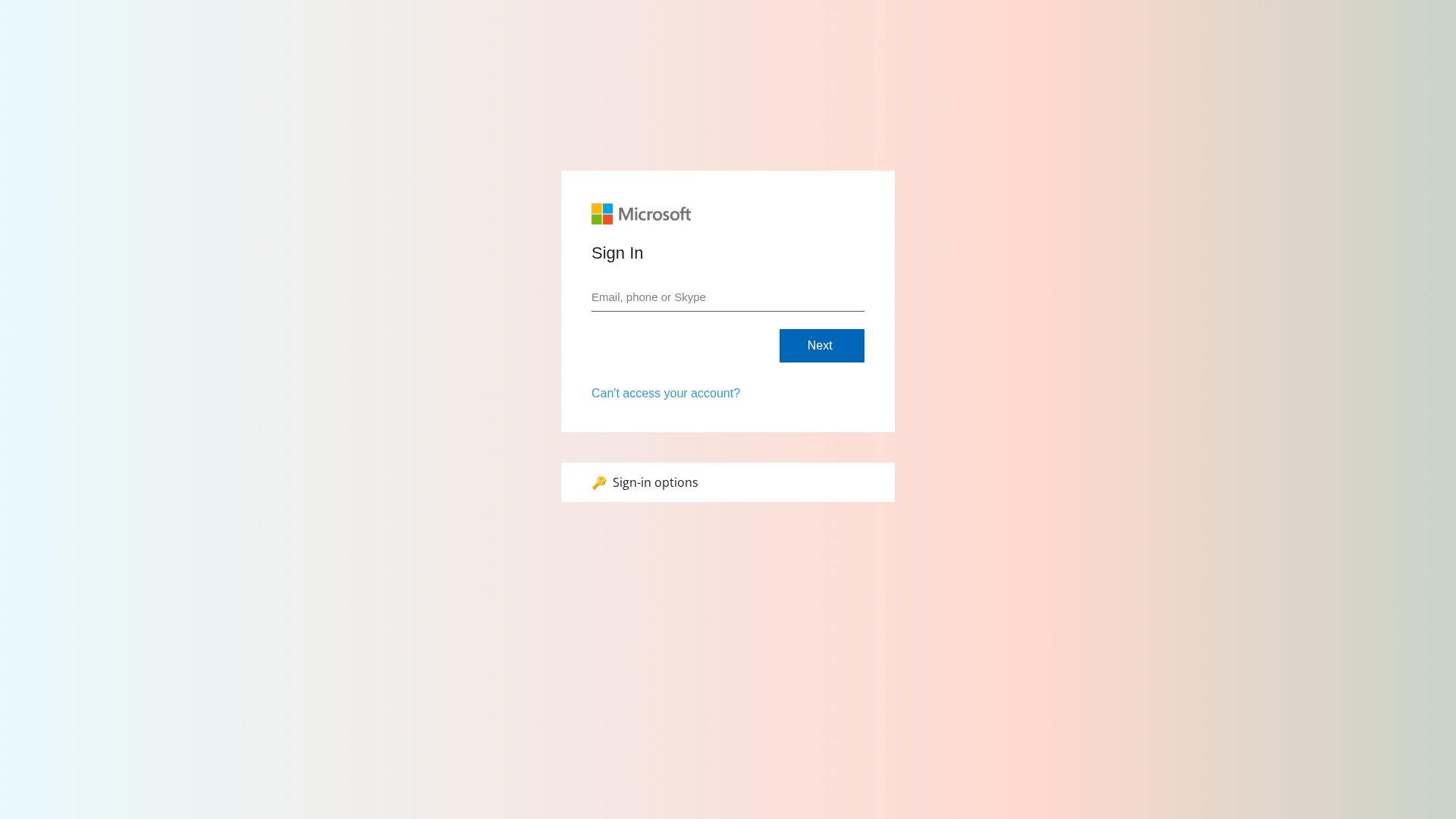
Captura Visual
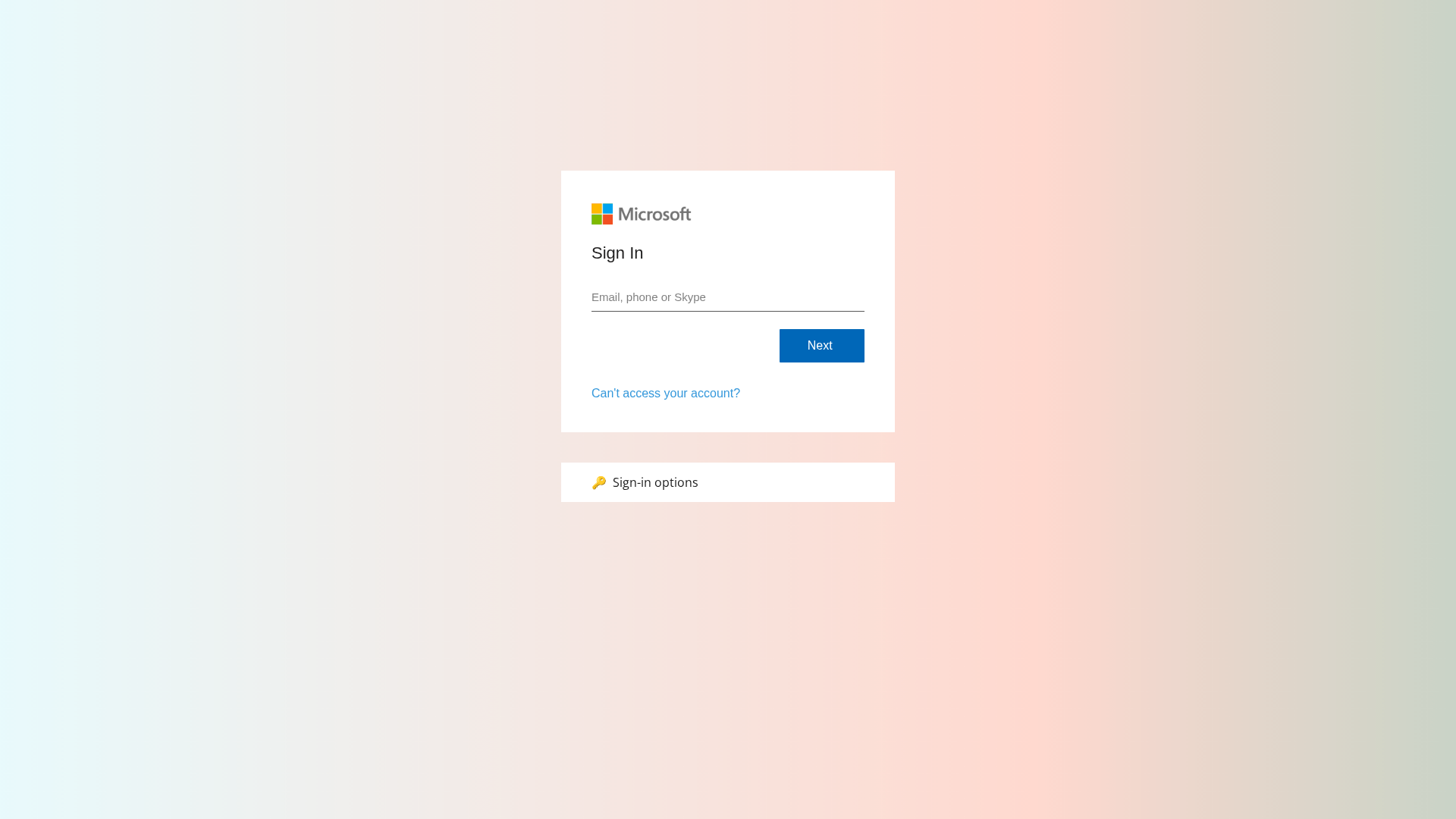
Informações de Detecção
https://ithelpdeskweb.co.uk/?r=a5715250-81ef-42aa-bdc9-c0cdcfab5b53&rg=eu
Detected Brand
Microsoft
Country
UK
Confidence
100%
HTTP Status
200
Report ID
342679db-ef1…
Analyzed
2026-02-12 23:40
Hashes de Conteúdo (Similaridade HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T113F1CE31E244C91B7251C9A4F6B1BB9A3B459385D70B0B70F6F0A23ABDC9CB04D942ED |
|
CONTENT
ssdeep
|
96:XNo9+uvTBSTST8FKF1fiPhevO9dShcFSTqM8V8+hucyBF+uuuup:XN6rQeQmfiPovO9dt0z8FvyM |
Hashes Visuais (Similaridade de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
dd88333366669999 |
|
VISUAL
aHash
|
f0f8f8f0f8f0f0f0 |
|
VISUAL
dHash
|
0010302430000000 |
|
VISUAL
wHash
|
e0f8f8f0f8e0f0e0 |
|
VISUAL
colorHash
|
07000000180 |
|
VISUAL
cropResistant
|
0010302430000000 |
Análise de Código
Risk Score
74/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 Banking
🔬 Threat Analysis Report
• Ameaça: Phishing
• Alvo: Usuários do Microsoft
• Método: Falsificação de domínio
• Exfil: E-mail e possivelmente senha
• Indicadores: Incompatibilidade de domínio, personificação
• Risco: Alto
🔒 Obfuscation Detected
- fromCharCode
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- https://a#б
- https://тест
- https://a@b
- https://a
- https://a/c%20d?a=1&c=3
- https://x
- https://ithelpdeskweb.co.uk/js/usecure.bundle.js?v=fbaff749-4ed9-4292-b9a1-20c3648c09f1
📊 Detalhamento da Pontuação de Risco
Total Risk Score
90/100
Contributing Factors
Domain Mismatch
The domain does not belong to Microsoft.
Impersonation
The page impersonates Microsoft's login portal.
Form on Login Page
A login form on a suspicious domain indicates credential harvesting.
🔬 Análise Integral de Ameaças
Tipo de Ameaça
Banking Credential Harvester
Alvo
Microsoft users (UK)
Método de Ataque
Brand impersonation + credential harvesting forms + obfuscated JavaScript
Canal de Exfiltração
Form submission (backend endpoint not detected - likely JavaScript-based)
Avaliação de Risco
HIGH - Automated credential harvesting with Form submission (backend endpoint not detected - likely JavaScript-based)
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, Banking
- 21 obfuscation techniques
🏢 Análise de Falsificação de Marca
Impersonated Brand
Microsoft
Official Website
https://www.microsoft.com
Fake Service
Microsoft account login
⚔️ Metodologia de Ataque
Primary Method: Credential Harvesting
The attacker aims to steal user credentials by creating a fake login page that mimics Microsoft's login portal. When the user enters their credentials, the attacker captures them.
🌐 Indicadores de Compromisso de Infraestrutura
🦠 Malicious Files
Main File
usecure.bundle.js?v=fbaff749-4ed9-4292-b9a1-20c3648c09f1
File Size
🔬 JavaScript Deep Analysis
Operator Language
English (1%)
Sophistication Level
Basic
Total Code Size
371,8 KB
🔗 API Endpoints Detected
Other
6
🔐 Obfuscation Detected
- : Heavy
🤖 AI-Extracted Threat Intelligence
🎯 Malicious Files Identified
Main Drainer
usecure.bundle.js?v=fbaff749-4ed9-4292-b9a1-20c3648c09f1File Size
371KB
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Microsoft
https://hhelpdesk.ie/?r=87209375-dd2d-4b01-9f76-19271d3356fd
Abr 05, 2026
Microsoft
https://pessoleldept.com/?r=6b2cc31c-ddb6-400c-80d3-28671fce...
Mar 31, 2026
Microsoft
https://gdprlaw.co.uk/?r=6f900ecb-f8af-4c52-baff-66204623019...
Mar 30, 2026
Microsoft
http://humanres.in/?r=2ae1eb79-d77b-45e3-9cce-2c36bd88eca9&r...
Mar 26, 2026
Microsoft
https://sup0rt.ie/?r=abc696d6-acde-452c-9573-b7347bd36b3e&rg...
Mar 25, 2026
Scan History for ithelpdeskweb.co.uk
Found 3 other scans for this domain

"Nunca pensei que aconteceria comigo"
Isso dizem os 2,3 milhões de vítimas a cada ano. Não espere para ser uma estatística.