
Phishing Analysis
Detailed analysis of captured phishing page
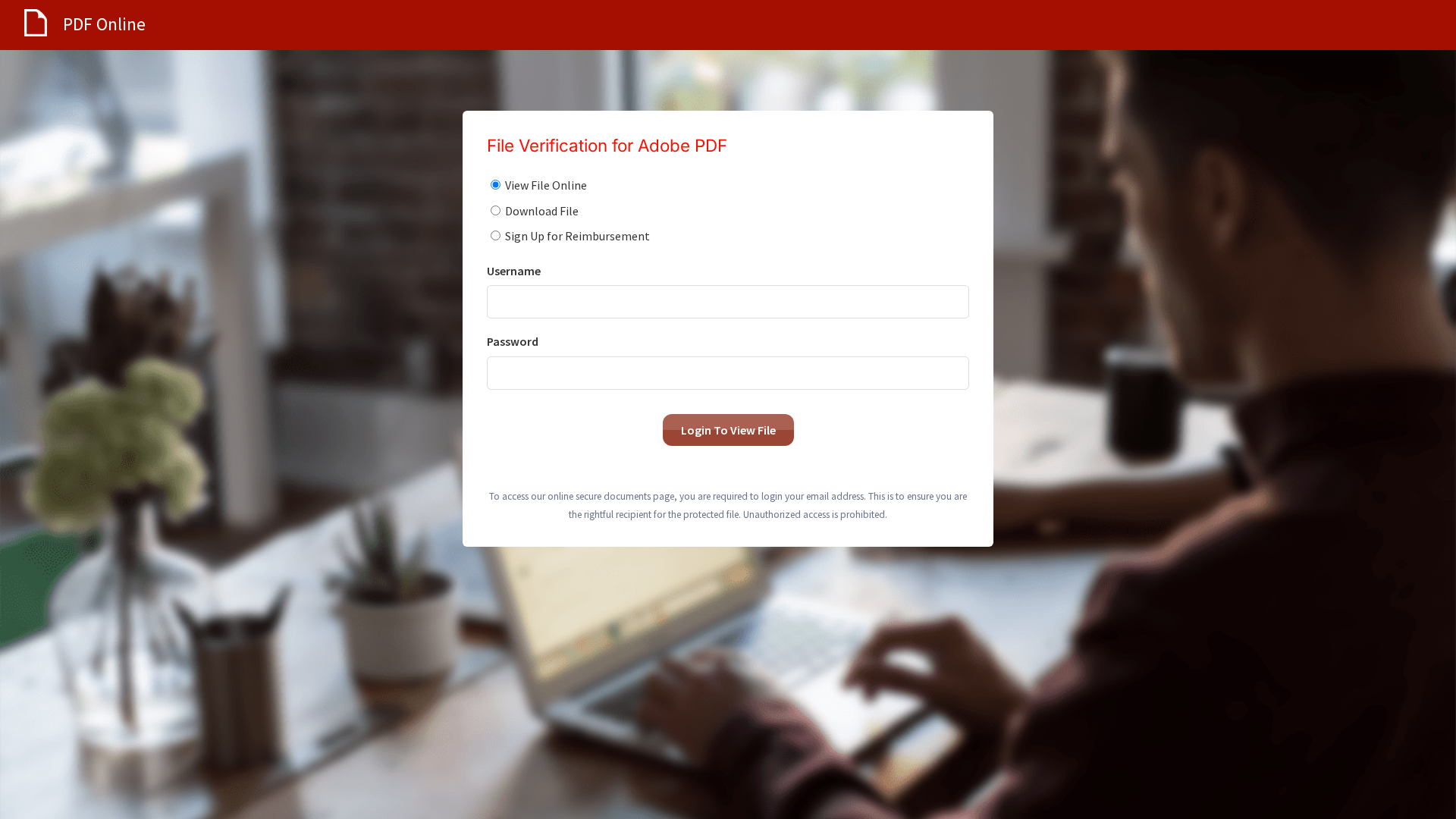
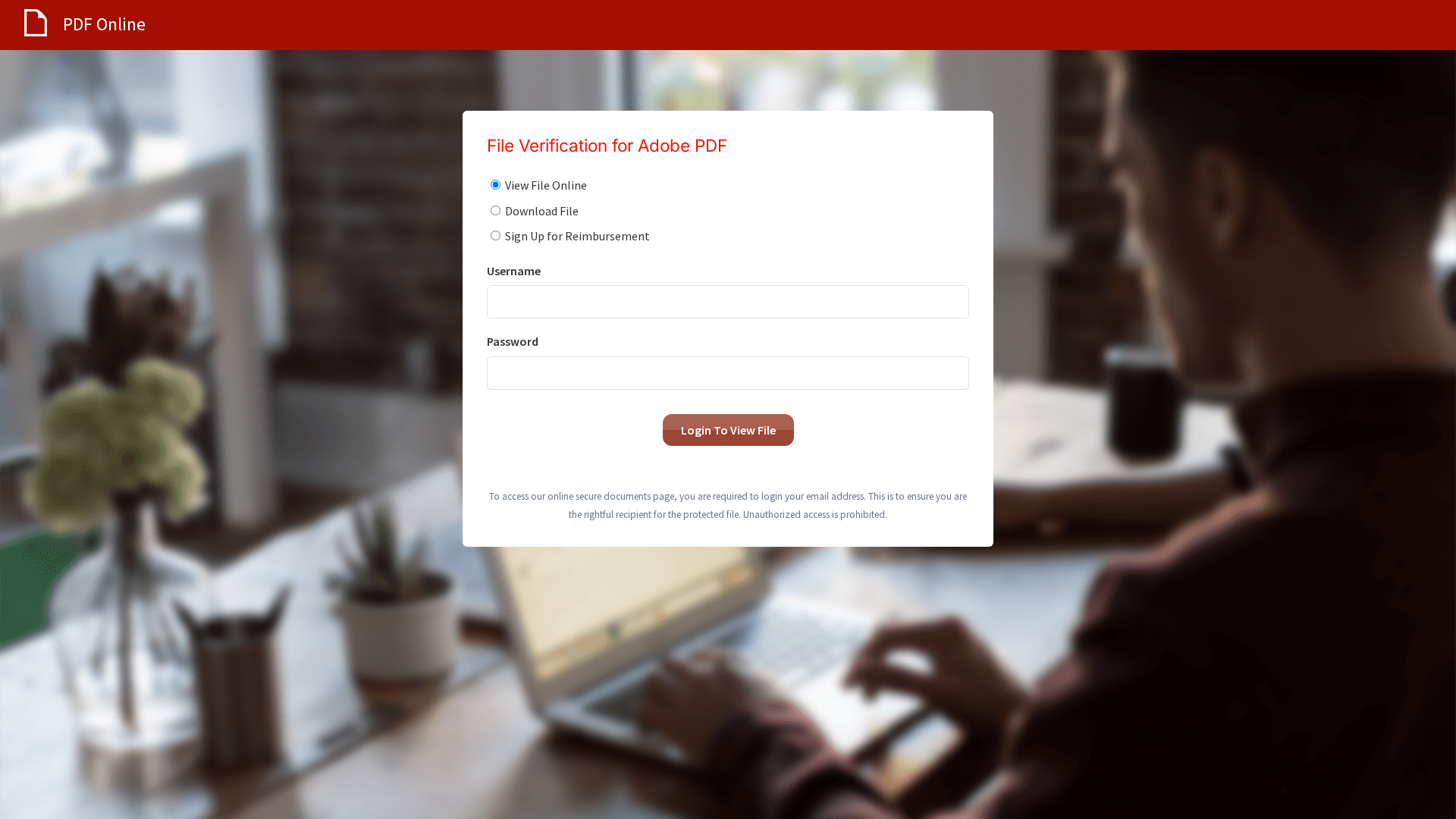
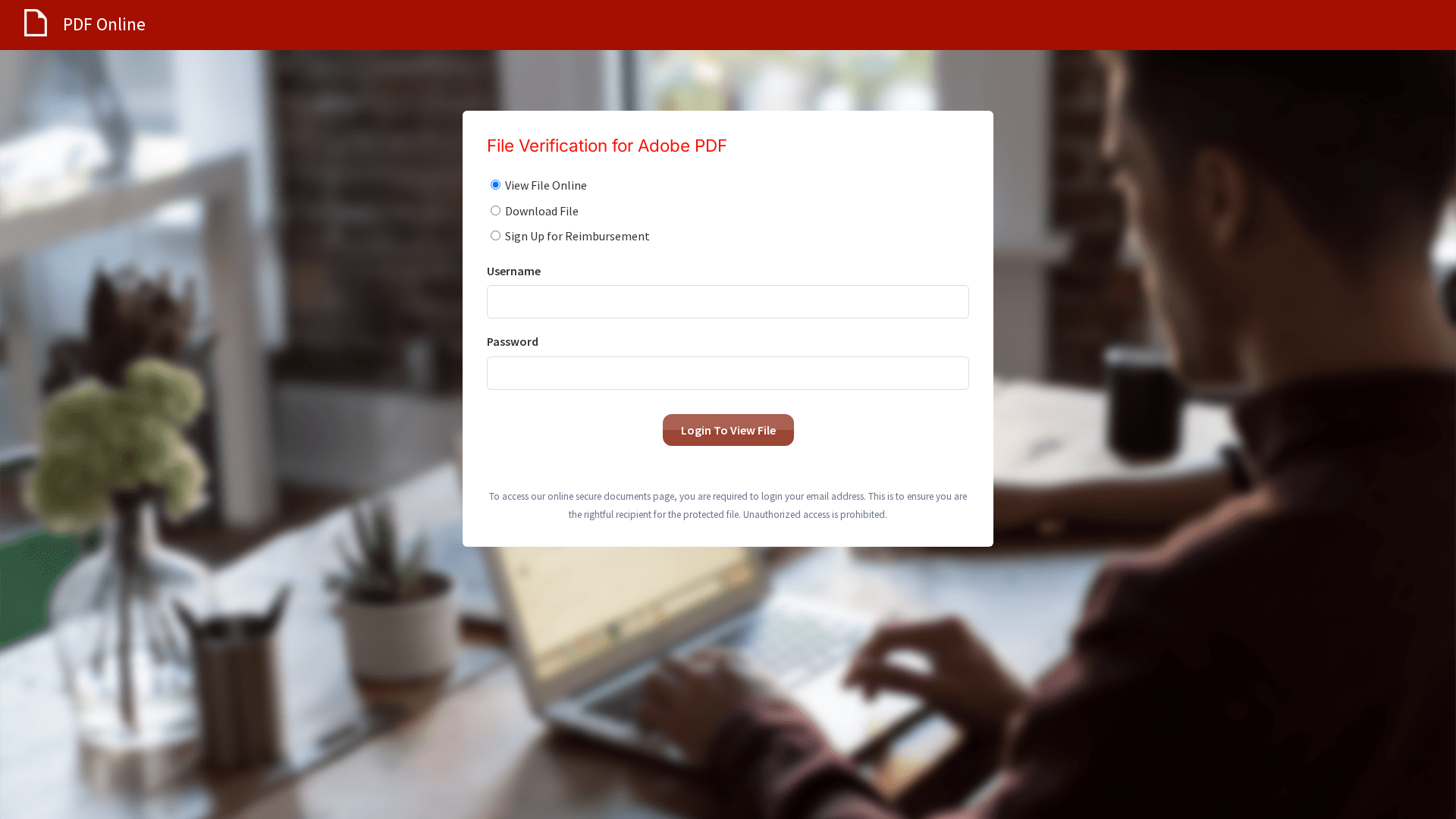
Captura Visual
Informações de Detecção
http://messages.319447.com/s/63BZGFSVBWSFCDX7Y9/584dd8/90eab167-7429-489f-99f6-ce86e8d0d81a
Detected Brand
Adobe PDF
Country
International
Confidence
100%
HTTP Status
200
Report ID
3833658c-f02…
Analyzed
2026-02-13 11:55
Hashes de Conteúdo (Similaridade HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T17061533190459C7A6252D3A8B3D6FF0465CEC1A6C70A6800A3F4E3CDE7E7D10DAA659A |
|
CONTENT
ssdeep
|
48:nICYWVBcWzcYRlUxv8Xhj1fvHgoaZ6pB+OTgl162phmzeVb8JoaTokg:n7JLREAhRfvHgoaZ6KOTg2ywSNqomokg |
Hashes Visuais (Similaridade de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
de9c73102738253f |
|
VISUAL
aHash
|
98bcbc3c3c7cf8a0 |
|
VISUAL
dHash
|
3038316868a02949 |
|
VISUAL
wHash
|
18bcbc3c3c7cf8a0 |
|
VISUAL
colorHash
|
0fc00018000 |
|
VISUAL
cropResistant
|
3cdcdc9909e9ddde,bc3438b6f4d43464,3038316868a02949,8b8b8383838387e7 |
Análise de Código
Risk Score
65/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 Personal Info
🔬 Threat Analysis Report
• Ameaça: Phishing de credenciais
• Alvo: Usuários do Adobe PDF
• Método: Impersonação e coleta de credenciais
• Exfil: /site/submit
• Indicadores: Domínio não relacionado, solicitação de credenciais.
• Risco: ALTO
🔐 Credential Harvesting Forms
📤 Form Action Targets
- /site/submit
📊 Detalhamento da Pontuação de Risco
Total Risk Score
90/100
Contributing Factors
Domain mismatch
The domain does not belong to Adobe.
Credential Harvesting
The site asks for username and password.
Impersonation
Impersonating Adobe PDF
🔬 Análise Integral de Ameaças
Tipo de Ameaça
Credential Harvesting Kit
Alvo
Adobe PDF users (International)
Método de Ataque
Brand impersonation + credential harvesting forms
Canal de Exfiltração
HTTP POST to backend
Avaliação de Risco
HIGH - Automated credential harvesting with HTTP POST to backend
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, Personal Info
🏢 Análise de Falsificação de Marca
Impersonated Brand
Adobe PDF
Official Website
null
Fake Service
Adobe PDF File Verification
⚔️ Metodologia de Ataque
Primary Method: Credential Harvesting
The attacker attempts to steal user credentials by mimicking a legitimate service and prompting the user to enter their login details. This is then used to access the actual service on behalf of the user.
🌐 Indicadores de Compromisso de Infraestrutura
Domain Information
Domain
messages.319447.com
Registered
2017-01-12T18:03:41Z
Registrar
Namecheap, Inc.
Status
active
🔬 JavaScript Deep Analysis
Total Code Size
88,4 KB
🔗 API Endpoints Detected
Other
1
🔐 Obfuscation Detected
- : None
- : None
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Adobe
http://319447.com/s/63BZGFSVBWSFCDX7Y9/584dd8/90eab167-7429-...
Abr 03, 2026
Adobe
http://ssl.lol.memes.pictures/s/63BZGFSVBWSFCDX7Y9/584dd8/90...
Abr 03, 2026
Adobe
http://profilemgmt.mycircleonline.com/s/63BZGFSVBWSFCDX7Y9/5...
Abr 03, 2026
Adobe
http://great-restaurant-deals.com/s/63BZGFSVBWSFCDX7Y9/584dd...
Abr 03, 2026
Adobe
http://learnmore.humanresources-team.com/s/63BZGFSVBWSFCDX7Y...
Abr 03, 2026

"Nunca pensei que aconteceria comigo"
Isso dizem os 2,3 milhões de vítimas a cada ano. Não espere para ser uma estatística.