
Phishing Analysis
Detailed analysis of captured phishing page
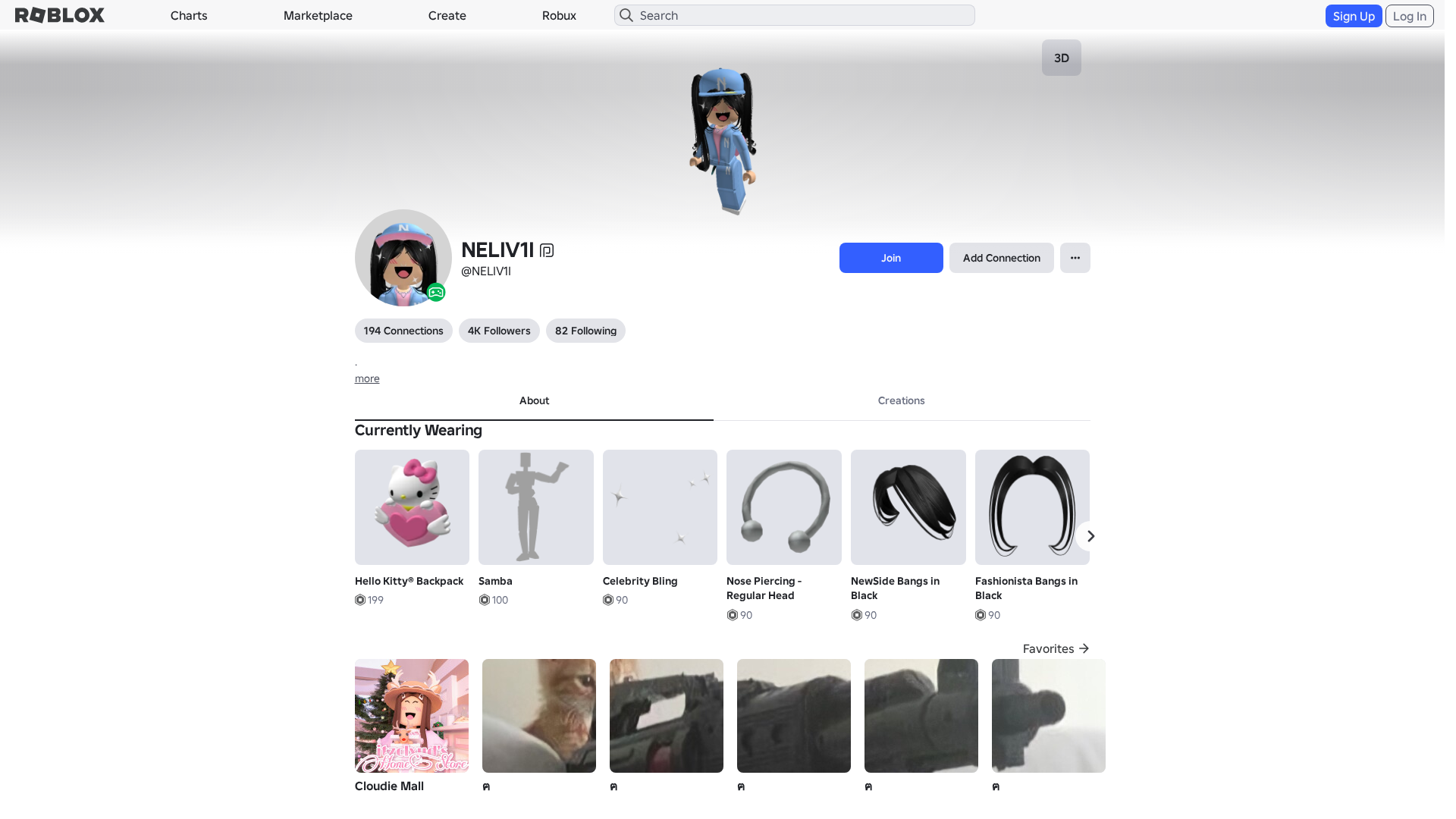
Captura Visual
Informações de Detecção
https://roblx.me/s/TEft4W
Detected Brand
Roblox
Country
Unknown
Confidence
100%
HTTP Status
200
Report ID
3b02ab6c-0ee…
Analyzed
2026-04-04 21:26
Final URL (after redirects)
https://www.robiox.com.py/users/277294125012/profile
Hashes de Conteúdo (Similaridade HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T13583207292542837617B79DAF064672AE2D7C70FCA8346E1A2F8D39A0FD6CD1E85340D |
|
CONTENT
ssdeep
|
1536:e92XWn4rmibeG+sga+gFfQguQgR6gEygmiglKglegkCgAsgXegVogSmgFWgl2gYj:u2XWniBV8zIC5Z0kVFwNNw1Hs5Q2Y0QX |
Hashes Visuais (Similaridade de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
a41a674bf3989c6c |
|
VISUAL
aHash
|
0000dfffd3fbc3c3 |
|
VISUAL
dHash
|
e8e8363036360606 |
|
VISUAL
wHash
|
0000d7ffd3d3c3c3 |
|
VISUAL
colorHash
|
07601040040 |
|
VISUAL
cropResistant
|
e8e8363036360606,191978660a7f554f,45b83261c99b1323 |
Análise de Código
Risk Score
100/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🎣 Card Stealer
🎣 Banking
🎣 Personal Info
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- hex_escape
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- https://api.injuries.lu/catalog/6718181714/fresh-blue-fitted-cap-jacket
- https://api.injuries.lu/catalog/6239323549/Celebrity-Bling
- https://api.injuries.lu/catalog/130433936882245/Super-Super-Happy-Face-Head
- https://api.injuries.lu/catalog/6869813008/Samba
- https://api.injuries.lu/catalog/6134532324/NewSide-Bangs-in-Black
- https://api.injuries.lu/catalog/124102129879581/Super-Super-Happy-Face-Mood
- https://api.injuries.lu/catalog/5915776835/High-Wave
- /login?returnUrl=
- https://api.injuries.lu/catalog/10385344441/Hello-Kitty-Backpack
- https://api.injuries.lu/catalog/3576686446/Hello
- https://www.robiox.com.py/NewLogin?returnUrl=https%3A%2F%2Fwww.roblox.com%2Fusers%2F277294125012%2Fprofile
- https://api.injuries.lu/catalog/14240606089/Pigtails-Middle-Part-In-Black
- https://api.injuries.lu/catalog/3994127840/Celebrate
- https://api.injuries.lu/catalog/4963346943/Nose-Piercing-Regular-Head
- https://api.injuries.lu/catalog/3307604888/Udzals-Summoning
- https://api.injuries.lu/catalog/139607718/Korblox-Deathspeaker-Right-Leg
- /login?returnUrl=https%3A%2F%2Fwww.roblox.com%2Fusers%2F277294125012%2Fprofile
- https://api.injuries.lu/catalog/86499698/Woman-Right-Arm
- https://api.injuries.lu/catalog/2510238627/Rthro-Run
- https://api.injuries.lu/catalog/6134536229/Fashionista-Bangs-in-Black
- https://api.injuries.lu/catalog/658831500/Ninja-Fall
- https://api.injuries.lu/catalog/2510230574/Rthro-Climb
- /info/blog?locale=en_us
- https://api.injuries.lu/catalog/973771666/Toy-Idle
- https://api.injuries.lu/catalog/4849499887/Happy
- https://api.injuries.lu/catalog/658832070/Ninja-Jump
- https://api.injuries.lu/catalog/6099260902/3-0-Layered-Heart-Necklace
- https://api.injuries.lu/catalog/86499666/Woman-Torso
- https://www.roblox.com/catalog?CatalogContext=1&Keyword=
- https://api.injuries.lu/catalog/3307608414/Udzals-Walk
- https://api.injuries.lu/catalog/4646306583/Curtsy
- https://api.injuries.lu/catalog/2510240941/Rthro-Swim
- https://www.roblox.com/catalog
- https://api.injuries.lu/catalog/6965372930/Swept-Bangs-in-Black
- https://api.injuries.lu/catalog/86499716/Woman-Left-Arm
- https://api.injuries.lu/catalog/5230661597/Bored
- https://api.injuries.lu/catalog/6711574264/Fresh-Blue-Fitted-Cap
- https://api.injuries.lu/catalog/7241804067/fresh-blue-fitted-cap-Sweats
📡 API Calls Detected
- https://ro.blox.com/Ebh5?
- GET
- https://apis.
- https://kyxn.dev/api/shorten
- https://kyxn.dev/api/shorten/TKvzwH
- /api/pageview
- get
- https://kyxn.dev${e.endpoint}
- /api/shorten
- POST
- https://help.roblox.com/hc/articles/30428367965460
📤 Form Action Targets
- /search
📊 Detalhamento da Pontuação de Risco
Total Risk Score
100/100
Contributing Factors
Active Phishing Kit
Detected kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
Credential Harvesting
Credential harvesting detected with 1 form(s) capturing sensitive data
Code Obfuscation
JavaScript code obfuscated using 212 technique(s) to evade detection
🔬 Análise Integral de Ameaças
Tipo de Ameaça
Banking Credential Harvester
Alvo
Roblox users
Método de Ataque
credential harvesting forms + obfuscated JavaScript
Canal de Exfiltração
HTTP POST to backend
Avaliação de Risco
CRITICAL - Automated credential harvesting with HTTP POST to backend
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 212 obfuscation techniques
🏢 Análise de Falsificação de Marca
Impersonated Brand
Roblox
Official Website
https://www.roblox.com
Fake Service
Banking/payment service
⚔️ Metodologia de Ataque
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 212 techniques to evade detection by security scanners and make reverse engineering more difficult.
🌐 Indicadores de Compromisso de Infraestrutura
Domain Information
Domain
roblx.me
Registered
2026-03-28 03:56:41+00:00
Registrar
NAMECHEAP INC
Status
Recently registered (7 days old)
Hosting Information
Provider
Namecheap
ASN
🤖 AI-Extracted Threat Intelligence
Scan History for roblx.me
Found 10 other scans for this domain

"Nunca pensei que aconteceria comigo"
Isso dizem os 2,3 milhões de vítimas a cada ano. Não espere para ser uma estatística.