Phishing Analysis
Detailed analysis of captured phishing page
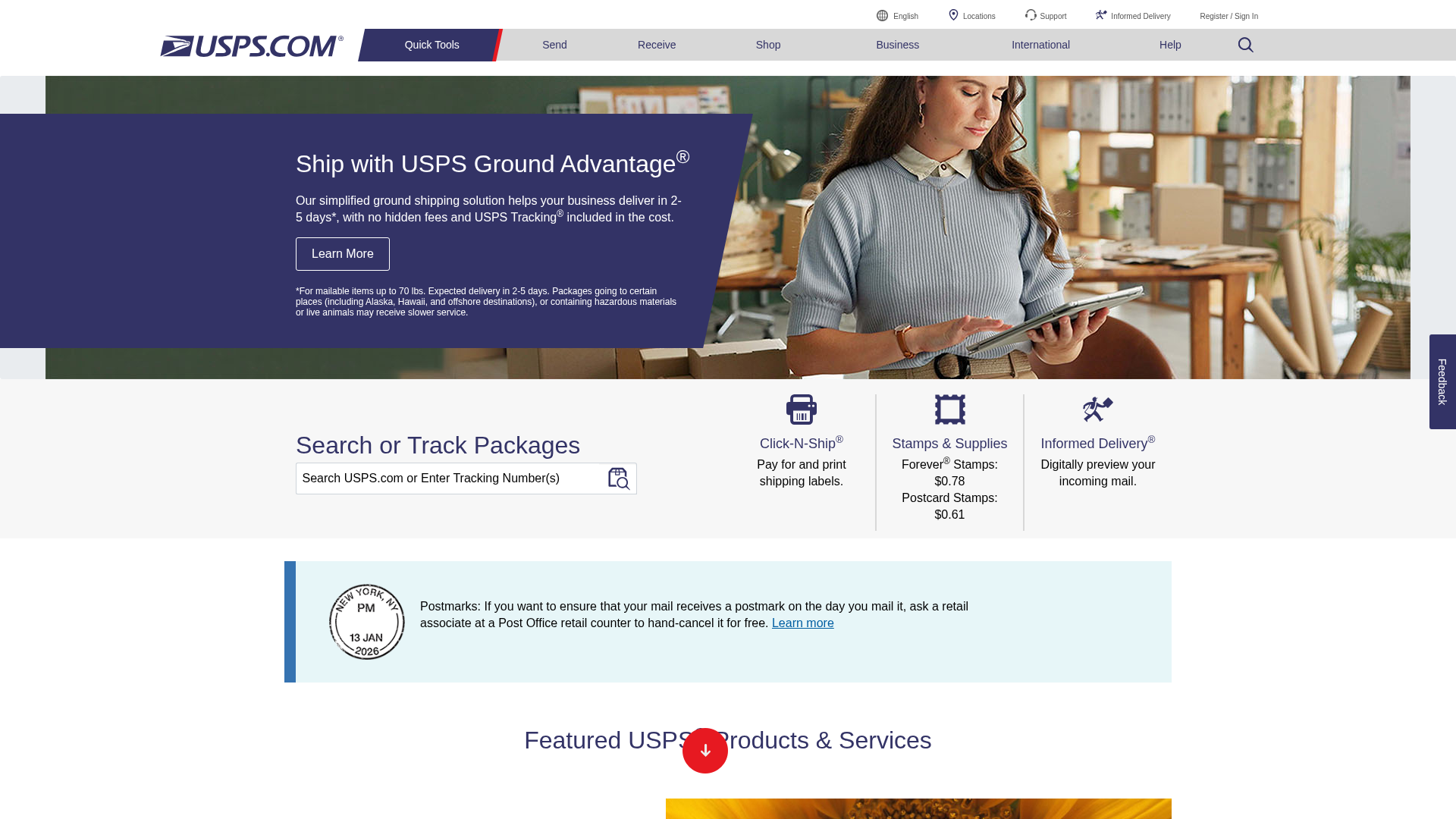
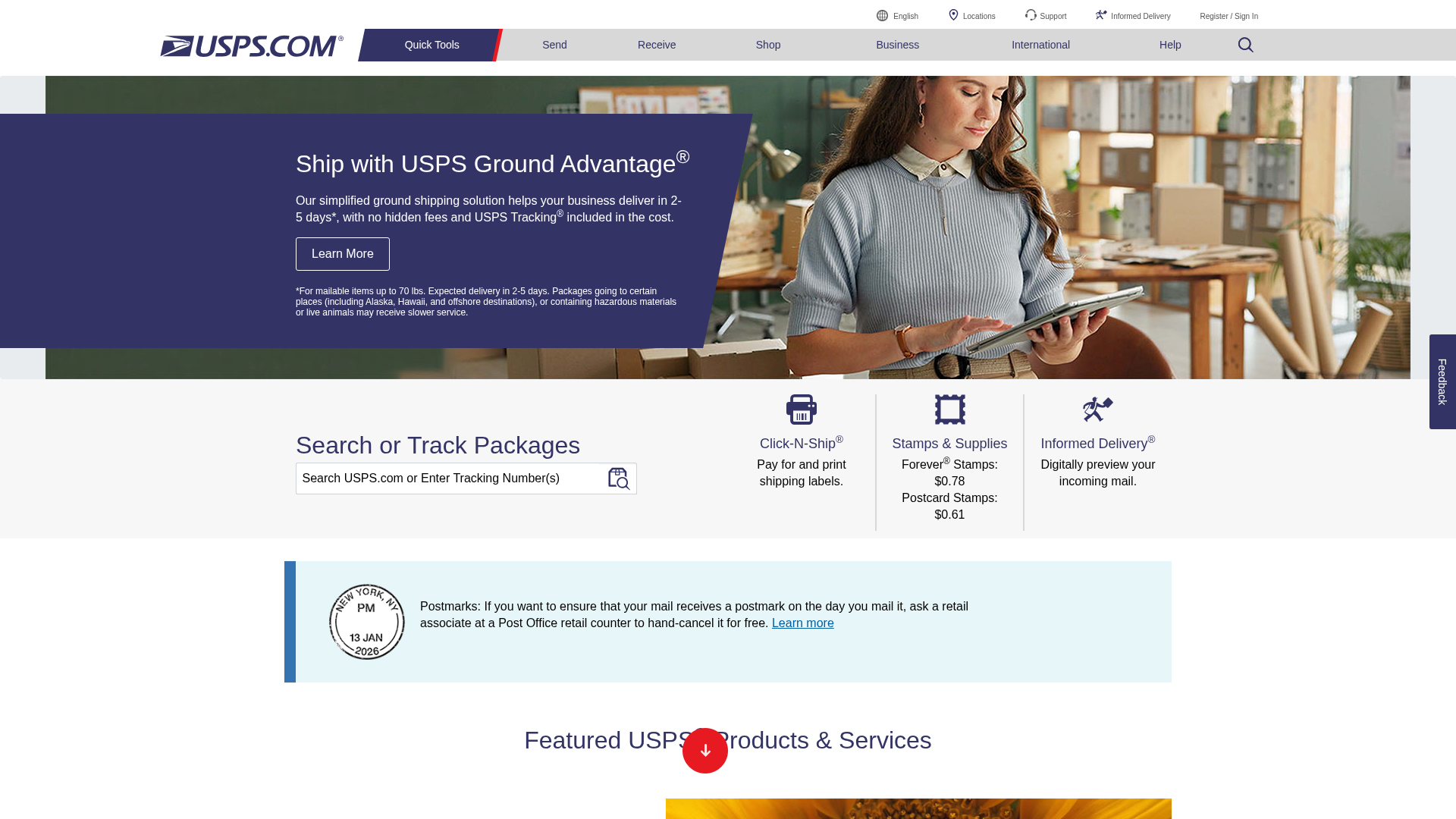
Captura Visual
Informações de Detecção
Hashes de Conteúdo (Similaridade HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1D15387738040352A121362D5F910B7BAD687C149DE3A0781BDF9C3993BE6E656C1DF2E |
|
CONTENT
ssdeep
|
1536:/wRVxzrKHcEtS/eHlSYD/ZSnDnFzzIree+UqWmvCE0ojOn9Gd0u:/tOe+xp |
Hashes Visuais (Similaridade de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
ae3ae4dccdd980d0 |
|
VISUAL
aHash
|
97000000ffffffff |
|
VISUAL
dHash
|
377fdd7f22272f07 |
|
VISUAL
wHash
|
01000000fffffff7 |
|
VISUAL
colorHash
|
06400e00000 |
|
VISUAL
cropResistant
|
377fdd7f22272f07,5b7b676c4e6e6f7e,5e51377f1e04e2e3 |
Análise de Código
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- document.write
- hex_escape
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- https://gateway.usps.com/
- https://www.usps.com/search/results.htm?PNO=1&keyword=Free%20Boxes
- https://store.usps.com/store/results/free-shipping-supplies/shipping-supplies/_/N-alnx4jZ7d0v8v
- https://www.usps.com/search/results.htm?PNO=1&keyword=Free%20Boxes
- https://www.usps.com/search/results.htm
- https://reg.usps.com/entreg/LoginAction_input?app=Phoenix&appURL=
- https://www.usps.com/search/results.htm?PNO=1&keyword=Passports
- https://www.usps.com/search/results.htm?PNO=1&keyword=
- https://www.usps.com/business/verify-postage.htm
- https://www.usps.com/search/results.htm?PNO=1&keyword=PO%20Boxes
- https://www.usps.com/search/results.htm?PNO=1&keyword=PO%20Boxes
- https://www.usps.com/search/results.htm?PNO=1&keyword=Passports
- https://reg.usps.com/entreg/LoginAction_input?app=Phoenix&appURL=/
- https://store.usps.com/store/collectors
- https://verified.usps.com/login?goto=https%3A%2F%2Fwww.usps.com%2F
- https://faq.usps.com/s/article/Requirements-and-Standards-for-Sending-Domestic-Mail#postmarks
- https://www.usps.com/search/results.htm?PNO=1&keyword=
📡 API Calls Detected
- https://www.google.com/ccm/geo
- POST
- GET
- https://tk.amazon-adsystem.com/envelope
📤 Form Action Targets
- https://www.usps.com/search/results.htm?PNO=1&keyword=
- https://www.usps.com/search
- https://www.usps.com/search/results.htm
📊 Detalhamento da Pontuação de Risco
Contributing Factors
🔬 Análise Integral de Ameaças
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 429 obfuscation techniques
🏢 Análise de Falsificação de Marca
⚔️ Metodologia de Ataque
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 429 techniques to evade detection by security scanners and make reverse engineering more difficult.
🌐 Indicadores de Compromisso de Infraestrutura
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for by-haixingtiyu.com
Found 1 other scan for this domain