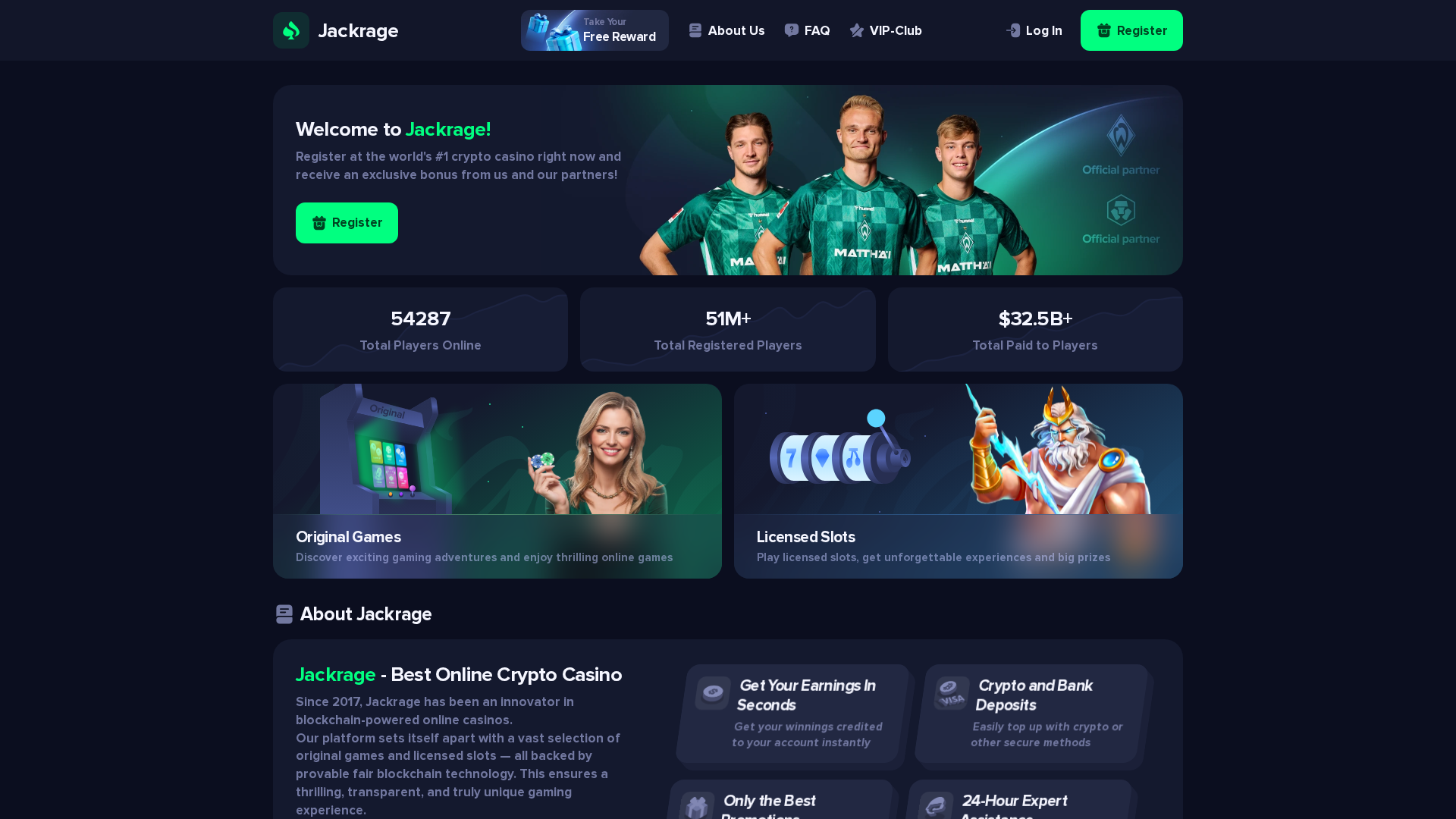
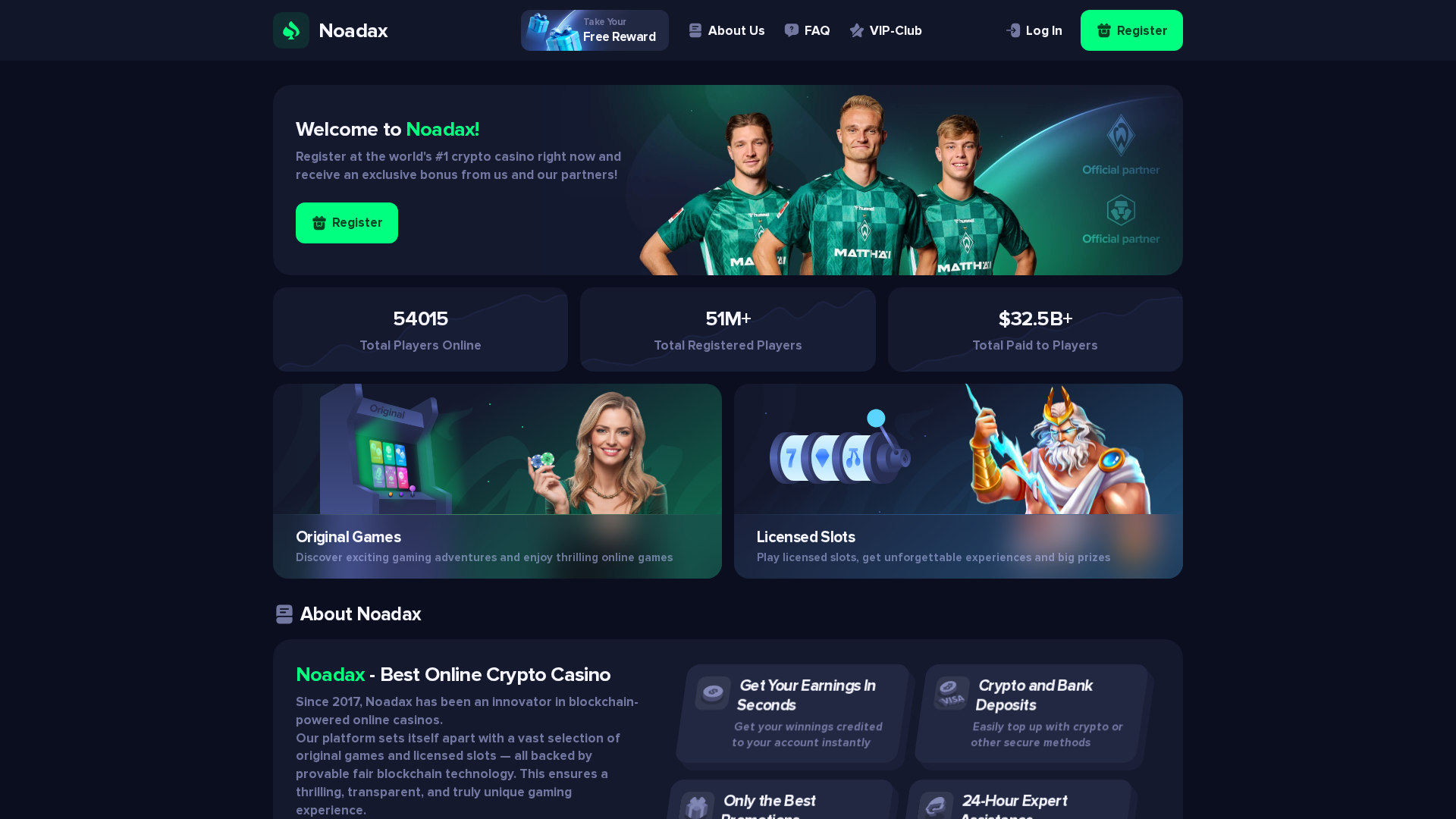
Phishing Analysis
Detailed analysis of captured phishing page
Captura Visual
Informações de Detecção
Hashes de Conteúdo (Similaridade HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1C45419BFA32452F9E106D7DCD952E038326E24FE3B5283A8E7594F36B5148DC8855D83 |
|
CONTENT
ssdeep
|
1536:l8Ucshc9BoUpQ5LToi0ZvqLDTKc9BoUpQ5RyiyOYjyty2ByayUY0OWIbZyfeYJNb:pc9HQKc9HQthY0yad06 |
Hashes Visuais (Similaridade de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
929969e6a66da496 |
|
VISUAL
aHash
|
123c7c007e76283c |
|
VISUAL
dHash
|
e4d8d8e4e4c4d8dc |
|
VISUAL
wHash
|
123c7c343e7e2c3c |
|
VISUAL
colorHash
|
38006000200 |
|
VISUAL
cropResistant
|
727130d2c96b72f2,e4d8d8e4e4c4d8dc |
Análise de Código
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- data:image/webp;base64,UklGRgDyAQBXRUJQVlA4WAoAAAAQAAAA9QQArAMAQUxQSE7yAAAB/yckSPD/eGtEpO45jts2kiQp/7CruttVe7wjYgL8k+GCNucanshxIQIsOGYAL+yIQcNlTFF5DUkygBzVGwLxPXw3R7gT26Ijx/Kec82lusMDCa6dUwFHuN5gsaUaa4cc8Ubbtmnbtq2djeNr27Zt27Zt27Zt27atY917rG3vtfZac6Yewhitlozaeh993l8R/fdF27bttpFtdTofokGqjjHHnFgASEoRn/Tw/1/jNM15Xak7FShe3Cnu7u423DbY8DHcxoDhNtzd3R2KFEpbCnXX8+SX52mTX35J27vc79kfEf2HxEiS1CjBZjHH1vR0D9eAwU+ritvY/5IF6JIme5PS6v90DeH2oLAUKnox8b86pKOfUKVt0dNGiv/V/Rnwd1IpoGBrkPx/de3AK4wOpRvoQ/yfDpvRuTSjSRys/F/dOPW2MgCGS/3/V9fr3KkAlEInba/2fzokPjeLSwHU6znK/9ON4zAuC5RCa9+GSP5Hh9Ttg660hwaF+9ys/k/Xbk1kzgTkD/f6P13b/R7Naq93kFnQlQbkIyc3kWN9/I/qWW3e4nDLGafIu89X15bhfOQbsxl/AxrcGim3mLvBiwCIWetL4PwZz3zHgjYcr2wx70Sue63E0ZK3yXF+23IvDZiA+G0SS/kt/J/S075zxnti/DZokZY5Cg3U75paaCiiIqQCCw38gy5tH/TzxvfYjslid6iCzQrCIqPW5tEOAuM1AZQ2muM9HPH9gJ6fGNAlDZkVIrPEHEf2R+yOEEJY3HozoPN3N1Rg+7bFWRrSgOPVLLCOyj/X+HC8wHuCnVuz/Kzoeh1sT+hcxmfMJn92qOV1SCR0MQWKLocKi+cQ9tK16Fk1a0yPYztjKaxxXo60uKLPpv2bEpdJWiXsnmCfSSw3A2ThpqqYfqC8ah4JIB9p9tW1tPCbYChxF22Mk6Az8Z/LrC1Q2sRPC5FgeQj/DwYA6QWfl1lYkxCNNjPchfJWCEnwUugu5FtDbAks37psLIBB6+8EW1hbCCNflgFExH4YtPFSHzzfUXVMBbCWSlhgYfWvK2ZACkvVfSwvY3hb7pkaeH6Af5wRtqEF8m/JCUuqv9s5RsFJaX0E7Qn9h4Z3vq9UETh+gPVzNQxan+ppSQ1WLo5muAtZ7KsU0tHC/oZDaz62ssPwLSE9msqqQFEKpW9qZ0HhcTKXSWGgStCeXTRXs7eGHMd/NPhJCcwJSqdbY0mN3Pcjay+wPsJGSKod4SRvhAeOx/Wwkf1ZafOthcW0xkHIbuaydwP3chOSWhc5ob9Ms8fwWP+dAw+9glFeFpO/hGQa2M7ye4CQVzNt8IQb9YOpcvyOZMYbZv0J1sHEvxtaSniOJGk2+6oSwiFrGsMNnXupHobvdDzIAjDm9GiwxEJaSNY4TEN4UF8qYBWpqGQE6KSl9lLsjs/v7HkxJs38VWUh9beLg5HaVsBZKdpmoqCPrqXA7siH5cJHNOyoZhnhNVYPg5wXKmDlwva5KNDa20Ey7D6g2wvoxzT1bCphGV3w4B8KBtjXSkjykDDmjK0swe1trXXMv1lN2l4HSwjFsMfw0vJMZyFP+C5AggYXejjhdip1oQD0D939mhbR+SDLsuGc6yLgBVC7FqNB562qT2B2FNV0cKjP4y0hGv0H4FztRQiGXU8dIvTTyXLsfknTr9DrvdB00VsZYfEgXfKR67SOqcKdtu0ymELFeKcXgdlbtz+yYG8AGLIDlJbP1OcLYcvHEn8p2NNEuE3yMTQq4OcpLxleR9U0BUCh9EMtn/Pgu7+jALQXkPfGCvd1HVMZxTNUNDsBum9D7AisjtQ1Rg8NPgAOV5dYOLtCiE1JNAf0h4WEUIT/jg5dcLqKDV4fILtTwBF8P9tZOOeFSBRvimiu5v0CiVDU20ijN1TxcB/MPnj8S64zo6YHWThnwYWSgJOf/zoLtWDteoHm0zzprsDrRJ4D8I0s8kRHC+cyLyO4X3TRraaCfcfHRV7k/t2CwOq47NNyHEf8MtXGoumvto/mxvC0tWAVDLcAPoB3CzywOrLVScwd66zp1Bstml5Vmy8otfyetxDsyj7ji3l1tBe7SgicPvLYhxyQp9pZMriPpFCOgLwWzFEULT/zgv6x0xqrfxSxBrJ1BUpnmbrbzoIh6gBSMfl9sWCqfabyA+TMd8bprcsUPQ2veqZ92MpyQTHhIxJpBwSblV2dHCOvVvOhlTNOv6TpwB+QV6kA8GOjjLBY+lcUIpF9WTA/kTldy+HX0a2tI8PoA9peoAF0IK2ODVZZLLWbDtBlCyGZHUvxG/hhUgiBz9vKMznWNAAgf/G2VBh6C43U3RIBr157X8cP+slEKT7HpiFgDwDMOaV1sLZQHGR3KmPnB+cGcXQPIfeizH3FE/rtdAk2RxaWwRqX3eg2NLBQbhvtphapgDQ8rCHkXpSGe7U8yX3d3xGbD/A8WzoGFPBmsrNFQqvXAIn8sx6CVhSYGs0TUHw+AJvPwGksdxTr/rNEzgYliJlxNBLxGwXdDSJpscPIs6WKWjhh816v0ts14RiUtMPeArkEo+JSJtpa4dX+Aj/rRu8kmm+zsCqBzS/ul6SjAQfU+/4WSNVor2wD2pBtYUJfN2Evb970wOa9xLoU7o+071wsjqBzbUsBJLIWOQv+fCNqiu8kv7ji88e6el8KgI5HFo10szCQhPyBWDg+Hq4QGLn30yKeGP9pSOByHK/pGIOh44HLLewsC1w630ZkTyuJ4D86wcokwLN9MF6Fy5HuzkAIOt3iCEtiXYNwbrFKA6/TBNgCfq8ifBpaPzPwJHmjJzbvnfoMJepip1oSZ4ZYT7ytgVZgh0nQDqtUBhWkDmbwRH+uPjan2h4KMNdcACSQjbeGWBDdoW+1qJvDqV1sy2DP5Kh7PAGvpxLY/LdTWpQL2V5jtyDtcDWL4SXfmY5cNN5pLC+LS8bsN/JsEzbb4PJWMuwlzb3ZBowJCy2Fi5lLHO6pOdYCYfwVXhae4bYoiyeZF31luLzTcCuAxjBLgzaxmsJCOMjl+dGICADdyqRek2z4S74DPjdUYPPeviRNc7cAnKxuGXTk1RJRh1PaMOsySUe9DTTPJmeGAy5H0vAFjXbjJUtrWAj3/Z2GijbJuWy2gT3HFPNEc9pXgsvbYMS7LwHRMzwsAezHZKH5BE3nP7cum2LRtn0s794aKlyOc3cdQAu8q/3kFsCULsvyUUk9JCXKZv9krXM8oQo6OONyZG7xRo7d9ID10bVgCwD3fYWoxWLs3DK7GvTvgG9VwUmBVri8IWbFwQAQQNZuQvzj90iHyru2ZYVTFF/ofY0IbN6G3Faj3jfseAfRv/of+t0IXQrCCkrqcZlVX1f4ZxmREgLT8HWIPTbHeuZLwI456DlxQP20pYvYv5egWjkU6tGOO35lhdTucRHPN/WamlbYvKm1vRAKAJBzQ/5ubCPusWumA4gUXXAuu+dP35jKt/fWcAU2Rz7yLWNdhhna0ADPXxgiEfW49QDIp6wdUpVdWvp8BCzXAogkbfDA6I84NDSf8TfCON9XOol6AibRqHxaIik7qtzT80R/vgE+R+I9gQRoe9eNXzbbEyKe2huQudKvLKuFHs3iO9O3syT4vFUEXc4HjBegOVrNxxkuUvG+DGxzFRVqf90yRLkihu+AlIP2BDaHkAx6kA8But0F9C8G+8lE+yKwbwyNuAms3+Bbppc0u8O1TsktoPBpiNwKnzfKOW8oeAzCit3nwz3E+raW/fgCVIqWO5ZlauofpHhCJnbG6j8pkOMf2bAQhEKDH6scRDq+CyjkC1HNV5XpEbO/1Hx7Cza5YfW7Ag/51cC56gFoxuzI+4PF+g1Lr6ZRiZtSptu+NjMS+aJ/WUVhhdEb6zq7AaTLsfGVdtyJEOXU/wey0cvlDw8HS8sSaZ8bsG0JuIexNRiTm9pb4fTGIeqnERrbMAn6GJF+IfvWByFwCTjUtkwXfkSDzYCrhOUu04sHe2H2J/lbF2+E/jfABqSMEOWDJb0vIVflWxRRtunxm6yj+TabGkitsHpT6VwBYAOgIxfudhPljLqLCjnGs2xx7pfLm1d9rK3wetPqGIUY35lhMhGOfG40ayUfcI1X3LuM1/hVrT+hrLYyUwWY4+k21sXsuM3/CfkbQE9C0DS0FeM1N5d+pxGb7K5l7ASy2id4v1EPptrgdaSdT3N9xlJBLawqwlGty0AlqawfnJoInM8bOuNIEzleb4Nn6WjYfkTWdADQL3qpRHgNpq35NNQHYBKim5d1Ueg+gD/U56XBBFZH1e4ndGLYRrZ+rocIPxFup5qmAXtXH1TApUhpOYaVOsP7iQoCr3dWlEYc+3PAHpX+9KtUdON9FPkegFYFl+2+E8fImdHIcOxL+TC/oYMEn+PcDjYxgI6Xf6Cy6KbOFYDKZO8yuWK9XKlS2Qe1nr77yrNvxbQgTXH88wt/t/aU4/JevxwjbCsLQKBeTJISIpveD7nW+iAC+lcSdn5+zfuOnzFvwcLFi39fvOnk8zQNRQvVALIo8djSATVtsDgS1ctCRnBzQmdddZWJa4h5HxEBoIsrryeBkdm5+obVrFuvYeMm9fy9guu2/WXn3S9p+cVanTa/QEvRQjeGjFvL2/vYSHH4dU23pjCDmjPKqR8NlSJ7sbcvCfkwR2cXPmKt3Wv3mb/nxuuP8UlJH+aNX/PEQJd5o4mbEoHFP+zwnrkdx4Zd8mpu+hCi+mX3SoNMGyfUS1dFLH+TqSUBXf4a8sepCd74m6qPjNzxzfzlvNIa2YtpZOHfAWtRx1jeQWnvjLJl4Nh1yYlniWoDVZ5ekNQCbeb7k4OCVZgb9ytqlN1YAABKP01Mz4SwH5rJynXAWYCCbtwfK4K6r7gYk0eWw+lZlPy7nBsruvoSWBubw9kcAFbEAXC6jUw8vxRVD2vRy0DOyWQBzWdf1QG63DfJJ8ZGyAiMjXxDPOf2FeS00NG24nl48GQtQGesF4dEx41fDHSFaKjkg04ynD3xkFtIm1igpM+4pZ74fcIDz5DAwGrD9rzMhuU3An8GE2ydPoO3Pigu1+NzLnZvdXDC2G3zo4AGHGOwZICHU+QiF7+RD549ffryc3qxkVeptySQeQUsv+7b78SkFZJ0BWpyr471wddU+ZdkQ9Nw6LS/PUTuntxuNylB1vRGe5ZqbDJ+w8VkA6ArWJNzY041AlfjtVYLuEdior/YhhC33YVa+BIOGWMHZ6ldUKet0doK9gkzkdrohZXtJLj66a7y2QAuwJcVUlFLm4NotfQAlxBS3dHFutafaXq6AjXw9BsLl9e0xtMof81GWsEApZ9rP1SWidmD9gu+MEs1nuuOuuRZy6/m0BW5IZ/M8MbSyKb/5P6MVQoAMnmimD16WGlHAQ0geQ2QMebHJOQYKjSg4NEMfxyNdNxH6D4kwO6UAorPVhaxM6l9zggtY9FnR+mNgK7oTd7Fkc4S/Ixk8GNooAOOcteY2t5NvNLzEeLBC5PRwJ0w+VzPqh62UtxM7+vwoRzbeoBcXEW8Mv8D4HMIo6LBP/2Gr2t7h9sSeBmiwwkaIAZ4qZhvg21E6/kg57NoU9oAgzbn8eQIJU6m5d7SF2COCgBDAmC+0aBwdaRYXbN3fgm/zgEr003Yi6ZIfcHnu/ume8uxcdt4K6x4ZQkANBvy7hiRGl+yoG/sBxiCTGfSYFWXT32yeVwdewIPE7mW326snF3BIvXroRqnAtYtfpjSiUr7YvdO7uAlx8HUWF4KeuiTDwcSohSbvhk0E9rUQlN5TwZVdpYR+Jc/eR60zLlqQ4hRnBbnca3Xm9hDKm9nhkuw7yjtDtMA/gKAowwwfu/IPRP3Fp3dRF9mex3ndXfeHPleLovjsk8x0GXdW+COeSsOSgbcQ4o5ANOQf8SLK7DcFp6/8++QUDtRt+opDXqm4y7mTN16JeAwDZX/7t82nhKsy9DnPNY0AGNwaisH+OqRbMRjjTH/xp9DW0XYSgjRNmbtH5yXJTVRL16mIfP2DqumxLltj+vsQAIAElJsSpWQiyKgharC9XU+Y9Xz641lTaoE+no5KeUEIb6GtC4qX8UrjzSU7xJd9+C3CDnGJWwBbJ4cW3gQKTF9ZNDPesJl6TNeLuwc7iATXa3X4DLb24eup8xVl1WTdqYqxm2V7b4DvgH40m//2tOXenyH/ySAz19625s+7RM/4WP+5z/+gz/2S99Rey9kHnOlzz7tbsBXEDLMX2ThlaLnPTwIbDuh/3IaAFaAs8fjir1//5NevyK/5q94m7U5n7360ls+6b/8jT/5+3/rr/nZ3+vrf5EPeM3ds9T1d9DmoaGKLg91x7Yd27r5ZOkqBACl47EVcNQV/BNfYv2/P+JfOpciB+rj2/ve+YZP+V9/8/f94p/4o77fN/+qX/AD75gPlbW/wZl54zrf2JdTCk/3cCOw7W2kPVQDjgKW+8/n//X7HLfUa778734ZVBg/dHHw6if9jV/5fb72l/V2UomUULQe/A0KTrgJhy+6F/r+4fCrgv862BG49s86L7nDm1PHe//Ohx6/vu3n/XccIiN3cMCzd71c01SkjF5pWh7PopWbEJANMRzH7hTf7yQjcO0k/a6jrkiw/p9P+HnHv7XxP3r3dECAdWQIiiE35dONJY2sRciYywy0+WhA0bOmjhJM23qOv09xFJ3cGt71Hz/v697vNa/90R/2fAidB4PAkPf5wlw/8XF5nb+ZmbTvK1i4mi8vpCOjCrY3dsS1H4WMew6Qo2z582C/6+d+zQd+wb/92Y+QdBuiEIA2fJluQ4gMWu7jzCGxkjjnINcRSE/egB7/RyS2PTvEeWQaoBCDicP25898jdd/wW/3rmePm3QiyX3IeLuFVNqnS4wQG/+j0zF+XKxcy/f4blOBR5N9CFzb2rT/QaKNAUfKO3/4F/qa8yEBIqYAsHRT/1aViAqIfpdoM/DxPGH6ywNtrHBto+p+j+RaowGMe+r57/y+P/kzJ4uiRR6GiOSR4uKL++VTnpv2wnUZzhmTeaohgW1btxFXKM6NuflbRD7uX/6bl7PdR7RHdf91UIiK5dqiWO51cbXW9jrCeU/QsdhSuaAMhm/LHKTYtvUa+5oReDRgBxTHXB7z/NX1z9VRGy99gh4wAzL2d1FxuxIOm7M4s0kleK33Or7Pg7hel1X4pI4tvv0zYHIBs3gFNHO841nZ2Y+sHo45WiDKdWe6iInBngc0qAXdDfuJfgUQWTTJD992iErbCwGAXv+gdggsygPgkTBa2Mp+/ism6pKFnaa4cu2mB9I86uJshW9bn5t5sOAH81nAYHn8FTL2s04wqfq3w8TEiYeXAHe2qnUDybrSz4VBgST5K+rJ8C2yAbf10EAydxfLzpu3n7UxJSH3grN42PTqcIc2Rw15a4SrFb5tKv3+HvDiAYLpYni/QWVizOzoIBoWaaOfmyXopHU1JRi3bbA+l3vLCXF0LgrkDyTxAxN6oKZcLDzLy9pvwu7Rs5b+mp4yxLO4LP2l/tZWGHecyL/RVhOnrb5x1xdO9BMHSN3u5EFyjFGQPtl3/uASLJYd+tvmACuM29hUOVDIGVXDK8NHgtp7hDsYqop6M0opDvK1S7yeNk9N0cN+cgLjduxaPs5DXAsxD9TjoRrcFEDL5/z9zUVBtrqsywFmCvL7elcZxu0QiikvjAil5nSgYhyoZphQLNFU3BYfUfClUM91/KuulO7pOMnTh1iCyZQKNCD/aW28e3tpoTtT2YGE2J6sFuyACKdAw7tRIuBSV/KITMpsoc8c6CvDuUhH3Ibtshcb64FyfJt2W/TsIgBcAE28v/kfx6GVEdDmqgHUlvq2Vji38ZqRxedAJfNtYbxd5e16Q4XZX3+fR5uz5v2IACnORdX6IMI645FgnKkTRrPQplIROf80l5h56h+A5RCNBR2InO4XVsn4s+RPFs0tLWdlIxXW7fiPKSgJoOV9cveNG4/F8RApOAaqmqUFfF5S1cwP6f4cIWdaz/6dLSbGVlAsxXC6nxPWxab2CzVsFURuPuZwdGibvgCBCDE+nGLeA9JpQiZt3nrnBRJY985JXRbnAkYZOn349M9sWINijTJOHeq7Tc37L3K1SGveyNneQIJ1O1L3h4Ul+M8fbQWB/KeOUjO+FOt2CnDnhvkwdV3CAHSyb33bDoJKeDnPHusiUSz/wB3SmPscb+sdhIsRNifAkGXIWxAsMdsoJr+gzVwTv8UH9/4QBWeKWD5qivwRCDyAyAVQLSwxALwaE2i+f969lYnmjuxzDQm8i/3Cd8+NDJeKVhAmhcAtzHi2t425xn1XPu+jtvMqmsQCJ4WRstGO+OE5t620L0fIMW/bbOer+Ft2AvALQx4qCzaFm2sCj2qRcgvGgwu1oq2VJs5UV5qpajczz7zDBT83OUjxLjb9P+y4rQ4f525WiKrC58d3b/3r14mDenZtF9V26NGfLEWsM0bYGljKyUu9zDVt71K0uWuKoqvb4l2Uvf6nusx4PDZxb2c8Nbx+gzpVKvt7urk4Obn6jL2j5pBWWsjC5T/5xUxvfslHvaPNHsb84d54d8Zek/8fiOvK4ew8Hp+rgKbJgimhShuVXCYhGA9d69L/Uh5TFUsh52YceDffTGO7MJ7mzoSBkT3mZVCe6rvhzMLighQSSSog/41UYd2ags13PXyg2npM+53x/TT5PcqJUXwSUie/iAat+6x6XoBYRLCVvJ5rpvPSZXum+YMGb3u74Vwc5n9Yt5mKxdA9rs38lWUUblFLzn3MKNRTpbIADAA4uD7ATONzXk2bwUYzvwq+hZD/+o66MP+BbA+3w77myN8U4hbaafOrlCIDrIClEfRCNGn/cjHXOyvMI/TtIfh2ZEWz+4X0fErO14lMHsDQo43deezeh+QiHckoV5HkcUnN/d1c1xN02pEOyxTUBZdaarm+M8H0ERQCriVnRQ/JQZabtDIc1yL3XZ9JQkFtcbnFAKX7kaMHJTI5pUJ0AABXROf9Ya5RTv/Etj5HHraOTkHu5bLGs9RYvTpZaM/3lmHazxw7fDUCVhF7TPiMOqBLFULKVABdqwRokZljtt+sWl/Xm8Xej8ucMO0ca6+hAAOMj/WPXZZIwCya+cqNm2K2r1/vtzfPLJJ7FtOO7D7pB7y0XA9Qw8JVqpZKYMEpkJOCMd7me4/FL8+gyyO9ZHqhL/762aCANevWqkO6hF4seGQDCUvlBI6dptc5PTOkxNY0HKUKAHpsw8QCqKbESxvnjO/sqzDfFw5rvsU89ubdc5dj2OGN/k1klKwXGA7P4797vJ1xbcIthKkZlX1DGwR7W5vzU6U8J8WbRfQZ7Vww7F2kLYmhmKXq8p1vhzwC9OGK9CmA6eECMJgfJDH3B+VbHwZ88i18PZkOC6umEqXvNUoFcA1gZbgMt2LdOVbHiBhm3MyCy/jPbOGWxUfc0epm/5R47yEGgJAl6TOBdMNkjmLh6t6xK2hSotvh1hrS9o0+GKBhZuzhw35UDARFMCVQhQwdxaO9zP4z6QY/0ZnFj6itTSV49X/V3V6MsIahT01LhL7xxbnVTe5tZe6RuIxOosxi+2oyVh1MVF+SRAOAvJ0nLiAHCocOAb7GZraT+T/d5lIGch7Zywobf5zLzkKEUvKhUUnxfqzasR13l2IAi6rhdhy32kAAtazgoYYhVXekOWH2P5rzxsgvjxzTzpykEBGLjSrlxSx7jNqtciC3NKwQuRxzyULzB3z5S2H2M7fWsWKz2JtzviaBT4fPfo+wcYV5JUHnOgVJJtDeCjD72C38YhahE1cocGkr87qfj1ZKQu+MRVUJoEU1FTfb/K/Id2fdeIFcH8x1g3HdoiHAHwKLMuP9aZltndFCSKfhR11bTPqZ7WD2w+lCg9AJSBwNuKQBiECkEC24Y/7XPZrtAmbxDej+CpXh0c989qu51xQuh6yO5fS0cMg6AQCAU5wxu4rS3FN5URFtHps3A5yx6EeqmnEGhG2oKeLUJH/ZBEDg1kRNdCfM/YDh3/kf9JW3u9Uhd9WT41A8++sBwst+Mkl6BBb33OzfZpjz2B9cuVOPgYZb9U/h8qo4dEi1P5mxDR8i/mEWzDgex1MQVRQMcTfztNlvLME8jvNtTSAGHdL6ImfxGl6+eEYEBSxlXCqMa+uY+aXawKu02WyKn851wZ7jyLu/RuGShlW2cktEekEVgpt9zHuv9R8xKFk0OWyBS2Xb93Z4JUlQTLVBgEtq9v0+lXDnzBV9PjKKTj7z0SfnkMAGUwlX9XOmyrzvwDitM6PQ6mut3CWYkwHMRweFMW0enEPzyAoy+hAo+sucDyAUR1Nps9qAmwMrYU4GfoeUmjwKUTTDo6ACuJXqDjY24y+3hRlG8wqtfjTHB3MSj7J+KG/rwqzjNfQarg0w36/QyR91ACBmh14tZQup3U8j5wMm0R4B5Lac29McCLzZA428EgkcgpHVwhGYh0bA+OgXwly/gsbe5ZEderUsy9kyVrZVUAideau7ixRj0v8rAACO2DiwQpxcBIj10/E4WeDZTKm5HjrqCsnEzI5TdKWpqwRfzqjXB5qrhDSz2maDfLm5kPsTZGZ6eTbpA6DNdPNgoCu+pNNdmtfhXzAx3tmcY8g7I83yKofUekuMDp4JzOu348qNmxrttw0h2PKqfu2uCTM/x0bsQdBO3hhmlrM1fHp8MW2+G+2nTSEyTPnW+QHSaFzwrm/0A+jMhiBMf7m/WX748EmvAG3OG+3330JVWBLlgC8ApXBEH5nIzDYMMeBSw5SiPdPdDH8TZeXZr3nsqr3gUCzSsJaneXEjJrFBGrKMSROrKggMidOEDPQoW89MiyVIGFIAOGAqKTplhnHe/gOajQgCJMley1MHdLFyXixWGJyysjc1lWBIwpYU8Y3H4/bTlh0XHHTqpkizu/rueTPFSJv/hsq7NlxJ4EaIupsMgO/ByoBT58bM9ze3j4fUaG2ugRYDDZV9/xd3OW6k2W7oGiNMwPRxc3AebhkfzqON+83DzP6udB1WsIaiZquNiUS7f5kWv6cLUGuL7umYMBVmpOVeQAN2zAAAF3BBnq0S6NAEnStSAV2wpYoZ3cCSKX36n8qnRQM0/XFaiAoz9mym2MUkazzGHSRISpGruISXKAHvF5rR7SunZo9yKFpUNJkHG+HFjt9vxTAAVMGowRB4qsKb9kFLc/ktbC0X307SQecvEmbxfJATTpy9w4hEdlkJ5yIfPjkUcA9ZANBFg9w7NhIz+F3u1adef51cTHHkI69sDFbv6n5GwVw/fv2dEQTwdEDbwq8bWtlixHNCerziDCTUDtPhsItYN1r+nBWAyiAL+7iZuU+I6sN+3/lMBzU7Qt6gceHm/JiWmWClwgJIBo/bNzSYwIVIWp9nBQ73qMaOmjwPsXYaU6DrKxyiztdTmLO/rL3qLX2Ra6BFTFNwa2ZNbDhRnc2schRSqoYJFYqEpEk/0t2cLbeCRj8jAS1uGlB8oaYCE+I1BPWSfME52uIBgKgqdpLUXH0qbXvkJ0DJIy4VCHkUsbiCZxDnBw2iDajOLC7NS6hs+WgGLl7bUIoHR2xuAOz4Y3zOuDdmEExbp/WsVIlUbo2F6wLM01/eXf59naajRVFD/ri2qDoOHEtRPQvygBvMcnW6PBiuRpZjeP2nFYhYqFTy2kDCDP3l1WnZ+WRS1GxQc4goiN7ZJ1CJ/ZAGR+tgBSs0QhSGyxK9kVIHUyqApeH730qzk292tcacT6M4TY6aHYBvFnGlR6HXGsNS7BFIKeKUD8ib05v74r6rnBIeJ9TwoBBbREkcDYVwTgTyz7iYnatYtbxaDDjyBC17INmGri2RX81vd4huTdLGgASVy0M+IJ/MdMF9HbthWRzxMe0J1u2USGbvsJ34FSv6+9XNzGPRDLtQSIuzxpj/W5gc62HTLhWUlLHc6whQuEhR1JaTfNvbrFzcIGLti1xSpAGM8XeXt1DhPHql0yVAVyLHa0dFcBjjvzuQG7ssZrwZ2SdRKWpLnJphaopEzCGAJMMTcaUvc7gNyVrhNjdQAb6ydZ+OLm7uJsV12E/NRYkcgmCFI8H7EhmmLqiMb7PMyLeKd91TxLS4oVgtvmA0lGbXkDruUjyH0/I8PtFUEB0z3M4Ll5b4+ebjzOmB51llLJmTlEGLtqbw7AAbPIfH2WLAXT6e6FVJp4KsC1Iz8bds/EMd2756jbbUxkBM1Aws/6d4nhCswHAz8nqoQxwX5wCBCETruC58a02Yh7+b38qjSm0NKDr/9JkUzgyByeCTl+7qVewycimamaJEVIvQculgS6AMX+8sqC3BbgTEGEoDDKCdd4px7enuOoQRhv3kKHVJLjKzcCZN4MYMkmFRYEjb3HtFIkDLDVbmccqIrsw2hBNfIbo96+pXuf0bQH1c93brCCfMVl1aGpZBwaAB2S6ck/miGPJ8lGZh7n1iyVKLUoDMPRXuOiu+BMpoAOWhZCy3mITTTZ6/5x3vnUcQqgHkv+pXzYnAaShr6ThCtnWiQhOjBGRRkMocfNbiP2YBYiDznkSpHCe/LkGXn2P+r3AFSiEw7/6I//bJz0F3UfW2VlhtlnbN4esDXLHgiYiO4QNKMYyrDrK4uq0ZIGh+LihpKDWZdrC5TO7a7d+fVG589AcKId8AQCuDJtdw+tyKw3JsjYOyOwWmzVC++3d8wy/w/f5+NgUAaiJS/6uK0fAewxlTLL/BcVPQ3q1686Hp5D1wMwNnQEma7TGW2pAiNTfGuqlsncI6z1n395n3ucgr6yZy7fAKinn2P3/L1/3C36jH7MNJAAAkffqUO52dJbiMWusRIwRvDxZ2JLOOo/sxE+d5wp8KwgyMPfoOYJwJQr2bX0tp52jv7Fu9028XkO8rA5jKSi6nFTPJ3v1ffuVX+GCHym1nbr+XZAAoyintuZlRfio8RsvLSGGDf83gKBK1Qq6JHmIWrgC7PIEmASANRTub2alcXBzsXMMG7vxkgOQZrwzh5n/hH969K41w+Gqpn/NVrQmJImTUtpvPfqgpwJ0VIHbXhLZh7jYE/qLDI1jpyVeBE9xInfA//zTOLPzUONtzqCJAGTVfBwbbu3i7OLk3WBSv5cofHirEmtzIB9uqdYpmYrRgaP7zt/yKYMZ+FcKuysoYLUMPp8eqY3d0C5BjLyTdoxFiA3mRAMfQ26REz0NmnpITph/fPQVUEVmY9nlTVTdnZwf37vvjDGbqSPBJ8ILw7O1vIQT7u+xarso2IHmt7uexPnYE5qJ3PK/Y8i8d0gdfYQF5d20lZuDI0848KjMr4f2tvu4OTp6d1t1L1lD88w0A81H2bu4wRbHnf2XWFJUonII7/LL/o4ZbNaVNeXN6cqQDzkI+OJ33vqDkOMW/lsjoRW9dZaYft78zyMzYt4+OVrVzrz/mUGwBxWF4gL4UQsy8G/g5nDPUbrDZdOONzHuzYWIz1oNeqfxbjfl97anPOnYusHKHzH+0e06nSlJ8dVW/scVoETZm1oB9vi5GvKDy0VNh+nFc/pXMf/X41i5Xl6aL7uaxrW3uuGyKKTXE7BhUB3LqG+Hcevm1xx9TiwGHTn3CySGRvtaYCucZlADbRuBmUC0e51nERTPzzUM9QeuJD0nD3RtXdrm23J1oFFeXbl4H05B+pw304XXljn79d37Uc4qkCs4O9SfwFJWXIZaxI8b3FJ+GUkjNN7NQO7rxuh/UuzvXb15I1gqVKcCMHFgpzZ8YVltqTNjXx4HjeS6dg1uN3f4ki4RKNsRs8ZdhKIh2/yEECYzf9Kb3UHqUmv9xxiVLO97TDKw3eHTftG76sjNZagpA7c8vP1Dy58JNvCRc2zU2aXRIgdFYjJ6zIgAAZFF69Kwwa+hNGclU9s7egbU6bXqlBSyduoIPE0Pk+GnKSU8BQC1DcS8Q8C8cfJDGguN1zcAAVdWB43878tkAK00EW0MTGxc3Bbp3pxZ18eZa+BJKlzpdx83a+aqQqU37atfwAOx0pZfVKeh7AXsPrYItxXo7lO1LZxszsGru3urXEzEaHoWLsIJu+QlMCqICBNrYc/OifLkdUapyazJ128m7STpAAyr75pyaNgRWwm13EWpsIDcN1qYh3VPgVpI7wMEMXLY+oNflXJJ3VgAA1DmZeXBpZQQol+XkbjOMQVbDHLKCmQmg1FemRNrLkNYEfDofeJOUbqQAmb62uiNWahteptgAjlIS5J7CioKAzgBmZqmHO5n+/RFVZzwjAQAw2yLZHlBk8f1ZHZaqKR5Zc8UPx6HO1BlFSAFE9RkOhjTy5cIg5OtLBA/5pistku/2dsBJY05h/rIYaGMtpwnOvrOUnhq7IP1cbyTkrsGOElOZWdbdd8VoeZuefL+hS53qgU5K11U/gTipPsPhv7rc6CmId0dPyK0D6i+8r6PVL351wUdIN8YjrlJIgnu6su0ahlwbhnb/Ah61mzibxoOENoFjz8QV88wFKu/94kF13FQKqZVEeSAZPWu4gccw7aHa2Umgfbmhq6cEdeFWtcPkg2kZdyYrsVFXfiKNH6wf9xBFcbYW88eBwKhQR+shhZXUpfagBpVkJjCrnOtMuJVtoPkA9N9u7ZgZZM+wrSygx6dC1Ax4yN4jkDKyPNCaNx8UWABbABl/aEwN5Ee+kjq0WX3szO4q2AiHh0X8g43jxwnKsqvmYG0kNwA87IgyK0LqEDp0YiNniel7NV3wVA345BRVnPVxa0cHyIGAXs+g+cGt95qz+/QNcukEcABz4sJ3f4Yo0f1OVrn/yh64CHnIT8B7q8g8WPF8GUWpE0c4IiDxCKlSa8mvHR1M3jwmXk6neBVHVO79CXZSiM6IlT9EyV5Ebj+EZJpuZwNHPoeurF1xEbZ9MgEQPD4o7aDQVjDHFwX/xm2DBq9cMcBBYspQBC/9lEdCDclpbjJmWcdge4JgFc2SXpdS9cLk0i06EEuwHLehRlBwY2oNKfqSjpDgon6Xv/KYDo8aH8Ffinl8VFTeV8vttKtrINVYbNi/Xqu5W1ZEmbAKYYR7x7UfiiiIrQHgyjTDj7N967hACgtZ8Ig7yQa0UgWeogtGyDt6hMUl5Dxe205O4K7rN/te0sJDAPCB9eOWrFvHiOVgcCwhj3VFWZGwqz16cNSI5dtn1bUlTNbNpPbd9c1II9iaBch5/k9vaEFhV3fqbSNAXvt6yv5GLYXwcEnAkKH7vKuVhwx33W5BrAEeB4ClADsra7idudXAcwjJi+kqlIooNcauGtRr3LqtE0OsTVJLEE69TqUB9GIEgNw7U4Og9pJErvoOVwm4x3uKvxPYDbcMKu94Z38FgbNQNTVyl5+Ax2xN4DZcynoXhNLMvubYA6uH9pq2799+wVKTtGRym/S2ANDokMUrq3EcEK+0P1WALLtfvmj6w7JGcpyFx0TAUWTQgLMYEMdCz1MRao5FIODaeOrxYytGd5974t9RYaboVXncew3JbUZI2al5NMyJY82YmPyRhFvdvBSwoPpvPbc8zvPIVBiAlCCmfH3WrdnuUmwFEbKFBoAjAIS7QJ8CaZTh1XuPfDAAZZQWv124/t/vPTr8e2L9ED+Tgyz0l6v5fGrKpOwbzHVyn33E4xxxcuJbTUjmPF9WwwFXIalzgwYcocAZDRSfHKLmhWN9MX/JuPcYOTdffPvprR0Tak4/cGR1R1MzDuE/6GyqHiBDfdvRjqtocGi8TEfxzIXHRS4t1Lmf2mN7sRGczaGB/uuyNl4SPIWsxQ9oyAD0GGK8EBWq+apURvrm6hipyLnsxI1to6XPPr26/k/jRouPHJkXoDQtrV33HfHFOobVkc4CSV1VR8Z1QKj+4lyaNo9QCj0ygE6Xvqe3B55qbXqQiG4PQZAJthuzFVVLCfqvCNdxltf6/XV6wpvrf4V3XHx4T09P07I/qeGOd1kFxYgAfeIwW+6b9zikYWSfmT2/AzxWIgI8pLOEGKL/dMVSbcBUwA0AqOsC+XYZEZR2afZ8J+413ipTn2SnJXy80Duo2/oTK9t6mhDkzttep2TlkYjZkXaoKfer2oVsIF72IoKA6oAm9WAdWxz1Y4psh8UA73A4IbD4YoCM+znaRtzIyElPfP9nRPUhOw9OrmtjOvLHteXjuLSsArQxqfgtHTgLBJntlm9GXtmBXjfbOALPeW3YK560NXvGUECt+qR/u1bCT0MGPwDcwQNgcahud8E9OAa51hp6RTR+b2HP/cOr9Dz5Mz8/M/Vcz9AaM47+1cvfZHwkCZr6LSklDamSINB/39jSjvt0ufaJaoFKqF4u23Ka4nsJjVycADYA2QwAgB97+3sRuKlu9OxkFhwzzAIglQRhICyZLUD3SzBnGLm22v0ltzg///Oq5q6RW7dOa2IybixHUWvL99QfPws4bMywuT59Z4iCU6Wy4VEaiI/HPMAzAFYGUhQLNC/OvjzEiSCwEs6rjILFC5gvmxBvMc8yFAHOR3GuQ9pVX/kqQ6PNz7s7O0Ixcs3q8VUlJuMHEjkXm5SSqYEDGMRtcUAoCGr8SYmR61gR+fRqLVQrQqP/Oc8NL82+zj6AvHZY+NDObsuP4ZTZgZwHKzx/uf69UF+oSTsz3CFw0O9/dHeXmQoufP+RlK1DqML7Zmk4witoWSJ6ZpV5hpZWPapt4p+jAecZUM1/w6pXb9574ZVMClUmIFNW11NhJCRDbqCHCjgUZyMtPgU6iJVN8KfojnRVcBnCsdfh6GydWlP4fnsH52r9Zk2oY28a1i5smpz8/jMtT8dpUerdwvpKbo3KmQ/1ImEMONxuUSyEg4VjgaVe3tFXIbdzq9K8/4Rl51OMDFUM0TBPNnzb0d0BHyFdFI0SJpybzsNnGjSrhMHF4rOyljIxYAgV86cv1/EHVeO/HySptWptxpMVYW61B07rGWRtElDW3pGQkqPWc1nUmL6yoQpBY4PzOWJh6PGI1dOoY8xrDbm1IFVgn78OPkjXM2QyRQOW6OTDfRyx0ViKXSkIG0yMknHeJFJggQ6JN94ClGLtzR4Srt7QJec/5WiLdJrk6wMCfBqOmdzCU2IaJlsYm63Wc+18JQsv1lQhKJSvSWBbm2RmYRkegKihOes3i5zh35cKIfOHVXNVSiCLW+fep2PytADBqAWPm9vgotb2fBFygEB1V9U8YFhA2ikXjhCSek7d+/C7tqTJj9vRJ8w36pfBDd1Mw8NcRr3I1BpIDpPm3kMZamUTlscqk4ExTU0Kl4Vgh97C71Z7I3L6QiBC9N929XSFZ12duc9IFJH6D81x0cB6rxCjgl/g0Mgjfa1hpXmFlaoyfm9vzfUVQIPWnn+VrSsqLs5+unN03cod+3atZ28S9kHYL32ZrSXhxiy42AVpZbTWaZZR9W/HqAZepczxrOiMJuBSQWlvTK8NXXQpap9MpmjAKfX1ADssBDE5FlrTDwD0WDAEk0sKbSYBn0yd5MD1rcBt/zj+6KdardUUxt3/Z3Td2i07tgmXEiYgi6Sttr7OM8Kt926+Bwr+EzKYkM/n+Uj8l/w01/O0BOk9NpX79f7u0fZSyI+1UXfA5jhOkSD/3zYEDnrJDqbTNBK0n0uWg9++Ll2D5lPp0+y5jFF72r5bn/NLejVZsTc3DW7QoFX7pq4m4XK+7oN2xqihh5h0e9uiVOaRdTrBkpX2dyRhZf1LDODMSc588pYI//otqsEsbNsXNpu92PWPEfwKAaVLvfdHnyrW7JX1Ss1+u59r5AC8n++GgZC7fC49X4sJ4KjKoDJsHJ0jddxITHU4u9iL8cdgG85adiP+vvg8Xa3T6Yoyv9xY379Vy3YdqjpKTcJ1X4ce+UHRNJv8+QEo4lzns1YqjXeGlNjTdto3M80Fvz94NoiAnGu/Na1EsMPCZ8ypF8kkDWDqis+0xUAdu5rMfdVQ+LQok/B6nqEIwRKSUm3qd/U4j0R4dFt24m58YQnagozYu2vGd2/bMcrf2iTM0GPkTejO/cxp7kg7aPeTTAoXVC214YpCs34qCDjTKCYWqo0tIftaP+iC1b7bQTWHZ8euVuAfgpYhlH4QIb6oQws2oRMyejHXJUslzlVaTdp17W16sV6vVxfmpj/Y+8fInh3r+gndltcvqfbq99UAsVncWFeUAvm3tyxZz1qWGqrhAaPZPvctuE0+wJRhX1Wojzk2jzNAk6CNDsU+SOtcgEYDAECAdYYjwAYufPGZbOBAA8m7IiVcxqgU2aT/6lMPEvK0Wp1WXZgf/+Dgsol9W9XwlAmLzMFFVj5Xyk/kUmzDPeljj4D9nhSGxQG1MbzEnpKB17gnQ8zBeMGTpUzx+vo/cFNowQor4ErFhi4q7dgwf4KN3L3TjSyoqJTR2AfrdgkQAO9owttwYEUpcLgw8bTnBjtyrqU51Ws+cPnhK9FpxZrStjg7/vHRvyb0aRXhTAiLU+0wV6I8fiPlLzEaNpc7opwOUvlKIUMVpenmWpr6Gc/Loujy15LLjjxoe+WFsVyNYrG55DVkXpwGO6laYjfkXCZMaOFWBYF5cB1qgDg/4L+CYe7/aWM5m3IJOjB+XMLMQO5NYmXdjuNWHjrzJC63WFMyjrY47+eLY0sn9W1eWdgwk1i36lnfqRxmlarmiUT2WuMlJNo8ZZ4hbMjyLt3vpVz+yVxf4SoJXrh9U/Pw1wAVAcnsMecLILrUdx1luGfILOS1FACMs1GSRthFw2yHlpcKoHbWR6nFU3fggn9OnLoZnVGs1ur0Br2mKPXl3qXjuzWqJBf24xozJ9QvjzOUD7+nYxnvZX87lLtN/cwcUxPPeFgfm80J5v0eqczg+QCnDipjLvSxX2z6vYUIM/7wxDwjSzqfKauAWl5l5rBlTMGw89I3qrCjC0p51mTsij2XL197mVRQrNUbSZI0anOeH1s9tV99H2Fn4D126SSX8phb9pMekEyrfZ/ojrCkWPmduQaa/5hxqqrdlu8AMDKAO2emVVkdo2hVMKMnAddyYK4l77kFIZpKceBsBxtYW/eDgaURaJs7Yh1UrfdkQj0ecMSbcbyuFuhsOFi9Jn+1Gb82tEV5azJh9b6rd++9+Vmg0RrIUrWk7seT4+tn9WropxQSxz4rt4zwUZbDcUJH32b+q6wFIdwotiSzn8VSSZSKnP9WTHxP0TLfPGRVsMRwKGPLSD87zgF2aK1XjI6ljprojXM+VY088K3UeTmKSQAvNWfDQ9RJTHiBMuwfiz9G/zHSBqU4qzduzYHLz15/TirQlrxRJUopsiD+yalNU/o29Bay9FS1WXpsVzc/RXm8ucqR5zONpVvPu1shXOZlYxJgkHtPJSlV0vMiSdPmfqAa7PURClMgUwwHMBmZF0dYs8eSuG74QrL0bAiTYBsU3q2f5XMs4OHTAR7lLrMQM6tmLsrefYb3dVAgqo9YffDcyy8JqYV6nc5AMfQbchOenV09s299T5lwM5PWm3PizuKmbpJy+KdLt1Mx6hJj3J9kzb1+vCyBScELO2kp4ZsL+Zh+XtoKi7O+6nEG2TBq+BkkGEyAnj4Asm83d4J4TZNDaYDJiUg5tsFryGeOSAEAqcQMRVOgm9mlvVfbBsUmlQf9deDE4/iUzCKDQa9nAvT5P14dXTezbz1nuWAtETFu793tg6uUzwueB6+NKzFm2lZ/7kM3M75SDNSxzGqKNjMTOfOIz0ZnfpjBlYY1UEheHJSr0dwKU7CRDb/J6lxrpMQ1Q6P+07DCAO72rOl4x4H/DOGqRlRCxAeaW5F2KHh2/X3v6Tux6QVqXckcSJZGQ2Hqy/PbF45tEuggFWzEPlsfHZ/dPrB8bod5TssosejnZdxFf8unegbGwrbODCHhv/H4Zson+0dfQZV6ozOkZLXp+4qhHDxvjmcgJP3Pp0LO3gd8vH+mFWyVnbTQxtxrhHTFPqeW0/89fSM6uUCjM1IUyVJK6QsTX187sGZ0++qVZEKN2Hb1oyt/DalrXy5R1pyabqTz3nDX7Q48m8uwKGXcGi4pxbbldRoAM7oXETIMdJg0VEzm/p5sJ5NGTCukSrV8jFJhmZdz1NUsimZS0icAHPIoMIWrnkdBkonGEO3jVk5Ihz8ix/596vrz+FytrmRqip0WypCX/OnB6TVTe9RxF2gsVcM/Hjz8d1pbn/LZsQlf/i6PLLrW35eAY7cyhmXj6IGejFz2HBSrZuYZj7ybNKvtpn4l9GGY4l7RE3EDQMI/dSF1lRo81zIufNDWGsvc9Heb/RSY93Uh4ylg3O5oOgCPh7JnAyzYytjytK+6uBMISKsMXHPi2sPPmYxpAMwI+qLMhNdnt87tJ9QsZNWm3np7fEnfatbls5X7Lrkck60/19ONY59Fn3OsfRbaXe2smSenbH6dB8wd53s+cwz1dgl7TwrhuS6rVOU3LIO07X/cXj2cgNIicolymcNUB7dATk20IWZogAzp15jrseLwtXvvkrUkpyVIXUHquxt7Fw2rKszZUJLAIee/XN88rmm5/UEf5PV+vW/Q7mzBIabSr/HsjcI1IayjQtPuU6LmDnBJXfoYyBXQVK3ijbjmTTL6LuB2d+bfADzUZdwTPjuCcSmDyCCzFjVAG7HNgn3n772KK6AA4FINKEP+j5fnNg6q4yFI/T+3djviXx75rUtY+X0iNkLh2aFHJOdR+RHJ7MusX48qyWcbvyr/fGOUKmankGQ+MV2YL6NL194OYbmNxOFIcomSD/jlY0LS72YuoHmFAUgS2mKz9W7ikIqilHVFlO2d3ZGuxtB42o7Ttx5/yGC+caSb0hf8eHlh2YB63koBcGi4Mi76/IqhkT720nK77FK4uXHW+VGETvymYVjKmPVozrilJ+4/+qlBy2Ks5TJ9FXQ1D7YWDjV4h2bM/SWE/ZUps54ZaPphc9wC4dT0WjbcsXkMcr9P22S1qd03KUVmpNxKAKCuPwDjpTGhUgTsa47acvL6gzdJRqREUPr8H2+OLhpQ31OACWyqz/vy9c7WiS1CXStUHQtV4KyTX7WMhYn29YNPeUYj23Kc1ndSwVSgGtLsrZwtThw5YM7pejf2+ZLNT+TR9LkGSszyqtRmG+ByZ/fEvMjzcc2EHulODDMjaWjFMvVqUSOUnUPKkL4bj1+7/zpBz4BTNNAXJD/7b/Gg+m5K3q0iZOL7+FeH53at5VXBfqEgpy6rb8eSDJuhFZ9m40pWfhNxFHpy0GR/gJkSi5ZWZ39R1F9fAb23phyvIOt2liqFOwCQlClyQ7TQ9hUlYkKSd3VHmanUu+OaUmLVFJpoylD88/nRpYNruvCOOnnQqOcJn66sGtIowKGCBSihqjJDQ3ECgLkBf8YMHWMGhrZkhV0fzFquSkbeIulN4RKsguK3N3y3g2DYHoPCZe19+AbgAnT3ZoeiWMil8ZIjV++/+lpkBKiBrsv8eHXL8Lo+thKeBAx6mBD/ZM/UztVcZRVvx23Pp1qkjDIrww5dDYfs0PbiNPoyqghoDvmx8rP+ZjWY649X5jbqUSHbxTmdewrMNNPGgLRh5m8CVwAVQX7Y2Bzl0swONX89dPXhq88FJLdVAFMAWZz2/vKa4S1CnaW8xpL59roR9+Pdyd/61quIV8D03vZd/FSPATmI5swDvcHwYCTLvYIXFILB7jgFpfftXJoN94J+ykxLgm8b5YyQAUghBE8dSDkxEOXZm61DZhy4+uDlhzwj3AwMWDKMRanRF9ZObF/FUU7wwavLxdiUmKtLhzb1V1U8bNbGomQPACi5rSRPxpONPsjPALMeiZN5uuSDjkz3qjQth2zlhFO6noO56xpj7AHmTZ/8k+0mdSTz/7eALnzwWzDC+p/Cd8K+K/dfRGfrAbKRgLE449OVLdM6h7goJTzwaH/2S2r8gzXj24bYVjycdiSV2h+ZafGYTLcmxCxN887RUnWgq0VNcaZW97kWc3HpOC7dEG6DUbBr9xEtIvCmXB+KyoanE4ZnL71CUmghVALgVGqM29vShuAuJisN23Wl5C1DR3EAoIKBoSDhwcE/ulbztEEfS+4edeJjStLrbXN71XQhKhzBV4p45CBLkJHLbQ0ZbQnV35BAr9VT2TPsGY6jGpqkdpNjlG6jLYiujDh6cTe+bcOWvvQZ//UTc3UosARyAbIfjvOScyJx6rPt8sM3nzO0rEIb0R6UOj36wvKBjQKdkD+UezQ7+C4l9evhJcOa+cgqXDvoIzB/+wabtI6QhFlcrH0QIGW40oD4QnspPkE+9i0N0ApOMeIDzVTBYLNqmAyf+Cd+7h+49jGbBJzAkwIToInfUMeee9lg2/6fq08+xGeXvKHYBrATQuly42/+M61rLV9nxD9UPi22v0hK/3Fh9cSOVeQVDGv/13k817wgOqNu1OEq2zVMkTOXDVqlSHhuqdWguAFje1ra632KtQSfoJqbhhrM83+1NY5Mkzyidj/79z/h2/yk1SeepeooSMJgshF0G3POdvXijh/rqH9uvvryM99QKhTwSD2py4t/eGDh4PrBbioCrchrveVJYkbqrS2z+kRWsBi1rrui0MhhKU6jHwzcsNvCJh2rx/CnwJxpMNKgtztjOdz+5lecguOyYm6HH3b8Mai9wLwrlEMwMbbIy3//237F7zx68b4HP4tJaDnDqRsmW/tqUlUVNy233nsfl1rIAiFYYafFFae8PbtqcNNwtO/otQlsv+VhYlbG871/DGvhJKtQy7bIeV9pgGApftycjyjzprHaXxd2HRRJz2HWJ2247ZmSwCd4rTNw+vWSi59kf5BeR7z9L37DL/mNOgyd+8/tuGIKIKWBM5mG5JVRrgT3c5Fve/T5R6aaRAZ+b525X6+tGtYq1JFAoXKXrQ+/5+Z+Or5ifCcvBVFxIEJ/i4ZlD68MfAK+KIakf5D1th5DMX2wCWPVMmDkMYzStaqxBxYGnKVl9gv3ZDDcwvGRv+0bfuGv1aj9oKlrLsYXU+jJgAF0Z8ZWlXPSeOuTr0lZWhaAV5oBqU59sHlci0CUHYbWgV12Pfqem//98qbpfcLsJBUHmz8/AZRMZSoA5oPjtLkapjaLbFQW/qRj+imYB9h64RQ6ngE8nH08Am1a18wn/pFv/jm/QNXm3YdOXXnmfRagkaRxjUdFb+jqwc3fT7+l5OgBvGBCL6xIbfLNDaMauHBHIWEX0nXP44TsgpT7exYMretWYXoJ6S/vdHALI5r+toapaYS9og4q1MMWpMun00cyRiQkWKVu9OAbvJxfD/v8I0SH7XD0gvQ6Nbz1737v9/8A16qt+o6aue74y0IjOxGAK3kAlrCM8zPrchwFIaybbn6WkJFvhOsE6NBk0ZezS3sHqDhbmXN4twOP47IKM14dWz6mqa91hdl1W/tJjjm/IPMZ5Os8w0OA0oP8sXZMn8QpXWLyE6b7AkHWBTjOumIyssazz9pgr/6vX/yBr5G7Ve84cMzslUdi8gw8Ke3TRu/o7wtvCZvmfz/7nllIlgBNKgzAATBmvTwwoy73jfIpXCO6H3oSn1WY9eniukntwp0qSJzKqy3RUagZCrfZE/DDrHBHdmBVbuiWo8JUAgBVMNEBw1yvfv5bKADm4pgZaFrFIQw50DXtzX//i7/WSubSqPvg8TOXn/2cRwH0gplmigGZ95Y0cVfCWqlDyy3PE3OKGYI5oFlwStck3tnU1d+W4BriFtHz4NP4zMLcuJv/TO8e6Vkxegm3PnE8dkTQwNSDnXE0ohCEozy77jTmTHDEMCz7zOG8gBWQPLJZSK73EnmffdoP+9CS7Vqfpt2Gjpuy4syHfF4w9egTTk2M9IC1Kp/O218mFejZaeSTWNa2F5Ufc25aPU8lR7nn6BfZa1/pW97PR7vnDGgWaFMxul1PAcCnxALma7uZqbn1TzGFJGTGt5E4hoUfYAGPFv/CAPLjhqcEZ6CxOYbrz3f/zS/C+LXamvUYOnb26hNvcpkpQI9bQFMFn/eNaRLopCCYw11De+75kKkhOWUCThlQLfqM19v6VnNRwMu9SqGN++x4VEJB2pujCwa1qepEVIQM7nQop1yXdqYmDXCaerD4XCkwJl7vjmGev56Y9ZIzEtr7pIJmPZThfR/5tUuPWLjVaNtnxJT5G8980lIsbSj6mVoM2Q/Xj24R4mKjkBIy60rBkYMPxeTqgHBpBzRZmHBhdpS/A+RfERIbr2otB/xz71tmQUHmx/PLB3eI9C7/vYSkyj9fSH4ZBwCi+Y6am/m10kiLP0wJjRRo3U77aG6EzAq/NMPvQByXR0w5CCwWDncpafjDxZ+/+QeXdqwDGnboP376H1uupGpg9QUBZ5JYxwYTzq8Z27qqj4udjYNnWN02E0/F5RsAHzsAzvgEuqzn6wfU8rCVslqJzCmgbochG2/FZhUUZn27tWFEt6Yh1uX+Uzvvcc81iOZBLZuU78aFpEk+A6URwanBsQCYKvXF1q5WGIaO50qdGebB3mWFF4HUp6W0cTA9/url312ntNBzqdq004hJs5Zsf52hK5HHIa1UAbT4JfPentswuWNkqJ9PYPUmHQf+dimx2IiYOhoincNIZHHs4WmtglyUEmYrtXYPa9pr1LqrMVlFxbk/nu6Y0Kd1dafy/rdDaKdTaYCD8rzetxV7DjK766SqBAzClDiG+oc4SklgTjuuhUUk5XOk7Nl/6CIvPRjiEd6g96jJs5cceZ1hYOqCJgQAaEKAIe39tT2LR3ZrE9W2+6Bxc9bfT9dxJodTBgBcBjJk3Fo9KNLHUSVlPWSfb41WfcZvuPw5V60uTI8+NmNAhwY+RPnGodn0zXGainRAA84mvW2XuJqr4VgG3y3wIouPAkZeuktBymf9p6yILC3xbDxCm/cbM23eulNvs0h+SQQ0VZT66f6xzUvnzpg+d+HKf468zzPC1TFTBVGAZAFKHX1kfveqXk7Wpa1E5RIc2XbAuLWXP+eoNUVZXy7NG9SpcZC8XLfy+rN2nMwz8spaBMuLE2XF3LTve0N0jdLtGJqJ6LUlit50T2pa4xgc/jLAw4Dp3WDMvnucKo0hUYTHcj52XQtJ6cMbOPnW7zJ0wvRF2698LgBwqQBBuz4/5evjC4d2/LN1x74j5+8mFFN808ttM2D4eXPzhOZhXo7WMolEblsptGGnwRPXX4nJ0WjUefG3Fg7v1izMRlKeqdR388mLaooWxlzm7ns5jFZvYDlT+bqhPY5BOS+bERuAWTJxXXCPIAfL/HGSgbRe1mxm/Jw0cvtKNaJ6j57821/77v40MkQDJBjiKW1BRtzr+9cuX7l559GLmCzYV3UgxyTgNBGV8/ro4j6Nw32cbWUyhV2l8GY9Rs/ceuNrrkarKUh6ump8r6jq5foyV0TIlP8uX9dzmgeUSQG1l3p1RXEmJWEMH6KccAzSMR/ZRReMFTAOeiuwxt44n7WrlxdRevdkTmH1Ow6eOOePDcdeF5MAMEEVS+qLcpK/RL/78PlrXGK6mmSnHhGAEqpA/e36P790b1bN39VWZe3gUa31wKmL9z1IKNDpdOrM91tnDGxX111RjnulkfNPXL8PvTc3wcuXgXoLgqw478/Q5dLDcz9hGwyfOmKZyawab0OPKSaAjKk8Zvh3LvXZ5ZFeEsZg3xote42ZM3/51vM/NRTPhPH8lfe+/U2f/ZlveOOb3vK2d7+KwIU9Yic27cXRZWN7RdWt7OHk4OJdr8ekxetPv05R6/V6XX78kUUjOjTytpaU366iy58nbr5h50ueYfGc3ITnDlVrcsplktQpYBVtRvuwjzeWwXUkT5/m+GbuPXY8XCLrZNfS1TlC7h5Sr8PA6fMWrtn9NF0PT6WFff7s5fe8613vfs97X3r51axYuxNUYcl5vr+O69e+XmiAf1DVqOHzN+27/zVLYzDotQU/r62b2LlBgH357ZU4j/rn0qME3uZ5ev4SaanqVJUUn+nigWVQdchBiH+YBZAdEZTR6L9sCZIxbkPXv0bz7hNnL/hzy4UvBRSaaHGZ+Mr73vfKK6+8+uyomUyyGyBK16W/OvjXrFF9WkfWrFmnQedfVu49+yoxT0cajfqi9Mc7Z/VoXNlFWX5xHLnt0qPk8gRc4Usi19QkHHh8k9ilDbDMhJJ6z/j79CWMIGFEmaHzn7ZlXGTAyTusXpuRMxcsW//fs2Q9RzrNffX8+cOvrJd3JoVg0HAtZMG3i1sWTRveo1WzFlFt+v669fSdz6mFBoo06tV5748uGtAizKP8TiyxG7Dp3P1Ubsb2hf22QNeYQi8wqLpxOR0RqzJ/5vUPV3TBMj+NV9CGUpC8+cGCmHMGEGqDIA5Xp4yZYUya4lAaHA4eQTWaDZq2YPmaPVdL/gM8sQbWvfDgUPsYe3uC0s7jg+vmTxrctVOnrt2HLjtw89X3bA0JKNKgLY69uHJku2o+jtJy+7Gyw9Jj91L5Fjqkuf6vhmnHYslZxIphQGgIhgpkXxnmo5RhFxwawpn2BI/BCg8ZhRPZEjjVUPnb/UpDQ+7iExrZe/L85Wt2nHicRPHSDs7/WKQslDrh6o4l00cN6Nd/wMAJG88+j80o1FMAUEZtcfK97VM7RwY4K8stsqbz9t/4KYiRnsAnGXttdoDp4IHi+53d8UuvQ7YBAMDtzcGcQ7o/dAlaoH/axL40ubZuAdXbj5q7fO22A1c+aAGaTkQ/CIqXnUBRBcj8V8fX/jph+Kgx48b/uvf+t8xiHUnTJeg1mW+O/t6vYYi7LVF+6wmO2HLxW3k7fuutPJyiJr8qbt1Jrku+MTeQwCsQsnO5NAAIZRTeNUJmqdGNSe1dStMrd/QJbzlwxrL1W/eeeZZDQ5Lu0C3IyORSqR1o42/v+XPa2Em/TJu2+OSb9GID89vdSIM+78ul1cNbRPg4lN+ZOraef+CJgZV+zF4qxEALfVfyJTJznOZ4gEvQNo+pnQy3M+UBH+S8/2+YnQSv/DHyCwWPD9wvXYGRJSkjiJnm0anCrq5WjI5HSMMek5as27bn+J0fFGAKE0XIMGXabQMsrJgmM99d3L5wxqxf589ffTm2kLFWzegYihLvbZvUtnags7TcIgsdvOJwupGjzFAIIkhw8lzhb1RtF54ayWNmMtriamECAFQm0Nya2DpYhVNwPpNf4rQwL/aOsssqO8a99hFqf9dRRd3dmCfhuQTVaT9iwdrtew9f/qCBJSeLUaGgaic87cU/X57funzFX3/99c+9JNjZdJRBnfbq8Lwu9UMrycvxHtt6QxfczTTyLs9offXKU/JNwIiBabYW6kxcMrUPl3epZiPFJ4P/iC4FcDj6McwMptNMxpawBmSYHb/qzfrNXLV196Hzz/NLCyMk/YUKDSkcqBAyN+7JqR3btm7ZtPdFJklDyfp4bkmvxuGeqvL8BUUNRm98WyDYVmzOO913g9yEajkRlUo/FWGHT/5dm1NIgQUzwgDZW5FLDqLyOrmyvw83uG73KSv+2XP47N0ULSizMqHWAKBJ//zw2rnjh/Yc+5AHUwhIdU7c3S1DWlX3tS3XB6pqDP/7pYZH9qQgOOJmxA37OulTDM/Y0IOhCwKAvD3KFZdQex9rFyJKAHvPLcLwcVing81fY0xo68wqhJT+dbpMWrFtz6GT1+KKSJ5RDsvttlwDMfXqcxLePLp16fSR0x/zYTIBpS1Ifnl4fIfIIMfy/At7yV1aTTrwhYLY8Mn8T17aO16htRQdIMj7cGSsPR6ZyHcj82LwfPC2EcM5t7CYoIKoFPoPrZ3Y393jUb39uOVbdx04fulzvhElRkFFlghmAGrkk+qM2A+vn9y9dvNbIVs9866rMj9fmdW9YZibshxDyPyjZp9JY1quc04FDG7RGbq/R/uCLpXMevB7K08c8ofdwnyIOyd7CFt0OAkFDMla4RzyHnYlNsfKzYcu/mfnvqMXorP1fGDsiIjTGrYVkBpDcXpiwtcPr14lFQOoTKM2L+Hx4v7NIzzL95O+yP3bzb9WREHMin9YrcEMj6Jr/xeewB0PpA3fUjjQTRwvA2TtHlbTnsAeyKclCgHYNnBfYhmYymaILe1hfeRRu+dvf+/cd+T8u0wdO3QcuUzYGl4GIIsyM9OTvn3N0MC1UYbClHcbRrWp5ecsJcp13no0mfJFzcc0ouuBa1Bfz+katQErkDmwLY2qPQs/mVTy4fr4o9Yg0fGUcEHI4/tB7YN10xwfIAU7BY7v7uwKW7sNbD5u8679Ry+8StUIXbRQVEGEAV12alJi/DcW7ISRurzvx2Z3bxDmrpKUJxybTd/z8NO3uJgLA4KZdXEUlUbdzb0n/oNtbJYJsuQ13h8ZhDs+CP2Ns9wKzs+ZdwBgsJTtiGPyGb7185XCflepWv1Wbj948vLbNC0ASMm+OL2oFYqyUADG3MSY6Pef0jRcwo3FadeXDWhS3av81DGTOETMO/sqPj1frdEWZUXfWdvdTSohCLnfiLOtf+BGHpi7gOtc9KUmn5f2/JgbqxvJCPQ9vLaV/CtX9vNwdbRVSAgLHad+hVA43m7OMNXzLoHVN2c93C4CPObzoBAVJMXWflG/b95/6nJ0hpYpjTXCrGqdSfa2Y8Ipiyr+8eHlqw/ckNrcp3+PbV3Lz05WXp6BsN3s3a+LKEjC9LEXVg1t5UdYSYNG/s13HXphtMlhcEl9rOQrfc0EpwnYQk9kqXWw+UBACwF17H8Le1SWcyJ1rNF76h9LVqzfsm3blg1rV61YtnBW/+rWUgt8VFmLOF5+u37odIDxIBl3AMFWRNbywNW/6VfNCfrN3NV/WbPnxIVo9sdc5vNzLm4pEVEZ0XUKVB8TYEj/8vrVp3QNly0oQ/GHg7O71A50lBPl4SixfcSgowkUgBsPkLqne0ZWsbeS+P6w/0wllxuZi0xd7h+uxuCVO8GZGu3lOW3q+NhIWE7hGly7Sev+K+6k6EnAaiiK1KXfX9atbdPIYFuZZT2qJPI2372Ij7OrAMgtQbgFGAK0jzrW94YlWeHed/muIydeZ+qRg22oEA2qPZ6D69WkfYn+zIBjZE38mYW96gQ5q8pBr8yz9f4MI9Jiivy6NbIk3r/ET3kfd8l/ejUiDLvvKMicp7+EqVg+3nnz0wwtQK5o83RNDUv7gLP3BLaDzoO/HhXWKQYTK9pEFlh9rXsLf44fs2bixkNH7v5UAxox7V5lZAyOtHIr1GQmfE4u5FRD6VNvrR4YGeJe5r2ELGzc6VwaOTsKnnoprF7zul/z/57fJ5+Ns5dqSHscna6DRwnqqN+PDgx0ULJnS0hkCqW1tbVKYaFud9vV1FKAf7FFuofSUZ7+18dhka7wdTmHNnN3Hb/2OctIA+HkT7hBGqJhqozq7MTkfIpTFJn3YtekJuG+zmU8sdSx0/53OUZ0Y+mS29aM+nG/+H++46EzlZ5NorCjzLLqOZjW4NTuLOHOKi14o45uK2Ay2EqArqDIQDFlcOrlEKJJ//T49u3bN9b3aN7994vXb966fefuvbt3bt88vrKfr9zyHOD8U0tDwX0LT8DWox1AZo8J4yjUJCH9Vhy+8iIhH+HpvIOyDeBsQRAOVQWAUZubq0bQp/5yZmH76oFl2yHcmkw9laKjediN1Bzbc+Lf/K/Dt/xFPXNVNmxWlZPWYHflVBVKe6OURiu4UsLLXnykMHcwGknSGH/p2MX3WiNJkhSjMebFXN28YEg9OwtzgOJGbqnj8YbmbsHfW4AaH0BwreBGjv/34t3XCfkUWxx+iIpkfT8CXBqNBiOCMfTJdzf1qx3q7aQsOxQBvf/5aAA0H8zrb590GipnLRmgS4H4NqebsMQUPVnd1d2yfIYY4rd4muFqjGfFxaJIVsAwMlDAOD/ORLtHLT1x6ebjD1oKSfRMYQhStVYOlYSaBlRRZNarfSPrh/s4W5fdaJ7Low3808rTAk/LM4a3LwBFCfRzXlK1XwY7WpZ7Ft1vaNleN8wX87SZc8qAPH5cxQvIKAfuot41avWeY2fPP89ELLDWfvgd8FuBIoVP/BXGnJ3dqlpApbJCEj4jk+RjCO7E02nh0TQIC8qxy5uf24PAllICrtEVX+yIJmAoB8KaAUkKimK0xDK0UQebyy1JFPPfcpdaAsE6l48GA1iZ9NUIdM3tERLtMXjJ1gPHTj7+8dKFYjHMuMEryNoFil5QnHh7edfalT3tymZEVfeTCQae6TTTtWPClTi7FwDh9QJOBQBdavLx0c4W5X1DbstmehpT5pkdcpkzOaYIlhGquI0TSlWTmkMWbNi58+i9//cS0kuU2ai83GrR5MDRpb/YMqBemI+TkigTxn+leAe/mOA4E/5Y1EiClp3C6wN8ASDt8mQvqeWIvO81Iwt3VO3pUzM7ZjmfVweLhMpq7YiSavt6/WetWL9xzz/9FOOViKBaULXDGLhBBAg4QBvzPh0c3aRagKu9pCxa+YhoZrrLuqxgfX/GVjY8zKmehCNExe2xCPnymAxO2B/OhHJahQUPjy94MTLQxnJsXQbklpvd5zqT4PDfeFctFdq1Uap1m7xoyfLf/4/e+mqtQMQmGd7PLU2oVFDFCWemtqoV7OUqLwukPe/RSOkWMp/GvlngheK2eULXoyr2Y9SM3wxNJAudFmEggZdEfvYBQCAzC6aQTBvlZ0leyvkXaHyk8//wcY/vdwfStLCqs8bbI6baLqjpwPFTf/6v+gef/LK2H4s1ht9J3wtVZ8h6tLJnoyoB7rYy4bGdeCWPTyaJuia/cOerl6+nIToKX71QVfl7OigsRlQBzwsvxsQpx5KDZNQcHbiOmWDUJ9dHLc6ktl4NOw0YOWnNlR9abtfnqQMAqJDD1ghbgdyQBe93joyqEVx638zCVit3qDnj6ocsUqBtVy53+VthCI/zGI8ICIsh8cIUR4mFCCGd8fnVcabQQQ0nEzA4yQbpotRn30f/KgWJ0qdmiy4Dpm26naiHxgIEpnyYLSBpZcOwxyAeCao/cMvCoDRxJ6d3qh3qW8lOLmBGSeqNXbb3hZbzZv6kYkzCMhQklQQlbP33fmFBOW0WUbEYlcQdKTSazpWr6okMJma0U5l3J/kqLcU//f/7rIewTqCYs/EzyXN1/X6NeT4HuhxdQ+xGawI92Ur30PrthszYeivFCCCaSxWgxwuXJC4xmCweAF3q7cV96ocHeTsqhMLap3bLDR+KAYpVAsU9ErwMIp3HAW9nqs6qjUq3MGUl6de8GVLN1lL8s/8/4TBKZKMrs0gfo7xHy0VwDA+G89ogUToH1Oo0eNbW+4WAI01o7s47zg6ygheKMffN5hHNa1QNcBYKovKUm3lADG7yJiLwLJ3qWt5ODa6XKefL3DDCQmxlP+TfLBMG8diBPa8QTTJ5vx/PuicOnrXaDJy6+k6uETmV0PQAZtKFi7hYSGniD/7Srm61AHuJEEjdmt3IIHmUIPfcyyb9Q/RKlANBDnrRjaEKwjLsfOHv+DuGaWMaL3NOR1a6hUYf9X4hz3TL7fxrtx88859XWSRqOiHG4FOuDarZmJ6MpeoMaRf+6FWvmjB3nOHSa9ebXANAsD87nVmJaSOGVmVdXWqdBEkN2cCklqGTFUu7sMDcpIZ1Q8tidbBkgUBmvBhXSWIZtp/7G37kux9G7PBgZBq38Lxaaf7GYX7K8edeW4LnkRznoAadh8377002V8tMHCccSeUWkuBQg4nMe7BhZPMqDjL+Y9h0W3AhGSBIR037xfOZcVQNf1xnWl6n5NQSF9azSFqHWpAJjmcbCToXK253NfdGhcktw/Z1v/MzVOxRZs0AeQh6PlnfzwLMfxDAtzhTuIY26DR0wf5nORQrmZCEQiVANXDgKkoYoH5/cFbHIN7BI3FtOPpempEjIeJvgs5c+CqiemrTR7FBjoR6sTTS2jKc4Ed+jDvmR8F0CI9hFYIV4dV9iuBdnqncwxp2GrHgwFs1AHAECRUgjAKAKLm0N+7c4m4eUr4vrw7r0vmkjltHSZMT2eUlvPLcVEmlrcTF0WgAYZq16h2Tdy5xMQQg6Iz/M0JhEfJ9PmKeVCMX6x+icZXugsfB/DddVW6V63ce+cfeT9pSqUjpRFcAAEyBUrp+TlVU+p21vWwJnrgti0ZMExpJe0otnCC6rLgmiJpSq0FrdE02PInXHj9hL5ywJLFNXSkWB73icy/Usgj5bh/uvn6GHHHkLjrirIEUP8I4/141uQC3C+8cWL/L6AV7P+aTXOUEV1oo0mAw6vUGquwOIALO5BRG7xvGE+cm95MNyGYQgVVnsBZRTfHG+dqpr6go9bvGdhYg3/XDrXGD5XYcMhIGkz2hcDQtSM2HTir+KZco3UIbdRu96GR0HoXs5IAyavKzM1LTUjPy1AaKEU/lIET1iRdnOkv41GKsPvl8gbGMUnYHHsXXUpJZHrmG0pxq7WL58d0//GHsrNniQbOGlTBazPldvFPIlCnOhACHcqw9wxt3G7/qdHQRQIoF5o2fpcW+f/Hk8ePXsan5GiMfDAO6jtInw3+y2leGjnXUwts6AdOwBxjoKs/BpcWm1SHpxMDzfnqCYhlAJ6xcRHd4Dom3aHsLmcXHD/yIxwlTD00OY1j7ynwlNky5W4KUQiTe3qtK075T/zoVqwMogJJXfvLb22cO7vp3x+Grr75nqUkOLrsC1F8P1kRGpqzzbwIAvADiEyDqApzyonSKoycqL3m+s8U3q1/xicdJx5/dB5I11PZZbMSYOtSXEACpvWd4y34Tlh39bgAo4sni1Ogbu1cvmDZu1Ijxv/597e3PQrJ8RLwx88EQ5HM6nZp/UfNcygAAROf2dGGZzz8E68RXNuCptpbe67V/6NMp3ofDeroq60zRZjJhV5S1EMm3dg1v2WfSkqNfiuDKmfPIT3j037JRfTq2iWrSqGm7gb/vuf2tgCoX54qCoi9/Il6VXBa25BvC0RqLaxxrLs/TBkC/+01h6dWO/jOfZY0WFEbeMeFSjF8XBAhhAKnKs2ZU/6mrz8cUcsmnDMXxjw4tGtyiXs1q1SMiImo06D7tn1vfdRQAQiW9RAw04jiMq0/ZWxlpu1/eYvU7A0dKAEAIXACYpo98SyuMFUX6pmpanaRzljQaYNeDpsgu9dZbMqxivToHYL8fRyvE/egvLaqkjP0Olh5/8Q3O1MppQ88pSmH4lFt3vK1cEAvY+tdqO2T2xosxarjq0qGPDi0e2qJKZX8fH7+goMCgGu0mb3uYo6cg9rAe+pi7C3BZC9Bk/tUa1ii3wddh61deMcrIF7YY7bOiWCxez+fFo5g4nUIDDF+xm1YuhVjFkgJxfALAJLGLwCIamb1GacjydHeCLT3+0htYw3K7hwwKN/akjhlF1Ov5rgKdixxQp8OoeRvPxxmgIUHpsz4cWjS0VbUgn0pODq6e3iVNeOtf9nwrMAIaAb8V6BbTvG3igHD9mea3c/nudxKd87Firq+RZBKqE8kCcwcT2SDgXWvCwuPPfpZ3/zsFzDtpm3HxUOq7TYV6kmX/Wp1GTV9x9KcBllaq4OuFOX1a1Ap1t1cQhMLB2dXNxS2o+cTz3wqpcrCbChhTBnlz4jc8lRT583yc5Wv8dmSQDHNmIdq+zZJYePz5zwJzwllnbEoKdCe0RAz1Y41AjyIhtfeu1WnI1KXHfmgBpD/twbpeUbWDPRi3dkhIFLYO9vZuoa2WXY1TQ2wid4X+OD6yyMLVNQmOEr/JuiSSb0oQDEuz+JGhMCY6wWCuvKLmxYJbpraHVK8cSfU9Qd0EbUuoW+o2bW7hDDUcKtL3KQjLjr/xRmfCpuk7BsQw622jWCzUsYbil7VthDGCzM6/Xpfh05bf+KFnpYHWJ15a0KpeSCX2/WxK5Cpbexe/GsM33EzUkFMzGhsEybwA6M60VcIT3vXfTyRfqeL4iHFp5WkVcIqpQUp31llriWXH33vzPFAgxovVoaLPLOVYaGPIguHeUoFa5+BGXYdN2vIg1chKg+bL0Ul1q/rYSWGWUtk6ewS0mbzt/k/NM8I0KNTz/g7QTfuowwkkgnpRPZrNUZ+JyjxsDjooEnKu2Vp2vP4fvjmaRzBGXoyjaUFKAADU1ro2AplB5RbasMugWbuf5zNVg6L3uwdXq1xJBd8AV9o7e9TuNmvX4/SXnokWsGNTJ0zygCTapfHpQoAsEXAmDEFPJvJUq+gUleBWYi5CDV2o2nVKGj6QuZJKjerzmcBWJTSAFgeFoqd+csKi4x+/BfzPB+HdcyA9VjIGJIzwFsoQKtegup2Hztr5RsfczVn4emvPwCBXGed1Epz8G/Se/e+zz3z3q1634t7AKVpTm41NryeAh1KAan2muKKoEuqV5LXbDa8tBdhAJaoBjwB8YCGyJ37zpCgD0gRWMAD8WU1p0fFPHrJ+bS5WYB1NNX6VoWXiazY1E8o5CaVLUMPOA2fu+KShSjUXv9veK9DPWcr9RR8uoU16T9v1nz7lnc/CbSJAIUNeG8S+SehFb7SI8qEJs+Qa6DtjUV7C8TH+hOXGP3srDBcExu14vM18vOrb1d6oe+M8hXJNidIlvEnHQbMPMavE6GMPDQysZCvltpeNV9Wmveb92X//ie94db2n2PX2eoa8NB2KsDVvCmnLtjnsoeF2M2ZXHca01yd/b+kttcx4/3/5tuPwgXeaHkFHQiHiQJZvyRvqSAmCEKj1rN6sU/95F+KKS9STaVcnBDgqJCj3fOET0XjAr/yz//6T3/WMhzKJtxrN0IYk78cqp9LzQGov+q6B2I9vCoAQ+lAV+7KxBLOIks3rVty4uFPN5yELJXhleR1oW1AFJx1w+Mj9cwgGv9V6KvbInHbeltjor/2Af//2de6CXc4BsWTQHB0jAiPAZOov9rWTyqQC2cI+KLJ5237Lr//Ug5IRX/8RYIPk0HJHnypRP+JX/YX//BkvPze6hR2AQsHBEEJm32BRDkVbrJB2BXBDWBZLc8HjIX7WMsLy4j+/wxyjecIfM0239Rw5IsIGkfBtS6hcKRXKGK6Vazdp1X/F9XQS0MafB1Bv8UHh5Bv5HX7Er/hz/+NN71s6pWq32omG9mJLhVe3nbkW6sb0RUxkMIy+p2MD4NOkEInlxX99p54kGI+tYNyMz6dHU066+n4HiUQqE+whvgNr1q3TaubNXAMAhW/6ekhRdzyGfP1v90N/0Z/775/+rmeydpp7ivp+Yvqf9/MoC7BkDS3jTpIb4gxvhoKYw71sCAuL//5O8fCiPX5EU8sw16xSbbmbUinYzFWVKlcJDm656EMBCXSp86tZo6mT2vl8xa/77X7or/7r//3T3+M8LIaRwKPoLRGnSX7zOY9EiTyklED1wovxpCarch+Z3DvMfF1JUFdeZ4ENiXcqvlmT8loONlUDswXfOzDtUvOVAoCfIQ1Z97d18pNaYjxMjppC5gE7arw44wrT0QCXVHCvlqNKKZg5bCr5ejn7tz8eV6A35P/bxg1RnKqST+XaUSNXn36drqUYSeQwBdQqab84WkxkVInvbNuCal0lrQusXp07vEpfqQlPZlYTd0r1f7FWahS8IapTlbupsDi68Pzc1j6E5cQH/o81lyUcgpPj7exdbkawjLm9fJRSwRxSau3kamfrN/deXI4679SgAMQ1UamTq2dQrfbj1559n23kMgoog22xifxC9Cha3q4wWHgb41JgFTgAJhpk3xvuo5IRlhIf/m45SzAMl2UBJ63pBMa/GrkwJhZqLGtba/s2Oy4/+5JwqJcPqjYbO3sX3xrtx6w49TnPgBwylc682H2OKPQ80OIWOA9HeEstJD74494jhjabRB8IKzAd4xdjqzrYWAnYSgip14IzN+88XtPEERWZQqGy96ndftSSC19ydADdVjABVCeQzdwEnIWC6y6PDwQUcKw6AEr+hk+J0gAkQGm0HTlwKuZAcL2yfKvuHtAeBBMIM1cASwxd3rkxThYRr/uQT3jP45iZc4x4fWX0GIDW5s5e38bTSdjKBYR1r4NXz++dUhfdhSUSmdI5qG7HUWuvfcrSAr5Fy8QK+sSLw1VjC2Tulh0DBZkFqqj0Z9t7O8ssIT7ppYuMBAxJZM40mmNKXv2lpqfAV4EkQmavW9yvkZ8NH2VSlWtwZLvRa8+8TtFQADHQovACFxSOfiFzAea4DsVZSeqhCu8v7xogtXj40E9/eRitYcqW75FUFD1xj9EUmGN4Xy9vEeAo8BJY2aRTM08HG15aCal1pcr1OkxYc+pFmpYqg7B+6l+IiFeBwyzVvDhetPdkjeNEK4BRkiou6DWi3pzjEyJVEkuHz3jf4WBlGKw16okrnGgKHoWDF4ubVQ5QlUfbeYQ17Dxp7anoXAMQUWtxeiaODiQFg6J9gwPDC5b3Ni1JZ/90993PfYEyS4dPfXmdFWvslsHSjsk4CAaSoYaKvDQyJKiWbTk0nszOPaJpt3HLjr9P1QBBgumxyS9MP5bKnZoUGKhOaQMAUQiZPjdCbtnwaSozwjlb/XmbYQSTSh0fGFy5jrO0/CFRufhXb9Zj/JozL34WI50dYnfixfTLZBiGzdXQoZfrRFRD6b8cn+hl+bwhxokLk0D8I8N4OxaXGcDk3JjqVWu6K8tjx7ZScK0WvaauP/kiRQc4zEd6xaBpXu+DbYfN9XdrWOcjzS50qun0Ty1SRk3931Nnp+JGL5K44wBm0tEiCrpwkHFzfrDccuFzfNpwk4sxqTxOqfrHGcPLEn/wIADw7Pem1er42RHlD0Ju5xFSt+2AmetOvczUQ62h+qMJvDAFqQE/JMUOZTAhK6kBAYoi7ZcZ1ZwlFgqv/1yf/T5jIjUEU2RKwBhvtowSIZm7O/i1q+ZaLl2QsPOu3qLrsNnrjr0tMCJEmpkXqk+pEeCrKnowICd4eA/QBFAFq+spLJZfGeMNr4iRRCAwJxY1xVIZzTDQ5uUk/VajvNaikrtEtuo8cPaxZC0AAsWu7NM9fsKeaTrwPQHIV3c8RSZ4NsvVMuH9P/+bXlFjAliDozCLAYKpRPAgGiiDXnu6t225vWyNY0Bk72XRWoaJAM/NurEhtnBuq2hk56RIqdkK5scPnPPLQ4pAhl5mWBsoqCYrLWYUyGKS96iyihNTf5KAR5P3aruHzCLh873RyHA7vd/dOVsn1N8aXLoBiF0SWn5PZvbrveZuHgUzXpnEx5VQ8Ywt6vlyeUgROPcnig+c47GyWlx/XL5CrQmluwO4U6j99ntllSXS87k/+xX/Thbc/c40WVOIAyAydZcGO5ZPCFlg310fdNxry95hF0N48fjimL3M05rRTMABRIHh54SaNpbJKO5jEeciTYdZgju1aGnIvdSsfKIKXPhDBzgTixXHguYa0jv/ucV+4jmCfq2bZzfz1yBLhM96XzZSHG53ut2TebY8Xg5D2mhdWgWI6vquXxfOrgxGGk/QKem1dGpzEwj2WlrfeXdzus5U8G2Zk+XB53uDEZAAxHMtg2blCHLnANMm1rErd3+Fb3iYqkf1etWfF8EfYHqmKcIuKVW5Vl6qii60k1gafMAXefPDuwkHShxXTFluJ+LNNIIMSjvKq3zhUGfSzh9awDsuTxZetJ5j7BycpKq0WDaICfjwu4qwMPjAL/X2V8VkYYwLa7TLm6xp7qKxBdT+2oryZLrwbhtjIfYAwsdrx2rvO85Qg1RwLefavj6Lzm9esS6VmQqOnY5dFi65LQZRJ3kpTr/gI7cw+KAv+45n6eRykNg2B8kaRLhKdJAxxL0c7RvwOZMBQEmyGAAhGDojBNV48rWkVqRy4XOzwnQ7C1JbsxNQRcj3ilYgKxiqOM9TxoBXGsjENtYWx88q8pblL58cDZ4jGqWul5RGbqxfbuzW5YYB8Eg2QhD6fX1RfiuesBSclGmFu7ylFgZf8i2vDMNhAArnlEWMrNB0PBvnWD7+yfhDn/MpLmvBLSQsFDbpfXnSTUO+ZyZaaLtExcjLbncTWZj2U0M7C+PjL/nWV/yBe3SQDL8QIGWPn8kNU1HWxohycAaIW5vVT7IBqgUAjW40y8LadX/H7z2qIQMOKzEXcYNeqsDuRY3lrMEEdSEEYezGFMGSAqzSjK+v4bI3yCoBWwpVPNyXsCz40u94NZisPDB+nBO9yVgqGZDXB5X1yIR7nSH/Ab4BAITZBTBA81zuwrQLjtfIGiSCIHk4g+gpGeXt/rBhylhdV2JR8MFf8d3Ptj+/viY7cKAqWQLTDpb1jKVDLmsAEMoya8UvnM8Lli1i6qCg9CzlcEm62E5hUfChX+Pl+fm4faeSbQXwUEJGDynTTyt1zzXys4JAUkTfNrX17jsv/WHtLn133KpyBMcQQL3D30c7WRR8zm/0Kg+zI0/ZSXBAYX6r0Sq6KMyAjDFZl8vudDjCdcT5D2X0LWzMDViauTqm2x0rGjFD0v53FsWSL76n4qxsnpRg2s6FuSmLqV5Zk7Ak+Nzf7PnDVI5Bze5kecg0voo1D/0xIxJA9HChS21oX1aXdOm35E4hO1H8YgtF29qQQzMGwdTwMQtNw5P+lzBMcoW+EeG82Xq9WQmjBke4gIJSLe/8cRtWAqAlBJztJbUo+ObPjiNpzAr2rFkiEXv4ALdWyjg3uCwckHAIbXs3B9D8AVDE7j3fIUTEKRd5G3JdNbaWiQqfZMiSIBMU0usC4Aeg3y+wtyT4XN/kVdw77mnsApGJau7m//0dd3zx1Ou+8e96OSzRQukkvQyzp5Cn9IsCNw8obJ4Jv7RgYDqFnG7HFe7zsyx6XkGNjKVAgbRCkuRQEkziq7/16wnPl/lbb9XFFvuRCWkUMTtAl2j2f1bMTtKyuR3nZaO5UjFTKBxJG2sCvGUWEE+togvTZW9Yo9TxbKTEguDzfKvniNnAGpZ5MGGWjB7F0mPPpGI18L9+ppvAo32RH/If3vjKXNdYnQpOA0DldOcRxKxTVWgyymExgFzHMhrTr8H4Z2Cg8lhp7Vj8iur7XhsLYuTP9x3CmcYevHwuW8r3/MUoiZB8ke//h/87D+iszpXVbwKkdXAK+t3xy0dSzO7YSpXHjdnb2gKdLUvzOlhmOfD5v4seWoIXRZL0eALJ5fmHLRau85rXfLUf9zfffKwxLAtRmr1F9X6zQKu81P4l+KVht0JKuXGvqsS9x2IeE/gxq8MKB1AlWDVhgGRljekMQNCwMVVQaX3sLQi+px5SnDljmBoaT6vkgUnx3sctCcFuG/Lz/fL//A4YMlWHrFgEq/ghhyo0QBCg2lgrXktGjBO4JdeHO+LarKz9TXMZgxuMrFQ8oQVCYwhj9gw3KHTBdnfLgS/wvY6ZJwkjR0sYAw7uoM90UgV7lOsP/io/+SPeRVLU6JEqf4OOSA2cYF4u7H45Ygye5TpfLTlPB1yr2fLIbEYjIyvVnuCEAtWRdNSGuOoyy+Hte+zbR9bMBUiwyzGmNxFkc+MDv+IP+WP/75VnvYeDjaJxlKWebUHyFP/YvPIksH3lK2XvblqZHaJ0w5wth7fvHc6ecTvC8ZtRUJlzSr8sRMab9/9c3+t3/vP/+/JUE2lNzC/+iC5B3jQ0AXwhEzUSikoGwy0/Pq3lGPtJQc26BrMBy4U7UE5ci9kUTnI57mpSC0MC2B4stRT4Qj8gHRtxcjkT5CijzcGRKbjgSRe+ndd/7q/2ff7qx773sSWz2gvDZ2KqUzTCNzMBDLt7hkoqkogMmmpU7khu26dnV4tU6/FmdRENFiEwOKgc0ZiMgUC1YfQcWC4jz5paWwp8kR+RZxLIATIzU7hkWRDqhUEEv9cX+iY/65+++vxQoyrTD52tYffDr8xlIT0yjCQQZd3YBK06C1UelxBaURPOwa0iGNKhXRKQFp3VtLrDHZE3rBJhIfDFf4ocFLZvNjAtAYa6EKXkxZf+8X/zDYORtNZC4zpqYuMGIkyh25Rbm9Ya7F/My5bF7IwVWdVNKnHbtzSWWAh8yZ9dOVowHKAgZOphLr2Aq+1s+Pz9RX/B/3nHq8fK0j1aKBbMU3SPd8dxHgCm6m79wVvtcL3VHG8HVMoJaIOloawc2gE672n0eJWlwM9HPaZhniwR5JxB4/LKtMEoIC/x+bY+hceP+HdvhUQdbHpap6Cuo1FbUpH27aFxy18w3ndZutkLVs1jGEJaE2doKzSUuSu8LAS+1M8fpk0HN7MLNbAGrzKlxpMtlDymaP833km09eIgNXv2Phalo2dXSbf7kTR1Ou0+E4KOwTiIT5UMw2xLiyCPNCMshLefN04k8wCtCHAHT9BmZr7RlMWwt74c+TwQ+6ar3o3wejXhFSfCHNKmdHcZtjkvgk7Ft+h8xW3uGgTD4TEv2RAP2Om/rNPKUoTk+aMgGSnPSHFmXs2UWQZ86V/M40Fpfu2CG1zaxPSAs0fRNCvDkPcsS8L/SJ+RQU1es4JOuUzMUEhaROaNK74lkf1wJYAIhu5gefy49bGHX8AA8Pu/8paPC3kr3w8qJKn0osLLO+lkKXD8L3jKmJz5dmgN4+2qGxersuQp6M8w7LMylvs0EKPOsF1Lc1bSSMa83QB81Opy79+/D9C0/jXQOGKo2fNud1UtJbKQb7tYBLzmy/4q1HnC2Z5XhxiWPi1Agdqpf6q4bM0g27m/AHd54FTLc/s/BspLfaqhkozz9tEutvuWtlVOWAJ8xd+Bmn4aGwIbKDAsPh2kqHBtiwAnCYoHEsoRT1E3wg6QIsYMPXiSAE2AMStbSnFDBV4PLNrGpjG8H8eOGQrl4pm4uA/nh7gFYbY4iazS8tJfQc1HN5klwFf9I/OYOuNhjRhuQI3kElHSEkYRdWdBr3oeShnCcI99Scz0rGgRp2hvLzhgtgTPdZZM3bnhCTH4wdVg4AA3PP5v/MWPYpGoNJxLNfgNoIzVbSwBvtLvUxNhKPRucJiuyZxNz2qMu33oz5YIVzVVNvyiRxSt96d9IcrYiykQtRGUpVT2ffbcISgQuAKIljY0Ne7dgrp7qLC0IIBs62wJ8BV++xmeTWL9DYZZL8ON2uK8xBX1OF9Vz6sBRyLY2Zdgkxm0nU9AbYc/FT/big0jMlBPMF9rAWcYnjNVYEwVyLzhILcI+G3LOMA4GGrMZtTR5cyhpYfmqUI+m+HA+eUc6QZu9bp2v5ICy+oPpPSkz4ePOyLS3RcvA1zxWVyr3m/9Iphcqp1+h20JlvRQ3rHKoRDPf/HKiytOOxXZt1zGgpxLXSSE5fA2DUeYVYRwYn2KJaiahjjFFRyuzVVrezQAkISJDF0YGKISlNAijWiBCLbODBaVHSsaaIHcz0UtQ8A2HVvJceNsYSUXEbe8h4jr2OOv6glmwqER27GUeahnc5SWwYy+0u9q7DFndDRr3QYIlpFs9N9OV3BcZbUnydIW1o2lEPtRRG6CUAEp0KXASa7mbss39p4Fq1Iqy7UjtJywcYhyKHXBaIc/mcbdNQnLgK/6xwvTusxrx7f1TRtdG97aNNCUJmRPKUkDYDs+r4d2ZYn+Bj1FeGmvAzdgeTeu4TE7KutQjac621sGfI2/uI4JJNMtOZOpM5NTYZIhFJTmUg3o5X9UVa4WQuSNdRpw8CpkRNqtcKpRwqBOLxYyOTOejL9V8n4emCuKtY5oJC00K1rvAHdu7J7V0UT3pcWp74YFKC0AvuZfdQdMDAuOBYKNhfI51YBXoTHzYF9PyHaH1H18NgLQ2++yMKeHczHr+zHRnvx+/Jsx46zjMAmVWRrlkBhteeVqtCpXtEAOtE/39nO2BFDTYMxgLz4pQVyQltwzEyKsCZZBbNqlMdNsNICgKmWIozEQ9p05aSGtTdunm6KZ0WlwYhsivOmwEPAfYhTBMQJEUEoUzzKXWF6uvDN97S2AHnNe0g3AcdoKVAo1caXK+GFZmIzZylynZCCrZSyJQwO8zA6IjsCYoUK6MhUMT1OQd8Xr7bDUOG0OmFO1okR3sbAOaabgD0L9uYT63CBp1TxuTFgGH6dDZk7pI7cRmMsqlEdm7fKTMajUI5fiZQaWPAoKDZDVY3s8P5PPpqkalNKjwlPyrR8qRQv462bPmHy1btG35FYQuZTjNq0duuitjUTs85ePM7yM5TDKHBFyKo2BXWEMmAUg2CMCwi37/M0/7Is+tuPr/dpPeg5GYWsNW64LdkmHamfE2iTuvv/IG86qOusv19uhbhooSFUej7Aotyl2mUAX5SDuee3X/vvJPEHx/MIw7zoLef63v9sHf8CX/Pn/+LOfH2rs2KXCdPhjzxnODFn5ngWA7ul//q965gS9NxwUx4Zr7oKytV3Qnpi1IYS45xv8a2s68BzIDTFbZoEN8CYPC/apv+zb/8Df87/fvlQ+2Q1BONMjCmXBrCOBXOLS5zCEdjLUjQpSwYZKzOVhAVCMrvjYBaMYdOLC6NY6lhjgObVdjxT3va/7Rv9ZDiHD/CzDoh0qWjgPmdCqGi74svf93T/2z56t1RUyM3Qlo3uO2m6CqzLrnV6POWiC/jxVP4d5uxm9PNZkMIxJGGW2u4OhYg5GW+OYaKNFSWKaycT92zf6L3JQCAZniD6jZqEMZjkomirnpfc+m8BR7XGEYxboQM7FKlRj4Z76TaZVstd/shEgzcHJ7yMCeXGKQ2COhAlMb6sU+2/mkPam7TzfRmdXvIUa1DC4cPtzooZQbcjYBrvC7dOwqaj6ImyvKesgp6iVsDVnab3HxC2YIcXQy07k85+G8Vrebw4NA80ZNGcER6QTEpZXnGhLsDW0l1jqAwcFQc/y2k3MU3sBOQkimr20A6iwbqhKpnjFdsbIbIPr3f9GjfUU93zjwy9Yj00/w5AhpnDYCwIskIxGHUO7WgeA8ONuBqeIQUJhl7AiUbnk+w6jjqCRT24uZP0eV3UNdsgqGcwWvjoSAydiL6GVVi1/VBH5/LdhFsfZI5kpLxnzaDrwkkLmir1MlTol4hKOujCqRNcnKwEvNrnT5n24QsV7WnI1PUM7vPXzfLKYIe6I7H2CAdU8m2fhetnelBD5TJOzIdPtNuE2VFws4dIvtllHqdh6TtLmNFe5WrCn2JtRsZWOHmp1XuopEfV8sw8fx0ARmDCrALx5miRCGtTjOI0/Ad0xG1LDB0oqixVUUaVXktXcobjZ5hcH98R3flA5+2kuFYuRGARBuTnonDYA4BKix0rFPR92HPZwXHDGhmGkA6zWrp9aMwQ8PANdpdmATjcDNJh9AKkcKffNV8fs9ELr3LXR++4LOuclzbrQFCZMk4t6vun/0VdcXOwgGGtcrWs/lIdidEYWRCA6O/1MRahOINCjyOtdUCJp2870BUiXy0lqMArgxLmwVFYpdNCwPu5oVZZS0plg0wI8ptZ2RMfLXmAj7vlfhwHQU8rEWF3mHHqWFekPrlndKmgdMoOExsCrbNldxe491dl0rDkHKVKnGB7SnYUd3bAjGvD4fl0xqlTPu6jZeqFJ065xF/V8k/8uhoPx/eOIwTJxpSxQP0F1F6e4hvwMQPPEqteuq5sKvSt+DyTFkbkaysju3WWhU2tgDaPGqxYjMHVwkXuqi/vJ/us4H420N9fTnsvlbs/5pmqtZEpSsSw6a9qDsYS4hynBjpA2gypQjUHW1FM8bAsZ5yknrVU9bDxPrcrEOc9BtUgF28bqn7aemcWh6ufwoU/LZKK+5789zJ8R1lFhHNlJJBnOdEv2oFRBRXitcS0Ha/ZdtCqVKCMLDMYI35zrOypkoQ3b5Ryh4qLQAbnYBtzrWV6mZe31B1kbfs8AAOn77UQ9/wN7vsA9DeSgJQN1DMakg4QvQIwQBW/PMVsEBlUFQRRhLk6UyEzDQt8Vf60gd4AtXy24hEkQFrIxY5ky/YcApfp0t8NE/WT/cx0A6/AypofZYs2WUAX1IJzJqIJZjx9QUlmsQ/Xr9EyX0f8i89XRYZ1Zdle85tLt3OcRhHjn9d/0f4gdoG4nh2eD8KCZy2jWUaozLfaihdfR4cuuDp+kzTf+z+54jEAEOgMXCJf16BZ7TW/6dD+lmJ+RvYWZ3z8PKFCby8EomB4ahVIlR3WuKMUIkFYNedeDVlmdupv+cCJ7hfEmxF5lv5yGh+KEmD7CEl0KAIiqKP2qUKmIH+WCHdR8DYoskkPuvGDkonMhr26WjDXSaIxT2FKubtcSklzM8KQ9fVhcViHwE6ExChEY/LQs9JooK6b3UBw5OeDjIE8x/4YYHeRcY2IAf7xskM3AdDxGMpkjQcFGpXE6gAxM9WB4qG1M1T4cJqF3dOGCTnVCBqA60w5jEmp0YoI/MgE3AiVp8Gl4nRFGsyRTwJ62KvE/ijlQD8EZzTGT2gb50T43Xjk10KBPXeCDupU8+ruBQux1HECneIybBjuBs3nmpXIoFXqeXArZV0jekPzVfmJ9lG/+4fbeg2QvaEA0qWY5EO0ZIS3WblRiOECLjBpskAd2sPf6n1I0uViQm06/EBhVE1aJRAAEQR+XqEQ63+KjxHCAN0lH0UE12FaBlgQjB75nxpgV4vVi8hcEUNjrbsGXtCjHFPXnDvl0GAOl189fssiYDAu41DMNBKWq4eIKbzQkRDofnWS6nZ4eSTuIp1GaBNIji8KbfQHBLXSuIfJPOC448eCzD5EJPmIWiBuhchyLwmKkFq7hpZCrqcYOi4JaOXnSGqiEfRbVTBRA4jo7qTjv+Sg5ockAwQpBKVLwEsvsgUm2BPPkTvwJoWPUw6B2op1zYIQz4/B7fdeEuKes7894kDfJGq+8yeQxRo5KYfxSqImr50CIcb7Zh81DmU4urIBx2kpm7UdoimWrIFNqwEIu9crK0IEJcEe920swWuvqTyI/NB/4NmRVjBPM8BQDwNpwqSh/+4jjvDjTLWf6iOnMqoHOtoNfNfSUvabYnkU1C+ICysrFNwmeyPPUW+p8oSDEkkg9pTt/qb+nnFVO6hUXjvAQ7R+DNxUG6LIJxAqaa9pW7L5WaBFWIWRemiDY3SSjDIW4L9/CWdp9DUuvJnB7sJ0Y5+Pk3n6IMzrR1DgU7BPjEMfiKweWEiWlJ8WKz+T5wKgw6sRQ9x14vHGYBIe0vN9YXxyjuJ2amN6Vngtu+kZw6etBYVZmba4lEd98y094HIZp+RkGw8w0O8TjqEZxRRgjiJpRbKoSWZ1RH6ciKhj9oIob0bOIVaE7aYTCA88n+FZTow3BFI81KtSYqmpgEigkbhvYPA54BjAy1T4Gdzc/HGsrvvlWn8Q0i8Wn0RoTyTD84LjGjMDS+WSMuLPfdhwCkxrr+zDyB1TVPzrJqtpaGGzRDfmNgobgp9VJzBoRNSBrMqo7xp2qzYtiwqNykA3AxWWeCCHEOL39RXs0YfjzXXJg/2gZnWNZDrxfyPQD4s/egDk8xK7ktgV7Ovd421ZoNcngnuEpx13Ywr6Lm6cgRDefuGXSSHYDh/GaFSPi4BcMD7XIWekzEA849wOiuhbB9n3G5UXkDQ7jURsWGB05OB2zJj8haWNCVSKb9/82n7KsPoxzgHPRs/LsEbT0YLHCkfWKg4jlVlJhQZ2e9Pnwccd+pLuQp+mQG1eHiZMsnruS5NLBwcCa/X7FTn31hlzihmw4iT05pZngJRHbfOqw/kuUYx6zMcFQOfpgmhcEWq6KQwGZqtrwMG1kEnqYSms0+UhjFQwdFnK4yclbpXopkh6naYG4hSzRj15oNArqFQeUrQktZxqJ7Ek+4Nt9+mHRzSBnMZwYCRyqmetAkhFBF7Lqh+ij8CDHaIXFN+JRB8B0RmK3HP9Swsm0Zk9Q9leAbyFfq3EkojqHqelW224lkRRnJsFM5kQ/QmTzGd5UI6ZUD81MwhwpBXIkJpoF7SSyoq1G2XbFWS+nmuxSSHJnfU9cMNXuEkJpfW35ZN4Rkhb1ZpAhlvRcT3E9+AO/w2cZcwf2RBoae9o8Od7QLvVtP7nI0TBKcFmA0SqCmmprYomHJtyk74ooAnMMC0U23Fke5JrkNYLFDXwxBWot7AxU7otLzFkbKqo7H/Ad3tTaW7AOUInR3tOVGqgzdlV36fjTBpSqK3bl6k9eTl/4VB5HBhwZcd21vTLUsZQzgm7Om+HaQIUFwDL8a8bhZH6UMM7tmLSQKO5OHBgcY6rmsCKXPSbj3I7R4rcCv0u4jKSl5d5f8WPeU9eNR2C6nex/arE6xYV1AhfGMFlc05MGnmC6nQGK3+wtqif79p/t7KvpoFoBggbiuZHavmUujslruAMPB68t1NWtjcFoDH4WuVkTBL0ZzWnvDNXN/ARbkZgY08scLl7GStb3zwzWjIMy+KqtSxk1vAqFaB61kIhpvu2nO+PBnAEzZmX6AUnQRczxvWkRdkaZFFp4iSkFTFWOTEqEm5m0SZD0lMJc8hAKazEGteCFppg9KiI7nd+OBQlL5YSY7vlsNjx33ruqXBmg3AMESiWNEe6FUeVbpU+teRQ0m6v5mzqoy75ws3780xWUxBV2BrZVaG+vvBrJ1N6CBw4img/6Tm9eRsQeFiSHaUIWgSBXvod2FkFwcTh1wquMsLK5HKfotIWT46SblyfiZ+CVea31SNHjV4ZSKGl64ifXiSJ8qlUEbGy7LBQiQ58cLBPPfPB3faua9TlMUQ7k3GCI5kgAg80dQHsy0aUi3Bq76Ix/osjyVvk5XzfAEHGjv74vbB92h1uxFFweczkkrZiDzaIJwpoJYirB8HPGtaQ0DZXimQ/5bm9fRskc2tmCmkhmGMGWMcYe8wxKNzZrVK1ewPVKBvFBMu5r6Jw/HYbswI0O8WrNzjDQLI81l6guSTUr9pCYOFFiGoyqooUKjAB0tSHEM9/zJTXQx1gWkBjXIgCCJQw+0N57FtUnCqNBhQ0PjVpJqWavn6KPat0z1ZMPC0TUznBuar/XFVOlkhGH2YtnPvi7v9veKQQzMz2VN5KLjrZQg3UvQPcmcvhAtzju9p9ZVZwOc2TqejZN14ZihUFt21IdpcoNeVFKKxHNO8c1LwygOzU4O0URoHJ1wpEXAMf+hPzB190uoPqUsCDkC0KlP7f7BAS3m33Lg8ByuXMes5qWqFCPFVPDkXQtFiH3ka9MTPOOC8d5Gg8AkiGbcgQyBBc5RNAwcxniI7EneLAumfdztnsmpUiw2VB7xc9YtbsYB+QtziXI2s2+pdp7Uigty1nid5NGcBUpe1SEiOa7vXNYcNbbsWbEoGcHOTvFQcPiIuRzTORD8HfiQBvi74qJHyjjbU2ZViyxQr3ZhzQ7usq+hrvewuZgSwW4ZTD2zUWOluT1ShHNh3zP96rhm3OZcwRUpnfUB7FHkmpRAWpS+T4HuW8vX98DWriGyk6esOQsaK1H8KvaCetVFzUkCzDy7rlJxDOf6we8z5gGwrNFAyG04sgRn0mIC6BejcwKiIBjiZa1DQIflK3E+FTlbfvyGDD6qFi6pQEorg6zKhtkFEUAKpRdA4HN2Xygq2PqqMQzn/eHvOrPiBwSdwf0WGFxsKH2xRvA8HqX1rBSN5YYtDbu4NPwp4iHTZxC3HVoLwp5wYk4ZrHxyjQG+2p9Wid78dz5fD/s2XEsnRE8RktIgzpnZEUWbQEZNS6go0iiB+qYA8OJaohUiBLX+Bvz0PQsHmms6on7OcysgDmMgiCKxYaquyzmVlj9wJg13Y4BomrO+CMinHSyeHQlqWjm8//w54jgDRE6ROPF0cmMxguiNCMrc3IsQWwBEWS/ZkNpF0a40W6V6ECVc1CZQMm4Wd8BgkURq6cmiN7pSFaTM76+kqxlyyj7VXlUGcZcrODF3gVWAPW7r0I08wV+lDqGXAUOKNoWcmfMiEKJiqLLWTiq2GI/wqorRYDqQhpIrscNNbcqjeZKhUihkK014S2zgHjqrAPlQtyW7nbROyJsRDNf+McNszB/nJpXR2Q/ZxaNGZaKqRjfdDFMm0o8aiJl0JNLgkoLSfr11D3GHtosu14+hBJkgj3kZGsL2/71rvqfNbIXzXzlX3a+ixI4DNrx4w6IFaRGUDiYKcpiIElA4f4x5CnTKvEe+KPUaot8loPIHhGveJ9ltcth5W1mwyqUKjS8CZ3cRPMPpfSd/6o5RGzdkNNkPeQyRfEQF3Hq800KBtcqwshImeuyt8dstnp2vN3snzqQLw+LXFZSROs23Y6rRhHWxddN8/umfd48RBg7Bf4SJvpIQdTkFOZeHxx8RvziLS5WeVAKhvkSYvnC9T/5o/WAMM1ZNNfZULlmHSFh3RmK4mGm+V/kR8pMG0JUOat6pDBkxhwzGsXKPPin4AUvcDtj9Ec3aV0uLZQA2tn2io/VJNOHj06bxNiVbrs6oX6NEMuzUv2iN+gcDwI3yxkjgmcAkzIV0mGBzcqKggUxptgZt5C4zkpvTc2T8lNZSh2GdiF9JeUiyEvvdeZMfnCgmVwkY/dr3r19n01XpOFQzUpz4tEqZwvtUUJU07m+tOSER0i77DbwVEraymupGAwg2bLGygvBYNAbFlMpGQ+6q0Qy/r/32eOyW4MG5oBomzeGC5Bg+hE2MG1zzDJHtVl+1h9RTVhEBXWxKgx6iFuXtMGNuXwk6wTErAuroBAHGD/yyJaQrBkJq35/1CquNM+fRziJ5KdX6/kPLkZYABcOBDXgS9IBfOQewUOkes2MQhdvxDwONIrRg42eOWuFTlDFYeFRgaxFUQYPt+qro4lHLe0X4+2cDrtLnflJO8UEJOwUcirjJhDYNJCxuDCKnjbNSwxDSMK3/l8xVcOEqO95ZXDMIxYM6CEmECw0AjYn3QKSoeQc8Y0cTXmJQSKpbYRb+Gdy1Gj5KlhrkkfUVu8HODUOpC2XiqjuaJpULHwBNKslaETBwlAxPKFEtfKHPbGAGLA1/qTUphsPrSrL3MxubP7cu5M9wjxBGWvOzbye1kCnZddQfQGqRzCi1QuTJEELE5SpX1dbIoK7QQspHi4xBbInbLQySwv1wFoKvkTFxPJJUNy4E3ItXRVal0+W0sGiubfkJ7l4t6sOgbhdJCe9XfF8Lsjbo7QdPd2uJN0XJRO/eA75CrjcdGLIsUFLLiFDWfK9CcLr8b0NWmGIogh5YX3STv/yCJ6IP1joPO3G8Z6mRLiKxYdUdbxduwMsJce7id+rvcjaHTQCdkYvsfeDfEQNiskY3FzcSP5SlMjAWuJXjFMcop6jo9AWPIsCQHZRNUrN2p7KbwC2G+0uCpcTZH1/VF629J3SqTKArAC/Zxf7id+3SgsSS3MYHpd5vV0w2lNgoBrTw6NNFEJhsCflESTCcW4ZHJLOVO3EsLpm9IDu2cFANcvWFLevarUsHVdyIN6iytjMRN8OIppaZsZwsOShlrQCi8jk+lCF6KX5UcAsOufbeUMiNCPVA6pCSokrZrpdMK6mz6qufA2jy3l4f1yxWUJzbeE68rQ8fJ9WXU6CNx3WJFiWQs0nf7szWvRWj1ZuSuDnoKDHyxlG5/zK57x31BiMR0mbOlXsedNWdGxWJ+6av+cybD25QAvCKjaW05mtTp3CVq7o9VxnsUvEjeJSr4XmBQ/uEJF7tMOi4lMVS3oxPJLL+n5/O7gWn1P1BJU+Xa+dtFpP3PpscavGS3MQ6p6cCbantITfNwaL21kRxPjPFNQHUDtiDP4EstxuUGKPJcItjBhF6OhZli55Qazkqh2qxCA+FVpXVMzVpUav6Y3qOOMFIUXg2J9Qy7zoSIsGysKCntNZXAzgbKzeg7TCEC5mF1Ti4vNPtbQhRC2K4xlwX5iHYZlL8U0hy5zMVBFZgX9iCdBMxRpxHh2eJ5h4TBxekicH0uNwcmJvK8JcntIYLfVnbkKI5gqmNSzxOmTyTMNQP6ra0deYwwuV4g2P8el0L5mYbWUOiVq4pzizsWadNDlcBjo/vhROhcHjJ6zMVtvD3i8CSh6/rnvnrw6UrinT4p17McHIZczwmZghGE1JQrH6lGPVrcUsLh1RvEFAnEErTzyiLP+iAL8GB4LvGDozVSnkcJu+VlgvBTf+xdys15HpCs7waRR7xYMGeN3Z179GTYafk/1F7EwkVbagZT/D6MhMkzWGeeLs2XPBSMmMnQiPQLcERoEpE5WNLenURFzTDFaF+O2qFQIVNJz4wAS3LqbbZeA+KvDfiK7sPV5Dcyqi8k+39BCvNaSl9e9xZb6hYL4drDABGowHAp1wVC6ZLVHBA8kAHCJsA/ixGo0c5XZFQ4x6mGoqtELGK8RisrTGRl/Pd3SUcyEsZIhjomqcUP2uMKACMCa4cWTWx2sR50Bjwi/VbcTrWz0oeBsAITAiWHCZbQZeSVwLLGqDx0pQ6NFt1iGQwpDPfWUPha3g3njGMOH0D7lT3IPgADrl4IcLdnTBmmQH6Pd3dxetg4mQNQjesTxkdOdKO2Cm6RhKoxwRDolrX0V+iWNJ9Yc4cI4n0iTn6fwxB2ft9jmqCWeCeuwO8wgqNM2zESBjf42Qi9aO+yAubzjOk/ONQdnzaM6kYVIMr8VHD57Vhjvwb14brHdh/CwvGF4ML1jeJ+CLwROS2VZLklGoa2M9RWvHuQ1nNmPMBYhn+IePg3DPogsxldlJCsJ3KqXlbV/w3JN/xeX+ieUr27NzCiV0lBC3O2J929ZYIVZbm3ANxcrnQzhGj89AYSCi4nidMIhGpWAx0VbhsVJz3zmZhFqVzfqG61a3EVuoT+XntFLi4uipKV0kBZFph27rEKhRkFm92ovujHeRiNXa0U4/dDRABD0RUxaBAlpgG4T+B2OIQRCht5GjHjA6DAIJGK9UNBBcoNHSEYwLHItRLgt41iORpCYaFGSS4hTBrTMPblHOsKJpcwKQKM31+CthlB2oMPHxu8NVIrVDSM/lAQ7X4SHT6TsBHsM8GnNmkr4oXBk41U0ImIMYvDGph1HglTGEWjBiAVfIMT7XreyJzCUNRhYEylqJy8Wa3fpZWQnUFvj4qw5RE923kmj9qNlLissbEFeSh9NyuN0RNuNWIYtg9gwOzVFU5iyTe5IMdSXbqezza3ch3FFPLtoSy9MqY+dUtZ9jNKvLmwTNFhYcaOAsVi9hb7c1EeoJGILSgCNH0Bhsq7DGJpq7sOHDYPMLzVvqvB9fywZOWw0U5qYOgyZ2qptYyrY8mTizhlitIk10usjL4+dhQc5PPLzjjGlnXW4SkhJEobpmSxQW49hmAn6rcAlB16MucIlr339tB3YvZGmxYu5KoRCrbqTKBoZlVhoUySxNSC8UYtuKhVCa4329xOokXsuzAbd3cLFyeP8M0riVPwdGCsbYLXAzA2CsojXn6ImP68L1MdnmHNDh5hoLMWpypaLCpD9eY8/3ObyKI/TOQsDi5pa5K34a7TpbIdh0Nj4wYasGn36PtBar5wD3u0cxcldNzRSSuUL9+oA4Wif0QhvRDBhzNmehgfJac4DtPmTwqsNEiGL93D+PnuXq1FeMk35BDxt4BGDMaXQGHatg+MZJ8X99PMTqyL6TjdyLO7AN9lgow5DQpmv1SmW2KRdTiXCSZ/JH/3nquFteMoGbsawrvzLAcq/khZvB+biFH+zn6JW1xerIiqbPYd7GMET+IbcC8wEefDVg7gNI8LVWHPlBDbILoQ+mircWsVjGIoJS0RXbdUh32LixfkMdVqcJD7gMjGcRKt2V1BKtpQW+EB+JQxGORfR6sJQKy5wYADRRdMH14U5idbD3TFg2T7dLZ1PGg2vMctBdjrebMEMhYNzOPExu3KuecKe9ZLyOmsacdDF1hVaxPaqjYRnBjrFhM8ZuDZOL1I+sI9KMy6gMuSxBDpJ0qdFgFICY1OV2lyUAkwgOaO924uOgNbPkjhM/S/aQu+43HGZCzG+8mGxxYLpYI3eb5slRkyIo7Y0LLVfu4x5uMpE6Y9mZvHGV1agxD9LsCsIclshSEEg8/mXgw/yD72f0UIkOaSTIbF5qJfEWRHaTTlEJUSV6++9Eky+eI8o7aGeYOVmyiBDJSrwgCwtKVkPdy4XaKiRAOMbk5VVtCZH6UeRLjoPlTqMaKWtIPOlciScaZ4qsiKh2ZlHYrYLLKMmXrsH1bqqEeiV57XbDa0sBNlCJisBLAXiJOix74jdPijIgdWCwbkpc8DgQKkCgedDLWyJSsd7yycZUoaYGMSbidgvZYdi1DJ8Jo4Di0y2EjNDfKnCz/B77JjjYqKYml0oPC0ZRZFWPfds2nFgMLpNQWetaOIrVE0M6/t3n64AQDMMDCdQw2aysBncsPQiMFW15pHjGvQ6u+s57z7bx2DKIZ+sTtJzgKKqFAsP1EX5itdfz177JiDMWIkLFo4EZMgQzUslgmZGdJCQs1czgwFril+SoB+oocahutVo12m1ZRkrQHaDtLepOIGdiUPOSNyAshKQfHfmG09lksKOGmMV1ZaL1xJB/u0zDGHk79w4SzHOY5TPJQgbCGqldqlih49wWAro6NyFLd8bz4tRxp+VSjRIwSChGIBZ+N3ILIG0FxrijIjtioGXv6WJvJVY7P2H9pR6S+XbDb4A1f4wKHIutzZ5w7OSxlL6yWgaseQF4c0dSztqZJjTO7LbLkJlupyiF6B/MCRKtt5zx9f/x+DXxEI+Qy9JGXYlmjSrbBtIA+545OpsX7sfj85bUuWHEB9ysDBzYw1sI9WVTfbE64P2+wI/0pmEJlOeXFmUVCVpcJuyscy4R0uai9QI38g/wEVMs4kB2fXub6+zqRgPsejAoKEqtFZJhFevVOQD7/ThaIe5Hf2m3Kt2SGy1lk/RfV6lY5QO+1Ce+YozEQ7IJZR0Kgze7glNabZg53asEHoNymCeBtI0Igv2QVk3JN+NksdjFevEoJk7HbMBpum41pxCrWCKg7Ss018KwFMJIWTBb1pFESSs5BbDIvDRaKVY7r3n9n3jDuNa4FysspCUTRc6Xl4Uc8zIlwczG4fKC/maN/ZiLDDaYhdwpz4xBpt0zKu/hfAfR2vt+3/A/vzrPpZyvgOTOok0egHuYGEMcol7cc5rhpLxjJGpnkJJH5r1a7yEVrXzo7/ukdRrGReeAqN6VS3PmR2jjwjQT7Q+KjZu0qbhRACat2Iuk0Hov0B0tP7c1f5wue6hhYyUxaMcReuwFmJXsbdJaD/0aWlVTahKHNJD7aluYeL3rjNd8j7/37LDIwxjMikfITEDgrJkTen/wmCujOslTybvmniYco6K79orwLNPRn0WnvFIVCb/TPEuDqpvOf7Ottoh9BIQv8Ws+c11tNcQMgINpsARjNIUxk+5oZ6Y8RqH98UOojEhQwGo47+p0h0dPazUFEOnEh3wY+cwc04tXAqrAonfbG6vE64DXf69/gJybxTECLnJ2FolhWZ+F8Xgjx5pl/RvoeR3JpIJ0iIePI+yegScr1YH3WuOfFmeTlzlJY5PS+63BZhC5mTXsqJDKxSOzQUZX4HAm6rzJvHTetJ92RNmIV97vC/3o93pz6Q4MpILl4xgcoy6li8CMqteulVYQMQSwpVJVuc+DQeBCK0u9Q+5qPH8WKkGXFGeq2webxD0dcIsZ+NoFQcnkjnM81wB+HGprJ2J5/df560xjoh8HoxzD7Q4DNnlH4ehlxKDRh1qltzivJtZG9w8ieDF5GdiaSjghujvFUEGHIgD4ic65291FKmafZe2Hv/Sch4ncsRF4fH8yitLEKiqWSDzcu07VDcXA3f+vwpk441jWKsB9FKa+4KZZLIIgzedhbjIx+1hXX+aj3su6xATTZrAOVCOMpGQOFSMYZ1lmZ0/SsCE2VgeR7alCibRWseGP60zL65ScWrqF4RYr6+n1J8RjcWge4qzOUUGrAMBfg4WfRikQJJDp87zFLK953W/6xOcPS6wyTtxweq4Gva8M9MGCP4crfyjEnkUG6srEnnovdHIxciiXF5EwJJVGBx24MQoZQ+EC2DIQtbb6VrAvTGUlZpuv9W9f1tOqwjHDCMq5BhOkIzCHYuxxHkAYSjcWxUrRDC8aj6KPgf1KepM4pq2MeZQ3g+5lQ3tx+2zOP+u/uIt+OHmkQwyyzz3czh31cOx22Iro/cDLC8WnOM9AbrZB6sT3ENfDNjNVONxX3D7G31f+5R92HAGCUXVYxrRpbc5a5oqwLkzuSB3rSrnKPgBTLjn30uMePeozZRvRAE4lm3VVDyEIS4SMWyKpRbFnzqQuApM6cVuksewS1wWuCEW6CiAgV4jcH97hg77+z/3nb3/+sNZTRsDxdjI88uzM84MM1hHu0Bi5U6nSyaC4MM+wHVuBYmlu7hdo324A/fj3b3kr4nj1+SWm/WBbJX5HKsHsMNICqwKdgRYUau0NdPe0V2FyhUsCnABOAWei5FaitnndF/2Rf/P/vhOMSWV9tQM5Y0QDBVI+CrGHXcsny5i5nDVmNZTOgxeyz5OkMMrpZG504KlaYw/4826QvZXIbV77eX77x1p/XdzpbXF0N8gBS+Q9FBKKzqTiBfdHWp1vbpuix721BuqdYcBHb+bskgGi948f9A+2jfg8NKyCHROY+SYiY424tLBQaFbsl2hhOnyjGAu8UNw2C/SuYynqkTQJBYR8mBwjdi102wJHxKw/UGpzSwimN+QZ0goGoMkntzeWiN82YlEe9zohaggGDcnU2CMIuojLWqAnFSSLW7ongFQVgV9Urhydad80OrMLAhOcqhc2K6ZeGSoTv9i1PaCjWLBdFmeeHlhZYECqr4FehKn6YkdQ52wZfihoeUF6khGXVB5LrCllNFVHlKA/QyjVMxX/Zo6dlfht3Dq8KgYcN8GCPwZmWL+AyghKnp6LTCE/IAkGnSyG1kRSqTNuoUMl3rgd5Slek9hRF7WqkIykkEobCIpBRPPTYgPqFHon/jFUOmCHaIHj13hbieDGfmQWE+7ySjiYxgyGuF6kSFcjC5x0fiV+KxxK4VEVeaKiaJWEQaURJi3nC8g+BraUEnFRlERslbcklNNtg0eBAtVJb/Cr3Io4Z1+EGMZKuugTxNEA0HOYMKxx0owyOmWseFlPgZrvAJPyQvLMItRtrBaDtXmwCGqALW3FaY/xVjdCFLe1DhVA6siYvAiUby/Kf+zavim72UNKvZgsFcWopjwXCmbAcCcrMYaDyReoLrZKw5w06KGKXEShKey9YrmhX6hM0DAslStLcQnF3hRuQ8KQdrBY0cmn5+sqlTjuNNwMc0Xk/KDCRQsHhxHsgA5+QGaqCFmHEYKALPtFJNgyKUEHzZgoG4NREgPlNBH85CMu4rhjPYHk9COC6XXHFPO4sxwwgoLichE4ZVv6YjUvPN8KFw2Q4ZUDunuyZBEzRU7suerKuxskE8VI2txg5zub7qzICVxGcJ/8rBXr0oAXmucPt3E5zxhv7NdJ3rQfGylFMVbh01E8DZIx4nG06uMKDi5x6icLmUtN5Ig29HyKxMg6vdzyWdWc+lhLypKcgzCWSxqSl1TsAp2V2yJHGAwC7D0/4QxyK8bEXnaEKMa5PSTbzengwJmH1QYefTrMBcGxEIy6Zonog0HQdQ1OzF44Hiz9movLNCm75LWsFZ7+IWwvF+ryWI0/traO3tozV2xTsauqthaLZFDYUg3ImukkjlHUNFK8g3L+Vg+icDRGk7xEoI6hMNMscYtFi3TlCDMvLE8gJiGmL+MXFQCqRrsqOglqy64pO9XkbfUWxyNKw/JY8HQUDu9ffpcwtiwcWlc61nCGYkHU+QKTZPxSVZicz5xt/6ItswPUVyvLRTGEx7FidL8g3gDH8Y19kE7aVEBjGAu+1EWXn/tgLHOT7aiZS7wNr1eA15kYTWjpoIPVIimsVQOktSewgq2/1A2L4Utje3E8otP4DHRfwNKgJgUHBCPLmS5bMFqJWB7IZEkT9pHzAvU7QnFsorlM1aRyunWTFobdKGNmD3dxjLJJKrpLMTnAyuLhCJT0I6Z/wK1WbLXpdiqeeVjhxeChdGWAfCurv/5P3I/UjbhdoeYoQPDLsf7iGLl/IuDpkBy/isUaSJHGYNty0yDLYbrdjFAGgWbqmAauqrxBZzlB6HnYfGRtQyMrYMD4pdEvS5S4BFGrqskWeTFKQnTPLy8A6bK1thgfOMXXkr9WEccTSuy+GlkO6I/GNDX0RphkIHtyAwSzIQcVgZQaUgsU+F1guHiJKAaPNGFgaIcGjR0pRSCdSoIEZRE2WDRsQmiQH1FUDOzfJfolBNQ1tSTieETlxSw0PwA9XgIixtmnatBkwgISTGTSCu3wi+fF8Oe+VA41KuZz8GnI0g4GOdJUKo6RHU6Bu0E0l0Z2bpzdd9WwqbpYazC5e89M+oPQLU+X2N8ZZyjJppGyrrYTyUh3/gAA5gioGZKgYGzAY/oWLp5MsBzmCPJL0h4cn4m2Y5Rj9mMWmUaHGZ8yV/5SBm67Qi9BVxkwOGs5BsUvBdebmbFd+XRgMDBTKYvU8rSrXByPKN32nQnHGZFhCMFEoYMZxigZx0gRorhFpUpPRCwijODE3nZ3aZQ8SNyzIER9jStLRUTD0Y5Xz5jP/VUime2J7IwnmA4RprgC/EEbgy06ov1i4zCCDXi2A9q4e/JrZ7ZxA4GOxiTF9kW0H5/TK+jnCDuR/PHeJGY505kcX+ibCsKzFUsEnxLiSj24s3OCWaBf52lwiNSalz21kjhGvjcJ7hGMhHCyMCYGXIU/WgEwqmi4naOe2TYIHJpVSVc9QxlqsNRZVwblNb+4Ifpo9GA7i4QkyI+3K7M6/SgerTHwWl4VV/8RJI5RnckE6LkPAWhVgIMaEOTVzHVoqtRRbUhzszyHF6ivjyGaIIjQUBhAOMdt/ZqqVOOa6oQorh1t/7CgrLaH9EiL4TrGH9N+DpVIlFCRzzym6flLn/WSQc623f13hNJbVgI0l0ZKKGEJG7I/XSr4t5EoRlopxsgr+4kHBAHBZU0YX8nxV0GlQomOp7Txwss7/u8/e9MrVoYyS1FNyTfkDXxuD4uSt0+0HbeuQ1Q5ndC6q9PBLsmsmUu3pkRhINkxcwdai2N84kguz9PjAsGsaxSDXbFUEClVqOLj5hL8Ds2Ad/3Tn/TzPuo9dj/tXtjKIhUi+LU/lg2CFezYyn45MFEipe9xooFQXZFE77RBhQ0520siii/iXP0HEMDRlo/LH9yIjwMht5EzbWSAU7vwjgyK5Qjgs7f8he//pb/At/u3b1uL6+y+npEScUvFVTO6rHN1dl7MLcadvcBqUlDo7LWMJdD1vV5+Y4hMFFMviQ2bdyEUkI5s75Ty/NkzCHcmuIXy8mf8mz/4Y775F3r9B33zf/bmoG1U+8+989UwxgCkU1pAnuueI+2PI+sis3b4GSaSSYYABPCSLFy6AN+wAQBJKqn5+ezKnSfvYlOz89UGI0kajQa93mBkNHpdcWFebl6RpkRATsrX909vXDh18k46CdAswIZGAhiyXp5YM7ph6ZOuKxucz+AwFKPR6WVpE4YCLp7vpp2XGI0hvV1AUY6lnlLvd0WU2IMXKqR8QbBliW8OF8dEJJIIzgEA20e5p5sZ2PuCWyQAMKkAcMJWBShNVtzLYyPqtRs8bdXh87eefPpS0sR8+vjpcwxTwdun929ev/Hw1Yd3T68eXDVnaOtalYN7XNUBgXwclkxNTsyVSeG2EqbVax1OQrIbYhMMCqLS0gztvsIQgJq3ZXs8sxetoNG8gDqPt8a0V8NX7qPjLTFrP8CtkXJRPCPnp8UoHsoGcMAhi2qQjeONJAawAYAJkshSVdrUa3Oq2sDPVVEolQqFXC5XqqxVKqVCJpVKiNJGIoEdXPPdV0QD4TaZAON1d2qEHLo3dW8ipyGcZhqYVqGWAq7yC+78VJt2FR0BK8TBCRJWx3jhHAkqBPVxD8crrMRwI9uaWBbxAds2OgsORUCXfH56y2APe45bqiG4GzSj2Qy6SPGwBYIgKvfJ8sY+TjICyo7vQlmSjg7uhK9kxveFDqgvdZMFejKuY8h2Vfxwoki+7EGv+4DpCwDFIQBgK+LhL6vKpvHVC4AxN+bSxqGtghwkZVTfJ3zaCxIAJGshJJLSJR6Y0zXCliN98oitcRCJbvtqqvF2BRWqlJt0cKrGKIbBShnWKlgMNANGla5FlANWDSardNv60UpSpbcKBRD9eLKtOCZwZ1YpHC/Anq4EmqEImWlURhrgUMWQj+bSgCpOeX1px4J+kWX5E5ooa828mazjThgAgDOJBZ/vHFrexlfGKVsetuUbxREAXIrnKRtT2fQV9jIEDkNPI7KdmoVU7glAVPocyWIuhCjYEhKYv+tK68jjr/BA6nb002nO4hjZpCck0xlobmDujIrAosOtGKJFl/H28PRGHmX9q8FIHNod/ZSnhf9HaGIBoAClL8hMvL+8k5ccJYGygL+/khxuX3zYZaZGv55cTweSpu9Co0eXVC3pQ6L+ESoNdCNEKxfLhPz5HA9xjJXXjGzhtrsqNOHEGPMezqxrXz7qv9s2/O1+roErbWxIUp//bu/gyk4y1C1ztzWfIScCtkMietp+GEEg6mQLulgOhZZFFrb2u0gruEQ2kogFeoqnRwABZnEQMYBI4CMTUMaCt/tHhzkoifJykS5nn5qjt979ka/V6XU6dX6hniTJ4pi9MyYN7dwkItzf3U5GoKaQUM1/qUW3XtTnOutYxs392manq5B03lytQFAu4nKJMV7PdLmuLSi9JdrDzO8uXv/mI5Kxsq35d6aRFsCv1YDijQ+nFgARAksJqU7/cH3dtD6NfRVEufqGOd9a7foOHT123NjRI4ePnzl/0e+zRjevHODtZiuX8koeIR12owhmnZM+/oQS6ZY8lD5/r21maX4NUVt5okXBAmxSGtp3S4LFMlbyejs+FPKJJIAErKOSBS6XMuYmx314fHnfujlDarqVxxv/JSRSuVKplMvktq4+gX4ejgph1LY6mknzh2DvDbfbdqLe2OCHciM3pVSyEVdEq0FRK5hbYQfRinmzeq2Y8nFFmJV4boKWvi4EvJ2dUQRSMmFRwwdQ+d+vH9k4f2gjD5XEpBg8bFOiMIwkdIxFydA3/kZu55DhZFfn7HquD5NzKKSSvBd5/zIbhL37vDpCRGMlb/GfAfB1WAhGmULIzCtdZYQpsrfHshgknL5G20ovSrYIPAG3xtVgz1xB2Ugk3xAeIuZp013OdrnZwjXf/64upiFsfPo+L+TwiZJ3wOX3vQFC+fTNwraBJuo30bGf/RoxcJp7ijvhrz2wvfvY1YxDb1rMKT9DkyCLakOOJS0HYEZmHmxCWInpRubRde0LdRn4IeSDShW939m1hrPURFlbOfYe4HT+zsajvz5wk//oNB/TXijWzu+qk111bhgMq6EF+p5ukkJyT0aVIqrHqj3leKIO8PMXkI5ZAWBOCtgOSxqznx1b2FRiwpYxfc+RcDOCaOKjZSG4EUpJEtLbHowOi4XyAhpiZzHJEFyDsRQgLDp2jWQMp3+2SXMoRi+Il6ILncQ2VlbWEdtjso2oXoG43UJBjj2ckk+Ksn7GX5xRx9qkVZJse8CIEBmIDnu5RHny/rxcFfPqTZ9ViyaJVLIqjwR0TXFfdPAT9kLV4euyhLX7YO2tfuIbKytJnVXRqA6Gta0cAFQuoLKuzIuqJTN1zhO5vhglPLnP/yoF0+zK1GtqjhFclbw21YbH4yQiHCulY+TCNxRPtxiPVLBlBfH3VjUL9Xawlpu8JWbogkz0aNm518atdcNfMUkOh8p6lFemT+ucW3nbdhzawR7cAAppxpfTpAzE90Redee9KqQE8DkwVAAAitT/fHFx9+R2tQJUEpO4jeDzy3de3g++gcymhLf91eKm0E42rDSLA6M4s0bolGLXDudZkGbZugzy3W8yK7HehIxcceS9EbCcgZdnMU4NKBGh//ngwMZZw7q2CLA2mXtFPEbHQAxrZQKsi2AIBdbKk/lw2jRgC6cwxubi8mNqQ8oYv5vaMSSh1dZoiug8Fb1ILtqxklZq9vutF7GZxXojCdBAPIHIs/e9rM5NeHb/6j/j6/tbm9bdwJWGvhMoQIzN1NtUN/8AZb8cIwjWwKAeURiVQ8+gjfpeHABBW+vVAKbqT8sUbET6f6oz7fTXzEK1Hs1xUX/c2bve9GlfL80Ktpab4D3ALgNeIJsV9j0cVfqnPWbfwSgsX6Ag+1ZXoDfqHfQZ9DF/IiDGjyXL5PaBix6lFhS+9NLLrz4+XfjKy+9990uv8PzVV15+z7ve+Y63v/WzPuYPfo/PecNf5Xfo+ZAjRCYEq2VBODx70wjW6n2K/p4s5KAHxRRhUSJnfRogU2+ZtcMwYIG23LUuNZxC/2WF0gLAipBIVYGRTVu2+C7f8Xv8xN//R375j/2e3/nbf9vv8iN/1a/+CT/gu37Hb/ttv823/pbf/Bt9uc9zy1/usut4AzDcHXcPwB37N6Uyl3pebZdVPdq8gcq54LugXkDUCvCd39apGFgEoxIS4gNf/yFf7Jt886/yhT/kA17/2g/8gl/1q3+Rz/lB7/+61732ta95za1//iDqHIV+iJfpdtVHfD2fWaQpOBqykRj3cWY8LLKtwu//6iGqi6g91VUe4yq8ivHLMjscFRm30ewjlh/q6LCRFUrGjmDZBnEAKzxJwWu3bUF/sfzBbf8TKvCW/mhRhRB2acIMxLzsiArZ2ODXxBSbFr9JicOQRe7QowJrSC5CAtiAfWp+k0bGlVNhXo51Sb1IEg8Z0LKqsAdepC8uO6OCV5wVVX3CYrMZiyGtugZ+Ya9x44LanXfpb/e4rExrq7J+T1z5SUrh3FtOsdqle/0Og926HzvtcBiSkEVZgOnocNrT1avpSAmqLa8WGCo8bQPO0kGyJuzve9jgYl0jsOmntATft9njMAj/WT8BLHoQmwm1iQZMutOMTTXUZWq4uqcQT9QAohD48PA4eCdEwSwxBzbrGklE7XvQlOoiScIWLIaV18QYHqHF8XawIU//z3ThMi5ZNyZjrsEsBZMGO7rYy8UNQycWDf0i4//GY7gPf80rwGDNsn/vsCcM968WHEIW0LQJVCxvd2uO+jGEdUf/a6sDFsOx86VyEHXGZos2dVwdSOCZPueG1hRadB1fOw2bgTm6gt26UFsO++/b8dibdeODbIeXkXuoumd5yv8CaaAUSF+PQcZw0bCrb7OZAcNBMxW2kXGRjPgtcYczFkNWbS3gFwdyl2iim3vi1+u5dQzLmhwwq+HI6J7FCq2qYfOzoigBqCwYhVSMoIWuyrD82O2OxSACZ5JAuMgcwri7BKtYgge5Ra8iYzSl39slwwnJ8v5D8FKuavoNjoyNFZRGiVm1a8LigB97vfEYnoO0lHAwCZajQ2HKQRjhmh8XG90cIENv93cI0XFrya79uQGw+3ElLVHxxWJYObXKNpTGlTgY9EmgNp3reLL/RCLQJ5dxonsLQ+y40IDuvodBO1aI4ahNWsFBI2Tifj88hl2dZMaXDzPervEwCO6hH2R1fPe4RKtjEp3nSjm3HGrcXKgoo9W4Pc01JBwIxWNYh3xVM8JpuR0HAUE271a2KbdVzJbS2xWnS8ThdiNnwazZ1b49q94Hk+bYvbicxWatVJT4g9XwGEqfV4XMALpc5PP9w96wAXAXBBwJ+PwUYnhhDb6NRhOJSFusI0B0RTIieaLSxx2sjcdQuD/MZ8AQDZBhyp3wnyHXAIwLEwONY9opIUHrIjoJCjVIl6JIhmNgTy90sfvq4jFkjueyAGoQIDfFEPU9TnfFTcFZIrFcLleu4bysDVEgvNj48shkDUikG1ujj92LyZDa7k1DDZplXwYoexNGWOxK4IgK9mTlIfAWWt5YbLkwEVZio/DKXOXtMpN6HzKbQrANo7+OO1HM8TQxexsSWAyJalMyO468bWoI1tuBf0rt2G6E4JOmA05ywW8rbq3KhF5VBErRCUpmpvuNG0ryG5GHZi64mKEBeZlFH3a3xGTIlyUCODxMPmqvMGcC3hd/laBjkrOPaQmt8wzlJVxVp7wCk26W2pEOR4mVXqNGyowreLu9owSPnRQinRULD4dD0qewjrQ7490yFwZKdQlXgqI4cZtQphqz5aXQs0rJdWrBq809ZQQeG9z/rZHD67EfsHHxPAqzMqNCdqNnJsa2pfGiQNdzokJwgWSesNp+IUGDKn3Fr25jIclC5T5eN1YlwWN0eKZnB+U6+e5e8lR3x6dlA9SihGUIVqi6eF0IWIIBlqbHqvINUc7j9ROcZXiMRneKoSHn7r7D7eydA/fAIctu9OA+EFCr2i57KKLADRrXkwvrSeSg4OnaKV4KPEadqwVcIbC+fwVcOMbbI4p19NVfo62p+yWlfk5VCp5+sJCWiNMFRGeoNLHfR3Qu2OjmFKg4zaWTwhcbZwQq8RjVL+ahhuIxjJsCzPPyycl5ikPHP5pMtKfEXIYxbjmGSnaEQRLRrUSyJImulNdb54Vb4zFqXMjlW2jcHZ8zXqTW8YNptdEQhoKcwkS5skZ3GhH0/K34/e4/qtngMaqd5wbynQjOZoYn/nyFQCZ4DwS9tviF0CguqaFx+DWFMdYsOxdidVP94dCfVTAZNc7lwEIDe7s4O4PC6WPy421nngonPwuLQHQXmkAabSkBs0r6odBnxwG7gYU61Z+Pbapli8eIvJgLDVI/w3nQ2NZ9YE6rZZedIrBfIjBFnTMWKM5sm24Xx2ZhAF2MlcaaHHVokmlGe4A65uS/TRzwGE1vFqLGEeP2udA8XZ+mb3nzmxquGLOEY463G8Q6Vl1OLO8qytvCxIUotFdD+d1gaJ1ov5zc1d4Zj50K1/2ZFjG6Sg98J9GAe+qCAQlweKtHhwwGxMTpkOaIKw1IhisVt2vJ9F8O7+vnjsfO/x3/0ShUjV8eMc6mGSyWp3BgQXJ8X9OpOSGCNujTZEOdwluuU1NdIC1P/86lD9zdV+2n/w5M8cFhJwBLFMviOcJg46Fyz3x73G4qRwbM94J4U1K8c9l2oM5IKJEVteDTfz74328BOAyZ/X9p0ACE9jXGtJUk48n6nEiM7xkAxkraNSGyIpeMYJHakKCAWrHxupDSSHa1xq+HDi0PkWAwVF7P8zkC3NoaHGCSEUUyza2qHF6xNzI8BKevzO1tBa+s+MpNWpO0a/IsY60nerBt1AFA3OEDG6risMseODbJ0DNDKdo21u3yTWdk3GSlOq8vsq1nlJYW6qw9MtPuyqbWdFon89++bfVsMNiYPqP0FA0B9FNg9+G/uFiLCdkfdALDMWSj0xpGxCNrz5kILkaX1O1HoQn0j9MHd0VhsFlJq67kH20wMhgYveuMJ+/b3/LmHmFxCY7NXOoM7dfvNyjrVEHfQ7OhhuRLB3d19sRgQ1peRI+VKSODSYW1xbTtEtskpiLvLPS6sMHLjmAt0kAZYtFRo9Ho1KZQWooI2l/W5Kv7d/byw1+4DfsOjUKynYmS3QnxG97pN/bxBwZDZPkCmkxPJV7FOmAhKZU4t+WCh3Fzefe2gcEE9hoSvk4P2X8YP/nDffUMYue4CxbcYQSSZTo6icco84MoM4rFwtIHSbmyY/OwCOx1FWdFq/NAgKJj/rjjTll23Uy68BR8DSBp12WbO6DbtBhWp27JW+bDXRtGRjrgLpwHvkQNNjAx5rfIBZjLwSnrWUQ39PqwemriKaFSDlxRbzDbtWcaiHoSk8BW5r3cvmpsQ2fc1R88+wcN0EpLoi1GhHH0XkG3LRuMpGYMEnh/P48THKkq2E0gAzPdjlowUlIPkZaCD//+Oa6ZO+6aa70NahbpLtSO4o4MfNz+v2WBDPaKmetAFtZ4NdKYjiHpKJmiMLhD1Q26ei0ujt27dEJrP8w1onW/84AdRGHEGduPe5RzK18MaS7KDI7pCFqBCn4gagBUe+oZdWuqqDQEBRgyTy+d1CFIirmeaGjuS84ycbkdagOG26yz40ahufVv0CNpuzs0hVSQMDb9pA2QJbahh6a0qfTXUtKp4kd/TulR3QZvEbo5EW0LDzacUGNu/Y9wPmXHKWl58Lk4l/NYTRWkOCPC84DRrtkD+ersfNN9WjezL+6asMGJQnZwHPfXgljCvHGYYxuobD1u5ZmKbBJBUL7Zap1tCVitThCmpyClniWihsmmMNEUjUjbjwSje7VzwcnknbP7NXTDW1cy7XHHyIgf7gAZMHPcbcQRubgMlQ4rnZv2PGIpVCLRIlH7kQXjSo3MnbPP7rDkABXXzSRYROUSRaj803P7NvHFWnOVz/9Q4uSsUtWMjTGQVfkAuE2fz+pI2LhyExH8vLYistoUVOmnWSzYXKIyAcObZX0bBWGtrsPR1DLdtSY2EgMj38k3LrKl19wAti4Z+DOxqAhDWlhBtUGt+gCSd41qGCrFWDOVet1jDQHA2wzC4+igsJNkETf2O3jdznqL450ck+DAba4CmU7XlIMdtMcpd6BTXAecvBU9XNgyVIGxkIe9VrNcH8idgruJxmDYBv4q0uXc1hzbWouhwAsS2LmMx3LSKiTMHvCO7KrRGL+7b5hSgrEuedDkqx4lAmSw9wyZ1ULd1i+L2dYpglMoKCSWRt84EhaCVKMjC+r+j6006/GTevJvzqltjbGw7f/TKMS6xa4Hpjf+51Nt844pc2tSI5eThMrX/SFCLaawEmPs3o72Uow1ZEM+QC0sDEXhNIKmHG7k/6jWKZqJ0QImoblMk2L1DqSVbKq9ot32nPyupjB9l1YznEoLnv8eZI2v+kMuawWInBkx7EUzQroob/3NuxdT7ZLWBWnWRbtj1TotJT0lptKI7Eqhh7r4Q02dCGzVX++jgVfYXeaNxPr+fBMKqRlu5qcoE6kX1fB0T6jDYZwtONXTnFwpCjwoISx2CQM27ziZ+2JsgAxX4dI1g0KCeRtqFSPB3DA+CB1u8ynLPmmwRmpxiBYuO+sNMFZbzGqGa9hSh03FkoyOV8oB65akz9zW0A5XUXmGDnDGSB7WIHPcbhPBQelK4GYFgzC11E6Cwg9GZQfFlMrCTbFQczV+7fkZvr/DQe15UwD1YogPrrqmX7fbnDEUHAfGBnf3JzzpfwQR1CzBod2rlUJjvGMt0rqzhV0KVp1uI6NayZuXt76JAk/hOvqrULGQ6Hbitld8AvnGxl5vxSKgbneyXm9vy9KK5e1RECvdYoy3x+Gp7yAnqi3LgoYh+cacjQYOC7dr55eHcmNnUL8BOA0N5YWwvr9gzStesrRmDaWUuuNUWy2BYzNYBWM9Bto/i3+sj8RSE8s6HdGxnB8AptPPDGuT6Fz25pZ9trHhYRpluFYZUSKlpPcPu1s/RhJ829GTNC732tFc7C/HUdhPeVLi6dCylYccJcf3z6CRcE/9EeSlxZJre4pSzyRfepE2yUeyv4+f/rTHUfhszSh312SC++VvYHCdtR6qZXg7Fs/oGXw7Szt3y+jC641wFDWPFHCsDlhXBpVrBpM1CEeGqNCusaJsSdsNsWtXrFnqrYyLH822R8JnqRLl5/lYg9MDG62lmTbs6BF8nmtc48cpUuw0mJD3u6XjCLBpp9o7xt5Pq4OZYtSBFHkFXmcuyO6lSh2zcSwCRhtL7HLcFW4uDRpspcK1uLW5Gn/6dgYgGDz9sJscN70kgeviAMKaAeGGCZNv0R06TvkyyWZ00e9lR5VUl4jMy1OTqKZGVwPZ1hbKKGJCS9S1LmiGQ4L6S1173ITzqG+6clEkdfbcNho7ckUVwtV+CTayGkPOnXsJWmH1A+iexfJqcKZsayulH+eNmXqd2yQaAHfwHhyVvYHkwWCxfKHeKpCrfm0Dxv5ri3MooC2CO1rkKmDBMeBeyYjpBLo7A528O/2dwiM1nClGc49sfcqm3vVqpwHXGynwEr4jsyi6BE4/P1wPrIYZAwNx+2a7h15eRk3DbEDN78Jbkz1lCs82f2UYy6kZvLIRyj3DSOXYThrsgZe+lC1sdj7g9HiGnXVA2Bv9QrBzTNBT9bctIAB1Txg/JggwRYASBVzyqYKz46tKrayklVps+6lFTisoiw+mio2+2GclS1O2xNbqVtaVYqXzQWqvVoMyKxzRjjV6EyJQ9vafDdyaQ1V3au5aANIdlQ58kJa6DsD6AC5M82AA88mnpA6NDn4oQig1oQABjC5iu9j2paKaRAV1pZ8NVrrMS5ujALJGw40Hsj2gThAsOI9BxwNeYRqtt4IPxrMc4vSfoGzXwqznwPB1pD1k0yF8zVe+phE0A7woVwjP0bo9qOaKn+eKk3Aa+p5faIFFURsnNz+t3/GRKRJf96k2EAooxc+Hwn9sGuduJwzlIM+dQnG7QiVUm8sWDgA78br/muOkiV3GfEOJEGifLj3mffDNa5y27MKrk9zhxZHcq/H6RB3gkXgA+KeKeQ5LvpRJOLZ5idSTqThpYv/ZKfB4AGyPP+xFY48MmAU5JBAOymjTeiVyPU8YYmLmaBzNGgop1KSrxhYWnB8fwrUORtjUW3wrA8EUXKkBzOmQC1HSahlS6K0bm4k88S4vjFQ3us7aPMSwYNiJ0+yjZM1riNV8m3O5VEPGN5bFi2ErhSy8OTQA6XIWE07E6bmSArjlA0QCjCNLefjdImADVLQPWuCjXmX3o1qUeFnj7ZxgiySCJ/JfF9eouir0Vq7wTZQT4mMq1f8rk+TvJuXd/jvKRVcUv0CGjVq7MXeEKxbi7XlK/k36rfb1DvsdJ1kz6sf+WuiOJa92PpWE6OVXexnwLve7Xl1o1PUmq/hjoAobfVPHki9MvwYs/wYwAfPEK4gCuJDCOeJzJ/+1nadEgG39wfd1aghr5RDweEao3IpH6z/ieA7MRmVgelPUy/b7ZcAlRz/cAxd1PDckwUMIwkg4y+Z6wh9jJ+dctLZrVpN0cMxDfX1MFX5HVaV+bX67k2/kayTOxIkKdbE+Kb5ilIpEzkfHfzXluGjKf7M4fZw7DOZ9cd/FFrmx/Tj16H9cHxIk410DPnDkvrfZFEDd9EUz0iPHZFoUU5R30/ekie3nhomosi9XgHUF3G1AdNTELEn3lFhln+YcjElskPYKwe0jVLi41RpTzvcV5vLGofOuphfDDAAHfZ2w3WY0iiV014jUZ1hZGxP1NjxZzBUKACAGnqXJpLbfAESk0XTqgCxWd8xihSErS1Ubx69WKDL3REkEcjCJ99BLOgomGwChs2fjY+dQ7Er5pObxCGsshKTvLR2PmJm2S4F2B/3XgEa4jBvfcra0Fe7axjKVZ8MpJ1NIbpfhNgAA3Y6AxYdDjh9XbDM06i3YVAUHdQjltJdGYWJrw/EKT9lRWmn6tRSiz93f0V3Q0sfav/nwhdH5xvJgOGiemOD6iGsBACBoMt4arsRBXbtln5l+XDqdsMjbRcKU6fqv7PtB8JuQJxByvjba/5NwsqMnIfTi1Tpg9rbzr9MowCNFQhmMdGnyIrBXS9bGrQjQP/71xUE4/5PA5foAAGGLKXiKYzEDz7SKlUrqSkPqudZls13hWn/0scQCtYES0rg0Gk5wf1RbPQ5e/MObhfF1WwzUK/U+n8kKFMEwlPfVfzVKnEz5c2vZXfKJkNZYcvZNvrDWq9isQJzZd/y4nJmy01aCfZD53s4T/sjeHXS+Ho6ejY+fa2oAXowKK8uLGssdvMI7nf5WQHIXqpw6nHYKG8ZNDYeGBKDW0ANjSn17AvsQ9LCQX0kxMLxd52nrForg8ua8WE6/uD2CXeI+OkQVfR1btYxPhiVkLs17LblZyNdcG+5q5O1azq4Y6OcHy3AP8irPizhcGSnGAIfmnX6GzrQYlF2XY+eC0hewhZyyZEloqnyjsh/96a0sDztWQgfv/6ymaMCd9kGgS6aTI/CQnEtwOz4pvNXaAfvc8nyDaC1KKKC3UO30u6u+RS5f6pQKCu/P8y4njqcKXPokm6IAV+qIZ7DHYvk4KI8p4Jv2/OlBuKfXtk+CQYDCtODicne/6e+MdCxH1Qca/pNGAQE9DVKG+VOu6uGv8lwva8wzr0qLYdc+EiSAJgKSMSnb1BFYosr6qp9DGn03JNSpFTHV8wb+DGTV9/BvDcfauUnK0z7lgP7HDYA7iZUH0FSUfjlQBKKoTPmrsgTvzMt3T2FpbAscHHKj3WGPoqMlg4rx1U+9EOUtK187lSu13Jdk4GU9s0GkTXNUzaXgr193ppsC7wwJPq9mBIAQrb//7p7sZWISXv6kvz6g3D2yKCFrcyCBEtx69Hq5ZiGEo+wEoNk/ejHeudCVMuyOBsndSaZ/x1OLZ6lLStl98Om6ZTO6+k7FSfuSBqCniYz7b3B5XMGSdjupBiwLlNHKH4Vc7CDkreRerIV1RlbV+GiARhQn7rabbpeImonlDmtnzDLsqs0GeI5tIQv8EpS5qEY5PZw2/BVAN7WIjYtiOErksDjwdbK1BONgExln5OnnXO7Ut3Sto8U2pswvr7+NGRG+PAmtlCM4QKWS7Ni0oOANtefz+IX3/JU4h3qJBlCmO8rgvkxjJTWJq6uU25rBdk2WJxkBWgk5W5LGEPWyN6TQm3ljZncXjNOxa5xsRIyUzr5YwOOGWjEbStlVe4xmQ1Hs8LrSUI5vOyYqSR9/oH453o/mWGdbipF/0dcJ5kLy+CtOMH5rCdSGqnJ8g0PLTFIo7EPgjoymoKH7ebgrUa4rEtS4lwt4258LW1bBCXW0g4vu7Ihx7iioUzEQCLgvnzlsLCiimujZ4eX7iCmh+P2dEdUWALXxEzx0i8tBro5gGOaHYxw6awBtMTX6ryPK/TVOiMCl76kyWehy0vtn0tLBpV4KbIP3EKHGFFcYyOuIFAhID/i7KwcWTwKSQva2GXZXcokryVL0eUFI+T9cKm+7u7hsykA3pwcm/FYJ25wSUm8DJWA4yZ9STwYVMXB+UmD5eayTFCJis2nXMPCxKlmCV172o2URsgrgiAG/Zpdh0YjPIFWiaNQCNDtxTQ1pwn18HMSFgRBc4I78HJRXFxTfn+lZITyx0thYwMccIsjzUgbRRoOklYbKY8lCr/eVYpq59j1NsoMBAItmHkB3pW8FOeFVWu9vA0B1wYWzBhW4FP+vWRdENEzkz+12WObqVvaLP1JMP0Zzf+t5wfHjqk/HpZdbQEW/1hwW0vCvNYJRndMQpz7CmhKVpEiHb4ZSuN1XVmFOCK/6RFcWu3CDhUoraKLxKiCf1cIwyL3nftAK9rCld9mF46lW1PD9YO2Kc5eMEveZ3/V8C0w43q43jRgOyG/r+Rxd/DT8clqIKmLySy26N/NiEf27Te0r0o9hpqi243OJP7JMX9KZMVgUN2slOlh+pM3pQM4hJ9zSKqrOfIwSSQhubyiwtozHX/yFkuy6nRqIa3AOrrwze79+rdMuS4mmj8GuRv9tTWNZxdrh0vVIyvM1rPH6Y8UYkwCJjIUtRP+2Dm65gr3viq+IoQRQVIBFIeCtLsNiBXSpltcqFS/ukWoBfaYr9ylgRLbGsoQVmtWQaavqVLRDpH6L373aXAl/WVJdMG7tt5xpDlilpoxDj2i1MOFzz35Uj6T+MNShwtWGq7c3PeqKzuBAnrGFRMtAKh6o2nuBMowyjyoTX2lBWRQI9+vBS7LoeQ9meVe851Ef/0jrnW7qIAQOs5kJV2JwnhpCgziSPY0hJcoZn5zz2+GvhwaGX3M5NaeIKUhg+wk3qCncXdVTUH0uELMFBr9cya4aODbA4AJm1mcdHxNBVDRkgQd/UlHfmHsLVhunLhaiFBIzs/0V000MxCU4dzn0vSRweDNN9R0cjs7pv/KLxQ5A9qUerhVvp4tNry86OsssYB7Q0sQITHGeE9LfDTDJeSE27d6phdzns7z/3v2lvcBAfaVlBdxulPvvKgA8C78pjzYj0Gn1LOh6jdztqsQiWDeK1kPiw6I41c2ZAd2HdRWyFlzAuBwS8DQNyDuKwhQTNRmad0leDd8nuOEQJIF/FvONdMApY7aBa0MhStS4eIkSn8mzN7a66kJ4nshiIyOk5RjN9Os2+MYHM4Mq4nFR246XDaXekfexZqNK1MYWMG0WFrljUqeOT0tDADDGE8brpaJkq1GzXeoyluT4SuNSqir2bOXI1k23E18RCdQPpletkOc7VPnjh2DeoTuHdzuOgl4dnTIfMvtzfgvCId3qi7QsAA0sgy1q93aU5sWUyhXyJe9xRi+gO45AGE5WeMzKOKbX/6CsAAiKFofgkBqCQx/A4sOiadSfxjgRFfZZ5lABg8DKWN4vVUpdDbiFeoUA48qqGITgzTr0NQUAUN0ZbJbcGgWW7xsK4xJXuO8FioyN0WcJumTLgd8MuWhB7ZjAN53oQFRQvxz2wIA6bUcTLi81deVyVoG21iewB9KB14CwhRTc6f//Z/6Jzk4V1C39D6aCMlucwfob7H/5HOZTtVDK/tb4A/tVXwSv9nuf59N/13dyr5heSdgP+aQRwPtwGA+3nW639RnVsZKkYi0620uCP76J7XQektPy0NEAlYHnKfk8P5kKNgLZCCz08dW3/+mv+SEV9obQDxUDXjDFwLgKLhQmAW+9DEeSO6PwB+EPDNBY4IJbUBdIEViIBBpgzhV0tScGYsdw8bb/cL0/vsS1YxLqo+uW1x7GpMYRuPPxzqtpUvzxdqEQGjzpMcCdfjPq/TKPint92zanKV5l6OMg7mRFsxwfycT74OsfSuyB7ZbvtIXTGJ/OrSqvqBAhS1P4rOPtEeHcf+fRr6RX7EmrbfHHZGPuw/2WbJJnViSiugnJtMqUV+PjTvC4m6jGSkc2qOH6AHg2qwI/WLx9/zsGqB2L8ZpOuBSWx86KIkrWVgxy5wX19hkgDg0vHAHqxDkhFfdFVN+QA/ebvEdOk8lHx06EtGKwCg9Uxh+4L8+Df+Pai8ab/suainy3s/Lx90gBy8eHYB3BZ5xkKLA0J2vjD2T9blkwUxRdHCyryB5Z90o+AByl5sCYECe+g7bqVIzk7DVcbkFgD4iIRRzHB9ebW5YWr16E2DS1ik/3AHooyBIMqFzQoF98lA8sPNLPg6jA/ihf8tVI0xVgLfGAOEp8gVyuQjOMNztL8UfrOiCXb8lH73zMeYWt0ivlrLlgCSZTKshQQ4V2XS7QWHC0t0+FvhqG/8N8IDhc6K63DGmaPTDe7i7DHygaPRWgxLvL37TfTjZzrdCbHn4jihjDBXM65EWg8XHW2Rnc2fj1Eh/xAKdgFbiFh59j3ZSZkG6E9EJK+EeNVd4N+BHytU67wLj79l+g5Wjbiu2MqkangKAF3oVFVcmG+TQH4P//xL6bDh4ByBhPlD0adp6IeLVYGFXedR6tc39ajd4FNFU/VkVU9EXwlAJ0i23FgNn6eFBNdfaLO71wCPKaXwxIEXDnv30aH1bBz+aSdT1FMR0QqQA1QTsn1iWXysLU6G/1xiEQPruKhdpE5G6O5sfU6tYV3Bfd5nwRyg3BntDwlGayMGdTiULOQoJFvod3SCqFHFtykxgaX+lqSJR53XL3nv1WhXPmUim8ocR1gOJ3WwIq/A1BNdxZxM5i3rYSFGyekdXgqqWK9MIUTdXd7IlFkId90grE5T4OUH/cUrXinxU+/h6JYm27dYyE9qJSWAzW2mktGgPt9W4EFvkmXoczGRbFt44/n2MCvlvM41A62uLGIXCau0Cfb72i5gcmpPhiRzyC44ovQsUB9/BP8TPe6O2nqPj0fqFHLTwJZtINCdQuzJcGhWkQoNXnWuKQMe2qjb2eiRQzYO8ahQt8ihqIBCgo7Hq+eMarkKBadM8Dnq8DdaLkPO0dVPFfEsW/iRAPQMpuosvD+oQoHKWKCgUVHY/EIH/bN/jzTpaOHe7BvNeeLfNzUcmp+IVdVcTJ0dFlZ0rAE6Gybs9wkpmAG67xe1cIMxl7OvpJf4+AVykvRubuD8cg3eBpeWVzpOFO/RwFd2Y6mYQHvOlUTKI4GHuHES8MIuIEXZjkUDXpW30wyEj1NzCW271rA+7a6K8OtjcJnhixA2mlOhjOnWPKeLD265hj/Ed8WeuCQd7qroP6KtYG81kgEEKABCdepZj9EfdavzEOXXrSPwI++HxAne5YySRUcHPq9V2A3LBPza3edMrKdSYst8EfOPY/ZzH819zn3fzkJsETaywu5izUUGVsOitLWmp4qWZPF7NAjj1w6rQ1Dubh83xzD39FoEDkP53vJDMNdeV7XaQERR2Q09C6yrQUWUQAzVglvJoqwRzIlC33fId6qkhl01B+8WVXIXAbzkXyduE4Iiqahvb1ylBTcUfo836U5dk0Aeg0z3OU1vb+aNyBfb3oYh4FWyfUHZVCtOQmBGRDDAe544JVyJxPC4JMhS/W26s3Hevg5A5tYXK6O96ACBj7xkBxhj7c6Tf6f7NqKEwE0rkvKM4yDuqOnOkMDYqD3VvA+E9DvPEKm3FLzSciAhH+hjlcWt0Zx3VteXj2lj/Y2MFUeKPHwdQyMaRNOoxpY4CLw6+v401i4dJwrIHX9LtapGocBQo27rCxHqO3SUxxfzj0DXp0l7Sk2Gjm5Rl1r77xb383V8JU0Py+lkbL9YTCYNJg3AliAFvezIIuyhRlzPTGGEiVA55AntlEKEq4PUEGO5zqddtSRXC2uDre/B++1+c2FS+CmP6ZAkiwLJQuwKVHEX6nhrlG20MyS/Hj3HDG3CLzjDSAuC7gSi7YfE/NVy+pyATfcx0Nf/c//UG342l/Qn4oDQB0A6GSL2NiIS4pXMK8soc9bTBGt+Z2CqAVZemu2nfAwJP+BGL+/W9/70d+7tsxjnLnmCL+jnihOUuQDWLsNxvg22ACT7bAGFPadfqEEBhsPlPwNAkHV4MDvBlnJtj99iTQXIIXv4QQpgPrgEw9v5w2mlxeo+13Ua0RpP6OJLAFkipztJwBAIODeG80d8IYZGzNtcdrUpzaEqAb0Ji9vI4peZBah7rF/L5zfJwiM6y6VlBczQynYeQJDdAvqIIvutZ9LwEEp22E8IRyGVgZy72B36TGaSpBlqO9V1tlSvyxUjc9hco8lsHCkK5ULajPRERmDiiFKhzugy/wW6/lcmKABlzqoVoIPMXf7Is8UsIAW5Pij/7zKCHcg+YM4Ru71hClDcafzeyxBfKpj1luymODcSH5qAdS33skZdzb+tIIJIcFF7/1DFVwId//rUSYEoiqOwRceoRrEpM4812Y7mWIDFtQ40wWs5DjKu6E5R7+US+ABhn/RclNCtI6Z6FGKcuj5TXBOaM+64MrxpSqfv8C+LnutB/Ux3HGx5tP1IPook97bbSDidn2aPywDHyiM8Ac784nC+cNyNvoiiuwrZagRQqDixmsHKUCR7gpDmgzQi+qucXXjOnjRiRF4PMv/ibGI5VRMXA7CmI+GqtxjM+Fk93DUenj7LDFNDOgrg54bkMdWcaWQORgC+1HWyq7cAsDnVzysOQBw4qaElNTpaBDCofL8TD/8JkKnd4FkxjoxfC5rgJTUGloQan/IsSON/ESuOFcOoeZW/GxEWhbi4v2B5icHf4uA/P4mT7gwKiguAQNIKndWfOCi7aYol/e8SgpTBjA8HEJs1/Aheg8eyq/Lw4yXdGLNkqTUzJ4jy3iU7L1757qzI0FCFf6JgWmIGTZd24PBsjQmXVF4CD1sGaY6uMpOEfX9sUtZGaP7tUCF4np8ck5WiFg7muBWZ0nrzDsVcQNGTtFiideqmG32A4K2K4KAEyFmnMonMpmEmSQy9MamqaSt1QzRTWplhvQnWwZpiiu+PgkK8a09RLWhpZpn7TBFN2AiwUMfy71eJbXsxUsGHWECET58OlfWDy1b9SZ3lITROQaI9Nv0H2QLSN3iAE5yZwZBeSe8ccSf0kUO1I5SkQR37zob4pO2CKabqc4CkdOBfPE5rN7rdMdt16JJXBolKTjGRXAdLsdz/OVaurtQLhdX/XM1BkYbrd8XEdO5c4OlpiiZXH7o+U2yzm8nXGQZC3k06kyHIGy1t8UxDsBGuOBOHwm49TZ9RBorampv305NHO63ZFgUTGivlzXJFXilXa/UCY5PlKJc74peKhEpPh4RwJDQPiNSaGRwdszjCeGCO0j0eNz0z72RC0Bk2r8OcHOJBULsj7Xy8r8sGSDmZzoKznUKS2pq8JwRFfW+SSfYqG7Lainr+S2hbQ90FBmX/aUmqYqpAPvCYlagI0rVzBix0N+mGyHIwjbahAgPirTbzxOYnybiCbmNv1PRbIKS7HmYpSpeqivUS9NvE+AC91xRC1B2zkvAGCUZaK/iVlcyURhPf69ic9P9foGGGII0exiDvcGSRkWvIzocinsqvGq7iGuYGWKD3QwVUc47abECJMTp5vTM+XH+AD88JLarfvB9GzWpi5smxcgSRhkEyEPJw23IZwqIHait8mqTzUj1jTB7IuepwH3W9vhiKv5FZDMghMKjYBrKD0tyDU8e1eBJz9VT8DBlgqTxbQvpmnvLYcFnjZAINwULsEP3TqnuZfRAKAUHOCcJyyfCU95h70ZvjUxXV+j4zj1Iw3K36Ly8Vdcx4jq07q74Yeu/4QMaBSU7dodHRu2Dd8WoK/7BeNSk9r9AsW7A2QmC+dpH8t8zZ9grjjPvAW2wldhNtgBRfczlNAARyDT7ZrouYARLnZdAL0lXxO9q0nHNRpud2w3y+66+CGOhMnCbSa/UcQzLH4EwjpIjeHz0X4SW8YJJxl2IGhlJkACIJURzFl/g2OONs+bbtHxdjydf+aunfy7VUxYmeA+N1Yg/KOv5jHk5vntWpI3Kn65EjvMlRh2m1locgFgApb3C8tC0j7Tcj+9Je5wMmG7+ivN/SbU9ix4FjsFCxZ7HO9a9K8GybADYQ8MULdF8222v5gKLi0udmP5oGIeqT5Dsw23ukusTBmxpSuAAth267ydeaxyzlbHD3NZkwiEdPPjoydn19nKw+1a+2Mp51DaU/yHjZcaO29/qEn7cU2mf+BruH6jy4cru8/jxK3uuAF51Y9qGuLO6H6NOBMlznCst1vi0OzaOHqf7sStcDNpTHnLdCYkp3BHhU1Bgu1iHR2aOgLeL8QNUxMOswBdCGp8SbcVJuY6XqGQtztvUfvQqQw8mWhvynCb8oblfqi2bkSNrr+UuJVVYpQ2BDycIMcN/6JqfIUtxsC73bkqOV0Ysg+dwqhjXeSmDPfp72lQfl2N807ysR7y2kApZqDWOm6H5fF21je3aV/EasgHl9hqT/ID6stlWJ7cBcFWJq1nZgz/fYGjK6W5Iwnz2BZO1mWAHb0jMF7FDbiNTWS5pTe1sAISlc1+2AuD6m56S5nkZto8dM5XWAnG7asB5vRUe79omO7SALyApM1+I7f3Doo1gwV9lK4qF61UgfwSWk6I3vNs2IaC2VNi7GgX08a8eDTLAs6CMMuOYWDHsGBxi8/3k2AFPFYmIEQI0+fTIutREco7R286M/DEh8f/vfT+xWBnk4bLrz/ghuXhXRA0P8mCpfwis2dxTfmn+2AFJJ3uAhRYMw7xkbFmgSjWGNx96HKe/P8gpgy9v9TN3qTh/OtPGvDwFtRTpF48iw66LkQolOAm+3gvnIDE8UIW/6X6eJA6kpAV8O+Xt93NTdu3YzvN+AIBoAjwDsJGbD5ePVuHNu1AZ5yAw5AUo+B1EuzdIlFbdkhDTlEEhR5tOg6g1hCz7EIvVteRmTQcp30uJ/YPcVvGqPT61M4oAiNUEQy+UCRA6XpP/2cNJ+dXkZi2RfO0mPJhZveOaTsmT9LWZvgAwrN/FsURBUwG5NZwKV3gxQLeFwGGSYFWpo2pMQKXpBAE2XE8PYWpHeuIS0zc2AAfIGt5mOnoADyGY1YHbMtSy+ihl5FqFGDtZDZ+64DY5EkJ/eI244FmqLeJ45dPvAxrTANuLl6MoTiYm7nkiV9ZAyNcrv63AlahyuXhCrPnLJPqon2kmvUfCCdqSiVjxcWavGZ2QhWbOmwnf+S1OBGd78+ElbPdxcUvCcYH13gZcZPiXBc4MtzvU5IUlwYVmz6I7oY3qnCgl2nDeuIHLodBoz1LttIdej3T3Yo+zfPBBkRsS4J7N8aIQhiBdrcLyEIEmDvhP8TLsABUdmdXE3erXWPfoa7Klat1SOxCBiq4Sxe34cUvbrhgGuXYR0Z+RD+zAFaZnwk/oZQRCklgjdZcKNi3lJzVsA3KUKPxe1N7U7dN8gLRekAg0zuzp7mgguM154xLITwY5YALKkb7nslALV8ID8MRNdGwZFKEIefypMcy6F9VV5q4S333v0cDxLxlQdhnY0ZAxXFZ2bW2z24NUuGCZ6sflQlzXYRYsI4xEuYRGbrjsu6Dx9gF231kpu6syVNMkD2SStLh8+OXVWS/cqGnDA9gXee5oSJVhbNvx3i7OyCaj92sTV1dtuZ7QLnwFUhvN0znudZ0bxsJHvis8qQ8imtRbOwfMAATKDCzACBXqhqzYpWxURinftFjbVypNhYfFKAg+Wiwybu4esMtRqYJWdkvbAb01w2CVS7Vqbhv39SEwALYtDsJuJyTcUjl0E4zrz7TBGTeGEfpLBn5rL+BsR19CMnJV6dexZc5B50ogHXPppu8rlXddQYmTM8RxKRQGIlBJjHH2jwr8SBY4Dcvr4MFIPznZnG6NtbzPMa+UhndeguYzxutuTO+B44lmfvqmD5vrb1Sz3Irfou98vPGrEFGKwhCZXE/c04VPHAO3KCryO66XEQIFNHuslkb6E/0lwjOHX88xcEEVixdWCY/nVPMiievwurko4d644GfQWlbNno8gB5V9NALR+g3Syo5tBqc6rBKxC9x/8m4QQ/dKjKW1ZCYPkJmF6Kal1c3H4KJQFCN8wxN//T+d+0dsACNLuhBqUeyvJJDA+jdNMcHBVK5Xe6WN/JadxcT6K2BU/NoXq6zYSQFJpOC9QyNKCduw99qpMICQ/o/ollezPRjuFfrmXbDBBJYxzBK7SAJPME/0e/yc0GoKazS4T8xF80nAIqEVtK5Y4QMasxc4jz/o9VlOADpnPdIhSHTWPtTPDNnJWsFPArGUkbaVEwW1jCzRHssO57gzIcjp8vzV483UZhCd/UZk8l/YZmulpqvvAaPRDYKvvn5+359ZQIHdGWb4gDLLWGloBC0TwvsMIRWUXYXMCpU5V1dIGjVrreXPqm5o0n0V+9RaYLtSTVXZfuTLJO0UZXKs/f+HD8sgOJkOsTt4Zz8q4rvmbdXPuKX2chMIv7jk0s9CLVU9TyBcgS3veYo59r3vemHe1rhAKwv58C8EsGJJ87qkZJYsxbiqsFWG5ynM+/5n7/lq5lCX5XI7OsvyjDV5xh+8ndywQKoruWySkUOjA8VOSiFBak0gy7IP5WRGYsbCUaFknx9L4AQ6ioFPH/DP/9V3/K1phCpV/3xhwuRzVlmubBFucf+rg//BvZ44JJ+l7JhcK4h2oevc6bO4CEwys0Ut9fTGJ6/501/+8d+udfcxKegbVvOOfbJiOpKKK6It0TxeGCFTYezrPTt//Er2+ABjqSyAkQoDjZwLDbwnvrTKAteLXMyjfN4/ef58r/hv7zhpfiU5GHmklzCGPNaD+BD9hUPPHDTfNKlMVwOCfR1goEx9pChIlYJfqKCp+Jb3vzecszzzrx6zhLCJC6fv8DX+k6/6W99+FvVxNiG9FD0EcHMhRNZmtTUfXaY4Eaqhj/lXldUjoJKXKIWZDmsvX0ahZX3+Rhd2/VmzP20oV8VWxPppw5f/Tt/31/2R/7lp+1fUWdIPRl0h6gBS1yvkOABml4FKGUVznyPKCpnJQMQkvPYcfT3Txq6orGLT2U/2zGuir2pLAWkvt/iB/+YX/jH/uMb2bOuRJQ5LLfDCKUA5ERSsb9KCTxA5WN6jtICrMeWQXFOFYKxPyY9hJg3EbiVnPXwPGF1tGA4VEr77czsRrYm9CqQVb/tD/k5v/2ffPIrD407VbCm9iiYhceQrHQew9uRmKBr5bSjiMtRD5N6DEsEqPJ4KTg6kwp71Gt50m+DjVbDcNqu+T6/pkk9nOlW/zv9sF/zH9/ybO8QQDCDxhr5xMumoovvtSMwAfJF30pcWNgHnx+ETSXCETN1ic3qbtvnN9tCfT0wwt+krvVIlPVa/4jf9mHP3db2xzFB+Sd07Cm0I+tMbStMgGTQRZ4+CyPgYOAREw86614w/ffCG1Uct6JXTU/TesElpWfUyN/zH94ppmj5OIKhQgxhPKuJLZ1bFwUAl+i0g/jg2cMbbYcu8Tmmc6YdAchiUe6AvyOVWtuit3un1XSWmdjqVU41+v71L9+4tnHu5drTbAbPHwolf//HDR88nOQiIxPAAAwDTfUkOUL34bjU6wTPwc04V5k2uRlAA31ezLXfG5ve62qq/NrMPv8pz73DjbGzJDNgLUvh7CzicIrj5NMKO2yA48S8Et9khwpcwmV0xFvngCvE1I0V93DIcBsyd2XopK0zpN8fF25tgk8gcqrZ/8iP9xH1fZiaFDcM7QlCBQQAm5ez5dgAWfeXcB/n8lbUBAeA9ATd/Roja4lPxxv5c3Wkab58um14v825xsdpVKN1ACDPQHtgDYcYLZBoWcDFHfi8FdAHe5FYYYMR620QZFHuzfSwd5Rt05mKXRICc3O/781ulO7RcDeJKUbq03rBAwOSKRFdtg/WS+QN100M3uY6ac2x9oQVNmh8hhsA24UBQijIeAPu7SFciiHVFlRJixV0nVYlXPULJlErnI4YoxdUN8nYR048lgZoK9rRS/9efk1WBLySmLO9vhU+wK5JDgkFnLiTjDvf5aSbV3pvcsyu5F8aV8kEjyT167XtMymw4xDPVUOPXFHP7BaHloiff4VjBGQhHwwlLsm1JjcLZocFhNM9HH1SfrKLvf1TT3U0wTtgrGsveKijgTC+4SYZZ7MSPAd7pxd8medphREalxX5qLtqAInxGCA/k88o1ECbccP+v0J/QMGLajamtmsbPPxKOsOEO0dk1pzuHrqkuj/SHidg1zW1xCEBKyAeCdOYHhk4Pw9G+njIQLiiLzq+4W+GnB11rU3rS+7Vcn+clqY5nfM4b3CjruwBpxzyZFclTkBe+Yuh1EkRWHfU46aaCMZcSyrB6fh0B0dCfp5TQ2ZS9744N5r9sZCC23G6dy0PAFcwVIAtGnDqUW9tJsUKz+tnczUDEj5IKwwoDWPUp1Ou2V/xUdh3hu+Wh6aL70zyJUxo1yZ07Dk1WWpCbndMhwPckK4QMlZ1KR9RTdbimoQVTmiI3z7wRB2WyjWDFaPu85kXbMbt/6EH1wfJTejy2L3d7ix+PogKScLhIfXgpPuWMCnYCi80Vc9SKLFhbBgbBdE+qW5CM3AjX0je08b8G61N6M0DN1j0FZTFlrB7ZDaUFGuC6lA/7+qMGXBe+xPmtIzTzUJpbK7KhoAn+t1+28m4dQpTuaUndRt+vpCHEceJTUaN9tyASCKAHhqAkw1VmAHpsFslbsl21Tn4E20IXJsqwgAE5eCXh1cxN+dYbYkKnkWYxn9FSOR113+mOPPfTNJ3hJVTJFt2NCjDmnCpFWZo6m8yMgAA2XOx9la07Qg2BCSBci43P8b8yX4Sk4jMdsSNPEGyOKSpFFaOaNnolg3Yao35k3wJ3IDHzCLEgmJl4KX0U8nb3stT+3a/idI03o2I7/Z4qrwtrzaFRgwvgKBNZD0dF1aoKtjtOQIgBKCfNNKDfrLLtOsg34BGZfxezST6ZKUBT/NLTctp6bDfajoxeLBz8dg0A3n3/JXYAUntPxEX7CwhmXMqgaEAb29Ik2uTHSChmZ6hk0S3WHOskynsVQUv+mkQPjsdpynP1qjCrVYCkrfbSbEDVp4DDBSK707/bZ9FsTeb8Sen+VtnSFTJgmZKsgMrfk3oLPqZ/Te/OJvAI2zO9ffnUTzzE9cCG8KYydsOYmqB/sMsOYEfsGuUaeRwVC6szw0298sktFLYKDkM4FTH4ml47FVnbKxhAq/x4tf5tgYg2XCi4LHWzLcjXxO0Q1SXAF0SXHT+3d4SK/yArPILHc1RsB4VIHfPec6o7bJz1HUe/9borww0eSs+Cucaoz8aUG2IiN1jBLC+7rNN3e/3pyPlSD0rHNE4zsrhVaAwjLVFYaJcmeAG/WyRWRCiYAJSdtmaus9cPJqtKABltLyLBA+FtARpFdVqX/9qhyVQNIgzlro3tycLi3PKZQoBzLn7Lh9u/s9A0N6uZur+hYdvpwNk+XeBaHb9J1ZoX/Ybr/SXYglk3o8L2V6KNbA8Ug6YfM8VbfRtp3HWazl5r6kv401bL2HjFjTkOtRiQLA8NpCrNWKDAdEcOsWiacve0dgKS0Codv6kSwAct0YcvE3T3ImKnmjxa4Bkr11lcIMmsGogKtJ2Sk1aSygdKk94wSrnECzZjck4YsKxw6URrC1AVPNpfiAKuOC+IQHbn9PzbQ6Yc+9rRBVOfE0ST3S9XycTJTky8u5Ym7aORBk683MZ5GdjFeKlCTAPIYajAa4NssUVVDtHwcoDLzlBDHsV2fM+TX96EVDHustNG5KIxWkmIXvY/VVT1L/NJbgCl78zEMtCWkeerduJvsH/s6lp+vTqpu6CL9VX5COVe7PDnVZ8GcS6i0Nwa3MvStHInBZihStQzn6L4sjg7qvOIyl3V/mVVEr0dhrB1ucaz1LRRrcdmmPM7+Nq4qixqphPhnKWJSM/vqMTvlTh027O2AJJj9MohSXOhmBQkByv0+2y7cFYyVCPLiYlkOzm6/pN0n5FNEq3OIAwcW+rNFwZ6iQZv14EtJCRUyvxYF0FtsCqxjqKj/9S2EwA7Q1nKZ/kv1TfyWombldXxCo9QHMUvCCTzRFWLfLpQprDSCSkyPnBBL7AaVIe8kbmjfrL2T4dTzJ+biI1bYT/iQT2yQamo4TxZzcb5hbRkNvGyQpfIOv6hMtvZ8XkQKGEgdkqGaVNomvyQZEVybj6k7XQhYw2CtNG2HIDbfKbrOteSowBUXsDvJAD43hYIRnIOt0KoCf+La+jtYl7JIhFGh5LrVOCAtIEYLhXTb0QVd9XW0swBla+I41wHn/lzPGai2E6T+ban5Jv+MVPUVcTN6ug+TmcdmO63SHaggCd8OWqNfMpG8b4djDWeFnZNoYPIN0qXqgy6DBIkeVCzvNqcZkxxhdqetqbNgJmJrJzjoNHBmNvUQER9i5eMgMldMG1OlZYA2nAA3hQIc+wMzBUkIodjCr1TGE2PKTJcP3agSbuAZHdRrwTKCd9xgmCkTr605+OeAPCYR56CQPT/oLu0VQ3Ak/uu7UDTNyBTZtuN4XyKVCTdsbhbNbJIeb6ICnewMq6pQ5s3gmwEdymwhPy++n6mrhVIFnT/aQA1gNrKirabIKyBySzOE/OziZWmAOpd5xODSvpJFszT2fnpdWg7b7jei9K49ZirY7XaCbqHqbu6sI1/9JRAMWQTC2120w2WrbOpz5mokZkEBS9/jUYd0AoTud4p8lwrplhZ0ZTO5cnIawmt52pO0srcFJRCQARsoFCNphTvGRF7jem0Hisj5sV9miGfrZOMFgwJAPeFjHsxHvgLbaJxMRRqXsmieZCaeaxPNed3CHQLCppQR0V/iD49nvru0Tr2LeRoMJ/kn7W1XWT9/yMzm2SjQhAr624OPv+m+PMJUVtuL8/N9CPwB/Ybv6km32UATXLvrp0Vb6lxYNwKMLkfUVzw29GdPs9cnZOylVY9HmrWrhY4Q8kQ//1w5Dqoe39H56w2CWcg3egism704yIh1oU+x0Mj4mmDc0UGm8ADpEenQPtiMnrAFTBpwlVrTEIVhF/5JVSMIPtjTgt25P2x1KeqU6YvCe42llIIbgCmkAlFEbqIUQzN+qzgiHiydRLPb2kOATVT/nIrc+OQce2oaon7rnFm3UIk7e3pV8KJ2ceJzo2e8itFL5d18LJCodAfJ3fPj5yiWb/qHM1eJpEWapp7APzfquXeMafXAhLA2xR7r9b3+StBCkiP+kgNhPQCUepPUAbQG1mqaKfV1ZWtcEiWH2+H/D/7GGfbte7vmoUcBe8JQ5wN31fTH8rTzB/at+fTUg4qid/ep6WDmRAG2OOLfVQ4BFe9xV/76vefDPdrvtcWljBnRDtVpNXUZCw/jeRZ1E5SSAYpgGEIecych24FcEUEYjiF9tn2UvxCO/3IV/js58nwy5EpkrsvU0q+tWSnu4nfAmkAAuabXUbxEwxfRt/k18ButRR+BM0nTG211+q7l02Upx756+h2ITXvP8f+PR53qNku+ExG1Vh0EE3oKDqPzWwocxus8GJKJNH51skss3EgIakbahUFa9//o0FPfEJr/sZ/7e2FcKt49vnmu6Ft++bXEwddc/oaOHHhd54QUeANe55RdobM9rY4hJe9yG//9P3vr6644Hq0x/d8x6mjpADhSjeIgN4oNlQvrs9lKKAoLEQVmK8/UsdlQSToPR9Uci/dORwu/ByY3FRC6lwoaW+LRVzI/5J2mzq7tXY899sllexG72s89HoH4VO8tnRpSC1+dhQt8dXVhCYBMemGgo1KAAnrk3G24b3RwpfuclM3Dc0r0/mpLPWsPexBudA3hnjKcUleI/njBbAJ3qYTB3bsJHujjeyqKaJu8Exh6WxQpSV1A9YgwnOtAcjT+aHMdrJCpeMWesiLcab1ZVN26qQvMshtSDDmh9KKDjSISxUuXCV98ba4RKkjV4DVuUOth/DPy+r+iVyf0w7zBbXKq634diA8f0xewTuqbGLvt9UadquAFT5ly8CZArs/PqjbS/aFTbDwwnWuARZiwRm6ABoUEHgW5a5mCEP7lZkxQf2ib6umZHQte5IFZ063NPEjTj6k0CZgjtWAWpVi0mIS8C4Q0ta8mSKCpsQlcqrIBUKLBFH/t3yZlhTz7T1+k39zsu15uMvCSaK+eh0Q5KJgdmCF7PwCS1TysNJExbg7nm71d+0TRw8L50J1JE6/8golhNTDo3HIUIH1f96HjbpkdR/jrBiANiRwJZxop911ygRtpcAxRpa23ooZXk/nOPv+7TctPVW/7OACZfx5QJcw09DHIstSaMX2+ASrEI3wQoYwdYo78I3/dlupuzkBaL+Jg0LqL95BoeCq0GI5goyiYUKfbFrbLEJvjO4nBbw53IfBrxfaMo2AiVt9hlQaN3jopBrhqk2Is9QIYeoOCtJ/zpgE7zHc5emIrnJ+M/NlNUT7HmaKutFLk2QjALQLivzPxdsgv88Wpw3mpvBpuxLXPqdN9XL3Ozj7iYSK1ZQOCCM/wAA8NcFnQEq9gStAz5tNJZHpCMxqqZS6mIwDYlN3jRQgSHNwzlfjdZleoW0Bzcs49oXwbrF+TWir5Gc85ZR/i6xuLfbP8z/R/vJ/ifef4z7Z/eP4D/M/8f/C/ul80vALsf/1+jt53/If+D/Lf6/9r/mX/2/W//Qv+D/8vz/+g/9e/+9/kf9f+0f1Y/9vr4/3H/m9T37cfuN7uP/W/cT3q/1//ofuD/tfkJ/on+c/+f/D9un//+7z/qP/N/+P/P8EP9W/4H//9ef92f+b8sf9e/5/7if+H5H/6N/kv/x/qf+N8AH/39qj+Af+b2Ev4B12/4yfqR88/j/9b/1PyZ/ez+ve8/5P7uv8196de3wLvmHMrXL/wf/e9hD+j/5v9mOgP9lewT/Lv7r1df3a//PuI/qx/6itxiugeLRttd1374l1b/YG+wN9gb7A32BvsDfYG0y5y0Asfu6MV0YroxXRiujFdGK6MV0YroxXRiujAKJ18mAAjeLTv2BvsDfYG+wN9gb64h4Arn3fORfGaY+6S47nz5dxU1V6wnQLNCUYroxXRiujFdGK6MV0YroxXRiujFdGJ+zLqzadE0Axb7A32BvsDfYG+wN78CNlFdoaJACufzxXMMCoN3dQhTrBQoaXUYl7ujFdGK6MV0YroxXRiujFdGK6MV0YrovI9dc8tuqvi7c8xpi1tvgiiUYroxXRiujFdA4dzlKHMvK2uiNCwUJ87zEdzh+RTHAPPw++FVWPLTmSem71N3qbvU3epu9Td6m71N3qbvU3epu7bsM5JmywSJtLr6svaD55VFVPv2BvsDfYG+wN9bOtLnuRUNNFTgGajVGRs/s8/4xGQYhrIeOJOBrotyBm8vA32BvsDfYG+wN9gb7A32BvsDfYG+wN9alIjxBmPASBRJJcQNIGxAM+xvzoJNT79gb7A32BvsDXhgp7Sjl/fiEYnkx/KrBDyifLCx7ZeEi2wBx9cWeSCiQ9Eh6JD0SHokPRIeiQ9Eh6JD0SHoi6ebV1pro53km6m3+bplAdQ8hRIeiQ9Eh6JDz/0PLakMdWQ12RMWhVLbJOHaCXaef/rw2u/AWcpseBFkq4SF8OqMPZ008IquYLT8+6xi13gv37sxQdrarx8dc10YroxXRiujFdGK6MV0YroxXRiujFdF5GK2VFxRAt6wySyqxT96FDbdGW1Xw9wRRKMV0YrovAgqQDCbvvE9GkF/UOSmbT3BJu8yozcekPIBAumtBXFzi9AAx/zClG3T4Tgqi8b8jmXiw1DKUAy7juAcY3jsueQHaD79gb7A32BvsDfYG+wN9gb7A32BvsBVnOq+6ASzcZMJhsY4YVSVoaE4/87AXyD/fBXyynNTKcOaW9Td6m71N3WiBEW7HgU+oRrsaAYIEakvTMF1CkaEVmrqkfSsLd0b5XdEEbifs9fMh6G2P4EfBLgeZmj+iN+WlYwCEY3mYi020fYiq7DSdkHCgPFEag5H0SHokPRIeiQ9Eh6JD0SHokPRIeiQ8FwGxr9RIGipFqZ6NxQygvuFTOj9jAmdYoNkmUBxsZf5BrjJnEccaiqSiUlEpKJFJgY5/MTjfL+NY/Q3PJHZKmCXOZn79EbXBaTVbmSl4yzWKyv/M6uppDh7O0MTbtNF2b0AUmhx5e2nry+76GrH0hlVdijoMo8kMLBd0g+5SUSkolJRKSiUlEpKJSUSkolJRKSiSAZJkmEGrspqV/f280Po3insPkklw7dOV+/f4UvtJshzlLnfrGV9K5+wN9gb7A3wFddrg4UDVLb99KEoxt8IZr3JRg5Xll88cQZ10A/VefJ/n0+z5wwMqqJ8g+wpwwuu0KxChw39VTbnle+u79rZfVAoW8erScfbVjAEkGdV9e5hauC66Ajyki+kkPOmCPokPRIeiQ9Eh6JD0SHokPRIeiQ9EhGLsxURICyjQNTu4s0EdxK3WhV0V77kaAsazOp1zydDmQXAHe7XUrE0QUSHokPRDHo4HoQ5ZKiShJPMhLRZo7XwJzmik/e0gKg6CmKi4TaPEwiv4nypowrf/sbNoVZhskW73aX3tk+B7vh9r8PP9wLv05QvfRsFOvmsnj+lvO3BEPvUq1pILTx8D5I1KffsDfYG+wN9gb7A32BvsDfYG+wNoNshwBhTpaXlI54r3yl5k8KdWdMQ9vL2/iCpl4VnKYIMJxqS2uiC7W8QUSHokJYMC3g4rvMhTaqO1sozVrsovPnRCoLEfyZVxyJFJyogUBs8x5x8MkpUEPmdb+OmK7qkn7gSOzKHlVmjjXxZklFc8hYuwuHGUtSTuUbKD/oKlp1pD3pN/B6aW3bFiW/iOO/ny7ZD0SHokPRIeiQ9Eh6JD0SHokPRE9g1Eiw/LG9QANTpd9St+ajZs1TMBKoi2p6hTrV7zN1pVy1fuHmuBCHhgPA32BvsBu3JJG3v8GOk5Me/fLKjpMopbyp4PId0Z/4YXCYM3UIngwLddQMjuli1fTaFAnvmIaEsP7RwET/FW8U9nCSMXRW6UEqyKZiQ2mnCZ77RPs3Qfn+nCfOGrMIo4N/NdVGqIzsIlt+hCYgvHaoIETs032KMKVNQf5oOxmlTl9Eh6JD0SHokPRIeiQ9Eh6JD0SHdpYoJLE7DMocFVRmA7v0/lDm9C7OzQueHayQWcjG7fkF7KPqJPjcDk1/kbzQZolJRKSV85bscaepS/cwr7KKGsX/7JXucSp+IFed+GnHPBlGHtFhqjEyLey9t1RaalTZOuGd9Do4elSsoybbIG5YS8IvJ9Zm1u4D5JuAp7GuPXKnvaPxU+6IoZb/WJxcJO2gmh5AObbH0TY5pda0BGa7i74EZklZbRQKKN6z7TKZwGBJrL79gb7A32BvsDfYG+wN9gb7A3v0K6I2riUD1AfJmkkhN9n+5KiKQmYqBe7lCUB4oaWe1kinW55WzktbwMP4YfCkDcU5u9TJp4KcLBvlhjFspQ6HRqHL4EU96rKTn579/xqBhVmiWdEuWeBzF6lXoRTFYKAQSRT5YwO0EBUUF42+jqp8f/+PtXm8bgqz8qAzHUxoH4tVU6D5tOO0oQ5f3sA0Q5J5Z4QmIx5WlqcHMUfpkv1Oa4y/j4QJ2SRzYIRJ69Ff2GCQ7SOuxu/6hQwGc0QUSHokPRIeiQ9Eh6JD0SHokJi/LIh2hTRanGzWeihUXXvdq9VumqupYZSQFiXYCR+ogNHwOTfwEt8MYbLVXP2cefCtP2veiQ8+zek9Ogv6JdGIAsX778i5IohtL8mKU0nV02HWoFZbVdAx2Wn4oc6o/rOkMyGTPWRutGvWs6ba+xX6eZv42m83/F1N/aXz9jeDw/4Xcv4a8d358gt5wA16dKKN/VKqd0jDlRPwgU4u/b+lST2CxniASyZdLcF0bPxe7To9HQQcBKl/duemXOorah1/7YOTgHm71N3qbvU3epu9Td6m71N3pmTT2nZvMwB+Mx0Jugyn0PttLQNQhrKrZVJmwpzpwPanZ6roydcDBpmuoWJMHFLEFlbOkDVmnxdlmi8tIE5LED1uEH2Pt7UVcq0T/+dtXLgi8QFukrXepWUE9ashHOgQyPFnRqJpS+1+2UIU2D0POj0KVp0YlFabpJTqAgK5Pp/brQQyT1jG8dnhbTzCw/14iEfsQZmCo2tIz0NtRuc8SpdYZ1SyBBFMC8ihgn/AQGmIdKw5hSltCEKkJGCdLPrK24kLcZ0Gp1nRfsDfYG+wN9gb7A32BvsDfYGuWT/lZshhMrJx+JK5NaH++Tf7AlNxOfs8MyLcCUxgBNckHj8418WYz6Mle4Eo9pk7lGkAyfOd4eOTEMDI6H7+jdTE0vq7eg0ObbY9wIhr5D69blw+YFrNez29kSLSODEWArTJbQMwV40OOlvTDaIR2Z3hF3SPahAQ3is8pK2EFErsAmf6PWRUe/+2Q6mOQr4EfwkFqZI5YFsKcrpYIVjB5AZ+no5oM5GcPWsrlj3+8pS8xmge0iLv1kCZQEpT23n1Ck07pPKAO30iWglEpKJSUSkolJRKSiUlEpKGjc0BHSd3o/gQ7tQArH1qZBlGAh67+AAmIXxYUu6tQxSRflCnchGh4py/tzS64jnexpXdTaPTPfUmCVaDpTppDtVD7j3K433Mz0tQNhmInNEDUt6NaZYH167or8QfY/KZfn5Svz/EYEhnbK46oy3PUvEgYLAMP+gklzjV2vPXnqgZSzX4HcSpGL48hohsw3uxBB0zogk/uiyeXjrLlb+RNCu9o8FnaWL9AMaKZf9j15rK/6ckH31ws2B7ICqzHLYv4BcJ3vRImcI3uFEOp6yNmFlhTtSUSkolJRKSiUlEpKJSUSkoc1StVv3idD0qyy4DKFUa4IJUmzUDVg7B11MFfwoAtRX412+uCyeVhGJQSXQtZ2h9OhXGPDH2FyDHskf/8mGVwH02kQn8OsOE0m9UJvjCUgazQrs6ecuRQMuFb/fqth75ldmZdvYrTNWcP3jpxqSW4gahK64tVDq2X9FsWLxHLquENJhyw8eM7A/YzL4J4j9A21gtECGMm7teUyNsgQH+rKCGtu2ZWVVH1swjKfjzppQHLcxf+Qk5vEjejkhtQ8n4aUzoFga1FTBiBq6XG00CfJLPQduwN9gb7A32BvsDfYG+wN9ga5J/7vBba9tgvSZIu5EHevANXxJkYIlYKo7IOm1UmggKupawyEfolm5RCCgq7Ki6LNltZG3Wp1Er5xpRZtGD1TLAfyQpZPLKCMlXnGX6D2jYrctJhr02NG31XQs/JjfZITVxbvAxUJ7AVUpD7h7KNG1VvG30XmpzBB/4lTCKSc7+c1sX3FqzKbzW2yXHPbsYGTeipitsaiLhbY1PoM7N0YjpjjIuSwq4G33xOxcOpc3hCxqoG4ZmN29EudJleowf85EZEcumSZMrUEllESLmv11ADbksuz6Z7Eu0eFhsaycWR+dMqL+1kou2LuacSmg2vcxjHpXdWCUYroxXRiujFdGK6MVv9J/tOKcRfihdbqFEqajWk0g1alzYcnvcscgBKZh+h9JK74wdDIkPWbd4pFvZhMWj0XJVN43OaEGnEmWXlloCW7o4ONh5lh9MRQmuYa7GE2dAjALJo3Navkj4tMs8nY1vciAvf+rl20Z3V597NE899+T14V4fOJebY68kUbFC+pCKTG6ml1ysFxQchfnZgq9qafgKY3hSkUbBC+YqINn5iejCESZSVfT0WJElj6Z2QbWsuNOehSlEDoJk6ykLkzt+oIYQctpSWs8DGV5xbHDohUPT0O8mhw5G2L/Hj2X/8hys23tF9o8a1D9HTLAquoRkdkigPfmwcihQn8CW1vEFEh6JD0SHokPRIefUyGwlur3z4SdF2F2iwb9yE4vPBX9JJsM30H3m0zXSMhRNkF0XXeDq0XIbhdR8ICLNrghhyOR5LRH02cHEQfZm8F61eGnIvdmBVfl3LbUIP6sh1fEHcqQ8YCK4CGqm9IVLYDHUnD1RNr1meeLtS7FMOL33iG4/sfQ+jk+J5YjOq1IotJrga5Lj88w/KiMn0Kk/jiFbQ3h47Tm3dQbrmAlyAA3dp/c7bm5MPOfyDvoh7I0qgG6f7Lx5eBzfI9TylMC+VIa5vVdvwBVC9m9RBXl3Nm6neNFB4fzPfFWCom0PMlOwDax0MmnEnpkG9eVwU1n6PhIerVUHpV+Zbe1/koS+iQ9Eh6JD0SHokPRIefhP6kdfCBNRvuQj8saIphWuLBDrXzHz0zi1+FEHndcfkh/6FokYixwFUN0gieijCVCtXyJqnlTU3iFm1VU/3EXveDoZFZc+bfqOLFDvS+H5/5eoqDkrTTkQle2Obk/GN3zcJIg/jRlmWxlBkWgeVRdJgj/NWDAGFNt7ZD6pPz31tGu2EjN68XiAPnzBQ/zLkLq5Y4UqcUjhshUh+DIz/MhFx5oBJ6KlClTPlsjhhi4uMm/mZfYyyEGEEh6CTfZxbip/I+l6mkZ6vR0KTLZ8DvAj9h55GZwgevHRrFbRtqw+ENz3Oxv/YkXQ9IKcWQmRU1jqdpkqc3lJtJcvwvytsrJ7vzDoqLk5WrYJRKSiUlEpKJSUSkoWn6+TQ6rI/x3RvfB8GH0xT3zc04dfgArR5HEdzw7vorBQ0DiRwAJ+QD3UDzey8OsYo8zXeh//uUBsSKuuEiRua3v79IwPykPAPEYzgc+PXPtB2azpiLUnlYzx/tLlBRIM5qucOAQi3lgLTXv3T6c6b6DKAj8fZIOK8Gr3Dzjt6+5tK/GlZTDZvdnig7uPEvdnAasYT/uajtX8a7b+70tp+k+MRU3pwNJ+bUOzS7MrJKww/q+ubgFAC522bY4LNEEadVLT0VVwGthTI29mToT+vNpHGXusloCcCEatOzGePd8MrdgBnA0AzP6mt+k04rmroLfYG+wN9gb7A32Bvf5aCA9XvC3/ia6nCGfAnbBnoGxSN7Vrjt72rrEHRsdXHmU4N+gNwDhfW5RFGCrnpb7vqbCRRUZU/styP7dzmvRzbyU+sBt93IC8tVX8AnwSNMb4QJC8lLLhb6gdyHOGn/ZrLG/kbFGMBfme3CSoYm9UB/fmst+tWdtSr9P87x8YSFeNldfClSJIShXaiQ1UBD7MUya3GiUGCC2Pjr0OnUSRxcIiQRvR2iLurfE8/9wQqHXEA3Strwjm5isuaxj3t4NFVRj68IRolghsyPYn3EFswVNbUNtQOAW4HWCAWvWY7Wnz6vOhbBZzXYRjofUJzGdX8Ug3kK/pQwraIrFP+wsP3/Fu76+WMRxrj0ru6DyCPYLbxKdgk0+iQ9Eh6JD0SHokPRDzG7lf3mPmHKwTxH7CHvV51sfCAAfM4NdfgfaJrxbvonxgMa6ZxdRlyWGit3PxowIQH95dGn4PAICZwqj0ESqZ8n9CRi5N8jRPJ2FTjg539j32Sv81jQ1EAPIYqncqltZSRIyXxXnPaJVLWwBwLnBhiuKVorZeVaGwWIZuiAQJzKCVmPZTRxE0YP8MJ/3xRqyHdOJ9MBFP8uk56fPV2lyfkpA0XbQdWaas1eUYYRZZ7syaYgYuhVGTma+7MOTYwN9j5IZuTtQUriPvG3owWEEMxjJ3feZOaVJurvi603YKxLLLxBznhz4xhbZ0dJTfwZfu2b3it0vXQqSnaTbPNjEJXKPFzMwpP8SBNVpxbpzd6m71N3qbvU3elpf/BoathWCG3nRJWpBlGLFNptInAfqr0HC+P/1vwRbEL51+1hxs192NeoPoZaIOYg1nfRenGQs+0o4u4QYTGk2GG1hWQ0s85Ub858ZG17VGVIe/P8/EBh8j5N6zigltEFSm4wT0yMj6Bg6MH0doGem9VWh2swdQA64uuTyiBhRMv6o3GXLBk/9yMVo4zVP5TuCu+Z5GkNq6JpiRvEyvWEHc0mrBFZZkBkES8zLOYbwKD2ofBj0B21B0ffLWmnv9IEJHocUHPdVzxYLR5rgk9gGn9qdI3p+7/O7nFfhpRv3/31517Gfb78s2FDESqbfd8DmcmjSbd1L0XXA32BvsDfYG+wN9gKVbiWP9+EfaEsT5H+4UagLBMruAVBJcOh858iyvK9ntm5mxNFbuE6kgZ29RalCjdppTaMM7JY6NH2IqoietkXGHIt6sJ9Z3z+atb9MVveb/DhGJuoyihigHbYeDqszZoitoMXgaw3EmsvQWSedeENRk2rA1WfiYT0Yt3iceouGQlbvK2vBLBUqweedCpR034nBVRBHz9eXXp+YIswTTO72Obf7QeiJ9Bn4e79gyinWO9RLpP/3g7X8p7LthTVuKWoLBp9T7lsViC6ictTnqEoGjcTa6UFsgJ8pGJfJ+65AeJyH//6zX/9Dcvznu6AP9rFnWbCUfRCnzuNKQNf71+5VVg7STbV9Bv19+wN9gb7A32BvsDYASFYjBwh++lOsmcn1XM8g3WHXEG7coSLzkeqmKEgrF0dLaVhmfh+9TOmvoK3GVQkmm+fNd3f772SY68PkaN3hkL7jXKplom68aZ/M3QFCX4Nxi6PubPeQUK8aOcV19DNVebKscGTAmeDFVLiOnoK2efb0ngY3NOlCJJrhCnYFKZ2ZijmyP6PbB8dqnNiOC8AFJiO9IYXVYK+soNwxmgHPyA/rk0Ildo9DxxpL7pb1mNlAD32sgr3jT4n0KUW50OAK/Es7ITHP9Pf79aVrii4lfX1Y80yGo4H5K6brPhogm2nG5mJipkcgGlUTr5bqQfSIyUSkolJRKSiUlEkG3isxxY1klCWlFHvVv6yfNxbsHVsNCJX7IXkUPcnfcQgJZPDUz5MS+sYkYSd0xR3/404Ge7dIqkFsum+IzkXSgs4vgOmYNAFVcL1pi3+QHGLXhCtrrWOOaZU+rmu6jpu0ggeU7Tg01nAGQvqMZ7qOYlVyqPXJpOyM1RDRSvgZ9Twau2J5yRJCmgClR/FOk0q6AGW5aBjnqxdnmQNJyukMjmyCf4OXoq+SNblTW4NI2D8Mraa64gOI/wN+Y7F1Ujzu/apbKtuIFwMLkhRH+AYkln9tWU8MJw2IG6EiJo6QClcmFbPheIM4qs/69BGv7LWQ9Eh6JD0SHokJNPWo2tubgcA6/n7y0l5gA0HDP7TP4aNIl5zrkw5tgVzlM5rSlAiv0i8JWFKftFi0vYrITTfv1JVC5bTDbdamANxKyo/9FTB66cqcu2PiUItclEcM2F1GDpxIroEqJHHRRqFKVK661c2qcxf1E8vjYZKudV46jew3ONvhDwYRM51oX3Ed1mGeferD27qhd00hdgr46hSJZ6h8W7Ut8J4nH/0QX+4VmktnncZRO0fQTH+FI8K3AVTz5QflxJKNKeCm4nJTDI9oKP3T+6v9zJNecP/SISiYOnr5gGZzgMIKP8iNQYdn0lmZGP2XZNiSA/a/hCnV2pFgUDSjXRiujFdGK6MV0XhS0+MWbuC1SwtrUN1HAaVWLXaU+PA5eFBRY7R+wwYhNwETK63qLTcyCyT7SbyKla9BmiXR00PP0U+M52B732sSHA4Mi7/4jUztXJuD8AG8vqe2ghEjyobTVRjiXekI7FvsTHU/a/ylsOIVWubCbKYHoeEHThCVgWls56WRFJZgeqSWx8O0HM5IZ3JrcmM6PU4NmKp/lKqW4KmXHCPA2hJ6r4III5H8dGBz6D5Ga1PIIJANj+Rk2VWRxBnU7cLIgylS48ELi++Ic2tWKUgDA/NYND8W2rvPxa/BRyE77b6jJOycZvOdIiv9pTogsnZnYcTsmZjQF4h8O2BM1YSzIMiA83epu9Td6m71Nzp1ct5iLhBaCTABhYmN0FJdBT6CaCTSv9VMrRYAh1j6//2l3f90vv7yIIab70j1z5slcZk6tb+dMQMlbOXWM9s1y5yZi4avfNbe7EJGKLITcvyjbHf2LjsAx/qlFvASlLT+1u2ChUWjbH6QrC6BSGg82MbDwBwk1WH29vYP6SHI2RMHHcDbsDun0amwf5wN2qX0oMHl66DoyeAN0UnhEMkF+5bZFookJjb2zJ4FyBHH825a0fwizxqJeBy9Hq4HjqyiCkIOv7DZtIxX/+dXra/mXFB4SeQE2EGL/alk7rcduh+HX2ikXWcm+jQ76x1OJmC+pTNrlKgOjHM+y8CcTDDPCO/d0YroxXRiujFLgZyCvo8jGNsjNOOab1qCWhNL2FKAHivRSsZspMN1lT5Lf1nGKMmci07q6BlOpHMp64qUWGDEmPmCdghK5BaK32+JbMAwGozSJRwwFLvhvrYh5f2o71CcSNqRWWJg5PHN8XUps+AywLT9DoUa8lZbEvyOqqkuDzmnk097Rf+4wL8+yVK1IaccY1CNfe1m9zpCPPJtFxZylbTpvBRalTsIT6RALxXMhqxVgplFQgzgAJwUftpVaHPoDKS4v2J/EN2ovqwN2wQK+5CFMElwtP4Mz8MsTASGTrdAgdpBlumOTvDgxU6gQ16h0dJqB0PFrrYGeJTq5+8fRQWP1N3qbvU3epu9Tc6dFBqdH9GBnJ3/W0GgjmpuBvIIt3Hniy5o0ImWyQAgPDbt9UVi5TlkT1d7KrghnP+VaoZkuvv0dNGrS2sYGR8PypnmFNDy4QafiNue4XdlwyHFtWdwrKXUNqPV2leExorVfnWV1vuMn4RW7BOMgvfVjz5Q5sRndxcAyDZjK4crkEomznEO+d/adbkMVHcmWLy2+FKcbVR3KHNyO/IDrwUiLqPFDbDVpd9N51R5MbA2QjmnvVAS+5+aSNyqGulprgsHDv9Zg6OzeGOIAz3qGhUcmk2soh7hQGUiyOr+qYolGK6MV0YroxW/U2s6ExtN2Y6P7aeUdtArB0spz3i5xKCVnKXvBUb5hF8ieMMoEdcbgYBIV0L5DVEMcZE2G280NJAPCKeSiiALADe7aasE1FA7QtXFA0VF5SYP3FT8IQPl0nZixhtkhnDUDTmo5Eb8IU5kwEOgdu8BNtwWXv3HbizrC+eajgo1awShMgxaETmj64Z0PgeHF65l73TKGd1wEFgfJaFpFA49dvPeFg9lNeu6B+dsMSFY4rYCWQiR2c0ArVzmDvHkvhPLMrEMgwDPCLlJ3asjLDnSxLFcq32UXKMCDYPrvoQlO3QhntlgurV9JCFi13n6iUYroxXRiujFdAslnYOqtIF1WGOwSJxHtEpe9ID59PR5wl2kiWJ6R9OuLsf3v+3E98vK94FD3GuU+3JVP/uexpA1nvbk1LnDtnaKfS79T1xHUoC/tROGGS5ni2iTVsMCiWugxtaAPdcIR2e8GEbZjigk9mH8T83PD2bML+8FPgAx2wf4z0DhdjlqQK88EFOResc94bz1KDUka2IGakMmyxHqcSIcT+jBPlIwGIaXKRy66d/aQgm2ZHf3Jlu8EWMh2VxKK1gtAVIgnOiePDLl7uy0iMqZp6EoVEId2J58jZ11llVoiL4Bb5MDzd6m71N3qbvU3d+NdwdZHoe52H4O8xlHUQ7xzQmaYCP7dBwLbU/oHUWo8VU8PbCtBMIRmdaC+CK3GSjYTSXLRktIggBupMw61qYOi2TR8PqcCG5ACWSulHP7h4f0d7SJDd5wDAFjzO7qnM/q+IJucYLDyG600ONrJWd2DNxoSz5lAdXY6jutdWlbhP/JG38Mny7lPbqGn+be2LeSRg96e03RUDrT77SXUtFcjxKpKCpia6dplOAW6oLOmpYB4bHFwT/71nnCpSbRI9jt0so8BrBQYt9gb7A32BvsDfYG2oUup6Rsh6JDtrxTIsmJBuK4lQFhYRI75l8CwhSiB5V6Z0oOZ09iRbulcMNOJ1z89cIqmVGIRxaIfuUxAVQ/1bOVo/lln/QwlDjt9Z6564Zr+yqtL8xXMzcU8Zq9m957bGsWJYZNpcdxawlElrvTDtFQV3y2DUhWLpJaUj4Xj4dgFiFMw+RURwFoZCWZz1q+bUSia4/vmUiBrmA3GT/X0pZifv6F5BIV0q/k7Pr13BIcT0SMimXXkOc69nZR+qRulvU3epu9Td6m71N3qbvU3epu9THt1mlzQfKWHn6zxOX0ZYXp4YBRFZIwhsPi/Go2OpyIvwL5KvUddt/kqH/Iz1SKj/QQF0b9Vz3JzXZ0SPAretVc4cPl0n1aoOPfOPm0K2Anwd38mnx7r2MX9OZ3U1fL7xtkB1AYXwcsleC2lS0yIJFfRzXm+kgcNkrP/pc49C1KWU+i0ugYQUkTTwf7SnkduYdPzmQSV7YyUVtNUIeHfK2DgUFstZD0SHokPRIeiQ9Eh6JD0SHokHT1ypneg3yvPfGBGrVkAgZgleagVD8BfPaOjx9KNiR83zzwBzovwl9cqdC9BRhNiMmEm727xsNFYsYtaqmQHXDjcU9hWN9utXsnDvyX/+Jv1DEULHyVRJr5+Xuy/qFGtlzf8f1BYO+s4LwTuVDfl9sIIfWH/K05XCZbnRGCQ9zvwaL5L85sGxYtyWOBDP+60RVNggN9gb7A32BvsDfYG+wN9gb7A3v50QIzq8FZTLW+Oz5vYK9A+WzMrlUVgvB2OBj2kWdHo8X5zXFvOzd7rPD2sRvdcPUI10i8pqR+7u7yTvRA93TaG6WCCd7DCtD8TnHw/yeM9yXqT1BBMyoY+eWGvhJjrHtF05q9uIROVlJhWMYj5WwAVoeOeRGCT0CaMQ+AHaIj7zjQFTiNQ4psymhNPrM4xKG0nX45NXvFbLRtxVbShrezXYV41E9gb7A32BvsDfYG+wN9gb7A32A8vEAVWz+6BqwKW5DZSJqgH4qQfSYo0vDZaP7meNaygYP4VlA80eRYmJuQUdzsUNi9rLj7XJG5W+wl/C+OxgxUbFvz0vcoUKSZJFv81E6vVJDD8HCxKR0fxyZhRgZSKO6owACbsqFDM/QFVS/FlqUwtKar0Y9Ws+opxJgzDic8T4AlC1kaVrM9Zd7dCN0Kabecd8dypLgRC3NdKXdcfXuwOlgMghnxPmREmaer1NVrJuI1yPokPRIeiQ9Eh6JD0SHokPRIegQpXJC3S207+u51czW1C3VwQNUekySPZKCsAVz7DTDdzdMLrBHtddDR/S9gSEaVNN2gMBSGqqc7XvbQBattUtUVStk/kx4iL2Rxm6NVpc9fptbJaZdxBO3Gjy0XtV1t2iHwIQt4mM2pIIC1K9WVz2UqShz9AniuDVwhZDrvjgIJ0sMdOxinXerPFmrgxDdtNupgNzLK4icJodUVVvfz5ynUxM+TTd6m71N3qbvU3epu9Td6m71NzReWyFlvMXpzDlOzGYfelTT1jxvMsucJlUvMu3tqiQJ2GF+E3Q+EVbSoqZ6+9OUwV7LkBHzILRRGpr+QQaZMUy/hkkt64nqs56HzM5UpQ9HwNpGcPzaOT2r8CcteZiFBeGsm7KotE4reNcimhWdGGfaWuLaHsMgCRGVv2p37KMLvAdixNt0HiTlFwhAFWE/FQPArUJes9nVpdrFbX084Pp9aRa5+olGK6MV0YroxXRiujFdGK6EfcuJgYYsBSUU2I/g1B7cdg2+oaFdoxVlo1CHypkFp1Lrwl9YS4e5rBYZLRkeYCVGHu5OxnwQZKYC9RSj4yD1Y1Es+DO8hmZ5Y4xl+li0+JK9moIaONRIAlB4LMqkjOWEnlBHIQM6mRKNJFTaRZUox3jGZqmWLxDHDZXOPlTXNoMiSl5VDuA+FRKtYh7cqPGu5fYKXiUrNFk4FyKJRiujFdGK6MV0YroxXRit8UQb8/JBLA1+bn9SodhMpTLGvmCB4hG442bhPv2xXpgmgKjW5zq/4OoDodbUaqsi3nQmS+AHI/xFGZA/qxcfpA6lnYoVHKUDw0+dzke9duZUveJ+dSyg7TYfXfRyTkpcpB4vLBB3LFsnGL6Mw+U9BtjUyNYxYTd6Zk1IA0oN0jj40W9nBdwtenhOHBSqS13XNBSg2c3Y9P6UDmny/mokx+w0cpKJSUSkolJRKSiUlEpKJRya6RaFGuegjbV1M+6zVTShLvUdY607L9a77qgFFqlVSy6a1+em7VPOVA+GCqmA75VpecQUeZw3GlXfpoatsxSiXGLzoGilYrDSKS7oGBCDoVKRulwcxKgdqDVP2cDQXOdPAS+DMcezat9gbRgObaRtxl7nz4i22cVQMIAch2Rpp8/vj6x7WyiHicI6gHUH37A32BvsDfYG+wN9gb7A2AXzK7gZVxE5S8m5/H+yfVe+fkXaCyrR/abhDfBN3MTtDChmQIXEjp/KI56STkaty7I+JGsXxRlHFg6xSYYBruq8Dicw0Dp0beN3QMoGkwtIXeaBQLhHg60iRrct1fivNN0Ogfv3NW7wZ3aivdil9BXnm3753BFEbn4HgVS4PMcoQXhgZjjKwDG5YXgeWJqmQUptyaSG6bGWp1OxzMOpi9qaiCiQ9Eh6JD0SHokPRIeiQjF9cQEv6sZWvC/YXoHSfGee9Fd+iyCVWa2dTzeVDypFPVN6YEjmUnCWpfTuZUSQo8EPk4yYKmc0yx0Cf53rTP9BlHISWcDqZhreQHy1dK+is2ADYpHuwFAyN1+dyXzOswJ/rmB779P1ytoGVH7A3vy4DUKBXYcCuxl6PENjElU8VZF3+EgF1p5UB1XTLCB6xGR6/47bt0g7zu1BjPOFTBWvX5QcVcYroxXRiujFdGK6MV0YroHGcskU9pPllzs+7Yk6KkyIK4JHZEbtfJnHAFmMG56hb1zwcZ4msM5oZEkKVqQpfYFNPIJItFtcdKT9KRjJJmZplFbHkogf34c25KmoJEJGMPPQYV2/fccd8REvMTO9Ulb605VIFWn1jq+y1kPREIAOGWWv/9di6u4+5J5S/dIYcFSE/EQSlVqPTOQ98h6MDPi4V6GLVE3f2J9K+SqNdQRktVBplV1rcsiUlEpKJSUSkolJRKSiUkqvVKmmzlX5AWCrEfAyx5hu+ZbadXPeuKC//Y03DYm2LJVfzSgwK/r9nRCWAsNyAZZWfSuaEf+aIJP64JK2ACS+4LvHgZOXTpyDrgcmCtmoPaETBVLmb7dBW1pJAknkDOf7dTuxeFtuwIduGI81+kyQoVnHV5zNbqFtbzuRIeiQ7VAzgrBCNI43/pvmH7j/DFKGeMw//8WXN/47uqU8OC6de138QwiTjwsAikyY9uUdKJaqq9uXlsE/liikd9XVuz7OsDfYG+wN9gb7A32BvsDfYDw7C9dYL0RpDEYam0Us46UOhvlsk/68gi2vbTDR607KXh0KyyG+e5uxokf5eQyUp+Dn47Ml/yFNX44FW7yawm/P85gGE0KxxEiiFEFZ8ED/w6I1/KlEC/0zEFlmPBhTAuA4zFV1ZY/4oCHokPPh0/F7e1pzV+mLQR/7ZDdseMhefVx/Jif//WivzADzz3GBlN8c3ZEyikwf1e70dcFIQVtnz0YCqNPusRv27sof5ZxTAdoA32BvsDfYG+wN9gb7A31sslOExbGiwOhtxR1IPPNXQLN2hvFIFY5mWoxOnq+2sVL/kSOPTcUirzcXjkmYRJ6b6SQ+ow+7yZn333c7PzvHdvabNXBYI/EiXW6Dc86xiYSJV6bWZubZmr1S31REacbHTLVXA4if6jg7YChM6jVABV6Rs00RPGwtVSnmv2BviM5C864pKB/6NkMa/++sakvS3O+RbsosdvuwtVRcBikRH8Kv83LRWA4W9Kx6UnvtxcSX2cs1kGzl7oUyJUQdFpOCird+7oxXRiujFdGK6MV0YroxPpUs4oCLeoLBl3FCkxkKudcaLkcrg2nYpTLxFyfPs2RN6WiZ6XYZIY+c3MnrA0cEM7gPuP4oZZrM8Vt1Uo2sdpNe7iwNLxBRsBu1OzWhUqnt8s2ocENaWk8TVeEsaid44IyiqPhQ5fcHIolvgoa/x+rRAJKTWh1jcW3Av39wu30261ySi8GQxmpmU5u9NcPIPU5TtYAsUJRcDL6ujfI2SUXCprbmWtv7fSbwfHsrVbH/EDDzmNB5KZTvnXXHVgVdM1xfFa4ouAq5TK9uZS7bZc55BhUXD8ZRCiQ9Eh6JD0SHokPRIeiQ9ENhs/1+fCx3NCu7klb9MNlQDapt86OMadEmWdH9VzOL0SP78hAT181frzfr1qgv3Pir31SbFXu97rA7S6R30uOKjypI0E4DDFP310bb1KKluBoAcffnQMlBS7bzk+EpWOFb/jdoI5cBPZwl78c+84xo+WW14fg0vvPHkuNGf4Xv72KeamUwaZqu9Td10nei9Hq11WxOpK8VWZXxuqO4+hoWEQ/+ozRJF/U0BDrQ47FgCY66+l4XrWK+LuHRK/X9/9aCgqreIKJD0SHokPRIeiQ9Eh6It5yuaaiMuRAS+o3xcXhpm4tQajj8JLsNDkOk2o5c9mGuhyRCJgnKR+CRdeYoIJ2YUANGUyaLBaJxafDKka1Mjgb/zIFedtiHV/C01DFkZYnr3lzxLpQvqFXBr8/o2Fo++cOrjabTHAQCtTvbKywyn362WZ63hXisIEAOhl02VkLv6iA/actN1pFRIZYOwk1LvSV85FnC6sl59rd/7LAFkyV0iuz2nawAHU3iQSiUlCgAAP791SEsv3M+VPmXivJdTKbEuuaioLnyzUUTMO/L/6OlVP4XUAUlnfgXfZbXME86DQS9TIiCxo8iuX2US+qQ5lKVK/GHn4rppRRvkWifO+9OpmDrEpZrvON/rGvyX49HGEazQqnb/kzV8ESZDf/9CcEbcAAAIbQFUJrXeJqqhGWadDSZji6L1vb3xBpbAI0WzKOlaYBuJ6ZSC3OCdXFOFEeVlrvfP2lPZgAAAAADsk8Ip7gkHs/hgh5kgeHERnjDxPeB7o8vSr3cxtlmti+XXrxpk0RtsFKwPq1FnRvAHSeCRDvOuCt9f/+FUxA+ohhqu9uL7TQkBGI3mN4TxjJkoIYuBiQ+YHotU9ZMAAAePNthXF5SGkeTeQDVmNWz18xYjeWoE8JZ7DqX0zN85zsEBxN5YKl2kDfn+1aNnvbdjks8G3sqK+ZyBZpoqHxCRku9HCxtyomJocGftkSIBz+6m09wtm7sx39+WHGiFcQZWEZflR15q3c5eGgbW1SPpD+WYfacT6KarlIwgO4K8zw1MH1u3TYcrdTyTzAyLvhd5ebw6c69ivUizaRYQydrTnbkoS3KVjWvmpkZSPF1blRDqpkXjbOG2scxSJDMXLXNe9F1ojbq/UraZ4S8icKEDqj2jJuRjGUumq09+/WWdcu+PU4EQ9R4Y7AAAAAwe3rXi44DHoWfgBbbPvXKr0VhbKLa7b3pu9WNE1S65Swc9JvBY4wXD59ZOzxsjQgEqz/EAy0TrELtOeOomIRPj3S6vWWtNl37ky5jLtwN5fQt1zNjMf8Ir6AACQvnhhJ75fEh/eaiZKUksf+thZQL8oiSqVvnI8dGEuh4UEw3W4B5rjLXww0bHuD1IKWAE2XIRJzz/n3o92CHmfpwVXILoDeGH5YKSYEY1jQ61R5eAt3RwMq8JTlTrPnvxfXr1ZyZO3fb+cQ75cHQkCqz8egnxO+IPaidb1+Mfs3SkWQopumLW0GBc2m0xl7KTAjhr/zevp6EnTTalXikkoNJPd71cCUBOyr9pOhF0H+SWV9hq44fr8urP9moQrgQFGSb71+F73bJOxPfag6xd9qxyWj+fyg7o8jNDN7c9MMBvkKDRNQrsFso/50u4yTTjU2N9cR5oxb8tZhAAAAOToGst2In6mGqypwBY06AXr2B+8o7l3/Npi3Z2NtpM5XKJ2EqBYccs2PFeRkuATplDFRq3wz+WUJtnPLesgqV0Pex6ood5XbjS2+GXAwkbkvJRJmGDG3RabtuzzHVgt30hABGs5sQtqjsm2X8lXg6wBQgL0DN3jSTCS6ohTQVs9no9vRWUZSSrImb6SnQIUiSuJTD6gn5SEdMSQs+8Mq5gXgcdpemy3im5RUdLDbSP9bKo4NceaCBCB0Qlm4aLgXpY51xpai6d+cbXTTrb0e85DRxY8Ml+5osNntbL97Id9lIopfJ+e2ApRcwsUCH+I3bUOypbiCvaWLmiAAl/7HsQjBgqGdm3Id40v8VBkLlIIdWZ0voTyrfMDJf8UfsZkQp0NqV6ZHZpPPJWd2BHZNW577jDl7Veyi7mgDF09/2K2P/5Nuhw3hfYkZDs9beOKVRfk/v8tBpUcOgAAAAPZ8UVIyEc/01AZINaVMhaqGGRI+CD5VVuNpEDFMAmwrNm9mGOr9+3na71bfQn5ZjSFmpxzpw5AoNbx9P5lmWQt43PqU+Rp6zW61mjdTE+/4qWU8qzkYrxQNGgAVmjkaPKOQk7loOP401CS+EoEsACvfNJXIm1cMkrNrGFwNApRcf02kqUNJTrmKHa6RsXIjlRqBCzOBPo2AOt4lted/JNIOKTN1YvejRLzzvAn/kU+08lNCJSmKyXVJ72jAPw1cbzWRyLJinUd/frw+HaF0cmJYY7y60NtstaNC8lR395BTpNdliqO4aBMjXHmMA54zziJn5f+mh4T8HZ+lDT8sgtcVu5omePDUZelqjGWoG3DAvxPu/b9f3V+2pJ+4s8b5Oqrh5gmKH/pVI1RsRK/Tn8RrQTZDJFCgm30wON+XpdppWI4A/mgCIxwG0YfPEqpz4YP7JPknXeojpvZ85NEgIBlJJyXeNG2k8xtWXnl8PMEmU+n43QLMnXZK/vrZk53TkYx1+j8CYr78arZkVvnV3IHc77tIz/wd4JgKAAABVbTmOOgc9e8FvGyllLZjRC2wzqiGzfI1AsJCoiDB5B7bH/GxL4azOP24cCDeZecufGdbVpOd+FRuvZbLWcdj3RBD01KyN8dUvrcTYscQwBkndJDHz28JXPOB9YipVhh5AOuXpf704cHmd5qba+9QABqXkZ0fBgdzTp+6p619XCqvtj0CW9pgVYj3xoAVfgCjt1a3xL9/lrR3Sfo32fMjKbjPldqwaGeIUe+Me6N3pNgQZ/uk7y2Dt6Y/FMqwjdMdDRBj4AblB9MN+E2jxubYAdfDiT7Z9AyDZUDXBWLVLqA3txuwio2hR0GicUnvLgbs6nOcbTWCqQydWr+sLxpxh5XGaPssFR6Fww2J2CRGkSGf4vT5tjJupNVCNKohfGosZMqVLA3zxvPB6RoAZtGi9XEsd0diuonJ6RZjmcHJ40IjtJpYooitUdhle3EvBjMjb31aPhqVEkxAM+0O32/4lx2tWV0TboCubJAAAAAAtbbI09xsHZ7LstF2eyUo7SVCf4/TV/TbFCyPGkCgnMtSKZDEWdvr9YgnpJQH6yjeKTLpuMkMSIC96u7qP0hmcR6r4I9YBksvi+f/UyMs4w+3vy3ApJEGzMhEBMMvyuyD2/GeAA1cNGnT8t09VJox43BXvMcc+Mh/CzW8LZA9vZaENJ7Uq30yLiyk826yfvgQ/gSWDHHbC0Yus9rnSINzsk4wzuWFKTV+ZnsUY6I9ZVQqBM2O8SmC0gf/cN5Dc3BoQfC5Sr2ASRv5tNoF95G0MlW+aUTaf2DmyOJBBm8tinIFJ8/KO6tlgSyHbnFg1DMMpk9o4T1coG74CjkJCqHlvCdkv/441I84ZJv+xDiJ9eY+Jcvk6GxyOa/EDehF90eztVbloeE2GE0lLtjc0SaZYtP/kVVPx1HK/ddRhfgQgdiQuGaHjXj4VGH74m8JwYb+JMhkuN8h/cTCe+mTpQGp+VABPfVk4fe0FbuVhnyaHbo+v6thHrjhSqB230T/yhATvFMWMcDd8gq4H8+f714KqHvZv7btP/bcVAOyGaiIOF+zk3OHKiarDsyUCwJhluOC9QO5mGEiK5xgAJYQpL2vf0skvAuphsk1cywGcmZ1vD8gO1WvUZ1HbKvE0xfbIno84tGDnNXuw3i6hgnLfrXvn53lCJQOGP0l95/0P1Fc97RUKdRT9J6rS6jgPJp49QraVqSZ8nxM1JS4+wA1swn/aa2MXYhJOprGdlo2BoK42CoRbyLSK/d6OwlhlsWzaE4uq9xHloAAADyenMOOCirklM08TYcuPL/23WBA2yDJCNDE6t4ZvqgKpwkmDzjR9Wa4kOFKbZTxu7tAvlZllqCLZXaoucLSIEt4DqWq7CCEN3Vum1l5ak7M9sGXk1jrQgIYKWtGgqxaEC8clzHRFleD1r+SjgP6LXzpkOKXdCy8C7zfrEWQlXnIYne7tyXWVrjLhtwCYygCCXpNXINkpCn/4aLQXVtsKqGFs8OGRe7T9Sf0qhWjMT/ct3z7kyZ3EiRsrxxuQEXYOnFBlEUK+mYQa31xtFYGut5kDW20w+YqPCQmVt0xOR6lTLHGikK4I7eR0ct6Gj/JqJn9rR89b8PsHk1s4keYbEKcXm3ikco4PDSNoZHKCc2gVfiB3rVrhTRWGENH2mDIDZWANcPlgkMCqo42g0yQBSf9vOq82bO/nVfVrohVg645ImFmmtNMLkorNxDQLQZOuBoCFurVCXaMZmKOON6Z+R3EZ8Q0Twna3AKr3fPcTSlM/OZPeHRYvLCyGeuiLoWogZtj48mZdVIdChbqr/87XXwhYAyj2lPvMTeEdUpzYMkBLqCCDp4aMfZPNZh2Na3v20w4zZ2V9phB5l1RPla/K63xCzBgyYXHT5F/1cjatYxH2jXDM7UZxsgWzBZwKc1oMQhT1Wox232VGSjk8xeKX66L/As/ZpQ8B3YaCWqlWI9RmEbf2I6qQJ08Zrv5SNA3ZY5OWbQcGWd2Sr51UILPJcD7EpHQZmYV/eEAAAFf2Mdpy8xDE0SPmRbBMpsoLXv7AOJqX/8xfVBK6HZQkGD5PvD9qSNo4gwUmom2R94SBInY4vY6nTmNxXYrPj3IeuUE9+CErr1sjHEk5ymihmjcASN49qwhNq0PW05lQmeb7ElNiu1Q0MFaBLuaQsffO0v/qSwHl130yIDArGJqF16Cc/L+2KCR0fmwdhML/hO/niUqfsqKIBxkQs8Ygwj9/hDc++n8xhW3RFWAywU82yKPN1X7JUvv0t4ScUuRiUEnchvuGX5O3/EcXhL6hxr/SN3aY9aE6n6hdnHiHCOAAICBhwcvj0ccV/kwbR7O8FEeSkRsdf8377DF24aBDhrHYrW4a0GO06CQ/v9+mcJ59vpzpCJ4rLpaIcdIly3pYHElo/R6rxq81CL23tIukO6UiYMui2hTNTg9lsSuiv7I2REsEni218tzheYdrK8m6djaTO4KES9RQO8fJRi/sim2HLRAzRv+KeJcBL3KgYKpcWdX8Nz1afjYYlpRFRDZzixeUC6qaFx7TgcDW5l9jAqeU6tsY4DYO43A73VX4zeoiqDu2lWh+0YTP9QYkbUCc2KT/SUFmAC9Au3x2b7QW3gfNcWv8ri0fUNAyc7oo8pXmhiMivL8trjskpPWqRLCLFdZTgiUa4dC0AibNzUy24LcW4vAa8aj51yE4fTK3k7cWZQQAa0LKeRmMlzAHhpLDh8b8Zh1NeqXKcINd36RxIDtTAE5UNLV4zMaZgQqqpdaVgpKx9jwknDOmMg1j4BsMWnOMn/h60CqCWG7FHZk7553Mp2R5xMAHFqjaEbDZUIHBybQsAAAABMbK19V9S0+cPGST+t95DYsDXbiOOcSqmr2di0nIrrGgH6VC5FuHtup5BQoAqzZ9nwQR+oiL/HPKKjC1FA3ecXkgsEubjh88IHIWUaMFoYOpz+0s5IrdRnTyYFjx7lfIOrgA6ktMXZfsrrZMHBploJ+nYAvvUIPPoT+RflUSR/XXMF/BiqfePxUfi6DHXFWU6C7oPEjDxqUCvhFEuOxXOJJ/xB0jZYCFgbNeyatbbLaQN2DIcXRQ1ud/M4NEDQUwWw9DC1Ie4E4QQvrh1cijdWPNDG1RwUCjNaqKmN4IT8NJbVRyEsjcQBLdx4R313pyrj/mGiWNu5L8akSr0ePjEdS6tpgNxw9bJBnnRePYErppVORouaYZyvexHECuzZnT30ccgLHxpadchxRZN6iw9jlAjKNDBxkxmIrjXfP0cCHkGYDxjPobyO8nS58d217vj2wmLoJFlMurknNxQjuZGLskzQVYi0ho8mEi4QPBa0bUd1AR9Yt/HzTtEI2NERTplL2uh4ObDgTDvfAQDZA3R/r/OGMRhd6r+siMmYbJfvHv8uPXPpt0nwHZddhjrwGO1mwIN+f848x5PfgAgYyXWJELhWEhDclVDvRWaaih5FSWSipdTOBJvyuCwn6+qq6WzANTyn5nmRKMPTDAShf31ahDWYC4IdOAmvc7Hz6vIRkhkfQKgk+Epap4uUNuSXGdk2xPEDNEp7OlwZAvUjHtesKTzHdWMeeIzmcVT7jdFyIC4HkVKxax6SWpD4z7fuqgHEByvmdnE7befzKz+OrOFPcZbl+im3SvwYVBu2S1K30+Vb5gFnL4OD9gqFbwmsSF5VuewdHpZ22UWMy9uFCjsDhTZU3vTZHzG42JzK0G5Yvz0MEAAAAG/ozUDQH/n/NRRO3Rs/+cYPQAZFxKqkRvPi1inBc9Yl1jS38BL1FXzRZr48kT4ej6/vWUWB1dZgvmxZthIaiIyuOtzeHJ7+OG+7t5Namip01qi/hQDOGPfzjDhkwFuUZjrAf0FhEtYgglwS0fMaYhlkU2+9zE4iXpsRswhJG6Vx7P60EPRZUfoqoky/zjf3UD29lh7qcybVUACc8p7mf3FjZqO3ozvGoHf1kqgp6A+KntpuDfvwlN6lHV+aJnA78D5f1qcNn0gDhCqKJ5YI0sqSFjbS47wAj0aMpL2cnQ4dwk6/EJsclo93QtP5wULnhkw8GQAOXSKKb6IXfqOk3xHN2pRu6m3tUBNVJB/VnZeHZA2rm3FkFEyyRymQr9UCqqmV70KlZJbScYzRAwALrKRmTmCgEq5ahhgVOZdKcpdAY+Ks5NlJ3rGfqpqJrg+ItnutPCVstiLj0TaD6BuKy5e6IIJAzMdZr2Yj6OsGtiBBKEsxc/2G6dEh7bO9iYujfQh84sp39+UCC27zhkbOX7Fb5YwvPTo82YTx0c77NNEPeUnpS2Cfvc0MD/6uk7j/VflyXmrvWMD6U61K8wRBP53byCyd2Ae5+ottPF80Kca+S/SUck1XNnLUSxyPYeFoJ493wv0aci0NB+iIK6OgbQEP7aaGX65BVDAjsN9TdBLkt9cBGYlwZYjaKZ53PKbKdWmDTtMA0aqqPNdsGi2dGiU6u8+figjBSaiCoE+wvsbsNb0Ilv2j8tkcPDhwZ6s7hvFo9qu48irl8bUj0d/+ynCXabrZ0eM/FwZ7PqmWEpURrr+GCv6j2ZnJrwL6WGVLNE79RC06j26vw2F3NfzsO9aY/E61ok4ot938mKGvUFJG8n4morl2Jlnh7JDfl8UIqGzLrchg4n+8xchSCy798cz1mFAh6jqF5YySfHYZ1CQSIlDcTXPobypeeJR5XU3S0LCIU5hZJunTQgUZ2J/lkWOyrcjdIxiZQuS6wp3aJNg5fXKMB2i9dXIEwAAAACs4ogzzFB00MQRsUYVmKkTb5da8sZwFoxnX/cpg+4G+tV4eDxr8rB+0D/zpMaOz7eScl5eZCglRRhMOPEPwyub5uWdEb2h07dPUgyiktNCjbf2FZ8Ft2njlHAkQoBArRomk+eNGLExpZRs78bcSPo0n6nc0feJpBpSpGSNW/W0IG0rrirL4NZbz88lXV34+rtgte0jxadjLeVaJNMx5UOLboxZiYgMtozOOR3C5EzHdzBLT/JddKVNvYsjmqN0xJWsuuOxWrLZExa+mbV5FLZJcUA89S1E+7Ma1bia5Q9WKnocdVj7Vca/IVkov05OOzt5r77Cy+sVK0pm25Cubwb3FbgBLJlXPuvWlKtdY/Os2gYsvREQhdYFGnHEI7QxijjunCYnMlPrWflYHNiUOAmRUurkzNTg/nftXWNxuUASPebD7AFqpTWw2NEgnTtKSMM/eN6Cq3UXReLDBhWK8fmHS1YlawYu1ZYGhiAIQxwjs8UFm4tne9jYkwh6kE0jHf5/S4HN988D+JoOKq6r4LMnCl9wxJnJWfIVV4/+/ShZreBBjqFIWIpWf5ouEYeYHZ9u3TzhtndSwwhQ1LGvO2WZs5fZ7F7eGngYGrS8XHbzyIQxEjEmd5Mq24xXDN+0ydsinH4MG2LyECWVzIbL1v/UkbAuLvwRg1Fr+9uQCZp4ND95btt0c7pzpzKiPDlWe6CCwShoaNJlhabNKPSKStIafxVfD/z7iXmHqxpNiGKsusQBwFBeRtMWe8LUwEKyxINHPebQb27VUJDZBp+cZgzbEIvzOYAWeIuVCTEx1vvqeJ0xPhFQcWitf7nh5Ef8CG21B0EEiVGRkxnqNWMIHjTjSpYujTFYF4bHBxMxzILTGvnFT5YzpLeEDeEPiTqeFgwPfcIVbQzF1S0o1jBHI4euUmKBzzmjweXgp3fz52vMiS5qLMLUKGOXQ73Z5X0Lr34fo7jhOZLXianqlmfjwMbo+4a6M9J6tl64qsvZz4SP0savi8wxT75wQcU4NBtlaGQw51gAAC9v0qlxOYmCngwmBBV0hQ4ZvgJekVx/YNmhqLMhbHpxe0LNR8MsWH3r37YgQyThyVLz33AmK3JegNamiN2tv9kLOgTYCgVPzgnPMEySwIZh6D3gQvBkeaBrHVBAUsWchyyOVfG9PDZ5wF6OKIHhhVCo8c4m1FlPXgGgZh+zrxmdMo7o6FLmzB+877u8pqDvXrzss/oOa7IaTzNo5cSlVbGQTRHwwCa0q66bKTIBbww44qeZCYlGV182yJ2GpifuzJ/JvnFYQWU4nqk5FeNVQRHy5LxoAO/C7P/yUmJPtQUM6PlO7tm/C2Kx3mvXntxIS7bhLl7cjpIp0svSdHW4rHxhV1b1M4UtHaLRNPuzHEv9P3naxA3Xd7JF00jRKL4LNGGCEFga9P/N4tiB2zLY+WEenIJrmxobk2u6zNdOv1arEZScMXjCBZW3ZZbe8IK+twVt5uh1TwFmAabea/r/e1EwPtS1WQcDkh5mYcvZkVaU+ziK1eAq6KfjoCYU8Uo4KrFH9w452Zfvi3h0noahHsJZ3zTzkZLAe8NWipg3yzgS/oV3ZaS9O9RqrH8zEChI7nY2AbDJchIBtz4YmXx2omUA5Ro0tfranv0hPOed/WR850kDv/fNZBHZIyY2AORTOgJAlplcABWnWihEInyj5tQWmFmmjplmpRstQktHtFUCCZuo6n64MXGnrTnp90uE4IcBXe8a5wKHu3Nk7Tl4RsYpeAP3JKQxBbOUojo2sGfQb7vsVO5kjqzcb76/BA2yBCuiYjKwVN6fTTeFazE06qo+JpGVXoG+y++NFP0GgNYbQSS4sMzv+cUnP+pLtbSzdkURyibKQ9POPPvRC4U/Arr3lG7Z7M3QHbXbrZHWndTpP5friLf5yvNuOWqKwPy86ei7oHGeVKfMOF2+u3+Xp669dlb+mOwgOro8ZmbYKSPc/iAHLfVuqGOjKKVLW9kAixoRQBOSENaidmEu33A/9esHWbFqrMYifqE74KkV9dkIp9poaSzbZAtPsFThLouGlHs1IHQXebXmDX7weuvCkLj0ZWRBLNA2NJuNmJ7rmftLnCqgmifHG1SoSe00+zAr++j3oGQuE0AAAFCb7gObuYG3uGHRdcrdsoWpqYiP2xWQWGEkjXVQpMJ3Twv345R7Na8a5bxWk0wbk91mq15OKiAjFepQrfYMsFOvqPsl1vCa6aF6+zTQ5E2hMMIqFx+YrHx56cbJ+rmU2WbJ+FY8SIcUGmHTLppQYpA/o1955zftnSi8N3XFymeM54DB5kgLVvphCw8mwDM3mEhO8dsz4wB4Ro5aYa43Sh2mOpz6idCYwVuhppG5KA+CKZ6gFN+dkd9Y+6CVd3TWTtoqvu7G51A0J5jQOpG5+sA2lcVLnTGmXn137DOx2fWrtQoSvoty9B784mtJzIYNLFLa8rbcWsItPMhd3vX0TKTI5cW8FrMz0BcSBbncq0Vr5X+qb60DAk9Ydf4gaM655/iYvukEic8B6qctOgaSR3dH7Sg6nqjoYKW+NU66v1xxX5nBU6bnoXT5emV0qjHmAftvhmgbYBfVFZKhJTTSuIxUsAaGB8MrJF64ZF+4X1BwdrsaRYnXpl82/uODLP2JBIL2QgEfaAiAR50eJBAKGwv9vGRwVw+z9qYo0NAzGZ7GeoZ4wxKgNbJU0FhrEiHQCU6D8eNzbxQ9LMVQ/iqwmgKGUHfHwxabMVQB2x3Ox43gbQ0gnNhqnheCWlHJbGMfocu1OL8lXaL549rRbFx7WwCOhlJeGMusIG4xqOqi014YVKmM7csKtEpgTYimB/8heJxjii8ECJIGzqDQ0OtJqnjn2oAPiCeJwxaBANsVzImHK8AVzXew6c7FZZ5T8xSZg6suD0beYb95ly+ofaCesk6zFI3g7g9cy8OJCY9QR7EwDCB0Hz4hLs520ZmTie9Mqj6Gx3vCjWnCKxNtlPu/gCtwoD/7lyBPtA7QRnA4qoPFxFoRukQubjJaCVtbV/FE7fvoYhio8MOITMKR20JtTE0srJVyPgy9W95wAMEztHuz0kyzPb7KLrjP9hAbLHbLG/wiyD+2L6WQ9iQkxcREEHnyklM+RtWVKp4bcAbvhhwYFNbvetFnUrUFHm5PanEiKobEHq9kl2TCWyD0mVgPLsa3H7ztDL9fQExqsf37e5veyN8yO+WqFNxCCP6geWso0YE8ASECSAjn67vMXgjpq9y2RrypJm/ki1vUD9HDm9IgdxvbBLg5zEkrxnksuZXwj6TfQbBYPGSigkhRwkZOpFXP2P3DYTi5q4DuzJoB+cC6rOGpAQ+BFu1oGsg/sHazPciXkTSoipBnyk6h9pSFK8PAVyXqGxkq8lS7BCcIRdHD0nvPQRUotRyYYcAAAIJ1OoAQOeR/yLDz09p/x8hFu/oSWsaPIZzsuqG/xvtuV2dVY+JrkupYl3cMBGT4FE5NVYE3kSa28H+UBNm4Re2MZ/qeXTrU9UyNpZPGjSfQ2AQrv2xC0ZApjmsQLM3K5fKh0LDGTYkBv4LesoP5DhS5numrlaECZq6b2jOP7uiYA7Asa/A0D4vffeLmqcMovW+MFu0QkEZ6aifg73m+tj8ReXY/zpT0X6DWFNVbX+eIHaez80a3hcQn7a3F0zojuhDP4iP9e9c4hC4vhzjQmWoPRriA0WtvvhiJRhNQ+CT8D9Uuq37o4dNbduJZ790FOqJpCpg1RYPLtHkWw+TwVbbe3chINJNBj1ecCZKzSNT28ob745d+NSIT8I7VW/4OqbAoQrDNHOr+dSO1E7+3EtyAth8xvy9VYInKgf9bzT3+Oi45LQQU1RYbatSzBzEZNcnuKRd0e1/AprIKLEXEp9LBKDXsFXaOFuEyE4kzZcqutsCGgOj5C8O7uWWoIIVgQX8MNmCaALSsLTVDVOsmbrTpo5I3oyxpvl1iQkzJ/ebb+GkR8PIRW/E6qgtQkAgrnqZg+boDhaey4HV9T/EFQIgBqVCzHg54CnofcknChuyMnuqibAu3srrK3ltsMePlx38idSetgaA2wYtVLyYgt3Kd/aXyxqTH/3LzEH9cKcrtw45wN0NgYT7tELjUNa/XwFKvXuCpQiWGfnG2sCMyUtrxUAIobR1CDcwu7n2TX6UlcK6AYunmTAkpiYpDRR6/p3YooCF/6tqE5xVYlNZ727FM10wGqsRzLXp80HXD+Yru43JVfZGX7y7U2SRhpJt6olHeHI1hzTbM1i+hEdPhaTYXLi835aQkRpo8QWG2c8zllZFp9CrYOHQtuGj5HyVTM8u7P5/tnhd5GfH83PcM7srKk0ms0zO5WI2e/qbohfJOn43KdMsDFpR3fUU85tXK4/uLAmcPVOe/8bz0z2ek8SNEUT0ACpNe5icEZ5KFuh5mH7kG2ZtMouWC6pcGkmOnmY3b0DCdHphU4iq4jgO17vkN35Mtn9Kg7orJ+pRMI4bAI99yAUc6tOQeeg97sY1LBxePWIY6KzK1X/16orlMI9a5Tg1/IrfVCw30xX+8iRN67IsT9Uj9H7q4iRRHQZ9MivYBtjQP2c6agoVVTRxu0tghb5bOupzGURBTMT19FvOmRkU9lkMQdjamjOS1TvunIYGSB4YI4fNd4sOna+BWEVi3MkUr0Osxaku6SFKJehJ8SdU3bXZgps04/3FBFMR2p28mSeVSP6kPueRNXYGpKjNgAeGddGdTbTi/brWALGANzQA9DyW3fBwo3LS19fe2Uwf4DkZ0KXNvI70tIlU6KRUqIBwHeXbN1WhPUDTfC50AgYgxDx+31OjGnw8sdK6LMap09fIOEq/wvJPv0XbiZ5g7tdxW9WBAHAL2rcQQRYMQdbijArSD2hpWDAbbLPgpmAAAL3AU0XIlUzxIGPShIn1vH7QPxt64+YYj4wyvC4KSlZspmBI1bzNty/MntJ4wUiBkbeAfbU3fS9HokmsqMQhAQ4Rp3zd9Ml1PHMfg0ttwOyVHgdf0LPzEt2N/ixwKdxRnK8gK7gmZthzBItc2cpijIukxDzFYVW+FKmg+EE3WNNK1UpnqGgrzivu+D+ALMqYA8h3GIZxfj1EVa74CG+Cknx7clnBzlvx3KbX4cUn/NPuzBrkMa1QJYXN9pqEm95Wp3e8EF5egke7NFPWJMHKn3CS+7fgAnv/OKgtq4TfrTCp8U9FvsrqTvC2NzWqEfOzuvPe3dBgkO9Se7YPSvW862lRYJ1iwID6mFr8WSWIRd5iqVJ+yRkQmRug/sgqfKYuZghD15Tyo1XhnSMnHtXghDD77eblw8XF0YvlhdLxDFP0oZRfslQ0GXXJFjSqxau7Nm7WDadb2Pe7GktZ/vesJc9P0DmgLLLRgnB2I2zi0iqZqO2Y7EaqtpwNAEUbJ97eHrP/fcoNkCbU6Shr5hxwOQyP/vvqETh2IjXwI/DuzY1WoIHyaY4vR40m2ZWQ3WD1mREWGwmoFg4sSFy28pEm7zNABaWPFm0EqyEWiaKKDP8y7ExkNnudX7AZzutoA5CBsEn/xjpcpBmhDbFyEloUJClTOqNeDbqJaRewb2fxp1+ZTFTMcaEiKrrxnhSVnWYb/9Ztfqvp4JGANzJBPI4+rl3xrhoZON51AexKu2Jut1Fi+AZez1AD+5zESTZjfkqLdN0y7Wjx3qqyabFbqFPbwcYlfVpYT1WL+LEvsitF/t4v09g2D4yZCHZXGJr8g5PHLzUgHbJRWSKWE7CdJ6MkwSLo1FVyPMnv4Ny8lWlUSCvu7Y51CnGtUa+FVd4G33Aw+vMdTNXNcxtIAMhMbPJpd5Lzm/JCUmfSi+y+TxPy5btytuDKGnaUQb/nT7TukPe3nTEIOUq0IkF9n1o2eJnjepyWb8WC2IpIASJPlADbXPsrsFC03bMc0Xm+WTU9DMlAOqHm/wCFeSXOYvx/pkM15rb/B+7ve+NiNSZp4f2LzgFT2B75a7XS1/kpEpatB8zx5RxCeK9+Mh7A8kKyRt3fOe60oaKxW8NhdjKW97duJrkTK2mLJXu0aEXWftOyRjrDQGcs4P3vNAaaHeCfs1w6TvGJ+aff9m62CFHafQ4Km8VRb/+AiHirnjGmgQ9U39NEl6cH2v8Cwkj6v3YEGobLUznUsQZfMkWRbDSXwgoOMjXUjbvh+aBx4Qb0Yj9DfhMaxldQp5rNuySLwNIGrlMdjUfG+LA+Ts5GUv2SGYVfXzfOo1qo9pU8m2wGXIsN8XU01RvXxAvwGCGyUdSz+4QkwzVH1Rn9vJxrWxVkqjOSI6fjPmr8SPsEsy0TjAKxJNUB5GtpeAvbRf9k6/CUUAuM9/V2F3XBUpHs2biRM4FYTQ5Gw5cAtzcJL1Tyqqqhx+9M5eG+Rtdtqc0CrdKh5gaSnvGT2/5BMYBTKIWoee5ZzFbwDiQWj+QzjSQwztW/jFnTAHkOPHl7P+MMoo4PqCvWaLYxFfKgqZgc/CLoPQ+WN2O4kcaZKQL6MGyuRBo3+CN0YDn+RaxwxIASV+EJfThuYSr3SZZ+yPKWrwohjknhhu9mD+tkCiit+haRjq1CHtn9356MMNEVcueUtAkkuGdBRgL/hHiHqWwP1MT8kUpJcr4CHY3rNdKTTNqgt0tRroLTie/2wcWdpAAACjBEcmUO9lRE7MAvoH8KB9j3OZyhcaNW9tRokKKQi+bKNnL9xQfq4JloEmLBTQonk+YN5ncG+xoalLUgexKAywUVruQO049i2RI6xWBAGt/vLbFcjjwbsBtkLND7fEwPsKkhkzYdKmDLF2mJnpoQuSmCEkqhmdsEPyi/fnLmVPgG0vUJAh+wpHfwCAB3cpVUafs2xRuACtZvFy6wdf40O+yJjfkednDrGi4hhdzbZIM0QvFmMwpGL4BF5aN9byT6K5qAvo+qNzCoQ52BIBEUdQ+WRinOx2VoqQwEK1d4Qf9NkIb93c+a6ZGp+gMp4LJt7rjqqqg6C0o4JLmz186w5aPJPpcYzgQz8M/yCIKPqFdTrp/KJh85ogrDTJnC9mxpme+HX7KaWt3lzaLZc9pFnxu3eoQD6itDE1SbKY9JC/tM2d7BegHh7/B/X9TLQhK3t8Orilz/Ij02xE66rKWipLI/Xpv2Ka/jHx+JcKkzM5DD+v3ymFjrYViGfOg9dTqN5MUohXAV71CbXb07Ol3Tb5pytsQl0lBRybyyCJWSuMMqDv4bNquqM5IOQAb9VG/VAPnvgBaGTZDmNLZzeJYaji9WQWSfpB+yGP030etuJlPFUQNHxz5a07+WhvGtUSXj3klC7DO0ZLw8Ezq0qQ81OTxXOgazgqNNzd2GC1pMJEZH1VhzcJWGrfXM6c1l4Hyjng6MprppGp7eaGq5xaN25iJTrmonGIZPpZPEFfkDG1Ttp67xbzCTwfzGWPHCKbhJHNiL+jWVcuCToWw2bz2NsCqFF/9vfIu7wA6NJvDlG+CNBD7cmZtebzZVDvbaTA8Tj7lQn3/8E+B5iSDVSrz6m2Tbj4Gn8PbyGxMg39Pg55Q7z2d6L9AcSVchVuRvRhEhip/vnUNPFQhVDppKRXNy4rd5ZUED4SIj0XYmoYQg3TkeYIJyqj5ZpOnkM8Pf6XQlAh5rXtncRUGf4UFI0QxVOrunZ/OcGIDMtej5wdORU4zN/jPuLJgOMSP+6qO3oamenTrFWQWTTYBy15dKejfXn9mU6TPaap15YYa+NDL/XUAfsJuxr+cjOnjQB+GN+ZJE6h6CA1TXdwqI/aB4zKkM90+qL69DGLpmyVK3xbr5Mn3K0vzEcIBX/NHh+WVtYTsft7cv/t3jCjZornjHfB7kN2sYIjTbjnQGEI1v0aC0LaEM2IHKMLOZ6Ah/2B2Y/RjJ6eDUh7/sCHFEvdpkELHg6/wglTs3YR1WyN5IeV10Vjo7zllzVb4jx53koN8S6cbNSgB21jCUDeVUv90oObX8WUYKAUmBhpbeOBPeRWZuXQ2vXV3rnp1awQnc2qcVLlVPTWO/yIAq+vIiKXkxtRCDBBe46xOmjQDJ5jeTD3GQNrcM27dsSxq8ktPJGHZxjyo/Piga5lbkS++qu37OUF9Hm99KuHHIvAsI1AB2lOS06zgDmyfo46EAeMcInDGWdGRDSOfZMO6uAAAAIKQqOpz8iOtjkWQ+rO4L3PdSypCN1YzCVJ+a6OuclbWnoLv52VLdHtNnlH3qvYv3oCjlnkrHSNlmlnMpjaaBqjuuwn9WKP2q0Hf0moPs2KeBUWxU1oHMY7KrCOu48PYrUg7RRcxXv6mkRc17y4xdMaS+kS1tZcBfi27d+xzEvfIQNAkbD5s+RzlQog808qodij9lXh+1u7fZMcHZpQ8khfaL1lULo+QWstR5Y/fvkOMW3ahOOOCtc2GEXhnutCgEW6HpF03LOkBBvzhqhn2FzP19xTuyFfPoPfMdUsrIdd172xRBXQiDmlLJRgh2+BQBy4jy/nZxoJiz4E8xMmfIjfC+ITTq+7yLApyg30p9X73C84iC3uCyg94j0GzaSlZNzbDhkW8guRQRDQEQVsDI+dJsi8+DcDA77yN5PNSn9nuaRLtHKzTnb4HJGEa6FRmqmdBx2waoCzclFDqEPsieTcsndyde5mz15/P6T3x91K1Iiyl6Xm/oeist51y5TssG2qIvv/P13pJNowugoND3ylMuX7bep5WVRUgCDw49l1f7aom1vY8dHcBnpwHYrLXx7AKkJoH+w5PzSH5SpYh89IvJSKrL1mbsrWgz+O/7mLV1SiY+8O2tB3PVR/92+uvMctgMHk9VLFFSE61aq7C93Xl8ckfb/1vgLhllFF159A9qwlzf8SWoineq+irMusL7nJMG6r5y2L00Us3FIdOIZUGxSttk/QTcmZ2c84P5TJC+vRf70ZQVDGs/MybGH30IgnOaVc8Filq2noZ6QxR1E1SV93PUfkgYXXb0RO2YPBsLMEvAKjKyYYvD3S7u0/FbKeOmjSEOS9QCV4uFhjVsdIDrCEwdal8K3gI9Qo2QUYvRW19LlGsfRK77bmFku9rtPzPkdqQ9A+rmLsqQ6GwxUYKkekcS7W8XPeJDml8Tbi+7CS0JFK/2lMZueUcFp8Ji+TXMZ/K8bqUSYloHKGoOe+Rwv+ujPQcGonAxcAD1IS+kGFRSPCoC2PojIalcmG1Sw25g7jFUs9mBk56TNFVtztd0KMa60o8NYeCP3Uen0Zvhci1ParjRiXXK2/Ehx7Yb4ZrrHhKZHuDihFPASOXw3+3CqkZAtWNeIHL6NWBvlR2zeogfi1KF8FBAkfN24CWpj78P5RQZdGG9sgpLEeTJVg2peGAXbMgR4x8hBrWt1PuuF0xkRklxTxNqR6T3BzpJPpRYuy9W/Mj5TiCVg+q1q9BOGQgLkFzd8i2VeAwvK5PhG/FAQUO/iXlou/06FT0jFn1lLdk8V7kqTYo9g55hYFRbIFINhdSRdOmJB8bFGFkjcihsPkhZ6fzOU3JWMx3ei+JQbYs0oksnVuA0C1x2//OkZXnkQE9nH0juoMoL7A7FHKUBsCK6hnO8vhn8nLoKPMVFD9nAcIxdq8hMk7ng2VihD8iTFS6dr1TIyeXyj63xFNOS8cdmls/DNrlucPvxEwHnSB8/WTGlKhg02f+wRg0FKUT4P9j+af2WvFbSTTKH0YuK3O4QwAAADagKOp0ND9Or0ZtuNVbfobXjrQwspngwi/3IBOEE3yVXRZfxV99bTBY9rzTtmV9FFKDj+xrU5uKk8tnYqkktpnthfnurBbLg9NbJ1Fv30/Agd3KmeVZrt+/isyzSHpcLAyVDHq/LeuVy536n0xBl9aoS4udKsp3Ij6c3DWrG0tJbzKf9ojsy5dNehA4UbgzrAv8T6PF+bXumJGAMCDCglPZiWwnPiuUyp2ewnAzD1kHx9uYPBb0NCwgW+EMmD+En27mU11VwjIVTcUz/bOHb8vtt3MT/1jjGrSiQxzZuMyDgFWyQx4oPizR2JUymOR1hIRhWjq4q8bdQQW+7YFPWvhmSH09/k+sASYgElDV138q1zqEGSVnoV/AYfB1LVHf/uT8e0qpG8lzEWqR4SeBX9JMMIaPqaYZgbBRMRPXDB5k2Zc1BAGrZY+3pSu0e8FolxvoejZstgFTKikrkal4AMqR7rxeWXJyeWeFQ/uEtUqdiWwyF6w7CYFU4U1/pc/P83HA9OGzH9SV1eERqUqqP5GuxJ0UDQkZ/SHxVxuea8aVmKS/7ctVF88a+f20CNcOoU4NBN346RE2ijejxrlz/iX/lUR6SJ29H/+qI+vXi/vDJ2b8NWGYD6/E36f94nwEYAZQKd9uJ7pLC7U7Wcn+Y96600PLZkRxMWJTC+BE6gmpvlRi3DUq8ZLZCyVAUDdcf2PEQ/EHlGDEMYnBJL7iyCWZIyaL6xM7PZUYBnqqHYHWl0GG9S6Z+jHvSWF436m8O+HRP0faqXaJH+Z51BhmQbR8E5eFbUs0/lhvlTOSqW4+f7EUmaati3JT9Gam2mp3UyB/JQGARQ3jt3vAyXM8ioexe7o5j90XfhQLM0LF0H+dj8roQf9X4hZX5L6J3yk3C5+3iqeVl/6ccX4LtdGHFRdHqN6x72zYSyeXgflEVN6Ld0jNjIIYdY6sQHy2wCnku4yf1o9ypJinCW90iggo9Tl2cspQqkZktsIIrEut/zhRvPfZOv2xJ9V0Qejtw+qirUAIr6QSRHturpgrY7J3rKsCuvYBAmQkde7DWK+mXz1HAFNRJx0JGX9z1YrrV3EgqLT1xaHqbtN8KAaBy44CZDvfVnKQG0Hwivtba+GDcK44RQapdKkxojGgRQVt+3pKPJAxfSiDxTmimB2+N1ysQPA9DScJGp/Jd069cQNa7XDkk3CXAXZqb27+9cfaBCB0AubYFEkbBFKu3Ck8iIvqjAGy79QZZWg8Hw6bn/SkFaKIMMr1zN3GOPnThgVOaqrTAuazPdxqmelXzUagbut1bPxDvzl2uzyYg2YJ6VbhYuw0G2dAx5IPxJFO4MfbpYMnC8/Iab7NLHCHV5/tptCiL2LBSaDVRHag9yBNVNL9OUL9v1QzaoTE0nEP1hip7At0xzKT32u3J9gQiI4SG5j2yx4ezSEO9vAhEjD2dipbcdmK3VOHXVFHcPqPXg8MJGvwUuYBJkVBziBvQMYcR94CXTU6P4gHXKYziI3Q1SJgLOE1z8levme9S/hbbM9qiBWinFH5zye8gAA3OZQYqAVt4apY9uJvZkcE12Qi1iq2XuB0DaUPeDpHZSAFKjNXt3cQTJai1M8U/rZVkFkI0bxMfGnYJDPyNc0CmbE9M/4rXhCoMfLxuifF00AAABq4ZbVSy5Gxsolq78kF2t2NRudNt4Uc818r0ePMeHNRD9BcPkZiyLaF5+oAW4QvuhJJX8zGrKEDU3+xXI/8vaLKlR4t4DMOo10E1y1zwkEVUepRsaJOdB/Cady4OXeKku7bMVQSvcEWKnY+gAE06PHRbxRHDEDuNSJ5qxnJa48vMPZJDR0bTYmBPW9qjfMlJCciXHk1SmZ2s7pyvJa5Xtf/lzo7Id+ZHcpSjd8DThHii6dBYi35IuxHPZlN+TbHaPalCU8secOStsybjOcy10U7hLYYg3qzAFWZRRHvU/oyg+u9lrx497i/XW0LM9x+qm8Lz8kOzSJJKFPqidms5Yw04Msh5maZvV5xtG+TR8ERxDNYIvRWps+/whxai4zf1ig4KnzI903khP8XonIeJRjHzV6YTk/Xbnf1zOYC2lFvXbvV/3tew/b1ymAkJtVAeBz7jyqwZSxU5vRUTjSyf9ROLcFpeF6cRBZhL54SdTNWzcMSswCglcmVyQQ3GywFKfRNg1c6PQz7jPGsoSClrcDJMWobFutJkv9RLbu+NEDJlwF/7tt9suVJm2wgFP4UhO5Bxc9cf+oTFUv6ltrMHSPvQDJ4MiB4QvoL2AaNtVKS8RetnUfeufbDZKAfj0JLafsihPoglya5hJv77+BuFYFfjYwpf4CMuDgtu0UGpAp7G+ZcB1Prfe/AvM2j/22nYqKlBrJ0lwP2+p2WQa8E+CJ5WbbORDAZDh5xjxj8/scJ9WHNeKH3dA/vU5gqzwqRDt7zs3D25nuux3apzbr44eqLAqFEsJN7xr4q4PyPy9mWMq3db9fJI7kIEX90mnxvxwMpa6qYnZXWmq+wwpER6Vllw1+9h1Atzzj5IZPR+S4/pgo9PRGnUgjMjxXtP/Su1wzrtRR2AG9QMuEcS1pScZ+0+hzYh7kiuGC9w7Rb0C02J4apZ+yEOWCnRWKlZ9HVhD2IZQ2e+lkwNbFDCBKqk/u3egNdZM3HCQD7LiCwtzmuiiVcxxdo1OMWmEvOuDCDiK+nw/DcKwRL9NVuyVLW3WML47Uig3zPzyB59S76SPW9/0fn/wcwo3odL04r0zCZNRP9RbDaaS0ZIk+K9B9bF9Vsn3RP06sm60dLWcLPbXnEtgAkd7ZHxNwR0bcYMtOEWrFmWvJ+6PSRH8FkDfWae6U9Ntm5un8yxefGZRDmLX/R6M5/7ES1eLzxLOBXuoKBlBpBiQixH2ybazsJbvFzg7h2vKuDLSjWKAqoTeEw57JASWg/8bdOVfaGHwmR/9oiM3FTSaA3lcsRMjSdIMPAoNUXS5exKGaaEjogu+N01M2UYSiUBzHPrxRv7QkeyQBW+HcDx+dRSLwaW3dkk6+LVe15FL7KxVzgyJhUJ3KH+ysq8sPW6mNXuseWSI3WPb1tkxMxq83XC2VjBeHMbZGA3nyL9NCPGI+p15lKmkFgg6xjgXvsK/fqGobtoBqHQC6/gx9NfSbcZ63mbmJkOLCyX07IjUDi9rIqp63H8Gk5kNHTv2xrryTsf5Q3YCKYzFPbwcX8zfDSsw/IjPQgnD9rbtD+mUFhiGXTEX4gRceb5FJJUCeQztf4nsaOpTDzKzuH/PZnEWZmb0gPr3dGHx08SGwS0xFDrumOSfpiTspb73ArAk5E3WxA7e/XBwdiuhJKJdFavygojxh5vZXi75irKtsJM/Ga3svjT7R1J1UW3sYeunGVhAb6HZh36vLsNnsP4s49FXDAAAAIFKqeyYKJw2mnacmC8ZRQIkM49yzld2NkyZQOwSoQEwRHt8DSVS/keP1VsVDtooOnWgT3IVI4Q3AO+QFlo8PXphTyx4JGGWthxqhEimUanCzSKhxDaTyFcyxGkQODHOWypdtcYaTnUbUmY4yYo6kNTmWzO5sCbYtg7WmXOC+yLJylGRFoQWAgqJ8DUNe9zamVTQcGrnI7yEg9wybrYxwBFi5bWY/OFEg3yw45qWmAnrWNu2PZhBmMNC1yZqM5RmXaKlK1HCIcXgYhsd84ZX/JuxL+06/WlJ8fXgDqgA7F5MCDaNtK5Ihq+wiyGA+q6wMsUkTexC/riVSsIu65RlgbHvvtHkQwn1Mx8Y40MPdtIph8M3d/i448Kmb8h/PMz7yhnzkV/IJYhfE7QHdRWaRdszxKeQALEeMuBZRnnK9gXy3rIZ9ha9JdRFqu9u5PDOf6DlWqy6OBXWsipIvXkyq6Ktj6bzp8UHzyKu7A/il7trY9v7C2jUcrmpXhSTK7WioMFahyt7fJ4I2I3QZk6lg7a20AOaoIaPoNKO7JhWfkAK9pf4bGy8wBRdcG5Y2WdUhYhMKpQFLd4zrukCqK5IpRyLcKANZBJZNw1yvxtXFjLvsjtgudALKX+LEPI4Uu1IGvG6K+EhOIUy0La2OOBeAQ1VpXt17smxl1Oefc7ygzToh04PEa2hjBYWd7CUItZmg86tV9hLWNuFI5yWElgUGxNtrsUnC8oomCZ98vLakNPvFC346xiab35tmM/5XGX8nIW1xA6wdUfD8Nl44rOf1rL/ThOcteFjLKrJNeZIGRBkwzL8HudjDo2+6PGv0+E5/q+W02JBgS/wuMXzAcjzVifiE8Z2cx/MzEqwF6wD6vDtv7IxwyG36TFxgQ08ErCcIOGkJ5QoXS8CYkW0PYORmmX3UK4JZGCyu5UGUY1/qJWBE1s5XV08o8TU3oPi02XwTUr72TCxxcZpnioAByU2Q3J43w/Mqpqx96FNWyYdCgBZZgQ3kyD+IoczKSxYhPDe1NTdQRLDbgy1VZH0LBQMtPnkvy+grnON1VriqqvYiWJUO864CGIUCM0z0gsYNyRqYlj4Vgyyde0CW5lgxVw7gEJ3gyXr0j/BLRulszFOVWzhWqSM3gWaoc8dVUvBAegX0j2tdwQc7jfoQ/rTBCrZxZebHT6hCQIb2GklBX0ARADsDERkUeGuLH0nc5JDZyCIQbwKox7EX8saSH2a9CWFo1Ya0umqLtmCutrlcHf2IfeTt11I+hCEQPXyZ6Ecmflx3Tp7RWpjQN8EI9xVv2tgZK4QSc1F/IwbIxT2EfIvD938vp9BK71mCvq8oPYKNIrEFnjslFm5uiTjPKFaCmoZWfmQKFDAgfGF/u13uqb5qqLzXPF9PWv4SNVwa9kOngx35rc52oWpijun6iLUG9psCSVWzw+nJVHTKbx4vnwTi3YBSz4z6m8iCJlNT4YGm2Bm/+SMemkxv31NmucIkNqvMEH12rC3PX7AMO5T0lywwT16clpV4So/k/Xa5UJfPQ3hfN24br6Q5LXcgCDIdq2B5kR76S+BnAUbe8SRR/suh2NVZVrCWthsGMGKEi1y5tlZTKbQ9JeZDdWLCxEQlEIguKGj/iwyQ0eYWh4pbyBbHPxAABTCmUudwxv3mqDC9mP0iTPH6MhD0uUkpaRWT20k3DI2lrjqymnvFfOLsH7bezEe7u6LRgbyslbL+iGjJQfh3KAU3BsUbIoKGB1Ee6jyt/hyGJftCalEnlhwwwzKgREc7x7DQGKnIg46ASQn+VYEYFJMWk4mOE0MrJW4mBwwA1RaI0lzql4QbSHsL0bsy3zRvU+i6nrtYDKsBjMQhW+98fENu7Fdp9wi3XpD2fdPZdcq+ila8o9BqIvUKuka9gelRepHA2ySwlmjVjE1zgpzevE6O5I7QcFkYXK1xhQEzTKO1fFlakZajtTNZdZZnQuhhsitXGZDneUtH0qNZ+u8K1Z7BUA2MeZVmXDP/exQywz23b3EnXQhvXvTmxzgi1AijXEPT5LH3W+rz82R4PPQzpNcTstVFahreknxPoMdOzjjdz+CgXfbOM8Zqc0Zi48JMgNaNRV28u4/uNA4j86NZobNfgLz9o0ZPcVhWGEe44t65NKPw+5SO513PluHnhA7fbvLXrdLBwdeho3hO08lYQD6M/oFk9RPc1zLI+w6f7xhFVVSYrLvEH0Ei4/D72rhJ6Xa6eA01zzFBls5tiRz0VF4p9se6l48oyQtR1HoEaesvKMC/OPmRo+D51jAdgc9njINmD8tZDnIKryw6TQbZ6s0RyNrHguegTel/8iEE+LXodb2+8VDB8WMzksjtuLGF9zrPg4f/AD+K/D7G/flVCLQF6eD1ve7KE7ufZn68PlTWx3ziADkJqffTIBwwB2tVigArMvb9MKJHhOm3CyFKtTe46WSVXA+MkIBM+civcFzDP5yZb54/ZnWiWIJ5+bKKLQsgGSvBCb1/ipz2cxiyaUxRnSvEbBFEV6n2/lo6HHA7DF0Yqge9bmOuwsJELQMyx+P5jkOyug1usIE476Lq4mh+YPmP5atvFnlDp2COyUs5TCNlCWKY7AIl/Mk8pWF0H8zM/RT1eLFbND201LRdaihk43kGuhB0yEV5O78X5LFLyJMX+atGgTOZw6JJiYTZDOUOboGZq7hq50Xo/xzh5BJ7kVPCzdOazEiZU2BwC7I1MGSVbzy4QyLxBU0jW+LQ7g0rgZ6hyxwNPBs5enVv1lJmdepk+JGbOZnVx6HUNEdjDinoXu+60dxNZCIWRtJbRb5kq2M9JVvjpYoTPYoooHlVar9+acCYysBnj2TDhpw+mMJYFm7JqFJpGiSZpfJ77bHFUjt2DECgHF6JxywcmKKrubjS6ifze3KRRMz+T9Dti5qu013wKpQtaBAnwQehr/QQFuHW549NR8pO67j1S92l8jKAO2E+1t/3sBtK8om8u10hZDn6mfFXUS8kcSd5QpR5IpTslwrEstwwHX7XxvBdXHsjWeB68R2UHEvVvFBvWCha20acJKHNyPgyJgfyUGHbiNRUhK0O4pNonC+BeH/ACkfx3dLr0ty5x8Y94CZ1qo+QI2xtvZhRBqcZtbD4uT5UBd8PlRrdf4ryBAMN51MqMdvShLT2N7PMpk67YgiIOEbVhAwduHk+XRGO0JT1AE0ys2nNgIwjhki+Vu2QNvupqPA/FuN0nrS/GofwKrUhcU04cPxEnrfDutiGkFj99+BSy4bfindknSRnbrr2uJGXTrGCNq9E4FQ8WeRt9ni/nRvhQLV6Xbt6kH3g/FVvZtS2RENmO2SNnrWuo6wD9xjJXSkJWahdLGaKHnRsGmsczW9AiT8672Z91D4GZStqaGqo89qizqGFTNz6Yz/YFRrvoaeapGZOxgGAY6R7gAT2O6ckJXJCe2EmukSaPXXuBYf3U6Bka7YvMt73FqVXBPtenesWP2SMeiPF6TG2qB/04A0dVg7qqlFK5mLV0vbn0juJfUFTlHLrK3HDTrMpeoFEnG0MCFmXnMwLhZLNm/6yaeK5dbzXG5sMPpYm0hh4e12BHZuZcBOXqRG6U8I8mCZ+Hxk/u5ivoqPKz5zmZ52fBaxFl8zLuhjWejP4ozE7kaSm+xJnIK5QF1T5Blq6dmlYjPOdOyig2cck+7PEwQWoLXPV213wsvl536hZld4rwoutKGavcEATXpSH+S/F0gAAmTtRfQH0wwLHAsikY47/HAayXjzngPElMvjy/l49bnOLqer5Q52vQnOh/HVe3Osd+xtdBmxPuakT3Fa37QjQCdjuZdkdRasW2hkH9vuA59s1ZXlYdL3KDQeKakUFLXZMwvfdSfBCdkcZC1N0kKw3Rszf34yYOp9OjeE2yfliTqojrmz7U+dGPe+MNL1acun0lqnRsTtBvd16IzsEeLrjSnDQSwHwye1nrYXFNwC0R70e7jffplgI+j7HkwCEkAhR6AkrJbyYa4d2UIN2OUna30gVVB84/JNj/N3yYjUB2lbB9ZE3hBLVrnPzM5DaVBVSuJoqC/u64ueNusPljEs6+7GP/+WnB6AHpqhpM1BmZBmTAVC+DOAKWb6Q7Arc+lx0czu3d5R09syrJoBR8nmNt2/U+6nVK4gGehoYaepDwGFJ8WRZ/e7mbG/tVM4cNwe5dKY8Td6eU+PoRmC4Mj8AnPA3dlaNMKEYwZFpf9igeYL7bmXK3OtoFX6SMrYBQqyTggGZlRnfP4jpERA9rodmumxdV/jf4q1OD5O2PLJWSNtKIcD6nK/JupcGXTuZziXXeJt6NPHQFlIf5qBraAbRkANtowRl5LDa+klF/92HGvj6DdVoSCp8tmhc+O2NkjQNOuRrl75RYH/SpDPQou3J6HVgI9NMrBVGFduHmoqMsgQ946GXsF/ZZcSXunrOoFyyjxB1YhLY4cbJ/3JOtyFg3gyHMC5FP49t3zv8Zh63yx9iDik+H9OZjcr59Zkzxs09PTTNx/kKgBLi1Wmo+5c9pXg/suaVCC/mP+zeSzgfg3Z1oDiynyuKJGe6g/cx1GiWLQ0gWcmNSfcaYQRrVzKoTpeDu3AX/4rXdhbxKI6gSXsLGTJfQvRm+ybqzl9Af+qgqeyAT8wr23DO/KC1yDYg7Gvx0naVVvOgYla9IX18C9ZmHfYTzpsHiWOwrxAfC7JDmagzJryn99IkbGOA3/8F96gN5/Tg8IJD59z0zAuObfHOZFAbltaV/4YRoAEhVyCjDrsOhHx7Marwy5DZUWFOg4bepFAI6vT/68ee+Fs/pdWHqaQd5IO8J5VcQ1CHwJhr/AZoIyRTpgCzBA1E2FM3yThZw0i6dnXnrKwZMyoKYHvYpD3F3hSIivFeWGJ21W/T+JEaIyyx5XFQ7wtxlvb0nmtP5K05r74kPNeVfEZZDq2Aji0CJx2KzTyTScINvceikb4nSSGg6VwpKdSmFdHUl3hr3PwEI+ynsFWye2GG5Y/PdbHmNyRSrOX26yjOYsZVIJhkjMYJ9aLZwYaACqPj2bXz+3Xr2Wrdm7v34FCStKu1rw0IXBs1fjlTUMUm0bJZAcdPkVrYDUj9HJT9a5MzWFEjf/Ux107xU8AUtq4eKAtabpVZDLy6V0D8caXSl474OpLQHvzbUjG7KdFx0yNRrvkgeQCbmvWZO60+BlBcaXV23o5VoPN3+aRGoz4vhz018v5v40NzCEkXH70zCmCwbNDxurleqcdq7JmuV3E3Bjj8nJalGchNT6i1Qu2HNEhIpVYWD4eafOkXsh2UGTIQ3GiCNTfzYG/ukCZDPbSlhKDFzQ47JMxE0LQd2q7LWihbFQDWyjqa3CEtKi9RCHFN7X10mOwurw7cguy/5PCXD2yL2XWOYjrqyNrlX/a4RGKgFWuIM6zYybp/UMceyC2kmJRmfBDY5K2lyCV8NAKC5WbkaRcy+iT7DGAa6P19pSx5+WD6OxGCLro7473/9qwGn1jrNNUda0KtXmDNMkceQVlIOut4bHkU8QAzV8qkT8cS2DidCU5GQDO8cdsS/UxV6PZjE07I5QRiq5hfOFt/AABx6Ewt7r6hvg2RPCpCpnzmNRnCOIFST7VPiSMw0XVVPzynI3pwp/YuKK9Rnqqk8Sj+oFPB65kgZsvstEvcuBjExOcoxpCEEqBPft9Vws7GL4iSp9SigRFTciroL9/nIpUcotXxwI3g+xLhWO6ag0aUq9YiXJuryRF++3ZqQAo13sybx0EbofpQ16ENUCkC0IjO3LFyyuYIMniuhbI+u9cJt5TMZe80TnRtJTsoYlUGsKuUTerrl3zwNR0s345IKlosBMG0M5jjAcMWf3KzCDtXdgKXXEiBK+XD6epq7za1kx/NEVrdEXMkBgQ2EufsTyV8YLvm1I05jPeCNGqFKtJOyt/iSA857mrvHRC9htEqECH37mQE97cGbX4zXxRxiRJ2pX1LE5mKsSK7KA8T+AsHXmGBRgVf+ATLMobrJcHfRW3a2yLFg22GIbpxjmmJPIOwgCJMy2ILNqC1PWBbgEYOgjFshIrIQVzBrcYdToO+PjbErwGCxUGZiFmHcb1ZYv4FCRYlAUaFu0h0E9IscdLn73w5eaMHiQmP+q7HyaFzwDIHFVBQKtQRyDaUmNRar7heBO1oRRim9rveb4K1JXkDmcs3WGDssOtxytkG0syHJdMaGWzYQIjT4hMuGXzFAMICv5PrylGm8V17WEvC1BDAo69kDWgtrduS2qkQP+2TG5HqW/1PRfRS6vnPNFXEnuaySRiAS4G3S3D+xVJCCh9TIclKCjC81EmVpgAbJSu0IS1AWf4SoXEiJ2qC3goLKOBkm23KHPw4QWMGxQNJTNnWViy/x/TqKFHi2WOZ8DFZTx9REFDKUUd9EZHwOJYlTjZn8jASRiJJ5qdJ+ddt15K3KVrXz4zUaTdTMHKxzU0VXFv7AyGrWLYDoHpIelnKWcqm9Er/7brXWccFXOgmtXTKz3ruvKutNGXJTyBPQShMcsS7G9pep+G2ysIN842OnRe3orcfMmAvfwMJA3PEklEjc2HwrT+Jan3ZRLv+IXKkNsfvl6U+pAcHfRs7xXo3mEFmwLfzOroirsg9i1Jk/2G4w86u8ZvTt+t4BDW8Omr289ZlSZT7T1pRlRI14uC9Ofvx/mSZuwmlKH8ClOMyOQgzWxUHgw/Oz+RQkGP8RV6Jnbd0Usz7gvfpeK6dtHvy/8gaCIS0iwDu6TVb576dt6XfxavBvo+RGWAVBd5FBi6YodmhVH5G106zOXDHt2vAYLkghX0RN9afWr0cXcuda/Hq126Da7d4aiIcUxQc9k3qaxZrFmPi09NiLtrPo6Xsz49csqg47wm2lrF/pHKD9sWjVtavw+ygFO6xE2EUjo66lvmJbW9rpWL02AYji2KoL77RuKfh9ylDGkwVe+AUtKXQIgzdhpgEl8y9BM+sM75DeDv+2fcCVrCWUgepFRimaLdY0gJwBB+eVO3r65XfBuHj5nQzCrPrdSZ1pC8iycarl029SY+BFcgQz1tGbsX8iG98NVoJMMzDItcdgx9dKGyxsFrTy1hRxALbWuYkfHi+QYTEH4pGzI6G/r0xG7cvlYWt6ZVRvkbIhb9Qk9+bwgkX9mUNw7u+RGSkWDd9KWfoUGHbfQWpKx//6pAD0eOERdZbbDksdMIibjH2DA+qaWNqE00yP82+I8lAC3w+O70ZwNrps4R8WFjTn0wRr3N2pNRH27uprGRSG04O3SGpc2w2P5a/uJvDHyOrKpms20XynOG5YcWbTkBBGZ78czgFRTU3KfdAelGW8kA5pZYc3AGghXjrn10vwEEmDHxuUhLdua53SwIi36K6UMcqOmjYzYfZRSdpskhoZQ+Otj93UPVPd0jluMpx2/n+gmTTkoRonBVnUkps4vjxoXPuR7XshkyhwXWO+a65sXTL/qAlMFSO3s/eDmaoFqUn6zwjVCKGMYL/EN2PVwpLiLHyVdsxapXk3cqpVUYtpCwERDi3xPzu4eoCE2nsXmNKU2svlR4iEJf0Rgu9sXafdWejmot2zyQ+PLfAutexpa6rnz2Sk/MnWyWUuMAyzj4RvKRQAAgHe0xApMoNErpDZpd9nybWhraqvRpW1sdF0K6QMgELPNzhuicqvtqSVq0NO7p0ix/X/GIz0PQQtyB7zKmA+VnQlEh4HYcI8fnvB1weU7IkGL9mmFOY85rPH1R54vpUqCuDwqiQZ4MCBAMizjbUOP6u21nXhcXdjsIJhdJSP4YBkopN5w8x4UuIsexeH/L0hp2fTXgnAPnmaAVYe+VxvaVZZaAdAwS81Vpa4AYgXj4+W5UvM0TPZLvesa/niavVOe22/22mELqkQfxKB57BWAjjQGZH8I23+gd968rIbI295cwYbAHg6rn1Vrk6lrmgZozZ4WjCULImTU7qvbz818g6j5OR1AxG0+Ezuag3cbpHw7mSFjUiwkBtN85pUPgjBEInms04t2saFzAExYr3L+KBITK4zWTcDu0TiIZQEjKSeA4OVC+IXwe9n7TiYFD13+f8bOudTPrba115l9uNfV1mj6JYioXYshT5DW/bEFRYAy3NR7MD144v70DS9mo4zYajOb0UyQHz6wrsm3V1GNox2DP9LAhoZ4WyzL+mZX/Z7mFmODrjDRBeWDEw0NemyVUXeYLGKvTOGH9MZxM8e1zibneDSoiQ1QTnRcc0Mo8HBpNvcB0XSNA2BxGJSGVU6CgMfimwfBgG0hZhiVxkl1XYdhdwhiE9/xR8xueNMiD+YQayW8UvPEcEnPXaZZao88vgOC5tDaR/lYVqwgkCGnYqdMmO4yP0H+DSKZBDpnjdoTHU19Ze1u3Nq12CmC16Mw0OF9Gx1pAJacAortJ7b5pRKN4hprg5n0m4qJIdqmVqj83e9m7eewnvTAHwpNU43f8qNe5p2H5M+qz84YQTfNx22c5AQAHkWcNw3pCitgYuI2IM8F2w6w23ulJW8ZmmWFcU6UGkOOPaPvaFOKMLSLpWsBjbtyZCaWeJc1ZuQWY2lP5Xirwx41EPa50I9TLsJWechwKovBSQscqY/GFbjU6mE7gsNSh+LhM6m2VaLgzpU4r6O/DN5zMPDI9+ZJKwBhEEs2Ew56reKZGj2uqO/sXu3MBqU+ew1ZVdIKsIubs0CJ5xKmiCBirYeZ3namgmhFJLl2VjX5eRzQfh7E02UCECBONa8pg0lDaPsYVXfknWsOGnF2KLU2H80SDydOh+M9SGPvUsytHHZCIXqOJdsxwy/S9lNfFaI4PH7TmVw8i6+8DCMEqL+rn4tH2HbU+lizwSzc60UNVJa/K86WP+OoS+rGcvoDUxVtWAH6d7bcTnwdFalZUKDb1WV+U3cF/Aow0d/hMWtZT7ct2MPEwoqk1vND2lRepQaPoSMuxwFon7Eupc9su/mpfwZQ18JdHtEODvUmEc8pTBKCuh0eYFtYnIoj9x6KpCEAzlG8wJQdZify4TDIijwA5E8V2L3VWrkyrc4EDA+vi72fBY9PhIpH3M4VlXD8MxMXovJ2gENkAj5q8hdUw/DuCBkY1zC7KjpGFROUhAbWzs/9Fq9e4JM8TTeb7G3OFGbljKVAj3zQYX15GGYZb/iUwI9lpX+Gf/ukGIS7QIBpe1JuDEo2CUOb0tBrngdK1fuWoZEIXjQK83X5TWD1zFMwtfI6wnCZq0qF9n2PIpOphOT75ktFp2NcShpYsxTi2GGr4siuS+6xbae7PEQr4ueNj5aCfH8YOWxZORxGKg/5AS3O9SdL3v2V5jvQMiBPiR9gJ4K0EBoGzVbCT3mFXFNmGCDWlNy6SFUjqC3NsTVzjjQiNWsc4jwI13WOJURqCtV8TVipWImmr7c+qmQUXZNxIkDRXacobNC/SLm727v3qaNQGVT+uCdXFaKD2UHskLrfGTlkC9qu67IwAASbMp6mI4aXNBU9D/AJMoZt1Q8OPHcLYmVOrHABxvHNR4YAOcPCcQXHB8jP5Rd03Eaqerpn2uhggAVF9UIou26d0WVYYz6u4Vjhesd3aAp9X1pYnJgPeuKCgdPtVYznAibBu9SGQPfTjnGJNdQU0TozCW7UTapE1BLTT51gKb8ZJ7z6Tf2wLS8D5W8tlhLWcmuWrq+H4S7p2Bclt55LUaC0AEtY/EdJDAwew04AunOQmHFGEiwmo9c6OnC/DWcqMSRScceEddClQ0iwiR9Iila2FMDwcWtaAdJTTN/rFvhmguVRb7TgRUu970moBHPJ4/bqtkKE27Dj347kYZrRWZE2S78TKJXeE8kGbSjXubbXHfi8Cm0plDP7yEssNF0Um8T46u6gDK0Qh+5W0N5+ijpnj4hHEVwc3hJu3kU005yT9G7OeR1RZL25zPYLwn/Bcsxu1YouVN0kUkNN1/++/lLHwzptkVueEl5m++tewv7j5LHHkmSgfY38XKyBg9J01u0rYzsvMzL3zAcNsVyAFKtm7lDZiJ8YtdiydiV2P6MKgNQtX16yl0ZdmJxugj7el0stDGPgkljtmalPH8aUmpeEIWv5FMV+16TpIo3vzCXGExJYMnCRuNA1yKNOuPqU5I6SkLVFByRPwWOLe8egfMw2g/HPUMC94kxLvup6dQe7aGHMAiR6WS2vhUmbV98bf+sad1IM/BBz67tsVjuBa4EtvHhn8UscsWGiLRLj8M7u+/ntpfjItLVGCwMVCHtdSVGgxAtrk+6ZwxhSsdK9KV9oopOwjGzbgINHLfpKgOD4SVRFjVXzfTSu8y6MmKbUuF9GKWifIeNFB8I86KxyW9h21yOScLoytpBudxYd/2KOTsIh1Qs/mK1bg68uy2DZ3IEzSwPxgXQu1uNqi37gJqadeG95LKXnZFDB9n+1VmGuNGTLfHTOE3N8mJeFMeHSNNKC/y0gzVlCP77ZxkhlMjvilmDmZsmlUFU4l3n8D/m61ChpwotV3ri3hkd8l5S4T7RqKOgCDFOSiXjXsp6fkENu0eXYi1drx+hZkL3EMCpM0WEJSzPPAdR5Kr3ew8aF10Q2Le6wQ3PEimzWLiCuohDu1Z46XCFljuP4MGDZccrny1a+WqGTRpr2aCrYYd93KYrluPpgnHQfzAdl1LxU8i7CnqEL3K8uJ4nmkIhxI0x6dIJtbpLNYA0PmqHdTkFsGsZf5egbkw9pSOzCePh/WmOzpBz4Vh1bBFU/5839E3kYhE5As8hhYwZVBy55NvL4rp1Cy3GPw133EHe42QubjIy2ac/1xozsa0Hoy6UNawEsyIdpS3eXjsJH4vrJj6r9QLIO5JEE50i2lJi3fzO0OVyKIpilika/uHB187GJ5cA93CJBo2kY+hCpo8cpOxmllX+e1eilefVFgdGPXt1P1M8kxwsnJG8bu7piNhcAQ6LKx+ww1bv0arwtZPVCKwbiQFb+SJJzoFzK+/r4pWB2nRAL72KcMVB6S2pxXO2GyPieHgs9wvvWtZR60QbLZgWH898AE7H8lqSc68P16rz2MqtM01Smiwtpe0U7snR+v55G87JdU6LRTyKRpVq4muyeiPYVukHsfG2TU0h2ewaoasKpNnprvtgbA06vjFUeh0JWd6vEJhSxI0x70SZmoAiznFgXPKpO7QaM6sTTTY1iFdLTD4ZyDP+v1wfOiKQ3LT3EiZSZRpi7w4C+5E3+ELAzfxnJyD+EHxo57jNrXe59rpBsxLTMbciOnzWVtfyrlOkjhIwobDOvr9JqlQuWS3MOxcrROgI4mbXPi73ml9mfOTkvj2hngdAOI+745fucJnRlM5MeaPoN/YI4rZyM2XOk+Pw6kAeIRS8ZjjVhLmJAQLBrkUjL6ucqEhdYkiFtUWVVa9c3AP+Hay8v1HvZ3nSgPImx2Tj43B8wFDuROP4sMkMQHkPjQk21CaIiiGH8RYvkd7jy613ZEHT0+roL6jlGE1fv7Ak/8isr+3WHsOkB3pChnYwLk2ziwRsObeNVkAAKgKFoOpYbPeQyW4XFuB2opMKDbB27HHZt7LiTLn2OfEl+NiTEFyIGqBBBHabs1VG/zZh5epGtngNv2O7Laf5EuduTadW3y+KMN3c5Pdx7gjoN/672QR/Ur+5IajETRxzDNjtzLqhVCPsWwEpo4NfEc/oWDYxP+3dKU6tp4d5dPp6nWbj03hxc8HNtcFEnZK2LLbo9pdYY0oVu2lswFWm2hSPcmTHUsNDhOlTy1i0mCQZrNo2NtLsrdYBUDqBu20yc6A84s0N7CP0Qiz6x4eQzkFW2rLMvn6igiidOCY3fRrpOuy1W1F6jtwYbDx5b1G5EBKaxORabc8JbFblr0VdAoBNxf/ms0wEAww/ir0MmnUTKIsORUsD2NMao4acpUkg6iy64B6HLJK45wbZdHKGu8tkzs8CcoNRWijU0X8ec06Hybb2gMHeEU6gjSKoP73l1epeviNccXfba5htwUyLl0g43OJxkdiZXmGLFpPsX9dD6zsdJV3/z5uddYdNOi/aNZzJNq6Pay0bSEVqeuLQ3y5rEgLgimhJ9xupc9pvTcL3Hh0a2vilGhe0GHT1901edM0T0uc0ZlKNybfM7k1PjSWkMLHgydhiOkr/nP602P0bEVudNH3RwGZHn7hxyVeIjmsnchxJ69q1iSA+S4BmPnErvF/mwr/L2TUAptqSELXTp6jh8q+k956xXzLP3dDEvZ+qDtJMgXbqPkhyunpir8Y41/sBHPdxUMRGqG7H8dN9rf3VCdioIZxWlfQB6tvyMWJTjLxm/O1mb788ixXxfuzjYFcUYKWw2x6DhDJHxXvJ9h6X1+bc/IwbqsvsQGWzzUJNMSj9DSGNKIjgQ5TL/f+ahmXldFoYAzaaggZ6qNWWJbiRvb8hlU9bU2TTOCBbheHKuFw6+tlq0StVcEZqpq+9zPSw/GnujObWaMLjJoxrdICP+UJxGIX2fuZuiY52q59S+ozH6ugMkWD7PEnR7smusTO6wKDadY0aX5ELMzGjr9l4BlnhS+WStQop7C5mm4+TURL2XO4+W/T27Bpg4rnFT0xs89jS7NN8YNt74aOXR1SApNh4GxUGQ8Dib5o9UnfhokRm8qn0AJsQUBQWNEBH4BwIIX6O5kVwINheowWXSro6/xJ3oSOo93QQvDcmxvTxhpdoPA2hKdJD/hzMDo1ljQGcxORMMlxFx+wIhuCxbLOEl4LwU3VWiVGivsL3HcfcnBhtJ/eu6Nol67czZMPHaoG4smtVkVi/QNcAWKLv2fSPHewqMrK7yMgY1apuXgOGH4BTWX1ACdcPDqBRrrDGpb4Xx/a+FnF9KDFqAD7nnjeM4fWLUse4XgsrCGugcJuuvlKyG6eH4Nyv2DTqOVLAmn5eunWxjeUoBydsoHwCttgeXQUt+RMJ7N786Fo2CSy0yn8piVeZTmjfKF2UE7IDdoZHf0+4ZtGe+uspcQpXTdon/E5Jc3qEIFzRJI3w19Doo2Q3ogEzd9X7V0Kt+TB6t2By9qvMJB/74EHeACxLuFAXBT4Nx6wLsVC+KJoUH0TlrDrHM1sHjvrF+QK1zVtdb40KnK838AKFLkgnn/jnL/XlkA9Wi9xNm3pbPmo2jGKtVV7x2g6a92QEMDU0VGEgUJXQnzif4YBPENZZLUBX+RTR0tpnhNzBxB8aLrlZ+szC24R3FeE5ZuIAVmlXfP8cHDrYTMrWmyvz+KjTvSxQ0injO7EOcuiUpiX3NnZLcupObhUi763f/tvLB/GHYeRyIqRqnO7Meb4z3/o2zlG732Fd60oHdUbsualY0m8qyR0XHs/JW2Pftc03zeDbFV+UbQojVbFQyytXNv1fi1zfUb8IZXAcu5cbXyyPpwhFK9w2rQbLff/55kfRJXqiNlSr5/R7pUtRz0Lg08bAzVCZpYI7mNl+ZxCCpCsxpopI7SeLFNi7e/3mGA3JEcXalTGsKz+JuOUPCrp8y+ZhEbjok6CEAFZtVCJnmke8J0hdTEUFl9MQzfL4la7pmAjz9GjaWsMnCmyIeF1QkLAoRguIpnprqJJMh/sHCmfvjhnWqHNTQ62YTwhk8NFOkfUt7CKWpaJN2Orar5czRwiSAZHn5YM+wAHffBaHDGPK/k+W2DTiPEHavQFU8DmV4cev3uwJNg6cJcY6cTYc5QqnhQnRhdfLtuYw8XcaY44xPuDbyHMsCk5+DXWExFC0yuSWPzD1H9TiUwmQIl+PRpqhfZ3uXQTMX5w2nYRrQg3ca7sh9hwlmNiETzimU47m8OnOIkUjHIXC+3DwGv9+OwgBeYsCfmJni/c5lvPgXr1C7BHpkxAgy8XkKEzPXEEApzUy5mpQxlSk9BXQ6Hbrn7wTynGiYTxmEtwbTQgtpggwU2usW+c3CnkMGqMP3hGcMwbgmTUJS9ONEsC13YPhnypP+6PIJX7LU9910uFctnnx/l82oGoQcyyvAbG5VTpg8JmhkF5ZWZ4g57TLV06yJ4g84zecXPIBneFex68s3gVLeWxOF+7v8hLFFLfm+qqN7lm5TJ6yoq+OYsuYp4gdeZ4EkB5b8yWL5aL1EVX4sOIon0Cf/qrwpRRyjyvSRV1iHI2bwHgXwTmrt9vfIuqyfOYDJSPHHK56oJ70na525blrRoqnG5ImL+pT1AuyctGGoeMfK+/SN8ysKRF9IQ8BX9ONoCVZKYYiBW9kHTCKpsZDcizDzi/Ur1yO6Osia39tS9z8G4qM69H1An9pxloF0b4dASlvhcPcQCUBdT1njqe0cvXwv7atbH4FGsHS76sl6u9X2ajCRiGsBlVmDW8pLarRexnFyALp+2oGgwU7umW+sPM//vwifnSf9iguJzXw3ENHwCGkq2lWNiJuh32F7TKlIJ/WDP1t77gDhZdDWViP1AtpWr5chr4bT1VQetjqg9SoS4YVct6alE//XQ7acBCNWHtrzJOyA6v7hncDQD3JRZKOzPYr1NmEViOZ9QHZ3BE+D+fihcVnVMAvIQ9XiIxZ4THNCxGopHMBTtt7Lcx33VorZFSs5DcPE19kCw+TBM8mLfC9bzkI+5Hc/X9oaZcKpR5xWoZwXPiEUvRLjIiFcWd1Zb06CbDXHrVhHBZWjt39Ho0254eEXfxpY1Zr6Tb2xm76Dflk4+AnPKS4hYiWlV4OLI5nB7cmZgN8pbxYR0NIDYRcsunSBFCTyGM98GFPEBUrviipEE6jZ3YEBaqs+VuJCubt4YVWZeYPoW8IneWfBs3A8iFLsFcWPEy+IpQQ2kMvCVPtMDHewHiZmeILTjrZmOrzuqWMQd5L15Y5mRK8alH4PiCJ7d2nm71qNRxc59dqM0k55X3TyY3XlixYkWeeAuhiV43lbGdVq9nzw+xO/fML+EfxFLuRp4EQrmDijlnSj8DSAmyBYm6Sb1Ko0Ikohhx4W2WhZEMmUIEkbkQmw9IPHZC26Evxf2l+uz2uvvVYNEqiQTR2AS9+kr5pG7kfBdKb9v++hDhR/vQY0CG+1Az9QumCKhMWN6nycEJP2QB5xVvzBFI+gH7VbvXKrTZ/QCLVXwO0NYWsH58gpV2Ma0jwZoXIM57aLiYd5eKd32TdtjkCuSKldNSEnXg5pe2VRsJPgeTcgWrEguuEU3Tp7c7yQDifMomK+BpWAuIG9mqmU3wzsD9vF9itu+68wTnMWKFUIMRURykLT8Z/At77kHBUhqkkjsHiTcrapo8iIN8zeQg3TQ4pJHH2C29IKFfdtR04CoyJnOzJW3oQj5nfnpQ4HQvnQRNfbUD2yi+nGG6hLyCa1IpaXfvfHCbG7HIeZot2IS7L8tfUPKYOj3K4O8L4NZT0u0UgF2W6vnFFyVHOs8FxvzEuksIoN2YYe3fM8P8JgXM3ubkNjeEzOlHbsq1VBvYWivE6REL4r/k2k4+f6nMmzXnay6anS1Kzm52/ZslIXk0gs34YzQufU4BRnFx8VTWxTc0TFPO1Q1xd8dz+KuXl/BqPasYtj8FOBkvRPs22YBHKJYO6qPzb2/vKcND5kYvzwQIdyG7V2F5DzhkgNSZqIGfofdd/GqhWay/A/y5I0fTFvZVdpPwLK8pBqkXCDtUJpeoux41saazrYjvDcjwqWLViIuu21rJd3LpWqA1rZUEhyWFnb4H79x650DT4Ig4NRlJvbDdxj5JpffblEyJgbK9eQUejb8cf7bsaSvLt4qcXFXW3b3hWbnScy57YRooxi/ZMdn6Yy6skM46z8SUJ/7kVel+AvGCNvHhibaiNrEWGgs/N4zZRuB3HN7vLPIVbjZErOO1h7S8wkoNbl/ZM70IxXUOIOKSZbu5vEKKPvwPtqVSLGbMVOz/wLAmlrIb3fXKxXg1sK2Yz0aPjn12uMABSCnMYJcSDtxV+IBfJRDm8kGDTf8Qf2wp5AhSaMmHGBWow/PWcQVSdHUHOG8QOaLg7umbiGFuB7T6bBPOCyAy0OfNUc/HtviJNypIBZ0JpKl2gfklVQh0QfCbzdVvWx0SCf/Qv+pV5mBX4Irtat5Ka+1BvRPfafVagcg0jRKbSC6sKyMPolJkKoz5EXZBKNlw/NDFsdtaYTTWg93gbHWxHPNRQ3l+tIbzoPgA2UW0qNVCc+L3mNlz4rCXHkT/R5eaUB3Sl1KRhCHhI4tardpd857NkP3XyJJwa2+EiKeVKm01ZVUHIXxDUszZJkppuzbH9lfDjSBzU6VZLNE05U99QmSzyBnp/ksxmfv4Qgpc+UOaAyXAHoV2d8oup2vJqnln5mjDTb1hdFMnnAY0bjNKap2MnJQPevUKDc9kaPHgY/qKLLlwRqAvTuDGcDwotwkO5/MN01c0Bkuotd6b39BKH+Je08LhPUYK5X1jNCkVSP2uahMEsqCcPENJkgC+MTGyRqYY2u0S7KNT/GgLvTa/I+KEXvKgMNueu4r1DTqafg1IJyubdQ/BhqzljUVZAuGmMwNvYqZmz5w2x5/Xhv0rGlncHeaPr29ltnYr1PO9d9RjY928g+nSoR9FvELBjWVnxS2wcUE6P12cyb1p2/lOPZ7g7eXZaRQRZFI9F+OQgyKKwUPv0eWylSaRiSkAXMCNkmPDqfgzvAcTqlRPlm2qiJx6S91qKF9R7ZzpEKQdri4hDEtJnt7XnmzRl5AEHwTIgfTzp5t5kCt02BigzaUGjjGwcxR8x8P0nd5F3q0pWhzXBqwvPafwGjpGkCacibAHtzzjVn0x3r65ayi6Tc7luCRw+1BdLD5++TtfW/Q58pTJyXcTBAD6tNgIR6eNiM35o/udVOOF8ntbFg/mdy0yf0OGhyFxxbzjFh5fKRn9LHB5hS2FAbjGfIpifKM6MIuQutZbw5WmLsKiC6+xV37i7dJhkTiGbIZ8+6Az4AghYjg3Vm5B47YnpYdvNwpn0nMwnDhJJpqZdVF3TY2WSgPYkVJxV86eOPlCnVdueACH1iVejO/eOXzYrvob5IDvAd1xAWC4NfObqeiNgl0UT6JDd9gCeRg+DfUalAbOn3cWkwhhOm/3ulCKmboQq+f43kAUENfSv5FAhqPd+scx93wq+tV/LRsDgWHombSoDXpGa1kF2LKxPG8Mu1178rKZqMAiVv8YQbSIFQAV6DtzBuXGVX0uO9okPPR9304PvNlqcrFlpJdX38mruo90hU87TsHxn3qDAl12LP7HnPU2pkb7WEQXMqt/0RGUAunhifMMpbYGhxvohG+YIzERfsJzHu71DOqzp+5SlivqQAstv/xgrwiQlrDj+QLwTRqvY1uVsOjN2RfViUzHAgH3LijZ3OFwWKkLzXdlkbkWkEcjuPi+NnKe+3ZTwFw0MmaEkGJ+Z0+/g2yKLVABSMDBuofxgH9EeOHaWuXKPgf7gY+IOok7kXyY0gf3BsqZDrw767IyTolCWLSrYyQY+bsePrPmBKKn4VE2SiEPsXvKROEhk6lEWY6j/H9M7K2RquUqXm/rTVhIoHZ2mDz1B/GZtbRjOYkW/o97FZzJdKOPAXr+AI4OQhwN/423T2QDK0jEzkommnHnOcklLCZzd+KDh/3PG79jjf89ZoUQ4lH4zAZS1ehHJE0UNag2sko1bSgZu1Xmzu9iSHp2w7jJExDEyHs2ax5aZWpCL1sW9O/G86o6/FTjmnz4eOz7LyL/oogW0rCmgUY83ovtbGnjvSpeq50AAA7G7XEIxWvaSY3XYVo+KPT8as55/BFsOO77XxubglP4sEBWgcX0Arol8ks831va6BjNKODYEcuBm/UG0q/+KRuF7wgIGcDBwD4l10pYrh6W02qGkEgb+AaUj6EXOJyvqqSboimIk5/1gAPrqYgvIGkNSDqB5kaiMUgyq5Ne6yjlnoFjhOfYTpdZKw2cb9vLujDF44dlQkhGqEkre0hELdM/goxwf6M8RhQgudEL7hf2Jm5bKwrMJrQMMlbKhKZRrEOA7jzlfg8tuaiqCSKB6CK+G2SyqI6cI57oaTb+Z0ecDowVbeDRXJ/Tn3xsNUR4f3z1I/hX1C+0NgBU3hNpgpD920qRirX4bY3T5Oy/HvnBAPmoJOJigrJTVswO2BwMQUDgRzvej7OwNWLhpi5taeBAdAGpiDvBEVur4aongo6VgnobBlU8tHCP7ZNdfntufm7ru+EKbFUQ9j1CwDF0EmHCkIyY7neSXQW64bHJBJ4dcG7llpXRwQ4E80hDDJ8TEwidSvE5J/3bCjpqznUcbXad8hpMQh5W+t3/5yRJ1IFqQSfFpi9SQ9G/NbYp6DeexxbV8bn7A+S2i6C05DWsjANUynrwytq/zd6IIdpi20+HUsvDeldgf8TYRdNx0tZfyZArgvd8/dMHrjLORw11vVgRKqFk9bImyS40DJSQvDyldvrMm1YWbBISSXfS0aA4Awd+RCYQ7hlsXEaCVa8JPPj+rpHMe+u72i2+ontL6vePBAZYJHRfiHoEcHAz/+GM8laPMk2bde1I0cK9CW3PFszTKCLzjX7nC5ZQfxXSGbG0sW0zHdClEkKTtVqjcso23gHHcTFlcYSOhEZzeIK/UleO3/yR1aD7rTot7bYiW1j3pgS4UWqW+XAB0SSpKrhhtrXClDc6JbfSyap2LFB1qOJIJ95IRARKtwd5zC0erMHZAEmBvxhM6y6MmFunWN3Fir3W2+ki9TcUXT2F8Ok82pDqnpf+F/4Bj7BzDXXtl/iTgeiuBBwN/VGhErgSsmvmBllxXyX2US5647x53wgRpSyOwEz054n7BRQmUCrYb0V1OlUf6m9O/wiTRhdI5SjHN0ioLFPKGVr9VJWKcIsBNJR4lDcSffQ26LjVZocKkJiyYbnix4A4l0UtWtQYMaJIJt6clow79drWJ3cbyeGRHqCabNR6wn397xu5D4AwD2K3NAKMXNyzqqddvWo8u+KZMOdaa6PK6AiraAQsoQya+WOSgEHquhj30PyVAk+qbrDiS3iUoj14KUB84TIw0ES381UvW0X34nzVwYIJwxypclDawXTDeQUKkgxNlU+3BYGvuEqsHCoEFvxrJZFZoEucrwjjVa51LnWqzVoOgWtTuDBEuGhvcsj4uIBvnV8AbTPP5Hna8948FjK7JuvPJ974JXZUSSAAYPoTFt0LNz5ZAj8ksshBJZo9nVsyJt+Tid+f10qGFCqOnAywkba3zdyyX8Ar44og+O+kbw4fKhO5tJ5UKsadiph2Cx8UfJs01UFgr/MRL3xrV/NUGYGBr1kDrlxr+Wy5BmH9XtOlM1/fZ5jJgxcVRloaoOuukzJefwoxx51oJrumg8gxVtbHkP3bChExYlE3FHpQGvX2wqf8Pp4UERPMFzi56lCxkESDJI+xML1NLPPrNyzTqhAlLALnxk4O75dnpv650XZ9poGJBYtSNPHcTqSGyaYqS7z+Q+sDDBdelIGDEbkCHzi+epUSDpCsTEUNsmf9mgU/iVJK5XYBeT4sjH4jrq8OcKQ7Ki37mLQ4ViruHPgwcGbdzdgmDO2N7wGwfxi7Q9NfC4sMfHwsdhZR95TCeXaIafyKrECqolrlQMBf3rUBWAZQxhLydbGT9EjTiVLRCVCWFG/1S41+dFxVBa4sh5bqIZuXdq3EEYjj9udZSTCJxV+t/Uxu4gpmXdc/CsgWVhbLpNEUW7PMf2n3eO2w1/CWZNE/aBLazIZyH9ee11WoBaBvB5NP+2LUivq+eUsplpGWQs8cdGmmt6d/59MeN3weZil0i6yULthT+XeW/W3QbbvROMVgU6G1cdH8/vGU51QPCXU3v5jfGCClzyPOf2otK3zI/ttp5JxqCI83Xma+v/oTTjvL5dNDdheXNqsQhEX9ZlXdMRPlRjHG0go7eRz6fyA9Aa3yj84rH7tvw4l+WeKcKALIQ+65j8NoRAHWxMRFGh2iQAu84nNCqrIB9CAq5OjASWbgaIzBorXKSSJMQh8XPZhrbiNikpMUXDZcglFRkJPYeEMOh3yRivxYB7y9czeuRS2sm7psZaf6BAyviDi8XUCQeBnljRsW+dv29RqBv790KA94zgf67Hxo2v8VHiFMNYNtNbRq4Bo+JmDmDjeiIPz8WXdhsFLWb1r5oVUlOZNZFwnPlZ2avcKa6wWFiLIWJtp/BYaz/MoEVsAKKrmC0Fs2WqUNfDHQ7ni/BYXDaj3wta5cjPoNrhAGLkv9v9lSMtd5wj5Jo+SVMUcyz+Ey6wwAmwpMAmW66qzwYo2BN4wfENeFaLOa1EQw422VbwC8k5Bs0qVCyM3Jugz94Ee/oH29kD7IlV8O31ZCDkrKxn6sVUgIPegytG/qYyvYs1d8ICGV3BOw1128PEsKdly7cfgYxHHW47Spzj0KAoDhE4K1bDP7CN+UTotE6mQtpJ8u2Ea4CrZxucm9RTnHaKDunsAX+D6BXHv0HKLEz49fZxQZdD5g+Bi8CDWAs9+PqmmAZwJSghGcAAAI2X93TPNLkeyh5X3rDaMYHJH4RgVY2DaB4kYbSJMe7mmwe6KoAjiwRkeoLm3Dbw50GFGC3RzCYt2LEtRbaGGHtL2JmY5LXR4ovMuyGGz41mgMqwBjzp4zRsCFKgaxTvcdWkqKfBleDH90+NfIbdvbQkQiTHosVVgDIf2GsLnZCbUImvQsxgTzELGjTOq2qzkLpRk2w0Fdf5EwRVzF6mVOU0QmkT5hFq+LSO05bGg8bRRIPCRT2/4bBm4qkVx2e3V5qvddZBPBooHG42g6IVxHHmS6kNLqWLV53vULcMoBOHdDI5C+qMcmMYjmr8sNRMT/Ma07XPZHKGlSxeBKmcSS25PzkpPm6cMw8JRHsn7nj4bPmx7Y8bHELq7axf02UfDwabBmb7B9OiNokvY/qAvy/DPOp7rKT5MSR5jA2HisUw2nPtJJljDdIFM09xbhyZAuBgQisnibJDwYHDhMuo+dM0jIB4PP5nTmI8Pw+oSI5GeUIjzks2bR1qh2aiS2yk0XXVcvf+RynHZXJ65j8NHvuA6/Kft85OZl7RT7JJLfp/WLoNBSL31eMPEWSe8nqL/XarK6mm2wM4pAcqLho+sr8DUpHRSlA6ydr796+pyiMU7/SvzBMQuQTBU4VUYYBsmOjFSdNxulwTpUFQzCW4pZBruJ0t5klliJzax7JfnbMd7HHjSNpHZXGgCzRnru7i9DWY2sDarIuEPeYQWZVF82t43r8dV4ehI53JwlmzHMmCJeGw40KQUJZcB/LY7CroK4eNPvcT8Dmp5NHRihR0OPHkmJkZqulCy2Y48EZ0npMA7JUNuNaFMpNwtSOjIqGPKnwlUwrae9lLNOxhiVxVDW2AZ2RLjaMfwnNh8KAeRIzMZFCpWKMXKFpYGWkoCVYsTH4FAXPYUjwbvvBi37I0JdTWmXmyLJjFNSQGnqJ5CrnT9Xiv5Y2fHlIHu+dc7zmiJjOxlt+NKCqRs2Fi6jT4I0epoX+0eOUmMIXPwiJIEGOmsipTnH0dXjzC35QDK1XbSnso7LDjL00gF4yZJSp6itE6zaYBbmakmPtRtP79a6CReV5MeJBEkrY0bd6LBUQmzRkwaYA27AU+sT23sxf4GXXoG5n9bGrRufh8SMqfuumdVcZD09txXUrXQxNsK/Mo0ALggPG2gDNirhcsU2aF2r87uXAx1rSlZj5T+mtQ37FlOuXvz8zMHyQkcei4JZDYbqHS2/hcuBWX2I2YSNBVt5d2FdJKjxRu7QQx2CUqLsf6LECx68m2uQZekCZ1a+yZZhIGGTkb+axtAcPVmOzpY6+WXdm+7U4T3k7z1Twl8B/xzneYofWwndc+gvKyMonOIAAIA2cnq+ikqpvE8Ilms1PBNZCMHsvOzbo+CxET7EqzuhhM61jCiFECCLvYw4LWGJxv2tceXvihHmDmcd2XE+Dol/J1sPzTbIHgoZMsHbU3mTxEhCwMoRH2H9ieDmEU1NjDwT6YH/s8hmuEu5Nmz++as6Q7Hq/cDIUh1NROfec71FWzp5tQAvBCF/cZk/vLeRYtpfvaGjQTv2ECjLi6V/ab2t2IReBOjud6Eb3WWTrSB5K+PCu7EXnnIOUYXZXbEc0FlqXzxSHF63y+AXqMw1BtZWQWLHFwIrMWiX1OupoPR3Aakg9sOUm3B8QTNolS5+1e01Frg2OiDi6ovgMVzdX4GX631G0dqnPwgHn0jNcBoSBujNEvFPF6ApvWFLiFyHgd4DzUqeFVlkWMidw+0k53CJ+D3z27WHJFyNmwR9LvvrtzQylXvWQRmqEftQJwIYuve9ero7ZSjLFuKPh23CTcU+y9zR04OnOcGz+vzswPErvUravBeEUBgCjlghiw6DIEAvre4n+1z+KW+rT7Dwbm1dY2Y3yR1aYofSrmw+WGnIXc0VVpu+nFsZHuNngfwlrYvPWTe2SdJ2wrSiaClPsFY1ciFT+VzHQ8HGNN6WXJhugWP2VeSeJMsfkJ10nV9FP9shJMtG6+qmXBsQePCiwVG5rc+v81CsUwRnXSSWngXFtVhRN/EjFu8zb+pBnmdNgj8P7KwFghpMxQNPlQQi9Ou1cqpJjlJ7mRnnE4V80Q/6g6lS+36zOW8TqYnvD5lqHACVfzGM3hGaza94pYwMaiUsmbXTcpgL/Rk0ojXlJPQ5wHZDU5atwxHkolKrWDdSVzE9QBH42gjKYQcBBl11OkKCCNadrWS6LCIyQQGtTtcGr8SafL/IwrbAjKnIAitihWuzgpSTE2FAHu7D5dxOVL+GOHl5nTfvWAtu++w0MAQMFRAwUMh82nrdrYyZ6ndUUkIQTjXDqBnfkTGBx7knpafLNPbEci2t26q2JaLorN3ThSggGLwbhv+DXUXFKG+e37BcdCpK1N/GfAkegU+aX8hXWj9YIIUIML1YxaH0s2sDBDNUYN4Jgt40lhB4H+f1sTD6gqPtu62MyG3v1LMMaBREFGnRzpWqks7iZM48JvYrG9Dl/wng5uK45gyhWmoJd0c5gLL1Au1qUcUXzMpALXcvBLKv6JBqqJl2Q1QoPUUJK4cytZT1gHxumgZEENJlx7l4pbpzZLgLL9iK9teD2h6b/FT0ehN91vrxVgOp3i1vMF10s+xXtrg3cEfqspa9dBsv8iLb9P7Iv8bGsDMdrR5tDMfmCbb8iowdT4nkylyv5eO/ADVnkkYySTOXMrCnao4g5P//8vWM/wODkNacEACymWjyt35G+Sg/wwI7vF0CdObLBZXDWefkgN/lsesV4ELbWPnlF1yzPdq7faWDLfZ2YLmMinouVlKVRPwqB9IzPoaw372VXVEcLxMYUK97HvZ3hOlHAoIK+BRS4qD9PbYFFPQkJGqEpBKLZX1AZFPV+RHRXzuQx7trwipTmh4fkzSH/Xd1g3bPDLhFJKoFDoppruq/yZA2JtSk1QZM0FInvmt4LLwFFd/Eg2KonSuZil7ehBxCMobP12ahKK122eQel3I1a9xscN1RM34D8V9vbmEXJCyHdl3N+VQKdviMCd07FRu9XsclxQW4UiG7cXr3h5QfqDs6D8GYvJ2O+g3da6Tz6gdfyxw3bulnqoWvKRcD7t4rxO11yKs5ZfJ/lPuq7xTzylxNf03fJ8t0Mt/QOyHdNeB34eWj6enQdTLRbg4QRUBVacSwNPDm9Ta3xoYsZAAiczNAFsqBr00by33ts3j/2e12e1YGgpiqr9nUCIcGccNYgokRNf6OnBCGMCojS70mnPy3ObASx++jTTaGXxz5NJ9jteV3hZWiVTCrmRgUaCIWul/AxVNMZs7FtQnsIV+WYRerclQRpnu/oSJtp9+ZhwUY0hHsjt4DuKJNq/xj7GWjY/lXaWuhBW7oPYbVHW7XL15pUrjlhivvSCd6QFHyhTtZKvRy4GpgSQE1dbC943XYvqMul+Vr39c3usS2+jzvUEVo+oKaVNZ4ZjsiDZb79UqvFtFFUVj7bz4RLyL2C8a+7X/IG9mmOcnKdCbdtQMefmz/LI6SpZ2dvF8KRGz4lOGk9QbKNIBxlmN0tIpKf1CoRAx5tZASwBJ7WyyvqQHjDwtEi8oTfNGJ3v7zef0gKzQFvbXGGy2qSAKT9WKwslbRh6arFbPJEpTI5lFYAxVP0FZ8bW76Fju9B3wvhUjNduDSWgIvy96a5p7itTbA6mbQr4vATNXcAn7zqjj5zFb411eVpBTCqm8T2eJ9edRemI54vPHQ0qTobSKZK8evGi8m2yXLV+3Ahsifw4+i4l1Q09oelet09szWkpTyQUBJsRVzN8sn6Sf13eRweTPhxrmJvb5eqtihexgRSuAURHIneIiNWnkyLGe0W/+m45jMrpRk3rGImRMY3jQ80Lb2T3dOVPVt34cJAe/VIvyKsb735kAJ29k/luoGqsIL64HIdAQwOq677HIHybM/GmmyIAQ8P3VUqfwv813ggo9/GEzhFXX//iWIh+isRO77w3rM6UgmhYj3mm/kQBkT1rl2aDR4fIDQPMpMuhfZfryUPprKeCKQQiNbDv5lbRbgRS71NlHd7s8A17DVT5OHamxZM+RS2wfoUl6Woi12NSMePkgAieNru0quvACh+QpVJD4dxl/hzNE1onmmI3jlkEOME4ClnZ3wm7JFoupUTnKfhkL4/NquMAFsB1O33KKyeyKK68iVn6dNiZeIAG2hBNujjliZoC2hnF0ztv81WBOmeqLEJnCjbwRLi0Dsfzv2XVD35vPs7JUbHZQ754+wsp7SY8aaLwFLgO1pZ9pzISg2F1h6o+IC9rVyw4Rl5s25gE0H8AX/IZMe8fajOcAzy9ZZ6uMm1qql+MHlCvKOIsbUPZ7DM5nxY6tGOID749dfAnPEUN4NzYzGtsnVZYLfpSAvPpXQhD2vhNUIpQJLzk7Dk+3ln2Mqkzq1iz+R5EmKz9FAnXxqU6WgnlGsDG+L3uyaDtPVGosUzAfRlDvJUWOhpZUswviNtXsxOLHLOiN91/FyyyxDzzB+e5rCPhorb7sNNIr0zp8Vl/hFoHveN2p6hSBqb8ooWpbLBxvkg4BN3X0J0yCVsky4lcA9Jru+mvYxN7P0DaHyN1+kuOyUry2V2QSnX1Xugfe8/LDXIHLJsEcCyaEuZg8/YmmfX3jwkMtYg6GgePB+t0jLyN1rVC6j/WL1NaYZv/g4ll0RMzezB5PaOEDPs4rRGqeSckS/4L5PxO2D9omcRdVt0Tsv4q/uhoKdcKAXYYREnh94H+1xg+ZtVq3wm0vYcaj87PkbDM+4uTS/wra4uvB032aHA6V/muV09szEkmyicx5wwkfHJddVj38Z3Qc+59WkCmDxmo3KubHlRsaNk8XwkzGMQLVnbVOj/LZDvgcvdtux8A2NE77AqXBTdSbe0z3Lh5qv1e6iRYYUoMVpzr5SK1z8YQKWI5YucXflrSuN6DgUuWidcPq1sWLrUA7f8COuyjOOP2RHFmqTWDY/kf0qJVTCOPVm4gpWjQOya8eGTb7JBMqCa2ndKubJehk9EQokk2y8q1llrNSpcmghSZ87QmO0fFr3c/NI1cZFQTm5xJS0qYvWrLECMDYLZp6qsIdG5MY4ZuMYB5xGCdT0XLlcdi/IrGrAqZDeyU8XVb8K9ds8fj2jOqtHZmk79Igb4NL36EMK5jHgqxZ/TQMQLC9D26LSylP0H6lsCV8Hygc2MtX0eBOpdVpO4L6yw+rbHAyreCZiPFLftR3y5XZMjmNYbLeVtTT93xQJkRPFzVs5n5jUxZ4dL4qmOm74HHwmd6azYhDSepd9vFTIMhfNeUguneuy6ReiR4QHDlgrvoBBcl4etAaZ5sSHZRGCGBwKC1v0xs5vILZJdiXqW6fENxb/qFIYG+VQ0P8jP5X0732Vsba7fESECnDPLlBTPVdO3d3vMXA77D+7ciCFhBzGbpXrAlGvw7WejvOIC4zqJoUTUr8nFxghbZIag47b2zkXPcstTuNhZMC6wDsFJRKVYWVrhWdnfZabho5Uye0pyTFihNCwN2ayzCufDvS+fOoE7dLR5KHCDzoWYmQRgIGvt4mVBJdpc2u6xxzn7ZLfhcxva3qbVe4JFKSwAAA97uuvF4ZRxdyUMaiWjVbkj3raBXirG90nqUyrKgH+dSmdZ61+L1GnKeAHLSWvSsyKrpvPvZLrcwMLMwaLgXIOZy+1DjRieKvqeAV4WNYWGyvXcnFZppZwDGzO7XXjGML75jye09Hryfq3D5eHDyxVa7IF6ec3TasUKG5MirXY98PRGP/wMO1E0tn6So56pdDejtbjXPUOKz2MtDYJ/kjAIxaXGvo6oJ6sh4R26LKLUvs2e1wOi3NfICOjY/mAS3D17dFeHCQCVQ4aJXJC1GLrZN+vowaQLlkA45VH8crpJSmvLbQdnQzkw5vrcuZbh3is3MVIx+JuiO2faWCNaAwvgZuaNhehOu0exfW9cHklvUcBkHUpPnMNafarGvO6GW2IawNfUGhLdomJtD1AkTDrX4GF5e3vIWt2G7ehDAJZOrHULhmncT8a2/XaA3JL2i2nigrCFAfru6scfJAXjhvLe2wJdE81UUuuwLFJr2g/bSgowZAJFjHd98vR6lz4jJJ5vsFO1h9qF4f+97v0nNVzXsge41v8cg+QvAfiNLWwWPRdRpPjZPehuCWJWGvTgteAfbmecCWnSRG35ppJplQJt68ow71P6d+KRd2X5HzDeYH/iyNMQmttnrIMiO0xAdG4ehnB3cwzWwq7SRWe23i3pNE+dwo53k72tdaAwRbS0wo6Fz5Ipca5Vuit2f64SQaqBBfmHeUcC9e+tmXoBmpyFNDNAC5kE4wUHviL8m2s5Ca0ITOnfNKz+i/VDgEzQvuMWWFIQiBMpl74NUZC/nb8gJGx/jlgXg1/KuUVQhn/J+O1h+fak3ki5eoWGa1RUdKYok1gwXG0SAygZbSdNwFVTiV65FuYryeAQ5NZ2QEbIQh5aGiWJ+1FMZCk8qN47ZU2pwHmc9i8GH8uVOpfRULln8FosE5lEacbRHtQSDP7QDJXj1GpzKLchBqfpmb814o71hLrcAmRYI0CEp8tVPzjpdP1XWwE2e4FzTSGB3NO+LQB1aHpbo5NQPhZiJTP/p19xXjDGxRRUYJub2/UaO5unAf4V8sjom2NuJgWSzaqF9OXXVoQAX4p42Rr/ktC2iIRSwU5diW5h+bQTWKcgcjHTPA85DU01ABe+RGFK0TIKm6hVhaoOZB67bjcmnmol7dW5epOuLHUVc7Nzqa93IGLgS2pDbR7f7h7D7w+pG5oG74cDA7WUZ5Xya3p65j/Hus5/MbVlVB/Q7JvHBGA32/ldJ/DlAcy8EudbryH+UwjEGuP/q61H+LkWMcP5ggQ0Ld2UteqjgGRTLnQaFKVOV02ULovdmjgx/VCfA8+A524vKChNgxfTWUN8d8MO8QcyEyjd4Gs+Rrmcz1GMbD4nFonl17dQDzF3fZEkrci17Z2rN58c+wygwqEKbFrfyJhCCwlSH3LNeaOPfjByXoCHR9sl9tsDdsr5EMMtltYu1r+Eg8nz0CeOI/OtPgVbVpTvTsVYcfU9aZ/Mvh1DB5a1OvBEnucVi38jfYFlAHa7kOiX5BrxlRvfbsw1cU58nvFv9M1IhXaILPWZdxLgkdWzKiyKv6SxXgNLcBu/hM9xV5qmEnRE67uAp7IwCfaDCE6w5aqIceYze6lezum7LCdw5ToYARsp4kiAYHInSrpi1NLChwYvnRm1Zoao0DDlUN1IUsPIDTgABBPVUQAtQgN78B93qDQDqUrfwITzFkDlFNS1tol3o3KnKJpEXgbwD7E9gjjt+6qgg+uPFr3WYd8DDPbCG2BZOEIVQF38niP2TfTbavpMPethhFCrlbiMohFllai5U/ZY98+wHnvTYELuUQR/0XzXm91vgveh5HpMCLDY9YhPDlmP5Q7izz9fyUuFde1igYpmSKQaLRmgRKZjXmhm1UGq1AFTVMe5BI6pkJtOU6RDahWA28aFLrZC1e8p4E5KIa+TJzNCqv9ERPgD/ELVU7xBflATY3J4DkCwwl3LWm3KZwHzqOZEyBieAuwawcy+Ur4Yzm0yngidfBnJ+fbkp2vk3XTd8m5Gr2Tfz1/hTt0eTNRVdqnxLp97HDMb21i6dKUT38f4ARL2CBxgGBEGOB9/B6CMH8hAQlg12gNkaaix8K9gS7tBQp8bt1Gurls+ibLt2C78D8lSdSJTiY979P3JxbmSy50DiIu+Z3eWLuVLUABfrpXW6VWVmOkmmcLogQzPy/LMn163Kn69n02gRm6ZWPmJ1ryQACya5tOyRNXq4HRtHFRbcEvbckx3RI3oFbDrD+rnINA2s9qSmKtMGSCQ/0Hc2r1dCINIp/5BOdET5TlGPl8M6EKKaW/TE6gr7M44+XpzG5Xczh/NeLGDxPJIt4ec8sPQvYKTjrOYnGD87IfAM4rTAsAtnewYSjbj+aJ8m1itFBaArlRaWAc5z/EGrM2bMwjwSYzbLjzcbcT4SSUfwl1CvR5B5arx2x5KGy2UszGB0M0EwxoD5minTneOGH60ELsSTwZBIiDW6bkPcAiV3/LhLVCgxp/+9fEV5kDaVZyYe9UnQ142ezwpWOu4pFLjetkqjel/faGw/SZeWXggeiRU9oEEAy8Y0UQxQaT8vqMotOG2RgWq3Chp6VS+8TL43u/iBCgBM19yWySBmVs9iA3ltoJ4Bwyg5tWcu/gEx9YqkCYQaIMGyDfKli853RjCwECzZbJ3iftEq0MoAy/+gzmsXEQ1blzZ8eNju0n22cioZkvwPo+RGyAR96uVpecpNXE9Vyl2yhb7yb2MtPerSzNHvnmJ9GiNsA32QDxW8An8lqH1+1+wFRydSWH6lXr6dJVtlRD+QukUMNlLtNPOuYtM//12IoZhEwdTjb5ijms7kswvHvg3aj1Vvp49siVNwDHf524pLL2CyQKgBWh+XbtpXSUI0nEV8cpZQPs2l0BO+co4x3ihmdth7E7z8pdjFIf5aTFcmS30Lf2Zihl6NNY0EakHEKF1LX3FFgXORejbWZIV3TTJ8cnKAlr6hXEOQWm4T4UYE/42SUvDbP556cLIcWrvk4yr+s+1kVHFNU+PZAsI9MGjaVNWay/xt/jIYNo859VMeQoYehrYvkYOkXIrAMGwA31cmxopeiinQ4b1FPm2shJYra70EN0IeCCRXRzNIHW1+TvYYG7eg4AAM4oMSkmQSj+1Qe+AKinHBjH2iXszkQCwNVIeGeKWlsfAAZ1JM8wkhBTJ3GxKuX60XKVjDSyHkejbdK7C2g0iYv/LVi0pwSNLagun0ARHLyRQzNHWTN7FR3drIx8Ssy+bNSXJa/ZrBewfOgz1cFWa14WSo3mRd/0UWdtsJaMcPoZMjJVoEUBWsjg1lEJo2Z7UW7SEONd9H2MZo4yjZKlCdoeoI1uxxvJU6hNn4zL8yAH13HLxeED2AHlXVHVTYtPZiaYkTZSFGMNq6DKj2OZXcxVaGDK8rmPufQokQttIvvOQa5TCIGPBxAn/KS0e455psfJ5QkX1CB1aLHN7dj9VOX/61hUnY0sfjqY4t0H7YIdG65Ba4Bg8v8lDTsrBzypQqz7j8XYaiGjz4OGhPEID7/3FNK6Agomz50sYzdLBb1RCm5jcuYGWTsUohlfUJMe3EsazD18eKzbMxq/xm2BX/icHAGhKsxZ6pEzbR2q3HUO0dQCP+5disC3aXOtAaoDWVhcxia13HU+n902zN/dNbi665RQXwnBdX0HoUbVShWv8VPj6XJlDfJXk0I1idNv2y22igxQkX9+egd+VSWSXtkyFQyi8KBF6N5BFQhEY/Jy0KQ6P0pa2E47rvdK3apyx4h3MjJjX5BVZmBtSxv2MFzvKeTZHFdXgaBBlraBN2wdFhAkyGAdXxmXCjT5c5geQkabvcRh+F2+3YsLqLsMfN1gMnBUo2qrvhaa1a+arV4TgMQgE2vSHuN0U+8YfLEjhKE2CyY3186yaAPaJZngbF0dX6iP6QOCkFr7UOgfcA2tKW2hIS172YyLqu22VD9pzP4NpneFyGcZsuzPGy+ADBBAviitxACQ1vIMjhb93wufbnhlEQkabF1ErPaa7G3zZSmBmBNOpjD/If+X3WCk1uJG9hbZbJ8X7XRfhzw8d2A8JILlAJagLVLUShiB8k7NXwrZkmbo/X5vLfIsIx3L9V63etzPsJhu2coIyGAYSQ6vWrGfG4s9GlO2TH+E46z6IsoTDUmMvGmIecxLhKMd1w7IOndNWbBC9jgEH4aAP2nsPPsPp6Q//Otv2VBoDE4kbA3FUYGPrAz9aOGqzlKuRQfmyA9NRUhfT2N8Fa33fcVdA5vCrxDyoOtNM4hDccC2glAydceGOcniNSHdF5PGOqquMSAull4/hKerfh1vWmoICOhMAk6pjD32sxjADiyI5DBZ28aKVhGp5pFlop4wr5u6r3KSd3EDfgcE0IBuRnxq18q1BVcMIF6XgQh0MObj16uWK0SuhzTQEnzPCb7rlsHq7wMMlR3+NnWoEaRPilXAst8nbCyYSSuSmpq6DQlVIsI5W5p2ZTCIsi4k1Erxcg5s+0rw3aYTnChJgV2CffBCn3LDCa14vQK8GnMXRh2Whz9nM6q0/K1ErAoPahyyQAAOV0kggVveqiM2YUIkXsDWt8LMP+0NBoylY1QFucEi2CY9a5zutjE88GyB7rz4yfWS+0VEcKA869dnfbviMTQvikMz46RhQlyrpjJ8ST1giivG7+SS12WqJESYVUeyPw5AH2vayn48FVGw23KkmVZTr9Rru2NZf3Cf1YsWKWd5SSC11is10jQE1z1qI3zzd23uv4ga2W/zAoiYduh+CZK/BaZq1ueECiQYcj/OrwtUs+yP4vtHaC34LHFpVNmziyVSsIAX+bXmi3/b/QAAAAAAACYyKu7QPvMAQ/s6Dvq4MlfTS7z5oE7qXZxbN1VLkaBS6vqDg5MyJhYUhqKf6im5wDhLTcrkRqgsuGq9L+FuNbAeqhWhGjMlnX09kB58tkqHlx3pV58CoAHV3zQ8khStzuYQyey0gTT8HaxD5l5XiUsoMq0/4F79VmLkZf8O/BfVgdSAuwXOLnVR+LbjSqZbb4xjlKG/QrkJYx7CX0u8tZUxSLIdjsAe5HT3DIh9gI/WICGJa1pmkljPbnazFrgA1cCAGIFPwrqntkkPNli/g+grxQ8m+QJu9L2bQCdP0jnIeNz1lx6pGWbCEvAY1SQNIN0FxjefsRzVe4REbDm336SQMaUFNFBqD4kOjJCKCXFKV7uXkchksRM1182830SZoxP20oSVO67a6LN7PwpuAGtJjF2nF3xwD/HSPqmcQmFiKowZKppL7vdXpeOcz3xV5kmRdvD5HJlo6yDAcl5Xi1TOYk8IaOlLGbFv63oLcYEknZisrewBFBW6ZgYJIipZrrPBWsdnJrPA+/UFrGPpjbWJ7XmRnylrKNvGbY+wlUwMAyx2xML1AzG4POnm9+OtODP/oZhx9O/uPXUla3IT7sCtU5S62xz+FZJzK9z9Oe2VRwEg0oeIIcAyWw0v0ufxGL4od50MVSCkZGIJySxV9A6N4AQTLDnb6uHPTGiD2YQss8An94YMAflmN7J4L/r+Y2JSbsVzuzb+S+jQZGOKJG9KfnwNw/+1dTivD27wBEiGsZ05axfN+xXLJ/h5nkpRf34AAAAAAAFnNJYMGdMARVJyc8Yt9D6UTuhbvcURjQ7p2YdcMRy3TKusoT+1UVTQE92g1EV1K6Gv90bm4zFqRe66pTfsJPkSD+Tqnc2tU2yuaJT8DQxjtZtomIhPgNrrdblCiQICaJYvk3O0Fo2pwLhW2AmfsqhYPyAD87nZi8l8lBoKb5gobt9+tNqUc9coJtMlw31P5sR1kj0lALDWwho5UviXgTIZcYC6GL7UN1cSQMM3Zb+RWP+qs8BiHLCBtcQtuzbe7CdJSquxZLdpdao+dagJI2wWMcSIk24ApYSWjzG3Ugc70BQj64erQX8cDy1RD1qpmQe4VYBEMIwyrPzqDi8tmjVEJqz59lHxP5IDDqMa6pNtwV+1VH+f4WyWIsxpN3yVJlTMODCFRAMZHv4d3yiiXSqUVrdwNrQNt4GWGn49r6V4RLWeNHShQ6zmAb7PAVBmtQXrY2bHFl7WOoS4UjQ/ASgdKibriEFJYyloWYQ2O0COq/Jcu+gVv990uso3bk6iuJehSL7wl3yIrxCOjQaUcLjToeockTPMbHunJApYEOrWjipzpz2U/Zj4j4PYsEaJoaQGzehwuqby8p1hhncGrO4NBHUOv4D1fN/vlxs2khatJaiHCBN7zWqZ6mYoxchJgBzBPYBgXLKNzR8bGzDqFc40Mr1Z9e+eY1yq7wZnfCNHSBluttl45FnBpV7SqtZaQCu/DPg8y6XSuN0S2YF4c83ITWxQ6J7ff7X3D7c870QJ7D4HniwoNTTieXiU2BgagkiUB9trMAAABI7b5NnSaO5nGgxWi+vof8sqbcvjK5FPevlczJ6mGzu/7PLiq5DY4vL4DsYWQM6uKq+hBbghFy4eAeZpfuQDQ3Su6ZQgI50LYMkqpfEuI5Jwa7Wb4kYv5C9oFrRsbm80KtVYjVKEZ1te2XIDpblfrvzUzTGBlB0mZ3JvAKLx9HHwY/PMxUQZEzZxrqIYsEBTmrbgYyQ7hfIPHBMCASzc18pdgoTGbFWy1+lOV8EIviNfXAeiZNyhs5EBzDizs94KJZvV7R9qM1zU0tikXWF+/nju0fGNaMmygHjcVVMu+A5oV6l3Uxq4hKoXG6UxzcViQKZI2tZE2PTNyuvOecS0CCakD9lae/pjRYsrMUtEzZaYXqCKcupoL91AMwsbOYUh8v6AZx2vvFatZSrSC8ZH3tH3qlehPSmKdnkI9QrCekdI1ou9qIZ8zuUCi18g9zDZoR487AeqBhE4HKUhi/pcuRUvGVXAnECNVkk1A1AFBD97sxOq3fhZiNKHxvqE06UUno1qrAhkT65bAOsNy9vuAaTp1tEBzpK9FHl3lpSftEVHObTVNVZLBhexjt/LKnZotKOJ6wCJDL9i4A0yoH9IrGmXgr9510I6JZJVKoTAod460FxGkAFkzgpk4A1Ctcu0N3jfTB+91ICg4jmxKNroyboIHwsyYlL47lcDAwbleYIHxhIdaY1KgbJINOXBI+FgeT5KPlDHcpgAAAM9wmt/0WVv/XhbKFvs60dWCnN0PxsVlOsZuSD1Wvl9udfdv7HlJCs2WCMgPvBhSZjZkpPEvGIjYOcn9YJR9Zfm2Ple1xX7+VJ+HODkijLAekCcUDuEVD2gVNggxXzgi4i+/PX3zXx3s/1fupXJ7rEsj+VXei13spCfJKKPzGdcYuB+UojM64LLvBQnkxUU5bKma+f7YM2w5K8GpCk97tKV5K7a5uTnhmivsD0sSHXMVPObxOHkdaZ4NNKIoaYTFkmVGtdJve1r3dzBuwcOgeUq1oicfYVM9mbZ8kkCwb3x8rpIMLYf+couN3oVM4xeYBhNzk2lyoFQmHf6QQcbtXDdyldOomMIq1qzTXAToT/nocglUZdDEPibHXfFyXTzHhYUrOUsqnoRbEKsaOrj9aR26z9f14W1V/JovvIJMBH/q1JFP391YeA0/o2TYSUrj8268+rThz0qcqQFHd/lFkdX6EfZ9tRlCk0pYb12yMmp9r8rJCpQ+Q5K8/ewgayQhm6NRz2/rqQwF5v5GXpsFLfwUDgOxZvb8mSB4a6Fj34rIX0QkQB/ekf9BuYvrDlBplEx/RScNqSAuLdsOT4mCZ+U0zcPp2VP2Klz+dEzdQbjQWasfXae8fG9uBU9PEk1HJc+GYDAYyycHTsJqFyL2+FYHoqFeUamX9XXRvavRrLeRFuugMW19mxL85nJ8UCwxHFZXchZ14/wnSEAAACeshhE4xT9x3zPKyzZXIBYeUt0M13YlSUhTXY8B4mN/MXdFi3wVib4Kqtc/Zo/SGnuBa5LxB2Hrc/cbZV57KqsFcSXErv3Q++kqa3OWGV3cIPKH937CLCN0iE285Z6WCwAi/e1mwIp/LhccFzWTCwS5gByfIrNhwH+5miyIkbP4rtlEB1BMlj4T0xl3eYA0uD31FmM5Q9PDMdcg3AeMb1fy0wVrNW88/Zx+/WnZdimP261kLWaPyod50dhlx3bDLaIrPQS6OMN+nl8JenCrOTABP+Tx5H1CunGeo77s9JYCKusPio0loXpLRXO85FPTz0YWlDXaNq1zCzLmsBfIOaz3X4R3xVmmIl+05n2FOv/QMw6r9NMh7AT+MYe/jsNBQqFir/eX7rCjxvMy3tW+fNO9XSNGnZSm5cJtZDam4e0Ml4dBEOe0YtnEtUY60i8omZpNBktQAKBgf1LAkFAInle3sJqq+i4clyHP52zguzC5G+QUyGDgy+e+3chOfxZlOdH5fd2aN5ojjkqi1wRT/PwvG3TJcDvAGqpJdJlXCmG2q//CJKJW3+pUsnxiDSGLQ47byyvL1RJ6q/5ZsiUlX7N92L2n3KzEEEWyQct1RRTg4Nd3paSgMLdYfKY4zWoErflxl8io1A3uBPwG6nTD6rNMHieEO1PCOB6BSYktAbNuazGL4L561Q+L4XemRvgVo1LOOxiHp82UxqdhUXFdW2qn1KWAAAb/+FCpTuWOsGadpVfI24dIcKN3DXIuULdvClBUFuKoz3ka/YGwNfp/2mGF1dqfEkelZqmi6fAfHvA0o2boxOGOUkXevy9pwsvZEbUlDJZDtqlGD0vkLbcpxjpjT3UXMt7Vlkiyg78rQSXZDbpNh1QDvXiiVvRBzP7Fm0qwbgtMdLV7qQ6kbrRZ5k6bIWkeVit3TYfNyIG18hpg+fu+ess4BJdXlmWEmFpgcTvhchIkEj+DHZvXamG3LTVLZbtHMaL8RL8GEhrw4Mp7NNvLDpzgpXmYs0k0Y7jF+qjXTYg1oHoTMlMGwIjGYZMT71SHc5I6ymXw5aFlYdEKL0b+RiTV9EoBsiAa4UmQz4bFNDDoWDFhhX1eIAKKJwphTg5KLVkJuf61SRe5j6g40kynUwFVqFgqzc1RKDyo/ODfbkTYdmXF6YVMCOlXFjP8u9R2UUQPdt2F/po9iJJW4ABCOitguZP7ajSar3lCmRJ3X6uO8G2WKFRlJw74D+QMaEEm2E3aalDCbmcWE+rKMGZRD1aJygreNWUV2r98a8f81k3B+Pj4dvXrDcfOF9fXMgiiMj3GFDteXMBnVqAYelze7kFl7rdxcYQpVEk2sZVSoq+RX0miSqNXpK40M0CQ01QmmH6kGPBgk8o0F7SQdaBYokwNve5tHtnwfxYpFbeGkn8l05oApc4lcwYkW4+GWogZ7HmLHOJOdruEErsU7dJZTqBIvxKG76kPql8DfmRUoZF9H5qQx9sGUbzxUculNvUa/E7XshG5wnT5Gvg5J3BAaptJNLWYKt/R0N7tL0rvLhcTulXaZs4Yxa019rYTnlG5fqapaIvyf6dGjnKtRZk+K1qYpw1SWTEFDSFogAAFXJEI86i3Hb4HeEmekzOcva84cLgSl9Oqcm5gThBpS7sXEH0VqMAGVOjVQ/9gYpxpEtCgj0K59gvaYwprx/PsN7sZ9ksgyFatbcB7dA/RIbBrRqR3nXz1iat9goV8kdV0Qx5Rm5qN5nCUEbPXtmmiMtRVGK3vgV+h0TLuNfrMIJNPFxQHwnkWhe4+0BXGk7v3ItkiqzBIikZdcJYWrg8UlXO+HC1/94wMW/34C21kYGLVLVa3LNUo/Rjr8gmItd01Yy/37zZrt9GyyCi0Zm5IP8esbUUdxoc5092za0xkvPSwATNOV6i90uSx36nrU0DZfy0HxExbEWDleSpxGe8BflJBZgk35sKjpOss6QLSaQv5xGte+dTHYQUyE3qz6T6mvWD9oLM7ycJul6VVgMk6FlygXToAGXQHasXVKGJgefAXf+LDpMrcwWu7YAUz/kdNawhduX2xf1qZxExqRlHHibzQ2aIoT6kw6qrR/LL1DOek90J6EkoeRI8AQQUuNhVxFvrGwCJUvIFn0w+fZZ9PF0g0TbDMzRzjXzX70nA7Zmm0om3ubOW6rUZ1J6kyT8eWWMtH21oS0R1zyX/yd7KJ1BfgqJl06f1325qdElQGGHG43zyd8Mrk6NQG3ZWy7jEgpeYAc+VrQnUounmAfU5l9yQ7FlZWDQFgXQ6w0dnIAHlK5M7TIc/BWgDOXhkdukYE0WeDFyzjIMK7heNMjfE031YEygF7oJsH02LPekO2ZtXhmo0TcxfMLqTRAx7EnN76+nWrsiIxYf0GWbGOKB0Z4GJ1A2LgCsYFP/aNS6WlRdl1yuUh5ja+z6CD4lnaqqDKasDRc7/jJ7pbuTFmvJRSfas0MHj9QW1Y4xn/7b9WHhPurpRVgXEICSi3lThAp0/cw42G9DgksffstYsRta3O7LQPn3vGvVkPiKV6sc2PszL//8lv3R//1esLSgYjqdidEimi8AAAAlFvwvqHwEgv0ZpZuv2w/HFURXXeL3YaNDR6O+u3BzRmAVw2bTBv4nBP2ftMM9gHeiIr8a8U/3SZ4GiroerIa0tpvRnjkoAQ5MRQRHl1eQ4KhmxrgcxdEg85y4FeDRmiBR6zM+TyMEAYpf9hP/5aA1qg4JE1N8U+MgI50BuJDU/3qyl+6am08sW127Jb7+2stL2zZfwoIrvyfqQ1dMcNuiKOpCcSBae/YximP8Yrd86SZQveeLuFC1nn/Tw6i8mn5AJRUfhOb/3kymI1gUVmWQKWuirjZubFkSj9W5kUvEzp9tvrTMneQDIzqmf2mz3HSiMOoYDmVmG7oJkzKTOSsp/vHVU8SbU9KDAH7m7AqEhxXh3QjRzJFLdaTsFfR4pvHJiAV40rKG3ecLrLPx/Xx1fUYCfpXB0XMNYFmtXD/4tBL/WdGWnE6am/117yLc+0CoIZz73c7HJYJ5ZrKhHUnLAAZDFeWrdwJPZ7/y7BHFHOIwSfviu6ikEIK/+oCKvkqufua9j2Xn+P+r+VCZ4WBwThA86ss4OtUSuI4OsDs8cWQ3Ou14T1RLEM23DBGCSZowpNXERe3ikdcA/sacN5RRcKWapMrzV0xokcRrXmYyumpcmfXTqzkmoS5UG9+k4RQ9Ucw17uOtswXHychckdLhQAFBYD4bUNXQcLJjQ6yqz/Myi8qqHN8tNNcD/J6pX53K3/PM/XNJErq7JqmCybasb1AMlRnBfiZn9joF+adny6Qx4wwnv8aC+cOYH43I6/0PfnnKFv3qI79iqCZgpjYAvJmBgpmV9okPDWgPON8iZ34PYfWP3ugTD5QlzhTtoyB22arGt+Ng3FwUTHgR+FBF2v+0kPcj6T8BFv9OzyC4k5KkhkpuPYW36psBLdTu4NV18t0AAAUn1qbuw6cLMOlMm6SuU/DC7zbe7r/h/MlfQECAjDgEsKBUKjA9r688CKlnLe64nos1MlqgxXSmm9Ba+oGerCHDNEcvCGZk410SXCjUMAVG9kipHxhB9R9qsImxeNsGi4TRNYcHQCmvdMztzSVM3I4OajX4f6IZb8J9Fq8r046u5t7cPRid7UpkRIrSWvgYK4cbpqtLPZuizhMg6M6XjXoyMm0Rm6GtzF3VXVjmVfScsFaNGldMmwprxKKUqyIFcL3PKUxBAzOKWqmgx3cxv2uWElcR8nw5FLQeTw5a3soAYVgjG4YXeAFLAlAD7UudTFsk31tWgbZY7+qWXzS7g7DfmCmH1SuIJuXqSoeZ5Z2xR9O9OenLO9xeMvO8x0/s95SgZhmKNPYGKiZBGOAQfTlK6+a6tcxTTpiOnMuLJeNe7+dr4yiefvXZmGILEw5z44fHr6FC8B2QVbw1a09p6fEOjytePmwkkuhCtSHMCJ1tNcdT1QGrwelUfL+LgNPEa4ue01bgcZhb3TRv0yCuNBN+PL8En/7Psbmmc5sFRmNwO0ohDhTMqwpnc94iGsSCG9LjBr4iIo/R7VEPMpjIMialfy4u691F+/y7x3GjdACh/fNb2JdQ6HyUX5hQx1exQPNO3nt3qQeeBeCAGqWLyXApAFuhIT6NzDEQaNlvpWaKi3WIltn7JhDvv1YxbS7ZJrVerJbhXdTzx4XFw3D3nZ97cAaWaRujCuTqtYIuQ1lCpPB4e5FkzZAvP+eWk62dQAqaCw1eiqxK0AGjWRKHq6VAeNxmYavqx6nNLYXw4zQUiTq8qzABVV5U+Yz+MWefyI2rg2AAAC1OjS8DgGhOEAdkiv8n/4leaZOqlNgtaUjQ5WSuVhWNOu5VhllNYWSWEsqNHtOpogwoMzQsjY3RoD2GaCrvMOiuZ0cSZnPqrVQCLvKXHKECNqttl0NKTH7LQgsXnEFZj98oV+pENc0rMELLTyYAg65p/ZI9yZAN9p+vKoNGy+iR9WsWN5bMr2zUOverSxqDAPO+C19s03feWhjgaMcob+Xhx1gWuxciugPcO4RQAL+AnxUppDEL0KH/rNgtqhcwXqh/IsLRhwLjnjujfELH7BuXynnzge5S1CcFzcC+2iuAX8vLbU1NaQgm9+hXVFCZpyYeC2ECKHS55HgaYUw/JNrZrwKsmdAc8wi+elRrHX2ABZ7OBHrVuAdyZvYheSpDpgNXbpTe0JcaUGso3AoNUqkj2r7JwjAUTNBxbSVnr5yLM7uhTf3v8At7TquSD6UFYDTapHzvzt0zwEjtJ5XxJXAh8FtJ3zSdQcYfytYTkgIchp1+xsRLXO5RakRr11k+VBa6BMu8pjx5s1hZ9CsAmYeLe8SzFQ5OfUag4uzXYAKDz+tUn002BUlOCjhuH1/hBY9eyxKhAerNAJZVocG5depP2PJmu0ygUOhDdfxFuiJcPIDNvdgh2HVgAnbNzylmlRtCUT7SoQc5uxvOCCje9sWPKXukpanFflvpjgRIM0kdeUFA1cyIBerUfwimGjXydy2KtxCVcJb8d6dd2/Z2zPtlgc9GXik4733JYDDaJ+z6dOSL0ocP1srjANTcAAAAzcpIW97rk3DAEGIq6x9UeTjQtXrQ5P25tz/iy3YM5dVNoTyPkz1uXg/jlz+LK3jScWPGEC3+wfFBFLn8gk1ndA1CjjxuTLPRSvluftmVzSO3NOyIIc78cNrvPu4oqgVYjqiI4lH8F5ToPYX0aLO5YVbH2CnodHZDBuqKRbJP5X7UvgmXM8YLrg/IMpKmlFrVqEtdgobPp/ibIVLUG7iLlDfszS4wAcx6KHd7dNWlWDhxX/0xPNb0NaAyLQhyf75Dd6Eh/aKpH61cFchws3vAzntD4F/52lkUEoRVGZszuOqXNjl5lTiZxMGf7pkAl+9ZtK/b5BdiQ6zKh6N58+ZcKrPHYB5H8xQMDBlZ70HBsalpG403gYjLpAeMkpaUDGa2OubW6oVDOojaejbQiFZ+teYmZi4T+INhh5tlNQ1C2Eiz1PR24oG69QOFHrtiLq06mOAwL77WNwl08FFho9tIwMUoq3rxE88yVbcmvA3/Jyh12fyRhI5lO7J1cddewLvBVH1r1W8wz+tXRfolxLa/9CM5+7q4e0EGXYUPlvS3ip+cG9s1s/puhskPgoZfCTn8LklUWP/9oWZG+8t/gLMlOB8AoeADd+yv6p15sCyRfLFbiT3HJmyUjN/xxlGGTVD7nQb0kiqqg7xiJomZThAGgR8L2ZC5MM/k6mXvnYoAarrly128PKmMqlIM8EKW0JjfaLY+B3a8WL3KDmvSrsOcIHWIiMfMVyJAK/bRb8nH8J1hjhILJnldIkQgXyAjVxolSlxk8SKfFLPlgIvMarqxcGXSfpty8rHIXOnWhp4vQ8I3f8GXD2Xg1waK5eew5jJ++q8skAAAAWsaZj2uBpbgBvCyENNPJwwctduPouLY2EbJqf0QWmMvKnMAo4E3S84YYqbz/8xEI69vgL7TjY5/4S5gpBeOtbNHcbzV/bvhHmIPuywnYpFFlPOqo1bOCbKQI3JoKlGx+5XC1C6EhjEsKCNfJyw09xhz8kq5Rhc4ulVcGj5u1XNdxK7BJnP47uclHTL275iJyU4QKxJDB+mKUJvmi+z3yi8DMna0s4huGlrkOhdqqijQpVxohIYSr23g4kYDFqhMFPN3soSLM2VwPhRGkz/4jYYJzk14zPtIuoYrNROd4884vRYE8CVdyN3pqjdeTUm0L6s9YH7jVSw9zGiQELm2nKfmwmqSCfKqRvS29dKlMmkix4kjKaAbYi+TwOf53vgNy0MQrj5udcyCFTmdcNV6mLjuSaS3ddDN/ThDDEHpQJtuZAMSkCGT8LQ/K+0mApLx7CPmijoH+3NY8b1l+4aUChCMHBmoaL6IYIjTlyDa6LnbMCIeFLg80IbnIJkuJgGwf1/9LENCKlonOOchjKgos7hFRZh5Umnb5o0oKhTecAEghGwlgkkqaGURS4A30VZUPZc2h+0RTqtV3XQIl08CL/oHhzDuNrbrFh6aHetlmroxlerCGrQzgS/ZmbQXoEHBHNaULEmHukYnEDJKdT055Owqdb7ZsivN8cjKsrPPP7W2B8wFEk8zsUPIzBRwuLKN27CORTlaKdYJYQt/fOP9ZzawC59SX6Okk4BUKaBN48bCWmJabR9lYKrPQYtafgtCItC7PkDUjXWkGIfHLID+V0lGPr7KKALo7CGMAskX4EQun9UDWxE5MGxu6xLCXmXKPCVNYwT3X3ruoOGMnuJdKmUmcBJX5JOPWpQ0MtZNmxxiX29Hfc5v9veFI4edBhcnz04xFMadaTPdrlvRWLgAAAHj/gAXpXkw9vruHNxJifyStqU+CLokYjtJxWdF2BIrY+pI63cTQrq1Zk5BK7aJl9bJyAi/M6FeHPn3OXqAtwUGQnAxwSY/17jUNrp4DOj5tNWuSlnwxL7SOIO4MJBxvFjeIWlckFUjWmPMS6rVB+JfVBmgfic0mKwqn5OahFPGyVmMSiFOy/MxvSQLuEUZN47TEnaQiI0ZnocC+o8lRfdblj5XfzyrunvkFae5YjJbhYSWalqnYsoZlm4SKDCcbbg30VHVOcuC6rjpE40EA1jkV1zzp9tdYR/ZmuDcfSxvei0/03SLP4FpOL96yzLiY/13+r3PjusBDtGV5KjcTJ3MXA0v6YdZaEBzjhkEaf5h2qhRJ8dBZi7lun8DhcbNehJxOEJ2bYNLJLe4i/HIQXFtftrASuD3bCajokpOT55mHjynrgDy9X8uMeVFBdi7tW4gHAfWvo5t2zVl5jmpqu0CfrAOtIKRGrYOigcHtYZU8igMTHMlKnGVVqUkL8+w2V3BuOf0n9huB44B8EN6fdFV2pILDmFi3wvz08RNdGD2ImtTtFgC6JN/LSMRXPMzXadVa1p/X7HDJCRvTrJ3eslRYWeBKGYnLT/h4UxnnpgAoIqmRwrgQLPkwiKHDbiP3I2NIzfOo/QsxzKKOemwv9qebJpzqX/0HljeMODkOTNFaG6wMg+4/fMAlPBfRnvGx94mpDNxXwH55Ntv1o1rvH+VYSKE1S8LOrIO3eeGSjpkStnV+sJGS/ERXNYpAJnY6JJn1iCdZg0GZjoK8vWzVg/B857UIMcYws2kQxr/NUa+WriPc2Y4J8UzVKc5K3S/hGcHgLD4C0SUJAuC6B/1jvXPofReWnATLVdvzCs8bZAAAAs/8caTltM5kJ7LRSvkRUv4NDQpycdQtcQukqx+ONkiDSgjtnxe4j/WKy85UCi7Jb+q6ZssLh6YW+cjSV1F64DpBi3oSlT+UgkM89mJ5DfR1Gv3+gllIFf7SGCKBsNLFs6/i+bWEosT1Z3Wzfu7fIIa8bONLXupLP25w24AKEU705SbaOOkAyV7wgx3ar7qxNoinjTlKTT8x/ZGN0IkHo0lxAzr2GKqAPYZ2XrsNFERq9hJ8b03h795kZJdEy+SS2XkzQDN7MOT4kLTbvyGRmStYQpRjsLGAHtxa90QvlY7uuqJrwOyHZ1oKf2lzbhUaF5RX7zh+PGdlgwDu9TBl4X0mltTMA9XH6bP2HDpR+HtAq0psYH+B+J67jsBuKFRiUkGbuMsiNGtg1pjKOyeVwxRhOTYGp21T9h6JWXeHV7HU6QT5v039bfstnMyUEosnhzJCg6i6+GbpPdCqd3nGk4tTe0ZL/Av45wFnVeBzlRAUioQsT3qevWtFSD9Cu4/GIxkpB9yIrUtWyGWgbbM3kpkUaVWNx+9kkj0angb45R18i0odFS6diUYyTX2GlBow1PHlKUIMzpdr+5DKf13UVPxndmKOPKuHkowk6pHo2SYwdieANANHo7jkhyFMu74H5cRr1FN1bhY7HGfd08KS1LxGDziVjv80z3Cc75iFtYzxesVwOFACMpL4VmhAubW3EPX7QEsb3PNRbaElaJ4Qu7KzreUPPpb/2VAVDo8RIoLnxD3ulD06zbl1DXKA0zRjyldE/tvc6iTn/egf+B+rTBIbR2nCnE3GkDA1E2gqjv/NDGSESqRtN8zM3r950SRfBUNqKAvPkoVwMfEnWBYFjxKYnYIA6HleAD96+hJ+n1U+m1bbcFik6RiuGteZ/McEUsQkvzN78IfMkMEn7AFDB9M6AhJsm7zI9rAopxdOCEUk4dNbBgTqOSw2mkp1kqHq+K7fEYzj19plZCFdbX/TOK7ecAAA7/8E+t7U0spkcNQSexU2XZP5TjH01/uzOSQoCK80T6NPXMyAUiNSfSC6LAx+SkQV6ZgLzGh3FpqQkkZYwZTN5GAavdkVL06Ky0jotsxTID7op34jfpXJBVODxeeJm6QV9nlK8ZOTQrf7IE8O1vIczi75Vr62Tw2W0o5gmzv+sFs5GHhpA7pIvs0Ho+9++Ue9D1ac03Wn/1jCZ0KhaiHY0dx7QqBOw7qFwRIt2j7rFW8vZS+JJNaYaep6t3qTYkqNQ+dQrYjvzUgGjgvG3Xz1mZO2W91az6vzP7AsfvssPnZb1pBdqc8b1/G9EUiIByqPgEd138ppGcQC3DwZe0JmMV8Lc0sy0cAe+6nb+Xzt/l/n7hO+7NE8uLrXarjmBZv3Fw7fRS5PD3xr7Y09QKlYxr8d5RdQXtKkqQnmMYO1GCN9IDqYqZ87JIcm7+R1F6lAwUSl9u5qVZlPNYiNcGfr6KDrEJRF1KK5ObAmOYScSSa6JMVHoH2Sdek01xvpsPPzF7xP1L5oPoAb/h+LlzN+OsKkEqPwVS/86zy8X6hwNNciUZVgcxnCGZXQnYoqbU/bOO5DgvGNtNfXEjx7mXQnV0GEOtRXqzY+Or7pIIACtBcamlMvF7zv3LJGfu6Fu6AkU4JFiDqpQjNzlMC503hFcHTS339YR4j73tjjf3QE7/HOV1fgY9oXLU3QPVgnHrWpphoSBIbidSiS9yCm1FhSaekv9IrTVZx1Uuds84k9O31Rr7X2yoVOCRgdNkWIL7iOimpDYa6IxUTP693W0nzE/QA4a3X021rIHx1tP0+KDSq9d14H4nxFx3gSPTt7DKApI3iCRwu9HaBzxnw/k/qphMeLdw2RzlNYnWFCbncIpnr1IqWqYJetKBUHefKNVes7ezUpZo9CD8yk9eopxkPt6Etg/oYYkUqw+P3AqsC0tHmH0CvmLP9Yft2HUhF4kRhTxtvTeI4xikHTeHuZr20CBisnVV9G1XvWVp6VnbsfOotKjkZqbl7gs96bB/k+4mxyLAzt6LCFz5+NxpskGq3fAWpEaqTdQspjBL+4rrNYg1AGhAcTY1Vt3AlwUYXPvKRQKptE0d7jZP80QraBoMv1BoDyNC5WghQdQdZYQZ49cSvxkYnl9UZJ5acBrSY5e1a9JtSBJ4Qso2BokDfqYf9Kqzjvu5dFtUJTvuyNikbRCyXHepHaQoGIvZqQHx5qSOA8mHLqjBwVUFa6loQnb/0aVLRebn238hpCl7cHRVExSWyWyQMOf0nL/xmkU3ujN38aEdlwWleuRzxmIMuYFb39Nok0DyL9PaA1Zf4WUoKhqnK7CApgAAEANDPNT1HSyutHGEQ5sghy0itWn7/EHnD6bVKq0kTXZmQo4DmJv8wwYvBRo/WM+cZO/6GPEDqWs7zTRY8XH/IRhZ9IDyeumsd7wOJBX5eDp+cnm66AsirCD1px5EfEGuc59dbqOAG/pzRs9VG5qncEFFLen+1tWAw+nno1yqK0Gz4D3eeFPskw+bWKqlid1Y+AoYmJKhrKx93v9SNr0xknrghh/ziox+0662EPRlkTXjWDGS+ismdDvR2ySwmieHtaiWWEt/uczGB/aLh6wOPb+1Xo5seiyNk3L3xM0TGenu7Q4t5XgC7ih0GurAeD6X925u2RnB6t8rpb+bfN5z+jex5MLYYGMbQ0TJbmG61KbsUjaxxNSAbwjLNq6vnvZknI6XeAizB5XDMkxFNHW1a8TGsyh+455aTY7OxB3TT8y5blWzW4BHf3x8NYj8mDPocliUH734K5638THKAb89lgmcfwiOeVOR7wh2Ya4MM9dp5ZgA56hSJlie6bs/vQwTayvCBazvNv0p/5qqj1+VOIQ4+otnUJ7tuDBlQ9sIMFNji16cdLltOV04OhqEcOOF3zoKbwseCwpKnVAAw585Wn3PsMADSyXAVFL0tB0LGEJTnkwSLOEOzd1hTRB5pjmJM+VybWnN0qqoUy4kjuaNPjFgzy24CKrIKTUzp2rffgJeG/na3nB0lHwFlTyLZdoq69F9pF5LDjUbww0oWbN50oTeZcUa8U8zKh2BelU5WBQS0YhE9Vi5SYQFPQ/k78hhE5Z3/YnfNjoGzRsQR+gIEe+pLJ4dPljNuOLq5kAAjW5+6j3fbhXiU7JBHTeETzGmpsrkVpN+A8szp3nWAWv2N1/POPUIMnOVWtHCwBDhT0AUi+/RfRZ8bPXFg85BBjYTY3gVEjd/ZHKJdb8PcCPlRe8Vc6FqoHIsk59hfCnjg/BM6lE1m1G0HSCB1VGtGYOpxpYbPex9pf6KwO1hez7wrn4hCrq4sB8Zfq31D7QRxbJOu4IS1i50BsCt6BycgB1kOc3nX28QFIAviHDwY8AQiyicV8rva5aPZpjBe7iiNXs7qwddhGqiK5cqnNGnF0uslygMBiP+OxOhR4UEQSA31hz6UF61WOFIzH3vugWgXaXuGmQRXlk+o/CBS/Sb/pKUvH8PKV8bJbF//F5Swg4qYbY5DJG6eFr0h1YPhnh8illfAMXO8s7wd1IKMUI5BcRSBfS27/8SQMMrx0SStgWVFe904yL/Dq6+OCLWuxExKENqp1LD3giK/50jXxb0zs5wRbXm5ouyar3HXP1ksk0je2RagCeRglb5mpA0YnkPz4+35+RW8ViKLG/q1AThPrptYZ0pnC4wOfxoTUsbazO5qflUfqaWB6OgUefV2vRsj2OCvM9QAABu6QoUNOfUpuXuLfzqE6ayNOqcydxHhej/7t/eZVxjUh5deAePHgdwgnPoj4tH+leI9JVDhiQMKno6Y+95sMAJ7gsWS5XpQA+bzJFZ/WBvx/2Thf0/9cJt0H5lYh+ASF6z+G8haqptmGAKlU2cEkf7JTZhJnK5kN8hUt+ixiszGAGSHD6UMQslETOqhJzT5W512A39yQ1rmBJLPDOQ3TSPRwD1V9s0IP6IuofoLz+J2y6NowhNtCNXrGNbAU8wLxYCSJZbu8Bs2B3LeG/XijpykiAJasU+k+/r4ZE/rSP6UKoEvbtZ2tb3D3Re/kCl8AuvA16ulCIpNBZINtDXvnkqxzIMoi423V2TO3IfIMlJVie4ZOmQTvYpim58hXcp6iYgBJkzpdN6U51d1byk7XUvvGRkq/+0MlzFwy5RGVq3xfQe9jcMVYwnpxZx0p2stg7g4gflRWH/ph07Xyg40qeEAFShcRNO49cd2Ssj7fl9yfX4HJ5JgSaJ8+dlkePV1aU0/NIA62icnMHgM2zMxiWFeSiPFCqQF9A8CxE+OH/5S9nKFreiL+ayf3WmMtehH0EDc86winh+I9cNXpZkrKPIHUqSkEQx7UG0CeOCQhiRlXatWLkVpR8W6uJR/HMks4KLkmUmvFk1Unk3OL7+Ux88SilFL6rLfZFJGrnpyYc67vf7O3dV4B3CHbqQ2mlBixWBzGiBbeUMJVgKm6/1zNJBl/GcbYzqHRAOX/31UJ1enLZI2pr/2x3EwCnRNK9W08TTFiYbxpqt0RUdL4oHnCsN+GIYAUH6WVylQJ1YzrZpGZKUEPvZgmSk2m49D8pn/iUac2myfFmzuzzOuJzcxniofolUXnMYn/Dk7Ti2vzKHSK7oFGU6dN3q9swGssmoZlBA51a9Wxmj+LlXL8/XdBJhswU2qvjv70/ltywPSsKJMiZwCPnqITYgUtLSHQZeK1RrZqxlI4VCIEW6rtfo7lqlm5qMrfUUjf51cJcPLfu7fb8siktry8isPI8+tMFC6HlYY4FmYAFYxtdYT0xinsvLIpDlNqBnqJo7jzF7ruuKfAEIQ7YUcPFcxCxW5u/OIXgYTZtUC4AAasT8Ukqmf9sWiMErDBwZCtU/yGe5l5wJksF2J9yZGpNRCZna2jCVRNvaIkvp3EpXASRFzY861GCkIy6Yw+njevml81nXl0HjG9G3SeN021bKIomkgxJs+Ykl/udVALmEcADHSBonW1Ly3QhExuNhF+v/qJc5Po+6kyajnk2kdomL7DhJ4ZG/btcrKnD740RA0wznActYaKrXqAgRPvqVB1Y8dptdJjHFNBW3hYnnR2GCArboF4mIGefHc8rnPlcY+wpqAzHpvq+bHI+tTLVQYiG+fognwugSE8fnB8B5Q+aNAejjqr5CXVq2gOz4GlwzihDDQjm6rxOZzqo25HXOzTz7RBD4nDNm4XIvzrE4h6RIJtuYFf/kmvQSw0yiBjxslTwDXRpgrt1Y/izDPvL77uUJsnCbI4FbWL4Za0CDcmdIweB2Oq2zT1H/Wguep2qPHHhuMG119VTlL0CjjeDrwDwCPx8thSHmNXhpZ1imF6m9fW4Rf99Qb83+FXQXzyPo1qwK/tvXDewaOPHk1V2YGAd25YSTDfdRC9o47iaUAjXLnmiLDeFyFac9ViaRaiycSSqcBMmRBLAqegu9thSEz8vDNEgr5qdDsDs2YwN0tPo8jJ80kAjuxmTN3zPiaQAAAAD1o4q3s5mVmSfzTmwDHLbJxOohSc+jbx9p4VCbL8V7/agBEjmLoHlnWL23smK7rO5fKtjA0CC5wLg61fCbmB1ZajV8+hoDbFQgfAsseVdTAYpkhiJb/cDidjLMaI4yabjesN6wfO3MUcQwPoPx+wvFqkZ9oy7w7tteZzTVHtJO4wG9XFgwOr6L4ix2SkjEwLJiFZR3lnRtwGWzhxuBSm3w3jG4KdiPEposbtghlfNkgrMO+Ci2++rgP27ckfqNaQThpgT5vEIbu8l24TZjSyUqENEHEjmZYq0SllBij7X8rzecyt7XWewe8IrSSXrXP8hH0eavjIdr7IkgswBUrNIc48QirbNQvaH1EQQO8+9j2zn/D7UUFLFWn4mDwifoK4puiOP6q5DNbkZGDLgLARLpzgNmuLXUpEQaxx5lvG0K2M667AItn3PG8htP/MusVnSuQAte1SClpvl6SrYfY/CZqxbLT8afuM/tHpUxM2/V3qCMjpvUo/2KfXpcPqTFE46R54sIW30QwxCLKPlladb3Cv0m0icbE3PjqcvivzLv6GH3xCDMo4uALhvySG35wdecYI/2voFEMY6PkjJ/HRNh2xoXw1xfnH5bP+FJN0E1t/EMjxsLf0l/983/gWeUSx0NQ5fQud5IyW2B9mnH6LwtKQhuVnRYSoeiSLPcf3qHkr08awzRLfcdn79iIUkCGLPjmsFF7Z8kZ7FQypSr4RkW8uISb5nvPcHxU91C3NqDwAxLJI7UFVoepE2osIfVJiy48J3f3JTLW7tY/M5WIVzI56k2MY1E9YPSfTTXV0okxFKzsaPQTVY5DTWfSt0l09ZIbJejkgX2JWGN5br7X/f7rzCDzHQkhndz0J1B/EY/FmzJvVxNWq8wiesgSnSSy8xFA7x1JnDqr5qUfO3sCTxTOo9Tl3k0Igd89quPv/C7pYVe8uyZ48P56PAC5YrbdsDzQ1CiFiUe/FP+DU9WuJZ2eNlGDf/j/MoHtm/hYdmk/Xvfe2GWd0zMKeijfsLdxLuih3aM01oARKswdz6eRwyYnyZBvg5M6tmHYWB+k+WsfL6Q4bwfPnaXokCkhWzsB4bvk+XxzOPk7lG31VpexExaoIIPx07wflkm+CheF6TfMlQYqiKy/WH0uSAm/gLGJcB2Q9s/LKqB06A5jWhX9v8xCzGNX1GmWI61E7a0FwmCf5/IB2tOwn9+JBOt0KuPBXmcSHkp5keoHa2RzR0LWS2d5fvFnXfpNuuwNXyxzTwq1fQffYTq/xNStErTrdkhNKPpj4A6jTUCqLWfkYi41hZokGPKzExJkBqzo/cYwJ3IAofIcDEHCzYWWRO6Dx8ut3aDW7ohF3JE+B9ckfBblUrOgkDQwRo5/tV5YBRPXXbb5b9v6tfYZygtAD0u0HC6OUGV6NNeVnNYw7GyvhyFzB/oa8Mobi4ixZxswCsuAo/5Sakg0rNMmZ1dH6FiK5MFmInbdN4EiaJY0E2KbYtt0gJlcHquN7J07nE8666PtljA7S7/R4GIhNtaPhd2QdXqrC6VMUOdjDokVEt1YrWtVDkWmL6eBbN31FhcBsgTtZ1owOLYdFgVnmP/LlB3xmTdfHzSG19p0x5r9W0PzVh70Sw26MZUKD2L4z4OGp3SPPXIHyc8cX+U2ibFYldkbFjzNXQwN2uHasJVv6o6xonZZJ2uONit3HrW2t3artft0O9fvo97PYqEnrAq05RQAAAQ+DYb7DSh1CbUKl3eRO8AaUbMrWd+wW2aWerDrjvxhufcpmXPLdxEjF0+WO+iqL1yTErp7b4/cI6r+PhuFcK1hOW6PWZaShRfgYHdkA5DrUDKp0e6IxyE1sqgw0kjXakZX92g7DHmmG2eizAT0DjDYSin3gLcWtripp6ThVvK7Mb/aMmXOpFEyAjJXt5jlCytiQ/8kp5oHJJLQ+fj7zoNzVKZG3H9J060jK9CLw2XksBLJRsO3JFrxDK6NsSxB/vccll6wSzH2JX/dsCafiOcN8EhvNt0KV7trdf9dvfCG70lfH5ueERDiafo0jwDq8UsgXWfPjJC6slbC20/uW0zopSYqdbI5naJnsto9mmHQ1YzRDX8+GhFc9a7FrO3XOpvxs/nfakGxkzsp13Hhm0XYJVO+lDF5MPA3gyFsapne0H5ToxCls1jTZTHT03Sdm/xaJs7ksY5xOfwHffy5/Z3nfypl2m6/UbWqagoUJjKb6n6sDv/Y11LQND1K+I1zuCbdp71R4GuyAo5Jk/KenAPAzV7UMHAJcrntSwwjiUaO8KLaHE2+syzdzieNWRhZhZuGIUbmKrtmyyrU+D1Fcvmswd81bYhYQO4Xc2lfwmjxa40+/Z7r2nPmGKolF4UE2TXpswv/+tMtqdZh5S01/iT+ftY2wgDrMag0ydPouxPoMAQPXNrnT0/u16QNIObqQ9k+ROoF2FGDJVvnmfDNBRqZkyvL14Xcd5qyTVca/wXaR7YX3bENT+cT8NDtE2v4R+9vI1O5TdAVNHsXfYffPzOi/R2rMG090Spi4Kx/n1HDZX6ewqhGHvLUeHRELf8gQHfVju/OgGcudM7uq7z/Li7+nplF3GsxwxG9oK/xTthzsk/AMKnSOr4nOwgoCwiz7XcCp8FzvmslNqDqK15Cyix90irqJ3WArKP2XzePtV5HLAS7SFIGtXG03aXjFNaZZQKgcB8s2q/xHFSzLbigE/WKZl1tQ1cVLnuo95GNgcL4ns9oSEfdaffi84wnqb0oL/4pv/0CmZOQ8CAmPOj5D1eqjqOv1vYP6s8fY0fVZEW7ng7fVwoc9ltZVYwKvmp7RM+8WoZBnM7eJ96JWdU77uI24Be2uNV9WwsJ97Puh8mcmy/HLKT8TB+LIv4pI0m93t6AcPN6acAS2KxF+6puO+mCQcTOw42bGyTFBvFYA/8Fvl5cQ0r3n41gz91fGKtvnjX6aCoVSm0pchxAS46ZGnsyL1kvqfEhuM7cRfh0eXOTrTynif6TG9Ky7qkVKbXBshouCWfbuOGYmHWuRBF4pWWnONlv+jjxZ3F/KjFpGxlZaTbxRpSmrLU7t5oP4OdtFEHPXc9wgHW7HE9gtv+Ovd/hdooGykLlxsM9DdX2g2u48+5bY01XdpB8ssXuOFpACr8cM2qJknuFo72vnDOGuhBVxo6yw8j3JpBgytD85yQKuuq3WWD1en6Vl0PFZCOFIoQwNJ1wpYlVUUimadyDj+hwmBsm/mGqcfwIAWaaAAAFsIC/rEt3XBphJTZAGr45JG2VWTZ3agAAVNBN8f4S08K4HFRDMfT2QBTy/ykL8Z09lDZzedo7fmVv+7Tn54q/5JQRIJ0TqFEr1PKSAXAVSGZSFg+N42YaI0trtohQphjjwmSklzXmRQFGsQegR7POhiEFcPfSy5HpRnb78Jg3YfK1QPmdBObhXN8uzmof85eNfXNWC8v560VRPl9N4onMgpBNatNVKN/7TpfPxyv/4PdreR1W3c7UZun+1Y9l8KkcoGxHeucyO++vaLqFoPjfz3x/4YOIt1LKak5vS8ibmwP2dpUXSKn/m+EXN3yCdyWIh5wQ55BWCzxEuclDg6ogcPMl1OVTUvlR1icTHgArjDJ8+Scb0npPR+Brbr7TST1U6WFxSL6MQ42/hgMuTrBaaAID1Q4tCKozocubgko5humXLunF3pfpqTj+vTUHp25PaSGnxZIZbbg8T6KxeR4M4jG/mfpigH33LVFExsLp/7S8alCpHfSdvnd7OyPkpT0JO7R2xPYgoiXYkIwqFWaiZk4TZ1SRN0o+GAXNQ6cm7kkqa7cAdiO0ki8A+DrzOWkxJ6RoWHPxG7AjDptmbMMh7AM/8yMzPJThg5JvVl+4hUZr/9P2WjPbJgaNBVzlCutKTBXlm6wcV2ERrwglPCK0Snat+HYBggf/QBHtHBzOC2AsGTRWWnPy4EHzN1/05+gUPqGffXKyIbg/TZLHJ61dsQm96ArPPk6VUzXU5J7nP+uLBUynWf1dGR4l+5Co8zbcZQPB7f1sE4DSG3Ka9GIONvRsNiAGRskWFeVMKDIJIoLybuyNcOGvVHFr1f2KDF/iqhXGBXeoQOLww/mlmF/A1eZprS+CUEdrmjuYrnQ9Yof9W2dn5S/5YQPAZUgN1JFmldEU+ISfdqpxzJwqIokFqR2xXl6xGbD9TxeJqhVAc7dehXsuZr5nhhWWiUIQsI+tac8eJeDe9DdlLeH8AuXHT9z8XizV+tYanudAD8tmMUKQ/XMOnQcshaj0VV5j/zhBiRuv7rKL+zoNNGr7So5NGwSPcmzRth1gvcafgVZMbEeMirKgBXIX5RZzLhunAL+CJbRlkjdVJIVSzWFw1/ABNdJ4FH/oLSPwXQkdv0gXOTWksI3WWV1LbTQga9VikC07MgbPAp5Ic9J1U9K5M9ga6/a0E9B+UQV49rjohCr+9xtbR680Zzq96x94TrH8z4TVw9WpDlCz1pMEBEFNxnChqeDPcyVfMzxLJ9QhCMoSlXzsAAAAAA=
- data:image/webp;base64,UklGRmR3AQBXRUJQVlA4WAoAAAAQAAAAwQQAwQQAQUxQSG97AAABGUeS5LZNLQCm4vL/D04C6HiM6P8E4O0rkMuI0wm5RrUJKLegSkw7qEF6R7pFDqxKyLyo0iLGgYi4KGgAWtt1nz4GKVA9EB8xkoS2MCHNMI5Gzg4wMwN7P0DJ1RzkeAWI8JmZByDPgL8cb5BbeMt8C11g9oR0wuCOexeqLkgSgQQJbiPepHoYt20jSeq/7Zldx3s+I2ICuH27md71MqusHa85yOiNRXeW2MIlSBrRQLbmb7blm7vsYFIE5RG1vv//XJLs+B/yH2BqGeacc87KOeecc84558zyv9XdVaeqzlPhe1qqz0VOoxvR6CeVho8KPBc5tZosWtSLnFYFzkVOq0ZOg3r46oDSjWgaOS3qQU6jA0r3XttoCnzliFrD7w+0Lp8CjxzRqJ1QbA1fHelokdNonFBsOaLVkUqDnEblhGJrkNPVA2qQ01WB3yKn0SDnL6jlVwWOnBbNIKdFPchpdMDR8m3ktKh1I9oDSo5oGjktajmifUBpnNCqpEeXt8YJxZbTolFJR4ucRu2EYmv46oC6yGnUTrw1yGl0QC1yWhVyRL3IafSAXuQ0KvA4oxl+UckRbYEjRzSNnBa1xgnNASVHNGonFNsZ7QEl81GDiAmYAD/Otj23JUkSqjnnnHMOTsG70eCcczaEnggfAuecc84555xzzpmw9jnhyc5Z2MuEewCB0BsfYKgJHOFvPeDNBmClN46wUy+41LrXBLZgE0jTW/KYwBIMqZcJj9ZSwPV+BUfpfYQ1gYTrzRylNzawJ1AwvZkj9cYGjtgsYEMIhF74BQs9cIQ39UDojUfw1hNHWBNIn4KHXtjCmUDaFByt5xIMrZdNIRB6/oJPIGHANwGHD8FReuIAC60XfAiO0BtbOK0nbAiO0AtLsNYLNoVwvfAJNoCGCV9zqV1qKjlKryNstF42BUfovYWD1hM2hEDouQRD6oEjRMQEPJto93+7/9v93+7/dv+3+7/d/+3+b/d/u//b/d/u/3b/t/u/3f/t/m/3f7v/2/3f7v/20f8O+kPW+of5w9X6h6j1D53/kX//7j+q/9D4H/uPY+NnOpFy9Uc8/WP+8f/Yf7w/xh/t9I/wh/9DVUfd/Xv/w81t9299+O/Ls3/jf+CP+0e9PFpJoWckUd0+/yf6k736J/7T3X3+dNu9GtswNOk/OLD7ty+r/l1lGP9V/8x//ebffeXh8vnnt1H8DCPavvqn+jP8Wb/93B/paFC2IWPJSlmNEArbZRyz7v81X/yT/JFXu3/n7g/7p/iT66o9c4j6H/3bf/a/4J/p2x2iDhURzo7CkClHKizJOOLtP+mf5k//p/72d77znT/Kq6dtLH4mEOXzf+Y//5/vJx6pbbsyqWFSIIzEgZbD4UoKZRke3P0TnP57/h169cm6al+e6UN/rB/8i/7A959SK1aSKTCeVSAo4JQATCCRKl4/ePTht98env0Tjtsn41l55g7pwRd/4C/+M3+c6rQliRCBAFooiY7kxARSVimiubRI7Dz68N13P1cvj7Q+bsXPzHH6xT/nX+pP+9UVTgk5HOkgJDKrkSOMEhHKFA4pq2pNYQq11qO7q+3R+m479VV7xg31V7//L/H7/ylPwVgqpTiVKaWEHJgSKWQJkHEKGSKsWmvtQwLKXB99WIeyrGfTM2ro9Ot/ob/kl1+UB2PKVDPMOiGMkbEZAEnpCJnAtmoKJca2BAXh3tfD0Xr14XS+iWfMyKNP/JX+Ip94pLRjtMhSuwg0WaRI0o6IIHEmrilLiaNYOJXCkoOeYSBrz8uI4/3UnhGjP//n/Sv/pme7AUdzSlnLcmLdMxQimktRpabUJcBEWAkSMsIIzcgU0oZkqLVf5L9t/8wXev0X/jI/8rnBssvk3gkyIRxZPS33VVPmeqg9E8JhSAQGh2QEEAYZiKTaEuGe2c/3y3/Z8hku6qd+5K/3l/6SiDBGkskozgrT8riZ+mi96ik7IpCQhWVjC0sibNUhPaIKpAhnYiNpmj5cv7NcRXmmCq1/8L/6N/6LfckqwpDg5lTKUaaxlLo+WqXs4gClnZIEhBAoIGxMlSP7ilIECkOEkVyto7uP3j4b+s7PSDF8/a/4V/veU4xtpwx2SJLHXRv6sO5pWthVpCTCadtKBVhCsiBSNtjKjKmmESBIB1jx9bf/FY90TJefYWL7Z/nr/zW+f4jAQUI6iiRFlFBm9pQPzBTpcFgpSQZhAXbQAWfWWhWmWBmuMkgZ2GSxnv/O6/+irx5vNGR5Bgmtvvibf+MXZWpC2qRUwJiI2rsclkESjlBKkgFsMEKyRIsqDlYOVWmc2CKRRWZ1xHr73Ovf+PjJVf3U+GTFqjwjRP3MX/73++qAKmEpMQIXYWdWHEIGSbi5VplwYCEJYQsQkqeUwA5jVJXYykSAQHIRffXuq5/9ibvnbVterN+5mgY/08P6G7/h135xcFcZizOFLSWOGckgyQlRgqJakQEJMGDN2BLCJgMkASFLQpHVIQGCSKz1owcvfvHJvzLjq8cxcXcqz+igJz/yV/3zPPAstVcBShQ2ZlYZSOnWpEEStsFhAqVSGDFbQFAJZAwgsCSB7BQSkolUZuZzR/8CsT9Z1aFMz+Tw4Ht/4ItD1E6hJ7YtgWiFxBIgJDCZQBAYg5QIY1uAZUEYUmSiFEZGCbKcJj1DBAbltHv9X/pv2q2X8WI7Jg3omRiGb/yGP+jDdBE9U0RRTSBKSEojGUkYYRDYIo1kOwKBRNo4EbIdNYVDmZkS8ozlHDupFEGEU9J5P/3g7O26/MbuZL1yIYWkulqtMrOgZ0S4++v/ss+L7AUEKFMurbllkhJGQkaAESApsDFgQQqDQUZGGMsIHGBAKcCTh0ZNSbI10iup5aP40nN3Tz41Xny4W2o41fp0dfnkQw/18oGyEs94UL/4F36x2zbCQQJu1KoilCmwAAQgsBJjYxAI7JBJBAgwgEEgSRgbgZBqZKhiKWRlpnJYnX747a9/Z335tT6cD48+e/dLp1/66vd/42wzfYlTu14+eb0cZ5e77Gci0Id/7l+4FE6nrBSpcE8XJ0gSmDxAzAqMMICxMQhJ4mBbyNhVzFoICSOBhNOSUGPfY7Aj2u5hDi//A/7x2/asT779hS8N3z66/VNXv/5H/pp/ru/9xjdefP17f+Y7+dm/wO/8eimntfmZB979c2zTxgJBStGMI4yUgBXkAYAEYGFAxg6TSieAbQRCFmBAQlwDIQG0gUgRUUc505TwssS/+dP/2lX92r/lz/gznz0dl2en6/V//s/2jfWLP/G9X3z7xfb93/ncUv/ql+9sPZZ4hoHtd//EJbKQi4wppao0KzMTi2KlJFlGCAvAAlFsqLId4VRKmgFzoFMghEAcaCWUTMlYMUxWBoSjxH6j/Nd9891fdapxo0crtFa//PD5y3703Fe/c/Xpf9S/+J1//p3VuHTxMwnoq7/3cwMhS5KzUgouISQRQIRrNUIIBGAQCBuE3VrJnkkC4jotCzGrlARIQoBSsgSa1lGUlDRhRyFGqFWBlNVZe+1IvZy3f94/5f3X/OKDZex7Lp9BoL748edTAEZK2xKOEJgkjFIGJBACMAiBhU0Uy4PMrBC6DjAFDAIhI0sYGSOTuFWpdUoq5LAJSqQQmIokUiTTecvhs8/38VdEuTWuluWZArT+7i91LBDFIkqYCA4UUawUYgYkAIMABBjAEsbogIONJQzgKkmABSgBCSRZOEsoHdWuNgR2GMkJoXQmWcGK5Um93S95/GIs37+dffcMAe4ffiElW3avhEuDMFWpVLSwEisFhhQYEBjxi6cx+0FIEtgSSEKylSBQIJVUqZRq7KkqLIEwpEAQLh51Pt66Wt5f89MvTMOyPDPAsKoCrMQQBYcjIBHTWBAykhMsiV8iJWpKYEASQiDAEkIhIyOLUnHYhJRhJJmUlDimSfR+mY/P7l29+E/4advTMwHo+e+/BCM5k8CuFGoVKZdCZkbUxKQlfglWioOvAyMQgGyBESpSIJtAJo2ElBKAhl4pq/Gl9uTy0//gYRo2fgaA118fAFUBgZtVImsVclGuqqQqCcQvJXUwCGRZQsg4bUUiAwYXSBRWSsxKylpT9iA2Gcd/v2PH8eKfHh01Zo0kR+8lh6FmTavWdSpBmfxSWUiIGVl2YogE5LBJERglBkkCMJJS9tn29Nbf8VvPnp3Eol9+4dmOMUgRJlvUjiPsUO1CRvxS/gDACMtODMYoJCOQEQI0gwGjoyebf9ZPPT/emxb8VAYEwoBbCVcMYCAhQfql3nfVFroGxsiAjJAxKQAd6PF7Pspru8W+fDAIBAjC2UpIYYQyQSJT/DLXYgawjQAhkRIggZBAEp4e7/5xVwt9/fmVkLGEI0xWAjEjKaVMftltbIlZIxDYgJgNAZI9/S//JWWBr+1LhAVplzIIySEQYEASv6w38owADBKzwp4x9v6Vf/m9q4W9em7AgMMVkykJh4QAc8NoDgDLRpKAmWLwtJw+uF9i86arM67ZotKyy0A6EIC44YwwBgRgI4cdsLw4fu8ljsUry4sA2wSCTCEswIC5ARXYUZBsgZDBDvz403tv9mPv6nQKCJnsylUlLBxICINuPEDIpYRACEDIIaaXXls/4uxhP8au7a4QEgSajbDSSCAD+EYEJKFa5UTGQorM8vilsjB/wqpsTJ1ffmcyYDKJoARgri3dsABCCR0hCRxG5awM5tTuWT+Wrr0QBC5WlRQ2sg22bMlG3MBm4kSYA4Vt2+KUncEwdu7qzs5ysRyuDnOwUjYCccOrBJCEQJJy/7ruDsMVO1Zu9+lzkERiSw5hG0CEAHzDg2wJZlJECZVNT121xomZe+/OFCYpUOyQOdDpSFm+IQKEARkLkoP06NjGtfvjJhbO73zQmE0JG1JYQgZsY8QNsGTAQhJgk63E94+J5O1YuItP7w04QRlKgTlYABI3yHYISQaawXZ+fn7DLMOPefP+5fuBTIAs0iBsbAsU5sbZgREIGwHbjilu6AmLMW/xxhvFqgWljY1shA0Iw40UFmAhkb4xWrPvHHy24hzjNr7zT98jkpGEBGzZZgakGyvA6ECLwBjxs5Oz84WQY9ni4T/5jrEEZE8EEGAChDE32LIRiUMJ2LBSfmVnERLD5t2dFwoEFBuMLVnADALsGyswCECSQzEu8/TtR9Li2vTGeWDRMHSwIwxpAxLY5gZbgA1kr0nL1dnZ5Zc+t7UX1XzyT91YaFCmTARZjBFhGxA34FJEoFSmEpP79uDV5xWLahcvvVQAOQpJRFNByAYBCtk3XkjNKclEiIh2Ppy+esmCul/ZTTLVJRw4KwGCABDI3JhLo4Qdzt67uGL9/Mef90JaXL1QoiBqtyVVbBkUCHOwb8TIHsZIQqrZ+zCsXiQW0R4+PBMmnYYiCrYtCAsbY2xj33CRFARKTK5W61rLo/Vy8cy3Xtg0LIwkFVUHsl04WAZHmLgBIylIWMrM9WXv03573BbOlv/wc2VxZs3MdJTsgZXFBgsLbNk2vvEiHSQEkmrNrvu62i2a+elPRYIUtVgYCjgSAmQIQIBtcyOeMiIFWKncl9PjsmA2vnFMMTJSohJpwsqCBcJGYJsbdKlGIAnJ4UKfXp82Xigr/QX3kHBih4obGVbDgOXAToQljH3DBeqlKEmUCbWflycPyyKZ9DMTEynJpE09a6ooZDKRw8U2MgJw+MYL9SqDVYfVkBy/PJwvF8nai58iIZG7So0yYCzCxszaYIw5wDdi1CpQCrJW2msf+MqLY+XJT6wdQkpXbBX3YnJKI6NCCcDF3MiLTCRswPXy+F+Y435hzOvvfqQCIgp1qFPNSFl2AKahgHAzBs04fOOFQAk6sG954/azxwtj46uv17CMgOWwqy2wgwKopK2QcDQACwzmBl0ySCjr6uyFo81yUexzn1i7G9cgyQ6yVcLYUO0qy3WasJBBOLhBlxFgJK0enNfnLhbDWry4SgmyalXCtZWSVIqNRBbCyuxLG8MB8o2ZDBYSIOXR0bA6nxbCNi9+2J0oZK16FkgKtRgQ1YlJryI4yMbcqKtgwJIww5PtJo8XweLJZ9YWVlcqklVRUSpkWe7OEkB3wWAiTAl8o5bmOpXDq092pS1+lf71BxVCDjtiF0GhkCXAoshFSg1jJVBJTMANG5LSksCy8rS+3/aLX7tvvCgnqDL0nIqoKXfLslScxVhbLKywIcL4hs2SsDBIyvroONQWvfbl3UGWUtSpjCWmAVlhI8msAAmFUkpJlGbs8A0aBTLtQBI9j9a32C963fnMJU4Ar4+2pYYii40l1EtGkVRVwFTLyLaLW9ygyZEkSAKTq7v7ZWmLXbvztzPAhHLsTTUodoYNlVIzkKhGuDpRtaxg33yDhmxbFrNKna7v93Ghy+3D7ZBCGS7bcY8HE7IjoQdpQLUEQoB6YkI+adywqwoJibCUqy/dWY6xyHXFqSMlUfp+tVeRKwjbkjMdoJSxSYsUys42N75xS0lIOILEOto8LNMCV+w+sxW2lavl2jFlBSkokCqpAOGGsBCqiFQ/Grhxl0BCKJEw9fIdlwWu+/XtlCwlW6+WLFchuURRSFZOFtQSGFkkFkLrFTf2QlJKGAynm/NSFrb89MMhhAz2cjwqSplKsVORcgFVDBYYCQtq1Q0e4sCwANXX78S0sLVfv26lUlipPa2Hg0IQ1SFNKOQGRiHSSIC48ZcEYCPJd9f7ha1y/HZVWkbyLlbHA1IlW7oGqQJIDTFrAeZmUAYQElkT0JempRezfHZ6ihCSai+1jiZshaShkS6SqwMQEjePNjZIJlMi8+72TlnMWm4+NwjJILXj9W492spik8UqBVFjZNYBoJsEUpIA1WqDqY/e2y9k+b39UaYIWZRYKaRI9aJQbT0bM4UDhbC5SZTEwSYQ4NX4cCFrem/bwSg0qoyXu6FMRG9Qe3iYLGd3yLIFxtJNAubaISw5cvVKW8Q6u7xrBI4aq6V1OpGR6YIzhtKUlkKEARzBzaMOMik5MHB6cbKAtTx7diVBOvowlHWLkBC40jIDK9WwZJDkmwkfJATYGHv3/gLWyXPPI4VKiSZW7lMgLR1yqo9I6mEBZja4GZVEAtir91vM1XT+rLBce0mklftaUdVDlVgXi6y1QWpGiJtLYzA2qBpIPb0da+X9i0ekpuqV1tW91kjwFK5SpWGSIgDJZPhmwszKYIyCtHN19kKs1fI7zyGrUCI0xODi6p4UUuoFiU5Apg2SuZmUA4FsQGQKq/uNGKty/I11yu70pixbVBMX0zK0bkBaBdsyls1NpZmVwEgKIFK6FcZW3Xr+QWRJV7KkKiWrwiKQa4aCVBMgS1RzU2kHkm1AkhVggqt8bFX5BEAokxh6LUqDrMDKQFQUQkggbjJUShhJAEJSJkIxG0vl9o0jdVVJSUpTrURE1ElW2jKZBYNsI3OT2YpLsRCSwTKE62oTx1BNX31XFYwyqVmyWjiZLNfAEoBskCTjmwxGhR1gkAARU7ifUImdmvpnaxAJiCplJRzyakyqkEkHIAksW9xsTi3wrCShFNEK9YTZ2Kn7z20zMy2rSMpqisdSm00NRNJDgDFKc/OpJpAQAiRwOBlba2KlYvttbNKpSqKMou4uJjkDQxYMCCCFbzok1ZopJM+ABFknT5iMkSr63EqJJKQa4JI29IZVbVQxNhIY0M0H2YeeKSEJYyuTmuGmFRwj9cUXU40sTrea4GpKqlYinSAyZA5AIG5ClTkjgMRAojDDG01M1Gb19eo0KamSTKWYiUwqB9ciiVlx06qsVSQ6MJGwg+c32jFR/4a315aR8ZRAi0Egq0AGSBI2BnMTq0xJSgmwDkBVdizEQvntDx0YqE61GHuSynQBBGBbIN3kgFKJwCAQipDipk0c+zTWz6zIUDYsoZbOcBFZEIBkZs2sb2ZAKSEJRFgEq6kd2diniy88EKAko5qy8tB6QLpKYDIsQAIjbnY1y2w4sdK8Zn/M03j6rJxKnMqIsPpSaLAtsCTZGMxNtGZEIB/+umE/ximOvz0ojSxnKoUVPbLUSYCNhAAJ3TwdmCJw7OLYwWKM09mjJ5kJEqjQqocYwhWlkIwCDJibbint0HEmd3dzTFPj4x2l7CqNu6yu42B116iAQEY26KYrhYQYntw9Fdt058MqUApFjSrkwHZGgkEYAeJm3AhwWNm41YllqhenkwW4OMvS1dmGSVgSEqTNTbkOQhz6MrVslGOX7He32MiKkqZGRsZgeiaAMQJAWmBoRqSIxnCyX1w6fv1dg2asQiVxFjlDgJAFjJa7LanEqnJ+HotKMT1HsREZaHQttWQbQkgYIAQCaZkJCOGIQVHuLBeWvnN8Nc5Irr2vlukVck1jBHJFPaUlBYiUak2Ih8cLSlOe3b5yYuSWlSRb0iWnkJAEg+vCaFELQJIC+fhxLCSFd/+YsxHJCAo9hikjUUoSRpZEpC7SsgIcCDsHTye7RSTvvnrywqgECdfQZNVEmRYGZAFQF0YLvBqDop099ALSuDq6rREkMpyVKWOQLQPCwsjMaLkLLClw0Kd7ZRHp7tPjujqgp6Cvo2MpAWMjCaOl70SiSdPZbvFo/+j2W+f7auMgi6UQKkojAIEQLT+JIKRRJ140Kpu4Bz1CRFBLJM1VFRAoZCNQXaQlJoGQMvt0dTUuGl1tr3ZPLrcpVNWra60oS8oiIAEZ0fJ3KhHZT3TsxaLYlXvHR9ucybSyKkvaAiyQLa6fpeUGxaHh/Px4XCzaH+3G3FYrKzVFWoIEAwik7xJayLZ9XQKJMDmML+/OFopCj64evLqWEqpVVWx3sCQIYYDU9UhLyLaJKFFaXMMoRKIMv/bC1BaJNk/G40eXqSohE4psxWkhcIIEYN9MmYOVwiUMCJAFKO3b/9y2WyCKdjmu1kaSiLYP5wpBQsgCA+J6GS1eGzwjECLKZADBDGktv3Wmtji0Y9y/PiAbGzOhJJNZm4TkQF0D0tKxscHMeiYuQjOyhI2yfXCn7BaGvNvy+oMqBbakKoEzEiELSbJm8GKY0cI1gAHNYEfp+yUgIbBRwvi4jF4UmmqJDzNxyDgrcqoiJZBSAWQbocW0fAMZJGTPhGqOjwOMAMuIHO5cURaF9qm3B8lBSqRkJCEQYJMgkJBbRraMuLZt9zZ4Ww0yQiitfnI/2oJQ2Z2vtzWLqqL2woxlLCwZYQsQklpEDoQAHWDjUFGqhw0IzOzxvWXxYtCybS5bpdilRA7YIm0hMCAQGMRNslwxArCjmCjjmFqpasYYQUrjw2MvBnl3rnGSLVWFpZwhkUEWspQW4mBp8YBA8kyEHS6FVEpJGiNsQLF53GIhKPb9dBcIqSa2cCQZWMqIAKHAYEDALR4bZgLbDoMja6ZraBaQBdJqtdvhRaB29uJUsBKypicrJUiMQJLAKCVxcyyQZCFACFuhYjyNMpJtp8jsl9yfYgHI58dcBClEZmKSTJFKyel0yiQHC5AWDwiwjJi1ncRYuvveB4UsK+k8XbIQ9G42Zc2UTYSxA7CMM7BAiQ66OZbAYA62MrKUItexpSxkkCDwS7e9ANR4vVhdzpSNCCSEpLSFwEJggyTSAjpYmglh5AhNKOq+QqZkOY2l4zdj8aec9ZooCcsRKVJIGZAoUmAhkDDQUrIBz2ACLTvBUFYbdZR2SRRRpf0Ly8Wf0TlBNUQgm1lLyWwKLAEYSTdPEmkwCBlqqxGJhhhSsp1CpHN66WThZ6Jvc13TRERWCUmWDNgpHBLiwJkWtAyacWBFn0aJvqlVgrScEuyevhKLPmfHd85UJQtEGBsVIyRsrmkh4GZKABJYlpD2vWS6EiuE5ERVZDl/f1rwmTbHrawUhIlMW2bWMgbhGWPABtxiwgabWRFZS3X2Qm01kcHpA8cXNgs+m6uLZEgLCISqZSdSljAKZAQYJHHTLAAJMCQYZxmKMro9SDZS2EjlzTuLPaXmrvWayqwuqCYIbKgIkus14ubagAHJ0LJOw2SZLIMACeM0060XYqFnilcusqPMmmGUYWwJpW3EgbYFIN1kOXMmCTHZhKe0e7iSMgRkWLc/WC7ytOnOx5bdoQMBAzigyhxoLNsc7JspYwnEgWnltLJqpGIQNsJC1vnTs0WepY7jsoqUhJQpOWQjAIFmwNgz4uZZ4JBtIZRZLammBbWRRpKoIWt/52Fb3CnlbHx0KQms2iuzBoyJGXCAwbPcVAsjZmbDpZCltqiWPchKEgmb86e7BZ64N54SIcmZwgZwSDYyYIyxQHCThSSlOMi2EVLWcNKFZAiccP7+xcJOrPR02AZpwgDGKTmUZsY2yMYH+eYKCYGwRFCFsnSCgrKnwHIa5fE/+7EXdcZejo/AtoUhkIAAIztsh7Fj5qZcklIg2YKiJFRkp6ttSAkpxs8/jQUdx3SVHRFkyhKIYgEYI+NAJbAR4JsuxDWNS7iiJrvbFsYSTuR874NFnTbsHj8ZlJiUolDFgRGYCFIREAawuUk3khJBrjrhUjVbwqoJlgXT++NijqdYrgZkYUhxoG05BJEWRmEbBNg3YUIiESI70QK6S2YUIwE2KOtXLhZzIo53R0pD2NgGA0IO2wY7koKN7Zs0MBZI1Cy7yZJRdTM1HQZkqO+/t5hT9DiHwJYIk4kNtmRBAVGsEmFbwtycSzKAgyQybSsha8WBw8i2Tl6JRZwwZ6/XZUGqKcnCFhIiISDqlDRbGWFj+2YMScIoIly7nFI0raodCNsGeXxtv4jTfLusN1ejITMlLAMInAobGZWwASObm3QJkKIZsBRljF5pRYowKUzsP39/EWcs52+3hxdTGEmEQUBghUgXZ5HDRp5V+CYNAoENmKrWoleZBFISJlm+/EYs3njpo0cPHzYLxKxAAiyHUxKA5EC2SzRu3gQohZQq4ew22ceoksC46OHXpgWcoL/3lRM5WpRSbCHIRCILslrYlEmBjTXdvAnJCNeaPa0qh1LGGRGA2zJ2n9ws3JhY6c6Vit1aKcZIgBKlZZAyNUYrSbg5R9+0IaVBpBKUXa32ytgpYVJEm/D7Jws3ZXf25OxpxOQYJ1fJOkgWDE7sbFFjip6aSlC4mRMhuyaQvQ+sOirKXUc4opSyvvXBoo190Z/cPx6WqNB7AsqaKaSMTAQUyjQEE9WKFjdxCCyESFIphZeuLXuqBCjd+u1/hhdsmi6ejGfD8Y5WGuCQyMRSpqW0IvpuSieRrhDc3EsSIkWg8GZqWWNaRRe1Zs/RfHNarHHZre+en8X5bopYRsqBsBESCYYi1SSGMhDCvrmTQQY5nInY9VqHuh2qXTMV+7b61vliTau7V4/v7B7uy7KmJMvYICACq0cGW8JSSdJhbvYDGxxOgXukydyZMpmMUtRP3vMijcvxyd2Hj32cWYf1SiJTSCmwbdrkUkVvSssJhZt9IZQKkQ5QxiqrlkWtpGzXGvuvjYs0U701jU9zQ2G1HrBnZCBsqlpQe26qik0owTd9iMwUShEp6rZ21T7Vyro6Qh51frxA4027dXR2lhuoqt2qWAZDSOFaq2oppRIBIUzMAZQpslZSdRiyGzvlWo1A3kv3YnGmeHlVXnh43lrvjYpqWgmYUJTsNWiKVNgUgfHNH8IolaGMVEa2bHga6pIkwue7/NhucWZ/t56WFy68armSC7M2BF0T6mkRjnQxIhwy80AJRxgDchmzsVMtskSxxjvHn7y/MOPdp2q7eFi6SxVRApIMpYR7OmpTpqkNhRRGzAklI5E1iDIOU70c+qTuEuHww+m1VxZmlu3sqW5djBRJYVETSeBCp0faKxy0orQQc0MhJClwmM52v6WHVxkyLS7GeN+LMuecX9bN26t00qkCQSSmqmWTpEjVuhTOaMwRhZISUi1KYtV7J9q2FrL2fnzn7tfKgkwc729vN/u+DHCmVEUmgRJRMGPglB0tsT1HAIGVZLpHdz9ODV7RSiq9OXn+rYsFmanZb5+0q52jEK0FIEtdJlpXMmJnizoFNsbzA2PhTMmZ1jroQiJCUO7Hm28syqyu1sTJG1FTdhmtIJAiaFFNlCCUFhYgM0e0cUqEOom8jkF5LNHA5eHJ/muxEGN4+Oj48r3dGlEKxQRgXIpqMpVRVLdkzCgY7PmBLEvhzER1qkM2xV7dFCjn7/G1cSEmtufHl2fj/W0H2dhWVdgad1Q7Blxt15CDYM4YkchIqk4VD/ueaw21TkjcGd68WIwZ7j3MF8/aGrDAzLoQoY49DNV9tEzaGLDnCLJANiackypNhLrCKZ3nyUuLMM7h4fmT7cPN1MC9VmFbgUe6i/vglCIVicEYM09QZGRQMJPUGI67K4PL0pm7KT6IRZg6HT/+FKu+dIRqZkI4gF4zqD1aqjmdRnMIKALsEFhIvQ5pHLJo4/PvjwswGsbHdyLXU7NV0UwqQTGIvioOAJPYksHzBUEnY8gqqaqUvqk5qLoqVXT6zzlefPHa4zvlbNtHm5rFkjJkEQMMtURxqBjMnDItpEzSlHRhu68qwoPN/umvvL8IM01vKV69tKXaK4BsKbro1SWcTEYi8VxCkGZShER2Ru2X2NBdvHv/H3Ky+FKjtTs59rMGWCkHCJkkacUgICUbQHMHIwuKsmRSquxtcTqLidi987/YLLx4O7L3uB9HZWKLCCWYAdxCUiWQAATgeQOIEAqJxFZfal2ylJhgt3v4ybOFF7Kwuf2Bm1QJUKaEXXo2wgnKKgUGHTB3FGJKVJwtlfvBHK/KPsY6pnZn5x99vOjiHvbw9P1zVwQGCVnqGSkyLbIjzzDjuQNCsnIiFOkhU2exStU1Vlw9/uhLiy6sCjz7wWtvDgmascOR61qqCw6G7FXMOZUhKFakKGQ5Xq81pKaq4/GFFxZdMiJ4sHzIcmRWyGbVZQjIlWqvHOgDPI8QIsS+Li2V3GTVUa7afhrNWG59LBZeKJef8suXV42QAamrFCxLVeoJIMxcU1lS2dYBmX1ydU+XpSZN5eRb04ILpjwZ3rh18rCQApTF0KXIVRb1TLCZd1pZVJdNKDNKGdrKlSNI766+tVtwMa7Pju0Lb745YUippkmlOpO6UgIZzQjPJYwkFTTsMyRpKMVLZ6lVZrn81smCC7TLz6w269fO7UwiZKtHKWolpcQicXBNzyMQWLUk2uWZSHKaxiHdMlDbff7NRReVFz98aRxPaldYUMgOclMqqwSy5IOMPYeQEWQJ18I6BGLsZJbuMnDytdcWXayvn7yxP+lR0ihTVcamo5oGsMBgbDyXACOULaf12DUk0tLbbY0arWj/ztcWXXjyuYfPPjzfpqTEqaKKkYYuJIw4AGHMXFJgI0XfXbZVSAlXvSqm3lyWt74SsS5fP378E+crZGxSqm5C2WWlMGJGQjbzSgNWLb1Qx4ZQerdSndYtyvLeD42xLT569zU9ulAWHIiahsjaQYTJFFgGJM0pbFlCeFqfdWSB+9XavaxaiKt/2ia2ZfhUO/vMW1lrho0UxtSekgxZBQgsJGHPJQgIIWk51DKcFSS3VVxmxGDr+MfPY1rK3Q/fqc+/1nKMBIwlZUoSRgIxa0CY+aRQGiHc6oYhlkaT4gHEuqDx5x/GtPDq/o2vls2yV5QgZTAkKUDCNoAAjPB8AlsqslVjW4b18wVkVg61VVHJH3onlsWsyybWDU5s6MiAbdVKyg4kS9jmYIOYV3BgSKHK5NOzphx7U8QQBD/1sZiWSsHbOaNMI3B4JmsSVq3M2gC2EZj5hZVFQnk1hHbUMH3cDKVlmPKxj8ay5Iu5/LPDXu1chEEW2CgTZxKBEIDNfAMQCZSjaVAbhlAoh3Up0SL2PxnDYvYX5oZ55VxPiOYIG6xMQSocCPAMNnPNRDJIFCqoNk8uua5DG13KPzqGxc6mzOyFh1Y99dpTCZTCSmHkCCPE9drzC4tAgc1yfXFaHGuXaRKRiJY/HbvC8wV3X///zF68sNxNNgfaRo4AhAA8Y+aaBiEZa1f3FTUPdV9WyAkMn4xdQbrLnHfOkU3nJc6X1JouYSNhg5TgGXn+gRCklYghLiFWda18ntoD6SsmZqVogt3u07o39tfW60ERtrmmJGE0AzbgeYYNCtRM3W9bb31CauVBxEqp9smYFZ5PhNefODd4a7HS5VYsCckIgVHig+aeNgZZNDLXTOpMQ+bemzEt2st+rIpve+uyu+x7D5f9KC0QB2AEIHFtAZ5nXFMWKKOPdegh9do3O6qlk/lYFYftKw50DT+N1qoVVLPWlC0JIxkQGDQz1zTIYJMWk9PD6JJlWrutask4XohR4Um3Z//6+edlrfG8FpGpsAFHSIQBbEkp5qBWOBPJlrXshWGsLQY/qc3L6OAYFS7ee3Xq9nf0Ewm3lRK+JpKNhABJzHrOYUAgjCVBVG/ZL0dND3phLCtMbIrR8YUtHbf29tbAMsKqQkqBxKwEaB6CZbmQTmFvctzGVJdRhkfboZTzMuXHpHCWe9LbRo9wfDKfX/VeLcDISMxKSMxJhSwcsoonCaZCL1MZImPHZMemwNebV6bKqzYW4TMOcARIErOSEaAZzz0AoUBKF9epN2r0dvyoe8myl/nYFBOm1z2tbDovjYJS41QcEZbNrIQRgJiTSBgRlFrEVFvNVupmPRb1VmM+jElx1Oj0QHZ71ksoVhFh7AhAkgAJce15h8FIEMVh7yXvq5vW3tbTKEUt68SimArGrnS3PsIeSIRajfvdFEjYgA3iQM1NkFOSXUNLQVbtLpcwlD6qlbQdi4JgeFWnOWHq0JyjyrXl1MLYYTDXFNcW805JQpIwiqpKn9ZeP6w1I7dNxQ9iUUSNvWPl+OCFM72KA+9ss1tOy7EgHSQO1EFzUIMwVIcDjbSzIbYatF7Zu1XzyrEoJu3twoY4J6QHqnZycX7VlCmbawsEoLmIBLLkLCQqdeoV9iiHbMsSWmJSFg7VeM0ttcvW9MOR3UXWOgwpAgHieucjB8pKKoCaVl6X6XQ1DSVXIYlJCcMR2DsX/I7dphJP3N67NFsg8RHUvASQktAUozOHEo8otdEiVUyKXfIwv6O0fKeaKyTG39wbFyOuXzNijiokKs7mSfK+PIjNrheuAjEp/ohg54YDvf2V7vnOzg8iqyiReYAAMSsJzU0MAojWJnWt22bbymbdtqtz18SgsFuGvzbr7J0yfiZXunc1kR0bzRwswBZ4XoIALDlbWdLvPz3Czz/fFLWqY1B8VyO72+XZrEp1msRrVyWAUvD1HCgk5qM+QKRrxSdTDPdOXuxlO0yXFcSgMHtAxR579Fy8dHUKox+7N0aUYpvvqiTQfAQJLDuUsSnrzfbpl97dlvRyiH0hBsVogIf3FxK75aLLEMx+5f2NZi18LQECJOYlHOhslGh1E699NtdXzkm6PRTEnigFODsO35Q2T/t2zQ7atT/wqmRPk4iDxdxVYBBgKzNHdl8fjzbr1dnU7x2R2JNFJ9cs+Fep7xyePOq9Bb/m1oRARjroej0H8QxIQla4yBk5vPhhrvdD3aVe3hObwlM970Iwev7QmkLXTz7wucuVVKuQfYAAIcxcVAcIwEENF1U/3L1dMmKKrJs7BrEps8NP60zmnFsLl92gvvztLqWQmbWQAMw81QbhsOrY6wN0TCrssYxvIDbVrMiYg32H1uS3PP5K+0fXVWALzQhACASaf3jGCLCLA4iSpU0rlWE9xko/rWNTsqsePd4zN9Cx8rK+zOzPrCRhjDFgZo2Yj4YMYGM3o1SJ3SSl8rJMWZYfk9iUng19HWdeNr91/ffr5WfvS2vZpJg1B1vMSRXCMhngGsK0PFs/9yBKpZbV+qVbiEnlsaHeMBlcUX6HhtT8dpLZgw6WxdxUwswaEht72l1uh2VMQB8/fxKbYrpTenK0NHj+iFsb2z+gGQskQAAG47kIGMsHQOBo03pVyR7a78ZWNjEqG0b9go6PrfeUGksnEkZgI4RkYTBzUSHCQraNrFamI5vqUWrdb02xKcWpdy69g6e2XYikvapYZTNrMysONOB5CIHTBmMHlNhr1ZxEOPr6vX9kxKb0H8z4qdWjp6SSXmW2H4lZG0BIYAB7HmKwPKO0ls7xLIbVeiWczVt95fPEpk51Dt04Gg73Bq5MHjQpZh1gQICYFZqDIIKiCOxCVTC5T4PDmyHLdvzkxWIKjxbsjszM3JCtOFSZlLGEQCAAH4DmIcaiRw1HI7Isp+2aYWieasd59VEvppiFoMNd3tE1wwrOgJeWJdtgQFynmIdKCgWABxh3TT1W6w6aqPX8YwsqYXy6v3t809OWlcDf5jiMAJeIENeUxPzUdarFCG8Yu0pQ2rozreOlWyymmvnkpHhTE36SmQcnDcooAMGBBgGaiwhQqSWAorZUbHuqT2NNordXjhdVcrJs/rShAVuLVE6zpVCEMMVIAAIw81EhSqiJKJ7UIlVq3UTdFMfyreWiSqfbvyu3JQUNsR2jAATCQlyn5iMGp6K2KHU/qi6HaaVkM0Sjt/YwFlSQXtc9sHKLBBrozxqQi7EAW4BmzHxUYGrUMjVymbUdkQN1uxprrserp15QUfmdxYEDXfMswpwNkVwEYWwAY0BzEhA4VGttA6ltpvs4VJ+r0269wYKqdm0fadOjBKx8FlgiiinCzIr5qSTIVt3LpLq7VE7aR4zHU4Y/9t6iisCRZN/kbgXwYLexbIUDEcX2DOB5CRbgdJlaUHKgZTfT6WmJ6WtXCytaap1htiIAprpFKhYuDmPEgTZz1CCEStSy2w7rksXLMl1u1S7eGhdWvHy1OjWSAmBcDzYVShobLAQwV0GW48rWZuWcpsiN61FMy1svxaKK6vIxOu+5WQM2BlhJ2IFsDjahOYltTIZKm2DTQzVHTUcrwuWNl1hUFe1fuHG4R9kCUayxcBEOy54xIOanlrMxXbqbum4Vx8CqxNie3vfCiug9/myYNGDtCaQsIYxxSGb+KtKT1Vte9iy4lHW4tHH8YMPCapXzC6neDWlm1potAmwZCzAW5JzEINnEpqf2ucrwOLXQOrOVk4+WxZWuwsK6ibnRJAPMQDY2gI1tA2hOAtgWbYzBYxnaUAs5WSqlfXDPiyuJPSN5PVNzgdBhNqEAY6gOM2+V5UmnwSj141SvdXQytYuP3WZxtTYwiWp1Lmk4DD0hDCBAYDyjuYlBikm99Mg8KlanO2rZH198/niBBc5oRYWhwJnMA1gBYCwjAIv5qUBTqSXHiFpXIc7iMsvxOF58ui2wuBPl+dHBnUbm5wcnGbCEg0CAEXNUJVAr3o7Fom6iXI2daay6/w4LrNo72B8WkwNS8bYPaozEgZnYMpqfSLYsMfVlP/Nyu3RfTmr7UPn8w0UW9KV7sm661w/yO0f9coBAKM3cVRCxnGJsw8VqxLE66rTjqbz5u+8XWgL0mOk4TyXim42DlRbgkIzk+YoJRyurM3Q5ZKjkFscy2yc/7YUWlOd7nQ2ljmSxw+0Hg0Qmqpaw5irIJlnve3nUahumHMbdznnxO52w4JIuDApXimNKD1pOgBACgZmvWq3Y8Tg2R1EY1Dh+vO/Ln/3ZtuiitjKSiY7hxHCIhIQIpQ7wHMUYe3Itj2o8O4y957JFS177291hwVWp2bFcX7A5t7ChnIk5MAOEp3kKpoQiaGu9bk0Udjo6Gq7+Ed/0ogsK6XSxmPQmToMGKSWIDrIpzFENgfemUS8n19aKa1/5W3/3DQuvZVXbuhCuxi19WgKBVItCpOU5ClZadWgFraaoO0eXY//7vMLiq06qwcPp2manK0kqLAg5LUDMUwM5une9bqpLjo1ujY9/dlyAQSLubK1u3X48VyeDbZKoAgeaowjAfZT7eloxPMhVmbz84CUWYbWdHi7sG982lRuR0hSmtLGozFMFMRFHMW4VUjo2j/ft/bOFGGTsdd2jN6wLuiYiIZxUQwTSHEVZQLGmjUOfwi2mMo1Xr42LMa7qP2po297CRBMSomWGSymq8xQgok+KNhpHkDGc5sO3vBgD16zyJjq6CkICpC7jCFXmqRJNkU2raNVhJmp56R0WZM3CZMVOzW2ewnazFRGlycq5iilWTsP2FIkpPO720/3NogyGXbVvaGX5qowBITlojRTzVWOGVus2qw3ZjrX5YLkoY3Z2mq1zA8FZtFBGxSVKKXOXcHodEbXjVM067Y9faosy9mTeXZicFqKRmanmaQoxZ3GpnaHul1XFGuqwznJ+3wszcxt9PRsM7Zdh5VBMtNHMWY1rVa7LMilFiBpn5xsWZpI8OxosHFiSGcqyDKIpNV8hamZq0GSwMlrx7vZ+Ycb4JZMeWbVn7FXjGFGm1uoqFZ6nWAPZqQrbSDHuix5uFmY4rGTmKlM8KkvRcoo2sVqnmKsKOUG0FiHMtB+5tzij7Gxpy/4V5n5hyrIvtth2gecpJBbkVFqmTBl3+7OXysKMDgt+2Z0ffuEKYj8W11IHpZmrSmChIUpNhzPG8eFjL8xAfHAus+PsIrW8KkDUbgs8RwFSM1s7osVqGFfnd1ic1bZGSl/x+pmWx7sIgrWYna8IIVUcdnOtI5v9Io0f+K5XOT2O4/NiOVarg+aptsHKXktpxTFtllligUbYBKbm1eP7DzeC0DrRjOYoICmlPqgYaTqZuFikQWBL6Nbq8q37k1POlTCg+crBIlopVcuL4sUabRto3rWTZaEHqyoDYq6qg3IVas1tc7XqV16kgfgC3Ls6mbR2qWtcDJ6ryIBkrTL3LdrF5nVdsUhblmj5lVfO98eqU5FKCQvNVYwJTKq0/Rnlop9OOy/SeEr01jtny+U6M4nSipE0T8HCpOrA8qzk7pVx3XYs1C5Lmd64v1lmddZoDkBmnmoMIAZvxl7uv/bqcPt4sabtl/tbZT+tzDCUMoVtaZ5iBAlW7s9Xq+XF3Sd65+TwGBsDiIg0azwtL56en4dUV7VEmHmrAQOYsqs5lp970N7bHwZj36lU+nsOdvvaLVfnrt/Q7XBzhbK8Oj457pG14whp3nKgbBzjtDq7nZ89Ksc+9MVhfnj74YWszsDTJnSyxVfjlXjJ7n9FR5GbJx5PTh63waRnw3MWHzAb0Uq8efvo0aru45CXnz543r7uTKKWdDMBABNm85uXXf4J3t1L8twdNRU2R2Lz8OlxDsKuBtvzFc3YliPCF8d6lBqWPszF/tiNt65IeFoW9TUABgD2K2NrH/UyvELX7na42eH9xXvDtlamRgHLnqsgQBaWVruLuPvqKss5h7jNwprbOwWlsURBndlkN5x9ycFKs6Psz69OIaM4DJCarxxoWcphefHh3QdDnj304a3sGccWqwp1NKg3c3HzpsGweeFp157fygoOFPNWGZDsYnw0XK5rObngsDZ3XHOFm1RYvIAR2ezey2+c5OYE0/7Rh706bDLnMUYG7GWrl+vea2UTh7X8vc+Z0YBeAiPSzPlVe2ezzQif8XaAJxuBPHdBgEyUuHx2vV731O6wVvaW5yghAMsiAkYD+sV1l6wKmw9l97nL4tYiLCml+Qu2gBJRjx6tq9UvxkNZnL79VR4WNYs0NPv5navS3Ewwdz80URqWlNhzFzEbLqSyV0GlHcrKPwfnadSVGwgQSTcbyur1jDIWdCDzWFuEI2XFBEiXOqzEAPuiAVlE6saTT71Wo3GzYcduFnj13GmO4+S0yGTWnrOAsZ0ORUvAtR5GYrbn++fzPWmVLHsFt1aqlgKpS+WOWzUavx/nZoD13Ouals0OS7JBSPMWEREKw7BSOLL40BHbPRs3bt8+G8+mfRUoVQ7KnWfetPxISS8hvPUqjfoLN5QIxnNiefHup/q4QzGaTBDzWZvEUl0NiZHzcBE7s3d+2b7lmlGHoRkABAwRLzF94YMumvEEAK959TSaIotMFKzOT764nnaZcmQqEWguA+mSqbpapwzrQ0UcP+NF+XAv2kP3M+qvhavrH//cGxIB9r88XwSR5IaDtkvrtbV5+9nVOKVdJaUBmzmsUFXUlOg9LfFofYgofsYLcM8deWZEVBjiTl/6Nt3k3fbfzkakURp94oCyMvnD9RhDRtg1U+bA1LwFK0IpJDJlymp1aKhywRe5doPNjIYU6Ts+WLYhbCpA4oY+K4sPP3RRRnGricCkzBxWDgYQNpiYsh8S4vxDrxo1jAYPPN833HT00KWudcX249toimVpTkk2s57DOOiJEhc6Nusnh4Qmz+thNEbNjKYs+l9cKJa1+sLddrFprTRWg8BGEnNYoy4HVli92n7wvA4DORvzGtY4cGnVqtYffzLdur3bt+hDFcVKAan5iyKZjShWVgfDg8NA4fBsBY1XA8xNJ3jKnyzW5NO6efNq2abUttuABJg5bAQQwobMtKNfHpZhX0nEKsM9PjceEUCakPS+XgVrejBcHN853jNkdiWmCkDzGAM+wJJInA8Oyzi3DK3UESoXHUbjFUETD96IRxcr2j4py1euhgdu0WVbEnNbCwdpG0kOqz7ph2R2vna5V2G11pGQoRCNW8DSlOT0b1ezoFXbD7tXjhmvpqxhqyZgBPa8xTMSESSOIrK+PRySue7Nyz/sJ6dyq89cnZG6Bb6LRi0AmJtU1x9cbTl1O35QLx++NuVmOQwpZRUYCUBzFwClp8guNVs1Xz06HMPv7jXwoYBa501vyTFcF286QGNjNG1x37DHF6vZtsdl8/D2m6se7imyCmQbJOawsq3SIg3Ykk4PyZjdhhEC6YNPUf3Jp58vS+Dhl0Y3MjCaOIfnrSxZjM8eP71IXvipup2OJ1dmwzYYNIcBgYttyyUsji51OGZUsCjD77/j8zf31lQXt/AX02jkjCbPB5NHLCXbuHlnuVpP33xt1dsUdIyxBQgxd1UXtktA2IqpBA+e51CsP8mLWZTjNw+/FX2LmAdcLo0tGi707LKSKCXeeGt1ebn/oTvSFIowRBhhiflrcHBMRgbKPvzkq3koJkyjrpy9ddObkAMw9tIFsN5wxYClNE+f38VU3vzgXF0lbCvDkoyR5y0uyAa3gt2rsp1NrD/TD8X4FakL2L6q4y5V8LVrYL3Mw+PWoRL4pW/Vuzx8rygzoxkXWwhAaO4yGmNiLIriXuHidujV1aEYGNTTv7XvIjX6YogFwV83ZxluQPvKm8tnj26fF6kEDnCkJBEIz18EBk+tOCIdTOcxPFgfjlH14fkr3p6ui/fBkuddywgDu9d206vx5q3mcBRHFJzCNoDmLSUwDo/FxTZErPYbhu2hGOVyPSC7C8EXEWsqaouwmT25tat3r947K6UIHBEgBAigzFesAXDEcrTBxmU1XHj1SIdikqgvm+3HCiyZjVUcHPfuvHlRI1yKsaOIAyUQIuYseQBRSoNQqi3L9tiPHnEYVmfqBWydgkWztUxvPn74+EjLqRSiTTZgh0PCknK+QunCxVFMIQsx3b+ndrZ9ux6KmauficOqNazUJ4+vUB7vW5DpQNgRhGwwc1cJO4hWaro63G69NT0YV2/nYRg1IcL1gLEqrY2VlNtvPp2W5yf75uKaGLCNZYw9b1HK0ZQxhso4RIP3vufNR7F6ux+GkSMa9WVYtCBhW8nZ+a2z893VScERKWy31rCcCaA5C1JEJG0puVkjq/G1T64uV585PQyDPbV8faxbzaUtJM7zKo4f3t5ENOQQlqMEEZbDZs4qCEOJUjttcnHmw689fLC9e1eHYGQoieaiHslayPLx41d2t28X2VDTNqSlBIznLwYBaqqp5USQ2j99Jy8vLw/DIDXRXBCv11jIVZ7fvto7prGhTkBNFGFji/kLAtul5Xaog7G1aq+8tRvWw6GYQqc0F0pDsM7prB+P7nH7YtmCcCMiQzjCNjbzWONG9po1FE0DV+8c19OjPAxTG0HzUOvewDq0H91W9eStVx6f7SOLC4lJ2SWM5zIiSpQuoR7h1lTHe8flwd3DMQPSPIB7ftoyNuO93dEqli/8Pt86Pxudtg2WI1wiQnMZbIKekShJt6b28sPx9HUdhlFbuHnA3qOzRVjH+/eWTx7+bH3821+eJtKBRUS21hwOz2c8SycQFcGqlnfemY5ePBSDEpqJN1Rhkbvj7TQsf/zX/E3qC3/PF5YudiulylJxc4CiaA4D2CKmtNJkdPnq02erzxwdiplvJnjf2bGIcvzk517c//yPv/zLX/3aD9/bl+XkEoXibCWmQEkLNHcx2E7Y1URpigvt02fDx188DGNvlGaBjNzA1lAuju8evfHWZv/Gp4++7yd30EZPxeCitmxRwLaZtxpjUKowmA5Fgd+55a9+9TBMZQ03C4KfnIc1nt8+e/x9n2yUb9Xxp9+Zpv1yjKm1qLSkNAY1y8xdFTbCqpTEqWJdittfiyc/l4dg8iuaBdJ5E1tCjd3xC5/cGaY/8NmLr5zXthzH0szQTUQpdoSx5i5gk1FMjLUalxpp9p+8WH+JQ7DOJJqD+u4VWKFXsXzz4Qiw+/tvv+flx156Woat9eTSBJQQ4DkMZEbL9N4ZlitAe+29+ql+GCbbHNBz59pWoPWL+48+NLMnf1c+dm9TSt1PxpWm1opllDKaw0SkKB7YTIMcy7Js2O/dm557cAgGbGECXpw6Jg8L7GufP95z8OO/1SsfnJc908bhihNiag7XAHveYiAEcs1xCVKZoktsni5f/dwhmEBZ2JLlsps4+qk/mT64FVzzzt/2g9eOd5vcLy2GEqXIbQoJbOatBiKTipJpRxVlZCW0/9jmS589DJO0MF6cZH53BVHfY+/vXZlrv/F3+tUvbDbLto+WZUyVEEyIICzNWwxR7UxqellS6aVWiOmDs+3P1cMvWlnY4gUPcRH9+7ShcJ1+/5f/9g+uWtudlbJGjIUSZYlKsc28VSJqQqZgu5+SZDmuquHe7fzs6vCLXbS+lX+Do9/y+L2HXLfv/b1/lzeulrvlRI4xTCVcwpNKK0aauzhCslFkPa2TwrFpKcHtV+ILzx9+SVesTnd9uxBRX3K5hK4by+97utntSrA867A9LQUbjYHNHDZUjVRl67KYaPvdhGDzxvjsp3ToZcG3OD3+Zkwi+mfdJKOe0/e9sRknebxqcbY6jZg8FEpzIM1hVEXOpNsQBreTUcB4a/nkMxx25cHQ2nTirBKivi6VtaBe37y3GVuUxzv2Q8djo2hyKiTmrlaCRBD0sYcJ2qYZKO9dnX6iHnbBmG1pOvGURzjqmXKfh/qPP//mprTl2ThNmVNQchmlkQn23EUCMGGskqDR45UlUd58WL+xPezCRVi4SOJJb2BE+8DYChGcfv6ds7If996wLnsNA60snTWFmcfazFpqNSOWalPMcPth/czRYRcE1iVQI2/DOCPqFzxGRH7yzd3ZSUvlak3UXiM3I70KNJcBKYVjUCrKruAuIY5v8+rrh12kM7CuYODcAiPquwaRHX/y3snjYy64XJfo68vGvk1OpcW8NoVRt8pUdqW7COz9le++eOhlZdKaRMTd8vgOor4EoURo+WOvXLQc5XUZuTzKVqaaNTHzWQkBImq3x9gvT8vZCFBut9NXD7ugGliSZlHVY1xmn31oEUA0IFHIq2UR4c2PvdTaVcuqlrX2VickQGk0hwFbkh2qk0rxbpVNM3Ex8qoOvRSsSBsBilMXTHb3jzpZrVEuFxKFrokzR4IoEyCOiH3fK21z1iZHHWpdhsmeRLHEXFaCxKj2JcWD62oTRpSLqN859NJ1oViQ0cxh5aRLlBsopcKQi8V0PN6dLz7L95yILmWbIzbde/pKhCM0KKfisqo2BqP5jA2Jk9N9m7TO8mACQbma9Gw/7FLbhchKEEgUgwEj9H0smRmhmOLOZ00+UyKKSK3HRsT7/nd746TXqKv0apel1p7hrCnmuDKOy1KkXI19b4x8POquDrvoLZE69DAvmi2e67AoAwifry0XSfQo3GAQ8eHolW99c9xmdoTXy9Z7pknE3DaYlat36sNqXwNje7PUth52QTkyoj/8sXfzol4kOb710aOIqiHifXXn4Qe3HlQrgmjLMvRKE8bG8xghIIWdD86cQ97eRdjA2XHh8EsuQvKq3HNcV7VYDWpDDAuseVHGk31ObiY0FPUAqYQt5rQSqFKKL7sZNJ1nJkC4uR966ZIIvQ6vnJLeOWZrEfWOZGGBdb0Zq49femHnFna4qilVM5jnyggnDKvJVfurgQNbc1sdeulTEQEe/+Vz4R3ak1TaKkSgRh50CiywD2ex2n740t/yJ1uLFkFeFirFOKR5jRCAU65PRMZ+NwiBQx63h15yQYQO3CMBYG71tGJrEB2kDjypwAI1tBjyaPk9/6s73RGZWqcrso2Z32pGQMnLQb1emiokilVWh14KXoTK73kPAHXkmCogEv0k9Zf+/5k2rDD7WHp/ML5/61c+LTk1V2QZy4oDNJ/BABk5cbm1i5xCQJP260MvSTdC+sM/rgYAr+9h4x6ivpSf+XRY5BDOGB483W3+ty9khtOrQGGMDCDmtmHJGfRLx6ZJDoPW23LFoddaMkJy4D1nFkHy/I969yEFiZhwdDj9f8IiawviVG8s2f3K9xvjFKtQbRGEcICY30o1S45adTL9QBbYWTyNh17ccqQKr8jKxQC509+gxzslo0UA7ddNACAq6JE3CtaoGlrVo8t7e9j9+HtjUQm79yySwcxxjUAZSmld9ej519PGkPZ6eehF1SQykGf+qEuApJ72B78uf+NAqmKD6yBatPGNQRSUwuMYaxAp8JMHbyyBi1+9mUyTe02Sg4TnNMKZQnJtQyWGB70akJim/ebwSwkR1nteDrUEAIU9d3um97x27GCHEW0gbinXFeQ37nQQDXX5NSvCGjUFHg33GsD9nx3HYqImVloBYea4koQoQ7gn9fn1WoBZ5b60Qy+YjpSoF6+zLoCuPvr3m6gm7FC80PZ9zl7wEqzTiIZS/hoVWKPicGyP7k3MPv3J1oqUWeWKA2FA85pMAIlKRaFXnzuVAI6GNqwOv8xIpORzXlo3AF5tLpVUQBAAvPGpMoJoqAc+nQ3LsFZ6s3Hgx356v5QykU1iSbLBns/IJFIKTyji6Lvf7TPK2pbt8Mt0pIDbvSaqPnVOn/11y4iCgtrV3y6ENYow6mXebhz8tW9eTMqaIhMsJMvYms8AVmbaEQLnq5+4REinucxDMIeUREj6XrGRiPG652e7SNMTweo3bTmsUgn05fJh42B/9GsXciqxwgUZsGhmPmtBQoajREZr+vKrAucR+810+GUoQKS9/3e7SJkdL05GEAX1yF86y4dVikBk2Jhrxid/rPQKM5RIhCDdmNMKJKmiiBRlWb501wF1WzePy+GXiVrE5MrbBJHpvv+jBNFQVr8CGpbJwqHg2FzHywxFrnbaRQawUl1zGjAhesGNjHEsugxMyC+9GYdfCuWIofNl6oqEWfUuRRAVOVSBZQiY0+nQXOf45tsWUMIuknUAKea3JkiyjVQX6G9XQ33A/ceHYDKJyAUPfNoIOCedpARRcvi+zzxhGYa1CK77PDRKMmSJKkhJRsxtJYGU8liyAtvnVhL93bq58uGXWi5y/nVOvfxLvkgN0VO8h3dZhMlioTyAOk9XR3u7yhklOxaZKYu5riSIuh8qV6UPw8s7q3/x9M034vBLMCcRw+F19eDBF2aHSBQBbni4soYsj5bHUfeHu3IiKo4oyjACnHMcz4AJGj12om9fuW0e/GB5fGd5CCbFkVtxWt2cB3/6pCC6BhettIQs8m4n6l5Wly9cNVqUqRQ0i5A8zxEIy+ydbOzL9f17obe/++zxe+3wix5BxDl+C9fBrHo9soJGLuCGQvUsL/pxKPPhNOqu9uDzb+2JovF4qQhmQ5LmNxiRluXRve8mLnt5q+XXv/D45P50+EVGRCIF/8b0kpwHf/0XDI1cpBxMmobSVx8v0Y8r+W2o7+s//+MfdQWuNg0lkpAw81uDJYKoLYYsu752f2Uz/OCLJ7fucAhmSCHya3qWUHmJHmeHaWTiXXi34v16uIGkdlYq6iEc7FX10Hpz76WPdhctj8PNiQWYeW4Gsw5y8pDTmD3XZ3e238vZvVuHYJCTBhjdvrjwE/yIFcyNS2qXnhXmN5xsGgg49C8k2nHezaHu5VF95/hOy5jKe/vSlhKAwPMcAQZbEOloslevv1J/Yrm5//gwTE03QPbkxd355ZpkNGqRzq9/pkHpL12X54Zyz+qVKBdOTqPuuXrdt9vDB623h/cVU0mEEdY8x1gG2elJw1Ra2q9P62evLt47PgyjEHn27zu2SM8DNzMasyB55d2KAPS53fdGgyf+fyHK+QnU8/LtyPuPS05nFy/3VYyAjTCe52AbhCMJr8qkaBqeO9XJ8dPxMIzDkQN2X8MA33W7QSMW4NC9Ht3Hoqlzby42mDr9eIluKqiHTne6eOf7hpXf/KmXsu+LwE0Y8DxHEVhQlMVyq0OJ/dvPHo8P39dhmGKDZD9BHEgf7aMRC5ce/15ZLF5funWzaShxv2cputU38/Fu2p+8FuuLt37o+SE2KGlIpOY6InEBlZSjMnqbZd+f3YwnH3AYltGgy44Frj+NG5EuHPNRbdSx9yff3+cGAi67nVhIvT2Nm81L03b79Hd5/LrPl5JKSYEl5rmJ6KUgZrLFqpbl8GRTpw+Wh2FsbghO328U++YbjUAt/56djLoG33nTVjR47aNOWIa3hdxNF69Nl8N737fL2KgomwQS0jwHC1eKlUHVXkmWdV2up6dnPgwDbgDwyXfwD/popKJXfs/zQ9Rd1q+8vd1gMn1u0iJ0GV1nUe687C/tbr90eTlO3elIJMR8V0kGKYeMV30Xktfa5fr+rcMwIRqU419kcpQbiUx8+GN81Dt51gmD3FDQp59iFbEbN43xzXjy+nsv3+/bk5rUSAGy5jsICRmlFb3nri7r6dTq5fC16RCMhjQE+PYfZa1pHFJ7lRBJ2eWt8U1DSemNS1pCVsuya3D2lfzUq8cfrdvNw7SSlAViDmwjS4Yhm53rZfT1cyevTD70UkADp+9xWuMQdWBX3RjMxikuzJ6TNGhwedITrcB3ilsAj7+2/vLl5qP99dtnEekUIDH3lQXGsilD99SGOon1uz+4eu9k58MuqoGwEEcjFNGZiR4fDBZm5myxMjU6Nbx/oVjVaISSOysX/Uy2HCUAv/bG9vfNO98zbW/XyTiRxHxYViBgWskuQzbwgy98/YvlzVvT4ZZxjxvIcGOA4fjhi1MKjDAMw3g8XuFkshAoETRKvf5ZJOo5ARwA5ZN3nv+Dywefb+uLVcgAxnMhi1BY0Aap9WpXSq3btz/x3PLO7VYIy8ouREGGsXdevNkXEaWU0hqNXd0rF+18DxzM7n/3i29/ef1j98acMmkykjQPkkyCIEIrNYZS1nVqWevdL3z/11ePbyWFrHRdJlFgscYIAEaTlC2nB9HNGBEcfPy7Xf3opy7fX6vUrABibiyDgsDUXDKEh6REt/ujV7/zideDTFITFffrB9ECYDRZUY9+ikQz3/GwpMc/f/YDr+7uXY7HBZEWc2OhkmmHcGcypPO07nc5roe6ff07/Vkv4SqSgo96g0SNpszJczLRLK09LPmNjz7+hZ87f7zdXzgrAjwvQiISK6MNxaJoyqHrfFvdq3r18z3rFnTSFYLS9ThVsT5IKZPlKMS8SBgksWR/5Sdf+vXfvnVn3B1LiYQ0N4IawpItovcCpWYlt8vpcuvUOginRkfZc5VQE3zPP6ObAUD+7B1htAmhACAsJlCXT37s9u/x5P7jpydjJhJz5loSEqdaVoUzIiuX03I19C7KQ7bYs3N4YdJNesSk/OGeVDUHOH3dba+vRBlehLNV1DW+p/ID9Wvvv3M/ILi2PSeadY0QZRWZiUspnK5j14ce+sYOBVzZv+Oo/cb1lBASDP2IPboZAJj+6x41ZqKJzxpAvCx1aj+8zN9/e++FN88n4esAz4dkDArKoDJUk5rs1WVdjsMQGvahRCScn5wa3twDdgM6gqf9cDlpDgDh7utOjXP0YAYQwkPdfvn39F+4fPjmOy0EOkjMj9MZykIMapmZ6h4nttW7OoTMLL7NKmDAdO/cumyDrTyPisifeS08aRaAnaO2j0YP8UVMNoG6lx/+P5z9in7rzfciKIABgzUvEkBqakdNxbWnZAeIXWSNYfYNlCdFP1Bs8gtbDw+bgqtICNTrdEwzAWB/1ZiJFjAsThL19Ff+Dxe/uT985+EUCiNAIOw50awTNEQVdBmMXYflPmsz+z6zMXY264tbLpfZHtvcMQyvrAkIJt7HNmkmQIp3uCrPUYJ9I259ePr/f/z/+bhGTThAOgBZ8yIBSawzSxVSsQj3dA8NMbZtjB9mjV1xfPaqnSUv8IcPbp20M56QD6x/YEmaCWCeevDNh+McFcKwgHrf+pWv/Ld+4KufOiomxIECibmx5aT1SghDViKLq3pNerro+IYZDM4Wbdtx7HmnUE7Muf2rhuO1qqIerC+f5GYCICisPuZv3JSRJqfjCanf8J27w2+9+LlHq2pxsGXmSGAJD3ZKCClMw+hs4vRSYTwV1aHWXrcPHt19fXV266Xbw+r53/Cjd3XIg80PaD4AEGSOf0O+c0o3MeMZ1Fev/sB/+xP9567WTimvIcQcWSapKplSYimVqqRcJg1DIgOrWjOVvQ+r7fby7qP10x+7P/zav9FvejEPd5i/OMrNCEAk8ZTf8+ET0rSSzFK31cd/z9/8c4/69jKQ8lrzZhtRGx2pWqLGoCGrSlEUVQkNW7mnEQKyrx8dnW65devd//X/7t1+mAObLzbNCkCkcPof/MkJaToGUH5Ql3z31/4Pfo8nq6QPU9rJgda8CSxVlVXaCWp2r7F2lUsp4IgoEVNXmHAEiWo/evu3/cb/25NHX/5P/Lbv9EMc5qk6mhkApHTl6/eTJ6SJsC9aYPQS+MHv/D/7Tc8OksntsgppxmLuLEtKqCZSCitW6UGJW1N1G5linC67S7hM47KpEllf/OJv+i///7781d/yB/wB31gd2sDuF6LCzQ2ITDzkdTun3DSMCIxiLJaLe3+v3/Ddq8ps9DUJFiDmzgqUkCiRZ3D2HLGKg7TrSjm29VFXVqWIHDymlMPzX/jRb7z6+vf/tv/Ki3lYgx+1Bs1Rte3rf7v1XhNgUYCAWQAzufe6i7/7eQmMrEyUzHoOhZAghYRJiJDQFNlqlxzqyX65vuwVambVMNB6FSi3n/rEF7/9xT/49/tV60Ma6H+kz80QSHDh+/3dndLooAGGaNsz/ZsuP3XNvAQgA0rErMVcCiEkS3aKsciZg6CuVV0gPLVhmEoxwvSeJIGE8/LZ77z74sd/79/1uX44Ay/WGtMcASRx7mt1fK2xCQABh/ux6fJL1uTZ4JmDE2tGzKklABnZVY41kVWVnspU2BlON09NEKSQ5CiBhNavfu5Ljz77B/1MPZyx81F28wSQiW/yNUYaGcDg/u7tJx88aqcTMmBIQzpkGYu5tRDXFIBar9GKag1Fza4UCNvYEVZNwmTKETbo8tkvPvfsb/mtz+swBt/3qOYKxN3w6gxJ42H4fqU7bp9xwY6D3bZhBoBAYARIGGtOhbimZ2RHrWabsZRK7bUKGzdySCbX1SqjVVJEmNk8+upnHn35R57oEAZm/0CFmymQBwdnBY2E/eL8/NTUisP9+cPDaYexWJG4po2Yi4trZ0+vcprUg16VMQUR7klAYejygI0BM9tf/erz3/ny0WEMHL2puSIqOTuBRsh2un//ijXr7IWO/ZPZ0PGxRDZcU0I21hwMCUFGotoT1TqqDzJl2aqIdAslNPfeXUoxjjgA3f34i8/9uu1hjM2P9JslIqXz7zLLDcfpqb2nrdkwtj80FduwMJhFADBDrjVrA5qDAUJYRO24ZjbXmhnLTetZw6Uph46tvvJULMCBAHT57Z/4dd8ohzDM0ZtMs6T6nf9fON9wnF/YffZDD45mbcMMhmEAzAIwwL4eM2vNwwQhR5LVTgqlqcox0WvFEbDKAlH75IJSimIO7k9e/f704QsMf/qwOYIjD3wDUEPD1fxlN28thj4AZiyRDRYVrt8Sc3KhIJRBWOGqya4JSfaaMqS67ZoX58djCce4LJJtgy7f/dFHOnxhHrWXLU0AcP1EznkfPxm64SR71LF704YBGNSffX3zdGHkGpHIWdWmoQqjrErCDqcU1Nid7aYWZWqkmDXW576BD11g6ra+xQlMvUSvfFkekkTDs7P7uh1pnxFh4bplEFjzMEiMXNa4VoyHGsWZVcikXWRVgihlHJfLpqEK20jK/tn1/vAFTt1haYAGTF0EgPdZ/vp3RkOzyWbjJ1x+eUfIiLhB1zIWRszFJdnuDD0yjUAFZ6bl4irZhey5qkyO1nJ12QVIArF99uwQRvyFs9nqADDAAoGR6oWPe7dtukE4TA8ePC/u7L1iwWZGxAUZC5ARZq6ekodIq4JwOjOllE0Xqebow+laXjZy1QcCScyYr76+P3yBHTt8y9NaBwYGteqeqy+9uk8QSTZFJxuGfmXnqo0749WubcV+n8GIPGOMkREgUMzNJFFdlMoEmUwBEpAiKREe6KtVFihTtILAQjj6p87b4Qv/EQtsddBuZq5r/MwTlw+kFCLJ/rrt560anQ+NH5SSWmkV5NkwGpQDLDAgC0BzMxDIpJSSTBVhValaAtuOmDysViuitFJCiW3AHp7sTg5foOdZjZUJwILAK/Ud8/eWB4KIFtfeeZ+b1FpDICJgMKPhSwoZEIiDrXkZAiFUUwhkW3JW2ag5iWbI7bqXYk9IwgLbvV++Mh2+wAnDVrZ40V7y/L/39UuR4Mra+3QoESzKYDRa4cSSmc8rJYQEEIGyYoggTVjoKDX0SjIVRAoIXKL2t/dXhzDi9y0aqwOgywMf/u/1Sn3CyTOu26oFTbE3LGFdhyysedmsASXYTgnjKJkpjGr0IdVJwJazyhFyONXvnvjwBdY8NGwGQFTq69/mYaouHD94yyXioqlWA7J1rVkxZ7eEMCIlOaIPVYEyU+vBWqvSM6FXByRWwtuvnurwBa4abg4AcA/84L/RJwAXB9P5wev3TbmCpqsMBFjXEp6zCZMSkKoStqoAZQZZ1z3qdqhKNddK4ExSYvXl/+qPPOeTi+57ZpsHIiN3+SYH/IWdtz4iG5STWgT1FzGNBSQz97eSa8q25MiUsRP16rpCNVoM3SFXGQvqt3/P/+EFFWqBi49qHgASHFpeGx7eHxeIoP4ChkEjAnQdMprDwfVghFGVndDJoUYOiqxURYiKHYLg9V9x76deYzOtSN8cbyYAUEllZxlgRJLBaNQyFsjMinm8DgQJAbZULUtkR12lDnhVrXCSYIRbWQ32wrH37mBSge0n+NxcAEQbRmQZjV6kxcFijm8BwgZXirJYIZxVpXZ5G+FMJIPcWhytQ7YP3nFtkVSYa3Y2IyCIVNMUoJn5vgwgYxJndSTqqTowpWNQyZQSFyRFWw2eD45fcfFGm1Do/3SDNCMYbdJGtkGAXDp0sVrXcVv3tWxAgADhtqmWBWbwfnf7bYd9MoGVv8GT5gO4TWo2wAeQZMkOq7Xi1FPdTzOSwDmsp0KqLEC46Zd/oGsXyIT+3ReCvlpm1qg2cM+i4RL1KTnGCCyMhiNTSnkAc+UO7/d3P02RSKDzNoq+YA62GCJNynW1jXV6WI7COG20ck/bdlIDAFdO/Xv//HqfRsiDpoW+YOEZSKGSaWk91G1KGwNCIrsoeunsYgAze7/X5+t2kwj0fmEKc6DlCHcjKqFc5SpjWE7YJEJpOUVlQy8G7JzxB3/sJQ6FwOOXqQzYdgSyZDmz9nTfk0pkkPF9MMviAIw+1Q/+RaMUYjonZAYntTrtNKRYdXopGIERMqFoFlkS7GUf/GucZhqGIQRACwhtyjWihjBKq6ZzSVZspxAcANB1YI7f/+M/1WRDGNYUIPSZ0CCpuqQJoWL1MkxhoBQBXPTBRuoAcHjFbX7bWMTYkRooYMUGsVVWI4QcElrtATsrGEYAhtQF4P6X6jdu57ox60XYKZYzIIH9RXITSgSSXamuLojIxIiBFuZ6gO1r/97JYV3YBADY7+ZeFzRwwSY3CcKA+qAawrapoBBABAb1Zeeq29w/viSTzQAId47e0MvMQgIGQ2qDEEoL1Y6EUERWMDCslEYEee//+4vzvJj5qYEAZv8FM5cGvtGggTuZ3ACSTJBUzZoAgxh+iEAiAN7/Sd9HPwD/YM/DhdNr9327K3umXBdEcJUQnQxkd1sooLqEAIds+1qkfuCFO91pDN238uf0KytO4N9dPZwZVyCC9lrQXIEFqepaXegoDdgY+L5BRLsfeY+Trl/+G7eft2z20f/FePaICzI4Ocs0B6UqIcmCIgkEmAFhcCS4uPVOv3HL+Rdsr5x5zqW7MlkQwt09ZMdKOROEGWwwgkVFJBIwzsIG9O90T3mW4zMhSOFRIciulFIFhSUFBwpERBBhZjadDz/g2qCFfCOTHSOklCxXXCcDGAIIGjDzgQYY1LCyFmRXSCIlUdN2byCLRUPKiA9y2HOY8AgwQlYKayjGYoQ5Ypw+9tEPCTXYMEV3kBBgLBvhagFEBA3I/gnL/swQNdjrMO2xDbIFGIwIAHDkgPy16fdboAX2aT4Ir4SESHGg0WCAuUE4/hTT52pSEF8G4iuRgA7GMBtjDBp27K6P30sKxjYz6REmkXXNBJjZcMMwHtr9EJcS7B0D7ZWcIGyQJABs0ODpa04/RAnWOMQH1RS2JNk2DDMa3lxw8G94hGADyK+QJAAJDDMao3PXc86kA/4KJj/XFNgkGuv2ox7PIwPFh5/ERKiRs3N0D8hg/i/dSrLAq25vyMDoRTeCZleOi5OBhdPPI1rmtKvIwOgx24kW0tcwFYg/3lqqxWcvUAH/P13CRAu7r6cCeKUeRbbyJ4dU4MH3MESL/UsmqcDOVyZOtIA1K6iAOW4HU63B05gIYPg4Q7TYP9mnAubHrWCaBV5rUwGkb3GYZmHDIBlAxz4RksX9e+mA2W+DKRbs85gMQPf4oNnLQjoAiAchWLwpTQnCZA1MrzA7RQkQHMlogtU9TAqA5B6mV/YqpgWY62ZqxfZGaoCeVdQKWONQg+xxWw21WtVNDbDvOGrFw1PkwL7PAtMq9M+SAxx8gE+snJ30gPftZ1LF/homB/BHkyKECrzP0AMgM0GqMGxThOD0cwcCETI1uEARgM5f+Bu+XwIiQqLm99MEgEcvufmSg1mA6VNllCosml52zaN2OszEie39lAEwGx7xFBfMA0yZYDYb0gBg6uxnPXWKmTJhs0MdgHDTfW7ebDNhGs7SB6C478cdPQtmsjRJIYDs2qOvORiCaVJ/mkYAZvuLdFKHzSQp300lgPhpx10zxUyQ4sN0AvAfeo/LiwQpu5MJBTB/2/+8lhyx32FIBXjD5yqJ0CKYQZ9WAOakh9SEFmHWpha49BM8cLUSUtRTIReYeLVOelBZhA5xP8GAOueev+jSjJAhWRglGEDtQcd9j2mhQijSDOgjP/bH/YuMECGnm2YAwem3/W1btJAgf4qJBlD6wV/3poAEYT/oplx90jfJUCDu8OkGMPNJ/19JCNAw6UD5c/5kTX4YU6CdieX0B4gXaYcwCHC6Qjt4yhCgIvHw4xQoPk87OAQBdiZph+9ToGyadrBDgex5Jh3GF/rDYQ9IJxsQYDNIO4zPBIh7fNphgwCbbiYdYAqENO1gQ4K6Q9JBg3neJx1sKBDiIekIHRKUzZIONiSoWCEdYBIUhrSDBoc27RASZIgH0yCHdDBIcFikHYYEcZ50iJAgEycdzCSIfdIRhjTIIR0aJNhkaYciQfBJh9AgZtoBGkw8hARxlnRAUyDmIukQoUCAQzs0DbJJB4QEsUM6BDQ4pB0BCWKfdAQuCRKbdtSEAsEhHeIxBZIK6dAKFJi7mXIIDcK8TzlgaJBjSIeQIM4y5WAaBMenHFQ4SzpE0yCnQjqUkKAwSzm0S4I4a9MOFgIEP6QcUhYQYPFtyqH7SBBMlnKgS5Mg3ycdGUWCjE06EpoEgUlHNSBB7JOOCZcEoUg6ugpMghzSUciABDPpKNMgph3JAgkC7VA1GmRIR1AQCsS0Q8qgwGLTjgQJYod0IEeCqOecLP0lQ4JYaEdCUyAhHgVFgRDQjrImQUI7EgEFEtDOgkuB4NOOMgkyIe0oVYUAgWlHtQAKLLTDJUGiaYeuUiAY2qESFIhd4tElBAiKdug5EpSlHWpGUyBDO2RCUSCmHcgpoT9iiMdEEvSXbeIxU1r6SyZFgBASD7ew9JfaBAVyqMeIECCfeARHQIBtph3oFQIUgnhOKAJkqEenJ/THoR4zZZBfNtRjggDRz0yC/ohQj2SO/jBTj6CP/hDQQ0J/mHwMgf7aTD1SQoBAPec0/RHykVP0R5OPrkCojyjykXOZ+oDJR8YV6sMEJAfya5OP5Dj9oZ9Bl5Afl3yoCVBfUfSjV1MfBvmUbeRHhHxgSAnxgaIffQGW+lqiP4Z+JKrkh4Ama9SHDf3wCtQHIQHJkB+lyUeQID826EeJ/Pj0Q02QH8PkQ2aE+ighH5ggPyHTj05NfSqgnyPkp8gERAnxsQnIRBJLfc0UaA/DJyC1hJAeQIR+uAkQX8P0Q41QH5+AYIb6OIaADFCfkIL0itAeAwI644L2+kxAxj3iQ0L7MsTHMAFJVYmP7ROQWhfxcRwC4s0J7fF9AqJKoL3GEBApCe3xKYhOgfYaEjKjiE9IQDBEfHwa4grpYRIynQTp9UlIpkB7bIeCJJO0h0mIW6Y9vk1CUkJ6TEhC+kB62aYgsoX4FCkIhoTyMLIkZEJTHjAN6VNCemwSsi0J0uuQkPEE7SmSkEKG9LBPQtwE6UFIQnSXUB6mIegC6S0yCUkx5eEsSGhCKA8qTEKqIL1FQ0K6RChPCBKaC7DU107awzSklCQ9IQ1JkB62mYSkqpQHDg3pOkJ5xKchhSEhPMwgoV6fpjw2DdHTivDANiQEnUJ5QtDQ6aQQHiEiQ3MgvMw0ZHwkELoDoSGpQwWmOzZoqOzC0l+/fobwaCoyXhayI4qKeGXQXSVUpEZ4HENEJEl3mEFEVYbuiCdERITuLBWWyYgmPIEmIpIUutPnEhHtguyKCyIqHt0Bk5GA8AgV0QXC49MRoTtkVAqgu+7SX2SLEBFklJCdPlDROQWykyQjJbqjZ8hIwiM7EDJSSi79pVqjO3S0nCA74RV0pER2eB0dyZEdMBnxSmRHFBkJ6A4hFbrDhGRIqA6EjGAcS3+ZELJj05GugOw4TEZSHtnxQEYzSbJTFjJSLpMdQlrLkB1NR9wy2QnpSFAiOwU6Ir1CdWp0BDNURwJCkqA6UIQkA6qrCUlJqE5ASAogupIkJHNCdVxCkhJZ6ktNQHQVIfHIjkdIAqojipAES39tpjqKkOyWVEcIyfKY6GiXkBiqqwlJrpb+YmuaIx4hGR+C5AoUIVm+R3MAl5BMJ0xzzCQhoRMdcQhJvSs0BwEhyQE0VzxC4kZ0dEBIYkl0giQhwURHUZLYEx3PpSS3heZoSlLug+Z6HiHxK1qW9sJLCiTXTVKS+0Sn4FKSey7R8SjJyRzFERQ0JbmYoThAhpSM40JyJkBJywQorowLJXFJSM42kNIJUFxNTA4JxQm6aMmAR3C4lqIl4xmCI4kcLelLCb1BydCSxA0ER/p8WqLXg97yEIjpZqY3ajU1mQK5FfQSEy7SG3hzxMTvZnqT7CImk1Ogt7UcMTGG4GQUMdEBwUlViIkKhNxIKktMyinQm2mfmHhPqsmNnmFiggLTm3FQ0zSorQQT5GSB3KCcoyZmI5ObgkdNFg7Tm5KmJmsHQW5TIKZ8nU9thFMhMYnfgakNZIiJyfAO0JtpENNlo/RGk5OtIb1J9hETnmSmNpwoEBMUQW5lwicmnKc36EsTk3CUyY3MZIlJfivBORISk9kNoLYifUxMbswztYGXAi21bw5BbpM5YrLxBENvMilawg+YAr3NgZbOP9QnOCMVWnL4DKY4aVLCZ6wDvZW+kJQ4l2SZ3mCcScnUeQYUB6R0QwforegZWrJ1kuDAHaElq3wmOFWXmDAIbk6TEn8dyekKSUmxGxR3gEnJPMnR54OU5uMER2SAlnSnmd6gNkJLJkMQ3FySluR9giM50NJ5m+Cgd56YMMU55NCSNMERTDMp4bRps5POQ9qioIiJ6eA2u8KnP/VSq3KPgJSOrjFtdsuf9MxHE4tKlGnJ1jVoq9fHeDi+bFETIS25bpDb6qoXARMFa5KZPCkxT+2jrX7LKUAmYU3odEjJmtO4rc47axoIStYkW5iUnNzdZpc6JgnosjXxSlDS8FQfbfWHvh8Ak7YkCQZIyeg+brP7fl0A4vstCckSKRkcQ1u9+iwKQMekNVU9UrIqzm10Ul0JgPcG1jRnSMkmG231CVnkerGmXqYkZgW32fWOAihuhxULDoCUTLXZya48gM2TlgQhJv1ooxd9xAZ4Wdma1BFaMsltdAhyPhBepa2pnCMlCNFW75UYSG+yqLkkKZGqtNUlEwyMObBk6cuSEjXTZpdIMrCxIGxFWG2TEt3XZjfBANZ4sOYhpiUjbXbjacCcpyxJ9DQtQaduq+vLA5XD1gR3G2hpX1udHMkC6aJFlXuJiW/a6gYM4ASKLWlCiMnutrryHAOmFsJYkPTFaYnZ3EYnEwGQPbgyhCX3hrTE3s1tcxgPse7aDQrWfCbTEmdzG51ODV5zbVlgzTIAWlocRdu8bPiLjhZYtDdETHrybXT+9k2wbCmniMmqtjoGWxdKCWricNucpUunQ0z6QXBXMjGJ0xuRaRBTh95Ab6EmIcFJHqEmaYqToiYVgpMSapKlNzLnUBOmN5gJqYlHboRHmJq45Ab6CKhpgd640+Qkx+SmdoScpITclHLkZARCbabT5GQ6ALGVAZ+cdCapDQZATkfK5OYIPclkhNgk++hJeYSJTblAT9yVmtgUPHqihkBrpRDQE71SEZskCOplxAYeE5ShqtAaRVHmUqC1GgQ1N01tDEFRu4TWVCsEBZ9FhNSMZynKw2qgtNIVUpQDfbQmZyhKdQup0XNMUfBZNKXxUiCpVyeFzohboilPOw1CW3BpSufVms5IVWhK7UpFZ5ByaAqOGRcywzNxorJnJais8IwhKoXbCZUBBkBV714QKiNnkpX120Bl1QBZGflLQmVKCbLinlsQIjNQJCs4fgA0Vs5kutJ7dyEynwV0Nbi7JjHinklYcOUIiUFfjrJsu5cmMRfOUxZ5XE8IjD7Hpyw48UICI3oXk5a53x0IeUHhEEir/vC9oK+rDW3B9F00dRFe7hMX9X5LQlwgV4K6nnITqGtwA3nRz5QR4jIyQ15w008mLnra0JfM98wIacE5ILD/4iLSIsnTKUzuFyYpC0a2URj8i9M1YZHL4iSm/DW6hK7o72dIDP7F42shK+5loLHul9wGqiq51UQG3+/RAqIi/OhZKqP+3kqhKZDbgczueWBNaErtIjqjH+9xNU2ZLtEZZP76aiEplzGhwYVPkiEoos8Bqf3O31nRE9T20JrqX+8VejLRRWtwytenJ7I+T2zU36sKNQmOZ2ID/1vOMy2R0jkgt3e9FcR0IEFv+n95nCmJ8HJDb/i40wwlgToeBHfjnRxKwqWVFMd8+sNMSPQun+Jg8yN9OiK4MiQ55pk6mIyg+j9Bc7/udYaOHOoiOhtfikmmIvJZbKLDx+41VEQ/Jaju6F27iYhsO0R2cO8dTEQuZbpjX7efKYjU7gLCe/Bym4TcEFAe3HuYgEjwN5j0ZMcqTD6w+kTQXpkUoR7ynwzxQXx3nGmHpC4F+c3eSDtEfWEQ4LP3kw4MPIQCmbVxylH+3UyBEJ91mEoIWBhSB9G3Ww4anN1JIQSCxYpAwAAYcM/58KDCC5Ms5EAWI4BABKICL6i5ta5aVymR6Etp+D3z3dXLXNBhKZIBASDCorWIVoFOlsvVTCrR11no8lKuXREsUY3kcqDFdooCiAAiWgVeIZFIHclU++bKXhXFYtZmUGg3KW1xAkAEIlqggqBWLs3l+gojJa/MTrxoGxDrZEa3tckiSgdurVTtKs1kJkq1WmBXQgO6nUyoNjGRJYh4ycxE15Hx0lxGOY4TgoKXViYgbVwiEFGB62YyubnO3qHOQtGAlqvpaRfSZiWAiHiZzMh451AqVwttUHT18IfsuyQLbpPSkMBNpo5sWd2XyNoMwn7kw/et3VD0Gdx2JICIDpKloW3n3zCRNqDvwe0eXhteMe8YAbgtSAOi3cz4heunq2kGkZeum453V+xP22xEuM1He5m51Jb1u8pxA1qfuulpVX602wlZwAKuhzaLCLiNQwQiqnBkz/kDKQckv+/4E1c7/fPxrG8AAddBwACE0aYpgNZBrbRt1ymdaQOyL4nVNx1IxnuydmgMIIsTMLMADG6rEAAaQblrfPmB3qDCIP7B+Pe7elo788Wsz8yACJgBMAzaKjVEglpu5sD6ITdEjGBty6Ovn9YVGPhaaQ4NmI0w2iQN1snM3MCFBzLzBrGEQerQiQ87c3qkWjVFx55Phyxog7TBsb8YP3/P6gAxiZmu3kO7DqWcsQsqGm2SoYjdxa3Pf7qzgljGIMk3nq3Q5miwcTt76f1PvrIVYhvDZe9yg0LboMHXwlGWV7de/uYHWxYe+Y73M2jFjpn8xcQWyJYBl/3xnVc++TRZhHzwcS5ap+MAAckvjjaCQLg42rh5/MZHX4rKImTluPtqtDLbB+la4mBfh74rxiBbkZRSpuXV1cOPfhAsSPa/jxM0WpMN6LqEIT8CJq8jQJYxLjhK252f3HvnYs2i5NafsVej9dgHkQfNGgnPGISuAQHyjNOYMA5cpt3V+e0XHl8mi5L+5e9yHq3JDurM9cuiCKyZ0LUAywCGKDbhMk2bq6f3zsTiZPbod6nRilyQxHfdsjAIAgEWRhayMQZHNKKUabm7uvNeEQuUlV90W0ErchESH1E7MRg5MqRARBoLH1ymNk7TZnPy+PbAQqX9JMei9djGKbC+KwZznZZlbGwSY0pxcynTbnd2+/iMZLGy+EUeIK1BPoimDiB/F8y1DbYMJghbNhQ7Wmttubz90smQLFqaT3AxWnXtA1RGEjlXHGh0HTbIlg2CYoXCJorDaUUrU3i3PDs/23QWMM3Nv0i33hhYlpyhD0RaxjmDjQ4yAoxlbMLhcAatNQKlSxnH5e7i9mYlFjLv/FE0Wm3bhNVrAELJgVZoBuGDwFYoKGCKW5FlRRmnMdRLTMcPT/buLGre8jMUWmc9GSW4ywYMFgiBQRhkBWDAFEcphGOaTEiUsrt/vB8ul8vlyCLnVd9Do1U2whY1AULgSDDIAgEGyzghRIQdY7gpyuSxtBjSsbvnSpyz4HnF59JojQ3KVFeAwABhsIXtJEnAEMYQJhwRYxmnUAlPJ7uLYZTqwGxZ8Nj7bwO0vtrsy2oL2ADGyA6MA4VcUVUEuAQRdovS2v7++Xj24GGsuwAKi6EdH85Hq6uJnbc1ZHFghmXL0YiQHYYkkcIRMTlaGTcX93xHVVyxYLruy82jxW/ANvJBRoCp0kfGjJNDCQaELcsOFRGUiIhS2lTCdYiI8PmVx5f9eNM52IsmLGgFNAceZIRlhO3+kfA+alcKjCxLFEumYMImIqZx52YSM+Kr8kCXnitBFGJWtfbQaigMGAFYQIQg9V2JqWioYJDJkEGBih2ODLt43Jy8NLRNVbGoILa133HQGigM4oDrNSiae+r6opw9SjFrwGFQOqyA4igu09nLr7Ewazo0Wi8NloJl77oOezp+GyJnsByATYaLbUeLi4uX7iWLsmZzt4/WSaNAoLBgz+V1XO2Hu06DCFBBNoRNa7bb2cMPbm3Fwmx8Uw+jtVCBwOgAg2WEwQqmfYlQYulyrcQgC2OFpYJLhNu4P3nrvWSRdnRVN6PV0GLWwjpg1mAwkWdXV//z3/er1ulqlVgWlgHZlGLb0aaHX7vaiUVa+4wVWbQeWlzTMhYYLDMb4/H/93dcrd+/In/rb3w3McKGxMieoriV5fFrt1Is1C5cc1XIrQlODMgYy2BhI8Ll1q+5twXOT4gf/tb/9YvCZJEEpijK1Mrm5NZblcVa++Q7FgSthgESlgHLImQIg6Od3Xrhh7lO/9B/8r/4qQoWVZigtRhv3//gIlmsNds//WZB66EFEMJWAEVZCMruvau49emXHyfX/0P/uf/S11eQiSyitbZ87ysPWbSN3/H+nqB1wVgGQhF2ROz3t7/1O15k7XwEP/Z//97f60hK4dBUvHznp8Wi7XlfOdBoTbQwOBR2KS5tc/xjtz76eJt8xJ/+b979gdOKpJhom9feYtG2556nKrQqGpmIEqZM0+N7P/3082vxi3j8L9z+hc8+jxvT+PhrxyzaHnW/gqBVMZBdWhlb27zx/htPV+IXx+lX//bdz/2up3l2/2PnYsHWufi+SUGrokWU1s5uf/A9+3vbFL/Yjq/8Tt/XvsSpWLRd+CibBa2KNi7j2eOPfvpjyS/2vr95yMItb79PQtCaKEZe7u9/81s7sRjtXHxxUtCaKHAZ9w/f/9mVWJDef9vNGq2JIqx8fOetn1+KBWn/ktsWBK2JGvBqd37s56/EovTw0XdQglZEAbxM5/pvHrMwbS65Z1LQmqihCuOXHe+xON1//zt4aE0U0eWZ73e1IHaaN33lmqAVUUTK264+0SCG2rn1Wg+tiqowffzTxhFL7dz/DI3WRFETl91OEFO97DglaEUUCc6/Vydiqu2nuasraEXUUjrl8UPEUvPmp9is0Ioo2h04Zjkjljq87u9m0HooIkHp/L9kEFM9/J/vtA6th1qScwOfZQ8jltpccKeMYF4ooryZ5d9vC2Kr+cZHeoJWQYGIKqQGjplmxFhvODopaAXULBJ4qZFDl40g9voEaLT0NWvNyUzuyPojMxXEYidVvCUnAhG4gVdYvWVXrogY7avd04rcYhPRnqu8zNC2E0txxG7PzG100AIXgZYgqFX7xldvmxAfMd07ejy0tAWideDWMqXpM4cKWRsx3rzs6Bpa0AIIRLm1xETv6kMjBRux4GOfPiktJZFFVFBOdI5v6S35IWLE+apQo6kKhLl5ZCDQot1yLdE3tOdIxjaIJXdqDG4SAoAF3GgMwJZjwDPRprIv5+ZG5raNlH3Emsvx1QvmfdM0GIDIYkxD2ciAYSuxwXZzW26WZ+dX793vrHlxg5j0gV9ozrhg0I9UAPmREEAM6sqIvDFYEIIxJhoZZMA+wGCwI1pbTrvjq7OTp7euptVqlYhhn36Wc446eoz5I2EMCF2XABAGGA1uwGA57NaiVoqGo4oBE0ATODylo7WxaJra5urx1fHth2e77bqzCC99xyzcksd3OTjQM0Y6SACAUW8RMHQtGxDGtttUYjk217a1x0e0tJHtEkxeRpRp3I9XD5dny+X52TKm5laHo1VloX7bTfsOh7oeYw40JpQIxBCwMCItMBgwELjJEaWNUTS5leOLR3feFDY1Aw5sKK21Mk7T/uzhw4eb3e64rI6261UXC/vqLx04Y+82LcBgCzCAHUHWFDAAYURUAEBmo0xtWu52m6XKIHCZlsvz40le/+A9Ts1ykxEAAmU5tWlcRivL/fHFndvLi00eJc8QmHn8c476Ld9eZxBx9njUhw/WInFrYyvql5ddABDG4oUBAVgWEdEItBqn3fJsf3FyfjbGHg0rTTmsXHtl9qPv8mOt85uGCEN04E1ny6vjzfnZ7upiL/WjzjMMVm+613M/+vHXlbvb79wb+cFf9fW7l90xnp2M1vDsz91dVxhmQBYDjUW1aKWS5UI545ULF+d3znfD6cDBsQPEdZ7tf+BJ3YYblUAgIkolPa+UKD08uX+yl3gGwyRkTbkUQ33w9qN1yp6WQd0+95t/3WeehAwADFlEKU97QVBOZUpdpZQbQIeXlY+grwfc+D1OTYO5MQgAgUApL5msJnJzqb6C5x2teCbHfPXX/8iPDuaLvvGhtE4mS6VEaqJQLhdqLLaPRnvLHzsh6wOmIUTAIhAt4lUzXbmJiVJnWbIhYymQevBufGohb3uu6krVygnj5A0af3jrfa7YWWQ24PrIYkQ0i0q6yWQ5NTIzU55LZEMsXfLAnr5C0oQ+oykf9YBTz+svhj4zhGUJIqJFa6WDRG6md6RaSgRih1g6peuh6duzN568qWM0G5pAtGilkqzK1VKpUM1ktnUqP14MDZZ+6qzbu6IYhjU3kIw7XlKel0y4gnb/t/u/3f/t/m/3f7v/2/3f7v92/7f7v93/7f5v9QYAVlA4IM77AABwPwWdASrCBMIEPm02lkkkIqUuozRJUdANiWdu8iP28VC5hroFnx6KzuZgyED5r91carnX+E3g+7UIX5wf6Xz3njWnH8tHAuB8L/w+g5yD5mPzeQnbfoI9Wecf/u+u7+k/8H2E/6b/mPWh/6v2q+A37wep39tv3Q94D/teuj+4+oT/Uv9l//+x9/ef2J/59/pf/t7RX/z/eL4aP7L/1v3D/9HyOfz3/Gf/v2AP/n6gH/t9g3+AddF+M36q/OH5f9zPyy8//0LrkcCfvvg72fu2f9x/yPQdyU7lnr/+h6F+EP+x5zfxPqB+Z//d8Xn8d/2fYJ/pv+M/aj3nf+Tyo/tf/K9hP+e/4/05//1/3vgn+6//7/8Xwf/r9/6xg+dj987H752P3zsfvnY/fOx++dj987H752P3zsfvnY/fOx++dj987H752P3zsfvnY/fOx++dj987H752P3zsfvnY/fOx++dj987H752P3zsfvnY/fOx++dj987H752P3zsfvnY/fOx++dj987H752P3zsfvnY/fOx++dj987H752P3zsfvnY/fOx++dj987H752P3zsfvnY/fOx++dj987H752P3y+UMKqCdam2mLlLNPgli8ZFhA9yiByTWdT3TbH/s6KykxfvnY/fOx++dj987H752P3zsfvnY/fOx++dj987H70pXNn9jQAcKMD7fxBe66j+z1KmQIPiQ1cIBPcAly2J++Pitn+upCZ9671oafj+gOVxCnTmVUN8Q2xfvnY/fOx++dj987H752P3zsfvnY/fOx++dj96cPtSp60qxRjddP7qcs9suOd5eMe7DWHuGMoelKzv23nERF4J/s9sFcs2/Cb94isMjvRqUusybLltO0msMshBmwYOl/k+qLVKmKdux++dj987H752P3zsfvnY/fOx++dj987H752P3zAawMe5EdVdFBkXrM3wVWeYYhhafw5cY4JQbvVCIA1sOSiOmEoDvvdejP6A8UXAPoN2n4heaxDBXexxQ9GcOcFmyLDIsmMDYA1sUWLZag6fXldIxAjWOUtb0Av2HYT2cGUD4MoHwZQPgygfBlA+DKB8GUD4MoHwZQPgwvoG8lO4M76/edNcTJq/6BWZrDiqSNAE8AZNIFmTP5FT4R89DfsG7R+6SsrPjAfVxdH8ItDZCiRcRzifKhlRU2ARbmtf5xRhOXAsdluZY/BxthWfNxy2QItpjHOe6glIhti/fOx++dj987H752P3zsfvnY/fOx++dj986NkMvJNuH8hv4Si6LRPMCKlM0XzD+DnwIyA9Z112g9C5QZS6m3msZ+JykM8J7MROT1rnpxy3/aqN9bxhbM6FVxKlvyo6dQyQ7TZSs9hzk/iE0BEnYKlDrDFr0nh7C6vGEhfsrAoo2q1hCQ2xfvnY/fOx++dj987H752P3zsfvnY/WdHjozKPg9c2uAYdzmlRMjlBHKLp56FH3JqKCFXPs9sy/RKsWO+NAGdR3yC0ylTEcJxm9xkdj17SuMvsPwf9Mq+jTXxn+/RQLuLSt5cqqxyXKbH1zDDeJLSoXADiiEvEKzLZqVEj89qtYQkNsX752P3zsfvnY/fOx++dj987H752PW2yQZc8EZ5zYZRcvXvCJ8fKwI7dt4R4PJDIgsnD6CmQIAQ1kp09J4jEF+mP+rCf9axyknQpdV+/jUo3jMH0fo3VwfWX/K1Wi8bU8auPbvfLOzlTwGmbyfvnY/fOx++dj987H752P3zsfvnY/fOx++dj2CxLh7qd9x0vko1jKbX8wtz0rq09yu4Op4lmeRtqta10tLLC2/dniQj8/CHkaTJmxqUFuoNaQJABYT15/rIFPFNFDUZHfFG77F++dj987H752P3zsfvnY/fOx++dj987H70mBRszzvQGkfIytWKcuFE6Z4jub0QLgMAhQd3iTyce+go+JEH0mSdxTMavWbFv9sd7Be8BfGv1B1Wt7+yYe38jeJhR6jnlXXqyhE8ld7Yx++dj987H752P3zsfvnY/fOx++dj987H75fEsdSe04v6CSFZriHUQ03PigK9dAb0wnf5sFffoUF9O1nZBlJyF35CCEDy6qT3NnmNkQg2V7WyK55z9t6W5govZ6/oB8nVAS5W54TPSjNpmgG2Wi7Dtq4uFR1CtJTH752P3zsfvnY/fOx++dj987H752P3zsfvQH9ZPpxF+fd1yP6guZAnWFRNYQnTN3ZncvshwrFL4ZSi628NthyzwUAR1Dr3NlIAj/nvzWaULk7GlILhp0CVqck/uP2ebW+OZ8ywnb7d0b7lMx5f2apq+PkVwIhdlYX2Y5orW4wgafo3GVpHI5QXY/fOx++dj987H752P3zsfvnY/fOx++dj2K+GYnB1L5OqT1rO79DB1JtSFHvWBQjU9MQlNrYkb59F6Hj3h2cakqbbTCNVBkdvuqVX3hHUEpRQw6PNlNfEg2DZAzzKrHUf+599HzWp9rJB22utf0UZ0pIRJ6q/vm6J8/o7nZ8fTvzHzu34BFGifswhdpzZZfZIgfFTZBRWfy7Y51QcQkNsX752P3zsfvnY/fOx++dj987H752P1K5M0y5uEdQQYJcspwff2Yx7TtBb2kCDT2JbOk5AZjKcm7YpP45Q986KLaCG/J0jJiN9p6B5ZFnF2hTi+I/+2oFXR0ab9NVZAjL1IE8bkKrri4eTz4FOtfAV28y//RVFblMVsri0/WbbttAbFUJWjou5yEEpU1UGjFLSbuQ9G2bPlFnlqeOS2aezgygfBlA+DKB8GUD4MoHwZQPgygfBlA+BaZOFoJvb4TRbf/ZYRQZ3IJ9i1VJDvKUWhWgVlQo+Hj8/LeCq1SRXswkOOF66K+f/8h0Cy6Lw0XuIAWnmOU5s39++Ymba5lk9VJFt7Z8xjfvjPIxKw33iAHFvbKWEkmDjstL37YJvxfpW8VuawdCfpxpNf3CbSok9nQ/DBQTODKB8GUD4MoHwZQPgygfBlA+DKB8GUD2qGCj/ywghmy8ENt8fPYYWOgSj8bOsCFZdZ7ElVxYes4bD5HVicYxGxyVYbT9XxVcg5erKYSRA8xHLovoot3S2G5uhJmYd1de+j+JgtxBwusfxo8Xq5o426Spnv3gD987H752P3zsfvnY/fOx++dj987H752P1QoKOM61g0xPhfnn9PrmJW+R93HI14oVaas4xRuODNnfXLWwk5/8ozHJQauM73t9VZIk95CFIu9To3p5V7TY1ABjXFdWJ0arsjWkzfzBi/H6ACCDh/FVBEaZpob9SNk0Y69jZt30BVQ1xJQVZ4s74zAzJMc/HtVrCEhti/fOx++dj987H752P3zsfvnY9OQkjNqMrgM28go676YS00p0BhJCTYDf8DirhjVPb3XjL/mt3IqXUf9kl1dqP+jQozP83rRYu480URqJv0s/F7iiiMxKzfT3ZZiycusZas66oHLVF0exEdRLbPYkUqXtbU1zwaQWQBWnruiJ3KfmZ0vWyVH28a9Qz2EoHwZQPgygfBlA+DKB8GUD4MoHwZQPgyY+CpTKRESEYzXxLzWtTbX2eDfnYk9VRU1m1FC+8Z0KS1fqX8SjJgN1bjRFEfZWkMDCBO0e579TSuqZ1pKmzkIwJ4hAQymr/mGULp6aIMYAXF3vvLtd3nvPbHpo4BNeBAK6wGsHTyRPP4EMGS+2wM+m4MjsIpKBPIOOs4bYv3zsfvnY/fOx++dj987H752P3zsfvnS+0LNZWZ/tbXj6+/GAFN+l8nN49ojtXuE6cpgSfWKPQdtsqJBGhc7x3DdHS7xOw94lZuDSWEwUq7jOYblXuy4+Abzvx037e+bdRwbu9GQUxXx++rfOwTMqwrE79oyWhW9Hoe6PMYK7Nqnj8mcdc7Vypc0UOUYODpz1i4YgxCqi3JtQuuqVKFym0F1752P3zsfvnY/fOx++dj987H752I87UDQLwzFsV127dzQDJonR4Fe8BP87H6yIypyc/UcGvNCWkVQceGkLGUJDHbYq54VyOBQWskJxj27Oh7Y3Cicxq/yEN9YqPq/SA2fRB3szD2kh5/E3vXBExDf2w7tffyiSAh+WZmuELTsPHmANwc+5II8llWc3p1lSCxTpaOJ1zAQB3Sm/u1faOIHoG3mglgk5jW4nL7TODKB8GUD4MoHwZQPgygfBhhfhMrVxBdFty0mIYT0jAfn6jmAmgZKThC3/0KGLJcdgOEiS/uXC2aHtETHjhPQBoKyGL8spNsmKc0NQlRZftHEqBcWPfn29YwWxFwpUIBTq/m+0RUIicpwqMaIMaJqPZIDtdb7K/vUG6mau/WH8j90tYX/lkch8cxRV799vKyC/gpxaas20uYMl09xSoXb9Y6SuUDNqZ4Slri4BYcmdhhtuESt5VO9lQT2EoHwZQPgygfBlA+DKB8GUDj4HIPRW9r2m+ae99i7akad9hrfe3MyozljAuz73NqUdGwNjBtnDdHNvxwWHT8eIDmDJ5r+zwX3hgiJceNHaGgow3gyMDCnKAz9gqANWfXISK0lZbpINDpyG1vN/ZN1kPWTRIxZeyteGCbN1KFukJmO5YAhK9pkGSfqcBfLlBfgpOGYDDO0TpNV2fUYphTZ6eS0WhWhQ30mqGEQdSoPjqUGR/piGPftC2fP6kqVUN6qsBGSEjdY1EiKzbKB8GUD4MoHwZQPgygfBlA+Br4aIIgO/XbiWiMaa5W1sIVfTAXMJZxUYpn0lI9/2hY3pmpN0WcPxCpR6tmvQ7xuSw2US/u6KPemmBZSXGWzdegDaoCBSCZ4y53at2+Ku8COPjHNvsFn1uHvWS8SXumEWAH0WQ7YRqpKB0FIzwuZ5MbmH/dJj+Lz5cfGz5bIz3uqREo5FHN6FBHeD427Wep1WAtTRjonHhHm5n34Dt6GjabBGJAPcdSfrxtF1owPIX98jW1cA/E2WXWIbYv3zsfvnY/fOx++dj987Eifj4JKIsLd0jV3IskrOTsALN198fsJvl5x+7rdZ7cVMDgIDLA80SrfWz2cuDicBBdvO98Ut/U2ffzzfgwTqjhiWy4KreSG3I5UbnGqJ2lv6qC4XfyySafn56Ha1hhxhZVmQrwkSPSbI+n936n9TDk9xrEuA5Sacx2Jlu57ENw8TjhhGf141VdrIla41UKhU7iFchayTBjpmCgaf0p2iq1pe8c4BzhKZs4isQXtsKnICqrwnT0iUtQwaRKShFOeOv/8beKDBMUzgygfBlA+DKB8GUD4MoHKpfmZCabXJNOLkS261PzJRRBoErEIqdgMWinoPrL2oLaeMxEMMu19uh7ooNNCfSxZNvwcPKO2PN4IW4mW2iHVGul6qdp1WOMrqTOmcjfmWZ15RWzlIpf9lgriRIpgHYF0viiXQ3rXnRddgzT44kE1C/9lIxtJrbbYMVK63WABKNDqKtoDZg9Etfe2binoKjXbRiZsZPKpCHXMmXTiDfzOkr1gy9nMJbNqDUPtt2YGW8bKr5ygfBlA+DKB8GUD4MoHwZP+/xT9FIQyuaQ+RF4qojznUmb6AMT2iSTAXoKfupb59gIB3WC9tkBWCRz8i3PFowXv1MttyQiRpqM8Znskn6HlkV8wNYQX1HhYX+0toFzko0FZ4LEZzAqss0wZFaSgXpAStWsgse35ly+qkKBWbB8cGEpbhZ6qgKusmm0LOx6DmXj8DIhI+4UpjOPI+z8sH4kNZ1zVmfr2SQr8Qz51brzNltwbg1J2CmCrrHYI9qtYQkNsX752P3zsfvnY/fMFT5O26fJoZutYdOcQa3aqrQRW1IcPCZ6ybFYWqHDux50Pwzmbgfjrz6DgY0LyX127iWry9hIN3gx5hCyTA4yDhrDNMlv+wrNJS3rz04A5ntBs6XPLiaAtKeoUPiMXimjqJlWfXC1DqyboJu+c8pFXSN2q6P5NlzZKJe4jh9GSdtiHYn9/zBUwKBve8RYQzkp/7X+ulJVgIFG5BhCw/Lz6b6nWNco1eg8fBOxEGFS9DyTYi8OmCTuKYaiR/z0edj987H752P3zsfvnY/fOxGBzfixllHIdqtSe/DR0xmsD44qsoMOSWhyjYD+Sus7cVLfb3cj/PjGjctpQw0HCoW9YguiFDGi18rdGuTc9K+kLp9M6+Ztyw7AzK1t9N0HGuImpvZA/oL4eo1RcrfKrl6D1xZ4qHhtC4UYgpePafxQcyEBkE5YOZlA3oafnsqv5MAWnE1Or+nzrsY8RA0tw2yVwLjP4Mr6hNCHG97iUImo4RXp8FHC2dQSaJzgFlyDA8CPI/lhW144d6asy2lWsISG2L987H752P3zsfvThjhaeP07x7KNTrR9KfRF78IHl7+B2Y3rHaQo76NZksuNE8aA57SfzLIvlAMUaJ5sNDWRmHb1mmVaK7THGEiGIN+qNu2/0qdcRtlI/iF8JkLqHYnRDQlUstqEREIANLLV1N1PXQtuvaN/i/YPWpDbB58ILyd8HfJ1IZ2CgPO/uJnISY1/R9Gs+zCbTr3CM4sNmy6A+RVULp+HBW8i1y4fE2tqIl+3pS2bwyuSWuJtmIuzuo7AzIN2yvm9Wf5by53oTlQRFYR/NZ/FQiwRHzYU793+C1PNQsf+VNWIbYv3zsfvnY/fOx++dj9eAsCnVuHeFZx3vkZNHVXLYoH9Ko3KpLfFNlkSgfs+w0e7xdyvjj6rh9NotcQNp6hLeiK3si/dVvjpxv1yS3o3L2X+Rp7Oh1hGFCqMfflGDCBHuf+iNCVxFrQ+kyD/QPq/+OvIEolPHWef5V6AdnxMPYXXPiLbPUlYTZy5Uji99FDsyXOiWKJrp2KnLYwf5IB6zcBNpB2NMduCauthg9QnyevzNLVUPOk2huhv2OjJjKwmUe6ha9wGzgYrU1dL6jvxU8klXtTXfcchZ+sEdvx3wyAqtrSver5hpUbY3BtYFWh75irK0baZK0ERLBILB9MoHwZQPgygfBlA+DKB8DdZcqIbwFccLNnOkoYNwjzPDeBlT80mgRsIBCsVUm6eSQlKqnrPAjUOlQ2/s/s1rZ+h0V40Vrhc2bGsLFaRhTKJLtZMnq2RMMMG3bVpzfagDL+nupm1rsq4j3xwMhmB9Qfl+DPPsIcgp7/IgWvxmpyQMrAI0oziFs93yCu9Cx1jj3sNLmbyZqn6+HkA6DJJkiXnc0vsTKXow0R21+62nBHz0QSTytY1IzjufCo1Yft3CuFg2FPzV4KT1ozIZvt2Uf0qK+5EEjoFK1h/uKAEpltma9gRBtBMv9FifZ6zUB8zN2NbpN4XgnJpn/o+nABj7J7oZshoLQr7wkNsX752P3zsfvnY/fOx6+Fckn3ECfFEbGK76M/IDzVv7cTYYhCfWTIcD6DTMO76KXp3umle/EafGoTe0nSJflCjfjkGeUvVUnC6x9j0l8ELJQLvtCiZT730pEpRDcaUFiWs3um/hujnVWa/DNE8mFiZlqMj5GTJyChbrUpRbz4ZGqdvS8PQkP9rNlJmgVDjXB/7V5S9GdZ5L1QxTvl49zQsN780ovbfvakFWciAgMuSfXiuD8aSpF2PyaTou2r0kXviTGDUDhCRalHqdAxz5e8/04DQftmg7R5Y23P/mVh3yObIBpgtIyPkyb/vN9qveionLBrXAZza1XzlA+DKB8GUD4MoHwZQOHB3QBMMuwoR50F8SQBuAVWp3/n5/3oXCrG65od1uyDKvc1HmlbhPkfPpCzyGlU7dpPMCpUfxjvBpRgTQaZAnssho4Z5SGDqDtsfD/yo/I4qKjNv4f3fVBHDMdIM6WDY3wP0naJI8OhWBZsfgs1eqP+jXtqv5LABBYhJ7tOP1V/RDED+5Tn3DroGlsCMl+yrVv30/FlVqY7JjWJOPKzZwNWrF1Cx8qPXoJwKgmHOOLcMivVGhu40PXJM7RN2xt9SkNToluRELpB+0zfMxaOi2aZleO69BwwcV69JJRem65yx++dj987H752P3zsfvnTfAev7RafTbXoCfvDscNPX5l+fHF4pDU66oPH1R6FTAqpW/1Twkyo1MGQ94un6LkKFxIlyhrynP2UXkpOnYD1u2B9TzH3n2/fN7G7+F/y+jPep/QI4+GlaCrN3cPhFCeFeAjiP/iIy2hTW5xqI0ReTYoilJqnREWFBvJ7be15gdfkPJi9/PQxoZjaNuDd9zYG3TPOBIAK5M+F696tdPJ5f/HsnveFYJDvgXSqZQFmwcWtg8yFW0/xLjekPkTNAGmETAQT/MjMCp7Ei4api3cvJ+1h7Kx3LHLGpt1N3byf+rIZnb2VJeZt62Ledj987H752P3zsfvnY/fOm+EK1iGYell4Mzk869692KDE/Xuh7tntN5u/BCFmK8T+ptbM4XsWLEpfj2bGjF+x9cLMYFQ5bOd9bIye6FGoILo47e1B4IXq4e4q1ZZta64v/Xw3TuQscXJV18ZUL6+bDqnC+hehuD6iQxgsx3PQGJl8ySz1DbocObARXGa1q9IJIo5SSIsw/Fw6PYMCGbLttgnY6kI/DhCqGbjhtQZKHj1uZXraV8VxFrCBXEpon0/YLv7ZfOQ4MQLOo7v386uW6+Qm6oP/+yNzcjiBwbzeF2PC/kZ6YJJJMX752P3zsfvnY/fOx++diLRY5dxowH6bH8eG3PAQ4uNi728KiSN3OHw8GklZjmMA4SCRMC1euetWJKtTSJAJkvtN5KqN5jtSq5EKABwQe6WGygkMR06QcobjYtdHaOj2Te6xkW89Rops9V3wSOARi5e75rDb24gpWI7jFz/NXuDzHEVB970OC02rTTb/+rwf4NSiV5Zxadi+uK7WOvxHaAZVV8kvmoyZeZbU3eHWXszxlzx29V9DA8puqBSsgyG2L987H752P3zsfvnY/emDB2LmOR3Xd1FRkaa+Bycb9ciHegf9WzOpXqgioLsgZjfEBNdQe8C2kl/T/wnTUAsilU7/gbMEQDy049grb1/fcRMGwamtySphl/nqWBHi3MWFTyYOYSEKuUVYYhNz6F4bi6fv8lG8l5v//+wUn/lEXWPYxuDdH2fbmi0K6MDakRtI8Dlb1X2n/Ou/7hIoWNYZDu1Z9frvbbLppyXXUe5XYTWZLMdp1bajhr85QPgygfBlA+DKB8GUD23NkwkW0THl3VuBfaQn62vKxzw97UUgMVaB4zFUaZMj/cJgsfwXgzgCCs76HzshwCcoldwgr0e6aESMruBbNMbzcOK7dlLRfP6NXlwmTOL0UOfWOJvNzLJ0boEFAl6k4EuMxi2x2bzNRAP9y7p1KnzwpbS1lyX8AcP9IXC85GtAOA8THIav+hWsQ9OsXwd3gQtIGF32KwT3OFyBWA6VYvY7st0MLVjOroblVKQ27ruL97mcCUD4MoHwZQPgygfBlA+DJ/toWJVgLNM6ocCsR5Kpk5zOBPQYi8CCXnOPQyWz35XSN8RrCLYwhnKskhmZczgpBG2sO9va4oFOqD5G5InlD+LYHN7/clLdtFOB5lFvHlHn4LPOTqUV9btwdDHS0aPcAQQ/ddkpES8rUuDelf63RSyPZdqTmYdroRYJEH5UHI5O03T//K740YSECP+6Av7gLXKLbLJInNETsfvnY/fOx++dj987H752JD20Mm2764Zgzd8iqvalFm483VZ4g/NZJOHNtKSHD34vGzsJQ4GOzFyZvJm455URtNmaxN6jwy6pYoRx2qwsgpC4ZrE3NAV9iC6gI1j6XJcgPPug+iePnNdnDmdIAwiFl3sZC2+6rH2sITNlKfPmWjJX+qMnwlnxhbgxXg/tfERN4cEwgHerW5zdyKF72b3MniFPHFsnwxsqr5ygfBlA+DKB8GUD4MoHwZMm8vTK5dc5QTV5K6nnlN+DUNprBs0X7rMsLLMfpmGO4vVUUY8owBhsY8rAGk663K2HaUWFtUxrNYpTqyD7EAqmVKJf8GTQ95uMmrC6MWUBEqN3DHiu//y7puk7J3vV5MKoyM/YdeZY0FD3EJU/73gPW+XOBLtA2SYxwmKCKP3zsfvnY/fOx++dj987H7073F3jU/5vSoJRVuCPfv+bfCw3Dy0Xfm0xll3wCdKt2no6zkiFH1OH3dK19Cw6T4s9jkiSQYAmkcTN3wbb/BZI4xR80uezFkyfV1I/demOW2cEal6NsbTpl0OPs7GTVQm1Tz5Lbu5r+/09BTviFMrwJnBlA+DKB8GUD4MoHwZQPblfwvlw53s+5XvhWJu1V4DYZytCqlra2cJVwR97Um355Z1ZE5fFkDYyOF4HbqR2MuGznhINM+dbahZbXRWlyTtKKo3RRp5wkLAe1n7fzle/1xF9LAhJa/AeKWxXRHgf0+E4+81BS9dFVJbXgfBlA+DKB8GUD4MoHwZQPgdLpsPA6N1sPNMBwULVrP9MW5GGEBZOCi9ffP1HV6qrfcTHrN69wa2eB2dN2OfGlIMWBNg9wL+fGTRe6Y9E5k28Zk0qTvomac9+2ZMxh60iXZHvWTrwV86HH733zj4Q5CQ2xfvnY/fOx++dj987H70gf+YEqGxJ8ZDq03fzqKSoPERygyT+ADTkQgNrAFgq07WkfLsMxWh4lkl9OsuvRBscb/h+/a1ABhU/3IIPnvrtysTL/5EjVB2WEB0i9G6YohDBfX+EBUCuOE4koUxEDuhqZmzvJEW6sVKK4V3ngYpnBlA+DKB8GUD4MoHwZQPbebubKMPEMnLLXOLvJ14SzTy2A2X0TkxcXNyuQ33u3195gz0keNVYndcwKQyUo0/cgli18Sran3vUty+iH0MAHw2Q/yYEWvZunDC+0rtSC7D4MoHwZQPgygfBlA+DKB8GGMjXr7lBGllv+8TJdviKeODvwzLZ2ejpeiT8IcOv2DNJBlPmKndZc11/g1Ux3jtbNmSw101zMBry7jYbMbXUaCooyGE0nHqON4dCE/Mda260sWyHBD+rVs0kh+lDYS3fo7CQ2xfvnY/fOx++dj987H6zyNLXJEuL2ZOwZ1ae1lScx7P1AZ2qdnb6AiSaoEMmunK2QTpphzioN3IwGZEoe4+TbZvCzMZE+WOoBoZlCjuJb4oLwdwpssr4hilID5M9Ef4A4MX+o8Dx6QQ3aZpP0gKi17bUNwdFpofBlA+DKB8GUD4MoHwZQPgwzHL/f3fM1+oxUAMFjisZhq9ErlkvJksE8+1hw/enEm5Ultcpvgh+QiXRSthcC5M9i+2JODXAi74K1PzesRm4Dj3f+1ZvKMRR4/etgIqAIMiYhOchY3cIEASRWo1Z24YBHt++dj987H752P3zsfvnY/fL8XJe0tHcSRcTaqpF2GV1KYkGyv268P93z6tyoScs4wnBGIeUoy/2Iwd+GSOOq2Q1vyN/Ek86bYEa48OK4qe33U/EY33cJgXqaFMJZPilgLcofastWgiYe81MjKQkP3ons4MoHwZQPgygfBlA+DKB8GFtAleXX2wjhTM+GsKDLqqkWguppnwnoeHTkJGhN+xvHXYWLE5SL1DzH4PLrpkfD9+szXZ6JsVD4425km2eANKSHktsUbA2SrUC/4i8KymtAKBwygfBlA+DKB8GUD4MoHwZQA6jaDz1M6x+jbI7LFjgc0OrMzicOb330xLwsnb42goyI4Ru4e5RP7A7084FKvbYhRKFN1KlNGL4kMRETXPQAFe3q74tVGhWvWbMGacXj/2yjFHlXz+o1RWAO4dWsISG2L987H752P3zsfrCf9sQloeNH0/0cvsGXtdzoZDzvwa7JJWdwzCESxo9xdCFvTSjIAlaWZgID/+Otme7J+u6/9wi3mvQnv/ybufZEFQnne0j9cRhXCB7/ci2dY5ZDbF++dj987H752P3zsfvnSnhKc3+ZhV+IQU+MfaSO4uQTxkEWgPEr4h0uuRwd2HXLupju+q1Cwmf/lTc3P6k+Lyu8ybkuBUh83DO3RWoMWKR1xdSU4F6691wuZr3BlsX752P3zsfvnY/fOx++dj9ZmmlC5ZqPDLBlvVV7RGRUBHZv12CYpOCQay8THx0JpPSQgOu8pvPtK8+ewJnnPU/GlSLlVhFUFkl49jsLppI69Bdac+Pbed8xv4G7qKyG2L987H752P3zsfvnY/fOlliGC0mwdggLpLtGJJvInpt3rVE+6BaslWoCURVg8sufB5Yq9QXFF6n6DSRIW3f5B2Lp/80pBR+68R5KzSVI3b4x148Bb0c3wLhuWn/rXEO8irUrApjpj987H752P3zsfvnY/fOx+9L2obGg3dUPdPWiOzTWMFrsczJjdSmGpu9h3ZkwYxttDgEpRoyetozNTyq3XRW/bYiA/cQf6E+0rwTkJNzLsfXJn/tydNI1gz1JOC4Pc2LMJUgNpSo9Y54GNTnbsfvnY/fOx++dj987H752P2/z3fScqV37tmpIGqYJTxShScFKmkYPa3zqvmLDNXUR1FMyffMOfQ8Bv/0Lwr6HYh4WbUTDvu15DVpCZYDaBnCVw3FUNQRBvYVT/JuTQNXBZU7owPfwgW3g5zCkivOP+DKB8GUD4MoHwZQPgygfBkyqGwUZVIUyNFA47UXG8LyrWus9QOwQMp6bIaI0/SW3xeIO2sD9fcuCnQ35ZAOzQuL4NKBOpqu2GUX7vs6z/1MMN+v7LvocAHwIht8jzh1gP3zsfvnY/fOx++dj987H75fA1N/AUStmIFAMp13tYDjEfEuH+tYQbaGjmEk0/w8soHS5+BbzU5pjO1q/pFiXftLNjn3cFA6szQ6e6JOAVu2RxYVdzFp/f4uSCY7US1PQ1E/EgC+bAwUQ2xfvnY/fOx++dj987H7503ysc301rkmBMTVlKpH6vQQ/jvKGUPaTO26blpMo+0fyVJvA/8PEQfjiH6W4AaHaS7ztkJeqhVrV8PFrRpDceIrulnM2sVkTz9am8JOStg3Wv2dszMl+txdQ3AR3FjN5nikQvhKBT8e1WsISG2L987H752P3zsfvnLZg88mpxy/7Pr8i7R3Gk3dzu58GDP0H9b/FK0PPRhCxSbL/wvkfzD8y5YXSF1uTTGVp5MzCbggIbrYC3kmV/r0OPYfRnFKSPot+aWdaRVBqQgtMcZIGNw1OvcCYLJRGxucZzC4KUB7go26cVTeZS/8MoHwZQPgygfBlA+DKB8GUD4mq11LEOPI3Em8GStvhHs9KseRXkYVJR4ns7EqvChLj/nn6t0saLkxy+15f7x9rhMKRcysiVOPyLIaTfdTBedNljGXeAPqx9XZGqU78yV3wL3SoYR/FN4ohoQUeBDX5ygfBlA+DKB8GUD4MoHwZQP2Q0c+bTdLEQhxz/7PZKC93ZNKydzonaZo3HvUvz2+5FXuUd2mfkHpyHfUz1ZBN9KbzWunVvTqSd+kKXc2aCBm9qeQy3UktXZvNERjzqA4+FIT+fDodKrD6IDWpKttadJxnc54uyug5yTETJxltUuNF0IQfjFHtj987H752P3zsfvnY/fOx++dj9YGSLPl5si5dcE5isfDeN9XJXTt4dk7FBWs33b8EItcylnbOp54JvWelq3P2c+FezzJl6ODHpk0Hepg9Q5FNAgSwM6YVVG3rb6E+kv6e9yA3eGkOKwxSLMzzVjm9USmECo9eq78H6e6xcaLnz6BETsfvnY/fOx++dj987H752P3zsfvmA1gbfouGqfldOm+6RGLd2NJ0ssrLWB3QEjdnr/QA1gep5R91o60JNyg2GDE+PO81XIkkqT0S5ApDmVxFREFQG6GM+oORWZKu5MhRRtMl+Cd/5BSuUaxKlvWy8fRsKOwcSYE9MHLxxDcW/JomBsubRpn0XnsJDbF++dj987H752P3zsfvnY/fOx+r5U1E/yL46QhrqlXwFgLZM7gKr27nkOTx1xK4rN/8/ibj/+E1MdXU9d+TcRSWX+uyKeE0540xNnfVnoXV/0E6n+oLAThkau5zucYxpTjqkxu4n6pITLKlaLLrI/q9ZaCVwDcq8mspc7+dkTysgN8vODKB8GUD4MoHwZQPgygfBlA+DKB8GUD2022uIPk2cFLsHLE+Tnb2tRalt2hnI/xy44V8OabNnT84bMozg290D+fefVj/xir1fNgQ0NhiBYHzfe0lgAA+mqkVdK1upNRZXmGvjdJ9Viu8jkhrCVYSgfBlA+DKB8GUD4MoHwZQPgygfBlA+DKB8GHN58CD5Efi5/sH2ml6uFIfvyj1dI7r7loEklRJrWX64MPxnVFoZ9L6ZLCHV9FTGf8L5qR/M0LTxxrW8OGs2RMd5k7H752P3zsfvnY/fOx++dj987H752P3zsfvnY/fOxOMV0fOmP3zsfvnY/fOx++dj987H752P3zsfvnY/fOx++dj987H752P3zsfvnY/fOx++dj987H752P3zsfvnY/fOx++dj987H752P3zsfvnY/fOx++dj987H752P3zsfvnY/fOiAAP7/RxgAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAEXzv07067tzJli6l243jF8Pk2mscFmqh21sh82rnsfqWvE6Lva/Az/pjXZae2v8mYo1PkIEwNlqca9g/SZxjz9uBZoYOL8fokU8ibH1RdNBwjlSIN+lyE+jnKHrvkPRPa0kqHrTBSDFrqzmD+3p9e5W2YOR8adfVCX5/U8t5ULiPwmBYzRSZ5feY8raN0J1iWEmcniuq2qXtwjRxLdAirSTILQdaBY2fp8IwLl724UzH2yz8+JiXJ39oSfiTPvu+kLfX4KGbVvN8fAKCNkJElbLSlbdHbWsf3fv9myr8calnzPv6yls+k0wPvK1afg+cLzEyOtUiupfIG+gAAAAADhuOyx+AtyvF0K4R5lUNyN+sbwT5INQtl2WN/XkvYmEc1bRjEG16ZODIGh+XPLP4MLNzwTqaedMOTP3ipk6+XODyAhFW4rRSJkLIUyJmXT2DJSxN4ihiA+IsIAYrB71ditU3Y5QiUdX6EtH8NwYqoRs/kjE0ZWtI6SC2/8soeD2kVbVXtiCnPsgJACsdMdscOk47ACU6zZXIEe64HQryKY0KaqxVDquK8EWs/8k54O6VhAPI6cAbET9Hf0/I4FxXUCVf2yR5Wm0ek5l5vYCgNZ9k9t3VEe6rku+pSx8nGIpyUNlto2sCBDf0vZNuVN9iFZxeWhjzrhhpEfAxHwlmYokP2ggUcimj3FUkOUF+QGHRxa+Psndpi2sGhlSMqEAq616t6p6UdkOz7i4m7nj0ImBOY2KwlTWN+sjE/wUDAXZ/cmNpNoky83Axi+tF8+8LcuVWZwTjjA48jpeJnLBDteLPrsrIWawOP8fOrO4h8aisSTmnzX87DvEfBbSc51c6MFsRgWJkRDkC81c77+fqvyjyNzLe2Hn+pzHB9A699eG9JkktEM7PCE6wrzy0TMSnk0VT376lPWJhqYj76mQytnTnfFNfskziEyiiMRQ5LABBpbrqP0dC9VGJ/ZU4wAAAAAg9AGpjvQj3EdDpe+PFkbdBBRm01qytLDCRDpItULw0VNpUM2afWo4gV5KXk6wbIdkU2O/Z7momS05679CVQXjhogOnNGcsMMNNmBGecG01k438yTyvjYOdo8bnvBempHEcHIljEgZ2qjZQvcbH5QTOUr15kanTWrLTn72+2V/gDh1WQQbVuM6Yf6jVH5gOfCNWqcenzPp9aNH8phyFQ5PBfWj6I7WNO10fO09Ta3EXPeegj22N3OWC5FeGJhBsHocJqIySkhBx8iQsWTmWHiQWy9HNFMBua9T0zoUXB3Nt/LCjPTSpKAuv4DyFA2szRjLTs4eKCKV52vLAOPCFqh+qf8xkiq3nCc3jA8uSEVk9bkJ5fLIj0bVZdjr/6P0c4FG390JAGnJovJ0LFqzQTZYvE8uHV3hBIn57DN2SONsHSJxUyPz/PT3y61jRF/iLGIXiEMyTym9bp8LRWMMYBMKpntHKvWrjKccmYxGPdhnWk6qmUfDBF1nX8zox4r8SZ+c892xz5qQUDoCXcMDYuRgaerwK1sOhx9Tuh9thXMXj6qyiqimJL6T06asXvO72jflOKL6wy1kb65vty6zGIW5vQ4TCBf58jSC8ebC4vDgBBjTUukW84SaKKyVfRQJ7SazI+H9zEArt622rgCFqAYYBQT0u7/lrLQEqO0ndyHIPy/7UHOrYf9To5c3+ynCpVmbFSslEB+TeJBRucDK2RoSasulQPiabDfNeE5Qsq9VgM24GtxRYappJAAAAAADt8wXZt5jzDhT/gohfUYyuUiMHZl1R4kbc0xHtSzdNj7UPM2Wek2DN0XeP2RGjiBiaiQ5mi9LgI2vp8tDt6Tv00nBYNuZ2zYg47pOClPjVl5fJMQuo91rWkQocEhgcIK0IePblx4dqOp83euvE1+gYw3F0/FSWZTt5oUDw5h84byZLx+OPhD/scAggrYgMyN40Vu7OX3zv8MUHB/sqTLKeIHTvrOcTL66Hudf3kyi8R/FT1vt5PqzGbtMrnMYJJutxcN4XXU1UcxJ4pShTkH28rF1i301IveuJtFOYSItixMLmXbK950FzjJ0sPjO/7PZpzvKE8AQEKURIa42NcSQtaSSn/0GGdbjaXrAHx4xjOCDuVd0maCcm0KKjRVIrk1USeVVLrNB5ZmTCo7CJsDx5MpscZ8A0HLKyZg1Gi479ZV1eWVGLFT9eVsz5rFOCbWVE7xzCk+swUBTRwF9V/NXNZWI2Os37KeWxYpv3/vMif8M6PuFS7hCGKS1dttLrl1C7Ay6hlbId0JakePGbHqbpvCle7hnmzo/hS/qwa/HJ+H5xc9JSVgnSd6qhdl60T7Ds/36b+fVAphUkuRmgWM02QFczBfujT3KZ+rR1R+SZ9Kgj0MTwwu46rvzOX1Wg/xMMooT0USK+2wPOZ1z3htpeHaj90MAxjHayOl3mK1eplM0o1CoRciAxb36pIuyjWmHn5ipDf9fszTh1dgvfAmdLNLWTAqfym3IMMgIOlB5q1iSgkklz8axVePaWcga9BvwNsU4t+aMekaarIsRt21cinlv+PSeBRaxSF6J9bcp+K0ZwAqzargNy6fKDI4kH9Av0ophKawUac404kx38j/EIaVjPNhfaW6RPHzwWyQXfb+b8TWVTef1H4yYJ2ZqqJy8SAXYlV+s96d0IXgrXpdZnydZAm0HeUDftWfbJfljuRC7oPOQfrLvEbxKNa2VLmAl05QskABf7LHgDdFbWn0aW6XEQZBLT1ar62fjxwfO+X246DUbLBGUryx6A50oURMdszgAAAAAHbzIQ8jBUFdNi5Ma8SIH1Mu0r2WTaOHmjtoKf8+u5vlfeouGFAqsIekd5kN1JJwGTHyEPyDUXPwspbU1xjvRHpFehFF/xHzSgZTCRi4Xk834Jv/+0wbVbQTc/tBkrP5cZqPuuRqYzLrhrismJ5tesrchVZoigT+b35AnbMxkFV9QAmnUaJgMoCbYc/O8RDTMkFUqyp8n/kM2GR6OJijo+AiNMkj2mTAwdlVzv/SfL2LU3NajmyNq5XaHTKt4KaCZ3VogJxzPvXf7tqzjlrQ7lpWh8mPfQXzirzoWWEHG4QF3g0Yw5rx2+cUrUvjonoB/LSP9E3SDZ7toTAKDCV2+nSCwHCN2s7hxl2LKtCV2qGjUDVsqbD0XGcIHbnuyfkdIxnDJAuDnINERx0NHZm4/imlNQpPKafTFIUWDSYc4QTLaGBnEekYkASig3+GSSJnJGoxlaSHzDY5rNwZGv0TRGINwgAZXwonDgd9UIH8eIYiJ0h2Zdx0fMpk3WXoUyKTGlwWqQDlyNQAlyak3O3PANfZITRa3u9awxgZaWtj7LRsh7Gz6qB30Xm50AwsHKGk6VHPGeaoVAwA/fcxzv0RDVNCTsKG10FQS/sI7fNnlsyUHcrzdwE439tLU+RH3wslvc/FUf4o/OSALLpvWNPcCrWtJbxjBJtPsMHjjTSWqryvlpjGkJcua0UpastnZAC1RWnn0Lm/Qjyx6mD3IlGW3TiUP69TrFjQyMkSQRlSM+7rrrMgrvU0oUCTaanZJRBcg8f9tbkiOHLEUyKYDOxYwOhPUY0y+jNlX4bolLzHAiiIt1wCn6uv2AMtN+0HTD5DTqjrBmDe5sd/kKnPwnCqKn4ZKlZ1iRO1E5j/GPcMEV6BEs3la6vJ9y3J2Pem4O3Kd8nsFT2GfwrVwXXxrAbVaz6FUEaAcmHGpB9iyAkxgLr/ELA9z/5pf6FGBaFOpn0jRGTNBgEJcYS0pxmR1cBB02Y7+6T2RDXMy5Sf2v21QGkhRpBIqoK+bE8PJpA/pffsbbH8+M8yuMpm/7MBVwAAAAC03Ye8yRWEp5K1bq4F+PxiW+oBND7lGa3tTYFsNXAXtrG+bowkhJMHCxm5kQ/WoIo96EyiSLyX1PrqxbV6p2jeDqMLAiyq3vsRwQjZ+tOoVR7uXShBkC/rN5kAPZRioYdI+2To6IsED5alvfRKLJbiSSKoohrijDk8IzmQWi87kMk1B7bbfQ6917PUAJ9bNWzbOPbqsSgaapGRBMG1rLLzzuIxQCc9Qd166BaJhLylV38Ly+wVo1fHPMZxkl+x1pVz0OgZPSjUj5Iak5ekuQCUwJ8z5v6nUokQtpLElRAxFdwcR5L/9o9sHPqaOOac26glbWKMN7WlRkyMMzXM1ZRAXq34d5p/41ez2vbOOjnP7poJOcy2y6OmSt1czdB79BIjJrNsvbQivt3rqa1bPDEwRPECbCdfhRnZZO4wm+TfJqMhnJX3JW0EPhZ4Lj+DimMcjx3Ht6Uc03wawVphJeypUhm5zJJugKhYnL3Mw0yeWqAzwhnA5V+fZSV7GggejkBmYUwtgXyMsYPGeshAwmcky8oeqwWiRyMpKV/6E2XXORrdRNr2METg4C273MiKJCq+Pa+F0kzvV+XigfZ+iytn4CGC/RD0jSEjpwPx087UJ/NIY589ZTU/S3avaX/SicAptnGCoaXjFyM/7YlQjSmCitHleBRRibKDcfLp26JHBPQ8sQPd4/wFkKNaxsJhoW2kUQWk7YZ9qCpRB1+/UbW4/iojOJWdAZm2eNJ4fXWV+BUCu91hIOiy0TCLkb7LZVi2Gls1BQ0DanIBPuGTubZ2SIFGSQSKxlEJ+hTxj6xcZI8QXwj6LY6cUmdcChOARtd2PEHOUFYMPWXjWw3BD/HVFt3FY8jAywfl9JkfGQ5Hj9CAUlLh7YxnjCynPky4bxBiULSxm4tiHTmM3akXvscHW7qay549xdZTQ9OoSY4iADcd8ljbBs9eMfpZnUVNbjF9mSrGL3iEBgDWQLV6t6eO5SjAB4s2pkMmIDUVXfBgUOhip3f1PeqEGIeQP4AAAAAO3hZ3ecpU+GZH9+PzLjCDatC+vs/b7E8245+2UT7OlfO0vdj8B9kLyJHyMUKbrS/VsBDmyvPnq39NxUbuKudW8dhiQWCPs0v9vNJfkqFR9dL45Q0cDAinSadob4qbNbnUHbtFtXRKCUNUdHOBuQejV/i6KJK4pCd2mnZQqt+hPZDd6GBB2nVbiYq5QfYUTRhBM080Qz4/E+EvgsB9q+3AVn5KCGX9HH38KV7k7bo83J9WT7PueM0hUqCrMPMTthFCnAct+sjqMcb6+qbnWztUoNH4xJNju0SzOu9idN0uyYx1qgaRrdPkR5jrJMQXW/iR8ndJ5/S+LPHjzguueFZUJLguQewD4Vcm+ozmEw6GTM7GQ8f0oqJeO17pnykTCg6/x+PqEUFQjQSCzS6S54yKfuL0qOgiM27Fe86V90J7b11oYIMloNukG84xpaqx/9w0kU5/2afEgxZqKvVHfGv74dFWjZ1GCtUOhhPxvsjaaOmq77WelBSm5oErbD5SacBSuslv35vebV2W3GR/lNEf5PLgVMg+kwL3FYqkXaGm1zrQpPFT6dZYSPrktYmVTVBD3wTLV/2T2fyT+SFevCuKWFtSSBe0VeoUWlR/O07bL2iZamYvHYZitrvsZCm8frNkn29TWxlsK9Ojdt+7wkMzbDTBctV8rJt3a9r75XEPo5pb/klY+WbuYjM0sYdmQBYgKSrEUsyoY1YYg9xbM/4bBWtSttRcrO/hI5oSV2InOHx1u6AFQ0TV+HEGJaKeM7WmNQGSHust1SGkngfboiqEiflZggDnIeJz+HwofeNMGfspFuMPjD+DWtgUj0JafoVqSubKGYXAjGo7SeQlGCg3HzJOhINiGJDtpDRktOYs7xY90B0pBXf/HhJ6cec24OAUEBX+Mis3th4g5S9mRHe7lRM3m6dQAAAACdzoVso3oTC2lCqhJvxqQAKl1dmV8p/UxwDLSZUbGooKDqJLogsgqFJoANDpZ0Kif1uOM12WH4xYoZnEUva7c5zVVtRneG8PqgH0RH3aLh7hVcXfG/Y5B9MO8/ftt31u+6Hnbrjm9vlNNLb5ZL/SF5jewZED941a0V/5TAJbrN0EMlcS2mso+S9juNksL4zgDZiOp+T+0yaiZ/IHQocURjYiuyc65z44G/oEiqMOIjBmYfeMqSdMpqXS0S6n4EoC4QPNB5yOeEJQOpojJTGe3k/Nr9f+6Q0It05VAZlgTFg8kbO62QpJUQpOWv/8B5Pg0oKUX5qyL59F4zqBjHgzPHcbStrAwua5Zd0Xn56c9S9+nqO9IqtI70JQ+L8+impkqWixo6SByZvsL1TaHNXB2xvXTa837+A+huZgEXlPZcCpgPD+uIG5gQaTo0JITpglLHymc0Cc70UDuov/tW8zHDggxx4wK+RUrwiRMoGFbR+sYHOYorVoCyw9kSf44UcUOVbVLoHfiTotGrNv9YqGhjgQNhj1Fo2FI/lwT9vDyWgDT+EL3zGcBwMFBmOoXmug/ftFhPLDp+mKBIZSohKcNFdZJM/DEqS7YeIDtaF47Jge3RHk7n4G/5HyVHEltTd0J6hgt77A1TWDQNxtwzDl/GT/r9QyvpW9hAPsWAjibRwCwzcW+7qxPa3C/P1lV32POknwjsrzVqT3tIPpVh9HMuqV83iRDQtPs4NLeLPqdqSw4lDs63MeiR4jSFTpyGkIABmlGAWDA+S0F/7FBM1ompSc6whCHNrtOowIjTz5lU772xsSlqddedqAAAAAczhQY/ythBnUO35T6TgfBqa4r/PPIIPjSQ9Kxcoc1j1S/t+NzFanba+q/DQHnJsR6zcnaYqaPiU4XSViPHC0aHN2fqJE4lGW7AJFZqGhEcnZgrTqq3Kxw3XNmsyaaEjTMe/H/ds1Dka+0nCy4j7AUCKvxJCn4BvWSrLVDSHwSOqcEwLWBmYxz8sa0qlFGmarEyS4KvTq9Iq6W4n3mpptCMkbaHeaSz6pNubmb/LZBUO4/KeY1NuS3GryHdPaEzSJdZOGuOKddPbAxnJOGnJg3t1miZkpJmyAejKUOrBY71g32fAhg2S99z+g9StHT0PyNmr6CdljnkCNNLSywILrx04yqXoixRGbjQ6B3cRNDrZX90z9I2fNihtvqFg7o/bWnb5atuyh6eu2jMpZw6xoZmJJ6n0cro8BcX92hezW9MnWi66OG/HxAeMnOnErZVzoKjjsYx+AWbmJuERb7ptwkTjjxOzM9N1csKIBvg8buVMBW5/2BkINQLRhQZR91wTLUAoDInFo83sTD5e/BhZXAQa2xde//7TAtC42aAF6cKBABEhVJKvDujVwo4JDhmjHupULRi7N3+5ZsDbzBchwFmqrtBSKm4afULdPcAlExRgTVWafqZYO0anI3NtUWKEKFVs1mxSpJcxotAELFEetdmGmw4LgYfsQpnuVzG5sfMEEQBgW0lz55tFznhx17LNLd1gIq9ou1r9pG8L6zCu41UW9tbcqzMbeUq+9TesOa9hYbD1/X01RxzUK2yUnSzdTDx+JbW4K86dDe1UciHcAAAAAACg/zij7sD/teJpk80MTysAMb7kt1OrqlNVzeKIhHnGJnQB9sNQLtYW05w4C1j787nx9pYe6SNlEUb9occUeHfOkbRpbCTnvM7RmhCoC6W7gOzL16jUFtldtNL6Ugt29aZNytJ7eXcQHMXE3F633gInn8InuoT5fJ5H7h3/lAzPKBNErsSWpuQqQdMZBIeIYRAPM1cw82yuqM4nu3r10OeTTdx710pa2kWyXc5NZE8xMHchd4dz8EU2Ki9SSXs3OccrbnCbnkNjPezIukkdUPVLDDq/ezdc/15pnGYlirDAyMhiHDVdvI/7MClmLRH5QrMkh03I5F8Kf4lpfDYGHJ5fAeIoKPFPVesCMIV3lYe5NwCH3SwJT4yGNjkPZSF/veNwaatUowsipPj7qRnpCNKa+JnhZ2yeEMn+JYygM1JAZPXANZlwvz7ij8HFm6/awiqv93/rR6S0dPg+RI6nI91PASMMVaQ4SR2gBi6/ooq6hNoGss32c432Jx1FYQ6ByvrQfvm7EHJvpXrk9Phwtv+43G7Vv2Ie2ldUpyJFcUrmF+mVT0xuVzszsHC+7uMfg+U3cGiaB7h8ABU5qACOeDh8BpuxGARXD5Jdf98TU6kV4zp0GgKyRLbngX0c1zxRIZnjwwIKjwtMPYbqJ7EhZ6ZowIn/NTnsebJUSnqIaIpVcl/XltrkufBiBxEOw4cQ/0C73F+EkoJg0Mbx5cogtVQB3npFdcnHyPg8kNJyOWtAAAAAOSzKz5Uw+oHl/HHvUeWWmps4HljNW8Vy6BPmN7YOTX8+WWNd2K5uvmTfcGWeoSp6Oa8/kzhFk7gvECnoGjU+Aj2wdle8jiJrbyFWXgPowGHwDrT1aDejACbqN635TR9mwut1hNb/cssEPNBnuZfdA1aUeKRIhXcC1PvY+9PSq1j6evIdHgjWtknd8GxwMEQOAC+LQpBNT3w5ISbwgoEHDDavoViox+3325ERFlPauOZNSqCaVR8SPXmFXNozC0tpJM7qWH7kRdTXPOZXB5qy02+MQjkr/BrgWJew5VMzeH1iO/W2+MfD0xI+VYjkNPuctbRFRahrhkLna3CD1KzDs+SjrMLOuJdPtGMIuImJ0x7Sdr/AbmhozYaUqsRev8WsyIPdhD4uTmjgbQo6BUApqV3gkV354gm8ObdnqOQXlpAMVKpFzsjr1D8DC6ka8RGDNrZBBOYLnEY2grHKELhTwf3ybl9+4359Qh6UYGGWeWB7b7HLcOGCbrYWyJ+nAqAgYPTs+3frvQMf6PTFf9M7RxKh2axhJK/534xrVk3lftQdQtYxujiuROEGzahCubkmVMCI5Mxz+Z63pVG/iwB18iwISwoJ2OH3cvpFuuvBbGm5usjh2UtyU3AiOdgryOQ66VmZ/0304L299j/IXsI/4IIUYa26wwmRikZ8shh24Q2HUFP0AAAAAord93Uo06agzFND1Upa6dQUaQJNv7gpfB+p1LOph+SCTfAaSZFAnYNMKbIRKt7E4RVvX44buS+L0zIWGULTquuftCvpXF7igbEvp5WMNf/Ays+4WLG8A8QHiY3QhzRVPFtVmWjdkZFirCmfT/iKsTrFWIF+Q1OUoXTEhuqHHdmqTA29bWaNGs71DTewEwRXTmjztZAHFe10QDLtIxE2vU6TFbluXoYja7QE/XqrgKygxAb0qLMXyVdX2QuByY224kW0I58EDPQfK7JxbBiA3HLanH6BM9otcqsbNf8OyZOVH6jgz3sh1RWIR33BIsc3cEXhmTxoYxdGFSC11kXLCSiyiFfoBA4ONQjxJSxs/PCYHo17WkSuHsgQixiSB60RYfTKjaH7BWPOwqHX6GkfvYIZs1ScIXYV02W/7PqJDJ6l/N0pikdJz6q+tV9u5bern/qj1Sa35S1mPPeHnufai/pF3xJ4Ku3gKD7QE3iLTt+p6iJxLmc7D6ollwD/1d0f2uxsimJZ4+df0hUqXf3zx0L1E33WYBEEsinCQ0Mus/r9dM2gV0/bL8XKKtx7pPTvU/sNjNium6kDdSTa6r8KYTQ9Kuj/2E8AS1L3vLPKkUl4t2462Ry/gUCueYLG7guNhbCBEjALeN4PVaKF5B5NWna6vd3XYT1IJN0yO9E/FFoD51gcI8694LBXcvoSqktyT8kEbaAvR0xG1s64IIj2gEtLAuAHgX13ha3Qg0xIDrjBLfaar+wT/cQ58iM1SkCQUK77eVYTTHN4cgpQZsh+HIwyjka3LZWfZBiWVDOkRKiuvJbU/9C4lemY3caBA496keH4H7NuFuI0GJbc4usdoUR2uONJCTx/h7Qtt17AOQkKz6ST/Ww4rfwoAAAAAJj32+mDNh9N69PjBsWpYXu5HpZvvGf23mIqqwL9jTpcrpf4IkiP68GtGPKib3koJEpyQ5jrT5LfxR/jozvNiX1XTffw/3BztfRwDIZRpqi2qxFh+0A6xuuYqNIww3g4cY7z5r5OvSsw+o5eW2Usr9dBAueVtiAB1PHvQGf6OOfD5eIMDbJ8/PwL3iC2RjCyfVndObiYe2XpHVnX1vpdK3Mqk1vAukaCityWQ3WKl6nRgl2NHzEzmBHuFVffF2Q1VLjBghyPO/MlsLy5EAwnUm/vGW3nLWwgOfy+E4sf/ya/TXWwPu96EQ8/ztjxooNUgpa3KL40z4U+r0E4B9FSWWMUQp1Eq+bXyYsbaAeRQsr4skEeVmv53EV61bwBpwWTH8qnSr3AXDOKHQXhcFpP4iihCw5Bd1s8rE8pIueb84mnI+psP6xC73tifjv+RMx5UxTewKTzFn+5uOsdgosyzQZyMOKkM64/z6Ts6VPcMnJc5x0a3Mq6AFVO+gVw50jE680ATi2WBAYxSnvQcUFkZdI39aH5vJ116Ccc4vypTk40/gH8cN4DEgiArxeVSJNaHmsTG2j4nfZQONUfjnV/f810SRKQIR80iW54OGknOrRPvjuvrYE0qTNu7b8xTCzp+zOGBKEUDDhmOavbkq7u6cr1Pd/ofLEsIsgy9KI1Yf53WLI8RFAbWE9JryFOKFtxC+BDY1XACArQDmgkShV3PnxSPaaHl30cqiQ442tXRYLQJiVQNchG0opOBdn8sgwQSVXm6uNdWTccUKX0/xexzJ/0YVUvNz8w1kvFirUx6NnDiX8ACmUtTuLSqWGFwzmQdJKAU8jxzO+uZNZiXgR8R8MwOR3sqD2vp8IgkCTNCYdh5AOHnWI/zlWU1MN6vtSR3eJoGC7dYAjjaT2Bk73W2NuqcB0uB8854xacN2h2qZ99HZbWnezrXVlNNgrH9z7JiSZHdivyEPJhjOi1+j7ahFMauK97BXJJXfl72lRAKWp0iq+qel9512p5yMmuAAAAALZ56viAW2uNHDUTEs6f9Y0cKsd1sTeU8dbCe7D0G5PU0tY/bEhVaGwBAnwulQt0yyuE0+mFlAnPMnmVdSxUEHcRfrKu1QrAvtfkkHAus/+FKoN/ZnJA5SfYhvrycB3CZkUUJhSVSTVQkQ1oReV8dBCnSFIG1uPkkgoGI1iQqAqV9INF6Cu5BwU20wKi8B9Q1ugJGCImGvk7jYPWel0QYXOHAtCJ1jf8mdVaIvatZz5td4zkKorSISLZRxX4YAl6GNs+bqE0id5szG+RQmTyL2/HEewUzSbgrPIcg0aUs9laG8aVQGkT1e2GtvFXl/H8aH2ytOOp3297YAcxYMG39sG6nMqWlAOOAjbKO7a3Sk5eaFYVALuZ5YicNUdYwoInbTnCVCEdQ0bT8UJVrsFlPcT5XbpQM9qaS//HjzfkEJK5ZAXOtq4j1yzODUotzU07f1PkMPI79H82oxQJDd3KvWRp0spRnKvjQByCGZGhj9fUZsOLFRy0nmVNhERQwsFN6cfB5KXZGTVpHT5cI0jAF8IuR3TS6d85zc6357pntMB8K/eFZ8jBgLhqalk2kfjHDOcbGZ61cEKx840xYpRV3Twnw+wP8cEqc6bnCyhelsyNt5EyV/cAFkdnDZH6ReIK6kTU9adnWjfysdCIgIDtIey7RFUmK7EPZ9qrRe9tmBvrw85EgUSqOZetvCxhn/dfAdvRIb6usFfGuRHwxdImG8WSgduM+L8saKJ4IJLeUvSWCRbnaFuJRRiY0rtllb9mrBfBhaUB7PIOF3QNGb7pqr+WLS0uLwelXC53cRS4zNrwOhKe2Wt3MRJJ1hEf9mfL1yiGy2tWSdxdIOrU5+bIEitr48c0Feak76X2jkYPGYstP6jSlWgrJMkII0Wp+2PStXXjg5If09eAcHlbndkKWP8Gadh13vzHqrGbCmzx96domRg9kIVf3SqiFmntYxcZ7qY6Bd12EuXARp+zf2RrFTEU7nHMMukGG/+UHHsoJvXUVf4TiW0LLDq6MObRG6O8ikWFDfT+I0VDSURDmENIQ5BXXcBvKRBlxfybzV9Jpy+A7egKv6xVmbjsLuQgbZ6KB+ikzwAC0h1oFWTkW1QkiVLF1FJOl5Lo+EeySuAJeQ9l42qF+U9ZevgLIJfgUOFKFtOJcDCLtM33KQdl7oJABewup6WgIt2ZBgAAAAO4/wDkLdtKjUvkfQrHXhUdteCidxYCWkYj0Km6j6IrAmWskrws4LzRfTvlLAfNLemYaWB4XfjmycIQTRgzFC9bJn1kJTYDyyL8NpaKSnh4zDpf7UcA8fLoRfRVX/QLTnYPq5xAD9OJpWiSH2+9mhZJCqPffp2R3WP+8RV+EmxWS105YKF0aljd9sn37JDudx/iD5qu2cNg6A4dgk9eLlQZwYvdZa3cNejwSNVSlAxLoCetxz2KYGZvRUKuYZFw8836o2KVTsxHh0aCYAiOyYvnF+OM6Xq87/jNw7e1T5c1BGeqdzYd7/WCxCnVALqmEkORPPQtR/lpVQoDyCeykNOwfaa8dEO8Q85d8FPbSLE1MnF8QnCEUsv1aqn8eoe+Zc0rhXtfRBLak1gJaO2yv5wWGSF7epq4xaMVN1J3YQrhddJdGEg0UUJaS8FFxfd7Pr03xm2//skTLgFQFZnu0p8vvFgU6Utd8+Idd5HsRQpRNlxxyXsQikPiu1XC3J+JNS+9gXAYKAoSuUHSTvg4t6sqCoVzKWY+uBIILYY4j1sRGfhTz7Q52bHUR3iB/LgP5ZMAJ64CO5bY5477NE3PrtK9Cj0vqLPvJz6miD7T1WzEL8L2FZcROnyvZrpwsrHDWZ+HNfgqU/WJPGe3bH9CgsO/ZBl58DO0tAHkWNYNAt+mhSh5amgHUxCa2rWqpysJgKodlbgKUAeTdK5ZbQY5s/a//HYpncQjkdBpWKnDdK+o2v+lcjBQr3tsPUQrx5b/OV48yfgReN0int6evU+lWrU3+ClvxFXzGIyQ333RgQIRMsUVXckAVKnHyfU/OC7cQwnif9pmkq9n2sBSPxNMdUuMPKp6VKM2KvBeO66enp8IVAnkwlnYUkGh6wbk+aOZ6OV2SI1eWgi0GzL/gisDTlo7YCOdXOVDngyRUuQqntqmgVRdP76hbmjSwWycSEoCeYaYaZjFBx+QUB0kOmAV6Lv2fQ0FzWWYnNtK/BCQAAAADrQn+fqF/uIkXZ26ThCJQw54lH+s8TtJrGyoUJGAbgaNhqXWDkz8nB1b2uOeftHZO7t6J5V2iACoyyTwCS41u7pLugylkFd/fXmtxf+YKU+J5w80xXtzDG5yiWr3SN1peUJKIfnY6w45/PI/ePPk1pt1zPQxVP/UJF/5eLGvNWx46h5VeZ3gpSgliqMHXzYE5BEBN2vaPdthmxOpwnigU8rwRhqRCrg7IMFPPOzNDw2LayTGYkcU63SmUegZfRMyHMUT4I3eGBU7DvBW57phf3j+FN/0DdooStdSO7r3K3xVVsWfN90h8/3j8qpXvUrhlpxQ3iIShHBvJ9SLkfj990rXXOz/bFHcM0ryH5ZQELYtluiQ8GNz4WO+/a6QS7wxtB8M62OFaSrmSoQY0dOzF6MMGEctdM3nmdUKV5+RPi2xTODmEym9XbAwpayiff/Ia1uesPuAmiQvueG6LYO1KTA43ywUkXOU1TsPOt8Pd4kaVdKffAXCVO39i4Oyd1LfejJbkwGYhWxCcJZgN9ZDY7lFxlhRhiPdNtyHDunw1XCzc7iweoLgyXoXvPTV6qVKpbMF+yT0chW057Hdjv4BJv/8uFMMOoxQ/EWIAAAADwSDzO7Qt3v4WnKphQpePYIiJYHAlTabnQ+TQnw7Y1dLajXn4cvuYmOTQFVVB7jNeouHE4Env1cAOlsd/9kQ5QLG/o+nAqw2ejNtVQJaky/p3L2J8YyA5Rk6Ty2jYG/x6lM8wwsYBnqjyGgfXaac/dtBQGp5Q1vSTZQRW4Y8ebcvFK07Pjrj4TP/pVI1g/CLkQIGk5o4X8HS2gDiF/T/2vfbkPKHNoWIGRuNmYD5ZeU+BjNUGv4SuLE50tXiZrAHTD08vLBEAATNMIBs52nwoElV30LXWsvvQmlJsrsp8c9Ql9QhYgy1IhVyzFI+bwQZBPjK9bm9Vw8KPkG5pB0AUEfn2fcuTYkY10oyTuwfYeOKHadhLGO2c2Vj58k0RG63pvt2Nv5h5059mSQVlMJ0bNYGpZVLTA1FJkDo2N9N4dhhxbGM/36BidehUPBB7QkytBCjHKEVzZMtRI6GbsdNxLJARQ6VX+O46zdrApNtZyOWQT2CCJSR+Xk7dreqyduQVtvUO/qg9EDLYC1n068RdCi9z2oWrU8M2PFpZ6zWYSTaJsRbZck+eYVGrxOKIN0zzGjYEm4WnPyr///hfv/wpf//CD8DyC1yeb1dLJwfUAAAAC5lhO/pH6Qgdz2VN9Q55uvjt9TxIIxwNOcvt5KzG/6FpeQsUSs34s4avkLiwkFUXREk0+KAwzUrARMjgoInU7AcOzGSgzP0+XDK78y5KWlys3NQnvWyNsXpZH19OfA00zMZvNgODbwSx1b98T60h3Npx6G+NL0zq9NVBXdeyfF8DUuB3C4BEoTl3+2lPXtNNSb7vW4Ir9sO1WqbtQb494K+fEp1/m6gKF5G9s6TR6eI2uKdnUp3q1RNrDfTi5Ok8PBCWFeywp29snoTjwcwyt/qm2sMhxNmyaueDV4lDp0/2yFSLaTWH/79JQwUDV7u2y8/oM5aV40kBWHJrhrsXXB9HQRzd0ZwtZSA8+6Uq4RinS5C8VToKeYGs1hEuBkslb4fF0cyEF7C7ysjll8PPM9R5LIJ/t3XP8sWvCnv+7uonqXMcwdnh26FSy6IooAKghUUmatJ2SvfG/J1B8ylFN5ljia3Dt7KUx8BO+8Ck0+nxDBkPaAxii6ztC6PBAdmjOXqBAPGc0TOAgRbqozSylUToN7M5/yU/q1YQsYLWjP5j/AuUHBf9Urlsy85nCwtErdZPx9GtwbOcqtqMXn/ZXovtfzULOrfPrLW6DWwSPdw9yOydpi2wlxbbtyiB1ASUX73Bsr51+6jFztv54aMTHwyKSX7kQrHJ0fdUnlMg/RvGlUB56D3zDHmlw0OiNQADqmPP1Sdvrlt2oqOW5TDw8NSp4bX8dZ4w9jgIbcfH2DE5cewrguMN5R/UjyD/mZ8sHc4QveGdMlyCr1fIkYiWyfPM4Z0yP2HPVfC+y8NdGM0NiA4zDBtBfxD+SdVWDj7ykzqnlXOQN3rB5yAAAACg6uh5Fm/pBXytt2qD3tRcXXYz0LCf1+PC31I04P5pvIg9/mZxB7EClsaovqd0dGyMj8brkOGsNxKpXj5sOCpT1EwrWC+U/j0CkhkW6sPdGm9piIvbAoSv2OXKFSonsALQ+gXRCffXVkOXM7rqvkt7KpCklKFYomV4z2ZteCjFHwWMKnoxeFWysfI5MJF5wWDjmcI2HCSubRRhVH2v5r1v5T0tQD7/BJWOVt5u7a/Kf6A0vRQtIstUrXCnmxCieM3cXRb/M7NFk02/A00U6gPf7o9lIoSAXSeEbaiw1iGDT8tSYiiwS+H6iCH8H1CR8Qj7Pf31UR/2ofPe6j+GYFLYDSCiYDXn3h/jOdGqSxbKFWZ0h0tlyI/yjxCL3nSBIhGNz1kZ0VcaqDYWy70wez6cEyEF5PhV+OzcZuElonAZoeNJDEBwrve35mf2apKVoMSf756PhoRpP+3MP/RK9fqxPG5LF3wcCBjntf6gKtZbo5drjRkntU8oaw/dv0XTvkn7fHlpJJ0pSB9dZ55b80kt7Dh0fbw4NrNkHGJttoJ8Yk7cwJ+rijrwJhB/VCcb9tgK2nPCLMcIf3a+s4DbfkqRggmAYFEFUBLAZnQve4Q2YwnwPjTdIA9Mc6e+ncEHb82OaI9dJpj0KkFMH6jkIp/cKK0Cdq/3ueYrhdJEu182UsApUMOeyjEpooOhxyFIYbYVWDp1rZ6Ixdju6dHHh/+AeofD9fbeM/S5MmhJkBm4cSSPtJBgw0x7LHc61R1gxbsGDBjvuumJPbui1ywfmLmz4WOj+MY0nl5+X5v4YGWGp/FdqKcW+I4VZrnhvROcVUq+YQqz++IhRwha2PctWmIzWJJDAMfmrobzAqLWCeMcxIkjKC5fLNGyqZCuOiZ7pqrJfLiFoff/zmg7h+V/+tFfP2NWq9Eq6ncpo8r7Amyk/15QOC2vcqluAAAAABSI9rCGTeEgIV13+NFhjhEZcZJF2flPVh3lx93m5+GlQVuImCQUPkSjelq7Itlc+u+2bMMGwy8Y6t05+huC+juR95Ad/xG6mRiOW8T8keHKhjPf/tItNzyGfMg8b9K9PgffJmNzK2VyU6SqyRzaBeCR8THFbpsJlvFMTK9qzEvzM6N2J3/rx1fu1XLiOCKIVxsjTYArxhQhYTYnfN9wbXPiUeEaarYXr42lD4nCSNGS/kLu5y3Ftl+ctNU75NvEvufChQPkT+2yUmSpeSKjgqL2Pt+pqOqU91Kuuc+Z3X2Su62DbLYSOqBQbV5h/2bDPHv6yvRUK5IPo1vWZnhM1DPweqr0L+v1OVL9+hm7rHgqNBrvJDTA4pslOAIa2k/VhcqCWCDcXh4XdmmFQKt7jh+P+jP04uCt3HJW0ERmwXkcr94KunU1L14+LAvWUB+dXJKs3Qa4hN7UvnC1ck2rUhOqNhg2ZY7U55ZYwaJeC/NhJf3crFkPhT3Z5AnNE+Zw2+K6ubq1yB6dA8CQdghOzEWT/mGJdQOi25sNRVyU8vk6ejfvTbQ0VOnzIVZRWk4yryc32MSkt7IElkx70uMaOiq+hh13XxoXDqmqou77x+OwJvTyIUoTy8npsvW84PGCDIb8eZeiNNyq2S5vQZx6LHh6wnc0OMhmEPDgqgrt60UdmzA7k979lfLqPaxg0sfqliFoR6YlYY0EobFoqxmiOeGl9Ytw4SHCUJYcpWu6u1GS4mELm9bUGduexKOmp0RA8ofzdw/qEfi78jdCQqsAZccjiPH2zbNjMk4UNA/iLMDYX/7ngxSchNB2P2+OK/1LDctFbmBZnsDW1otSOGj2chql9LSFRIjhKp/aN60kFgJcCpnCXsEaC2B9mxyNtMDD7aDubrEzTueGrZVDEMJoQ2VVNUW89M9y83DLd+kfUZxcWKTyi9UDxG3I5S7jJDkMcMevcv1xxfcaUuV89QHXN+crWP7cNrcTlu6EoICeD5NO7HM8PSGDrdUnipxTVn0X9/DhK8IVv2vMQxObYqDXRFEcGv9RPgRzJNRnWtPnrZq0ht/GAQZk8sbL79HC281eaoV9DW8A8cSbTUkPRc/tzU7ftUW6s+dSGiPsomEapXsiumxwhwDtvTyaI9ZZGoyRc3afKbJ8ISfw6EYAP3AeYPdu2BtMJtYa9MUSpl7Il6phxJLK4yLs21vgAABbf4ADx3qFPnd/f0r+q6S/YzycApgQ5wabTI4jXaFRkfAeZB2Q2+qaWnRBNSNZv/a0uTlGixabcovDWVoVrfq2vGRJXbwggvjRaEVZePFT8XbsDxBzp1eiz1HUN1MRcUx8WbfwZi1nAM2/CEiQ9yH8/FYot7OT+MgnDXgag0DjRWJrtScu7JblNI7cp60R2DxLSyHAtWQ1yPmR8op8J98BS7PwylH087b9IsmsUSdG5RocyZ3qFiwn5ZQAANZPoJ+UJUx/x0Cw0fGkUac3Wi89lrNphRtRyvUTsck3ON7Js1be8AHb0g/KG5NLmSGR8RkBqmjuqUTvabdfwQHzleZVCZ2uZHKArU0zKyNCMQM3+U46UKFRJruxqeXTwbr/bmqOK7wtfD1ho+kePB64jzsP5ruI/8f5BQnUPvPIdV2LDMVrQWYhlGtJeGck5sBgMMi2zvzeZHkyV7X7pjTH51jgDpZOTUNmA8QGBJdz9uSAWkwVVcdxxdPpKSEo8Rpz/KuIXCgLeXS5ZBM46d2cJUzSf2+ZqcmYH8EksLQKJn3QQubkPfKtbWUEYL1t6ZvGxuIdrvoCosSINlVo5SKwI46XJMgIuAeeiAVg78dPMjvBlU1hRlPtU4Pz0H22r/1bUDqpQMGxDMeKSOgjkHyANFzOmC3XdXi1G4mTOuF0o14bl9ZjVZOg2duORhDhDLZ0Fih8KmFumPyLp23S0gwfNvxSLaqvcfyRoCSD0lC7/leml1T4oTeEE+1bzRGH5CZAGzByPx9GSvLwx3otQldeoSpstoAchEKugci24EkYJCfuBx5ClymqJCqQLzE5+rD7ddnO/0DFBh2i678x0V6qox3SaUm93MmTfD5ipCaj5NNnE7JXMWI+BZ+vsxMuNH3Lkb2lSSzz7jK2uQFy+s1ssk/AIf+1pI6VgCIpYwcvSv3/HHylOCr2xr582CoL5V/9DmNjcApYAE3HZ/ng1a6LHj5XGoOCzSaTQ4eej/TnKu0fFQ+8V7L+5ufKoN3uTqM5udeewC4+LnVVNSrHKYKjbSLRNdcrfCI8xfWEa1HT8heecPxyAsfMjdJ6PGkHxYlnLuT5lVBnJjm5G5CDkmxxoxojqxWVsG4y9cc9d/IyRgOf6swagCSE/isYNh7g2cE318KWGY42GGZ0VLwN3avCm72AaDSzIunE3SgtWlL12HrsFBi4Vb2mTC7RYA3ElLnx/O7o10qeNkcMDcCcEgIGKnyrLIXJyDymzUsArHYTcUo7x/ZRwPZ65hWvrJpJ1vb+8+Ep7gXHT2Sc0K6T2+eiMoYGC4f/ZVs1IgjW8mTsSGYfAAAGr0Y9wZmPfspr9xVexHoqssUBwITi0U9QqePtHWFCBETpFwf7b7iAULLVLmrlz/tMBLQ8nGdYg9EO2p+0Fa7oOJWMD6xAzfLQIT0xXCNkFzvE7ez48v+6Tlj/IG+8+rWxX+PA/bARGzmorPtHGjIsxAegeKzqwTuV7MAjnsMCFwa74qz4pFzet01+qwfJGRxr2ef/QlmssVCUoQ8h1l3iJANG+pXOVCzTJz48BTbhU+/T6rIQh1DMqSrLIsTBfmYZa3X3b5MGa/BLjnOSHF309NwGpqtezeb9lhttrGsjcEPc8b+2ZDz8FAl5VR/GI+gIzVkcryjkXTPkofPNlM1Nf4rn8nPJdlBQwCZzmUMm9WRumZ95QsfSMPM/foirUhaLY35TkpI4QQ6VIS74P8dQcxaEIkxi/gHfB30Pb37+AearTCh8MQIT2U137EGbDyCh4BynSYXAf8QG6URSHXT8phZuPsCOZmaF0asvUv4KL4bQjSvtownj7ZiRRM3Q5pnIx/G2ee1Q3WtJSLThrn2fRVARHZLrBSrDpDCwRxoklJ61C834T1oYiGJREgTK0vLUEaM045/7gFPZv0cIixp2gLuxOmNmaOwy5duYFzG1bAgQD80dsrcuHaClkJ3knMdzdS9PIsGLFoFcJX5mH8F6cU50LssFbG/3NNFazZASKbmYb+KQBdk1N2/7+w3BB6lOfIS3A21VL+8BK/iwJvRwwmg6WhWycmyNfwZo3RETK5to50b304mdH425W8Bg2xEvvbHhNh6xKk/0wuTP7Z0JkROCrpXmm2OillZi1xZWmvP8MTY61yfcg4Q/luz4awmvfZaBqDG/YWk/w5Pz+B4QfdNi6hpBZ70k/V1pfjrZ1FmyBlu8MP4MnkKMxewEBqTWnJ8fvAc3qqch5fvVkDrWSVHWkHgZ8+aKDNZDqJ/pGXwPqn13UXbnhrJXhv6YSPsks+vr0l3ckZC8JLdp41dCDpCII0v5vrXi5ZUaAG9yXMMQRilZDaoiINZ82ZZEfIz+1Sb/x3HL8HxVxpI73q7LN7BmRI1tqs0FHXXfQVclkEJWBOLUyUDjZFMdykL3cc5aPTQ8P3BSbHgYSmVa43qDlhV1OwnxBsB/QhPBYihqy2vfeJNwp02DUxuC2aunVb64BV0li8TeTIx0CQsd2EdQJyMV6Aut9RwtR8M6K1BX/YWMx8lT9CmMHTjkLfQyxwX0Lyb7mDFdVHrSfcTz3AVl5TQzOnPMvrwiKlA4+7Jbrj7lYHdLBTjtTFVpd/mLM2zzVi82bbINcr39dmesRK5p5fq7g4RPskunkb6aeSktve3c3jp0Na6fwXGu8ZzpxNPIVfTn8VHdyJ4hCFMyaUh/roCiA9Kf5srJHtYJRHI2j+dccZC/4czBNlu8RE/TxVsEoMWcakT5ozF595OH2ZGQ2bUJgekb9s5/5oQEezSSHrzXCuAAAL/RcCM3HG4S9uIugYO/oLDnIXok7vBcGbNlihWum60lo2WiZJNz45fwFw9axW6715MZYJFXKEeeU+qKyv7/cCu2fDjuzKQLqBXAnSTm6S5yP7gct+EsxwwTB8S/X2ju/oJqZBr+zKN+iNDjH0pcEFlvLO21HepVQPJqULQNjnys4mW8wnJwTkaTxkw9L7GT72Ub9n9cIofn+8N19b2cN/ANwAXFuvjRZUNZ9/GZDb9VRTj8fXfpzfUyFsqYa0/uVERgqwFySrgjk5IBxx4W4JrzAhRiM6ErsYg/tSfYcKbX4OIQ7AVln28OHAwHO55g53bLKZj9NjQkvRtvRiXELxMmyb1yQJFUueMk3dWzjgQGditHZqAItBhK0crkPx3Bjd41lv23X4Urge9WPK9gpQ2AZ+QyQ/L3Pzu2WYXOp8nr43aSV0K/Gp9EexTMoICCQZO2GkjmCU2ehws8gqT3TIIp0diV9KqA5RQk9LfJZIvhARHTrXge61jIVrKypg/Z6jB2plGak7TCRr55V75i+gD2LIPglnnv4i5kwJCIzsP4yba4EWg5cIWernXlnO2B6LHNinpxcz5j+X7G8/5Qdl2Lr0SQoK71i09zsLlhWxrLpMg+I60GemIjHBr9SyTsXLFYMAiHNG1oUjYVNy2ajhnUrm41L93ix2rBUa24dAPBnAQfp/W8V+CuVTvbfjMT+EB+N2qZ3GG34mT7Q6xgmTnk2y/Mm5L48jnk71RQE8M7fA8lSPyVojI3zCyp/J9hi/+U/wNI6lMeOldMDmMU1heXJ3eHa0FeohX4R7LPMqSa3TiCiH7DOWaFqk4nthO1OhAj/bqfTrg9P+R2WYxxTS8D/U3wG3TCAclqGyB5LxqnFNaD2YxB2B5nHLiHnl2k6wOdXLvmj5aek5Zu3Syk9r1zSsQpzzhdvngWY/S1jP6LAcMkDFliGUg6jSMW6EsbJA+wonEKydLeYRk2sz0LhyoOQE3bhgCWiYoYebUIGede5uxhLuI+5MEAQQYtNemmzNFwMa6iC+4pFqXfeEkwitaSAEoTOd9uPM4mVabTLo4LEhOeRPdjXNBCqALCumsLNTFyAMSzKOTh21DVMvqY/H8yxZGF4jFtfWf7LYE8O+YBHS+zRrPAjKPXz3xNniJyNDNCmkh0j0LzZDpAbVOwRncmGRP4lqtXiFGmt+3jxKxRI4KNB2aiYPsVe1dG5Ad3I4CiWPn/Z53L6MZ8kLXe9pVwfLfOx8rZgNvA7eC9VH8Yx+/hQV/XQZi93Ssc9gOJgUZfd4CTC25jkmC9UP6udK48tKPLquwHOyzdBZIO5gsySz5fsS3tKuPFIzv0wkYVxTliz214SlZgqlECEN5fyRi5XYqOTCqQuCbJRxsERK45o0RV20YvFYPCsxvMPPFBDcS9o9A+00fBSjMhkPGyRoAAAWIe08/4xkvnUvXDj2m8CLHKEXHMRidQkwDI3JG4h+4RGRNjBAaeJO9V/3+1hnmsKAnSM5Lueelf77utnZ9lCpFCdqKaPaIAyJxt/2VIwWCbNI0ab/Ce541SzI6Sf7f/9DMxeUeJGExDPLa5ohXFpRwpk6ZCHbjNd4Mym89D8dWhTp2/7pRxm7QdI3jZIJpGEmDxvVxkRZWhWjSj5qTDake0CxJZ9Tb1UMPRUm1umMf8sgH2z9otpielQjMqESzMG4sjYh1qPCMc8CAYOZO8Y+VLjwL7vs72AoLHyJgu8wsq5ih/QR+Zo5k3U4LpNEBNZ+mRiMhZSpnNWeIYJKinSF3+bEksYPf2sd7o3JVGOFXigLeJvzX9zUqorVBH2FCKGa69A5n+HxbDhax6u7I6YPQWzwqpreA/PaoT3Xcu17ZS6T32FF25yadsT3GCk85JvOITzvKXoOkiVGoFNapo3qDQC44/AhhWa08jiLdox5fxAX/bu8/9Y9yNyiD9KTjJjkgos41nkMY6XVZwmpH53sYpodNv6vAwKBItbLxY/d3eLhjSirAsJj32N4bj47qGSoJ+uheiPzuC54fygTxp0hNTsHNE2agfaZatX8UWjD6MqSn+lV3wx3/DsUrSN/c4cajhz60HtmXoTI1nXN+VAWtlazKsaxt/pxSlYIp6kn8N0OeXLZJ9DJE+DqrlW0+U6ykf/jcxIoBGMGH58W7E2RM0eevme0KxD3OajvwVLMJMeRupFAuqsfeJivjgylLmJVNMH5tpPJajP4SRoX/1DkxDOniOGLR29Y466jYC8VD2IYJZOwExuVonXSAhQe5oXIxyiYELhaL1z/yLmI0JGMUV+lpwcTAfzd5HzRbkeQ1xwqGx/Bi8K27XRQ9s3g+S7c45KjN8oGNNLx7qyoKsipDr1smkh3kn/Nnug1Z7Qob0sxrC2VHQ/hoONOCo/lZ53bitjIS7aJ8otxzp4tETT8ygMJiUoVnBZcC1B+bTYzGMmuX7YU/E9MNzLWLMjBmFEEALB2mrZInGrveglIV3/KiiUeX5VpfN2ab4euE3hs7jYuW3HIjuoLl+zj2FXTexeC8/jxm8kIKbBRGDZaUTgmecgNr9Fw7JLzBfWbyUItp2y2G/njb03LGbmG7wVC6WTRMDPuCamwJYPkY+pVVol9K8/oPtblVd2pP9TB7caF2lgxSoaAxxZsJLLhdlNh26mT5z2pj0Pn7qzBY7lUnxHIYRKHthEEZSJ6wJVTGmU48B+hQaUjRotiydW648jQWPyZ3iKU+2Vp6WFs3bk0eG6HU4rH/owg0Iuzy5IR++2TMaKt1tImAQK+tO63TjsFoCZZwkB6cnWudVn7u0fKMGPQmPIBMK1qpnDLu3cuXipO5YBq8BguNxmH48XUYZKE+9fL9+JgBsVQmRo4kxQrd6kgnH5+gFhHRPDNMu6z7lVHIELWKB2ajJ7lu1GmHoTpCkdHBXADkTf7tdpYf31SLfxl24P+bWElsaOhO4ex7d9L96bOWz0xrpf+03+fosOzTsHPgh2AmP27kcNE1b73MJ83T2DhWMovHVAu1fYAAAWZNcJFhKroF3R4XqfRvqdxNQSwhi+Nij5U1ARGqPFUXQ8n3TSsUIFzWUUXsyrtctt3fnVKWSDo12bdZbLI2DPZMprrSnSKvvopuYedfvQM2qt/7fy1EU2jeo7iN8SPHq+w+0rFmpaZzXl1EUu09sel1/YdTubjl5/QITGF08O09XvSiVSwQ8w3xXKl7HVAL/8DYr1XyX0BVOsq3AjbE1FoXfl91Jtj//nIEEEn+7GnVd7str3Q4mqJLNJ3oA/UkSNZF+7co3OxlxfNAoMq2a5kHEbNHV8f17f3/vaYdMQeXNTVI+CXfkA9j4VeKd4cKSTz5xh4uSM2tsq4RySre1g9N/EQMzq6+JLMv1fyKH6r0pKIiV5c5kySjylyYKZHIpLlYjS1o+YDiBfrxwCalnrQeLD2yIRwCi+aUzDCiRGbzLFDEHlG2K9HIii8L3xNrynLfIRswgN+xcU4tPMlTZuVjfq2dJ0Ce5UGjFXMnC947lyg0QfmtXOesqexJWPgulF/1g7faBOP8X4eGErbnHaRy9W2LnULc2FnmTzA1B3LRYJxpbTq4dUhaCxsWXfFBkqaWqSUVau4KAgMW9XBzgf6xNi6vCzvU97buoTQCuXnP5eqYNAT4vzLLMWN3KMFijCUCGEOnFZar9FZ4el8yWYc5B3DnkwREvHwkn9hZ8tMI/49EUog/I3NIDQyurRtEgFDL262IkEyQdATtb4ozXzK3IWdDu0VaVcxqH7g3Xsm3P7MYKgjkiqfdYZrZIFErUJW3zTg2kSrq0933rGJ0/D1mHw3uTB1guoYusnWWKELLSXEB1YvozdhbcB6ho3L4TxVJebeWDWqwcAsR2o+HhaZGHPNOvEZj6FYS7DS26W4ileIE5r5y/a1v956erum57w4TA28j4ytNS9/IOmN/L3zLthPdyuBg4/9lEuoo9+LLLc76uRKKrSiMmEJFtx4VsCYTvlMEnL5JnQDV8rE7ws7621b4Iv/TnLl2lp0iytG7LHKy4D1ZIYg6zFzIYj+79zGmO1j/SSwUZ+pdNE7pcUZ0/l5sfJVxZbAuxeQ27dFodTbQJ5nwIJppUDoCUHyy8qGGRUc0VVNvH8Gxi2jU9ili5YXC48lPdbH4bMQ6Q9V1p89TGPiu9LLuxm+ECdBnyrWICKrG7CV7mmqRaqxHZopgRBcrxj4cogNtexApXlLPrZCclb24U6VDeR+/Yi6IlZlOOKMN+s4Pg8K537oI2wjU0DJHBbHnyBeHWFh4g+sO469b18OSSyHv3aIEyK5O4IAv2wVQ1HlOBomSD1rQEMXXp8HmgqwVCEQFvz1qQtem4A2BoeBs/3AQH94etrVQR9EXpcFzGq5bCOx9t2Gfy064VPq7fU6+uqoW0EUv0cXno4hQ0SyrB3swX7i/t958/NTQsup7D2uHvtrSjXPlR7Lece8MDB22IH3nUpqhNcoNNAG4GhKewv6JBL4SEqvz/gFdBmcSPNqXtwLni6ERPHzy1nnrJBbkTSYNcDxD0JC6jNzKVln1cu96pXvp9/Bl6Szk8dWr1EVXyAXRODrBwQjY/5bxzy2pz54nlz6WuLLYSTVn6CXr03Ok+HK/RTr6vwAAAVIcgVH5h5h31oy+Xv0l3WsQYD6YKlHbGfccD620JzFTijiIzclhaEFIYcPWlDyz6N2alv7FmU1lGuapJ/kUOQwWBoyJgex4V3yAmiM6FiIjZ4yBMoyIs0UuvOwmxqS+It0xCBng5FG78wmLEeJN9LcmFtE4LHyioyhECh3W9ztn8ajvoYccRktLet1w4r3CmLs2CQ2XG6V+xT/82mOGEMmjTBgHZrrC5FQvTCb1l2eDLKQevz9cv00ihF5NvD+h0EAINa6eDhyrVw2YRGXoJrgTKcHv3G65ZQDXcilv+girMPay9TmBJo+U/rDmUQcDc5krsN9SZSTf3G7vaxd0CY5/CKkGskTu9b47uPNovP9YKFxuFqvQQvJ1fezLu9SRvdeePofPTATH3Ei8PT0z0KOP87UmW0nP/7H5ATOc55uGdMN1PZM5RLOGkG6dh0IANGEeSdsWqT2j1AGo+j9B9u2tci3hvgTSAYwN6LqdHCAubDOGwaJjZMCSUHSbsLBEcrn5OohqArsTuo+qhDQuiLCs5yn5XJRU+9LTMOM94y5qvjW+T4c38ZT/8kr2lV9bGF+mK8cAsi3BNOXu6KZ+KKqQfy1KfCNRn4mSV3fkdaIhkW3qWy8ZweiikXCnO6ys7XcAjhEnol1v954W9GLoMx473/jIdtnFsTGi9N3DwluvOZUsjNA0zIIGEvW/c0GbQUyFTQ0N9DL30f0HZlHbHrT1vGy4V7Qnt8refylY25WgZK7/oojQpV9XRrN9IwhfBsjZd8FeAf+FHZnLobOzFpgVb+g+lcHZw5uDim2/5w70tFhgcfvddtIZ4esAeqPz1RAylm2sqluu68/lWpAyngEGs5TPLqcDCJjPlZpAHn32d/wqy2Q8xkANxxI7bEIO1DDE4pDwuFiUkaFPz0q8JPrtsn/BLBdGRRXK9qyDun0fGJxNdeerXRrfsnPp+YkHpoT1/QHmGO7UzXHkbW3rJIRsWxUMTym/hQgFcPNUpKXnavok5n16dZL1D/9aUTYI5KAP/uKu8dNLhzRtfKBwhCt7tW07J5y8XZYKhLdyNgl6Q9J+scLNn9ba/XwXp+tdRccxLJYXekPnHiUgDWhoNeoDhpXbF4qFVNJMxAJoT1NtnSB4oY13NBlESJ8Tuzmg8yKAGJRCDm01SA5MDxdQ6/cBYUnyN9fbfVk5ZvSrO7YiFz75DmWMpvPw0EMI6tMSrvAWFvupTNjXn8l++Yf+n6x3XFYZt4VJDqclopa0kVeVQRjEqXetzZf2yMRIB9aeD6tZpTAIQGm4LMsHonNMofACThO6iYfqWKcmWlMM/X4K10MdunZZ6bdxyGsnHm3tyJxSm6KfZFPXOK0WQnvnsU1ohi+WKqge1ihQoGRosFHHnB7YlQZmr/glW6R4ABFbS669fB4t2cEZAu9ukCsVY8fw9CRTwp8eAAALezfbZGAaihNwgxQBfwiLUPTkTRfzkXx/UhOPShiGVMNmcZyaNUc/V8MdXYYblhFRaBlfdNkRRWkejcVS3mmai42IgAGAF50h8wAwLa8Nf90aaaunBOqSjXQ98CD4x0K2ab/iNB5OR6DxnFL9RS2G+Ep0qjb56ZZu5WQ6kqPSQHOQVswPg3r5cH3cDUhzl9UVPrp6D6Zfc+VEEscXkzqwRqEz3wd+UPvNvDdOyY1nK9Aury6igE8vrgG8t1l5/SGsS/bvBBFW0QracguiCQE/aeq3FHg3VzNDBe5hqtQyve08/4OWLY4r7xgvNlAzifwMTh0D1V+nZZtLx/jDgnBxJQgeDCt43GFCnpvxR0Xe0GoXl2mO1y2I9xNaC17iTsIv/T+41r8whcS1pHEsamlJ3ZXAcOD7Ke5bsh/PnDFNGRncx7AH6OxP7wT7/3yQL+/7WXID1zFpG5R9HrZQ2FG7HV73hEqt4O1jht323USNPYbpmY0DfpRtkDbvonbw/Jl+37DfobO5SayrEK99VZQOgC0Qm0VXruUNo3sAHNU4GB3R3DdZYqRQuk1N47oXyaOphN+LarNwaHgqnrjOgSc7CnujNtchzf1Y4fQCz/QpqH+pCt7Iui0Et9AdP3CShVo5eQQkt6ogsc0oEpi9wj7JrexaZSdAAZ1jzy/pg7qTZOnIqw4+0AimF6mA0zMKXoqG9CnniPb1238Btdx0xpSzy0IxgzkOSLRSFJrDRC0Ix9O+1CaB9uix1S4MqfOzeF87wmQDhUypND0NzYcct+l2VMskG0gZKNRiIbV0aZuwD0Fibgsh61HlgSsLtLH4hIJlTLNRyiqWIeaVOrVdGWKRPMKgtKqBYriRrN7Yqcqp3jz2XbAFPE+3hgZfWHdzi6WEarjQT3reHJqeDZIPTl5iLrjb2K1tRZrvcYSCtBDOjzy6zzwUIkv6KBT0jV0qdvonJJ6dFTiFLCJoTQP36jESAnXIMaZaDUOFi8xYb3+KoEbrhD4ctRBnD+jUp6M4qxzH9Dw0IuYsEs78VaVfNGipC8flc7rURr4bmw+he9t5OZTaxF9L0ARXYYk2zogwaLeKRmvigHF5Qc+eUsn5vyp4JZQ95TUzfpoxpR/anb4XxY21YQIGYWguZeMaGSOUxS9kRKfVCiL3/bYLb5bpYtZPcdtbpRskS2ffqitLIUMxGWKl4eovVyH8KlyMu1xzrcxs3QWRV2FUUSNJhW9K10B+XjeyPX5AD1uI6Bbg7rzDWAQhcgZyiTgXwPjYsZ08dlKw1N+7y3IHYx6iM6e1sXKkLkqH3TxnsqTwtgQ2avnBSHZx3NUZHOVeNbvc+edRWrLqFIyDplL+CgnvCkVEeq9/LjtltgJJsevGog0I13P7bIhY/2QNoW6YhRjtAkf3pmY/DGLIu49KpMZs6jW/ZBoKOwbSSn60nyYSNTALdYrwttEQd+si/GAAAEgnZgGewELSx8COXr5WN6aQGbSTM6C5bZu86l9l90SWNp+Lv1/6/ov4n00pBXbs+9pRc3x0YiBGLmm5PO20LAlOZjiZ53XwIybmHxQ3jYTwsRFKFdwGyP81q2U8ZooL5gkI+iRCJQgLlh5jH2XVmAqUvS0KjtK8oT9qNa5Yo9Vz5MDPonUL9B7TLxbag3ewali45/s/IjtW/cwRa9eIXxOFX2LV0AxS1toIoc9gxC859ZRundP5FCqg4N5sHCbbxtzNoSJ/iJtBrhJz07Cy1MB/GWk/2MbTr9QNgq3PSnAUal0Zs/ZBNKezcE9AwX3nY351T5DbniolsIjGFHJaAv/se0W0C8SXWgJ6ByBBjWlABJlb2zIQUN7LzfQ86OJQcfeLHzLJcXPGHTZguKG+6V0p62QxkcgJtF/vM3kNiTJuRLQ1NXw6Zelz+NFNeFiA4441UgGcsKsG/U4qK2YFLlX+QtT5cLGPYTPhbXRVvbhNdBsZcH3MqKSzQMBU7XUXHfBlqImWDbUbemsTlOJX/e8IIWVcyD/lmUGK5kH512yyr8jGZ18wrddeomX0is7tPe+MAWcTdH0Xok3nGzeo0RpNHYxtPReW6a1jaaonucVAjEkOD4BBIopFYZB+S5EwnDErLiDEkkQkQVCKLqjAB9PmZei04K+z/bD0MIM7dooogpn1bpssefYZNDNqQvOamvV31VSJZ/VpOIoY/LOOLeV986e5OuxrAiNf8+545HCoJOzfZjdFJhPCZj0drrU+doI2X9nMTIvE4cTKXY6DH+HKTruJCfFOPAFbAWYi1xdiG8odZ+TXzCgz7k70ckYHNFdZlTtFmFnXSkxGZ2LD8NO3moBIBzaLV2aSe7GkY11koSlAAwgieFLBQPAsUVPiL5M0t3ZfJC4rsIG8tIaAPWwrar5hulNKdwwInl7CmDDvcjNtsmU2DyuQVmYJuvCJWwZ7tVVATE3E1pMHeUy3/wUpvzsJfqxOVVd/mXn0MDXhgCLy6hZs9AZDe7ieBfZMCEgN1mWCtFEsXEJZ5Ii2Dz9ik2tTcbGxlQVPRSBSdLZRp0s+MQpdBdR2OHwCV2iAiftjO0oFcdTRZIMvrq2skB9Ja9IvOpUhulnmPOB4KiYZNNB1ZL5dz3U+tCB058x5IRNRcEAfizb1zsvQJcG1Sk4db8oIdv+PThVLKYk4X+NYK+xYZ5cuizUI//kjveK4+blkEKEYtk2u7afjLuiZNckYJmvkjFOMc29KbQa7EvQMAmZublOv/AcTIfvLxfDe1f6i+mkZPotrIjUMHaz4aYZMOsaxLSipflchg+Cplq7aqy4+0yfvcjf5QDLoaqw9diU2WZ0YbmV9ONir4Oij0Dj8KzEAbxwi3XZvRAPDIYv8vvN36+83jckECBM5XXR566Z1SpMESx0RHJWq0eLNOhwTrHHmMVs8ky+JubjmtgyXRjzKNrMFyYaRfknKrSbbTqTG6QHkjzODK4dIEY0ulEeJzI8aBY3p+GluAqakVOnKEyPej01K1aE/2QAjL9sXqXCIOvG1NwHUnCJmbIAgWrKr2KmRUduAMaG9XU8nl+e+7oAAEx4H+gCAyna2uVVgNG8eaZRW+xRk11z6H7gDGe6avnFjKuw2H0MhBMxj9Iq37q0gTavApZQMxYzV8aW46xScWOdNDyvFM2xKveALnDDScIJwg7HtYDMYAyafxZuhqoQjnp//HK2uYHO4gkjPjIQ9gZ+2ZZvv2kC4J29gUrm06fBzsR94mdya76/bWiWtkBqxA6GBrcoTCm5E/Dc/KgHPyqbYeZCcXrryojazmtG/1HiwGajjckSaBoFY2OgvFmSAV+a8+MahdGHZR7InVEPxuw8jjpvtoxXYIE8X7KrSjHiMHJwpnVnICgo8RQqgw3IOePc492s6yrKUmyoZsAGEY9iig7T4M/4yW0Qwhooh2kmSomvuxqZjW4yK0ox9u9Qahgtwy34OHTqHRKQOcyrkSd/shBihxixK4lLdJRpRuSrRjBnTbXnvhTrUfwSVuiWoudM2+t4Hu9UV5t31a7bFYNaZYhPL+kcdn4k1Vw/uf9Ecnv3CaPnDbGvYq87VU/wIV/mPWO8AxKbxnoLAdaVHTynUu8QrVl5lStXgescHPPXcaUJRsuc9qSpd0k+ALFKiSKKPgQ+K6bdmarOQNKy4Nlzbm3RNYZC6jE9lcpVwqjsLHCcsSz3Ki1/nBJi2QGRFsiTQInSB9PlZvgOUYwWj8NikzwkfVGcX1KtdXzCJT7Zeuoi3QxmVxXYe1hCvg0pCWwMRJUsYk0EmEPY/D41TmIl3it1CyW+GSLS/Xtt8p1NTJkfUPRxqQCLepEGa5F1jFSKP0wVHnRj0MFTNquOu0wLmj5MjujuiYk74a+QQKGU6pSzNQo4doVmyaWHdduoJjhEAbuNfVE94LYalplsDEHy2Jmh0kfRVH7+1vbLmVuZs/p52f876897hgtJi1/rZQ4I0Nx//c4KXytSf+IVxa+Nu6r348Uc2mn9pyLKqV9oNNHG6Ux/D4PdxmszlxTqkm78iACFn+6K7Kn7YPpZ497eDPEZhOr2remT/4sBuby4glyhf4r6nI44G4PR/BbPUo7oM6IYUd7oo6iPlNNVvxZpu3yoZO76jTP79FWfjeLRHxVNoaNNvAevtKWNGmjYc6ad4kebERgIVGhQJGtJjASWoLCEUEvr+F5ORzV2AeY2XOV8x74ecXLSMOhVnuEbfb0ds568ZPqpDkrgJFXvVosz9nq5sMvKIf1za1xKVNSj8fl8dKkynW4xh/vrrhLV1rkNVkpy0sBoN/ijV1iPz2gm19NHshVxPgh73ZfvnxJA8qZYE6SYVQ6utGY8z2pPyR+NCydLTIR9IGUahBUKV3LCemlJb8ZLuAaT6sfQZQtFYT1jxBvUs9YMxQbXHunnJylOoGxfZRYJ2CA+XQty0WfeZyYNZ7KFK97TbbwyUgfE20hCQdn360fSmiiFYTZpUdGDGGk7BD8lu3oIympg9Vhh7xQoVz8EoYSN2kZbeaj5skoIRi5yf9P9viPrCjy9Y0jk4ZR8szNCJ0e8qA26fv23951Oz+HXnNUmzVG+mldF/k0DotBHdpw2S5wmndyoqq6u+lQnnIezeCiRHhvg8j/RIc0OROAGsEV5p6BaGhvxKxbog9qQn2s1bVDItyKwRW84fPshidhQYREo1E77e0G7EETuR02T/xAN1DBcR8QXg+ipaNU5dmjRJghVq6aajcXDneZAwwowNhQAALnRauAA1iBHIYdsDn6fr+v8T/8eQh0f0CiJa6NH9o+kkAIPyZpAYPQXioFyOt6SWFMSk3iE4RBUflX41QnnkJ7tuVPovP3kTveahO5qBLhFONNceMcee1fMdkletWAtMQoYnr5zttmbxTYyi5tvmzMZ7Jc1LjiYGwb5vyzkK1XjOopjHNXAIOvgZaIzWwW3v9LiOcXoLK8dbR/k0hVMyygCW5BQ9khnChXAag9l8hddzZ6wz0Da3v4/1vAUR2LpWaYXYqBhUA0uGtduhYVBrVBRk9z3zAuuS2hv/Q5nvzwSM4EDFr2VZ5RCd4E9TsrmuNkWzst/ej0roeQpjraQ2NT+VClxNE/Nj7rw3uR0ZC2x/m2r/eAo2IN/IsYH1EqV0Ojf2PALymD3Ereg9jdiYT1da4xEQdVESCMSm6fxn8blcpQEgAEESTsquzkOo35FGy8X2wE0G8ZHNXonEWBd9Y9b//ZQSb5DRKRkeCstrGtsuqJPYg4d8Ke9Gd7g7+E5TDrK+esboJBQjzCrd7XEM4GjfuXTGyf4GbMOSckSZiJY1UXKsIIdn3TaWk4DsldegQOFoJGwPTaOa6ylyLZEwq7f22jkkHsCyMYl3EcFYpVGcQuN+/MDkjp6PDlOl2JQ6cCphG9xcFCXawAiEi3UvSds3C+DOzJKikXGvnxRIx1fHNanNk0DA0GafSpxcJMmPDIeB6r3I8aR0KO6EhsA1Fv1Roj1SfwBUTw0TIJchAU1ei4+HoiJTX368c+K+MiY+QDwjDWQEOyt74iFYAwterXB2uGfrPcwVQgMkAgxpgGBRoAUyoh5/w6S82RK6qo96V3MKPFAo+boyYluJpC7XetQNgu+R7qi7JL8NNobxXBN93tt9raRgJD7eu/Kb6VorJsPpzpvfQR5JZjD62wGsv86HBat+MLcPMCt9nZph+fmMajvT9o7Go8YGipylYwWFiGq7QaB5vIO4e04IVhaszBLOrIq2sh4yMKDnSgF9O/gg/wAZyCD4bP5/Xd4ypxWj9y3s99fY4LKkihDGL3auGF1/9VUvEJI8EkuIX2uHMPfJL4r0U3ilagzVI47OblJC77u5dtPbeUOZ71IL4t1rsk9UdzjndY5A0vrRzCyXm5IyTBTsw4eRZ0vU2Nc4xXb+bwVgKy3/N6FfrhwK6UCaXOJx3+Aoprl8zv2gtXZz4WEpjv6gZQQP0NykVqbg94T10ddOT+YucQi52Z+ZA34rEJLdqGWGqlkOAMCWVJGCY2Mv3uhmSUkgaXsMOCTv/i2ouODir0lpglKHgYBH+H84TITUGvsfGtxxV7AyRQzB/Dc8BQHTwAfRouZkkJKBXgJeR3AH9b+ZYoafQau8u9bZ6URZp+oTMAo5P5wtoMGu1cWKXiSykSVKD3W5kfd+EscQjHrY4h7kxCQKaJGBKtCPSefF2PcaM24RGiGNcKmgP7eG0+lTa0k9h/Z2Zk10R0IFhiOSiUi5iVP7phvqSibv6PzOsuyD636x9zQpVeIqVl5RaNmzBYV155sc0wpyJPbnDpGVPhBHXHsIgRsZ0TuQjQ2HVt+bnN0JKmJgIed7jYcv6pCzjIkgThVEsfmQKhighso67dLpL6cHS5COUQQsJiMqDZY/5geLRGcaaUEkrKKy8ElFLvPFUT++P/7dr6SvqSd7TdPixnBEBdP3neQ1bESq88q557UhHZl8A943V2TrRu0QicId8X7v+JDq2EGYP33EPydfsO1ZCh9haEuezu5PSgXEXHd6McA192qSRBg5bleRFMtvgjLPDY3YG5FX6mcWKieeK1Xy28mEtpokzuPWHYFWtKQKhWScYaWnssBaaMqPvxMfJeNDenAeXzQgZNNnk2+jstLFbkxYoCWP92RIZpl5HwCTqe4RrCt+ZTLDwdjcNz2cRaAL/6JFav8cjP6cyqN8RgyDfyrdlxNtRhGzm5qtdQAAEVaaczWp7cMJpvSRhWsB7/DjV90/Z8TcvXyOBkaTxzAspHBlljMHbdGN9Pa+YSdcHkq94V0OcOszQjfFKpm+ZMZR/imORJDCT3UkkEorLehaHYrGyPBWIBOd3FZwh4wh1ioV5Q4S8sGLJ7pvJUSH3U2us2FaZ7NPcE8kIyHARHdBwnOhPWhgpGx8z/H+A+m/wUZGi8iBcuUyRxyKznQpeItsyudA8qQSA/CEzoVlVGoUNBz3OrKEIc8TUcICWH/4YAGet/8HXiv8hv2lglwmk/QegWRkWqpPXHzMOXKeKrIBqG+2WwOpgR7zulerdc/8vsVqirPC8KQlS9oGPB5mkezyIMg450x4h5cHNpJdJNcw2zkLu5kdwNyXflNz6HHi1R3pF5ZwjMUJ8RHLVHrmp47FevLQRl0wfjjM6vA5T19+pLKiq8r4Ns/zxxjkl0Xov4COmrM/DF5Tul5zWhYdmFZvnmh3k+dgCJjYzcwQQcV2tJx9krbqSbHEZ5gK1rMGBt+f++ethT+cHOncxldl+mPoVQacw/QEEEqelZ/FLXt5LotYlaRQ83TtpP3AEVOG+9WWS+VbOwUR7r2KsdIWTOks0QKr5K94UZB2zT9O9t+COU3TKnP/poUPgVQ26K1It2G+ER/SZ4uiK67OrnZ2sTRNaE0r5ufrySFvj2jF15oGsPP/CvW34uuNXEMYZjFP93rERfKVMuIVH4sKEjNfFbMCHxFIfBf2XQ/OCt6uqwWX2kx8IoOV90zDoiThNWC0LqicfJgR7Nd+s0ROf7LsPYTe7CbvW2ZMps91bK/33mi0lztCOvMsF5UCivfA/r7yNHzionHi70oRW82yyCi1l3GmQ8U8rRW5SGnTD0DXAd80qvIPqqbyychwvha+uHOekHDvLv8B2a2QiacfcuvLGMZ7hB5YviTbjDKzFk1C5IUJ7KZTGywtGAh2gm9SLLAdB2lvPahI/cQ0dzwumTuqTsIncYxu4V0cdMqgG/8KAb9oiuO74yVrEKkMZcnCs7IO8fD8oO8JDvy505xFkNnXiNFQtmOhIKlNXd009jlxEttMWGDemZpoAIcCcfNN/m+NwM8TUGfLEtKIXbpM1W+f2UGPseDb9iEdHYBtDtIDk1+p1Njz8uZA5Y3O94oUmRZrV9+IvG8HLwuOkO2JysWlRTpICKciB7gS09a6R+r05z3QlS3by2CRcTeIGEBHuiJR2nPBX2sN7YvSmBXWRNOks2L6vf+xZkVygE2zib1sNbtrJr58B0+Qfdbn/3lx13J2YbJmK+3FJJelI6eHFzJ4rnvtT4xqF3S99y8rQJQn12f9NLF5DARR8JzvM0t7Fz8/EN06K5lLl5YlphJqTG2d5A1BNI+m2PC37osR1y8+u06R0amZSmIUu6td2QeuAjDAJsj6TtKCJYznaOwVI62QTq5fSrfy8WgQd9nMPyS5ud5asLJh00QcmYc3DGvrdxUgc2Vkmxn4Ko3SuAPXY6k6zKPcPF1UUK4ZxOpNOR0vewEyfWIa9C+DgK16IhPeOWkrsl6BNqqI06Ys0qc/2mj3r75QpKjqYMi1Fc1JzAUJQgEHxgj16UczpYr0IJQ45nTHiUycAPYD3tc11uXj39UMsjgHdIoCEf7mLuyTk3cUvah4BFYigjgtmqhZM6WvgKkee3P2pVlk9lk7SxFROHST9scKhaVHLs1JYNbbhk+z6BMfiGWZkzpCuOpiui1/tcSI3qglFBt+W0adZ3OUxuugy0mjwH/r9WM5nc/je6XxvZljqv/1Mb4gkc431kTwqdOTTn/15butAoLnyyIKOZi4Iah52KkAa/a3psgJzmVuADqzwjZ/eIiTwt1ANGXtKjF/j8s0MmgozqeXiEGLKroVPcpQdDYfzZdSJj6k4dJ5VsPv2eYghdXkelJgUt60Ar4/VJj2600zTPWZzJn0aPQJYs8L/JqkBTZXlsvMzqnlew/KwMKCE1ZX03EcCaSjkzSt0XpTKlU8gDHmkEqc36AIURUhOliEK/DWBNcpSPzXnYGdX9oisY+7jBqjtjaA8V+6P0RHyrLtD1fPIbf90GzXBDHlS2JtMvrN++sR973zxBOXG1bmIf9PTwPwel1uDCkt9igq6TWyPj3y0l/tE9W+i8//bLxWFPTUpiL/1/VlT+Ny2t3qv2O+oXzmWK4fIc4AAAl1XfMNr1SW6nBNfcz2CJVP4EfifSBCKwYaoMOUsq2WWkUwqwm0/hTuSnZvgMWW49VQPIbiUZZsXrmDWgJ1Nx3VpeZQatS4w+4Xpy1qHCbx7IN3hmKsDs0xLc6dIU9lzHwMIeQf7Ms+kjSs62k8L+vvL1jmNjpLZDRiwO6GDD38sZLHq4r2LkuNOT4XO9dvlJ02BdPe5s4qXQKr275cRCyVwYq0JncL9pzutmf5O5JkMoHWd+M2pWscezuW2ENLOnohKaQHBkz0FZoTY/03/sKMC45JR15qGcM+hn/cmVNbAxZnoPRa7+Xw68JWvm9xLMSHmUCOJS7hjGv4NhOi32enR3PsTfqyGRbpxclR5bsUiORZeR3TQNaipGxG9I/aEp/m3eXPYEhmHj3OmWJgS3MoGpVkriYjyVzlvkLl771XIrRmQiTUSZHY6db0MBTlidq2Q/rrVCTU2CMPAvYVSJbqB/bJh6iXn1EcboxZ20bYLr6kyWzsi2LT/OX2yVj2ItjQeaV9WrveMXZ0jDTesw/3Ck6SacbywuvuSzFPibyyHpRokFi/RbQGS1wWQZ0GCB/CxOUDvyTTu2YZF4RdMPpUgF6vDI/FxFYH72fgAiwaBE8IfWDDsedqQuDTWpnojK7J7bo7pyp850lfyaLRiPM1fG3Jr9AVF6yd44NtuWZCsbglerKNtkZV1cl4u1uTu19uEQs6I5hYJj77VM4/uQb9vZftBqXw9pPEaFSQ8SpLOU9XUMjeku15MKRKXOrGmkxuRj97izqourjfCnKrXTzBclIdNAdphtlpQyLaunWF3d1P6ifF76CJv1iMlr608BQzUIRI+zyKA/FB/KgerSRYD5c+OJBiy+/8DNfiBaZk+xEy1hpxbGZ9fpu8KDWBESc10Zqpvv4sKcbCv6dNkJ+g55I7ZfEBBCL+ftEGD0evGL9DEhv6l/rLjRyWouUE8X4rbyhFYEKc/ct8t8YXhT+oVreMST7tkeDt2nOeqMVe8I84Aqn9Pk5w6azowG+kXWKYxS45NXfCYSbllQ72ByrggdHTqBsif+8oNStOin3L5rj+Xj7GYDr5erqm6jvepZycfpUEwAb8hyRTksyq6mxoaxO7Uz1gQlG+JLS9VHrJAA5+dIL1pFyqzQu1rqbvVLnEyyBu2klDb9uBTh6+CmobJIeSTNN6do0FosFAJfbhuZOebMkfYlS25ibyHfuTdVLDTGoFB6eiReRfjwt1jiNJXezjpoiz3yKIss/cFr8qn8gOrNq8XXd6ZuDdbw/i6kGC5/aJ+bYndTSqDnF91IYlfzSpFhgCIubE7naz5PvQqf6xSWqhWqAfcwWUGPiGziyKGn/0GeX4GTjCtfFy7kF+1EFYPeRqtVG1DHxRHNIhid0dNK5qsWvEBd5ELUW7NxFJ7u79qcMqe02ukHTNxd4ZjxZot+YOZ0cyoHdYuU3qbmTcldKja/JD73QpslDglH45KA56n0W1Ei4/pINxLqGJG5/TG5BFAps6E80X1MxELf7YbiPo1BFI40SBG6g08x9FST+EjCF2Q2O80WjOdXFfZJIOs78/6h5/KKaNVl10B1mHGUHAb2v4KU6DR3SCcUK9IiTr/MT+z+GzmU1afI/IRNXhsehRr/cQYUS3A2q3sSwY1irxa85DPacrCcfVSpLaRsyV/8EWVZG1mvJfAIfEQZFEBYNlFTsxD+ROwDiaAW2Add1oO1Fjy7MJTCD+uYJ3nr8eZ8UjO8BDI3pDywAPcd4f53bR1tXNJvWMVPAog2W+xuAzNCFteqka2HjZsbI+1max0iSOEzpjgDwxncJdSWIkS0cfMqYt9U0xao/RpK4CvTEw7xM1IJPJAS/zzAYVGj1jrY+93Um0M1q61c8rcCE03URWUcXxEgriolWwKmOhYOcCceD6XocjjSEhOvFD1XyOjpE/hLfDV+v0OZYtKbK4I5ys7urts2zEhPIJ46ru2XrEcy8X0ZFUXJHhdO+QN5fh3QUZtTXPCR/kY8cLhnb8oeLqHE1fUS0gpB93GbtKeaUh0LS7xI+0R9OHavDVXYmSbgw6WAjiH8B8kryXEGN2lGiyKiXHj5ag+UGxXQ6nyLzHsvb1eBzZPcToarFJC2qsjop9TlY14haaoh2cwoiu6ESCD8pOZiiwQQp1u3pw9B51xXJBybkGSpIENP0bZ0qLVu/5vYAAAD434bt7Z1R26AL5V8tB7aaQv9ljqWONIMipGEhe8wpCWB9IbUSIQhKYzJAakdNQKNI4h+JfOmanSYzPrZSj01hYy6HMBb/xXPI8y9i4BSpV9AoBKLtY7KKtRJDSS/+O0m/y6+PHckd6nolRTq2IfgCwUvwhyG5ZuMEBT8v6oDgCJ0NOhyuMCret6/ugKE4l7ZzyRaLKEufKlikQ+bpBkfWwG+NyxaAOnehM734EbTLzt/fPW9BLHft7NRTDGMIQn6EvmDs75Saf3DHAMR62r7aaUgemKdG5feM7bwXyjggVxCSr1mGxdUhT3FATWAhgNOc/fdmu9e+ivckX6RZGvZqWDMLI3sz3MO80+dWjM0QYsrXeAr8ad/cTdEpcSy4DH2uVp0hPivSjoE1yFOUbcMLCSlVLY+Ni/hT9dgfw15ZxU/UNlifehiiRVojItTNNONjacZl/Vj7aTerSDKVjuHEiz6yGMWMuAzmp1hdj2PtkV9CDGcXZAylAzp+Sm2f9DwTgNM3fKnJ1SaBzj7nMJK9ZG0NFFrpf36u8LW3sxyKW50jmAnwF+VZCQodfMN0Zq08/v3on9NrLDv4K31lFrjgOOxMKbXeV1BAT4sB6WG+XcPJ2vtptiTDN9+gCAZToBeBXuR3FMdZ2Z/BNU+O1WAn6b87vLC/ZJLmxhBYrgfjRX9Oaniqru462z8Z12VtXR0dR8FLLHB7huf8tVd5fJ0qvfiv9rwKspj3MECe5+FcTDuq2LEErp4O7pJUzZ2AA5MoT0yugf4Kjgoxbt10MBzzqbnuZnEnhaCOC6LlHpO5t19bo5xu8kChl8tOmG7Gl2cfkoRp5z4sqrTkwh/QjhgAZBLDPDfu1DCM3mRb+s+/GKkp6V2KXmNyS7p3mxudp6k7pPIH1tu5HOg6Y0tnLjuGzVaGq+ngMehIWlvAB0H9pyfyz+tbe6BbIA3Z2pGeN9kTti1QZfmq1k8b4yihgaVTrN2mktMM6B96BL5pMT4OQOx3TflrObyHspRzlV5rNnRihUOexqczrHY9q15RIRlDs5Bksd84qXoOZO7Rm1lq25Ieu5O/rqUIviN2kbVcBf2TRJr2Xr03Lz4xYePFjGqdAMc+PeDJuWdLgMs+AjcQEliW3jyy3Ts7I8s6Q/AB3d26d+POXZRMploDy6WpGrUoXb4KiJD7HNnf4CB24gekLSfdGbp/Vu45tnuYL9dOSUxdFk3+ucwPpzCXlH05tBDIXGqfCyp34e7g+DyZa80SHlKfEXme0EK+4/n18/zwPFXpAhBEWM6CFHPPcre43At2JKGL9Ml4FxlrRA8Mg95fwM3pdsR0YD8hOfXlu1Eqh5p5DXdgRRA/WdzpPVAG2YUFoYy+VCsYNZRSjkjX/mxJwSouwtdNksUniE2rfj0nDu3BlkVWF6UnmDH9HG3k/zAXPuiHCNIZDj3URS84qRn7XTYt3nKXuZ1Wjp2fOG7aSYglU+QI/wzuHLOBkev+qNur1Ot1ohYNF9xmpkIXN8VK78JWa2T2S7yE256x2d3P/moPPa7B1QpDlqyBpANlgYdRiJR16fk8DwuWmCuRDzJq1yVX7vctLmBWIYgPOFxAfrzA9Qcv2W3h+xQYErVZgnWbIkV/t0EE/OlzhkyGwIbrpEj3tipav/JTgHvL/Jbgxno109zEZ1rAOpVc0JfqCuZ980YoIorUPGujd4v8bi0sRGrjgvEaLqPrNct1o1rO9AHLppQ+mNIA8QYphxfJk2m/PhkaR8wIqqi7UwWmzeDCjKq416cC+6u5/Dnv0MEafErv2D+QHr1OoNSq0ysJjkrsj82uiURvqxe9ugkVoIGjBLGQUOTxizSAsdxRdmCaGeEHagVFgrNrpQHjICGx8iJqOXtBnas4m/gGs6qhTE+vCczKaqXcvQa0YKf0B11jkSpVy/504mMlubeVuLN7fmdIY8zw1ZvnOHCKOXT+OwBe1ajfLaTMkcLMzebZ4O8hspN70iTUo6w8+ESER2RPAN9mFu0i5rD84/wfK+mzf0r2uVIbmUBigu41QsfTfkqvyMB3mrq4m4CmNzd+gvVsBBR892SnFuaSH5GCMVW0QUKVeRBNYFZkpwC9UYGakXC4qRzFqi3hlav80jSD3RTx/AZiUDwM07J5WYFyqa06bIMwnSTEIIKHaMoig2vwYj+p0v7OzSteSLV2/kleUsA97RjLbXMi3768cBRZlXN/Vq2PMrDfVnMRj1JmeYpcwyKdkh59gQ7PdhVZwKwQdgMNiTLY8mMITgGN+pJ0zioTN+sQ2fe/0K+3QktiExLl+raQulom9DW+CeZ4HhJWWkz7qBjuS3nVOIOG3iv09e1Z7f6nkAAATZkRWY67Zz/8g95jn4FDGynb8tIxTCduyjgIqMaSJ674RU4fopxhPpy3Q5fq/YG2K1mn+BDzX+uf5sJ3kZyomHBmFWiRHPhZD6Vz1VH0AIk9zLOjgpv/02vSJ9r0x7Dz4jdIkfhaNYXoX89kBDi/cewKEsp1kN+Rxu9z9iaFcJEoAVPGd8coIYRADHpFRs0zFjprr6fvPDaSP7GrIYQMizKaZpEh2Wz0Dw3ZazvWrutkuJ+25OL0l2yW1Eg741DMnV0LFDvxIbZM6KrP22am4QjLww7ZI2zxSj9b67R8SA8agKwWIcWvm3o3vbr5uslkr/QClDIGUmRYbA2EN4NOgVCS0k1FOz+eVJDJeSBLY7r1CoW9CVgA5iDe+CZPrTxNFIu4WisaXxXAPXVUbwM3oaYbWg9lhgeqTU9H4cW+/rCCAKK+64c8wJOoAQHQVKSHGORDGOcicjjnbfjFXGdhINLBeV0JKRCb2UIalm+7hMlXXJPPNZXCKQi/taeD7q1aLiNFDzYFy1NKf7sXtS2d+tSz+ybP0FBO0PSUwDYzicvuTYMLJ/2+CcomYtGy8giIfiMSjB8Zl+Di8Qkpvi3dWmA4Qe0Jb5SZoSDEgcEOzxUkud0iYtM/R85LskMBhNKycGGOAx7t1saGRsZ1kZJxCeIcOJRkoN8UWhxy7BdEutDGQIq+6NL6BVyt4B5T57bzoO1G6x2XJDQxphnQdiHzGtS1WJjYxUSU9TnZyyLpYURlKSNkLvKI+DFZdfx1DVsjK+C0Snx5LNiyPaA0+pCmZYUUbDkbKKcbhEOraT8ZtYzvxL+6JJK1rIBA7eXmqfgFdZXP0YHV3NNgGZQTj57nFTN3ew+9hjtFeSI+d6qLHKhiCtBjisYrdr7Sr/mFIKWHAh/AXragTqj8WTEb1Sx35jU6I+M5NLsq5Xuf4LU5efXCK+xwidmvrByf84u7kfL+zko4/nBDP1/yy2LnWMAjFLvvxDRPhgXb1Et5MibX1O35LWP5w1Ft1y8GEiR/Vfc06lwf+7aEipd3InWccn5doHAMj5mbsRxfHD6HV5gJPfxbE8v5k/tPx4m7+E78uUDc6fLsQfejiGdEiqcHp9U0ipJftwkC9SiV5J+/BV1HAPZmMWyO3KpADVY04ygQTjEoG/zOQnNYG01IMOQ+5ekZSaFRzso1+DcGPZkT+t+HMOBLH+1fFexlOg6PtAsdgOLyuMs/lmhz9N+aI2EJRVr2Sgdh9KzmzHPVnz1joweUJ3NF1HXddoQ/qp4p+kaDBbDEJIhYEVLZp2f7JoO3YCVAhj1tJOfNJRJM/vyXQgiFxUByc5/tXZSblrXtVbl4KQylvr+bxVUR162E1G/ao3Gh9640AU1sDX7fhdOTNiiI27LYDroKDoxcDbhUgcy23g/9Z/cI0SR5IKAvtY5dhnMwK1XhuLj63pQqgM7WpiCRLANJEOr6bgIceoXeHm3BsLrae8nA9um8zNXycnXZWqjbe7JZPEJw6WiQfFtdKpFRAuqQXFIJTzDHonTcqB1CLyVyXgdAO6S/uAv7ECAdec4MHxphhZLOL3DF2e1pXKVJCc8f84kRv6l/7dXvJJ0+RWg7dKNiJkYDtKWDNXFjdAOpRctwrZqSZPwe5TqFP4a9wcTQMsMy5l4JSbYq3rIakcSPzYl5HvhRE5LbCLrUmAj/BhZFRNYgADrz10VvGwNj9BhRDJF1QKbzGsIIh/O0+eWQdQo+BEOdZS8qQxXsUU5ZptNfQ0yKfZJODWvCrZdzxsSpNu+9bnhZQ6KcyF6qItDff1qXA1xfd96vWF6K2L52F/FKDBjPs2JurO+y2M6G90Jq+IXwoHkOM/88Z3P9yuFdo+KFFgvyFWHfSYM+nxzW5RsKw6ICZYxL720ycvCm6Sf0+4mK+msKGbDaqAL0eznyDFC3xG4n3g0JnE4yr0+miUF51ejtQaBgiGJidk7kbBRRVTxYf0eEMSIbaa7bAlTLm7q2O+OPrxOdSb8NsmNwffO0j7Tm8jJD0KEN6bknkuM+tX/c+CM787xqD/swaDDXoi5Fhk8c6HHs1PJdovcIcpyTv4jysYLqt5z+1GVYS3Cg5DMmY7ilUGcb3enqv9tDu/Tp5rdg/YL4IYIaOzi3tH33oERap6q5TxgnOgxbkDnQcRThNRvMVX5RRg8anQxIcZIVWuRBtypnolmUVETrAdhBoAAD6RBpnytEWLsob2S9lb9S6lC3YnKbOgWxJLlDJJ4NHxOIF24gDtZUEBi+Ln2E6u4LCziPBRQWN9sq7eiAtZNlvwt8n9famVKFZxUxIMoXnl7IyyRhcFYknPoQkfjh7lelOIW/6bdq/7IZBROsFsBlJrRdCJA88dME1yrfDcyxUoQjUHbnkqD/KCLQtyq44rABkfE1UImQYA7VGWeJqdpw5K5hcKU719L6GGeuTp6Xo30ImGrn9fdhjQLYDdkIZSfzX1OVkxqjLJoU5K6uNBMIkT6mPT5YUWyw1k1d9Ehb3ttcSJXTLlvdgr+WzDlLdqeqsJ9C44Wte0oZqTa3kldod2B9X7sY5LJrRuK7ECtaaIej0muR4qBgUVS4HlJzvnqgP15evwzhufTowituBlMO2trSw1JSe3mCxV9QUC5SwV/v7rrvx/lfhnqyLwarn0pAUIv9IZfZ0fS5OQLyc2hbhJuMX/zScW5cAhG26NJVCcx9I5XuTM9I/3N/8Qzl19YFpNVITX6XKIEGQlJPucflclheR8/MCPfg4mYdiX4HmDPpMhG4xY7QI7/KxR90F6zCg06LL+OO6c3MeUySqWYR/iNBuYcODCF3gp/bUSy+k/sX0R7AqKhhr3z1ITDpCHq/dx1xtRcTnGFVpkk6fS40zcD7fNUdcH96GYD1yA7RHE1lXsdvWE9R7DzLGfD+aGg87qxB6ZboeE0NWGYSEtsA4mniAC9PnAu0I5azl62WmTuit6GyNRci0hWmSXMYF8tgUdmWkJrCbJJLoFZ77zcKonxmkYWDr5kPgIqUhUwhL9lnpl47vV1ThB5TaLYPjuyh+SHOWlo1o8Tcwhg76VEZfZqDdh5Of0Hxf3vd0NMVkbDprSFstrz2iR20v6Z59hqHjzLe5wRnPBQytxpQqahfL/58AhGbW8ttWIfukCWj0KZP3+En97wwb71+yM5WLrpJPKzfaBghtX3M8sf+DpDIYLCeqMNjBqlWdKwFs7NEE6bDvtXUc7bqLo3fNfBKL9XxWxiHgjr/y4ob1vE3k3HS4XTP25a7O2PdPPFs4E/byGf5LOPz7KHTHkBpZFOkskOqLh8uNDTHBt0knT++w1W6J1/O8/2j799SzLR96Q1TM+mjWZhZ0hz0j9tylTxL/z+QM5+GltZT+t3w2MXAeplUCnANvHBsZ32S6560yMTg4O8o7hevR+GXJ0gNhIZnTtHeLO1Kedd4sYuvJtFO1+3JrYgxh9MDPtuEGbu91j64unxRr7auKdmky/E2Sjyb04WebZiVtXsK2amvpCUZWG7MfBejfFK4CPkiEf0GeU9kjWSr4MHepHxQWvecHP0tYiWRZNOekoVAFcjK85hegySyek7Znhf9iBPxWLGG8/FZMWHGBYO0LCGb25BslTYlkAJK5JZjs3t2R1w5FjwFrT5pPdTM3SFH9rvXEofF5/ssqptZpJu4ofOrouE008sIpDKjHUL9fgJjZT6WfhxMWnib74EZfCDFp+PYT7orMs1DLnFjsE1zi/CjgbtN1SYI1stSF0W/ZNVKjjhIXf5p7VjZrY13M1A92WntDv7FIUKJVOPva5Uneps9a4J0fLF76VtAl9AecD1T9klCa1lPqnWcMlkoj7Adqt+lmdbLbbM+SCOLbutzBiCCxR+Wpdf/lR0MbnM+GJWIF2ruL44Iv0kzKCebo690IUT9fyIsN2eHh1sp8l+IuNO9pbNnIsdydYem9Y+LpSE3p3W6XKXJASRw3rhUQYy4FO4akR+y1yg5fMvOzId6CpYcFvbOSQzWfU0xmUJKmQHy0Ug8P5e4AEn3fQ98LeD/5AU49KnSuT2AXZ5ZebNHwTeQQe9Uf71Jrf0L9si+5y+DvZEs8CBzDNXo9cBG45TGjWNgmSgO+/jPUBiLbhvSvLJNWIbH7hYOEMNICM1LAjSryez4BavM9cbghO0d60JMqFrL8dmsxLY1/UK++JPCSPkkm16LhE2mXR/c6gYnD7Xw1rUKKDpq6QQDNhSivuWiugsUqOgGteMGyhWgPX3v4iUTb3f8sVqKuNujasHuXFfLdNXZUZD9lpcMioyV1ZwPtgg7P3KokyHJ1YxdpIW2UgxZQLMMT4x99AJAXvAoB/XjzdbhU2O2gO3IjDWTAE9KANE298v6JzjlDqdT+3Hbz3cxB2d4vUXnyR8NaSHenOonDoO83gJFDPRXEkmJ1+NNydKqdYE4PeMimYlEOGWt0koPIzP9IVbAaR6dq1bwQe9kHiKpQ4hdtlo+hS859aOWg6DmMZSM2rznkgFoxRWUI1uuZh1v+9LE4/gSNrH0VrSvUoOb0ILlhZNS2S4vVWhTs800eCgvFiIm1nFiThecZLgmJcPcxxt2537KRJkmE1p+CCOZnxwctVx2Ci1oCXn7GBPtW0uOfdJi2Dp3kpEfkou3KAcu8OTNTGWrKDAxEqyY5uSOtjUCFzy6sGPUezSEfci1uOpcZ3ntS/O7ZIGDVgbeqcnyX9K+9FojGLIT9e12swAAAdkwGpyNpC1JI67ufyZql6BQUFsQCst3skjyZ7QiFHosQ1axMjBeCfzEJS/GZyTxjQsDe94UC7qDY53WeLvwR7YaL1UX/zUQwX1DbLiA/Zk7Lma8XHgHZub2AwtHCmEBiULuy9ib80tJBAHvyLyP7ZPhut/ULIGtPmWI6Ncb8JDYZ3YwM1jdQ6pT64ya/jiNGYT2AS60ljs9yV88kR1Xb1pNYq0znTb204d72H4hJkFNkzWC012MMo/fy7958jdIkMTrCuW9vUUCK7PWpzjNj+kBXFNLzgoHfZoyclDplTK6zMEuRbPw7dkaDScv7vP4/9QUYVXp3VkitupfDSTAUopY9dFLkBwz2CQzIfJyRAllqa3oNwVgDcpPDEYHlN8S3wtB+aIrhUintLjQA1yKF1kwrJ2zLA9uDGOnQwGqN+0fYxt0yWyyKF75B2O8wNkUUR481kjAcAtcM8rQtUo//uzJz+9aTIsqPyhqqHGchjvfpm4Jlal01a6h8g3ZZsvndjCMBJDOeanUMLjvH7KlUIhvG0cNqZIzB0A9YcpuhVmkhDaiu52zzN0Qbvj9wzCLLaw5Zbi04DROdiTtbKPN/Csxp0Ef6I1oVQ3qLLB+BDQKr0VJGTK3phLFSrvNan2/dv2exb2RvbJmJvY3580lqQMvTWccbOmfM4ywLrEFPthdx/JvsOUP7WpEkQWsTBKPhzVEevKmGX2FieHAM2oDM3XOXOXBTItxiokdm9dyPEUNVWn97GcYREwRd3c91b+sg4qJTd5p4mXKjL4ACjfs7SS99G5Fh+07ExGiF7H3UV7BW5QGIDohiaamfHt44E8LrsGZpPOasoOCOZ/MkU/cFAjDOCB8fYSLdnAL+HLV0JvaYqoAHJSn91rFt0vcsE0wmZqVbEcbuLlMtFjw7hJdgG1bgx0yyYp2YgwW63JC10k4+zw4Xk+G17L1IyA+75/0Xuivhg+Nb4V7LbFAEbTpjnziKKMc9PXluHzq3enGP3m72Gk0/r18yaX8g6VgQIetWPJRC9+2w/T0H2jioZe512inZTkza4LLUKyAQdxApEGKABOgBfooYapHqG96BjRj6Tql/E62kQEHtsZiuXUictioKFgY75bXf6V1ZPuAwAYLdBCQ/Dwp3MTaFXIrOnyrqyxGEvHsSUKYoLywBUIIHtdcrWUsSHZo77N57UFJEivAhKDQNVh4ostm+m1Hhg3Aql9RehUvVOBpZhk6XsKzXExfFoXlg2FpM3P7WZCb3v26LhHZ1JV5i18odQmt2bYMtI/YWWj4NzdU0LH11HxI83my4k4nwmrYK6JEQLYv4ZuFjWZfbGD11cOMcl91eG9B1MPYcvbgoLnLWvw9SGkZa7yhD6nCpvuX2Hv0z5PZDnK43cjTL42vgDaDKn6l/J0JW7rHEWKbhYUHot1fsFhpqo9Mwucwo4RH/wC0be+lWD7cdzXefK/5uHG/1nOZ2ROphylAroqpw25ALTO8p+D2llKzLrms0hd34+Z7DWQwcDA4Gu9hxKw0HCaFzF/uqctd/7GxrC2rpXnfS7yh3ezK5gqamkqW3Jiopk061XrTvp1xj823LiT4b7YnWuYx9Zb111ovvFu+ke6eLknEwN+h0h5fLF1BJrTG4Nss/ivXjCleXnVfFdPOfDOyMnOLGfLw50zcUitFLBikdUT88RY/eIfw8wAxE2i4gtD8qH/uRlBOp0LVje75BTx3NurwMuZI73q5Ktsxx9Qxn4lTLxTZhBIdvv+euBsBEXxAdaThYGve5CLXexKEOIf58+8zw1GEZKb9f8IzBjhANzHQvGMulkV6DiG4zvrFU/70KhNYAc0+hy8e2YTQkG/UrNja5vewiCx/IJVOGxCFc6ApaVJEAAHAD0Zg70gKtJrHDGc0Q1lWNRhwSKvC0Q2l4EtMMVOJhn8Tleoklq9s2u5N4VCcYIHczdeEbcvCgQiaPNzdRg0qb212I9gUY7op/qgXCco0mTt/0jOvPxbbr9iJXsOHDEaZ4J+9l1eYzajcnN4NTkY/YmXRuztfsy8Z358bSLDCFci4eEMXxONzs8Ya54oJQs/fjMWS+i1IfiL/IkBUBjZu8MzHxHsNr/kP8ARmOa/kjCPEdVt34HvluzgjWZuVr69h6jZJdCTPKPImn21GOTbfK4BuzFbvzygm101GK67P44TIhS150iypi2bx0tTTcqz4QV4QVas8QmpR+TnnIVNrkoO7gCgHqWwasf0PyNW3bXrJfStxkfvI0W1Gz6eYMNl11wAvY/ED65tye29uQAFqIsH4iGyQXBsRW8n6q+Pc2NhTYd8OeOQC84Vn6rpHy3DVxl8lVH9cUwn60+dM91lmfKtjTTsfFQj/J2Cr1QFt/yLPmYUv5qAgJJamHEbeB/8Eo4q8NVzjbb0pjS61pNKDg8vpjBjL4EuDr4uXMNS2qPghO+UdMb4BXpW8mWyRHsrIeEFKxbtgTI8UWQa/bDclKz1CRRKbgBQMSBLbFrabSPgbb4l37aBKzjlYrIcpqEglilDADhLfMGRerzaJMzkcFg24XepfLJxyb7IK6lrypU/BxpoKZ9cu8Rw++89kiWa4OmqvpsjOgvXwDALFIGzA2eD6UdxMw3krvVy+IK3i7/udYtILp2zZGfxVAkLoIe8m8RSrmrEBuaPiHFT/YV1LERl+vkcQH0zzdCMMc0EoPlN1vI6cb/5NeeLS4u1+zfk7stVjO5lT6Q8kCaXveWUKQf0EmgFBxLaExM58mBfD+xgpuTYq9rmUE6fxG+CMTIA3wH8Vzj/1cXF1pWcFkHSR4a9TDuZJKggLRczXF930E2h0o3mcPwgiz6X3zq2IS/31LOh0+wmUrwtJV2qptgk1xTlAQpgTqzLbFnMR/Wf343xVzwrxG8LXULQl4soKtxke1M1ZRFfR1yfajR2fM5eBx3FM3vm23Bz9U3GNaPuVfIf/ZT+7dX4uYrcYyfEDXFciets9rERkGpY+K3Gi+STduHETyQWJ2Akchtc/7BkiyDroKFftn81SXqabDXzkEdVRhmGwEHxaRDIkfBN/Phpghag6Tn9ryc1fA007DTDVa2Efvqj9PYfosQKpUOWWU3KMDtzcmNUlIDvR3Q1Mbvza3oOuXU4Re+JxlfSrbfwEAfmYh6qG4wpVyRAgcFdYVaLrT481JjUS72S5POy7FuIfTC7ryyefxEDf80O7gYa4Q6kVMPrTKuDO80C3A1svo6Gw9gUqQg19Y38Gx2PBKodCkZJ728yEIEN7spRstejdLpz3Fq8Q2u0tIOeSHxgYXmrj5CL9TNaAu2nDdCEHqKcMo1nIEJQ1rso8pLLTTMzT8LlA46mmlG8Yz7CojMTXRfl0kZLn35WCchp6K+dwDaiuo3NrHfxzkDdlNYWIeIOCep9RWPHv6FyAW4rP6cgadaV8fk8Ejxw/wAAAVL8q0UR4oNk5qoUG1lr90wL1m9KE+mDuf3uCiXwLwc2wXjDRoiFH9VYSVKYDGvzxJNIV6nzazlL9o4VCzt7a/yevo53wK7pOtRcTwRAPNREUxf8dbtC3GoC6HNhrX5hPK/L/gntJXPzFjOhYLrvR24LL3ggLEVvuK5BtE51KWg6I3livdliIe5qh9wy2qbOum/gzZNDoLetWXYTjFnZdGbTup1T79XphIoyEw4FVsC9aa7zXwziCeC+9HctrgyBn8+3i8NKmZo90/kMpS20653Psi9priE5RuwF84ChBoWBdRpxdVmhuKbpfYTgP0iSMZO+GRm/bDZLDiCeProyXYhhN6lMalw80fkShUmiShWe4tdEH5ORNXNQ3tm0PWmJFkF7Fb83RLREyvWDOzNryFLy8QBllmA3ZNwi5lBCyUqz3YJyXVdH5XfZ1OJD7rfq8JQqME/tob9NvoAOL2mOUYsp/HH7fBe6bcrYuEvecqrBX+GWyu26qUipH2WEOHqCq+DQl7t6gWlqR58qksoEmC6K3vr927bhBVgqwQQqZRvBLCyTWYeBl9c6WrJ1jPNnNRNx1EcAdDmaHNDPaHAH9mGtPtBceTMSf4Oop+YHXBR3POeIj65VxSma/v3FghfsH9wXtd+7ddVRTrIJRdIFySAt2ZmTU/6v/nOcR0CmRvGZ1bs+50/rUcpKV+II8pRrUKD5edxma9gcbP7VqqkZa1m8b+fQELBSOzQ259PhlVNkktOX1EOyTj/1HUTh7O3Udq4fE1L8dd9u2kwH4x/gyZBgc6KoQZE05q5FhxkmEAPul78kAQBffPL1l7vjSeexoZpeKoiopCBDspQLtNmIWlSAnjbKJvwt9HY+tGxxydotOYeU9jfHpijP5LR55MbRtgJpFlj6k/A7ZkWmkSa6bipEnC1P5xG9cmgEsiy3RogQZsYrWY2yt2w+ZOpytUf9Q7lR099nYSraHv99EvrAzKtyXZgoaXbGvAyLmv8iekdUzDnpPypgyOZMKC7j0eKu4k6xEF2UFbAufO7ddfdkizvStnPTufIIWgeMKNaFzuKkAR7pVEWydvhYl1+9+hPMg1fFR50amma2FAygRYVYRHkxNPqA7El65XVEwQujrJs5GWBcS4SSKgBSKfqVEPqjRXAcWCoprifLGeBYuBT5TNj7QF8x5k6frH4YIG4C0M0eCrw2NTFdX9fY+cekrq7iwp9P+aNhhXrFeI6dNc4t24fr+7yaW18F+2Qe5KTIC93KT5NGAY+Jd4KYehC3q1xfcDfGk5CjLRppJLXMkI/D+QFpuOfFIcAkID9bBuYuA1Yc7bn1HpAJh/ZjqdP64XTUBJtgw6/fCzgX2DXpXCiGOJrXo0tGzyk1xpQEAnUnnRMUpvff7bSHR3kQHl9IliSbDFM6uJ1nVS1ZUUnraNECewiAABElD5hO6jWqkQQgA4xrCXClwhvsGuXyYMFjFe7D7xuYbyxzWct5AJZ2PPBM13azznvSERTyVxDdqyks1J8M8SMSo2bEi/1Nnucl2kxB6H0hMcaRITlpKD0eVCOQkX4EAQFbAT/ThSX2XlQ7QQWeKbrlfkoUtoIUHLn8K9iqem/GEmtIM3aXjYLs5iG9WjzBD1+4UGy6N0ebLlvf9gqGSC7+o1O5AIXcr6YuvRIjLxB1dbqB2mjRn9TokUGxaxNZbmIaT4TIcCdQYJlcUDncxGS/wwYJ8m/s3U0QlZo3O5f1YV+eZp+x7qhh3CHnGOBweFnbzZl33BYn+Zl1GD8gaPpPxRz2AGC+Y2NgrR7zJ0WDQEi5a/tvolUrM9tVsLyNnvLyOmXziZOFfHPb9b+C+qzKuzpiHn1hB9D/oNonoqCVgnzppaExOtLU2nzKMOugNkE9oB1fgO/hMFtA43PrWQyyBMY1y/aibHYVbRuNj/s/N4D9r1tV0o7Q+T3yGCzJmCKbLB6USzi5Oq0+3d+RTA3DnXs8sz9F3UJzQgozqZmCaX3YacVnp83gLJZnoLhaMShV482HQwlIi8eupugHWJf1KdMGQPRiAzDoTM+2YG6VcEVXmc5EN8vb5MM1raXqYXt9uvlFIv0EBfpUUTZHp/k65s4t9NvgsJdmWL5LYysmyo+CRwYro+wVbBnla+gnKPBeSwCXCyH8RqR8VrMse5cPqUKWIiLR98+44hVHdtrMcUmjQaLlnLFSjOj5G0l2fXGHa0SnA+0Bo9mk9lWSQKnpi/2o1X/beUVWeYhv8ZYyAgN0wIfxbJ5i85CCCHnG4wzWUWabK6KN/QxGGkxORg/KcWHMlbxIx4Bdbf4AkcfZrACJM4o/Lgx9pjLTb+pqIFiBQQ+YvEovfHs/C0d4+6V55LMg1gB6lMmU2PfZs+YBHbimS10RRxoJ2ppFFdZeQDvlUbC199vkDZBeLfnjWf9T0FgIMopFhhbLOdzfw06JsS1g1c/kIOhhSGtH0CyGLwYutvG4VX61KeJpOXCAW/5yI01Mgb3pXlLCyL3olT3u5vjZsBm601dhfP+RL+hmdE+Jz11EZH1A5tNZdEQ5gQ2K2+AAAEOMmeMpjXMWL3hHRF75vIDspf5sR1LRuOlM3qsbo+G1lS2aqFoPndD6azxBeccute4KImEoka9F15bQXuvulZ94T0lGPrlOjtVSf58HMltg1RTppntxZwsQeZjL5F3jfWmz6So3awUNeRMnHZofluM9dfnbwg6KLLPkBFxChjYGaMj9PWj1gBY+Cym/8vOgBy5B9JsulYEZCxs7/8frL9N2Yybve8G9zwQBBMRz/NfmzOu+Ac44HOD8PJ8IFdjYWs9xtYo7/OPjJKBP8vesGy6JysVIghcQoSo5lpLAITdtCwqCyOUrjV+obPYfc55Z9KS7VWTVPb1Xlt/r4eJKnhH3hZS+o7zr7UeKZcX+SV4/9n3qK+jFCTV1p3+HJnnp07DrgxM3E1SPt9t3NgP3N+cl09KK492YW6GIe4bWKyMW2zuIVPQPSv+xnatQMgg3VK9QKZtFEo0bY+uvlgkACVSLKmDPBYoOIrLraVNSMlMo1qCH7vJsbg8+mwEANw21TdS4NVG/BVozyajN+rAshY8z8khU+G7Rc10M9+fAXKVcP71NwNN/Z60KQ2p4R34miQvhxQsaDiHptmh9iMCJCVeB6lKQLkccjlRTq+jMNnD+udE7mkbNvnjdOejV1G3UCelgu4iZDpTedhYkcio4IIM7DVigIdQPcoQPRNJhJI2DzzcuHd2r0sVP+rKhHP9pJGXKCYp/e1Pef13Qxc5K+91vZf2mqoY7ENDQ18Lg6MQjPAVmYRPOHuIP/jbg2VRIsTK5I8pCZr0ZMw2U5AIOH1O4W4LoCzS2giW9Q51KQdMxsb6K90O81FRMBN88rz4i+odHqYmvUzeOUlZs5BgO4TaHyASohQmAtk1qKyoB7bSr9WqNoTtry3qCdPIg+ByrCIrZ289OIAirduzs5CNZgWXVUhc5bUXVzslR6Gw/1yIcAu5i687OGz0xF2PEXRkK3H3V/Vu7b0UD+sNJ1zGw17n7MfJ0dhYkK5ajHNrWLRpx0Tzqxiw426TlNV9HZi2Jqv4Ly+uKPwQHy20VbsiqvvAYOnsVpGX8Ofipu9eQ0LW4yAAAJ7BB8NGkCgug9UKaxLis5WCpxiDUmkfjcwOp52b9fsL5gPWSuqnPSLgkp81WDGDgpE7QfyM5F6MWKnoWQSc7XBRzrk/ddkywNaUL8xZvz62JiKicemhY8Yn7xIS+WEBnpJV4SqJfD7aDh6IivW8AXB5rjpreF7q/6l3+ATH2xccmex4+9knM1RfRFPbwIM/JM1kLCOO7Azh39P2VaBRIMXF6nlNeWVvXm961My8MQmzhCxI+Q56f4ylJxe0DCeyxZClKvh+M8wAiBQY+MTRVx6ExedYThReTrZyOTjmD6ruLd3cNeJU7DEU7MLefI/Nl8Q2ns2nmle2TjqY8AOFpggFeeVFr4q7rtyCbDm4wE3fQ+MNvAZSrFcsLlkdSkKgRV1fFOj5yNixbTNYEIezjLS2HcbKEp00UklGBmvAED63jTBrn6WQeOyDmC5XYQPXQsLAb2NY/Mk3/yo8DAc1d8HX1S2vsTE4ZHV0HrtPfq3lKz6ylw3ATOPAzEOlqUaLYP9S5UK9551utZtiw4PjPPFrCJEkAD4nsjrlnVZjbxUeX4CECpsGEv+YdYrP3ZnQuH7At9F8gpJO2vz7OGgvWdCC4OPgAvIuU6An3ftylZgdaQdTtTec/WB1rPklIqpFhfL+l7hHDb/SeDb3ikMTIv9pY3C/CCOegrbS/r8/6+T2m/iXXSPe22prvqeYuily7EoXlO3LcKVVdNafnPsFmTVv18ygDcWnObNsm86mmyfeaGSmb1CTkfQQZmGDVBVrU1atp1hgGNDPtM1ldMLnAmOOnHXYuf/gJW6EIQb7Gx5VpuktSx+aOUrcJX1qk6sPMSurVCm3HGdgFAZr8Z3Q4A2n9t3gCe3dM5xYyAulXg9XqmxUvo//z9jBwgeS9cFj5Pv7MAAAQ0ce6KShy6t/GB+QCADwIIxmF7r4MYGOzeOGMQNkjyJ8tS2870pMLocMs//e5YlUitc3lxRmjVYkW2BM9HxagGf5mcA74RBNQtW39XCEwXsuFy52xtippO7im2GMBqGUiYQcx/LN2IY9GmbVdN6u/gVGna69bA7aDHJaWCH96075IRaSAdpdElqSESki0T7IohJ4g1wy8RN7mJZcmuZX7/5MPfV840rHy5xPgMq8IlNb0hxkvyuHhzyqgYUE7ka5wHphwIykaHFq7dKHtWEU2DBy2lsjTA4n2k8Dl62mYjncMf0pUSRLcrGApRQd8jl5RoOAM+t5KVe3xBckrDMq0FXljgq+vbKLI6KvzuIQlwOmzTfMnmyQzHWzyboLuChBagkvsMG+6HnQQfjLPY6iFWG7CZ08TIPC4byhfDzwIOAlloKKKiBQOcdJKD/igdYg/UD73ljcdPV0aK0Ww0wA4B2PJfiDyEZmJEbikYf+JtgmOD++DzJyVRazJ/PVEujrw3GfMeoNvAa0xXQBVyFQS2mOZKYi+bMkw2Ux8DoTQiXwhb/oddpP1kcRInO+FhWJWukxZtpL6zvs0ZBKKe7Oxt69ZuiYfY39bk5h8LL9pToQ2hfmp7w/sjs5sugyX6CA8qRFR+0nVllC3kPwGATCQPYJ7dMSS2bD7j9hYABoHWMbj7Z1dEmtuxC1jcdiTeYUtrG3YFtom4mqafbV3krDfDiYbcJEl/yQPuDEOTbcwc0xmJcJeObexGGmGbWq6eXjZ+/ZjO3M8QYRTGHruSefDk0hkv+NbYrjhNOxOuoLhNAA+LE8ADIPI1wNIVMTnZtyz8Ef7p4qhlqESUcifSuwTUngeLIvA2LgfgudQ9RObRWMSpGKhW96CPYC+KskxuwOCRfucJAAAQ90eTus803xKJbwun8mvAAvOqTtkJYJUdBHFwU0Fj0easzDlm96O6f8PLOGoWWKYeXYvviYLdiy7eI+bz/BDjLWsh5d/Ch8pC8HdetITMG41mn+9ReHpvVDD9KqgdSvP08Jv4NFMAyxAKGyKLsyLgqh7ARnkewfnS0t/Zx4pXtp5gwVLPTjzdt/lnj1nHRgYszHOKZwokvKhm1Dj4LFU+2Lp/N8zSot5MaqZYSvnXQNm16gTeAOH6T4jU2Tssh+4+/dVNukGyrN+BFLlTTyFMh8TWuFkiJCwCFgH2YBoamZ6phLudhzSp9q3+0AZPz7HaqD0jsfmjwXma3wOK79xPTVChYtI8WZq9L+kN8h+JBmEC6mB47QZSXVPKecGF6eNnuBnXpf4skfAARcgDEUobi+4j1XuFQrg07nV7OmOji++UoHgEWL8YHLbE6lmiArqJAN1LfaReKEJU/vPAE9Y8AUKrfIhvZT05RtfnpZ0su7fbexzzetrorX3q9+zNNoGrsGxPseWaGq0+b6DvCh267h8uqCMgA1wLKa1kksHcct6zwl3fx3OjD/o+vDel/UdefjP3Pqp6DKMD7euTo39XXcRZdMR+fnv8fefb/RO9rKDHmAbAtDTEFcrmxRCcRU/vK8YTqIQDq/zuUDSSjrOY8Ok8BBB+uxIJNmBfYZ/PZYJst84Eaf/V1yyBjGruP3GumuOh/8z8UBIpxnVICcvHhH7iT3WoifQxSCbmsk6VJdUauQIwbeIGNTVcbBSCfxiCW9bTZvGPPnYe7GawSPv28kjiLKCcqpzS4l2sB5WogPpEVqloToL6a6JGNuBKEOGmCYt8MBHuLxEyc6qhhgAAC1VmYX71t+t+5dG7hq8vs4T26XoDgjJDemKUn370sRZXmO16lOD2ns59nj5hnU8vIxgeDkh2NVhr8ldK7ei7MJtvqNs/QwaqaaynmJK0XGIE/rm2zdvlWWR5nWgylRyBVUtfzJ8plfzO0WWNqgw6xtXYl4LGlBF8k2HLBz1KTnvDYe0jlnzkcW+h6VkkPq0YPYx0Hgbj1ezwxNb3iUh7D+6nx1nMnETt5VT5zM0venF0S0lDCRiCx8f97DivERcdlQtQPVHmo2YUD5prO7RJM1BrtAmEeD2Iv1X2NYhmkieyOsgndOIhhqigXINhQzOzo5NiNpClJRUcJ5Tce+wEy2ONjKhjubAVh1lDPvQvFswmqa85cFlGfrrGoGGEn495Rt26Ls6B3WoHIylKWYkzZkD3RS/fAiLr7l7bS658x2zzEbPwPkLGBomv7hds/eLEd0PUrpAHC8iV16z7yEbME93aw/4D270BU6+BcuGmi8SNSbZ0sKmGFZfOzUqCV66D4QMtDODitI0y2tpiQhw5g0ful0h4yUVZMOJZfwATQ+i215s9S7XzwpuPT7vlQv4hZ3EjnStG9SKjjtBSQ5NyQ6bVCoR+FAI5bzlPgfhSiDpceV8EgYW3ZJwa/62RogZzEvgeVQTXcYJYb9Dm7yUxTj+KvP2/vzzNqDrb3nVotySkCmvvnMURzu31y4hQQs+XOHfXz97ui46HphMAAACb7XKx7jc6PjMoxwk3Mjn1NiBtWzfRN3rULCBsIInJp1TcHN97GcAScpytXyQISkybv3irk61oodkQmRBlSDdCmx5A1mUe4+oXmvdv7eD2Y1AmkbjcBPcffFNuwlnnzDAP6133UvFVFFXQnzWYpvD1vUL5MA07fMaljXXVVHZjr+3iPx+FzTwhBM6fO7bQsCk/3vofHuC0o+cnvxNQCDulv7EOuKTklYEa3OqfeHDQ8mpXp0XjM4LnDWunisPuHZ6h1y8tE/GxcXKgP2FhddswruD+kFuPJAbRGT9JghhMTkU81q4PJCNeBtPB54OnRx/DKY7cP9JslBgSfaitTxy98D0p8YYrlNSJL5wWmexHxuAYs4JjmHSP32Bqz5TfP912hXoE1fqNkPGDodo3Z3KPxrYMqE9E3/Qz996y6nq0HUy3nLjwD+PBugXUc6XfqB+vNpIdriryi/xaMTFym6RgNakfpfNFNnU0COLQzXZd4YvA80IG3dSjuPccSPZuZnx4Ng7vZdSzPmUrdPe4aocjMeBmy9XQfNhs+EUkFDzlDx7YLmmG33nPHQ945mswJeBUFi3mI7QCb7z8gpqGaZ5TUJ+1AwHnZO2lWE7iyZ+0GJ0CB/Fl32PP7nT8iaUZxd58Ne5VrcMePkhBQYVCrO60nH7KPrSm7BfunlWRgtkVr01e7GXh2+2KCGHh8TwsqcBasulsUkQ1euAQN0O1VNH/BXy4Sdxdh9BfBgAACbgd3eFZxDZ/779f5yOq9KprTZmGFLmSxePO1w4YfvLNBE2GjIbirstEu2xgV4VIaqAUe7Af+00hv2VhWBn18DeTeeGlWViiYC3IR9jWkQ0jSwwgVsdS1Tb/29QaUpa/4NzdggB45uHMhtHhdllFB2kjvXKoO4Ga7oPvVzXcfSCtO6xgK7rF+5RNeIZ7wvnfRjK02gGBiB9VraNHtJPDaczyy68YRGWWW29PQJnW7pCeh+O00gAXDx7TbEd/FeJQ0dfEr8DAEPMdwksuHhTkeDqxJc4alhyAobNC0BS6yIa2Ns49tFf0/V0HnLzqVsqqk4kVZA/TLtylOj7kKRG85IYOS/vWklrM+E1l8QqSL+8XkDxcvjdtCQ/0CDXRPIStGRz3MRYeV22uMWuXuYrfznLG5GtPEFO3lqg64HH/OiN7H33dJdUDS4sZdQ0kTHgNzKssANGtoqp+t6EYaUBBEOfiorGGtmRiBUUMjLBGBPBCCUDjzPxgoJW3iKdNkl0Wgw4qCs+GIpOgbrhig6La4ag+HVfYlOnBEZWrEe8sYm7XYmdi/8sXllZScKT4PDx0IRkgxDGKdVy9NUq0nLpjXrj6/Ex4TEZIzYXh3s/Fsh0sGxJPBEA65j0Z2T5swwg6jf8xsmMpYAAAPERkDb7HHEcQThR3keviKPLiIbO//BIHg48Relm7zNe+sSjl+7rpMqLkfeG/c5mdOk5rCl39NHLHTbZnNINT6E15AOsrkj4GJPk913dTF2PA/lXareHLNOk+VcK/jC0/H1TxUAJ5RdZwxdjVSH/QtraKY53fRSmUeh2NyE8uemUTp7M8z7FKb7Ox/55nsNno7dr+7U3S35nlTB3vWEgriM385S6MG/bilV648mkF7V2DKRoXMWXMRULgmVAwOuNIjKCi8gkewOYFJp6M5t6G/45Y5kT+UxXuI8mKZA+Av2B5KU7Ql+Wy8tq91vu4YiMHPVrcKgyFdzysmiKFK5lxWakXoL6yDuslHJTQBhuw333OnEWtGFANJBKCHa1gqW1JVkHONqBTFh5n06tCxdYHLgu0BEt/dJ2vomeSEuL91+hPGaugPdrO4Nx1LiubXXGecS4r+OFWmJgDj3e+DxVs3pAv2oTO9zRivxei5Rn+cIHZEo3R512oE+IAST7mnfrhTQAHX8pRsKvtytXehlFSO13IR4v+dmIy6+ENrbYWCVi32Peayo28JZNXAZvHaxw0dl2S0XrQmH5ZaP2l4AwAtt1zy/CTjQOCVpEK03xtsl9rhQsViG1pYn3N+EkgyzfxIHwQZTQvGRVtDbIJY/CXIJIHlC4zJIFFmNONrpOWfThrx054NXZJZZ6ifDWFyX+D1VBPc4PSQAADJjY/++aoozxlM1+GLM6AWlKrgGNMnZr9nMda1NIJnlqDKulK8duPh0hRutjg4cESf6CJFRZ0TnAzg4iDpEZ+owLOq3QwoMMohmYKWMXnYcP1u9IKItuxD5ptRdqYccgIUSfcqmokf5JbXDHjXlW9ChosC+jKofgJrlmoTE0JnooQoeJz8HQYYjkTCnLLcRB3rMHkYbpF6xT6cCf/J2LQ3u0wcFAAZbOq0d1wY8U1X/lB8CENlc2V4804FG0peSAkEvwN+Ay4JSrFt65A+fiscjbiengKlRL/gbjnd3cF8YI4CkNhqTHkrzdOEOgXbUtfvWCtLht2UBoHHnnQwmFgYoRly2BzhIIWAybFq08/v/kk9W1PIoyhl5rwiLRODZ5t+FnvP1jlkqaSpDDlu6A/yV6Rdp0T5GLwAjSbcciM7X+3xJUjzN+nWVf6LhbO/tNqb7DDP3AscSVmzQ2unVNFjEhXQ4mUBQeWbau+L5nF1APh7CyLih7iD3Ru4hBvSPdcdE5ZDX5TIj56VkmaeEj7Pb+8WMEkTJ3LvNuFcOIO4L273AFtcvUr5L9wDL7G5kHDLcrb0/YS9T4tAr2mXw4jTYalo6SCdZLFsZOYKa3ghoRdJKWOa6bgNqAS0FHAHIPGnSJRjwkHNwXLxHm2IVegad+sWeVoP1yKCtZI+CAbxRgD6wAABGx6PEWe4CxG5CHlf7wDdknaUlywgTlQQCr8+jEZztDdY8PW6peKa2yiJ2ezkMttKRD+TM8aj9T5LrF9xriGUYVYmIv3ttlAauNmXzJ3oUQAoz1AJtIZ1ffFgY3G27OTY6no1vUcUtZA4Z6nDVpTZpaPh2t3PJQnaeNRRuhAOqWfufEpuBdanNiJWxK9PExawvPFTzuVdAJxfINQ2RcNNRlW+xYXmn5IEsxUxXeABh2Hx1FhSylTV1X/3GjUiB1B++AIpjPpTfVDeshwzxcnqxK0wNX3E9LaG4QAFHAgMEyKB/aiquvKoNzawqcKZlh8qRjOcMkLnL6drT105klNyg3S40ognnsjKqKj79MCGztOLewOReqfBCY0qxp2DXM8VGbbFNIvXsrIbMC1O05tvvGUKIb0yIZxw2vY8++FoVNJb+AMz0V1bGQ0IuITNrAhHpfFTQrbkF4Tv9cm/LWQ38RKLlbUVjrGVBH/N4/gUscoEaAZsGF+lNJ042L5lLGBxOXazmtZra44OVHpJVpltIFv2jm+PMrQWZTbTZXU18Plm7Qbw8NJ6iM62B+s2ZSOiFMi7i4wBmjqb0uaB0JnK0i6PED23BTC+0ettEjCh928Yv2M4gZ9nnc98UIB45GFTkcAABCyyDS4W29fyDAj+IpZxaCeAmHGRb33yP5xzvDSVocQI++d38Y0tcCBAuO4LqIkFdR5rbBzHknFDGmte7PbjGKp8VKG4aZSEi/+5LsvPWQe6rR4aYUUwXCWrpX7TP1VGUehi1EpKUqxMiMgvgpXFxJYf2vztksFX62Dk0BRJRO401DJHr1Q7PxhSlkmfYdSR4pcBr55EmHeGmSrUdhs8N1q/6YODeMRThIaJre93YqM3xDL2CSh8JjQopIqKklkWOUqbUfgKjRPy6YReSiz3Zk3veW76izimVbJEROk6ZihRAHAyxZ07yO6O9xBKqNddjJ6L8Hl7Pi+cwj5B0AlEJXQYpDOZJtX4N6od5k/4g7YS4krCGB3m3Vf0PKAP4A2O1/2Hcbw8oM9ZazoEoN0yN9aotnTiYFg0mw+24k/HvXr4N16l/lJq2AOsL+sEeh6UphFgshvBqntibnsDLl4fVbyl64JcyVFiIWS0ch7dODXSDKQacX9l7Zqwmu6wdYecfXRHUHD2ZGgjVrRBvAevvFassy582VExN94GLGvJpXMtvlXyJdv1rl+3e0dHT4w7AnJBh4kx7f+JdXDqR1Z/0HIhVtnl8ww8Wyu0py1biRN0gCYawQz+OsMnXEO5AAANk5iq9YRH15AJ4Qr7FZKnzXFC7i8VcUVyrn6tOUMAVjZ/lhB5hqd+QD/uVJooRRIuOMok9sSvhbB/gnbMkVhP3Mh8tZXYS0Wpv5OcK6GmJ9H8SjXJMNyHmwR9krldHutvDWQTOwtIes1NVKwqF9vQW26eZ2rTDheycGBhe3V4847jIrMja8hlcKmqjRmhkjSr80gM6z8vHLlMUP4SGN14WDmHIFUnm0r+c4v6f3AAKCrDkk2+2+ckCwbrULC4auKX1dRHLU9WVbvkvbRmDA3PZCO6I3jVUFOTKHsLBIHHnBcaNK1z+/qq19a5hi2Md6hvKpdPlhCvsJzJ0RHKlfpQmG/l53k7H5rCmkVyEX/KOsjyYy+QE17DkRN024EDNGcudHSMUC7Y0qwGWA97gLrR12t88GWE29hkweftNQn+aG4F+96AjVObY/23Xo38X8BU5u3Wc01hffn6OQPsdmC4jBO2PQY6ih6WlSUeWHi004w+/JYVZpXkbEdTzS35rOMVAbv3QsvAoP1fNo7GxenA4+VuJ9OevHUFSCvRUSmHIkVmpOeNRRhrvwzmNYERwulZvHk05CzsHgAAX7bLPJAO83X8jLeYGXgXo23F+33h/73IK0klEvxjt9QsYfccUn5QkPhWEDnNrN9usAFb6ue3nfNf815zLmsuWSF8jAPh3Q+/bWI5/ynmO9KJfz6tGBPRRWOBnxPl4fubU0kF2YLptLsbCaBOKZ4oVXxG5Q+JkNhdrhOWQQv83PNjbgGsvPMOyOz3UdCgR8y1n3m64kB/7nIcs40xkKUlcHxV40SS4sKViz9WzLmpb4D2LqVqtzubwvSIlo/NHO5m1Hktlm77bYawYTL5/6yXnerug113iQThu9KERFgi6ySrnCZ21zBsnPDs1oH/ZkoSZUrQA8olC/EzAWpAU8xjTI0hMufi626wlrLeZp1/EaxjXf4yGr1ap5KoneoCK1Y4JIY/0aNqZTjau2tPonwv6O6e9m/KHxSsLk77xxozH3VOmSHwLwZcvyTd/1Kmpdm/xFdE/6jNa8CwtrEF11Yl9eopRzqgPAAgLCI6Lzn20fasuqKP/qOeVZWwxMcbVQHs8JDuwAAAHMLt5uZGerdA7JxyN26967513V7h5sAU3qQWWBVa3PWIeRUkSFQDlwDkcdKZ/tm13MEK5kILvtQLW44m08B+BNZC/DxPL/+yiUAxlJ4wkhrRAKpTmxNGuVLTccHmgOCEAcR6CwvFWJ8XBb6syiVczknrb6e9HeKlQnOjo0U2UB4t5ejyAB4c9bQwRdk6vSuqNGoQTfAI1/VRN9F3kmRdYMsbJI2Omb7AsUI5dU4x6qn0IAiNceumc3JzgGs5vY+6LVg7qiekJz7hFqm1K+8KZLT7FtckjHgdZzOxf1BScgvJIPMpbCWejiilW8+pdKwLyLFQk6nFs/4eLWZ01h/wGzi81fhCPego4QuVbA/6IvsLpyHIbH2XuXHv/k6swktDNShC93F3d0/Kdaqt+XOpTPwg8w7kgBnP/GneUShSWSdYWOvYbEElaNmPjLB4/ARZtuBhUgBveNBdF5DePo/Cl9qN+fgx2mhKJAaPaW0vAo+njIAACOOddJQJ+qaXR1a7Oc9xQis++AXysJaZkX40Etv0xf+HXzCqI5ZBglFGBoXXFcSwZHG953llcIaD/BvX2boOwHpbaRQrGwb35HSTNBEgA02uMK54NAjcAvwsBVMJKcU74eiUf2ACE2QFLiAIymX3mJC/y9weWgSkuGwhdVp7aZfdWc8XkVEBFkYAFHhIOuSXKrVD45EUse7LtGFINJQhviceV5ZzU9yg4Wb1u8CrervozDg4lbrXog7RGhdCdvEowHkCtKcEgH34jgl4s94HdAHyrU+wxTbpTFixOlOrYFSVBio4hO2s5rwXtBeA+7yCl3dPB838Sa/H5fRL9tRRX1hR8tPxVmWWG/cSH4O/ZXlEedMNCoj+tBYVbF87es/AQZrEKSvrTtPQBUgjDGQpUu2/qd/z2DjtSZe2HZ0RLGEXVbdUX6kPHPYOlTKCAXxPhiPx7dXpCg9hqIzrJ+uIw7/Tet52c+QwHgB39weCGyFrd8gvwcUBsnqA3Ll1TDW4eIBLeIuSuKMVUGsmwuoVKhj0GFwU7BkdIOaFnNIJO0+JzDvVr7xGFA7RqGyJMuwdAAAa9NyfhvLPEPZl+HhkYKFJcI/PKu0LB3gedojaGFcjHeTjzo8AT6FeNTCpSJSaa0rvJ/C0kuMOlebClsD6oNfVR6h+wpBd5qTWM0Y3sDwWeWkD/P3ke+Skbf9rCp6KWOCk9ewKKPJFd5K3uSzupkA2UF0C1lN9TbJOCeJ9YK/jIHnMDyJre8sYToS45c1rE5AhHRDBEzrXv3GpGJeeXZoc5zKGixK7iIUZtLr1wHTZ+KlS+RC9g2T996ulBeCzj2BJMLQuF1WSYnzGLqIkduWpWieTRwi8tPCAvr9UMCzQ7Ktm+X9GAQRQ40+/zfQhRFSOMV8dTidKEkOyaTTa2zNTV8w2SGFetnk27llDURe73wBlM4GToluuM0BHV93fGzRHggjopcb7nywMYWauEIdF8XB6HZULjEAa9vcII9h3CAaJdvm3Yj3Q7PeWkSZ3XPGoSokcWY45y8be4kHZGBw+VXCL2V9685GIvWwdjoMwxr/4skpinuiaQTPpnUwPYZvKkmsCaq0QpvmvVQGLwJolBkAJjWHUFl+ycs2R6LfsT9oN44s0RLHN3m1FqJTXXm5L3kOAAAyXl1gnG0S2Z4pzd4aU3itk+NRfjjvrUMhDpuFGv+y9I+cZ1ODJKogAEWyAmZB3JS0l0Bf6byqkqb+dI2vSkL7yMVFuOz71ZsAEX+MJgSZMxddPsXGSP5oDatalbCX27WARcffRNtRxTAWcLKVPLJuskBckaXB6UjzQyTyWchMuLGyc8iEUwZ0RP5UcRKfJHtGqFAr9ShrmVOaZzCjPUxBxNNkSecmh2OPvg5JbBBZeBmZa0o6ofaatNDLdHDb1y9U+QKouCxxZAwqh0/WO5WptYMZLFYfgXKFq7+g1akI7sh/ZkuO7daOzsZ4D8kIkheypmgivl5JG93mtX1f6xb1RpjL9OLcEzLZE1bo76SWIMmBPR2weGSSoQAObJ1W2VkNfGsNvIthzy6Y9oCmT2bCABmrjD8tcTtbKCS3UofLUfLgm8RCa53RmDsWVmUVOlcEKJhc5jxQbsIwilAS30s3I9od050uxmDEn3BQz1oDJJCt76Jv7bHkjOxCdyFmN2dQBishDUc8mGiNvllDtfInZtcbnPhfqam6XJ4kNYbc0IUVUmL11a2AZ6V+aq2tX/t/COrkxwgAbWOqPc+e2ulWEXdaSFbUnIk6eyRdJtt3hxRBnPScibBbpX9z6rWin+KQ7Zh53UYMX+MzX1ZjJqMFB+tumUzgrw6FHruK37/MfsrNOMXy0hIalQJ6QOoMFM5WfoKnKiWudI/5J3X020QOlgiLB8skfaudQ7i6P5/N7jKexgT/Sv9PJC+bnU4dUro/jp8VcxtaRqC50I/JKFLAAAYDRfAaZL7Zp0ytFAl5mEfR4f6fJvQejQHXqZPHblJhEOJ+T2a5fK8qWYfAsDn5oVHnhCkHlqgAgxUmnCInSGljKp4qFdgwzzi6fXXOWW2n9hvxywzy2FXM9W3eQSQwDu6Wux5HwueJGp8AEDC2sJYv/Otxlh7UGvJD/FzCb3M627HFSVdn1i4b/Gky61uoXO6rgt5v8BqHVbqnufYOiDgOSBdUG/wTTovhEecX2CYdASaf1lEfUohk65WSyAtrGsFFELWNTmV5dMYzB0iO9C6bYSq3fj/puuV5vnubWk13wRwDK4/qRk5WBJvoqN0Zat820ulVgqy+NOdU5WtWbFlQHLk/i1YSJYxW71tUHeUiG3arirBcAn9Wgyi2lCxFBUTQ026xSE15UOnkaK9jqVr/x1r3/6T6++i9Ta4rdSagQOV4rKu8cu2HvlCFezxvwXy+vztnJ9pAL/5J7jPYPuWZ5iGdWLxTXCv0/yLj94OtZSjUFkdtPdfijZKmioVypPDSi+1tZalFLh0FTkRyf7ZKJ948HkXT7A8UeCQ3bzAZjhdqOnZ6+3NrloGYOFhxOfgXvCcwKDGcqGoElb5oeoR2R9ui3XWhYcPMEWMdSbFiizlQrCsLRINCSgjkR9q1sdsSzYEfl2WUPQO41bLoD5tdKO3WnXiLSzsf52PYKQ918HjKyCxxyC0PwE5n1houBHv1vGCQeXcxeDxxBruNU8KhJ8qShmucUQiUk1t5rtL8OVmN6zXSgN/4711xZ5jpaOpu98dwzZ0Wzd0PbdduaLZ5cZETSYqr+9Rhv1tD5orIys5ZNzgJUeRdj9nAf7l2aGnaBG02CPF0AAAZKkDZ7FcOvyvybha1ASnO+vBhWDs0Td64Lm9SNnRv5g8/B105bSkNkCvBKqkybwnghnzjJnpwn9M5WV5vZaKYrRKAUzZjnnJKAIHCGCRWMBA6ikNfYjBDZT0I+GSXa8ADEnVZmm2qHzDnfRsX0+twQGVN/bradjydDLxf1ppRI1KQdf0bWrPVn8f2duPTQI422bQUCp6MOeqHpa/BgWguiKirT9Y4XwzK5CJO97SdGE6ziGrbP6jo1gPug/b0ZPmvaWd0ynwfmVTGYwy0qF12LMUNyN20OdX4ArNOfjY51Sx11FhxpHpyHxOX2uGgK3DVJFlWQXSnzJC7EbgV0wtRrYGXyA5q0fnWtWdw7NRuA1kN1S6SkHkeC8JLulyz2VD1vn6A9geuT+0Ebs9N8xYpZxno06Gfff3JH4zK8X8CS03/3mLR5Af0jZn3rhC799HG/0Nu80aB6ElBy/f0FprBBBxIXvVj32XJFFpwIjUVe2xQoEJ9fYepwOH9WaMEIH0vwVxicjX+rCcVvp98JtiBTNz16YfQErQDja/m0PXsc5UCfvNUz/opZB/23fI6bo1eELDLyU5K2VurSD5OIu5VaX4n1mIGggA94xgQ4tg3g56FP/2kdVFwqdryGC0/QtZ5q3K8S4oIgr5p8SHnBiG+R2A42YLF3/96qPQ3i3ngI3K0ew+I4hy4V2XYNThs2BZy7ctfz7Py0WWxE3vQg9NAAAE4N7MFMyKhaZrzgLfQKkIA3qpwqppL+Rgkv7aJuDaXoz+uUKyH+lHRuUP7nIZ57gNvXEqwJaaR/+bnmdYTKemtwEIVJFYCZZkgEtmN0dmQpOAuLAYpIsicU0Om8SmCG7oRGVDRgUawifBKvk2gWJC5tKfNYBoly9XTuF3toavgCc/l8tdldF9XlyjeheR1I4Xojj7FnhVGAFujPWBzid9BmVOXebXfaDBCHhE9smM/E42gH3UOmwFzbeiJGyRYb3y7sWrlgbP3kPwFZdcuVtCxvhZ7uLN07pzwgB0CUxhDay00iIPbiPxkl1fY14OItvCGjSWzUKs7hd5XZJJ5HJ5jT6/Ekt2ibGByo0i2YUULcOneYnvoHB4ZqjBczzaNiAgvy+w3mLsjZdq5s6QTPuaylcCfHrwy0cQmm8zWGmx5FPUoCVffOzZB6pq0m+MdPxW7jdvXb1kM4Z5Mgcyi4cpdN0dA+JnwtZqA/2XS/mODBZV4GvFndLt5VUTiqf6WWXDlY0Kvz9nCkWACQgEXJigysFNekxZ1cjJKrnPP9J61AxYQyYmVmjfYXPNEr6qe/BrvvL6KKDkkCWDus14j1E/QtCgUkAA1Sv+zI4isqCodVC1ZE68bicVYHbjmsajwAAABA8vNQu0z39SjXZlIVkQ5sqcqXWJ9f+RVVMPCM/zY2CwkH0gY6uoBTiVhr6Ncb34m/8MxjkZwuXvWfwnmWz1bf1Kbg+o5bxZTditd4wspUG4U2dThRLmJ4TXgVkqHOMT78ZyWWCsoMwc0wuZJkRvOyYcu3RfWH3Y03V7wciw9Nr6bBwvtkHropmTXLqvTID+/Ip3Va0wIs2XruyuG4pywNhJkIo3X4O3aQnfFmSFmoeRUBzNRpWDmM57A0JNfQMJfiakufPJwyua6Xh8LLoUpbwF7CgbYcaxrZHzMRCWrsQ59s4mXtJjJTK/ZWFVGfTaDVyMbXE8EB/Wy8sYzpvrbgfIAjUzUR4jLkCvtzkgg47cxm4thJO6i5vTih6W/vU6Y/sfDUVU9BYtKMDZvZSch/Em2Giku3G9moTCnhjrhn/qdUMeH7RrFEcWLA+RkzTUdmr08UjbQGMFaSrrFWtcgIgrtvoBR/0LjmST0P3CdOOSe8BgjmideKTTwICPVB1oGrWQBxk+KH4WkXnMx9QwOezlVEd2W5I+S0GpmCEcowdX7NuW03QAPsUXoYROn3jwXiS+XXs6pgylsg1oqMRZZAHo/5H8SIGPFZQKCocIH3CwKnbkfcJLkyko8E6YaUjLjVSdZcVQGcGPaqM5shdN731kY8kcYKjvOYHwMogdZ1u/eKAAAHNj5UraqbwPGhUxin206TRtcHg8R6lIYsAAFhrnckbfwZ+Li693AoY1jz0S8e0avsuNxGjp9jeMmsREIZtUH9fnwsVywZGqHdQ/qcOQz83chrJMgTv5AYssoQaM71UfAT6h8svcj9Qt/PNerebRhns01q09yeTe/jPJ96LoKNTGrz7A+j5Ym4RLULpSRio0PbG+xwXw36RrBr4uCe7AY/WTmFfLsXvecWkTiC8S0hrDnQnz1xlttr/1F8Vnhd0I+QspiXTQ1bVRuULweSW81PRTvH0ykHIToNBYggef8gV/hrXYMROpnYeCjaIgG39x5gsyGUJpiWOSdNs+JQouvHHzF8YhfgyKpBl726Yz2QUKZU+8yscpv8/7WVUPFEIDZvr44JGh6PuETpkL2HGJaIyRLaSi1tTiwL8aVE9bD4THmCO8Sdik18LIbD/Z2qKZ0+s/Bft1C05HZgWim8KOX6KSLord3p4zrECwlvcJyvilzr30hjGgBqXfRKB8ybmEjRlz3KO/KcrAo2pa0IDdvCk+8W90C1dZ36wmkoK1VxTuP4q4c0L7Kn2Hw8OyotamAKLEGNMo9k/O+JKNs2S/j9UWf/Rr1oHxmhL19nhMVIyxsG2t1Qx+BlKRAAKIRWeiQdWzLKsMwjDcsww4tw1+KFImB/jl8j5QDyknQiL5LErl4IVKrb1v8rpThHe8W49FIuoVq7mKqLIz/Rl9aBn1ROFithcvOYUfgriV7O6gvnBmXFlIHNNpOBqEMqQV1SupiUjKLx3uUdlfBusENRGE0kPp0RNaP2roFlgNsKUgA6x6Eg2qXitMOIeAABMdcg1fFN0ZIFENF5wuYrbZv62AAPVlF9Xtj4+sxirAmqqO8oDWiY0LchGIQvGYv6C6xFKqM9sySN68yH1ePH/c+12lFdi2hEd9Aan3wIPWtS1hwSopMM1fnuIvEQGHxYoPl/x14sNHRGIrk+nsDAbdyTnOLfUzqUTTdu7l7wTeGERmXBDWbDcn4Ve7UyGjEo5mCk511TDkx4aTVDRn5lrXBRmlBjiNLSTcsovFx84ArL7Kitqi0u17RRoy9SRb4hMAana3pnF+Q4U2pTr9GI606GyJ0xzKRxwmsRCXcpTvMeZ0FJQ7GAYaFdcji0yPCq4YZcyAhs/5VE4O+2d7dtQEkfG1v+y9InyzsVOJ5WKJvDIpEeWyYmBETJV1fJhDSQE0hijmKkuy+fbAyGffzhwbZP9LtDnhWjpLVDlWhzf1RDbmN0mle+1tthVVBLW1R9F9baVhz4aM0jKOrRpvaTsYW1FAjcqkwBi7HEvAB+1/GK8FjxSKNejxIE8J+D9PEtbn0NhFEaztDHTZzTKjX91XlQYHQemhskiF+2xr0fpQBm2sGPYO46GAcBWuUEIjQIgN+cX38XFWrS5z7RTGEKkmjja/yqo+Eflge7nEYasV+kl9K0njSdM+Xy9yto+MUKoiX+foHJ4ZnHeEn48GEweqymiePnX5bd4+UB3SSSFMqokkH1nWJdVtl7XDCtmS4aMbduduEFphRK9cER0LZx/7i0LHT/SsJyVVLg93/uX+f//83Veiw5YsZ7sp7tdTbmgAABLTDHr12DvCazjzBk5AWDAAEO4hIj4tKfrxle/aeLKICBLlBWCbzlGkbzs2YShdxdY8a8mRMFf/pvxL6RcLc/U6o34am8bav/bepyn7kcok27jG5CphEOaHBz50PKE1rNBSCydxb+jAc3qsTgnwgQOpx8tpgcqWdeawan3uexYq4Q/yNJZCS1K12ILk+HWZFCoz52vwMBIDsFX4kH/vU5ChJP2pXn7F9thb0otu57p5q8CT36xjGWWxT48qqAb9QQkfZf5XvWORm4UJcSMJf1vmlPNFn0aY1EcFcBUo6EF19z4BFl7dMeoqKi9uz+WLXG1Leqsu9DZ4He9csUEh8maKyhAGW1KqrtcBEuSkr7Y4i0/8/FnfcyaTZn9JB5qCvDidd+AlBL24kUPwKeRcdVisyGkCEpZAccC6MwsMskw77KU6o/QTC9tmxPEOpVyDCHM8oykoHnnjGJPfX8HM+SVadiWgWVNLrlpWnOsMXzeamOSFkxNsSWfvkyxDG1Bd7pfgrb+L8fpyaw2Bqhll6VzqRwg6WE1ZTGyRE/TyJhDTosQASTQbi8WXraJh19rGcmBY3kvwVVh9mqAswUzfVPtp+iKdC2smWvZHpxod1EmgVY2aiHpm1shuTEMYqGoeO3SnH+EZRsYj8oqLAfropAGfaLCqQ55e3lsL35OYiu2+sepyHVzIPxtbAI4Oh49w3J20xtf80g1BH5Ks6g8zdfkCYT/9ZndOFtot4hdGcZXLDT6DBDHNJXzLwK/2AzLdNbtoW9pNaBqeoHVf0HiV7M5mJIAAD/Cj5vPz7wQ6eXaoPVnEuGOAXLEC+wSuxi+BmApHTBzxns0bNepOOAsl1fFFqkxSMhFyjD/dVH//4/gB69Z1/jK5Im21Uz4wgkP/GHNQ4CZc0w3VMzUPFTkKLwk6N2XLdaZ3Y/ALpgKfELg19l9hEzR+xHZXQweZ+ZNIw9Y65rmkW1OZkjW8nZS9HwRV0Q0cc+hWCg4LzerXhnhRueEa9zy3fgp2lq7kR5BJl/F0fP1h6Y1mn8rsxoHIHh+czXW9S/q6RLhjZDoNlvaxTwxldUuHunfO/LdykDe+nhD+P7wfNXU+5xHnNew8P4ma4bbCEzFDUzaK9qwLKRz0f2HPf1t5N6XqCJEjFTI8PSyUrL80LxokG8khVcttNDOWCgQr4rHKALd8wueHI+nvQlj304lPtsamb/jfZ3XfS8n2+NGJQS32sqtdrJ88jFAIo7ntbp7XIZbnXaWiYpTRREmuaQUUAWAmzGtMq2/SFQcXpUhp/SRmdQReqqb6K4cVMHL0K6VHpeXzm3dLuvQ2S+oZXTFRG3/g/Q07Gjma3mCJ8yXMcq36HkRhm6Rq/tjjqYPnYfVjNLwnOpG06/4casOfVNRUz2Ywhm7HoYaNITcyiYz6jZmiwTGaP6p1+tFRAfmPZG2bNHCsdnO5cNTAwvoAQAAAAOPx3wMoV8ztUo9lRNlA6oB0MN+yo78n5IGeO96LCHUwQkjusothlBxRPNuPbAbEuxyW+Y8l9r3AwakUvXb1b1j1+1MGUoAnPSy51YGNRCJEFYyBatojsKHXugvuTZftauo1MGbRp34bB+ijtUCHZg2Z9Sq3fsmFaXZL2UyPwwVV5VOFaKZGd67rYeVVaT9IFclpQbcTfPDXwroAppqyI05Jrz8ixETUf8QE51F2VpXgDUvtu/LvPuLpOOYlqwpZOBuCSGyAnCfYK4dwadPqFzpmppj/JHUgn3i+ixqqS8v9iqdWBaWKcoBkZ4xiejQkDN3YWCFgdPKcYtZje2GgthcAqTtoafvJSj5mH04SYF2sslxEYGNPt/L0TqRswNH3XZsjx7tWI1V5zfloOPp8ZQHPg2ooNM88wuTgBhX9WvSP3J6YNbwdoLfpQXc3cq/2KjRX8LuN4kGw7OuVGqzQMwOfW2O1yuD4UYliS01AhtmEaWHmGNbcL1LvK79yU88BQAJoSAAAAAEHG4x4oaK1+fzHlbJJv+YYx6qgdbbKMouDafk7dJrL9Q+syJx7o9vgFs7/JMXoTIylOIzFVXI66RQZ027AjqYAyuR3v0uVU0ekGyRPuSduLmn69tQE8bDYaZI8FW6Ma75qYpwWu2YZpIVSFDwQHTIW6XX9JiMMKM7TZMlv2xFDLP8Wz6PM3mY6JfFKRaBVKzjRFPtn6+LcMsRd4WMzHwObSZk/Zmru1nNd1xgQ0XgjyKOLun6KRTxWYogqL6fDcPzRNG/wFJOqcHgDyuoKULlPsGpAyJAX5S7z8qDnM3nrhIqrLp5o0RXxPq6R8Si6+/WRDOpicoSVneOEJ0JID9ms3+SnrZNLRYWNL1X/A8mKbOr9UUDl3uGpw0O/GOpODR7P6eVLUva57+HUJOfkZzC8qdKK5inQKQuqtZ2ojFaevGhEKK2l3j/nBrIB+V6s1VLggguX+qTiPoq3YyUGEmu/U4cFVKMb4BpdbPaHUxSLtsFhvlYwdcKkHa05rRlA0g4Yhz6eSawc74GSTY6HVFgAAAAAAH52TbIWRLMnL5HQKlj4JG8JBd0WN2uiA22f3LQxm369Gv3SkIcRsFJtVSwWwxjCYdpZ7aY8kCvOUosL/UStddrTtVKsG6r3OdGbhjY9BbUgndVUdPl6gBfewZjKL7eIih/q0TjaTh55RsBCfO5cRJkLwIA3cSTA0g1F1Gyjcpl/9uSeGHK5UdHp08q68NC+kdrnPuTnVb3+gmKoparBlhozDWRI9pc23NsrJ6ni7tJ036xaErAOoAp3orGNO0yB7H2z2+9H1bUFq2QiSOLtdOB3PjlBKgmA/Hfr67R6hwxukOhnUN4NxvdGFYFXz7NzE6IbEXgYuWgoPIcETbjR/odkS2ELwcLQXrayt84GMVmE7AnfJ4e19Vp3b4B4HcUDJARVJVwk1Irf1vQN/0LNPY4pKE4EdgR9xRMqi6AgkbpTq07RpgXlt9DrEKvFMwdh/NRmRAhU393FZ23KwMjZ8K6d6tdDWHzk1oERlo0TjFPFoqPWMjLOoT6rCHzXZ7BGX2bNvOIpavSOxQ39vKsNVs0j8xeJWCEbHGvwlMNwplmME/VlfVpGFahU0BNaOdfUH3maE1sIgbIt6IhBtzljV5xlP4ticAAAAAAO1wj7Wjw9ti07doVawGbX2ji+Zuq+Drx55fTi3g6YMtR+hhan+nsgSRYewFB+Agffr/aN8ELcwF1ts0ThshaxeDgPWWl/ETDg40OvA6iRrLU0UmEOWHqnJkGItnminA81Ot+vMGMQxJDh6jrQwMjop5ni1Elw3LiByRGkdmlnUwiP+xQTwNMfSFoTIkjFMX+3oEhNeP4rK3btJ6YlQRo2U897Wg9Gf0VFs67Njljhw/xM/8HpzzleeSHK12p/0nJcdSi52n/njHoSiCRnBb0OWn5DiOhG0iW9PwMkSH7L0eGlyTbj6yLhmQNoC9kI4dq/v+D97Iv5n2TlQAK0bEx1NFayBLgR5m7AoVEQ/RKaMVCK1Ag2V1tRA/DUPqmuzflOqU6YGXEgpD3DGT+8ssq2DR2ChX3r/whYjbB6H8redTgGcZ+dF80TYHfyEJ1qgEBM+2FhuldvUUVCK0DSiCrTb8YyaVn7Ov2tKv9rqYogpplHRVy6PYKkdJrljvkwekbodR/eEeANItA1x6f+xSaMas83P8iX4IriCm9CBSd79hDEpajvXvSJ5wAAAAAAABBdzLknechLu2C/gen86jr9grp6TZvlgP0Crrn3JjOjAKS3yAi0PujrI0s4reuXUOfd4Px3EkahVQ31UOzgkh+rVWjA3ApHbXszBfflNG+QhbfNeirgfl61MGEgVdZ+L/ns4XJ4jqayvyjheMWePhh0m8XguPM6C/eTPtkJ7bHVszy7FnwbrXLOEDo+KTil6cA6magoZqLRcdHyWkh++EQgd9fpu3fT5g4Ep3nrfSV5yknmyKliaOdo5f3VdvFK3DrEP0zbOHygKFc+oUbuWXrVT4CHw67F5w1urnAXVJjJQAE86PbpfGyeVoDlUhMBRTjUN8IIAqrFNWqtzd6QhwCZRGDvsacZwx+KARmI3mbdABOZuwERsnJQkp1rMWTSXOH/0s0TPa4b36nGoInKWegKNEdOfmdB7sPZVLm/gel7rw5wm/dqRkFBxuboh3OfXyrIBtpYKXWogsnuZ1i0rUwDgJ2ytGKft6yebeiWY9Kt+br1yGv4WXaDy3ygy0bR+tBo+hD7VrL+i6lWhY3ZDLFP8RmRgUXFL1TYEWBjMEiuHaGqQDT/tIV0X1yeZTNZMqy4K49Rw3uOtWOMeryNdRK/xrirBJEyAAAAAAAtojf53cLrzYIRJl8/tJGNLgKfG7EyihwNSgVCoWkzJyHK9T9v6JpDiwEmNY9gcAasv4bzoE3ddlDUKbqAtOsw2VTLkzNk3aeUvp9NxWjl2pTtL2I9CZEvhMdezzyBB+8NMna8VHciw5fI07tU93D6q6ezgSXaJyD+5HbYMSRyv4NThk4OJLIXvWUBvmtg0TckfKf4QFgGLD/SSKmEAbRz9sVE5YXnx/tqRDFNg9fgyvTZMcrqnH8u73J8QhffYEf9gI3imKj3FsNredTCpnnSJJQxMzWc/tVqbbaWahoX8oybjKhqSKLSv4FS479Xj3777Nj4FZwXziS6ymsph4SWdKgjaCgui2XGJQil8qs9G6+qWuN6dE/Pj3Tbq0wyNuhQqZCDuj4FOYfoFBDakIjbwcmc8kUsrkkG2+/s6PsHkRejL8wSCv0zmeWRe0+FuaV1oTRii6nuew47Z/5JxRDzXouAre/a9lX//dm6lYAsBpSlYC+NtAPAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA
📡 API Calls Detected
- POST
- GET
📊 Detalhamento da Pontuação de Risco
Contributing Factors
🔬 Análise Integral de Ameaças
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 75 obfuscation techniques
🏢 Análise de Falsificação de Marca
⚔️ Metodologia de Ataque
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 75 techniques to evade detection by security scanners and make reverse engineering more difficult.
Drainer supports multiple blockchain networks and checks for high-value tokens on each chain before executing drain operations.
🌐 Indicadores de Compromisso de Infraestrutura
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)