
Phishing Analysis
Detailed analysis of captured phishing page
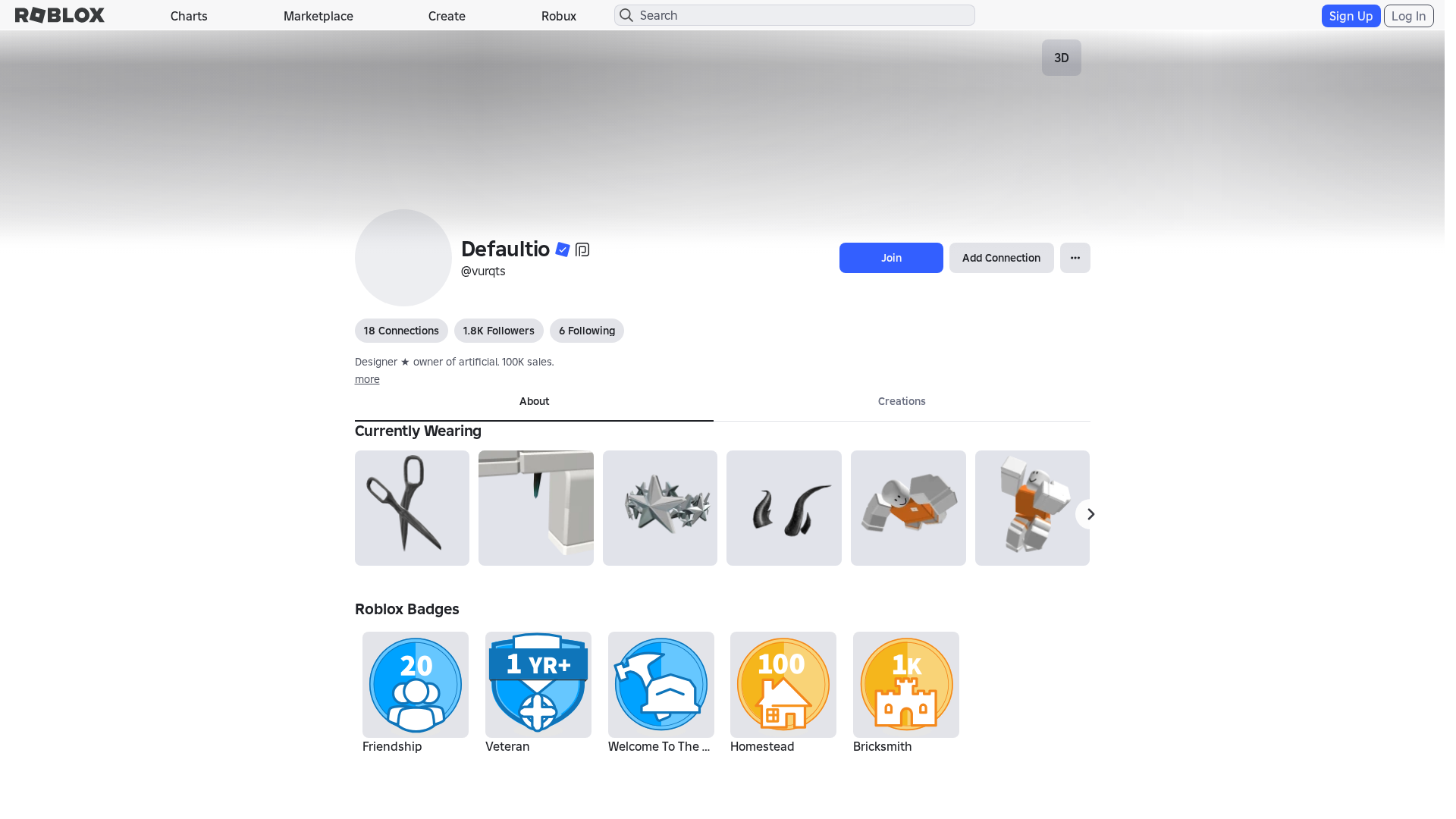
Captura Visual
Informações de Detecção
https://www.roblox.re/users/5704265775/profile
Detected Brand
Roblox
Country
Unknown
Confidence
100%
HTTP Status
200
Report ID
4dd49f66-165…
Analyzed
2026-03-30 20:18
Hashes de Conteúdo (Similaridade HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T19F83877292502437617B79D9F065771AA2D3D70FCA8246E1A2FC93AA0FD6CE1F81740E |
|
CONTENT
ssdeep
|
1536:ZBMXWn9rJm7+jeXvTaf+YuO4eZJZx7Hq7Hv7HL7HH7Ho7Hdz7Hv7HM7HL7Hk7H0K:/MXWHm7hLmruOj7K7P7r7n7I79z7P7sQ |
Hashes Visuais (Similaridade de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
bc0f1331d390cdf4 |
|
VISUAL
aHash
|
0000fbffc3e3c7ff |
|
VISUAL
dHash
|
be3c363016061c1e |
|
VISUAL
wHash
|
0000d3dfc3c3c7ef |
|
VISUAL
colorHash
|
072010080c0 |
|
VISUAL
cropResistant
|
be3c363016061c1e |
Análise de Código
Risk Score
100/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🎣 Card Stealer
🎣 Banking
🎣 Personal Info
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- hex_escape
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- https://www.roblox.com/catalog/124133969040178/null
- /catalog/139607718
- https://www.roblox.com/catalog/6550129/null
- /catalog/658832807
- /catalog/11573370910
- /catalog/658833139
- https://www.roblox.com/catalog/18698660019/null
- https://www.roblox.com/catalog/15093053680/null
- /catalog/439945661
- https://www.roblox.com/catalog/13112718134/null
- https://www.roblox.com/catalog/139607718/null
- https://www.roblox.com/catalog/658832807/null
- /catalog/4637151279
- https://www.roblox.re/catalog?CatalogContext=1&Keyword=
- https://www.roblox.com/catalog/79479709542439/null
- /catalog/628771505
- https://www.roblox.com/catalog/105907355922978/null
- /login?returnUrl=2785344935925744
- https://www.roblox.com/catalog/11573370910/null
- https://www.roblox.com/catalog/658833139/null
- https://www.roblox.com/catalog/123530341978004/null
- https://www.roblox.com/catalog/126354114956642/null
- https://www.roblox.re/info/blog?locale=en_us
- https://www.roblox.com/catalog/439945661/null
- /catalog/6550129
- https://www.roblox.com/catalog/4637151279/null
- /catalog
- https://www.roblox.com/catalog/117863280989654/null
- https://www.roblox.com/catalog/628771505/null
📡 API Calls Detected
- POST
- GET
- https://ro.blox.com/Ebh5?
- get
- babylonjs
- https://help.roblox.com/hc/articles/30428367965460
- https://apis.
📤 Form Action Targets
- /search
📊 Detalhamento da Pontuação de Risco
Total Risk Score
100/100
Contributing Factors
Active Phishing Kit
Detected kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
Credential Harvesting
Credential harvesting detected with 1 form(s) capturing sensitive data
Code Obfuscation
JavaScript code obfuscated using 229 technique(s) to evade detection
🔬 Análise Integral de Ameaças
Tipo de Ameaça
Banking Credential Harvester
Alvo
Roblox users
Método de Ataque
credential harvesting forms + obfuscated JavaScript
Canal de Exfiltração
HTTP POST to backend
Avaliação de Risco
CRITICAL - Automated credential harvesting with HTTP POST to backend
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 229 obfuscation techniques
🏢 Análise de Falsificação de Marca
Impersonated Brand
Roblox
Official Website
https://www.roblox.com
Fake Service
Banking/payment service
⚔️ Metodologia de Ataque
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 229 techniques to evade detection by security scanners and make reverse engineering more difficult.
🌐 Indicadores de Compromisso de Infraestrutura
Domain Information
Domain
www.roblox.re
Registered
Unknown
Registrar
Hosting Concepts B.V. d/b/a Openprovider
Status
Age unknown
Hosting Information
Provider
Hosting Concepts B.V. d/b/a Openprovider
ASN
🤖 AI-Extracted Threat Intelligence
Scan History for www.roblox.re
Found 10 other scans for this domain
-
https://www.roblox.re/games/80094481358254/Sword-F...
https://www.roblox.re/games/132949000120744/Sword-...
https://www.roblox.re/games/116881334009378/V4-2p-...
https://www.roblox.re/users/7843616099/profile
https://www.roblox.re/communities/4333423243/Build...
https://www.roblox.re/communities/3297083824/Pixel...
https://www.roblox.re/games/18737532107/Dont-enter...
https://www.roblox.re/users/1499510197/profile
https://www.roblox.re/communities/9161997419/Blade...
https://www.roblox.re/users/2292934203/profile

"Nunca pensei que aconteceria comigo"
Isso dizem os 2,3 milhões de vítimas a cada ano. Não espere para ser uma estatística.