Phishing Analysis
Detailed analysis of captured phishing page
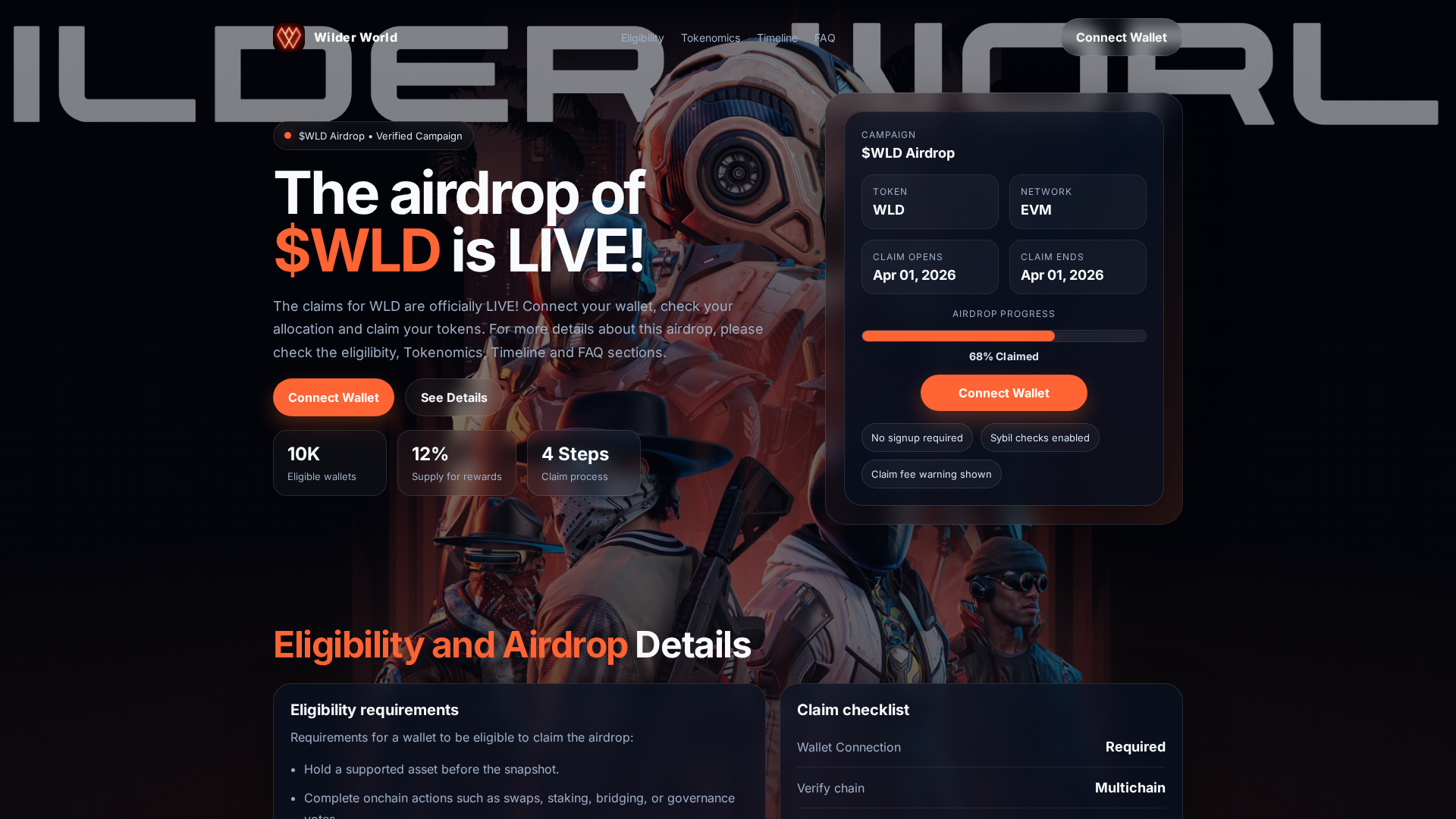
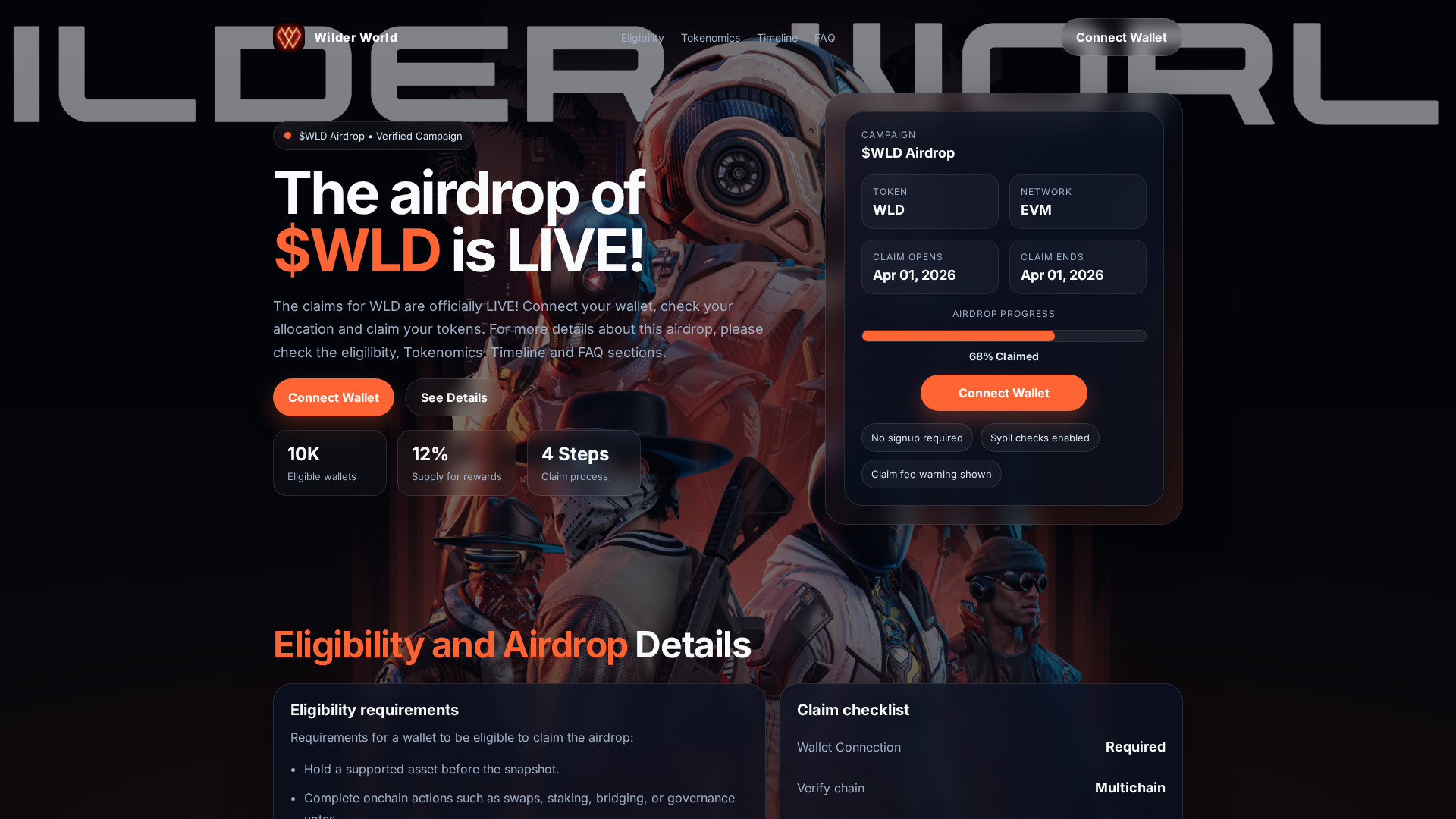
Captura Visual
Informações de Detecção
Hashes de Conteúdo (Similaridade HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1BCF123B0B059EA37119782E1A7E1A7ABB3F18518DA57031112FDC3AC8FE5E85DC62189 |
|
CONTENT
ssdeep
|
96:NaZNzl4N/YsOoV6LqJVZTAwaAd+OQg4MIHFgSNzHYiG48rhrDBO:NaZNzl8wWV6OJfTBaS+OZIlTiA8hrDs |
Hashes Visuais (Similaridade de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
c7c5a5bdb1940c47 |
|
VISUAL
aHash
|
ff7c383c34383c20 |
|
VISUAL
dHash
|
c2c1e0dccc61f0c8 |
|
VISUAL
wHash
|
fe783c7c3c1c3c20 |
|
VISUAL
colorHash
|
312000c8000 |
|
VISUAL
cropResistant
|
c2c1e0dccc61f0c8 |
Análise de Código
🔒 Obfuscation Detected
- unescape
📡 API Calls Detected
- POST
📊 Detalhamento da Pontuação de Risco
Contributing Factors
🔬 Análise Integral de Ameaças
⚠️ Indicators of Compromise
- 2 obfuscation techniques
🏢 Análise de Falsificação de Marca
⚔️ Metodologia de Ataque
Primary Method: Search Engine Manipulation
Fake Wilder World site positioned to capture victims through SEO tactics, typosquatting, or paid advertising. Serves as entry point for multi-stage attacks including credential theft and malware distribution.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 2 techniques to evade detection by security scanners and make reverse engineering more difficult.
🌐 Indicadores de Compromisso de Infraestrutura
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)