Phishing Analysis
Detailed analysis of captured phishing page
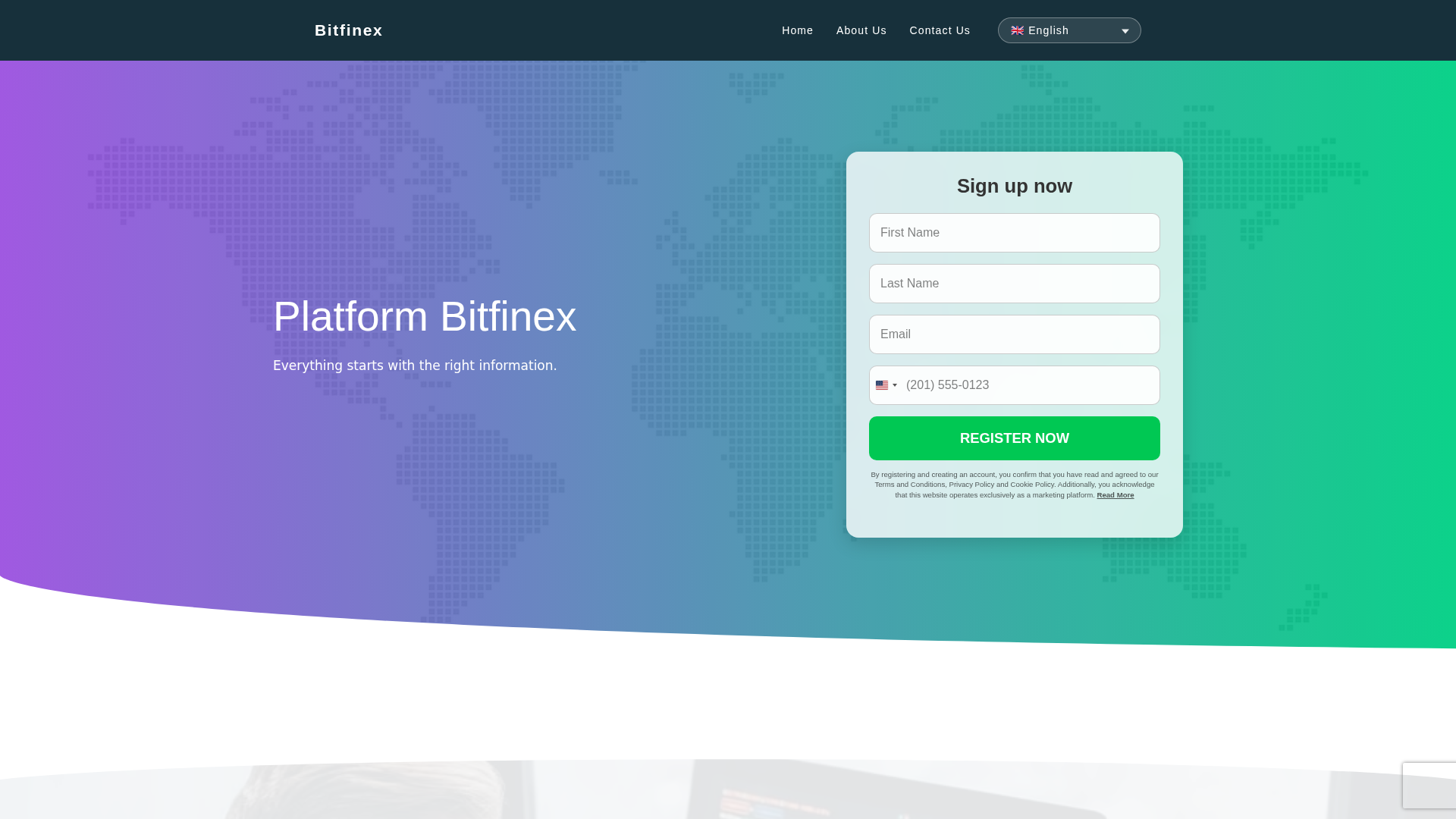
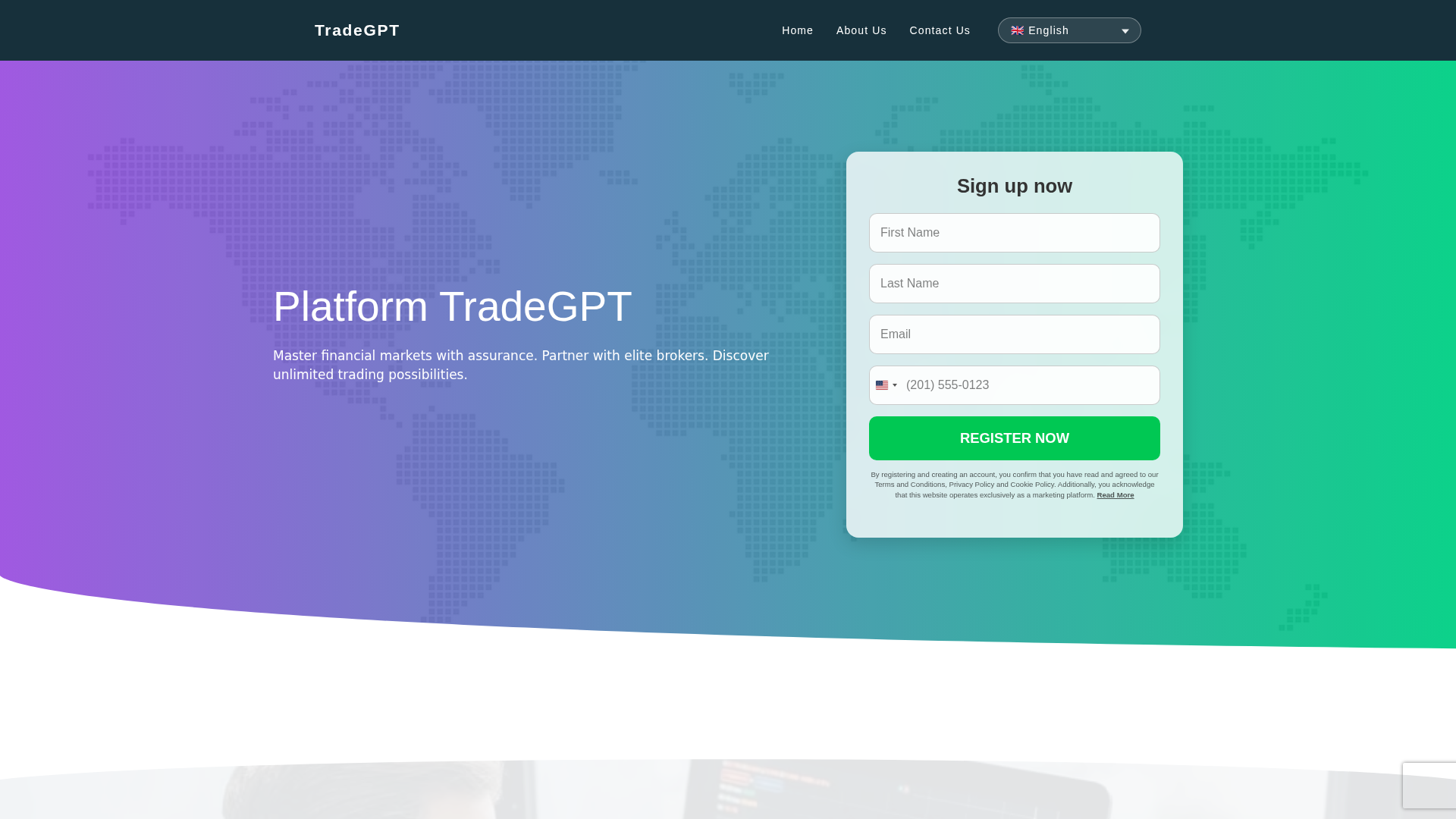
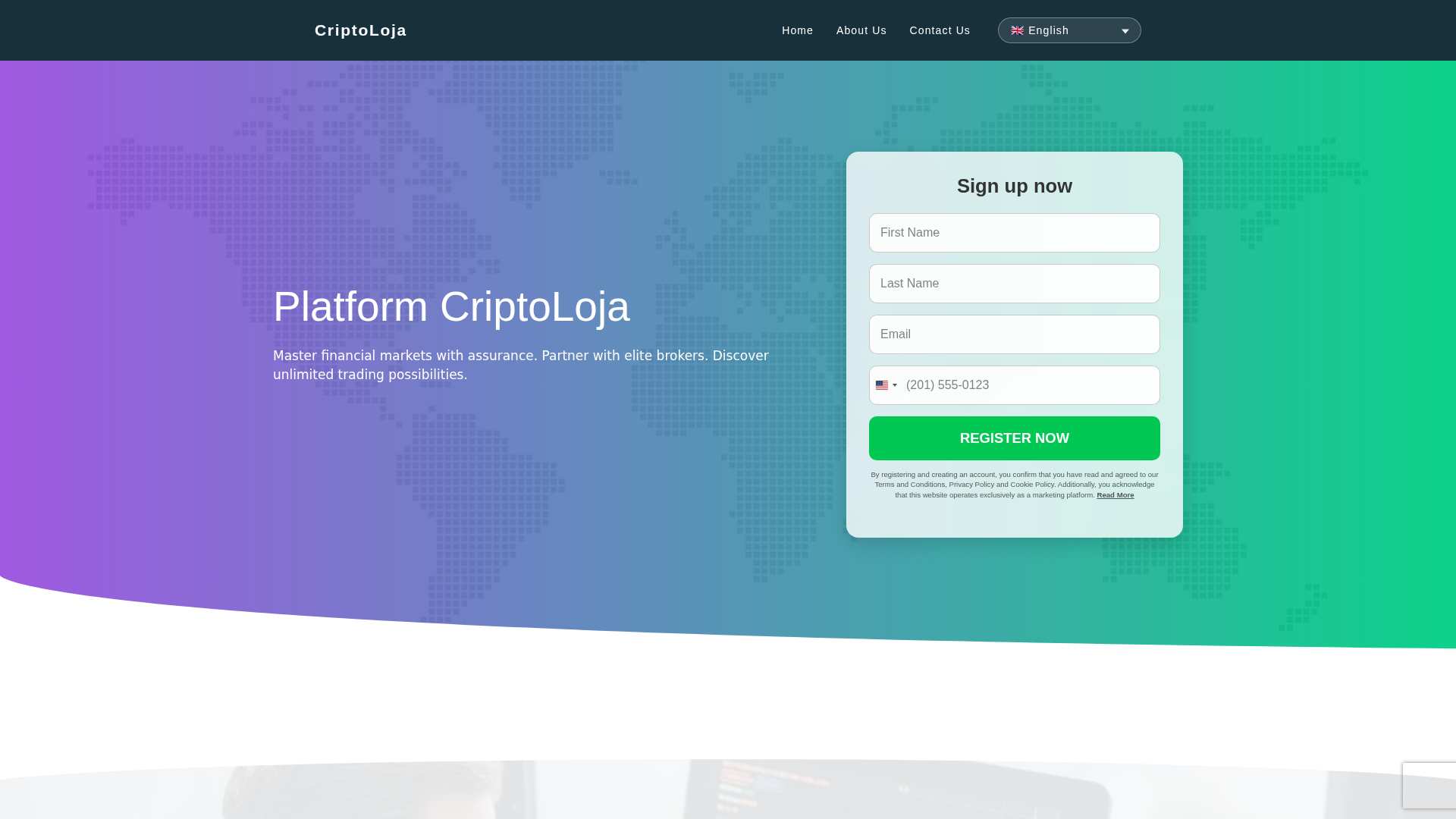
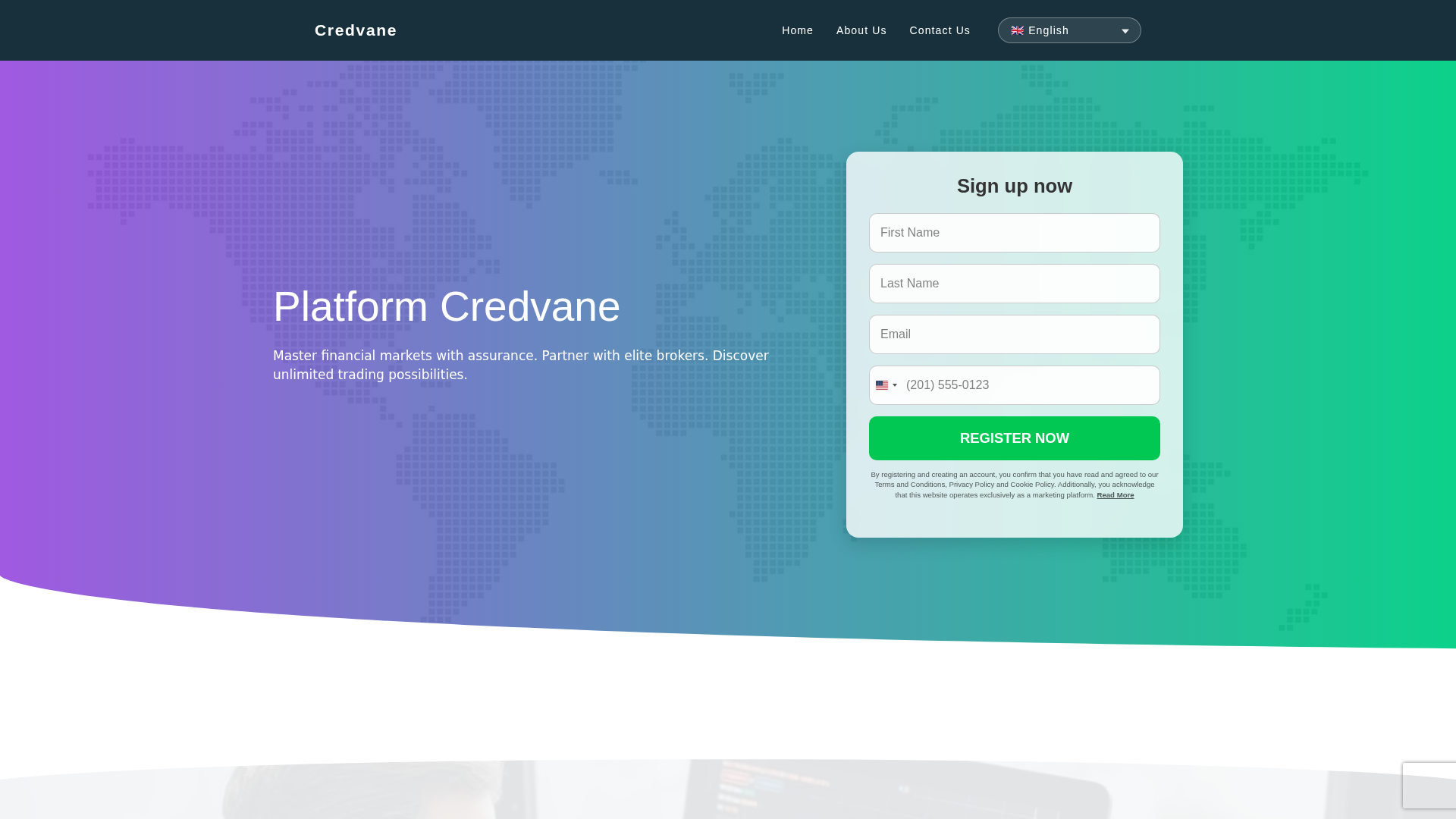
Captura Visual
Informações de Detecção
https://tecfinanza-app.com/
Detected Brand
TecFinanza
Country
Unknown
Confidence
100%
HTTP Status
200
Report ID
50f443bd-bcd…
Analyzed
2026-03-28 01:05
Hashes de Conteúdo (Similaridade HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1C4A3EF234259752A4477C7D430BA1F3BD1AA994BFAE709400EECC7F62BFAC50702B659 |
|
CONTENT
ssdeep
|
768:TNc9tMbXReQ/GJi55RPGOrbi4LKn/sCY9qcnM0:O9tMbXlOJi55R+Ovi4LKnTY9qcnM0 |
Hashes Visuais (Similaridade de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
9612ed690d773692 |
|
VISUAL
aHash
|
00040e060600ffff |
|
VISUAL
dHash
|
d77cecccbc0c0326 |
|
VISUAL
wHash
|
000e0e0e0e8effff |
|
VISUAL
colorHash
|
02003400400 |
|
VISUAL
cropResistant
|
bc6cecccbc0c0026,dcbd6cecccccac7c,1c07432513161c3c |
Análise de Código
Risk Score
100/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🎣 Card Stealer
🎣 Banking
🎣 Personal Info
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- hex_escape
- unicode_escape
- base64_strings
📡 API Calls Detected
- ./form/handle_form.php
- https://amos-mamaya.fun/geo
📊 Detalhamento da Pontuação de Risco
Total Risk Score
100/100
Contributing Factors
Active Phishing Kit
Detected kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
Credential Harvesting
Credential harvesting detected with 1 form(s) capturing sensitive data
Code Obfuscation
JavaScript code obfuscated using 61 technique(s) to evade detection
🔬 Análise Integral de Ameaças
Tipo de Ameaça
Banking Credential Harvester
Alvo
TecFinanza users
Método de Ataque
credential harvesting forms + obfuscated JavaScript
Canal de Exfiltração
Form submission (backend endpoint not detected - likely JavaScript-based)
Avaliação de Risco
CRITICAL - Automated credential harvesting with Form submission (backend endpoint not detected - likely JavaScript-based)
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 61 obfuscation techniques
🏢 Análise de Falsificação de Marca
Impersonated Brand
TecFinanza
Official Website
N/A
Fake Service
Banking/payment service
⚔️ Metodologia de Ataque
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 61 techniques to evade detection by security scanners and make reverse engineering more difficult.
🌐 Indicadores de Compromisso de Infraestrutura
Domain Information
Domain
tecfinanza-app.com
Registered
2026-03-26 21:02:42+00:00
Registrar
NICENIC INTERNATIONAL GROUP CO., LIMITED
Status
Recently registered (1 days old)
Hosting Information
Provider
NICENIC INTERNATIONAL GROUP CO., LIMITED
ASN
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)

"Nunca pensei que aconteceria comigo"
Isso dizem os 2,3 milhões de vítimas a cada ano. Não espere para ser uma estatística.