Phishing Analysis
Detailed analysis of captured phishing page
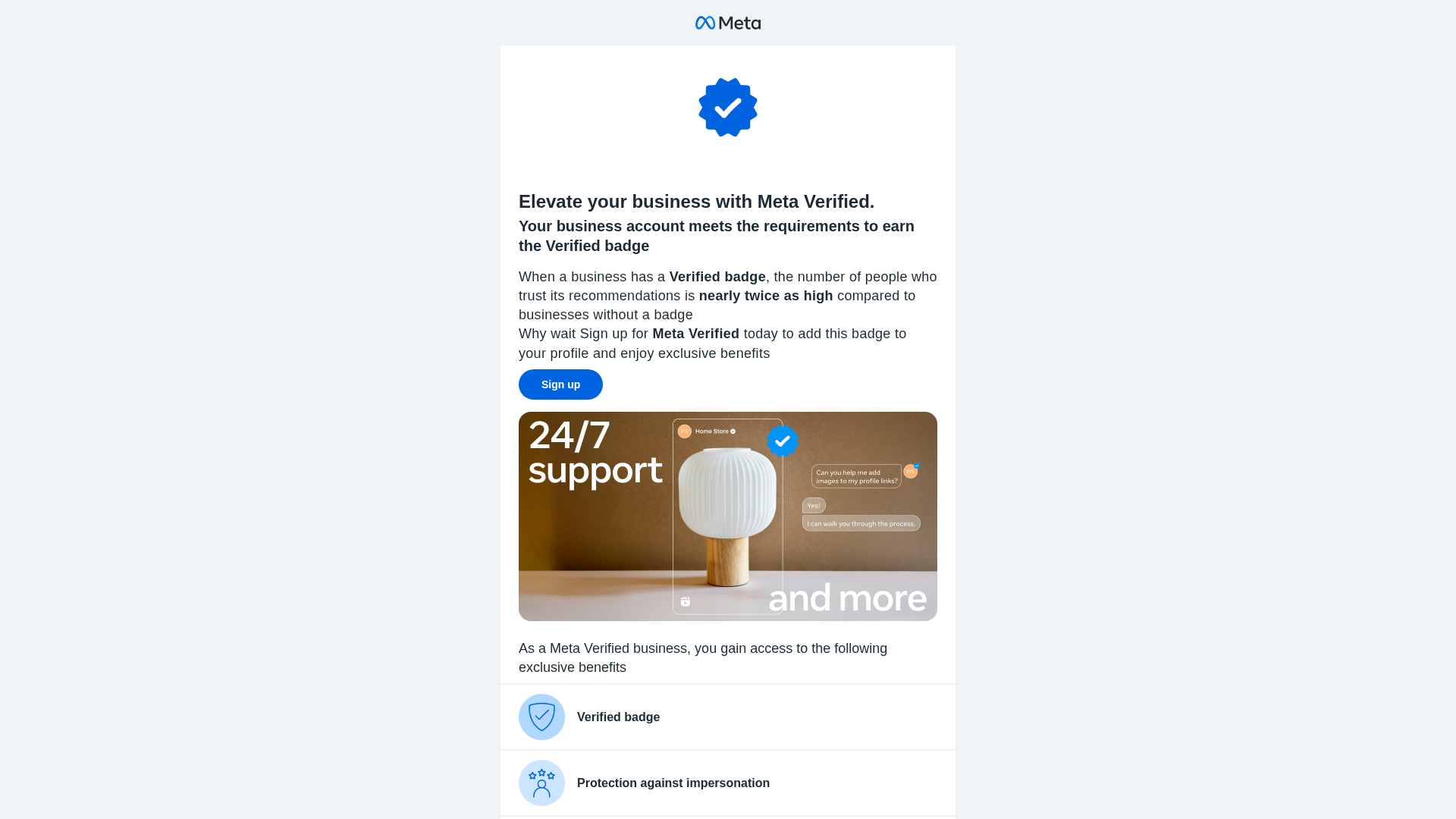
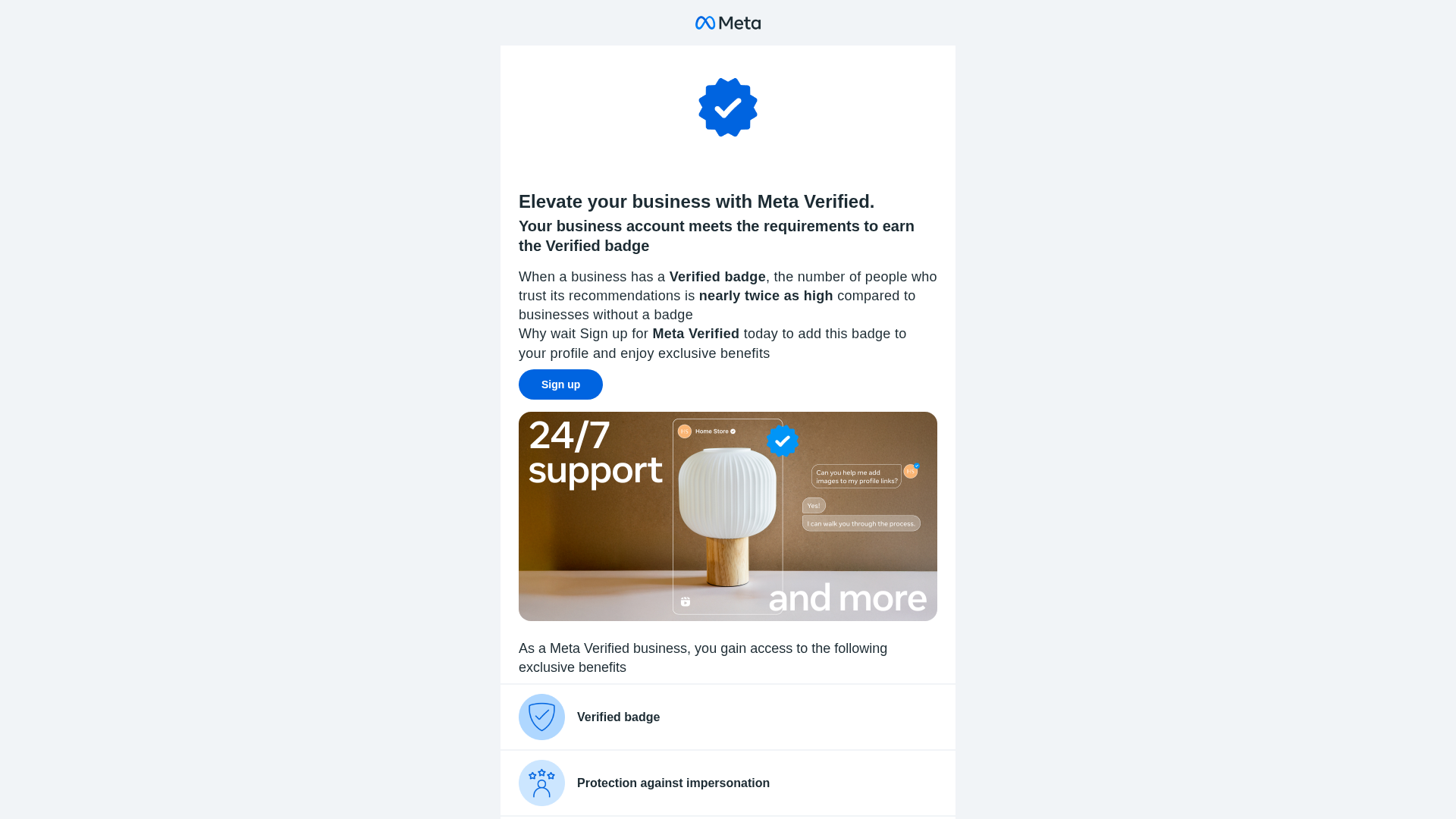
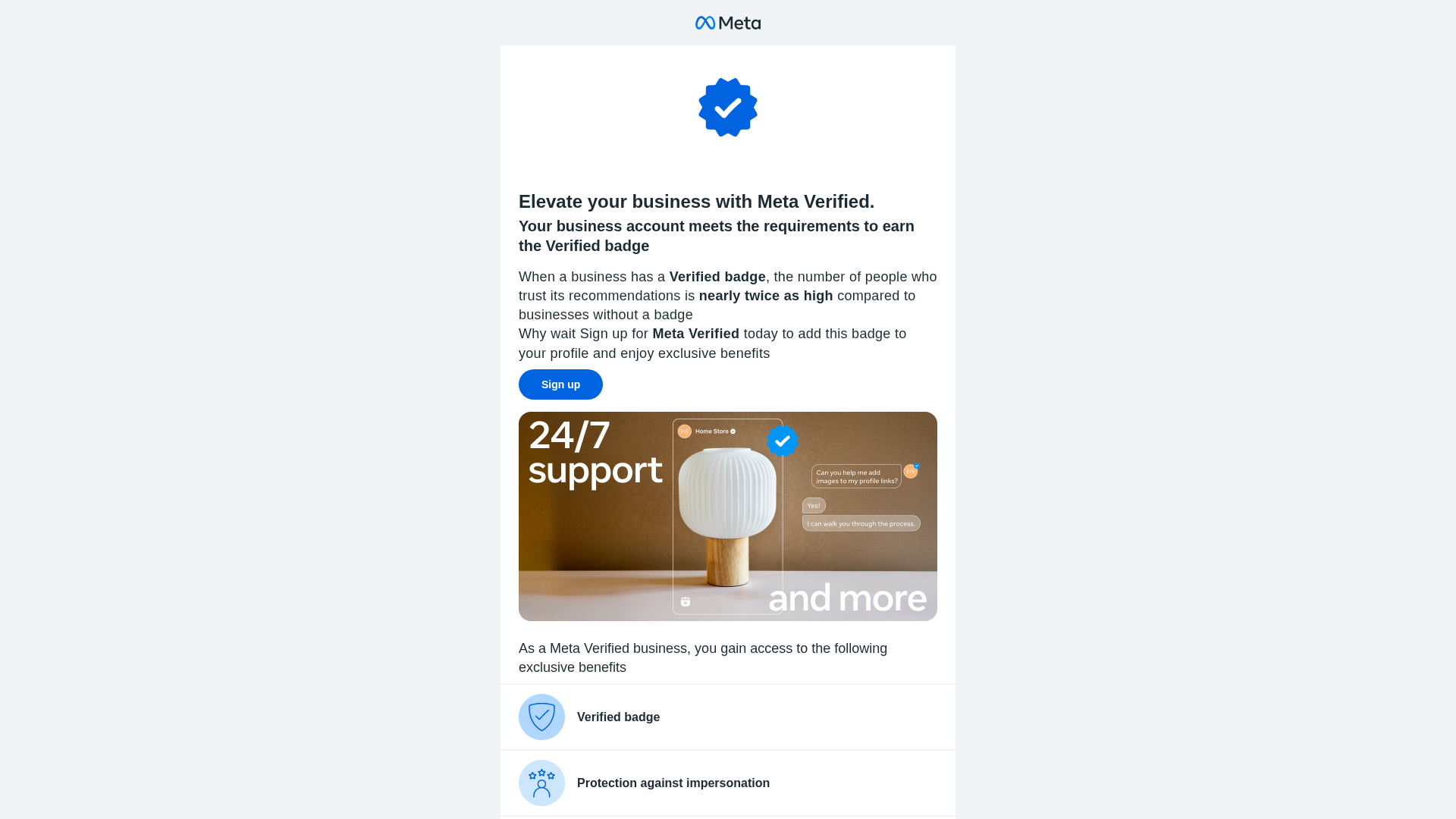
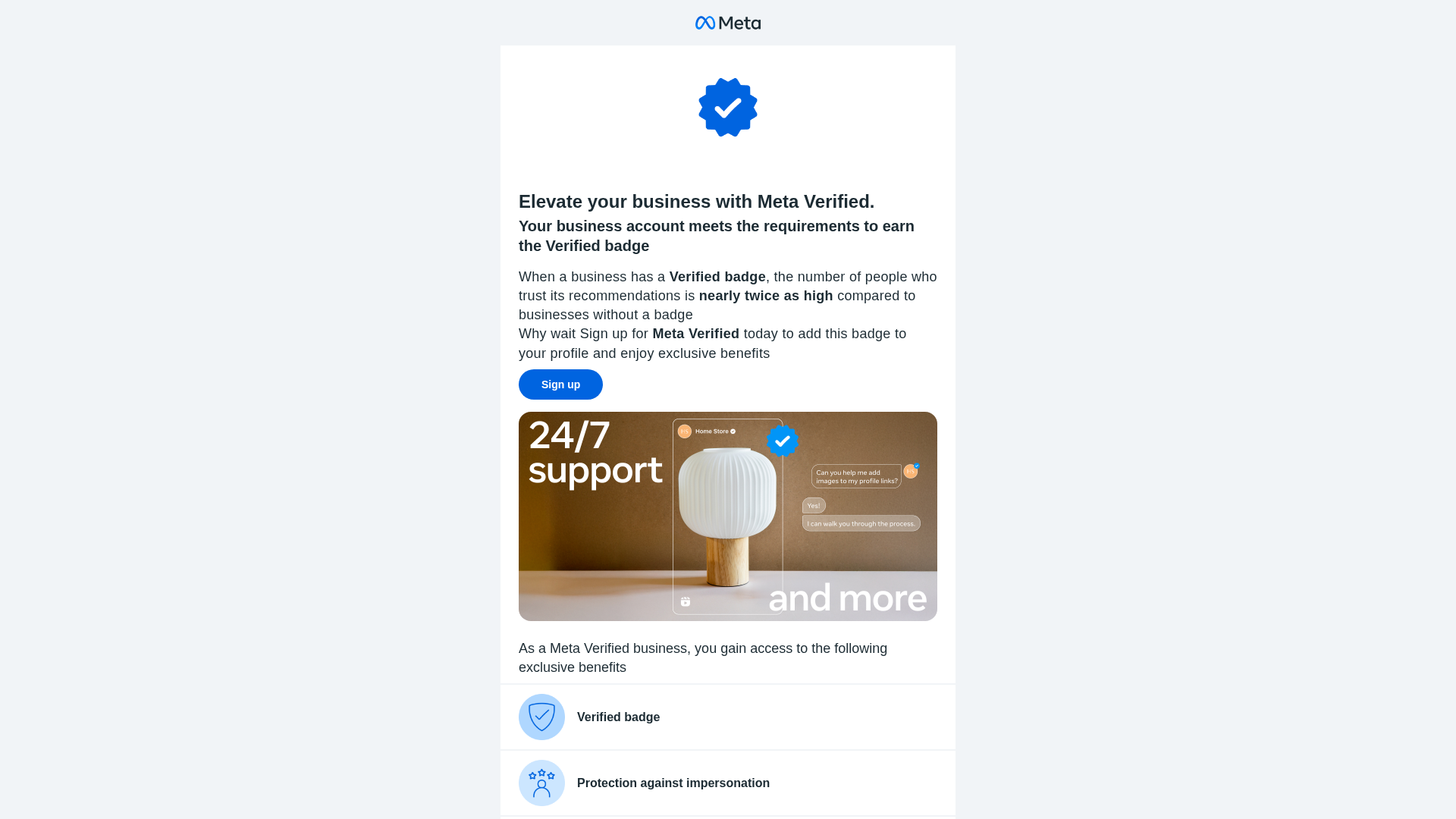
Captura Visual
Informações de Detecção
Hashes de Conteúdo (Similaridade HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1BA725410D904991D01DF8DC5E1736A5822F843AEC31304D8FE60ABFAA6EF839D777669 |
|
CONTENT
ssdeep
|
192:PPpbmWkEcGMkRY/zO2YzorUiXwHBw+FhYEUCpsdxEH5LgnttAjg+ust7VaHa4Xjf:Jbm92UGYEROEXUac7x |
Hashes Visuais (Similaridade de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
b3cecc3364cc3364 |
|
VISUAL
aHash
|
ffffefcfc3c3ffff |
|
VISUAL
dHash
|
28284c1c5d5c1818 |
|
VISUAL
wHash
|
3c24040cc3c3cfdf |
|
VISUAL
colorHash
|
07c00010000 |
|
VISUAL
cropResistant
|
28284c1c5d5c1818,b02030f293b2f070,c34f3f3f3f3f3f3c |
Análise de Código
🔬 Threat Analysis Report
• Ameaça: Phishing
• Alvo: Usuários do Meta
• Método: Personificação e coleta de credenciais
• Exfil: https://financeroutine.com/, //translate.googleapis.com/translate_voting?client=te
• Indicadores: Incompatibilidade de domínio, JavaScript ofuscado, vários formulários.
• Risco: Alto
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- document.write
- hex_escape
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- https://financeroutine.com/author/roselee/
- https://financeroutine.com/
- https://financeroutine.com/money-management-tools-apps-track-spending-effectively/
- https://beta.melroseplacerestaurant.com/media/2025/11/favicon.png
- https://financeroutine.com/?p=1195
- https://ogp.me/ns#
- https://financeroutine.com/category/money-management/
- https://financeroutine.com/wp-json/oembed/1.0/embed?url=https%3A%2F%2Ffinanceroutine.com%2Fmoney-management-tools-apps-track-spending-effectively%2F&format=xml
- https://financeroutine.com/feed/
- https://financeroutine.com/simple-investment-plan-long-term-wealth/
- https://financeroutine.com/category/investing-wealth/
- https://financeroutine.com/wp-includes/blocks/categories/style.min.css
- https://financeroutine.com/wp-content/themes/generatepress/assets/js/menu.min.js?ver=3.1.3
- https://financeroutine.com/#website
- https://financeroutine.com/money-management-tools-apps-track-spending-effectively/#richSnippet
- https://financeroutine.com/wp-includes/blocks/paragraph/style.min.css
- https://financeroutine.com/wp-includes/blocks/search/style.min.css
- https://financeroutine.com/wp-json/
- https://gmpg.org/xfn/11
- https://financeroutine.com/build-wealth-in-your-20s-30s-40s/
- https://financeroutine.com/category/financial-literacy/
- https://financeroutine.com/media/2026/01/Money-Management-Tools-and-Apps-to-Track-Spending-Effectively-768x512.jpg
- https://financeroutine.com/financial-literacy-vs-financial-education/
- https://api.w.org/
- https://financeroutine.com/media/2026/01/Money-Management-Tools-and-Apps-to-Track-Spending-Effectively-300x200.jpg
- https://financeroutine.com/why-financial-literacy-matters-todays-economy/
- https://financeroutine.com/media/2026/01/financeroutine-512.png
- https://sw.run/js/element.js
- https://rankmath.com/
- https://financeroutine.com/wp-includes/blocks/latest-posts/style.min.css
📡 API Calls Detected
- https://ipinfo.io/json?token=0916643fd922ec
- https://www.google.com/ccm/geo
📤 Form Action Targets
- https://financeroutine.com/
- //translate.googleapis.com/translate_voting?client=te
📊 Detalhamento da Pontuação de Risco
Contributing Factors
🔬 Análise Integral de Ameaças
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 285 obfuscation techniques
🏢 Análise de Falsificação de Marca
Fraudulent Claims
⚔️ Metodologia de Ataque
Primary Method: Credential Harvesting
The site uses a visually similar design and branding to impersonate Meta and attempt to collect user credentials through a form, or by redirecting to a phishing site.
Secondary Method: Javascript Obfuscation
Javascript code obfuscation attempts to hide malicious behavior.
🌐 Indicadores de Compromisso de Infraestrutura
🦠 Malicious Files
Functions: iziToast['error']() - Displays fake error message to manipulate user, URLSearchParams - Checks for malicious URL parameter (utm_campaign=lnnf), Cloudflare script injection (c function) - Loads external challenge script, setTimeout - Delays malicious behavior to avoid immediate detection
📊 Diagrama de Fluxo de Ataque
1. Step 1: User lands on page via malicious short link (e.g., sw.run/Verifybluetick) 2. Step 2: URL parameter `utm_campaign=lnnf` triggers fake error message after 2.5 seconds 3. Step 3: Fake 'URL Not Found' toast appears, pressuring user to take action (e.g., re-enter credentials or click a malicious link) 4. Step 4: Cloudflare challenge script loads, potentially enabling further malicious activity (e.g., keylogging, form hijacking) 5. Step 5: Obfuscated functions (n, c, u, p, o, f, i, r) capture and exfiltrate user data (e.g., form submissions, session tokens)
🔬 JavaScript Deep Analysis
🔗 API Endpoints Detected
🔐 Obfuscation Detected
- : Moderate
🤖 AI-Extracted Threat Intelligence
📊 Attack Flow
1. Step 1: User lands on page via malicious short link (e.g., sw.run/Verifybluetick) 2. Step 2: URL parameter `utm_campaign=lnnf` triggers fake error message after 2.5 seconds 3. Step 3: Fake 'URL Not Found' toast appears, pressuring user to take action (e.g., re-enter credentials or click a malicious link) 4. Step 4: Cloudflare challenge script loads, potentially enabling further malicious activity (e.g., keylogging, form hijacking) 5. Step 5: Obfuscated functions (n, c, u, p, o, f, i, r) capture and exfiltrate user data (e.g., form submissions, session tokens)
🎯 Malicious Files Identified
element.jsMalicious Functions
iziToast['error']() - Displays fake error message to manipulate userURLSearchParams - Checks for malicious URL parameter (utm_campaign=lnnf)Cloudflare script injection (c function) - Loads external challenge scriptsetTimeout - Delays malicious behavior to avoid immediate detection
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for sw.run
Found 10 other scans for this domain
-
https://||sw.run/verifybluetick^$all/
https://||sw.run/mszhm^$all/
https://||sw.run/mexteadmca^$all/
https://sw.run/
https://sw.run/Verifybluetick
https://financeroutine.com/money-management-tools-...
https://financeroutine.com/simple-investment-plan-...
https://sw.run/MexteaDMCA
https://sw.run/MexteaDMCA
https://financeroutine.com/daily-financial-literac...