
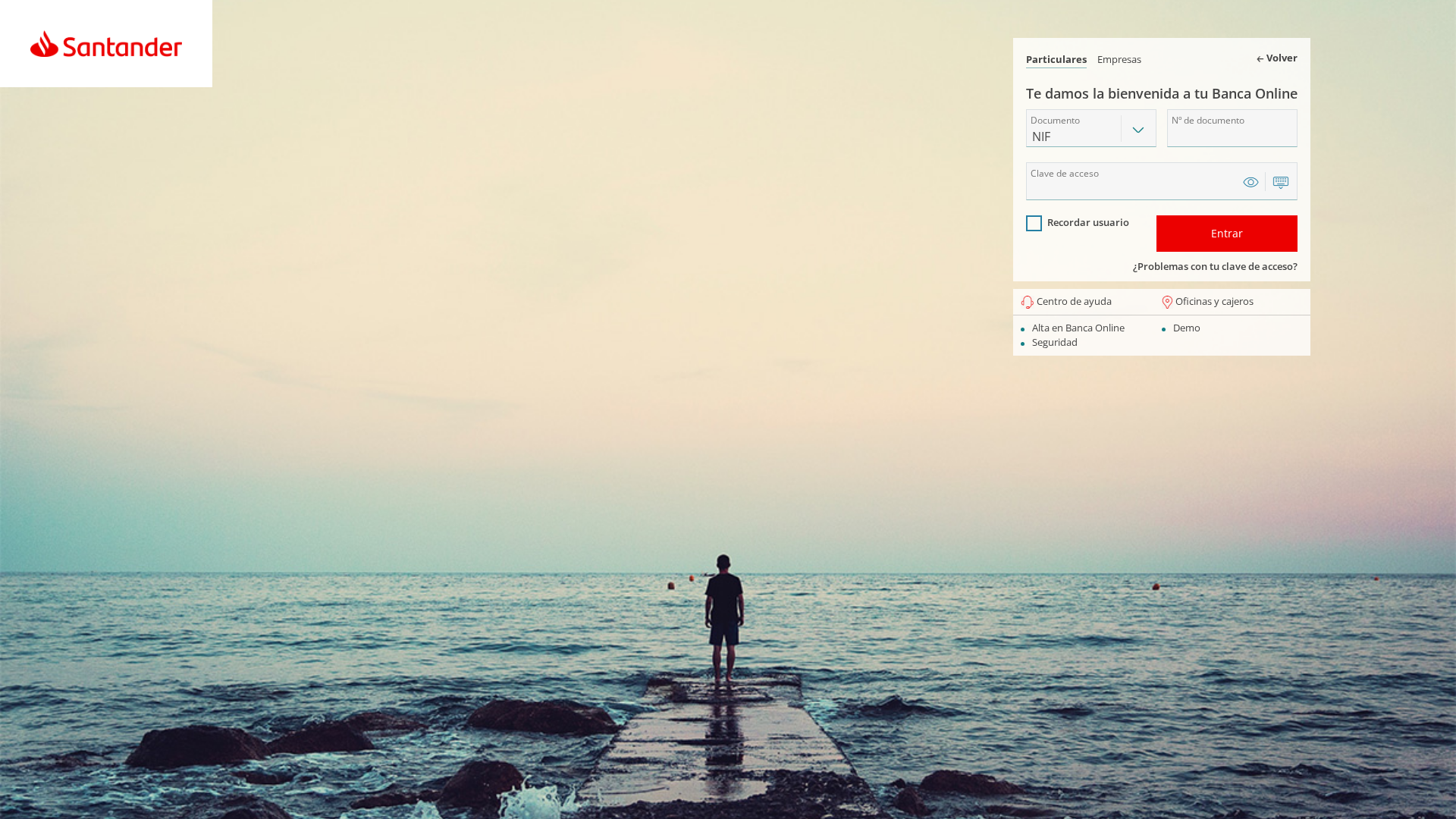
Phishing Analysis
Detailed analysis of captured phishing page
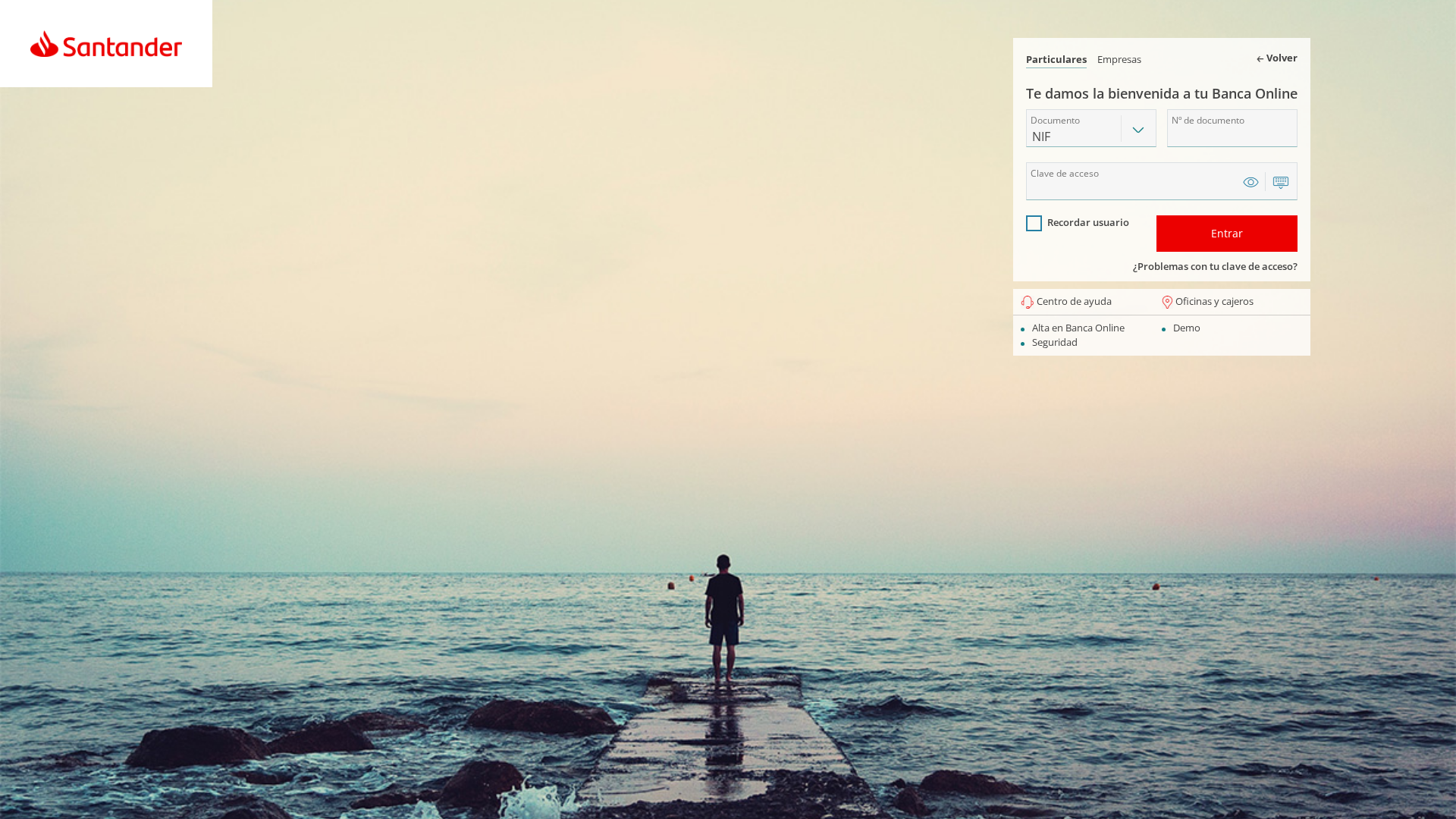
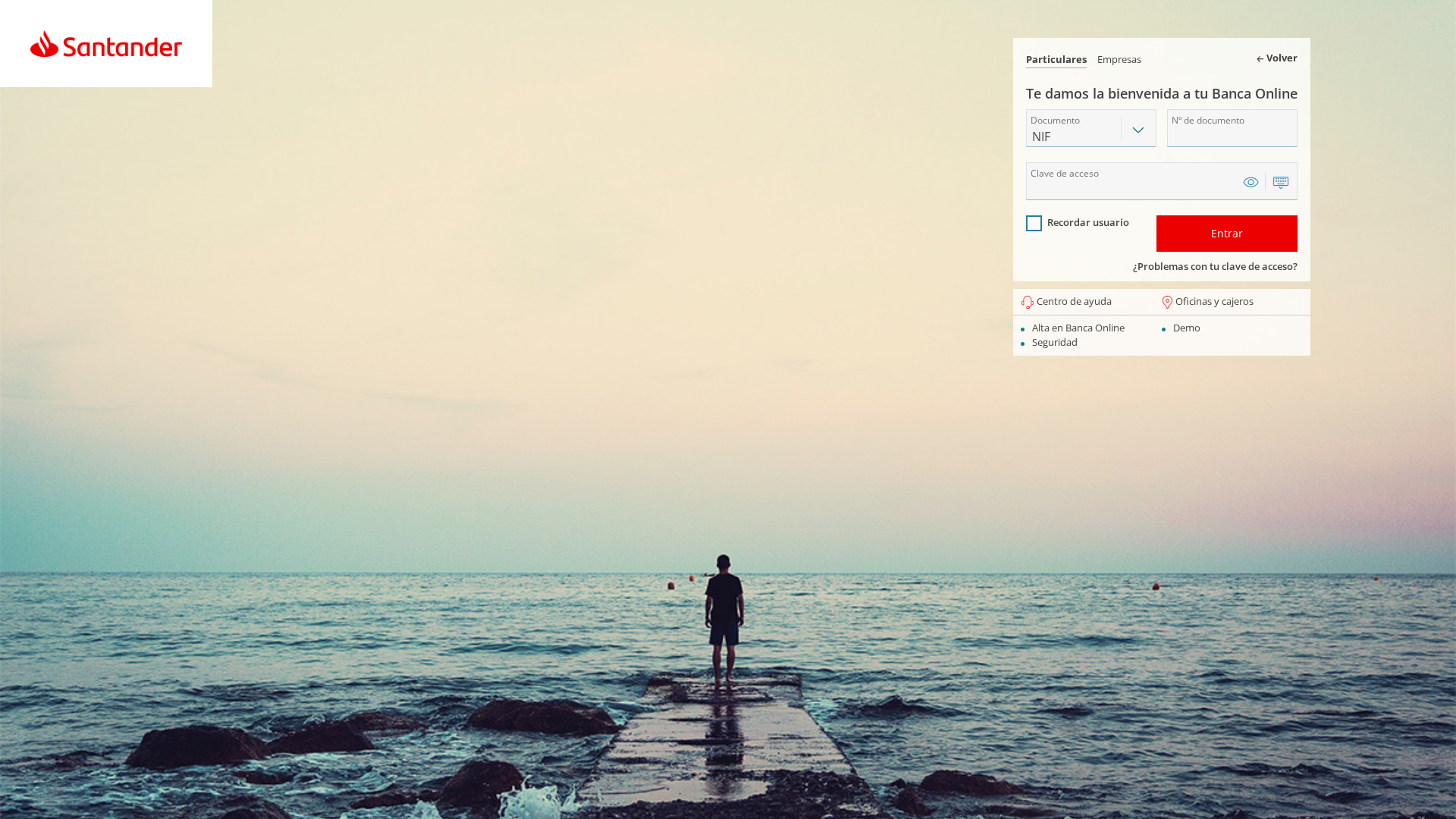
Captura Visual
Informações de Detecção
https://maq.khd.mybluehost.me/website_38190c3a/in/login.php
Detected Brand
Santander
Country
International
Confidence
100%
HTTP Status
200
Report ID
55ffd852-60f…
Analyzed
2026-03-04 22:16
Hashes de Conteúdo (Similaridade HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1F151CF206189BD2F048392C48FB55B8E67D58361CF530B4512EDD39E9EC6D98DD2B845 |
|
CONTENT
ssdeep
|
48:RJoPDCSEGquo/vGjnYQZV1wpuM6e1e30DUH9Ab0GAkxo9orVClWTbK:PUuSM0YcTwpu54NDCjGAkxworVClYK |
Hashes Visuais (Similaridade de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
d4e83dc12df14a5a |
|
VISUAL
aHash
|
ffffffffff200000 |
|
VISUAL
dHash
|
26c4d5e6f0e88874 |
|
VISUAL
wHash
|
fffffdff08000000 |
|
VISUAL
colorHash
|
07006000000 |
|
VISUAL
cropResistant
|
26c6d5e6f0e8c85c,c8e8c88c1478f426 |
Análise de Código
Risk Score
76/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🎣 Banking
🎣 Personal Info
🔬 Threat Analysis Report
• Ameaça: Phishing
• Alvo: Clientes do Santander
• Método: Roubo de Credenciais
• Exfil: ./Assets/php/config/func.php
• Indicadores: Domínio suspeito, Obfuscação, Ações de formulário.
• Risco: ALTO
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- fromCharCode
- base64_strings
📡 API Calls Detected
- ./status/update_status.php
- http://localhost/ES/santander/panel/api.php
📤 Form Action Targets
- ./Assets/php/config/func.php
📊 Detalhamento da Pontuação de Risco
Total Risk Score
95/100
Contributing Factors
Suspicious Domain
The domain is not the official Santander domain.
Form Action Points to Exfiltration
Form submitting to a php file with obfuscation
Impersonation of Banking Brand
Mimics Santander's login page
🔬 Análise Integral de Ameaças
Tipo de Ameaça
Banking Credential Harvester
Alvo
Santander users (International)
Método de Ataque
Brand impersonation + credential harvesting forms + obfuscated JavaScript
Canal de Exfiltração
HTTP POST to backend
Avaliação de Risco
HIGH - Automated credential harvesting with HTTP POST to backend
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Banking, Personal Info
- 3 obfuscation techniques
🏢 Análise de Falsificação de Marca
Impersonated Brand
Santander
Official Website
https://www.santander.com/
Fake Service
Online Banking Login
⚔️ Metodologia de Ataque
Primary Method: Credential Harvesting
The attacker attempts to steal user credentials by presenting a fake login form that mimics the appearance of Santander's official login page.
Secondary Method: Obfuscation
The use of code obfuscation helps hide malicious code and makes the analysis of the site more difficult.
🌐 Indicadores de Compromisso de Infraestrutura
Domain Information
Domain
maq.khd.mybluehost.me
Registered
2016-10-05
Registrar
Namecheap
Status
None
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Santander
https://lms.khurasan.edu.af/2/login.php
Abr 06, 2026
Santander
http://ggg.ixo.mybluehost.me/ryf/login.php
Mar 31, 2026
Santander
https://ggg.ixo.mybluehost.me/ryf/login.php
Mar 31, 2026
Santander
https://ggg.ixo.mybluehost.me/ryf/login.php
Mar 31, 2026
Santander
https://encausticcementtiles.co.uk/santaticket.encausticceme...
Fev 18, 2026

"Nunca pensei que aconteceria comigo"
Isso dizem os 2,3 milhões de vítimas a cada ano. Não espere para ser uma estatística.