Phishing Analysis
Detailed analysis of captured phishing page
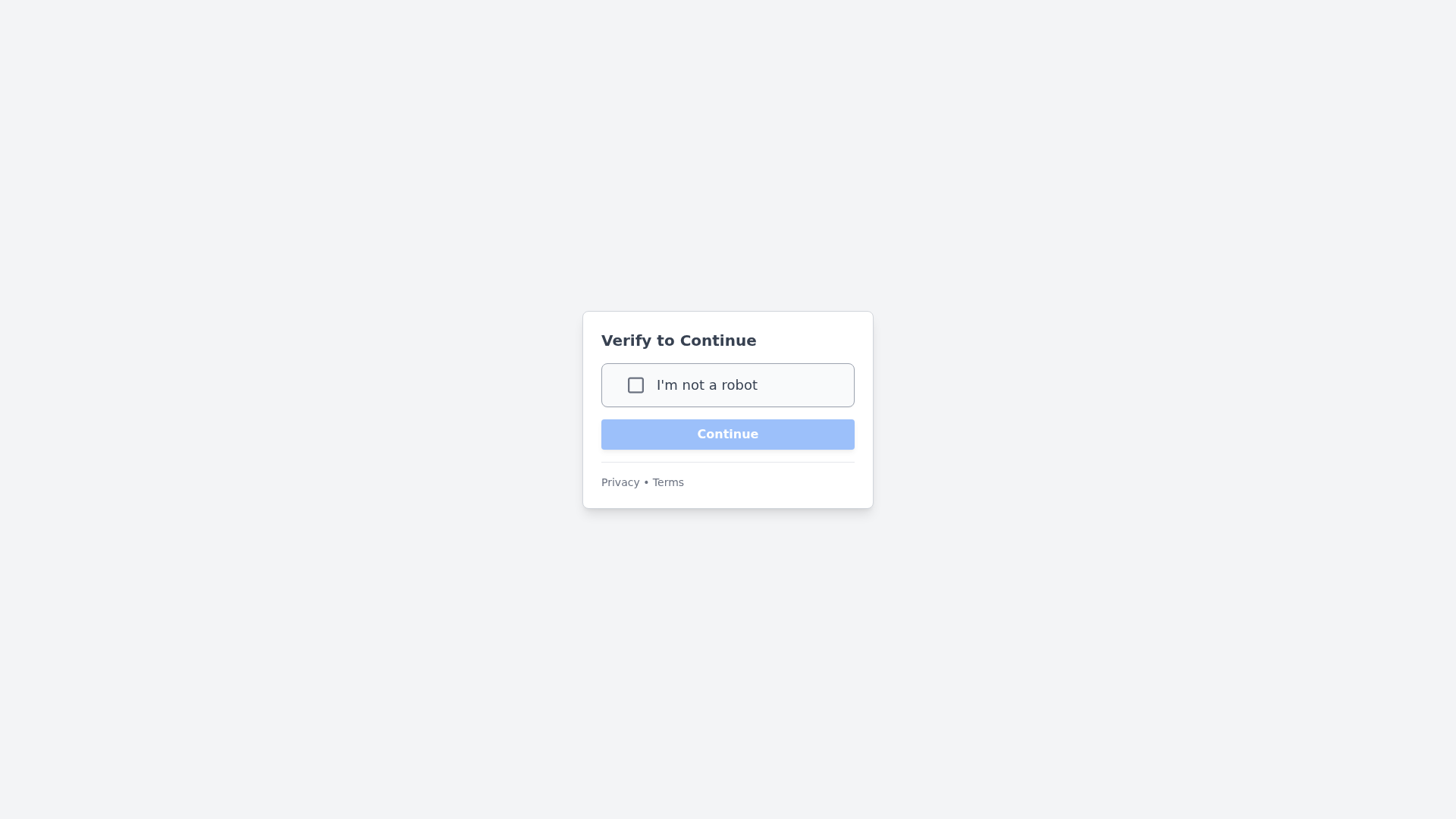
Captura Visual
No screenshot available
Informações de Detecção
Hashes de Conteúdo (Similaridade HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T12D516620A0101C9B23CBC9D997B8274626E1C331CE432C896AFC52FC6EF7E9165657C6 |
|
CONTENT
ssdeep
|
48:ioYcMWupUH56sAd8psAQ3sosCSWA1qJV573n3nol3gEOTg1atSdWCqbhkvMBcpKD:i4HuiofAgVTSWkO7Xol3OTVCD4cpKXuS |
Hashes Visuais (Similaridade de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
b399cc6633998c66 |
|
VISUAL
aHash
|
0000181824180000 |
|
VISUAL
dHash
|
000810324c100000 |
|
VISUAL
wHash
|
ccccfcfc03033333 |
|
VISUAL
colorHash
|
07038000000 |
|
VISUAL
cropResistant
|
000810324c100000 |
Análise de Código
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- hex_escape
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- assets/login.js?1710922708
- assets/login.css?1710922708
📡 API Calls Detected
- POST
📊 Detalhamento da Pontuação de Risco
Contributing Factors
🔬 Análise Integral de Ameaças
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Banking, Personal Info
- 86 obfuscation techniques
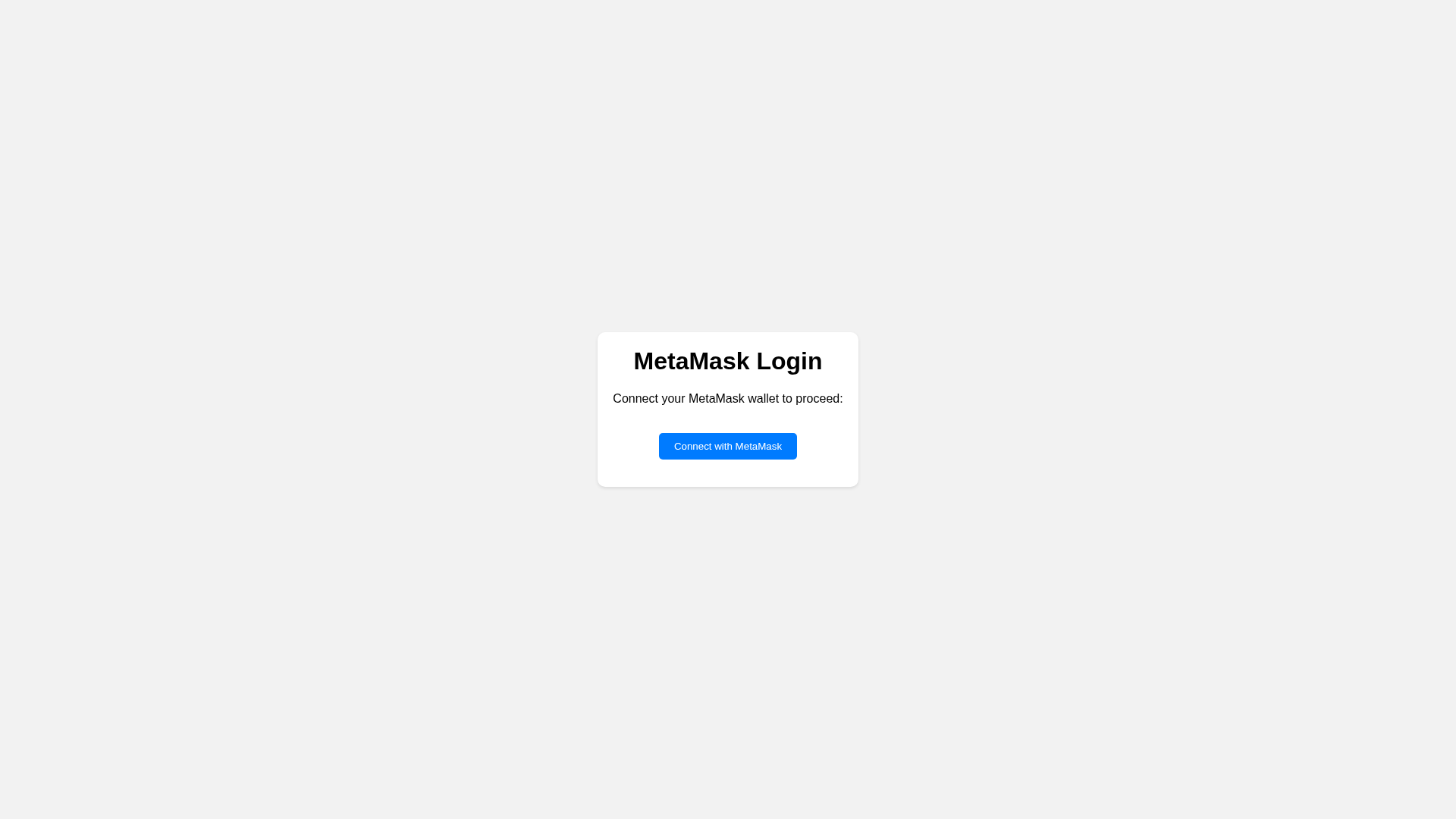
🏢 Análise de Falsificação de Marca
⚔️ Metodologia de Ataque
Primary Method: Credential Harvesting
The phishing kit employs 18 form fields to capture user credentials, including usernames, passwords, and personal information. Data is likely transmitted to a backend server controlled by the attacker for immediate exploitation or resale.
Secondary Method: OTP Interception
The OTP Stealer kit component suggests the site is designed to trick users into entering one-time passwords (OTPs), enabling attackers to bypass multi-factor authentication (MFA) and gain unauthorized access to accounts.
🌐 Indicadores de Compromisso de Infraestrutura
Domain Information
🦠 Malicious Files
Small JavaScript file with high obfuscation, likely containing credential harvesting logic.
📊 Diagrama de Fluxo de Ataque
Here's a generic ASCII art attack flow diagram for the phishing attack:
```
┌──────────────────────────────────────────────────────────┐
│ 1. INITIAL CONTACT │
│ - Victim receives phishing message │
│ - Message contains link to fake Banking site │
└────────────────────┬─────────────────────────────────────┘
│
▼
┌──────────────────────────────────────────────────────────┐
│ 2. FAKE SITE ACCESS │
│ - Victim visits fraudulent Banking page │
│ - Page mimics legitimate Banking portal │
└────────────────────┬─────────────────────────────────────┘
│
▼
┌──────────────────────────────────────────────────────────┐
│ 3. CREDENTIAL INPUT │
│ - Victim enters login credentials │
│ - Form appears identical to real Banking site │
└────────────────────┬─────────────────────────────────────┘
│
▼
┌──────────────────────────────────────────────────────────┐
│ 4. DATA CAPTURE │
│ - Credentials collected by attacker │
│ - Data prepared for exfiltration │
└────────────────────┬─────────────────────────────────────┘
│
▼
┌──────────────────────────────────────────────────────────┐
│ 5. EXFILTRATION │
│ - Credentials sent via HTTP POST │
│ - Standard form submission to attacker-controlled │
│ destination │
└──────────────────────────────────────────────────────────┘
```
🔬 JavaScript Deep Analysis
🔗 API Endpoints Detected
🔐 Obfuscation Detected
- : Light
🤖 AI-Extracted Threat Intelligence
📊 Attack Flow
Here's a generic ASCII art attack flow diagram for the phishing attack:
```
┌──────────────────────────────────────────────────────────┐
│ 1. INITIAL CONTACT │
│ - Victim receives phishing message │
│ - Message contains link to fake Banking site │
└────────────────────┬─────────────────────────────────────┘
│
▼
┌──────────────────────────────────────────────────────────┐
│ 2. FAKE SITE ACCESS │
│ - Victim visits fraudulent Banking page │
│ - Page mimics legitimate Banking portal │
└────────────────────┬─────────────────────────────────────┘
│
▼
┌──────────────────────────────────────────────────────────┐
│ 3. CREDENTIAL INPUT │
│ - Victim enters login credentials │
│ - Form appears identical to real Banking site │
└────────────────────┬─────────────────────────────────────┘
│
▼
┌──────────────────────────────────────────────────────────┐
│ 4. DATA CAPTURE │
│ - Credentials collected by attacker │
│ - Data prepared for exfiltration │
└────────────────────┬─────────────────────────────────────┘
│
▼
┌──────────────────────────────────────────────────────────┐
│ 5. EXFILTRATION │
│ - Credentials sent via HTTP POST │
│ - Standard form submission to attacker-controlled │
│ destination │
└──────────────────────────────────────────────────────────┘
```
🎯 Malicious Files Identified
Similar Websites
Pages with identical visual appearance (based on perceptual hash)