
Phishing Analysis
Detailed analysis of captured phishing page
Captura Visual
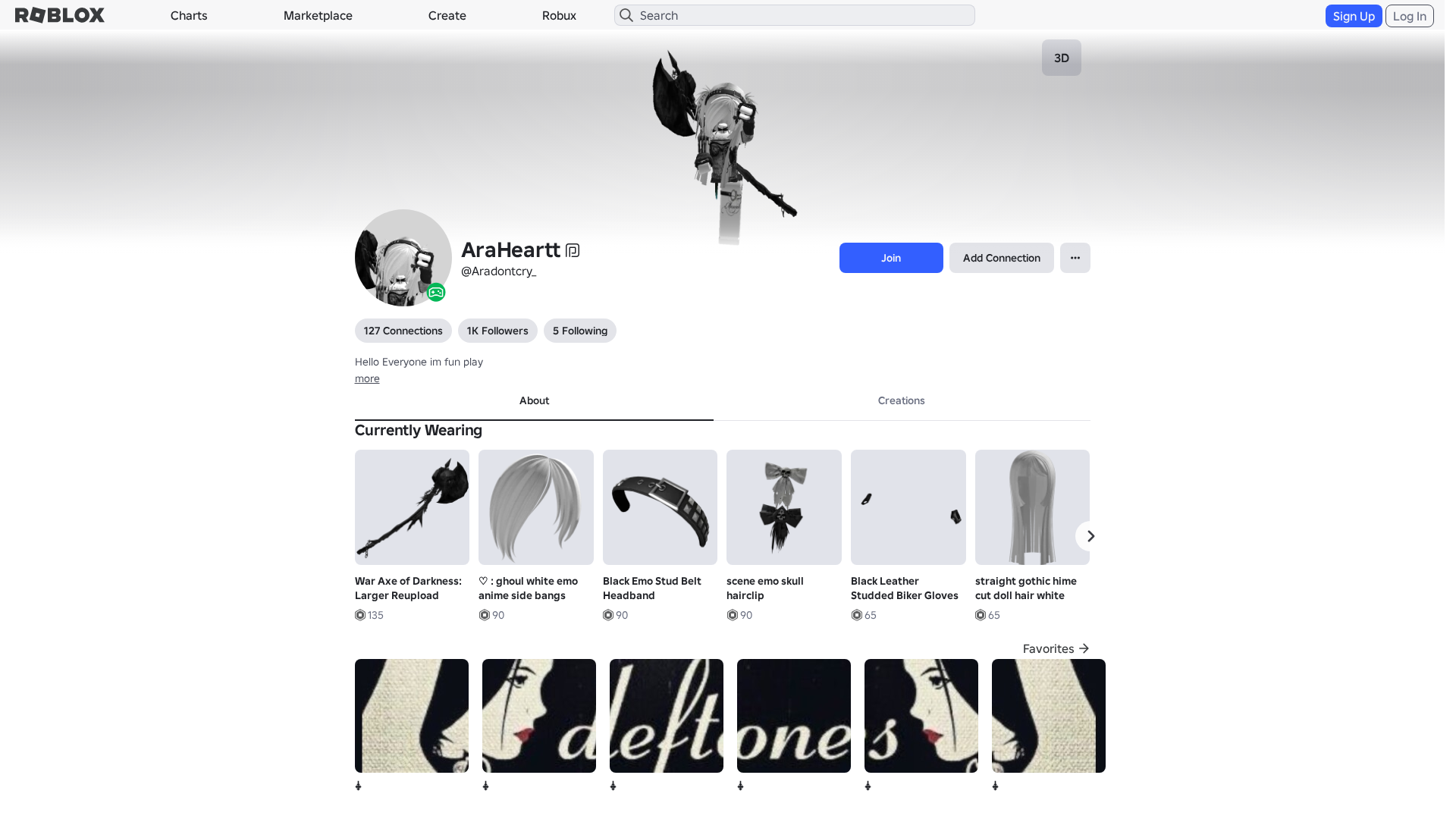
Informações de Detecção
https://roblx.me/s/cLMt4D
Detected Brand
Roblox
Country
Unknown
Confidence
100%
HTTP Status
200
Report ID
680b7dda-a19…
Analyzed
2026-03-31 23:26
Final URL (after redirects)
https://www.robiox.com.py/users/243671918813/profile
Hashes de Conteúdo (Similaridade HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1EA931E7292542837517B79DAF064672EE2D7C30FCA8346E1A2F8D39A0FD6CD1E86244D |
|
CONTENT
ssdeep
|
1536:+6fXWn4rjv4ewGsg4wgPQgYCgtCgW6gkOgwXg+sgEYegaOgzFgl1gBkgzWgn6gjh:hfXWMvuJ+xaYQFOYKTsGhPHEbI5RPs52 |
Hashes Visuais (Similaridade de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
b49e675391ec9c24 |
|
VISUAL
aHash
|
0020dfffc3ffc3c3 |
|
VISUAL
dHash
|
c8c836309a1a0f0f |
|
VISUAL
wHash
|
0000dfffcbc3c3c3 |
|
VISUAL
colorHash
|
07000000180 |
|
VISUAL
cropResistant
|
c8c836309a1a0f0f,4e4e4fcfcd696ded |
Análise de Código
Risk Score
100/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🎣 Card Stealer
🎣 Banking
🎣 Personal Info
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- hex_escape
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- https://api.injuries.lu/catalog/91325819213930/Little-Demon-Exorcism
- https://www.roblox.com/catalog
- https://api.injuries.lu/catalog/3576717965/Shy
- https://www.roblox.com/catalog?CatalogContext=1&Keyword=
- https://api.injuries.lu/catalog/619536283/Zombie-Jump
- https://api.injuries.lu/catalog/70743723096841/Head-Pain-Headache-Dizzy-Anxiety-Emote-Animation
- https://api.injuries.lu/catalog/619537468/Zombie-Walk
- https://api.injuries.lu/catalog/11138361726/Chain-Around-Body-3-0-Emo-Y2k-Goth-Grunge
- https://api.injuries.lu/catalog/87939036754320/3-0-Demonic-Shoulder-Hand-Grey
- https://api.injuries.lu/catalog/91977661719010/War-Axe-of-Darkness-Larger-Reupload
- https://api.injuries.lu/catalog/137722157875140/KoRn-tats
- https://api.injuries.lu/catalog/11101586051/Ive-been-split-open-CanU-see-my-organs
- https://api.injuries.lu/catalog/86499698/Woman-Right-Arm
- https://api.injuries.lu/catalog/973771666/Toy-Idle
- https://api.injuries.lu/catalog/628771505/Black-Iron-Horns
- https://api.injuries.lu/catalog/1365767/Valkyrie-Helm
- https://api.injuries.lu/catalog/5915779043/Applaud
- https://api.injuries.lu/catalog/128086015688807/Zombie-Robloxian
- https://api.injuries.lu/catalog/110096711981486/Full-Body-Piercing-Choker-3-0-Chrome-PBR
- https://api.injuries.lu/catalog/79405777737801/KoRn
- https://api.injuries.lu/catalog/63253701/Skelefriend
- https://api.injuries.lu/catalog/8650652210/Black-Corrupted-Heart
- https://api.injuries.lu/catalog/118807721083478/straight-gothic-hime-cut-doll-hair-white
- /login?returnUrl=https%3A%2F%2Fwww.roblox.com%2Fusers%2F243671918813%2Fprofile
- https://api.injuries.lu/catalog/16553249658/Mae-Stephens-Piano-Hands
- /login?returnUrl=
- https://api.injuries.lu/catalog/11573370910/Anime-Mood
- https://api.injuries.lu/catalog/134584040095037/Little-Obbyist
- https://api.injuries.lu/catalog/619535091/Zombie-Climb
- https://api.injuries.lu/catalog/619537096/Zombie-Swim
- https://api.injuries.lu/catalog/15093053680/Headless-Head
- https://www.robiox.com.py/NewLogin?returnUrl=https%3A%2F%2Fwww.roblox.com%2Fusers%2F243671918813%2Fprofile
- https://api.injuries.lu/catalog/18837037240/Black-Leather-Studded-Biker-Gloves
- https://api.injuries.lu/catalog/86499716/Woman-Left-Arm
- https://api.injuries.lu/catalog/619536621/Zombie-Run
- https://api.injuries.lu/catalog/619535616/Zombie-Fall
- /info/blog?locale=en_us
- https://api.injuries.lu/catalog/127661669981954/black-lace-knit-arm-warmers
- https://api.injuries.lu/catalog/182509980/Death-Metal-Headphones
- https://api.injuries.lu/catalog/95124530227940/ghoul-white-emo-anime-side-bangs
- https://api.injuries.lu/catalog/129199219729775/scene-emo-skull-hairclip
- https://api.injuries.lu/catalog/99482053255919/Black-Emo-Stud-Belt-Headband
- https://api.injuries.lu/catalog/6550129/Scissors
- https://api.injuries.lu/catalog/1744060292/Poisoned-Horns-of-the-Toxic-Wasteland
- https://api.injuries.lu/catalog/86499666/Woman-Torso
- https://api.injuries.lu/catalog/139607718/Korblox-Deathspeaker-Right-Leg
- https://api.injuries.lu/catalog/104725162009226/Cute-Choppy-Messy-Scene-Pigtails-white-w-raccoon
📡 API Calls Detected
- https://kyxn.dev/api/shorten/TKvzwH
- https://kyxn.dev/api/shorten
- https://help.roblox.com/hc/articles/30428367965460
- GET
- https://ro.blox.com/Ebh5?
- https://apis.
- get
- POST
- /api/shorten
- https://kyxn.dev${e.endpoint}
- /api/pageview
📤 Form Action Targets
- /search
📊 Detalhamento da Pontuação de Risco
Total Risk Score
100/100
Contributing Factors
Active Phishing Kit
Detected kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
Credential Harvesting
Credential harvesting detected with 1 form(s) capturing sensitive data
Code Obfuscation
JavaScript code obfuscated using 212 technique(s) to evade detection
🔬 Análise Integral de Ameaças
Tipo de Ameaça
Banking Credential Harvester
Alvo
Roblox users
Método de Ataque
credential harvesting forms + obfuscated JavaScript
Canal de Exfiltração
HTTP POST to backend
Avaliação de Risco
CRITICAL - Automated credential harvesting with HTTP POST to backend
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 212 obfuscation techniques
🏢 Análise de Falsificação de Marca
Impersonated Brand
Roblox
Official Website
https://www.roblox.com
Fake Service
Banking/payment service
⚔️ Metodologia de Ataque
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 212 techniques to evade detection by security scanners and make reverse engineering more difficult.
🌐 Indicadores de Compromisso de Infraestrutura
Domain Information
Domain
roblx.me
Registered
2026-03-28 03:56:41+00:00
Registrar
NAMECHEAP INC
Status
Recently registered (3 days old)
Hosting Information
Provider
Namecheap
ASN
🤖 AI-Extracted Threat Intelligence
Scan History for roblx.me
Found 9 other scans for this domain

"Nunca pensei que aconteceria comigo"
Isso dizem os 2,3 milhões de vítimas a cada ano. Não espere para ser uma estatística.