Phishing Analysis
Detailed analysis of captured phishing page
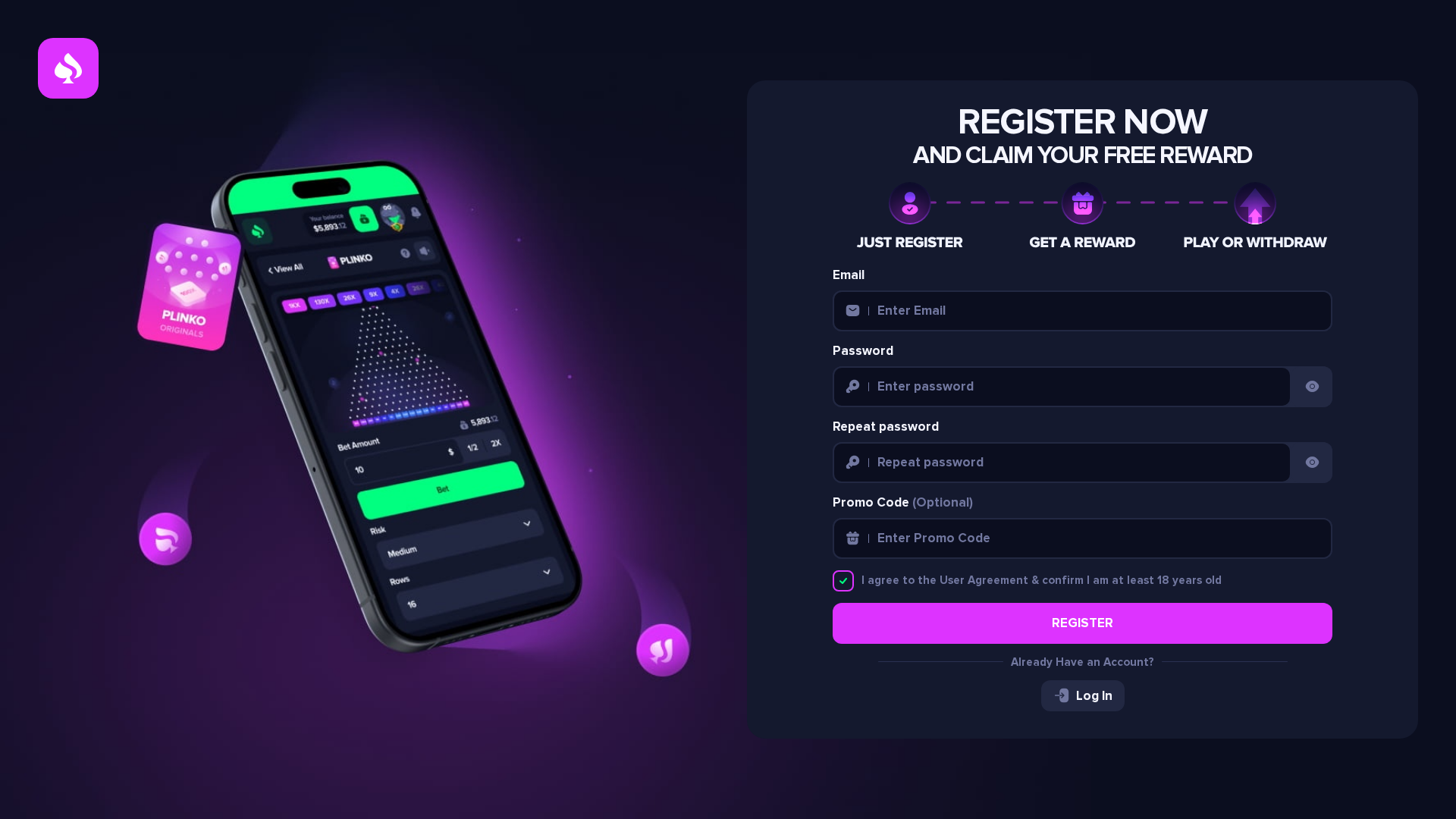
Captura Visual
Informações de Detecção
https://betplayer77.com/
Detected Brand
Unknown - Gambling/Gaming site impersonation
Country
International
Confidence
100%
HTTP Status
200
Report ID
72970c25-ed5…
Analyzed
2026-02-22 09:38
Hashes de Conteúdo (Similaridade HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1AAE229B4A230D335B1C24BE8DA6525287A5FE1DCD7C695B0F388AF15B0D6CE8D5260CB |
|
CONTENT
ssdeep
|
384:4r/aMJguX8FRhiXkdvNTDhPhLxeAxeDWNW1Tp34PxeeJEmuW3AseyRWVGMd:4r/aMJguChhPhleMeDGCSPxeeWmHEGW |
Hashes Visuais (Similaridade de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
c0303f9f4fbc6849 |
|
VISUAL
aHash
|
8066e2e070fe7f20 |
|
VISUAL
dHash
|
7cdc8aabcbccecc1 |
|
VISUAL
wHash
|
8066e66078fe7f60 |
|
VISUAL
colorHash
|
30000000030 |
|
VISUAL
cropResistant
|
7cdc8aabcbccecc1 |
Análise de Código
Risk Score
100/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🎣 Card Stealer
🎣 Banking
🎣 Personal Info
WebSocket C2
🔬 Threat Analysis Report
• Ameaça: Phishing de credenciais
• Alvo: Usuários interessados em jogos/apostas online
• Método: Site enganoso imitando uma plataforma de jogos.
• Exfil: Provavelmente enviando credenciais para o invasor via WebSocket (wss://gambler-work.com/api/ws)
• Indicadores: Formulários, JavaScript ofuscado, idade do domínio, promessa de recompensas.
• Risco: Alto
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- unicode_escape
- base64_strings
📡 API Calls Detected
- POST
- GET
📊 Detalhamento da Pontuação de Risco
Total Risk Score
90/100
Contributing Factors
Active Phishing Kit
Presence of a registration form, credential harvesting, obfuscated JavaScript.
Recent Domain
Domain age is relatively new (63 days), increasing the likelihood of malicious activity.
JavaScript Obfuscation
Obfuscation used to hide malicious intent.
🔬 Análise Integral de Ameaças
Tipo de Ameaça
Banking Credential Harvester
Alvo
Unknown - Gambling/Gaming site impersonation users (International)
Método de Ataque
real-time WebSocket exfiltration + obfuscated JavaScript
Canal de Exfiltração
WebSocket (1 endpoints)
Avaliação de Risco
CRITICAL - Automated credential harvesting with WebSocket (1 endpoints)
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 73 obfuscation techniques
🏢 Análise de Falsificação de Marca
Impersonated Brand
Unknown
Fake Service
Gambling/Gaming platform
Fraudulent Claims
⚔️ Metodologia de Ataque
Primary Method: Credential Harvesting
The site uses a registration form to collect user credentials (email, password). The collected data is likely exfiltrated to the attacker.
Secondary Method: Malicious JavaScript
The site uses obfuscated JavaScript, possibly for form handling, credential theft, or redirecting to a phishing site.
🌐 Indicadores de Compromisso de Infraestrutura
Domain Information
Domain
betplayer77.com
Registered
2024-04-18
Registrar
Namecheap
Status
active
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)

"Nunca pensei que aconteceria comigo"
Isso dizem os 2,3 milhões de vítimas a cada ano. Não espere para ser uma estatística.