Phishing Analysis
Detailed analysis of captured phishing page
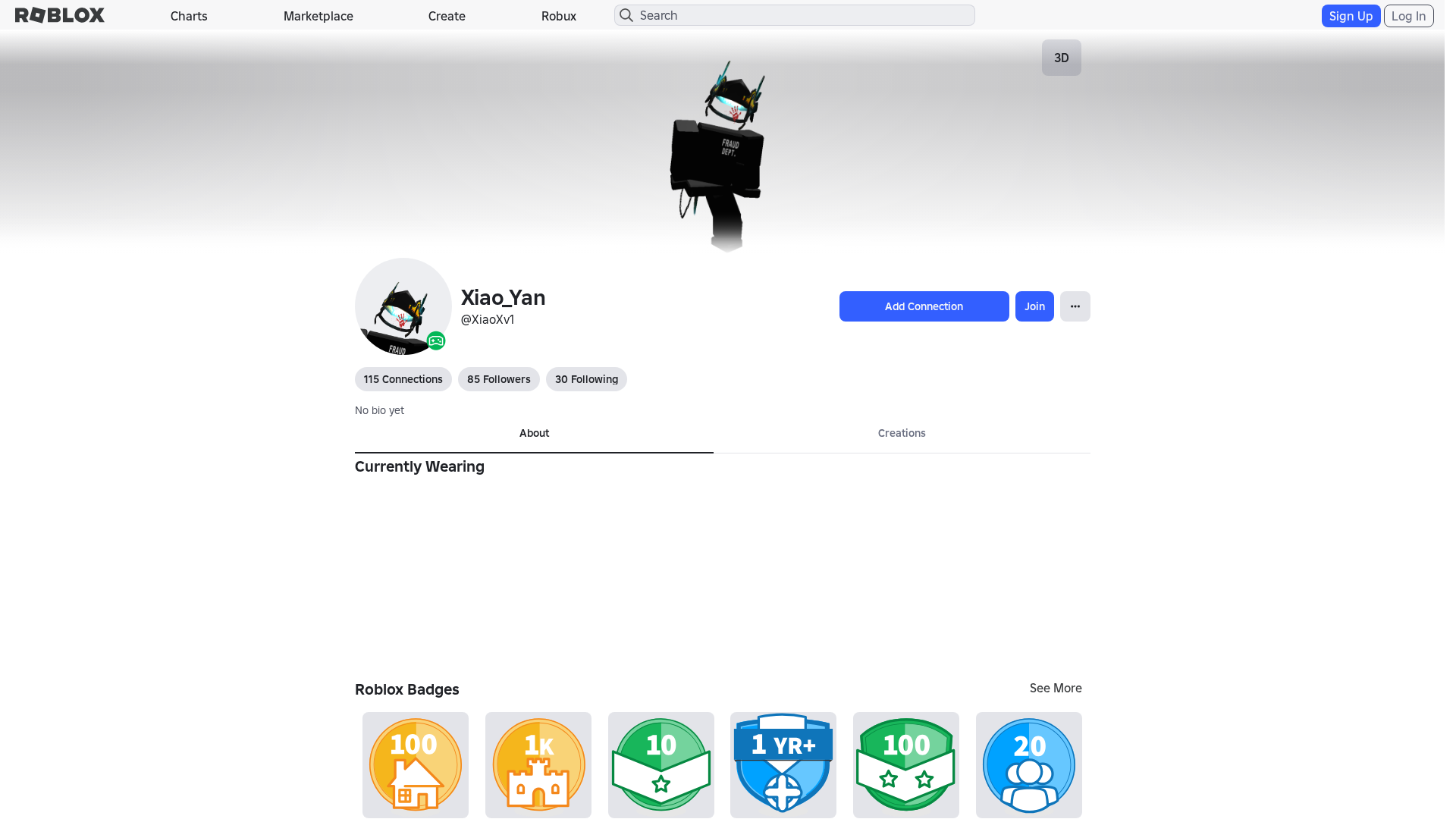
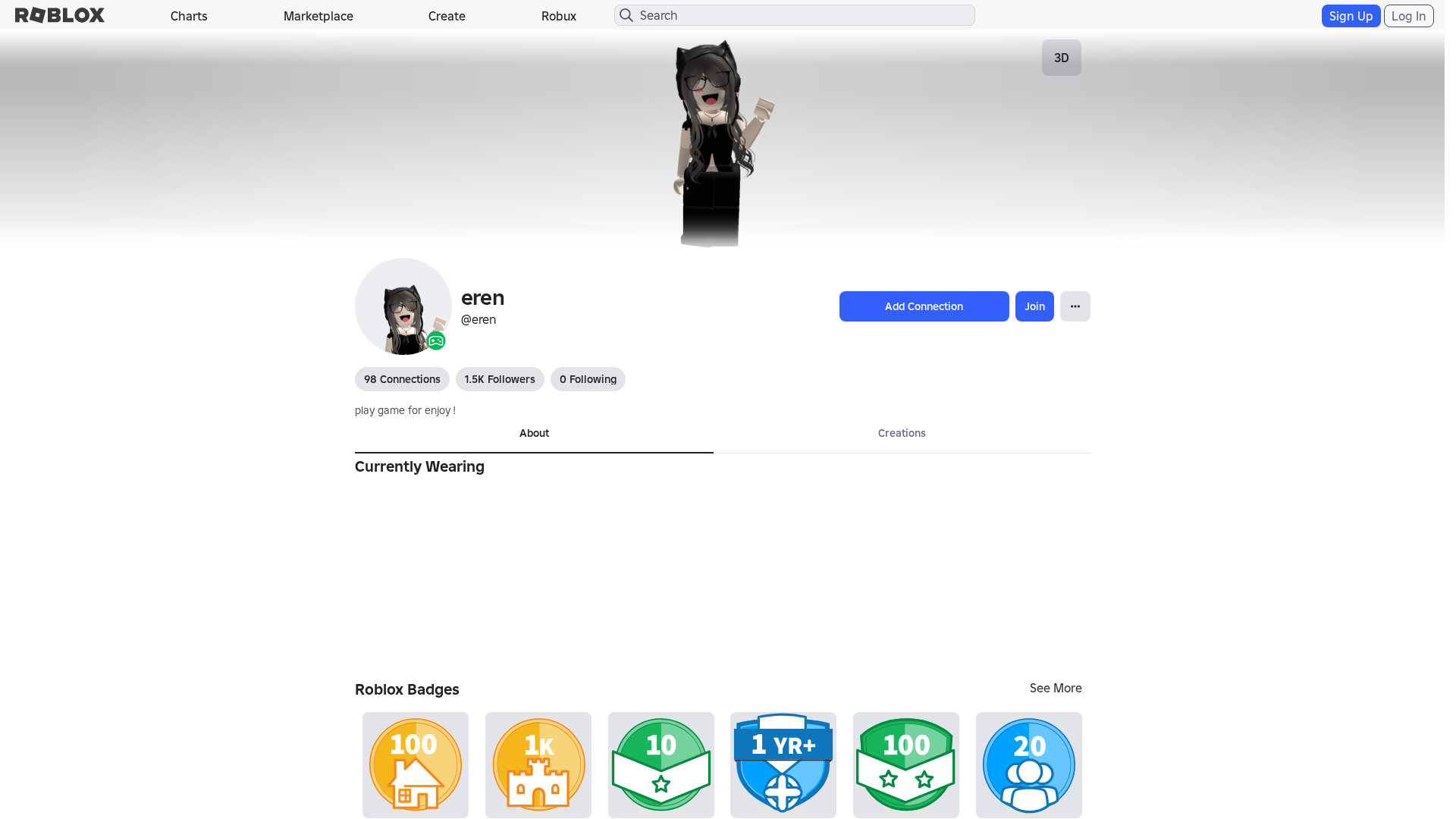
Captura Visual
Informações de Detecção
Hashes de Conteúdo (Similaridade HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T13193B8B29251243320BFB1D5F1297709A2D3D74EC68287D1F2F8A36B1ED6CA1F817856 |
|
CONTENT
ssdeep
|
1536:OYMXWnSras7uOQHor8BPmzzXXMd6MiucCOK:BMXWds7uOTkmzzXXMd6M1cCOK |
Hashes Visuais (Similaridade de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
a41363933cccecd3 |
|
VISUAL
aHash
|
0000e3dbffffffc3 |
|
VISUAL
dHash
|
c8c8ae3638002606 |
|
VISUAL
wHash
|
000042c3dfffdfc3 |
|
VISUAL
colorHash
|
072000082c0 |
|
VISUAL
cropResistant
|
c8c8ae3638002606 |
Análise de Código
🔬 Threat Analysis Report
• Ameaça: Kit de phishing para roubo de credenciais
• Alvo: Usuários do Roblox internacionalmente
• Método: Formulário falso que rouba credenciais de usuário
• Exfil: Possível exfiltração de dados via JavaScript ofuscado
• Indicadores: Domínio incorreto, TLD de país, JS ofuscado
• Risco: ALTO - Roubo imediato de credenciais
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- hex_escape
- unicode_escape
- js_packer
- base64_strings
🎯 Kit Endpoints
- /catalog
- /login?returnUrl=
- /login?returlUrl=1568847022
- https://www.roblox.com/catalog?CatalogContext=1&Keyword=
- https://www.roblox.com/info/blog?locale=en_us
📡 API Calls Detected
- https://ro.blox.com/Ebh5?
- get
- POST
- https://apis.
- https://help.roblox.com/hc/articles/30428367965460
- GET
📤 Form Action Targets
- /search
📊 Detalhamento da Pontuação de Risco
Contributing Factors
🔬 Análise Integral de Ameaças
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 862 obfuscation techniques
🏢 Análise de Falsificação de Marca
⚔️ Metodologia de Ataque
Primary Method: Credential Harvesting
The phishing page presents a fake Roblox login form with 'Email' and 'Password' fields. Submitted credentials are intercepted in real-time and exfiltrated to an attacker-controlled server for immediate account takeover.
Secondary Method: Personal Information Theft
Additional forms or fields may be dynamically loaded to capture sensitive personal information, such as payment details or security questions, for further exploitation or identity theft.
🌐 Indicadores de Compromisso de Infraestrutura
Domain Information
🦠 Malicious Files
Large obfuscated JavaScript file containing credential harvesting and data exfiltration logic.
📊 Diagrama de Fluxo de Ataque
Here's a generic ASCII art attack flow diagram for the phishing attack:
```
┌──────────────────────────────────────────────────────────┐
│ 1. INITIAL CONTACT │
│ - Victim receives phishing link (email/message) │
│ - Directed to fake Roblox login page │
└────────────────────┬─────────────────────────────────────┘
│
▼
┌──────────────────────────────────────────────────────────┐
│ 2. FAKE LOGIN PAGE │
│ - Mimics legitimate Roblox interface │
│ - Presents credential input form │
└────────────────────┬─────────────────────────────────────┘
│
▼
┌──────────────────────────────────────────────────────────┐
│ 3. CREDENTIAL SUBMISSION │
│ - Victim enters username/password │
│ - Form appears to process login │
└────────────────────┬─────────────────────────────────────┘
│
▼
┌──────────────────────────────────────────────────────────┐
│ 4. DATA EXFILTRATION │
│ - Credentials sent via HTTP POST │
│ - Data received by attacker-controlled server │
└──────────────────────────────────────────────────────────┘
```
🔬 JavaScript Deep Analysis
🔗 API Endpoints Detected
🔐 Obfuscation Detected
- : None
- : Light
- : Heavy
- : None
- : None
- : Light
- : None
- : None
- : None
- : Light
- : Light
- : None
- : Light
- : None
- : Heavy
- : None
- : None
- : Heavy
- : Light
- : Heavy
🤖 AI-Extracted Threat Intelligence
📊 Attack Flow
Here's a generic ASCII art attack flow diagram for the phishing attack:
```
┌──────────────────────────────────────────────────────────┐
│ 1. INITIAL CONTACT │
│ - Victim receives phishing link (email/message) │
│ - Directed to fake Roblox login page │
└────────────────────┬─────────────────────────────────────┘
│
▼
┌──────────────────────────────────────────────────────────┐
│ 2. FAKE LOGIN PAGE │
│ - Mimics legitimate Roblox interface │
│ - Presents credential input form │
└────────────────────┬─────────────────────────────────────┘
│
▼
┌──────────────────────────────────────────────────────────┐
│ 3. CREDENTIAL SUBMISSION │
│ - Victim enters username/password │
│ - Form appears to process login │
└────────────────────┬─────────────────────────────────────┘
│
▼
┌──────────────────────────────────────────────────────────┐
│ 4. DATA EXFILTRATION │
│ - Credentials sent via HTTP POST │
│ - Data received by attacker-controlled server │
└──────────────────────────────────────────────────────────┘
```
🎯 Malicious Files Identified
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for roblox.com.kz
Found 10 other scans for this domain
-
http://roblox.com.kz/users/148545229/profile
http://roblox.com.kz/users/77847908/profile
http://roblox.com.kz/users/610068118/profile
http://roblox.com.kz/users/346442339/profile
http://roblox.com.kz/users/441311283/profile
http://roblox.com.kz/users/112610331/profile
http://roblox.com.kz/users/454211500/profile
http://roblox.com.kz/users/277299660/profile
http://roblox.com.kz/users/630412925/profile%60%60...
http://roblox.com.kz/users/430029405/profile