
Phishing Analysis
Detailed analysis of captured phishing page
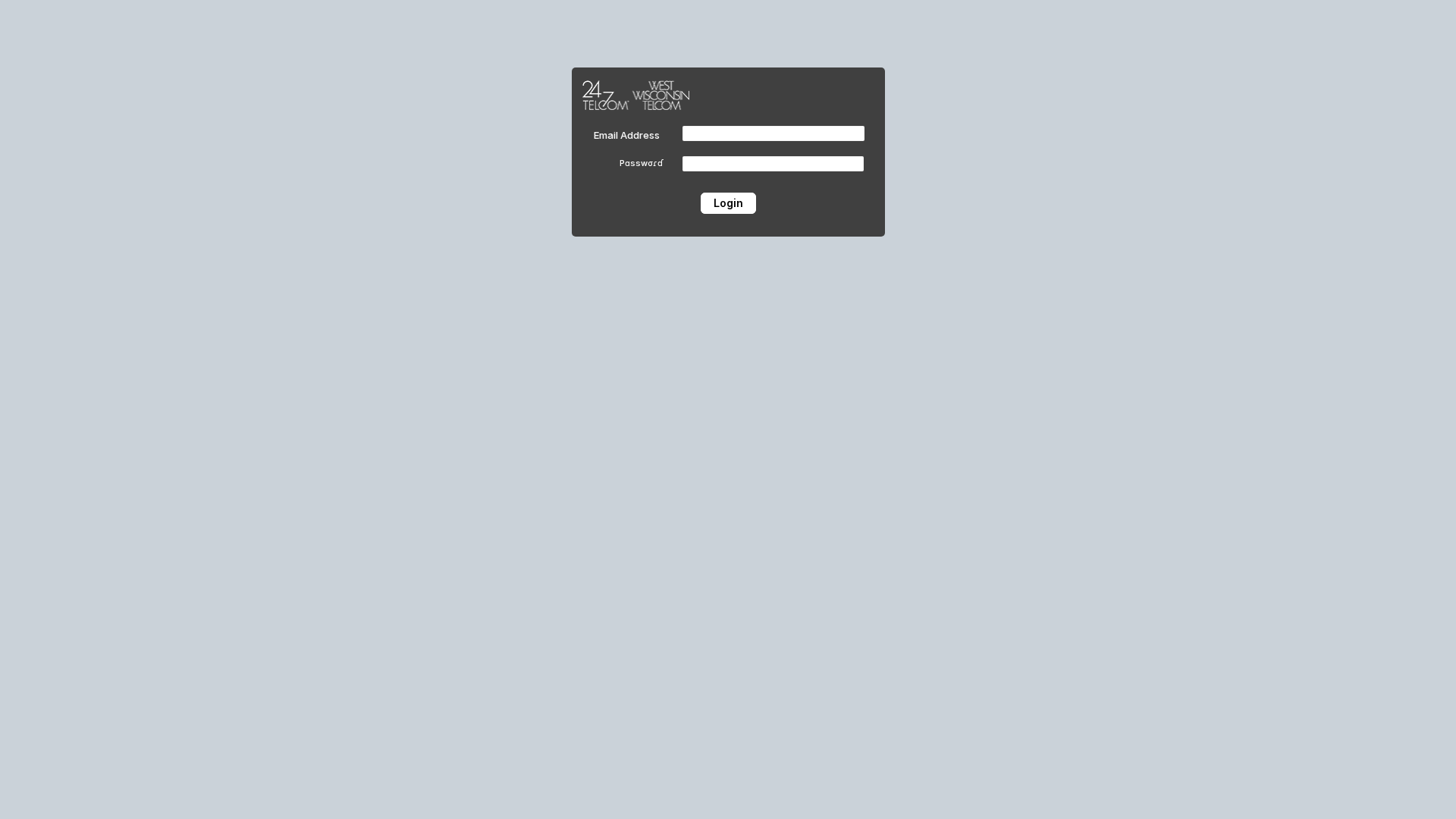
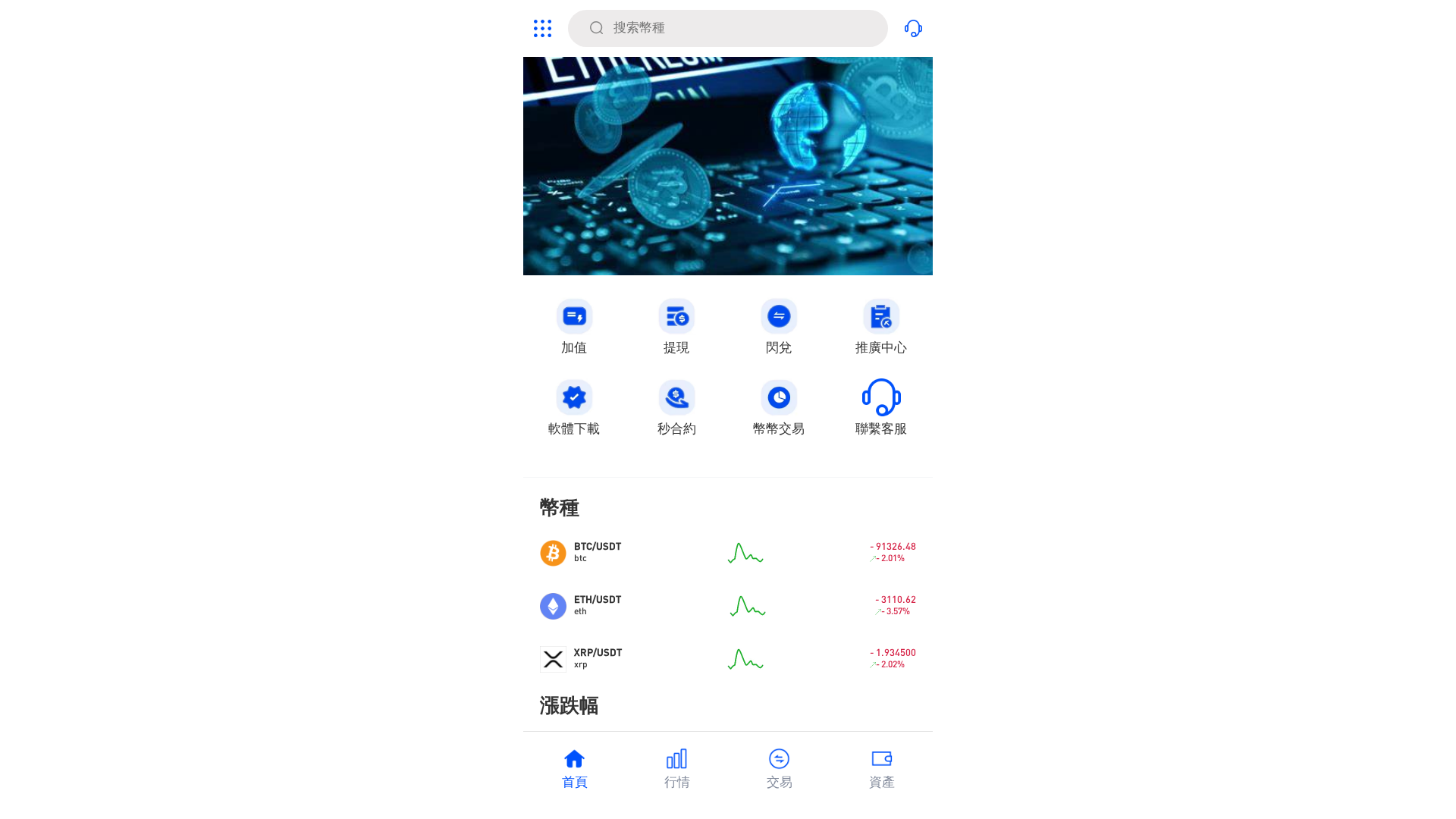
Captura Visual
Informações de Detecção
https://grateful-aspects-830309.framer.app/
Detected Brand
24/7 Telecom
Country
USA
Confidence
100%
HTTP Status
200
Report ID
886441db-3e7…
Analyzed
2026-02-11 15:38
Hashes de Conteúdo (Similaridade HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1E0225233B200DD294A9B56CCF1C49688415EC346FB3108CAB1A491FF7BC4DF0699A7AD |
|
CONTENT
ssdeep
|
192:skf7I0cqcechzz4vy9AKeMcnthWeNWbZfMmUU8VCosIW:ncqcechH4vuffMmUFCosD |
Hashes Visuais (Similaridade de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
b333338ccccccccc |
|
VISUAL
aHash
|
e7e7e7ffffffffff |
|
VISUAL
dHash
|
4d4d4d320c000000 |
|
VISUAL
wHash
|
0707273f0f0f0f0f |
|
VISUAL
colorHash
|
07000000000 |
|
VISUAL
cropResistant
|
4d4d4d320c000000,4049b2b2beb2b232 |
Análise de Código
Risk Score
76/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🎣 Personal Info
🔬 Threat Analysis Report
• Ameaça: Phishing de credenciais
• Alvo: Usuários da 24/7 Telecom
• Método: Impersonificação por meio de um formulário de login.
• Exfil: Envio de dados para o servidor do atacante.
• Indicadores: Hospedagem em Framer.app, formulário solicitando credenciais, Javascript ofuscado.
• Risco: ALTO
🔒 Obfuscation Detected
- fromCharCode
- base64_strings
📊 Detalhamento da Pontuação de Risco
Total Risk Score
90/100
Contributing Factors
Free Hosting
Hosted on Framer.app, a free hosting provider.
Domain Mismatch
The domain name does not match the purported brand.
Obfuscated Javascript
JavaScript obfuscation to hide malicious intent.
Forms requesting credentials
Login form requesting sensitive information (username/password).
🔬 Análise Integral de Ameaças
Tipo de Ameaça
Two-Factor Authentication Stealer
Alvo
24/7 Telecom users (USA)
Método de Ataque
Brand impersonation + credential harvesting forms + obfuscated JavaScript
Canal de Exfiltração
Form submission (backend endpoint not detected - likely JavaScript-based)
Avaliação de Risco
HIGH - Automated credential harvesting with Form submission (backend endpoint not detected - likely JavaScript-based)
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Personal Info
- 10 obfuscation techniques
🏢 Análise de Falsificação de Marca
Impersonated Brand
24/7 Telecom
Fake Service
Login Portal
⚔️ Metodologia de Ataque
Primary Method: Credential Phishing
The attacker is impersonating 24/7 Telecom to steal user login credentials by presenting a fake login form. The victim enters their email and password, which is then sent to the attacker.
🌐 Indicadores de Compromisso de Infraestrutura
Domain Information
Domain
grateful-aspects-830309.framer.app
Registered
None
Registrar
None
Status
None
🔬 JavaScript Deep Analysis
Operator Language
English (1%)
Total Code Size
26,1 KB
🔗 API Endpoints Detected
Other
4
🔐 Obfuscation Detected
- : Light
- : Light
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Unknown
https://cdn.gosafemode.com/screenshots/e937158b39e7.png
Abr 08, 2026
Unknown
https://gfhfsw.weebly.com/
Mar 18, 2026
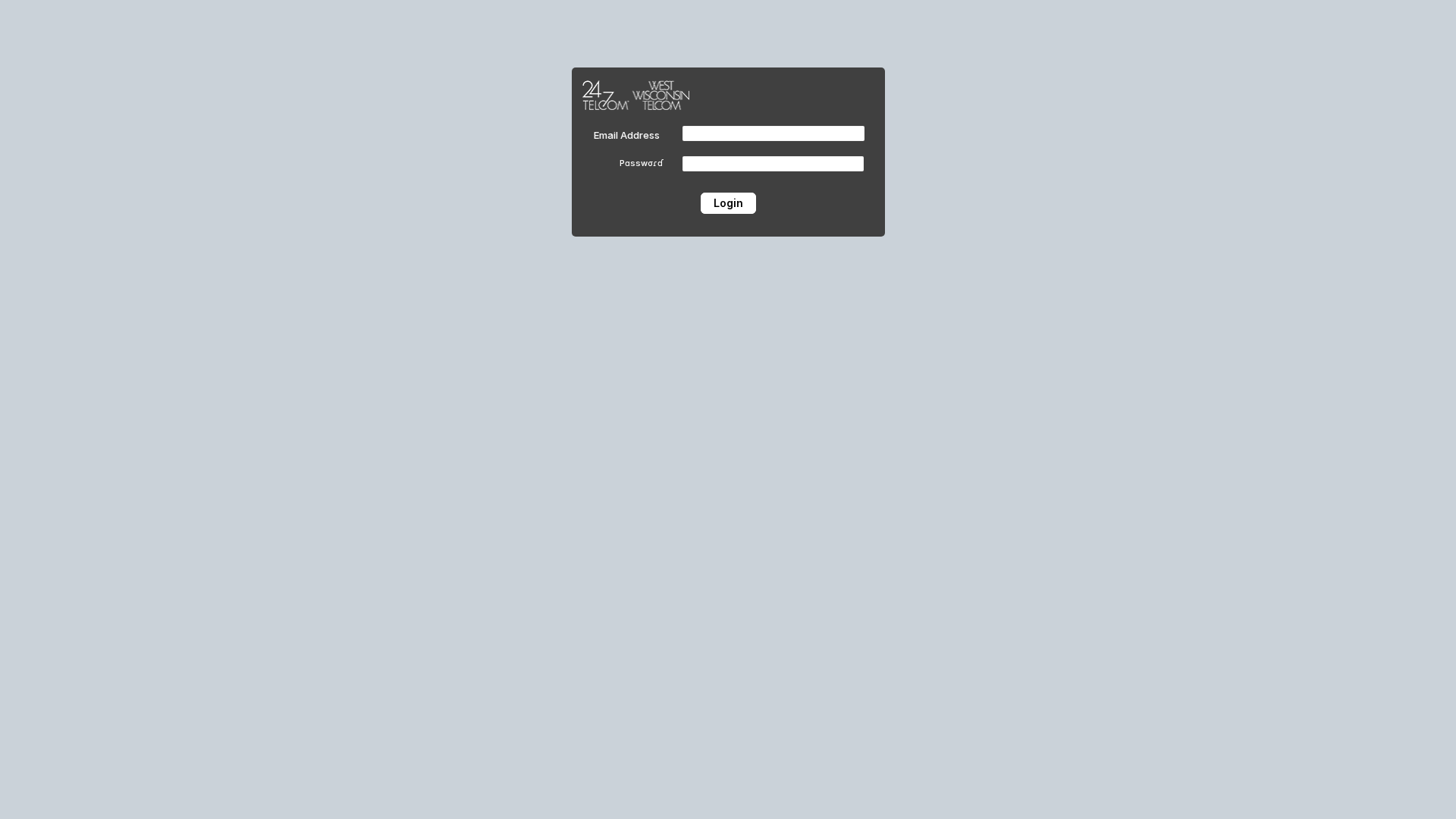
24/7 Telecom / West Wisconsin Telecom
https://grateful-aspects-830309.framer.app/
Fev 11, 2026
Geminis Pro
http://gxh5.geminis-pro.com
Jan 20, 2026
No screenshot
PancakeSwap
https://pancakeswap.finance-beta-service-alpha-online.pro/
Jan 01, 2026
Scan History for grateful-aspects-830309.framer.app
Found 1 other scan for this domain

"Nunca pensei que aconteceria comigo"
Isso dizem os 2,3 milhões de vítimas a cada ano. Não espere para ser uma estatística.