
Phishing Analysis
Detailed analysis of captured phishing page
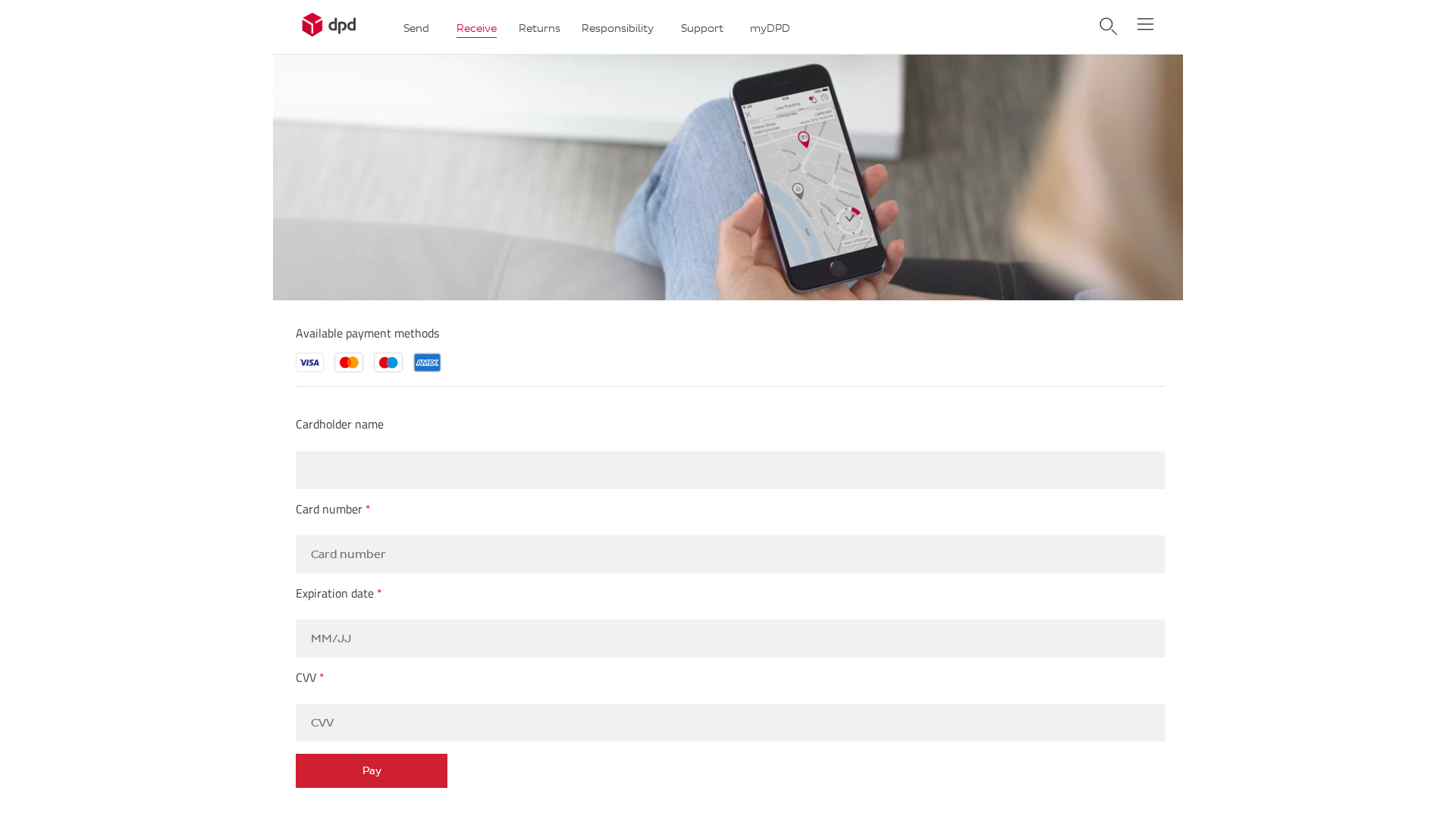
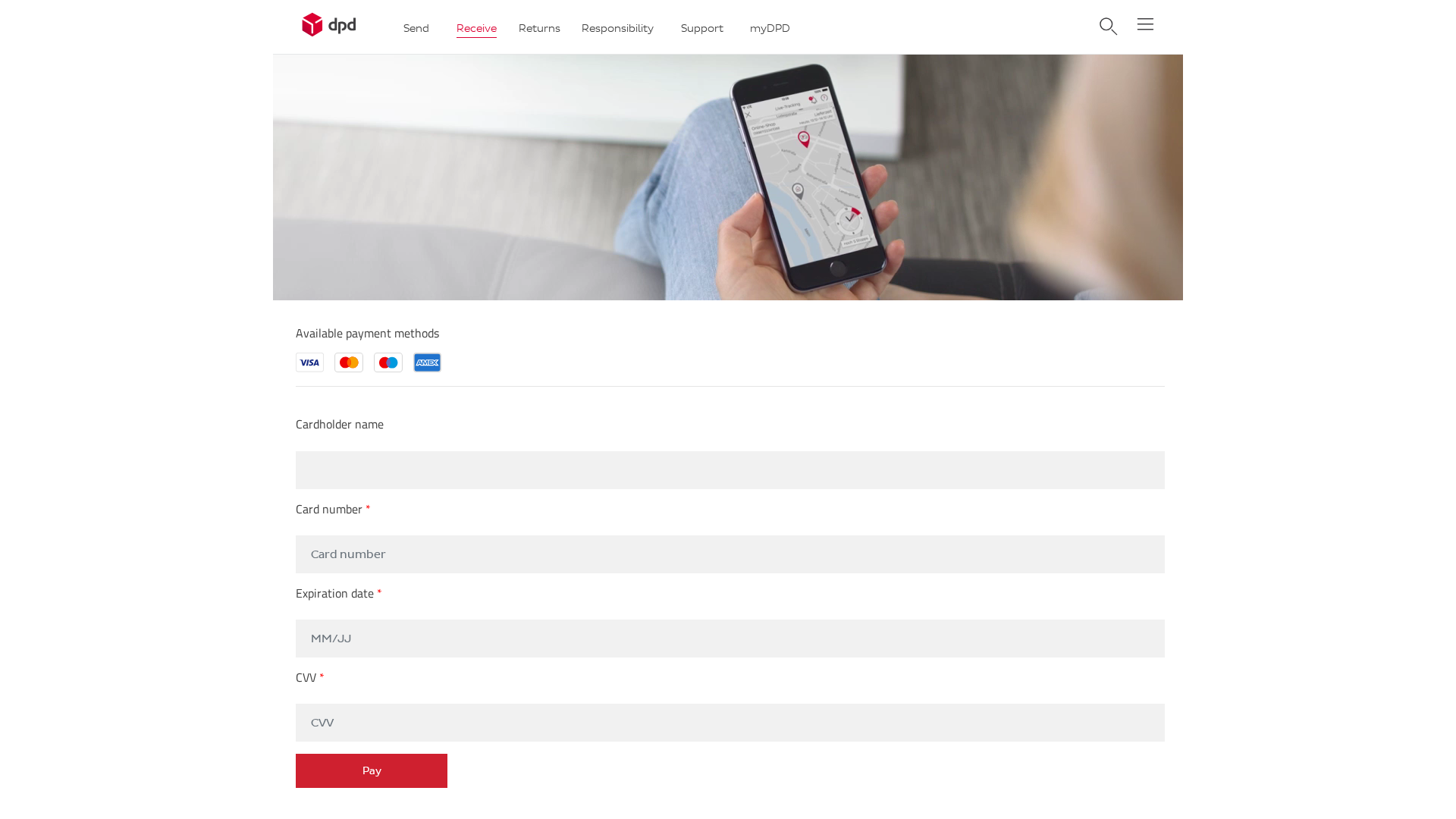
Captura Visual
Informações de Detecção
Hashes de Conteúdo (Similaridade HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1FFC2227094B5A57F009F72D1A738A705A3C39382CB520BE567FC936D8BCAE84DC23569 |
|
CONTENT
ssdeep
|
384:2x8xw7pvKpJrVUatKroxNaNp8+XxFUH/JO:txbrKr2sRUHc |
Hashes Visuais (Similaridade de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
ed6d6d9392923c30 |
|
VISUAL
aHash
|
f1c181ffffffff9f |
|
VISUAL
dHash
|
230307233b23032b |
|
VISUAL
wHash
|
818181dfd3c3c39f |
|
VISUAL
colorHash
|
07c00000002 |
|
VISUAL
cropResistant
|
230307233b23032b,67e5258787c39767 |
Análise de Código
🔬 Threat Analysis Report
• Ameaça: Phishing de cartão de crédito
• Alvo: Clientes DPD
• Método: Imitação por site falso
• Exfil: action.php
• Indicadores: Domínio não relacionado, pedido de detalhes de pagamento
• Risco: ALTO
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- base64_strings
🎯 Kit Endpoints
- ./app/wp-content/themes/DPD_Login/css/styles.min5b21.css?ver=6.0.2
📡 API Calls Detected
- https://whos.amung.us/stats/
- GET
- POST
📤 Form Action Targets
- action.php
📊 Detalhamento da Pontuação de Risco
Contributing Factors
🔬 Análise Integral de Ameaças
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 22 obfuscation techniques
🏢 Análise de Falsificação de Marca
⚔️ Metodologia de Ataque
Primary Method: Credential Harvesting
The phishing site attempts to steal credit card information by impersonating DPD's checkout process. The user is prompted to enter their credit card details under the guise of paying for services.
Secondary Method: Social Engineering
The attacker uses the DPD branding and layout to create a sense of trust, tricking the user into entering their sensitive information.
🌐 Indicadores de Compromisso de Infraestrutura
Domain Information
🔬 JavaScript Deep Analysis
🔗 API Endpoints Detected
🔐 Obfuscation Detected
- : Light
- : Light
- : Light
- : None
- : None
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for 104-248-69-158.cprapid.com
Found 2 other scans for this domain
