
Phishing Analysis
Detailed analysis of captured phishing page
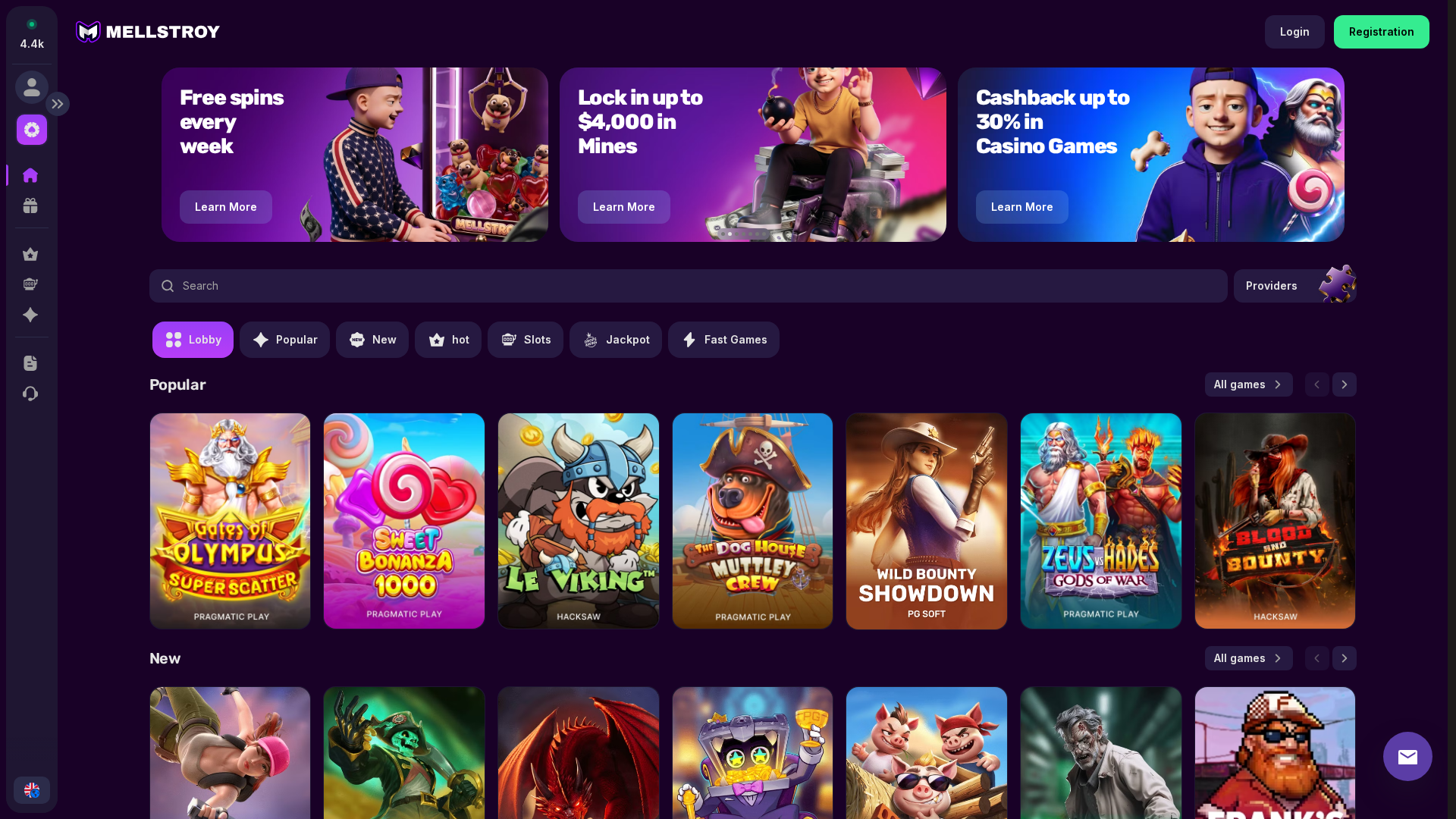
Captura Visual
Informações de Detecção
Hashes de Conteúdo (Similaridade HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T13F142235AD02A83713335CDA7162BB4571D7C10EE7072A81A2F88F89CFE7DA9E0556D8 |
|
CONTENT
ssdeep
|
1536:1sW+IAZiR0RwRsR0RhRmRHyGT50I/9N6m1ELjbYUjwTAWyhgHak4j4u6:aW+IA5pTib+T36q |
Hashes Visuais (Similaridade de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
912fb9c2682f5ae8 |
|
VISUAL
aHash
|
007e00007e7e007f |
|
VISUAL
dHash
|
dbded0a684d89a9a |
|
VISUAL
wHash
|
017f28007e7e0e7f |
|
VISUAL
colorHash
|
18200208008 |
|
VISUAL
cropResistant
|
fc6cf435b73149b6,d8d4a55d1d7bab2c,d3d425337366d6e9,97a9bd61c5d6d4d4,31311b8e0e4ed2b2,bc7172339194b0b0,dbded0a684d89a9a |
Análise de Código
🔒 Obfuscation Detected
- atob
- fromCharCode
- unescape
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- /game/play/39314/GatesofOlympusSuperScatter?demo=true
📡 API Calls Detected
- POST
- get
- GET
📊 Detalhamento da Pontuação de Risco
Contributing Factors
🔬 Análise Integral de Ameaças
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 151 obfuscation techniques
🏢 Análise de Falsificação de Marca
⚔️ Metodologia de Ataque
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 151 techniques to evade detection by security scanners and make reverse engineering more difficult.
Drainer supports multiple blockchain networks and checks for high-value tokens on each chain before executing drain operations.
🌐 Indicadores de Compromisso de Infraestrutura
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
