
Phishing Analysis
Detailed analysis of captured phishing page
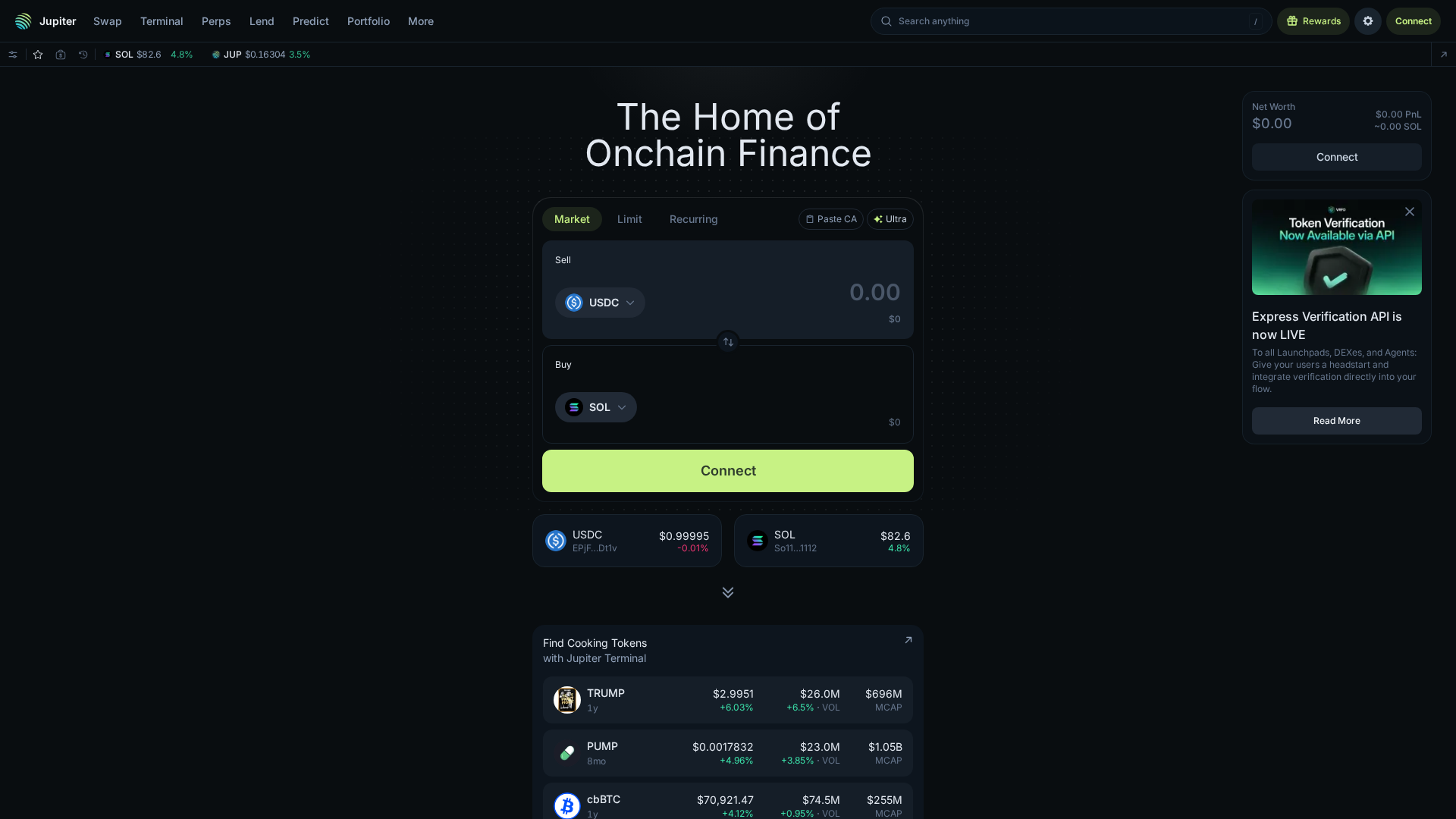
Captura Visual
Informações de Detecção
Hashes de Conteúdo (Similaridade HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1BFB3E7B95051257F10378AE1B0A9E35EA0CB831CDF63D894B3DC53A62FCBCA29E1556C |
|
CONTENT
ssdeep
|
1536:lN/jlpKeWe5SQDdi9CujKg9HywmW8VpiPAqEOwA32WZasvsz9JVIUMMMg+IlvHOj:l9lhdcCujpzLmOUuaFFVE |
Hashes Visuais (Similaridade de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
8d2376dcdd232389 |
|
VISUAL
aHash
|
0118190118181818 |
|
VISUAL
dHash
|
13333323b3302032 |
|
VISUAL
wHash
|
ff1b1b1b3f181818 |
|
VISUAL
colorHash
|
380c3000000 |
|
VISUAL
cropResistant
|
8208104d4d081082,13333323b3302032 |
Análise de Código
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- document.write
- hex_escape
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- https://wsrv.nl/?w=32&h=32&url=https%3A%2F%2Fraw.githubusercontent.com%2Fsolana-labs%2Ftoken-list%2Fmain%2Fassets%2Fmainnet%2FEPjFWdd5AufqSSqeM2qN1xzybapC8G4wEGGkZwyTDt1v%2Flogo.png&dpr=2&quality=80
- https://wsrv.nl/?w=32&h=32&url=https%3A%2F%2Fxstocks-metadata.backed.fi%2Flogos%2Ftokens%2FCRCLx.png&dpr=2&quality=80
- https://wsrv.nl/?w=32&h=32&url=https%3A%2F%2Fraw.githubusercontent.com%2Fsolana-labs%2Ftoken-list%2Fmain%2Fassets%2Fmainnet%2FSo11111111111111111111111111111111111111112%2Flogo.png&dpr=2&quality=80
- https://wsrv.nl/?w=32&h=32&url=https%3A%2F%2Fxstocks-metadata.backed.fi%2Flogos%2Ftokens%2FSPYx.png&dpr=2&quality=80
- ${this.getGreenCheckmarkLogoUrl()}
- solana:signAndSendTransaction
- /send
📡 API Calls Detected
- https://cache.jup.ag/top-tokens
- https://x.com/search?q=(
- /tokens/
- https://api.wallet.coinbase.com/rpc/v2/desktop/chrome
- https://worker.jup.ag/jito-floor
- POST
- https://registry.npmjs.org/@reown/appkit/latest
- https://errors.jup.ag/logs?service=dca&accountID=
- https://fe-api.jup.ag/api/v1/chainalysis/
- https://worker.jup.ag/send-transaction
- GET
📊 Detalhamento da Pontuação de Risco
Contributing Factors
🔬 Análise Integral de Ameaças
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- Kit signatures: angler
- 906 obfuscation techniques
🏢 Análise de Falsificação de Marca
⚔️ Metodologia de Ataque
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 906 techniques to evade detection by security scanners and make reverse engineering more difficult.
Drainer supports multiple blockchain networks and checks for high-value tokens on each chain before executing drain operations.
🌐 Indicadores de Compromisso de Infraestrutura
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
