Phishing Analysis
Detailed analysis of captured phishing page
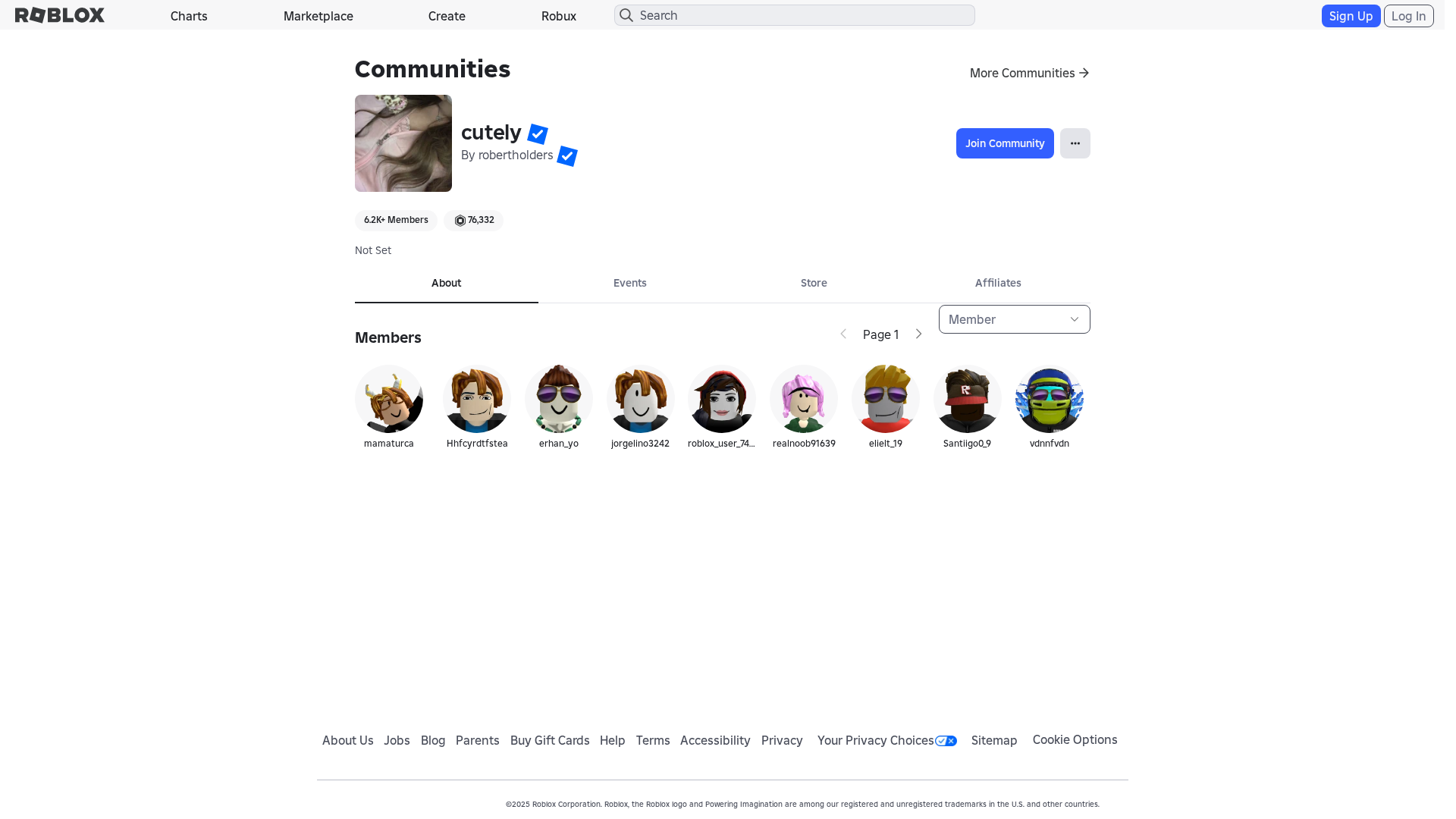
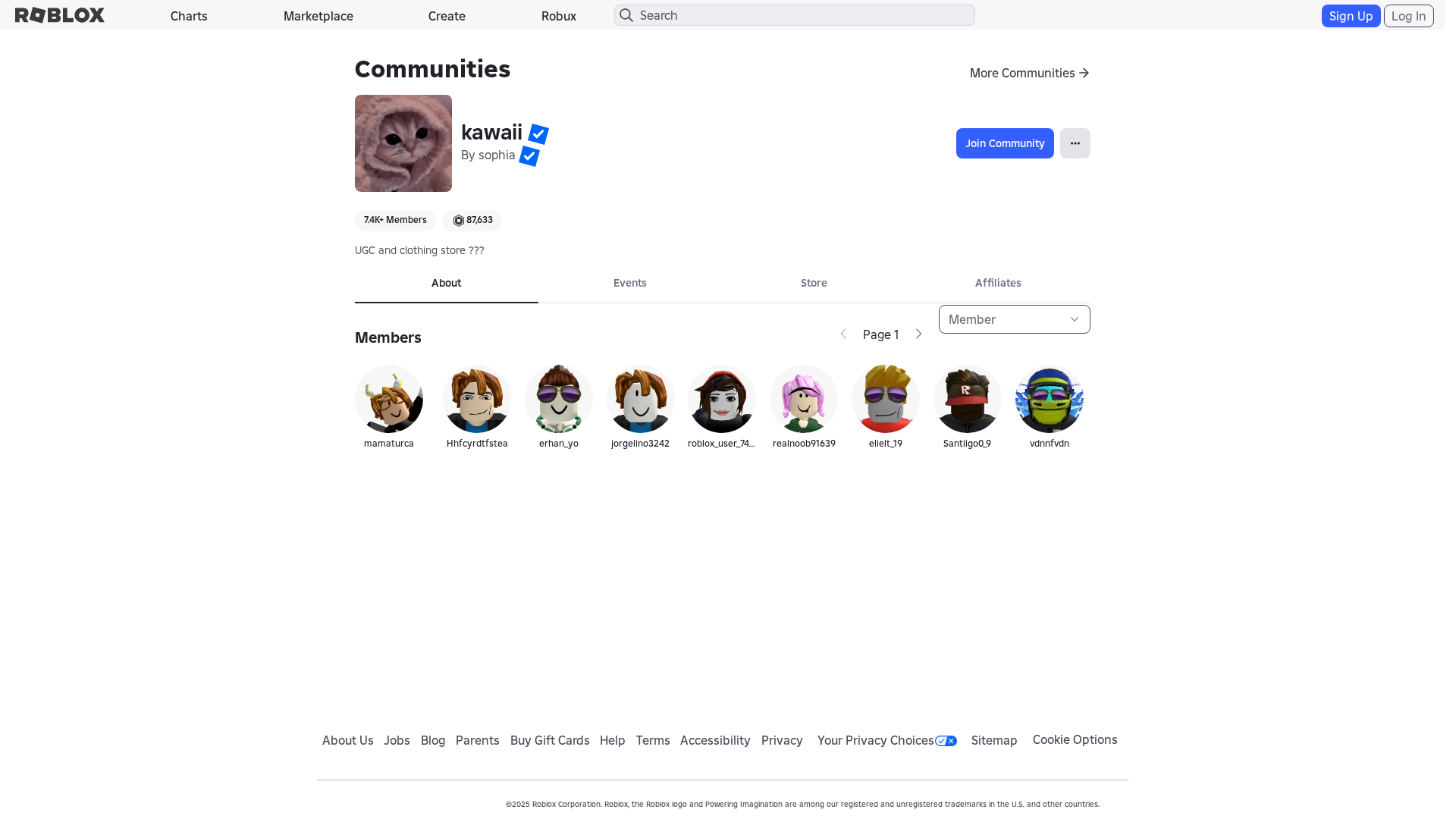
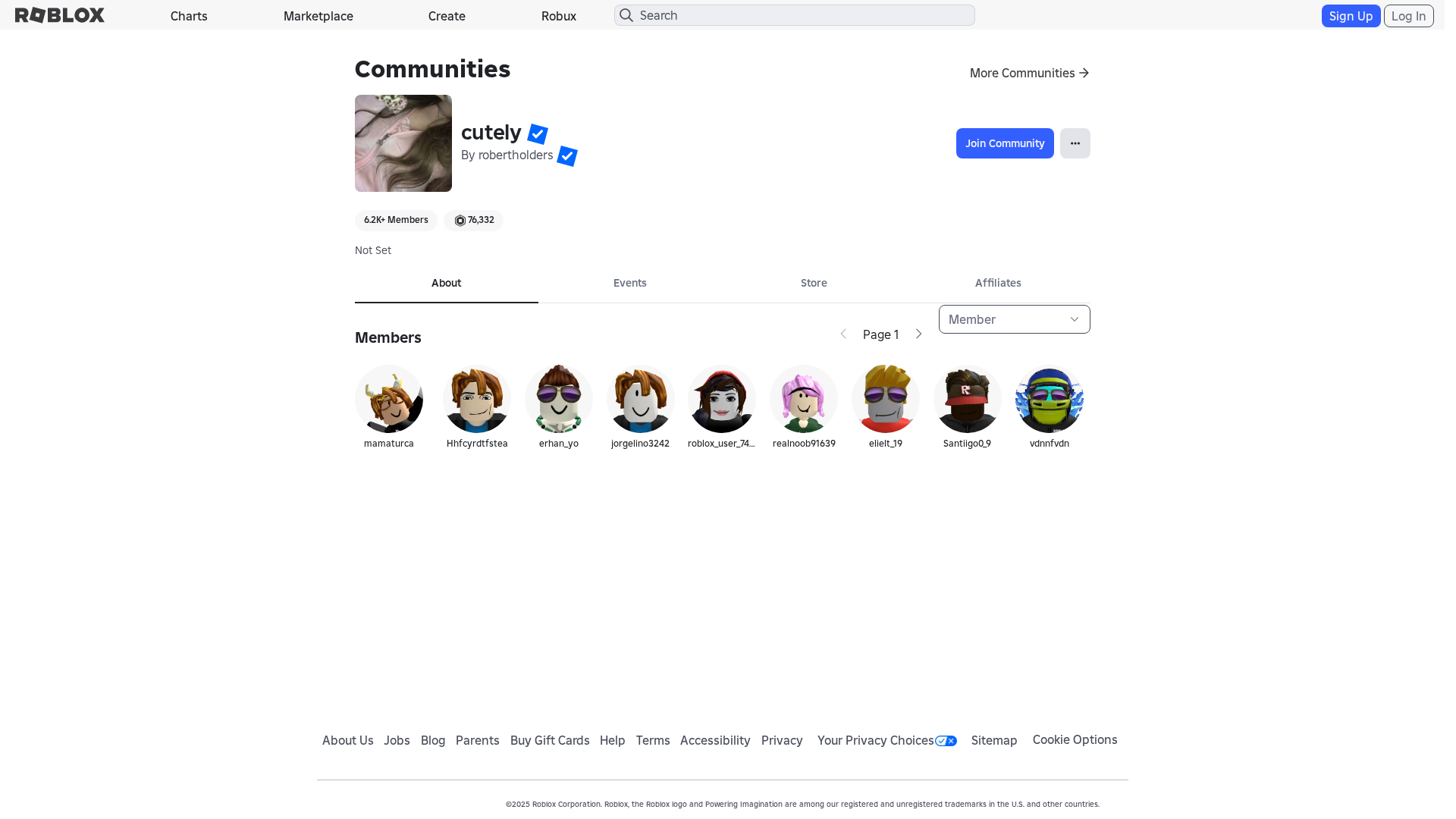
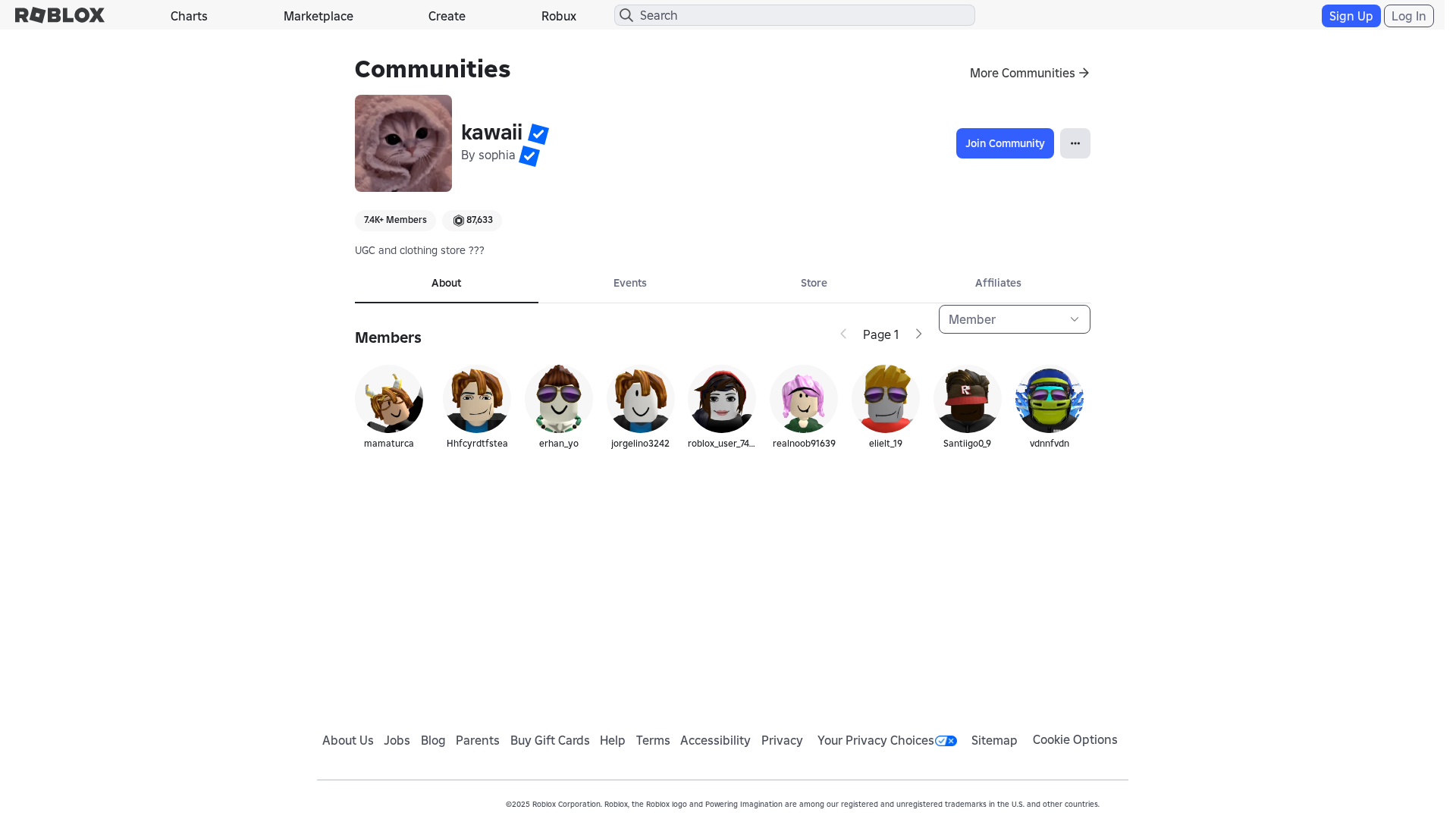
Captura Visual
Informações de Detecção
Hashes de Conteúdo (Similaridade HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1E253E9B193106837946F56C7F574BF0563E3DB4AC68286E6F1A8A32A0DD4CA2FC07527 |
|
CONTENT
ssdeep
|
768:9iqXWZyjLHUaSDzx2qf2uuOCuOosHMMSBmiEI:9iqXWZyXHNmxuOCuOotAiEI |
Hashes Visuais (Similaridade de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
bc3c9e9261c3c3c3 |
|
VISUAL
aHash
|
1a9bffc3c3ffffff |
|
VISUAL
dHash
|
b232201602000206 |
|
VISUAL
wHash
|
008b8383c3ffff81 |
|
VISUAL
colorHash
|
07200010080 |
|
VISUAL
cropResistant
|
b232201602000206 |
Análise de Código
🔬 Threat Analysis Report
• Ameaça: Falsificação de identidade
• Alvo: Usuários do Roblox
• Método: Falsificação de domínio e potencialmente javascript malicioso.
• Exfil: Desconhecido (Provavelmente credenciais da conta e informações de identificação pessoal).
• Indicadores: Correspondência de domínio, ofuscação de Javascript.
• Risco: ALTO
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- hex_escape
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- {{ $ctrl.getCatalogPageUrl() }}
- /catalog
- /login?returlUrl=1937185965
- https://api.roblox.com/accountinformation
- https://www.roblox.com/info/blog?locale=en_us
- https://api.roblox.com/auth
- https://www.roblox.com/catalog?CatalogContext=1&Keyword=
📡 API Calls Detected
- https://help.roblox.com/hc/articles/30428367965460
- https://ro.blox.com/Ebh5?
- POST
- get
- https://apis.
📤 Form Action Targets
- /search
📊 Detalhamento da Pontuação de Risco
Contributing Factors
🔬 Análise Integral de Ameaças
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 182 obfuscation techniques
🏢 Análise de Falsificação de Marca
⚔️ Metodologia de Ataque
Primary Method: Credential Harvesting
The attacker likely uses a domain that closely resembles Roblox to trick users into entering their credentials. Javascript code is used to make it more difficult for security tools to analyze and detect the malicious intent.
Secondary Method: Malicious Javascript Injection
The site uses obfuscated javascript, which likely facilitates credential theft (keylogging or data exfiltration) or redirects users to another malicious page.
🌐 Indicadores de Compromisso de Infraestrutura
🦠 Malicious Files
Functions: submitForm(), $eval()
🔌 External APIs Abused
- account: roblox.com
- purpose: User account management and authentication
📊 Diagrama de Fluxo de Ataque
User fills <input name='username'> → submitForm() → fetch('https://api.roblox.com/accountinformation') → Data sent to phishing server
🔬 JavaScript Deep Analysis
🔗 API Endpoints Detected
🔐 Obfuscation Detected
- : None
- : Light
- : Heavy
- : None
- : None
- : Light
- : None
- : None
- : None
- : None
- : Light
- : Light
- : None
- : Heavy
- : None
- : Moderate
- : Heavy
- : None
- : None
- : Light
🤖 AI-Extracted Threat Intelligence
📊 Attack Flow
User fills <input name='username'> → submitForm() → fetch('https://api.roblox.com/accountinformation') → Data sent to phishing server
🎯 Malicious Files Identified
0c2a7c793ed0761b93b214956992ffb44014abcb404fd8bd2f9a7eb32ea0a600.jsMalicious Functions
submitForm()$eval()
🌐 External APIs Abused
-
Roblox
- Account:
roblox.com
Finalidade: User account management and authentication
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for httpss-roblox.co
Found 10 other scans for this domain
-
http://httpss-roblox.co/users/1721859/profile
http://httpss-roblox.co/users/2058347444/profile
http://httpss-roblox.co/users/1776344257/profile
http://httpss-roblox.co/users/545015728/profile
https://httpss-roblox.co/users/1567517298/profile
http://httpss-roblox.co/users/1338275603/profile
http://httpss-roblox.co/users/1776344257/profile
http://httpss-roblox.co/users/2058347444/profile
http://httpss-roblox.co/users/1721859/profile
http://httpss-roblox.co/users/1092230912/profile