
Phishing Analysis
Detailed analysis of captured phishing page
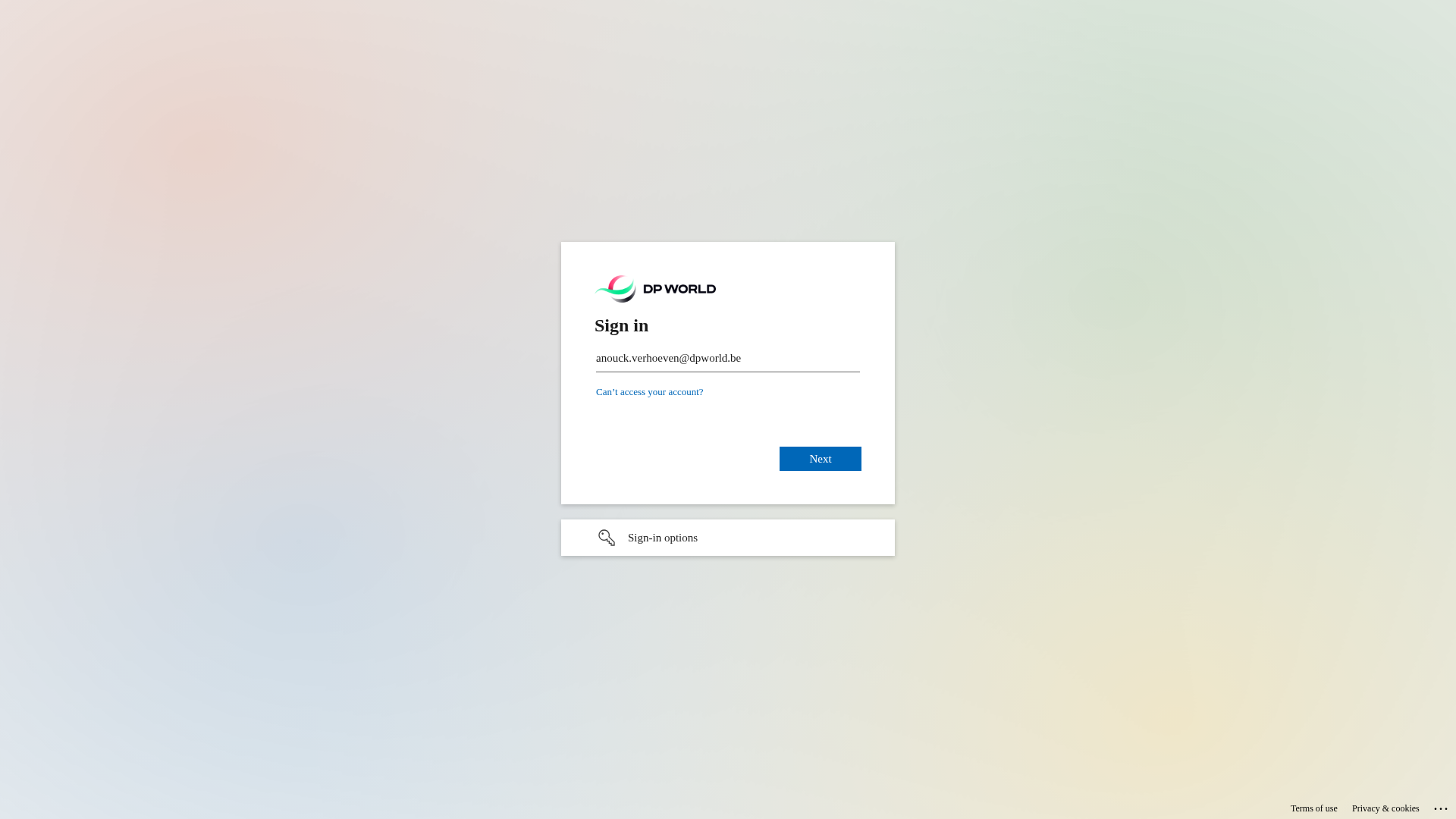
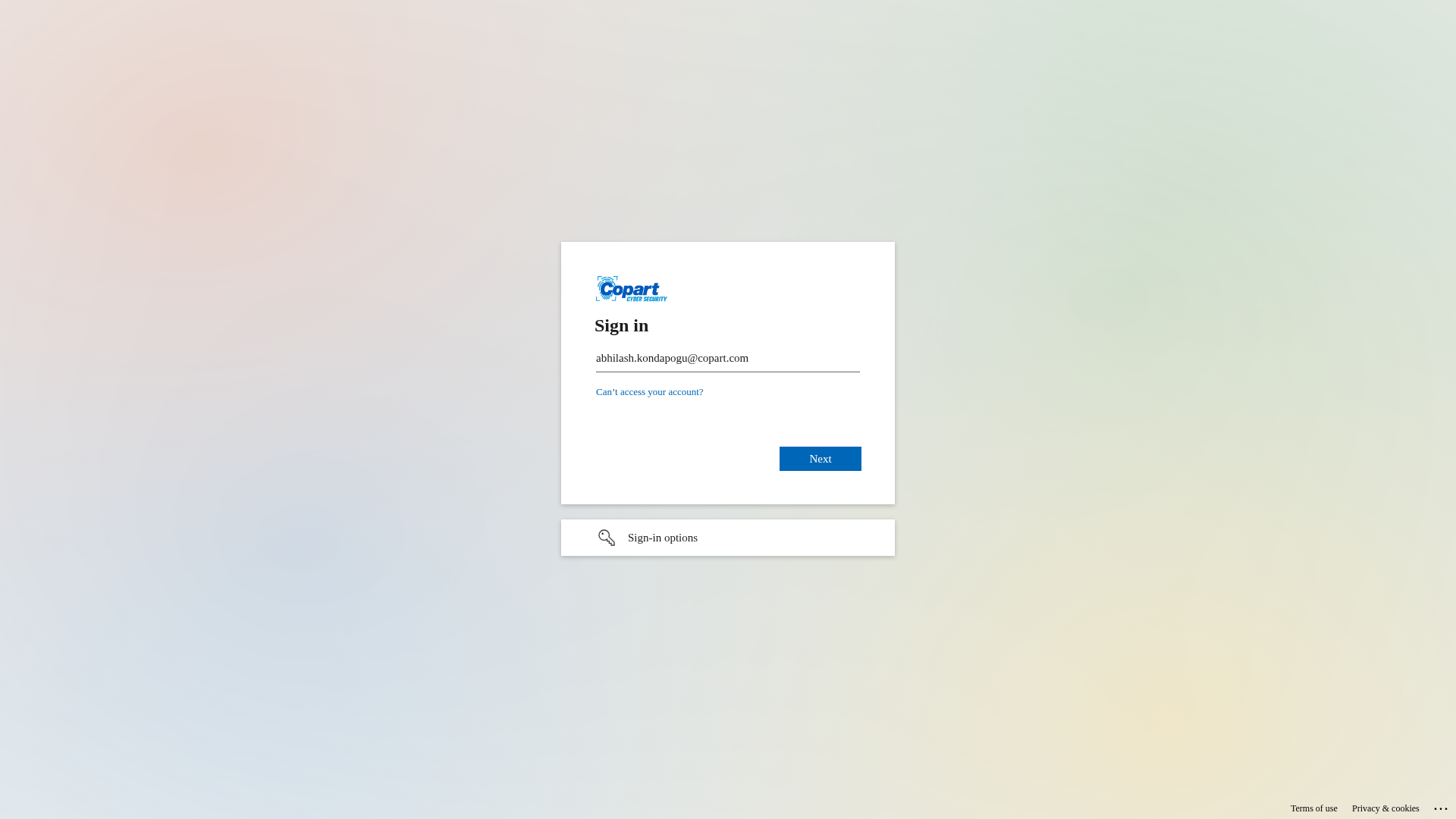
Captura Visual
Informações de Detecção
Hashes de Conteúdo (Similaridade HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1EBD10F7060409D3B42C3C7D8B3B96B8B3794C346EA97565A67F4C35D1EE3E26CC1A226 |
|
CONTENT
ssdeep
|
96:DIpkCGTHRPy9OkrwkMAs39TbJG9KjsWsjOJx0U2gs0sjOJkOVJQ6Q6ynQjNsjOJV:ZsOk8l9TbJG9atDpkOVJQyyQjtV |
Hashes Visuais (Similaridade de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
9c497326cc99d9e4 |
|
VISUAL
aHash
|
18001818191f0f9f |
|
VISUAL
dHash
|
7161713331727d38 |
|
VISUAL
wHash
|
191818181f1f1fff |
|
VISUAL
colorHash
|
070000001c0 |
|
VISUAL
cropResistant
|
7161713331727d38 |
Análise de Código
🎯 Kit Endpoints
- https://login.microsoftonline.com/common/login#
- https://login.microsoftonline.com/common/oauth2/authorize?client_id=00000001-0000-cff1-ce00-628975298370&response_mode=form_post&response_type=code+id_token&scope=openid&msafed=1&msaredir=1&client-request-id=d98292e6-fa3f-ce32-1255-21bc5137cc6d&protectedtoken=true&domain_hint=klp.no&nonce=216376187722.ec82d3ed-b372-7cd6-3e42-fcfc13352e79&state=YXJ1bmRldmkubXV0aHVrcmlzaG5hbkBrbHAubm8#
- https://passwordreset.microsoftonline.com/?ru=https://login.microsoftonline.com/common/oauth2/authorize?client_id=00000001-0000-cff1-ce00-222702038275&response_mode=form_post&response_type=code+id_token&scope=openid&msafed=1&msaredir=1&client-request-id=d98292e6-fa3f-ce32-8163-21bc5137cc6d&protectedtoken=true&domain_hint=klp.no&nonce=549041763484.ec82d3ed-b372-7cd6-3e42-fcfc13352e79&state=YXJ1bmRldmkubXV0aHVrcmlzaG5hbkBrbHAubm8#
- https://login.microsoftonline.com/common/oauth2/authorize?client_id=00000001-0000-cff1-ce00-668604993751&response_mode=form_post&response_type=code+id_token&scope=openid&msafed=1&msaredir=1&client-request-id=d98292e6-fa3f-ce32-7154-21bc5137cc6d&protectedtoken=true&domain_hint=klp.no&nonce=488276081147.ec82d3ed-b372-7cd6-3e42-fcfc13352e79&state=YXJ1bmRldmkubXV0aHVrcmlzaG5hbkBrbHAubm8#
📊 Detalhamento da Pontuação de Risco
Contributing Factors
🔬 Análise Integral de Ameaças
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Personal Info
🏢 Análise de Falsificação de Marca
⚔️ Metodologia de Ataque
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: Two-Factor Authentication Bypass
Victim is prompted for 2FA code after entering credentials. The code is intercepted and used by attacker to access victim's account in real-time.
🌐 Indicadores de Compromisso de Infraestrutura
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for authentication.ms
Found 10 other scans for this domain
-
https://authentication.ms/3ejxDgiR00pfew
https://authentication.ms/JpVBD5ezQ8YTOw
https://authentication.ms/rgMIktWwmJNq
https://authentication.ms/L2MoeYOKmp4GRQ
https://authentication.ms/SCExRDDMAhF0?/:f:/g/id_
https://authentication.ms/FQXXJbjMQUwdPlw
https://authentication.ms/Q0geWwh1if8
https://authentication.ms/KdRxhBr-pvsxWA
https://authentication.ms/wSEhhsLwlTzsj3E
https://authentication.ms/M_WFL0TUfH3JZQ?0b80-4d97...
