
Phishing Analysis
Detailed analysis of captured phishing page
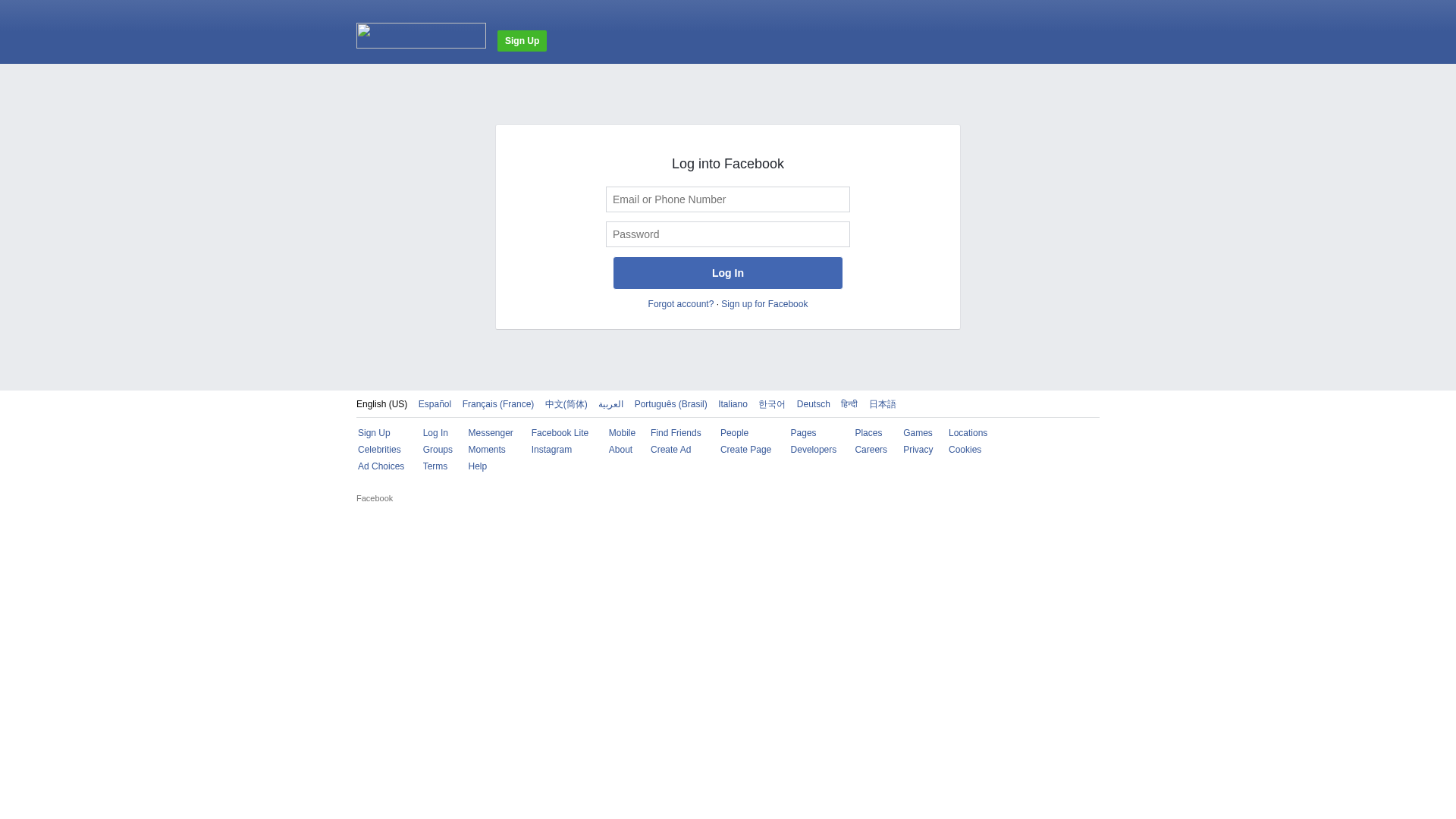
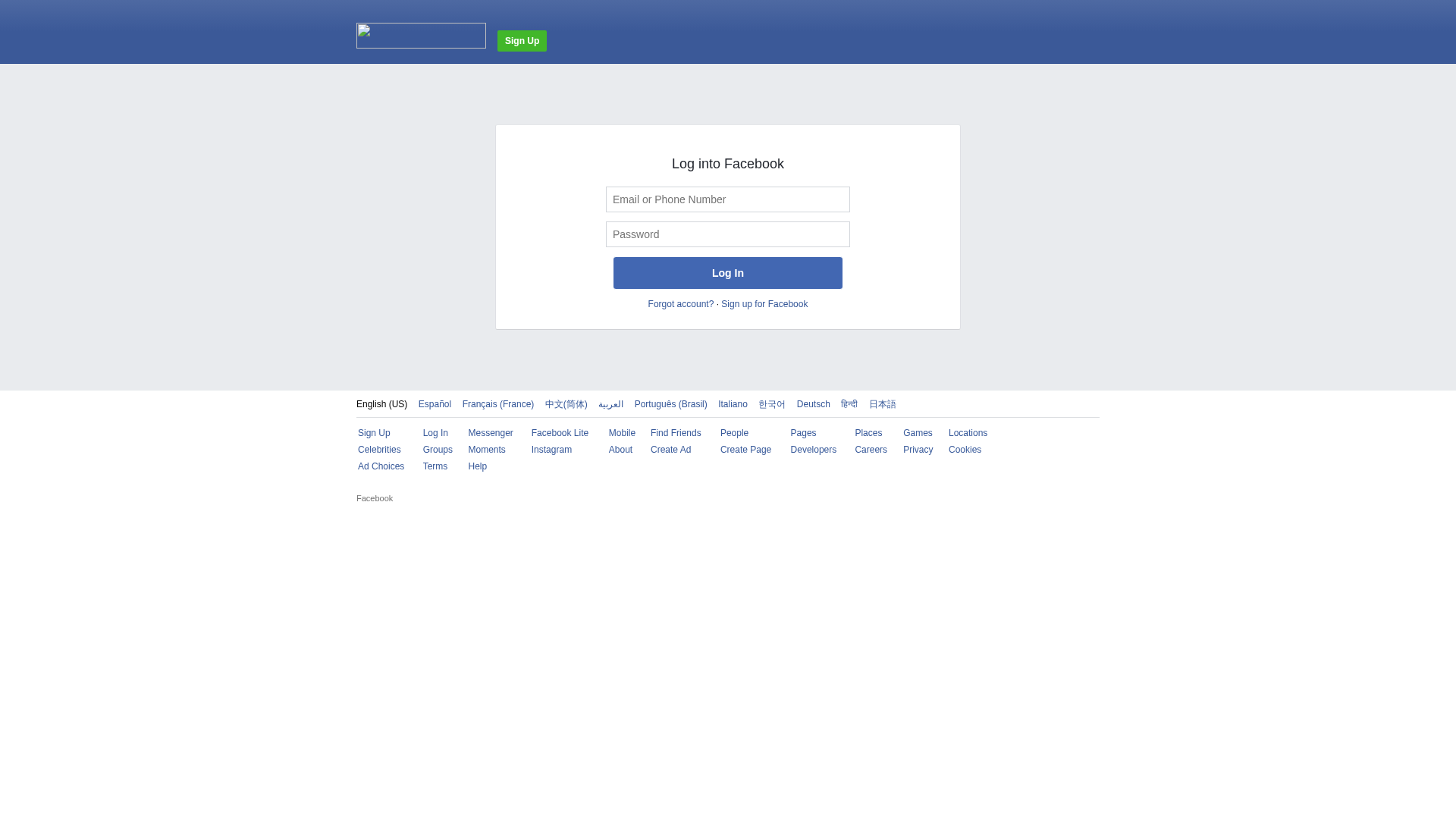
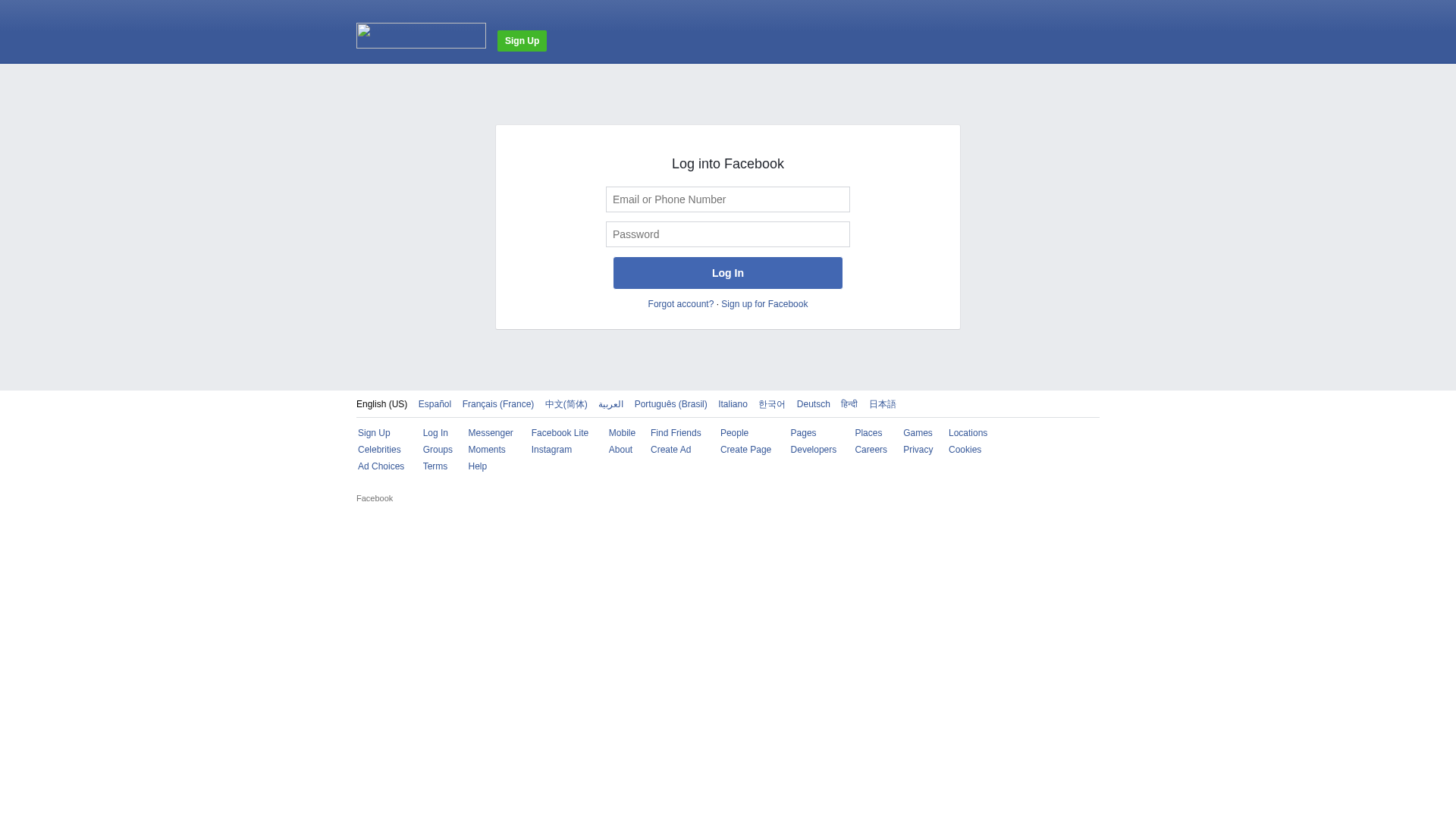
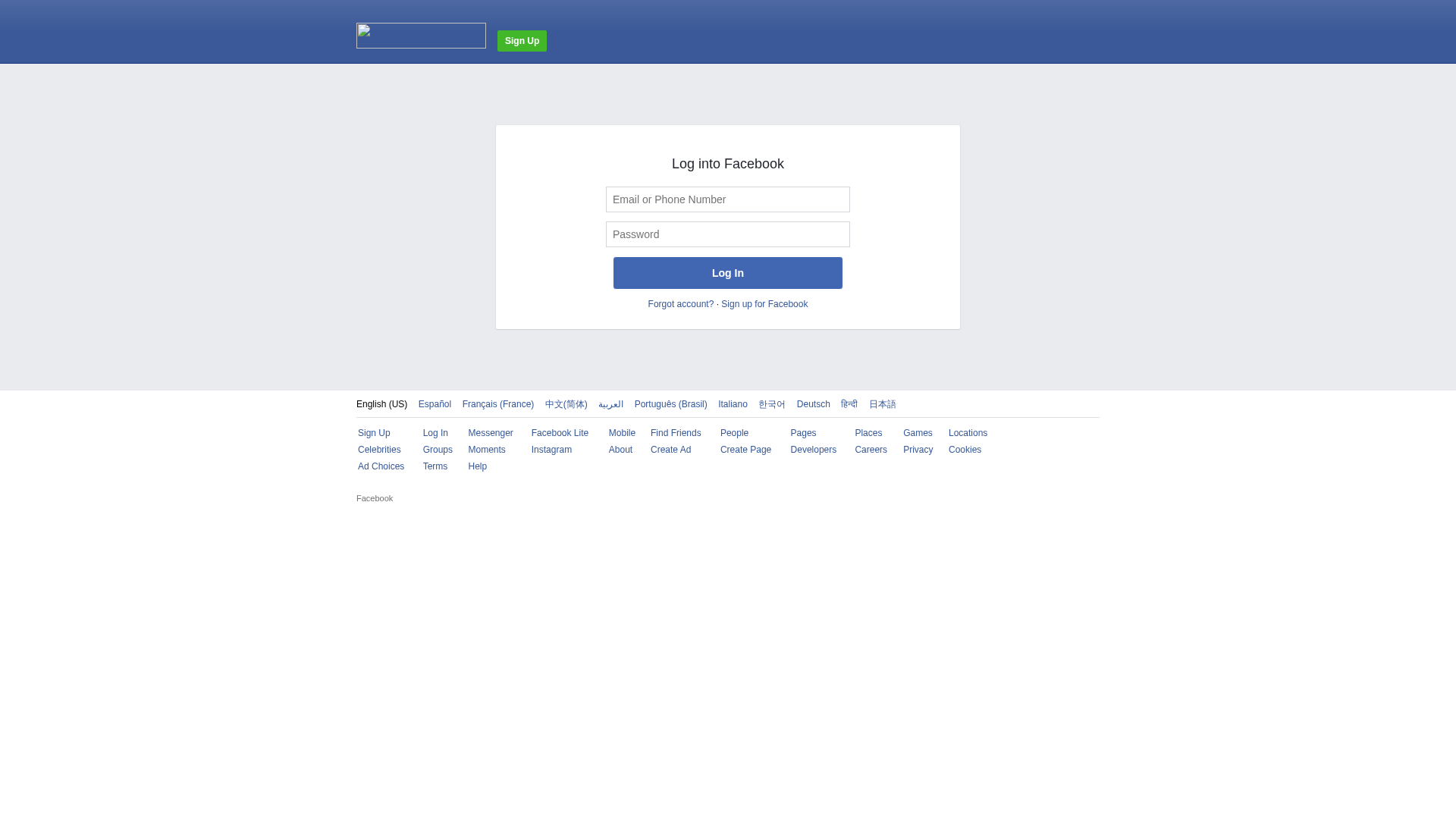
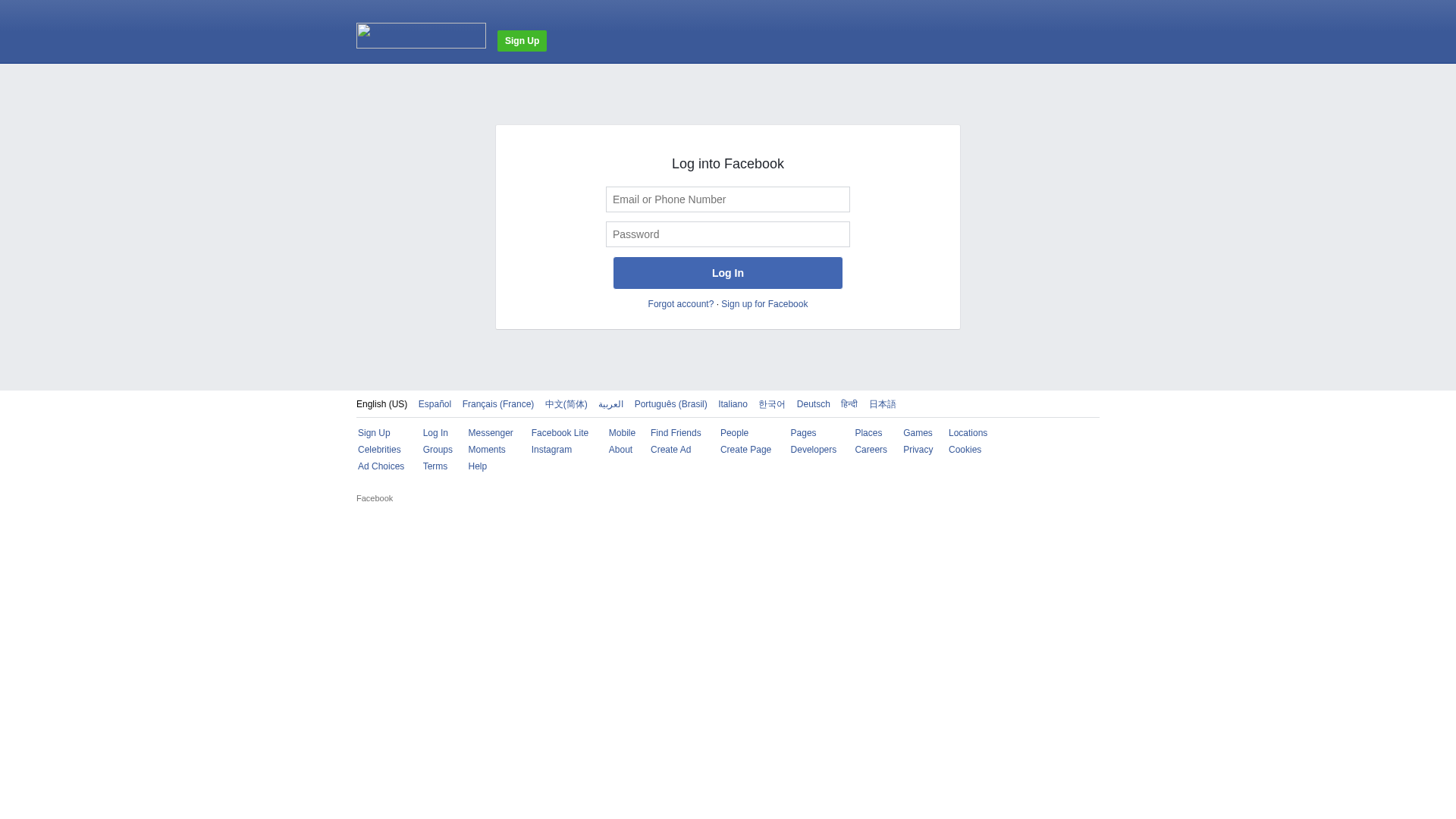
Captura Visual
Informações de Detecção
Hashes de Conteúdo (Similaridade HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T19D32443995823B0A653AA4FCF961BBA7C37241364B120FF05B94167BF54DAB01CB42DD |
|
CONTENT
ssdeep
|
192:Q5A70FBYAUsInNgjeJOgALl63WvIBIWIVI4IAIWpI+IaIUICIrIfeIwIqI5I4IeR:OjUd43L7N |
Hashes Visuais (Similaridade de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
b6434d4c3c676732 |
|
VISUAL
aHash
|
00ff24e7ffffffff |
|
VISUAL
dHash
|
4c20692836000000 |
|
VISUAL
wHash
|
00080000dfffffff |
|
VISUAL
colorHash
|
07007000000 |
|
VISUAL
cropResistant
|
306868362c000000,129141c2e8684820 |
Análise de Código
📊 Detalhamento da Pontuação de Risco
Contributing Factors
🔬 Análise Integral de Ameaças
⚠️ Indicators of Compromise
- Kit types: Credential Harvester
🏢 Análise de Falsificação de Marca
⚔️ Metodologia de Ataque
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: Standard Phishing Techniques
Uses typical phishing tactics including brand impersonation, urgency tactics, and social engineering to trick victims into providing sensitive information.
🌐 Indicadores de Compromisso de Infraestrutura
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
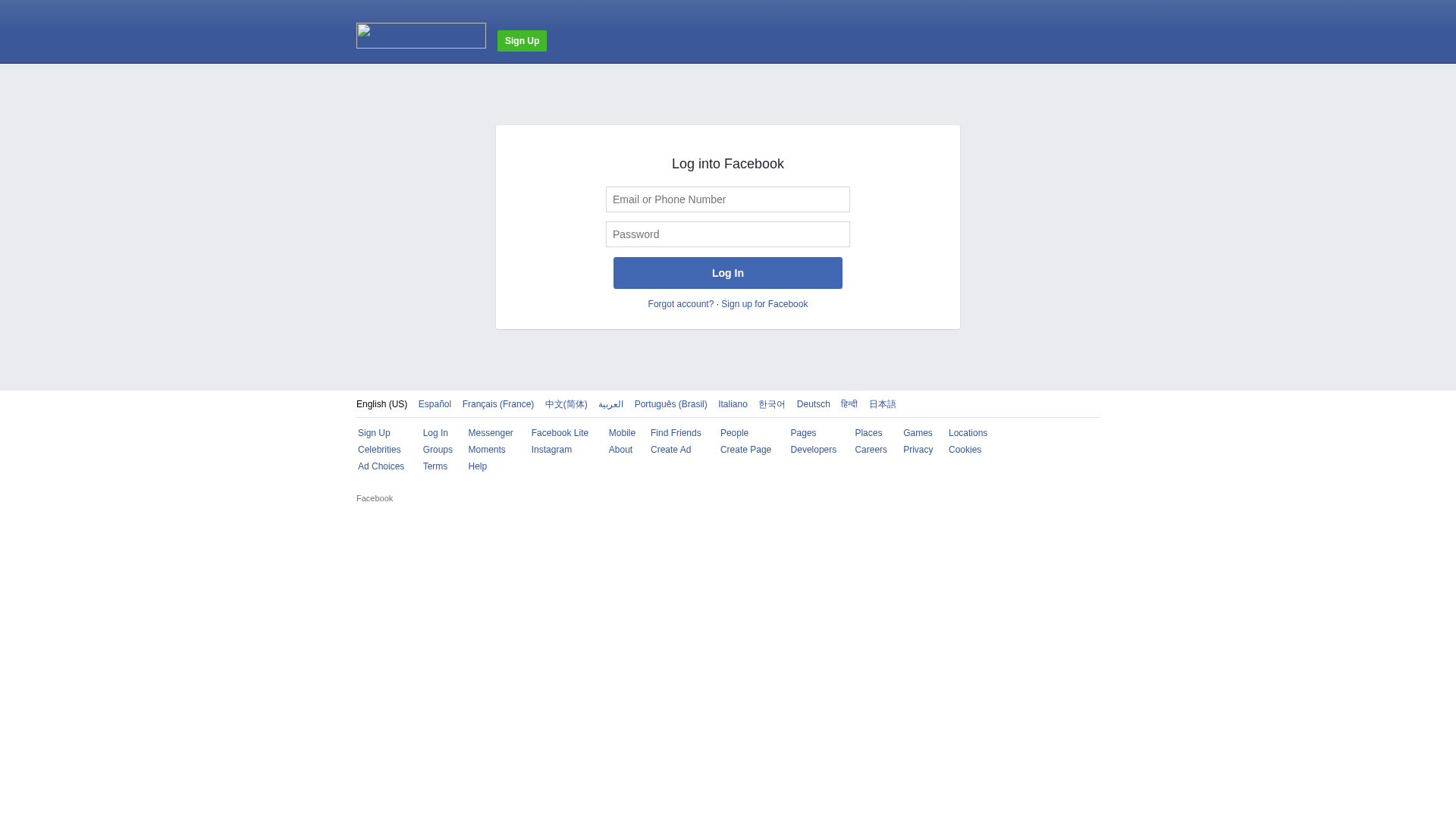
Scan History for hh.voicemail-system.com
Found 2 other scans for this domain
