
Phishing Analysis
Detailed analysis of captured phishing page
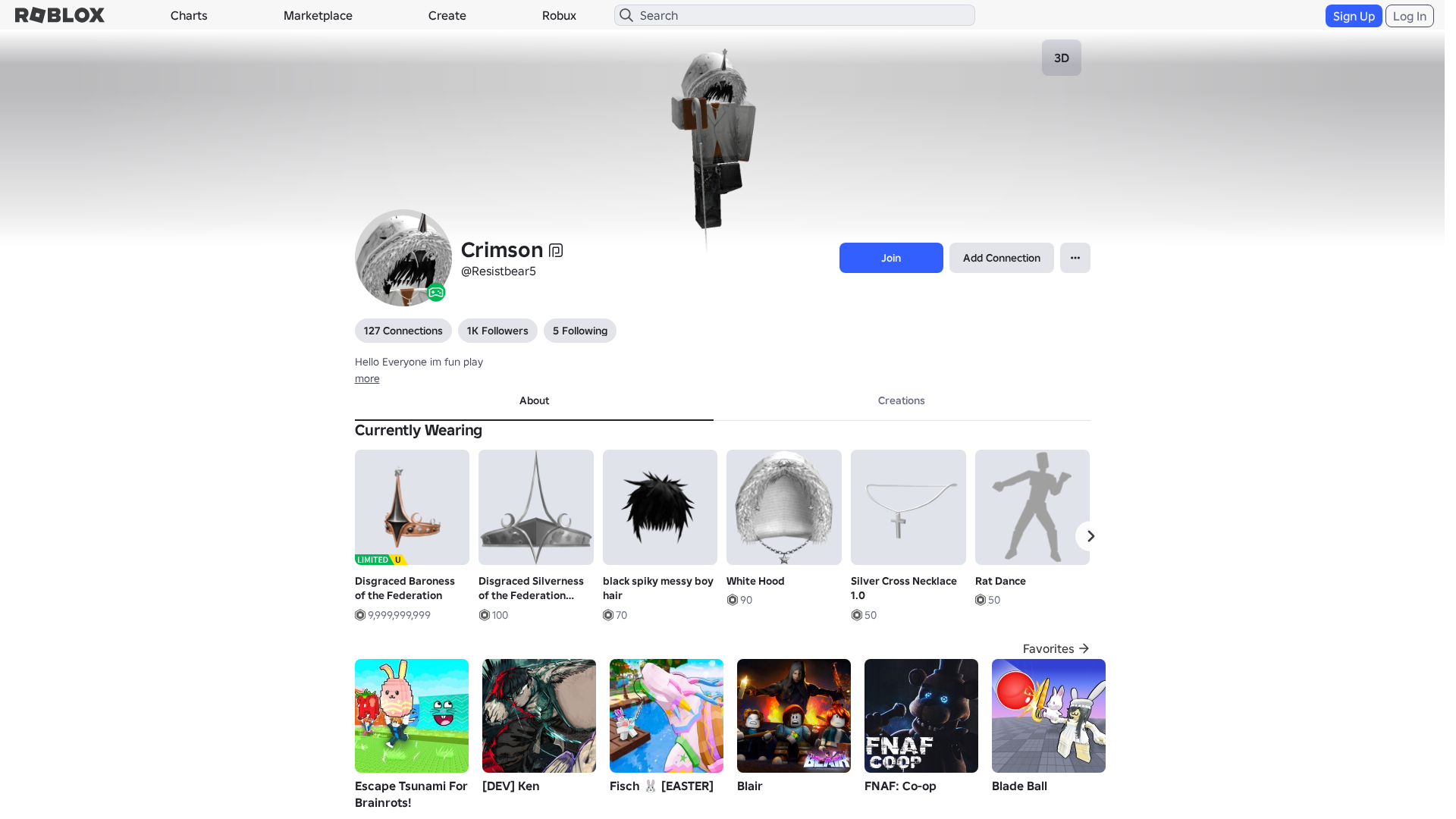
Captura Visual
Informações de Detecção
https://roblx.me/s/users243672918813profile
Detected Brand
Roblox
Country
Unknown
Confidence
100%
HTTP Status
200
Report ID
aced5cc2-be4…
Analyzed
2026-04-04 21:24
Final URL (after redirects)
https://www.robiox.com.py/users/243671918813/profile
Hashes de Conteúdo (Similaridade HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T171A31E729254283751BB79DAB024672EA6D7C70FCA8347E1A2F8D39A0FD6C91EC1340D |
|
CONTENT
ssdeep
|
3072:lKXW0DqjBpqrlgmB1WymH+fHqzCHk1uvarrgBODqmj1voY:wX/DqjBpqrlgmB1WymH+fHqzCHk1uva/ |
Hashes Visuais (Similaridade de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
b4936553d9cc986c |
|
VISUAL
aHash
|
0020dfffc7cfc3c3 |
|
VISUAL
dHash
|
e8c836300e1a1616 |
|
VISUAL
wHash
|
0000dfffc3c7c3c3 |
|
VISUAL
colorHash
|
07001008040 |
|
VISUAL
cropResistant
|
e8c836300e1a1616,07535d1585838f8c,71334dc989356f4b,7b3f66361bdd952d |
Análise de Código
Risk Score
100/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🎣 Card Stealer
🎣 Banking
🎣 Personal Info
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- hex_escape
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- https://api.injuries.lu/catalog/117091974006042/tornado-mart-japan
- https://api.injuries.lu/catalog/109359129538345/Disgraced-Silverness-of-the-Federation-Addon
- https://api.injuries.lu/catalog/4390896732/Viscount-of-the-Federation
- https://api.injuries.lu/catalog/106537993816942/adidas-Community-Animation-Pack
- https://api.injuries.lu/catalog/1180419690/Disgraced-Baroness-of-the-Federation
- https://www.roblox.com/catalog?CatalogContext=1&Keyword=
- https://api.injuries.lu/catalog/81500432784353/R6-Torso
- https://api.injuries.lu/catalog/78755795767408/Aura-RNG-Fly-Idle
- https://api.injuries.lu/catalog/5915780563/Country-Line-Dance-Lil-Nas-X-LNX
- https://api.injuries.lu/catalog/124765145869332/adidas-Community-Animation-Pack
- https://api.injuries.lu/catalog/120307951/Noir-Periastron-Psi
- https://api.injuries.lu/catalog/111968802067441/White-Hood
- https://api.injuries.lu/catalog/14618207727/Default-Mood
- https://www.roblox.com/catalog
- https://www.robiox.com.py/NewLogin?returnUrl=https%3A%2F%2Fwww.roblox.com%2Fusers%2F243671918813%2Fprofile
- https://api.injuries.lu/catalog/104929891852793/JOJO-Pose-Jotaro
- https://www.roblox.com/games/6730460146/NEW-ADMIN-TYCOON
- /login?returnUrl=
- https://api.injuries.lu/catalog/80432799757663/Blocky-Right-Arm
- /login?returnUrl=https%3A%2F%2Fwww.roblox.com%2Fusers%2F243671918813%2Fprofile
- /info/blog?locale=en_us
- https://api.injuries.lu/catalog/18742165661/black-spiky-messy-boy-hair
- https://api.injuries.lu/catalog/85092320680319/Nonchalant-Sit
- https://api.injuries.lu/catalog/76672609579386/R6-Right-Leg
- https://api.injuries.lu/catalog/117849292432710/Blocky-Left-Arm
- https://api.injuries.lu/catalog/31046644/Crown-of-the-Undead-Hoard
- https://api.injuries.lu/catalog/93993406355955/adidas-Community-Animation-Pack
- https://api.injuries.lu/catalog/115715495289805/adidas-Community-Animation-Pack
- https://api.injuries.lu/catalog/136084918174993/koaro
- https://api.injuries.lu/catalog/6202629757/Silver-Cross-Necklace-1-0
- https://api.injuries.lu/catalog/24123795/Al-Capwn
- https://api.injuries.lu/catalog/101573394483995/Effortless-Aura-Pose
- https://api.injuries.lu/catalog/123695349157584/adidas-Community-Animation-Pack
- https://api.injuries.lu/catalog/98603994713783/Rat-Dance
- https://api.injuries.lu/catalog/117302755748327/Coffin-Walkout
- https://api.injuries.lu/catalog/99223542650102/Korblox-Deathwalker-Head
- https://api.injuries.lu/catalog/126354114956642/adidas-Community-Animation-Pack
- https://api.injuries.lu/catalog/187848395/Workclock-Shades
- https://api.injuries.lu/catalog/553858732/WC-Ultimates-Peridot-Panic
- https://api.injuries.lu/catalog/134444446333310/R6-Left-Leg
- https://api.injuries.lu/catalog/106810508343012/adidas-Community-Animation-Pack
- https://api.injuries.lu/catalog/501755654/White-Sword-Cane
📡 API Calls Detected
- /api/shorten
- https://ro.blox.com/Ebh5?
- /api/pageview
- https://apis.
- get
- https://help.roblox.com/hc/articles/30428367965460
- GET
- https://kyxn.dev/api/shorten
- https://kyxn.dev/api/shorten/TKvzwH
- POST
- https://kyxn.dev${e.endpoint}
📤 Form Action Targets
- /search
📊 Detalhamento da Pontuação de Risco
Total Risk Score
100/100
Contributing Factors
Active Phishing Kit
Detected kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
Credential Harvesting
Credential harvesting detected with 1 form(s) capturing sensitive data
Code Obfuscation
JavaScript code obfuscated using 212 technique(s) to evade detection
🔬 Análise Integral de Ameaças
Tipo de Ameaça
Banking Credential Harvester
Alvo
Roblox users
Método de Ataque
credential harvesting forms + obfuscated JavaScript
Canal de Exfiltração
HTTP POST to backend
Avaliação de Risco
CRITICAL - Automated credential harvesting with HTTP POST to backend
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 212 obfuscation techniques
🏢 Análise de Falsificação de Marca
Impersonated Brand
Roblox
Official Website
https://www.roblox.com
Fake Service
Banking/payment service
⚔️ Metodologia de Ataque
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 212 techniques to evade detection by security scanners and make reverse engineering more difficult.
🌐 Indicadores de Compromisso de Infraestrutura
Domain Information
Domain
roblx.me
Registered
2026-03-28 03:56:41+00:00
Registrar
NAMECHEAP INC
Status
Recently registered (7 days old)
Hosting Information
Provider
Namecheap
ASN
🤖 AI-Extracted Threat Intelligence
Scan History for roblx.me
Found 10 other scans for this domain

"Nunca pensei que aconteceria comigo"
Isso dizem os 2,3 milhões de vítimas a cada ano. Não espere para ser uma estatística.