Phishing Analysis
Detailed analysis of captured phishing page
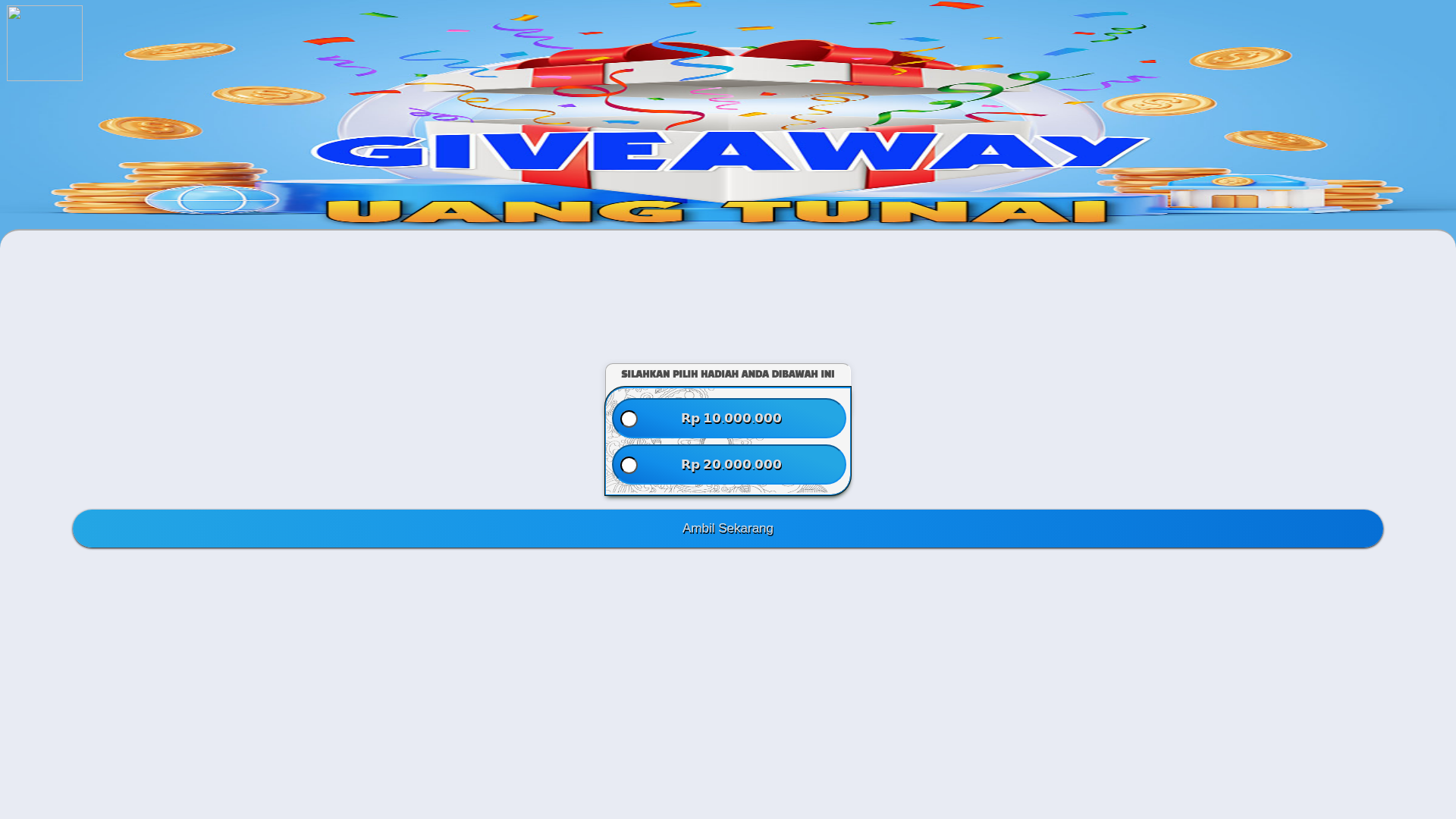
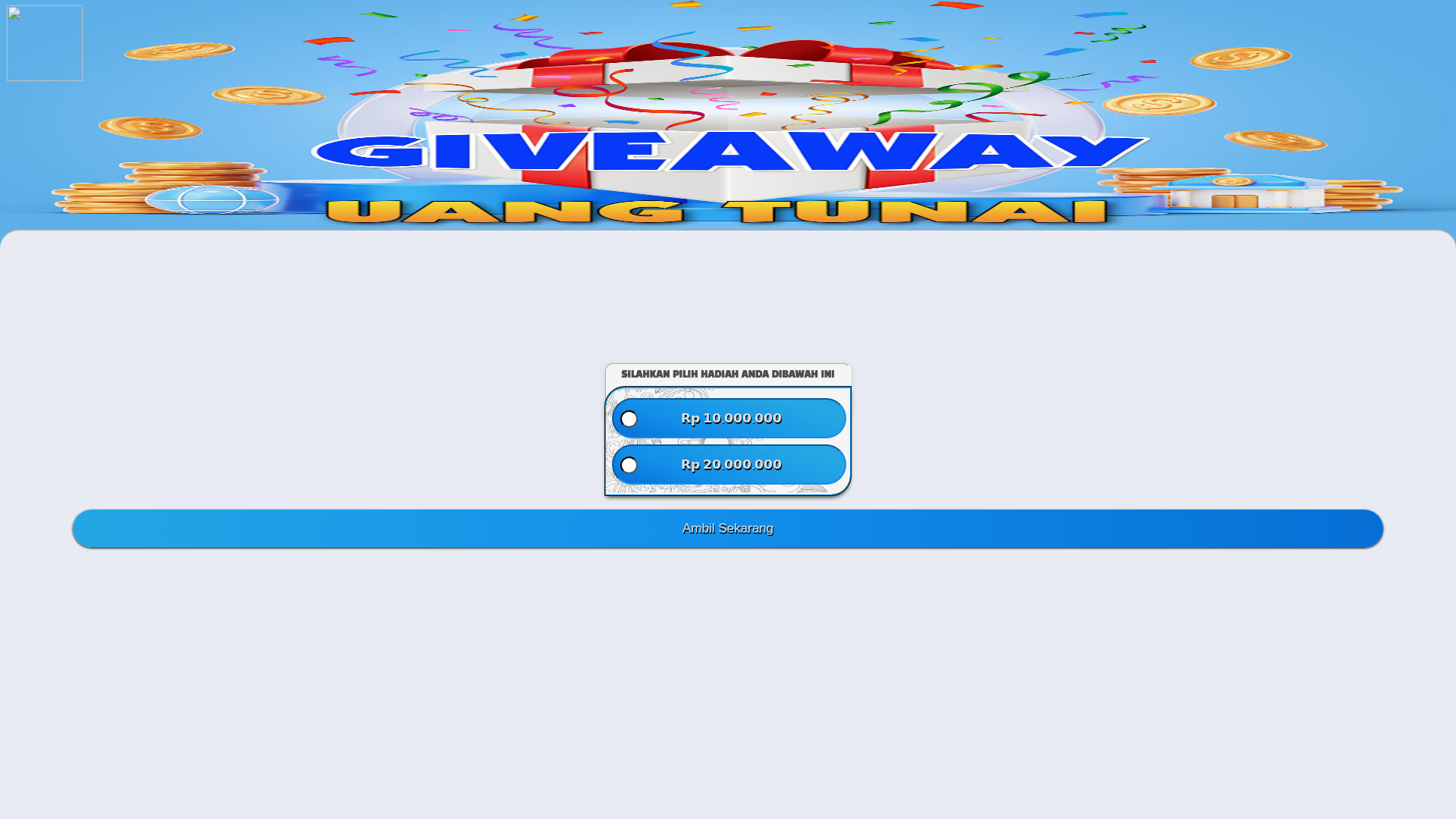
Captura Visual
Informações de Detecção
https://fqwi.qzz.io/dana/elcf5/
Detected Brand
Unknown
Country
International
Confidence
95%
HTTP Status
200
Report ID
b3fd97d6-288…
Analyzed
2026-03-06 09:05
Hashes de Conteúdo (Similaridade HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T17EF1E8A2A15C48083226C681BEA1FE486337CA46CB5D193AB1B62457B3DE5F4C1373A1 |
|
CONTENT
ssdeep
|
96:Crhvf25BPf2iSiSz5TdvVXZXh9h1kD5OEpdjKlVZsquTn1P/y8tj7PadPOQie:MU/SiSphFZvkDZ1Kl/squpP/y8tvSdPz |
Hashes Visuais (Similaridade de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
f3151d62e68c4a37 |
|
VISUAL
aHash
|
0000dfffe780ffff |
|
VISUAL
dHash
|
d49632cc4d118401 |
|
VISUAL
wHash
|
000081ffe700ffff |
|
VISUAL
colorHash
|
07006000080 |
|
VISUAL
cropResistant
|
d49632cc4d118401,0000202000000000 |
Análise de Código
Risk Score
56/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🔬 Threat Analysis Report
• Ameaça: Phishing
• Alvo: Usuários desavisados
• Método: Sorteio enganoso
• Exfil: Desconhecido (provavelmente credenciais ou informações pessoais)
• Indicadores: Domínio não relacionado, sorteio, entradas de formulário.
• Risco: Alto
🔒 Obfuscation Detected
- fromCharCode
- unescape
📡 API Calls Detected
- POST
📊 Detalhamento da Pontuação de Risco
Total Risk Score
90/100
Contributing Factors
Suspicious Domain
Unrelated domain with no brand association.
Phishing indicators
Giveaway incentive is often used in phishing attacks.
Obfuscation
Code obfuscation used to hide malicious intentions.
🔬 Análise Integral de Ameaças
Tipo de Ameaça
Credential Harvesting Kit
Alvo
General public
Método de Ataque
credential harvesting forms + obfuscated JavaScript
Canal de Exfiltração
Form submission (backend endpoint not detected - likely JavaScript-based)
Avaliação de Risco
MEDIUM - Automated credential harvesting with Form submission (backend endpoint not detected - likely JavaScript-based)
⚠️ Indicators of Compromise
- Kit types: Credential Harvester
- 4 obfuscation techniques
🏢 Análise de Falsificação de Marca
Impersonated Brand
None
Fake Service
Giveaway
Fraudulent Claims
⚔️ Metodologia de Ataque
Primary Method: Credential Harvesting
The site likely aims to collect personal information from users, possibly through a form hidden in the page's code or a redirect after the user selects a prize. The obfuscation detected would likely be used to make it harder to detect such malicious code.
🌐 Indicadores de Compromisso de Infraestrutura
Domain Information
Domain
fqwi.qzz.io
Registered
Unknown
Registrar
Unknown
Status
Unknown
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)

"Nunca pensei que aconteceria comigo"
Isso dizem os 2,3 milhões de vítimas a cada ano. Não espere para ser uma estatística.