
Phishing Analysis
Detailed analysis of captured phishing page
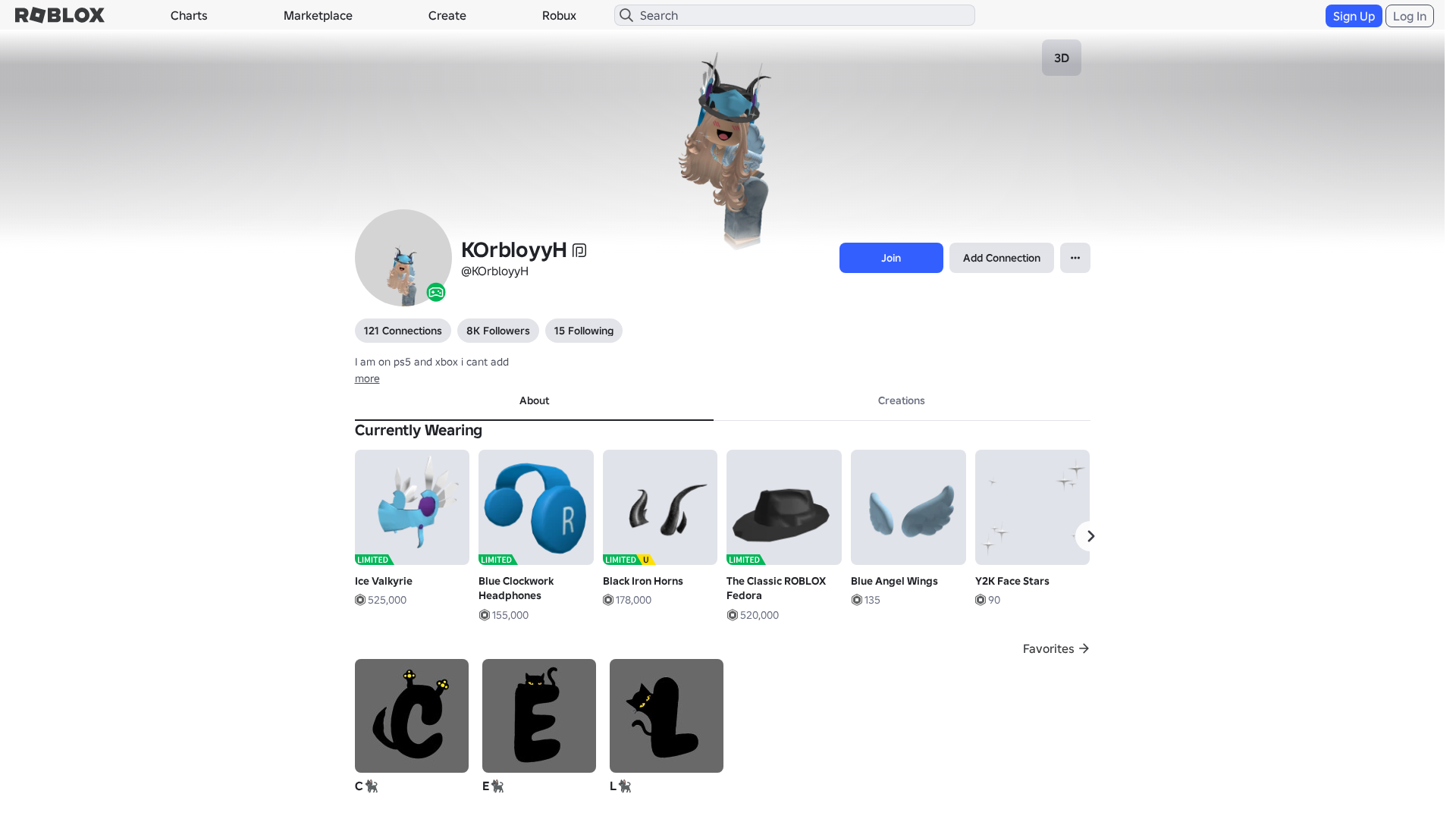
Captura Visual
Informações de Detecção
https://rblox.me/s/7jJos3
Detected Brand
Roblox
Country
Unknown
Confidence
100%
HTTP Status
200
Report ID
b430edd4-fb0…
Analyzed
2026-04-07 09:27
Final URL (after redirects)
https://www.robiox.com.py/users/126874490812/profile
Hashes de Conteúdo (Similaridade HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T100831E7292542837617B69DAF064672EE2D7C70FCA4346E1A2F8D39A0FD6CD1E86340D |
|
CONTENT
ssdeep
|
1536:telAnXWn4ryqilbehOsgcog0T3gkUgqjgzEgM2gQmgKVafgIOg1YVg86glUg1Sgw:0lAnXWHqilwwL0Ku4C6VYlBfdyc0JuBM |
Hashes Visuais (Similaridade de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
b0463367d999ec38 |
|
VISUAL
aHash
|
0000d7ffc7c7cfcf |
|
VISUAL
dHash
|
e8e8b6309e061a1a |
|
VISUAL
wHash
|
0000d3dfc3c3cfcf |
|
VISUAL
colorHash
|
07001000180 |
|
VISUAL
cropResistant
|
e8e8b6309e061a1a,484d8713535b0fc6,468e9e9c9e9e969e |
Análise de Código
Risk Score
100/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🎣 Card Stealer
🎣 Banking
🎣 Personal Info
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- hex_escape
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- https://api.injuries.lu/catalog/12731825880/big-blue-bow
- https://api.injuries.lu/catalog/1029025/The-Classic-ROBLOX-Fedora
- https://api.injuries.lu/catalog/79131329994586/Kemono-Furry-Head-Pats-Pets
- https://api.injuries.lu/catalog/126354114956642/adidas-Community-Animation-Pack
- https://api.injuries.lu/catalog/12625283415/Y2K-Face-Stars
- https://api.injuries.lu/catalog/124754866635882/Modern-Woman-2-Torso
- https://api.injuries.lu/catalog/130433936882245/Super-Super-Happy-Face-Head
- https://www.roblox.com/catalog
- https://api.injuries.lu/catalog/103168660352906/True-Heart
- https://api.injuries.lu/catalog/120037539988659/OG-nya-san-russian-kawaii-hip-swing-dance
- https://api.injuries.lu/catalog/10203909727/BLUE-CLOCKWORK-HEADPHONES-BCWHP-SHIRT-VALK-FROZEN
- https://api.injuries.lu/catalog/74277551575520/Funny-Goofy-Wiggle
- https://api.injuries.lu/catalog/139607718/Korblox-Deathspeaker-Right-Leg
- https://api.injuries.lu/catalog/16744212581/Bold-Jump
- https://www.robiox.com.py/NewLogin?returnUrl=https%3A%2F%2Fwww.roblox.com%2Fusers%2F126874490812%2Fprofile
- https://api.injuries.lu/catalog/17402541939/Blue-Angel-Wings
- https://api.injuries.lu/catalog/16744214662/Bold-Run
- https://api.injuries.lu/catalog/86499716/Woman-Left-Arm
- https://api.injuries.lu/catalog/15880450837/star-tattoo-belly-shade-piercing-cute-y2k
- https://api.injuries.lu/catalog/628771505/Black-Iron-Horns
- https://api.injuries.lu/catalog/137525589399948/37shq
- https://api.injuries.lu/catalog/18538164337/adidas-Sports-Fall
- https://api.injuries.lu/catalog/16744204409/Bold-Climb
- https://api.injuries.lu/catalog/16744219182/Bold-Walk
- /login?returnUrl=https%3A%2F%2Fwww.roblox.com%2Fusers%2F126874490812%2Fprofile
- https://api.injuries.lu/catalog/103155280474275/Cute-Kawaii-Legs-Up-Shy-Kicking-Feet-Cat-Laying
- https://api.injuries.lu/catalog/124102129879581/Super-Super-Happy-Face-Mood
- /login?returnUrl=
- https://api.injuries.lu/catalog/18105944281/cutecore-black-bow-leg-warmers-skirt-emo-goth-y2k
- https://api.injuries.lu/catalog/16744217055/Bold-Swim
- https://api.injuries.lu/catalog/4390891467/Ice-Valkyrie
- https://api.injuries.lu/catalog/90221568176994/Sit
- https://api.injuries.lu/catalog/86499698/Woman-Right-Arm
- https://api.injuries.lu/catalog/1743903423/Blue-Clockwork-Headphones
- https://api.injuries.lu/catalog/13864155985/Horns-of-the-Fallen
- https://api.injuries.lu/catalog/15083127542/Long-Super-Model-Curly-Hair-Blonde
- https://api.injuries.lu/catalog/125183511213246/Parking-Lot-Dance
- https://www.roblox.com/catalog?CatalogContext=1&Keyword=
- https://api.injuries.lu/catalog/100597438247721/Sweet-Hug-Pose-V1-MATCHING
- /info/blog?locale=en_us
📡 API Calls Detected
- https://kyxn.dev${e.endpoint}
- https://apis.
- https://help.roblox.com/hc/articles/30428367965460
- POST
- /api/shorten
- https://ro.blox.com/Ebh5?
- get
- GET
- https://kyxn.dev/api/shorten/TKvzwH
- /api/pageview
- https://kyxn.dev/api/shorten
📤 Form Action Targets
- /search
📊 Detalhamento da Pontuação de Risco
Total Risk Score
100/100
Contributing Factors
Active Phishing Kit
Detected kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
Credential Harvesting
Credential harvesting detected with 1 form(s) capturing sensitive data
Code Obfuscation
JavaScript code obfuscated using 213 technique(s) to evade detection
🔬 Análise Integral de Ameaças
Tipo de Ameaça
Banking Credential Harvester
Alvo
Roblox users
Método de Ataque
credential harvesting forms + obfuscated JavaScript
Canal de Exfiltração
HTTP POST to backend
Avaliação de Risco
CRITICAL - Automated credential harvesting with HTTP POST to backend
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 213 obfuscation techniques
🏢 Análise de Falsificação de Marca
Impersonated Brand
Roblox
Official Website
https://www.roblox.com
Fake Service
Banking/payment service
⚔️ Metodologia de Ataque
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 213 techniques to evade detection by security scanners and make reverse engineering more difficult.
🌐 Indicadores de Compromisso de Infraestrutura
Domain Information
Domain
rblox.me
Registered
2026-03-28 04:11:14+00:00
Registrar
NAMECHEAP INC
Status
Recently registered (10 days old)
Hosting Information
Provider
Namecheap
ASN
🤖 AI-Extracted Threat Intelligence
Scan History for rblox.me
Found 10 other scans for this domain
-
https://rblox.me/s/AoBdgb
https://rblox.me/s/0AA1uD
https://rblox.me/s/BLOXFRUITS
https://rblox.me/s/VKvl9R
https://rblox.me/s/user-214761231-profile
https://rblox.me/s/roblox-com-users-1834383
https://rblox.me/s/users-463538495178-profi
https://rblox.me/s/robIox-profiIe
https://rblox.me/s/WHzLfQ
https://rblox.me/s/roblox-com-games-2765465

"Nunca pensei que aconteceria comigo"
Isso dizem os 2,3 milhões de vítimas a cada ano. Não espere para ser uma estatística.