Phishing Analysis
Detailed analysis of captured phishing page
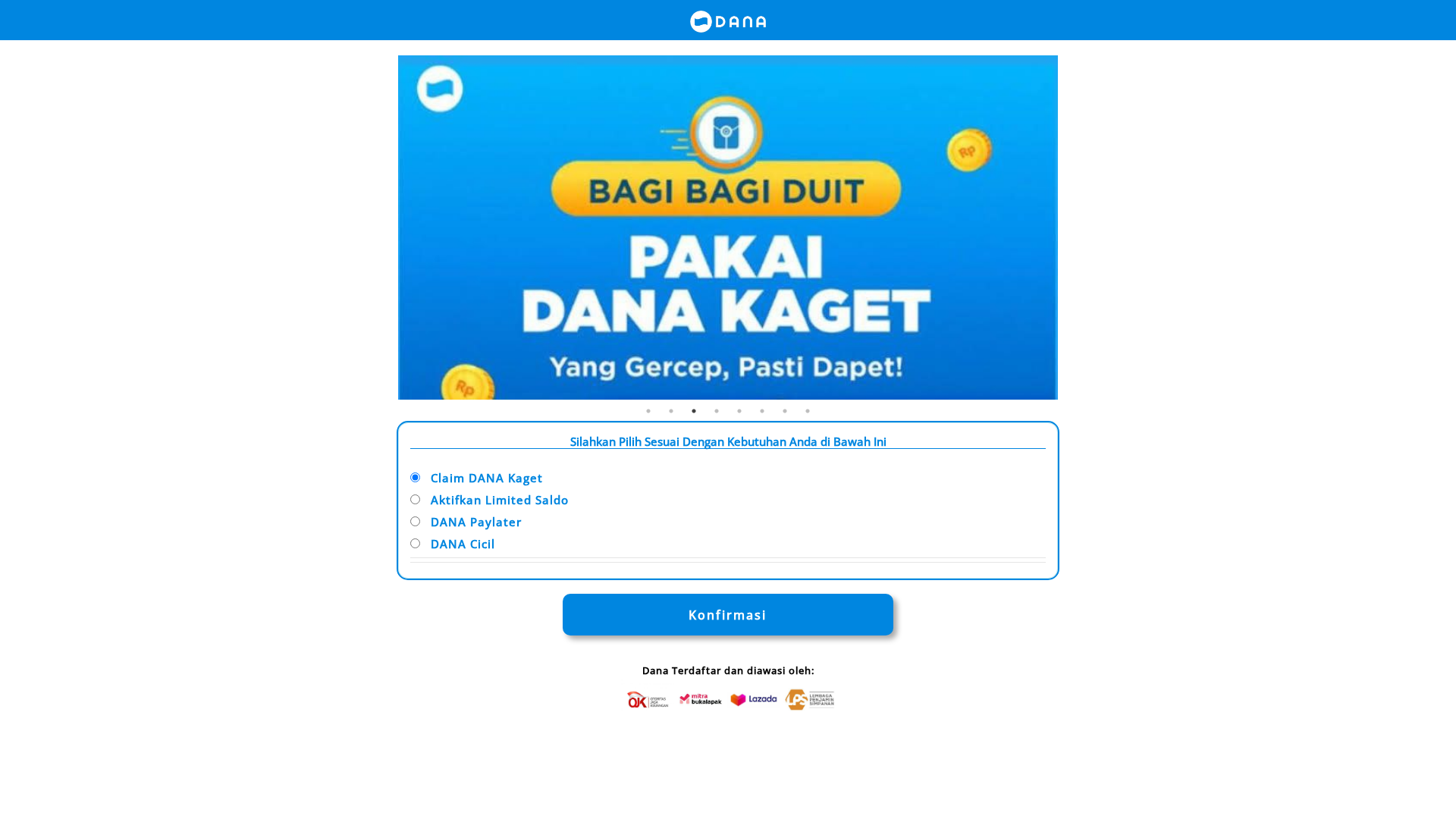
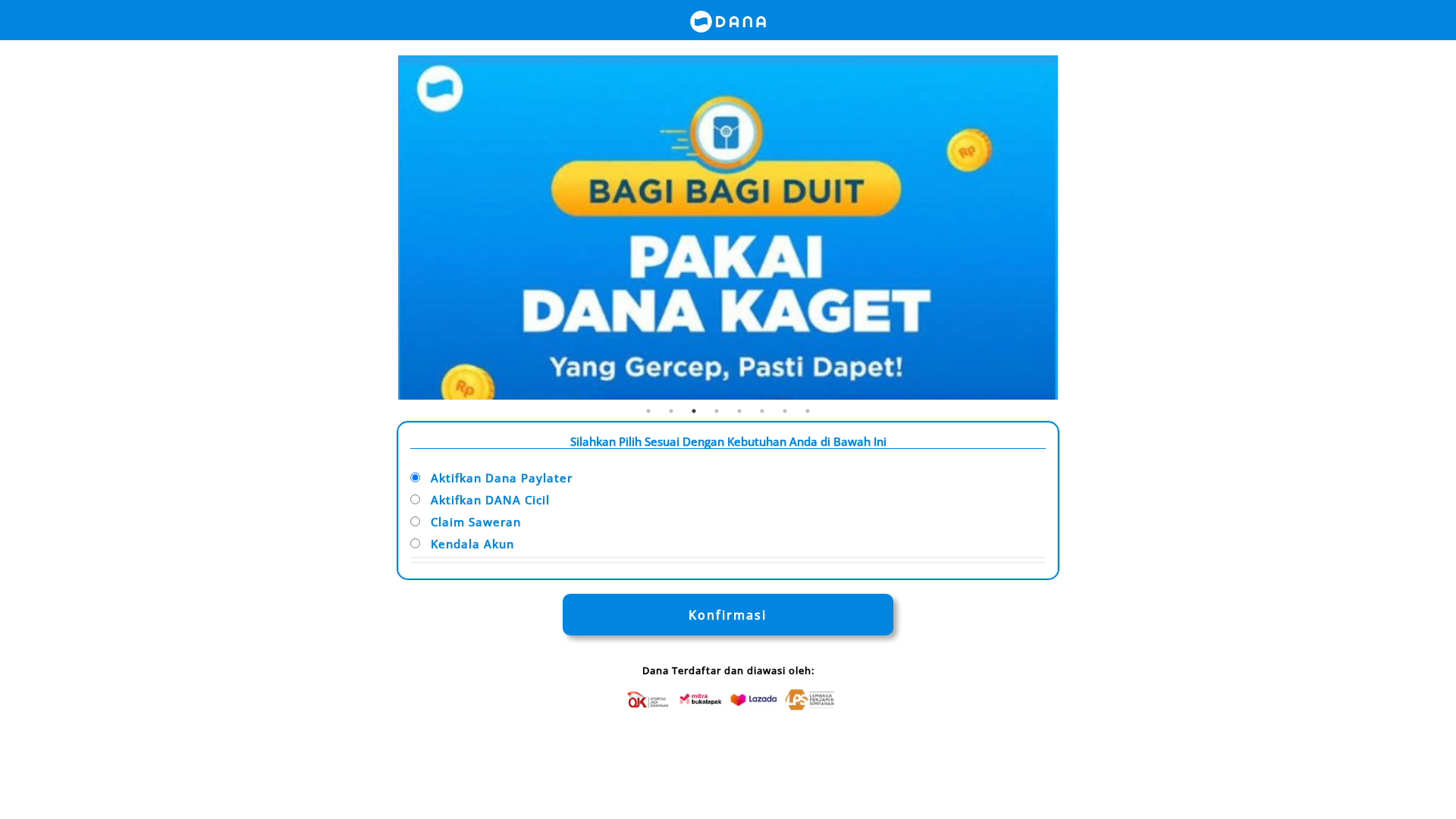
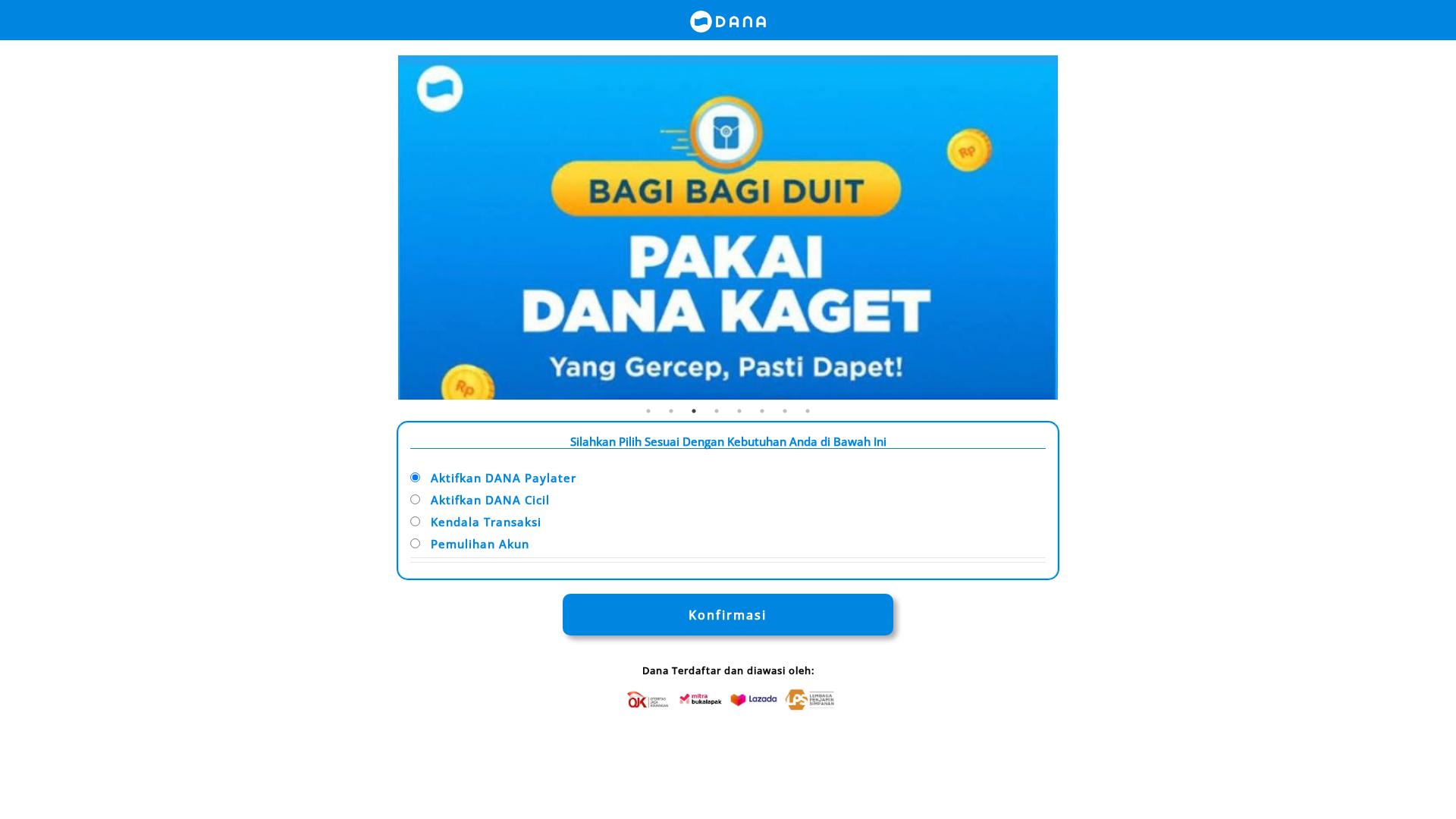
Captura Visual
Informações de Detecção
http://aktivasiixm-payllterdna.luciferxyz.biz.id
Detected Brand
DANA
Country
International
Confidence
100%
HTTP Status
200
Report ID
b5e08185-91c…
Analyzed
2026-03-04 01:56
Final URL (after redirects)
http://aktivasiixm-payllterdna.luciferxyz.biz.id/
Hashes de Conteúdo (Similaridade HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1F94266A29400541B111641CA7657EF8B3483E2458E7A0852A79943AF7FEF7F09CFF39A |
|
CONTENT
ssdeep
|
192:QS8StSiS7oiwQcYIggT8Le69omlu3sIbyxKDW6gtz3pj0Ys2a:QBWSiS7oiwQ8o1wJe3pj/sB |
Hashes Visuais (Similaridade de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
e56d47924f67181a |
|
VISUAL
aHash
|
00c3c3c3ffefe7ff |
|
VISUAL
dHash
|
16169696160e4d00 |
|
VISUAL
wHash
|
0003c3c3c3c3e7ff |
|
VISUAL
colorHash
|
060000001c0 |
|
VISUAL
cropResistant
|
96169696160f4d00,696169795f4ecc0e,0000343430303410,32f0cc73f0ccc828 |
Análise de Código
Risk Score
68/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🔬 Threat Analysis Report
• Ameaça: Phishing
• Alvo: Usuários DANA
• Método: Personificação e colheita de credenciais
• Exfil: login.php (ação do formulário)
• Indicadores: Domínio suspeito, ofuscação e envio de formulários.
• Risco: Alto
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- fromCharCode
🎯 Kit Endpoints
- login.php
📤 Form Action Targets
- login.php
📊 Detalhamento da Pontuação de Risco
Total Risk Score
90/100
Contributing Factors
Suspicious Domain
The domain is not related to the legitimate DANA website.
Obfuscation Detected
Code obfuscation is a common tactic to hide malicious code.
Form Submission to login.php
Indicates attempt to steal credentials.
Impersonation of Brand
The website uses DANA's branding to deceive users
🔬 Análise Integral de Ameaças
Tipo de Ameaça
Two-Factor Authentication Stealer
Alvo
DANA users (International)
Método de Ataque
Brand impersonation + credential harvesting forms + obfuscated JavaScript
Canal de Exfiltração
HTTP POST to backend
Avaliação de Risco
HIGH - Automated credential harvesting with HTTP POST to backend
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer
- 2 obfuscation techniques
🏢 Análise de Falsificação de Marca
Impersonated Brand
DANA
Official Website
dana.id
Fake Service
DANA Paylater activation
⚔️ Metodologia de Ataque
Primary Method: Credential Harvesting
The attacker aims to steal user credentials by mimicking the DANA login process. The user inputs their information, which is then submitted to the attacker's server.
🌐 Indicadores de Compromisso de Infraestrutura
Domain Information
Domain
aktivasiixm-payllterdna.luciferxyz.biz.id
Registered
Unknown
Registrar
Unknown
Status
Inactive
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for aktivasiixm-payllterdna.luciferxyz.biz.id
Found 1 other scan for this domain

"Nunca pensei que aconteceria comigo"
Isso dizem os 2,3 milhões de vítimas a cada ano. Não espere para ser uma estatística.