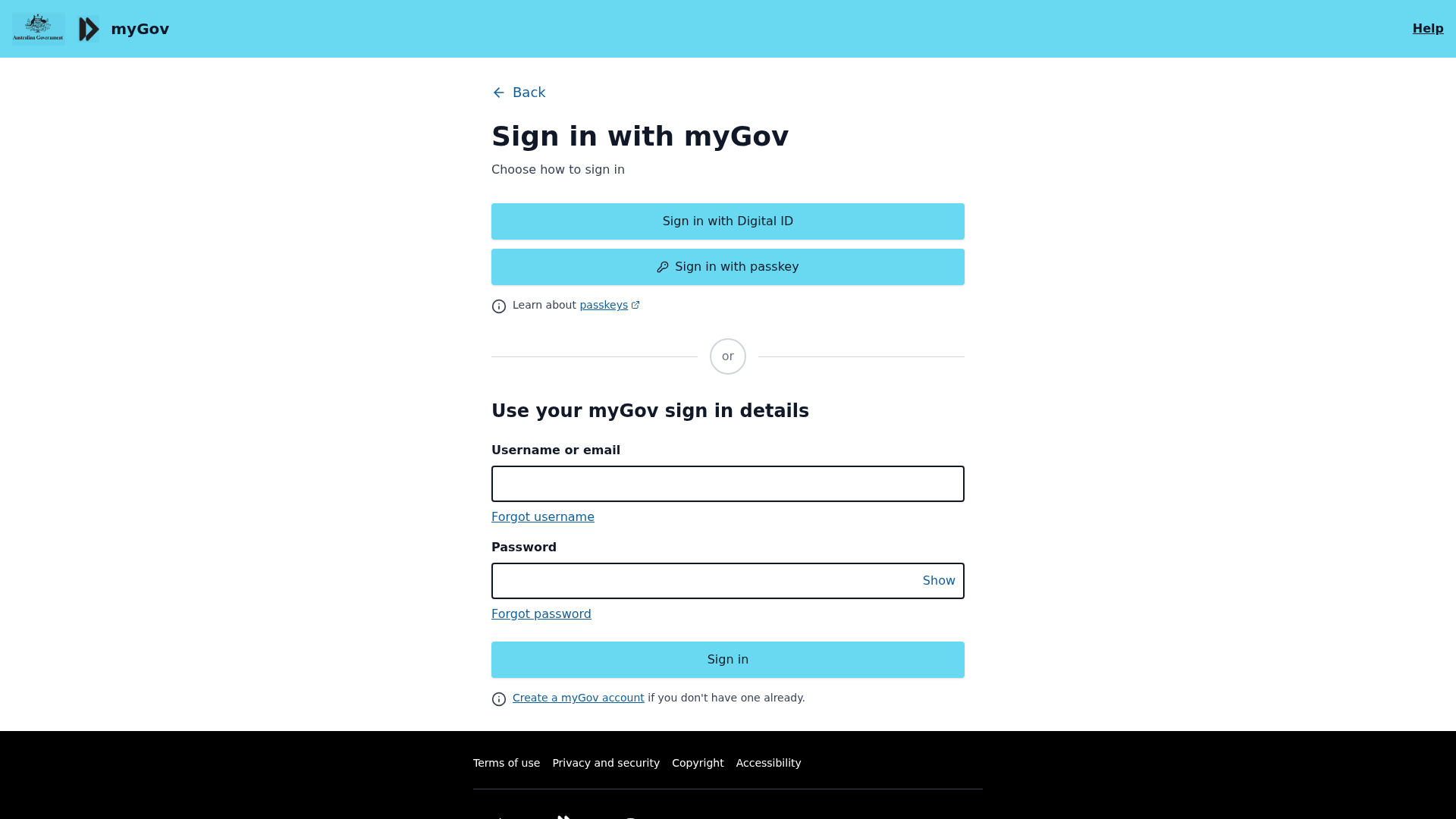
Phishing Analysis
Detailed analysis of captured phishing page
Captura Visual
Informações de Detecção
Hashes de Conteúdo (Similaridade HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1D722E83612101E7F5A03CA84F6D4B319A79FA256C677D849B1EC835B23D6E21DD231B8 |
|
CONTENT
ssdeep
|
192:8XOdeNuELeTEKeoe2X2XS445iPxOYs4YgAlXU1jRXVRXJWYThkkXGXXpRDeJW:JePeZeoe+gxOYVYkjRXVRXJWYqJXDeA |
Hashes Visuais (Similaridade de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
b3b34c990de44ce6 |
|
VISUAL
aHash
|
0effe7ffffffff00 |
|
VISUAL
dHash
|
da1c0e189d140e20 |
|
VISUAL
wHash
|
00c7c3ffc7cfc300 |
|
VISUAL
colorHash
|
06007000000 |
|
VISUAL
cropResistant
|
c2180e0e1c16160e,2000606008600020 |
Análise de Código
🔬 Threat Analysis Report
• Ameaça: Phishing
• Alvo: Usuários do myGov
• Método: Coleta de credenciais
• Exfil: qtrypzzcjebvfcihiynt.supabase.co
• Indicadores: Incompatibilidade de domínio, Obfuscação de Javascript, Formulário para credenciais
• Risco: ALTO
🔒 Obfuscation Detected
- fromCharCode
- unescape
- base64_strings
☁️ Cloud Backend
- Supabase: qtrypzzcjebvfcihiynt.supabase.co
📊 Detalhamento da Pontuação de Risco
Contributing Factors
🔬 Análise Integral de Ameaças
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Banking, Personal Info
- 8 obfuscation techniques
🏢 Análise de Falsificação de Marca
⚔️ Metodologia de Ataque
Primary Method: Credential Harvesting
The attacker aims to steal the user's myGov credentials (username/email and password) by presenting a fake login page that mimics the official myGov login. Users entering their credentials will have them sent to the attacker.
Secondary Method: Data Exfiltration via Supabase
Stolen credentials may be stored or sent to a Supabase endpoint. This indicates the attacker is leveraging Supabase to facilitate data collection and organization.
🌐 Indicadores de Compromisso de Infraestrutura
Domain Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)