
Phishing Analysis
Detailed analysis of captured phishing page
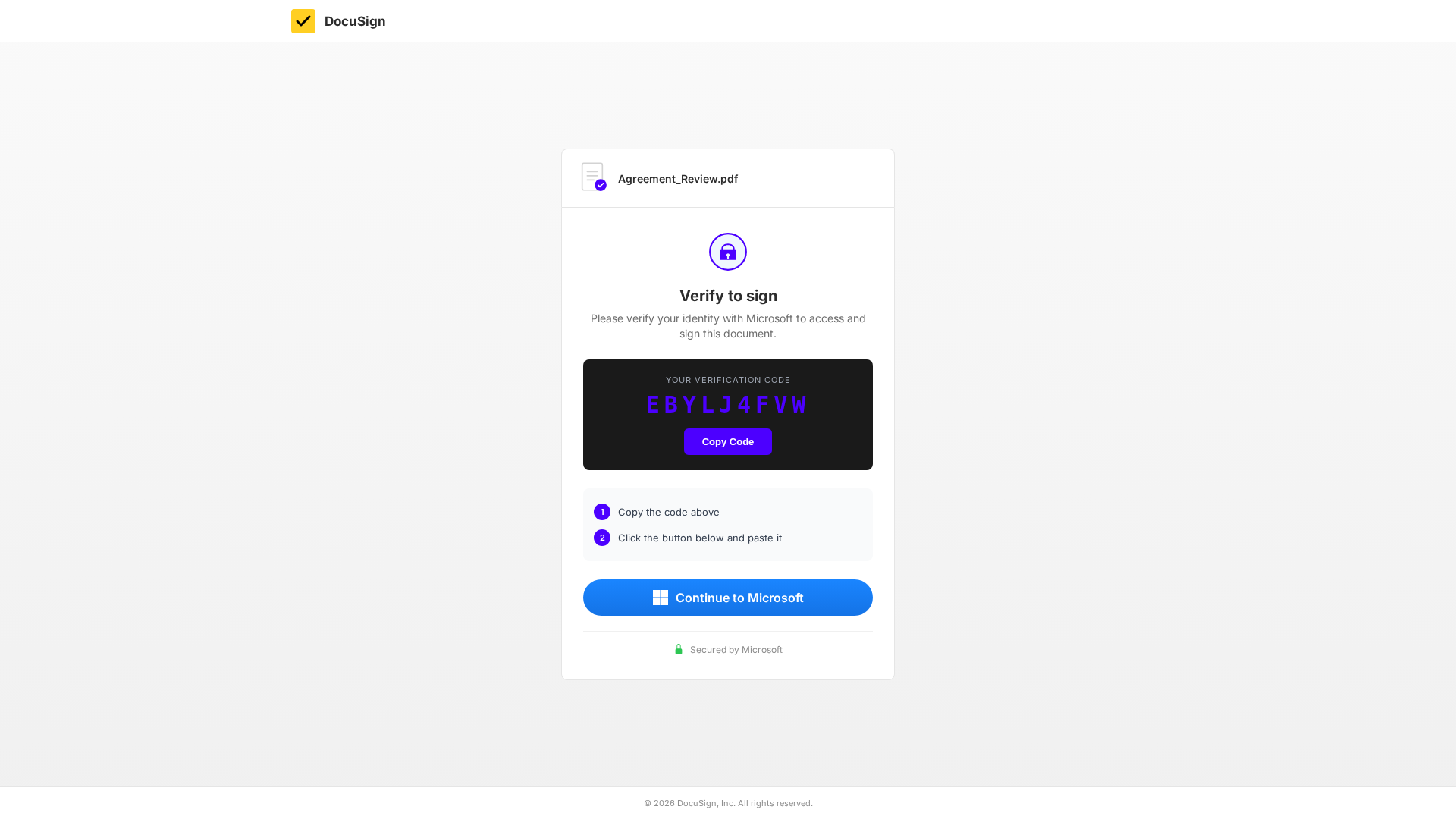
Captura Visual
Informações de Detecção
https://pd6w-iubf-rxrt.accountant-fitfranchisebrands-com-s-account.workers.dev/35ee7ff45d1c077d?email=%7B%7Bemail%7D%7D%20(https://index-4eo.dianna-mudmedia-co-nz-s-account.workers.dev/?email=%7B%7Bemail%7D%7D)
Detected Brand
DocuSign
Country
Unknown
Confidence
100%
HTTP Status
200
Report ID
bba2bbe4-a9c…
Analyzed
2026-04-04 21:05
Hashes de Conteúdo (Similaridade HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1B0811471921C2C3D76074AC5E729736631AB539AEB0A31143AB9037487C6D6EED770A4 |
|
CONTENT
ssdeep
|
48:TU9q57ZAuK5Leb9Wws39qyPMrCgz2i93SggVBGF706vV0pAe8rSA4ie14nZY/aba:TUSKtNg9Wn9Y5gLGFlV0uU1ubo5MA |
Hashes Visuais (Similaridade de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
b39c9c36260e9d9c |
|
VISUAL
aHash
|
ffffffe7e7e7e7ff |
|
VISUAL
dHash
|
204a224d4d4c4c31 |
|
VISUAL
wHash
|
ffffffe700001800 |
|
VISUAL
colorHash
|
070000001d0 |
|
VISUAL
cropResistant
|
204a224d4d4c4c31,616949554d33334d |
Análise de Código
Risk Score
71/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 OTP Stealer
🔒 Obfuscation Detected
- atob
- document.write
- base64_strings
📡 API Calls Detected
- /api/device/start
- /api/device/status/
- https://microsoft.com/devicelogin
📊 Detalhamento da Pontuação de Risco
Total Risk Score
75/100
Contributing Factors
Active Phishing Kit
Detected kit types: OTP Stealer
Code Obfuscation
JavaScript code obfuscated using 4 technique(s) to evade detection
🔬 Análise Integral de Ameaças
Tipo de Ameaça
Two-Factor Authentication Stealer
Alvo
DocuSign users
Método de Ataque
obfuscated JavaScript
Canal de Exfiltração
Form submission (backend endpoint not detected - likely JavaScript-based)
Avaliação de Risco
HIGH - Automated credential harvesting with Form submission (backend endpoint not detected - likely JavaScript-based)
⚠️ Indicators of Compromise
- Kit types: OTP Stealer
- 4 obfuscation techniques
🏢 Análise de Falsificação de Marca
Impersonated Brand
DocuSign
Official Website
N/A
Fake Service
Token swap/DEX platform
⚔️ Metodologia de Ataque
Primary Method: Two-Factor Authentication Bypass
Victim is prompted for 2FA code after entering credentials. The code is intercepted and used by attacker to access victim's account in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 4 techniques to evade detection by security scanners and make reverse engineering more difficult.
🌐 Indicadores de Compromisso de Infraestrutura
Domain Information
Domain
pd6w-iubf-rxrt.accountant-fitfranchisebrands-com-s-account.workers.dev
Registered
Unknown
Registrar
Unknown
Status
Age unknown
Hosting Information
Provider
Unknown
ASN
🤖 AI-Extracted Threat Intelligence

"Nunca pensei que aconteceria comigo"
Isso dizem os 2,3 milhões de vítimas a cada ano. Não espere para ser uma estatística.