
Phishing Analysis
Detailed analysis of captured phishing page
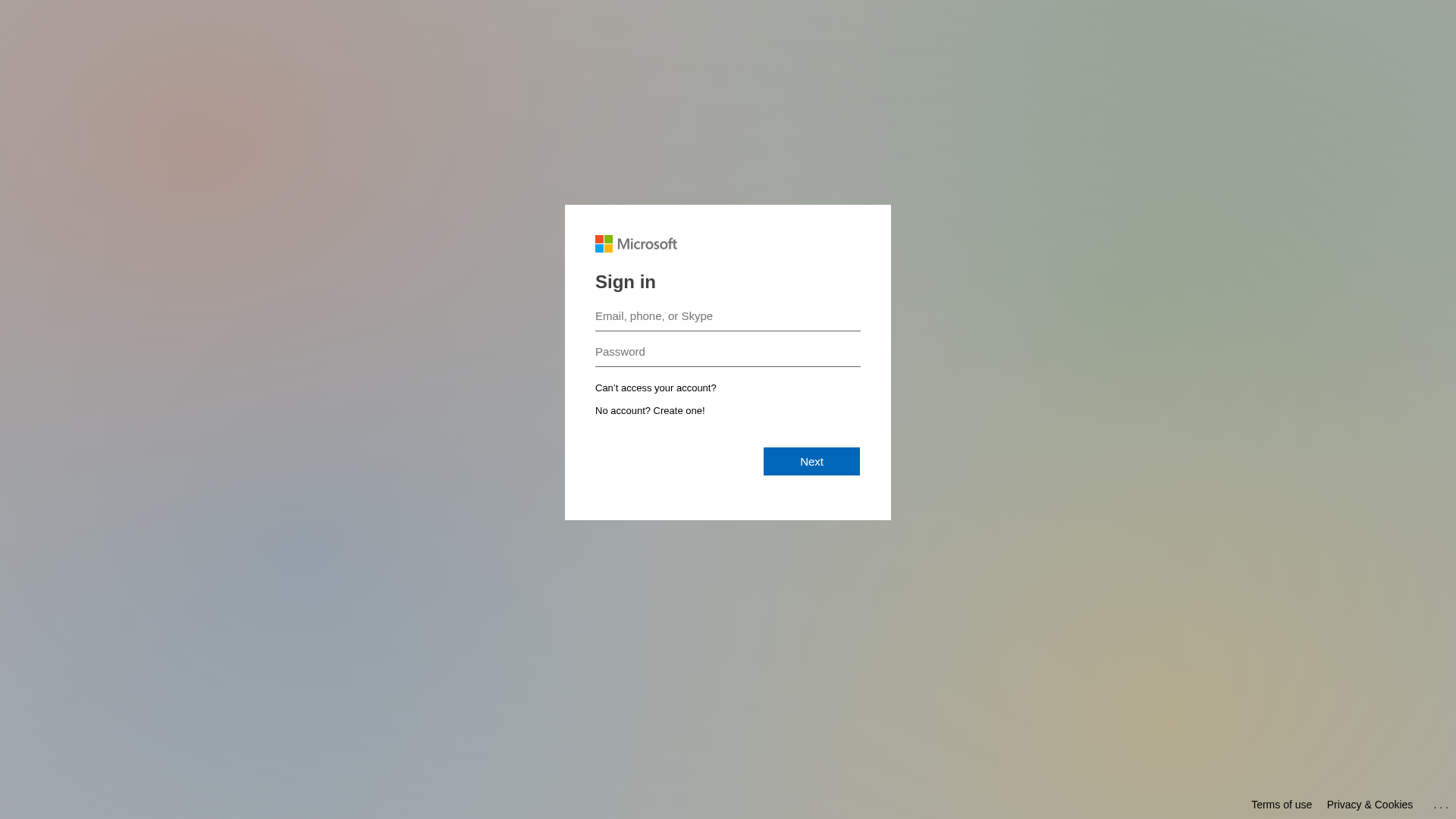
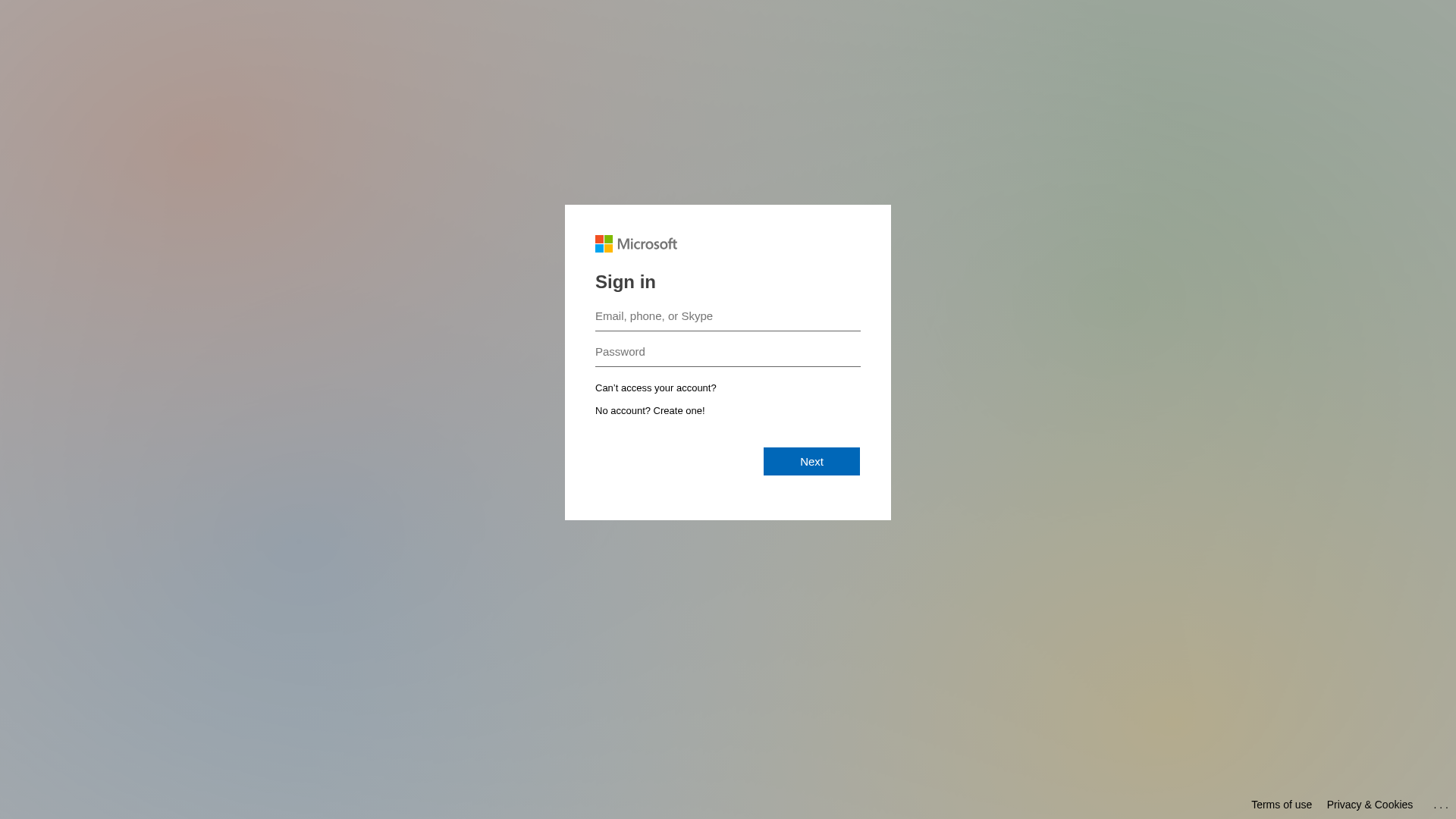
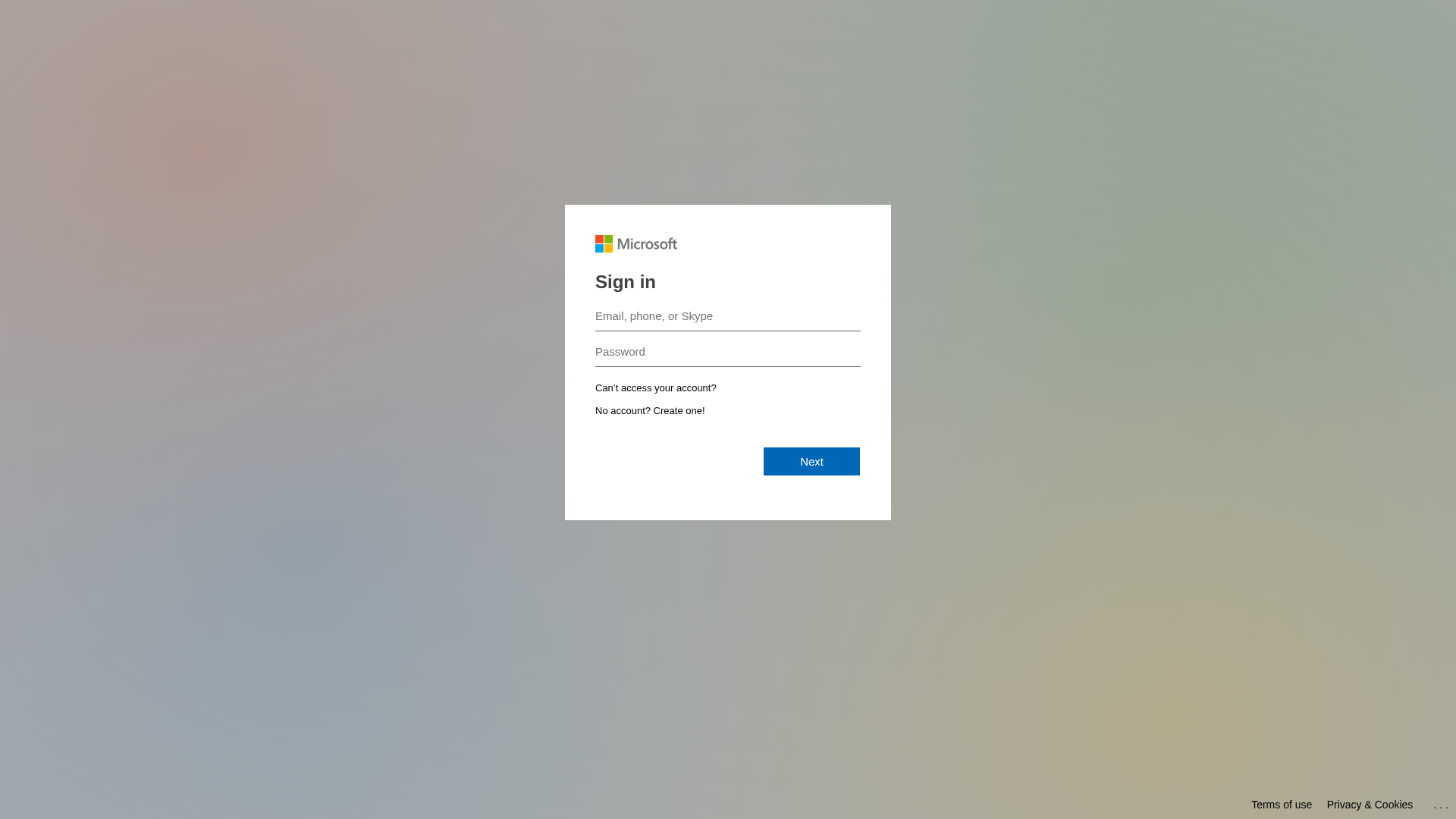
Captura Visual
Informações de Detecção
Hashes de Conteúdo (Similaridade HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T17641A81CD2010346E357EE90F962FBD666140BC0C7134A7C6AB9927AB1CE17553723CD |
|
CONTENT
ssdeep
|
48:n0i0Hls5hwhjO7c2ZgV0jxJF0jIPcU85D4c5hkj0:nfjhh7xg6jxJqjJTt4g5 |
Hashes Visuais (Similaridade de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
9cc97326cc99d98c |
|
VISUAL
aHash
|
0000181818180000 |
|
VISUAL
dHash
|
6171333232327c78 |
|
VISUAL
wHash
|
1818181c1f1f1fff |
|
VISUAL
colorHash
|
070000001c0 |
|
VISUAL
cropResistant
|
6171333232327c78 |
Análise de Código
🔬 Threat Analysis Report
• Ameaça: Phishing de credenciais
• Alvo: Usuários Microsoft
• Método: Suplantação de identidade por meio de uma página de login semelhante
• Exfil: Desconhecido, provavelmente para um banco de dados controlado pelos atacantes.
• Indicadores: Incompatibilidade de domínio, Formulário para credenciais de login
• Risco: ALTO
📊 Detalhamento da Pontuação de Risco
Contributing Factors
🔬 Análise Integral de Ameaças
⚠️ Indicators of Compromise
- Kit types: Credential Harvester
🏢 Análise de Falsificação de Marca
⚔️ Metodologia de Ataque
Primary Method: Credential Harvesting
The attackers are using a fake login page to steal user credentials. When a user enters their information, it is sent to the attackers.
Secondary Method: Social Engineering
The attacker uses the Microsoft branding and interface to trick users to hand over their login information.
🌐 Indicadores de Compromisso de Infraestrutura
Domain Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for outlook-office365.mgamt.com
Found 2 other scans for this domain
