
Phishing Analysis
Detailed analysis of captured phishing page
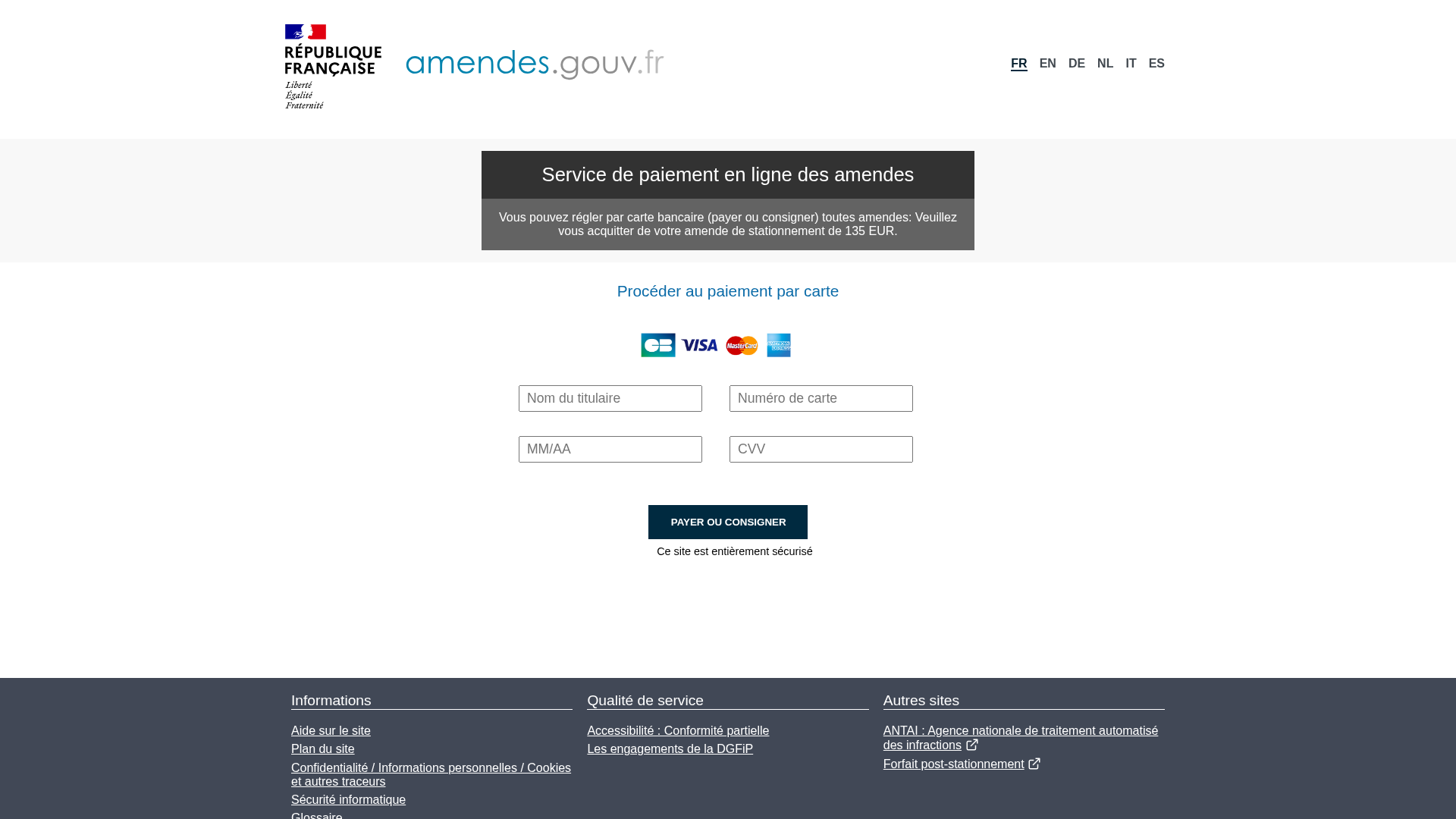
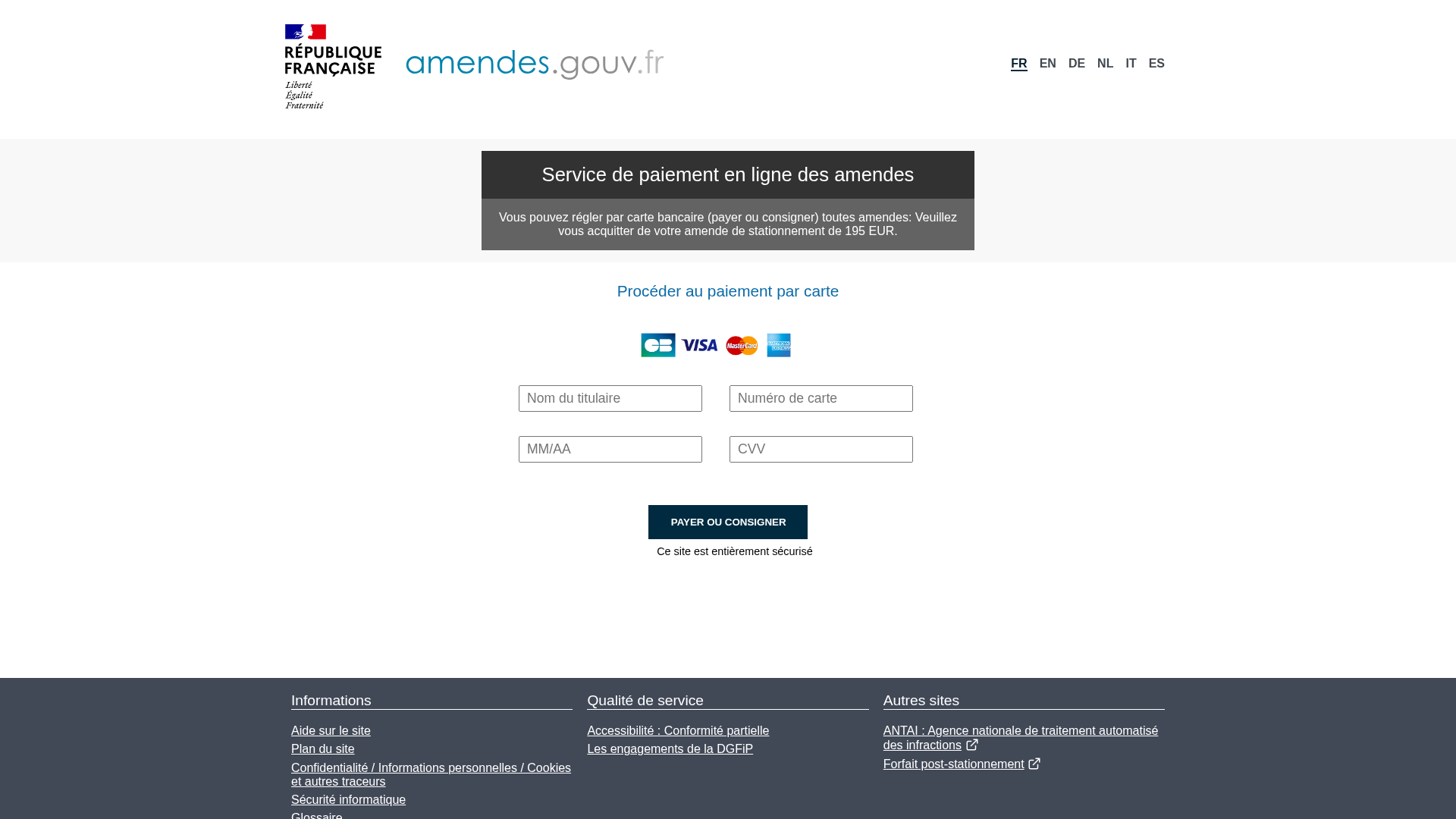
Captura Visual
Informações de Detecção
Hashes de Conteúdo (Similaridade HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T179E164726158343B027792CDBE62EF29C4D7C12FCA4E2C0196EC9B5D1ED5EE0E94425B |
|
CONTENT
ssdeep
|
96:cZfYIkzIoN5W4QkQC7JXntEGvEhW8jAYrZiB7QonZijov5K03nDRA1Uebmw0g9If:oAI8IAbZl8l9YTZSovVeawRY |
Hashes Visuais (Similaridade de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
b2b51c9e1b9cc334 |
|
VISUAL
aHash
|
ffc7e7ffffff0000 |
|
VISUAL
dHash
|
238e8e000c08b0cc |
|
VISUAL
wHash
|
9fc3c3e7e7e70000 |
|
VISUAL
colorHash
|
07000000180 |
|
VISUAL
cropResistant
|
230e8e0c0c0c0c30,13eae81380aed4d0,a0e0f4b4c9c9d2d0 |
Análise de Código
🔐 Credential Harvesting Forms
🔒 Obfuscation Detected
- fromCharCode
- unescape
- unicode_escape
- base64_strings
📤 Form Action Targets
- infoz/cc.php
📊 Detalhamento da Pontuação de Risco
Contributing Factors
🔬 Análise Integral de Ameaças
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Banking, Personal Info
- 38 obfuscation techniques
🏢 Análise de Falsificação de Marca
⚔️ Metodologia de Ataque
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 38 techniques to evade detection by security scanners and make reverse engineering more difficult.
🌐 Indicadores de Compromisso de Infraestrutura
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)



Scan History for antai-info-amende-non-payer.wasmer.app
Found 4 other scans for this domain
