
Phishing Analysis
Detailed analysis of captured phishing page
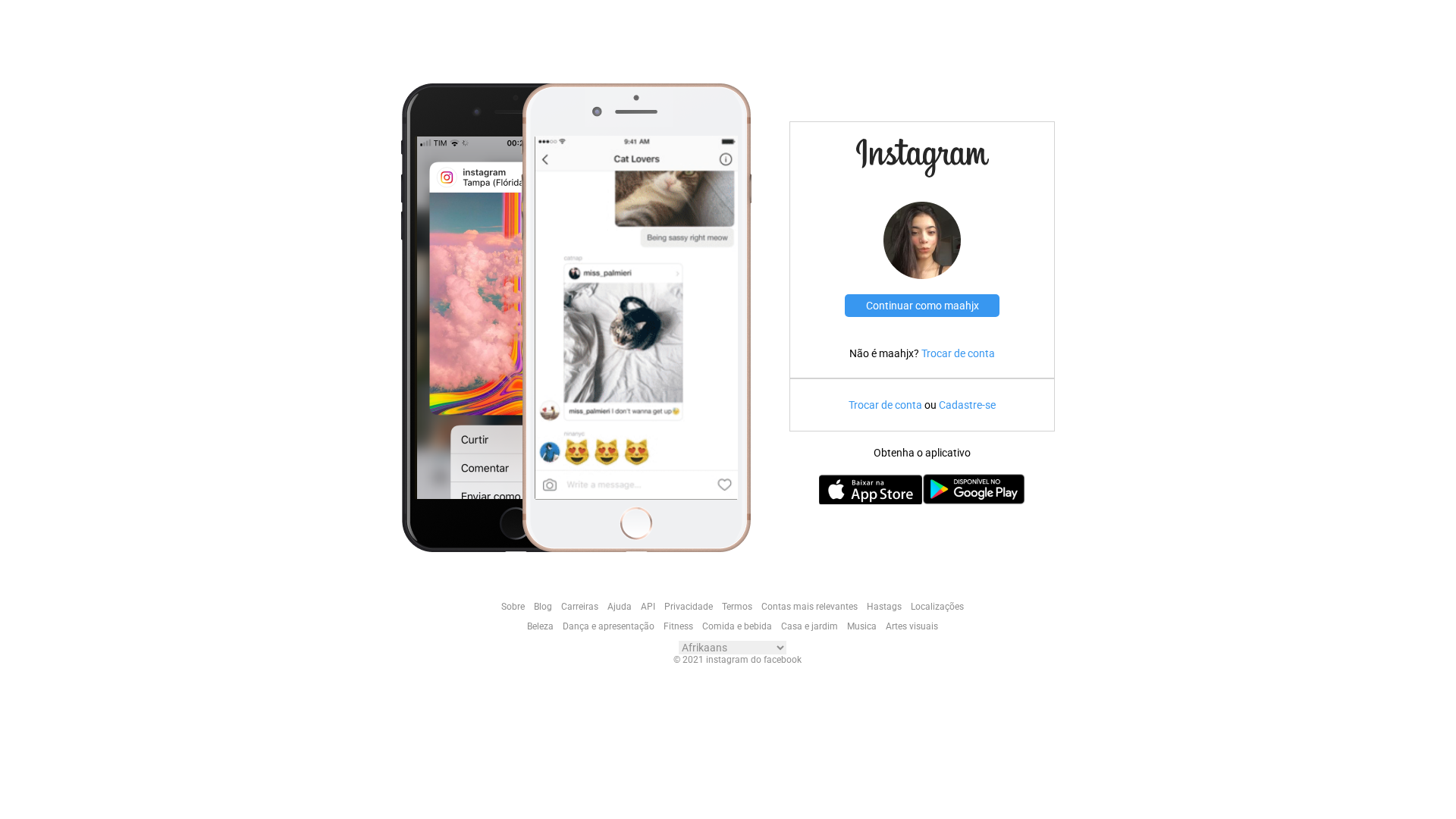
Captura Visual
Informações de Detecção
http://instagram-clone-kappa-eight.vercel.app/
Detected Brand
Instagram
Country
Unknown
Confidence
100%
HTTP Status
200
Report ID
cd3f3961-491…
Analyzed
2026-04-01 10:18
Final URL (after redirects)
https://instagram-clone-kappa-eight.vercel.app/
Hashes de Conteúdo (Similaridade HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1DBE14B31FC44A87504BBB8F490322D9558B5BF06C275A584B5F582E86AEFD34E3AF138 |
|
CONTENT
ssdeep
|
96:sX/TKNrbzcobZyplMJ7zId8qUifTR6M+2uE:svTKNr1y4QXQMeE |
Hashes Visuais (Similaridade de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
b838c7cc99c3e564 |
|
VISUAL
aHash
|
dfc3c3cfc3c3ffff |
|
VISUAL
dHash
|
b0beb69eb6b60830 |
|
VISUAL
wHash
|
c4c0c0c0c3c3c3ff |
|
VISUAL
colorHash
|
07400048040 |
|
VISUAL
cropResistant
|
b0beb69eb6b60830,59c7d3f3d9e5f725 |
Análise de Código
Risk Score
50/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎯 Kit Endpoints
- data:image/png;base64,iVBORw0KGgoAAAANSUhEUgAAAIgAAAAoCAYAAAAlprK8AAAACXBIWXMAAAsTAAALEwEAmpwYAAAAAXNSR0IArs4c6QAAAARnQU1BAACxjwv8YQUAAAwiSURBVHgB7VwHTJRNEx6QT397711RUayIPfaKXdQYe0GMYmKLYjQY0RiNGsUSsYNR0dhLrLFgUOyxG3uPiF3sDfefZ/LtfS/HUe4OEPGeZD3uvX13992dnZ15Zl6d6F8opZxCQkKK/o9BDvy1+PXr15d79+69DAwM/InvTuHh4S7R0dHtv3796h8TE+P248cPF3Lgr0WWLFl+5cmT56yLi8uCPn36HHAKCwsbfefOnfmbNm1y5k/6+fMnOfD34p9//iF3d3fq2rXre1dX13k0c+bM2KxZsyr+zVEcxVRy586tFi1apDLFxsZOu3v3LjnggBHfvn0jJycnysT/BL57944ccMAc379/J2eHzeFAQoAWcaY0AFvGNGTIEGI3mvLnz0+2AiqvcOHCVKZMGcqVK1eS9cuVK0f58uUjB+xAyZIlU9XYad26tbp27Zpi/1q9ePFCFShQwOa23NzcFPvoavny5Wr//v1q3LhxidZnz0z6T83ny8ilSJEiKlUFhHewevz4sdLYt2+fYi1gc3vVq1dX7IqrnDlzqmbNmqn79+/LdbTp6empevbsqYoVK2aqX69ePcUaS+XNm1c1aNBA6uHeRo0ayd+sXVT79u1Vp06d5DruYQ5AVa5cWdWuXVuZz02pUqUUay+5v23btqZnYW0m4+nRo4f0ldoLl5YCkqpHzIQJEyCA8jdsnWXLloGxJXvAC0hdunQhX19fYk0i19glo169elGFChUoMjKSypYtK9cXLFhAjRs3pkyZMlFoaCg1b96cpkyZQr1795ZxtGzZkmrVqkUsWLRkyRJicog8PDxo27Zt8r106dJx+ka9AwcOkI+PD82ZM4cGDBgg1/GMXl5eVK1aNWLNRhkJqSYghQoVIm9vb9P3hQsXEmsQshd8VFGlSpWId7wIBOwSeGEbNmwQIcyWLRtVqVIlzj2vXr0iPz8/sYFYq9C0adPkOhYbLv6bN2+oadOmlCNHDmkDdk6TJk3oxIkTcdrBb6gPeyogIEAEFbh165a0BaMOJBPuzyhINQFhVS+G5IMHD8jf358mT56cIizt+/fvZfeOGDGCunXrRqz2qUOHDqJN2NahqKgoYQPN8fDhQxEqDimIwABso4jGOHr0qGgZZ2dnEbjnz5+Li2cJHz58kM/Pnz9T5syZ5W9oSraH6PTp09I+NFFGgd1PgsmoWbOm7GZM/Llz52RHY6e1atVKdhfHd6hjx46iij9+/EgnT56kGzdukC2ARwTVjx2PdtnwlWPi6dOndP36dYu7F/cEBQWBNabOnTuLcAUHB8vxM2vWLGkPgoFiC+rWrUtnz56VMTArbXM76RGZ+PwOxK60Fthto0ePpp07d9KYMWOoe/fu1L9/fxo1ahSxAUfZs2cnNthEnS9evJg48EPt2rWTBRo5ciS4ftEu7JUku0/sctggWBDsYLTz9u1bETa4vjg+Nm7cKN8hONAkEFj2nERI5s2bR8eOHROBOnPmDJ0/f17GBe0CQY6IiJAjDG1DG1jq/8mTJ9I+nh/CfvnyZbp06ZLYNxjD3r175Tva+NOBI9cmL4YnR/FCKHvx6dMn8Tys7d9R0rkX07dvX2KXjuwFdv/Lly/JgXQMazUIqx3FalXZCxYOxWo53e+iv7nYpEEaNmxITFiRvVi5ciWFh4eTA+kbVnsxzEiSvQBJtXTpUrIH5cuXp0GDBsnfMDDXr19PvxMFCxYUT61NmzZioOP4vHjxovAzMJj/WFh7xKxdu1bZCxwv1vRpqUyfPt3UHuh80N32tmlrqV+/vimkgGdju0qxhyPfQeUb67LwSAjid43VmmJTLGbz5s3KXrBbbdfA2d1UBw8eVEy8iT3EfIhiVvO3TCLiMTdv3pTn2rp1q2I+SDEXI3Gj4cOHK3avTXURD2KuRrHr/VvGmiYCwraDSgkYg2rWluLFi6vXr18rJqcUE13S3qpVq5J1LxZMB+aSKkwCSuod3PqE6ri6ukr/zLAqDgEk2t7gwYOlLvMvSY4RGjGxfo3F0vNgEyHwaE86qU1GKkillABoclvRokULyfM4cuSIxEBiY2Pl/NfUt0bVqlWFGOPjSOI3vMPp9u3bxDue9uzZI/kiGnjbY/v27VIH9gQCfWBmQYqdOnVK+kwMIOV4QhP8fd26dRIoBBArApuMYrynRo0a0j+SxzFGkHyg8UHyabi5ucl9IP046ixhAtQFcQeA3Bo7dqyEHWCbocDeK1q0KNkEazUIs6EqJfDs2TPJ77Cmb122bNmiOFaieNHkTEfYH8B3Yz2oeWY0FTObcgxwCEBduXJFrgGPHj2S0D79qy3wHXVYqBQH3iSPBTksAEg9pAWQhZ3KQiR10AcH+SyOmT02xaEIqYe2mZaXouefwxLqy5cvcmweP35cMUMt40QeDW8CkzbBnAEXLlyQehoYBwupWrFihXxnIVIs5PIJYM6s1SY2HTFQ7xz9VCkBnMd16tSxun8cL0zTmwxT3iHSHtP6ceryTpWFBQ4fPiwqF9eRI8JUu1zfsWOHqT5rR7kGoWDtI9cw6Zo15t0oPJD5mPAMTMGbnoujwIo1pNxLyThikJeCRCggMDDQlGfCIQGTUDE5KdfYe5PvrDVl/rApcA2/cfhCBAzPpAUKnxAwCJqXl1fqCwgGHxoaqlISSL5Jbv+YKGD+/PmmazD+MAEwWI11oR3gTXCEVXFAMc5voPi1MLD6lWt6kQYOHBhvojDxWBRoUEvjgrAGBASYhAyAMQqBTkpA/Pz85DoW3FwAITAAH6fyvWzZsqb2vb2949RFQhYMdggN2tHFx8dH6kO7pLqAoCCNL6WAHWKNi7p79265D8cGdgoKB8hkYiAkRkMR6hjGI4fv46U66omGWsdRhGscgZY2OMobr1+98PBMEhsfMsrYblAxMTFSf/Xq1SaNkJCAcDBTruNYMW8P3hkADWUcN44pZLfpejgioVUBaNioqChTiY6OlutsY1ktIDaF+2E8wfiB4WcvEOlNbjQZBhiIKAAGHYo52E6QsRnBcyNRWiOM+R7awNN1LUHnssAgTgwgyObOnSvt4BPjhUHNi5bgPfp1aEs5KPqaHqNOJcA4jPk1SLtAQdISGGoW/HhtWYpQJwWbBAT5HpMmTZLUPHtyH7CQOm0wOUAGFyx65JrwuR8npI4cD3ge8I4gdJgoDUwc2E1kjmkgPRDARBoDhlgI80x4JBrp9MPkenHwNAAsvlEAdR9G6BfXKlasKBlxxufSmwCeDZDQfCNRCUKoPTDzbDhbYXNG2a5duyQjy1Ygl2LixInE6i/Z9+gUv0OHDomQYnfpgrwU7CpPT09TTqoGXrXo16+faXIhMEgbBJAXwh5VnPrDhg2L41oOHTpU7mG2lK5evRqnLhYbi2jMIsMiIz8GgEBpDYlnBiCASCzSgKsKbYAYF5KYNLDYiJwDTFDKZ2Ibko9fGTey97AhjLB5I9uT1Q7rGzaAJcAmgAeBM93Sb+PHj7eqr0KFCoktAUOR1bbFOhEREdK+v79/HBsEY8AnXD3mD8SYwzWczchQ1/fDBgFg2LIQqqCgILVmzRoxcnE/bAjzPpH9jt/hToaFhamQkBAVGRkp7cBlNhq1INVgO8DghSutyT3mbxRzJPJsoOxnz56tWEMrPhKkHXhcmgzTxBxc4BIlSsSbIz0HzN2o4OBgIRLxibEllyAkstNINRaWcnlQDSai1NSpU8WzYDUuBi2sZxiD2iicMWOG1a8/4JUCTAq4hoQelHeO1IGbifa1gMBT4SNIFkwDHAfGaLwfAoJFwvs22qMBIJi+vr4W+/Tw8BCBAC+jgb8hAEbh04W1psn1Rl96HsBjwAAGN6IBQeUgpFD3RiHDM8IQtcRG49UMCCmE1rgh4eaDFU5zAdEF7cAfT4ge5rNYglRpGVTTAgJNAW0HXgKuLybZkoBqAYEXg+fAeN3d3ePxGZYKCDu0Cy8KfydWFwuFsYGPMf8N3gjaQL/20OTQSvB4UDD3trSR6i9O/e5iLiBJ1TcKSHp9prQsqf7ilAN/PlwyUoq+OeDV4D0WFJWMN/rgXsLjcPyPB//BBa8tZlSAO2AvQ/7WLzwlBpBa2DC2vAaSEYGX31xAOJn79hkJ5hxHYrCGk8nowEYBJ+PM/9yDkDjggBF4N5m179P/A5Nk78LscDZEAAAAAElFTkSuQmCC
📊 Detalhamento da Pontuação de Risco
Total Risk Score
70/100
Contributing Factors
Active Phishing Kit
Detected kit types: Credential Harvester
🔬 Análise Integral de Ameaças
Tipo de Ameaça
Credential Harvesting Kit
Alvo
Instagram users
Método de Ataque
Phishing webpage
Canal de Exfiltração
Form submission (backend endpoint not detected - likely JavaScript-based)
Avaliação de Risco
MEDIUM - Automated credential harvesting with Form submission (backend endpoint not detected - likely JavaScript-based)
⚠️ Indicators of Compromise
- Kit types: Credential Harvester
🏢 Análise de Falsificação de Marca
Impersonated Brand
Instagram
Official Website
https://www.instagram.com
Fake Service
Credential harvesting service
⚔️ Metodologia de Ataque
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: Standard Phishing Techniques
Uses typical phishing tactics including brand impersonation, urgency tactics, and social engineering to trick victims into providing sensitive information.
🌐 Indicadores de Compromisso de Infraestrutura
Domain Information
Domain
instagram-clone-kappa-eight.vercel.app
Registered
Unknown
Registrar
Unknown
Status
Hosting platform (subdomain)
Hosting Information
Provider
Unknown
ASN
🤖 AI-Extracted Threat Intelligence

"Nunca pensei que aconteceria comigo"
Isso dizem os 2,3 milhões de vítimas a cada ano. Não espere para ser uma estatística.