
Phishing Analysis
Detailed analysis of captured phishing page
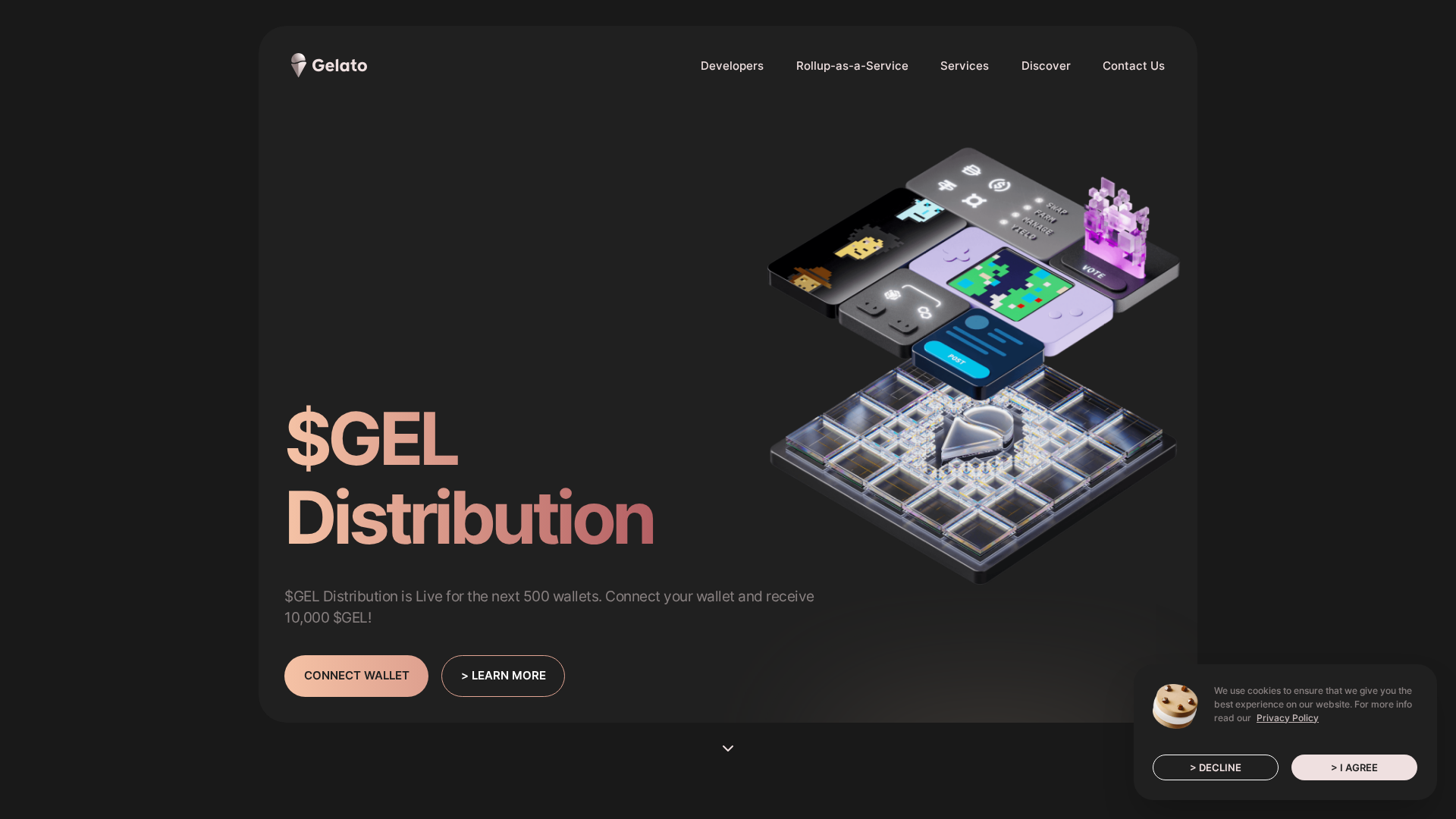
Captura Visual
Informações de Detecção
https://gelato.pages.dev/
Detected Brand
Gelato
Country
Unknown
Confidence
100%
HTTP Status
200
Report ID
cd9d6ac3-c62…
Analyzed
2026-04-01 11:38
Hashes de Conteúdo (Similaridade HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T18DE31AB5321411857103C3E4F211BB68D2DBB39BDB26C5D8E2EA9760FFD5C3A951BA80 |
|
CONTENT
ssdeep
|
1536:ZvT4s6w6gU1nd7FrD35XAgGbMuk/kqj5j0B/4pqpqsq7LnaiL0N:xT56+uuk/kqj5j0B/4pqpqsq73AN |
Hashes Visuais (Similaridade de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
92166d49bb6d1e92 |
|
VISUAL
aHash
|
00040e0c6c346203 |
|
VISUAL
dHash
|
d0ccecdcc8cdd6cb |
|
VISUAL
wHash
|
4c060e0e7e7c7e03 |
|
VISUAL
colorHash
|
1e601000040 |
|
VISUAL
cropResistant
|
f4e9da78e1e933cf,a8e454ccdcf0b0d0,d0ccecdcc8cdd6cb |
Análise de Código
Risk Score
100/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 OTP Stealer
🎣 Card Stealer
🎣 Banking
🎣 Personal Info
🔒 Obfuscation Detected
- eval
- unescape
- hex_escape
- unicode_escape
- js_packer
🎯 Kit Endpoints
- data:image/png;base64,iVBORw0KGgoAAAANSUhEUgAABNgAAAFpCAYAAABOGJULAAAAAXNSR0IArs4c6QAAIABJREFUeF7svWmTJMlxJfjM/HaPKzPyqqvRaBwcEuTOiAw/7M/bf7J/aLkyQy45GKAB9F1VWZmVGZffx8pTM/PwrK7uAQFyZoQM687KDA8/zO1UffpUVX366af/N/4ZxfM8aAD9MEyO9oDSgDukYP7mb1em3/0zizxv8rcpCj2G8TsNBc/T0L6HOIxwc32Bs/UlfM9Dnhd4d3ePsqzgKY1BK76Auc1grp9WTysFpTW0p4G+R8+/7TN4rqc98yy+szbP9bwAvs/jHpQCuq5H07TougZN18n1WZZhtTqD1hq//vU/4e7unfxt7s56mLc073N8U3Oktw2hcXl+gziI8LvPf4uqrqTuq19e4Oonz/D42zeoDw082849u6UbcLa+wcvnZ/j8v/8ORX7Af/7b/xNeGMs9Az6vy1GpDhg0hlLBD4EomyEMKnSlxrfvNggjvjObrkeazTHPMvRdjb7pUTcd6rJD23XopGcGQLcAOmndtm3RtR2apkFbDdImDduo69HxlHYw7z/IlZOBMu1xaW45xKO2+Y9DSh+v0Whwc3aPpovxsEvlu55XSRM3wGCe27GBeFD+Zx2eFva5PG98II8ocBaYuqhjDfXTWnu8c9/ifLGD1jEet3P0Skmf94rf25exF0x7nONPDnMwjd8ca8cxyaexDvKn1vI8pThuFbQPKI5f1tQ21OH9Pfyu5IDA/OYX0u+sxwCFMAoQxTHaaoe99CMQdYEZ8Z6H2SIGfB97APdlj2CXw/MipPog7Rl6PE1h0D6a3kPXh/i29RA2LYKzEK981qVFVdbY7husZjE85aGz60ivemjNmngo8hx93cjIYZ9AmRk6DBwhPYZ+QN/16JsB3cDPQNv3fC1zP85ZnsMb80sAPltHaelC1lPa2zMjxRzT8HmK59k+ZWfadh88UwXTzFidraQeHTwZB2MXsk5cX2zfa91B4Tt03TmgEuQt50EPVddIdQXPH5CXHg4I4GmFeerDCxV058n61En38Tv7iL6F6g/AcAB6z8xV9lAfQAcR9k2PotzJtX3XYuhMP3L+d9ImdgwNHPeDtA3bSZpImo1rjB3EbAM7Btlcip9lcGs5xeM8UIAvi4cax50MvF4hCCKs5gnarkTXx9BsQztF86LAbJGYc+0c6ZpWPvfdIGs4C+dn1fTYPrR4DNnWHRbzEGmo0WwbeNsddH/AfF4CqxX6foUIDVTAvgmAPkDHdaZsZB3syhK6A8JVht27LbQKkC1b6HCG7968Q1kczBpvBo60Sz+0pj2hMNixKs0gQ8jMdunxySblZqlZz+16ZjcYTynsDu/gxTP4OrRLu1v3uZ/JhBzvw3WSY/MXv/gUj48bvPnmDbwgYNebusj65dY+c6Fbo5+sG7InDbhZr3F+ucY//OM/IY5TW38zsJWsTe4IFyjWhv3Nf7m3mfXFjYFxtbP7o60RPlbMG9o5yfe1bWz/l2NVWaKud3Kc9yurBgoBlucXuPrkOVb6a5TdNfqglfHr9aHUS1pZGqSX7aZDi8ViIeP3i6+/w5ffvkHsL/DiIsb5xQV+//kXuLhY4R/+8f+DCuz6KfUx7yH9ZqeCrLPj3BmkLdiO7IP/9H/8Z1lLdtstiipH33Ed8UUOGN+bex73uKZDNzQiF/AY1yn+Lfc2k8/KVKalTPPaDU6a2Mw3tx8FKsDj9gFNU2F9fo6yKrHZbtA2nczjD/exf375UID7Y8pRiuJc4Vi3A+VUTuVU/szCNSCmjAaFjiIsBSTMEXse4v5bUWm4g1GmE7mPkqrW8IMUVRKi0RpB7cErOCdz6KHEPG6wPo+x6z3stx1WV5cIuabqEkMzYLer8Ph4L/uoyAenciqnciqn8kcV9emnn06Rsj+qUBD3PU0sBD2lSnPwqUz2P5DPjurA8TM+vPQjQB3BDaos/P2xQkWQIFcUhlguF7i8uECWzQTgedxssH04oKW6RBCNYA4FfBHyh4mCIpqE3Ms8zdZrMM9V2oAWAo6JsunBC3x5LgE9zR9+MQxo2hZtawRr3ikKI8wXc9ko7969w5dffoG6qkRxUYoKiKmTeTvXAB92kUaazLBI53i8f8Td+3eiUEXrBOefXiNsgP27rYAQIo/bW/iBJwAXpe//+J/+FnGcQBMOG3ppk25gXWt0NZ8QIE4gyqz2MhQqEGG+LR4FpNTak/fJ0hRt3aGiEkv9hru+6jGoDsPQyvjg5syftu7RNgZ4FHCtpZJBRZbvzLsZbcuJ5ANfXwAmaXUoAWCscsv+kd92LPC3Ym/Z7+S0Bmm4RxYP2OQBijqW+zmlmUra0GtRbFwvi44jzzTHRMXkONAKg/QRn2tANfe3qY/rGfNs873RdqXf/QpZ1KGqE5RtZPp7BARdX5t34ovLbe3Lciy5tpH35Ki0YAfHjHm+rZutr/wIYGSBD45pKFTbO9Rli9n8AlGcijIZBCGS1EfLfiFcoBXadoAqOyRxCC8KBVAxmF6JYniPqrpCgBqP7ytEPhD7rQDSrGnZxqiTDBmVV767V4kavN11UGEGz/cQ+sDQEgRy/afQy7v1AihVVYuiKATGErWcc6PvBIDhT9daEI0/MofN3wYUMZNaFFc7l8z8cmOGzUHAyDxX+lcpA2Rx/fAdwG6Oc4xQgU/iBGnsYVCeVegtsGA73PSTHU9cF9te+kDOVRpd36HqFNqqAWrzTmxvFXqilKeqhT/U0AHQebGg477Ptcr0nbwjUae+hKcrqKEGegJaAbpBYQgCtL3CvihRHvYy/2V+8Tqpk1tOOJp6s+65ueeADjPo5P2l3WQNtLibm1dq2nb2O7anoL0Ks9kZ0oCGCfZRCAwBNOvXD8irEnESIQh8GbsaD+i7FP0QCThJ4CEQ4JM4nRKAaUswheO57RGFHiLVo26B3ZsS5WMOpXqcrRok5xqdv4YWDWNAyzXXIM3G2NFsoHQIr+mhWq7PAWo1wA8HhKnGNm/w/v49urqS9xRDAeei6Sq7KNv5ZlYLOxcH871dP+xKclxT5MIeqm9Q1zVUGEJpX9pD+uKJsWqyL9n7CfCmB6yWcywXK7x9d4/Dfm/XnuNOyDXBDEUDZLHu5paDjPmXL19iv9/icXuQuSL7l10zzBR0c8SuTfazAaG19IGsOgR+3Npnx4xbq9z6NS3j/jmCjQYsl+nJsdl2Am4OfS3H+c7sOz9OMJ+v8fwqBaH+Fi06Alyco0MEPWgou1a6sVsdGsFtgzhE4Buw63DIcdhVIMb/m//237HZb/Hs1Us8e7bE3//9r+26dayjvZlZKMb+Mes49/Fn18/x6iefYOh7bLdbNHUtl1AOkHWDILsYcIzBqW2PeyB/eJ0Abe7eth1MG5rWMtuK2XfGeSb94skawH4MuGYkMQ6HA/Z5Luv3aPh82gXf74yPff+hmPFhMdPKFjchhg8+mbFL+WAcH6dyKqfyJxdj+NAIg1D22F4MmNwvE/h9jqC/F2NkbQ1uxjDo2+t6zJMIrQ5QUhb1BnRVjKGK4PUV/OGAJCgwX2j4oY+yD9HXGlGSiixf1y36pkNRHYSocALZTuVUTuVU/rjirVar/wt/QhHlgEqpbxQxK4MeJS0ne9vzf0zUGr/74Jrxg73nVL47njM5257ghFsq6PvDwYBPcYTFfI50lqBtalRVZes8oln2MQakkc/CBKCGQwWVyiKFf8NzGhVTp+DzO/nbAmQiFxPsM0K+KOrdgKapURYl2qbBarXCq5efiPK3z/cWWJm+/URrG4+bhuD1eXnAbJ7hZn2DqqxQbHPs3j6i9Cqsf/4cTVWjKzsDKFBX6DtLNFS4vrpGEvhoCViQW9QPovxReCeLR8cG0BoI0jUl4kAjTWNkSYKyyFFVVPI9VHVtgEUq912DXrWAagVc6wguErSxrLW6Nky3hj8CrhmCkdMJXPvLW9o6HxU+o4AQaxiVfVE67G9r4TfNpMe7VW2I3d7DMt1jkZUoK22ea7rVggvscwIYphai2BrMzja5GdBWh7QVNmqz+df99QOjXICDAGXtI/S3mMVUhgJh1I2KqZs3FtAw/XxsmKOCb747frSgI/91YLFtUPNb3mxUssM4Q5TNUVV7VPkWs8UKWaJRVi0aAR1IdTGMriRLEMSRqT/bhcjr4GGofcRei3pXYT9EAjy2FREJhabx0IU+zmaRKPqhBuoaeLjbwwsDJFmIUNifTnk088jAVU5B6+D5nLMJyAFrmsIopRwzTS/KN4EjIcLY+TYi5ebFn6wpU8X1CM66ccZ+NyCDJbtZJducL/NfacwXC6SxGye+ATKlzc2cJwDJm2sy8VSJoTOCrvQTlU3PmAW8wEPvaewjH63noUsDzEOFmBTAukOZm7kREnoL+W4BVN/K3OX7sqXqTqOqqcyTVcT6GABO9eTU9YiiGDpIsd+XotyPirwFisyocCCOAWsdoXcEbZyCb0f1OBena6S9xqx/A+BFOFudISEoqGs7bUhxU7K2FHUtgruAqRwwZNn1CQYdYhiNFRZgIqjGdbbpkGggHjr4fYdQkUHkQ3cK2zDEToXYpxmw8zHsgVDnQFiiRYi+I2hM40ZhgG8/ERCXeKeAp+y3nusB23OQ/j0/X6DsgOJwQNtqeAPrZdqexQAdbtYfQTQ77OzvIzOL4BtHQVfuDWgUJpbtfRxjBo+azmjTQ+47A/4o5EWF3cMWF+uVGGnI9JQ1fQTczVy3M95WBljMM1zfXOHt7Vtsd2SwOiOBnSVjX5saWPOB+coMBHPMnufWQ/k0/jlZtz5YCacr5JMyKHRthTLfym/usbxf3ykk2QrnNzd4vo6knxr0kOUJIRQZmxZcO958wHZb4s1+QNsM0G1jgE+lEPoBbr97g6HtkcwzBFGMIIzw+z/8wYCItqFMvzmw0O4Nk+pyv/v5L36Jm5tnKIoc+90ONZmXZHJ6vhjWzD7LtcoYkjj/zI/ZDw0TxBgLDJhoBtYTkFPweGvAs+skASutfVRljvywwzxL4WstRsMDwTUaK6ag14fglvvK/Xx4/EfLuBF+8Hl6zE4AUepP4NqpnMq/ROH8D4LAGLRovCZ4rZYIvRRB9x1UtwPNQcZHRixd4M7pkYcmHjgdwqDGPNEIggReHwBejjZq0Q4RVJei6TSKokZdNpjHPYZUY/d4EIM4/VtE9vYihLEhHtBw99QodCqnciqncir/YgAbiwEnqLh7ohg9WXQ/IrS5Qx/KeeqPlfU+Ihg+EeWPkvxYt7ZrkecUSnOpY5IkhkEWBQIOdV07KpMfQiQi/FogTSzZok9bIEMQD6Ncm3OPTBER1nmd0TtE4CSzjUAUH0Drdd00KEu6T/V49uwG5+drcZ3iMXHLc2Z5h6x8r2HMc6umRNkUuLhcI4syVFWN+rHC4+v3iK8yzC6WGGrjnmnuoRAnMcq+FEBO2H0dmVW1MN0CP4QfUFlwCq9wL9DWOfq2luOBF6NvB6kvmSh877qpkKSJAK5VU6CtK3R1h6ZuUFd83x5NTUXDgJ9kj1HRMK9C5MCBHo69dVT0DUBorPhPgTfnuumOifQxUV4Ns4RA1r5IUFUDzuY54nBAUdISyHMNsGbAVqP0jWPTgQ7T0SpKxPjL9rHpKzsk3EUfEjlESW3aBE3rI4kPCHSFrhMfu7GPjQXyeI/xhhPQaDpO1Q88zAEo4tooIKZVvmUcK0TJHKuzNfRAF2YtVlHeQxh7SglzLfCMFVQRNKUbX0tAMAeaLdrHAHkdIljOhIGVDyHy3sMhjDGLfCSBhup71HkpCuHqYgU/pKsgAd/azhEDBBDk5TwQRXJ8bQNYR0EkoERRNmjKGm1r5g/nmWEeWq8qOw+PTeac0sYWsmPJjqsJcDRdeeywGQHYIIhxtjxH5LVQ9C9UdGs0teT4Zd0JdJkLBA4k/QyDDsTaTHjFI8gyEHgDAt0hpGOH1yH2NM68XtxJI9Whanm1Rh9EaMkibRr4fotOkbWiDfuTaKUAdj5qnt9at31hfbHinrhb00ttvpqjHzzUdLele6l9VeGvSduZETzCCBMQzcy9CQhjj7nWkivM5BKAlS7jF+dn0D3nnGHssT+bTuFwqNBxzMWpgPBdVYiLq/IDYVgaAMH0AR8h4KnSaHqNhmOQ7VzR9dzHQJfZ0MN7rbAOCcR4WC40VOSjPtQ4bGr0hwKht4MXE1zUqPKDZbLRtS9GN2iUHEg+HWnILDPdV9PluGlxcZZivjxHyfs1FbQXCEtOe+xru84cp+W4Hpgfu/6zdQUspHHB3MP3Q9N2IxLn2tKuVbaZzdXHY3K2nZv8f0PWVFfj6vJCmIN0D5RzLZNOeKAcb74W98FZmuLLL79C3xuXT7eaufFwxGJYXzs3xnni1rkjuGqHymRMTFakCfg2nifrmpuf9j37AUW+R77fmHq7a1SI1fklLq7OcTUb0A4KLZmQPKePoQZf2JDOhMJL6r6VvcjvKmSqw2HQuK2ATBNw1fj8N7/Dr3/za2F5XVwukRc53r17M64BvJMB0u0R+96um/j32fIMf/WrvxHwerN5RH4oRNHkfudzHAtQb1zX6aZZO+NSR1DNAGudM8JZQ527t2nvCTta3LEtYC9/mz3qsN9g6FssZjPZr98/blAyRISgv679bB9M9qGPlnFgTT6rD69x6+L0JkfjzvjbrimG1X8C107lVP7cwnWAhnlNH4Oa3iGUl2L46gIRCqjmDeq+Qw0CalpY9YAxVFHP8TXllUaMlWRiq7BB5ndI/E4MFDQcqbhGG9AoHgHdAm2ncchb+GWNbBVgCJXI9X3dI9Y+vF7Bt8xgzvzRe+lUTuVUTuVU/mUBNleMsmtYL0aptNqGldx/TMZz3x1V3I9/Hi+YCo7fM9ROLNr2ewq0FGwpkO53exRlgTDwMZ8vsFzMpb5FURrr+URIHZkeDqixlXqqChnB0lXLsdp4r+lnOYeCM5lePl1JjfBM0Itx4VinOIrx6tUrZLNMYu3Q2i0xTOxTjODvFDMjdLtv6eZXlKVgLNfXz5FGGfbbHcp3Bxy2e8xenWN1cYbicYeL9TWGKMRvfvs53ry+xe7xHqvlTFxNAp9KoLHEs4qMmiQgpR7Q+gQXBvQlXW20sACaapD6U+kPw0AagQrGPFuIi+Hu4SBKK1lrZBUQIHAuMq5tx5YckTMLptkGN7Gfpj9HoESYHRZ0Mwqm7SNReK3WbIV/HmvhY3fwBWx4eblDVSuUZAI5ppH7+XDgOdLGtFhAy6piNkbXREmWG1rGk1NcLXg3KB9Vm4ir4yy5h6foLhseY37Z2GrmXk+V+VEnciCkAH3u5Mngd0CwU/qtC2U7EAxZYJX56KkEUkAjIONTMDNgRxDRhU0iyAkbC22Jtg8Q6D2q2/fYP0QCTkbnGRZzhcjvkaZagI+zmRLGEVBh+7hHmERI0wxtRxdMwzYcel/i9nVtLTHC4BkmZdXU4p7KcS+xpej+2HkSvyubp9BhjP2Obgrk07lJd1wTpsyzSeuZT6N7o/lmbGnbYWMbWjYXQaPz80ss09QIo2PAP4q8FDwbA555vmGmELCRexDpIrvMQva2T9vWKMldTxdTJUKzR+GXTDfPx7bTCEMt7LYo0uh0IK7abCfVkS3aQZH9Rldt+kcOLTQFXS9AXlVo2g5xZMay6nmeh0ZpJGmI5XyGqiSD1Lg+yngQdo9BiR0m4lYUM8dsC7nvjg11hCU4f8MIl9eXmCWeAGIc4859ertvsT/UiNKZKN5NnQuLyA8SxCldJA0QJ1G0CAhJLC+uD2wTD4OvkXgKrdKo2wFe5CMMfQQKmMmlCgEZSnWPSA2oGd+s7ECSVlvlaLafI9A5svUVejVDQ4CyLOQdojgTN/Wiq8QllwCoNAdBvYLKQ4+rqwSz+RKHXY6uLxHwRON4LC0wGldkvlk2paw1PQK6MtZkqvYIIrL06ALtrj6O2yPsdBzMU1B4CvKYbwlEk/zXYfO4k/h4bH8akuqKwDXB2AGzLMGrVy9w9/YWDw9beJqsy0l/unXDFtO9tv9HtpqdN3YtM6DrZJlxy+AUz5mAO26uuX3L3Y/M6u3DHeo6l1ATAjwNHuLZApfXz/DiIhUQmmtVR1AbBNViE/HQ2lDMzQYc8gd0foGWcS1BpseAuT/gZjXDV198gW+//BpXl1d49uK5zNtvX3+HPN8bMNqtGRbgOnIFj31EZvbPf/5LvPrkJ8JY2243wkzje9DVnfNf7iJgO9nZlrHdWnCttWESRha8vbHrYwuqyetYxpqe/KZhjnvs4bBBlsZi0HrcbLHbH6TPTX2P/Xhs6GMffbS479x5xyrZ4g5Md8anR+WzuLaasBzjmnEqp3Iqf3IRHUHToFYb1v6gEKkXmIUZ4v5rVF0OcrK5PpKtJnKmdqFpeviKhr7WhEjgnsS4lN2A1iOY1iDsGyS6R6joeA+0YYEqIqN2DvQRihao9jWCrkI6H0QmKUsCdpQtuL958MNQmMGGHX+KzXYqp3Iqp/KvArC5QgWeCzaFQoyKHH5U0pt+831xbvLF5EsnuDtZ/mhnn1w4FRgFaDMxm8qqwm6/F6syY5DN54xrMxeFmfEGhqlVfgQIj38f62Ss3eLmIW5uRhtyzBphvLm4UI7RYAVqupPQOmUUMwJPrbAQyF5bLhb46WefCevkcNjKoyT2yvhu6vtMK1tHCvB0Gw2TGJ+8+FRiu1X7Evu3G+zrHNc//wRffPEF3n3zRlyswihGmq2Q7wp5h9XZmdxLYlHJK5jEAFRM+MOEDWXZozj0CP0Si1WG3vfRdAX2jAkk3nR0uepM2y4X2O1zbPLcJhRw3UErGoEG2478LfqNA9ic4mHBNMuqsqF/BIBxsa8EJJiI/8JGEWbc0Y1XvrGuhHyfqvNxt/VxuThgvWqRlwqtsDtczB3XxS6Al9V0ZUwxvs6oTk5Qr6k70bGPnAZqYgXZeE1sXIIsCFA2KQJ9QBY9oBsI/n3AALAA4eSjfVn73k9cs74/XczVJhkAggxXl2uEjK1BcIMCmVyv0TUDDlWNRnIaMEA8qWJkYdA6CvhNif3rAbfNEo/ZXMZwNvMQCMtTIehaZF6PsG8F3G12DeZnK4kfxkDhZHpIXC2JuUYfVIV28IXhSKCNge29IBRXwrojW8gAfmSrqE6jGZh4Q+HsbCF/Mx6IpDn5YFpKl4xtdZwdZs0w/eJC37m2e9K6AxBnCzy7XEMRwGq90RWN44/uzQSNPT+UOUfXNnFnDDinTVxKcSMUBp1hXYqboNYolEYQ8hyFulPoeiXzJ6SlmqgRFFIq1aBbh2HHkfFV1nQt7+ENDcKwl5h4tDY3VSWsOT9MJVnH9kD2q49AG7ddsWpLBgeN5TxBPF8gP5TS3gIATtdS0yAjW3RsTouoHNvItBddyhfna1xdLsWlvGJSAfaR7ZDbxwM6L0KSzlBXB/RkrakIaRYjkDZhQhr2BQE1Ao09dA8UDRl8PgKPs8PNdw4xjcgDfGG6ccx1AkzTQFJ6ngCUkviBRoLugEOxxX3+DH3pI2zeIk5KeFEqbqxV2aLOD/CjCGE0k3ABLUGxiC6hClrWAg9l4wsIevFyLUB0yZiAAihM4DCH6ZIJS4acJI3pcdjt5VkqiGzKl8kslYvciuVANGcg+AAkHv92M5kKjnk+353uh9tHugxmmM8WaOsGrz55Dt9T+OKrL4ydS9afybph9+VhGu/RMZMmm+txzrgJYz+PG7EbO/bdpmCc/dKc6f4bkO+2yPePwrjk91QCgyDD4uwCL26usIzJeiSD0TBtFeP3MZ6Q2++MF5QYpd58d4sqbzG0HQKvgw57xMlSNpPisMfb2zfY7Pc4W1/g6uZK+mG7eRQWtek/F0+PNyVIJqksjCGJiYFWZ/irv/prMTg8PDyIIY5znXs3ZRzudS7higPW6DLaTVxCDbhmFd1J6gHTxGbPkXa2hqSnMfBYX8oAHZbzOYqiwsOGrLVa7uvAue8Vd2gyjCbbw8fLuBAOP8JWm9xEAOXesGddZ57KqZzKn1yMbkCDJ2OMMhEKj2aYBy+QRPdQ3TscBoWK1OvRIGCS0fgeQ28M0Ay7wAQqsrSZWJAiojEkbEPGu0ZNYwDjmapWjHJDRy+UEkN0EIY4erK8I6lDu28xjxrEC67LtRjKWS0mqJIECpEHX2LSGmbuqZzKqZzKqfwZSQ7+R0UsmjZwuAOZpvLXU6X26fE/ukxv4izl7qATOqcCpv3bsKOM9TlNU1xerHF2di6fi7zA/fsH7PeFESdlE7MgjbjfHKPuOMVjVD2d25lz9SATR+KmmFgqFET5DFqgafUmeCDspsFm1qQwLsCChySJJdso4wd99dUXeHf/zsa8YzWOL/UhPGCEbcc8UVivryRWzetvX+Ow36GT2GiMw+ZjcX6JLE2QeAHOLhe4vrlGEIZ4/e03OFuupL4m5pNJXFBWOYaugQ4CySYa6QF+x3fSaHSA++0e2/v3Aiis1xfSDnxHus+QXfeHr17jcKjhMa4b2TzhAI/ZEoVJ46ptNAGDs9mYazbbpiUPjUqfA1dHpcW6qxnB3ygzhrllgUKbVdLFXXOKJgPwrxfMiOnh7UOKqjlmgJNn2HoZ3XSCRjgwwgJnTvlzLDtzgVWgJhlHqZybOFNUyG2weNFEO8yiByiOw3opMdvMGLPjzbp+HZXZqVJmYrkZ/eh4Dn8RWCMb7ez8HBnjfonUZjI6Sow9BtpnVjwdwPMDSXKxfXhE3zVYXzDWxwHNY49yF6IJ5/BepOLOx/aM+Q5aIcYgrKo2f0RVdZhdXqD0A6RiX+W8MYCZZP608YlU15J8hZ5xhWqCzIzZ1UH7iVS8rgpp11kcyzjrlEblE6iimyUBpw7v3t2j2G0tMHGcDfIzoqQmxh6/HBNQjBjCBG1jCSKsL86RJgEaiTXiIWqBgGPKa1G0DRTdBTl3GfOIBgUmVBGPCTNA+VyCa1T6yTBjP7d0axTvcLpRmUzEbHPGkyNrTcaDncdU8RkDTDNy6+MWAAAgAElEQVSrLoH3km7EtB6LlQABk0ZECl4cohpClEUvoIoo/VGIhi5jbSNzmwlVZEiY8HjCRPX6DrvNAQ/39xjayiZmMM8f9WtpEjvhnox7U0cvTHG1XiKJIxmDdP+sCCz2QP64Rdkxy/BMMpmStUbIKctiJDZtLcc9XVg1rewlY855aHWILvGQBgOigckv2Eq+rQIBFwKdpAAykLsBMiUhBkE6T6NSPh5aYH9nMoX2bY9dnqM65OI6uIoKXKw7hPMUrX+FqolQ7Olu2yNKGRcOqIpcmGcpQQOGG4RHh18UQ445QxFGCe7eb7F7uBvXYcHyOffozuwDJWNpki3m8QKz/7n5KPkiZZ06rtlPxqrNQiHXiJvt8SwH0Nk0OLY7DKhnYkjy8hZZFGC5WuP29tayaE1cRflPPJnd/mj8683qZNYZA6od9zATVN+cK1mN7Xol+6KszdZVmnCkZZ66seOAOnu1zO/D7kHGspmT/BUinc2wWJ1hlZmkIgRuZV3k+zPWoXPbtPtBP3R4e/8em81hZDWzGkkW42K1wtdfvsPnv/81FoslPvvsZwadlaRGGrPZTPbft29v8c3XXwpj1tzfzFvjYttLmIRf/oe/lLiLu91OwHwCmSbRi80uTiVW1jKTuMBkDDdAsSQXGQxTW3proniOgJoD9+1vF2vNtK1GWezRNpXEWuOaud3vzVrwxC1rsna5xc/9/vCUJwLXOMl/5KInF4xnTllrbpycyqmcyp+rLxmwngnRepGrfGTJDWZ+i7a4BdOo0LBIw5SRZMyuwAATnpcgCihzVJJNnUUAfWHV8homGmKoCsok/GGkiwFBoJD6TJ4QoGxDlDyfOZjJMm5ToIoQdAW8fo9Et0gXPbD0kO88tAcTG04q0tEo1aMaGpH1uQ6eyqmcyqn8ey//ogy2aXHuMy7T5kcRNVusuP9E7HPFXaZ+6KKJ9f3peer7F9q/HejHzWy/Z3acHEEYiADORAiMQSasBnH7OsbHGg3zznJsdRUJkm7BN+ufOKr6sglaNpv8J7EUbPwVG7xYwDdrBWaSAbqzsk6sx7PnL7Cgm9KhQF2XFjv8sDXM5+GDr+gKUzcFXn3yCdYXV9hsHuCFEc6uzxAuUlx9coGbi0s8f/5cAiX/5vPfYrfd4OFxBz+MEMeRiRVXMKU3FfsUYRiaTKmSDpwB5wHddVhmCbx4JXFh7l/fIYh8xFEkignPv7m+ECEi3+TWZdIBkayz9fuxSoao/NqAKcxYKkkwhfXl3m8C2NrAZ474YVhr5m8HqPVjXKIpuGaBh8HHNg9RVwNeXB/kmWVtYmeJgizPMHQPE3vp+xqLa3dRlCxKYRTniQsnP1s203GcHPuKb111qQRcz8JHBB7ZZL6th1PEzH0EuH6iyJobmXY93pN/BnGGm5uVWDerxiCG4sY3EOTp0fQDAgZeF7ezXBTMNJ1hMVO4++KfsHuXo60JSsRILhOcRT3iHog8D62vkFFpB7DZFcQ+BFyLQh8p31Wa0CSVILAjmTV7hiunsEjXMGaGbBFGZICFJnh/yQyHTHBAxRLYMbugEJNcJkOOPANKLRYZdJSiLMiCa2z7jOiZaS07b0WNHgGA8RRpJYqDQTLHi+eXSCP6CxpAj0OF2FlDFlnPmFaRyT5LV9ZBIQw9BB7HlXkIsxTK+9EVsfXRDD7K0EPiAZ5krjVuywTgBBwgS4/Kv403J26S5DV6CrWn8UiXOFqXRV41HdtKrDCmDGsQMp5bzJSJEfKyQ1tWkhGWzKxDSffsGnEQiosrcVVGYSs04+/5OF8u0NJVuchtdt5je01HpW08y/bRWCzJWlvJc8hONC3OpAUd3t8/EH2T8VPy+WUpyRaWiwgxWUGtggqUuLCgY0biHnkTYBNGGDIPa78XJmRLwJVuxMxUzPkr7vIE3Qhk9AJYDkwQQQYg8RomgMhfI+xzLM/OsclCcaXNEAizsBDXUYXNY49+t0HqfYEoYebQFZohQL7Pxa0zyWYyL/dVyVBg4jZa7HZQZFhWsQDTq1WM5WqFTU6GEjO5mrUpRCvMaK6bmjG5ZGn6YI1w4NlkbzA2gA83x3GhO64z/Diha7oVn+uClKaSudMS5CwrzBbcxyJUbTNe4Bhb5o7HfpWed8lVnFVjMocciOK+H6+364+xQZiMy5OvzH3Zhoct9vtHNKwLk1T0QBhlWJ5f4OpqhWUCdHpAJ8YWslY5rmwiEbmPAXSqssCX376W9zPUUBprBqzXNB5k+ObL18iyFGVb4SevfioJRd6/vxcDFvetsiwECDs/P8OLl69QVw0O+V5YHsY+w++u8dd//TcCjj8+PojRjbIC1x0ayAQgJ7hGEE2Yaoa9JnHWXHZQ/rZA2JHtbNrDrNcOyLRhD8asz5LFQTKEMm4jY61RDtjstiZerCSBcI37ZKJ+UD4mSU2Pf+y74/HpaJRhN15ugVGR6U6x1k7lVP7cIm7gTILW0tDE0Bcavj7DxXKNmX5AUzwYd1CbwMCsueZaxlellTLymTiFcVadkcywainbDmTa09ijU8Nqp1FbhGJjz+HaRmMAM3NHsgcEQENLcYU+6NBzI0SEbvBQ5T28vEMWD1ApXdcp67QYaDxVvtFl4sSskZLE5cN97VRO5VRO5d9P+VcD2FhEObKAh8RnM2jUR+W/D0U+9ZHj6qNS36grjIePXJajQv3kJvZrk82rF7c0ujjSTZNA23w2w3K5kI2MQjl3IgP7WAXEAhljNYyvzeQhU2DNKNXjxufitEkcMnONMOpI8ybjRVgFjNnUSWZQAn1k2r18+QJJnGKzfRBl3DGfBMSx9fqeiGyZFbvto8AIwmgjc2RosbvbINYxzi/OsCtyfP3V17JhcoPP5gQbnkkyBGYWopKTJom4BRLwIjhGJYmRHqgYMbYQWUmJHrA+X6CL5vj6q3c4HB4lY2ScptLGzGZ3vl6IG+c+3xkFwyp2hkxkg+wLM8uxwWxyAxEsjnGjnLJqhH7L6xDw0ry+VV/HLJPmx6m5biyYfuOvpvfwfhsiTipcLRjLSOFQCNbiTh4V44m/lR0Tx2FlcFfnNip3t1dZdooMA+MmeIwEdtRrCWLUHVlcHWJ/KzGFOsYicx0qDzMA2wiKjFPKvh8BG9/HigrsmWFAtC7TJL+nqzTZG74v4JrE+mAwdwRgKD2ve4/iboeiWmJX+TjkFbw4wGI+QzMQWPMQej1iZoqtH9E3DZIkQjibCZBH5ZASnEcXIgIrvsKm99AygyupTh3ZIPRFZSB7hZ4ulwLg0lUyQtkMqOgCqhXCOJUYfnlpWIaSgVTektG6FHToY7GcwfNCSYRA1pS0pQtGb9/6iK05hiHHBjNLhlhfX+PyfIFAaGbm7sYlehA3awqQZJ0y1iDHOZXvJDLB2ui6KC7VhOm6BnUJYZbtowB+rLBg7DTGmmPuA/L5CMQzU69kdaUgTOGYTrOMiUciI1k0FHiBKFBoIo3CC6CZYELylJhUoLRmE7hka4SeLzHNGt9HTpe5qkEYx8KGpAGhIUDlBQJI5VDYcrzrAWdpKAYFuiUTvDDucccB6QBI/kc31Jtn10hmMWpx2bP9MAzY7Ha4u98gI/NVaxx2GzStwmK5xFnqyXynByfnkt/XGMoGee5jgxjlPMJZonAOBlNuUTc+WrIpLXhJYwTdiAmyEVyjEhHFAQJmr/Y8aYftlmM3QpJkCFSHNdePWKOMCdIFyIYAXeAhbxQ2Ww8PdwH6fI80eo8k1YhjJnpROOxKeN4gbq1c38q+ho4UlnGCyAsJ64qbDdvp4mKGMM3EbbQuNqjaHnFslRi3MDhmmV0TDJh1dAE1a8GHHDXruzmCX/Y3ASaOei62I2uXY7BFk+fi+s7EJc5dr6oZ4HowDFDfk3hdbi06zgfXx+aZx/3tQ8Vo9PUcPx/3WfPZAUcm+Y85v65L7LcPqComGDLgERXC2eoM6/UaV2c0LPUyFuUqSWBAl1Drum6XOxq67u/e4839vdlD2T59iyiNcHN1ha5p8P/83d/h7f0t0jjDZz/7DL3uhBHHvZOF8Ve5NxAkYxZvAmJMLkS2NduKCukvfvEXePXJKxz2B4m1xjANZPFJXFKxElJm6E1WULqE2kQGLoGB7Ol0CR2ZiK6bjmzAKbDmfktIDUXWboki3yFLI1nrHh43kgWdsd1sK4/dMXbRcdM/lh8F3z723fGGT7rZ/e1AYJHjjGvYqZzKqfx5hesK1wsJTyNqQorL85eYp0BzeI2i7lAoX9Z2Ya7JtOOJGp2ixwEQUiiggcka8AUwkxis/F4LI5vAPWX3IIgk2Q6/P3p7UOZgCI4OAw1F9BDgHG996J5xXkt0IU8PMagIdeehPgBe0yI+B1TMPbE1MWW5RzJMBI3rwUzq+pRxeyqnciqn8u+n/KsCbN+Lz2aD4eIjIjzLUVz//vEfFBk/EDbVx6742I3tKQICDkZoZgy0/WEvgFoSJxIPbT7LhAlSMBOcVV6MTmLdc+wzR8F0wnIaH+cYbGNcNiuMWwDOAD8mqLGw2eTHuK3Q+i6W97rB+focL15+gqapJcixAdVcBRz442poG0WABiVW9qLiNQbsWa3W+Itf/hLv7x5Q7Qu8/OSFKM2Xlxf4+WefyrOZkZSueAw2TwaRb4P2m7hyfAbraIK209WK+YqYJXIZerh4donHvMWbb7+VbHFnq6Vxn/M9zFcZVquFtDWZR8JKEv3MAWvkihCoObpfClTllD/LGjy2KduQ3eYygh4Zg6OWMx1xTge0bUZ9yLSkQt4l2B40zmcHPL8osc8N02p0hXFVsB8dg2QEcCYKs/EvdaCXeaicLy5b1kVYIE31vToOCND0EfSQIwsZM5ABZW0gaXExdRkxbbVsv/M5fjLHs2eXoIMgGXEmo6PpsYaMi25AlGVyXV3sMHSk+4eIghz99h533zW4zTVKL0EyXyE9v0SrI9yXDeKLACvd8kI83j6gHyKkSWricZBqyMZkIouO48TEPmRMqsRXaCT7o4lrhpruihUUx43o3nQhZYwthSwJ0BMwy5mB8QAvDCUo/W67k4D+URhSBRd311wrbLXCPPVxsZwJ+FOR/TkCls61+thJ/LPpe6TLNZ4/u0RC1prEK7MgKt0FqwZd3UjWQM5Vzj+6DMaJL7HACIr1kq2L4GCNrmpRVQF2foQ89vEsApKhxmDZbC2zYQqAbgADAgTMsiqBiJmhizEZmQiA7syUSaXdOqR6QBR62EdkYvnwawd20P3MuJaoKBABPPEGRKmHnG2wIbuqRzybgTzcXb6zbnw+SgLcEteMwvSA5SxGmixwKGv0ZAIatNuOR43F2RWeXc/kHQ4cgxSiOde6Fm/v7jF4IeaLJbYP77B99xbJ6hLr8wyxT0Gf85aBl1t4XYlqB+zqCPdJjHAV4EXQIupqErBQ9SFU6CMMDLhmXG0bk4mYrDa6Fg89woDrJBMZHFB3LWbLOXo/lCy3pOoxF2uqeywCBZ142CYBkj5EokJ0no99q/FYhDhsgLB5jyTeCtuWfV1UQEdX0ZBg+wx126McWmH9eTRsSP8wHg0EZCaw7GfnqHL6lBJwNWvQcR5b1qpy67zTkxwI71iuk4ucIWq8g9lS6KpMmFZmOgd0W6PMC/jZAj7ZlQ5olzZX6AZmeq4kNuB8xgyudBkie5LgqGNgO2Btgss82T6PC8y4q032WbfnOTdjw1pjrLUH5IeNrM0SsLsb4McLrM4ucHmWYZWW4n7bSXYYjikyLX0B16b4EBlk3373GvuWLGpmFDXMtcv1Wtad//J3/xV+EOLVq5e4vn4hMQ73xcE2m4l9SFemOI4FECPLkFnwWC+Co0xi8OL5Czx//kzCGTy+f5Qso5zz3IeN0cusq4ahRtYa2SYTl9CBxw0D9chGfAqkOQOSyEAOXJP9Xsv1+/1GxjtZa4z19rjdCGtNYv6N/TA8/T3Z5n+8TASkj37+8G93jt15uW/TsGGBwFM5lVP50wvXlSBg0h8mj2KcxgCz5AqfPDsHytfIdxsUNOZIHFUj74nhQv43rDTfH+Abaru4TVDOYlzWThkQzQ8ZviWUzNfce7mdM6My1zvtJRgGI0+aDPMGtBO9hFnNdWviuSmy55nYoIXyG5NzSjGmaCCx3Nodk/nUCGY9+qhHeSiNbOsxSRZZyqnEhqP58BSf7VRO5VT+vZX/aQAbi4BLVuAmS+mJJjIpUzHwh8W+Dy6YkNXMOT8ikH5ERuQmI24fHYXdPfYMgu17yDKCQUtEUYCqKsXS7YRMCX4+8ojMzc0hslCsVjSCLe51LZeJ9GwbJ8EAQuYbgV7EFc7Eb+OzRMEnyFcUct7zZy9wfnEhrk1knjhwypHZzPOmoNDTF2YfnJ+fY78r8fl/+53ETeA7UrhnDCoy58qyRr5vsNkrbPMOw/stBnrPkc7u3lfcPI07D5UkUbQYtFx1CLsKz9ZnSJbXePN2i7fffoUkTRDStYzAgKdwfXUh55JRwCqPjDUqgK7K0yyhRl09tpfoNPZva5ETMJPKrGtn67I7MkUmzBAquaNznDA4SJcwkNemiLA7aPzkMkcQdChqCybKPRw45vp3cg+bUZftYyE+4y5th/ux7dxQNN8RLnHurgLeynglQJFJvKjY3yDQDLIeCzIyDR3mxjOzk55fPcPlIkBZcgwyq56L88aYVA20FyGIE3ENZJB8upGlSYeg/T0O77Z4e6ewa32E2VzGA7Pb1nO6h0b49NxHf/8VDvevcf/YIb18Dj9JxYJJVEgyQNLtlAw9WkoHKtYSXk6C2ce6xzzQ2EYeDhwvpQfVkM1mYozJOzMbYAfEHrMKhmj6AEWeS7r4bL4UkPv2/h2qukQURRKP66AU7mU4DrjMfMzmKxTiNloZTG2kkhj2YYcQL148x+VZIgkY6P4gPSOs1h77vJQgvhSEyWBjwHMvCJDFpj05usg+81nvpkJx0Mi7CLskQpwpPPNa6JbZdRnDiy6cBI1oTSZA06OpGrTMrMv4Tcw9we9s5l7+Q1Ycj7PdJCaU6rD0FLxI4y4K0DY+/JZh+LmWMlmJRuQbt1aiaTO6Yc4D7GpawsnKYowqBvMv0bclIoJ9vYdHAqwyPjrEQYf1cgXlJyPDx4syPH9+hXk6oBo8lBTCBVwD8v0Om7wQNhLbeL/dYECCs/M1gnonsa7ovkq2rGpL9AXBDbLWUuzOY7ycAeu+MsBk46PRobiVh0yMypEwdMJGZBxKWvgZ449rrzAT+xqHzVsBXbM0FVCWbCXJnCpuo8omQWiQkVUbaBzmPkodINUhwphAm0beetjsFPKHBrF6QBjmSJIAnZcJYNbWJZIsE9fgLV2VfQOocnbW7QFDSRbCDMs0wPn1JfYljSHM1HpcG8x8pmvfSKO1c9+c89SNxoJpkz3jOL/NusbbMPFCW+xkngXZYhKR5xir0biimrWTDKg8L5EmZBaExhVJ4mgd90O5empEGP8wLOnxbdQUZLP74OQazpfD9r0AgeZ2XDd9zJZrrK7WeLaiu/eARvcCRgIx9BAZcM264Qu+iAG3t3e4vb+XtdFk1KahZ8DN8xe4e3OLx3fvcft4iyhKkGYZtts7k91X2OEEvlxbm/0xikIkUYTdfif7G8GtqiZLvBRjEo/ToCWgnM+4iVwXLLDWm/nKecv249g0MSU7ifdnMoe7TegYZ41/CJzpwDXJpHzM2FzXBQ6HHWZZKvIGQyzs81wYh6b17X4hbeyEnMni/3Rrn5Tp4HE/kz52nz8ox6eRPWq+9wgynoC1UzmVP6twDhHcpyzWMDkSQ1B4Mzy/foZ53GD/7lvs6x61yH2Ohm+vlTXEZC32yX4Xq7DdKUieH7hxRmJMoDxhErEYYxPjwbIwEQyNQl5IInEAT4dgcAPKUBRaSYYTBi6NdyFZ763srSLfd/zdYvBbdGSWi9k0RFNp9AXltQHxivJEh4axliXOr49BayQJ6+yLK+oJaDuVUzmVfy/lXyXJwR+72fiiUTK75Mezz0xUlCefP1o+8uVR/P8IwPYDQJuRQQ2tmkricr7A9fUVZvO5bA6bxw1u3z1InQkEWUzHPMkxokY2k1O0zLnCAhCZ2wjXnkQbpU5tmGt0FZEU3cyoKK4YBoihGxmVJDJfhKEU0I11jvlijvcPD/jD579FVeZyLwPRmfd23jrGrdK0tROU5SvPx6sXn+LFixt89cU3+PLzL5HNU/zHv/0bdDXw3X2FWdci6HL0WYQ+pUteixQhAi82oBYRMMHzrAKoyJepJS6SBD9lVId0hi/ebPD2d9/BTyq8evlCgqCzDckcofL87u4Oj49bAzA6N0C535Hh5wbCCLARhOA7W5BSulVQrKOq4wC2Y/daV60Juc38NoNCgMqxQ00SikVU4OaixuM+wt02FgDEBf82AWdJ4rft7a6l1dG1t1WMDDvPBha3AcZHspCVp0bXIZt+fVSPZBg1SJMNui5F2yeMVCvvR1fJdLHC9XqGgdloq1IEoNBPBahlHCZGKIuzmbiD1hwrOkQaA9Fwh/z2AbePCjvGrIpnmMdzhGGCLonQrny8iAZkfYm+anB7u4fKzlCRqZgFmMWBZLcbmlaURyq1fhggjE0mSzJ9JENk18FXDEpvEnl0yscfOo1+22Fe1ohViSDqRfCjG5kKAvTM5shxrwc8bBtU+y26usD65iV6gizlAatshsEP8ACFvR6Q6A4L1WKlFPa7Hu/e3aKvc1HQaf2dnV/j6owW1g6tRM7yxph0LcE0CsEEIepasnnB9xHHJuag8nlej6GrJFtXXdCNMMQuiuCnGtd+JwH1u1qh6gNKz0bYtexBstaYWZDt1dYW5GBMtJjPiCUZhSRKUAz2zgyRJjYbLdW+18HzGfw4wHt4eCiBeNcI+2s+awXMYjBjsi2pmjMrbKAb3A0KzZaxzWpESQgvJMPvYFitSYZHrj/+gIVqkNAtmeD3EAnIuEh6FARM4Zt2YpyVusV+84hkxkQovmTrbOoeQZrhfEagREH70pjoy3thJpVVhLyLsZ9HWC40rkHkjwkQNGoVQIVMFMHYbJYFRKu+xLdiPMpKYmWZDMR047wXF9GL9Y0JO8C4WPSVsQxEMgBJEOwI3PbMLtnCD3qxqvNZ33UK+WOP4KFGVRXYVAd0eQH69i6jCteXDeLzBVS4xqFOUee1BIMmQNkxQ+7mXvatVZQKKESgkmOGczBMWxQ9xN2+KBiE3xhuZJdwjNlxnTLJAWRFkjXLZpQRRvV0zzIIkWGs0u8yR8UssCmzZR6Br+/HZ5MNafK9W0JbLOcztK1GWdXC+lUS5NLcQtYfF6/QbB5WuTuyrsxX/Gz3NBugm9lBQUB1TCbDNlnKPnWxiJGGnF8arSZ3jfElY2MEsKxIZefD7rDF7f17m5iGAJcsfbg6X6KoS/zTP/6TAGGf/fRn+PTTT/Hdd1+b+KQE56WdbLxG2U8NUCb7KvdUWdN7Yb0RnL2/vxcmmgHNj+6gJo4QWSEE01wSA8NUE1DNumURZHMJdQwwaNrtCLFO9vxxHzD3Phw2ImPMkwTb/UHYdXyeM/uMgNjwA/LLtMM/KsVNhZzhB74xhqAPvxQGH41pLtHJqZzKqfxJZfTckRw9tcQuZqbO1dkNrs8j3L/+Aoeqk/AbInOOS69jq/siM4lZl/ujA9bEE0ajVYGsW4HsoZbdrBgfzXigtNyDCLgFzMTtw9dM1BSi7xMxYDIOb1uVsmeTja88hg/poWOTQMjnPgcfZecZxh2NlFzzuxi6CSRhlR4KRLpCknRQmcb+0KGvaFRMoSgfiZdJj6KuUVeGIfzUuHQqp3Iqp/Jvq/xPZbB93G3UZtH7CKFtKk8e1YcfKRNB82hwnV6pJr8mQutH7kGFgfWjgkdGG4VwMmbmcwJbmTA8qKDwdGHjTR46Cq52k5TPVrgenjzGKluTxxuM5ijyirIgMaCOgBuVdIIodV1hMZtLEgO6A213O7mDAfNM1lMj6rvqSW1HYIdP2T5usDsUSKNUMv397D/8DLv3e3z1zR/wk1cX4kJWM7b7TCGISnRVhce7HQ6HHLM4NYGZp7WfsMuM6xCDwjdYpwFWz2+w6TTuvn6Nti0wm8+MRUtB/l4u58j3B5M10eJSQl+3fXVk+vEfo0wZxpgVOORFDcA5tqF7eWuNd1lHx1BuY83didMeMqpS3fl43AaYhRWer6nwD5L50GWZBSn4BIPGoTV11Z3+2L9sbDA3Ds23R1aIu04UTneiXEKGTgKlKkR6h55BbHWC9fVzXMwjYX7R3ZBp0wmz1G1rsjvGEYIoRpXvJUB/GEXI4gKqfIM33+T4/YPGFjHSaIFlMoOOM1SLGNnaw0u/Q9yXOGx3eNgPyC6ukM1CrGYhAgVs725t0g4t45J9wSyjdEuT2IIEDbVjZVn3R8ZgUx3O6WKZeLgPfGFl6YJvyCy3rc22q9ETv6ULa9/g0DTogxmGOpf7z7KFcefiPAg8JPCwHxTuGMxfdViFCuvVEj0iNNWAm5tLnC9o7W0FNCLnTjJ2kUlGNl/IOFtalHdxVw18pExjPzDrsEbAOdXX6Apm9/SQqwS7NMAyVbjUjSRsqCuNGqHEhgslBooViimYkpHFc5rGupZZcMUCGo7N6JguBN7phkomIN0Sjftjh0wZJuAh8bEnQHUgq6yG7xG4cPEcCfJppF2DdDag8QIUFHrbFnGaCLg/lHvMOCM0EzJ4BpiTsdkioett16MemEzAA533mn2OsqixWK3Q9y2qfIeuDzA/m+MsNtlVA2b1BF1CaREPsN93yJlI4HKG5ylwzhhsdYeqCaROEq+FsZplTpMB2aCT+FY2Ng2BjZ45HQo8vP8GcZIiyc5MQGe65cnyYdxQOVcIpIonm0d3GSVuM+xLxpPxVYOV1ghTD7sZGVMh5jTnh54AY9tWY7tT0EWOUD8iSWpEjLPGhBV7sijpjnouLMq8reHHxk4vAC3XCSzmvYkAACAASURBVGn+AVdXS3hRjHxfSHxCl+XTzGm7xltmq8HFDIJm1iwz4+V8B8rJitCjLQ9oyO5NGN/GJdYx7z9Zduy+ZtdEt8jZvYl7Q1XRCNIhTTjeCUhyzh1jS7o9yd3LgW6TTdWsUgaRE1enguAaOmF+sSJkRSyWF1idLXF9FiHyOLYIHjOSXAQlP1TcDGAno3/oxdDysOG9LChJ5kXg4+L8DL//wx/Q5CVWyzXOzq9xvj7D27ffiKuyM2S4tnVVNXFWCWZbsFOZ2IDz+Uz2djHOEGSmwY9gnAUQJZYRY6xZl1ADrpmMoVzvJM6a7Cm2Zy0g6f4167zNDGrZaiZBKDP0VRJrbZ5l8rz7hwccilwyAI5utq4fJ33342UqRbB87Jrj2HJ9/GF5ylo7gWuncir/Eqw1MlLpVs61hobPX372Gfxhi7fffY19yz3exn+dJEAR7xAJvWEMzkY+oH8FQX/GYfUxeJFkCw99s++Tja6Y8KAyeydDYfBc5VOgoVGRBgHac8jAt0ZdGhQCJkLwJUlOP0mEIFgg4+XqFpFmCA+y3SzjzesweFw/ycqLTCzXZoAuOixiDT8D8rqCR2Mis4TT+Or5iGJ6sTD5FfehUzmVUzmVf5vlfynAxuJAEwr+EnfsB857KvT/eDHy6FSYdIrIR4TWH7mxgDcUpttesnkdDgcRQBn7hUkQ0iRG1zeoSgJtVB6s240F18YnWkHVMNus4jOpiwODTCZBOWLdXMx3DnwRt1GXLEISCTbIi0Jc9C6vrnF9fSOKwV6ANvuOYz2s6G+VJSqk9kkC1iVJiM9+/pm8yz/8v/9VNvflcomqq7E8XzFsNnb3OxwemZ2UbrQFbh/eo61rzJLEsBicdW3SieZZjP3Twh8q3KwSZOtLvN83eLx7K8oRFX6RHZTCfDkXd1zWicwBuR1BGRknRxTWcBuo6NiHTZ45bWFpv7FK7iQDPk4/j01kaz0W61bIuu2rEPvcxyppsZ4XKEpPQC6T9c7dcxKXzd5UMoFKfCb7ySnNT55pB+HIgrD1eOLeasSsdghR9zEWizmur59LBqi+Z2BwOzboesQYaBS+0kxYFnQJ5fE41oj6dzjc3eGb7xTeNhEQzrHOVpilC7Tsi8sY13PgEiW6YouH9we03grz9QoMV0ZgTTg7dF8MA2weHrG5ezCMTHFrNsKbEQZdEg+yrwh6WKCtMck2EtXhLNToEx8Pvo/moOGRfeVV8JhAo+P8KiUeyWqxwHKm0YYBDgWD+eeI4sRkS6QFtqkw9wmceWBEo4N1WV6lMc5XMQbdoqTFlwkFJP6IRFC3gXlDAb8M2MBYa4wDRgGWAi75NlSsa9RFJ+6gRRSjm3m4CgfMCbrVdBv00TGLZ+iNro5kQHKMU1knC0aEXirsFg05quhmjBuGk3H/IJ4uLhri/qjRMrhxZ4Vj1WJJxl7kYRv72BOgzJUJTEwXVYkPx3f10Fc9Zn6DONWo4KM+MIlHjyiJpX+8qqSjnljKBWjjWgyNHZ/T+9BMMnE4wAtSJGmKIt+iLmsEUYLzVYiI49L3BCgjAImmRlX02FQRtrMF5qsQl90W3uFeAjkTgBxCH3GoEdJtFhaApCsoAci6Q1Pb+FZNj8PuLep6h+X5MyhFZqNdtiUemmESmUliHC+5ixjAhHPBuM4SaGP4MonPxjFBhWTmS9uFOkTmM7C8jwMUNoXGZqvR77YI/b3Zl1SNzo/R1a1kJg0JQjMpQ19Bk9lIRYae0jSANAMyxqFcz+GFmRhoxL11XA+s87hzzZysWKMnKT8RrOY4aHNJEqPCVJJyGNruZH16Mois8cSC+E+2NbfgSLwdAmMtBt1J1l8ep5ujQZds+8pRC7LIjYYn96HbZFkS4M7lEI1AMj7DGMv1BW7WC5zFBKjpDsoMomwDciQJxjJ2p9ujlGTOfPvuVlxMjTuoaQ/G9qNL8u9/+1vc3t0iiFK8fPESPWoctg+WGWb2DrOsmhhnGEMAmMbhWJplGc7WazmXwHxbG2DOGPlMYgXeQ+KscZ6KG7cB2foxkYEFQu1eLbuzM4yMMUNNEiJh/Nk1WRi0wlrbyrq5yDKpw8OGyRRcrLUnG8IHnfcjx8Yvptd/7PNxTLjhMp5hQxu4OLCO6X4qp3IqfyqwFgiDm4nKuGZwjfnk5U/w/HKFb774jWRepzOlGL0F2HdMYSvn04vGuoMawzDjIdO4q9B6scQ4o8u/7zHzeA9NYI3ZpMkSI6AnSVfMZOfeZEAzOtzTDdRAbZRRtKaniESngKKBRGsx5AyNJiHZJHMSG2orHggR47NRpKVReaC8VGMIbcZRlaLpfBRVB6/usVz2GOYNil0la2bIrKaKydISxFksdZNECCc226mcyqn8Gyv/ywE2V8Tdwm5CwsCaLLhTEfGfXZ7Iq+opmPGRcz4mmzqgra5q7A+5uP+EYShWcGbhCwNf4qNR+KZJaCS02RuoKbhmaG3uxhNp1ykvR5dHUUxEPzgqNvyPDApuvtyMaZ3nBs4EDaSJP7u5wdnZGo+bjdC5TRgHaz0fM8WZe/HeQRjhV3/5l7i+ucF2uxWg4urmCj/7+U/x5vVb/P1/+Qds73e4uLjEPDvHu/t7CcJMlyjuvdtdgcf3WyS+hySNR9q3s8SPSgNjs2lu6iViT+HZegEdr/Hm2zfY7x8RRwHiNJPrmS2VTMGmYty50tzDsdQm6ug4RCyLxbSiEUWkWe3J0swjq832vQOtrKJ7HAKu80xgWfXkbUR1x64KUNUDnq/3ItjktVHSRL2X1/1AWbIsxpYKMx0VPQoVR+DV1MM+ifEwxqFgQVbN36YPCcyoIMb1s5c4n1GYsUHLLXOEwsqhqoWFRkZWVRxQt524Pc6iPdTuDV5/k+PL9yEKL8YiWeCCrLUkQ3EWY3Xl45OwRdLn2Nxv8LDTyC6ukWZ0C7YZQgU0Mm7LBI3EHSuKcf94j3y/RbqYmTZ3gJG4+lpWFoE2j24NBItMUHpyp2Zeh3no4TALcD8ECPYabX6PqthgtlwiSxIZ88z2mKJHlnkohhDtgXEJa8RxBq19lPkBy2HAyvNRDT42VJ7VgLBTKDrDBqNgyOeS2sR2Yf3J7KNrYRB5SAOT8dNnsH2Je9ViIJsqV9gjxiENkaQKN7qGRzeM2kM90NXRxFoLHWuNijnBNMk26IKjG0XdDY/p1Odhl3XZsBcNYE+wjCAPWVkE2pqOrDsTZyxSLRYE8+IAt0GAtvbgVeynRhJIcIwxNlndKPhti1nYQKch8kajKytR/hlnbxYOSJhUhbEGmZmU4CS9Fg+F1HmxPBOwszhs0PUhFucpzgIDKnqBJyCvYrKCnDHpGGstQrEK8TIDFqigBx9lm+B+X8KPQ8xiPcZaI2uNbVMTsKpp0DDs4aY+4P72C0TpDGGyFEu8sNGYAIFujcLoNdlehdEmoIeJd+ZAF443A+56qG18NiaXoNMrEyGsQh9t6qP0AsyHEEkQsrYSC0dnGYY+Rbt5i8XZHVIydv0YZT5I8oUoicTyn9cFWrQI6FJHwFYiRysMjcIs9nF2eYVdN6A67I5hBSy7V7rfzRX5cFybCKK2FWOtkemXmbialpV8dEF01gO3p9gF5QNy9nFVPn7mXbjnNnQ5VRBlrW0Mq9yc7Z7iDBA2iQMzmtY12movaxTbWeKTdRrxYomzs0u8PM8kKQSVOaFBEFQbyFrznmSD5sp29+4Ojw9MiOCAMrqRB4gXa/zh88/x3TdvMZ+f41d//SvJ+nn/8BZdyyyh5N85l1vLxOBa6/ZMESMGWTNfvnyFs/MzMZRxr+b1xnjBMWhahfOSgJoB1gy4xnHFc2UvdhnAj6LJ2DauV+T5jAk4MteMmxX36DzfYTHLZJ9maId9znq04/7wPaaa+gH5ZJRfJp39RKb53gVPyodXGddlA5C6bKmnciqn8qcVcUknSFXTYEeXUCVu8r/6i59hc/cNXr+5Rd2bfVncP8lUowwncZcZIoaGNSc/mXWXwgHDRjQqgI4SREEkLqGMk8ZQEJLwhvEkG2cQOOoVo2QsSaeOhgeuzQwZQEYcw3dw6os3kbjJM8SHJ4YYieEmsonV02gUU0x1QKCN+6kWEFD5JfqAd+RexYyjCtVegcT6+blCo1vsd4UYaJOArDwPQcRkQpGssaf4bKdyKqfyb6n8bwOwucJFVpRKWlE/IkriB0TK8eAPnPT0/A+uVj8igU4PSwpsxgWqhSVGwM25jdK9URIRMK6NDcI2xl2xqsr0pu64lXDH3wZYc66W1ko++ewYcmZDNpuysbq3JjlBVUlihp/+9KeyaREQdNZxF7uBCkLbd3j54hV+9atfCXNhs9mK1Z5nvHn3ToJ1E3zIshn+4q9+gW++fI3H+0f85KevoH2Nx00uAe1ZyDh5e/+IfLfFYpZIoFVu38YZ1SiNtMo55Yyx2qisZB5w9fIZDlWAd2+/RV0WkpVPsl5CIaPb6GqJ/LAXdx6+twNiHdlP9DTrXmVcUo9NKnKJoTWMjBBTHQOEiUOW084EgTv2uWGbTYaADcDNYF1Ucmmle9gz82aN5+e0GipUrQHZRAmmy5VVGFkRj26k0g9k3PQSBFaSU0hiBPcs97djQFpBSJ7bo2uA5cU1fvJsLcAP401J7CnL5Ck5/rpeMn9yLFbFXhIzzJIKcfsW+7c7/O67Drd9hDCd4zxZIItm6BYZhpsIn86B9VCjLw+4fbODyq6wuFggCi1rzbKxyDQSlhEZWa11fdC99FcQRXj39jW0pIkPx7FLwInFsbKc+2NLQZOgR+dYWUAWKXxbNsj7DPNgCX+ooTUzYTERgJJA9sxrvwobDFmMstJoC8OiYawsunh2ZYm1pxEJfOchGSDuC16nMQsZT40xS0LJmjnUrQBqWTbQiwKNYjB4Zs3tRHDtih5l7WMXxvAzH9dBj1lfoS0H1F2IjoGFI8YRo6uZAe7YTq1kwGQ7GdcyYWSJNdhmEB4jBZo+l3FHWVYsz2Yku+D4YmEWlpBIweLOybaTBBJDi1hYWRpV7GHD2HwHLcwzrWqSuIQxRAZcU3SIhhqzrEfrJ4i0Quq36GuOT42+prBMPJyJBLaI6JKZpqiKnawvBGKfnfXwyh7FwIQZBCFboClQHVoc6hjvsxTxysNPvAY+LeqVJxlCvSTCaplKnK66eC/vwyagIkI2WNOYGFcc1pvHb1E3OebrZ8I25Fom7WeHvE3ofJzzAi4bYM5kBSZbyiaN4ZgjKOdzzBGgpDszFYMOvq6x0ECaeNjNA5kviyDCsxWTa1T45n2FQx2geGyQqLfwGY8tDdCQmZCTstYjTmeyZuVVAS8h64DTtbPgH91UFa5WMyzWF+IKWNeN1ElCJNh4kDIGhJlm9gq/z1FWBXSwkBhzI/5mXu4JlHLc045bijl+3DWPjCS30kxZbgZU4bxJ6Jqtycw1+7Asm5NnsB4EPhmkk/ckWCTZXXWCxeUaLy7PsY607C9cEwQwQwAtrDWbxMC6Jh32OV6/vpMYey5GKEGu5YJgqsJuu5VMn01T4dWLFxJnbbd7MGEThBFm24T/SExLM57kiCaw9v+z9ybccRzZlfDNPbP2AkAABBdRFCX1Ys85/v9/4vMZe+zWLlIksddeuWd+574XkVWAqHa7x55xeyokEIXaMzIy4sV9993boDcY4PXrL+T5C8MWk+vJHJGMKxoY8PqUsmQt4+Za2NiSUGOAZN2/7cZVr8+dxho3qJ1GnfyhQNtquZAxPx4Osd5sMJvr9yCjTRlvD8/fg99d2492dr8fxjSPn/9v3aP6mMqMP7DWDu3Q/iPKQZlQ4JzGNYmJvy++eIVp7OKXn37CguZLoq/L601/pHqH8waNjsSYgPGBfVeNGZhkkXJQAdZ8BGTV05m7pZlSKWX/tpS9204YRredw+20JbGHGBroesnCUcJiXA8ZnwprmvOBF8Hx6FBO7TUmlbSahKCbzD3UaaMchDC4mTX25Pu4QYaWruhMhTpcHxyUmxY930Uy4TqdY5MxAcjPUO3pOA5lfRYQ0E7sh3Zoh3Zof8Pt/5rJwV+aCSL7QN26LLj06bYffuru4RNP6mJYvaEL0N6b2tfZux7f3mvc6PL7xVGIk5MTHJ+cCNjG7Djdz1arrSxMtlRENiz2rQyIsn88lmUmt4wYvjA1+B4GSLP9QfFhCeQlY6+MCAEVzIaAG5leHGM8USHyH3/8AVcfr4yzWo3hcIw//PHv5Bho2sAFmrfv7xcCSE2nI/lO0u+K7eC7777FaDjC51+8xu3tLc6eneHnd5e4v+GGR9kkAnQ1BS5OJri4uEAQCo9cF00NFdTh09WFXDZodQjPC5BVId5+vMLs/gOenz1BfzRA4BNso868j816g7fv3oveDzct1M6y/DgTNehniMGBnkhTBdux6mykoaWWNuSwDBDte7tB1TPycKuqrCIeg31cN6cMCM4nK0Shi8sZM3chPHNedA/L82XIKaTuuxEiv0LY+Kp5JZRHo7Nh+lIEzQ0IyMMI4wmeP3uChIwkUvMNrZ+DhhvcrKwRshy0abC6v0QUJogGCWKWg97NcbdwcZlFcKIQ03CEXthDG4UoTmMc9yHC825V4Pb6Drk7wvjkiNJUKtAv57CWTKYwPCq6YBktoqZGWZdyXpX8wC8VYEsm03yNs7MTxEmsZZYBreMZSAZ7ovSidy+GAkHbYLu6Qhi26E/OMHMC3OQOkmWFSZsj7pFipgYJtImvixxBWyKIHCydEJsFhe1zhEmMMIiQpVvRW+v1Ynith7xoENKh1M8FEGM555YidR5DwQppGYAoGUsgvJZAItmh6j6Z9nwcBy36bSYlgEXloXYDYW+xn+R8WQCybpSxZjbtAgjL+DdaToYRYxuDWauxKKOA7rzGaTegjpsI+XsSgFojBGGQkpFXKlMudGr4YS0Z8NINcMVy0m2LwbZESAOJuETj+UgLR0pGqWHX7/kibKwgHUtRfeQlmYEcTzl6wyHybIMqZYluhOlRg15VYJVFcJMYcejArQlAtlIuvWBAPvXxNGgQEYDMWxRNiGbPRVWAVrqJVRVurm/luo3jnoBovE7Lco3F6grjozO5YPJCQcqq0quS134QsU9cI8LOOVb7hOxPMaOgupf0m6tjTjYLuqkhuE6AtqRbcFnDbyuEAQ0keB0GmMPHbMlMe4sga7ApUiw3G9H+8totjsMCp6dbJJMBnIDJgb6UB/shgbe+CDjXVYaE7EceasXyeA/rjEBnhdG0h2Xa4N27d6jStTBaqWOj8wRNNMhaW6P2EvheJAyvbnNkZiICoHZOeoir6LzXzVr7yQM2gvlm7uKT1KjFvtLO4ZyzGkQBXYA5xvR5BF8JGNPExpqxiAxZAwHrn5xMcTyMRDCbs6QWs+v6tSt9opaPupp+vLwVZ1OHY9qsu0zoUGPvmz99g7u7GxnLf/zjP6Cf+Fgtqcsms7rO84ZGpuXUuzmec7SAYK6Lly8/E1b0erUUhjebMswUTOJaWQhzVZ1AhcFGFz26gnK+E6DbSjXIzq/jDXIc8jMVUDNaaxbqMsmv7XaNskyFtcbPmJMhvges2fVm7+Sa89SdlodBSPdce9/+Ex+/Ufupd9i90kgPUGvt0A7t0P76pkxpAkqeMOEpG8P559n5OU6OJrj86S1W2xSlyMjYuN2sWYznjQmSRKX7msISX1EeIhTzJ2pRcvkne4wGPm2ViUwMWceSuJOKl/0qD+ycwB5VV2hSQBNVkvAIGWeTiW5MZ8hgcyORHmlqasgxbsiAOhPNYZouOVwz6UlFV1JWMdQBslKraphckTit7QFlCL8u4LYZAidHf1DAHTm4nlcI8gj9ZIQwoJspTdwoD5Niu1mIrMyhHdqhHdrfavsvx2Dbb1qaybJRgllWvezRnuIT9z1+/Fdt7wkPADb7Ts5vvKn92ftuDNLXRp+NG+Fer4fxaKQ6YlkmG2r5FCPA3H2eyVw/APlM8KykK+tmqZshWTZt6eiD9zEaV+I8qptLLsxkSaSyqaC4+7mAgMv1Ei9fvMKXb96IrhUz+gLKNTVu7u+QJCzNZHmfblK4seV7bLIUR8dP8Pnrz/D9N9/jpx9/wuxmhq++/hyTkxHW6w2quoRjHP02aYr5bCYbGbLp9KvaDYWoPpkfXfB5mD4anEz7CIYn+Pj+F8wX9+gboIQbMrLipkcTybZvt6mUi3VdJjcsX8OBW2lpzgNg7XGzuzp7vrtnGfaheYl+dS1RtUHJbvtoQDbHxTpPkObA+WSLXlRhm+/07liiVPosNeSGzIPLkjgBTs1n7rMYTFmqBCiNuhMePznBq6dTeCXt0tnHGoyxkflDTbGoP0RVklWVIYz6qLMPwOYd1rMKv8yAuypBvz/BSTySrGoxSuCdh3gd15i0KcrtGldXa/jjMxGtJ8jkW9ZasytzLKR8SoFaGSdk5FE/S0TnrfA3EEWh6OktZissFzP0ejS00Kyplj7quLdlo9zGLtZbBNEIcTgQADZxGox9B1nPxy217rYM4qqOlcWyv7JuxZEzbksMhw5KLxabeLp1UWMsDGOk21TYOlHgI6CumJ/D91IBhwKCWywtLV0g8rS8k0L7OUGmEJsgBPouTqk9UudillDUARo6pYauZJIFJKHIiXH6JfiorDUb8CpMKkwYug8SZNtnw8gGnZeGSSLY8WhKRsnM0rS0gRfEZVbLOVh+Rm07stNYksgX0SiCTEACvjeRj7T24WSuIJk0oAj6EZKQzoyFjHPOH3yftK5xs1yBlbsEOtLNHGXWwO8leDIu4WwqrHM6zfpICOblBbKNg3UV4b4fYzT1cE7WWpWjyFyUCOFEASICXV3ZrHEILenuGaOtPdxc36CqM2TZGkW1wWhKcI1f15bWGvfGzhTCXK16MRqNxN2lzce03NaKtitT0JYTcj1hCU7rqbGD1Wcr0iWCOsfRsA93GGJLAwYnRD+kIyxQEjguXKwWLtxsBr9NkcQtvDhGSoe1bYYwjOCHCbKiRNHWos+2XK7FWTliVr+la6yDp+cnor+TbjdSXuO5LFulA3AOJxjCc8mm2zskRUX2FiY7b5nN2N5ytb/S2PvtW+1mGptJMPOdeZ5ycDmedOzR1Je/q7qA77ddcofMTwpzD4YTPL84wbAX0jsarFyWDSeosxMYg4Td1L9eb/H+8kbWJ5Y821l82B8JC+Of/ul/Yr1mKeUE//AP/8DUEbLteocRynvpt7UAoU45vK3AWH8wwqvXX8jzlou5OCezce1QIJtJES39JAt9Vw6q4Dc3qpzLug1rRx80Y02+wg5Uszpwch2pdSw2LAd2VfeNOqnzxVIYv8qa3rvIH4xbPLpv/6z+ajA8ePHu/P76lTZVpA+YEnSjtXZoh3Zof33jtRwye9jQFbuUOSMKe/j7r7+C2+b46YefJIlXkxVs9dVcHw71aqmxFtDtW5PBukppok60n+sQrc/1JEIYBBLzcG336EZepMgIrkkyYLc22hVif6WwSQEzcZk5y8xBUkHh7BhtoqPM13BlpFmRGsP4nOMk4c1j5fxvNS1YPsP5pYEb1fDFlTpQjVuaWbk5mojzXiRAIY2e8spDswUmAwfutMR6kYoRWj/pSZInDGJEoaB2Enfu1vxDO7RDO7S/nfZfmsG230SHSCgyCmztt4eh5ifap3ca+78+HZo+ftPfeg8JrLlY+gKunZ+doT8Yyob67u4e97MlipK6Mrssty0LlDczgvvdRsQgOZb9pj+GRm6YbXazYDc8wnAxuxDJxBvBcL4vs0N06RwMBrKRoD6baL/Awf1sIeDVsN+Tz1ZTh3pPkF1LZmqW0rXApD+S79Eb9PDu53dYZkt8/cffCUjxy9v3Am6RYtGECh7wO746P8NkTL9CAx7ua8EJk00ZHE7DUiIHXuTjw/0cH398hzao8PLiGQajkZYPc3PUtLi8vsLNzb2yykR3R/vQln5Kme5eqCGfZz7UApgPQpFuSO1ALnlPYzqgL9WtitUlMiGK2fyZbW3ToB/lOBlvsc1j3K0HCq4yUCGVvmiEsUIsJKCKRWvOH0cGj4V9R02wqkXYn+Lrz07go0WRURyWZYt0b6K7Yy06ZkHcU0A130q/hhHLHBfY3m3w/kOGAmt40RBx/wI9loP2YpRHIc57wAQ5nCLF3dUSdTzGYDoRcX75DAOGiNZaBxgR7FHBXVrNa+lUJcGRBnrW0MCDFyrjyqdbZQ3cXN2KbuHJ8ZG4c7IsgLbxHMtlsUTrDeAFibgPkiHnUDeOrCyWIQQU3g/wgYDjusUozRF7BbyoQeE4ottF8IggThS5aKIEy9RBvc0FFAiSvjAKWWpGptkwchB6SwmKCfAwa9p4PdSejyYrhcW19UKUiYfzsEXYFCK2z/trOg2KOD9BBOWlsY+kHwyzz5aTWWiNRRiyWRf2Gq9NDYrNkJKNOhlQ4gImOix6vTOQtWCulpE4CAKWVLjCnFM2m7KyRJ+F5ZUVg9wGgct+a+B4IZbwcF8Ck0w12KiEiCCGS/08Mmoc4Gq+FjUWmkLY66n1Y4yGDnpVjjWrArkh8IGYLKTMxbaJsI0ieGMP5waArAogb+iE4SmDzLUApCmbtVp0NDEw5XwE1u5nlzi+OJPxw77m+OeYY39ybFU8NlPSLf1AhlpAFhv1B3UuVDaRzCDCZhOHSjrAsn/l+Z78JlNPGG2iPuNgnZZI1zn6cYQ4YHaefUeh5xg3rYvZpkUy5wYqxSrfYLnKUM4zMW15elrg5MhDxLJshxpfZCe0iHuxnMcsXYv+ZC9qRLAahY+69iBemhHHSIC373/G4uYd2jaG51PHklzfvWnJOiIbQwO7TugNHUc2TWPnQVsSal5p3seyps3CZedBrVUXZpwK/XMnx76DgPack8TJzvN0XaipkznE2ekTPDmCuMGWAgB7wnTz6DorbEK+vQr+l3WFj9fXWGdZx9TmS8KQa88Y33zzJ9zcqKz4xgAAIABJREFU3Mha9eb17zCcDLBa38vXFNMCo/+jh6cHr+wyw1wmSOm5eHbxQpJcy+VCDBMsy0zXRwXW+Fwdg4WY+pApYQ0MCIBzfek01/bDAOkmlk+ZRJaM7R2DjcfJpFpRpOIQyjlhsVoJa83qC+l77cUXj2OKT7b9gGP/G/3Wix6+sX2Wuj0TTD+Ugx7aof3vNsbNwkunxETDecHHl1+8koTS2x++xabkyu8JO1bWJrJF6QcUhAhE40BBrJZxjUwPmsysarrD0yyJMhYBAjE2YwlniVoMDArkEm9ZVM7MgXwLKyljpQKk0sMYb+1NOzKX2QMxa4mUhhqnYyY/GHf5UFab58ayVlWtT3UO2c84Fdm4qWq4uY0w2ZxI11+ufXRp5zpO3QtKvDD54ntjoKYeZykAZOSUGJ7UKNwKy7sWPS9BbzgBah9FRUCxxHq7wZZmOmYOPbRDO7RD+1to/6UZbPuNa4Zq1ugGXu7b4591i8Un2gN2g11kTAy6yyY/YoY9ev6fvS3fT53KKGa8Wq8luE7iRAC3fr8nf6csiTEMKNFWsm9lM/Ld4rd7cxE6tSUw5iVKZtlpK+g/tmRQwTcpOzOCxSwfZeDPn/VqLewBlo5eXd9gOh6jR+dI47TG51JsnBspKTslI6cuVWC8bbDJNlLqGXghVquVsFFOJif4eP0ez189k6BgnW7R+jVCbrQBzJcrbLYbjIYD+W5yXHKk3MQpm43i7VJiJ2VVDQZhhJPzJ9jUAa7e/YiyyNEfjjqHM5pL0MmVbqM8Lu3TrjP22o7ZZm/vene3W+3gMlNS1Z2LvW/bRSJyc/ec3RhUYJQlovNtjMDP8XScIc0DAUAEUyEgwg0+WTOixaEbUdtY3kqg4+nZU7y6OEKbMZBSoEDBvRoZSzKDEGFvIJv+Upz3WK68hbN5j9urAu9nLtZBBGdwilEwELCpOjlG+DQS1tqw3aLcbPHxaovo5ALDUQ+Rb1hrsskkYKTAGvXWlI1lNrRSe0uATd31CJqoRpZxmxJh/r3OcYDBqC9gBtlKLEpikNmUObbzW4TxEGEUdwwQbpQbw8qiPhujT+p8jT0gjDxchSx1NK6ZZE6iEcMNxnIM6LyqRp/gRT9CVjBbmqJuClRlKmVu26IGPJYgq25Si1BKH5gdpmh9GcSoegoaBXWGKndEQ6wV1ppHopuARhQlUa01ZWTRTKJjrRkH09YEzWTWEFgTAX/qpBhHL4V3rU7d3mjtSoTt7GSSxQSaJKjeY2UZ0IlMQMn6mjJIGjk4KJBQ1w4NQmyFteayjLwh4BshLVpcLZZS5sf3aCnK3IZwhj08HdRwNjnWmSOsNurLUbA4S0OsnR6WowhHExcXbilmDwW11qi3Jaw1R9h9Wl7MslmWsqiAPH84n/B73999RNXmOHl6ipbAY9VK2Sv7SplFhr0munVmA7EHOOgasAOe5C/Td2xtNzcb3Ua9Q5/rtiio3ec6GIz7qm1Xe2iIfhOkdCoM3RZ9OrX2CGQGGNQBwsDDZuRgk0coUxfpiv25RC+aIUkCVG6MNNXjjvt9YS1kWSV6NEHcCls3IPOy8QTkifwAR09fY5HXcIpMSmV4+owpsWnmy1u/l27i2YFAdjPVHbe5tW+Y/IA9pXd072MvXJcbPgJRJV16A32K58pcSxrFaHyCFy/OcTxpUIhhCV9OzVQfLn8ItJnP4DXNDdLby0tkNIAwEwPXckoOlHmJf/zH/0+cVoeDEX7/h78Xt7r1ZqHfZ//7GsMeIYkZyxnew3MruqNfvJG+mc/nsl6wZ7jO8YefK7OncQTVsVgacM2ySnmdKrim6ys/zRiS7Ek3KKBmWGxS8qXGDJs1TSysQ2gq4BpLuLry1e6kPVyFdjd341r/styT/dfh0+/Rtf0U0K5JWapl8D2kex7aoR3av6PxGgq8QNZ6q1t8cnaGv/vDl7i9vMS7d++R0hxAJwmJxeu2lBiApZ7Udw0dk5gTBpmCUNQqqxHCCyMEEcE1lZ8IUKIV9nyKvCyRc40Uj5adCZoklO0cL//qHzIPW51Iy1wzcz5/dbOImRJk3jCmYaKV7Dao+FvkAQikKdmB1Sp0qecniBJbTR1dlq2aiIYSJowxWjWHCyOaZIWAW6INuY7RQCiWuDijHEPuYHLqIW9LLOcbAQTJYqOT+yhRwy7O1QeQ7dAO7dD+VtrfDINtv3ERoC4XFwhx5PstCvHjKHM/rnwYyz4IWfX3oyD0t2LST8S5DObJ0OklPZydn2JqtNAocHx1dYM0LYxmg1nkRDTUSHGxCfimGfHd7kn1mewCqaw5Zc5xAefnKZNDSz9kMWXgz/IegmakWhvtF2bejsgk8gPM5zMtJW1aFXgW7Sgy1wiqkXWjWlJi1d3R7rQc8Oz0DGfnZ/if//i/cH9/hShO8Pr3X2IwTnD58RrVJkMkoq9GlBoljqZjPDk+kU2nBgUGXqJQvwA3NVy6n9JjsPERJC6W2xrf/PQDmmyB8/NTcTTd9YGL5WKJD+8vVWenixZsZ+624922c29MkLaviOXec8wxWi+9hz/6y7JpHnyS3RGThWNYcNTyejLOEHoNbpcJCrL0HG6x+TTdhto9JKteo/ER3jw9Qsj3yHl8O4ZcziDMDxAlfaHfl8zqEVgLc/j1LeZXGa5mHuYI4McJJuEAkRcLWOIchRi7GfrFjbgF3t9nqKMRRtOpCuZafSyCIQbYIMiq5aCWtcZjIryqwaGAIN2Y4eZUrxuOQT/kj2qukZWlx8rbPlazFfL1BlHg4uz5CzmPZLN5ATer/q9ZWdTKouOnzwDVQeMFuIOPRQaEyxJRlcN1c9QewSy9cgOWGvgO/MjHug2wXlcIqlLKtihKXxQEu1v04xCJn8Fzt3T+ABofjdtDG8QyBvO8ReUGoifIShB1UVV2HzfrcvzCsNJNuUBmUvbM0gbNMpO1RhBAwSKdrwRgMmPJjmMBF8UZzOgvilOw1bDaMbI4zijarzpjhsVK8wPpO6vPBtTU5SMjrWXJa65sIn6kZJc9XC1y6UuWsWWp6oyVxRpeD3g6GGFTEOTkhdEo6FIwnxxhO0wQDqm1ViGuMmWtsZxFtNYMsMZ+IGDBUkID1JbM6DNJ0hKkW2JTLETnjcdbG3BNxhv7yrL9uInhhWHZS2azoPOc+REwT/vNuq3yR8HrnaYd2VUESNhvIBugyjGaTOGSieDymtQxxw0MyhpBUyJkWWTIC5lMQB+XhYNqWSFiX9U53mYl2tkGfrbFtLfF6VGBwSRGGzzFqu6hyYAodhFFsehHVkWKXuIS0sVmmUtfeF4srF83CXC1XWH2yxXSnMw3gt1GL20POtHNTwef6WplwTWzXsj93cTULSxmvrGakmbRMQ971O2TaqdCtRI5znwy7njuSnhhX+b8i1OW8tTIjd4lGW9kH1vWoNeoAEBBTcf7WwHYCMzx/QhgcbNFOYKffvoRN5eXwvx49eqNrA3z2Z0ayZBtJsYFjjDYHs61PJfUSyMrPMTpORnjA5E8oPQBD051DVXviMcp2ocsdTdsU5mz6AAsgBuvZQXWhKFrlgm9Ps13sSkhs0gLw8MAfnnB6yZDnxqYda3AWlGoHmoHZtnfeyfpV23//k/dfhS0PADhHoY63eNWa+0ArB3aof1vNa7Rch0xEc21HNQP9fHV6zco8y0+vv+IDdmqnTu8XpnUN+Vc1rI6oakk8R3TKlRMu7jeqWs51yCfpaCMhRin05m7KSURqdUkjZbu2wS7veKt74r5Vws2LY6mAaQmf813kq9nGOHmZY9jWbltlVwCw9Bl+oRJIofrVSwaa1UTiKO2AI2sEGgLkTtwGYtRdwEOoiSQuK9pfFRtTT6/VAtU6KEtfPglE1QZfOQYjSu0YYPVlgkQF5PeMZKQ5aVS64J8uxEJAa5Hh9LRQzu0Q/uv3P5mGGyPmy3BsoHjXzLZSsbZLiL2xqM4tkvo/+rB/Tf6jdumCWOCGmZlidVyje12K2Vx1DebTMaywaPAM4NxzSpZIeoOTTPZJfO380ifi/9Zbad2TzuhcyjcW0ulZE9L8gT4Y3meT1c6LSMaDkfiSrRYrgRoI52d72XL3Hgc8l4mka/4noJbm3QjhgcUkz6eHotY6Xa+xZ+++Wc8//wFpk+OkW9S2VRJ1oslU3mOxXwJ3/MRxtHusGUvwz9Ypuagdsji4Oe3CBwXz56dwg8n+PHyg2QJh/0EAXUajN7X06dnkmnbphstv7NBhT2n3bm1/W1o8+2vYTjtO3MedveY1xpWod1omfOvmcLuLToxWW7yyXTZFA5Ohxt4VYWi8WXPK26NBohoW24yX+HVkxb1hv2vJYiiFYUWW4713gBR3ENBMKSoBMDq+Us08x/x/sca16sAqzBBbzDESTRCkAxQnvSQnAZ4GZEBVqBIC3z7p2tgeoaTJxMklAJhoCUC/WR5qZYIWWsCmrXWmIIDgN/T6rEZIX9zm2CI3czZnpTxadwwLQjO+8IkwmA8xv0qFZdAz6frrLJAlJNkmKosp7CumQSOSJWp1DVz4FaYBi7WPR8bIiCFB68kIMCySI4fbubJxPEQOx5GA5Y4eqhK1+iz9WUMrreZnA/Pi+D5BKFyCWpZoiob04gCw+raxVztDjRiP7GM2jp3GdYaw26jW0egUsA1YWMZJpYAkYbBZt1wTcCsv3Uu28XPxknUuGXasWvZbASjOsdRea669zJA911+Vi7fledYsBSPwGSLq3WOwWgi/btZzUTIOO4HGA0ieFWA25sPEljTaRWFi6KIUIR9bI9iPBsB504OryiR5R4KJ4IXBYjpNst4XkpvWTrMPmJ5CMvxrE5MhfvbD4zPMeBJYRlirow16yKqLD+CbPqjJXt7WwhTqt2BF/t9+GCzYfuto67Jr9V8Lt8l6Q93JZUGa5J+84mzqvts1Y25ErFbYkrAuOdhyex6FeC4dRElLraBj+U2xGruocmpiniNQZDB7feQlh7arJRxFPUGyDZbzJcLDCdDxIGCnnRoYz8MQh9n5+eAm2C9WQvgreLX3RJgj8ywGO08Z+eoHfi2PyFxXNn5yz626z+Wh3IOYP/UCH1fHXvJxs1YZgkMpk/w+tURTsYhKrdByU0S37OlKLaCa3a+lKTHaoH3lx9lDRRwWMC1GuPpRDQRRWttuUQ/GeCrr/8eVZVhtZx1B9iBXN3SaFy0pcxVwbXReIIXn72SNWo5n6uum5QDByLYLcdntNaoESosWyN7wGtC9NbMtWjFwe08JdO7gGu6Duj6ZcBwMRshSFtjtV6KK/Kg1xcdVrK16eAszt2GwbJbw3d9bzr+0X079pl99CHr7XHbrVG/etRoxFpzpANr7dAO7a9vajDmS8wjc4bn4rOXL/DF6xd4//5n0ZXMOY90caOdkxnPGrkMJsTIqCWvvCC4TxdqJpojYbaFsS+yB9Rk8xlHFJnMv2StFYwfuph/72rf012zM4aukWbasfPXXlJeHu42Opqwt8lkG7PqpGKeKzlB89mSXmW5qq5bdD2V8nthCbMShXlKGq4xDtE+Y6BLx1F+pMyjZDg3lCLJgTCXtbZth4x2hVFfpw5GsYPBCJitV0iZqPcS0TCNgwj9MFLZkOrAaDu0Qzu0/7rtbxZgYxNmNbPYokvm/plA9GGz+4q9vcZurXmIknSL1q/f5Nd3PXiqKWXi98vyQkpguNmI4xij0RCjkeqhEXCSl8lGgovx/veyX3THZOs23ntIhuarLOhogmv7uHkPyUAJS0YLa/gwM/lc6MmuOD4+loz7YrmQ72UDdAt22D6SJVg0ovT9+J1Xm5U82B8OsVzcIw4TnB2d4+eff8b06TGiOESZ5Xtd2mK1WmO9WqHfY6keARazoTJPks8U581agDApKer5ePLkDEUb4uMvPyNbrzAY9KX0hWw7MnGo8UUWQ5qSzWaZD/Y4bL/unasO4bN37LY19gW777TfNDAxcUx3nwVAuvsVkSRVTkrJWNB4OtzKhjSj1kYLJIMp3nz1Cv2kRkGGEwOvSg0qKsdHQXv2wVhAzmK7QctNfVQjKG6xuFzgp19CzOsIzWCA0WCIcTSAQ+e6sxhPR8BTJ4VbbHDzYYnMHeL8zSv0Yh91RoF1srcIOpVaDpqr7lVty0FdA64ZNpYARdW+S6YBY40IPRuDzK63DePKXg+2ywnaDUY9of7TibYqSoRRpOYVsjnVc2KDQn5HEfOXkjBFmCijTzH/JHSwin1kbQg3d+HX1GMiOmbYpAlL+UoEZQo/dlC5EfIthc8bcX7kcVGHq0UfAXXyXJ4lljwQ36BtvZZXsQ+4QWfpogCQskHXoFNASAHXtAS0sX0j/cO9+K40VAEjM2S6y9hoA5oAef/x3TMU5daetUCEEfS31zuHn+gUEpLdSClH6wbKCIWL62WKvPUwHI2RZ1sUmy0Kf4jRNISTb1S30XcQD6dosi02sxUad4JiOIR7EuBV1CBpMlRZK66rTRgiojkEmV4CqBJcLIU9xz4qC+0DtrzcYHZ/ieHRSPT4ZCwVCq7tA2uaKGCgvpdE6JAhk2gwAPp+JfIOpDRC7gJ6qrkIH6dz6Xa5RjIciHC0sJqEnGvnB1pmqmaYb8ZcE2ipsoC7NY+xQt+tMQl8ZAMPqRcgrn30fA9FTJ0/H/crD4ulC6dYI/a3GPZXqP0B8nWGbHWPaHSC3mCCDRMajq/6e8zP81wWDsqsxmQY4+nZKTZFgyzbdDqVv56NzN/dsmduyFrx6Dlm8HR/iTakvpYYregmGtYXgdBskyMIhjg+v8Dnz46EjVw6tWj4CWuN5cD8LexK1QkkS/rq5grz+cLM4QJLywZyOB7jh+9/wLu3b+W7vbj4HC9evMBseYOqKoxpgNFYbYWvab6simnzUfIiyOp8evEc0+kxlsulGEVIHEAmt2Fxsx+YnLHO2pzThJlr/taybZ3jRH9NLyYzviwuZjafdr0z7qD8m/puabrGaDCQv+9nc6QZk0n1w/Pz8BQ8ChLsBz14Qvda7Y29dWvvGWbEdwDc/nOsfAQdQrUk99AO7dD+atYaq2UaR5ysmbwYHw3x5vXn4uL5/bffYL0tRG/MXpcqWcB/ufYSNJMcoQGxVF6DcyfZ+i6DDDLjE4JsZK6RHFygyjMxfWHliXpH2RSwLvL7CfZfzwtmXjFzmEhvWJDNzGV2/tfpZwfA8Q5dZvZ/qwYmtXTFaI1ztKBuUhwqVQGuz9iGwFoBODEcd6jlrxLPmaS0p3ESYzNKmgiznEuuU8AJMzR0LUUilSt57gjQNu75CPuN7BfyLFft1TiU5LoXjeS4akqmPOyIQzu0Qzu0/+vtb7JE9FPNAj7UEVIW1799WCbB3d1+HP6aRz7xyt94qP3t+7lxYRYsiWM8eXKCo+mRlMqwrPHy8gbrzVZYA3aR230x/UfZB4blI7/t+mlAJAG7dBNAAW91XjUlo2KEsDNB6I5x73P4nKGUa/kCjN3c3u4Og/t6S/YyQKB+N7NAW/MFtBj1h5ieHONf/uf/wmJ+Lxu48dkEX/z+DVbXM6F4+wTEjMMfy1Epcv384kKYdTubcbOQE9wR6o1mwKgR5lPTKHfwpx9/QXpzhaPzMZ49u0AQ0Fa8lnGwzTL88u6DiF2TvacHbgqsjKadfI4cmAEmbefsb1psnGKZFKZX9veuwkTrGIfd3meHj7IsgJ/hUShWu3zUX0upZnz8B5xOPJQOdTrMeSXAQOFcYceMZeOYp1thk4Vhg6idY32f4cOtg/uC5zvEsNdDEsUCbjaTCMmRi3PaqVcplndL3G+Ao2cX4izJDCkZKyI+m60xu7tDvz8SjSlmVeXaIfOnA9bIblP9MCnhE+CIm1XV7RNAyQReMgY9Owb3yh1lY8rSbmZyjYguy8aY5XR9pJsSmwUB0xjDMbX2tASS41JE6V2WjbrSRxRZb0qWEjeInApeSOOHABvHx4fShbuo0cszhG4OP6EjZizaiNsNXTMpYA+4kym2C8AtMgSRhyCKRM+OIMygFyD26MaZwSG1iMCHE6H1epplTXNhr8ECkAKs7Rif2j+m9IPn0mqIWRfgvWu7uw73Sp7Zb4w/tTROtdW0ZFTnEVtyqxqGpszaaJbEkSd6LQQQxJU0CNA4CebLLVbLHKPpRMC/bLsUN9RomOCMQNGmxoY6YXUq4y8gsNuEKIJEjEZ6vRpPY5brAlkRoPYY4LqiESPF7lZrjQxNKQdV5h6PlQ6hi8UNol6CXr9nQFoLQOoYsvp9qn9lnCsFaLOsyJ1TqArKs3+0lEbMY6wulmHKqsOqOoYSnCIYEsc9RIO+EeOXiUuD/JYGCCwzVRMEMZAQt0kdcywbLUypssdSZbeGH6qBxNbxcVm7yDctonmBrNriXV2gvctQVEtMyhQXTygJsEXQG6Idf4Empb0JEA96ei7SNUjGjTiOUo4fasERTGrQH7hIWx/vP37EbHYtFTuWb9Cx82S+0Ulnt+o5j5aiPcaaWTfY+HwFsJWlwXJJMsFq+Oj3x3jz6gi9oC+MtcatBODSuiHVkFTtS10cWKJ5e0tjAm66FBziSSFLmkzuH779VkDpyfgEz5+9EHOLtNjqdzQuzXpt8PwS7NM5mPOGOJeixckJJQLOpCyT7tUy34twP1mousmVUk8Btk0Zt4DdhlFq3Y+t6YgxNeDfXYeYjrMgri3l5+6Xn7fdbBCFAfq9BLP5QvTW+Fn6zc3kv9/7+3f9uSDB3L8D1XbndPe+j8/z7t06YNkk0g7t0A7tr280LeO0mrNknrXzAP7wu68QRw6++eZbpFklyRedK+yrNIajdAfXkZAPypymiTjSoZsmQO1EItVCQ4TAYYk5kyihaBRTs6yUWIIVBBovWAMDBdf2vmQ3LShjroPaTeWDKgDYBIgpDzVmcfKz/142wN8tJ/oRDHDlTvN+/Jtzs8h/uJJkqUs9zDges6YEdcNqAcYAqVRGeG4BL6DEB1n0lMLw4bVkrrkoa+rGkiZObhwTbz24JSUFMnhtjh6LSacVMup53hcS54+PT+A6EfiyrCqwWt8h3Wz/on3foR3aoR3a/4n2N81ge9zs5lUDzL+sbPRBnGs2vI/Xr71V7Nev2f+bvz8RX7Nptol6aJVsDFjKyAV20B8Ioy0MuHHPZDNglz/RLpMA37AR9E77bmaN3DGHuvVytx7qYm9Em7nx0OerG6eli6vraCVOP9zQnp6dYjKZYLNcoygLs5m3m1hb9qL6ULIRkqyYbkjIRCAzjYy4JBlhs1ohXW1w+eEKwycjHF+cYjlfKVPFRCZpmeL2/l6+NvtDD8GCDmYDx/NJqrlby08SODg/OUbUm+LHmxvMr6/FaYnureyPKIwwnU6RxBHmy5ly2MyGaZ8T0J06w3IxxZ5622bxHpxgc/iWMmKd+TpNJIuXqCufVxcCiFSS1dPnVm2JoP8Sn7/8EsPEEb2vWoTN+XmuBCaOEyAeTGUDTlCyFXA2h59/xPXlFu9ufSzdWECLk8EASTKAO+qjOYtwNnRw5mzhZCvcXC+QB8eYPj1BQnNHMXlVE4OmZLBHcCHB3e0c29USUa+ngaC4hNpSR8My4u+OlWVLHrWkWEgnex1gx6302W542lhTfrTMT7PCLHeN+wnSbY77mxvRaJJzJppdWqbMYcizQ/0xAiA1GW2NK6CPQ3Uwp8bUd9AkPmbUMil8OGWL0CtQl8wKN8gaghcBRgHLoz3kXiSsvYpAG8s0ohibbYaciWU/hO9TBN+YaIiysKOlyQyEq1z6STfryoyRTTz7pDSsNck+q/GB1UpRvtRes/1l9FK6eciwi/CInaWdZ380J05DlSSillmhDwvbxhOg5vpuKYAJS+qotZZvtij9EY5Oezj2Cca1MgbZF9RBy1i54vSw6SUIj328GjoYIsPyfoVN6sEdDBDG1uxBU9tSNksBZpbN5oa1xs1JvsZicYXJyTGCMNDxY00MqLsmIK2yjWypnij+dRl7u3GwgIedp43zbnetCkm022jYAcdS1fVyIeWgZEvq8Nxd1dLPRhtMhaMNSPHIQIJjDhxz5E2aMcdSZbqgTTwHSeThlkBtHeC4UrfVLPbhVQXSxT3SPMFgWGLglUh6Hq0nUGwymTvj/kC05rK8hB+FavaCBl7roOQQqxtMJyNE4xNJxNCIopP5sQci5AKzRsn/u5VrN289nMcUgGQZsCZ2OHayNIfrx7i4eIYvX57Ad2KUHOMggKRGBuLSKudC52bOAVcfLzGbLWSOk3mT85/vy3z+/bff471hrX355R9wcfEU17fvpWxT5mPLMDTGFzw4cd4Vaz05iXIuLl5+jqOjE2GtbTZrYcuJpl4QGHBN1zJhrZH5IdpxlRoZmNJs8WeVUmJlkoi2qEkM6GfvwG79rftRrntkfKbbLcYjZa3d3d8La43vba/hXf/u1piHbf8xPV/7LDUbZejv3XvY278V0cg1bEwdDuDaoR3aX9+4bnKtEJCL1QStL6ZTf//Hr3B3+RHff/8TsopzlFmB9tZvSn0wIRhEDoIuZuccRg1kxn4JHD9BHEViCMZ1xXN53bpwqi1KmnbVyt6WV5rkktVp/lWTeWoXn3d3madrOKGJ9/25zewsdK3oGLryim5V3c1o+jp3z8FZJAG4XhodXib+wohzDxlqJinC5L5L8yoPNU2+KtqPmwRja8pGXbGYkmQZJT3ogO55hZik0UmVjxatJ2ZCUdVgRCMElLi/XsKnZjHNE6hLPEgwDBKjBfyXESwO7dAO7dD+M9t/Gwbb42aNBoR98xdOtgpkmd+8w77MMk1+M2j+9EM2UP7VbXH6dKVMajIe4ezsDD1ussoSN3d3slHhYqNSCHaxM+8iK6ep6dl/X7twGlez3W0aIOxYRPJe/GzRYlOHOG7MrLsaNxuhH6A/6KPX74vr47tf3qEpjabMnoaDXYDNngquoXKpIKousGGY4PZyjpvbS+nceBTjxVcvEfsRbt5tgNwDAAAgAElEQVRfyWHwZWJVTufVJBF2Q39I30NL0+Mn6hNb2pW7FXw6GtLsoglEYP3t5Rzv3n2Hod/i+csXUgLHTTt1tghEfHj/EVfXtwJGCHvFlCDuEB8D6j0+kY8yg7Z0cfeY0ekxmmt6Phh60a2RzKpE7cq5SfUqwBni/MU5vhhT4LZF7QZSMBD6A2wKukS1SKKhsNYKlpBREylsEFb32MxSXN66uK9COL0E4zDEwI+BJEE9jTAcOHhKR8cmx/31LTZZiMHZOXoRx4BhrQkYYkS+qSNG4MyUFlM7aD67RBwF6I8n4rgpAAjF6cX1UIEkcXoUZpaCS7pJNZ5+lnUlTCyT4ZSxp5lLGSf824G6eBqwrBP051ltXczubmn2jqPjE2Gx8blihECnASPmz34ra0fEf92KEFKFIKATKEvZAlw1HtJ1g+G2QMuSC5pnJDGCIMQgrBC1qT7XT7BMXSmXDNwGUZIIuFgQdPMcjJIWgbcSIXc0CWpq6PkOKsfDcrOWst0dk48/inoJWGRAf+mmzo/Fsv3MaLPXqr12yDA0YGxXvsGbxsHLstl4HfthH5N+As9hKYl+rsC0rof5OsMyq9EfjOR40u0aZe2jPxzgZFihzlzkeQOPjr+9ARrfwWaxwbpwUQ8STHoNjiiyXBB891H7ocxJZMjFAdmIgTqh0RSFzsNkXRJYJNDRFlgsb8QNrc+5zYCyqmHDclAtabdM1h24pk2K9/Yvz25CtmCIukhKf3QAvG5WpJTPYblzqkB1wjJyM+6ESWz7eTfm5NoVgwwds6KXEyijjUARx+j+mCsIgpcVAqdGGFSiCdO6Ecgxu98C/qzE9uoX5EgxL/vIsgLjdo1Jr8DJkxY9zm/BsQBvBOvo1kmgKE/XoMJZzOulKIHaQVu6KMm0I8utF+FyPsfH92/pYiHHLr2iVUl2MTAbrh1wY9cP6U85PgJrLOnkSwgwl2grH+FoiNfPphhQv5GlsWI8I9YFCobR2MCWwTuulILeX99o6abZ5FGImyY6NDP54YfvxCl1OJzii9dfIs3WWK1nhlVhUkn23BrWm2oKmtY6OD07x7PnF8KsW63mAt7K2De6SDoNc45SXTVJGIlRC4E1Miv1upTrTjqgMf9b11DVQtTJewdw2+uR1zWB6SD00YsTMTGgYRE/yy4D+7382637kL3nW4ba7tHHj/3ZZhJowlA/sNYO7dD+6qYaxQEqxntMyDUtBuMRfv/V57i5usHt1bUkQchO08l2V/kg0ahUjTgSm9rrWOB7SSD5aJkICBjL+PCFfU1xf5qhFCLNwGQAF0Q6jOaUAxGAziTjJEbbS1ra+cL+vZdU2T3DPm6S6bbaxYBlXV7ezndS+m+/txF6te/V6T/rHbouGxMXcRV14IQ8dh9+S6AthOuwL1mV4lNKVLRvGVO6TQHXq+BRfzRkIoYsPr67i5ou3mL6wDCQK1OIporgiEtpDr8tkPRKeIMa63UtSir93hiDwUi0mhl/bMoMq/W9lJT+pXu/Qzu0Qzu0/+j23xZgs42aLNyE/LuyGt1i9SjAfVAm+DActq/7ZPvEU9kUiPBEo+z0yROcnJwI6EaK+MfLK6w32Y45Zj/XbtDNF3sQrouGzX4my2wijZ6QsMGkhMpVC2zStEUAmVtV3aDYcj++MZ8zHA0RRRF++PEn0ZmRsjUVR+s2cPKbP7JpNd+o+2KNZAN9Z4D3b99htVoIiyCaJPj9//g7LGZ3yK9XkhGrhIpOB8QKo/EYz1++lAyVFe3egVsEqri5LMXV0WsieK2PVRnhu5/f4f7uHY57fbz8/KXQyXneSUkvihxv3/6CxWwlAIUwJ7i/E4RPz/k+u0gOgcfbuYPuQhsNNHbHanoFvkM/qBw1wRiWFZIZQi21psHk7BnenI8RtClar0XLkiOqL5ENlXooMxe90Uj0N2TTFDgY+HMUq1tcX/mYZSE2XoTRsIexGwnTpB3GwJGHl0GDuM1Rbre4ut4gPDpDfxgjFMHcx86XtYrzW4dQYZHV5qhqMeVYXl9hOBnBoVtUSfBTyxzV/IIAipZFatmjMu/4ah1nuvlWkM0AQtbeXRwCLTNEATYpgZSySC1lVtdZlh1Qz+kek0Efk/FYXDwpAiyaKDJuKaBLXTagrMiebMREIiQAG7RwfB+5E+Bj7aJc1wjTDQYDH34vgZulwiDy4CGJWviJgyV6WC9roMyEgRRGiTAymVUe9CiuW8En26mlZiD1EgmgutgULe7u71CmqeIFNkjttBA5/1iG0f6MYsY1+8GwgZQgapk8NiA285EVCZZY1BPwsUfnVY5az4ATLZBnNW7ma/hRD3Gvj2y9QJURxRlichSi37DEtYYT9sQMopbj4wVRYb4JpKx2GNZw6hJFHiBviOwE/F9NDNoGZbpEvrmFH45RI0Ah4Jqyh5ebj8iyLY7OzhSMZWkxgTUCbLZk1mifEfyQ6jzTLXLTXlemi7QPte86ZpEUKOq1p1pdWv5CgI2bFhq2xL2JgoAmyc+pyWpoCXvrkVMrQSSZ14xgPwEcC+z6XdmogrtlCxS1I6XKHsFdp0IQ1eLkvG2An+7p0DpCsqSw/gbv0zWWeYVgUyLBBifDFMfHmehWFu5zbNNIjEaY2OB32W5pBOMgbCs4eYWmcDFbUD+vwJMnQ3ijEd69+4D5zaXRAOScvL+xs7OZ+YuEg6ZRlmbg622fpdlb2dj5QYLzZy9xfpToRse1641vxqZusqihw34m4+7tu3fI00xK/nUNgRjXMEnyzf/6FsvVXEwyXr58g14S4W5GlrHytWSmV7RPN3t2TiVQxr1d0yLyI3z99VeI4hiL+VwMUYghk3FH1oJqxSnQb7XWupJQWctatJzjdFRJP0l/mAu0K0e2cgFmDdAxpZmjNE1RVjkmo5FoqM4XS+QFWaImmWR7fD8kaD+16D948BNtd+Y+9czHEYd+X73eGeP8dvBxaId2aH+u2TiZEiXiBk6dMAR4+eICk3EPP//wM+bLtUp4yPOZmND1SCstrCSGWBoYDTZ9XNZ9RCLVQCdyYUMz7mdUWOWS1JREp2Vxm7kj4DznknHfomzMTP54zrHNJr337regv4YRpgrExl37+wl7FHJT50eN5yyKxvXQHqsemyTCJMG9Y9yLaZfkPjWWcwm0UaOTMZqkPmM0tafJOGpgsuy2zeG7BmgTaQa7t6DuqaPac5KYZsyVAEUi5lNoUoRtgVG/htMHZqsceebg9OQYvaQviUaeq+1yhuVqKf37F+/9Du3QDu3Q/oPaf6sS0U81BupcEHTj/5cHoXxu+xhYe5Ql4l+66Dx638cfs7fYPX6YQT43BJv1RsSaufjFSSIlmkkUiqMjH3/4PvYTHy0aZnHWddFsIkzWft+t0OxLTdtltSzjSBjnUjJViUYc2QCnp08wnUxkc1EU2d5m1eoeGaa6+Z76MSbIqFiqk+HJ03OMBlMU2wLpaovLd7+gPx3j+PwIRVMhZ3mb6Om4skG+v7sVAIjlb7LBlViC/S0+iarfIJ9BhaAWkePg6ckUQe9I2DtXHz5Ilo1adwQSSVU/OjpCHFP7jsENoRl+Q6OxYzcxXfBhMoNdQGL6WwKKvS2QBC0tYpdGDjQyiBgiyfuSExhEfbx59RLPj0JaBQoopMlJH2XloSoCRNFQNqdllmGzuBOB+r4zw+p6gffXIWZljCZOMB30MQgSIOmjfBJjeuTimVcgKLeY36wxy30Mn5yh3/elhI9OpCI8X6uVOo0M6Ooorp/8z9kJ9NNCnqwMHlUQDjC/W6BIVRuQoZeUhnbC8zsxeg0ytStUo8OMUcM0UjDNDt7dVlHGhwBWdrNoNsFmI8/XjId95GWFOcvPJPPqaXmXMUKQUlxTNsrxWHsUpGcgx4xnjcApMfYguimSXa6BoadMK+pqOQKiAU2Woe9n6CcB2iACyUMEOjnuoqiHrKiwLfi9fNngSxDJg2YpqecI45KCxiyxY3mahto8VH2OXgl6/CYm3YHhe/ftDbtd6y5zAgoN3KiPJ8dTw0DiaxUA4Xm4XaRYpiX6NMVwgHS1QFV66E+GOB46CJ0aOY+tDcQhlczGMuUcFCDzYkShB6eoJJDNygilG8FPfGWsidC+ArUaasfYLC5R5Ssdy22J+epSANDR+Mi4NppyUFteTHCW/WGZQxZc60QNOYbsRGI3FPa67DquA3z0UdXB4aalSrkRou7eyJTsPOxDe052mJ3ZEEn/GRMJc62LU6sBBLsxZzYhTDSQ3ci5imOuMjo0y5tfpK/OxyMMez62fR8FQgzdUEp4m8DBtnawWTvIFjXKNEPop+gPVKMx26ozWtzrkfKJvKoFKM6KAlm7wihKgDpElTY4ng4xPJ6gZFlvnhp4Untkf62RGdMhmzhSfT/2S9MgXW9kMzKYnuLNq+cYjwegZ2lFgxBunwiuiZnBHtDrAnd3M7z/8EGYacoAVH2y4WgiWmvf/uufkKZbPHnyFK9ff4WySrFY3XesCb3uVZ9NrvXd0iWgNQtCL04v8ObLN2K2MrufiRkQv0AYBIZ5reXjAqiRkSuMNWPQImXaCuhq6aTOdbuFfDe2zJ51d/EJEMvNXSNaa2HgYTjoicg2wTXOofLMT210H7QHq/yj+/Z//7n3+PUrpHVaa+oQ/m+9x6Ed2qF9ujFm4Jzi0reTi5MHHA0H+Pqr16jLDP/6r3/CNi0FsLGToM5V/FcrRIRhLw+ZeFf+4/rBBGAs+q5SMcLrlfFKkxsTg0L1Spm43Fuf+NZ0DKW8A/VyaQrQScR0887DZLrGDHp7f5ujc5t5jV0+u3VzL9awiU97p43fzG09MqMlK8fBRNNudupy31ZmQVymdd10WyrX8jhUk1fKYanD3LLCiEYIjTqVNoYhTf1bI1/QNp4xuKH5UoGGSS5qvDkBsqIFsgbDPk2ZXNzfb5CtM8R06yagGcTo9fqyLlqJgEM7tEM7tP9T7b89g22/WQFxNsuK0K3+rslGde9O2aCYv3eLjy42e1u/X3/Y7qm79/mNh/V+XXzIKqAm2/nZmYhDU+iU4MLd/VxK4XQzbcpqOp2i/U+wYNBuQ6qLq/ug7MUPCBQEUkLZmSEIK8j2jxWB1o0ls3tJrydOncwKvf/lA8oyF5aHkCfMN7EENlG4MZpv4uYnoq3McvmYjk6wXq7x7t1blMxkxR5e/v4lBoMJrn74RbV3WJojG4kavhfg5avPpOxIaeyqb6YbNRYnUgw2hecEcOtYGBet7+HD/Ro/fv8t3KrAi88ucHR83J0tjoWPH69x+fGjsMuEOdVtwmx/mv4zbL39cyWfbhgjvtcgcHMUVYjaljmytMv3cH52jpdnAVCoDhdLCxtxi1UgyAv6CKIeijxDVVII1kXPXSO9n+Gnn64AZ4wsmSLuJUiCBEGUoBzGSMYeLujoWG+llPTjdYFkfIzhONagTPqGwBpBs0ZLEOjoaDXTDKgmNk6t6obpxrSVslE99y2KqsZmeY+Qm9uYZbe2E4zumh2K7BUCrjLU2F9askQgQkryzP223FHdVk0g17nSGl0oA1ywTFYBOu3T+e1Cylunx8dGe4NGCBrgUvdESviMKD3BHOqD0PUx9Gh80SArPLRhhLxx4G4oeM4+C7GpXDSbVJiFiUcAy0Md9LAqfeSrHFTMCpNEQIq8SOG1LYb9CDFT1mTOUWtMAGaOSxc31zPM7+93AKPVXnP2Si329txyN4FtvWg77a/uerUgiedjfHIkwA09Fgh+UESZwWhR17i8nyOI+8I43W5XqPMKXm+EychH3KoelScMJA/wI0Rhi3LT4DL3EUx8nDBTXANZXklZixd5KsLM4LszMSADkkL4BDRU15FA/Ozmn2WcTZ5+LmPbGj3QCEN/VG9NjluCaS150X6wjpEaAMscxHLwjmm0A2YsIKP9Y8cSA/sCRZYiSoYytykbaaffaPtWndR0orKsNmFaSuadTARTqmsF/I0JgjiLSlmlJ6CrGCEIm03B501e4vZ2julojNhjSbEKOsMNsXB8XGdAvajhb+k+ucL9OsVyTvHsAtMkxflpitGRDz9+jkU5ADKI+QaTLWVOFlUm59knwCM4PlloQg5A3PewKGv8/PYHlNuN6qDZdap10UtYrrNjULJ0tipaeGGMi2cXOD0JkWceWkHkKVodwG/UCMIS2dhX1OP8+d07bEsmghTU5NmIwgTDZIzvfvoOi7t7Ycm9/uL3iAIPt3dXMs+YUb1jRcgJtLOxgu3cAJGB8Pr1F+K2PZvPujIfMr2FjS6GNTvWmgBrTAyIlp+Ca8pMU7BR6ZE6c9trSkaVZWXIWsUBudPopNYa52I6hHLenC8XwtAU7dJuff2NNf+Tbe9i7/7erdf7kcH+Mz912+oXcS749yQMD+3QDm3XeO0wdpW1QrRoHfhxgq+/fCXr3HdMEjARqWIn+hoT92tCUWUtmKDazWla/aFgnA8vDBDSyZePiURHhZaMtaKQRKe6F9v31ADBxlP6edYBm7E5YzagYrBh5h/lrndTaLfGdcdo/zbz2i6m0CTCg+fqdK6xuiQ6zNpsWHsNNYKbUgyQ6BKlBlXGmEZeJweg38OCjVKloXFg4HjwEQkwR+fsCj6axkMp2q05KdGEOOEFNA9y4UQNu1DWIeraCXGNrD+vFlmVuiKbLYBblXDqDHFYYnjkIkOL+49bREGI0+MncOlMSufriuzjBbbGcfrQDu3QDu0/u/23Z7DtN2VMUKPH6pF9usm6I/v/vQXs8XMsA8fcfthM4Pxb8e+jzXV3N8tjmkY2FWvqOlWVbDRYpjkc9MWOmpl8q4awW1DNu9id59772W+oWe9H37fd/XSLvAk+tHyPrC9ltHFDQzYddXDoBHh+fiZgH0s+dcE2m+GO4WQ2McZgwWrdEMhZpWvRvmIJKBoX2+UGs8t7rNdLPHnzTJwwN5uNlmYSiGoazG7vsFmu0B+pWLntY/mPm2CH+lieLKaijFHT4jvCyfkxVm6CD29/xmx2gzgKRUCfbTDoCzMvpcPkNuvYRBos7U6Ojgeb4bOU+Qah7+BkQLekAmkdSUZOgimOsaCH3339Bk97Fcq00EDKODiRNVK1EaL+VLQqsu1K+i1JcsT1B9xdLvDzrYdVeITW9xGkKQb+CNFkiuokxvHUxQuvhF+tMb9dY7b1MHl6jj4tzRnIsf+bUsA1KQcVfSxm8OoOXGM/sdSWwaRsUqnJVjQCrnVGBka7yKcJAxystwuEMh60NMsOLTvm5LqSLjTIhYyjvaxolyFtH42/vcDS3pYO0ycoqNIiSmKEcYz7+zvkWYo46hldMz1mDfjUEZHjlyW4ZcvzQ8DNReX4wkjxQhd3oYei9DBEjX7MbKsrAFRuDB2CukA/qhH0EmRtgHKbg84FUZxI9nW13cpr6GhL8IgupmRxcVoZDRIkgwEW2xJVkRuQx5Zm2ChXr197+Vqmn232NnuM144X9/D06RPRxysMe5PlqoQb7tdr3C23GE1P5D036wXK0kOP+o7DBl5dSYDP/3ieeb0wm97kwA2ZVSMXZyz5ELDJaJX5HmICSlJyqeBaLe6g1GNTcE1dU0vc3n+A3xthPJ4C2b2AayX7m/p+RruPZaJyTi17rdOAMSXFtoRYxowZH517mcVi7Pxlrn2ea7KNCmrLtYj7Yx2bHXBh+nlvqOrbmbnOOHPIWDYOpt2mwaTk5baZH2XzZJxNbeLAdRpxZOXfx8dHMq/ReEM2QrUDty2RuDUmgYem72MTB4iqGDEZrj0XhesgK1xslh42mxKxs8UgWsBPBshKH3VaiKlGFPVRULDfaRDEARy6aAjTmIAQRMPm4uIUbZBgtV6ZY3HR7we6WhiXzu1mJedkNH6C11+8xPTIAVXfck6ZWamOqkxUmNJNZSo7AnZ9//OPyKpcBKk1adPieHyMvK7wz//0T8g2WwwHY/z+67/HZrPAYnW7Y1IbrU2dIxRM1blU+5ZzzdHRMX739e9knprNZiKVwO8uySCyTMS4CDvzAnGs1Tmulr/JWmM5kJGDsOe9Gzd7m0pZ2/VHp32WprdYLufwXRfj4QjL9Qrz5QpFqTzp7vrdG0m/fduOOHv718/SkWzLeHev+K1GUJrjW3Xn/twzD+3QDu23GuPaKArEvVyY/LWD84tTfPnVK/z0w/d49/NbZCz/tyWQ5hqW9YpJGCZZfJJ2bQyq8yHnfMoluEGEkCYG4oLewPVq0XRr8hwlDZXEzVhZayZa1jDIAHXa9LaA/pS4oYtyw4oRrjmWHGBTTCaGMK/UuGIveDWmBt2fqoDwYB6S3ZAxE9K11cx3TD80lSShfI+MdyZgzBy7F7N001H39Y20iinBV6OnSqRI+HpNqDGhxVL/WBPOYoRgF1zGHexvuqEzic04wZf1zqFztBgh0PQsph838srDdtUgqiucnAcSg1zf3KNxG8TRQKR3omiAKO6hlkoNZSIf2qEd2qH9Z7X/pxhs+43rAJkvZLRxwdu/v/0t0wO2Lmh/GEZ/MjS2b7b/0OO/PxGW84ZkfQIfSRLjyckTTI9YEhZgm6a4vrnBep0Z1gsZFruFeg/O0GVbFtIdg6NbPEUzwhgguH7HYFPmkGWzKXND8mz8XzYv8uUQhTRCGEr/fXj/HrPZvbjsiY4DF1PRvLMaXexHw0jbO1CyZEbTI5xMT/Gnf/lXzOa38t2mF8e4ePMCy6t7LO9WUhbI7KBunR2MJmN88eUr+Z5CH5fNm7UR1LJgLuTCPCOY4AHrCvj+p7dY3XzE6DjBqxevjZOqui2y9PW7b79Dyt2quKPugge7Ybd5TIZRz85HUuv27nItgItm/YA2CPHi4gXOpwHq9aoTf2pdlp+xjC5CkAzF/KEgU6KidpOLXnuJ9f0cH64CzKsIVRJjFCcYG9ep5dCF36vwu+MQcVui2Ga4mlWIp0/QT3zRWtux1nTDyXIp3YhKwQJqU3rZkm5PsM0wQMTEgDpZYl6gLLfuvAlYp3lWbpC5wS7zLfpxD3BVY27/QlFAVuuFLWONwI2OOyPg3w18HY960/S3KTnma+T1wmizzCJat3NM+sjTLX758TucnD3D6elTAYWoz0a9LLLZrFYWtTxKundVtTDeIrLpdJRgQ0H6ssGoaBHVDdbUeKp5XameoNc0os8WJCG2Th/zTQsnyxEELEHsY71eCxvp+GiKOIjg8zPZUy6QORQrBtbLFL+8/yhBpTDzzCELG0bGp2W2GbabFVk3wTY5eNOTY5yMWTKoMGJlS9+LEjf3CyTDAcIgxGYzR5nV8PojnE48BGUpoCLBMWoDEvDKUw+NH6NKfASJiykD2LqUbLLMJwK+mtsCPBnh+IqmATqWCCgy+l2tbpCWGY5Pnih7iCCuZJQXCJwZ5tmxaK+0NTcHpgTYHB8dc81hq9y96Nfs5i0R0lf0SzVhDAvQFN6qDk6doshzRL2JXMNdisDOeQYg2s195jHzuN42/W7AYBlvZLPJvGi1a8jm2umz8bPJZCuKlYjfP714Di9QZ9ndmHME1Kb5BjUBg6ARfZrSTXDbeLjaNojuSlRZinmxEXMJ5DmCeovpqMLFEx/RqIcieCL6bG7dIOnHMi+nW2pWUmvQRZsWgGjbeKikfBjwRh5u399hu703GLWK9JON5QZDPHv6FM8vBijdFjlxwMaF0/istEedFTIvMMlBFgDL9n969zPW2VbZqKbOM+xFGI8m+NOfvsF6Qb24AK8+e4OkF+H29grgfGeXO0MYEJawZR6bgU+GNrUOv3zzpSRu5vO5OHNyXidLi+XG3NxpSXqzVwqqAJtskMmuoK4f1xs7o1hGhjnHduZWFxBdvDVJps/bbFei0Xk0HgugdjcjY7xUF+MOWDPP3g8STNtfe3/14KeX/Qfxw58LwjRpRa01nV8O7dAO7d/feA3TXZ7oWEUN0gYY9kP8/o9f4/ryI35+y4oKNbKx8b1cm7JAq4mBzzhrV62pVy7Zsy2Nj2hUQ/MwMve5bHBtzVHnZGk1KJmktuB/5yiuV/5eetvMTfp9GTPo2sn7bIzPtUnnOoJuNqCy88uD9Y7HYoKObgmUuKyLvOTfnUjKLiFBIIoVAQQi+aXs4dogvmnoQM6yWjpLm8CGTcjDu6oPE9BIko8dw3guRAivjQEvFFCS/cfjpM4lTR+cJhMTCE55bkg2G2PCQGQLKFDBRBe/A7VCa/ZRMYBTRECzgd+mmPRKhEc15nMX60UlVUHjoyl8st9qIF9tMFvdIcuzgz7boR3aof2ntP9nATbbuIhxs6Qsqx11eD8YtoupYggPs872vk+H0HvR837s/YmnPX6q/S1OnH6AwXAg5Yb8zUcWiwVub+9Fw8GunA+YafYNzd+7RVcZfNbwgCCblIiS8i222spc8+ieJ9lyU6Znl3cCM8YwghsmMuwGwyHS7Ra/vH2HbcbyIWWDiEaOsKZsjk7VUBViMX1ouvzs7BnSVYn3H39ClqWSnXr+h89wPD3G5U8fUKRZx4ZSNoaDz169wPGTY2FUyL7JgGyqVyGQkmTAiHh4/Ak8fFyl+OG7P6HcLPDy+VOcPDmXTRzfk/38/sNHfLy+FsCATAZ+Z272NVZwEPkFPr+Y4perNVaZcVYlZ44AzuQMX786Q1KupARAuttzRLS7diI43gBxfyT9V2RrCWt60Qzu9mfc3QAfFyNs3QR+P8HETRAiQTPtAycRnictRu0W88sfIGSq6CnGpyeisxbsaWMR4BBQrWxVj0gMK3astdYAcI0BTchakxK+jpFkgVEzgAyLzBJCdF/sIM9Xog0SBnRopKHDntmDsYRXwMaGXjsG214Fmxm6NgDUoMzZ13Ezdu/WBIHjcbuaSbnC0dFzzBdbpOkaZ8enYhaiZaPqNsrsqIBSzI4ShGUpsPSBqKhLwMes6IxuoAXgLmp41F1zcnGqlRJnnnO3Rdzz4EQ9bNoA9+/mKNI1Tl+eix5URufHtsYw6RF6xdMAACAASURBVCHxaKrhYkutKo/BeIMjB5jfrbC8v4VDOy2WP3L8S4RsOsGCjbYktAXCZIzzsyPVj2xpx6BBKvk097OFMMmGkwnKIkexXaNoEoyOe5j6lWwgCPQFPjUQK1SZg7wMkLoRykmA07DBgFowHCc1BdZUVw5VCZ9Zd3FP5BjRMuGq4JgybrN1htvbtxhQJzLpdRprHHfMHHM8OXWDo+S9gJv3m2NUNEqwk5KpRxFQzRy2FuLYmdWqZinHqJX8h527eEnVAmw2ToIoGcjYtyCKXqY7QMSOva6L9zca9rlmnMn469xGLeBmgTY9B/wh4H9z/U5YZScnp5Kk6IwQuBkRsI/6kHS4bQV49JsKoU82qLIdSyfEjxRjnjfwZgW26zVusw22WYZewVLXAqfjApNJiHg4waaeokhZrgtEg74KY6drAZWpl9fkNVD5cEIfWb3B5fX7TgtwvVnKdRMPOD+doz+okBMIlHFGVoAelwwYztnU/cwrEfj/5fKdApXGvITJlqOTEyxXG7z9/gfZYI2Gx/j88zeYzS9RlnRutQZ0ZrNokE4RBpdpQhMx3MA9vXiGzz77XEp3VsuVHJdIGBjpAr6ZAmvqCCpj0QBrTPjIWkSNSQGizFhSD56uDMrKP9omY0L2fCwnb7Bc3CMOmcxKMF8usd5sZf63bFNzRe4tqL/VHq/enwqtdvd/8lk2o2eewOMTJvnBIfTQDu2vbozxqMklc0kL0c/8/LNnGA8G+Od/+Vek21QSI4wN9lYSs4IIXU3ANfdB9YoaPjVOCE/ANQ8+2VbMRLJCoFCdX6ki4LwqcZSZA63sgWHn75p+OmNaTn/W+MAaDZhFS374WgH7xATBhg/7M4q+VycZYGMx0Y81dz0A2Ozqq8kKJo4lWbr//UwmWb6PbIq4H2AiQl0O1BRsr/rfvsyyiJm8NAkscRyFD4/22I6Pug1RNb4mROscTZnDaQtEPp3ONUFFMycmvGyyUSoYHJaNsjpmCBR9SQq2zRoxCownNHeKsNy0KNISo/4Qk+EETeuiqUvMNyusFjMxVuuqMg7t0A7t0P4D2v/zABv2gCybKbdAm10fZK2wMe9j8GpvubV/7Xr3EzH2o4fZfr282mXOfDcxHnARRxGm0wlOjk9kM0BdgZvbeyyXG9kQ2I2rvFp0w8xCbrPre5+tuhCGwSVZKgXYhHHk+cbdUbXZZJNpnYjkvbWPbD8xa0ftnCAMcHd3g+urS5RUUpcnG7FTy9SROEGDAz1SfYDvGUcJnpw8Fce4jx/fC9Dm9wN8/scv5Vg3NzNUVJ+XzZqWzLB89tnFM0wnIwOc2M/QziPwIc53suUlkMiNr4t3H27x4cOPiNDg4ukZJtMjKT3lezIo+nB5Jaw8LbRi3zUYeBRQzXGf9cV+3HYoBXKfvXiOs2GEdn2DplnCIdDixWi8BK0/gBeP4PshiiJFXZYIoxZRM8P6+g4frx0syxBtLxZx837Qhx8O0ExjDCcuzoIacZWi2G5xvwHKZCgB0Ek/RC/gxpjgGhlKBNeUtSaun+L2pHV5IrsrelkKrNH9UMpCrcujBdYMGCrjx8RzEgR2ASHL3pSN0qBCUa0RuszaxkYfyQAVBiWzAJuaQuxYS/K4AUp3V43Rx7Ig2x7DiOORKvLZZoF4MEQyGEqgJUym1sX8foHA86TstxcnamjAclBhv+lGXUSM2S9OoKXibS3aJnSwql0fVw3ZQQ2CVYmwzOE6RN0qcZkle4eaUmLEEfXR+D0Um1SE/8OY4BFBx62A9b0gQd34WHoO3vstfK/GU6dBL6sxu5sh3a6l3FR0wFSmUNlPdi7wQkymU4zHPeStB79yEZpNwabc4n6xRtTrSdlclq0FDHGTAaaDCMwHCwPRlmJUDfLcxbaOseqFGA1dHNO5i6Bb4aB0fFPyItL3oudHEJBMJZaFF6ZkVgTj3RaLxRUqt0GP7FWy6aQ8jyWhCrKpsLzJulcNkmCDYbzAJo+wLAdoWzqLKXPYEVbn/8/ee3Y5kmRZYte1OzRCZkZE6qysyu7p7hnuHnL3wx7+e34gd3dmmi2qu1TqzJDQwjXPfc/MgYisajUz5DlsWFVkIACHw+FubvbsvvvuhfxoiYoZMmwftCOhACcE0Qhkp0izHC61C4PIMNrMlhYQsYM1+5NZMGk3qz/P2Es3tdsYPUDDolRAfwtsc12ky6WMS4P9+5IN50eLAx31MwmyCbgbmD6n+mx57SDTVQN8mq74G322kePjeg1kkwrlfI3pYoblfClGMlGZoROscbhfYkB3z3gf67wjoCgZxAFNcNJUFiME3rwSIi1wfvFR54/Kwf37D1DUBNsznB614AYVcod3ri8OoQTYFDjU78oTsl6u8OnDW8ynM1sjKme4004QRjHevn6HyXgkLNwHD58iCX1cjy9lsWXSDYZxsbkmlV2UqYomWkmChw8fodPpYjabSoJGyBACVrIEUmkZsiA2JaHs19T/syxblpKKlp+Uw9ruYzUdN4Dp9twn86npEMvFHGm6RrfdlgUWTQwogSALra3F559v20HB9sryFi9lq5l5tFnQft7sYk+0jpr+vGu7tmt/TZOxWVhrgSSMiPwfHxzi6GiAm8tznH+8RCpl/zZw1phUmdaaWGF8QJ1fu4HqlGkcUbt0B6WWG2No8s0ZY+So0lzL141EgmgSyxFpJYCEvfbeb1i9mogQU2DuRtizJnFsxqTNuLQlUWPifE1/bMVczUng1ibpKdurjvN2oklWMRLXlzI3q3mKNtmPrdgxY7jEhs2HiBuQyEUIBMmEgI3zTfyo7zelnzwOfsfAaOE5VGdjyW4sYCUlFjhnkilfZtSDzelTDo/zpk/5FV27CNjGtCMlGUTTtRLGfoUYKGgoVsGr1kicNTo9F6DhUNaCW+h5YNko1z1lSUO1T5guabK2a7u2a7v279P+rjTY/lSTyUWYEFwgmeC+/vGw2awZdDLeCn6dv5TR9hc0w6uQx8IAM66ei+UKi/lcmGFkjwyGA3Q6BNsyXXia41EAwwKDm4B/+/M3R2jLt7Yfb4f9W49l4WIYRWbCJmhDbTiCYL1eX1gJXHjTeU2WPhJAcAK3y2Fb+qX75d9c8HKRM51eI2klePTosQQk85sprj5coKhKHD45E5HUdL7UYEGYVBkurq7FNGHQ78MPVHPI4DYWpZEIhHoMhJrILznqxxgcnyItQnx48w6TyaW4SUUxNR0c7A2HGA73sJxTEDyT9xeFh0URbfUID4PeAb764hHov1cs1loa5UmuEpXXgxPvIW4PBSVI04UAAq14CSw/4eO7Nb69jHFTt8UZci/qIYm6QL+H+l6Mh30HR84SfrbEeLLAtGqjvbeHYRJi0ApQ52ssxxcAHQzLGmlGTSJjWMBlrMvjYGaOi1IjCE49ttT8EBgh+0gWqwaQk4yp0exrrn5tmGDmXArzUZ15gzARV6ksnUtw6YdaTiBdxWzOc1f/SJ/The9GI6vpYHeXnHWN9eQaebZG0j+UcrwNx0kDyFaLTrMBLsc38t0Cn2CpMaIQNFZZewXdEQMGxsYKXuiFlbCi+m6FTuRh3AqwdAN4a6aQuXuepxWyskDSGyJKWohdIGz5WNcuskUmmndxqyPHQxan45SIeUZKBzM4uOHH+BXudRN02n3MlxlKgnUNnU/vzSjp4+z0EF4rwJjeW3QSKwhq1hgtRpitU3T7Qwk61wtq9wVo7/UxbFFAmMAW7ziqtGXIlyx7jTD3Wsj2Qpy2gQFlgNMKae4jZ9Y99ERLUB1CaV6QCYghjDQLrknpxhqX1+8QdRO0W21URa16MvxpdPu0dEPGD2NokBYRpmlb2Fv3+lckyKEsCeCbhYAFU21PU/G9Rr9Fg3v9TqvlWMpJgqirJe1Gn6+5ze24J++xv293JTM6mnHIdC/zSJ4z/V7LeEwPM+Xx49EnEanrH+wro0hKro1QfmndUflmI05NxzhZQJAgSOodLTdc5NSZyTl65EicEsPQhdf2MU8CtOsYvSAWLbx15WCeuZjPaqRLepFO0YoWiFoR1qmPbJ0JyBbHbUxG15KUmM0ncryRF+Be7xR16aEVOjg69DhMoBCNSoLyHCfpEmpkBoze6M3FFd68+lY0DpnUUejKwf7RgRzDt998g3S1FofQFy9+hvlihOnsxi7RzDhiF3FmESjsYjO/uC5OT07w/Plz+Ztaa6noikLGDsoiMJlj5zsCa/ZHytnJWiMD15SMqnFDs+5TFqbtC2aOst1BfggcVxXGY7qaOui2O5jOZuoQys7Z9KWfmKjt7Wof33qh/tExbGv2/ZFX7zTrEGoSXTtwbdd27W9rHBujKBbH7KKmo7iDf/yHF4hDD3/4+muMR0tkAgIZsMncqJpIpJ6qJ4x4sVVpdDk5H9JMKZQ4IojoauwJUz1g1JVnMofS/ZnsZdUe255hdGfN0GGN1ni/Bw5Cl27tKqfCpvH8FnPNMK5vxVemsQKT+myMx+4m+rfHtGYstIGX0b1lMppJyYYta5297RhqH25VIjSfL1IgHLvrxmWcAJjE/XfGSVV/0GS4MtAqlJ4md5l0I1DJ/Uj1jNG2ZQkpXboZVwhI13wpvqdGIDItvkgpOC5FSXNJbpdVC3kVYLXMEaxSdJMV/FaA4eCeAKNVMUcSzBC0D8RMbtd2bdd27d+r7QC2O82CDOo4aoA289p2XK26SWbu28oq3aZob7/rzlNmQfATYfytTZs9mmPjYmO5XGK1XMhxttttAbYo4J+Rls4yGzkWoxomO7ETud2xhfBMyZRZoTbbWA67XXjaR/b7OtuLKFPGUxZYp5kwpPYP9rG3fyAaSSy5EXFY2b9JtzUZPLPwkqd1kbdaLzGejnBwcIjjeydC35+Pprj+eIFomGDv4THKlG5MRXOCVlmKy+tLAYtozU02VZMVtGCl/Y7Ur3CA2AOOhh10hscYL1OcX3xAvlohiWmtTqaNg/39IVpJLNpsZIhZkMn328Kce3LUQTpbyXcW1yQJcCLU0QH87hEicQhdoCjWCLwcMS4wv57gzQcXl2mIOqaVeAfDoIOg04N/0EF05ON5WCChxtRigem8hNM5EiA1oUYUAQeyk+iu58W4GU1xc30j2TihzTumNBYsoSLzw5oYkLXExSrBNmUnqWi71QXZ0l3bcqja1gjT7KZh9BBA4DKdVvcRhWZTZOsFAssas1lTC6I1IIghW9ouph3jTq/Xq1alGVbTS0RkSLaHylwUxt7mNpMjNTumyy3B2OvrsWzreWSrsWpANVDUqVet4gnyUDyYGlQESCjmT4WPPZbdxh5mrQB55iIdLVBmNdqDjrj8RpGWARJkagUOvCTAqnSQL6kb4oiQLu/BrFih4zlIKERfOpg4LsYMxL0CJ4M+XL8l90uV53DDCMP9IxwddzB3HFyyVKJ0EOcU/l3jajGCF6nt/Go+F4aoG3Wwv5cgItgkGiU8LxnqNEc697CoW5ixzwx9PPBzeNTPW3tICa6EtLL3hPlEGEVNDDLkBNgyy1ojYFZgtZ5gvrzC4HifHNAGnJXtRLvPlhabANiw8hRA1zLqDBGWaQvd1kqCXAoai/bX1njQ9LymJEbHoapYYb1YIIz68EO6BN8O7jU7b8E403vuDKybIN8OcqZEXfZj+nozzhpGgGENsE+PRyO0u3tI2m0FbK1G3Na+ubmQJHgfSTmkMU1gAoGJfWJsPvUYqZdGF2GirryHCrTdSoC2vBsgDwPETozED1C6LlaVi9Xaw3wOZCsCbTP02mtUYYLlZI2ri7e4ubqQ+y1s9zA8OMLh/r6U7pD1yP+ClmppkkHoyI/VM9QTSQ3KV99/j8vz9wbzZSrAFefoXr+H1z+8wvnHjwj8CM+evMC90xO8fvs9SgGljGYRF4sCKhqlPI6FwhRV0C1utfHFs+cyN0zGE00UlRSs9hCKdhFpfWqEw7kk51hVWGBNTVpY4i4grkkENYOAYR3KwwZk2wBsIlvg1EjXayxmM7QTZbleXV9jJU6lWl+qzNufmLPt03bCspO4eax/3Z7/t7fafq5pzYubOXFXErpru/a3N8bESdKGG4YyxjLB+PD0EC+ePsbrb1/h7esPoLIKh18mb7TYkLcga8tZms6xSFQTZCzQ8Z3AEfdFE4MYfhwiDAMt5XRKeNVKYm8muaWMnWx5Ga+2Yqmt1nBXJaYi+1nqQaV89ZYmKzc2casNvJv43Iw3NrbV46QcigJVjLEkQmsMC3R7yQ3pQUiMJJUoIo2gurXWoKABHvWDmjGuOYbmMPSzyXBX4wKeOGr8qnSDTfbbyVnH2M3gqGWzjJsLlA7BuVq+A+MZiWtEqiFA5YYaqxU2xrBAIj+HGru8FtScJXhXIPCWqANegx7gxlhWPpazGn66wgpjdFs9PH/xC4SdA6zzDDeX1+Ise7J/H6uCSdOd2+iu7dqu/e1tVyL6JxoDdWanhN3GCdOeNBsX2wnCPt/MRs0zW3vbCsq3AYWtCHw7GN+ekO/uhY2LGB4fy8T6vZ64erbaHcnuUyj64nIkCxHNgG0tYgVos3pXplRUSkRVM2sjVK+/xfVNNGCMs6j54fsbEfAGmNQSRJ4vauiQidZud2Qh9cdvv5XFu3x1CrMK84M/gmwYi83NN9SlE506IxwcnAjd+1tqp+Up6iTA/S+OcTg4xIfv3xqGGQMD4Y0hiiI8fPAYRweHqs9za4XD8092V6FZMikc5UH5eH+T4ruvv4brpDjeH+De6akANATWmM28uPyEt+/O0Tk6wVenh8B0Ig6AKopPUIustQh+e4C41UWRr5GTzRT4iP0Z6vEnnN/4uJx4KPwIUZSg67aQxi20By3UBwEexNTGWorg+XS+wtodot1vIxI9L542LUEQ0XnR99joX93cXFBvFoO9AYqawvXqBirb0NFRtIsMIELWmi37vKPxofw7E44ZF1kB1oxDp12DWrYkr6MNUrmIX2cLoMgQt/fE0l2DRLvP20Gh7dB2cWqDSu5vPbsG486gu6+lD/Jm61RqTRAUXGIZh2q+mbIOeFhMVpjPxjg8OEIQR/IZUegJEO0FDCZ9AUwLurqydDRnoFwiDFiKAKRljpvcwyzowL/K0apStOICrZ4vJcAlyxgkjub3r8TYYDwuEFQZ4iSCT5H49Vz6eBB1cFG5GFGUN6jQdXOcwUGr9jCepdjr+shQ4sbxsWDpXuFij8c1I2sLGPQHWFKofrVE4bQwHCboeORAASEl1NinsxVW8wLLNMDMj1EPAjyKKoQVjSkqZGWAwg8Qhi5CajYrNUvLiws6BGdYrynIzNuRAFiK6ewS7W5b2IFFpn1HSjeMQ6gwloRJZBxCG4DWXlpjbGHGNylBR4phZywaM5eTPmoy9WzwbvqDKL/UOVbLqbiMkTWo+9yUp2j+wPZTG/GbX7Zv2fHPbnl3cJU92k5t3mvcLslGJaPWdxJ0h3vSuzXYZ3/TwJ+lKlpKxFGEpTGy0pCxk8CzarOxdJQGMjzp7HPKnszI+Msr+EWO0CP7s4Tjh1g7Ad6VLhaTGuH1Whxrp+sZ1ssUfpEiQYqjg1LMNy6uF3LY66rC8fFTHN8/EG2ZbrTCbFmimK9kERj12f+5pQLf1RaIdvHxEu/fvtVzIfeOsu/2j+9hOpvj9fc/yDmjTuazp8/x9t0rZPm6GVI55tpmASbZvwy1BPVcHN8/wZMnT8QdejqZSH9TIx+6g2oJNzsP9dXUyEB/c/zmPCYsW84VMs9sXT4BSjfzqk0Y2blN2ByUFChzTCZjRH6ANs0UJhMslkspP9V+seknP91uTSRbz91+tNlCj+vH5vRbzWitCWNjp7W2a7v2NzfeZ4OkhcyI4fd7Ib588QI/fP8Glx+vkIvBvEJeNKtScEcjDo7hUtlPoEgpaw2AQ2CHY7cXkrlGiQMm45hNYSzGxFQhTtY6F2pQZVloPzV6MJ4ii4rHIFId21taLbM7z+l33Iy8d0cbPqXTnoOAcbULKbdUY4TNBMgxXs3AdCLVqVS3a0ZC2XRrcWLLPMWV1M7RCnRpfLdJpNq5vCJQRZY0T6yJDZplUvO9dByvPeqTMizjTBoiqGgcxUQ3Ey+eaMWmrBjgvJCl8CuWjRYib+H4NZyA6wWmANU9PmN1Qp2i8GuUTgtYJ6hzD4NWgYPDCMlggGxVIPZ8kYN59+4jeq0ARw+f4e3rS1RRB2X6Ftl8pc7hu7Zru7Zrf0XbAWx/QZPFkdEksmWNdpIwJIdbM6cFC/SxXWbe2Wj7zzsz7+2n75gq3HlOwDHPRRxH2N/bw8HBgZQ50o3n44dzTMkeMxOuFXBVgEIBLXlsdNgki2UnWat9ZUtBBdCzpaH622rDabmUHiEDDC5aLCBJnYNutyPlrK9fvcKni0+yAOQiVMtGzQKNrCtDBWnOmF1I1zVa3R5O7j/Ah1fv8PHjO6HeewMfX/zyJbLxAjfnV+ooar4rF2Vk9T19+lSAPgY7GlSZpQ4BCaeA4xRity4mCJWDVd3G168/4Ob9G/h+gScPH2Iw2JMJVhZhLKtLp5ier+ASPAq5H1KlXDhRF3GnJy6W+VrZGWFUIq7e4foqx8crB7Mqghe20PVbaHlt+J0WykGE5MDDY2RwyzXWszkmaw9h/xBJTGFzZYEwKyeC9eIOWopLIZlDNGGQ/5wSy3yCm/MPGHb34PqRMNfINuIpFzdRAURoE29iJ+m/RuODGImSavTaW/0Rw75hqZv0D/d2f5Q+LqWYlo1IY4cSq8UNWlEXYdTW7cyNIuGZ2a4BVUw0ScCzzDJk82u0+/viyiod07hPal/e4CZWK0synYaVtgHaGGq5uCTzMQjQ7fYQxoHoVzH7TMDDuo3S1VKcHxmBZykW4wv0uglavY5kTt/WHtJ5he4sRy9YI+7UqIMIFZlAnod1DjhZDieqMEpd1LO1GCrE7ZYcM40Q6ALsBgnes9yTGXK3wD2nwonjYVEVmMHDsvbRqlyEWY7pfIJhu6fGDvOpyLYFvY6AcXVF3RdiupVoyaFIsZwC8zzEtBtjr+vgEBlqKVnxkTFQNeWgNMVQt9kNu5EAbSYlxtSGA1arMco6RadDbUPipbac2GjKsARUmFpbQK3JKuvaRC+WmhIQHjW6Z/xfGEjUeslw0LvBfB1jtmYfUd0XCf7zhYB9YdKT66tVy9pvZNfSBy2goq83/cJ0Eu0idhxRjRk7WNshl+euqAh+NcsK1Z/L11gsZmh3h/Co4WO+i2pRsp/R5bJu+hwZjba/idOopi60RNR3EQZGp4dlf8IU8DZ9jvelGCGUiIIcXuig9iJM4OND5qC+KoBZhslqLsDQICrQba3FUVoAqHyF5y8fIcMROkGNGGvMJzWq2EOZjeC5AeJ2V8+fHarJKswLfPPtD5hPF+ae0WG43Wuh1x3gm+++wWJKM5MA//ir/ywaOx8+vFXTDVOkbSdAnhP+raxUnfU4ziRxC19+9RJxnGB0c4PVaqkJGI6j/qYEkoB/LiYtxqmWOpHGwIBjOUvcZdQRrR0DWskYZdgUfELmsS12hXExpoECXVT73a6UmN6MxzI/6lxuXPa21092f/Z30+wfm9Hv7rLL+RFgDT+yO/vYSjNYM6Fd27Vd++uajVUl0ee42PcT1FGABy8eIw5D/Oa3f8R8ujQxiB09tIzfaq2RzUrAy84bMrQZuYPSoZsx5TBCE/syMVvAKcn2JmNNGdzUGpZy0C32Nu7c//a+V81OT4yoyJ4301SzrU6VVrfSxEfNaGIYw/YZi1E177eMOX4nlk+qNAZTCTovGdkMM27LriXEambUzZFI/G3+Fi8xBciYSNLPtpUOFtkzb22+vcaFynTm5GME5uygvf29lLouTDjHmqw5AQLHg8+S3DpCVVGWwxMzBJrxMO7xsBZ9Ntev4AQOgtgkiSpPgNE1JVLqEknUweHhA2SxiwOPWm1czzmiXbq6fo3ZdIVFkaDV6WO8GGD4ZYgX3v+Bf/51icmKlRA7I4Rd27Vd+8vbrkT0L2i25GebsdXMe1vMB5mU5Tn7TjNdmYTYZuL6kXYn+r675d3gfPO6Zs24IFkslpjPyZip0DL6bO1WjJxBgJRTGkbbNrhmj8suiM3kbT/A6rHJf00AYbJzJpBQ8Er3IS6kBojje8hEYIlnlmdS8nl0eCTHu1hR6J1aC5vPVnFZO0+bCELKjiDMtdHoGt1BH8+ePZcS0fnNApdvz2VSPX56Kic5XaZy6Ay0sizF1cUlsrRAq9MSjR/uqzFsoCgRp2LqZAg1XXU0jvtd9PYOschcnL+nrtEc3U4XId9flXCCBFG7haxYK/MgaiHs7wu4VlIvaLUQRKoTjFHMP+HduxrvbyKkiBDGXQyCPoK4i/qwC/9ehLNejeN6gWq5wGi0QB7uI+730YoIhvAICYaQWaTCufw+sgCV4y7FyIBaa1WdSeATBl1M5gssplMBPVi9SuCI7DUCn9Z0QrWRbGdmPtf2XwZmJugU9yyCQarDT+01vWSmT5h+oRlbc8lI8XfoMNuRsszVciLvp/h7A3LYPi50IfN3DSwnlxLABt0hKlGCt9nTLaqoOeTm0AUvYmpas7K2RlGO0SE42yZKjtFkJP1GdOOaN7O8wAJBQF6sUTgstRvAdSMt4XMKDJ0KcexhkfiY0XVzBXgFQdZCma4sN/VcFGuy00qEbQcpAqTLHE5VIk4S6ecsN+y7QKf2kZYupnDRdX2MAWSVh37poJqN5d7odwbCFFrPlii9GP096nPRqctDFDjw6wIOj3eVYz73ccmFxV6E06REr0pRphXWZK0FAcLYF8dZcsVQU8eK7EeW4ZXI+EOQjSwhpFiubxAK069FTBdZqnps1JRRx1nVZZPFh9HcsquCxo2TY40A9moQofe5RXW1UVdlumrBd+nutYLnlsK0Wy1nqN0QftQxlpDbbzMGKVt9QfrDrb+2wDXDmtNuZ3mZ2gcFDOSIZ+l11eWNOQAAIABJREFUhtWwmBKsd9AmA1NAYOOcIg7F5rMskGRKQW1/033YxYIFHln2qLp0WjZKh0otrxbgWv5xUTie6DzWBavNMyROjiGB426AZStAv44QuhOU2RUylsinJebLQEqWO/0DHLUCVMsMq7WDivcp+0qVyjn0A/Y/e+96knz5/vvXorVmHUI5dp+cnuF6PMKbH36Qcsr79x+qQ+jkQsbfprzI3PfCcG7Orz37vLYlHjx4gidPn8lYdXNzI1pr3JYLVbr68XNFWqAiwJtvtP+oIylu1WrOIkkEOcfmc80YZecundI25a78T0DSosB0MpKxh2X+88VcXEI5J8k7bfnST7VbL23PvhtgzU6V23OyXTJuz9mfNanIVx3LHbi2a7v2tzWyX8MwQufBAcolx+MMZ2enePbVC0kIXbz7gDiMsWKiqWClg5btg4w0cp2Mzlpg5gAZlYVRyvuTupXU5VVDGYl/aB5UZcKgSinFINUANUprEGWF/c3x6e8NaMUxisk9iQWE/m7mik26qElOWR0anU+2ByOTqPrR2W77kZnRJFFeS2JN5rKS4x7dsJWJZuN95w54Zz/qVjp1M1Xq+GYHO5O8btYT249F15qSBNxM0USJweUr2kSEMgZVm03Nn+QyCaSnMa6uX2ph6wvIyRpeL0DphKJ1K4Y3YmSlRjqM6Zk/ZSw66Bzg+OQYdSvCIu5iVHkIyhLpZIHRzRLd/kOsrz9hvxuh7U8xWaU48/9vfPymwPUkQVk8hc+yY0cTRLu2a7u2a3+u7Rhsf2XTxbQ6/nEBwCaLi1sToJ11mtnnpx9vP7X991a7G6g7f+IVsimoE9XtdHDv/j0BhthG4wkuLq6EfWKdyYQYLosundhVV8t+FzPRbn0VYb25WywOWy5q9OrUiXUjkqpub1ruw0mJ27TabfT7PaxWa/zxj3/EcjGT9+nCVVfSlgGhs7tdsOoCnc/zMx6cPoZTuvjmj3/EYjWDG7g4/uoEe919XLz5iGK93gQlFQW0Azx4dIaj43tmzzYMMgtkUjeQCqPFrQN4FXW2HHwaE5BaoZUXcOIYfuTL99IyWhdVToCtIww26kTxw6KoQFiMcXU1xacbF7OCs3yEjtdBO27DoynFUYLDvoNjUBtrhdVshmlOoG6AJGAJH1lrWsLHhaLqpilzTcpwhbHG8IPAmlmMyrlWxppsnxZYzCfivuj5HdSluuTKV240PPRfBmGFBC/MGlo3WV5TBii1WM/rdTBnTwJKzWiKhkcDrlmmkpYcW0ZJuiLYt0bS7sOhRp0WJZgY0kVJnbrlAkl3iNoLN4vo5t4yIK68wUR3YlWlwZn0ZiNy3pTwsWxU6moNoFp5mE2Womu3f7iPTqurmWlhqJLBNYWfHMALYikbzRmwZeo2Grp0fiTVJMAcPi5oJjoq0KlTtNo53JjgrS8gWZZVCMoMYVRg7kSYThzRP4tiD0EUwXNTua5l7uHaCQQ0m1YFevy85VLKUJwwwmw8kQxs1GthLyaB0UXFcmNWGtY56owllDUWRYxxN8S9joM+MqKpyDLaHARyXBFBUinDZgBqwbVKDTGkP6kYc1lMsc5Wcoy8trJwEIdZBdbk7y3NPoOr2ihcmI0C0BvAVAPpeis5vbnnGpYTX+Oh0WHTuUYSrzDPWOLcM4G+ZvF1jDX7bcYj+zFmwdGALp8nDvRfi44pC9e6um2Gl5WAMAHLSbIVoqQj4LmWU5qSoYbRuwERmZRXFqXR9uP4yh9TjqmMNjvGqgYg2QsU9KeDKxc7NN1gyXFeKNPULQoEKBBEFdzAx6IEvv76DbLplSY58i4yr4sFajx/3MFpv0Y2VQaxikt7qEPqvM3lmJMokWNephle/UCH0LmW44hztovYjzE4GuKHb7/DbDqV0vynT14IS+9mRH23zVlUJ4fNnCfJFqNpRzAxjJS1FkWhyBUwwcJtOG+y1FjnB9VaY6m76qwZl1ApC1VAjckMrcwxCQEzJ8ll3Zo/ZaG4fV1A1tqscQgla200mQhLUxxHm4606UufTaV/ci7ffu3zLT9/Bbc+wGr7UPNox1rbtV3721rUCuFFD5EzAXq4h+XyHC8f09ilxGKWYTGZYL28hutwPo2lOv5iNCJ/TMtBZdxopq8m2UgNr4JxbKA6paxgIeNL5tySTu1Gg1TMVgyj1sZVZoLaRLCbUSHwQriuGrUUooGpAv3aNnrPOtSp0Y/GU3YXtgJja/gyZazN5zXDjHnGln9yRpBKBN1HQUDKxPvymXcAO/ked4a77SWOPWw7/duj2EzS9nuZOdjECgLwmVhVjY6Mx73MkfZr2vnclKFyjg0ccQ/1GZuTzeaoCzZB0KwOkOWesM6dagWvLozbaIV4kODo4AwFlkiShGqkokE6R4iPH8Y4GnTx9MkjvPnhA77+8AaD9gJfpO/hhgV+mA2lLHVy0wWCZ3AeJHh6UGB+8TWuPn2SOHzXdm3Xdu2n2g5g+7fYf5O1IgsBO7mZiWUr0m4WhrrF54G689MRus0k/Vjsf3vusyWjVpiUGXwyiCIMBn0cHh4Ko43lX1dX15hOF5vJ10xkylrSP0xuyZSRGkcjM4nKQ+vOJiAK9SiUsaYgmwJsAkLaBRjLf4q80WejRlqn00Gr3cL5+Tk+vH8rTArVBNIQxTqn2m/XTOHyuapz0WsPcP/4FJcXl3j//q2wIKJBgtMvHqDKSsw+jQRAMLqtMpHTNe7p4yfoDnobppM94ZJdE6siXRRT8NYFZuc/YDruwGGM5geI+i3RXlL2BoMEHylL67wasTdFcTPH1U2O82WJ3KWORBdtv6Muk/sx4v0Qp3GBTpUio77SNEMR9tEddARYE23dmvbkpeimSUAnukTKHCIYaDN7Ivotmmyqw6bi8zUyloVy2xLIiiXKaoEAsYBbNoCR09t0JK0DJTAlzBoBTTXzyaDMyJZvwkYCLRIuaf+XIE3QEgOKmchVMFlhh7lCsadgPsvDyG4jE4sL3pwAaV2riYH9JLNQtp19O/iyDo0mwWtADMtkMSK+jvkuFHk35cwVM6MIRNdjPh+jznMM+wNhThVVhsHesTBrtkv4RJ+NJXxFJYyxwK9kv2TXXVU+5qsKrUWBnruGH5dAEBAyFbdM5BlCtwAiH3Oy3tYF2kklJgFO0EExIXhSwk9U+L6cKttola7gC93MRxXGGHop1kUgWn6hV8ItM5TrCsuVh1kYo+j5eBjUCMq1XPu0ClD5dGQ0WmsS2SpQq/2JoIaCGzzXFTIUxRSr2Rx16cOLE7lnWQZKkFGSworPqcYM71Jzze19qbe6YatJ/mEz8Mn9azpIc6+Z/iPjC1mu6zm8IEASBeiEazhehZt5hMqJxOlSgBH5nK2yvG0QzQb5FvgyfWj7GDajiG5vj5/9uyoXSPMaUdg343gJN70BqgxOtIeS900zPurCwH60PGeANrLRyEiScVD02cgU4ACkfZRvEn02bwO0CZvL6rPBRcaS3ILyPiW8MsN8do73Hz9gtS7QShKEj38Gp2zDXcyxN8jRwxplHWG1YtkjPyEUwHmaL7HKxhj2u0iiCJfXI7x+804vppTEAqEXoTsYoigzfPfHb2R8Pj6iXtpTXF6dYzod6fGb6yu5iOZ7G/KeYYHSlXT/4FAcoGmaQM0zjkkC1tPEwABKBJgEWKORAQ0MjIkBATYB1aRvGRC3udTmOjbX2p5/7XsKsrmy6J3PpsL85fw3I5N3tTRJCV1Qbg16m3Zrkq1/cr628+ztbezzn8/Tt5oFimU80iTdru3arv11jfdO3Krwq8c5lns/w2++OcDL4xR7gwFG7y8w/fgRi2yJws0Ryvjgq4kRf1oxUtfDYjmXGKu0Zi8mFiSrmgZAXuTB530qgvsVnCqXShCOVznHKhObSvwvlLe7ZeZmNJBEpYPQo0B/jbykwzeTMZyLaUq1PXroezbzWxMBfTZibUamJghqntchjqWW9m/OtDJrSVKJn8qEG8fOnHOrPdTtT9rsaGv03YyGn42gUjaqx9yMjJtBWvagFQ4SCMjzdcH5qlQGNBM9lpluS1LtZzFWZfJOtNY0lvRMHOdWnDM9mf8IhmWMjYoMiVvi/sNjtAZdXFycw2EZaRyjm/SQTTNUboyTh4+FqfjN9x+wqN+ihUusLxzZl1cAh70Q6B1ivlxjWbRx+POf4/RhjDOnxOWHD/jNb3+H6+trTTDv2q7t2q7daTuA7d/QJLB3PVksWfBIn/88AL8bqH/WtmP5u5tugW34/KXP3t7s0jDMkjjC4cEB9g8ORBON7LGL8yss6XootX8iz60T3VbiyuaUZGK8pQGhn6iubdb8wDDghMHGrJ/RUBA2hzKnmLmTUiAp0aFDXSzi7dTiefXqe3x8/15BHlOWRUCkOafb87354jzPBNqG/X3cu3eCd2/e4d27N/Ji+7CLkxePUYxXuP50oc52JuAgODAcDvHiyy/gUUWfrA/u0NZ/yWKeC7wSjldj/H4sJbZcTCZ7fTh+BC9qI8uWIJzCJppCbo7R+w/4cFmCEuBVGKHl9ZGEPQS9NurjEEddB0fI4OQrTEczzMsW2vt7iAIgFEKh1VqzRgb6oy6NG+24SspGjRi4YbdJmR+F6HMCBrZ0TwMalpmW1QpFlsLz2qI9Vokehu3HCkhZMErL+jTrKYCWDY1MfKSLYAVJxNXPBFf2IlnOjgRe/HyrieWxQK7AckGFKV+s5eNuX0oxGjaU0VNpILatmI8dVCE4E5qqPaACb3yrcf6yOoP6nOrIyf5cX6zo2edQupjcnEtAdnL6XL47u4NoZfF1LoJ5noiV0SWUwERRIqRpQVCK2HHuBLioPMwXFYbzDG1/DT8pUIUe0tyTMk0ytFrdCPl6hZzWZSzjZUZ9VmMdAKPrK+zfO0DiO8hWayzStWTRCSYniYekE6OiFgkyVCxNWXuYlRHmbfYnF3t1irookKZ6PF7kitaanAr2E/YnAdUMA9KYXJDZWNdTrIoUftBRkHY+R7Y4R1a14YQ9U56nwvJNuXiTqTcAx1Yf0iz2tpCxPuY91yjD2PsMdHWci5Nq0huqFp4A6xVCJ8d+b4I0d3EzI+uR+mxkjtoFCB1giWmbkcGALZY8p13R1P7asdHZyvi7uh/fIwtwgTAcyEKsYeyad1EqOwRZoAXW1b4wGEXL0g7IZgxUNpsuptQIwd0AvKKvRZFnV8BCq9GmiQga1RBoo86PdwvcXeU1vvvD77Gc3sjYc3//EI+e3YMTtHBTlGhNF1gsKA6dw48SJO1ImLvZXFAcXE+n+OHtN+i0E7huhcViJX1ar0SJpB9jr3OIP/7hGywXC0nCfPnlz1EUGS4uP5jTaspiLcAp39fce3ZeqsgmaeH5s+eitUlgbbkga02F+0Oy1ujqLHOANTAoBAwrWbpuHEI3ZVb8beFXO44YRrW5pI0Yt7ikcpxyMJ8vkK6XorXGeYbloI3W2h3AfrOK/ZEJ9kdn1Vtv2H7nrfbjWyrjly/wfGzdHLu2a7v2FzZJAkdDpMseyvQT2v4c/+nLDlqPv8L6psL47SdcZA5+8d/+d1yeX+Ldd9+jqFIE5QJuviJ3CUXuYYoK+yf3hOE6GZFZb/R1nQhe4Eo1hHXXdqscVZlpVQDnTeNizKZJRnnUTBqWxSXRC5nDAVlWTHgWt6Jn4nEiAeIl4mLMZIMdnzb40uYddu+bmXf7OTvHGQkAMwDxMSU9NE7bCCRgixUXuKKqZmRDXLhMQmqV5tbHK+O4+fStYXRzfHeP1TzbyO3qDrfgQ90b5ROKTGVmpJ5Tn9eXt/ZkJBdkNxxCaRzE6oqK1SZMKHmilUcThH6ng+R0iFnso5s5iNYZsMxwPbpAmmZ4/uWvxMDn1euPuB7foF2cYzH9hHkW6VwNxvZDBMU+Dg4iDO6niNMPuJ6mePwPv8DJ4YB8RKRlhU+fPuC3v/kNJpPJrnR013Zt1261nQbbv7GJBlnF8herz2bLWbaBtluz1d09mN/OT0fqP/LS3bb5BDvZ2mNTtsB8scBivhBmWbvdxmDYQxgForMjpa5GE8F+poheyxxn6O9mArcTpF0w2OdUhsgsvq2roD0R5qgo8C3sDorgk9VG18IVHXoq3L9/H8f372MxW2K1XhheuNLk9VR8niXSNbqD9XqFy6tPODk7xdnZY8ynU8zHc9x8vIB7kOD4wX1kyxxVmmoA4vA9KT5++CjZxHavYxwxTQgiEzszm7ooXrK8EZmwMIacvLtt0Q2iuyhZgS5yKfeh1lnYGaD2XazWPlrBAfxOH+FRF+FpiMdJhWG1QLlc4Pxijqp7jO6wi8SH6GM4IjyfqdZaWmAt2ljGmZVQllOidnIRn2dJXZ6q0YGI02cFUiNET3BNXOJtgCI1eAyTAnh+S8o1i3INjwYCBER91RATp1BjaKAOq4b9ZPrUtv6e7fcWdJGr02j16cWxfVK19XQ/YpxQO6jSFYrSRV5lCGKWToiXq36SKTezHUevx9Zz9gXz2xAsN6+bz9fjsMdKXSjtjwK2GRuspN1DELXx6eKdHJfP8lTzPSxTjv2F2WyW/5F1R1cuan44Jcsac/RcoB25uG4FWFMMd+XCzXJ4Xialnu2wQsoyucJkyw3o9/Z6jPPJHIfHh3jz+hN++DBC/14foaPXnBn3cl3CW6wQEX11PcznDm68Fqr9EE+SCu1qjSKtsc4CFGEoZaixxKk8fiMabwwM2FeEBSnl2imy/AKFE8L3W+JmSbZRSv0SN0HizFCtJ8jpaEoky55L+bUpxVThf2U5WlBLy0INoKbozFbm2lyPMsdiMUHtRoi7Pd2OnUhYkBCXzekqgosCh4Ox3Ad5GRodFnP9hTVgRj0rumzGKe0x+khYr3IcBuIjW9KvEHhLLOdk1Pa0XN72KwPi8HuWcne34MJHP76U48lFyU7Hp6afyfHYx3qPyH0iQL0KytiFj3ZW7bcCXErZre5IwCKnws3VJb754++xnE3ht/p4+Oxn2N8/lOx9kS9QzNYCwNUB2bYEiz3k7CtRiKhLHbcc49kE8+VUmWIlNTiZ6NDS7eP7x8hXFf7w9TfIszUOhsf48uU/4OLyPcaTUbMwku/DwxcpAAWzVHdONyAAe//kAV5+9ZU6GY9ukK7Wsm0Y+AhoJmKA04aNy75okgIE2QoCwJyD7HjSjPWGkWgYqQqc653O/WsSQOebyXgM33GkJHQ6n2Mym93WWtsePW4NFvYJ2zbj3d22ecX56V1tvW6fJxuU50BA+x24tmu79lc13r+seth79BKT5BlW40iY2S9fnsFJ9vHpd7/Hxfu3uE7nKP0Y42WNe8cHOHv8SJNcdSjj/ZjVAjlL0Quk87G4CR/eP5NkVppXCCNf5CJE6oDVDGSEF6kwm6k/KkYrDXN7E5EYYYQmocj5hmWl3TgwiU+zpRm7NA5S53Imce/vDxHHMZbpWuOmz8aIu6POnXHH/iHZJWWRE1gTsyBVmVXA79Z6RP/l/MYxXpl+anKl0jF2qNr+pDtj6K1m97l9rAbt+1NjntH+5DGriYAmRreTtTp+6/xpQguZKxjPlS4Z9UwWFnLcp2enGB73sGgFmAQRllxzOD5W1yvRPX75j/8Jjhfif/zmB8yrC3RXnzC6nmO+rOCFgSTCKvQwT/pIn3dx1QtQnC9wv/iIn0Vvcbm8wKvzNfzAF+O14aCPxw8fyLpmNpvtykZ3bdd2rWk7Btu/Y1P9HS48jC6VCQ6aVP+t9hOB/O05sAG87s5tuol9tNl0s9nmNXneLE7IYOv3ejg6Pkan3UJRVhiPxpjOFrJQsfpp9nhlL7L2UzF6xdVuT/gMKESLzei46ULI6rFpsEF2hpQIGUYJz08m5gu57IdgX7vVRrvTwWjEUqZXWFCPSpAQw2qQDzMlOoZRJ+GOACy6eI6jCKcnD5GlOb779lsB37zEx/HLB+iHCUbvz5EuMy1hlHIlsi8iPHpwgv3DoYI5sh7WulKWSF6dvzH6PR4Cp48ocdHth+Iumc/f4eLNAosgxNHREEmrJQsqxwkxWSRY7sc46wADctrIDDkfoYz20Op1kYQufClnY+BWoqLId84yhEo0sqiXJyCBlMSStUYWHVkf3A5IpSRUHVtFK4smBsJ000W7npVK2Dp80iWrbT1TbSYvFjCP1yWMWwgM8Om4Go4Jx8Z0KIlnZPHLTKeCBdZhS38My8UEaRqTNflY+CrcJ/ss84WU3QUENYJQmDrpcoKqytFq9eH71GfTogZLWdGs7FbpQdPlm7qGzXY2e7xdXqEVenJgvEfF1THUEj4t1ZKiWKyWKdaLJQb9PpIk1m2FzcbSZy6OqbOmZaMZBeuzUry5As/os7kBRghwnQP9eYFBzMx0CtdLgHWGfJ2rtlq6BLL3yBIX313twX+/xGLQwcMnSxzVayyugWhwHyEdwOYr3h3IyHCKPSStCGkSoeeVqPNSFhC548MXh1CjsSJaa+WWvhXLhjXzTvCmzM9REkjkT+kIc439jf2O96MsJGjuUBWIMZH3r+ouKmrn2XuNl9S17qAbxpoOdZsliMGbmr8JWWXrGfLShx+1JWMsTFFxod1oMSo3Ut/PxU4rWiLyM0zXMcoqahhhdiVg4/FmmJWFgr6m/dKC5xXaSY1VmqOqqeVCXoMdI3V/6qamZT+C4ZmuSAA8DiboJEvM0y5WeUdYb/px7haTzwK4Rg9QsFEt21dWr7/RaOMYI6CXjpVOneP9x3cYT2fy+U+fPMbByZm8Tl24fLHAiotE6fIunIosUBWQJqjKhIgbOkDi4be//h2Ws4meA7mRXQyHe7I4ePvuDaaTCcIgxvNnXwrANZmy3KU09AYDU4rZ3BYtwjxPAJj6nk+fPReHUGbwOdYycUJ2qIz5wpZTrTWCXQqqsTRKy0Eb7UgzZtn9y/nUE27GkQ24ZucykVZ0XDHEYKKGi+UsTSWRlGbKWtssEO+2u4y1u1PmZt60T29vYOfZ7d/bk699TsZgw3L/fNG8a7u2a3+uEbh49PAhvvr5z3DZHuDypkb2/hMe9SndMcPV99e4yq6QU9eUJlUE9bsDRGGI4+MjnDx6KO7wN6/eYTqa4GJxiWx1hUgSNQEqx0drOBR5iIvLC6zXM010FjkKaqUxtio3c5JSu3Qmk3vcRKE2/mRcGUXU+aLGaXGLhWWbjGgGKbIeB912goODIVbpGh8vrtVQZ0MWu7sD66HTPCExOOMFxk4SL3IXZvLa3tKMiZu1wyau4kzGHADjGxm6tmKrJlfb/HN3dJTZr4n57FPb83ETkd0+pE0Yx2Q+k/MS90oWcguwIwnAbGgyqkpe5/zq4+DgHg7291HNrlD5JYpkCCfu4XJVIfs0xYtHjxB3Enz37Tku6wJne++RffMB44WLdREicyK04kpYdGl8ioedM3ROVsgjalcXKF9PMMyneHI6xv5xgE+jDm6KLs6ePMW9e8dyTNPxDH/45lu8evsaWZZtfcFd27Vd+3tsOwbbv2OzgIMKrRugqgHX7s4qbH8m6NY567NNN0/bqf1OsH/nLXaSElZFWQp7i26jZLYQSOh1u2i3E2QFmVN0WrKT5TalmyCK/WSzANnKtilDyQAuAr5stOnkb1viKHOiLjYFdDOC1wSwViyhyzP0ej08ODuTz59N56qJZnSArAaTPQob6NiQgQs/ut1xkfj4yTMEfoj5ZIrJ+2ssl0vsPT6WMqZ0qdlCYdMVpWgpzKYzMWAg60K/ojIlZrMFCupFuCGidgeuXyNfKp0e7SFmToQPl3NMJ9TqKpG0WBJVIwoKDNouhk4qTKTrmwL+4AidXgutYMNao+g8LccVcCyaUgQCa7VLd1OWT2nmtRC2WoW1/BjNNXEHJatqU+Jq2TANEFkSkZvCabdRRX14fog4isVhr8jGYOVS4DODx8DTlMyaq09wTQI2+a1sGyvuK/+b69yskk0AtgnKuLcC2XoiLMYg6aH2mClUtlsQJQgCakjNUOQrWfTrwtoskm0A9iPB6iZwa6K0z24a+Sbmetqjkefl1NhzBHH3StptAQt4LGEQ0UT0lksk90Cmn3V+rMgoomAwASm697qlMNrCcoV0laLIjIZbEEuZ3PurOaarGp3hGVZvf48nhzHw8CGe7nuIPr7COjuBv3+GT5/mKB0P3f0hUjIXRR8Got/mrplBJXgRIPcCBKEnDqE8oxSb4eKAIKx1By0zfb+LBbL8HHXQFTCwYlY+r1FklTwWII4Brmj9MdD2kFYxQr/CIL6RDHNBcEvYTIa9tnW2K5telmuyEaYX8JOgbZVhvpgIQy6IOwr8mHJsWVA018XuQx8LCFv4wtLrxguE3hppHm6NUWb8s9XCzRU2v+U53o8lopDHUApzTuuJ+bKC7dKPpDtsBKYb8M4Ai0UVY7lOEPlrdFtjcf2sqK9nToIuDDbfQ8HurSSFPV/sSwSz7SKkrrFYzvD67Rsp4Y/9Nr568QX2D4bK2EsXyJeputtRM475ego+1yzuN+6+rhrvvH37Hv/yu9+hfb+PMIqQrzK6vODgYE/Kor779jtxWD48uIeHj55iMrnCYkkgztAHt0bUxv3VjAZyrh3g/v1TfPnlVyZBc4N0ncprHDtpskNWAscKMV2RMU2ZlGqqsQHW+FsZftp0zDKl3XLuNXGjrFplrBH4pu7kfDaR795qJVgsFpga1tomn7U1XmwPC80DM15tb7f13N3RZntU2Z6Dbr1ompSdWROgHbi2a7v2V7dWq4Vf/vKX+NUv/0EeDxiXlEuc7CU4/3aJt+88vA86SMtQEl0cN9ZuD5VfwKvnaK/GKCcL5LmLwydnaO331cW4HSojraRaao1qtcBsdI3+cIj9gz1MRiMsmWgiuGblL5p7XUsp7f3eDCtMXgc+OnEoWm2scLAbaILHDvRbzKxmj0yWVhjPZwLOPT47xnyVivN7kzi69WP/1d9MtBCKigMHOQU4JE4yGrhb/zVz3Nbr4DKDAAAgAElEQVQxsFnutrDdaAjmMhYUcQk9Qjvom7dYcPAnBlfzp5lD5GkLjG1e3jy4863M2kDJeIUcnIpdGLd5eYupWqhrcTp//PwrxPtdrQ6offhcw2RTXHwYIXYT/OMvf4F1muP3v7tGdFLiPx/+C67/5wWuZg6yinP3EKF/IkZknldi/+UxHvzTPSk/Ta4nwMLDNPcxrSNcTDzMrgrcT0Y4i6Z4++Eab85H6Hc7IvtBuZqDgwOssxSr1WpXNrpru/Z33HYMtv+gJmVlBmSzwNsmzr4buv9Es5vZaP4v2PT2M/VPPidC20GgNPnDAwG1WD5KXbbRaIx1lje6WQqsmXm22ZfVUbK/tiZgO7XL5Gi1hlSbTUA1shusELhQw1meRncmsmcqWZzFSYL+oC8LlTdvXuHi/JPuVQiC25boyqiwc7rO2fq363vY3ztCvzfEuzdvcX7+EY5fo388xMHDe0hvFphfzQxwwkBFEDdZiD48eyAAFD/n4sMHZGIy4OFk/77qNzlkk7GM0kESlljUDs6vXaz8BMm+g6N6hpK6bagRhwFqtw2v3RJHRwHWRENNHR1ZuifC86K1RmBNWWtiyyAAXNVorcl2LAUtajkm6+DZMO9MUYCygrTvEbQSlhFNFjylwTOI4qJcGXQ1smwhWiMsxfDJbpNzTMaa0eAzJcCGv2YcDUz5X7V9/S3qon2N/1LHigCf67fpEnF7U2F46CKUfSXL1ijTpQCjUdI1zDPpsU0/bFqzyjX9WsoUTamzRoJ6fBq5KWBgtAIJkFndOWGyWTYbs6aOJwDViuwxavwNhwhFt03LvNhvhVFEcE0cueiCSTFklimw7DlDlVqSTCVaYVSAGc1LBEkiDJvXf7hAnPh4+bM29iKKsHt4P47x/Zs1Bh0X90/3EHgOVlWNQcdDsF5hvVpLDQcZT6JTFrvo7LXhBjSuYEmLZa1pPyH4we0YqBbFpQgae2Ff+l1p9a9koaE6eqqPpSLzWrpo720yWyv0wgla4QLzrIdF3jGsVdMNBPhW7qG4fvJ8W3QLJfL1AlmZI4h7cu40cLflxHyP7S2bZQfvS2OpYJht+mrkUsQ4RVl5WBdtVATpRYvL9gntTwLdi/Erz2GK5Yo6dQSVA1RWO43/UROtEYS2zWTthUbAE2GC/O0htc6QhDP4XoF5uieAZwPIkf5pGHFWC5DAkGfZbMblVsa/Ari5GWM2m8tuO0kf90/PkCQB4shFns+xKvRG8KhbyP4pWKqamNizlhUrvLs4x5s3HwTc5TVpH/UwPN5Dt2zj1ZvvMJ/MEEYxnjz+QtgeV1cfGoUeW/7UJDPM3KXXVx+3aBLzlFpriTCftcS/ljGd8wnHbgGDTV+S8mRj1qLAmjIUCNCL46k6o+hplfHAgJ0WXDMAuhCjRRfJkYVLnq2ELVzkGaazuZTqfz7H3pk47cO70+Kttln0WojNAr9mNtza6kfebZINMkbsgLVd27W/upEB++TpU3EibiVt0RctsoXIKqwuP+F3X4/w+849lIdtJNUK7vUc2dtL+Bihbido1yskNBfKPbQiD0fHT7Byutjbb6N/sIeb8TWuxh+xHN2gvLlCTTCrLJE5JaJ4gOOzp8irFD98/z2qgkwkHQdUBgOfjSeM81tRKPMtqwpubWSGDI0wN6C9Pm2327DIpMTTq/H09BhuGOLd+0uJyfkGnYru7MWtEYl0RS3jrGWYb/7V1kzFzadvmsyTsv+NJAv/CXyCbR7WOdnemzJYmecNgPbZ/raIwRJO2w9g26Lk2c/QjW3MZs6EnXdl7sn1vFPeYCsZ5XkBju7dR/fkGOuQyUAXUeYgzB3ML8+RpiXOXtDJOsG3311h7Wd4efoDgtev8fUfPFxUCQr0gfIEsb8PdEOgPYJfv8UvT1Z49uQSa/e/4odPbVz7e5i8mmM2GQP1Em62RFKucL81x7P7Uyz9Dr49r8Us6JTzaqsl893V1RW+/+6VJGx3Rgi7tmt/f23HYPsPbKKrw5NMZ0Ir9P3XBt23V31/sjl/5tnNlKgleAJsZZmw2dbrtZSPUp+t223Lgma9zow4Od+iM6dW2pmZ0X6XW6sNq7lkVre3WG2WAbVhs/FYuChjUKUaNVw4lsKkoz4c28nJCfb2DzCZTZGKjpotB9Qwwh7G3e9PkIisEOrz3D97gNN7J7i5nmB+M8Po0w2Swy7uPTzBcjJHRZSErpaACHRfXV6LxsNw0MNytsDleIH5bI6zo/vqCOjQobGGX2dIS4q1OjjoOQj3Y5x0fXSDCsUKWNEJkML+ZQqUBdqxkPgFcFJtLGqoERBhtpTMGvXm5Mq5JjDChaqAajwnlpVEwM0uVA2vREq59HxrOMf9kRG3hBsmcJI2XD8wJWrUFGPwZHTWxNUwhBdESNOVgCEs1SwrR370euk1E1jNaq3Z/yQmahAQ7V8VEPoFOvEaWeai9hJxirL6bU0AqB3FhG3UBvMRRC1xg1rMxmIeIQ6LW91r+0IL6Gavf9MRzE1jupgEhM3nmE+2iI1+oeZGUzFdslAJ8kbyezS6VO04N2xAAWHXUefEuISxlLguFpjPczg52Y16l1Us2+y2MW23EbfbKFY53l0vkBz28dXzBFGaYrZ0kRU+OqGDo+MWVkFLtit6EYb9EMPAEQ02PwyF2ZjOV8go6L5cIF+V8P1agOs8S5UBKf2DqF+NKp9gtbiEm+wZrTVTopdbgXkF1wRUY9meYZ/q0GXOoZQ7usJmy/IYw2SGfnuC5ZqcOS3jUNDVgDFyXc1CoMqwWEwlOxyELKm05b9mW9tlty6vvt+MHeb5BjwXbNdHVkRyfL67VDCQYMw2ACvfoUQSpRh0FmDVTU3jBuX5qS6bfD/tP02P3CqFlM/fWnRsABd7UD7ysoWs8ODWM9G7gxPKvu1daDdujsxqrpklV57m+PTxUlhr1Hi+f3KKvb19tFoRkrDAOp1jTRxNduCDHYqQOAGtIOI4VAmb0Q1dXN3cSDltFIdoxS0V/Z+uMb0Y4eLiE/J1itP7D/Dy5S9wc02H0Cszjtsx22qe2bJ8c28Y7J6l91999VLmjNH1jbDh+J4gIIsyEABRWWtGa03ANS17V5dQJgtsUkBBVWEjNKsr/WzpOY0piXFr5tiBCuPxjZRBd6i1NpuK3hrZcXK2DaC5Ods/NXFus8pt2zAob0+5dsa8M83dbWZukyTSDlzbtV37qxvHnoODffzX//Jf8OKLL0Tug0nXxXwJWg19+D9/g9/8+hLvPBfHjxZ40L7BcRZivz5DWrHcfoJOCUR1F25eYp77mLsR3PwKXzy+xHXRwsfrFfqdNk6PT8VgoKhjibHSciXJtpiavjdk5JZ49uXPJCZkxQcTGjZhpwerv9utGEkYYbHKkBsjHx2FNkkK+3vzY0CqW3PJBtjic9fTOZaLKZ4+PEGv35fSd87b1oma/3sBDcrJMq/ks+1UvfmUu4/Md/isbTmyy0FpcowxAHXi4oDrF40JtGp/a8xuxsdmpm722nzq5ktu5sPmhTtHaOZlJeHxHFJOQbVpJCYoPeztH+HR0xcSQ9WhLzpy1FqbF8DlD28wODrF85c/x4d3I/z+2zFOX17jV+E/493/dYNfv+viquqhqB4gwHPEw32Epy20vmij7gDeciISFtUihFtSS7TGw+MMwZMjjJw2svE5Srp9x23cFAHeX7UQVgs8OqGBRoXf/PEH0brudCO02l3sHe8jTBJkNLLI1RBt13Zt1/4+2g5g+w9uMidQ5JjAxjZQcBcpuNvsS85PbPoTb7+dI9s8+/kz+heZBFz4ELjigiwvchFc7XZ7wm4TIf80148TGsEGSGlAsq3JdrNe3tDLTWGRlhVKuegGcJOFiSyOdBHFhaPowDkUli0E+KPLEsuAHj18LIDLbKYZIZ3klV7RUPC3NHvkW0rEwTKmkWTivvjiK7hugMVkitnFWES5739xiridyCJXWBB8S1lJ5unq5gI3o5mUrwaBh9P9Y2F8+aSv1y5yNxRTg8qrJYsWpiv4Ndl/AUq/g6A/0H0yE1eVWC5Y8qqaaamUexo9ImE6kZRP1hoXpATXCikJFAMD/hZHUS3lUw0jqxe3Aajk/5qA3UIWfH4yEODMd2kwoWCQb5hrUnYlGlB6DXlpCayxXnQxHzeMMCWrGRaRBU9N394AJJs+RjbXcT+D79WYzEKxUW8WtKb8zu5EWYhaQye7EtYSQWky2GLMFjOU+Ur6hRyLAB7mustCeXOL2O8gTzcHpj8bENY+3iyn7ffYAAqbbfi5rU4Xs/kKi9EUnk+WEs+JqftjsEkh5NUSK8/XktKiFgPSPPDR7rTQikMMaVYbLMT19GjYwUm4QpkWAjpyf2Q2UetluSxxusfK4zb2wxR9pxDwtqLZgOshbsUIYl9KqcMwQuDFSJdkorE0meCOh3SZC1C4Xp2Dyn1hd09KWAnoqg4WNdcIrqlIvdxL9reA4eZaNmwsU5rnUnstwDJtI89CHA1HgLOS0k29jqrzpdehRp7OsUxpYtGDy9WAOesWlGX/tWOI6b06tJjyTNvPzGW+dT35BME9lmySSVblqfzNH9XKqXB6wKB2iatxV3TwNneJcxtnsaYaFly7M3RaBzP9TLMXk/HXbQPUTkvcN9PZDRw3kJ+mNaXy+hEs8WQZ5Wwyw/X1WMbYdjfG2dk9hEkLg14HfjnDmtdLbhUfDp3SKl/OjUoq6mfnToVlusRguIfB3p6Ujorzr0fAvy2sCurBEPj55a/+F9G5fP3mOzGZsOeS11v2a5ikarog4nfiVhwGIX7xi3/C3t4ebm5uMJ1TzLmShEgUBqLpxvepiQGNX6xbNPsZDQw27DW93vWtBIkZpLd0PM1r4iit/W+1WmIxm2DQ7ci216MbrNZr6b+W7faT7bN5shkxbj1nZgz5ywyJn23t/CS4piY+jYbpru3arv3FjWPM8yfP8E+//EcRjqfW7Hq9QMG49P17fPPfv8W3kwKzxEM3LHGaedirEoQHD3DwZYlhd4XZ+RrVeg9Ofg+LKkLpVHC9ClkdYXJe4Nh/i+MHK7ybtjA7X2B/fw+Hx8fiLAo31pGdOsQEyYoC88trdLo9HD+gXEklTss6H7Bk3UW33ZJxjS7YdrzQhK+JQ3WAw3Z0ZMcXO9pIomdLL7YByDi2lzUuRyNhoP/Dyy8RxRFm84XMYFGozsmUE7HzGf/Vkv7NOGY/UcewzfFsWn2bZbb9PcyUqFrAdERV6FBi960kpux76ztsvu3WHNuMoVs6vc3f9jndh1wHtYpuzjdZ5K7vSwLq4OgIacAaEA9gbgXA6GqE4tMcP//qZ2glXfzm1++xDkv8rz/7PeI//AH/818dvFnvYVGfwsVDtOMjdB91sP8owf1ftfDiyMVhtcT0/AZFSkZ6ifE6Q7pYo52+wlnntczfpd/GnIk1+WIBMtfD9TrG9YWHTrjAo3sJlrMCf/jmBzESi8K2SNJ0+n1JQNHFdMdm27Vd+/touxLR/5cbQRqdpEyJ3a0Z7+7fP9KcP7/pjz+9vUzYfrv+K+whj8LUrpT/MJPIBRXZCQTfLs6vRMeAkyCdJRuWhjBANN0l7JQG/LCT69a0q6t1+Qwpz3MMc41C8nT7ESMEA6RQtcu4dHKRxvcS+BsMBqLH8Yc/fovzT+9Vv6eZmDffT8rUzNeTwMPIsfO0d6nxdvJITBCurs/lWkT9CM9/9RLzqzEmV2O4YvigE73BUQRc+d9e/lIXzA7t18mqoKhsjYrMMyfTTB8DxrJE3OnAjVqySKyKFDfXI+RVpd+RTAc6UlIzSP4rUYGW8Ka0SkA0y24rUWQEUeiEqYtUfj9bmSlXQhbvZFGxZGsFNxyIiYBqWvD8smxJQTUFFExgZRbX3IGUbUnplpZ9rrM18mot+mgumTkWjBI2Jj/XLphNWWhVY6+Todta4sMVKfix+mttMQ6bPmHZJiaAEjYYQ1uzoXUIpBoHz8xsfo2IoBvBGlPeJ13MgKtbV74J7MzpMYGaBV51wW7ZMfpxukBX7UTBF03ZqAV7bU7aw3wyl5KV3rCNXn8PZZZiTYpR5Yo2H2LqQznwCX4FFDumuUQBz82A/BNq777cT+fjGkEAuCybZGFpAQXoPA8d5DgeekgRyH/Sx1l+R/BZRw/pIwSEs0WGmlotUktLR8wK0aCN65tLqWqUK0t9NTLWCHiwX0k5qGEkmlI9KQclLiVsPzsy1CJTZtcJ1s3VvkYgOPZXOBxMcD1tYb5qoXJ9VCUBxxX8pCN9z5bwKgNS36+YbbPMaPhDDevr1jhilxAmhS7HoigMAU1rtkADjbwEDveBTlzg02UXtRNJv9dLvxW0yzLKkvPMIscMGLZcVN9hQFR7bKZ/WdUwdeXcHCp3tZhPhOXV6dCpmQCgGYuob+NFcIICo/FETnhKLbSjfUStBIPePgYJmYiZLA6rmg54ZGYQnVXwSQ9MP/1yNMFknCItZ+jEMc4en2DQ7YuhxX//13/G4maEpEXmZEfK5M8/fUC6XplzuK17Ztw4jQaPXgI95kePnuDs9AwTJiSmdB8u5J7gglgYx8YlUwTBpSx5Uw4qTEm6WG8xYOUc2drdZm6wpiSOlcWTc8q+Qy0jamgmUYAojHAzHkvShf1X71vnT0xzf2o+/XwuvPtbjq9JEG32tL17GYuN1tqu7dqu/XWN983R0SG+evECvfZA7/kiRUH2/XiOd799i7cLD8uEBN4SruOh593H3uND9MMVnh6fI8z+Ba/e9/D7T8eoD57BqQfwxpRqoEwHdRrJoF7CdQr0gxTPTqdwTh7gzfkDBHmI00cHcjN/ePsW05sbFMsR8uVYEhlO5Yq0Quf4GIPDA7z9/lsUGUs2HQOsabLAjgnbMJM+Z1ndNi65vYUCVWZmMQOPyi3Y1820Bwf3Doe4f3gPyyzFt6+/A6tXbRm93Z8mFrcCHynt3LS7KhsmLWa0SzW427DgzDYyhYstvYB6SchyWCAtmBDeBhFN8t0+ZysbzGP9rgoCWiMkfc7MbdtjrCUjU37AcbA3PET/5B5SxljrAh6BxTCSKpvJaIIHj7/A/nAPX3/zEZMF8Pxnlzgb/Su+/rWD7+cR0nofdf0AQWcPvX6M/YdtdB4GeNAB9pDDy+b4dD7B11+/F91nx0lJRkfQSlAt1zhOlnjy7ASL8BhvpzWulsCExnDrHOB1oDdQscYQc5wd5mgf9fH2/QKfxjPsHR/jaEgjBEp+lBhdXGIyvpJ5ftd2bdf+/9t2DLb/j8pGZQFvxDqbkP7uYuHH2q0VwOYp589sdnepsZnO9BXLXBDNrrIQ0WiWaBIAayUtdHsdk4EhXV6p6g1gYffVfBfzGXaSN0sUO4nqX1ZHjQt1pd6rfo1uqaV3vjiPcgHMBRWZEWQykJFxenIP+wcHWC1XyFZcNG4HLiYqaA5i+yxAdL4uRxc4e3CG05MzLJcrLCZzXLz5hGi/jaMH95GLQL06nEoAVVdIOh2QuNZOIgE79NvpuZMSQpZwEbxxciAHCk6+4iKp7ojUfqKg/Dpfqz4fSxGNfgZdNEVrRNgfdH2skKb8zgTXKDxvTAaqzeLYsrEIjEgBVbmU4wzigZSDyiKVuk8CGtVaEmoAOfmR022BDzXBEG0nKQ0lckG9sQh5kaIsl6JNJsAqP1T0uSwowiAox8mAQukFPow65E1tgC8LqpmuYWNAi801KkzNVzOgpvlNll0csZyDoNJMihLJLLMAjV3+CqPI/K3lbrYvmOuk9c0myrRR4VYgaftqc3ymP8rm/JaViMazHzhVIecvTR24JaE3BcwJJrQ7iQShClqUaiZQecjyAEhLrMYeilZbWF3LVYB56SP1IilJ9eME7soB5imCegY3KqW81qfuiJs150RLG104ZPZ5LDlW4MPvJFgvUnTCEEmnh8UiR7ZaC9ihZcWmRFuMKsiW1D6lPcKCjQoUKfi4EVo2Z1m2Y/k0/8tKF5N5hE5nLQYEy1WG2apEJ+mpeYG5rEK2tEwxG+Wb86xB+GaE2lydrbHE/JZn7NtZNhLRjYHgWAUvdHFyuMJ8scSn6xb8INkS7t+81+5Vh6dmZ+bJrdLVrU/XRc9mjLHH2JybZj807Ygb044yXyIIY7lH6bZZVClG47EwVMly7Q8PELW6ODw4RNsjQ7UwZhEe3IrQK3u7pgcsJu2HATq9rpiijBYLREEHVZrDD30sszVGV2NcMxNfkaXmyDg+Hl+LqLcFCwW0lGu7uU+03FwZpUnSxsuvfo7BYCiuzrPZTM43x+QoCmVc5pcluCYJADobm9JQAmziFiqMZeNqbEBG26/UV8JoL3LMNNqIymR2xNFuuVhitVig12lLf70ejYQBINdd9mNBra0run2BtkaHzWNzj2/1qe1Xmrfe2fPdZueuHWtt13btb2tMmD57/hQvXjxHFCciC5GnCxkzz3/7A77//RSvESFt1fDCDH7Vgh8+xNl/e4rHvRHauEQxfod338d4dRMgGLbw5MkJ+k/7cA5jDIMEdR1hVQQIWGPvFaqVOwlRXU7w/N5ruPsefnjjS+x19uBU2Oo5acMOZQjWEgvTlXM9m4mD8+HREe6fneDi44Uw9S3dVueD2zOXjinNRLq13fZMd3u8sRIV9jlbXSDJv7zEx6sxhntD/D/svWmTI8eVLXhiX7AnkGtV1sYii6REqafHZszGZv77fJqx91rvdaulFiWySBVZW+7YEfsydq57BJDForr7y7Qkg5dlJRIIBAIRHu7Xzz33nF9/9ZVossq4bG7381OYf8uka+Kje+OkbmpK/uBJfeyqaoAlmsw8mqLxSh3RwHcl3mlCpPb9en7fTXjfX9uopO42btuevfZz2Zj4dhw8fvIJBsfHQEgXd2qbUNPYxOL6Dklc4/Mvf4WiqvEvX1/CGxb4Pz/9F1i/f4n//nsP7+M+suoxzPoJnPEI49MQk09DHD938alXYYgEoCHBBlhsclzOYkQZUBQ+DHQQRQbsogvDY39gfBvDdw30gwph10VJpnqeoBSnehcJHMxXNeLVAkeHFkbDHm6uF7i8uYBjOsJQD7t99IYD+X50vt7K5ezbvu3b31PbM9j+C5sI/csqvNGl0q1dF+yG/TsPt+uEe8/vPrXbPpw2P97u75xzHkEk6mCwXJRZRgJtLCGdzxdYLKlbprL3Mkk2n6xLl9TXMXYWrHoxt3uw4g5H1oJizgmDTkwQCKwpEwRhwBic8MjkyhXjq6xE86fX76Hb6WI+n+H1j2+wWs/18egJfcdcQr7VznlrAJ8w6OLo6FhYH9+9fCngm9PxcPLkBL3hEDev3ooz++j4CKvZCldv3qPne3j29BnOz05gGnYrvi9mAAQtCJYZJb0/VZmmSYCITD1qdeSIqa9VKwF9zwv1aauRJRGidawNDHQpKN32mK3TblaNfpWc8boCFSgG/QpRVmMdO+LAqZhYClCidTs/n86gYnTQBH/6P6W51Syu1d8E2ZrPavoTy7yqIlH7sUNUBNsE7CsxcBh0xFimIdIyVOdeEQv1+VZZ1iYpqbqGflFnMxXwp/81AdfuIryN0WokaYS8SNANh8II0hdUAxNqQ14TiTvlOJrPaTpew5jRgJIs7NXiv/3cZrHPMjVbHYPtuOgGXTgMuBOW8NL0wIRBB1cCCZYpDrGKnUlgJ6ZGr5QyVMkG0bxCnVgwRz1g7KOmvoxlIclr+LaBsGZAaSCLaiTvFgKuBn6BwdiG1XVRlZ44lRLcKmuCubYwhXhf8Jz0ex3kizXskoEwg9AabtdFXBa4u5kiZhTJUyTJ6IaxqECVJgBW12nLGGvCYH1bK5YbgRNDaWLRXIHfNSfbMUswPjDQC0tc33ZQVo76OLJAdYZc1g/iGKoZl022vu0reshoB7JdWEvxPNUNbaA06dRmwq1LDMMInTDD+6mP3OigynI5vxxLXJf3mP4muqxTdSVeYzJm1avq9265StNH9QHqh7trBW5DFmsz5slX0F+IXYCahqZToBP2EMWJSlCUpYylrt9Bf3iAwyH7QsLKYlksUSfOBNmPmp2gh7Sc1z2rYAeKzUWQmcDp5fUdRv0BLt6+ww+vfoDp2Hj0+BzrzS1ms7W+HxQ7QQ2B1A5sTnQzZ6hteL89eHCOBw8fipkAmWtkEnNcFXdQ0RNV7q8qGUCHUMVa42JUOe9pxlpbErq9uC2g13Q5zUJTPAt1v5VFLsCaGIs4lARYIRIzBQWWbs9/O5p85O+di/SRbT6YWe/9/eH0eq9poFAxXvestX3bt/9sY5x3dHyE88fn6HY7CuznPJbmWLy9xOz1CpdGB5vAgO+m8JldzAcwJ2f48h9H+Mz977j80xy3a+BmTVaQgbS00O8O8dWXn+HocIzY8HBTGbjYAHibYXGzRjyfosxuUFKqwSjglDlOgzU++9zArfcFLt8NcXTQwXDcx3q5wMXrN1jNZ8iSKcbjCYosw+JuCj8IcfDwiZRufvvdd5IsaRhZ99rOnNA+1Ux29+Lk7TYqZ9AMykrj1fOYbDGxKURsVCZh13Pw6SdPcHRyjN/85p9Fi1Ic4HfGLUUS/ktjlP7UljrH96vn6NzNj7JoUKUE0VR8JCG9mvMYHwaODdcxEcdMqKjgQh96G+PtssDbWbX9wvxv15V1e0xMfo8mJzBsG7VNN/EKJYG1u2vcXG/w2fNfYtDt4et/ewOvBxyerzG++H/xu3+1cZn6yHGE2niK0BnCO/UxeBpg+MjFJ16NUZ1wUYEstZDUNuLawO3tAj++fQ2T64uKplMEOIfo5yvY9h28IEN3kMId5XCYZALNknzczjqY3cSIwbg+hJW4qKsVnDLCURBhclaiQAevXkciUzM5PEd3MIJtAGmd4+7iQgwU9qWj+7Zvf19tz2D7L2wqC85svAKXfpLJuJf1aZ77C+uIv9A+vphodvbBFhqcItjCkh86xXGRw4U1F4Z0HO10AtGBSjTNWVsWK4UAACAASURBVA6ppau3K9idAKOd9rcBhCzUt0GGLPhLxbARwEK2U4s+MrGknJSLdYqDF5lkfyhAy5LPR+fnwiaYzabtaWt+C3Qkek88lm3Ew/0WRY4F3YGMGp8+fyFisSuWXt3MsVqvcPT8oZR6/fjyFeaXt3I8QXeAwiiRlBFc34fn2mrhRVYTS5dYOkqnP5a6mlJ8qRwd8xxdv4bld8VRkbS0aLOS7T3fF3CMP/PlEmmiSvmU1Jcs4dV30WAAPy80Izw8nWO6sbFMenBtlhEaxFYUa00AtgYwaTlKci6IjTXsJcIU8lhYhQ34dr+fMfAh46qk/2lGnTnqkxkY+QtZ5N+lA9Rw28BwlyTWAF470msKSJGgTn0f3V1aVpxGu5oP33lMUXUPru0hTpbI01hYZe1mzfnZXuQtgPQhwLYTBKoP3+mpDeuGQE5RCxgy6g1glpkEnw0QRW2zhGfFcuCHXWH01GUKo8hRkbFGCHKRYj43ETsdVJ6NsO+iZ+cw8woDk2UrQLfO4RomnLwS4GQOB0U3RFz6KJYVbAK/boTctlFVrmjzlWWmMsq1KeYFPCaL50JfV5A1F5WwawOjSQ+mF2A5X2iQTGvqaXBRrm/DXCNAuHPamz6hflQJNNEjAii2QYZlLP07CA6Q5R6SzMDkIKXfo+izSYjdXILWAIV/63GA+2quYDM87Lx+7z7WR2VVBqyygmtXOB6txDXsejZkyC/3kyVi8wQlqV+4FhMPXnPF/WxYirusSgX+yMfv9FN1rLujZbMEaLZX4BC3a1INslVtirFrfziQpAGdmYssFWCr3z2A7Q/w4PwIBwEZYBktTRQjkU6kla04a/z+Guwl++zdvMT72EBIZbSSzm6sHFaMsu//+A1swxRQliLQi40q6Wy+gxpL9TVo783miyrArNPp4osvv8JwRNbaXN5PsIxsNddzZXzl2/icGBjoHz6WsvZK6UmqclC9GGzPWVMqvsvmoHurek2ZiABxtEESb2ThzTmAJaEEJdmfG9BbtZ3BqW27g07z98+3DzkTO6PGv6O1pkvH923f9u0/3Hjvcox5+slnODk5hk3jkiIXw53bd+9x8ac3eD8zceX6KLoFQm+NIOMIe4LB2QhfPDZwWn+N2csf8PWbHm42fcQ5jRAIvtjwrACjThc934Br1hhYJiaegWxswwg9dP0e4sRDFjMpRnXSAsvMwZtLYJC9xsOnC9ymHdxcJ+h1Ozh7+BCO52AwGGC+2GCzvJZxwaI8w+0dsqzGJ5+/ELb6cjnXLN1GSGA7V+wMefcHmHsJnaYUcxsfe46FbuiIqVUsLgvcTiWCKDVyfXuHy3fv8b989SUm4zFmHK9zRmjb5FDD5L8/rjUHsoP+7SQ55KjMCpZkjNW4/GEpfvP9OC7nWYGO58K1TXFjVTE755StBIfSK9XJy1YzeXdvujG+7oT45LMv4fYGynFcA391WeL9j1ewnAP86lf/gPVNhK9/O8PpJxv8sv9PWLzpYVU/w+XKR5SeoTY/wagzwPh5F4Nfhnh2ZuMLuxDn2SKtkeQucsuF7dsIXErf5HJtN9M5yszGsT1Eh1pvRoo6TlBkpvS3LONzEUojRplnCLwKpuehjlmpskEZUA82BGof69zC4k7ERXD+QCXAr66vsZxNYYchQi9Ef3yAUBt6EKzdM9r2bd/+PtqewfZX0qS8i+WC/KfLSP/d1sxL9f2/dxcLu3v66aLhw2fqn3mOx0c2gS3ubcdHRxgM+8L+4CLs6uZOyhopoC9L812gpPm/can7YO9qYtcMp9ZBTulfcSHj2FtWG9lsfI2LtzzL1YQkWmmmmCCMRiNZOP/xj18Lq02BNC1FY/frbD++0WcTcf0KDx88hmcHePntS2zWK3lDSaF5BjxegKPDYxoiokOXoHCIB2dnAgpmizlcamhVPD6ye7bsnJrmBabwmGCVBhyrhBH2MVtusFosRDyXJbhdaraJy6eFi8sbTKdrob7LudFacwoZKDD0NzCR4HpzAFgB3AZQE/0wiNNeA5wQ4hPGm7D5GRRpIXPRXdPMtYbJJEHV9uyo66YAEP1tZJ9lkcKr1iiozeZ27yMSLSOoudo8H2p/jb5Hq3clAZjetglC9f3QXh8BfLTyuTzZMOIM5NT7ipYIg44wlcg2bMAaBUYq2KNd3OvjaR43C3++i+BHw55TwBwBDgeTyQShxUBSCa8bFrXJKB5fY83gMuyK+UZJbZayVE6odgmripHOgSjzkR304IWmMCX7nkFaGwzbgEFTDLNEXlnCcIzY10ugcGo4ZY2ImjQUb54u4Nhr9IYZTIIP9gTTqxmyIsJgNIbjdeQaJnEkILTLwDSpUKXqelIjMOhZqF0HP76+wnq9VOeQxhfSr3hOtqXDzXVvGDsqi636jPQB9pMyQ5RFsJ0OHMtRpgUCXtVSzjvobBA4EabzEGUdsFOqfbflxaovbZmSzf2qr03bD7cst10GwGi0Qs+L8Pqa4C7ZfWQx3h9jJINPxmG8hms5oo23LUnR4I7qsPqnYUhtXSnVmKT7iN627Yo7nyZdn+MI2ZMsrfc8TKd3kgwoswL9Xg+mESI8OMDDkw7KbIOCY4Sw+lwB1uRoZLGlGQ5GjYgmM3SQY9ml4eF1buHQNHA48jBbLPHH3/0Rq2iBRw/OMT4b482PbxXrTO9b3ZKNxmHDWtMunnL+C5w+eIxnzz7BerXCglpraQbDImuN7qDKBVv01Ki3RkCNjJMsl98EwoS1Rhfkmj8CqTZXQJ9TfU3ly+nFll7UidZlVWG5WkiygueNi8UojpRznl6d/nT2+Ng8uTv77W6j+ub9PXzsufvvav+mmYK5B9b2bd/+s433L/VIh5NjHE1O4PoOzCqH6xiir7h+O8VqUeGOchRBDdtJERgpkHeBwxOcHxoYGhnsbIbV3Q1u5jaW+THq8kCSW5W1hOuU6Ho+nj87x/HBQAATx6uFfc7SvSlMXGUGNjcl1u9jzC4XKFd3qI0pKnuJ2ioxsnI8f5ijHj/Bcn2GybALi+X9Ro3p3Q2m17dIVlMUmwU1ElQSxTIxmByhMxiI8crV9YWw+ps4Yhvz7owoOw+Ne0CXGo9ooNBxXGEGpwRc5KWd8XR3NwJmVTgZj3F8eoL5coObqytESXJv+228o97XxuZ63pOZTsu+KH3fBgDTTOdmwyYp1h6H/nY6Du8GPrJCxeacB5tkpP56+h1bcE1mCm105VgWHp4/g38wFEMnmR/KGmZlYE7X6qzCw2fPxE37+z/PUQ4K/OLsO9g//oB//Ra4SDo4GD7HJ0/OQNWYZRwieNTDwRMb536NfpVJKXCemcgNB6ZjwqGEijjAp3j/7gqXby6xXifwKN9g91F7NtZpjrtZhCxNUBmFcm13Kjj9AnaHLPkKIc2mCh/LpYUsS1HY1EYlMz2AkdM0I0XHSDAZ5+gMXExnGW7mMXyvh8nkGL1eT+bQ+fwWt7e3QmrYA237tm9/220PsP2VNdGf0Ww2YQF8NPz/oDWzZvP43kOCdruC1qrtLkF+uihRS9rtlNxsUmuwy0G/18XJ8YlMDDzW6WyG2WyBnI6p3FgvttVDDQypiOCe0qp8TpvJ0wAb/5byULWgIXuNTA2WJzUuo5x8OSGpMqVMmEMEAJkhHQ4HoiH33Z+/w3KxUIvjHQBoF+prj0QWcHqZb1p49PApXCfAN3/8A1abOcajY1ihh95JgJ7p4mRyhqDTwZs3b3B99572QjgZH2HQo7C7EqNXgrbKCEFEYinMBgXWVaUyvChdDz++ucZmvhTQ6uCoJ0BhAzD+8ONbLJdrmCJWq0Anx1gjobOkRV08miVQs4gaXVqg39xdNPI7sVRVgSTCXhPcRPWvRn9NgSj6/DTXSZ5T15Dgze75ajKjBAloQ2DadGmkIn5TJ6ezti0/relHmrWm0Ij2KTbB1HS1gABi+iop/SnND9op9WxAM35/slySZIFO2IfjBwIgKj0TtYemb6nP31nwayBOwLX2KCmeX6M7mmAyUGyxqnCENSVuVp6BRZqKzh1LjIuC5QYpzNqB5dlwqjWy5QbxmufNg3c8Rm/oqKw5tV2orGWTgVUjTktUeSlGH55nw7UMauaK9grLAR2jQFwAt9cbrO/msIwYgRmjquc4fHIGw3uElB+fxxLsu15HShDjeA3fdeDQGCPJBXxiwYdhmwi7JtaGiddvLsSSnplnMQ1o6Yv6HtF/N7eu9GGe05KlFWtZuIjOmUBkpjBQFcKpLrBigpXo+THyLEWahjDJKmtAO2FONn2gYZXpV3h9xEijuSs1sFsDrp3g/GCN24WFadITEL4F3nRrsdTdfocSWbIRRhaPW+4n7aQrD/RKQDHTtJMsmVX3+qmGbJuFw87ncCHG0ZaMWrq9cQxiUG47PoKgC9ty8PDhMQICqmR62QVqg86gXHDaupy5ltJefib11FJEov9SZR5M6giVZMF2kKQFvn35LRzHwPjgBKtNjFW8xiZa6ePTl1KOSQHUMgsQANOLNZb4M1Hy2YvPBUSbTmdiICDC0g7PkS2i4jwX1FRTZfq8F0pVFiruoI3zLMH6clsG3ID77Unashb0ny2InsUbEXzu97ti3LGk3hGlAFpZgftNzVTbkag5/z/danf7D5sepD7Yw/Zd+r1iaKNYax/by77t2779fBPQZTDAwfGZ6HLaDD6sVOa+24sLZNMMiyLE2gVML4dvxrBKIHfHsJ4M8awzhZduUGxyLG4qrNcm4jIA8ieiTVrZJWp7io5biTzDo+cPRffKIuupKOAaJRy3kjLDynBwW5t4mxlIriqs328wv52jWlyismbCSOqGFn759BydIEbVT/H25jGCysH4dCRj3OXbt1gvbxEt75AnEazaEOZwWdkYHp3B7Qe4vnqL6Xym4wkNJjVlGjvz1PZ1ncKklAhlWRwbm4hJNzUXEkC7PzJt0xfbnTIOAo4Ohnj87BHevrnC+8sL5RCtj6EZB2WO2ZlXm0NkeoejXMEYURI8O+UlzRHr77Iz0+6kyZS2mmeZolOcFAU2SaZjtuY76zLWprJAn5rhYIhHT5+i8n0VCGqSQbqKcXN1g8OTM3EQffPnGW5uEzz41SUeR9/gz7+L8M0swLo6glGdw7cG6I4cnD31MXrcRXdg4IwJbcoXZDWSiuWmNjwaqzEhXVcSE0TrFfKsxOW7S1zczeHbFUbUnSazbFPhOiK7GtjkKeoyg29AYjXLMWB0E5hhgq5pwKpdxFkAGs5mdYzU5VzvAVEIMwfMKsKBmeBkDFh9F1e3Ca7vlhj2DnB4ciIagJlIetzg7vZagMo90LZv+/a32fYlon9ljZMNF6CSvVF2a+qFn8T2Hywb9KLlp+3+VLwLLP104bFdtGy3apraWgCZigL8qZSNssQy8AP0ul10OqHo8CRZqrJhaibdCQc+mKwbtszOZ6nc2e5iWzNedHmaqjxS2yrwjUCUKjXiApAGCGmaiKD42YOHcG3S95fKtfXeirildrSHsz3KGrP5VMqVnn/6ArVhobJK5EmM28tbfP7iS3iBh5cvX2I2vYFp+rDNEJ1eB+PjQ4WOVIVon8llEbxBl41J+aiB2qqFnYY8x9GkC7fTxexug8U0QhSthclBUGk0Gkq5VLROBExkdJKbLgzbF6aSlM6aNeigTrdEKQeVr6lDKO3cqLRoFTuSy2B5bqdcTzGPtpdILW41QCpB2fZcEXjROBkMm+6iFqoylmCF4KQ6AAWkbpewagdq0a9OuD47qre1xBYFLjQ9Qm+qQZ6m1zYvbPdOpk3gd5EkkYj6E5AlSKkYWc3+9Ce2faD5BA0KNEwpy8Xk+AjD0BB9NLo58pLy3OZmhVmUwgk6cBwfeboSzSjb9OAyY57OML9bY7YqkRYWLJasDDw4dYWotGA6FnxeL62vIppThonAIbORx1DBImDJ62OZmFHnTUSXLRS1hcV0jukyget0YBcxAmcBO/QBqytlxQQryLLzA4o150iLDHZIvS6VmaYrWpEYcIoS48lAnD6TKFLlze3ZVCw0PmoYjsKC5HUgY5C6Ym4Iy/baspjm9/YO2l73LGe/t2GbBMNT1JXVuvM2/aHtb837WDaqy7qlb8ilKkRrbdzZ4M1NB3HRuz9GSv/ZuZGb/toeC8vMKcxMw4dE7k+1451xSN8LzTuaPWyHo23/2/ZGBfySpUFdyNvbKTbrtbAZw+5AwLxB/wDnp2NYZSbuawoRpM6aA5P9SwAolkGq/d3O5pjNGPQLdAnLy2C4HvrhCMtVJP3gzfu3sOwQDx89wOR4LGziOIn09WvOW3OPKbCI4J0kSgwTD88f4ZPnnyLLCsymUxk72RzXFb01lm0KO02SGDxnTTlogYrakLqUn4sh6k02SZlGy1CSFq3m2hZgk37P8rCqwGa1lKRSGAQCrFFLiHpurdvcdhTYuRqqtUPJ7rjwwbb3n9m977e99eea9Ek9x3xsv/u2b/v2843j4cmDc0xOHsAzfRhZhiAwMLu7xc3rd9gsTVyjiyQo4LobhIhh5B7K8Bijhz4eu2/hZBdYrje4vAaWaxtZZqMo+/DtLg66No7NEp16jcqgPlYHJ0c9DLuexEUVSxZZUZBTD7OEZeToWAYmtgmzbyIZuOgEIQqjC8wtPHwywovPnuDPry7wzZ8vYNzd4rOzaxQ9D+8uLVhViQePH8L3mcQyJElW1pkkGqQ8f7NBsl5jfHyC0wenuL29VrH8z45GKjZmwoNjzKDjyfY0CWqKWPSQ+cEoeD/p0CSlOebHcYrLyxscDgd48eI51tT9jJM2XlOs/p3j0PpqrsSLhqSAxcFz5xOb/3c/VbHc9fO78ywT32WNNM8kPu13aZJF3Vi9R60V0ZwVatg+f/4pug/HyHwPrmGJAil/bm5uMV3H+PIXX8F3O/j9b98iCiz877/6LcKXL/Gb/wG8WvcR109gWs/RH4wwOetg/Hkfw886eNoBBlWEaLZBVTko6CjuKXCN8TIdy6LlQrRSLcORMuD5co1lsYYRrmEP5gL65qXSfmZsy5insE2kjE2ySuaqOvNRZh4Kg0BuDs/JEQZMTIWoUhcVqx2CXPTjjLqHBBaWmxJllODo0MRkQkmGDS6ur5DlMfq9vvwMDg5k3cK11h5k27d9+9trewbbX3HjgoRlo8KooPaRsHI+Euj/5fXFR1vzlp8uPj6y0c88T1DL0uWZh5MJDsZjOI6LOIpwdX0njoIKLNlZODcLamEDYWcx2IAfagO1GCN7RH1//uZkLPo3osfmwGagpFlunICoXyDuddSBgCEuVYNBH67r4YcffsD7929bRpb8bll1+pj4347YvRyu1o2QY6pMhK6Hs7NzXFxf4FdffSGLXboEffHlM7h0GkopOM+yxRQeHfc0qUvIiATXyDyjaYNRIasj5NFGyrmGfRf+YILXFzHevX6NuuJzHh6cn6qSWZhYrWK8v7gRrSMBFgmq2ao0VGzCOcHzW5Dyrs+1uEbuAGhKe+0eWUlP3mrBqWzeddmanAKlQ8bvv4Vdd8GUpjVOqCks24FpKfMHVS624wrasFh0trOJzhQgqE670SzCm64mMaAO+HbNCaSLqOcVP41ZSWpflVjHS2JS6IUDYa81fUz6ShsqNo8146o2EA5HOOx3BSzksVaEDgSdtLCOMxSGI2BylkUo8gSW6aEbsKxzjmS5xt2yQFp5sK2uuEeGgwCW66AKLQzdGi7PkdzHquyOn18RJKormBVZOzSP0IYUtFI0HdzCxHRZYPl6hkHgK+BsvUBZzeEaGU4GBfpHNir3GZI8xGaTynVwwg5cz8cm2oggc5cupRlBXTIolUlBgQzhKMD1fI35zY2iVso1bwo3lfYVg1FmenlkjkvWGsv6mv6hQbbm/tbEW1kkyIlWCDkfUrOtrjO18FEwo7r2DdjbgGzNGCGHUCNwU5yMNljMXcySjri8tWxJ7p/3gpQ/E1TdAfX1/hqmgO6q8ra8TuEhh2mGyp1M93HJsTfMKQ1SsS8oPUO9W/0390UglywNCvNHm7VoQ1Jrxed5cgM8PDtEYLOkWJYvilEpLrtqfBPGqf4uUZri8nouiQoZO4Wta2JyOIBRWfj6D3/E3XKKh8cPcXb+QMBUbus5Hrq9jjDAfvjhFabTqXLllE9U4yN7M1mGnW4XL158AddxxLCGrDUy0VzNEib4xquhtNZyMVsRd9BSgWyiMyjzkSoxV2O2Yiyqc68XY02CQf+n7k91RFEUoSozSR7w8xfLlXyPn2Ot6cv2kec12/BnJqzte+6/9rFprX1ND4ycWz463+7bvu3bzzbOsZPxBAfHD0QHs0wyeEGNNN1g9vYK9Hea5j5iz4LlxwjNDZzUQVF3YR4NcdiL4JczJHSkTunIaAG5h6rwUNQeQivA+WiATt9AlWdYRzMsigLDkwmePT7B6GAgSTKOCgR2ckouZCXssoRnF3xJXs9g46IycDMrcZJkuLpb49/+dIOqWMI0lrCMBL5Z4HF/hSef2bgOvsLN+wFOxx35jMV0isu3PyJP14hXU9R5LQwmJlEdd4SDpxOU1RrfffeNlLrL6CiJVhXbMmgjuNYJAhXfxZFO9OwmFlqe187/u207PjHuk78kkVuLJu/j8zMcHk/wh6+/xXyx2Iln1bTpiLN8hUzi8V3l1WbfamzfPt/S2fXkqLds523OHY18qHovdexCz8UqSlHSyVw7xz8+e4iDUQcXyRvUozP0zCEGpo80ifD67RXOH3+Gw8kIf/rmPRZpjV/9YoqTu3/G//wnC68jH1k9RmWdIeiO4R93cXjoofvcw7OAJgaMRTMUuYm0cpDLpF+hF7jC9MuzBCWrEFhRkBTYxDHmiyUuri+xTu/gOBGCYYRev0I672Gz7IizaG1QhsRDWplIOCemGdy0gMcYxjPghAXcXgLHy+AaLsqsg3XG8lEgqTJkvOZJB17G2LwURtuhm+LoYYG8cvDuTYZFkmAyGePs4QOYpi0g6e3NJebT2d4IYd/27W+o7Rlsf+VNXB510KKC/Z3J7sO5cHcN8eHjDzZt9nJ/0fIX9t+2ndcJamnB680mEi0xlnB2uz0MBizdMhFHiQYGtYSqFqreZtR2Pv0eTUr/pwExWcDJ99mWrbWTfQPKiLC5Kuniwk9MGPTi8fj4SNxCubAjY4egVSMt0QYwu5+pj2fLqlEMlWdPHuPrr/+E+S0DwBSjgyGePnsgTCT+HSeJOCqtYhNZkaGOI7gBAacGWCL93UCc5UJLJ2jnd0IBWcqkwLhnYHJ2gmVaYX67wWw6E3DECz0pITw4GMAyLGQJS88M2HQtb8rZWA4gl1Az1krtCKodTptz2ABszTVUYNoOyNHSzLRZQQOuSWCogqaP8T8ELKAWF0HOPG7BLAWy6airbTsBmry4LWNuADAFk5A5pZlM8mLDJtrpK+3fqj/w2nqeL09Ta4xhIzXCtsyk5lrry82AzzBwcnqGceggT0ylS6bBSro7TjcJ3LAHz/cQrefCJqTmWz8sYCV3mF2vcbXOkdYEtfpwOx3YYYCk48LpWTi2C9h0iswM5LUjgaiwf+oClllR4EqJNZs2ipp9h4Aug98CVnyHkCWkpwdIHBcdwxGdt7ywEeU1ZnGBZJGha7yH57O/HaAyQmwWCfIyQafTkczrer1BZTHgdSW4pP4Nf9uFgUG3g+54JCAimZoNMC6/ylSE5003EIOJLTat2IENuLa9gs2lVtdj29UI9gofC47D+5XlDzwHqjy16bvqFtfXvK4x7q/Rc2O8u+1JeZCAYdxedcUGwZE+v4XA1EHsDmHt1dfAOe+jhEBXlcA0lyjEXMCSBYB6/3aIUbvT90TLdqwEvKfD3O3tDdZrgkQJep0ePLcDbzDE07MRLAbWZAgKkGbDqj3lFCoA2xZcu50v8P56qlcn+qzWNc7PH2A522CxmAlwzVLf82dPhK02p26Z48k4TNdP13VwdvYA/f4AN3c3qCTZsC11fPL4CT7//EvkaYbpjAYCiXxBujIzacFjEodQXQ4qzs2iuaZ+6ODcGNHoUVID1OqRmqc0QKkTI/KvYYLVFVbrBWwLwnjmom+12SgmQMtaa07+h/NT87i597ev7G7z88/vXMsPnlcvqvPNe1Ppzn10q33bt337SOP9wrnm/PwxxpMjmVOpteZ5Na7fvkNycYtV7GJu+Kg6NXyy1soUZhqi9HvwJhYGzhTlcoPprMYyBrK1hSpnZUQHpekgcC2MQhv9SQYzKFD4K6yxQlLQqd1H1/fgC/tfxUIcT6SSwDZRGBThN1kDKbIWTPb06hIj18BlSNftEIHZQUHmURyirMguB2apg4vLAmfFD3j4dIkfViGmlwlGBz2cnp+L7INZU9vTRFqm4nbJpOn1xaXEeZ9/+aWMg2uymtvYhgkNE/0gQJqUiLPsfnJCx7RbdthPxyL1uk4u7khntPNhXYlZzfXVDT799BmG/S6iTSaMLPKrepT9rFRJ6NZt1Lg/fzcJzZ2QSW3QaHk0b2mOuz3g9gvQJCpJc3Q9B5bDxLCJL158iqD/I+C+hFmvkGw2SFMHqxvOSQa++vU/IolS/MvvLxA8qPF/nPxPrP/b9/jNH128ywZIjSdw/Mc4GIwwftDB6EUHZ88cvLALdKpUNE+T3EFhurB8C6FnIaAkS0LpjrWUw4IgWazY2ZznojwSBnWapcgTIF/T0Z1loRDzICZdrbqUOJnhvENzs8BFJCZEBsyUJgU1ypxmXw5Ks4BtFQitEh3Kf9jUibVQOTFyp0BVd2BUATaVgcVdDdeKcHrmYhD2cXM3FSYiyQQDVkEMRwi7obDMZa5sA+J927d9+2ttewbb31BT5ZBKELoFmBqkamdB2Lbm74+sEz62dNhu+sGr7X4/3LleZOu/ORkQhDoYDXF8dCzBFiculkxRjJtbapW19tg1b6pdtMr/zcvtR2njg4ZFIkBao8+mGG2iDacXRXyfZvTWrgAAIABJREFUsC0044I7I7OOJgL8ubu7ww+vvpdSNy5WRTuqZbapb6mqxxr0TUURsvg0gUF3iI4fCAhz+f4Wrmvh/OlDjMZj3K5SRFmJXp7CRoHKd2AEdPw0EZohsQqslhHyIkfoBLAdD5Vbo7RygFm3qoZDa/bQw11U47tXbwSsoiDw6eGBlIyK1FVZ4PrmWphUZJzwpDEgVOCHdvAratEoEZBWdDcUS0tMDjSY1pZFKlTjJ32qxUnkMxQQ17KV7gVjakN5RghhDDQiMVyAycyfuvKyqWazNN1IxWTN/tQ++TYaNbQb6LKCNvhsmGs6oBMAV5c5yCJd2GoqcNzEK5RpIm6wtsfMtr7GUnxnIugNcTzqokpXiBMbvuUr5qhrYJomyCtD3sv+wuwqmWm9wIBX3CFZbHA9y7EuXVgO3XX7cDwPWeDBHVg4dSv4FUXuK6SFg9K2pb+wrJdC8mSaESQtGJjRCS3wUdPYoASyVYpkvcRw6MILHBiWjdhw8L4wkc1KmPNUQJVlNAWKObw8wsCtcHRmwDs4RWIeY7kxUWw28EMHXtgTnT8aIYSBByNP4ZXkUvlSmF1Rvy+wsMpyvHv3FkgjlNkarFC1XE/pq4mJiTY7aPvIDvtMZNp2dNuartGUYTZdyyDMRmFjpUuYZxbKymuwNumnnlXgqL/EKjGxTLraLKNB5u8vQJpFRbsQacfE++wmeat2tTVJ5StdGC6vQwWXemdwUVihdvTc2Tf/loUIRZdpJVnj8PgIVVHh9u4WaRTD67iwvQC+1cPh8RBdu0aW16gt9jJCdywJJUC2BZzZRzdpjOu7OyQZWWvK5IDw1Wg8gW+7eP3qR/z5zSsEfohffvELuCHLbmhioO7jxWot42qv19XzhClalASD3799hx9fv0bgeXj+2Qv4vof5fI4oitVY07DWBAwnC7hUJgZ0BZXHHD+UQyjBOikzbceO5vTohdhOSae6B5tzx1IgQxh+LBEmY4PHT23JjBozAuTuXLvtxWuv2f3Xts/vtt3rvPv+3T3+XFOMZq21tgfW9m3f/lON48jx5FgZ7jhMEuWSPNgs11hdTFHGNRami8IxYXsJnLqEnbuozQBO10EQxDCKNaINwRgtfF9S26yDyuB8DPh2Dd830O2XCA8SmHaGslxhducjWfbQHwzx4GCM8WQI37dhuw4MhzEh72k1d+QVVTkqGDTIymP4DuCFAWrTESOE9ymwuSiwvsqwuJxhk1wDxRQWVjDNEhMnw+dfJChGT3C9PIVd9nF8OBRzl9n1LZbzGyzWU6ynS0ny0nzIMT0MjobodkLcXV9gOrtByLgQJqIkE73XZoTTxfxao0zFpKzqlxisjZ90QlTOvI6Z2qRPE781r+p9G8B41Mfx6QSvXr6CWVSImddr02J6P7pqoZHVaP/G/WTTTuC2+4w0lTTXSRd9wFIGa9R4dP4I4xHBy/cwgrei62rAw/VNB7PZIT799JcIO318+80VUrvCi2fv0H/1Et9+D7yJAkQVWWuPEXT76A189I5cTD4L8KgLDGvO57mw1jLOs44NxyLAqs8c5zDKyCQplivG/opBzmuX5htM11O8v1LSMCXlEiQ5VUhSkjEZtZUdk8lNF4YZUDQQteUgsy0kDJKWJew0gYkMllcLI9wNK1h+Bssq4RievC8pTSRpiRnZ4bULO6K+aiFsto6ZYtyrEfYdXC03uJtmCH0fh4fH6PT79MbCaj7TRggkL+ymNfdt3/btr6ntGWx/Q02VQdKtUzECGvDjJ+uKprUroA+e/2CT3bdtN/3Ymz7c4ZZrpP5SCzQu3qh7RsZDEIQCCtH2nFoQXFA1UUIDtzV/Nbtu12UNmUwW3Drw0MFEu9AThp/+3YrCUpuMgBtBOHV8BNqSNEGapGLM8OTJUwE1NtFaFpC6LlRnArfBhjqWRiRcCbSS9cGMXNjrSYaQ35HA3ZvXrzE+6GHsO/I5Vc9H3WW2MMF6EeF2tkFKgVSzQL/TFfZLs7CkTYGI0Jsq6MnTCgFKPDo/Qe2GiDYR4s0ay+kcQceDLXpPfXh+iCxeoyjJBhJzK5RSFqq01lKU8OCgrJUOhjg9tijH7sXfLmSVpfoWDJGyAh0tiY6XBIDN29T5Uu/VgYwOGMlmk1xxEYtQby3smwYw2/G6aAOxpmRTgWVNMNkAIsa9ILJ5cUtybIsp9I0hx16XoiflBx1hWDK4ch0yiPhxHk7PTjDp+Iyj1HWwaLFOwNPEbZQg6KgS4/Vqjiyt0OsEOAiY1nyP65sNLpY5sqqPwBkjCPtAECAZ+TgdWTg1M1jUBMwYcnkwPAe+S4dPnkdqW+VIkwJFXiETcxDAdRkQmkiihWTsO6MBitpGRR2ZOodnFDiwALtjY9XllXUQ1j5Q+khyE3elidtlDWe9Rt/+Ht2uj7LTR7YxkGxWsB0L3d5QdLeyqhL9NikxVhdaSjjIiByNekiZec4oUKLcJ5pSQ2H66PFolyMm10dr/ulLc1//bue6NNeJmd+ysOB5Baw6RVlaAuQddtfoOhtcLrpIi1D20BStbvvAFhTXe9RjotYI1M+35eDtViq7T9ffmrXVhoVc2BYD1CZrN2IF/+p+3Rww/+L56fQ7OD45wdXVNRbLBaokQSfoi4j2YHCEx0c9GHRS47gizqmulA6ZzJvzXMvpVJ3+4voG19OpckNupKJtE08fP8XF+0v88U9f49HDRxiMhnh4+hB5SQaCShrIWTVNBL4vzOHZfCHfjY/J3GW2++BghEePznF6dialq3fTqTIyIJTouUqrUAxjyPjNkeWFlLLyt5SF0sxAl4NKYkefjDb5QIdfSXzocax5LI7PyqWWp369WIiZRhD44lK6Wq/le7SA+L2ZqC3w1bPL/deaS9LMPNsZaLdtB5dm2482YVVu9Tz34Nq+7dt/vPF+PxgN8PT8kWhgqer6UkrnZhc3WF8usUpdrCwHcCMBGxyjhp33YHd66I8r9N2lgO/zdS1zJTVP69JDVndRGz664ixMF/cKrpfDDlcw3GugniNdV1jPfZQVWdEOfI5pWp6imSKUfqiKLKQ8sCyQcpwUqQMbRlHCNAqERoVD24QztBBPaGAUIixDZEkXcU6NrQLkPr2981HczPBs9A7+sYG3lybMwsDh6ZEwjSzDgx24KKS6wIRNsIfHuVhheDzE47MTrNcxFuuNmo10/KLCzsYcSMdFzdjVBsVqRNtiW3qEbOKpdqjUGzSJDpbKZgmi+RRJBsTi8Lmzj7pB8nbbNgm6+1nbXTcv6DlB/38fd1MRwujgAJ8+eoCe9z3M+kcdhz6Va/36oo8g+CW+/OJXmF1v8G+vljj6ZI1/HP433P4/7/HPrz1cZhPExhNY7lMEp0McP+nj4BddPH3q4plXIqwSVFmlWWt0C7fh2TSg4PktUZc5yow6yjmypBLznhw5kjyVc14ZKTbRAst1hDzNJXEm+qOcHySoroW9XRNwM8k+o9QFYJcF3LKE6wDo2ig8V5jwVQpUBHEzS0qbea5zxLARI7RLhC7gslqB+3UT0aQ1qi6yOsA6sZAtc4wOUhyeBMjSGu+vrrBeLsVhm/fZwcFQEr10G92DbPu2b3+dbQ+w/Q02YSTJoqBhDfxk/fHxtvPavbn4g0XKTxcku39tJ9ifvsamFiwE1+iit9msZeFCNttoNBBadZokwpCQXbXgTJMR0wHDDmDS1nI2QJpeLPOXuFtWOwv+ZlGtD41ZJ34+F3yciLho5AKTFP7jk2McHh7J8TDAE95UQ33X72/gr+bQWnCgrOS7vfjiU4wPJ3j5p5e4uLgQICzodUV0vCRYE6+wmdP9qsY6yjBdLAQkHXR7sG17C1JKMEjeFrWluDKtUBo1ijjHgW+Lvl1K3aw8xnI1Q5GnUhLhui66vb4AFdEm1udMgxzyox4VbfnnzvVqQYcdwKw9d+1Sehs60ZlLX4ptKPZBkKVZSs0zXLjSOZIAQlXEAmZI0NcAmrv70DttCXTt07tonMreymFI398JNtt+oo9aHjbngQF6CNu0pFTD6/Xx5OEJfIJXBcv1FOPNtG1s8hqb0kSvP0SepojWS8DyMBpY6NQzLK6meDdLscht2MYYoTcS04My9GGfuHgU0BJ+g5L6MWStOQ4ciuta7GE8QQz4CGQQfMvl3LCcV0mxZYhWt+h2hwh9T4FfFstbDOSlhbpgwJgjMCsMbSDv2dj4LqzKhWv5LGQGZdZmWYXpzEZQztG1pgIK5V4HeVygSCIx6WCAFqcxcmaXXUsytgLwGjXKKMN42Ef/6BBZbiCJ1uq6ySnVoHZz2tvTvBNoa8011ec0FtY+0V5J+SGAmpVkh1oI7BTjzhpr6vTEfdGgU3vaXtemb2x7hLpn75d8q9b0iN1eysdkzxmVgcSm5h3/LlEJ2MZSIVfKYg1GyXTR1OUzZEOePzoTZtibN68Rxxthj/puiMJ2cf74EcaeI2MLWWsURSYjzqKRAZlp4sxGmhSQZhl+fH+BKEnb8hye0cFwhEFvgDffv8a7t28kIdHpDeD7DuI4ErCLdT33QUOVUCB4xUTCar0SRhpfZ+k+xxsa0hDYImDGcYfgGoE4npCGtZZpE4OSJTOiZVmp+1Y+T7N8m/uq0UDUgFrDYFOacoqFR7wqTmJhBHQ7gTDgpvN5K9q8TWbsNnWF71/x5ve2A334ru02qtU/96qg8Wo7NV9QYNxuHU33bd/27d9vvG+DIMDR4SEePDiBZTGJR9ChxPJugcXlNeJVhSlVLn0Ttp/BJUVa9D9r+H0f3X4EJBSWL7CK+DydlB1UpY/CCAX87/o1PIJqdgnHIWs3QVZtkMY5oqWF9TJEnjqiker6tuju+h4lGJg0UJ+lNE0hhlx0/uTfBF9MstssC0VloqIkA5PXZiFukEcEZ0Y2qqGPkGM4OtigizwjEFJgXVi4vDZh31zj05NLJIGL69tKSgAJtNE12qDpFB1GixKWXSMcUgy/xPVNigfnZ5hMhlivNjJmy8jWhsBaz7IZG3Ucqs57M3w14+F2m+0vZailfqtKgJ5rwDErLOkqrqtE1G52Z8cmzNrRet79rN1Nt0GX+pzdOFk/x1G864eitfZoANjR7+DYKUyzguUkmK9TRPGneHz+D5iMx/j9t+8wN0v8+sVbHPzwP/C7fzLxbdRHVD5GaTxBr3uMg4cdHD3v4OwTDy86NSbIYBSZmF+klN5oTQwYq4pOikiWFGkpbvApXdv5zyhg2oy5KqTZEmkSo0gNrJcx0oxsba5jSMfX8x4fSl8iMMkfmlCVYmBAEM8qC6lYsemG21GOtWTS1XmJOmM5ggOjUiYWFV10zQwdp0LPtbRkRI3KKVAyMqk6SGoLy5WFalPicGjgaNLBJs5wcXsjRl6mF0glTZ96gzTfyvZuo/u2b39tbV8i+jfeuJBiiaQsepsF1+7q494qeNuaP7eQxP2/t2+7/9e/33b22Ghg2Db6/R5OT0/R6/Zk4ppP57ibUsxbb60dRz/MuskyXr7bVg9NZesU/60xQmjLRVtnUbXoZOmoLDaFtVKr0ifRMCil1JQi22SCURz8u2++wWqzkg9QDBZV1No2AXaUOPzR+AhPnzyVp8nGIKjomibiTYJvvv1WNLW+/PUXwjx58/oCs9Wac73WQqPwRYnTgwHOj09gG6KipgwQNIOsMhkEsHyKZaPE22opE0xqB+/evkZeLAWk6fVGGB1MpASWmbfrmyvMFixn4AlUwUGDfSjt+Qa9avj+O4wife34+QJitSlRRQfiI7MBVzRDSEFcTadpixjaj1A4miphZVBSVol8dyk5JNimAzHNW9OBnDr2FjzWvbAxt5Jj22HMNEFdA9LKXgRc1Tp7cvn5vZjl7uD4+BC+Re0zAlbUxAIMt0JS1VhEmbDWCEvGa55jE17PQ9+aIZsucX2TY07fVKOLjscsYogy8FAduDjrGhiA4h100rWRGzZsam8QWBMAiCV2Wiye7LWUP+wUXAhUWMzeozsc4uj4WIAbwybjSYG+pS5vKXJBr+Eih+OWAgjSVfaitjCf1bDvMmTrDZJ4hXk5h1snGLslJgcFOsMuDO8UUREg3aSi4UdmH/t0HC3h2AZ6nS6KdQynZEpWlQ0aHpCYwKs3bxGtZrCkDyixYgHPJJDXkJt0oS34o4inui+qomkJSIWp1fQ6radGh1CjTjDbdATkEr5o6yQqO7rXX7etYUA1I899pK15TunFqb5AQ5DCoiGGBatU54L6cOwjql8pJ2CUkWjsjCenGI8PxShlvVqjLHMp52W5yHB0hPNJD8mGjLUcpsO+S/CKDFXq86hjoZkBTTOotTZfrFrGJoEn17VxdHqM71++wuu3P8h+f/HZ5/BDF5v1Rp1v+Vqa98vkCsc6un2adjvOqYRFLVptHHv5XvY3nmOOjQTkuS2/I4EzjoVkq4nmGsdFgmoljT3Ue5ofBXrra9beY/qcN+CaNofg2EMDA7KDaaTAUpnFaiVjLPe7+97da7jlQ+6+tr3au3PV9vHOM7pkVnfL9tWf9JdGP1DPG/u2b/v2H2+8Z5jwo6atQzMBOlU7wHy1RnR9gzyuMM995I4J0y3hWgUcMpNNH9bQRWCvsLxdUn6UIgHK6IbJo5pGB6r0ruPR2KYQYApWCcvMkWcpsjxFVlQSN7KJCzNsSRD1BgHGw7Ew6nzXhWnwNSZXDWFv2Y6N4aAHg4kF05DkFuUffDqJElDJKth1AccmIKaMEMhYe18ZuF7WyN5mmN5sMHt/BxMLOLiDZcYIzAKfHkR4+MLDhfsVlld9HI5CDEZ9zO9ukMRLFEmGH3+8EJBFJD0MwPYsHJ0NJZnz8rtvhUHchEANgNX8yfax0bFp23lPx2Qyb9boOAZCp8Y8ZdTK+LKZmnf2rAdIFdepObaN63ZmV4nu9Ftk5topQWiMbkTGQbPjHp49wNmwh/Ld79HrLlExdxwAUWni1fUhjp7+b3hw+gAvv3mL1DPx9DxAuP6/8fJfpnh1M0BUDlDVjxC6Y4QTF5OnHQSPXTztAUcoYJQpiowmBjZqxxLNZ7qDqiqKErVoARNYo8YaZQ5U3EJzicrMUdZkaOdI8wTRao71IkYYHuD95Ry3szvUNYFPzld8D2NfFaWKXATDModCbDQas+AZdIrnWsSWpGDlukhyD3FkokpjuAUNlQzpg5ZXwewkcALlassS4lXhI8pdrIsSKePDzINDLeA6g1NFGDgZJkc1csvE+8sNllEhOquPzh7B8GwkWYrriwss5/M9o23f9u2vpO0ZbH/jTS2AuKBTQNtHQbYP1ysfmaE/uhBpJmv9+8OF68d3qB/rzSVjU1birLnSTnHMfBLU6nRD0eRhoNMul1qxVbVvBZo0jz8WF2wND5QcgXZA1Gt8+dFv4flRjCqV2StKZYHNH7JSHj1+LEDVcjFXpY9mAzZt3ZUYtH3yyXMRC6f+FVkh/AwyUu6mMzh+IGyfXi+E5wb48ds/4+mnTxGGPm6nSxgU2dWgwiqKxBEw8F3RdOPzUj3WltXpejLRZKqQ5jXsqsLx0RC105fFc7raYLZciLYSv0On28Gg11elaywla+Kelim4e7Gb2oQGWmtKKnQwtbOJPLNDTRO30Z3s57aP6IBMu4fu9gf5i4CAY6HOM1RVIQ6MTZmpYiC1H9gmSRUEt+2fck12Pqv9Gvfeo3EevV1Vmej0D/Dk4QS2ZCJtpnJh2hWIgN0uqTVmo9MfIs1YjruESe2UgYVudof59QLvbnJsKpYejBD6I9hhB2XHh33s4pOwQqeOUSbMiLooXReuZynWWlumoLWtWJ6Zl1KmyfsjKzNc314i6DjSf1haS/kPBnYSyFKri2XPZNiRiWkpsWY6gRplCRs5hiYQhDZWPRu17SAwfThmgCK3sMwrLKIC6aqAjzUCv4DX8ZGVDrINAaQCXkB9NgijzRDBe2bqKexroSqZ3a9xeDiA1xtiQXOEkmwC3W/ulV/ujCINQK4xXaXbpoJcycSLpS1Pf4Fxd4V1ZGCV9wApLeablPtrO7rsXNv2Grf9rkV8t013mmacaMsam77UMIFZldruTd+f7R3h4NmzTxCGHfz5z98jplGEsCEDcR89f3KO48DD8qZEhhSmncO2qNGiXELVF1Vaa1me4eL6CpsoEnBfzkkN9AY9hEEHv/2X36GMN3BsH88/eSZsX4JU6vw1x7MdB8U0guXgLEXVZeEEzw4ODsTZOc+ydj4gW42lzgzw2QiiEVBjPySzg/2Sz4kzqPw0102PBG2ZOGG0rd5aWw4qZd2qLFRK6OONJC/IOG5Ya0ysNKD49urdv1wfPmq22y72dn83o8L9/dzfwwevibMyZRb2rLV927f/bAvCAA8fnuNwcqi0XJmEMCopl0+vplisHazotOhXcNwUHoXhyxAmZTTGQGCuUGxSFAX11QwBQMQtugpQGh14roeBB4QOQa4KlZegwgJpHCNJcmQZk6SKncbkF4VDZTihbIJtwnNs+B0HBucvi+L0iUiWBF4Ii8BHqcYzGdkdC55DZvBGNFdNz0ZeW7J/gn9Ma3lGibFpYuwbyMc2vK6HjhOiTlykImavqgNuUwsX7yscFT/g5GmKm5UDqzQwHHXhdoYC8ASBg6IqkJcpLLKmawOxGBEVeP7FZzKfriXBqxJOW8MX1e4nkXaf1RrGO4MjHw98JoOBRcbEkZYGaffwwWP9nrZqZGc+VInPbVyuptEmvmvM19RzOZ3Ygy5+/eUv4K6mMN7/Hh0nlutjecDbeQdz/BovfvV/CTj69W9eIzuq8Q8Pf4f4D7/Fxvg1vOFTTOd9FPFD9PpjTM4DjL/q4eSpg8/9CkOWgzJ+ym2kNHxiOahjgHgX4ywmxii/wYQzDSSYQBKZAzp4WgVqQ10DzntZmgkbcrMssFhmuLm5w3gY4vThMdabWFhvkpjjWkCypNtzp+JczsMUY+GPTmJT7qMqYTuVaNoWboDCtGS+JZuOST0ad5SFg5RSIUaJrlkgsEnA82BaHmqnQOrws1WiblPbWC4qWHmBsxOWL1tYLja4vL2Wz/XDHoajA3QHXZGnYQJ33/Zt3/5r257B9nfUONFJoCCuNlr8spkvP1yhfGRd8tPlznZZd/8tHz7zczvXz8vMrSIAstmoGTSZTHB4OBFjgiiOcH19h01E50mKv2orcY2OqUV6K+p0L7vWfqouT+JfBCLI/Gm06qjFJu5FwnBTLDcuPAn2ldohj+9jecFwNIRjW/jh1Q+4eP9O2Y4zOKkqnJyc4vknz5HmKRbzhSzUuKic3k3h+T4G/Z4wNAgoUvfr1cvvcXV3g7PTUylFHY5HWCzXeP3Dj4qhxNJVlv9VJXqOixfnjxF4LKXSbp+MO1nCxVJR6ppQKKyuYJYGfEkIe7iYr3Dz/kcBq7gg52cFYUfOFQHNNxfvZH/iYtq0JhJoT95Owd8OwLbdpGGwqWsqdPYPspxqQ76ueXLywhaWlWd1fNJU4VbJCmlRwXGoIUVGm9Z/2wkAW9ba7rFIplVlE9UiX70iv1vZEOauedgGLL+L47MjDDwbZabF602yvyxkFInfRACDoIzaHKxhMRGGDkJziXS2xO0ixzwl+NlB4AzghSHq0Ed94GLSBcbIKHCClKw1uDAJrDn0ieQ5UsAay0QoGJ8z+04woyAQF+N2dSXb9oYT1CyR2SxR5SmC4Ql8PxCgiwsBy2Z/YQqY5QdksxnIaG+al7CrAp5TwHIIvjmYw8E7fqVpAWMeI2IZTjxDXq3gI8OkY2A4dhAM+pjObZSFAdfvwKfzqeuKkQOzt6HjwqFIf0qNEpapQoJGw7NwcTPH5eUb1GWmgJXG1EAujwZl7nepFvGuKRpMVmZZYdRJJTidR3TS5WJJw2HiiCvIsn6/7F1fW70Q0J+1fbb9oGZQ0K80W2i2pLxV9WFxE5VjbZzU1KKkqgspWzk7OcHl5RWmd9dyzVgKRZYbHWdPD0dARAMLtcArywJ5HQto7Pqu6CTKCzVwN18IGC+HrSi4sGwXg9EIF+8v8MMPfxaA6/zBE5ydnWK1mcuYo5q625pFlL5l1T3FwF9n1sdHYwwHQwGzuHBQTp/UxdyCcmTL5RR6psCyBteEraZLYgiIKedqfb5lsafuR3Xf3GeOyt1qcExV33+zWSLwHBn/5sslkiTVrLXd8qGfzhG7f21HjQ/nlvtbbffz4aOPNOl6qmx3z1rbt337zzXqm00mhxLDuLYjLsSMs24WdyinCySRhXXtscITppPDQQ6j9GB3+ugOKoTWCmkUYR1R15MZDSaIaDBFkIpmNylct4vADWCzhNDMULixuGDnEVlIjNeU/EjJ8kdJyHGOZ5knczKmJKcODnwcHg0kMcSkkB+G8JxQNG4lDaBZq0w4OCzPs2mSRYOdGnlZwSAVj9pYNEIoKExfwHYYP1motBHCu9RAel1g+j7B1XQBzO9glncwLLrTF/jyyQhPnj+DUV3h1WIgenPjw47EJsvrG6zIlpqvkW6oR+cIAxlGjs4gQHjQw8XlW9xe36jEpx7qhN+r543tTLfV0lC6ubXop/ZdW8byqKADejNPqnfs5MJawO7DGXY7X6st2mG7Dc2aUbqR7lDzOhODT548g1cVKK5ew81WCBzq2NaY1wHuzCMcP/9fEXb7ePXtFWa2hV88+hGddy/xx+8LvF92EJcn6I3O8MmTLhwnREw3buqsBcAQmcRSeUZ7IkuZGIjOGo9GSScoB/sKeabcQUXigPOnWYreal1xviNQq16nBm4UZ9hsFBBLuRj2bZojPHgwFkD3+maGOCNIqGQ8FKhIp/kmGU4xNtGZEF0Ew1TMSZdsNhp+WJ7EhUXuoI5SmHEEuzbE2d7yCOxmcMIYvk3HURuW38Ha7GOVOiJnkmUljMyGlVrC8A+QYjJI0RlYmC1KXM9X4JU/ODrC4GAssf5mOhcjBJIA9hpt+7Zv/zVtD7D9HTYGEASJ1IIi3DTJAAAgAElEQVRJAR731p9/oe0ucpqSnZ8uaz5YJOmFLj722r3FkN7CJBBoiesdy0b7/b5sNl8scHM7Q55VAijwyeadivtwH9SR37J7tZ0qy6qV4yjZPvzHx+IwqgA2KaUi8CYcb7XoaspGucAls6HTCTEcDsXp7ptv/oR4HePzL79Av9eTRXIURTLBkpXHCXA8OhC9EE7mZKlkqRIK9zwboW1jNl/jzes3MkH/8quv0Jv0RGOJk7rQ9nUUxfKsB5MRHh+diVYYF7rM8kppqwixqrJROQ+1CaMw4bgmMscSp8Akmgntvd/r4uz0DLbtyIL53QWdq6ZqISyXZFsmquIzHVYJLtEurRXA1riH3lu9qoV/kxFVu9RXpo3ndoTaGnyV4v4CMFRwijVsw0FuhYjTRDKPBNkIIrVXXQcvOqbZBnXtp6r8qnyaMLy0jolmz5W1gYPTB3gwGaCmZZYERlxk1zB9G3frRFyggqCDLF4hWke4Wyzw+MhHaKxxdVXjhhlQ2Og6ZK11YAQ+so6P7sTCE6uAWTAgM5CWLmqX2lZma2KgXKsI4KoShTyjM6M6u9FmidnyCsMDBTKrPsC+acMxbKSrqejKdIdjWQhwQUCDAvZlQwJyE6XoshniioaigGtQbLeCaZuoWDYKCwsaHsxz5MsIEU0ykjtkWOHABXxzg4NxB/3DMyTlCGlEgLGC1wmVYylZfLaBkDpoMTXLhFQGgwsgG8gsBz+8vcBsdgmT9vU7ZS2qE20ZZc1DKX9GBc8sMXRjTDcEJTsqOOXd0DhUalBHFg5EmvUiQ3ex7cjULBzaIWYLz9wfdviOLRPVMitEEpbaoNwxYTa+wvuRpZafv3ghWifv3rwVhgOZl7YdwrYCPHl8ih5LjGIuKmoYZMTKvcUjLJAXK9E0o5ssK3ovbue8PEpPj/otVSmOd6htfP2HP8jnslSmNxigrDLRiFQ5CdVX1DisAWQxCFYLTX5ngmdMDDx69Fi243ikSuC3d4kCDsn84LhErTWCa4ViqrEcVBi/2vm1dajW42qrnafLUnUGX7EBVTkoN4pptJKlGPS6SNJMxklm7OV63R/+P9LUBtsS0Y+3j80/u7PMz71BzG9EE06VpO/bvu3bf6wxfiJ79+zBmbDACMhT4D1j0mZ6hyoqsEp9ZEyOeBVsMxXwoDa6cA666PcTuJs5onWOZaTAMaOyYVQm8pqu0QFCmzqWGQxzJWO8yTJ2SsJnqTDcaOgo5X0cr6TMXwFsFixdAloLwGZ7HQH3R10X/V4ggBUlFMhcI/hj8rMZA/C3YcI2CdCYsF1LWPUE0XIZD2uYNo0TDGFKkY3kmGQkcax3RDLgsjbxNqpRXxWYX0S4vbiFba3x+achXKPGd9+8xNha4JPnBbKjz3A9fYSuTRBkhCyNMbu9RLJcYH4Xw8w4D1WiG8ZxODwcwx14ePnyW2Ewy4ilZTG2TgZ6TG6mQbNCxzExcC2s0hIbITA1pf077aMDpd5JyzTXEypZdLujq04OEcyqWp03lQQ+OJjgk8fnuH37HcrpHTyjhm/k8NwS19YB7JOv8OjpY8ynK3z74x2Gj2p81f09bn87xb++c7FCiKJ+CjiHsA+6OJ14OHzs4nhi4cip4UMBZ1lhozDpEGvCtXg1ZdISJmWly0EJjjLmqhrWmsnHucy7TAJx7qOLZ5aWwoqMMwWysU+zDJmvNzqnw66L48Ox6MVdTm90glidd9EelVhTmX+JQDGvExP4ksynRm8D6lKcLUDqeihiE+U6h5WmcAWYtGH7gNXJ4PoRfNtANwhQ+H0s0xCLRYa0WCsjrLgHq6hFzzg0Njg9zOF3Tdzc5riexbA8H6eMJfp9SfTP5jPcXV9J0m3f9m3f/v9te4Dt75zNJpo8H+qz/RTzuv/enXl4u5T5ubfvPrP7yod72DbRCNK6PZ7nSknT4eEhwjAU5sXt3QyrDbWDdMaoyRJJBNCAheo5+RT93WRp3SzyZWLjJEiqF3XZtDabzl6SSceAqmE/cbFJVocsClkCRvOAbkfKWVWZa4k5XfoY6BnAbDqXhS1BQn4+38esGUtFKV5PsXACdPy80eD/Y++9uiNJzizB61qEFpCJlJXMrKom+/TsmX3Z//8wZ6fPtCDZLMGqlEBCBEKHa7HnfmYeEcjKIjk7PS/DMBKFRCAQwt3D7LP7XTHCarZAkaYIOyGuZ9d4+eorYetN7u6xWSfaS0+95pbj4Hx8hF7QFSYPiUqyzWYBti2Eqh3TpzLghS7u0w2uLq+QRwRGgNOTE7S7bUnNpJz0hklEGhzk/5rHaDbxCoRofOJ2ONwW1mrYhNu/UtVYw07Znhp1ArbAgEJXJIMS7D26BqPpQ+QCFO2Of13Q8J2SPVcAj4b5qM6renU8PrvHbdhIDTuOVH7WRgYCv4uLR0cIHEdYa1bFArqG5QNpVWKRFMprrS6Rxyuh7fshENQrvP35PearCrXdghkM0fU6cIMAdeCj6rs4JmutjsW8NsssFCZZa9prTRI5d6w18f4Q9pqW3tU1lqtrlNy4eC2VVtX4l/EzK/JMgj4qdCBd3sML23D9jvbPMmHT28ZSBs004Oemg2GfwsCjnxe77uLP5mJtOLgrTKTzCvUqRxovkW5uUOURoixDyzJxMjTRH7ZQBUNkRSBsAT6Px/dcUmoRC4PBLg1YlCPy9WqmYGXbWKS5sD2jjfp8EKRrZDi7C0WdZ/7gmgk8K8cy8+nIJqwoBcARYNu/7941tH2cvR1Cc53ubnkwDynQl0N5qGyl3gIWcQfiUHgNBz5ymiHXJc5OjnF6fIrrmxvc3VyjrihVclEbZHAc42LcFUNsYYXqBE2Ca1J0y45EebwURYRP90ssI0ppCeirTZJruxgMRri8uYFVW7ib3KAVtvDo0SPEyUY2lNs5u+GRNvLMJsyFRbyARiaOjo9EGiIpw0ksm1BhFNLku+Q1p9LOCP6XOsRANh9kUcr12AQm7H229VTbTLN6Rt1KbBXYp7wvszJHHC/FWJxNAfpRxonyWttuAH91zfjL48trzsP1ZL8J9PAX6pZm/hIp+mEcxmH8TYOfddf1pTbjlwDpXAvqCtO7GcxogfWGrDUHJZOvnUJmUwa6wPfROmJzMUUxXWG9qRDnnNNIc6XXmjKB57zaciwEVgHDLgCbCd45agIctYEo5voquY3KXoCAV8U1T80rArBxTrfILLbQDkIMWe8ELkyXNQCDfGxpfiqvSt6foBxBNkux3Ai02bwPv5sCtHFezbhmczp3PGkkcp22ubbSD06IycyDtHFTmZisauDjBp1WgXdvJrj7OEHtTFUyKSo8G0Z49JWJlf8Kq/kQnU4frbaPNF5jdjuRdPN4OYeT53A4d5cmSttG+9EIUR7h+uoScRSppEldaKnpTTHHWUaFLkFAA4u4WUv1jKgnx/358WHFvlevc4kR2wdVUzb33defCsinm558btcLcH5+gbZn4/LH7yQAwjcBV16mjaR7iuMXXyPodPDmx1sURoJnX03R//BH/P4PNq7yAJnZQWk+QeiN0T4OMHgaYvDUxWO3wqDOkUcxopTp2gGswP2MtaabmGxe8itn8ievFgJrKvWzrBVLm79vmG30vmUjPM1Zs5fSFMqzSKSVbLTLyiKLbS013dmwjVY3wO0iwnK5koAEqhPo2yrHqaqVYkJM7kjQNFDREM4yBWSzyXgj+930UDg+0spDEVkwoxR2GYsToW37sHwTTriGF2ZoMznXaSExulglDqZkgGYZ3NRGndHnzoJdrjCwM4xGDFYyMLnPsIhyuEGIo+NThH4HWZlifn+P+Wyqm29/fe09jMM4jP/1cfBg+z94iD+PmFtzg6FYDA92LRyfr7yfjV/bCj3cLD28ZX883Fip+6mNmyoEuNkjNXu9Wkl3KWy1Mej30NIeQjSClw3mVhvV7Nj2tFJ/4Vm3i8meYfeWraH1Z9wcs/hqQhI4aDhLerVaeHPttVYLCLeYLzEejxDQ3L5kEZiLFIreByk9HfJM3gs7SPz9OloJcMIU1flijuVigWSRivdTf9xDp9MR7yubhqciZTWwijdYpysEnicFoPhw0Vyf0BMLQ0kcZfpiLt23eFahE9g4Pz8C3Jb4ZDE5kNHw7PB2e10MBgO4vod1vJbXxuJSjoU+rs3hVDhGA5Go4ygsFw1u6f34jqW2R1HZv170GZB/mFUBu+J7NJGixbwl/XfqeZVxOwsQ+rKkqpMtQIE6H40ksHm6BkxtCkm+NpUORdbaC3x1NoRFqW3BY6WewwgtLJMImWEjCDtI4w3yJIbpOOiGMYzlBDeXEeYJi/8+zNqVc98enaIYhAiPHLzwC7SLCEViIC5cMbMlU9G1VTIl/T9qppWxkNNfLPoIfBTVBqvNDYJuF67taWN5JRctCgWomGQNkQGn2QNu2EHNQITNvaL601S6UsCLOkMKrGbBSXYmgbu8skT2SX8238gwsGrYLRvLwEQ9z2D7PZgWgSJHElPnMYG8DF69RsuPJUwjL+jPRsDTgNdqCxhDmQRlyYqppalkRQ2zyHF0MkYQdhEnKWrxVKQGVF8E+nxJmETGa89ChlAYe3IG9zYE2+JfBxKoDvyOuaavqK3/2/ba212q23+oa6T5wyZtVr92+v9IiAIlkQT6PXz96pWY8v/8089YzKYCzNuUcThtvPzqOcb9EEmun1/74TVMWPWzel3z9RpvP90jTgiuKWYc5Sm97kA2lf/27/+Gye2tzG2vv/4NPM9BlkcCbMtncvsuJCpafdZ4LcuFX8u/KR9+9OSJgPwynzCZk2l50kywNcCmmLScy+Qr23mtiZRdA77bz7xmrHGoJFAlm5XvOlRBdfDlZQmzL0s36HXb0hiZ69ehpPM7cG07t/xibtgf29niwe/0J3d7RptH+GtbBL03ejCnH8ZhHMZfH/zM9Nt9nB89QrvfRlxlMOsC96sVNtd3qNcJ7mMfMdnmfiUsJbeihUEb/sjHeJDAS+eI7hJhraXi4WnByF26mtFnAAETQj0y1wqRlNZ2gqKOpX5KUqa9V+gGAdrtDpYryswbuSRBpWaGUPMh55mLoxG6gY/JOhWpJ/3ZmiZdU++ptUDL3vW6oCTxrNNqWYdlndHNacdiuqgKxLI9F6WhvE9JSzbqAi5Z2CZE2le1LdwbPty0hapuI0kC0B01s2rcZxY+3VTopO/x9MkES6ONu5tSkpyPzk7hsqnmWWCuENMsLauGY9SYfJpjkSR4/vQJBsMhpvdzvUbwvatJu+0rf7hVQtaauZsx9f3UjKmP195t6seHs3Az0zayx6axqlhrnzGR6xrHp4/w4tkT3L57g6uP72T9kdXOdLC2+hi8/Cc8/+3vMJtG+I8f7nH0IsM/9v4Zd//tEv/tbYi7uofCOAG8l+iNRjh53kP/2xBPL2z8xioQVAmKlICZh9oPULHIKXMEtMug7JM1Nte0NEeWsJlJWE2x1gi6EqylHFS81tgMpRohLZAkShoqPriUk/LvCoaJUUKqrCNUAbbzXdskBZaLCKOOg36/K2BdlTM1tmkA6gqmqXe4dAtOR+UJTTAUy84wGJzAWriE45mwPEf5/hFGrjLUeY0yD8SjMDNyZMYaTh0jsCsJimPdUkRLFPTXc6j2CCWpfrm0UKYFjoZAb+RJevj9ZC6ybBIXKO3uDYfScOM+5QCyHcZh/O8fB4Dt72CIp450YqTHsvvF57ucZv/SABif7Xj2ypoHG6GHmyLjs5++9CQP/80ChwwwsjCiaCMMs7AVotfrwnNtRIzQJj1aTLT3QZ2H/Pft5k1e/8MtmPwkrBCdsESwQhteN2+gSSDl8/MGLkYZF29qFHQs/fhoJB5y/F1RVLKBZVEoG1mm/7CbVqi0SLazVJGi5J9xmgp1++j4BNE6xu31Ne5u7+D6Dp589QR5nAhrSWQLlnKJWiYMhsjQCgKdRMkvJdukhCJN1nAtE17XBSOU6qJEz/cwPjvBKlFJmEvKWjdrAdl818NoMEBV5dhEG308m3So5pw3hdrDYq05zw/lZ5+d6wfXigKAVFeTHbYAKYul7d9oRozshvl/DarZti56My1BU25m6kG3F+jemWWf0kDtdfDy2UuM6RNGAFFqJMpHLClIZpsYQasv5zles5sH+C0L3XqJ9c0SV9MMs4Isoy7arQHa/THC3hE2foXhoMIzms7Say2hua4LK3Dgs/MtkfCKtcaCnAUbpXjSTRXWEVlES6RVgqDdky4nf6fANQIelAI3aY08BgqooRRTzgvZY14bdR6jiD+ittqqc7oF2lRoAI8Vrxt2TQkelRWvB+JcBczkFh1UCM6GWIY+fLhw+B7ATY+FVVlhtSpRx2sE5kcEgSnedWlmomTR7zjCpKOBfUbPHNcRFtRmHSMtE5hVjl7LE2/F1G0hms/l+BfS7TbhUKIhPiaU7fj609kYL38+R+yujZ1ecTfvPLhBvjcl7v5D6VuaX2wBHzUHEIiUAImiRn/Yxbdfv8b11TU+fnyPJItQk0VpOOgNT/D1Vycw7RKbisiSkoYoedIOcFINgBofbm/x8eb2gSckf0UJzc3dBD/88L1IUI75uK9eIoqW4p+4NaDem8REna3sbTTwpgINRuMjAdcykagvhZXG56DUWDE1FHuNc5J4rfGapMGyXGe8FpkUqvzZ1HPqjaf+xCtgW70xBZQZsDSQaNlq7lyvF7SbQbsVYk4wf73RXpb75twP5/rdM3x+vtWZ/Rxc2z3C3nzxi/XmlzfI3K6ZKfvz02EcxmH8+uBnhYD9+ckjHPeOUFo5KvplZjXurq7hLpdYRxaWVYDcZTMwh8c5sOrAaA8wGlroWnMkiwjTObAhGkTjzoI+nwFKKxAwqetaCD3FeoMTo0SErIiRSUAQpewQj9EV/RuLFM+enAjbf5NmarVvgrDMGqNOC08fDTFbbjCZs16oNQvN0uEJZBvr6U3L/uh1IO0skfPp2kNkhio4WjWwFHBHqxV6zWWJag7aLi0NLFQEQJIM2WaFrm9g5AfotUzEYwdex4dj+YgKF1lly9rIuXeycvDpQ4kj8y2OHleYxy2spgn6gx56/aEwgJ3Ql7pusV5glUawqgz5ciPNqK+//VYsSDbxRuqasw4PQYWbDesE1ciRWvPzKW+L/GyXwi+uuc3cvLesbtfNxguXNSm97v7x23+CWxf48fvvkFLKS59grldOCPfoOV7/1/8bTuDhX3//HiujxP/z25/Qe/8v+O//YuDPUQspjmEaXyFoXeC820Lv2y7Grzz8Q6vGuE5UHZVZUmfResNzTZESe7aBaEU1SCaswjTjOkdFBJNBGWJArzXFWiOwRj81gmkpr62E4JqySUjpQ1rWKLJaM70LBbA1ah9Z/1SDiU008hOoMKFfL8Grs+M+Ou0AScLn3msoUWWiawFhv3Ep0p6mtHiRZC2y/Mn2ZF1m1dLQrH2KYClR5sWfomYISOKjytiM5HsrUCwXArb1To5RlBQVrwE7h1H7qAwCbTaWcxtuVuL01ITnV4g2Ce5nM/GabnUCSf9tt3sCKLLpdgDaDuMw/veNg0T072xQKkk/skY6tF1N93eue2vvLza1X1ya1dg93P6DPnyEZpMl/2o2P9tfK/80skj6/Z5IHFutjjAx7uczTO9XAhY2jAQFmulHE1la4yCm1zf9qKpOaBZMzTwhY01LvLgpFQmp+CwpxgMfi6ydnGmXZSXdRiaMkuniB75sai8/Xor0kuUYwRLFWCOkoKRZTSFjGWrTKy9XL+BB2IZZ1phOpgjDNhbxHMePR7g4e4T7u2sYOX2h6L8mvToBSrrtFk77R8iTEssklSIrdANhYNEfX4oLkdkRADDhejbWOST9cJNOYNQ2ht2OyNEoMeR7+PDxI1brpZh/K7N0veFuqjTNammOq3T39o+rSEr13+2jcAS26gIBoS/bwrp0t0CIPMI2jECdQ92T1IBRc6zYvVRApWX5mi2knqCRhrHAZKf47NlznHUclJtCgAbBDcnQDwNMNgkM25dzt14tgKyQ4q/rTpFP73BzZ2FVWagcH22nC9tpwaLXWsdHb2ThjMlT0RI3n6aovRH6RwO4DlRqlVTnKiyjkYSKLFS81ghzbZBlG8Bty+Fhl5wAnHxl2gOL5s2SckvjW0N7rikpKFlpKp1RfbeY3JbST49ktiMx0mcQgsS/E1Ag6mGQS2eKbDRZZ1hMpzgadBD43HyYKEwPd5WF6bqGM8uRxxHidI1VEiFfb2BXCc57NYbnFvzOAEk1QhQRSKzgB4F0dpNoI5sZh6a+xVpkODSSVteBiaw28NO7O6zmH+AUG1SlA8MJtCm/AkVFTVHvflYXxx5VTaGu+nzrfM/t1NIgs7v5ZTv37E1YElCiaVlN955WKYWw1oDXr7+V8/bDj99L0S6xryX97kK8enmBll9jRbCyNmGWJuyS58AUnyEBQRWeieVqgz9fvVfXpZwrvrwao6NjAeJ+//t/R5alsoF99eK1nLMoXQtblWDpbi5TABflqrtDwPuQ8eDgyePnct/VaimbLb41q2Gt6WNLhpoC/lP5Lumgsokg4LvzW9uCWgLsauNwvVFomKPKb0aBkZx2N5u1FOedtvJO5PumFF6Bw78E1rbz8d40v5sFdp/jh+PL68fn69AvBtkCmrV2ANYO4zD+9kEwejw8wrAzkp+LMoLpmphM7mGnMZIIWNYuSjYfbfLPKQdtoW6N0Rq7GFRT5KtbrCKygpStBcG1snRQGAzrcRC6BEhquBKhmaE0NijqBFlWIU9MSc7mPCIWFWwOCYuZ4FGNbifEyegI99MlpvOlhMi8fvwI98slbuZrWOJ3Rb9dU1j6ju1JoijXJ4JkrkhFDbiOJf5dlqvuK01V1mdcu6gMkFRSU2pDqgl4/8afjWxfhjLVlo11TEmsBZ/rNHI4bqVDiBzMYOJdbiC/LbG6jrD4cI90s0Zm3MMwI1h2iRMrwesnK9gvfoO76RnMqoXxqCd+nvd3V0g3K8wnd7BZ51V8PS7ywoQ1DDEc9zC7vcT7y2vkdKHT3rOyVujv5t6E2cyiu7HfoHx482406zAZbWpuNW0HF0+foW27uHz3BqbnYL6aoShJSvThhQO8/M23GB4N8cN3HzErDHz7+gpH9/+Of/8fDi4TpmGOUeIxAm8Erx+gc2zj7HctPA6Acc0QgxxFxvqBBZYl58zeq7PYQGatlacV5quVnBfxa6bPmkGeGL3Y2ORuFAQV0rQWKSjrMoJyBNQYNiV1V6nCedhw5hfXSgWHKSsGsXWgR1oJZFUCnz4gBBMpj4WBJ4/GWEYp7qZzWQdlRWPvk49AoLZSjED1eDrziAw8bdNiM9RNlBshKptWFWSopTCSHCYZ6a4pQLZRJmh1PbTaGbq+g9ruYJ6FmC1zJPkacjUmIYy8Rl5lCPIUo9YK3XGJKLNwM2ezrUZv0MOgfwwv8LGOlrj9eCPN9wPQdhiH8Z8/Dgy2v7OhNmBMaVLFhVqV9RLcICa/+KOHt3/pLg+3Tft/1jzo/tarucfeX+jFnK+Fm0BKLul1QE8EUpx73a50jJpobREVqj3h7hEJRDTPud0oNrjP7rnUfpubTGXoXTWbTu1xJLWFmOYr0E38p+h3pSWiZPHw55OTY7ltPp+jKCmL4yZTs4kkZUgVdwRO2L1SgJHa3MpibBk4OjlCtFqK3KrbGuD2+g6dcQ9+2EIaJ6q7xpCDusQ6SXG/WsJ0bLR8F50ghOW4ILVtJw6QHTMqs0JBppFRiWzUcofSFY3jBJO7OwHnyKajbLXlh1hvIikuVNdSHyn5oenmNRvh3X+Nz3a9zW/I2KLPWsupkMFDXJERKOZk+h4KCm3u/3BbvnfVCAuIxv42yjyBQUP5PRCP4JQbDvDq6xfoWTmyeI2ySgUwoNlr7jiYRCnC9kA6hqvlAlVto92r0SmucPcmwuWdhXXuwgm66HhdmF4Hdb+F6jjARc/ASb1BTYZi4cPuHaEKHJR5jIC+L3wpLAileNNyvEwVbqaZo8pvkBFo9bqyUZDf0YBXZACUhdIPS/lgCaCiwRR20oXR1ACb2+PG88oaviU+NnV2L8BJSQcP6borsIT3J8CYpWsp2HrjAcqaslGyDeh6lqFj1Wj5FtYdAjMOwspBy3FRWjYWcHGf1MjXgJWv4bsrtFs2sjpEFlNKUcn1yWucQQA2wx8sRwNO5BLS3azGYNCB6XeRFpS+FAKe05uEFaiyeNHd9pqMMvV32/O7d1XJsWguzP25ZHt97t9bsyK3NzQSVNVJJvjMY356eoKvX3+DD+/f4/L9O5GqG64LNzfROXmGf/iqB9MrsGGQhEhJbdhkI9C7p8mvFUCrwtur9/h4/0nen6QOU8rtOLh4/ATX7z/iux++kznm0ek5Xjx9LlLbjH6DwlJt0kEFWtORHZJ7phNVyaStcXRyikePLkS2vlwtxU9N/CQ1a41/z+cQ2bEkhHITkm0locogXLF1d+Ca/gw2c6WWgOrpU3Sg6jNIBm6J5WouXkVh4GO+XGBJ1lpR7FhvX9jM7c7W/icdXwDMfgnO7f/lL8C1PV8geS+68dLIYw/jMA7jrw9+ZtqtNo6Pz9Bqd5AjFzP/dbTBaj4B4hSLyMHatFFLmmYubRTL6MM5PsHotMYwu8T6boZZVCEruX6ROc3QJw+VFcJ3HbToJyWhigVqK0JhrJEXCUhqZkgQiTsknkp4izRddNq3ngXIVJotNuh2Wjg9HuBo0MWHT3eYrmJda2kJuzQElI8aOV2C1el0ZGGoaY9Z6V+QXSQTi/qHLLlqEZW/Y+3FtZySfD6SpNOjFjP8wHPhBy4qi5YMlJLSt4zNwQKBAYwsA3bXQt51EaQerNLD0g5k/bDJ2asNXM1CFDf3eHH8EWbXwc3cAZJC0iB9vw3LdWB4ykqCATLEnDr9Ltb3C4T9IR5dPMJ8MRN2Muc8tZbu1sNdldVM6LsD2qkw+JoAACAASURBVKyTDw7y/j/2imceo7DVxevX3yBZrWTNTIoSrU4P/d5AGnnDR1/ht//4TyKL/O7fPgFHOf7r+e9R//Et/t8/BLjO+0jqJzCslwh6fYyftXH0dQuPfuPjtVuhXafivZflNnICnp4tbDVbGrxKXlmzcUmJJ/3TcgaSkShA4CiTepcnlZJRYW4zzIchBmmFSLyRlbKAVhziPSpfWg4q/22ULNuDJ03xYbsr8miCaxYTZptjYtYSYDSdb9hex8XZkaBnccRU9N1jqC9dkzQ9wSal26yFecezZNcFnJLcyBqm54LwndyvWgiLzTYGQOUhr2qxhTHrDTpmJvsAw/TpaYPaiVA7BszKQWo5WGYOkoWNwMtwdOTCrhl6tcFisRKlTNgZoD8YSXM219YOh3EYh/GfNw4Mtr/jwQWEmzTZnOnN13ahbXY0f2WvssdJejAebrT2H/RL27C9mxtAp96ljbY7bRwfHaHX6wnzbLNe4+5uhjTPlRmQ1BSa5SJ/q16PeriGGaOKJ3N7P/WkypxcdzJ1CAK7YsoLjZtXnS4oAJw2pNe6LVsz7fi3P795gzl1EfydeDMpXzdWdVzQCXaJMbmst+w6qmRTpoAGno8wCHF/N8WHD+9lue+f9vHk2RNkUYJ4tVGdXSlAVeBCN+zgYnSCUEIYsCsTmDQqPhSq86sDt+BLIeji7ccbLOd3yNMEYejg7PQE7TYBIODm9g6z+ykK0VTsnz3tzbT1XtO363+o29QPrlMjsOh9YSKpmI6pzY23Z0j/4RYEabbdmn3Y3F7vlYi6qGESlCqGyfBxcXLxGBeDthQLLIJZYBlGDtNvY5PWqC2aHHtI4jXypIDj2+i4cxTzOT5cW5glDkzbQ9cP4NFbLAxRDHwMeiaOrQJ2zoRQesY5MNgBt02qcEXyKhLTLJPkMm4odqy1CmVGwDWG3QoECCNrrSSoxu8FX67yXiOoo6ShSgqqpHi2Trw1hMXG7+zQKoal6rorXyy2SQ2AwCON+B1fmHe8bquK0poMQacHxw1FUkPJDVOoWA0zqMC1c1gOPUZsTOFgmpooZwXMFSWgMZZpjM1qDSuPMQwKkcj2+n2U7gBx6kknWFidriO+MXzfNB/2bALJObKIHikZfCdA6Xm4vlvh+vYacTWDl7HTz/tpiaWWxoqod8uu2l0DzT/1R3Z7i3ysdxfL7lrSf7d7mC2qBNfz8OL5U9k8XX/6iNVyA4tgpQM5l48vLjDsJ8gNpsc6KPiLyoVZWcJcs8i2JEPUMLBczPFpcqW86Ux7+9zD0ZF85n/6+c9I6IHit/Hq1Su5fuk3Ka9ODOnU3NNsYtScpGAvbiq4Bwy8Nk7PTmUeWtKnUss6FAtXBQ2I/ISbQZGtk0lJcE1JQAgmCmttG2jQHK3ms6jAQgWyNZuuhsmmbk/jCHWVIfQ9CXFZrlRSKeciOeL78vFfneHVrfu315/9Fl/4u/37fGk0AQ0qOfrgtXYYh/G3DH622Tgc9QfotPvCuuFmvywTrGdLmFmKTWoiKl3xBjPtXEIMzDqE2R6gO/Jw6s9RLae4uq0QUX4uJCMyz1xUhi/Af0AWmM2EcK7bBUozRl7EqMRwXiy1JO27SUVWNZueF7dzvnzAxftq3AsRxZzXcrh+gMl0JQw4zsf0GSZbXoKCTAeupIeqBoEtta4Bx+Pv2fgkM2ifKa7qPkkcpdySIB1nRgb7SDACU8lzCRpqdUJdj7BxymAlNq/Y8KtgVwUcposLq8pBalgShHCzqpFf57i/WmIzmwH5DDDXgJkhMDM8GaxxdtFF1j3GavkUYWAJ8MnaZTm9R75Zg0av6/dXAqAI4z3wEAwJxJl4++6dNEkV3YznSddUn3kVb2uupnjb3qrRn+3d1cmgauP88WOEjoMPP79BnOWiFiE333R8DMcnuHj8GKYb4vbdPRZVjVevP6Bz+wN++IOD98su0noAyzyD7ffRPvHRf9pG78LG07DGkNYRsmYxVdZGbe+x1mS9KlHL70vkibLVoDpE6lwmhHKdlHTsRO1hYCKNY5RkruUl4oJN8VLsW2SLIxepCkKghFgANqKt2jqBaxrX0XbYQtsJMF/fyueCyaA8MvRca1xSGTom6hLakVQ1xv0WwlaAZVKIHQQrkEZaqxLS1TovzyvXDenWguSJ5YTL647WFJYvjfg8TlG6LZSJBTsrYZkKVLTJAm0l8MIUAa9dM0BW+9hkBjZ5gYhAY2UDaQsFgcg8Rs+OcNRJYYf0iDUwWxewLCUZ7fR7KMsci+kM93d3B+noYRzGf9I4MNj+jodib6nFokn1VL/Qd/gMA8Mvl+RfvWvDR/jyRgtf+Ovmnnv3FrlALR4Ly8USaZLAdZju2Uav1xGAMEtI697R2eX/KrJvK1naMtr0e9aIkNrwyYLXJOmxSCQw0CQ+6o0pKeVMtqLPEdki7G4ydTTLxDeOFPPz83OMhkPElNllqYBzfE5J7JNFXXkq8XYWdp7jwGUxIQAnAZcEnW4b7aArPnSb+QY3lzdw2z7G5yfi88YuU2M6nhQp7hb3suHttFtSSArLbGtMrh3mZRGvUDJZ0sxxOmih3Rsjzips6POxmCl/tm4Hw8EAg35fPDUoL1OBSI05vDqOxn7RJl1TBYzZZoaLo1yMgZexjbiiAWsDrDWw5mePt1fkNadv+/Oe3Gx7Mwva0kS7M8ZXLx5j1PGFCUZBLLf6juejsH0s0xJeiwmsJeLVCkVtgv6wfn6LyacI76Y+Fl6IsN/BsN2G57dQdVqwTgM87hgYG5FQ9JPUQUaQzrfFa83Z66aaho2itvDpaiLXpefRly/HZvVWiien1Rf5AZM9yViT6Hj+W6QJjdE8iznVuWdxtz3K8t53wHADOm2llLxvUxNbZDDSq4O+JQnizUr8RVqtvurq6+Nt6U0GjbNyAm7cCBWU8WZomQVGrgmjbWMVOHBKF63aQhg4qGhYHAPLKZBsNvDMDdphAdP1kVAKFDNh1JXEOQLes/laBQNYFXxPAWhWUaLjOjg5O0NZBYg2My1H3p1/dR2pW5rz3lwozdbgwZZAfkfZjvLZI5i8/bv9q0Z/zgk6n54c4dmzZ7i5+YSrqw+I0xyW4UoS6vj4HF8/H8IP7pGZGfLaQVV7EnRhCXNt50fGueH95Ud8mlyqDrTMN5Vsvh49eozLq4948/NPsikY9Y/x8ulXWMUzkVTKqZPCnCddqK5bQFGdXgUy8rMxHp3i9PxMGLMMLOFGxNhK2puACHU9Ke9HJVUuskJfXw0zV0ebqQOnD23jL9MAttpDRrrz3KySIqrmCFoaMVV5sVpj/bnX2nZu+CVg1pzLz9eA/fP08Lbd918D1nZzQQPWqeNxYK0dxmH8bYNAdLfbx/hkjLBFU34FgC1mc1SrOep1jllqI+Hc6DJFmTx0B6bZhX8+wnhc4Si/xvJmgauZgUS81uhfZqGoA0l79MmypyTTLmAxBMBkiMFGgqtKAiXZjrWmHCn0/K7noP0GH5tMF+fH6PsePlzNJJl5k5C5lOJ41Ee7HWLDQB69LhDwImTBOXtrg6LrO1XTcQ4npsKmpWpwqTWWIIhiM6nEdsI1pszjWcraMxCfNN5XJPMC3ilWOOss1oaFYSGjGZn2PqWCoE8mlG+i6NswaTvhtRFnlHzSyiIDXzlDI6Z3Kdqrazx+do+b6giryUak+IPRSOSZZLExbEEaWqznSiCdpmJuf/HiKVoMeSB4J7WDZq9tj2NTvel/79dacr9mcuVfqaY1Q3m++fYfMLm6xccPH1AKIAVJxwzDLh49/Q1ef/MNNpscP/35DsFJhHP3R9T/8QH//IOHT/EJ4org2yP0xj2Mv+pi+E0LFwwxcCu0qlSCAtLcRmbaMF3WWXvgWqXknjkZaxJiUKqEUMpBTQJsKsQgFxUBryn6jJZwHA8R/dayTLHWGEykz7c6zyrkSNMVpUqVxrXYzADnp8cwihKz+Z3IOQUM01WsqmgbSry+XV6viSjJsdqsEXomnj55hPUmQZkVyjtZvppVrelyNV5/lJVSpVIh8GyEtODIN3DCQJh8cFzkhpIIV0WKiiy8wkeZBSpAwUhEldBimiz93AiF1/Q8po2Hi9oMEIH2KA6qBBh2Cwz7vJ5KzNcrrBYr8WZmCEJ/MJCDlSTJQTZ6GIfxvzgODLbDUBeC7L0ZY642kA+vki9cOF/YBO3ftttYfeme+gm3m6T9R/j8fqo4EtaXZSIIfPR6fRwfjQXUIMg1mc6xWkXauFYzMnSxtW+g3wBqinmxtwnfY0k1RRqBMHY0FbNNLcYOaeueL69DaPvc1OY0KK9gOy663bYUrNPJPT5dXSGO022BI1IrkZySnWTCZbe0qSXNhsFDZooFy3AwuZ9jcjcVKakbunj29QvxFrm/vKVBipYzqAQs13ZwdnyOcbenF32Ny/D3ZArR/NVkoiGdGgCnJiAV4Gae4PLyA7JoJR3so9EAx0fHUqAwGOHj1ScBjxTLT8viGtmFHEse3xrDVoThIMXVfYAo9bchBttj3JASt1q95uQ2LB51722h1zxLgwloWQcMD+OTUzw9aaGkpACueJOoa8hExPMBG77nI1ovBXxjx7rjLpFN17idW5hWDurAx8D14BseKtdD0XbRHti4MDOYBVNjmXxGTYsFj91uAW9UJDz9p5QkVMnxWHRu4jU2ayZ8zTA+fiqFPcEmFo8s6oqqYa/tfLBY2PP2gtdi4+cl1yGZjcoDhobyyl9LdeENS/vGkNXG28RrSnJlBRROIso5M1hWG7bTU34zDGHgNUfvHKa+ccNAUQPBv5xpCyU8XhduKeESqfizmZgvKrjzDGUaIU1j8WeL4zU8M8NplywtB06rixhDkfmwIHU8T1K36ooAMxBI6ldKioJ6jSlg+iZWlYl3795jvZxuAUAFxmo5bLPT2tGt9rzXdDgp8R/TQmXQo4/vyNReMSplrpl3+BC27+Di7Fx8ewh8ZWmMmpLvijKfFp49GmPYWiIpl6BVYGXQh4gyXAJs6pgpMKtGtN7IZ4bsMJkX9Evttrvi+/P9D9/LJpLMs5PTc3iei008l2aAFOOya1OmyGS9qcdWb1PJTiuZYy4ungora7NSIQacY8h6FZaGMDjVZ1/5q5XSqab/I69J8fWTDUoToKElUHpabw6vnu1UGIPeUCpgvhIZfp5HaAWhzHNMUZbXofh1DzZoXxqfg2pfBtt+uWLs3+/Xh3ov6vr/Ky/kMA7jMHasNc/FaHiMVhgKy5lErTTJsNlM4Sc5FpGJyPBEamZZGSxpKnXhdHvonTkY1DNkkzmmixKx8mtHzUZLxUYFvc8cSXm0TYY1lajtDAUS7ZvF9VMDaxrsEsfV3YSkh+L+cJ7ptgI8ezzC1c09Fut0lwxK5q70D2u0fQdHx0NM5zGWa6aCu7BNTxpKfH8S/sPmZtNUIMuNvlp6jXU9FSpFH1HxM+UcS981gw28HC5vtzxZW+R/Jtlvpnilbn1PmTxPEzmLMkJLWHUmLSyMEjbXVmm4uuCK9z43UN6UWN2muLy7Q7m5R401rCqFjwRtJ8Z/+W0Aa/BPWCZAHNkYjfuy7s0mNyg3MaL5BOlmATOn+a6LtAKcsY/j0zE+vP+AT3fXihK9PbYaHNqbXHeHe19eWsO2XLx4/lJqj3c//SQpnbR2yAwDbssTD6+Xv3ktvms//PEjItfGb3/zZ/hvfsQ//6kLZ3yBvLRwO+mj9AY4OWqh86KF7rmFVy6UHFTCoCwKkgHWWDz+8oJUnSWsNoJmTJTNuJ4pUK02C2oEtn5pPD8qVIogKEMPuP7l6LZ8iRGYTtmY175+0jMSoz8lQ976s9K3LEGvFWDQ6uHy6p1SFJisldSqJCx7PsRWYKP1xU0JUDbPwccuAbPAcypQ4gK3t3eSGL4F2OQ+6gwoiSqPuYPnz5+Ip+nd/T0s1xNfQQJ8gIfSCJCWFvK4AKICDlNIG39Bv4DVWcO1M7Tphet1sMlDrFYVknIjDdWyIJuNMbUZ3CLBcbDGYMzwIwu3sYUoKdELA4yOxwi9AMvNBjdXV1iv1gfp6GEcxv/PcQDYDuPhBSHgkvkQaPt8H/Qru6jPN0b7G6mHZtZ7u+W/9ID7d9eeO/L6TBOtVoij8RiDwVA8BNhxub2dYB2lAlI1SXbyrPKi1EZeSTz1Pn7rV7Hb2DUgj4QfiHG4Tmei35Fjw6eBrkOGjuqOyiJf5NLl5BM4rotOl4byAa4uL/H+w5UwWwQUkUJPsUYYxc6lU2og/YKUwa+K9DYoFTR9XH+6w3w+VcEIvRDPv3nBtRt3V5806ND46FXw3QBPHz9Bq91WIRb6van3x+KEBWoOkzLKir4OlHKE+DCJ8eHdnyUF07WB49EAR8dnUjze3UxweXUlr4vHXZ2mGgXNXyvgbLBEUhi4XbfE5H6rG21EHk1Fp0EkdT4+A9r2mIbqJv03+vWzbg06R3jx8gRBFaMUXy0W2OyQh0hL4G4a4fjkWNK+EgKGhotBJ4OT3OP2U4VJ7CB3POkIh2DhEiAPfRgjB0+CCu0ylkj4JHeQ2w5c34Zn1sKNI4DDY0MQg34nUvCxiygbBDIEVeLncj7FfMlAgTFQ2ZqtRjBN+bmoFEft/SHSYWX0r4q2BtxV4JrIty0FZAiYps3mjebfBOEksIT2G6kctbDdVwwrspiSJRwngBf0BVxzuekRialNZEJSx2jUS2ImgTarKOBaBNpqAdo2hoePhYFiVsJZMj4+wiZbY5JtUK/p/1HitG+gf+xjnVu4ndsY947l74OwJazOmICf78BlelaeyAalzvm5qWEEJjaFiR9/focqmqPmHoWvRfvcCPCs8bVfTD9yORE5o4m2YqxadQmTARAaXCPIRpnF8GiAF8+e4t27t5hO7pDXJRyCsqWD4ckZfvOE8t0rSUI1mMxlBiiMIUy7q9iBsqGzBLi6ubzElMUvAUu5Bmu4XoDTk1O8efcON9dXsgE7PbvAaHCE5epeXR/6jahPD5Eh7RckQLeSiYikxwDOTs4xPjrCarlETCBQp+FK84PnTUBDFWTQhBc0YL9K3lVejyzyeZ01EmSZA+RlNJ+wnQRUgVRK2s6/jzdzeJ4jm+XZYiFsVl6/W4abPhdfAsPU2XvgeLmVj+/u8/lQtzT32z6mnvPVUMeQ81ATUnMYh3EYf9sgu6rbHSDs9WDR3oKeoCiwni1gFymSdY11zTWSnqdkXhUwag+wB2gfuTgezWEvV7i5rbFOlS+kYCFkrYFBS7YY/rOpYtNPk8CakSOnXUFKDzED7OdwPlPzUNPy5PSoagX1s/q801v29fNHSLMN3l1PVBY1Aa4m4VjqNEFBFIOoBHo9sr3GuJ0ukcSllmk23mnKk01cLmVtNTXARhmk8m5U1gyA79twbR9FkcJv0UbCUYw4LRtl6IDkSAvQRpsPBiGw8WWKTURW0rKBaemWgERmTtkom7BNEIKNG5i4IjB5VWB9neDT9B7V6hZ+EOG//O4F0sUSk8s/49nFCvajZ5gsLsDs78GICfAFlpMJ8niB9eReUkarmuu5KTVK/3yA7vEQb9+9wWQ60XNo0x5VgKYcZd2k5RBnk9rA06fPMBqN8eN3f8Zms5C/FRg09OB3B3j55CuMxyd499M1rqcpnv0uxvP4n/Gnf6nx/SxEVXaQGqcIWz28fNlC5bdRPevgRafGaV3AKFPkDDGgwoHHrrHd2NZZTYgBm0bKM02koATWDNoSFMJak+YmFQEE1siCS8lwo9KEKbSq8WSUGc5P+4iSGnfzpUh61ZtWb5hNZbIMeSGfHJ9gfnePOF1JfUVmmPqfutYVyNaUt7pe35OAKva5vqrlPooJyWvs6eNzFSh2eSfSZrFq1dc7PXWfnz+DH1r4+e07JHGG2jLF248NOAm+oo8zXNSWj8LykBUGsjXpizncqobLB3QMeK0MXmuDwKrh2wwkaWGTe9jEKdI6Qg4XWdlFnbLZWaCVJhgFGwxPLfm8TJIaSV6g6/sYHZ9Jo3qzWeLq6pOEuR082g7jMP7nxgFgO4wvDvF8MtVmWG3QPtsW/XKX9Kujgbr2b1FDL+7b++AL99u2jPSP6veNP1q308bJyQk6na78jkyLu8lcbQilCNs9X/Ns8nCCHWpWh+4oqWfTkdt6A6p8joi4Kc80gmX0nmLB2jD++McEXhiAQGCBhRiTRgdDGpPW+PnNz8gSmqSq5FKmPon1gk5SFABma8RbCbOJ9SsBgnbYExbN+/f02FjKOzh6eowXz5/j04dLxJvNFgRU4GEloOMT+mI4KpiBdHv13ti9Y0HBkIhEur+03HUsD6uygz+/u8JidgOjpLzPwlfPn8PzfWFevf94hdl8rmVhim3XshIxsK/gSamxS3rUYKiWxT44pfVn51UqFnV+VAnY1ECqt8eE0GdPn+O05yDPEilaa7MS6rsTdDCfxzC9UDrS1zcfYNc2BqMeOtYUm7slLicWVrUNJwgx9AIBVyrfRzb00e+bOEMGM0+QphbS2gU8h/+HK5kMPCfKI0QVb4opJGCZsCUrGJQrCJihfOBY2F3eXMMzLQRBH5V4s6h3Iz5ZjceYBlMbM/tGfCDHQNlySKGnvPwIrCm5iqTREnjjRsAxxXDZdn1hN7LA53UqmwFYwmgrkhit7lBYUZTvymbAVuxMPojyZ4Ocxzor4dBnxilgs51supgYDq5jA/Y0h7VMkFYRJvkGcRTBT1dwiwn6XQ+PXo5R2ueIYh9VnsMPPJHsJvEGFf3gaMZbpCizXIG1sjGqgaCF95M51h8/IM43MG1fgadb4+Gd15oEODyYF7hzpARVXVgNq5JAm2m7ePX6K0kBfv/uDeIkltvs2oTttfH8yRGG7RmSPEFlZKjQA82GDMpWKD01QtRuSzZKNNe+fPtein8pjjWDbDQ+lg3f99/9SVhrYdjBq9f/gNVqipSxezxXUpw37AHlJbQFjfQHhp//bquNJ8+eyVtarekrlMmnQQWtKKaWALPCWtMSUAH3NdCmfyfdcz60AGvqGpP/cUKRqUpdUxotE5Ba/Wgqr8IsRrfdRpImWCyV15rMIbJJVce+YbHtILHdWdn/mO+Dbbvb9s7fZ7c/hOHUaG5vkk8PCaGHcRh/++C8EQQher0BAi9AUVFmXkvgj5FuYOY1lqktXmGVS+CpUD6T8OF1ehiMK4T2BNFNinkECTGQvmtpoCh81GSKuTSkr+FbZOKwsZchQyJergVZa/RZE1mmBtcUqqbBNXmVD17v0aiP8biNDx9vkIgFhLQi1dSp10f1XYNtErCimMuc24ZHfXnPt/cLqctk/RRwTgFtQtjlvCq1HQNp1GORLTTotuCZfG8Me7BguipNVJLJ6bNp7OSnkjpqsMml2WwC1HGttpTHKucrxxMbiLqoYJLlLUCb/AK5YeG6NnFHz/nrFFYV4bhT449/+IDldArYGRwrw+P+Es9fVliHv8NqeoTA99Hpt5HFEZazG6RRjGQ6RbxaSwqqU9XIbQODxxdMGxJ/tk20kfVesbtVtaZs1tS6GbS6ePHkGZJVgg8fP6CoWCMSELTgtdto98/w8uVXLMjw9ocb1G0Dr57+gPK7K/zhjY+7ooWsPIVlHiPotzEYheg+89A9tnBu5RhwkaYPbE5Iy4bhWnDZdFadbhViQCa2AGWakS2yzcZvrUn5VKoRAd9436xGwhTaQoFxBNek3tJhaWRx91s1BqMOFssCd4uNvCez5DVXot/tIPRsXF9f6ctQqohtU4pX39Z3WYNsWzMPrTpQV/BOkbP7j1576xqdkKz0c0znCwkyq1FIcNHzFy/w7uOPuP5wh0pkq03yuertcbPAZhIb85bpAZaHinLh0kGWmSg2tbquqlzYl25Qw+uyjsoRWAY8w0OOFjaZjYjhSgwMMQPUZLMl9PAtENZLjLsxul0T68zCLC+RRCVG3QH64yNptNOb+frTpdQ5h8TRwziMv20cALbD+OtsNsqb9IZN/eKzXZHGsbZ+F/jVu21/2r9rsxnb/fQXRgO26dfH1+Z5Hnq9Lo6PKX1oiXyLzIv5bKn82STHXEmf5Ln4VLJ+qm6T6jo1PdWdAezWm0gXcwQlCKzR2N2RdFENsrGokk5XJSAbn59/x/u2WgHa7Q42mw0mdzeShklwQYpFMkxI3NFJoYrtpDbDDAtXiVoVLMtFvzMU2OTnn38SoM32bJw8O8P4eIzJpzvkm1i9Bv1+WECen51ieDSWLq0CKhgbrtKWCBwJ0FZnVKwpIMcJME08vH13hWgxkzPSawd49PgRgjDAarXG5adPiKJInYAtQ17bvmr8oDlPOzp98489dosurLfNaCm21T94HwJRndExnh134ApzpdrKQsJOD6uoRGEwISlAnsaI4hi17cKrJ9hMLlFkPhZ5G4XlouuGaDkBatdH3vHhDx2cu6Ww4YqUwV02SseRItmjklKAHRZqupijB0tGlpDy5BNzW7bMefYoZ2BhKOCa9liravG122xWCJwQnh2Kv4Y6n/oqbEBe3RZtmFdyHrRkmSw1HhfF2NkdKzLayEhjwq4pbEp1DZp283nl9UWvQFOeI16vxPR+MDwSySLDCBrZqOqo8x0byKQAVrJRty7gOuzEm8gsF9Paxt2qhj3LYaUxFrP3iBMGIhD2K9BvFzgeMpCkh9weI45tASgpy+TzZAmN8mu4Dr3fIhXMwLdeEQS2JAjhcjrF/dV7GOxSywHSnmx76Iv8U/7DzZr6rKousmZElDWOj08xGA8wubnFbDpRdiuUE9YBzs5O8bjH6z9BacVKimR4jBOQ4yAde0MlpRa5gcubNZZLFWPPa5vfPS/A8OgIb9+8xZKeN3WNx4+eo9fvYrmcbROC5SNBJYmWrQvept8DX7NINy0TT589R7fTRRIn8tni7YpB28wtyiuz3F5rSkIj84YON2h81pq5rPkmr0GYls2BU1/CJtXgLRmQTDEO7biR8wAAIABJREFUXFeuH4Yp8NzK69PzLL4AmPGWfYjtL83guzVgB9A9hOd+ZYgUtt4Ba1tG22EcxmH8RTko2fTtNjrtrgoGqmh/kCGN2BghwxhY1A5KNmzsUvzCzMqD7XXQ7nvotjcoozmWswpxrhtCJVmuNNn3YNkuXDJn7BqOVcI0aNGQIasy1YiSYJ8mGVTVjzI1bZslu9Yr5yKGPT0+6WND24/7pSaw6hAYoamp+zfqBAG79Jwga55qQQkriEEHnTCEF4SYz5fiSyn+bFwTRQWhmgach53aFMls2HFRpCmyopb6ynEIvtFmQds26MaUsvEgwGYrRlzNFFNlxSDhWGxiseakB6+w1Hl8HXUsaFtBiMmuhJ3EdXoJE8ucya011pcJZpMMk9k9qnwBw4hh1Qna9grnR0tcPBsgsZ5isT5Hx3cQdENEqwWi5QJ5tEI8naFYbySQp6xtpK6N9vkAnmPhzz/9hDQv5DXTnICNULLzjo9P0O/2cPX2HdbRErk0XgDPD9HpH+Hi6VcY9Pp4/+EOk02Gx88WON/8K374fYV3qxBJNURqPELgDTEcBmg9CdF75OBp18AIOVAUiNYFstqA7ftweWwb1hp91oS1RrCMTEfN+qetCcE10XOwocQ6THmtMUmUagNeY2lRISO4JiCust1QIK4CuBoI0aDPbD8UGeh0kYmU+KjfxWa9Em9UXkZ8ji3bWzLflIepsqnWDT+xitDXsH783erIoZv1TQNLNwnV1V5iOOyj3+0ibPekfvz+h++QJJm6NnXSrXo0vWZatZKJsgYEfYAdGBatOKg+cVFWPtIEKJICdpHB5n6BxFO/hu2n8LwMocmWYShAW1SY2MQb5PEKddhDUfaQlxXcNEHfjDHupnDaNVaFiVlMnqYjAWz93hhpXSKezXB7d4ssVaqJwziMw/j1cQg5OIy/OBQzQhcjKubuS6iZGg1Qsvtx+31/86W3eA+2V80i9eVH2Pv3dre9Xc5kw0mAZb1eCaMjDEN0Ox1J9CGDhZHdzUOo592xMRoWlTKE3XtFqk2qn0mDi3pzt5WfNqa5+nfizdEYkOvXWfD50xS+72M8Ppb7EXhp2CWFeHI1G+gmKVQDZZrhVNcFVuuNhA88ff4cQdDGcr7A/HaK6WSCkydnEpAQrdfyd003bblcYLlYiDdWEPraN0L9XnyXavp3EOCgx0WGqlwjNHOcnZzCCodYLBeIswTT+znKPBVG3tFYgTRMcuXGfis9EEaePntNh3nvmD84jfpr55+kQcymjLFcvHzyHE+ptMxZeGhTf0odwx4W6wyGG0rgxWa1QFbk8FsWRvYc2f0GNysHE1LtYeKkO4LntCTlKjsK0R/buGBnOI+QxhYSymB8Vwz5KQk1+QrIECKAwah3/cViTuAL+oBQskAIVHteKSPd3RdBD3a5fctHkqWI4pWKYSAj9LPj01wnAqg9OIY6VlIDvPr/4geDKkXGQtl2tmy4LVAshaEuLtlhNWuVkOp44gVC+YVru4qF0LAb5X0rZiW7oDSsyWsVhMCL00GOjlmg79vYtE2s5ikCo4V2awTLchBVwDKusFxVqPIYLWuJdrtEbgVIY26ycnhhCNt2EceJvBbKrbnh43tm5zafR+h3HRxdPMF8nQjjs9FffD4LyM86CEAudQGuKriOh+fPX8BxbXx8/w6r1UIMr2EQEO/hm5cnOPZXyMoUJVggEgQMYRiBkhwSxOT7txwslhnevpkgSRgsouYGgmZH4xP4bojv/uOP4scW+C08f/5a7rNcTeUzrcBklcqswDV5wRreV58YftZbvS5e/uYVPHoerpZIklilw4n8l5s0VcyrjQMB3uaL4BrZa1oWysK8mbuaKawh78oT7s9bKvhEGGmmIYEqBKi77RBZlmO+XEhwigCKGvDdn5Gbc7A/vvT7z3/eXyqan9X4fBFpbm58amgdSKn+HvPvMA7jMH51sA5ptUMMx2NJMFZp1Sk2C6aDLlHHJWaxjchwUTs05y9BMTzQhdPuYjgs0bFnWE7XmM3pR6pZPIWFvAxQWYEE24QCrlWw7ULsJ/I6RcY1UaR7bDapuV1A8j1WUDM3bWtAy8DTk3McjQL8/OkWqzWbhTqoacuw1WuhBi7UeqkbnzodXppQwvZWIFoi5vcJjoZ9ODbXohQm2VDSUdRJkgVwPOwKq+x+tlFAokA6qoGzDUSQnptqvBlNQrv+anq+wi6mpFE3OzjvE5gzNXjD22yP8BqlpCpkiMFETHkcMBHUtxGNPFihj67dwpJm/ZlqvvH+87WN2V2MXnGJ8/MJFsUIy5sUrUEX3cEQJUE+14PbCjBfLRFlEYosRrFKRKb71evfwPco+1/KCQhaHbx+/TWi1RLXb36Q5POcdg6OA683wvH5C3z99bey5nz/pysYnQL/17N/Rf6nP+O//ynETdKXEIPMOUNn2MezRz10Xrdw/tzBS69Ct05QU+6ZmShdH3bgCWPQKHNYlBGLpUGpQwyoEtDBPDy+FoE1st0Va03qMN6PrLVEea7R5zYrmuamUggIiKtVEcIw4yUkexcTSVpguVni/KiH8aiHyeQWcVUpf1rFVdOdd3WZNqDwjjnf1FbNZbxjsDVgngzdTN4rdNVNZi2NK4aJ1HmJsN3Car5Bkmeq1Nsu2k2nmg1xyp95AapcBh4V1utiicE2JEHxwELtKBYqE3nrnLYXvL5CVJkLwt5VncEuc6yiNRy7gtcdSEViemtp8lV2G5uSQUYOyrWJYSdH369RmiXWaYnVYi7XZ683RGswgm9Zwoo8sNkO4zB+fRwYbIfxNw/lC6VSlBRTYm9v9Gug22fj4V12P+2YEQ+3X7u/2h97T7J3dy6kBLg6nTbG4zH6vZ5snMnIuLufSfeOPZl99oRaO9VCqVggD5+RvxYOicj1NF1bpJ5KYsCCjqa5AqyR1aYT7aRvphkn/M6NquN64o/GcXdzLQut8vHSHTctDVUsJy0ZVS4QevlWjKRBty+Sj3c/v8H9/Z34RQzOhjh/co5oscbinj1R0ThuWXudbg8XT04lZYjMOT5R8126iEwdApODJCZKCtLcdPHz5RSTyTVQZQgcB2dnJ+j3ByJLu5ncYnJ3D6PaFREKVFBHcH8/rMMRt75wD7bt8ku+Tgut3hAXZyN0yinS2pcCQmSPfguGFWAVJyJnIHsriWK1mWjlsFYT3NzVmBDQCQN4jFkvDGzmGbzREO7zHp75TK6KUKbsyPvIbVu6qZS2iNcaj0OlvdaEsaZYayIBFXCNB0cZ7ApzSDqnqqhu2G2Kgah8sAiM8GGzukaarsX42XX4PkgpNNRx00WbLgm3x0y+b6UttYBGlO1Gm5V0vfm+G8aVYkeR8aYlzRKOQJkkgxB4jaogBIJ+m02EzWKFbq+PXrcr5s62q7rvIhs1mUJFgM1ALmlVFewqh8fErmKB1CxQd57iNlP+bOYsRppssEzX2GQblEWMrpvivBuhP+wArQtssjbKrBavG56XPGO6VqKkN1WB9f0C6WYNp+2hHXRgtdqYrSN8vPyINFqrK0WAq2ZTplM4m+MEQ3wPn5xf4Pr6GvPZVJLFTJsFvSe+PE9PAlTizZcDVsZeMAzTh2m4yqRa0naZAFfh8tM9JndLkYTLp0+6+R563R5ub29xd3Mj7NQT+qWNTnB7f62k11twS89lDaC1d355SVBuND4+waPzc6w3G5F5M5mzCXLhHMO/4nvkdSY+a1oOSolXvWWt7TNvNSirn0euK33MtrIsPUfy80aQbhOt4XHuch1hp0ZJLM+h9rA7YHP7tr7w72bO/pyN9qVZ/K/+bgtOquYDXwHn1MM4jMP464N1hxt46IZDSZvkXOfUJdI4R5EtZFO+WTuIwUACspcK2JRV1j7qoAuvayA0NzDjGJuIwIji7LDmKEsmZHqwXFc21x5tnygHNVMUdYKc6ybnpaxCJWE+277P3md9b37SzYd2u4WzoxCzeYT7VaxAM8ovNWNbQAxpEOyS0aURJewzJfsUcELXYlKPSbNEsX7YPCJI1nY89AddYS7dL2difhXaDoZtD6s8RZSqmo5rrbJhUMb7XAMUe00FGzAUQQIOyFQjo40scPFjs4WNLRJMMtqshtFG714Lhm2p1HCpgUwUtY04SuHQBsTj49K3jmxyB1OYeJ8ZSO5KrCcxJncTlPOZrK0GIthmipEb4evnK3iPnuPd4jVapYnhuCvHajW9E7n/bDpHcX8Nr2LN3kKd2bBHAcIzXxjtZmXjzdufpVFYm5kAW+iOMBhd4PmjJ9IUvnx7i7lp4unj9+jcfoc/fRfidt7BBn3U9TGcsIVez8foRRutpy6e+sC4zkC6HiWMuWGrxihZ8zK1l9gs58izSpKpeW6kAa5TPEHmGhlrZLFrBYGy52DaqAo8EAmppGarJHYp2wX7VOuHVPNi31ErQI/XTWXCdR0cj7vI4gSzxRTHow5M08HV7USaVVJVsHYr1TUjIRy0XJCLWK2zsubpPUOzqu9K2d2V3oBlOhpBg3E6bIhqlbqGY5p4cvFYmKZv371FwrQoSb4lyKg/eIIFK7sVinAqNt3IaKOnLlUyZN+bNir6sxkOispEkhkwNznsgt5/pvgqG/YKeRWjO3ARhg5g0suthSQhEL5CbhrI6w6yzEeVlgiSCAM3wmiYAr6JRRpiVRjwzRoXx+doBy7+8P33uJ8uvjATHcZhHIbMA8+ePfu1OvgwDuOLg4UIiwflqaF1gnuY19+6qWo2Z/vo3Jcf5vO//sITNViNmPGT1m+j1+3g9PREJJp8rfP5HHf3THtUoITCNxRLRNHVq4deCmqfuaV8CxtFQDYdzy5+ako6KuCapFApsE2KPcGNuFlUm2OlFzOFUdahlC7P8eHdGyyWK5VIKEl/ahOuqUnSjVMx8uq1NhAgPUCORidwHB8/fv8dNtGK3rk4eX6G8yePcPXTBymsJQBVM/D4nsejAS6engsAQ3mjAtlUTKcARzW/+HyMnzfF7DxCiB/f3WI9uxQKuuc7OH98jm6nLwyfj+/fY7WOlKRxL8V1V3g050b+u3fOtASQRvW2h4tnTzCwKpRxCkNo8RUMx0bQG2O2SOC2OiotdDVHVRrw2gV6uMLirsbbqYXMIgjVRscORVZbByHyQYBRmKO9uUFLPOl6iAmu+A58FssChig2msjutByURRwJepQoEFirdVpl43slaY1UPwjQRhalltBISlVTpO1YaCz26QeS5nM59p7fVwCb1FBaIqrltUqWrGQzvCZ73VBYjBELcvFOU95ZAoKITHLX5ZdurQ5CkGCNRjZKViWBGy1nWa4iRKsYJ8dH8FydnsbrlylU8hyOPAdlo3FcYHY9xaDD69aG7SqW4ax2cJkYcO8K1MsIabHCvFgiWm5gZEzlMnA+ttEbe6jdY6yjQOQi3ATanocsjVDkKULPQ5lOxdfHJKOQoCL3SIGHj9MVPr39ESY9XApuqZTpsjDFKO+xTTx+/Fg2OVdXHxBHibzXmr57YRdfPR2hhQzxhoAbpdtM46QUkvJY5ZejNmIm7u4jvGFKr7D61KaOYNbxyZlcu999/0dUwpBt45tvf4vlco7FainMPyml93oOQhDdaxzwPFEm3Ao7+PrrrwWE5XxEyZZ8nm2GmlB+pD7/IpvZfqnkWbnmCNqLxLup6feARj1NKtBRvZJmS7v7yBlYR2vkaSqsNSYdrzbKa60BtRqQdzcr//rUrn73JanoL+fzv6XQaFgDEjBzYKwdxmH8TYOAP2sKr92SNYOgF/3VNqsIXSNDlADrykNhsbFQwrZT2IYN0xnA6YfwnSWcOEK0KRATJONcxgYLg19o5GU78GwHvsW9PW0rKONPkJWZgP85JXq5qqGE+aU9YT+n06o5kpJSC6dHA+Ip+DSbcerXc4+adxvWsAJI9m7XvxMbBc1MEthNM9fkZ+2NSwmpWlRJ/XGIEqI/DlTS++1EkkWXkWIGqYlz17AxDTZMCbAp38em5nXoU0eAzdIgmwBtSjYqtWGtGllNmjXXXtaFKnGUr9EW5g/tOGhtwoAmMo5omeCaJSybvmeuNM8uYeBTbAAfM6zfb3AZMRFzBbvasFUGy1nj1I7wu1cbzI5eYTZ/hjZcjI/6IvtfTu+QEjyczZFP16iyCq1OH52LgYRPuJaHt2/eYba4h+W58PpDPHn6Co9OTnBzNcW7T0uMn6f4xvkf+Pn3OX687SDN+8jqMWx7hN5pG8FpCPexi5d9E48YjFGlItfMCgelBhjFz5ZJnWmMZLOB7/pSv0Uix2UaN8OFlCqAIVxc8wRAoz1HRtsVFWTALwHbqDAQaemuIU1S4raxxLWX3np7zcdhfwjXLnA7m4nHq0Uwry5k7T45PsZsucZsNhVFCc+bgMQChDHsQ9VnitXdqAX06qab6Wq9b16DtkHZv+6bVVHvl8R7t/GYNU188+qV1Os/f3yLjIw2/QzyfkoNsDXPSosSkRtw/0ERpy0ALpuj/KosD3kRoF7XqMlYzWcwDB+e34EbFvCCGI6Vo+06qGoGIfgCcsZVglyajD0kqQUzz9DLIoxaK/SOSmRmidJ7jJPeqTQbf/jxR7x9+1aua8uwxef2EIRwGIexGweJ6GH8Tw/pwJTcqKqCpunm/NqG6PNN2v699jdfn+Exv/LX+7ftPcLeQsbXwkU6TVIJPSAgwkQcBiH0Om3kGZOMuHBqgGf70IpxIv4K26JOg2zbpVOHCTSLn35pzcZ0dwyazaoC4biIcitMQIbPn8SxFMWnp2fCjlks6Bend82aSacFFdu3u2WhaA7POqbP1xJPX3yFdkCJ6AaL2zk+vb/Ck9fP0en7iCO16DXgDZMdb28mwqYLw2CP9SJlpQAV0kWTEqCU6HnGxz8+7sDrHgsww2N3P5sjiSP0em2cnJ0hcH1h4xAIaMyI909ovfddRKWsLcR3Agj7p/jm5Sn8bIJ0RYUeu5k1wt4ImelhFVdodQfYJLF42RGMGHQiuKufcPmhwIeVidoJ0HO76Jht1MH/x957cDmSpEeCFjoCGgmROrNEV3eP5C2Xu7z7/++W995yuUuOnp6qLpVaQAOh45597g4gs7tnuLfc45ADr5cFJBJAKA/3z+2zz6yBvFlHcBjiZb1EDzE8K8DlfY5xYqPZqaHus0CQoAiBtQxFloqVunKj0plRBn0sCdWlCiboY0lDoYV1eX54Tan9wX6mWIsKKBXgRmJ8lWUn4OV7IUjuT5OxNslQDJ212PzafVUxvga9Bh4ep2KWIAyzNSCs+pjApjrgU6nVTaZVY7QKgzGALcFCUEcsQFSv4ermWoJxz4/W5TwS9LF8gBq4yQJxUYgbp+X6yHNLFl5OlaFu5+j7DpKWiyQK4BcB6hkd1wKs4GBalVjMC5SrGKF7g1a9QOG1ECdAFcfwwhCeH2K1IjhbgxdESteOaX46giYlur6HvbMTrBYWZulMFmQMkBmO97pdvHr5Slhr19cXEnzT/ILaM/2jE/zotIFyxRIMOnepTDYzvsIQ0wRALoo4nv3u3RVu7qZ6YabOrh94OD05w8Xnz/jw4Z1cm9OTl9g/OsLt/SXSVGm3qABcVnnq6um+LuWe2vGWz1++eI0X5y/kPmUppghwc59Ey5ELX1VmxH7Gv62z9Dmz+exjLGsiwKbpIbLJZ+OfJAE2rxmwlkA7GQEE9TzbQS0KZGyczxeyDbn7DQtVA3PfM8puNesH/tf3/taYrcZk056P5eZlLUUgWkY7cG3Xdu2f03h/h9RI6tDIpibjBnVEk0WMKp+ihhyjmYs5jYjcCoGbiWamyAuEEWptT0r6q9kC00WGREocCTBQP8xFbofiml5ztdaam8OxUmTlAqmUYDKeIflbJZTWsMB2iZyR5dAAFnVd+3t1zGcr3DEZY3JQ8h7NUtsa157EYsbyQL5WxRgmsbROglIjTctgiGO7/m7qrvG8lNkSrf4AYbOF6WIl8zW/VZX3KxDFMPDUAWndLT2XGnMiSQZINkRHavrz26MmmUp5oeIcju3zyVSSlnSj576Kk6ljoaAWZm7LebdLzgs5WpaFnmcj23MR90K0gpq4m7JkNymY4A6Qpj4+Lgp0p7c46V2jrNdwf83r5KLd60t8wdE96DTR6bdBwtPlt5/w6fICo4cHnL8+R3//AJXfxtdf/wTtsI5vf3mBByT46dfvMHj8Lf7uHyK8n7YRFwMU1hH8Vg+98zZ6LxvovPDwkyZZa4KwIk1spBVdolwEBCLJDC8LzMePYvTA+IfsNcZYUkXBJJ5INhTCXssLAnRkv7F0tJSS0IQAW6LYa2TUM8ml3Gj1PKVlURyCmuskuAI4CYSeHvQRxyMpj+SkL8YWuoyUhbs0HmCi9eTkUEpNF/OV9KtNJGWu5ta11dOY7h56/ld9QIXahsGm58O1bqD5LvVPmaRB5DvyKhPzMsZmy9lSOaTrPi3bMOsMcXw1TLoShegBq37rVNRRrOCyj+aUjClQegMUZUNiCDt3URL8pDGbtYRjxag51NvluQuBnP1xBQQZSpYoOyEWiYO6VeDVUQ/TzMPMjZBOl+h3+2i1W2h3QzhWXX5KUGpGGS3t2q79pbcdg23X/pcaJwiXqUBxuSt/cP2EH1iwbaavH/zYs08+f+2Pb0wmXMdBvRah3++h1+vJAo5i4nd3I6ziBKUJ6sy3rZEJPU8aRpueDCUYNGwhMT+g5btisTHLKbobutRLmDICQqqSTbEgJ1uKml6Uu/I8tFotcSf9dHGBm7tbybTKNiR2I9NOORuZU7Ce6HnO9WRLIeNeb4iH+wdhlLHkrL7XwMHrQ9i5jYerO2HNmAwy/9XqIc5PDtFu1jaMK2VfKkBZIWWjmqVYObIwr4IG7kdLXFy8F8txzyYrroPhYCiA0v3DI+7uHwUUMOQtw2MxgKFNI4DKhRW0cP5ygBbLaFcxnGAqpW9u0INb62GWlwjDhrwWx3MUuYNm3UJUXOHxOsHFfYWYRpRhA3W/haoewarVgH6Ikzqwx5LXNEMSu0gcT/RPbKcSZ00fiYCuDNgY7KU6qBNwTBhr/ClQkdFHcEOcrZR7lTg3Gs08nUUVcHQNThlhZqXbJWUnOjCSDkUgpaL71QzIU4ReQyj7PE9cGEgZ8H5bMY1W1HxRphgbxhqfmghrq+/qDqyka3SwuS5l5n1A8WdeJmoEqtIWvpnHPZ9M0AjraLXawgqzrBST6Rh7e134tS4qm6LJDIa5yyWcgqLYGTy/EMBzYYe4z6nPVqJ6TJDPl1gkM8yyCVDNZaE36AD9vgcnaiGuDpDHvG8AvxZJ30uSJStz4PN+i2k0wMNRJRPUGZlnFq4uL7BcjHF2eiwAL00MqHMnZ67idw3x5rgNz0pEc4WsQyGHklegnZEth+VRjLVt3N8tcfk4lSBeSoM0wNTfH2A+WeH68hJJGqMWNfHi5WvE8RSreKHHBg0cyX+adSG/8H4VRwQJZPvdHk5Pz1T5zkw5hEogLlprqtxXjE0ErDX6agRrjYmBKjcWYE20YtRAoAS+zZignij2qNIFUn9Ur1OPjuXP9SjEKklE0zHLlDblD+RFpH3feG2SGH9sDH8+WuOPlIQaHRfVL//Izuzaru2aNAFnXBe1dgcR5zyOl1aBdBnDKhYChM3nDpaFL2wXzkWuVcGvIpkysmqGZovlnhbiVYGVdgsmsygvXBRVCNtzBayjNqlLGQU6ZpO1lmV6jOJ7OQ+qpKsw/9fjjsowcD9LfU9HvoeDvRqmiyVGi1j0PTkecxJQ49b2BKbiHJMgUHkL9b6127iUgRqNLTLHlHal/Fj8cZVru1shpQA855bAV6WLOVloLg5P+pIke/fuRgANIQHZuWZEqcQov0cMFZiQkXJRfidjN2ruMiHAR8VQE/kQU+bPz5HRRiMJxnQV2c91FSP6lHDg93tyvBxN6ToqpggpZRly0cqSecr2xXH0Y2VhPKlQ3Oa4uZvhYvwIezGDV67guHN0nBle7k9x+rqBm+I/YzHyMehEiOoesukMjw93uP78Fr7t4nq5QJmkwr7rtvo4Oj9DZzjEb9+OMXx1j+HiN/jtL4CLWRvLoo6q2Efkd9AYNNA9byA6dnFWtzAgs79gghJISxellIOqeZ36rslqiWy5QhDVVayVqmSRcgZlfFWsk5cJ94cumUUmIBeByTTJRbaByUyCauwz/CcmYOvpTwlgrHuGTeahhb1uXXSFZ0sm8Nw1EmbrihDOzWKhQKYm+3SWYq9NB9Qu7h4e8fA4Xle3SEJYYnCjDapZmloH1iw4zK8mKV+t3bf1zKl1djfhvJlNVdKc91Gn0cLLl2e4vrnF5+trXVq6YbBJ6K+cF+S7JS/qaWCZ/a4EspixWQuu20Ziu4hzS4BNJ0lZIC791fVK+NEcfpQjYn+mGVVVxzyL5FzkVY7cbuGs3kCnS5UYxejLueAoAlR5gVmcC5NzMZvDtfZx8uMS17/+J3y4IfNejSm7tmt/qW3HYNu1/6XG4VO0prRGm2JsbAAuaVtrJvN0+8/bzUyY24vD737y+eP2hgwqtnmJwBKDQrI1louFMEaazaaUkHJSIdONIuKi52HKRZ9vwgR6hphlykTVfC4vmmzUGsJaC6WqVyT7JAGg0gfhfrFMVBz7ilLK9Xp7PazipdCtiTao2FRpoUhbH6p6YsjoNEAYTUZotQkEvMRqtsRsNMPD5R0sz8bRF6dSAkmnQgFfSMbPcwHElnGGZr2uNafWB2xyxeocVoqlVaYpOjUfe4MhitzFkppe8znGowdEEcsTBthrt7GMlbmDOV+qiziwCGAVJVqdI/z4bADnMRXBVyWTEaDW2Ufm1iRDG9VJVV8ioWup7WKvPoM9vsaniwzXKweJ7aMZdFFz2nCiJtxuA95hgC+iEq1yjnxJrbUAeRAgDF0ELhBYEHt4Bmq3N9cifFxZHmJmR1l6R2CN0bUIw+YKEE1ZNqrKEwRXCOPPAAAgAElEQVRg46KCmX7Rx9JGF1pvzVqLLev7QbP51uYF60vHLHMgwTM1zOwqEW01L3RFu2xCzZWSpSeGJaqvyRY7aa3vsVWKs06gm9dMf5TXzH6uuZGyMwSEWfZIcfvRwz2Wi4kITe/1DsWYQIR0DZguCxZbnOfy3BGnTbsqRKOt7VSI6i4WTQKZAaKKC7gQRexgZVeYzDKs2K3LOZp+grBuY1VGSJc0EqgQMggn0JZl8GvU3+Oig5ppFsqsksBweDBAs1nD/d0d7u9ukUlZN7PSHvaHB/jqyJd+R8CMhyhnrlKub8q1jRlaMkktvL94xNXjXDL8aiFH1mCEw4NjXF3e4PLik9yj/cEpBoNDzGa3SLN4fa7VHW0gJ32vSydQyQYugM/PzqWElff0fDYVkNYsjjn2mPGJwBoBL8NcY3AqrDUpEVXsLildFQBX74EB2EwJ+xOgVfUVns/pZCzOsVEQiMD1fMHFC/UoNQNEf5/pLs9HXesHXt9+v/l5+q7vb0+2J1+gtD134Nqu7dqfbpwPavUmolYbjh0ACV2LCzH8adpLYbDcz6i1xtJOgkIlPBm7PbhRiHrDQuAXmE9XWC4SZCWTGJaUomVlgNJqiF5VjfOlQxMEgms58nIlY7NibaukkiSktnk+64FBMpPrWHDQjjDs1HD1OBHRdGUoQ0a2MhZiosG8Vw8JW1GIGWs1S02/bsTszVin4jGd9IQjcxWlBSokqIc8ET6ynIiVeg8BtdHjBKWd46svz2XuHM9W+vN6XNXbXudcdQm7YrjppKSO8ZQHwpZurgQ+FpJ4Bc8noOdL3MDtKkDSzCLqeMWJVPTfbOQUrGfdrLCYcinL3bMs1EMLyxbNngJ0vAgLx0NCoDN1UOYuHucO7u8THAW/Q/t4D/Wgh+xmAtwkiO0cs+W9MOYajQ5my4XEPE3LxcP1LWaPE3z59TH61QJ/9/dzfJ7XkZcd2MUpukEP7aMmml83sXfu4cdhhRYyVGRbpzZSlimStabBNepnzMaPUqbp+xHSmIw0aqspcK0iWEuXUNFay2Tuow8E+yMTeGFQE/1cmhgwAUo9WDExYCwseWAlk6ESiQy2eN54ugrUQgeHww7ms0esiPxRbkCXUJjzbUzG1vrHel6dxwlm4wn2Oi0cHR1hMhnLHGxAXYkPt7r4BibbxAEmHhM8T67tJhbbzJHWVnLU9GjVj+M0xe3tg2jkfvHFa8yo05owRtK3lTyqz3C9ItLAsk2y+zIpb7VroS7dLMEibwKODo2lHBc5ccpcJTDLPECVUbuNMQvBtxR1nwl+D67XQq/dgt9vY84S04Il2w5WixTX9xMEaY5+zUfvaIBOt4nKmsBPPmHxsMCsGCJwIikj34Fsu/aX2nYMtl37F2sSJDCTSCFOsctezyjffe8zWMy0daC2tWAzU5qe4n7gE9b3/259Nzj1PQ+dThv7+/uSUSTINRqPMRpPRXdrnTWVmUxlZddz6RpgYwhH8IPHbMoTVEkCAQHDHpLMqgZJlEaIWkiqxS/ZULmwpwhgcb/ogFqv16Xc8sP7jyJEbmRE5MiEfa1VXdVOrrEUeY+YQHnodvpwCkfEU1erOezQxfB8H3u9Pdxf3iBb0FGL2WUV6Hmuh8FeFweDvgAQoq9nLM9FbF2Jz8pCv7TF2t6rRZhlJd59vkU8u5fJPIpCHB4eoNXuYjKeiCj8nBlE22EYDSeKcLJ/hG5RYTXO4IRK8yJoBXDadUyWmWQ7eepX84UEQY1ahah4wO3VEo8zILU8OFaEyG0CXgSrVYPb9zFsW+gjBtIUceIisUM4oSPZOSmurCgQr8ALKVPIC9HdIJsxojFCvSb+YUpDTbHVlNmBMjGQ68UgT9h+xOjUa+LGVG3r8ukkvLI302ZjGzhGXUsVpIt2DDPXRYJut4miiDGbxAjcmtLZMIsJczdsBXWme2+6uAZMhOWmS7Z1xaISf1b7ZHTamL2WMlXuA1zkeYLZaCyMtL3OsZgkiEiux+BMmXtIxp1sNhYaldRaqQQg9aocgVvA9i2Uto8RXNzMKuAmRb5YYb5aIM0mSAo6qubo1mzsdytEnSYyv4NV3ABl1vyAOjc+siSW/sZDYKadj57tYjQd4+72Bgf9fSxtV0CwRq2GFwcdKUydL1TpCM+B8B30/Un2AQNOHuvjbInPdw+y0JGTIufLRrvd4hbx4d0f5L5st7oYDo+Q5ymWq8k6K62uninpVedbAWvqzuT17Ha6OHvxUv4+m84E9BNuI9mucs6VM5+UF4tjrXJQkxJjGhlIX9OLAA3cmXBcgPwtU801oKafq7JXYDEnWy5BvaY0VmbzuSQatrrKum3BhN87Lpv3bL++/fv2qLw9hv9QMwvRndbaru3aP79xTP/ZV1+iDCNcXNF8KAMI2qdzEcyfrhwsKw52HOdLVR7J+dL14dIwmyWeVYZFkiPOKmEiW3S+prGNUxNtsNDxEFAPzKYuQUahCHFjJ1stp8umZrsLqLT2Rt5EZxx/TcBSq/noNkPR25rN0zVyZmI7PYDCtyvUw5rsF51I1Z8MM8mEOsrUgM+VV4s8U5qjnHulkoDzL+MDVwoAG5EtTLxV4RFykzJEAmpV7on2qzJo5DYTDAcqwXl5eSvxoBpYlWapAfFkr3RsJ6CFmBlwjnTg0CxIjBJskf1Q+8x4xodNYyK6totz9bY+20bLjfsvlDWB5wh2QmIQi2xxkClUCSjJhOAINj7TCOE2x+p2hYvpDJPpI9zZCnvNGH/zV+doRW3EH2ew41LcYm/dGON4hjdv3iAKPMySHP/069+htrpDxiRmSRZ9gIOTAYbnR3h/OcX7txWae310D2sIXwY4bwC9KhMn0CzjPrqoyIYii09rrS3JluY+0608h5LcYPyoHVwFYNPuoJxnKbkhIFpcIkmBrKiQ5Ss0mxHK3ME9zRoo3C+nnz3OzH+qQoDxDGOw0HNw2G+jyJYYP1BKxEHFtYhonRlut45rhRGuWeP8nfvHJDKTrEUmMR5B5vOzY3nfu7cfZJ4mI00x2bbmvDV+puZOo0GsJCJ0N19PiipG3ILjFPC2nmzlDlJPWerp2Hj54kwSjm/fvsV0sdD9SiZRAdfUPcfjInBNQw0P7GoV4zdRaPOlVJhQW2pFFEwB/RSsJIdfJIqh6roIwhxOsETQ9FD3O3DtBkIEcn8lYYjYcTG5vECt1RVG/m/+++8xn8d42Zmi2woR9s4wS0qpfPj4aQQLRxieRxg9/h6Tm6udPtuu/cW1HcC2a//ijUEQgwdOJMw6fc9K7jvN+sHlmQnbvvuJp+1PvGf768UkykEYBBj0exgOh2I7v1ytRAthvkgVKCbZKqUxx0Yiv3xcM/UYeImQqhLN0otcg6iYMkEDsGnheQEgN6Abv0+syll+KKwSSLloo9lELYpEX+rjh/cqmDX8c51xU4ezWebKvsliXE3cLIHc2xvg8XGE288XwrTyGh6Of3IOv3Rx/+FS6YvoQJeTdOB5ODs8ErCHrD5xaxS7eqWlIa6ock0ZJLEcwIUfRrhclLh4/xbIl6gcRXM/PjoWsO9x9IjLyxs0hic467WQ3K4EkKqyBE7dR9RrIJFw2EFYa2C5nCFjyagXoFtbIH+8wcVDhYe0guMGaFRt+HYdVq2Oci9EtO/hzE0R0mY+tlRZDK3mA7qdifeqCNqKiYG4UtElVLueidJcgfH8AflyhN7gQGXnCawJwFZJwMcspriEGst0/SNnW9yqeLlZgqgcPEX01pRyitW7AWdM08y3wkYYhej1G7i6vhHRebdYoBbVUXnN9bU1IBu/T5kfmDvDqAPK6kubWay7o3qiwRgBdqVkQfdfAk7ilEaB2gniPMH+8Ez1dKk7UHlbLhpogsBFBMtiWApNth31TChLHBcWCi4EaGCADD7LRj0HqR3iqnIwGVfwrlbCylzNxojLObJqKdemVy8wOMwQhm3M7HNkK0eYagEZbLaNeDUTNzeW9X78+FHc2o76h8oUgPZYLuDlC8wncyVQrGAsybTKoUuJLK+PJYDVp/sJpsu5HLc6XxZ8N8BgeID3n77F6P5eruOwd4jB/j7uH680408XcuiyRrXQUtdRyjWkIlTd/+cvXmB//wCTyQSLxVxpn8g5pNaaUkPmR/I8E8ZaIYYaxhFNl82Q6SAuZmp7al2qHfN0NC6vMVg3/Ux0hpRAMxmQvujg+BhNJoiTROkjyuc2/XAzejwfZ83vm3LQ6jtJD/Xq9me/F1xbnzP1BhGL1qX7u7Zru/anm8QK+r754uxLnJ52cXd9iQ83E9TKmTCDJ5kjYIcKPQiZEXTy4IWUrciFacxkCEEyggpM1tF1sIAvJWM+2SaujZpXA9Nhub1CVqZaC7JClatSdhmT5ONKK1XGFC0SZcA2xjoHvZaUD15NlrqE3uBrZhTRbQtcOOr1ZUx7HI0QEzxkqaeeh+STWs9UfUz/kwSKAteYFOJoXQ8C1EIfS85LtqfnBJ0z1WOnRHbC3JG0mjZ2KHB0MJT559uLKywZC4pwg5rfiWg4BngTlvqmLJVxIOfITqOJvKDZTgmb86VHxjL/7olGqJj4EAQ13t7aMIEsN3H9ZjmjdggX2X9ep4xauNoIgUCb7QrQdsuE0NICbnJxvm77C/zs5R7mVxNgVsrcnWmWWPjFCjerAcLKR7ce4e1oiYODDL2H/4K//+++zI9O1RAzqBwZ2mdHGLw4xlUaos4YqyrglbEqB81dFDT2IrAmU22FMouxmk/g+w3pJ9RNE2Me/o2gpqWjrZKO5KoyQOIr7dpOqYo8Yd8skbGfiWN7goN+F4tFgscZk0PaVVbP6TxNBMleHh2g147w9tu3KAtCqaosmuWMAngZRqU4hSpGeGUSXBpcM+7vMgezJFXiXiaNfbx+/QoPkwkuLz5LKa9GtbTe2gZc20yAek7cYmKuX1YTt+Jmatqm3DnmPpBYXM+rfCwrki/xox99jXiR4MOnT6JHbLMW1FImSKLLRtkPSS5CKgxKTznLM2ZiybT8nbqKDs1OIhSJJ8xCVqV4RYF6o8LRSwdOGeDDH25gB44kCvv1PcRljEXh4ezVKzEz+e3vP2BixRgkjFkLOEmGjpfg7Oc/R6N3LjI4Hz9fIvf3cfBmD87tBX7xi19iNBrtgLZd+4tpuxLRXfsXbwIa6QlM3Au3cYXt52a+2Vq8PX/8zgeefHLz7u/F7WTDW3/Z2hgDAC5wWTZKthgDG1rGd9ptBL6N1WqlJi5ThrD+SuUYJOWkGjQzC10dZmwdvxbE5eStywlUpZfJgKlJVErvRKtNTah5RrH9VEC37l4Xh4fHWC0XSgxeb+UJbc2cKR05CsggeFiO6XSCZqOG81evEC8TrKZLjC8ekVUpzr58KZm6eMnJWk3zXIQ/jEfiPlZrNgRMUUekt6MsmvT2VaBOwf+WY+Hg+BQJPLGIz7IYD3ePsKsKg/0DDHv76AYO4qsVnNxGZqeI9mqoH3TxOM8Q1NvCJppPR6JB0mrZ6FqXGF/O8OGhBM3AI7eBZrUHy2/C7rRQHYU4Hto4sWI4SYxl7GKJEE7NRy2wEBiHUDExoMZahjhl5lUx0STwEwvTQoSHbdfH1edPpJOhrBxkGYM/w1rTuliV0sNScZEK9oSZKGYWBlg2l4QLIhONqfICayscY4x9eNCXxdDFNUs3GGR7cIKalA2X2QKOS40WA3Ko7eqiFRW/aQFc9a2b/+Vduo+Z4E8epe9xUVGt9clmszsRvW639nT/Nf1eHYbK9PJRayyyVFG/h8fNkltZ2NiOlBsx22yVLEvK0LFL1CIX064P2w0R2ZGYIKBwZOEwS4DxmIFsgp4zQ9R0kFWR6AIx/U1G5831Ja7v7tA/GKLX6UkWmQs7Mr18p8J0tBJfBKVVp8E/fV34yIXNdJHi7dUNkjxVpaL6ftnrD+GHIX77m19hOZ/D92v40Vc/lRLh8exeB8h64ShB7IZVKNeX54JM0KJEu72Hn/z0JwjDCI8PD8KM5LkT9znPE3avGMTQqZalVgTVc6O7pkpEhbVGQLfSQsEGUOO2ZeFsCre166zRK9LMCZZsL+dTNOp1Ae8o4MzSX7M4NyyMrTt63V/Wx7k+vqfgmukPz0ee9Zpiu5kTZlbVz1hrqux513Zt1/5Y4/3K5F/U6olg/KtXr/H6yy8weZxLQsPxXXTrHi4mtpTd0cxFAT+uSkJENnxL7K61zIF2JacmU+WhtGsiAxC5Pnwvgu+wFHSB0sqQlToZJaw1FdMYh3O5vTWjl4wsMwlxPqzXfOz365jOl3hcJGo00eOoGcvUuLrB3eXBsjBdUty9EDZZ6IVYxmT+riOczYizDir1+ELdVAliKnQbHP89LFImNsyYp3Up9Y8pATU7Yf7ZjivyCBw3T48HqNcCLOc0imIhq2JGq13VNlAEcZi8K0vUwgCNeqQShJSTkHnW7KeZgZU8g0mK8FGSdXrcF+F/OT491m/FFTRCEMOEnPtBdneBhmWj71vIWg6OIuAwsjG/WMCWsl8FHN7OElwndxhEFTrODZzGobia7jXmiB6+wWP+CtdTB55zgEbHR5HOxEl2fD/D+OYeB4c1nPgeXIKtmS1aa5UpB3WM1tocySpGENSVOUFK4ErFEjSLYn8SrbWSWmeZADuJNi6gsRQdQinrkJUbSQSpFGCCbh5LmXKnHaKyHCQZ3T8VYBvVXHz9+hRlGuPj5wv5u0p8q/NnlgAmChMQTS6Hug+MYZAqY9T9WidOTfKac/Tt7Q18x8aPvnojunA0D5P50VSWbFUnqNDv6eyq/mYCNZ2MJ0CmP2nm0e3kmaqc0ToXZYmb2xs5n1+8fo0gCjGZjMTwQc39WmLB3IoE2kpLWJoSBzIhzu0RoBWgVJUdExwtLAdR4OLFaU008B5uC6ySGEW+lONMqxyd/VOcvniJx8cx3r1/j8qZw51fYTLNUIWuGFvMl0Msb6eo0g8IIx/D/h7KdCHVDYf9Dk5PXkisNV9wfaCZ9Lu2a/+O247Btmv/25vQ6B17DbptzTvStn/dBFPf/3z7taffsL3sMy9tf0q/+OxLBAS0mEGk2UATR4eHqDcaksUajyZ4eJxIxk2JwivhegZtnMQ5sbkqMjQRog5CdSC6niyVToRhrRnheSVyroVJdSDIzyv9JWbvSBF3EEURmq2mTEq/f/sN5tOxKu8U0G57oaqOU/Ftnp4nvnc4PBTK97sPfxA3TgajnbMezs6Pcf/xFsv5Uu+y+iSDkV6/j4P9geyvaO1pzREF4omlllq8Vw6qIoBvO0hbPt6/v8BqPkb/8Bj9yBEAhqwmBvrJOEGr38O0ZJY3lJLQ2WwsJQJB3cVeeIvV7QxXIwuPKfUgfDTQRuC0YDVryIc17PVsnNgZnHyFNLYRlz4q30MY0Bbe7BtLEIzTmRLLlfMqZb8q+0cNkKpUQIc4V+UV5lMK844RhBSEDlAwy83PafhJE5qUsQWz28JYUwG8Aiqf9tw1y1AHenR2ajTraDWbuL66luBdIkLNkjTlxvyK1eIRgePADZpwLE9tX75IZfI3kJ3apGJRqSZ9gOCuPNGvayDYdgrUwxWmiwqe39XlLsqwhOLLAoyzX4p5gCppMSLCnslcS3aejEwuaJhRt2VRkXBBluYi1Ow7NK1gQt7DxPKlrKW8z4FRjGQywyKdYImpBLsdP8OgW6DTrcOuH2H8kOPi0wcMhi9wcHqIhMLMyBEGwGwyh1NViEIX0zsCbFpA2JEzLIGmYa1d3d1hGa+0Q50KpIOoht5wgG9++w0Ws5n87fToJTrdNm7vGKjrRdx6gaQZD3pxZO41gkZ0AH31+jX29vakLHq5pMZZoZgJ7gZMUiXG7GcUdVbPea9zYUUjjzU7RDLt+h4zoJgAaxunT2s7E25byLMY0+kMUeBLWe9kOlMGLmStrYG1zX5vP9sMiZtjNcDaP6dV33lBn7ut4ZfHbsqRd23Xdu2PN96vQUjWyRGSfIYoCnC4v4dudw+Txzu0gjqKykM6y+E0CNyXuL6fYzS6Ej02J2LZXgGL44wGO5R4Fe9FMo8DWJ6LkEkdGhg4LCelVEWKtEgl/nFBfS/qu2aayb6d19tIU5jb3HcdHA5aohf1MF6KuYEpl5OxxYBs+gNr6Y3nMZnMWxZqnov9YR+jyQyzhdJGW4d362FEjW00Hug2fGFYT2kMJILvKumgZDoIQCiNNn4FqxM28aCeQzUDT+mpFciRCwu41+livspxfT1VRgoM+kSnVc3XnmfhaDBAmi4xnRP4UlUKyvyA8yXnVUuxv0VuQbHUyCyyWTJKHlul5llxldamCXw/9XMVW3xjhEBGvZJlYBkmgStgPs8xv1rBihnWlEjDEkm9hm/HqSQ2T497+Pb3I9Fh+5uf3COKLzAqX+Mf/tHFyWEX3eMGrm6nmJY2XnVtPHzzBzxeXUt5cWFZaA5beP3lOaJGG26ozDEknczE0GohMSyZ/3T9JOgjcQrjKzHGULIcTCKRrU05BAHXtKYtwbVM9Pw2yUtlyKWukfDSJe4uEHosJa5jtMrx4mSImm/j7afPylaIwJrGo1SGWfUmJbGw0VoTMzZWI0iCWMl8aAE9bSbEGE+zx+Ur1L6QfcfvPtg/RK/fw+XFFW7uH7bY6zrRb+6RJ316s/Yw87kk600qy9wIConeMNoMmL0+F3QHLTHsNvHitXJQv2IMyY4hjvdar7ki21R9jrGp0aijGQJ1oHld3ZJ9z8LxoI9Gt4U0CpAUFZJliXQ2x/TqEp3BIV6++YmUgn68vIKFJbzZHdLZGDOeMzuUiptFPkBs9+HFAXrZPfb3PuJ8UMHqv8Q8GEjCle9rdjqwygJv//AWv//mGyEy7DTadu3fa9sx2Hbtf3tTorDKNU+c+r6zInvaDHtie4Fnfc/fv79936d++P3CANKTLpkeMy1ETuYMAZB6PUKWpuL8JyCZdgtU2VgdaGruh849qsnUzM0meDNzpDzqYFU/XwMwen8kINTzMSf8LKcTZiLmDMeHRwj8EPP5TMoGDCPFHJ+ahre+T5hMCvyhnlucrXBy+kLKT6kNtRovcHd9h72zfbRJxZ/NVbChg1GCBePxFA6BMCIbQsvnpK1YW8odk0yvBItRgXgJqjbg6LSL9l4LrTLDapIgmyvHQjfy4NQ8xEUOt9aBazmYzccoCxuNZoF2foObj3N8nFSYsaS1aqBV9eFFbZTdBqyjCGddCwdWDCtJsVp5SKxAvjPyLLFbF1CJZQh0hkpLJIkqRxCNK6mtlNyzaHyJHhsDPAZ8EvQVyojCriNerZClEznWggELA3A5tSpIYfmFBPG6RFS5heqgRp//9bXV5Ql83N8fynZu71iOqC70NsAh/8uGbPghF1LAajWGVWVw3UBfT8Ng09vQ4NoaclsHeds3G7OaFWphAt9ZYTr14ThNFSjre1QAW91ZN0w2A4qrvr52TjUBnH4f38LyGS4mKi3ULBn3jM5dGUI7R89zUDRcrCIPnhPAp4lC4gpDYk73sFUF361jdP+I0d0VTl6ewat3ka1WiGo+GkEMaxVDFM2qUspcs4XwoqRcZO0mYTuYTBe4uLkWpirvXQNM9gYDYW38/ne/FfYmWWsnx6/gODmmswc1JqzvXQN0meujADDDRO209/D1j3+MIAilFHqxWklWnOWgnkc2nQbX1uXJ/KH+DBmRLFtmIK/AdHUdN8LgBkwz9+KaLbvOzqsfOrWR4driWJXlGJG1xgzxmrVmetVmdNgeXU2Qv7UeeNJ+aKStfqgMdP1oFjW8HDtwbdd27Z/TeM+2Qg9/+9MS+dFPMB1lOD0YICld3E0XSOYzxEmM1pKaacoVmUMVhfy9YV8MYapsAYuMI4JrBCsYcohDqIfSCSShGJJZ6wCek8OyWUKeCAjCRBSBNWqUhp6LTrOOVUyQTbNqdTmour9VNeNes46jbiiOzNNFpuIDwwtbgwZb445mcMl4ZBIGuskQToObvJIxvNUIcTjsy9hK9q/+OhPdIPI8DDsBpkmG+UqXxgrQYrZoWN7bYMYG6FBgh3oq+6z1Szl0M16YzOYokhz7+x1J3qRJikKVCKDfamG/18Td/QMmC8YUKpEsZX36eBRgp+cMU/Zv5kxNpTOGDev3GjMik8zcnl+1EUJW2ciSDJO7GPOPK9gpy3ZLZH6J+osBVo0GDrsNRM0Q/+0X93COffzV+a+w+PWv8f/80kY4+ozz/9TAh6yD2TjBwX4Th/0IQSPAi7MDNOs1LGYjFEkJxBbSmynKfIWwEUqCTXT5GJfSaCGmCyhjLG0U5RSo7FzANTHt0WZR/IljMtwqKQ8luGZALqn0MPOKXIP1RKhibzHhspFmKVpMpLoWPn26lsQtAT4m3Phj5jidDl1/p4q7FcimHtRfDPBmElzC8leXZfO4jolo1jTFw8MIh8f7eHF+JpUakoTfnlV13LWee+Xzmzh9O0bXL+jHTey4FX3ohCvjtxxulQuLj5Ii1Az86suvMdcVLk++VTanJFJofCKEOeNGTs1cK8TZURdZOsXjZAa38kRSgnHP+HaOw/OvcHr+Gpdvr/DrqzHqnQr+6CPalY3xUjnx0jHWqgIU/gC1l21MTwpMMgvLsYvVdAF/8Rnd5giF2xVWJI1YGMecHR/j6OhQko2sIBLQc9d27d9Z2zHYdu3/16bYWyqgMSVsm9zPP29RZ6aozQz4/N1bDIr1J54vH5/9bm0+5noeGvWaTF40BWBJE50yOanGcaqs5UVYVzlFCh1bf43CHNTBmXlafb8Kt0zJgmRWtU6d80THQ2Ux1SJfAX+GzSZZbWaBmk0JYC+vLvD54vN6Ia2Ave0089OD2z5b9XoLNb8mLkn393eynUa/jsHxPlwnwP3VlVD0VUigJuWw3sTBcF/KICRAZBkbGWnTJdKYAvVN+LTq5HFJILjCchYrnRMeE+3tGzXYQQS3yqQfLJYJbC9AM5wgvQ73o38AACAASURBVJ/j02OOcUU1Nhde3kTotuG3W6j2QnQGDvadDKGw1iwkpY+SrDVfZeFt0dDYaK0JI00EdnVmT2jy1NtgSYcq+SRIKZlULkTEyIBuoqokRjRqcpbqzhSI5jZhWcwmA5aUR9AaQJ1PdXWrzf9rwESdeX5vp91CvdHE7c29uGOxrGVjMKXuAtU3jLGGWaBIHQaydIUiiQUc5TnbXB1zZbf2QgO467JhGlk4CZr1RywTD8tVD46vgFz1n9oDlhqwj7Iy1eEP+7mU9JEBwIwnAyoy25SGCK8hM+1kL7hks6312WwxDEh5DlMKNecIbAo1FxIox06Iu8LBZFbBvk+QTBZIqxEatRjTx0csljHazRpOhhaC9jGcoA03m2E1WqAMGljZhWRCWdowvytRCJOLiy9lSHH3SC1FXjftgssS4zBCs9HF1fWFmFvwWAeDIzEViVcj6eMGkN5IdxsQXt9DAoBVcL0QL07PJZNN5thyuRAWpK1Lungvm/uXCwwuVo3WmmTyuRBhxl4vujbXcGOqYgA0MTUwYPYWsJZnqRyj5zgiyDyZThE/Ya3h/1NTI6P58KZPP33lTzS9iOFO8Fzs2q7t2p9uvldHnvfRwh3anRRRdwDPrsMJWshXKe4ep/j6b/4a97fXuHh3gf3BAG3fRjKzRE/tIh6h1ivRbnm4u7jAZLSUUrGidFFYvsQcAfU0JdnJeCRFiRhZThMDkUxbM9U51rHEkeTqTqsuJgQXtyNh55oRIar7AuJM5jOMZqlm6mgXTnX7q0fz+9axyjiiJQ7W7zePMt4q/1B+H2Ok4aCDZruNj58/YrXiXOLgcC9AnBV4XJSqEoBJPIk9mHBRc5e4sUtJoS65VNYIGrjRQNtanN6wndaYimI6ERDKcwSRg1ZYwzwrsd9pYDyd4WHOWEbHAWR7M4aUeE6ZIZDJLGW7fCSLjcxmX7HFOWcqfTZXhOjV/GrmWJVUEe1T0RzdGCEkSYbFdIn4IUZGPwYpV83QPGmid9CR42UR3nVRYTzJ0IqA6OoC/+XvZ7ij7ha9ilYujtsRfvpXTTine7AKC92oQGQFAu6JS3pl4eHiGp9/+QkezQiKFWLfQvfFPk5enVLET/TKhHkmDuwE1lRlgMRhEouV2lRKJzPTSnS8xDSD86MY+6g5UIn267lXKOOapS2lsrpKgO+zS4mTxGjMDxFniTjlkr0n8zfNDWQOUhUL+kLKdgRE007qIn+hGWxiLESGp3n/unxUA8malce9Ew3hEghCDy9fnSEMGvjVb34p6wPpTVvBtgHJ1mXUclg6aamT9QbYVR/WoLBJ7PEeoSt5kUqSPaMvqAYjuetkrJ+fn2Kv0xVW2MP4UbM1+VXqfQJaM9nJHK/v4uD4BM2wjQWT7NUD8jSFa4dI8wj1Zh8vf/RjXN5P8e7Xj7COWziojbH67f+QihA3DJEWexjFIXw3RjRsoPPiK9Fijh4/4XKS4e4hh7ucwSsy9OwxXvce0GGs1HyNeenDL0t0Oh14bihxyx/e/QGXV5c7oG3X/l21HYNt1/5V2GycRGThZSjQ39M05rV+vv3aJlAz3LHNX9d/N2nJJ9+A73zD89c5CadJhtl8JhoEfuCj0WhImSYZM8vYWE/rReSzgMxQnjdL5s33G0aH/m39YfP6hvGkwEjFZlOTJYMCgkLMXvP5oD/Ewf4B5qsl4ngmnzHB4pMF8ZMTrCbxlM6ICXXWajg8OsZytsJiusD4foTCK3H26oXogNFaXRbrNoPvFOPxGKskR6vZQJ4lWI6WKG0PUastJZUCQFF4nQGQHaNguYldoE4b77ApJQa8/PEyluCLluq+nWL6MMa3t0usXAtB1kCQ94S5FPRasE5qON6zcGgxS5tgGXtYIYRd81H3WRJKsI86aYq1xnLQJGWWVLPWxL2KWmssgWFJXr4G1kQDhMGflOspME702ST4U8wox4ukTCHPp3DBsgxlgS7Ax7Z1pD69JvlsAia+6/D4UBhLlzf3NGGVN8qndQC/uWJbpXXb10/KYHy4foQ4XqDM5sLCUrStzftkl0x1BAy4RkbEHKF3i4fpHoqqo0T+1QpH6b6sy2Q2Gd51Nlf3dXW4WyXekm2nyLACksTF6ok+m3Fas1A6DtLCRpGq7flWgrZToRY5GDc9RJWDfHWJ+5sZiqKJ3HMxSwpYQR/t3h5A0I3lNwQD/RpyOd90urOQJRYKHaxOZwtc336WLDfLhNh4HP3hIVc9+MPvfidsL9+NcHr0Rkqj4niiTsUam1bHqLFzHVyrxsC23e7gZz/7K/ieL2LcS2aOy0qVzlJrzVHmJYodqbXV+MOyIzEJ0YYZPGfCRGTfNNdLh9cGSNOLLDIX5Ng1k22xmCGJl2jWuSAvhLXGY+Z+bDNGttv2MLDNYHv+9++OlBuG259s+vxxjKd+464kdNd27U83AiiDsy9R1r7GZOLAq9vCNIunFSLLxujhAjcPN1hZFeKM88kp+qfH+DiZSOm8W1i4nz1ivrxA/PCA1TTBFy/OENYcPC44HzjwPRsRXStFl5JgQYK8XIqLOaURChoZaINyFcuYOcHCMs7EpOZ4vw8v8MWd+HgYoVUvcHGzxIosJxl3tJSGnstMPKJntvXgIt+/HlS2xqv1WKsZcppQTaBnvogxH4/xxesXAlTt1S1cT+aYsSRUROP1J8VhyGxHFfar3dBjo972kyTC1sbNaLc5Co2eVQ6K2ELUClFzIc6o0yVLSQlgqoQc4zJJSNpbHCrtBL2eT7VDu2KpGW1KvX1+bmueFadpXhcN+DDpuVrFmF3NUY5SiUFEyL9mYf+LPmrtumYA0jMyR6tcoh+6yEdTXE4DTLoNrDIHgRUhGDYQvemhCoGTIEc7KuDnqewGZTEqsd620ew2sf/qEJN4gtFihiK3MXlIcH19j6hTgxv4okNXWRkqKxettSIlY41awoWUjTLGiinTwRJR9rWM/Y06depcsK0TSaobaX1bApOKFS/xsJSCauMCkW+wUSQpQt/VCVQVFwhYRvBPxzTq9GmWvhH70EnwzXv0j+4V2zOe9UQeQr3C3WUy7+Z+hOVijJ/99Gfw/QgzniMaikiybos1uQbVFMBmuv46Qa8DDflt67HKCR6WqNwAOfXvtGO9/JEsy7LCeDTG/eMD3nz1FQa9AaZS4ZJrrVZVNkpuZ6PfxsGbL+BHHVipB78imzUSwDbJG3jx9c+xf3CIf/ynT/g4AnpfBuhcvcP8m/cAmljkDbjTfUTLIyw6DnK7QD9K8J/PL3HWybFMmoBVQ4k6YgCxY2GRB7ibNpDNphjgHUKPr7dwP1ugzBOEfojh/gDdfldpvmnN2F3btX/rbQew7dq/SuMASiBDsbYMhfrZ6u4HFnzPXzdh0Ob17TKodeiyFVB9z0bkZf36mnWkykYn04mUiYoWWqOJZqMuZV6kN6svV9tX+nJqca3mB12aoAGK7R8zka/nEU0/Vzibfk9pFvob3TZz3hi8EGjj+Ts9PhXXyelsKllCtTCXrUv5poIgN/p3m8mc5ZMpFssJTk9PUfcbWCwXWD4ucHNxhcHZEHvDLlYU+RXrJDWxZ3GMx4cRHL+GoNmC36gpZ0nqcgh7TQXZsGM5f9TwyBMXjbpyHlstY7iej27zHvOrKTLbR6O9B4cZtKkHP+vAO9iDfdhE98DD6zBDPZ8iXdpYZiHKIBBx24jxn6Qlc5RZglxMDBjQqXIEKQilLoXF8lQCa9S+ori8cq+i0K44V1EzhMGYFhomUCROUpqWL0EfRaCDCLkEj1N4ridlourybfhOqvpXL2CqSthRB0f7uLi8xnyZKK01qVI1/XLDXlpnSZ/cClvln7qv+EEoWWzqs6HM4Drh01BQxZ1y7d2qQC+8w2SRYZ7uw/F8Ddaq+2F9J2wHeSYE1SWxOrbX21dljNK4jhH9Ed4ryghBaaiYnK1a2EhZixgh2MhtF5mUjVqwqxyhncKePuL64htUg1cY7L2Glfuw4OP8VQtvjhZI72Kk1D9xaDfvw3IjJHku26cWYp5S/LnE3e2VlHhWyg1A9sMPPeyfn+Lu8goXHz7KwXQ7B6JHuEpY2pHKe41uokqYq4WhKa3mjxT/WDbevPka52cv5F4j2EzBZjLhPN9V94DoKLLUWJeEpsqsRDR9RIdGMddkYSH3ul6YyvCztTRV1ELNaDXMC/Xdk9Gj6PpEYYDxdIoZnUpZOqU/p/E1PQKo58+H1u0x8+mY+rR4xYyhfzTcNf1Cg5nipqvPxa7t2q79cOP9fbC/j7/+j/8R9ZdfYDpfIbRX6PZaaLg+7DTG5egWE0nqcRxwscw83FxdI6y5eHN2gnqrjuVyjiRPUBYpwipA0+4jWXno1EJ0+x0Utg87T+CwjpAsI6jkF9lFRaHK/glYmPhjawRfjxOMO2gKtddu4nDIRFmBjzeJlJ5KImdr/Fo34zL65Ki3X9mAa9vRmWLCmXjMlOiXwuBx7YTPMBgew/FCLBZLxfA3Zat6X9RMpvdND2Cb0c1sdzsu2/p/fSyKqc3cUb1Ww6BfR7paYTJNESfUMWV5IqML7p2W/uBua9BsU35oAB66PCuXbmEvbxlfKYBHAXQiFWCMhjYELKzmCZLrFFjQZbpCUmXoHLUwONuD43uybQkt+L15ipLyCKsY05WLOArQdm20rBrCZg0vhnUMOzYatoMwyRDQ3Zu2CBbZ8eq4FAFcxX17B310+l1h36erHEiA+093IrMQ1kK4BPKyWOJiMYhi4lKqCICE4BqTl5REyA3gqFw715fZ9CFuU/8wWWWqOsR3VfcFdVkNYEUpihJOmUk8XFCTtGLJJo0StGCu6dcG6JRrYz1Jiss/HecYxroOilS/0NlLE+vJXzRYRp3Ci8vPYvDB+IDJT7LaVcyt7wq9vwakM3O06ffrOdaAwBWdfzPR6ysdAmsKVFNsN/3Z9U3D8u8Sl9fXEgt8+eaNuNMvVwsUmSWas0en++geD2GFSlcPop1r4eFhhvreMV5/9SPMH1f4zTcPqI7a2G+MgV/+DosRHdoj2E4P9nIfWW2I1V6I5qAB36Vu8xj+KkGtnDL9jEbbg3fUQ14EYsaRBxZiavAmNTyMAyC+R8u+FL3YZeFilq5k3GqEEfrDgVQAKAOobAe07dq/6bYrEd21f/Um5YRC4992+flOVPb81x9s6qN6gvze17ZmuPVb9Os/sBFO3FEYot/vod/vI/ADYa7c3j0gXtHKXShnG4uBLY0SCfMk8NnYD1imXFTsxI3umiobVVp1Sq/OAGuiaWL0nDTbisAQzx21nprNloA5FxcX+PDhg7g1iW6Fpt6rUPLZMnkd2KigzPMDDLsHeHi4x/3trSzmndDG+Y9fyAJ/dDkWJo5oQ+lQg+6T+6enaNUaimm3FsTntXzAbLYQ4EVAoITi8h6a/SY82Pj04SPuZ0uxVQ+9OvpHLXTbDaGeJ706XkQVGuUSeVJilXrIBORyEboM/xTzh6CZ0fdIU07KulzBLlE6SmuCJgaigVXoclAJ/pSbo3JtVIGeCN+SkaUDJ54glp0wkcsfiUmgNGBWLD9ECS9qomJph2iu6HJhil14wMnxMUajezyOWKro6oULt8NuYnRhVDBtGGSmUEVAPVXFooK9LfdKFfCWsk9FnmC1HCMMm3D8ug7m1LWJqFNXjDAvenDdUESnVbynOuamq5tvNQEbz59anDB7TIBMWFSmxMVVJc1S4qyFz6TwRqJ7VZ5D4WcyJlwCT7y3GcxZ5P9ZSLm4yCvEsyU+v/8VAtfFVz86hxW0cA0Py8cc+9Zn5IsV4LdR9yrEoyXSKhBWmu3V8Jv372C7BU5O9nF3Pcbj443aZ540OUYbw+G+aAq+//BeFjCBX8Ph/jnSco48j/W51aLAcsq3BPhFh1B1hKLK0R/s4/XLLyTom0ymSBLljkcx6jWYZMBvlsKkSmdNOYMyq8++ZYBu3pMKyloH2TIWmOBanXe5zqLvp/SMRB8yT4W1RhbtbM6yVA3y6+turufTBePmVfPa86De7IdaWj9tz0aNzYuyGT226EULx/FN1L9ru7Zr39c4XjBhR/2kL794Kff7h/uJaH16HH7u3uLjb2xcLlpIvRlcSzkal46PxsCG7VmIZjG6tQEaB4foHfUxm89xS2mHeYxWZSP0qXMJTJIccbSA7fsYPUywGKu5ndiD9ilSwMJ65jBjIhN66h7nX8LQw9FeHXGywt0kwWDQkrHo6o4gv3Y436z4n40lRpNsA3E9GVe0O7Ka6/TntP4nX+ewPtiLUIsCfLrhgp+sdQdnJ0c4PT3BN2/f456u5WQ36fhJxkQdN7FsVECardcFwDHJSC16K5uXp1vmPhVQp6O6A4wnc7lGKsZRbs+MOYKaj6wClrFigPGcMUaR0kYhGtHdkjIL6kfmVW9jgEDjBG9dMso5Vs2vAM0QAjFTSh4SWPSmsi3EZOS7wPCkg7DJygHDsmMikY9LxLMxynGAbBUi228ADQeztMAqdGGnrG+0sC9SFQ7yyxjObAGEM7R6Jdx2iLIaivGFAIyVclGVWCsrMJvN8O2v/4B4HMMq6UZboHXUxPlXrxAnC0wnU+6KGB5QD5QmBmJkIDqv65Sv6gWbakn5UcxxVkBoCRaJY838pj/DTxu9Uv3DhCA7sueUossWk9GdcSe470a+RaGVonNnDBAE6DMMQZX4UvlPdYOoaW6T+pRHCds0YLaOrPXrloPz40PsHx7h3dtvcf/wuO7xdD8398D63thiya9/qkIZw1lk5qlvN0ZT+nZ5koxV95pO8sumShwcHuD45Aiz8QxJPkLsNhEFISrPQW55mI2XSKYJ3nz1I9i5jd/86gqLZh0vzz0sv/kF5hesigmQWC1keRth1gU6IaIv69h7EaDhpBj98rdYjj/A8ado+Q0EfhOdWo6jswTj4D/h958D3F3eYV6kwoK1FhmiJEPHmuKwNUFv6KKoHWLh9KWvUEeZyeMid3B3d4ury087Rtuu/ZttOwbbrv1ZNBG5JENea2U8B4NUOGOeq/+f/m7WfGYifjJdPXnf0089/31r6lu/pDJfXDgzW8qMHQOger2BdqspWiB0KRTWEz+kokMt0qoDSSPYul6Tqv3Sb32yPZUoM5818JiehBlsaAdTe82WyRDHK6RZhl6vh5OTYyyXymJbhadb2eAnbbNP3BMCTbPFVJgx+4MjrJZLZHGG0fUjkiLFyVfnItJCwwWZ7BnUlSVmozGWqxherS4lcorQV8HKYiSLlViFO5GHCpkAXatpioKldsd7mBWstQjh2wMsnBpWvoe2O0PLytC0cin/WxZkrfmIQgehZq3RxKDKCylhZdkBM6S5ATIosOuoclApGxUdEO0SavRAdBnohrVmHJhMNl5rp4iOig78CHboaMjzQsmcJssJgExpvehgrdlsoNfr4OPnz1gtUvmetSbbugxR92BJT5vrsdEm1L/qgM1cexXUsV8ZQhu36wVNcTArkqnocdF8wc9nwk7MnT4cx1dOXCb1u+l56z667g76iWIvrNc4WqCZfWQr26733xyH6WISoIrujypfUAs09cM+69oVbm/u8OnjO+ztv8Lh0SmskougFDWK7y5vEE9SZDmzshmSwkPQ3UPkFSiTWBxJ7yb3Yo7x8PCI5WomzEC1uKukpLu/f4RPV59xc3EpR9tu7qHXGyLOZyhLGpaYshs1siiw2+y/Mq3gopPA9+vXb3B6cob5fI7pZCL3G/uH73lS2qU0UgjYKgMD/hD8Fu1E0U+k1tqGsbZh+G00gFRZp3YJFVdaXR5jOdLPp9OJLLzCIMB4NhOmKQFjNX6YUe+7Y+LTEXDz2ve973+u6Q6pyBIqSeISRP2f/6Zd27W/pMYYZzgc4m//z/8LB8enWM7meBiP0Wk0UUw+YP7tP+Cbdz4u6udYngTIghxOQpFTC04zQTeNcdLZQ2G5GD/MYa0czOIlwlaIg8ND5IGDBW1gilzm8OXsAuX8CsV8glbjCE7/CJPZDAVLsbbjEf2jSDzGIkDldvYHXRx2IlzdTzFakFkCzBcJ5ssYp/stDPptjCYLPa4Z79Dt9jQy2340v61jJ4UerOeMRuDj/KSN5TLB5V0sCTQjzzCeLnB9c4f9XgcnL44xnkxF/8uEPAIVauds828N/JnxX5frrSMA+W7FWgs8B+02NTonohfL6EMSn+bzGgASOYosRVMYbbZITsifZKBVxkoyjwpoqdwg16wpPnJeXcMl1AlTc6jr1mHnFhZ3NHVi2SZ9HDN4TQ+Dw444eqr9LcQEqZRDXyK7G+HhwUeah7AjD+2DADWnRNMDDpxSdPsOrUyAx7pboXAdzDMLMWpY3tnwkwxhY44UAarM1lUTBONYqaDYbb3jHqyGi/lsJNuNFxmur27gBREODoYSJ8+mK8XYZnwlUhLmPOtySxPXEOw0jDn9aOZkgqbmyqm2SVSb3xVQpr6M2m6UCvEtC7WwhjSmzqAB9XRfW8fXmr2mgTcdoq37noHCZE/0fWISY2ZvVL9dB3WSZByNp7i7vcOLsxOcnp9hNBkLm1361fPJmN8h5a1KX86xCm2s5a5Bwe0wTSoHZH/0OTAgsY7BBJBGhWWWiM5uvT3A/uAYkxlB1xxpYmN89YBOvYevfvQT3H8a43e/GcH/so83jREmv/h7TKinWNVR2ntwrH14XhfO6ybaP2/izSsfX/kZWvEUNw8jTCeJmIAw3lnxJy7hzDJ0nUu0wraqPMhtwKX5RYXUCbEqapguIswnBcL8Bm3/AaXXxZLOyFmiStm9AHvDocS8O7fRXfu32HYMtl37s2qS8dMLTLZ1Rub5+7bCMxMwPV80mqlx0zZg1fciGOtv0e94HiXqCVwyoq6DTrst5R2NZlPYUCybpOMmS0vJtJGPSwndk11Yf7UszCV4MICZAs0Uo01lXuW5LhE12VhhtOkgVBb2FObXRgjCtItC0YkiyPbtu3cYT8aKAGUmcyHnmCBlq+nFsXIGBdqdPuzKxdXVZyxXc3l77+U++od7mF1NsZqQHr5hPTHTVm93cXJyCpeivcsHLKhjl5Xw613YLMdj8FvlaJQhasws9iIsozbGeQSr5eMsLFEv5xjdLxEXFbygjrDdRuQY1lqOiq5UuTIxMCWeAmAYEwPaw1fqPWILr4V1M7LbRGONTCNdtlEoEGjjlqlBD9uwtjbXTQIYicl1QKbPWZImSOIp6mEDr998gYfHR4xGE83u0iUiOnAzIJv5TUKltYj+Bghdl0to9uM6yNNaJebtxhBDBYA5ktUMbrGAEzbhBh3tWGau9nb/NqHm+uJv+gH3d73I0WK5sk+aVSl6cMyyqyy8lHEIa4Bgk6uz/9wfflbpsHmejcB3UGQx3r3/hEariYOTF7BcD2kOOGUOO5lgMl6gTFkWwZDYhw0NYHH7kYNaw0c2HeO//ua99Hu1h9w3dmpH6Y/MFri4+CzMsTBsYLh/jDwnUzJRpTOauWaanM+t0UF08aoSw+EBXrx4JWWg48lEOQlr7Uje/+IQKqw1ij+z7JhgrhJt5nggOjAsCSXoKwspbk0x43hKjcuePgDtGqrONxcx3I/lnJp0qbgax8Jam6syU21s8rxtX8/1QvJZez7SPR9hv+819UFTMqNLbvQCURiK2+y/Xdu1XftO4/3abjbxs5//VOZIJoQebh/QaNRQZEs8fvonXF+McTFvYd4+hP2mgb3Cxf5lDx8XN0D1GQ1MUa72cHbSwt18grhsYuhVaHfrSIM2UivFcNgTCQYu8GePN8hHn+GkMSLrEF7Yxipw4A1rWCUTfPjDO6TxQs8OarKr1v+XaNUbODuIcEfAZsZxR88LJpYQcABohra4aVao4dPlrZpbtcD6+vifwyO6nHJ7JpJ4SINrlGE46YfCIL64paKTkt9gW8N/1HvV+Abnl8FwT+KB6WgqIKGUi5oqAYktOVZpnS/CZZTdkNI9Pe8aMM520GvVZcijkQHnOtv25H1qGNRgjcgoqMRTTr00PikzYfvFCZMuah50qRMrQB4ZvjQC4raVPqliybOKg/gVmW6WVCQ0ojqysZ6zYCFmjOcC7X4NUVSTigPOOXTO9H2e2BgOYizfV3iY15CcNxGQ7R9YOAoVc5yMNLuiURcdPB1YfoBEXrcwYkbMsjGdlgg/z1CvFqgPV7CbzGoylgglmcmjoO4ax//VkrIkGUaPE1z/7oPM14VLXS8XB0c9dA+6+PDxM6aPc1guyxz1PKgCYJWYEyahdmKXa6A6h1wRTcwzZbJrEEwzylQ8pTTVhMHG92qNO5bgkgnWrvvICgfTRQywsoHfzzCU/7TpgTJZ0JUMGnjVnLf1ZKj6tIkdVMJsu2+rxJnuE3oS5fc1ogBnL18iqtfxq1/+EqskFfkR0+14n/DNAd2AK5qVGPDMsNUMo1OVP5tIzgDGKobUXVi7uw+GHQyP9rAsllgWNqoswLDZk315++kOJ2evRWf69/94BWewhy/e+Bj/j/+KTzf3yJwa6s4ATjVAHDRQ6zYRntQwPHPwwilQK2OUcYLHxxXef7zH7e0tlqsMpecgckuEISsYEuw1gWYtglPrILMiTAof9zMm2JeY5UAWO3CXBcJiia4zxkF3jlq3g6x5jGVJ1iZdjD3MlzQRsXF1+RkPNGQTk5Vd27U//7ZjsO3an11T2SijPbZFe37WrO953F5QfhdQ2Ibb9LMni9Tn3/Cs6ffK5F1QHD3GfDYXxgrLM1vtFmr1SJhkaZqoxbIcyEZ0l49PNikZ1M3fJCQ1ybS16KqhwhuwRi101WLc6J6pGZYsO5avJXEsGgzHx8dSzjoajxW4JYexcZv87vnQv7IMIV4gy1kKMkCt0cKMbomjOSZ3Y7ROu+jtDzGfzGVGN0FyliwxGT/C9jyEnoXPN494GE/RbXaldNCtbOxR8yOzMHEKTBYV3DRHr06xVBu1KkG6oCh+G05YE3AhQvqRRQAAIABJREFUmY8RiRU79Tu0iYEuVSAzTUIjCeZzKuehLDOU1HAQW3gaVlSiA0JhXbLVtgE2nSLUsboBOUUPX5fobp0eidhM/tIsLhjcuOgPDnB8dIi3796LHgcXKwqPVdnotQulvr4C6OntGnDtaS9X8IgOGdevqay8yWiq7Lt6l8q8M+iGE2EVz7U+W6T6itETU3v9nStvFlVPIegNk1Rjy/qNapEhejKGzWaMHuRQNu5X8p3yd0uCo9+/fYfjoyM5V8IQJABXpSimN3h4JDitXEZdmlhUnnbdZdBdiUPYdJZgZEP1TRpw2Kr8ww9rONg/xKdPn3BzcyX73GkOsNcfIE0nwmaUvZHTv7VM04YT6nV1Juka/PLVG5ydnsr9PR6TtcZFCYFCw1pj2Uypy44J9GbSFwVc02YZojFjSrS3zolifyoAd/2a/jHluDTimE7H4hBGwJxOW7Sz53fLKf4ecG27fc9I972L3efPfxBQkwc9PmoA0rDWduDaru3aH28Eoc9Pz/G3f/M32Ot2cP94L9ISnlfi4dOv8fD+13h/UeI+r6N0a2jXm/jaddBvDdH6PxpoNxIsrxdIl104tX1whXqXJqLDltC9Oc3Qykao+U1MRhnibIXefh/tTg8lAuRuDV5ZE/YvYapyThdmB6fnB3DdALPVSpnUqAkJvuvi5XkXzTDF289jzGLOOar8W409mjmj2TM0SRhPE9hVgpfnA6S50q/dQACqbThEW2PYZrpZz0/9Xg3HfR839zM8jIsN0mI+q7dvNLBoDkBNstl8JWX5UcNDXpLFbhjW9lNET4/3HJ/NvCVzdm4jCjz0WhHGiyXmSSrxFZnMa8cFSeaofTDHwLlBACKZq1zESQkSeiPfRUVzH5ZYOorVrUT9FbikdkUddS4CCjYO948QFC6KhxROrgCTVVXAqdto9eoSi3HSo2M0E66+V6BKR8hGI0z+UCFJavB/1EV7z0LNt9CgyywZ1y6lGSyk4uJJcwRPqi9YosrdaTkW6ijRqVdIAwfjxwST+0KkGjzrHm44h+NHKCsfq2UmiWS/1hTwj2ehc3ogFQPVgsw4H9kyxeJ+gcPTQ7T3mpIcSrJCafVqQEiSmHQitytwN0y1wLo/bAfH66TO5nH9uulhKlBWLHshDdpYJpmAj3utUM5lkmcoJEmqyj8lplZfruL19VUxW9auH6YcdF11sBaXUF1I2PB65l3fIrbE5HcPt1guFvjr//Af4HsB5lo31a4qBB5lTywVoxL9244HzZrDeu4yTsdVjRLrHWW3sn0Pp6+O0KWpGE+mS81aH5O0xMX7a9TqPXzx+hzIEvzTL0c4+vkBXgf3ePt//x2upgskZQd2fIR6eYw0rCN81UHrRzV8tW/hpZXApcbeysYiCTDPHDyyzDQGsrKJVdbGKg0k9qYuY5zlWJUL5JiL4VnkxGjWCpGVqeIV7LBAGthY2YEwLWdzH9lkjlpxg7qXAEFb3Ho7tUAc05vNLtqdrjieMh77oXXhru3an0vbAWy79mfbJKtUKaHT7SDteVPzy9asvCZ2b7/DfMPz59j65u3ft95jJks8bbLAzgssFgvRR2KwQKCt22lLmSV1knI9iepk3SZT+mS76zhhEyBonYh1ILHO3G3K7kyA8f+y955dchxZluB1rUKrVJGJBEACJIu91Tu902d//H7a/bK71TXVXVUsShAqdWboCNdiz3tm5hGZBGt69kzPtAgjAYTw8HBhYfbsvvvu1XhRLkoXhMYIOMgkWjWxq3q9Ls7Pn4sS0CVldkXgojTDHiF8dROhQoECm4gmSODg8BBaqSHaRFhcz7BYzjH4bAS34SMmvSyZmqT7tpotcDuZM7OH9tPvdOFS8GZUSHQdC4MciCiZK6zaw0WBeBbD8U0YjgeyGiKH0aZnwzbBgvJC+LRicI0CeBbMJWCNgDcKT8nsgMtBpSZbTP+SC5fYlkAPEoIld1Dh6CXPVGa3heYZBXtCc42C5a3D55Z5JMoK6f4XsAwT4+MDZFmCj1dXXDqsEp/qPip+pbq6QoFLBdbiOtdXvr4dcgEhA7qajySirvouic/Lv9WhUtDtNPg8w4iYdBozGra/kMf9XQBA8tXa7EAElpQxFXGcAIbqPUgdFd5UavlwgFpfK1muoINLlT9cvGML++fPP4PvN1BRvyBwLJlgfUtmAxU0x0bG4JIJSzNV9Y0oGTErXFzf4Jvv3uDq4hJBr4XB8YAXcZ0mBfnAm59+4CA28Ns4OTyDadHvYF0vrFhQuu77Rn38KnalBeZgOMKXX/4GjuNg8jDhUkxahBGbgsR32fmYFkNSX038SYUmovxD/ayqBZbrziBujWTA1gCb7HvM9JMaQZtNJB1CfQ7OJ7M5Usp60zWSBgy7bfdZHeB/ou3E4p98/qjViKraUvUJ0acJhORF56/vYd/27T98o98qzb+/+eo3eEastbJkwD5PQ0Szt1i9f4OL2wjXKw+p7qM0AnjVGO2DERqWgbPREkf5/4HsQ4LbsIGyN0Tl9RHBgaHbsK0KtpEh1AqsKmKEbNDQY+hwsZxumFXePRrB9BsILTE+kXwXeR1kUYnbSQTH89Ad9hHpFRsYHXcCHA1dTGYrXE1iZgbReKnYtZ8aOASIpSFMKzzM1hj0Guh1m5yTIqmC7Xbbf9VIJTS3xJxI8/3ZYYOp5R9uIySZ1PeUM+aj7GSd0FHTpRj9KPGTJULDyzBkEksyjwSXW0V2onCQGdIsAKyj2/EAPcPDImJNNfo60lATjGw5x8kJUh7Ro/PgsVnGrBVMdmc0rRIGlcexuIXYmuIocS0FMEj/9Qc9HPZHqBYZsCkYz0vJNZYcQZsmGt02LIeYzAnPl56jwzXuUC3/jIcPOSaXJmJ4cM5a6PcNOFxKq8MyNKouFvxEQ0NCuqKaAccxhPkQlyXyxIicrkWuwSanasPAbVHiYQmsp4AWTWDrdzC9EoYVIC50TngZmgW/0WQNLaPh8dxM9Rs6J/iA6IHY48Dx8QiOayJOE1FCy/dHgmySwVYHWTtxsgyltvGUAlbUfKTMJeiecMwsIiwZMjM2m4FKF2M0bQMN32dwkPRLlQmYYphzP34clov+I++9CrHqGKr+Qez8LOo+ue2r9NuJ0wwXHy/Qajbw/Pw5DAI3ycSgTEHVx6pv0OdYd62WfpA7rXeuUoFSUoSOxjTQG45wdDKEq5NcCfVpE6Vu4PZ+Bj3z8MUXX6PMNPzpj7fQ3Bj/2+sSfprjn37/F0zCCrk+gpafQwsGMI8baHzZwvMXNr7yCrSKGEVSIs4spIYDeBZg6UiiEDmZq7CchodcC5BnJpuOVTTGxCaSgsRhEqBaQ8838IwMuuWhTImlmgJ2idS2kFQeotzHekFuvWvY5TX38YzGOttlPUnLNtBsd+CT0VyaIs8FiL5v+/avse0Btn37V91o8KQF667Iv5zhftF2X/rE27vT9T/zU9sQSjT5eCego0aTNTFYlqsVws0apmWh1Wyh02lxEBEn5O5FpYvqMyq42gW3tl+5zcaJ82dtt53MnfjO7WPxMSHcSwt0YgDRfmjRT8dFTDsSpyWAbHxyiuVyiSSOOOurJurtHwk67Bwj/UOssDDeoNPp43h0zAYP8TrC/HKGwihx9PoZijhFlqQiuCJQRIYMhAeOGgE6joa5YSBhcSkK1kmzyRIgiiYMB+6uF0C2RLNhCcH0kjLtFetdLZeh1FlTwRNdFypZIP2HTDLWqHQ0RxLTv5VwScuLGlijP0oPiy+/0rsySw4ySQeE2VKKKVbfFAWEMcLJ92Q46qPb6+DD9SVr0DFwoioMFKiixHFrQFSV6G73ru6CemUnWSnWFDKwrMGvR7CNCvVVR5D7ZBDE4lKSNI2RxCuYhmQbPdHsqj+vyl92KwHl/ggkFl2/RoLrAxCabCKDysWQlTCCoEB3Opni9uEag+EQB4fHss9WCPwMyWaK2UOBjFztNAuG5sAhEV7XYPCa+g/p3hVaiavbCUIqwcwqJHGK1cMCd5MJusMh7j9e4f6WypIqPDv+DMPOCMtoyuYWzBKog3KpGyhLjQQwKe6NbVj4/PVvcHIyZrCcAV0qvzHIIdTm3zSdE4HbBJpTH2O9NQJ0Cejl/iXKQoVhRvG4DFsCaqLUW7EjqRxIinCTI21VYjafsjmE6O9LzvrT+MK7kGXzvxyltoH47ginttP+KyPboxGx/mHsfFreb9Y+omPmfvR0j/u2b/umGv0+CKR//vwZPv/8MwSux+V0SRpiOb3A5uYd1g8x3i1MrMsWKsNBYbSgeccY/udTPB+XCIwVsLrDxzcmLpcOtLaGs+cj+J/3YTdd9KwGqtAANjRv5ajMHCsyNchKmNEMbU9DntuYPyzhNx30hwegVWpS0riVIQwjnluzKEe+yXDQa+P09ABhluL99RwRgVQkyM8yAapW7zFrhv4Vpe5ybpCM7NU6ZsfRk0ETg+GAv4skG8SwoT6hdkfjr46TUQdNz8DlwwbTFY2jwtxFtVpFQfwl96VYdLStcPyUAQVrYdGHaMQnlhQsYa4jScuCLUWJItL/dHQ0mhaW4QabMEcpNTV4tlCoiprXdwyC6ksiH4jHBJBQXFFBtygm0BkMsAxKyBlCW03GBZlWwLctvDgdk50B8nUKsyIReiAmd0ozg91x0eoPOLm4XiVs9NR2Ypjpd1i+fYef33Rwt2kiaXVgH7bR6RFIqGNl6gioupN0MJRthVbBovmGNK54/pOaoDRfaQS0UfWAhhUlvwwTgeMiti3MEmAxdbG8M2BE12gE7+HYGhw/ABEMp8sETdtDs9ViQLXwDei9BooygZZlqFYlllcUgxDD6oSIVYjWG54HSddee+IQWl9dBWwpN46dWErIX2zdVpVTa+0OynJoYu5XZZaE9cabBG3fhm1b3B8oThZsQhm87bZ6XyoBuTuXyn5Yx8q7neLxaah+SjtYrlfIkxC9VhPnLz9jg5D1OtoBaWXZqIy95YHs7F7GktzFKxieg5PTY7SbLaAwUJWUPNSxjCLcP6xwdPA5Tg7H+P7na9wuI3z21QTH0e/w+//rApMY+F///u+geR3M520EjS6aX7Yx+DrAl0MNx3oCI6OKGANRZQOuDZeBXZL1yLBeLxFtFrDzBD0NaFs6myhklcZJcOEma6BIXCS5gbSIUaYRAuSwLWJ3ajDLAq4eAi6QWD7CykUYuwiXFbCZwM8fYJsWcstjaY6mQ27yOoajA2b3kxQO38N927d/ZW0PsO3bv4nGrj+8wBNlo7urwk8t9XZfUwvJ7Tu/9gm15ae22Z09tw/F3CmOh8tG0xTr5ZrLNMnWvdWislEqdSTwJ90CHApsk7tT+2GQRUWSKksqZ/a63EE8lUw2lb2TLzJriBbBJHYvWEAMtGUZM4no+p09e4aG38B6RSWgqXRq2j0/FZ6ol7bvETAXZRGOjk7R8FvYhCtE8w0m1/doHnbRPR4iXIbMBlIBSdBpo7JsvLu+QdBqwDAtaNJRlbPixJTLC0SbOap8jTypkJJQqlHCtHWkGYmcZqzxxeBGngj9L9NAXkastUXAWp7QNRZ/CFhjORRpZqD6j7rDXNKhgI7dLGotelzDXVJ3RlwDCuCobO/0/BiL+RLXd/fCbUxlTGWAJs59C2FUv+iM6vWdvvYoeBMviKBT9C/xj/wcf2wHtONd7vQn+QYFobZlQ9dtxNESKFPohlW7Ue1+7BHvsy5dla/UoJsMJtXN3el7InMsvpvux93thHU+Tk+P4fkeB7CUPW64IdbTBTYRR//MttBLmxdEbMBq6tCbFuvNtHpDmJ4vS0dzOLaNhtfk/pzFKZYPU2aQeW4T588+Q1YkWMbz+qrUV6heBemPmHb0frfbxxdf/Q2DWgQIbsgchIwsTJOBNWatSaCf+h+z1gi0VUYGVBbKILgoCRULAHkt+WuFtiIvAJmBtjUpYcDN0LmkexOu0fA9BpFn5FRKoshSa0059+72j+2vcheu3Y5eu0uFx/1q+9q2t+58WlBt6+3EohLsllonOfZt3/btk43Gi063i5cvX7ImWJJGWCymiFczTK/fQY9D3M9M3Kc+ciNAZdgo9ABmZ4Dzvx3i7wY/wrz9M5Z3Ea7uQjwQEwQZPF3HuN/EZ10P7Y6JdccEfB8mfGihCS0lBnuMwiyw0EyswxTeZomAygnXFpIoQqsXoDPowvINmB4lvyK4hobTsyGGwzbSWQQ9aLGLZJomzAjfxis7Ews1iSoocEkOd7LcXSRdpssNsjjB6fERHJeOgdgu0qRH7rfV9HF+2GbG/Yc7Mova7rfW3tpOQI/ALDH6qbpC9TmhJSYmJ5FGIbNM0ipzHNIB2wFn9ArdFrldF5jMYxb0JzYbj6aUCJTJMB7T1ZAoJznBfhLHsD158YeHSZmsoyDMsISDtmC900wo5CgOj0d4eXyMcpMij2PEZJBDoKcJ5A7Q6Hfh+k1MlyGyAui2C7T1j8im/wUXfzLx9nKEtduHddBDe9RCs+Mi8wwGsPqk+1akbEBALqB8YDSPsuaZYGwLyTGdrzkxrnUUXKrpUUxoa4gcHYFuI/BcLG0ds1zH/b2L9a0OM72AY16j7epw/QYmaYX1IkG33YLnejw/W64Dp+kh3YRAXCFdVJhcL+G4Hs7OD/gYUjLNqtmRYq4RMYeKeeWtVPesNl2St0NS1eTbMqEmWGDinlGil1xniQtpwgTpeq1ZU7XXayJoNrGOY06C19/LwZacB+sbv9vUzRbXVcXs4pB2OgI/FeJy9E8n8DHqtbBar3B9dY+7+zucHJ/g9OwMSVIwEC368C/nWfUN9F9BQKjpoN0f4Pz0DJbpoSRWvmahzArMVmTm5ODl69+iiDV89+0dvE6J/3z6Harvfsbv/uTiJm+zVt+7Cw2How6+/KoL78TH8NzGl3aOBrPWKsQpgVs2bJdKWQGT+n6ZIY9DzFdrbMIlrDLl93zu+6QVSCxJC0XpsFkVxUtVQoYZHrJCR1bmsLWMdeeI5lgZLgNtjhWjdDTEho2o8hFFNjbrEkZ+A7ucQ7M85IYN23HYgZfKbWmsdRybxw82y9u3fftX0vYmB/v2b65xyRuVjZI+m3Rn3C4W1bQmXhFT5LacTbyjtt791Pbdp3t69PATm/Mn6t2pkk3STvIwGg7Z2ZMW6lEUspV8HCUiQOQoTKv5SDWj6dF3KFFd+UeWg1IQrwJUYq3Rc7Z+N0xmwxCLTQAzFS/YRSkbgVSUWXcZ+KPsz+XVFT58eCe1ohRTS4EPu+e4G2QIwIdK5g6GY8ymMzZCKMscpmtg/NUZTN3C6mGOYWeI25s73N/e8ueazTaenRzAb/siOKGS03WEZLOG62gcqDEIQQFSaXG2tj/0oNse5vMQeZmiMkoGMPUS8IMWA5eLxYRBOQqkiWnDrL9cAWsSauHFgSzPkyWgusza7mBT3KhsQwGnKkhDAQz6bXiBj/cfL7dABB2rDO7qQHznJioQo35pB4SroQzZ7cQ93iJt274sM6BqgVOveMT7DNbwZgrxYqsBKRgsGE7UJ6s8QxTPYFk+bKvJSf7tXsShMfxUL6TkEexU5yjdHWaCcQmNWFCJa6sjovKn9RLtXof7mW6QWYWHdrMNPSLtIXJ8NVDSAqay2UiD929IswkdyC0TH29vuNT6bHwCz/WxWhCja4G7hwfkqwRUePQwmaLbGcK0DMTJnO+1OAPxr2AH7txZFZQjZy2Q16++RKvVxmI+x3oTcr+h3xeBa2TkQOdPQRuBaVSOkGY5B+IMrrGYMhlsEJKrdNx2xhkFivG/VN6pSkOFHhDdH+FMvIZjE5BHJTdLwQAg1u7TTvnXh6FHo1b1V9771OfFizt9Sz6nhahw1FVuH/u2b/v2a41Yaycnz9HtdZnNm0ZTbFZraOk9mjrwMCc9JBuF6aHSDZS6jcpuwxsF+OIAOAvukd3+iO9+HmJFMt9ahZIZsgWaDSotO8TJuM0yCqXuYQoDH1MN6WUG7TpCuJwAxgS5HSIhuKSw0YkrHOkpEjIaCgbQghydUZfnjM1swmymKsww+/YORuVgZWUoA8DqeTyOX3x4z8AMNxWIUKtjHjH+88vVo0F2q1dVaei2XZyODzBdZ7j4cAnHsvBs3EWRRnh3FQmJU/UlPCEIUESxiGiCq4fDHUKdAjnUnCiwCbEtc9pqU6AKVlXCsnWU5AKvG2g1LFw/JGKe4GSfzk6d7KJKSRCuqhRC/IyT8P5ZrU04mSoNA55raQMRO4lEDjlGihiVx1KeS8hxNEPTd/D5Z8+RLXKqSOUyuQwlkoIkOWIErS6a/T6z9qdJgd7AxolxjWr+J0zfp/h4fYJl2YUx6mI47iBo2iibBrMWh1oJneQyqDQv11GR66dJ51ahJC1Redgkm1GZNO+YfO2J5a8XJRsyUGmtJstcZ5WGywQwZwWW6wQf1xuE13P0lgkG3hynZzdoHmvQnK+xskf4MDHQSoWOHmmfzh4eYFkVijDF7M0EyAzklQEykO+fNtE99HF9cYUwiqATuieTryKmUow1movYglTEcrtJZXrOTEQJrtX/ycCFHpFenGnDLDSE+YqjI4oVaO52XB2jXhNhrOH+fsIVDsLpUxM6ZyoVJ5PZdd+W/z6Kn1QcL38Mim1JDuDPTo7Y7f3y+kHETpS0k/201fDx4uULWKaNP/7pGwb/CPytT1HunUBdujoExg8PT9C1bWbB02ES63K1WmE52+DFqy9gmDZ+/ssVlp6Fv/3yAp13f8E//qODj4UHoAfTOIMRBGgMfQQnPganJl67gJlTvWqKNLOR6pRkNFm/j4A1vsgErqUplvMNLm8neJjdIS8T2O0Ifu4iX3qIcxNhaSLJbWYNplUCs4rhlDk78xpOBdNPYDk5689Zro211sImsYE05pLeMCetPxNWVKCRRWgYc4w6MSfstc4YpduGTZUOJbCKYy6pvrq4wPR+wrHavu3b/+y2Z7Dt27/JJthbpJW1YyDwKOiTMdfOW49Bop1g7slWj//dgnTbnX+i1R8ToAzrs2U5C5PHUcQAAOmzNVsNnmwT0tGgOk86fKWhKj+rjquOVXfYS3wU0vGIj00uguvTZn0x6XAk9ZoIbGMATtMYOMrY9TLhSWg4HOD46ARhGLN+lahCkxncJye4LQGhp8K6fbVawPddnI3PEUUbRGGM+c0cWZVxZunNtz9htRSOmr3BMTqNJgfrdJytfh/ThweUyQZBy2XBXI1K8agETacSx4KzqvGiQJWl6A48wHIQJRugIlH5DIvpErZto9nqcuZ3SSAJWd5LxpogFMkFgCoHZbaaKAdlEIrj8scQrDp9WiCQIymJ25+enWC9CnFzfyPL9ShI2mGu1TvY6rwocFSxgJ62ulfVX7mDZNUB2raP8vbbt8V9Ufpp8jXxWGX45cvy/DTdgmM1kRU54mghNFiU422N5G4RXaWNswvmbfcrv0keB/XDdThHGobo9AawbZfLfmmx0G94yFYrMu/iMhFdcwSwRi6hsnRFo8DetVg35If3t7DhY7XZ4O7+ljP/vV4fOWmG/PEbWW6tYzAaIStiRPGyDsbr345kR4rfkbwwXAabo9vr4+uvf8vnPptOsd5EvCWxtIjJxuXJxKwk11liTbJxCZWoCtYagdbsEso0SRVsy2ssAU2xKBNHINxXydRB9j9d54xrRJpJgcflU2RkQN8hXG23jBBxdbft6Wuf2mZ3291RSz0XbXtNtjtQvVAIRauxY9/2bd9+vdFvZDg8wOnpS/iey3PU7c0llvN7dK0UZWrg49REqAUoLR+VQfpIAYxeF+NnLp75KYJkheX1Ct9f2ljqJrLKRJlaSAoduW7DsH24fguW1eTxxdAy+HqFkamj7BpY9RweM6vIR7rQYZQxLCsCrVnvoMMrQjjRBIYWsA5WUcbwGl1masVpjJJEx0kMqiDKU4FykzMocfLihJlVlNRikEElWHjc2JoPqIFlG2fJsUSCXqRHdn8/R5NKZ1++QKNBDuUPuJkSg0k5ectd7ZYL7rwuhkXtUWloPVDK4xLOoY+DP5E8FHpu9ImjloEw1XA3zxhEEnPoY/aLmlWFFqkMxJhVvp1j1RBaJ1i5pJTKQilJKAyTOCFcGax9R0DQ+dkJDjpDpOsMjq0Ll3OtQkRyHnmFwfgEjuPj+nKFNDBxPkzQj/6M9eWf8P0fO3gzOcHa6KN5PMLhSQdWz0HeMTB2NfQo7VSkyDOd+w+VBBMjnKUvqpKlQohdXmaUNKpgkQs4S4tIcx2O64S7Ov2laTl8XcfQ1BE2dOSOhZ7pwvA93BkGlnMbD1cdJA+AY/0ARw9x3HYRei5uZhmsAugNexwbkIRCY9xBjpRZa3puIp4UWN1FODo5RKPrIww3PLeqak0hOSHKWAXIpnypVAJYstcIYJMmYarUk+ArChTojreDDiKqvihjZijWEhukz1YAs2UM1ypwenLIZY1xknGZZt39Hs2N8m/ZP2u5BMWY46dSawNAv9fF8aCHy9srTBcrjgPkB2UfJ0fXHDc3t0jyGP/pb38Ly7GwWs+o/ESy2QTQTK6zx2djtAcduLrLfDxybiV7rw83d/DsJr78+ms83K7w5scZul8U+PvhH3D/uw/4f3528FA0UVhjGPYzNIdtdMZNtL8I8Gxs4XMrh1XEyAmwrxwUpOXrWsxMI0CZqJBVniNLqBomw2oVYr3YYB1FyM0QVjBH4awYHBP4Vg6dXGtNOk8LCWyQ/VdWpEBeQiNDhNJgdm5ZRmgaKwReBjgejMqCVeUw3BSZZSLSfCSFj3BtItms4JW3sMsUcHxkuoV2w4eWZ2h32+j2+7y+YZDyMVth3/btf2jbM9j27d98o7p8ChBECeCnB1S10BYLzDo8+pWl6O6SVO1Pvi5ZYTtR1uNV6+Od8uvEWHEcC51OBwejEXw/YHCLxI6ns4WgNVMZGQFBooJteyQ7mbrt0hfbAFOBaGwxsQ0ZAAAgAElEQVRyYEgNNrKFp9IzErGl7KUSKBZsHF7EF2QKUDJwFARUytrmAPrHn77HfDFj7RURu+wEt48e7ZwoC9RqGHSHaLW6+PH7Hxl4Y400ys4FDTT7PRbbJRFjysweH49xe3uL9z9fYjhqckDB2Wo6Jxm76JSdokmWHLRKyiY7sAMLRjvAwzLB/cdrzrJmRQZDK3A8PkZZGLi6uMF6vWIwSUXpdO4SM+FyAQp8KTP9+F4/zrjTuadFhsODARzXxdsPFzA5YqYtdSnsL9mRfJlUgC6uGUsoy93zV8nSGN6iBlIVKKMC+m1nUoBmnSGXzDJxndShb5lsKtBTYB2DOYba3eNyRU73UcY8DlHmGwRBG5phi9KL+oDVUShmowSM+HsVN4zvFNIsxiZawPV8BF6DQU7ba+D4ZAAjWWOzyUGSexzMazbrzVApD4fBfNlKlKYJt9ViwJQ0zt6/u8JyEeLgoIdGw8Gbn35CeD/DWicdGk8gjfI4RUz7uLfynZHi1PQ7oXOjbOzrV6/Qbrf597derznTr5u6YK1JGzMKzNhUgxxCs0yAarlgr5HGHLEkBZ4nXULlrWPNIBl0q1vDv0/JcKDgmvaz2azguDYzcZfLFes0MuAuWRL/3LDw6SilXnv6+U+9xu3RUCf7baVK8ffA2r7t219r9NtuNJoYDI4QBE3oRYrb+T2i1RoHLZNcVjBZU3UcJQ5IG8ti8XHNa6J5YOGwmcMrMpRxguU0wjrJWBS8yFxkWQuZ7sLSY5hWjkbTxeHZIQbDLuyKSE85bKOAYVXQTAuZZuJjqWM6B7LLBMl0iXIzQ6HNEJkx0qqAV2r4rNeGG2xgdDvYhB02OfCDBuIoRLiaI5wsUGwSaDn9/k0UhQ5zYCOyEzxc3WC9pBJ86cAox7vd0YXnCTmH1o3ilLJA02/i7LiJu4cZWv0DtDsdfPj4gYE3ngvlZxTjrE481XiGYv3TXChnH8lYqw+FGWti3qpnKJ4bC5wOfRR5hnlUIE4NAYZx0o0+JzRj68/J+EqdkGC8C8MHwaYTrHEe31lYU7wmIDwxN9E0a+hCX5PmnG6jjyouUaZirKcIiXzQ07KE1xXi7fd3IVaGjvEgRbf8Gen9B7x7Y+J22sfK6EPvdjA8aqPXd5F3dRx5GrpaDqPMhTsofSnFgxJYY8VRYmXlGZIoRZoUdQzr+lQlYHOsSBeBy2mZzUaaJyVMir30UoAkukV+kLgrgc0GwKrEx0WEu9sFtNs1GkWEcesO45cL+N0BSv85JmUb6UJDx7Hg+SaiaM0xB82Z88s5stsUZumxbpgW6Bi9aqDQYjYDoEQYGdcyA5Al2IQW8a4uGkNqHFuJblZpdEUFKEdMtH67z3HedL7k6gfuPztBmGLDCXYhSYSU6HcCdNsdXE2nWM6X9f3kZDZtz/eNGObb2Er1UQXo0LG6jo1XZ2PcTO+ZicgapkpypP7FqOS4AK6pGbqJw9EQ4/EJHmZTvHv7kUHA4dBHp6chySqsErovAzScAZus6YaJ0/MzNqj4+Yc7FD0Tf3P4F5TvrvHdWwP3iYMYQ+jmCbSGh85hB62jAIdHJs6cEkGZoEhL1knLDZMNGGzq5iJbLftPweAa9Z8kyRGGK/7dzldzpOUSlr2E3kyRFSbKxAcyG3pBcb2HAi6DdlFhcGJcyyIuK7UNMuCqYPkpTD9CYJXwXBOa4yPM2ghDE3GRYVNpSBIbRazDiSIE1RI9e41OB/APDqA1jqHpNhyd5GZyLkWnsl9ylSdW3750dN/+Z7Q9g23f/s03pa9FJVZCn+2XS0kJT9SrSfVMPN5u9fRTn3yuQLZfvP/pjzCIkNOklDLwQ2VoBNg0G01mr7CeFDNiRLD2aM+PE7G1WLt4LIME5SrKfyRNXr2+M4XT/yyobhJDTAQNpF9GJgj0x7JMnJ4+g+t4XI5HJQQqvtxy5ET0KzLEO8eCih0Xl6sFXn72GVzbQxiHGPZGcFsOYidG76CP0+PnHGj+9MMbXNxdM707TUz4QcBadUmeCuaP8C1jZ0WLgRm6OIXIrm0KdBomWgcHmEzXSMKU7z8J3VOZ4fhkxIue1WrNjD2hsybcQSnYqo0MVJCjMDV5TZmGX5L+m4Hz56dYzua4fZgxS0GBZsyKk9urq6xuSr3fX0E2nvY7dQW3V3LbxRjwk5Gc+pyUvK+DTDomodElt2HGXv2xeu/Uv1iZRkaktG9yxzQMh/XviBVoms72N8L3nlcXW8BIPWZXTspG5ojiFWcL260ebJNYayWa/SGeHbuIaMGWyPJIYqyRsBqDeyLDS/eFQNL7hEqedQ5M6S3qi0Mqfxl0OCD/h9/9Fzw83LMhwudfHCKOC+6f9Qkqfb062yvf4uMmU4oKB6Mj/OY3v+Hjn0ymiMKQrzGXQFCJpvxNqJJq0o8jMIwe0++EATZidkjHVPWfuol0fUSpLv0RpZXiD7HABLBJ5aCkydQgRl+aYS611kQppixnwl9v4o5sH+/2J/V8G8J/YoxSCYJ6B9seTGPGXmtt3/btv94oOTU4PEZ/dMLM69VqgqubKzhahdOui8Uyxd1aQ254gOmj0h1UJNTda+Po0MCRM4eZrRHFKWbzBDEZp5D+VkZi4D5gtzBwLDSICeIU8DwDRwdt9Fo+lzlmusF6RmVO43EOS8vR1TU0fANpz0LpunD0BpKlCT0u4doVjoZNLKIl3k0KdNMb9EYrRMQMmSdwPQ+Nbo9EMKHbtLiuoFNpIC2KV8TI1xActOF5LURJhLIgF8ZtjMJzxY6chZwteD4i1v7zcR/DroYf30+w2GScXCRjqLPTZxgdHGBB7qpltrODLWi2O1xJOEO+tgXhVDJDzVmqEWzUcnWMRw1M5gkmmwJlIUwRBMuZNpdMKBUQ7OxhO8qLf2vWer2V0HITU5pgrgk2E826lFCycHh0jKbholiRa6QE1bQCSZWzmUD7cIRKM3DxEAI9Ha/aEzjL/xvX383w52/6uNgMETVH8M4OcXbehTewofUNvHSADjIgp7lKR05sPNPg621K1hongShBlBILO+dYVDDCBEjEwCFfaAEtCna/EJIrqMyY2HgFJfZyOHqJjq6jTTpZgYa2Y2MQeCgDGw+Vjvulj8W1B30zh29/RMdao9UOsChsrNcZm32Q5hnNqW7Hg9v3kGxCaBlpwFmY3hKz0sD4xYgTw4uF0FNljK2OcbdMNvGmrBiQRgUaCjZ4Oj4cM5Bzv5gJo6Ba2mJnTuT+ytFRzcRfhwkWqxWOug0M+iP+fdJcLayRtuxK0ctU3Kb6pHhv2O/hoNvCx6sbLqulWElc46czszwmmQjmPxWwWG5wcXWNbqeNV1+8hhtYsFtkipTDtXOYVsrO9fNZjsPRGMdnp7i7muPt5RKDL1L81vs9Pv5ujj9+DDDL+ki0Z3CsUzRaTYwGTQy/aOHFkYFnRgonj5CmGuLSQmVbcG0DDsnj8rkVDMxmxLJMcsQUa7Omccpxy4rMzrKQ+1aRaCDT9iI2kRWioqHQiIFXwKxK2OSGS5q7FEdbxGZzkFAVANHdUgtV5iAvNeRlDj1P0TQT2KTvp3tsCmKaMUq7QGjbiEsfcepitaqAaAq7vOcYK7cCBrQ5eanraPV7rAdIGrf7stF9+x/d9gDbvv27aQSK0MRLwcGjsrknTUIjO8/xK8vR3UBt9x215e4nnrz2eEf8Mi3yyZ6cWDNxHPGcSjptnXaLRToTyZTZXTCLKVxM/k/Ppw7yxAwtvp1dDHeBNvmcGTdbTQgCE1irjXS5SJQ+z5lFk2Yp2u0OTsZjLnElWj2BCoIp9+jAFGwjn8vgg50QJ3BcB0GjgaSIed/r2zV8LnFxMJ+RltaStTg8r4nnL09weEQ6WhbSmCbwEiaVVVApnVkKLRCDHEcpHSucGqNVyZTw49MBdM/FahEiLXJsogTL+Qq2beDoaMj9gLTnCF1iUwMGrHaYThIs44eMaomAc3jUZyHVi4sbxHnOQFCtCcIfqj++vRm/fLEO3n/RGxXbbOcDu9uoJOtuSFjrolWP36N+ZRoEIlGmXJ5jbdagNhcLCbGLR0sDBnUcJ2AmWZqs+HsoIyoUaHYXLfIXQdnkEnxv42QDw3TQCALBPDQ9jMcjdIMCi2iDpKIsOjEFLOiVcM0UG4pMcF6ViDYJokLHrDCR5RW0LGVWahzG+Pbb7/Hjjz+j7broDFuwXBezaSS2k2enfgeCpSDPTvZ1Kpe2bAevXr/G0dEhZzPnM+EQSixNy7ZgkukGsztJr1CaGEj2Gv0GKDgngI3GFy6RqqE18VunbxXMhh1WqWSrMaCtGyjyFOvNCrZpsN7aksSBN8IVl69pTdXYtk+NPH+t7Y5I2zv8qQ0lAFkD5CIY5hJWZrv+c79x3/btP16j33Sz3cXh0TnsVg95vMJkesWl8Yddj0vqPt7F2BQEVDWgGQ4qzaXJHs2DAKcdoJ0tEM5jLCMNq03JDtg03sSpzgtPzXExcoGOlsNCitzI4Lom+i0PgedwqRjr0JoEqhjIc43yI6Bnrl6gT4LjTQNx14LmB2hZLgLfwf31HCtisGsVbmIPi/sSA/sC7V6K1dpBEiZotolJ1UJFrpumYDtVCU0OFfKQXMKBoNeF1fZRkBFCRqVg4to8HcYoudXrNvDspIP1coOfL9eCHSXzIJRcvL+7Z0b9V795DcshUfONiINUgkeCD+Jv5Ssq00m8jUgYiDFUzVRibCNDomHHQLNh4v1tgjQXx6S23TYZE9QviW9jtpT8jq0uqfqE+lu9pwBG9uZkLbfAb+HZ+BjVKkYZU9lhhdwoERN73AD8bgfNXh+zVYxJWqA3muK8fIP1xT/g+794+Pb6BHNzAHs0xMHLEU7PAng9A4OGhnOjgM3loEBKrCHS36WSUJJ9kHpZ5KRNovdUGkrxJbnHUukjS1/IgkrF8hbHLsEjqa1K/YwSXzl5ehcaNHJh1QpYZA5B85ujIfN0tHwHzaaHVWBjVhiYzRsIL02U0QKWeY+um8EJXKwTDfEmQ9AIWIqh0XDhdxwsbmewiNduGCTBxSWbhm1hPD5Enqesz7a98HLOZ2kGwWAT0YD423M8HA2PML2/wWxDSTTpOLEby8ikUn27d5JMYgKtMFsR8BTi5HgA23UQhSlyKputWY7bGEQx/Mmk6GQwZF3Bi9sZ8oKjAzHlShMzNeuKniLeF1UD9JqA8fiemCah3PCMDbqdEzQbXWTJCoWWIEtsZNkhXn/5W+iWhR9+vkFqJ/jq5SXaH/6AP/xew9uwhag6QGE+g9cdwD1vYfA5gWs+XjVK9KoYZZYhTm1kmg3DIRMDileEqyz1nYLMw+KCndvpZ0vb5BWxbBMuaV6QZmxO8VjGCU+u7qXyUAJMKRmpFSg0YiKSg3DJzrUWwbb0HaaF0rC5lJn0/6q8QJlZ0HILaVlRITFMfQVHK1iLl5K/5IlgazlyT0OoEyvOQxw72KwzIHqAnc6hmyZSzeZqCtcyYWgGuoMex2Ep6dsqPcl927d/4bYvEd23f3eNgwNZKlkzux4tPFW49qnXVWimpt4n7/BMufua3EYtWj/VPrFwZpdPyly2WxiNhsy4ogX8fLHAw3TOWUampsvgUuhKyNBR7k8BC5Rx5P0q9hsHm9KlUIJo9H1cnkfOiFw6IF6nRgACZXeYoVMJJqDv++i0O0jSBG9//gmTyUTqjj29Lk9PT7FwtoAcHY+lm/BsDw8PM5ycHmD84hnCRYaDkz5vT0YFlCmkLH5cAl62gW0BlSEmQ74fFOARvqEcHEmJtjTgNx2Y7QAfrua4ub7msga6XH5g4eBgxEDZ7e0DNuuVPOe6nuDR46yiLL+Gw8MD3E1m2KzD+pwFaLM9b0kOlJ/dBmhbIFRuIMtQn4RzHPRtFwJCzFktGNSu62x6zSSTCxPOkqt7IcJKy6SAyOYCldxMYDD/b/s5XpjIwHlbSioXLYrxJssj4yxiEdtW0BG/HwVWyxiwTDNsqMxD0+AHHakrBjQ7fRz3AxTpBmRBkNPncoe1VnQu8aXdE2AqgvvcLpGXNugWk8g26bWtPRd930e2XuHNDz9gupwz8Pr8xQEeZkuEETEciA2nrqrMPMvf5ZY/KH73g9EBXn32OQNm89kMETmWUeGTZTEDhX4TXE5SlAwE0yJXBIuks0avC0B3W54iAWW6/tLoS5yXXLTRY9ZYYy4AX/8wXKKocgSehyiJ2b2XgLWnWmt/bfjYBuW/3O7XXq+bGq/UD3LnuTI3ESWh8oT2bd/27ZPNdT2MRidodgeIiwTzuxtsFg84HHTR9mx8vFkhyjXotg8YNkCloYYPreli0KgwtFNUyw0zT0Iqy9ML6JINQqLglWkzCN8xTXQsWmTnWOcpokhDo9XC6VEXw2EHlm0DBkkgCFY1VRySdpSe5qx0ZDqlcK7UTHzYZJjkFrK7Cun7FTbLCUp9itxaIKfxTwP69gZfjSNU/S9x/9CHZ5loklFDkWPxcM/gYfwQIgtJir9AomeoGgnaIwfTaYzp1axmb4vhV+PSw9fnh8jyKX58T6AZDXQ7Omd1FkkAFPTho8MRnp2d4er6Dm8/vJOAmYLVZILwUdy1NRtg9jIHRAKg6DsuTkYWPkwirCOib8skE39c7Wc7J2814LYsbX5fVaVSqSRvJ7Q9eTtO2tH4KRIUPI9XGtzAw/NnL1GEG5TrkGMqOn0i63SORoh1C6btIl4neIgL2H0N5/oFipt/wvufDfx018MGBwDpl447OD9qwO4aMNwKz+g4qpR11LLcREEaqgSsSYY+XwRytybWNWmtsW5oyVIaWZlBM4QAPBku0H8GHYsm5BEsm9hvorxUlY3SBaAoLMuFMYJRkBNqAdMquY8Ta46IRLcEqqxKXC9TfJyukX+Yo7VO0HVXOHs+QWdYwGs+R2IdI89seFaOh+kCy1mM1YcHOJXPIv8Z9WnLYGCQDD56xy66hy7evvuJdUop+cfxF3shiPmf4gnLNNDrtZHFG0wWkWD2y4oDkdQjxh6VgbKLlaxGkKkyObWrtQKDk+pxCbQbDsaHQyzjEh8uyOBK9D8hgyJkMw4GXTQtHR9vZszEoj6t0nEiySrZb7LrioTglgPH36WL7/SbfZyOdDgEBjEgWkC3e+j2z1HpJeYrDc1BDz/+dIG7pMKrl0u8WP0T/vInDW+WDqKyiao4g+v10Br5aA1duC9cPG9qOEDGmsZpoiGFBaKrOQSs8bWk7Cldd9F30oQ0+6RLOpXf6jkMm0BcGx8+vMflxwliYsBlwiCKNJOV8y5HoHSOVMLuaNCob8GBlRNQRjCbhbRyEVcmHwsx5fRizYCabZqwnAqGv4bn5Gi7FieBU9PHJnOxDoF1kWOdaUjJCCHJec3Q0pY4aEVoH7VQ+SdAcwiff8slsxLpflx+vML9/R3Hdvu2b/+Sbc9g27d/l42AIrWAFSwtNY2Jtrug/WWopYAJ9e7uVvKxtrvs3X38ZEefeq7KWivhhkmW3QQYBb6HRqOBhu9zcESMMhHsieOpM7W762X5R8SMImDY/VKeriXIKB6W28eSvaSEzI0dwI0yPcReoxLC45Mxmq0WprMZM3nq79vhNYmru0WH+GhrcpvGYAbpWYQh0clLVFQi4Dlod5qIwggbMllISqxKHVYSQSPbetNAScwxjptllpgdO+X3UdBhFKxnUkQFRv0G+sMBlquE3TKJlr+cL5CkMQ6PRvBdynSRFkaxwxcTgRDZiB8edNFsNfHu4xVyKj9U923XVeARgLa9sRy/qbWFfKvOV9Y3qt6L3FYGwyooVsezU4G8/Zb6Ju9cY7GQoExhZlhItRR6XkDLRf9Umff6GOW3198ms+2Pzo/KcnWLwVDqK7tgHEVOaZogimM4boCg0YZe0v0xcTA+wFGQI9xEyNnKgBY8rmSuEdgrM+PkEFrlmIcbaHoBw8tQkEi3acHzHPQbPr7/5lv85S9/RpGlOH82RtBs4/J6wgGfuv7iSLe/P5W/pncIDKP+9vrVVzg7PcNyscR8PmORbV2WD9iWLUSdCVwuctYlTKgsNEuFEDQDzoUA1tgpQ2qtqd+jWvgp1oR0ceXFl9RDpKB/vSLHVoP1WObLFTbU/6kcXLI7PjU2PL5f28fVX3n/cdvpm/xQjldPgDZVlkpMVlEyvm/7tm+fahRD9AYjnJ19zmPfcv6Au4v3cC0dL08OsVnFuLqPkRsuTK/FY1+l+dAabTQGLg7cHO0iRDxJMAs1xAxgkKZjjjAHEsNmQMwxNPg64FoVqiBG7IaIKmLVanAMGpdNXtxuS/bFuEpsb9PUeM7MKh1FpiOi8rp8hUHDx4FrsS5T1Pdgey2UoQc9cqHpK2jahplzH25saPM7jE9ukJseltOcgaHOYMDHBo9cJwuEyRpptYSTRShmazQcYHjaZ22oNMqYqUzam+cnPt5/uMHFDYmNC0Y1T2O78cOWqs3j93Id4erqGoNeE5+9eMGSGmmSyJhHGSrIHfAfldgQwFZF+rOGgc8PPeh6iTe3G2Y7C6Bum1wS37k77+3OxeJY6nmWx86dubJ8HCEKHbCK5SjIhOfs/DnGwwOsri8BdoOkRFIOLS3hlynuwzWswGZzqGle4bC/wXD9f2L67g3++FMT309PsPJPEBwP8dnrIcZHHqqejpFb4UjLoeVUsqghoZI+y+RyYVux89k9PUORFshSmq/JsVsAJHQMZNhEbu8EuPG8Jq8DzWNc0pdLaZHajXsrXUB9TDM0BvSImVVlBGDlrH/r6Rq6hobU09ByLBx4DsqGh4kFzCMT07sA80UFr2GiHfQ5jpjczNhMQc+B5XSB1lkf4y+HiLn8mGJkKq00sFqXuF/O8eLlOQ5GQ8znE06YCSK8cNl9fn6Gfi/A7e0NwphAYAF21vdXluxy/PNkIhUVDDI62ukf/IgTaRpfx/vpAp6l4dXnz/kYo4SkHcgBNMDzkzbuH5Z4YGBvFzLbmncIx3bR5+nKKca92FL8nk3bx/HJGU48DXpMyW7AMEkjFpiuMtyvNPR6R2gHNpbTOVYW8HfjH6B98z3+3z/7uIh8xNUBnOIz1kPuPmuh87qB4xcOvnILtIoIBZV6phZy04HpmfBMKgsm1lqOirSZ0xxJUiCNpTyGVgBGiUon+4KEqxbIuKzfH7Hu5HKy4BJMAt6JGcsJWTYHE2sPKi/m8ghah5iktVugpNiPgDQUonSUk+k2cs3l8lJKcLI2b2ajJMOOIkWZJ3D0FIGXwvEtmLrPWpSalSI2DSS6izz3WLctWa7h4yOMfI3Y9FFqFnrtFh+D7zfQ7Q+4D+6NEPbtX7LtGWz79u++0UKWACSawGqxyyeks8cQwxNg49E7+NUtH+/46euf3pwCMy4jM6hc0mNXz36vzzppBEbd3j0w64ZozmJ7lezdWXLL4HQ7qW/fpX2LgFYwVAgA4AwlA2riurDmEmtESetwLpPLODCjPVG5Z7vV5OO7vLzC27c/c7aK5e4endwu7qhOUoEQglEYBDnMKsDVxykHbt1BC6+/+oIDi+liDXs5R0n8q34DlUOFCQnSVQrXdVi7hDKPBJxRrM0m8vSQJnACejIqkbDg9zxMsgIff/zATmk6MaaKks9hdHDMTqAXl++FLphmsBjusONjto6QEHOw7hgUtAtQR0GI4vrLrKi63PWNEfde+Fttg6w6aNsBeUX3oGe7QN72Om7Za4/Zb+oYOPfMGfuCFEcAotNTIFy6yM1U9AGpL6MKGsR9ULtSLmzqP/F6zXxUiCFrsmhISZg/2nBWstls8/0kLY5Gd4TxgY10fcllKprmQYPHrlECDJaLFjqPCpgsVliFMbM3SUjXsjX4DRvdzgGuP97g52++QyvN2Vp+/PIF+qMBAj/AdDrF9z/8gIzqRyhQYydYUU5B3yFDZ9aaIb2bzz9/zbqC8/mcBW/p1In1Qf2DFo20D+rfvAAhUVxalFDGnLK3xFzjbKzQg+M7wccvryOz0wTbjy+nAtaYyScWgXG0ZjFt0lgkQHK1XjNoJ4aHXwfWdn7Vjx5/un1q9Np9vrOd6m8SWFdaa/ty0H3bt19v9Pug5NLh8Sk8t4HlfIbZ/Q2Xip2fHiInQGi6QQUbhtsErYSr0kRuOXA7Dg4bGtwiRjpJsIlKpDbRZ0kzK0dIDBEaUQgkIcYHM7SJaZXD8kPYzQhFriFaOkDqIXB99LpNdBsduK4NxzFhuyZ0ZhyRhIJgHG2yAvNlhMB2efHqGBlMWonqNlLNwvtSx92sgnaVYHN1j2R9j7hcINdyttZ2jRKv+gscvTSxKL5AtGmw+7nn+1it5gzcLacfgOWKwRFmz6FE48BBafbg2zbubt4Jd1DWI9uGAzXreGeGrOc9xcBXJDejwqtXLzipd3Vxy1ICPNWpnUk2kJq/aFw+6vjwXeDDfYKMtMMYgJMzqJr3OGDaHpRiFdXzNIdvGptOMQNK9gMmc8nvEuOmZJxz4q9AvzfAy2cvEL//wMw1vdVCqlXIiN0d9KBt1nD0BeZaAykZH9Cin6oXAg+XP/6AP/9ljWXRQqs/QO95F6d9B0bLQMuuMCAtq5LKQUn3lBKPBkxLZ9YaH6HUWSM9K5rHCFyjRCn/p1GiiBJJpNMm4jpChjgWtGg/FizDUldRJMTIm9Kg+VnneZpkOihxpIwQMjJC4FJA0v4jbS0yQqCPE6NNx2UJxCGQz3LcrmNc30zw96+6OGwWuJ+uUKU0B1GsBRi+iYesiZ7nYtBx8XC/wNy2cernePv7H7Ait1UyPyLDD6fC+MUQs8U93r55i2YrwPnZKX786UfMlitYlExnyQMJnIkAgctid3qctCIVb4tqBJWAFklRjlvkc9XX6MOcmy0LPBsP2awr3iRYzG5xOw0FUKlmbRnr1TOz7Huq9/O1Vt2fv8pgvbeDVgBs1tDKDLafwrBLLjV/iJs4ef4VJ+p+fPMBK93A//7sAYF+jJuLa/z+5/gsVC8AACAASURBVFsswzaM7ABttwd75KB54qJz7uDcrdAhsJLinMREqpvMQrNN0jjeLSUWbDUyMSCmIgNmOoFmdKNJKoP6T4o4SrDZJJg+UDxY4dXrz7HehPj22++wClfi7FSMQ+sbJn9S3ARodgXN1qA5FMDbMEsLZmFDLy0UhoOkcrGmElECUNMNzDKFZxTwzAK2U8B0S9h0Pg0dltNAhA4mkYsoSrAqUoSpA3OtwU1i2MUKHW+G434JsxWg6ryCZgboNxpYzMmYgeR6QlxeXGC5kGZz+7Zv/x3bnsG2b//uG01gNHgqNptqn1rj7r6mYKonmNiTrXcXt7vP1Sa/XEzvLmrVY3InpGzRerVmq3IKeghYIH02EnwPw4izjkKcX4BmInsr//3Ut+86XHLQKGEIFUjsgEMK0KHj4fJVUwB6BDiQ608UkR5FhsGgj/F4zMdDAKCIGwRbSn25OCUJ0MjzUyV0lHllN0cdCIIWKCb78Yc3WK7meHZ8CNP3kXsmND+BnoXYzFIs5xmmE7omBMqYKIyKM6nkbEWOS+RuRV9jGJS9LZEsyS2txOHzI6Saw8dJx0dA5XQygec7OB2fIo1JkyRlsC6Mc85A19eJgzPFQBMXkK+eqgGVTlYikNr2AaXTIl552nd2Ajx5jcTWiuUmI7EaVBP3S0bxKnSrP89lw6JyBQldSALCOMjbDezE50XpSv3F9b3f9gP1glp4CG0+ynKHZG8fhfBdF17Q4GC91Bwcnx5jEGiI1gv2LdC1ABp8pv/TwoquEGttaBWSLMXV/QRRIkWsKWRLM/h+C+1GF3/4h3/Ejz/9gChP0Do+wNH4FLbnMsOT9AqphPr8+TkfJmkYEqC6ZWcKNpZlOvjN1/8LxicnmM1mmE5nXHpFYLXrOKy3tuuky6y1OGUdINJao35O4DIBbFwWWl9/cdm4jFKWX9NijB/zwkM40XEZEGksruZwLKG1RiYGFHzS6wJnfjoePO4hu2+JLrLTN37Rnv7inzxX91UMEvxYsHql0cmv7nff9u0/dqPfhmXZODg8xsn4OYP5NzcXmE9u0eq0MR728XA3xcM6heG2YTpNVJrNQBsaZBZg4cjN4W5CrKcFNrmGIqA5K2PGzaYEctuESRqQhH2VxLihsSxGUYWoioR1z9LQQBkb0Ei/0jRgeTZc0k7QhWkNORPWi/mKWCdrZhq1mgEMS+cS0CzXGdCg9y2tQI/e93WsexYMO4ARBkjiAGXhwLCI5ZtiHjmY3lbomx/RHeaYrzyEyxiNZoCg04VhuoDjsUxDGerQrQDH568w7PYRz+dYlDqitGSGXh2niJloO0yp2EC+zs/qmEaMvZOHKdIswfj0EK5j8ViqhjSRyxBzW+Bo+PzYxyai8kSC+8R4x2O0nDvVEYg/ymhHDZlbGQQ5YyooTSZQPpEU0WneIb1YA19/9TcYBB3cf3MNffMAOBoi20JmduEELXSOjlE2epjnHpd5gkottYpF47MkxtHxMRpHhyRyhfHzAUZDG25Lx8iuhIkBGe+kBGyZgG3CtqRWlpikhYkBzWHEWkuIMUdzNLGOcqGDVZG5gTLtoRJAYRQgvQyUUXl9jWhufcRok9tqu0YIpM9Gcx4ZA5EGIOmzEaNNr9DWNZbbiDw6BxNfjF2svQp3doBuQqYJxHSsGIjsNk0MujFuNQe2psNuuThpaDBj0tJ1YLueAPxIH5QqIZYpfMPBZ5+fo91t4Q9/+B0WG0pCk4ES1QerqU/Jbsh5nI5fOb9zfKdSj6pfbEExBRLJriHCQRkvUcKRknX0a6e5nzQL5/OVKDmUy4u6v9T9fPdblPQLHyQsy8fZyQk6MFCuliSEC8uMASPHNHNRBi/w/OUX2KwjvPn5Bu6hhf/U/Rbz7y7wj99OYLcH+OqL10DaQJH4aB/66Py2hedjEy+tAn4RIUsqxJmFwrJhu1QSSgIWlDymRCL1mxxZTOOHKCdmUJb0jjXBeCRgltYncZwhCjNsVhliqjhZLfH2/Xs4poHf/vZrZu4vlmG93lLazXWsQYEi1UrTH+qjVIFCrEyNEu80elZwNAJraeyykZU2isxExaw2cBKdjF1IF9koQwTmGn5QwvCaLJFiVBEbIcS6h1RzkSYu5iuSIAnhl9cw9ARh5cK2PQSByzq8VLXiegHiiNZY+7LRffvv1/YMtn37D9VESZQsNZBsjidr3EfBmII6dl//5ZJ4u83jKExu+XSTpx99ErhRqaZt2+h2OxiNRnBdl0XZCTAgJgxpmQjGjPwOesBBgwwiFCYjWXT8Nv0r3Tm3QMFWe4mCd6ELp9ht4hoJbSoBQNDebMuET6LJrRaWyyXevXuLxWLB2WMpo7IFnNhZS1rYq8CZtdF8nD87h+O4+PbP32L2MOWMPGmlHZ2eYHjQQ5QsMbldIU5JAFpkXUkc2W+66Pd91lcjNpXBmWbKuorsP2X+SH+kygggdOG0XYSGjg8XVwg3i9oEInBs1mcjna3pZIrNJmIxOw5K6RwEo32nfFME5KJ0RAFwu7dfbLe9ndsbrko1mQGl4oy61FEFdlt20bapx48BtrofMtgq9CWgmawGojPoppzRxA0R90TpxmzjvaeLHpG33jKzqirjkkkKqj3H536SazpanSEOusSqyFBWqdDBAbmPMs9flGZIYwfS7ZguVphR0CWDeToHw7RwOBqx0+u3f/kGSRKj2+5gdHSCVrvJ3xtG5GxrM4OS+qpj2yyOTOXLHz5c4u7uFmWV8bkdHh7ixYsXvICYzReIolgukk04liX0GNnEQPRnNjKgfsVloCTrl0mtNWEMsr07uws/df3k8kv+jtRCL4o2nOX1XAIGydRAsNZogfLXWGu/1n5t2Khb3RnqH/zjT2rb11QXpd/2Hljbt3379UbjXItMDI7HsBwXy8UD5ne3sGwXR8MBok2E29kKMFzYXpPHvZKAD8uC27LQtgo0CazfFFglFTIi89q0UCVx8AqsAklxCH0ZredYt4gYJAlyKoUiRja9QZpRrLFqMtuUROIbnSYG7RY8LnEXAt40ZzNzqczR7bZhODY0ohMRy5jYRgTm0V8ZAWw5LIsWsAZK3cJ9ZeIyAlY3GcqLkN3Dy+wBhfUATcsYWBw6EZ6dlLB6Q8w3z6FVFoJOk4Gd9XyCZLXAweEBoskMV999QIoSpu9CtztYIcNk9gFVwVw9cYHrMUtMjk9SR+rlR42etlo2Gm0f62WM9TJkxMc2TBy2yZCnwsWUrgHFM2K+5TFbJow4FmIQSSFJ6ljEnC40UEWMxIw2jluEHMcWaBGfq9NfmoaTgwOcnYwRfZwheVgihoFN8haDs2McvX6BWdUGKU8ZeYHrKMJRL0WwvsPVhxy61+DYyKcKAhdIaBZtdlC5AXQHGFAQUhAgK00MSCdLuoPqu6w1Tg6VDJyxQyidEzGPdJrPaP6h5G3BLpDMUMqkbhhdP8uATYCdTbIGNJdR4oWV2aTJkS6dUMVcatqiEoHmERFQks8kOW9TFy6hk0GVQdIdAnyKK+BhHmKz3HAFQua4aGsNYJXj54crjI87cC0X4XqKwYEN39pAsweYTcggxOIYJ1yGyCmJSgWKsyVHOOQQSfsLWjZMD7i4vML11XXdWdR8VzMmJS2S86MqG6yAOFniu5Nx3pl9GWrk5Ctt0221cURlqssZLm4n3Hd7DR9HhwOUhoW37z8i5thDHYqK3cT+OCqSZgekodhpD9A1bVTrDbSC1OwoIZgidR2kjUMMT57DMEzcXj4g0kucn7yHd3WLb743cVvayEsfRTVAr9XFF1920ei4WAY2jj2gVaYsxZJkBmsxGo4wwDCeGGCIflFy3yDWGpU0M3ONeKkl6dFSMlJsRyZk0YbkY3JsYtKOpBJskZh0LBNnp89xcjLC5fU13vz8hs9ZALPyNyk4knJdUkGzyLWADA/ouCyYpQ29cFCVLlLYCEsDMZUjJxnsIoZV0fUBbKeE5RRw3RitJuD5AQpriFniYxXmCOMUYQZOTphxBSsP0dDmGDY3GPQDVO1jaI0hPNvna7JYrrnS4WE2wd3NLVc/bOV29m3f/v+1PYNt3/7DNWJx0ABPjBM18amQ6zGIoXKY2/b0+fbVp48foS+f/NQnN6eHZONe5MwaI9dDCpD8QLDZyHyAAYI0E8cn7bsoCBThgNxprdEinhPzTU1qYsNdy3OabAVbixkuai+sz0YGCeTuxJFn7TZKE5DruTg7PWUAZLWhkjhyExNXSAEKKjhlXQoNOD4e49Xnr3kbAuia7Rba7TbrrNw/THB7fYuHuwna7T6XXFCJXxSRhkvFxgxpXGIxJ5CRronDx6es0YV7I5UzEFhIGbQceZhBS0ocH/fgtTpswU40dyoBnK2mnGk7OjhG4DU4G1dVpO1RF4TuAGLb6yuYBvIZn64qp1Q6YAJbFEG5vCc1s03uR3aLbQ+roz35VO5gB8jbLanh82X9Nb5RHASK4ogaEtppSptPfJeCASU/r/4esSgRIFOax6yrQe62rh3wRrrpY3x8gq5bIItoGZXzQs6AzyWh4vrTfRBHGqcRbiYTrMOUM92Mt1Ylms0m39tv//xn/Pz2DX/f0dEY42fPmNFBHzYk64zYZavNhgWM6RzoN0F98fj4EIN+n0GtV6++wMnJMbPFppMZ4jRjINhxLHYqowUz3W8qO0hScs0Svx9hZECMNQokadHxONAW916VGYnryk6btAAxZRkN6bjlJdbrJSwq2TFN/s2uNxsG7/iK/zdorf03vS/73LbfqEj2CbjGfUkYnezBtX3bt19vrufh6PQ5Dg7HPAffX3/EdHKPo6MTDFoNXFw8YBnnsIIebLcBVDZK3YXBiR8LfTOHu8oQrkpEVLIZEKidMoAfVRpyKUZP+vAaZRyIlV4krDdJ2oxcvSd+tWLOYQdEgWUYFhkHkJSEAZ2GSSqHKyuE4ZrHJTJgENMSF8nV+lnCjZucuA2klYEiFckoAykaeoWBrcFtkz6bC9t0UaQuytgV+pRajE1u4u7eRj5dYNx/h7LlYDbVYVQlGq02XD/A7P4Bm9mGkCDWYKNkWB7HsCsXo6PnTFiJ4/XjJI+KExh0eMz6+eUMBiRJiXAVwXVoQW3D0jWcj3zcz1LcLCgjpuQw1OSrmpyXd5hIv9z7dt5UsBI/lwyc+jndsorK1Dz87ddfo2UGmP30ADMuYAYG9I4Ft3eIxugIttNBgxJ2VgnHSTB0UmQf5igaZ7ifJLi9iTE4PmK20IIqBMhFdr0BygQ9x4BRVchSICVmFjGiTVUSuhWiZ73QRIBr7HJN4Ag5ihPzaAdcI2ZblhBIUiDNKb4kZpqMK2QoU8ckjH9spR1oG9Y0JmMA9kcQzDkVd9H0Rn2MnNYLXUdJ5YCokEQxJrMVokUImyojqopNAHTfx6wq8ez8EPMI+Ob9At3zFXD5O2zyOcxyhqrZxPXGAtWitgZtjgvIKGQ4akErRfxJIF8WlchWJYajPs6eHXPCbhNFMt6V8ZWcJ7dEtm0nqLtJHQhtOw4BYcqJnebwz56/YCmRH396i/kqrGUhkjTHZDLjROfrz1/AcwKOW8VX05UQjHeO0+RXW14bnZMzeOsc2iqE/v+x995vrhxXkmiUNyh4oL27lkac0cx7+/b//2n3vdlvd7USJUoUeS+vbd/wQPl6X5zMAtBNSuN2fxkhyb4NVBeAQlVW5sk4cSIKwqsJiNMvGl24x1/i7PwFZpM5Pv10h/ZxhW+6/wU3v5njf36IMDVo9NCDZzxDozVAeNBFdRyi3bVxYafKXTYpEecOSteRccMVd1nVd8haU4BZpgA29h/2VTLKyHqkiYaUJGdSMkpmG9mWZLAxfmLiW4A1dgitT5sWJe4fxri8vMbJ0T6+/upLLMngXS4VWL1mSrKzaZCNrEdRYalQmBVyzZojmMqqdqaNeZ9XjoXM9JCXlvT5oiB6RvdkD3FJY64cXhWj46XaZTmEzf5t5cjcCqkRIK1CzJc+5pMYQXoHH3eI+blGgGbQQBSFcuf3hgMBlKXyZQey7dq/o+0Atl37m2xKa0zpXwm7pd5e4w36ef34KWxR76fCuU3ItsnGPo4S1/tvBZGPULXtN9ePCXYRAFgsllKSyfcm0EYtMWYd6fBJwEvcs+rX6wW2fESNDuk/ylFqppvQ/nVUJSCbuAmqbQK21eWRnHIIKGgnUgHQCMBI2WgsQEWv28XR4ZEACovFQt6jFn9XAB7QCCMB1obDoTDeFvO5BL0s2yRTaf/wEFGjAZtBS1nhp7fvxGTh8OQAUYvgF8sCCYaw3KESivr4YQ7Pp0acuwZ26iy1waBUBOdVMJHOMvi2heF+H5YfYjJdABVF7RMpJyRgQpCGb8DgrdafkxKMrUulSjI2vURDGFsXrw7i1IN13FZvqQO7dRZ1q2z0Ub/Tq4F6uwRmGzBl/aqtS8y4pV4IrC+9fu2jPrD+lM1xq7iHwQat1hNhezXClgBoRWUgbHVxftSHmc2QFHWG2oUJf9P/CKyRBViVeJhOcT0aIStZJmogF+t3G8PhnjAu/uv/+18ElI2CEBdnZwibDTEZ4GtV471pwHUdBJ4nwBrLVGlewGBwuVqJLh/LlbkQvb29xWy6kIUAdUoIDLK/8pzxHsk0uKbYmJn0I5Y+sIRJMrn1ddUsQwkIt8E10aZTP8Jc06XmaRIjSZcIA0/6DEE+lsMqtuIWTfDf1bbGCXm6XVK8tduTbXI38/xrE5P/Pceya7v2H6/xfu52Bzi+eAmv0cBoeoWr9+8lufT6+QXm4yWu7mYw/BBuswfT9FDyJwwQdhwcREAUJ0gnBRaJgSI0Yfo5qirFqiyxIrjtmLJoNMlAJ0OKY0+eKLCfuo/rGVgpoiuATTNk9ZjEH58sIsdAQXZ3EcMLQmEEi3GSWu+uzbEFaNMAkTCfLFP0u9LCREmgjQtYI0PTBPqegWLgwG76aJihAtliDxVta4wUs8zFx2sb7eV79I9crOICi3kOJwjR3juAGdgoAlNAgnzBdIWNrCqwnE7RbvYR7Z8IMzmniZFm5+mJoyaH6X82f6mb2srx1JJSxKOeiyw3cDVPMV9q1raOrcon8+16GtXu5vU4WO+2TktpIwY5zzJvKvRIDacKsuRVevHsGb56/RrXV2PMRgQPyNTK4Z3vo4q6aPV78JtNjB9iTIoKA/8Niqv/D9OHBG/NIa6vCuy/OEL/ZICHJEer3xVWTp4pM4cqzjEbcS4zETQ8rZGmdVFZ0ifAWoaEAEmi3K5VOSiZR+xzZEsWay02zn3cjwwlcRXNNSOrPrnVFrNLwhod+20bA+gEoSR/pWxUx0I6CVn3TwJt1IOdJQuMZ4kAezJnGiV6gw66gy4K34YVuJhNM0wqA786KHH/mwf87k8BssTGfFUgNAIcdmyUgYckB+yGjaFniplCMwoRtUKsEkov5HLvJrMci0WMl6+foduJMJvMRMAej663juElPtuK2WV6VT1sezrl6WAJdLvdxD/+3a9wd3+DH998UiZbdcyz/jHF4ZzgUjOypWSToE8scbt6f0kymyb2Ts9RRF3kH8ewY2rKZsLUS/wAzv45jl5+hYYf4P3bT5hmJb754i3aV7/F//hvAd6tfDEDqKpjOPYxwuMe2q9aOHjl44uowqCKUaYs5bRQ0TlApCoI6iuHUMbCJcX9E8pjaIdQSn6YBNcylAZBs1TiJLLW6CKaxAVWy1zkPWL2u5zgWiHxfqXd1VVIou5BxnBXNzcYje/xq6++xsHevjh4cpyj5jHPRR2ri/kJT3pdMcJqAqtEQbkX8Rll2WgBn3rLTCjQCMEMkJWmVCugsFBlHvLcRMpjShJ4+QztRoJGK0BpNmBSOM9NsHRsBbRlPmZzC/F0iai6hF1NkVge0tLGwXAgkKgXBOj1h8jSVGRKdkDbrv1b2q5EdNf+5puEeFIeaSo2lwY9tpe1G+Dj59s3gWD91+32S9ue/s34q5v4nIEx2THtdgv7+/uIGpGwuCaTKe4eRtT+F1q/ZNw0AFQHkGvS2tb7yeOtdfp2uagqEVWaLwRDlBECSwhUIEyNKgVakPlDpyOaF4RotztyTNTSGo3uVcBbWTg5PcXF+bloZ5HdU3+529s70XRpRk1hGPF98yTD6P4B19fXCCyKJpdo93t4/eVrvHv3CaOre54MwNGCskaJwLdwft4XV65N4tWEIToPFL5nqQUdkijM78Jt2CgjC28/TzG++QRDNEoMOIaBg/0BwrCJD5efxMFMdD3qC6IzuesrWgek9dmVjTqYk6zeJoBX23SwLyzBx31oA2duF6Q+7jvyWr1akFO73X/r67ilNyM8hvpJDRjVYeT6AHQpDHXHRLNYsdYs25XKJcsNcHF6gobBoI1ltGStOTANn0u2NZhnmNQHBJZJgqvbkQTy6vrTNTRBu9NH5Ef43be/xXQ6hmNa2NvfR7vTk2BOv4kqUzFUf6v7n9LyMCVjP53ORZjZcZjNzEVLjOWYZKOxrJrHztfItWJ/ypW2YSalNKrUWMpoxB1UB5drkLM+Q+qKUE9EtrLf8z85Nt4nlhzzajlFwM+zbUymUzEzUBpn+gL97EauL8zWjfdvbTXIu77Yj8cY5RCqQPFd27Vd++XGsSVsRDg4PhdHvOVyirubj0hWOV49u0A8j3E7WcCwHDhRW5i6ZWEidz04ERf9JZrUT53mWCZ0yTNghBxfMqyKAjHHa+Z6igoGSecEwEhTkzJ1loSyrFExvKU0XSe36sSXWowClER1bArOGzg92IcfVDIH0hyIOqQsQzQNjsfUclOJANe2RbfKdi0lVM/xjCYMWqSe7pplWsCpcrh2AcslSuJgDgfvCgPzuxLJ5xijmxGy+QileY1e18PJsIm76884bF2jfbqH2+UXyFceev0WHLLZH+4xn95jcTcTB0jGJha/ipWhOdxD5pq4uf4J6XysgMZtEEyPvzVzSJXUqbmTM/HpXgOBV+Lt5xgxJa8ME0FkCVBAp1UuyplWUbWefDeu3GuQRZkjCaC2LvtUbJpaQmEzdmu2kRjaSC4Og34HX3zxWhj09yzpqyyYcS6Op4evznBTGWjmJpbzGA/LFP1ejn76G9y+uce7ywjX9xFeXXTh/+oUt4mLPc9As+eJTumA7tppirv7B6w4x8GW621bFRzGSJ2WzIsl5zABzQpkOWNV7fBIgK12CCXzkEBapiQRKO+RpZUwmhSQy/0VICIlpxYdaNVcQeMEec7KBTrdsnRPXKYtbX6gJSCkhJZavaYwt01HxYnLdInMuEbi2oiTAYxxJq64nX5HlQrqekFKO6wqG2Wa4v3nBb6fpri/jOFPOXmtcPSqhdOhg35QoRnmcP0VYJ6hKG2Uym1CYgUmdG8vb5EtcxhkNMWAHZgYHLcxmY/wp+//hDjJFLueV1VXaNSAyTrmWhd28N9S5nGWxP76m1+hzFf43R++R845VXfUOh29ZrvXP8pvSzrMq2dniNo9/PTTO4weFugOe2j3BhhdLpDHY3FTt4pKkuXB3gH2T84RNSNcX95iMk1xcrHEIPkWv/8fLj4vfKRk9qMPxx4AvSY6hy345y7OI+CQ0igCiplIKxumx/7DCI3xLwceNe6I1lrCRCP7SSXHSlAWorW20ehLRZqlFOf1pHYVJXOM/YsOn5TWIFgn7H9lprE+C6K7q4B9nu1OFOEf/u4bift++OENlnGi4sXazaTaAto4UNgscaY7qNIUcRizlx7M0kVWuYgrR8CwJCuAZMFCUrhcHxFP9CpYXo6mW6HbtmA3B1hUHYwmJaaLBRbIMc8CYGmgsYrh5XO03RnOjpdw232U0Qu4ThOtBl1vx5KUZQXF54+fdkYIu/avbjsG267tmp5YBSzSguVPF6xsm0X4Nuyx2f54S/1TL7Kf/mzt93St/QvPFeOukGwKQSqKjtLVK4oioTZnWSqOiAyuxQVTf24Nqaj286Out9Ugj8pkKpBxm+m20bJQIFwNvLExaKMuFgEGbjs9PYXP8pmixNe/+pUw3O6pc7ZcyPmdzxdYzBfoDwfwXVdN6qSdx4l8P8t0ETVouZ1gtliJLszVh0ucXBzh4PQQi2SBKqvgCOioAq3xdIE0T+EFLButvyIzrxKJCUhCu3OLWd7EQLUycDgIEQ0OsJrHiFOKS1eYT6ayyDo5PkEraslxEshZM8h00K+CzPr0bdAuFXTVCwZ97bfrUrYCMpUp1qUrj/+ss/Xrret+t4HPNviebKkfrz9OZevXGOAahNPXUxYwWhCN+2t2INmAXMqwxKfTG+L1yQGwUmYQJp3CLLIFna1MpDr/DCjvxg+4f1AAqtLd4/8lTo7PMJ5O8Zv/+d+FlUhR2S9evYLtuUgJrq373mZxKWUHmv1YHzPBrVanhYODQ+nvXDiwz/OLBb4nJaWir0jORa4CQjItyZqQUhopLaCZBbP81F6r783HJeIKbF6n5TWDkxohSpuQJiR5tkSz0ZAs+cNkImYKaj28zVrblPc+av8ecG39ftvgmn6u+49cWQLkO3Bt13btLzayYbuDA+wdnQmYMBvf4/bzJ5ELeHl6hJv7KcaLFF7YhNtowxCNSQdlw0e7bePAKREsMyzHBVICDg0Dlk/QPsOCLG8xPjFgEQjKDAHXkKcoc22sopMwNXNDzb1bY6C+rdWdXcK1LZydDIWdFNOa0rDXrxXRUNEl2ExENMUT8I4Il7j5qb9zjGKMQCDFoJg4pekLU+ZUs8rgmQWGlgE3MrHquvCDEJ7h4mAQIHQMvH13h/Eqw9UsxOQ6xknrDZr7Bu4mHrJFiqjdRthqi7aS5eTiQJ2QaW+xnG6KfLFCf3CMRr+POa0mM+poPgmL9G9F9DbQDny8PHQwni/w/obnrp43DQFVOB8HgWJ5ETgQTdZ19lABI3U56vZgXyeb1MdstEt5FksNwtHE4Pnzc5wen+Dz5QMWaSLgUug7ePnyGHtHA4lFWpaBKhHpygAAIABJREFUhVWgMAvsNQrYD0t8/1OMP75t434xwH3YwooJUtfG8xMPge+gaWdo1W7fhiVaUtQZRUE1t4TioFhMEtxNVsLmJqOSi37RxOUcbiumD38IeDBGzAk2ahCObLUsq1CkjB+VKQZ/ZK7aStbVEiPSdeo+te5buj/WcYqOhfgfY2ZJvFoGxqOZJMAIRC3hYmr5OAwiNJvhWh2WnZLmBvxNYDdZFYhho+PaCBsB4pYHu+nAGZgidm/kBnK6kS6u4FifUFot0S5jUpdTNPVVW23WYVfiDk/pQsZ34/sVPNvFl1+9EBBoOtEmBPpcr7/HGkzVfUXmzxJHwz384z/8Cj/8+D1+fP9RGGuK11jHKnUX3chH1H227kN3owlm0ylevnyJs/MLlKWFuw9LmHkKw05EJ88NGxicPcPJ8xfyzlcfboWJ+PLkDYq3b/G//tTEXeGjsAJYOEaAAwSNBnpftDF44eHvvFwcQukAukodZKYD27fhEySVShY6oSsdY8ZSK5Z4JqrvQJtgVAZ1H1WfYglxEpeIeV3IWCNLUpiPqgSZ11tp1WrKWX0edNwj95CWClHJSFPisA+fPsHzPHz15RdwXA+T0UiNeU/OIcvmmRg3RJtSnW2lB6fGSlt4sTkso4BNJ17bQ15xDUENwEzF1AVL4Q2sCEBnEzTMJRqhCcujbqQDj+fLq7C0XWSGhyTzMB5ZwGqCpvEBMFeYFzSZa6IZRZL8pyYn5QMomyLMuV3btX9B2zHYdm3XnjRZTGt9trpk7V+yJN4s17f3f7QK3mr/knfcaltvwwmMAFcUNdDv99Glq5dlSTaPGggEqhgA1gHoNlioFSXU4zqSqqMNwRMUMEKdKclaSmkoAQblLMqfuuRMwByxa1dsNilXBUSTrdNuy4TK8lYy1ziB0vqbJXQ87jAIlHV8rkASUrG56CAQInpYVSnXgayl1WSBRZII0NXqNnH27Ayu4+H2+lYCNWb31bEoGn6vH6LdaSmwtC6b1EYIJqMMxgYZGVHU0jJgthzcxxk+vP0JyWoBy6bTZIV2M5CSRhogXN3eykQrwbdmidWaHo/PrQbN6iz8E/dPsYvXx6SuwRNB53qxpS/JZsGk99d/2O5jKjjfxMI1blb/VQCj9TPVnwte34ourKWcc4JmwtYruUgM8Oq8Dw8W4hUXbiUsAk10niR4KYYWKqDi91guVhhNx5JRFLYX15JliXarL0HW93/+XrKBDIhePzuH47my4BJX9HXfrN2m1H2nuqRii3Gb4znY2xvCth0k8Ur6OPsOgTTuJw5jBKF1WXUNpslvZmuZuZcAUQVrdelvfR7X57I2D1kHjApY4zEVBUHkhZSs8kTPZgvEaSJMubV+0NO2vij/yvv9aXsK+K8HGnUTbpeDCjj47/28Xdu1/6CNY0oYRegPjsTEIC9jjK4/yb101B/KuHI7jmFYdE1uwjTpbadKrtzIRsurEBHkmBPoMlAFBgyHIEeGmK7LWvvMknmmVGWbNDvhWMG5kmPUWgNVgQ6ycK0NVtY1nkwyALZj4PCoh17o4vKKtgEuQi6iAweOb8NxyDyiCL2enw2K/nPMsrWbsy1gGhnwZLORAUydUmG0GdoFUkh11IPL4Ro5LIdjiY1YjBAMTO9SxPMco58Woqtl5CNUzoT1rvCqHPvhHOcXdCJ4hofZETy4aPQjKdka392K3upiuUKW5sp9sTLgBh7cYUuSJZfvPqJMaFyg3SplXqzg2ibOhgFss8DbqxhJzhOmYhvRk90y7+Hc6LpQ5ZZ0HUxVbKOcv/WYqMd1MTKQl+lSfsYG61lZgSylaeH04AhHB4eYTFcYj5ewXUPANJpJHB7tC8uar6G2lehbZX9AsmxhtPBxs7Lw4yLF/DpH1WghaJu4aBrYC20MQyAIyO7zJFbLWXKpE4EyfBNEnc/wcDtCwjkYDvjVzZaLXs8XY4RVwiTTUsZ9caEXZhGrC1g6zB8mmji/0ytB6a4J84oTr2aTUTfNqhls/CFbkjEfY2D9d1ZPsH8pJhvnRMUqt032Qx9ZmeFhskKZUddPLHHhhb6YFtGkSMUrWpKFLDACHHQTzxysbBdTxnlxjrHloJkB46qClyawVwsESxPGssS4vEd0eIe9lo1GI4fhvUZp9lCVdDuvpO8yJniYLDC5n8PJtVYqKjQGPuyGiXfv3+HDx08CLusITcUxMrWqsleaaP3q9UskqxX+8P2fhfmuISBdCaKTzXUyja12fReGm2xQ97Xl4GB/H02/gXRaYP98gCQv8PanN1I63uofYu/wREDV+9sHAb/2hg9oLt/ix+9NfIx95IYFs2jBxABO2EFw0kDr1MWLDtAtUyBLkNJZk+A/zSrIWhNAmbrKWqdPSj2pvZdLvEtQPc1iFOVKEo0c71hOnK5KxATYyFxjcpIaa2KcoeRqinXSU8XojHskiNMabPUaQq0jGBOtrWdVHF5W4q5+cHSAvb19XF5+xoeP74W1q4BPgWx1goHUOl3K4dBdjZtsWBW5nSbMwgFKB5nhIqlYLm6jSlIYBV2UE3hOIaxdO8jhuyVagY0gCpC5XSxohLDIsUhSLMoKcWLCXgJhukLLmGKvOUPv0IARnQH+icjyMOydzqaYrVaYjsf4/PESaborHd21v952DLZd27UnbZNAVkCbbNN/U1NqDXBsQxxba971s21opW7br9kuFatf+fPyMY2pPHo5s0lkfRG8InOM2U2WjbZaTQmWqGtGQEHFlDoAlXh0G5xhxrd+X73PI+hGLQDqrDqnUTGI0NlM9TIVeNWlfNwvTTMslkuslisB2OqS2+lsLmw2is8L+EGtiIQaB6liJHFCZ5BIIKt2bqLTlU+xelNZ0K8y3F7dif7GxRfP5H3jVbIu+eCCYj7LMJ2tYFPk3ncVi0sCQwUaqt+sNFVBVbmsEJoVDk77SMwIy3jK+BZxHmN8P0Kj0cDR3gEKCeJqhyjFCFCPax2++t+tPqBZUrWGyaZf6DO8ie/0u2zR2bZ33WJGPe57W03237xIYT61HpuCrQQ0luvOLH+OMi9guoFEMvxGvcEhXh/3gTkzmQTMyBwjwKrMAgzRXmM5KAOtAg+jMe4nY8mUErSSLleZGOzt4+rqGt999wexP++2W3j14pkEtIq1Vn/Jmj2msp4Su9bltVw4VIWUHx8dH0ufIQuS/V7O1FZZswTZNWtN3EFZgqX7EzVqpBRUv68O4NTp2mis1ZbydSaW4KAAzeD9NEOexcJaI1uNjDx+jnII3dw/v3hNfulabTdFfXu68edDBx5f3/Weuo8pcK12ydu1Xdu1p40L/v7BCVqDPUl2pPEId58/YTAc4rDTwfXtHBOy1oIW/IALWxeF6aAKPXSbNgZmCXeeYzUrkTLR1KJDaIECmrUmzBEDNuUJUuWsWFFKIU0E/CDmU9QLfM0A2SKr1ROBnnsrtJoRvvnqHIvpBG8+jJAWCvjgGEsDBMkXcQzS46YSx1Ilg7Lwl/BFjcsyDoq4vWIIcw6oNcdqfbaCRkKl1merChSrMRrVAr12G1nHQ95toGM1UKYhikUgi2AaIcxTA7dXObzZJU72rjB1+ni4zuB5FnoHB5Jss8xCAL7VIkNJ7bDlFMl4hMj28Pz1BcqggcV4ppJmJjDohnh+ZOHydolP9yohowTjN+Wc2yMdH5fUZioqMYHwIkpCkNFSi8zrsXE9JmuwbT3RKs1VRjqW5+Cbr3+FVquPH3+6kbnQocmEa+DVixPsHQ4VuCYumnQvXwGr7zD7YGA+HWCZV0jtDG3DQa8zxN6ej17oYRA48B0bDsXdE8Y5iQBSMCi7wESWngvJ1nEcBGGA0jbEZZvzcJlVmORTVKWBbrMhWrPiLE+WUUq9UaWxJgAbzQxYBqyZa9JX6rmG+AUrhoWFruLA+vd2AFL3TcVcUp2V/wVBA63AR5rdYJow1jQE0iWkFYUNtJstOT/qXRgbCB0JVj5HsiiwWtj0coDT8tD0TViuiQOWPQc2TpomQpdaqxawsJDdpLidpbiaRSinLfpswi3+ANuhjEWAjAC2Nrei3ljQ8ZFSezdZwa5MZNMKySLH4dEezp+dYjIdC5O+Bs0k5CqAi4szfPPVc3z3+z/i3YfrdcWC6hc64qqesNbW87aOueScmfCbQ7x69QzmqsTVhwWSVSqafSx7/PKrZ4g6QwwOqUlYiEOoFeZ4vvcHrN5c4rdvItxWVB/z4GQDOO4h3KMeWl+2cPLMxtd+iUYZoyDTLHOR265ira3BNcqhEFjLkMWM43LlZs4EZMXHqZhAOa6L+WyKgiw1gmua3ca4Rhi2EjspBqyYXNQsRr1AquNcFZKo2LLWiVTsNZ2E1UYYfM4xisnW24c7DPpdvHjxCvOV1piub2htUCFnUw1nqrRXTDwqFDZ/F1L+6laqJFyWaa4thgVZ6Qjgyti2KFgObyIRdmeKRrFEx08Rhh5cJ4RZUhuzRO4CK9PDqvCxXAWYjSpY2RUiZ4pFZiE3HHSaTUS+L2PJ/mBfhhNqA3Mttmu79kttB7Dt2q79M2WjNdV5e81bT6uPAbW/trR9DGytZ6Y1urL1ym3QTR5vgV7Gk+MrmHVKMJ/NBVSgBpWUjTZCARRE6FWyoypYkoCqfitdLvL4bbfUv9aBvt5BLwbWrqOVFiom401KMOk2SiaRAgDJJOJ2z3Wxf7AvWV8KzDPTyMCCdGtO5lK2lxOsUABIDfrJZ3AbmVa2jWbYkMVFmiVYLVa4/HiJsBWht98XCju1JdYTOyAlA8tVCj/01sGwiol0uYgElYVosJFlUKxSDDsOWq0h4sJEslrKVZtNl1LKMhz20e/0sZqvkBUK1Nu6GutzJUFWfdnqE/dkT2lbmm6P96qPU5Uw1KUc6wivDmzqoO/pQmPruToWzdrTpR1cvKhyCQem1lpz/AbOTk9wEFEwOJGoRkpqxaVVZa5ZIsrzRdYCdTQ+Xz+I5ppUiHIBVxniKNdq9vCH7/+Iq8vPcB0XF6dnODw6EEOLtYmBlKjU32XDGpOzKAFvIdfs4PAYvcFAHF4J2JJtJwtGLpy0fpqAzboElKXKzDqzn9VgrepXOnuuT7KK/bbvhVoke2NsoNxHSywWUwF4WYI6nk4EPOZ7q/5TX6j6hG/dq9v37V8E1LYeb29f952t9hfein9Q7IKNWcuu7dqubRrvj6jdR2/vWExQyKKZ3F4JtnGyfyBi9bejBQrLgx/0YFkBSsNDHnoI2x72fQPNJBMmSsoypsiEHSq3xrgqEXMIsCDOddRaKzjtcqzi/JbmAvpk1J6qB3pNUlvPrbqpP7NU38brF6dohcD3P77Hw1Sx0iXJIVCG0sKSBBHHN10Kqiq39FxkaimANQ6gQBZhMsnCuXYaVfM45026VJLJtCorzBYpbIMu0p6w2nrU0vIt5AMHRsuH6YTISxfWwkZVGEhL4IbMrc8V9vEGB6crPKQhxtcrKXvsDfeULpxTUgpOasDIDixTE5O7GXpNF6fPTjGNK5z1eX6W+OFDhjjX2q+GAtdkVtPGDdszpwzf8tBEQZ28pIIbOmhEjrCrFAFdM970xKmGTzVH8j/LAJ4/e4UX5y9xfz3H5ecxvEpgVuwNW3j+4kxMJRTAQrhvBTv/DvHDH/D2BxvJZQfBytdGOC68fgfdUx+dwETYMdCwDTRCCyQfJZMcOUuHywyu/SAi80ZB0JLsIIIhKulFZrkXBqgslRSLrARGNsV4lsGzHbS7PcSpctgWpjZfS+Ya+4OYXmwSf9uxBWoHUCaSar9LvX2TlGUVh477RHrAQ6fTg0cG+uoP8Pz/CtOfInYPYZc+QpYTB6Ho5NZzta4NRcXE6wMQmz6MhofCNtEI+NmAU5WwyxyRQ+4lY0kDueugGLq4GoRYUgZibCKoGljNbIzp3pu+h29donKaiFPCLYDtuhLXeq4Jq+EhoUZYShDGRDxVYv0XL87RG3QxX07FRZMlrL/++29Ea+23v/kOKzIGdXJSxV91SYA+J/XJ07+3FUAMO8T5y+foNkJ8/mmC8bzQ5hMFGm0bjVZDMdHCEE6VYDFLULaW2F/9E/78BxtvJhFixtF5F15+BL83RPRlD8PnAV53KhyB1z5FEluI4cL0HPmubm1iUPL7Kp01AmusDskZA2kDDDExKBIsFjPpL50mRf0dPDxMsaT5QZZLOalKTOoxRX3rdUyrliz1GkbHr/p0SDxEkJgXte5jdby1NiFTzuujuwlG4xFevHiB8/MLTMZTZGmsQyhDxi95L5UPoEwcTMr1imFwhczhd6rEzdiuSjgsG6Xepe0iNZVpQSW6l0xy2EhzE4u0kGRHUE3R9AsxVgvRkHs8t4GlX2FpBAK0zebUk1ygVdzCq0aY0bjUCbDf78s47Pp0ju7JeMvEe63rt2u7VrcdwLZru/bPtDp7p8oiNwHdL7X6r4+X2GrrJo7e/uvWtvUOay7TL/zt5x+i2DuK3cNsJkX9CbK1Wy2xrKYGFVli4uak32DDbKqDKfWjJst6Lz3R1ce5ZrNtQLbafVGwASktoHAugRul0yai844jYBtLBFvtlrzHw/2D0oUQTRDlHilBs86QMfivwYN1RozBadMXlyjun6xoiDDC/e0dBsf72Dvcx2gyVdku0ZigvEuK0cNUdEgaUSDnoI6VFKDCEJZOrGRF5ciTFBZSDPs9dPf2cMMAKF+IGPVoMkISL3FxcYpGo4XR9GETeG3REOqrWv3i5arBS11qsIlDNq/iKoyR/tbrHz/Yes36Gm7vsllAyAJKZ50l9iEYRdDYZoaUpbBAf7CPL857MGKWCihmHwNcBaqpYEmASGaFqwK39xN8vpuI8gudQbl4pD7QYH9fArVvv/2tuGcRjHz5+gspM6G23iMQuT5oLVisDlkDbHkui4aziws57hk1zpJ07fbHRZIq/1RuoCL4zGwty5TJXitqcI3gm8rcbgc/qo8//lEOoaoDijkAneFWC+RpjHbUkIzuaDIRQFgZGWxp/Ejbrut99CWfPN+6WPXf18Cavm7biPajMUTtv+5fHJNsW5hrPzu3u7Zruyb3aBg20N87RthowzQz5MkEDzd3ONs/EHDh081EjYleBMdpCXMk8wLYXQ/7LQf7RGbIWosrVKEFK2LdZoasyrEig4mgFO/MzBBwTcpC0xSluBazHFTM7jRjRrFna9bpZo5Q80KBHEeHA3z57BDv3n3E+8spslLpQG7YtlKnr4i4alLW86hiqvFwBWiTv0kdvi5jUzCLcLRKAjCbMi9+tsy9LHSNV1JGSk2s0nKQsgyWi9uqgGfm6FtAM7IQ77nwowbc2EexaCI2QhRWhcQErucuHt4v8Kz1HdonFW5mIRaTGM1OG93+UI7D9OjyZyMtclgl3SMzmd+/PNuH6bTwbox1kovfV7Gt9JxZ6zc9GUrrDfJvZVDyDnmco9slG8xGGlOnVs81AkCqlxJo7bW6+E//1z9iuSrw4acbGFkui3Y/MHH67Aj9vQFMhyYXPK8FTHxGOf4dJj9E+PzmGHcPDozUBTIfOGjCHAY47Lro2EDIc0aNWMuCw/nItjCvTBSeh2JpIp9bcGlS4ZC5b8pPzPmYbDzXke/F+Mf2HcVEyxXww4X9qMrQ7TTRbLWxWMZIlythqUvlgE5krWeP9Xyn3GlZDioAG+f6rdO4Ro3ktwJmu709DLpNrKh3u1woBqS7QmYHKJMjhHYENwiVJm+awRSTogLI6GyZIp0AiePD6HqiEVYF2jSBkhwFsegStsE4lYlZC55DQBI4bBgwmwEiw0SYpsjnOa7GJW4zD7O8hJO9RbORoDAjxDHZTARxfYmDTd8CIkscJhW2Y2M1SSWoefXqBY5ODtFuRfj2f32L2/upxCOK9ak7mTzZzM2bp5rdtwYjDWH/f/nqDJObJW5vVmp/I4Np5ujttXB4cYG9w2PMFwtcf57hAyq0jRn6TgNvP1m4WhAUb8DLD+A4+zCeD9D4sokv9k08d3IE+RJZQm0xF5njCDuUrDWLiBNBNOqoieuncpgVQycCm3TkNFOUyESnTMVKHM9S3NyPZew4vTgRxhrLv9W4sGHGr3OG+oHiqtV9iXFlHQ+pcG77t5xK2aAiX2Uwwm2qFpxlzVfXV5iMH/DrX/89mq0OxrOJmDGoenGd85emwFoaxogZDPUWrQI541ImhKtKXEdts4Jt2XToQmpQy1lJzUDGMRdJZmBJ59ZsitAco9VKUbW68B0mXko4TorEtZCIPhsdpR0spwu08RFOMcYks+H6DQz7Xbk3Gs0InW5XVeKIFu8OaNs11XYA267t2r+gccisSy7J6lGh6mb5/DTOW89Jf+H9Hu/98996Cttsf/pG28/1wXCiJMjACZxC7HQ3ZHlju9WUElJh3tRBQa1JokPuGgTchP06VSVzxSYwl/9qZpkuGV0DGPJiNdmKCQIzcbp8j4AHS+vSNBHw7+BgXx3nYi6TFEEYvoGAF0qcSyZgvp6aJxSvd8TJlEZoJprNFhq+LxpYWZKLk9TDwwPOXp3DdmysltRH0EdOwdNljPv7KZzQge85moZea92o7ycAEl2MzFI0KpCkeH5+iNRpYrWcwRAHpRK3t7eiDXN6foayMKQcV4nGKjmJzTVTC5u6N2x6TX0NNwGMuhrqX+rfGAwAdGSxtWRQ2jH65Uq0etMRNj1IRza6jEGkLCTDmaOUsg0yswDLi/Di2RmOBqYEW0VJYCqW96UuizI1qFRZKLN78QpvPt1jluRK44/k/AxotyOErT5++7vf4+rqs1yz5y+ei2YaAUlqgWhRHfUd5NDIRniMLSl2m4HTi2fo9PqYTWdYLOai91EbazwqB02UZp9yVGNAqX7IWpMgUbT8Nudcx3nqDNUsNbJCBFBTDDAG9hSLni+mCH3lSkpgjX2VC4d6gbJ+w/ob8fF2XLX9/Cn4pe+TTT95cjM/2X9dOlHvIQAfgWz7Cci3a7u2a3Wjhli3M0C7uyePDSvFfHQn9/zJXge3tw94WLBEz4bpRrDMBkorQN4K0Os6OPGBRpwjHhfICHC1TJhuIay1RJsYGBqcqbh4E2tOVRJK7SIK8eckv3Ds3ciqqbm3ljSQaU9R2cLQxddfnMGuVvj2Tx+xiFkKpe594V3pwYe/hcmlk1/iBChuzaoUkMCCJL409Uix1NRgpOYpNWbwcGoZJe4n7PLFXLFrZO5WRgiVZSkjBDFpUAkp3yixb5lwmxZmAw9Gg6wtghqesEyKqkBSWbi692CO7nDavobV9XDzYKNYpBgcHMBvBKKrStCMjPtv/v41VuMZ/vTHz5jNVnh22kd0cIzJaIEyT2ReWhNndEJGWj2BbMdQ+vzK9zSA1SIXds9gLxBgiqxCxY4p4BkWvnz1GidHJ3jz549YPszhV2SzFegdtnH0/AhhqymsLMpaVFKk+Eesrn7E1Q9nyK4GMOcsSzSxGEbI/u8+unsOytBEi06vVQajTJHGBkzHFm03Xr4yYEmjgcxziUGhZBIpXUjZKMMhlqlmMKUKgckuisMzoSSO8U4Ay/Zg2B4KxyePTsC/Ya8lINd4NleaZ3Iu9C9+X0kgKXBNtMhqZ2x9UutpqzZxYn+yfQ/Hx4ewHQ+jWaHAVgrMWx5W2R6S+BS+24HlOEjJUocJz7fgGKkAJckiQRHzHnIRdn0Bzdiffdb10R1X+qWJjLp5BKkp+0odQIPXQJl2RY6BMnAQBy6mdok5GZZLVhfYGMc+4myJlvEBXuBilQUi0k+Gke16KJg0jVwUrilOmYyFyNhbjhM4MMWhNSkTTOcLJYGiy6rX506OTyVj6+6FdQVBBdv18fziAv2Gh7dvJsKAE/1dI0OzbePw5EBcih3fx/3tPR5iE1nPgnXzEZfvbnB9e4NXL17gcH8P2dSH4XTQeN1H95mLr6MK/SoWI5A4oeaY0loLnG3WGqU+cmSasUaDCzEkkHiW4xWTghyTMqRSAqpdQRNqSJYYTWN8/nSDQb+F1y+fKROy5eqx9ZOupqifaoVqVQWjk7dyWuqkpQD2dSmtAtfqzqWg3Jo9quKbJE/x+dN7ifF+/et/EGORyXi8NqKq4y7plnUnZRwkCxqOk6UAbQS+LZZ4C0jL+JWyJgE5wciE3cnyWeozeuJiuygKGMkYPfsaHTeH2ejBgS/vWxIrtwzklS996n5io0jm6JqXEivPE0PMD7qtpiQqWt0Ogp0Rwq5ttZ3Jwa7t2r+yCYCkxW23F/D1knm9rt7a9s82rV+2CRpV0PvX36UOAuopTGfGdckmwYF2u43hYCBCnQS5Hh7GmEznqjSxxsTWb62ycptttUi/Bt7WrJ06SKu1FhSQJiK5BNYcPidwwfICLdzMdxExZyUI7wc+Wq22MJs+vH+H+ZTuk1rDS0+olQYzOeky0yrspXXwoyftSps73D0Iy4jHMDzZw/D4EPF0jikFmSV6rPVuSikROj3dQxR4MIQHrxY4ojVRMgBZYLqK4bgBgqaN0GsgLkN8uhrj5vYjrDKHWaoFznDQQztq4fPNtYigSga0vlryserkquuqmAKqx2w4inVGvS6ZlOwzV20sRdoqY1Sv2sR9NG3YzgoK+CaY3paWGN0ypRSHCTwLbm6JIG5vbx9nRz4y00RcVLDzCg6DjWKFggLDBkt76chqyft+vB1hNIsF9BOQSzQ1bBzsH+LTp48iWEsXqv39AxweHEgJLRcDCl9ksLnRc1ELQxUgqdJVGhNkGO7tY9DfEyCWwGtdhsk+pcw3DF0OyvKHVMpBCXor8wLNyBCHUFU2VV9zdSr0SZRF8QZgU+WpdVlxieVqIdeh0QikX80pzK3dqerF7eOmr/b2LbpmM/6FfbefPkLlttpTwE7uRdVnNkzaXdu1Xfv5rWOi0WiiEQ1gGzbsoBLW2mKR4vhgT3Q1p/MlKgHVOcZFMMwW8kaIRs/DoV+hzXLzSYGUY0WbOj3C7QLhg1TfmDJ/0p0xr1B2QxALAAAgAElEQVTRZY8GPQT7S+6jx3gOG6IDtnHklplLM8sIRJEBcn46hO8a+PHNBywSNU6IYEJdgrWef8nksrX5C3+r5JRIWNQJKQJjZJDb1AwzpbzdcZXBgWK82prNbsGsLClB5FjN8TzwXDiyHw2AiIRsjBBSbYRgFjk8I4fNRJDNRb+Ny8rC9RwoPqaYPSzxcHOPLHmAaUxhYwnfSHDaW+L0hYFJ9I+4u2qj03DR6baRrWZIl1PM5ktcf5rKKVJC9BWC0MTRxRAPiwxv3r1FMR8/Goc1R3sz1m7hIPWGWupCmmmgFZgIXBfjOEEr6OGrr77G+w83uH+YwC0MeFWJRtPF8OIAYbcL2/aVaydK+M4I1vSfcHNp4POnI0RpHx0nQmHZmBz5iJ6HOIpMEGsNqVVapqpPUMfJtuG7jI2UQSJDGTLUqCE1T0rM7udAvITrFAK8eaEJ0w+QmQGWCZAsKQFiyzVk4okSG3S4dWxH4i1eb5a55UYJ+nbe3I4xurlBTpmQWoZBT098KDlNPR/ycR1rrOUtTBfdfcpiNJHlFoqERj+csAmyrbDKlvAaEYIgRComVEDIklwnQ0W3Rc7/BB2nJdLcgd9uoNUgwMi+xc/Xkg36wDKy2ISMVcIuCrg0V3IpS+GgJPOsMnDLqXhWYTpN8ZEuneMpzCSFY8UI2kucRAmOeiWM6AgP8RnszECjReA3F70xqRwgKLVIYBcmjMJEGVfwOy7Cvosf3r7Buw+fhUuqIwU97+o+JPWJWpsYLtp7e7johXi4nOJ+VYm+IvVGCEwP93vYPzyEHzUxG88wmaWYtR04s1ssPtxgmREcr2DmTThxB53jCGdfdJHTrKBp4oA1kXkqrLW0IrBmSWLX4j0vx8DrwJJOMvgLcfuUcnGDpetkdeXCWqPJE2MmATtTuoMy2a2Y/9Tp4w816Bg/USfx5fMThFGIN+8+4P5+IYxAxW7VAD0fMY5XdekaqmfTGrd6jKvvx61nKg6u+5cKyNX6Qhi2rFop5VjOjo9xcnIq7qMfP30ScJzjpHy0LlsWYE9qRw1xsS0dE5WjxjWndCRGrypHjESSkmw0li2zdn8Jv0okce9S/89ZoBeVcP0cg06ILDjGKO/hfp5jtlhikVJ6xIK5LOFmGRrFDOfdWwyGQNl6htw+QL/Xk/NxPx4LQ3A0HuPy02cpw90x2v52247Btmu79m9oMpFp3RIGvY9Ww3odXQfG9bJ6M8nU27YXyWoyf/wmm7/95bYJLLfX78LyKQoxQJgxm5nnUirTajdF4JN6bXHG5YMCLmoQrbYrl4x3XUqx9f71ZLEWOq2d0Phbl6VIeWdZl60oPRGyyhj8s0kJQZYijldwHAdHR0fw/ACz+UzAEhoRkLFGENPhQmHtZCo5bAH9NkuVSoDEFgV/QS2EBLPRDLfX12gPOjg4ORLwjoKnqlySpQg57u+mQk8PG6F8nrAASorvqgk1bEQIWVLqUNujgGPG2O+4aHYPMVkAKbUiaNywWGE6n+HoYIBWqytaeFxM1YG+5inoS6S28/i3L2md8at3VesB3R/Wa4et67D19/qdychTL68Fi/k6MrlyWPBQmi5z4TDdJk5fP8PZno05mXp0mass2CVdVm1YdJyzLVQVM57AKk3w48d7zOJs3TcIlHZbHQFvv/32W9zd3cOybLy6eIZuv4/ValFT+dZgU31s6vuqKH57IXR6eoF2u4v5fIZ4wUyy7gfCWtQGGgTR6DpL1hoDTwaNwlRjfyPIxlLjDaNy+8zXLLBNmZW+b6UMliWnKRarKXzXFQHgyXSKORmfolW3DS4/vs+2LsjmeZ1u/Vnb2rYGz9V1/cU7XAPnbAKIC2ttB67t2q79pcb5pNPuw2904FgGXDvD6OFK9LD2GhGur68w5SqeCSDLh2m0UdptoNfAft/BiVvCn6RYjksUgQ2zTdaR0i6KjQppXV5HsgQ1eYik5IXoSxF8ouRPpiWbOL6ZJcetrbFbMz44vzIZ0Gz6+PuvzjAd3eDHd3dIC+VYLP9zTNdOzWqbGthVUmCL3Vy7GGpBcC5AhZmmWe2SxNDPq60d+VrOyRl1NG1H3lclmerxqT5WVUJP4I5gHh2o89KidJiwuh0zR9us0PUszHs2ishFww6RVQGylSOMJhbojRML11dAL36D4/MJ5mkP+WQBww8QdQfykTYBFdtAumIpp4E8NzG6m8M3Kzx7dQYEESbjiSRB1KKf30KX9W2xZyQBVLME1+dTnT8SxarKxjfffIMXz17guz99xGxRwK88hIWJzkEXg/NDBK0eDMNBvMxgODna9u8Q3/4G3/80xIerNoqyBdsJUXUCVC8jdA4D9BsmPBPwCLEWKYoEiAsHhe3Ao76YMkCVkmI2MhQZhdFxNoOFRc6y1kr/5DCKRM6v71gwPReTRSFAWxD48AIfy/EEWZGi2QgQUCuOgYxh4iOvVcPDaa+DonKwms00ELsRnScoIfPaFquNV52RrRU0cfrsBFHIJKQt7+vydZYhBlPLZIFmpw/LdDCZLJFYFnodG5GRIF2mApSlSYki5fcLUIUhvNBB7qjST4cQI+UbRJSQXVi5xhP0YKyXs18SIKH+HllJJgE3AxHn6sBA7Nvoez5sz8PKNAT8q5Y25rGBcUozhQn2GvcoGyHGYwJpBpqdCCYF78kIbFCrjfdwLnFltqywnGXoDwc4Oz/AbD6VygTlLKvm4fq+5X3teS28+uoCUW7g7qcZWJRLU4uyShA1Axyfn+Dg5FQSlKOrO8zoWt8FzE8/4uHzHSjzxj7oxQM0yj24+10kJy2YAwdnYYVmvgQpo0liiZ6Y7bMclLGwBucZ6zAOirmPYvGLbAsNTkzFsiVrjcBwtqXJtiQjVwNtlE2R5IDWU1bjiYGHuwcs5ws8e3aGg70B7m5HAm6x+KEObUyVBlavWYc76hxt2uPYb3t9U68jJKm8xtwUGM7+yOqF29sb7A37eP3l1xg/jCSpuv6wOqFcl6HWNN4aYDTVbx6nS402DoxMkjgmCmprlq6AdqxIQUFX+wBLrpfSAn45QieIEQURXKsBI6lg2wUyz8TStsnfxXwZYPZQISiu0LAnmCwyFE6IYbcn8SPPZr8/kO/MMu6dEcLfZtsBbLu2a//GJlphKpWi2VWPmSx/bYldL503+/zCQv1nf3va/sL2zbpcMX6oz0bgaLGQP6my0RZ835OSTWqh1ZIb60Tw08OpJ0rNtKuzeut/620aWJPJXlzL6FZmSMkJNTmUaL56czKUmOGhdoEqGz2U/cheYvBHkE2xddSiQg5HT8g1SUgBbiqLRc2YMAjkffMkw8P1SDJJvYMuur0uYpYAsMRFmF2G0ODv6VpmGHCZgZ4tJQBs8dx4vgA7ijCnQY4yR2AnOBo24UVDTGexCMby+z6MxxIIHu8fIPAbcq5rRqLOg26u95Zo7gZrq/dS4cimEz0tGVQBRv0atWsdyKgLr7KBuQS5LNsgGyCvTES9Y7x60UEU3mIKC/RhskoTdkkmA5kRauFGx1DCkZf3I3y6m6tQihnCikGWhb2DI4wnc3z3x+8kWzccDnF2eorSMhCz1qVmq22xITfy+/qcaGC23e1ISSgPfaI1zrg/Abu6BFJKjKm5pjOxdEwj0MZyUNXPlIV83e/qTiuaattsh3oh8Qhkoz7cEiUzk6EvwfdIHEKppbENfuprsK5pfdJkm77xJHLf+q0ujhYG/jmc9pfubrYawGagznvhr++9a7v2t9l4b4RhE61WD7B9hE0LeToWk5ujfl9K125GUzieD9fzUVYBYHWRRi00BgGedwz0KO59nyOm5lnPhhVSuyhDQr1PXQNFBQGDzoyitUbKDcE1Gh+IxA9KjjEa6DLpJMqFn6gdqMWgcmVWLpkvXhyj23Tx7R9/xP2cQD7HYM0gWq8j65FzI25UC/XX45uwg+s5Q2TXNBNduzrX5qIi9i1jaYHAawgLhhqllkemmhqnOHfIOMoxVWsdKd9pdfycSwhcGraJjCWTuSmlsUap9Nn2LQOd0ELadRCFPqzKx7IIkJMBVQJJYSLzhwirNoz7NzAzE5OkgdVkhVY3Qqs3UOWRPucsHp8Syk+WKWZ3Y/SaHl68fIVF5mC5pD6bYsevx+it6XO9Fq9Ly7i5LHF+fo4vv/gC9+MlRrM5XM6RWSGSAP3zLjoHBGjb4qjIz4/CG7iL/4affkjx+5+OcDfzkZsRrGYX3mkPwWkTRt9BJzQQmQXMMkWRlkgyBwnnMd8WUIlMNVXSpyQ2DDD5pUDOJedOy4Lr0vXcQcJzlZHARJYSC0Vz2AbEsCF2bdzOc5hxiVavLcm0h/GDzH2R7asSXZj4aBi4dwx0Wy6Ou32scjKdYuUYu9Zh047qEpKQUeVguHeA/tGelPj6mQ2/ABzq2ZYprsf3MFwbrXYP82WKUZJL2ed+WMGKE3GiVKxME2lmITFDgAYNTQeuZ6BtFTALsvoqZAUTm4ohKWz3WieWfczUfYxgbk7tLGXwYBk5GqaJjmNiERDJ9DAwfFSuCxbXxitDTBAelhYmcY5G+Q7Dzhix08R4bMClDnCnKcYHYtoQ+eKsSTCLbLYsLpHHJS5enKHf72AmsUC+rn4gk+7o8AQXhw1cv7/D+CYBfAupvYIbmDjY38fJ+Qu0Ol0sJjM8jGIkTQ9Yfcbi+z9jMk0k7kIRIjAOELT3YF204X3ZwJd7Fi6sDHbB0lobSeVSJA+Oa8IjOCoHkQtrLUtYcqzANUliI1fAGo0MqhR5zvfIdCloLnp+q2WBmGNVVkoyoODXErMoLZRSg2eGxYpUXF6OxFDs1988h+e7mI7HAjiKbIiAV3i0Bqjh7rrVEe9aJUXXbeiBZr3fduJ1DcOxWqGocH83wt3NJV6/eoWj0zNMJzMkSbYGzUWmTbLJOoJm1Ycuw2FpfmmRVch7soSHCo5VClBY2j4yhCBZmJIgYoKS033UxYKMwXgFvxqh5ZWIWhE8y4WZF7CtBKlnYGUGUtUymwSYjlZo4DPcYozxMoflNXAwHAp7k+uIfr8vxAEyTndstr+ttgPYdm3X/p1NAllx1GT5lgJP9FL7KVyybk8gk1/Yur1of9p+CYTb2vTzNbwAbSzHnM/n8ptlBVGziVYzEkF7cWikoK5m4ylQYjN1bjCFutRy896Cb9V7ixU40/sKjBAARDP9JKDTemosaZBJlLpxKV2RVJanP+hjb29fOYwys07mmsEyxU1urD6q+vTU2nDUC2Gk2Gw2EAYukjhBskwwurpHkqU4fXkhC4T5cibZQ+o0EJhhyexkMkPQbaHZ7YjG22aBo75H7XAqovl5iqZd4oA261YT89lEjBUI/lCvy/VMnJ+cCWU/TmkH/+gErnuEBP7rS6X/rgORrd105FO/VINp9Zdfl5AqeE4Vn1Sy0GOprpkzU+3h/NUznA1HKJwlVmWTXA+Yha2AtXVkpYwq5tMFfvjwAcskV3qDXHQVFfq9IfqdAX7/7R9we3stQrIvX32BbreDyXKmOkXNfJBuog+6rkXW4JNgT5aJo7NzEYelQ+iC5hySxWYAxzIYleOXElC6gubUv6M7qHos4Jqw1mqjDbV4VB+hWR8aSJXTpO3RFONULSwq7RDq2cqMYzSeCuhKMK++Po9aveERcLa909a2pwNAfROt62/+cqtfphxmDTEJ2ZWE7tqu/bzxvvC8EM1WD4FFhz4LgWfg/voWrbCJpmHg8m6EFcEw00ZRuUiTAJXtwe60cHgQ4oTljvc5krmBMrJgtSvASWl5I+6gOcdSflZuCquXP6AWV0omtgLfCmGbmUprrdDOg7UOUc0uZuKjzDAcNPHyYojP7z/hp8uJgAxqcanmMqWXphklWwkYAdc4PkoSRI1xmzGpnhfXa10YxOxE901pl9FMgKzgQa8rot0xSwcpRcAfeUFd4qXnVHGjpAuzmgPVnPsYaCMAQEWynGBiznLHTPTZ9mwTfstENgzQcQP4dgNG7uLZSRttr8Cf3tzi8zRDmI4xMC9hh01MRzYSmsrs9RC12zApZuBTN0ux/fi940WCyegeR/stHJ4+xyRj6eR8c47q8V6AAhWISRFbYSAKG/jP/89/RsMNcHl9h6QsxKCHDJWo6aN32EVrMJB9H5YprCBDz/rvmL//Ad+97eDTQwerPIDpthD1h9h/1kf/IIDVNnDiVGiAwunUmbUg6l4uS0JNuCwDlBhCOzMaNoqSwuvqvFJvLDAp6G8ioyabY8MxyPyzkeRAkihQTrlE2wgsC+3IwoNjYfQQwxfQqI2kyHE7vhetWq905P1HMDA2TcycDM8IYDa7WMy50KeZAEtDCZmossyg08f5s2Pchz6uEhP9xISfEJQAxvMJ7ucLtAd9MVi4fFhh1fRw0XPQZiHiKlPnuaJRkomUemFmiLQZAJGJY6dCyPOTM+FrIRdDB1XWSsCZABtF+tdQsRyb7mMWS25N5HQTYTxjZLCNAl3TRMszMG/aAmR0/AYyJo2psbW0sVrZuEs9zNMEw+pH9Do5pkYLs0mBKAwQhqEk6gzHgNFwRFeLGorsQ8spzw/w6qtXaDRDietMv4V/+PoZkE3w08dbzOIVkpLxQoZOr4vjk+fYPzpHnqUYX00wtVw0GgmWP32H28sJZpmLpAhhFUOE/h6a+wMYr1oYnjn4O69AVMUoqIuWOshsB45HYNaSVChBVg48BUEzmhjENCpQ8h81sMYSdjLxGU8z8ZmkuZSDLmP1Eyc899XaHVSYrevbRsd/emxRBlemxFvXlzcIfAtfff0FSpSyhuA14/ijEu0UDtleFOhYrDZWke11Gel6lFoHOjqi3fxwnFNiawL+5mWF68+3mE+n+PJXX6LX72M+pcZgumFgSuxar1tYg60ou3JuCLLR6AGFdhwlYExWGl0+PMSmJ5edbLYqt1DlvO8MLNMC+WqOqJqgEVYCtDlWKJqBpp0g90wsTA9xEWAy8RFPl4jKMQzMMY5zRI02Bv2uJN4bYQv7RwdYTOdI0qQ+A7v2H7ztALZd27X/TY0LYgaDNZutLlP7a217Hb6Fomw93tr0sydrBGiz7Z/5QIIVBJ6ms5mUiTZCLk7aaEYNoZRzcjZIzdcZIQXgbFhr9Yz8iAq+pVFR56iUnthGY0Fl3tVsWjOHRLTe0ueK5aSirRXL8/2DA4RRhPlihiJn4MUpmrTvGnfUnyiObOqw5PyzRIfZYdvC/mAP7UZb2EizyRSXHz6j0W/i6PkZZquZmBjwFfw8govj0QhFniKIQtE54WeoQEJfRyl91Xpf/IxsiUHDQP/gGNPMQLacy76LeCUZ5cODAdrNDpar1brU8IlAjCKzrRlpT4C1dau/9IZOL9dAg6FyfHK+GXDZqChwwkVbZSFqH+CLlwM0vWvEZoqkaEqWzyxcWFIeqj/M5EKmxId373B5f6sWi/KRpSyizk8uxLH19999K3pp3XYf5+fPhLG2jBdqsVcHUlK+qo7x0YJNynArNKM2zp+9kM+jkC3LhSWgppYMmY763uE5YwDM6795zFIImhco/Q8lglu7hGqWyBY7TY5Cr1LlfbWhwSpeSja/3W4Ka+5hPJHjqNmQG9zsF26obaCtbjWAVqOmP3+RDibrcPKv3KiafbJhre3aru3a08Z7IwgjeEFL1lTNtocsXiBepjjZ62H+MMH9YoVSVl90YoxQmn0s+31E+200l2NY4zH82EfJZEQbMMMcJcdJsqb0OCDkrtwUwIIAgUH2C3W16GmgPGPUOCqAll4Y1sOBMCyUVhBNdL54dQLbyvGnP3/GgoLu4opcY/Zbc+ajMWTDvFWsI+UqKnEG/6zfY0ueVJhzctwyJyp3heGgi3YU4vJqhCytd+Tcq+clqWnVzpo6ruD8KgAXv7scVz2fq13stRECjXPIaDNE19Q0MoQGMHAMFF0LRcPGXmShTA387pOJVeYI026emlgkBBfeox08oDIGmBE1qwr06PJKYX8CoBT85/hPnSjDwWqcIZ8scXaxj8b+kSRHmHjhfKrYferbSWxgWHj98gW+evkFLj/dS+xT2epUeaaDTreFzpCstQjzaYqpWaLfvkRj8k/48c8ZfrjtYxo3UFUteG4Lg7N97J+24PVsRD5waBawyGSnR0Fho7Ac0bEjMEXWmiR/aL6TEQxhmT+F103pl+JDIKwbnrMSDdNAYBsYeyyTtEVLiot9xjTULHMCHwZNmgoDXWqttS1cUcphnCDyPTTaLcyXc8TZAoHlYJFZiMWQw8StkcB1cpz16YbakDJAzqGF5eHw7BitYYTf5iamiYmD1EQjNmDkOS4XNygCskLbmIxXmCYVuocNnHtMzunvIXatKcrEwjL1kToBkq6Lfgjs04Gc5bKMkVhaLOx0mldpo6aq0KWMBNn0PL6ey5VWHJOyhWmKcQgBPHGKRy5lqz2yu3wDi8BCy/VFbmThWJjzBp2bSBfU23NRpXMMnUt4XQfjxEcRl2iEAVzXk7jXbjrsEMpJnjdPASxGc2F7vnh9gYN+A3/+4zvM5jSobMCzXViBg+OLcxyfPkPYaGE6GmOyLIS15s4+YPLTR4zmFVZlAKCDAHtodIaITjrwn4e46Bo4Y5FwTrMuQ7HWXAc+dRO11pocCHUdCfiUlEFRZlullIMyJlbloMLqF9OnDElWYJWUWKUlVtRcI2tNmKnKJEmqxDfDy9oAQ0s56vFGbaPhVbxMcHP5Ef1+G2dnJ4jjJeJlrJOYwn3UQ4Yew0Tr7hGCpsYTMX/gwzpCVAPl02WMuos3iWXe10ma4fPnSwFXv/n7v5dRbbKYyrkR7FmPXfJxdbKVzi8CtJUoafhgcS1BIwQmA5TOnyOOH6zacJGKFjMZjazCVUDbKktgZDM0rBXC0JSyZLNyhVFp2AVSy0GCAKuUjDYDVjpCZFwLkLbITdGabrUiNLwSy1mJ0eRBfcOfZXB37T9a25kc7Nqu/R9oDISpl8Sm2G31wP94zb6ZZp6uyo0nO29Kzh6/hd6vHqx/cXGvX7F+K7W/LFB8D3vDIfqDgbDaWLJ5dXMrWmZicEDRfpmrtBjp+jD4ZrVugwKJlF6F3rIuxdNGBbajfxRoQIYSf6TMRQN/DBCUCQIEaCHAFgYhRvcPuP78CTQdr93TqK0gZ6KoNWeUYKzKmDGDphcEMHA0PBb3pqubSymJJXX86//0NSwrwO2nd8hTXh/FPFTLkRJ7BwMcHA7gUKiYLmAE1xj80YWIAI+U4Sh2F2OxIGhiXET48fu3WMQjodAzfPRsExdnp0iXGT5dfUZaKfFcRgJyqfRlqfGz+vSph+r41xdO9iGAq8IPdQ1IfydjjTu46viLEpbfw8VFF/vhe2RVgpXRQVV5oPyxxdVF7QJKPy3Dxvh+jJurSyViXANTVYlOfyilt9///k9YLGdwHBenR8/pgI5lzEym5DHrSGldflk/X/dZWqi7Di7On8t7zCZjpNo8gAxFKQXWDqFVzVrjokQs4wvR0JM+UrvX6r6yKQ2VldTjk6g/n4+EmcmFYMlSiTkajVAy5HejkQBsvEfrkqtHbZ2VffLeT2Oj9Y0hT/BvbTVAT3Bt13Zt137eOL64fiAC7zYAv+HDMSFjyqAZIVktMFpkKOVepqaZj8rsAB5BkQAHbaBNkOyuRGGZuC/vYNsV2v0QmV1BqWsq1hpy7WxI8IyMLi5UK2qtKfdOGXJYG1ovXKWppIeMxVKfmeNwv41208Gbny4xWyo2luKNKd0glT5SyRtVs1UvVOvxvy7hV6AcHT4lwcKVZ40m1ekt0X6TYi6ZM/vdAEfHA1zf3GM6YZkT514DjkPNMxO2wx8+p0GRKbqjTELQTIFJGv5HRp7JR5zLHUvK1tZGCIYt8z/nYRrmsNzKLnK4VgnLyZHQvdAOcWsFuJlWqD4kuL+ZY8SEVjaFgzECc4b9xhQHrRx2+AyZ9xJJbiPou2h2FEt8OnlAGqdY0LiImqB5JiLurW4LvdMj3C8SvH/3VlgngnsaBfb2DvHixSuMHxI83M9hUyzdK2D5DkKWB0cRolYH6SoT1knYvUd39Ufcvlvh7W0HizyUcmLXbqLR6qB11IQ/4GuBIy7OaWJArazMQUkxeLo7EvAR1rbUn0lSSFxl8wKOR2YSXcylYFSMAaQUl8Ah02NWJQYABIRnMHFJUtWsgrtIYZUrDDqWaMPy2qcF2f/qdXMLcm6dZSYlobymy/lUnGVnbgPXpoXcLYV50zBinMBCv2pgMl2h3XLxsSjwPnNgpTZO/n/23rPLkSS7EryuHQ4NBEJHpKjMLE02dz7s7r+fD7tn9+xZks1u9pTOEilDQQOu3efcZ2YAIiqrh1/IqebAuiMLgQAcDnNzs2f33XdvZqMpJYRzlF6J7sEAq3mCaVwhGoQ4iSzFjPeVw3uVM4GZIKY7ph1g3WZ1hL3pH+p85aWLSsYddcQMsMaEJfuGpY7UVN1WgXAs8juwmsBirGJTC1eJ22dc7/NazKY8gps027B9YYJe1RYWZJgua9xNE7xZLFHczeGmGRpuglYrxWE7xtlRgix6gXl8BK+w0aTLaJEhTVfKdCnNkc/XcCoHVunIGG4OPPQOB/j+h59wezVDt9/G8GiE3uAA68UCq0mMqhXBqsdYvHyJxQriVFnWDTj2EI2wj+iwDVwEOO1bijlbJigyC0nhovY8ZUjC4g6JZ+h4qVj74pSeFZIU90JP4p04XcGieybBSzE7oAEUS0DZnxXSrEZWVDLuBFyT0nUNPEnIpucYAafUVLMF2GSm1TPPVn+OCUiWKp+en6LRauHrr7/HerbYoPtiUiCgvtFmNliXYbSZ46rS0c30pp83IZxJxqt/FDAn79MvoLnLyfkRzo7O8MvrN3j/5g3UoDRJd/PhujxeyJ9EankYzmWUR3FVLFwFYoSQ1D6SUrH27JJGCBlcl7F0DS8o0QxydCOg1fFQhkOsU2oGW1guY6yWE6z8HqROtYIAACAASURBVPLcQmuVo1GtcdAe4/JRjWv3CUajcwyDBuI0xz//8x9ln9XsdLCYTqXUfV86+p+z7Rls+7Zv/w6t3inxEocv68N7821orEGTzXMPd/Bmg2+YObsHfMiaeYDi7T6Wt6rfCWRQ6J+Ub5aIEvBqNVlG0JasNEVe1YZfg0E7ugnqUKas5UOfpiA5vcZtmgK+HhxDsmSKzWaMDAj0SNCVZVLKOjo+RhInUt6qDqsAJpYlmA/Y8OdkbdWZq7rGnGWADR+nZ4/EKW21WOCWlPN4icMnZ4iCBtbzpWZtqU3Mar7GZDyHH3gIGySFm48xV0dT0Om+RL2UJINXrXF+cQQrYNnjkgrYsukajyeywNPBTvRW0kQrx+g+MOVBUn5jjm9UdfS1Ntdcv0l9f8AVYJEsQBrOc69mYXBygi+fOIiwQsYNIsG+0odV8zVaIFvYXA6KysK7V69xd329vSi0nvc8PLq8xGQ2xbdffS1aPaPRKS4unojLapKz9FWrcBi24874NUGV6M2UJbq9Hp4+eSYsA+qaMMvKJmCrgGvKIdQArVIGWjDI1xsUuqFKubEC4AzQvDueFD6me01vRBXjwxFGY5osUeQp2s0WkiwV3TxhPYhG0g64tntA0371+MHAftj0eTy8Nz7YTF8xDpT7YA+u7du+fahRl7HZ7sAlU8V2cXDQQzxfiA7aoNvE9c2dMFeUIQvn7TbgDhno4pism1aFaJIhv6lQhhacYY1210PtZri5u5KyQb/RUEy03BJWEgXWrIwaPbU4iOayE9VzHkXYWRIq4vJaCoFJGbIpqgJ+UOOTZ+eYr6b4/qdrEW6XpNVm0dIbQXms57edSU1vRTesElUOpVlsUsZl5j0jrHXfYfqjj07RDIFvv32DJDXrtQL0FCimNZiqXbFzNRupKWyb0BPIkJtnatAJg0idJ5lXu0YI1M4qLAfrvMJqukAUhIh8GwPbQi+0EQ98eFGAFsXC4aOofRRViUXqYL50UJUztLwx2p0ARd7CfDZHq9NErz8QgMDzbJFAyJKZMJtY0rWaZGi5Hp5+dCnGPUm8wueffI6js0u8/OkGi1kKLy/g2yWiThPtfh/9/hBBGGE+TTH3gOPetwh++Uf86WUDv4yHSIomULcRtUYYXBzg4LyFauTiogkcUdeppH5tjbT0hQFJ1toWXNOsNeqepQogEdY7U1qba6bKIKk3Wxt2FjECzc6iWUKPchqhhTnLBeHBL4HQyyU/Jsq07GvbhZWWGDYK5G0X40UFKy3QpHaU68KJ5+gyMWV7WJcuUjgY2yXSOsN52MCPSYH3uYtm7mCUWXDSGHk9R7PfRKPVxPh2janlYnQc4MRTeq4EZGk6QAi3SHIsEw9p1EDSc3HesnFk5bBLOldayCoP0ICZZ8C1iklKlTSj+zt/BIzW1RIyHhk/sy9kAVXu85K45hjbmG2o+9SiPptdoE2XWI6JgKw2D8deiMoPENdkQNlI1x7msYdpbiEq3+Aoeosy6mGxduDVjugTqwFvoXfQxXK1Fm02Xuf3N++FxX9+eYaLxydodQ8QNpuYMSG9rNAatVBMfsLdy9cYxzZSi6yoHjzvGP3+AYLzFvwnAT7rAEfIYRV0QqfWmgcrVKw1UScxJgYExqiZluaiA0etNd6DZNpXVSZOn9QIXC8Z19RIs0o01lgWSoZqRqMMMYFSsdNmTtEBiZpPWIG7nU8E/FS5yK0ZhmayCbDFKQ/A3d0Yy/kMn3zyAsPhQBLYZNWp0MjsL9QMtsl9bme6zQN5ehMg7cRdOwy3bR3Q1vCFx5zN5ri+vsLZySFefPwZZrMl0nWs5y2etImqtBYmf2TDQK3MGqXNhD3/ztJR4m+VSlyIMzLZbASPa1WeW1En0EFS1KJr16xW6PqFsN1WSQKnNxBmMu/HzFVzWr/h4/z0FFbRxXXuYBEATWR49uQFTk9OZB15fHYucfh6tVB63vv2n6rtGWz7tm//zk20LrS4v9Es0Fv0XwFUH3rONPXcb23XzeSsQRj59Te297tP6ZcQ+KHAbq/Xw2h0gGbUlNJKak9MJwu9uJsyz51NgYYFDddKPWOAF1PaorS9aPetABVlXsBMuEunSDpkEQTRLqMKaGFAoUoy+bcgDNFqtQVge/f+DWbTuWI8aRhDzBV09kzORqMvCnBTQAevQ1dcfhr45YcfsVzOUDvA4fkRDo6HSJilHU+2i7oco0SnF+L0ZIhmI1T0cYrisuSTDkwEsLjhMJ9rO2g0fGReG2/HK9y8eQWrzBXBybcw7PTQbrfx/uoaq2St+khnFBVGtXuFdQbOiLjyD4xBxVFSa+uIwyZLPSkn0cHFRReDcCXac8zoSZzClDh3Yo6D0nZR2Q35fTpZ4ebtlTAOtkxFS8CwRtjAtz9+L7oSjaiJi/PHcJwas9mdsN9Uf25HgAIJd5hr0v0FwiDC+cUlGlEDy+UKSRzLdTLAmtH8k2tOIK1SmxICrPwR9ppcVyMYYvTw1DUvJRhXZakbgFXOR4OlNp3oqIsTo+H7AuBO5xTKTWR8bYA1GdPm3tm5l/Q43vx9GyLuPP/rP+mr95t3q/m7vsTqPpFSr7/2jn3bt/81GzU7wzCEYwdyT/cHXeHf0sH48rCH2/EEy6SQUkWRA7dYktVB3RygNWrgsgW04wzxVYmcrxlSfD5FhQRprctBXaBY5pjdjEXkPnRasFiSTjYPdaC46zT3uTEOoPaYcSxmgoTC2vLHDGenQ9l0vXx5hYwLjSb6ynym5zBxvRNGtGZ+kJFr2NfC1Fbzq9JF0hpssn4axrgC3Lg2S7MhSbOjYR9nJ318990PWCxqUsIVICPrcaUcJAWg06w08+NacH2l3+n5rmK7aR1UstrIdqaEhHy2dn2U13ENpymNw6tiYxknAuhYBH+yAj4qeF4O23NQ2wEol/5zZiO5KpD+vMT4eoFZtkBWLRDaS/TCOS77BYbdJurwKVZiwVigN+oIC358e42UGlhJiuV0CdcKxDCB6/OzL88QNiN89+M73E5iBJaLRlUgCl20T3qIOm2EjSZWiwzLCmgeXGO4+Ee8/N7Bq9suMquFtGqgEfYwPBmic9hA3bLRi4AzSkZUqWy8U5aD0gjJ2xWhV8CqMK6pN6aZa2Q9cmQwcRn6njJ9YmLJ0WuzFK6JD4UI0DtlCdeuxL2QG/4SHiY1MIkrDOISbTeHHUqGSvq4JHOLmqlpgjAqMC4jLGcleBc024Hoxq7IaAtDTJwQ7+jt6hX4320fr2cZ/NJBx7WRZjFcp0Kz28OcJhA50Bn5OPMLlJkPNFzyQeU7skQuT2qsCh+LhocwtHDEsVUlqhyU/SOVCjvAmgYeKybPyMqqFOOqoCUvz0kY8c4OsGzGpY4TWRUiqLLiVUmZNml6eQWvLuB5pdLQtT0kBBIrYB0DyaLE7SzGzWSOar5GUCZoNGJ0WjEuBnP0D9pYWn/Aau1i2HQQepkI/H/7lzdSuln7DharmQCKru0LcPn42YXouI3XNRr2Ci///N8wW9XCWnOsNjynh0ani8aoDRx7uOg7ONXAGitqk8oVYJbusuwfBVhT41ez1tJtolGqM0QjsUBZU39NuYOGniv6k9fvbnE9niDXerlVzrhUVTOo/2n9Wx2TKIddxdKV/L8AbIqlxp5VM4uasDYglYDxjNGUQYRUGeQZWlEbL148l4T8V//6Z2HKEUqWz5SwzZSMqrpUHt2+h6WZGGuXPLCzI9rEmdundHCuHlYlwtDH44tH6A6H+Nev/iKGWZznNkJzUnGy8504XXqcFzlWHNhks5Ue3NqjFQIy+FiR0ZZbsNMYXpUisHP4AZ2qWRafoypWGA5cDI87iK1TrBICZTkWHnDuNnHSiVDHply9wKpIcZcupPT06HSEk8OBlNqyBBXxO/z5q1vckdUrGsD79p+h7Rls+7Zv/85N5neCIcxear2U3b34w735b22xP/j8vQ359kgaZvgrb9yuY3wdz48TO6nLZF/xcbvTRrvVEp2KvMjFdMCkzCXw159tmGzqYLosb+dLqs2HfgU3IfJIM8B0xl7RyrfOVvIj4AvL+lSWM0kTYTAcHR4hov36eCLgygZk019LAUW6ak+eUGfB3+N4hXi1wGjErOJI2FSL8Qw3V7doHbRx9vgc8yl135RmGhdHujDd3i6khKHVjpTWgwArKttvqPZGn4aBD/I1Rp0AveMLTBY5inQlJ8RsFx1dj4ZDdDptLFZr7RKh3ZZMhs6wwjYljur3ULKMpPxLHa2ivtdAf3SKTx934GYzZLQgszJYSBW9nxsjZsklsPCRk7X25gq37+9UdYD0MxB4Pi4vH2E2neG7b7+VMolWp48nl8+wWN5inSyEoi+FHJv4ZxsQmTHHDSJLGYaHR3j27LmwE3jMjIxIzUJRWmu2bCgly6qz/eqHmcGt1p0BpE1QJWw3c711OYHRsTOgmmwgAcTiEErWWhNJmmIym2utNZ3B/dBd+BDk2qZ8f30vmd8NUPeBe/k3gbYHDqF7cG3f9u0D5aB+gHbUFHfFqBPhaDQUoXufYu+BjzfXd+K6SCYALLowtlHbQzjDIU5PG3jkFXBuMqzHNcqeC++Q4MIaWR1jZVVINThSc1NaugiCDrLJDHEyR01Bes9D5er5RTwBKKKtGBHC8mDugqwPR4nxD7oNPDof4ub6Gq/fL1Xp4MZJWc1h8n+Z25S+kmHsmNXbgO6KGWamFwW0MYbgD+dPx2yUpSyqQhh4+OzFY5T5Et/88BZZQdCLZZyK0abWKBWPsKRzU0klDDYF7Empqy6tUmw6JmD0hlZvTtW6rY9jGG0kE2UxsvUazVZTNv8UqWdpIF0t6QZJBMmxMjTsGocE87o2skEoov42xca5uRXtIw9zghVpgqbzHpF1hapqYL10kFNU/uAAfiOS2MBvNpAWBZpND5/9lxeI52t8/+MV5quS+voI3Rq9YQvd0wG6gwNYlofxPMO6U+Gy+U/Ivvkef/yhh+tlB0ndQu320O6McPh0hMOTEE7PwmVQ4wDUGUuRpQ5SsrJ8Fz5NDITJpTVBqROn9cSkpI/rGqUt9I+wVCgtIYwavZ7p8jthZ2lGG4G7sqR7pjo23TMj20KXxgahg2XpwCGZvyqlvJkgiUdGF2ykyxo9J0a7bWFtkbGfCzOn2W6hG1jo1AVWMxspXJwyLljWCKnJ56xxeNhAEDZxM15hGgY4HRU4ylIkRYBG5CGwtWYaHSwTF3M7wLLl4igABkhRSTLLFfYWTQyk5FHIRBxMqn/IyiKrj5piBIEI2DCxJkDzRgdwu75LbCqAto6xdAxpGIBGA5DfvZBybkI4uWiYtW0bDd9C3bDRokts0EDuOFgVForERZoGuEtCzGNg5M4x6neAKsE65fVycH31C6z0DhdPn6I/aGM8m6l5qajw9u170SE7Px1gMR3j7e0SqyxEaDFBPUL7dIjwpIXocYBPm8CwilHnNB5wkdu+uPfSBIOC+9I/NDEoCok3+WNYj9QOE521ukBBneS8EEZblpZYLVNcX92hM2jj8OgA8+UMi2WsGFe83zQbVgi2mxhJzVtqDlFmBkpBQ89nmgWrXNd3QyOTSFal76ok3hJH07evX8OySvzdP/xBkqKr5UrkO3b9uZRTrSlP3UZEJrrTZ7eJgyTu03HvRpNSXmKAP7O3oAFGjdu7MWaTW3z2ySfo9wZYTlYST6q5S+nMia6ykmvTZf/ag8uuxKiGEzxBVF4Tr64F3KXjqDImscXYpirpzko9w5Y4KcdJgraboelz/rXQR4RBu4uSpeC8Ny0L01WMd8sSbuXAn47FFGaarNEMfXRaDaymGZLag9caCgM2z/aOo/8Z2h5g27d9+w9qXOu4YHKmF/HyXQBKv+aDG/Gd9tt/3wEINovVv6E9QAB4fsyarVYr+WH2utVqodulwK8vegEEPxSIZt5nQCG9VKrdwQZzUIsgF1il0aYCJBVAbUoJ5fGuWL3K1ivmn701aMgY4GainXJ+fiGmCOt4uSkVVe5D+rvppL76A4+vQCDm81bxXHTSnr94AddysZgvMLue4ObmBo8/e4YgCrFeriUQNj25Xqe4uaNLqIdGI9DPKvFqlgUp+3LdpbUlQZJXJLi8PILTOcSSZaOlKoWY0WQiy/Dk/Exeu07WG6BoNyhRwUUtwU/DoVBthZIMMpaUMBfotvDxR+c4aZZYTc355rAIsNnFhhUlFH/HwWKZ4+cfrkUTziFlgwouVYXuoI9Od4A//+u/4u7uDp4X4PGT52h3O5jM3svmgH2rdN9MCZNmHGqQlH8pClVy8PzjFzgYHmAynkoJMgNHAknUYXMcV14rwSOzteISqn5oaKAcQpWRgWKuqfIGFXftwlcqalLsPx2e6VIHjlFm7KPAQxAEwsRcrtcyhqRPd7GyzSDddPp9kG0XYOMfN6/bfdPOy3/jnq7vxaock8zMu3tgbd/27TdNDJrwgwZcO8DBQUfcD5kA6oQB1ssFxsuVsHhrmrtYESwM4DYP0D/p4mJgY7BMkV8VyOHAHllw2wT554irDGuyPXhDEiRKueG2UCclEGdwrICZAGQFZRIorE/HZUc2rsRSZJMm5AfFWuM8RU2zk6MOd9/45dU1D6OY2Xq+VBpGGqgybGutH6mqg3Y5uLtJKf2jkbZNeahOdEk5aA2cnBxi2I9Ek+hmlsJytPvwjpwR32NIt0pmwJTjqTXLgP6badewhfU5a2q46JgaIFAx75i8Wgu7rdFo6AScWr9IKOI6ThZgUTtK066iqH+BtgX0AwvVyIfXC9EJGghrTwCsovCxSlxM5rU4njbdV/AqulV3sF6WYr7T6fflswb9lpQL//TzK4zfTxGGHryC5ZQJXnz5GO3BEG6jhXiVY1pXaHffYjT7f/DjP1f47qaLpGqCLhd+NELveITjx120DlyMIuDYLuGXZGWxPE+ZGBAcCQgQanCEQF9FJlamwDXGUDTjUcZMClwj29qYKQqeQqYR9de0eQT7lmOEa72UqomwvyWbcYrTc8V3rApdVhtQY81zsC5tOBl1YAul+6oWQSQEV7IKXT+F16YgOxDaKeIswSoGnKWLIKtw0LaRLxIEJOQjwxJM+BVot0McR4C3KJBaDUQNVhuQXlciScjS8rCOXDQjG8dOBY/lsrmFrCQYrRiNBFd3TR5oDFJI+aJa84VZxb4hYMe/00lUu84r+1tjuGFMj5QDpmjh6r7SsLH0F1mdNZ1YOcYK5STJMUawhKWjngHaohCe4yP3HKRljSKp0T04wLB3KHEDXUipPcizT6nh++hjDGkQ0u7gcHiAggW8y4Vc7yyJcf3qPQbdAR4/ewTfi1C6TYSjHoLHEc5HNp46ucSBLJcl67H2jQkGgXENPJY0KGA56A7wKJrD7CeOJRo9KQ02A67lqTY+KIGb26nMi2dHxxj0uxKnZ0kuMZsJU7bgvEpicwsiBC7tCqzYrXxprSR6pf/NZKF1bgVkUwkBxdbUsZ9lY7Fc4c2btzg+PsLZ+ZnE5KvFWmut6QTsJqm5g5Btorp7qXo1X25WA/MXU/6/83oTMFsW0rzAmzdv4DsuPnr+EXzPxzrmnkWbjKmcvXm72hPktRgp8wzJFCSgSVkV3jN+XSFgHO2oe720MmQVY7YAdanK0+nOTJ02ugVnMwddZwCnsuDyGoo24gRJu42jywtc3a3wKk3FMTdY0Bn1DuNVjoOTU7Q7kegoR50zhKND+HUqlRZ7fba/3bYH2PZt3/6DmwoWWO9P+ruzrUjb2YDvbtsfbuEf/r59/e7WfpsF/zc1/cFkM/Gdoo2RppjNF1ivVwKudbodWby5QDNrozLbKvu1WQCFhq2y6ZtDG+0Yvcir4EhrM+xsMjbMM51Bl5Pios9SQi0KzOfJZotXsdIFOzrE8fEJ4nWCeK1YYjy+Er1X9HMFqklooB+pPsmLDJPpLYKogY+evkASp1jPV7j65Z2wnM4/fiIBrbglGSCQ2g+TJabjhQjlK8HiEnBK2NRgYImEbHrEHlSy0MkqQdPKcf7oDKXfR7JcKTv7ssZ4MoVtlzgZHYidfF0SsNPXjWKsdY0GoyCUSEuCZa6i31suDo4v8Nl5F9ZyjTRRos4WSzfcDLbLrHUp4r+W3UBR2Pj59QrXVysddKl0Ikt6Hj1+hNubMb7/7jvJ+F0+eoqLs0eYzu+QpEud4tNXeBMXqeuogi4VgBVFLYHVi49fyPihTkeeEuyjmLYHj0594lZaa+HeXAFrzPhTq4ai1aIZYjZ8Zru5G5jpj9sMWh1mCaBLFhiwEhA4RbfdwpqstclUjAzMBlPdEvo+4S+KzrY57v07ZveOfADuPXjd7nt3DrnzCgMiKxMP0Wbct33bt/v3iWWJEyCZNJz7W90WBr0I49sbtL0ASFLcscyb84Sw1gLA7sDxRmgc9HF25OPEz+G8TyDE4Y4DZ1jA8pfI6jXWZBlrgMiizloMlDHprgWsmBv9GhmxNIr+hyyys1AlMTwBtHjfanCNLn8sq7JL9AcRBv0Grt7fYjLPlImMnlt2EwNqvSPbSbFzjfO1eoWe1fScaqYpw2RTMmtcSxUrQi27NZrtCB89PcdqdYe378jqZjmnMULY8UDYHFQ6eZNwknXSAH96U21AM8VsU2VWW204vY5unLw592dwHSadyCZR7HTpX1kPtXaWQ8ySmmFkoVHfiDgKmUY5htTOiiwkAw9uJ0Lfb6CGL2V0dOZcJC6mK55zjF7wCpaVI0maqPIE/XYL7gq4ezvBq9s72K4F5r+yxRzraoz+sCcgH5fqOnAwwP+H+Xcv8ecf+rhOI2QOQdwDtAdHOH48xOgkgNe1cO7VaNFPtiBoZiOr6TKphOh9rZUlrCuyslLqaSlmFhnbdHgkeEQHVAJtkjwigCQL6Zbhz25SUghGc3XL2lGsSFs5tLKEtLAEXBKGjV0hIqBERpvjosgU0Mb1n8L3PFhVKmfX0LVQZmus0wwoXaUZGFcYDjx0Ox7CyGNdKgqyyGw6fabIkoVcvyhqCFPeYeliTqDTwcrzEUcOjjwLDfYP1/LCQQ5XWGs0dnJ5X5hy2dxoiRXIBHg0DpgEjxS4ptwvNegsQO5uZYJmTgrpj2w2xZpk56n+0hqAUkrOEmoLFROQwuJiLEYwt0RgWWgRFA0sOJGHQRQhCj08ueygedaBz3JwYTR5ArDVyRT9owgpTQqgs4eWhaPDEMPhAbKsQpkl6Pk+sFzh3ftrKRd8+myE+jDAk6hGv16jSqmL5iK3PDihKgndALMCPBZSDsr+YVwkJZi2HjsgsJajzHNhRFL/S0C4tEKeVcjyCplo1KpKi+ubGZIkweefPkGr3cB8tpA+E31jrV8nFbRaK1Dka/S8wt+lCl4bFkicrm78zf3PuYAJWQKR29hdJa35ao7j29tbTCd3eHxxiefPn2G6WIo0iNoXGJ7a/aaA0vvzlLxOhdHbaWvnkfyrNjnbv+o3LRYrvH33XrQbP//iS/kbNdukaUMH+VpmfhVjGDW3VXQcFX028m5zeE6BXtOVeDq3W4DTQVnbyMnG9Qqcn3XQsCz8/OMa0/kMyXoh/ZyWa8zrHMPjx+DM+PaX75F47+HYKcaLEON1inQxhlcsMF/lkgC4OD1AtxvBPTrAH55eouGHIq3C/ci+/e21PcC2b/v2P6kp6jsXPw14PNjeW7+xrd9s4jev2Vl0dlav/yGLbfPanc81/9EAGBd7CvjT2p4ZNLp6UkOMZaP8Gxd1CaR33i+PVCpsU0qqQCMlkrp7VmovYQL1rRCrLOhmcdcAirDZNCOL2xJqd9D4gL9TNJQZRi5wfF5ep5lV95oWa1WnqjogyxLM5hOMDg+ldHS1XIrpwd3bG/jdAEdPzpCtEpRprr8Qy12Au/FSXJqidlOo5Opw1SbgUyAWS1yZheYmLsagZWN0eollyirSGLVbIS8h2b9hq4FG4CPNCgHBGISRtZZzM8YPZtkIg6WgjY8/OsWJX2M9ISOOn8UgMhdwzXLJXsi1aUQImjx993qGNC0EUJNwpmbZzAH6wwP85U9/wWQyhu+HePbRJyIifTe+VpuHnWEiAdLmuu32bQ3fC/D8448xHPQxnc50mTFZfY4Aa9RQYuNzzO7noi2y3XjI5kPrEBkKxYew4d27w5SFqoFmSxC6XM2FvcDM5WQ+l3JcbnjMJnU3GNsebHdM7DxnfQBc+yuA9e6r9f7p3vMCHIu78J61tm/79qFG98BebyQJBALQxycDWEWO+XSKg2aE8XiGOYWqZL6l/lQEyx3Cax+gN2rivFejHadI3xXIqP90ZMNuJSjtFWI6CNO9k+sQ2UNrl5X8qJIKFulm3LDS04CCSEzqEBiqbNHl8ZxQAWLlWtgn4qBJ9poDnJ70xDzlzfsJSrLcNOP6HqhmWGsi7q5L383ypmaze1PL7tSk1hLN6NDJF/mfDTx+comDfhs/fPcD4pilhI4kd2SZsx8g/XoirzfTn67ZMvP6bomq0ZjbMNkUGKSAN/U9XOqrVdQOy+H6/ma6JB4n30/q+rYlkKo0TZX0kZ2VS2mXLarpNjJhioyoYRpZWHc9eGGINkLMHR9JQX01YBXbmK4qNAOa7vTQbfaRv4lhrwrEVY679QznZwd48uIpsnyFq5srXBxfioh5niXCMkF9ju+uA0xn7MUugvYRhueHODlvwRu6OGgo1ppXxqwIlZLV3KX7pyNaawQhyDoyDpgbcIRrmQCPGlwjx5yaVVpHiwko6XcNcJiLLMQ2AhVESQRtNcCkutYsGxVWtuOIwQBBI4JXBI1ClkE6DmLfxo3lwEsc1IVi09ssYXUrLJeq6oBumHRN9GkA0KaWIRCFDrK8hBX5aLYdxeQUzS+eUwqvKFE71I4Lsc4dJA0PjdDGiO6ddK/UrCyy1j5o8kA2ljCzWN6o1cCkfzj+FWuN4Jowscx9oUEbZfrBTtjcJJs+kzHGe1gz/V0mlQAAIABJREFUqYwurQKUtRGCa4sRAp0dKZsrRaRWJTIbkWejcCsc+CkCJ8EKHpKwjYiun2mBlz9fA0EITK/QIhuPxidkMdUpqsxBavnoHzB+GiHJC0yTCUorx/Rqgtn1GBfdJpqBgyypkFY+ELDfHV1OzHMudDmxLpclMFvo/nEKDcxSNkODj3QIFZBSmRkIuMcxxdipZr+pxB1H9Dor8PrdFULXxqefPpUS9sliqXRvxdRAJQfM/ahkQkysrkE1GeN6glIImsxhAq7tsG5VLnybJDDXiXHe1fV7KeWnEcLo6Bjju1tVQbCDmCkY3ox5vY/YCdF2H3wo8lJx1s7A2HnM485nS7x9+waHR4f46KNnWC1jMXRjBYipZJD3m7dvSuR5JQqEUYCD4aEYpREADkSDT51nELh48rSLsNVHNglRksVZxEisGIs6QffsEofHjzGfXuP6/SsEWY5i+RYran52qbNIzc8+yskQbjVBEKzE1C1otHEckjFdotsd4OTskehcTidKEmff/nba3uRg3/btd9C4mRCQxgBND9rDzfpmPfjVwvMbf9FvFF2DewvKvTdvP0AHdwrk0oGLo8o/DkcHGA4OBCgg/frm+hYrblBEoFYt1lLqyCBQH4z0fdLQJazXov0qsNfPmfIXsrbcrbCyAomUE6SUO2ohBwXKqKBWlef4UspKbTY6C/3y+rUsVkISMoS4nU404NsWNFIvosvo4eGZBKVvfvlJsoeWB1x++hitZhM3b65QxNkWPJPsoIXDUQtHo65opTBra0mgyEjDQZXbUrKgGAPK+SvqNjEpbfz88yusV2M5A2oWM/boNGmmkCKOSUk3AQM3hgGORie4PHCwvkskuLXInHMLOC7Bswy2k0oGm7I7ZeXi+1c55muCb0qbjIGR4/k4GR3j3bv3uLpi+SdweHiOfn+A2exa9FD4kWqsmA2dvl5ag0NewL2E4+Ls5Bwnp8dav28hbDS+g0LOFCdmk4CsZKZb6awpdyujs8ZrqDO6BNZ2QFV1Hg/CJ2FYbC8n38vrRZZfq9nAcrXCYrmW45r3bJrZbN4DXvWgfwie7b5m5774a/fmr/6m/8hec3aMPPZt3/bt1+3p+SkePbrA2/FUyghvrm9w1OlhOhljwUyE1C4pcK22u7CDHnoHLQxaNZp5huIuR146sHsO3FaO2oqRoRAXQWI5cifGNsq1jZLCbVmGOlNmMIVno/ZpBuDBqSl8rcX8dcmeTTEpm2WCROVynJwdScn/+5sFaoJNmgWm2NiK06GSBqoUXtz8WOamzVnU2qrmO5n39Jqk5ljdNMtE5mABZRzBG87PjnB+coiXP36D9ZpyYHyeM5B2INbzprBKNG6jxMc1eCFPaFqQXndEB4qbR5aOgfpu6vvLGuwaJjkQNDwMexGyZI1alwOq0jMmDlj+z3Nh6b6SePAock+Revatos/I9+A3zkTUX5TqEbCczytgeR4KywcVQl8lFtJfMkxu11jMxyjnEzy9DPHFx+fI71LUYzKkLSROgSwC/GEbfbpneraAOussQUgRcfoSVbkAFywjdBod3MQOXl1nGA07aPZcBH6NI0o91Bkqghk5tbIcKQclY80R4IidqYEhAT2027Xoh7Hfd0r6BICr5XVk9bHb6b7peR5831NrshH1Z39JfzNOYlLKhiM/XDOce0YIuYjY18oIweUPL7snZdB3NDtKKzSrBNMswfuog8d0wV3Hwo4q6hqtyIIXllihhaZNt8saTesaRdrEPDbJnwIucsRZjrhO5dp32n10GpEADAIMFY44mDrUEWP/6PEs5bLsk8yYPJCJpUX6dbmslM/qBJswsthPAh4o4yEx8RBzA2W8ocYgTZFkZG76jP8zZY/KbIPj1RghKDOmvOLw4j8VfKuE6xWIc7LBEl0CzSjVReWEWOYeJlcznJ31ccNyvvcLXLxw8En4j7DzEvPg/0CedxCSqec56jvQtbZM8OblX7CejQXELOMQzU4fH335CC4rHRjTmv4xrDVh8TMW0mWX7Bsy1wR8U8CsMjNQ4BtJTOuECVeyJkthM8qcIpGPuZVVrYYQdKkjZtc4HvZwenGKH39+hzETqWIRSt0x5cop0mMyq5picJNA1UnPUjPVjAGZBtkED944umsjBRNoCztM/62uMewP8OmnH2MynuHrr76TMcFzYLJDVb1owymtP6yYZdt1QcAw+U4qFr0fue/y3zbRvMxn6pZVrFzec48eXaLfG+JPf/qLqnhhlYd2GeM8bJIInKsuzy4RJxne376XhArHk5N7sKoAZ4d9jI5bqNpNMarI4xr1JMcvr97CajbxyWefYbaY4vW712iGKZrwkK5SXL37ESG19yIX47SD9+4pfGeIYLrAYf0LnvTvcNQKMT36AsPTSzGR4Xfm+Gbi/+uvv8H3P/wg+599+/23PYNt3/btd9AkM0wbd9FJcO4F2bsb912gQcMQ9wCIXzcdQOsl6VeFdjur2Iaw8xsfxsWWCz4BjCSJBTxpNltSOsoAYkURewJOOkMlGTLJTO18rhZbVouqOQv1oRLvSwZpy2wz5YJqETcgmGKzCeimz5+sNeqx8fwG/QFOj0/FYWy9WCqQTW+U5FPVevrrzpSPqbBYTCU+O7t4JCKo1GKbXk2xWqwwenKGUERJF5oVpZh+i1WCu8kSYdCU8ibZLglAtM2syneulKFEHBcIqwInZyO4rQMspxPQR4uft6gqJHkubkbqFC24XhdPPzrHoZdjfpOLNT1LUh1Ps9ZEA47ucCzDCXC3sPHNLwmSnCVMyliDYS5dVPudIb7+9mvZtLJzLh69QCMKMZleK005+dBtXtCMMR16qUdVDdf18OnnXyjW2mSKxXwpwBmdYam1RgBWcDiOGykB1e6gzNxq1ppxihWBaB2s6cGjf9SF2YxSc1IatGWgNp/PJZsYBj7upjOs18ohVF66Wx9lBvi9a2/A5p1BIGnN30DTdHs4fB7cVZujqT4ja03rIe3bvu3bpvGe8Mh+0uYnoRuKm3W+WqD2Q/SQ4/X1BNRgNyYGsBqwvQOE/SEODgOcNlP4kxjxXY3Cd+EMASdcgxDCuq6QUPbAriiNhnplI6cUJh1HUzJwmMSwUYY2bJawU9OKJXSlcrqTtcYjG4bzrfKVYYnmaj7GfLlGnKQCCFkiwK7WKT6Qh3peM4y1qtqCXWp5M9vCB3ONTEn6f9tJWA4deR7+t3/4ElWW4Otvv0NWGT02Lbtg1pvNXG10lVRiQqs5yLElHba1gtZnokAkUwmq4hI1Z3LeHo36aHkVppOZAAt6R2oOqkXqdfmolhYwWmNKFF2z2PU5kGnkuIqdlVNEvOAaqYwQWizH8yxkQxd+r4Gh5eLvPunhfNjF6vUMVlqh9i0sywxex8fxoxbcIJAyOt8F0jJHy/kLkttXmN1FaHabco1910W9XsJFgtEogt30MAqBgUWHx0TKQdPSF60sxTpiNylgjeAIddayRLOu6DBLIIJlZbqkrygzJYFAkE5AJq5/imWkaUb6kipBf1Wftu1/Uwa5u1YZhuOGnUUjBMMAlL220mdrUEM3ncuaaJUlOjHP2YNbBaj8GkE7EhfXxbRSTG8/AfG58dhHbjcQtSJZV13HR2F7UoIoMRhjlrUqVaMeoeP6qNxtuawkUjf9o8tBM81MJ+jIkjtbs7IqVQpJ4FHKanMFQAoIqW4ZQ2JXfaIBEh0IbkTuzb2hmFVam03HjbvlyabUlow2q86wSlLkiZKMEFiwpvN7A26zCde2pazw57slGGZ9+UmGzo//L779aYiv/+ignb1Cf9RDYTekbzhG7NBBu+Hj9PgYYaOLLI4FnPaLELM3C+R1IaA0gckqp4YatYQJKipdPmH0EVjjj+4bYwKRZbUuByVzrUbGuYQxlL4mgvdiC5ip3APnKgVS0mE2jjNcv7/GxfkIR6MR1vEKZZ6qElHdXTqVrpsuEddsQjJRFXNVseU2ci6Gmasu0r0gSJ7VF4jzUhwn+Pnn1wjDAJ9/8bnAcSxflSulAbXdQ9yPlBS4psLSh3OlnndNqGj2F5vQju/lA5ZLl2KEMBnf4e///nN0Wm3RXs5LOuKaudLB6fk5Br0+3rx9g/lsIsclN7W0K/h+hCenQzTDGnk8R5nGAvLS5ZcSLCPKq1yc45tvXuH11QL+YQ1vcotWXWJ252Icawfp0kdlHaLXPoL/OMUqzBGvbaQLF/N1ip71Ful6jMoK4fmBAGxMohwfHuJgcCCGXUxo/6pCZ99+V20PsO3bvv2OmtCvpWxUZYUf4gG/1e4DZ+Y9W9DgV8DaLizwwYObiduAZXrF0uwxTvAsG2XA1QhCtNst9DotAai46ZDYUQMKysVnR1xZ/mt9AODQodGDBVwt6LsC0eqtxgHJsNu4cGVZpheeCienJzg8PMRqFSOlALOJYney+9sT2mbu+Cw1ZRbLGbqDHo5PjpGuY6wXK4zf3gKuheOPL0VbgyCeORqDnrvJAstVjChqwfECFYBoG/R735elNSy/zRN0XRvHF5eo0EC8WsKucziOh5obDng4PjrCi8s2ME8Qr1SmWIA1LwdcKmmXUnLDvqDT0cu3Cd7dZpKZ5W6GH8lF+uToHPPJHN99942UHQwODnF4cI40WyJNlmoTsQvFmuu1JTroYMzF6ekpnj//RACuu9tb0f3g+7g5JrjG78vgbKOxltMhixsN/pe6IrrMQKJp4VXoq3O/nzZgnwGnZJOhvhfZcmmWCLOQrk40MqA+H6/9r7TWzDE3X0Q3Paa34/3X5/BbbXt33X+ZeZ7DimNTDE32bd/27V6zqe3khGJY4wURXnz0FFEYIl3lwqZdzSY4HbaQVzXWCedCB7Xbgt0aojts4qQL9PIY6bsMSeoAXQdulzpSSyQ1BdvpLki8p0KV2ChXLNOniUGOKiPDyELhWagDsnsdILNh5wTWNBObG1UPsMgkksrPGuvVDVCm6LQHcNwQBYG1isxhPU9qtq6SOyBjjZthPqfANTVfaPF2zmvGyXPTtqu9mb44O3qWi2cfPcLp0QA/vnyJ97cTKfffiJLvrvN6HlfNzH+GjbzdeMpmXF5CTc/dk9AQIDU2yceqCvQ6TZwedZWxxDRGVnGt0Rtwfnql5nsR2jf6bPL4fklfqbWz7rlnaqCN7Da6ZxYlyxwJctKkp8CQBj92ibZfIBhnKO9i2L6DxK5QuDaCYRN+vyXvs7MEXuSTy4U6zvD2xwTV4A+YLUrcvYsR9jsyHsgAohMk0iVcAnQyush08pATQPKdByYGqqSPoFma0B1UJ4c0eCTgWqXWNnHJZFkkwTeCa/wR5uJ2XTCDpTaArAEk9ZIj40hE/U0dnrnGW6CNAArRIwIsXDspaj9bzJCuMwEKGHjQgddqNAAP8IJA2ONZWSLolAjrMZJFgjJZwgrpNO6ipEmR5woY5QQ+Op2G4KUEEvnxPCdKhhBM88lcJHAlCTfFuiIwRFafuIELq4/9wxFsymUr3T+VHFOVzipwTbTojP4qx5PuKwHP9JhRTHc15hVNa9snBgwWco8cRN8bMtSZ2FshtzMklouaLsA1S9J9SRI3Ql/KN8kwHNcFWg0Pz9rAL98s8E8/95CFXcROA69Wx8hSF4OejaAZSilu01Zjhx8ZNloYHB6rkl4yYwsPd5mDlymBzFKcj9kH2S6rT+4yXZHBPiHjkX2Z001S/xRq/BjWv4CPuiJCTVb6fpYEvQIVpbRY/sT7y8Z0Qgf1RORUmlEbWZaKdiDLRU1fm/nLuITWNDmWfjWVoorJtiEAGODr3vzxcDdinrYwm8+lauLs9Ajnl2dy7dOYTEL1Hbaz2P0jbA8vX1YfbufV9yhvO+jr5myMTq8lff/m9Tv4gY9Hjx7BDwLROWu3e/j88y+xWi4EXGP1igHsbNfHweAUHw0f0YYAcVGLuQGwFvmCLG7i8qMnyOMCf/nqHbymjY8fvUH+cor1uMJysULkdjCpW+J2a0URWi8e4+zZKQ6XBaJ8LrFsZrmYFm3cjX0gHqO9eI08niKmdqIXCMvVcz2MRiNEzSayIpPYdw+0/T7bHmDbt337HTZZRFnO55AOv7uV/+vt4Ub/1y/YBtz3IIKH7JqdBWr7nPmTBk/KAut1jNlsJo+brSZ63a6Iq+ZZKiWa6hMUzdksyLtrpcI81IJqEpQmkMJuFk3vQjZA2wZ4VIsmy2sFkNQuR6T/J+sYjuvg/OICjaghWV1qf6kAVX2O2gLocsd7Ox31mOKsdMG8fPQIw+4Iy+Ucy/EcN79coXd+gNHZIeLVWrRYGM7wDBiE397NqBuMIIrkvFQgxA9Wmw8RIqbjZ0XnLeoALXHYdtAnLT2tsUgTRNEBXjw/R89LMZ+QBcB4uhJgzXJzKQ+FS9ajAhnvZgW+f7NS7nVSSkHifYnBYIRGFOHbb7+T7J3nBji/eAaPWf5kqQsMTL/fx5VE8FouogIEG0EDX3759+j1BphOJ5hRRFez2cggM+644kZLbRUpJdHlECwL1RsTJfCtUtXm2qrNoX5khp92ppVzklIQT8wtZtMpGkEgZajj6VTGIc/PBFH3xrn5/d71Nc/tDPPN+4wGyQfvIPPuzVt3X6WGJlkathgZ7Flr+7ZvD+4dy8LBQQj/8AXW4xq9kY8/fPklxrcLxIslur0Wbm6uYacRbhMHByd9BF4DKzuE02jj8CDAoVfAuUvk/QX1agb0OohRYIVlXSKzawWOUFNqbaNY1yjiHHWsgP6Cmo2hA9vjPGnDym0g5zaZRim2LuWjSzNEM4zaa8n6GlGjA9dvi5Og3P9cdxxfgBWWYxH0yMtciYFLWSKBNVFnNzOEXuJ2F0LDc9UMsJ3lmCtUr9vDH778FNPr9/j+p1eIWVKpJRjUy/W7ayPIsPPvjuipKoXi9pSMZp1eMsypzQ7WFFzx2HTHtvDs6bkYEbx+c4NVUglzTS/PejMuHtOiPybSCGYh16ARE0yG1acSiAps4wOuUEqfjSWY7Gtb+rSwlBECWVh5kqC4TYF3a/W7C8QsVR31EfZaaLRCOWNqU9V+gkbxf2Hx+itkQYzvvGd48zbD4Ukf/Ysh4grw2k1h3Ft5pvpP2O+pAE+O7wsbmudBUEZAUoIhZB6lBfKEDCyW8elyR10SKkkjDa4RIOG55JsSSQ2OGBKWXCsVQ6mhsAl8NiCbYgCpZ5Wov9Gz09dIg6RSQVYniMsl5kmOig6tNeVGXHQ6bbQ6EXzfQe7ZiBlo2EDLzZFPlpjMKiSli2XuI4tpKQE47Yacp+fbaLA8k9IVoQKhHF7IokbIs8iBRZIjqQkaKfOFdJVpVhajjloDj1zjCx0PKFYfASNhsGlwjeCRAGwaPOIJiJyGMeHQwZ5UkEpXqf6SEkQTn2xGrwba2Oc0jpBAr8QypRtwBcutceN5iJ0AfS9AEIQSn8kYpNRIvUDXdtGxa0xXBVZugKwTws99OH6IweM2wj7dHnMMo1jCObKfhJ3KK2I7UjLd7nfQOewgTzMk4wyJ7WCaJljNZohCH1GzgbLOUdTKVV60aQV0rFWsVGhgjcUKxQ7ApTW4VL8o2Q8DrAlrjfcQATYBYAGnVo+VzAr16EqMx1NJIF8+vkAYNCSWMrIfRmNNmZvwPtWfq+91c99vE+Dbs9EjW4dwD5KT+g+Mkfldr69vcHt7g6dPHuPR5WMkcS4xnKn4UG/Z1kzI/bI53sPE5y4ct8kg7DyvATt9zwjsKK6nS7y/uUY3DPHFF1/i6OQE//LnP+J2zMoOzeS1bLT6A5wfP8FJ+wSe7cm9FXgB1nGMSQkMz/4Og+EIr75+i9t5hssvx3hq/Quu/rWUe2ueNVHEQ9jJEGkzQhJmCP0Kfz9c4sXgH5FVp/jx1XtUnaew8gbSoEZs+5jFLdzNXdjxLRrlT5iTKAAf7W5HgO2wEeDw+FCMSLhHISi7b7+vtgfY9m3ffqdNZe+0K6Uu89uFCPCBDb714N9d/OD+M+bZncf3Fq0P/P7weZ01JKNttVqJNTgX+lazhW5PlY0yuyLBtEoj3vt4+Y8OJnf2GurQsidRGgqbrKZebhVdXXeQ/koKWCGoobRM+EZmmfn5/Ol2ujg5PRW6+3Kx3JSq6NV7C+Q8WK7VydSYz2eS5T87vRSdNjqrzt6PsZjNcPLkFJ1WC+uVomybUtT1mg6WC/hhKGWj5oupMholdsxPchg0Mas5oX5KiuPTLqJ2H48GDuJJgvWa342sxkr01iyWgopWjhKLplPp66s1rmeJch6VTuVOAji/vBRm18tvfxAr+H73EKcnl8iyGXJq02z6X3W8Cm4MGKXdu7Rez/HJCT7++FNx5Ly9u0PC8ihLsdZ8z1M6emT/VVo7RDRWFLjGMSJ6IQKs7ZgZ6M3cxnrdlPFKdtrESkqDr65trFYLJMla+jtJM0wJ7hbMjmutIvy19iDL+au76det/sB99PAOMkcxQKEwKvestX3bt3tNtMycEG3fxaenKwwvOhgcf4KPTk/w89srxNMpUjvAbDmFW5Zo+m30D3tIZiliGswEKdpdF12W4I1zpKUDdGw4nQKVvUJSp1gLZYMbSyYtHGQrC8WqRBmzHJQbfwuFb6PyHWF4OCyxFCBHJSlYAkpwQdhrJJBXOfJ0DNQJGs0hKngCHsidrkEp5Xpoo5AdaYGG70kyJBcdNh7ElI+q1242pdbugqdZTEbDlGwY38PzZxc4PhjgT3/+M8Zzrq8E7YVmooEIefNmI7pNUmjgQc/nqnxUfY5anzRYI8me7fpviGdMNvV7LTx+dIyb23d4dbVCKdxp4/6twQxdRirsNb3pJthgytfU5+n11ZTOGoOngu9TSRbDZtvo3Yn3QY1inSF5kwIzsrVrxKwQ7vg4enIowvxEmBTjp0IUxCjf/hP+//+7xr+8HWD2M/BxO0fv8hjLyhFx/0HHR8OzpDzSDUO5bnWuzCHYQeJsXebKiIHQDIXJ6d4owJDSChWtLCkH5brG12+1slgSylI+xVpTjC1hrmn1gy3uoGFM6RD2lxkf5rpslyuzNjOOUsRIM2aAOE2wLhcovQypHyEoAwSuh86gDZdrsiQTawTIpZwztIHpJMeaxgS21pWyHJS2i9L20PKBRujAt6hFx/Wan68cccMoRNjwxTQoZtliZWNdVFgniYDZ3PCLIVOtgTVh9VGvboeZlavrrn7YR5q9puM888X0sN58TxnRpnTZxH7mlw2gq+59iQVsS7SuGCct4xxFTnMIJglreLWFQz9AxPJOJj/J1NT0QoKhHP904s3gwHMstBHAajfgdRs4jTw0OXYyIEhyWHWMkrXnTiDADSVnNzk620Jz0ELUC1DHCcr1Cm5eYXG7xHK+loR02AgljiIYS1myvIBoshHY4vUWcyyjDabu6k2nGLaaOBo7W4dQl3Ew40reS8ZYTO7z7f3P5CdjOOraPX7yRMp2l4tY38dqsBoDA36+mfPk0zddvj2jbey8bSaW3n1e/a4GNvv8/dW1gEOPHp/j5PgI0/lUSqzvH0sZuqhP27L25JM3GpI7rzY3kHX/8zYVEvICBU6yb1jqf/P+vcxuR8fHkgQm2OdGLRyfHOJycInIa0s/K/3fCjezCZaujcsnXyCJM3z38g0aoxovLr4B/ttbfPd9D+uMxjhdeDhE7I6QDjvw2hFaYYrSXaBczJBPFrh9f4Unjwc4//gYde8A+YqWZmvknoOlHeAuaWEx8xGWd/CqdxjPE1SOh1arLQkdsjCHB0M4jisyOXt9tt9P2wNs+7Zvv/NmssSyLDBladbYf2OzfvWbWRIftt3n9WPrr7zGBD6Sla5U2eh8LpmdgOUF3Q66nY6AXmSCSQC1WfT0Sqi12NS32wJmKtDcKSvVDkMKbNspGxXARr3IsNmoYcfFRjYVoCh1IWYMLFs4PDoSRhvLSNdxovtyewYf+rbmVMmcmi+nCEJfwDpmvZNFjNu3t1ilK1x88lgtcqu1WvDV3gqT6QLz+UpsuP3QVzEBASSHpZ0MBpUWhl0CiVNK/w2aLsbjteQVBVhjGSjZanSuk7hYlXTMFgV+ejNHzJIXvSkgENjtD9GJuvjqq68wvRvDb0Q4f/QxwsDBcs0No87+yoZhOyq2X1r9xvOPWm18/tkXGAyGorVGmj/7ku6gQRCIFh/72jiEsr/5w8fU7ZEgW2utyXXjsXUwbYKhDXls4/apnrf1JoClpfP5BIHrCGuNoOFqvZbPVDHTztXbHEwd4142dfO33ZvowXsf/EWNeJNNf/h4eygBeEUIfG9ksG/7ttt4TwTRCbL0kYBWdqOH85NPsZxeY3Y7wfTmDov1FKdPX+DJ048RFzZu1ytU+QL5LEMVl4iTBZaTdwIANDoeCu4i/QwxVkjII6JOGufx3EIZO8ilJDQT92dTDlrRQZGC+7UFuyC4pswBuCH3PGolKq01blizZAYUYzRaXdRupICS+0uffJ5im6uyLbK74qSA79OsJhCRbFnPlKCZYrnobekWFjM/6qhk9p6cHeOLz57g7evX+PbHN+JOSgBQvXkz4ch7VJnhzpT2q/hg549bcscWZJN/lSQA2TiNho8Xzy5Rlxl++PkdlolOcOi5VGZwAQEVy0gZZyqGtTbg27DODdtcfcwDoE2MbxR7SYTUdUmfSD0kGfK7GMVdIp9RUKeqaaN/OUS3H6nrJcYPZNk5CO0Mv7xc4r/+3ME4aWLtdrCwe3jn9HHeDPD40Efbc9BwUgGDBNDiQuqH8KKGSmTS9bq0keU21jmZRaWsNXTfTpMctYjyKXCtJCtLTJYIrCmmNsE1amaxtE9KSMXhUUlHqDJaLXVwz0pdlQ6bmMf0l2H2bftNXUOyvCjBwKFwu1pjtq5RZS4KAkK2g0HUEHYUmTeC2dE9lMcoGWPwHIGUTqQSb3iwal/0o+zAEaYa9dR8mjxIIlOVn8opizuo0r7lms8S2oSMOQ0csr/WWYxmky6jIdLxiQ5yAAAgAElEQVQikyoGgmsi0i99otwlpVRYgDXeLwrAEWaWjgd5woyfhKtlErGatbdJPButXuN2q2NHsueo6dhu+kjLBHFG518p4JTS5dBz0QkC+DQckluIgBpL/dhXuTD56hzy/ZyGr2LXjoeDnot+14HdsDFo2GLuEd8VWC0tlFmKhrOAFWSoilCYn/JpxI7ZZ76Nw6MGgjpFcRML05Tff3K3EO3eg4M+wiDAYpUqgFJceDXbU5e9yvfdjBkFDolShi4HFRMxAdd0aagGjzg/KX1GfW/tTA4ca3Gyxu3tFdqtNp49f454nWI5WyuQX7h/nLPM56uBuluBfj+KMoGbjuFMbG1yCfqxme9IiOSYIsvv6upKKl7+8Hd/h1a7jclkqrUfjdSHOf7m7PW/et7UH6hesaN7rAeQnPNOTGgqHdTraLBRYzadYz6e4OziHM+efyrj3806cHIa39QCuq/yBD/dXePoycc46J/g+7+8wtuqxqefXuFk+kd89481ruMhausAq2KE0jpA0eqg9bSD0R86ePqRj3a8RDy+wnx+h0UaohE0UaxiXPj/hIvhEl77HMWKmWqiuBVS38UaIaazCKspEFVjWMUEd8s1bDfCaDiUuSbwmuJsy2sfr9d7x9HfQdsDbPu2b38jzYBKitJuCNT/9rYbTO8G9A9f8evHD1+zfe8GDDEaGCWBtgTLxUKCT9KX2+22/JdllCkjPC3+IswkHUjJUfXKbbLy+qAmjbsB5siA2jQdkJqAXZ2Tth8XHTu1KeF5paTrJ7EsqGdnF+h0uphT5JSlIiyz1Auyyrxvv+32W5vsX4b1eoH+YIBep4/1Yo10neLm9TWCToiz5xdYLdYoWCOq2XWkb8+mS8RJhajdlEVQQEOHgSU3CRooqlnmCPheA8tkrUpAmA3WjDWm0ViGQFfSN9cL3ExWGzCP58jvfHr6SEpBX/74g5SWtNp9nBFUXIyR58kmCBFgUgcf96687n9udI6OTvHZp58jK3Lc3t4JG5CNASHd0GQssmBCHLG44cgFXJPMPQE27RAqIKyAa8otzwRBom+hy4flXw2W8X8UCmYUtlrOkWcx2q0m0jzHdDqT81F9q8/9Hqj2gfbwb/+j1++03TGw+5y1wzIVYI2g57/xmPu2b/8rNN4PnU4Hg8//CxznMeZFgi+eH+Lw5BA///QWyTLHzd172eh5sLEY34JktbNHj9AdHWCaEujIkaxmWGV3yItMNG+YsOm1SySVj8yhiYGqdLdSB2UMFKsCZZKKi6OUL9KowNeueTRJppFBJTtUKQOlkYEryQ5uw0uky/eIGi4QDkRvTNI7+oZX841GFriZJlON4BoBA10qlhSQhNNhvwnPoftfpkpFpWnWruFjCPWLjyphzHzx+XOETo5/+fO3mMWFKvffzCtbtrUsjzIRbTMkypH0VxdB/9nMWmpTuQHKTIKjynB0OsT58RA//fwL7ubUGnA37n4msaCgCi2uLkfRZWs7WqmGsbX5r6w1eoO/I+zPzTvBTwIOItFAR9CkQnpdAXN1fvSBbZ200DkdyByrXFDJDcxg5wv4doXbSYz3bgNhOxBh8HbQxOkowtFFhH7TQ+RU8FyyqWxh2PHzaknE0aXSgR8FAloUaSGJLpZZCrCW5QgjT36od5RX6QZckzWPYv7FFlyT8UYtMa0xqjSsFBAp/ah/FGBlrohekXeu20ZzTOiE7Cey1h202xGKOsVkuUaeW8zRwSkrhJaDwyhCILIERgJDvRdVhnKdCXBEimZNUxHbwl0UIOz4mEUeWq6DRkQzBJZU5+ISyriDjE4y2Bx+EePeLZfJRtT04bsWUpZeS2jC2C9GXVRoRy3YdoD5MpF4iWy3jYuu0SXELqPTdIAGRDTj0rDid4e/eakiUKnYkPEdIcR+d4CmJKFvYPkJCisSP1S+hsy6kHqKNF+SN5ty1BpVmqEoHFSerzSQXRuhR7CqxoFTouUALZRoW7WA86ELLC0PqeUhKUKsZw4aVQknSJCLWxfBQ3WNHTsTsHrBEshirpzm9XmnaY7Xb6/kO50dj+S/KyajC95rtoCPapCoWFhYV6YclJIZmvEpZaHGFVTHv7xeKtVn7lr1neWR3MA6dqZJ12KFq6sbnF+c4PT8BFOyiTNOlJqxKnOU6nvKmshR5bx2qg/Uhdvc50Za5F6iXL/RmLFs3kM1sySWeafXYUL3c9Hhm8+Xqq9MdcIuurdz7+gjfSCk00/oe23DfpOn9Rys53X+oXCboi2YZYWUrvqhh9V4Iff5m7tr5GGE55/+Pd69vcOfvrrF4Dnwfx7/Myb/fIU/vh5hafdh513Y1hBVs4PwUR+tzzp49pGPT4IEg3SCl9//hPl4Db+OBPhe1mSBWljOAkT1CpFlIQhDcWQm4E9/4NoF1r6HZRViPg2QzAnqzlGkU1zP1+gPDtDvtQWsDKImer2h7Gv4Y/ZF+/Yf36zHjx/ve3/f9u1vkBHAEkzF5toFnB4gATtNhyr3FqgPveLDzQBdW8Dr3oftvNWUSRJ0aDYaQl+mKCd/Zynp9fWdOBsp6+utE6cBJ2TRkwBkJxOms76qDHAbhDHIoN4VBbMZfDDLRBYZ+0f0wPQBmOGRMg4RwVe6IgTYoiiS7NkPL39AWVMcWKL+7XfefM3dvjGLsnKnarc6qHMLv7x+LdeC2c/Tjy/R6Xdw/e0vKKhFx1IUTWnjJqE37GB02JNgixolLMdgJpWlSlXpI2yGuBlPpBxVUfuNYL6L2ZRZxxkq2ahorZIKOD4cwfJcfPPVV5INpBPYydEjWC4t6VkWu73yGzBy55uqEh8FGLVbLbz45DMJRsfjsRhF8BLQ6Y8ZdKV3p7TWRDhZwDWWxCitNQbO4iAmOms6vJNxYSJjNnP9zR5RaZdJYGg7yNMcq+UMzaghJzqdz6U8VUqHjdba5uR3v4gJmHbaZtibdKZ+/IHgY3OInbea53dfZLKn4pa6b/u2b/caS8efP/sIH3/yCZZhhKt3S0RFgun4GtU6x+SuQpzNUFsrtaRYAeA0ZGPeCi2cnh2hfzhCGqeYsJRofYvbu1eoag+9Rgf90ILP5EXQQhLYiFcJyrQQcXFqMImxgGvKPXWShqAaTQxk7qaDJYFxwdlkfkviOwQeHQdbqGxvuy5pDMts8hQwoBJKAhBph1AzLyiRcG5kS4SBhYN+hMUixXhOGQFV8i+lpZqxRdDhxfNLdBrATz9dYbxg4oQsGyUir+Yjs8NVANl2Q7t1CpUcjJZLkDWDGnFcH/klNxGAAeTUJpgMq0Gvg6PREDdXN7hbkNmtXLCNbpiAZtqsAAZc07pp5jPlc0Unk3OiAq88GgWISQS1qWwFZOq/KVacA1QummFDjBxYDlzTsCKzBdByWhV6p214Us7J81EsLjLm6nyBmmYVKwezwsOq1UCZlBjXLtyA4FONoV+iGbhoMomVZ2JG4IasM1Wuzg5riaU4TLG9RDd0nQrzUUBTt0blFJJMihqRMLMmd2Nh2PFcjEC/6GRJyatiUam4jP2mwQXNKOJ447jzPa2TZQATbdxDbEj0OwVEIb6pdL063R4aDtfYt1jXPtKiiyrzxPG2GTnCWhOjDglVFBQqcWG2FkZeWthwslrcWO3AlvPmfaFiLzrdWvBYllsAq3FKIS84dgnfKhBEFWq3uYkzWMLoMnajY2pR4eY2RkUg0GZpm1rsee8FkS/unPFigfc3E6F0Ma4TcFML58tY0gk4bGIEDQuRmaXHtkOWvxnbOvaQpKiGkPqjAXrNCOU6gWfT6GKCyrOwtI6xXHtAYcGNlxhZ/4TUegSrcwHXI9uM181CmtQAtfd8G0lWIfLVPcRRb+cpHIf3qCVzAi1qpWsJ3JcVFmTv3+Vwp0uETgI/SuEPe3AtWmfoMmjbxo/vZphe/4AnFy9YTIrZ+1uk60SALGU2kGNweojh+Tmub+e4mS1RilOv1vwTuRg9FzEGkpGrWGoiGaLNSbbxCkFrRfEzlQOq37VbqwbD5dgSI9fI61wYrM+fPBUNyW9+eIk4SbTsiAE1TfyowHW1Fdj5XJlXjKOHidE0uL7ZN+yAXvql6in1yPMdPHp0gdHoGD//9DNev32rgLpN7Ga+o7xr53/qWaPrvNmryORt/qr/q9F/Ze7loXdwiLODETzXRkzzgCKD33DQj4ZYLGPUYQdVaeGXb+6wPgzwDxdfw/vxPb77McA4baIRDYCyj7SOUJ500b1s4uLMx3lQol0ukc7n+Ob7a8zXLqYzmrEtYJUpbIfArA/XKdFpl+h3LYSNHkorwIrxfmphMUkkeU134zx1YCcFoiLGQZOapQCiLsJogNHhieghv79Re6x0vcT7q7dYzOd7Rtv/hLZnsO3bvv0NNi5iXNw3wZnBuX6Nd32wGQDh1697CCcYipD5287vu6DTzgEN8MGFnIAWxUQJrNH9RtxGe114noM4iSVYUwHh9hjq8U4Z3ibjZBZLs7jrD9SLtimvUBuc7XeQjK7OVlsWg2l1Xvz8LEvR6/fx+PFjJCsKrS7lXQrTUroNGzxR4gUD7KjFm0Ei3X9oQX96cirOYVmcYnY1wXQyxsnHlwj9hmwSJeDR2hHrdYLpdAEvaCAI6TbKYxtmogOPosTJWnYvNQNKx5Xv9P7dHRZz9TwBRQZHtuvh8vIRXr1+hV9+/FE2Cp1mD6fH/52993ySJMmvxF7oiNSqdFXLmZ7unllgTxiOxg/808lv5JEAFgccFoPd0dOqdOrQgvZ+7p6Z1dMr7O54ZsSmz/ZWVYrIDOX+8+dPnIo/CwdmFl+q2N9hiW0Ond47+uI0wKOLR/j85StJBr3RCaEE1LiqFhjfEhZkBNNyeq1pDxrKashYkzADLZvS21dsOXXe5Icw8ZR/yJaqz0mXmngwyYkecf1uV3xm6LXG7bOpCeQOOPbHft9pn77eHz5vmj7Dm983PzfXGk8JUxD3CaH7tm+7jffmweER/uN/+Bs8ffwYrt2gXK/RFAUW03uUyyWu3gdYWAOkoSV+a7Ku4UWoohrjo474tMXvZyg4YW75MvEM2y2EnY54nPUIethqknJzcwe7zNHpREiSCnmWoyFDWAyJCDBp1kXFDyFgpfodAdi4BuNwkh2jyu4QhhFqp4Vapq47fdPuOCCMNSVrpPc8+0zTt5gkZjUsqR6Fvk7zeYwgcHA47gmzO6XZkl5YiqIQv/ryOeLFDL/7/j3WmQ7M2YB6yh5he4C3Y6xZfVGfrz9xQzYxckPVZDKsfU1VciGN+i08eXSBbsvHTz/8hDhrJHFQgS96bN6ZnH5cX9jG6M2ASbqLVGOxkpVtPDeNeTpfoJE72/bRjjpA3iC7jSWUggmiaVOifRagO2Eat7vT/5ISVsMp75DM5lhdOygzD+5RF92eAye0MRo6OA5ttLpAz7XRCmzUBdMKyah2hGroOtQBOgIscXuKYa1kd17ooKQVQ67SqGnhQPoX2SG2FaA/HAhbbTlbI6+YJqhlfEYaa2CH7crYlnkk150GJeV4moRszTLUg5AcLgCuH2EyGMPOE9TpDH7wRmStqd1F0XjweE0jFzDJMOJkvCWok5dIVxZK+LBDH5XlwPf1/cBt1zkcK5fgAu4nPfY49i49LqIx0dVFmVncPBwwqZBeY5Qq8xxm+h5Q7EyGNkmKeenAgY+ycfCzXeO7ZoV228dFf4w8q7BexTvXkb5rTD2i4WT5XSSQ23vPeMnJq/SDBJzg+jg8OUErCLFeU6Kp/BDhBsiqFu7uU/T8Pkp6LNYpeqOv4eE7NNNblHmEhiCboJo2vIj7T/BQIe7Ko8tCUloqcIBMUtdDoBBlBJTTkqFLj7vQxrpokCYVepMWHJfgmpaeEqizXCSlg17vFN3eALbnIncj+IMDdPwCzeoWNj2DZ1PcXN5hdHyAo8lA+jIyJTfHw3iuib+aqZ+Mf6Fm/Oljq+5RXSfrvssEFRg1gXnMgG1s9M599+EaVVHgs8+eyALnYjrdyHgN+8sAZKZSN+CYShLWv2/+7XYcahvy2IOiTN8LUlfXuLu/x/XlB1xcnOPR4wvxPU5p62K2t7mG9PfY1e9vFkX0YxvXji0Mp/bBghu0cXJ+gcfDsWKAOg0cj31XhTdXd6jQw+HxCewyw83tGs1Zg/80/Fvc/MMNvn7Twzzvo27GcJsjWezBZ2NMXnTx+tTBEydFUMS4fDfFh2WAzuRC/O4I0JcVGZBdlEUbjSSdWShKFymDLZoVbC+GbyVouQT6fOSZDbdew2V4iO8hdX0skwjpnInLM7j2DPPlElkDnBwcIfBdWTzp9sZod9viz8axZ9/+57U9wLZv+/b/42b8GVQhyHSv7cD2x5p5/tOvM8Oi+X1Hi7czGJri6OOXbsZSnXTGopPSwsWSDKQcAT0yul2R/HEgJStJVjA3g+5WAqOaSUfYwUw2K2qmIjVDrZEiblfZ1NfXprBcSddsNwJRac5JWiKSj9PTEwwHEyRJLMCb2Sm1HrxNMVI/dll8ylskSdcYjbpodTpijJyvM9x/uIPXcjE6OYDlOpKIplbNaPLaYDlfIUkKBGFbVsllPdKCrPyv8kxWpUkVpynuzc29pG9xmVtNXBpMjg7RCiJ88/vfY7VYCsNtNDpCuxsiqciW4DflBGezO5vTpvBIs4pYo93p49Wr1xiOxri9u5V0WH5H3/Uk0tzVEx2eM34PgombMIOqlJVak/q6u2KqS7vN55qVaJ7DbQGtwDWy/ZarOYLAE/8bAmv0ylPpWTuTPdmuXqH8M9sD+eYnwDd5+OFbHjxmmBx87z4hdN/27aP7xLLQbrfxxRcv8O/+/b9Hu8sUvUwkT/RjSm8/YH71Du/vLNwfj5Cfuog8iGSTE3ivlcMrMxzZNjoBU/wchANfvLDiNEbQjtDrjWH5Piqm8i1nuLudyURwnWZYrTME4zb8bkv6c964TD60BUTh1J1omr0B10j4ET+tbA63juGFQ5QNJ8aaAbYzwVeTP81c40JEZWlwzZhum35OvVYBJJryoT206Fm1XqUYjXoY9Noo0gIHxyM8ORvhu2++xfXdUhZXTMqnGUoNaUN+SJe3eeaB3cL2ROhXS9/PfdfcFjKVrAaVRXkk00n7Aq4t7q/x9vIGoCRJiG56wqp3a9NH77BjeK41fKT7RcV4U19VBx7sjsdajiYeqiRtNzbaYR8dv41iGqNc06uOrOUGdVrAcwq440AYRZw4C9uEYwwXi4olZu9yzNY9VEEbaPsYjFxEFhDaDTpNCd9u0KqUvNYVk3YbaW3DCTzUpY0qbeAyC1ZSQC0BSYVhRbAqW6BKc8U4l0U51gpKNkpvtaSs0R50BGiL0wzrOJWFQnPoleWCBhEE9VDXkeA4vO4E4DXXltr+9gSrcAcLrgAx/T7BjRmKNRlODuD2UVgBisJHP+yKKb5FBjxtI0SuzC/KY9agSGtUZOp1fZKz0Pi2SAkrsgyZupqJphlFTY20K7LI2rLQJevQZngRMWl6jJXIM6aWO3A8RzxVje8ZcwtnSYXADSWpnEz3omS6d4B7WEgCGzN7BRsZDvo9dDt9JCklqKV8B1XnbRctWcMKRqRBJH2FK8mrjPva9w8O2v0+Ts9PUVse4lxluBNIl2s46ODnmIEqPdnm5SyB1+ui5T6BxYTg6B2ccoksGYOmGbbvCmDG65JAIbF5ASJ1wVLqAK2IzDY5a4pBxu9d8V7g5W1baPUsSbWNqTuXBXAb3NNkGaMXpmiCQJJebdeFG0Xo930MxwN0+x3px6qM0L6Nm6tLSaw/PjnAsNeRGpnMyI3nmmb2bY+VCTMw992mJ5LaaxdEUz8Jrhv/SM06kzeoa5Hfmwurt9fXiAIfn332XN7H2lh5o5l+QdEQN73PrpR0w15TPzc+aOqkmx/quU0/u+lh5H9lU+H6+lKsXZ49f47BaKgTM7lovHmTlgpvr6NtaW760e3nyj8+yFCPwRhPDs8wDjtyX9JngGBxnMW4usvw6PFr+K6P//r1z7gvEry8mOGxV+J3/yXFD7c2inoMu34ELzgETrpofznEo89C/FWnwqBOkC5WeP9+DYxOcHAyhBcwdCdGw9T7sobj+ii4sFR7QMHkaSYBO8gLRxh0lIOjyhGWOUKP/ZQDFPSRzGB5NSrfk8TR1SpAOm/gVSu4WGC+WMELIxxOxsr70XMxGo/geYHMbfZBCP9z2h5g27d9+zfQTNKmKlAe+rPtlN67w9fmpynXf9k+8egW4Xr49PbjNk+rl6vXibSjqsXAf7lcSqR9u0M2Ww+tMBATe3qkPZgoyGfoREkzSJvnzeRht4jXKJIAO2Ka/LCgMO/gMSLIRrBNCiR6w6WZfLcoDPDo8WO0Wm01kLOC1ZWLmmwYOt3HOyzTCkmEYgrZZHKIXnuM9XqFxd0C99e36E56OH5yglh8SVj8q4kcpZDz6ZzjKwJ6lzg2fMfBPM9lYnB7NcOCrDUj2+Hqs+dhcnyMdzdXePfDz+J31mp3MeGAapcoa0phTbXFqd4uS9AUQXJipGh7/OQ5nj3/DHmxTQgVY/IgENaaMLW0lElkNJsgA8pE6G1DQ+fdlFAtf9pIB8xKvWFF6H8bRpryWmN8fLfTknOxWC4V+CqyEXPpfXxNfnQdfvTUn3jgjwJrpojcwXCVr9/ea23f9u1BY1/BFLj/9X/5Gzx59FgeY+BNWWQo1ndY/vQNfnp7i1nmoo4CjCY2XkQW2tEpmqgDJ14iLHKgaqPndXE3XaNyLAS+g1E7g9sG7ucVqiLFoD+RlGXbayMIujLh6IAywD7y0sfSBnrDFlquhSJuYHPSLECGYu/IBNVm+M0SKAjmt1A5bfFMkn3ZgP9qcmr+NcagXQNrhGM2XYUZRB8kJKupnnJXo6m38mdbimfnCudnI0yGXfztP3yLvCRjZrePU+9jn2+bh8yYasZF+WkANv15H73OTCxlTCRYomuEL19+gcip8c233yPNlSSfb94sIhkAbQe8M5Ng0xcr0EM9sAH/hN1sPt94dqn95jEoqhK97hCnJ2dwVhXyD2sBCwj6pHWJ1lEbQAo3WIucMisblHYl8sW6zlHMbrH8ycHKHSB/1Ee758LpuIh4bAks0f8sz2HXOdKMklQPhXix2nAD+q0BTeCKFBJMDE1zzrPhuGRkr2HlUzhuLb5dTKklE6kz7AsLkVJWSksLx8WSSdGeh6PRAP1uB9P7mTCsZaFTT/RFwqiloSRFUfYp0k8NvCnlweboqrE9rxD0+jg7P0CCBO8WCziVB6/2xVg/s3tYzjy02x0EZJhVDaKWkjoKo0sYfqWwprjvTuCgxXW7xkZAsFDCIdTnF3Sxq+lB6IjvlJH7qhKHHoWKoZXXEL81N+Rxo+WD9tyT726jaLdwnTkgRBH1eli3fByOfJy6NqZxjcQOsHJqJE0K1y1xNBojYn21WG/qMYa4ChtLkcnUP/ETU4CbuZt4/7lBhKNHZ5gMe2gY/gEFGPJFlPyGbQJ8HkYtFzOnkXCLQdfDyGGacIH1oo/ceo7SfwTXvUaY/IRq2UXmE8DkcRJTN/2JSkBMxQWvQVtLLiU8oqlgU3pM8Jy/I0bLUyz7mRNgjgD2usab9/donBBp7sCLC3T7tNho0CbQJ3e6DSeM0Ds8RjgaIV0vUGVLlFWKm+sPKOIaT59doNsOsV6tBAgVgE0JARRrVtd1Uu7t1iy6L1Igt/KKlJp4ZxFg213pG1qQYcOGtLBYrnF7dYvxsIuXX3yBeL3GOomVeH2jJtGfZ7aiOxKDqZlti62ueoHup7YL2Nt3mPJU3xMWff4yXL59jyrL8NWvvkR/MMTV1e1OXWk+V/dDutY0HeJ2cZUyZ0uYoUenF3g8OEbgeBugkPXn28srNJ1DPHn2Am/f3uB3l0tcvLTx6+j/wZu/+4B//NcY45PneP7iGdarNkq7C/95Dwd/3cevjh08tVbwihSX72aYZS2MH52g37IR0o8POZL1Ckm2QJGu0a8d9HlDBhZy20JBVjSBNoaCZAGSPBBAP68zeE0h7El6R/IydMsMnpvA9iwUXihBCOu1j2JRILBmqKuZnLvuYIiTw4nI6t0gwGRyIMeDoKVauN63/6/aHmDbt337N9IUoKR8GiiH/LhtpwO/fPyPAg0PntlU79vRtPnTGzQDnGI/FTJAr9ex+MiR9dDvd+F7rqyQKa8GxVp7sCn9efLoho6uSQKb76cLBtmG8giTwkN7TpgvLSuB9KcRc3r1XpHupJms8NCY++T0TLa1WMy3e7+z0iZb2sys9ERGy2QoP4Vd4/CAsd9AlqRY3Mwxv5uh/eRAUj6T+UpJZbiaDSCLE8xmKzhBiH67g3d3U8wu76WopbSVH8DSfzAayer27/7la6SzlTw37B+j2+ugKJlSZVbtzARRHx8WLNrrRJnPVpK49eWXvxaZ7PT+HtPZXCWVuS7CkEEGKo2Vj0li2gZcK0QiKobO2iNE5KHbym5TKsnRMUWQZq3JREQb8nI1bbmYIww8hH4gCaEE2Lh98/oNsGsKJ71Xqoj65eX557SdM/fJ6199lJHVKu8g4w+zb/u2b6rRx/KrV1/i1YsvEHoBVvFSJmFNkWJ9/T3efPcj3s9qZJYP2G1E3gAnToQ2fb+eljiJVpjdlFinbTjeAeo4wE3SwAkb+F6FZVajVWU4HCTIbR+zW7KAK4zGBwjbHdhRG03giUl/yNlbzYRFBTQcdMm4cSRZ2WFCqKBCBcr8VgzPLb+DoiEjeEMFUXIr5QKuGWs0rSdLWTGhKODcBhaYLkgPRFukTX5Xk0czbilZllcm6PkNbqcZ5qsUr18+lUn7epVs+iOuKakNa3nXdo1JeUOZmesO0KWAuO1YJJNcYcKpY0LD9JOTY3z26Bg/ff8DPtzOxbtURkXzwRpQU+EL27FODR8KKlSkOTVZllFG3qcAQtXfm+f0hL/muFNJ4NCzJ08wbHWR/ngPLHPYgYWEY0fooU6tKlQAACAASURBVHvQRWfQQtDvobA8AWMcsu8odazI3HbhRT3EMdB93MVxq0boWIhchlwo4IjnJi0sYYCQgsX6gsmYIv3kuaVBPRNJCbBmBbwW32sDyb1Mfi3PQ02wFRGS3IMXBpK8TfDVYvokEbraQWC5EixAhpcdeDg/P4Lj+VhNF7DrWjzKjCRU2FBSb+hxb8POUmOgPj3CBpucH6Pf9vBjco+7soZrRQgKF5HrojfuSuKp2+4gp98bnaNCG5FVwK5iNJRBWvx+lEQzBIiLg8qlix/uWNqTywCkPC6uC+JKDkOW5GQRNm4EwFGAbAPPKWHZBSrHx3svQMT03cZCuozhuw46doN+y0EV2KjcBheBhaCh1LjBeeDCKWwsShcLy0FsMfV3isi3cXp0hrq2RbrG9EuCY0qtaYC1rUyU1zE1BZODQ1xcnKgF0tqGr0Emnk/PbdBqKZ9a8YAtKvQp36THFRpJw4XbQlm7WGa+3Pth5MEJr+A5fTjpHE2+Rm7T708xXlV4Qi3SUd6jJMbWDdmCtniU8aDRK7BJUoQWrUJs6RtCXrephftpgcFkhHVa4l3aoOrbcJMlXPDc8oDz9dwO+yBlw9E/v4DjBSgXSzkXlCO/+WGKMGrh6bNT6Y+4IGzcKdQ9qmpbqfg2JdjWY00W4HUyqVIWGPBN2X2YYALVZ+3WQVuFw3Q6x9XVB5GNPn50jvlsiURCr9RigFnP3XYouul+ZCst1V2NfOz200zXZWoxtS11zxpUP8lz/PzmLXqdNv7qV1/JvjKoTG1C1dFbLM1I58134pm00R8f4sn5E/S9LhxZwCCTjAs4M9wkBR69+ivxQv76v7zBquvhf/vyG/S++Uf83T94eLvsY40xrqc9LBMXL74aY/Cki4OXbXwVluhWMZJZjLe3OfzJMcaTNkKHbFmm1eYouXC8WiNO7pFn9F8r5f7z7ELw+9xxUFgEvi2RO9PbucrbqEoXeZOjrHOQY817uW5cWIUDv07geYmw1FI3wKIOsJq5KNYpPHeOMp9jukxVEIKwIXN0ez1ZjGeIC9VFm7p93/6Htn3Iwb7t27/BxmJYGQkrP4OPQYSPu1MzJn38ml3gavMqeXKH3iM/P9rgw408bBoAYxHl+Yw/7+Pg4BCdbkcAm9lsitu7uRqLxdDWrNibWYb6MGX/rJKVpNDXxb0xvlWTpd1EUUX/F5mo9s+S1VMD/FVMA6O3CLdpoxVFGA4HAkr9/pvf4/7uRoFxJllJagVV2ChAcCuRUUdOFSdR2EEUtnFF2v96JY+3Jm08+uIJsmmM6Yd78X0wgA5TzuiBUlZk9GnD38aCEwY4PXuEN29+xO37S/mMTmuI4bCPrIwVa0xP5KRQ2lY1+nQo0FGZyjZ4/PQZzs7OpUBhahTT0GiITcYaDcpFRtvQwNkERDA9rdow1oStJkEG9G5THIWHpdmOd5ApgPSEULxWbFsdj7pCr9fBYrnCKo4FWDPv+fjS+WXbuZo/dWHvvE5PNaWZy3JTEJr3m2ZIfjqUgtfJvu3bvm0bwfdz+uOcP0IUREqWVqXC7Mint7h8/x63axulzekkqQtdOPYZ2q+PcGLPMAwzjKxvcfmhg5/nIap2H3b7CFjUyOM1nGoO254BQQkv9OE1NkbBCoOTGjfJBVZLG71+B71BD8vVEslyjnR6idXNDEnhIJZpdY5Bp0HU6aIqbBTrKQKnREMPK0pHNbAmY4gB1whE6D5UWB4MRuBkWzMqVL+/7VtVX6L9xTYdrIHTDLuE40uGscPAmxBTMvmkg6NfZYnD8QCHRwfCnpjeEuxRvZN6zYaftulHN/2pgF1mUrzta5VsVe0eJX3jXh/PP3uCq/dv8eH6TrzPFMNKAXbyT1II1abN75sAgA3pWZv2G7aMyCsVyLZhwcjijRlvuJ0KF49PcXp4hOTDAlgWktyaVznqwMHg0SFqN5DJcujVWKcVgmABe/mPWCRPxLpAebcFKPmlQh+u7cFnAJBra6CCY49iz6VkvTUWIk5spTYgYKrqFLK26LJAbWXZ5HItTL02rHiFvkUJLVPC6cMVIqe0Ly4x6pA55iAgaFaVemHJgat9+grHwpVDx60ah2hw8/YO8/sbWcBSZ0WdCDk7NKM3/qcM29CjZtjr4ex4iPl6hnmeYuF6SCofh02As8hHu83gJgJHCiSx3AYOQxbSDLADxHEmyYQ2a5ZRABtcaOMCFQ8YAb9IAECDpMqniqcX0SmGdXDfFTNG3NhIWOc1m6vtNDxhloMaAeLEwv18jdGgJd5RHPu7QwdumQprrm4o6zbMdLWoR+DpbVbghzJF6hQInRhDFDhsOmjbPdzfTLGe3QvYoZh9BkRmMmsNuzXAo4sDXLEuKx0Mc7LrGth+g0YDoLaAQ2TYcV8UgEPZZVrUIhlmdsZNEyFqHPQCxdiTEA56yuVroLlEE2dYFX24LR+hH8KyQyXlIwBFaTjjCRiSIWy6AsuiQjPP0HUKWO0SpR3Cc9uoHSY+Ku+2q7sESwe4cDJcfX+DwK1wdERGpYPI78MLFchf2/TIcwUotjVL7vbNO7z/9i2qKkThtBFHHk4uejgbRri5vcZsrgJihFVHhYEOMZCAC7HqYICFBtjEF7faAGwq3Vb1UoaVaJJFpXrTdbqyGNEAHX+vyehz8dVXr1CUNb75/Tfij0b1Il8tvowawHtQ/psU2k2nqVQhqukn5DWmilb3rulftz2c9vFtGjx6coHTkwv8+N0P+HB9uWWq6T5QKlD9GVG7g9HhKQbtiYSD2GR0ORCA9938FuMnT9Dr9PD9f/0Zc8vHl6+ucLT4Gv/09z7e5z7icoTcPYXf6aHfDTE4aWPwLMDTDhCu7+T6u50lsNoH6PYiDazxeyppe5kXYglzczPFzewW82wNv80+yEGTeSgyHymBNHqzlZSJ1sKydesSdGfxgwp2UMD1M7FW4CJ4VfvIcoLqXPRORTKedo6Q5R6sNEerKDAOVhhNKgTdHpxgiJPTx3Ls7qes+WshNbx98wYz47O3b//D2p7Btm/79m9aNtpsJG1Grrc7pv0hBEOVYZ969OM3Wn/6zdYv3yKFn0w6KqRpLrJRAjdkQ9CfrdNpiXk+V1seMsoN7fvjDzRDsWp6nW6TWrnxmNCmrtsiQn0xkzoq6ZgyKamQZsqfjc+dn18ILZ0gEP2ENNlBH1MDAOpdN3/KQ40AZXG2wnA8RKfTQ5EXSOip9vYabj/A4RdnyJhcpveVGza4pfxu2eidHKDl+Pj6X/4Z6/lKvBSenL5AGNEUdbHZ9+3/68Je6hBTarCQbsQj7stf/bWsYt3d3WO2mKOsG/g+k9JC+akKSJUOypX+nOw1Tiw0yEajVkkDEw8PY2qr+Rq7/kHCUlPH3axKk8mQl5lIQttkyfk+7u6nKp5eJ2U9YE/8oYv0v6F9cksff4QuDnnPUIq7lRfs277tG+8H9tGfvXiK07NjuPRlKgrkWSwSztu3P+PtuzvMCk9YL7XwNSJY/VOc/6dzvDycwZnPUCwT3N66mObK/2l00MbBZ0NUBwEQBXCtFqrch13aCGx6S1VYFj5ubx0MnSv0DoBFGkp/2Gm30ekN4HptOK0QZb5GtV6LrL3IyZrO0O/1EIZMgiQLzSQQElwyZDDtswa9eCDAg2Kr7Y6cRtC0QxbbdBxmjNHzP20pUMGr15h4FuIqwrJ0jXWaWaURH6/7u3scTYY4Oj7E/XQqBtXmU4Vhp4ErNdxsAbRdgdXmBWREyWoG8OLZM5weDvDd77/FzV0s3kNq/N0uDMlkVy9iqfFs80GalW2YyGZk2f63qSg0K1n6fEmLbGQc//L15+hZIbJ3c5FwNp6FzK7h9QMMzsewfV888eTo1QV86w7V/VvcrU/xw7/eYb0OEQ17Yu6NKkNT1EjpnUcLA5HtlaKMVBNvxb7yyVYUFIGAC/1OjaRPsROrKoFbxgCN/gFM0UGztBEnOTw3pN2/bDcIPdhOI6wRhiNIEBEX5fSsnQw7FAQfbLyzCLQB40GIw+EQccpFqUwt7G0W+/R6pD5dlKAenZxg0PUxnU2RcyJuBcgrF6ftHo5bbQH2hLXIya/4uNWwywR5Ri+0GtNVjtqJEA67cHxXxixK4Hg2CKg41TXiDxnWjo8gUNuSeTRTywWYqVDWlrDZ5DqjPxuP8f0SbrNG41E+7MGyfQGOKMUN2iHu5zmuLaDdy+DNblBkpHQRnKPk00ZZ23IN0HuW+z8MXJwRKciBaeViDg9zq0SJAuN2B/3eCEnMoAL6venriuz8oxNMTgb40bIxzR0cpha8vIEbAXbLkc8iIFyxbuN55vGtLeSlg6yqFYDGYKsUiBwXbtuR6yYQcE2rECzue59Ln8gtX/xwA/teQBjeLwSR6VnHb+W6BA0zYdTReN6puNhQwfLJuuzC42dYFiLeYmQoRT4mvoPbWYl1bqPb7SGvI5S5OpYEw0K3hu8yuKWSe0dk1ZaNaNDH4Ggs130550XeAmHILEsw6vdwOBlIgFhOeX3jbJhpRs2iahkdvqGQcR12tV0kNv6RZgHWdCUbxhkf0Gvbqg9QjNQPl5eomxIvXnwu4TD388Um3VRO3aYn3GxCS09NZbjTNp+rPmS7FLrTv5r+VL+fN9NsvsD9/Q3OH53i4uIx7uhXKMaE5qMb8Q48OOhhfHQE2w7hkOmpd+Z2NkWMCo9fvkKeFvj2Xy6BIx+/fvwtnG++xX/+bQdXZRcJDlFFF+j0+hgddzD8oouTJz5ehiXa1RrFqsDlsoEd9dDrBmgxJVj6n1LGRvpt0muZSdLLWYz5coGiSgA/RRMtUdgFSr6+pI9aA08IEmTT+jJWlWYxWzJefKnXCXZawi6tkK1zOH4Ij3YLIKMtlXE5d3zEGcdIMuKWCPwZ4vkSVUNPtokQBrigPxoO0epEOlRDyZz37b+/7QG2fdu3f8PNrHiy7cpGd+rw7d8fNQ2XfPK5Xzz66dFy+5wZ8HZ/apkECwyuCrNQoMcEB1ECbUyQDAKu0CifLzPoms3JJ5ligP9XfwyvmeJgh7nEh7QPhRmA9YKZKoDFY8v4s2nZaJbJKhe/0+npKSzHRayZVrveDtu29Zcw+8g/0yxFTX+28SEcyxUAcXk7Fxno5NEx/F6EOqtQi+8b323DD0IcH5xJmuf7n97IxK/dGok8qqyXyItET77MsfjovGxmfKpYPX/8BM+ffy709Nu7e5FiEvjiam0oUeGuXC/c70wmzYUMuATaCK6JHFSnhCoWg17d1CdAeXIYfzUNrul/cnwBxOuVJI3Sa40gJmWpLIoE1DKSkD/WPvn8H7tWddMv2PlK29fr46QYKMoXhkEG+7Zv+6Ya718yW0/PTvHo6bmkX9LUq6YBd5khnd3i7Q8/4XpRILM8Ya41nAy4fTjjEb562cXr9m+R//w7XF8HmGcFeTbCkODQ1Gm5uOjaOAxdtPoekr4P24vg1iGqlImG5AgVyC1gugpQzdY47lwi6hWYLlzUXLHvdtDtD9DqdRF1XBRZguGgh9ODQ6zu7jDPEkSdDtzAkn5tI0EXZgYnMTThV4mQZMWQsaKSo420yYBsqvdQXYrpZFVAjRptlPTKqmK07QSe28Ki8CRXUM1pdya1G0ZJg+lsIfLa89MDdIdk5q0eBrzoDuyBjFODdHqtSP6mp9rReIgvP3+C2d0tvvn2DVJ+OCWDYklgQEN1XmVv1Fd52AxLTwNKZoKrAEa9FZFeqkcpuRKvH8fBo0cn+OzROaoPKzRTsqsskGyBfhvhcIBw0IVFdiPDBRpaweeo01vc/HyP98UYuXuIwycXSAobK8tFq9cSxhElmDbBoWwBErgan1wyggu2jE22Rb6kZvSQdWMptiDPR1rkKNdLeOVCEigbxwedsCj3rBsbXhhKil+cZCJPplSXgCz3qWHaLE3shJFFkNSW4AABBxkoUAD3loV720Li1jgfddBrd5EJAzxT/mZ6fOM11e6PcHw8QZrFmK3WKInVwUPkR/h8MsKkFQnQxAk2vegI7HhWinq1xHrFFFRXFrmK0kZGVpVnoReppFCRndHSgIFOVoEmZsqlK4wv3yo0O91CKeN7rbzZiDahRFxWmC8KhHkJr5UBfgTH7chCmNhquBYzRZFGLk6cGvmHFWbEKnndwZFjzhpL/O5cJfMkRic8UMvC2PdwaHti9j+tHCwtB1NUcnyPBgO0wq6cJ/pFnV2cI267+H1lIc5tjDOgW1USJuBG2rdQJHP0WuQCJVm0NkrKiX0m0paomQCa1ijJeoxc9HgcGTahASgpjwU4ZYiDL6m19HBzvEvYuEeTt1DwM0JPEnYdFHBFzqr8/ZK6QScMYPv0D+R1pEBc9mt+U6PtKPly4CvFBtmjDQFIMpcInpJpR1PAsoBdpkrySksQrUDxmJp8OEDUD4F1CmuWSd80X6co1gUmh0MJTWGNmhBo0/e1Adp4LlTIye4i85ZxqsBzVfds6mT9t9F9mr5C+e6ZF9qI41SANqo9Pn/2TI7berFExXva9FeaCSfvke9g+hD9EZt+yHQ62+cf/LVTGKq1AAXoM2X16uoa6TrG06ePRQbPfjNjoFq3i/OLQwxbBHsL1CX9GV3keYVpvET/9Bi98QG+/+Y9Lhcxnry8w4vqH/Dj303xjx86WGOIyj2H0znAaNBB73kfk89beD0GzpGgXse4vUuxttuYHI7Q6wTCOCvTWMIJWDMXcYU4KSTkhgDWah0jyZaoi0z6DUpBuQ+8D0tdV9NZkNxh3kNcfIIToKx9FHye8vA6QFXbyPNUfCRbAxdRwDregu94istrFSJ9rd0QqeNjlQRY39toihgWFqIWoRT5cDyW/poLB+PRRHyXKRvdJ47+97c9wLZv+/YX0MSLgSviOm3UtD+NZXzqFR8/tluVP4Attg99XLjvPKdW+ZVfGr29aG5PA07S0CkbpT8b/a/WkiapEjhVva8H/Z0B2vhl/cGmqe7qfSZFSRciWla5kZQKo42FOw2QS/FVIyg2GU9wcX6BJM2QxMrzbEO5kn/6lweIj2YINA3SbA0vcDHpj2X1KI0TTD/cIc5STJ4eot3qIFmt0B9yhcnFD99+i+VsBtcJMB6eI2w5KEumOWkp5QZK1BMlw4nXEybuY68/xKsvv0Kv28f9/T3mi6WAZCz4WBz5ZGrZClAk2MXAiSwjsKb+8XF6wREYY/GkvEnM5FB/kJ74mXOqzMLN7yxwSqzXSwm14LnlZHJNoFLS23Sy2qfO2YNS6w81fQ1scbRN21x6f+jt5nDp80hgbS8J3bd92zbeD/3eAOcXT4SBYdVM2rNRlBmcqsL7H7/Hh+s54tpFTX0ZJ4hWG449Qv/Ix2cTB2P7CvOfU7y56iGmHI33O6X59G50HAT0d6InlFuja1c4CBx4Aw/zXoCm8dGUERpaW6JE6SRYWx7uFyH89Qpn40tUQYDlkvdxgd5gjCgigAPxprz78Xs4WQyrbLBepwICtCZ9WGTiMg5UPG042eH4oBkkD0B7TTvSQJI8pkyElFH4zljEvq6pCwTNAr3IRly3kInM1DTji8mtq0n+7uSSbOHpdCHMh8ePT8TPa7Ve6/7R9JGaRbc7K5aZbIPA8/Dq88/Q7wBf/8s3mM4TmdDzeMsu7PSDaj+2DHG1PrIdsNUn7B4FNbYZJpvpcA1cV6NCr9vFr379CmHpIv35jpALqhBIPRf9szHCYQ+2TqTmWENWmdfEqFa/w/z9Jb77XQOkFpJBF4vSxuPzDoZ9X8bMVhCKvUPVFHCqBOncwrysEfn0eCNjy0aVFyqQh1YDYgfhaOAoxXyZISxLCTyonRCO04Lnh2gIRnkOkrSUxMieUyJbp7DDAG6LBuIOkNITEBIMwJG38VxhQXESy8RNBi3EcY1lTYaeg1u7gus1eDzoI4i6WK3Wwo60nUiAo8j3cDNdIidIrT2/joZ9nA57Ao4ptjcBqhqBW4upebrIMY9r5AS7JaCJEsk2hm0b/cCF2wC+w2uKLCOeGhu2R+l1BCty0QldeM4bAZfqOhDWFdlN4hlHDzomG5CxxURZbiuKYHs9uaYNW9KzKtnXkc2zbWNFH7WaUmFfajh+Z8odybZxacxuZ9o3UHlg8aYMXQdHoYthY+E2A5LGxcJuMLcoMwXOekOMBy18CwvvchteYcNLapx7DUYjX86VhAOzppUdLVDlFrLagU3ppQbQ8rTBunSRNQ7aHRchWWv8jlahWHtaFM1+guCfIn0SSCXY3gXQRZozbT5DVSs5n7xeDPV83FkNxr6D0Gf9pAB2qcvYvxkAS5in+m4nYzTwYfNCsh1ErDlJssyZoFsjJauyKsQ30HXZL2nrEQY4+A46kxY6fQf1fIUmpcIAmN6ncizOzg/RjkLcTe91V2CkmjrMQPc3Uq3teJ8ZSeZGrmlWnB/c+Tt1tv7LvJT/Zoslrm6uMRkN8PnLl0iTRBJlNxWdqY91P7rT3an+Rz8nz+jjpd62oc09+CYw/awB+mnan6W4vLpCUST46svXGI/G6LghWj6DPCq4bg7HWmM+TVEGLTxlYMMyx+9+dwn31MHfPP5XNF9/j//7n318SIdImgt44RO0BgOMxm0MXvbx7LGP10GOVrXGahrjamGhdTBBvxtIOAYTiymkJiC/WidI4hRVznqZ4TglsirDOlshKdcS9NYI+GujKDjHUGNQ5VCSXcBpmChbSaKy7dYSqlKT3coUZoKFGRnaBHZ7KEXbTQakkr1zn11PgXAKECbY7WNtUU7uIZ0R0J3Bs+4xX67RavcxGY1Q1iXC0MdoMpbrmedxLxv9b297gG3f9u0vMG2Uxaj4zuwAX38If/j089sifPu3WQ0zg+kfaNYnftdAjAICawF4WJCSZRD4PrrdDnqdltDeuTLFFXUDzG0GbrWopYoZLfFTY7MpJOT/9URkZ4VPKPQKaBP5qGEIiDExgTZV5Mj3ynMVYAAIm200mmAdU66RPvgeDw6NflgZGqvnKbPMyhTddkc8ZpiWSVNSAm1NYOHg0Qmur+5x+eaNfK9uq4PJZIIaBNa4nmo+S092jMeL9v7ZTIQcBycn5/jixReyKnV3dydyJHrRhUEgQQacPHO/BUzLC2GVEVxjGAXTXSnjlYKTwJr8M+CaWm0zFZJhg5jvAyOJYbx7zkIjl3PIz7ifaSr/rtxqc6weXjwfA2Z/7mXV/LHXmY0acI1TEc1a27IS923f/rKbYq0FmIzOcHhwKjIkj8bgNFavC2SzKX768S2WOdMePZlYkxHUWG2ER0McP3Iw8lLY+QqzyxI3KxcFHc0tG2VuIa1dNEQoPBe+14Yd9OT9ZMbxM7p2g8PARj7ysWyHCMoI5cpDkxEQSFE7OVZlgLvbAN36BqPJEnnZQ7Fayw0+PDyTPjAcDcRvpljHsKsKVl4jocl+GMKjhxNDW8S7SAFrBA50bMCmf5MJ5mai+FE3pSfTMkktFui7GeB0sKoCNS4awvSm5+bWdNKyGZs0YCfP2wpou7ubIfBsHIyHOvWNbC8zYd9OhOWvCji/OJPQhA8//4DvfrwVM3ZSp7bA2q4UVI8g5sttgDXts6a/pTwq0i4j39f61u2MXMmVLAsvXnyGi7MzrN7MUK8y8VrLnAr+uIfx+RH8MBAARhJVm0pkn3YRYz2b4efvMvz2xy6mTh9pu4ez0x5Oj0O07UYkdJTcCTOIzBV6irkhCk4gWwFaQuBay3ON7ckYk+e1gHJ2kyhJH5lNhYewduBEPhy/I4xtrjeSYeTaNSzfReQ1WGQMpy0RhQRPCMzYWDuOBCiEFuB7/D6MVDBgLJPJLRxGLqKylmCOFLakjd5Z9EGycTqeAE6Iw+MRrmMuJFIeaZG3h7bn4/HRBGEQ6uuIx5NbzQVILOMc67hGTFsm4jcIkVWueHcNBp4kXHpExJQieWOlpfxDGdCjUkSFqWUFAiKnK+5nhVboCNDs2LleWAwwd4Buy4MXRCKL5bZEsszfKfuUxUkV4CCWqbWHKowY4aFBOCXCriobWcK7KVWyT1m8VItvvIQIhJ3wM/MGywpIbAsrqxTgfVF5uMuBQW5jUjV40rYw6lKyq5JFFetUDPWQZC5yx4PvWfBFKkwGvoPMc8XrbN1y0WeSLBf6CAZKQAGZfCLtgCVgG/1kWSNTUtwgTVnn0KvQwTqtJW3VJRsyJ0hKphrQa3jclY+v+MfJeeO2VGKnYqoSbyNDyEIdOmhHNlqhDb9FENKCRdJZZcn1muRMkiTGVsIuKV8ma1el3srdR3VHN8DgIEB6NYVLU0KyHAsLN3OmtLp4/uxcQrWSmPROdZ8qQE33QNoLTY7gxktxWwupVyrUfwPnm75u54XCat0UU+qau7uf4/ryHb54/hwHx8fisUs2osiVTZ24+UD13m03qn7b9Es7Cbu6et555RYcVf8z4CiQcwyyanQ6IxyfnqDOU9RNKom7N1MXR8/+CuPDI3z9zz/hbVzhi7+6wRfrv8c//59r/Pamh6Q6QeE8Q6d7gNGkje6jLoavO/hyBBxTMp3FePdhhczvY3w4QFv6HoYY0DcvF6811s/MGSFwxnACLggQjk7rVBaZk0It1pNxS1Ya7yFhT0tILyUUlYxtvDhsA7QJYF8hsHM0RYW86aImu5ZhCCWZwDZq+odybG4KRFaDduAIS5cnxyFQ51nIPQ9J42G19FHMcrTcJYpyjsU6xXAwRrfTlXlOp9PFYDSWeyxN0g0Qu29/ftuHHOzbvv2FNgJHpAZLUpruPHfBjE91p7vAxS9hCDPz+OjNH7/p4w/5+DF5XAFkBDwIBB0cTARgIuCVpilubu+xWsWbqHuhrhuTCLNJqRHMFEE9asAfeZ/WLyqzZ0sM/m19TAyDjb9L0coCQnuScTLGRzjx7HQ68m86u8e3v/+deItRJmDpFNTtTuqvpic69s5O8/uErS7sxsXl+7comEql+HXiwzAcHojko6qzzZSMK9NCkNcTWqxGZQAAIABJREFUHUmd20Sw8z8IePfq9VdS2BFYI52fk8jQ9xFwZV40HJSDMtxBS0KFrUYqPY2cS1l1U6CnPqC6IFITLv2fOeYbw2ypjmQixUIxTmJ0WpEcz9v7ewFNDZvyj2FZH18SHz/2qed3H9/8/CMXtZmkui595/Zt3/bNNN6vve4EUetAJsWtvoO2S1ZKCbuu8ObnS6xyTgIUG60R1ksIy4/QPXEw6efKTH5pIV/Rd1ExxarGQdJ0UHtdhF4uq+5eYGM4mGB8cgCPYxKNycnkIPPAp4+Oj8Ry8X3lYH1do/mQIL2fosrukQULFDYDWhq8Pj+DzVS1foo4PxJvrHanB9cPkKzmKJIVbn56i2Q2E5l+6fgonAqtYSQG4ckqk0mOSW3epAYbBoUJFTBrJdrgn2NPRZ83L0HjRohzBdRvJPTimaN8kcRnUiRkJuVPL/bomad0VzuLP/I9mhqjQVsM5ef8jht2nRonKEV8/fIFptdv8N2ba+2ZpcWrejFKAhr0yMPprkCIHKf0rpmxSPpwmbWqEASCIY1VwRHpPMdDPqgOi2QsVgXOz89xevoIq/sMzZwMMuXT6XQdDE8mknCnJJL8FGrWVigS+hLVmC8b/DhN8P2M6Z4tYasdHDr4akz/MfpbUerHMbsRTy+yHdUYrr4Dj4nyrvoRTdbDughh+4F4b1lVBs+J0XgtFHUPP6QlHlF2Fygjfp4P+mwJqV9OPC/ZRpL8bm/W6NgEsCitVEEdBMRinvCkQttOFROu8RRTThI7uR3KNmt8t6zwjh6sAeA6OU6tGie5hbf3MSwyMrlg12R4PO5i0u8qY38BsmhMX8FtEpRJhiINUTQ10qYU+ePKaqMdumjE27zGUcTaRTNn6Dcm54cCMwJKKsxASF6S4K48VIm1rRY5lmWFw0kL1SpFGAJO1EJJa3ZJAVWgkAKyzHiqmDbqciEr0kWcV7hyLAxtGzFhq7RCa5HArysJF6idCjT4IBjXblOZG6CxQwF9yCStKMmm353v4TezTLZ15FQ4rlyRAEeNhfEACAJdV0mZxzdmKPMKMULxyiOwpnyq6CnnwI2UfyrvELemrJLSua2agybyPGahXwq7h8EV3G8CXNzXwCPDlrYeNZazQpKKQ9+BV6yRM600XsCJRgL2bpMu5QRKf8jjwzqKdZrrcV/5G+0/XMV2Y9p8ycT5GrMaSGc5rCJF0DCFlUXJGkGQot1i4mlfahRJj5SADuCnH/4VrSxEbTHxlgmUPjICdWWB87MOBoMAP/38DnfTW9VHyzlUIQfsg3gvyeXKbyJMQNMVaL6bUSYYtSj/Ez3tzsKA9G8f1VXSb1XoRBFevX6FJC3w+2+/RZykqn8xtDduY1PAfYLZJj/5GhWzq3oz/UGagWf2QLZpWzg4OMDRYAyv0mxCK0fniEqQAFc3MSbHp/jh+/d4d5fj8CsPv7b+L7z5hzX+6UOEpOkB1iM0nRF6oxYGvRCtZy08PbRw0mQi3729iTGvPBycHApjTYA1BkdwEZoL0qyjU8o9K2GjNXaNxqlQlIkA03Eyw7ufbjFPYq0IYS0s0RH8sgL0Sl/ETBGfoC7nI4EAsOP2EJ7r436eoEAHSeWgzNnVJvDoXUkpsk8Mv4Af5Ai9BqFDkLyFyutgmXpYZwTzSmHhZqWFJivRSgsMvBhHpy6ijoPGO8DRyQWKLMf9bC7XDRd33r17K2Fo7D/27c9rewbbvu3bX2gT6WNVC6hkJhJqZVz9/EPYx6Yef/DIp/7+BARi3rz71IOX6Cc0O40r9lzpoT8b02446aOhda/XFT+gJM2lADImwhxo5a0crDUwZlbj1GfpL6B484rtpRlsUkgYPzHDbNMhBlLQ2wTclMkxHxd/tjRFUeTodXt4/OQZiqxAnJA9ocx2zf5KvbUpDtTExIBjbDThrusMh4cHEv9O09pO1MVoeIjaSlHRyFkXPQbaMv5mcub0RKzWAQNPHj/Diy9eYh2vcXc3RZIw1t0ROSij4LkvZBAQUGPIBBmDwqIjY61kEU5GRymv2VDEpQBT+7Vhzek/FLhmjpNif8TrGFWVY9DtIUlSZUArXnqKoaEK5e1ZN+2Tl8Wf8fzHV5tcZp/asCkWG058lOfevu3bvunbhAbdURu9/iHcVhdFU2Iy9BAy/a9pJO3v53c3SMWLilIpThYJKEXwwwidUYO2G6Nc58hjC0ViKRZso8zU4zqAE7QxCDmRzIQ54vsO+p0Ik36EwHPguEwfpXTGFiaA1VA2VWHi2PC6NpYDT4A8v2ojTSy0/QaPDge4u7vB5XSNclngsHUPN4pAMluZZWh1e/DCNsJOCL8ToEozNFkB1/aRxQSFAK8doCajV0AE4zP26T5EdeC2BmnW6IcVEkTISxOMYiaEZrKqmb8mGGfjR/Txtnce3XR2FuKMXneUQ5JhU8kkm6ypR4/O8fTsAN998zXe3i61PNcsgphxR/WOZsvCJ9nMbg2IaF5lwDjtGaZ7ZzWEmq1xql4hjAK8evkag84Q8/sETWKjzizkVo5oFGB0cSDSJm5b2DL0TisWyGZzpCsLy8TCdVXife1gIgl3PRx2AhwFFnotF05dC6C7YRBKvirZGDqlUk+uZfhuOigKC8u4QFzkCOkPxvPLz7fbKC0HA8dC4CvwUwItNoOGHucoD64JLDpYVxZWXgCff9PLrFYhCREX5DwbcWmjTpjwR/aX9unbjDkWenaDMbEueo3RR862cdgAq1UuPn/d0MLzkyE6RLbMvggLKoFdzRBPU8QrBSpJ2AZlqlEL7XGAQWgLay+KyJ5RA2kjEjP1HWybdR33j3JlnYApPq1k5ZPR1sAiu2ZWIuyGaOIELnLxFKMtBhcbN/o/vT+SzrkjPVQMf0tSXMcOZaOU1lroeyoRk0bqZGSV1LRJ1oSDlMcsz+E6hXjjUeJIbzkyzwjKJksgLWy0HAuDEvALwG8qAcELMvoIJPJaqBLkMTOCI4ShA4/AE8MaChs5P8On1NwWQIpsHlqTUZZMRicXV0v57iqMoSILLKdZvFRlUksycAD5UgEgjo+0qqT2Yz5J7ZS4q12M7f8DTvZWscvc/saLkECsYnla4JoC5dnCtrJVQi2ZbsJO1IuQtssACAtVyxEWUkDJbt2gKC0kBVDZZL2FcK1C7ntuh9y2d1dX6B9MMH50IkAO0bqmyGDXloCnlCgen0xwcjzBbD5HRhNGS90/u9epqutklWBbs5qeYluyPqyldFO93E6hq7fDnwQwL99dCQD1q1+9EoCQ30OBdPrdup+SvzQTzayTq7rdbNV0TmohXfWvuv9qbLSDNi5OzzDudeCS8UWJrc1E4QI/fZjD7Yww6vUkLfbDosbnrz7g9N1v8E9/X+DraQ9r6xyO+xyd3hC9ky6GFx0cfBHhi36Dg3qFap3g8jYH2iOMxz1JCGXwiQLXSsVao2SXEvOyRmUZcK1A03COQkZtgvW8wGg4QFE1mC/IrDVakC3YKEeDf/Cer214boCTw0NZYL9fTWFZDNGo4VGSSja47cv1IIIQIXQ6KCtPZKMV2aDIEDQphq0GQasNy47QkCHJRGvXFmB2XXpYUVm8TtAJlpgvbsT37fDgUK4Xjt+j8RitiAqUfRDCn9v2ANu+7dtfeDNpowJSqWjMTwIe+ORjZiLxqVc9fOWDl28+YQdl2X39Zrze+rMxbGC1XEkHTzNV8WfrtsW3mRRmMZfdIY7J24VFvuOdowdmBbAIh38rh9Hfy0hHjZzWMAn4ThZnhtlm5lBMBaWXGFeHj4+PcXBwhDzPhLml5ySqkDCFjZ68yJs3B1rF2dNHImxHaPf6sl9lHauVMA0Imdc+lDGq7XFtstPt4vXrryTlj15ri7kyyVZyUOVfw0Z2mvispYrOroIkWAgo2rqsom8mhttzIuCZYTnwO+iJhQHYWJwTZEySNbrtSP6ezudYJ2o/FDCoJq1mD/7UtWZes/ueB889/Iq/3KA+9hu5g1wn6jzy577t276p+5fpeZTWhN2JeDGRcTLp+7JaT5f89+8ucbfKJB1UmBgWl9pdWE4IPySAX4m0qYhpoO6ipHRUZDAl8spBbvtwfQ8jzwW5MhaUNJP9SCf00I1c6VuZwsfJAxMIK4sTBpozk6VToGPXOPItuH0P61GAieuj5Yb48GMq/VjllFg1De6WHrx8ikFrCTsEFktOzgq0uiOErR7cTht2y0UeLxgmKQsbJcE8uLDbgbCByECR/mpngUYmmzKmWHCqDF0vEQ+mZUlWzlbKpBZDTP9kwArVWW0npabz0pw0o58yfRhfvxkvyNZqBKQkF8euc7x+/QJ1tsK/fvs91rlKnN7N+9Eiqi1OsmvApr+DTPA+8mbb+QKbRSfKColk1WQ1WxWePH6Mp+dPUK4TZKsEVukgX1fw2sDwtIPeuKcX7/gpJexmjib7FvM311h+6KCahkrCymuhP8Th4w5Oew78HtCiVJPSVhKVRDalWDNkUioXeB2yQ2agmMQrcIRHPLstkDWU4fmoFjk4B609n+RJxd8z9YcOP6KcUORZZBbyu1I26hFEI+NKmczT2J/SQWScmEJdnw6vXkd8vqyqhGOpICbKD7lwSZC45TXo8jstOJbbGDoN4nUuQBF9kgKRW2syPfepWqBcrrC48eR8ElyuSxdVEKEOffR6PoZkkdr0rWM6bYOa92HD7yIiRXVeScaT/RTxrvYBI9GuglXxy9APzoZfJEArgmctULRSkTTHa/rK1uIDR1DMqBtE8kjWmpZZKl82ddHU9LWzKqkh5XGCW6GDuuNhCVf8wgjo0VaM781y+qBVCENP7slG0j9tLOY1rDV9BIFu3SAoK/igNE6xmFICGTXZqj5Ky4PvE7qiNK9GTiah76KhJ5pHElBBZB05+yDLg+dRmaAWBHn+ZBlQcMMKuQSb1HA9BlqkQD5VN48bIrMC/D2Zlg7lwTayyoFTuui2Gtj+Fdz697CSKzR5G7XXkhpJVBFSF2mLETkuFkp6BIqklmeJIFsNXy8Od8hA8lzUfJ24BtZo90IcDFsix5c+RxY0XPHW8oOxAELcr8rx4A466I9bIscny421/Gq+Rh7nuDg/xnDUU+mVcq7UvaJ6gU2xrVM+d+9/de1sF6h1X7b5dcczbacDkW5L/05T/7dv36PVCfH58yfwvADz2UxtUy+0yvZ2GWzyXfQi+VY5vwH52Xite06E08khTsYDhPRhpLG/w/oVuFqmyDsTnD35HNc3S3z98xStYY4XvRt0shB/+9sal6shSusRgvYphuMe2qctjJ53cHHu4HM3R5SvcHebYpo56E4m6HY8+A7vHMU+o99jnpC1VkqqL9m0tU0PtRK1TXZaLnU1U0TXywx30xXeX9+g3YpwcjQW6fCSaddawruV3TLDxMfp0TEO+n1c3X7AIpmjppKFHRnTeiketpiSqxUYLkMQCBjTkpB+ogHqwkfe2EibAla1xsifo9cGIr8Hm56JDJdxC+mDM9vDIvWxvK/h5wTcbxGnibCBD8YHcuy5GD0cjxFGTBzdByH8qbYH2PZt3/ZNFdk7/mwslAyotINf/KKpx39ZtG//ffwGvbUNDeoPfMDHm+TLmG5ZUXKYYLlcyoplu90Wz4BWK5KBjAWYfLLIWvS30Gwr81nbAmI7udmAa/xbryop6axaFd71HzASUw42nECwSUBDnglAxknq2dk5+r0hFksmZKpkJ4F45OO2han6Kg+LE0o0mconAOCDxtcodpiqM9Q+yLe2LTx99hzPnj4TVt30/l4mmywomQrkB542364FEMzSHDmZa3muZKFcqa1KlbymJcNbiZL6bMMSlCKaNaNORJNQCBaSlIhIaEEhEfJkHc4WC5GEqiP9aUmoeeiXl8J2Ymkeaz71uo8x2p3Ht79uC0oj/30IUu7bvv3lNt4LlJQPxxO4YSR32GTsyyp9y/Vxe3mN91e3slLOSac4u9v0J/JlMk0ZZ+QygbNCVXAC7mx4TnnRIOPk1/WkH4pcGxHniV6JzM4lhY8gQBi4ImkhsGbrfsXVTBMGJ+SWI0mNdlkJm6ODBB2amw9amEZd2G4HeRHBjtkhJCjdHIvcwXxWw0+vcDi5RVwdYL1YwXZd9PojeGELUa8jTIPFaiYqwTK3Ea8KOL6F1rAlyW8ykWSnJx0PAYwGfrXGoOViXUZI612JuaBR2wWKHfba5k8NpknXv5mNbscYtRndY+mx0kxr5dG6xEmvwLsPd5jPV+Itxsn8lumlx74d86QHbkcfsbt3PM83vathlsi312mLnJD1ez38+tf/DoHtIr2/V6mrlPPFjQRedB530OoECuyj9Aw57PRn5DcJbr8p8fZrF829h8hroRqEsActPDoMceQDoQP0aSZv0/ZAARPKE0/5YlGa7Dock8nqUqw41i2cX1rVCnaZwUtTWLEFtxvAL9YouyUW80aYQr7LZFuzr4LMCbCqgCTliUVgjFeviwYRZY4MMtCsp3Vlw9XHVPmkcRGPieA2ioyT3kzdD2KynwvQwWsqn1tok43i1cjiDHbVIKJfmOchEzmZYkglixLLqY2mJAOMbE8f64MuukNPJJIR1ag8IlUqYDA92DyfILRKASV5keOyUnFxkq18TsW3rI7RZNewrQRwW4jhoWitUDotlE6FuB4AhU/6vDD/Eqbsupb2btMgnVlYlITLrc0GU07pBUW2GE+7R98320KLstDAQUHvsoa1TSW1h98OEXWYQpyrC4yglOWIFJPSRc9r0GP4BVNhCZz4tTD17EoFYzCZ1fdUoinB8bx2EISuMJdCu4ZDSWhGGagrn+2FlPAqAEdKW61yUJ5XglnBD7n4SAlmDBV7Sj+8QJh499cVlpWLkWvDq22ETonaP4ZlPxIg1vHeocyHyDPNjiQLlmxL7Ren7filC+GyAoFluQ4pTyZURDkzkyNdIPccYd8N+w6GXQcFZewE8wVwcsQapVwt0GlbyCxVd9WeK4zPVuCgP+6KbyN92CwChqixnq5QZw2ev3iKMHAwu59u2WLWbj3JnybexXgzmkXInRrYPKfVFKZbNM/qDW4KcJ772XyF27tbjAcdvHr5CvP5WhbN5fPFUkW/x3RED+o38w30ggAstHuHuDgYo+0x+CyDbdHMn4EUDd4vLBx+9hqhF+Hr375B4lv49aufMb78DX7zn+d4P3Px+q9fo9U/RpYGGB520X/awfHLCK96NY6aNcr1Gld3BazuGINhR+49d8NaK4SZScYawbWirMT/jP8a+qdxXKpyFGR7UdWyLLBecdE9R1aUsu+L+RKjYQ8X52eYLVaocy5cqH2djAf48tVLLOhN+e69LN6j0uOPAHE1GmGnUdDN8bARRhvDMyqGlFRkirLvoT+bj6Jm0Ecjih+3XKIbcu4UwPXbwvpkepDj1Kg8HysrwGLto5wSxJ/DcW6xjBNEUR+Dfl8scoIgwoTpo64rdf4+COHTbQ+w7du+7dumbYz+mWnFFeQdkM2Mr7u4xOa5nd9/KS5t/ujg+eDvB4X+LxAX+d3IM8kaowyR34c+aP1eV+QfBJgIxG1AvAeFgd7Ybvja5hXGY0JPPDYMBAViqee2jDeRSAgYqRhtfJxpowwTIMuOoN/JyZmsLiVJoqLYRb6jPtlgdltulflGXCXWq4I7z2y8ceR3Ixdt0G538cUXr9HrdHE/nWK5XCmfFddFRK81ndgm3gvagFVMoItcBm4+LqwEARM1uKYLqA3jzEhAheXIotEw0dQx5ufF8RoB2QhRhNv7KVZMIJKVaf1a6w9fFZt9fPiSzWO7l8HmiGyquo226ZdvZpNdMdf0PiF03/Ztt9FY/XAwxqAzEO+pVttD17fh2w7KOMbPP/6EVc5IwECYarYVIs1TCkcQRKEYrHPiQdCJrAJJRLTp4VghpVzF9gVYo1KPRuws5BHlqIMUaUFPGFcSFH1Hsddojs65nkxKNcmBgAUBCMqlaFa/uo+V51krwJDpei0bGdMFwwg+OsAikoS2BgmqOsVyRZDQxdD9gP7EFVP0dB2LXL7VHSCMOuiOeiiKDIvpjHQj+EkHWEawBx3UQY1GZGQWnDLDOCjgeG2sCgY67IwxMknVzGg9FRRwTc9XH/RLu03bBuz+rV6qjev1IgonVCfdHN2oxPWSJv++jCkODfrZjwsLxPDWVP+th6tNX6p8qbahByYw6MHX2llQEhN/sqUCG1++/AKPzh9jfT1DuUpk8p2XDsq0RtgUCDs5lq6HOS8XMP0SKNZTTH9MMP22g8VPHcxLB+mkg+ZFH93zEO2uK95+Nn3easU4qi0PDdnWZI2RoqHZOwQl6qKCXWdoaDwqhuYpmnQKu17Acn1kwVIWuepWC0lg4Te5j0dcWJovxHCdfmpcYKG0i0wgypwtVzGHCKyIvI/AHsHWQoG5ZDN69NQis03Yz5Qv04ucrC21EFbSv6124fMaKFcg8kOwjQtq6X2NoKOAGbcVIVsWCEOCymRwsW6oZEHMj3wBn2h4X9gegsMOjgaOAFWUvLq1Au3ywkHROHB9V4AjsvR4AikApI8Tf1deaY28ps5XsIq3sH2ang8BO0KaeFjVkTBE7SKAV7gIyKiijFdSSBukCcFlHmZKGSkd5fXABGFVE2xYYLZOEq0YGKDc6oTBxYVIvtazUVFmS1/HSYheN9iGAMg5VOd4vloJ4kWgaeDbyKsE1+spuv02HCYpCnPQhWcz8bXAKqtRE5Bi/yL+kPR9ZH1DYM0T3zQCcd4mE1jLcAUYZdqp8RckVTBG44aYuR0ElSuekivLRlFZ6Cb3GJSU5daw8wxFUeNf3AhzO0RYU7HwTPz4WsH/Djt3RSZdmTpJ3/8K+mb/xwU+9TzZqJLTQJk5wRJe7k2NoEng0lCfNi6WjRV9uFYWLm+WKBCgcSIsZxmCiDL7WEI4xIdX6ksGKPjo9vuwPQa4JHAJvpQWZlcrhO0QT58/kcWP6XKh+lvtnbu57Q1rTPsC7lZfBlx7wHzDxyy03f5ESz0JtNXA3XSOm+tLPHt6huOTE8Sr9f/L3ns1yZGdWYLHtQydEhqoYhU1lz1v+9v3bW3HrHe7m8se6pJQCaSIDOlarZ3vXo8MJFDs3pnpMWsyLiyRGcojwsUV5zsCVFMoMcGHEznFFNZTPCExGgjdAR6dnOM45KiRwTALmGaJqm1wndjA4DEeP/8cV69u8NW7Fc5+UuEX1r/g8r/O8U8vh5i3E9wUR7i6cDA+8vCTn43hnAU4f+zihZnDLRPc3CRYNQFGJ0eIfUsB/pq1RuAqJ2uNPyX7EDLWWvEabA2yYUvUTSHF6zwtkW9rYa2mVIuweC4JtRz3GiyWG2yWWzx7fI7pdIyqbPGrX/wC49EAf/zTn7BaJ3pHKGkOE2dFxk73O/otMnGUzFEy2njddB0cnkSUQ5sOqtaS/hKs8RNoazwkDP+ot/DaFcZRiWgQwHAi+TwmMkmvrTwXa3hYbxykc8q/5+iwwDptMJseYxBH0l/FcYTp7EiOLdddB6Dtw3YA2A7t0A7to9ZXhpVsVPlx9Cyw/WF1b0mwax+uHz6ERT566IMN3ENJ5M9PrEr067iAI7tgvd6ICacjaaMDjMdD2GRTEdTSskT1kruh//5b7xYdPbimmWFqYdQjYWqfKOBNT9Y0m40V4jvJYScAVsYBp2lwdHyM8wcPBHhLtqsP3quXqajPtcdk0HeqBZGeYOw+rAL7WM189uwzfPHll7IfGCCQ5ZxsmCIHDTwyTFjpJ7tOS0EJ/pGxViopqJKD0idCfS9+vZ7s18N5PWsNe6CaVFP5KH0uigxdXWMyGgqDby4JoWStfRxk0B/huyN99//dY3fH58PnfqopWcPHB1Td7o+hmtQeWGuHdmgfhBgMR5iMZjBtB51jYDIMhYUWWibevXmL+XIroJZJigfZaoYr/WwcxXBNoNjeAGSMCKNN95ttg4LsGssTM/mAxuBcbErX1aAxCrRGg5rSt5wAgw6UsW04XIQbKqGPgL/yfOyBNsrvCqRFDW84gGEFaEsynUqEVoNTy0AwsJDPPNhRDKsMYa581ImNTVdh65i4zgPUywIT/xbBwESysVHkOaLhAEEwQDQIcXQ8hEE2UuLCrXx0awtd6cEfufDdHKENpHUgrBLpy7XVgOq29T7YMYDvWGv7LOhdf94/Z3+c03KhD/pGo0Xo5nh85OB6Y2CREjJQ/ZuwyyR9wYZnkfnMvncvvGA3lvSLXu5PvWyWvr6XeanPY2qGVv+Zu67Bk6cP8cuf/QLdpkFycUMaDhoGDpFR1DbwQh9OVKO117CNGFXt4KZssa5rBAEZgjHyq0ISW9sXI8S/nuHpmQWPLEGbfkb0JStQFQaKzpaiEE27O0uNNRyLyNJgY3GN47BFZLdYwqxew3QY5zhEY4RYVyPY/kgAWcfwMa5sYViKt1mZI1ttUTYtXM8XhhHHSG6Kx5LzBg7hBJLoxVe19BCjbJAsmQoeQSwNnPDxrKJROOdJDRzfFmmjUS6FnSmAtEF/JBsXBc/3QtLQL662yGcjPDyKBMwS+auwwi0JkmDqoT8NxCcwCmz4AmDTjIvjtoGitdE6jnx/hgj0cwblhqESWmUMFeCNieEGlm5MPh5sI0JnesgZgkF/OobdGjZcApd1JmCh79eSBUpWEecQlAbT145BC5xbyFyHoKJQsBQSI8pL2xKmaQ8a9fuM+8olk8vuEDtk3IjWFBc2E11t9Z3pK2YY2NzOUWS38Bwmwa5xuVmgbjtETDOkHF2YXzzbK1hMk21MZPQjRAFXBz8R5GxsGy6LBJZi/EnyOYEJndaoeJEt2iKHWaeAwfAB+ikyhZReaEwypiq+o8oUy8UNqnqLLN8CI6KdDsqFBbvssC6BLI4R2AFs8wyGk8C2fwMzv0VNI3qD54GtGHMyp+Z+UQw/JqsSnKRsloeR4RhNRaC5hUFGsMkjYUnIxyJvEcQDbPMa36cV/Flf61geAAAgAElEQVSL/NVLpHUCr7mF7TDmgSmv3J+2AKdeHGF0NEZX56jrXIC2umixvk0xmk7x+Ytn2G43SLLirnC7m/ep/wio7joiCUbZm5r3SpEP5qt3/Zb81Us9dR/EG/Qgu7yeI09u8ZMff4bxdIrVYqMLsuoT7N5Dv3FrWDg7fohH0RBukwFmBrC/Myussw6JcYInX/xK2IF/+O0bFFMP/+WzbzD+3e/xT38AvimmyHAKuE/gDmeYnI/RPR7DPXbxLKwwLDaothkubkpY42NMxqF4rUm/Qz9iFqQLgmuVJOP2rDUFcjEllP5r9CcjuFagyAiw0S6lREamG5M/6ZMofqSiEdb7osX8diNz5x9/+Ux8Kn//h9+Jh50wG2Xs0zudfSHXDHLpKVZ0w/AXW30Ocn15fRHXN5mO7bksg6ngjor6bEpIPRSNh3XVoEi2iI01RkGFKI7Q2QPxDXS6RALWSsfH2nSxuPVRLCrE9gp5thCw8OT0XIJQ6NU8Go0xnkz0moxj0KdWhn9/7QCwHdqhHdq/6c+m0jT3UR7tjfAJ5OPju/bRj3uQyQdP/hRKcu/+vTfsFzd108oiab1ei2w0CAIM4hiDAenPZG0xJlwt0Pa3v7f2uMe6uycJ7e/tcRwxDdaxWhqMVEASGVJcjLKOrHxYRGqhvdgePHyE4+MzbFZrqdiphY6q0inQjT/aCFs/pj+OnuioD0H/tGE8xC9/+WuZsF9f32ClzWM9x4Xve+LlwUa/DfFaE3CtErkqJRZcBIsUVbzWtJ/NzqdO7ytd5VWBBKrKKWCiUqkKIy9JtwgJ5vmeAHxJ2rPWtAn1B+Syuxv7Z8H+Ue5/axLlx2fA/v33T7R7t8VrjRNZpzcdP7RDOzReC4EfYjaeIvRDASIC8YLqEPoBijVlKe9QslugKTbBNYvgWiDJfFy00lScQIPrhDCkT1mrhFCm83V8gie+ZAJYkJ0iVXumlzEJkUtbF12lGEqWoQA4m0wUh4wcJiCqhTC3J1du2yBNlsJMGkShmKLTPLym5yMlLlqeFpkNZjRZH1oohz6MJkBbh2iaQPx54ObIOwOLrQMr2+B0fA04IZKVSnJj4qjrBQhGAawIKPJMFtpu3OD8JEC28rDsQu0pxoXVrmfTwiVtVqU6ILWo1kBYL9JUWNz++HI3NgoDpL/J13b0nSNrrYJt+Hi7gOw/9bb9e+uChChXydAlCKRDcXZstr2xe2/g7vv7HhxU4Jr6RLQ9CEMXv/zlz3A8OsHm1QLYZOhQITNalHaMtGkxnI0RTqe4SQ2UXoyx1cGrbDg1JZUd8prjlY34+QCYuHBOAjwamAhMwNWstaZskVeOyPlsl+cBwRJ+dz3mE1wVgISsDQOupxbcZZvBdQjsjNF2EbO9BZTICzLPDBRVC5vegJ4L2/HQooRD4K110eSlJIZaHoXQpmyXi2kuYLm7CBpxZ5YsUgmwozzoyLSTj2QayIkymyZCk35IBUo3wK0VIuQ1ILwpShMdjAYu0taA7ZpoBx4+H5rwRXXM5EoFcJK5pMDRDjV93Qx6zdKPkIWwVpiCjclEU0oIed1o7a7Q+gRqlSOtAlFLmNUGRsfkcTJTHJRdALO0kJjA97UBK6MCYCHXZZonaF0DcF3kJtmkDAhQqZqlzAEJBABFUxDhVJ+79+fSzH5h0glopFisrQbahMFFwCjP5DuJjxiAWFiqoplUQRW1IdYfVVMizxNhGypo1UAczWAS7OK70neNjCwB9sim6+AZW5SLHJVYYiiGoRAfuU/pGyjJnkw7logBAawXaYFqwbTFCmCqrOGihYO8Y0hsCxQdBtyhNdMU13LZ8Kt6PP+YPFwAbmog93xcA1gQbDAieMYYFo7RmTFgXsNsSrSdp2WwdxMZOVZynrFw2QhQreu3hNRo9McvC9t2hfln+zaSqsaiM3AWmEi/XeH7iwJhGGGdZyLNd5mMbJPdaIjklapX1zBE5eCGMZoiQ0tGG5nA2xqbTYZHTx/geDZCkmyQZpRsCg9S9S7sj7jfiOiIR6HuRPg592TrvTC9L87uI267mde9KRifQqbmxbsr8S/8yZc/krFpmyTaD1H1WdyyG01wfnaOMVUgZYrOzQG3EHBpkQeIj77E+aOnePWX13h5neLJz3P8wv1HfPd/3eJ3NwFuMEaNp4i9MwwnMYbPhpj9OMaXRwYeWQW8KsPtIkNuhohGQwxCRwpIJs8fzpMrWqpwDs31BI+TZo9JP0vvNeVhzMIyi92UjhKIy/makgWnVoA0nocC9uprVXVtun+rgcvrG7GaefH0mQwj6njczcdV96zGCPkRIFv3/fw8ZIezT5UzuYFjKSVLZ3niS8k1Cef+qNmfuSgMG5u8hllliO0EA7+D5Y/RIhCptG1WYqdQUjrauEhuLek3QnuDbb4UxufJ0akoYAgaks0WxiGKXPmz/b0DbQeA7dAO7dD+apOJhZZO9p5jGvPZASH7bTeH+Ogh4xPPuP+4/vkAENm7X9o+sqdBHO3PxsFZgLauFZbFZDxCEHiSlElAqaewq4XRzoxFb1V/rj35qFTx9X3qOToAQYNdIqdV80tpyp/sLghBJssEufICWZ7BtR08fPwIYRBjm2zEz2A3KZEJq96U9qrr2QXy3jK5N/D5519KYinTSq+v5wKgcbFLaSaTVUX6wBQqUtk52Be9HJQpoUxLq0U+QtmPgGviK3HHVusXbztzb/2b29VkRmSpSkodDQbC1LvVrDV55Z4peH967E6Te+Da3b7/8P77eJjc3D+p9HHpWZX7rT9evdfaoR3aoakLhwBVNJ5iPDyWayOKfZgemRWckHd49fIllttMsUW4uBXmmkeDIjg+IYMOdqM6foGRRD/G53qo2xy2XcFxAkk+U5w1SYFBzUUzQX0CD4YNS4nZdlJzjiv0kmKaKEEICTHUa/fNaoN0m8oi0bEpJ+XimnJTmlwbaGRBSSmUAaNphA01tlocByaaUxf1JEDgRTDpz7bmhktUXY5lZeNq4cCpbnAy3XA5gmSt/KUYMuMybXTYwR2VCAMXr16myEsHbWlLCqrh+8L+ZbqkWniq4Jwd81l3VD2DTW71jGVVLdGP65KKZrHoTkwWtJOowvkEeLdwsMr3xkUZAu/GxB12JptWZvfcwzYXf9LpKkCkf53qO9Vr+nftf0titWHiR5+/wI+//Bmqmwrl2y2JiiiMGoXV4cGLxxicjODRk8ewRC5UBQ0eeQtUWYM6LzEie5Hgkmlgsa7wrqjghgaGkQWfABFZayLnM8Wjr/PIOiLY2oncSQGVSpqlZJtkkJew6hsYzQ0628GlNUWbkDnkwLBcYVrybAwcSj8pwSSQRa8iZbtgERC2AsAk6LFEs+mQJR062xAWG/ecYqlzEaukhJJGaZsin6aJONP9VKIo5ZQt7GoFNKnY0svC1vRQpZSzNrAcSniVp+AoMBDYBWZ2I9JSOQVYjHPo5UqZKpmbZLNpGSEuUc7nyJoIju9IkqmA0ByH9f4hAE0YUsIiNNtwvd3CvF3B8TboHB+dEYqfHSW1uWHCqzuMG2CbpjJ2c/5AEM6LyZpyEcJH2Rioyf6y2C/02a1Eg2pW7XBN8MA0EOjxlSCdnioIYKQkpGS7Adu6w/aKLKuUylQJT1GCSJ0syy6kY3BHjYubdwLGq4KeApjZ0dAfkuETneNw9ws8Iec/95/IxzOgcAWAFNN3ZXAmZzU9sAgssOhomR2KusDlskSyaRBULbwwQ+04yDoPZWPCKgG/6sQP0PBoQr/BepNKKqNwqzpgMphgNBlgRRAi6RAlHZrMwHsYuLItuIYLqx2gtY5g2mOYPD8JTraF6i8FPFdXbMf75FLu7ycjmH56npLMy/5kUaMW4Hka0E/LwrsW8PwITeniauOgsEIxwfdQITRTeHYCo3ME6CTEynMxnk2lX6vKAij4fUxsV/Tza/H0yUMcHU+wWKxQs0/r04X3Wl8kkH5GT00VaHiXQLqb2e9N4u7+1P2fBpb6HiwrMrx5/Q5R5Iv3GPvC1XYDw6N08wnOIh9+vgK6JTorRePUWLcBavcxnn7+K9Rliz//4S3M8wD/8OzPwJ/+jP/nXwO8zibY4hyW8wTR0RT+syGmXw7x4pmLH/slRk2KdJXiclnBmx5jNAjguwzUydGUuQSgVD1rLadXsSrESDooQwwIrLWFeK1J0EFeIU0bZFmDrKDsW6eK0mdUAll43at+X4FmSgXSF7K5T9iX3iyWGIUBnj5+KDJ2hrgpFbX2b97r++lLKNJRstTYfzG9VHz0eqCthWd04j9Z0fNRwLyOxoXomDbaBsgavm8Bo9xi7G4RRw78YMB4XBhtAYsed66L1PGwLB2sbg3YxRaOe43Fdg3XG+BkdoSmpu+zg+OTE0RRKIqZfl3w99gOANuhHdqh/buaAEtC+1dpkft4Rz9+9oPvfuun73orn3jV/r16C7vZ/z56soNfPt6EfhmBNrK06ENG3zPbtiQEYTweCFODJqO1mH/021bvvFva7CE/OwBRP0MtXhR400uAesBtZ2a9Y4FxcqmlTxYlB/xcDGhIBeyaTMZ4+PCx3M+qrVSj9MyDizUtqFKW1rLY6jAaj/HLX/0aYRTh5obm1mt5v11CKN9HAD1KQkuhptMHoqrJXOPkQElCpYKmAxz678a37iUmahC/SwuVVDDNRGmqCnmWIA59uJ6L+e0CKRNcZVLcf/e7I/bD58PHj+0f6U/dvt8+ZB2qyZ8iZ9Co+uC1dmiHtrtWDANhEGI6nsJxQ1mITwaULdWIPR+b+RXeXd2KsTrBGPZAlDUZjgfTp4ca4JAlVisZliyTZDHFhNBWzLaNIJJ0Z6/NhHUjAF1ToaS/FFfFhg2ThuMsQOx8GVVBQsYU8VLiQpByMqpyGmxXSzjs38KBLAr4ucl2uWNMEBhh4qiJ1iSjiebOXIHXsiCdWMA4tJCMbTSBD9eMUa1teBXff4ParLAqAqwXwNC4wnCWYVsMUKU0zDbhxwM4DH2wOnROjU1WwLIZ78wEURNuNIQVuajIUpbv3PdMeiTTgTm6g9K/9R87kK0vVOn+niCmUeHBpBG53dsls1PVwkq+s5brf9D77caz3qu8l3ZZoFW7JFyK9PYOpOuPYd9v86NwbBiOhviH//JrjIIRFt8uYSwVsyYj2DKOcP7sFBa9Pclg5Fjl1Bi57xGnKd692gLTZ0gND5erDJOBiy6lhQDZEyYu6e/VbkGnPH4fLh7plWV7ljCDyCDj8aU5Nx/r/ak4VpX5Fma6gO3cwHAmdA9EaPT+fdp0XyorinlGn3rKFIW1IZJoOgXS98qCQcDVoZdVBbuzUOUt0qxFxSAEpjISpBSQQc13TH2ekZ1V81yl5xD9A68XcIwVDJ/b8glTIS9pYg9JS2wExKABeQmjWCJfrtCsvpIgD5ihnNM1pY5MArUdmJ4HfqO6o7fbFlaRI934aBxDzPv7YCHKyOjbRgYZrxsO11VT4fubDbaXOaZGCnv4Do11ihoucoJwjQEGBlLWyBX5m3cXalGuz8em7DAMIrgEwPj9yVrjnE8ks32wUyMA1KIwkZNRKEmjDXzOPZis0Cexyr8KW3SYbxv4WY3Ar9B5BmqDpv2WhEuYNQEhA1WeIucxN4F0napgk65BFEZ4eP4YXdXg8vJSjjH7Awm9kDkKwwhUH0LGmDsM4DsJTPwB7SYSv0bXdzSY2WJVkEnkoK06KTIGTFGMSqz5mXIXdt7Bo21GucG3b27gDxwMhgPMJmOZqxEAfvbokVgDfnv1Gq/WF/DaGpHrwMga+KkQ/IQtx9TYxg4UI0zA2gJmdwNUa7QIxdcPHfsZ+iuydGFhw7OaUmFK9sljky5CnYdkKvEcdDSATEGoZbniVZj7NpzIhM8zvTYUaJrdwjFrNBa9M9VcVHiVrg0v8IT9WxO40cXzZElPRQNffPFUfLxYNFXJ73dy894nTRVX7oqbfY+ymz5/NJnTfVN/U/9FNqnnuiJ9JsiaJCmu3r/H0fEYn33+BQZBCGtTokspNaanYQESlheY4ujs5zg9e4jvv3qNb5Ylnv68wk+q/xPf/N8Z/vVyhG0zQ2OQtXaO4TDC5OkAR5/H+OnMwEMjg5EnuJmnSM0Y4+MpIpdScQXo08usqViwz0UFUhacNxNY4w/7UsrU1dxaPI2LBlneCHOWP2S50aevbnpgrZ9z932+3h8aKBOmZj/PlvOZnmaFFJem4xEePXyA1XIB4mLimcd/O3IyAX/FAjUalbwsHDmboQuqEGB1TFglyGbApD+bQWCN/mz0HuxQVyyQuSgaIKty2E2CyCnhhx4MJ0DD8a4rxRuRbPbCtLHMbWRzwOtWMMwV1tsSg8FISA0MO/N8H9PJFBbB6zT9u/RnOwBsh3Zoh/b/q/VpoyqSXQ0Qfw0o6e/bG1buAW09MLMPveDuFcYntizg1108wO5hfT87c1ZPVpuN/CYIxYnScBBJVTVL852E8MNtqKSeu8+iDVr1Z94xzDTY1oNfXEjdpY3e7Q0OmGSXcXLPhREf5uRHJe80ODs9xdnZA6mAcVBSe1IttMRomHIBx8Vnn32GZ89fSLDDzfWNDL70LGKQguexcs/FSisgHplrkhIq0i0y91QVje/HqrpiWajBbrfHNZgmlWM9ePe0dLVwaZFlpO5XIkulX8Tt4p7Xmj5W+0d31/Yx00/Nvz56/j1m2h7w+akXqIkgF9rKwPru+B3aof19N9dxMRpMMQjHqISdpZI8iV7QO/Hl6zdIOLMWg2yCazQjDyRN1PVNWmrLorxraZBuSrKgYbYCAnCRLX5HHv2/NOONUqu6gt9shY2S1gRTyB5huiL7Q1WJl2tYKvdc9nFRqdhCvNjzZC0pbPF0Iubq0qez16oVCESp4H1/Nm6bTDgyqshEoT+b0ZXCYDqxO4QDG+nYhedGQBuhTXwYZPQ6GbLWwE0aoLjN8XBSIC8T5A0lpnxdjCAcIAw8xCOqUQthAjPV0M5rGJUFbzpGaTao6IHZy372sDQ9jCiWUf8A/yYW2PeLAnDVmA1LDAMDVxsLm4LAoV6Eyf7abU53gRqg2wP15H7pu7l9ilmJDxrwjAa2qxL9aOivt7r7XJZp40eff4Yvv/gJ1tcZtpcZzZyQMeHyKMD48RGicSx+fSZtAOj1gws4yf+B7/70NdJ1iD9XJ/j6uw2CUYjzB0fIKE4cUTZXwi0aBCKvW6C8SLAyHcQB4NmWMBEJQvCcJLBKSIHBA2Rz5U2Jt9sEZlIgtCsYPqWSp7DsAB2BKXpYdWRlqPOBi2MCNII10J+rrtDxvCHIRKDIU/5lXNi7fij+4V3eYJUCr7MOC6NF4HTwOabWNPzn7lSSNfEaQ4UFpXpXCaIqhTt4g9ZmoqQP0yXN00ZqWSIna21T2CPbRYrVmmMo8PobF4uFAz+kDDlQx5LplAIwKtkog5FEINsGaIMIYUQAckvDOwHKeJLR/kJwIxNIyho3qwrZskBYNxgFCeo4wcY8R167MAvAL1v4TQEj7OCGAcb0TCWzvsjhOj4enJ0iCgNh47WbFSyyrgxbpOIFze5tfr4SXWHA8mI4ro9XKZmJZEk2CHgctY8ZWprPV7BNAl6UivP6bFHblJp6wrohUEQm4KvvvsM///aPWMyXGA4GmD06kwCKUTzBbHKE2+s5bm5uMDmeSmoogUXHUcma7K8IzJhGgFvPQ2YbGBgFjG6NpoyR5sCq6hB6Bl6vOyxWLeq8EYbOIHBhmw0Mu0TTkiFF2TIDWExUto1VVeF0Esq15HgORqNY+gImofK8XC82OJ+cYMqArXGA8dRB4BoIuhZD+knCwVXW4BuCvDaN8tkHBjCtEmZzhQ6xgG8d/fBgY0VWrgGENm1GNIu3I7ewT2TeK3wym7cGCs+TwAgn9DGkfJW+XaWJtrCwyjtknPtKCMJKWHSSWco+uyV42sIZBrJvmiSTOSf97jbLFOFohM9ePBYAcL1eCaij5oEqnEEl8d6pHZRAWf+966ju5ue7koguItD3Lwp8uVYpo5RnKXIoTHeAcThDmzU4OTtBNBmK2qNpKmQIgPgFHn/+Uyl2fPP1e7hnNv7h0Tew/vg7Ya29rcaomkfwzEeIJ2OET0IMv4jx9LMAX/glhnWKzSrB7RZwJ2St+eK1JpQB7bVWFgwwaNASJKsbGRrJCmu1JJR9ipKCVsiZEpqR5UZgTYFx4qXHdGUhmvYsZl080D52PUApypC9glNfdBIlCjqsN0qV8+TJY0xHI6y3iaw1VKlLMeBUGISWjgrFU7HSKaFtTVoZaN9Cs4ZttnAZCGIRaPNQahksGNhTeShrBwk/f1nAq1PEXgU/dOT8oQ+kiVwSmVl12xouVmsP2U2NwKTcfINtWeFodiyKGno/M4BuNmVBhMBv8XcFtB0AtkM7tEP772azcdDkwuaH2g7A0T/3cZK/9sju8XuIzAeAzu51d2BcP0hxEOIEmWEHZIlxVhBFEYbDgVDRSZOnkahsZ9/HtWe29ZvsB8J+SSK/+oVS/6G4AFV39AOIgG369QTAyKZTkkWyzEgjz5FkrNZaePL0iTDUVuuNgGJiotyRtTbCL3/5K2GtXV3dYLnkwrMVz7OQXkSuqs5ye2pw58BPkI2MNUojmOZHNoAC1j7MqusXZXdsNTY10Kv75HM0jBhfYRSHCDzltcZ9umOt9ROt/hh9Cm29dxj7o7Z/xHe3f+D1H6F2+gX9+UDW2gFYO7RDU439ShCPEAxUiIFhN5iMQtidCbeucXn5HvP1VtgqBLhopU45KNMxw8iD7zRwKqZnSu6erP5ogk52UVGTKGFJcp7nkFWhFg+UaJJtUlYm0sZFTcZSnYPomUX5OhEKYeEo7yquXIQpJ0UIQ/ndFDm8KIIb+BS8qGtcX+dsHHcazQxQXpg9a4bqTvYDynC9Miw09JqpCLpUiM0G566JZmqjmgUInAhdHaNjEEKXwfVrnByf4s37FFZT4Gy0QUffIwYbNi3CeADPDzCMGPJAz7BcmAwOPZ42ZKJ4cE9nyMkQquix+TFhbWc3IAst9vG9z1ALxyrw+NjCOnUw3xA00iDkLhdUAXLqnntyz/7ePqzA+PCHIF4tcrtO/Ots8cjSYCUaPDg/wz/8+tfwrBBXbzbCAiQRsOxqPPxyhtHDmUgZOVpS/kS5odN8j83bP+G735r4+vsTXF9EeHocIvriIZFSSdUbjzwMKdOMPDiBDcugAXcBlwCn7cC1G9gNTbF5jE2R81VMCWW4gVljnmd4tcoE1AlrA4FHis8RbDKDyPTh2GNJgK2cTkzMM2isL+cWB8ZCkkBpNO8HlNsRzGvgauMi8Rq3XTgim6uwWje4bSy8Jwvc6jCgrJBzHb4BX9MsACNBg0h8zbzOhDWYoTanMEHpMz2vOgTcP46FyDaQdSYS7jNK4SoLa4q2zoYIphFiYczRVHwjx1ROZ+17RQDRdEMkroXIY8IuC3AtqsLEpujg0WgfLX5zlWN522JMkGUcKVkYvQa9GEU1QVCY8Hmc7RquS+/ANZLMgBcEmE3HmE0mODqaCjhtFnNY+TVaJ0ZaczsOHMMWUI+BUVQuuP4ATVFjc7NFkrYiAeWCvGiUwbpL9h2PAQFSw8N7YRTSD8yVkAKTTDrxRjWQkGllQoJQFnmKi3dvkSwTPD49l/3x/fffy4F98OQBsjSD53mYjAcIXEdYc2lSwPI8GI2JNO3w1jMxNCy4dYC69tG6oYAhDNcQcK1o4FHGVtBfqoYzCNHZMazGgD/wYAXsyYiRWlKE4GsJwqHOYTq+9HGUmba6n3MtAm8D8b3l/C7NCQTxqBioFgmM61aYbEvOpWT+58E0Ihgm/QBttExd1XM9v6ODYH8lk6lLxhP3lZJysu9UWLuaDLWOgeMQCD1TPNlcxxEJc9taqLYN0sxAVrjYlg6qjMflUo5xXlrI8w5uHCIOHEmRzJMVzFJgbVDFz1RgMglnsyM8//wZ0nSLbcIwCAsWwZtPTNTU/FH1S/2KQH3SHd9YCqGnRzMMogCL1UrYz7Il7lPDwcnZM3x2dozVdYI0yXB9fSX789Hnn6G0XcTnzzCazPD1N68xzzv85Ms5niz/Eb//xxR/uImR4Ah19wJheIz4fIjB5zGOfxzilzPgARJYRYaLqxSlM8ZoNlKsNRm7akkIbUqdDpr3Xms6SKDj32TRmQqUzgoB0LOMYWY18rxW/UzZyO++2N7L/z9a3ug5cy8L7ckKQsjk0Ci/e2sWNdbdLtZI0gQ/+uyZXAcJ0WMtY+9ZzX3nL0nC7NvEKprMUOUZR+aq+Iey2GIRqOYhVd6X7OMYhGBwzKwZjGAhbcjEyxAZBUKPASi0oHGlWM+ACZK5K9fGFi6WCxf1skSENbb1XNKgOZ6qMQoYj0cYT6ayLiE4+ffgz3YA2A7t0A7tv7uxkySAI8la2twfe3P7vgvdH1v622rMuYfA3B+JpDLz4f13r/khUE4/S6M+HCQJQG3TRDzaOElkpZTgFeUgTN5sWanWaWU7HkCv29xjtN2BehrY0Wal/eKvZ7WJj4tMljWrTdaVypuNMiqRGRFoqyqZONKfjZWep0+fCYtsvVnj8y++xI+++BKb9QaXl1fIkkzS1eI4hM/qn6VMSykHpW+DUNXLEjV/alZlSWtnSig1C/xRjIb+6MhibAekqcWcGtR7SShp6lvZ1nQyFinofLFQIQl6n3zEAFQ76e7n3t37wNonh9ePJiKfeqJ6Ui8JpTRWGIIH1tqhHZpcB57vIR5M4LgxKIwbjVzNGKBCaYW315ciB1FZwWI2BNMM4QpbxoBjVMLqqWvFoDJonsyctLoTuZlBmRH9svhS9oECQtRoZYHBxTgNnGwJOzBcD01Jc+1SpIU9E4J9EX2leJuSOcIFZFFZ/kASDPuQQo1I7YH4qrfl2oyqNElUljAEleapLAwMkR81ZLTRn62mmToX/iUmpoGxayCd2IZJL0AAACAASURBVCgHPkIvxGnoYRJEePXuWhJHV6WN2yUQVLcYj0uURog8IYhmIYhiYcpGAZknBBMz9VVpmL+pEYQRnMlYCh51lfeazbuvomWgytCcn7fEUVxgENh4dwsUIl/t+7+Peld1dz8W7hIR+mJJzxLRzAb9iDAdyEIi5tRy+x1i15Zx6Kc//SkePXiK1bsM23kpzyu6GtEkwJMXxxJ0wONM+pZAB3YKN0/w+sLFN/9vhG/yGBmOkR4NYU8H+Pw8xKOJhYnTIrY2sLiE5bGkXYLHAJ5IPKQwdDH0udD7Rxj5BEVpwnQJJBHc6/DntMPLDWDkgF20GJIlOZkKOHE3F2C4RSPHmwUkJnvWaQaHZvpkT24a5J2FiMCy0cG2W83wUOwSMZ7XsqzBwEHoG9huS5FAzmFiTtaKDUwojSpoOfEXmNYRLCtCbhmIQlfYXLSDENcjsug0f0e5kxkityvILi9MkWa5vo/hwMIstsVPTWUU6JRJHi3BntU5wEuFTEmCozZctBWQZwa2tDUyW3y7KbGdNwi3JZAmcI0Kg6MhWi9E2zlwGgcRF8UMMLBMJGWLrORYCWG405OR3mRV08Cgn6ATIW182WdxHCEICUxyQc1z3xUwssy2KIoENhrEDTCCiUkcCMjJgl7keQIccQ8UHfAd5bJpIxJz6UVoM+JawqKU65/XVDiQJF+C1ExhpPVElm1x9vChSJZ533g8keAqnrN5UeDN5QU26QYVGviUpqeSS4Dc7jAQ8NVElxRiOG+HkoqBsCkReQWsgIbw0osICE/W/ypZilQ3CAOZMxJcdD1PJJ+bTSkpi2R4rVdLXF7OcXx8JPuICgLuy6v5JfI8R1e34m03jvla8p0MzGIXQ8PGvGzxjmeF6Uqhw6J1CMNwk2vY7RawAjXlkXPB1IEomtHUg/P6mnbILEUDV8ITVCIpU1ybgYu54wnb0e0IILlIagtzWr1V7+G7HWwvgseESq3iWCe3aJoUtuXvUuq5/4okx3ad4MmzxxhPBki3W1Q5+1E1MVNTLt3L7IIu+2tT/a/k7x0Cz8GTszOkaYbrxUIFi0gfaCAcTvDliy/gVh3m1wSwmYpZC+CUWTbKysbR2QOA58blNcqRhf/t9DdIf/8K//THADfVAGX3EI39DFEUY/woxvizCM+eOfiRXcNvMmHmXa5bhEenGEUuPAZlyGS9FsZ1xaRPeq1xDCMgTeaX2Qhrjb6UZIzm7AOkWO5ivcmQpAzt4ZjHbTDE4C4grf9u/Vx7N5nVWFjPdFZTcO1xrH2cd3Pr3Y8C0cjUvZov4FgWHp+dyzGiGkft7Dt7FgE0dfFGEke1VUErEbDKn0082hjOYjORmanIdOy0VbAQAwpqgm4uShYI2gpmW8A3CwSOAZfs4Zb+khVoYEAPTAJtm9bC+taElefwnQ2S7UKA6aPZkRAH+Bmns6mQHAhU/q37sxnPnj3724cRD+3QDu0/vHEgYOWPrff36v4NrMT45K3uE3/fh+p68Kufcey7q97bsL5fSPb08LBtAddOT07En41V/OVyiaubW2U0rYwmZJv7gFD/OXaf5gNWlgKk1CCnfYVEDkW6PyeSBNYsqer2EkayL0qdOkSAjAMuWWmz2RSBH4hfG73WtlsGCjDEwEfARTLNkLUcVFhrwlYjU01Jvqq6VCwPMit4HPYMf3fLNfkSPXNNVdBkei+pgZxwFsjzDYaDWL4X/Tj4GZWs9m4SdXcYuB0tmf3EYdzd9dfuu3+o9TFTn2xfDqwmMVLlP4QYHNqhqetJrmN6To4kCbMtyXS1hNUi+EZV4v3FW6RS1ea1pCShMGPYro9wYMKzCzT0ncm5QVsMk6WC3nUoyLbwbJF8cSHKxYlM1Fn5r+kJ1aGijFTkngq4kB9ZHJBe1CFLt7C4jWAoABulKr7dCtDQWKEwz7hgFCaaJrmRCENpWO9NI0nGgh4pkQz/0Q+MPmz0F2JIAo2WSQMgK4pyKCYhMqnSbGp4lMl4nZjir2Dg3bpBsjFQXpaoL9eomxtU4RotZTCdi9ju8GiWYnjsYV09R1s5CCIfrushTTdoigTb9Qr5eguUNszKFYkQphbcyMX15RXyDX1qdNFGh+NI4rVV4XTs4GrTIRXS216/2i/S1Cr7rmPUidPqbw0+yg2VDNEDkdIfywP0z+nd3fRmug6O5+IXP/05hsMR5hcJGgamUkrktHjw/Bh+HKhiUdPB7mrY9i3q7X9DunmO687Gnyob7+c1jJWB0XSMo7jFg6mLpxOa6ou5lwoqYLoizxUyeMTfUzHpbrsWE0qz2ks0mwArMm5MA3Fs47dph1VmYZC0mCDHo5MA4zF9q+jNRTBXA1myk8TdW7zMGGywvM3RtA4cz0RadojcDtMRQT4CwZoRKaEHKhhATVkUEEBmUlm3mKcNvpqXWNoOoqGB/92v0W23iMb06J+KKTjBCW8voVpY/dq2gtviuSrHqgPWaYX3rQW3AxLbwInRYupbwo4TYFB8UQUD+2BBzd1HtqYkqHY16D5WXOdYVTbsiY0UHZLbDCNaRgxqNMQeTQ+hH8NxfGT5VuY7cRSp+QH3U1XJ/CDPU1imhyAKxTqiLJnEvsVwxP7Dge+5Mq+Y396IhYVh0C7dgA8PJcEZFwgIkAnMQ28zQbuF7UO2m8xBhP3D4qWgmbuxntgWfwgy09OOAGPO/oWJkQR3BD9sYdlKETCMmVTuCph1s1yKxK9BLRLI0PPx4ulTARK2zBHweI7VcLsUbpWiTQ1U0QRl3ghYSIl3XtGjUYG5N5e3SNNStmN6rQBVD05PpC/tuhQXXYbv//mVMHCarkCVlBiPBmJAT48tgpSrzRKb9RplRuWci8dPHwijjXO0LeXH2xZZxbPOwsYzUXnAFwGZiy2uW+Axfgev+2c01WdonJ/D9CfCttwBNDq4SooSGoQhKEgpret0MG2ezyxRmLIfagO4WNXobnO4SYmKAWB1DnsEPDweIQ55PfS0Xwsv375B6Lg4mp1Kn7u8ukVyu0KVV0rPSPmqF2B0OsFis8ZX33wlxv9qriymXzsgTfkGE7zTHpQWcHY0E2nv9XwuGgo1/1VA45MnDzG2fSzeJnJeVVaFlvJi+sxFE5w9eCLf/dXLazSxgy9P38FPHbz89hp/frtFWh3Da89gDSIEJyGGT2KcPnLw3G0QdhnqrMDNsgLiMWKGJRBQYodBVUdTo6Ffmqg/CJZRktspcI2+lWA6aI2GrOyiFYVIRYuAosFkPJVr6e3lJYgTyVRbOpF9xp7ujLUtS/9jsM+S/bCvKLlbT0gfqf5QTLR+3bE/FHQNxoMYs6Mp3l5dKy9nOaR3/fzdqomAobZkENaasn7h+Wh3DsCQGcND3dBD0kZRNDDrQtiwPA6mQ1l4hsDLMeB1T89JO0JWB1gXCnwUP82WASkmkJWI2gLn4xSTYwe1FWM8eYggiLBar0UqykL+YrHExcWFWOb8LTLaDgy2Qzu0Q/uf1gjqsJuUFKQdIPJvN+OjIeY+oNbfz3Yfkfkr77P3kEyEWWVtW6k0ckCirwPBrMFgIMwwDqYErGSBwhdJZbyXpO63Oz+2fhzcHx44aRa/BS0d5SRRJY8qyrkshhkxz6o+U8QIatWkmufYbrdSob29vZX0USaDSjXZ9z/wWuPnJOglcdgML+BEgEl9BNtI4dYUEPEp0gCgqpSpir3860MM+kWwCeR5gq4pxdhXvNaYEErfkX1p7v392jMp9nfS/t/dDz+mi6GfbDumhv7dMwVZ+T6Aa4d2aPo6EZ8gD95ggMAKpF+bzYZwPC6ADWyv3uPy5kYWYAT1aVRsGi46aySvGYyA0NqgXuXIC8V2MSiNQouyoVTQFtaJ79C3iAUCrruUFFJ8H8nU4IJNgC4t3dMAm+hdeAUzNCAgYG8jSbcIHQtDj6wiB6VJyZ9iQRNcU31Cn6qsGBVqBceFhwL5e7kk/yCAQ0abLOhkbaKFSZqVK9skm41BCGQw1QbqdAmrSnA2ojm6i+3UhxUEMI0B2g1TIAt0Vo7CaLBMTBS3CY69DayRi21moi4KRHEMxwvFyNkLbLRtgW1WYL1di2dl0AInp2OE4xFWqxRtU6oFUFvhfNAi9Dy8uSUwqYod90e9/XY30vXM4f6OnnO9x3a490JxSNojgz9+/Ag//+LnSK465Gt6IHVIiwrR2MLzL0+FAanCJ/h6+pD9Bfnlf8X8zVNUV0dotg4GDr3tAnjRBKNjHxPPxnFoiwG7LO502jbNtfmhGHwhmJMePzyyd+oWVuuh3ZbIUgM5nxrY+HpR42zT4rHf4fFZiDjm51HfTUdsiFyZi8yW4Rfcd1IcUtLgdGAL482MCbrSB+1ujFEZR0xqVGOeWuuqdD/lUdVi4Ft4PnWQXGQCjJwNLBjLDTyH5uGBDl8gmMGN6RIQf2sQRHmY6t2v5xBHgSFyvnO3hU82HQ3V+Z0IRnFbZKoRBOzHOoJr9MoqG2HNuPTP46VpL+HSX5Beh5aBo0EIJzZRO61IYR3DR53mmM8XAs4VZO+kKaIgEDCI3ktkYL5LC6TLJYzpCKv5HPOrKxwfHSOKQykGcg7y/vqNyN5owq9kq2Tg8fXkvSrJOJMKHGsF33uD0F1gYFJSdoGgmcOrr+HVl7Drt7CbNSyjhN1lcOpMWEWOkSBqF4iqa4zLWwySBZwyhWlsYdkEdcmyA3I4IotdrksJYxCpr21jGAzw/Cm9wlSKfItS9QVMReSCn/vX55zLRV2nqCSh1YdjOfAcS4qWw1EMz7OxXDOl0sKjh6ew0HtNOhhjjeurtaRJtgUlyIYADJPJSOZV9HSzXQej4Vh8/c4fnQggxPmZzCUJNFLKlxcotq30rcRBXbKzyCatDMTuAKY7hG1dwKr+gDbrkBlj5Supr0OZV/Nc0uxGMovZl5HVyJPFQnPn4WewcMHgBxu1SdesBt7YweOHU/h8Y5Eha1YrbV5c2n8MBExh/0nwfTAdSGpptlnAcGhF0mGzTsT/jgnDTH2+vr4VBnQ/L+wvMyV/7yRMYTqOJZl0s2bSrmIY8xqLRyf46Y+ewVpnWLxTUuHKZhBGBS8MMDl5gvNHT7BarPHy3QLxYxM/G/4Gt3/8Hr/9KsVwdIqnnz3HNotQ2z6CHx9j/CLE80dkrRXwmgTLmwTXiYHo6BiDkLJistaU1yOLQgTKKAel+oPXnvxjUi5DDDpVOKL6pSpaFDlTQSmZ7FBULRaLDcqqxuOHx3BsE7er7e6iZ2pv3yur8DBe63pckvn4HZi+r+7s1xI9E1n36ns9vPpf9cum+L8tlmvMpkPxc95sElkfyJY0SN8fE7LCe+moWoyoGrvCWWmjwH6moYUkLNdBaTkoOQYzIZjpCjWDEBxJAy+7EjZyBA7XJwTnXKCh9DSDYzGkp0NuOlhlHtLbFraxheGusF4nGI2PhMFGP2mC+2S0iXQ5y6UI8LfUDgy2Qzu0Q/sPaRIxrgccYVLpAeRTWMr+/f0i4sPW/QDAtv/c+yjOvbb3kh7k4kRzEEWYzWaYTCfCOFtvtjIhIJWd6Usio5LX6oVdvyldcVEVbLVxkVf2b6dp3wJuCStDmdeSgWY7StZIkEhJpiB0aQJqnNj2oJ4fBDKZ477kfQTPOGnrATZ6hAg1XaQOisWmEov6aY4ea/v0uL3Bezdcq3kW6opMulykZI5FidQSeUlTUs1a04O23oF3+/RTt/FX7v+h1/5A60E1tePVMTu0Qzu0njXMpDsmBToI6FV1HIqM0eECfbvBxbtLAZYU5MR+xELV0OwdmD54gEGXo9oQECInhLNrTojZnxgoWO62bJlEU3LJHDqBgWqmqLXIya5h4ICkJqt0RZVCrMC2Tn40o5evNpSZu+9UwkqrEQgwIv5PBML0795zTCM1ImnkJrkoEe97LvAFBFQMNqNjUh9/Ky83LnjogSX9LL0ZqeE0lYfYJiuxXWeIfB8hFwP8LA4Xoi7edxbepoB5VSGZb1HfXsGslyhQIqW8z7HxIK7x/LGFMjhBuonh2hb8AUHNWsIZsmyF71+/E8bNhMBhZcF0HIzOQrx7f4vbq68xGxt4t7DQtKKxVcEzigqs+zptPaBRRDXG3MmPpPCjL4D98UbdvmNe7zpXstmaDvEwxs9/8gvUG1vkoBaTOsnkCFrMHlGmFwh7SXBRAmJ4iWb1R1x+b+O7b4YY5DOcBFPUIxvFqQvz6QBOaMBpWjhOC4+pkFzAK4M3rrlkPJJwABkL1feinLBl4h2TDJsaVlUAmxLrdQvjyRCv/7LC1OswejaELwEalgBh/FxqVGvRVoyhZHqlTvrk++q1I73ehMHIxaGAtJRFKsBPUv2YiEs/OJuLTO4DMh2F2imMoLZKYdQVrl5WWJcGzn40QpB+i3rkImufyGcYEMVolRm5nJ+dCpDgdSD7XtHYZL8zaMKWFD6yPbhzHTRkUIHgNSEKJv7RM5AJhrUGJVUaJT2/WEATohAZevUGfkewagJayxpkATqhjItkHE3Gvlwrq+UW19cLYVnFoYfZ0UhYaeLl1XGOs8ab90s5VBavQcPA0bPn8EIXEZk8TSsFth3rzKC9xjtJvezqDlkVIMs8FDVjH1wUHX33XGF2eqJv5WtM8Y/zJKFRAd0E5nugV5hMPB8oWdV/s5ZXl5TbtUhzghsNaIRolDn8roZDJtbEQOMHqK0BysZBV1Kq1sClz5sNhEYFuAG2NGa3G7idgaJiyJMJpjZstjnOJz78QNl1qKR35UHGfo3Hk/cTQPnu5XdYzLc7Gw0FZAOnsyOcPzqVvotzRc7JKP/1XRdpmqNgKi1DSlBJWmmFEp3nYL21kDQWxkeeeNEN2LeEliQ8DpHD7l6izMgq9MgvguGPYNq+8rHUjNW+d2Txo+LUum5ht40CNxxeAAK3IW0NrIsOg4ZBX+w7XVzT27esBWBOk1TYXOwfVaiIIRJq9pkEyJQpYI31fIn1imn36prmpTeYxBjORnj56iW+e/laziF+NoKJgefi2bOHuLy8xvV8qVh3fB9RHvh48uQFRm6Dm+ulYmey5sGrxHMQj45wevoARVXh3atrYOTj+dnXML77C/7lz0PcViHqdgy0xxgPPHz2s5EAedXDGJ+7Nbw2RUH/tkUDZ3IsgRYuz0XusVax/nh+Fbnye+ScWphlEmIgXEyxO6CXGtlt9GIje42sLhaaheXW8PxU/sZkbk5GAR6cTfH+aoX5zVoAYDW9Vn2eWgYpDjF5nVo/qvtzVXTfiXEErNd/6QWHmqmrEVx3aOpc7QcB7UF5fEKQ18PrNxfIqW0m01S/ls8lwLZjw/F0llRQ7Q9ICxthlio2W2V4KBobWQGRz7pNJ4FHlJMafgU7TBG4FQaeA5tJo20I2vRtljdyPRvREbrSR8HOviwwRoXjaY74iNLSGaZHp6LooRycn7+oa1xfXePy3TshDfwttAPAdmiHdmj/YU2BWIo9pUIRNCj1b2Arxr/73juftN3tH3q+Bsn2ny81ay5SXSbtxTg9PZOUTH7W5WqF65tb8T0QltedyObe2yj/iR7NUn43apDcsQpo7qtlo0rqxKQwVoKVzJF/CzutUZVPMtD4GCvO/b4TUK0qZRLOvzkx4CDP3/xA4oEkYQZ35qo9i6O3nb1joGkTaF0Ny/JUaOtMFmMVjOmrSraigD79NXcT43/nAfvrANsHd3woA/1QGqoXTXtg5KEd2t974/Xg+yEcKxA/mcZqMZ0MRebNBe7V27fY5JUs3FUnoL3W3CG8YxcBVqiuL4HGR234IuWRtMSOiwYLteUKS8GT0rtKsDMJtlNi1hkCDNSEzbRfY88QVoUF3WH0IJj2WqO5fGAzTdBHZ6j77n4UEEeQrgfW1MJDTKrUIsJg4YaLX8qiuA+U/F4BeCbMHmgThgBBNgeuq1nCshDewvAiuJ4vwADZORZlVmYFx6WM0UVtuPi2NTFftrAvCmzeLLHNV6ijFWyHVX4LEQw8GpWYPhwgaY9R5a4s1sm8KOgLVWVINltkSQKT0rDKRl6WOHs0FYbNq/kKt1cXkqLIRdB+v6r67l7Sz9ZXdXYrsN1vkebv7upZD3vaILVFYR+9ePoM5yePsb7MJTSAy7qirhCOLQyOAnhxrHyr6gqu38Jt/xnp6xtc/fHXuL42sW1K2AMb09MZwi8ihEMTo9iER0IMPT7LAo3pCzOL8jPxIyJrkL5kbSvHTX0VJmDS369BSyaXQ+NsE01dwMxrpK6H2zc3aLwG4+kxNmQMecAZAVMBiLlIJnChFoZKQgn4joGG5yiRuKYQf6GaPkKUM7u2MMIIUBA4IOPS0GCWMDVtst8c8RlqK8p5mRwYINts0aY12ukZauMKl90U520oct7O7uB5HcYOkyxVSINiBpk6wY+AM33XKHfsJGGWUtuK38JzZV5EYghN1gWEJIOH28krkVy5DIXgJjXwJ2AdTFxtWmRujYD7fdOgLjQryDAwCk34PlNSKX80lURxk2A8HsqilZ6zItlta1y8eoPVdrs7vwhSTI5P4DIAo2GsCf3xFrCNFbqqQFHbyI2HqBGjNm24NpkqSmbHeQf7BF4bTBLt2TfquiaApWTfPQtRI1UKYNMn/9084w5oVg+pWYAC4gwkPLzbGtXNEnZ9DcdMYIURan+AbR1IYYDdD8M8XN9CzX6Gqa5JBa/JZJ8mXYh1ViN0GhyPfZGe8jtzke9apjC5bq7meHNxuZP+8VztC6gCouq+7uz8CJPRCJ7niwxVjl3kIt3WqLeZpDEaoaOM5ptKknyrxobtENwjC7jFKzPC0jHx2G7glRnGLhDbX8Os6F85QGNFgDuQIq18O23pwXNOwkFYTGFqZd3CIxPJaaV/rDpbjrvdUZWhQmUSshHpMXg9l3MlJPKWr+FELYzsFnYcoOxOdQFYzXsN+spVHVa3N8jXcynSdBwjGgOzs7FEwv7l66+wuFniyfOnEkTxuz/8RTyBCSARWENtYjQ5w5MHUyS3axR1JsEbYolIp0ZvgNHJOSbxGFdX11gmLY4fpnjY/gbf/kuGPy4iFO0YbXMCz5rBm7gYPhkhfuHjcQyMsgXctsJmW6MwYkTTIQKmZQr4rc9TzVoTuSfDCCgIpUzTJPuRyg8Gg1UCwNVFK+xRAmtl2Yp0vCLLjQC90KXVPFulhLLHrnF+PMJwGOPN+zm2Kb3JekYxpfD6jO70ewrDV41tApvq8a6fC+8Y2nuz4n5b6qa6dnYzZnpNl4WcX8+ePUO6TXE5v0VN4FiHsmk8724oYcel7BIV8M4xUwlHYbQOWsNHZdoCtOXMuCgaOG0N0+5Eamr5BSyffmsmnKKWvsqdjlE0oahx+P2Y0Fu1HnJ6AhYNZlaK87MONlOU/QmOT84lKZWWOCy2UT767vUbLJbL//RA2wFgO7RDO7T/8KaMrGUm/kl/tr7p5cEHtz++pdGs+0/+AM3ZIV57z/vElvce40SQ/hnHRzMcHx3JhKmqK1xe3WCzpduJTBmVh8Ju0FPDn8Rm7xY3aoEpA+QuIEGHCuwWkkxfVdVTBbBpkE0SWdUEUyj8XAwwyaekDKuS3zKZlWRQ/q3kU8rHhb+VNPSuGra3PpNFqB6ehWBioq5apNkagzAUs2MmhBZ9ws9etfYDe4R7h2H/7t3T9p6v5827SvgnD/xe60G1fnLNSS0rqod2aIem+hNWqT0vEP8jXquzSQw38EB13ubmCrerNaqOvBjt90gJhxPCHcSIYhMDc4l2naHMW5jtRgD9tAukat3wNQTXCGiwIKCZB5w8M5FTFlZkfPSAmGb47nzBpHO580xTwLgBn8w4hwveQJg59D9S8qe9wkMvY9fS0N6rjCme0hdIQYR9NaVeSn0qcjUWcfg+O382Am3cFpkhNuoikUUNvTfpJbTzZyNQSICm4H6o4VnKn430vqXh4KIEFpctupscxe0SXTlH52So6XvUWRiZLR6dVvApp29OUDcWwtCT71MVKao8wfJ2DsfyxW+uXJWosgaD4wCF6+DtxXusb2+0R9V+P6sLNH1nLZ2xlsnuLbzU/5qz1ktM+/5aFnAGTk5O8OzxU6Bwkc9roQtVHCeCBoMjF9EwguX6SgLXtRhGl7CSf8Xbrzskrz9DvDgWxtXVtELy4xEev4gwFSZhh5gyxzZHXTGcwYQXuGKfTZYSATyCpfTYYuqkKYbWDUyepKYy0+ZCVzy6tHG4eHfRpyzJcJXkeBxPsGmAZQDYbocXtoHQooxNsTEJsPLU4HnEhTpJZQQaasbccnwk+9KzhTUpkKX2heJ5RZCPoJdjd3B8ohFbGN1CQFaYA3SGj1VWwOwK5OYQ25bJqRYmlD/xc5sWEqtD6HQ49nguMzWT56AKkqAkWYicukCUVS0aehu5pqRmktUny15iLDx8DIsyWGCjfJX+YybaWi2OlQ0DpdAmtpsCBWxUQkGqgLRG4NfITBfrtEEQdJhFDjxPBRioeQG3rbaxXW9wM79GlhYSOuGHIcIwFD85UMJMvzXKrkUrZqMj1ZXguMV0TS3/7fdhw5RMHkMFMBLUVrJGHeokvpAadO9lcP2k5BNzg/35Xj/+f3Cuy8RAvbcUIyVQoEXD45RvYTcLmF6H1h1JX5a3ruxniwUIbqABHIJcdoeGclqyWD1Ltufyu3Yd5qsVNqtrrNc63ZbglVh7qO8h5Dy9L4U5aXYIAg/npw+ElStKAzBdmSAFmXMl8rZExXmV0M3k9JfrgOETnN/crj0pWFCd3w5dnHgdjs0aXpfDYvgBi6ttgMb2YdshLPrhtY0qMLATJMDK5FJ+1qqF09Vo2acwUEKAGV4kvGaUkf06Z39qIi1KbJYJJnGNZnmNS1Q4aV/i9METuMFz1F0ooK6AsvTMdEyUm7lIivNNATQ0wjdgMrjjZADTauWx33/1Fxjix6ksWRie8fmTU0RGi+v3qUq09EoJTbG9GKPBCSZHxzK/vbleoYlsnMdfoX39UF5VUAAAIABJREFUPb761sFlHqDqpmjMU/jDEYYnMcIHPk5PHTz3aoRNhjIt8G5Rw/R8xOMYA15jGtAS+xRRfhBcI7jP488QA6JN7PdqYSAT0JFCdt4pIK4iENdKEZvnOvusvvDcF+v7MB4ZAw36Mpo4PxmhqGrcrhNJG5XrgcOK8jHQXmzqPN4viPeWCP0VcJcavTv5dzWUPgBDGHCNAjJNk+wwie7AeDjEMBqIPPx2sUQrWvj+dXqd0kPXytJUimxkh/O8prmE1bowGa5iOigMF3luCaBPdq9NIJennss+MkHgdQhHloD4LE6UnY+0UEUcJtu2TYiSv6saflXhbJhhcsQUlwjx+AyeHyNPMmQZ07mB9XqDq6tLLJcr2ef/GdsBYDu0Qzu0/2WNFTEuuEQSs4fa/BDu0t+/P/H6+NH92z/U7m9lj8mmPVSEEi/SVlti14+OZjg5PhEWBKsr9JtgVLlUEHX1td+U2nrvTK3u530cqHZAEZ+jjBi0J9q+VJRVU/W7l5Jy/wiopmns4g9XFMJakyFS+9yov/cp57oS1n83PRncLca0J0yabGRROx4MsFipCHBOItREuGe46a90Hxz7awdm7zm71/5AUw/173M3m1CTDi7iDumgh3ZoclmQEWNZCMlasznpJSPHxnQWi9TPaQu8e3eBVBYPLGaIyRQ604URjBGNfYzdAna+QbLOZW0u7KmOrIcap2GC28rCsh0rXzF6qNE7SKR+XICotEOCLQYX2tKVkTGkJedSG1DMIvZz0qcZENaaZxtoHQJrtg4n6UNgFPuNjBCVlMdN9elydwbwXCBJMrM2z1eeNp2wUYgzEIywHRYtlA+X4rBYsqAlo4zebxHTPR2ygi1YsghQgAhlOFyYUvZEjyWyPTwyQFxlGD83bLwpDJRXDarLBMX1EjXWaLxUFmi2YWLqNXh8bNDUGKviRNgKYehLwWM9vxKmyO3qFlVWw2ktmEw1bYH4JEKCDt+/fIWciWu6GCO94q7/7TtZ1bfvOsm9RxWbRTEfpP9sG2HpPX/6I0yjGdIbpsKRIU0JXgVn3CKaEVwbif9XXtSw3RJj+79h/fobfPvdADc3xxhnM5wGE+BJhOpZhONTB2MampF51pWysCtzE0VrwfBdBAQ6Jc9Ce+GRCWUSiOmQJ6V4z0lohTCp2LdbIBaW50q6JTJjx0GZZQLaxK6LhgEQlomFb+DI6zDgF7QpM7ZVccvg+aTHX5UlKx5JFdfwNkR6tz9MSYYeTyMy6wzKMSsYNhkWBdw2FdlSK0Azfbly8esqBGA24DYZQtcW6RjB1IqhIj6lnTUzcBFSLms5kl7rCHNGl4tUcCmqlqw25VEkR1Q818igseT1FtM8OwVwtbaDK5iYVVzIUkJKjzZgm96iozawjQQM4HXHpGDX5HMcLBoHo8DCOHZ3kkf6LOVZhuXqButlJgD9YEiw2VEsuzxDmRVovQH8YYQgcGS/cbsSqFTu2U7wOuX1q+cV+8CTun7/fTOy/5GmQpzI2GJSumL4SRCAYaDkoj7JYeZr+HaONvKQIkRTE9RXbE676zCMCR4BSbqRY0MFw3aZ4vvXLxUjUPz4enZSP91RYU67QoCWPjP0YDYjQFQKCEX8ioCkJ2EvlJ8ynTZBsqUPmS4kCPuW0maeJy7WaxOZG6BxLSQu2UHAidXioVHArlvkLc/VBAYlfJSeW75IjKUPVoaC6vzvWpQswtaGyEaFlSwaTeWh1zIdVAIhGiQZg7EarN7P8fL9EsPTAOtyhUeuiwejAcazERr6dXouAhYwdKGF13OWpFi8eSvnBjoPNVl9voXzB0eYz6/wlz9/i5xhAKfHeHw6QnE1R5muxeespIrccRGMTjGbPIDre7i9XgjL6eh0hTj7Hf78+wpvbmPkbYiqO4HljWCfxTg6GWD8yMOPYmCMHEyWWG5KJF2E0XgAYuVtTa++XGTJPE4MMJAQA2GtkY2oUkIFimoZ0KMkoQTDhK2m2WtVDyBTEqrZa2rCr/thKYKrHlgNf70/ZifX/8OHU2Rljcur67uXiU5dbUc837RPszzUz9v7vn4vJVr+311Quten5LXKxAOQDFxhtWn+s/hAt8BkNBRm+8X1HJv1Rj4nP3JPcxAmZl+44XzAYlK0YrQp2agNq3Ml5KQyHBStg6JkH1jBrjaw2hK2G0gQguk18IIKEe0CLIYjhCjgY5VyDKAyh+zZSAJpkJcIqxrHcY3ZmYHO9hCMHso4TYseSTY2Ggkg+e7bb5FQf/qfrB1CDg7t0A7tf1nrKdUyIbsv99sDbO5PzD68fbcIufv7E+DZ7q77i5K+ffhmvXySExTKV5hsQ9CJLLM4ijEaDuC5NtKUZtXaSHRvS/vkgl7suMOluj1Gwo4KflfBEtq5nszJ/W0n/mqSMspJpESBk77OyPA+skknEu0NvD2g109+ObPa+SJptggnE1m2RRh44slyfXuLNM8+7bW23/bv29/9++1TANxfmWXfHb07iahizymvtR2IeWiH9nfceB24joc4VEbUlN/Fw4H4KtmtiXx+gbfXN8jpqSWSUFskmHACGIMJJjMLx/YSzXKD1bpCSvRCdG30lTGRwceyiTGJgMfxEhmlTq1a8FPyJMwILrfF7FwvLEUudQfgq+IBF9+2ACgm2T1mK5+7trggZIqyAteUNF6xXVTRRclEVeqo8rXa9UOqrK8lNbov7Re++keWFNLfqH6RC8o83aIqt4iH9Nb8/9h78+a4svtK8Lx9yx2JhSBIFmuRZLvt8UT0H/3dJ2JiomNiVo+77ZZtyZKqXFUskiCA3N++TZzfvTczgSJle6bbklp5WVkAcnn58uVdzz2Lq6U9mh/QHdhwAlwKICi7K2gsR/lkiUyuQuJ0mHOhPHSwG/oI/Rh24aLLiCRVqJwcu97GYmfD2m0xH6TowgjVNpPeeXw2h+2SEejCCxzxFqLcjGuzYlPCLVu8enUNKxljtdqInOl4s+ExPKSl/rrPNL8fKgqvT4OLswv8D3/+7+EUIeoFwRgbJRdzdo1wBgzORwgHE6RZhW3TYTjcYFz8T/j2F0v8/T9c4H5zhdqeopuNYH8+wuDzAQZnPkahAkydLhOQqax8YTYwXTYmcKaNvAmz8lRriyxpekQBFb2bamUkTl8nerwJOGRbYjJPTzL6VlUiLSLroUFHMMTvkPTACD2SBtjUFu7pI9gT3OQ4QShVbTrJyCt+YYrVSDBLzkVvQBk/pL0fHA2/ukp8kTZuCLsMheW9tl18RxbaYoG2rhD69ItLUVIC5bvipca029glU7FFxnbXWMgb+jnl4hknXHdNvJD0UprJi7SQSUuNsPBaSl0J9DGlledfFUBfCfDL7zWR4ATlM9dIeqqNYrtRhusF01JLuGMbHRMrGy6Ge5zPGIjEeUoun5Megat7pvW9E/bpdDrDaDxSjMpNju26RBONMLqa43waIQkc+LK4VucuUw3OHciyZ0qveJaZpF99U6TVA0vttw/7/7+LAvS0KSMBLAEbFN2MrJow9uCPh6j9MZrChpstMHRS2GGCtqO8VdWB9/dr7LICPiWkVY0wiSRFtSgIHBeKImsM/I2BvXlvHZRx8/wG4/EYaboTo3Yeh3NE3/PRsJ4Lc4jS3VBu9GcjYMM2SdAmDmJMJxMU9RbNtkUEB2HN1GMbH3oLmQMMOhc5fDjsfyUVmMBii1bmdAxkUZMtcuc4z5QcVuPdxWRgl76KymePH8OzCpXWHNoi4163TD8NEPeeBJh88AYo/RBOVyLpdxjav4HtjBQTSSIoHQHFRmcTGnuh4Maz9ltcrTMEUYwvv/wMI4J0NrD4oUSNFrXfkUIIJ0wwnr/G+cWNzGIfbpfoQxc3l78Bvvtb/PXfJniXjVBjAvQ3COMpxlcDnH0xwc0rH38adUi6HG1W4JYnn8wwHUUCrtF/kTf2DZRHc1OcYSrse2Tm7bboGWRgQgzqei8bLdiuGHxA3zWCa+IxSu++wyb2vnbribdSpXDcU9dWpNB6vr1Zp7I59Pz6TMa4bZab6GPznx62OO9VXnSP59mHP/b9vVmntBW6mixUBgT5irEtTzChE6quFmWF9XqDySjB9fUFdgwTEP9KDRAKw93geexv9jZveoVBQI53Evynzr6F43UYOJVIkEtrhLZ2hBndNZRa2xDBbd/C7itEVo049GA7gfLetHPxv3QcH6VrY106SBcdAiuDZS+wyxqMxzPxMKW89dlZAscN8OHuHn9o5cRgO5VTOZXfSeEgoBgHOv1tj878ltc8xuF+/MgxINP/FoDNHMgc7elD+iWcVDFRazKZ4vLiHIPBUAbcxXKJ+/ulkoYq52UFbBmgaM+OUztJalzW0s/97icXAAdDcJFUyEJTGaSSWk9at8hB6bcmO2id8mQxsycBozTz4xG5XEZFZcwrEg1OwpQclONqEkcie91lqUru0ef3Izzr+CvZX7Mn9x0/9+gLkimoLGp+/G31T15wANZUCtbJa+1UTkUV+kOG9A2TDQkLQWRhNJqBNByryvDu/VtJ+SQcJD5NBNdsH3YyQjRKMAkzROk9VqseRUtGGxf4NGjuwSwwSuIo6zD+SF5f4zxYIrFyfL0YoXQSYdPQnYVPEPaFSSGW12hgTdqtI4CJa9UIyJZwAmHn2MJs0mCalo26Ri6vE6eFuXbUAbG/Mn2eMOga5dtF1ELkLtyh52cRCZgl3k8k1jlWIX5eQTKETxktmVLSM7uygFCyLhWCwNACApZkLanFtKNko2S0VR3sukHAlESfMicXleXju87BYt3Dvi2xvNui39yj8teonQYD28WffXaFIttiMqmQ+tdoCk+M/8M4QVXmKPMt6qrA4oMyd3aJRVUW4oGHwdUA7x5q/NOvf0XDG7UIEtnrodc0pAbjS7UffLoe0TDGz37yM7htguKugdc7KKwOFQML/ArRKMDofC4G3+u8RnRW4Dn+Gh9+cYt/eD/GbjlDjnN0QYTZzQxXLwc4G3mwBsA5AdO+EMZLVTko4cGSa8jvu4fF+ihsaiNtbEQyVzs+8tZRUr6igUXmg02ArZGESI/sC5epto6kqa6LFkVWwmkrBDGl0D6qIkfARRkXY7WLzHOw81qMnQZjOIhGobAl1YCrAFbl79WLZFT80STAUT0mElKG6Qa8sxYJNf1/towbqHtETYustrB6uBUQWliSYY9oYCOyz+FLmjfTBjtYZLzU9FNzUTH50rqHvQ5gnZ8Lu431msxw+q/xehAs4/rWCZT0kkAJATMsNkjCHawR2akj0OSIV7QiFi5sJOUb9fb2vdpI42LX7hFGLoLERRLNEDi+tJcPizWKLMX5dCIBG3xqmhUC8hLMW35IUUYJ5ldTnEVKBq5Ao/8P5ekc4XdQBKiQhHgNuMsGKBmuqo/iBsFmV6JcPmDM9jyZonFCJT/vatzd3Qtzhn0RFQtxEkvg1Js372STU/o4M+dSllWYnU1xfn4uzJo8p7JBzdno3TsejVXIl2MjikIFWEi2RSQyfgIcRV6KX1fRVPibb77BfbfBVxhjMp6jtgM0pYOWYO6wR1wDbzkXjS3c2EAAhjpUcPot+o4bGlOVrK5TmykNf990GBHAo0xY5lcqeER5XOpAB3Yblo3ltsRy3SHtHJGNBl4tXplRb4sU0GlXOBvtEIyeofemsJxAzXWlb66RZiV2yy3SD0v0bNSs1ww7GIY4Oz/D27f3uPvwPcOrMZ5eYDZ/LunRi4cVytbC/GyL0e5/xy9/HuNX6zE6eOgwgedMEE4GGLwaYfjCw5dJj1mXi0/kZtcit0IMRjFC6fc1w9lsCgkbjdYqyl6FgI8kw7oMMejQ1vQ6pP2KYqwxzICyToJxClhT7LK9OlG+fi3b1G3lYGugQgZ4TU3MmcJjlSS0bRj84OD8aoZ3twts6X3Yk6mtQD+16W6IbYpVJs1KrAOM+YKaSbPO1lUp7drxKOFU95umt5eV6s0o1SdLLIx89+dnEzi+L3WbmxSSSGs2Idgd6tdwE4iMUBWCoPza7N7D5WQuoPF9VqOjtUDhIc8ttEUNt23g8XnMFgkaeGENL6gx8G2EbozaCZFWLrJcfR9d56PuPGYmAWWFM7vE+aTF8NJCH7zEbDiCBR/f/HCLf/j5f5ZxOw4jCV9jKNzvezkx2E7lVE7ld1YMvZ8U94/hN8fFDCBHGM4nHj0u5pnHrzLo2SeOaJ6upYqSplUU2G63krSZJAlGoxGSJBaWGXeSZREk27cmuVMtfgwrS21aHbEyzBtpkE95nerFpNyU95AEF2gZxN77QR9ZoVj2QX5qdpCNLJQ7nTpYoa5LpLs1BhFT4gLcL5aywy3+GOY1H7t8HyvHo/l+VP/4aw2PTy8NH73MPCYTPQ08Ui57AtdO5VSUr1QQhvCTBJ4GYuaXUwySEZw6w/L9G9yud6iFreaI/LIT1loCfzTBdOZg2K/FDPxho7yqKGkkoM4QAwIfbhDC50SdAAInhOyD6hbLNMCiiPHZIKXbk3gZUSIi5tp6U0CZbfN9KbdUck/fbmTHmqmGLSf/vJ/ekjqpTzwntU+TAts0a01uBrDTCwbdLas1h/GqUX3gnr0miweld+m4iCq3iuERDGVTQcJmNJtKfmoZpbyebLZWSeAMVMW3lCAFgoD0wHJsVGSa0COcCYZ2hZltYRTZSKeeeJc5bgK78nA9dXA9jvH19+9wm7ZIdz1m1hLxiAlpgUjw6PEZJgM5j8EwFBlMRtaSS0lXj/yhwCAGLj//AjVZK6lK7iPTbn8x5NrYRxsTCkh6/cUr/Oz1n2L99Qa7JV26PBToUXkl7EGD8dUMyXiC5UOK3G3x4uJbxG/+I375nyr88s0c6+0Ncv8C3tkI11+c4fNXQ/gzF2Hc44XdwmtLMOyzaDwJwKCBfEgZIcc8PVbR9Lx3XNQ9mWtEslq4ViUL4D5wkHsOKtZVLqgoVxWpX6tYH+JFamNAc/qgFQCvTJnkV8OLInSOhwwNYseStFL6KzluBXsLPDRsK5ReKukTF+ACxEqQgpKd8pJVfYvbZYFukSMOalgBpWI+GnigeOo9tZSVBZfpA3WGjYT96AVqa6MsgFHEFEMbNcFYWUyyXtDtUK1qbTeFmwVIm1CSTQOnVb5s4vXXoKVMrWewkgpseKiBzYcWUVohHP4j0xrQWlORjFJSarcWAvnWewEcmeibZpksMgmTRGGM2ehcNtNWuxS/IRuos0VCKz6tcp0FfsfidolFH+P81QU+m8dyrRVs/wnW+pNi5mePniqN1WxuHs3gPjqZM7MiAxqYucxR+dHB//li+gvWI9N2ZU5pwA9pO634c6XuAHXawctTYU66YYjJaID1diWgF9sW/dK4sXF5eY4gCASsZDukPNTzArx69UJ86zabjdh2sK/e7rYCxp1NZ/I3+xWyo/KcTEJb1A9MzCVg7LkufDJ02lYSN5nA+TyeYzhMMByT0RZiMvGRlwWstoZdtQg2wIfWxi23CriRwXYkHpupAkht1a/wVjA8w+oxlPAOPf80s1Fizazfcqeat3JsePB9TMcegkEgjKiYXm5kRTYOdnmPt1kLu8iR2O/gOUtQrM30XdZ81jF4DqZXU3T0u2xKaQ+r3Rqr9wtcXJ3h4tkVgsEU0/kzVEWJ1cMWzgB4Mf45ql9/g//776Z4UyWonBEcnCMYnWH4corBl0O8/szDT/0Gg5qs5B6L1EIf02PMR+gonzm2pY6gWVmjyDkvp6caGaWUBfO74xy6lmsuwJuw1RrkGT3XdHCY2LFwjKRh/8EfTZqHulx6I1ptDO19RgXgUzfDEjTX3Einy6bD/cMSZ9ME87MJ8rxE1VTqecIiOyh61IaT/nl0H8FMnpsXRgKoHsbKI322mZ/reb1i2akb+8ZtnqPIMrx+eQ3PZuJtqeqFnoMrYI+4INlsemztOgRhjM8vn2G5vsOSoWh2C1dL/j2ffoKcKbjCfLcqstmolgnRdB4q+txZTMhlsAgQB9x442YAA2ZqHQDnYNfS03WA53POf8bIBQRucDYaCFBKcHY0HuDq+TP5ngiy/T77s50YbKdyKqfye1FkAUYz4r2X2ONipm9PMZ3DfccTPP2s/V0fQYDksU8iQ4eiTUE5lFEewR3Jy4tLnJ2pidR2u8OHu4WwApTEiYvAo3PZj1jKU0HeUdhsajA0ng0GLJN3ksFWgY9ka5gF5bGhmexOCZNkP+6rbTTxYVALdG6JpcVOnhNHoey2cvdMvNbMeXzs0n1kcmyuwaeu0adepx7+FJNNLRpNEuCpnMofexE5qB8Kc5azV/pBzyYx/CCWienq7gcs11uUHY3dNQOWPYATwfUTRAMfwyhHn6XIUvrxqAWISk+kWo9Al5J6SeIfQQL2NdrnkbvJAhdon6Wh3WHslshaC2sMYHkBISxJ6+xlIStRCwicEp4XorOZSKrCW+gnaXw3xdNFQhMUc1cx5g4sOLM26B8x2BQAc8xgEz9KYZ50VK2oxWWfwWMSnB3CtgkYak82GjZ7Wi4o58P3Ueeuz0Tem8AOrzdBD16bx/5slqRO9hUZYWRddbJDDyfAbe/ifdrD+bBDl1d4eLtG22xRBil6p0diuzinl9KZC2s8QV5y8ejCjyj3slHkKcoqx3a7QL7ZImh8ODQH74BkPkI38PHtt2+wffggIJsYUZu+VIaDFuPJBF99/iewcx/tgkEUHTbNThY1NgMtLqcYTcbINhU2dYez81tM87/C7bcZ/v67KdbZBdruDG4UI3o5wYvnAwymHsYxcOYwTZSSoh5V7Uh6pAKNuIgk00LVG34/9Cwiq8ILfRGJ0rifaXw0xPbIVvMpz/KwhIdNaaHfNfDKCk5XCzgWR5TQhjLepcuFHKNJplikgFdVCPweYazSHm0mgHIR65aw0gC7JMQ06oXlRgYdrxMTYpuqgRsySZZG9RZuqx71qsUkyzE5W6FNYuQEs3qCUVQ/WfCYJMkFo2Xh4WGJxWIloDSN7K+vL9UG1SZD2QKjmIEIrQCvLheW0oC3aNIh+kGC2GddZ4Oi15NK/avKWvxWmSFAasiut5CnQLTcYTD9Fk00R4UpLB3UQQ9EsmvS+3sMLsaIYgIbHTbrjTBGk0GMXZ5hvViAYtc4HMARnaAMrMKcWbzP0I4GOJvEmCSUr8qJmv/+leUA9Kof5o99yz1MufY/f6xPeDzleDKv2EujD/OT/XPURX5yNGPR0f/ocb4H+z4j/WOXR6Cfz2m3JTmCUmdZT7JdiruHhfQJUUjw3EUUUYJnYXF/L0DtdDJFURbIs0zqCOWkeUFgPBIwTnlG8vtWQE0lxvm1hE6MRyOEQSDed55Hk0dL+tyH+6X0WQxhIQDHvnHJTdC0RMU5Jz/F2sPK8ZFGFpLQFl9L9kWx0yBhP9yHAjrTm5NfsCvzS/bhClzsmPypJ2oEj8SbzWJfZ6MSSiUfYscGYfBuVzXaokW1qSQNORdZn4VhUGM2uMd4nKAPrpCVHmzPhc9USbKrygzvv/kNYx6wqHKs01o2F17cfCYMLtoMLHcFhoM1vOWv8fWvS7zd0ouStvpnCNwJ3PkAyfUA4ysPP417DPtcNn7Skvh3CJ/ppwy30Z+t5/hAO5WCrDWys+m1Rkm82mA5hBhQDlpJwFhZdUh3lPR2Indnv8K+R4JWhAmpwXqZqmtQTebrajNoD6bpubfy5juu12rjQ+S7EgSiZN5kjjN042wyQBAGuH3/AUVBFq2MwvJqkZEfNyJe17aS+qeY1roFS3U37di0RiWTlzXAk3aiPN44figGeEhQdToV2SjZhCaAztjYcNOfrNeX18+w262wTHeoCetS6k4PaUlK5qZ4APQ+6t5DVbkko6Gnr2fHMYEbIYAblvCjElHQIXbJ7kzQWLGMBRl9Ju0el2cXuAzJjvRl84tXpOorvLu/x8X8EsEwxG61Rmt56D0fXv0Gv/7VB6y2qQLrfs/KicF2KqdyKr8XRdGxSetXcqKPgWzHxQwdZkA7DCUfmzKa+54Cap+YXj55ipFPkM3GyRLZbPTZ4CJ1NBpjMhnJIi4nK4yeKjLiKUNcdYKHHaY9qPVodqtT+tSvGlTTBqgcFvViaj90Gzbcsd+a7EId0rzItuOuahJz0WlJkpD4xxmvtf15/DPF+sQk+BiQ+xcCauY+wyIRSdnJa+1UTkUK20JAM2c3hmfT18rDxfkMQRjBKra4e/stFmmpEkK1NJMLGdsZwosSxFGL2Nqh2pbIik4m9JxWixy0tcWw2vV9kW8yWVF8sPoKXUW/Rxo6K3NvA3hzw4DGxmkXIiBDwS2EhdETyBLQyoJv1Qj9GrY7lGQ+0uEUG4lg1cFvzQBc4glJ1psxSxfQ63E3Yvp+Q9g1Gwz8x4WKPE5iWtsi6FPp/yoabdPTSj9fehkZU1Sa3rH3pfjP6T0O6Vs7Mow6YbWpBYgKUhBWrSQ+K78n8jLodWXVhCBrBPU9Jm6P/myETRzD9Yew6hDOhi7eNUqrQt52YtTs5A+YDjJYQYQ0U94+8WAokjT61IVxhLKphF3BkILl7T26qsBnL68RT5/hYbslaqTOubNE2vqzP/kzvLz6CvW9BWSWJP2RtVYHLdwzH7PrSwRBjPu3KYpBi1fz/wL73d/g//lbC79+d4lFeY3anWN0PsWzn57jxbMY9tzFZdTjwm7g1Dnq0kbReiIT9n2msnJRRQNtptcd5Fhkf0g6tkmhkwAKG63rCmOyo7VY2yCxa4yYRhi5WIlxuou+skV66vuUbzVY7RoUjY04STAfOeg8B1nRq7RI+orFIRrta0a5E1MHR2IaT9DVEr83CUIIXDhWBcf6AY4dIrRjdJ6LgJLNoEHlkmERgmGCtIdq8x3+8e9/ieV6gWQyEeP78WggrLGrqwuhpfzq6zu8v6thoxUZnRcwOdURLysykawuxC6MsQ4cTPQGGMfcqoSEJdAfrW/0ItUh69PBdwxjaF0EiNAxxZTWgkLNAAAgAElEQVR+W2zbXSdjODfF/DDEIKExPxNGudEXCQD03Yd3eP/uFq7tYxgnyl+Qi17fQ1e1uFtXmLy6xM00REQ59J7l/snZz5Ny8Iva/75vg5ybKNsK4yNrUn8FsJD7lRx9L/emp5U8pu8zQSZif6EW9SalVDFWVftVPosGvDtic+r/qSmQmgcdF/7F+sgEVPrnycYC+y3XRph4cMMAm7xFneUYDBPxQyNgvFot5XAE9gnyU7UQ+D62m42EGfC4mw3TiXtMJ2Pp3/jZCJjtEynpmavtPcqiwsNiKYCbH3nCHl6vdvjmm3/Cy5fPESWxgLhURNx+eCPMOBKSCQgNkgSD6QCrbSbt3yP8XAGL2sJ72IhcDzHJRlaPXZXCTX9ATxmn0v8p+wDNduV9EojSGi9CdZXspobv9kriz/u52RC5WI995I2DEBYSxwMaH4vCxyLLEXRLREkkUnuLjOCeQRwVttvvYbHdI8AHsvx8B1YT4v7NO/R9hedXZ7CzLX7+9wW+zyKU1gCuNceQLL7PZhh8McBnz1z8NKgRNhmaxsK2dGBxkylyldca58Vi8l+J5LvIGWSgATKrReeQvUo3MLK+CKzVAr4VVY/1RrH+BomPqiqR5oUEUfT7OmnANXovKtafYYEJQGvGBUnLVddUzfV1yqeueNJODMtaz4pNwMA2L8Qj7uZqjjiOkO1KFaJgbBjIWu9teExNJgOVgCzBNTm2QtAUcVR9t4/XE4YJbqJfDvcrEFA9zjFvu9kJu/LyfCphKFnBVFCC0B5evHyBVzdX+Pb7r7He0jtQaZ33OBw3fUTGqhiCrt1JKrPD+uB6aLkJyPWQgM4cO31J7a7aRgHbVoUotDGJJrg5nyEaTlCFMayGSbidJIl+82GJ8egCu80Cy80WyWiI68sLmed06QqwhvB8hvWw7TFN9fennAC2UzmVU/m9Ktz5k81XnTB3QHIeF/OI9VtBtqN7zUxMRqYnU8vjPx+9pXquoWwLlVsv2mgeSgkJd8WikOa4Q6H4t12NomJHr/aQjt/rELtt2Gv6PY7eVwbl/Vh5bK6qJ4tm8DQpc4YJwgm5uExbyLJUZKGc+GV5geVqLRRr2eX914BrLE/nrE9f+pFDHYNrZu/aDPbms6j0VD1hOJVT+WOXgwYBomAogBl3fL3ExcX5SFha2cN73N4tkNLfSphVZFgxkXMAz58gij2E/g5ukyPLVPqZTHyZACisNRe2F4jXGg29ZWFAnZ7I/hpUrYVWTIJUH6L6XtP/cpFBxx8fJSKReIR2Ls3YBUERSgYH6Gyav2vmGiWh+nd6rSkzdO05KeCaWpTIQuK4az5aI0hvoftC5VWjWG1qYd/C6QmcVKitECU96GRxxFdqGG0fIMOnaybBkefNXj6qd/vFAl+ANgUcyKJBJ5byMrha2kogJa96SRy0Ow9J5GPsdJgGNvqJg2pIJssAXemLPxflUmQorDYWVksbEVKMhw1asih2DRzHQxjFYvocRgGcyMbdeoEqoA9ShGZdI6KE7PNruP4Am3yH+XiCv/iz/xFenaC+I+PBRtkDeVehDHPE8wRnF+fIsxbLTYnBzQI3zf+Ft399i7/5OsHt7hJpd414PMfNl3O8/mqC2dyDP7HxhddiqEHXsvZQw4MTugg8W/x1yFojAEg5FmVVZI2ItIoMArIhZdGprhnrkCzWXRuN7aBsHaHH8LsbOi2GgYM0dFGyThA0LiHSraK2YAUBZqNQPIFitxfWD69ZXfRoilxYYLYboGpr7BxgTDkcWXN1j7QCNgxvIB6QboXN2NtDlLaHe8fC2PeVWXtHFoYLX5goZHg2iAcJNmmOb777TgBCbp4RzGKNIM46myZIQguB2wgDJPI9hJ6vFpKs332Ah7set2MHPjrEBJjo8dTY2OYE2CwUWzI2VFLf0rLxrnMwet8h9Gz0PuWtKm2cbDnfJ6PJRlEX2Gx3suCmFJaL3H/69i1WD/eYTGeiAJA26ccyvtdZjTZO8NnNFCOdpHqwj/gXlCOQ2oBoxjJD/a2tK0RSp4Az8Y01wJr+Wx7bW1+o16jnm3RGNZ9SoNvx6xU4p6R66nnyu/77MC/S86dH5DUze9Kehfoj703o91J0NSsh6EkJ8i5TwNl4PEAchtimqUhFxQqErLW8kI1OguJMBA2jEHEUi5+UCqEimMg+VwNrTz4TT5fSwPVqLXOyhw938llubq4k1ZbXiH5hPFbFPsi2cHP1DMPhgPp9BIGFvmhQlrV8/wRCKJcmo5SwbCkm9Q1i9xYoFsJGpnUAfShF3i8drKpbZD+zfnOjhkAS0zMdhjIQLrYhnp8EIs89C8GAHGUVeiOJzpSzk2c0mGGUkHWqfTQdC2VnIc06jOavMZ1dYja7QttYsOsCTpPLBsLqfgPHG+D5Fy/IfUbVRJjNLzB4PcH0VYCfjnpc9hlQVchqB7vGFSAv8ui1acD9Gm3ViBSU4JokhNI3zFYhBgx8aNtKNgAkRZTPLTu58bqkKW1TdogHLkajGGmWy1jJ1GMZN/TYp2ztlG+nCvQwP49ZbfsQVz2eHI1Buh4eSGkH5ijHnMWKNgDAs6u5XD8yItmf02tsEAfI60IxyveBpWYRYTbZFU9NVXPryWCqFC2K2alru9mc1z+50cXgnXSXYhjHmE3H8rqf/uQrYZD94pe/Ep889SaKhauyhNTuFEG2ltddcd6k/rj0/PToOegJ2C+ZHhx/SebtXLStK0Ab/WDHcYBJeIa+DQQ0ZvdXuhbe3r5F1jt4/bOfoHMtpKsNXJTIl9+iybZIzq7RO0OkuwqWNcbk4iWC6QRtwTUZd1h+9+UkET2VUzmV39tiEubMZOrjUNuhHAYa8xcO9zx+8FA+clBDsX702PHrju7n+XFn8/x8jouLS5l87XY73N7dC6NNBkAtf5Q9LIOyPTrDwyTx8AD/Z2K8lVeaHkIPk2Sd4qXut8XTochzxGEgLydrjZO9Rwmhx8Vck4+V3/bYk/L4sh7+egyuqRmG8q9Q/iincip/7IVylWE05GwUdU+fJQtnZ2N4jYUuW+H9hw8oJL1NTaaV+1QAyw8RxD6GTGVrMmE6VGSgiQ8kd3N7lC3dhinfcYWFJXJKHqWrZdFRc7ErgL1J8FTSj/0uumwQqOQ4ActE2kkpXqF8Z2wftZOg9wLNaDukgwrApkE0SkVNGIL9xGuNxawbFPZ+8L6RBT0X13rhKmwSUoGaHJ3jysSfKYxcnJqljFwlYRUoyY4xOufnpxSUzC+azRuGnfL/pGxOgTzkBIpslMEJBJU8D67nwKKsjEmXVYW87iVAgRJIGjvTFJwgDrhIt3x83VgoHzrY73bY3K2QbtbI3B1VvIgDC/MIeHFmIzpLsCouYDWWsFfIhsqZfloz/W6DzTKVoAKvCWBnPfwrH8nlFA5DBh74vSspZkpfvT6DP7EwvbgE/ffffcjgXTb4KvkrLH/xA/7TPyXYZjPk3RyNP8H0aoKXL8e4mHnoBxaeEzilyLCqxLSfsknGLZLpI8Aar6+wk5S3kRiEk/VInyMaeetUxdAPRFbEukDvPQKqIrfVhv1l1aMvyG2hbI7hCy5SK8COvoAEorIKfV1jOAwwpQSTLBUyulVtRGlZuN90sMoSPuWZUSigcFMVGEYO3AzYpRbeO8BXVz7y9Q5R0MAKB/ilHSAvbXxZ9HBiLgZ7lOlOUjVZG8lOJwiUp5kwOn/xq98AQY9//+d/gdD1kJcllqsVAi9CFAfCLGK9I9uJpvhhGCHoQyz+1wZv/sMQ3VmHP7crDBiCkHZYLBtMbiLUt1zYd6jHHv5zHyFa2nj5XYXkdYMCBRarFL3bYTAYYDqeyrWUc6s7fP3N1+LD+PzlDf7hmzdI6JFYlUiGU3heLI1oUzT47OVMEl9l9P1YgNEnmWpCoT+wb4TRo3zoFLB28EBUbdTME8xor+/TAMOP5hH7eZxq/8dzh2P2z2ET8jE4KPOGo98VyPFEaq4RDzVl+u0f3PQ5LIpZRNCmwmxIzhalpTXW65VmNqlQK6aBMlmebN7lYoWGYI8OY1FA4IGtx0Oz7+JzTVI8AS3VRynZ3l/+u5+J7y4ZzHXbI/A88XMTn19pZ41slBKcoAm/25VYbFo0gxCXoxCDgOBqL2EDtlsj8Su41hpWs0JXhihxCYdsWdsXhmlHwEQCcRRozD2FslZSSZ+yQJ8sST5IYM2Vx7cVkG1abDPKaktcXUQI6H/WMwSCG6VsTRaKpsR95grjjfekZYNgFGHiNPjw3a9x92GJ0B8hcQLxJRs9O8NwNsG3hYvRhY/PUMCq6U9mYVeTiRmI1JoSQpGkE6QVqWcjoR9kpckGCj3WnBY9WWuSEMoNABViwOfyd7bpuu5lbFSMSTVO8rNezBK5Fm/vNhK2ojz3qOJWhmpSz4QBpubcClI0jDXNiN77gpoaZen3IW3N2LwotY7AUZqFS7CKbWs49HAxHclnz9IdbhdrVde1dYz6z2zAy7vrdzmEqh1X9z0/wXhD6xbH81R/68A0DQnKJpQFXM5nMvZ9/cOtWA7IhZGnqY0nNY8/LFN6j/J/tYnmkb3MDb2OjDv28j7KxkVV9Ir5TRa202JyGeMnzxM83KbS5saDqWwcpdkKi6rA1eufIIxjPNy+RbF9jzyrsEhd9GmKiEOK32B+9Rlef36DLO9wX3qwzkO8RIZvf/Vr/PJXv0IlRIffXTkx2E7lVE7l97YoBoKS6kgipi6fmjIdL9ge32umcf1jBM0MjsfPNS82j5vb8bP2kziO98obaLdLJaqd7A3KCSbjsfxO3zOZmPGQ2qxava2eYKq4H8WO05Ncc9Z61FZEuP1C2HlktKr2oWxJBG2qEqPhAFmeY7XeCLgmkieZbOoPcfxZftuF/G3Amx6SzRR5D6A9OcDxEprfpWGtncC1U/ljL5KIFcVIgoHyX+lqXF2OMRuP4BUFVu++x/v1ToAOZYCs/cOcCFYSgl75IytDlxXISwphJPtLFiBky1S9Dyf0xMibYJhNWV9fo6sr8SNqKIkTwMuRvvXAblE3kbXI9rxKB5UAEjRIvAp2kKBzRrDcCMOgE0NteuswjZNMGo9gnHi4qeMbAM/+CHPtURd0zEhRd5j5vxoL6lzkUZ0TiqeWkXeaBYaS06v+1DBetDp0fzNggVoI6ZQ2Le9RW/NqkSFBMyJ7Uu/d1hXS1YPIdelnyc9HZhbBR15vBiFwsRnaNS752MBGNg6BgIEPMayaACXltZ34d20oE92VOEu2cGKmbDpoygphlMD1YtiOh8EgRtFVqPoCMY3Pz8YoPmzRp8oHb900SPsSbZhh/GyM0XyO9X2O27bFi5e3eJH+R/ztX6f4qzdTbLMrMDPUGU7x4qcX+MnrMeK5ixHBNYchBjnaisxsD7VLTypXGFX8bi0CXAQRRA5KqZXyXBNQAVqOpb1CVeiCSgaXsUcJoxQLUKR61Lg5Uq/r0hI5UGAXGDJxlOCn70nS4sADAvFC4yKeo4st3wdZkwTSHC9A0TC9rpKFcjKM4YuNaYqoK+FtAH8SqpRW38PW7vBN5eD5ukMovlgplvdrYUktNyupn/RXJRhMNinBDc8iMzSAP3CxfNji7dt3+Pz1a0RxKM/lmH+3eC9+b6xvq3QJP/Yx+8kY9UMJL3LREqDsc3j9Dm7RAIMQXruENcjxYEdYFy7m2xbjZzbcgYcPdyv0jScL8rxMZdOMCZe8hmsGGSy3Yrq/WCzhdCXqpsVofCbMOwIsfRjg82cD8acSVrtOB/5kOQKzhaUmkk7NSJO5DcGhI5Bbs9HUxp8JG+E/wxg1AJxOYTQ/NVPNJH0aSShvvG8vzzPei/o1wpg7+imvFcmp+l3ORTR9hmm3pwrtgQMWBQb8+EKYuZwB8gLaT3oOltsMgUOvPFtYZTyM2kBQrHvKP9m/UbnAc6BPGeeBosCQczKXV3lvmeu1n9lpRhEZng/LNRIytJg4KmwysnIUQEg2znZboi4IUpSI+wplVWJ+nuByEglQphIvG3Q0jC9yPCwqtPYAbjiU0BGZQtZrNL2tmMoO+2ntvam7eVGTui5apvmSAEQ2FxjQ0WnpN2XdDhKrxfmkR+TbWHuBHJNgGplXP/zwXozsR26BLohRwsZo4GEiwaIOxrOZeNhVRY3FtpAUa0oPN+s1Xow8XAU9+jqTpMkcCsSOfAapkLXGPohy0EpSdzmGsQ8SSbHDW4MWlZKD1pVsIInvHn3ZCK4RkGsUu5ssZeNpzG+k6h2styWatsLlWUy6MvKSTCzNwJW5tgJEDbCkvNcM4GSAUw0qH41ZCsNS9XAPKeuBz4x2ZvPbdwLxRS3bCtEgRMHwBfolC5vcrBwOm19m7n9QtegDG3bbEQpm5uLm/Y7XQiq9W/u5EkzdFeJP90KHfJB1qWSgRi571H54GAlE4B/0veOtpSGfzEWkDnkEbFUYU0NW5M0Yr29maJuYOyao8wxFvkXZ5PAmE1y//lLmQ5vFd6geVlgvXaR2IAmwTcMtiAT9Zo7GDnC/u8VsHGJ+PsB1CPHmOzu7wMWzG7EbSNP0dxaEcALYTuVUTuX3vphJm0nuURP3j2NCe2DqR48+uX8Psun79j/1Qu8YhDsc+NER5aZHG06sqkrR/+l1RrNaTiYo0+Q5p3kuMgi1q2Qkp3ylSbfjYHUEWomESe/by8CmFqt8TCUXKSlXWZZIU+W1xnQq+nwwZYyTVjV5fGp1+q8on7rITx7+FBZnHuTALGmCpyCDU/kjL2wLYRAhjMcCEnDNNRwEmM0niF1g9+4HfPjwgA3ZWaAUlO2XIBfNpBN4SYBB2MAXo+1eDKlVP9FIH1QQgnIDSXlUPmsEKBpYjZbLUBkqXjB6oq47IvYTqldVbAS1ONfAmGMhcUuEvoPGHaARrzWhsKG1fUkiHQaAJ2wxLTNlv2her+X++8WsuhJP1rv9k77ksFAhKEjWnWN5IkVVO/9q7XKgC5g00P7IXE314bKY0otdtbhXABB9iNRDcgcsyoModzGSF3nvDsvlnfSnyYBeSwr04U3JRi1YngOKq2pJzuTCtcLIanBG5sXYRTUm22kALw/QF454l5VokDY0qwfscodxkqIPfewKMSQV2ahLbzbfw3g4QkpvpsU9BiHBhqHITm++SjCcR4gmI5FXvt3WiM4rfOb9b1j/4u/wf/7DAG/vbpBXN2gH5xi/muKnX53h8jpEMLZx7XeYohQfo7J0UHVEtegDyAAMlSorBv1M2KsaVLkxESegQkmW8jkSBpsY+ZuFpaXBGAO0mVAdtdTjsblgp7eahHWUNqyuQmLVSByCaEQEXPHhkaRXAp2uK4t5jqFctFEqFtLPzPMwkKyBAk1eoqGhWpwi8Gv0fozOukPuxGgQYdJTottiOFGpohw7N5uMMAcqWj0EgZwX6ygTZG8Xd6jzHNk2F1YbNXlM5GTYCGVcwq7veizWSxl7Xzx/Id9zb7Xwww4+W27DdSeP18KJKzR2CDfIUFtDNB1993qMnAYxwwdsC1OyVwNHgIGL83MMh2S3OiJJi9y3KNeVsJzEk7XvcTa/FO+1Vdng7HyI+cDbz0s+CaztvcyO5J4GVKNUsTmAaXsJp2HnGMjKMNw0C0aB1wa4NkC2bmt74G1vhyhtc/+Y8eDdA+EKmDAMuX2i497n7eD5Zhh2ylpEH0ODd4e+wUAZe7zhI5Mb1TcJiYcsLsfBJsvlvmEU7q+FOnd1raqqRlGWiKMIo8lE3iHLU6mzCuRXEybjK6d6avXeCgBRGyc879Vqg22WCouNXnvsW2SDFBB2KyN87bKGE/kYzkcimSYzyqEsmPXQcpBu6T8WScokWT0Z+xonQUhmJ7vjtgTaTEAbXnNCM9rUUfpOkR87TAJ2CIuIpyXpa2REC1BSF4jsTCSA/CSBUKl8fPdmh3XZIhrPcXdXY9v5mCUFRu33AtC0nZI5CzPYCzCeTRCNh0irEj3NGWHh4T5VG9FeALgB4sgTsNOWPoghBpUAcwTXCKwR9CVrjWwo9kG0ZmFCb81+isBa2SmAivJ1nQ7Kz10fMcnYVah8nxYDboSUNe63qbCwbi4n4pPIDQU1hqkhT6WEausAU/cNa21f3YwlgRmfzNimfipQ+jCf5lz++dVUNsjvNztsd/Sxy3A5H+FsNhQ/voo7YlreK3MCGU91GzdA2qPxfL9CMbV7/1O9rV7UHIFy6vWK0MA5wmaXST9zfXkmYzyZsop0d/R+5p+w9LgzpT52x3/0t0AjCdx2x40RD19+dYmz6zN0IeuvjYHLTY0e3nCI8y++QjSaIF3fo1y+Qb6okCc9mqBC77ew6kzev7WnWJ5NkTkOBkWFuPoGs/I7tHaCBj4ay8VgGOPm5jmeXV2gyAsURf5vDrSdALZTOZVT+YMo0mlLB6kkhp8qx9Omx/jY4Tc1oBy/6Ml9BlzTBzzG3p4WGVz0YpUTMKbccdK1Wqrdce6Ej4ZDiYLnAbg7yV3hfcYPD84dIJmsHA2G/E+fg2LLqZh4l/HcQsXnLtNOGCODQYL1Zov1xrDW1ERATeI+dT3++fL0ef1H2Wq/pZC1RmDtxFo7lT/yIiAz22oYw/PYF3TSRi/PphiOEvR5irs332FZNKgtLnCUtI4eJkyspFTGjy1ETg7kFYqSQBAXIJzEtpIWWlk+3MATWZ8kfPUdbErsqlLkMZJkaCbFxwvw435nD64p5hrTOYd+wxgwNFYoCznxUSOIJjJL9Tz6woW+jVASxvg+7h6cM6Da8c+nXbAAM/ueRfcvXNTWpTaYJrCmFyyyjD/4qZksGbOQMfft2VT6mPKqvbxNLfL3AQiy+NfH1Ads8hxlsUMyHMMla45pojIG6aQ3SY5TLBSCLXDJzFJAm9WS2VdhzHS0wEFFs/5BjKCL4DDxs+xRW50Y3+9KC0XWIWp2GI8rlH0syXuBBwz8QNIt//Hbr9F6FoZeD2sxQFyVCF4E6AMbAwKfcDCfvEHy7f+CX/4ixc8XM6TbFyjtS+BiiBdfzvGzVyOMzlycJRaunQZeV6ItOuS1h8al4bsjXmvunrXGhW2DmiwQMkYIvjCR0NbgGih7U6buyptLJ1trhoOAY8Z/R9AUfvcKbCOYREDWJpvNcVDVDDvgawiYOCIzzRxK5gjW9ZJSaHu2BHH0DcMQ6IXlILBqNDn9miQfl3AEKitGaYeS1Fh0AcraBRqy5WrxEOT58fjjEUMmWE97XJ3PVTog67Xo5lqs75fCEOOiUS0igetn13BrD9kqR2v3GA6GGA/HmM/nUoco5WT6Y11Y2K4KDO0KvnyOALVN/iXbdIC+DySkg9o7MmWqutpLKsPAx3g6UDJbvsJ1JMDi7rbGYrXRF7fD1dkcg3iIddXhfBIj8chGVX5RHwfXFFClwB+y7o6k108YagdpqAERFAi9D18yYLV8tYcQEgOC9U8AMmmq3aFNqvZ+aPPKZVEx3VWzNj+1/+Ix005jFo+kq3uWmAmFMoCdaetmzmJmg49M2/ZF+i5CSpRi2hZ2ZSm+W4MoEN9d1js5T+meVMhHWZJF2WE0HktIQlGU4tmmzk/5XR3PmFQ/aDZO9dxUgqlarFdbSSGl9xvbCtlD3Fdlgq4zTBCEChxmkf1WbbIvFgCBh53UVQaExBI4w/e1eyZS+7qvrmA3FWraBIifmKO/G/ZlSlYv4DpBO1tDSD2Zqy1cykHFNcCFZXmS5rjMewQ+2UU+/unNCqtphFfj79G8e4ff/HIFO/0a47GP1hqhqdUxLceRoJLrq6l4ghZFJizVPGuwfUhR54X0Q76v2jrBfQLOEqayTwglG5ghBg26Vj1HZKAaXGM6aFNxPq68/shaazUz0havOtX3c3OE3sl1uUVNmWNA50RHJImJ7+BsPhS2IufsKoX6KMhAV2SNB+/rmQKIVTvYg2sElDXALHmX0sf2GMYhZqMYdw9b7MpaWUHoIIr1LpOE2mcXUwzpDbnLj8ZrZfq2n8/reqtH2P3PfR3XANqhuqvABXmueWw/NutXE19tWwlCIOB8Pp/Jx6Fs2tg87J/LemhANukHIL9ys4p16XJyifOxj23VwO9dxDRp84DtZgtvMMX05qX4Ru9W92iKCttNjYHnYlBV6PIfMHDX6NsSWRWhT84xuO5hJyU2eYX8rkK12yHo3grT3mVQDNPYHaUSeH79TDY+siyXBOB/q3IC2E7lVE7lD6qY3VAlNTriKutiBhzz++Hn47/M+PNRxOkIh/tR+QQ6pRateqATM+AWuzTDer1GXZUyWeZu9Gw6QRRx8qR2eTj4m9dz8mFYJY7xbtOyJZFatA3yIkfVFDJpj0Im5zVYrjYiG+B7Hqjij07uaGL58Y+lnnEs6/z48z712uPCQVi8KiQh9Mff0amcyh9T4YKXDAfXD4SZQPCC5vjPLy6EubN7/wM+PNwj0yEGkvrGTQQnhBNEApp5bg2vydFQ3klWAR2uhUlB1porCyimgRF+JwOIu8admDzXKGkuLBNys7hTfZUKNzM9gpagEgAgMOYCideIFIhync4KpC07DDOgBNSjDNQRCZWAErY6d0qMAoe+XYqZa3bbj/vdJ/sI+wXofhEqpIVaFleOH6g0N1lvd0eLbi091GCaQm/06+VvtUNhwDXFMjCg3CFZVEnL1ALTAHgElqp0K4cIxxM5YVlQazBBrJVEXaU2PUTGaAzURTZKbzRHZKOUNhFomzkWothGMfNhMwjBilFVHvpK+cyVLT2UOtR5i/nIQxQN4OvAU77Z93ffw4lijL0hIgQIhgWs6QA56wvrU9AjrGP8lzchvns/wi57hTacYvpigi9/doaX54GEGLzwOgx7stZKVBVto31YPqXETLQ8MEYkxIDeRSK10gtbMlds43NE1ohOS6SvEVlVetFPs+7j7+JY1qe/GeXYJB5Qlpi0EzyrKLdtHfFlY70KSbBxgJoHpZm7bDIxiKKVlEN+hnqXw+l6kVZxAZwrT3cAACAASURBVExz+MWuk8X6eBQjTxv4Nt+jwe2qxpKAlrDApTGI3FekeYJ3KOYjvVN/ePMW251iMJnqxBdlaSaeVJTu+lEoi2/VLpiY1yDdlUgzW+SaM79DmaXIykxdWwLU0vpsVGRVbDYIWddaXiMyOujDpRgtBAsIOrBtkWl3+/49Ptzeq81F7d/14rOX2BQtJtMYIYMMPjb2my9BtxuRaQqgpkBRJWvkTTOtDKBmwAMz99gzxTSgpjJU1Pf6iF1mALwjVo8Buo7O6Ai2+xEIZmqJ3HUku9sDc3sGngHuzHkeMU/1Oe3fW4Nvh+Or95CrdXTJZO4lmklKJTtpf1Qf8CmDyMcuK+T5wmTVHRg/K33SmADK15/NzyQBN88zNCL3NECE/cQzzoAT6lqw2XCOeHl1JccjaMTvh3PdKI4lbOZ4i1P6R4dSVQWueFYnvoSNy0ARYOi5iD1HggmytFJty6E/b4CGRvQd2ZAtxMOeJ0LASdql9ogTZ8UaeWPDrRs4diNelL3NhFKG8XhwfBtbC0irFoNZgs/tGu//LsX7dICFN8L7zRT5gkECLpzEJ8EXnm8jkL4GiJMIk9lEGHblNgOKXgIIvv+wFJZuGPmoSm4oNUo2rPugzvRB4rWmmLUFWWv8SSZbq8A1Zq9Ilyam/OyPbYiC0QKCyEcQeMh3O9gBP48K5ZHNKZuejD2qosJ46AujjlJTnoP60s33cAB0ZYNB99edjGm6fspdul7q+hzSSmYQyzW+W2TKC1Xm+0b6qbbgOdasybLtW7y4IYjfyedTw50BuQ7txVRmbtirzTRVwVRdVc819V/q0p5RbjC4o35Ehm8lRi2rVvrDYRJhNhnJxoOAzarjPDqG8pm29PklSYLnl59jFo1RE9jNMmEEs9LVaY3h2YUwsNfrJXabHUIG1xQViqbGNt3AaXwUCwtdbqMuHSC+wPnnf4LLosQk30g4R0p5fuljsfBh7e4wTL+X+VHBwYPJ402HOBpgfnaOKAyRsV3+GwQhnAC2UzmVU/mDLGbXVMmRfgwKydrxMNw8ebV59Oix4x/Wp0E16xNBpGaydjzJ5cSUk4PNLsXDYoHFYiGTdw6kSRyLx05MsM3mZ1GpR/SQkNSqhgugQt/IemtkEUv/F991Zcd7s9tJ+hFBNhnczUD6yXJ49BhMO/7dTBuOr9/xxPi3FU4gZNGkvUo+Ptk/lVP54ypJFOM//OWfIxydYbPNMb+YII4CNKs7PNz+gAXN4rnsFzCastAANn24fBeB3YiHEwh4NHrSTK+TRiUT1k4An6w1nzb9nJRzwl+hpaxEFhp6cScb49JDyTlxon+A2w0QpvrSJKwwCjvkXYRcgDUPtkWJNxdoGlzzCK4xyEDJQWVxoCWhBNo4LafEhwCYcJb0OmDfJzxhsBn4n+AWJaEMIaBX0F4GqhfOmoemmQIq6fMRO8V4Wcrx99Q2jfTovsws1DXTRoJDeR+BjjJF1xbwoqGkoInERcBCBQgZMM4kIBoEYQ8YkZnFxTeN9wmUtI4w37iYja0G556NKHGwnAYI/Bh+x7AEV5hP0cDB69efw/MS2K36dipwodCjzBx8/vInGJ2do5tEuMsaJJOBSCyZfSisCNfG9fUFZs9usO2A2fUIf/L5GMHUxfnQwnO7gkOJWAEUrYfW9eGRtcbQB/HoY2BEg7aqUYnPEf2LuJBV3jp7cM0AawQAaCJeE0BT35OqZ8o3VHmOmmt9ANqUhE+BHSZxlGwhAWs9S8AoEgL5IhcNAo6PriPm4y6/867Cpuux9WLErQVfBp4ed5sUqzSH1ZboPB/DOBCW4NDfoUsL+G4AJwxwl9eICXj6nvIWk2+ZwGqJH969w/c/3MoilqcvcrKjhSfH2bxisl8tINciq+GlrkiyuRilNQQZQHa2QhuSteijrBukXNTlqYCyy9USjdPCjiifs+C2mYA39JGjLI1titeOISTvfrjF929+QJZXUqfUCtmS9MZkNMMg1u/3Ua+1Y2BNy0AZUNEowFTkoPS20kCV0n8dgVWyqXfsm6b90jTQbICFPehFdqFqmrqJaSDo8RkdHj86X2Gcyi+H52s8Vr9Os9s04Km6BOtHIJ5qkhr00EBh/4gJpx7TaPrRDFH1k2YeJe3YoyyZoQCdhAxEnK/5PrKSLU5L38XD8sBoo3qBrDPfd3F1dSlJo/Tm5fcuPl76dQokVYmUBNgpTf7s1StMZxNRIhRZJt/nbD4VEEqBuOymVX/aybyyEIYy+0oZOtocVWnBdx1MYk/YnkVOUJqeir4AFxll3pR+upEkjMp5sT2TscrPIheel4atokJn++h7R8lRGTTgKoBOpUwz8KbCyK6QhD6mroVNb+OBYwUI/AeI5xN0kwFau8U0aOS6eK2qc6z7bESUxQ7HA0zPhqiyDNUmR295eEgbvLtbwvcdjMYJirqU5EmOlqy33Dxi6nBd9aiqHgXHRAle0XXW1MVegUTihNx24rF3PqfMPuOwCtfzteUK+0EFvqkwHlX3uMlAiepkEGIQR+KrDHrZsU3JeEQvOAP28m+qWY42hYRVqeod68h4GCGJfSzWO2SFGnsVInWYhetWoS1ebAmHWSx3iD0Xr67P0XBTpqgUWMtz0WO7+qcCLA5/m/FXs+/2m2xHwJuZCZjpgDmejO3a8c2ykBP8KguMBwPMZ1NsNru9G5zqI/VxXA9Xz1/i8uoLxM4AzFSO2P9yE44MttEEZ89vULc1Ng8L+Y6uxg267RqLskcpvmwdmt0YKSbYhARYgVfPavzlV+/QWZdY7lwU5Qx9Sf/ADpXt4r4IcLuy4e0eEPf3SGtSMkO1frJsjCdDXFzOZR5DRpsEkfw3KieA7VRO5VT+oIvIRjWo8zFw6FAOg9bjR5/MSvfrv+PZn/5pXvaR56j3NsfWEk29uylmwS0XJLWw2lbrNe4f7sWomOwzhhKUFXfi1E0SpyTmXg3c5n2468zBfZdlklrGSbJaaBpy+GHx+uPyo6H76BF13o9BtuNXfvSAh6JXrRzARMJ68lo7lT/yIos0LWXn/DmEg0nkwY88oO6we/cNPmxyZHDRUQbKpEWb8p8IjufB8yp4tImmPEWkLTyQCTEAKsuDFboIxGtNAWv0WuuqQvoZKttEjiY+bGaqLWej+ilp8moybtybfafH2YBm0Q52TSgLMHq/ScCBpEK6WhZqi2SEixIB5rTvGv8mI8kwNrg45X00pjfgl35bvVFhzk2tmFv6DBFc8Xx1jrpf2WNo+he1WHkCrmkWiPRjXBhpAt3++9BSLePLpo6rQQQukOsWPnawKAW1Iw0YmCMqgE2BbOr9BISg7Ej8sDSCpL2MDNAmQQiOjRpMgaR/GL+RCrHd45lnox07qCIPozDCzTzC65cXqIsSFt/XJnOwR2PZSAIL1WSCu0UqMpyvNyWm1x2m5a+RrhpYwQiu5Ugd8+gzFtn47EWEydBDN3Xwld8h6XK0ZYOi9FFSchwoSa8vjAN6ndXoBFgjE6cWcE3AFzJGnEZ7rWnGSNWKZExSRGuCvYYloi8TJU6K4qe/d7UeNdZ4ezab9tIz14xPl9RXRY1CR0Zn3WsWIL/vCmW2Q5NmiKsGg4rPj7ErWrzLMsSzC3RWiNWqhTcYYTJw4XUtNqtemHoEhRPXxpTm6ZEvfllRHIkX03q9xTffvhF5p/EtFVDHMDokrVt9Nt4ETMlzBBYwv5xiueXrv5WQoSjxEU2GaF1ithlKesNVBMR7GetZ5xynRRD1cAIXw8EMYRKi73J89/YtZtOZXJ/dlhtzS6ljZj7Bc6Ksj4AkJVuy+NXn9qjsJZvdEbCm5iGcNygJqJLrmjmEYt4rPzN1OzDWFDigQa29154GFfTXrLHI/dzBMHjkG94/Vz3D/DRV5HHR8w8DnOmmr0m4Hy2qWR+CT9RPIwc/Atr2PkxPpaMHYEFknVr+7XsEBJT3Hw3TkziSOppTamb6VQ3OmM0DXmPxzSorYbJdXl7I+9elqlumj+Rx+B3Mz+d4/eqV2Hus1xsBAyaTMcbTqeq1TVhIT9CXrKYWd1smBzPgwFKSx4bML8rmQgSeC89uRVZN9HXVA3nZC3uHqgKC5lQ8dPT1dNjXkk1WwmpS1L0CmSyrVWCv5ePBtrHreozDkIkhcp1ZP1g5VBMmc5qkPwWOW0xXthJYUYhx5GIwCBB2jrA1vX4pYLYFyvgoWVVWCTKtti0ksxGSsyGarEBfMTnGwmqVY7PYYjIdyqZOXmWaWUtgrUPNxGx9YyqoYlMqSaawn3mKQsxtcHkxRjIIsHjYwJKxTQcYSJ+tAH/zXRrASHVgFvK8QlXlOD+fyZYGv2Px7JQ2YcYmVX8M0Gv8CwmihqGP66sZdukOq22pAD/54BrE1xsUcpeeQ+zbt7ZJKOoOi/UWk2Es0tGsKHUQggL45ZWajauHYVW1zUH3ENwRS008ofmgYljy/M0YzosnoPD+enArifWpkpCXm+sLuYZkGCoAvEc4nOPVZ19gej5XYyDZlT39CXPktoX5zQ2iZIjN4g5N3mAw7jBz1nj3rsQH0nkpRaaNwm6GZTJFF4ewwhK2l8Gpd5i2P0iSrRO6GP/pc2T+GPWulhAm27OQuh5uUx+b+w5ht0VTc1zXoURS+xyMxxPMZjMt8S7/m/iznQC2UzmVU/mDL2piqOQjXNSaKZNZUD4uasD9MWhkFp1PX2J98ldzHAPsqfvNrtDRc/XOqCzIJBpc3QimkZ1GDw928vyd8exyq6o94Cb3y6JZJ2+ZyfMRuPao6MXmUwbZ47/UGR9PiNVzPjJZ/1H58XMoFzDylVM5lT/WwjbnuYEsciCLlxYeXIzPplhtNrB2GebDCPH5DR5y7rhTYubJc+F48IIeSVDCYWojAwlkK7rVZvPkFLiwfB8+JX30WmPbo1S0rsQkueJimgtCAb70RFtP2dUyje1d+7fwMXqkORamSY/Q67AtA9SUDZLdIHJQF65HXxNXZHxcoHHSTN8ok1Kowme0FPQIYDPJZ5RM8h0d8d9SvQ7vN9nGBG3oo0NgjYvV4zXvHijQAJZOKDCI2x7A2XdJYj5ttJWmO1KLBrPQ4nNEFsdvp+8R2xvEbo2sjVBSVrKXFanFkbmp9zMokjqObKBI0qIxtjZX2DCzIMwsGodzQdzU9BXq4FglpnaHSUAgtsbI58qcHpse1gyrKCqh1gmn0Q0xrjOcz0fo4x43gxrB/T+idP8d8srGm68fMBvGEoigrrWS7dJvLGkruGSo0OetCxjNiTBQ7EIJMSAoS0YT2Wr6RgZIZ2nGGr2OyBjhBhEZkZLep34XBhS9/TQoY74Ic63V92hYE+p6KSBEe/Qc+7PpkAqCCJLMTQmWTjXkSym1LDdbkap5spGjpLHLKkUVhIiHY2zud1jAwvRmhOeTAJ6six209FnjdRG2IoM5HDSeA99z0UvwRyOLxYLMlL07qq7Lwsw0q1T9eXR9mE2nuLi8RFEUAopUdY9fvv0Noi7AcODDd32EToQ8L5DmhQaqWqmb/PzjaILJYCKspHerB/z83a+ROCNhp263O/h+gMvLc3i+J9JUFiXH5iLaFUYN2TePiwGSWvHyEraa3IzPWnsAp3X7MSEBxoONgP7R16JqvQG69Pdq2GcH9tvTs9hfMFUPNLh6PN94erx9u9c/94fdMwjVHfu30n+bKYeZz/AOc9x9eMKRJ5wJPZFj6d8P8zfzXmrOJiCbzx0MD01VIysLjAYDVGUh0kTFsFWvlI0IYfuo69a0tXhocQ43mUxxeXUprCseh+9DtuPr168kJIFWIrT/8H0Pz67mykNNW1pJvQEBd5XOXPY2LI+BL0wz9VDbAWrXRck6Fbvg6RJQJVBPYHro2QhiD4u2F0ZzEkZw2QbKUjZjuJHC+tTZPZy+hE12m7CiPAH4q77HtWcYe2wO9BxgGALZfeq6qSaiNpQ2bHNnIQaJi3bk4SxyYHs+6lWLYm2hKWsE3hbwyUb11MYQ01ZFKq3CdgbTAUbTEFaaAmUt38X9hxUWyxRX51dybTbrQsA1Bv1IMqi8nieiRhaOgezfWd/9wMXlfID1eodd1sp4xumqYaoR9JRmpYMM9rNYqUja489iyAmEtcXNhtnZSP4WTzJukBlAWMYszfzVG89fvH4Fz2nw5oc7YaITFN3XZNO96Iay73+kLtqPQ4hY2W0HadFgsdrh6myEyTiRNYRYxGhGuRp/D4ndqoqqcVcAtqNNNwXi6uftaaUHpE+uqAbd5J8+LvvzdJvK2HBGmW8YIh7N8OzmBVzfg9NTtuyKTPpht4E/neL86loCBzbrJezAx0W8RPl+hTcrC7XTwcssWA8J1u0U/eUUoy8nmH0xgr3boF1vRTb8sPVQbivUuzW+iv4PvH5Woh5+hmxXou1zSci1PBc7y8WHjYNqXcCpN+ga+iKSfe9Jm+SVnjLZdjqTz8A1mOkP/muUE8B2KqdyKv/dFCNjUNR7lc60n3QdTcD00PXor0fP+leCRAZU+xg49WjSqGVaZmdZJntH8fRKdnSIqt+nVh2d6TGwdvz+T8tT+efHJKHmOnz8zP/5IuCeJEN5PwLzTuVU/tgKFz/TFzfY3g+BLpPkrMlwjIvnz2V33W07uI4v0gfuxF8+u0Q7mCrvHi64/B6hU3G1IGwXafOU7nRMP3PQEoDzXfg0ohcPG7J7KOmrhP3QyGJSJ4wZ1Ygcw7DW9A67zNPVNH4Q2pjFNIUGspoGz8qLTQIWHE/ANZ6rS3CNwJruW9Vi65AQ+kgmsv/dTNC1obKexHMf2fQflMPTt4wAvbz2WDemnqTBNaE+qYXOfiVjFvoHmouShapkvD0d4EiqxudzyRJ1G2GUjJNKpEzbJkRLKdRHZGcCnAlrx3g47Zf+ZkWvUhH1Ik9YMprNJn2+1A16UmpwR9L5KD0qUOUVfDEmpy1Nj4yfwQ1gdY54bPpRjCItUToeAu8H+Iv/GV6/wNfZl/j736SYXkzw7OW5SpmzaQxOVhrBM7UoouyLrBTamLGfJtgnHn2EF+nDJWw0MloUI01Y01oOqnyO9IaQJPS1Ijsma62psQfXZGFrxrrjxekeDTEgm5Fb6rHMeHVxrBOAUjO+G76/pRI92w2KKkWbtfDJruFi2HWwrRvsWhvBaCrXfrMuYY8iXDO9kP5oMiaxbkoeoiwoC4/Sawtu6GLgQvlAaX+/IPQxHo+F0UBAzIDHqsIa6ZMyRnddD8+fXyOOEwHmuAGm2lmPi8kl4qDDb24XyPtW2ImTyQRxGGK924hcNCZj8eoZkihEV+RoditEgY/EmUudUEm11n5jjT5GFxdzAR7rqpTzMAEI4ucqbvemregAAzF2N5t5JhH0wN5iUcCa8s+T626SQDUD59Csjhad+69Uf8v7h9QEx+Btn55QGEDr+Eka3jJei/qYujo9ful+71J7aj09jaP6p9hLh896ANeOQUHzi+kszXFUH7kH2VzWIhdlVgiDcBSHWG23+pofM4XI5qVFxr7zk+vO0APO78iaGQ4H8EMfl5eX8h2T0cQ+YzoZYjoeajN9Hos+aXTnYj3uhG3KKslxxqEhPyV7iYtJZCOkTpjsIa0iVp9ZXUtubAR2iwGf41lYy0atjSRkn9eKT1sSBVhXZJS5sC1fxiC+mPLvRH84BYCLoaf6aHwD8RRVm9vcaGEjJrB/4VoY+Bau3AYBvbh8IGsdbFsbeR+iXDPR9wGeX6LufPT05Goh4QTClCaQTHuFOa8V0KUZOmGoObh9s5YNqefXZyjbWnklkq2trpT6Jz5g9LVrBYhmDMx6W0pgkLQdCWvQeJVmrBm5uvn+9daOqkv7WB11D9sM7R6SwMP8jJ6XufRbct2F5azGqulkhK8+f4V3797i9i4VIHOvnNdVRM3HOV6Yf+yYNLim+x91wRVjXAH/7NNdMfkn6/nynH2Mj11aCBir2OTOvh3wA6v2tH/TQ1vZj5OHNYH8Yrq//V1H/aCpD7p+Z5aPF9cv8PzZBTIGE1St2BxkaY686TG/fo4oiLBePqCuOgzGBab1W9z+0GFR89qX8HYxmuUIq2QC+/MZRq8T/MUF8NLeIl2tsX4o0VUdCib4di6y2kG5szDGCiOHidsRyhKyQUCJM9sIrQW28LBad2jzAp6XoypKhGEs14jMO4KSw/EIYcIgjlI2JP5rAG0ngO1UTuVU/rsrZiIprAqhUZjp3NHoeZiSfWRydTRrezJRfPynGg4/8rR90ZtSe7BP3amlJmaxoXdMZfdTBx2o3zVDRMuwHr3Ho4Hu8IgRX5gzOjzj8Bzzuzq1g6z2X1z0Z+KOrZHBncqp/LEWtt3ADfHFyMNPv6pgzb9EhxG+eHEOJxrgrnZx9WyKKPREhhf6TAX1Ua4X8MoW06tnGE4i1Kt7YRDVmiRFCgkXHcIo8ygHdXVCKFeKDfq2Ql3Wwlrb79zryfKP2rOWr8jONmyRPk0jLkQ6bAoHTc+UTsXWUXITxVyjDxGBDpmwaw+2A7DGp6ufsiwwCzF5G7NYedLvaIkJAxj6rhF2Dt/r0Yz+cNJqoqsBq0eSr6OFzxESsP+sBvA3TB1hpOiDM0aCbIL/l703a5bkSI/FPCP3zNpO1dlPN9DAYDiaoZFX1KWZ/p5+mR5kJrsyma4eLpchOHtjgEYvZ6kl903mX0Rk5Wn0DKnhG1EBVJ9asjKzMmP7PPxzBxw0eY2qdjWoZUADHXeblDlJ89H70OCeOYxE1ebYJn1UwIFxwUTTZjSmZLXJtOPo4FCbs0TXaECRl70YemGLLOYx+jBEHwToWwd50SCcOQizr/GH//Y1/vmfEnz7bYd1AFz+1QsMg4eg7xEsKNZPUXOmnhGpMhEcLx3TdeWUCREwYB/ExIAi6qU4hDL1kymZHXqXaaGN1jmiHqgB1ujMp9OxetE8oq6cPAw4o9OKno86Nh13BF3kOpjrJZVGXz/JNhOgbtAu2DTJ8F205RaD+x0Y7zveCl7vC2j0LqvQh3N44RyHx4qJ1FhdRNh4BQ7vC0lrDFQL19W/syqAslVIQqbbMpWW6dT6HhF+E1YmxdtB0fUUi+VCWORNowXqj2zLQdL5qK3F82DKoGWkH/YHaSscDglUxbMZtg3EHTD0BswoXn++EfYQUwaFOdqUUId7DGS5tWTb9ML8EPsj0lcloFWSisbjLZcLLBZLQU7oIB4EEfL9A5LYg+OGx4U66uMRcKdQvjExmKZG8oZo1qF9WDbhRJrsI3BtnDHJ+3ajSZs77n0sgnNPJj26LU431IxG/XpyUPvW2H+YCYfUl+c9m2Xljq+t7KJNGZ8idOYYE3x+Ekgf02VtkR5p7NMchIE2cckOmbjDUwyfwIp1MbW/SdxomcZLlpR1dOViArMRqlIA0SgMccj2EuzzPPeHDLNFKmnMBM7okCLp14SnaKBBEF7GBaZUMilTmyKs3UE0Cl2Cb7zFBMjs+GEYnARbCYbRm5p6hTP2QZ6Dqh9wniiE1LtUPv5waFE5HhKi2ARlHQKFnlk40ICbbuRKNNn0Qo6SFHGOHTyvtnNEJ9EdanhMKa9JhKOBB3USPPRk2C181IOHauujL5j2mlFpUuQHeP40KGC9dIV5Sua0h2g5kzZKUxOy3rKsw/fbveiZfXazkfOr6CTs6bRuAlyzmY95GiEni9ChIUMg82kxozHgugBtbN82W9NUHlvTjqCaNdCwn+jrUBQtiqwQvcd0HqGsK1RNg9Dz8NVPvhSH0n/++l9xoOuEAZB1LdF9odRRWRhi0eDZMDLEjoCWzP8FXzsyyDQ7jTYJLraHUhrv5WYuxhBFqRlaAhKbxTQ7vOp9T2v5WNvHP1pnwQJwk3Zgzl3GO/5VHtZXN3hxfSugJqUFlkkkqdT7fYZwtsL55aVoCu53WwRBi03yHvX7D/jmPkRPdYzOQ/eY4tCukd2tMP/pEl+89PHzqERU7pA9lfjwWGG3r9E1rG90kw7RDREOjcIu6zC0j+ibFlHoI0q5GOmgpdyCW0lbbN0Au1aJO6nX1yh79t0DoiCAH/poy04YeLPlGeI41qxfCvT9B8oJYDuVUzmV/5RFB0N6qY0rwubd6VTxE8V5/vkngTY96Dh/cg8fTQAnAdlkWnrcfjKBmz40qDbRQpicjj3Ec4BNn+QURNTAmX5tn9vA1K6VTWC/f3eRCaSkQ5wcQk/lx128IIbnfIaujFFmBzRZi5++mmM2W+Dtm+/gzAu8utzgan2nWWOeh0YpZO/eU0gNbd5h9+6tCJV/9tPPhBWUZwcDNnjo3QBe6CIItBC8y36E6aO1TkljcKwn5Nat89g/mCxJne5jIlkCOsuFhzBoUB62yFoyfTxhb/UyiafWmitC0L4BHpiOpwR008CaBtuOfZX0JubYgps86yANm85sw9S1tq3hChsvELCLq/dmo2fBuzUzsCmh2sHN/Cbbc1lWmcnV0mLpmg1wBMHsqZAFkmPh52gwQ+fO4LgzxDjA7e/RDFoLT3/XLoporSrtSjjBAQx4JEESI18bdAjQZuUArI6b0TnrB2ErthmX2Vu5b9RgLgZglkQ4S3VqMQPczh1QukCaKAzvH/B//l8dfvN0gaZb46Hf4LtmhfX5Ei8uAgyBi3m4xZx9smHgEXAVhoZh4DHwPTgKpWiZtaLZVuS16ESJVpBJCe0JrpEVKSYG3fHRsj5qRovWnjMsa3M8DXXo/2zgZzE0M/yNT8agjdVyvNd6Gwq6E2OqdjugruH2MdSQYHBDvNvmeCw7zC6uUWU93j91cDcJrtcKM1Uj2w3IuxBijVBRykehqJh65EqQTwAsoPGECR7Zdgh0sS6LqL2YdmjHwbOzpYAgDJ6ZekWx+s9evpC0PuqgMp2I7ZnAGllI1F4j60bfe7rBFkgcYJUmRreuRRSFiGhswH6DgCvF1edrqDhG2XZ4ODBN2sOL63OcrZbo0IqzXhhFaBsCwbWwSRarpQA8EVlx9zv0dzJbDQAAIABJREFUPdszU08DSccamWsCfhpgxFxzyxoUYG3QYKAFDY7pjsd7MoJkk7Z5DLWn84rnc6JnMwt7+HHfx+9Ovzc+tw6M5jCy949+g2miPyzypmm/45u2X7QZAQYmGPsTwxYe+63jb7R9HLdkvaZTc8m0xLLBapng8fFpzCh4tohqQAkxQZDFUcNy7ckUJTOxFlCI7F2yxtjHzkIPg6RHN6KN1rgBIoJdPL5S4sDJuinnaSQOmeLMNG9W5q534Yee1G9JsSaplUCD0T3sxLiD6YxA7CqkLplnRkeTdfmpZNYmIneQ1GOeP/sBAq+s2+Jc3bWaqSZAkJ6jileBp6iKJUznliTsimwzR4ANmi4Q0KM+29x1MHc6hCkZSAQWqSvcS731yTUKKijXF+ZRWQ3iHky3XjmWpzA7X2hDsG2JUPko8gaPuwxn5wtcX6yxz3K0fY9XLy4kHXu7r6WdaUaqHp9Gx2eOYWN6q8GUxjqE54605rV8OB0HiIV2DrKiRllUuFwn2Kwv8OVXP8E3f/g9Xn9HQX6zX0m31jvXw+UUHrZzfRMTmDF9rINqygrXnafWRTMnzfrRKxwOjbCU7y6XaOg4Sh07s59pJbfj8bHYuj6enAb4nrVr2271tXDZJ776Epv5RhjaHG8I+hZSv3ss1pcCFu/2j1L/lqsDFuVv8fobH29KJWY1OISotmfYLdZQP11j82WCn686XPV79FmNfR5hV9OgoxGjEbK/O0o5dHMB2TgOl62LrB3QqwJulCF0ayxCnQpKximQCYObzMza8bAtFLodwbMStdMJmDybJwaIdhAlKVZnGwQ+gcpcg8t/QTkBbKdyKqfyn7rYiY8eYNUPJnXH8vGqzmQLPR8bN5kMiQbAOgJbI8Bl/tg55aj7Yctxbvfx0Y5fl9mtPe5H5/PxtpPBb3oudgI8fe8vBdb4FZ3+cHIIPZUfd2Ffsrm+Q3L399iVc5nkvfp8jS9+/tf4wzcf8O7XX6OtHrAZ7hH79yg7IEzOEacLaao9XdGKHNune+TNFtunDyjf53h5dYP1zS221Mfp6LpGvSkGA4PoslErSwAP0ZthF2E0VyZdio4DJswOEyDG1KHZeGjqGk9ZIOmhX663EsiIPpciwEBwzaSDkqEqRgdkrmkjA6Ynaa0a0/OZgEA/n3Z6NlAwAu1wRCOOKa9eGB8dESX41EL29lwl8DArE2N26Lj0/0NdNM0eOTJI7GKGLgwi2f83SJ09QoKbXSqr/jwSg59GJRhUjKX/BDVQ6Jv6Rq4WndbJPiOghqmeEz+z7BUDtAloJJmERseqG6Mw0Y8hqOoyHZLpXRK5OpIWprW06KLKJN1OUljn7oAhz/CHg0J+vkBDHSTHxeIyxeXPU3x5NxedsZU/wOP9I/DKQNqkqYnxhKddCisCtmTsiSYewZQGaeTIcelY3aGS9wQMatpRZ42BkjjzdWTgUNfLSBkYd1jt9DgB1Xg/pb4anZ/JgDnBM/SFlwFFXx46fC6WMZo6Q5MV8DuCULr+kU327mGPMF0imS3w7TcHPM5jvLiLcBcUcMst+nrAEKTo4ljQK4LYVRAi8wPEAVPgmGLLtLqBtiLC6BJx83bQjL9JKjLbU0t2pe9jvVkjSSJcXFwIwJVTE2qgqW+D7W6POCZzMDaOtLw2WkOO14hO3wTLtdlIKOlIARkTDuSzpikR4AHbN3/Eu2/3yLf3aLO3GLL3CN3vkEZzhNEMj/cPAsyzbfJ7dIMk85P1Lp6lApgxZddrd0QjxKSCeq0Ehp8B1sRHLHNt4gRqb4mu7UfkQN+747v6/bFhfWIGMZ0d2Y1syvbkQHbTj4vpt46fPaM/fnKWNEpZmb/jXMdQuGwfId8cCW16VjQ9rvQRsORKI/Sud/gDkI31Ypvl2pii6ZCTImnTcydnamdk/A5Zktb8Sf+cXtLiyXIjK3GWxlrbkgYvkirZCMtSg3QEgM05EhTjjxatYQdV64g2ZzsouKEP33VksYZtgOxMork8PrMXyT51DDvUnNnYdxPAYt+zXsQyvxOX2Z5sPIWAOpFGq5EghGhcwQAqlDoROQGt6ygsNuWgpskAmXqRNuTg2VrmFM/VI6HLdZAT+G9oGALkOeA2GXz3QQCwMPDFITk7kI3qIopT0coKZgGWFymcksYs7O9cfNjn2B1y/PTVLV7ebvDuzQfsSgKYZEiLe4pehJJLc+yb5B2Tdik1xdQleye19qB+JQv20pcbnUlTNy1ATSAzL2ss5xEeHt6jqth/GiaqMRTRD81e082L/1o1Us20NpdJvycnSs65fv+Y4XJMF9X6p+Ze0lSnBR4fMyxnIdarVPotURAwGnmyW9m7YVcagHW6YKb79GNdHvNZRbMRWF1c4sX1C0QqNH2mTu0vygpxssbi/AJFvcfhkGPoSyzDDPWbR7z+kOBAdmPrAfsz5M4lqrs1ki8X+MmNh5+5JfwqQ3FwcegTDGkMP/LQVDm6jn0vf0iCzkvRdy7ceoDDlNHWQ1X7on0HLwPaDF6vHWMbsiSdEvBKuOC4GCBTHg7ZAJ9OvE4pZhFxnAgLXMZgB5jPlzg734jpzl9ihOC8evXqh33kqZzKqZzKf8LCwUPYGOLW3T8HscZZ2mQeN33/ExPCZ6DX8w/M4GnTZ0zakA0MDathHKA/MVXVu3l+3I/Bu09tf2So6X8nv+oHjLZ/b+F5CnPFZSrXqZzKj7sPWS2X+Lu/+1ssbl/gV4VC9l2B66jA4cM9vvnNI6pmCziZBFFkFKVqhZubDWZnDZx0jXh5KY6SdX6A03b45g+/RpbfYxNwMueIgYG7PoMTBvjd73+HrmH6R61Thjqm++lWrVewbeg7CUSNzppdiWawcrUORdD64dAJw0cm1cKH6XEZVYidCu+bGfpgAc8LoLwArheKHk4QePAJ1hgzA/WMaWtANumr9MPG1KPAMnWEhg4+g0dJKTfBwhR94V/mGlEfSLSPyDDSKaFkfUgaFsEL48wm4IGkxJnPLFvMAB0mWhetMXc4CBOkaCNZ5dfBlGGUCBDG66WZWbFqsUo+IG8DHOqFMO1aOurBE00bXgPRoLOAo681kcjcEMDG16wVhpQKgRheBNy2c8Xpj7TCGgOqvhfWGlfO7TVrJFeSYW+DItshbBw87Tw8xbEEeMVjj33ki3PlRdris4tIdLhEv8yw7YSByBQt2raBAYfWhCPgc6gHlAJgsD9v4KoDkiFDoM6xL1psd/fo6krAGjLVCNIwWNMGDtq5VafA2jp2ZEGISDivA1OYqQ/lGhdVkRMyZgFG10yLixudKd/H+WqFQGVo6u/QD0s4bQSvo2PtgNxNsc0qRMkcu/sS966H8xcJ7lQNr96jqjwcCu63Q7pIEEQKxaFDy4A8cOErgoME8HjOTG0jAEbcQd8/VuC86hD11OIh64umEnTKBaqixtMuRxD6IiJOcIH36Wn3hDAIRZxe1JO4T3N9eJ3lWknqq2b52fevLq6xvFjh3bffIcsr/NXLNb7+tsPZy42kNUUGtN33DuptBewOOF9HiGc+vv3j92j6AWEYSjovQdPFfI712Uo04x6/+VaC3OXFBbwkwu5AF0tqyR0JKdKerHmHaXKT1meefPTOCDiMTWq69Z+YjDyfW9geSj+Zzj9MGvnkfZmzCMg1fuv5/Ms+NT/qh0efLCc+mzsdv6PfOPZBZN1wEUPase3nzCKitGV52AVaPQYcihZZUWARefjt7/5g+kS9X25nmb+i92UlPowRjNQPWXjQID/3KQH9IjIgkF58YD2lrib1CMWd0wDADpmPBmBjnSCzlO0qdLVGm/2VhOrJ0yFgx7HDd9jmByg/RN33ognKoxNQPxS1udf8HTTo8RBFCj4ZvMYkgw+Ce0x/JCuscxVKz8WCm/MgUvQ1qg1AG5j3ZZFb0mfZdXggF/PA9YaiR5E12BelpBG6ZYnIbXE+L5EsyfI8wxDMsa19dEUvi0Q028myndaRrHs8vdlix3RoVyEKdZr87fUZdrsMD/tilIlhrXc6o3fG+b+Ze8sCjhjWaCkCAuR6AUfP2Rkr6N5V51BrTU4rX2BSjg3wpLNm+EaHNPFxvl7gw1Mm4B8JgHqObkFNK1swAdXk+ltxODNOjxIxhrFm65r57liJxqIZ3LqfbnCxTuT77+8PaGiEIIDfEXqXXU3AIx0nmIUju5XELD1Cprhf3mEWhMI+Zz4yPyFApfwEy8tLWZzI9o9wBhfL2QPU9j3+8bUv8xrqr7l5irY/Q325QnI3w/raxxdeg6Q9oModFGQhx9RUc0Qnk+7ib9+8wft332P7WMAbqJ+WoGLKZ8F+jiAe04NpXkEWZwt3kcHzGwROgKYOUZZ68QNkrLkUCViK4U3T1lA1JRcGpGsfXuBhni7ghaHoAfL+uz1dUiu8ffcG9/cf9H7+HeXEYDuVUzmVH1XRqxAaaDsO/CxmWjIdrCZB6nSTPweCjdtNJ692lWv6hn360WT0z+/7hxPH4ycfP7cMlmNq6A/G4X+rmI3JZBGH0FM5lR9xYXD7xZc/wf/8X/4XnJ+tEDoDzlzaiO3x/vff4Lu3PkqcoXZiEVZne+vUErtoBVxHOvWF7lltIUyFdLmStJflGbWVztAVO/hND69hus4W2+yAFz/5HB0Xex/3mpXCvVqns2mjt4GvAYskbRQKsyTE+czD/lBiX7AXmKhgE8hSCnkfohpiXEY1UtSoBwJsZJkR5NDOdTYlVLqkkdVx/Ct9E7V9zAYSDjA4qUphMAhDy+hOSghpz915Lpwkv69nWhInw0YYx2iuaRDRpP5bhpt1eBvZbMf+1ekrBMjguhGKJpYJ9SgSLccz2xm9OH5EKC2rU/guDRCedApdS6DKuLiZfnW0O7DmB6NLoWW9UBcrQcDgqNXzerr0FSa9ZpHGki6owQANBIq+0lCg3X2Pw4cO9VOALk0RXcfwAwfDZYCLucJsQw09B3OTPqZ/BIE2I/XNdB05yUZW47VoPakjrQ6ELSjG8Lt7RF9XCN05ZvM19kWDwzaTgJyMl65zDGPNAmwSGZqg0OgFKTJrtB4fgTVJx2Egb++vrR9mBLK3KEpnOF/O4Rwe4bZ/hB99jSE4x+DOoeT69fjuYY90HqNpFT4kIb668HE5VHDKHfID0HlzIA7Q1T0in+Cig1a5CFSHgDlyElQZZ1gBmTSDzyGIxvRQZxDXRToRUlMuDBnQCtULfd9gdzBukQzMlSOpmVpfyx01Ae21EebauJBm64MNVIHDYY+n7RPqvMRydQlvvsT15RyLwEE8kFlHSNTBTNFh1EWyjLHNWyQh06tWSOLUCHDrecz5ZjO2QT+iEnyDrsmg/BRxpIXiyUK09ZLphVaLbZyKTCcq02LIYx8/f6549oOvmG3s/Me0a/PccMJMVD+Z+Rx3bp5PXk/mSCOQPy3Ppkh25mNf2Q/lgM++ZPdz3J/tz/T2Fvp49g2zAf9QK436W9T5YhqvBlZsOYIuplca37cLEcI6Nv2WpI2ybSaJPoYswur9kXFDwxPqM5IRpt/TjFmeo5CzBBg8uhpoN2OyduhWrMX7XaaGgo6hSjZjunjI1Ma8RFkP8INYGKqD8oFIs5tFDXCgDmgvJipdT51AD50KcPBdDKGLlerg0ixFMpENU5Faguzz6dJsQGl+V0jKBLacTnREQ1ehJ92OCzh00nY8FEwx7IAs80hCghr2UM4BMdlycYiMaadME08TWQTq+hbxMkUa+Oj2pQA4RQO8fdojDD3cXq0lVZTOrTToGZnXYzdmxktTMce2+1FV1G8ckWbbvi3LUd4d+zndJnndnvYFlqmPi7OFsBJ5HUemmD0ReWrGIFPPpaaYBSpd52zds6xDC7iZZzK2ThhpsrCm04+zohVW6/X5XFKcCYbJeKYRZs1WtT9iimXb48q0YsB6c46bmztEBHhlrGI32aBoWsSrNeabDfJ8h2p3gB/2WPnv8fTtAV8/+qi8Hn2tEPUrBPMZus0a8VdLvLpQ+FIV8KoceeYjUwm8NEASEFQexGG2q3IcDjvsdo9o6xJ+QBY8nWE7OJ5mMNKhu++UOHQPrSugGln+7dBCBY3WCux9DC3H4xpwcxlfuAgGz8O2d5Dtejhk+6lasgdmQSRjAecANNahCc58PteMwEY72/65cgLYTuVUTuVHVyyzTFYvP9YRmwx6z2eMH83RJl84DkjHbcy4pIsEO1NB3+PDzv8+ngKOA92zKHo6aTQbTd7/8939v1GmJ2DORzM19OrtqZzKj7WQkXB5eYH/+vd/jy+/+qlM7Nl/FGWGh9e/R/vbX+K7HfD2dgH3ykMSNXDqAc2Qo1+46Dc9LocMm7gXsfW68REwbactJIXBi2ZieuAv5rQSxcP2AY+7R+T7HQ4Pj5hFM6xfvJAJdJFnAkMJQGVWxCXKkgm/Zq5x4kzXwstlIsDN/Y4TRgJE+qE7FwPEyKScK+Y+8j6F48ZYhQQrGrRDIEAEAxNxLbOstGfAmumjTOc3phyR+tQ3suJNoE5YGeazH3YnpucSeRumPzE0o4ZPhZ4uo/IFm8JnBcVtmqhNV5yIUPe1pHr63oDWScRxjPu1OnW6XzVB9Ph7jDGCed10McqK+no5nI46XNTxcU3faBCH8WFF4vmEqXwJ4iAV9z1HQNEeFV0smZYIzUKS4HAScIqofZej/v4Jb9/EKNwlhjjA4jLCWUipc+BSNZj7DpZDg5S/R1JzbGDLW+iO4JoNFKm9RiMMrrrTFVZSczudfsZArGs9dL2PphpQNT2WZ0vM5gtkVYPDge6GOm6n/t1xfNEBmVw7ddTeEUKYwTCPouGT8cvcM6ZtrTcbpL5Ceb+F13Rw/RDwqKszQ+cs0CpPmC4P2wy5STO6TQNxJuyLAvvSRekmiOaBaEY1jYu9b/QKlSNGDExnbcgcJPrgunJNJKhimqjo0/GUaADQwVN0B+U5ak1A6k1x+7wgUE7QULOZgiDEbJaKk6ikedaNMNt4fbXmnggtjfX16HhLlpE+Zjqb4ebFDQLRf7OX1Lr/2jakeUy+r3C/b+GSvRbxNxAn7YRNPpslWk/NHpsAfluhqQ/oVChOqgQZ6CTLNFubwmgDwx/OF45Aw6RJTj4+ggkTXGFcuptiEccXn15CnJ6BfPvZ8fSeLUD1fA40XRC15/mJidl0/mZ3MU0/tX3Y5PPxHCbIij20/HTzHX5Zp30S1SrQNYOwCAlmWZDEgme6jzJ6XpZZOwKeui9jHyxpvmEq+xYgSuqC6aPErNMI8ZsDcPFC+gwG/1KvNNOKPQxTMAVHN4wqYZ5xvsvFIMIxBFTqBoe8hiPC/64YBBDoShJfHHbVWFcItHfoWsJ6Poo4FKOCTQDMyaVuCb4pdATECfiLTFsrhgqiJ0fWLumgnqsZQzw3LjjImfaI6X3gOxgihcr3EKtQGHqVQ2apg32u0Bw6cRP2nT0SfxCzgqcCcGpH0rcls8IFZqtYWKtdQWdoB/uqxeP2IKy3zdlcRgimMRIgH8XYTJrxCIibxRNbBfS0+FjjZHsDwI6Td2vcMq4TPR8bs7JBlhViYEP2O9siU3BlWDPg2hGrMfN40weM831remYYbRZ004tVE3DtGcPcmh5xKxd7an86Di6WiRgu8f5LfTDMSi3XYOuYXlDieQVpjPObG6xWa7giSaH7trypUHkhzi5upBLut/fSly7n3yIs3+I337j4vhEuHMJsCbe7RLW8BK7W2Nz5uHPvcTmU6CqFQx1Jen8cu4hZXbgi1TXoqwJ5lovT7tPTHkXXoIk6qLQCggqDqsUkiMx4uqyToc40eBG6bAN0jS9OuY7L9PwOQcA+NxB9TsmtZuqo24smaeO5krJc7xq4TLPvC7mmvO5k8bd9J3qYZ5u16LRxbkItxT9VTgDbqZzKqfxoi9UgsW6dUmSkM8/1+GtH2R8UPfzpQdkOrDLIPo8p9N9xAjpZMbYg3Kcws/EUnn+oj4M/Wez63J/Z5NPFfsGcm6Q2nLTWTuVHXgiG/M1f/wL/9e/+C5bLlTC5mI7w+OEtsjf/iP0ffovf7hTKVOF2s8dNUGFWXGLoL1HXB8z8SgMjvU4R/EBHw9THWUxRdQ8FU8/6AkGYIoxTYdssLs5F56fOtki9AEHjUjkYy/MzXN/c4rDbi1C2TTGho5vuRPTjfDXHWQx8eNxr9zIGNRJfmr5Bgjc9saYui560s71rdkKNGI4XYJOQ8USnRa3/pCfwR6aHXeG2gAD/kj3R1SWC0JM0i2cd2vC8W7VOZOKkKavkx/5W74+AVo9iv9VacwKSEBDRQerIHuKuTdoO6oOkuzpegrKjTpW9NhrxMUo75iDmYBLkmjMz10gnybho+hjNEEg6b10X8IPInLMJsriHnlrc+jotFyucpTMEDXXlenSKaZkDqq6D71GHj06BTFlp5NvK7eDUewzlA4rXPR7vU5Q3a0S3CYKZhyRkqo82iujKBt5QoWXqCjxUBHo7DXCxSEqmnJB2/SNrg8GQE7hg/NyLKyaNOSgOPYg+kOMEGLiyjwCN8rEjGyYKcHW2Er3A+/dPonHDLwqrQlK/JgEcAT1DpBPhcKlbFoh9rkRPIGpxtsHl5Rke64METnHnIWRw7kfIhjPkNXVwUvQNr70vhh4iCt93yPdMZ+0QJQl9YBFELlIfqCsHh9jFMlKYya3WLLWa+lOhcd61ZEg6y/WUY2dKnGYgajCNaWO8HgQ8+XtcCdZ4nwiu2TpODSgGx2y788Vc5g17ApEW9DXjuwVhNYNtUt36Abe316LdZuvcEeR9Pg8QHbBhkPN/OFSgJeNiFsEPQwFNqf1GUIUsIWG39j1aaiL1QFlkcv5kJoWuI+56BF4ICEo7Nedoqruux/bYdooiv8fOcKbQ1zjV0Ztb4G0EqKbziUmjnxxEDjt577ivyXlMJzF2/+ZLoxjGM8xsOu8xQL/5XM+jDDvMNnP7ffNctx39fDJFM/dGWqvpSvR+aIpB50LP6XUK4Ec7ml4f3WfZdzXARlCUG8tcCwqxT4MOhcpjX3wEV4QZTBaaPgPdBgkasJ6z7yRQJ/dfM20k9VkqHFPq+czMCmlkAmqdVWhaR+pRVdZoegd+7GDm1uJ4q4/EY9FMp0NVKjHbyZMAs9TBtWrhdTXamlprLgYy0Hzdxtig6F5LQwWr9xcEmgXN3yRmDVSZpDSZnJy+frFSSAOFKqYGqI/UC9G6HjKy7CoHeeahK1u4zg4ujWoiH3Xk4SkHvB6I01juq8sFiLME/tCjPnCM9LArGtHMW6Yx1psF8pzonEnXtXXO3GgBPs1fecvU32O90g1Zg7D6vozNY1pf5S1bV7VWJcH6qspxvpkhSRJxoLXnMBZjZiBfNfprzkcaa2PfaoAx+5nVZ7MLRUcwzuCJdNPsBmQ52YzAi8ulAKvU2JS5wAgQ63NyVI/V5RJz6lB6ETxipWQBt5WAa9FyjbPNOXblHvk+R5S4OA/+CfffZvjNwww5R9DWR5Cfo4/P4dFJ/fMEX976+DKskHTAh/cdHkqFeD3HLAQCpk5zjGf9qmoURS0sy912j32eoegbOGEFN9yDfPCm1QscPC8ukDiBj5ZAW8dVsl6Y41xAogEI74hyawQh3UY1QM5vSoq/14h2oUsjBNcVOYVmxy8XGDyygIHFPBVAmdc3imMB2kI/Qp5nn0wbPQFsp3Iqp/KjLnqiY+j4n2Jq2QnoJwbQ4yaTWep04igrQCYIG1dy7UTrBzv5wd/jnHIyhfwT5/AfLsNEp24iyHsqp/JjLGwDV1dX+Ntf/C3ubq5l5bZHJxO9h29+jd3rr/HtdxneNLG4vYX9HO4hReLMcfbzS7z46QPyfYOwnwHdEmo3w3bXYO80ohNTFj3cpsQyrdG7HoqsxtC2iGdLOMqDH8dY373Q7p51h4DMhKxEWZV4+fJzEXvfZRlaurqZIGE+i3G7SQW4+LCt0YnRgWGtSRdldK/MZNpOwIfBAGiSCq71gwY3QNEHiEOFVUiGFdf/TYrNZBLPhwbDGP9TkrpDEEVat8gExDqIn6IHk9V+Y8Zgg155ZaJszaFwRNA9LzIc9judrs4sUnFCNP0jt6dgfPsI3wtQIdFMCe7/Bx3mMVXeBsTHuJiBq9ZAGkN1c70IgDLpKc8etIaZ648gH0W9k3SJm/MNFnSsq+kQOtDPACXBj7YWJh8BK6YhlnWLIPIQ+RWc7LfIvn/E02sXWRkjfLXE1V2ApeoRU9eN98rT51V2BHwGNI4vguap56CnqLkBaVydgyUAMAMpshaZEskUrjAcBDSlqVxTVHJ/vCBCK4YZvTDq4DJdxkVI7SiljQHuXl5JHdxv95rdxSDO1AMGzATVyP4SJ04T7MnCjBHvtmlVKkhwfXMJNxrwNttJ+k44BIg66vJ5aCIXiOei48NotCRjK3CwnPlIyUppB8yXC6wWK+zuD2gPHWazGC08lJHCpTeMek8C9vG++R5COTfDfOyYokXAQDP6yKTTtbBHyUAJCiGF3QnkKo/xGYqimtQcM45Tm64h8NeIk+fZ2VqCvLIsj1V8YiCgK6J+zetzc3dnGKF/fjwXPEgpASsoLJ9RDD4vkIQKyWw2BvlirGB04PigyYXH+knTi6KA8iPRVUw8IIoC+bwm0CZt5znAZZmP+s3jsqBuNHYSxG0s7cf8ALPZNG1qfDYBKSw7zOzFHMMyho6p4uLOqxvw8diTi3U8yhSgGCcx09nYR3/tK/n1zz617DA5rrVUHQXhj4DZqIklYDKTOHts2T5MP/j8jIzrpEkntmCbdabk/l2zP2F+OWyXAVrDVmPKN691bxlswqYkC7OBIgNnIBvLlTrANk/QjyYpFhy114+/oW6oG8e0ukjOrSgaDFGIWaxZX21eCXOIwIPTtqgLoCh97KIQ3czDbTRgMdTomx5VSyCDiyjsL3SqNY1qtPswDVLIFtO/l0Q/nZrJvkK7YZNxxD66azlwcISqEajuBLnOAAAgAElEQVQeS9FRU9If0BAk8gI0jot6UChKF/sn5nNzoeARUV9Kim7meyizHqHnSz/LYwaxj8UywlCRZdqhHjw8FI2AazfnK2FwFRWvn2Zn88aJ8/LouMnHpN6O1diAT3JPdE0ea5JsaBaaRka0qW0mbVOYdYcSXVfj5vwMHsX2i8qMxbaamvGVd9+M0Xbc1Wmfz9mueoxlrzwd06wZgv5rGXvyHYKcrYPtocRyHuNsEUrqed3qNHimfiaJh6uLCG5XoGpbUO2TTgllW8KJYqwvb4Q5+PB4D3r3XC4foZ5e419+E+K+COGSEElNV/cSznqN8PMF1i8j/M2sxbLNRHsvaxO4yznmYm6TU5APAc056JhcNijLTlxis0Mpbs3UPKxr7cDN+sn72lKelt2+pKxqWQCOdYpAm/K4KVRFhw/qrdGN2UdHOQZVIvA6xNRscwM4TGF2aihVa21EJ0ZJrcXKQblnSmmFAxfvfM0M1i6+CrPZDJvNubSZsiieGSGcALZTOZVTORUz8eNKMAcfalo8T3iYoF0y6fp4VmwGNfPPOBe1e/nIRfSTufvTt6axqJ34TT78D4Nsdp780Wu9+mkEVk/lVH6EhW2Nk6af/dVf4fNXr8SqncEz/3t69w7lN/8vvvvmPV5nHkoVYVAhvGYDlf4E4asLLOMaX4T/Avftv2K3czHQxXB9iyzaoKkiLFum4NSAUyFrXWwPDpI+x2LRoGoDFPuDpNoQaCM1KVzECM8WKOsSQ1ahaDO8uf8gE8kXX3wBRSv64oDPX1wgcjv88c0TSjPHkwDLTPj1SrhzBEhGFpIW7hfXSTN51+xVBnIeOsdH1buyurwIqBXkSIBudV64r74h06FGGAdQPtNBbaBpg1YT6pm4RU7LnN8IrNlO0wbqIrJs3B37AZ7vCePi8f69gIxME5JNuXJcPiF0WzRYMkwbU3xG4OwY6Zs3jt2fDY4sM+tZXWCKlsnAZVglTnZhKrouef6kQQwvFgD25mwJT1h0BDiAcgCyohLjgnS1EWHxbF+i913MkgFJ/zW69/+E1//s4t39DIdojuB2gfOLkKowaBloe45oFUngRFaY66BSnujoUACaZ+sxsCC7TSnsOwdD5aBlQNExUO6lLjXUUWsGrXtEs1GPdaZHXTai3eUHAaoyFw5eGoTCJuHV1UGjwnyV4Pr2ClXVoygOoAmhTplksKxTH3WMapiREwdKxhsU3r+8WiIvKEZeYKDeUu8jGJgOptAlPpxoho7pmAzIQyX6hm7foisHPL0v4CDCYrXA9v4D3j0eUOxCbEsHyQxYuGLXqlNuxeWPLK1BzlPnVFbCNCLrq5SIyxUWnEP2H7USVQl6QoTC5vOkvdd0Em0Z8/G6TIhYpo5wDCe4LeYHfYfFYi5ukFVJ0e3KYFGGuWTTzgCs1xusqDtnA+o/W6wDJZknRuQeDnZFLUAIAz22V63jNU2d1hlSDOapoejUpa7LTKF1XcSqQzILxf2RoAx/73R6o+ctuoUeT3JsmBpsGr9gyjjpMdfHvje29Mm0QxqnAYDshRUWqW6Yzy+LAdzN/o/t1hi5mFfDM1bdMLlXn7jIuls0bd/uTX/P7kOqkf19R5zEzL90P8oNyQridX/cbp/P655dn6l21xFUHH/bpL8kc6crSqmjA+UDaJjAPlkSKhWeHCUgmq92cFSt0+BqUotccQcVPUTlC2BDxnJD/KodkGeF9OXUwiRzteoVAorwJ0xPZT/hoqgJGpMRplDULgo3xG7uY506uFU13LZGVSs0TiDp6IGv4PN4os2o3XMJOjMlVRtqmHpk+jBJvTb9BIE25WldOTLoep4oU+idGgENH7jQQ/Zu5CFxQ0nNLl2FfHCQFT4OW08DbcMBi6FCMndRwEOTdwgpt0AzEBoNLFIsZgH6rJQ+sHc8fNiR9dTh5fWZnBPdfQUoNUCbQFWjXqduDfo2as1Jvsk+3tabKVPN6rCNRfTNzFNTJ/lo+wHbfS7svdurlVw3mpeI1qnRieMih4A9siDGBTA7Ruv37L4sa3ikEstYbwiX8tKyjI+DrWWwU38vL2qsFhHWyxj7vsJqlmAzd+E5GXxk8PsMdedDuSGW59dI5wsUB/bBJcK0xkvvn/DH1xX+5SFG7ToCrAXtBTA7R3C1hP9qjp+eA69UjqGokOUeSi+Bn/iitRapQS8m9S3efv9WFqD6lmn+rbAhq7bBPj+gqEq0LZ3UB1SFg7qg1hrNkHoxqWCv5yiOIXpcop6mCkKZv7SNgkf2WeehbQJJee6HBp7LR4eIY57vo+/JaKsBlcFTlFTgYDdgt+2hsg6dSzfTEqEfwPeZNtoKi3uxWMhCC+uKdRw9AWynciqnciqTwkkBH9YpbhwadcQwTjiPEz3770QbxAaMhsGm51bPUwbME3yymJ1PJ4DHGZ6ZiP4lZTJhnBbNWvP/8v2eyqn8JygEUG6ur/Czn/0E8/lMgyvUqeo7bL9/jYff/R7fPHV4HCIMDmGQAL2zgbr9HD/5X2PcOW8x5FvkDw2+eRuB3JcgDTG/u0J7PRdWGphuuFcYyhZ+SA2cAfvaxeFpwCq6R7QIUVUKTVUgiMggmwm4Fy0XGCIfu90eRVujrGpkD0+4ubnE7e0NHrZP+O7tk9ZOMZPoUSh5ksKpV9It6GYn7JrNJivjnNSL+51xfBSmkmYQkHGwiPUqMcXvyarq21pSMwjU2ABZ5vq2n5ROzAS845W2E337HtNCbDrOsW/UfacV2NdpfGEyk9+33d6jLUvEaOAGEaoulXQP28seWSTTPlYHs8dtJn257XOn533kgJhrqF+QUed6MZIgxFc/+RIL38PQkbXWo3AcFG0vAa0XRZit1rISvy0oxu1i45VQ+T/g6Xd/xK9+dYl3/Rrd+RqrqxWWy0g0+WgZSEdAjxN94/houYgMopnKwtV6Y1sn4JJLQXNX4eA5eGIwVitJkXEdCpszjVZfEbJPGBRHCTkjLvKcRggdYoqGU4g/2wlYFvm+0SgDCsfFwXVwfb7A+XqD7T5DR507o7UmNUpuqQ369L1z4wR3n93A9zvsD0+o6dJpUlJnyRKBF8CPeC09Cfpzz0UQkdlGxz0Hj1mLogsQnC2EUUYQcbZcSrpZ1XSSFqraHH3dIIgDqc8Ef7XmVDvqVNVVJ45wlINiak/geejePSDwd9peVATWteMqmUL9oMRZrqsaFBQEnxgVWDHxUVGCsCRZcRVZgQrr9Zmw2rL8gI4pSrxrJshmO7q7u5X688OxdkIjGz861kWCKm3vSCBO/byCzEOC2uJiq+v9KPE17lIH8lSRU4p1oZIcLyeIBViPvA5p7MH1A7R07W20P7HVkzLTjfH0fliOb46A0cenb66b3d10znM8xLRnsBpU+LPzoukR7abjcwuC2vOb7MvOyybvHNv/JwA5+8piE7K9YRXZvpU/6eHhcTQ6sL/hWdbCZG9HIE6/tsw2+R7bjauQ+h4CxxMXUTm2ZHwq3CsHD67CGTiWhJLOyN0TJBWZE4L+0rE6eHCAd0ULr6wQhGR2AUXdogtDzBMXM08nwksLduiUSL01H50boox8dInCC79HOlToKrKXfPSeJwYPZBqRtca+h/2HpCm3mg3LFGpJnVQaYLM6hLodGF05k+5K91amPXbKQdtxPHGECaecFpEDLDymjSo0XJjwQmHh0giBygd56aGlcU+fwW0PmPst3NTHodaLDEyhJjDFHvTqZo1kaNFmvRyvGhTe70rEcYjr8yWqpkJLAIaMNlt/hN1taohNJ/0TdcSol2nwytTpcQwx3x3HYfsdprE3vQBtZ7MEy/lMpAR6cYU1emsjoGbH6KMm8nEct8CdlXA4noeur9Ntx3ePrDbHRVb0GOoGv/j8BeIwQF9n0s/wWjXuBeLZOdaX1/I7sn0m4P3ZYotg9z1++U2CB4K3ykFULaC8c/TrFYarGc4+j/C3cYNZk6POB2RthCEOkUQuSFqmWQIZ15xH0GSDTNt9VuLp6Un0Md1AoWxK7LMtyqYShiQBY5Ef5IMLBAR3hxa902JQxlFIrncPz+0RRb5kCdSkHNIluiXTl4sLAWr2qQNlAGiIVIvbuOfRtZt9dIsVQTQuKjJdmQZI2x5eW8NRFdqhQ8T24Pmm3WqJiNl8LrIGJ4DtVE7lVE7lE0WsuTlHoK6NmcTokcxucRxonw+b03JMf3i2umknwc6/Obc2T4/HHdfDPj7Uv6fYU5wczGqtncqp/FgLJ62L5Qqff/Y5rq7OtRA8277jYX//Afe/+xW+e7vFfeuidhnUEFyLofw1zl9d4u/+pw63xf+Od69rPD12+JD1yAxbgcH855sEXy08xGcBirMIpN2oOgX2DlxxbqsFfHjIQ1TbGuv4CUFClzqFts4RxTNZwSf4cn59AT/0hFnz87/5a8RegLe/fi3C65vbl8gOB3G4sr2Snmgrk75ngS2dukcwjc/HVXJJDVRwPc1i0+CaBd709nVLXTSFgOkUQy2pkkwvtBmBo2a77aam4JpJB9Ur8iPGprskE2SafKoR1NDOldrJSwMIOkDzHQpfAw+7DIMK4DLFUTpSEzRKZKQRh3G/EsDKiRzP0UTl46UZ6W5aDF80zEyAq4OVHoEf4fbuFnebK3gU+nJ6NKK15mC/pytfi+X5OeCEePtUok9dvFgcMCv/GdW3/4Df/WOAX7+/wy5ZY/P5Ja4vF5ifRXDmHtIASJwGTtegbWhS4OpAj/QsI8ZP/SUGGQQUO6YOMyOM4t1Oh1QNmPkutqGL3eDByZlSRS09sjQYiNA5ltpRDmLPQZS6KGiesSdwA6TzuaQP7g57zWZUvjDDmAD3LceL0MEXVysEyQJFxpX6RgOqhiUhl0n5uLi+wsVmhv1uh6Ip0XgUX/cxj2Z4udkgiUJhOxbtgG3ZIk1dnPk53P0Tcqb9MAWr75FTPBsu1jNfBNgZ2M/nEVarUIIcv9tjyB1kzYCQjBrPSPFR446MGmoMkRkS+EgTH2XbCyNu1t7Dn/0fgH+N3llJqqmIw1PvjgzCrsbTbmvmAXouYAGcEbQWUXAN2PJcyVwj0OaHAa6vriXFLc8PhsXDdKIFLs7PdMqWzCkM/DKK4Zs6r98c269ld1HLynFDYRkxwqTo9tOO+j+tpLyRUUSnWqn+Y6vTIEfZEJQTOFBEvclyYqqg4wZyzdLIwXwWiug99Ys6HmTCrhrBKwOCT2Yzz1CuZ5/I+0cWv/mxx3nUCL7ZRDtTDGDw7IuTqdfYbp9Ng/SbI0Cuuxvz/NnZPn8tjsvTPsqc37jJeNTjHM+m5xmVem76cP+A1swZ5Yp/vHiqd27qz2T35pjWAIGgUJrGyPMc+e6AoPOgerKzOviDQlg6eEenTTVgqR1tJI2YDDRh1enDoKFBB3XHBr14WlUNGrLf0gCbYIDPNE1zjoorJIqahQNUGsJLPcxDYMN+qG1QVS5qJ4AbkD07Ya0JGETWWi/pemKGQMMPETbU/a+QkE2/K6y2zoKJ9loMMjb54pJCt1TXAG0QRhOBtoWjsCJjl44IoYeZFwmzvCVrt3ZwOHgC3nTtHm53wDIcBGjLSgckt57NPESKAv812l0GnyAiU0KVEsfRw0OGRRJjvZ4JK5WuwTaTQ4BUq+NpmGW6LuhbasUEpB8wANo4oNgtJ3Xy+LE2MbF9QV40YpRBnbjFLJUFAUqraqBNj72WdSZSNhPDnnEsHVnpx4d81571OOYaqQjzPi/9Kg2w9FI0TxU8f8Dy8kqYhZWzwub8DulsKcAaF4viuMQS3+DN6wK/3Xko3QFRGcGvNsB8A/9uhejzBL+4dPGSJgJkrZUBKjdCmGrWmj+Cs1prrSpb0busaxq4OMKGr9oCu+0HtE0t/WhZa5Yf21lvNQzFgUcbg1DzT5sdcbGLLGatqemqBkE4wIvEcxd1x5Rqpo1yjPHQtYFm5vt08m4RuJ2MoV7g4qllPWGdZfq2EiOZp8ZF9tRh4KKK06Hjd7ggJS7q9KkKsGLa6Gq1+t+m7fxUTuVUTuVUPkobFSFaPSh9NG16PjHUbzwrxwnXR29+VOyAPZmrTiaVz4G9caD+c8XuyB7Kbm8npmSn0N1PuOSncio/zkIzgYuLa9zc3ArzhNrLZNY4vYuH16/x/vs3eF86orM2UFQeZLvM4C422FzEeLVqkGbf4dvfA++zGHnvoRGxf660cpXfxyKMkAQDZm6PTeTBW3rIqA/TRGjKEEPG9L0GnZMj64GnnQevLnA2K9G5M1QZU+TIMlrIxJ+OVhfnV+iqGr//x/+BoSnQlk+oqhK3X36FlPps251egX7GWDMTdQkWtL6LOHQa5pqAa9IvGO0vamlJKqAkleoVdQAV01kcso1CpEGvgyaTj/Is9co4depyBNd4KlrpjEVvc+wjLdCgQTKZSMtD76HJdhiqA/xwBjegIP4MZZGjyJ7gmUmuTcgzyxv6KAa40N3g1AHOnJ7pBolPTANhOTf5IifjHdLlCq9evkTYOVBth8EdxCGUzJDH+x3ixRJn55fYP5V4X/W4vnFxp75F+/j/4O2vdvj6tzf4vruAd7PB7csNzlcJnGWAKAUuXOqI0Tm1Q10z2PQlFYvpmGRRMs2RAYAEtRQ0JxOK7A+yLI07H+0DWZcWLif6Hr4PFerWJw1NTBfooikae/xxPoXvXSR8OgMeGoX+wADLQ5SmEvDlVY6A4usMtuDgvQPs1YDLGLg+X6PpA816I0uOmWrRHK++fAFnKPB02GlGGXXzVIDb5Rrns5mkPjGo48Xm9xaJg6jNkD2V2Oa9aKeRHdPzfODigtfHVQg9pkYy4NX1KQ0jxFECehaG8xghmYVkYEqVVsJyIyslXdDVtYHrfgO4G/ndIVOj03u07leoEKPvlQC2qtemGk+7vU49Er0sXX90nXae1RuNVxvBdNlOM8vYRihkvtlsZNMsz3BzfYc4Zh21NZ/bE4TQjzHNc8xNtLH5kQFDgNEL6WDqoCW7rqUuW4ksL+S+BgEZGPp8xNVWV349FRgcCdzLopE6RKMG7U5JGlwgfULoAvPYQ5wGkk5I1hzTsizwrENYc26mXYw52IbgP05vTFuy/340BRnBuGkvMZ1RTac40zmP3r+dGel7ofsc0971iU2ONGIc5rnpoWwjt39kfqePL3uwu5l82d4POU/r0gjg/Yf3wiITsGwKntovHk9F72fyvk0bvbq9RhSGeHj3IMxJ9kmdoiNmj91uKxv7ykPArHgxFenFhOZ4SnqvlaNdTcmC407KsoUTBUgjD3NXG3sQxJDSk+WjHYk7OJiFDuZej2Bg2v8wstYI7gbMlpPvEBgxjLWmF1BEtP8E+NByCpYFOd4ruSZa7F+02aSLJmOMoKgGRsmA4rkMZE1Rn03yW7XZAhm6MbUufeqzsY5TgzJA67kC/medi0PhoapaDM0WqqlwtlggiXqonkDIIBpZr998D0cFWK1jLS8g5iYDyrzHfltguUyxWc9FtN+4tei/FhIc0V1TYezy+gRQs/VC7uvIJDtWubECTNqHTe/Myw51mSPye4Qxmdlk89nxWT/sGCpfs23CAmzmPwusWdBPa7NZNrue//O17wDrKEAyBPCIvQe9sMCogdn5KZaLjbTT/SGXecJqvsXw9B5ff8cFHAUloO8Cg79Bd7GEfzPH5YsAv4hapE02stZ6svFjF8S42KtTD1NcOMta7hkZzOyrpf4oMtFquB4XhBrRvW1p3EI37NZoTY6ju9GBJDuNqcZWwpXjkeL9Za3uoMiKVD0oP+gFnmawsQ7yH/7fBegrDx46LGcBmmELt3OQhAk8PxVAliIU1Df0VICW6co1UBxq+HRCVWwPWpZArvdJg+1UTuVUTuXfLlrjZDgGpJNynOYZiv9k8mTHT/33uLZ7TB2Y7MQOmB+9lpfT2aEMkh/NWP9UcT4ezPVznQLGAPvf2sGpnMp/zsK6v1idY7P5XJglvaMZS7M4Rr7d4u3r3+NhmyF3mJZCtgxTyCL0/gLJ9QrXC2DBIGSX4/6+w0MVoVbU5wpQNgOKlsCHB9dLEM7WUG4qATwl+Fdug7PYQ3cZIp/H6JlymofAnnykGp1byyrp43ZAig+YLws0XYSmyNF3DcJkrSfKnov0fI2qrlAdaqDq8fThUSznX37xmQAldDiUVm5F1U06kGbgaCcyYakZJqvVYRufizOl3pZpHLxGYRhofTaeLbV8PK4LtxKvaMFoc5FNcCXJjXIo20Pafs4EoSbAZLHpoFoI3AAcVMpqarT7DwIKOMFcu+fpKA1hEAkYkB8e0TQ5fD8wrBDtUGoBCyG0TQJ+W8bk/hE30WCJDqv0qgo1fW5evsDVfEU0TTauVY+8G/B0KJB3Ds5v7tC3Ct89lnCXDr5cPyDe/Xe8+fWv8c+/XOL3289QzS+x/uwCt5crxMsYzpmLqwg4o6tlW6GpXVQU/hfNOQow89r26ClCXTZo6W4mqYd056M5hQ5MCbS1DgXvyXYjdtUgRItzT2FIPDzQda/x4VYE2hiwdghDX1hfZLYMFbAJetSJwr4AULaIklD02fJ8J6k8TFljSs0eCu9EI6jD9SLExeYSVedic77B1TrGw+4DSrq7KZ4B3T1T3K7WIuitr69Od3X7Al5Xocsq7A49soYumB6tBtCQNeMqBLGHuU/HXbrTcszSi14MwvUikYs48SVtlA8Ba3rNxiHQlMS0GSUrIoPjknF5jgcCBmCbvkODBOhc0AcBfY39YYd9rtNCNWig65H9b4RgLGhlXrOdyCKcgAhk02h9Nu6H+jyrsxVmSaSF6iX1TDN5RN9RUuyoYWVANjFIOMJQtr3qqqnvd8TfFcSoi1aCVWqpPT1m6GvWfwKvnmyn3dGfz0vYGEXwPitE40iCQRO8s13TZIXPI19hlXrCjqXeEJlOImnXNmNK4/MZhGWr6fmQYF1yqYxmm21bx5nQ8dxkW9v6nk+ijpDXRzjVKOSvP9GLCLbbec6K+8EzexCLx40t316rKRoyKWahgg/bV7Jv+vD+3txTHGuK6dd0rTFd3LO0UeNaSaZzEOH8YiOfREksCxvuwkMztHjYPyDwfKnPTVdrowACUJRaHHtUDX1ycefDoOBt9whapvy2iGJKDbgIhWGqJQTk9/VMCSVLV6FWLnzq/TH9re8Ma82HImuN7U9Ya4NZOGrFyViYawKKUNuMDwOQGF0/0WCzFc94B7AIy0hS+7TrtIBcArLpeya/j/psnkI9uOjoFkNNK9DpccCC/QKRGqYZegFSP0SjKGLvYFe78MM5Li9vEJDVZ4xZmD7OtOpWJfjiF1+JvuV8ESHguE5R/QM5gi6yqhNw8vJiiXkaCngtbtbsW6ybsNU60xw0DcKNo4X9XKeT6iptAbEjGCy1RExMzHYyxrLvbkTsn6xlAt6bGesC0DDzURxEj2YGdm182l5MEzDA/9HYQGumGlab4jhBMEhh6XnwO8CnE6fXog0dtFGCcL5Gki5Q5hV2RSUap7G6x4c/7vF654PeFGEdwuvO0C/O4N4skd4l+Ooc+GwoMBQFcrLWyDZMAmFm0yGUC0SD6KhpIwOCa6K1NlC7lGz+Bv1QoyP4xm3yBnXeID/UwnoOAh9lQdDZ9ATWSd0AjMLMJwtZKO+21ybgS3CMfV0rwJ0X0/2Wv4PtaIDTAptVjyTy8XZHAwY6ZB8QoUYSdIhnKRwy/GgEgVocVbloRAOObdGj21WI3EaMsHgHfI7NJwbbqZzKqZzKv6/YFWYNTh2zCeyqkS42teP4PT3POk4Np8+Pk97j9tPvjlNOM4o+m/N9PAG0k5lns1A7j9QAIVlrH4OEp3IqP6ZCp7Hl+Q1W6QUCurcNHebzFGmgcP/H1/j++/fImHYQzAy4Rn2nGE4yx+VtjE3Yij5WX9UoixYlkxIIOA0Bsj5BB6ZzMmWN2aAzrC7W8OfUUnPRcFW+HRA6FdbugFXqIluH6CMCbSn6Rw+qHtC7OxRDhYfcR7YdcDGr0HQ8UoK2LuCHEYIokaY+Pz9HsJghz56g2hJuU6DfFjIpvH3xQlZ+qdmmtaOOK+xa38UEioa1xr5tIMhhUlEkHYXMp66Rya04L05W5bk/slwGkHXUysRZM92oC6XBtVFs2XRPNtjQgafV57Gv9PtmfiwBWH14gtdQUHmJXlF+X6d1ydTZMibI7ggjceE77O4lGCRIoGfehk1hzkETC8wvkADb/B67+m27UIIJUDi/usLLixsETAdlcOkNKDGI2HxWVZivL7BcnOHxTYb3oYsvrjtcd/+C4tv/jl/+o4t/ffM5tu4V4hfXuP38HJfrFO3Gx3Kh8JnbIuhKEW4mW4RaL16og1oKYEsqVtugKWtJ3WQwImmLIuLPe6iBBaZZiTkPGW0D00bVyP5IVS9AW5242BINbfgAArcVxgjTxSg4vuc9bIBNOuDRV6j3DIY6pLOZvmnFAXNHIXY85L3CvePigWL7bo/beYyyeMKuOAiwzLZAPsDdeoX1QjMvGUhSU4qC6Oi2aPYFyr2LshuQS9orgcUFnDBCGQQIPQ+x64qRg0cEUNoqK5MnoKPO4tIgCTXwmkazG+qqQV4y3YjpvB4OT5m+lt4aWxXgD4OLdaPgDp5mOPQd9vsHAZ8J1LI+UUdKA0karCEIYPHZETyawj4GpLEuf2QdsgI3FIavKgFQItLDTBvUADCBNQIWJrXOuoD2dn/afECGfxswy2CuzQ8IgAV0EyUg2VCDqMeucLC/f4TTZwijAP1Axos2pbCnqmEW7ZXL33nISmT7g4B8krJnwHaCdEz3dWms4TN92cFq5mG+mIvLss7Q6kfmlgUenxsgaMabfhwnLFNoTBuxHPsHXSwMof+1wJdN57SA/BFcGPlrn2ANPYP1f8BI0+Qee8J6Ljd8Yju7L2cCeop7YFnj4enBpEMe53u2D5kCinqKZoCnCSDnRx7OlksBnrnfMAzhI0CDDvPlTGsN3JQAACAASURBVFg21BXjaSinQ1PtMA+0+6EwccgeJSGHZia1g6R+Qtg3GOoKTVlAMcVNFlKsrhcBMqDguOW7SF3tolk1DuqeOpC+pIMGrgbD2U4I8lMnS4C1phv7If3Q4BrfIxOJ9VkYlKbTFQbk9DobIFTYzyZt1DKPea1ZN22/1DN1tNeMNrJw+ftDB5gR1I4VOmOEEAceXl7PcPeC+o5kauv+QXTYRNeNTNelOCf7QQjPDxGlHi43MXzPQV2Wki9J1m2WaZDn7vbcGCE0Yx/LvwS/RoabAdWOxkFa18zWH8sas797/GPety1BtZk2d6HuquOLC3jeDGJ6czYLMLRaT9FUxLHu6rm91YEzx7Mg8LiYppm2omnaD4hdhaTr4VOTs28xBC3qNECw3GC+Opd+Ic9qNJGDVboDnt7j/UGJrqjTUqNyDsc/g3dJcG2Gm2sPv4hqpE2BMgOyPgaSAEmkRGuNzC+Ch11FExg6hBJco/MtISnNmuvJ4u+pxcbPalRZjWxH59cWZdeiKMgMrnGxnsOjOUajWdP6WtjfbJsaQTbdFjmX6LgwI9psTDtuoFQDL+glHdYNHLy68bDbAe/uHbQ1dTzpOOqhdir0OCB29lhGHaJ0hsaLJQ16wAH0EHaHCLlS2O57NAdqkzaSNnoC2E7lVE7lVP5/FOmwmTYqYJXWLrOr2D+AwOwkin8sd1ne0gOi3WS6ud7HdCB+DtZ9BLFNP9CP6Q7tpg5XBL0Ta+1UftSF4HIyX2G+vEXspaAeLi3LNmcpmv0j3vzxj7gXp8cYTpDCUaGsUkJF8NMYm5WLGdMEKLRbMcjp0KgWLWrRn6HxwSLwMXc7eGTnuAPSJMDV+RKrWQA/UGipY9YxWGA6WoPIaXDpK0RzF0+LEIrHrUM0mQ/VVlgtfaxXCX73JqeIDTazDE6YomQA0LeI41RSvKgjt7mhCLGDqsqAwUW/U8ifCpxfrjG/WCKvKrR1owWTjbYkJ+CarabZK9alzKaFclLM3+FFvA6TJXOzOm/CC3lOlzulPLR1ja7p4NqUTaOn/LxzssWaGehgUwt+6017rmxne0n9Q5hIAKgjVqvmbhkiJmGEQKCjEIQJuqZEXVJHTAMFNjA3WTv6+2MfPAnabcfsQLSQ7l68xIIacxkBHrLWyE7sBZRw/Rib6xtJu/t2W8O59vGz5Fu4H/5vfPfb9/iHf73Bm+IG/dk5zr68xsu7JRZnIbB08aWw1uhuSSDIQ0W9NAqb08SAQa1cDKaD0pWvRVVzu1Yz/KhtJCDLeCuesT94b6nLRE0xCjQ7FEB3GswVMPcVHkMPBYGTwoFPgWdFGHFATLZb4KKuHZwNDZIFkNGZ71CTwCHOm6y4bl1gwcC8d7GDiwPZoMrBYbfF4JB1Q621BJezBFFEgFqDEqJphxxO/R7ZQ43yQEtT7ZA5wEe3nmN+FmBBqk3KVG2FKCS7rkdb84eSpdbB8aiy48GhmYEwzfStYxskYEgMsfyQSRAUMR3oYYfQP6BLHPx+iDErHCzqAa5PA4QCD/kWjSJzJRd2zjKdI0liubBFQTrfkSUkQNIUNDEMK4nz7FBtUkY1kKZTNVfLBRs8PIJWZg7AoJ+glnZc7EamvK5+RvtvbDe2vY1vSqHhRZT4UFEi94PpeyLifhhQPrxD4D6KcUQz0FyiN+6v5vdYFpoBOxjUZodCfjPBFN5zaT8SvSstoO8EAqATAJ6nAeazCFEciX5WI1qJR+dUO5HRKZPmhD8G0izuYraZzn3Gc/wY6Bo/Pc6Gjgw/+8nxvck0aHLgI0hx3Ll9f9JPmeD9+Nlx35oNRICtwNPTzpyvqS1mAdYuptr+TeCUKVNW6hQEdKBbaOi7whLjtuyDYz8iJoBsx/5fOytmewJmCsVuh9k8Rifi7QSTqdvZoHNbtiaETicppC7vCzXS6FBKh0XOWzuF0nOR+A4STbiS/oQmH9T6DGliMHEIFe0rAdZ0KpxNA9W9r9EpJFhCAXoBiqe//zkgJIXrNmbezDqv9dlsndRXhn85w3YnRggN9dk4dhJqcjpEdP32HLSBg/MQwgynOy6ZReTC8lrv9gccikbci5mCz9/H9PEoAnwocUYVbbdFImAf07t5SblYsd/vEPkBzjcLucYExG37llRv+U0TVrh1Gh0fx3ZmmbAWVtMA64CALFy30XqXsoBkGXL60YDsux5JqBD5ZJ+KkuKxPj8LEY7jssb+2A/pbajZSCfpiIszBBmFjdXRshX9col0dYEwTlBkJWhMG85arKp3+PBNhreNL/OWtlBIohT+LAI2Z/BvInyxAm6dAkNJMMxD5UfCPE5lkUiDs0Nbo6N7LTUxWRcFoCXrkay1VnTTeG0bjnM0l8laWbwsSmpoclGJ/SOZ3IMwjFmHV7xfsoih02hlTiKsPdNRcL4gEqla49DU2lHvkPdz7bu4WgDvdwq7lgxtV+oAU0r7jgsXofzuamiALsPcO2CVKqhohtqJMHTU9qtA320uRpQAirwT7cITwHYqp3Iqp/IXFFlplhVf6kaQKTEZPCeTNjsRH1lrk5VNC7jZyacdUscX06fjzOQTLDZnEh9OPuKROAEkuDadpJ7KqfyYCut+msxxtrlDnJ4Js4YgzdlVjNjv8OHtd3j34VHs3FW0hPJiKBVBuZEIgVM3aRU6CJkDWQ8Cjkkw7Nao2xyVuH4FWAY+ll4Pty/h9AxmOIn3sZ6HiKm9ppSkZSim5SkPVe2irwd4Q4OZqnEdulAbH+UqRhLHuFomOHyo8fbdHoVbYN8qvN8qRPUemxXTJAIRmh/QIEoXkgbjhSlWV7co2wrZLoNqQ5QfHFS7Hpu7S8zXqaSNSgxoAkQGL0wLs8AaV4cJA3iKTqcBHIpgD8eJ+lFU2V5fC3Tp4EL5gaQ41SW143Qan+nwJgEHX0tenryvSTs6CHW6DnVGafseXpxI2qDuKo3GkVBFOuMwao895npJUR5ZhAnqOkNZ7+GSeXfsam30br5jFkEYbvBEHIXPPnuJi9U5nEMJh1pe7oCiG5AVLWoCJhfX8KIEHz7kOCQKX5y/xfX+v+HhN7/BL385w79+eIl9eI3liyt8/pNLvLxKsDjzcJ4A19SXEdYaUHY+Ws+XdE9xhJQAXK/2M32PATXTaAiwEYQZ3E6LLps0QglkzeINtW14LwjsMCgl24JC3gxKWWe5Xx8N1q6DWaDwGHg4NB4U5XWE4dIipA6Xr6QtdAUDkBpq5qKkwUdei5sltQqZ/HnrEZRRso5P8I7C7P0QIlQhNmdzYT1R94vnR7FyNFv8f+y9V7MkyZkldiLcQ0fKK0u0BDCcGaMZ38ifTzMajWr5sDuzxOwMgMagRXWJK1KGFrTzuXtk3kIvH8gdLsyQDmTXFXkzMzw8PPw7fkT5UOD5UaGpWcjwOgqBKIHKY9zNNGZMpFUj8q6Wz0JRKVkbND+XIrsZoLoBgRokVVQM+S2gQ9BHdT/B6z8hZgBH6yFINGL1D8DyR2zxDcYqxrIm66rEw6cH9BlTERPUu0qYEzS2ztOZgMNJHOF5szNAwjm10Y7haSi5sST/N/dnAa4sQzSOUmR5IEAI+88V1pNht4Bsp7TcCYuSpcQZ62l6xzNAyRbSSeAjn8XQTNkdFOgHP09i+G2A7eMWY/ceaXKEH4ZousgCaJZd6gp++zUBDzJ2DvsC+91BmD3DSA8jA7gJe0cFGOndRjmpViJBXMwizGcpopQbE2QNEe/rDR7+cgkz9Z8D+NzP3XE5Ztf0uwnIdP3h/sRMROenRICOs/PzGfxgvz1fe52vqV6uoNzvzj/nCUwxAEtVlNjvjy/Wb9Ma7/yl/uzfs/nKBw6HAs/bnTCrmPrZymZuLwbq89lMrqPd817ScNnvWZogVRWihBs3JvWXzJmWyZpRgoHzsN18IaNYdS36okBV1eg1wTsC7C50wMzjHBOUpRvWGtmzFliTEAPDrjyBawZYk7FLYK0fRapsfAtdeqg9L+Mv9ImyXm2258RrU+SlFsiWn3LbhgpNrrMp2zOS9raj56QFiIYeYUfwmpJQH3oc5bjqfsSHj4VI1clC3+8LSVEunjfI4sKwnStZJcucxn4iu31+tYL2evFs472LY7g6lMiSGFfrBVpKFHua4Llkz9NNkRsbBuhxTEE7ruV+S1a3PwHpZIS/vV+hq0oUnZH7mnFmx7SVk7vMUBKo23pAFnETYUBL5h+TEGyTr87vz3bsynU4DkjJNqZRJ33duKvBsIvrJYLlDRaLtfgyFkUDLwOW6gPqn5/w/aOHQoVQY4CgyzHma4zzBYarGRbzHr8KC8z7BlXh4zhEwlrLhbU2igcs0dC+aSxrzdzLJAyDSeT0WkOLobestaoVf0iy28qSMmUCcQZcc4xIR4psyLArG0SxwmKeCttPknSndYmDaIkam4fcb/iRBm7nBFinKaqmwHPZAcGAIALCKMKgIgkXYj95EqDATcPQ2De0DbzmgLlfYE4/tzhHhxS9V5KCCN9jsnyAbTteALZLu7RLu7T/L83svlGuYopTsyPpzEfMc6YSzq4lJrDtFzCv88W1a5+DdtPPzBfT606bXmeMHceyu7RL+2tsNENeL29wtX4FTdClHxHFPm6uc5TPT/jw83scqlaYYyrI4RFU8yMoHYmXVxYpzDUXZJaBwEV+QJCjEtklQw2gNSJNLzIu8unz0grA1dLbJFDIY3pdKVn8cTE+mTkzWZHuZY0nxULg11ioDnlIs3gf7/0EQTFHdwhF9uP7BTrVYNsqbJ4HLPVH5PMD6m6B5lgIAy3OZmiHAfl8jsX1Cpv9FkPtw2sSHJ4YLd/h7Re3woKqykqANW9irxmPLI0OIVlEND6X3XkjPpmE5cKWsl/KfOYWsxa041zk04cklEK+LsnmM0yYE/PnFERAdhmLDqm16gZdcUQQJ/ACKwd1yIYt3Iw/Vi+G8kaXZebWE2vCAhXCMo7F/L1pduh7enDRn82VzOeLcV82TebLOX7zq2+hmbhYNSZdT45HIVyTczbi6uYVDvsKPxc95q8b/Mb/B7Q//nv88T/6+E9/+gIfxjcYrq7x6tsbfPXFDMkyRLrw8Fr3iFFgaFg8BKg9+skZHzR6C5mCpJ88jhoxfybzxO7gU2bjiaDG9pe5x7DYM3IsA1wyOY3HRaCNoK5hf5h0vpGMtrFD4PfiZeRFCs+aQK+GV43Qfmv/3vRJQylp12GedBgjxdODPGI90qCvGnhtJELGxGdqYSXyoYCAWJygksAFI2XtikfsP3aoDgnQKlRMOQwyNHc58lxDp/RTImOFCaqVsOiEeWhBKhUaMIPJdiakkO86CDLB4lu4A82/g/Lfw2MyaLBBEB0wBDmGaI9m/O/gdXMB57quRIMG2V2Oet/i/b//AL+PcH23wnpFv0STcku/w+fn7WeAkAV+3FcvgBwZ2Oap7r4MH7N5LtcbU0XtM8wGnTXsluLxDJgwYNLZrdxKnM0Swn0OuwKw4QrmfBugLc1ieGEixt+B6rGcaUTJHMdjjMPmA2L/Cek8QOunqGtqD+lRZxhT8tFdcW6vDRbEJYMU9gWOZPnRt02ABQO2eZ6Rkoo0WKRyPpJIYz6LMctiRFEs57FtW8MemZYzZ+CA/dLhmOfPMJ/p9HmmuefPXuM/87tzlO78d58dp/mvO3nu9SygZ1/bPVd8sChZJljhK+z2x+lzTCNietvTQvCXwEQHEAoLRwIxCpRVKQnUIVF3yxRLswSL5QzjSJ8xs2HQ1B5IoiFTlOzETc17lEZqPfPqwUPrR4gDivhryR32OJ8UpYAXXkAAThsxsjCAzRxySghlaIcJCxGeMMciDeSt1PDkuXYGrlmmlvzfShinPjnbEDHydiMpdixBPk/+3j5Mn7l5zQJtPmWj1tdMgDzeWynWc0jWiF752BI3SRIZ49vnAq3vYbvZ4qFvMbYbKK8WmTWTIRteB0zETkLEqcbNIsUiibA/FpIoHFCqyvCSssBywTkrRUk7BMrKXdiF9TQV3zN7HZgQMcsYFRaV2RC5mud4e7/ED+/eSwLyBKy58WD7xCQVn0BdDjzOyQQ008D0HwNvZCRbtuf5dULQLhiBeddC0/+Mc/swQmcpkptbJMs14jAW5mo90pe2wuz4r/jxhxofByalB1BDCA8z4GqOfJXCvwrxzczDq6BFu63xsOnQhRmSPETKTSLxWuuFtUZGmmwQUQ5K1pr49dl7GcjQprTfyEUJrFV8bmVkyBxzZG/zGuusn980P9k1BgFfMtyyKMQsjVE1pDrbo3d9IYsU9g/PgYeb5RpJqPB++4Sa5psStsHk2B6BN8i5pjTZWB0QmBsk8KDvY3R9QLdUtEONYCyQ6UZ8PlUwk/VeR6DN47UWwfv6668/vztc2qVd2qVd2v+LxiJSMcHLLRLsQpo3Bu6uSOEnP7MFodvaPZuFT8u7l1+cA27Tz86fd/YaIgFz0o5Lu7S/wsbiZ5bPcbW8hwpCWSiRlrXIY3SHPTZPj9jVFaBTaE1QjRAazftDqMAAZhmxM1vtimREcwHLHdhaDJO5Q06ZCvel6T8WhD3CiDKeFtWGTLdAZIa3Vwssl3OkCU3juRgLpAgi46yj7w0XZvUA3TYY+wPCcESU5zh4Cb5rfBSPPYY/HVB/fAK8Jwz5E/qgg98FSIcBb+5C5PevsTnOob0OUTqHDsluIwusx3Fb4fv/6yO6soQfjeiiFPFdguXcx9PDI4piQKwTYQUlNLdRiUj9WMywH2U+OSuC3JrVFeLGzNlIz6REnJ5rKybK99pazMCTNMU4SdT43FHCB5iQ2ZWFSQJ1wJplaUnC4mQ6b1PEesqoZDvazqnGs80Ya5+YQEaOxa/JEqrQyzmPoFRkijIWyQPZTyG+/fW3CAnxFIWAS2SKkPEQNg00B8PNGkmgsT32+AQP38b/hPHpH/Dj7xN89+MNNuMa1XKJ129W+PJujnQRoEqBr0IP+djYgoPsMI1RGGsGWJNZWuSgHXphi5hUNTle7vSPxg9sYIFkBFkC3AR+iICbKMJQIdCkhOURBL4wsSYfLXoQESghlsIEv84wGYJgMIWEH+I4+nhoRiyLDiH4u9aYjDOsoyGY2cn4ZbRFTXks2YVKYVvPUQfAPDMhGB+fDiKx0YulpBnSny3xByxDha4YUfy4x6BCFGQ63Ge4Cul5BERS+FEy26NuFXodiLyTMkWRQ1mmHo9ffOjqTqSPmpK6+gE+ficS29H/O8BLBRQCzbJHMscIXgao+xrvHj9hHqWGOKk1Rnoc+QrL9ULMxI2U1QQVPD1t8fj4ZEAAGa+uCLbjXUzPLUhjgUBxNuPXloESBjGur+doel5bsQ0xGAw7sWU4Af3eCKA6eajxRyMDkdec+CBOTBkDlpIJYzwT6a92+kwvFw+igBJwZGQK8bCTYAuoEBUTFw8NjsUGSTIgnKeo+xkORQvVtkZGyiKTECbXLYJjOHDbjFfxovU8CVQI41jkwwTUHZjg1j58UMpLDyYJqBg6mTuLgoyVUsaVCV6ZJoQX8/j5EsbAXW65c7LlOH8Gf/Ni3SNz0Dlo5opv92sLVU7dZ+c4AUccG8j0/zTHEfDl+dCaQwhBkOL33/0BQ3da4zlPSWPcd/p4FvuYvPjkE1v/LPOeHD/mg/J3SZxIQEZGSR4F1r2HYt9jbFpjiB9phGmENGZIASv/msJzHCojj4yjAJrvS7psy+CTEl5zxNBRbqlRMdQiCcVnUeaKtofnE/Q1fm5MChXZL0E1SYkxGx3CWnOsIvvgeDPzr3uc7gWmD23/cc6XfuQmsL1uuEFtYWOy0Lhpw8Ph+GcgAUEPMiU57sne41zIewFln37n7jsmwVVU2JSJAnjsBhQlN5MGHN/v4NVHSakcDgVWcx9BlgnzM80C9FGALIqgR8p06U9oqIVlecCHn9+hbxvZLBAi9aCQL5dc9OPn9xs5UEJGsv1hZdImLZV9RBYX/cUoAx5xM89xOOzxxKRSfnBnGTMBra7f3Fxi/N6m8SHPk8QK+P5IAjBqKhhHsuQDC2oqBJxDmwPGZg/NRGq+TBwhXt0gTueI8xx1WaFqe4S5h/X4gJ++O+BjpaDTiKshdGMML80Qz1KoLMAq93Drk8VVoaoUKi+ETkKbbl0jD80mXd/SM7RD09I31I4R+vTBBG8M00ZSi7rpUTWDSRMVxqS5DwqwJvJQA7KZnQR7XU0zjQFVxVKBIHRK1ib90Aq7iefw7QFJEuJuscD7T09oho5IIDw+uBzjNU2LBdZwXgR4EYTvTfZa5aErW/h9b8JF+DdxjzArkUcFFvTbjWeo/Sts6xgHCY85XBhsl3Zpl3Zp/6WapIdZfzayJjjhO2YBm1uo4j+7QDxhZdNC7GzR9/J5rtI9/Yx/R8baJSH00v5aGxefURzj9u4VrhbX4k/GC4O70nmksPv4Hg+Pj1KoqHghKZ+eikgZgx9GYgzOsAPiKVKwiC+VWYSx1G/HEQ0XWbIQ5s4nixdTzEsUI1q0xYimMYmGiiyEgL5FLAocq9UwjMxi2pNFO0EUSg9HlXLP2fqzNbjlYm6mUaxi6CQXCZ6/1/CPvez2PgwJfixDBFWBV/MthiBDVXLxWksKGD+4p0fcf70C4h6H7YitnuG9F+Lj4GM5y7FKQkkuI+uko6+IaMWcafMJTGNhJH0sh2A9TuxOshRMrnY8A9fccYo5dKBRHPZ2ojKyT9ZsZKyNbY0gTSUZ1Uk9p+ADB5px33uSH021ni3+nX/bycNtQvfsf1nme0wcJeN4rEzyJoD7V6/x5dsvMB5qKVzJfth1xtg6KluRE41pj72aoWwaZBHwJtd4+vkJv/3tgN+/v8NTcgPv7hp/+5t7fHOXI1wHyHIPX+sBUV+i4w59E6BRoYQYxA5cY5FI6ZZ4z/So6TkjXmt2p98jMMhHK8whKXiFqmfYkCJBMgZ3VjLKwuRkoj4JZYgvS+qmN/mzscZgVUzghaF8c+1jGylU5DCyQGf6Jjl7oZZCfaxL9GWFgMw0+olpoPFphu4JWCiJnnGCmLLMsocqBwGhS29EQn8p5SG5ztARXFzEWMWUI5MdygRVAz5WQ4A+IKuPxY69RixowuJ5INI9kNHmIQwJGAWoxg6hTjCqbzD6KTovQEdJrB+LrxOVaJvtI75//ICmAz4cHiUJl2NvtZgLw4wdSskW+51eZD+9e4/9fv/n913LQJ8YN2dhBy+louYuPp/P4CmynAjqmmtCCse+MwbfAhpbsGJ6DfMyDieaXntaDzhG2/jZesB9WPNzYTBqH5pFZ5hhlGvb9OssDbBereAFM+yfa4y7d5hFNdJ5RNQSJG+y8PYp1zsD2uWdzj4XP3vTNDjs9zju92jJIKGHEQFfpRAQINBkUzE8gidUCzNrlmiRdkUEOyUZ1vTLNFinucQen2VDTX1j1z8yR0zPP1sQnfuoyZfnUlQLmE4vbv5jn2ZhHvdKFsywQJwDi/jgPSDSSoDFp8fnz8C90/PNtyfpn0l0tPPk+RLOTZa8b1DuT0bhOKDqGuRZbgBM3o+0En8wBhHk8YhI9cKQ5p9yc6era2ESIaLH4SjAgKcJFgDHjszpWEz9+f5kUvPao+8Wx5OOAhNi0FCWZ9wtB5/nxUhGXzAueyPpNHOy8bYy4JLrdzdo3YA5zc3CRiIbdWKGWp6bueCNRJU/levFvI/4TlJ6PDJ1kvNfYOYF6yHHjRvXn2S3anxEPh6QBykUr7HYeEyi9bEvPFSdRptG5tldg6R9RjS+wzhS9qfhEdSjxDsMsVou5LVLBiHYTaV6V6OrGtzcr0yCK5mgmpscxtNUAk9kkHLsDpgx9RTAw/MeBXc77Pk+B9fcAZzuu1Yqase7k4saQNb42FEuy7k9CuiBSJDTxyyKkewK6OEZShVoxgrx1WskV3fIl9cmdft4xOB5WOUVku0D/vCuxpOXiExSdVwT5YiXObJFBn+l8WU6YD0W6MsOxypEF8SS4JzoURJqmeGye96iqAo5XwTOOJYca02ANSavi9ca/S87VLwv1oP4mJItyQ0gYa7JOefwNQm10+XhghuEKGj6YQKnKaOVEI5GpOrsf7IwyZS8vV7JXPT+4Vn6SK5BmcBMGI1sCCiOc7kpClzKIBDaFQSxBz+M0Q6BqAN8jv9Oo+9iNJ1CywCQ/ogYJWbJiDhJMDDo6pIiemmXdmmX9l+2uUUIJZpclLrC5xxoM+3z70/NrrPOvj+BbOfAnHsF8U7SZsFxaZf219joNTifr7G6vkPKgnI0xR1lnm11xMOH99iXBAwy6CgXnzVPh/CDCCoKkdJ/SXuILUuBCJtHlM03vCGuiSmBMmmCFvipe4xVh6FoZTFZkyjQmEQ2roaZwMfCiD46xvDcJqdNlQblE5V4cMUxPws9ZpiQpUBfXd+rsfR6XEce+oVGl8VQQ4KunqNrY+hggI4q7LsRm2cPM2+PNOdbKVQFE608REkmBVA6S7B+tRD56q5t4UU+btIYcw8Ik5mRalqSAj3UTjvpE15mk8rMD8zi34Jw7ng+LxrFU8yZfnvQEWUWHZqyANGOsauNlD2mqfzZ61iQwpR4ZFCdMdrc79ifIgWdlEfmayuZkXMkH8S9jvFioaSNBdosjfDV17/BLMrQHUp5DkMMik6hPhSI8xTZ/T32tYchosAqMv4vY4+qbbBa3UJdfYXdmCC8XeFvvrrGzVWIfKGwDgesCU61tYCtNU3mCSyFCqzxyAA7JfOZYoOplywuJJHPpwyZfAju3p/ANfohGZaICbFzMitr8mN6XBjTpgBm0StSSgGFBDqVwp1gz+A5oI1BCD0UZaMcs6GPQ6hRkaXBDRu/w45pnpQ89z0CTS84Hw0CAbqYDMp3ZmmidYUEZHT40O2AzNdYxkzGHfCpbrHt6EvoCYgdkhHa18JWqDstPlIqosG6bzJoxWDdFPZEw1hQjZTSEgIcdvCGLeCH2KgFwoFpmgo/L4qzZwAAIABJREFUeAo/QqH56ScpdFk4Pz5scKxaDO2Iqi+QxYmA3m9vXkmABtkU0h/9gOfnDT4+PJzAntMwPrUzYOb8Xvz508k0u77KUbUDEjqqO+81eq7Z5FDD/jmxxH5xMXD+qmdvIk8df2ndcAZq2K+ElRYwSMP4UbGv+Hl4DubzGPlqjUHlKA8NvPqAUB8QBj68mKxAsv8YzmLASs6AE3vOvoFbd7C4LcsjjoeDePKxkDahByZx0ySUUgtM6aMWZlIaBciZYEhZuOcLeEFZ1nQoL7AyB1qdrZ2slNPYeb1YNJ393jxn6pZf/PeMkTh9b0EQ9zryMCwiRc8yHSDQGk9PzxPaap5zNj5c/7jfna/h3PtTimafb4JnzPuslnNc39yYVEyC5GSF+kz/JajSiRm83/aIfKY3j9avkUb9HWaxZ5jMrSdJjNy8COIQzQAchlFAt4ByNmEZkvxGsKNFENKXkLJRAjadBSvJHD6Bak7G6faPHWN4GsJn4K87zNO1ctqcccmrZn7ir+y/vu1Le844dqKIScQUF9JrTVOpOp0XYcH5JrlamJNcc3cJM1gtkMfQBg9+T9ZSgpFs3DRBFgwIuVlU+yhqD9vmCQoFIm4IabJZjf8o3ylKEiRZblhW4onZoaxr7D49Y56nWMxSeSrBIZPAba6xLOUaBDgeChy5eTJJZp0XqfnafO9wtxPr7/OfOaR5Aua48UB/MSjcXS1wvVpieC4xtkfxBQvmKZLbb5Eu75AyBZNS16pFlHZY+k/Y/bzD91sffRhKci36BCqbIV9m8BYR5gsfX6gWIVlrJWNqIqgkRBL5oHKf84EkhFJy7NGOYcR+Vwp7TeiT/oDB62Qs8Tn0kXPgGjeVGvr3cT5keAbnRvHmPGdAOjnxWSqqk+Xaa9sFOpg+orVBI/PTPMtxs8pwODbY7mmJYf9+6kCzWUjZLAm+bqOOG54SGDNytBFoAwIG7ki4jy8gG8ODvJYWH4YVXDF1uimQ+gUy2nxcALZLu7RLu7R/m8aFtEgpeLOWm78tDqfFh71R/sLfuoXri2d5fy6VELmC+CddvNYu7a+zURKQJCmu7+4xy9bQNOAePAGsAq/F88MnPO+3aLgrHWYIIuO1Rp81FZO1piVdMWUCIRdf3N03oVACOvV2T5M75OJzwgKDfiLHHn1h5Gqy0zrSp4MLNEGKzIJP+QiTQMIOWDSxObNeAiT0NmKBSbkVF4niz8ZFKX3DRiWsHprsG3P6AatMobqNUc4SRCqBqkKER1YaJQrV4lMRoNg1WOoH8VOp6lRMmSm9DONU5p6rZYgvshD/7as1iuqID8WAtlMIeha6lE7y+3aS8whJSjAcw1E7B9bkGE0Va+t/C5C5wuEMXLN1ipFXEdTg3EgGCxkZExPIgWhWbmUldVLM2X8NEGHf6Yy1ZgC580LPfAbugBsIg/5dPDc+vvryW7y++wpj00mqXNF2KPoB83mIPpsjTZfI5nO8fzzgGIS4WnpQxZFxEvI6se8jZZqi3+GrNzO8Xs0QzIyE5kp1CClHrUZUbYCWrLVQi6m4+NOQtWYLEpo/NxV39LnT78C1zrDXuNvPFFHu7NfOC8lK76QWPbEEJ+nMSZVrwBxKlSyg63yMRAZpfQCNPxu9pMjiIEjRIfR7CS0IvAZjdYBHRkzXIdApBp2hYvACYnhRLoAgPdf8QCFkIbXbY7cZMSZLdPTg80eE44Djppbd/mr0sRtrBG0F3ZMlotFSMksfw5CMJ4KPLN5toUWRs00XpJywPx6gKQkNNvDUgponpJ6Hg6+FlaobICyAev8s19bhUKKxABYPPkSIL27v8er6Xn5flAVmeYbjscT7D59QSGqoGe8OtJ3mGTuGzplH50z08/s4fz6fzRGS/eBHlo1kNt8oezLSUCt3dgCFS990N3f35dlY/hxRc2OdX7iiffosn2228Vu5pin/JNjG4A9OchY2JxMxn4XIFnNE6VrYtEPZYiieESuy2zxglqFDgr5gMmVrWKscR1x/OBDAsWtGslJqFAK47VGWlfh+ybMkWMU3MmbNuTEUoCoJNWZxhCRj0IxCK2wpg/pPuOZ535wd2zl7zLChXp6RaeUk/oIv+8cR3k7gmnvNl+DY9C8GpJzTNQFLH89Pz/Yas69iPRDN883rOjDEyU/tf6a5zAEFBCC5IXN3d4MZZYgSACASCfmcBMUZAFK0BMlNCm8nXmw+6NfO68n3AsLMSNSDCaqJYxwGH4eyF1l5EMc40ryfTG5eewQMBcf2JASh6VvESSCbQ2R0GjDYeH8Zqb5hT53G37kfoRmQZyNxAhpPZ+xsHE+3CnfBudc15ypJY8RRa70nGeZgxqt7H5GZSr+KEB7DYAC3lhs6HOti78AEYh+l1ggWAYIswuwmhV968KuBQZCotz2eC4WiVga07DfQmtenQjcQuJMVN8IoRpSnwtQqjjvkaYax9VEdGuRphOUyEzYbz9Xt9Uw20Z73rWGof9ZP3hm4eBrLdlyIdPoEIMnv3Rc8JvuleGBmM6zjDJsPR9RNgftvbxAuGHQRIVy+Rra4lXFVH0uMysMyL+Fv3uOPPwObkRt7AVQXYtQ5gmWO+SqFWmu8TUeshwpD1aFoI3TC8tdItE0IZeKtyEAJ7PYmjEeIxQGKkiD7XlKfeQWToUZAra0ZokLmK9cZfJjNBvcQH0rTES9Y9Hb1cfrZ2VwjrEcBpk3/8fyvZjmUHvDpsZDkVWNxaDvNXX/GQ8I0CUOwG1TyMKJfboQRaKM9QpAM8OMQvReAgbKS0E2mHRNIO3rA+Si6Enq8SEQv7dIu7dL+TZtZVJvlE1lmIuG0Md+ndrqJuLnfTfrTLo19iBeIlWxwcXrxWru0v3bW2uJmieX8HiqKZReSfmp5qtEUGzw9PGHXVAKs6XAukhlejlGUIyJzgnLQgMAaC3sPI1kbrDuVYT/RI40yClNTmWj3rurRlB26uhUGkomat3rHs9KBy2eCamHMlD1er6b0i+IAVVXh4dMn5PniLDWNzBDjAcViQFlz+paJjg1fvkPk1bjSHmazAIdFJIwwHwm8jYLi4jQoUY4eng8xmk2L6/wZfpqhKjxhSiVJQpEYqqqQ96Accbc/gO5amiYttZJwBzJK2s7IhsynNoZE02JXVFMGWiDjxFX45pnmWE779La8ZS1Jvym+t0/ZWmKeYQMOXIElaYp4Ca4Z9t+J4TMBa87kyBpnu02M6X0taCXlIM2eZwv8za9/w0w91EUtgGlZG3ZinqWIwghX8xR+AmyqFtmswuvsCL9uQdLdu+8+Yr1e4iqKsKsqVJT60ZsHLWb0IlM0nKvR1GSABeKRROCI8hlfQhk6DPTe4s49x1HTnQzEScmwrDWyI4S1RnCNhUgzGpNoFiHCiPbOzJudVtEUamYsmuJB+sB5I0k3GLDCeUuJ9wzZWyKXNfJLMhLaqkS/P0IPHQIpXChfVjgQ7NKxsD4lJIMywFhBDUxG/Q940CH21VIMwX0dIMlijIFGMosQ0DeqHFEHIxJ0qLcjdiGwYJqd1gzlswmqHfqOfUHwxdwrm6HGz48F/OcaWfYD/HiPwf8GvRfiR/j4uRuRVB4WdY++3Qp7ymASpg8I0iznS3z91RuRhz6XNX7/7hGzKEVVHPHp04NlOfI6s1RInhORpp5qsAkwOFXD9qfn93MWcz5ur5eSdpdEvObMGD35Chm53cmz6mzMvgB83E8/p2V93uy19hIRtGuJl59tWm9wHSHJjBojwz848Y2cBcnOghTRs1mC+XoNL5yjrwLUzxvo+hPmiwrJOkefzIW90ZEh1dK7z/r+nRYwp3mC6cBNheK4R1EcUYvcjgCdWccwaYH+iwK4MdlRK2RxJOb+ZLwJI8Z5wJ31uFsvuTNhMDQ7J02H7p7/kgVoSvTPz98ZsHZ+5i3YwTERUead5Fap4OPp6cl4Qrq/Pfsb+WznstCz9dxJdmuTfymfnc3w9u0rRAwumDz2uFnLa5sWZHYtyGuDGzGejw3VElGAmgmJSSBeW0yKbI/cEKLHZoM0DoEwxEM7Yjh2SCkF1AEOdYvOJ5AVwJN0WXYTkx9LjIOPLMsE1GtLhlTY68mNVUth+2VwzWwCnMDE8/NyGh9yNgkyyusYkIMgDccBWWGx/08Y/J8w4hYYOTa4UWLmQTLbzNv2ktw9UvJHOwbxRKavlpkAmd5NJtJCt1hqH4tYYc17GAF+P0ClI+w29APz4XX0cIywachQekaoyDrj+DP3OvYZx0E6y2QThqASPzfDIupiRH2ssZynuL2f4+PzBhtaNlgf5hdBPLYXp3H72biTsWGtGtwv5auzZNLRi7BcXyNuRxyfaoyqQz3sxCIiyRbw0yXyxRpNXaOua2EPr8NP2L7b4g/bAD19LkcNRbZfnCNfZ9CLCOnMx1e6hRavNQ8V056TQMIBIiaE8rPLPN2LLFPkoA2lksaHbnfYwAvI3kvsBlJrntfCMLWZxm49VR0jUuZE2xNyPdBqx/m/2r4xxht22NjHBEzbFCbOQfc3DHUpsT8M1sLC2XLY62/qa7dmccPXhsbIqeHaz9wV+F+RjQ6D2COEtA0JQ3QEXzvfrDt5DGOMrovQEPi9MNgu7dIu7dL+7duJaWGozuLPwOKEO0ek+1vvNGG7iYzCeTkY9psB1EwykQHVPgfpLu3S/noar4d0tsB6fQ89C+FTQlN6mOUx/KHE06f32O6P4scURguoIIWvIgTJDFmeircUmTVZyN1+T3Z1KQflotCw1ih9M4tZKQG4nuTCkAlXNXdsaaDOrdoOoHeHXSybOuMEfPB/MRf6tM9RAfJ8jl1xEAkOExsPj++kaKBskYtNk2hl4uYJfoRiwqvQ+dwh9dG1HlTfIvNa3EUe/KXGcZ1ISmDfZPAOAfyeBVOJYvTw8BTAqza4WtbiH7f5tIXWoRTNvgoQKg+v1nNJP2WSGMsXSlObTiNIYiT05GkaY8RtF/9nNatd49oFqtS2tuAyeIKFLMzis6tL0nqhyVpjbKFlXcnfOuaCkx45tprJMRAmlnmO0RQ5lpvzXZsKO5tO6gA3t0DmnPnt17/CzdUtikPFekxM+JmcFqUZrldMQZuJZHi7KYRhd5d+j/Kf/2fUDzN890dA39zj/ss3eN41OPQ+VBqhrbmNzYKPRUSFvm2hVYgxiOHHGrHs9POc9rLT33Onv6IsmGEZPToWWjQQd3JQGI+a/gxYa2oDrolHjSziHSBg2IMTQDP1g1S2Mo4l9c+OSyl+xHjbDGhJ4rRFhjAnhbZVoixLjCXB3F581jwaV+dL9EECFWpJVS3LVoC1FI1cF4MO8af/aYPqYY/buxx9PkfAe1RErzSFOPSRzEIksUYwdoj8EYp+glKwMaWNHoY8BA9tZVh74mPq9fh5d8Qf3x3h7Xos2x7J8o8YIuDR+wY/9hpx7eNtBcy8FipXEnxAX7AjjcTGQRiKX759g9VqjqZqsH0+IonoF6fx4cM7AfcIiIkhv8VwHWAwAQcC7Biw4DO468W/cjWMI2ZZjtlCoR8i8cdy934WpCbU4MTWOPcOnJhX9v1egsUnAG764WeAsrs2zA9On9Rdny/QJfc7y7Yyawz2haXvEnC3Y0xCX1ItfZiubtCoBbY7oDo8IjwesJgxlTVGHS9RMqSi5EVLTypK7YxVhqltDQPFgI2UOB7Fu60uCpGHSZImHzS0p3dlQPZfgDjQyJNE5iRuevA6c3PROaDlJiXDfjodn2NQTT5u0xVkvnqxlrL9dALHTkAZvyErarlYWMZyZwG2Z5mvJizEggTmpV7K0ty/ct+xYyrg/UAHePXqFuv14uw1CPJU6IfQpLwS0JPrloW+JxK9WI9Yh57MNXxNgvnzxEPRDChahUHFAuhH3QdkUYVFmKKJNX4qB3jFgDSPMMsjBNygopR4pLUA70HmHJLNHMYM7MlQ9QMaGhzis/nmvDmqsjsKC3xMbKMzMPRklTe+YPPN53ORlqvuCSr4X+EJq/dL8SBtyIJkQA3letzgai34SDmnMec6XavC4KXf1iipkG3FBGWydHmuyOT0McYKi6XGfp2K/+h8HBG0QF0O+KHqsK25AfUM2rV1Y4hW2FC0n4jkNaI0gRcHArTJHY/S+77Hbl9gliRIQ43jobKbewaskYCzs/7jtw5Ic+PtxfhzfWX7j0DibH6Dm3SB4ueD9AOiAkNU4e72LdL5FaLZSvqI11fve7jK9/A2H/AvP7T4yPGkNHQbw/NyBKs58nWKYKnxVTJgOVSy1inaEG0QiYdtok4JoSL1bO19jAmh3CTyyNiucCh2yPIEmpuD3BTqPDQMCmiN3ydZ251sLhh/PeepKuCa1DemPhI2swPVZMw7Sa1jap+86Nxwu73KJRzn4ekorGwJOvbP+3S6sCYvN/n52Zg1t0xjJ0GPNrl3yjrCeLR53IoaewQE2hL6szFtlOs33q4I9GrUXXwB2C7t0i7t0v7/btNi+Wwx7G4sn6cFna3wTl9f2qX9lTZeE1EU4erqFbLZGoEXIRi5Y62xSAJU2ydsN88oW3qT5VAhvdYi+AwxiCIkiUYW+BLrTlZZ39OXgwttrsS4OHYcLLPcEsyBHiGy62qS/1oWyPSEIuPI+YPZi9oQiSzA5hgP/ojXd6/l+/1xJ2Abt0i9IEacLVAfHnHYPkMHZHT51jfrJOnTDEKwslGyjGoaVbcjgrHGQvW4iRSKlcaQx4hUirGOoY5cfNZodY3O89AdCjTlFq/fsEBNUZcsUGnImwlgE4UsnlMUtTHkF98ub0RL+UmeiAcK2XqTB4r0z2nBe5KGmv+KpFbs60ZhtjBB0w8DKZrNOtYd3wkMc6AZi0hKOV0yqGGqWfDBRLhNaZrCArDFysSas3JIMU8fRgHVfv3Vr+V16U3EJfKh67BczJHc3yPwI4RhhKashSUTJAXy8X/Bxz/8M377hxneP4wokiscB4KiI+7ulogleS7EVRaiqhu0omfkYtwXEIVFKo3/pYju6f9FYM2w1sRAnOCgMB+ZhEfzZ8daI7DWoyerrh2NaTNNn0VGY72PbO+7UAk28/PTfcWcBTOOHPPQ9JYxjxbmiQUzOf4pyWybByB4BuhLSKiVlUmUYgxys+FjtcI8H2RlqqrGoeigY7JvBvzLU4ciu0EzRrjONHSuMPM3iAimspjiR1K++JGFNF3ndZcGyHQN5dcYGh+snVWkZTPpiA7/x/sKT5966OMoMtVF1CC4+k/4V/0Nntt73JUelgN94VoM9Vb6mn5+88XSAHtBgLdv3sjr9cUO7aEUE//3nz5i8/EB+/0Oj5st0jhGFNr0Whlv7Nlz5MqMeTfCHWDj/jHA2DRL4fX9Gu1A9lpm/oJF5Hm4gQQcuOLSGcNb5o+bfNxa4SVWZtcMlrVoWXrmQzj5tPsbc125ecm9rgF4pv+4Vz0VmA4Ik9RSLamNXI/YeEspeBOCTHmI9XKB8PoKT5jh/fsO4+5H5DT7XmpE6wy9F6MkSNwN0FzjiLeYm1+NfI+vSx88Mtp4Ppq6OaWX8gPxc3Ajkh5RfoBZFCDJMynIxStP9PZubWRe+TRHmV49O5vmGO2BnjPXToW6k8C7dEoHwJl/cyZ6+gGKY4GQY4YbF8/Pxmd3Wp+5TYcT2HMC8izIyC4VqwBuqmo8PW+xDBLEKcEPsknJlB6x15Ewh8ik7umZaKVsbu40lzpt+U2itacCeGLebjaOgiQUQ/+6VEDHCJ0auT/gJtEY4wCrwLCmiUYMQyUgAgMEFG0UrP0I4X++JEHOMEmtFJCzvBs79l8ZizxYs5F8AhwtWGQ733X19HuRX/Laj3B7vYDm/MhEW4J8/hzw16jbJVpu/NBHkJb5vK/0HJ5GbjxIgi8BwkFYkXxtEmHJgq2UQuR74iNIz0duoPh+L0FGCW0cfA83DE7hhhK5SkOHuutRVCN2jYddxfG5QaaOUHGIatAyTzOh3PO1sDPjPMGguRHXmuRVAE3RCXPu7naFvq1xPB4lbXTaObJNiIwyFk5grwPZnDSSB8S/UDrG67t7+AVQPFbwdINWH5HMM6yuXwmwls6WqMojqqpBPBtw5f8JD3864rudQsXj7SgJnWPMZ8iuZ1CrCMs58NavBdCtSiaERvBjstYMw9+f2MX0CyUb9SzEAL0Aa2SKxSl9VpmUbCSgxP64MdQOPqpmFEb3SIZkz4AGHqsNEVEn1hqHPzcYzYA5rS3cd+wPi9vKpsw8jvD6eoaPT3scSjGvNeNs6kM7d9kx6dZm5n9Tfu3Uz/LvBLLZZcc4nJJieW8duSHQIQxG6IRzWWiCeCgb5X3swmC7tEu7tEv7y2jni+hLu7RLe9m42J8vb7Fc3RkwaqTsw0eeBtDVHsfNE7ZFgV7F0OEMUIl4rek4RZRGmCX0WYN4RgmooBRCSn00nZ5aWVhz91kuQ6MqFNYPWUqSekUAhItMAXQsK4n1nQBBrqp1RRuL2h5ffvkKr27W+PDhQRLIWKOKD5gsoI0MNUhnCJIExcOPaOU5sbAjCHpwSX0ypzfsCQJtLaUJjYexGxCixbU/YJ4pNMsQPRO0vBTqoLFKR6Cp8dACz22E/VOHhd4hnY9oBi2eKGQKBVEkRW6aRUhmlBqRNcEkU1EtQtGQnKl0BLYYP+nqSMeQsgCOAJTO74tbum0jqZUs1E8sEStlPMXNTcXZBBBZqYaFCOy/BkA7gXFn7DUB3Rw7iyyvAVGQ4Dff/gazLEFTV+gwomQhFAf48tUNrlc5ZqGPJlZ4JhNlaJCrBuXHB/zTP5b47fdX+NS8QRmtcXu7wNd/T7lNBB30WEQDMrsLTglgxEKLQCUFuL6HguCTSKzYvyxue9RlZXy3bIiBgGtWDirAC3f7Zcd/NEl+LE7ke5PaJ75Holc0bAaCv7YemIS57IpJDjpt3hiwcXqIEbjp6DAO0VHSetgLEKroU6gieEEKnRBci6Vsp3E3UwzUSAbICNV0ODL1lOeJhWbrY9cHiBchFvMYqaZwmahaZM3QeV2N1taARaKGH3go/BEpmVKDSd7dN6N44TFE4n9/X6PdjJgfO1z3Ha7nDYJVg1IvgfEbrNtQ0n69kOEFHUYCC7HCnkyJUSHPmGhKzzwyJ0zAxq4o8HHzJJIpghj0U6Ln4fNmi0NRIIkjhAHHuQWobB9OmJYrdl/iadPXfF6apFitCYRHiKPwBXvNJIiaJFg+zoM7zCg/vc7pmwn5ObXx5ZrBgdAOXDOg9fma4rM/sM2BQH/2+me/l2JUbC2U/VdP7Da2YByxZGDKOkO+vsWQLHFoIjxvG/T7HRK/xCwdEWUxCqQC8KqBc5kBFOAYdFYONwwt6qoWVltDVihZSva4JNkxoF9bgIzsoJRemtp4E/KFz5Ikp2MQVpQ7bjf32u/OwYyzP5yAjYlJZDY/sxlBlEhAQLJy0yQSwHyz2ViA7cTmFVDSveu0T2qvXzlsS60BJLnx22++RhK24gvPTR25WQRKvEH5SsLmYWgW/ycv7VtQjNMsxxdBMKa0KvTaR03Fw8i/56D0Beigh5ph3TL9NJD0YNcv7HsGuAxeAD/K6eouYRj0cyPgxn8Hj3JiD1kaU0gsLFxuCJlr4OxCsHdBB6K5cWRmKtfX7j5AdpmHfLHAapFJCiYfYofiKfRjhmNNv0UC/Vo2ejhH8vpldpABZ2i9YjdZBgKG3BCi4lmLVJQplzLUlC+WC91AsNHYLhBo4/wgGxEMGQoD9MqkGZe8fbbAUGscWo3HqoZqH5EHJXSsUDRKEotjSnJlbvMQ5rFsqnFe5+cYex/VvkMcxri5X4p8syoq43zIDY5p3J3AWAfqTn3oE1xVuL++xzJOcXxqDNM3KDFmHtY318iXV8gWa/mL4nCUa2WdfsL48T1+/87Dh57+nwphNcOol0hu5gjXCdKVwtu4x2qoBNAla22MIgmViDXA7Uv6htIPlOdbggm44Wi9Pbmu6YYGYcJ7h7L3scEkgtIfUFjX9v7Ve+K/RiZ+GjPwx5MEUR4fATUubySMQvqD16xhpMvd3W4YGGDZ/J4hUl/cLdAPDT5ujiZd3PWfvTmeQG0L+kri+WkDdOp3N37dWLZ/P82n9uO4hG9ujNHyweSTd1DhKIxsAq68310Atku7tEu7tEu7tEv7i21cCCVJhuX1ayTpUnaq6QmTKCZ/dmg3T9gVe+MPFc7hazIM6OWTIMxT5BlDDGjaTqDKGmwHxldKAsRAGZOPuU95XoO29UUawJ1IE/tuimExvRU0zT5syqEs6s4MrvmDOIvwd3//rYAq3/3wXpgHEhJAoEEYK66CNjHyNIsJ8oUs9Ivnn0RCQYCQrCWzCOcidDRAARej2kdP/5jOAG1+3yH2G1xrD1GucEwVIm6+9hnKxxjoyESp0JBtcfTQH0sskx38VKFqtLAFwjCR4AfKV+bzlEQfNG0l8faaRX5L3xEfYRxJPw09uWBmAWoWnaaAYj3nC7Okx6gjYS2xWxwA4NCDCTqz1bPDKF3R6eSl5un0ULMwm5wL871hr9koOpsWR1jy+uYOX75+I6yBoW9Qj4P4E72+vsbdzTW0+ESxxuuQ4T2W/e+BSuF50+P7B43f7hUOWELd3uDVlzkWNzFuQ+A68ZDwHIxMRzSAFwFEhkhw556L/01Zo+7pG+ah6TrxKssyFh8BWhaHXieLcwHXCKxZII07/rLrL2mipmCWNFB+7dhOrhxwoIcrXO3jBLTZRFgHLbgQBNu99Hcim5PpukNTC0gi4RNgap5hiUjBKEwm6xbkDZJM59Uteo8+M4xKY3BBgEJF6LIEaRBgkQVQgZakNTI7eqYtKuOzpKwXDk8dIZqE4ABT9wYP/a6xKXUmee7pxwKv6wF3QYur6wrhqsWYhGiHayRgeiPlvbGMLdooEFRlMl2sIknJe//pj5hlC7FaoP/QH/74r9hs9icTbXu5Uspk0kRHPG43koSZ5TMJJiDoPGHn8nQiT31WAAAgAElEQVRbwU1g2+l15LiGUdgq7Ealc8PCkHNhvNcEXBOA7SSNckCyA8Xci9qzNTG+HHjm3nfClt1ZtmxP8+UJHHTX2PQaE9PNMd/scZ0fzC+0ifnhilTLtBfWvQ1K0BhFqjhPtHgZ5usV+mCBQxni8FQiaJ+Rzz3oeY4OIYaa4459RRBn6trpfdhvBENLBoy0tX0/0x+UZtIvMonpGWkCG8j05DVlPrDpi6mIlo6zs7Q7f2fAxol1dSrKJ/CR4BqZa2Ei83Ff1dbig+Beh+eNCTlw3Sfz4gRwnxXvFkA5vQ9/5st8xuNcrijDJrjEtAJSf2wSsgNbyC4b+RgMeCSsUl9YymLqHyrZhCEzi+BZF/Be6SET+SrTFQdhK6ezWPitRqJ5ks41Am5pY7nATSjpbyVeZ5wdlH00BPooG83NRlfdNCcA0c1PE1vIjK9p3pJjNqCcpHuStXazFsC0JzjhGEW8N3c96oHsxRxjP8r55V08jCghNGxcAuQCrg1ksVJGbzagWgbLUOo6dpMUlTA/WZT0heTdq+3ZSfxsBmiLfF/8tQ6Jhh+GSIMIg1Yoea3WlDkG2NYe9ocjonaPdVaiDWMcCpkgEcfxtPERJpGxMSB7m/NbDRz3PVarJW6u5yiKSgIkZLqzoI+Lb7DDyFz7IxDEOV5d32GoGxyKylgJqArpKsX66g7pfCVp4QSmm6ZFnnfI+3f48FOB77aa0Q/QTQi/WwNXK+R3M+irEK/nHl75DYKmRlX5qKkIoNda4ElypgnkMQnWvC8Jc433I65cRrLWDlCBDx0R+IS5b7UGWOPahaCazHVymzayUNk8I5hLxaVi0ifZ0WY+lIRrub7PNzfONtOsryjHx3I2w/U8xfunJ/ERnEAx52voOvFsajuNwbOHmx+msXkW3GQh4emMyDrDMdrsph93WT1uTrXw1AA/Mem9F4Dt0i7t0i7t0i7t0v7iGhc8OggxW15jtnoNrciGMdKlPPQQdAcUm2dsyE7yY6hgZv2DInhRiiSPsUg9ZLLI5sqI7C8mHvK17SLRKgG42G4GhcQHMu+Ium5BCycuFKXItrIAMpJEwmhBHeOpYgAw8XtSCq9f3eDrr1/jd7/7Ix4eD1IIcadVkQEizDS3aLQgHRdo/HuhqTHhbCFBAPX+SQybR09JAeYkleLPJkEIJr2xZ+HUKfFOo/9c1GwwDwB9t8JhniHSKcY2hF8pqLFFpxoc+wHP2xZp8wEzGsaHC1QVtYMjYqaNelzokgVEg2uybhoBGKv9AUPXIssXIs0hYOTYM/x8kgw6kHFCBCW0So3T7x2Dxh379CMaCvN1ZC3rUIOzhbX7WhIhrZTU/sws2slgYXhFgq++/gbLJENFOY4acCSTQCl8e/8K88VcwAG+fD+28No9us1vsXuXYPuUoyLgE3M3eo55NsPtF3Pc03sqCxBrTUgJ3lAbUJXSILIllAWneF4ChhqEklpWtcYvjcVN0xygVI88m4kvWt2U4t8kYJrs9tt/CeYKNmnBtTMj/EkKKOwaa/4s9YQFOcRsxl48LmX1pKCVz8p0N/oApvqIpvlRpFmaJtdkeEQhijHAQLYKZYFyzjjueP30QFOhLDw0Rw5ThWAeSXE7JgqL1Mcq8RCnHmYaIo9lMda3BpzgdSPe6WR4WnBJwBCRRxl5kPb2CIseXuWjpx/7+wPuZj3m1yX8fECvMwz+DM1hwPHQ49jUOBZ7CaYIKT/2GCZCP0bgcUe5qEKS5Xh+fMYPP/0k7yeS3Qkjc2waU1wRiIt0gLqtRfKXpLmAEq7/7aRkSy5bfJ1hUXxGoAK8vp+hamnQT/DBjP0TuGb81xwwP41vJ/F1498V2O47W/hJ/7kfymvb8zxdR/b5Z4C1veLs789/cWKAnrC4c0bNiy9eNDsMpd+cZ5L4ygrDzQK/wrIckGpgngdYrmeIshXaSqPaHBCMByQ59xEidJznWKdy3pHgDbMRYQpfM0Z4LZRFgbamjNGMdQMuE2QJkEUKaRIL24pSb/azPXQDXJyx1Fzf2pJ7ei3zcp8BbEypTmMMBHkI4teV/J6grAMvnzeb0xhx58iM+NN72k4TCwH7ueV7ez3z+BbrpYT0CJuKCDQZr01jQ00oG2UACTeCgIAMQOkbI/Eke4iebCKrFIb1iNinwb8SOTY3A+g9GCdKAkj2BJPYN/6IjrLGrpHNGxOCbcaE+HQxuMImNNIVQdHbavBQex7eCQNb4Yrg2AB09Maz9+4JSJRr3Jwvdz+Q5pMJN8PNaiEMYBP+Ze/HPY3zG7kfcg1AT0VeLwRzktCwozmjSFeRRdRRgu9jP4ZoOBfEHmbkLAs4xLFkxxPv0T7BIzvGNAFIZRMhCd21iLwRa6aORj6OMf0jQyR+KGsEyalpydwj0NZjX5RYjAfMZyNqX6EquJmgEEWxrBO4keNH2sz1tF5QPupqQN8CN3dXyBcxdoe9sYUwGK+AgAbL4TmNsVjd4TpLUe+ZYl2j0yX81Mf66gazxRXS2UpSfJmITHRvmewxPn2PP/zk4ScGMfUdgmoOT90geLPG4iZFuNL4Vdwj7yuxhJCE0CBEHGvm8oislYgZ2aOS/mk3Gin95B24IQuvLpDmibk2yYzkaSAI6lheo7U0sFOOsK9tYozMGQQ6aV8xcN70kIplR38+zdrNCbuBJimy9IMMcH+9AsYa7x42whYzib2npHLzj7uu3aVmv7Ggu1w79s0mUP0Xrv/purVzyUuQzRhT8FjlPsntPS5EyIq8SEQv7dIu7dIu7dIu7S+pESxIswXm1/eI45ks0GnsmwUBUtVgKJ7wtD/gyAVpPBePNXgRPJUizFKsViGW0YBIfFoMy0jANaYh0keDkgtbOzpyDxfPRe3hWPlYR0fMgk/YVkySIqvHgDoEukRe5xgobtXVd1jOM/zd336Dh+cn/O53f5LFpvHXIRuAKXk2KU3WjQYsmgx+HaPNGtP7MaWtM7Tlk3i08bhGJxu1i3EWKyIbJQUkUDg0AzYPB4Q6EwByqTpcxwrHdYh2kULrDF0Zwa/pP1PLov/TNsSHZ4XZcMB61aElM4mJgD5341ORdwRaiRRrs3+E1++QxBn0SK+UEHGaYKTshl4vyqSEslhmOpspMqfK3fS1fGmBNbeb7UABAyGYIn8CAk5ApPmVWbTLwp0yIPFJMRLEN6/f4O2rK7S7n1DTL097KIce63SOr+5fC/POFHyUEG6gqn9B8fGf8bt/9ND/dIdol4JmM5RF6i9v8er1DPOZQrgIcBWxaArgMaTg2MnufOD3IiligpiS3DCeT8NDCHwjP+Zp9bsRWvOYdmirGqFKJT32WAwo9zR3Z2FqTe8pdSNrRbBOC6zZBFQjC7NsBwdu2IEgfmlWnuaUaVIo2GHVDR7y2QpXeQrv+AyN/xE6+gFjcA9PzcRnqfAC6DQT+V1dE1S2xcXQot3Tn04DcYKGjJYgQEZJDIDcJ3uSUuUBieiyyIOjBJkG6+Lgjk5YoTRON0xHMYgnIKVH+PybvkYXVFDJg3i2dQiQ+AcEOTNAFEYvhadz5PO1MBS3uyPKQwPthSjKg/gyUurMww11h8fHn1EWLXbbPbb7nQUxzPgypZIrYm3xZazqbNHl44svvsLrV/c4EFDmCZp61BVup0FrakZzbd9dr6DjHr4mc868gTDWLMDGOcF56Z0HdJh5wUDRrrY0b/kS4LL1oU3udSCRE0Da13AgtptnLFgiM58reE11OIHX8uypGD4B4af3+PPP8nlzQJhIvWwKMh+G7Wa828g6yhKF5SJHnDKYJUS1q9AXW0R5i3SeoPUT9E0vTCI5p1LUn8Y7C+66KCUggQb8Ucy5phPjfwZWkNGWJTFGHaIsSnsAVnZmwSN3LO6ITvOPAQzd7/k1pcZdMEPPzZ2mEGYuZd9MSORGDP9qKwDbKUVUXsm9+MSScSPIDDjzNNs39DgMyCxbCnDPa4gAO1nLmoy2kVJQY2sgMklK7gTMMmElfDEyjblZI/1FD0thP1MezQdBKUoh7WAfR+Mv2vt43pYCjvheiKE4yiYBX9BI9vgZXKIlNzE6tAICkflFxqKHd8rDVg24TQPMYiZwkrlKOMoBGLYP7KELUBYmuL29FkBUe9rKcU0CskgOux5RnMi5JlhKiwGSVcm0bTsfA6WYqoM/1GiPEFnjUxhhzDTuwxHx0NCdQMJ6RsrRZW4gK5iyTQIh5tw6NvigFJreR99wA4DQXYvUH3GllQHakgBLHSMMY1SeLwzlulYoG4VNXaMttliqHdIFk5ZjNMUgVgSUoPM9VUxPSgPe+4p+hJ5Ii8kH/OqL15JKu90+T2sAnro4X+LNm1dQ5TOawxNGXaIMOmTZFa6Xt0jma6TZHGVxQE3WbdZiMfyIn38o8LuNQjm00FWAsL6Fur7D/IslkqsQbxYe3tBrra5QFPRai6GSACkDaXi+uXnF+YpBBrzfkV1N+bG9Fx32e2FKUn4/iMeaAdX4ECno2cbBaKaV0/Ul84NZt0xsfAt80R6Bdp1haOS1hmlsgGbKvznnEVibJwF+/PgJh4rrGKLQw2kWPLuu3bVm4X4LmtmBZsekG5fO+8786HS9uhd78b15M7N2ITORagfeY+0mIWdxjp8LwHZpl3Zpl3Zpl3ZpfxGNixsazs8Wd0jzG2iyt1jYMMQg86GrDfaHHZ7KRuQ6OsrgjTSXjeEnObJlhJvZgHRo0R96OmMIaOLRW9/KCwRccwswC6xxociizsi3gF0ToB0CfDl/D6/b4tgGVuLpZAEGqCOVgIXV3/833yBJQ/zjP/0ehwPlJoZxIMl8/FJkkqdFnll8ckfcLM7E1N+uRs89s1SYwdMZ6uMH+WwjGUaWseVStViglcedAF3zKwIQCl0t+lAxtL4hgyRVOC5C+FmKqE0wPkXoSo2tN6DWwLby0ewbLIMNolmIpguEKUHfNR3GstBeLFdIsgVaBjTws3FpWw3I6NuWxjiWjbC1WB9Odl925/mERtji3y2+X4AJ9veOqSZfGuYgPmet2WKWhVicZvibX/0K4aDRFnuRaxy7I8t53K1uMecOvw5M0TdWUP0P6B//AR//Y4rv/sMah6cIqvAQrxaormPE1zn+9jZEHntY6QG3fo3AY9rliKpi8IPCSNCI/nV9Cz/0xR+HrISuakTe6xNgHAn2UN6jpVBshXVhUkGrZsB6NYOOM2wPR/SUXVrPv4ndJIbKxqeIhbbbnfcJ4rldd2GsGLN49yBDzD7V9GMQ4dWrOyQE8oQ5VMJXH+CH9Mf7Br23wuiH2LUe/ljxzQbMQnoa8boo0JYMhwjQRzHCRIm3j05oVG3AiL4iQEYGDBkOlFYFaOlBQ6aoT6aPAYD5e+kkskhChYBMG8qn0AhQ2fU5yjHBqBNEcSqS3rElSyjGoGNEWSZjhWDvcjUXIIEj6PWbO+t1Z1gp/aDx/t2zAMgcJ8LusXOLexjAx9ZjViLJ6yvLc3zz7bcSxLDZbtE2tT0fJ0DODVjH8uHr8dxoX+PN/Rz1yGKV4IAZy+K7Rmkw2UgCfrh03BOIPL2sqxFt2ri7LE7FoQVmzgCwlxKm0/VlsWrzsAD+CWw7vf85EOd+aTYATn8zXcMvlKSfFZ3/D4CbS0c3smaOX7I+RySRJ559i+UabR3j8FzAax8QLzrxAezJKg4DkT0aBrFlPNoimUmGu81BJnFea8qr4Y21ANyZArLZQmSRDKcxQJe7NkwxfV74n4prMy/xGs7SFAc1k74Ih0LkfvQCjSKa2/vyunw+JaLsTweaCTRw1lcOApWzdVbou3Ar+qFRlp1EqWFndQzBIRuTjGweWCAgkQMJyf6hbLNpTMKwIa8av8ae8LYW5yx5D14DLWWQJNZYibbxh/OEhaXDCLRle94XxMyggxi1p6ElAIXsVSP1FhxcabSegp+QLSfIPTK5P3soKXtXLVY5ffFiNA3BdsNcdY1WCcvVEtfXM7lPeaMyrDjersYW++MRyg8F5KPPXTeOiGJaQfgYWgO06oCRRi2GssfxGOLgxXjKQ9xlHm69BgNBoUajY1BDpBEFZMdSQmoSwI23qbVdEECV4KSxjhA2OO/FwgZnkFGHzAeuyMhNfSAJMA8Y0hKiAscf/e9ClJWP3b6G1zzjOt7DzxPsK42h7iQkiJsWQ9sgpcxYE/wUPpywGatjiyCM8dVXX6DpGhyLFtevvsQqiVF9fIanDujjAr6f4Ob6G+TZEtl8LWPreNxJiuUyecLw+AG/e+fhoW6guh7BMYcfv0Lw5TXyuwyzK4Vvog5Zd0RTDji2MfokQhIrSQgla433SHrc8dzRa43+aNwQYG9VTYWqKpDOEhk7EtYi9gUGzJX1jLuFD4ax1svP7Dxmk9GtjazZKLIAm3G+Jf9LCVsuYvq2HgU45KZEEkR4e32NzWGHD487kS2bTTgzrrhKkHn4HD9z1/l0jbsv7AbFdD+wa8Gz+4Ncu2YJZwC289e0XzvYzYRaOesKGj/QI3G4AGyXdmmXdmmXdmmX9l+/sQCbzdeYL+8Q0r+I/ix9gDyJkHpHtMUOj8c9ao8LZ0r9yFqjD1SGYJ5gufCwDmqoY4e2gHiUefQ4ZzqoWHSRjeaW1Z5IQoi0ycKdxrys92lAL0DciLZXeC5mCAYPr7IP6Jmu1RI44QKMLKMWr99c482rK7x79x4/fXgyptAuFl7ANbf7b028pyWffVgG12TrJlJHV3BbsI0GzuEc49iirWimzUWtTxwE5X6PrimQZikyst64cKXsxdfy+Wkm7A0NEq/FrR4R5RrFMsIQphhVCq9RSFhIBbWYyz/vFVAdsWCRkGrUDYGjTnbifRXIojqNGR5Bo+gG8/XSMErKBkkWI4wTkY2e+yAZIOIlK+asZD8DDE7m/KbgZ6qrAdME1iRYQSBEQFEjofz2m29wtVgLyMNdb8qWDp0nEtb1+hZpvjDgFvW+QwHd/js8/+sP+OH//BrdD3fwmgTHQOH4xRrhf0+T6BDjSmOhCOswUa1FyUoqDNEz8YzGNPQ4iul/5wte5FEmO5CZQFPtwEhpukZ23uktZcASptzRg43skwC9F+AD2YFJiLurlfTtbn9E5wIk7M6/XcGfAUNuXJnCXH5mDbyluyUUwyAHPFc393dYX63QVzz8HqH1Q0P4CofuN/DVW3heDBJxmFo6HIFjM+KRIJA/IAu0MOwGSvAypu3x8E3qnrw/fYyYV0t/IvJZ4gABwRT5HYs2yskGSaHj4TBtNSLVsadxdiVsDlhZN0FHyrx4DYX0cPMjIEkwBAofyxGHopainmODxzyf54gTghAGsCE7br/b4/sfv5fi/BxBMYCMvfbs556MtAW10Xjz9i1W6yuUZYXD4YCmqWXsnA/dc6DkBM+YYvJ6NcNsEaAbE4RaW7YlQUfDYCO4JixFYYqZYszIne2rTnrT09UxFX8TWGMFdmcG+u5P5FXOQB2bqXv6jDKgzPPMe9vnWAmxew3zmewnMB/Mvq8raKfOMJ9RPs/0n19srjCVoprSdjLbLOBmPNx6ZLGPxTxFls4xdhHK7QaeX8p48XRoJLyR6Vcpxx1w6tM4vcN+XwsrKNBMh9zD7yvofsQsTSXgompaK8c/6zsb+uGmYynSRw9RHCPPlziMiYAIBNfGlmm3WkIVsixBRXacPbrnZ+fBZkC8F82csLOecIDpCfjlvY+AGUHagImpHP9kbQtoYKSTDhQiQERzdX+sEPBapv8hGbAN/cdG6MCXa1DuHcx3tOdW/McIsLHfOS/5SkzZCWQTVKLEmiDULCcLUKFXlHkLYQ8DgScen0g0jccbrzcyseTRkonqC6O7QgOlRyxnmchdm5ay6FE8wm6vM7lmmSjp8WHBiYKWCJS9hrx/0I+yl8+WMa2YAKOw83jMDbyml5TL4xDjgQDRQuGt7hB3NdraE4AbYYCIn9MnU499RrljK8CR+ITxZu/CeGzYgjCr2G8ELsWvjmndJj1TeR0WnHO48ZD6iBKCfrSiiKRfyH5ruxjl0cPzvkLYbbDOjvBijQPTW9sRSZbZM95DRbxRe3KvlDXBANTHFvPZHG++egvF8bwtMMYNKs3NrbfI56+Rza4QxpkkhHJeSdMOSfUTPv5U4vsdw14qBEWAsbmBunuF+dsFopsQX86BVzgCVY2iClEr47WWkSUq92jjXWhYaz1qpliTTS2bPD2qmsxGXn+hnEtjY2DsGaYEazvuJ0sCGAmoXPeWESl+i5bRasanvSrsPU+uIMpG6WHajMhChTxPEGsfH7bPKGqy601gzvkcaS4zC14bsuV0Hzy9yS/8++Jrg6qdA+12UngxP5ifOpTt7BjkW7NryPn1wmC7tEu7tEu7tEu7tP9qjYuWOCJAdocomcPjApneUL5GHjPGa4vD8YBt3cJPFlA6pbhMinJK1rJViFU6IG6YWjeKfGOMyVob0PuD7Mr3RDskIdRICmURxKKktoUvi2HFFLazNEp5noe6C/BczrBKClwnH1HVI4YgxW9+9QWOuwLff/+zyChOu6FmxWiYGgYEMQby/FdNPjwOaDOFrGNonRgnhqVlPLAIErLIhE4w0Li/3WKzofSN7LHMlozOn40FFv3ZfGEbNK1Z4Cv0yFWLq1CjvwrQLiMkYYaxC+GT+IUWnd9i31GCB8TtDotZiUEnqGhORnAkZcobpREDgojgEbDbPhlvKya7kdGQpPDCEHVbWHnn+fLbObLZxbRjAjpmjTwMK9BILo3/nfEiM8wSeist53P8+ttfCYuM4CgLS/pME1Qi8DJbXiEMU2EsUN4SBT9Bl/8b/vDPW/zpu3ukz2vEowZChepv5rj9H67xxcLHkHi4VwMCslXqViRAvQqRRBqFooTGPMi+Yn4DGXSmcDOeT2RWkOVFH7O+Nr8jC0X59A8km4oFeoKRIHEY/t/svWmP7Eh2JXho3ElfY3kRb8vKyqySptFo9P//NINBNwbdGI1QI6k1KqkkZWXl8pZY3Z37Mjj3mpGMV4XpaUGtT26Z8SLCPZxOJ2lGu8fOAsq9KHNZ5QmurvYo2gHF8WiPkS0WLBNI5vYWHHJ+RQqy6YTfXXu8doI0x7uv3osnXU9pZy/5oOrbl8UovS0QbKWwl9Q3eFingUg9x1IDF8i+zCmf4mEK6CFII3UCAbzGFDjVfQA6Q8N3I6lzktZG5grBDJFi04NNgYcopA9chJogoRT8oTAg7j49oT09wie7g8eI6YG+QZ7Sm8fHJvFQ9T6+PzS4TFRO19JYnawTuSZa/PDDj/jppzspDOVIWEu6CcyYQDbFp/SvBqw3W7x5905An8PhgLqqbIiG9RISkE2vYU0LdkWV254WZm9fb6XQTtPVVGypPFS915aeek4eOrHDHEBmf3a14VS+uSpygmVcRfcnfnada/HjDOIt+9nMXFt+CRvDfp8Zo/iC4aZbfgE82se8P7U/i+bOiYLDlJD6IgEUVoqVkCWRwXa1QhCscDyUaNpnxNEA4+dII/ocMtSin0Bo93YEiY9HhtKESKIGXn+Ex6TlIEG+XgmzkiEWDlebjqsqrDXMIMuRhDuUlMDHAbz6gLEt1WPO95FmsQDEZCXy9XzZ/f29Mv6cCbs73u5kvqj0Fw9PxbweC0pe+cXgDTnP1kZOHDgJIsthJjhJRuAfYLz/BNO/gglXAgyR0ScAxgS6W5BuFOKUSPflONtUxdCUiPweERl5vrJMc/5O43qRrjLQgB6fQOL3SIzwd+WzcszgGzFsJA1VAg7KWMmgRo8aFeLYYJNvkaYJdmuXChrIfZXHgDLXsi0RxBqqUpfCgUZCVpVRRhP9HBlJMIoU08Opj1BHKap1gNvMwyVECyqLX60JxXA/4jqInAcGE2n/oz8cAX5doJr7toxj9kALaGglzrD+bJTPkqnHBOXAdFjRk4+y3YzsuFBCVVrfRzGSmUxWYYTn04inU4F4/IyLTY02TlAcdRExyzh/4fnsJVm3G7hP4ign7/P08Bnbqy12V1scmxJX+7dI4r2w1sgkJLhmwhHb+A79w0f84wcPd1xQaHoEz1uM4Rtk37xCcpthdxngl3GPvC9QF0DZpRgTphuTkW291jg2tXp8JCHU3k9lkbGt0NYFQkljphySMlv1O5UxzNqjuatbPMmkA3h2MWhmWAtTzfoN6o3KvsYyyhxAJsy0YRCrAN4X759L8TRjWiv3zSWWy1izYJa5BQqH200qftvH3fqFG1vltS+6pd2pqV/qH7n7q9gxuNCUiZ7qBh/9mSoHed/BOwNs53Zu53Zu53Zu5/Zv3ziZEnPqfI/V9gp+nGohzgls7GMd1SiPj3gqKrQmQhhv4Xkhy3R4IhmLsVv72I4t/ENLtRl6Yj6JAlKd16OVGZ413uZkihNCFrqy4q/ADSEcqj9FgCKr3aKSm6tQzqoMcGwTFG2KXXrCN28j/O4fP+D+1Gqankt01A9m510WYJOps2awyX44iZObY84vtKwXKyGzXk3iMWZBNhYAY0efuBZpGMpkj9489P6aVuRZolhQhrI5FgoNCwX6YHUDQq/BhRmwT3zU6wB9liAMM3RFJEAchhq11+KxMjg+dlibR6QrD40XoS8bnSxHPFe6kkx5aNHVAqjwKIzNCLrqpKsVehY3Ldll9vNKYemKfXshvCjkrSRUgDU99iKJleOhn+nN7Wtc7C5QFKWURfUICW0g+4LgWrq9wDgGKKsGXtAi8f4byh9/g7/7bxH+8OEGfblD6KcYLhIMv85x9e+3eL8icDZgPbYwfYmmNKj6CIMfIU5YbAKJMDboIWZQEwC2K/gV5Z2s2Fhj0j+tacUfiPIkinTLUuWB9O8RJhuPlQ/EfoSVb5AI8KqMnu1+jTxfoyzIxuDfzTIWZUYuJI7CjtTHBDrmsTUBNtfXePPmhrQzhL1BJAAv/Y16MKWhCRTck8u7I2gBxKYTj6aexRtGbLIEF7GPz4cW/8TazbC4HhGRZa4dNG0AACAASURBVGPNw8XMXd6X3le+FvA0HOf1SukzQwVGGqdrQURfGtOTWTagZUAEEpTHWiQ/9FEsmwCno4ckzZCkTAm2/U8kcT5WMYMUYoQERZtaUgcJjj88PeH333+P8tRIX5PO6wohKbT0mKlXmmX4sbAOQry6vsX+8lKSXguGYthkXMeEUL8/BYknzzTLzlAAT6/RzSrH1WWOdoyRROF0PTtwrXPsNQHdlqy1l+yPF+Oj+z7VcA6Sn/9i/l0rwpdbsb9/QTybK2IH8C0envrin/jZPj/3V/fCPw206R68+OdPNscYcWCbaswVHSVDa5MnSCKydnp01bNIj3nfyDJK7zSEwp0zVxSXTY9D6SM0MXxQ2nmEGdQ3LUxT9ZQSibF9b89H5AdYrzYIkh0qQg9tB687oW+KCVxjWjB9wxoJOtD0Ty4GPNzfW/8l/exa8LtqfnF2J2TPfe4vDoaAFmQQNbJd9iu5fq3kjl9PxkdNrzlvB89LMeIKI9m0A9OBQx0zjDLghN0nYA6PZYDBIzzG+4z14OOiyBhJ8jMDBCRgoCTApwwjHhsu1pAVV/UGXSkiPgwWwaNnFoETfoyA7G9JBeK9lvCWEaBt8DqkBO8EVCPNl2w0SisbAUnptUaGJ9llDATIskCtITwDruFwYYiLHUVh0IQp2jyCt/LwPhwQk7XWANUQYrDAK8E1Y28YysoiaNmh6VpJGnbnwt3iycjSJOuZ0cb7J2WjZMcO9Biln2RHv02mebcIMSDzjdwbyFLbxLEEG5D5VtM3rjNoKh/HYkRVPGLr/YDVukc5ZmiqAVHIv8/kvrDZMoiIIQWV+MO17QGfn5/kOrve34hFQ5TmaKpSmNFJ1iFpP+Lupwq/v+cCYAmvDuE3Nxgvb7D75R7ZVYjbNVlrFbymRlGGqEyMMAuRWdYavS95vshaa+pWfDe52MIjxFCjujrKpUrLjtEG0rSyzkYW+Qy0T2MMF94s4OTZBR/edxRcc+PYvCghY7LtL9NQImaYBps0kTngx8ejzIWYDh2FHvKcR1494aQPcXvOO+FlR3oJfrnFlnm0XFhY2D+akLnZV/PFyDuFIth/XOf1Xv6dXXI5A2zndm7ndm7ndm7n9m/bhB2TrbFd3yDMMylwhjaQiec2YqT8Ez4+PeHU0e9pBy9MJNkSJhG5z3oTYB/3iKsafTHQxQljTI0JV197NJTIkQUg4JpljImyhjN7ayZPthqLf6mB6NHCL+dhZY32pU0zMfR9gGOV4/GxxNvVPTCecGrVj4e8AFeIil/bVKjryj2ZSpr2Nk/SxAvHraTayap8cdLPtFKa6FoSGCWt1fNRkkOz9QqGgCRGlMd7dE0Hz4+tFwo5AATZyEJigWSskTP9ZQyGRsy1EHsNrkNgmwcot7EY3AfIMR4C+PWI3q9QDCPuDh6G0wlXa+5HicpbSfFJ1kMQp+LPlsWZeOUwHVMm09z/chBpabbZoJE0sloZVw6o4DF44fNkwbUpKdQyZ8girFtcX17hF1+9E788sjw6Y2T/GGgQ+wYX19eI8zWeH0qcKOdZ/Yj04T/hn/72M/7ud6/w6XiLdnwFb7WF/+0O6a92GL5KsdkAW3qm9CX6ekDZhOiCCCamzMhDRM85nhUBWjoEHs2YDR49g8fBh+kCSaHj81KcjB66dkRAaS79gtIY9eALmMTPHmeZgFJ1cUQSBUjJYrOJZLVncJcGeH+7x3q1FTN/FkJM+iO46hhYwgpwABsvpQFI95d4/8uvMCQZhtZH0grPE15IgIzgTitJoWS/MBmOL4wlqKBHW1Q41fQYIguLRRtlw2SSjuhOHZ4JRA+PCAiwhqmwYOinpCBwj4AMy5EpqL340dEDijIw9uuuaoGygO/Ta40gcwQjwNgJZWuQrbc4Hhrc+RE2txvs8gAhtVkdCzwVVatnGcMVGHhgpBhlYU8W0d2nOxyfSwVn5Lp56a81F1rCkZDztN3u8O7dO+lXx8OzABoEasQzkf1UJGkqJSPzUBiurpp0bAslFMoA8u7NNXp/RBQxkEUeFGNuFq+aHkoJ+pK9Jp18KjDlXzveaNG4GCxtITcDadOnmv9ZsN4c0KZln3nx2uVm3S8Kms1A0Ayu6c9Ltp18CZPUBb1Yg/HpuQX4NrHe5jd7sc//n2Abx26ylJmiTMnxIHLBPM1Rk8VUPCGh5D1OkK9i6RsSKiNjrW6eY8ehHlD1ZBkFGNqf0FVAlKyQeHfI4h5p6CGJgFUSwYxrVP1KTPqNL4aFYgtAFpdvVMK53awE+NYzbK+JocfDw+OUGurGcXt0LeCmr9DPbaVs9ld3iDT0htdIjySJBUAkIFSWJ4RhIn/EZZrCM/jOAK+4nDFu1Gexr8WYnn1gJEDp5MBk9Y2jAPkqLedjBAX13kO4TAJSeJ+QJ0c8DCF6Xz1HeeyDUQG3yPfQGx+nakTQ14gCisP1gtGxmiAaQeVGQ15GpmdyH32E5JPxnmj7c13VAlZSbttUNTrPR5IZZD5tGtQ3zfd6Aez7qsWp8tEwIXYV4CIasEdlGcahLhgQmKNvl5j093IsNAGTwB0BmV48MBWM5YKa9VS0AUOUPArQxmtIIUgLENnEUbFdMGh6H2OjY0gAStaBdeAj5CJMEohNAxdSuLBXUHZfhShOAT6f6M95j8vwA+J8RNlkch+72seIQV84DwcGZbBnRQav37zFh58+YBVsuZyIoSsFfFqFT2g/P+GfPvS4r9RPLqwuMPo3iL66QvR2he2Vj2+s11p9GnHqYoz0sSND2YKPnqSrtnJ86lqPERcreL0U1UHu40meWZ9By/gjq1lWHwlqWwG6s7jg5Wb9ypwthrEYlP8Sg5r6/zTaycKQzltCE2CdxjiVJzzTZ9fOo7hxnr+66oRdud8QqGx0bmTHOwWOZ4381Adfkswmgbj3R0PsRFubf7TjsYQg2AfnMcbBaW6sXcB3/NznFNFzO7dzO7dzO7dz+7dosiIeRtjsr7HOL2i6ImyjcQiRpwZr74Ti+IRPRQUTkU2wktVyj0meNBfOItBjNx8bDCeuSnvo4hFeVGNAi4pG64S66L/GIk2ANQ9E3EZK9ixrbWSaqIalabCAJK4p+UUmSZNsRKUS0xqrC0oYI9zVK2zCDm/zO5RNi2ZgSqW/rBSVxea7ol3BtZmFpFM9N4WUaaJl3kjBwrcn0EF2gTeiOjJ0IBXpp0e0kK8huyDNZWX78HCnn5ksBTUzWxQKuiJPgILFTNMyMY3shQ6paXEdeOg3Acp1LNJKjDnGE5NbS2y2IfabFb77wzPCvhbJC43z64ppYw2SfCWTbhp+5+u1FIlNUxMRxEiAoeqQrTLE+UaYH8J+Whb2AlwpE4TfLWnPpquSceTj6198jRVlp0yYYxHgAwU3U9XY5DkuX92iKlt8PrZIr1u8M/8HHn/71/jN36X48eEGj+MrdMkO6+sdrr+9wP79CsFNgG+yARdjBTQ16spHxcCMJBKJWhxQZkSvNxYfHrrBqA8b0/jQISf7LDL4QBmZF8GjvxrNyaEJaFSQsegPRpq50xg8BrGm5lQjDAMpYE7FCUVTIQlCGPr4jMATWEB7yDKDb2+vpfgrikLTT6Vw0UKZdbFG8sV4/fVbpFd7/G3tIW58rFkEEyjIyegk58yIaTrZdJR/ikSIhMaaBVYrm3lkf2qAZJ0iWzHcwmC9CrFPA5HAwquQHAfcF/SgG8SOjjtBGS7Zg8JCaQfxjyKziMmOD0WH5qFB7hcIko+AucTpVON0qpCt1lKs3D+3OK0S/HLdYkfZVOBj6Fsc7p+FOSGG6UOAMVQWEZkMqyRWb722lfCN9XqFsmCqpDLQZi6RhkMIcNt3UvgTWFtvNzgcjihLprgSbFQfLAHHLIDGgrOjfErARZtia7c3D2jAKk1xe7tC3UfI4tiykHj+9Zg4cI3yOwFQBMhS8Fi26CrBBfo1FWpfNA1AWRZzi+LwxY7ZAnBZWS6/KxKngNjEw7Ofz6Jj02MLoEzBMyuftd5LTkL7gu1mJWYOaZsxtvnnedf++HO6hwUUonzUhBh5D/B6pBGQJxkOR3o/HhH5IbI8RRT5AmYqeGR5JEwnJIjaErTbwR+PGIg4+zmMyUSKTEZc6e9wbGPZuyBsBQzhIgFBNYJrvO52242mGUoQjX4cXhZ9V+Hx6VlN3idmon5S3Qv9T9mV7iQ7po/+sUqHdUHkYr/HZrOVPs+gDcriiqoSv0Yy2sKaa0Qe7kyPLYWaAsx5kMNDE06ywHmdWTZzOF0XHJuIJFm5m5XjKgvWpuiOIzLeX0MFsznetLVKJ+WqswwjpnN25Qh/bAUD6ToPpcg7PaT0RQtHWTwoSrJ+dTtyp+Nxadn3Izl2BEyMSMBbePRxDCPkTPvmGEpW1clDMcaosgibzGBHiWrXoKkNqiESz0d6rcVcgJDFmU5kp/QRI2gkfphkjwqIpvcYfk0s6sWlJ0mQLqFazrHERMgZ5P4TaGPAC++f9AgbOk/un8brkHgGq8CDR6AtDbHlgmAQSco5j19fhHgqQnwgQ7Z7xPuLrTDUerL4hPHX4en5A1b7K2Fa/vz5Aw4f7/Du9rUGhHRCsZdr9+enEgcuZDUZguoC5uYG6dsNspsYX61HvB4L9FWNUxmhDlJE4hdHWwPOJTpNCOV8hV5rFY+XSq27scHj00cJ3OA55Hgl4Jpl0lMSLOp7SaPlY/zdelpa4GpKYvb00GrYk10gnEComWnqQGb+msehbPfARVMB8bnIoQDeNE5yP9sRxanEfpsjiXxZ4CPffQqAcf1r+mmGwUS+afdlef7nn61n7jQns/9JyrTKWxVo0+dm5NCGWM2d+gywndu5ndu5ndu5ndv//MYCNl/vsNpciiRxlPz1CJHvY5+18MpHfHp6RuXHiLKdMLK4Gk8mQ5AmyDIfG79D0LSoqxEd/ZoSZjbVKFiE0P+CXlGsGphw2HnwaNxufbo4UeRyKi3eZGFUVZcKplk/KVtF6hzJyWhkRibl1BwJb/9ejJarFa6TBtfpZ5waTtLJqPCFbSDglq1iDAsH+dGyj9y0T+ZkTvIwr7CyGF/lEZ1QRAbjs8i04JuYXS+AP0r+knyDx4dnPNw9IuIEX/Aq+9msNM6tyDP5kilrTcPENLrm1NiZDjexQbsP0a4TZEGKr65yVM8dfv5YokKLzyVweGiRjUdsNx1aP0J1olxwREZJKOUjAyT8oOkbNG2ByB9hqh5j2WKz2wszrCpYdXCfnL+VDTKQEANNJWOxfPvqNV7tr9AXhZgtN/6IwziiLjpEHfD67XsBHX/6eEK1Mvj1xV8i/O4/4zf/14C///Et7qp3qINbZJs93ry/xLuvtwjfxXi3Ad6bBmF3Qlt5KNsIfUTj5wApgTWbOjeQKUfflyAQ5iD9xNpOiysWK8IC5HlNfNwlIbouhE8mGIFeFrmS/knaQCgS4XVs4GcBDqcedVkjSzMESYzn0xHt0ML3aADu4ZnG6R5w8Fp8tYtxe3OLovXQkAlmPW1YVK+vb/HNt6/xox/g+8rgqvGxqUeRu8ZXAfxMi1teey09q3xPfM3M4Ik/H4tPAp4soAeTILrI4Ice0kDZPbxeePnukhgrMtd6Ru6l8Mnu8+nHRBluJN49FYMmKOuiPxFK1KNB2fqIya6LC7TeiO8/dBhMjiDKcHooMUY+sosYb6MBp0MD09bi09bUA+5Kg+OQSPGXryj3Y7gCk2CtYT9ZMgmZPQpQXJPBGMcCWlL6RHBdHPxYVLYN3rx9J0EGddOI11rLhFDBC2zCpS2WHJOoFXBNwTEt7rS3OfkoDbHYa3/x5hoer/EgFymhA+cEXKMEywFsrni3gQMKQM3g1QwLapvLvOWDi98tm/EFUGCfd7uoTy3oGPYRNvlMtj50+6JP8P+ZRaf7N4Nn7jFlLenrNEDBSrwnFtvLr4kBaAFGty33plrffvF5bZMFCT+A5zPYhgN4L6BBHER4fK7RNT3SOMJ6k0rCJo3sudigwn3ZApqhFwDdDD3i9ZWMjz391YIAVRfDCDB3wFAfVBJqrQWYGkrpuY7NM/Co53NAU5Z4Phb2cQX13HVirxj9hNZ4/cXHts+x35jRx6++/QZ+FOLTz59wOpaI1hGiVSQyxz98/4MAI6EfIm88hL1KNFXSSLSb7E7e4EbU3ojHpsIG/wTPy2SRQg3pXdSwhqTIHnAM4He7qOG3LWjVpjJRg8omeY+8tulF5hh4MKi4wFXXCPwWJqGnJ/s++4tu/7kkk5p3tB4+gSRKSbsS/nCSsJWEAJnvoSoMvDQSD0iG8rRFj1Mdomb/Xvm4jEYkQy2emxUTvoMIURKI56Psj5j061hNqSkZuiID5nVHian4edrFEssitWdluuE6YFRAU4JKXMMiGLdYqBJ/tsDDSL87BiF0BiMDHmhT4fXIfQ+b0MOY+UjSGNs0QxOHYKh3cRywTi/w7dd/LnMeLsbwnPO/gAzKdA8v3iIlwzpbSdhHztRR06rMkj25NdhebrBf79CcQgzvbhC+zrC/8vFtWCFpSlQEJYeUgy6y1CDh2MSRkEnPnDs1BCg7NJXOiciSfD58wjBUWG22uljW0GNQwTUJFXLzILJ6Oa72ZHaTscsxltePXfRZMrqMznD0SC/YXfab4Gt24Y8LVWXToWyt/60dEdycgGOy9iEFrblgWbaD2DPsd7S40H0mIOfeZfppSQgWEHke+6TPLr67B6flCwsCKmBvFQfuHjB9d4D+/HdsZwbbuZ3buZ3buZ3buf1Pa5x0RHGK7f4GUbqRgkUKlzFEFnTIccLz4QGPdQeT7gR88ygpISgRhIgE9BiRcYJMHx4CR2Sf+WSH1Dj1o5gMR5TxcHIzzHLQgZMuiZnXXAQWwsJC4zcleU0FJadzopJxhZI0KyVxYJbMnVwxquUt51hPTYqyTvD17gmRV6CoVd4kbDMp1qxvltQ2LkXLTcr03ZcT0IAsnSzE0xN9oWhPz4Q2u998+ylt0/qW2H1kkmeSpfj88ROqqhGJpha8CmY5fxlJfvM9DAGlflwFVlAo8Brs6XsUjehTDx/HBH23hteGJDBhMLSu7vBEgPPUYuvfIVmXqIYV2lMj5vNMi6tqvncsxuJdq6bxLHfbA5HCFpurCyl66upkj7cWnpzMk2EV+zG+fv8VQqa+1QU6f0CFEUU9oK8GrNd7XN28xtN9iZ+rDhevnvDL5n/Hj7/5gN/87gofn9+hxA2i/AIXN2u8/mqL/HWK/MYX0+fNyFRA+s6EaL0YHuUz4SJ1joUYmRD0penon6YAD4t3sll6wyLek2uLLIbE63FJr7sswD2llR2T3HRblJvRLD0iAEe/tQ5Y5Z6k3B4PlEL2SGl8zUKzPiIhqDWSTefh5BsUZMt5LW52KyTZFs9MRPU8fP2rr7He5/jbekTR+LhuDVZtj03uId2HtoDW8sZHi2BkuiL9wI2wRmhyzWPQVmQcjghXCfIAWEea7uezaLXSVbIJgiBAmMbwIyALyeohKFBLIUpQgBLhMPQQjAVMQO+1HF3kS0Lh6anEp2OE9e4WTTHi82MPb5djvw6wkcoewrIjww4lzaw9ZhEKa4fgccR0RZqgOz8qfi6+PwM9Ag9RFIiPEK8/Am0syI7FsxSxqyzHN99+gyRJ8EwAvyqVLUSQQaRzrhybmUTKOiMDzbJeHCBmgStXQNLX6v2bDU6NhyzhuKWFKMMtCLBRri7gmvVfU8mzg2i+GGccCDMNnNPD+pgdL5YgFOVR0198IWuaNuTGrEVhOD9u/9qyTJZtgobccLcA12TP7d871pYeI1eM6587UM693j0/V7yL35ef1xW7817MjxMM9WPStQTkTsm+7T0cy1rG/yyLkaaR9FsZWUWWqMeEW2uYmllXwmj0GGwzxnJ++q6ANxDMUMax3KMCg816JQmmZIWxaf6NgjQEUqvDAUXNhFL7eSYmzReMmon1Mn8kdz55ZDgev7q5kvF9tVkjikOcDgVOdYX8IhPJKK/9dqjphoXYp/CSASKET5R5IxLIIMCJY3lbY5X8Ncz4HTCswVxkYRvJlzJyZMy1F46AfJ6HWqSAvVoMiHcbmddGwCVhMVWDgEncGSeJH8ZAwiccaCpdyvdxd2IvNmBSQM/rtxskKCHwe3gdZa1kxo4SciDHS/zA6BsXo88pa/Sw8xoYyhkrDw1Xx5JwGqt5TiiTHNjXWjLWKH20fY3/eXNYjvRrmoi9sCXQ8zSfi3mFi4s8ArS5BTh785X7pw1CGAP6sxl09DflvYD8ea9DzsWAyIOX+tiFkVyPt7cJ/t2vL+GFBj4XtYSZrtYNz8WTSD6P9yXKj5+ELZ1fbbDLGENAWLfVVOrUw1B18Hsfm4sY6crH9dbH67HCUDaSENpECWLOmUJOedi3KJmlRy3vd+p1x3usAI1ocDzdSSpqKAngyrQlyVwAWe24lhFv+7O9XuS64eKHpNYyEZVBT853Fotrfx7U5h7N4+nJPYjzkoILobQccK+w76sS9IWs3vbhaZHD03sGFzJ220Q6p9gfOGXAbJo2Dy7Lh7747vZ7uhbcGLsYNtXybQbunCJhsvuwz58BtnM7t3M7t3M7t3P7V2+cdNBnZb25xGp1jSBI1Oh/jBAbH5nfoG0OuC9O6P0UQbqHMZEkLHoBzczVkDcxPQKuSHPC6w8CrLHAKLuWtbgAdrSy9miiLIlfo0hB+4ZyIfVVpi2N4YxWM9Stw7Hup06SFOhSmQEnc07asyyC7V/LczYpziV/cjV7DPG5XIm08M3qCb6pcGyYjhYIC0jAGRe4YAs+smD0vTVYjfuwXlFqOuBwYIBC+MIM2L7ZNOGUIkFmpbqnIqygL8xmJRPhh4dnmVgHISV1WpCoVEiJDASNCAIOxpfENE6s26pA2Je4JFi3DtFuKJvMBDAZykCKg56gaF/g6fkAc3dEmrcIU4NTF2Kw4JofRDLZjdIUQUym2xFPT5/R08y57pDmO6z3W5F6Nk0jBQ1TNq/3l3i126F9Osh5roMOJQvZgsBjiqubWwRejB8/HtFdNPjz7W9gvv8L/NVfevjd3Q0eundoskts3lzg7bc7XH61QnIT4d0eeI8aQUc5qIYYUJIUxj6SwNNEtYESmhZd3aKpWOwx/bEXFpicP2+UokhYiXLMDDqyusQsvMPW9NjEPto8wMGP4HchvI4BCp0YcNMPbyTDZqBkx0OaeygJLJ06SQiMqc8aWkRthZiFHAIxXH8Qw/EOm3jEq4s9ri62eESPP1QGaR1g3YzY+vT0CZCuKafTNDdNyVPAsGkD9IbG4WQfCAUHRQkcB2W/5ClBah6HTq5DJi46zo4kh1pfHZUH6XVPjyXKwJ6qHnnsoTw0mnBKP0AT4ScWjU9PiLI14mSDnz/XeAgjXL5N8S4dEJJZIf2Oyas+iK+RnVJGifhAbTMfWRoi4vkxZFqqTxB7j4AA4t1jWacEAIR50iNfpdjvL0Wa/Pr2FnXV4Pn5WSSk8lor+3N4E/vxDK6pD5b7fWJfTQWi/Xkccb3bIlsTTM8R0R9OADTrvTb0UnSq95r2VVewzoDSLH1yW55HG8cA0b91hasDa9yPCs/b8WTRXv6++G3yapufnXbHjtv6d/rdfXL3uSd8bNr3+TPMTJcZXNO0weXj+rvwpiaQY379dHzcXi+rXVcAC52INKtYWFv+yMUBDwU9pVoFn/I140M03FJ98eyXgImjMNpq+mTRwL0noGRlYHL9+gIoC7gmWuj53GjYgP0cXY/D3RM69jfrwTiN1laq6nb6xblzn89JWS3YcnG5t9cyP16AdZ7D9B6q5xp+wPAMwhpkTpHh9SDjSmhCASdaMtoMgXAamfF4dAjDawG6DB7gjX/AMOwW4TvqbSgAMxcPBJEgcGLs4oFKTY3Xy7GV11AeKsnDfH6Q1N8k05RlZRepV6QSfzw8H+hVxqGSASaU9/tIV4l4pYlPKI9hyzG3ln2nBLIRBD/ALuyFtTZUIyr6XAYEgQK5v06sNQLZBOUEXOMcwbLWCKwJO9r6HwqA6uSOem70+lwyCh2LUjq3nu+J0aYgO4+HLogtgLbASOIxx8u+Ff8IGI/hOtb7LgK2XovXeSsrYw0DmwIFSz8/HXF3ICs5QtzfIVvnkhR+9TrDxjTovByDT/8/iWdG19bwRwU7/d5D2LYYq5PMAco+hZfFyGIyfd1CUSOeeFwoYlAApbMiozZkotWouwPSPJPwi46sNd7bBVxT1pjrq3ocbEIoD48k1eoVzXsZh3CmPUcRrSLUAmK64r3lKKLXP68JditKcnndLkafCZB3Y670h2lI4PPz+CdzNnsei6qTe/kmi2X/6qa1YJcbSV+2STk9bW65uuF22fXmxR/PT019egLZ5EF94gywndu5ndu5ndu5ndu/auNkI81WWG9fIUrotUQWVgxvCJH6DWKUeDg8oeqAIL+A4YQTAUay1qIYSRIgC3sEIu8axXerDwgM1WJsfqTEjSlexkdABI2TNMHdWNxSCmInSxGJcCwMnCE1kSydtOn80H6XosBKKb+YRM0fap5040VBaSfptgiuhwTPbY510uH96hOOhS9plJz0BQKwWd8bIip2csbtZFmIzSYWbyh6y0lxJjKL+b3djglLRiQ/dkIqRcOckMbZO9MW83WGsqrx+cNHAb3kvQYWafpZFTBS2SgljaWY32cwYwB/7LAyLS6IxqwDFJsIaUDj7Rjm2YepOpGH/qFd4bH2sfVbbNMTxihBXRLo6JBmuRTANFRe7XcIExpoG0RprKBUP2CzXsNkNObv8PW7G3RHyrQKYSlWfie+en0dYffqNXaX13h8KPFDN+L2q0/4xfF/wz/+xSP+6p+3+Lm8xdF7i3B/gZtfXeLbb7a4uI6w2Rp8G3VYDSW6ihKjQFJp/YkJQZyT6XdMVaM/TS/BCSzahPkgVageJ7lUKGMiJCWgG8FJZTHQn43m0bHXYuPTm8tHuNRLVQAAIABJREFUkQVoPCa8GURgkUwOG4T9QL+kpgM2LJLXwHPnoy8IhvqSrBc2NdKuQmAiVGOAgxRWWsBSYftz42HVBci7EdtgxNVFiDBiP1NGEkFaoBGfn7KLESZk4WlhyqqxGkN0BJnSEMc4xJq+abym6KkmhbV6/A1kYor5tzjdyPUuyXNNJ8ye5tji8NxjvU9QPFeSsMfP91i0qB8PuNxcoDz1+LkYkb9b4dd7g71RLysLWcCYQApV/p6mNLpW0/OcMjKajLOQEnkXvymLkNyYsSa/Q8F37k8YEigM0dSNyIcoGZ1ZaxpiIF5rNsRAgBMrMV1+UTalrDP9zE4C6SRKWkN5+OX7V6gHgzRd2b6pyaFTsIGAdU42aQEkO4hYXHD6XYAfW2TaQVR/e0l6mr479tqSlTYxvyYAZ3rqxXimr7Hjz4z3TO/pKlP3uNvNaTszHGGfW5iL2z+QBYrpGLux0j6+GEcdKDczipY7pE0/1ssSWfuip2EcBNrISpTU1gFF18LvA6zWkQBVBFac8bowAa0/prLVlGHMhQ/HXiMTcrNZSyKnfSPLsrXifAKEPM9HMoBOktSsHl+Orae7O30ke5Dd+Zz2Ydo2gcAeh6dnrNY5Ikn55XXZIU5TrHKGO5Tim3U8FJJ6y3vJ81OFNIkQZ7GAfGRvhUyi7A7oiyf8/LGHCa4RJ1f6HnUAbzha4NxDz7FJkkCt35hgbQwzMCKHZ1+T4Y+wG8Nd7JhXBj5iz0MWK5OrDQjykb2qUv/iWMlCRbb2UHmByA1pDXCxCQVI4/uSoa6hA7zPQxhtYOpw6CPlYkavrLWK/pYxE0IXrLXejtUdFw4UyFZGFoE1Xks6dnNhQRlZ7n6pIPfEzLWdYnma5Mq2IKH0EyuddRJvCbmW+YNLHLX+bL4eMy64EGhjOA2GRgCwCJWMc/ycDDlv6xH/fH+EMSmiOMPv/vlHdD0XBQ5Y9/8VufFwaHOR5UZhiIB2DjVQBiuYNITpTvLeImWuQ5yODYagRZbGEkahXmuUzGo6qCSEsm8QiKY9xNDKVxiGEh5AcK1f+K3NgPhCBm6Ph7LvX/48eGSwMZl0xG5j/TEpNVhIJl3/FetOb0TD25CsF7qBY9Hv7ZxoGi/d084/Y2pWgGrHZa6fVCKjBq4uVyjJLLWo4BdD4/yzledPf+PebZnKvBx6ZgzN3gvsXG05UJ8ZbOd2bud2bud2buf2r9kYYrDdvUKaXQrjiGvVI0GZocMqKtC1JzwcT/DiNfx0LewV8dWxK9RZPCLzO4yUMnSU0pG11rI6EClBxUKILBzOYwZKZAiuMcSAsixOrNVrzURcvOe7axIlZ2c2iHFiqtmySVdC/6iqU4+luXCci2LxGuJ0XrzPF3JP+/dktJ36DE/1Cl/v7hGNJ7QD/eSiiSnhJvGBB7y63qBqazwfKg10cEuvVoKq+2NX3V3x6r47uaiVsemncObuowBr6+0ad58/43Q4IoriqbjVd1GpJifblFeNZChQVMgF925EgAY7M+Am9vG8DYA0RYgM/TFFO6RokgJ+UKE4+qiOlDOekG8GNEMqaXH8rHG2Rtu0shK/v9hLCmg/qKyKgFaeRVhRQvp8D/jPaNCgHALUpY80v8Tl2/dSBPzw6YjhasB/2P5nDL/7a/zXv0nxzw9XeOrfoMnfYvVmhz/71SV++SbHZmdwm4y4YHHT1qhLg3KIMdA/zEokyYiiLIxMCJolk7HGle+Wq/xWYuTc4aTCsDNy58njiisW2B29a1hcNSxfCbR12Fp/tqcwQFcRlBzEGJyBlyyQo8BHMRgEdYuLrEIXRwJO9mQBZjHiIERYFriNyXDwFBQbA4SUdJK91pDRRiAh0KuZjDVhd7Tw+hOqA1B6qfgX0uSaFQjDLXoEiBOm9hpkhvJWyROUYqeq1ROK1xOZQSFldCy22Rcpx6aEjCENVOkNJwRECQ8tok0GUxSI4wJl3wuzZrPZ4ONdiYdVil+8CvHW7xEIwMsLz1dgmEEGLBSFyEZ2XScecgnZOvRyouE5ZVj0ZycoEgYCfDDBr/KBhmAuZbpJKOeCBSL91Z4OJ2GuUapJMIXXHsE16Z+uvzhQzQFqjrUmXyo1kr5uQWzbEaUP79dbXFyGqPoUaURfMJU0CXvNhRvY5EInKZzBpOVos/jJ+XZNQNeikJMhwI4Ltp5zY4QCNzN4p89pJ1csTf5ifjsrS18WmW4Am1gYDiRyn/oFYjRvyqX46Z7Mn2c5XurvDmC049TEZnv5nNvES9DNfhbZkekf+xgBV0biMqSAFwTTRShl5z0jQpoQrE3lNfNR4Gssk0vYOGRwKbjGdGQGGihc4/aNn18dpjRtUu8zxYcn1KYX83u995AxamX89kM7LFPP0XzsZsaL/ZkMpX7A3d2jsIBogu8WRQi+rddrAYyrY4VTWSKJY7x9+1rCUrijlAMapkV3I+5/5udfSfr2/eMBZclwoUskGZlxlQAwArQLe4iAlQJO4jk2jogCZekS4CFDiSEvEgYkEkggHjv4Y6GvpZy87+GZQAz9TyWDC3KudWE4tbLQkGYecnZYbp9WDhwAed8PEgmSMIY9e1BP1LYR8EwSZMNIEkKXDGM+R9YaGWuNTel1klBlrXXSdwmsOUaW9ENJ2LZXzXRduz4hN+3pmlIZpPYTlQRaVhWPBecaSmG0/Us96Xgfpz8bF06EFTiSoV8L6CjXKOWgo4+TifCMGOvVCsehx9///iOi3Ra/uirw9N0/4K9+Czwfa1wkR0TpNarGoKbsNc+QZIEwpIOI9wGeNwXRqqpAdyrRlDRS6IW9RjB2Yq3x2vRGJFmIQ3GQv2GIR2uPEb/k+Fg7CZ5XFzSkbH5vZnhaEFbTQQlcW5CLi6DjiFPZIIlDrPJYrmP2Fzk+BNc8gnxkR88dwb7a9gk9J/NQ4MID7Bhoxy43hrgzaPmY0/Z4r3g+VrjY5xK401jZsPQzC/Lzfw2YcksFizbNudw/458cA78E1nR8sQmqX3/99cvR8tzO7dzO7dzO7dzO7X+wsUjJVhfI15ciCRHjW4rAmFrol2Kk/3g4wgsoGVzL5F2mOGTIBEwHBFK/h98OaDiJ5Wzb78RsvmoHlJ5BQMaRm8lYYI0BBpSZsI2c5TIkjgWTzIX0PfifmzMrW00nVo7FplNlW1zayZ28hUv7s3JQNYpWCZlLvHRFlLJb7FSMEgHrd2NGg9Tv8Cb9jOcaeO6vYCL64YzYbzYwfouHx1ITSO1Ef66HrQH1cpo3FcFqKixgnciaOMHXwojfOdnncSXbR5LwRFhj8OMPP2KVrXC134tRNCfWq1UGI8mrBPcIFnlSp9I42O86BT3iXpIoay/G3/UG1d2A7lOF9qcHoLhHkz+iD3rxy7rOQ7y6BoLNDYpmBa+BpJkFUYyieFYpIvdZ6qkKx4cnSYfryb5oO0SbHR6fBly9fS37/oly0G2AX+x/i+jDX+M3fxvi949bFO0lEFwhvtzh6t0K7y9ThBcBruMRl14rrIi28VB3ITp6iEU+4oDAEU+wGj8T4Gudfw+LtQlSsyAqSX0wklbIfSFLiqwNMi2YmMmCkYgZzz79xriSz4NH+WMU9gIGw8T4aTTi1bUqOuRdjSRv5XgOg4+CWEBVS6KrlwOPXYr6qLLLbe5jqEocqhj3BKIjYE/vtCe+x4j+IsAYGVzS20foBA3Gkt5NKUyaIInFwU9AqoZpqDBIE34eBeKEccWUujhi/SpsUce6opQ3iQb4Pgs0Zqqq3NkMR4z9HYxfo+3XGI49hvwWfk+5N5NRczx+rBGRWXe1RpBlCvrJNtgFyfggs6VDUwJ+EojvIPsxGXTG8Nj7CNJImDE+Iy5EnqrXjXZQNS1Xg20Wm/SmEmohilODTw+UTtEDT73a2EdUrvjSV82lhE6SKEUbLDBmATIx2Z5Md+Rt/pdv3wLRiDS51n4qyaFk9tVyLanROj0jHXC3CAGQ93Ujpx03pGi0rCZBt+Z+70pIV/gJE9WOBRYqm0A4+ckWhktwXhcXZkDHvX75d9bCW7dkD/OS4+YWEuwmF6Xpy8fdfrhvsn+LfZ/GMOsFJj3MgV22aJUi1QXCyEPqlyf/2e/zB5yhs7oZUDwe0Ff3oOmgidZYpwkCJg72RhhnBNMnAG/aTU/YY8rq6fQ6XZwB93204GlT1Lj/p5/x5JWSSlsUpSwcqCE7j6+eYP08OobI1tx9Qfyq9DPJWGjfyv1d7424vrzAxW4n1zCfIRuP1zA9EymVFJab/QxcRFI20IAf+xH3zx0uTYhV4uNQFnI/2NP7nj6JQQszfEZ33KE1MTwmOAaReEqSUUbvORt5LR5r4nva94gIkPA6bpkk2cAEvPdFwjw/1ASfIHLypqrk+o4TGv8/oXg2CCMNRxHmGn0gKXsk64tDDxc7mmd4dU0TTvQcR8lWDRLEvDeRpUjA2nqsifTaBhaQsea81gRYI5hG1przUJP+O1mv6ZXski/ptWevJQFZRSI8CmArPnVWCqnXqHpTgkER9NIUH1P1WmPiqgC2fiBgaMdxkGM1U5Xp9ccops5HlmfiKdnCw/ddB/PUi14yeHrGb79/Rn16RnV/wGq3hzekePtnKX7xloFBAdJsQMR7+EDGNNmHnrCFP/3wA4KxRhpl8IdMwNCK95FIfdEItsVZhGZQII4DgTD65EtTVt2cx/Ul4beLFFOOjD1W2hvMZHWx6McWpnJstJHj+zhgs0nk9+JwknNKZqRb3NP+p3MoBfYsULrwvlN5PX/nvdqFVFhm+UALED2xBAt1Psb7t26f1wTBYrLht/sUnqE64KT9ZDHre9G75R83P5wZxIuhbPF5pxHBPmm/23HlLBE9t3M7t3M7t3M7t39x40QrSTOs9zdIV5fiiUbjMzNERA2wjQo0XYHHskaUbuGHuQASMoE3AfyQTB5KwXp47WBDDLgiXqNvOpy6EW0YSFIU8TPxWiO5pOFEupVJl0x4GCjA+buAWk4+qRNEmSjaCZBZTIimOaUNCnCFofcFS8xNopwHiepM7URN5lszu8Itak4/U3LjhTh0a+TRiMvkM+g+9er2NU7lAc/0WmNaqivm7Dcxy3a/ul12s0E32ZvndPrd/bwwVNfCXXQ+cjy266145/A9mf5o/FA1M1Y2KpNpG4JA3zFOihtKIFsDQ1mJaXFjPES5Qb0KEcQpPC/FeAzE8KjzSpzaHoeDQdgW2KSFJMSVtY+ubiQ5k6AOyxQCVJSSNlWNqqvRD52sON+8/wq7qz2adhTW2u62wi/M/4pPf/s9/u9/WOGHxxsUwzWQ3mL7Zo9vvtnh7asUwYXBN9GI9VhjFJkgYd0IRG+TmJJinn8WYmRCtCIZFePn2hZswoLgBJ6ArfXhsswHt/o9F20uodVeOzxm4rUn/0igAYErsgAN/dPMiDwwOMQGRxPCKwwM6RUsdm3aqDDgyg6532K1TpGYCt2pghFP8RBDy+118E4lYjLgvB6V8XFPk3cWcsMgzLGyDkU6x3qWbBVJPg1D8dsjSB35ZItU1r+IRtv8W8pdPcQ072fxJmG8LJp7CRAgUCvS1vY7mPEnNZo3N6jJVDQJAnrOxTmqJoE3BBjIqhhGHI8nkXRR+ilScfEx0rTBuvVQMw2QjFQmo7Kgh5WmCSPNgJZSIv/rybxhaWp9D8mEkw7B4qtU6a5Pz8JAAHpKRiUIQYB851uoBZn72QFoE+gmdCoHsC+YEtZ30bXtKserm0zSZ8kkcmAN2XIEZ3h9i+/TBKbZPujAEDeuuDHHSQtdWbfEjuyjcwH4oiS025irQDuUzU+7DTlwYUbd5jeY33l+flFwv9iOBeSmAtOROhabm8MXXLPMvGk8dcfXjV12lJ1Yb/a56Q/+mD2nx8RRkvURNo5bYRKjHxM0xRHeeBDGjOkJIhkkaaLXhIB4en2EQYg1/a+Mj0ZA28UJ4Gvd+1uGD8eF8qcn1FWL+/Ie291efCT1OtLPs9zPxS/2u10UkWO5AEYF+9HFIPaQoixxeD4iSVNEEa9t7mIor1XJozIs+bqRXp8S+NBh1fdYByPKwKBoRlxtEuQx2bUtTifKpX1hqfGGKZ+HTC/2JzKwxODfpWdqYIF4L1KKTVml3EpGuRcrqBRLv+tCHzXvFfR9gC/yexxPOJ48dBHljkwcJbsMGJNYADSaQaa+Lv0QPhqDRO/TfSvSb4JTlLjLeGwIXo0i/ZbwEWFpW5axnJN+Bo0mvzV7H3zBprR9ZSntc4Dti5Pkml6brl+6p/mYgEDC/KLMnd51lXiY+sEgthAtpcud+rPGaaYM2pH84Sfsx+8QJ5eImhZPDVDHFPT78J9TePT+e79GlIZYBT2ytINXU647CmDvhT4iHjdjsN6uEMYERzln0oXOiHYbDQMvRvhpgFP5hKGvZKe7how1LmTZ8Wliitp+Kf1uPj7eF8FMgvVaFrcdyKbj6Y6fJ9+Z7NmInHm738CPAtQ0PXzBNXPH14610sUWY+08xOk8a7H46U6CPrxcpHCniYBsgTgcJO22bUdc7DUNuKV3nR0rX7TF7/Nix7wPU091QKJ7AT++HYq0T5892M7t3M7t3M7t3M7tX9iCIMRqdYHVq1tEIY17CRqEkui18guEfo2HY4GOJr4pV+IjlYYxSZTJn7FBagZELEzIWiPA47cYhhZFN6Agg4FyPhYjwljzYBjlXhM04GSdLDcaCVPyIwIh9ZFy4JplP0iNLVO+RXToBJC5QtfKoqYp2wKAm14l02qdZjn0yz4jjAv3xemZsDOsHFR4NgQBc0Sbt8Lkevjht+iaAn6YyfZ1mzp5owkxgQTBBgUkdJM/3aNp4uceE2+geYI5m6o7OYsydCILkrDY4cMETcRPSIoRK6OQgk09uGSVPtC0xY7FZ2cwSDpmhzWlhXTi3wSotgnCKIffZMAxlNVmipQO5YjTc4+0P2C1ajCYFGNdI/Z9pGmGx+c7FOUBF/sLBH6A5vgEhD0e0y2GvsEq9nB94SP49Jf4i/9ywm8/XOGhfI0qukX86hpff3MhXmvrqxBXK+CtaeCzyGlojB2hs7JjJg3Sv4xgkxhjUw5KD7lKmUY9V77FGJvFdSe/i8SP0hoWczwvpETyAuNVQEkhV9YtWKNAm2Os2EAA+rNZ8+uhpT8bUzwJtJEs5qMMA1R9gKH0OONH6LcYfTI3EwkHQVVirDrx7QmML4ECx1ODLA/FP66qWnnHzAeiEih64F5SBjvsklAYYUSrm8YD6GsY0cONpKtGWCJk9lVDJB5r9DcSpau9/uQaJLBAFskwaopq4qNvSvjmEV64w+hdoWdfp2x0ILtPU1WrnsbnAVY5Qx4akesEcYIwTCRxMQxiobkce4My9nDpj8LEYB9hkAGLOabzpZOZuUq+CGZ0TaMyM2HXKEbfGnIFWWwquEbD7kpAwVqAPAcyK3tM2Wr9ixCDmb2mfUmrTFeUz3I/fZzn++1rLhQQIN7J5+aTBPolOVTM1slysl5ubtuu0Jdt2W3bTuzGoJfjwALYnYchV+K9eET+whagskXvpbx82sJiWzK+TfjUDOBpIbl8i+V76SuXhbgraO3mp0r4y7FTv89jlRuG3UjrRmV33PnL8CeOm3vS/ahAkN1ruyNcZGFqL6IVmoLp0w9ovBpenOP54UE8rcgmYpAOPa7CmNeQh4aolQMQZfvz2Kvgq57L4u6Erqjw6ekBnd9ht93ZoBYdKyZmnNtveyKWkjLZY7lH4Y/O5STDs3JKptLm+UrYs05OynsDx3CyJgkuEyDnPWboCUBx4cnDJomwyQO0/YiuYt/SZO5TUaEodOHHELiT+4wCa3L6CDhZb0LZ3bGVEBK5w5Kdw/sZ7x0E1zwNC4nRI/VP0r9pNl8PwLHq5FpMaYpFb7w6QOMbrGIdA2P2e+snOlomMKKUaTYqRzU9fN7LG00K5dvzvEra9NBg4CIIx25ht5FBSnBtXgRRwGZxvbijLAfdXfNLPzzXjyyTfb5M5/HB9lXps3IcPCSJj6GrJXk6oD+bk0Ay4CYMBdTlMXXsunHw0bdrmJHJyPRo9ZF2BvG4QrvLsbna4HafYh1FSLmQU5ZoucBAmj8iYZT7HsEqZYTJuGccO5j3MLL6eFw7+M5Gw4QoqgINwwzIVJaFBV28kOOkl7fObixzT9h9Eu6jrDWd42jHm4Ybd8jkALvRaVRJr+wH35d+EyPWWSRhMFzU4qRMjqEcRsuAc6+furL+oEf6i3FoMcC4U8bNyTxrqOF1pQDnPejvy+sWKIpK2IabdSrsRS7COHXDcmt2ljVj+osLYfm59ad5eWPe53OK6Lmd27md27md27n9C9rVLsPrX/wafZ/AiLyRDLIM27WHddjg6fggE+x4dQUTJIBH2Sgn5b5E1VMhEnsDfMvy8Gw6aN0yxMBgoM+TT+NkT1aBRSNG4/mmFfCDVQGBNaZ0iReI4Eg6SRM4y7NG7RbwcsuVrsQUdzY7k9MaeTYcmlZU5W9dRP1yddTOo+wDypH5YhVcntNJKWeu6TrDm9dX+PT5ThKvgjDHJmzgNZ/Q9pGar9uXyjRXtj+zG9x2lwWZTvRINXJFgJoDy3NOFsOiqx2wXuUidzzVpZV5LEga5AH1LAC4wK6gHI+fmDgTSGVAA2UzAR3ZfGFEkYIQosHW73GR+DhtQ7TrBHGQoytDeKWHNihQDjUq+oVFK6RhijxlMl8op7NpT1LsnSiV8WO8+uqdTPCrMUE1jqhapmuOiLe/xMNwg59/ijCur5F+e4l//9UO169TZDsPvwh7rMdCro2qZvKmGmOTtcaMBrIhqF/qKa20jDV+MelRWGukiJmOHI0JWOslMEMlUXL4ZSVfz4sW0dY0ezKG1oJCfP1sKAKPmYCT9GcjONlpAcTrfkUpVRTgEz17mgBD3UsCHHKDnueopiSLRTZlzwHKOMSHQ4vmQPmVwY+Uib2KcRX3SDAgPfWIRx+XSYyu6vChrsV/ykQRgpgebL2w1roGqFofHSWvcYAwUKmRXkQMDbDXnqT6AZFp4Y/P8LweT8kWA3bw6b03hDgWDKqgEq9DL+bwRiSp9NuhlCrKEuRZhiQKcffTIz4ce2G00GYwzwy2RMPJGLKeRpSDs7AT0/CBjLxazgV9hKq6ESAtTjLZNxeSwGRCQ5nb6AtwzFRW+uh1ZSkfyXmsqd+aBdosg21mrvG82ArKgj5TH7OMCgdI0Rfv3dsdTm2EVZpNYJzIQZ3MmDInAfLmKl33dx5jdNt/7P/zEk6z48qimHMjjduOFnxqti7Xpi1Q9cnl+9kHp83P7zOxcyZgYR51XhTR0yumV9mxUDvExElxY6M89fLzyMNzhTo/7p6wNGGXuKrHXQ+iJDdPr/9ig64otzvK9yUwHKQ5ysJDW9TIt2s8f37C8eGgjKqqEjDUY0In93OiKLvFFrtNK+2V661uUXx8Evny7z/+QaTi+70y2Hju9YMsP5v34jhoWKeyYfWcWSbbdK5nXzgmgu42K7y6vRWgTWAIMdangb5eU4cTQRQa6Fci5RYz/LJHkGcCZsT+IP2SYSzPZC81QJpRMuejrCoBFQm6CTuV91Fet8J4VkBexjQJBhHHSskSon8kQo4aRsnPZL9RstdzO4Qz6Pnmiafl2HFsY/hPCDAF1A/p4oAIJXqyhQX84CKOmvbLUSIbjPAbxxS/FZkjA3HG9igsMQJWYZyiLBv1+ZL0YCsLtcARm0i7HVi6OCN6H9UvJwF9ke697DbzsGCvrxl1TxKmdg5omycBEH2CjQRERY5vkDNBOwjknBschHnv+aMcl47SeB6rJIbPBRcufN1mWOchkpsQNwnHyBDtc4fjU4t6DCVVNU6P6JBCEEyGFVAOy7GPDGh6jfkeyoaLmi1WDEjwAsRDAlMHcs3WfSvnnZ/TpUE7MFnc4gjsuuNi5wjyu1y343xI7CLMdJDGGZj1Pe4TGcm6EMIvgqglr4dxxCaPJd1c5anqhCtbsQDevKhgwXY72kyLEtP44Vi39nGO8V0p709wvacygPMj+wfcKo9XUTSiiNjt17IfFldfsNas35t9L2/52adBwS0oLMYJu6dsZ4nouZ3buZ3buZ3buf0Pt/f7CO8vVti/3eN4CsRX7Drp8PT0AUXTYrPfwSfY0nPyzBCDACb0iRUgNgNCFhicDLNCZ9ph2+DYAXVAPybDzFHQoMXjF3WjlIaIxISUHnrr0GPMAnQE1mSSZBkAIpWwWWlWailNvIemUkYfWhRTMnG0s/OJWSGqMUf1sK+2hasD76bX2u0pC0AnjvSaefvmlezHzz99tl4uBC98lGOKIEqxC+8wtAf0Q6QrxS+nj/PsTd52ZrtMe/1FoS5sBHm4xypNsNmucP94RN3SB8tVHGT/aUKmmycL8GDlj2Sh6XY1Mc1YsIeADEHSdvSlWGNyJl1lrgOuUBvU+whY5YjETMzHbgu8+eo1VutLpEkmE/MSNDoGfipCfP93JS5fbTCYGP/nbz7j8s01rpi+2QBlP6IYe2RDj/dXGW5/9QrJOsY3rzfYXIW4yQfcooZpK9RMnOtj9FEsBv4JvW0sA0oS5+oWVckQA/Vb670Og9dh9HuMHoGRRtggBHPki3JlK/NTINUWViKdfDHTn1b/5fjJbN2l0tpjZoMQKHzqKH+kbBSthHnsA4Mq8rDyB4xNjbEa0ccr+FEqYBzZDWOSIQpCbNYxhiTCkBh8dTVg2xxRY4Wa5uwJsE0CdJ9P+HwccOh9fD80iMYaOZkw6IXNxkKNTAiy1mKjTAPxuKGBt/VaEk8zorHFCab/CSY8CQMiHSP4I3WnWnAbyn56bjNAloQaKMIUXx6zQI6+JvAxlZZy4HYQ8PNjWCMvCwE26PtH0RQLMg0kIKuAqXZkrSkQSpPvOE2QJgmILajnIP2rAmXdCdBGfyx9f4ZE1GW18FAjUOqAtmW4gS3GFwEhcwk5g+quQifD9t3tJeKc772RkAqc6pUHAAAgAElEQVRlgCq4xuPIgIzJc215XUwy0Bl0m7v1zIJw774YnRYdW8H06VX2OmTf1HFhhhFeAltuhFpWgi4p0T5jr3G3jy/HGbwsgucH/+gddHHCVZ/Tll7+4WK8nDwn7YPTvlhgbUFam7fj/mh5fuy2FSCZx2cCPlGeIlut4JFFdSqkw0ZZqgsaBAUIsEmIid2OA1y5b5btyHNPAO3w85Owqiv6X91/EJbM7mKPuiaDjYDRckd5L9Adme4b7ryQqWkfU0BBWdAEs8IgQBxHeP3mBtv9hZx3yRkQr0CDw0igyhe2KAFm8SurAvRdiBMC1COwyzX0gx2LrComcK7iAF0UoCg1WCTLyTonWbZGI4zmwN43+T5iuOXiI2UfngAkBN3pOeZsF0aOpervqQDgDBoeOw9PCT1XQzxmEXZRgCAJ4dPz8tSLl5sAaGTbjoEwo5VlSvzQR0MJeU/pK+0hWgXduxL96SAs3Hy9FX/LU0kg3rpnWlm3YxHqNwV/J0B7wVoTNuDyutFf9DKYVlPs73a8oL3CJk+QmB/h+f8Fnr+HZ5gkHIJkrW6MJEFbGtlUZNv1tFAgQNujD2Id14cRSWoQjoNIel8FA7YpcN1X8McAydihMhFaP0SQZiiPQHM0iL1Swp/EUqAzaLn4wDHHBKjoLxgS4AxEXi9hFsJODhE2IUITIFnFaJpKpP/CVuYHtH6H09zJrT/aBcjl2CTjugBX2n/d7ZBpzyI5hgPNXvZ+wbCHEUXVIIkCuT4lfddSKLUX/LF0c3wx17HjpRuebH8aWs4DqAiI0YeJnDuVduu1+3JEVaCtLCusV6nMFyibddue23w9TAsAy2FPFkDt8/ZPXV7GGWA7t3M7t3M7t3M7t//fTTw+ohBtt0bzHMI8VfjzPwPyMMHvvvsBDf1dkh2qekQcB7IiS4kKJ8lhMCKixEsm70wU44S6Edbaicy2yCDxDHxWEzRC5pyn6TBUBEkGWrthJLAWKsNKJQ6CeLwoYtQzxrGNLOCF5d/MX65AW9R4+iX1lfsjnfopw8BN2heL2ZIq6tgJOqGnzPX9mxvcXG7w3e8/oCkp5ZFYAgv06b72NLnvV0gTD9n4s0jhaMirLActBATysxO4ye/ty0no9CA/Cye5HV7fXAmz4vPnx0kga83ZJtmaGNbxNU76IiCR9bAR4EUPhshGrWm3Y2axSKjJzGp5OjukpsGlD8TrAE+bEG/zATc3O/jbPT6HvviiNaOHpmoRtyVeXwLV5Q4//NUzPjwc8fV/jHETfsTh7mfEyLFb5bggMNsPuK8bdKhwsw+QZQHexiPSvpSCpWwiNH4sZvk08Y7kGPUYJzkoDZ4JMFnWGpkTvPbIvKL8qae0T5PXGgk8oEH9KACbeq3ZY+wK/8X5cPWyGDS7xEjrz+bOlRT6RkMoKI3umIpJuTM31HfwywIoKwQ9nYh6xH2DcWShHMCPEymGeY35ZsAmKrEJDmhKD88FZUGjyJD8KEE9eAjyEFFZInoeUAceSv8I81OFxyhBzmIuDBAzlU81YfLZhXgTKCOFfadoO9x/qhAfasS77zAGV4D3CoMXoWfogAUEeHFQ/ZUlDD/Q61TlWzyeLLaMgHDiGbSKcbFLlI3iPyOtSjwdaMatfk0sdHnt0/ONX5LqyihCP0S+ikWiXBcj4pFptKUAbGRtUNpHPgbTDsOBzLcez4dnTc6zgSQO8HJMuZnFZvuunKtlCakne/Zv0j5C4OOrr25Q9gFWaa7oGXuaTTacpKETeGdBIMuCXI4yS0jNCqSm4s6WrtPuTMW/BQImYMZdh+67HQfnBxbPux+nwtT+6fglajaPf7qHM1Nt+WfLo7UsSfWxmUlr9/6Pmr71y2cWNez087JEn8BK+59+ni9eYMdoMi4xVpJSK4nUVYfOjCiLUug0kr5JOZ9Iv5kC64bXea8IrnGRQt/Lw9PPT8Lc3b25wt/8P38jwD390Xa7nSQmi/G6nOvF3cSet+V5cfeRmamjnmwBbROiCBeXG7x6dS0gm97PKDukJJz9ZERCI35Z7GCqrt5P7tMQeRogZoekdFzyatSnQIbwgSDLgDwEsjREw8RgMt2CEFESo7G+VKn4o7kAIHouklXKxMkRCddk5L7EPSFwREAxkIWM6cYobHRlkPM+cZtSDmrwJurF3zEPRq6Voe4IDoboaw9+1yIIWwHa6cHFcB2yvMisG4MAJaXuoA/rgNBrEHLRrvfQlpWwYbdkEPajpAbrYXcgp7vA3XG3j/E+LEEHiz7oADd7XlxzLHU3XqxWK2xSH359QOj/A0xwhzH4FnWbomBKdJyLJ1rb1Bj4xRQHJojyiJUqyyXIyD5OhhUtACp+Hs5X2hp+Txa2D5NGeOLCRezDy3wkiYeGoTr9gKZq0BQFvLEWNQCP0939nYw/aZYgSdZik3GoG4y+QciT2XdyHftegKALkKYJ4oxy4VqSPekRQIs4sTewrD5VALjj5hYZHGClDHt9qZ5vJpu64zlOA437Tcc4PQNM3B4laVbYygRWua1pQjafNScjnbvPy4GKY1JdPso938QbWbjUqYxLHXXj2ItLwf7jiVy1rGtcX+ZyH5UAlAXY9+WoPc01LbA47ey0UKlsvzPAdm7ndm7ndm7ndm7/3caJFmWMnIRwApaZGCs/RNUN+PhTgTQy2Ny+xRhnaBuCRCE6BMwiwMXKSHrjQO8NTkbEtZ0Gxq14R3Us+pnIJQEGXOa0zIG6xciUUF3gxhhpLLzFhHR1ffL90C8WI7ZEtDuu/7i5tIBgTh6pFdU0geIDbhqoPkZ2wucm3tOkXdtyfjX90vdIkgh/9s3XOB5O+P7HT/ApVeBOu5dOS8Izn64ZYjRmg01cIGjv0Hb0qUumSZ6r09y/KmiZP6P8JivEvcqKri7w4eOdsLYo4dU5oAUV5LixaCBrScFK3Y5l+9mZo6amzhJIPToKXE4SyJCG/ioblRQ5NIj6CuGpEA+gOIhhVC8iZvpedRKDbZOu0Rw7vPKPuPnzGG9uW6wOFT79/oD09X/EQzGgPFXYrDPUo4dnghiUlXYNfJrady18RGj6EEMYIaZXn/h2KfuK4BpNtem1Vte9Js+x1GQipmExSa8/lYN2DWU+BEoGNGRAiZePSo742fUU2GP24oQrMCnHz55bHl9NPlO5rQpvbHiEMNpoQUbPMF4qNZqigWl6SQTlY0z0a5KNSh/DUABEIj0BAcHyHuXjAc8PTOVtESURfBOjZ0HKfUtjeGmAfJ+KuXPU9oijGmkf4tQzRRUiMxLZDAGklgAkj4uyUjw0uD9V+OG+gV8Au6GGv/8Og/9reEalmSxMOwca8fqgj40AduIAJWnBwkogaBESeKM/FIMT9OAkcYA8jOFTGhQkAgyGAb2mNCCCwRZ12bAeRLrJkGWthEa0Y4Cx7pEMJUz8jMFP0Y3qv8ZTEY1AXZxwd3+vYIFN/1QZlKVBOQabBBxY6MaCX4uyTc6rnPcFuMa/v764xGYXYxhjRMLQI0Zp00IlXVL93ViwKvivF4xasr+oGqd+bbuvHXu+LAJn9pP7rvXdvLdTrei2YYcF9xr9pg+6PxPWyhdj2XJ04dgnw4Dbhy//1P2yKIjd6+YP8Ce2vnjADqszyrf4DJNH22KvX4DbjiTHLzJvaPhOgIDJlt1H9NXfo2sPeHiM8HwccapKNPRhRIf6VMv4EKUMZyEdyddwDAkzmEE7STW0Ua98r+eHg8hM1zcb/MM//jMeHu5k1wnuZFmGquZ1v2Cw2fuKstZ0X2XMtiiOjrPz73EUwQsD1KcS33z9Tj6TfFaOZW2Ndogl9IP+WQJSWxAgMIOwOC+CQYJCAsrTZS8CAdEJQeu1xe3Ry5RSxgExx+/IoCDQ0fTYrWNkIe/xAUrxD7RJ2MMADkHincr9l0UXHhvKEiXTW7YvTDB7bxE/RtlPvqKVRQOyV7m4wLAcJqg0AeW7AWoG6JAJ3fXwxorGZcJ+5dyhlsCEAUEco/eYwkzleczAY/hjDI/3TH/E01gKsLRebcRXk7K/F0CM7qGeBwusOUDNpda6czTBcO6ytAwv3sMv9mtGMaCvWwS8HzIR1eR4PFyjaQOk+UbmFh2jkdtRzidZZARtaLMgLLE4pLpWxhOOuY+eJyBaR9Cx1mCcIYmRBL54h3I/Up6rbkQeDQIklkWNStTIBmP9jOeHnyUUKElWcv+qCL5RihvnAiAdqhKGPps+rygG1gDxGCJqI6y3TBDn4kYFw/uygGUWbJw6nu1tViGgx1O/eE1K2IQ7ynZRgs2xB9mmEcgBaXZ+5dJKDRe9yJp215Lr7fY8ulmafJddoiy/QV89I0tWkk7PkJxpXJnO3TRFnMZBeY+pD/J5+pu2st/rNdnigVgSzJfQdJXjyyZAnJ03uXGT5/YMsJ3buZ3buZ3buZ3bf5e1xgKAPi2coHC9NTUhNjQ5Js1sMCirEXkYYu01yG/2qDjBZCETUBbXo61bbDb0xKC5fAHOncvQIPRpdqwr0tyOeIDRa60mu4iGL/SgooWbFj/CahMkyZZDnMRbKpn6ZCgQ9MIrw6aEyWR6Ltmmydf4RxOphUhzKmjnwnF6nXDFFhO//5e992qS5DqzBI9rETpVZZZAFQRBEmRbm83Mw3avjY3NmvU/7t1Z27Hdl32YnXmZJtlNNqFRAEqmCuFarZ3vu9cjEmT/ATIcyMrMSA8PV/f6/c49AgM+/fQDTNMEX3/9PfKiElaCjvZswWUHrCYsgUW/HegNDoo+BbwJFuEGTnONZqApfGhqUAMGjJIoU4CbQpefdfnoRGRQt7c7M/xz/sRjapzhpzKECXLce/t3KTqH/fEJ0cmwuXhBlNJmvIB4eVQ22gce+sFFWWQoiwHTMJX7hl5qxTCgcT20eYcpGVmeL+uRvejjK+Tf/jdsX32F8LTHd3iB929yXF5McbJaYFsBZRrh+SxBQ++0TnIkxcCZgQWh+H5R+qJymKEjsNagKhrUTAkle4UFoUvQx8hCBwIwLMRUDkrjZ0pC5Tu/CK5R6ijAoB2hm7vGStoMs0/ByAOZrblHRBopKaQWaNP1RM7X0R/sRoIV0HniM8gEwD5O4SUJPBoUBh5KpsYNDqJgwPYuxzoDijaQe6JsIuQ5EM8m6GaheBomUYepGeSTARHNYqRBCI/xurMYi4ib/QFO5aLtPcOmG+Az2bTp8Nv3Ne7XHeJqwLTpMFmF6Ke/xCBG0VrrkGlB0o8UKEwNZPtrcy3emgpl3qDuPEmNS2mABxd+16hc07gR8fqHcSrSMUqFtF8hS0/ZOiyWWXx7PdvPHVyXHoUx1r6HdGCBDjROKiw/ti63bXB3e4ttlu2T/SxAYmXPBiyzLENhVEg7sI3fMMjYTg/T9Qy7lX3ehx8+Rdm3iKKZphFb7zVhrpkk2kO2nNwiBsg7bH+26dpGqK+YPuSgrzkA1cfvlkWy797G7/Ku0TjfrPOTlVTIZ4/V/O3fKhzHrR7s98Ea4+7+9P3mEMaCdFzHbuSgsViayU8X2bxK/7XfZJAkQWIPURwgDQk6D+iaUvq7vM4BZ43Az+E4z9A3K6FT0s0rTAlEO1jf3Ov1bFtEEzIQtf/0glCeK9KOx3RZBWZ5rxBcy65zXLy4wKvX7/Htt1/LJBP/fnH5SIFh4w0qvn7jNbUyXD129YOyoJvpmzEgSgL4Ie9lF1mW4dnjqUgLrbvn2omQ0J9R2NiusEiZmCnPM+Ptx2Ny+1ok6mRFs221BGCone4HIelxn6U/l/mATgCwaegiieibxnNBsNIT6SbXkTAQl+mrgfoKGim541MivgcPRY5HE38ZCnj6uZRAcvKsbuX1ZiCw5NPUUSZnyDRmRk5EZlZNkK+WiRBKw72+RhT2CJIADf3MBGhjcEUqLN37cgCCCKETA0OAJnCQo0LrVFjNpiIdzYpGWKUCwB7IQXkJOJUgGI6MC3Th/tv7bn8L6pTSdJpiOef9Qsawp55kDtO1E9zsTuGHc0RxgrbJ0dWV9FdxqgAjU7h5Hsmk5LkN6Y0hwTlMegZmng5xCKg2PKm+jwl9LE1fSwE9T3bjubivHTgtk27ZG3Uo8y12JeCHU3hdCd/LxRPQ9UNhbJOtGUYR4nSGTVlhR6Av4USUTgrxesR9hAihHCOf+0zYtOMMST42k0hyjqT/0RPEsYZIidlG7Ekzt/0wdmsmOdmMNyR8yo5XLMZmTzonlPg3TlDwPpP2MWa+73sPM36pdht55gfJDIP4+yrQZde3y55Iu+/R9l2fBhzYfeI9zjEbp5zOzxbyXtpJ2GnQw28Hnd/4TccFDi4vro4A23E5LsfluByX43Jc/vzCQQdNekNKE+wA3AyOQj/EzOfc9ID56RKnl0tU6w3evblHla/x4vFcDKZFxsHBhw+UZSVDpsk0wa5uxA+EKVdCTeLgzQBr9IGSWcGAHmbGcJ+DFzNre1C/GK8rNeS3zCudITWDIcMcGuvMBz/sS1wpd8ygzvA37Ir7DzMFs/1d60P1eFrOU3z2sxf44fsf8frtrXqpaab9g1nf/bZ04DnOrJstykCvJ7NgAjfwsfJeoa0q9M7EbMcUbZIix0Ke5vk9FksWFjFe/XgtA1k7ItVZZI4iORg2Q8NxIExDa2VcjZidAc+EcWdZd4KrqYG0JKGJBNKY+guw6YokZrdbw/EoUyLzzsHWbP90FiKKQ1Sxj001oNmxEPARNbf41//2Br/7IcGr2yluXi7w4SLAs08eo6gcZN6A6DTCU4YVuMSIQkSeL3IlcifICmibCnWXifE2k2arohLvLguUcQ80nbMV2Sylu8JaI6vNgGoiDSVrzfqu8T47MMvW20mBNRnIG3BkX0hYkNfWxAZQJRgn4KQCcDzmlt43u1JYJGT/IYhFouakU3QiVVOWSeh0UkAwDLHIS2zJ3tAmaCRYDAIJsDhNMXcGxM6AsM0FYOnIFiQTwXPhB2TGBPgxcHBK1ghuMPSUMznYNr0k4H2fdfjtbYfFzsGkZWBEg7NnUwRnlNywqGTxofKfg/pTEuZ4bnZ39EcKUZQussaDx1AF30M4NCIvq2nCPVC6M0h7tmbmLOolsMQEceRVh13B9EAHWcVAE8piQzhegq3j4SVcnDae7BPfwxKvLjIDiKtUk15oApCMMmgDgxtmBZM99234z4DnB3/bvwhM0xQXjxaoWsq2It0uATbKi4W9ZpJnLePT/mdvIrMdy8A4PI/SPM3fD1+zbU/6pbGecx6uYvs68/5DdpsWlQcbPvicQzbH/oN+sn3D2ny4mG0egH+yGAaT/XXfe45UmJ9uyH6q+UUnS6RG5a5QuhgGSJIA00mAaexg4jYI+xpOlaPKK2RlJwVxXlUiA6/LEGUzh+tHCJNAJHAE0sIwElkdgWumyxKMikeAzYXnh2M/LvfNeO0GrNdb5NcVnnzyCNkmxz//yz9LQiP7PYJpH330icjwBWATSakBJUbyjT1Lpu+2QI7cZy5Ozk7w8YsXcsxnZ2c4Pz9DHFOWWYt3F1cLKdkTb1HXyPcG9GRyS5aIL/cGSVsN/b/YKsJAJj2I13QeATlX7DbFJEDYRvrc8+mnacAPffIpCEXQmD5j9E7l611bq/cY++xQwxaE1SUhOJrqSwaSSMJp9eA7IB7YOWRm6+eHCYF0yXMUgJ4nh5MHHps/Zd4tZag6XSVM0Loh/x0h2WphiIKpx5lewyiZiIw9a0u4MoEQwmW/6QIVKs4aYTWfww9T5Aw7MUniOilkQUEF2kYJpAE8za7p9fN8nCzmmMTsgxiEoYAM75VMPGMdpLOlnIuq5ISRK3Lb1ONEjbb10FX2XlNLXBCK3kcZBJiEA4KB/aa2AF5TTjRwwsgdOjNZpJ6eLmqReTJFdhPSew8yWcWJOJ5rTnJyLqgpGAZRwHdLhCHlwyGyrEVT1gI6+kGEzTZH3fdI0lC8Nrn47J9LB1VTYjqfoOkqtLyZmBwrqeJ6rzEdlYwzMu8EfLUTkIcN2vzSm/GMfUZKmqsolvfPEOku7MnW1iHPNZ2EUkYwwVxtUtq/cL/abIN0MsVAL7uDDucn3dfBctCP2Wf52Dft+zN9jvOzXWwznkMPq/nE+GtKBIRp03Zi0+6/udaej88++yWm8+QIsB2X43JcjstxOS7H5U8XykEDplBRQiMDCRvTrkPxyE9xuvSxuDwH2gr3b95gu6NPFoveFm9evYHXZ7h4corB9VHsdhJ8lcNF0dQ4YcJgQMZTbbzWyBribKGy1pyQxbiRJXLm0wzEbVlm5YoKZAx/UtTZQnNfcOrwWde1UlDrz6bHtwfZDmdX9yDKvh7Vd3O2nUbnH3/4VJhcf/ziazGxJ6NBp8h1ADfOq47+Pntjb7vnyqixxZeChPUQIhsWmIU9JsMrNPS1cmOS93SbPcSn5/R8LoXE/W0OT5yNDwadYxWrYB+xt/0H6/mwk8xi9i4DYlN00eeOPwjYRiaEAdoEZOPPGlWa7XK5dsk0QR04uJZ1BgHEphGTzFhwDVi4t0CYI0zmYkj8++8GfLFboBhm6IIJNoszVLMFLucBHp1HmBMU8m7g9hzQq0SJnkHzJAIh36JpULs9mqFBXe/UvJxeZDXDCmoJcegZHuA06AbKDslqIJvSMNeqHpWRhiq4psem6ZLmytjRt7mcthTQlx6eL4O8jQAbX+QZTOl3E7ko8wJ93iKghERWoZddhCCK5Lq5Rn5pAyrcrpKgj7LzBVQiFtU1lF4zOjdAOo2wiClv0xS9lii2QyYY2y+LZDIdtNBmGViTrTZM0WUDNjsH7zpKQ4HP39VY1cBZV2OVDjh7MkUwjRWcluNkO9Pt2Paj7A+9f64JgsU+3MRHHgZIaUpOtoxIwindozwMwmpxOxaPjcqZB5p09yKvEzlaXSPblOKl19GIfdMg8gt0oYPbPsCychAL+NKjoYdbdo9NtkNRZoi8CJNJiihSPymCqDz/4i9kvLsInmjfYblBh4uVB5q2Zf8lYNn1ePHhM2k7UTRVLEkAGTIfmYZHlg4BNg3FsMCeFJUHIL7hsh0UogeMC9PH2CJf77WD3w/2Vmu6fb8iTdyyQvZrPVj/QYdm+4SfvPTnf7GrmzeYbY3nar+zutiDHV8e/tzGZJEunV1LECAim5H9xSTCbB5jntaYRJ8j9v8ZofMlvOEbuP0tHDH5C+A67AF4uytLOooSJJOJAKEElbVvp8yecmwXcRIJG0XYavR1JBBkYqY5icTrRVas7BIZt3WDze0OZdbi8UcXaMsG//Q//yfKrh4BJqYhf/LJx9htd2haejkq882ewPE02+eHeZV96PnFKS4ef4h5msAnA6vuUTF0pKsRJzOAbYogmqOecZSGwlogNIWmanpqFC+BOmRAkWfpe4jIVjP9E6XZBMIpsew6MsTJPjKps5IMqoCRlUJqMifBQu3b2WdyXzgWCF29p/XJSZSHk2EahFAwpIDp4JSsmn5Qds3YCIScUNAHCCm9Klhlf0cWLPlYgy8TA7atkqHHxGciVUyrThLONoTISqDJKY+nvJwBByWatkboU3ZOsJHcrh6FU8h5PVmy5yPDkJ9ijluwHvNwtPfvQftnG55OJzhfzSU1mGwtaT4uUFYldkUBJ0wQcwKxog9oAycIMU9deAzKYb/OuZKuwVD1KKoAjRcjj0P4qYtTv4YjidY8bnaMZIk38MT+okcvfo6UyXpoyNimGmBgWmyNoMmRTGLUqxlKP0ZY0peNIdmteKDVPGX0omu38P0KcRJgcAOs73K5brMFgyEC3G4zPlpEwrpd32PX3mAVh5g4IZIwgZ/GaDo+M3leOJtH8JSBE7QhVNsOPXMjL2zfvrHvHMYJKWPPIf2BmS3Y9yt4MFYjkMkAG16vls9xAbM4rtypvHnKiR9KUx+CY9Jfmj5HbURMRzv2f3uw/+G4UHf3sO/lTxwT7PIKKdnfM6YRc1/MemZ7Mn7qgaePn+KzX/0CP/z4I7746psjwHZcjstxOS7H5bgcl/3CgQNBGxp6y0BUPDmMhEIG5ToCmc+muLi8wObtS+Q7lYCVFYEKetHUFFKgKTtsbrc4iz0szs6QyWxtB/JoJCUyq3B5wrStXsx2GTFP1prIQWWmmCmV6uti5TU6EDbSA4Ev9jQjGSIrGjgWsjrWN78LNcLEy5v1dPBlhlmHg69DB9txltIUvRyENx2ePDnH08cX+Obr73Gz3uqMv5GdyL+2sDoosOzrDwtka6RvPkGYHIZRQG+pIURFoC3O4NZv0XT0dAvw6OIcbV/j+v2tgFBSMLrKktiPJ+3PFvyxh2WBSbOfY/Ko1D97mZyAK/uBsZVhKBOAZtQD4jCVAoxhr1lH1qGLq0mshatDOWJv6RVwGxfTPsPNfYc6ScXTKmoiuG6M58+neHwWYxYFSJwBkdeiaSN0BJhoZ+95MstPthrZEMIOcwKRUpLYSHP9qs0xTUKESYyqrdBQOtQ1Uly3jTHPp9S0HsTvS7zWWgUEJTjVFNgjDmAqK4JVvC+ECfHg+hqZlgFV9tLATgrAk/kMrrNDme/gt2SmeVL4UTpUIRZWgYK6BJM7KUp9p0VTNKi29O4BPCYexvT7cdHMIwkyqBYRVgENxFWCrKEfyjSTAAMpIksFesgMEX9DXgaVHfm7Fv1uQDgJ4d3kuGwanD2PkJzPVN5l/KcM9CuFn94uxnSdl99IzhaRg9RzEHnA0meh6Ml+F4VKggT8aToETGz1fLQtZWiUI3XCUEgiFlMV/KGGt91KsIOftZjEt3AW98i9GeouQtoSmGzw7tU79JNAAhSy7U7qqLprkEZTAdlaMjfWzDw0LE/ruTYCodoexlpQrte+39B7YF9AzSYTPHlygV3VY5ZQlqbbYuqpgLZkrpEtSYDFSlHHkv2g/Dz4QLsr+zLP9hMHHmgP3qTbEiDkAfirf1L5u11rXFu3Y1B2ez/bNeUzZWJhf07sX/Yv7o/AnJHxtz/Z/4P+9hohq/8AACAASURBVHAGQXoRYYZp4RxGIdJJhPkswWKRChBP6WcfBqh8DyUzbhhg4SwwOPT+o3E+U2czwM/Uf8+doCOA5sZwA4JUkUiPtUu3/bwBwOXS0jOSzx36gypQL56Cko7MUl4ZaVyZjFH6Zw6uJwnHbV7jN7/7F2yyjZmnIEjW48mTp3K/lWWpLBcCD6b/kEM3QJO9p8hs5HX6xaef4urqEeLYR0F2mT+gcTp4WY6bHZNo6RVJ2XcsJvnsUyjTlF6CfRSTQ1tKZK0XG73WyJD1wO7ApT+Y+A0qmCU5DiKPVK8rZYjr/f7e85AwEbppkHGyyw/F0kGYsAN90kJMyIYSsFo9Pmm2Sey/bHyUCNBEHpJgQNg3IoUkA1vnF5hW6kiCqQRASHAOQXWhRIt8lwBg5HuoIhetTyaaL+tIWAyBTloYEDUiiOYw9dFFHUXY7TSFNJml8F0fOyaLAoi8GD4nYwaGKDAWp0ASh1guTmRShWnlMpYZfVD3z2vp6fwYj85XEgLAxGQJ2pYcpQ7r9QY1wx4mc9l/smf73sdkFmJCpm7roKGjhdfC72pUuYOsjbGJEjjLEE/iHpO+QFMOIvXn/c7EdN4m3C9Hzl8rn0HWMdsE70GGP1B6T7bmLAmQ+AOWniehNW+nIao+xlDR2I2QNZ91g7CJGQ7l9jtEfov5guu5wsIk6DlfnKBuO5GO9hMfQepJwIVP5jGB2aYVphqfYVXbIWGwFW0ZeF8JemWatwRAjb+NkwuwYyw5xfpd3mX7LjtuM7/Z/mR8VZ4vbBsBuqZAnW9U1h3GxrdNOkrTvmzfs2djjts0w8ZRljpe7f0Y6cFix4V2CtZxBOglqGr7ETueJBc0jiP8u7/9W2Hb/ua3v8F6t5Mx89GD7bgcl+NyXI7LcTkuD0MMzPiFoIIdVNiay85c5lWOu+0GXu/BIxOtovFuJgEGkZGVBj69SFI4ZNasc8ynAcJ0LjI+mqMTyCHritXB6dlEpDf1wJlm6ksUWBOWwzgOMr5JZnij8M/wp2Oj/Ssj/+PBq7KiAocP32M91/b4mi1Gx3qx6xH5Lj795AMZcH/z8pUYrUv61uivdihJ0EJv/zkHg81x7GnDBvYyKTtAtOUZDXwpG3X8KRbuDWazBO+uMxmMcyAuAz9jti9AkHmv3b7z00LcbHosLqxCzI6BtQZ6UKTqFwG0UJkJoIyLGh6PUI5IV2bugLOIsh3DeESjxtic/S/u4WYNtq99lOEM6SxV1sFiimQWYTFLcDFVJotHRlDBgqOBH/FjyYTjvVFLoVHVBPZCJJ6P2A8llUyT8loM7TXnn5Gmp1LUZ9uN8VcbZFaaIBMLVBZ69F2RgbnI+nSwbs+6XA/j4SOBfPwys9fKgNoXafaaqv8XMJutsKJOqvoOrvNHeDT8p6THcZG3QN6H8OJEzfTVFEm301doixaNE4EiKdZM6cRHRM8cF1hFNLt28MitxbuN4Qfcm74lyOiJPFhYByLv8dB3lHwRXCQITlfqEBUlXQmQtq0YcUfNBsmiRZkkuBkCkXcFFrA2u2UBKHvfyO+Gaen2DTynhSO+dgTIAymyRdcrZu3cB7IK1GOHhX7nKtMz9Fqgy6UwdPwafvgawARu6sGZ7FB7F6ixQCOG3jWyYoPoNMHmOsPN51vMopnIjy/OzqXYcZ0tWu8dNjdK+dGcAYOcmqu0r6v2skgpr0dMXI9TepduwJPHT1jXwfdTkWopWEJQzcpDTXLogXebnGvbdsyd9bAn0kYlWKjtXA76hfHW+jeWff9heyj9eb8l8/ef9gMHRuDjrStvsuvtC0y98Ad18k8/3Lw4nkvbR9oOw3URsI3SgH42wXIWYzmNMI18JK6HgPdIo5L4XmTEel/RY6wdKAAmaDBH15yjKJ9hkz/HJnuGrJ6jqn1J47VyR+mXDnZIi2dz9AddMq8Vf1aZMgHiXp57uvuDAGu8ptPVHE2ZI7vN8PU3L3G9fm8mecx9Mgz47FefoWG6McF7AVpVmswPGEE2bSyyD5dnF/jVLz7BZJaO1yD1GgzlNe5rF5s6xMT3RM5HZndWtQgIwoSxgELSHRFQo2yPVCLxCSCgpfe6gGjGP64TaSYBdw1K4IcJQ7wVu6vxek76HmVBFmYPPyTLjwEwRPn57PaRGkcGfhF4k1APyjWdADt6X6YOll4vPoskuzGMRGhRJgBEnuDcH54bemX5ZM3Rl1UnciiFJOg3cZhwDJSRJ+nJbkdGGyc9KOwnPk+gjcZwDaZ+jXjmIXMC5BvyvIDpYi4Ad55nylh0Y3g9WY4OqqFGDYJzKZJ4Jgb23I5tO3JVByCdLXBxPkND2W3vi3yVz7CyyXG72cENyZCN0VaFYUPGWEwjoGn5lIPvU+bZos87FLsAuyHBZhFjtXBx5VbCWqsqiQESlm7MUAnpAFrxqKVtAZ/nvBZMXhXmHDphavdk0oUJOvHUoxNcI8+EC85kTHzcx0zAjOEU6n3Ha0j/urJ20deUGm+RBD2iNEbZOih3hfjGRWmKmp6lzSAMQVooOE4Fz2kQuiV6NEjTJVp0qKpKaYlmECj/Wg9cu1h8Dbb92XbwsAcclfOyOdODmEkNO2qTJ1DXyjjUjzg+1PvqsF/UrZuNyTe+l+y2fSc3AmnjWNZ2aPst6Tp7796xb/xpOMY4rdvj8aML/M1nn+Hly5f48uvv9DHO+4iS4hcvXvy0Lz4ux+W4HJfjclyOy1/RwoEDgRIrfVKwZs90GAcmZrEghAxmHBdxGCPksIYJmmSvwBcfmCSZSCJTldUi26NEdPAHLD68EiP0mx9e6YAmdNH3NU4msfizvXlzh7ZRQ2cZNRkPNutvYxEga75rnL9NfPx+AGVnKTkTKoCaFM7mywAntoKUoeABLibFmil+BX8hAIYGl5dnSOhp9eU/I8NMpCEsqqz8ZayVbVVyMJbbn0M15LUDOYHDhC3IZDK7hhlsis+NPSwDeLIw8nJE3R2KykORPJLXXAIsslnDSpHDM9shwmXZFLINc53Hz9KESH6ETvDrOaK8iIw0ShjprRZGqfprxZG8p2xqNEzQ6x3MoggRZ/4JnjhMLy3Rtb7M/vebd3j/xkPXTRFOYqTP5wh89TzrPQ/bzsGKssaGMk8P1U6DCsimoh9ZEvdiAl2sM6RprCAOASjmlla1FDecWS+LLbwhA4YthnaCIFwhSCd49e493l/fSLqbDR8YvecMKMKBPq/lWJzLOSDDRY2tWTcSFFKwzdw/AqyqyTfPZDyd4uJkATfbwskyxJM7ePPfoA1OkJX/C4oiQBjNROJJVkIQuZikTDhUOSi92imX8qaRDOOZDjpn+xDAsxXZqOeTORjAYZwe4WhnIEFMgg4oE+vKRs4ZKy2y/uilQ8ZeS2MgV4tzV4zLmZzWA+29yuKcE9z2EfoAmPsDzgKItEsCCMRAh0CEcAnVLJ+gvANJ/STIxlYw+IEkhYoNoDm3LPgZpuCUtRRwfhIo26gnw64UDyfK0MhI2hU7lKWL5XwuPjheQBYHsNuuMdQNvDAQkKDNOpEer06XiKc0sad01JfztLm+wat3b5XrKt5x+zRYsoEecK8s88E2UuOfJkw0YVEG+OUvP0VRF5jPVqP5PQHLplHvLQEwmVJLqbH5u0hTTaWpTFDZC2WGml5Af7ColP3ngCN2WEkevucQJJe2fMDI0L8cHt7Bxg6O++CPI1AsXeFBv3+wP6PX0h6THItmaSMOwwci+CEZifTg0wAUgifCzrQV9SiD1z6HQRUK5OtkSt13wjStKL017VMVZQey//EQbX+l7U+U+WS9sM8iiGxAKZH/ux7KskFeFprY6VD6q+mv9Ggr8hzr7Q67usYqSfDyq28wiRd4f3+Du+2tkRSaXaePaDrB3/+vf4fr62sBW2goXze1CQKwnb/e+3E6wSef/hzzJJVUT8bK8Jz4zg3Wb97h1SYVs//gdI68nyLIeySTCOkkxMAJp75DmiYquUQBp+MEAa0C1AxfCv6e2+N9S4DShReF6k/Vkd3WoqSEtQVismsCspBcAVVKJhiHEXpJwlVmWxi5SEiFE79TPic0bbkuKDN3UfgMP/Fw4fWSSkzQp+4UPPNFHq6gHifSBAwkONcPknrss/3CRUOsjJRnAnsgu5WWEGQc+cgHD+/Zxrc9/F2FvqswDAVch4w3Td8MAhdR6qEJYrzNfTjbFpPQQ5gGqKpcwNE0SRGQtUgAy2vQuvSD9TDzpmiLHuv1Gk5NL7MI54+m8GMXWR9KkEDEl/sO22INioKn86U858jQh+NjMg3huwFE4UkvuL6VbVWFg20XYJvGiOcengcd/K5CUzgooKzb0KQqS1xPRzuDCnleS6Kz+K4FDqYpxxW0zHCRTKZyrdwwFJZ4X/XwhhaR28FnsrofCJP7de/h7aaH97qCV1MCuoM7kDnOSa4aSVBhugTCZIbOP8U2c0VyLSzAwMNucyf98zQGwm4rPnJkwM2cFlUXoAyW8pze7jIJp5LnnyTaWvBM1QHDAZB/2J+Nv5vmof2OakdFFirjFPNFSfHQ6CQTR1d8Zss4TAFkDasxrGH2uQIq7xl0NqxEnm8mPVo/2CZJm/GkWdf0+qZ177tlO6ErvrRixTBIe/7VZz8TcP0Pv/8jakqlTbL6yaM5zh6dHBlsx+W4HJfjclyOy1/zQhkfJaEy2DAgkP0y1YkBevaFmYVldKHMjlKpEIvFibDV0rMYk8kMweAgL7dqCFzV2BQldnmGfH2HKOrw6OmVyELrJiMkJzPpu12Jk9UEkwlTEjMzeDPyxLFotQXMvgTU71oE6WBJzfdtPfeg4jSzkbZIU1bSw1WsZNPO3E8noXit3d7c44dX11hOfJynr8SYXZI+7c7YL7ORPTPsgF1iJoHNUFS/HzIe7HdT/OuuaMqiLS7bIUSDCZIISLsfkdf0R0lGM3TLYLPHqJ+7v2Z6+LaINvso/xhJqGGTyPeO8pEZkijBJIqRJJH4t2ycAdvegc/ksaqCn8zFP6avK5llbzuyBEs0rwq8+SZCPjuDe5oingRYJgNQ0iOoQ4wGc6+DR5kVQvjdgJKlKE2jE0qWPOwoz8lKLE/nAuLUjYumLKUI8aNIcjLouxZHsYA1GWkPXShAbda1WKxmmM8WwkQoOaMv425r8k1wzpwbwWgNS01YnQpy6u/K/jC3ztgS5Do3PS4eX2G+SLG+38DNWXyS3dnL/t5mP0NezZFMVsKgK4oWwSTEjKGxTYWmZOHmiGk5TZTCWItbFroshmlmzTpJzMxrB42vqXz0PWLuW+ipdJrf5f6oG/Ei0/1n0itNr300BK7JNmlrOA6BNhpFR2jdCEHjIM407W3TA9t+wFzACpUdyyka9sAri3t+FtmVVesKwyCMKQ9VNpEtvHgfkQ1CEJDgZBT7wgAjwEaPLF4vMpjW6xI3GV0cEySBi/t1CT8Kkbg9yu07XG8pd/KleJ8upjg7PxGAkrImlVgOuL65wfvr97Jj6oG292gc2RaHTK+f/i6r6dUVr6yTU5ExV12ImOCAyIApK2afZ4INhNljww0OuygL4GqbMx+4/9H+MLb9caf+DXBNy1gxAZe2vQfDHoBP42YOj3N/xx4eu6aK2lXMvpkJh8PFHoZ4cInMMxIQaL5IxAh8tYwxTYMRXFMbSu23LTtEfnapE+ed6qGoGWzRYlPWWBc1tnmJsqIsXD0eubeWMbqfDDj8ZxTB7vvzEXizbdN4jTF5MC/xZnuNZluJb+R2vcV2vRbPqs16h9++/AY//OFLvP3+B5ydPsG7+2usd3emjzaYoCnyf/3rX2tIDEE6MpisRJQdiyn+CZY8fXyFX/7trxDFsUgs6YM4UApYZXj7/Q4/7nSyoOgc1EWDaeDBmU0kpIB+bOI/Sg+t9U6gOXo5SqEvfoss6unVyH7JE5CiKloTQuTJNUDfoJHwDU3g5rSE43fIq14YTgQXxXONbwsYIkNj/lbAOr1w3NcaZe4gH0LcJSHSmYcnbiMyyLr2UA9E4n3xwtM0Z4IYmhxug2N4/tkvSBgNJysMGMp9JjuVDFyeN0l9dbXf6Ql4xT7CIVSPNjKOCU4KIGJYsU2FZVTDnYW4bzwMOYMRAgmxYFo5+7nIjxH0AVyyJNGLbHTwHCwmcwEiLy989B7E85RBBV6v4TnbYoMgmQhT7d37t7L/nGAiE58PCj/yhEU21IWEDmyzAFs3QbZMcL708MxjIEeNsvRRUfJrWGtyjng16d3YtsIMI6DMMAQC84PD50MuMuYJ7QEos/Xpn0eJJlOfQ/G6bSgfNv5sZG4vXAeLxEN1EiAPY/hlIIb9PFsE5nYNkG8ZrLCG724wifmsibHZtmjLGrPFEr4XomXwD20oog6T4D18Z4dw8BGVHYLaQThj2EupfbjpVyRgnB3EOEE4jH2HHWVI2zRsfulLTNcngNqBLyaPhX9oaWSnA5iD8Zmlx5nJi7Fv2o9XH/YFdhhk2Lhja7Z9ou0/dE/lNyuVt32m2Q7v4ydPrvA3n32K715+j6+//k48U7l2mgT44MUMs1Od5Dky2I7LcTkux+W4HJe/woWDWwHWREOis/zmh1FG+HDZA1IjDEQz9SFEGMxxGp7AbQM4YYPZskKZrYXdlA30tGlQU+5CM2r67USRgCJpDKSLKRAt8fbNDfJNJrIIoh9BMODiYimmy2/e3cJzOZOpAzQWMYbbZgZDe1nf6K/GV1joa3wYRZw6UJIBvvHTMkCUsnH0qLS2NtvjzKjT48UHT2S28tuXbyRNTIpUSfpqcBLdY+Jv8e39HHCnUhDxs0W6aph141yuOa+WKSeDSsMYPDjF6qO2H5aqG5speiVsQsyvDw4THRbeHZo8R44LOPFEQR/zbmXIKdj40Plkz2KTT2TK4wgwsRhxxYtmdXKCKCAzKZHt1g7DKgZkeY6grTFJl7K9Jt+gJ1DU51iexBjyNfIfU2T5FPjZOWaXAbymgxewOKLXsgM/b+C0ZBb0IouMCKw6rhhli8lxmQnLIqRkBzX6toHnOwgiD30QoyhYmFVwhGWXiNl4W5USLEBZaJ71kl7aJT5WPqGbAbd3Gb78/BsBBcn6IxZHcpYct6hQ9PxbZoxKXa1MVEE3YfiZ80k56NXVKd7n99jWHVY05C9cpD6QeQVuuwDp6lSuQZbVwCTEydRB0lFq1Alzi/5AHgvGOEacMNXQQel5iFlomyvJwTylsSxaafpNg3O5diz0B0dZbGShDDTW7tT8m0GloSYC2hsmYwpe1iKoGvReK8w4ggbsDxZeiH7nIPd8JCtfvAZvhh6LyMWcYJ/jjWbctqhhkVTT2JshFGgNUKNMQK4vZTNx21bszPUeIrDHkI6uFnn5fdZi8CKU242AflcXc5b2IlEjS4HbLKoMP17f4oPLx5JiTJkOC2UWmXme4/rmvQC7ej5sEizPh7IVx1YnleBPAO8RDDuUaA/41S9/hrxtcDJfjewHCTZgwIaw2AhWasAB91N9qrR8VDDO9CtGgqiSQdN5EsBWaq6eq31Nuu8LzPSBtVC0/44InFlP60Pbb9vC0HD1DkF26ZDMzwcF8cG7xs/k/njS7n1Jm2UfEIa+MKlEhiVfe4nmg3MqL+lvBKEk5bOh/yHPHYECbUsaLmP6RitBHvf18JAsYKafbYvewyKY7ZQTRgRcKfsc5boG+CSQ9j/+3y8QXPjwZw5Otj7KKkeYxjh5do7/+o//F55cPcf55RX++NXvBDA7hBoFwh56nJws8Xd///d48/qNHEOe5SjKUuWVJvhiuVzgZz//BWZJKP01O4/OqdAVG9zcDnibK8AY0dzeI1uHJxvwZzOcnS7gM9igpCS6FEApnU3l4Mtyi3kaw59OJDk4cHfibdlWkTCt6OlF4INMMu3DKRXsUXQ9gqaXZNJqoHQ3HlN3yWgNpiEiSjLZrosdfLKj/ABl4aLoAuzI+pu6eOz3CJgySQ/LLsBAK4iAwJq5EyhZ5b43DYqqRdewzfC5OyAkIBX6kqZM0JOd7WDSRCkZZV/jderV6Af03fPROQE2g4M1Uzk3Heo8h9PkCMlmozSVKD8nEJg4PXGx9WfYbV2EVYdkTl49UOYbuRfTeCLnpnZadJTmOsDCDUSuPoCTZL74VZZb+qn6SCczVATP6kqCZRz2lfWAxckcic8Jhg5DVeL+vseuDZFPYsQrDx+4Lby2RF06KIeQJnOIQ1fYdwo+kk2o56hpWxR1LX0IHyYVP6urMZ8tJWBK2HpyT+sECQHJsmrkvIikl7JZ+qVxDwM+W5lcECJDgO85uXTXIb0tUTQMg9mhyDIMVYW5n+P8Yot0kcBPnqNw5ugLF4t5In05n6PFbo3AH5AGd0jqW4RtCqeaoNp6KHwP9SlTSTcawMHLOUrRYUc3po/T/lWBtXGQI2xL8QYVgI0sWPrzdujdUJjrtuFJ32nYaQJASlIzwW39nexI6beF5WYCimR9sknVHkC/K9tNe3ZlwekkiOmZ+cyyPxM4NY8MpnrTtuJv//ZXKIsCv/uXz8W7VY7GGXD1KMbZKXmplUxaOc70yGA7LsfluByX43Jc/poWKwelWbwWwVrkSAlmWQIHRY4Mk+yM4GGx5jlY/ewZgi7FqpvD70IMQY/eH5CHHbbTAlnp4v6+EDnedMbUwymSKRlMoczE09C42LRod2s8Pl8gXayQbTP0Zqb2/n4rBfnTp4+kgKEcS/zZbKF6UM7ZwnV8RRgUBkwzYIk1/7fHKQCKfbfxArHbpV/NxfkSVxdn+O7717hb52KmbMtIPQ8uijZC1kR4vtrAwwZF6TNf7mBbezacVbLafbTlqD2ag4Mxxaleg/E97sNABAsE0Gur6icIOLvuX6MrdmidRI7XFufyDluJm69xMGxCQq2EVn2rKL87xepkiSROxAuIgpUCZCW22F7fSsJaMl2iLCjJKRAEMSbzEKn7Em//9Z+wu54gb5aIP1zh/NLHlKAkTf49F1HgIGFx5dKTjLPxHrw0QhS4AqqQy7be5AiHAKtJKAyMpqjQcNafyqe2h9/XSNIBvR+jLljE08A5QBBNsNtRUtSLVx11PJGjvk9keqSpj6dPr5C3PfLNbrwnCKAJeEQAjVIzsZFSQJMMSy4EB+Xu4QDeC3D15ClmsxDX+QYFGSJDiKQNELQO3nYV6mSByfIEu3WJuwZITyNcJDW8aodC5KAskhUYrjqyEGM0NDGPPEw8pn4SsNSbiHAGwT0W0cJEERbEIMwG8tiYDlj5PoqW7D9HzK5BZgiLidFvr0fkOEjTAI3joyejTfz/BgTxBIQ6EfZYTn0M9wVudw7uXQ9vmFrYdZhwH3j44nlnWo8cg/oJ0XeJvm9kwXHfuI9yn9PvrdHURwLIvoTTOri5z0UunqRTVLtSmHTT5USM1X0jB5Lbt6cHXYjlbCVoKK8ZmSpt3eLt23fY7e4NOGZZZAYkP2SH7bE1A8zsgRzTq5l+TtlvJ8s5Tk5n6BEoe80wkyhhFAYb70VhB2mKq7YbW7TZpqX7L+C2KTLHnTGfOvYU+yZ/2ExNv6s/jf2XDWl40Gdru92D8wcMVvPSvgDe74Nlw1G2S+n3lOm0MxaNCc7mkRqrBxECjzYCHhzq4jhhgYO+1XBmCRwwgTPLcuy2Oe7vNtIWq4pgAjlYJoTFehqZfvnBQZi+efy7mfRRFiXbowYTUK5NFieBYd4L/BLAtyMI2qLhdTHrShtxgP/+u9+g+fef4b5/iQ8XV7jb3uDs5FRSRc/PrwQo+OLr3+9vFPOv3lP6TPm7v/877HY7Aaj4BwFFjBcfAZOPPnmOn//iFyKHJHhE306v36C/+7/x+v0Ctc/UXQdNpG2JwHtvglvOFjFOprEwUQkU9kGIsgW2my3aocV0tkTd9rgjoBf5SB1NQBUfu3ZA2XByioE3/KI01kXlunjPoISKExEMTwh1n5kMGUZIYk9CZWDOc1m0qEsXVcvQiRjraYjTiYNL8REj48pF7URwmPwaUu7IZwzBjE6kpjwHBFM5eSDyVRuOYxuCmXTSYBeV9pLRxkmSlow29h0ML5WQhA6J62DqOyhipqTSZzESdjS7NwJmrsu254gMM+0KLGcdiihBsSXy2Mm4w6X0NN+KjDzxIjitTq15nloN8J5uiwJlliOdzIWhWeZrAf38NMIqZdJtiuk8Qblbw6FUnxLStYs7J8XuJMazpYOroUJfEVwMUDMhWtoOmYN6jjhBRCko24OkXZOxyf6Ez1ZuN+glIZWMQp4rSY42oUME58gK5YQJAc26rkTayShonrOupXetmCaIRcAp/fwmLm6njC2I5L/O9bDuHdzkHt68CzFkNO/f4HR+IaqCG1oz7DiJxfCGhbAEs9JDH6/QD2S/NTIO8gsH3ZsS/jRBOOP9VI/9nyO3kkmMlQ5G+z1DSlVgXgdco/SabGaRfPLayCSobX57dYH2bZq2Lux6CSfZ+8qOvqhjV2q2Pfa5/FknBWzPOvb5pp/cM4HVH5OE8A+eX+Gzz36OL776Cp9//VL2n335ZOLh46cTLCIeawHfLeV+paXEkcF2XI7LcTkux+W4/JUsnN1nUWIHHBYkkqGLpP3penbQsR+u7GfxbdFB36uibfHZf/oPqG5ruLcc+AFlssEG7yRFNPVmyN53SF0XIZMC/YkYGTNqfWgHNJmmOopvUddjsZwgPT/HmoXZ/Z0UsEpQa/Do6kykmvd3O/lsoz97sIx1qwENyU6S4kx8qtRj7M8Vb/Jew9wiQBAHPh5fnEpy1LubjR61rbDMB3Gg15tZ0I5+V12HRbjDPNpgm8e4qxbo6TMlQALfZPzjxoRTLYBlyCiFm14UHeQZ6Ex2zQgnuBETXmAHgnYAKUChYXBwuzNvC6faoMAEtb+gmMWAbfYTbNVotiOjUT2fPJ7JbILT0zP1/fE9meEve4iMKb+9o6EO5qsTMdcuswx+GGKeOoid71C+fYUfXiZ4V57g6skEwAVABgAAIABJREFUSQhMlyvMlitsfQfLiOAQQReMJRYLSA7OmY7GgrPc3gqTLEgWyEEQBWjLDh39eOocbtDB9XUAH7oOosTHECbYVWRLVgJE0SdFmFVFjjgOENEnkOAAU8EAFB6vW492XeKHH37E7v5OmHFyHsWyT+4aAx50yHsXU59eX/TbGrA8v8DpaoG63gnDqZbthggbHx5ZauGAdLVCWw24LRoEyxiPZwPStkRTtsISEH+xmoWnK5Lfll5IqYdFQJv/1kiI1JdI/W4auNJ+1VtMmDkOJbQDnLZB4NdwAw+dF2LTeciLAV7ZwOlYFHXC0mMhS58sT9JLPTEP3+UVqrIRORmLO5++gmQmOgP8HMhaD+8CYEhrXJQD2jTBLFXQUuok2b7esw1NuH1lWjgE28h03DRIqwbxihF73GcyY1pkdQ8vTNDWHfK8gRd7mBOIpxyKxSWPryUriE1PWZy9BKgoY4aeSG/evEFRkomo6JlN8dT3WEbDAdBmcCf5+aDw0gqO5eF+/Z9/+jG8qEcYLEQeZqWhBPrpv0YggV+SRHuQIKpWkQqsaXqm+Rjz931723dgKtE3va19eSz2DjzQLOnMNOLDLlCb8P495tXxZ8vSJUhGEIbMo9Bnfe4jiRnUogxWFrBadfKThNppvrT9SIFMwLvrUTOZlww1pvPWjQFETXlr/NHGIvmggNX91f3X4zlkrxkg0X6ntNBTVpowStkGzLWUdErjmzeeV3PU8pqwU8mYZRCHi3/8x/+CJorw4aPHAtpenJ7h5Ix+VAU+//xfcXN7s5/4MNdIt6VMvJ998gk++uQjvHt/LcwiytLJ5M2LHLPZHD/7+AXmMzKItfinuXyf32JzXeOOSTCBspGEYeykKL0FoqBHXZfCqL1YMvEyQTtQjqwSdpKUbvIOeVaIbJQelFEUoW1KRL6DOaV+BDYl9AHSH5Kww0KfDM93dYOw6RF7DD3phS1FKXo6CcQLTKSZfCYzuRUOduscNQF6YdO6WLpkEDfKWuvVa433j8g8paFp+IF4ENLLTYDGDi3d9g3Iq84DGqREvz4C8gSHPDKzaOYvjCVlNSkpq4fbMj+zE69OrscJjWrwcN8BVd6jzxs0THcc6G7WyESFZRinnFdJU2zLSPzWQs+V0IbYrRG4PrIdj3cAiWucLCCwRvAtSqfoqgpNXcrnzVIXbu+i8ZmmylENLRBqrO9KFK2LKp4hPAlw6bcIxJPRlZAGNixOItlzJPLOjiEwbCsKxJIhyfuXYGfTUA5vYEc+G5xQkrl5rhS+phTeFRVAGNJHzxeGH4HMnteZTDxOeNSd+MExPIbjMa7TuCHeDi7utgM4y1NlBX7cbdHcbvFk6uLqcYLN7Q2myQbzsyka7xy7OgUaV6w62I4LsgCHFvHQIqxquFkPp/Clv994DYKLCYouF/uFjgxKsQnQfgDjs95O5JKWbCZn+lrSvz0vFl9Q66Mr4xxjhKv9Jxu7TnyIz6C0ee1z5TloJ2OE3WaZq8pmFiWCYbhxM+qFafpc6awtW00jU8Rjs2sxnST45KNnss0vvvhGbE5U9TDg9DTAxSxAQB9Tr4ATbAG/ED8/uIsjwHZcjstxOS7H5bj8pS9k4XCmf6xfTNFlCxgtpvZV2QF5avxBZV97CoTbB3j++IWkYX318ivMfnGCbsiRra+xiJdwhgD1ekCTu5iEM4RhhzSkrEtTsvqaM7kcXLEo46jHkzEXB9KrxRThyRmur2+xvqU8lPvXMVMOj68uUNUdXr1+r6CYQdVUGapTkfqNBaP7EGDjH4QFZos4Ozuqx8+B1yV9nXwfP756KywcDUcwvJixmjWFtJUgmYEeB9IEBS/SDImf4d0uRtEt5LPtwM6eZysNG/dGZBJ7jyh7lSyIZtQW42sWZFOvK3PcikHIO72hx9y/g9NssetXGILFOOOr2+RO7PVhUnj7AS7OzzBJpphQDuox5K/H1nGwzipkr2+xWq4QT1Js7m/FNHu5TDGLbuFmv8HrL3p8f/cYxewMF0+WOE1jMdDeMbxhAjyfOIik2OCQllIKU3lJceWgyXfId1sk01MB9gjEEkjrnAjvBhebfECya+GWGfyBg1k1F/ZZsNHgOg7QhxG2O0dkPvTnitM5ur5Fle+wmE8w8WL6PSPzXHzh85gHPCPQdp/j5csfMJQ7ARroDaZ3jnqQSbIbZajxHBdXV/D6Alleyj3bug5qAwR6mxLzkxXCNMX9TY5dEuLxuYtzbNDkA6qe8CL3eZCvsgrRegmaqY9JrMUsATH6DTW9J75mbBNkh1GqxIKTIAhBPgpqwiRGz2RS0jnKFuHQIIpa8War3BjX9KrbdfAr2UO4lC/5EMlLSL86AgfFPaoB2NYJmpzrdJL8yIJzaCoByN1ywC4qENU+3iFGMHPx1G9EMt2QyEN5nNxcNB+PBJzI+w5f74DTmwbnTLF7eo3GeYS7e55fsiJpLl+yNEY89RGzmHZqeCEBulBSScmGqmvqcBO4nZGZSVfE+0gLrdvr97i9V68s/s/XDlNhtQDbs9u0LZrGTJDHFP82mZh/WUym+Pjjp9jWDZaT+WikTfkfQRUWtq0F2AzYaQE2lakqSHfIqNN+w/So447sma72Zdsl6U/7/RSs4gB4OpSUat+nax+CTQpqUBLoI448AbxJepHCX/TQ6uU1GiAJM24Pcuk+aeojEw7pkWZTJ21wxEN23f53+XxzQPvjMYl85n1j/2beL+wPsulomO+RYcR9NPIwsijNOdQgAXvse1jRbo/feZzD0ICYL/efIvP//f/4fwQwj4NEkwCfPMHd3R3u2J8JIGT8K+38jfkYAiHL5UqCDd68eat9L0NX8kK8Qj98/hir03OBI2nWL/LX/iuUd9/g1fVHyBlcwpAUYe7x2CgnnGMy6+AVWxStj7wJEHcdTqYe3DjAQIappKvqs6ccgNtth2xLZm8tEyFkok5CtRogm1MAyzDEwEbJ0AB5PvnCgqIkUXw8GUQSc6JD+zm5bzv2CxwjdLjPepF+puw/hxY9QdTWQ0ugn6CsZ9MvLXDEdtGNQDNDZAitK7hsJHki+TeTXqZn5fOZ15hgHaWN0ucKwuuJ5J1AGwEpt+uFkeUH9I9Tz8bd4OCuceBlPWoGBFQZhr6AP3QmjEaZccnEQZ8uMLQ+pn6p81xuiG1GphczqWuRspJBy2vDkBzKFoM0wtLvUNY+BjL1fJ7jFi3TXTMPGy9GNQtxGTUIiw1Ch+BfjNbzEEWeBCjL01bAR5Xikvla1/Ts03PDfNQsoyRen8sEKNVawtEU9jAQawxh7Q8a0iSJmkxfNgC5HwQCTtYEOHmmvcj0xy2CvlM/vYhBCBEaJ8Arstd2QHxXIfUyAW3/+NW1jMXmboGrywyrkwjR9ARtcI5dEcNtOemWypiFLDtGvKfs5m4ykSd3Hhn0LkqnxWQZoBkabHZb2U9t6RZyt+xXvS+bphD/ziSeyqyW6U3MJKBNsN9POPDetb5t2g+YoAMDqkkfTS9ME2pgA2kUlFMJqCDP5mdtV+Z16Uz5GgcnA549ucKTJxf4+pvv8MPrd9pXDj2SwMGTkwTTjn1TCUQ7INpg8OnrR8obQe3VUSJ6XI7LcTkux+W4/KWz1kQ6Y4YvAjQd0OpHgEl+Md9sMWRfPwBl5PtAFoyPoavxhz/8Edkmw2o4R7yaIT5bIWei2hvAaVJM4iXydYHivkBRroVFQLlfX3VoOYNrADLx0AocRAE1NyX63RazkzlWF5fY3W9VguO4uL1bixHyxx+/EMYE2QOaNmoGczYB0xR3UtDYYvGg+FNwSr9LCeIBn3z4DPfrHV6/vZGBrfVKs75swmgQbzMtY9VE3RS0ZmDIz8vaEFkd4WpaYBnf427HqWQdMMpY2QJ09pyLXZuyCHqPYhFT7RomCQvIsbC0QQfyaQeF+biu2aTjoewTDG6Cub/D0KzRIFF5nZGwKWhKkKLHbL7A5dWVyPAmEQfTUK+1bsD16xvUN1tcPX0qheb1m2vAjXB57mGK36J49Vt8/tslvi8/gPfBY7x4usAyCNGECbJVgIulj2dhi3ZzjWxTA8FMwCGeEwKSdNerizV2mwKT1QWcMEIrRtM2BY8hCD2mkY/r2EfNpLdM2V/kbLT0wpFj8eD0HlIWONMEu5IA70YYL+lsid0uR15nSJjOVzH9zcEb18Et/YFi4NPzE8BLsLm/lwJS7iODg/KT0pNHePH0AqUAgaSjkF2mIFi9KxH2Dk6vLtF1Ln58lcO5SvHzsxbT8j2y6wI1InhkQbgDutpB0SaowwT5IsBFDCyooWTgQeMKU0TZWp4ABXRT0hQ7LdAYlMDrLGwGmmB7TPCkOMhDywvXdAidGjMyz2IfW0qhGlekR2SPUq7EAo13E+/5ctchTXxgMcW2pVl4IYlyUZLSVQ2N22IRe/CIKMYRThIHkZdJwiGDTZyAQBtZcmS2UHpOhqCLvnMR1APmbgeWZjeZhyBeSFDD9qaGO4kxPQ0xo5cSfaoqilTJZKT/XoWyHIQREoOsFF+KRjGRZx8irFQX0/kU09kUWUm/pMbc11rUW89Bg1HsGREjjm1LwLH7k2Lt6tGFMEpcN5FzqzI8BdDVc60zDBR93X6egnf2U0wDN3JV/e3gdfvqsMe6bZ9w2PPab3pYpv0fVJ5jP2ImU8IoEBk0g1hWU8rbXEx8D7FDaVkCz0sBN5YkW3oGMRURDNeQSQjeaUzmbZEVNdbbBrf3Fe43JfKsEsaayo0PpZtmIuNQ9mnAf5V1qrTTykJlvsT8TCAtjkL5SqIYUcjwDkIfej4ZJDEmBeqJ1XNr+uSR7Tdy9/RJwO0QZGnRqBG5sIJcfPnl1wJiNGRk9Q1u725QlNmDsz2y7Cy4NtDrK8B//t/+MzabNcqyEpuF1hjU8z74+KNnwqzkxA732alvsf4hw4+7S5QM5nAVpHe6GbrpCSYzH6dxhbj8/7C7jzE0NSZknnECoPMFKHKd2hB61I/KGwbM2O4mkciqV1MPE1LQRA7Krlx0hdIf9WjwdgDCpkFM2Rr7B4L1AYMomPSpYIWMBnhf1zTKd0WmzuChqdsg4rmridsH6AKOIzxElM9LYraa9BNUExYjAX8DEFESqsBHNzKHhCikAw97BxuWkQLiNnlVOM3se10Iy43gU+e5wvjtW4KWPC8NIrdH6nsYKLUNfPGC7Z1A2JQMC6AvBX20GKEzSxIBCrXRa6J4zjYsh+4gnc2FsVsVO8bEYLF0Me0qbKsQThIiZABPV8vkw7qIcB/GiE59fMAQgKHC0IbYFGp3MJkE4nup54gedDyH9B4kW5/ych5fj7rNkFc54jQSBt0IvEnAB5OeB53okRTn8cZU1iZBJEr0DSjE5zkZnmL70VOiOEh/TLktpbQit6WFAIMQPBcLMuX8HndM+G4SOHGMYvCQVR7uNxGyHZ8idwi8d5hHDhwyAbf0mGwxmc3hugEKMi5nERyG7NQ1mqFDmXe4vrmG07V49OgRyrpCxbaggx6VdnK/nQ5VuYHnR4iTdOyP7XHannEch8qYh/fv4SSiXd0A6mNfftBzmrGePOWMPMMMefYetuMTgEuPOHAlxIABLv/029/jbpvLWJBjpEfTBE+TOcK1ixAF/HgDN7oDglLmKRRd5yTxUSJ6XI7LcTkux+W4/EUuUmiZ1DtbNNjCzEAxDwqzw0HLvryz73nw2wEbgUWVh2eXL9BmOf741bdo3BKLv7lCv0wQfeeie09fCprytvCXCfyQJskuXKYOdo0UyRxEh/4gs9QhBz4cm9ZA1TloQh+rD54IKPfd11/JAI0rDEOL89UKj64u8c23r7HZ5Qg4sDHea5bZZUMNZBCmDv5aCI77Dzx7+gh1WeP162s4jMAbB3wG1BqL4v1svBbcCnyNwQHW3Fx+1oIwdQs8nq2xKQe8361k4GttduUTWExY2ZjsNA/ezlhr1U2DaLlalB2JrNOCiIcBCcrS02M+YJGIJAyIhwKp8x7bykcfXUpRRoAwjBJcXT2RdEayF+quFpZVGE+FKfH2+hrnl08QxRFef/cavRfi8aMYK+8lqve/x3dfhni9fYLu4hyPP5zh3I/Q9TF2yxgnKxdPnFb8aigvavpAZrrrpkSc+JiIz02GYrdBFNIzzoUfxwijkDwtkT62RioUUPJCBoPnY+tEeNW4KN81SDdkLeSIUsobPfhpCi+eoG4GYXNVbo+72xp+WyCaTuGHiQBkBHDmsym+ywf8SFZERI+vCh+gwXkX44dXt7h/81qwh3gyw/MPnqJvctytC7i8Nrx3WPi16qezPD+H70R4/2aLYpbgxRMHZ/13yO8C7HYQcC2dRfAHD00fonYj1IsQSQJcOpRx1gK6SYFLU2syReReFmMrSWfNsgIVaR2mDQSRLxIekQsJQKISLwYJNhVZaw3igNIjoPNj3A8hbooBcd5I8uvMb5HEA95s6J/jYjJNME0o5XZwmzuSSOi2JfzQFaBN/I66Fq/mU3xALG7YsYZEUTFJ0EESKttT0ldD3rE+3g8u6vsSXX6PeLKQ/uL+tsY6jnG18nAR9vDECFuBqPubnTJdmCpMLyayNOJAQNPYI6g2iOk0mTL0nBNTaWmTlG922GQF3r97J8AHr5H6WB+EDZjWapr3nyxcl9KsX/38Q+yaBovpUpk6ZFywkDTBBjQBJ6BAmSQL4lGWZFlsBmyT3mAE3vbQ256VYb6PfeyDvRkLyIMuY1yL7C6CpJyUCKAJjrw3CfoOTiQAmlGWK2Bsw1HYn1CaRzAIBIlaVJS3kWHTGAbgCJZp36LpfwdsM/ssEKbJHp5UmbqZjDHrOweTPSpNDQyjmLJLc+6MTGtf9NoJBdu7GiDUPLRGaNFQAu3eMPgjDEJjB9CibCtUPLmdgwAe/sv/+V/NNqxczPbxunGVYpttcwsD4WUX//AP/yDX/ObmFnEUmXCDEkVRoOtq/Id//2vEIbfFCRIfN9cN3t2ruX7n5ZL66Q8n8B4v8Tjawt2t0TLJNHOEPcq+JEkSBKtL5PSLZChQ14jUL0wGDD7ZbIHI43TySAMY9DxLdAiaroY3eLKtjCb1jYNTFIh9hpjQjy6URGP6VBJIZZvns4IAUFk5qJlyGToiJ6VknPcOmWyUcgpoNLLWCDCTkTVo4qvIo1VyqWxuw2Qj41DiYJWpSamuSEL5TDZtXMETvbr2fmZwgYQ0kGrLe1kCXmi8T29Ujh8YmNSCikJ4BJIC7HoHd6T43TeSLj10Gc7Op1ikBDzVu0ySul1gV7TY5A3CIBIGWFMX4lkZpiGWfoZsw3EH07I9kZ4SWCvqEDs3QbMI8DgZMOtKeaaR4daSbRb5kija1SX6thS/NrLWCJzRBoP7zb6rHRrstrfiQ+sz3KbthBVaM22V4LUJ1ghiAs+eymgpjRZprfbxjh0bDCoblfRWYbNxLKXyfMlMkGAoV/aT3nkEChlAxHYRzU+wRYBXnNNZ98C6wcv7DV6v7xFlW6R1hpN4g8vLEvPVFPH0KTbuI2RbB/PARTJLUVW5PEv5+CzWOdavX2N5uoKPRENmPCBa+LjZ3KNryJwlcF4KeM9nqkXL7B0gAOLYkvW+1slT639hFtM+LXNNrQDU49ICj3pPGubyOF4zUlEDEI9/Fx/TBk+fnODZ08f48qtv8fbtjbDR2N4Cp8dVmiDYatuIowrB4g6Y3GGIGvScxOKw0Qfy3McXf5gcGWzH5bgcl+NyXI7LX9IyhhhwdldMcZVdoF+Wsn/A6DLvU1nMIb/C/myKJKmhzLvH7WlBtNndiY8a/Yk++9Wv8Tha4eXvvkb7pEI3a+C1DsJVKsUCZ1gbDkxloBKIHCwOPCQe4+s1yZKDpIYDv3ZAxRTD6xsZX734+COJpy+2mcgN8qrG9ft3eHZ1jtOzFTbbnQBx9Jqy/lkGjTLF3kHB13eYzxM8vjrHy+9fY7stVBLHvx2yIqz8yJIm9qWdOY9aNGsNYd+oBSfXJ6h0k8cIXA9Xkxv1KupZDo/6ViMT27/P1OEjHGB+PdiH/WBzLDgNI06um3mvdV1jMdmSlTJMkYY9ovYNqsbF5dOPcX5+jiQwckHfk/RIzrq///6NMLEunz7Ddpvhx5e3mF/M8eFFiaT8H3j9h+/xuy8u8Sr4CNOPHuGjyxmmfYQdk9quYnw4HXA2FBjqWkyxKzAEI0AUe5ilIdy+wvWrL3Fzt8V0shRwhIAa8U0WDZ6YritASiYU/YU4E0+T5cRtcEaztnmA6yREW4fo6TfWdQiDHmkSyj1VktHWQpgeRRij3Obo60LkQL4X4H6zxiOmi3quAKAlfNy7A9Yo8WI5wcnyApM4xeX5Avf3axQlzyKLBDVZzkuCVzFOLy5RbRp8v2sRvpji0+UN4vV7bO48bDJfUviGMMaABL2foksTlEsfz6MBy6HEIDLIQM6RE9IvTsE1yaKVxDmVJdLfhuwMYYSItNamwFrbZgVQKOFiwcXAg6r10FcO/KHE1GuwiHxsKT+Dj7p1kYvKh35wDB5J1WycPk++g3gaoiYrpNbCUeRJYYygLEByYUq2U8mkVuCeDCHPRVeymGNQhBb979dbuHWJyWwl4RivdgNwkeKTlYsVgR7BjZWhwBs3qzt0fog2DnGXBliEDmaJj0gKfMpnldFEKSEZeWSzSoiDpHuSpeJgtToRoGCzzQ0Gs2etaZvZ+3NZBq1te1zn0ekp0imlV6kUr/Kenv5SKgsV5u2BLEmZrPsvZZaYNm2QM9Oy9+DUwxmNfb86rneY96tgGNmMZB+lgYdpGCDmdR58DG2Mjh5+Q4jOCdG7kbDQZD/Yf1GyGFCCTyZQj13VYZOXws6435bIawusCfqmUj0TJmBZapqoS78sBUis1xXZk/Z3Aih8L7+HbOtk0iWJJBHzSyZAhLVKGaE5fxZ4POhz9fwdXLCDU6Xn6JAVuH+QEUAU9puY++smWym+GQTgoK87fP3tt/vN2ctu+tVDcE363r6XNMn/9B//o/RD1+9uhCkUGPYamWzCsBt6PH1yJRJ7Mo7Y29HvazpbKKOKsvbwDMurGM+Df8Jw+w53t+xzgJLPTQFlPTi+h9UswDT2UBD4AT3ePAxkPTGkQZT09hlswQl9re4GAcTJ0pMk7g6IyQLzenherY8+oYtp4q0kbPOadh2uKf9MPJwRrJXbjVMtroBrDCNi4III+Hr6rDEFthMGrZjzE8ggw9rVxG0CjJZxKEyrA3aawMX2YSrY2sPry93jM8CgJaZf0+tMcpY8D9iviHckdb/KzGL6ZMwghNBDRW9Iz8flKkIc+miCSH3MBp2XuFnn6Hp6WvJjyRprMDA8ZQHEVYl17qMPyabs4VcV8nsga1LcpqmkKn8UNgiaAmVJhngIN+a6LiKRhHK8pZ3K/d29sFwp5df7vEde7lBWW5H2cpxDLzZh/9GTjYEH7PskPMb2UebEyL1+wNo0dhHSDAwDkB54BD7F85U+m5J0zdWZLEofVRfbrNSwA54TNIidXoIQgtRFOeVzMMYyTFD4DtqyR7ZLcHMzkcka13uDifse81mIYoiQb8jiDCQQgt64TgAsLk51P4ZBEk8JChbbEqvVAukkRlFu5D4N0+nI9rVjJz1Oc6zSZ+szVsasth8y50Ptd/eTvzq0O+wk9MsqFMZBn6yok63ChjOBKLx+f/Prj2QC4De//QLbXa1+cAOHGCHO2KdmPYK+RczrP9nAje/hxPRaVfIvJ01ffhvj62+mNDo4AmzH5bgcl+NyXI7LX8rCAQO9lSzR4EGC5r5yGwcjtr74KdNgP6ds1jODEzuQcQ5GNjobTSlOh3QWC4Piy89fosy2+HjyMyBusX6kaaDY0ayeAxdlGlDtxYFWGNCPigNmzlAPqFsHFY2OhR1BaY+Homhwd3OP1STG+dUVmqFFmZdwnEDSRtsyx4fPnyBNI0mws5Kg0bvMmLBz4E8pxYfPr5BXBd69v1V40aR+KlND1hxZJuPQzRTj+7On0k6RPtj3GqNcjKwZHdSVXYBdM8E0aLEK1qhazmZzRtpux7DVZIw57Mebh9dMiQD7IsWspSQOOxzXRFTZF7sfI6hAw/oQ8/MPcfnkORbLlXoxEYhxHJA7dPPmHtu7AqePnwl49Pq7azA24NkzFxfu77D9+nP8yx9S/H7zIbznz/DxB0s8YmIbDbsvUlydBXjqlYjaCk01oGxDdEEIn95ZPkziXCvsCD+MgDJDcfdWTOzpJTMwYVIuuymsHLIZCLR5aDgzT8BICit6xnQ4izy0cx/3UYym8OHXHZKglMACkfZ5nDP3xTMm+f/Ze7MlOZIsS+zYvvkWOxDYc6+aYVc/k2wpCoX8L34V3/jAN8qQIxyyq7q6OqsyE0gkgFh9NbfdjHLuVXV3ZPMHcsQNEogIDwsPdzVVNb1HzzIiYOSjXG0oEkM6GkuhONQFrkMH08HDqnawcQN8Qo0s6MHl8nyRaxE+KOuiaGppy9OzK3j0h7srsZ5F+Oq6wHVzi/K+xXwbYFsGImftwxR+NkKUJQgmPsapgyu3gcs2qh2UBEb8AAGZYj6hY5UX9ZRFi3k8vYAalG2LnkWsFLPiciTXWT3HtN/YOoJjnu3N4qpyaYbtkUYnQNuJ34l3YhEF6H3jLZO6SEdkPTmoylauB93ixmT2xSGa3hf5ZUt2BgF8KYZ7hDQgzyv0Wxdu4MCl1Kyp4IalADYefeT6AI83NVYnCd6chXju94gogzJziTBjKFmjAfvgIEzIWHPxhIbkjjIIeArlU2RmdEzzJZDju1gzPa+iLKwVKSBB+8CnnDTD/f1cCts9gL0bMXv4ao98yThiv/zyzTNUfY8sSU2xN0g6Io2vWTSrRMswdAR4MAPVpoeaueRw/O7mV/tC7Bxq5ln7lcx3LHoJoNEHi0m9foLQi+E4EYY+RNsnaLoQzRBJMWdmHGXvMmWWdCOP0ukGZVNhW1dY52RLUZYkSqa1AAAgAElEQVRWCltt559m5J0yvxx8/WtwTfwsZa73do+J/FNYRwEigto0xY8ixEGAkCxMniNkESPxJMJhit7dPci0ly2KLWi0azATZuP8up12l41BGNo/2PsJvhAElKTboRfGJ5lCTKzla/jhx592Nz62gTyfYTQfAnuUhPmBjz/+8Y+SBnp7cy/9je+Rz1OV3DhQQ3eOnyfPriWRkjQWeqcJk3PoMR0nSCZT+DEwKd9ic9fgdpOhaMheMl6KNIljy/oEarjZ1GNEiWDkYRtRnuYhljAAzoURSgLdJhNDXktOFhENIEPzntj3OnhDh26gcTzBYnNP6SjOryVtUoJE6AcXepi5vQYWqBhPJZqeKz6RvKdp4IqVp6vfmjCAjHepgGsWeDasRAHyDIApI8VcI/1ff7ADjswHH+V81or/vGEomh7OrkBAl0Ab2UUNpeudJ/2KQDvnzbhnmAO/Vy0gvUh5t9jkJdZ5hTibKPjPMUDp+cjHxKtQbVrkfQAvGJA4Her1gEWdYBllqM9ivMp0w4jAE73ymO5KP0h6s+l8rQmhZAOS1UfAVJlrlaRvb6u5sNICzrkCqhHU1s1GMrrkXGFfab9U7Mlsltl2MEC+yEaFmmoHwSAgLcFJendqyIq2F9c6ZU5fUSDKUtnAqTu+fw2hYTRP6vQ44T0284A0xKmfIglGKPwAD44rQRHrRYt+yeT3JUb+GtGIARJAvW2E3U6vU/pSOqELN2E/bND1DeIkxmw2QTHPEXg8L0HVNMKs07WRXbvYxFGTEGo2RO0cZPGzwy2Ig4WumcbtvGDWqtJWduI9+Gyn4aHFi+tTvH75BD+9/4CfPzyIjJojIAoCTL0YQUVpcgfHbRERXItquHEBJ8rhhIP4mT7OQ/z1hxEeV7TgkO23I8B2PI7H8Tgex+N4/FcDrkWhWbTKIwdgmH5vz/tcimPXHtbwfo+0HYJpuk45/F5lHrqAoQ+USQFzB5FtfvnmC1Rljr/9+W9wPvQITxOsnxTwChdhR1kXd+x1F3tLBk9P0MUT762aRbT4W+lurBR48CQlK1836PIaVxcXmJ6dY71YiaFyy4Csx4UsJL/56rUkXG62xS51kS+bS7jrp6e4PDvB396+R00PL/Ec4mEKTnmDe28fW7hZgOrw2C3VdLW2WwAfYF/7z+Kj5mDbRdh2MZ6kBYJhg6IhmqSyVFP37Vkv+4snBeLBpTFnHi4rTYEidb4pHE1xIotWrsn9CC9fvcJ0GiIKK32vQSzAxHJb4+7njwjCFJdPnuBhvsLDwwYnlwHenL2HO/+/8PZPFf754zPcpM/x7NtLfDtNEVIOOh5h9DzCFykwI2utaWSHv3ZCsAKhrwl9xAiyUopBMETN6xu0IPiWoqs+oa5XcMOx9uDegJWaSyHXlbvyvc/ETVd8yliFhU4lxSFZTuU4xLIN4awY4lnA81oBBlicko3RFAMmQYdgHKKsXAlVoAQnSjPUVQWvKfEijYEKWLQetq6HUxY+JdNsHQRRiDyvEKQZTk7P8bgocNsNOHkZ4av4Ds79AvOFh21NEM5HiwQuAyPGGcJRiNHIwcyjdJWstQ5V46FxA9ntjyQZk9dZvY16puvWKt9j4UJ2lngauR1Iy7PpaXrBCU6xsDUokfEx4vWltRmfewjJuCAjxhW5UOLVmPiQ3XsWq3zaSUx+KGWqZD2FGJhKWNMoe0Aae3DCEFXrYqhKJLGH1CcQ0SFM/46opudVIDLbMH1APgxYzUtkBM/jBO1Zii+TQZJJFfAyIAvfLwuYwRG/IEkApP+TU6IuqIhSKRv7OgF3giES+mBMxCnLEg5bD2QxwR8dfwSD7u7me69Dw5TS700RuhtKhoFKn52zU0xPEvQOmR4qsZf0UEriDMC2k79ZiZGBNBSgMSDbbrI4mBN2+I2OW/7P90vGYkK2VxwhiRj+QIZHhgZjYZ1WQyTSYc5/NH/XDQNNTPSZVBiR9SnxMSirAtuiwLYsDMNKwS2ZHsg0s35oApBZlto+BEaYaPK4mtALWGUlagKm+YhZUCcx0iRGbDzTyP0l0EBAQz8r64k4gAAjApbruzZWRaZUtixgM4HxMAZJOm/vQT77T+889Ops0DHFj+BKQFCNYDEfVtk2gWnZaOG9iRLftsbbdz8rmLYDeC0dSK+VXNOuRzYa4Z/+6b+TNri5uZOfko3Hl8h2ZXItAy70Xjpg8uwplgTH5Prq/YLtxY2dyF8i9XM0DhOygXXhoRliVLWBhTxtFdcN4QYjYAgF/IjcRoA2Svt8LIQqI60qkl1P0ohzpv8GqcgY/YGy8Uh7I687r1nIDTcHXcN7K33U2G8EmpIQESYH+wIM035ArwqBMk2lNqCZAGuaFCuSUIJoMsiUSSvCUMtYk7FBcG0/xqRNDUiqY+9gjBiASPvnXu7L+c2yHIfP2GwGOBKgjcmiui4wU4lKUblZY9YuHLNzrhF4bbIRavo0lpV4YU7SraQsr0sfjcdggg5u3WOd+8i9DJtpgtHMwyu/RkipceFii0hYayKl5T2N85eR8FvQrCLgz9uu52CTr1DXBeKA6ZKOgLJk5tNagOCasNdEGmrYsAb4tusNy/rbzS+m3XbMeaEAm4cN+Y+bEApqD9jkm904FUiLUvHQV1Z44/LyS3iD5zTIXGAauuhGPsoswlmUSgJ35bkoqL4tHRRFj75YI3BWOMu2GOJI+nNb1kizEXyuJ6oaTuBJCjmZaw+3D/AIgncO6mWF2flE+kxJmQLnGAsemvuCZZdJMrSdJw6BsoPvTc8xmxNmNWQtNMzpsoyy3xgJPzdwvvviWpQe//K3t8jLTmTT/PkoiJAMJfpiyeQJeC4DNhoEYQ0v4FzDECHeBxz88D7DD59StK2RvcsGp3sE2I7H8Tgex+N4HI//KsC1WME1u5qwoNLhObJQs4sQ+7j8zC7gDkA1S7HfgU4WZNtT9oXB4NK0nV4hoSywkjTFcvmI73/4XhaQZCw9O3uCmXeC+b/dobou0U4knlIKLSa3SVQ9DaMpL2DBI5UYTX65kNaCTJJE5R3qgnq1aEHzmutX12LcXBdkrbGI6vD4sMDZyQynpzNU3EFuWDBoETm0LW5u5vBdynn2C7jdZ13d62ebcmAKgx1L7DOkzUozbfW8e3j/xJ89qO9h1bAQ8nESrADxCeL1kz9qQD19Tj5ir8Pnf8IUKXLNzdObQtXu3spPBYhxcHJ2ji/fXCFyPyAN78SLh8XCqhmwXmyQ/3yP8+uXIp18/8sj2gB4c93gtPkX3P7wd/z1X0/w9+5LOM+f4NvXM7zwI9ReguIqw5NzFy9d+nqVwlorGmWtccee0l+mgbKYszv8LNQq+v6wKGFBRqlgNJbr3aw/CnvEcePdzj13t7XgY39QCVvvqWyUvmU0vo7Ryi68P/ZxE4fYbny42x5eX0v6XEDplO+hbBz4Nb21OiCKUWwaYRkEcYSAMtKiwMwfcOX5aHsPSdPAKTu4fY+LJ1OMT2cI4gQfb1doxjG+uKpwXvyExSf6+vioen6EcIIRovEY8TQWH5qTBBihIYUTdUVGow8QnKBxuGFB0FdJ2oigGn2xKgV1xFyfHFFWkGS2wUrs7Fg25teWPWIqLd3BN7JRBiGELlrfR9l66EoHbt/CZ/uwj0Uh2ibA0GihF8e+gJJ1Z/yeevpB0YuNsj9PUgwpV6VgtqN/X7zB4CVwwhW6gCD5GdqyFeZdX21xQnZOyCJeKmnt1a6DtupRdR4az4dHXSyLc0qlWkfkqfSXI7jDruC75FIa82/2bUkwpDm7I6w1h8aN8vQssH3c3j9omhwfNDI1figwqW1nQTF+x2nn9YsnaN0eUTAyYB3BArLXyNo5ANh2nms8xXr7mLF5+L1hRUnBSIBKWFARsjTGmAVolMD3MnT+BI07RokE245yT08k2mQMUdYnLCL2ESn2Ogw+580KdbsVUI1gtQA+RuqorDPOzRY4M585D5p0P/58B6S5h+Aak2vpl+YLWzEiM43gXxyJ0T3nZHKWBR5iSqFDE30doxb4c0Tevf9eN0r25uLqkalTvX5tmMMHZDZttwOPNfMfmVZMlhSwiSBWoF5Tqi7URMDDmZ1/n/eZKIzww99/1MfMPVKvl5krOUcNPa6ePsV//0//rVxrgmtSkKeJPA/997ZFhVqibfl7CtQ9eXotXoIOx5+AP0xJNlJb52e4/Z/gli+RTE5ELi4BLB0l10AQqDE6gehkNhFj/a7z4HQDyrKEu13Bj5aAM6I7lzCzC5rmd2QrhnLt6eM2BLE+Dze6OO45/iVggBtfzBCmv2Nk0kJ7SQsWoI33XfZnuTBGWkzTLM5HwlajJFTli3SYMwJaHUsE2AygpgARu6uOC3uP0nFhNn3sKDTM0B0It0uC1X5g7oQ6xrr/H6DN3g+kn+ur4kYVwTX2NY7JvCiwLiqEyVjkyfT75NqBjD2/XWGz6YU9zGRUyv+a3MWmS7DNRhhmobE5KCWQqawD1H6EMPGQEtSWttX5R1hr5p7GtQbfS92W2KwXiEa8D0Zin8FNFW7o1Vy6lJSck8Wuqatk55KFJnJh8y6tAuGze79htGm7KZtN2F+m/eT3hAUIFGWJMIwM2GS8Mdlo3Ilh+1FCS7lta+wXTBDCxHMxiV3UIzJpI5wECbooxML1UG58bNYRNmuyqyv47QKzSY0hSiQIgZt6k+lYwGiGhxRNIyzq3oRMBF6IuqjhNh5GY961udHUCkPd9gCdv+wEoAuaHXNtPxGY7/e8NXsITGzOUyBOP9h29KK8nCZ4+ewcn+4WePvxgVFB4l3IDbwTehEwZKtfIvAL+B6Z2JqsHZCxRluGwMWm9PHn9zHm2xAu+52ZvFpvQB5WR4DteByP43E8jsfx+K0fURTqbq5hRnwOrn2+CLFFxX5HcF+47Bclmvhkf26JVMIesKmcUpixQPMQxSkmk5lIAn78+/coyy2imNKlRhbzDWp8+vSAPN/gfLjEuIlxd/mANgG8FalVRn7E+prSAi61WChQJiMLJrtTq0loXEgTnmtrH6uHFpEf4+mrJ1Jwbeko77pYrXL5e9dX5ziZnWC9XMn75q6jhB0cBB3w2JEYDChhTU6s14ndKd4116/YKrbsMM+g59nievfM9jv9quk95G2C0CezaSmAUw++N90JtQCf/dO68DbfG1moPJPdzTaH9W1jgRhHCb769jucJS3i/j8hDD+ididYYoz12sHduzmS0RkmT66xev+I9ac7ZFcDvp79C8r3f8Lf/+TgXz+9xt3ZF3j93Tl+N02RDDEWswzj6whfJT2mQ4GubFBWPmo3hBdT3mZ2+IW1RqlMjbq0aWpMnWulsGjJohC3LhYYPpxwiqHboFq9RY9MvMIIGonkyhRWmprJ5Fl6y7BgoR8X/1aLkdPgkkDSOMQ7P0S/8eHlNMWuxLOMAEJDB5oCiPsaoxMHjReLh9rQsRhLJTCgKba4CBzZ+a8WW1lA9xnZfj1iv8f4JMV18Ijq5mfcP0YoagUsOzdDkI6RTUcIpgGizMGl3yEUU+wOVU22RAg/Nqw1kWDtWWt12Qm4RtaagM9CsOmEpUkWlTBETGKfAOL02iFKYct9kVYpw0r7jgKUPINFC1MACeqJP1vNMcRWI7PFF0naIz2yGkdS95KIwIkn7DlKt6PYh9tVGMoCTttLoe/6Hqp2hLIaw48ydJigacdS6CYFvRIdNL2DTVUaQ27DmOKL6XrcdpQleZgQHBUvejLoXDQDwTxfgDMFYXphRvQVQyYaTRJl15d5g7/YwvEIdiiwQZne7d29Mb3W4BEB20xh/9mYNRX/dJTiyfUMm9rDKIl2bDdK40Qe1xNoMx54hoVzCKSJDFKQBReeHyCMIozSCJM0wWyUYRyNEEYjZWl6GRonlfALAomEDvncvIBsoyB0EMUDIq/RvutsxaB8GCr0Xb0D3WQWM+2pPmlkTRmml4BqnspprYeagD+6KcJ7hoJrCvolSYQ0TZGmMZIoFFCCrEp6XJHhQlm262mxSb8z6z8+uGYrwBTDu2nVomjma3u+TOECxum9xojF9PTP2NV7NrDMfUZxyD7SETQz6JwkKB/co/ZT4d4Pj+xuvt+/ff93+bu712tZa8KWdfEP//gH/OEP/42EGdzfPchjBNdkHLQdiqIUBpuyAk1gxtDj6cUVEhbY9D7lGLI+TzKXP8LpP6Arv0DZBJJIenGewifrdrOS9hXgNfRxfpqKTLzqWvHM4nyZkpkWrzB4M7j013M9dGRuMfWTYQQMSBDvSUrMTVo15eSUCxKM66j3dBDSiJ9SU4Hz1TyKiZwOU5gZOtTUwo5l+/Q90yEVMCLIK4C+kYPqyFEQWQD9lkNZwTUFnQ8Ym+YGeXB7tVd2L4G055v7mN0Y2HuaGkYbgTbxNFMQlX2a6wUBlZjUaoAZgln3y4WY/EcJ2clbtGWBKpkgHgVolgU2HEIO2YWAXwPbPMaWssjTBKenHl4HNYK6RLWlxUAEJw6QcDPEeK2pZLZFw7lavNS4GaJA13L9iKYrMZqOZT7oGHbQMDlU5aBpMAgDdLlhIIJKaWXo2xWCGSh75qZpOkv0Mumr2rSCuMk5BCE5ruX5KB4PQrlXiJxXUgdUaiveiQzfaDmeXWEmyz2R6dMt/3KF2Gkx89n3PWxHPkI/wRn9Q8MQq8rBtgqwWnnYFmR3L5F4c0zSDn40Q1NW4reZTk4F0Kd/qJ8k0mcElBs8eIOPclnLfHR2OsW6KNFyM1UklmYcH6yYLKP18zlmr6zY/X+wrrXYmjxLz2vt4M2zM9m0+fHnW+Ql7SgCuL2DUzLte2CzyNG7Wwx+K6ncA/1QI7mpyhPRUuHdY4+3j+pTqD6/DJZxUKYtVpsV2k/1EWA7HsfjeByP43E8fvPstSjUYtvaclhmliJle8aaWbPYAka/ttWQPcWYeju/Yq/ZHVWz0GHB4fshxuMpRqMRfvnlLe5uP6k/E53qdQWNtmtQtw3i1MPTyxfCmnn/7hd0P1cY4g7lmw5e7cBvKfHRHVsuoOumFnYTk6e8wZUFv/h0kX4vsk/1yqBTVLV1kM8bzM4ynFycy84t/y5345fzJYahwRdfvJaCaJtXyryTFekel9Km2ady8v3v/M7sQt8sbi24pUwV+6Phs8LB/sCCbPKwnqJnmWvBU2nGX/QJTqIaQZsLuCAgIuUu9sWZfNLdNbYvSFefuyWmBeG4yH7x4iVev3yJYP0eCf4C+BsUXohVe4b7D0C1TfDs5Zeyg/zphwc00wRffLWEc/d/YvnDAn/76RXe4Q3i767xjy9GuOhZhKRonif4aubiyqnh1BU3fFH2EYYoRBj7SISRNcChHFQYWQ2qkuBSLxKjznj2cGdYQCMmMhrDbFbYbpjBTy7Q5Hdo8hzwGBBgHJ1NMeFY9gJRGY9yVKalQRhY9BgauwMuIg/LLMC8DzHMB/gNC4pGTIkHGr53Dvpth7FfI5qE6ou0pS6RyaEjlbC2HU6fnAm7hXSThlLGfkDYc2c+Rd6OMV922DoRnGSKyWiMdBrDG7s4lRCDCmhKAbPIbBuiQNLhJCF0MCEGzYEctGokMESKTp/Xl6ArizeaixPoshJFc90l6GDvMWjxBSnsLPNj1yu03ehrx2LDDT20rjLLQmFlAGOvJ90N1eDDa8jSoHSGYBdbldSLShgy6sHlo/ci5Hy4ocyIoSQ0uHaQBK34s8U9gZkAyWyG0A+xvF2hLckGCFF7HsaRi7EArDoxiecTvZ9CH6EYxrcKPjYMeWiEJcKhTf8+lfdVwsrJ3RAhgQRXZXdkZjzc3RtQ7fMPlXUagM1UrZS6vnp2jcHvkcRTYVPycfGFEzBYWWwqhVMZnErlHDHE5ibHOEswG2c4HY+EnZYwNCLMMAQpOi9G41I2TDaRuDbJa6AFHq8FfbcYAuM7BfouR715RLtdSnItUyrJJlJJp/vZPCwg1QHzzLKLOUdKKIVsVJB1xvlaPxiCI4AaGXQE1BIFkDhXDS2BZgKYLJwZf6EJjGqH6RxsPBg5oY50+ZpXS4rN3TxEoNPMVmY+tROYgFy81i4N8k26qWFisl2Y3ifAmfk43MjQuVTvawez68FXBBU4nmoBiCLxNwzEvuDh8QGbTS6bD5I+KKBoj2w8wv/wxz/i7OwUv/zyESuGc3gWXGMSJVlMlZGeWvYaX78W9Pf3dwiTGKM0NYmVmmBLzAJOiKC/QVs+U2YiZ6jOQZZ4OLucGRZUJQA07+WbskaRs99zChiQDQ3cMcfamTCgCEoEAnDSa9Kn3Z7YHaQDv2efJtOuRd32IpcdjX3xdgsdSbJAN2hQAMMwHCcRhrNLJqJPmwYy2khnYiplJPM12WtyGTwLrBmPNQP0WzatlYLyPzuudmPMIB1mWfDZmsPeV+V3bdrvoQRyd39V30f2VYKFHV8HAjiUiJrJbbFcY1UUSMZMLGYS8gZ95yNIR7jMAjgEDWXe6OEwqaUOxbIhH2XoLmhzMOCs54ZRh20ToY0iAfrptbZjrTU6F/P+QBmypH8OQFlvscofJS06iiINg6h7tPzomDisPml53qIpcjy9nAowV24baT/rayjrGvlaQWfrQ6j7bbaNuU5SpjIZivygF2LTVHDohUnwWdpdr0e7k+2akekCoRj5k0FG6aMn97eanpYNzf/JTq72QQgjD2UaYObFOElTrH0HDB8tixCLOZnILc6vniF/+AFpmmPdp6gXlbBf0/FU+jevTzxKZD3YVPQMVKn36mGN89OJgMxsD7217QHww3XOjs12IBnXDeU9EGmBtV3n6nucTmNcX83w6X6OTw+5bMSwgbnBdRV7WD5uURRrDEGBIeox+C46Mu88H43L8KEYXBq8f2iQc5OWmwTmZtsFPZbhBsUvOZw135YL5/Xr1/sZ6Xgcj+NxPI7H8Tgev6mDyUf0ydgbAhtwzeA8dtlxCB7Jz4Uyr+fbtcu+RlFmwB6Y2yc4qdzIQ5yMMJ3NMH+8x/39rew8MvJeYCAr6zD6DxZ6siYagIDoRkOAK5LdzLvyAfjSQXI+QvoYwV9TTqCLKi6f+Z6yIEbixUCvxQmdZclsQh9ydSN58PzHvxGNgOmTAHVb4fbjBwFGuFill8zJ6QRnZ+e4u3/Eap3D5yrJLNDsmv/w8x7IsniZSUQzlYC8wkNTYlNBqHRPPcT0fXxe/pmKwoQjmOLBSDxoWx71ChBunRSuG5iFtWlAypAsDGq0EAebtrKIvnxyhRfPnmF4WCNscvjJBl28QeO3uJtHWFfnuLh8BbgBbu9WWPsevjxbYtr+Gfdvl/jp3RTr/grPn9FwPsJk9hKtkyG/iHE1cXHp1fDbmspWlK2PPvCFFaWMtT0jy0pnmorFBa+mNehnu6mkraGPUksvIH1vXhQISEeJFYtJ1BXq9SP8MEE2uZLd5zBgX/MlnMGhy7DjiTyM3n0MLfBa+oa18EOCNT5yN8DH2kG3aDGtKiR+iSDuUZPNJrv2NELvEKcOSi9GvmEl10thxQK2KHJhfsRRjFoKJTJ4aC/nIvEdFB3wsBng+jHczMdJqD5iTltJG9UDpVn0qnIlwEFc/0QOSnDRGF5XnYA4LBoJMpK1RkFWN+zNxeUcU9DyopOJQNknQRMWJzvgWRie9GlSIIaMP84Tcl5A+R+BGF/AKOE0sJiSBED17hFGC0FLEGQju6UUwKWKEjrmwakIVPZwwkSAFo71slGQLGCAAhmIVYjWjxF0tYBPKAoUixxbxxf/KSQBTscukphzhoICwmrj+xcJI5VMWswSUGQhSxl5ksaIAh8OJXRuA3j0EozQuzTW9kT+RL8gz/Hxt3/9iwknYAGsTBE+vcwrZmTacTNKEvzHb19h0zmYTSaGpUZwoUFV0W+LnBCOQhay5ABpIaXsKXr36FgmWCGjn0mMklxoGD0CHmoBLamwBAyrQjcChK2oLCoZ6Tbt2RSKlk28A9UON1CMpGoXVmDl+/K4zslM+5P0TyOT4iFpf4YGo7cBC4vta1th8pr7gGWf6R/W/xQ7M0CY/f7zkw6Oz8tNKw+0TBwF1uzr+/fn8lBAzc7M+pnvoaoJpDXyu3yPDCIgoBhGgTAsbz7dIc9zPH12LfPGZrPBfD5HVSqoNZ3OMJ1O5fGH+7kAJ+yzURLJfY39h6w1CTaoa9kUsG9VfaLsvN9LWurL168xnk52czOcGmHzgG4boe44Vxm5Jq8ZbSppDN/x+VtswTARJiLznTZI+g6nF2P0UWRuHYQtRRArzCR4EdZCAO4xFFukgjG72DCMwKTPZrGLKOb4DtB3CnRyDiDQLqOg5UZIaSTYQu2SzSwxoveZUBugILDYVAdMTd3EESLfYYiBbBqYe5oB2uzd8QAC0f8PJMOH7cm5lQC39GkylQ0TkPf5UZYgDJTp3dOrznAEq7rCKi8kmIcbf/R/lY2IJMMs8iWwQSwIOt6zHJTrtbCvej9DMQ3xLAXOnQqDAGcealcTzlW+z5dmmdhk9SkjjXMC3zOZxo+LW8SjGJF4V9KqgonDVNoaEJKBEwJy9Rgsa61tMR0FSLIYy3WFJZnSTICVsWz8Z0172HG/e2zHSKU3YCqAWktGWuhIsIG9F3Buol+fiqK5Ian3g4gbGOx3cg8lC5ySYwBBJJ6XlMX6DCnwO/hhD4fSTjfEXe/iJh/QPTZYLbZ4XG2A5c/ICN76PkYJvdkGzM4dDONLlPlzDB2B6khea1lshDnH9qjWOby61/T4zpPNGX/qw40DLDdbfb/SR4zCge/FbjAYF0eL31sAXliAZhOF91JuZJ1NU1R1g4dVIWsE/g6BY26ANY8F1tsCvVcCfoueYSCh+v8qiBfAaV0Uyxx1xXCjw5Wcgzyq5Gf9irJ1yr0DjCbZEWA7HsfjeByP43E8fssHF/RcUPEgs0LrMl3AHi4G9ky1w2LF/vCwHNovgtVId79DqAUDF2g+RuOZLLhvPr2X5DgB0ULsnQ0AACAASURBVGSBowwPgk7WQFsLaH09XJxTPjaKRsjXWyy3a4zSEfzzEOvLO2T+FHjvw28N48FAUCyYR0EGz02UASLhBAFcygqhYIxkPBJMIEMnGZCcBljlC6we76RQ4mKfbXV9fSkynXfvPgnTwXOZtKaNIAWBlTKZRduuKuXr3+3Mm538PV5mTzHsCgOdmXNt02uxaE4WXI1/yBb8ysrgqeHQIBpWyNsAnT/aSa10U9oWtHbnXv8Od/a/+vobjAg2vL1HHLTArEYdttjUPe5XHqLpM5yeP8VqvsKnvEZ85uHb+E9oPr3D2588vH14iXx8idMvZ/gmjSRFiwGU7fUIX50EiHsWIWSjuaiHAE5kDfotsGbT1BQ0IuAlRYVrP9QUmubkZFmwqOwatqORMUoiIWVUCgqJvwl8dFWBavmAZHKGZDSV60hWCkMKtCgJhDHDFEqa9NPvxutbRF7HcD0pEO6dALfFAO+xxqgskETUiQ6oafAtyaTc1SdI62PVRijXLOMaDJRNCVDsixk9pX/sB6H0dzKS2O8Ih6n8Mhy0UKvIiOMCPXIRS4FnE/m0jVQq20lbqQSL/aTbgWvKlFKGhJhh88MkV2oBRpN7VxhKAt4JyKaybSmsTFElTEhHJYEi06QpPUE2fhAgI0DMMev4woxj6EAYsngku64SMJDXQYAkjwwEFmh6rYShxHEgwSSie8ZyXQoDJYxDhATd2TcpWcpXaDYtNkiwSYC0K1nRYXI5QuAEUlEOZBmKN5SjwCNZImTSuS7ScYKGqW6bGqMMcJJO2IucB8hK2Q6usHmo6CEw9rcfflDWH4HLnWG69rUdIG58IN88f4HLq1Oa0SGNfDO2KcnV8avXjW+VyYXKsNqLG+00YedLiJyOTCZJ92trNBXlfkyNrRW8MziRZWDo9GrmXgvM7OZeM+blmtticz/Pa8InC2sC3aFcWz4m742ge9sdyFfNKzZpyYcwmH5v5ifLApEPe9aOIm1+boNxdtsv5gl3r9j8lha82v4q9zuYAvfn2g2O3X/7e5AFaziX8Npy3uZvkRVJNh4BRJ52d3uLD7cfBbxYbbfYbgo0eYP/6X/+HyVdunc6ZFkmIBzHA18TAdRNniNfE5ShFJqgZLQzyadnZFmU0hclaIR9wTBB1WpArz3HahInePXyBUbjlPtICGlu35dw+y3cis/nCoBBOXzHUB/KSsWzbhCmL/2w6PdI6SMlnxcnI9lUEKE3+2SjY4PXU6TBkrDsSir1fEMPPpVU832EtFjgBhx9FrutgC8IY9nGEV9MzscSLuIIgMh2HaVA6NUiMeUlYBLw4JDBk6CoB0mi1Q0RsUvc3dMUUNN+ZWXY9l63B0VNP9v1FpV57hjduz6vAJuASYJuUd6aYTKK4DsLbkGhHzI4A8cpsN5sULVAmmUCfjZ1ga4LEI1T8RJT/0b17utFzgfM5zm29MucxHgZdEi4qVUOKLsIg4DSek/jCBdvPisJpRy01rmZPndFucam2mA8GUvIhjCMKau1LFcLphFg07BRHQeGVSbXsW9xeZJJyvTHu5WwmEXWLV6He6Bd1jcCrPF1sW08zE4mCvqShUY5PeWfkjirKcvKdjWbLtxwMbHqBK0Ccy/gPYv9hCg6A6fIAPaiWMBBIlLh0CIKGuk/jqeS9l86F/PHDsVPd8iLCnN6cq5zhLIFWuFkvMD5RYPLaYAq+g6bfIRgcJCNU+nHm/Ujp24B25pVjqB3EHQBys2A3C0xfTaWwIhtXct6U70M+T6sJN5+bedf60lr+16PUewiEylugU3BscsxxD7H691hfbdF3ZKxtpXU5Z5hQJRe72QDHrptg2qZ7315Td9t/Q7rvkB1U4H7PGxPbv7Eo1Dnhtls9r/sevzxOB7H43gcj+NxPH5TB8MNbIEl5vCyHpUlvwFrDhgPu1Ws/twuFvbMA3PGgbeFyoLMcxpPEJ40GY/xD3/4A0ajMRaLOVpKi0wSFg8t9A3jwJhP2yKPX9dDJZHts9FUvp/fPKL7xGK0RPsFARgfXmlevykW674S5pPDgALxunEwcCVOAgkX4pTUUfrGx+kpk1PuFWN0PlOWQ93K78znK5FSvH79DEHoS3HBxa6VW9lDATYLUxrjcmkPfewwiFDazTxgy06Vxvy63Nz98LOiY/+lthkBg86JELs9gq6QYmagZ87uyikKyLZjIX9xcYbf/f536OY58G4lxVWXOtjCxWLZYVFNcPr8G8Rxhg8f7rHGgDfXazyr/gtuvv+IP/19inf1F8DLF/j6yxm+CGL0TFK7GuPsVYbnfo5h+Q5DHaIaErQezZuZEOoYHzGysWp0lPEZrzV603AXeSDq4bEoJZPIJq4dsNsoszGgrEFid22kXZPssBDRaIqmXKLcLITBAIcpjzxPUzPFNF2ABqVA0COFRuKMmHWGBiO3wyx0UI8CLPwYbRlQnytAnMNETLEuctAWPRI0iMdqDk7JDNs4TkcCQBVloQUbmZSULBuGhSR3iiERxBeu8ZmQSsms81mIAdtIGFkiLzJtxO1vV5zWMAiwQ4ZDv/NAIlBJxgrloxpioD3FohIEflgsSxvKUFU/IAuOyK8Q3DAyIWFLSVvzuql8SRIHWZy59FWqRC7I9y3FDE3b/QTl4EubStHWNmL6PLSVXA9N9XMlQU590Qgw8TKRDRLAy1IJvgh7Sr8r+KjQlHT8UW82Xja+N/oadcY0vGmBKAmRjCO87VzkHxtkJa/NBm40oHdTAQaZLEuInQQEAlkfPnxA29QKrBlJm4AgytlTaZXtZl2H2eRUC/iArFjtyzUZhiUL4R5b+vwxHELAEaGUHI5mGZUsuAmMcOMh36ywWi2wXi6xzbcCXrDCVhaK8T4zzAzdiDiQehpPNRtSIMWy9GvPMBEJaocmyVOT+ij1JODMQSCgHtmcrU071QJ0N54O7gLy9c5gXt/HjhVyULTqT3YYioDZ+piVhGoNqoxeNqH2Vxnj7OPinWWlg7ubzu5etAMSzLOKj6B43xHQaIQ9ImE1BNUYvBBGqNoGN/ef8NPbt5ouK4wnD4vlEu/evcV2myNJUvz+9/9B/OXWm7U8V77NsV5vsF6vsVqt5TO91djPkzQUeZ/cT1uTRlrVqJtGgFjbNnLdKHETgE1lzWdnJ/j6qy9E9vrx/j3uHm9Rb1sEyUiConl7EusFAidOJ+mJHIYyVNlPCVy19LvrMZtFOJ1mJt3VJCr3tSbqymaR3vOVAabMpiF0kMVsHxd+TBkpJO13qGn4z74QwOs6+H6JgXNXx/fIcUavRwLugZjN+z4DeHid7bqhF89FssCimEmqnrD5LLPw15/3x6/HiH2+/fLj348i89kwwynMTLIMs4zbLI9wvI+AcyIpv/QzW6xpIRAiTlO0NcM+asCPMZ2lGAWaEE4XAfH2bzjTCOKMvPMwTYGnfi3WAUy9rhDLhlES8Z5mE0JpX1BLP+aczfsVQdamIyg7F59ZMiB5/TQR1MzTBliT+5pI0MU20QDMphHsePd8lBVB3C3OTjJMxwkq2lwwzVXwsH27ybVwHcRJgskow+NqIX/PrlUIIgkoegBw7kxbbdsbINtaDYg/Gzc+6UkX+BJiQgknpdt+ZPzZRDbKVOAWgdNg1OWyAvKuT0V+OwszNKGPomH2lI9y7WO77tBgibD5CZO0Rh+MsM7pHTlgPJnpSok2IPS7dBxhgj2sHpHTZ3PdSvIqAxOE6d7x9THIZj9fKnvUto3dEWCQwoBZFkpowe1jLmEgCk8CGZPF8xyPN1vxWkNcY+C936ddQoBWNut8tI2DZr5Fsy7175prQJl54daYb1fob1t4Pcebh9EkRZhGcg+QJj9KRI/H8Tgex+N4HI/f5sGb/mSSSeHFBT+LBHn885NMYaXAjQXMdj+zTIHd9we/av//FeDGRXgUpbi4vMTlxbkUej/+8AP+9v1ftdAxkksle3FxqYtSPibFpZU0maKMu6dD2yNf5LLor1EBr4HwTYr4XYI4V78nAbnMAiYIEnjxqUhFafpMYEB8Y7gzO7jMhULYkw3AnVwgOqGnRoeb9+9FRsaFWj/UOD2d4unTK9zdzfHxfo5QEtYsMGgLTKOD4QJWZEyGyWYKxl3BsMPMBPHYMQhtUbmXy9gP+4umnc3vW36NFAMiCQJiVOLHVHoj8UqRopZeYFGAP/zDP6ArOqw//ITEKeEMCfohlrSy+7bF5NkzTM/OcPfpAXdlj7NXDb5y/2+sfrrHD29H+GV9gnzyApdvzvG7cQSvC7GcJMgufbzyuNtbSNpj04bYbEs0rovZ6UgM8wkasWDpmmZfhNS85uqtBLc9YGQpWCSeVsJO6sTUX0EjMaExbCyaKlPe5oo3DFlXlHqpzM2TZLxqPUdf1phefSU792RwUf5I8IFSFVa0vGpkNrDYofdO6NH4uRVZTOlGuOk88U+bLkuEwxZ+RD8vnu+K2To9wJKwgZM0WJYX6KpewgDCOEZdlwIsEcBNWJCzP9F0W64fU0tZyLJgZRsJ4iAFu20jMZ4m4Ez2IVl9ItFkG/E8LcxEWsQizQAU0naGfcVFv4J81rTeADHyoSwGPzCgg9BAKBUybDaRCamMiOfKOHQ9MbfHkKN3+BoieC1BS14Xzi+BAGWt46HsyPrpxLctqAqUZYuMBY14QZLpVWOTO/DTWHbzw5BtaTy+TOHsdCWGssayiyRpLxFgz5E+IkyRkt6NA7JRJAmVrRPgvnUQbgZM0SIYU97lkxenfkQcX12LxeMCqzUBdMq4mh1Iwz4m8luTxikYmwEpOTc9f/YVXj4/lbmpWZUoxyGqJTBNOuRkS5YOvIDtpIwxsuLEJ7JlMIWyf3RzwUJEpraVdEyzcSGA++F8arEmM9PKSYahYU7g3yIrTQIHgv1mirIblVknSZZkgwi4pn5MjhSVB0CqvB7dAZDgCzNP2RJ1xyIyAJvMUAevcRcCs7tFGIBtZ1S/n+cMJ2nPwjPPYd+TPSyoxv8o8WRiJkE0ARIDT0C0KGDxzYALbqxoeMS2zvH9jz/g/bufcf9wJ3+ckserq6f47ptv8erlK3ks324FIBNwU+ZsBevkWgnwoeCjMjt9AdY4lkScKdLgWthECq6ZdFIx39fXvvPJ8j18/eUXCIMQH+9/EcCuKtj3evgMJSgjXL44w/MnY9QSTtHCcTgxEVTzVNrsuVgx1KDvkYYurs5jDG6sTElBLJlOSiaP+teJjNA0vKak8roSnO8E7BN5cx+IRG7TudjmjcgCUTbwuxpx0sGJ6VcYYVuT3dVhFHvSLmwDDFsB3yVQhKDe4Em/6tj3ySAfPDwutyi3hVqE2Q5vwNz9Pom9Bx4sN2x/+3drFfOYvOVB1hiXlzN4baHv0y/gBi3aIcNiyaROslqnaCnFL7cYuhDJNGFmiq5DPI509lNfwMntskbHjZXUR8J7DiXCQ4vWpTcmQVvDWjMbD5yHJKCAvm2cR2hN6A4o6xx5scJkNpX7BOdysr3kM4E1yhN7skZtsqqCywS+9NB1AC+tMNHEVkHXEk3Xyrz69OocZdng9mEOx1N2NpmNEe+95zMJksq53jObbvS/VMBV11YiI/VNoIFIRs39U5hfYkK6sxHgVeC8R+sFSQlm4A0Bp95BUddwgpiRo2irDk5do17eYDxlW88wuBGWg4efqSye96gXBW63a8xXCwzlEtm2gh/UODkp8eKqxWR2gU3/GvnKlwAYsvbqIkdVrKQzLB8+ISUL2RnD6QOUdQsn85CcJpgTTCW7TjZvdXNCO5+2K9uRjgNZGmK1qbCteX/lWBjg9x2SrsbNpzXaroTrM/l00DRyskfFk5Djy0G3KdEsct4x9QLZsBu/x6LdoL4t4ba6ATKZThBGHA+7rRsBW48A2/E4HsfjeByP4/EbPbgYmE3HiKIAAQuPgsVuvZcafQbgqKRHACFT1Oz/t1/ZAnAHue3+F1Nq4iXGTDsIIsRxIp4T9GK7uDgXqc1f//JnMXwWvMh4YYj8z3hByQLPFm2y42pBJyCgoWxeYVPUAgR0cQf3PzL9KUX0MUbY+GY9pZwJLmiC9Aq9nwjow/h0spfozBLDQ9S7CHuPAlJlAvgdgtMAj4u5sO54nqwvhxavnl2JxOSntx+xpceUbB2bnV9TyFjQUIp5FumCux3sFO/aW3/PmqnrL9mf2vP2stCDS7Rvm1+Jr7iS5zI7ahYoWegECV68/gpPrp5KEqi/6WRn2Qu2GLwaN7mPNp3hxZdvBHj95ZcFvLME35z/CP/xn/HhBwff/3KCx/4cwdlTfPnFCa7iUJ53ex7i9Qg4HWoMTYW6UjnoYLzWWIRU+Vzkk0GYSVHMEANKOlhkyGsnaMQP0F+KBYj6jSnAVqDM6UuWoywiYVCZylyKAQUTFFgT2aN4rnkih6IsRnPwPHx6/wluU+HsyTWy8UzOFalkqL4yAso6nshGCTbyNXgsYGgmL74yMRaUu7DAnLeINyUir4ATMslW5TyU9nVFickkgT8+x7LxJRHUF8O5EMXqDuPJSMzNJYyDYI+rfZ7Aoqb2OWhKpqiy6B6EmSASYzF473fgo4BLlIPukuWUDSGkOPFeM0wssspEGkhgjWCayj+lwDLm9gTOCLARWxMAnh+mnBMWgHj5sSTpxew+iZnWuoHjks0XoHNGGFhE0JVJUt8os+qFUcGnoawMXYWHFQEsIHNrTMYECwZsKSuOM0Shh4RStIHjibZ2vrDNrB8YgYOf2w5p6OFCCiECiwOKig5VHSIaIAkAr6ydenCwpZl71cALc/G1GyS7UcG1x/kcG0oC2dc6mnerGbk+rzgAGlBlDzjJ0O57PHnyGm9eXnISQjM0WM4HnEdAy0TalmUdUwDrHZuK1+Lw+Izt9SsQwdp0Hc6tVt5k2cICrBFM830FmMn4k5RmV6SHUrAbNpo8g/hiaj8QqZ9hutBEX3zgzNykIJvhmO0YbJZz9jnYpo/rJCTAr/Wm3Hmj7QE1O23tmLkH95yD28vB93sWCIELsob5WUaykbIxLIcbF2Sa3d7fCwNsuVxgPn+UuXSUjHF2eoqnV9c4v7zEeJRJbX17+yj3wKosJMDg5uYTtmWBb7/5VkBjXl/XtKWVcgrwIfO7HUcqMdWAHQXhJBlSJMYGpDyQzVpWCz8naYTfffedgDBlU+Hd25+xXRYIuhDtqkc6TuGNfLg00D+fwo9jOJyDhgZeQ1Y3ATJf+vfHokDktPjqyT8D/VfocYmujxUMJmu71xbnGBKfU74mc19u60ZYpxynlKC6cYjGcWkphYIMNFd9KvtNJWOXoQd+7MKLxwLMmbcoG14dZe7UfZPV1dfiQzawb5kUV1o0EGwsqwaLOX21KgVWd4PA9BGzDpDrLwCv6RiH55metNuQAnByeoITpjZTui/rB7Jle5RNj8d1gygZC2OzLjcCbjlhiknmybzGAScYIdmAMje2KJbAOzfEaOTi2nWkHfKqpSIfYeIj8gZhunHSHwisETjnXCxyz1ZBsgFYrW8QEPiNEzNf/1oKqp8lUMUAbDrH7O/4dnyoewZZz2Y9I6EpNkCix2Sc4PzyBDf3a6w3FS5nYySRi8eHBaNflAEnjC7LUlOelshCJV1awVcF2NSrU+6hBmTj7K6yUe3U/Cfrp4BBKJ5Ik8mu4zzKTRWC92UN8cT1xJ+tkfuo6wXo3Bg3g4tP6wHOosVyvcH8doHHJcGoGolXYDbKcXFS4NlFD2f8NRb5GTNqkI0TBFGAfDVHRzkziW3rLRzih+xznYNNXmH0lIExA4pag3c01EUy5qX9TkaBtP26INilj1NZMXErFLcFFtscA4E1l4FFDA0hQ90RmbZuTgDNYw6nZrKuSeNlu/ZA4ZVYLpbASjdM4jDGaMrEcV3v7KxC+AV/9chgOx7H43gcj+NxPH6bB2/00+kY56cnsnjiwuzjp5v9brFZx1rJ6B6+0eWUfeTw+cwX5pcPWRVGIsoFHP2Q0hESSubaVlgSBNpOTk5wcXGBxXKBf/5//x+s1wsDrBnfoF15p8wKAQwMCGf/LmViWRijWLbYlFvxLulHPaJ/HBCXY4Q3MYLeE2BCK0Ex7sIwukQVpLIAiwKazLvICLT1LiLxZnLhtKygBjgZgGmMx9t7lPlSABDxhnN6fP31GwFACLRx51p2Sk1D2rACZWrs5U7WNF1/aozDnYNz5BdtS2shrowRc469PsPnANtuIS5eNfpzLrzPz2f49ne/R160+PjjA0Z9AH/opUgo+hKPnovzF68QJQnevrtB7vv49nqOk+LPeHi7xA/vx/iYX6AIn+DiZIYXTzPZ+a9PQ5yeenjutMIa0BCDAK2k8FHGp0lqUoTQQ60ssLh5Bz8co/dGJGQI28ShJJSgkUgdCbp1IvljMVKTBVAXUih1xYCG6X5EaIxnHwE0MtJUDqc77wSRCLhRvecGLrqS7KYKk5Nz+F6IoSqxfbxBMrlAOj5VoC0k24W79jTzV38ZJoDSq6ivO/hdh8hjgckFcYRHJ8BHspQeGyTFFoFbYQha8ZdhEh/iDOnsDJdjFz9/eICzqTEhiy/VNMui2CCLQyRhKJLSkkwoFnnugIlTInRCFNsaBaPI2AdEMqtjh75KAqARgCQAx2JNZH4EVRgYojIekTqa3XR2GV+khmZHX5gKe7N7AbNFwqagpfryKMigFBG2cSAyI5c+c32lQBALL9cCYaHKYMkEZAJeOyB06IdYCQBe1h5y2jWxqKyZgKlFNwu+bBIhCVwBVAkMiSxOQMBBXrMt6gh+FOy7LGiaFsW2wapkAQScTVK01YA4oszUww3BpsrBGatjv1APra7D/XwhPn2TyRhlU2DJJMHVVvodkQlhAxLUNMbXhwDbbu4bgOfPn+Pq6VMBtxzLdqK0XFh1BLk0YEI91Iy/4k5Cbp7n4GsLph0CMhZcE4ahz8AO+g3yGrKPkqhkGC/2ec1LdD5HtXYJw8poUrYofyQMNoJglKPpmzQbBPv3TYaOwhkGVDNzjJ1vTNSCYese/NnPNm7Mezt4r4eP81z+DsFIZYwRrFFAiknT3Mzg+0yyCPliJQBw2bXCBqWvKDcFbu5uZNPm0+2tAEvXT66Qjeg51QhLrMwL5JJIoptHHO+8D7HwZqjBcjXHk6dP8ezpE8Pkc5AkCUaTBOvFWliNcm9ju7GfULou5vSUtdKmQGXWe9m1dhQFMRQY5ZjJogjffvetXirTR/J1gZ///AFhTHm0Cydu4MS1MEUZCHJxcS0gjd814K1sACW/AYqyRb7d4MlZAMf5O9CToXeFbniNwUn1egjDkX2PKa0cU9r8VQdh+nGu4CYDGVmevZ7i/yWOkcirDlVeIo5dJFkgr1f6hOkABNg3W4Y5AKMsFNYtZdSS6C2AhrEnoEed+IH12GxqLFdLkcBL23yOsynL8le42q8lpfw+jFNcnU0V5OMk0NKzlZ25w3KzFiZrNh6jqQrxWhscplRGSMXvUENf1C+xRk8msutj1XkoIg8XQQ9yv00krpr6i2crLysRsD3LWEJlrDcmehTFSvy6GF4hc7bMh5y7NZ2T7DQyYfeMNeM1aO/3cm+06xwVVssok/WBjkXhoh5s5Mm44/3+6kTWeYtHbgyuhMUtLEoTAmAWKBqAZO0KxO5CfezkPMNi03uBzj/KdDNAm/WT7PU7bmiFPlmkvIE4KIsCnR9glM0kCZns4q5sEdDn1DcbVgxIcEJ8HFx8XA/obhusVzluNks06xxR3SBEiWm2wfnZBpdnCZzxF1jlM/p/YExJtO9hs3qQ683wg2aZYyjZNwm0uSiqEumTEXIyXenRig5ZHIg36jKvxSqA75fXwO8LhOUad7cVOrdCF9QYPG6Akd1OH1/2YXoMOqjzCn2uEmIdY3qpWrR4LOdoHyu4nW5eTWcT+BE30/Z9WuXMBjTlXHT0YDsex+N4HI/jcTx+mwcXEkw7O5lNxQeEhWEYhZKGtivEdoXPvy+O9gXSZydqIcVFoTV7PQDZpDj0fGTZGKdnJ2IWLdKGtpW/S8Ph0SjDt99+J145C+76cekmC3ObNGYKSLOzu/+7So8hwJVlCcbxTGUaRYv2nYM2LNG+6kQ64BUqpZIPFgfVBmHfYghjiVfn2tynyTN3prmTazyp1IOFvlEl0kkohvncoWVaIYGF2093stB+88UL8fBYrtb2xZlKgYviAxRM4Y59Ibtr3T0z77O23wFt+5/YK2GBvP2f0+fR9D/KoCJ8+fXXeHL1Ah++v5NC9eLpDFVVgE67H+sc7WyGp6++wLas8fbDHOETD//h9E9wP/4FP/61wfe/XOBT/QLt+Bkurs5w+XSM6CJD9zTCm4mDJ0MJpy5RlS6KIcQQ0kTcQ0QVk7D21J+KPllNRXrRGE2Zo97+AofSTBoFc3+9V1mN+KtJsUJwjRKYAeWGWIqDit4n9L4zQIWwMSyYu7O50rALU9uiydVwOJ6M1QCbrcRCYDRDV66RL+/hhSn6nkADDcG5OOdCWGUwvKbiz8ad69aTcAMHDVKnw2noosl8PPoRhioQ82L+nMbY9Fg5G4colhs8PUuRnM1QIUBNNsjAdMtU2Gl5kcMPdYwUAooBDSVwQ4MsHEROzTTMtmMiXythCMrq0w9NmjMsCCnWWWtY/yrT7UxnUdDGGlnvwfAdsLM7+aC/GhA3HY0xzUI4PWU3mrQrrAbHR1nzOrMIoyxbz6dwTkMaGrTrQuRSPj2/kgBu6KGhtCj2sEl8uIEn/kcWZJEiRi2jBRiilM0yNljAesIwpMdTD6fI4awbAcQoEQSZQBGLOwI+HtKG8AZB0QFVUWLVFGh6sk1KlNstYj/G2ekZJvSGnC9Mu+3luHZIWm7Wvm0G8ex6+eK5sDhExizMMfO7VhZ+OHbNdThkpCnD10h1DehDsJhzM4GjLEsxGqUyb1LyKW1kWC+c9yyjV//U/trtcvMIrhhGsQVahMli5guZi0yiIokRBQAAIABJREFUqUXG9oCiff2m8LfeZ3KNNFFWIRj9Wt/Zr9NJ97OVGZ4HzDR6ltXY5oX4zrUVi+8AWZJiOp1IYZpEsYBPBLP8KEDEubpqsc1z/K//+/+G25t7kXWyeJ6Op8KUZiokMRaCC/f3D5g/LqTgJ7OIY1+AYwn6IfNHgVTOjQTbHh/vURQVTmYzjMZjjEYJRmmMUOTbTDWsdgAqgUDxezKhELb59yCptoVcWwEL2f4QphNP5XNrFo0jANfZsxP4iYeqW6N3O9R9h832BkO3xMcf3yN0MgkLKivtN4Hby/ui1xnlnb5/Bcc9g4P3GJoxwLnZpT8aGW9k0PI1KFdHxij7gkkHoFROm0QBMF6/liy3XvtRHDEJnEynQAByj/dQSk05JkUSC9DjPhAmrqZNiqeqmYuFNEWvLzgomEYcujgZZ/K62Ad2S4fdGLEP6Cd717Tdkuednp3jfDYSNr5SZbWnlkwI3TIhNEWYxCi3awFAvTjDbOQh4GvmWJN7FO9PDarcwbYJ8BD4iFIXFy43jbjhY14AfTcl2ddIaztlu6p3KINndAOQG0bbYinBK0k20RCDlusHsrIN20zANbMBwnmNeKAZv7IMM+ND/rKoGvegth2ju84m48w+5OBsOpH+8PH+I6bjCWYnMwGfyZiz3rT6LGZUauT47mntPcPs+5lNQWsbwp90n3m02Stj52aRoq5yYZemDBMxIVKB52DgZpfrSTBHRxY47yNug4njYha7aKa+hGpcerGM9S1ZwJ2Lug6xWntYFwzfuMFZNoczmoBLLQYoZRz3YYSyKuExfZT3F3qCopeU1r7UaxP4Dk7Gkbzq5ZZhRBqGwEVl3OZoHu805TQoMYRcG3KzMETr0FaE4DSTaAe0i1zmIO+QUewC+VBivnjEsKDXmos4DDA9mQj4uFvbCT5qAHiLdnIYHgG243E8jsfxOB7H47d5cDGQxrEsei4vL6VgG2eZAFwEusiK2S/u7CrXstF2JdJnzAQLrh0ujne/Yz6TIRDReypJBESLIyaZqn9LUZZYrVaoqhIXF5d49eq1LHrmj4/KAhMmhS1Y+dxKubdggaaKMQ2SxsuNpEClYaJ+SnOgu+1QT0p0rwY4Wx9+rb8nBVBXIdhu4HPxGUXoJPWKnjKUCCmzRmUT3BXvBdxw+0YKv2g8EdYL32VZtHh4eEQSB3j18pkUW8WWnjS2zT4vtD/bljff7x4RKZ4+tm9lu4z9VZHBL3SVbBbnuhhmitbF5RW+/uprVMsGi/cr8Zhr1yVqsvziAb+s53jyxXeyw0xgbYEGr15+wsv8/8Cnvy/x15/G+GXxDGvvBbKLp3j6dIbZ0wzh8xRXFy6+9hvEXSEG/yxMmiBGEPmIQ0dYS2LQ39VoTYAB20gkoSxCCBTEKfrqHu32kzAcWIQ0plihWX1dG+CIxQkXpQ6LHTX43kOR+z4mAJuRHPFbnz5uNRkgBHQo+7LtvDdld+MEXpig3MxFuulGYy0sJPzDJG/Stc/40jAxrBkIpqjZMiWvU7dHlnioswBLptT29BVrEPZbjOIYkzHpj54wBrMIUgCUjYt6W0qBR1aKsGCqUpJD6QlIIhX/fkupJApkUQrPT6RwoceTmNGzvcgKsIwIE/qgJv3aRvvjUF5oin4LgOyKWYO12TFsdtm9IMJsMsMooHnzf5b0QjhTkbsSlW6gu/uDo3IbnRrUuwxNhZ7A6BCjEQacI5KlAMDYH5C4A868ASnlqewFrP9ojC1sCld8/ARPJ6hE6z6yQDo18iY7kkfnbRC6H+D1IYIoROAtMSQdWjdBO/gCrtZVgVWxRkVLqXmLIWcRXGI0TjBiceZRjpfg5uFBgF473+gwPQTZrLbHyESvLnF5eaFMNWETUhqmbJXdGN0xR4zXEecsK8slSBL4kmqZpomAaZQo8uuA/l6+RCIa03O+HhEia+FrrpGGqJgLaAplnRJsUW55tNqndnOGecz8yq661vetcJkFN3Ydw1Bcdk5su85yCKQdHLZ2J/uYMs9tiSIvRP5s0xOZZMrgBfqZWQN+vm8+E6XkRVGLpxwTaGcnGYoVy26GghCknuHs5EQ87W5u7vDjT+/w6fYeq02Oum12r1FZmgoq631j//o4d4oElObpIrcNMR5NcH39VMzr+bcYqFHXWwTdStmNwkCtxO9J2Lac0+T5zHMbLzwNnjD3KGGO7YHH1WYj97ihY5ogrRM06IPtkE0m6DwX7x9/Rr2q0dcpXj7/Bs+ePVW2kE9jekoFO/VucyNNDhXWZYShv4LrU+74X+A6TAFlUqGCe5JILHtHyizm6/OtN6YAR8q4dJjuaEAA/kwZcHyfDirPh9f5yPNKvBUdJ4DTk3XLSZiGZirTVC9GPqabSdJDaH4PYOO4eHCAccLwgEQYRwwb2XXP/R3NfKP9i2zLKE5xcXGKNGJKKBlV2hXJNiUrblPV8OJUfCwZZNCTxTaKMQnkIWFYBUwe7iq02xabbYC5n6Cb+riMeowYDlECVR+g5yRNMLkxXngSPKPgKsMeJNmZwJnDuJkKZbVBwCApMTlkyAYN8LlZZD3WDIBv2MU6VxyMHMt0VItYwzZULz872g7Hu4W9mT57Ms2Eqb3c5PKMm9VW2nR6OsVoPEK+4WaTjgm7T6mYqpnv7GsQcM3Oc8biQuTmVj1gfCmNN6WCVEBZbaVfUqmgVo8KwdtxR4YZ2XAMzKBFhwQhNFxbtQjdDmeugyxzsR0HcHnv9BP4gU8bQLQt5b0hlrmLZV5i5BBA3GLwM2zWvQCY2WQqDLum7+GlPhzK9ZkyHTjIJqG2T9VgnjN1lXchwBtq+KsNVndzFNw8imsg8tEHEeogQMN1qlilOOjIWtuUcg3Ezs34W9ZOi7t8ge39Cm5JpriH8SjFaJqJFN+2tTIOtS00cGG/9jsCbMfjeByP43E8jsdv9OBChybrTDUkqEYJAHftx+MxZtOpSJxoHG3P3QNq9glMzbJ73PzAftpXb7qY/sxEV+V31kCXfij8YIElgFRRiJcOn+TFixe4enItoBUXbbsK0KZByYdNRbPJbIbpxmWMT3bABK4ToC5qDPf0yqjRvCzgnvhwVpoeaBlfTrMFNhspaockFhRHbZwMuMYPsmn4OvMSD4+fEEc1rp8/Q9H7qIpcQKJ1vsVyMcfL59c4PT8R2VFRVfBklWyrX1MZy3GwG/2ZFsa08a+BuIOf67MZA23rfTQAcRDiu9//DifjE9z/8Ai/gsofmRLqNLhdL+Cmp3j15e/x8PEBP737Badf+vjd+D+j//EH/OWvAX78dI6H5hp9co3zJ6d4cjVC+DRF9jLC75IeZyhFZlkVHgpEAKWOkUpCyTqCJKlREsqEUPqtGZYHF+Y+0y9bSc8avBRDH6DL36OpctRdiFqKFyOvM5JHWdxLQbkvAnasLAGPdJFPlkTsAhHIaOrFjFrknjvV267V5BpL0cId9jiD58bI5x8lLdYNUgWLjA2xFgi029ICgbKtpvfQNq6kgCZOjZk/IM0C3JEosn7E5ekM2TQxIIimtfGDQQ9pQgZHgHLboWf/CAgOxTL2nK7GJGaR3MFlwdzRY62WQngyPUXVeVivV1qcUb5qCmL53oA6Gg9i+5At+lX+qSwaU+groWFXoO6+MSDOeHaGi0kGr63hOjk8j6l8IXr3nNlrIhW632oKaBKQUcjnZtHVoq97kCg5eKEUO0y5Bce71JOOyDvZT1gY8SoSpGP1QdaMDBXPFfaCsGlMQeoYvz2fXn2SEgcUPDdawQ+3gH8CJDTvn4kUjFdvu16i6Qp4cYDivkJ+W2Kb13j95gVms5mk4BGcCODi8f5WADyV8Owlkiq3tP3H9L++x7fffiMbBgSKCLSo3MsymQy4YxiDNgGQAEochQZMSzDK1E+IoJv0E8paTSFmh/8hdCWP7avx3evBZ6wULcqFuSfTjd0gsR8WhTsA2A5etgW6dpstIovSy/Y57K+jSZ7A/LIAHWRerTfIVxvUZS3MQYaUJGEsYKIyn5igqJJaggAVgx+YKFxXwgyUpOa2lQKbclHeG96+fY8f3/2Mv/30Fu8/fEJuUj0Lw07T+4Blzh12an154uO3e9jOxwoikA3IkJFvvv4SL189F5ZWxcTgoUPoVVg+FuLlRX9G/n7MDYLBx7bIBaUwPWQnuVYQ24Jr+/TO/evTFG8ytvlBCSzvxQQ72C6TbIyz0QX8IcE3X32Fs4tTuTByHSiHQ4cOLWrHFyCMDDu54gL20UMxges+N8DMv8EpZ5pmy/stN1skR4UAm1odiISRcxQBIYOdCPhY1ZIISu8omQe5ndU7WKxbDLRa6D2slhvxL3O8SMBH3gfIQiUAKFJKMn+Uqoc+cOGQ6kb8Ew5yTgVui0niIYszAew47yugt794CgC5ODk5xdnpGJ0TCEuIUlXOa3mxxcN8iTiZCGDZVjm26xx14+DJxQgurQcE3ObmSwOnqrAlWNOnWIxiXEwcXDo1vKZFVXqovQBuxPAcMpk1xEJ8QTt6K+pGkNynml4SpZu+lMCBKNaNBnrBkX1NT06y/VwCRWRLWq81M27kPdo5UcaeAcbtOLRwtpxnehnbRn5N533KoLM0wnw5l/usgDdMC5dxxqXNVhhd19eX8sS0HpANIysHMBYVB3dXMzysZYUB3g0zehf/axYdBM+Leos45aZAqBkbshlC6S3nb8MKl+RuE7bjuwJe1r0vQJvD140aidvjPCDo7CHPQqQegdEYReih7B20tYdtGWK+GVDma4z9G0xnLSpvhO2yETYxJcESHNG2CLMAaRZJ+jtlzpu7CiEDFnitnBr9fYH1OkcXbNFHZK1F6P0QhR+gJDOZF6IeMCwKuGbzR9mWuuGwaTe4e7zHsFTpNpmws9Mp/ITj0TYRW1bBaa4F1b7DzqQ6Fx492I7H8Tgex+N4HI/f6MEb+unJTIxc/SDAs+un8jjBtvF4IouB+/t7vHv7DmVFjyVj1mIXgIY9piwhI2cwBYcsJHZF3AHrzVEfliBKpCiJolgKTEpTKevhefTNodcUgT8uGCn1IjOEHm0//vgj/u2vf0Fd1ybB0Mjb5O/x7+wXKvZ/W2D5XgR3CHD/cCuyTh79sw7xVwnixwzRA+ULxt+Ju7pclEYZ0ucXyJIAIWVnw4CAO/tljfljgcYpMUppfE/PkTNksykKJ8FP725QbbfiF9XVNS6uxnj5/BmWyw3e/vyLyPlEMsOGEnsfBUb0MItbY6Iusg0LoRnWlZYXZu27Y4aYNyyL9g5vXr3G8xcv8OHvN3DWlNBRqsOiHXgoV2LA/uLNd1JA/fTLHVqGGEx+QPGvf4Kfu/j+0xR3wyma4Azj6RXOz0c4v0xRPQ3xJgMuUZJWgqYYUPYB2oBsRE9i7iWDU4zVG0kPoy+N7PALA60TDzEF1jS5TsCzyiRdtpTj3MNtF8i7KYqeKInKTqzZswBIZl2vF1rhBPbRgCwMJr+SlUAvNy/G4NGTyDCFhFFiAF/KgoyvjKSNsuATDxpCLB66TY62WCGdXiBIUgF0mASqqaSBMDTIGiIji++tZ9qoyBMr5PkNvGSM3p1iW/s48c3r4fI6TBUAENbC/8fee25JkpxZYte1CB2ROrOqS7QEGo0FMNjhcoeHv5aHj8U32j98A64glzOzINS0KtFVlVkpQ3q4Fjz3M/OIqMLsA/Q5YUB2VmaG8HA3M7fv2hW1sCEIJs3XDYo4VZKikJ5JLBwi9PohbKNBXKRS+NoEoEwDvm9L6uq7d9fIVgtJvSUJQhnyaxHRhlTKIlf1IwbBCaOG0qgWBBAAWUcZ6PPE59pegNOTY+VNlNdwJeG0gOmmKJoAsPvIyW4zLNzfl8gMi7Z0OAgMBBZDFujRxvNjwQ496R/0syM7j4or8rLIaGTQAK+iAtvJQoUw/XgOKNMmmFGkJco0E2NxSm2ExtiCqqaFTBJoCzQm56uOpMjSa4oysZ8uXyG0KcNTabEMf/AsC0dHEwWK1KX4mbGf3N3c4+3le5W6WrN/tp6P/LlldCiQl8N2NBri17/5Rgo18d8ik4lF/MaonOxXyj0JCjoqgVVL6mRMCwqmmJdKlrVN12wLV2KV8l0zVYTRo/+2Uco3HzFaW3Btw0Jr/6CHjfxHATXSXzZ18hbQaEGzFjT6G8moZoPxAQS2kjgVw3yeM4Iv/JzctKHnH0FR+mJ2yeSU4AyywVIB02RWqwlelPJaTPyUtNWyFFlntF5hOqWRuWJWy0aNBhE304C+6ah7zvazqQRSpRtXGzLtnUkxdlQHUqxPo2pwcHSIzz/7TF17ytp57Y0K5TpCvk6QBF2g8WGJOT/BJEdSbx0beH/1HrGe+wVQo5chmWZ6Q2hznHJx1P1TwFrN0Oav2Y8GwxEePzqT8AWet26vL0CNTQYZ5dC8Z1QFsoLiOgtxnMGzMpmT8sYTkM3xmJpcoS4yYa35QQnH/D/RrP4BcT0GXEtSJ2E4yBJu/hCQYcqtAcN1YbuU17Lvl1inDby0ROAXgMsNLh+N7SKtLZGiM2mUXlRkdhOoG046MDxbmKdM21Svq5nnngufqZP6PpHmpgQpZMQvbB4D80kr9OBitcyxXC6Ebsa5lnOb6wQ4OuyTHoSclg8MGxD5aoXpei4hCmG3L4BWka9Rm4FIcHnbmc+nCEIH3cAWs/14aSBpPESuD3to4cKqYJV8HoNRbDRMfqYvp0jcCT6yjyfCQpN7dwseEY506SsZyTVnEi/BYBU6s5XpcyOEXF/fsxFn9L5TpvjsA+ZO7xBymR7n2/t/q9VsNxA1GNbUcOmJ2ethvV4hyrKNHFzMNVoVJ8e4nmd4nx0O+ugNepjezxHHie6fm5Guj0eHJekbQrupKZsE3GQSL0/6nKrkbQZweCHnWdKKrU0YgpqLKA9lnzPh+SptVNhjJu+jPN+UTDNDo4RDn1MGIXhM7vZQGL74s10vG1QPJdbzCPPlHOl6LexDp+FabI2T8Rqnk0aCEFbRiZz7ftcHKu7wlFjFqRxrsY6BpIJdqwTvpFyiSCoYdobSrVG7NgqGNBgWc+khZMdlDidSG1wKFFXrzRI1bpd3SKdr5bVmGOh0Owi79JVT86z4dwqLj/+T2A99ltXszevP+8Xz55/vAbZ927d927d927efcxuPBlLgZ0UmBQE92VjADPo9nJ2dod/n3yvc3t7izZu3wsxowbK2sNXVuwBBrceKtBaE0zDbRoYmHkMsMl0x6SbIxvclm4GFL4+DixcCbet1jDRJ5S2Y+nZ0fCxMjx9++AGvX/8oC0slC1Xv0S5Z1E/qGBVboAXaGilwCUTcT5eIUxYkDYxPKgTP+/AuXXgrpo2SQaI+BtUy4WSI3lEfntOgWa2xnMZwexaGHbJdWCRQt8CXIiPDQTgaY1EEePv6SkAmJT3KcHF6iNPTY1xd3+D6+k4VMjxSXTS3FXULpKkzqIpr5X+iimSyv7QStC2BpZF50B908IuvvkI0XWH1EMMnH0e8dIBVlmKGHMefPEdvNMSbV1dYNyaePlvjKPlvePghww/XHeS5h67XwdT7BE7/BONJAOcixOHEwBOzhFmtVYhB7sjuvk05qANJKlXSIoYSlCKZEcYaQwlEJsTEQpUQKiEGLGBl51+Ba3xcyfRGYasV6JkPoPvKvJigrMKNGEXEcfTwEaYN+53aDWcfcx3KfRKYVgjD9uUsChjbysKkMNfpjDo5kwzF1ry5NfRXyZlMwLSQzW7l2gSDQ7i+L0CMo9lObdqomB3XwP1sjXK9xsmwL4UiC1A+Z2mbSFYV+lmJ3pCBC2TjEHypRA7LwtQmsOQ4WEY1iiQVuZbXCQUEJwuDEm7yJzPuutPzzTbgWwYGaDCPMrz58S0qsk6lAFD9Q/Vj1ffVbjsZKC0zSQFsis22LZ4U8GBgfHqMQb+LpDQlMc8pSvhGBcOpEZOlZTnodUKsKJdhkm9tIF2VSGAhc0wMe8DIVYw99nWmy9XCnOH7bvlPBNOyjP3DgO8Q+JPeLKBPRRSOISKoURC0sTiGTSVt0wC6VIymgeUygsOCTaRckETW26t3eH9/C7/Xxf0ywiD0cNAZ4HB4IOB9ARantoBf0WqF6/fXiLNEFbAf+NlpXyUtARQWJT14yhpf/+qXOD451Ab35AxqCZxOmWz5IPJM2YxoP/kO4LUlisi5V0N755ftzwKy6ZRODcK3eI3MEXqHQzY+NKbWuqK1FbN6rnrjXaZKC8y1ErHdn9vjVD2J2LryPhMmD5kreS2gKednsixX6zVWcYTpYo6Hu3v8h9/+rzj96gJmvcK7P//fuF0PJHXV7/UkSZpHm6f0LZphsVhivlyo99cy5o1HkT7iTUKyJvdKP2gxvw1rTX+0tp+0EtEdcE6dVoJcFTrdEF9+/pmADhnnLKYaM62zSZDOE9xn7Hf00coQBhZMMqNhI2Byq1PDoukiTMRphbu7e2GBC4jQAtcbgE1P5dpQXX0GxcxtwU2V7Gvik08+Qa8XCIBM8Jz90SLDp8klQMUhTZfhA2syADl3OvB7IRrPgZvSK8xEYxtqXi0LuYcFTARtGEJCWXIpQQANfGFjZXEuncYPA9moIBM1rW2UaY2gyOH6CeCGgOFqLz+6UGZISxvTyoCRVnCyFKMO5z1PgxeNbAR4nKedBq7NCAICbgxEUTJj8aPLS6x5D2BmCYEuo0DAY2l8ScJcLVYYjbrohQTpPZF908uN6Z9pEiEpMgHW2CQhtDJghx30Oe+Yik2HKkeyWCKiP6PbQ+L2EQ1sPPIb9OsMJe9ZpYvKsgWgdGkLwRck0Coy0xxxkotkmfcfXhOmYzN0hkA+z3dRZ5KiLPk7wipuN4WU0FUSwiWcRfnFLmidwL7SrmV2PM0UkK5nj5Z1rcd3C8CTfZvnGSIakRG415ufakzU8rrtRCGzghj0q82Bsikx7nFTdYCbu6mkVTNlWzxIW3+1ncGkOVty7blBw+9B6CPLE7kn8pwxMEfCc2TDQgUhqKhiMpLV82wCrPJli0+aae4AbbWBrFAbVk5VSH9xKCaw6IHm4qeacz1g3maYrde4imbIVmuEWYnGXiH0UjyepDg9ctH4vxN7CI5nOxiJdcVq+YBeJwDyNZY3M7lfrNNbNKUt3nClDeQWgVcDuWmjYbARwTVtOddSfHl+13WBq8s3MGN1zXzPQ3/c03ikBlXFx5P9iNeE4JrarGnl0gSeu90hfvXr38iaeC8R3bd927d927d9+xk3+t0oVgYLRbKMmNrGwinGYrkUyQ4NainFIEujKLi4pO+EWnS1S66WLdAWLKq4VPQqRRzQxY0uMOT3GlRSPkUqPU3o8UI2INPDhut6slAjG4Tmx8vVSh5zfn6G8/PHWNGvLYk3BVULpCnGgma2tFhfu7BkgWQ0Ai7SHyNLc9QzA8X7DMV5AYxdmFT6cOtRH3uZpFjPVpLwWFB1Ouki7PPYWGSQHcVyge8rkY3I0wq+0eDo9ACl7SGOYjmm5SrGw+0UZ6eHODk5kvMb0Xhfzpcha9D2LApDYafIbY9flnHt+ltV4VJwc9H6/NljPL54iruXdzDW9DIheEI4rsJdGiPvhfjkiy+lOHjx9g7GpMLXp9/CvforXvylxvfXY9zmR8isJ6g6T3DYZQHswf9qgOdD4MxIYRQJ8tREXHkoXRdeYCGQhNAd1lpKeXGJLNuRg5JmYBFcK4VlVBOMYEGY1ygYYsDvlNexsKWXWA6s8wBl5WPoP8AxYySl8g+SbWF9PhRoJmQMeGYs0hzYPRiGq43c236hvz4YAbq4FcBEfRfTYTJ+RJ6joBEr6MKyfSTzO5Q5ZZyB8sshyCJ+YSyaSqTJWiRJnUEfRW2iqAwpdD3HRI8H4hm4dy0YCYvcXN6HoQ8EmPJGSXjsqgTX/qBMNDdQxqmwtTy/gyTNpLjvhb5KfCSgQW8jslNcG4fHY5E+rVaR6iKSDKo+M99eBTuo87AFvLcyNSn8jQqW28X5k0fiYYhGAc58FUqp+aCCP7oBGtOC0+RIcqZ10lctlyLWJfOUu/i+iSSukVJGxwALFhe2AUfGCT2MVOFIyZAAnQbZHUo6RVoMJbcE1MRUWlhAynyd461ggl07NmiDBwPzxQqzhzspKBk8cnN1LYEd9GZK1jHsjoHD3gSPjpj2SaBUpXGSOfD+8j0eHu5FHijdgt2ZF0S6g+aNtp2kxbt49esGB+encG1b2Cwq7VQDupT8mGSNcmwrBpVi+6pOp+ZD9aUAL4WIign8zjy501W3792Cbi0yt9Ol2+9tUqiSE7Z8mPb9t0/agGx6clHJxKqP8HecM+kzxvvCcr7EarZEHmeoEpViS9knQQ76UQ5GA3T7XXRo2m82WEcLdI0cj07OZKOiytdYxEDphcJgvLuf4u27d3jz9i1ubm4EJCXY0HrUbYCCtu3iD7tN03TUVK8/0eZ+s0MHbP2ldphA7IOn58f44vPPEdiuzGMcK4aRoVrHmC+BmKxWoREqwDjL2FdLhD5BYWWuRIkggUf21l6/Lwwwsq3lEuyCfC3Q9sEmlPpsIpvTXnwX5yfCKBepoFxGyiwrVCbHeCHAKSWO9GAkQ7ikfM3vIAg9hCYQOfT8UpsXBDv4ugwEYRoyPSQdn7YM3KRaAAXtGUx4oavBkdYbkDJsEzHZrByDXig+Zqr7KAm4VS3hmAF6tJ3wTMUQL0pJ5FZADOAQuOA4zmo4TSHAmlKEc1yrxFLaDDoEfohTSqKticyokSOT1530O7CdSsA1/k3AnqrCYjWTyY3gWimMSHrzuej1uwjom9UC902Baq1CeAp7iBUDEbrAk6BGWNOTFEhrT+TrfguuyfqI4Qdq0yjNCKQxJVWNk7DnIisoS1abdQTh6DVJ4F2s7HZCmaRtadcoCSpnOXqBg07Hl/Mmnody09L3n+bDPruznSabhf1BH9F6iTjh+2+Hg8znW7xdMZn1DbC1OpA5goBWViBFdFHEAAAgAElEQVSaLTEa9+F1AglC4Pqnfbl2HbLdGFDzFNccjmsg5hqMAJkeYhwf7VzCuV19b6XoCgBUYLFO0BRgWadFo5EgBG4uNTZlmRaKykRT8FoUsMwCY9NEN7AQ90hV9zFsfJSug4ivnVmoUhOdYITJ4acoswzp+h5W6CBOLTR1gcNRADtZIM1tZMVS7pNZHaMxAgHXmODNJG/mghpxAX/NPqvZ7Xrckp05zda4/+kSyBiIZaE/6KE36mymHXXJ1IaMPFunynObcDOXmyaePfsCX3/za/HqvXp3tWew7du+7du+7du+/fwZbJQx0KCZwIcC2wRUEKmdjV63KxLNk9MT8Uibzma4uryUYlZJylqwQ73mbrGwgYY2BQX/o43V6RdDlhAX12SQ2PxyxMeIX8qTTaUJMqQgS1MJQeCqhH+nZJQ7t9P7e/z44nusFvNtYSvF5A6TbQf8a4+Ki03bclAXpfjGJKmSKRmHDazHLjpWCO+9Izvtkj3IQpmLJNtG52yCXj+Aw+KCEra6ksh5+tPQlZ6AIWrq8FzYnQ4K28PDNMPi4VZLQSiT8vHo0RnKSkn8FlEku5tyDMqFX7FkeMC8Jrom3jDdBL9UBc7RwSEeP32K+D5FchsjIOBHYMKuMC8irE0LBxdPxET/+uoeiVXh4nyKyeovuPq+xOVDgOt0gtyiHPYQo3EP3SMfwaMAB70Gk3wGO3mAFx4iLXwUwlqz4NNnTUIMlMSPu/9crGc5pZ5kqan0RWGtiRyU0jEmX5ZbxhofS0CNUhoB6Ch90qAGCwqCV02Nnhth4K2QVB4W+QiNTsKjn5zbMM0vFxkJ5STibSISLeVxogqWNqmLi13dazWVjQtf6bkCQilvNdmFJ6ONxabIKNkXLTRpijJ+gO300Bkcw3YMVNlawK7eaCKSF/6bUk767lBaxPpbXTAlR1vCQpQ1CPNaXo/AlOESBLGkuCSQxddlymFcmIhierqUcD3FmqNsjGBTGHaUKb9eqxeGZLAKwPn+/QPm0wf5/MIII4uR10KPyw0YzfGnWUmm5WJ8fIDhoAujJnhGsIh+fUBBAJwVkfY8rCoW+DxOpWtscqLSIdYrFrgVwn4XVlViGTdIHQtWYGDiG+gQYASlgAoZpcSOwAWZPoKrSaoDXaVYVBVwbIJWBpo2+U6kv+pcictfyyozbdzd3mJNDx2Zy5T7HMc5+xw9Hx9fnEhC6N3DQpixjx4fYzFb4H46FWaKlD4CehLwJ1NJsdcoAePv5b3a1FptckdG0de//y1GviuAI4E0gdZkzLZglZ7/dDdoAZ+PcbFdzGxToG5AID3upXZtAT/1sNYX7oP57YNX/uiN1Oyii+zt3M0xR0CIGy3c0DBKgjOU5RaKHeM0ODw8g+tZwjC7ebjG+9trrNeRlvI6mAwnGPQHeHLxBL1OV95uvpiLp+B8tZQ5PBKfSi2XakE0GaAa6N2drP+VtvlE8uE//NsuGLfd0Nl9mGL3iFl9XaPXH+Kzzz/BuN/VTDbtWVXGWEYlYtMTY3QmFHJDpA0V4SaNbTZwzRqOQ7N9speZQEzaEsMxaPlINraJNEsQL1eb4vxvm7qWKgjBwnDYw2RyIGEOIlslC4nkKz32KE9cEdysMri8B8FBWkEk5MeHfXjcbSDrk+OU17QxkTDZsiiF/WkbnHNzeT9KFV27FFlelpgoDAvdnoWstODyeBxDQPtlU2OsZfYqaINMZQ3Uy4aEmlDZ3xfLDHFhgfiHr60vFWBJv0ogTgs4VQbPbyTllew8esUJI0xkwpXMnfRwyzjurFJ83/oC4pDRzc9HeXGGOEvFSJ9XOI/XiknLTQ6f87WjvFNrnqMKVZJjEZlYWD7KgYMTstbKVFh7WWHA9DtwfFtSr8WzUMJ5yLBmmIwKMciZFlqVwoTiPSJOVnI/acNlxAaB9zDpS/rqCglXddZ2w2wD8kp3awSMDH2yuRxMZwvphzJfa2mpPFxNOvI69G1sUGG+XOmQEw3aa1CNTVZBGpzdBKBoWX7LRFW9jxsKKsGUac5+6MJoLCznkU4/1setX4KflyFO3AUjWAsClZyNKYfmfVNk+CqAg2NH7qEii1eMNoGbBLDi/1SYD/sl72+2o1Jn5T6q3G6R08OOIHFZwkEB1y3lPlhbHpZw8DYFomkJzDIsoxlOuiVOxi6idYyXb6/h2QucTkyMj74Wxne6IFPSQBNYiJaXEoYQJfysIUqTNgc1MloxrBu4BHv1PVPGommgaCpcX18inUcqVdd30Rn0lG0B2aDcLNMBMXyeYoW383XLWoPMPV98+QvZ6L69vRPmrkyDT548+WjW3rd927d927d927efSxsN+xsjZe64kqnQRsazcWHQhh8w+ODRowsMhyPxZLm7ucVPb94qrx0d+Y7dAuID2WjL3FBrFQVYtKDFdqdcwDbTFnBNEkZ9V96bx8BjIuMpThL5zpVN4Ac4PJggDEO8ffcW33/3F1kuymu1y1hZGLbF7FaCoYpdVdTx8Clxms5iVPSM4t8f1wg+78K/9BGsLOXJZbaLzRp2r4Px+QSha8LkgrspYYuHD4sx7sKLPkQlqdmBmO1mjo8fvnuPKl+KF1TdFDg7OcDFo3Pc38/ww6vXIqWTxDZ97GrHu5WY7RTnLGjtBp9+9hl8J8TD20vxN7FLH44wvQq8zecIDw7w6PFT3D8scHm7xPAR8GX4F8xfXOO7Kwf3qy6SeowmeIRBd4RJ10dwHiB84uG5V6HXJGi4w72ocR9l6E7G6PQ9eCxcWGEJEJGr1M+0EMPnSqQwBNfIWOMOrmKtKXBtm7Ymnmu58iHbSvC2RYgqPDVIIcEFDSb+Al13gYf1BI3twagjJJULOB3F/GlloJrZJdia4GdaNqOWvOoNWlabAD26bwjgxn7fFgwEmtu0RwWysXAt1w/IV3fClBgcfopO2IXlKOmLYbGiZBYmXd4V64TSSAWYMtHPEAnSbW1jEdfoLQv4ZorAyVFZBiq+hxQhCuSjGfhDxuSyXDzQ/ICBCQ0W9w9i2nx4MEZTGcKCW1gNFkaNI6NCtcrw4tUljHwtn6EdlxutIPEqSaYEwt4YZ2eHKOmTVVjoVgZcMgpo2s20N0rTbFVIkmHE/khgwa5z+ZyLhxhlbcMdMFDEQFZV6LFQKyus5wlip0FoZ3AzG944hOeSq2YJ06yhh44GQVlM2Uw3tpiEyES4AtksQ0gvng6vD73v2L9Z6IgDFqyC467G68u3yMTERyfzKXUpDicTnJ4cSpH89naKVZHhoj8Qf6blYqFZfsponu9ZbgA2VWAz7VYANpH0KsCrLZD5mK9//ztMQhcUvnEykdmHIJzS5G6BII2TiZ/d7u/aYc6ftdfaByiSBtja95QABI2utS+xGS87T9ugSh//UsaC6o9k0EbzSB0vi+WK45hG7Qk+efoIL1+/wXevv0MislluDAwwHrKvXODk4BAGr2OaIYoTMTWnYT0TCh9m98JsoeG8YikqeaYaczsgkwb4tpJP9b2dp/Uvd1hrO3O5/qWcHflouwCd/qw6qU9+o+dOzkj02/zk6Sd49OyRMCXVeeamS42CTOPYhBk6cOUEM7iikMTf2nRRkOokwJa+T5JJRiCdoEvYQVUaMEsyjJS8UBiYBKnmC2H7tUw2AYtU6a0820wLh5MxJgdDPT8Z4lknbFn+m8EYlCAypbGkDDLHuqRvoUrjTeM1TgdkoDkCTsk9RGupCf6ui0b8DrkpRIYW/RFLpmwybIXG70kmY6o7CJAuGETRwAzoGKY8EzkHKhJUhpo0H84LEtjCNQCPV/X/VVYgpTl9Te8ybVpfZlpKSQkgfRcrGGWBwFEy19rwUFJKStCOk29dw/cNCZdY8R5hNehyDuNnKSrE66VI7w0nRJ4n0gdzeBiObDiVhcqxENqcAAo0RSZeocvMwZ3vozOw8NSkrUOGPKP3l4fGoWdaDo+ye9fR9zX6KarEa7KsBWjncXVdrJMlyroQiSrnXgKvAswra7aNRFt5pbVjsO3b6hct9s7H8N7F72T6TcZ9REmK+XQpgM4GqCsbYRYSgJ1Hc0mNVd2onRva12/tAJRMcTPNtGuxDXt2+xiCgu1govck/UZpy0EAbb2M1fEx8Mmy4FsVkjRHY3Y0rsd7pqLMtvdesog/3Kii/QKBNs4DvIfa+li4saJ9Ci3KeE2xErDF65T9SQFt4s/G9Oi8gpUX8OwSrku7AheV6eOhMXEfNxguGBcf4eomwXfvY7m/+GGN3/3yAmPDwjrmmoQbd0DluVguX8n7ROsUVUPLgEIcP+yCad/KDK/gXYYXwXcwW97j9tWVWCZwXhkMuuj0AxSbTRAdiqOZqYoErG9Euj9UTYNPPvkUn3/xJeazuViw0OeYG8w853uAbd/2bd/2bd/27Wfc6LUmbBIutHXyHXeQ20SptgxSLDOa0zo4OjzAxcWFSEfJSnj37hJ3d3eyfmhtclo2glrW7Rb2eoG3YZppYENL0ORn/V5cbNCbjWAbfS3o7yG753UtixEaSUvymWWJoezBwUSe++KH7/H+/dsPjl8KUflhe1y7MiMBXCgztF3kSYaH6UolCJoNrK9NBIMOgmsXXsJdUwX4mDr9q3vYw+R4AAcWbJG9AQZ9umkUJgbvis2A2oXlugjHY9xFOa7eXGq2A03jgScXjzA6GOPd5XtcXV3LAk3cwnT1qL6phRvBjsOjMZ49eYb5+zWquxQWzaHdWHZgF5GBvNPByeMnAga9fX2DrG/iq9M38O++w/c/Oni3CJEUfRTWOfxwIqbUg74P97mPxyMLZ8jEPJjFdla5KG1eB6Z8ZWjyFbpBoOSzWYmc7IecclD6qgmxSJhGBNZqsG9pTzZhrZUiUypZ3xSqKCGou2EcbV35VX/aXLNWMtYgNBLY1ZWwGuLmEI3dVWyslpkmUkjlfdQW3K1UUl6xLXB1Pb9l0LTAkwLZ+EWpCk2cRTIlYJsCgnks6WIFo1pLkdAZncMh85IMESa16tAOsqDKimbZNAxvJGGP0JJ4HzFNznBwXVlI5hWG6wy2wUI0h+my6CSr0xUwheAFOVbzlE7dC2Ev9CcTKSDKIpaFucMd/crAtQ1MrRoXRokzSidnKS7fvoFRp1LYKB8exYhgwuD5xSn8gY/rwoBdOegXQFhW8DomrMBCTumNMAtp3k8JHOVcZIYBBQNQTH5GA9PEQO56OKBsLnQkaZW+S3Rnj+IcTbVEufCQugGGYxO+zWLDQLzOxIyd55Tdp9MLRVqUVTUWKyBYV+j35jC7GSrrBBUt0Ani6oRDoyqkgCsqMgtuJYmxbBgUEeDJ2TmCIMCKUvCGwKCJ2+splrMbDAZ9FXhAWZdm73LzgIU+mSoC+nJubJlrbZqoqJrUBEL5+te//i0Oh77IpMhc1ETJrRy0nYvaolv/Qr3mdiJSNZoGXTQDQjHVdgC2nQd/9JsP/qbmU93BKUcrC2FI5Otciuc0ykT2LpsFbo1pHMNDg6vFDAuyOeoCpyenEpZyeHCEaB3h6vq9gL7j0Ri27cv4oGx/vYpwf0dPScVwlPHVjrePivn27xv8b/fvG3Cs/VlDaRqMUo9VDCplU6DPZvv3FrpoUxBFYisJFvJK9HsajgYIOj1h/fYHTP8k+K3APKtJES1KpLDhuXRXkwxXNUc1FuyAXmsGVokpTDyGB6jwCb61AjVcp4HvO8r/sabMUTE0eXgMDCEQ9/7qRjPTtB2C40hy8pdffCbej9Kn5ZaUoCwcPhG13OsYlqG03ny3rGR6pyEZvoQIk3WGwDThe8psXgTXtZLuyTEovB/rEkgzpo8yRMiCZ6v7aE2AjYBb2EE9X8HtlyLtN50eGgQKqyPILCCKBtYs3pMVkCd+cwS+eayE5ZRxloBmaVoJYC8ydQKWnBboJclQhDqDF9DMzENe2AJMKjIQfc5s0EWBMk+Xn6tRPp1kwtF6wBNFb4PMdDG0MuSVJynBHs8VWc1JjnVsYmUFiPuueK31yHhOK0mqLm1u6FEOCpGD1mWGJJrDNAniW8LK5nzAOcD1ySgssSTbnBtHOuSEjEbZmNQ/b8brFrPa6dt6RaQ7/6Zv82edjM37ZTd0RXK9XJBJuZBr3glCOXdREmuWvJKoE/hqpxFhs7akVI619iB2308NRH0wrc+bYltpLakKUKgbSdzkPY8yeov3azK8crKhXe3NqPjTao916/2mNkx52FzPGR+GCYn8WAHKvHdqh8J2JQYVhMCxRqDNgsEFEmXJZLM12p8t44ZmBc8q4HoVksLA/UwxwG7dEcqZg8U6gmcs8KtPApilgcWiEHq4DW7eWChdG7PktRz7cpWgrrhBaakQIT1/KBY+EBkZ3rz6Cc08lvk59Dz0KDV1bdk8U4w1vTndJprLKWllvgTLawxGE3z5xS/gep4wrimJ558pCacfn+O4e4Bt3/Zt3/Zt3/bt59x63VAWPFmmjeV1kclFQlsItgs1LhK4y85FdOD7kixILzTX84UF8tNPb7GiDEYAiw9BtQ9ZCRrQEHabfpy8kZILiKxPGzyz8OCCw3O3YFsrK+UiNM8zpCn9UAhSWej3+zg8PES0WuLbf/kLouVUsSY0Q0SBMLq4UyZw26KsLYRpqmzaWMwTrOJMFp6VW8L9xkHPGsC5bnfxLYliVwyrGsePDzHs9ZTUggbBlIKyiBIvFnWMVaNYO52Oh2B0jHfvZ7i9uSKHSIq4US/A4yePYTsuXrx8hflsCVMZs8kRCtDimPjm618gjxqs3kXwaspYybaqsaaBONY4OH+Kw+MTvH9zjdsox/nTHM/LP+Pln5d4MfewzvtImwPY3hmGvT6Cro3Bkw4Gjx08tyv4VYIqL5FkDgp6zPk08mYhR5Alx+z2PYokg21WcIID2eWmhJCfQ/msicZTZIQEbxlkIF5rBf1/WNiQJcQKi+dGJ6xpuEAxOnQ/0WmfgtdJKhpT9HKk2VyKvtABxp1rpKWHRTGCYXgqyZaAmE4NlMWubCNvtTMtwLaV07QAmy7+tbcb/yMsNr6/AGxKEqkkL9yFt2CyQKgqpIsrOO4QQf9QxhSZCNzhLtk/LAe+74vRNn3ZZBeerEdTgRv07VoZHn4qTTjTEt0sh4tYJFSWp3znDM9HWVtYz99iVdDf7AB1lkoam+MHyESqxBTgEFFt45XRILKBkVHiCUr4tYHLqwir6Y2WsTQYHJzh7LSDqGlwV7kwKhvDHPDrGv0hxzrrY2XcJlBpRtcg0aqhpKcTJalJgqbMwSyPyg0Rdlnum3BNpq2x+CA4p+VtqJFGOSrXRdcnU7MUc/m6sWUOoh8iTfJdFvUWvaZ8kZrRT7DjztD4MXKco6b8WqTW7D8VkCWq4PW6wo6g+T6B3+GY8Q9Auk4xj1IxXb+/vsRyORMQgMl5k9EY48lYgJCSIDE9BMlYoSSMwDBZlwSONaDVFkvt/MiC+5tvfovJINSgqkpy3RTXrfVQ+8MOA6ud+tQ/FJim0ga3bIfNn3f/u30Sdpsq1kngqxCtIpG+5VmGMilRRgz+aOAELt6+f40kT5HWuZjQnw+P8e3VS3R8stMmWGZLAdAPRgfoBH2EHR+BF+Dm7g6r+Rq393cytttaveWF7qIHG5Bx57/qYeqxxubcqEH4MWPtg8+183N7TuT5eg5Xc4Z6QQV8kk3motfpYXIwQrfbw8FkDM/j/FAJSEbJZJrTuJ4BJzWqJMI8JQPVlnEpOyRES0hDpH2BU8GtGepQwAp7wnpimAFZXxJmKwelWEl2Kx/1PMB2Za4LAxeDjifpqEwanc9X8in4flEUI4sX+F/+3Weo0RfWDpmT97mFQcdV8lANcDNZl4wgAtBlzTmx2AB4cWbA8Akm0Msxg2WXMNxgI4flxoz0MU69+hy6IiNU91tUsciyayuAUaxhuHztFLb9/6Jpfom6OUfVKE84PkcYuQwlkrAPgmL0GrSE9cXX8T0yrjiJ2EgoCdSBrUWcq0AICwK+kdHM/uTZTEv1FRCugWoCbPGyRmXUWEzv0T88QMf3hMkuTFPe++wandBDVZswyIBiGirDDFYNVoWLh9DDeGji3CjE8D5nQqjhwfQILtJbjk2F85B5zteNI/qqMdHZFzGzF9hYJ5HMC8JkJetaEbg34IoCWNrwgVa/3a552p6s+simR8sftLfj5mkK3OKxjIYdBN0AaVpg+jAV9hPnVK4vFDDGhGWd+KK6/u7A0SNTj5nWGq0NKtDris3f27WRsO7ax9CjLRGxphM4kgYtAtpNMqh6/c14V+lB2uRf+45ZW1a4vUnsVonylGfyPrqBpBoFtlFm6pLR5ljC0LRcR92LyPzXQQhpXsPISsSrG+RZitC3cHh6gsoM8KI24d7NMSwiRIUFb8hkXRvpMkGdqvs7Gc5Xs3dwfVM2bO3alXWdzOt6nuG68vXDW0xfvZf+y3v/cNSDH3Kjapu+rJQfXCPrfqs3SOSc0jkEjXitPX36FPP5DNOHmTDBucHDkAjf44aFKfecPYNt3/Zt3/Zt3/btZ9xYjJPNQM8dssGUBGorEf2bAkcvFMX4mKau/R4eP3qEyWQii4y7u1u8fXspXjWtbFT4GO0ic8OqUIuzdg0qcgpjy2ozd5hsIlHlLjN3NOnPJmw2R4Fw9J0qaS6fCJDD12ERNR5P0Ov1cPnuLX74/q9SBG9Av/bTSD2nIB11nC2gqH72+J6wcPOwEINvSe48b+B/4SOY9mDNTTgscNrPwBy2jifBBp7nSEomd9spFTLotUWATVhaqqAkQy/sDpGaHbx5e4X1cq58X4wSF2enuDg/w3yxxMsXbyTVkKWU41f48vnXiC4z0HXapdeJ1PsV7uoZ8qGHsyefoskbvHl1DePAxfODH2G/f4W/vnJwtwyRVQMU9gk63WP0+wG8Ux/BhYevBsC4yUlJ4v+RVg5q8cMzZXefcigWgcmKwE8oHmhJHGF5dwk76MHu9FETMDHIBtKFCv39xGOtQpnRn6ZGXlEGpKQ24nK9K7lrC3Btvi+/IovMaEQCZZZrZE0OyxvAMramyh13idBZIq7IyhvIgl2xIXXR3nrw7bArWzBC3q4thDZ9tQXaNCi7+U4mmyoSJG3UtrdSVEpdsgRFtIDXGcMLWSirXWsyWoLAlxQ08QSjfxAL5qKCVZdwrAq2S9mKB+am3iYN3GWBMI7R6ZQwfZpJO0jIArRChCLJAWY0N1+ncLmTH/qyuE+SCIHnwPI7+KlsMLUaeFaNkZHhhJ8ts/HuzQ0ODgbo9Azc0U+qYnFqwysNjFx6u9FHjuQGFk6Uf7GCoPeQhYzJfCxibUMkZkmUIYlLkbF2pVAg+5TjkumsymuGACLHvPKCY6Ks8niUkAeCkxnQWI2EZSRpKbI8x2eUoo8FyCIBRlWGml5RjacKxLoUA/0kzmWsNyETX+nx5su8QgYa365NcZzdLfHqzU/CUKPSjNeSDLV1vBYm5eHxkWw4pGkmEnSCfTQdp2xeADaRiX4IaLG/sK//7jd/h2HPh0XJ8oa1ptLhWhBJla5b3zT5LuC8+kExrtRM1IJFm1/twHLt+7aNACB9DxlAQCYZwbSaMtmSqasF1ukKWVngYTXDo4tTkXb+lz/8k2KnODY+ffIc47CPNzfXCNwOBt0hwn6AKI7wMH3AYj6X+wPPgz4QPVd/eBz46Hd/8+e22v8APNMG/y040P5Jj8ftr9vCvz0PW0CD78lNGALY48lIkq8JpvFe0Qbk0FeOrCeGhNDs/vj0RF6R89OSnnAzAreGADyySUDwR0B/G5aAMDmaNJHUaYIvoWOKT1VpBYgKBhkofzMxalcEWDVuKP10XIzHYzHplwALy8a7yysslyv4jkoHPTk7Qp4tMBleqb5QH6HBCJWhPgM/JBmb7K9kLpE9KugAwaokh0kPTAMSqBP69C+khLSBlSuZp0HWNYcwIWl6HOr+TwBRsg21fDevM/kcJvi+3MTK4bpM7b2D0fyjgFB1/RXq5gvlt0aWsLKdkp8zhq2YZGAxdIEMoxKuTfatIbJ5MnJ50GneIE8qmHUuQCF5pQSnA6q/DU4GarONcnyGuTw8RCgMbrZ5Mj7LIsEg7ApzVYnuea0q9L0GTidAXRAgq7E0A8Q9BxdBg36Tos5qJIWDmht3riX+mAKniAyXLGsFqtMDjhsG3ChLkwVczxXpLP0oy6wSqSjXSgQ9VfCrHtct0Kb7sKx3hJhlfMhcay0qdsd027c3AJvq74HnSfBKb9gRoJUMXW5SSYInwTX2iV1g+iOWbGs1sRl68ke9HpOxrDe22nG9ObJ2HFdCNWRiNDfGOO9aZPfxSzNJFfdMEis+nBs23qfqXswp39ascGWlsF3jcRzIPbtpwwQUs43rSNe24Ll8jqX92WwBeLkBOr+/Ex/bIBhh1HHgOoWArMtFgmyRI+V1Yx8l+9zxEQw9NEmBYpnLeLqev9fnrb0G7fRDm4MSb16/QDRbqGvhOhiPh/L6koqubmfS/+SMaU9i2QRoNw3pr9ft4JtvfgffcyVdeLVayTXgPZ2b1VzP8ilcw0ooyt6Dbd/2bd/2bd/27efbuh16ITkiuRQZ3/8QYNv9oQUmFO2fQBsBtouLcwkeoJ/b+6srXL2/1jvcatGll5sq4U3H1dcf7fSKGewH3mxbeaptkkXARTb92RxZ9LJAlJ33hpKuQhK5mHTKtwmCUBU2gY9Xr17i9esfN9SPzeeRhXxb2fGIdotD9TsugpyGBuozxFkmslHzokH3sy68dyGcSLH6JHBAGC0NOv0Qk8MBHM9EUxJkU2wt8QgjyMbzKz9wwegj7HWxKl28evkKTZLIgpmP+ez5YxwcHYkJ+/Wbd3CMHjrlCG5jwq5oKm5g3axx4yQ4efIcnU4H71/fYFE3ePRsiZPlH/Hi2wI/Ln2kZR+FeQzPP8Zhh2lXPqynPg6PLTwxSzjVGmXaSFJnaTpSWAYEkowGVRYhXrLQoEoz2VIAACAASURBVIm3JSmplHpWXHxb9FFbIIuuYPl9mP5AFbSlSrUjwCaPZZpdxYJAAQ+yMhVp0XYx3wJrXBCrFE9V1PgGpT4JDLcDkxKKTQHBxEXVr5qmRN+bo+NFmMUHKIVpwYX7R+CdLiGU8bAqAFqctWXitIWRlP9tCq7+SysdtRxokE2z2cTcXiVuVvEKVb6A440lkdP2TIR+IH1J/NlkF14DbZSf5ZRrsRgtYbpMvXNx2VhYrIH+PEczfYnuGBgdXQgIRxki4SN6/cEqsWTBGuWSekepCYGgdL1Gtxegsj28rRvc2+wvBR4zMbExEWUZ5hVN0B04tQW3ajDpWghCV5VLYsel0j4JrualhcaxpT/QJJ0nLctMLLMaWWNStIkgsOAbNRwyaiwmaKogAkqvyLDk55bLXrP/VHJe6X24WgNLA3g0tnD7PsbYMRD0gSbwcWk46GUmugR4nEKPdco/Q5mvkvUai+VC2CRhb4C+Y+GH1z/gy199I4Bby66N00SuES+1sAy0np3/Jci3WkcyhxwfnYn34yqKkSSxYp6WW3BchQ5sDcIJpP/d3/0e424ghafEnKrJRRGgJIVQMYcUkNZOQ7tMNv1qm98rn8f2+FrAjeOKcxzBmSxWcj4ja1AaObI4wnqdoHaYYDnEDz+9QNmU6PQ7SCLKnxr8w+//AZ9/8RkWsyUsMlNNE/PlXEIIbm5uhcWR5un2vTfMm49uAjuF+M70Kd9cz1E+eLpI3TJ3tmN897N++NpqPm4/72Ze1hJOvh6Bs26nK5soLHZ7va7cC/hMBjLkhQpo4LnivMMz3wtDHB1PcP8wR1UkOD8/1xsuCjheFDXyaC3XW109E4bD+w3li0xN5mvWyCmRoxTSohSUwBtlixYaK8CqDFGlBGE5vwutSYzPh8MQvtbLyrxjWbi8vEOS5DCsCuk6gRcMMDjo4mjowjBewWj+DFQcK/8TSoxlzmB3pWxXjO4Neo+pUBCyhzkfc94MA4JG7ekle1bJFy36pEpSL9mi6p6scLbtNebj1/yMBBAZuFKVSPJK7BlCn/diuh1+C1TvUOa/h8V5Cn1hmmWGLedCsn71azGkIOf8VDawG0ria5kzKaOmx2TMOSyrYeUlgoC+lJYCscpU5hjShZlCvZjPMLs3sFoZCJwCy6xB9/wIz859eHWJeJEKmGcVhTCcascWRrblelh4Ho7ptSZrAxMpAUvPhGfRG07JWpkqKWO8KLfhPARH6garaC7BHn7gwhDvPIbO0CeS/aBNnm7BXnXWt3ODZnHq86vGwpYt1o7/doS32L3ONxI7DjK3lpGSg/I9KJudHI5lw+r9+xu5jmqu4ODTYL5+HRnBG4BNA9my5NnOOvLOckwtS16ztQmect4qYwlqEh80PXfJnM35sMiEaU92dgssb4NC9Xu1Fg06ylslyrZstlY22jLCFfhsyAarYofLGBWWJm0aVBACpduGTblnhNV6Jcmxw8MT5ATj8gJutUK0XCNKhd+s1o81/d5al8cGZo/p6C5ml3eYL6PNPCTnj2xPo8bbyze4u7yBUSnwt9vvoNfxFZSr16wqZJrvocZSO8eTRS9MRsvE8+ef4fz8EZaLJRazGdKylDUzgTWZt8R+oZY5k+Ax1+J7gG3f9m3f9m3f9u1nDrD5niM7+22KqFpcasnBv1JbbQtC9Z0LGDG+9X2cHB/h4tEFPNfDcrnE5eUlptO52qHUzI5WrbeNrtfftQRQMd/UjqdarLWyUbXTycRRCUHwuFupQDbS7HkcwlZIM2R5Jp9FUlB7XYwnE2RJgm+//Sum03tZ3Clgb1sM/+0n1atFsRmxEHqBFLDT+7kce+3XcH9hI+yO4b2hLIXbpEo+JviZaWB02Ed/1BUZJJd7SuJIHxsl9+GuuyzIDfVZvOEIV/cR3r17LY9HneFwPMKzZ58KgJDOc6wuU3iVkgjdFVM0B308/vRzrGYLvLuawjjz8PX4W1Tf/oQ//tjBtPKRN32UzgUG3QP0Bx66p6GEGHwS1DhAgqZIkKUOssaV3X0uYlWSWo10dS+Ji2E4QMYgA+7gs9AkYGJROleBQp26zlDM36FcR6iDc5SNLUAIGR/qq/lATiM7vLog2LAouPgmuEZfGKOBawOOwWOrYXpkhPESbcFf6SEtSKrtY1yzxMh7APW78+gUpuEoMMsu4KgScFPwtwBb2wN2geBtYaCLJDnOtiDVaWksClggiHxUsdqYkiaLeZpkJ/dAmcDtPZMx4fmuSE64YJcq3bCFmULQMc8bGEUJ1yrhuCyGbawaEy+jEnbm4jDPMQhT2CGBK09S1sqGCYUM2ChQ0kdracFM6eFGhk2IjMb0RYpury8m0C/F4KbG142BVZRJcWyVJvrCUiwRhgwXIHOALVcJelWJOPPhdhx4PMcVE2MrwoGoHZUKSJ8mas4IyFYJ03QrDUDyI2rmSskkRPJAueNvCgBCgJhMuPXbBPPaxNG5j+WLBUajEtY4ReSMkBRddHOyHdjPciwWC+RVCtuzMe4dirSGMkgWxO+uLuWcMgnv/KzB7XsH7y81K0iure47m4JXIFP5vJRZFXmG2XyBk+NTmWfotUTAnudBAWUt06yF5VlIVfjNN7/GYNCRMSyjRlJGtW9by9Jq50wtH2qhJN179e/aKUj5W5GVxsKMKZ6SdLhOUFD6BwcO+1Jo49sX36N/0MPN5bUwQh5ffIIXL7+X+fDk7EwKdRsh+t5QmLVZHos0lr5OTP+sDAInW+CrHRO7Y2NnhGzH3vZgN8ydyeQQf/9vf4NVGuMf/+lPSFdLHWizHVcfvp6eA1oj8J3XUt5lNHQfYjAY4PDwAL1eX/w2+UhlPl8gyzJlcUCvPO2bJ7L+qhYQdjg5FAbOZNLFYhGLkXqn68v1bUE8vldTFUjLCg8PsYA9nh2hyRPEuQJehNFE5TsZyZwbLSb6svBv0GFf7/REWskkzryqBFgbhq4CTDQbTz6nYeKn+xyL93N0gwbrvEHphTg9CXHcYTIl74NLGM07VNkEBmaAeY4KviReC6uMbFUtvWRfo1yOr82YDb0vpCwQCPZL0i6PvYZFxphZiz/crGnQKWrxKiOTj2A/NytSHmnJ81HBCmxhpIlfnGaME9q37f8PRvMXNM3nqOrfAqavZKrCqlM+mcKWa9OUublUVLCNFmjj41zkFcMgYgk54XxY2AF52pLIzU2lOAN8o4BV3KDGBHk6QHwU4HmfzyfAqO6jOcdGlAqgL0nMYphfIwwAP/SQ5RZy04bHxFR9X+PFlORr2QiqkItPaCObW2Q7rtdLeD1XktNlc4jnJM9knsxqCxEDzSV8ol3P6PmgvWXsXPPt1+aGtxkB7QsoBpxCeSh3JTi05M6DvqAKpFf9z/MsHByM8DBbSFKmmCgI81HPKDKe2lfXfrNq2tJDVrPa1OXabnDRBo/3PNo4FAlsP2yNUBVjkvdPORw1bvKM4B9DBDoCwnHsCetZxpQ6brVJphnhguMp/z6Rh8q6TgNt+l5qclxpZptstApbmQxxrgnVOUzTWNZ4B+MRBqPBBgAslgusGKhDr0G5Z9Mr14ZNGwf9ubm5QsD8h+gdmrDAOOvpa6CY1kkW44fvvxcpKZ8S+j4Gk6Hcy1R4gRoP4p0p50+BkhtGLTl/ZYWgN8BXv/wanTDEw71irZH56PmU29OrVbHEOWdx/S2bAnpjYA+w7du+7du+7du+/Ywbb/6Ur4nsomVpiFHvthDdbW0J9q+BUsJm405fpyPebMfHx1JcPTxMcfnuEut1LIsm8bfSnmhq93f7um0hpsLmWgBE/VV2NYV5ogAK8cqxuctLQMiVn/n+Uh+w+NKLFYJu9OMZD0foDwaYTR/w12//jCxZi8xCAVzbFWhbCrYLVPmFTueyXBuh42I2W2ExW6uS86CC99kAvXoI84q772TtKH8vwgkEAg6OD8TAluWOSX8YFjMlV4E815S2MrmUi2QbQSdE7Xfw5uoWxWyKjjnBgMXaeR+mY4oEbH69xPVygbPnX8hnu3p9jcwx8ej8FoPpt3j5osKraYi06qEyJ/D9UzH39kcenMceLo4tPDYLOGWCImuQFg5Ky5FjpSeNYzTI4znSKILt0HDeRppq6YyghxVqW1IcRHLHYlf8q7IKVZbCiq9QmhZWzQgFE91K5SGkkYTNuVXnXhxbNsw1S8LIKgx6NvJsjaKiJISBCvyDXtS2HbLd9ld71RqMZaFIo+QEw849iiJAlB2o59MjSBbT7W62Luo3RYnuf3onW3XHtmJqAYYWmNH9VANtkphGFodmtElKI5feRYZ6fQPHGyIIT8QU2aF5M+UuOm2UlUOpU9Iob7KKEunqGp2eBa93hDmDEHID9qLAOM8QhCyyqbfxUVKqm9GLJoPv1YgsG4tlA7tI4QVKfkJvpcBpUFh9vKlrDCmtjjLYJcVgNYKJg4CMs5L9lobnPNUpstRCUnsIOsqXikAx+wuBPa/jyOeVc59TQk3vNTJXyIKhFEj5D9Kw3OYhsFCt1G49fdc8z4RRPQgQiXWOdBbAORugnl7DniQo7CHSZoI6teEaNcKei/ubGaI0g0XZZpXA7XqYDA6E2core319g9n9QsadY1pIi2Rjb6QAVDXnbGpMfR35ewYkcFI6fXSOyegAL1+8xIyhAEWu/CkJwig9WPtCquc1Nf7Nr34lScb8JYHUTfto/lS/0sBaC2jRFL4osFosEUeZ/C6LEyymCzGoIiiBgKEOFb57+1I2M/7ud38vjKxBt4Ppao0XL15hPr3Ho0efCAuL/kj9bojVMhITbRZ4JRGizZzWHtiWwbQFzPRY0Czl7Ty/+6/2sWw1vCDE5599jkenJxJuQYYNxXfv3r3Djy9fiB+cSupVn58vropUnld1TbhBMxwN0e/1xUuz3+tiMBzIO/D88IvzOQtRxbbWKa+aHdhOBYpZbeBgMsGwP0BGGXBa4qALLKJUWKb0CesyhKMNImHSrxTLPK4UUdpgeXWJlJ5clGbSX7AwkEpArSFMIpdkRVczb8iytWr4gQenO0HH14xWOyA8hj6l4GJEzyNVIP8sr7FeZyidBkehC94dyH5UNgE82RUcewXT+H8ULlw+Rt18gtKgPL9QrFBhTqs5hL2K8k9FDlZ+h6ZVi6SOcwtN4bkpQ8DEgNqQEiZslnOwCvCowHNOnmo8ceI2OJ+J35qW9Zs0oCdI8iMM/GcgeoKi+D3K0IOtwxf4OjKH2LJbIkm/mZ7bzLKE76pBWdH6wEjF484wXeWfmBt4iEpJFb2+XWP+w2uMJz4OPj/BaTgH8p6wfC2HQJqHhqnCQosFUgYSxClQEugyUEqoQo1Bz4EbhGrzTsaxYqyx/1BKzv5KEJKwYBQzVdhEwDHHNREl9CKjV322rEt4ZoLArrHKmCaqGFlka21ZY4rRRK+6DYtzI+PczEYKVGvng5qp4LYECcVxKl5visnOj9f6umlvXB300OkGElKxWqVIi1pZXuh9QyXYJLimE0X1+6g75Q4I2+pWDd57DdQZwU6CxwSAeOVU4rDmJ+ov/Xy9UZqkS+kfbtBTnmriD7edJjaMto1CoU0b1VYgEoagvdkslTaqNq20TJTPqbmO4ByQCruT/ophl5YhDgxDSeSzmh699Bus5HzUhQGrUhtGyke1wf39Df7wp79ila1R9wz0n47wbHQOP/NwefkON2+uxV+PwOpw2EfQC+R+IoFAWvYvLFANJPP8ylkVAJJzSY1nn32BT548xWqxwGw2Ewk/xwLZoFRf8HPzcdwg4NqbdgTCTubGMJnde4novu3bvu3bvu3bz7d1wkB8IUhLl4JFgg60RPRDwsKmGf/aT7oOU8UNqfxcnAxFNkqZJhfmNzc3kpBJMEao/5oaz+9cF4onjF6daq7b5hBatgn/TgCrZc1xASYMDfEKU2Cb+LNpv7VCMxwoFeIyKAwCjMbK9PrVix9FNspFtMb1NgveTfm5qS+bDwpPJ/BhGzbu38+QpolaID+ycPDVY1hXBYxlQZte9Sz6tpQVwk4Hx6cT+AF9RmoYLILES1sVMpSqcKHG96F8S1I3b/oU2AngVFHGeREip5/WaADL9nH9sMabyxXOngJPnX/G1b+s8NdLypV8ZMYYtvFYiszBQQDr1MfkEwfPnAqdOkYtxaqLlGbPLlPz6OnGRXOBh5u3MBsbne5QpEyURkmBwYWkRXNqSq/oW1MIsEYGAI2qMyaz0bC6qNGlSb99h2neRVR0xbNNnQ8utNVOsCq3VcEntU9ZYTwMMeq6uL65EzmkYjRqLxv5Z8sA0KWJvljiWSNG+upV2Z94xB0vxiCYYhn1kaInBaJcYSFpqj4m1149a9OXW/mUqgZ2+rkGTzcAXBvEIFJmCDvDJNBmqWKCnxu1Lf5xRjkVia7jj1QQgquANrLRBGiDgVVaYDGP0QtC8U5zrBI2JVuWh4fGxk3SoLcsMDRihN0CjeWjMGywTqaBt2eQeVJjUfmo0xKjkDvjFUqngyiivI7pncBimcLOG7nmN0yPtYGJVcHj+CrXiCPG6vpwfYYZlKiLBoWt0jupQ+sQOGty8WFLMwu256JmQU2mIuvqih5gDcyihI1SfTwCASzeajLrXsI0pzCcz1DXb4HMROH8GqBXEmN40RUT9zQr4DPR0VbJcrw2V+9uBdBiCiRZoJJoWNW4vrnF7GGx6RAstFqPJLlyygZLXTedwMfGOak3GuLx48eSjHx//4DFMhLmJn1x6GWmpK1av9Uyn3Sx+83Xv0Sv25XXEhnwzry4/bfqTyykkjhBGmdIoxhVVmG9Wsvno5H7/GEOMzAwOjrCn/7yz+gMBvjy2S/w3/7pv6DbG+B//rf/Xgprvm839LBkKqhfo05rfPftS7x+8wZFztCHlk3EGWTbdz9o+pj09PfRY3YfqwHxD35UQPnF4yf44osv4BI0Myt0Ql9AVlJui9qFH1h4+eMLfPfdj+Jtx5fl/YFzMAMIBsMhDg8OhNnBIlbmbMo7OT/RD09bFxBUk+uo8c328FQaoQboDUOFMxyPhfEiR8jCmIEA8QNWZQDb6yAgjYkMOZFsqo0hJRmm1+V/RJMcIWn+PW7vp1hMlyhKG0VpwKIXoqkYWQyl4WYEJYecEIKOj+OjMYLqR5juErX5G4kQ4PmnPZsy9SfrisdTwqxnWN1PYdg13HAAwxvBpPSTKb+8BxM/J2PbpBh8CqP5j2iWYyTr/w0Yc7waEjpCcI9zCPsnA1SYxCl86ZKpnQxCKMSLKqDNQkdc2gXMokxTbOMIiuc5nIa+qY4gh8TNlc8YJbJK2i3ySw2W2Y4B3+T5+88AgzSi3yImczckQETAi2nJZLopCb3S/NO3SklPeT9M4xJBncDxKf1nsIGHuDQRwRcA5WEa4dvrBTqNi19+6eOgXmAVO7D5+QwGIqhzW8o+Q6Clh4R1a6SLDGlMlm2DdbEWBuN40EVv1JH+QnCK9ymG7vA8cU4oygxRukTYCeQ+wPmkJKNtkxCqZKHcYBKWZFVi6DMAwsYsdlBUYmyn70EK1JINmBaL14uZXfaqgqFUh+51PCQEWrJSHqfSbZUXWxsRKtJtjc/x3kapYlUXCBl0YzqIGWZCWbTc+xQLXK2lNMClUbH2GOTqayuOipskTI4Ou/r128CCahNCoI6V31p5teYEy3zaYB3NZG3mBz0JuFEMXp1O2sZ4b4B2zWCTjTW1WSUsNsuEQ6CZfV/Y4fTWtGWOZjCLabnoBj15rWHfh1GlWGYFCjI1ZSVBmbQlCd1c2xVpiYYyZXqWzu9wf3+Ph+UK84cF0px+fw2aQwteYqBaFXJemD7N4BvDVpsA8lHJYNaembIelduA8qXktMT1Uac3xC9/9Y3Mbw8PDyK553PIbBZLE7K56ZtHKTvvA4lirnFeZJ9kn+NGijUcDv+Pndl33/Zt3/Zt3/Zt335GrQ0PEPmDprhvfNE+qsU+bsbf/EstAlt5FHfm5ouFSKxYDBNoGw4HihKfpBsmyMcFaPs70vu3b/LxwSgOlByvTt1rE1DbhwtsQ6YbiyfualJKQqPrOJadwpPTU5yeXYhxdRSRKdDutOodWr0Y/vC91dJYGFtlISmFvusjS1LUixrRTw+oj1wE50PUSS5gA5/OhSTPw2K+EkYEWWpctIpsTcz4tya/YiSNQnb77XUokh7Tr7A2a9xFa3SOz1EVJop0gYNhiMOzAcL7/4o//XOEf7nvYV2MUJon6LjPMBoP0D8NEXwW4uLcxnMzg1/FyBPWRR4Kx4fNhFDXEN+sIp5i8fAe3XAE0woQx4UC13hujQqNXQBmIb5TJZk9ZJZkpbDbKFXkY+WrrLEuDMRFByMnwtCdIspNFOKrohf7cr619MMAPJMMvBEss8bN/Rym5WlPPu2VvEE72zJ/V+zZXh0NfGi5KBfxNMVP8hCDMELHnyNNPQG9Puha+pg2r6P73gZQ2PnX9p22xyH/EuxFFUTqS0mFhUHFbuAEsNwRmnyFMp2jNlhUEnzTnIAqR7S8gW25GI16krLG81UK05HlTYGOWWHkmliFjnj2NSsTRkm2SA7TIYPCQsmU0qxGl2xEK0dCcE1Myz1YsY24MTG9vsJgECDwbBhMeS1trCsDD2S0ECywHVSmA5cFD6913qC2PWFLsPoOmH5KIIxhAJmNUmTbFlxdLJFPQwDZpf8dJWykr0iyowkjX8OovhdmTWM/RmOOkOcHSI0TSVgs4SBLOSZsYT4lmYG6qLYm+yysRn24no2iyqUo4xVIkwx3dw9bCXL7YOkPmnXYAkqb9GKVvnj26BGOT44xnyvGAYseAigEGMjqbeVXm+u9eXnVSSgP7YQdeV8JVdCoFZkxWZaK59liOsNyukS2YmJkhjxRwTJvrt7B6jmYPDrBH17+ETkKPHr8BH/4638XieMvPv8a3/3wPZ4+eY6///3vYVkOmlIleDINsyxp5r3COs0wOZxgzBTlNWXVyjOq3bhomXrbLz3f/g8gtU2TX7bjQ8/LwjgL8Jt/81t8/ulTsSNPmBRbAp6RoC4ySfZ1aUxuAEcHB3h0cSESz1/84it8/vlnePrsiWx2kH1MII3nfjFfSLBLtFqLHD8VT02yyNRGDIE0nl+CkerepTZUCEQR2CRQNxmxuFdj0SSw28yRz9/h9oZhAEyS5d+UF6IA4JpJJ7OFgO8/Aqs5kqsD+P0eOpMxlnmJxqzFhN+2eI1VCiIBJzKPRpMRDntd5K9vEdp/ghmmaIynMAxHQkEIVrE/Vznn9TWMdIrp5T2u1w6WaxN1nCOUMBFHJWMywIXpnK1pOvltxl9hEOROP0NsNnCMXIJyyHzmPZWbHNyr4RiVUAGjRlLmuJ4lsOMCHTuFHSTUskrYitK5mihqAkk0yjdhcww7atNBwT8VEk75roOcv7Rp9G4Kw5nzVlk9IoVbGK0y1ZXKn4weWbxGBEVJDVNTLPsOgRAgLUyYVQ2XclOvQVYzkdGV/k4wfWY1yA2Oqy6enXhwkhjrzITle3Bc+rQZWKYlPLIIaXhvci0jBGXFJOImW2hjvZqhjjN07S5qJhLn3PiqJeE5J/hCMMsE1usFiqZE2A2VaT0tDQrNXBMfReWnKGsk6S88PybWhQO+xCSg/yUBToWoCdN+M770GmLjPavmDLXEUkEjge9gvU7lnq+e0doo6LXY5oq0QNuWvM3zyj5DJh6xTcocC0kkVg9s71R6a2CHQa6SP7ntVaWxktU6ZOHuTAqbzSw9/rd7oDt3Xb3JZQJ+0JHzz/OpLDro37adVdrU+FbFoFje+n22b4OWKMyxzo2QMi8Q5wRjPfEY5Zpu2Gf4zQorsqrb+7fcTzmmlTrA9EzYvinqgf6wpxiipiFMMoaUUM7KdSqiGshr8fkdTcYYjPoqlVorOZQnZSMgoHwcWWC0fpzqwB8/eYZffP0rsSu4v7uTzRnOJ2TmMniLG3A8JxKek+ZyvxKVRcYEbnWfURtC9Z7Btm/7tm/7tm/79nNuYeAjDLhzqhhslEI1HzPYPsaYdPvbX+0CYuqfUhDR0DUIcHZ6grOzM1kc0Z+NaaOrVbRZbMmSTRZcalEnDKR2bbqzwJNCSK/0ZBErUgOdNirGwJT+bNlsbQqbGKsLIJDJ52NxMhj0MegPsI5jfPvtX7CcP2jmk1pCqpXw7ofaOAXJa8oi0LIQ+gPEsxj3i3sF9IUGBr88Rj/oony7FNswpmPxecqFikl2RxiLBEo0IIoVxe8ioStQpQnc+UDgNmfkIzydoPA6ePX6FvfrHAcXEQ4Wt+iffA3PC3F1eYd//uMUaTlWEqujLrwTDwfnDp67ZAvEKBNKJ1wUpgvTt+DbBNboY5Ph4e4Kns3Fa0e804qUshmVUEbWWmOSVUQwRklqCpGElkhzAmqVsJVkx59MN9HbaFCC5sxmgdPuVIq5m2SEmiwFQc2UeffF6RAdz8Wbt++FWWGLJKUF1pTMRkqCtmBpF+TtunyDeGjYTfcT+q20ck4+1rUKjLu3Uiw9RMciFVOyoZ3+pylO6upvpXwtbaZ9PT5lUzsITqqK4ZZJIym3Um8p2Yvj2rAtJQ8xeF6Texhw4HWOUeRLYQIenp7BovGxMqJD3ZjIWMiKtKqCY5TiYURwKjE9vC8NlIsKwyRD4CQM3URuOfBNnYRZEuqyBcTk676/rrBYzPD46THm0yUepgk++2qCbgmk6xqRYWLtA0ehiYBhBha90iD+RaFvKf+iJkNTkNXIopsgGf2qIAw4dQG091OjklLrXGA/uHYqIGNZpLCaFUyrg7KycHO/hLlewuk66AwOkVWslCnF5nuVmM8TrGKIf10nMESGRyhRzrfB48tEGhotYy2B0uy0torddhORbMm4lQCCGsPRCCfHJ8Jam88WApq3SaHcBKDsKKe3l5YkKjBfy6y05xJf6+xwiN7RsYAtrmXLtSRAJzIzLfEiILTOU/zxz3/AaDTG44vHJ+eo9wAAIABJREFU+E//+H/hcHyEs9NH+O7Fd/BdB1999rUYmMscKKwOG19++YUAD8pjDEhlCmngmRaWUS7HZCJTvdJ04HV7mM4f8P2f/ogkWu9sXOjOuvNt+0Mrfd3p8zutLfody8bzZ5/i2afPlRyL8wE3OFiQlilWczJba0yGNmwvVJ5KMs4Uw4h+Zg+zubD2yEzjdeA8IyNXS7zVZosaQzKGtV8TwVTFHNXHp8GCXr+H0bAvALNKlqAeMUW1nuPudoVVpny5eN0C18bocADTc5WRPL0MtZ8bgblO8Fc40QvM3vw73FALatmYHHZoMYjp9XtqRZW5ICx4nS6OJj3MH9Z4eLXEWZ3h6PP/DhwFqIz/HYYdoIKNpG4k7fP/Z++9miRLzivBc7UKHZmVmaW7WgEgABLgzLzsrNn+6jXbh7E1cmx21wBySYIkQKIVGl0yVcir1dr53P1GVDWww1fAwoHsygx5hV+//h0/AkWBOgM2mwI1SsCu9HmhN2OM8WyEwKnhjQlkRXAp2ZP7MY/dO9h1hry6ghNaCOzfkHaFpv4cfcDk3BZ5WiAek6VFll2PtOiwLSrM0wqTSYt+NgHIWNb+ph0l/o0Fwk6UxQUo4Lj8PgdNSW+oHtZ4hIDMcSKlXQ/H4nVAfzW1OKRsKjvxPq0K2h0ony6GnNDzjKEL9HazbYY6ELKLlFy0bOH3LUqGovhkhBMgI5uci2+vkFufyjkvqxb79VY88pSMnYEorlxr47BFNPdwV9o451jEcTWMJXVSqdcbSTmuMm4zUAsbupfAlXFMDKbF9d0aXqDuAwTyyb6WlGtuo77eBeuSG9AxwKbHGs2cC+0aCWX4rYu8UZJRfdfS/9fA2tE1R6+1rCxk3sVjxCeVgb5Z7Ozf918T4Ewb6OvtUVuifucx6ZmS7JJfbksfUKxsxdZVzDoulukZDhdPmhqOR+akYqkdJK2aBWeGiuMFCs3iVvuirqsPvUoJImXZVoKRonA0pJWq46KAQWUNoe6d5nMhYKmHKT0NCcgK075GMo0EFGdKcGwVKJn2qtN1u54GaY7ISAesTq1L4e2bN9hlO7x48RwPLy7luN6+e4eb7T1effMtQqZ236/lbE6nM1iOSuqV4zow8A73ejk92kGFY1c0nuDHP/krGeNuyVpLU9k/MtZMkjE/h4vYXLgRr7WC90/FWuMijnidGoYcR7ETg+3UTu3UTu3UTu1Pt3H1lECUkd8cBw8MBdj3a62hvf+ULtKOAA7DMCMLYbPbYU9PL9eVtNHl2VIkXzR/5WsEeDB8JM0MOf6CYZInf70PsCjpECd62ufGPK5Nya0j9sMAuLWtFNZ5kQsA+Pz5C4QhDWlv1AxqmPQdfb9mgZh9VPUoDeq5uupiMRuJVJI+aeWbPfblHsEPF3DpH5IVunhUbye4mO5zjEaJ+HJJzSyTTyXr6ijZqWx0Xo3a8bG/p+CoxHzpY7HcYPL6/8Jv/iXFV69vEIQOLi7O8NGLC9iNK+l14V+M8MmFgxd2Ca9JxXw7r0M0fgA/chCTZUDpVL7DdnWHyWiGvtdea2WjJnxOh96l0IYsEjUhrMtapKCU4DB8oNastUZMwCmpUSbjZhWaq9YsMlfVmFUXHo/vpfAprUCYJ588u0CZl/iOqWg8P0ORrfxhhuS1ARcwRYXyP5FeJ940x9I9c9YGEY40AlZpkcgq9/nkraSgNvR4M9pBXQQN3c7Eoh1fDv0f6g96y4bqSYEwhmmgUsbYx1V4CEFl1xujKVvcvfonWd0eL5/oftyq/dKgnUtggkCGsE1YBCqfNN+qMadfXuThZeCiL1yM/AaelaJGAFaxXevAIcAG+vv02AY9vnrdo/7NK7y8yfHmUYDy9rdIbA/T8zGirsNZ4sKtOrzNG2ytFhHlYAJa97DbQgpjAWkdJs26CGnwLqeLpuE8JwSLKdtU4SBk3rndDnZ3L4hR6U7RY4R8V+K7tysEyRm2WY1s6yIcjRGErvhZkaXFvkVPojhwkSSh+EUqcIVG8xbWqy2+e/laCjBzRo5OgRznA1tCBY/wD8q7Hz95gvlsjvV6jd1uK8USxwiyDQi8EPxhoibZR0NogUiiNLvEjE+WhbLao7RsPL94DM/zkee5kteFAf72l/8D95stzs7O8Mtf/UKKuBfPXuCXv/oHLBcL/NWPfobtJsWEnkL+CK+/e4m7m2vs9wxbuMBf/vSHcv6FVcPvZ5qe1WPk+pjQGy8MULQMkiAriSwkX1g+szjA48cPEfiRsPKEGXHM9/wj4/owvpnDqEEsvj/yE/znn/0cL54/EZYSwzl4bBybYFaGzd4SqTCRqjxXflsEbIQ5osdcLnSEEc3TXey3O1lAkPAaLQFWKdGukvyLz6ZiWRtTdLNpPB+U319cnmM6HmlPJ55kBm4wSbDC67WNDZmeBKzpS2U5qPwEo+kUcUCwhoyyFr1OqJZzns/ROx+LPDkrGuS2h/tKgRMcY8n8KrIc84sllomP3355jXfXBeatjYVbwrty0UT/G7qe3pW0n6dU81tYDXN2fVRJgIIMqpaMOvYmIgoeRmdjnC0ilZTYZPCQou3U2KmO3xi9NUNGrRuPEeXWXSrG//SMa20XCSl20s/pj6hkcm97C0v6k85nihknYxK1oZ0Ek1D6aSTELPz7kqnGPbLCRuvamI7IJNbXuBx3Av/KX4whJQLWaVBWXW+KgsR/CC6TxO1Q8k3WsACkLrayyNDK+8NILbawH/BcoON5OJPjQMiHlxrvM01GgNpBZXlyXTl9ACsDkjLFxL9B6XrY1TZiJ0PocScJbChfNMWwUttJ1hLBtqwoJBzh8mwuQHCe5gIqMulafLaOgDS16GjGc83YGhb41FhNcLdqeZ5aCa/gtSo4jWHE62uLRyZwPUSRj12mfFwNI2pQDwwPqXFGPL/MXc+sOupPHeY6w+yL+8zO3sDpCb7zs9ScR84TwX4Ozl0p1y9Za/J6fSMTQElPvw7fpCc7w1YcNb1ocTTyyu9kMEbhGG1bI823cF2yuHhG1ccMFgx6J7htamwIMCEbuGuwY7IvQ3yCUNJnL8+ncJu9pFa37EME1uSHkm/Vj2WcF3DXw7/+5ksUFa0vYrx991KCXZIR5yE2/vmX/4ScLF/PQpyEsoCjNK8GWDswW4UlLfiymmfyOQJ7T55/hJ/85C/FX/jm5lrYypS2kmUXhIH8znGqYkJoXsqiDec6BNfoJyfgGv0AZXw9IHcnD7ZTO7VTO7VTO7U/4RZFIUYJpYAsCJn4qNPyjhhB/5F2KMfMRMtMyPTvnEBJNLsD33WxXC4kbZSG1vTYefv2Ld6+vhaWgZoImrcdARymsDb/M0wi47tFOZSwhlSxJmmjLMz4nSw6PUpF6WmjWHIEFUUKxtVj8Q0JMZvN5bXffPMVvv36KzXZPEqJOsgijmafZmqpfw9CD3br4ebNClVTyWpx+NEYi08u0b/JgU2uouC1XISr09FohEdPLxCykmFxIqDdFv4GaNwabTBBi7l8UdAB87MQK7vG3//9V1jdARPrCstzCx99QvAtRh5PcBnb8JoMTdkhrwiI+JKuSNaaWt0vsd9u4IpJtIUsp5+a9n0hG4WFqs0JYC0G6VzpJvBWFR0qGt1XWkpDrxquvGuJrpGfDIUFz6HM31lssijpsIi3WI42yK3neHlTikxMnXQl3Rzw1QEcOTIxl3+/n9CoDj/NrY13nzpvbGTBGO8tZdes+mQSbTCNVrhPl6iaqfSh4bQakE9LTtWnm0/8oA+qikE2mmyGAZnVq/78fpfH3VMAr+t7SG/foWVRfvkIXbVHX27h0p8tiOEzBIG+Y8afTeTEDEKwUJElWJP90cBzmdbZo7F9VNkWVV5KeitYhDJh17KQ7zMJr/DjBE2dC4D5+9zDN6vv8NH1vwJtjMmP/lfshQXX42oWor7OsacPUmShD0o8QItxOIPn0aychTfDMNiPFKDGJD/6P3EbCbLR0J0sERbsTpbDG6fovQiwJlJ4Xq8qeT2TTlfXG2RwMb4a4wmDGygHpSRPwj9Y+pF9RCSRZu69AHpk25R1h5vrd9htt8JwUswO41ekOov0Zel32sy7B+aLBc7Pz5GnmUjDxeBeQlponK78GzkOckGAiaUFzacJDFGqqHRiQzmrvB7JMtriYvYM548v8H/8t/8dn3zyOZ49+gj/4xf/HRcPLvEXn/0Fvnn1Uoyzz2cLrFeUKhfY7LdI052wjyi9NGyZ+ewB/tN/+TkiptJyzKNcmGABaVQMmPAJChNsU32LwOW3ZYcgbTAL6HFZiql9wwJRgFkLX3/9O7z89veaoaYtlYbBaxim1QMGSNAXnecG+OSzHwiwpmwQtVzKrdAUGW7WNhrHkeRhAe0ZDCBFKOCRGeIDURih7PmX8qWUa5KAd57LwothuZlL72hThJWmClAF9PGcLeYzOZdsBHt43dnWCu3m/8Hrzc+E4Un3MgnuITNJg2TLiznm0wQtxzpBQNRiAgM4yGZjMd3UZAPyXNvYbgqs8wa1Z8HvGkyCAA+WEd5+d4+vX+0QWzbOKIONLYw/W8KaLwQ0E38sAoxVoUh1HhN6OS602KZb3K/pDcrvd0WqfbkMkMQjCVEQIJceXK0KCWESr/L0VAzhsqmFTeoQ2N3Y2NQudq6FR0tfWMQhA1Q8G3ca7HpAap7ccxTDiTJyk6Qtixn62snyCpuW7FELBS8Zp8dlYAAi1T/lD547Ag/sX2S0CdOObDN9P+X2dgzFoZechcCz4dQtvMhFbbviNUbGMoOJ1BkvVBAOfBVSoxe3+J08ROu0xJrecGWH0OkRUU4b+sjuCpSv7+B4DWaTPcJlhWvnEv09cJ5EAqw2vZLbVkWhgKqOnpEFfIsAbqDGbLdHENvY7Gvc3d7pvq/uxQZQlyte5iMHmFoN85pRbe4R0k07RG4PP7CxK8jQVIgZx6lRFCtwr6m13FBdd0oNqpnfZq1I7qfH16Liv6v7rLlANMdKv0ndH81FTTYWg55KdHYEj4CmzfNcwnbJBFbJnhI0JPt1xFjTcys1JTOPHthn5i/lpnC8KnXEe2O6rZ4H5MVerqtktBC5tAxBw3ta8SmjpUUjHowFdvsCgR/K/e/BgwXORhVS5htQaimLbh4cSr31tqqwFDXmc8E0DH2Z1716+Q5ffPkdHj+9wmIc4ctff4EwivDg6gHevvkWb29vh/u0GoM51iigiwxdOf4cQ8z3dEzbnuCv/uqv5X03lIMSqONY5xvWGpnwamGZiz/CXJMgMW2tQaWI/h5hXerzq7v8CWA7tVM7tVM7tVP7U25caWPaXJpzgquT2WTlVnPghwnQ/7wZoMP8Nfx5WKZUEAXZO0xUCgNcUTZ6+RB+EGCf7vHyu1fY7DKNa1BqotlLetIo32HANiMp0JO9QVqkZamcxDmDZ4+rwhC4ki9sCOWTxOJLJdSxoO/kuSQZSUADJ03//ptf4/7uRnxNJHFLb4tMGo92dTgCmt7Eh+IkRrZucbdeCQDR+R3GPz3HbDRD+3IHmtocJsmcILZ4+OgS8ymZCjSe3sHJMpRc27fnsPwzfUh7MMBzOfXgRsCX1w7Wr4Do0QLhIxvPunt02V78bHwnQIUQve9LiEHAIpR+VakCY5h4SMlWSZ8urqZyqu5wBZusNa6wamCNE8WKyaydpEhK4UTfnk551LCYVMWXAjT0+vSwdm9JNCjPvTpPBNmcrsGjkQIh11iibgMpItVcfug8ugvpgy2nwFQlWsahixpTlKs9PC4C9O8GYDOTaVVCi+z1cnIPy2qxSs/Q9uHRKdWfYCSqqgcP/U695LCn6ruMXEYoaFrmiqEvEtgsd9cYLR/Bjemxp5kQ/NyMk33KS5g2GgjAJsAwfb2EeUmwiYAJ5Lx5XQPfLpCXmazU0wxaigR+vReIRJPsSBqA19lOMKqmBbJsj9myxu+vp/jyX+6R+zV+/OPnWE4i8YOJZi7Guwz5psUqLJEgQ7ueon8S4QF91BwWL6xmWiURJGvR5fXlCZjAffz9ukK4anEVZHAv36Fzn2G3s7AvWoTJBHnRYLUuYU1CPJy5SLiPukCq6X1Gw+6OwCKN5D14ZMvR/6rvsN3mqOoCUZQIO+DVq9eoq1IBpCKnUgxKc+wJ/vp+iOfPn8r52ko6aClgIIt5bjcBeZ5hvpbm01mWYrvbo+D4ID51lM9r6bzuDcoE3ELsxnh0dYmLhxf496+/wMX5Bd5c38h5pen+ZrtBnvLz6MGoPkMtZCgPOPVxCkj50Q//Ek+vLgXYNoUf/RrJZGqEMWgp5pDGdNU1pa6EVwRgtzWSvIBFgLwlg4XjOuAGAbK6xq//+dfY3Kmi0jBqBRyXa4qeUB5mkxkWyzPxmDxfnokEnxI9AVOFV0SiWCappzvaihM41gAAK3YZDyztvSXoQSdgbBSHsL2QJE0BS2WkoPE3wz12OzTUIw++mgZQO/q9U2y3J08uJTSG51ilZpZwmlvk9yvcZjEssujoTcUav41QOTGIU3dFikfzEONRLKAjT2fJhM+G8sUWOcGtxhHGphy3phQQlcdvdbvDtq1kzJiHMX7/xS3GLXAV9Fg8GcF99EDLu83YVaEWcEWZg4nXv2CFNXarHVbWVAzayyhE0Nt4gDVG4xg9B3UCdKItVowj26rkvkYQkMmfHAOqitd+Db+skK9t7OBgchmi26YIYwdIgiH9UY17PDfsCwSqeW+lnE4JZ40bP+WYBObkPWSh6qJfjZ8GxDD3WxqyC+FWrn+mXkqCMrNRmF5qW1ivM2Gthb0NDwVK10fZOJJeLgwr+ovaNKEnWEzGjwqrkG/hyRF5nWJK+x6ENUuqdFPbshiQVTa+u6nQWja8fYmFnWN+vkU7neDNuoNdeIh9NX5yrGU6b1GmCCMfXksWHe/jauwlgy6IWglR+O7tHdLdTt/nzeKMvgcRzOUz8j4NVn/I6hruFB2iQF1jVaMsLLb7TKNw6jgqcMwsBugObfr/sF5ggDY1XpjFJXmr8VsbhiU1oHT68ymD5d++lYv3YMVkTbIgZRN6sYCQO5gGykxI0DCxMYOofkz9V/UpBbwdjou+I6pHZH1KmaFyWykH5SndpStJgY/iCVy4AsjOFxNEkSuhA/v9TmwJZIE0GeOTxzNGXqNgArUwJJXtAdlramw0SJ2FVdqgr4FRZCFIImHCyuJd3+PNy7e4eX2NL778LaLRGA+fXiBNr7HdVod7vKbdSzI4AWnt7yv7pOWbH3/yuaQ1r+7vxeqEsn3uj4QYMLFbQnPUvFKBayYltBTAnIw1Baiq8zLcA3STa+2UInpqp3Zqp3Zqp/an27jaNhnHAiZJLLwAbO+HBfxH2tE0a5hkfe/JAWhTD4kvlUtPjTGuLi+FVcLJxf39Cq/evJNJiQE2VBS6WWVVE8wDyKYmi2qOpQtSSZUz6XIKcCPIZlhtwmyTYkC9l/usfJbI/rBkokRD7iRJcH39Dt98/QX22f6w4no8m9b7djQlHfaZjBWCXKvVFmmWK1nT3MLZj5/Az200t7mk7cm+CAuglQSrswdniKMe+/s13t2lWMyuMJ49EgAspvwrYLHVYM/UyMBHE87RLiI88hr4dYFiX+NmX0kBEyZjREmCkGyYvlEpbgXNw2nw20giHosYESpQmiduQzRg52vIWmul8CrqVszu6VstE0Xt1yceKIMURukhhaumixKyS459VgRgM/gTWWReillwj7Txsa8m6C0WmKZkUQl95oCriahKAOWq9+EZ1utmFV2tw5tyQBnc68JoYB+ofjIAZ9yOoMR8fIO6irErJmg7yhGVF5xiqEmv/V4/lnM/MCyP2gCwKRCHn1Lv19Lv6DXGipvJmpI6KvI3FXLB0AGr2sB2QjjBQiSHnk9wTjEw6UNDkIPpcX2xltTRrvcFXLM7MlMAZxSjEokUUPNcM4SDrJM2he94SEYj7G7vhEm399g/mdwGOLMQ86mPBT3VyOrhOS9TdNUW+XaOdOnjMlLsud72FdhXMOyig58EYh7Ofvd2TTDWwrNdg/PlGtXiNVab5+i9CTw/EL+m0qIkNERC8LUpEAU0nieQwyKpxC5X5upt6GFkd/BZfCusBi1N1ftOQhB4FgjWM1Bldb8SKQ6ZQmS5SZFq23jw4FxS4eipRuCMwLr0UoagCBivzO4JMrM4IsMlzwrssxxlVQrgxz6viltjF67GIOUP5uBsfobJWHkN/dtvf6PAZ14sujfydapgV6CRAtoUmMR+dXX5GJ9+/LHIvRWbQQGZ9KnLYhfjyMZEs2lNMax63GEBgj953+Mm68Q4n55WpJoK40y6owXb8/Hu3Q1+98XX6NoG48lIxuDReIKz5XJgYPBYmO1VQQ+qkHXIJs1TbPc1GgKfgzkRC2BXPp8sqbZmQp8KiDCAgVzvkQsvimjvLgW4SVokuMhQg/1uKymrcnXpylPOY9fj7GyG2XyGgMwneSP3/Vco7iysdmNklHtThsgQAAmOCVFNZwijHtOGQRA2Rp6NKPDRuyptk76QXGDomXZrMZXXQtFQbuaIB2FPKadlIY4c3L66xWZfYjZOsPqHd7i89BE8O0OfJNJXea2LjxilefQ2s3xhHwpTrKsFLKOFAJlS8/MM6bpGGJZw/CV2WxfjkPJ9NV62VqjATEmsJBDWSuongTUuajg0PZT7RguXY0bWA5MAfXaDauzJ9XXhc6xg4ixvckrGyPuisL55jfC81Ez4VeM1fTR5DPgcDf4ZBtPRN1Lk7ZIgoAAwuQ7VIoeka3LresrZW+HZ8TkuVm03e7nP0xONUj/bDwWw7Golj5WUVF5/PJ8axOH5I5BNywHPJUNaSU3drhRvsaJyYYWhZkla2HQ9RnaPTWkBb/fw0hXiZINobqMMRrjf+fAqnotO+jrHn1YW1QoRz7uUFzIYhsMQP9EBRjGQVy2ub3ZiVq8SebVsX99h9DKLgcj0JaivSDPnkXkJTfZ9tJ1Ki6zkPOjUa33PHMz05VrW0tQBSFM3PvPcIFXVX6CSjQ2uplmGxu9MA6RxwDTmHHVNoFctJKjtpB+bAsKUFYMaXMQPzviPmvua/l3dStX907DCzThkFprkNxM6qo/JcM+1e9RlgaqsMZ7NJPyK301Z/XpNNrIl/WRxtsTDGedlFaqOIDwBYQJYPGuafivjL+cfHSomPpcOrkuO6TbmYaNSprsOX/z63/Hueo1nT69w+XiJL776Fpv13cC1M3MXtbCrt3OgEVpo+gbT6Ryff/4juWesVyuRhXJc4N+cg/EezlcTcCOoxutU/NYkEZkJobxPc96kziWPvZo7mqNjDrF98mA7tVM7tVM7tVP7U26cmISBL94zB6r6MFtTd38zWfwQP/gjn/n9l5sJ2vvvMoUbJyMrml5nqRR3i8Uc52dLYWlwEsOVfCUZMaEHRqZhpolqcngAW9Rk2NSchgGhVieNn5IqSlXNqAEOHZbAL6FslaAjE6bIZnvx4hO4ni9eRix2FGCiCwK9Ld9rUo/QMLlGMg4x4qydBdKuwf73axR+i+DjCbzeQ5ORoaA8ogj0MXUw3RW439IDqscsniFKRpjHHsZuj01RYcsixGUCWwOrzDCqMwFFui5AjhD+dCagYpmuURWcDLLIY4pVjZxhB7kCE7iSyoTQzlI+a5STNFUh5sJFWqPImBDaKvbaUYgB2T9GSmPWvQ2oJGCCJHbRUFoX0RpgE57S4aUi4UlrAoDAMt4IU6ZslXxFWBdH/UXzGY+8aEzimCnEdV1zlJ6mp7PDa6VPGAmantpy+9reRVqMYFsNzsa3AhKUjZIsmTNs3qOKrSNJx/BMpx83zDvVN5tigzrdIBot4PhTnUh3XBjp/sK+7bqAO1LFVPFOFZjwtXyIn0+AcY8iX6O0LFRw0bcsimx4YYQgovTJkUS51iFzoscdpU7pHcZ+hCjxBXjNmdDYEUgBHj6M4c18nMd7LN0STkcPQLJcbNhBCM+P0XoOosRF7BJw2KJrmIoGuS54+hsb+NWmwfVtD6foMcpaTOwWeWDhPj+HPzmTNNH9fUO9IM7OfEw8wGPqXVVJuijlhXVei6dUDZq7eZhSDklQsdXArhRptrBgGdDC/rXbpQj9QHwdWc8ReGutDqM4wfPnz8UPZ7PaSBHH4yiBKL4n14cwcyhz1mEGBJXJiqNPTt1UesHhIJtX51yDtQZgk4Q4lS757vYGm/W9nFTFMNNji+73uqdqVhYl5Ql++KOf4sWLp1SySaFPmAJOgNLykc1cPAltjBh4oPmZIhsVHWGtWXW8HmvxFKPvWUyQRwIFWni+ksDLdst7Wjluzz7+CD/4/FM8evwIy8VSkvV4fLbbHSp6CWmWr/RDvluAxBLFdoeVgJ/0S9QG7Lyg3BDhKMDYJCpavvgxmnRnxdogS6pDX5VwCf4xSdZyFZuvacU+YLGYCBC32e4O8jwy12wLz58/UWb73J42hVX+Eps3Dq7zcwGUBI+Sw5rAdkP4cYCHow1G+RsUGwqRuR8jkZe5NvsxZXoMUnDRuY7IlilPjuwKjduibCyMQ7Jg+JUEJiq4HGsjD+PIgfvRJbp4JBJEgjYCDsu+uuhsxWZzbQbXFGhKCyUCVEzlJHCXbqTfNgz2pB2aPQFcAn8+urKDY2VwHEoweYwUAGyTeeQ6qBhuQtZ13wg4RfZoRVm/C+R+gy/bEIu+w9hPYSOTRFEGy6gFp0MQC09Ko2XODS0WCBCUZJR1qDh4uJ6kivK8kQUreLWORua4Jue2b4Wd6zqd+KqxTwsexbCPjotkLvZVL6AqGdEdd1gsIxTjh4CWkHPlHqFM9nnN8Vpo6KvlesLGos0iE5VbN9Djm9qXCdmBVY9l2KJhAum+xf26R75tEfQcHWnB0CJKHqhwnpysOgdBkKBumZKaK+acumFLIFFTSDQMzpcj8RTMS8rVW2E1SRSAllOaMUHeqpntamLCTmjDD7k44mC/z1HcWcqpAAAgAElEQVTUjYCH9JOUOQa9/8xNxXh+CdhmqNj6s4+fO/7OIxabArLMveQAxiWeK+EzaV4qQJvgqjbaMPdGOhroIU3fPw8MtOHDzcA13Kz0o4bVZx4b5niHBSzF8jvMk1RokYeHjx6L9xkZnZvNGrt9KWELXjjGx48fYO6nqLs1WpssuxB2zx/vKBhBrXdVXYm0o3yfycINxk4lMlgrjJGvVsjSnYzr6/UKo8UYL199LdJ/BQxSyqm3SVh5Jl3aTBQUE/DjTz/Hp5/9EFmRiYSYCwG8/4hfJ8E19lmm1HPOxITQrJT5I+e2TI/nYpgKyeE5NydKzw9k/qECe+S6JHvuFHJwaqd2aqd2aqf2p91EtqbBNuVzo4t/NYN6/8XWfwxg+/5zBmQ7fkaDHtpQuNBAGz04xuOxJPxNJ2NZ+cskIEBJV9QcVrOUBtNrA4KYz1deGupbDNh28PFSLBItMdTyQgOyyYq6nuS3NePUC5mgnZ2d49GjJzJp2u92g/+SrNCKn5AmFJjdPbLioucGi8VkHGFGSe6+RLuukL7eoF06mL24RL0uYNG/RstOBATUSWTnywd4fDaRlf97BhAIC0EBMj0noC4L2QZNVYoBejROEHiOyGOSKECR7cXQl/5X/PCc4BqLI8rIHEpD+bdhrXHVtZEQg6LoUFa9gDRMJCPYKfW8JrTIHFTOiSr7zYoyLX/Eo4mggCZ/GTmHkYkaSYk5Y1XnI60jTKMCi+gWm4JMHpr083so4VEH9zjQwExW1YK7Xtk3BY4qz4c+YP57qBVaBo+p5DGdMcgeRqlqmscYRymW4xWyIlT7qPuVOalmcd8AJWpVWpt9S32lVuvz9RthOAWTSzFZV1ut9noIgtCfofkMqnhwPFjeBFaboy3v0fUBAjJ/2hQ7+uV1EayOq/WuAEXJKIYT+iKX6ijX6iqE7R7F7g5Te4/OGqNg6EFbw+tq5CXhAkcMpJPAwZSsn5oIjyN+SI2wXOhZqP51dUHrsOBvKVFzccdES5GxdfjFfY90Y2GZdpjXLUZ+i3zSoo1H8OIE23cpbhDAu0rwcMKUUu1zY3HVv8NuR2moj7TzRQ7pxz6CmOEKBCl46CllU5I51+V1QvapYkgynbXuekkDnk8nODtbijTo4aNHIj1nQUUAjUdd5OK+PzAOJcVSs1fJyhSQTcA2JQ014JAZdRS4qsYeA85Tch74HkZJgt9985UUTCJD14DBwIoYRj113i+XI/zX//q/II4JPhAwsdGLD5iHrU92r41HAqwpEI0XnoxrEolYoisKxbzrLSnYq5rbTpCQzDUCa/RyJPhKgEqFPghAbjmYxiHi0MWbN9fCaFuttwL4kOX30bMLjMaRgK8MMOk8C06VYrsqkXdkA6tjL/5m7INBhNHYQeJs0e1u0VcVwpDMJDJ3FPhoindeaQSyCGR2DYtqXjcMOPCQJJ6AGERX3t0wZVd5GUk/cWxcnNGHksefNMYa1+8SrLsR2EH4mKiWMUZzNscy7hB7e/S7DdbbDruawKUHbzQVPz9KQem9bxY2yMTj+az7XvYxaIF5orzuRE4JC+smQ8ECPhjDms9gh4FI+znuEvDkNgobkuef/ok8b02OKutRewS/HayENdlht9qiIIu4p3+dh3A2RsOkXG6DZaNOO7gtTdMpX3WVV6B4G9JTlGOuI2ziplLFu8skUYIzdoSk9pCQoR7RV5L9/jUclOj7eBij2Zd5j2E/bcky0/2j6ujzaAuA6vvOEHBgwBOODX1Npp5K3CVYJQBep7wMxfRfwA8Xu32OpiPI5KHKU5GOW70PP4wlFVeNmpJ3KbQuuZ0z/ZXaXl7hnmLWSvqo+Kk5CAMy4hST05N4bgulYyEvbfhkDToO9iAzM0aaudi/3WHirRBFa9j+FLYTocgIoufwCOgEEbI8Q8P0TZ++Xj2cjiEAjlw7/K7FMhHAtMjz4R5mbgf9h+k3Mo7bGI8iWVxjQruxTeg6C0XVCMsxiRxJ66a/l4Bb4runFqHeu0/pnyFRVN0w9PV0wOH4l/KwVffdUeQir3K5d4uH59Hd1lhvvDcb0zgaN2D4yKPfZJP0Gz6A1dR2vTfFU3+oW6UGkfSkiGPv5dWlSPTrqsDN3R0aBuo6PqZnS3z6OEHPuYrcQ3nyR3C6WPzWVKiEmkvQX/J+tUZd5QhHDdqgR9V74tu2mE/wr//vv+Af/+nvcH97j0cvPpLv/OKLfxOPQkmK58Kg0efq9FQ5gvrYUuYejSb42c9+Jt68d7e32GwYhtNLfw658MRxRLPWCLoRXCvzQnw7OY8l+07GSM41DGhnJk6ywGiuRfWvAtpOANupndqpndqpndqfRWNhoFajTZKVnh2pZdkjgOz77/0DD33wvEabDg+YmdzwIxPIlj4uTI7aY3V/JwXnfDaT9D165pRFJj5gAoDpiajMUwbZn5qumzLWfKtMJY/BNf2/gcU2FH8HyRelpO+ljZbKk0n5/zzF+cUl1qt78X1SKWrHE23zPceHzUitGqpRcLYcw3F8VPsK9bsc63f3sJ+GmFyeo75PhakioJ/My5lmt0da0jRvLFI/NQ82ZtAG0Gql4OgbGo+vRZJEP5m2olTUox0T7u/uRZLICaLtW6j6DJ1F812y1mjEy9XXBnnRIq96KQBLAmuNZq1Jna88X4QZaM6hnvgqUE0Zr5Px4Go5qBQlYkKuttVIRtV7Te9Qxfe+DpHWAa7GayQepbU0T1Ig8KG4YGF1BJvpk3tguckW6tccFT7aD0bZQltwjVZn+GzdGy0bWRUjLSIskj2myR32eaJXuFUlIqdWLhYN/Gl5h5GRNvkWVXaPZHIFy090HyPzY4Bqhu9V5ErDHlXVjvJy69E5AaJkgShU/nY7SsGsQBhrVsfC2EYSh0ruKH2CK+UW3tytkG/+EcvgHNXdGKUzhhN7aEob+52HTR8K6yuahAjI5KoaAeZaSThVW+g59DVTMmo5W8L0YhFCeXONXWrhOwBTy8L+psZ5XuEyBtooRze1ES/mwojZ7hv0yzE+vfRwyTRSAz6TvgKy6HoUrgc7CuCNHDgRpXyWmPyL5K4lO4i4EsE+D2VpwWFVRp+rWiXZss/NJjGKNEWWFwiCCKv1PYo8k2NMIJL93iOlQx93FexCcFnJ441EnvJIjkUyJurOY8YX1d01I0MDbJTxxnGM/XaLzeYeHveFCwJ6PDEgm8J9VZ/hJz44X0rYC0EDy/UF3BB/rcjFs6hHREMhbpuAUa14gVHWiTJHtquwT5naS2CDAm9L0vV4vYrcX0vNCEASj2Ohzb9H4xHOJokwMFh4X1/fIk1LSdETQNxzsZjPhZlBEMQPemSbPe43FdVZ+vM6zdiLEIxCjOMSXnWPbLXFZt+h4Ploc4R2DicgaBhK+Egz+EXxmmGSZoe8A5bjkUhH5Qv4urbF2+tbXCznePToIYqsEPbRxeVChYjIooYPdzYWyV9W5HJYHXeE2cUIT/wv0aUblJst1imQyXEjmYr+ciECz0NP5iSBh9aGQ+m+sP6UsX0UME1WMccEHNDnuqyAOJxLEAlBNC7A0F+T55qsqpbgM0FpyjbtCqhKZDsXpRshJHPUAeZ2CavYYbPVtgwSsmpj5ovCkzuB1nIk+KPIHPQluUdkcrfoGZpARpyAuhb8wEHjesgrC1VWCEOsZjJlXQiI6FCSacewMBbwloxCjstqjLFke7lNZI6q/dQLA0xxlcfpE6UYa2QTSz+mfJgLPCLvVeNZ74XIYcOnb5vjyP3jdp1pOWuNtirRdwwRGclYJQtIcjHUoO61pFMCJcYEdFtPWHrcTzoPCj+a0lvur++Ilx8DFIRx33aSlBmw3/oO7nk8LAdj20Ga99i0Nra1hd3eQ7GpEeMaQZTCDRP0CJGlhYCj8XgiTN00TcWLLQoC8WdjPyX8V1TsEw0uzscoGgslTe3NrUAOpUba2h5xHMIPPKz3W9mn95q+VTHcpihaBB695TgGKTnuMEvSjHvJWZCFosPjZgajP07f/9RTBDlHvgXf7rDlhMH29PzneFvNFWgCEfRnyMCmFuz4P1lSMiCe+Ta9TcNemfeb+diHk0F5Xs8SbODswTmCMERGiflmg+1uK5JyJDN8/OxS2NNZodLgmTZrIVbMNQq2ZQhVaobb9RYvX92IvQWPJa0rgrbHYjrF5u0Wf/+P/4jnzx7j0dUjXD17jjD2RVr+9Nkz1BUT7bdqYVTbT6i5ZK9Y+Xp/Xnz8KX7845+IVQCDDLI8l/kfg8E4fqhkZxViIIw1AmuUhor8uBoWbMzB51kcbPxkcYbXsLo3KJa/WsiSkK4Tg+3UTu3UTu3UTu1Pu1EeyuKATYFsZiJnliP1hPwPTaCO2gf40nuPq7cfPfMek+3QZJJIoK2uxRCcTDGuEnIFcXm2kHRFToK5nbIKKciWKngP36QnhrLZQzknzUiOFMvI7KtOpNTgjbxWgyWGzcbHWOCQvUbqPxPxPv7kU3iur9kxZBcMeNHRsvIBSDHACreBzJggtDA7m6Gjr1lao3qdY12uMfnxQ2EsdDk9Z2wpVt/e3eD1y5dYrzKcTcYSTiBgFpVZ9IyzLSQEzij1dCp0NleHM7TFHj6DDChPKmqEUYx7TmrJEaLRcBDJhDPfp6jyCnnWoswpddCsNUpCBVwzx8f4Tx1RuAyTR6+cc9FZsR6UHbphsIms1hwfWS3WZ8ccc+1lI4Vf72Kbx2gaG1fzNXqU4r1jOqE5j+rcHfoOwRoBASXd8qgMOUpoVBN+LX3T71UJbnpV+3Dq0MHDrhqhqgI8Wr6UleiqVJLIQR2jt0kx9CzYbY1i+wZeGMOPZ1quqrdDxz/YxwWN3iZVJOn+bPoiV/WnE/hIkTKxtfcRxQmsmsUAGTkdPEpUBHRmKbgV6dn69kvMgm9gFU+weRfCihJEz0bw3V7Amy7xES59JGNLEh55XVGaSUZML3pZyqHoY0YQr5TCjSv/UgT3tniS+ZMAftnCWTfwxg6CtztcjjN4Zy5G51NYTojN7VZCNs4exLhKLLgEh6SogN5edh8WSUAYWOqnbxFS9kzgAQS5LPGeapk8R+BbQlJtbClv3RN0quGFHqLQFrYf+/N6k4qch+we2yZjjbJZFkX0rmN/bkUeLaEu2k9QGVBzH9Xjkhynja2H8WEYSw4AG9lzDGmhHPXly98rQID+j3J+TSCGBlC7Fg8eXsnveZ5hOR/j8uqxlLO8dpn+2PnAguwgw4KoOlSSsMiOWqHZE9jskfNCIwump1wQsDtK9YhROSKXIlCoghQMaORiPh8jpnZYs2/ZX3dphtlkiidPLzCdzeBZSnpLkFCsyW1KgyMxhs/oRydjnSty5PHYRuLsUO/W2Gxr7E0ASt+h7DvxHnKbHJHfCmBn2ZGSHuvrd7qc4dGDGTxhUSuWKPsGZaSjaIzpLEEcB4j5/WEsIQkC+GrfNo4tZBiR6Qw7RBxYmPU32N4W2GYOisYVEE8SKluCM7YAEPQiF7kfPf+YGkqvsYbgP0HlVvadrEAhTarOKqwUpvdSBsn0ZP7Oa5V+T5RB5p6HiMm/vTp3XdFjnwVYByGCMUM8GnhtKtfZbtchzUqRPXbi9+bDdSI5Aq6lJLYIXKxcD2Xroioc1BUXOrgpjWyDyD0tBxFDBAKCcq4E0IhnGwExJ0S6LyTowaZ21Akgam4JuqEvn4b5pV+axQVe9xA2G4WhBOTIipO0VTKtLPYxMiIJeqvrgwMRGawewcXOxd1mj8piyISLtsmV11gfY7yIMSJoSVhNZMNkYDbIeW+iTJigtPijMkCj0imvlFPSB69WQATHSyYW83zSWoGSXmaBkJtoNwiqDIFrYzOhRDhC0nnoAxdp2yPLLWw2DtrtBonzrXjdhdEEdedjv0tFbptMptLnt9mO9DgVDlNUyMsd6qKE1dhYzCP4oxGygsEnDP5Q4z/PB0Mq6Lu1z8k8pN3EYS6gfG0PQL0EGTW2XLu+p1jkJqBHBQPwrSZ85HBvkKf1PcOkiQrZ3e4wCSxJg6YwlteJGrMO86LDfEgFkBzuYGbRTr1UW4YOQQzDnVTftw0bV91H1b/D7VB/k7yLC35di3Gc4OLqSksmS9ze3Ato1js+lg8e4+OzEFbZoZTruoHNBSTwh0Jd7QpCUmHX4XffvcNqnYoFBfsWfUJH0RTz2Tm+/s3v8G+//hfc3N4gCEfoJBVaMSvJbuaWPn7yRHzfOLekFF4luht/zRaT6Rw//0//GZPpFNfv3kn4CsdSMqKDgAtZCggVCw32jawQ1lo5sNYUsKYWZ7TtirlvGNaaYUBLWA1lofxd+YFKztQJYDu1Uzu1Uzu1U/vTbxLYJYXZISb+0DTd5Lj9T4A28/Ph4weE5cNn1BRkmNcJu6QTWeN6vRaDXvpdzGdzzCnNsTlhopeLYZNoj6HhOxRDRMk41czRgHBqbnqYqQ5JUUdMtqGYltVFZcTMCbMyX25kBZurlUzae/z4qXzPdrtRAJSm/A/fdbSXx401CydjnJRPp2NJb6xXFXa/u0MXAslHZ3j7zTts7rfoK82ScHs0dSHFYRiHYtcVei5iMYBvhQFDQVDDia1doMcGbbGSIjQZj1GQWeF0qLsd9um9eHcl8Vhi5+l3xwRXFrdtTU8RBa4Z/ylz3IYjrbQaCljSfxp2msj2BFjTxtAsjAbmljaMGQ6MlAi6YNAEH2EPKH82Am0seh9MV8IAzGpVPOiqQ/+jgTdDuFSzfg3iqcfNWRiwY/5+7ImlmZDSE+Xj9HVACWPvYp1O4dsNzqZrdG0lHkUSTNCp97m9hSK9lkm6F87Fv0ivh+tvGNBFs3lDIXLo+IohyOJ+MjvDNIJaDWeIgRPK8y398MTvpUQwmsgqel9XsMj+3N7BQg4/H2N18xj3WKIbh4iXEeZBI5K4sddjGvaYokFE5k6jGCxFZ6OjTNoPUFcKlKHci/yZhiwBCbkoBICyKMnkwQkJbrCI6eD37+DMShRtKN5fgdMhHCUYTz2MbRbIYpU+gDssoFm889hKgUHQrq+EkdU0LiwmkrK41tI1IxWl3JEFfkDvQNcWaaZnl0BLVgn7ti+yrOl4isVyJgWYKooY0KHBM2GqmUAXBUSpxQXlKaWKI9KetAfYMCCqsAABXaTP03vKRRzFaOoKN7fXAlwb6aiSHalCeDId4y9/8jN89vkLPH74CFFEv78WF+fneqxQcvdQF4QE1YqSfZQgPx3Ya+T7HjkN2X0agRPgUQEGBMBb8TZr4LY1XCIkDpMweX12WM4jjEaRDtI4KqY5Rjoq1MCjDK/thfUkqaqUXeq95tjj2xamSQjLDcQXK/EL2OU90t0e25ysNcoVOT6x6GVHJmONjDobbdHC7SskEWWL9M0LcL5MsBhHSvY//Fdfm4LS837USyIl5cxhFMp2quuFCJRh6JEJ0iEJv4Bt+8hzB/dpq6WpriRONh37GBl6BFlDOPT2YoIlgSixBuBxInD1Cr0VM6cZKcd8YX2R0VuJV5yyTuB4osJE5JjRAzF0MSGG1VdomepZUKYYYjvyMRvbWFjUY3NxhmBPgLR1xERfxkSCsUEEdzxVTL+aoHaDwKowdXv0oYfMdWVfCAKKRFPkqL2wDYXxYkNCbNzARUnXMb6GoEAYyDWWEskTKTkBSo6fX8HqvkG7nQu4Jb52YovAhQlKFpkO3Mr5621XWFzCHmVoStmi3pK5zdTbRvd1B1mWY1920j8qGuoXW8aPIBlPMScYz30RwKFGT5P7rEfR2mg9H37sIQ4t+ASZyKQmI8+KYIU8X/xOAlnsWCqMqLMd2Vc+SQ853rO291uEDJAJbczpyxba2Ijk2MfICtC6NtK2w27vYn3tAMUaoXOLIO4EaGs6GzkTzB0LSULgrUFBgNBjH7Qxdsk69wRcdZwOi1ksslwmxYYRrxd6xuZipaAkiOq+ZqS4ZtxXgL2+K8i4z+OuEpRtix6R9OkyAJu+Dx2BXOqPgx9tZ/cYBUBfNpK02due+lj9BYc7rQHGNKPMsJLlohs+fTBjG67F4T+HzxmeONokEzygbu39IB9++vipjIlZlgnrf7tPZXwJxnM8e3SGMV0JyIhlXxKmWghb+qheiNFzi3e39/j962uRwQvYxrmIY+Hx4yvc3dzh73/xdyjqAp9++gM8++i5JJOShZqWOfb7vQ606pHu9yLvfPrsOaazuSzk1gWDPRz84C9+gufPX4gX5e3tnYClHJm4gEIJu3htaq81Jk3To7csyFqrhLnG+clBCaLuKwfwUv0mTDX5USxUuX451tg28jxFke9PANupndqpndqpndqfQzPsHt7oFeBkgAEFXPzR9keeMnOv9yZpH77iaIL24SzO/CYplS1X+zOJROfkZTRKBGSbTMgsKiXlT3mxaZmCfrf5ffis4dM14PFe5L35V8mp3j8GOn3P+LNRGtSZSVYmRfbl1RUePnyM7UYl4BnWippSvcfd+96xIRuIn8dVVYKIJf1h7gpsXt2hykphUTBt9exsgeX8TEIprh5f4cnTR1JsUEjB9DOufxOQUFpVma5rmWQhSXh9kWIUe3CCiUx2mybD/fYe6bbAaDTC8uwMcZJgu02FXaHMls0E3QBBeqs1qIlBEkobJE541TeTCSJwigbSvudTYz5mkE2Yc6GZZJKwduiDeetjnfs4G+VYJhtkFS2mXOXPRobF4eQOHz90L9mHY0MbfT7kBZpddHyOtD8NH+gEZFMfzqKpaSPxZxvFJWajW+RlgI5m4HWJbH8DN5zA9SZ6A9S2q76gtojSSgO+Ktmg9m3Tvj085k4Y4epyicApkbHY7gNYTAhlMdm1yMoKdpDAi2Lku3u0+7X0n/3+d5gE71C/HWG9GqN7+ADRo0gSSKMRmTz0NHJB2ozL/kBGWueCDu4szDzKFB0LgW+hJ5OKBlw0KWcxz8RTz1VMH67UdwRveV34yLtGihNvnKC0Q9i16jcVAZ+mRCiKLwViDDrithPgJfOUiTrPI0ODWyrGWGwGvoDCItljH+8LOD2DOtSYQIYAj6ND362eXl0VNWLCkKp7fpeL0PcRRfTIIljjK39BMotE3kjWHAsgBaYJQ0f26PAYQThld6bZHhwY5FTqa1qHefiej2SU4O3bt2J0P7BeTUKt5eDTzz/GZ5/9BCFNz10yV1rMZzGm8ULYd2QNqeJbIB9hDjF50aPHFxm9RYWq6JSHIg8WGW5NgZJG9zwWPCYcBzp6rjVyjgK3ERPx6SiWgpZA2tay4Ct1tFxrBAt4XigLJquVwBG3j9IljoHKa0rJ5Ll9Nr3+ghJR6KApa9zerpA3BNUctKWFvLZRtPTDI3uJCxwcEFw0cITZxnNJRuYiIfOMxzNAQUlhbyMYAF0F7HHxgABk35bC0gx0uIEiTZG7SZBLG5NL6MTfwmPSc/EJwrM59hkDXWx0BNY8V0zxCR5b8VhkaW3L65Hva9CWKaz0X2F7X6G3nsPqHQRMJqSvEgEVSu1F8iUjAQJKqDsLJftZ5CAWb8ACTVZjV/jIwwhE3B75LRKyKvMOWROg8QM53zzhTUl2VwPPVYsl80WMMHTRuA7KyqFdGdyuRuxUmPg20pCgnydpIsJYbMl4JFOKfU35/RGATnhcAxcFPcR2lXwHmcvsFymlja4Hz9nDwj+gz58jbyM0BAvJjGNfIIhVqXRpfrb4sGka0V0F7G5qhGWKIHwtPm1NH2C9q1BZqq8W+UbAc9+dYDb3MY70vaKvYXcZmpQMLwJoHix6ziUOYpd+cyWaskXW+GijEHFMdh6Pa4OagSyVYpsSwGIAEq8P7m9R1xJGEYxGSmLMUKS+Rmx3WJKZHzvYhh5CK0QM9ksbq97FO56nnYWwvkMQ3goL0A1GKMseZcb9i+DzuNUNmq4TBqarvfg4TvMaDinHjDwwb3e1yRTow1TLowCCA3R1mE+Yxr5s2GAiEe2ZpkEWbarCS2RRwtgH6HmNZqTKvcTpEFkNirxGR2BNy/mHlSHzX3UjlJ/h1vTBPdPcIs0yp0n/PJhtDJOqgemm92K4x6nvUuPzdDYVcC3d7wR8ur2/F18z1wmweHCBJ8sQLSXEXAzkeYYPB4Hqy/wCzdCnXP/3b9/hbrPV0xp1Tx6PRrh8cIEvfv2VXNs399dYTJeYzQlUH446bRAY4MIFRP4QdGaITVnmSEZjPH/2XHzhPv38h4jjROxJ6LVGhjMfJ7gmacIEl3UAjlhpEFgjI0/8Oo3Pml6gPpovqVu/ZjN/kHBP/0NhOoKJ2FsB7S/Pz08A26md2qmd2qmd2p9LM0CCyGaOGBsDVDEsJx696fj3Dx768F/ziWZuNkAauoj7Y02Ar47So1rSAemFxonKZDKRxFECTmSskKKvGGvaS+0DYEt/mOyGkYNK0yDK4ccAjiYlTb3OTI5Y1EnaKCfCmknEFU9K0D568TGSZCwyVk6+hkN2DOrIduhJl8yw1eNlVcDzbAHROAEuc7ImeineH1yeYfnwErHj48d/9VNM51NcX7/Dr/75n7FNN/AixTrh5NMx3yffyZAAFhxK4lOlOZy2xHg6R94E2G4ybLYZbt/diw8I/XGuHl4gigPcr1IBIhR2yepab78Y8ZI5YYx5FaAmoJrGT2R+bN6n9894vxydDP3vgTWpagPFI9OWzUNRzfTIbe6JVPRymmIc5MhLAsLGA++PVA1HRYPCzTrxVhqAN/P4UWcxn6TPvEb+1Ov5k5UhisrH+egaaFZS4LjJlbBjjHeaAHmDYfRhFVv+0pPuwzFRTKXJfILLByNUdSEJplbvSaInP4vFcdl0CJOppBUW4gkYovfW6Lb/J8Z+jfW3C9zeJwienWH5yMPUYqHrIODM3bcR2BZK+v+QaUT5TUQgS0lVCORShOv0NXyalvdAVdBLRqUE8lz7BI8ITkiRX6Cm1xPlYHBEMhX6MSICQ5R0CQORoE8HvoLUG/qnsRsVjY08cDBjij7qd9sAACAASURBVKiWzdD7qWaoheeI95fqt4pxxmuhIctA2B2HlFoWNcxmtJxEwBoy7bZbJmkSnWCftFH1NpLEx2ySwGExWjC8gCCaScDU17iMA6ZA0smXhsFm1MtHhSZZdfx8guIslF6/+U7k7MpXTp3j2WSMv/7rn+PZQ5V+WVH0ZCmgj4eujyORR5o0PsqpmCxAEIRBBPxGAl4qfbOmuJw8PJRNhZyLD8Ku1NJ3YbNoLqhtIRqNEIcsWDWjV0u5WJgL8G1AcnTwyTCsVwi6nWL7OWSZKcaHSq61Yct2cse+htf+3/D7JwiSC+Rlj/2e7FkfvSSzerBcW0zpO4K6rQGOfVxcXiLs9nCsv0HvXAKI4fcsrRWASXBCjc0V7O4Wze4W2WqN0E0FcJNBiExLxj7IIVMLHtwzG9+izyzsf/sM350HeLiIhMECAkd9DdfpEQYeZrMYvrCf+Fkt7rd7bG82GNkVnPgGsF4Io4jJi53tyrmtKA8kW85m6jaPNYMJHMQhfcfIIC2Qby3cdxHScYB53OMBZZjCWvNQ2gHc0EMs12AHp2tQ7ffCjuPmM1lyGntyrfqUjVGy7bioGoeHAnZfYeK0IkHNAhc5wRTKJ0umXZawHfrHacN1Ljh1pYADbRKhLHo0NOdnoqlHu4AaZc2ggDGAS3Q+vfYIglcQyzUCHPSXEsM/EnHZD1rcw8JtZSMpgFGbwZ2+RNY9wTpTCbJ1kaEq9sgtH+F4ick4hN2kykPRImutRLoDtpWLmoygyMc05rmv5LmisFEghjMOMCFwxY3R4FolgSNk0JJV3elTVyFLN4ijEKM4UJ5Yto2arNia4xnlrpWk7859G2XioPAjhH0oUr/GtZFXDva7AOUacNo1fD+XcA74IfI95dk1oiQRptq+SFGjE8aqeEiS8U82Y1liOvIwnkzlOiTwYkIQ+PzA/tY3liP4ZVh4Un8b2wMCzGRL1vqHzyrfWfkckY12cOm5igYZZcFuqCdWOpzKfKj+RY0v+i74IfgmY4feFj0fEXBNWGz6/mj++YB8Lp+hJzZyLCQAwMHV1aV4UjK5k3Oj65tbuAJ0JXj+8ByzqENa8ILi/IJMUbJKtW+lrWwDeMGttht88/odyqZW4Sf0AXQsLBZLRK6Pv/2bv8Ht6hrT8QyffPYZLIcLDGoRRe+ZxrZshCFDCRysNxvp25zLiWdaVWI2X6Asctzd3cm1zsU0Aqq8hmQBQtuWEFwjc02krlxoIuiuk0EPoVrDkZGlAvnvkFKvfNeGxVr6QHLsyFJMxwkWsxn2vK+fJKKndmqndmqndmp/Ps1Q22UyIB4XR7CYQcb0n99rf+Ax85bjp1Q59P/34sPkz/ywcfJG82tObjZbMsUymTTRN2gxm8hKOwMSlDT0ALCp4vn7322ANjWp1bWkniipZFPNqtLpqmZeKlMmR0nDeJxEelY3MpGkdJQMjWfPP4LnBbi/vz1MUI+2wfyia99hywholU0hhthn8zHswME4GaPIS9i+j5//9c+l2Pjl3/0S7169FQbAps4xjWZ4/vSZ+A31LE4JdHUuPIsAjSdeWjRSbi0mztVo9xnmgYeLy+fIChd31xtc329kQjybxpjOxnj29FIm5mu9ciwMJM3kE7BRjHmVLHQILjD7NICc2rfliA2I9/qEAjTMUwbzHEoQZSkkk3fzmrqzsd4HqPIWibvGOCmRFkyFdIRxJgXFUUc9BriO/nO0NXp7ORHWRKYDvmzSaDVzRhcjLOrp3/LupoflzXBxlsN1C1StMvA2nz9shT7/CuDQ3ygr8Wr/bD/Gs6dLJH6FfcP9Vf4zZEyQKbTK9nDiCTw/QrreoK46YRvG0R6j7JfYvLzAd29GiBYN3PkY04s5YgDr1oMV2AgdCj11cAYJdwQOPBsR2WP0sqIIzGqlQGXSKI3VyUIgm4PyQylsWORRjkePJgIUXigSxqogQyEVxhvTfqveRTwZCZhH35rYD7DZZMIoovSY76Uh+ZjphjSS08df/AR1aiABCLLn6HHEwoZMLbJU/CCWABIymKht7dwQlTUVYICMObLfOsfFvuhhE4wMmWbpw+353a0kzJEBSyYYfQfVda2YU6bfGEBdnRsFsiknJNUxVJGrGAmOLsT4GjIfGBzAVzCZ9Qef/Qg//emPkMSxNu3uENkpmt0aBRkoUQSKueQ64Ukhhk1jefHT032HMsZCgX2jWSyA2qbKUAvgLcI96VeEGdn3yb5LkhhnTNtsHDjsWy4BDsX0Iv/GJjNNKEncjxpO+w7F7Xd4/SbDepvDqXZIAsoXffSWJ9I5MmNZ2Kpr+xp291uU302wynwslkvEiwm2eQGPIJbXIXB78fUj441g1MXVGc4XM6zf7BCVG3gJEY3nwjhk6i3JkhJuQF1sVaLZ7bB6t8Ft5iPrPez3Ftq8h28HAiDSd84mK09CMMzYfA276VFcP8NXMw93oYWLyMN8HCDwHZFeEawc0V/OYZpjir+/vsbv0hoPWgdTL4eV7LEvnyCvbDmHrU5k7d1AJLO891gtk0/pFWaLp2BDT7XMx10YwZ64eObXiNocVd4La00ArNAhqUwlRHc1aloM5BmqksxAGt1bwtBTKaRkA9MOwILlOSLhrCobFvsvSky9Dl7oogvIDHRRlQ4jmOFa9JNqxEuzooE+md6+hSh2kVse6rJDlxcC9DruGLv9CI1tI00CjLloRA50awtgU/S8dhkIQraUCi4IbUe8PjkeRomD+/oCZRfIfTJLt+gZfuIkWF5OcRYpO4Nsm8GqCwnY2exd7AjqJyHGiYeJ38FtMlRZi6yO0CYx4rGLMfs8Qcu2VnYMTJtkGiM97zT7Ms+3It+bTudKZid+fJacV8oSCe5yIaHXQJtv1Zg5wCSykc88VK6HRR8IM3LfWdjkDlZrD9W2hI81giCTRSYCzemuQN/UiCdTuU7LKicpU11DNZmWofjo0YeO+zWejrEvWgnAUHMM5e354T3HPHCQfpo7BkcLNoLDBNlrdC2DWlSwhOs2CGwysGo0Fkd1gvpq3jLcV9+zIGA7zLeGRZ/BQkEthMkdUoPwhxvg4SMG1toHNziS5rm9ZHEtFmNcMZSEqaxNjXdv3gmYxfvW8vwKz89i8WUshfXM+xFBtRAO+4UA/uoeVTUVfvfqLdb7XIFTcv/tEU1GOJuf4Ze/+AXubu/w6YuPxZ+XPo2b7Up7qWmGsoS/6GOhN573DiY2s89yG8lSJJs/S1NRI0hoBtmufgCXbG/Zr0ZtM4HeggnrDFyhHFRZDcicWX3JEfpoAnDUAsCwOCsLQ4q9xvnUbruS+97Fg3MB8pmout5uTwDbqZ3aqZ3aqZ3anzubTZnFHyCR76FfxyjYH2nW96d534M43v8cDYK9/yZpXE3kpC3PC2zWXI2sBWyYTqeYz6eyIklpj9lmxXDQ32hmXFJIH0APXVLrOe4htUtWQOUhzXTRPm2yqQIyaZo/vTl6FV7A7eKk7Pz8HM+evxBZQp5m701Sh101h1UjMAro0UBb2wjAYtLSHi4ukeUV1tsVPv/0czELJpPlv/z4Z3j65JFMuIlXMAXU44qtU2sj6kYlyLXG/JxluYWq7tBmezy6mmB2+Qj3qz32WYnXb99JEmmShFiezfDo8YUw8sgSpAG6AGqaoSaG15rJxia/6z0xR12Tv4bTLbus6gjdtDfNkbziAGYYpEGfIcpJLCYUZnLIsnaGJKxwtdwiLZhK6B0BekdqWe2FYw4+k1g1pAZLfFJUsIC2nxm6nO4pQ/cUKRpaFNmtfHg8eYC+85EVI0R+jsV4haK2UdVEibRsRvsDHvVord6lT56N84sLXC0jYWe0dgSHUhndH+7oP9gB08W5yJZ26xR+EmE+dxD3/4js62/xu2+W+GY3Rz+/gh0/QhDFsJoe+zjCOAZGfSnFrzASZF8JfhAgVoEM3A56ZrGIdFEJcFD4LlLK/iwGGoiOWVgsjRwUdU2w2KYZfmuFqOi91NOBHQiSMbKqRus4wiBqNxuRMNKUPCVgw9Q/bge9nWhSTp8n/k0pqpAUyFSpUZdMaGslbc/2AkwnsWIFNjYsrxWwV9iabS9AoOUE4iHF1NwgpCzvHsVqhxA76Z90+FHdykE0GmO6XIjnDdOJDbNwaPo6F4828+9RnzA9nO9iUffxxy9EJs4i8/zBJX72859jPl/AljAWdey88lvc3W5wW0Yo8w6hxVQ6Xuuqz7EY479k/KkUXnaTEnZVY73pcLevhOW0mE2FeVHuU/Fc02G5YjJ/uTxD6Ee4WRFB7JC4NWyfekIyfHht2JLmKQwPAphphptXBd6uHBSWj6oPkFYMPkngeJ6EaNiBL6wUpjfKNdnPYfV7NHdj3FYh3uwq6UsfPz4XkC8nGMwAix4SjvDk+QPsmh7ffpcjyHvMrB2c+St0zg9gWYopJ0wOeg82FfaFg/vcQ974KnCDclXLR03G1XgiY7DrtQiCThiXCqNnP3oK4AL1roWdWliFDm4oj3YtjH1XFj74Xo7XL+/v8N/u1nhT2XhYO3jcAP4sxq7/BHBHUgTXZLA1NtzEx4gBGuxDDG8oa2GZuZ2FIrew7kJsJgEuhbVG4/4aeemjZKhA5CFk+AyZOryvtDRCZ2BLjqwqkOY1Wvb7gMCJShZURGEFNLi2kuz2roO8Jdhui9dibOUYUR/J68v1UMNBVdpo81b86hrHx2RE9qIahiaBLT5neeuizhu0dQ6fMlayDFP2/16u56bgtQRsmh5532HkOkqOKuHINlZksbYl0rqH60fIsy0aAr5dDH82x4NZgIQglwyVNNyvQavUvPNQBAHCUYB5RGe2Cn2eI0td5E4Mbx5iFkD5KnIBiH6kdaMTGflvMwBB2/29pIAy7EWFM6hAG4Lksr9k6olpvI2asGHDkASO9bV4aC4dIElc3I59eJaPxAkkCIFuW9vMxu3aRp8V8OwVQjdHPI6EnUl/NgK1ZDVxIYvJtUwLdcjm1hJ/jj+Euy8XCSyffoCFLFAI0Gbuc+aWLzeagbatWWNm0c/cM3mzYiiJg87ewpfFvBJl58J2g+HDBJIj6KxnEH9ohmUeMxOPIQ3UfI8B0g6rS8Nn6T/1ZxwsFxRrlvdk4POPXwgbN91vsU/3uLu/l3RlJxjhxfMnSGoLRd2gc5SHmgoxUAtj4h4gY2CP++0a3727Vop8HYzEqcHjR49xv9rgd19+hdX9PaIowvLyXOwKOBdSx1gHMmkvYS4SyUKJWACocZ2LJvP5HA8fPhIAXTxMRdlgy7kVBq5m0gprrazkmhc5KEMMmOg8+HXqOYVZKDR3BwJo2kJgYKyJ15pSP9RVjjTdYMnF4fkCm+0GN/f3os7g3PHEYDu1Uzu1Uzu1U/szbTLJ04mbQyKWmdGZ2dsxEsH2QZ1qHjp+6eHRP/TiwQjkQ0jivWbkm5yM7HZ77HZbeZxeYovlQgp/Yb5ULD20Wfcw4zRg3gFaO95GRdozlDZl1itTKBOCoBluA1imjw9ZBwocY9JkqVOrgKfPn2M2W8iks8zIMiAg9f19PPx5AKnMBHdxtsRoNMNv//ULvPn2FXwvwOWjK3z28ScyKaRsYbvZI1s3+P2tJWCNJ/FkXGHu9ATQljS5vhcuk/I9szrxeYu6Gi8+eQx/PMdqvcP9aofr22tJk2Ms/dXlOc4WS2RpjqouxQeK6aWK1KZSRAcDZcGVFFCowCpDCdOd5Ggyf3zsxb/EVCDyuEk8MCvqLZy+EBZHbwWoEUkWwrYMsc1CnE0yXM23yFkk0iRfs8UMo86caQHgyPrpWKBr0/TjbXuvMCHzSP0mTJl6h6op4Plkk42kCFAni2buEbIiwmy0xXi0R03/J/qJabNm9fHqF/bdZDLHw8s5nKBF1XhwRCbjSkG8z3Ns9hWS8UKKlNX9CmXnYLkIMQ9+DXv1d/jyVw3+/fUZ1sEZlo8f4Gw5RTAZIV2OMZ+HmHYbYHeLrvfF+J9yt16Kj0a8y8TbiH5dPRkfnsg225LEqBqhXSMMbZS+h8pRvkVdpUA0sqQozeTBJWMrCl3xOqs7WtHRLyxVckKyP2iuThZbFMBtCarRBH2N9maHLb2hAnrQuHKNdUzko0l0TeYcmSs0WbckBKR2fezu6P3UwIsrWC6vQRpn18pjzXFEvkOw3apSZKstdoWFrCOrFWhTJQniMehcH5ZHjzYHZ4upJAKziKLkh55hqqv2A9hlWG5GAmT6h4wD+nEeV8rVP/vkBR4+voRDGS2ZGBwn6hzlNsfrlY/MShSwaZNBRZktpZcs0hWIznREmpSL7LOnHK2AU+ao9kDa9bjZtQJaXE6ZrjnCfkfWrApbuVjMcJtZuN52cIoe46ZGmJToQ3oC0p/JJP3u0TeUljliuH9HybAeazrHQxPEiM/nSGLKecmauoZnbdF3I8WUo3zNfQErmaDIqv+Pvfdsk+VIr8ROelPete++BhduhjvkclfPI/1q/QF9k1lpKXIcAQw8BsA1bctkVnqj57wRWV0NM6S+LiuAvt1dXVWZFRkZ5sQx2GbArWHhJkoxc10czSYCVsxnU7iDPj5bVrh7qDEtG8ySDOFxgHr8d6iNkQD/vOaMBDC4+DZdmAGlyybShnJY5bXXOg6GkwCzgScAsEnD/SoT6SnxXwJxshlke3BmNryqxjCqpT2/tgysKJMm+Gva+MO7B/zLNodZWfi73MAr14F7FKAMRjBt+kKVKAuaN3niiRbyeJJgaQiLiiEjqF3krYtbPmdg4dwp4VEynRnIGiJFDjyP0mzlqsd7rhGwqBBGVlZkSGTBrvoX01aMYHq/dfYF3djEa0ZmFj93Q6CN/nYZpbcFPLOCL6m6DnLLkvZOwZofOiKHFeBJD3cEo3uBKcEBeWVJ8iFl25Q4140haYgCvFOKzZAT1hfBvXUCy2lRUu4dpRJwQnZQmi4BAvPhCItFiJlHDzjlu0mmlzANyxwpJfxBiHHfwdCpYfF+iCtsywDNMMRwYKGnZbMKWGM91dI3kalLL7iawO12jaop4IWhjDnE89n/MpiDQBsBTKk3nVotIDVZ+LYpvoxlqV5DoC0wasxtE07PQhTaCEwPQ4dsQwsRTKwZUrFkOEcOH7cIAluuQSweh2RkufDDgfi/5lUusmoGZ3C4IuE3Y7KlC8zGffHvi2kwSfm3vhjdBpLqTBQ4piYXe/3LXmfjEa3OGxQlQV49krUd+LxnY7E/zZEpjoysOkKk2yh90ontplyPc7luftc90CFxuzfdzQUJ7B0vjsQ3TAFRKW7ubqX/NgwX5xfnuBqPUTP/SeSdamOFf6PNhARCSXuhDLPE9+/eYh1Hqq/SnpL9wQCBH+IPv/8X/Pj9XzHoTfD3v/sdwn4P2zQSiWb3odkOlHpBnTbbhqQpa0abF/g4Oj4WOw9uGnJDVLHLFNtM2gtZa0yqLSoZU/il0kGZGstkW247yMG0/FdNAtS8RwFrsumqWWtyX4s/okorjaOVtCWy1vjqm7s7UWSQIcfxhOUAsB3KoRzKoRzKofwPXvR8f0dr3wdBnszq9CRsfy72S+Xx7/sTuL1X/ZRNsgdC/bR0Uk76r0VxhCxJ4brOjs3mkomzTZSfjH4HlRap57fdbPRxztg968kkeOfFpME1/klNhjp2k/Fkt5JFvKNECqRCBF68eA9u4OP+4U4mhSLV2JsRq+PqJC7NCJNllkGmRCZpfePxDM/eeyaTzy8+/Rq39yuEg1AYP9FdjduoxbzJ0SMrZ9ZDIcZFlA8pkElANvFzIeyoDZvrAtu7Gvc/RjgaAy9eXiKrPSy3sRgTx5sH+I6LsBfg9OwIrmOrSTA9bjSouPNn24FrGhrc0cFUnXV1rAAMVbed/E6u5b6PiTyvY0NUcEE/H4IBPupa+Q11XzTrf9j6iGMX7x3HCL0MUUowUX/GrsForxkuPFVumzo/tcB4rHOlFVWPc8HIaXeVbwjxwXJGSo4qiqXHhs9X1KaBOA8FPJlPVgidBFlGhykF8kobsiycnp1jMfKQbbdImIpGuRL5CU2D+/UaFTz0RxMkcYTNKha51+mYDKB/wu2XP+JfvxzjdX4Ke3GE8+MZhv0e8r4Pe27jud+gT8ikoQF5H3GaCwDh0lydLl6kqNA7puICooYlUjCGGFgoKYEqGWTQwGlTDGg+7lnYOjZyAnEFQUbl50eJJhckTIiz2gpWsYQbWJL+l28LlNUWjhOgtRwkVQOn5yIkm8f4EWbpoUBfwCUuNphCSplgkRHcqIVdafke+gMPt6aJ7zfAIG4xwApW/xuk5QBxakrYAz2Z2P6VVMfGOmFgAuVZvMIE7zxkbYBC2Jc1Qq9AEDBrkR53LTw3wHg2lSCRLVlhwn7gQlkFITze+90a+JFZye9cUE3GU8yOjmFzccWkXrOBY2VAEWG1LrGiQNemiTeBTcWK4/3v9EMEIduzKSmgsmkgAQ7sAxyUJRehNuyCHmmUJZnIKgO32xJO3eL87EiAPXprfXHfIk2BSdVgYhQIRjYwnqKmjExuFAKkJZBvpF1Qpmt7BB8o2SJbyoFh2egNbBxPAwEoWgI2ZSAsTWEZUpJJiRMBJ9fGYBKKf1gaZ5LQuOSmRpzjZDLCXWPgL6sGdtTioqiwsEqMng1gnS5EGiqLat73NJGnzJHgmKOM6x2mcVYM2AgErHRMB6OgQeDyblb+aXSgknFJpF9KYqytD2GFBrzQwKRuESxrRDXwxjGQlw3++hBjXlv4jWHiYuzCnvZhhUwOhYBrBGy9vouBp5JV5X01E1UsCpju6odIQgcXATAGrzPHIILRLmyfgQpkrVEOyqAMAkdK6sz7jWEDZMSkWYWq7sKFCOApr0Vi14qAo7yzdgCZlkAS1CbozfsUBfsmMupKeI4Fx1WSXI+pok77eM21ZyavGy3GAt9E6bgCJFY5zQBb9AahJLbaTiIeisxKsB0DVpMhoe8kj2U5SLcR6iKB2QQIhmMsBgwQ0DI8YWLR8p/HLZBuWzg9D6PAgEcftixHRNaa24c38jCV5FCiZAzt0Ky1opbvVdkKY7CqS0TrB5F6U7qn7kO1SaUPKcyxqlL3qoCKWu7NOiMLkFLilh5tTJZlCEvNMbFE32wxc01UAxtb10G/9TBwfZSWIW2GuFi/P6WSGmjeoO/Zwqbdbk20WQmvxxAZH3GeoGwLuTfYkOh52hBUrUpJ+JyMR6gMW+Ynihem+w+9AaWwQQV/6eFRrrnJUACD8sQYpRnIsS3T1RtGTFGXEUrsBvhcJXHvxrIObHwE33aDmh4QdzDubpzWY3g3YHbvZez/qmTC/H51dSGfmfMcsq9uHu4EPOv1Jnj17BJhnSG6KdAyYddj/0tPs0drDQEA2xZRvMbr6ztJbjW5ISVhESamswXe3t3izTevpe16XoDnzy4RJzGyMt2dcDcn63KPZQNNrA3UPcCbarpY4Pj4ZHeuBMxkDifR43oM15u2Ctxlmm0hfQLncnz8MVFdf5f7U1lm8D+ZI2uQjffbjr0mSbc5ttsNZpMRxuORsNbu7h+QpKn0K49bgMYBYDuUQzmUQzmUQ/mPUtTEgrvCGprodmB/Df36lfL41A6R6X7dA9o68OsXXvnTh9UcSQUOZFkmCVCcDHFnnrKg8Zhmzg3SJNeH0fIufaydPEwmmRpQ07+rj6gX2HpmKgv5XQiCfl43OerMbHXaKB/muYg/W56LOe/V1XOZyBEQVAmFeld7zxBf/av9mQRkU4yWtOAEnZNAA6uHewRMSnQdbDZrBLMhFmaJ1i5gHvdR+DVMOxF2WxzRF8kW6YxIMbRZeJFl2C7XqPMGbo9Jk2RobHF53Mf45AybqJBU0+Wavl+ZyDIGwwHOT05k8snI+85j5FGC2dWjcNB2xsuPgOVjfcrur5ZmGvuWbArxEtaFjxy+mQnolOzAgk5IpQExCRQwUbUm7ta+eEBdLWJZwG9z+wnrUs5MBxDoBqCv3yOzrrvWNOgma46L0JZG+gwV0N59u/bX/dB9AJHxWEhKT6Rts8FSgAoalnu9Ia4uzxA4DoqaQIVNKy0BE9KsxDJN4Y8mssO+vKOnjInJwsXc/hr56z/gyz+b+PLhEoV/jvnJAifjAYx+iHruYTE1cGWWsKsMZWEirx1hjwX9niRy1vkKTZGiLChlVml8XJjS80wlR2o5mmOigC3vQdlogAIjBh8GNh4sF2VtglrRtqDVfAXXozdihYdlLszJXmij5YIyA8p0g4YsGddDWTPEgEbzM8DqoR6EGASuWpSKNI6NgObqLfyBj9DX52Q4cA0TDn2lvBrbdoK86YuvT5EUqAoiARbcwEO/58IJHWyjrYCfkqrrWDACGxYVVTQN367gN5/BNB3UbU9Ybbxn6c02Gg9R1CXS7VakRkqBpoDfHcC2A4FbCTX48IP38N7770k4A4M4CJqYVYJ68yfcLx2R8NGbrDG1Xw8lsfJZISb5PRq0M6DEtiVBlAeREAZJcSRbzAECD55vwK8z2JTLlS2WeY27eCt1+8WyQZABJ02FUVAjPApgj0ORybGZk2nC60Dz98YMVSosF4CU/ZYNKqOHYBAAfoDAtDENCS4pmV1Dk38JEqlhtwVsk/Qugtc6YdVqMQyVj1cZZ8gp020avN22GNxXuGoKaZv++RD2KNyxVpj0aIpJuA3TZd9EAEgt+ausQNm6MEY+QqdBOQzhl5TBsk9jH6sX+vreNwn4CrOS/a0CaykDN7wW49DAYFXAyQwMjBb9zQYvvRynF3OY/R4MyxXvN8p7CWYGoYuArDD6J8k9TcBTBbiIH5tjI+xbOKEXWpWJNJMSyJasNZesNfavyqCfHoJkv+RcsLOeCRwxGKciS5MLd9WW2P4orxPgganIUoed3E24hTuwjfcEg0nYrgumsxaUTSvAyFVCaAnJMCi/Ltm3tFJnEgyiezb68IVWA9e3UZsMWLDgmQwsMVHapEzdS19QmyG2hoWsdaRnI4usXDqhkwAAIABJREFUJTjlDDCeBBiGCkyQ0Bh+J3s7K6UN56UjCcU+QZOqQp7WiKsAVZ8sXwtDspmaWtWRABpkrSrPO37uqq2QJmsZ2/rDkVzrqgO8OWAIM2jXDat7i9XOsYXgisSh6Doj0Cb+bAYqAUqZ1KsSSllvY9PAyDex7TsoHBsjuBj0LVwserhZF/jhxwh5xDCQN3CMAoPAEibsNlFpw0HYl/ZCZiJZ1R6vpYB9DCHhcwi0uRKEwGtPwLWbM4i8eY9b1oGE7FvNOkNSkgXc33mUKRY0v2w0JuuaSbE6RZ0Hl3tCp3PrcVjNUR4HLHXfqL89nXPsnqJ+74DT/WK0GA4HuLo4Q5pR5htLcECyzWBbARbTE7w8P0KZMYmW6lZuDJBtSiDcFQ9ACTGwFJD65vYOD+tYfS7d3/phD8PJAp999ilef/2dsMt+85vfYjKfYBNFak4hcyLVorts7u6cleWA6qMpJX4u4VM9bNYrmSOKf5ruv+ReIytNGMSPrDUC4mRUcmzjPds9twPXVH3puY/2W+tkoWStEVyTNOa2wTaJqG3A0Xwh1/H65hbrTaSCa/bfS3+KA4PtUA7lUA7lUA7lP1hR8kh6OKm0vB3Y8O8E2Yx/69Fu/rib5f38Vb/0HjwPSroIaMVxLLR77jgOBgNMphMMB6H4s2UZpWDqXR6nZfo9dsfupIHa5L5jruxmwWrx/RiE8AgadYa2DEEQMNLggqkRg1wmRPG9Li+f4fjkFDEZTEyN0rug3UmIwHIfexTPMLXQ4vNptPz3//g7jKcz/P7/+T2++vpreGgxvjzC6GiKAhHqfI31XYrlbY27dYp3d5yYmhgPXZk4EuBL4g1cmzKngZh4WxZdtlpkSQm3jPH+8zO44wU2Dxtskwx397fCwCHrZjqb4PTsFNs4wjZVnmhqB12nkukkL11zHTz5uFPfVaaqQDR0fOICQuqci4USfSuSZMSoDlEyZYztjwCPvlbquXuLAFnsAVHu4H7jYj5I8PIswiY2UFSUpahzNJ7s2qsp+m4hooMSbNZFtUVREuRgSqUCK7o2os5fSWH1mahT4BSczC6eS21gm4To9RwcnV1gOhsLG4hb+uQQkv1Ffx3Kcu3eGIPJFNEywvo+RW8a4nSyhrf67/jhk1v86ZsF3lgn6C+OcbmYYtDvIxuHGJ67eC+oMWpTAUqz3EFpOrBkwW+AS2NJeKVPUxYjj96iKm0FIAkDS6e/ygKe6X0GXLI6LPo+OagyA1ZdIDQLTHwTTejigQBLRaZbC6tK0ZQZEkpMDVfYVGO7xahvIzNDVHmLqogF5LG9AAnVUgalx66SVQug1CLNG2zjHIM+JWgEEpQ3F+U2CQGFukDJlE53IH9P04LIINzAwaBnaZCwFRBmE+VobA+2S1aOh8AtYLVk7tXISwNxMkaZtPCsFG7wAMMYylVkPQyZvjmYyOKHi0deUbnPRcasWBfsY07mR/iv//l3wiATSZqAHw8w8mvcv4txm4zRsg+gD1tdSRps4YxhB57UNcE4Sr9C3xJWEr8InDDtkgA9iYK1sHIaAaBax4PpOejTw2qzlARJKvlGPR/OTYFzN8PoyIY96ZN6tAO9jTYX366mMWGy/ghkEcqjN2PVIqfh+xSY2DEmYSryQqvkYlgBbKx69vcCkFaMLdWBGLIwJXtGgXXTiYeZb6C424q8dHRf4NLKMDsv4V4eyzkROOSuBIEVAogNCALznFSip3hGli0yhniEwLi9QZulOPYytBSHl/SC451DBjB994hmkZnE8+L7cQygjK8SuSPbP9Nkffcd+qVYlqHvXsMc5vD8IwFCCFhRkss67we8Jzmusd0pQKOmnydB8MaUZM/ArIUh2jLYJnNEvuz4ymuNvFrh5Ym3Exfq9A9TcjMu6htUqATU5OM67VAz2BjwQakor4/0JiSKypdi90ofQ2aPBtromSayUcdGSrZqRhkksW9bAiZax0LSkrEFYaZJjoZ4AlZyL/J8XMtE3yqVTyBhCsNAbgSorQGq2kdU8No7SJMIVU7GkI9gPMRs4EiiLz+r1JOwGgkgFtjmBkrXhxfwOZRLAnluIHUCBGMXM4/OBfRae5SEFnkp9SRAh9GirHOs128RBD24QYiSGz9SD7rfZT8uvnCKSSW/6z6Z/ZrIRoUdqFl8WuovslHWMb3lDEs2OeTityU8VJg6BgahhdQx4Jsm0shCZHpYUlq+tXC3GaDJYxiI4LtL9HxX/O6yqILZMrl3IGMX/dkkCEMYbYqFXjP5OafvVh/+aCrM4pp2Cxowk0ss4Zn0w0tRZilKO4TpkLGmxqlGM792w1dLVjKtHzIB8Rpu2OyDTfp1T77pYa8bjx9LN5btvVgz4brXsU+4ujiX72w/BKvu7x5k/AwGM7x6dYlB6CPiXia98Li54PTguNzdKJCla2Hvuz5wv1njh3d30icIOCWHMzCdH+HN27f4/NPPMB3P8eLFS1ycnyLarsUvUwQCAq4p4rx63eOn7awhqqbG+cUzXD1/gSxLsdlw45XAprK1kPfQ6aCUfnb3Kp8jXmvan40guGLXixj9yeZax17rgDU1XnVp85ZIZuN4LWnS08lEWGuUhG7JWmvI9Nwvj1ftALAdyqEcyqEcyqH8ByyKvaUMo7lbp2drfwtBezLp0/uqP//rL73W+DdfpeaCeqLVagYFk58IItFrg0wTAm1cDNN4nQmkZDrIdKzbpd2bTKo36g79eMxHGUf3gfm3R58mTafbvQ8nWQKyaWktWRKc7G23sSSgvnz5Hvr9IVbLpUzmuPQV+Kgz993NihXAxp3U2XSG//o//c/wPQ/RNsL87Azvv3iOoNfH7//lz3j3+g2mixMYtYPrN2ts40LCEMq6wcN6i9uHrTKBZhpc6MgCZifdkEpUXlkNfXmiDCO7wcWLC2QVPa8ybKINHu6WEoLAz0azYD/wsY7WqMVTqNtB5yLxEUzbwU+aRdYBacrjjt+1Pxqn602OwM6R1gHShrIgLnrVC7vEx581AlVRClQQIMzEKgnxsPTw4UWMnse0US50VGtRUheCTOq4asebn72WNE/x5UIoSXKqGegrr78reUt3CgqckuvEHWx+rrqhggv9ySlOz0/QmD4cO1TPqyj9MbGON3jYEhg5l0Xk/dt78Tg6PzMxMv+I9Tef4l8/8fB1coJ0coKrkyOcjUZohz1kVz4+mJo4MVIYJRPOTGQt/Z8opTIVk4bsiYaMJ20YXhkoGxttuQSaXMBLJZlWzMZuIcp24BFc8UxJ3KPklfiU0+YYWBVGoY3Id2RhX+Q2kpSrHQN20JeQBYIyDMoYejb8oY+UEkMJ/9jKwpNSJzIeRALFOyhOkW0TLJMMg4GPZE2JKoEmSOJmESfwHQeW7SCNc/H4CgYuhj1LJG+8orLQpywri5G2HnoDC/2BgXjUh5NwfUc2EfsGJtEa4jmXJTW84h1c+3PAmAlgRIka2+RiPsd4HODd9Y2witTCSi3W//7v/xPOzy90u9FSrPYvKG7+iNfXE2y58BWJJQEfCkPJrOthvgB67VokpJQ+MunTqSs4dgXLJujFe9yQQAGmIlNOzPTfSlhBCth2Qg/+aI1R/QP8ykc49jEwt3BOY5TeDI5mK7H9kV3TVDxjBgaQxaMkhQy9IMuyaCz03BxB+hWSVYYmLeCbLioj3FkCKAN5hT6ynWS1IcAfoRwuOcl0YwomASHHWqKfvoXvD6SdDJ/978DAg2GdwjQpKebnIa/URGO5AnRQSmkR9ClLYYKVhiWeWU6ZYr3OIUGbBELsHmqbAC7DTCyRzNoWgTbegAQACc4Q6DQV+5EgJlNU2Yic7+D6X6NsTxA5NjIs0LN9aacmmV+UQguwpoNbxCeTOrNKEkW3povaNREyPThrFUMUHuC7CBggQDmoIGKlfA5JvxQvt1pYVwL9kcEowCSZhEoOSXYZO0Tiiww5sIQ5R8xdj2h7AFu3iSPH0ZsEPE/6ZBJoq2xbTP0dJpYS7GPar92ikKACSj3ZF5ChzJRpFdBDUFO9kwIVRVbdGni4XWGbMKXWQJKQtWbA8kYCog4YbkmwsK4EEFW+UzVQpYhzB3bgSqgCj8+5AUM1as/GqGeiT+m9+NEx7IGMNV1Hcs81aMwW64drVFWG0WQuQynrSTYDOqBDkZfUhob8oLdvdjtSXUCJth3QjDDlp6k8unjdCbSx4gt6p9WGgM0WQyrSCNPQRj0MEfcDjBoX08ZBHnoiG19HLpZxjTKKUTvfY8CsiX4g6cvZNheLCr/XR06/PRrWU4pLr9hkK555jlUIe5BehbXpIkkJjtF8QG0QoIwElDTdwS/Md/bGHEGK9DjLwADDRtvEevzWm59PXq02BWXs02OymtqoFqCGL/WzeprSivKeIjNwPBrg/PxY/G752tXDGlGUorZtnJxe4eXlCGkFCLbG+m1t2MIOVj6btuvC8cge3OLN7QOW65SGC7vNQyanDwZj/OkPf8T16zcC4J0sjgTw5zyno7mrjTV9zhKqxJCcroLUuOsFAT7+7e8kZGX18CAKAoLv7BsU04zPUyEGZa4ZlBVZrJq5RiCOLGINRHcbg6q2eGwNqImnZada0LJQLRNmqikB6LOjIznv65sbYa1xHH68Cr804T0w2A7lUA7lUA7lUP5Dlw5YEl8eLYn8BRzsZ8X4tUf2cbTd/GMP+PqVV3Yv2R26o//XZPTkWC5Xwl5zHfqzjTFfzARkSpOtnrAbTyabuyNpsEiVDlp79F8S4EgvfFS6qU7C7DybNPBiUZ7p2CLN4gyRZtcE/hgPTz+ODz/6WFZW6/VKGHOcAKqjarZW20g64O/+4R/x3qv3sVw+SEoXn7fZLLHNMri2j7vba5ydnoBqn5t3d/jotx+I1GYZRUpew/ooKrxbRrJxPxgM4btMzdKTVfGtUpNzcUdrGdjQolhnOJ/6WFxeIUkKZPkWd7e3WK/vEYQBemEPV+eX8BxHdmmFQSDn3VWfujLCANr9/vh3Knp4Pr5FjyB6BhEA8UTyqWf7GshQL1DX+hHs6q6Xuna6FWiT5pqSjBVDL0x8eLmBZ1WIE0rcFKi0W6Q1DSaDGp7BdD8HrUk5qORUqv+1v9zuWJo593SiTKCBIFsN2x/j5XtXmA97EmIgSa4EJvh3q8Xd3Q9wenMxy17e3iHNGkyOXZz2v0L57v/FX/6c4dO3R1j5Z5idXuDFYop+2Ed2FmJ6ZuNju4Bfb1FkBtLSRSVMGhu0WiNAw8VvUxWoGRggvk/8XgiDpnV91JTAFUtakQuTiOCSWoxqxof4PkFSGA2PbDQbWWahzVu4bYqZU6HXc3Hvuai4kGoI/roIQ1v8lFIaXbsenLbCwKrh9HriKSbMjCKD63loTRsxE/tCF15TAesITtAH7gsEXipyZ7IgCACnKaXWNYzAxWxowze4YFJgBFk5ZHHQxyxOLYRhBb+4g7l9h3P3B1jOBFnjIzGGaCsCqpW0HQrqtsUAyXYMs8qVjBIWevRWslt4joc37+7k3qkbGmKTNOfgxQcfIXS5uLJRVgWa5B1uv0/wdnuG0mDWn2KktBgiG88xCVr0vS287C02D6ks6OgnBm+ApLHR5GQClmgIjtni1CZAvUcjdrLXbFPYVZKyynvU2cAa/h5Bb4XGP0M1WCMypnDaAA77DiaRWpQ1KYaZ4fC1vMkKlFmL1PJg2DZavndZS0ppxHAQAqH+AE4vFICaGAThHDLehMnG7si1UYlU20ToKlmnkmgDJqXEvc9QW2dwzy5QmedorSOYlg/DoNdgKQtRhmpQskdPPKMuUGeVhAYwMKOkBNQD8pg+S5XywjMM9HuO+AiSick1bErgMCcYT+8rtRDeGdsL20SHr5g0/p/j+m6MxhkiWTWoNw0GwwC2wz6FjLxIwBU0GmjindyUiHILK4JDnoG+sKZ47/L8LTiBjZCsSQGNCDgRWCuUxxqlZZQCEtQyFLBGBgxZTCITLWrU/OJpigeUArUF0Oz6GnMPUOD4QrCo0rLRnc9YBxqRpUZGGxmoKumYbcCoK/hGBcc1kEk4AZk1Sk5Y2x4qi2Ew0mtJPW22GW6XsZL+EgysmMbdw2g6wrRHOITvS/YZxwV6JVLSzbGWtefC8y05ngIBlVSWQx7riZm0lJyz7UsdEdTIWQ8E1gyk2Rqrh7cYMBzDY6oy2UT8UiEiwgDUY+0OZ9KSQjUW8JwJLmkHAQ0o8fzkOjBkRdj3asxg2yALkEBbTU+7oka8reFZHly7xsBocEQm79DCeuBh3Lgi80xDJpM62KY9RNdDVHkJx7hH3yvEu2+bWSi3hYA8rh8KY57gTtD3EPY92ASWQXAywtA3sFgcy/1QRPdIsxiG1YdtM51ZMX3VOKnHTWGt6UFzz8xfNovo/2gEKq22SVQ9KJHsbj6yGx73fujmPXoWpMFKHpubAwxYsPDei2fyHM5bCLA9rGIUTQNvOMXHHzzHcORiyRAM2XCwYDU2bPq8inzycY/y9v4Br2+XSnIubPMatWXiYn6OdzcP+OM//7OEtlycneLjj3+DGpSRlgJmdW6t3YaosMcYCiJvrlBXfsbnr97H+dUzsa+INmuRePJFlqWsAPh0MiVFDpqrICy5V2vNWCMATDBXe3Cq2tHzvq7C5D7VwJqkqD8mhWZpjFi81sYYDQYyT7t9WCJJUsVYfTKF3Z87dFelPTDYDuVQDuVQDuVQDqWTjSrfiW6S8Gvll+GyJ/DYT37VwN2OSfb01cYvTFOMnzDtOLFJkxRRpHzPwjAUf7bhsC+7lWmW76SGMm3lISSqXU07d0d8tOnqDtD9oP6g/dnkSxm07Z7C96aslrJA8TYiy45pfttUDHBPTk5wdn6BNM8RxZsduMeJHOWk//CP/0Vey53QIuM+sYGbm3s4jofZbALTMTA/XsDzfXzy58/ww+u/YpvmODs7wfnFKZJoizRO9QTRwjYrcbveSqoXZR2ckGtO345dJpNXnQiabQ0YSYXLy2MEoyk2UYqsLOV86DFFRl7Q6+Hi/EIkMgxl2K+s/R1zvTKSdsL9YQK0p/MRjDbFtgAKStH2BStybZ4CaRp32/nmPUJc/OMjwNZNysnculm56Hk1Xl0kyCRJUUlqyPSYjmokW6Yi+uLFpBZwnceK2pXvFiBPW15XNKjSAovjBV5cLWDWrqR4Kg8nBZpsoi2iqMBgcQaUGdL1ErXj4+R4gyD+73j3+Tv8+csRXlcnKCdnuDw+wlFvgGYUwLjw8GEfWLQp2rxERmN1uDA9W1hrbsdakxAD7s7rhbAwaSh3qRRLTxJkgcpkaiI9w2K53mICzlVdu+f7RJaSacC3DTSurfzZMvqwEYzMMXNbBD4dg2wEFVMNC7WobU34BN9KiKeNZ9APh+gfF89AnScCSnARWhQNKsvEYNITLzPfvQf6b5G0IdrKE98jn/o+z8HQI/uPZ8UL0ohHHshCKG2krG/LRZNEWK02oO1iXdgw6gy+08BfBIj8AUwCdTSSI0NDuFgE2ih1CzAZ+7p9KpbP92/eSR389j99LAsu9hWXJ5e6v6DMzsJtzOAB1qnyk+Ni13RD9I5GeDaKYCZLlPEWq6hBnAMFMyIsB9ZghIxMNsp3KxM22WwEnbT8maAHwSTf0gxJLeMzjBFqTJE0l1infbTmGEE7FHkvWVDShTUdakMgUqhAyFMDleMh9G20liFgc1PG2ESZMFzJzAgDG32foKZanEtViDpKgTpsCwRNHEtiPXabEzyvuvUQZVcwnJEAaJuY/ZwrDGKDRvvyPEKY1W77oMgaYThavvJh840cThkj2eZKWlmrz05rsMAh20vdjAQOc0I4TGIlkMPQBpsJydrTUa/s2f9/typx/UMGMy+x3ebYGD7MgYeBwzbED0gWkwWjcaXOee839B1zTcysBg4pPLo/Yl1yc4bMMQVmUGpL5osCjsQ/Twe2qIRHlbqrjNIpF22E6cufhWW460q0a7/48OmHuv6t23CRjSMNtnWdjWaddufGlEOyb+rWEsZqU9UCFkrfIOEDvKYEQVpYMs7ZUsfLdSxtlqA8JbwQb7yhJITSk473GgFoyl/LvEWmJbP0eWRghss2WuYiCa/pam9q2a84C9J3jMAimbTKZ62i1xqZvkaD9fpGAO/hZK4Y6EwOpUekAGtKnqfktOq+ZF+lOvduU6/rkzWAJl5luv726oxfspujogF2Ywr7ItMl+y6U5GLKak0x3C8xNIG5ayIe2Ki4Qde4CJi261pYey6y1EIWsRNJYBlr9P0GrR8gSVo0RS2pp47jiwcs+0QmkArwpIHCJk8lUGIwmaG22RemCgTqmFr6eY/A2t60Q39mNfzo72SvGZSOlgJo8z7pxqldMKiqqd3P8pOeX6nxUzF9F+MRTk+OkKWJhE08ECjKapGtnp5e4PnlEI1bYWuqq8x25dD+oBFu2g5gY7DAt2++wyreKGao+AwaMl/wXB9/+OMfcf3mDXzXw8evPsZ0MUOabvXAr89XByuofFG9raVOVmSnrOdXrz6E73tYrVbI00SAVZUOSna+AhoJ1KogA3XP0iNRpMmyIdv5ZOr7a09FoI6nbjS+5w5gI+RvM/23QUzpPhqcHC9krL29e8BmG8tx9j/LY63/fJ4sn+358+e/PoM+lEM5lEM5lEM5lP9QRZYHlB9ywsVJy9OZ4K+Wp/OODlDrQLa9iUj3+N6r9qcp3c+d9/H+24ipt2UJi60/6ON4scBsMZddRwYjXF/fIk5SFWm/A9K6Cb1mFeydo0y4tNRwJynqQiA6DzbxVtr7Tsmo3vXkzjxj4rlDy8kdnz8ajzAcDhFHEb788i+yWPvwo99gMh7j7u5OpA6c2BEo5GLuaDEXZhwXagxRSDOabpdKJhU4qAoD33zxFeyehY9/+1tZRHz26bfIi0zVkZ6UB76D50czTPuBDhpQslf5+PI0pttxYkzgyYVH/6yRjbskxvfffiseXH7PxtHiCLPZHJ7nC3Pwh++/x83tnfLT6nIG9kBJLlvPFjORmb29vkFW7U9n9+ak6iSePMYFWbfb3l393Y8aYFN+abICE9kmn0DJko8Kp/MIvaDEKpqKH9bdimCLSh3lC4U9IACb0iAKo0S3AxHLdeYvclBxtcJgOMTLywU8J0CROuKtZPJ1ZoOEYRNZCb8/gmU5WN9GqO0Wx8MNjPpbFJsHfP2ZjdfJHHVvjvliisV4AMfzUC88LCYGTlCK5xklagXZRg49bpguqBLnRH5FqUupJNJM4+QiQ9gzmkHDHXrq+fhpawGRmNzI9EsmB1K62IdpeZIeSi8n21ESHwKx/NAlyJgjMFLDLkuEdiHYQGV4kpQp0uu8AMwK4aCHrDWQJxncuhBghvLQxrAQpRWyLcWeORzPgeMxrZK12GAQ1Khamky7sJheKvIe3iPUHvF8lGF7TUYeAavGRe66qHwDI6tGdH0tEh1Kfpgi6PLLMjEbRXCHBu6y34r8sC7IKlALxvlsjEFgSnoqXaIEZDVsfPHVj5iMhljMB4g3KTZJhsV4CNveSxbVnkR3yy3WkWKvDAc25v498uUDHmIfSU5vKQUqsD/o9T2cHc/Q+iGixkFNgC+v4GrjdYd+YExN1JsXu/ZtGIiLFq+/uRFmkhf0sbrfYnQ2xulYpXCqG1dBwd1Ckb/nlSNgrE/vKvo2lQXWqxzLKEFW1nBtC6N+gOk4hOW5aMlUoyk8WZcMb2grmDRWpycVJWkibVOwPPEPPi+vGvEyGroG4rIVwI6+eGwkagOGoBPl8Io91rQZCmMuMktKw+kjuM3oo5cJM5dgCvu4QW+I0CX42sByWxi2i8JwYJQVHGOFpg1g2AHumepKdKCpkIi0lgmpGSIjRJ6YEsKwmNgSyqD8NZkO2ErIwCP9iWA5AVPNSG4s8VdSskQyjNXn4L1G1gv7aYJG4tck91a7Y60xTVIBRpTlkgVESaSSkSqMTI0dBJYpf+V5UK7KNqJ8MXV6t6SMUsKpJOgidRTPPlPSV/lcvo+EPBDoCAIBSciapTRRkcp0/6ZBKJ4f+yRK+3ht8iQSsMEweugP+xiGKtyCQCqaAmVK5hml6JaA7RxjQsqO+RnJSqsc1K4LPzDh0ZMtZ5oxX8/wCc1IYz1paX6cLVGkGwyGM5gG5cOKNSQ+anpjbMdc69J3eX043mq/K/XFJqnN5W32acoHS1hOkpotWnj57BzvbdMSCbaMB20l9gqK6cigHEP6TZQM9eA9QZknj2djY7i4KwysGRq0zrEtM2wybpKksIocQzfFfJxgMLbg9I5QkMGaSV4xvNBHUxfIsy1cp0XPZ4gMEK83CJxcrndtBEhKG29uluJtqi4VG4n2gdVjpzDSpEtQgGnHqt8fI6WPlxClWiwfmLTNsU8AVnm7DoTUDFR5HwUIcwPyaD5HWZLVS6ZigYflRuwPer0xXl4tEPZLpIaJtLVQNY6A0xaDe2pTJdDyPOoaN3dvcbu6Ufhx55lqWZjPj3B9e4fvv/lGjnFycY7Ls1NkWS6bnnK37Tb9FPgv460+d358AV1NEyenF5jPZ6IKoP0G50N8aueBK0CmTmgm4MzNJs6TBBQnc1gDbEqRwO/a9kOz/+Q6qC5Y+a1piai8P/vVIkGRpxgNhgh8Hw+rJTZxLPXGvuXnZTe5le/qSPo6HjzYDuVQDuVQDuVQDuWnpZMjKEq+XuB1c4p/Y6rx9NGf/7gPpvzaq548XT/QPcaJF+Ve9NdiGhV3VpnYSGBrMh3LIiOSBEFO0FRaqir7k6RHaYYsvtT8VO0q70+CJamKZstKqqoeUwsbvoO9A90UY4GTPsoItkmCMOzh5cuXuLi4kgXczc2NTAb51m/fXWM4GOL4eC6nwMfp40ImXJIkSHL6pK2RZDlCfyggns1EycYQVttH//CB+LetV5zAKwCIE+uVTE4L9IJAzk2BVwSYOFV2xFBZ5KNcODUtym2NgWPj5PIYUW5wilUNAAAgAElEQVQgizZYbh+wWa0wGdP43cTJySnGGhwkkNGBp/wchOrOjnzEWYE3NzRKVimM+2XnsyOVp6fVXX3/BFh9vDI7aFS9Q8dw42eVhZaSvuSNjcGIBv4ROVlYR4EsIDowtWs83SnJQqdrYASUWlM+g5gtW7ZIZN87n6AofFSFI0tZRfxocLeOkDFgYn6MLM2xvE3hTmycju9gRP+Kv34RoSx7mB4PEeEMz4+OMRsOUU1C2JcePujXmBEQKTrWmgfTd+AyxICLS7JkaHKtPY1E+pLXYvRMkKAxuejn7woQEPaMyKbUIstyTBgOwRQbTREL84HpjqJ41kwZkV8JS4bMJ0MYQ2SwpCUXWHy9LYtW0zVxzcUqUxutQgARAgOUqNJMWqSBlJ7SJy50UTBIgeyOOlM+gK6HlJJJ04PDhbBOhCN4UxDkIdCmWT1ZaiI3fZRc6IcmZmYOJ08QRVtkaYWabBpmVfD4lYUktWEWhchLTccHWkdSVi9PJ+i5JsxagYUEE3n/06/P8ntSV4ELxGUjTAnPU95hqgvSJu8ABn0fowFTW1s4+T3S9Qa3S0eOzToqS0NAbwFJLIfObAJEDOwaPk3zXEqTufg3JAmXCZcEI3khRA6r2cLkQ+SOjyKhz58BTPo4nVqg6lQtCNWKkH0PgRmR0Zp/hWM9wDZHIqusskYYnDSlT4VNROYd5ag+THoyCgOFBuRkgfA+KGE23+oFoaeyNUUarH0VZeFJMKsV4I8tLvQo6FSsGjG1F9NwAkmUpfP5G1j4X2FlTLA8QVWaEqyRwUVCCSWBcXoBOi68YR+G76GqbUnHpP8aU02t4r+hNd8AxgW7JoRkzORAlBQwKYOsWmRbMitdjHsmpn6tGWn8BLxqtmJL8ZrskkNVf0EJmizwxYOOHleNsNUIOgmQXTA0QwFHAgxJ3Shmn4S2UBKqwbW6bPXPCuhWC3p+6X5Gb9ZI/epk7G5QkcspQL06F+G9CbNQeZLx/YV0JlJmJUPz9dhCFhavrdloyR7BVZMs4RJLphg4LpqiQLZdo6kpw+1jMvMxCnjleO+WQJmj2FaICxOp4cAMPAxDG6FVw+Tfskb8H42+hx5DOHghahVeIOCjAJCVBtfIzmqwWV0LmD4aTaUPZd2ogAJ6ranUbH6pMVYBTMohQI2fKgl6NzSo+tBedZ0Pqkrd7JhIasOEeCHZm7yPuLnlSYjAY9gLNxsIWjb0riPgxiAPhrkYJXyzwtimBN3COnTgtS4Ghg07MLG1TcSFg2Rjo4xrmM0dPETo9z1khoc0opTZhN8bSJskO7OoWvRDsqt022pTOKiwmE3ghUPpx3jfyMeUD7BrnPo+1InYeyPekyL3NMdVtoNMmL+UCe8sKHTddC/l5sv8aC4bd/SKZcXeLx+wjDJYdoDLqwu8uurD8FJkRil+iU3jw2gcmI0t5yKQpmmgLFJ89e1fsNmupH8Ur7SmxXA0wnA8xT//yz/j/t211PdvPvoNFosplmsC5QSwVRsXh0ANau02XnnCvAeaWtJG33//I2GtrVcrpGkiDEXpM7gppF/De0L6Hg3yqnRQzVyT9tbdi50YtAPVujlAt5FKKxR1H/H92VCjeCnM0cVsKu93c3+PTczxXIH7+oLhbxXjJ885hBwcyqEcyqEcyqEcyi+WLmGTO7Myz/nbONtP/tbN+vT3HatNIxwd2PE33s34pZ/1TLXz2EjTDKv1SnZMgyAQMGgyGclEjGwwKbJjvge4qAef4nt6YdvNp9Tup3qs2xkV75z9tFFhQSl/Nvo6ccedi4siz7FNmC7KBKpYPDy4GI02EdIkw8XFuUwoyVDibi+fR2CNn6UocwHUZLe2qrDaLDGdLjCdzvDXv36D+7tbbG8jHF0tcHZ5LM8pqlwvKixhNKxiJp1S8ukqbxcxwCd7wgVqPkYGkoGGBtoEL7Iazy/GGMxOsV7HSLcJ3r5+LWbrlKsSRHz16hWKokC0TWSBowIG6A2XCdmJgpKfXatOUro/Se127mW3fe/Jsvjaf/LjolVJU/UOvdDSKrw4bxE4Db76wcYy7glg88HlWhY+caaYLJxE67eRf4REIj4/CuQhWMf3c/sDSU+bOCay1BfAga8li3CbbXGbxginx8Jqun+3FHP947MIs+afcfP11/jkLx5+TOZ4V5zAtKb46NyCF44Rnw9weWTihVnArriIVb50jevC9W1JRLS5s9+ZhpNBktUCZIkxOOVpVovWZGqgXlCI74zyNerS0WQhKvIx7QHl+CRvwCzXuv2yXegETQ1rCjuABuv0Z6MZv2ki9BTYx3Oa2A3SwEJSWrAIljFFl4tn9gfiEcVFFD2zVIomggBlYaEuKDFLJF2PbE0SSVyfElFphXKvEFSgHxuZMR4lp76LkdvAb1I0GROEW2xTpuSW2BIbqCy0ZFgwJ7C1kFSuSLId08F0NsI0TOW9GGZRWiFMGp4bhoQNsFbIDuQ/Jj3YHIYC8GcmVXZJlvScozeVTrazNghcpkWGuF9nSDK+l4dtrtgehmvDlPvdhxGOlYS4bOBwAU+MDRmc9i9oLCYSEkzl4s4hAqHSNil5orubbyAc+ej3bZyGrbAP5SpKP6KAF7KahDQmfdU72OU/ofjiHJUforIpc/MEGFNJfq2kHjr9PuwwEI81Gr+zrddZger2r3Cc/wOwJ4AxVzLdRrGHBICi3FGSJdkmG1RZKtdZwBH5DLa0JXJTREIr7JIKhvEJ2jc11t++h3xowSHg4FloKd1qKAIFfMfGeEBpqyVgMBlK+bJC+vkKgf8pzNATgA2Wi7S2kZcE+VyUuWLgGL6L0K9hGTlKGqYTtDAcxSgrmM7goSIIaJrS1rr7XpFflaed0RJ8pXyQMs8SBZMHCRiRMcbwAN5voASb4DXZlwSVyFpTzLVKwCP6srGt0Oep7u4m3b8Q/PppL7hDhlQft7v/FCu2Yy4pCSQB9AYlE2vpn+fyvq0UMCjsO81WMlssoy0SSmttG2m0lPttaw0xWAzRq1KERgrHpiddjTopEMfAprVRO54wL0eeCjyp0xLb3EbuhfD6DobSJ6kUVUlKFRkeAQ2y/ZRhflFtsV5dYzAcw3ECaXvicajBQQKFapNOM4mk81HjgQLSVJ10ITW7AUCPu6Ik5fO7UAipxVb5r7EX8Bk6oJJhpSeScVltoChJvPK0c4jj0J/NNAVoI8OUb26BAD0wY9hGz0LqOggbB2NuKHoG1sLOdZCtHVRpAbO9x8hLYPUdZKmLahvDIvM4GAjDKa9bCX6ReYawJ1tJKg2sBouTY5Smi02y3Z2/aphaKCnjXudr2k2yHjexlIeb6sfalnYFKkxFgn70+MbnkS3IoIz3Xz6XY9AbNs9SvLu5l5CWfm+Mj1/NMe1XKNscpQSceGgaD0brCngrZyRAVIv7m9f48YdvZR4inohCZiNL7VICkv70hz+gKSv0whFePnsPhtXIxqLsIkCBq6wLYSdqFFVhrZSGK0D5/OwcV89eyDgRRWthhcq4ZCsQjJ+N7UHkoJVKCqUlh3yXsVDdi8I4VZO1x3tNb1DwPXYea8LAVexHgmt5nmG7XWEyHGA0GmG5WuN+uUSaaa+1J2Xvfn6cVPzkb4/lALAdyqEcyqEcyqEcyt8snCArOQsnkd2+6y9NK3762C9MQjrEpQPa/o3SPWsfdul+6IIJOAGL4i2Wy6W87aDfF0+zIZMas1xAKyVLUSbXO2StOxU8XQB1n0++78ktu0WDLCI6jx49aeaOK5l0nZyUk1F6xnESR/CNE7iryyu1OCgK5PTfyjKZlBII5HkSQFHMJOX500nLkiTGavOA0/kJTk/PUGctvvz0c3z/3XdYXM5xeXWJPE7RlEr6RGPzjOyGzQYuwRzu8IvZPw2FKZvj5NVGw11+p0Vl01eqgt2UeEZ/tuEJHtYr2fm+vXkLz1N+TpPJFC9fvBApa5xsxLic76eAse66cMmjau9poMDj4mGfpabK/s/d++iHze59uEiuMRtv8fI8wutrG3crLspp8m0hLR28W7mYDTK8OouQpAayQkf6KeKIwnjlV7IfFNvnw48/wLP5GEg9oHKF0UaJHoMlrqMNzLCH4ewI8f0G61WB/pGJ0/4XKN/9Hp/9qcVX787wYF8iGJ3g/dNjDIcLrKdH8E9cPDOWGNYRjdKQZg4KyjYZYiCsNS4YyUArUReKrSZfBUEJej+1aC2y18iU4S49pVkKXBNQQBa0amGpJCwdmqCMwim3apyemLYb9Ub5IrWUQWq5EvYWoqZitFEmRk8qsoFonN9Hjh5TSF0HG2Ed0Q9KnTePweQ+/sz3oncY5Wb0T2O6JY/B+ra5AK+BpK4FaLNLMhRqYU5lkrj5T/CzLQwMBKBLGg8Zk/nIKmL9WBZyw0FZu7AbW4AHMr6Oz88xG7hw8/8NhvM1YL6UdiDprwSTddoc64OiWK/+FtHrf0WAH8Wwv0YI2K5KoisI/DkqBEDu+htY2/8bWB9hMD2VlL1N0qCxHQS+KT5irksmi4/JYgg7VMmZDCfI3j3AuPsnOMPP0VqvYCIQ7zGCppL8yEohU1G8giyuJgWcLpjYJ3rATCSBDVuiYUtgg8iUBUqIYdQ/Iv8/P8YXoxBlr8LIpv8hrQBTmHUpP4/6PgYEuWzK5Rp8FwPLHytMqhTO8AfAOQbME8YcClDGwxJMIpBEyWjbpERfkBQt8owbC3JXIOfNQ7N7nxsKZLaxDThK+hjbWP1whk9dB7dmi4ldgwSqIqPEqhCQM3ApuWaKaYXPCgM/ftpg/jpB7/knQNhHY34Ek+EJ7D8dE2sySBobQeDBMyp4KFHnNZbbFtuKCbi+JNHS77Fygb7HgADBUIQtKYEG0uc0SoIoDL1GwD0yHHmvibxM/AwVuKbkoKouOnBNfMQEzFahB3yO8k9TGy/S/3fen5o1s/vS3Zsis3WIiTqnx1RFtekgY0xdo98PETAFk5sWrQoxkEIJaJZhuclgOKEE/ORZjLol2DPCs3kAu6iQlkxKbdCmFYq0xbqwkTJAJfQxCi0EJk0yU6SJha0RwBrwcQMBNx8EWCTAT3l6iSwvFDONZ23WWEc30icPhmT7tIrRJvWjNr12G1Cdh2kXIrRLo96NCI+bbLtK6rxS9bi798X7xfdDAajTPFFyWl0x7NME/OQxFGV3l6ZMcMfh/WOrYIuCCbqlIQEydAAcWS0WnoXtgECbi37rYWrbqENTwkvi1EO0NpGnvL8itNmtsMnaOkCZFyJNdZxQ7AMqAjj0Z5P+mLJsgtQxRoGSQBaNKZtvaqKhZxkdY7X73Dv8Ucsb9VxJVRE/F6F5aczSd/MVZdvg2cUZpsMBtvFW5g73N3eIkxyG5eG9Fxf44Bl7EKY3sw2zdny0BNcaRyT8kjBsWciSCN9+/im28VrJmjkWNjWGgwn64yn+/Mc/4ubtNRzbxdXlK5yczFAilSATphxLknir7jXWvQixJSjE2LXxsNfHx7/5jQDo65VKCN2x1jjH1JtqMuZpoFdJk9XGE8+HzFIJT+lYoiLr1g1M34ty/2mZMecvBNZ4DM7heFwe6ng+l3Z+fXOLaBvLJuLTsj9PNX51zvLTGcwBYDuUQzmUQzmUQzmUf7N0khdOUJR59iPba3/68TMgrJug7CNl8sefgmvtT5+we8bjI09f2impBDzQjK84igWQ4kRtOBhgNuUuuy3eHsqbxvwVgOfp+ag5b7cjqh7YSRC0ma5MHMUfS4EMnEF2Xm0CtInHhy1+KPK7Y4k0lBM/+prFaSJhB0z2EvP67r12x3zUrfI1cR6LQfuwT/kmwHVSvinx5u4azz68EoAvjRIlyVB0JkRpim2ew3FcOLa/kzNpzZIwI1qa31sVSrNAlm3Qdw1cPXuJrLCwjba4v71HHD1gwECJusXR8QLz6RzxNkYinnJ781A5d50IJh9C16uwFdTPHfuvK2rx0IGuut41ICZLrhZwzQofPIuE/fTVjyNUpatNxTtmh/o8y9TFfeTgxWmM+YBAoCXhCOocVYgBGRajyQK//fgKZlljmxoy+ebmO7/WRYJN02C4OJVd/ft3K9SOg5PjFfoMMfj6NT79coh3+Snq4QnOj2e4mI/g9EOUlwHOpyYumZ7ZGohWGyWX7A3g+TYDHJXnlXitlZJgl+UEztTCXhb6FhcrBGC6Bb+SZhFYK0WqpiTLmrymvYkem7Qs+ilHYz3bLmrDQ12mMCrK+Aj+PjJMhJsgPkAatCOjkYl4pYmSzMSasqoSvmsi9xxkZMGwidaKyfZ4zVSoCL2kXI+CXVdYFnWdy0KNXmRM46ttC55LsEx5C7X2n2G8fYfbr10Y/QDuKBDmTl0WKOn/BPpPGQgcBWAR3Lm4OoKxNlH8GCPsfQ8jZBV8DEZXlmSYaVkwF5pms0UdfYpvv4zweuPj9taClW0Ylalkd64HWWkRMGJKsDBgCtj1NZLX5/hh6aE96uHymGENucjpTKuRhX7oOhj3PVAZ2hQpfvj6BskXa0wHr2FOU8B6BRg95ATKDBrWt8IYUp6QrXipufTgsg24jgEh2JQEAUzklNy5ltyLhAmlW6Dcs3mD8vsXeBd6uJ46gm3RxJ0ejBUTZ+sSgefAc2ys6hKfWw5uYxuTJVmJCaxpgdb+zzBM75HkodNYBbyoDWH2EWxNKh0rarswXRuBRztw+uEVsMRInPcT7e/PYPbPJTBluyzxYDh4zbr1TFyOA+kHyXByXB9rGPgUDlaJhfFnKSZmBv/9AJX7vwDgOakETUrzApNeYJRJUq5WAWRT1fSIIyrswp/2wJyGkH5hTMLWbZitWvzWukRPgi3a1051Uyo5lTJhSmmTMkPdFopBJmyt+gmwJuBRt8Eifb4aczqWM99R23fu1almA+13jbv7VfeCXaoyGU8MXnAcTMc9OHaNipJ+AYzVOfO5mw1TWfm5bMTxUgHV9kAY25M+gzYobLUkjZgC2rRoseVGikeWpCvhIk6TCysrzTykYYCwb2NIkFYk6grM6MIe5IvHoNdbk2O73aDXH8AREF0Ba9IPyXcl6xRgpLNdkN875tLPQYjHsaFjHHVDrmZwaUYb/zYaDrUkM1OMqF0QQudvqGWEBIsl2VUFWAijTQNtlLabjoVSGJ9MhFb+dJTgTkwDfc9E3LOQGQ7GjSMpwaVjIrFNuEaD1T2P3WAQ0mOR0k/VT1JKHPT7stlDsKhlCJJIqglKcmOogJFvMO778Edz8UosskQBWDpbU33gvc29PZbfblYkDUk9gyAeGXEc159fnaMkc7iqkGUJ7u/v5b4M58f4uxcTzHp/RMakXwn+IbOV0npXWO0c3xQ43OLh3Wv8+N23ErJDgEzaK/3Rzs5xfXuDLz75RFjWZ6eXeP+jj1C1ZCjnaqzvcK6dJBTKY1M2i+iHSv9H4OTkDFdXV+KzFsWxtCM+k16EIkOV99EybAkzUMAaGcZ8TNhq4umn5mKK7ti1Jz2z0PceP5dKCVWfkd/J6ku2EcajPga9Hh5WKzwsV8iKQifvPplp/sI8VR3nl8rjK4wDwHYoh3Ioh3Ioh3Io//7S+bF1PhbdRPinkNVuUvjTN9CveYqe7T/r5xOan/71yXF2f1SeLFwQkQ222Sh/NjK4JpOJAG0EndIk0Z5e3bLn8U20I8ojviXz3p1xjHqGgGDqd0mtEiNnLiI0m00mlgxKUGljPL6SbjbI0xxJmgjAcHx8LO/x8HAnRu6KJac839SnUeekfGr0QpHAJv2J6kw852bzCbKqwOr2HkVcwvItjM6mcG1HJCJcZFIyxZ30ON0iLTIEbih+MWqWbtBaS31+8QciIEM5DW17apzMRpjPaJRs4vbhAeu7JbJ8i8APBEjkZHk6mWB1T4kSJY149M15UsV7V1AveNSje946IjvbPWknV6E32fE4wek0wffvAtxHPeW7pGbwjwtaeZV6DRPwbla+MLHOZltMBhnWW5X06PkB3nt1hYuTBaqCyYM8OmVoXEgDqzyHNRyjPxgjXkZi5D+YVzi2/4Tix0/xp08d/PV2hpVzieDoBM9PJxiPB8A0RP/SxftejUGdoc5qpAQBgynsHs+5hlEnAhKRtabkoKV8cUHL3Xj6rEFYa8pYXQA4AdX0F5M6C7JGtPeaxnX3anMnc1bsR3U9xCzcoecWgasUZpv/xJ9NAXaykDFNuK4tslH6sxWFYq2R3dizKziBJamZRcP3or88U0AfpVm21YjRO8ELSgFppM8whbrMhJlEwCYj04WgmWvBa76DlWS4Teb45naD9TLCtK9AagaF0EuO4InvWBgfDxGcjfFN6WD5Q43jqoQ/fQ2EF2jNKwEeKEliO6IXUV3UWK6B7360sM49kANVtAHibAFzMIHXd+VaeH4pflcSMsF+xOjBNIYo1jbuVya+9hysHRNHswDzni/ytEr3LWTt3d0s8fknb5AsS8wB9AcpsDhD2X4gzFFKFm2rRUUgi/2mYyErGnhtBtukHBAw6hhtmqNxA9i+BdduMLAyAS3IFOR1gTEAjFeoKMd6W+C+NREFFlLbRM8xMQ7oLefAdBTA9UVpId606N1XOG4L9M+HaMIP0Riu0sKKHJRSXfrldWb8QEJmV81ADFfqxKM/XkBPQm6w8JqrQAS2HzGmJ5vGtBDOHPT7BsxtiTRusKwtPMCEH7gYhiG+by18lVio7isE1xnOggKzfxzCHL9EazI9VDGV1Ll5YlpPGaswShsDadYKoEHwKQg9TAJb/OJ4/p34mX53hDzI5FPQu1qDE5xRUlid6ii3Bv0EawQ+wXoH2zhRDBmmhFbKD03M+fXmkvTNAiRphk1380k3puShsriX3Q+dXKzPQp7ZPb0DnHTSISHFfq+HSW8N07qneFgzc1XnRhbZOsnRNjaqmtLrSCTTbn+M+SxAaLOOlGyb95x8nLpAVptwe4q1FhqlGNtlCRCjBww9TEMTPfFa04nFwpBlwqjygWSfQ/inKDbi/djr9VU/oRNC2QdR6qfARuVf142NCsDvALPuo/9k3NVAeFfUZdkfK4DBYIAg8MVvVNjdHROw89rayYH1Ebh3IW1TeWvqfxRzUQiYCmhjAyHoTUZbWxL8KeEaFSaWgbBnYy2+ah58BiU0MdaGi03RQ7zl2FrDtGIE/orbCEDrI08VOBP0BwJupSIHJ2OToJFqD21bwmoyTCdDDGSDiptr3KBSfVY3VEr6924eoP55zHZXdczfGfLEsUdYa00tHmbrOJPNg4uLY7w6dWDXb1GZK2lTRjOG0fbFWVTmbhoVpo3FD99+h/UDvcgIrBnCfO0Phuj1hvj0k09w/+4WvtfHhx/9FpPpEKvl9WOD1sAqi0rqhtxjMj/S4PEgGOLV+x/KZuN6vUJGIFLGKG4wKFn840bpI3NNNpe0/FiY3DuvNT0t685C16GwVHnvSYiBAtv4mTi3IiuPl34+ncj7XN/eivKBkmwV2fG0bT5pi7r+/9Zv+5uGBwbboRzKoRzKoRzKofz/KmrjUE1sOYFUk8K9CeFueqIWPY8Tjx2y8vO59k+f85PyS4/usJtHxEbtftaU9zBwIMFmsxbmGiWaTPIcDHoif0m23EHWiWzd+3UTXQ1M8Ls4cXSLq26K2/3eSWHkmPVTacwu4t5QO+tkBzDNKy+E9UVQbbGY4+zsFEmWYbPePJEZqVrbkxqJjwi9QyhlsyRRsmhq9MMenj97KRPJrz/7AndvbuCNQly9/wLxJlILID0VpG/JevugWEFe7ymwJpNRnbRHA2Iy2riUdRqczkfojU9wc78SH7n7+xsMer4YlwdBiOcvX8q5cydYfL72Fgu7i6xlL8LY0I9TNqIrXl++Dm0j2GbAM2t8fLESH65vb8aoG0/51ugDKLlvB7Cp/7o6J6iUlS7uY08+74eXEQznGd5/9R5cj7JF+kfRC4qSXhtxliMzbUxOzlCVJVa3EfLAwcX4e3ib/wvffJLj8++G+KG5hOmf43Q+x+V8CGfcQ3sR4NnEwBlSmCXlvkzp8wDPhecZ8MlQEglmjXj5VhYQBC0pG5RUNJGDEq2gpxOZJI9pfeL/VClzdS786QWlpFj77XKvFcviTP+2s5HRqxH6rdmeSiZkEAKlVQ3ZRZSPkv2hJKNMouQilKmd1PblsFHlBmio5hkFhi5gezbuTUeS7Wj+bpD1JImNSj7qmDXsOlX+QoMeIgI2BJDKHBZ9wyh4pEG5fwEjD/GQbLFuSjwkOd68XsJvgLOLY0RpIel9p5fHWNsu/pWm/htg9H2GeRDDPj9BaX28Y62JL1y7RlU6MGwHVi9A1NbYkB1IsJopxKdjnF2M0LNa8e5zEQtji7JhAoJEkQx3CHsWwDArJD9ssXEc3FB261t4Nh6g3w/Q8z189uk1vv5qDac0cJK3GC0A/+O/R+O9L4wRhnHQVN9qG2E0EijkpajNFtttCTNn8ECJdFthW3voDzxhrFmUcWmWTU32h04v5j1qT130xybCZYk2qrGCiTvbRE4inmHh89LAm8SCvaxxtMpxGdRYvAhgD3wF0gvbR+g1wkKT+6mTrxJupmLLcCWZlaBs37fg2bpdCZOOwAbvX1NSGk2TQAwXyAQxGgz7JqaugXqZIykNXNcqjfQ6MjC5LXC0TXE1A44/6sPu0aCey2HyzrigVkwWdX93LDCCnibeWI5IhhE4YixPWTPRFPHNY9BLyZRaHdZA8FDSRbkwN0UenSSF3C+yoBcSFJ9TC0vTM1oE/TGy3EASJ7tFvEq/1EC0AGOP/X+3uN9nzEif1PXX3ZK96w91/9axuQQosX0smH5rL2FZ/43GiWiNc0nB5fNWcSZgNo+Rxku0RQHTCtBfTDHr2SI1FwN5jjt5AVvfd2lqwwttDHiv1kwPLZHkLtIgQH9oY+wYsFk/EphSoSBzjaBaofoeAg6m3Qrbx3Id8azasfm6Lw2sPQKQeoTsQgz2WO47AKz7Vbmq6cCgru/XY13snTkAACAASURBVIWMISaO5jOUVY7VMpLfFbimGUv6WHK8LnlT2F3qnflcsY/oNiLEykEHIWjZqHiLWWSLWhLOQfCU6b8EI6fs9+wSd6aJUbDA0AjgBA4iAlK5gygyZFPL85bw7Ad4TF+uPSRbhi7ZCPsjBVhSiur5am5B6XKZIlq+EX/Cy4sruOFQEtAFFdTjmGIkPxpVdKCVAJlNA9/18fz5FdIsES9Ktq93t/fI8xb+fIp/eO8UUzdTXq4m6+0EBo5goqcT0DneKG+yd++u8d1ff5QxReqDvmmOjdPzU1zf3uPLz/4iUtjJ5Biv3v8ARb5EksXSDz0CnWzvqh0qW41mx8zkcy4vX+DFixeiIog2GxUeoDchqYjgz2qjkl5+KsCA8xb6ralQK2WbIex+AaS7ca+77o9y7O6+6+5FjmPCWksiSQjt9wKZpzys1pKSrtQH3fj5a3PQp1BaV7rp69PX6rnI8+fPf/lVh3Ioh3Ioh3Ioh3Io/47CxC5OZpSv0ONEen+a8vT33Ypjr/zsgd2j7a/8vHvOI5rzZDLUAS2dXPT05BiLoyN57P7+Aa/fXIsPmmHTR0zvQWqZw+54slW6e0e1k9yBOBrskV1qMlPIArEt8VwTmaijUrA4ieNzKOHkhJGTYk4gKRml9IWJnYyF//wvnyOhGbLkV3YfjMdXkfISK89FrRgH6z+Lp5iJQTDC8vYO19fvhG3AheuLv3sPo14fN2/eCd1EJqEikeSk3cbR7EoWAg0liZYC2rhYNgw65FeAUQrrw6N4i3Kw/4+991pyJMmyBI9xAuqcR2REJCnS0yO9Ivt/+2Mrsg8ju9IPM9KsurIqMyMzgzsDNxg3Wzn3qgHwyKzqHdmZ6X6Ahni4OwAHjKip6T16iHOAN+8f8e79T+ItczDo46tvvoLnR/CDQAqsH77/Hm8/vJPJsxSbMg/uSs0dNmDnt7M5XVoUcV8o7bsZp+j7BX6cxCibcFP875zcTTfaTIv5OfKZ+ogwmdoWfhTj+c05Lo5PBDTI1qkxZbOxTgqskgzDgyNJhSSwlrk2xkcJDou/x+LHHN/9fIi37RBWdIqjwQgHgwDBuAfn2MfhgYMbO4dTZyiZxFr5aGiA7ZOFROmVMoXIEKlFdtUgTSZo6zVad4SGzAYy1yRvjUbi1UaiJpJC+hzRXLyThopEzTBFuOe08RLmEVlfRg4jxSPlysou4vOOR3CJ2BEdv4hC0IQ+l9RNx+0Jg8hyW2E/Rgy28JkSqWATM/BSKvTyGl5BI/8cnt+i9UM8ND7WWQs3KeFRTuoU8Dya0ddY5RasqIfYD+C4Fh6TBkVWwqozYbkR6CRTT5hRTYUffn6DT4uFyPasykPcevj6qwv4x318m9qYJRb6SYXjssJlWGNw1QNiBSJYgNGDzJR4jFWV65mMq4/3U9zOgMxyEJQNzo9dnB/3BVAsjO+Yx6RNk8bKfiBeRwY4X2cN3n/M8WbdoD6MhKX1ld3iv/39n+EVAcZNheu4wvh6iOjLSwH2eG54PsUUv9SwAgVeWChbyGtI4m+es7C2UDg2jvsOBky+YH8x4I6CloDD5EieNqZiktHWkpVVoy0sLG9LfLAszI4pawOqWYX+ssaZV2J0GiDokdnHMYpXofqH0aeORTBhLfF3E+CNYGuNx7pFzHEMLVZ2izFN3I3JvgBDtbLAbIfvQ2CCYB3TJcnTdCRAwKNHnW/j3XepsNh6sY30hwxnwwaDL2JYoSfjn4Zl0PuvRN0SABRkTbq2QoEqERRfSvJACeLJdU/vOn4mgT1e5wQiLfGfFODI1m3jdcQkTDJ5XZ8gSIm2zoU9yXRc9pm2tNGWHgouLPgWkrSQe0O5ztVw3cjQhI9jwDVhSBmmrkIE5pqTTmRYfSZopUtQ3C482LKtTL0e9yJYax6vEnb0TtMxrS+RpEyH5VjsIV+vVC5tBYhGA/TcUt6ISdK0IBDwqWmwXqzgOD4sj6iahSbNBbxl8m3uBkDfw9gHfGoX6SdH83iTDMogA0kAbWpYLkM9GLjDeA7PMKs5hhlQzYSBCFjYBQBtWIFPBnV9aLMQYJiG8rRysoRRaFay5N7UtDg6O5D+QzN9AcUlerVjcRML1nAhXtvSL7l4IfcbHm/2a2PYz4PEwBqorYXPMcfXezTDISQ8wqJPIWXHrTBeXWFQLtFUS/RHR6i9Pt41NqYrIJiWyNM15nmK2WKFKk0waFY47q8wPAYGvVN43jnyyhdfr3jUl21Kk4X0by70LCZ3EiQTBj14DpngLlrfw4f7CT59+iB9XvqIANmm++uBluN0dnYCz3WEdSa2EUu1jaAn3/OrU5yPXWHuc4FM5xGBMPG4/7KQJrZ+lmz/jz9+EN9PxxxLsjZ5H+RY/e0fvhXfubg3xPXNczi0CFjP9fokg1POmS7IKBGOwm4T2ABerxXGh8d4/uKl7APZyJz3sB/IPIlAuekbqjxQn1EJHKmMx5pIfvVxDegxAKv+4dZBo6OymetQF0npLVlhuZjBdxyMxyOZ6zHIgN/p46azuR2bg7+IiP3aDLR7xmzXZ8/vAbZ927d927d927d9+//dONmjFJIzQ06MdBVbm0IBT3/TP3ryDk9+av8/AG1PQLbPX/zZXyjA5Ur4weXFJcYHB1Jg3N3d4+PdgxQYlI8oNkOQ57Mt2C0czEozJ+6CcZhiSozVHQXaeCzE00kKW0rmPEnk5Ou4skwmG1do+TmUmh0dHWI4HOLnn9/i9evvpdB1WSyZY8uiTRhXZkLL8kH9s1iQqcdQ6AXwEeLdz+8wXUxFnhGcxPjN3/0WVZJj/ulRkjM5CWYByu3wgz7OL54j6NNkvIFLg3xJ2uQElKlelXjUMJHNbVnU+rSGxh9e/4TZw3tGPOLZ9Rmurm5k+waDIbI8wz/+0z9jtZqrZqQxPmly7LpCa5dhRRcb/bXvlXg+XuH9NEJSxgaUMICcsG02J0CfM0xDlX2ZCqxTBqHFFzfXuDw7QAtPajo+HsR9kdR8vL2F4w8xHB1jPpljsSoRn7q4Dv4F67c/4M/0WUuOsAhPMTof4zwI0Rv2wQi+6NTFF16FiHLQgqCpi8L2jbxPE+xYxLZdGmFh0j/p7UTWB2Wg+aMWNvRMEsYSi1iTWihSLAXYpNAwUiyyLERObI5XJ9Fj/2ZfU4/EruA0aagCttHo24BxLEiFdcN0TgttvhJgAnYM2wukcPd9A4CwgBcKBdMjLSRFizqr4JclwqCEGzCNNsS72kW9auCmTEwtqDFG6/mI+z3EoSmO6SsGYJrWqFYqVXUDX8zLWcwFgYsqW+P1Dz9hmtUoLYJ8LQ6+/D0ely0u5wUu+jVGZz6iUWTYDzzLPG6U2bJvK9zhEOPiLtVrfJxZmPR6OLYKLCwPo7LGSUhze1+EQVXLoAMy32qEDhMBCS4HIjUmkEIzfCGYOI54uSVBhJsTB3/6f/6Mm9zC+bkP/+tTtL1Y/OcENCKrqyYLlKARwTpl1wkAaDsCztAjqzDsI25v3DTCHqT0Tq8KAh0EH5X5SQYkzzyB15LAgecLsMLHMWuxWLVoDxzU0wRDFIhPAO9gBFh8XScJlWjFDuNWQKhjQUq6Hy8hAjs6fpLh1FhkjhJr1cdEcCeXMaV1BLk0YbIQqVgjclIJv7BaFPcrrFcNml6AIGvgnkUS7CCwQVnI+9Jzj/1YQlikADerByIZ436z31AuXgoTmN5RduijgCNefpIVIRJJyq+VwdwWDHyoYHke8sZBuiabrYLHwBbXQ16kjE8W+WSAAG1iI/ccvAkkrxdXlov5dIXbT+9hJ42ATvRHFMzGIB+SIdqFHEiitEksZIiCjNPmLmGkajJmMfC018fJcQ/k8dRFiFFBL60cVm+B2gnwsGQAR4S6yFBQDlo7QNDH8TiCL8emFR/HfL2G5XuIIhdNXuFxBfjDGIOAQCRDXirkSY0mcDGIbUQipzVgPxNUC6Yz1gIsCVPPbuGGNhJKs0ULbCmLqOGxM6w1w1ZTzGeHzW3Akq7fdE12uXv9FgfR7xvmkYIsYeDh8vIc94/3WK1SOEzelTRnc7/vPPUMe3nDVubx7qTKZvwTkE2YjHqn5OILf+JiINM2PZ+eqK7crzm2tSY85dPdXHz9jgY81gUcn6BUIGPRax7TaQNnUaAoEkyWS0yma6Ao0EOG86M1Do4b9HtncJwrLFc1I1kRDfoCUJKByK5PHzeygTWTphuvHNSOg9dv32M5edTrTUYSXVTp9UPcXFzicfIo+08LiNmKXrMeRr1DfPlsJPeaQlikvM5dOG0kdhBMUrW4gCDgbYsf3n7E/S3lkioJJwOQSasXN1f46d173L1+J9feq1df4/DkBPcP7wUc1NUBBUh5B+d54TlQ0FRPrrAy2wZf/uZ3ODg8Esaa+N8S0CKjzFZ5quw6QV7xOawMO1LBNd6bNalXWW0iJTV9hqOP9J+Otdh1JjMnk1faFtLVElm6xuHBWOZi09kMqyQRpmYHij2Zh/4CXNuZbcrz2xe0n81qu7no5nEuiIzH4//j87fct33bt33bt33bt337722dNFKlTGbl+nPwa3dS0zV50dNX/Vvt81dv/vwJ6tbRvLbSzTTNMJtTNkpPmZ6sbI6G9JapRbopb2AWNnffrnt//WYmfN3cy/zTpow32f/NMdFnZeXWrN6S3aYph8SoKqRJKiu8JydHuLq+ERbIap0IG46v17/VCV1Xf8o2mQ3j+3NSmqPE8dERBr0jrJmKtUzx6aePsGMfl9+8QL5aCYuoA6jqpsB89ihJZOGgJ5IK4hYyeTYOQvwn/CqL8qUCHjJcHR+hf3CO+SLDdHKLyewRoUvmlieFzauXL+G6PhaTpXicbByRdhNHKVXhlgtBocFVb4WhW+DH+RAZE86k+GI5r0deZDbdZNocAN0NPfY6wdZJeBgN8fVvn+NkOBC/se4cstiYzha4u13g9OQMoR/h7n4iZuAnpwmOy7/Hpz/e4U/fn+JtdoF8fIazZwe4iXuIxn3gIsLxsYMv7Bx+laJkWmnlo/Z8BKGDkDI9oR+orxFTD8kSoHG8egjRa62WhFCaxxNIs8oJrGYtsi5KMWl9xMdZ0GpimqbwbYydjcE8fcy0kO9YNEZSt9NXu2PWFbkCbJjrTXzTBOEIUDZE+si0qNC07gZAEZjHyH7Jh/BZrHkOCibyFQ6QN9Ifxm4jIQ6pz+RLJiC2iJlY2A8EbGSp2CX49mzKplyUBLBy+tGlcP1Q2HK8Wi4uTtFzgPl0gcBxcNE/xFFW4yYscfTlQP5Wt4/bVkjyIf2pZN8lXVABCMr/eEk7sYNL9w2C7BOOnQf4Xh9lTmmwOV5i6q2Sx7y2eeqkx6v/HcEvD1HApNUaQ9SwbzOMj1w4Pz/i4tUx7JfHaKNIwOSqoDEdwTUWs76RXCuoKeeQfk/8zFqs+BFZFUKnQUBQqOL1VtFJS8+VJJUYpmZnHk+lbg1ZEGAQBE8+WTBVQIkjENs1Qm+F+GiKJvRFQogmF8BE01VNz5ATb64pYcsY+SeZyJRw0ReyrpGXjkgEKdHcXEQmfVZNzJnXUaHkQoHriDH8JqWW+x3cIQgrtH4P9igQdqDIvSqetxYWmZWS+KhsY/VoFKhMQxRA9hVBa5sZBygIRHsufI9JpkDuWAgJrFBhLQwzZYOWLVAQta9aeHYFP3SEpVll9OYrxRzecUPMVzSHr+ERZGsc3DsW3rscA2sMQxfjwRGojs6SlWHRap/Ri0sBJR2TNehAWYJd6a1gmCzEGC+qeEjvzAiZZ+EtfAwqB0FBYMhBigjTtSey0SJdoUgTNFaIcDjAycATmbkomHl1NYS76VEHZGmBrLJEDj302fe16xBwan0Hw9BG2HmtlVuvNY5JZMWyxzFwg8Q3JpPSK5GAl/QxYRaR5amLE50klE1gfgO4dAsncvuUoZlj/nYc+nXgosvsbgUIoTfZh/e3yIS5xwTozVHsLgPzDtu7sPiVdW+7Qzbf3BU38lFzP5bkcVVkqmxUGZFNXSJPVhiNBogGEUqCi5KarMCua1U4tm14sYM1B6cmQB8+7NBlti+yykWycsV70MIjbPsRw0EfrtPDar6Wz+8Nx/K5GTuy72l/N5JXAcDrGicHAwwOjrFI1iiKVO75p+fHGPR7mE4ncm+jv+wiTeFQKvrsOW5OfTlmJZepCOK3lJmHsOm1xnu5o96JTBX9w59/xnyRCOgkx4jhDqMhxuMj/ON//QfM7x4ReCG++e3fwAs9TGf3m0RWWYwxhC+5VI1Fg9HuCojIRcLf/P4/wQ/omzdDmtFrjaCfDY/MYLkfKWNNF5EoUVYZqEhBJUVd73O6ULt73k1CqLnByezEzAXkMZustQbJYibbQ6+1osjxMJlIWjuvc+01m161bdav9E/52v3dTFWf/FkHsm0XlKWv7iWi+7Zv+7Zv+7Zv+/Y/sulch6BQJynpQJLNK57++EsU7hev233ZX325mZA9wewU7du8SOLgHQe9fg+X5+c4OTmRgosyhrfv3mOxTlVqwpd3fyZtuwQvbyekBP00ZZd1/l/KJFKPN/18JsTFUSQAlCaMcoVdk89o5ktJCQsZ13PE2JkTVRZCf/r2O6yWC7g+V9sNhLRhcm03T4+JAiGyaS3Qj4aYPSzw/sM7lY36Di7+5kYSQB/ef0S5LjaTVd0fG8eXFypD4b5xYkxwhVI5soTAQj2jCAxu48KrI9h+iDcT4Mcf/owiW2IQh/jqq68wGI3VM8718NPPP+LH1z/CIpPNJNCSmSQJcDRTtnOM/BSTNELahltvtp0mx3nn8a7INWvWuveipvXw/IsbXB72hQFGTxkx+XfUZ2wyz2HHYwz7Qywe50hplB9OcBK/RfLuE378Ocan9TlS7wjhyRhXByEGcQ/1QYT+oYMXXgWvTtHkLdLSQ+V4sAMHoUNVFvdnJ41PPI3IEjFhGJTeOjyOukpPULcqCZYQzFhh4DwiyQ6xTH3iAurDI2mhWxmWfO/2lUw0OW3Gz0aCRwjgGgmV+dqwPaToNlJjpmYKeYMMET2KVW0DZY7AKuF6MWw3FpYHJUlMByWQY5GCIYwPC2syOrIGdlYgsgv4QQPL9yWFL1k3cPIaB0MyBnxhi9peKMwa8SVixW4BaUMvsgZtmUmhG0SR7AdTC5kcunqYIm59+PYa9qhEEd4IaESvMU0FZsfl9rB4a+CwsK9L1A0/C8hbGwHWyKffY5EAfhxiMH6Gyo8RKplLACIBwg3YRBYIi13Ke/2Qx4nnVAFCq3mP+jFHHb5Asi7gjgeyvSVT6JiU6doICDJRlmaKaK1DLZSUQImuScFRR7wiSwEDCap5kY9V3WIgsm8GD+jYIX1A5FMMQykNWGYjK8gq4jEgw8qHTcC2LBBQ+sh+VvsYhhmsdi3gWYO+sNEEpZHBix9AZqSajDOkhOBMllVoCsIuFtzYQ0jZbEc4NYEuwq1hXweBmEoYj+qPpV5XwtiyXUnoBAFuatMIyJWljE3cN/phNZRzUqLrQZi89PSjfF3ANfY1u5VgELaKbMK8ge/TQ0uZf3KkjMyPASB2QYl1DsutJFCCrEYa4ZGZy89oPQ/rzBZGm6SVxoEG0KwT+I6PddjD95IS26JvVzhDQ3t42IWF928/IVtSwqzgtEpGFWSSf52M0dplZ+kdgj5cJ2cHiKMapQu8Q4BPVYDfrx0M6gYJCsAPkdHDcb2AVdpwe0McDR0EPDfCvpKrFFVay7mnxx/7GGXNntWg4D74gVyrQhzesLjYf8yYJGEpCqwJS8iBJPOma7qLcX8cATnEl5HjFplFZpFIAxm2TCX50bD5NK1T70YdW13YRuaWKeDM0wFd/cTor3h2jof7e6xXqST6yjKdsTPQQ7kjr+3u68agX54zstGOzabjoUmQ5D1TFvzYX4znKvsfE1ptLhjYWC1niOMeBgcjlcWL3NFC3liaclnW8NtKriuLN0bbxwQu3uWk49awFxnmaYLJbIlinUmQwTBY4fwsFZAt7l2jqEZI1wX82EcQRxIWVGQrBFyQIpNdfO90HOb5csIYKa+dMsNsOpH7SJomWOVM7XRxMB7iy6sQVR5IaAyvEwquXduDS2CN449IZ3muavzw5hYP85k8xmNHTMxxPByenOL9u3e4+/BRjgsTQo+PD7BKFqiE8WrmU3LyDBtTxic9vw59K8lOczy8+vJLHJK1tlyK1QUBM96h9N6kAL360SpwK0mh8rMZ38Tv0NggdBEiXR8wfUYAOvPgBjtV3w4slnNJUx0PBrIoOZ3PRUorwB0XY7bvtOmDTzul+cCdJ/W3DpTbfdUv/vBJ2zPY9m3f9m3f9m3f9u1/eFPpiGFt0TzXpI9u2i6IskHEdpGx3QefvuzJ2+Cvtyd/vQGTFPQjqKWTwbWAXgxCoFSTTAzKCaSAl0JuZ6LPv3+yeU8nXwoEbT9Y6pDNvnNiu6OTMawN8YSRYkgnoEVBb6ZcCs5nz68RhAHms4l6npjijoWNMCo4y7R/eYD4LS9TYW4cHR6LDChNU8w/zmQievbiCmEcYzlbUcWiBUzTYjWfYfY4Q3/QQxTRfU3BUS14+MVzSZZTgbphymWLsd/i9PIZCivCdHKHu7sPyFYLHB2fCPBwcnKKm5trLBZTpCkLBHNgLGDkJPBR4j4boLRoBq2T165I3U5uTfGxc2y16NJn69pGMDzC3/3uCiPKx3IjHeV2OxbWeY7JssH4+FKKq9nHGR6CCLfuHayPf4/yY4qwb+Hd7AZ1eIWz0wNcjnroDweoziPcHNp45mRwyxRFamFdB2iYEhs5iIS1RvlVKWBNlTMhVCWhwgLhtSA+dwSbOn+Zrf+RruC7WK5DOFjhcPCIdUoZmx579ZgynjP0W+I+G8lwdwxEotwVml2S2+ZrN7nVeNSprY+y4bRSNiCrRzQANY3D6kSktQTFRA5mZH8ERvh+Pn2NaPzPVMyaMjUys0pmdcIhsBkQWPNR53qt2b4noQk8JyL9KXPxy4oCG43roWQ6ZZ6ibSu4QYyCwEjsI+p7sOIUpRfCbiLZfoKlBAhpYM+NEY+ztkRTFEgLH1bkCwuFkl1eT48Tpui2qFoP0WiIgH2bkiXx6SOIpX5nKndTcMcKHPh2Lu8rwQeUVjoeKs/CuurBG2iibZnlcr35gY3AYz3OkA56PvEjyOSRHoq2VqZSSxBO5Frkq1kShOAEnoBGDMRQLyNaIFKGpTJygrbiT5SX8J0cLWXItoKeRekIc66uCrh+gLJkkjIDSgL4Hq8pH5ZFMJ2XM1mryrxiXyFDh8EBlFiqryNRNguVJM9q3xZlqLojyrFuhPlqCdOPw6NL+bHja9iAeEUpeEdvqGzNhQMTzEGwgkCiz6CHBgWlhxXldtSAsu/QSN/FunHQ+AwxYEKtoRsJLkCQ0xbPPgJNSrAkU7GRFE0mHMxoWl+RqaZebI5bGfk5gQCL1FAEbougZyFrPKRLAn4Nol5fmLZNukKPbDLLxbq1UQq41cjfHB0MEfYGSNZk5dA78GlTm6tutNL7BoHQwcEJzi6HCP0cjWMhsTy8ZT9sPRxWJZKmluCPJJmLx1dTh4gPRrjo2dJnqJRk2qxV5chXDZKcfoIe7DBAwD5n8Voq0NY+ssaVcYVbbfZaGYaUqBNgy8ngU9CMicCUNCcE1wTIJTat8nQNM1CwQ77M+CDydBP4wL7EfdXxQFlO3Z1QAJgOITGSwg39WMbrBgdHhzg+GuPNT28E0GNn6mAQOZ7bEctwk7tbeLe4svmkDXt50zbba36XN9m6q/InmunfPzyg1xtLMjbPaTdW8toQr1OTxF2In58Fu2aYS4WeU+PYc9D0HMwDD/3GR+h7KH0bc7LUMg+LJRcBErgWfdfWcP0YZeagTHN4gY8oHgqjnuOvG1K2rWy6jkK/Xs4wn01le9frHMkqhRdGeHl1hedHPlaJi1zuCy2cxoNj+XAkfZbAoi68kEH2L9//jGWayBgpOSWtheHBEEGvj2//9Y+YPzyK196rl7/DcBxhvmCSbXeYzYKeKBN03FDvQVUrELAdjA/xt3/7twLuzqZTAddE6i0JoQTMjSS0C++RZFDzswC4BmQzQQYbn7VuEa2TW3e/d4tHxpuWr5/NpjI+HY5HOt5Pp8Ja46LGbi/a9IVfbU/Bte6nvwyudbOPz95iz2Dbt33bt33bt33bt//ZjZMhMsZ0sq4TnqdT8e4h89gGZNv88pexOPyV1q1ybl5kZuW7bDbxbXEQBD5OJdXzCr04loSp2093Ih9U+n+HYv2FTTf/q9Eyf1Q5aOdLQ9aJ7/oiDZUgBM8VKQ4noFI0spAzbD9OQGXFlUmagS/AH6Wib9+9w6cPH6SwFsaJzH1Z9CrwoUQDA0iZbRMwjjCJG8CuHDxOpnh4uJWJ9uEXp7j46hrVwxLzTw8K2ph/BH2Ozg5x9ewCQeijlThEIj1kvFQAJUr8LvIRrp1z3yIQLvv29Y9YPr5HaPt4+eoFTk7PpaALwwjT6Qzf/fl7rFZkghAg4iq3elRtALVfOand6r6w3gxrTcC41hKpzNWzazyLfeRldx4UvCzQYr5KEcSHiIZjzKdzLEsH034Jb/0HHD7+hMnjCO/mZ/B7PfxvX1Tw3EOscYbibIjxsY1Lp0RYp6jyVpJJS8eDFzBZUYE1VqaUbFVkqxUESGtUZImI1xq9jZgUSvZRZ+RsZDFdQqiRg0pRy7OV5TgczuF7Fm4fB6gaQWrkOHSZsJ0sRoqPrh+zIBSQzYQddBLSzhtKChQ9xx2zTQ6k/I32WfZF9kteE+xWKJdSuLmU+DG4w3WFIUOmlk0zf8P4oH/RugCalKmYtYBIUczgBAu3RQtnVeI0rOBHBJQ8FFkujBueIRpoC5Bne0gqB2VWwW5y+GEsxvTsHE5LmZ8Hn0wPSoFY45uiWQphu0GVVkhLH14/kNTLxm7hV2vMZgt8vJ0J2OsHHq7OjzAY9dE6HJheugAAIABJREFUsUAQJIAIyFNU4j9m+5QzEXCgT1wG2KH4mPH8rNYFyrJFEIVyDlkY0jw9cHlu6RWmKZh8zBMAiewSH0uLbCMbA7KjpIAkfdBCSSleDZEWq4JWrzOCbxnTL/MWrqTpEWBjKiGBnRphWInEuGkpdfSQFTbWKQFeAtgcP5ju6SIaxBjGgYQ4NJSUij8cgxQM/MJUYvYLuZaVycbjXRvAn0w+2V7pdJSasc9QBkxmWKk+g9J1bEwdFyMegyJDXlQCupFRwv7G91MJtSXHkWBWlTFNmW9LNlGA1vexjhwcB0BMsJTgM/3HKJEX6KUWrzY14+dY4MrhIt/IJRjH3bI9TOFgWQBOUiHIcnhuIYy0RiT5yuxBVYBdK0UgzMYmKxHGnjDxKJPMKJWO+5g7jiS+hi6ZbJQIN4gaF5NpivsP79EW6UaeppeXKbkJ7sYDnJ+NEUUNaovObg5Ky0VKH8vaQj8jaElQsUSWrdBWFrwoxMGAARMuKrmHUL5aoGYKaNYitSI65KMXuYjotVXTz7NGXvtookD9DqsS+XIh8kKP8mEBNcyYxFNJS7fAQVkyyIA0LNuwiHQsIpAuIQ4Eb8R7TZmJPNidsTwXWzpbLpWab20SlFi4vUl2i20qMWwRxTFOz44xeZxgwZRSl9e43kS723UHXGx+NgsJek/r0DUjczerLp3P3YatK9+3TLYueIc+pNl6JffkqDeSbRUwiDJGBiF4tHCwJfyo82ej56EEIeQV3KZC4FYS9MJU5tzy8a6xMJ81cCY55lmK+/US5SyBk1P4m+LseIWjU37OCG15BthD2G6DcNQTRnO6mgvjnyBdvk7xcH9nwMwGgRfj7PISH+/vcBZRrmtjzTRpBp/IchG9UR3ZfpGECrZb493tLe7mM+mbJvJBrsne4RAfPnzEw/tbYS8fH17i8OgYZbVELfp4s6Bijn9375BzSIM6PlHxWvTx4tVXwohfrpaSzK6sYmuTetwxryVFnYw1fomnqPqsaeCKkYYKft+lyJqzv2t50C0cyVqSKgYWyyXS9Qr9fiwBPbPFHEmy3vjbmr/EX5xAPmm/eOCzZ7fPd71TPmN3vmJesmew7du+7du+7du+7dv/1MY5CCdVnDxJetQTkOtz8KubvXQz+c/Rlu1q9S+f2bzTU4yue9wAOOaXzUeI2W5Vy8SMK6GcJFKmSTYbPVlo2k8GDmVxasC93Vx9TxOKYB4TwprIn7AtSpptsSGrwKZ42WybTH5NOAILSuNVQrCNE24eP0pZz64uZDKbUz7CFWUBncyOCNamkqDOjUxrYxZOJfI2x/nlBc7PniFZrrC8m+L+9Ue4lwNc3lyKl08tEhQtVtKkwO2nW5no9/t9ARllEiwAFoFBpq+as2G1qLIG7bzCF1fn6B9e4X42x8cP7zGZ3qPfixWccV28+vIVoijC5PFRZF/yeZ3kR7qGUg+kYPpFU4BNTxwT5y7x+1c36FUWvaaNtZRoRTHNc6SNh+OzZ6grCx9uZ3jsxYBzj/Hdf4F/u8B3P1/gtnwO9/QUJ+eHgHuJMhpjfObg7KDFpZPBzlOkmYu0DoHQR0RPIzJ7WGFSjlgWKLIKOaVbWSmr+gyeoFt2bdNMnyweDTsQX6+iRpFTHsgUS8NyY8EkPlxaAa/SGPPEwdVpAtvOkTDisEvHk7qj68eGQbIDokl36ArS7lra+dZdIN1xNodyUxhvGG98Ty8SxlKTL6UT10wfFT+mrT8bG5lgBLUsn4CEjZDMGpe8iBYjFt+Rg3ntwMnVrJ/FFuV+RdaizZUVQnlt0DYIIg/kwZV5gSrPUJY5cp4DsjrDQBhTkjzK65F+4QXkMwn8ISAYaAso4fDvVjWWSYvZPBN/tcZ2EdghfIcybYJQ5rjRj02YZbTOTyXcoXFjtK0vxXeWFZgvCmUQirSTrEQbvZBRCfTYM9JdCXuh/JP7Z2PdBFgGHg5CICbcy7RGIoPiHycwlcoda0olWXhawiJiuqvvkNnkYu64su01ATc5V5TZ6nnQ86SgQBgSlHFRVjYsSQp24PoRFqsUJYHAQGWkCgQx7/MOVmqjalwBLcm2UiCEKbDUlKpEkP58tUkvFaksBeN5IX2VwJV6blkI6X+U5gJGuJ6PqmI4BPuEL4AQlbPCzmN/qEsBrNF6qN0Qy14Iq+/g2q3g17yeLBSNJ5JOmwbwLMp5gZu+09ouXCLc9L0jo1GxfmG2xVaDkWtjETqYk1mXO7BLsuHIaNMKPSe4XTAgIscgasSjMlm3yJNCZItRGKBdr9CrK0R2gFXjIIGDNcELu8IwsnF6doq6dpDkiQ7wJjG6hovjmxtcnwWwvBIZ5YZtgLyhz5sHZ13BKy1hGCaLKaqcIF2A4djGgVOiLMgeZF/MYeU5VksLM4ao0I9tFGEQWghRoMkLZJmN3I3h9gOMQqY9k82WKZjBc8fzZCmAzPua3/PlQCXrhYQ2qBq62Ulv7KSgPNRGrkcPSAbF7txxRZoujG6VJ+rIrOPH5q7W4XLGH5Tvd3V9hcEwxs8/vxOQlWCvDNcy/G9Ekk9BFnOf3TDHu7bRkD7FSzogRMIoBAg0PoMc66oSy9VUQn28mMC5/oV4HMoCl4Y58N6soK7xn7S2/pOUHpeVg4YgblPCs0sc2hYGsYPV0JfFpgMuOEWueASmtYPFPMDikeNkgrg/h13PUVUh6lSBSaZ5x2GIu48fMJ08iCyf29IfHiDuMQSmwHkvwXJJGwVdUGOQgU0mI+E1goQCrtmYrxb409t3WBaU3WsYE89z3B/I4t6f//hnJPS39AN8/eL3kjKcF4vNEeT9nvvdAZTyqNyneZzU0uDg4Bj/+e/+d1n445yJKgACs45h1doE17hY2PD+RnBNGdu6uGRCDExqKDdOZMhmwiZ4dQeO8gSZ0BAZ6gR05lhU4/7hTllrB8paU681jnXdIu52nvfL9ovZ4s7vv962oO9OH999+WZqae0Btn3bt33bt33bt33795CNamLck4nN53OcXXBg07a/fz63eTL3fvI35rHNg2ZS1U2+dozgyULiqugqWclEcTQc4ujwUBg7qZm8dea6+rnbAqCbfnUeIWqKbcDEHU8ets17KA62xUA2Pm7GO0xWSdWrKctymUBfXV+LHGO+WAhwJpNZs2cEHORnI+MQyYVJ9+MzCcG5IsHl9bVM0NerBKsPUzxMHnHy8hK9wwOs5nNjAM3tsbGYL/FwN0U/ihGy8BTjZC06lP0CZKsUq2Ui3mH8rHHU4urmOXInxvThEbe3H5FnKxwfHYv8dTAc4OXLVxIsQZmuTp7NsRFWxNbPSEHMroAzfciL8fU3L3EzilAuaPitPmtMSyP7YpqVCAYnGAwOMbudYkZfqRMfg9VrhG++xfS9j+/nZ1jHVzg8HeNq1Mco6sO66OPwKsB1z4K3vkcym6NuB6i8CE7oIvKsjddaUxeoKOfN6o1puBxvSrbEa43eXpTuGSmoMNt4LpW9Rm82Pi6m21LYanEo/4TN4WCe+PD8DGeHC7QlE2h9s5Jvet4m+GJbhOh5Mz1N+tgOK9CEjzy5PgxI1j79z1wjZC3ZgBdI6ixKyka1eJVC3CRcdp/t0dfIYc9igaoJcPQXCtsSPY+G9QQqyZ5Rs36COhRmlXkJixI95ow2LXq+TZqNyC15gDrpVGNROluZ1FQTS0rjfBbx7Xv49T1c9ATIynIXSR1gXQNpUSoQ6TPpdQTbDWAR/GkIsqnczy7ew27+L8A+Y/6u4AZNbWM2o5+QAz/qidSO8lEWz32XYIZK7wSgZKlLwK6yJBxg7gco+jbO3QZunQuIWtQMDFAPNYL6wuDsPLIaGy0lny093ZiySe+wEn23Re07SBymmoqpkrAL7c5Dj2xCIbW2CNk/Aw9l66FKCZqkIjEn62ydksmlsi29vv5PtAsLy4djrAcWQgFqbSmGCRzDMJpsBrK4/ABVBj6S8bVoEDilSDDJYiQTc5nmAuDxuPF80s/LDy30Ik2CJPvSoQl7k6NOeB34SL0QySDAWdTiFLk5nkxU9OD4ZEryeiPIU6FIy42sjAAE5ckdM4kAK6W+ZBGKdyQqjGyg51uYxS5WjQc7c+AQPOQYwT5H3zYCmkUFvy3QH1goAx/rpXpixb2eJpOuFxjSR8pykTc2FrCR2xYqq8IJUzsHh0jzGlmaIu4f4YsXVxhEBQqUWJOxxnPRuAgIkGaVMH0JMKwWM1g1WWsRDnoNrLTGsvFE1u/Ray2psEwdpLaHJg4RD3wMpC9lkg66bkKU9BTs2YiZoiqgBQE6gvwKZFBiWpWlpGcGcYg0X8i4Ral/XSmoz+/CWOtQ9nb33qEec9vxYDv2dAsrOsZsA2i6RMmO3CMS2zDEzbNrJIs5Pn2615TjHT+trumYZe6XuxMBc5/u7rHyv3zbMtg2XztAjdlKebiqCEiWiPpDvWeacU8WK8yCRTcP4LHgMREg3HiG8tOpRCeATnC9ZLJySd9KlSyHVokj14bfczCLfUn07tscr22sWiCpXMwXrnhOen6BQTxDUZSw2ghtu8abH/8k92fXG4ic/vD0VBjvZIxLP/cDvYaFJU+GKZmdtlxvSjxt8f72I95OHmWBxzFzC7725OICD48T/PzDTwKSnxyd4uXzF0irBGWV7gCTWw/FXU84OY4EHR0XL199jS9evMJqtcRisZD+xuMrVhcmuKmRxUEuHBkrBPFaozem+kZyGzbBPSYZdHsf6RaRyDjcLlzqApKDZL0Su4lBL0IYhpIQOl8sUdCj0sxbdvvBLyaHm7bTv7aQ2eZPdp/ZvvJzKfLTt1G1gr0H2PZt3/Zt3/Zt3/btf21TWUArRfJmhXR3tmL92kznV2dI+tRn86cnP1ufTZQ2T+7O6rdMuW7SR28UyhkZMR8EAQ4P6RdzKMUcH+uYaMpo0y3YneerP1YHkm0/TmsCM5U1E2ABHgUEMxNcM1HTsAQ1qqbUkAyEPMuRpmv0+wM8f/ZM5GGTx5kyiQiqiedTJ8tRQaH8v2OBwwlusppLWtrzF69kQptMFnj8+Q5JluDyb14ioBn4iqvSOrHlZz/cT7BYJBjEfQQhTeUp7WiwnCfI6xK9Xl9kVrbHFL8SbZXjctjDxdULrCoH93ePePf2J/FL4vaTGXh2do6LyyukWSagpvrKdcdwQ23QYo3H3HFxen2D3706ARYrJPMJWiZJslhzWiwYLOAOMT65kiL/8XGBtBchiCYIf/6/sXhzh58mB/iIS7jjM7w6GeG8P4B3NID/IsJXoxbnzIXLcxRlH7V/iFJOWo5e4Aq4Jqw1FrFZiZxfha7QM8SgtdVrjebtnbG4mIszvY/MNcNYE3mhsEwMy3AnDa+rZ7n/lMTlVYj5Osawl+LiIEOWk92goIUUnbtS0J2+2L2PwLTa8bbd3lS/0k92+of+bPqjFCs7fdKlB1mAukjQlERZXNkOSXsTNmbHfKCPDosrRmM4KGsHRQ5hZYU2zcItpL6HzPLFYJ9f9FIrCEwRwKrpMebA8QKE9OtyfRQ19X/qkURWVkpPKQJ3IS29CS5wtz/Czd9i/qdzpP0QVujC7nkilauTVJhXfhji4GgoTJ6G1xZ9p4oWq08ruPkbeL0f0Dpfo237SNc5lutcgDUSLchia0MbccRQC0tAOwYPMGmUrCVKtFA7WLU+1n0fJ3GLYyKAZYm8dlEydZCgEZMzrVauZfYByqMIuvJc+/K8jdbj6xVos8oSsV1g5EG0pInjoy5ttAXgVjV8yiNtgkqFMAHZLwK/hR3aSKsY2SoTrzOPgGUDYXl4Prf3EVbpI2svZL9CgjRywdNbqZX95Vgokjm7RYYK/8xzuQDGeYU4XKLxaixTSujoJRmoTJpeVfQn9F2EdgmHMlsCmZSf0SNvYWNVhZj2IwRjB1+4JcIyQ5nTWD6QfadPGwmJ4iXW0NewQF4UIsEmKCSecQJ6Gb8sMXRXoK2syWhT8JTswiMbGEYOJj0PWe3DLmw4nW8bla4ENOlFl1foOyl6Y4jUfb3gGYCkTZMiZ61XiAXV9LFubEwtGxO7getbuDo+EK/LwxFB4BwZbKxB5psPEDSjdr2lPYCPZDVDnqxhWSEODlz02hJJaqF0PfHwc6oKSQosaw9VECIaBDgILWFANinHfwdrv4dg4GHsW7KPyqQthWmdFTmKnH1TWZVlm+L9/WsiIIgDgns2ijwX5lrVyUHNIszmvmGSHDcglIwhapQgQEh335RBZMtyUozO+DkaLy2ypvv9CG/fvFVAyTCTZcnHjPcdGLYLeXS/6Kfs3q/Nf5upwtPnzAhotougWCsgEgNwPD/Yjn/yxkbaKl6m5ruw2qXLSqIzGXzi9WfSNNnnuJBAKX3tOigaW4A2iyxJZOjZLc59G+7ARdILMLJijN1IVOEpX5H6oHKTzHmORfP5BA/3txp41IS4efk1Do6P0Y+YZOtgmTLYBPDcBmlSimRfApRMejTBt0WywOsP77DMc7keyPDl8WdyqRVG+PYP/4rF4xRh0MdXX/0WYRxgkU5lMUgPhLLTeOx4HcnIvwOUcu+Pj07xu7/5WwFLp+K1lso+CFNWWPcKWtYmuInArvj+yX2O47re83QxSVlrZFFuzrHcxzprAxPMY+ZYZK3xvjmZ3Mt9YDwcGm/NCZI0FQBvg6TuzhV3fjQn/rMnPgfWOs/Xba97+sqnr9/O61RmzPkaf9tLRPdt3/Zt3/Zt3/bt36VxUs+JCVlZv7okuDu72Z1x/8prP3+mmyJtft95y+0PO6/aeYFMKDlJrMlKyLCYLwSmiuMYo/EI49FAJo+rJBVQYzP9l+01kzJj1r9polrcZbF1hjPGPN7MZLt/XVIoJ5zqHeMIY4ysgopsDgJABaUaB7i4uECWZVgu5qZ46dait3XEE38cs7+U3tFY+/D4CC9ffYnVcoXVwwL3P32COwhx9Zsb5AkLX6O9tIA8L3F/P5FUUkpaFpM5WsfCaHwghupkebAME1jPqlE29OSqcHVyiNHJFR4el3h4vMNkcieT5I6ld319jf5ggMn9o0zAxRjZFHA6wSc40sM3X73EWc9COqXwyhVfO6IkWVsjaT0MTp4j6g3xcDvBPLewPnQQzv4BePMveHsX4uP6CmlwjtPjE3wx7CHmubwe4PTSxSuvQFStUKwtrMsAlefDD130QxeB66Jc3aGmHIxFUlYhZZABJX+UUhFYswmwkbVWaRKfMNVUIkNwTTyQytYk9GmRoYWtSWiUgrPrmsa7T64PXblPiwir3MZBf45BlCPNKRFyDchGlkXXZ5QB17UOwt6AbE8ffXKddD9rOmBXBW8976R+8QKAIE8+FxBV/Mk6ybMwXhQ0KiqCYb7I3UrbQUFQiKwsFOg7jfhArX1PGFtk2gjQVjNtkyyHFMO4hu2pbNoLPQkokATEIhO2hOOFSAl6ideUDdd6DafOsPrpC/zTQYjKqTGmb5fVCluobQoEnoPDQYiI8kI0eGgavJ4AflZj7N/C7t+ibn+L2ZLEFBeBHyJNMjE5D3qByA99q4Br05y/wJoZCFYg6X2U/90HPvyRixuvhl9l4OHJG09CHAgakd0nfFNew1mhDEbj5cbajEwjNVgnYGWhdmwTIEF2aoGeXaAfuMhDD3OaaTHkoaLJuXq7CShK1g3lmbWDeBwiiXy0OVCnmXgF+kEPaVYjLwfwnEsk9HmMeJw1VIPgFFG6wPelbzLBuPNuiymRrYAe/eoiYFUGcP2+MlZyylxthAOml9pyTpqSzL1cAhEYPLDOQ8y9GMtxgOd94KTN0BYEhTyUdiAsUUrxdhN5Gd5QlAXyku9vpPcE2DgkCQbfGdOTQagBILVF5paGV/B9PLvGIYGDwEHqu2hqV44JZd42A0jIRqKXIIGSrMRBVMIfelgWDqqkkHRnAm11lsIrUwxcgpUE2RwsCepZZGlWWDcFcl6rhL1qD2Fjw01z+EEfVZEjW00EHHV7PZyNS1TzGgmTUwNbthE5j6mDxPbg9CKM+mSt1XCqDEVaIylDlL0IB31bgBxbrjWGzRC8LyXEIBcgn/tkYTp/i9X6AWdnX8hYkueE/iyxQFitM5RkvRnmmgAqgix1IJneizZrHuK5ZsAYHTo29xNlfnUEOE0/DqIYz188x3L2iA8fbk2SZwfqd2+667nZWSjoHVX9uHSxqbtXy8+bOUEHomnQifkrfaUANDZcr5XFG7IGzZVnrBu6G313UzRf5rO3L1FvTEm4FPxty2jjdUqvRrI76e/HhYSK8uymhmsV6NvA2HdQDl2krosjhJIiXjQlBpGLs+MRHh7UkoIs59iv8OzrV3INjYMU9SzDuoqQ1bnst0tmaJLpMZKUdt2Hu+kDbh8YTGBAKcJhtoWT82vcPjzgzfc/yHg8Hhzh1atXWK2nKOq1sWXQJTgykh0BtyjjVj9YfSey1oCXL7/CC84RVkvM5wuUVSHH2XWYbq7BNWppoTYImozegWsqNRZwTTzZFNRVP1U9dXLehI1t0tjlZz3fBNfWSYL5/BEjprKGISaTKRarpVp3bCc1+Ldb15f+0rP63C5/km3rSLfzaPeQyHN1QXWzJV988cVnUNy+7du+7du+7du+7dv/2sYimvNv8aEykgQzu/4VPG13jfGzp0zrnv+8dW/Xzcnkd/ljM3HvaF47H8/Jk+d56PViXJyf4+T0BK7jYTaf48PHTwK0cRKof9etgD7dgG51ViaMxky+CzdgwSMgmvivqYRLJHBcFTYprLpibQA2epmY6Hl+bhhFGI/HArJ9992fsZwtxGuo83nbsNjMPm2OlUgSjW2+5eLk6EyKqNd/+k4KsTYALn77DKenx/jw3VuRUukiv24Ht/P89Ag3z6/gGArUplijrx2NysngkfPpSsKZ3xvgzWOJ13/6Fk0+x/nJEb785hvdP9tBHMX4ePsJ//qHf9FDKImFLl48+wI3Jx4W0xVaenkRsGDqXNNgnlfwx0cYHZxgfjfFPKmRDV1U6Z8QPPyMfOLj03qMpXuK6GCMq14fIydAdRKi/yLEC69Cr0lQ00Q8d1G5PpzARUC5nazdq0SNhSwltVkyhWVFqFp6V/G40m+tVtZWpWmPnQyUhS6B2oby0VILtXrX/8wUdfQ543ctkMxEXgy6lTGhXAwjKyYzxylwPFojK2NME5Uhqf+cFqTyj0me8lYsQTumiK7wbwrYrq/LJWA+e5dBIGltZAexj7KYZLiB6b8EeLi/+Qq+F8PxelJsiRG+FHku4l4k54oABi238qIF0hKBVcDz6TFmI7Ei3Oc2ikUFKy3QUmrYZIijDKMB4MVD2Q4G0Fb+GA9pjXC9guPU8CN9f4IXZHzE9QIP/3WAfzjvozh0MIyBC6vBhVMLgLycJTg9OxIJ1h9LG4+1C/exxG/WK1wevkMS1UiqLxDGfWGYZdzeXoi472LQtCho2l+xD7aYZzxaARyHUkcP7cDBjdfAa3I0RYO8pL+YK55wvhxHnnMFjYq8QJLk0kdE8ulApIFRGIosTJgQncF6S7Zci4b9vCoQBiWcwEHmRHigF1Rawy9qBA3945hU24ghe4+pl4Erksl1BTzS825VwJcACRtBGIt/4NKzMRjEOCbrMm+wzCw8WEDktjjzGpQEF+mD5DhgVt+bvMZ1sobje3AJnJINxVjT0EffbxEan0r2ofUyQbog1S5A4/lYUWbNcwJqhAlSOsjhwWZoCMc+DjAcLwhSG2P0otJUZYLZrfGJ45gY+BwDXHgOTekdATrIcOVxE+ZWDZFhWxWDAmphABGwbWwFJx+LFuGqgl0U8GxuY4OK7y+MpRqBUyPuO9I/ZzNIwEZIRqTvIGNSIlrkvSHe0VvOBV6UBao6FxnpoHWEXUh0guM9fb/I9uW4cXLUIqpKTBMXNQFkmtWT6MhrwDHHsedj4BE4LVBnBdaFj4JsNvZD+t514KP4WxFQq4Q9SGZsUTNoZYnHyXucXFzCtTyRoau5vPFVaxoMBzGCoIdPd3dqTk+gioxaAzhtADZzx5VTI+C9Pi+LApI0ogAEX0+ghmP/5fWlJOe+e/te/P3Eq3PXRqGTtJtFgW4QUoacjoME+XfHKLl89MnNLZt+BSo15UuMpYLVYBD5KKocRUX2JSXR5oZsWFHdeCcMSI6xZEtKHzf3ZzGgdHShy6Rnd0xJhs94ZKi5DHFhf6Psm56BlIY3aIsaflPB95jkKwg11laAd5WNdNYgnj1iOf9JxizeRxfLCtmywtlFhK+/+Qphk2O24iJGDUQ+5quZSEFjp0Y2JRNyLvedVeHi/d2dCWnQ/SHrbnx4iNq18e0//pP4nLmuj+ub5yK3zou1Sr0Ni15ASwOuyajdzQ8ouW5qnJyc4euvvhEG9nw2l/GPf9t5xXbAGvtPlwzaCCOXSdmaSNsxIvl+yhjsgHGebQUDpYd1rH0zT6HXJn0cp5MJfM/DcNAX+475cimLi+zHu33HdK0d4Kt7cBeA284Uu77dvWL7Lrt//GSZ9BczS7kuxO7kyYv2DLZ927d927d927d9+/dvMuEzhZOszHZTnt050c48qvvlV+dTvwK4/Wozf6QT7p1JWPeH5jtBI04OOWmkXxjDEJgCSlDr8GAM33XkMU74OBHeUn26VXpTWHToHn/fzt92fLE6Had+eOebJoWO+YPOv07fsBUTYRafNBmm19Kzm2cIY6Z1TlE36o2isIlZrTczaCmRzGd1fLckWcl+fvXb3wC1hdV8geXHGe4eJzj7my/g+gHK1Xp76NpavE9u7yci+aSUlv5sakZtAEUWJ5Iwx8KfLJcShyFw/ew58naA+9tPePfujRi+D4cD2ZfhcIiXL16KrxkL9//8zRfoWSWWC0pBPdhOIAyWea2F58HzF3AdH/dvJ5j5PvLxGs6n/wLvcYnHT2PcZ2dY909xfnaEi0EP/YM+2q96uL508MpK4Zdr5GvK6QI0oY8wciXEQMC1hkVsIXJSDisoAAAgAElEQVRTstYKemMhRNWSQcdjoUmhAgYUhklSbFkk8p2+a2SwiSRLJTTqX7btduI7xwLPVJhSjJoCUIIbuyKTjALbEi+yRRYisDOcjpcoS/Xn2r1MOiaGnmFCDhqu0bUNTL0B8Mw11eHaW/rjpvDaoalswGfbj1FWuQQhsDCtacgvKbjKMlIGXit+fcJq8hzkjYMqV/ljaOcidatjD2tXPcoIotYZfd4Ivleo0hxZHWHQj3AUQYAIso0YysEACT+IRGK6rgP4Rw7aWY4stbC0bMwdiictnEQBjg8HWLU2fkxtPCxblMsKx1mOoV8g9wdow0uRka1XGRaWh3AQ4DyyEJl95UlbrwpUFUHDCA5DBPo+xgMbV3YOh8mMuS2m9m3gIRBwTWJQFDQq6SNGWXGBXEIAFOCujQ+UXtZqus5f2B06g3VqJjO4AsS0RYPQyjB2G0lXLX0me1JGZSGnWsrlgkAIz/im8RwMPQtxz0XWuChTZQJyX2PbRZmsJKjCpRn+skGRArdNg9PYRTqv4XGMciwkeYFxXiAIIyneCerUlg9v6OLQMxAH2ZQ8hwS5igqZ5aLpRWh7Ls7CBuM6Q53XWBcBSldZohGDKyRYQX3EeC3xOmIhTeYa5WGdv6GyrbQH70qURULeAULcF0mItgXgIXDWUOtNI3aLwQU1RpT3RS4K2xOPPadgH2241iD+h5RSlnmDuMkxGgK55yNf1wJ0cv97kY8Tr0FT2VjVNkZtg6wEjnkNrFYICWL6FharuQSu0lj/clyiXgLT0oXjMTu3QZNx7HFQeQG8foSDgYu+U8EqUhTrFqs6QjOMMO7Z6MkxYsKqkeBxrKEclOMLxxWrwePkLYoyw9HJpYTeSOqqSNK3Bv78t14XWCdznJ6cSD+gx2hH5lJW4FN/RT3mO4CD3kQ2gxjDRsnye/nyOe4fbnF7OzUhBsrs2eFnb6SZYgOweYsd/6zurtUxwruXmPue3mK7MdG8toUAX73Qx4psTSswXqb8k9378eaNVJrfhTHwA8yx0ffVMIHNPGDDZtPxW1+m+8CP4PhGhirl7SVlx2Ts0qKwLRHYFQ7sBqv5PSYfvkNRUDbtYZaEeLAHOLs6w1dfXqNNucjjwPJ0gcK2fWRFKiy90CUrNUZtufj4MMHt7EFYeqJjFvDRwcX1FX56/wZvv3+tIUAHZ7i6vkFZJeLlJlYTZoGHu9aBiXr4lcHKewT367e//T2e3TzHcrEQcK0s6f/GMdw3cxBef/UW4GXKMe+BlSaFysKSAOWaHq9WFd31qYCeAGoyZpjka7MA5DKkZDHHYjbDaDQUgO1hSouKlYB9mz6wudv9yoTP9JW/9ILdvvb0911Q7fM3NY2gprHv+LW2Z7Dt277t277t277t23+oJiCSmPbyiyugTyfFT9sWGNidSv2lV3/edglyO9N4/flX5m4dwEVz3fOzExwfn4h0lMAQmQDTyUID5UzwwGbStsMs6rxFiKYQLNlNzJIVfX4GDYwpgzOAo7LZdNVYV46NGXNdi6E1PU7I7ojiEOPRWF7z408/4v7uo6S1ycRZJHz8u12GIHa+kx2ispOD0aFM3m/f32GxmEnh1n95iKOrE9TzDOndErZMlhXE4VufHB3h4uIE/UEkE2qjxRHPFBbODWPXxCzZhme58MIQs9zCj6/fYjq/w7jfw7PrS4wPj+Ss8rjSV2hxe4flIhMPKZosU56SWxUGh5fw4yGy6RJ3SYXhoYum+A7Fu9dYPMR4Vw5R1KeIDw9wOgqFsWGfxBgeOXjuU9KVok6VaVTRVJ0sGin0uZW1JM6Jr5GkfhrfNOMbQ6+7qilg1fSNo9zOAZW0FSWgZLBJQduI3JESGfE0orzN1KTKCOkYYw0Vl1IDUtpmG+aZyk60flJ/vaeSGvlfiqISR6MVGqaPZrGAP7sg78YzScrALUNkU3Cagke2R1iW+nnSRw37hA+KNw7DLcjyYDHkUMao0hhlMlCGuBIWpBP0hE1E0DUMPGE72jTXt8nKciT5cU1GX6qsrMDP4YZk8IT4UHvIVkC7zODnGSJ62rkNosEYh6NAwEx2r8KisX6LIs3htqWYaLvhAFZdIO4HyNcWbucNppTGDTzEgYVRXWFZUj7YIsoqhE2JYVQj6jNMIhQAOKP/WORj1HMwbk1KppEyU5I0ma4BJ4IVemgiGyOnQa/JxMuNXnE15X0iBzVJsxzDROrIa1VTZrOCIB0LXoMviNchEDjKyqK/E1lZ4m20w8zilcztY/qqWxYInRJe0KL1fJElrjOIX1ngNBgNAmUusi9T9iXYlEosFwVBtErltjYkOZNgn0g70xTpQ4sZAhw/C1DdrxCNapR+T8IpCIAS3CFbyfU9AZJ87oUAkHrt8Hjxp2VSoHIcBIGNSGhaJYrcQQEXFgFIykEJyO2y1kTuyGOlyZeyuMFrkV6LgnEqKOB7vrBidUylxJVMY8oCyXDlcdNjRpCmalR6THaRQ8koE1rJLnJ8AQCnlLCuW3hpCbfJYfkE91UxaTOB1akRRhYyN0CWexgFCsZxRWFW+Jg2NsZ2iSpZwat5vjyRizpOiyjmdeUhaDIsVw0aSYtu0JYtssJGwUTUKECv56FP1lpNsLrCuvCQ+spaG7EvCWuN3mqdj6NJICZTzgLSbIbZfIq4N4DnxSa5Uy0IuoRMgQ6EvbQNwCEA0o9DjMZjLOaJGO0rgKEJ2NpJ9fruwCeDhxlJOM+9i4uLc5Hrv//4UfqJ3Ms6QqK8lwHmha2kw9PGM3Jjn6BjW7fA0Mke5e9EEqn3UfVu65YF9NrsD0IZr7OMsl9S0nTBQtemrF/e7zdsYXNv79hsQl6jNFLlxgoGGVabrCBpSBHHQC6u0TfR9cjsdeU6JTjLsB8C3XXeiK9hvvyEjx8/YJms5byMT8+Qn36DcNFiFC0w8gkq+bKolGe0ZHBhg6s8Nv7447dybk4GFh4+Zvg0+YCy1rRv7qDVtDg4OpJx5YfvvkeR5ZLueXVxo2NqqbJgAQg1VlxZyWQCdgsnunoiY8Dp6SVevHwpx3Yxn6MsCl2MM4x7mdsY1hr7Xsdck9+5gNBon6tk3NsuEnZgJa9VOfIGUOsCevQewyCfEsvZTBZjmD6+StYqBy3UE3JzIrcTrG17gv7uzud2X249Ya/9WtPn9XXbpu+n/bNbSP31tvdg27d927d927d927f/UE2KQDISDANBV6cNCCSzpM0PuxDW5vv20Z22ARI+f2Ln6Sdva14on9v9rBMvTvIIaq2YwGmKkV6/J2mjvV4kDJU0yzcAh6wyb4A1U0Bs/LK2X9vJYBdS0DH7tAhSyY6Cjvp+Kh+lTLTzXiMAQGkbgTcWPKen58jSHEsTINBJbDYHqPPaMpW+mfoiy1OsszXOzk5wfnKGbJlhdTfH9N09vLGPoy8vBByR9EezL2ma4O7hUYqL/rC/ke5IESDvTC8nfl6DulXz/9CycX11gv7wFI+PU3z48AaN1WI8HMlKNd9jwBTXKMQ6TcS82wp6OLx+iaaw8fHjBEvXRjSaIZr8M5Lv7/Dj/QgP5Tma6ALHJ0e4GvXQG/fhvuzjxZGFKzsTH6WMrLU2RC0gASWhCohYwhBhiEGBLGXBYxg0EmLArxKNRYChFkP1PCcjZga7XWK+6oA2A3wKsMhiVlfw9VAb4EurDWEotcJyYCHqqXF1V+zJZH6H3WRtC8ZtP7eRFCFIihjHM4RBjYzsie5sGoS687SRAnkXP94wp7rKueuF+gnaRcz1Z+pp00t3/G8Mo80P0NguivxBfMCoMxY+hDCM+BbNhpUnYCaljraHPKcnVgMfOQ7dSjyK1qGP0vFNIAqEeegZFhm3iXvXZw0aOpjeLZDnBXyPgadkrtD6vcDZgYdjbuOsxKKm8X2DOK1xXBS4PrQQhZQB9gS8ZrBJYTvw+gEuIprKd9ev+i3xhPCcEhzy6Y0V2Tiwcvg12XI2itaH5ZO1RnBNIC2RyxGoJSOLAQ4EaplELBJvPsc+ReBkYwyv14xIiYX5YcI9zNkQg3WRqdkoXAcZJaIF1WQ5AqegokykYDw6QSdvpl8SUwdFhq39JrIaxIGN2vWRlRZ8u8ZBjwzIFk44hR//N/j5Aex+ANf5iCa04JQMHlC5MBlhPpNUfWXYKT9S+1hTVAqqkD1l2wjaAmFL0KjFuvTR+IGw1kKPLFGTyCs+YpVhf2rqoF43dF8kyGZM0sUg3fRMI+nT8VKBHGEYCUVHC3vt8ybx2LCLasuWxFZ6yTF4wbNKDPhegYNlwOAOT7zQPCae8pqUkBdNvg1d+stpiU5mloAupQWvrZFTtgYfKGqEgSNgYl02WGUEIkoMBj6swOfgIGAevfXKIEAwiHDYc9EzrDXaPK4aZa3xnPQZYMExqWLIg3pbEYihDF3Ae6vGbP5RGJFcnOA4K4CHGMrrooAwJQ2a0i1aCVhhACu+52K2QL8f4vj0CEVFZhyDQcxt0dz7zJKJjGGCr5U14kEf189v8OnTezw+ThSEkiFBX9085a5tgYoOsBPwrhuDutFk+/Muu3Z7/+dYpatwvufiYBxhnaQSVrEB157MBnYWE3b+7wZU3aItk63rT929WJ9VRptut45pvE7pqUkgUxc7VLbIbikWBnaL928/4P27H3W7Gwsvnl3g1atnOIhcRNYj3GWFvLJQ1DW8OEDcjyQFWZBwq8UPP36PxeQOy9UaD9M7SWWVOUVLoNbFwckh3r39gHc/vRFWaX90iIubawrFdeFt4/Op4JR4F9JLkfu2uQm0YoPxu9/9LS6vb4QRTwaZsMU4zzCLfTym7E/iK7r5ImuNCwgqC627AAPTvzr2tEpAdTGG160uLppFRmGwWQLu0i9z0O9JSMpkMhNZKD0Y//u91na//1s/bdtTUG3zoGGUqx/uXwPX2PYA277t277t277t2779h2xd0dkBSdsJlmlmktNNjruf/1rrptvy8+6LzZtYf+2Jncc1bbSVyeViuZJkUc91MRoOMR6PZHK4TtcCdAnzp1uJN2+jn6OTtl0Ar5ve6b53iY6dZ4qCezJlNc91K8Edw42/E+AjEMCABk6ar66uMRqNcf/wgKaqTF5BxxB4miC52RCzSas0kUCDm5tn6PUHWExmSO/XWDzOMHx2iKPTYywf52YCylqpEdno48MUw8EQfkiApDvoZuWXQJswEsi6a1DmQM/xcHRxhcHhEU4GvvjI+UEgb0p2IBk9x6fnsII+4uEhZo8T3N0mCK8Ab/VPaH94jbtPNn5Ihlg7ZwhHxzg5G2E86MG7GmDwLMDvwhLDOkGdlkgJSDk+3NhD7FvwjGE4wYhaWASlgGsi7WSx0IUYWGS2qMyPRQVNxSkJnC8JHqY4H98jXUN8rKSAMedL/nXneqMiVmCSJv3CYKsa2PQlo9SToA5fJ9isAgWbHmmYb8og1EbWG8hgyiNJ6zwdU+5locjdJ+Da5orpildzTXXFqKzca56FbJcWwKbT7lxk20K0A4bMF8EA9ne3J8VdnS+EiaGSO9NnO8CIslHbEqCt5fXSuigzpvHVCOwUBz59yVxJlST56SgiI4iFZW32hWBmgeVkgqOTA0QHQ+S1gyYnOyxH3Avg2yvYXqum8GWDHiqMkwwH7hzx2QhBREYcJC3UikKMhi7GBKgaBdXkPAkDk7vdoKosuB4w8JlQmaHOyEbzUbke3NBD6GmCHyXPwjbqGJAScqGsDvLJCK4JyFbTZN6ksHKsE/qk6qylPjVFfHeQJd/PAH4+wXXPRmo54mWGohVJM4EjXvcMVmAKac0amZgDmXAG5BR2VlUi9mxEBHd8AsCiUwbTCyqvhh0ssEr7cPrsBWPxlXLaHBYZXQQR5ThVG5aPbHdN/zcLOTu0b4PBp1xrqAobOVNU5RjZ8MRHjPtdCQDJ8YrFOo+TgGgyoCh4RHCaxTuPn4aDmMuIm2qSQPU8GdBHwEmjaxafpq6/kS2nXoL84wq2BCFQdWqjROS0GDk2ysDGTPqcC8aukjnGRNreIILkPch1Y8A1WLifJfjDv34Sr70PP/wJf/zuHnX/ACdjG22awaXcmV1okSK2asSjHiorRGq5GIxCHISA32Ro0gzrxEMS9uCOPZxwXJK+R/CiNMeHYxJ/12NUlQlu735Cf3yAOOwJa5ZSdAVw2X8Iq2zvJTomdanV25vh/8veezBZkqRHYp468+lSXarVzKyAXGDvKGDGn0/yaGckz0gAO5hVsyNal3oytaD590Xky+rpWQA04o4AXozVVNcTKUJlfB7+uTum22V5hnS3wRHNfI5PsVyuVJOOTW0BGZvVWbd4+vwpRuMYv//6a2FQCStKPrA/vswTg+enlUfQZ49hpZlnnr0WO888ejSaF3Su8kQv7uh4IkzR24ct6KcqoKsB4ORzFowbPNL3c50d38O39Zr6DS5TT/bZqD3MVpr5vLAADUPQzBOe0yHdrPHVl7/Cdn0j46NxEzx7+Wc4OTqG0+1QbHbYvQ+oRojWJTeVafFA1bSI53QcdtBmJb57872AYgSg7WYWzzWezZCMxvjNl7/GbrWRdM+zqxeYHc3QlFudss19yLxO4M+4ng/UCWQOoknRL3/534ue5cP9A7KMDqFMU1VnTGlXAbDbHkwTp1D+lv6mm0kWWGt5dHnwm/o2/UtBNvMjhgYKrPE6qbXWdhVOjhbyzL+9e0Ba5MqG7xvPtOXwZ9B2pifZD3/0e/+JH3z1jxVzOK6v9IH8j5dDiuihHMqhHMqhHMqh/P++2DRJAjLclTerR7NKerxU+tTCabAs/kHpDzH80AAU2qNHwy/sizUioOve2ekpzs/PxRGTi8+bmzu8e3fb737KctNIqLnyDwIpRo9EY8R9MGFDAbF/t2kzupNsATUCT1wA6996YeLkJaL8BIQchGEowB/1cd68foWvvvoHYYbwvBrTmJTRR5XUPWIxSfrYZIHz02u8+uYbvHv/WphmyekY5798Cee2wsPrd5raKxpzriy0x5MJPvvJS4xHkbJ5mHLF5uPincE1XxM3xBCeG8Bx13h3cwPHGwkTijp3dV1iOp/JlVCYnTv3rx5SHE1+BefVt/jdH3x8mx4jdc8QRic4n40wn47gn47hXYX4+bjDtEvR5mQR+cgZiEU+EgIAEnwzKCiFjcHglYw0casUdggdQgmJsC4ZSFTCruHnRHuGwvGFGhqQ5dY1OS6PtpiOGvz+TYSsipVRYZpU2WjCUetTQX2vQ+MH8Nqc4lnwXKa2qVOdtr9Br2z/s3ivbaU+ZUuDFh0aDSbxGvNpiuX6FHmlwadFIxTYFUil1yeyqZ5ySNMn+6DYoG771NJ9OqmmVZk0Z/NjOVdMdW5ppVmmSCan8IJQXUGZ/mhS+TT90WdiIbIayNIGQVFgFJYIIoJS1B6LJQV2JIFcJcDShm0EF7NRKCmYDvu8A6RtgJFfoSObs/WRJNRG+z/Rti/Rec/gpW+AaA0n+DNzXx1qm55WF3DDRNpIGYAdqrQSQKaJAmGm0I2TKalkaBFICqKh86VJdWT6nhGdlzQ+MhklBZjsIab2kdVG5latTSrBL91SdUzTQII/2p5ap+KUGngIyCbhZ0wKJFuxaAlktejyGl7oiLkBr6nsOuyKDlHdYBzrfMA0TLYb0yal7zF1VMTqlU1JY4bbDys0nStmD2umHU5HuJww1WwHNEw3DdDROdUL4RBxNMmoaeWhpg6WpMdS8w/ITao0HVxJ7JLw3mqtGaanpoOSsWb1Jg2wRo0nYf5Rx9CwsAQfU6F5OrOK86qkzbPOjPmG4cwypY31RkCQ6cxuoH2N7dsQgG4IUnXw6hqhW8EPqcEWoHZC3FODLe0wIwMv5Bilq2oruoHU2yqqBh/e/QGTaYbX1RxvXsUI1iWiP1/gP546qDcdaDvR7nJEuxxuE2IXh2AG93jqYjqLCcWgzXcodw523hjeLMRR5Ig2Gx1fhdln+hIBtppmF4RL/Ba71Y3U0XR2oqAHU/WE1aYAo27OKG9W5AT2Qop2wtjPBVYD1KRxNl0j/fH8ybnwj95891rmQQ6AtuwkZfHi8gLff/s70eUjOCQzhTCl+L/B5o19pFhAy7LCzLOGqek659g5Uvu7tKEVwBfKqhXVdxCHAU6Op/hwc0varOojmjmpn5/0YP0jzWl0suI83j/abTX0TDU1cthfsQKzPDyfbWTUyxwnzt7Sw7TnywaHMS3qWry/eYeb+xtJ1azKHH/6l7/A0cmF6EV2mwekeYdCQNpWXIBFq0yWNSFCY/gUjAO8uXuH3375K2GqCfAHdWY+Pn+Cb7/5BndvPsh9nsxPcXx6hrzeSJqumk8Yx13R7WSqtLk/viddgKw1H3/6Z38pbuTL+3vsslQAM00h3a8prAuoAGoif6DgmoD/wlir9+6gnWFK94CpkRcQkM3822ivERTc7lai/7qYz6W+7x6W4vzK/mxboW8oadMhlrZvq8cLs+HrP172q5zhFtbgX5IZazYQ/hnlALAdyqEcyqEcyqEcyr+aoimRdLgywZYFHh6tmLU8/uvHi/2qrPk//tLHoJoF2pyPln5i0KDAQZIkOH/yBOfnTxBSPDrL8ebNO2y3qQTtKuZrDiMuogpQDE9ouUkSWMjnLChi0ykUWONCnwE3F+ACsjEKMNdDkE21krhg1uviQprf/+rX/4B3794ISOaa4FrPq3UqO96P0Bv9RfzgyZNr+J2L77/9BpsdF/QdFn92gctnV1h+9wHZ3cZoq7iqvQMHl5fnuLw4lyCX7eYaUXK3cUhIEq0Who6u34ipAhDg6PQMK2plxXNEsY9294DxhFpRDSbjCTa71/jNf/oOv1nWQHyOaXyGi0mC6HgM79kIp2ceXrgVvHqLMncE7GI6aBh5iD1yqlR4noG+BLAlDSOMngzZNQwoDbimjCNNz1Jgje6GHaqSAbqCKG3N4IIgQYnQS/HFdYosDfD6foIGkXHkNOmGBoQk2ChyVa6D0vEQWQbYkOVoUns0KjKBgGEH9BpeQozTFB5NBTadtKlwPl9KQLPeTEHelbj6SRxqqSiWWbf/vjIcDVhqgwujn2OD4EfaST3uZnSP9MMKANMV03FRrD8gcENEo2PRGyJIRg0jjw6QHvXZFPgoRZ8NqDYlAhp1eEwDjaQPPNAZ8sMKyO5x8eIY8MYqtF8VEvBRg1DcXonUUcfIdUXfysMGq7RDkXmYTkZI4hYB65+cMJHSYiRFFokBQAnWeEy/bLGmplbkiQ4WqytlHykbAbioLRYJEGpMDNh3mDbFPlLu0xxVt0+So6UfaX8jMMsgUsccQTMyX+msKq7KAloQMLKJ2yr+TT07gkaca3iNVp+NR8priq13IrYuYB/hDrqQ8jgFXSmZLlghjImTecJCcpjeZtglBLxXTYPffVcjqXIEcYS07nD+NMGZXyAIcvhklTUhmioU1icti7swoU+naEYJJ0fmLe0rymA1jrb8vOjRmfQyCdRVOF6lvnjNltlHPUOytlpl/9EBUyZp3RxQwFF1ANmXJFXepMuz7nhAGWOsN4+abb6AcqIb6AYC2Ig+W+egIshBfba2RuRTE5HjP0JVdXBojiD6hHTccNC5Hr5/d4+7+y2ury9x/93/hkXkIbj6C9RxgKPiAdtyhGAyg9NQ860SpmOV0YygQ0dTCY4Tv8FiQbBohHUVwE88TH2yENUhlAwhziuahmcYjwJeZ9hsbjBKOJeTHaebAUxHrQfgGllVwiQzM7pkHMqoVf6SPIMsuD6goUoKqZFX41w3mY5wcXWBm5t73K6W+PzpMwFpX7353oCaFrAxfbwH1UxKag9h7LERa3Kg4NngWd1PRVYL0jK/zSZF2+H88lw2Mu7uN/B86nIONgZ4PWbu6c9o5iXBvgmSyXjSKxzCKva5Z6UY9tRco6og16Up0i7T28WUxjzPCbR1vqTZvr95o3O4rAlC/PxnX2A2n8kzJX3YCDBddY2wWdH68AUQ1jRppo8TIF6na/ztr76C/8TH8fkpsjcPaNIKRycLZEWFP/zu9+JKy029q8vPAL9CWaU6/4pxg6lfmY8Ns1PwUwX1eJ6r8yv89Gc/R9VU2KyYYl/I53rXcqkCjkHte5zTOF9x/iIgKH1u4BIqKah2zQDTtuKCzfFmnE5laqWzro+2KnG/vEPo+5hNJlhvt5oOSq21Rz1m3zdMM31UzLPuh298spgr61c7LMO/BGwzfUDMHIbX8E8sB4DtUA7lUA7lUA7lUP5VFUn1MUCSFWp+tPiyi+3Bd/iyqpQNPmaPZ/5nN9WH7/3RF5xP63RwgcoULeqIXFxeijYbF+Hr1QbvP9why6s904cACxfsPaKiQVG/o2pFUgbnJ8AIu7A3GmwMzhl4iyj6YIHM+rGBLINWAnFk1zGNdbvd4re/+y3uH27U6ZFpaSavZ6itZe9rXxwEQSiMtiZr8Pb9W2R5Cmfi4uSnFzg6OsHmmxtUu1zSDC0rguLt18+ucHSiIJ9o1pB1VXtoshJZvcV4kuD97Z24mH7+/BmiyViAp2++X6KJapw4bxBETxFFiVwj3e++e5/hD69KHIdzOE8nmF+G+CxuMGkyNGWNrKRTYAg/8lVUnYGSTb3qTQxaBUREK41ufAqu8b+qoOMbg3Cjf8R0PxEZZ/DBIFRd+jTNj0ANoQ7VGptFKS5OUyx3U9yuYhH4F/CRbW7aliBMECkAMWRdSE/r+7UCyo+cQE0wwzjaxJQKshHwEdDHaN91QBRkmI1ycUvc5BN0ZPEQVLJGCzJALJBjrsU6mloAzrBd5NosoobB5yxDxX6GZgjsl6GyLcVEg4BKtkHgxIjHM7iGlRVaYXrPAh8ustZBUbKPdBhHTDRtsN0uUXgjZE6I46ZBEtCkgqL67F8lqixFXiUKCoqDrYdtEOD/+C9v0O7e47OTC3xzk2P6+Rx/8zJCHCgzUgNroXJpyqPrCUMtddhn1O1R24b6XR2q1rZUM1YAACAASURBVBE9MqaCUUNMTAzYJ4SRZUBa4xCq4BrbT9OoCMhSxL8m81GAZZO+ZcFyCvUTNJJxrMwYAdu6vREF3xcWoIBLvjK4XF/qjcGupKiSRSQkkFrSKVsvFKdHV9InzTxJSh67QV1hnWVwWurH5XBC4K6ZIm86nEY0m6jQ+lOUdYXEp35eh8DdqRkIQfIuFjZb5zPXmewwnZusE6POdapJJ6llBKUl1cykMPI/yxQlSCSBvIJqAkQahpvoT/abDAQczaaLAI80NrDufhxnClAq0KaAP00QLBPQI6grbogeWmuEULfwqIXlkQXkomvMmCCT1WmxrVrcrWo0on/X4qu/fYckC/Cnf/MEV0dEXz+gdhMUwj4kEEpzjxBpSYvNAOMyQ36/E+dRur4u3Qaxl+FyMRGXUWGPVaUCGhaEpZaaPCiYjnwvgEgSzaV9FfxQQxUCYqq5ZlIbzXwk4Eovzq6MXWcIsBksie/JeYwRhrDPWp1veP/z2QSnF+dYrda4fftewFT5vrDVbNtoKrxlTnHu6R/PdgPLpJvq5LFPEZVRaOYPmbksm40sPxoDLBaYz8f4cHMjjsG+R8bzXstL5yQLttnnpgHq7PNa5rP+Qfb43D2LzTC/pAJ0bMoYNfObPuM1RVnNDajR1+LuzT126VZPS33I2RM8vTrHYj5CW2fYFvJYk+c3n9P8FAFcMtgUpGStlHjz7g1+87s3WK3uhBnmxR6uf/4UiRPjw6v3eODzsQNOjs+xmI1RtQVqzkE8qzQf+4qBkUxd2HYmMEZjkr/407/CdDbFlq7oaSr9jexVCxjy1oV1KynHRk9UwHDdNJB0UAOCC6tTANPhWskxoJrRXbNgm9kc3KyWIrPAzQ6uSx5Wq49Ya6bNfrQ8WpQ9Atc+/c4PIN4BvKbFvrNnrQ360T+zHDTYDuVQDuVQDuVQDuVfXbHaKJKSoZHCfo1lAvwfgGg/8pot+6XXPhDoWW0fr9oeAU77A8hHjcMWDQfWsjOcwfcDzKlrs5hLUMhFrQYuJi+GRdf2ZiGoB1QM5VGejcmKMIGTXREae0p1CLXBCy9T00kJwvF1gm15miIrMnHpfPkZ0zdnuLm9k/RHWVS2AwaVxCh6PJtCKIFY2yDPdsKAe3r9TBwF89UWu7drrG/vcfSLp5LOmW0YtFsh/w6r+5UEaFEcI04iWZzny62YQgTxBG7YYbum7gowO5rCIZBQNzg7DjHDBt9/+Wv8/g/3EiRMCL4VBY5nEV5ezeEejXByHeJzP0dcpyjSDrsq7kXVE9/RlFCmXpG1VpQoMppCmJRQss/IzqE2HE0MWjr2EQzoUBQKxDF9VAACsqZMYKuMEdsw+mNZNGUd436dYJ6kuDxNUbcQ11LRFTQ6UgRV1NBAQTINBvbHkpa26V5WU8ek4thA1ja5yaiSgFjTP/kng/kAuzICugrHsxu0rS+Ol494AqIZbpmS5j5sHxiC1n3XHwLbJlyhHpHR/LHV0SfXyP268KOxBGj5ZmlSZgPRlFIAkcGaglmB4yAKGEgzLXONMttglEwx8h1Mww5lEKBqXEReB6fZIW0CuNEMHsGgphPwjsH+OKzgX0zxsExQ3Bc4+dMEf376JTbrCm++3yCZTQR04QWTSSeacUY3iimNTAcl04vsUwW/WwXXWD+iIWYZaQRgFWATBqTREGPKljI+yG5Th1lJ5RNQRIHZ4fQl1Wra1RpcKPCwD2I5PlRMfKhrR8dC9hMFsFqHTCkPVaEMJY/jmJdDjT9pU/0OAcPVroQbEgB2sKbzZx3geJLgKPLQZg42GQmBLuIkkXrICuY2Rwh8tlcBp6sk7VvyTdn3faaQehI8iwCZ6BtyDJk6qhRcI9NSHSZrZYpK3Wg9KYCtQKWYEve6YfvJSXvoUAfQ/sOOAwVItIsqq0vGq6S22f6mrFJuMrAbuATT6FTaEiRjsM0r47wAlHGEchTBaVy8W28RLKb4q7+a4/rIF/BwuWZqci0AvjsZY1UA5C3HiwhHPvszzSEiWoIi2+xQb7bolrm45nLeCUOKzzvI01JMO6xJiusUSIslXC9B6CXClhV9yJ61NhCXFz0wBcr2taF9Se/VpoOaSjKfUq22vd6nzDWGkcrNiOXDLW7Xd1jQzffsBGmeS5/vhqC/TWe3bWD+aZ8be3Sr2z9fZc6xV7l//gmYbDYALq+fyKbE2/c3oufoG/Zh3w8s4N9PZjrv2Y0Afcsc+aNHt8H49Hlrmb/2Yh5x3cw4NZsd+pkO29UGd+/vxP3Szn00Cri8eIL5hI6/O9wtHTSSYsuvcH7R5wONQjiueJxkHGG1W6EsU4zjSJiNxN/yXYrVuwfcfbhFtt1hFM3x4vonCBIHZb2TduvTcgl2yU6iAot8DuncovqN5xeX+Ou/+o8Cfq2WD0jTzDDcreyEK20pcxWBNdlQ0jRl0VljGre8Z5i5BoS06yT+uBz/3BywQLhsKCngTqb6w/JO5s7JaCQ6tfcPS+R5IXPm/inzifXVozJ8v585B71n/6oeTdtv/97+332xz9DeNOofu4YfLweA7VAO5VAO5VAO5VD+1RZxlDOssY9Br08tj5w/8t7HxS4YZfEoL3ziAx+/NPi37PQ2DbKswHq9ln9HUYT5fI7ZbCoLVYq0a9BumUH7RAW9AF3A2rQbm/ahvy3NwDLeTMBtg3ZzHRI8espwswtoakClu60YITBt9PPPPpfXN+u1sLgkpcYuV+16d7BitfXBRfd6t8J0PsHx2SmctkO6SvHwzQd0UYuzn1wL86ba5j1ww8Bweb+UwCGiRk3TIpofI44SSa9MN5ks4OcnczihL+l7XU021Aw4foF3aYfffp1L3D6bkclGAfAc8xg4ZbZcVUpqZuFFcOIAiUnjExMDAh10dMxr5OaHLCIF1oxDqOhrmbTRgm1UIxeherJpGHRQdN0IiVsjCtaHBIoWjDKpluK66CItY2xTHyfTLU5nW6RFoBpbkj7D0EfUsfsA1IRz8p/qJ2kw0wMyFHI3bBNpDwFB965wEj5IcGpf035TdgF22QijaIVxSJDDQ02WjsnTUu0c2/aDwMUcy16b7QB636Yz2GxtCxb1oJtlqeyDcAaVHsGKYocyu4frBGg77ZsW+CCw0TYl8u1KmDnJeIG69YX14dY1YreF35Uod6xPT4AFto0b0/+zBZWhECbCFFs0Oa4+O8L8+QLnbYrXv87gLP4EzniB714TuAgQj0Jhpti0TIKNClhTT91DSzSUt9BQHp/agWStKThL8JXnpiGICPPTHVQ+w3RHw24TPTayHTsBSAQwIthjKm4fXBp0zxicCPBn8+gMCqv1qvOfddfUYFcFxwnkkkUr6ZBkeYn5qic6VOpH0MHxOpSuj1VJJk4k44IuvV4UYjRLMAqN3pSwdKiyDklzbMkcSmJ0YYjApaUm03sLOHTdZBsKnlaaa/YkTb0qaWSgbFoZbwLeKADZQdm1MqYIGFkdsYEjoU133PfJPYPSYDhmswEDwNFUEseGncu1Oo1OmflDHKv1SGwr0fqyKYroUDAlDg6iyMeIbrbeCnVYIwmn+NnCh19mCL2KlprI0hJ57eKhCBC5OU4mPhLPwzwgY5b34grwSJAtmYXoqhSjMEYUJihbT9KPQ79DnIT0V0BVp0C7RFbsEIYzqVvWk/Q11pdhrQmg9vEcYQekYV4JsCYs1yEgoSznhiCi7XMGYNPvNHCqTDaLwtFcxgWfEXSZpj5bHIcCkrDP6ZnsU8q2ivZna6aiAKhtNTN9WdBtwKYVfpfTYTSb4OL8FA+3SyzXO50vjbmE/SVnGTJoDXtqPxfvn2P983+gzWaP0f8Wxpde435KNv2P12sexnRyXT0skaY7YXnxw37g4MUXX+BovsAsAYoyRepGEJnRQkF2Avhk5ckheSyXumN3mEwSnJ49QZJMRAMvGvminxqMQxQ76nMCp4sneP78BbblPeqmkGeMzFAE11o1MVDG8f7eCbqR6f2Tn/wcL158hs1mjfVKHUJZT2RyKqOO85yC2qK1JnMbNUdtOqhx95W5ZgCuSb8yfUzkBxwDWOvzTcA1pq9nGXabJcZJgjAIhLVGiQmy42T+G4zn/VxoX+kb7tEnhu/+YHn26AjDT9lWHnzDdACRKvjEuu6fWw4A26EcyqEcyqEcyqH8qy7CGDOuf6JB1rMYHoWsffljy6fhosys1fc4mvOpT1iK26fPo2w2Bo01ttsd1puVvDdlmubRAqMkQlkVon/CBanujHMn3R7NBDwmMtRLMOCNFageRA6q+aSBt91ZVqacfscPAgHauEMrTqN5ge1uK0Ha1dUVnj17gSwvhXmnbCqCDXqOAZ9JWQGDuiiY+lSkmM/muDq/xuZhg93dFg+vP8A58fHsT75A/rBVlpzR6OI9369WcL0I06NjcTms20LYbJ5fYzo7hRfGklZDF0/SvOaug2fnU7nWbbPA5mSGadQgqEupJ7qfUeOIIAtdHUeUhWJ4zJSWukBd8J4VYCObRhJCBVijQL7RlmFgkVcoyWwrKklBLAiimBRAqWMJYNXpUS0ihtpkzLxTYWxJ2zTubUzL3GZj5GWEp6c5kjBDlmlbCDlKNIxM+GsYSXJ9TNNiUCPOgAZwMz/SX6QZFKDTOMECZDYgMa3Wg3Eu8jpBUQLTaIvpOMUuZ8BnHEdts4qOkQa+8sv0gr5v2/HVf2HoEGhYJQOwzQapxmpPAks/iuGGI6S7B9TZDq6fCDjE+yrTB+TpTsw5CHrQ9MIJKUBPBgsD3Ay7HUFTX9NtCZQEEbYNtRBD+GGEqshQNTU6pmzHwMR10AYTvA/P8A9fUscKePbsieiHvW8dTCIPbssgmO6Skkgn/Y9AA5l0vAsyH5kSSr21QlKLNfBkUCymGFZHTFKsFFwjqNb/DFhUOrYJ/g7mpW4PspkYVoEIaQADGA00twVnJXnMaJkpgNWKthGvm2Bg4/rwWoUmyJ6ikS9TKQNqk0Ue7qApzwR+4qbGLKjU0VROSQMQjo8O3pTgZYdJ0mEsl8nUygCNO4Xr+nLPZIB5ZLU1haZK09EULvI8VyYggVP+EICUOlLGmoioD8A1qRvrsGr6hO1bfSfUTt4DM8MuZjqeqTybiqsgP9+SsVQzPTuER0MIyRBmX9JhU7UtiraFF8WSviyuik0Jv9kiaUZYhB6NWwVgbbMMza7FKnVRJWN0cYy2aMQ1NIx5bgKN1G/rJJVV2HK+h/FiCm/E1N3KmL84yIsOeVFhNgkEZCpBYxdHAUhqPtbDlFDDVrPujeJurRpce8Bf00Hl3/K80vFomU0ESJQJuR+nBOO8rkS23cIJxnCDWABjrWc603Z4uFtKv3/54lrG2+rhQfUdLby2f4QNnlHmRdPZ90/pwV/m17OnlwJ4f/f9a7knmdf0JgY/BlgzxxdgzfaIAXNNzjx4Tvcz2X7qenwt/WPdzHf2ko3M2Ha3QZau4bjGnIMmIkfHOL+8wpOjBSK6hHYBWklXJouLz91I5qm6ylCVdET2sFqu8Pa7e9y9u8e75RuUdY2zk1Mcn5wg2+X48tdfIUl8nJwc43x6hWAUYJXeK4BM9qe5Jl4snzm8SnnNGORwPF2cX+GX/+G/E8OF29tbZGTPc73EVFWz6caxxbbU9G0FxMnc5mvsV2KgITRSfe6IZIGpsV4z1OiuOtxUMkAbpTx4DQ/LW5CbSbMlOtU+EJjMuZGmm3n7vmHby7bE4x6yb7DuB+8+Asz+qcVMD+qU+s8zMvhj5QCwHcqhHMqhHMqhHMq/iaKAAzW3VZesT+MwZb8Q+6eVHpuwzBy7rrOLwf6Anz7i8FVlIal7IIV8uevNBTbZbIvFTBh4u4LpGo+veR+p7CPLfhnag1xcaBtVG+MWZ4E6BYPIpLEHUBCS2kCyuBa9nE70TzabDcIwwGeffYb5fIHlcomqIjPFLGpN+o8GZXIkA+bYa+6QVznSosAXX/wMvusi22ZI323w/s0bXP7FcwTzGHVWAGSkGSYOHcTub28QjsZIYhf372/w/t0tnl6/hBdElChHwAClrVGSXdYAMWqcnwW4mPs4C8la67DcVhKQMZCvqxyxrwBC1xRoCJRljYJrdAklWMWgW9JBmeZU6Q59QcdCMnk0NaaoWmTCTmIwbgAuAUdMLCptYMwBjG4Q72vvqqkmBsTQhGRJgAchVmkiKXuXT+5R1Uz1MQ55to7JfGLKqgAyTPtSpomwTdjGPb/NAA8GNFDGmw0xbQBt2o9Bl+nDknrVeSirSAKgJ4sl2tZDUwV9/+4DV/70A8C09wAQ2msa6RVIq1r22uD1PaCkzA25FIlcHUSjMRrHw3b1Hm5bIl3eoA3GSJKpCNBXbSf9iU6Ufpthm+6QlQ48pvIx2HQdjBdjhNMEZRRgwzrdpnDdALFbw3fVMMF1Kvhei5Oow+lLuqv6KFAjPI7wdOwhYdBa1djk5L/pOSWopt4V2SdEQejamZfCbBQmkQHWhI1F9hqZbUZ0Xp33GKjqD4GMISNR69KCHhrgaUb2Pojs9bBMndrgWutOv2tdIgm+sHcQlOQ4r3lM6pFxrKlIn/wmW1DbtkHQ3WDe5hiT+Ud9Ofa1vEbQ7eC0ObK0xbakW6mDeQSEgYNAAGtlUNHsQTXgmPoYwvUyOK5xlmTaV9NKKn88GqOkJmRTKgBpAGteswXWWEf9/GXZVMbxUPpbDyjv5z/zp24BmGl5DxaZ8WEAa9aXECq7Dn5Al2LWU4OKRhZ08DWH5xwihjVRZJyROQbZtj6adoTOjwQM5ziqOgerTYj3dYgyCTGdJZhNI3TEFzcVunSNwLkD6IDchAgcsnl5LNXGkjsTswoCiQrujucJtg+pjNEFWbpegt0uFwF46UPtvi8x7a4H/e2zij9GYF56laSFmjErn1FQxfbBHsCVVGIXZb5FTsB1NDN9j+jjgBFnfpOR+ObDB4xHMV6+fI7dbmfE8q1DtX1+PX5G2rYUbTD7QfbjpsHxfI6XL57h+9evsFyn4i6t/XwPnj1+9g76gnU6Ngc0U9ng44P37GX1bMf+yvbP+n720pmtLErs0gfUdBt2IGm8HEuzxRnOr5/hfMrnBFD4PmphdIZwW91EkTRMPxDtOHgtnpzT9TrAm/sb0eNzmwSx16JsWrx59VYANjp7klVVVSXylpsFel7VvNN53G6EaFuaPt524tj853/xV3j+4gWWDw9YrZcCnIkWYUi2Lum63LwxTr7CMt27HxP0tQYHe8BbdSq1B5HhOpSOUMarZ377ro/Ndovt9gGL2VTWOPf3D/Iaz9cD3sNi/7Yd9fGb/Rqm7+ODdz5VzAwweJbZN1SywppF/X/BWhuWg8nBoRzKoRzKoRzKofybK7LAowugWRTqEmsffPy/KboG029b5tD+qIPFof384HzD89qd4ygKcXp6gidnTzCZTAR8u727x/KeaZoaHElILYGUpoAaGou6ORp9EwFXTBRgF60U+FZBYf1hXfihpoIIsEbXUQbdTBelNpLo/SgXi2k/R0fHiOMYr159j6+//j2qktEiF6J7ME9je3t3+yBJ6rpzMZ0uMInGuL95wIfbd5J6Gl+PcPzyCqPKxfK1ijXzOybDURwl65JsNAd/8z/+TxKUe52yg5ioVXcV6rJAXXIBHwgDaRwzB26KFIGkzdTbe7kq3UV3MRnRaZLpWwTR1O3MgiFM8yNrTVNi6A6pZgdMiaooRk8JKWGP7dNihgt7K8qtQvQm9c6wRdRJ1bBH5D3TdywDUWqqwCzZYhJ3uNuGSPNYAiZhP/WMFArXW40khRo0INDgWIA9AfQU8OzFpSWdypzXXI9ysjTYsNfFCJzHnoYZkpCA4hhZHfVB4X7AmDuXLjdIwTK6Oz0I0qcw6+ft5yyL0gZiZEiJE5848ikQxPvMV7coshKL40uE0UjaK45iJCNPQE/qitFNkQLwbtFiMookrZFsCZ6rc3JsuhvU2QXcNsfDbYFRCIzCRoX3uw5pnaAeTzCLHREZT4KdsEtu7ysEEwaDPtityECji4Q487kUKRdOm4AuRV5hl2bkfhkZeQU6lNFiWUbKVlOQTANfK0A/TC/u28S4sgowy7qxQBIDVxnLxGKYLq1AOdkiKuTvCkA6HY8xSqitR0BMU10VYFEjRgaUVjOL/Z55iDwW+xgrj3NAVgF1UQGFUKqkvp1InUsnToWAyFHkonFjOC0NA6hjpiYWmvZao+tyBC71F2kQEqJrlMXWBgGKxsWG6enbzZ7NN6gbxRwVFNP5ey+8L++ZAWbTOKXOpD+rmYIOScOiEVbTY/dH9rPF4gSjoBJWXtPxPgJJbyWgkJUFxuNEDCREy9C5Q1NN0TqxgIy8jpBkT7Y4XW/rCkvZBnDgNq2k1kZOi5Tade92SO928NwWT54UiE8CNN4JnIbgBufeFh1dWIXhRrfRe7jBCG5Rwa2o1eWjcDtEIyCIXdxtctxQh6yuZCxTG47gL9mWOkSNbp/VY7RAuJhxaEdg1eoMbgBeAWhZb6RB5siLEl6ciNFHzx40Tsb2OUog1uJtmsWsRgjnZycYjad48/Y90jR9zArak9N6wyE5hswTrdT3Tz7/Ah8+vMPDmmYBVsPLzGN9m/Ma2JmN87HoWdpnnW50qGut1ZPUOcnOTZ9eAWhlWQ01+T/RY7lGHc9krDFlnYAUD5NXTOMc4/TsElenIwQEHAnXc1NH3FUjeL3eod4w+0+RFZJyHSWRpEqSyXh78yDzWZMX+PLv/x5pkeGzn/8Es7mPv/vbX/dplrwfYSzqzKrp4sb1VY0MdAw9vXyGz3/yhQBZmxV13fj8VgMQ1RgjTqZs1z4dlGxbzl80RJK0bLPJI41sQFgDYsvNCPHatIc8f3g5enyCddvdClHoS0ooNxX5I8AajyWA74BpvX+iftQmtnwMtv34J/fvD1dfj97QjVgDMP5LlAOD7VAO5VAO5VAO5VD+zRUJIowDmOqL6CLLLreGv/9YcT4BsFkgYb82s8HNp4/mfHQ+y2Ahu2VHAePNWo46Go0xn88wGiUoqSOW5wqeDXd15SB7JSJZ+xonLwlSzaJYGVCGCWLYDiJ+3acWqpC81WAJAtUe4fcJtjE44mKY4N/Tp88lEFxtHhRw6WtFAyO5rH2mbB/DVGWOXb7F8fExLk8uhamWP2RYv75HPelw9idPUWYlmrzuU5h43QySeNTr6yskno+aabYAaMRHdgSDHWHNxJpyxbQzt2bKJTAejTAZxUi3a7l+ghLUuWNgQcZK2TCorgCmhBKss/pQhdFbK1RPi+mgpdHL0hQ8E/jb1hyk6PIVFXRWtpqCI1oRFjCxbndaN3Y3nQd0kZUR1msHJ9M1xkmFLGOgbwAHAjvSviZd0NS8hFRSYTZ+dAfXZvqGZfCYfqtMDWWfWH6ZArJ820XZRsgqH6PwAZM4RVkEaAmc2BjVdujeSWHQ3j8YSb2gkfmze/SaZRhZIIVvKBhJNtsE8XSBdHuPfLvG4vhEgNQ0I8OCQT/d8kyK3SRBEFOcn+6eLbqagvst2izAyGuwWxfYIRYgpKaMUe0iL120UYCTWSxgW+iSsdTi4WaDZDpCPIoQkgVr2k9rSYFSdX5luzQIwlaMPKiFV5Y05mA6qNERM+YXlGayoJGy1jTLs6+HXgtqsAFggPs9QKBpeTYwlK/2aeM6n9A5ZTFfYBQRjmRhqqMG5fr5VgNKaT5CXVt0lSfMKQHzxbFUT+6FHhrPxSr2UTI1chJiETmIqYeY18h2mtIZuhW8kP00EOMQMrw4zzQ09yhd5IUnDqcK5Pt2skLgtEiSETo3xnarQvkKpBlmpF6w1pspNiFNDW33wEkPvljgx6YFiqmKvXedL0Wv009wenSMxCfYmhuAJhLYmcYzWVUhGY0UVKlo+0gAa6wOqT0jVdAJQZZ8p0aTt5i4DZKuQVjXCF0XTUWABdiEER68CJvxDM69i24LhO4OiFNU7JeVJ2Bm25L156EL2J9qdEa7kUCWRw3LypPU0enEw5PzY2yLGulug7r0EZD95Cq7ljWhLKLBRoB0HX1qadez486AY0YAv85W4v4axmOT3m3HptZj92gY6yuPnqGOg80mRbrd4fz8BNPpDNvNWl1t+8RR87x4dMxWnnsvnl3j6+++w3qTa///iHXUg3vmPxk7lrEm/WDPZDN7Gdr+A3DN3pa80oNtw3Ps/2HPRZOidHePuio0TVgccT1MF2c4vbrG8xPdXKicBqWcKxRQme1mHZjl2YoODw8ZXq8gep4eU6/NsyMKA7x//RahFyAcJxjP1LH3D3/41tybXlQPrsnGh16tHSa8L+ou/vVf/RJPnz0T3detgGtqXuT5fj8HSNqnYatxM0lSQ41TqDUzENaagN6aF6u6drpBops4A1BTNgAUXEvTLfJ0g/l0Iq9z05CAOtmOCsT2o7X/vS8f//3p0n2i1R73lWHZdwY9v/svCq6xHAC2QzmUQzmUQzmUQ/k3W2wajKQCSARpQw0b1n662GWezc6U1+zi3L62jyz2v/+RNdtw+SiAmBgOlKLPRgCK1yj6bIu5LLqzLJeFr6b4WG22wTGsW5wB2fYRlbLTGNCoXphliRiBcauhYhbOBKKoz8aFJ0/BBTbBLAJtXDg/e3aN4+NTLFdLSVPS0Mxehy6ah3UzrLcs36JoclxeXmI6miHPCqTvN3h4f4voyQRn1xeo8xwNRZfNAZLJCHmVoSkaTCdT5EWBoizgkz0SRMLGE0aKxzQ+MUdEU6Zombrj+gi8RLSy0ryAH2i6cFmXmEzHoptDvbiGTLhchd3VIVTZa8Jk653SNHLp050egWrKjtEfgmhGGFx28g1DzPwtn5G/B7mVBkhgaeBjtRujrkucH2WSPrpLFcwUsX2j/bMP+xQosxwAqbdhdPjolwljevBiEC33GVr2My6KcoSqJvNvA9/N0TQBRKXbnF5CZHs+ApxyPNOX7OEH7MY+mLKp33e4nQAAIABJREFUYgbg0/4pB1RwxQTgeqgO49kJTo5P4HYVipoaWL460hqNu3ESCTCsdU2mGVOaKKy9A8ot6nsfuzJBdDyFE3hYtSEyx0caJFgkPpKQov8N8vUOaZ7i6OwIfhjDo0C/q+YjijEwhVfTpKymHoE5GW9thzhM4IcjZBl1+0pJabV9x6at6/1pxUgXN+CF1tB+YpBffR+zwMDjerW/eWwCWnEyweniGBGF9l3OFTTQ0KBfGSotHI8AFyu6htOV6NpQNO3E2Y98IGE40ViC8ABBImDhNRgFLk68Fp4AkWS3kaXjog4iASxpNhEENWrHR1sTCCJAXcKRlMcAaQ7UbDOP6XHKMgPZW1WHMPYwnU/JXUK6zWQUyH0+crI0VWU3FaTrDRhNFnDr62m4+WD6lKAYLiazI5yfLuDSMIG9yBiMVJWD5SoVkDJORjIG2zxTU4gw7DWlNPVQxzU1/Vt+t3RRBQEcpgEXDSpQ9NFHF3pYOQ6OExfzqYejBbX/fBSrHNuHAu12h8hbwRsxZbZDsaV2pJqN+GRtUouNJ2E2IfsJJzhqXeatsHHPT6eYTqjTVSKrSuoiKNvOAPxSF4M0bY5ZO67s84BPAN5b16pRiB8mstli2Za2o/WuwGaAW3BO2bxDKEPbgc+Yh+VSDGuury6F6UTdLQXzLcBPJmAjkgRXFxcYxSF+89vfa52TF2XatH+MDIFoY4Zg3xv+24Jog8ePXnP/otUS3bOA5fsmNd8MTp3emhbbzQPSLfmJ+pqAmE6E0/NLXF+d4slY27ykfic8eF0iqcZ6jeYGug55U0j6bFgXGHktdo2Du8rD3OMGUYO//b/+Dn/35d8jy1I8/fwC93f3uLl5N7gz8wySelCdO5k6xahD6+DJ6Tn++pf/QdY693d3AnTyucGNCLqYi5kO54yaY7RCaU0MjKmB6EXKc8+maTeDlHQDrA02i2Q9ZdnINE9qO6xX9+IYPJtOxPzijmZGZSEarz0w/qh8/PcQtN2/t3/t42/tny/7B+AP/63zCNOfNSX0XxJcYzkAbIdyKIdyKIdyKIfyb7pI2G6ApWCgO8YyXGZ9vIizxa7NH73/6IVPL/3s4nq4mPvB8Q04RkCH4v6r1Rp5nknqyNHRAkeLuQR0TEXjPdhdff3PhJCKcOyX4gOmkwan5j2TbtVrQAk2Z7Wg9NpE+Jyghef1i3EulLnwJ8PuZz/7ubBPqKXCBbkmwOj5NTXH1usgAGJA2jbYZVsJ6J4//RyBG2BztxJ9tuVmhaPPzzGeT5A/rHF9+QKF4+DLf/g1vv/D97i/eY+zs2OMkhiBH0qKKxfKPlPlTMpW7baofdXCatIMUejBozMfddfSXLTh4igyounAZDyXFNDVzUaYamSuVRQQpyA9U9y4w8/6NQLSGmANmDMmJcZqAwnbyf42WZUWZJNqMZXRA5DY69nYwJftRBbZ/ZLBcoWX1yvkuYssV6FsDXb024/iB1PfppHNW3vArQe6jO6ZBpQDsMYq5gtLyn46QFaSyVNjPvog3ypFn00/K2FeH5TaMw40oOREe42d4f/73iHsPNNJJW3SuDu2DmazI8wTT9OXCe7VrQDOUt0U5o8jDZQICmFLe0tUTYjQXSJ9vcTmjlpZDkaXU8ynDrygw9HEhR95OJm5iIUAkuPhboN4kmDMNOKGrDUe30HT+GJ20ZSluDk6XigBqbj+eq5os7kU82oDdJUPz/ExnY3h+BFW9xsDEJnhL9WzBxbtYNOXlaHaMzssMGsB3L719EuKa1pwJMSTJxeYj0bwOmqgGXDB9VB3ZN5UavjhmfRDYZDQ2TYQJ0thSA3AcWoBylzU+toVihI+tdYaB7UXYlO7iGIPrc/6p3WIj7oE2lKdJj2ywkIfTeejpoNGV8HnmHM87PJC5rgkos0vmVnUqPJQuWQhRrKhUBSdGFdol9GKU625PdlIbRo6FXQ3Y06q0bKTPgJkZHMlGeH6+hyjxDVaa56asboO7lYFNmmF8XQuxy+LjaQM+9EY8SgQtqQmwrVwyK5lSi6dYuEJIFaHHkaeg5K6fMTDkgBR4COiJqCk5OocFRedpBxnnYNlWmOVQUw9yuWXSIIUoydX6JyppAmW6U4osGEykT6XtQX8UM8r1926KHc6FC+vxohGM2zWW3RditANTeq71pfJ8NThbYFLGUQtAs9Bna2JucIXRqEj+nTy+f7BYiE0w4A1LFij+DkodlNH9erYFmQB398u5XlydX0hEggl9Tcdaj02oj/62cvn+O7bb7BcEsxnkuXHc6XVe9ufpwefh0C0/awFzvr5cT/n2PlOp3Dbb/aXr6/qeCjzAg83b1GWmQBUmvrtYXr8BBcXT/H8PIFHvUKHJihEuZhiHMs4lGe03YPoGmx3t2jDDJXvi5kKk6UXIXB5PMWvfvUl3r56jedPn+Hy6VNkdY3ff/01smzb+5gooKnAlp1/7bTL9/wwwF/+4q/x4sVLrJZL+SGAJjIZZJD6zGdWdjvbQFhrZG0La42/yaCkiYE6U6tx8n6106flGnDbAmqiKWckKMjE322XOJpPpL1v7++xFq21ymwq2Iq25VHFPz7fR598/Nr+X3ajdN89PvVNo/cp+nf6HP2vUQ4A26EcyqEcyqEcyqH8uylklnClGBhLQFm89ovrTxfz9uPXTMAnZY8ofPSl4Qr+h289KsJGUQ2nLM2wXK1k0TsajbBYLDCbTSSNg/o49iC6i23SlfrUi8dBkZx+wFYTQE1SD+WkGnRRA0nf7AMUglhMrRVR/kadEunQSaCNDmeff059lwrr9VLOoamjel09P9CANcMAiUDbarvEZD7D55/9FEWWI3vYYvX9Heqww/VPX+JXv/4KN9++hds4SMZTjMcLbNdbeGGAxdFczkcNLOHotA4oC06GBsMcarBluw7ptsEoLjE7GqP2CdSk2G42JkWGjnw1xpMJxrMZHpYbrLIUJArSwZJ3QM03ggCtDeJU5qrXM9Ngw6YoqabQ0DlUATfTTloZpt0JdKlujtS/ZR4apqWAn3CR1R5uHnxcnaxxNKuxyymyb8SYNd4yxzbtbc4hAMqgg0lQaX+kSYasNf42V9UZh0nbYMK4c9B0EdJqImybWXIvjpH80f43OIk5oJ7KNrgFhRiM7a+pB1/tNZjvkG3lJTNcnZ8gEEMLpjAafSXHQ1k0WGc5WjdULbGGYmEEjnxQQszLUqy+B962J1hP5/DcEPO5B5/HbR0ETYmJ1yJsatE5dPIW05Nj0XNqJIVYNbvaiozXBh2BqcaTYLuuc/hhCDcIUeQFiroRlpYAbWSLNQ7K1kGUuDh5ciIC8XTr66EIG9xbJpAZoz2HzaZfsR1Mn9Ioej+mtJYIjgOj+RGeXjwRsAK1Ol+qSFNnHG8ZeEcy9umey+YJokAMYJTJwY9zxGiflSvyXBQEdkKyURwUNfscMcQQcejCDVRnbESAk+6YAcebCqSn1I+qGmH/RRHgJpGwCYs0VRAgGKFsHKy3BXwvhA+mXPoCUokJQ+DhaD5GkEyw22SidaVg9h6s6Bmh5jUppp/u5zxTXwRrWweL8wtcPVmg8z1kDgXnHQSdK3Ptq7s1On+E8XiKPFujZUq+m2AyjRHS5ZSAecBxUQvLiOAv63lbeXBDD6HXQpJL+Tk+Tmjk4AE+jTBk/qjg0VHVdbDzPawr9hWfeXwImyXW2Ro3m+doUg9R+wbxuIAX0ewjQZGWUndBkiAIR9hmO1QuEIaeaH25HBudh7T0BLi7evkERUswPldDAjMsFb/WTQhhitIdlMdBg/VyDTecAH5omN6G+mYdXAiYme4p+wyP2Jd9VZtz2VFMAE+1QvkfwReCOQ/3S0kZXMwWwvL84ovnaNoSv//ma5lYHzG+DITcTzJDvUf5jJlB+tfs6/v5y26E6NHMc8h+x7wx/Mz+qx3WD3fYre9krPA1YYnGcxyfXeLl9TkWo060OemEqy7boSjweWbsSp90OzFi+f6btyhS7T8RnXljYDY5kc2ddLfF96++xWqX4vLpM5xdnMnzf7V6UG0+Y16kmxkKLKv+m9Y1XT2fXj8Th1C+bx1CZbyJiRFdaPX5zXUPgbWCzDUDrompT12pnAQBxF5j1MzbVhuyf86pMZFoGxqzJK5RVqt7cVg+ms2w3mxx+/AgjHOe185rj8vHf9vXBgsF0wtsy336dXuVw+/tP/sD1tonz/svUw4mB4dyKIdyKIdyKIfy77IQZJMFKAXlB+ltnyp2Gef8o2/0Ii92C3sfKHziqz9WhElGjanxGBfn5zh78kQWzeluh9dvKCBN0WKegoGWpnL0F/JICN9eo+7iSmhixcFFd8mTBSiBJ/7NlB1dnFu9FrJ5uPNdyk43hdsZeEzGExyfHMsC9u///m9xe3/bO0My1UyuRO5/sATuHd4UjONVX10+RZcBr1+/wnazQo1Kggq6hy5Oz7GYjRA7Ps6vz/Dy889FrJmMh6vzC7lH6zBYdTXyfIe2ruDHIaLYEZaSXxMobFEFU7y++YD1uw/wIh+XF09N6rCLMIqw3aX46rffIN3VEizT6NAZtfBLggDKpBHtHZOephJre9dCAmrWJVReN0GhhEJD0S0rDm6dQEWXywiPG4aJfNqkTPK312X47HKDpgvx6masLJxBnQrwJ0L3+yDSNITRqLL6RLxfXqsRf5fuoe1hxarJ0CG7RQFCinXvRcPJuJuP3sH1RtgVMwHahAPVp4l+xCCxfewRAMt7NcL75h7IFXT9EOdXlxh51NkTa0qBTVnR7A9Mo/PJXgwiVEWO25sP8NsOpxdHiNwlitsOu/UIzWQG/8WEkBnKzkFMdo7vIGKKcF6j3t5huytw8vwZlr6LObXcXCZ3aXok9f0YbNalAUgCB60fIss71EIbahFEE3QEM9ItQop4RzGC2kPtOsiJPXoOIjTiMvrmzXvkm5X2e9NgNhxUFq0yigTgNAwtAscWRLIgkwXSnXiMy8szjGMPW8eHUztIKgcBg2+3xqYs4AWx3EvD1EHRV/MRh/ynzR9s4XLOIyBGVmDrCbuG/V61u1Srq2TaY90hjlzQG8DCfORRpaxX6s0VFbIiR90wvZvgcYvAbTGKAS9JkHUxdlsyASv4BKXiCPluJ+DoYj5HFBCcYJ93ULmdmEhEaHFzv8XtuzcgRU6Zijyz8Pb6Ka3f1LAAm+w3KLATRFM8f3YuWnpk9FVMr2RPrzpsmLbWdpjOF6jKDGW2gesmmC1GGHsEMRzRQAtcAmoVqqxFUfsovQjdyMM87BC21ILkZZEhqPMrAVnaqtKAgG6j2qYNfJ/abx5qJ8Rrnv/DFkHFem9ws1qi2GQI2gzHcYbLsxzB8RFa/wJpkSBdZXC8BslsIbe6XS8Rhx5mTAnNIBqJVddh1WzwZOzDnc7x7XevsVveqjEHR49aPstckvgQV0cyVP1oov2P86CMSzLY1KzDCntpD7UAmvTaXn+un2hM31BoRke0AjX7x6OkhBLSLVOckJXt+Vg/bM38RVR7sJEhuJX5tgVz5Lmlba4bScqc0vlW5y55zzCq9O99Wi+15dg8vjVtGaQrWlXRMs+w2dyjaeseWKNf9dHiCMdnxzidBiiZQikTLUFOpqyryYIei88IbtLU+P71O6zpgMrnqnGHXhxNcTRb4Mu//R1+9/svcXr2RFI6ecSizOF7vrD6yBT/7e9+i2+//YOkK8u1EsTnWCao19ZIkjH+4hd/Lc9hpuNyXUAQjSwtHkeeVXyWUGfNGPjIb2tkQKa26LSS7Wj0D3lf8tzazz12nPXzUc9m87HdLdGUubDsuTa4f3hAZoE1x3YNswb5ERDtn/Le/lXLWPuxYwwes1yLuEZr7b9BOTDYDuVQDuVQDuVQDuXfZVEtGgWzRIj7Ewu3Ty0PnY9e6F9zPvGlPgD5dPmxtzSNkymLldja51kqgBuFo4+PGKA4yHMGtrXRljMLfBM09IH5R2dSIMQEhFZHavibcIdxOZSQiWw2sog8AlVinSe76HmumjJMB/nss88xTsbCMmOgoCmSH5//h4VvC6jWlfjsiy+wODoR7ZhoPMLZ9SnC2QgXL87x7PIaV9fX+PDhA776za+xXN7j9m6JZDJGHIaizcagncBEkkwQRRECBhkmYCSzyKlKnMxncJMj3N6u8Pb7t0hGkaSNsg6Zknt9cabpLrcrDc4kuUuBKc3N0nq17qC6qz8A1ySosKYB+qOYiq1rY1agIkcGZDNMkwHIpilBpjdKFfq4X8eScvf8cicNyLRR6wcq5xkyM2zH/EHzGxDH6FtpcD0A5sx36KxoATM7JOR2HA9FPROQdRQtEXg1qoZ9Yn8Ngw/35x8GalIGw4zhfDiZ4+nVXECxrFTE0OrFMaBluiOF11mqciPXP5vPMZ00ePeb/4LNDRkZCdp4hPHlGMdhg6h1kLBRfAcjuoEC+PB+KemKx0+vEAYuZrx18XBwxcyCDpAMXqlJRaCnbFzUjQOvrhDHLZxwhLJ2kO82AsIl45kwO1e7rTihciyw3wTGyZDjZj6fwIun2KxScdfs2VYWN7P1YwPaQeC/bz6yqYDR4gTPrs40zdL1RQuNfdzrgKIukbYNgiiR81Cnix2WqZwRU15b49pKsLgpRS+sbHwUXYAiYppjJ6LrKvanTqnSzz1yc5ge2YpJCkWfyOjiMVMaIVBgvw6I8fe6UBXbTRCtCpHfIEoCASnTrEGV5YiTBH6cYCVGJAXiIBJmGaegwnGxdYBx4uP0+AQVfOTpth9vP5zSBvOrgOAeFkfnuL46Fi3GvQMlsboa7z/cSOr4aDxCulkLO9FPpjhexEjoJtw4wtRz3QpOXaLYNdhVER4Iok49nPotvJr1x/sMRMeOddY2TJdvpO5zsvn8CC0ZkC0NSwCvrVFtf4+J22J2dITllEp3AaZdIGm1WQescuDhwYGzfo+x/zWikY9wukDRhtiuV2jQYjqbC2t3le7gxa5oCG6WDwjIbMpjSec9P58imc6wSWvUBQ0DOE81CNoS290WYTIWQHuvRqbQheGfmXnfQmuWsNY9HruPBvtA3HEwX3zMN2rzFGW+Q9mQfQXMj+fwAjonUzdTG1cZtvodfYQo2KvsWguO8XWC/3uM1XCvH7Gl7Fjjf9w3sLpu/fv6Idnk2K4fBFwjCMVj102H8eQIR2fnuLpYYBp3oCWBbrYoE1GTf+05FLsmS/r3375CWtS95llbtbi4OEfkhXj97VvMpmNUaPDzn/25bCi9+/BO6pjPoDTLZBPp4vwCT6+fCttsvV6Z6ybLrMb1088FmON57+7vhfHO54ayzvUZzWeMmBjUrdzTnrFmtEWZ+s1B2z9vtC56oNIwsK3RijX3EOmIBlhv7sFpaD6dYrXZ4N6kpdJgyelZa4/r25ZHa6hPvD583/TAvpb/UXDN9FVZ0/03AtdYDgDboRzKoRzKoRzKofy7LbIAJotIAmIaIVhzgEc4gJSP8SL7N3/bz/44pvRpoO3HPq6vG7dR0WfLsV5vRJ+NABLTRufzqSyCt7udCW51Qa9pjJY+pcfR67MXbF/hatSYHgizSn8L8CjMKiNEb3RXuGClHg1/8/tcsHNxz9RR7ry/ePkCcZTg/uFWTyN0hIGb36PgR69ALpMpew/3iJMQx6dnwgghc2T5/gHni1NMF1Pcr1b47e9+I+lvDPFnswVevnguwTpNE8iqI8gXkolD2pOkgVGQ3RGwRLSFqgbj0MHp8THKcIZvfvcK2+0KSRwhDEPZhT86muH4ZC48os1uYwSdLTPNaK8ZQE1/bPDGHxto9lGoSdFk6qe6O0o9Nx+x2KyQuA129rFC3w947rwKcLsKMEpKPD3bSZ/dZmRxDPuNfnMfOA/7ptVQ2l+bnk+/xSvsMTVJK+Pr+4PLMclwcXyUVQLXyREHKzluTaBNiB3GmGEQqD3u43o14sYXhDg7v8DFUYKqpf6cauQIK65pkZG9FIYIgliYRk1VwHcjhEELr/yA3bs10uwED7mD3bZENB1hMZkgbV0RmQ/dBjFD2OwWRZHi6OQI0XgsqX1kaomzJn+cTlJE162LPAOavINTN9SNFyZT1ZANRs5PgzghDSYRECXfbETjKIrHkrq9JnjhK6BloFnUvJ84wMnJHJ4fYZfm6CSI1zQy9hvbzhYs6IEko6HlBgnOr65wfjJTdooivdKfyEwpi1xE7hlUlmIWwvRQMutIwyFDziUeB5diW3WFPHWQIsI2DhGPCDTWcKpCBPupn8bjkvlCwJopjgTUCdzQiKOuKajI/lgjcTqEoYM8cpF6IbyS+mZkfWk/qlpNMaUuVRT6SMYBSs9HuqnQFTUSWsN6PjbrDaqmgecFqBqAs9kdjUvcBifTCLPJHA0ZgzLP2boZTL5mNguTOZ4+vUQyG6GQlD1lShJMIADw9u0tjs8uBCzcCWDlY3G0wAnblCmlHMt+B68p0KUVtrsAd+4Y+TTC5bjDoivQFjXyyhdNOur5Bb4CNEx7bOoKRdkKeJQkIQKy5zwPWdnifkldyAWiMELkNDhjH0lcaQPXDTFyItS+i13p4Pbex937EG7+gHF0h9HYkXtrKgfb9U765XgyR8kx0hYIRw4W4zEiN9ZU6pLsbBenpzMEHA8CJK4lrZEmDrSS0GnGpJtbcM2w/+QVy6C1Q9bMYzrI7TA22oEGlOPrJWeMxlOgTCmFcFgv262kBMejuYCg/HhGPTa0mE8mMo/SzVL1CK22ngGe+3bWM/0AthkAaXK5Yohh0+b1NbsRIbfcp8ir5t/y4YPMLz7TzkXjMcLi5AlOz89weaSssYrznug2UmuNzF1lvzu96UWFN6/f4d3djQxayi6wn03mY1ycPUG+y/C//K//Mz7cfcDp4gw/+ekXaB2ypT1hoZH1xec7+xJfIyONt3V1/RQX55fYZalc+C9+8Us8vb7GUrTW1CGUm0JMB6WRCNuDDLXKGBiwTpkayjUE07lFi5bGJ8LSs2sda1xgWMziEGqYgeZ1BatcFPkOWbbBbJxIvd7c34tBE5lx9hnvmGofPO37dti3yL4Mn3OmpX7wKQXXPnq9f7DZrmnWKrKO+6+jtfZj5QCwHcqhHMqhHMqhHMq/+6Igh+q+iOvkcAE3KM6PgW3mR5aI/T+GH+4++cVPLzaHVA1dBGuaZo1dusNmvZaFMBfm88VcHLvyMheTBKbeWFF1WZQazS05mrmmoRj9/gosi824jnIHnAty85pdiDPlj0E+gTZxDuuoz1Yh3aWyY356dooXLz6TVBG5ToqCGwRIj6EC2FJfNqCT1B5HHFOzIpUAiIHAyek5/uxP/wTv3ryDVwOf/+RzoRx98fIFfvqTz8QdkUw6CoOj9iQFzRcmomEASiTFtmTA56JzlQHgdRWeTAI8eX6FV7dbvHn1DZoqF9CS10jQ5Ph0htlsjM1uLXptNFRQ5poKwwtrTVIwefl7HoMGF5aFofesfcvUuXF924NrA7lw6yppJc0MENr3RTLxOg/rboL1EjiZ7nBxUmC1pRbO/josSGbZHP3fNlAxJ7RBtp7LsOYMG0SiyZ7jYpN6TYBtrrhDjKqO4TtbTMIVajpTdnsAyIr19+c2f/DvaHKEp0/PEDbU8WJKE0Fc/VxekhnXIZ6QrdMgJ0OsdRFFMWJ/ifrhA95+X+HNzkceJpgdnWF8eoGsC3BT1ZiehZg7BZwyw92bD4A7wXQyVjYmcx1pLsEUSaYCCprUCBgX+S6q0Mdb14dX+nCqFkFbSIpe4xqWYQWEBDjGIdogxmaZos5ThKMEUTLBcrlGmtNQg3pfyoTZOA5WnovFJMDp0RxFS22yrQr1i46TTTXeB6eWCTaj7tPzczme+qcq6MDC87RljTCKhYUpxgJugGQUSno03TtbpjqKC2iJOq2QFyFWYYxi7OM6AhKmOhYt8jpAQwMY3pwAdxU6BuFtg4rMPo/6bZ46ZxJ8rU29ocHU64RVt4p9ZG0AvySzjh1SNy6YHulFFN93MfYchBMfaeeJoyYbIJ5OUFF7arcWExqPrqItsKSAvEtzgBYn8wTR6Ahrk15q5wwdZxyv53h6NUXhe9hQaL51ENKwtCrx5sM93GiE+eIEN2+/wfbuFuOTc3HijDxfE1TdDoFXwqty5CtgWYxxM4oxOQ7wPKgQVCXK3EHRhSB1Jw6owcZx0aKrChQF9a3IFqLTLJ1lCUo4qIsNGsfB7HiOxg3Q1EQONfV07DY4Dj3UEx+bOMCkiQRoK90A68bD3SbE7qFDVN5hPFkiTuiePEYmTMAdoph1MkFG0K+rxZTBk2NTd0vBzSToMJok8JIz0bsUgN/MkRbIkLlI+pzqfjkfzUN2DthPHMNnm/23AmOhyAToPC+ZnyU3YHIE02Nxf+6LMYdpCKjucgTU4FuoqQPF9q2TqO3v3aeejYNz70E2nWhk7pNTKAO5Z7tZljcdL5c34hIqs5zrCDAaxEc4OXmCiycTHCcbFGBqr/YxR0wM/AG4pu7k6+UKX3/3HdKGbEEXtUxkDi7PzmQz7D//p/8dyXiMzz//HOcX10ScsUu3/T3wPsMoRBwTuC+xXK6UWV03onkahTE+/+xzPHv+XO6BDqNkj/M5zedwQBdbY5QijqB0wSbwTqalMNbUAVkcUOV5Y20vbP3snx3yjONMI+m3BKv039xMW6/vpU0Xs5mw6u+WSzF9EdaaOY5tlu5TQOig9M+8/vP7v4Z/D4/w6J3hB+S2OiNzYXRK/xuXA8B2KIdyKIdyKIdyKIfyiNHW9QL/KkY/DEj28cWjNd5+g3z//nAXt6el/PGy/779/P7M1v2Ti+bleoWUaUIe2VwznJ4cyzXnGQXCNU1jf0Sjm9IjNUNjB/2cpokM9KGEPWfYfaZOFCDTT3Ahq4w/TcPgAr4sChFZJgj38uVnol2zWq5R2rRRwyzQ5bcCThJE9RW3r2EKL5+enuH+Zo2v/u9/QFk3mE4nOJrPcHQotPTeAAAgAElEQVQ8F/ZDlubYrks8rIGHVQX3bgXEDlwqLlvdMaYbCp8okJOIMLXLe6oRNim+eHYNf/oE33z7Ae9ff4/xOEYYx3INDF6urs7R0DghZfCk/ylrzQYm+iNApuGC6PWrGL1Uq6k74joSDAiQpcGshqJG2mjQPhqgPELaTD8kckIWn4/7lC6pLX56tYPjtshyUq5UN40XJdiRfM3o95jj9Iw5o7XFcwnMt++s5jJMW5l2l09ZQIjpTwLgMjFugqyMMAqW8N0cbRvLuWzisu1vAiY6Ec4ur/FkQZCJ7wZ9mi0DtU1aiqh7mIyQ71bCziKwRtZeWH6Fh1drvP7gYdMGoku1mE0RxiMU8wiT6wRfHDmo33+N1Zvv8OGhwfzpF/DiCHVB5bBaWFwCVrceOp+GDQpE0DmSd8JUyePQxU3sY9d4QO7BLWt4TiVgsdatJ8Bc4nuI5wnyxke6pmNejunsSO76zYf3op/EayeTcuUAN7xbr8X53Md4ciJstrbOtQ/ZsWUMB+CN8Pz5Nc6OY1SOh5ZAsSFIkomySVP4biigF1lr7Ft07JwmZNeovqHrNQjcioglsq2LbTvGwyTCdOTgyi2FtVaUPkq2QegjCpneSoClQVUUYqpCwKjpOkmpDSRVXB1GJFGUaZ1MDe2ou1bj2HeBxMP70EdbBghKjpVGBNBjpqoGrGEXbt1hFrroxgHWOVBvc9GySyYTSQdtqwwjn2CthwemBUvw32AcNbg4PUPjRJoW19QIxsd48eICkxGQwUPOdu1chAToHu7xkOZYHJ8IQMBUSt9f4OTkGGGxQRCFiCIPblfAqQtUmxqrTYh7Z4zNWYTPpg5O2xRNXiOrQlReiCD2xVRAtmAI0pKdVZUCNBCUJPNPAvwmxfr+FZLRDONkBFaN69Nx0kXVumgruoKSPVli7rY4jjys5yEKJ8DYiwUsq5iuXjI93EFxXyLCHeI4FdfVyp0g3aZoygKTGSUDYjykayBy4BuAP6+2QEkAZoaTWYjFkyfYFjWyXda7EuvYNDOBYbhaHK1/HkjXHD43hhs0dkZnt+f8QDU96kY2yLcPqJ0A4Xgm84F11rXHlsNJWi8dbBthQk0mMeIgQEEqo4B9Zj7aT4H76zBzWA/kyFTZU97sk8/OaD27inILm+WtXC8BJFE9dCLMj5/g9PIM18cE4muUfE7IhgodQ2P4xshAtCzNfPX9q9d4d3cnxyUQxfk3jB1cXz3D3YdbvP3uFd7fvcN8fowkibBc3aprZ8MRSvb4HuwicyyJY4xHiaR+0gWYz3dKQRBo47Od4BuZadzcIrDG8Q9jECMpoRyzMm5r2RjiXMdNCr7HZ6o11+lTOM2mkW4eGfaaOGRbh1AHabZFutvIs5dGKDe3t8paa4iy7+t1v1LBD8C14XuPy7AF9Sj2aAph9j3mk4V96r+2Q+g/pRxMDg7lUA7lUA7lUA7lUD5RxOae6ZAG2OpLH1HsMTMblDxaRP5gRWkpPbp7/6kyXKj++KIU/aKSui0nx0e4vLwUoI0L6pube7z/cCfXrCyzPofCHHS/aFUhbGWCWP0VSQ+RdBEusgmi7QG1wA+E4acpKQpC8tgCWoiYMlNFmDoW4ujoCNPJFG/fvcNvvvpS0nF4fI2DlD2kAvpWt0wpTD3ziupjUYLPnv8ET5+e4x/+7tf4/utXeHJ1ir/+H36BYtvguw8FZnWJoN0B8wTNxIUXlJg4CQI3VoaSQS2oLcagCm4BpyslwAX1kRhQhFP85s0aH379HaKjEp+/eC56brwvpqFWZYl37z7g9vZeXS09E7o5BDMpiG9CzT6IZJ+xJgwMBNS9Vd9i4LbXX9PvWSzNgFk2gh2AnjbYHXYdjX0bHI+2eHFR4c19gttVLEwjFbTX+xeJcabM9dGzwdEGujv8W1KBjRlGnzJkNcclVdbq8tDdU8FVFfBXwNFDilGyQlXNUHUjEcPmfTadg8XpBa7Oxqh2KbI8BZwIoT+R1Ky0KlA7noAsFBsvixSuH2OcdIiqt1i/vsfbBwdrLxbNrMV4gcgfoZrE6E4DvAgbjNsMdVbi1es1ouNL7P4f9t60PY7kvBI9uW+1F3aQzW6yF21jW55r3f//4X6YsSR7ZNnjKzWbOwEQQO25b/c5b0RWFdhsSZ7HM7J1K/iAAGpJVEZGRuZ74ixVjlN6a7kW4k0iwCRlvbQScwJP2CWNYYp0ri4bWARszAa208CwbGSGjVeViWZeo59mCKwUjt/Acl0YpgvDc7W/Vo2czJJ5gXyzQFNVOLq4RFkmSNMYE56Xjo97JlDaDXyzAt3FJoaN+aLE1fu3MKpMQMYaDsbH57g8cVXQgOGiaim9NGE3yoidO+E4nvzcVC0M10bo2+KRRxCQIGJbZTDrCkVsYNP6WPkenL6JR2YFu85Q5iaKxkHr2go8I7DG0UQmXFlIiAr95fgQx4Gw4gJP+kV4WwIUkekmcZ2wUcO1KwG3G9PBDSzMEyBclAiaDMNhBTdgFIOLkvLtlrLbGo5V4qo2US/4uUqEPR+WQxnpEhaBFj/EvcnU5wYjowTdq0Iy+WpHGLtRUCGtWhSGg7K1YRs2qX3iW9UfHYkccbOZgXkPTr+P834gRbnj0NIwQZ3ew6gZYuFj3YZYjXycDoCztkBblshzCwWBTM8SzykJe2D/1tUW0KB8XySi2iB+cfdOPAKPjk/VIoRjix8cdbo83+gpyJRX7r/dVHCtCrbbwrBcJIaLl5WJ/K6Ge58hyRMs0xWqdQKUKY57Kc5PS/hHUxjeGVaphyLJJV007A/k2K1mN/L72I/gNC7QWHK8aqOBGzZYNw1ePX+FJF4q7zMykDja9FyuVgYUmK9ClTW7uZO/i3xcfd8CXvophoUY+QZpVcHsjfQVTEMlegFFPaLnHg3xbwEZ+dZgMuohy8lqZmq2An2YFKyuT2qLHTikgCICLOq6yDUfed7UoAv/jkXWJYNQ7rYsasXosuH1RiIVPp+E8K1E2KqVSeSYQRWhloXyHOxYXjzX73F9dy+7TQBa7BvzFo8/O8NiPsff//e/l2voX/2Xv8bjR4/w+vVzFNTuysKECn3h5+M1nNdUgmVdsJACP1uRE/uBj7vbOwGzeE3Yl4NK77WNXHO7saiuw8pWoqGfJFOEJSVcB0+oi9a2x7tLibI+UOE30scMSalqrNdzkTv3/EAYa7SjEHarbGYfCOu21W1xHxjbu2HaPts9pt6pftu7L+nkqx/fAHWXUG0zQG/YP7cc9FPtwGA7tEM7tEM7tEM7tEP7RJNaQ25K6T+mpSoP7xMfAGFb4GP/pvDjG0S9cvxDyNn+Jn7gJbopSSvZLEmqCkp+ON/3MRoNMRz0UFYFspw+N0oCI+KPnU/0jlG2/UP6Gb2TndG1/k37qVE+ih3LqjNBlqAIBTyJVKWskCSJFBWTyRhfPH0qBcByvdqCeer+XAF63edQ4Nou9VL8k7hinhQY94foDSI8+9EzzN7P8fLdc/zk60dwnBp5YKLptbD9GE2c4fZmiSzNEPmBFLnqll5TgDq2GOsrScA00JQFzvsuxk8ucLMu8OG7N8wmxXA4EH8Zfi4y6Hq9EGm8EUYMP6+qT5XMs0sDVQWpkqiqIA0WYN0f7GqEzrmoe48ecAK0KTB3Dwfdst3kmHQSru6oGQZy+rPNXIzCFOeTDHneoizJ3KO/FI9/JQUi5WPqcHeFTVds7cbBbix346D7FOoHJZNVY0W+d9izfHwXWR3BMlME1hx15QLOAKcXj3HSt1GWZIE5AtwaTH4tS0l0tMMQjsuEyZXI+rwgQN9fA5vXePUqw+9mFhZmgFEwwTAYwPR7SCchhscWPrdK+E2G2Yd73K8aDC8fod9zMOm7It9b3V9LOiiPD6VTPFo2JYGUORsQWbEA0aYKNaD80WwqOEaNKc/70MJ7zwFSR5IbbYPBIioYg15XlIQxzdOoUyzzAoYdoc03AuD1ekOsY4J7OYaOCbe1sGwMfDBNJChxFBg4Gh+haV1UpYHPn1xgMqB/WY2Cnmdk11C/VzC4IBeWmhxvnte1Adt3EDk2GqYkOgZcobhlqJMKSepgY4WY910cRQYuKJstKwUaGS5MkTqa0hdkrbUsymvl28QvSrBV2AmBenX0BR7QDB72Gwv9hvI6AczI3GJWZImB2WDkmpiHNjaGA3MDuE0Byy5kHqLkmtLRrDIxqEtEQ6A0HfFn4/EP+5T0Akhj9CjPNR1JhWWUQEXmkVHDo/S2bpG3iuHntgay1QZFXmI0OUJRpMg2K9SGj+HJAEeeg5bHgD5rbS2sMpQWlssSqekjO+/jWdhgRNlsVivWmqNYa0HHWmPyYsXPqJhCeUGPq1JA2yxbY373Cr3xEfxwpIANIi8kY8lcSSBLsTW7/efxLSsTLUM2mgqeWeKIAGrfwqLnwG099BiY4Jkgh3aWW5gvTNjJBr59izAgcNlDWtrIlyvkZYnh0Ymcl/QwdDwLNkFSnvetibzicQMuL8ZoXQ/xmoxBMpG0V6YsxnQzhJa2yzHXXFcd1MImj2znCZWYWqYbOY5mGKkQFgHqdvOIYsOquUS2LJPc/lVUzWdJKu6ZGPQD2QYZbpTxdnPRvjOkWgRQc1EHICnJI/eZkzRkLMTLe5HvUoZMjzS6Ko6PTzA9muJ87MI1GkkCbg0mdPgiCRXgbrttSm8rXN9ciaefCl5Q/eB5DiajIf7lt79FnRaYHp3g5OQCo8kQ796/lHOrI1ip+wp9rRNms7rOKaYzzx8Dk+kUvX5PWOFkh/PT8vrqdOAawfhGy0GrjrGmfNYUuMawom5RR4t89+ZxxVhTx6QD1zoGG3csy8iYWwtDmIfm9p7pyyqptDtG3RVgd+R2rf2Bx3ZXrU/f32yB1u4FH91vsal+YqiD8x8SXGM7AGyHdmiHdmiHdmiHdmh/oHX+WbyZ+6EbOuNPenDvjvEHGGz7r/yhG9UHbU82ul6vsVqv5fVRrydSKHo3lfQPyksNqO3kod32t0DJ9rkO8ekwn+5n7dMlq+Gd1LADfJQnElfgO2kJ30WALY438vmYBHpycirMmM1mo9CpDlTrvL+25YwqwfROikRmMBrg2ddPMb+d4R9/9Y9wbA+T6RhJkWE8GcNocyyuV1jNgWRTYb5YKZZBXWIQhUoqqRkTux5Q//OZqi3hIcdnZ0P0j05xc7vG7c07mE0DP+T7FbjEgszxbGzilRTQBr2utqCj6jT1FyQ2QMsxd3LPTpYpxapCpbYglXpEfz61sT2gSz+jB8S29ug83wg4JC7i1MJxv8DxIMU6ttEQ4GhYlGn5Vye36vqaRbD0DVNXWYzTx0n5IKkqcq8o2jtOahfV51MQowbrDANF46KsexhN+rh89BieJODZiv0nlDjFHDMcH16vJ3KmjGPCMhGFBrz6Cst3H/DdOxtXpQfLH+K0N0UQDlH2e3AvfDzpNzhBhjJZ4cPNGm1wjOHpFIFjwCGYoQMMHMfF/G6BD2/fSQgHPajYFwSI2LZJsAQ9mPxI+WNN0EOFbfSMClPXQtlzMKMR/9qEWZKxlYPYbcMEz01MB3lMRwP0BzYqx0G8ob9ZgiAMYTuuSLzsOsfAdpC3JmaGiZhglVlh1A9wMg5kDKb0bmvJniFTi0wrfiIDNuWmZYGS8jnLQtRzYJMZ5RCwIfBHQ7sc2aZG3AaIgwD1wMIXboNek6HMWuW15rpwNSNLSR3JeCOgRrCoEJCGXlidO6ACQvT5r5I6FNCrPQjFn5AMIUOlZrLfDLLa2G8iD7Uw8xysCgdmYkhaKVM6CbLyvSUBsqzGwC7h9dg3DopNprzMghBmVcPOE4SmI2w+fhXCtjGxrgGnoZS3RLyJ4XiRME438QJ1XsKNejga2fDIQHIsBFYjKaptkSPdtLjPfCzGY4zGDk6LGZr1Hdq2hxwe4DsIXROu2cgc0DYl6qKQ+YthK0VOQKNBVRRYzd+gqhOMji7Fr4vHjecWWaxM3SUIL9OrgGy63zjmSImzHgJtlI1GqDHxTGBgYUMGkeEh8gJhRcWtgbsNsJpbqNd3CP1EtksQrLEjNEUJ23MleTfNS5RtBsth4mgr26fXGH0rh4GDs+MpWsvBerWRxQAF+vATKlBHHX89Z4oX5x7bVv8gM0cVi8eb4fVh2K5C3jrgXc5F5eu5hca0rL6b47tAgt28ZKKpKY+kByIBLOU/KMmX3QS2vY7tFgjk4W5+JOjLIAgyADNaF/Act8Xf0fZ7mByf4vJ4hInX+dAxooFbCni2bWXwPFjc5HI1x7v3VwJuUynN8d8Yhnj7cT74zf/4DT7c3yLsjfDlsy9R1RlWyzuRoKqphowzdb3jPKi6Twv5hQhKQHGAk/MzWTyLNxsBuvlCWjHIooQOYSKYxnFIcJfnrXitNTohtFbHTjH0dB/p6+z2S/qpk4SqOVk8A5sa8WYpc2M/CuWegmAiveG6a0fHMO/a/m/dYTE+gY11r+uu77tH97ewd2w/2oDMQyRa8h7DJmP3D94Z/VnbAWA7tEM7tEM7tEM7tEP7I00wEHqS0QT/o7TRrnX3hNv7/v0bxY/vQvfvIP+EG8U/9goWcLy55s0/08gISLmuIzLN0XAg8hMaK4sZvniy6e3qH5QEUN94b6sUBcipxzTQo2Ub/HudL5vCWLq7b5W4qaSlaqWdq+udj0zgB3jy5AnGwwlub++kKBDZocirWHTsCi7+Tqcaz4vwi7/7vyRAYbmkmX6NR48f4ctvnuK7b7/Dr/77r5BvFGsgCkZ4d32FNCvJu5FUu9l8g7ubGcZRCM+nt5Ne0df7qmSq/JuVJLs1TczaGo/PTmEEE7x59QbxZgHPcxGSmdG2KmBiMEKR5UiSdAdQ6s/fgWpbdpo2/+7gM81H03XrbpAo0E2XIFvllQY+t4Nge/B0kbp7XPWZjXnsCuvji7O1gChJqfWdXRErb9pWTPKNx4DG+vyV4AsL0c5oXLXuM6vf1TjX+9QBb6YaD4YX4TF9+PqR+CkxfMNkUdS2KOmHxSI16MNyXKTxCmXZiNH3wKXD/Fu8eh7j+dxDZgeYRCMcR0NYUQ/5aYiTMxtPnBJ+FePu6h7ztS2sNQYPeJYWtnVMo6oWlhyLZSeMcHV7jbLIEPZCPZQFVtz6Kom/nm2iIehBKaNOzXTIyrJqDHwby76HWe3AXRpIV+8koXEwnSDyKaG0GNSJvlEjGDhICDSuY8AoRXJMplm2WePINDC2HMStLWb+BFvsCkhZaNNvjXo4IiF1A4+egDyPikwYdn5oIXKobrbheSYowiUQ2OQFktjExgyw7rmYhAbOzRzIc+SZo6SO4oVG0EilHFLqSElr590kRbsU66xk9bmuMDXFvCEWQLoWx7NICxWriP1mk1ljidOd9hkjUFvBN0qMHBNmYOODbaNObZgZ59FCvAMJWleSTAu4RY6hX6CNfGxSA3WWSTEdBCGGboUeWWqFILSEwJQn3WojQNeQTMCSwNkCdetjfBpiajfIK1eYXL5JZClDucmxWduYmSHyqYevogZD8sNqF0np4y4u4Pd8RB75n4rdRxCVrFwCa3mmmEMc51kyx+zmNYLhBJ4/RF0pRpJpK9BR9R99/iijV4shEiKgZfHCBCTwwzRS00LRWqgL0S/CMXIMrAZDz0bcd1DYLoYtgTYPaWtimddw+iM0ZYB68R7jI4JtQxiWj2RDRmIJPwphMowjXQtbl6mnZkVPQcqBmawMjCP21Rnu6aO5Wgj4I7PVNlVUgavbgGRhw6m5joExZcZEVh+O11PP7S2QbGeP/bWbvWlsO2/ugWu79E++ydSyR/qRGfApjS6Yg9otdHV/pZsjJbJCtsFrTplvFABoAFXBwA4L0XCKk9NTfDYJJRRCOK0GvfMcGC0ZomS2Cu1Psl54/bp6f4U5zT71AoLsu+0iGp/gN//4a1y9/YDLy8/wN3/zc4zGY1xfvRaWs5JydrO4BrM0uNZJVWtBjQx8/vlTjKdTrFYrYX8TNOvY0F3fdwmhwjBlIATnOPqvdQmh/Npek/Vf/YjVx8UE5bO2+06pahwnSJIVRv2evPbufoY1JaFkD8omHvDLPmq7a0IrP3Ui1O6Af//nbmvf26bx/Z+76yLvYziX/0dvBw+2Qzu0Qzu0Qzu0Qzu0f2MTk2H6Demb2k81fR/+kcSu/f6L8BC/ePD0Rw9/4iXfa7wBJQhI9trJyQlOz84QBiGKssDV+2vczlcqpU1kX93NPptO/etugLefTT2iAglUkii/2yIJJQtF+aA49BqiEbpI7xS4JtiSFAWqIOBjQRBI+mkURXj+/Ds8/+738hmsrqhjkikLNcvEj7/+ER49eiQ3+kwq5Y02ZVnzxRzjwQht3aIocjz5/DP8/l/Vdj776jHmyzVevLhSrAkBEpQM53gc4atnl/CjQH5XnmRK9iSlllmJRIi7apNx1XqobBu/f7PE6sNzjAZDXF5ein+OsBppQh2neP/mHdablXhQdZZ32xJCAD3F4JD+kAACBb6J4nPLXlPHQB1k1fciGerYQ7o/u9cqD6P98cA+V6CHMizi36xxMthgPGhwu4wwSzwV+iCHshX2nQBvFolQZEAYMByyGUo0RSRAG/2buo+kwFmd8GcqJo6AbDQ35y+1j5PLC5yOQ2FS8L2sUpnqyM+1TnPAduD3+iiyWCRQBN96/h3MTYL5bYHvbhvEVoBBNMTI7UmIQTr24R05+MKtEDY50uUSs1UNb3Qipu+O1W6N58Ufq6QnEZP0CBiRkVVIwAXZlUmcYTmfYzKcYjyZwCEJjEmXHLe28spin1D2SJCRhblVN8ory6E1k4VFY+D1vBbJ6KXdIPByuKEJ2L4wsgjEoCgQuCVWhoPFsoWZp/BCT5hFRR6jLktEUYCN7SI1gaOqRFLQl8vAKKAUktJHSlYLAasa20ToM7XSRG07iFwW7/w7OYoUSGsXceDCDUxMrUI8zcrMQNE6aJz9EAMOOrLWyIBRgBq/OlmZyMzIatMMI8Vl1Oe5yIMVk5fyWIf+bY7qN/Fn42eGIexEekEZ9FmjP5tTwXQoJ/Vw1VpIkxb9TYHQyuF6NRoyBGsbZV6jzUv4bgErdLAuA/hGA8+o0NLvzfSwii00DgMWYmzSFFFvIPNQFi8EpAsGIY6CGkVioLQD+L4pAKlRZmB446oOEA98jHsGTpEL46tg2AMBSNeCqIGzBG2+QuRHcr5wzilkTClPK8oV726+k+/h8FT6UYzkuYBhGfACW/WL6ajzTcJWlGcY2UGcK13XFD9LQwaVSjpmcEROkI7+bHUpY85xaUbpYGO4eF1ayGcVvGUKo17ifrnB9TyGhwpH3j0eneUIxo9h+ieIiwhF3ML1TAS9EGWZIU9j8SSMCOJWXExQHp2FacILDGyKHK/fvMFmtYFjEWTnnM0jqs5fRbgiSEMDvjUSJu16fTlflABWzXedT5qCeHatWw7ogJ9u/upA/312rOqv7mfV52yBw0RaW4JvOksBmf201LEStmEuzEy5Ttm2gHKmFWB8foKLUR+R0aLUE7Cw0gVUIyuKG1KAOwmks8UKHz4st2FH8knaFpPBGDd39yKjXi4WSNIYf/XjnyHJlX9kB/wp1rdmAMoCVguD6cUC6pE1XWM6PcWjx5/J4hiTtwmWSX/zOivJoDxOyhKCbEgB12qCvJVa6CJjjc+R3dcF6+j+lmvBlrmm5nDlW9d5alL22iBer+B5NgLPw3y5FDkor9l6Iw84Zw/vQLZLRduZot1BntvX7L9v99rv3Q19vwmorxJC/zMAa107MNgO7dAO7dAO7dAO7dD+jU1kGnWjfccEGurIS9vCQd2Y7oMlnyKr7d9m7vuhffpV+9//mGyUn483ysvFXG7A+5SNHk0x7EeSEpjlykBabp+FDSVv3m1nf8VaHv5YKrrnGSZ1hE6X6zzENAtNScG48qxMmZm4l8Qp8iLH+fkZnn7xTNIiV+tY+lGAsOMz/N3f/QJRv4fZbCapgfwbs/uF+ModTccimxEgzLGxvF/g1csXCKMQR9NjrBdrfPnlEzFCZ7Eon8eykBYF3l1dw6hKDCOm72nWnew8KzxzTy5JRlsDszJwMYowOXqCu3mKFy+eI/Rc2C4BBwuO6+Do9Bhhr4/Fcq0827S0eOtnpBAxBbBtFaG6EpLCUqNtXQm6J+d9WKLuxkhX9HbFnDzcJSd0Bm6GgbQMMF+5mPZjnIwKesCjbixhMmy3QwmpYHKOHKOCrB+HRTRBHm2Avh0N0mHq8xuEJVViquVN8PXXX2DgOGjrDlBQoAJZICzGvf5IPt7i5qUw5qKej77xHpv3d3j1rsHztYs26OE4mmIcDNH2IhSPQjyemvjcyOEUMa7ffcAGAwxOTxGRkUXWmoCopfhJFUWJnDI+bf4txSgBI9Fb1pIO2+uPkOQVZte3IjVWSatKViqAwh67SFhplolS3M8NLO/fIzRyXI56qIcerphGmthw0hom0zn5fiZtthayooVfFpj0W1RhiCSuUadrSar1KOFj6m6RYWgxgIJmUS38yoCPWPaLbLqSskEf6IGJlQ7guZJkaTaFYq3Ra83wsRm4OA1bjNsYbV4jzx0Ulic+bb5L2SwBVRr073mIkQVDNhbBUJVrKKxS+V1AaTVGBcjoYmHJEhIscy9dmMwsPX90vna2ZmWRCViRCVgRLK4wNFv0xZ/Nwap2gIRJrQUcM4PhGChhisE9Dej7ZJFVKQzKdcEkUwICBvK6QNE06I9GKIsE+XqNygxwfNxiUGfYxDYQBQi9VoU6bCqsNy6u6Y937OPzoMKwSVCmlM36qFxXpKwqIbQB1ZmOZeP9u2tsVitYJj3y1L6m6T0Wi7cYHZ3CCyIBPASoLBV7aAse7Z0j6kud7jydhHWk++4BE1AAoc6fjaCjhbbkvism4JEFuKHBLkNaBPCdHmyXwnYLqyTEh7mHapnCM98hCFYIoghZ6SLbZDImo/VxR+AAACAASURBVP5AQOdNRWCToEUH/huYLzPYKPHZ4zO4vRGW67UwAtVHV8EHPMR8DVlrlenDdXt7acXd/KW+uvmim6G6i9/+tUseElRSrUrsWE2awatfLIsWXDTgeCKoVJVwbZWYzH6UuasxBLBHW4jPnAAyTQtazPnRCF88ucDlJJJjxOEoCwWmreSgEpKgQSiy1uoaL757j/l8o8nZ6prnuwEGgxF+9etf48XL55jN7vG3f/MLnJ4cYbXmdZbaYLUApRZtdNZMt9O6GySAyHbx9dc/EpCf12j64REwI+AnqZj0hawbkYFykYBjTMZaXQkQrRJCKwHFZZFPEr87aS+BQ30N776EWa6Da7gQZtpI4g2yhF5rKtDnw909YrLnNMin7gEeHLHvQWe7Y73/yvYjBtv+s3vXs/2bGjz8WfmX8vru/IeWg36qHQC2Qzu0Qzu0Qzu0Qzu0/8XWFZhKErkHpuzdK+raQQMn3Ts/AiwefP8kErfbHv60JvJNsseqSrxUNuu1GDwzbXQ8HgkDJU1TbVysvGbktnjLJNg1KTz2cZ5OEtp964z9eZMvNjnqiW6fpWjgTT2BBC37KUTSlki/PX78GIPREKvNCl8++wbf/Ogb+Wzz+UIKfoJy1x+u0etRmtmXwonJarkADBmSIsfp+QW+ePoEv/5v/4Bvf/d7xKsYP/7pVxgfjzCfUTZWC1jComq+iXH34Q6u5yESf7YO7+JnVuEAEhAgn58FjAnmOp4cj+AOj/Hq5XPMF0v0I188vigHoqn9yemRrLZv1rEUR11XSdd1BSML6dIShoQ2b3tYdGx/2+v0rtDcGwXCEpFxpQqhXWHPp1XxuS1qDAurNECStXhysobr1kgyVcQRXKzaBqWjTLGZxEjwhhJE26zFs6wLnlD7oyRuZHowOZGSwIvHj/Hscgwzt2BUyiuoAxiSrEJtOPD7fZRZgrrI4fghmvQN6sV3WNw1eD5rcdf0MOxNcBaO4Id9JEz1u3DxtU8wJEYRr/D67Qbe9BKjcR++zc/KTlVyODI6WITm2hurkYGoACMeH/rlkcnYgZBB4KE/GmB+u8B6vUAoqbEEG3aAB/dYyR+5n8D9fAPPH8NzIpEODswWE9fAOnRw29iwYhN2TY+xXElNKfurWpRphRAFekMHpRmgWGVo6hx+FMG0HaRxLHV5wDTBuoHjZLCtBGaVw3McWIaDuDJhElA0a5gEmJIGaelh5XnAwBQmnVulKMhaq2mM7whrzSUYJx5YpbD7CADTY02lDqpjTiBZ/rVKHqpkZ9o7TOYjBRQo7KADcFWIh5I+KoamyB9134lvnPizmagZICH+bARzK/GLG5mA71m49i3kpYuW45H+YTbg9gKETi0AovKwUkEq66LAzXIFw6M81kOymqPKW7jDHs76GRoCaYUDO2T4QwmkOeK1Kay1D/0AFxMblzw2BWWz9HKjv59i99FrrZPNCgBZVHC9CEZj4d3btzCsBuvVBzSUvE5P5DygpJbsKMro1JhjsIE27+/04Z0KW5/L6jnsgZR8kGws1XfSbyRDEvwnwCpSZRV/m61n8NscR8MBmrGHzHMRmR4GnofaMcS/bp1a2MxbIJ7BQYIobGEEAdLCQJnmEoTj+T1h/xX8LFaL+XIl3m8ca1Qm90MLFxenyBob8WoOmyb7dg2rTWXRwvRGws5TCy371zK13/uAyG6hQM1VAshsL3G793VznppnuglPfZdHOJ+J5xsfJtDG/qvhMWiEhv8EDR0CMmr+KbNckorH0xN89ugY/cCWoAgyWWXhBw55mToVecfw4iLJyzdXct2U1E/9WYf9Ee5nS/zq179EHK9xdnqBX/zd/40kXSJN1wKOanhV75Oao3Wv6MbzqkJ/MMZXP/6RjBuyaemTykaPOJUkSoYmr92l+KcyuZOM3C7YgN85cARc09deJaNU40x6cQ9Y2wYcSaIqgbsay+Ucltli0I+wjje4ny/k73XBTtuFwj94x7EDRfeuWuguqA+O5d6z25cbn3hYS1vFa01Si//ztYNE9NAO7dAO7dAO7dAO7d+hEUSiDxFvD2VFee8GssOjfgA72z25//sfuK/9Q7e8n2qdLxp9ro6nU5yenWLQH8rN/u2HO1x9uBepkDC6NFNh9/GVhFLBb3IHrwpuLXkSqYmwAbqAA/VFmSpX4uWLwBa/FE1K+eqIl4wqLFgs0y+OslEGI8zmMyW5gmKtcRWbyahsqvivpPDIc726XxE4KORDn45OpFB2Ax+vXrzEMl/i53/3t1IIv335FmZtwrRblC4NnBqEvoenjy4wGfUVQCjSnv3OIyuBRucEB1xVNDkuXlx/wNWLl/AiA59dXGAwngp4wf2kaf/b91e4vvpA3/49z6DOMJ5f3JBEDG6PvQLiur+/xxTTRalGP+VxvpuqKQJpW86IooRstyWv2b5Nj5qmwShMcDxKsUoC3K36ImsjyMLDb1UGSocedhac1mVpLf5HKoFUgSdM3KTfVDA4xs++OoVZtShyV0sJyeBqhGVUWTacsC+gRZHGwhB0gxJuOcP6JsWLtxvUxhLwjjEYPhFGTtkPUJ24+CJsMUKGJt3g9kOM2p9gcDSEZzKggF2gWWs0+S4bFHklIIcwgwgYGWR0EESqUGSFSsUUzz0lzbM9+sJRsmcLSHN3ewvX8XB6eizPu7Yt302LKswFDHcC0wmksKdc0KJvnFnCdlqYjoXScPGyMmCuGvSTDKGbw/Ib5DCQZbUkeFLKSqZU7Ye4X5to0xSua8ANmLxKU/dUUj1HIeCaSxh1ibZhRISN2uyh5thKmL5qInZ8VKGFS7eF22So8wZZZYt81HUtkfhtky/Fa00BQQTXBAxicb6N3Ki1BE3LIAslPZMhyHOd/eSSXaW9FcVLigkPBGgVRUfkj7YJ17EFvGefmJ1sVJhGlD9S4lrDaWs4VgOL56DlYtbamBXASV4hcnKUHN9uACMrYJaFsCTf3a1l39qm2DJrLCfCaNTAS3OsE6C2THiugcBskcc2ktrHqu/DGVr43K7h1KnIZrPGBdEYjwERMoURTFS+feLVJQAbQTN1Dq2TGWaLG5xcngsgQ6lelZNdpOS1HA8CNHYMPkvLZ91OQqvnQbJuZea0dtJR7f1HRpbrqjFHuS2/CCeRS7ROKlkwGAQ+AqcSdimlpYXp4W1jYrZu0Z9R6rrBItlgvkhRzTNYVoYvzzJMThz4gyNkGCGObWHpqaTWFlm8lpThKGjgcv4rXJSNBc4Arhjdufj2xbe4v34BAyEs21d9JUChsU2q3GdAb69P4kDQLQuoQJWPIZcOcJQFge2CQTc/6slLryZwpFkiQ2SqB6XnDGwgO4+efmpcilde3aIfjXFxfoaTIwOFxRRaInIWrNaG3TBdlTMBN69k+HlZ4O31DdZpqhM/TQGw+r0Ivhvin/7pN3qO8PHXP/tbRMMQi9WtZuryEqGZnbKzai+7FF7ue93yuFl4+uSZpCTPZzNZZOLO89wR434B9BSLWxhrZJpnuQ4xUFJRgokE38RrrWOQ6oUx1dGUVCq5bOe7JuerLHoYSNNY+owJoWSDzxcLWcDidVXt90POmj4I37uuPLxb6Z7bHun9K9on2t4dRrf6qOWgimGnQMb/rO3AYDu0Qzu0Qzu0Qzu0Q/v3ko2S/SJsLcV+2jLX9C3lD94zbp/Y3iXvUd9++EbzT74FlZtX5a8UJ6l4vVBOEoYhRqOhrGJXZYEkYXqfvinvGBfdPkgQgdpcd/PbfVr1UXesDSkS+AKNM3Ypm6pgV/3TFet8LWUwSZoIo40mz1VRiaz03bsrTCcT9KJQwQBSzCpgjUCc+NGQkUOfKhY4XJnfLCSN0rNsLFYLwbBOT87w7t0rfPWzr1AbNeI0Q2PTmtuTfqHXTpzGIpURAEFBBgIIKaqZjZoyIpb69Ckra0z6fZxcnOFuU+Ld6+diFj8ckdmh9m80GmAyHkmya06gYP9obYMWdo/JI1pWtH1qj/q4BciEYbAralQ9qiRJuzd28p6Pho9Kj0Bae5itPQRugUfjDJvEQ0UTbb5W9t8W5o6Ys4nvVlf4slCEhCF89vQZvr4YoIkVw0+5c4nIEHFdwPBDuGGEPNsIc4bHO/RXaFdvcfWmxKu5iZUXwuw9xsgNUSUFqtMj9D/z8bVXoddskCzWePchR3DyCP1hiECz1oxmx1ojcNqBawSJCK7JF738yPKQMVJruaj2kWJvCpNFFfgElnuUSbXA27dvxefJsjxUeYrN7BpBbwLHdXdBCGSBmMrMvy4NmHUNh6mZNtlCDq49B0XqADFgVvT0a6R/Cc5VlHzWFYZhgyYKkBIYSjJUJb8SYbPEeQvYPQHfxIOvcWGUMWyCAa6P0g1QRiae2CWskqCRhZSgkedK4qJrKdCIPlSNloRSOrsF17o0YIPQVaUBOHolsr/UeSRgs5ZpdTJwNW47k/7txLD1W+yM/KVQ7sz8BUDQ/abiClGRxUqLJ9pktQUiUwVDuPUaTVHApPcXJaVOIODS+/kK4WACoywEdKxaD844wkWUo1nlWOcmasuQsWHmBpKNi4Xdw2IS4HJk4JFRiAw1TW3khg8zcBDQA00CVii1Yx91Mjw1poTNiAofbt7AcFscnx2jpgy0YHKo6isCu2QWiaRWAyxbSbfMh4oBJWflPmqv/cRU76nwnFpISYphyTlRhOpmi3S9EqCyP+6J5Jay0Trn8S3hGCXGloG+b2ERUeroolc7sF0L66GJNHaQJiayVQ0Lc4TuHGHoobRCpOtSxkfQ6wtglSQFWtuBFyjfPKfi8VSgr++6OLr8GvOE7L9UjPkJJHXrAGpe2eEpwuTq1gLEV1NfUwRkUy9SstLu1WqS0lCR7pntxUZPaRxT/MESsJ/XsqZM4AX0sFM+XbyGkAI5np7j2dNLjEc1cstALZ+Bfng2TAJs2hNPTXcGFsslvnv3DhkXSIioCzuzwXQyFfuBX/3ql5J8fXx0jp//7S9Q0P8vXm4/n9p1SqI111dPup0jGeef8XiKL7/8WhaD5vf3AmrxjZbliE+cXAuFPar81cha42u4gCT7SvZavRtrCthU46pjA/K7LHJxztYyWQGsaM/QNFiRjUjWGu0MVivZb/oLKtaaZrjtgWgfN7U3Dy4oez/vwDJj+6ody/1Tr9tv3Cclj/2PnRD6p7QDg+3QDu3QDu3QDu3QDu3fufEGkavVvE0UCeYDStT+Defe7ewP3bd2YFv3+Ef3nv/2W1EFENBom5LLi/NzHB0dy004V7Ovrm+RJaWsIm8lip1Up6t59GfaAS8KOJPV/M50RoAIstaU0TQZHARZ+Jg8rlIWpGBgQZGVhRQNwubwPBwdKbmleLClmfShmI0La43m7IW8lwwlFh5MXJSaVj5jIwb+3DdKR3/5336J+/sb8ST68r98g6OjAV69eo8qTuHKajn3lRY/DU6PpziaTERK2grAxiJZ7bg4VRk1HMrtBIByxFR+ljT4p//5z0A+x5PPn2A6Pd5KdLgPd7d3eP36nRhZa43T3iq/Anm2Xd2hkrptQ0a3lm07YEO5xan/9UHYjpGuuN1KfWQb6nX8JvkGaOEaBU7HqcjAbpYRSilEHfX+DmzUmyZINDi9wJfnE7gs9Eoa5yt2CT9DRhDXcRGEfWEDlWksMsnQS2AV17h9m+Fq4eAeHryQKY99+F6EdhTBPvYwNRIE2RV6foSr6xRNOMJ4OoZrN7Dlz/A401tNeYcxTIDFa6MZNQTW6BfVtASNFMNISUcJsik5o9ExrTxLgAjLUT6BDK5g8W4ZNmYf7lHFCcLAxcnjz/T5YsISdlFnSm+gaJiSq1lZTQXXqWV7jeXimqystEWwLOCXqfizNZZKn7RaenxRvmnADl3xIlstS3h1DstsEPRHyDLlSTiMfET2GqaZCbLZNDZaK0TrhgI4pJmBSrPWBFgz9sIetnJQAkYaBJLxw+zEWjyjyIYhu49f9Hsj001ko9JX3bBS5zWZMew7y1FzCPtMAAlhy5BbpCTHHGCUOHIO5Jf9iQAJSmebsoFvVkBToC4ykbJKoqtlIq9NfFizz3wB2Jk2S2ltWS7hT32c+gHWGbfFkdeIeXyVU4JLP7oAvbGNz+wSNpNDcwNZ7aIV2awBR4A19hOTZpVstszZTwTx1cmWJAss4luMplPZ17rgcwpU4zhSfUYGGxcutA/lnnk8GVX8UvOeIQme/J1sNjICFfjBPuO4Y7+xq01Y9HVkWEqdoWlKDCcTWI4nfcdkZIK0cdHAKio4qOA5DTgkW9vDPRy8Tw20ixJemiKpMryMc+BuDS+PMenFuDjJMZiEyJzPERchkNfwAxueHyJPN6irTCSiDgGZRQarMWGRTWjVQOTh7XKG2+dvUZSxyMeZdyCKcZlbNLwo46bd/S7Jo/paocGVDoDrXt6BdA84bnwp5xe5VDC1lOAsp/pCGH98D69jZIKVTSVea5dnl7g88VGbNQqmGsv8aAO1A7O1hIks/EGmwJYZbu5uJESH5zTHLucNP/QlJfR3//o/Mb+7hWk5+MmP/wrjcR+3tzcCyMt8wWsYsXBhh6k96T49fSELkXt7ePTkiUhz58uF+C7yVfvXQe4bxxOvZWohQM1ZZHiTTcn5rUsKJUOXk4hae1N9rjxUFTdSW8CJHYI6byGsNQJ2/agnyaMzstbyXDHtt9f0799JdLcbWny6vTFR164d2PZDz2Pvse0Gu/YRa00WJf+TA2tdOzDYDu3QDu3QDu3QDu3Q/jc08TBqKV1RXldKyrGHUj0AzPbYah+DaxrAUu998O17P//htnulcDMqGqEXWC5X4gHFsAB6sx1NJyKL28SJsFpUkpv6HDuz6h2brQN31Mfu/m93gJT2ZhNGjLD8tLm3fCRduGvgTaRVLlf0KQVTJu/8TFyVn83mSLIcrchlFCNpZ/CsqttODtkxk9bxGre3H/Dsq68xGY0x6k+xvF3gt//yWzz75hn6kyEyastY2oqsxkAcx7ifzeF59Cryt0bbbDSiZxlT88usZP/KGvAME188PQfsEX739jXmNzfohR4c0VhBpK+Xl+eojQbLNVPpVDEtBdIOL9PST80elH3YjYctM2ZvyKj/9tghsv+qmO1YMtIf22JsbwP6bzGRb5P6SArgcrSGWVXIaoIhCoSQDFF6/hgefvz1l/j8pEa5ZKFH43wGfbSo2xYJy9jBCK4biHE2gVDbNdFzblHePseL3zW4WntYuxGGgxGOvRHc3hDpWYTRuYOnbo6hWWAzW+Nf/vk9gsdPMZ32ENrk1xAwJcuqQJkXsu0sU8w0+oaJHNTkZ9TFqE4RFQkfGWwCtGkTcMFCOlBQB3MIOqLTA9HC70XojceYrRNkmwS2JBcae/5sKllReWUpVlYJC1XJIIQGVltiYNY4ppl/5CAxXLT0Bqsa2JoYSO+6mgy4xkRg2BgNG5SGjapkcmgJL4xg2Q5WcYy89eScsGwCdSnMJoNBsK01YQeeBG5QEsqRiW2IARkw9G5i0a5ZL/TUMzpgTRXzAkKSlVXuinzxBqOJuialClSyDTHRX9t1g44N2HlAqeFFNiBBTVHLC9tG950kEusgBLNEU2fCHqOclSC/6Ti4WVW42RTiVWXxPF7OUDWueNgN+gHaTYPb2/cwmfppe2hSJn0GyPwe4pMAn49MXCABMoZ6uMgsD07gInAIrnUMyELGBX3U8oysNcUko3H8zdULWKGJ0WQk+1nm7B/2FUE1BbSR6cdzn+C+6pudD9bDE02D4/I8x1BnGaC92jh2tVSXbCRuazm7BywbYdhXssotE1AtQFCCS7kwx1BV0NuOQypHZJY4di00PRtrhmGULk4p9Y5MrE0H89jD8s5EzaRW8z0GTgqz18c6t9EmKbzAhxv0sFkusUw2GI76CFwFURFML9MaY8/Fo8+fAGaA1WopgLdcIfSlYbtQIPtCbzkFhHVznJrSHvaTurLsQWtafqouNeraaMo8z98reK4jEmXO9xkXXwwLw+kZfvL1KY4GDkqrQUlwjYsgrQOzcWCQiSyAnfL0u5/d4e3VWzk/BCCWnIAKR+cnWM6X+PUv/x5JEmM6PMHP/urnSPMNlst7OfdlShSAtpt99R5JaAU/tALCjo5P8PnTZxLos5grSSjBY9dxxA9VgDHxVeOCkWKtCdtUM7M5j3VMUl7r9OmmrnVKl6rCHDSQJnM2ATuxZDCFVb1aLcRbrxcEwlhjSmhR5NpL88GV48HI3Q7c7RFS37/fdo89eLbdu1l5eFKopzWrnoy1vyRwje0AsB3aoR3aoR3aoR3aof1vat1NJFfhFWNL323u7lt3rSsmtiDWJ37/A+2Pv+L7TcreukaSKtkoPytX2kejEUbDnqykJynNonXhJHfxH33srqLuZEJaItqliSrpqP57Uohqtoe8RjMUpOjWjDdhBajEURYZWZYJ8+z07ER+n8/nqqjV4J2SHO0qO9WNynOm63MaOjuOgzDqYzG/Rz/q4/L0Er/7/e9w/uxSGCN5TO8dHfLAxNL5HOvVGv1oIL5S2w7r/hyDBGgCRL8v2lHVDY57Ps5OzrHOgLcvX6iEtvFIJTQ2DYaDAc5OT5HEa+lX8R0SbyG14e0Q2P6xvTGwxwnYgmodxejB43ttyzLcf6z71oGcCvGg9HUzrwG7xfmQIQ22AG08ZqPpGX76sy8ReCUKcRcvgSpV8l44KNwAfn8sBV0ex7JfYVDCzm7w4eUSz197mLchmuEAk/4QY3+Ilimcj3w8GwDniNGmG1y/X6EMTnH5zTN4dos638BoEgleqCsFrBW59gkTmVqDhsfA5FhQ8ikCIcIuEvkeQaRWJTwKwKv6VfnWafmegEXK9071uAIyWqZdDiKRhl6/u5HCmV6AKllTs6Y0mKuCEMhcM1HULGzJ7CEMm2PC5Effwip0kFUurNSE3TSwGSpBKykynAIfxSYVppsd8l0u8piJpC2iqC8sq3VKMLEHxyEYXCkwpgLakrmbBDLIeiLwrEC1znxfpfFpOagEdtBfTUtmKXOs2i1o1KWHCiC2B66pblEgumJzdj2lpY8aMBfwYTvG1GuUdJuso84vSrEI23qNFrEkZraWJ55kZWPgapagMhwMR2Nk6QbZKkbpkcnooNmsFVvVtRENpqjjDVZ3C7TeMZJRH96xg6+8CmHNUAwDSeWh8V0EvqVSWcVrrUJbKXBNpOYZgQ2OoRabZIb7+3eYXBzBdZkcqsHHLbCm0qOFSCl+WDokQnZVnWndj5x6lE/l7pzsFlnkm5bRSnqtDjeo8wKbxQrhcADb8zTgqby2VICEoovRUJ+JqhxztaOkygRmjZoAXIGB2WDsWtj0HGSWi7BhkqyFMrBQFA4+LGwsFi3sao3IWWHUi5G7Q6SzNfJ4jnB8Bj8YShBCI16ETLmtYHGBhCEaSYnpMMDx6QmSskUaL7WlgNpT9dPez91U1o2K7oGuZ7ZgTOdVqZ/RJ5gMK+63p7zs+GRdFsg2BfxghEdfPMWzR1MBmQujRiHH2VbgWqt87+RYmJRrVnj79o2wyXhs1FwAeIErSdC//Yff4NWrV3CY8vnFT3FyfoK7xbX8ve5Sx2sT/fMUv1el7woICKbgcv6w8PjJFxhNJljMF0jjjQByZHIznVbJUNU1QbEgFQtbwDUuHAnIrXwRmy241slC9UyvJ3YVZGDurnlkxpkm0iRGmm0wHgxkjN3NZojTRJhwex28d23QPp7b37vn1T7uILbusW4ju+vu/vuwf9Dl992zHRDNRQPFeP/LageJ6KEd2qEd2qEd2qEd2v+BpmQQlKOpFK8do+2Tr94Ba1sA6VOve/iOrn3/RvlTbXdz3DHJuKoehD4enV/I6jt/p4fY1fUNVusElkkjZuMhm62jLggjS1C07llpXUpbB3ZJ4qqWx3SSUZGQaTmpYgLs2Asd243MtsFgKH/uuxff4er6Wnk6CQmku6FXoB0ZDepj8nFt9kzmAhocTY4wnkzwy//n77HaLARIOXt6jmc/+hLzqzuUcSzlmHhiizdSg/FwjMcXlwKwKLhCwV3yMxkoopJTLB4bBlzLxmrT4Le/e4H8wxVOnxzhs8efCROKDCv2xWod47vvXmITrxULSsuoukMjJdUe6LMrzneMg22Rhb0vAiFagvWQwdZBdN/Ha62mlOK5sQN5I33qJsFKUi4HJ3+Do6HyzaK0Tw43i760EPabF02orUWexFJoel4Fv7rD/EOGN7cmbgua3rsY9CJEfgTPC1CfBBiMTTwyclhlgtn1AsvKw+jiFCGN4YU9JzGB2KzusZzN0R9NUdWmBlcVAEaDPRr0tx2jkWARQaOChvVa+qgTMVWAhRqPlOjJeCMwJubzZH3wZyWB5Je8htJRwxbZ6GqeIV2vMRwGGI7HJK2J/FE8g8Sg3EYrfQTkVD0yCIHpsmYF2+OQdHBvuLjJDRjzCr00gedkcCMTQRhgvd4gT4mYNXACCxiMJQ3SKugz5QrgUuaJAI3Dvo/AKIS1JPmmBM2MEI3LJFT6aaUoc3q/6fGpWWsqIIT91OivPd80AmsEjzSA8D0Anf0mRbySiiqFnPJWI/tT5jYSHymD5DwhkvHOx1DJx33fQxgQLE2FQSesUddGhQizeYz1phAfw7oukGxWqGoP0STCac/EellhnZVoywQ2wQrDQdp6KNwIrZVjNKxx7hmC/aaZg8r14Hj0YtyFPez79pHhyHHC8VzWKe7v3yMaDRGGvmI8cuzQi036qUtL1f519NJjKETTMfTUubX1pWO/cK6jHFmAfh0gIzJ0ykPZX+w7kh9ltkGSruGHEfweWWtdGIIpQRKUXzIwgUA/GdHcL3b2dsw1BjICpEWjpMoWxxzDRjzEhoOXlYl62cBb5IjLGL8vczg3axTlGtMmxuPLAgZWiCYXKHrP0MSmsHLJ5KSkkNJRzwc8IqUJ+8aSAAgCtlHPRNza+Pa777Bclqu6hQAAIABJREFU3sn8J/PTdr7RAQh7ElI1/+zk7ML60pPSDo9RMxpfovrKEEYzQWSy1krDwXR0jG++PIXP8BEGmpil+K1Rui/jTq5J2jC/hUj17+9nGuTVc7hhYDqe4ur9Nb779ls5P6bjMzx79jWWqzvkRaInYc3SVAihgGhy7PS6GecQcprPTy9xdvEISUI/0aViacm131bm/YRJJVCE0mSOL7LXNBhelZJ2rcaZSj3mIlc37vQFQPehTgnVtgzSb/Sbq0ps4g16YYDA93B3P0OcJLJ9NUa/B4X90fuG7hr0B+8h9M9GJw99+LDagl5UU3PvXx6w1rUDg+3QDu3QDu3QDu3QDu3/UOtSv2jgz8V6MRfG3l3t/h3u9gZ174E/gcnG9qe9qtu2Lnx0KhmNvlebtchjXNfBcDjEeDQUltcmJrOJkjAFfMkm9lfBt6jOngxU31TrGkWBP5rJovpDsfz4gxQR8r3ZFvNsBFXoSUM2GwvVi/MLjEcjzO5nqOpyB/oRRGMB2wF+pgVbfKKUWTy3WeRk6y1xen4Kz+1js1pidb/C1bv36B+PcPb4Asv5QopqZcRtYEV21R0T5FxEYbQ7UB14KMY3rOlatJaS4UWehUdnp3D7x/jdu9e4f38Ny2qEJcF9DMIQZ2cnAubMF3PhsOwGw+4Iqp+2EQc7OY9mL2yPwV6Rqg2Pds91j+kNqpfR04gsFvapjcL0teyI4FUOs/8j/OTZl+gFDlrbRcWkSYMQpYkyr2E4AYL+VOR9WbxBa5noBWvYyVu8fZ3h+Z2NlRWg1wtx3O8jjIbAqAec+/h82OKUCQDJCu/fLVGGp5ieTxGKhE8bz1PCyJTZhmmfAe7e3yOJF/BDBl7wyCjQiJ5hAq6JzJGsLDJBOnCN7CnN2tKFqRp7XaLhQz5Gu88uki5TDEX2iec7CAch1qsUdx9u0O8NRAZJVoliA5LRpoz8lQzUQm0SiLCAkoyXChGDEBwLRWjj3nFh5rakkfp2gTLLRYKY1xaqysHQNTAYOMhsH0VSoc5TOJ4P1/exXsXIGkvYdba9gWEWyr+srOQz8DX0vsvLTAc+ME1VMUKlrygvJRhJUK2TbcuXZt0+GHF6FBGw0GD1/qQlw6p737YD290YFJAP6EU9+C5QlbkYANJrjOd3WRl492GBmjLZ8QTxZimy3NKf4Og0xNRMFAvODpDbvgCnaWWiMkKs+hHCUwdfDiGhGPObFTapA2s0RKDBtV3YQ4GyKJDnDMVQ7D2ecqv1Heaz9zi5vJA5TsllNXNNM8g6ia2MIQlw2Qty0bv7MTgkwIeWZgvoIH2heaPagIwPNWWB9WqBXm8C23O1dLvboPqZXpDiv0VQqzO33445xaB0OFfa7BcTZW2gLXkeEeAtcGRbAtreBjbs0sV5Y0lwQ+o5cOoEy9s7pPkAw2GKnpkjDF1kLVmVTCIl0NYXyXGWF/IZDaKYzBlugSI1YFYNTs+O4fSnwvplX6v93g4fNT92w2PXW9uFlL1XbwExesuJbYAE4hgo80xYWLbTx9MvnuLrJ0ew4KGiNFzgLUpB7b2xqr7IrGWi9GKx3I5fejby/On3h/jNP/wPvHvzBrbt4q9//gucnp7g/fVLCf+QQywMQgWkqmND9qvyflQrMbUA8l99/VOMJ1PMZneIN2sZL1xQ4t9hP7JJiIEkH3ceicpTtOm8JIWZrQNG5LtK034w35NprVNBJchb1pFMpGR8Zgkmw6Fs64bHNUnl+sm3dmzK/b7eHQn1XUC4PTbbD4JrCuX7xFbw6ZdvWWsqLfUvuR0YbId2aId2aId2aId2aH+GJoU45VGUgdAku2vb4vXjJeC979unPw267b/j061jfO0z0HbblBVx04TvueLJdn5+LoUIi6zrDx9w+2EmxbSSpuwKyv2/3cnxyL5QXkMsCLqEsx2rjWwXGqJT+tOtypPVRkknWWv7K/4sTnibTqCrP+ij1+vj+voa3377rbIJI1uB25YPolb1hccgBYjyeGLjd/4dSp88t4erN3e4vn4rwE04DvCMckjbw/sXfIzG44YGJGoEvo9nz75Cf9gXtkFXPEp/EmAzCXKUkmjo8G/Ujhis/+7NDG+++xf0HOCLL59gODpS7AbTkv27vrrGi9dvVMoqgxU6uV0HWOhCW3Xy3pEVz7W9skkz+XbP7T7f9lVGDbPOlTG5FaEW4KxGZRewnSN886MneORn4nvV2Ib4hHnOAOs8QVYY6IUj2WYWr8Xo3PcLePkt7m9ivLt1Mas92P0IE89HzwqAXojixMdpH7gg66qMcX8zw6Lo4+jxGTwbcMkAFJSmlGJTEh3pISYgB1lYrSTHzu7ewfdtDMZTGY8dw6hjqynATYFG9YM0TPapOnfILCI7TUzoBZRVRSs9+IXhphkzYuhvK9kVzemFGclE2QZY3s3R5AXOH18qVpHDIASGJtjCLuJrCUbmNQQ4o7cdYUrHqWG6BDQ9XDcWVqsK43UhiaV5U8CKQniuj8gtEDQxLM9F7kSYb4Byk8CxagEZCXBkaQzPNgW39Mx7oA7R1iHq1kJLsMW0cL9coUjWCijSKYSUAyuGppTzWxaW4AUyH+zkyDKmBKDuEglVXxEvULiylkHKydax2XThT1ZsMMDRIAKaDA2ZWXLKEKmwcEvWWtViPD5CWWTYbBao6xDj0z5OvBxZaiPLa1h2jaA/INaK5f0G68pGNQzwOGjQa3JUaYW0cFF7roRE1GWOnk+mnaNZayXKjKEY9ONT5KaqTfHh5hUGR1OEno+yaJVUT5hEHEvE5Qis6YURvTjSsVcF9tCgi8hndcKqnGfacJ5SY1koIHuNixIiJdZjzKiRxBvYpo+w11P+WbZmAsqXAUPYbRx3TL/kuawYUNKverztsyjZpxQmF3rMoazg0rPMKcXbrrJc3LY2rlLAu8qwvvoWiQ3MygDxJsFJG2MaZji9AKJBT6S367gnia5+RE9JF6mMpQyhY8NIUwmXaErKe03AaeH3PdysYzz/f38rLFSFle0k2GqO6kZWJ49X8/H2NSbZeqofpI/bGukmhmVFiKZT/PiLKTw7QNFaaIxas/14bhpoOAd3HpatIay12+trlY5MabKWhU6nU1y/vcG33/6rAMRHR2f42U/+Cm+vX6Iokm34xIPVIR5DkWo2ezCUicvHn+HZs6dYLpdYLedK0iv74OhEce7bDuDeyUG1FFQvAnQLU2KjIHOWSj7mZ6i/FwahzzcmhJYV1psler0IvufjfjaTxTCRU+9dLnbA2f79xa7twDX13P7P+gXfv6nYf+zjTRrqMUpchcH3Fw6sde3AYDu0Qzu0Qzu0Qzu0Q/szNGGO1I2WS3Y3nh9Hq30KKtveLX8fXNNg2Sde/cfblpmiawphTNSI4wTz+UI+RxSFEjowHPRQlgXyTPvS6PfKDbnUNnonNGPt4c8aAJIVbf6s5TDCglEsEdasnYeaKuZVUET3duXNlksSGv3injx5ImBMkiXKx00KU4InChBQX/pnytuEWqIKmbJMMJhEuLj8HAW96OZr3Ly5QVIXePrTbxhjgHKRSPnGgobFwtXNe+RlgajfF9koH1fAnir1lF8Vi7AcrVnCNehrFuLo4gvcbUo8f/0cbZZiNB7L52KfjcdjTKdDJJtE+lVqkc5jTg8PCZzYx9ak0/fYH3skNgGTdNGkyHFk1NBYnumDGQzDBcwQDcFD2UsT07On+K9fnWJolKiMFpWY4hOoMbBZVygyE1F/jDxJxLjb8g0MnRmK2Wu8fd3i9SLAyg5wNBng1O3B93poT3qwzjx8FdSYNgmy1Rqv3qxgjR9hcjZGYDPJlPupJXy5DjGQtFidnkePNRbSZAAOIqR5jtu3rwTHoteSmM+TtcYUSDK1CCY1e+AaPdY050fnomqGzR5ArBNXBQ7gIdxjdCkfQQWtqOdbBL0Qjh/g9bsbJet0fBWCoD211HkBSVll6mZj2shbE7V4ZdVwzAIjs0EUOPgQOahMB4RHBkMy5XyYdYU4qcTE3keOQa8GwhBJYUs6K3fDD3so6xbLdYHaHAooIWOkpWegJQBHPwphuD2sVwnqohQWlABqcq5qH0QBkbTH2oPxpb934JoAbAqcVzPTwzlD/UfwjucxQYwzjHxXsUdtSuRUumFetnh9s4QV9NHrD5Gs5sjIlgomOD4NMWpTZGkL0/Ng0PeuqhF6jciJ09LFcGDgwsvgFjHyxEbc+EDgwfcMBI4pfmPFZo54/gpNaxNnEvYVU0KJm8xXr7FJFjg+PxPQiow2pq1KkAHTZwVcY16FYtMqpp+en4SNpmXn3Qm3HTt6LtRejgpH6pi8/J+QK6WcCeL1BkFvCtt1NWi3w9IVIKxN8PaYgN3lQF07lLedeqMK6GDjMeKYI1jHIAQCX3VpkToFh+PIqjEwC9xWBazTxxgZQxx5FmK7xrr1sE5cLBc16nQpQQijKEHr9REnrcyPBAMdJ0CSFeKFJ+GwZFlVLRbzGIv5EkcDD5fPvhK2YJ7Sq1FQs92ctTe6FCtLDUL+Iyjle8w0JiHPEhA5S3PYbg+fPfsKXz+aAqaHXPqD6asOTDD0QDOA2d+Wgbyo8OLFCyzmc7WQw6RoQPw8+1GEf/mH3+L9+7ciX//xN3+NyXSM9zevhO0mTENhGYr5mwoL3Y5zyrF5Hajh+yH+9uf/Vd774eYG6/VKFp64OMRFIF7bue/CWiPI24UZVPSyLLZSbSVf51gjWNgdd/lru37iSUSQVYNqojg2TWGa50WKo+lYtn9zc4skSwW0U+y2bvlLb+cBgLZrO0j9+8Cbap3n5+53fPIWxdj+rFjDTHp1vidN/UtuB4Dt0A7t0A7t0A7t0A7tz9hUwiYNkJUMZgew7d/sfu8udncDvp/W9QduYn/wmQdsqIePCfxFI+ayFI+ozWYtjJ9er4fpZCwMtzzLhDkk79h+5G4/duvfW+BnqxFS1WQnK1PeRkyk3BeoqQ3yfyUZVZ5tiu1Av60SaUqPnBbn56eYTCbifVMVhfLsEW8tJWntUta2gIAuANiqshDWwunFBUa9KfK0wPJugatX7xBOhzi6OEHZVEiKTDZCkI79wYRS7lcYhYpFoguYjlFBxlkpTLRS6EGBZeGzs2ME/RO8v5vh/evX8kmiKJBiybEcnFJW6rJwykRGJIDFtpjXPbo9ZqqoVIX83njRrBFVuKpEVdNo4Fs59xYlQpFT8aixv91ogL/+0VN8MfXQUlao41gb00FRWWhyD14whOt7Igddz+8ALDA07nD3boFXV4GwYNAPcdTroe/20PR7KE8DnE1NXFo5vGKD6zdzrCof48tHiCIHfmc8X1doS0r4KiXho8xTUnhVkAEI9LUVmlal7Anr0e1hfrtAntMzz0bdGlsWmwKO6CnG8aTBJH3oTV2AdwWj1OVSrO6ScbtO7EAPgkUyKolMaaN5AgJkGY1Hfaw3KZaLpbyLTA1ho2wlfMr8XHykaEpP0KMy0QjQVsI3CkwtwPeVJNqrgYFbocpbYSIZfigJl0hjRE6OXs9B6wTIswZllsL1HHheiDQvkORkSTGFl9JoXUxXLVzLEH8xpk5ybJPxwmcFPujYa3oq2eIU+wBuJ0fTY2xXrHensu5djpmmhRsOcH56JOcgE0AEoCPTpjXw7m6NZVxiMJoKoBCvKMd20Z8OcNJv4aFBWhqoDE/kiLZZo0gaYVPGdoiQIGJeiOw2LX3kjgsvcBBQTihAbSXjCbDRtiFW85eocmbcmsIQvJ+/hOcHGAxH22RQSZzdyooNJaEVUE0x2PRUtd1jAXO2o0rPUt003M0x20UHBVDyB8uokScrmReCaKSZb/p87eZL+VvsK82c67y/ug8hiwPduGTQAsFAQXE00KYAXrJuedzJvKwpxW0sVHmD5e1bCXx4NBnCDy3kDEJoXYztEF5gSGjCpjKwXpqIZzXKLIZvx4j6poRRZHEpf5v+jNyPtKphuQ7WBN3bNcZehLZy0aQ1zs4nCMYj5EWNNE/U+dCNGjVpbc81AmBkB3cSfwJdvN7weIzPHuOnXz3FYBCioMxfzimmg9rCNFMAuR67BnB19QGv3rwSWwF6KEq/WRbGR0e4ufqAf/7tP8lizOefP8OPvvkZ4nSBxepOwKit92W3WEVGXDcEOKeIFYCBzx59jp/85MfIigz3t/ey2MOLjOe4kv4r2+IiFT3WBFijNJSSUAWyiRci5yoeY73Ysw2K0KDttn+0qlidgwo0Izst3qzguw56YYjZfIHZfCmebTs886PzdNvbu8fUCO7GceeLt3vHw+W6vfbR7cj+z+2e15pi8P3/qx0kood2aId2aId2aId2aP9B2tZAnF4tUtl9oglD5eMHO2BlDz36xH1xB8EYP7jdjza8Q8W20k2m600nlI2eSegAC4Xb21vc3jHdU0miVKGofWv2tr29jdfFv6olOvBIsYkU24DyTRuu40nQgrkNRFCFOt8owKSW2/CNNACPop5IRz/c3uLN6zdiCE/5HskLst+yH2qXVBikAnGMLRjTwnY8jPrHmN/e4cWrl2iaClZo4dnffIWeF+H983e60GJxrAz2bdvD1z/6GpPpRCUp6n1X/Un/mwptQxacC7MORQLauA6+u7rHd7//V1hVgWfffI7p9OhBUfX65TtcvX8nTBr2i0iftodFl0m6Fts/9GpfFRjH7nKtEpZZIi9d1AZltyZQk17l4tHlOZ5dWmgSAmpCfEIjf8tGUdI/iImGoQBZVVHC9U2ExhLz1+/x+vU9YE4R96YIw0CANSsIUI9CRBMLj9waUb1Buknw7rpE//Qcvb4rclBlPE/vIXqt7YznWYh2wBpZa5C+U0y2Wp7XclBht7UKWFrP4JkW/GAsz0sPcBvaF0w90jE/BOkQObHItEWmrGXDGojt8BEpsPlbZ1Qv3vIKLKPn0pZZyQTPxsDibo06S3Fyfg7P59ilOb2W8NFQirJRwxCPLEpf24KsohKuXcMwCULYaP0AOVNINxVao0Aw9rFKgTbZwGszBHYDy7dQen0sEwv5OoWFCr4GaZm8SQbTMPLgs7gtCFZBpIAWwZn6/2PvTZscua4sweP7gh2BWHMnM8lkilSpusqsp8ds/tv8tPkwM9+qqyQVJZG5kLnHgh3wfRu7974HIJNJit3TZVZV8kuFAoF0OBzuz5/jHj8L8PbNDdaL+U6yRSEhtI/Il2rfWysJpDpHdViJ2h27fcTnrwIxSYY4OTtGL7CQVCbc2qQRz0zDOMvwbr5E2BvxHLJez1FlBO4OcTy24NTkjVbAtkhmbbHHn+fUSFY1LgsH7sTGuWkgLxukCY0JwAls+LSPWV4svn00noqsRJoTI02CCao6xeztP6ExXYwvHjIYS2OJk2YpDZQZRsR6lImBmYsqFGOXGHLADhUQTQWP7Lz91D7T8lrFJBYGUQOjSpEmCYJwwDJiYkhp2a0w3vS+VX+rMck3CjhUQstGxbuOAHz64RAEJWO3ycPQtuHSmCMJJ0uVbQZS55sUy+UGk8EIrlnBtwuYLr2Jh5nhsGy0vilhJzE20RrTVYzVIoFT5Tjqxrh7K8LgyIfl38FNNoKTVvBojNF4TTbIyww2sVGzEk1Gp7Yj8xaxCnsuZlGMp8+foUw2wtrdwTwGOqGv4Wzep1kao8gaeIGP2/c+w8mRjaywSQfNn8lsHNi1DYv2oZoKaX/RzZUXr35AVMQsA+eMiKbhcJVuMMDvv/09ouWKmWcPv/gNfM/C1fUbIYzxxVFBpgQO6UF+IG+lsdTrdPH4yRN4rofZbMaBC3TECVh3WaorslIOFCFWJI1HBtMEUCNwjW62HIYW7AAuzXbUN6bU2OLQEd42ubamSYwizzAZD5GkGWbzBbIi04Q7he1+Ghj7+Pov79x89A1h//iQ8fbBood1gNbVCjHWN8L+FqtlsLXVVltttdVWW239OykGbggRYKCNGFCHxjW6Dv7Y9Si689sns/3MK3ZfoX/9V9/9ksxmqyrE1IRttsxACcMQg0EfvW4HVVUy80r8bnbduXo/ZeytfNC4Dj+e/uxKHqNaDtXc7BtZDXoQm00SC6XpoAYmy3KkWYbBoIeLiwtejjxxGBzRQizNblJeN9pQmgBNZsWVFdbRCn43xIPPH7Ff1Wa+wuzNFFEe4+KbB3AMB9v1RmRHhsmvvbm8YoPv/qDP3nH0XpKdKN5JJnFzakr9IyNrariBST/Aya0zzGoHr77/Hqv1nNPfXM/nQzkcDthwexMniBMCUj70YNNNvNqBOymQGM9XbCp/1LWQUkBE5TNrjfvGilhGQ/z26y9wEZZsos8MHA4tJJN0ExU8BL1jZoulxLqpyUotgZf/iOvXCzyf+Vj7EzS2BS+K0HcGcE+OUR6HOD8ycNfK4eRr3FyuMU98jO9coBtYzJ6hY9GQ8TyZfTNrrWT2GstBCRgjSahZoCHjcvbQksTHnNhGB0AcLU9lOwHyusZ2O4fDjTUhqsoti/ER2V/ixadZWdYBO0t2om4IxRdqN1x2TKNDCZ+iXqpuXIApP/Th+D6urq/Ya8lzA2ZC8bHh4A4FVLMXl4naMtlHqihMlIWJwnTguzZMz8QNyRxTEyOjQhASCGSwIXpCcti8hl9m6AY1nG4HUeWg2KZsPk9JlCRhXG23qBri91DKpHKMNxzFuusi7A8wX0YcJMH7hMBDBTIyo0ZtKzfrmuWnxx2zqlQDzkwrwO0NcffOKTNqUjabN+DQ+zcGrpYrzDYpRsenzOhZr2eoSw/94yHOexVRSAkH4vOooghWsq4nU/sUuHR9DAcmzgzaf7KNxCC1XQuBTRLcBgZJFKucGZ9pWrI8kJhpJJPLyxhvr14iGJ5iSD5uyQ2DaQWx5BisJRaYYj6y7FLPDfroClCjpeaCf2nppkoOVWNE104iTEADf441sxGD3phBUD23CYhL+/BgVlZJyvyMCoHR8nkG7plBKYvyMVLvqcMqJNmU9oksS9uabFd8g2IyGVNqAIrGQkkMypI+Wo6OWWLiWij6NiLPRVD68C0HdcdCAgNJbmG9MLFdpwgQ46izgBn2kMQmiiTlMe/5HWQk6zYbuIEHVLmwuEoDaUyAnoXbd87QeB2sVgu5AWMAva7PNyoYyGnoHF5xuu1ofI4nXz/C+MjAxiiR1gaqpIDZWDz/8sjWJv+Wgelshm+f/wV5lTO4JsfJwMn4FOs8xr/80z8jT1KcHF/gt7/5HVabGRbLm90x06pM9mfkcX8wBxh0fSlx+/ZdfPP1b5FlKb9fQUxKkuQ6LhwCNOnY8jVE+UfyjQNisBU8vxVlwcEJOixDDvn+GDLTcTeGdgdZhoUpfq2073zH5iCDq+kUy9WK5wW5tmrwe8/YVR/ho+8AH//r/0DtVvTTbxD0/cAkljkBjX+j4BpVy2Brq6222mqrrbba+ndY9AWV2FfU1GkgQb4X62aMlzpozNRTh/90uL5f/ue/Umr9zX4NEkRArLGQUz2PJkd8Fz/abvHu/RXWxKyxySNnRx/74Lv8js9mfALgYKN5CoGwmSXEkkBmsAmTjdkcxGzbSc9E40bsFU5us0yWM1LSI2336x9+wJQYOxzvWDHYwWbvDK4R00k8d9j/jftm2TYCDo4mZ5iMjvGvf/gjprNL3tbTh+e48/gBbn64wma6ViBfDUvJeo4vTvH5w/sidyIWBwNeEkYgzTKxs+qdcTkRTTYl8M///Bck60tMzvv44jPyf5MUOtoPy9Ua3/3lO/Y+IwBJ2C/7Pam4VupRiUf3j5FEMV5dbpg9xXgTfXrXw8P7D3BnYiNfbZhVRYwuTps0bZaPeuEArhsoQ/MKnmcgbH7A6mqDV289zOsAVTfAyA8xrDuw3A4WfQPOuMLvhja8OkO8TnC1AsLjU4S+JXJQbipFwkfAWp6JZIoYafT+FfkwEfJIzLa6RENhB4ppxEEGJOMjZgibgmsplwCjmjWY5MTuiNANeszOoa6TATb6d8WOZNaZJBuwlxEDS4pZqbAmdYLI8zqgdScpVSb/DNwqNhsHIRDzqiZmm43NcoFXPzzD+a17ODu/w4EJJP212JSefPsIbCXwy2AWFTHaPMeARywlOVLYwMZ1VmOSN7CLEtskRl0mO9mz3dToeJRT4SE2+piuSlgkG/VtTqnllN0iwmQyQeiGzNbjNVNABQEhTY31KsEPL1/DNkr5TKqvp3OKmG182mvGqXawU6ws+l/VODi5fY6Tvo+GmHzE0GOwHMi3Ma6Xa/SGQz5ft+s5M5Ps7gC3jyyWepaULNEUJPJFnlFwg4XGCZF1XPghcGySGVrB4DSZ/hNDtIZ6TG9CzKCS5MU1jyceL8z+LbFcvgPBtMPxeBecQamdVrWEgxvMkxMU6Ij/nErolMwCAsGE1kTjhf2uhPjIn1uEwgrAZSCLGLUiW9f3DxhcqhLkaQq/e8Tnq2ag8nTKfloKhJedKsddhbR8wGhT7GYeaxwIIz8ip6S5wJJ5tuZoBQZqKHkzTWbI0gh37z2C6ZDnojBTCfNNCdfMa1h5Ac+q4HqUDGwhNwK8qy1cbxp4NymyOMIs2yKarWEUOfxii8lRgYtTBx1iUNkn2G5cEuQi7Ab8WZIt3XwomUFZbygJ2OQ03ZLGVABYfRvvX7xBnCx5v1R1gWS7ZUDKDcd4cP8u7pyFiO0GOd08IZlx5QB5gzLJ0FDYTNCFZzlI8wx/fv494iyBTddMFUTQG/bgeR386x//iHi9gW25+Orx38HzLby7fM0Y/K54zpd5YXetUs+XDb1XD7/9+mv2y1ss5sJao+uMTdclZd7PKl2ZyzgZlD39JNSA5jJJMhZWJB9fdU7tMTV9s0RdF1VwDf1FY2q9XiAvMhyPx4iShFlrBNxxErkapwLMqhNY4hh2V4XDOuCSf8hO+6X6hcU0G8+mea2tFmBrq6222mqrrbba+vdcnBh3mDb6c3eQ+Tv1oT/Xz9y+/ghs+1kmJuazAAAgAElEQVSgTYESHzxWoIO8WAALktl5novRcIizszMOHaDm4/r6BlfXc2al6Dvq+tVsIM137vfvLqsW6powRYSdRqCdAI0CrJEEipprSwFuBKaJLFUaB05lU2w0an6CIESv38dqucCPL16wlEm2gRgrIjFlRoH+uJTgqbaYl2NDeBO3b93Feh7h1ctnIsdxGjz8xy/RC/q4fPmWmRzcBBOAQab3lo0vHj/E5Hgin427cgLc9gbaNUo0JklUTdj047t4cbPA0z99izxZ4IvPH+D07PYOeCRp3fPnP+Ld1Xv+jGQCzk2YNp1vDPSCDPfPj/H87RpRSr4+vEVoihre2T38w+cnsOIVS5XYy84WL67K8GG4A5awsQl3GvF+7vlXaJYvcHlt4u1iiK3VgdsLcWx0YVsBmnEPxrmHu36DYbXC/O13WG8NmKNHGB1TiIH2xhIJHzGmSMJHnldZIYw1AtdYEkqMNZbdEgAnktAyI+8iJQtluZ8GRg98/jS7UcmT6CfJVsxu8jwCWUkqJ+NXy/J2ibPaBFyztT4Ok1CMkF0zzK8R9o2AdQpko3FI49G0EK1n/BnGk3uYLVYs5zo5OkEYuLBJ0uhYLIEW2SgBbeSFJ2bxlC7ZkFaXGG8Wne8O3sNClADWuoSVEJCQwrALNlqnEUfgZdixiCKFdeng+sUNmirDyd0zBvOSaMXb2gtDBKbH3llbq8GlRemtFU6bBu/fzhAtZwxuchquYqex4lkjArwz6HwTf7CwN8HF+ZgBRZPZctRlN8ibGtfXc7JJw2A0QpJsUcQR0jrE8WkXY1NYi/QC1xaPxzI1kWQeYttHc+Tg3K0QVBnKvEFO8aGOC5u2g6SITqMALJGBZuRrldFjATDyKsbV9XOMjs/guh6PJRpvBHqIbK+BWVWYdF4iyR0skjGKytsd8EalI3NSqsIrGGjTclAFQGrUgZhvGtRgGXFTYhstYVhdeGGPGZF6DuT9qgBd/h+HU6rHu5sNO7hlD+x+MNYk8ZbmXpHNq3TmhnwgbT5m79+/xGAwwXh8BMc24XgkG6U5lYA2EmibKBoDGSXuZiWcqoTnVrBdGncE2Lr4oTRRTEtYi4w9Bt+nWw446eQJwk6KW0cFxmMP3nCCdTZBmdBhMhF0u8izjNNrPc+Gkeeo0hooHZi+jXW2wNt3ryS21qAk3Tlsy0M4usA3jy7Q6VZICXxm8MaBUdNNGvpcBITS9grzdbVc4s3lK/ZU1DccaFa9uHUH76+u8PLpMwZAJ0dnuPfgIaazN6ho/tcelXJAFC3RVGApHRNTkqvrEp8/fIj79x9gs9lguaCUW5Jzy3WI/cXUucBjmBiT7OdXiIS9FHl7zfG8B5dTlqgfHtvDI66fl+2gsb1a3aAbBAiCADfTGbZxxOtnYI0Bxd1U9Yu1B9MOvwF8WL8Iun38NAPsf1sJob+mWgZbW2211VZbbbXV1r/zYlkZgUqmqZIRNdD2KZDto6d/AUXTix/+/ZN/2QF2moF2yJbToIUwywhoOz6e4PTkFJ1OB3me4/p6htlsKeEF1Lju3pCaon3TQevmxketnr7oC8BmiWyH00HFf4i/0DPDTf07sdoYkJMNY1aaAmOoXaCkz263B8f1ML25xutXL5jNws208sOh7SB/LN10CdtEyeSURCvs9HF6coHFdI4XPzxHnqfoHQ9w66v7MOsai9fXqEjupkIYSK7V6/Xw8OHnGA8H8ll3TDYBMUQyKs06QRTkn5XXBr5/O8PbV3+Bjwq3zk5wenF7Z6BPEqS376+4iWQmBTXsTY2+S2buJbZlBwWBEtxEksl9B4++uM1pgeXmHfvBGbaHxu6gNDuk74NHLBvTRpJuUOclgqCCW1xj9naB11cGtqWPpheiF/YQuh3YnT6qI5/9sy7MDG6ZYLPcYJG7MHo9bgCPuy5Ch5g1BJYRm4OAFWJ3iH9aRcAfA2uyDwgcFa81MvkX9keRN5yUyaw1ZoBofz81CA/AUcHXBLygc6VsKLxiA8+y4bldiiUUAFd1sCLxlQZXEjE12LYLbt0DH3pUshxUGaDTM0pWSe+HgtIhV+iOxwj7fREJswGghfVyizxLcDI5Ruj7cBwavwR6kEegbEdFABHJ/EyXwXSrqeDYNTPkctPBTW1hvq0RrAp4eQKT0mDtksFJAvZ8x8A2TuAPJ8hMD8UmhW1U8EiyZ1LAwZaBgY4ToKwdTG0Dr8k3y6nwGUoEWcOgeLQkw3cCZxmxkPNEIU3sHeaFuLg4ZpZo1thwSxN+QwwWA4toiXmUoNvtM9gUJxtUmQG/38NR14VZC/gAq4LdFDCyBlFqI659rIY+TjoGxkYGk+R1hYXCcGG6FjzGSGsGeMyagi4k1CIvCNxQcmETeH/5DFbgotsfwKyNXZABvSeBbGIsL6AYjSPfXGMYrBGVLqZxHybJD4kVxjcPJNCCxhc5nolMXXnTHcIQ6m/LrFAkG2SlCcfvwLbJgU6NFwXZ72S2O6qg4gUq0HY/1tTwE8RXzYd7BuXOM5DZvorZZtqI1gv2khuMTmFbItXlZFGHGMcWJ81alOrI4C6JtUmmTKmb5AlYwiVxuFPAdimF1MMcDq5SA+msBNYpFtEK6/UaeZogLHN0nBgXZzUmkxBGcIxNOUSZ1pwE6gUhB3GURcJjw66A6/kN5tMbBQ7buHvnAUqm+FY4n3horBKFQcwx4sQ5AANs4jNHY48Yesk2wounf0aakh2BIKF07o9HQ2YgP/3+KTPiws4Qv/3t7xBtV1iuZzwP0e7UQQY7SSYDpkparxhZdMPo0aMveF8RkJckCf+bfcBa46RtlheLxJ3nNeULyh5sxMKla7WSk8vx3weq6OPH14vdCFH/DmC1WvLNjtGgh+02ZhYzseO0vFa/Tg9CDeIeXtf3jz/+l49rP5/KetVyP7O4MOfkJtjfshz0U9V6sLXVVltttdVWW239Byi6S04/YnZNTbtGgg5BsE/coP6F776qxfvgJT9d4iPmmv6Orm+zK9GUAD8VoijCerPhRQlkG42G6PU7yLOUTcylgdSr12CdABbSOBz6yCnATMmymt1n3n92/XLdYPD/2Lhe3OoJsCjrihskYhkMRyPcun2Pt2WzXpNglBs3WYVKi6R33hk2K6ANBoo8xXxxg16/iy+/fMI+YIurKW5eXSI3Ktz9+hGnNpKpPwMwpsG+cO/fXyGNU/R7ffbr4fdSDdJuH1CTZ9YoGSwxcDH0cXTrPrZbA+9ev8FmO4PruMxioNdRiuuw30cSZcwWoQ0uCgepYuLIZ7BwNLnAb7+6g5AABvbHow6gFNaaPYTVOUXQm6CqcqTJhmVw3WAFbN/i2fMCT298zNGFE/Rw7FPyYB/GaAjrlo/PB8AJIhhJhPlig401Qu9ojFHg8k+VbrFdXDHzhPrMJCtUQihBaxUak6TPxFoj/zViFlUoCIBLqWGtuOnPVboj+2NxqiM1xyK1VYdMwFAaPzumD+FJDTM/SSZWmwaSeAGHgAZX2Gw75gjvfu3v9+HpdDjs1TCQ8c6/D0JIKjLjv+Yx3p3cYumYJI7qk6xBEBCo5uJydo0iq5hZxf5sHLLBUZAMnFYUvuA67M9W1iYqCjyoyD2vRN+qMfAtXFPyY+XAzG1CIjidMs8j5FWD3vgUrh+CCG1u10ZM3m4RpcdW8MMun0NRsoFh1ggoaqI0sTYMXBPAZ5W4OyTG5xirTYq6zIVOerALgv4E9+5MUPoOFsSWIjCJ/LyaElfrKdKqwXA4RpUn7P0FBBhOhhiHalzWJQyzgF1nyDbAOvERuV3kRx4edBoMmgQ1SUULB5XtwiWghlTMdA7WBbI040AMYqHRWCLWGoGRSbbBzfQ1BqdjdIIOg5XMlMwEWKNxRDJcGj906ARoM5CWHlZpBx03w63RDYqcDqcroBVPIZpxpgEHDbLpcAcZC0adIonmqM0Qrt9lwFXCeGWJ3bn+8fSsn1MT2X4+kwd7fEOx53absfeSpH+o8gw3Vy/hdjoYTo52vnk8d9IiJAkt6RoiQKUkeoqklaSVFMhROyTjNDnltiFZMgp0zQoTx0TTs7EOHPQaHyPL55sb26LBNrOxXtUokgSusULPj+F3fCSZgyxO4AY+j8fFzRV+fPkcSRyxXLcf9HHWv4WmthHawPGJidpseP6ridpIwBp5RjaSQivXB+DNy1f48fmfmYnM8m8FS52en2E+neHZ06fsjXb3zud4/PgJrm7eYL1Z8l7n85xufPBfxPxT+5X3iQLuTZMZa18+fowsz7GczzlIhY6T6zpwbIe3h+YwAtbIY42uJZwUSjcRyGNNSULlRs/hEdTstf2PzA/yW4JULAbV5vMpXMdCv9vDdDbHYrXm+UEvpwF+Hjvq0+nHh78P3vlgYB1e+T+q3fX94PfB4h8nhLbg2k+rZbC11VZbbbXVVltt/QcrSZfT/mz1X0fTDp4+/Jr98SKfXINGG7T8btcd7pfmRk7JU5k9RB5ojsMm/SQbHY1GvG7yjZneTBFnxc6ket9Eyhf3/VtKmp42nWbAjFglWjqqQDSRiiomG+8TJddjPygB2KTpUYmhps3BDP1+H9vNBs9fPMd8vuSGgaFCptBVkia4A9iUHJDlosKAIH+5i7M7LGF89eo1Vqs5m9Pf+uouwmEf8eUM8TrmBkR4V4DnOLhz+y7uEBuNzc7VJ+emXbGzTJL+EK/EhMPsJwdXiwTfPfsT4vUUF8cneHD/AWxPWE60/uurG/z4+hVq8uThfdXA9fq4fecObvUtRAsCWBqYtkrlJNaBN4LTHTPLhYA1Ylt4Tg63vMRimuHNpY1F5aJyAwROiL4Rwuv34JwGsI8tPDYzGGWKdLvFJjFg9k8QhDY8gxJCBTCiEIMsLXB9vUSaRjwOuLXX6aAkka1JukdACYEmAoow64j91iTZUcAqlUp7yHpUmAUBa5oJotM+tZeaMNJovwJxtIbZlAj8AIYd7saYxGQo/siOmUZKScUIoTch4zLNNjEEmKD3rCjxMF4gGB7B8Dp7mSCPSVP82eiH/NmIB8WSuA22yxiT8Qj9XpfBCtpGCkCl9FE/ED+zspHUTEobtYnNZpWcVQDLxcywcZUZMC5j1Nfv4FgGxrd68IMAXki8R1M8towa2xqINhmQ5fACm0M0KKmR5Lie62NpuHhDZvxOjZ5V4NwoMakczBcJpjdXQJ7CDkNMTs4wGtiYNhZmlOJYGhgVBqwiYeZarzdgOXe8XrPS1O32MB64fM5ajsES2CKLUMUZkshBZAXY9n2M+wYuyG2ryJDlNnK4sDwLLrGeeMoheXGBMsuxjVMUmTD92Maf5ZgzpMUaw5MTVHkj4BoBuQVQceJszQxa9lgTpJ5/C1igUztruGaOcXcJ1yywjMfIKgob0XRGAbLYm67Zjw0ay1URISXmYGcMgyTs7MWmWGk8ppS8Vo9ZNe7k5N/PuOolB3/vJaN67GkoRQI7RP1cJBFWqw1Ozm/B9SnIQgAQke3JmENtsYyX/dl4fjaFRUmhGrYtnoCUR9sAWUWAXQ2rJH+2Eo7bwLBdJKaNy9LCctXAWGSIlmsstltsowg2yUbdFCejApMjA/3RAJFxju2cQKp32K5XcJwu7K6Ho9EEXWLTRjlskn4SqH+ueawkc3XRNCJjFe86C1EU4/nTp4hWcyXNJNaaiW6/x36DL549w2q+RBB08PjR1/C7Pl6+fq5ANX2B00xhFTRB8wLdtCLA1TDQ6fTx5MlXCMIA05sZ0jTh19I1xrZs/k3r4HmKAlp4zpJwFh5jNOeRtJSBc7khpq8fcuiEta3ZizLPyI0g8X2skUQJz5WDbpeZcDezmbDWiI19MAYOUbAP8TC54aXgxJ9IPn/ueV7Dzgbi018StBSfmNQtsPbz1QJsbbXVVltttdVWW/8Z/Nn0nfJP+bDh57G3X7XI7tv7wRL6fT71ftRgan8232PpzsXFLZZL0l3+6XSKy8sZMytYJkrthWZ66HZBM5HYxFsDJ8JkEDmoNIvE9mKJqPIhYoYfG4LL3XVuZhQbjSSI5JND20fyvF5/gE63y2bwf/rTt7xtsji5SYmPGyXckYyRERruP8gzTNZJz/tugPPz+0i3Mf70pz+w5NTpejj7zS0c9yZ4+ZfnDO7x5+EevYLnB/jN468xHo54+V0vo2SpJBsloI1kejYs2JS7Wdl4frXFs2+/hWXGuHU8we1797k5Juklff43r9/g5bsr9G/dx9/fGqGYr5AVJEEkYJFkeQ0quwOvO4Lf6aPIYuTpFqZrI7AWqG7e4s3UxdXKRuF66Po99M0O8k4X3qgD89zFF16JsI5QJzFmywSlf8KMPvLScnicUDgBeV0VzDRillFZI00zTGdX8F0Tg6MhykY8xCot4SNAjT2yCBwhvzXyLtLpnQKuiRy0IZWtSLp4mEjQBaVyEvuOVKAav9DeVtxEq2RHes+UqFN1iU73GDWBsmrIaYkwr1MBHLuek483vacwk0hclywv4To2nP4xavUa/d47+R7JmB3llUVjUo9TWFhN18iSCCen5yxjps/m+w7CwD8APSgEwUBB7KO8glOXcN2KgbakSDGrfMzMDoLrHF3E6IQVOgMPhuUKG4mwYmK5mSW2TYPlvIBbZ5J46nqSEIsaXtDHm8rAlLAYt8LYKHDfAILGwXQW42TkIjVrXIPknDaMysRRCWSLKenmMByOsI3WzJIsrBAnky66JOMkYNkloKxCncbYrkrEqYuVH8Ke2LjvVHCqBGXWICk9VC4lqZpwOW22UUAtga6UEJwjiXMGzuhgF2WKxfodBsSodByUGSWsyjlO0mIC12heJBkfs1HJCksRYPmsU6nGBEjLeJFT0DEzjHsLZlJN130Y5JNH84caBwxw8dyQC2hrdzk5U4aoGjsqWXYH82rGkRqT+xnzMDlSgbkKQebTSY3x3Yv4/bWpfYHl4hqe20dvPNZqyV0QgkhHacwJyEaMVvL1oh8CPemcIc80LR81HO0JqPzZaB/SmKsKeE7J/mwkLd8YHl6XBqKbGs4sxTJaY66OvVOkCJHi1h3xcnt3Q0EGBgjiv3fvaxyfHDHbr+dlWG0LFJuIz4dgHKr9q3wlOc1WHr/+4Q1ev3qlEldp2+UGx9mdu7i8usYPT5/xcbt75yEePXyEZz98h5LYl/tbNwKhK3CTjyUfa5UGbFq4/+Bz3L97n+WvqxV5VBZ8zSHWsABKKkWbJKClJIPSY2LjkTdkwd6fMsAUqVBV88GxF6nvwbFmcNdEVWRYzGcIfQ9hEGA6XyCKY2bJaaBVs9Q0oLZ/h4P3OvgX/ek/qI9frErvl921/qOX0HlEwGbrtfbXqwXY2mqrrbbaaquttv6DF/kqUTNAANLufvbui/LB33/lSzZ+9uldZ/dToO2wDt9aPabmisMGfA/nF+c4OT6G5/nsn/P69TusNpG6uy+wBcNbuqlUr9fG9Np3SJLyBHDT4Bt1LcQSYj8yBbRpwE0Dc7RCkfZIM0Rr8lwPg+GQQQ1K6Xzz/i2apmTfHwJcpFkigKxiqSN/zN2+VSwE1OiPyPD9Ln78yzNOqaNmzDsJ8Jt//C2W726wullwM6cbLdqO48kJHn35Bcs+tRxV2nM6iuQpRc1Vziwei9JGGxObPMQ/f/cUi8u36PoNHj74nFMSqdlj0JGawWSFzWUC03QAl7a9BMh3KRjA74+k4Y3XzOLxwhRB+RLvX5f48QaIjQ5sL8TQ6aJj92EPO6gmAQZjAw+MFGaRIFmtMU08hJMThL4JlwAKJXMksI8MyMnEnplplQ4xIPlViVUyw+LyPUa9MSzX5+RHAteKTNiY7J3H/kWKXfQBqUIa44q9mNTxJwCLGZ0NHAZkVQiBGrZse6/AOZGBCf2nQo54M0MnGMH1O7KIBkTU+vU4l7Es6yTAt0hilNEU/fE5atvho7Y7pfhlCkTRsi8GPMQzkA3ZGfyV9Me6BK7eXaLj+xgOhnB8h88VkqMRyEaMSxrbNFqL0mCpI/IM0fwKR5Mu/E6I0vTxnMC0RY3BNsPIT+D1yDDKA4lLCUBI8hpmXqDyGywioNmmIEJO0A15nyfRGr7vo7J8vKqBpdvAsQrcMhrcJdZdXYCyN6PaRr82YScJttEGR/0xf95oNUNV2nDHXZx0HAanHFdYaxYxFbMM21WDZRFgOfRwd2DgqElR5wXS1EFuO7BIDroLxajREEuIwTWSCxfs30dsHkJEo2gKmBV63QGPF0ogFWYRgR2UOqtYbsRa0x6LxEIkGbjyVaODROAan18sl1TjjdOEK/hujOPBFPNNF+uEUmnJ11CWLdIlkrRC2B3x1KXBNZ4TeFKoZSzyzYP9eOA/1Yje/dbGk7vBrm4zMC5PgI7NDEB9JlBSZknJnnGE/vAUJoFjO2abmvMIoLTEF4/Sk/cgG80wtLwC2ugmjaMYbS6xtMifjWTUFs9/WSVjzqAghKaE5xWwXAON5eMKLt4Ri/J9gWaVYBZvMF/McNKpEHoR4jhWfqERvnjyCDkuMAoaeEWCJamHQ2KATmFaDoLe0c5bTIJETMRJhn/983eIN7EE2dD/SqA77GIwHOPbf/2WmXG+H+If/8t/Q5xucXX5RuZBxQnWCDmBWCKnlbRo2tdVVaAT9vG7v/8HTsSez2aIthHvY8d1JIhEndt83aB0UDUeGVxT1xFKR2XJsQLsZNrSCbHqmiW6SgFx1aHUYNVmvUKRJTgajZBmKabzOfuX8qYfjJefq4+BtEMg7idomV7XIVvtU4vtnhYJLd0AaOvXVQuwtdVWW2211VZbbf0nKGrkSZ5FxSmLH4Nr6gs0P/yF7+t6UeOvLfGz7DX1Tx+ti9l2jo1et4ezs1NMJhMGGiid7vp6ig3FJCrQTO74K9kf41EqKU8BKMzeUMtIP6rNv4ndIMw1nTpq7qSkAkJSwyQyHvHQkQbQQBiEnIBKDf2PP/6A95fvFONMScFIdMeNtxLgfCDtUubUhoWz89vohz38+Ow5Li8vUVk1zh9f4OTiDJvLFVbXM7UdwgogX67z81u4de8WfGLBEPtPswkY2CPfnZzgFRZPmeQPRcbjmwJ/evoS2fQNOsMhvnz8BUtQ6fPQZzUKYD2bMwPPCSn5cwjbD5HFESd5UpPcsa6wXczw9r2B9xsXRIvywx4GTh+WH6I+7aI7sXHXLdGrE1RRhOk6h9mZIOh1OL2SvbE4IbTgcIKMPYnKXSiBDjIgwKJqCk5+TJOSvY2qLIHvd1A1NoqCEgKVyb82WJNDo8YVgWKcEbFnLnLwBUmWDNgMlGjWkAxEpQZUjbV4UekShiWljSaosohlw7bfVUxQtrTnNxfZqJI/l8Rau4EbBLCDvoR2KORk/7YKNNGkIy0L00EltL2uBkFE6kbjhvbZ9Poao04fo6Nj9l+iH9slcIRAD5HMLaMIVW3DsRxYBOKawiwiMG5tuJjmBqptiXGWIXRj2IEN0wlQGzY4yDHJEdgFUtPAYmuiiQu4jgGv4zPrsCA5qOdgY7i4pFHnNPjatnFd5yhrC+MKyFcLmI7HwEaSblFtc5RhF2dDCy4xkBwHPpGh6gJNkaCIyffNxaXnoztycGqXCEryZASy2kXj2vJ5CRRiKaewIIlRSixIAmo5nZGYkU2EJJ3B8wIOESB2Xk5BGApYI1kxAegMrjGzVx2T3fxHc4c+NsqSUIOyijmmTel5vDUluu4GvW6Gbexju7XYR8x2ezBdX61Ts5Y0MKvZUvtADZkg1LhQAS961Mj5voPV1DASb0g9l9LTEmjSYD29RBgM4Pl9NJYa84zySdDLPt2WQDZi66rxRnOgGm/8Q5+eAgTofDL2slHHtWAy0EasShJ8E9AGFEUDg4IQDGK0VTBdA6XlY1o7uIwA9yrD4uZPKOIpAzNZUiHKXUxGNe49eoizToB4XfC6GsLwXBNlNmPgshuOGRATuzUbP/zwGm/evWN5P83lVHS+3764i1evX+L9W7oRAjy4/wgnJyeYL68RbbdyvmlgiD3V1P48BJBoXmoafPnFE5yenbFv6HK54vciwNEmsJeDc/Y3ZIhdm3NQy14OKh5rNK8JkKvfqD4IKpDzXwBDLQ2lG0g0Z5Gf4Ga7ROC5fO1erdeIyCuUE0LVeOUBs9/4n7s27+Wevwo12y92eKH+qOhaJ9dP2f9t/bpqAba22mqrrbbaaqut/0RFDRYx2uiLPkmjdvUhzvarS8EFyrflUwt84lkFvH38fof+bBR+cOvWLQwGA2bQXF1d4/pmxg2yAA/EsxBvKuq6NLAm7La9oT2/HTMVNBCnGG8aWCPmxoFHGzVOWgJIckFmyJTkB9bANi30en0MhgPM5nM8ffodN230OrE210DNgV+c3i+qiaY+i3yt7t15gCYD/vDHf0aaJTBDC/e++QzD3hhvvvsBDbmpc/csjTSxRx5/9SUmpydqvcrwTfgTAEgXl7E00aocWI2N2nTw5iaFZeWwNzGcQY9ZQLQ/SdZEVRcNnA6l61H4AoVPNAjCHE56g8urDd5MLaxLSmUN0Xd66Hb6MHohqosQ94fAKTIYRYzNfI1VHSIYTxC6e9YagSHEQpIGVIAQakI5HZQTUimllRrTQtL1SgkvIPP5PKWgiakCnrpoKkvktLIDeFv1+CsNA4VBLDUTNgUBECjAMjhhPBHAppkhfFQIXNHMJfbf25vEi+RKg68CFKcJMQwzdHoTwHTVkRWgg8ZfQYy/JELQP0LDzDDFllNgiUZBBHiV9EntsyVNv4xXkTQbMB1htdHYJHYRg3mVhfV8izKJMTk+Qq87ZAYSGf0bSFGUMdzuGQzTRU5gGctGa07V9O2KCGtoTBdz2LhKG4SzEkPECLslzMBBbbjIKhN5WsNpUnhBjTVcLOcG7DKFHzhwfA+OmaKp6JjZuGwcHPs2ZlWBEYFe2whuJwAsj9MVq9pCMOzgNCSgy4LhOvAYeM1RJRnirYlV42Pd8w9E77EAACAASURBVHCrb2DcpGiKgk3wC1NYa75irRHwIUCtyIv33nwi1S7LOdIiZ2krHd+SEkQrAtfkN3v2URjGLhlYsyA12KEOiSaVaQBfzVkEoMtsoscLsZ2ESVbnxCS9QacTY5sdo2gGO9BMUgTUHHsQlCHvqeTvDGztMyMkAEGvgLZDp3boOVX5hKkVm+wXtsFmu4VrdmGkW/iU/OsFrF7Xb0zzHv+o9+LfCoQmticn19KcaJLsUXm0sWxUzgmen22ao23Yng2LtMgE7hoWyFosK8G+k2ZZwjMLuF4Fw3WxyIE///Ep0tUl6toCqh4ia4isbvC7J30cd2tkSzqnKuU75oLyWKp8xfuhG3R5pyw2Wzz77gXiKCESHZ+jVWNiEPTRmwzw7e//gDjaohP28PCzJ7CsGjezd2ovyYkoNyf2+1e4bOJLRh+i0x/i8ZPfwPdczKZTxHHKSziWzcw1YZY1Sg5Kc5rMb3TTgH9zgEHFY5IPvZpbdoxENQfp8cDnPYOeAmbSNW2zWSFLEwwHfWRZisVyxSxNfZ3de5zpyeWnV289Phg0/qQ89MNHuz8PL9m7Ve/Xr+0m+EbNp67vbf1itQBbW2211VZbbbXV1n+yoq/EDFrYlshGdfOnv0If/n3whfvjr/AffrX+6Rf8D7/80y/1+KM3ZEDs4LUMlJkWwk6A48mEGQhh2EGWZeyps1iuFagmwBqtl1kWSl+jeEOKtaG8kRTRiNsMJTESeQ4ZVBPTSd6TgTYFuOnmgdMrqYlSfmi+52E8HMILfLx98w7Pnn3HyXDcJPM+U4mWhKHsOG57nyQNxo2HJ7h9fg9vX7/Gy5c/oCgzdE56ePCbh0g2CTZvFww80fay9BE1JsMxHj16iMGYgEeietAbSuIfRwE25C1UibyL2Gx2jdmPLxCtu4BfwQ59+MOegJkKTSCpaJJnrHALrRmy6zXeXRe4SmrkVgDH6KPvDuF3u2hOQ4QnLj73SgTVFtkmxnJdog6P0Bt2GDyx1bawhI9ZRiIHpVRVBrPIQ44Myw1J1GPZqDIFJykf/+RKBkqMqGKNqoxhmz5MM1TGU8RkO2xWxWCNfaUoX5DZiSINpZ9DOEJASwHYeEtUEAgT4xQwu2OeUSABN8CUDJghzpZwLA9B0EdjyvlTRCtmtrjdyS5lVgDk/Ymzs7HndEnWGQrwwc/TFgvowWAbAwcEeAjYJuOVvBT5k7E/23azglGXmIyPgHoLir0YTc5Etkagh5LwFUrCR2ZrlDTqkD+bbaG0HNzUNuabGoMox8imRMcKje0igyNspCyFZxWoAxer3IWV5+iFNTOPTK+P7LqEHVawAgFtqjWFaDQsY3MCi+WxZuBj2CSIS1+CCSiIocxQJg3WsY21F6IeWnjgVnDLBEVmICXWmuOwN5tD+4LlxSS5K1herMcTMYXYb69OkGdzlgqidmEHPh9Tkh8zwMapoOK1R+OPWaaauahYZQKq1pyYqay9djOYDA6V6ConHINmMlwMTujcxBtOfu34NoadmMM3bjY+YAYSeMCvVYEamtzLLCZ9M2AP6OkADvWk3gC1PXsjew3bmHQ+1RHSnMD7oQA1KGEkN7K97pClvTK2ZXbcvZ/2JOTgA2I5C9OZwRMxbOPxxrwv3nAlG+UbIRZcko06NH+S1NjmcZg3wmZjcLfMsF6+wvOXr9hPsdsfwP7s72CWXRibBc6PKvSMDGXlcOIxhW+Y8Hg71yRzzeY4Gg/gOS6urm54PXziK9DQNz0Mjo4QJRGeffcdz9unJxd4+Ogx3r79EXG0OWA0E/Cldqn6YbzeqNWfNi5u3cbnDx+xFHS+mLPsk9nVrru7JnDwirom0G8G1cqKb8iILFQAX5Ga6oucgHLa91GOqrI1UFJxOm5FXmBNslbHYin4fLnENoqVvcOBb6QaC3I12T+WkaKvpfLch8DafpsEeNN/qdd8fIHfrUpY06xkVWmmbf3PVQuwtdVWW2211VZbbf0nLQaylIyOPIl2X7o/RM4+ANwOn9L18eI/i7Hpu+CHd713VK8D3agqBs1sk02db9+6xbJRkkxut1tcXt5gG6XM4JGGUiSi3ETuyEHSwFIzTY2/vN++aWVJDoN5cieeUx05BMFiJodmc0giHfk2kXdYzlIhAjzCbojxaMQeck+//46lSRK8IKyIqlINjGqud037LpBNto0awouzCzx/9hwvf3zBy43unuDek8+xeTfF/P2NsJiIhcUG6iaOT47x5ZMvGFDhxl95Q3EHyfuU3OsrGA5w8+KGTblJWmX3BiJhDPuIN3O4Zq28yijhM8Hl87d4O60Q00a6AbrmGGEwhH3UR33u4n4fOCbWWh5her1C3PQxOD2CR3ZuTMZRXmtFzobyJJvKcmk+BVakgIZSmGscWiCG4LKcmM9TCqSkg+rxQX5VJcoqRpGlcG2SX9qoCXRiVqZq+hwtgROwlU3dObVUgSJ7dR83wQyCEhNFMTIOgTFmkuyCEpRfkjKIz6sU0XoJz3IpzxLOYMjyWRnKasztBYFy7iggmYc/G5urlpbGFjX9GvQQCqZiFynGpUo+FWmzDYckY7aNOm+wml0yQHBx/pABOYd+XAFIwF5ZNn/mvDaQFRXMooJnVHDcEqZjIzM8vKtNJMsKR1uSjSbwOhUK10KaWsxGola62/eRxzGyUvYLyT/rWYmN12Bzc4OjO6fo2gaidYS4yNGwH6GBTs9GOAhQNQ4cZKjSDGlsYVX5iIc+LvoGRnWCJi+RpDYK22FmFLHWJFSA5MU5AxgFeffl4slXV+LZV9dLJFUBy+qgKhtkyynS7SWIm2cQsMQSPTneAnwruabSgTK4oc5JOrb8LJubifm8TFeK9bQLIxH2KJ1vSbJGmlcIByM2/2fgtqoRWAlOBmtsUgeL7ZABTxoVzDQTqIWCO2Gp/cRMSYGxZLypcUhm/odzr4xJ8Ymjcq2cze4dd8jScJZI75idJIvO4GPJZ15cH4t/GqeFKkhGJ1ZKCLOSQO59AQ0GrfchCDT3aFYbg8pKNqqBNgF3bU7dXEcZvv/2jzzPUPDE/YtzPHpyD7ADXKUFeqsN1htKjShg+wE6vQBFFIMyRkiC+n4xw/fPv0W/S4m+JTPJ6GIltyxKDM5GGIcT/OFf/sCJz92wh7/7u39AXqZ48/ZHJbXXQSgE/anQACWnpcMoSds0vvv4+utv4DgOZtMZkphSdBsGG11PwDX6mwMMlDyZGWyFXBdECkpjVdKeeWbh69AOWpfxpFmS6uaQXC9q3peUHpwnEYaDAZI0xWK1Qk6sNeU993NssY8um+q5A3DvA6TsV7z48N9U6SCeNiH0/39Zw+Hw//xrC7XVVltttdVWW2219R+vGLpQ8jgCk6ih1/IZqkMVyqe+on/8vfwXgbbDOmwUDlkahytQEi5qjKmpWa3W2G43nIra7w9wdDRkdg+FIRBbgEEJWoFOaNNsMsn7lFWqxoOfU02y9uJhrzV+LO+9l5DtJTm2RZIoaU6JuZBnGeIk5nXfun0bk+MTARjSWJmX71kCiu8iW3HQ1NByZAZ/fXOFO/fv4t69h1gtyIttjssf38C76OP2w/tI1gnqLNsBNpsoxvvXb+G5LoJuR5gN3HqKOTk1w5S4R7/JxwdIYLs+TsZD+L1QgEJijOUJHPZpokRJA+FoghwN0jRA6BzDHx3Bvuijd9/F46DCsN4iX63w9jKCcXQXg6MuQhtw2KOKvLEIWMvZcD4hmWcmKXrMWjNKNGbBjKMqIzCtRJYWDJqktCwBcpzuSPJlaYD5mBDgwcCiA9vuII7nqKocluOxPI2AADouZMrPDBxuWoVJRwAbFbPVmHikGEzMZBJPt72k11DjQjXE/KMYiLyA8qNqyKssQlWZSKocbugy8MVpowxayJhRq2QGk/oXWScPiD0DSeC1ffFrFRCox6KkXQo4zd5ZdNrYBsIemeh7eH/5mkM2bNuXZlitgPYDj132pDNRmyaDbXVpsnTUNXKMTMANbdyELtLYIUIczDyHZecw/QBdt0CyTVEVArDQOgmZ+P79DabbBCcXp/j++9d4+maJ43sj2OSnVxaM8ZZRDmeTwAspadPEemPh0u0AJz6+9At0SkqqbRDnHkrfQ+BbAq7R+cIebeT7VrAHXZoqeTEdVzNGnl+jtgNYViDMNhrPlYnG6sDHClWyRF6T76AC79X5rAEmjk0hdiOzHDXwKQCX9lwTv0r5LaXmiTLHej2DYXcQ9CgxgnBOpQEHAZomFpEPz8lx3J8jK2rkpSdsKcXkZbCMx4ECztQYOWTz8uZqhq8aR7Qtvkuej2vEsQnfJ3BNxpGeS5kv1VBKq4Ws6TEzbxxc8mcht0bh4imJNDPsZEzKUJfnyetQ5q0dL/Ng4pLtpnOVwUsec3wGMWA0u7rEH/7lv7Ps3Bue4eGTv8fx5JS3s8hWKFcpYqK6UfJobQOljTwuYYU+vK5BtGHMljOeu+jmQKkYwszitEzcvnsbm1mCP/7+98izFPdufY6vnnyN12+fY7maM7imDrmab3lSkE+9890jdmODB58/xDdff4MkSXAznSJPU77RQnMrgdl0A0ISQukGi4xHBtiYuVairAv2YmNfP5K+K0moXDcFwRW2oAJS1WM6J+lwFXmOxXzO8vZer8NyUALX6MYDH0te7tCB79Mlc85+qQ9nlY+X/Ojh4cp1qIYaSyR5JWCtBdf+11TLYGurrbbaaqutttr6GykGKWxLmTMrtsYnltPfxX/u9752MMNH9Qk6HP/9c2uQ54lFQN4/k6MjnJ+dodcXmeT1zRTL5Yab210iqHprzRZjuQ4zUVQzuZNayZvsk0jl9cQoIGYbG+ST3xCx2RTARi8gSSOxCwioovehVMfhaMjecdfX1/jTn/+EOM04gZD+XbhS/ED1LtSMSdOkn6Oi9Tz+8mvMrmd49vQpy+0aF3j0v3+NsDJw8/I9irRgU3tqGqkJpkbwyZOHOD6WpD3RzWkGVoP3r79n+SVMB3ZD0lYDk2Of5Z/57Du8fBojDX3cvXuOIAwYeDOsAIsoxOY0wGfdBpM6QpOlePtugSo8wXAygm/VcMx9oqOY4NN+IbBDgWQ7r7USNYUYkIyKwJKcpJ+yD9kUvNDNuvJG0/uJ9pspJuEmeWjFc8A3UTtDVPkWtmvDC3tw2UOPUQ4xpmdAToMTmrEmzSLDncrkXtgtitGkx41K5pNjQrJBoVPROouE4g0LhN0T1IzKmOITZ9TodEewTI+3l3EWligrVpQ+wvp0EFRl18vSA8265KU5IEH9yauRZpw9sFwTjqfGI7P4ROYbbSJsliucUHprJxRDekdYoFrCRyyroibZaIOaZKN1AYf92YgR5mNm2HibApNNgeNOiizPYLk91OsNBwUYnof5agXP+BFxr4t//WEI78cFNmdHePL1DBdJietrE/3z+7DLAs4yYU+4mIIKAgudfoCiE6Jn5KjSEmkhCaEeJYSSNxuBTxxiQBLQQ681kQzbJnnzvUZh+bDdUMYNpcyyv1+NLBeGKamnrapE17hEXDhI6gEay1UyYJOPkWXW7Nn4oZuZHJfDeUsDvSxFR4Vku0BeOfB7YwGgmLWp0j51eMbB/9PnGYYbBG6OeRSiqIJdYie9Ix1bBlGY8qSmJN4uGQt87HlM1iDnxF4HmK8SWHaHma3a5l7x3xhEFf9DeS37ATLYVKLnTdEPYyyTIaJ8KFI/PR8q2bjBoKNIZSXVVqTK5EHJScyUREyAsmKy0XwjCc3Exkzx9MVTRHECCxae/OYrnNy6jYrmpDxBulwhJukuzxsWzNqBWdNn0GBwg8ZugI6D3//Tv2CzWKoUVgK5DJyenvGH+fYv36JMUjhuiP/yzT8gyraYzS7Fv41PfJnrNQtVX0XkdgvJvSuMx2N8883v+NnpbIY0SXieoTnFpSADAqTpBg/JwJXUnUA2kbTrAINyZ7PAt1N00umOGsmw/I6BJtMMhUbIHt+sl6jLHP1eD3FC6akrScKVUbC79/QB/rWbTw7GqHpO8yP16w+X0Td7FH16Xx8vrq9ZDOhT0qz9k+tyW//z1TLY2mqrrbbaaquttv5GSjPG2PyfABxN3NnjULvSjz/13F+tnfTqY0zt59Yg7QQzeaqapULrzZrb18APOAghDAPkpQK8GEgToOwDNshH6z9sRgRkUaw1BmD2Jvg6vZJfoaR+BL4R8Mb7SbEbqKkkaRGljX722efMaKGGiWSRusnibdu9v9omzWgBpdJRoMM7+KGPzx8+ZuBvs1hh9uMV0jrH6eM78BwPyTqS7VDN4tX7ayxXSwb4SOYkwI4wJRbLDXudGZbPbBvy6M9jC3ZlAP0TzGsP76YRlgtyKG8Qdlz2dQq8AmchGc8nyOMaV9MS7uQCg1EHodXAITYOeQ2VOSoGG+lH/LGY+2ISY42YawUqYnmQHJSkgBnJAWukDMbR61nNyrI/+s9kNgxxbESqx8ekzIBiDas3QO2P4Ngu/CBkwKVIpwImWY5q0jU/R/YxgWoEzjDgx+EeIg/V6aEaZNNHhB8xa47Won31MuTJglmATjgA7ToeHwA8v8OJldvNEqgyuA6lRwqyy3itPt7adI2bcAmvwE+G/x7aUxtyAA6oY7obsALUqifgeS7CTh+L5QJZuobrhMzao7FL+1L3/QSiENOPqH6lYaEsTT7uRlMgNGqMrAZ+FSPZJsgLg9lhhtdBQ6y1HxeIKiAc3Mf2z/8Pvrw3gvHwc3x5AphPXyC2voI5OMcPrxYUh4r+2RhxQzI3g0GWLClgxhED5VXjoaBEUc+CR4pW9sgqUZcE1JbItLw4l2NlYIY8ew/Dn8CwXAaCS5IU52Qur3yxyAOLJaQGitpEXHUROAVGwQ0DTFkd7CS3/KNSOtXO3o0aDcwL00n82VAl2GzmMNwB3LCnPLYUW1Cd1PLwYM4xxD4/KT3EmY1RuIJtZsgKl5l0DO8pX0bZAjnOMu8qsSdPHDUCr4JrJ1htKBU21JGju1SG3X+Kdbt7rWLSkpdgXoaI0g4CN8IgWCLNHdQ1hWTshp8aU4rZSSCdVp5roFGDYaayFZATBMvNAi9ePGdGauCE+O1vv8HR0UCuI8kKeZTSMBPAHMT4dBiEI1CV18dTaYW/fPcc//3P3yI8H7DfJaVpEjh6984tzOdz9lprqgp3Lh7g88+/wHT2DlEkQJw+jrv5T50bavYWPqph4NGjx/jyi8eI4xiz2YyvGwRwU0AGhezQvCvsaRmLciNAs9aIlUuJteK5JuzGgzNUs9Q4eEdGl4TwaP8yE2WVY7Ocs5ddJwwZtF5vNvwesqI9uKavf/u/9KfU143DK+fHaNknar+CTxbvJ5bPSrr2/8CVva1fUS2Dra222mqrrbbaautvsJjBJbopZrRpoO0nmNj/kvqI0fbzS+3em778u66LXq/LbLbRiKRy4mOzmC+RcMMk209AFzcjDGrIukRypR+pN9eSHu5vJJVUvNkkCIFBNdfemYBr02tqConhQGwzaspov/W6XQxHI5Y3/fDiOd68ecWv5/1JPmRCcTowwj6QiandQQDe2dkdDHojPPv+KS4v3wAucHL/DMd3zhFdrbG9Xu7ZEZQg6jg4PZ3gwd177JNFn+7Nix8ZeDCMABdHF6gZ9CrRVA37pnlehU1l4+21gSToojdpcFLMmeFEzb9PgJ0zhNMJVaIjAWsq0VGxjEjCRz5qzFBjrSQx11SIQSVpj9So0n7K0hoZJTwqY3DG0ZSMj1MEGWhRwQOUBplFAoaEfU7opE6atpsSAh3GDygUYYuyiBGGPdiWpwA0k73c2NCeFWxKbslvpJpiBt3ooQCgzDDhTliODclBHTNjcNByBswcJNCEFlaL7ZJpCejIsxhFukXgdeAGXcZQhDlC8jYlVfzUyFYMS2ZQ0jjg9FL5V/bb0mORmUKS+qiTHy3ynuNQB/ISFL+sPM0YICPW0dHREftqOQ75CjrstyfJpGyFj7wEmqLmEARKI022GepM8WEMYhsZiBsP87iEF3YQRSme/f4twnGAv/86xMSPUJQWns1C/PB9hJNTF7fvTJjxFwE46puwow3SOINREbuKElEr+D0bvaMeTJL6srxYGEIEmBFIw3JQ9hfMURTXKA3y+Rowg4hYahWNoUJJiquax3jJ7DX6+8COkMILrAJDd4Wuv8EyGWFb9nmOk+ATmQeIZSpApKa+6mNQIY2WKJsabjgSBpy8RMAVArT4CRa2qhJpMa2Tj5+WDTYNuk4Cj439bcQlhWUw6innvkr6pDGhmWme16AXJEjTAmnWYwaZEPE0Q1Klgu45Sjtwjj8+j3VlSq8YVjy2kcF3V8xgXMUnYMNGRoTJl1GhsUoWTcPbZo9KGXc2pdwSO5IB2gaXb68ZrKJz7Wh0jPPz2+h2PXgE5ucrxKUjUmUC1ihxlI5RoYAwAqKNBlG6wevL93j27CWyJAfR9frnAxzfOoWf+3jx9DtsVit0eyN88cVXKMsMNzdvVViEYqMeglwKXOaPrT7zYDDEb558w0Efi/kC0TbmeYFTUR1HsfAIhJf5ilm2ik1ZE9OWxh3JzPmaSJOLGBAwhLm7ZijGGm8X7T91PVFg+ybaospTdLsd5HnOQQb0Pns7ApkTPpR7fro+vhYfgrv70aB3zAHopl94+FsnhDJTtk0I/beqlsHWVltttdVWW2219TdYwvSR5pEkIvxlXfRVu2/0H38/P7xn/ivwsp/W/pb9Lxa3U0rGmqYZ1qs1Mko89FwM+gMMBuSJ1DCjjDo+hq2EPqYALNV6KEBt5zunu+ZdEyKPtWSWZYaVsNukYVbMEALgWEZKTQlJ1iokKfmzJXBsG3fu3sXR0TGuZ9fMBtLgzO79D/bnwYfk911vFlitl7j74DPcvriD6eUMq6sFppc36J4NcPezz1gWSGAYGYDTNm42G1xeXsPxfAwHPWzXa7ydrZAkKe6eXrB8lCRdnlXBagqkZQOrBk7HJpyTEA96Jvp2hSIxEeUlbNtEnsfMbOl49s54nuSgWUq+ROJ/xSl6DN4RMFJI6iOz1sSLTS9LYQbMAuF9qfb3bt8z7MiPiypl028z6MIMezCUbIsAJvKNI6814ldwyp/lwXZ8xMkaZRbDsQMGWThogn3XKN1PuUlp1hoDINp/TQMT8otwv9Ap0AlSZCm50XdYesfAHW+vBmA0jCHjwabgAz9EVmTYrOacfshy3h1NTs4Sfaw1i42fU+NfAy17YtSBF6D6NwF0xPNrz7RiNIWPE0maSSZK67y5fsfgLslIaezS8ROfMWHWEJvNMiqU2RrbdQmjsAhjYdZWRdLA0QA33Q46YQebbYo311v0Hkzwj4882GmGZWQjL22MfAOnd7vYWCFy8vgbBDgeu5g4BnyPwgs8Zu6kmxjpeoN0s+VAC8cmYNhGnqTss0bjhcBX3rPFFEl0BTM8Fq81DsagcSWBGOLXR8CHhAvwD4MfezBdfOYtJFWILPdx1Flj2JtjG7moeATpo6fOebU/CfCuywTb9QK214XjdnfAB4Os2rtvJyHdD2OZX2R88XFTyBu9rKpc5GXA63KMLapapMY6h0VWROO1QD/M0OuscTWjc7vLkkwegSrMZS+BVGNDrUSGh2zcntu2n92E0+igKLsoSgNGTVJFCiBxZL+r8bXzE+MXUSKAiCwJZKL3JoDq7av3nPBsWA3uf/YAw+EROl0fgZMjzjaIib3IgKWNhthyFJDg2nB8ggRJnuygsQ1MZ1M4ZgXP8+HYDrbbCMki5pCXq7dv2PPywf0v8OTJN3j37hW2m9mOFczngQK5BHikuYU2fC/V/eLhV3jy5DeItxGm0ynSJOW5mCT2FGRA7DIaSxRiwPJ/5bVWUGALgb8M3lI66AF6K3c35BiTNFf9rW/OyHMCTNI+m89v4NkWup0Q8/kCq82a34P39m5dek74mJ0mtZ9Fmp8+uavDq/LBU596rOZEBl1br7V/82oBtrbaaqutttpqq62/4aIeoqzqXbqmUndy6S//P/lu/4m//yqgpjVZvxZkO/DWoqaIwKz1es0NkO8TsDREvxcyQ4B8mRjIUEbmujU5NKPWdQhoCCayF2+JZErJR0k2qpgr8vnFRJ7kmQT4UEtHjROFIMRRgn6/z5IkMt/ZrJYCXvK+VA0ws+0UwKKlYczEoN6xwnw65bTLb37798yKWE3nWL2b43p1jftffwbX99iDi9ZIclSibl3dXOH65hLT2ZL3T8d3cevonH2kLNJlNhYK02UQhXzGqdEP4jUcYrfBR+n24Q3GzEqzIMmgUbSFURMAUiNJhL1GDDX6j+Sg4rVGDCPVnCoQTtg3lSSFEnONwTXd/6q2n/cn7XcCWTZoGgt2dwzb8WATe5B9oCg5kcC1mhygmA1FLDMGjGCILJJYItuFApssCQdQQJQwBtVx1eo+BkQ0SkGu4w3uHae8Tcu1y3I2QUR3lCgllxOgYmeAT02qkgTSNrthgMWamIAJsy01YKHBlw/74wNfJBmceziEGD7qKUk0/XAxzYwTIETJQRUSZzsWur0hlqs10k3EDTTtVwJvmdlEY7VMEccRUtsGtfpGXlMQJArXQW/Q4XFzQuPD3fI4vXXSwwW27ElFslF6zrYb5JmJaFvi8zMD3UEXp36KITMlCVyw0FiSvOsEFvI8g+914Fg+sogA1xxBJ2DD/SzOYRgltuvXKMlsvj9BXZIUVLEgy4/ANTofy4PQCk7m3LOGCNzQCZm14WKb9VDnHm4dX6FBgjgjuaaS7NJvZZ+VRWskZQG3M4JJ+01BNRpwknAAJSfVx2MHsh0Cdo2yBdPQlhx4SlYtGg9GnaLKM1SGHBs635u6wt2zGEkcYboawrQCGb+Cosnn06EHu4G0Q173Y4eZVOqZg7lb48PCdCPfwA7yIkOyvIZpejBsGveKmaf8EPV8R6w833Exm84xvVkwi3U47uDe/VvM2jwa9WCXSsjlvQAACKFJREFUK8R0/jMT1IHJn9OGSX5tal8QwysuU2R1gfHoCEeTCeg+AQXZuL6No16HgVS6ieJ5Af7r//Z/MHv4x1fPUNf5PnBCpfDS8aVHfBOEttuisVGi0+niH//hv7KVwPXNDVbrNQOydFPE9z2+McI3lHhc0TxFNw8k3Zh+xHONwDXFWlOXKQmW0TJcYbGyFFTbgDKrVPz11psV4u0a40GfgToKU0jShOcmWdfBcdXMQ3UU9e8P66Nn9PT1wVX5g3/4cGUHi+hrHF27+DrU1r9ptRLRttpqq6222mqrrbbki6FhcPPDEiMljTmEw/7a3z/7vAbVdpSTXwOyyVqUkI2fYSaZbSMMfFycn+H4+ISlnNF2i6urKeKUZKPKTFyZf4vFuTIpp+d2wIZe+050pfooi8FGWzETmLlGXmy2xQ0KgWzs30MMLGZBZOxJRk1WGIaYjI/guC7+/Jfv8ObND+pjEGRG4Mx+P+iGljp94nkQaNbUxKBqMDk+xp2ze/jLn/+My6s3vFz/9hAPv/kS68s5Fu+v2ZtNVIv0GgEWu70e/tvjvxNgiZt5gtrIFL1BRX5pRgGDGGi1AZ+SCrs9YY8RaFTEuL4SkI+kVLRylnqVBMZRy03MDkrTo2ZUGdMzE0TSQcUrq5FEUQKAGBDS/lANS0QJuKsrSudMYXljlg7SfqPGmVhWpkVSP300CGDDLsyB/mZPJGKrKfAuyWKUdQzHCdlon9AJxgt4cTqyxLRTzBeFYJ32E4R+jDfTHkoCBWjfs9TrwBNJycB0cy3eSrQWMs+Xf2PVH0k6DQtFnWO1niL0QoThQK9kN8o+PBsOGSwKL1EphPRv5u6xpCmKCnrfyJPyk4BIOhdonPIyZG7FI8jCajZn8HV8Mma5XJGlSGICgEzKwEDtWwxgeV7IzB4CFOyqYN+wungL2LeRRhnerWguqGFWOZzGQloCqUsiUwtjM8fJxEJWu6D/OJnVdxkc4b1Gst+qwnYTId/kaMr9Z+52KtjDPi6v3/JuYVYRS0HJ/4q8DoX5yIw1nQTLj2X60IRIvQdpf/A+0+xB/iVjrqpz9Lw1TsYbXM8CLJMBYNko8whZksLt9JjpKUmfKtWYPQEVfMUsN7U+GkcaJNFTCM8zeyoiMQL13CeRGUDJPoqUCAqUxYYDKO5eNPDtEi/fDWBaPkwy/VfE4Z1RvhKE7oAe7dnFEtOPmE8MpskzvM3qXgaff2p5+s1DzWiwXs4YTOr2B3BdT302SvYkjzIftZVjOV+KNL7McH5xBj8McHR0hoHbCOOL2I+1xcAq80xJGqySlQUSbPD2eo7lMkFRbdDvhPjs0QOM+0Ns1lv8X//v/41qG6HbG8DrdDAaH+PVD89RFuKxeZhsqv0tea27c1yAsMdf/QZ3bt9l7zaShBLLlsNyKCGUgDVmq4rE//9r72p22zbC4JAUKUaKXNqOXBdO0F4KBA1cBAjyCHmQvm2B3lqkP+ihQFIliitRiijKFCmSxczuSjKSoj3lUPADZNjUikvut6S8w/lmdjTKkIkBQTWjq6mHB5bBbC0rjBOo01G0Odd9wppRKFcqqQ2wrUoZNZzcH+rvWZqKSbxryCI9Zh8eQDW35W655yHaj/x23G7/feXuMfvv1bu4m3uAxAdCMrvo4pMEObPf/VujLrrooosuuuiiiy7+/8F/xqmzRS0nAkp079uHE3N3m4yUz94V7zj+ET77T8CaC9P2eBHCxRC3rPMGkz/fqIznbDzGcDTCwzDE61dT5EWBiItbu55gIRqZUDWPs3b7tfpfgiTMFr5FbIf9ka3F5lJrYrkQF8pagBudq4AGACwNjKxTaVsIcFpnhmFHTaxvr5/g3jDG7y9/IjIoFMDs04xDux8Powwl5MCv4TUB5rOZyl+fPn+GH76v8Nf8ndhsL9c/4umL59J9y2+W5hT37IgGq3yNbVlgGA9UOlmzlJC6UVx01xFqiozLlbBAWfjAYoXYK4E4IRKAB6djTCYTnSN3SmYjdZh4bhrJZiejiVrOj9CrIMONDpAVdb7MeDtwTIcVEF4gC61Gu7tFVeWIB2cAXS+DRuWVgpN6LF86sLcOmTcOfuYMuagn+GtKvfwwQq+OcFumiP0BEIVqV0laXZaihzngAUmc4WyU4ddJghoUYHf6Smxt9Nhs16Zv61hIfh8RHsKVDR0RDZ4lihA5fdSdOk8ukC5vZNYwSsZi8CnvbofqzX5Mk81MOvUjCS1zFPJIlX4Wx4skRPZnkCUBfCxRNs4GYigSBNVIBZHm3sn5KfJ8I/bM/dBDXsQIDeKIlqAoyxJHCcI41NmXDV8c1xj19hLRrsRm6cGPYsAvUWU9bKn/H5JZGMELQzRZi3pRoX+yQBkmQDVEjAJoY6NFJ5F8aigO4CU+iqyAT0YazTGiE5TbAg8ffIFlUyOdvJY+mXMKNYCHybXJA6Fdd90cLlZhijZFGmECWTxOZovAsGX5rct7uJ16+PqrJbavaqRZjLIqMBwkNt+trhPNExkdHDJmxtxcmsIubPvDdWx/eAeXUekvCvjroSp5bZnMK6/eAONRij5y/PH2En6vr7OTU6c1ZBAs1h7duchwdXNTYBanpHowRyFrXcOS1WctQ8mS/Cwe2Nox4agAn51fIF/NsVq+QZJcIgxjtLtWbMNe7GM6Xar/bFPg6uoKuyDEYHiB06GHTbbVvTRoffTQR08gvhmwmgmQvmeg+fVulsKPRxh6nyNfTPHzL7/hmyePsVxkmL2dYTSiIUOBoiqRzufq0xynQ4ocTGn9Imrm1FxHBHCvH1/j0aMvkaZzvH+/FHMMCGVIQrdmgrJk2hqzjAZVYw1a9vNMCnpiFJpbhb0fS2eT42wANWaCIJUrA9aQB1B+V2kqE4N+L8QNwbXNLSrdK7g7V55uwU7rcKp92McWLo8fQmkfj+N2d0pIP3xT5y9DnC7wKeNvanNG0dLFctEAAAAASUVORK5CYII=
- data:image/png;base64,iVBORw0KGgoAAAANSUhEUgAAAMAAAADACAMAAABlApw1AAAC91BMVEUAAAAud91Ihsjy+vobff8fe/8cf/cVf/8dfvtikL4sfuwifPJAhM4WgvJTiM4wf+Uke/n2+vwxf+Irfes3iOpEhNNJhc5VkNFEhtw5f9kNeek9gd8yfus3g+I7ft9Ag91Ch89DheAvf+k2f+QWg+03gN81gOs5gt86gNY/gtoJfvEqf+43feXI4/tbkdp1odC43P44ftFosP8+hfFDi+il0Pin0v0AaO9Yj9Ow3Pwcff8Zfv8efP////8dff0cfP/9///4//8cfv0cfvsafv76//8cfvn9/f/0//8fffshev8af/kaf/z/+/8fe/0XfP8Xf//9//0efv///PoefvX///r///Yjf/8Zf/77/fz7//khe/kbgPUAceoug////f8je/wXgPsqgf8iff4zhP8ngP////z4//kefPkvgfsAbOYnfvoXfv/7/vUAcu8ggPoffPcAbewAd+cUgP/7+v75/f/++vUje/Ynff7x//8nhf/t//8jif8wgP8AceUef/Etff8AbfDh+v8ggf/6/vAAaeobfPv6+/kAd+3//vIbgv8bef8lgvzP7P8riP8df/8AcvQleP83gv7/+fkQe/4BefgngPX/+fEihP/e9P/H4/8AcvgBdfMAa+AAdN8Sgv8Xgvf2/P/x+//d7/+32v8fef//9/4AbfQdhv/W8//V7f/I6f+93/+aw/QxgPPn+//n9f/C4/8Xe/grhPfn//+UwvurzfY3hd/F3v1OkuIAbNpcluXr+/+gxvwAaPBupe6x0/651f2n0P0tfPcBefJ+r/B5qudjnuUFe/4Bdf200fX3//SjyfSKuvJIku9bme7O4/2VvPYngvAXfOGSuuwAZuYof9s5iP8OePYYd+9nnu3//uuu2P0dePqHsu1PjukifOkDf+jZ+f8Vhf+g0P2/2vd6qvP2+vWHtfkCa/lgovP9+upuoeVCjOUphuR/tvlAhOnB6P9zq/QRgPkxiPIHetmUyvw9hfRJh9s6j/ZSmvfb6PoAWdUUNgEkAAAAOnRSTlMABQkF+Pr5+PgU/vwe/i/++Qrv9f5nOihYj/x61a2mmUlv3pr8ysW9nYf95tIvQR9R2P7bzLbdqIN9DyMOigAAMRZJREFUeNrMmnsIS1Ecx2fuNuY15P1+v5/xz+8c53DvdXPvbnezLlYbxsiwbCxhxmiRRlsKjcQSWeQReSTvR5G8i4hSHskfiFL4x7nzKOS1F59W997ddfp+z+/72zl7mMqm7meaNm1a17huOmDA4OFvn71+fvVdJrMmsiaeufPu/dCXhx4PHzxgQFPj9U0N6n7F9P9Qp2HLFm069OvbdsvSWXPWX1x3QDI4cODN+VUTZ82a2LZ71w5tWjRuaPovqd+4S7ee9puZTHz6wgk5RkSOCAyezwpJnRUil0oFJ0yfNG1vk2GdWrQym/4nzI1bdOy6LJ7Ie7CFIWNKsebzLfAgAFFEoCgaIYKqrV1r4WyumD8RP9i+d+tBpv+D+i3btL+ZSCDK1auHKbjdsa1uAEBFoHgWDrNTVRUIwRhrQYdDjG1NHHzVq0tj0z+kTnHuB7ZpvyFRWMnVs0ZlDPn8FARMYzQkqF6vF0ERNZ/PO3mgYPjgnRLgwAIHZ4sVMvZeXVp9GqsUypffuF1/eyLttTbQMJFDMtFkmRAiS8ZEUwpfIBr+9IS3eEXcbuIL+GS5nm3ro3izjq3rG+PV1ENRvrl1h+aTcqF6nPZJqxEYQyVCXsQQeZ4n8AmmHkTvFCkQ0DAACIKIwlkExOdzWJ2JSf3btaqtBbOR/BY9DuYwxxGPB8rA4+E4MZVp1qll7SwY8lu1az+p8MZmy0L5eMBmi8XtHTsXx646xiw1bNc1nrNxAKwfKwClyGZLx+0damHBzMLTrmumYLVGA4GAgqECyL4dJHnToRRudhhY5RwZ09OifZx1rl/APj1EoRJIfgEolR1cONGkU6tqFoGN3LnXzYLPIYcR8obD7ikqVAAUY6uHCzl5R4N0ol87c7UsGOlpY48L9WRBFQUehREQAhWByJIESJVkTkwf7NG5Og7YmK3bH0xZLFmvGwmSIZ1gWhn5GMuSAMQbBp+DFpr0rl/5TmAD1u9ozz3goNoQLjWzfetKF8FIf9dExKFA9SFWIbWsm9lkrqz+Nhse+RtoMQTVJ+zMP8r1b8nKXjn9DXtOzXKBpH9rDQzQHe5G3cmy5l0qFaM6LD7NClIDH3UhDFWHGQCV6Ml0vCNzUBn9Xc49aqQHomHX6gUEqo9bW6s4G/lRvMcgU51K6O89NVsPU03Dgq7XwIDgR4iXMQ5aCs0GVkB//V5xGhLAgAgi1AABkEgogGhN2VuX7aDhkIQNa/APQKA00Pe2K1N/42ZrbG6sYag9AlZkK13ShsWgHP1pW8wb0ijUHl7CO0C1xjuZSqdls0cccuq6EEZQe9QkoVLSkulduv7mj+plQ7quq14E/wB/UsKa3j3RsVT9t7dyMtVkDKJTgJpDNJjiJFiIcolSalCH5f9RPRkjwBSBRKDmyDINe50qXeuzZjqVoL9VszQXFBD8c3YoPku8z9+vX0PW2CAkw78HQdRvm9nlL/Wbe+RsbkkX4N8zBYlOdfXe1kzVX+x/OsQ5JOq6+B9ESFUpRRGhSUuT+c8NtIkTjEO6jsLwz1mt6ZhK1nSzQX/qwGxqsQxJsqYJAvoPKrBDS0oUy7ZCrz/cVJjZApaO5lVMERL+gy4OaWiKE2PQcr2ZgT9q4PaFRjwSgUEI/B0UM0DwO1VVFEHkjSFkmefZAWMoCYmwLgYKmutgiz8LUcepkg4lYhggvKiiz+GjlAKIKs8TopW5p8VSpFlj5uD3DTAVWX0alAJvCAXRSxVF0TRfdIEvgDEFJLJqEAaUAQ12b7Cs52/bwMxW4EdEjpZowPjtBSE3YEwESXKyh6qqXm/xHgPKgESdwdXxNr8xwO72KuRlGsYlVgCYfhdyeVVV4LPZNDtKkhQCQnheFMv8eKDgrVvtnU3mXxeg3c3IgqTLJZRYbiafBhdOYixZtmzhwoVLisz2hVaqZS6KCK2FN41y/dn3pr8MUL+UJeRHq0vbP4vgmT5pyYK2c5fPXbp03rxV8+bNWzpr7snldxvMnLnGU+6iohCnU5zEQvTrLcQOJbZVWyCJf6ZYhC9hQzwh06dKm1fMenj16Y0Tp58c3XT9+vWj2w/vufL6atulszYHp073/MGohFBGsaE8mAf4EgVBQpqOLJ4jP99SsButN3gsgBD8aYDyeWWtMsWNduCV3sia0PKJD+/dOLPx+JjRI0eO+MzIUYsW79t1/8q1tsfmeCYEKUVho8/dCH3vJuY29GvsHYz9p2L6woMbVq+MpDw6QVCkaIZyv1iQ2R66f84Cf4OmSX6nrChUORe4tPPhhTMfto0eN/7yjNGjR49ijBkzav7IyZPHzhg9YuT+3WdP3Zq7LpJM+jRCeBF+aGo1FAh6JmRdb9afnzNn4qyTOxe8mDfnYurb5BG3vcXPQ9QuIWl/F8uPrJt3UFt1HMDrqKNV651173mnd27Pkfde3nsJL3lkkEUSEpIAmYQRIIQRIwHChlIoU2aFUCKjrIItm5YCQgdtKaWWCtZRrNrWqrWuP/zFFm2BGrzzd8cBd+Hx+/y++/v9vcCgHxmBWwIVdyozJ/sbSbHcYACblskFGIYJBAKxJDw8XC6TibKyxAhmbTpw0JwZN+wPs1i+icsmnHH+sHdmVfXUhrO9340e3b97V25D+eHvz2iu9b63vP8U6Dhez4Kzb/6PvprPp/mHaorMF0d31SJZqQYD2DpBkmStewEBuHVJLCZwA/g5PBwnHUO9UeOQMI8CUxlLCSIpfPPkl7sPNTY4bCQO/s6AC/ALB/N116ZGvPeuW549/t5aH/5/a+XzfX01qOmh07tq9LFyZgCB9znbh7q+/mHwxOTYiR/ANa263LYaTEDgpMGA4wIuF3F82Z2/NzGCh9ISl1gaLSXzQCeJAbNhgiWTAVmKvrV9ae6QQtA/xgzf/MXKGQWo4u/Jvlv43wCovkdCx/PHmm2ILJW01ra1bx87Z46KilKa3EuZlpZmP9Z7oM5ZSyASkYhJMJkZMXjb9mNVkRFsGrzEo0m9zjlnvyXxwkKRSC6XC8Thovp6i6O3Ih66yq+gPnder8Z/+r1bIin/bUWW+Eed7XcQQPPJ1vYD3eZp+/oW7YxWqwWhTKstAO6fUTEQtXF0wkliAqAS4thCC5PMHe3JLPHJWfKwQM2pQ1nhVlwikYiZTC6QgiS8xkJ87QoEIYT6twQ0oLa5a7kV3OCuAm4DWcwqcwYWHEahCtVFrtO5RGwhQrTtHuwJMbfMaONZOZX5FWC5XPnHO4Q6tarAWJQ8vbHrQp9YwrXEGHBLKdK559IZVpwPjeP2RFKdn58GpnD81a6vbXgMl8AJAjgAuYApSTXEYF+74vOumuhSvSg3v/f4dQRA59EZq0xMAllhYSUJFVP9nXipCG+b6K1KBievyD9zxmW+uLO7t7d3/uyxi2ZTfkVxqPFdbUHRwKnT5TZMZIkh9KJYOdF0ImpLUlAQRGNo8vO3RsSxwvw4cJL9S7LQ4nZfegQIQCAW1XPxr11SIUqlQIsBkx949xf3ABEs72Nl38Lg0VaXQqA+bHhbSYlyvhkPXxC3nvytqlI741/hsm/85nzXUHOus6ysrKGxqW7P4cGDp5SmF0o2qQuG05Tnc3FxoSWGKdiXKnfMmT9We0WzSyrPfrP+09A72VB05HBg9QQmYgICBAkIYAIOLpMccekoKJW2CODnB8rLzSs4ouc33xoZzPNabQ4ERbbEJ3/XiH1biueeN7lmZoKrenae/qjp806DHnGvAPAFfGhtY92B+cyQvZvf99YOp63rdwhEXFygJ0qzOn82f7LjR03O3pOOuemUiEQYpXZINdUTIOgtSkAv5mK2QZeUcpUEQJbGv23TU/dfIwLwy8tPZd/qD+5A0Fa5f94R3+TzDnxBbhs6WzU8EzddPdlf3go2rRcDG3QTgO+z36aKMQx3nvzhBVdOQqR/wfGob9pJpDCAy+WKMOvQ1F4V/OkLe3DHiCk+3h+mKaKFn07V4Uw3AMIUgFAgIlpP5EuB5tP+BmBAWyNueXfZ4OPezbfmBcJ8aHVZEOyz4wPT4Vp9Lek4as+8dCnNfmKogUQQAdnnbCzf1dzc3N7U6M6JcMPCghgh+3aN7D0Try5KKHB98mWfxGLNkGDMQqzumY+N60zVJ4nW0agkDUp/5oOipLiLvyMyN4Be7wbAy3rdkewfCTDoUDTj5uylabW7E8dhwav1Qj4t6zN/thUuIM5vprfMfDwwuceJIHjf7xPbRyYPHgGJdOapDfMnTnftdtYgCFlbz9XXfjWoLN4ct0Vb1DPXRnbWSAQSYPx1U5+07Cg+V444x0KSWPytieuTlKNtiEym1+vFYixAHI43zOfroKsAaFSUxqbk/LRkevZECetOBQvlU1eVC/F0oSFd1qwFvLF3uuDSmRcON+BIbe6ekbOmtAFXfmViXJx/R3G+O6D1Hv2qjUAKa0kx0rb/nFIrLTK2TI/lYqU4rhdYJdiEmac2RvU2YrndJiNECUyI+q4NscgyxHrEDSBJxRt/uQYALJZ/EHT3e4/+fXf7ig+9mc2AKSBeeIi86DYO3zs0JeqATVKKNx1MvtTSM9lsxWy75jaaoyriE4xalVrnXmqV1phAdUWZx/Y3kHhGYX0Aeei75Pd1n0pVyZON+izg8A0ZInwoLd5YEHW+FSnfWWxcr0oeK8Nk9fUSAx7DFAeIJQtY7s4KAHD1gr39oLvzgCe9CuAOkMatyv8rtm3z8wsNNY+0CRbwQ93JM+uqzzsR8qvRDQP5EdoEqRA0ICCwgJmDdFkoVSV8Ot3TvceBFFpqREjZyED8cIdfQlR3LlZokYtkuMC6PcSoVvfswbE9eyNn7N2NmIHgcuXhIgsRACLxAnLos3EdtKxEAcHs4asAgAmvXZ31RicmUgPj88faAjLw3O6omU+q+2sR59HPBsaTdpQEspY1ZoOEuoThEPt35VZ5OFcm7ztcFWcMglqqunMD6g1cJhFDOkarjAmfnLogsHYpK8/mEqmpBoJpAPKRg3hM1CCHpsbdElgG8OGzN14F8Oh7a4WrAuDRFYnx4xtzkQWkbCxkZu/UEI5PzCePJ+loCsUyFwxT2RweT6NOP7Nuv01giamR2PpNPF1O5A7TZJnewuWmimusDWPKloKK35ySvtGLFwJKM2QyIgtrmnMi4SCZiEG+MhevBEC9s+WlfwDuv8dvdZUYNRDi+1KSh7AFsnV0uuCTc3VI21y1Kb4kMdKbEbQ1eikAzFBw+GFhUvV41VEHVh+zL9X2c8jx+PQP1Ge+a63nMmdnmRaifOoTtSpteyf2e5M1NjYmRhyL5Hb/8V0Zkhpbb0F2mz9eCYByy3sP/gPwJJjGr0oC8BaILzUdIGfDbV09LTqe+WTumPLHllCFggpvAzXKCgBsNvsDRlzStqgRh760vl5s2/9ZeooXK7TqMJ4akzEr4QYAM0hSr7/YTAboM+QSOR7OzO02X6r6wYHH1mdgQ5lF0hUAhLd9+MjtfwM8+uFtq4vAKIsRUTHpmM0i6uxxOz7OLv71p0y+Ljgsmg9RYFag/7Irrd7BVCpDwfD3l+ZNjzok9dxCrOnXYimYnvpUnSRrLKIspgUrGzxjvNQz2hdQKsflknA8d95kHJYmj35O1ocT/ZXpiwXNNYvmN3zfIsAd9/Bv5qyyhPRNt+/SpxLOgyYtj5eYWFws1QDhoVSFIghaAfivFwa8Yf7WsNCWqrlWayrePJ/JgX0gXnzmxkY8gytmYgZs1wtFBVUfkXI5cEsipHG+wuhdFJ9UNepAvsW7kr2FK6kQ/ebNzy8CPPDuWv4qs1DYN+ooGcu0ne/R8iB2pLdUClNgEDyodDpoNEAcmAVDflQYDYOowCi8Fv8tOML0UGlal7Wm/1TlsMY9uaNKXac7LRYJV28QkwfsPdutQHew2FgQ0pRqkPr4hJZUj5TJPv+mQrdyR2et9LnLLx2BC0HvrQ4ARWFN8dkGPJZov7iOxWOzfZZWhUFb+Yz1vhy2QsGBUNjnmlOD1MVTXx7uKc6+cmFZ2HHxJJkBEmY8Q99wbK4PNwD/H1PT9IvSiEIcOkwVwsndXYOZFOHKAIHbNtx/GeDGV7NXKQGUuil5O1kj6jtRVcALYzOW3Z0O+gBc7dJkZ3MUvjCKLrt/cuepyhxhEP+KrkWYJz8nmDKCzCi1HGoT1OBcEU46eu1qFPIL4qAwPSxv3FWpuI5yB2nWGu+9DHDXOhSGVgNApUZkHnSIRMRQTwFM8VsOgMJx64VF46b8j4XecXGMrdASgAg/SBgXtzi20qQnb8e5BhyXl9ZjWd/G4IQcTyXnokDgdV9qRv3jfOkped7XibB58G3vPnYZ4Ml3b4ZX00ykpVPV1XuIWa7jG5MapXDY9GU3d1lbAk3VvaPf7cyM1sT5LgWAWcG+CoYmcBFbWtndgISHywRAjVKzmMxYAxk727jOR+gGQCGItcWfTrnuDXn0Fvj12/8CeOy929gougoAuvT4WacgK+ak0uj+dfkEjV5y3Dx4odVa23j+1MfCHJ/lFxIT74wuQv+WV4dyP1EKyh+CJHGxvhA5NEHO2r6eNvIgPw4leivEYjFAQ/o6IYnCQI13uQFufCR7vQL2DEClpRvTDpMZ4tZvXAnpDG/3MG+J4klfuNjVKZiVhMtt26s/FgJluWYxvFCOAuX50RZ5pRW9ZZJwIoCQy5hMMdn0yy+fy7HcqfWBKEj7GewgPw6d/cF1bIBFpyg2u43gpvvX8RI9A4CSzjuCcSQXL0QuKI0axmUAzlV4qI+62PylLTaWS1gXZmtHTSm+SyKzry+KxgX6KOiLPktapJxAFvAAuaS00IJf2Pip/Uui1HY+RJUDXDNrC4PtBzTjehKgg2zicTfAA8PBoJbxUIn5K6LROGPmiA0vJLoGtJxlfJFUNB6kpp37wmN+n2jCvwU5THGE10qCvOq9gfXDFaf7JBkCnIgFxcUvJm3FiVYZXl5dAqMw7OVJIyhro99wR4IHVbd9wPYEEOnHR7cYlUO4XNQ6n6lLX6rc633R+OKe/XhGKXFy4x/dTkTuGDNJPTUGPms50/25uB4AiEqxiWPslNCpJozZOmhSpdM9zTQBn4az82VgA09vXhvEYHlQIUUYJVja8VOZIAtrDjmC0pYKwNtHGmzv6jQs4LuPVc5E7cZSyaNKFPYwd1RXTJ20MkFZQIhFmLN3PKWl6mc8ljwZolIEcVgUDwRQoNcGkFK/+Ih0LYfm6dNsPhypcp0mJVnk18k7vJYqJi1ME2E/agXrZPWnBaqow1aDfAKkkV7/1p1khI5n7iFFOC7AML2esI3kU0pMk60iufPS8ZJoyMOWqF6Q8OaZt9eseeUeKexFZXnIRkHfL9I4UCcWiRy/Facwlj0tO6Jqrk8SS9RNdaiKtAOjDhzZlVis+1efJuVVf2kT1WMydwMMk+F7lLwSjbkJkZBfh6g8A0BBtLXuO5nvvLV5rRewaU8igEJ9jzjFMiT3hQiYwVlymhFG5VwtXot9NTWuulMBat4GAmk8WKn7t6gY4R2yn5THBIDugx4ggCfvHA/dpOwnRFhzjwqieDhSHzdACuhNvPnW5tsAANsDAP1HleubNsKK7K7etI1x7achobHqtEOSagVtHm0RQ6H7dG+5XuA4Ydr0b/vX2Y/Wlu4juSKBu4dFMMW1gxWaCOUPNhHm6B5X+37gAQBE68Cc129a83OPDqXRqR7qAZjyY8HAUZwgkf4QNYu6CECFaUH8Lf7GtMEyYgFv3lBs7MiDaCm65DpCZB1RaoQrP8wPgn2MVQds3EKSFOndrVwMw0TY4Xw49Ph8GS4nj7q0vmxPKkTnUHkbb1/zWo+OR2N4QZ4Exi9InsCYMTWnXe8Hw4u4aLCCz/O5VDX4OV6KNx87ruJRwBIa0/rJQqzfnr4IsDxqaENGWhEDLsqqcS5gAgy0gmXEUGZHaPBD5fg+pM6u8oc9Vof0IP6G29f89pAUpQTTKJ4A8pKU5RgTr+0eT6FSFgGgoMgtwdqQEw3WVKL5XH4C77KDKxj4GnTd6uxFK0cCfmCcdmDQgYhsZClWN1qGyP4CwMoTj4dKQ3YTqUjuM5GhqKc4wKJzoHtuX/NrIgR6XVSPJqOLPNeIEYRzJy8PNK3+jkWszy65Jhtk3xLtG8w7eFd6LwWuwTZQ2n4/vjIAPV0LOnAIl9g3i7SbjzVeBmAiDQf3aqTKw3gW4pg0qTwA0CgsWnrePXes2UTngWazp2zam6cyTbZhBuKQGSg2n/JPQvlT8mQuAvRnp7KlY+uVw0moOOiU430nKlYGCNpcMVkmERExWeJdl9J2ll8BEHeOgfJr76A1HLHOpWk9qBAD2CWduu6ONTCFD8Ew1csTQEHaHAnq76/sOtY/ANQObcVG9/4vnFO2bEOhKwA63qkmQkbO5a/0trSQt9k03wj0n1uIt+80D5vrLgNgYnJUmScsnu+TCbCPQrQsDwAQCnlT19+xJgcCQQrUVx4+DgC2E8x92ITSyKL4wVf2As7/4AXcvZHKI+k5iwWAlzChqo6IxbebIOEK+1fZf8kVMElcRLQfyf8pzjR0BUCEH7ULfT/+3onLkF1Kdfy/n6kvAPD3AQAoFESHYQjyAIAWRO3HsH3YR8odLCoH/ivMwDxV5blmrJQs/z45aetWSmTiopUWTHfhWQToSWmWNydVx78HjsbA5GLtO/MTIrJdHyEy5l8A2Ed29EjRZ4fwGkkjGHVA/w5AAQCaW+5YAw6MtopymJIQMkEI5OR+e8m2IJDXJyqi4W3GvRuayVTk0PcVavcR/N2ZY2vTfqgNIMvXFZfAYVQWx2txvAWzeDs+O9WMZckM4UT5BuW7jIi8/EWADOQrOy8iSNmMZYgdkxXaf5cADaVBrDw3wKoWFU4IaSYEMnJ7yJGcIF9gPpHUHOMnx+rwUvLC/NLEOV3lmmxDSOc8AOD/A4AG+6I6XzAEC98nqMfavzdtiqaHCk3XAKSwlUNYobhzdEDL8xBb2RSW3+oBhAn2Zlwgw/dHleQEMbwZECtOfbx6N/Et1nTQtGmJDHnq4xt/R4AbqoyA+XQWh7YYenw3Se1DROk+m4VbfmxczeDnhULKiSsAQPPNRQDgI8Kitx34vwGkCfZdhCCD+CgtFI1mwCgjXd1RPWTNwJrmk0sUS6QN6eKU5YiFnKv0QyH23z4aQuNDzXsIkUhmwdrP7Y2gekMUXZF5NzDiywDlD7kB9pM1oOE7raV4AoD+M4Be9CdrVxrURhmG+0Mdz0FHHK/R8f6h44wzzvgjyWZ3kyy7IWxCstkNSUgCSSCQECDkIJjhLBAioBwFpBxKQRQoQi1CW60VLIKl1KvFVq22jHfrfR8/fAPWKJij6vujQ2co3Sf7ft97Pc8LcshVxXNDAXyyyW2Yxtupsb32l7IeF/E2ZnfQgqfhxLstvAgAhUZj3x+AOf2wadcXHU1qgZSPQrtuzx8AvMiecwBofPqYVfW/AlCtvQEG+bDQL3ILUmRV8oofyqCRf6TiaXRbwcZiEW174VmKAZdYzELh6P5xu/odFeMD5A5nLbZ9pUMjhwyGhxo7ZprDACIu5AoDIA7ZyxMGkPgh1pqQsYYsMQBoyrOPB4IwpXyyqtTtfmJD1JQ1vlU9X8YSg18tOuRAI19HpXFAAsoOUE4c/KdJnsrj64VCY8vekT8BfGhQAIBpamAYO1RRrpLEPQMPJXyNiuEancWUudzq09vU6agjy7Vc1kWNPGcvh1aPtHUjALSt+rMJzvv82x0OuUyMokIxH9WUu96Du3XJh2xPeqUpE1VVSmCXjLF3YRIAIOsAShRFYvDMARr70FClkcRO5tLC12iigUzMbzNMm0gbt+OXxTfQR1v7vqzxICML1cbwjbz5u91VJ+8e5RhqvteCCvR8VF2ZrqmyfzSJBL3w+Sf3mOuBYi2U8uSC8pb3BiCPC5sHiiVFZyoM7hmC+NBg1sQOZBl8iMQXJZpKiBVt9nEMsdk8nzTsbrXY52s83tW366yQNvzTd7v9VRXbWQZ/tlDOE6ihgM9rrao7O0lMUcPI10nh5xeGe8V8ocVf+Dr2BwAtNt2vyEL7d2LtAKChKjaAzAxeOJVINJmDXOjYMg4ATPv7ja11L696fN0LrijPzxOnC6z2aSyXeNdQpBJU8h8XwvMvjCBLAdK0Z6bHKAQDAKJ0vuZkyRwCpIg1FyKO9vME227YDoGMmAUXip/MCS5LNJ1OKbDaDzyv1DHIUH++65sar6f77LHvZGiU95WhaOtbphBs7NQzIgDglldVPzdKfBxsh4F87+4U1XrXSpReYO79YhfCIGEjtWXzJSreYvIo5uPwWUOcW0gG+ngpD9Lpn0/wEihopAXmE8ndSi04fnLdQjejXT1Q95ZYKo125N3GigMTCFbz08E0QSUqMBv2juEe3AfP32LNAyr7OdKm2fAcFGTrAJRTbxeqeL17JzCGo150taninEoBkJOhoFkrKaWieNdo+taXSpoxrzdUtrB3hCRXD9i/Ez6Rqo6W+rkfLDnSjbDU2YYiqUxeXjgzRgwMBPHtnxdan2j8o6BDhekZDvtRSkmuA8BG3u9ILSo8S2EkR83VxQEg4cnToKRMtKgXpGe0uT6Eot5HftiME93w+WfKU8WyaFHD/eip06OIDxsvbCrOMFev7AQypY7a9UXhd3lPQCnLX6vmhAVbTzTMIk7sjzO8PWkx9Q3X6zju5cqefaFNEkfglyXOLgAAP/Ql0lZJ4Sus9qNlNIcD403b/dELbY+gUrUsCmyRhG/ZXbIH82BDrq2VVS1Je3AYhEH+2WOtRHmZYv4fY3CFufDIIGLDgJaCkdpw/eBX972IOUk2sAwAEmurPGDQSOM3tjKhEKmDRgJLmDh88mW7NWaY5Genthrt08D8fi2pfvfJG4bw4ADkb8ktVkhMIyZQdbrmKZpS0lwII5346y0FDhn0p0Mk8nw4nY7b2PI33n/Vlvtu2CqP31oU50mbGr8awZR0+zs1H/U9reKrYgfu+reOAZeAm/zJcrB/DqjUa/mnVSb66z9DHQehIK7FlWT4DXCBAy1pWcePrLIMjQDRDADEbS2qboLu9NWWBJq7otTUO3ZXD2HYsC80ctri2HT/b6QkZec/+dnz73TtmP9t5VAZPqAldn31pLW+XsT7G4BwHlHL5pKEEu7S5kt7MjVPfhMI0TTS/KY0B02suXvvXYm019PQ1Bt+ht6iidGyZZ9Ul0visPIfy3b4G0Z1Hnxk+jWM3QHxd6alTb+2eS5imsbew9iwjcslcIxxYoddikrHC/vxkJchhuz5lgTb61tuf/iC+AOOZzIV5tJLd9poXZnX1LwSJ0rKBdkyqRUmgnT7EoWwXg7Z81OL8eTGqJHTc2QEobEQAIAR69RH1arK0hOvIU4vQz17zCpJcMCx5cZERkzCK5pa33wx8DGtpch26mhdbAdN4WUUo1tLT23HfEFbsBbDd371pHGbe8NFYdFXjANtgcwFhQfto5o/78jp7H0uQJtwdsc3dqsiwRHTllsSGfI1+h3975aFPCSuhbJs7LRfExNAOq9U8a3jePLXiAnDiYn9pzuqstxp8g1D2Za9q7SzlqGVNiXdRU33Lzryq3+ghk02dvJIiVGR6JDvkkv50cesaGqp7LGMrCc681+YK8MmjnaDs3pp6lnXj6X8x/j86DNZSJfrc1pmjr7WPDZ31tCRIxRKhIJzH16lusBd75cbPigbJmtDJh3BOoMTB3r8pUUHxyDa65DRu4X+iJIhzph1y10xBt1CfXF6gUWvMdftD2inln87TPl0Xg8x8vkN+QqJLJ6bbu0w3JB8qqRQ8ff3BRLFdL7e0fN2zRJNOp0mkmSBR/Tmor+z4dVJBrQq2KG6cmkkwY896L5qy+0xqAZimZvf2urfbfghwE0tuz59v4Zlap0EPtvXZNGrhfFmm5nZi68sAlNoY3FRoNaXXnHqNeIMrVzS0jTJcYF5uyPt4b7DVEgHZ/iTurb6SKEdh2qw5bqmC3hRyR7pbmmp37Hv9SldYLlOYrS/S/hCS8HcgeU6a54gXvjLKtUXWSytrRv/7wKFXF3Utx8/00XragmaNjmR5u96qooWZ7qBK8ogg98df6k+4p8xyR7gQtcm8aLTbWA1gCOn7/UdxNTrdeqtWwsXajitDfpqI8+5gBAgikfwEqrVkLptYmPKBY82fASKDpLUOXNpn9NWdtRgad1dvYzTJMNiQ4XGUmFsABG6DZzjO5+KSngSZ6qzquqAGRx41v5MEU/WuW+OogmSHCDGVo7n18cVacEZynz8240i89RikD2MsFocJ5Qsawqdob6eOfhgamf/doQhaSVESqs+8u1xCE8A4ProlDNRSlH+sfkaYJ/UKYog/yw6uHcVYo9uwIe/u09tRuMxpIBDB02kjR8e6jjx/U7CRxI6HU1zOh039aXLLDG65gO5kBRh3UcO5tdvOJXRKWcA4JamCzM2AhCd01HnGA4MsoHxfSeb+HlqgUBjOIzRREhbW0vtN2Q5QO8OFL/oANIywoTMvymOwS2L6ktehNhrYkIc8OSWoKt7w2KVpalkDOM4JYnvrHi6tCDOWqkI6Q/+uOSejE20y5SUMOMa9T9t/2yVLfuhwpIjWc/hO1aaiWBQqXOyO5btDkd2tjQrlR9L7hoxIZD5ZFIe35EVFvswNoxhaPB5X273208aG8vhBTAhlmZ3zFe35QE5hrfBotMut9y8mfi6VjahlqaKhUEEPmtpjmL99s2srP5oqpYkcWJYWfOlS+p4ApVlJih+1ZcWuPl5xTnyfeMBJ0sSThYciPPQZeOuN/T+vJUxjNGRJDG68ohf7+ZtPAUxiK9brnl0E/V4rcaUvmQ/Mmoi5/qLzQrVOsHkiqLWJw/jHtoJ6ctSzSd9J6tg84k4YVm8olH/9PGSHwLvcBTO1hIEXERQKZzq3d3Y1vc65fPgGFk2vs+s1ys2iWFiUI+BuvvQJvI3ABB29r7ajA1Ml8jyG1XrsCF2qRZnoHPzTgi4587nx/t7zBp+eqLKUYHeYiz8/oOpULuHcoZYUvkO68Fq3v7U+q35lc9HEJ8XtH41ew9u1WcposaxCPk7Nv0eAFhKe3+gAtPfux9szDr34lrRxzKBO892dTEk1sVQ0ysg7klQ7p8mznqpqSV5CNc5vR6SY+jcXKbLNnW0r0qgNtbNUbkk7vURh/rM6dD5jd7sjNDvI3bdJgGEBH4CVEzvD83tO7V7W0Tg18p7LNNhf29qoJ3R4XSXj9r1XN3xp5sUCa156Uw+Uf3ZGDbM4MD8ggDMmoZDUx/s6/Sn5L/w8gRBYsCDrQHVkhhutk166WgCCLCwBGXrBZsPMV+YUnhF5Yn8Z8TZknNejKIpaQIHkLOCw4SN1gY9RPfRN6stVpUi3mtQqMod9jdfn8SCWgzjfDRpY6EQxodOqc2ND25Leg0nSMTJ4O8aqvLUIh4acy1BRIICtkkEFFkRgYoezEPNishFL4TpLEwlNNtKpqlhr01Lk14PQg19VtjiKPej9WJpmAQuAs73mvHCjHAJ/B3kafV+q7na8PZOimvXLhEY3Q5Z0JKXUe76qsVYjxqBF84FaY/unecXejR5sJIgzIiMWAwRUESGlRmWYUnlG06CRvNP3pFzfOVFPOTDQQKtdZJ499xzxz7VWHNSUUWaLJv/ZwBIS1tT/6fJRDlWh8t+5IMahIMBMackSLjxcZsPgwl5uVzIbyr5ZgxXdnk87GxdU9RXuVmGtVkIt3khxj/+OOnTDaeHkK4ggeE2Hch2sMHDrza8cLLcalYpFKgc5UvA1lbDKBR8jbGtfFt1/3OHRwLcGR9OsKSJNi0tYcO0ElqN+SkCgSzbfOynD1ZtZ3w1r75SFCVDjCWEA7t1XYooSSwmocIHDybN4hwDBaM31wkVAjU4+3JJnb03v60t/yXHGkdCpFr7lRVt+SeqXae/ebcby/V1+Wgc55RMO4NTOh+2c6bF+LhUIJaAHqKw4uxOivjAVVUcBUAsKSJ8ffltD12QuBg0rQDNbzg9V5bLmECLROdSFIkQE9v3H5jZd6y6o9iRX24NW/5Lpb0ue8MVB0AnimOEZ5imCRxjOScEXA+LH1rpMaZk8FJkEPMlZv+nl41/vbdXL4v1CBExaBQ5boIARCkn0QeP949PEWfC8QCUj7CPgcAGJkdnlz/77nSDwQVyersBJJWfnz26Z3QSR7gQ3J2YbqnWSdI+JYWf0U0d/r7XmK1vFT2WnqmWCtAi8yuGmROpedm8mBaR424SRKeDopuXoBQlDxbImE/1vzdCnXlHqeQ4xqR01mpJBMF3TA7+umf20DTYodk9rw0+T+SyuSwD5gvV1taGOBMN+jYbtTrveiX/GUlqa5qbn1kpf0JQeUeOoNfyBD9aLRxPEA03aeIA+AWiPKEiR29f2EUpg1hY/25ilFqopnQ6BAxfNyRsmDdoIwgvCTBZEvwN6pggi+9asKv89SdTYY1ceCtU2C2v0Kc2FaPu2D4QkaT/p6UAkOpJxahC4y9M2j+BcF4cA/5AWIIBpiVpkxILmxJcC7JLjMCJsMwfgi8YpxsIYhPjSZ9qiuqh5hRl8FAeFC8QPEQCNC1FFFfRHHUpQLg7kcc7L+NnOY73n91VhoAaCYSD7cMkPC+IoJUmcs3OrYiBL2kwBraUeD0eJLDrLKxlEDbyzt8iaxmiLMYQpp/fT9N35rWcXh5EuHBMYHyQ35gQJWjJ/2bsOyE2DM1mc/qCXmr0ve8rwosx0H8FAE2NuhgDauMroZ10PqZQqIss2+w/HR6Ee0aLh4v0XBOg+DsADNfB8bXhFE4jxMizyZ92ZKYoGoWV579FKrKaJNpymIsfOT8fSpcVZ7WqOhqSn20OYGywjMIJrdZLnnvyNVNiHg9JahnohwWax79yLT6iCrdWYMSZoCW4HAbsxkdTzm+/ULE6PV2uFz70UEdf0kdDNTjLhXw+rZf4GwCQ/7dD7UvgE0MfXerq0DtKYQlSMVz9vH9hqvX1PNGXdJ4ngN+rO5fQJoIwjvtITGy0xkd81mh81DeK6MHZcVY2S3CTJUoIJNA2JtVCm4qtzcGyplUJikhJKajEZzxYjPiCqCCoFxXxIIKCiF4URRBBEfWiJ7/ZGFcPspiJm+RPCzlsl/m230ySTeb36wbAjc/j90Y7x/effnn97bHdG9bDNIDlZ8t6mA0QWIrgPszGa+cvPr4Z35dvHh/0RiVVv1DCf0AHkASIKtu/Iao4DuNwjHgROoBDvSf3t0z5fPv4sSu/IapgDd146/WFh/c/9Ow82TXgxzyXoG8uN3P8P06BAm/LpMOMdCrDwxok7B8SgDUl1Nqb3xHvmfL+3aU7Zy9SRtjxG2fvXH/34mvL03353tYQAyqvCAlLaZCwv8zjDAumjYRaI53PT8UByNBD6RI9/f39+86dyLf2tYaQLqWNGdNGK3CxgfLQpu2Bzo4OysmjoLy2vo6Ovr69bYQ+gRoAyqOZzYAqRG5RhbC5YR+6HMCBwUEZQIXdB4qyLJZQVGFCF1VIbRXLGGCRAIekLq8AxoQALlJFLCI6cvjRKYAZFqmtRJ2DtqZSC/C4ZUHksJcGLoPXi0tw1bDgOukB8xmAqYhgjItXu9BPogDkS8QebC0AU/ULGFk6shZC5XWyD4YsCm5ZxXUGgzoFlBdZC8fUVyU02KxBg/Wnwd6wr/qwzQu1CaDbRUtqGpxN46xpdLmK3lVqGB7/G75fRBWPiu+PuEoSKBBSBS1UECjUoMKivZ0H+gniVIVFyRKRrbxUKYkIJmIsRlWvIBEpWeOSraDGhecW7OFJsLt0jQtUMKGCIh3RF+R5T5BFpAMVVFBl5KEqo7ApPadWZVIC9kpdfITKpNh0XpmK6byabJ7Ls8oiVJMMFarJKr8ccaKVXahGK4A3OMiOEVXaNRuitBvP8f6mrTwxH9KUdmwVzDJWKoijXj42fhdWFo7T2p9Z6+izSQZpHfEQluWgLaU4RzNrHbUXRo2KYWJNxIFYM6qJNcupNiWGFJCInclmGqjatOxyWbMRclnJ7j4ULa9cFjJy1E+9r4BYo6/3jcyjet/aEywL4e0cFSx/1BEsMymuJ/9HxbUAimuLjuKauYSpBcn45v8hGScgGc/pSMaZ11Poo+X/U/O+WF/zzt5HrgYl11xm0X5wj33YANE+hJ5/7Kx5SuaAiSCfB5UhPM9ZLLJyeTY0v87lL1sfjXMtj+SyFssgYk8AWSwJpc5pyPC1EsY6Fj1JBkwmEggwjR5OIabSk+ZA85TQPUwljJo7f3JEabdaCc8XP0PC8BAWKA4iCn9sexPkmA8Qt4Qe6C58EoWItMs+xpeMLJ81zbjhayVAprka65JvwmNsfkykdon4JYkQWNQJxljD/FEgLyEqHZLe3eDVfRHRJkmyWrJv0pOc08cyDJ+1hFFTlzQcTeYEk3UM/e7AGVjREcb+7nY3eNSKN2PkM0Cflum3guAXKkU4ustushzOpesaXdMK56pgoIbGV8lkmDdbrerlTWQ300ZRgyDFByLxY+z1RqN2u+lwNnn10yJX/YgqyTSHs+FuWzIXwGaT2SzBVMD+aJO6kUcUOX5oyDuMseAfMptNlk2J5qRytWHx9JUjqipj6x3zG+uedKSVtt5ULpPJdEluGkEYBD1810BbKJUKpDLpbXUT1sxx1I8aUZUZN9UxY/a8pTNP98d3HHlwOO+hyee/3DvYEo+3zFwwb/YMR/24kSOqKKN/ZeLEiaNH0511K1asWnfp+uf3j76l0wNdA0r62bfvq8ErtXbVihWA6aaHQrQ/ZBvAD2f7pPtrtOliAAAAAElFTkSuQmCC
- /blog/nft-lending-management
- data:image/png;base64,iVBORw0KGgoAAAANSUhEUgAAAMAAAADACAYAAABS3GwHAAAACXBIWXMAAAsTAAALEwEAmpwYAAAgAElEQVR4nOy9B3Sb15H3/bxJNm92k7WTze56s/v682aTbBL3ItnqXSwgCjsaxd57712iuptkq1mNvTd1ShSpXmzLki3ZqpbVK/EALCBAtP937gNAAsEGFpBUmXPmMJElG6T+v3tn5s6dSwGgnvvznwGe0Z/BmH+A5/78Z4DnADwXwfOFAM93gKdRBBRF/Z+R8rH+XvAU+ph/gCfdexHqz0z852b+iyG46Z//mZk/BwTPARgrsf9s/fr1/1BRUfGPDQ0Nv963b9+LJ06ceOnBgwfvtLa22nd0dHh2dnYmdHV1LVOpVBtUKlWpWq2uV6vV+9Rq9R4zbzB4pUqlKlAqlZ/J5fJFHR0dUTKZzL2lpWXu5cuXX83Pz//9li1bfrts2bJ/zs7O/qf33nvvH0wg6RWMsV4gMM59zD/AeHZTsWdnZ/+iubn5NxcvXvzX69ev/49UKp0tl8tDVSrVx2q1eptOp/tBp9O1wHrWpdPpbqrV6q+7urpK5HJ5Hk3THjdv3nz/yy+/fLmiouLfCBgURfUGxXMg8ByAwQieEf2JEydeuHHjxn/eu3fvjY6ODi+VSvWZRqM5ptPpaIwj02q1N7u6unbK5fLF9+/fd/r222//euTIkf/Mzs7+TX9AYBwsMmPtY/4Bxpvor1y58u8tLS1/VygUHkTwWq32FAAdniAjgKpUqqb29vacO3fu2H399dd/I+ETRVG/NABhmlP8n2cZiDH/AONB9FevXn1JJpO9p1QqQzQaTZVOp7uHp8jUavUPcrl83cOHD4Xnzp1767PPPjOF4RfmMIz1389zAKwv/J+ReF4mk01QKpVBGo2m0srx+7gxtVp9kcBw//59j1OnTr1JUdSvzHaGZypMGvMPMNrCv3fv3h87Ozv5Go1mrU6nu4pn2FQq1Vetra0Lb968abd48WKyK/xfAwzPzK7wTIieuEwme1epVMZpNJrGJy2mt7ZptdqHnZ2dxXfv3vXeuXPnK33sCk8lCE+78H/e1tY2taura6FOp/t2rIU23k2n03Uplcq9NE0nHDx48O8URf2jYVd4akF4GsVvFP50Q5hzcayF9SSaSqU6QdN0SmNj46tPMwhPk/AZ8Uul0ndUKtVqnU53ZaxF9BSYWqVSnWppaUlavnz5fzyNIDw1wr958+Z/qdXqReREdqxV87SZTqfr7OrqOn7//v0giqJ+8zSB8MQLn/wFKJXKYJ1O9w1ZscZaLE+zabVamVKpbPzuu+/mGUD4VW9Vo7HWx1MNgIn4f97a2jpRo9E0A2gda3E8S6bVau+1tbVtWLt27X9TFPVrExCeuN3gSRT+z06fPv1btVq9/Fk5vBrH+cEPV69e9aQoijTh/VNvYdFY6+apAMA03JFKpbMM4Y5qrBXw3MDkB3K5vLqsrOzvvYRF4343eBKEz4j//Pnzv+/q6soDoHwuvHFnOpVKdeXChQuub7zxxu+epN1g3Ivfzc3t5xKJ5FWNRnNgrP+Wn9vARtP0qlWrVv3JbDcYt7nBeBb/z8hNK4VCIdLpdA8s+Nk/t3FiCoXi0L59+yZRFPWCyW4wLkOicSv+a9eu/YFcJxzrv8xnyXQ6oEutRVunGpL2LtyXKXGbVuCWpBOX73Xgh1ttOH+rHVfuduCmpBN3pAo8aOuCVK5CZ5eG+fNG02g0d8+fPy+aNWvWv5pUisZdSDTehM+I/8GDB3/WaDQ1YymGZ8GUKi1a2rpw/YEc31yVovbkHazZcxVpJd8jeMNpiD/9Crzlx2G/+Bjm5BzBjKxDmJF5GLNzjsJ+8XE4fngSC9acQuTW77Bi+2VUHb+NszfacEeqhEKlZf4b9+7dW5iUlPT/9RUSjbnuxpn4f/7w4cMJGo3my7EWx9Noao0OD1qVOH+rDbu/uYePtl1CyPrT4C4+hulpB/FO3H68Ht2I16P34bWYfXg7YT8+SG7G5LQDmJZxELOyD2Nm1mFMzzyESekHMSHlAN5IaMLf44jvx5sJTZiadRjC1V9j2bYrOH6Zxj2ZElKpdOv69ev/ZgiJ/tG8SvRMA2Ba4mxtbXXQ6XQ3xlooT5vorz+U4+j5FqzecQUh676BXe5hTIjfj9cj9+KNyL14P2E/ZmYcgt3Co2AvPgbOEr2zlxyDw2K9sxYfBYv5egws8utLjut96XGwlp2Aw7ITsFl8nAHgtYQm/DVmPyamHYTP2m9Q+9VdXL0j2VldXT2RoqgXx1NeMG7Er1AovAC040k3rQ46aTu0tx5CfekG1N9cgurod+hqPoWunUehqNwPRek+KMobDb4PipK9UFY3o6vhBFSHTkP15fdQn/0Rmqu3ob0vga5z8JXfWy2dOPzDQ6yovQDxRycwPaUJb0frBT8pYT/mZx0CJ+8oeIuPgrv4KNh5x8BadFTveY/dvjdffOyR2xl9yXHGWUtPgL38BFhLj2Nq5mFmZ3gj6QC81n2DhtO3jn9eUDuLoqjfGvICY6l0zCAYF+JXKpXxpHiAJ9C0D2SMWFXN30BR1ICO5SVoi10NmedCyFzSILWPBz07HJLpwaCnBYGeHAjJpADQk43uD3qSPyRTAkBPDwI9KwhSm3BIefGQ8VPRGpiH9sx1kK+tgrL+IFQnzkJz9Ra0ncoet3o6ujT46qIEn++4DM+PT2JGSjPejdmL92L2YmZqM9gLD4OXd5QRPnvRETh0c4P4LYHABIDeIDCFwWH5SczIOYq/xe3HB5mHkVfzw7n0NbUOBgh+Y5YcjzoEYy7+rq6uZKIjPCGmk7VD9c0lKOuPoGNZCVr9l0HKTQI9KxySyUGQTAiAZIIfJO/6QDKRCDsI9IxQ0LPDQM+NAD0/CrRNlP4r45GgbYhHgJ4bDnp2MOjpgZBM8YNkoidaJnhA8r4nJB94QzrNDxLbMNCCVHQlfAhsKAEOncS9n1qw7dQ9hBecw8yFR/Fu/H68G70XM5OawM49DN6iI+AuOsIAYHSHhUceuxkMFoNgAoNdHyDYkq+GMGli+iG8k3IA/mu/vuKdV86jKOp3Yw3BWIs/gwx8wjg37cNWqA59h8619WgNXAmpbTwkU0IheT8QkomBoCcHg54RBnp+DKSsBEg5SZDykhgw9J4IKSehD4/XO9fgvDiDx0PqaPj/nBjQrChI5oZCPs0LeN8dmol8XJgShHL2EqR4l8HdowrzvWowO7oBtjmH4bDiJOyXn2AEzck5xIBgCkA3CBaNzG7QFwRGEAgEcxYexYS0g3BYdvSabVIhf6whGEvxp43ntgadSgP1iR8gX12DVo/FoGdGgf4gBJJJIaCnkhU9ClL7BEi5KZDykvVCJ8JnJxo8wczj+/A4vXOMHtvNaU4MJJw4dHIiAXYQtNwwfOuSiXVuaxDmWgRPdgF8bDchlLMFCW5FiBeWIMSvGuLoXXDMOsCIb/6yE7BfdBSc3EODgOCIVSAgu4HNkuOYtegoJmceuB31YSWXoqh/MTTUjToEYyJ+pVKZMF4TXrLaKysPoDX0E9CzoiF5nwg+DPSMSEhtiGCTIeUk6786EMGbij5xRAGQcOLRwY4CHIKgZYfhlGMGVrmvRYC4Et6iagSKqxAuLkeMqBSxohLE8osR51aEOLdCxLsWIEpUCr+gOrim7GeEO3/5SUaYnNw+QqGFowMB40tP4O3kA/D67OTVjzdXs8YKglEXv1wuDwTQhnFmmtst6Fy/AzL3XEg+CINkSjgDAD3fKPoUSNkpkDoYhG90KwBAVnwZJxZwCAEcQvGtYwY+dV8Pf1EVfEXVCBGVI0pYilhhMWKFJYjuxWP5RYh118NAvgb5VYOfsBesRUcwf8UJ2C8mO8LA+YDF4VBfiXFfO8GS45i36BheT2xCeul3PxSVVc4ZCwhGVfzt7e3O4+3yiuZOCzo+rgZtk4yWd4JATyeiT4CURVZ5InoieHO3DgA047HQOIQxwr/gmI7P3dYiUFQJP3E1wkVliDYRfoyJR/fhMYJixJCdwb0Q8e5FCPWqhCh2DyPS+StOgJV3xAIIjlgFAnJ2MCnjEN5NPYidp258XVhYOMUAgWlOYNUS6aid8NI0PU2n08kwTkzb0gr56jrQ8xLR8lYg6FmxkNomQcoiok+F1MG42lsfAJodhxZOPLqYcCcYN7hJ2OK6CkGiCviIqhEpLEOMsBRxZGU3E74lEBg9ivx592ImPArzqmR2BLslx2Cz/DjYi8huMPrhkMOyk/hrXBMWfH4KF6/f37t8+fK3e0mMrXZiPCriv3fv3uvjZTyJTq6AouIgZJwMtLwRoBe+fSqkLOIpemfEPxoAxEHCjkeHQyx0rFBI2bGoc1mJKGEZvMTViBCWIZZZ8Ut6+JAhEJciWlTC5AoJroUI9quGS1oTbJbpe36GUh2y+JygFwhIUjwr9yheS2xC1Ze3tQ8ePMj39vb+iwkE3U6MnzQAyODZVwzT2MbW1Bqov7uKVp+VaPmbH+jJ0ZCy0yF1MIp/dAGg2QloZcdB7RCBLocIHHNchDRBITzEtQgXliPOEOb050OBgOwCJDlmXFiCBNcCxLsVwid0GxwWHoLNMhIWHR10ODRUCMguwF5+kjkoI7vAXalSd/Xq1byXX375P81OjK0CgVXFT15NUalUa8Za+7qHrej8pBaSd8PQ8kYQpKx0SNkZJsIffQCUDtHQsMLwIzcFq9w3YIG4Bv7iKqaMSZyEO8aQZ6QhiDaBIFJcilh+CZKc8hEpLgM/aR9slx2H3eLjYA0yHLK4bcIMAnJiPCPnCFMVOnRef837xIkTvhRF/bsBgn+yVhep1cRPiO3s7Awf81X/2x8hEy5Fy198Qc8kh01ZkNqnQcpKG1UAaGbVj0c7E+5EQOZAwp2PECKqhKdHHVPKTDARvqkPBYDBQBDFeBniXAsR71IA/+B6JhQiYRER+IDh0FDaJswgYC87gT9HNyKr+iI6lRpyn0BaXFxMxq/8m6GBzthFOqKVIavF/ffv3588ltrXyTqgyN8HyYQItLwaBKlDhn7VJ+IfZQBodiJkDnHoYkVCxYrAd7ws5PDzIfCoR4i4EknCoj7Fb00IoswgILsB+XVmN/Aog0tqI2zJIRrpCB1oJxgmBKSB7o2kZjh++CVuSfRtYXK5/OvY2Ni3KIr6V0Mr9YgnxdYA4Odnz559eSyTXu2tFrQnbkLLX/wgmRwDKS9HH/YYxT+KABDxyx3iAFY4HrLjUeq6Gj7iGiwQ1zKhTpKw+FHYEz8WEIhMdwEjCGVIcClgEmWPmF2wWUoOro7DIfcI2LlDhGCAcMh+6QnMzDmCDzIO4esfHxcLb9++vYmiqP80K4+OWD5gjdDnH8hLh2Mlfs331yETLEPL//qBnp8CKYeEPET8owsAs+qzE6ByiIKWFYkzjtnIFhRC7FGPMFEFUgyrvqn4xxUEHmWIcy9iQPANrmcETBJksguQvqLhlkd77SJdegKvxjch/+BNaLSPe12PHDniR1HUfxgqQ8akeETygZEW/y9aW1s9x0r8XQe+hXROMlr+Hqhf8UnY80j8oweAhJ2EDjZZ9SOYGn+Fy6cIEFfDk6z6ohKkmK36Yw1BVJ87QSliBPqQKMSnihH+vBUnGdEz5dIRhoAcjP01dj+yKi+gQ/F4yqVarb6blpb2viEpNl6oeZQPjBcAfv7jjz/+RafT3R8L8SsrD4OeGAXJ22H6VZ8JedJHFQDaIH6lQywj/vPcDCzjb2GET5LdZEEREknp0cTHCwTRfUBAzg3IvzPJOR+RC8rglHkA81d+OTwI+giHCACvxTchYMMZtLR3bxKWSCS7KYp6eaTzgRENfdRqdd1YiL/ziz2QvBUK+v0oSDnZkLLMV37rAyAxfCXhjoYVjQbnFYgWlcNXXIs4YSlSBMVIEJTofRAQjCYIMcavohJEi0oRISpDqLgCAeIq+IqrEeBaAW9xDeanH8GMlaf04ZAZBMM5MWYtOY53kw7A9eOvcE/W837UV199FWOWDwz7fGAkQ58Fo/70kE6HzrW7IHmNtCmTg61sSO2J+EcXgBZ2MtrZ8YB9OO6zE7HBbR3TuxMkrkISk+iWMCs/4yMMwXDPCWKY30cO3YoRISqFv6gSYnE9hB7b4OFRBx8P8n1UIlRUhkhRKeJdCxEmKIN92mHMWfmVfifoLzEexG5A7hpPTj8Em7xjuP6ws8dft1KpvBETEzPBkA+Ynw+MGQA/P3bs2H9ptdpRn8vf+fkOSF4NAT0lFlJ2lon4RwcA2oGIPwWdpMpjH4ZzPH2iS1b9KFE5koXFj4VvAQSjGRLFC4uZ0+YwYRlzCCcU1zHtF+HCMmTy87HKfQ1K3T7EPtdFOOmcgbPOSbjiFI8fneNwxSEG1a7LwE47iOkrvzFAcHjYl2oIADPI1ImsQ7h4p9dued29e/fKKYr6/wznA8YpE0MOhUYk9FEqlatG+1pj54Y9aHmNiJ90UxrDntEDgHZIhsQhBWpWDMCKxF7n5YgUlTPJbpywrG/xm0IgHDkILNkJYg3CJ63UXuIa8MX1THt1sqAQa90+wx6XPJx3TMRDbhg6OIFQcQKh5QZAww2Aluuvd54/wPXEbVYYogUlmJN+DPM/PMm0WQ85HDIBYHb2EUxJP4hTV6W9/r1rNJq2Xbt2kYnU/zUSodBwxU/m+MzU6XS3R1P8ipIDTNhDTyYXR4j4M83Eb10AJAYIYBcJOSsOm9zWws+jBmGiSkbc3UIeUQmSGC9FstjERaVIFJYiUVSKJLHeE4mTXxeNLAT6f16MYFEFhOJ6JilPERZgs9sqnHTKxH1eJDo5QdBwAqHmBELJCWT+v5wTjA5eCNp4oWjlhULGC4WUF8qAcMsxCunOW+ElqoVTZjPmLT9pKJEOPRxiGQZwTU47iOOXJH399eukUulRiqLI2wQvDTcUGlboQ/6jarW6djRjf+WeU5C8EwHJBzGGlb838VsPALLqt7ESAbsI3GKnYil/C3zFNUzCmyzsLnayyse4FCKcsxVBthvhO3s9vKavhdeMtfCeuQ7eM9bBa/o6LJim/zW/uRsQbL8JEbx8xJJuTdIeIS5lvg4lHNL/vmIEiqqYuD5MWI7V/LU47JyDB7xIKDlB0HICoSBC54SgjRsKGTcMtInLeEZ/DICG64+bjjHMCba/awWiPErByT6E+ctOModlPU+MLQuHLASAPNDRdfbs2SyTqpDxEs2gd4FhJ746na73vcoKpj71I+jJcaDfi4SUnWMQ/+gBQDukoIOVANhH4DRvIeJJ0iiuYVbtFBGJ64sRydsK/7kb4D1jLfznbEC0UwFSPcuxNHobPs/ci41Lm1D4yRFUrj+Byi9OomzNcWxZcRAb8prwSeoe5IbUMGFQqMMWeM1cD8+Z6+BvsxHRLgVIIP8NsWUQEPcXVcNDXIckYSEqXT/Ej7wEKLiB0LDJCh+KNm4YWrlhkHLDTTysm5sDIDMA8JNTLNO/RHYTUiIl5wRE0LZLTgz5Ug0ZvjU7+zCmmp0G92bt7e3f8Pn8dymK+oPJAdmgd4Ehr/5ubm7/qFard4+W+DU/3YeUuxCS18hfjKn4RwcAEvN3suKhs4tGo+NKBIurEeJRhSRBMSLYm+EzYx2C5n+BZI9SrMnai235X+PLpiu4cbkFrXQnFJ0qdCnVUHUR10Cteuzk/5N/plSooZCrIHnQgQtnbuPwrgsoWX0Uy2J3INK5EN6z18Fn7gZEOOlhIIdqpoLXg6Ff8UmMny3Yil0uS/CAFwM1OwBqTjBaueGQMUKPMHj4oAAgoRDJCX5wTkS4qBw+4mrEModlW5n7x7ZLDDX9IXSREgBmZpL5o4dw/nb/t2Z1Op328uXLqymKesVwQDakhHjIiW97e3uQTqfrGA3x61ra0Ba6Fi1/DTKUOk3Fb30AZA4p6LKPg5wVjzKX1foSp3MxAmevQ7DtRiwKqUPluhM4c/QapA87oNFooSUT4oYZGOp0OubfQyC5dY3GgR3nsT6viRG/z5z1CLDbhBhyw8sQ8gSJquAtrkWOYAuaXPLQxomAlh3ArPaPBW/u4YMCoI0XwuQAx50zESiuZDyanBiTfMe5AB7Ru/R3CizpIjWDgABAZpDOyz2Mqw/kA/582tvbv8/JyZndS0Js8S4wpNW/pqbm92q1ugGjYSoN5Ku2o+W//SC1Jye8owuAzCEZWvs4SBySsNplHdx45fCavR4pboXIX3kQ5768wazgo2n0gw7srzuHFfE7EWy3CZ7zN8LbtQzZ/K1odFmMDk4EdEyYEw6aGwUpN9LgwwNAyguFnBfMALDDdQm8PGoRJi5nDs1IA10cX38J3zW1ETZLTzy+T2BhOERmkH6Q0gzHZceZseyW2I8//rj2V7/61R8NCfGLg90FhrT6y2Sy4NEaZdh18Du0/DUYkpnkrm5uL+K3DgAk3m91SAYcYnHTPhXpDuvhMLcQqR5l2L71KyZMGQ927swdrF92EDW2OWifKAbmeKKTHQaaF2Mi/JEDoJMXBCUvAFvdPoFYXMfcIzBtoGPGsXiUMcO4yKUai+4YGwAgA3nfid8Pj0+/wgOZZSOj2tvbz+Xk5MylKOr/URT1+8HuAoNe/desWfO7rq6ueqv/zZJs/3YLaJsMtLxDVrGF+h2AcesCQMTfxk4B7GLw/dxUhM5Zh0CvOuwqPIV2ycBb85jYt2ehzlyNlln+aJnsDdqWCDZK7yMIgJIbABk3CEv5X0AkrmdCH/P+IdI85x9Yx7RQPwqFLLhUQwAgY9nDN54B3WH5wMDvv//+Q4qi/mhyQmzxLjDo1Z+mafJkkfWHWqk16EgrQMufAvTit80aFQAkDqno4KRAPS8KR6YkI4Sbj8/XnoL07ria5tKnqY5/h7awJZB84Al6hi+k7AhIHaNHBAAZLxRqbgBuOEUjTlgEb1EN00JhDkCMsJhpoxYkNOhbqI2l0QHCITKa/bXofcirPg+50vKwUiaTfRUaGjrFsAsYy6IW7QKDWv3Xr1//okKh2IpRsK7936LlT4GQzidizobUzvoA0A5p6HRIhnxaKHZPSkNu3G4cO/0QT5xpNFCU7QHNiYBkohi0bTCkTjHDBqDNkACfcMlAgKgKIaIKRuw92qnFpUwuQE6cyfAt+yVH+509ZATAYdExvBHdiM1N16E2uQ9ggelOnjyZNZRdYFCr/927d2frdLo7sLJpJW2Q2mZDMoEcduXqxW9FAGjinAwo7RPR9m4gds7ORXHBGdzv2Y/1RJn6+x/RFrsCLe8KIJnlB6kTCYkihwxABy8Yaq4fStw+hFhU328rNUmKmVAouB62hrlDfecDZFz7UczLPoKJic1oOjf4NxHv37+/19bW9t3B5gKDqvu3t7dnYxRM/lEdWv4c3F381twBeBnotEmA9FVfNLl+jMMHro1yW6v1TNepQOeGakgmL4DkA6EeAsfIQQMgJQkwNwitvCAsFGyCSFzHnDL3BwH5tXi3AmY2KRm+RXaDviDgLD6CqanNmJd9GJd6b4Tr19RqdVt9fX2AYRewuCJkCQDMqe/Zs2f/rlarv4OVTXPlDuiJsaBnpUJqn2N9AHiZ6Jwbh/t/9cXJkI24cIXG02jKHYdAzwtAy7tukDoSCEhybDkA+gMwf1xwSkSwqByBogom/u/vdhm5UUaqQuSU2G6p/pmlvgbykldq3o7ZB4+Pv8RdC0ug5nbx4sUNr7zyyt/NzgX6PR22NPz55cOHD4UYBWuP3QzJm5GQOhDxZ1sPAOK8THTMisG9v3jjh4wy3JE84THPAKY68R0TArW87qQPhZyiLQaAxP9qri9qXJczDXW9ib+33YBMoSN3CITxDZi38mTvk6kNAPw9ogHpxd+j3eQ65GCss7Pzp7y8PAez0+FHPUJDBeDnJSUl/6pQKDbByqb68hIkb0VBOj/TIH4rAWBHxJ+FjhkxePAXb/y0og6tgyi7Pcmm/v4KZOIktPydZ4Ag0iIA5LwgdHCDsJi/kWmsIy0XFo1dIQmxexEiFpQziS6TEJtBQJ5rsl94BG/F7EPZkZvkmbUhW2NjYyJFUX823Bwz7RHqNQyyKPm9fPnyuzqdru/2vBGytrB1kLwbDaldjtUAoAkA3EzI58Ti3p99cH1lHTqVQ1txnlTTXLkBmSgZLa856vMBJifoGwBj+HPWOZmp/oQKy7tdtBl4JyhjBm6JY3bDZsWJHq/VkDfLyHtmM9MO4HQf9wAstRs3btTMnz9/gsmlmX5LogOu/oSeBw8e+MLKpjp2AZL3YiGdQ4SabT0A2JnonJeA+3/xxsWcSrR3qvAsmvr8T5A6R6PlbVdDdSiiHwD04U+h28dwF29nkt/BTqAj7xWEe5Yz9wXIRGrTUIi8VPl29D4IV55kXrcc1velVktXrFjhRFHU/1hSEh0IgF/U19e/pFAoSmFla4vbBMkEMqKciN06ANAOGVDYJuHh//rgm7gCSNp7vrT4LJn61PegbYMgmSiA1NkIQU8AFNwgtPDCmJtjvqKaHgBYAgFTESK5QFwD81KN6XNN3LwjeD2iAYsqfmBerx+uNTY2plIU9b9mJdFek+EBw59z5869Ze2ef9XXVyCZmmxS+Rl5AGhWBjrtUyB7IxDHvT7HjfvyZ1r8RlM2HIVk2gJIZnoZ8oGeAGi4vmh0WQhPUe2wxq6Ql2pCvKuY98rs8/S7AGfRYczLOIhJ8Y3Ye/reiHxPN27c2GZjY/NBH8mwxQAQWv7vvXv3RLCydSyqBP1urFnyO3IA0PYZ6HBIQ/v7odjLWo7TZx8+Oe+yWts0WnRuJpOz3UDbBkLq2H0XIFciSQK8WLCRaX0gye9Qp1IbX6rhJ+7V7wI5h5gnXN+P3wfHvCO4OMAdAEtNqVQ+TE9PZ1MU9SfDhRnjtckeYVC/4c/mzZv/TS6XW7X1QXPtPmR2OaCnJvWy+g8fANo+HW2sdCinR2H35Ezs2HZhWFWGp9I0GrQnfwTJBDdI2SGQ8vS5ALkSqeP64UuXDEb80cMdzS4oYSZQB6Ax2XoAACAASURBVPjX6OcALToK3sIjeDtyL9IKzw65/Nmb1dTURFIU9deBTob7O/z6h+bm5j9rtdorsKIpCpshmRAHelbaiANAxN9qnw7dvHg0T0zFqqWH8XRX+odump9uQ+ocCXq6xyMA2rmhUHED8Yn7Ongxw3x7Ptox2HCIlETJuEXn9AOwW34C89IPMOHP9i9Hdq7ChQsXCt988813DZfn+wyD+q3+nD9/fiasaWo12oLWQjIx3iDy7BEFQGafDtgl4vT0dCR4lOPyg1G5wvDEmqK2EZLJAtA2AZDwIgCOL844pzF3i/WP8w3/kQ7ylCtJhj0jdzKPeU+I3QenxUdw6c7IPhza2tr6g0AgmNVXGDQgAG5ubr+haToJVjTViUuQTk8FPSUZUlbuCAOQAdgl4af5GQiZuwH1O3+05rfy1Fhb7HK0TBKilRMCDdsfn/HXMNcse1v9hwoBeZIpzLuSOQR7K64JeWU/QKUZ+awsPT3duY9q0KM8oM/wZ+3atf+uVCrJyBOrmWJDgz78mZ3RR/gzNABI0qu2S8ZD+3QkzluHjMR91vw2nipTn7uMlnl+wBwhvnVKZR7jNr5QOVKzSMm7A/H8YthE78GkzMM48N3guz8tsV27dqX98pe/fM1QDfo3kzDoUR7QZ+9PdXX1K1qt1mqtzzp5F9oCPmcAkNr3tfoPHgCJfQaUdilot0vBx7wNcLMtxKWvblrr23gqTbnsC6jed8JHruuZxzz0YxSHN5C3exhUhCT3Ith4VMHj81O4b+H1x8Ha5cuXy15//fUJJodixg7RR3lAn+XP06dPT4EVTf31FdCz0yGZRB6lHhkAiPjldqlQ2SWj0Hkd3G0KsTZ5jzW/jafTrv2Eb5wz4etEHtp+vPqPFARknlCk41a4upVhS7P1Fieapr+bNWvWNIqi/mLSG9QtD+i1/Pnee+/904MHD8KsGv6UHoZkQjyks0i5cvgASOwz0WaXBtgkYJfTKgTwqxAy5wtcOWP1+ztPnSkB5KbvQyBrC+IFxSM+mj1WXAofu82IFBTjp/PWe05Co9F0eHp62hvKocYpct3Kob3G/2Kx+IX29va11vpgOhW571sMydsx+sa3PuN/ywAg4m+1ywBs4vEldwUiRFUIttmEz2K3WetbeKpt+zkJZkfuQ5xzPjPtbqTfJ4gSl2EBtwjrHJZC23zEqt/L+vXrAymKMuYBpuXQPgH4ZVhY2O+VSmWTtT6U5sZDtLqvgOSdWEgdFpp1fw4OANrgZOW/6rAIiQLyunolIqavxdeNl631LTy1JutQQbDoMKbENyLMrwrJboUj+kaBfkhvJfz5Ffh6mh/w6WqrtqQcOnRoxa9//eu3+soDeo3/8/LyXtJqtbes9aFUxy9AOisNkg8SIHXIHRYALfZZ0NokosU+A4vdCxFFniLibEWuRxmU8mez03M4tmnXJUwK3gGbnMPwjNmFVJeCEX2og9wR8BHVYJlwIzonc6AJT4am1Xozli5dulTx8ssvTzTcETDOEX3cFtELAL9qamp6iyzU1vpQisqj+urPo/h/aAC02GejyzYFKttkrHfdiHBRJTKFpQidugaVq6y7tT6NdvlWK1iJ+zAvZg942QfgkrYfcWRcOzm8GgEIyC0yMqGadJQe5GcBU+3Q6hoC9QXrndHcv3//xN/+9rfJJucBplclewBAtoV/vHLliqPVPpFaC/mSakjejobUlgg/Z0gAkJW/0y4dsElEvdNqhAmrkMovQaZ7ESJnr8f556XPQVv6pm8wKWQnHNP2wzmjCeycQwgOqO2xCwwVArID+IuqkCvYDLlTALpmOUEyfwFUh7+CtUwul9949dVXp1MU9XfDJZnuc4PMACDbwj/du3cv2lofSCdpR1vwWrS8EWkofw4eABLzS+0yAdsEfMNZjhhhORIEpcgWFCOetRmLvSugfEYvugzV9n19G9MjdsMmfh9cMprhlN4Eh9xDWBC9CymuPQEYLATk1yNFZfAR1WKvaxbAE4G294Z0uiu6KrZb7fvSarVKgUDg0GcibF4BIncopVLpR9b6QJordyF1XgrJW9EmCfDgAdDZJOEGKwfZfHI5uwJZ/GJkiUoQOn0tCpcdgO55v7PFdrtFDo+FhzA1dBecDeInzsk+ALfkfYgTlSCRXzRMCEqZse1Zgq1ocwyAhucFCS8A0smO6FyxHjqN9QYML1++3JeiqDcMibDpyJRf9KgAkfioo6OjzFofRnXqCqTzskCTBrgh7AAS+2yobFPRYZeGz103IUxYiUx+MeNZghKETFuDw/XnmdHiz80yW1F2Du8Hbgc3uRHOBvEbnZd5AOE+lX3uApZCEC0sg6+oFk2umQBPCKljIGROQaA/4KE9diG0MuuNniwrK0ugKOots8Y4/TVJ8woQiY+USmWztT5MV/NZSKYkgZ6WMmgAiPjlpN5vm4w6p88Y8acS4fOLGABSnQuR4LAZNy4+geMMx8gav76DGRG7MC96D1zJ6p/WpHcDAOzsgwgMrkeaS/6wXq8MEFUjT7AJCp4funjeoB2DIHMJZgBo9YqF9qb1Diybm5tXUhT1Tq8nwr0A8IJKpfrOmhUgsvqTNojHFaCBAaDtsiCzz4LONgVn2MsQR+J+YSly+YXI5BchixzY2G/CYt8KKJ6RESfDtRv3O7Bg0UFMCt4O1wyD8E2dAJBzCJ5RO5HqVtjvC5b9QUBaqUnsf8wlHeAK9eInO4BzMOipLpCRStB56107OX369GaKot4zuSDzL4/GpZiXQAkAWq3Waq8+dn6+Cy3kBHg+CWlyBgWA2jYNd1g5yOMXIFJYgRx+IbP6E88mJbbp67AhvQFdI3iz6Gk1jVaHZSVn8a5vPXipJPTZD6e0/T0g4GYfgCCxgSmFJvGLBw0B+XU/UQ0+5K+HhueNTp6/PvxhAAiCdBYfMpY31F99a7Xv9eLFi7UURZGmuL+ZtUT8skcJlCQIOp1uZG8nGK1LhY68Sv3kt0fCHxgA2i4bnbbpUNmmocBlHXOSyIjeIH7iOcJihEz5DFWrjkI9yi+2PGlG0qM9J2/ig4BtsIltgBuz+hsB6A4BL6OZefEljjzt6l406HeMo4RlCBRX45xTAnRcD9COwXrxGwGYK4J0jhCqw19a7fu9fv16I0VR5DDs1R7zgnoB4Lc6nc4qGYmurRPtKYWQvBllFv70DQBZ+VtJydMmFUe4HyJcVIEUQQkT+hjFz8AgKELYjDXYX3YGGvXzElB/dv66DLykvZgStA38zGY4pZqKvzsEjunNcExrQqRXBfMslCUPej9e/YuxQFyPjfxPAe4CtDsGPBa/IQmW2i6AdKY7unYfhLXs7t27xyiK+qCXUmg3AP7BCIBWq2211tjztqiN+hJotwS4/x1AbZOKG6xcZAj0Jc+FZuI3esSstfh63yXmYbnn1ru1ylWI++wk3vSqgVvGfjgTsRMA+oGAk3EAYb7VSHMtsPhV+wRhMUJFlYgUluOWYwTUXO/uqz8DQCCkLC/mLEBZuctqf2UPHjw4TVHUJIqiXu9xR9j8EIxkyFYD4J5UfwmG7AAWAEBCH7ltBpS2adjo8gVCyCkiv5AJfUzDH+LprkWImb8B35+4PuzXGZ9WIz+XL7ZdwOviavCS9sE1fT+cUxsfA9AHBJzMgwgOqEGai2UA6P9ZMUTibdjhuhjgiCHjkcQ3qCcAbB9IpzpDmV9lte9bKpVepChqsuEswHR8+ugCoLklQavXpwYAFg4IgMwuG7BJYUIfIv40Q+hjBOARBIIipDrlI4G1CVfOWC1/f+Lt8Jm7eN+3HvOjdoOf0QTnlEYGAL33DQEn6yACg+qQ2ssO0BsEycJi+IprkSXIRxvPHwquL6S84N4B4PiCnuwExYYSq33fEonke4qiyBNKb/boCjU7BbYuALclaPVZZREAZPVX2aThrn02U+OPEZZhkZn4jZ4jKEIydwtSHbfi5qXnZwC92dU77eAl7sXUwO0QZhrEn2IKQN8QcLKaERhSj3SXQiQISvqFIJF5Mqkc3qI6fOOcAh1ngV78fe0ABIApzlBsLLPmzbALJgD8qdvM0PEKQLtdFnTzU1DkvI5Z/Uncn0PE3isAxUjmbEGacz5u/Wj1IdZPnMkVaoSvPIZ3vGrBT98Pl5TGR+6c2hOCRyAYAGAbAXAtRKKghPHeIEgwACAU7cBG99UAxwsdvAC9+McQALlcfoeiqKkmp8HjGwCy+utsUvGtwzJECSuQLihmQh8jADm9AJDC3YI0p3zcutJijY/+RNuHxd/hHY9quCQ3wi3NDICU3naC7rtBNwAYkRsgMAMhRVgEP1Et0/Zwm0l8fSA1in8MAWhra7tmBsAf+gPgX6yaA3j3nwMQ8StsyRXHLCxzy2c6PReZib8nAEVM+JPK3YJrP1jvjumTaNXNVzHRqwa8+AbwUxvhkryvGwAu/UBgBICT2YygYDMAzCBIYp5LLYNYvA0HXbKZ1b/VGPoMBACTA5RaOwcgALxtcjFGPyhrNAHQ3pGgzYIdAPNTsZu3GmGCKuS6F/cQf28QpJMKhd1GXDxltYtsT5wd+/YeZgZvh13ULkb8rsn7HvlgIOBkHkBIQG1PAIwQMAAUQSzajlX8dVDwfKAgJ76DAeCLUmvnAOMAgAcytIWs6/McQGKXA7VNGm6yFiGdX4I0fikWuhchh/gAEGS5FyF69nqcOXT1eScoud11UwZuXAPmhu7oIf7BQsDJaEaYXzXSXQt6AkBCH0ER/JnQpxxXHaOh4XpBxojfAgAcfCCd5gJlce1o7wC/G30A6Ha0xZBH8KJ7PQlus80CbNJQ6Lwe0YJKRvy5BrcEgsgZa3Fsx3loNc/2QYC0TQnPrGbMDNwO9+TexW8pBE5pjcwNsUifSqT1sgOkkMfyROXwFG1Do0suwPVCOy/QsPoPBEAQpHaekM5wR1f9Xqv9PO7evfvVoADQ6XSDf6jVAtPJlejILIXkjZ6tEBK7XKbqc5a9DAmCcmS5Fz8SvyUQkEQ4bNrn2LX1q2e6FUKj0SH6o6OY6lcPl6S9cCMHXkmWA+BiBoETUzXah1jPcqS6F3UTf5Lh6wLxNqzlr4GC4wsF1w9SXoiFO0AQpPM9QM8SoGv/Mav9TG7cuHFksCGQdWqJGi3kK+vQQl6CtM1+JH7aLgedtpnoss3AGtfNSOSXdVv9e4DQCwALSTfolM9RvKwJqq5ntxt00aavMdW3Fi7xDY/FPwwIHNP3wz1xLxPnJ/OLuwFADrz8xTVIEZbgumMktFwvk5XfAgBIM9wcIQOB6tgpq/1MLl++vKcPAHovg6pUKqs1Zyu27mcew6PnZj7aBcjqj/kpOM79CLGCcuT0svoPtBPkkunFc9djVVT9M3kfWKvTYVXpWUzxqYNT/B64J5PVf293AIYAATejGeKYXUhxL0KSoLib+MkUjiBRDU44Z0DH9UQbL9hs9bcAgJlukHH9oD7zg9V+NmfOnCkfTBn0dwqFwmq9qV27T4F+PwH0DPIeWC6T+HbZZKDVNhsrXfORzC/rV/x97QK5pBTK2Ywc90LIHlpvzsx47e3fuv0CpvjUghO9G/zkfYz4jT4cCDgZB+ATtr1b/E9KnuSOr7e4HsVuHwNcbyi4/qB7iH8gAIJBT3FCKz8cmivXrPbzOXTo0BeGk2DLDsI6OjoarPkcKj0jDfSkJKYSRJPV3yYF+7kfI47fe+xvKQRZboXMLvDDiRt4lmL+qsarmO5XD1bkTr34Ex+Lf7gQ8DKaEOZfzbRBGAEg4RA58FrG38QcdKk55MCrN/EPAAC5Evk+D20BSdDetc6IdGI1NTVLB+oF6tYMR9N0gbU+jPr7G8w0OPq9WEgcFkJjk8GEQcvdC5DCL2XCG4sBMIMgV1SMsKmfoSH/a+iegZZo0va9/eBPmOFXD9uwHRAYxW/0YULgnKo/NY5dUIZU98JHoU+wqBpxwjJccooFuJ6Q8kKHBoBjIOhJPLSnr4RObr3Xez799NN4k27Q7pMhegPgzp07i6z1YbSkHcLjI6YSJHNYyMT++7mfIF6gH23SX/I70E6QKyhG7Jz1WJewE1orvDgy3lqbG47dwNyAOswNrIcwxUz8fYAwGAi4JP6P3cMMHkgWFDOhT6SoAgHiWhxyyQK4YrRzg0HzQvsQ/wAAcP1AT3VC5xqrrbfkTEgXERHhbXIfoN92aOZCzPnz54Os9oE6u9CRXICHb0VDY5POhEDM6i8oHZL4u0EgKEK601akO25Fywi/OTXerOHYTczxr8dsvzqIUvYyT49aAkAPCJL7dk7WAfiHbkOmSwFT8iSrvq+4DkXuJO73goJL3hIjbwmHDB4AUgK1WQB6lju6duy32s+pq6ur9YMPPuCZ3Ajr80LMozvBTU1NLKt9InIx/ou9zLvAmJWMZu6nzOqfyS/BIveiIUNgDIdyhUUIm/IZjtZ9j6fV9p+8hbkB9ZjhUwtxSiMjfveEhr4BGAIELinkEGw/orwrke6mD3/8RXVYLtiIDq4/1Bw/E/EPAQCXYEhnkgvxXlBZ8UK8RCK59N///d92FEW9b7gT/Ep/d4LJVIgXc3NzX9PpdFZ7UVSx7wxUk+Igm5KEj9wLkCTQ1/1Nfag7QS65OzBnHTakWO+K3VjavmM3YRu0HTN86hjxE+F38/4g6C8cSu7uJPkVxe1GCr8YKQJ93E92gVuOkUyjm4QXbiL+IQIw1QVtHlHQXLPeJaYff/yx6eWXX7YxXIrvOR+0t7EoNjY2LyuVyvPW+lDqc9cB2zQcn5SFJFE5Mtwfr/4jAQGzZbM24f41KZ4m23P0Omb7k5W/DuLkRvAT9Cv/oCCwcCfgZDYjMKgWWc75iBRVIlhcwzyaB84CtPLCIO22+g8BAMcgpg26I205oLTeHKeTJ08W/f73v59jGIti/nD2L3udDDdnzpz/am1trbfap5K2oiP4c6yb9iESyU0vRvCFPQAYKgiLBEWImLYW2zccx9Niuw5fwxz/OszyrYU4eR/c4xsee28QDGI3cDVLjEnoQ0KgJDIT1K0EvqI6NLjkARxPtPNI0kvEHzosAEgTHD3NFZ1WvAtMrLS0NO8Xv/jFDIqi3jWMSP+vHoOxTM4CCAC/ee211/7j5s2bK6z3sXS4lH8Y6XPXIdW5AIv5hVjEADByEKRztjBXKR+0Pfkzgmobr2COTy3m+tdDlLQX7uSk1xIABrEbuBrE75a4D+zMZviGb0eGSwF8RHXMYZeO4w05N9AQ+oQODwDnYEjnkhYIMVRHrDcanVhYWJi/WRtEz9GIZsNxf/3P//zPv//yyy+9rfWhiCRLCs4gdu4GLHLayojf6CMFAUmKo6etwYWSE3iSrWzXJcz2roVtQD1EiQ3gJxDx7+kJQT8gDCY5djJcgklYUAZ/fg1Wua+DnBuALp6/yco/fADo6e5o9YiC9o71LjDJ5fIH06ZNc+rzPnAv06EfnQV88sknE3U6nVUecL18pw0BUTsQNX8DVpiIf6QgIH+e9BRttvkECnYadFKrNLda3TZW/YCZXtVgh2zXiz9uzyMfLASW7ATuSXvBzjgA/4htCHKrQg4/Hy3cUGiYDk9z8Q8RAKdAyDj+kE5zg3zpWnKaZ7Wf37Vr1468/vrr7D7PAMwA6HYWEBAQ8L+dnZ1nrPHB6vdegY17KWJcCpkzgLwRhoAcqKUIynDZPhfaN/wg/2I3nrRDro+3nsYMz2pww3dCmNBd/IwPFoD+IEjSi98xrZFpovNbUIdEt2Jc58UAnL7EP0QAnA31/5nuUG63Xv2f2IEDB7a89NJL8/osgfbyQoyxFPoCi8V65f79+1tG+kO1timRnteMGc4liPStwlLXAixxK+gBwFAhIAl1tLASRc5robFNgmxaHGibVGivPxl3hds7upD66XHMWFAFp8gdEMT3Iv6BIBhKOJS0F06ZjXAP24MYt3L8wEsGOD4mFZ8RAoAcgM0WQuYSAvU1615fXblyZSJFUTP6HIzbxyN5TCXoN7/5zb+fOnVqxE+Evz13D3zvStiIy+EbXM8IlkDQGwD9QdBnCZRfwvQUXWYvhMYuCRLbNNDvhKEjbcRZHnG7cacNYbnNmOlRBdeonRDE7QY/dnffAHQLhYYeDrkn7IVLWiM4CU0IFNfgG16aXvxcInIi/hECwClIH/5Md4N88RrSw221n6VSqZS6u7t7UBQ1zeRtgO4VoF4AePRKDKmVrl27dqpOpxvR2yVFlWdh41QIQWANhCHbkOxRxgCQ51Y4bAj0q38Vip3XQU1Wf/t0SB0yQM9OgGRiBJQ7T2K82unvH0CcsAdzvGrAj94FIRG+qQ+4CwwjHErZC9u0gxD67cRhbjZ0bF+0ckNAc8NGGIBgJvyRzhJAte+wVX+e165dO/bee+85mrVBd38dxhSA3hLh+Pj419vb20esmP7goRxxaXsxj1cAn9A6uIXWI9i3Csvc+g6DBgNBpjuZYV+GC+zFTPhDEwAMTgCQOWZDe7tl3PXy7z16HayAesz3qYUgdg+EcbshiNX7sCEYIBziJzXAJuMgOBH70eCYBx3LB22M+MMhHWkAHMkNMBFaPeOga7PunY2Ghob1L7744nxDD5BxKG73BLiXl+K79QRNnDjx5atXry4fqQ915rt7cPGoAE9YBq+QOghD6uERXMfM9l82AAADQUBW/yhBBba4bIDKLgWtJuKXsjJA26ah5Y1AtCVuhG6cXJlUKNXYUv09posqYU/KnHF7IIh5LP5BQTCEcEiQsAd26QcxJ/4wqlw+hM7eFx2cYGblJ+IfUQDIZGi2H+hpLlYdgkVMp9NpU1NTIyiKmmnWAtE9Ae4DgEctEeQP7Ny502UkHs0mvevF5d9hLqcACwJrsSBI72QXiPSuwHLXfCzuJwwaCIJs92LEC8pxirsMGtvkx+I3OjsT9JwESF4PgHzDTnKTBGNpt+93IOvT4/jAtRS8kG0QxxvE3wsAI7ITmIs/fg9YKc2YmXwMW4WrobPzQScn6NHKbw0ApPM9IeX4QXvVuheWHj58eJ7D4YgoippucgLc85HsfgB4lAcsWbJkokKhGHZrZYtEjoSMfZjDKYBPSD0DgWdgLfgh9cxXJhl2670kOhAEi92LECuowGrXzczrke32aT0BIM7JgGRyNCQTwqDcMXYHZN98/wDeiXvxgUsp3CN3QkxCnphdjwGwFgQGEITxe8BObsK01GP4fMF6aGx90MUOgIQb0U38IwoANxDSKa7oWL7O6j/fY8eOlfzhD3+w6yP+158AU9TPGM2bAtBbHjBv3rz/uXHjxufD/VAXL7eA710FDr8UXsF1+l3A4GQXIGM3VpBdwL2QgWAgEMx3gChBFfbzPoHGLlmf/PbmrDRIOZmQvBsKemYs1MfOYTRN3qnG9qarsPOpwQxBOTxi98CDiDuaiH9XTwisEA6RyhInuQlT047jE98voLb1hobtDwkvssfqP5IASO18mPhf84P1HsMjptPpNB9++GEKRVGzB4r/+wKgWx5A/mBjY6MH+RcP40OhYf9l2DoWQuxXDc+gxwAYdwGvwBpG9CQZzrMAAuMukEemFfDLmTzgFisHCrs0yOwzegeA7AysdEi5mZC8GQipXQrU31j3L8RoN++0Y8WGrzDZrQw23jXwjN8DUcxuCEnFpxsA1tsJSNjDSWrC5PTjWOq/FV22vtA4+KKFET9Z/a0EAOn8nOSCjvQPrf5zfvjw4SU3N7cFfdT/u8X//QHw6DyA5AGLFi2a1NHRMeRbC52dKny06ijm2G2GT7A+/DF1z8A6uIVsQ/yCMqx0ye8GwEAQkB0jUlCFQpf1UNmmoI0Rej8AEHfQh0Mtf/cB7ZAG1TeXYU07fvoO/JL34gPnYjgGb4NXwp5Hwjf1IUHQzy5gCoEgbg/YSU2YknYcef756LDzh9beDzQvykT8VgKA5Qt6Gh8aKz6FarQDBw7kv/DCC7YmDXC91/8HAOBRYxz5g3/84x9fuXTp0vLhlD+j4nfClpMP3+A6ZtXvDkAtBMF18ArQ7wKkImQpBKTpjSS/J7krmOS31RIAiLMzDBD4grZLhurIyIdDtEyJotrzsPepwXR+GYTRO7EgdheEkTt7BaBfCGKGCAGpLMXvhkPyfkxNOYYPfTdBYesLrb1PL+K3AgDOIaAn8tCRvQrWNrVarVi2bFkSRVFzDP0/PS/Bm8T/vQJglgcwfUGkg27btm3uGo1mSBdtr1yVQOBVAWdhGbwDaxmhm0PA5AIh9Yj2rGDmA5kD0BsIi90LkCAow1L3fNxnZTLhj178FgBA8gE22QnS0fJGAOgZMVBuG7n7A9+ef4iEvEOYJSgHy6cannG7ISIij9r52PuAYDC7wUDhEDlQY5GEN/koVntt0Ic9LHKdkYg/0kz8IwyAYwikNl6QzhJBe8N6L8Eb7fr16ycnT57sZhL+9Fn+HAiAHmGQm5vbqw8fPtwxlA924PA1sJwK4eFbzYjf6Oa7gDCoDuKgOmbI1TJDe0R/EBAAYgQVKHJZhy67FKYCNCgAWKmQOpDEOAOSd4MheS8Eik27h3VE3yFXoXzHRbiGbMMsfgXz1TN2N0Smwh8uBDEDQ0AO1EjMb5/SjDlxh/CFaA267HyhdvA3EX+EdQFwDoXkdXt0rinGaNi2bds+pyhqniH86bv9wUIAuoVB5F906tSphMF+qC6VBlsKv8E8h63wCdKv/qZuvhO4h9Qj1KeSyQVMK0K9ObkET+4TH+WuhNrONP4fBABGCLgZkEyJRMtb/uhI2wTtjcEPajrzw30kLj6IeaIK2HlWQRS5Ex7Ru5ivBACjWwrAUHcCEu+7JTWAldwM+8gmlLqR6pgfutiBJmGP0a0EgEsY6GkCyLhB0EmtMmy8m8lkslshISHBZtWffsOfPgHoJQxiqkHLly+f2d7ePqhkuK29C3nLDmAOayt8g3sCYA6BRxDJB+qRLirBhy5b+xQ/o9qadAAAH7VJREFUWf2TmVEqhbjOyoHSLtVE/IMEwOjcdNBzYtHyTiCkrlno2mNZ75C0VYmNpd/BMaCOEb9LUD0WRO+EKHKHXvxG7wuCEQqHyK+5xTXAJakB7IT9cAvcjR1Oy6Cx94eCEwwJ11jtsTIAjiGQcQIheYOFrqbRuZZ68uTJyhdeeIFlCH/eM1R/ul+ANwt/BgLAPAz619/+9revXLx4cVC1rBZJJ6Ljd8GOW9DrDtAbBMLgenj7VzMl0WWu+b2GQvrwpxxrXDcyiW+nXSro4QLASoGUnQbaLgn0pDBIJoeiIzcfmuv3+vz+9h2+hoCkBszlV8DBuwbCiO3wiDKKf8eoQEDifFLfd2Imw+2Ba8Qe+C2oxwHeImhZ/pBzQhnxdxe+FQFwC4fkdRbk6R8Do9B2IpfLJStXrkylKGquyeGX+fXHHuGPJQAYwyDmUIycpm3dupXb2dn5o6Uf7u7dNnj6VcOZ/zgBHggC8tU9uB4RXhX6smgvVSESHpHqT7XTZ1Aa4v8RAYCBgIRFKaDnxEAyIQgydjI68xuglj1u4Dp/uQWZKw7DzqMC9gsqmdBNTE51uwl/kBAMIRwiIY9z4l44Je2Fd+R2+PluQ7R7Bb7kka7OAHRwwwzx/igB4BoOeqo7ZPZ+0N7qe+EYSbtw4cL+l156iUNR1CzD5RfTAVimh1/dwp9+ATAJgx5dkiH/wpdeeul/rl+/bnFz/Q8XHsBZUAq+ZwW8A2rh5V9jEQRiUhoNqkcqEwp13wWI+MmLMKmCUuYRbVWP+H+YADgYnJ0C2i4R9IwoKN72ATwy8XDbSawrPw/74G2Y5VEJt+B6iMmqH7kdoogd3d0CCIaaGLvF7oZT4j5G/B6ROxHjW4FwfjVSXEtxlpsOHTsQbYygjeIfBQCcwyC182VWf9W+oxgNU6lU7fn5+WT47XyT3v//NRt/0mv4YwkA5r1BJBn+f9XV1SKFQnHTkg945Nh1cJwL4eFdCW8icgKAhRCQqpBXQC0W8Yuw3AQCAkAqGaTLL2JanwkA3cU/MgDQDslQOCRAZx+Nh3ZJ2D5vCTJnr0GI/VYEicvgFVoHQdROuBFhRu1gQLAmBKRlwi1uD5zIPKDY3fAJ24Y470pkuxUhwrUa2e6F+JGbxKz8rd2EPwoAOIZA5hQCyd9sIF+5ETqFVa6T97CrV68e+93vfscxSX6Ntf//MO/9GSoAPZLhF1988U+3bt0qZ+abDNABunvPJdhxCpgwyMu/2iIATCHgB9ch2K8Ky10LHt0cW+JeiCRBKVa45eM2KwddPRLg4QOgYCVCax+Dhw6p2OP0MdNyEcUn72QVI88lH0td8pn2i0SPMoSS9o6wbXoYYnbCndzmIgIfCIIB8gGy0pMQxzVuD1zjGsCP2Q3v8O3MuPJkcSkWuRYg27UIwYJafOi+Cfc5sdA5kKGzJNmNGl0AXMIheYeLNr80aO+3jNrqX1hYuIKiKBtD56dp8mus/Xfr/RkUAH0lw6S3orCw0F2hUPT7qoFarUVF1TnMtdsM70Ai/MFDQKpCJL6O9ipnqkKkY5TsAImCcnzuuhkS+0wGAHrYAKSglZWCLvsEqO3jcJedjt1OH2OxWwHTapFqeLbJ9BIO+d9LyJ1ml3wmJEtaUIpI30oEBNfBI3w7+JE74U5W7ehdcCdhS8wuuEfvBD96JwRR+hWdfOWTXycVHKPYY3czv5f88wUROxAQXI9Ivyoki8qZ1T7PuYARP7n8Eyyqw1bXz9HGDofWIRhSTpRB/KMIgEsE6A/cICOHbJes99CFmel++umnExRFsQwnv5NNRp/8YaDkd7AAmHaIMifDZJu5fv16Ebl80NcnVKm0KCw+gzk2m+ATZAqACQQWhEPkcEwQVIckj1J85LwVS9z0CfAmly/QZpfBlEAHAwBNnJUGGSsVraxkdLBSoLFPgNI+HlfZWah1Xs0IPEJQhRS+cXJd/0N5mZ3JJZ8BglzvzBIWI1lchlivcoT7VSEosAb+wbXwDa2Dd1g9vMK2PXLv0G3wC93GgBMcWIMIv0rEeZYzfz5TUIyF5J6ESwFyXQqRzdx7LkasoBIRgmpsd1kJNTsYKnYIpJxoBgDpaALgEg7pTDHo913QtX/0JvGRO7/r1q1baLL6G09+jZMfXugv+bUYABMIjMnwo11gyZIlNnK5vM9Osq4uDb7Y+DXm222Bb+DQADBCQHqFCAgZwhJ85LIVCfxyFDivR6ddGhQWAECuRxLhy+zT0Gafgg77FKhYiVDbxzM7wCnuEmx1Wc/MKY20QPi9QfDonQJyUu1W+Gh3WEygcC3AQvcC5PALkUVes+EXM07ETN44znYrRC65Feei/70kzFroWogcN/IGsuH38YuRzi9FpKAayYIynHDMBRwC0MkOg8Qo/lEDIAQy53BI53iBfpsHRen2URM/mfl/6dKlQ72s/qalT+PJb6/J71AA6FESJdvN+fPnV/V1cV6p1GD9F1/pAQiogfejPGDwEHgx+UA9PANqmXcAMlxLUO68Fgo7cgaQBol9BgPBY9cLn9wNIBdkOu1SoLBLRpddEtT2iWhjpeASZyG2Oa3Cx25bEc+vYIRPHucmifZQJtH1+YSr4R1j8n4ZgYOs6EbPNTj5Z2R118Oh90zG9eInf54c/IUKa7DYPR9XuEmAgz86OJGQcGIei3+0AHAOh9TGF5I3OOj8JH9Ub9h1dHQ8SEhIiOlj9f9389V/2AD0UhJl+oPILvD++++/1dbWdqbPHWDT15hn+xiAnhAMAgRDw5yPfw3ihOWoclyDLtsUpguUnAPI7YjQU5kdgZwNdDGCT4HKLhmddslosU/D9+xF2On4KT533YQ0QQkT5sTyK5krlSS3GIk3CgZ60Nvcsyxw8oZCuLAaG93WgOZEMuJv5UT3FP9oAOAcAamNHyRvctCR+zm53Dxq4ich98mTJ2v7Wf3/xdLVf7AAmJZEu+UCe/fujdJqtT3eJlWpNCgqOYM58zd3A2CoOwEpoxov0DgFbsc6l41om58KtU0yFPZ64ZOOUP2hWDpusbJxjrMYjbyPUOi8Dh+5bUUGv4S5Pkleok9nHuUwNtiNzHj2kYSAhEsZ/GJECiqZnGeP83Jo2cFMsks/En/06ALgHA6Znb9e/CkrrT7dwdykUun1CRMmCA11f2Plp7fVv8/S53AA+FlvuQCZu37v3r29vVWBqmvOYb7tFmbV7huAwUPgGLodvv412OyyAbu4n2Kb02rUOa1mwiIyGYKs8GTsYha/hGmYI6KPE5QjQ1DyqJXC2Fna1/S5sYQgl1+IFH4JwoTVyHPPx7eOmYBDIJRMvB/LAKAX/ygC4BwBqa0/6Dc4aE9aCR0tG1Xxk9h/69atKymKsjer+5tWfixe/QcFQB+5gHEX+GN6erqdSqV6aH4O0NBwCSx2Prx8qpj+nv4hGAQIgTVwCt0Op6DtiBeWI8uthCkLJgjKmdWSfCXCJ0ljLp9cnCfl074v3Y8XCMiqT5wM940QVmOT21rc5cQBDkHoYEeh5dGqP8oAOBti/je56Mj4FDra+h2e5mYoe7INLc/TDBMfTOv+Fsf+wwXgF8a3BAzHzeTY+S8nTpzIMf/Qp76+DZ5TEcQLKuBjBsBwdgPjTuAeso35fdn8Yn0LtZv+pHiJewHjvbVUD3bkymiBsIhfyCS8ocJq5qBvn/NyKNgR0DqQ7soYZuXvKf5RAMAliqn2SN7mQb5kPXTt8lEXv1KplLm4uARQFGVn0vNjbHk2r/tbtPoPGoD+TocNzUevPnjw4JDpB79xQwaRRznc+CXwJYL3rbIQgoFBeAyBvjqUKSpm+oaMU+b6u0swmIkT1oRAv+oXYSG/gDncCxbV4mP3TbjISwccQhkAaCbkISt/zOgD4BoJepoIknedoFhXBl2n9d7z7c+Ki4s/NSS+xo7Pt016fowtz4Na/YcEgFlCbNwF/sWQgf85IiLCRqVS0abzgCKit4PFyYdfPwAMfyeohzioFskepfjQNf9R28R4h4Cs+qSsSyo8McIK1Lp8zIgd7FB0MIkuWfWN4h9FAHjhkDpHgp7oCumMBVDW7x+zYWKXL18+Ygh9TMuer5qNO3k879NC8Q8XAOMu8GiKnCEW++vOnTtjjR++o70LS5cdwNz5m+AXaABghCF4fFhWzxyYxXiRSXMF3RroBg+AdSEgeUken1zqIe0MtVjuvhXnHLOgYYejix3BhDw0J85M/KMEgFMkaHYoWl7jQuYSCfWpHzBWRnr97e3tfQ2hjzHxNZY9jdcd///2rgUqympts/Jftv4ss9LjhTCTkH4vSQr8CimKgDgzclNAEIGBES8gKHjL1GMXzzLrZJZ58ngi0AQUBCozl5505TE8qUGHYxLpsV/xis4MgiPCzPD8a3+823bjjHIZBkTetfYa1DUzLr7ned/nvey9H//dcYdtTQCTKHBXQty9e/fhZ86cyeGJcH7+T/CdnA5lPIG/2SRoIhESChA5p1CKBmyAjun/92g/wf32F7eECC0lwZvhjePcLMldNCMXhSEboFakokGRJHl9Jnm0d5aNCTA9BeqJsbj+PwpUp75tk83s97K1a9euEqQP3+vrbCbxbbb3twYBzCXEjJUvhIaGemm1WqlBVl5+DaFh2QgN24E4lgjfhwCtjQR8W6Vydv6drZWWdpY1jQTWIQB7D/u85eE5SIzMx/uh6SgLXA29LBG35cmokrS+CH4bEiAoGdrgFFwfPR1qj0jUZhSgoapFh4BYzQ4cOLCtW7duU0n68JMehtFVR+K4c7MSX6sQwEJC/DsptHr16mC9Xl+j0eiwbPk++PimQ8V0uxgF2kgORUkbagoRMbcQKTG7pCnSd2mP8VvtQALWaPsjmzMKz8NrYdn4e/B6qaxpkCehWsGAvxhaSfLYmgALoA1ZCI2PqlHyRC1F/b9/AfTte3hweXn5P1xcXCKFqo+p9BE3uzQr8bUaAe4nhViikpeXt6ihAQ2Fn5dJBIiOyYWS9QRaTIKmjVOLO8uYJGKNuFWRWXg3JNPikSutOZ793rJnO5aE70Ja+C5khmzGhYBXYZAlolaxEBpFGrRsSeC3MQGCUqBVJOL6qFCoX4mGbnMOjDZubpkzjUbza2hoaIIw7uBhQfq0KPFtCwKYSiFeFXLs06ePy7FjxzacO6c1MO8vV2Q2RgFTErREDjVxU80sIUFOjN0l7TBjPYN11DNoq0jA9P6KsGwsnJGHjaHpKA18HUbZAujlydAqlkCjWNwIfpsTIBnaqUlQe0ZDPToM1QvWQl/+a+PtfO1sdXV1NUlJSWzQTS40vEabVH1aLX2sRoD7SCE2JjFk7NixHuXl5Tuzsn80ek/6W2MUMI0ALZVDzSABG6dmZ5Cyn1Nn5Uj7Ct6R+ga/J0JrSfB62A6sDMuShuzWhm3DoaD1uCVfhAZZIqrladAolkArgd+GBAhk/5YErTwRmglKqF3DURW5DHX7vmPX1KAjmMFguL1p06Y/CSXP8XTBxXAad+DDbq2WPlYlgAUp9CQNJ7EhpReDg4O9jx8v+2buvMKGyf6f/hYFWiWHmrfH+M6xKxIRGpPkpYwIYY0lU77brLly6C1aHPhscpPN8H8ZsgHXpy4DZEmolS/C9TugX2wbAgRy4C+AZvK8RuC7RaBqeipqs7+22b7dppjBYKgrKCjYYmdnx5LeySa638lMw6tV0qetCPCI0CDrQe3pO/mASqWS5eYd+0ExdRumh2YhnlWEmkGA1uwnEEnAfpamSud+3pgfzN4tnUzNdnJJe4/pzrL7E6GxqrMmLAuvhbE5pFysDstC7rQPUaF4FZAnwSBPgVqxFGqz4G8jAgQthDZwIbRT5kPjkwD1uFioPaJRFfNaI/DbubpjamyS+PDhw7see+yxIKHeP5a6vVz38yNO/tsa0sfqBLAwMfq7fICFssTE1NA1r+8tY1GgUQpZIEGTI0HLSMCJMCuhsW8QNv9zKBPysSh6pzSMxhJldm2TFBVM7i/jUol5eXYla1o4A342doV8iLMBKwFZCiBbIOl8Bn72qm1LAkjenkAvXwCNzxxovOKh8YiGxluFGwvW4XbhQRhv2HZ0uSlmNBoNJ06c2GNvbx9KU5486eWDbs9Z0P2PdDgCWOgS87FpqT/AxldjlQsjUhYWnA4K3i6BX8oH2kkOcSJEMSLMbyRC9JwCJMblYsXMbGm47u1prHKUifVsyG56JlZP/wzLI3ZiaUSudJBvngT8VYAsWQJ+9e+Av8T6BAhgaxG0QanQBqZCK0uCZoIKGk/m6WOgfkWJqrCl0L23HfVFJWjQd4xLAc2NN//444/7HR0dw02aXTzp5fX+p6yp+21BADEfME2KmZ57KSJikVKu2Prr1IBtUiSQBuVsQABLJJCIMLsAs+YWYAYRIXLe51DNLkBqHNsjvANLpvwNad5bsGzSx1jvtQF7x6/BeZ/FwJQUQJGCmsClUAcsh3bqMminWokAAQTywDRog9IagS9LhmbiHKg9lFD/b7S0mMevCl2Km2/8Fbe//BaG85fR0e3kyZMHR40aNZPAzys+vNk1WEh6rar725QAJlHAXFI8kKb4Ro4dG6tMTt59Oij4M6lTfCcnaCIR2oIEbMXMKZDuMZ45vxBTlbsxMTQHPiFZmBGThw3rDuP7jftxRbkO8J6PhrFxuOEWh8pRKlx3ZV54HjQTF0Djx+QIa24thTaArSXQBi79bQWIf78E2iB6ZUAPoCVfBI0fq9owsMdB7ToLatcoqN2joRmvkqLBjYS3oPsgB7cP/BOGsxfxoFhpaenfXV1dZwnlznEmFR97M0mvVXR/mxPAQn+gB+m4vqTrWHLjEhaWFP3mm3tPBQRth0yegZjYPMSz3WM2lkPs3rLYeYXSBX7sMj9Z6A74Bm3H1PAsJCzcgw8zivFd6VVU1bNauQG4eBHG73/CrfzDuPnnHFQnvYeqsFXQTk6DZlwi1GMSoB4dB/UoJdSjlVCPim18ZcuVee54qMfMhto9DurRMVC7xtBr9G/LPQYaz3ioJ8yFVrEQVVGrULPkfeg256JuXxH0padhvNb+javmWnFx8dcjR46MIvD7CuAfQTKZV3x6mia9DwwB7kGCp0xJEBExL3L7ju+K42fnY5LPJwgIbMwN2J+VfITaytGA7SiLY56e7SVg9xVH58I/ZId0jeuUaVkSEd7ecATfHD6L8xX3B1mD+gYM/7mI+hM/o+5QCWqzD0D3Xg5u/vETVKd9gOqEt3Ej6nVUha9CVdhKaIOWS96/KmQ5qsJWoGrGStxQvoHqxPWoWbYJN9emQ7dpF2rzD6HuHyXQ/+sXGM9fQUO17TejWNOKiop2Ozo6zhDAP542t4wQyp19zFR8rCp9bEIACyR4XCiPSj0C1uaeNStu2tGjJw/95ePvETlzJ3z90uE/JQMzInOkAbr42bulV2miVFpNG5uIZdGEESmhQLqfgC12SnVETC4CQ7PgI8/EJHkmFKHZiEv8Au9sLMKBQ2dx+j8a6HR37fNvnumNaNDVwqi+AePl6zCcvwLDr5ckouh/Pgf9qV9h+OW8JF2kv79wFcarGjRU1aChto6VSNCZbP/+/dv79OkznTS/OfA7COC3esWnXQhgoTIkkmAQkcAlMDBQdvLkqcLTp9XIyCxG0oIvwPIDH99P4OufjqCQzxA5MwfRyjzplIm7VgID+m8rdvZuRCnzMCMqF8Hh2ZgcsA2TZBnwVWQiYPoORKvysWL1AaRnluDosQqcq6hqPei77C7T6/W3s7KyPujevXuQkPCOMwP+P5iA36oVn/YmAK8M3ZMEY8aM8SkqKtrCjlW8crUGxcUXkf5pMVas2C+dAjEtdIe0yX6SXzomTf4EvlMy4Cf7bfnKMuAz5VN4T06Hr/xTKEI+w7QZOYiOz0fasn1Y/94RZO0sxbHjFZK00WhuSce3dFnbWHV19ZU1a9astLOzCzABv5sZ8PNav9XLne1KgCaSgOcEIwcMGPBKTk7Oa/X19VX8gC2tthaXL9fg5E9XceDAaWTvLMUnn57Ahx8dxZ83fIcN738nvb7/QRE+3noc2z4rQf7np/Dtkf/DqbJKXLxUDbXmFm7erJPOLO2ytrcLFy6URkVFJdF4wxSq8/NS53BKeNsN/DYlQDNIMITmP9zT0tJmqdXquy7wZbvM2JlDjBi1tXrpIu47q1YvHcnIvLrBYOwIA44PpRUXF3/t5eWlJPD7U4fX0wT8YsJrc/DbnABNIEFf6hM4UXh0k8vlAeXl5bY7ebXLWmX19fW3cnJyNjs4OITTVOdkmu3h4w3DqM7f7uBvFwJYIAGvDvWicOhAHoJ5itH9+vWbkJ+fv7a2tlZ9v0s5uqx9rKGhwXj58uVTMTExyUKyyyo9XnRr+8t0hOFgocnV05YJb4chgAkJeHWI9wmeJM/wLHmKoeQ5xiqVyojLly8fN3cOaZe1n+n1+tojR47kOTk5RZrofV7pGUn53SA6xOoZkyZXu4C/XQlghgS8T8DHJnrTLMjzVCFiv0T3xx9/3OvgwYObb9261fybrLvMqmY0GvWVlZW/rF69+jU7O7tAam5xycP1/gjK656jPI/P9rR5k6vDE8CECJwE4gDd0ybJ8Qj6pXrGxsZGXrhw4Z/19fUdb8b3IbCbN29eZ17fwcFhhuD1fUjyjBX0vljp4VOd4mxPu4G/wxDAhATiFOkTQnLM84KhpCeZrhyfn5+/Tq1Wlzc0NHQV821gdXV11WfPnj2uUqkWmnh9bypxcsnzIkVveyHZ7UFR/s5gW3uCv0MRwAwJeIWID9H1oV/m86QnX6JmiueECROCjh07tqO6urpJV7d2WfPNaDTWX7p06aeMjIwNdnZ2QRa8/mgqXDgJkofr/bsqPe0N/g5HADMVIjEvECXRQIoGwyjUsr2j45YvX55w6tSpPTqd7moXyK1nlZWVv+zduzfD2dl5ptDR9SOtL3p9XuV5VpA8ot7vUODvkAQwIYFpXiCWSk2jgSvVmr02bty4uLy8fL9Op+tKlFth165dO8sG2AIDA+cQ8Lnc4RWeMeSARK/fnwoYXPJ0GL3/wBDgHpJIjAbPmESDobSJ2p0qEBM3bty4tKysbF9XRGieXb16tXzfvn2ZKpUqWdD5/gR8L3I0ruR4XryH1+eSp0Po/QeOAE2MBjw3GESVouGCLGLheeI777yTevTo0R0ajeZMazxiZ29knTt3rqSwsPCvERER8wWP7086fwI5FjeSO0PJ8QwkR3RPr98Rwf9AEMAMCcxFg6epUvQseSNnKpmOojDNwvXElJSU2V988cUHFRUVx7s6yo2m0+mus43pW7ZsWe/v7x9/D+C7U/VtmCB3BpADsuT1O5zkeSAJcJ9owGeJePOsH5VMHSk8j6DqxBgeERQKRfimTZtWHj9+PLeqquo8Hj5r4N5+8eLFSwYOHBhGVR2ZoPG9TIA/nCLs8+Ro+pLj4RWeB8brP7AEMCGCaTTgfQMui/pTeBaJwKURe7AT+vfv769SqeIzMjL+VFpauqe6uvrB2VXeAmOzOt988002m8/38fGJE7z9FJrb8aZdWh4kdSwB/xlyOLyp1SErPJ2WAE2QRbyBZkoEZ3qgL5Nn86AH7u3s7BwQGRkZu3Xr1jd++OGHgs6QL+j1+lsVFRUlrJLz6quvLvfz84vv1atXME1pysjbc5kzjmr5rqTxh5kAn+v8XgR8LnceOK/fKQjQBFnE8wORCA6UIwyhBzySHjiXRyzsew8ePFjh6+sbkZaWtuCrr776+Oeffz5YU1NzBR3c2PmalZWVp0+cOPHl1q1b3w0ODp7r5uYW1atXryAC/RQB9BMFb+9O0fElSm6dqKjAPT4H/hOdBfidhgAmRODRwJQIPCLwHOFZesBO1LwZQVHBjbzgHTL07NnTf8iQIUFeXl4Rqampybt27Xq/pKTky4sXL/6o0+mutdcIhsFgqNdqtRfOnDlT9O233+7cvHnzOoVCMdvFxWWmvb39dLpZRUag9zMBvSdJQVcqHQ+n6OhIya29IHU6lcfvtAQQSHA/IvSiB9uXHvRAISoMJS84isgwhsAynsAz6dFHH/Xr3bu33MHBIdDJyWmaSqWa99FHH72xZ8+eLSUlJXvOnDlz5MqVK2U1NTWX2KBea9bt27dvaLXa82xrYVlZ2SF2pAjbXM7uzZLJZKpBgwaF9+vXbzrz8N26deOyxl/w8t6CvPEwA/oXyQk8T9GxP0XLpwWN3ymB3ykJ0AQi8GSZV42epgfOo8Jz5AU5GXhkcCXweFB04ITwJqD5Eej8yePKKLlU0JpqhcU/Sy54dg52X6rciID3pGjmTlWwkWZAP5BKmVzmPEWysUdnB36nJoAFIpirGvUQosLT1MkUyTCYwPIi5QwvCYRwJ4B5CqSYIBBjEpHDl5ZfCxd/vw8tDvSJJNPG0fd7UMRyI8C7EIGHkrx5QQA9lzh9BG//hFDO7N7Zgf9QEOAeZOBE4PKIR4WeAhl4ZLAneTCIooNIiBHkWUcR6NwoUowhQHoKBHmFwNrcxd/rSZ85lj7fXQD7y0TO4SaAH0xEfpbkDff0Iuh7mHj7/3oYgP/QEcACEcyR4TEzZOgtRAdOCB4hXiDJ5EwJNSfGS0QOFwLoy0SU5i7+Xhf6vBEE9GH0fc5ESkci6UAC/AD6//ahnOcpC6Dvbs7bd3bgP7QEaEKuYBoZuEwyR4i+5FntCXQDiRjPEzkciSAvEEhbul6gz3Kkzx1E3+NgAva+ZgDfkwj92D1A/8jDBPouAlgmgkgGMTI8akIIHiGeFEjxDIGPE6Mfrf4E0AFElOYs/r7+tDjI/0Df1VsAey/Bw4uAFzW9KG8eeVhBL67/B0X+fqC940WeAAAAAElFTkSuQmCC
- data:image/png;base64,iVBORw0KGgoAAAANSUhEUgAAAMAAAADACAMAAABlApw1AAAC/VBMVEUAAAAAAAEAAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAUAAAAAAAMAAAQAAAAAAAMDAADwvILv8etcXFwAAADyvIAAAAPwvYAFAQACAgHv8enuvYMDAgMCAADwvIXyvIIHAQBdXV2DVTLwu4D0u4Dx8esBAQfx8u7uvIBbW1sAAgDxvH3tvoWCVTTuvn/uu4PzvH3yvIQLAQDwvX3vvIcGBQWAVjbyvoPuvoKCVjfxu4ftvoj0uoSGVDHvvoVeW1mEVC+FVTQgFA7rv4MODg6AVzpaXF4RCgcnGBEXDQnrv4zuvYt9VjmAVTIbDgk4KiAMBgPx8ekKCQkPAwHsvIcRBwTrv4gUFBMWCAT1u4M4JRru7unxvoXqvIr0vHovHBPwvoJZWFh4VTxUQTJdQS4gIB8/JxggDwh8Vz1vTzcvIxr18eblvo7wvojrv4Dyvn2rjW1cXGBROywqKihBLB8cHBpALyTnv4hoUDskJCTswZCUd1wrHBTdt4uKcFaCaE9cRzVQNSSnh2VqSjQ2HxRLS0t0XklkRS4nFAvu8+zu7+vgt4TyvoBiSzl1UTdJMiLz8erp6ubbs4VBQUA0NDIYGBd5UzYvLi3z9O73uny0lXJMOCjqvZC8nHdGRkXjvpT2u4CggWGHVCziu4vzu4dVVVV8YUlzVDw3ODdYPivX2NTnuofOp3z09fHl5eHTrIKYfmJvWUQ8PTzquoSxj2pPT05aOiXxvoresoDkt4rzvoTYr4T0vYDBoHtILBvKysfyvofsvXvHoXe6lW2JbE/f39qUdFRGNSjYsonLqYPmtoLHpn94WkLQ0c1TUlFLOi/ExcKqqqWghmp+Wz5pamju8/H0vIJxTDCEg3/Av7u3uLXPr4dtUz/47t/BmG6wsK2SkpBwcG2ZmZWLi4h7fXqge1bsz6yjo6Cwlnh2d3V4ZVJjU0TswZW0iV/15tHXq3lhYl/v2L2NZkPUtI/On2z24cPqyKGenZmFdWi4pY7UmGtjAAAAFnRSTlMAIO/fEKBgv5BwMICvQFDfz++Qj1BQIpn5rgAAOTtJREFUeNrMWV2IElEUbtPa3f4ogsbR5d4dCqnLzQr6HXqPoYd60qKBhggffCqKGnywdx80ggZHNAh7EmRgJAyhiLAXn0JRMDAj+lsKC6IeqofOvWr/W2pj9e2g7u7snfPd833nnNlZ4jzcK9bMzixbNe1yLRU5lrpc09PLVs6uWeFe8n/DvWJ2ZhqiXhxLp2dmVy/5L+FePrNWHBJrZ9ZMLfmf4F494xJ78PUh/oDvfrF22Zol/wfcs0w1SPwOkqLG9IxummahrEcUeUDj61NXLf/niXAvnxa/BhJDasQstxaeP2l2ala1WiwWDWo1mk/a3VYullZDgxP7NKaX/0tjr575xrFKNBZoNyuGkM0KBL6SmGiECAIWCCFUsG2tWnv8vJVRZQT47Otl/8jVIB3xK4RKTz9amp0lmEODoDHBFFMC8TMOFOMg+5ltWx+fmt9IzrV8yV+He+VXm490f7NqUyEpQJQ0iIEEbLwAocMHDZIBDHrEgkGgRgVqFztdM/TFD65lf9cNUzPrwI6AbQBz4XHVIBoWRoNWrSwUQmjbwN1/kcLUsoFjRVlvdwyNgkQobPOIINRoPDdlcYAhKDgsHjX1vALuBOkIGsYjpADzsykc1HpWUtHfpPAl/HSgoVEMMVAWymgKYgQwZeQ1Wqy0TWnghdklk8VqF5cOIPq0YQiOALRX6+py39CuSTZo9yqxj8hCkQqsnjgA1imyxsuUjKQJ62i2rx6ktCxKQARB7AQBWIj1Oa0dQ2iSbWFquh++2rJsgTdX7AwB3vHA0MazCJqcmdes8/EMh+oVg1KeeMEpAtDyuJTs2lOFtYQJJMG9HtaFhWWzownQsyYCKEtCJRfiFxLXux2VDys+EhJRF8TP1CM4D24EgVbbsV6dczkoo+U998qlZpZXfDgmADZAMXF2cnJvTHVMRit75g0FapTyGQ1PigDm3bn4VBU5VjpV/LkoC81B45oYATwQU6fAJCuJq9zOyB8ISIVatr8+nhiBwboascrIx6vRlBPxA4PQAuWtC4AnSQDz+LFG7Y+KJDlg5RU9+6Y/JpNc/IDJE8C8LTR1xNvyij+NH/p79Lll0CTLAUD4KwAOlRT8FwaJS1f8YflEkhSKZQpPHhjD2Zfyrz8GzhIr5+PT0fKx4+/ddqX1aFpBovq2IfxNQF+rtuC2eXwGK0QGKVr3+wNxUwUmz4q8D2P8u0s7ISEMVi62WE8DFY2pfwQJiIX9HoZwShXlukX5/0fwryVEktShKc9oQwg+YDBm/UQo5vH42QGo6xJKWfav+4D2+IFBAU7NFgbsog9yMDVe/JLuCXj8cPjhCHhSihR9IJDgrzLQKceeaYIjDAjWMIUE+MboB24XN3A0z7bfzw9QkSeuSpFmkuCgsChAt0pzEP+fFV3YKWKrKAQEgMFoU8UqPtHG6pAADw8e3lgq8hmkhBt2ki3/06IK/i2Gow8IMAhy/Imxg5jasliKigyrRp4/UboO4X8FTqSgomi79qsNxg01Z/Q6KyMwBgadhFUiMZSPK6POptAAAGocIgYK33Eo6yEx88SgixPAfqVJgt+1vbHElBU6YsTjTyniSA1tig9AShzCDfi/CT/AjkBOkZS3teTid4aP5TgJQsQJAAGMO8ASoaZLKdi0gsTbwdQoBpZLEPzPAIYOm0AhXKM810mBgGd55YcXjmIuXcGEMaAg/stBYDMKAQLrUr6WZSI9DFsWZreZQxt5PTsZmYFAwLMY/OWoiPSFoi0k7d4VCXwymtWeVemC3CZZzHEZMCIBSns0aIOVDNgx0K3ERbR+aANIUbbTiwKopdKSqLZqED/tX7RSR884AfiISjYWtFM9BINkDPlT44nqU+sgY7hgPgQEAGuGvYNJ11mUi8J/7pw/b6qiGGk9qAo0C4OX9jImK13aI1DUZUMgEPujR5wBiIyOIiE43XpZUuRIGcoIZCCQh0dvQ9pgGX9SF+dVfzHAoucOwmsqKm1TouXu8yfPuxkZxVK6TYOJBNZOlVHzzft3LzjevXv/BojwgsoscTnIpUX67QHDdMhrFGOZzdpZqlmP2zlVRmqJzWF8BgACz1QRMD2UgOQMBP8b8P6WT+mDB6hIMfPxaOP+ZYxPPXrzGr06fWPnpt0b57Zu3Xrm2IUPL969eXRKA8NfBnACnBAGAjQJPLLwwKYDzzIXAvVUQYfpXVYLoIIBgIDVm0xnhxFQzDMEASgOLLvhXCETS0cyqbAnUFaf3H/06M2LD9eu77l0a27zli0bvPPzW+e27jh89cShD4wD7H4CWEDcic9jP9Wqj9ulmNx/+opkRY2Z8W+KYF5WLSvFReT+jYAAChPQMCnwcA6A/nf5dPfU+xcXduy8e2fPeUZg04bNR4/Nz815N+327tq848KL949wIiFAEhLwxpAEwzS6BVlEoZCSjuh6plDKxWHZAOj0S+Uui5EqfaD8dqRYwyuQyf52KEDsvWoLL/AWjpovbhzduMW74d6e4xf3b2UENs7Pz+066/VumN++a9fO0x/en7oMtsbC/fuEcL83SyGfrEQK8TxsGwO/Ot+TL1uVE0tFqnV5P/vVY2WXKLER1DMWwPaRAzevbNmwYeO+h0dO3t4KGdjo3eL17t07B/HvmJ8DzJ94B4bGCZrUmItpJSVJcgTc+quqDa1Y9Cdpo8U7susXTzA+cW4tUE3VYbx3nV6nzqkbe9zr7rbLRjxkYzDZZI7JNja2wTYQRAgtBHkNs5KXUJjQQKgEQl6ahUkRYplKSpaFaVpZZg8ys4fl6f22c6rTOf3+V1BEytEPnJedce/3+3/f9/u+/wN+BbEx6P8T8O4P0Uhmh8u2ZTf/tpiSy1XC9XdER8JuKtaoklBKpViy4q8/P0fgLF2K6N8ShOf17BqrmcEEUzMpFHz10EP9PV9iioKu7gIZHPG/CQTVOB7QpMTKlRQIbJtLyWNUwpAQoThcQsEtFCUUiiVx+1Qbf//8kXnI5nXfdbK68l3kef9NILg/i30v7LtKwZeN/5nHl/NqiFD8f0AI19CrUjTRd0RrkANrZRq5XAbTJXESsTB6/Xph7Pz5ElyELLvz21+XHj3a/nElW9gYAeCJ/02gkS0MO57Vld7/nu0/GuuLBQy+NsOQJGB58DSJIJFBYLUxThgplrzCVb0VEisRysnYSyQYe0iqTCPDxXphHBULBjN+sOnK84IDuC0mIczJveW2Dtvm9pMshPbGi/9dQrMg5wkYEvI1TeAXyunVc+NklFKynaub/wQIhIDAJAjhj9se++vXk4xuc0BCh9bRlvVFoa73iK1w4XOnyA7O5VM7AGBtPR39CUBQQsJ0cwHOJwTEKmH03B3008/fFiuJnoKAUSaULDJu/Num6wHnQAhAg3p6dJ1BR2yV7be8UwkCgov/LQM6sfqTXtiYEJwAz00fICATQnmeqeIenSt8NTxafj6B+TI5lbhip5ZMOCICkTbUR4bRdUQE70ovxCmer1iss1w1pQPQxH0RdvzDdFF6TX9QBNKAhEXgAGXkwLKQ54Xrn3VoVy6iZKjA4edFkFAOAp/mcj2k1gbk2Q5WYOvA3Rt1NVhq2dIFAhCiKR3QiFX0sC1fZ9G6nryk5cun64SIQhB4QiOO3c6VJYe/qpkVLY87j8AdwhjJitV0Vn+gxaW/C8kOshEdgsatM25dd5KdUohIDbB9h9p46y0HP/RmcF0dy5dPL5WD0Upwq2LXi+P2vJt5v2axTHN3NHU+gZeFlPFtK9ML/waEXYU1vSjUuH+P4Id162bc+l4lXwumaqN3tZPFwfeHqj4rcDK6miNkTj8d7LI5HnhhvVi1KT33RaFYRt0RTUWdn8Rx4Xeu4roCHpq8iLzTPVdeZfp3YWS58Wtmiraa3wj+7pFbHnruK0duq93uy3FwXb15CUiFpEADKLhX5/10TnTUwxvYVSmRStnsyEhqFjUOJSURCmXGZ7/ZF3eolOuA0AV4V4wiv77Wm164dx5pZt/LOn9mcx0hVX7wkbAtjVxRt8msUOcXNGt1PUeCli9PCjAVlgd10qWPCWfdvj2zdOUidNAxFCUGgXEQfU3+tO2Pxck/Ml15MGuaZbKc7l1I5kIPtjeyyNfrzkth6cmwo3s3p+W02g0KhcJQ4iviuJr+iCAMVWAEkMM/JQs/OpFj/SD2ZTTQMgy7khqDhhLKhC89Wb1pftza1JmbkyCP00Oejf1y3a3zyAz7i3SGOVdJLyNLWZWfPHS8kqto1dvteoVZ4dGXbHCIbI0JgRJI2mXj/l6RsqfCsTp5/R1i6lxoSAClvJ46nzLuzNTtmrbCBQ+xNXsx239w3YxH2ndNTuMrSBt0auEnhVyR26PW6w0Ks9mk0OfXueisRqRBYB7YLKVTH99Yxy15WLw+WjyJgQQBlLKtYXsMlXI/Z8tLmhaBBBAoFPUc3PrQ0aNkQvfd5I2nKzEZZT75pAv295n1apOJZIFabdH7i+n0Xrg74sJyjY5FIOW0GdyStVGL42PiFktQhWUx4wTCNYuEt+9wPimX31tGFwZDo6cBNAab0cWFbv5kK9b5wo6+Y2OQxue2QUzNJ51cbqu5T6FXEPsVaoPabFb4vLRtKOnCCQeONayUpjm6altioiR+jkoSt5iiUHXPMKBkJ2rrUhbFJFfhoGzSNFwAFU3Is9EAV/nx50tB4KFeAfL4solFgGHyargcn4GMvMIE8wkUZpPHl8uxnWSP5oIFX8dI4YEdK2dRKo0s5TcjJsNK4VkC4o9SBrT3v0C9tDuV6QlKCppeDPXQaaXa2urqJT8dX7rw1rD3YfCEUnAtIVBOW/1uxL9eQV54Gga1RWHwN2h15f0XUD2otE0koDnrqofDxXLlqwu++SNFFY7lCOEZBwjXv5WasXM+9dHu1JmdQUkRCdOQ0KDeNC71p9rs+pJ8/47jnz8Stld3TikQhYaKONrVNOo26A0Wi55AreCjCGLUOpIWWtlL0oBMcyarM1pvBDSKMCvS1VYfMq6Jksjjb/eVxMqo2UrlWQIqKnq/y3VCFadcUcX0BC8PRNyIekSgCCccsTHWgZIWb7FPoXCPfv/r0oP9IpY+o0M3S0WhIppuM3jUJIDOQg141B59lQOJkIfmDuXn3LoQQQYfc4fGLNqVc/jEAgRNvGbOiYIlK7Eip6QmQKWU38M5TlB3KZPfYHpwrwAJAMFHCtm0ArvHnsMVeUx6vfuD35e+H8rS9HXjVYympQI6w29B8pr7+vrMBCZCYIyB25+rlXYNJfHDTW48cR68PCkvryOdrtj5zDLqthDq1Tkv3pOz4U0jkvYcAhr57AeYtAcW7YtM3sHURATkATwLPk/KK2e5inyFCYriaOoz2C36+34/qBNJpeO17Aaoh0Da3G0woASbAd72sSjyWAxqkyK/TUszlY1BCVAbDMxEgYaLe3S08+2UlMc2brw3OXnjDm/Lm5q3qNmzZ08kADr3SOn7l939svEeSDMmwwGBzM47dGxpvgF22d+QNqjVBpPFvv3XcpwEuXRMREMFNB3K5nYTcw12u50fdj2gACwej8dkMpRUN2hpXWFvEgDNHJtC8o/o6KK5JW+qJDtzOEdVXYXX+fqCRdFrzp/IzH00jV7yc2T0nD21oVmnHXABFgkRxAND6bSTjD/ie8DLNSn6zBaP+76/daGiMSG9SSSlkcbOAY8H9NQGUoYtZsBisfC+wFtwSPdgrVak6xo6ArvHClswzGisCaWtq99M3Jc4oGV12gxX3f677o4UU+cTWPSslbYe0kTOSa6j2U7Qh/0XIhC8PLgjjcv1W/pMejQ49gqu1NPn8Zg9+X+7RKKxYnyVVCoFAdZZMJA/qlebTRYFsgG5YAIUALxhwZX9cF1pppZzdPUMHcmLIKGT17i5Usem1T3+TLg4Mm7/4bqyuvsP3ZmYuJiaEzuZgFIoTh7k6J/uVcaq9jtpXSMqwQUaOjIR6K9J0zr9BlOf2eDWKyytrrQms95jNusHvNLxqfENsF/Eeb0Z2VZnQ1H9cIHf19rtthv06nEGSAaTBTzc+QVFxdkcw2ZlVdbUlBd2pdNcdsWmtao1QrkwPM54+8O334tQUclkc6jJiBEqjQ+4pK5t1DLJ/ANpZBP3Qg1KcN6pxi5a62yxww41ItrscW/QFrnVMMribqBFght4AnCFiM4d8DUV1I/kOq0uR3ZxcbOzqG1DQdMxMEFtOB1ICgSUx93a1NYAEijrUhHrSN3x6DPyJ4QY4DXi+Ph45SzlqzFYTMT/kwnIYpTKJ1dzdMFuoyR69080k9WbRCatEGGC84wn9I506qSZDQNui8mC4URke/Td2V6fxURK1AgnOp0E15GpgDY33w0JMtjdrb6msraKHKfX4UjLsDprc0bKBnmX6FHkDB6FxWIwtDZteKOigQt1HNj9ggaN/uRop6aATCYPMX5apeUOJM+NjDtURTPpQ1j9I/Ol0wR4DmNsgkl05fVWzqQzNuR7+szjdQnPT+WaLOgy3YZhLSuaeTW/JA3Q2pwWX2trvluPHtTghhR1tx7zD9ZX5DR7szMzsr3W2oaK+uFjHjgBlcTtLikpcYpcOzXUS7OpgEC2CajkQ+9qHds3xu2LW7kkQ8oW7kpIIDoJ4L9xAgDZG24s1LFc8eCo3jOxsCqqs4uQCwa74VgmK+LboavIeZzK1Ibm7GxraWlOBexsOua2AxBSu91d0n1suH6kCHGjzSgqcXvgSaS3RW0oS8NatBL6HhCioiKjX1bdubEl03VgRVR4yr33ebVax1BCHqQeIHo8BvgEvXmNLpTNQPhAxxE9YzArLCUNta0KEwi4x7P4SoQSnbr68ChG3T9cn5qKNMjQal3W2tSKqno+fAgd9+hoSavb7rFYTJDXvj6LKd+q3a5RwgEBElCGfKSUJK7YP5g9sGfFAuqFjZuq6FBsDZLwGc8DmI/v/s1ZyDFtrr9EbzEj/scJQNnVpgKXX2GC3NtzGRHfz10CAtKMnDYMvN83cLgkPz/f52saxqg3OK3WbACeSa1oKxsmXOwGpIJdj2ptLqnQrppLzQ44hChkOXZrVLt/8ft/2b1vjWbBp6WhIp2rpzEvOCEIPdZp7BqqsbE0l9E86IPyoYBhvM4QwNANeAsspKrpi2gRcwmmwwICRkoopzkcLmtpVdswkR+kbEn+gK+6aRABlJvrLM7Ozsx0uGpzqt7YUNCN0mCo0+6IRQQFBhm0dQ62+u6Owpbli7vfirtLGW28J5OZKWLJDtnmjsbGxt6hTmzbsrDE2+BvtaN6IW+JmJ8JIbWpryQHBHCtr4eOQoau5gmIQgF0F+ABaB1ea3NuRdswYdLqdiO4ulv9TTyVoobmYm/zMIqEpdr17rLwaTA4LVFxRqMwmjLODQ+PVq5cQrNpzmwtx0l16TZbOitlaM5hzan356PuYl44Gfq+PvdwE8kFs3owDX8FeDU2JgmkAlbEsvyVVIpXzPHxM8dlZHqLm3OL2gb5mgAmJK27fb5uUqwHvM7dFzR/vKmQy4XiqCiJRBYjjNw3a408XhMllN9Zps1eMuAfHmlotgLNDW31g00+4nwyofK49Wb0A+rxJEYwEQLdHugSyPldIqngeqjoTAHGHYPPn7IXMbp0TJ/BByA+ARsSXlym1+lsGCkraPL5BkoOu/WoBwNW7+NypYySjG3C3D1LLBGvUWItaBEq2+xFMplEpYqKEodTMfFyJfZoQmJkFGp2ZFTULKFcg42aPc3a+nyYi0FpHWjtRmB61Ih4fJFvNV+8EEXgA1igH+jk1BYYj2DyQMdDoaPXCBCEhYWFXVk6MlEmPwkYQMBfwxUTwZJMyS6uzc0ZGW6qbrFyq+JmvSqT8KMMwyLDY2M14lmz4yTGFSu3vb3zgU33H3j90Ve2PXm7ca4wUiiLvw07fmd9I1u2U5udb1djRD08SNuI6QdJVgWMhPxMAF/IEAAGCxYe0AwZ3E4R0dHLYSb94dbn3jn+5dcn8zo6u3Tj1hIC59oPlwAkzMCD42iWLVsQLiMEQqLlc2IQ5ymPpbwUGWlcu2nHu83QYo7/9m7YsWnlvcYFCxZHYst1Qn997wHONYK0AirwzaNtA7zc5PfD0QP5+SWjJaOjo0TGDYAerrK70ROBANzWAFsux5IQMjfrvaNHw3CAIWzd1q1b2w++c/yLLz8+GXyko7NwEgMeyHiwmEkIWp8NRwgJqZD18XPQwMWAhPHhTfVIS5bF53ShOh0jAF1OW7X60Ip9iKczfcbLkarHDktrVh/+rLqlqWCwrL6+vq2ioignp6EBmud0NjcXE0DF8drc3JzbAIBqPdoFg8kMMkWoZNeCAEOn0acIAZwSw3FJ/OP/Tmxhe/tzz30hOAfI8DEi5C+JBdCrAxoNwj9GCA/IsBUZr9y9KcdFMzT/SUJ1nDWjzV21Z4FkUfxZApo7PxPp3m3BYKOJAUoAvOJlDAOA3+f3t9QVDALDoFg/MlICb5hMaM0IgSvJujpdWpv+5YQ/b5hwdu04cy4BgCfAMyCh1PJCeKI4JCY8Cmk7K2rui/fVZnChIrA712vECwzrfHpt7FPy8RBSapJ9rEiL6pLpIHARFDfXYqhzSFCNtNUDgwUtLS3+lupq3wCqLAknEkIgoLa3wZZLTxNYktG1BYZPAt7YCwITIZoEpiol/C4QSEyksD284MnVjpk0iZ6zBHBBiCJjUGnSyx4/M1PA8vsLB2ishswcA393ltyUQArQQFoaT83rhcxCBxFhRSPDxwgBQz1NCFwimElbf6rS9r7z4BnDz+DWLeXktpPtJ1eYBRFkPraPEFBJ5CHolpdwNJ7NmzL+cZ4BODAMKZa099FnqLHmQ0bJ91thNz7A208wkTbvYunp35XChTwfhgUv7TBPoAwELrkIH2QylnzmpE+1z8M5yVvmnWUwb8a89lPEjCkSgdwNjxBxe8SJVAhKwW1P3La2mmN1eJc3ZsIv4ZK8h+FlsLTxmoYKV5LjHxJlyIupzNAPp3DuCzpeCXRldWXZbAKAAffx5/F1lX8u0UFcZBZg1VChHyTsQAAzq+JjrV7mZPsMHEOakAMzcHCYLEJOInB2lFh2JrdTJYmNp9Ys1ghVBzJYKR7735A6DyUqhaTkUWLlH7nsybB1QNiMhQuhGQe3bNmy94tCvvpMcSeYynvee0x9zGBSFMAyngBEo2K0yRX64cJ588Bg6ZkD2zgv2W5DLZgaGCUQuG+ZRBZPKV9SqfbnQl6Bf+HAyxLA/Xin5qM7okOio9fITozQNQcXjocteSS05GAPbj01AfImEyp1urub7OYzBAT0P81dCUwjVRiO931GxzDMjDOdmdixTpix02Owta2NoRqgVYrSVkAuBUURSoMKyC0qHoAYvDkEBPGACAiKXMouKyCoq3gf8TYaj2jURI3/KwrKochi9I+7i/SY9817//29N1efk/jMeTfH6r57/I6T/gQAtOCTCyFG2lAYirroU75WkXCOVrRyfm/SbwAiNgGwjI6pWLSmdAoOIWPS+U2jifr4vt+5+mC60eEIp15Cha+4yffALbj+vCufgRpuzm9LKJLcm52UlP1CTjz1wGOIj7eqzNDSefyBTScggnriY9NUGjRT6WnM1TFnglgy4u9EQyXV6lMcmGqTJMs3l2aSdz0X3qAZFsAAW6M/iN5s0hEmHZN8wxVPXQ8xRw75O4DWK55KTiq64so48tpPbgMWJAiMHRh590Hj+8WrN7kRlOacn97ydmDQTqJtnHU+hgSn+/uLG34kCgwUFZ20x8pxmOxTcO79M0pNzCfh7vof5PG7NgeAhpt66ZWZN0NkcTMJ1gLMKMU3nXtGTm5uznlXpiZe+NrLFyPeNSLkof/gzyt3wd3eAABDXnLxVy3uaYNBxGwOYj4GslgdmIqN16+GhOoZEiapWsZx8Bp2hf32/FdTo69+ec2OldM+hg7SpkIm51zalHs75PU5yIwiR8Y/c8Xp5795+S1PnXdp0S3ktW9BMxCROR9/7MVnX3772ZdffOfOCyM2AnDvs6+Upzt9HE5jRgzva8qN5ylU6N4QAEmi4Ijk/bm31Lr0BGvIwJSnZ24+4+E4ErZL/NmJPv4aWN3NJOmpF7L9qeeefe49j5LLnjiSvPzVM88/49Knbrz5vCtuz+R11772+cuff/rQnXddd9lF51wLZM57L9SsuSXIqt/90ztfdksNdoj6HWnOTvH9kdCepphEcmMASLn5+MyhrpZvvrXq5TY1I0OZ6X3mzHNvjo3++KTwsl1F8dwTmwIgM+95M86Ufe5Zb95QREYBgEMQgHPPP//Mey69Alrc99T4GfDlfELcNaW91eWzs+WzVb2P5sXF8xoK/BY4JEbHhP3SvR+8UlXpxC2s6rOrqkUyywHZ6a5cKvKT6G3gJZDhDHtlDfLCTGLFC7vddlZ1Ylki7VH1hcRAa3LOeWcUJZ3z8ev33XYSOE7kiCCsPPW+F5+k4CtW7xZI2DdTfEXpU7eYci89955nbr+e1EEwdyREBZnnQSrx5jMQkXvzEiCCz6upmur42j3qdKZZxrHpgq87OlqqauISyUhYycjGQbhw09tLg24agmMA8NmPBVA2ka16wsj5OkLZSSRDMZE6hGBZ8+BD0D57102vRtOYVV+YXmWKefXsc69Puujtky5AnPCw87zgqjuATvBSNEXBiNG1wl4Z7ir8yGcOQaye+NQVX8VcfkUTjwAcBC/FXYHqz/c8WpwXrSO91bvTA2AiBMMbqk2xiFkuYHFjzvS2rxf3QGWQgcCE0V2098vytlHMqgUAvoU3v1Ehq0nhaKdNhl+5WwBCNOirhmR04TvHmDL3NLt9aRbjH8u+Qkrfo0lF5515RU7COZ8DkfSkW2H8Ybr+yTARz950IRozCumW/1AMmeS9OpaHNLpu7zkJV16RCvp2ECrMRcY8fP7p0FG9tCYztyjUHJzs7OyEBFarVeAqTl/904XgOHtYxWKvDA3FkIlXZ9dUhZrTHDYLgWZAsS8M22xANBNouUfFMzImfZVdTSYGAYBJBtHEv9CvmIEL/gaHiSvRqCDcP76Y6i+6557zSivO+fzikwEAskEIxh13XPzsJ48gv4u6w0hIEA15IfjKi/JScxNNNWdekUmSQHw6DAKM+Bug0nZFY2rmlbv7sswNkgHMHJbmFCXJjKnue3KGRaKBwC1vYE5XcKAqNffLH9wlwaBo5HAthhAUqEatVbq/00qnOFIgZddjbF+5l4wMe98IMvar9nzFYBBSUqCwtev3OgYAlszu5ysSL7/yPKjb53334n2n3geOGLYQ3PbiBx/dew5vyi3Ofq+6qral5YsvvggtDQ5l740zkWFJajrlrBfieBMk9UdHkAy0zh48tzGmuLZEb8ZYloAhEARhDrd5FfvMTECmRbOEI1icw7a7OrN1RC7U0xiHQVRJo5oVR+hFzKI3w8RZg0E93mkITHl5lPXodHxdpcyxtJlAGecq/4bjslwuPT1V7M9tvfn2827P+fKLX976+OOPP/wUjkO7iK8ofqH2/eYxKAc0NKAL07I90Ne8O1SVnZdIahKzzz/rygQdGXE0FLbIyMScs89/6pbqp90B0WDgwt0V+IyAs3CP8SxZBjio6mCQ8M7778/Ql/T3Xv69rceiOC2AEwuL2dzXX2ktxAkkNGubzLB3JUREAgDK+66SYaBdcFMA6ip5Qi55urlSvv+Nb9+LM/lj4i4vejQnp2ju3liKoRLjvlp6Pj8gW61ZIoGGYjDghDaLUGRRO14w0DIE3bimN3MSQcEOh9IiBKNFV+TkvtANHAcFIzhHj3FZOBi0IOEWqxbdfXTTHByBKTbMWtJ1ee+YqNdiCABCy+INn91Ybi1UXAR6K6sqDdqxVrSAKL66Dc8woLdpCTQJK/TLV69vrZl93se5d7+QGm/ioXzhj0/koW+QV73Y5lG0DXpRzPpz4UzBLA0NWna0vzfGFBfDLPMl9meiqLnWpOoxWKMcBCn6XWY0BgKSFLSGJNCG5RYGq6oyGi0MW2+vvP2G+iBdAG+BQhYAwLJmb6n2NajhVBGGKo9y07XQQyGZhEWXWSIwW48Dl2AZrZAn0mfK37smLqb3aXvAvjDzWTmSwcHi5GsGmxvw8fE34MpaWGfh2wOCoZ9tiiiazVkE7Wseio+GQuT+qLzOUFHXJl+TbvwNLEFs2m5hVZYTUAGOc7Bln71aT6/cTqhRL/w4/IdSNQ3v/DYTLB/T1CcTBsS7WSPOgoJpz0DtC7PDYTaRrKqsmF6X1DvmYXF8+cqbCu60j3bFRjGRh6AGBwCILv6hABO3UKDlOAGoTCIBKYB75vvhP1xDC4MXVxlmBG3s9BRpojRkr2cYirnq+nq7L6uhwedOt7MrfJD06stnyjxG7O8El7Bh7dfZUQxz6HKLKfLCpRIfFJq3IKDacG190NKgD/T/aMFWBXz2H9gRhBMz2KvIKIqs9TkBALtRz8mst8oWAf99/IHPmtplTi3E/3YQoNNcRx6oO2oxHR5FMbHtu4YLCOzvBBZ8WEXtJWCuMkTP8Apm7dr5g6R9siDEw1cvFrANGwEQJXAzLhlbAeD89oYZ2uoDtukWAOAs5B9kmLp4IIRd0bO7CrYEgADNYiEMzlcEAZWk/ySWP91gAre1J0RQefNAu5GwtWLRKqyCE7KPFX5Xa3nmM/F+ucSa8fczMKnl1HY/EAyWG90Qzl3pKmAJbEtTAOHn9zdOTKf0sPq/+gQt4pbmOSrS26zFAMB6qQ9NeKAML3T+Pl716V3SG4LLtZWFTODuaogsUKMbtSmjNK0dqrIFAHDLwaqq337Th2lZmYYFtTlWK4Z3Z1/I7K2XYN7gc2smAPs+aY9ba8CFlSWUpkhWu2CQVexvJUsc/7qUosjjlxlzACChXR0Hy49k1X5uLBbRabeaJUnvsmMGPPzWDQEEMYO78UKmsc8ADmzdmyzYbEKvnJFByIGVhZgGmbJL6FxjhdZ8NMxiowlLfiq0kE5YZr1GRkWYqmRLUAzkl31dZi9w0qJL7BS0TpkGe8mq8ppLI/uBm/U0i0kYeCgbJ0nculYZDBr3XBmtGUrHifUQtZilfuRpi0H6IwAjm2UNODq5lTeZMWgM2rRaDlOc8L9Q/lOC5gyB43BJ2x4fSWp+28hxDDj87LayqdnG7Lxbbrk8+73yxfySlE7OhQAgx7q5wBtQ71RhLWsbxsjZjX5PaurScUgVAOhaWdeg5RyQFUGswf5hqUyDCy4sLBQDZWVtY88/P7D4Q36Zx04UGtg6MgKpwLISQNKXG8pJiI1mmOhEiOOTclur5tvYQoPAqphkuH/zla5iEGf5vqlNh/GvB1DwGcN8mY6L4sYAsDWCgltJ4FYAGG1pxK5dwcDY7trq0kcvj4tBklpTHaovGS4rglT4oN+p65DTkH5eB5VZ0n/NXi/FMCRf0Tugv7/TptLwnZsDYFm8sCR0S9Lseh0QAMAIw9RtCgBEu2bRcYYM2OCxOiXTw+7dXTWpMX4GyrARKE2GBAeC1d4ffvADT/HEVep3JINq38nXVLUMdFeB++G9tyQ31SpGFET9lVkgWJbO7+WZcmydJwP7jgAM9WmtaAlthYwAWRoE3Y5VpqN7pjQziSdRVZpBHVRoCkFtgYn2z/1M6iI1q9TpcMWO9Ia6S2RDoIpnmJh3+6u9CdUDAZEzgr3cdPx6zIa5R5qGKtd7DJzD1BkSlFgrbg0Aoed60ktKfCt0Zbr+1Weuf68OZKixZs4bRzJQD9fBNACNhYds+8g/bgKloviiKRtuVTIKenmdrqhMn/5ub8LD3U6w0+ZNr641wzh7eoZ99IYAnACgsQ/bKgAz5pt/74b+FZtFP/3Nt32gs87p6VFPemV1kiYqNhHKf9RvHexV+vqB0OWmvPM9998ve4TRIZMuuiqYIapt7TnfeMAhSH8VF5oxbjIjQ1g/mt8AZC9wWwQAcWL6eybT7AoAfdDl86gKhvf0pAgGXxVJxS7NZpK631tY+/2Bfg81i70ddkNGUJYCdTwT364vlG09nqdnPLReZLFNxQH+zBXUs8ZNAbTWj9NgyLcgnACu22QKWfDVtBllYRazK9iQMenpJXUVHWkDX8WG22pAnV6zAULzhaywXGdhSZ2GyVwQZZsNx7YvZtzBivp2XlMMsZBgY7VbWUO0/dvvPxvOWvd71AfF3KUk/17Amjb+TV5k5NoNEGCHoqLq7IpidBQGvqSY61VRtbH7BqAHqhstPJXXrGihh0xsBUCa3ZOubhBUuvAUo7PsGjJuxJ5lFOyLeeS6nWQQ0EV4B6bNik1wVkEWNU2AWu7jDGCiNcRr4iYUTGCxLQDACdGpwvhx7TrzhMOOkOYYvsajpGGsNfCuFwD8eUcroi4mltvNsqczq5xP7LI0QCdxXwCAH6P1cjlPxfcrBOT8+BayDRy3YFAQmMTWA+jBgs8nmGp7WG0KS2SN+NefDQCuQOOt1Ls8Dq429qIWDieIfQKACQKt9/TyFD9Di4JxKwBwEO4NMHrrAdA2OlhritmtuqT7WbUvh19/NMBhaApaAkG7g5tJuHZKwAgJzMj2hRUEQp/eCLT+EVnEt7YcEQAO/toQQEk1720OBAvvd7jb45j1pyUdeByEpHX5+ixj2vu35C2m2CBUNu4TAAOhH8smo8haWS9tCQCkIhwIQa9/BaSshmxMD0DxsqftSyZyg7MZjgDncMuM2Uw7+zPj2qE6t68ABGLXGNRVyM9kq4RvEQAgQKNdn57q6eY4crBANZhZtdJLRSIVXjcFEJ++J+OY+LQ3ttbRQ0sYuy8AcNCi+WJNJDlrh5Lpn4IMkQ5X29YDWPlnjaRZCHEkPm6K7TEQTnsvyax44T9bUh3wl1hMWzLHl/c49ObtAljNSRfzAMD3HrHQ8Id1YdZDzZOzKNjWBRy9a4hvfVrUcqK+/kZGt+GpAPtB35QfauOsBUP8C6OcVW/cVwBseywAeMFjkQDAnypaWSX5LuIffJVWW1bB7/FZuKxJezkPkfR+Gx7LEMnzFVNWAhs0XV+GWQkjto/iHIHesKY0Pa3wT0bUrgrTXU27bdiWRZqknydNU3bCLAkTedD2OWiT09lIJromXzS2JMUNWIErie8jAHtIAwBauzGJoLmVL8PtaufCjUmzo/8AgNlXTVWMsWJQUqv5SGrjCUCGiImMbXGq/QnJIRfYNO2+aYDiGYQZoCoqMUnEhJWA20DT9w93fTkx/Q++jKico0qHWehUVMZpVs7F2MgQaZhrKu1tXnKoLAsCgH0DILv3aABA4uI4bnWuAgDrlFFYkh8sxLYsFvsSnxhypmnptjqwQMfst+kRiwDAVB7wZFOZ3VmFuG1fAdxAQYefhADfxf4BADh5SR/cJf0DK9TXyt84AQBsX8Qzf3nM1gEanoybsC1R/s+chYZ9AsBhctnNFCIxz6ZhMjjm1eKJyvakpPTYtnwnMPvuJKbKZaW5hWJosR/wV4/YAFMKjKqBTF1RSRBP4TDWiTKl7QRF05hhHlwmsMpLS4IBW6H5z9kXt6Wlb7USGXCsT/4LpuRmqyuYXp6oifrrw/KOBFZJzBdlvaakxaBW4Ljli20DAAuBb60/itJEMUWVQdmGE9tZhjhtJQzSaEuFv8qTFQzMVPAktbEGr6ZmJEkWvzuVyzc+rUBkqEV94O2IUcGHbyZJb2wUVdEexG3bWo4OAQuUiER9Np/3gxPT1xeZSA1o8F/KYYikWld5pSl2yQ4ZBkoLtqnE8kgClRTaG0WZ6lwZqm07y5DrFAIBDM6pMA26RcK+xw+co789dBQyGzJ+qf0Wqrhb1OINZigKbWMOoPNVn80wqZWDFKWLmSjM2k6CTRMGnLaw0PK/pluvd+1OZda4gE38MSQGec9X8Xx1iewkzGYtxm4DQIqvKlF34aA6FkfqontLRL15GwCAv2PQjuXw3t0ZehfcEF3kVg4/PhoaB2R2R54ppqXMR0OTflsARhcrGMbb/IY6BGTMuBZ5F7ENAC4XYXCHkuOX5Iysjl6/Lmprp9YeD4REf/UPXrKi320XJXw7RiitzctEx4dkqWA+FegerX1OcRs6oNpxfDGOr/5alHxLsUDlP3RrR9YeA8Xq5NBSgunReTuqLJpxkL9vYBI4wopzwGyx1j9M6sicBUkqKChPhIbDZ26ZgByN3tJk0mHBUdJjTJ+jvP0cMJVyoUC91bOnQQ10ZMUX5QlkU7OMYaI53N3+a3uqNZuBkJOSYnDYWGlXdy9sjs6cMt4vqBKsYZ0ut0XF8Te0GK38+VtYhWU3UF4QGkN0mfpSPn6KlezPzwHv4rj9/sGxzRp+7y/lsf6aAVkZ7TH+vTMwouKB3mrOUD2Cob7Kz0QnhzyI31rgmkllovnUCZsnHTNIeuuf6ScLC8oG6ej9QKYF7kxBW29ibLUHp2G7luYfneJ/hCZCF13z7mBFdGq7T1FV+u88Mmg6IrO4giIucJV1sGoSq0cFTJYJl+KZySUp8pndbR4n3FTXnwF8/80G5v+NTsGAwyTMl0YzdW5hEvH6IyOO+GdHl4PqlZaE8siK2oDLijhHOLQ6/qq2b7TZWJr2GYT5unNg+09jJWfAfKJkVtT0qngG+M2VBUajwLF/BvDjArtB+KbKuEFwflvKk3vTWbqv2q/R6Y78h4fHA2Uy8dXK/hp/UunzsrYTKG8CpmwOQMQcoACS5Etvn0skeT67O112stAhlKBc6Z6NZxhq7nlbCutcnUYttoliQVNSFgRP+16eb2zuxDvKY4E5esyB//T4fsh8kqvbPHvi+YqRMh/LocrlpqKqrEMAEp/4dVUuzzCmR+u1PjuYMIPBYHaptvRZIDEyFe0e1mklVgBoNwHQkGXFhNFQnI7MHusRPEvxUVHbeJzLftD5i45dctvn34tPmmvpcCvYX9T4WRsqLqfnj3ihJccnlZbgWkVhYSVjApQHuDcCLXE8r4n9qj4o06sAwCpthEDEWHdljZ+ML28TuK+/SGAiYfzbe4QLH7OU76of2RubUNOeriDi4l9ogSu/pTSXAYmvqpetaRZcgD6zD9QbKHNsYKomMYqivLWrnDPEVqNXEaySxRS1b9AbTVZ09WkFX20MyZPbfQgHtDdjy7tlpa2lNSG+eLDZKWGjHp9sFUGyLGgAikigQhVttwNrOjuGhIXCe2v7iELCgq26P1TnliurY4Cdn9zY75PTLFlWKxBUgfBktbpckGvRIkGIwNc0N+AEWxKquTDaXzPvcVhKvohF22a2NX5wBxqgribvaXY6ep6eKc2LSX2hdsJNa1McMPlQshjnHEZ0HkODiKUtvF9VnAiNNh2fUPNum7NBWjdV3PRYSyu0t/im2m6LQdACrWYciJFAhBQEsK4c5KCIqaq4898vhZue91kJdKndXTGayH15EA3ajOZ/YZ7rFH3u/q69sf687D0j/U/7VFBa1smmpWVZfX0TU4M3AG+SRKz32Efb8+0qKIR2fT9TstbXFsVTVPxc+e5hp8L+7ljwZZl8w+HoaXu+fM5P+lPLJwL6DEP9rJ/XaPbluWSgBxDY1dTLbrdRGO0YrIkx8f684uy62a7aUEsoVFteVVrkjePR0oGbG9NaO1bQMCk4jFpivY4UGiaBfL03AbQ8ry40sSA79SDm3zipTqdvbCDUmMfzsXnVA6POwDC3sCee0e3To4wAwTGRFMnPLbZhEngy1d0/e32MCWrmPEhiIuKUR2iQUAwV7+19P92GDlExbKTrol7EUxzGgr6B8qYE8BS3zA0Ntj8/0bwwPLywUD//fPtsY3EMqYmtuHKk3lOATaa5B97zQxV0/fi34Q+Y4v7xDILGhZ40payyvDTThMZ/zt0X6sIbHzUUmXRNXSgf+gBGmoXuprRxbwGWzBtCZ8ro189XtYYPNzEl5e0tyoatuMVxSYi6y99SWtvtdoJ1zTKMd+9FdIgdeSAZBLK5XW3suBluIau4htPLOtq7ekvhBBOQpqL39nRNdZSpBJGVpRUIVmUJ8wbkhBS0mxsReGHhq56vO/prexubMnNh3AhIbmpraVXLfFmB0ym7fMHCXYFaOPoEZWA780g7XURs1YSKd0I4kWaFuq+TluXh+vr6p5ub68fSVQxUsFNgZVkroJNhwCiu5wNyYGrgJcBHW8Q0mw1I5cMLEwPtwK0PtUz1N/f1qdNpqKIq2wsIfX1VfDRM75EH7tBDBWGd8MVTZWladPwy8MSMjhStZN61y0wgRrqCOKAY63A4RDpFQD9ihHZ9pw5AoH9EkUY9bQU8Ma5F3iysygS8psDag8/BNt3+R3m0B/mInXusI9BDeO9gPgvGulDCaaNDKIQMZn3JZXvdcVhzEudwcFKhRCjGgrZQEw8XBPO5Y7LfMTpwscmlU24xC7rpDg5tkQhvod8BQdR0GgnQMxyToq+7CrZM6SKhgrWDcuDxgACihK5uiIfT0qwuWVbhutxOAIA8g1Vl2eXyqUbcCTuIYtG27uN3+vn1B8Mk6Hh/9pS7wYD0GNIXlMbsgJhBj9CXEUA6c7/bmMwD/e04YITutOx3UCQDxjvhy0q7uVAShBQHUswdEFiMXErKpJSRQecPglcHQtYh/84zlg8+gKKAsBxT3SEXGjIgYFDVnQCgqhwybWaxrb2IpyB52X+1g7HjkxBFgphaW7rTFRznbLYdAcBCNJTVl9/eGGMiqSgKjP+/JyccowPGL+VvXcoPEIX4tvs3a+JUSIZCRckw+EjdMUCj+VflsAPCm4Pja0ITARxH6uyAGA0VoySJIAgjUm6atq7nO0DWgg5JMuLoncubokC0FhrHA/lfNMbzFKJhbei7dnodLZ8I5W8tH+hLUxTaCsmjhHaTsOCgBSFMmuE2DOXgJVB+ZDZpBAKjIa/T4vbmQcgBNOHhb7J6dh4CXA5yd2/v7vwS165dhbgYppqwRiMBxHwYZec6Hib8SkB1VsIIOMMAFVEfDLrSJ8qLknm0m31bjxbfPgRgPoJZTdi71F/iEkXYJYZ2/WF0WFBrZyM+Fno5jDQF4iabXXaVDHRlV/DAi4ZHsB66veFvHwKoM9rpySeUwuFBBePTo05gurwBmaaThpx/XZQEMZw1DYavQAinOFmtYCzrbn8vl9dQaKv6cVtcPDvsFsJnXeiiTQnZVZARBGSFQ5txDbgFBILNNRs/MIvWAN5qfNwiB8o6FssbbzGhkB9SukMOg+H/F3LUQfsDABQlJSbMDXUtdrtltG9XC/o6jq2RcbA4nMVsFuVAd3+ozhsDCSnEDBB0HgqG8z+TAw8+RMMwMAxIKxPjb6zZU9v+bn6ZXbaEC28WkD/sXPGUdcxPdVXX5MXEkjB6BsoYmkMOhpv/38p+Bx8JexOWT45g+Pi41NbGPV0j7/f3N+fnd3fnw19jlc0Du98f6dpTOuetSCYZ8rfzcfY/5LD/fPS/ydEHHRuxKhAwwWl3MV5vsbcYidcLpyLEhoe9KgccetT/ZfS/TcTRhwKIVWE0aDf8ssDYGQTs99eOPfS/XzibaPVhhx6y/29H94Ql/HBe9ANYm3CocMihhx3+Px38qmIffvRhRxx0yCEHHLA/sPxReHzAAYccedChhx39bwz9V33qXJEkLKahAAAAAElFTkSuQmCC
- data:image/png;base64,iVBORw0KGgoAAAANSUhEUgAAAMAAAADACAMAAABlApw1AAAC/VBMVEUAAAD///////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////99f4pLS2D///9AiskmL3IWHkL///z+/v1Dicf9/foVH0D9//8YHj9BicolL3D///pAishBisX+/f5Aicj//v8VHkUnL3AYHUH7//8UH0JvntQPH2T8//1AicwmMG78/f36+/k+isr5//5DiMT5/PwmL3X8/vv7/Pv8/fdsnNNEicJkmNE9i8r+/vZFib8WHUdblc49i8dgl9AYHzxnmtNEh8okL3MUHz77+/329/kmL2pzoNUSIEj2+/lGh8X1//5Wksp5otZ8pNh2odV+pdkXIEz5/vr5/PXz/PyCp9k9i85AisJVk85Pkc4RH10SH07w+PkRH1VRkMnu8fNUj8AiK2QOH2fn9vpHjctKiLogKV7y9PZNi7+GqdlKhb8VImfV6fHm6OwdIj/9/PLg8/hKisYaJ2xMjslckr0ZIVMnLUbd7fOdwNdblMZcl9Nil8I3ZJ4gLHDp7O+syt2OtdEaOGYdJVi61OVDf7kVLlohKED3+fOyz+IgMXLB2ucgNHcjL2/t+/3O4+1qm8UZHzfJzdQ1O1HV2N+Cq95jl8vG4OxsnM9SibZ8gI7Dx89ol7vh4+nb3OGHrsp2pslBeaqEiJYSKFHc3+ZCgsBDd7UpT4dwdIFYXXEwNEuVmaYpMmR5qd19psVwncElSnhRVGpCR1o7b6JtcpDl8PTP0tkgQnE7QViSutSqrrumqrYdJlGixt1im9WArs+ZuMq6vsW0t8EfJUV1o9iMkZ0jP4JgZHZJTmKhpbMyX5UwN21qn9coMldvoto5bq2Di6YsUZNkbH9KT35wpM2eoKszPGW8wNBZX4U9RXOxvMxzfp4zXIhRWIEfIzlgjbGPk607ZpSXnbaBnremqKsjNGnUVnY4AAAAKHRSTlMA9+8QF+m/HwUxCijYZI8539G1Watt48l23KSInX+YVFCTQUhNRddVbKCYpwAANWtJREFUeNrMXAdUW1UYrqvuvfdWIrw8kkheEiT1hL5H8kxiStLSSCG1SXA0iVCPORBPRJAT1ikyiqegVEAU6LCUQgvWapcFaW0trbV22VZrHad173H87sti1j0+kdYehe+799//xQl/P84489ybrz376nMumnjWKSfGAGddOvGq6y+78KabTz9pwv8bp5183WVXXnTpJSfEjIMTL73iyotPn/D/xMnXXjHx8lPA/TegOvG8iVee+/+6izPOvO76S6iYP4Tzr75xwv8Dp5179UXnqWL+BE644uxTJ/zXOOnsiX/g7Eeb08Rrz5jw3+GkM686D3HmL+GEU875r7z63LMvUIwmJJHExMXF/SEN3MRbJ/z7OPPKs0B/FNRqtSbBnKARAC0CKA2BIEsSExNWF/mdcdH6W845ecK/CISdi8YMmOAKBVqtOiSAsE9ISIgL6xkTVMH+xv2uE675FyXcdNU4lh+XQEnAX6uhKIG4JAgKwgiEC4GRDVUMrBwoOabXUAnX/zsxCcZzScx40IArTdMaVq1mWY1GjQ8tjEqAXgMldJxErZYMUUzT3PbKhV16ikqI+Vdu4eQrUSmMB4laEkcbzWZar4cEcBeIu6CBVeAG8Ad6SBomwGAo/sS6cIVGoUjAP5939oR/FidffGnMcSAhPqx1ejxer98faGsJoSOwxe/12nmn08lTwwVQmZm7K6WN8/WCAODymyb8g7jhguOHfYlW62yt6mioq+/Z1Xu0trYiiNr23l099TsbOgJ+pxaQDHEBNnOtVTpQoFeowtHpqn/MFU6NGr9ETVFw0hgaEYaYO6VVa3HugY66+t72Cl+hyaQTK+UiJgSx2OFwlOdW1Pb2VEOFV+symmmWNdAKQ0HX+ljpcp6KkUQS+uUXTvhHcPpERcxwAZREA6s2Go1uo91bBfLdnZ35Jp3OIZYBIpEIn2Tk7xDEOpMlv/O7nuqWQJndZeQ4eHDe8pLYkv0sNSw4/QPxCEXPWcMCJuIl4HQaS0tLXZ6yhuq+ikLGlG8xMThtnRgQTp4RA0qRAJlOhz+05Ofn+5bV1wW8HqfbzHVtk0oru/Sh6PrPXcJJ1584KuBLJCTiEPaDR2sKLSYH+MpTU0RiB3gOhTwoQC5mRCmpqalpjM5R7uvuqatylxZ8khRvXbyCThgqADjhHBR5f2fJfN4Ib8W3o4zu0lLO3zEI8gyjVMrS09OTs7OzU9PS0lJTUkQpIlFKECKlEg4hl4tSklNSoMNRZGJSxIXfNbjce/YmZlg/yaNpSjUiUZ916t94/BdfPipeIidxdm+gblcNjN6kg7nA8JOBFCIArENuQHTIxGIokMtTcT0MYxKnOyw5aaaKar995UBSbHzJfq97pADglLP/tvO/4sTRAR8pyFNW1+6z5BDbFqWmyOWMTi4SDhtWoxMj7ABiAelBn5ArlQzcQJmcDsGd1VXevFUl8fHSD/a0uvSjBACX/T30T584qmSLoTS8PVBdYWHSckymHFEqOXjBunNM5eW5c+ZMmz797SDmzZs2bc6chx9+7LHH5GIdbkKUnCxnlLKiar+7aUNlfEZ8/Kc/tZR51FRCOBJFcdFJf0fldqlqOHvayBlc3radtfBbRiRPY+RicTKAgy/PzZo25e4777zz7rvvvueee6ZMmQ7+NTVZEPBw7lxoSE6WwdDEIlFhT5ndvWiTNGPWrFmvd35X3+J3lxpZrRoVx9/sCDcOr9wkGnMC7/GUVfd3WnRixEVYNswdpuOYmzXv8OEjR47cCwFQIPCfjvPPysrKhYC5cwX+sCVRdkp+T4DniteVJMVOmvXy5qKizu76gNeQqWbj4tTDbuG8v6jgjLNPGVnsULS9rLm9EPQJGQgQyZJlprlzDh/Z+OC+ffuC9MF/CgD603D8ubm5OP1yMeEPHxBlW3q2NBlXLC+x7t0bn/H0gnSZ2JLfXR3wGM1xanXMMJz31xrOi4edv0IhUWtYvqrex+DUEXVIVESZUJ41/cjGjfffd999D9x7L+EfOX/YD/jX1PoggBgaQlVKCpPfW2Uvzdu/vnLdG4szZq1xJCdnJ+sshUcbvBzF0nEjhmF/RcF1w/kbFAaa87fsKjTJU2TgQr6xzFE+/c599z94//2gH+YP+oT/NAjImpPr27WzopwIECl1suzstMK+Fg/HLVq7fPui/ZXxL3+YTr5OstKU317n5zgjO7Ltv/ZP28+1qB6GgDUYDE1bqmvkSp2JhEUxKW9yp+x78KEHH3yQ8L83wv8e0J+O8JNVk/Wwr7u5bDC/XEy8FwLkhfWBAs7A5xXneXcsts568xV4EJAstjBz+6psvDrm71JwLc5/+A3w3paefCYVuZQYv1xXnjVl44svPvSQQH8I/ykCf5g/8V/fO3meDkRcGU4ZHlBT7bc1lRq09iZu0TZr0rNPMWlpwXKDkTOW7roy7eiR6pl/Lv6Q81ephIaWNIIqmI8QO0mhnJySlmby3XP/QwA5/n3EeqLmT+Inwv+cLF/u3P5AqbtsV75cJk4W6Uw1O/2lLoOZ5nhuxTqrNPHNBWkQgNNAmcTkMDm++iotmjeJglL9NT847UKh/FEpNPo4BaV32XmDLdDT6RCTooaRI+qXT98o0Ad/CAD/SPgMC8hC/PH1dthLza3N8HulzJTf2+G3m9Hz0xy3+o29VuvLT+XAgsLVnpwRm0xHO7xuvVZLq4aWFaf+Yf43hsofdIhahUpldMN8evMtOqVQjzG6udNgPIR/0H3Bf1j4CcZ/38Nze9uaOF7Pt/XnpKZZKuqrPC4Xr0E2zFy5tlEqnfVmkViuFIUhhwQmp7bZ73JqNTF/KR+cOjGUePVoZCUKhdntbW635DBCRSliTDVHCP+w9w6NniH+oI/j9+1qs5dyvMGY12NJIwaOAtbgRC+kn7+20WqNfXazg2SSKJQMbrhm0K/VaCXDFZz0x5r3C0IXiMzo1BrNRr1/Z40uJwflJL6JuHw66D/xROj8Bf7Dwuc04r2oH2oHA3aXVo8vYB8s9PV1tPLGUrOepWnDfHL+SU+ueUWWnpYWJo8P3IEyJbu8fouBV7CKYXXRH6qfr1GESx+VQsKVNtnLBn1pjIlJTZUrxY6sI6APIPqM4k/CT/j425v9XCl6Zq3b7Kzr37mFRweKoVfIfmLjZ72+QA7OYftRhnUkywr72uwGlh2WEq7+Aw5w2YnR1kulMjd5ywY7dfAw1PpynQnW/0To+JF8Rx8/zp/w765v8fK8MSFBrXWZtYEOP0froQbdtMA/PnbSs5vForQ0mSxEHKlRhFo1VWlyKE19Ad5gGJ7Tzv797XuEP3xAoaLt/p0+i0WHQIeCufztjcLp4/gj/KPVD+E/TeDf34B6R6H16MmolzY32V12lqL0KJqplQcaYxMTpbO+tihlzDABCM9EAIqLwp4qG8tKhqWDU3+vA5AEkJBAkkCMhjegeKv2idGJgH+yo/ywYD7R8BP1X1L8zxME5Nb0V5c5aSOtUKip0ITXHKeRGOACdMHuAWtGfGLi7NcXMCKZXC6LOLAyHIvESPGFPW023qlJoIcU1yf9Pgc45wRBAIKnKo7l3VzrYIWFlA2kN4T5E/qj+C8L2v80VG9wgNrBDj/OWj10hktqEa7JbZ9/aHFJfIY06ZE3XwJhfIwNuTi/r8rjdGogIIJzfpeACwUDoiiFCuM+lue8dci+OllyaopYl7VROP8w/aj9w3qWLl1aWwv6NbX1HX4PT+YWAm9ABShUlLHJbVv0SaV0EgRMffOlHNHxoNTBihDEh5VGN/0eB7gk9D3R4GEyy/nrKkSpDOl6ReVL4b4j+d8NoHYDltYQ9FYH7Ii7NMoBFpYjKMBRKJB9jU0rl6+XoolJSkp8+iUmTXRcyLIL68tIQvtjGfmMC0L7N3QvrIE1eJprdSkpqWS6gOj/RNj8R6Uvofmtaa+vQ+Q3mxPI4JDjXJxeT4ZgNE2mcPSKYwPoweLjY6dOfXpzjiz9+DeAgtc36DXSMUMx8TcFnB3NHhSPWW1bLZPCMNnZIjEJn2PyB/17YD81te07O8q8RnOCVotwyUOBrWARGwMXdnOcnbftWddoBf+MjMTZT2+2pKWny44vwCFO9jXbhwtQXfybJWjU8TQ87+notohSlExqtsw0hZh/pHoYVrzB/tv732nxe1y0gSU7Gmxl9BxvW7J2P49UYjRyBVv3L15ojRcQO/vNBbp0GXJYEMFaAp9HgITVmubWEaX1ScePoFecEOGfgLKrqiffhACEclE8bWMk/JDjH1q8QUA75goYOeu1vFNLKWAuZiNXvH3d+j2ZCGg0Z/vsYCPoZxD6sXu/eMnCpKOEUIrxF2ZFDNKXCJ8xDosEUySdFCXa7vYW7BPgj7+zpDg7ksIoSutyF1QXMkr07Jg5wH7C5nN/lP+yZYT99OntzVV2vcZs1mgBA+d2c57iHQfWWw8uoVUKzK9t+0sE45mUOFVa+dE79f3ttZ35+UVFDnRGqKDlqdmpGKsCIpQqoiBI2SKT6Y6WOXmbQoOgEsINx7uAaApO0Do13oZOkxznIhPi51Dzj9gPSb5La3sbUKaBvCbObDRkZrq9ZR0/bfvWKt27oYkIMLtXL7ZOmjQpMTExae+63Vqjy9Na1tZS3ddf67Po5CmpKKJTsrPha4xShFsIK0AkUqZb6lGDSBRx0cn18WqgmAjQUqgDRy0mJU4C1b9QvoWLzyj/e3D885b21/ldnBGmT3bEZndrVUP9d6/PTkqSblvE0SqV3mzc/q0UAqZOTapcuzVTjyil1zqdra2BhupdtZ0oETFyzGFEmDNh5pI8zJWVYl8DR2N/Q/2Oqu7c86MRyGWk/YM+zGzlaWk5qB+eeChU/oB+lP/bgoDqLajTDBoWolnaXlXXW9G5+empiYmxq/I4Gv2oIW/dwvhJiZMSS7YdW8EZVJSElKhY0xhd3rK25l21WCvkmHTJaPoZOW4gClyB0tJbhZqElfy2H5MaIgyJvZRuqLDkyGUQQMp/4r+jm6+3py9dOg3fAMavps1mg8ffVt3uy8+xfJ1ozZj06QqeM9K0reBQpTQ2MV66/pNFNjRH6LMFmAFar3XlVbXU1xaaGHiynMzpR8SinLn1XnRBmt8urM8dMoWg7Pay/iKdTokIZBL4D7efu6PVf+1OjzEB5mM2c962wQomVWwxbX5WunDh4u02zkAjBG0dsEqTpJUH9hTYbHGoKkLVEUahBJrMTN5ThXsgs1Y5BhcjBOiSCxu8vFbx22XpOUP3/56yegxQZGKMQnI3vhgNnw8E6UdnVzXd6BrNWjVrNHga+jtNohSx49WnZ03KWL9hPpeZiXyct6qxxGo9+PMKTsFyMZSevDrQAIS8RkGxPK/m7eTuuvNNqETDAkJltkxssrS32bmYIbhm7A08CUHBCbeCoj3Nvpy0lGQMo+YeJvxHN7/h2VV3lQE7R7XG6G2pMOXkMOKiD8E/ftOhvFKaBfhD67+tHNhRzBnYTIWCJBgKiMPfQq0nPENQsAbKgGvoI8seOaAUhTck2dmWovJdZUYayZFstgQFY13BadeEdy8KBavhAn2WVLkO48zyKQ9Gi+dRzSOq5+4yVm/Uq2muqi8/BzOeBT88PUvaeKDL1tRE0rl996bFa3cUZ8aMBvgThEyK0mc6/c27sDLJMSGpYRIMIMVlWyzpNc1eo0ZNoTiUSMarq889KyQAMlnWW92Zk8pYkGeQwaLhJzr6jzaPuAHERDaBa6gQ6xxFm19/OaPk4IbVNs7GoYzADHTV7mKbATPb8aAKQqHWGPjWquZeX74Fw2MyekWHCQmYaBf2lbkShNcv4waiM0IhSCJB7WJADWdKS9Fh8Vh+BOOrcWYPmB3Oyc2taPa4SPy01XUueOmH1z+oXD9wbKWNt6OlxcG6l6ws4OEJEDAWcVAK3wNqKHi8HYbUX4gdlY5cAuxIKU+WYWBX56ETJHCauPEC0ZmXhgMolWC0t9bn5yiVsKD0KRtRvUWqB2Co/UMAFi9HMe0h0fKzj7765JPlG7avVKhINWTAbeMK9HpOj0cpIwWwCoBVqAwUed6CNAU/oGjEVVbvLas7il2/OGhGYgYDbcbRHuATNEgekDv2FZx9QmQHozd6WirQhJF58sP7NoK+YP8h+uAfpI/ZJ2b/WLzk7txSajTwnoLiFcXzkbpojSYBIMZN2uEg4oDhk24Fi6pDwfMKA2fQ0wD+LQ3JcDzCcbXPZEKRgfG9WJmcnZam8+3062k2JAAYVVZHN3kwRX89eTEgxub3baF6DvO/m2DKcP6FnZ3d71R5PR4niy6eQK/H7IcIUMRFMVKALW/3z9t//rlr65IVtkw2k9froZECf5wyZ2za0twOT5AjDGIOjrIux9Ib8Jj1aswIxu5sTo8YJgSoOyrkKaQUdNRgdYHJLZk9B4vPZfuOEPMHCP1cCNjV8FNFZ3ddwI9UQNizsAlKQpEHcSrCmeRdBQBrGqIA5sPyeVt3rzq46eCBAzsWrZxv41mwx8OtOGQLA1bQ9RglCEu1nNRsxiIu3NlKgnVcpCgdJ4kpWLW+dbBQLJelJ4tMy4TiWeC/7PCdy9rbexruWxoanZPNo6+wtw1eV/3O9q75KNsVlESCjDlOwIkb4QPQJbEVL/p5+UBl5cG1+7cv0fK8YEu4EN6NS6g1yZkcHS4gW2kSm3rLaKR7jWTMCcWpl0ZSMMvpA7WPORjYjzJ3H+Efat5x/P2DgUD/0mnT5oG/sHr09bZ56UxPK94z8ZK4P/F+F37M5a3sWrWpsbFy24Htq0nAcnPFPxe7mpq8Hbvyc1Bi4+EC0jPja2CdWrNeEinpxm5kJFqzvdqSUs7gCsrf3heZPRy+e1l7f7Pf21KL7DXn4TmC+eTWB1o5GtagZfW0MIL4w4BxGQwcP79r7abGhSXrD+zYWszhDc6mY1u99qYtdT6xyMQAyuwUS5+XlYRTMXDh0Dr0qqgL88Yt3fJsFOZKTLEi1edhOEBfnT/TXlczD9HzYeCxwtrqMo8LAhB4BPp/ij9Llh3IGbatGwYqpdKSTct3F3u6NjWuO7SyqZTM9IkAspZgKloMeEY45oDizGgjoLXbG3yp2TplCuPABYTD57Kl9yyry3Nn8g01sJ4g/+7mApZOoGDMCfj8F15QKwBJjMK2ZMO2kpKMxsUHDpH6b/3Aniba39FvEZZo6PoLB7167ZB57xAbujAmAg3v7zPh9LFqyD2yL1L8tC872uwxIhD7+2uE4W1Ff90WuzsOLxzQdGsoMnmL+WugSt0Gfv9AZUmS9dttq9ZbUYKv253Htw76TFBAUNthCD64G5kKTroiJgLa3lGbpjNho5gzfd99kei/DG2jHanH7qn7qaLiO7xWavMYDHqFBIevolAfS1SkIvtzzEP/HdfU5C5Ysn+bFajcS+anexevWmKrqq5gyFMYC1O+066HgNE2dPKQ9wRm785CucmUnSwuP/xA2H4wuh2sMmaiNnY3FbQ11DV0bPGiiM9k1RJEd4R7CJAMDfQKEv8lKgDCyO8FnrAU/GbUTSWE3D+TM5a6ubyuA40ZUkxfMjIy4pP2HtyR56/zMRjBoMLbtQUChreWUQuSBL+P2X8USTgZ/WmWsHlE/D+8rH3KfYEmcyYyv5FTcCCujzkeQAVt2I79q5av2rBn5eoVK4rz8gqaOCN81ZDJQoUgaLzr0s/fv9gqzZiECV6s1JoR+8YKW11Fjk6G3aivze4Cz1G57KqwAGJCAR9eHaIOLH8b/IkAFD8IoHa3weOy28HE7daazb8hwGBbuWrTtwtD+Hbxuk+WH9vTVVyQiZBLG1TAcQKTzbbowKdPP/vy7NlTk0qk1pKB7VsaasVkOGKp4w2S0dP20xCDIgNdvi5fp8MsSzn3cHB0hdnV20vr55e6nU6uadHyA6tWujX0bwhgSSO5FY4Yj1kQjhLPskoq129bt/bQ1gKeFwSML4Ll3PbV77y6+Ycf1rz57Cz0ppM+WL4Se2Zs1pEKeAgYOSE6XXABSfA1SmuPhbzoUYrnHAkKuHvZ9HlHW9xur4e37ThY+VbjMWSumOMDucnN8Xldm0qkiVAAg54Um5SUZC1p3HZgw6L5NoWEhM5xBFAcjaXQzoqiIgv6C4h4edbeA107fTmMxdTdNmz7etLQSlpYaPB8oBsvP5OzdeXzDgeL57sxeK7fYsa2tGn7p6//sPn1VQUKdczvQzEuQQqHJEiSSmMnxUut1sZ1+7vm8yxHj5M5JJIEc6ndjzdJmEnlOIpeem/N0y9vO1Tvs5hMhc1Oyai132nXK4I5ER9aZ4OPIY20ae7boeYRw7feBju2XfTWb75+KT/npR9tKH1/nwBu/p71C6VTCYiEoJAk6bdokvN4nh1HAGUuNWfiYUBfkSMZFZmjvOilp17/4KvefJPJUt9KjVw5YakduneJhNW2vpOfIgjIOhx5N7O0p8puUCgKPvr6u5/e2fXdl3oX/zvTLs3xi9Z98Ojjzzzz5OypUxNjk6AhER9J1srFO1bmSWLGAloJOjMT65yyvkKHTJyOV1JMzisvff1DhcNiOhoY+q3PD7rA+aERAV7icgGkYRnmk47pECA0v/Pm1dZ5MGjULvnkp4Y8rvXLYkrNqoR2EW4vZGDijvhMPsJls/APKhaLjSVvvD958uSZRMVsMm6MxYIGCqyNB1dt5RUU8YXhQtAKkSkLXequ6inE1D1ZLE/Gerfopc2v6HS1DcQJSNKJOsGNwTSGhTRbamxpZzAOwDrpnnDzPm1Od5tTbzY4v9wf8KA5z+MJSyFxkReMQgfG6g0sWaxnsvAjCjU9RbE0+mAJ9mLc6s/fn3n7jNsnT74DIp6cnRgbPwlRCQ8NSg4eWo0tDjf2T9dI9MamwK5yBjNfMMIA2/TKAqW4s7pVk4CHdXFBIz5deBdHRQSY7Uh65Fmbcu49wugc9jMtq7tVqzdm8igSbQYDbTMMqRmwzTO6C/LyilevXr2ya8exDcd27FmC36+Yn1dgcxtxvKWl7kWfvzb5rrvuuu2uOybPnPko0RAPBbAmaeXB7Xk2o3nMOlyi5Y32qv7CNIyJyHwKL0zw4Ci/x4+GWwIBkXLojCvDpqdhzd76fAjAknZOaHYyHZVbnxPVfiZbjLLdzhk4PI0M184K2/wlu3esWvvJwRIrgRSwInNZKwfeeGPVoT2LVhTYjE1c18Brd0ABNNx2x+13TH70LVwD8Qd8Klm7qGDsTkLictpLjYFezLkYHTxBxuhg2kXdAUznKQzpwl6MSi4qgN7SZ4EAPCabF55dQcAgjy6dJQ0vrERBfiWTEI7NLO46tnzdtvV7k6SoWxAuMYImpEANSNr7weKDSMBdqz15P346E+wF3I6PmY+TW0B+w8KjcWB3Ab7aGArMeper1NvQbkpLVYrxTADEspNNFW0uY1TARBKELo0KQDNJVmIYw8yL8s+q1icgxVHkmFTC0hTtB28r3r18YHEjDh1RJTG4fiG/xsaDmbALg5qFVmnl4oGvDn32xuQ74AS3E0DEXXfhFogdTYJg6bb9xZkGapSAOLMZKwS7v8Enzk6RIw/LRWjxdcgEhoS4sIBToqWoRJNAaQxttcSC0vCcLMg/izwbgwB1DCW4LUUEGBQFq/es3WaNTZw9e/Zbb731zOOPP/6ogMffegt/hFgTL4C8SIGStz547f3Jt0++447b7gAEAXAHcguQCwUl67A2GFXbUbRewWLP6N3ZqcxW6pTBIZGpaLCVpyIV+AkIQ2fGRASwmmZfUMDct4P80TxCgBECyM/KBH9MUpG5csM6aVLik8+A9syZM8EMhysA/OCnEELiPujhbrCZnP34ZESh2wnvsCHhV/jCk1NjM6QZ5BI+40c1ExInViZuO49NqQUTe7GICHCYLD2tTomECAiHoRvD4VehNXLVeB2Jnbw4d17w/Al/X7WeVmPoJOF5snCxrd6wqXL2M4Q7GAfPdAZh/8ILL9wWwgsvQIWQvGLh1dLZj06+LUo+JIH4wjOz46UZ8bHx1m2HCsh8EUBaiP5MWpyelahcbe06k0mZBl6IqKbeVo0a5hAScB0qobDNKbRmV31IwMPzpoVfbc8trGY16hiIRl61FSxZtXjvW4/PDNHAuRL+M2AcURArEe4idBOxU5+EgtuI/Y8A7Ii4PQytEus0bD5wTqqRpuTyYteFUbNIAFPhpyFAHZ0wXhY2IdyAq9ckCEiHAIxuMTt5eC4E8Bq1iizcOduS7wfeeubRmZPBByDUZwifwff2CMBTkAANIRGPPDNzMjBKwO2TH31mdiIQK23cv0Kt0cMyRgvwtNYXRh7WMZ1l+qgAEkevD9eAEOBpD93AHIzessjoB7Nb06BHy1IqzJlt2wc+eBw2j/uPQmBKLOi5KEK3MwOfhIt4EldAhI0Ebm7m48TQYlEdrZqv1o8RTVEhuwJH0xixMiggv4wdIuCqCROuCJscfL6106QLCgCCb/7LRUy3E9N/HH/XgQ9emznsGCOWM+P5IZhx1+233Q6EbgVHD1eHD0PPCMAvBF9OJJlk4dr5PDVWStbTfEsN1vmCAHl+m1qNUUhc5OHBBREBaqcfQ2klBDz2cJj/Y+UyeWer08Vxxd9/8dovt70g8I+IAMfnnnv+3TVr3nsqgo/XrHn3+edm3BYWABC3IE48hgKYERSgW4jPKFk1nx1DAIXwiHF5WIClWTtEwAWRubpaCwFl+bqQgFzCnzz6d4hSO6uc2IN+9OnMOyLfNGIDzz2/5qkPX12wQBfFK68sePXDDz9+993nnw87RJD7KBPCPcEeZyAaQUHsJOn6YwUxqIlHTV20Wr6tAsSCAt5xaqOv2c6aMOH8kAC1QuIsw2YYm0FBwFzCH3FLlJrf4vQE+n6YPAMXLrDB6ZLDB/13P/5wgSNdliyPQCkG8ATllVdefepjaAB1wXRgSWMIgHmRrzdTcOWp1m27FZSGGpmSKbwf8daXY0+A1kAQQFGaqIDzwk5MqRSBfOHtpvKx0PmLsOURpVqqyxraixZ8DLuYATrBT8R6nl/zKv595TgPliDlFVzEXTNeiMam0VcQvB+SEZKmShcuXoKHpiNm8aQA4J1t3Zac7Ox0RxoEIBHESUKzoZAAQAPXbrMogwLC/HGgylSmt7rbonO8uuZ5fCvElhmIMzMI/49fdeBhAASMA/SDuIc1zz8neDti13hAMHoGCQGV7NrVHD36f5NAs84t9YVYdKSLmaECgKgACm1Ch0WkJALEjwn2LwZ/hzI11VKIB3qM49WPn7+LHNkM4DZ477uvOmQiKBgf6Uq8FCl66t3nZhA/Pg4QbOHJ0gxpydpiNo5gmIAE2uDpqMW0AcY6vgC812gpEsmJANFjgGDKYh15bsOkpqDJcSz4+N3nIIBQAZ/nPy5KTjkuf3wh/HQDXh68+9wLx1dwB4mmifHIB+sP2RLQIIwQYKQN/p5CnQnznnEFxGl+ZeXcYhopozgejPdLvMSNd12jD66zbcdpt7QM0wnQlbZbCEEa0pTCpuITSCBprQgKa4qshririUXTtcUb3najkdXVWguuJlohivES4xr30heiiS9mo4/+zwztDMN0qKQnQdndBL5fv3POd77znXM8jr8TTicZMQCsVnJbeG7ubKXcNir0Ou2hfJIc5D75AHij2I9STEOhkiVI/+IbU/PuigC0q3C6YzDkgMCd/YwqHAGgEEi1v75XUf7cPWytCICUyt5zK16z1FDxhFluzKELfn2XfdgMV0MeBioNBFsjOfmePxLWLQFCErl37bXomK2nIoH05R5D3ER3tNHejb1Y1NwHO3iGLmfWFiMAy4+FtJcA7GCA0BshAQwjV00GTSV63sUiEBAtNPacXut3GgNYSezd6N1ITkXHcLgZ7AHMZDJAWaPDp/qQEVC/Dd5H0v7gz4nuLu9whxbgSqVJz3Eqk0zQjazbXl4Cii69aPOyE5bTDoOASsPBk0t944+02b4FAP0Xz4wdiaV4fAamT6dHRQ64ojCSFSdP9Jo2RqUE4L//qWedMGMAeO4rv5ThSnZDyY0iX/mdWFj0SgDqwjXNIlGIl8+vAeL06SK2oArpbO1HCVG8aabHbQTQCDMIhxl27lwfXVg04mkf/QWZuhGo0EO7y6HEleVQgu6Mrs/CmWQ+hDQS+SID945cGbqFE2tr+V3VSKvdG+o/H4s2zRj6Ilw5J3nkBoLL75Ir1SatUYX+aIt0DniUWAi5uetLuXXo0EfBSCFvbmm1GwOgwzlEjZRwQlUJanND5mwmFh0nLTIAICXiWPbgQi+SP5vSlEPvv2dFKPE3AJpde8rB3K0KgOeRd3j0FSExZ6wZ8LUwBrThhpxVrd9cj4gkXYjEm6ZmeyrvAd2axwZoC44ec8GTagB8g8/8gk7AiZdR8dGsikZvKauQa6/rHza2mnC2kPFtgUBOFXW31QDYzXZ4gZFijpRodt62zwCAPBGuZwujfm323eRqHnr+SWv9xFN+D+o2lQvNDsUGHI6jrJhb8SKG2QoApVzEUJ0K2VuGUTWzlsEWjM/Mz1cC6KG4bv9PPENW4LM4NDFR8+BDrz+2qwNXShXAbWg5V3khxzdh6o2Cihs3J0CBZCdZpbQM273WxZQYaxpvmq0IsM+G2BpbwLLBuS/7/JodcAHgqRdaAWBxKQA7lEKbBqhZ7wIrirliPhRCQ52hkPlWL04UP1rzqyK2gOzYUCguZbmTH2lVCCkHz9AnHRMfPo4yW5dLSatcUlcC2G1p+5QVOT61iCAfADUTOyYxOFu8MsDUrM2YYAwpMUwrsTi0AP69vl+6Jr56cxDNdet5IdNlSC1eWzqxMSriy9+QsIyd74DXqDGAvdVbEHkAjM/cayywApENLuzVADS3+5s9P09MfPzm4AOmEkDd5chOX6cAmN49ig5BtGiOtFhrDbArv8ry8WhT09S8MYB7Etn34PKJBm2y12LyvTzxwfND/j0AKEcSqLcsmTmS5t8BQOQChXQIALWTero151fDfAwATbPGAI2UpeAO/6C53FPB7973n/3g5YcGLTimlXKJS3eUANArMn0ySE1SuWLCXEsAZMbrnelUmAHAuBqgUd+MAzx3cGGvBgAfu+m5t/99y+PBI5P6mfIOuVoLAarFcmAhyCLRh/PYW1MrtiOfsJbhZACVEczO63hTutow4ZPTGgAXKvwf//rr59DkUo4zrlJqjiEA6MO0kwDPCpHVRadd+s01AgiFzMlckABgBIobmpnRAZA96dHjG63YhKJRy+hXHz/id3nKKnT1huZt3ER7f12mHWCY3FLajGCtsyYA9m4cjd4lXt6BcQWgZwpO1a1jxhER/Td9FtQiKV6o7ekh3+jHzz+oppKrpm9WhtY5TpxhGeAzgUwxQdXXNdoBZyiUTrFBLcBsEyJsm44ZD7Ast/Ai1qMAuCxPD7UdeOl1j+ahG3JjXemFuc3Rt3BQAuAjCEtDNQKga+VIMhbWAuybIqdq0zNjHMbLx9osJhWAo32w7ZX3nzNtbvK+64LyqMd7Gn6YE0iFeDaCA7lzl7kmACHnSHo1UAaYL20AAHQPZjcCIu6L4w4LGlbKwZzD4rE8/K1PDbBzvWROPYDqBJ0EIAgzUsNsqDYA5q5iTmDpHBgfL59k8zNNkE1mbJN0CDH1j70mNUAD3iYtvc1qu5YbOSjDrkjf5zgJQMCyfKyQ7a8JAEaZZFMiJwgUSjRFozKADevXB0BQfYjBvczjJ4DKckO5blddLXZOAgjg8xLRNO6swfoxdCu/FAuzASYiAUzaZBc6JQFMbc6xAOAIz3J/+poxkkCTJ23Q6wW6rE51czs2BwCWAQAXiC0lnCFziHrJtnsAkAMydyRzTBifCkwgGo9NuiVPE43KADo20INbAced6fPvwaIrF8zeXS67vFgF8OIZjqWnTxZv8BEcB5g7uO0DrbuTDMCbT2YEjhWFSDwajYn8JLKM+8cOxQlAN7ZDLh534+D3ozQ/z1URoE7pn9mhAjhAITU9saPkgSeCDnRjhULbjYFQPjiykooJAn4gH4vHI2JkzO3G016MAEj0ABoJYG7aGOB6VQfTRQqA7/hykABEAAg8nytkR7YN4LQCoCO7GuEF/EDsaIQX+QFp/YwcmY7rBKf0GLJ/QAi+UxlAW75+4fWKa2ob/fwgx5AhCxBOiKVWEnjdcTr/vz0js4qsYhZtZZzAR5ggx1I/+iHUDA2wQTYWNwBwHxK4d6b3GAIo822Vw5gq53ynDnMwAbnSEIYwkCmmR2DE23BIZsxsSqYGBI5iXAAIYXxzhMo88DdwSZCKAIwhgLa1++qbVEWr02epmoojZ8Sx2Ac+U8h6sf5tbEF/opiJ8NTLjY8DVoWfGhgYkD+ZgAwwtRkAJ4H7yJYAOzeOUyz7prY235e/MSwBkMAfh8VYKpmXEtFSA7+sTeSbNo4GUgdvEq7TvLgU41F6K1Ipulz8yvM8/QEs/DrAvB4AsqQAMGmmeBoMHLq7bAPNJsex7znp4RZCBT+ciNBuKdvR2umkA8Eq5UXp7cCJlkdZwEMCJBJkt60IH+D+V3O8wIoAYAUCwA+lUJH+xFUEaCQA22RAAIBBA+Odmk7Em0oA/gbH6EIwwGwUPpdKJrx2rBtvLuCQ3oOpAV6WTgAAizaH9qcFgOZEupiJ8bBfikzUQvalAMzYNkXTtANbAdTRXUYttzWsA6AZoxdTHDUAGEgQSSXTXnoykgZhjXjNtM5Sngtk0vQekElzU6357BJVbpMq6gDwAgcjVmIhPQDOEODiCu3cAMDXi5//xmp+KUoSI5lCMt3vrccarfWUGMWiZaXBd1Cjzu7W9ZQjPUSlYlg41Yey+jvAD8hudLYiwD/TuysD7NzUzXqr6i3BR+mVjQhwhdiEzOr5LI3KwGhamkQLLZKF1B8DLmjtTvvISBbl2hGGg1QEYOkgg0xVBjg6uqciwDUVpvLIggLRTzU6FAhAi+DIeWzDShr6E7J6zST1JNI3GNcM1epKLyYLmYhst9L6GT1hoUEyQE9FgJN9looAN+oNNlOaQO5vO3GWgWg3gdyfGIllCsWVbDrRAQSvIl2JRDqbPI+mBdCyYfkohAfCaa4DIMZkgBl9AHih4J8+LYDxWICdCkC7H/kVgWHLv5rCO8R2IoSTYrxMahU1QiuLEwlZJrIryeLSKhpHyHChNOQ2ZREELQBUimNLGqQDQLmhI3xwAYUfu6vxodpOFIij4bMzHIovFALJh8sORcD/I5BcDhwlyWDpEZxSEm0JgNEX/CsAcDvGBqB+RE8QSsz96NO8EWjmJBlZAezg1y9IhYUKS8BS6SuiEhGFotUIAAEg4nJGgRDWrw8gfHHc5ddugDqjaGgFGM924NODHKTCIqAahMCwJKTuoBGEagEobRPHBuhZANkAEiuHuG+O+SwmgzhUzwouUgDa/aPLHEdLMxKRBCrDymuvGkAciEv5CdoAnZPYZts/ICW2duNcMnJB2rPgdlUfhcV0CodBuLo1ccRKMFUC8FKCiDZAH8A9Fjj81wFLO1VJ02qqHWp+RZ1ixg88MPr74a12QFgXqBpLUuUWiFJ6gjZAF8DtRmYLD5Xt7Q4dgLqrjIaUK+mV/5q7lpgmoijav9SqWCgIAn5QEiNp2piaTFqQaGoXxXZjujDRtrFLxZXRkLiwCwMmJLqzC9dssCsNLgwL0dloKjHARt1oGpLGJlAgJISN574Z+pnOjGUYlJOIRjb3vLn3vvs+9zz0sGR/etVcB7ggQCDRMIEhIsAiYBjDLUvgZWA2E7ouS8BpUAHUJURwUMkKz324Ic4Bg/IMvCIYAeBvhntZXqMyiCKARXAdAR84JZ+Nf8R5hWwSsqvqXJaFsumqcRjTGb43QhQEdAARAMlAjHYYcVypdGnlPHZVXk1xSilUFZZuropAePr9uBcZEnlbFwKY2mkix3IeBF6onfP1z6Ylm4qNqrEfcIouBAIhMPh9gwo5jJseIEcjB7rPTlsHlC9hLo5/uyr7BYytf9eKNAoE3MQgEn77eTxABHSzP8aquEcTitdW0GHzePDTmOwk5m9A79JyWlzYuOnMyZP6/pUZrxMBwX4xgyoQwFE37kpEz8mg09yI4DGeGROEl/DzYijx7TPaffTiEID9j9QPuxHCMVyViPpVFsLq6GsXJJeoddyDyhpvDVGVOQjsavwpod2mBETLMJ9SCkIIv3yOW3MyLmRsa1AzuK3mgJzOXodQU6DVTSMDahiLBdAO1H9H8J8J2YGfpOvxwSDqoM8Z7pzMB7CZG1ZtNlaOFNAnmEBV5L3FlmQaCXhZvSTarzQBBOH+tKv4+MO3OCeXQRvXznbY/OV7UiAQTy+8utWPQaSeKQ2A7eBQiV/Fa5fkWLiz9Xo04pYJgD5D4+izlj8B+VA8Pf/hQuxOzKuRALXIDG3nT8UJjPwHSfTxbDblkbG/Y2dvD5QVqygKOC6x8HUwgNJHKwEUoJh/Wf6/qU4gufw9FZUhwA7ENIl/s/bhSPgN9HK9Q1qzJ8zHmZhQ/ygSQAAPJ5c+ol/wYn0AN+30+aKuqkCmq0SJqdlxjfMB1f/M/Scm0detUgIFbw7wubF4dMQjFf6wWXb+AkcXV9EZcKPlN5zNLfVTg2o/cpH66mW7xBYTFxt+il7qWpKtIKhHi7WU5nPTca5+O+iYptcGu43VonYoTjObP38M3WJbbuoEwEBc5+BHICYm/5vKl+9ZRxwaNPlcVi6DOrU9p2OpMEAkQ40znF4rLd3AKRHQHyAoBu0ggWI3Jo7+hHLxQxyCgG8gWcqm4D5SWB1a30A8UU7HsB8ygqnUzObSYgzzKqBCYHtDCScjrPaH+WgcGv6b/flcFnrDUuUcd2fz7h/yAgHcuYuMRO+m5zd4NPWT/SoTFwmSsMqNhn+CzKcqUwGsoXry/EB+fQbL4Mglqf/37uYhxBOmcib1k4rhtbsPVnLLS4vUdz6kTACBEriNwg3mP5lA64kqBmC+j8Z/OhSl7n2J/5P/aIelp7LRQn+uobF7bHOZJwpAQJrvRWDZi9F/eJn5jk/dftbUOJlcLkynolE/xPZqx3/XD3r1mCpKUn5SVbsWCc8UVnmeZzodMgRiMeY6T2C9bxhQ7BgQ/596/PKlqUR8ZATSQ7XiSy1m/d5zxAqBpFRIlv9qei23mqQrA48XqelcDGmELPCQWU+OP7zd2y0NWepEIWZCOy6a61cL2UQIOgY4VK1u3eBceryN2NRrkhExml4p5YkCU2PAtxBwXzAd10HVILSGso8D+JL8xkomHqpPn8Yus04P+h6XUvDHw5H0Sm41Tw3qLAf62HAGmSaAOsh09hnwF6k45EvzD+6FovUFnLW+ftYeylYJgfAIpdSV9WIStoMA7h4qJUr5yoGUHIJwr/zG1kwY2X/EIyFgbGnW803r1qO1LnQN4pBX3PHMVKHIB8U7PuABy+q2a2XPwIhCkE8mi1vZtAdKPnUrYK677D56uZG1ZqVMChboMr0b/7K2XiRPYtVkQ+PvCzI1kCS/mlv5koqMeOqbxvztGH6dcbCjU0KAw5V+jgslRufmC8QB8DVGAMbzxdzWVAaeGIpzdXKqRpfdoD8O9la9S89h1wvaupAOe/rUw8XTc79yyzwvkACLuh50Xxls7PmNwhuIUUOaHermHNOdqUqfpjbKnvqjydxj8tfqdpNyNNwX00NidOb7u9KqyCKJHwMDovTHTXL7oAg+v1rMfZzLQPSPRGtxHuqXJk8b3Gev0OeSpKMKG3puO5Nd2SzkNoosvQJgwqiwgg2Wb5TWCwtzJHPsUToB9h9qazLsISwnnQoMPB7ISEMfPjGdnVqb39osrOdKG0UAZufWC5tbC2tv5t6OxhmuKtlvPeIw7DEsh52cHAFKhUz0LBqFrmUqkUiPZjJjY2MZAIphCSwmIO5znYC8KUuAM9l0M199vS9HQXjyCoplbtIvqgX9GkCwXiQCogy4FFbXGXjPv0CTvaNdIQ6uYAPAXbZPomoJim528Cs3/CZXq3Lu0Z+Co8NplKHgFo8VBFRzE/i4/eyf9YnfarPD/H8Kc1tLu78uEGC8shpqWa5fApPziN3wH2Dp6+o8t3uYWg43G/4TDh5odVlNuzCeMzm7HBqqNl0DusvWadRmvunQ8ZNNhv8Pc29H96Edc2i3nTjsMOwXmB1ne47twJc6jx+2W/bD4NdGhL3juO3YUavyx/AbrYeOtXSdtBj2LQ4e6G3tONLtsjmriRhNZLjrdE/bKfs+Nr7CwmxxOOzNzb19p1qBM73NzXaH48Ce+MwfwMUlUY/U/9wAAAAASUVORK5CYII=
- data:image/webp;base64,UklGRoJAAABXRUJQVlA4WAoAAAAwAAAAfwAAfwAASUNDUEgMAAAAAAxITGlubwIQAABtbnRyUkdCIFhZWiAHzgACAAkABgAxAABhY3NwTVNGVAAAAABJRUMgc1JHQgAAAAAAAAAAAAAAAQAA9tYAAQAAAADTLUhQICAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAABFjcHJ0AAABUAAAADNkZXNjAAABhAAAAGx3dHB0AAAB8AAAABRia3B0AAACBAAAABRyWFlaAAACGAAAABRnWFlaAAACLAAAABRiWFlaAAACQAAAABRkbW5kAAACVAAAAHBkbWRkAAACxAAAAIh2dWVkAAADTAAAAIZ2aWV3AAAD1AAAACRsdW1pAAAD+AAAABRtZWFzAAAEDAAAACR0ZWNoAAAEMAAAAAxyVFJDAAAEPAAACAxnVFJDAAAEPAAACAxiVFJDAAAEPAAACAx0ZXh0AAAAAENvcHlyaWdodCAoYykgMTk5OCBIZXdsZXR0LVBhY2thcmQgQ29tcGFueQAAZGVzYwAAAAAAAAASc1JHQiBJRUM2MTk2Ni0yLjEAAAAAAAAAAAAAABJzUkdCIElFQzYxOTY2LTIuMQAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAWFlaIAAAAAAAAPNRAAEAAAABFsxYWVogAAAAAAAAAAAAAAAAAAAAAFhZWiAAAAAAAABvogAAOPUAAAOQWFlaIAAAAAAAAGKZAAC3hQAAGNpYWVogAAAAAAAAJKAAAA+EAAC2z2Rlc2MAAAAAAAAAFklFQyBodHRwOi8vd3d3LmllYy5jaAAAAAAAAAAAAAAAFklFQyBodHRwOi8vd3d3LmllYy5jaAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAABkZXNjAAAAAAAAAC5JRUMgNjE5NjYtMi4xIERlZmF1bHQgUkdCIGNvbG91ciBzcGFjZSAtIHNSR0IAAAAAAAAAAAAAAC5JRUMgNjE5NjYtMi4xIERlZmF1bHQgUkdCIGNvbG91ciBzcGFjZSAtIHNSR0IAAAAAAAAAAAAAAAAAAAAAAAAAAAAAZGVzYwAAAAAAAAAsUmVmZXJlbmNlIFZpZXdpbmcgQ29uZGl0aW9uIGluIElFQzYxOTY2LTIuMQAAAAAAAAAAAAAALFJlZmVyZW5jZSBWaWV3aW5nIENvbmRpdGlvbiBpbiBJRUM2MTk2Ni0yLjEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAHZpZXcAAAAAABOk/gAUXy4AEM8UAAPtzAAEEwsAA1yeAAAAAVhZWiAAAAAAAEwJVgBQAAAAVx/nbWVhcwAAAAAAAAABAAAAAAAAAAAAAAAAAAAAAAAAAo8AAAACc2lnIAAAAABDUlQgY3VydgAAAAAAAAQAAAAABQAKAA8AFAAZAB4AIwAoAC0AMgA3ADsAQABFAEoATwBUAFkAXgBjAGgAbQByAHcAfACBAIYAiwCQAJUAmgCfAKQAqQCuALIAtwC8AMEAxgDLANAA1QDbAOAA5QDrAPAA9gD7AQEBBwENARMBGQEfASUBKwEyATgBPgFFAUwBUgFZAWABZwFuAXUBfAGDAYsBkgGaAaEBqQGxAbkBwQHJAdEB2QHhAekB8gH6AgMCDAIUAh0CJgIvAjgCQQJLAlQCXQJnAnECegKEAo4CmAKiAqwCtgLBAssC1QLgAusC9QMAAwsDFgMhAy0DOANDA08DWgNmA3IDfgOKA5YDogOuA7oDxwPTA+AD7AP5BAYEEwQgBC0EOwRIBFUEYwRxBH4EjASaBKgEtgTEBNME4QTwBP4FDQUcBSsFOgVJBVgFZwV3BYYFlgWmBbUFxQXVBeUF9gYGBhYGJwY3BkgGWQZqBnsGjAadBq8GwAbRBuMG9QcHBxkHKwc9B08HYQd0B4YHmQesB78H0gflB/gICwgfCDIIRghaCG4IggiWCKoIvgjSCOcI+wkQCSUJOglPCWQJeQmPCaQJugnPCeUJ+woRCicKPQpUCmoKgQqYCq4KxQrcCvMLCwsiCzkLUQtpC4ALmAuwC8gL4Qv5DBIMKgxDDFwMdQyODKcMwAzZDPMNDQ0mDUANWg10DY4NqQ3DDd4N+A4TDi4OSQ5kDn8Omw62DtIO7g8JDyUPQQ9eD3oPlg+zD88P7BAJECYQQxBhEH4QmxC5ENcQ9RETETERTxFtEYwRqhHJEegSBxImEkUSZBKEEqMSwxLjEwMTIxNDE2MTgxOkE8UT5RQGFCcUSRRqFIsUrRTOFPAVEhU0FVYVeBWbFb0V4BYDFiYWSRZsFo8WshbWFvoXHRdBF2UXiReuF9IX9xgbGEAYZRiKGK8Y1Rj6GSAZRRlrGZEZtxndGgQaKhpRGncanhrFGuwbFBs7G2MbihuyG9ocAhwqHFIcexyjHMwc9R0eHUcdcB2ZHcMd7B4WHkAeah6UHr4e6R8THz4faR+UH78f6iAVIEEgbCCYIMQg8CEcIUghdSGhIc4h+yInIlUigiKvIt0jCiM4I2YjlCPCI/AkHyRNJHwkqyTaJQklOCVoJZclxyX3JicmVyaHJrcm6CcYJ0kneierJ9woDSg/KHEooijUKQYpOClrKZ0p0CoCKjUqaCqbKs8rAis2K2krnSvRLAUsOSxuLKIs1y0MLUEtdi2rLeEuFi5MLoIuty7uLyQvWi+RL8cv/jA1MGwwpDDbMRIxSjGCMbox8jIqMmMymzLUMw0zRjN/M7gz8TQrNGU0njTYNRM1TTWHNcI1/TY3NnI2rjbpNyQ3YDecN9c4FDhQOIw4yDkFOUI5fzm8Ofk6Njp0OrI67zstO2s7qjvoPCc8ZTykPOM9Ij1hPaE94D4gPmA+oD7gPyE/YT+iP+JAI0BkQKZA50EpQWpBrEHuQjBCckK1QvdDOkN9Q8BEA0RHRIpEzkUSRVVFmkXeRiJGZ0arRvBHNUd7R8BIBUhLSJFI10kdSWNJqUnwSjdKfUrESwxLU0uaS+JMKkxyTLpNAk1KTZNN3E4lTm5Ot08AT0lPk0/dUCdQcVC7UQZRUFGbUeZSMVJ8UsdTE1NfU6pT9lRCVI9U21UoVXVVwlYPVlxWqVb3V0RXklfgWC9YfVjLWRpZaVm4WgdaVlqmWvVbRVuVW+VcNVyGXNZdJ114XcleGl5sXr1fD19hX7NgBWBXYKpg/GFPYaJh9WJJYpxi8GNDY5dj62RAZJRk6WU9ZZJl52Y9ZpJm6Gc9Z5Nn6Wg/aJZo7GlDaZpp8WpIap9q92tPa6dr/2xXbK9tCG1gbbluEm5rbsRvHm94b9FwK3CGcOBxOnGVcfByS3KmcwFzXXO4dBR0cHTMdSh1hXXhdj52m3b4d1Z3s3gReG54zHkqeYl553pGeqV7BHtje8J8IXyBfOF9QX2hfgF+Yn7CfyN/hH/lgEeAqIEKgWuBzYIwgpKC9INXg7qEHYSAhOOFR4Wrhg6GcobXhzuHn4gEiGmIzokziZmJ/opkisqLMIuWi/yMY4zKjTGNmI3/jmaOzo82j56QBpBukNaRP5GokhGSepLjk02TtpQglIqU9JVflcmWNJaflwqXdZfgmEyYuJkkmZCZ/JpomtWbQpuvnByciZz3nWSd0p5Anq6fHZ+Ln/qgaaDYoUehtqImopajBqN2o+akVqTHpTilqaYapoum/adup+CoUqjEqTepqaocqo+rAqt1q+msXKzQrUStuK4trqGvFq+LsACwdbDqsWCx1rJLssKzOLOutCW0nLUTtYq2AbZ5tvC3aLfguFm40blKucK6O7q1uy67p7whvJu9Fb2Pvgq+hL7/v3q/9cBwwOzBZ8Hjwl/C28NYw9TEUcTOxUvFyMZGxsPHQce/yD3IvMk6ybnKOMq3yzbLtsw1zLXNNc21zjbOts83z7jQOdC60TzRvtI/0sHTRNPG1EnUy9VO1dHWVdbY11zX4Nhk2OjZbNnx2nba+9uA3AXcit0Q3ZbeHN6i3ynfr+A24L3hROHM4lPi2+Nj4+vkc+T85YTmDeaW5x/nqegy6LzpRunQ6lvq5etw6/vshu0R7ZzuKO6070DvzPBY8OXxcvH/8ozzGfOn9DT0wvVQ9d72bfb794r4Gfio+Tj5x/pX+uf7d/wH/Jj9Kf26/kv+3P9t//9WUDhMvjMAAC9/wB8QTTBsgDRMQVsg/H/xdkRE/ycgdssGbUmUtEXa790rlNcmbQP6i8TuguKHH+6K5EybZGZmB5uZJsnxuctMEk6SVxbAT64TcpfMZ67th1nMn/+jbwiJ03NOcUYpoG57WswqLPB2V5L2Xf3Ytmz7D7VbADCwgBRJkiPJ7fiDGwgJoZ4n4xQJ2LVtu0omYCCzzWS2+Q2/6L8qS0ALSZIa4v2ZHmEQNryw/xMAW7ZsmyRJGgOeTTQmoYGGmNHAdJwkSRJCqOkcXM066s4B0HQGmGZLVdVLVR1NAzTBMkumnToqVNVUdRo0pmliCEdNVUJU1Xg0YRpSBAKW9UxVEwHTEJKICFtt9ac7YgAYhy1EEUp1NQkBnAZMCYRnnrXVEiCgJghThbAFKHxGJUiapqlBUfSvisYa9OPzFQl50oSqR30ooqUGDRp8nkGIaZrGK3gF0oXihCmF/9MYUJJ0CFPSY/+2HGBLviQ9koQ21KGgbRsm4Q97fwgiYgJ4KtgyPbBsIPTKiow1laiNcuu51uz/J0mynYga7fsu+2S5DNj3XR0gq/uc48GHXhtkhaCODYcG/OGkgl8/ZIMcqAsHD4wLfzhdCBe00utH0KBJm/5pa7Hgbg5opWXDGZiCo11lQ7gjeOmhF96hdWHBGRvCCu17W3DpiB3aQxv+qHwoS7SMBWND0mkq+LNDF8qLfTn4wEMDtwvpW1LBpAp6qMS2kSRJkqL2Pv/NvZkU5UiSHEmSmcWC97Kw/BOHD1+6QbaRKjCB92d7gROYALz2/y2zLOV536ravnf3lqq9u4/7OW3H3d3dz/jMcXd3d3c/Z3yOjPscdx077tqyXXtbVb3B6bmH31oTzTXg7u6Rhy4VPjjULTy4E7pGnePuLh2+OC8OdQNI4XoyJJtoOkTDimatjdPpTl+c0RvomAsgPGMx0hFrFe52YpxnLe7Apa8BzRwyTzfOxp1Qi0tg0o6I3LNDOIRnUpyXUGKIOiR1h9gtdNk4u1Ocuglcb8DtBjRy2OlOcdeOcB2JST1ySMlYE9YiY3MLFNxGkiRJknlW1lz/f+rMblWGm3db2962zbZt3/fjBAgWlBMgqSRXWf8Fyy/JNgvYARxHTMCv/Pf1K61mnoAaVUzDXIEmUIkqYR/UX/y+0JiKBx6oDwadNaAGmHFfocqxqtEYTTJEF0BFfPLKNMQr1Z1QnEQ1ZaPq0O8cgbjWZIZZFaqvqjdtdeMNT9O0bnZjutjr8uAPBsisTayK1XhVVmFXUIPV1WeVVVs11Hh99ucr6GU9a1aN9vKzly9f/nnDqhOMgAGf2Gd//r+8fFlRNVZn0AirCNROJf3RP//yj758+eeDXn016EVQExDWX2OXqQFm7Lr6g//8P//Iy89q6c//0X/88uVnLz/77LOxQXUTE4ABDDyZi96qjWixjKM7PQUDgc4dTBof1HLB7NGxGcyEJWdPYA7mIlVLVJfmAUM8oyaDqVXExKTZ5taUBEFrhvB7No8NztvuCnmciPTR0v1KVIVoe5BZwxmildPfgGzEtohpaCaEHNViAcprURP4uG8HBc9qbNZpe0s4UGpFiJZObjTMOBvi2pmbaBZ1FrltIw/PDY8Lc5jJgNfQgJHlHgjwXmgHJqxnhnooTnnoi5qnA41zAENcJLhYxTEMxsm6CazpgRaL+WJg77XITFqM16DRlxTKJcQi2M8ELmSA/EGwfEJh0wiQMaYigDjKoZe0H59PLkMXu8j4ARmwZeyqw42j9RNjlzcItofLQ2EyPNByz6PY7W7HEX9UhMKcB3dHYmKUNKGHG80CjE2DeYGYZ85sqPHEoA4mV8X/+h8wM3pd2JxJ2smNZRiFlGbacruldcLE1OI9N3zsV6Eu7q6ZHFlaB0wqsxUKNo038xlguUZGurmTHEcoc1HzslRf7Px2i2FIsosJY7Zxjq+bV0oT0SQ0jV0vtoMZYholOnpjHdp23h07zKQ2dSo3PPZgcdKHwBZPuaCfNwTWsoWTL3FKXAUvd/lhu3PouYCxmfRLferKGa1lp8BdbM4++VwkILQQXe7ALEDYlFdgdBhHg9ZH2CYUOa2hAMyQYEzWmFxQalIY2HfNSyTObpGewrDetEcJGpAlgGIxR2ECHBAmh04MzIAJ13L73vxFu8sehE3x4aEEWQB1JkAYMLGkFh/XlDSTuf+3dv4YjaxcL0oc5w/f5qrF6mldwjIKy8I1o1zRqcDDJG0ZZyFapjZ24zS6ACJ9PGuLyd/zVNIKGDAD6E9TSEApbnS66b57ToYd0tIkPHKdvijZxmLl012cxtC5A5gcQBc6mPqfWtxUGBxgGz5pvJnHD7a2mDFCT+q2qAgJGYCHwKhNjmdF6jAItPs0ksU8tyW0NAE/jXSr15eyKLW6Z4gIrci4Xo8u8dQXfILu2/ujExLpLIhkmRKygGHGtY1QB0w85jketUA7malUk+/b7iZ1xSTn1Nn1xbA2g7Jgx3m/rgFwTn8cwRQdvXxegDY6XkxGYCxnJh93u9x+Q+Yj6HzOWy+2LRibAp/CDC1npa310nre7e8wpFxid2gRx3kYbobYDx0jPbHWZjiFCZalWwxAM247ni8o7AhOhwkEuRMc98uYc2KiSI0oEUXaMJwjwIKSc2gieTUUIVyO7/Mm1MUSYfMwFrA11eb6sclGNacVy9fgpnirDowOaG1Lsbr4bkhmDd157A5fCwMNLiYmYRgtgMvmZXX0Io/OWFTYYYxB9v58KaMD4vh86hgxgXsW0ngcnRi20GORQDvcTXbHLB3wUKT74viP1TySDlNN+vYABwwcLwK2G9AUhp0mEeCUJSk8qAxOCiZF9c3+hPHRTX87Ii6GMckTnFPfHeVsc5yNnnwLgjB2XSdTspMwNeBwrPbE/BDBEQyYuF4bLgVeSinloBhG2Ge77gEwhYGBGUB0FIPJmVIedocEbUvetYGMpw8Dr3bbEW8VeCIJW0I+vPvesm4ZxsQdaAJPdcGmaQCIs+u947EoKfu7YMhjDIw+Os84TiU5HcxTgn6Ir4dk4qnebiNFO2h3HwE5kKVrR3jFi45uHG+HrQEttphmDGBUy6sDTDGOz2M5/0A3YAwsjwGe3hA+lYdixsG4re9phrtkU3HkhRYw4cf7dpmKMoRb56uCNT3HHKjLgfTBjsO7ZT0exTQtYAIkgIu9tVXaKZNgdBSRRKwAThCdFWAuhuaRAmwP7UFLsikZvYoDnAWKrM1phYuYY/dEtHlmlyXHm1hbqAyXRrx5b/Jv0AIYYG6A6zdSVCznOMb4PhLOOf6cE2EFHEZ24sbOvlgKSALJIPfzIXx8hEJ8b395stk0W7E2J+LA2wSYC5OL6xdAa38G9T3bGGm/iOdvVVqN/amM09u8rQ67sb3v2298gAFItIB97Qmo1bM/y7CNRUj7E/OhYbJuyfRbv9/9mi+y8N4Y7wkzq0ntiT1B9l7xqrttVFr4q620w4a/+v83v+j3Fz/SHLbFmH0ruCcbNUrFwcU8hOwsXp+tIq+XnmtLK1uZzxoyNcq/W03lVX59zMUbsGy5mhbmjHcF1exAngXF73lA2zl7aRECQJIxQdF2WsIlqS5K5HMUOJhbD9JhrXNtY5oxisEWRgggpRou2+TPLbNRSq9ZlnM5cZvHIwPP6LfpXCstbLYtbJmnGJclaV37dvaRfj8uM5DDVD30442lwwBKBRV/Tv25XrYX1DG8+vW910YsAtOYz9VaCqjIfQJaoFO1jqofn2x/j176AdRx/v0zbabUz9Ncc0MSdq0x7jBANOAp3Lk9OrxeuFbtXfVil4KxE3eKkukDWT3ddncCQfgcV4eyhgJ4wFjyenjq/fUJHELNxTuNogLRHdxzBdxlL1i7hS+XKHXZ6fPFnilhl+V8S4zgh4OriG2hnxyo7LPABOtdTZ3wfQs1siasQNgJJAP8Ke5VOBk9po3uLtmHJKDdRSrCxrufCO9mCUOGZbQ52HJVwqSSguVl72Uc5kAC+0VDESBsCXdUnHpKo7YEKhddQeTirKlOxJ4lZ9+pPrP3Wg7ftzgsaYOdT01YEV6+cXMERtuZ8LQQvpcrjgoJDMC4VjUQnkbP5uOwr95pnKW6qQ7VNwgWGNNllJMPg3upnpZ5EUYV5LeMNp0+eCecPwPNlLq0A+8bSXAvybn7irGyEgJsWr2p+rkto69AADBisFSujEJ/nom8N9vniEIwk56I+4jRD9rOPwlkP7/XUeiTiHq1aZA289zWU1rZq+vQdS5cnFo2u2bn+/Z8ns9bpgvTZJYwlwxFWjVxm9VT1s58pgqI4A16b3IR3n2hkla2Ldpiwf5B7v4x2ltwWZVw0zJaEqpt97EmQQAQJWAVKfX+/IzOJzq7SOLANkHCCmTN7dEZNZ8/s8cQWlTeyH78WKC1sVR0HICG2XCbR5kqYqDZ7xrh1aHt7og3aDYEcQUK4q6jmiJ+QLvSfqIluty5dY4zWXH6CDpAztxqZxWrh04hkAqqkkSzZmrwrLEeYZaAvoQeBpr2dzhZFClN03mK4HYACcVq0gwRU1yF2+WW1p7b2rx3NASUqRRSAnrF3qqDWlk1ZbswA0wPdHETyQ7SKLe7pHaMLhaT1UBw8BRYCSskzAEQqI6OqZ3cBgFJokxQniCERFm7Al4aeXrCOGUwixUwQAJMQxaoXm0hcPc+SYBNi+TaHk041AgHVQSZ+jyOakpr2rOLVpLZhIvogq4ZbKarDp8fHFtA0VmaxxSE7a25FVCzAFIIQiHbAOpy0WuWcBGwGkWKASSX8CdRogOAu1RVxTL3TDUh0iuCwWEfZxsfMFUEQEhgmJTHeDvdoIy9FpgAHC6YSceukJXRk6mDyVjbm8e9eYKmcNhsSpP0FWAR1OMphEf2FOJkj5BtUFFGIGBDHXoJoQaAaZDtJZkQNRRh46aUVfRzcO3I9ZrvU1MIeLsga7eSmRlW1KRda93nrUd6xOz+sDB2y3kAjDXckGVxih1DILD8JB9llDrsVFPSkKtyHf5EVgFsVzZUuYCcnrJjQUOJKLCJFnjB7oZaICQzA0nXyXh1F0SwtA2wmnBYwCSjAQTwOvfs9fxQSsYJy4Xbaop5CeGAbPv87bAdJMoLwgSXywON4hGyi1pnHnE/VVnWxyDUIgFqwLW76LI7QaFcBtXbHCUh5eYi7bkGE7ArFpZrCAkvAgFCoDb2+5jbSacAMDZbbg9zdfi8y+h2kS+E9TYummNMB4QNGgLKrDOuD/G6z0gd8FGb7LaAWuc61b6mCWZpHEELNdBeBayuTh2i6ZHdTYtUbx61glUR4S1CQNb9zNbMBioCCJgNIDDm1rbTugCIyzXcz3PtQ4SNhxLuoklmHw9dvTl2yMT9ygCI1W6rl2ix9MHtYAx5hbF7GXNf1dU4cDqTaUr21mhxCKwsEJLaDlVjRR7BZju1XCg4yAALF4YXwzUJEIbRRo8DwwTWA8a08fa8nNVpamMXOdEXjKBgmlfulzTATSlht2KEdiCz2SkgFDoQe8aqffGDqopNEVkFAg/NaaDzNZjBfok4PqEUmeqlzZAJSI1K2h+2EhaeRN1u2sp3UkPYIQkwqRV2YwLYlbVpVmEyk2NwYzfWXLpyZhzapdh2LMv+bsh2YYFF1IVKCQckEDqrtZmzZfeAsLYWMih0KHYXsTPvAyrbWBqnOi3YPimzfp2dN7CC3GdHfdYtgbZhAEhUKWeq3THuPA629+riESAZgLHnRkw1Kg0zFejNDJRvo3WSFpNAiGvNT3klakGrU2S+0KLdTnKOkU7NcSwPa+YSlkSHWVmJKBRQrNgk8cjG0jHhUIZVBKesvvfHHXWdkNIboC4UM3dO7+3F2mRB7/iG55JcdLmf2c+4os+1tQO7rCjWgpuJ+EPCSGgjL525RuKNHC4vBTWKAqSi7UBN4B5fAsnBpIpjYDB1ZOVRNe2JR94NFjfCSd2a7HYBqhQJKBOL7TvpnHOLVo2W0u4F9GKT1lOHRSwhVMXS0t8CBwkMsIvUGXvVIYcd77q7vcgS+roGOIctiwVbDJvdHt1NTbkhGHoflRCwCjxU+OBHPpMve+L5jmXHscBVcyZ44aNgS0meKqABvWSSAa1Z7lsi3fNbZ+WnUmZ0eACqykQVJ9L2t1/Kvtgu3Pvs59133+GWazYZrA/LaUqusT0DfkschMCoBMzI7UCBXPzzRUpmA0PzSus4QRbrOZmTVk41oXVlILCqlPWgxUiVEQAHgfMOmiR/nucqQsaYgAzIyrRUA4c4jqx+3Wbp7XLBDD7B7YlomJYBQACpDosUTIISEGE2sO7vlsxT9jwbjz11qsSUQaSCBzKSgosouRx4Qvj07FbtnF0OuYy0TdqXuCy2uYuo4qKyiNL4VMh2ir1nQ0vnjJ1Mwnjl6NnFuoqvk/0TMEOvXYYohyqBcY/6GnvGFCBiTFWnCa97ytupEsw3Le3UPsXUy8zA0I1PNiy1iUq13eyG0mGsRdLvb1E0NRNHb/jQVdsIC1vss7D07j+wGibz2GyGs18a+MOsopxVWp9LK4xFsvTxjQWklIUjYfUJu8uSgNdN9jH81LHnsqBT7PlDMCsQDaNURJVepp8rOstuorK/BnoCA24I05k/oSkeFYQvB8aP0eSJIUAV6bkYYNbT8CiP1nKU1SpSLQSxPYZa5QvZauiLJtXQ/6FmbA30jP7T6kqrrBdMpKNBWPcMeog+AvuKMHQjgG0qs6JSO/Mw3tTGvO70QO26Hx60c1Jnm8YkQkAQpEXGfx90j6m2CYF2tEBcuGDzFIwXarsGVD0YszFjGEhmBoieizz+U/dxs2QrpNxpSZGCxF1a+lnuZtCArHIlgNCSNOB1WXGj1YHAGngbhGi3UqeLMMLBrLI6ChiVIAEUAJwneAgNImq7RQfmbfY0X6c/FQEVgLMeEQU2ncokkp9fS4fVJRAEfjnEwtpA+HqnUpWYBCqI3iTswmavh5t2ufCHbmxswpxne1gWcMYkIzD+llAdHAGhXYIh9NAKbdR6OYMBCE01QFgts49ZFWbsSWeTWjAGBoqdel35wrHqmBJF8G/7CObLJ4l6Qs2GspMTctZSvwSWjh3384GtBSbMDAEmzLgAeD9O5DRHeik10UBlygK1ExlLYYcak9vIORJWh1MS4P1kQMzsf46fPXFCVzftgMmuvp5NjE0m4KPb4xd4psKo3oEMKk734QHmwWgwTS9Z54+Kei6hpBp44MWYl3XeOuL1FQ+ne35t6fsqMwPoS9fOnOUuQxsCA1R6+H6HUqtVRNrdmvSSRDWEytWB4uUK+c/BNH/FA35kRKiD52BK/0SQGrVEfSMDFpQ8AQRaB9i8A9zGcBUgtq6GserlSbm9LBwbY+OFf4dryCuyM1pgvCu9MpKWiLVeZH9/tV3ELlkzqcxd1CBnBBjqwYDRBZDUg920QVs3t7QmoxZQSofiBez+Pplj5TlwfjDVOCp74wwvsiGtycb6OqqqdpyPm4xo8xTBiE927zue38OkRvAMo3SbA8bMKvVcBEUViKUbCvVF3/1et5h1DOv+/92HHvsBp2UqWkk+TBCbZsDYcAQQvqpVRMkXpyIznosljoTCVZPyc0HgfIXPV00ogerAMHuDbXSG4aoZbhE6WywGeLIIs/WzMdo5iWQO/nY4AHOEoazeposN2ihhDMzh1ZwqD727sc5qNYlDfn+q3YwrP/10LcsSySLQJgKXfsDZvMeMtBvdDoGmRmTttDmLHcck4GcA4xyxlOJ8qhCR2QeDjVbcz9poToF8MYn6dRlxkyT0PVIM1Gsmys9hpnID2NEc0won/cEin0bz7vIqlrwKYJ/fb2E9O8gIsygOGJsyA8dnNtug67ZvksS4uPu8nDnuluV0KOCjm+agS13ZjnM+0Az4ng9unaIPMHnIec/2DevWlYiFglOilElvXU9AAURGx3W0XjpnnrdLyRNWxUUiTIQEpG4A1Rr7CFL+Psrs2EnWgPWMJEwSMHqRTcAuvr9TTW5CNoJoGEo0IL2oHUOwe3yUcQ6m+cLgtpzzvmx/R3/67cwVeqHefivz/zsKviG4zlCzKZ3RtuB4YeHFfRzcioPVs8Kwq3uLOBQ1W4topkEHM2Da5+rvuoUCQN/rhNV5omA0nlNMAgHCcM1ocoBbqgMs3irhYjUnBUoW/6l0VJMk+Z9zNzqgd5t0KAH+q8Dv6S+/oT/5B1wxv6kf9mTmfEw6RNv9e10WvEE9iMzTE6CqQ1UZJ9lRraoiCOd/25Nh0veS29WQYMlzA2AufVlf6Cspvq/ItLjEphCYRI8DExOTYoqggKZL8QIsO0ZyN5mdz2fyhIWL1+ZlSdlKozI+AbauHLK7zbmd6F5ypHOPDRztwJrIjgMa17jbJyCmwE5CslQlwu38RAGzq7YcTQ/TUdbzRPhs+i9GLjquAGwBCHZaUkVWjNUzBwCBBNCPI+644ziftqM1AFCZQDAADuS6NKkhpO0E9kZimLGW3M+OlIOqMUo2H8sMLEmm47dm7hXh0I0tewlnxVWuFqh2u7NQQBIo5U6FbDRn2rE0272mInJOjSOn6XZjoOqsKgIAS8X2qxEefkk+aA26lsMpcRMYUu+mxwYBE0xAtWdqRweTx4DplMu4NMoHxmVeaifB5iWGykv9TFn1MasI+15Bj6RKlCvrVsZOuyhYKfLpDXCtQOVeAFyx/3xB/ilyqixM6nMXH6E0ZNeO6GzZHdFL1QIAgIOoWUdHPC/CNkQWXDM5KCOX7z/ql0rhAk2AuZvLASYceP04P8D9t2w4bRF2+/yjEqTPZ15j7eBqIDP43vrDkQYP0M8uobYhBHpRwBEIQsEddxW3y9FLACcFBUUTpzDriGV0vULYDmizahFvq9ZBwwsAa4qDaYeJrfM4jXyvVY8N0gGpoNw6LoPiSDaN5s4EODBR3YOgFu2apcgiihQHX3OsF3lwXNi1XnNoPpkpIcDo+gT2VM2PtmeERGKtyo+dhTCB3sBIpkgYWHje62hmWKAaRJARWoSDqHoMS0XiNVHnhGItbdVwebkWJGckdJE39LCRhL88pSjytnVxH6iQQAK5+wjuwDSBQ82DNDUNhaG1V68aBmK3G8qudo5QSvIQlGlFyHc7lEIpsGXsuxOr1gusLpN7DSVElNzYWuwA2ija1mIaJhQBjTKiwFG+xxrw0+NkLbU1eJVNou2f6XSJx3Iv90e+pqrdZsNbU8LizcrHqMTOEA8SCD0yMTHVAAcYMVv71W63cVe6miyVgcHNVVK5zQYkVeAlDbesgKsQ1Ol2BIB1YIleIhdtXR4ESb0RZvYDPxCshYmQ4o385d+KUCIsMFOmqeNfdcaJZyzxHVO8q6jlt4vaVXlULqBrJiEtbuptQBY9g3kBiqPiQnIcdxygAcDlW2hiZ1/YRTdk7oTtOVKiJu0RqgdMVqAUSsImFajcADYGcMAVAKKA6oDrGTIaqeUxTuHzOSmIpRgYkF9hCLmI3CyuHBK3DPb/yPQyCTAFNpk+L2iDRuTbSnSSMMSsSWw4MG24wYtH43gsh1ZbT3NABDE2i4+n7rjNG+RWqNpUC/ED7UJgC0jYFZTZVai45uN3gLUDCbdQLUI3JkwDE2ZSxjHjZcZ4GB5o/I2uEooiKSHtqyVjhIfnYQWqnA9jPdxEhd7sXG8TECYZo7uciQl8A2M8jjxWRFKUmsCWGNzdvJSd2mN3FTwSZwCAXOiXTQsCCaImMKSABFS7CvBnaJNpDMJCEGa7przcQ5AJnAAgkDJZocmw+yLmTqkaV+1OMWUGfnCGzsS1Xmx2d9yd66f5sTgYNkT6NjPSgwm6hxhcsZe33tck9poEGM8GxsIEUaNMgv6FoGRNBoVThzJ76qpFH0VUJ1iJ3dFM+2IoO2EvRy0lOmzk/A9IgoJ64hNqpCmGWpgmwMTI3PvE5jQxMYGPbnqFDcNaPLGhmKsYQxJkNXUOMYx4qzLF+zEhMKxEkjwjQ1mo8jKOb3TSXAx9YjgajiFM/BgTKh8YZSVF+KRwhJaqXViegLD62kYpORIfr27i4GIc3XEHd8dxgHneWtciKEkkbQEsEWvXSWzvtk6mBDTuEkEu+HZYQUmZDJmraAhVzWRGywCVcGTozQvgo5odqEcSvlYI3AuFB7g7egaDMidwdNyWUfM0yXGunSZgAlyMwLZ4SVsct1QZ9odXTu7WQ+cVqcmN206gScAgU1AKQHAppLwSlZfJoE4KNQvV7ivIXSVntK8TKsu5cwVumwLvz/0Toa5WYGdawChr0z0CzaOLpEOPjwIB7tMEk8OEP1gOZAaeWWriYDhS+u2pATkclu1IYYRdPW58TSLzDhKtgsiyNoSbl3FnU1Flwbiew0AFjPBplbCWqAaqyJK0UtEAes1IXUVf6mSJi2H1VAZfXs+0EWXuxDZsRKO4uDPhODiOgyFuB2KXw7FQoCaFe0Z7cRNhy+ytjYzmrY1JQDMUUsf1C0TBavByBOSFrAqmj4nrtdY+JyOmh4l8YgUe2ALQxc594MesfcZrEKHt5/N1wnx+uuo7UKB60FgDo3lxVUO7jp6BH/ZZN4O8YIY7OM96Y9aAJrSQOFaKAXm0+qZNAsWQcjPJoUApjeu9j9Sz94GDiv5KvW0EZj+tlCqp58bdGP3104+foEbGLjF0BoD3yFDAQF06D9fad4nf5BD1X3Hn7lvXD/b3/W7x3iYtqEQUFTq3vt+1x1ufhoDTdKdJIMCdCabpmi+ggJtyswgbkW3dcq/T7njM5xQWlMcUlGVX2bz3ydJFA9NoE5claNKC1V61Bfppk7iT7XmZhVdqWBKlDW/qyBrQJfNhiUXVcrG4sxy9YrYLM/a5roNTnF/m7y+HW4akUjO31dSmfBskZ0vvhc1MTJP7NLlPGxdwqAl2O+ahSEjF/Orm82Jq/VAXfTRYCQYUj6ZBJxN6q0y1ATdgI7FK3dMO6hFVInAYDO8PCciaV22SWNuwAIBYcCT4Xj2YAhvY43r0tMnPp8yO89AqxxUMUfOYO8bB41BU3EZ3dyZ3wJlAABPEcCpsgHNpyeA2ameb7cHtTJ6gQIEmaX/ds9uZeusQAsD2YALLw7REoARVyMLbjME/1Vcva3kQi/5K1PGzWylyz4tocqHn5WRY3O+UObXcmog3Ps64YHJ33GGaHMAA98zCTsam20kPJ9bTIoZM4axFigOlOH+l1p790wxc67Twl4+7LrEckcTNYHc8K8HgcDUrLVbUMPVvK693l81QZXeNNoAOPu4hw5kwWqJAcTDqAxGkfIw8aQGpRow24c7Ete6AMdnIzODIxabl8OMHTiFHh4OoCSkUeD+hgQKIMB2md/QBhFWo2wh4WhLI4xTyz3vzNdkKCiNmm3g+uwVP3bK8vJoo9jxJduKSUs81U5/PzKKdq3tst2Ow1K3l7KXhwDThMAETwBZnnt1BRQVtyG7xamoPn3vaGQfnLuDSSrnXayuTCi/eUkRcQB4FVJWAIhwQdT1uImwa45pcW2agtw4IQ0tB426f28dAb1rF4I0q7vLR84qpnMX5oOAf+M7BJ/AtMEw4M0g6pMT1Ucg23k7jLoWDt6NN0aBAcdnVAtVhUz3geRywu6REUb6XSyYGlRJkF5CnrKmD2iVAfUDcsN8Po91Evv32aNbqRZqP+LL4Ju8xMIHhPm1YpNk1Rlcf3KX9vOLUvEyoGBSUaVDAGEohH7qFu6TY2PcjHiViiGHARaE8/9aSlNlt2JVprHk+0zS7CgHZVXnlNJ5koiUWD1HoyAagaVYTMLCduF7IP3a4VexK3YpNBRMQUzWmoFRRSrXY5/Jq6EeXm7s7o/m7keO8oF214RshlbE/ZTHzljKvjFK7whTVrvLo1GX7roDYEsGyRPGYcQ8a0DBmJoQ2UHwdxa00K3T/vBdMgdcLVYMCjfNSfOi0c38s5qjd5S5aKHJgwTNPuEw9Gf95VgT8vKCYKmuaythYxLfHHhbamFpfmvDkQCw1caMIh50cNFwD3Mhe6j2Nu8En8EYQK7gVKICCUgULjDmJMrqcTHFMubn1EHWJY5w0Cr0QggLVWyDb2cnACkpRUPpYRvkJLRBfW+52DWCB2ePQhAdgQg6QCRjqs4HGdlcdXq9Wlu/wMuZEWZ5LhYZYIA8uzTiO72SeGmYnFMERR6WQQo028rp3BRRNEpoqa0XhPT0GM9Fm0CRY5nZW9EW4L17kJzBU1CO9fLEozTIOPvVJZSFyCEgHM4oneurP1qPaILZjLOM16KGmeOflUHYjKubuedXIxncX78eUhfj20rqH3gG/m5MIMhPpmk7evuPneaNnSJG1YbYMgoylK2iGf0HtrMsIt35On8c9jh7UN4BJO15IqV6Vo2ubN37z1vDKLu3qwY0C6FSCbg3bllVkN0Bg/vAx1ajZGCzMhl2bxiBjHN0lsVuyv7EuKp9/8kQMH4REDlQm4XeHXzm1VYSp6KMUJdV1iCwbpS2/u82N1225kTywlGI5kOC97PyiFkFGR6LOGjRrupQZxsw+Ru9PEsZm/C5t45twOUKvK+xoRcnKgMV2yWRZicuWnDfoZUC0aW/z8To091n67IE5tbdHKHbPsZNUEY3j3KZHKPJrf/g3fP7zOy+/Z/M3SQZFIvFb0i/qf6s+/458bLjFLR3o8zvoR32al077hwOfn+m/P6M8cwWw8EeBF0UhPA8RraEMj7v0rtuiKBWvGXNNJ0l5Wmq15noCwUD1wq8ywKgKCVXIKndvcZWhxIAlYY0ACewMoSKGyWxMrl//ukwOz2Gyr1+3bv369c/LOJ3xGoyz/zjT7E1zfK3uZr+iFKvVo0nbhaWwaQ6qNStgHkUg1fo8JryOnPNK7y/CMfrP3y+8nxeuCv086HjK5I8LhRaElhgDiX0ehrdvAwIeKggwgZGeuUyFtQcx5rwS4B4+6VKxlQR0MkiK2UWYB6UbQmUWyxARFPFZyLkRUvnkSHtCAfxujPsHrFs/Orm8+TyBxro5RM8+ZoYKc0DXc+BYOZbTM2GoOIVFCtqtp3/9GdmHBNxleYAM9RWHl5yvF72O4XUs9z6+KtBBZHlGEgNfbF7DSh5sOETgwxsAd730YweWEuuaSazkuvQABaA1xxoV8A2RFtZ9nLl5lzaxNUtRtmmR0KWL1e0NmFzO3GSgDBM4jEZXxd4ZlS7GrkL663zYXtNNZJ4q2EeG1tM7y02Ouo4dUk/kwGFYdG/OsdgEGmI1v9fAq+6HqFQKaFN56Cjx8zK9t4YmQt/RfZAA53t/HzHdVQJDPfBl4VCgOOvEPvfLUYeAvwrD3YD7SybHCJWMhBK1mVnmRWUMwM7b7nMzZmDnKhi1NY/vZSk5SIlJzFP3MlHZD+ADpl9ScM4vZuh0TYwzEFZVslte55zzZGJCW4jpkxXn6BKs2PNjdtZ6t76znXbP1QgAW8GJpt/fceN7Y/rx14dM8So5X0/r+upPCz0ctf7uk/8tSlMbbUOzKyz6Grn7m4Sr8OmPz29+/8PLYjNh28RPgiyssZ4WqE4AW8KKqZIwZMlWK1gwUYtK3zCrBB4YmQKnSCIkIOGcc14tjZgqILuakvNN5KGZOOfDp8da2rdzcDOsDt+9gwwH2xOwDsggekBAn3M41ImK9zH4x+HSt0Scc64OoMiem1NmK5pZnGY5OzTKGpHpntXhCZhaUZFa2mKg3Iw14hSZGic7mBN4lEP2ioByMIDrEFcCFpXc0CyBb8Q/gfO9O7TIeiD7X+d8aompFefzQ6CS7baQn1ZL6YJNQ86e47BqcHJIyoedmgtOa8QZFjwn9HHtl3p+P+dGYVUP5e+vCj/3hH2X9zERcs47/uphM+siKHI4lGWtQthagYT9KfClQU9AE954QrWpMBk+eXpmRG1OS+aa6fWiMQagLVCtRA9FOuw+c83+1iFxGWXLGAAw8JklCDVmJzifzcDmgN9gRTtEZMBUgPMRskd3GTieLLmnh239at8Xm6rK3env9f2kfn4fUA3QQOX3UXj/FXN/+f88kvy9jeSc932vUv7+axC2IrfMQqFqoiIZB1IfeJMeunSA0kACE6rFmh6hlLOumSqlAMC3Mt3LQc/5yUSmWCc9iLKmFCgGBR+GjGgHTGTmfDJbwupVuZWoLTjPwTnnc8bQbwaOq3pYwtzWziJEW4VmqJCz9AuBvl8D4RD9/qvxLGOcc76NSP1Gwll0JS+ykUom8pgtNUN61TRNm8m1qliPnO9lMgQYpEs7RwOmABg/faDrSBz43+o7hqU8LYqj+DWwAvhDYGK6Fz4Fv8EEcHmpMJdUQ6ZAui1gAMB8/gTgzKz0kokyocwQ2vBzSP6fhGaxMeCk20SvjQ0GKZ932KtwChCa2p0TpoqMvjbMk+YSPHWuoUefyySTCQyhsks5BdOAt1pQzbinntOUK4D9R/DDGACGfKAMgApMqZyJBI+TP/MO4Q7mibTnUYKwtIRKqIBsYpd/i1XAmrKHKujaB4icIP1/p4Qi+mb5O23wmdZXuNGFx2JePYD5B5/0ZbItP3OUYLxKz/11EzLsaadKAvnskHbz+qaDDCBBKYBcEAjTMAzUALB2vYkTR1GoUMfZAA4FOB/EHsA+zD1WoXJecei91gOiqmckjEcstoatgR+tfPU1nhMwyQxPqpNjX38RrktfAkZ7lgtRZ30ZsJ1Y7ln8f9TWwuGQFxKi9vnG6ynBLnZdPbxkc3Zk0dLe3bVdChgaHgsQoT54Z0Nnnbn3BbCtts4+dhERIImdEAGAAXNKdGfH+cdMzG4wNt1QjgKBbbvQHA3oHhw4OgS+wI5zRbPuKRzWgFMR8foglIMVyNSCWM1DcBjLboOHnSjHgNfXcF8Dlh9mnlPolTgb0Zg5lncbRjVh0wwBH70EE3gDAGI7etmDgPOT/AEQAbUdw0iUtc9KWIsEsAHWT/0fgfAKMQAoBwFElsB+JDC+LeecA4lgMJtNOgUlr7mfTUC7EP0tYmE0mJN532IPFXa6ERwo9fY7ba4Be/n6bkETERdDaPs1PQqwviBm3QGpgieojC7nO1ZxtIFdDOAlmwJro42W6oCPxXuKgBRxcCkN6eJcE7SotW/crX354/+8HKyQvFQ0wIKuF/hbHRR1achHQAFuFP+sVguWAhjafH7hZHRvszjYQG4DHnhVME+5NZfo6cUynqXb6YerOqq+5g/8ktU9djVwmj0VR33/bdGh1Jxh7efU+eu4PFpaM8M27jbtP+we865WSDrPqodLTRwkmO3yhTsZfySHM6RzhdqZ79gP9BtwMdDLXRSjISNqmNKEuofHMwg3hvIvbksarB2cUbes6Nk0hTjsa+fBuh20uYXRAYD5fOB/rcJbzh5ePgLdhtOYWW75ACr3PKC3j/EQbW90+AGCBdqXN6coaU8CfUz2loRZRGaVUE6zt39zEsuYiEdMs8y+Cek7dDB5RfYW8GrKDa3rfzHY5i0/DLgkIgnXEzE/8EyY7Px/sPPfQX78f5Y7Qu/UDK/ELPcnoCpqv1MxFemvwS5WTX+0Q9YFyNr9j+fH64s6wW0A1sIgI+4V0V2qaiVAKguIHEXONnI2OfA1rSJfQBY8EkqguMzCIsB3KXcY6c4TOcN1Xdd1mewjHULM7xZaXpdm0WVmaZQn7vy0qKCsuEcPTLMxy7uWKn90DkR4rXrEmxE3/BrvqWvKOw8dkOJkEPXDon7K+JsR5RsJqFTgpha6Qk/AqXIq00xcrCI/oA0wqlQdaAZuCkQD2vNdBC12PwIFrkgUAxpR3kHf/OZY3mm+WQNb3wlfK1A564MD+B/4Uz/tB5Ug5OeTHq5IQaVd/tyfunIcKrG+g34az9Ug7O13rz7p/srXxL9YKhUser5QHypHmKFeG4i3YV4/oT/4GNa15tPnJMa2AAXogQEwwEZsJ0Di6VnIDMSm9oNwtA3Bi13DUJpOVpsltY5HxL97MkyffP2IEHah7yWopv0en52wDtKs234ObRsoa2JQkIDdLhHcamsaAC7PAJECdE2M2rrwQQiKXxQSiwvz1efRJJgd2Xcu9JLuu5aZmfCWBvhkptXubyenXQ9sHQMDdNti2I5OZoD5s6Cg5kmBSYTHMRzuzIBL1B7TnU3HF+uLd5cnSktMRYwCuFwu9GLS0jSLhCFuQtbywKKbo9rYN08DCARiiwGDjFfiS/VolPsJRJF5HmIU8ULCrK/NN7J5p/oq6o2zZrtbVYZGuABJPXa5AAurMABDoJv4BJ+82fFs37i43swwAduJa2cgnpKxZEgIkI87XFuESdLjN/3JhI/r7bjyeew8GLYOGAZcLusKwgSYjKfe23Aab3M3RORAAQTDzgBxNMCdAL+GRTl4imso4cRIghmj/usVs0uyWmLcPe+Gd1neXA4J2IZAbJowkAmMTcXA3czQvrEdYIDxuQE7a18BuPOMsZWfBCZ0HMt2jBEaxyRQeUd9D5lfLB4/GfVXuS2u8NkBgwmZAInrzQSYiWHc5XDXtmVNWCVQbmXHQ0klIE3PMMRxPQcgIS2WmQGrBNzq0Qd/vs02Fu/vKFESnyeBWW2gx2fE0zAzgUGQt/j6kT5Ovh0Swmui0keig4EcMq6JiDUXCYFUWPG20CZgcXp4d+XW69JcXni1+fALFeMnlfIPWsBMkhkXDGFCgBkgIMlzNIImZCxrAqTAxiJCAoPkqX6cMzDgaBGWGQHDkCCzBjBzsxxfkTm6Pe9s/bD22XF8eHgA2cUAQzxV0sUAmdqA71tKbbJrVwTEG/oeQWHDaZ/mvsjZlGSBVLDu1S1I6MckLNqPch9k23G+s9IIwfRwMTYlexqot4sJIEgvaid13AkkP4AEafDAs6fIQBKYzn7Aty+wN8ELBDc/tuvY8/p2n62IufdvH8YiY1MgwK4zEJIhNj9+e4zTiooAla1EUa8ifHw2BYyYQC6ZeUkVq4lsdJh/YnTRXgFvyz6CrV5Vhzs7MnoBiS/RDFAPwhrgqD1pcLVWTQg8khGMBTSJ4fg0WinOyKUMNosSYgAYyk+Y9SKqnW4+d/9v8a/b/7/v3gvt+p4v4wUQAuTrCqncp67QQUxZypBKM7Uw4vvwpzHDEsoEKEW7abSiQxmH3vNQtpisteeFtmW3RPUDrz549Xq68OU1DCoku8hMRNCSN/5d4e7BQCKyRTA88ozbhXkUvQzKtqCJmsxW9tBwWIZWFwuzEnNrj3R351ZUB1WyLxNcAPXfMYkoDWgeho9QZwYEHVF6XQxm2rd2/wxEYmP/iACxaL5JFebl+Kg1g0xDAMJmtXsPtRXsy2YY9PoO/aUmswVEtlFNAKMhhemFfeES4pnPOxgf6WWg8L4BLcujd3fbs1wE6pAu1gNC077EV79scAH19h2TgceEoCCIGyBkYGbbli8xA5OpBwSL+obneWp8sXRbB2vJN2OPSQDbXjdjpfsKmEGvS8MsrNJ3X/nd0VrH0BrsApAEQfds7E0Avcx62dIzd1FSsfMBPcfGh6LX53sWAb3R6L4CmEFvZ8nWrdFCewuIEZyN+eIc7vkSI7HerO/NhMqxZzY9XzL9i/vq0Jq103JvYmGqCYb0/suvABfoEYi0vRQ2poAAQX+5jGMDfD7O/mzEtgBIMrROFOD1UpM3ixNjyNDxNTq/HtIEooJ/+ZWhtw9WrPv28P5Xm7GK7f3vff9H33+/wtVsX/3we983i+7VA7HtvhS2iwlAAsFZM+PjFO//aOX2/lf/zd97/8EbIEwK7KAPyvtQU0FJTgAAADhCSU0D7QAAAAAAEABIAAAAAQACAEgAAAABAAI4QklNBCgAAAAAAAwAAAACP/AAAAAAAAA4QklNBEMAAAAAAA1QYmVXARAABQEAAAAAAA==
- data:image/png;base64,iVBORw0KGgoAAAANSUhEUgAABQAAAAUACAMAAAAvOg/FAAAAAXNSR0IArs4c6QAAAwBQTFRFR3BMMTE0LCwuMzQ3T05VRERIODg7zrfXdm58aGRvybDTaGdybGt3wqzMx7HQAAABzsTqGBcZDypKExQVLy8xx77mbGxvioeKeXh7KCgpEi1QPDs9LS0vNzZEaWhsy8LpKiosNjY5cnJ2b29yQtR2dXV5RURSkZCTUU1SGxsfLS432M/tAcPpMjI2fn6BOzxNCAcLIiNXh4SIfHt+WldcYF5ihIGFISAjZmVoT1FkSUZK9/f5Q0FHPz5CLS8/XVpeSNJ5Y2JljYyPEiI5Hh9OJSUmTU5b7/Dt5ubmZmqAgICEhoyeanCImJido6KqYGN1s6+xlJSZuLi7wb/DSUpXc3eMDg4ReH6VPkJXgIWZPtBxRUphjZKlpqq2GzJSWlpqISEun56hx/DyrLC/LzNLyMbKTTZfraaqVlJWGyhBU1VolpurG3Go4N3es7nJ5/Dzu8LTzb658e3hVVt00c3QSklShYmO2cm9EBwxf4OKwLbh4dTJ6d/R2NXYw8nZm6S6qbnZw7SyVjtoBsjpJig2oK/KO4Kq2e3z7NN6Dw8i55Tv8enUcTsLw67IRi1YdIagLzla0snssqrV0qbc27XkW2KAzNDd6M5t5Na9k5yO7aP0VEhFx5XUrMfjvZ5ZCyNDudTrZniabFF5f5Gvu4DLopKlvJzE2+DpYUNz0tjkjJy2jJSCy+PxQTUuNEJtso+534PpQVF6WWqT8OO/Z1dP5MXo8bX2trOcrp6N79HzvOXxhIt3HXm1krjWh6PMpXCvo5nK9OX2wZ+n1W/i1LyetV7FoYuBlH2eWSkJl1+iNS0bj4W66NOjfxufU0EqrH+2ESxyknNvdXBhF1OQfIBuoz63pZFqNR5IhdrwSle0UGCMQrvnQluPgmRKoeTzURV7qQzCZYe2nYBORtiBx654iWAhxwjcpHkkQTqReUyNxkbXXtfwbFQxcb3hSoPPdmatEgpGUoJwJGxHZJ3UDSacC5vQMKJceMGLfmOJu4OP8dsb2w8ExpkjGK/dIszPONCxK/hgLwAAAQB0Uk5TAMPfpkBfg/wOI7m8hUZ+/////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////////2grhhwAACAASURBVHhe7L1vbJtXfu/ZTORQfyz5epM+fAxniJgES7mz4Qj8Z9Z2SpAXrlj6kiNKHfcWNXvBsKq5VSUZqEKsFpCy6OzcoC+U4EKEgAUUYHrHoarsXQj7QgvIQCroxUDQLgotWgw6QIFc7MvBvMosFuibne75/TvnPJQcJxkriZzzlUQ+JB+RlBJ9/P39Ob/zG7/h5OTk5OTk5OTk5OTk5OTk5OTk5OTk5OTk5OTk5OTk5OTk5OTk5OTk5OTk5OTk5OTk5OTk5OTk5OTk5OTk5OTk5OTk5OTk5OTk5OTk5OTk5OTk5OTk5OTk5OTk9LxocGjgIuilixcvDAwNPu10Jycnp+dCg0MXLkay2TZrvN3OZEYAg0/7RicnJ6dzrcGBl0byhXZmPJMZR7XlIvPiSwPOCTo5OT23GhoYyRYymQw6P602U/BmwSHQycnp+dTg0MVsJgv0Y993Uu3MCxdcQtDJyel5k8LfSBbwdwr93mL84VfWIdDJyen50uCFkUKmjfyzdRPg95bc4gcVAp/2dE5OTk7nRYMDI4VCO2Mn/p4gOKNdeNEh0MnJ6TnR0MVsgejXDuLurfGg2vShfOKLF1wc7OTkdP41dCGvYt+Mwlsf/k4TNgaqk98aH3EVYScnp/OugZFMQdc+2p/GPvMwVYpHBp723E5OTk5fYw1dRPxlbLydpjZf0tIQMIHt9lsZ1xfo5OR0bjV0MQ99zxle83Ya+MydbQIgHWWImtmXnAt0cnI6jxocouhXqr8B2AXAp2+1M8y/9ngGbrTbI64g7OTkdP40cDGbyRTatOjX8C4APusIw1/tE4GEZB7HCw6BTk5O50tDA8VCQRlANHsaa5p47ba55jPa4xIG41UbE4FAwIxzgU5OTudJAyNZ8m9MOTzQFCTECQux8pFpt238jaMfhAi6ANcvuGqIk5PTOdHACJg/4F9bTJ8BHrm+NnFPINg2/CP3pwT5QwihUc4FOjk5nQcNXoDiR8F4urZ2f4LAcfmSx9oq2i2021QygeoH0E/dRIyil8y4zmgnJ6evvZT9A3Tx2jdt68jYsQNsy/E4lnvhNlFO3QQQFjT22pqAgMCnvbaTk5PTV6ihl4pFMG4FBFxGh7Ti+cT0tbHXpc2U5EAXk37jBcQeeD/moGGhc4FOTk5fWw1deIFRRqaPnJ+5hGJHhvGXyRAZ8WyyepD0Y94BBQvGAML9+JDrjHZycvp6amCEMYYEbKOIfW3+olVxFOy2+bQMM7PATk8iXy37RvuFl1w1xMnJ6WunoYsj7UKBjN24fOpDSQe20QW2LdC1qfChUdfWDxkXSCrA0xdcQdjJyenrpcHBi/lsIYvYolC3LQC0wl8sfmQKhnbwBTetu/gOBmCGsoEagNBd3c5edAh0cnL6+oimXgGrOOfHBpAQmMHWlgxHxVjlNQhsy0GBcdfWJMz0CfkHcHQu0MnJ6euioYtFxSVctzEugW6b4cdWkMJczT4An1jAJ6pATLTPoSg449oCnZycvh4avPBClvDUzmj6YdKPDd+44KtdoOpum6JcjTYrzaeJ1+4zgAX5IikEXnjaG3NycnI6W8GORwIpnfgjANJC3gw3uUg9Q9EPF3gUrIUepwi9Hh/hJX5xGrAAJrB90fXEODk5fZXCHY9A7Tb5P8kAQrmjrRv8dDW3bS4KT6Zfpp1VjMsy+goZA8OM1EJgk+G8Q6CTk9NXpsGLeUr9YV6unREDOJ7hDmcEF1c1Crq6odf5EtIK7O2EcGT6iHWKgop1hUKWuQe3OQoGgL7gCsJOTk5fiXT02y5kZJIBR8AZbveTXJ6wz0CwwIAjkmmm2Qfmbjkm+iEMs3x30XVGOzk5ffkauljMkmPjXuZ2WwOwTdk//KTsnR0CZ8T8GdCBtbOVFcYR+TKFfhjSN6hnyeadC3RycvpyNXRhhANV8nmQ8jOVX4pyWeL6ghm/go5r1XWWji0DmJEDtH0W/oKCJ2oXHQKdnJy+RMnQU9Q4LeqltR4W6E4eGPgVyMFBoYNBCHUNgF2WiFhgT2jYB34zm9XBMZ1P54xccG2BTk5OX46GXsqz/RJrh9Yvw6t6Mf8n9Q74ksnOHO4y1jIU52bZ5zHjsopxWXUvcBBuagcoMTI9i1RF4Hw41XVGOzk5fRkaulgky0bDCrgEPJ6hxW4IOm37grFvgQyephleAsCg1ptFHiL36C56lBFY4G8A4mV0TIywxCpxIT8y4AJhJyenM5aKfrPcogeNLlj9GJei7zi3/BnwFew1HWL/slzmYPuWpSMyfnKIpxAKkXWZgiZkBq+gEJIVggIK3cxoJyenM9UQtP4VuLdlPKPLHXShdzHKZPSyX2Zlhjqms5LVQ2tnZB/bQiRmdJiM5xWoN5AAWdAgzbSLrjPaycnpzDR4cUSn4ghz9AHc4x4/vfrDinwz3NKXYQ9o4lxQkb+yxSJTrygPaiyKF8xy0UQMIoXH9M3w/A6BTk5OZ6PBgREMQKkMwcaPgFcQGpILpAeJkgVTyc1gHVcsG5KuSBcIwbwiYLFYlNsB6WCYOShJxGzg+QCNF4dcOcTJyelZa2AkT70nurVPvjLiAvGrbY29AgBqz6iRxUArovJ5Rb58Nl8M6CT+AjEzITDLOKS6MZ1UKLjOaCcnp2csWPhWsLgmw140AwNAzGClFi6Ff9TSYtMPLZ/iH4qui3CXgmGeEVjkcDgb/N7ApR0q88luYKqTk9Oz1MAI9y9nuPsF14AUdA2kHcRfAZNzdMTBqri1onwY+uXzEfiKRISC+WLe8oEmVWhUyGr7Z5tKPE29VMT1xDg5OT0jwbpf4//0Qt+CHutS4C9t/yT/h98WLPgC19DpsbwIfEQiHh4QDAGDKirOaiNo+CcHpkCSDQhdY6HoOqOdnJyehQYvjHDhFfFnN77YVV8bf3CZ1d4vQ+m6/5Al45cV76csn+Je/nseKOYBAdXn98QJ5tkGWvyzbKDExv30yyJiC25xiJOT0zMQJP9g+QVVP6TZhReCCAQN/AKjC6RaIXwC9BUl6gXfh+SLxaLRaDwejSEFPY+DYTy5qG0gHZyokFj2sig5QzzVIdDJyenXFKz7pbVoDDiBnW0DLf4FAViw+ZSVoi+k+9DsofOL+r6f/MPlStr3o8JANoHkATEcZqpJ+hDiYyPyiHakDN+FCHzaz+fk5OT0JF0oQq2BZvdZmGtbZpDBh0UP5KT06NGVgZREvirGxXQfGT8/WenUG6uzrfsdBcE4MBAJqCHIQXO2KK0yQLdsMW8HxEUNQR0rFyMRuPeiM4FOTk5fSAMj2SyBLGNVeWVXt4J4PgEgnUmdyTzCRfQfmH6R72HYS/BD+i3/Ub2xsXXr1uT29Fy9U0nG4zFKBwIAI3nujSlKRhAIl89LIZndnj4Q0Apsizgl4Wk/ppOTk1OfBgcuFsnJMfkKYv5OiGccmLoHLfgI1n657kH0i8f97/vfTy6nSom5BYU/0OJGq5roLCf9qJUK1DaQGqY5JBYvmC1KSIxBMpFQ7sNSMiQJXVugk5PT59SFfJatXEYHwKbcYdc9ONzNcMwLXc/ZrJQnpCoBAANfB/Tzk8t35+53OnfvJqqt7cVbosWNqWoJAuF41ItxGAwUJHpmqXFac05HxPJBdRJdLdGULLiBqU5OTp9DgwMj+SxHshnueQ5wr8Cuj7Bn1z0yfa0phL8i1n0jngp9/UqnvrCyWF6amms2Vsu3bJELhFygCoS5QRC+EV2gLgzjlbjBIqYEsxb8+IYEzcobZkfc+jgnJ6fPqIGRIq6xgNaXjOzhGwh+qeiRLciKN1rsQUnALLe/ZE08CgDDlpdoPF3p1GYnkXarq1ts/8pycKu82gAE+twVE8F2Gd0drcknyosVJGeoCyb4okVMFlIo7HpinJycPotg6hXGsIHFv2DzDAMLtjIFGfNyivvj/B1l/+Lx9PeX6y3M+i3emlzUvq8xvS0msPywAYGwH416XA3xrHKIxiCTMMtHeXksn2Uakl/M8jJjtzjEycnp6cKpV1lT/c1Q5UMveTvJvwIveevrfJGaLBU/IP0X99PLnUT9/tzC/OSkCXu3ZmrV+3O1hRW+b1LdcTe87EM1RBKBujOQGqkRgoaIOkAmNnI9WMfJwF+wig6BTk5On6qhi7x0wwKg8X2n84/KvllrzQeFvpiJK+ribzy5XGqszm9Pv92sPdzS/FtpzFXv363fTQAXhYnTcxAHR6klBumne6P5ikAoEMzr+JftYbGo84XFonxPdsSlAp2cnJ6koQsRyeUV+sYbWIfAvAwDkrar5O3ZzGA+gSDSKfK9CC756MzNAPcmtxcWVqj4sYgEXKgp/KmPem1GuLj1cK7USTIBPXSQuhRikdDATXtAio4JkRIlI4QxF+iqIU5OTk8Q7XhEU09FOu9HJeGslH/Ngg+0fv0DX7LGe1Hv8+/Hk6UW13wnyyYCViqvtObuJzqKgPWGWMPJmVp9OQkNMZAHxCA4ol1gRF+clMkJEgWtG+ABFQJdHOzk5HRCEP1y8KvhZ4Y7654Xgp4+1uiz418JQRFUHAD7lVIt0PUyubUihm9xozV3N1FKJO5WGxtUGlmcnUsYAhr8QT6viH7OINBmoSQFdZRclCwg3cgWHAKdnJz6NES1X27s09iTtb681LcgkS+aQIYebuuL5JP1uFyMZTrhzAMFwM7damtDI3BxfqHR2hArWFYITEAcXH17lQi4tVAtLfsIQC8vTdFcDeE1IgqFdBQpii00IXJeU9CKk+EeQKALhJ2cnLQGh0YAX5jbM/GvVfWV9b5Z4/vI/IkFLAgBTYtyvijtzx4u/yjV5xpINybcw0attrDCvTCT5YeNegIWhzxgAq406p2kH+dJgRwGI/BokKBgkF5EHwYRqNOB+u4I2EC3OMTJyUkE6345+g1UfsX/ZQmHZP+sjr9CX+iLbcg0q4DjX2yAhgpIBfi3oIu/yLytWYXA1raYQkXEucT9+3Mt6glcnKmWcFEIrwzGXhruiMGaCMGQoEhUZBiakFjC5j4V3fo4Jycn0iDUftHL9QOQ8Ifr2zjxl80a62cHvnjN5CuaPBw1AKoAONlJqPhXOp9l4cfi9kJjrrag1wMrBFarc42HdGt1LrGMq+IIgXmcnB9hB4hrROgl8hqANGbVzg0WgwCMFJmUitOuLdDJyQkWvjHWMifoZzk/iX2Dri/LRV9rHoHhTYQqIIp/lU699tA4vZbuA5xcmZmbqz3URJxfeLtZW6BbG7U6NAPyoGiPVsWJGSTDF6EcI9nDvH4kT7FwoIHQAiGMYy0WIxG3j7qT0zdcgj/s7TuFfpp9mYL0OgcWe6ib1PLMjS95m4DUAhP1k50qI28RVvvOIfMEgdvTtbnGgiBwcn6hYQBYqviKgBEvhjOkKez1IkI6AaG68PiK+ReRArTOFPJXhEwghtDFbMR1Rjs5fYM1eHGkgCOjsnbsm5X6h5i/bEEGHOi2Fwp4s1z4KMoyDLsDBSPS70UUAJfrC4K7LeX4qol6/X5jVjfBbLdqzcbqlqwD2V6iSskqOkAFQNg4hGgnSUC0gpp5yD2+hIKJhh5YRiax7QTJm3qAQM8VhJ2cvqmCmc8F8n8QAZu1bhk97yrL9i8rpd+sXuabzcoUqqJed2ZTRloAEYBi8GDi1X2o9tarU0t6BsxGC2ZjyU0i4eLMHM2FwcEwvC4Yn1KzMM+Wz7BRegYjGBozEyVaJvTlOYuIBtEtDnFy+oZqaCTC0S/aPwZgQUBI3i/LBtBe72HyfUXd+Fe0FlzoeJN2fovF05266QAsb0zPEQLnWgaBq1O1WivQKD3fUABM+tFo1NNpQEEd3/DIyQnl6DCvgaiZmRdeEpbpqsgxctEh0MnpG6ehCyNk5tjsmZSfPe0AayN9hV8ZuMe+T8e+lgMEj1VkXFESsGQNf15cas3Voe25birDgMBmDW6KV1xVobICIC4IpjowM88zTk/iX7F/ebJ7XkRKJWIBtQukdCHHxPxNxZhDoJPTN0pc/MgK8ayyR4ZHHUDXizXdniX5vjyOp88K+nTYm89Tqwm7LmwDjKeTy51EzfTBlGdrSMBEvTm9LatBoDO6MTMvlITO6NJykgEY82hENFs/vAL2UZjreUI7j6mY9+Q2RsqcMMQEIRdTiIB5oqXriXFy+uYIF74Z96cdoJDPDnwLdtMLmj3ZoVIbv7xWkagSwVqtsCpG218q2s3M62Lvw0a1frekTGBtRqzh5NbqjHaEcHOhrgAY55kwHAQTA2PsLvHLjnbpQOrEHpWM81whYeUjcgbZQVxW4hDo5PSN0CDNfC5K84vMtZf1vlmY+ZLRIW8hawwghb15e9wKATAi9i9C5Ve2W7iKTdm3eDQeTy93SnVrEmB5tVWr1ut36/drM7oJZjJwvdrsIABhKzkhoMdcJRuItzxtDPlOPkc4SNGy5AbztLQY2mEoC0iPF/MXHQKdnJ5/DVwscvibZehx5cMsdstQ+s+ecZo1Q66k5pHX/SYCvYgYsYgk51AxZeLisBxYucC3rWGo8xszU41ardZo6e1BEH/lFQiEYShgJS0OMOYZH8hcxQOgY0Q5Qo6EiYUS/PJb0rEwvS3O/UVMBIw5QkDg0353Tk5O51pDuO4XaFYoWMSj5B/fzHDDM5s/6nS2Kx8m5OXMH8GE/JSuwjJ9vBhthR73MRVYbcwuatotlstboPJiYEh+ozW7sjRV7zD/YvQc3qmKiNMkxTxdI/YM/XSIzM3SlBTEWohIOcOsc4FOTs+zBi/kCWNU6Miamq+Ufnm5W1/Zw8yXN/k+bihhfES0sRLU2FBSAMT90P1Kp1S633hoG74TgvGAiT8KL1eSin9xrgJrBxh4Xgag7KXuaWn0ReQmAY/GKEQ8esMIcJMgVAiMjDgX6OT0fGoQa79Fsn9ZBp/e2ZKBSD3Puu2FCr39BQ+p9BalmwTxp0FClxIDI56UBVQEhHrwcqdUrS0sncJASQEuzlYTnWVl/4h/DECpBUvST4gYE/+nLaJVNNEhMZPZQwR6HABrVMulp2Ji1xPj5PQ8augiziqg4Na0/pnSb5b297Ayf/Z0+6IV7+Y51M3n0VF57P6k/YTZlzc8inlRmAqj5KdzCoF3q7Xp2Y2tRd33t7i4vfSQC8LbDcU/tH9xWAgS60sAElD1fTG+5Cg5FonxvQJKLTMwIcIA5P1GTIQMD3huVJaT0/OmwYsR2CWXk39Zrn0U7ACYg99A+CulXzv41R3IlPXD9jqpzyJT2HQJnohVMSAgMND3k5XlTgcaoedqjUar1Wq0arW5al3dbm3Mb0/PlRB/6P+8KNMOP8ULYulDXKHAkW7qbGEEGQjHTDbPqoZYyNPTFfCHgmO3Ps7J6fkSRr952BMjK33OAZEVJPYJAPWIF8n9FQl34qAEJ55gxIsEKw+eAArpBQCMIgJ9P51OVioqGO50SqW7JaVOCY7VZ6J6v7RcSSr8+WT/sAgsbTAxc8Tgi1mvQpT1zBWJomD9TiOUBOQeakGfZ9eI854bmOrk9Pxo6CJUbCGgNe0utqjzOVuw418Jf/M6+uVJAoYZxDoOeyNi+5iAQiZPbCDWgrEYEvcRgumksoJG6riSW65U0knM/oH/iyI3Jbpl9PHTRuVeOgeuIzEBpmEmtMiQI+W3ZVioO2JM/MtSP6jrjHZyej4ECz+KMvaUl7pl9EUWW58LJvwtMP9wvGmeOmBs/nGfi+WuxFvR7Vgw9RawZ2wCoSkGIKgwqED4/TR+fT/tq8uk/32fwl8QfyMjkMDn6cZAcZb2dZSPbW+Ibyki/lQ4zQ4QW6Q9nceMsLktRpwLdHJ6DkS1X+SfXvrGga+ed5W1xx1k7VF/Vtufh1WPCOX/NP+0rBuxAPoMvRSXoozAeJxsHnIQLR8j0Wf7F42TAYxq9MXY2dEz2eDzYuwu+Yvv9ZiEYh8ZfXnPM7Yvr0mYjwjc6WbRuUAnp/MuWfdr5f70Edc+yBtK2wsRsKjzf9L4EpF+F42/JyrCMa/Gnx0DRwmBWBJGAMbR8PUJ7R/FwB7xLioH/JQY7RLtotRkQxdsHW0ICpE9LxZENhY+ImwEIyf1fC4OGRobG3Vkd/omSOEvXzTZv5MIzBRM1o8AaNhnz7cn9kUCvSVUiLUjVO39hHhyt2AQUBUzBBQKyrXcipL/i9rTANnsYV1EomnIKHJlJSoU9RmfBoO6YsLYI/aZPGZESjoRc4fc+/wtDhkcHQ5114dHn3aek9O5l4p+8zi4NKvRZ5EPc39wEeQfM1BPOuDN1EzqT9PNph/ZM3NtM9Hcb0erzMAoOz79FSX8McGiUYllY5Tiw5bCmDyKsTRyzyhuwmgJiG0ACgPZAHoU1BvyWQxEg3jx+SLgmMKfUs8h0Ok519BFSGQB1QoZTb5CXxG4L/GHxY+8jHyBS7PIQ+AnUWVUF2kl1LWv5EaEUcjmjSAW1SaNw1ZBX9x6IIpej6fBRNnJxYiKzE2fI2gEXzKdTmJtOQl1ZDaE6kx6v+wDiX3co82UI18boSqOVLrlR47kR54nBA4O73a7ofX1zd7wmEOg0/OrQRX9AsGAahbuCjIDS5d8LQOYl9Y/bnspauMntVM2Y9GYRpTEmR5DxjOH1i0xgJS4i0m9QgJezuBFJYNHT0onSuwr3xbX30oExIaaSq5SSaU6y53lZfxSNyuymEQPVBAnysqTw9NwNyXuiOfpA8DkyIXnpzN6uLvTUw5wc3OztzM29Byh3cnJaHBgJCL4y4jvy+jpBzzrxWr84/UeZtZVnkcFiEti7xTzpJUlHrBrgkE+x8TA7L7Qx0X1J0viXr7FLpCfzjwt2EAmo652SNibTmJLdalUSlSrc6RqtV6H1urlCkXD8I38trQLpB+K84CetMiAyADmPUl6epFY/vlBoALg/vHO2tpmr9fbHB5zBHR6DoX4s82fte4NkJjNWgNPzTYf2SyOOhUDyDDgdW6IthiZLx+69aRlJUqfMQ42iYQxwxtxf5S/Y9zFBHn6Wgq4cbF6nAGM2afGTMUEe6krlWVgX32u1lqY3djenkdtb2/MLjRq1USHbaBmqYaz/EQUAiPmpDFG2mKIjBIgPyc9MYMKgMfH+4fHm0DAR73h0eeF7E5OrKGBkayKXglwsstlhsodBWu5m5g/MoBS+KD0H0059TgK1FEt0gdN13JlOemnfa5BYJzJoatnyhZSvZD4lwkqEbQYPjaB+EQS68Y0A0k68xflyNdPq3cRLiXqc42F1e3yYt94mcXy1vbDRh2mytDzevTmbEUi1nWwEGIgqE3ic4FABuD+4f4OEHDn0c6w64lxeq50YaTI0S83Pmf1tIMsr/mw+EcTsqyJV8U8zzYVB8gERCuG41w6nWqt9Xb9rgoxkzi2wBQcohzpxnTkaygYJfLR41wHPgWEcb4jxtSjVCDhLyqBL01UUPSrtWY/Zbrg5FK9s0w2VfKVEgr3Q5CP8zYF8ZKrI1AeeQ4QKADcPzo6OlYWcAcQ6Na8OD03wtovt75kdd2jIMMOCsGRL2bNR55WvBVpgw9rzW/E4you8S/ZuVt/sLS1uLXRqtZLJVi8iys59Ppd9mvEQHF/HMrGdP0DCsFSDI5HpQ4st7nQERX8mdOilPiD6dKlerUxs2JvJnxCi7P10jLzmYkai+koGJnHq4U9iYE5M6j5R3aQT4ieewRqAB4qAu4f9zYVAfePnQt0ej40eGEEm1e49S8jEw4yNOuvL/Il/BVl5Kl0PUvcR6OtGH8YoPpp2OBygfb1KK825uqJjgqG05QR1P6NSOMZE+dp+kR1lGvXPDQI0frFpA/QuEZ6UlP4ULGvCn1X9QYjSLvFrZWNjY3ZpRUJiLdmaqXwsk+NMnHOLpIjRSPIpR0LgMw+3mSEKMhLX2J4dd5HZZkQWAHw50f7OxAGP+rtuLZAp+dAAxeLUvw1VV7Z5EhaX0RFPe8P0cfBrydD4mGRrEcBo6BHgadUb5iQs7yECOyoSFiXRNjJceAaY9Nl/FxUs4xNX1xHvXFyhfQAYy8mEbEp/EIKspSYa1j7K70zv7HQatSqc9X71fr9+txcrTb98GGrCXimpkD95sSaRiwfyAVuk/LUsa9ISscAwXONQBMCHx6BCTyCXOCj3mav51yg0znX0MURD1bxm/KvLv7SvD/j/4pF7f6K9rB7XvAr/oe8XzTK46ug4aS6aruurRntAiESjssgA7RvBnc0EJoJKHaOPkwBBC85/hUqRjX+CMLQ9afeRaI+t6C3VF+cX12oNav1egK3W1cfd9U1zRmEd1ZJQnO0ev/4/qI6CDYVkYg54BjYFD+sODhGV5Hz7AI1ADELeEQIxHrwo2G3RNjpPGtwpKj+cIt5whwP+GP3Z8e+2v0VTeCre58Jf7R1EEe/iho0wBT67f6oPrViFx0m5x++Xa0nMBdIVituShmsmIah6QGMa+LRhXzKhZzFTGQL6GPtt5Oo1mYk97e4slCDN6Bgl0ggAEulRAJgWK3eTZQUAXPqjYc7yMI0xumcnfT6CBiLRbgdRlwgtQdyMlCDEgrC53ZxiAHgkdFxDxqjNzd7Y+eX7E7fcA0OjMCqBur+y9JC34z0OduTThl/NOk0q3hp0Y8XR0QkGCT3l6yU6rXGVKMxV71bulufa20QAhcZgQs1doFJX6ohHM7KZywWcHTxuAW8uIlwo4JAPiMqJ8JDfpzG6edgb80l2Utko1VT9OuAFP7q1VoD3mit1lQR8mR5aQoeS5SaC9tb260qdkazO/WkJTDYGeOZdXKxiGQFpT6CNhAxWDyvndEAQPJ/h4I/LIf0NjfXFAKdC3Q6p7owgpv88K7nJgTm1W6FPgOYpcKHBL+0xznHvxz5AR647gE0ubVY3p5daMzdV5RZ2A4gcBtMmDJbuQom3HwOgy0XiL4vLsc60uX74lFTAJbLeFRTEO+iNb/k/xpC4K2HtSrjDzYZqc0sbS2CtjZma9oxGQAAIABJREFUt/GMcququFhbhfMXp6u02wiaQM+uBaOkd1uY51GVRCJgTxtFTCFGLp5LBJocIHwYCh7tbMICufX1YecCnc6hhkbQvIj/k+EHfeDLSt+fVfMt5s2qN2KgmCDI2wH/7i+YckN5Axg415gJFmChJ+ZuCUsOaWkLFP7pnF/U3GnAZt2O27ckMNY4pO6/5WUV/86y/9tuzRH/cJOl6oLVEShHq00VCz+kW/MN5QGpLzomYvAB22IxKxsoTJQLbQEld6j+gRg5h6hAB9gfApMPRASuOwQ6nUMNgf/zpP7L+MMgOAC/opl4hWvehIIRKX9I0p/+/IF/qfutlcVbk4tScrg1Wd6YrjVrDd2AvMgIRDPGcXDcioQtiEWNbMdnoBeNStLPfiQel/rvcqqjfB69l0XkH9KvA2nB1VO2Gt5uVFVcvMCPrDbqygPS6uAow02bQGvpnigSOOBwmM+GE89hW6A4wKN9Y/5A+/uHh4eEwK5DoNM50+AFmmpi4l9zafOvKHu95XnRBy56w4F/OOs5LzYHUaDAk15ONMDrlVenZ03P8eL2TKPRaG1oKOKd2BNTolKDlQskpOkQN26RTlc3ogJLsYA6OUhukkdeqQC4VJ9rkflcXBH+hTudUr3xUHi8NS9oLi81qvcTio0cMm8tzCWWk77OA0pB2LOygXZSkGknu5zomxwuwzedt5nRkgM87HOA6ra687i3DtMCu5vDjoBO50hgAKFRNy+sk8jXILBoBv5x7Tci3s+LSOsf5f/4bz3GAETulRdqtcZDXQBeLK8uLPUtwljEnhiIg5mAUY6EBXk6p8f4M5EyEtCMxqcjX27QLQBgbrmknB7TbQYt5x+FOynYab1BSb9bWw9bjYa8txUVmSfuJprMzMnZGq4MoSSlp/uh2fwFkoKRE8UR+d3ouBhj5nPWE6MAeCx9gDoHSPTD2sjx5nq3u97bOVc/lNM3XReyRShaSg2YvJ98afhR70tWD3rO88w/qn0A/6TxA3NdioB+upOobRBvHtbmqirwnWfbN3nKCtzJrZkHTUBgRSaSkuWLa/YJ74ztE/k2/3jSadzCIBpAqACLAVxtNBMKgDAHq363Xm3M03vYUqSuzbEfXHzYVA4Q1ozQu962Y2AarR/VeIuZIDg4NME0xvCJeIM4GDtnbYEKgPuyFtiOgI8If+qxnfW1Xs85QKfzpJEsLmzIc39ztnBK9EvsMwP/VMAMWx3hkWYgj/9jIER9v9JJsLcqrzaq1fsqAl0tB0LfgCZVcEypQKoGcwIvqol3Un7wEMkXpStDQVQaM4ALEs7WsO+5XlvdXpmuzYkxvLWtbszVFsgCbtegClzV39SqljrSDShBsNAuYADlLjv4NQCM0L8QXgRj6Ejs/CAQALh/EoDEP4W/451j6It2AHQ6RxpSbk79JeoRqEI9dIDs+2TZB+4Skhfhxj86ApYvj5JcAKz0cqc6ReZqcqM1V61W52rSB3hLg9Byg4vbUA3ppKgWQnlACjkpzNXGj3AYjWrExTl1aGFPzCAZwHQlrCLgJeacCrcV/qqNDXzR6VqLY+Bb8+ABCYeLUARWZ0kMvLVAAIQXltldnrS/MAElxaehGNF36ruEivqbY+elM3o0RA7wSBPwUEXAhwZ/xzsOgE7nTEPZbB4TUrIOjvGXpcJvVrAH233IxFNuecl7esFX3uMCiPxZR6EKXIG+O+55Ua5rrsqLcC0XuDgf6IlRoFQExGIDsctYPJ0X1LeNAWQC+nEpoDAQ4/oSAfg2ReS3NqDkYmq/G43atHBZRevsALegDbBTrzdlfoMCYJgdIHZoe1IHge2HNQ4tBAoBRZQvlDuYizDo8JwUhCUEPrJ7ADEAPkQE7iit9dYcAJ3OkS4WskX1JwwQy9vFDiJgnld9UN8zApBSf1D1zUe415dWv1ltHrwIGAkomJlU9k6qDaLFrdmplk4N0l1LjXqnkhT0se2zUnwc3PqGbnFNOnZ+hE8BYhx2T8e3EgDgfZ0RnFVxb2P1HX791Uatsbq1tdGANXJ3E/cDITDnAKUSHOWFcfxTyz8AMSsRGOsrkCAVGYhiCSPeyHkYqzcUCuQAGYJMv2MEYM/lAJ3Oly5mC8VIlAlI4S6PO5Cwl9v+8rLRL6f8IlbkS1f0Vx2jP3qEUTKw9rb8EANgXFnBuCsvtWrQFmgAeGtx4X44l0sLvPpsIGPQF48XlEVGSf7hNQzA7yTqDc71KQBW67onpgyJPzMgZnGhdr/erNVhhTC0SJsiCC0GoRg4Rsv0omwDpS2GHCBc/oNGntg+AqQpl0T03sjwdQ5cYB8A+/i34wDodA51MZPNRrw4EDCfF/YJ/ND3ZfPiBHXTs5fnL459zYov/kPnCahIwHq1ta3XvQVYB3ep0LhZa8n6XBjE3KiXchwDS5R7Mr+n2cYmkEHpW7aPAUochBC4XntIr7HVatbrdel+KT9sQOmjwZzGBmgFvzCtEW5yfnAR22CS9FKySFlGBGJJOGrcXozjYPaEEhH/g+cJKQ0c+R8MGJX1NUfgkAmBLQDuCwB3CIBrbstMp3OkC+OKdpFoHCbaSYdzcNyfWfQr6T4ygXKA7BP6yR81D0GF5Rd3E029+m1xY4Yj3sUytxwvrioTWJuiJNzidkvRJyeb8wr0OL6N20izY2A5FvQZBvLdUATp1JsczS4+bCgHeF/KvZMbLRX2agsIAOx0UkBAK1G4BRMCK/h02IIdEwZy+g+5FhWHF9Nwk1+JXNEykpghH98fV19f887o0dA6FXwN/g65B5D5pwC45gDodJ50YbwAbIvj32Ukr1N+tOgjSw7QtL4YcW8v9T7bXb7whx0lAwgOELYeqrVWbrHKq7OrZSDhtBSEJ7da2HyyMTm59RBCT5pDSvCKSzArB3bsG8ShIaE8oh8DB5jqKBAz4+bBAlabemFweWVjQxarLK7WYFBruANvvaohudqQcQjUlg34w+HTEv+KteMDz+T4EHNcDcHqCd73D/ILIyDSmJmvNQIFgAZ/bAGPgwB0IbDT+dGF8XbRKxZjfjwa8XBfH8r3SQhsp/4Ci36lBkLVj5jpgOGAEIAE68+gl/ihvflQeXVhdha672ozXBMpw1AsddpUU+EvDGNhhICWwSMD6JsL3yahPgr4QyMYBQMxsLjOxly1OjetsWxpBTyoMoAd4J8EwFgT7iyn05KPjMajekyX2bYEQEZbyFFNROf7PCAgpwbIIHIjTESTkr7pa9EZPXj6eyAAHu0f/ktfBLzPFRAC4PDXPJJ3+qZqaGjgwoWXXnrxJdTAwBD8f36xPV4AfEV9P4rNMBFu8yvKrD/d9QeAZPfHk1909k9XgNHzIA0AO0ngX226f+81KH3MVaErZlViUmg6hqQbjMXiuVi6kOvLkRg8E+saieeLGz5aXhFi4FynRJ1/wLOG4t9C39uCN1KelXeC8S+H7ouLD+fq0p+oRy3EeEZ1TM+v1lGw+ZfA4xDZ4yOxh56uhujiCF589Z3Rg6PDoVNH+xEAd7rd3uHPhX9HXAEmAvbW1pUDdAB0+tpJse+lF7515+V79yYuTUyor3uXr3zrhZcuDL2UAQJGY0BAH8xIPhLJB2Tm/SHp8mT6InyHZ0e/8jcOkV6ci8BS4AgsAZmEyVjQGM2Jt/JDGE4V7uT0FiE+2z7LysUtq2ecX4BzQSzqhKAP02ByKeUBqfKrgFu/rzOCW1uTPCNma7U1RxOiFf7uVxuzHBZPPnxbGUApzUTteTSxmDW0K8ZJQYmGBXPaDeJvRpCoHTPDEgkY/aoLwqNjXaXQKZk8AODxZne3213fOTz6ecABogFUAIQiyFf57p2cTmpw4KUXXn154tIJTVz+1rfG24VMIQJ/tyrAiyLShHk06VmCX5r6Yjr+Ihb7xPHwHzY5wPTycmlOz5/v0+LWrELgnN4mrsUDsSD+TRveWYHtaV9PUrzvDHjSZGU5rDzg9uLk9nQTRkA3FyC+3XrYaLQWZlYfPlxowYB8mIsPg/GrZusQFTFDAIwlECwCKxtoJhUS73jJMm3hRCaY7Z5mYBQWD2PpmEPeiP7dxcQMUoz8FSJwbLirELfe7Z6cazUa2kT8dUPd0PqxGECTAuz1eqEnAXDITYt2+moE9Lty+RT6se7duHaz3c7AiuB4peJHaZo70Q529KZsnzg/4wQDnS+eFc4RD6gPeu5h39rf8sbGvCyGW1x52KrVpgkzs3P10jL0/zH9TO3DBtlp0Ev7AcXNfdY3w75LygOmoK5Rq4LHK2F0PrNQq1ZhN7hqvV7HjUFgZ5B6tdlY0ONryjNzyD9Zn0KTuOIyqjrGPpCGJET1sCwjCnFjnt7aWJAn7GMi4j8f9PhXg8BBhT8gXHd9PbS+1utzgaOhXSX0h+rhzR1cCWc1wfSe5AAHh8aG193OcU5fgRT+Xrn3RPgJA1+7+sbN8Uzei1ZygECPqhsy6DlPWb+8F+Ftf7UJRCMYk+hXjCClxKDw0KmagdAg2IWopofiA1tWZhfwlMXZOcWYnAqA075dAumPd/uVNueekLaQaT41mczlcupHTNEmTcrngdm7X79bh62QErQxUqJer9Zas3rjuMntBc0/sn8yn0YmFNLPGxMaYk3EpmCUOScOj7cV4S8LgRQCk2n8KhaHDI11d5l/6+ubvbXezqjlAkeHd/f29hCBin9AyGPdB80RcG+9d1oOcHR4HZ7UIdDpy9bAi689FX+ge3euvvHGzUzRS6dSiMAIr/PNS/ZPjKB3QjHBn6Sz0ObEqfJabZhhyzj0T9mtuVrLzAOcXCyXMchUBpDrHzoCDrCs/y7f7/d+FOmmzQ3f+hZwgIDApAJgRXEwt6zcYOJ+barVaMzNKQt4v67Qd78+93ZjenW7bBA922iq4DxnKjO6DyZqXB+m/4SLbAljulfaWEEIhClQ9mLGL6vftcTJ0Zg88qW7wMGx0K7wb20TtvtV0tUQZQ5394CAgMBQKLS2tq7i3WPwgFIBUQYwtHYSgKNjiEt4VodApy9Rg0MXvvXy09AnevnK61ffGM9kY+lUuAIFYR37gv3zdMvfk6T9n0eGCEJYZQFLieb0Bs3EX4SJMOS0VIT5cNskBxe3Z5r1UipHG/CewNopwkQh4Q48Ix1Z3tE4Q5/upMxiGnOB6XQFtursqBB4dmtxcnFre2NpdgY1u7GxVTYj/FXE3mrWE50Uhb+83CSuh7PykeQD43IYk84YMYOeZ2JjhKQni0h4PTH9/uiK/jWB8y9+iQgcHQ6Rveui/dMiBJL9Qx0c7KmzFOpCKhLu7RzvH+/vcATcWz8JwLFh5B+qG3IIdPqyNHjhhc+MP9DEa1ev3rzZLsYr4VSOAmGq9ur1HsYB6qQfXkVinvmgEJia9tKIwGpLIRB24ahDzBkuYfCZqDZmlpA1k+WHc4lERxmztK8NoGX2+t0fci6t7R6RkO5Om8dtjKYZmGm6SibRCHbq0hTzBE1uzeJEhBS+NXoTcT8e5ak0RDyxfVFMC8YlII5SPyAViXVETHGyH4/pu6KUEeQcIaISH/Aonva+vJ6YsT3Nv82dR0w/BUJl29Sjwwcaf6A9ODPUVU4wdLyvayBrvX4HOKjsnzqL8dfd7e46BDp9KRocePH605DXr8uvXb19+2Y7H8+FU0k/CjVL6vbzZN2HlD0k8WfGPbGPiYkDlK3YcC1ItbXQgsJrqbOcgt3Gqc04Ua01pmcWYDppJ5XLJQlnTzCAaX2VJu4xz+hWUhtC8XnsJE8YQfx+AmCi9YQKNWhxa2OhARt2hiEyp/oHF4E1/6IiMoNYHObKCCJQLmP6GirBwFBmH97p6c6ZGMfEHs5TRHB6X1Zb4KDO/232tKGDvub1NXgDUBtW9KMPRiD6wN6hHQJ3gwAcHFM2ET7X1xT/dkmnddg4OT1bDb30+ewfaeL661dv3xzPRlQcnErD3yDFZCeSf2z95FibPzxCBHAVF5pPljui3HIFtVxJwVqLUuJuoqSoGE4hZJ4Q/ga9nDFz8OTqA+CXTIuSxg9qx2c7QiZjEnpiVHS+feqE6snJrY3pRhN3TYe3Jt+MrTVxntIqDlAuDQ01/sQLalfIvxc6IyaAJPeHp9M/JB43y1B8PPKlTEmAAgi2+AH/jmm26eYabHQEABwcVl5vl9BXVvSDo7297loPALgvNZDNtVCgEXp0GAiK6m12BYC7u8OuVdDpTDX4OZJ/fbr8+hsKgRlCoE8IjMSCAOT2P7P6I2ZyWOhtOEyMEnMAebkUlF8Bc0lFLMUfdddyKqUMYQoqsxXO/pFrC2JQcGZHuUmfuAfPhxjEsDYpxJOYV2hpvlkbRWUBoTG6ObWwurQNeT/YFL28uLW1sjQ7XavW62hXlS8F94dPEBcAsgO0AmG2g9oXij2EbkHsGIzpe+Jojc0pUWqN4ZhYCsSmUgKPfhnr4wax/1nFv5jVYwKuYfF2EGehQrjb5QiY1MW2F8sBQlpQAVA/53AIHeRaTz3nDuyYRPxTnHUe0OkMNfDinSf3/T1NE9dfVS6wXYxVSjCWiqYkWIrBQE+Tt9d5P6Ife58oT4PhJrzva1SxTRMGAhvxgaSm1AlpKBo+4pPgc8CzwCXl9RCvHBfzNxA7NQLZAqbx9VPhEmYj52qNRgvVeDAHvdDQHlNSsXoF4vKkvCsCnlkNHCfWxaUvJiZJQaMYmUNZOMwn+3xKXGcPo1xM4X9MolQwoX9c0AVeOGsECgB7QCsGIDavhEJjCEBI5fXEBbL/21RwU7jcYQBu9gMQb8MTok0EBEKcraJgB0CnM9PgS9/6TK0vT9TEjas3wQRGU4mScoGYDNT0C1wz/PhTnUdWhv6yZXhBmh2dMXZpX0CI4EoLYSwHmLaO1ZOkNQipmwXTeAp4GFIrm5bTEExSWIzfKslAeQExkvgkykKq78SpfyoMB+apy06Cg/Xwcg7ZbLnROI+mMUMZbMOHP3IwNBYCsvUTx4gWMG7fAQ4RDpB9nikYU1mY6sRn3RODIXA3tAkbG+2gqeshEUO7B+XhUXKAQMd1JuAu1IohBLbWgWyudUNrIQ3AwWHyfzv7h4dHh4fqGdfWIc7edQ7Q6cw09NIXjn6NJu5cu337rUweEAjDmeMxoV5EWz8yKGwBuXhJ+JOaQFRGEzCMGHwclcIX1ha4+OHbSmtaBciFQEI3CbSrVJa5py+HYTTYQYyDjV1Mm++3nwwRiMrlVKiPw09xk/SUurWcgueEV6hQ9CtPxEUQEwXzYVTAFqUbOr6Ny2+CGSg1ZD8u1RT2h3h6LCZl46ikFOQDs4Nni0B2gJuw9bmCGeEvpPB3C9J+w8Ohbqi7tra52et1lQvcg66+9TVI8VnrQNRjawEAKhySATxSADwEUxnCMNg5QKcz0sCLN7549GvpHsTB4wXPJxcYj4sj8bht18DPMxEwZrPiEtQRKxA6wI40W0GhU1IOg24vSCpfwlc6J2mE1g+yiIpaSrncMmcZ08RAfm5f7KZvkReRRpnDCkXiykqm0PQBSZMVCtd9Q1JJAVIvtJUKZMgRA+2VIvyYyAKmr38lBpx0EvIvHpVisGQaYvRvS/QspwUOrlEEfIyL23bWYEHwendP8e8WGr41WAC8tgkIXJPFIgqAoZBMw8ckYNcOgQcxBwj5P0Lg/gfKA6IFdA7Q6Uw09OtGv5ZefvX27dvtrFcpSSAsf5Me1SolRkOvEo9Jl1tUAzCq/9qlic8A0Di0NN/hBy7l0IIgBs0U+VaSaP1SMLcU0nVwjRDUOUU/bVPQwNBiajKtY2mMxfl78fvZ9hk6C5zjui/Rwp6FQqKaH5cfnxOE/Jugx+SZDBN9yQpS7lRPSzD/xmA/YfQse2KGcYXb5jHNd1lX/CP7d4sKHmsQAgMAgWnrXVjYEdqEqgdth0kr4dYgUD4JwP3jXu+Dw0PFVXXO7p4DoNOZ6PMs/Pgsuv4qFISzUUCgCoRpP0id9dPZPy+qe3o5HRY1f/Vx7ZwYH0w3bcg0ZBh54gLTYtT4vjQWNwh/GPaqwLUExQpYwVaH9J2ioCYgR8LYFmO/pFAX68j0OqIk15PF9VlgNoqbONjXWUEtcXVxHQnrG/xbiPO/CGmroiwHlDAED8n/tkggTMdUFYmdVU/M4DCaOuUAYcz9cUgZtYNbBL+D8t5BqAfL33rK/61vrkN1ZB0aZJQt3EX3J22DCoABBxhCAILgaqe32UMT6EJgp2evX6v2e7quX4OWmGI0lUiEEYHIQPrLZJfCWXrqeRP7h3/P9NeuCWgwmD7lwreONA/TwkNt/pK0lhfcXxg6qaV624KNjMLhMA07oIIIebe0dnu+FYHLk/rkAtOQEuS0IPvGvrcGMtbN18ZNiAhfUU01/atgLlLYLN8J0bfva5T6dkIQfsUMO2nCFNsd022BT/s/4YtocHgdPN0OOsDDfeX+DqAlUgDY3VG0gzrHJvQ0r1MMrPjX3SX8IQA3n+AAKUju7Wxubj463t/pdR0AnZ61VPT7rPGndO8KpgIj6XCiXpKByDHqdfaoa03oF4NSJuX7yfTIn7cvWS8dP2oAaRylDek0FdN8M+0DnNI68VdZzqWQf/Xaw61FVnkGx+mnKqnKcgW795La0vnSH237O2GjUFIfpM0b9I3i9gVD3YIfc47vDCT84uL75KeHZ07KM/CzIviQfz51BWI4HJN/YiLsCfHeyJkgEAG43ttB/O0f7nJP+MHB5MFeWYXASDgs9QIoIUEIjYEru99BAD5CNq71+hzg2pp2gMc7j5R93Hy0jw2GbjGI0zPV4IVvfe6Fb08XEBUR+FYmkgwnEiUaCcptu+xUojFe88BpLDY+8oet8WccoGAHDzVxhEGaRmmuk6RpxQem/hCAUPsI414j1qytjUYTRtlDIhBtIHXFVKhnxhCWOafJ5xMMzevrd2akySVM51vs9/gnJdcrNBQGMgV9y+zBm0gGXsScp/hHqUD6xXLY63EoLEb7LFygAuAm9gAC/z443tO/WFz6oQC4I6HuJjpAin9XvrMr4a+i23q/A4SomACool/wf48eHR/jOuPhU4fuOzl9EcG63zOwf0RAhcA3bt4cz3rJUj2RwqkAlN9iCkZlxRfnvKT4EbfsjeV9jMGylJacXzotvlDAxPSCWX6KatT2kgqHYYHxnOxYxACsq0A93EmBQcRIGE0g2kcd7jII4YtbXBh4aU3BQPRruTbmlG8+jYsTLyhMjDPOGGp8Aj8V5xvlhfhl5PfF/454skLOqrSTDWQXOPCMETjYWweDBsvgoAsQq7+Av8mDybK6CEEp94Njoh3k/zZ7azgfdbfX2+EmwE0Y9xJwgBgcq2dTYe/m/6D4t6MIiKiEdhq3e5zTs9HQS6+dHf5AL7/2xs232tlYRSEwXME/ceNTKOqN6foHPKR9D0OjjyNGfSg04GMzBvGvn5TwF1pdcjkFuTCNUrABuN1qwhqODjyaymFHi1SEK7SaN83bjfDQQWgolJdMYlGEw2JxpbYEehbyGGp4HTfn+EzCuI6NzWl0ArwsohnfUhC0cf2Pid5cTvcCQgiMicAotwU+7f+Lz6WhYaSSGD0s/qL/u4UOcO1wB9j4AU+9Av6tdXe/U977TxjlMv/QAeroVgFQnb8DfYXqMTCAvUdAwEebcPbmmlsS7PQMNHThhcufhrEvLMU/2D0Jjy6/AtUQaIxWCAScxAWCptVNd71RLr/v7z8g47EEOj4ONWDPp+WLX8LwF7yfcn+dTpg27egDIGytWS+VSoqA4XBqGXujk0kuCqep8EBsNYzTzPN9GSxovTmtuHUhVk5+LLo7YPbkh+bUn9DTpydOkp3FH7eS1LE5vqT5tRIFpequ8acJiG2BzxAgg2NQ4n0kge4BeD9g4CSEwOWDroIf8o/6/Xq48Hd3d29+eHgYu50hNF5b7wuBj2FW1uHh+m/iQCzoIaR8IYTD0EdtVs05OX0xDbxwBsk/0IRcIgQnbly7+dZ4Ox/N1e1AmKNesn+67QO9oMUKmyC+0EcjhoEDIEjqmJdZhWULLn6oqDaVAv4h/hT/rO3WFQCna83mXJ1GDgIClQlchn5B7uyjVW0SawvqJC6W+/RbChozv++W/un4zn5jKOTr8770+pDPVD9JDoleSdJyGD9NhZG4QSCvDGEGevLFDIxHY/HYs3SBg6PDPZqEBTRDB7g3j0t/98rlvYO90M7hIRIQ+bfWwxII7JykvhGLHb01rA4bAA59ANm//cMPYHKq+lLPrgD7iKohmzB0evjT3pCT01N1NrVf1IT+0Ah862Y7G/FL1WoiBaEb9/uRCYxFrcY3yw4FAYAMENCktR+zH0lyjx5aQIp+aYp9ZTmFyb8w4G+uWWstrFrz/Ca3VxdajWYVZxlglIyrQypQDuGFHTzWQDu8tHld39fmL20eMIrrK0M7be/MGdZpcV9AaD3AExzUm4KWnRT1LSatmDiuk4AxJF9UMn9UDvFg22FqQY+SD3yWi0MUybChZQcBeAsGHux2u7twBU0xeyHC404PlsBBD0xomNJ4o2PgAtd6KgRe0gAcHB37AFtqjvZhevQ6EO8R4K/3CB0gtAQ6ADr9Ovo1pl49VWIANf9gZPQb4+PtbCxZqtZLOCU+Hue/V20AZdGDAWAfA3ybd/qaI15qWqEPKF/AbfBvOVr4kQOuJRKwn3BrdmVrsW+W32R5axa2GwYXCCaQl4ZQTwyuIeamGMuCSqitQ3F6q2wBDdBsMQaDPs9ATh41UJTvp14eLGOHIUzHxkXIUCIU5bkCFaaYLL3xOB0Ykd5o/K17z3Za4OjFnR0BIC6AwxGBu7u7ZQqHeyoKpiUfsAZkWG+ZhCYQmv66KxICjw6H1nswBWb/8BgM4joE2Oqj9wgsIHrNXu+DZ/fWnb55+gIzn5+gCSl4TIif1Pdc4iwgHb5yGxDoJRWESrhPkInZdATsm6KAMUpBUdRJFCLXRdZPglNM2HF8C2IbAAAgAElEQVTrcyXJIw9SOEK1rvA3Nau3rOzbcB22G56ugQ0swZxVKgfTnAQ0X/KibPj4Qmwf328MoD6Im2Md/eqfL85VDyJnf4eLAT2BDpt4oIsbZ24BplMQ2uf4bPqFcls5W7+Yvds6FUTwkqLkZ9oTA4Ew9PtRCAxDn2FMtDqehHpI9QhNIOJvbThALxz+HOourWARBDdY6q53cWnxBzwTdYeMH+43QplG5wCdvrCe5bpfptyEHBkQym25dflVRGC0Uq/WwzTF3pesH4e+ftACGYskIEhzNk4jkNftUiRIgbGMOOVpBTk0f8i/2tTsp0yyvwUbGS3UmtUErgxRcXAlp0ex4mxT/fJpZl1a6iMmSSjQslkW4FqfTMJTfhCRDrPhVbCJEXoYYU9i2ogYGQgYrBCK+ZcYxcI6z8XS8JOycIyzgRQrx58tAkfHLAB2cYLfLq2IO7i1u7sHDYGQ/zuxtQe4wNDuUmhsEA5x6NU6zldVAGy1WlOt3s7xo00R9c44ADp9UT3z6HdCuz4p/cqF9n94gMvj2hE/XK8mwjnaLYj/aDEfyFYorrlghYMaC5blksO0bwWoMqSgwvgDbGDry1xtxuwq/ATBZkZIwA60xKRgFjXPt0IGUkDsy0v7lhH02Yj6AYj5/O7T6T47a/ytdT+vOukDJuEPenjC4QSUsJu1ZrNZVcLtiMOQUSBHDV+SWo1Dqk/zL6pbYsQGejw9RgXCzzCYHB0jAO5ZAAQeTkJheE85uZ3QKZv//gaGvdDfDPYPvg8XF69vHh/3pnoN9dXageUg0BCjPrHW4gDo9MU0cCatLwZ3VmWlD4aXJu7deP2Nm+1CJJ4CBCqs6MjNl7S/RmAf+IQGAgXf9N/JiHtmIIWLFDJSxixMnS+rT8MfaBFqwjjZuRMOL4dTVETRNhAHKxAELdLJeC7fvrDfrg5uNc8DLNSnp9NxZnpS0xB+HOIf0e/Bg6mpBw8e1ACD2MGdyumWQDHU1GcJRg9BJ5GvF5OSMKERz32mLlA5uHlYAbK3G6IhzgeIv4NbkysHB2u4v++TvhOi32GcLNj93xmA65utBzsPah/Uag92Dv/laGcT73MO0OkLa+Csar9W5u/SvcsT2hJevv4yPw7Hl6/fufbGzfGM54er1bryLvyXG9dFT22M4ifxwJ84DZUi0CRhj/CHSySSVu8z9b6EufNvI8i/xfLW1orSVn9FZAvCYBpuL5OyuCMmLZ8UBPvs2Tgmti593/JxcQuI9s9k8z3O35Lm78SX8Wm8AiX/wtDBCPibmpqenpmZnp4GDGLADh5Qhu/LEBms82Kk69mJwBgvjPN0IIyG8ZktDhkaGx5eQQcIE7IYgNAVeKv3AQKw233iWt7BoWG9ubDWg9rOBx+oT6XDw/1N4B+OhVlzAHT6/Pq8+/1+Hhn3d/21169cpsN7d1595TVaazdx+cadG9cvv3z9+r3L/8fNTKSSaEI1BP/8dcBrfYkftMQuK82xJgAQC7Tk/pLs/tABUu8zjGtm/jUC/IOdK6enGo1ardFoLKwGQ2MgILYFUpoNyyG4gQjTFdHE0/h1jyC8I6RQ2nDaOEDfvvUkCULpAMhHkXyK+Af274GC39LKPGhlaWlmegpYDYMcCLvxQDdgNCp9z7z8mjnoRUxiMMbt6M9mZvQo7AB3gBHwLgKwq3OAPXX/2uZ6d3ev+4SFbGOhPdlcGLv9EIAKfjXEX+oDKIWgL4RScsgB0OnzSuHvbNb9ipTtm5i4fOWVV15/5VWcr/XyldeUXr1y/d7Ey3euvHbnxo3r9y5d++hHH/3BG7cLESgIc2e0xIY4GEoXS/vwwBdsk9gDStAbEEe/nTDs2AGtf7XGko2/7YVGbQ7TaPerc81mrbawUbYfbtVqc3PqwTqVhGFfOnriNJsyAqGPS+2McdP2T94sVzXSnN0LKuht8SdKsnukK/XUkIEMQ+k3jPZvanp2Zb4MmpycLJfnl2YVAskD8rNTDIzsoz3UafGbtANabYGmSRDP/fUXh0AVGOaeHuidfwmAmP/D1hh1BxBwt3vaDueDw7tsAKnMgQQM7aD7+z8PDw97azsfQA1knbaQcwB0+pwaeunKWeKPHeD1V15/9dXXXrtz7/ond//y5YkbV5Reu3LjOlwrB3jpf/p3H7355psf//jPX7lZjObqzXopZTJYlvmzcmQcH2pTJZxJU9hLcbCufZD9k9hX0e8+bN22YE1/Ka+2as1mHZSAmahVhZbGjN0ZvbHQEtXqpU5Kz0fQkpgb4OtTm7TYPDKnJkXY5/1OOltzAjwzm1syl7jzCLW+AP9mZufLyvwR/+B6hQioPCCwk397gsCYfHFR2LOqwHJM/KNv+PVc4NDYGm72sbaHKUCCWbdLy+ImkYA8A2FPGcSTLnBoGDZAp901YdFHr7cZUg7wg2MIfsOHO2uh3geKfZtr3El42ntwcnqSBs9q3W9QEyr+ffW1K9cv/fu/e/zmjz7840v3bty4Awi8ckNp4tIf//BN0vvvXbszXoyHFQLDmMQXC2OHwJoTafFX5Pz4Fi/S4C5Aq/yLNQOY+lfDqacL0wtWkFueVfaviiEuSjFQIbJmI3JysSzTArcb9UQ4TP2A6Pwky0ivSUYwLUMSxA3KUTotZpCXqPhBMey4l0ZYDl9kG5PmZ0H+rZTnVQCs+HdrclJFwfNAwAdNDII5mQC/P9NcHiMIQsGX/B9NCuQUoHaC6hRcH/JrrI8bxaGAONgPELe7xzuZl7ER8Nat+d7uLmyNCfRTXwehfgQO4RPAsBhFv+Mdmp61ibm/w0PYEiS0ttPj3dJDDoBOn0tnNvXKiB3gxIQyezfe+PH7iLkfffjLv76syHfnDoS/E7/88Edvih6//97Vq+P5eLgKCKykDQBP1gc4z8a2SmMQ+UelArv6gTWDTqle2ygzxyatMsfiBvFPAHgXVwdX5xozpxaJF2eUBwzriflp8X/0qnhEhi1tWVMkdVoYyEj0NR4ZfnIlP5y6hBdJs5/F8i+KAPhAxb/K8ykAwo+DAITbM9NgAVPcWOn7wRxgnE0g3OXRmCyPLyOexMMxyhTCuV9wcQjhjxJ0Kmo93umtw7yDPRgHQ7/8+d2dYwXA3XIZUoTqkX4EEgBxdD5NVXgEYbDhH81NQPg5B+j0+XSG635ZVvuzOv7zjzTnPv6bX94DBN64fu+//5uP3wzoh79/+3YmDyuEcX1c0kJef4bMTwtm0r4UG9JSBdauLAkb9kL9IxzuJKqtU4lWnq7RDuZQ47hbIgZCe0lj47TTF1cVX3QhxMTAUgrBL/FwviahwTT9CFZILOjrvwNQzhOp01zL4YV8BoCTZaiAIFEAgEvzCMCmioFz/OvTrTBmYbBM3Y7xFizSFh2TcTEcBkMF2Yt/gZ4Y6F7m4i2Nxdr/+X/+l8MeTEY9KE/ygPzQ8bEKgffm93BIAiBwb8luCRzCnUVwc2GlR7isbm3zkPjXWMP1clD9CMGGmQ6ATp9dgxee5cKP0zURaIJefmwA+It//sf/buKy8p+/86G5F/SOcoEfffLbVwteMtGExSHSFEN/x5aIHuSrfEz9kfNLSvxpcUnqvyUFwHdOA9q2BiBuaV6iMBjqJKunnH5rcpVybLlkgH9ptp1IYT9pwnNiWVpPpBYass8T2GkGsluk6FcAqHmexCnWOQLg1MzKJEbA9MbAAaovAGAdAZg2BCT80Re1+xEJhX60KkSuFBkhJJaC8IXPi0Dl/7q4dmN9vcdTD46Pjj4IHfBQaPVmd3uwsVtod34PxsOUFQHLCoFd65XIAdLmwriJMBQ8Nol/DwB8a2vo/7oEQDcOy+kz6lnt9/tZNXH9+p1P3kbYPf74Z79Q+ue/mLj0bzko7tPHb39y9WY2lqsrJgECg8thGX8aGWwCkxxtpqVTjs1gktqf0TMlEs2WldUz2moZAJZQvLziSQDEJGBKpq9oPnH+EbcdwR3aafsRHf+aeBffdTItjlB8okEjx7sQ8qaEgAhbWINSoSIIAHCaaiDz+MbKmAOcX4JWGABgxXKAtIm6CYQ5Etb2D4jHFzEpEXMQjAj8nItDRmFqKRKQxlbtwNiq4/3j0N4t2BXpYK+7sw8joWFvcxiQhXUR8IArfQAMEQBhL0x4Sqiq9B6op2vRvATiH6Bwze0M4vTZdMa1X9SEffDyndfuXL906ZO/+/hNwN+vfvHPCoH/+h8XwPGdpscfvvW/KgRW6k3ltHDAyQn2SWCZTgsv0DBRDyCHwCJ0gMsw+aXZmD+NaOWZRm1OAAgeEB1gtdawRwQaKQcIbSYpazkIA5Belwog+LZMk4yOhJNp/dbTUunRLtAXK8seNo20o1mstH8xLedL0TZ2YAGBgOUyhMDQBVMul5dmprAIEs5JAgEpyHnAuA6HOco1NhAPuReGLSBXi+H8kQufB4Gj6NbWsUf5EQ1GhYaV4/2dEHRC7yqo4e5usBUIWL8ydUfv7fUDEPfWhJ1F9o/h+dYUEZXhm6YJCsS/jd+EYQoOf06fSWc59UrLXgSi8Pca9DtPXLr+3sc/++dfKfsHBPxZIPp9h7/4xsc//j3lAqEnBgJhsDJpGxNkk5JpK6JMkpVKSsnUwl9S5h8kqg1r6rOllRZ0D+siMODvLhjAh6ZSAqtE5re2tle2t5eUASyFmUsGgOIEMXYlHPv0llg63qUCsS9n449DzKSsXdLiN3pX3L0Yfwp4SZiBQBNgqugBV7AJEIogZWgEnNGNgGyeuadcV4KlKxDo5/GoLF4GbNk/TgnGouwCvdjnQeBoD2kF1Qvyf2AB19ce7R8d93b31oBnsLmRAiCFwABACIH3loIAhKegneX2j9d588xQtzs9vIaJv7W13wx1lxQEHf+cPpMGB1688yngelay1gFfv/Laa1du3Lh86dL/9uGPVAQM8PvVL37WV/ywSEgcfH/5d95oQzWkWS0BAtM6eqRgMU3BJdKEyZM8ISIUzQDEKnD1IfYMb4HKWBBZJE/XqNWgyxkrwOD+YEpg46EVMG8ttFqNRk2dN1fFRcEpey4Mv4N0UkoVFMqyC0zzgxwYs2/Fe/0k32bxpkv6p6G1y5j1wxmGOImB22DQpSoCziwhAoF+80uzyv/BymXKUaZ96iKKy4IQC4DS7cd7g1BphJaHeDwvPyrlEFodEvvsbYGjilwwtp46+LCFRfFvbed4/2i/t3OIw50lBN5V4MMRgRADn3SAGAEDMde7XRiGD62Ew6Nja7NoATfUnaHdg70lty+c09M18OLZ7HjUJzMIEHoAod35xsS3f8zM+1jFv0/Cn633//Da1XGFwCYgEO1WWnvAtCTNJNWH7OlDIIIPu/V4DTCGjdVmszlXqwUboSdXpms1XAcCndBVGBFdaz20SsaLsw14nFfDIf9S3AYj8MPXlxRkMsnhL4W7Go74gM/WlR6XH8NPcwDPJ9L7zuG85xTuX5Ki2xWe58C90IDA2dmlFVwINz31QKZ3pcACoqOEpTQxLxIBl8dLQsQEchpQSMfH7AsRhXQv+EAom3zWmdGja1i/oMl9OzvHvXXc6WPn+CdHR0f7+yr4pe19exQCY2GkfLC32wdAHHVFBvBwH8oqyux1/013d3gQ1hhDBLz7b7ohyCkeHDgEOj1FZ7nu19aEDD64fOfVV17BjueXP6GCB8S9jz8O1n5FH/fZwscffXLtjUKskmjWAIH096xjRl/opz+f4AErSWsGllR40eDZEw/KSwsNGKYyNweErDVas4HVwBQkJ2STEJ6HIHuEJK23oJFMDPTlPWoEpq2ThIBJ7QktjFO5F8CdorVvMIYhnOOBNrQYjkzg1DRMQ5iBYQgYy5cwQseZXWQuo148pe6Lex6lAqW4EddmkNBHS4PJHMbYD8pdNKL7MyKQALiOrXoKf5vEv94jACCGvzYAy3vQCkgADAUBqL7nGOmnvqkr87R2d3F8Ku4estLdpR7Cg1u7Lg52+jQNvPDl1H4ndAh8/fXXAYBgAP9S4Pb4JP3egc/HP/vVD371s8fv2JWRxx997w0sCKugDjuPk9xdwnkzP+C1ggSk6DeXS8oQVBgCjVsAU5DbnGssBWa+lLdXZ1SUC5qe3Q6OSd1u1WgaTAcmqeIWHDIfHy1msBYix5QM9C3+pYPvEb+B+2P4fC310+JwZzCuYbZ8wEGAIPNPPKDSVGNKCeZh0S4mKawcV/D50340WgVGTk81k7EYOjkAXGBCgqIckhGBRy2CGApHGYDES3WK/5lGZY2ucRNgaC10fNjrIv7WNAAJfwzA+T3sgIHicD8A0T3u71sA3IAFdQjAobHQbgj4KQQ8OJh3CHR6kga+hNovybzMBI5+AQd4/fK1Pzy16UX08T8r/gECP2YgvkkXH33v2u1sLKVsGTV2UIiZpgoq5tAovgwWPirYLsIzALl+wGEwbATCG2E2VvunQU8ulmGpSN+9i9tTNYh+wxD7hnmXzBztrhlcEMwWz75XqMZzDfAceVi2WxdnKOnMCiX/0P3RzNNSQiMwR9eEQFqzAqYVONikHUwwP5nUXeR+vELTsuCy6XtcCZaCcNTk/pBzngTDaAxxeCDdxEIJfstpCBy07xvCNkBax7G+Q1vDoQP8yb7iH+6HCVlAqALv7hL94ONgtxwEINROYDPMfdgSbh0Ho+6uoAMcHFvr7oqwhxoRWHYIdDpNZ7bf76cJW2Bu0Jrfyy9f+rfvffQYgmD6COLvZz/4wa/o4xcfBbtjPv7wz6+1834YEBjG0maS+owJKUFDhZse4VclyR+YqaPMmWIKEYw6/arNQB7wiVrcmKoxWQg81AGD+4MEXj0Qh0tEK8fSphjgdI4XE0v1hB6sJHnTzhS7PBJO4oI3ry5yYYyMw+hmgYLIQaxjw5uEDvIkJ0z9eKw5OzNdS2fTU4qAD5Ieezlqi5Fol8JdLviC8/OIf7h8OIYr52J0PvbEnEDgwIvWfUM97oJeY/JtbjIAf7KPGUDiHzZC71IfDNrA3b4qMJPyGL9BAa+7AtT7zt7Y6PAB4ZC2WWITCBCcdwR0OqEz2++3XxMT/RuAXLpOAFQEvPR/I/kYfhYDP/rHv/hviYA/+NU//sl7ZtXcm2AD33/vqkJgutSEFWgc3CX9pM4ABlThrB+vmQXvB4EwZtOofErCImqzNr1y6uI4W/MPG+KsOhyD5rgaIeGvVQvhd0Sc1l9pgRzXhNP8VnE1nXyj/lnwHafI5CH+qrJQWcEPGhXDlBhUnwlpW1Q/zf9MGUp1L5Z+OFsKLdAPZqenq7cvXfcezMzMNKPs6uIxYRqQL0Y+UNKCuj8mqv2gWR3nn4LAgd/6tikSKwCCA+yu92jfc9LaJgIQcEYANBZQfczvHfQDcGwfyIdzEJSJ7CLtVAz8ndAUjFg9oOEyWBhGApIJdAtCnPo09NKds1n4dkpMLQvgpBFm4jqkAFUIfOn6L98X5gUd4Eef/Paly38CCPzBr/7ilwqgf/IenqmN4H95/70/uJ3x/ESz1kyQvyFo9Pk/gVGFp5VyCjDJa0EwBk5RWNkpcQUB5v71bYhpaxF2BKF5+LhBeo75RwVafhX9+ubt9IXG8nDat0J12tcIO/ty5lmoah2WkX8Y40KE26xWpVWRQmHMDpbCYmkRg3gT3xn1RVKHjdeECLiauXwtNjU91YxGPNgCU/s/6fPD4xiC0bS+eHpNCJVOYtxOA2PzA1XXgd/57h/81QhXYofWiE2buMd5C/Zu24Sm5U0wgJQB3D/Gw16oO78LAIRLBcBZa3PM0NjoxQ92jpl/PS6CdEOz2M4Oq+p218heCgIdAJ1OaOjsOp8n+ghooY/vuHwDayDX71369x9+LPQL6Ec//lN12uWJv/7T//cH//p/TcCQ/IlLv/xQHuYO6Y+Wf+tmIZZO1GrUFmggEhQaKnJVFZobIAEwWUDMq5kuEoBLrbW0dToCJ8srM41aE7GD+MM6LGqZAmtemqb9nn47Nv/ScpXWF9oD5jhYz8nPhFDNMaYpUIc9P2DDjxpxsJ7gfGCuwz8HMzBMAOQEIJAvmpuenq5HY4kHUCR+kHmtmCu2M5lieKqW86QPkJKAUXF4zD6BINeC2RzKFRLQCwxMHfjWd9/9s7/dp8GmBEBYC7JJBnCztwktLMoCYg0Y6QfqUSMgNEOXdw8sAA6NhRTQhsdGxxCAPXaAMFR1STK3CoF7IRyStcku0AHQqV8DL55d8m8iiMCJvutL965fQf5dvjSh22D6i8Af/fGlSy8r6E388v/5xb/+xV9PvHz95Uv/zSmrhH/4+zduQjWkRj0xJnjUIWjFBMDUoZIT9HEZmEygdNHB0hBGYGNmtX8bkMlFRb9Wo8mJtQ7tjU6teOo5oX5B17kKA9e6APgmbaXhLhP+VvQnfHuOUpX09vApKfwt8Y5H2OXCO35gkzNxDpbDhUtSJ2YGhnOCUqgtx1KzM9PNeKRerU/NTM80x9ux169eHa8rHNYIgCYVyPP/OMyNSd0jyr0w3BgYY2OIHdV+dMQErATAo50eIBAAuI5L12hgFSyDC6lgdx0BuG+E/IM68DymAXf3hukZR0N7JEDgDllAMIChUGj+wP7vpEzg8Q6uu2MA3nIAdDIaeKb7/fbr9LKy3Hvvxh2Fvzs3rr9875OPaBLCyfTfm2++/9EnE/cm/uRff4FDEv7jnYkb771/2irhHy18cnu86Kfq1BmdooUYFYsmEgHrIDjHJWDBC7rAVE5KqNITU63Ozb3dWli1jCC2Bc5xXYGqD6lwThtAqYGQAuwjnawOV4IBMhlV/hF0jA58DnP5Q/CnaAVdzitLS7PY6NzEjdrZ+6VSnA/kHynFQTXN24+mp6H8UUkkklUFwKnIzcjrr/kPZmam6tkMgY9bYeIafZIT5BsMQDGHyMA4nxePp+PaBQ783rvfBQBurm8Oj2IXDM6yWuvBxJZNXMPGAFQ6MgCEEsY8m8C93V0E4OiwyekhAnsYAgP/5k+Y9YPdHq4zUQCEKogDoJPWGa/7DcS7ExNBHk68rPAH9u/liW//+LHh3il9gI//7k8/If4p/X+ffHQa/pTeefx3f/kGjIyu4rATXo1G4W4lJ9ihkQFg0SiuzFEVRCu1zBUE9IBhHnyAM/BXraW/9oxodoyYQMxJCpD5ilEwvXaFwZZMMhZt4BkSWvcG3iK9yXBKB+h1CH6nZ5dwzw/a8QPm3T+omSg4xcgMpzhqzvFrcQEkWZuCBmnlHLEFJjOeuZ1WRw/ib1wbj/FELN4wLirLRPQEGAmCoyY2jtLSEIQjmMC4r3tiLvzOtyEEfgQTq3rDPVixFoL9QDbBAcJUF3CAXUwCHuEHXuxgM8u88oCQCFSHa7gT+t6BrmkoBM6OjQ0rxO3uLq3If6GAC9zd3Nl0IbDTCZ3xut8J61Jfy47o927Avh8Q/f4uVXUJfKYMEhDNyEL97HGgD1BYSNc/+vB3Xm9H/FLzAbpAXCVL4S2Ek0kCCjKFG2A0WAwAw6YSAp8y+6UPgKuNGk/IouxfhwAoz0JPWqFZqzrutaCXs9YJW3ebMyvkUXPiAsmuSpWawt8HOPJ+sgwT7xdhsS/MOmACJhjJOf2eEIDyqlgAiadqTUQgaLqavXo71lT2L5EplJo5L+JF8vF4JIaj8gMpPg5zrdZA8H5xwSJGw2gDccYCdUZzDhBGHmxu9o6PN6EIQhNL19aQf93d/9R9BNj76f7RkfhARcCl3V2BYHd3TOGPJ0QLAA8OdpUL/KDXXbO3sdJSD8Ou6Q6ATgENDr10xut+LfT1Vz/uXb5z5cqVG9evT1zi6JeoR00wp62Ee0wIfOKQhDeZge9/+OdvtCNJKQiH9Zo0ikZzOUaiVD/ok3mFZRDGHwSPHTKBPP6vMWtaYiZXaURgqYMrf8MdDjVzFAbzk1IdpCJxtz6U4DapI/Rkjh/kU/AkeBqK5Cscp1dyZt/2Jox6WaJxf2AAJ3HzIyQgRsFkAInF/JOGw1xK4bXFflL9O1GCQFr9tqLtN97Igf3LRRPQEFgvFCKJqam66e+L8ldMVz/E7mlLKKaQ/aIUhC8MqWDju++++7dHjzZxB0sAnYpZcWIVOMCQ0spuqEfB7xF5QFoUApNNu7vU1dztDo/BLup9AIRh+aOjo2OnDTMDPnZ3oRfmcwFwcHTMrR1+njV44YUzTP6hjOejUogBIES/UPt9eeKXPzZpP1wH/CQAkgt8wiphFPnBd955/73btwuRdL2G6+PCGoGGeUmmAnlDclk5dG+pHDOQjCC7Leo2mastGAAuLmG1gYofoBx+GugQApPEOSZaxRxQeYPdXkWCc7y/ojOT9LZS/C7p3fLbAiJD+o+2/AD+4bg/nnf6gOYdpMI5znAiTZPqh4JwPM38g0EMpWqpEsu+9cZvv3bt5s1sdXZmqppqTk9PTU8/iI6np6BGEolxb59J+9m4CwjWxmlWagD6vjdy8aVrCoB/RQDc7D06+ulPf3rUCxEC0f+FumvHRz/RBKQgeB8QiDsbhbp7ezjY5RZsFwd90bs2AQ+Gh35jbDIQ+TL+EIAhAiA0Q38mAA6N9boht2rkuRXs93sqtJ6pJnTEa8fBE7D4g2q//1Zqv0LBIN/+Sx/iPj5p/+xsoETEj99/742bhVgKEMjLM3Ja7ALFFYpFyuWkEZpiRk0/UIeAEwAgjL2XtRfqBZZhBRo+iWQBCbZJ4ivFsNr+UdIxWTG+L8cPyExTeAYMgelZ5T3qFh0ozUAAXKaJ9zjvFCzgCgw8nQYAigPkVCS+CMAfKs1muFYyVQrHs7ev/e7V22/Fle97ABupV+tT081ivqri4lr8rXFl+TwvJrk/nhsoTTJRU/TFODkm7JNzhYH5b7/7XQXA401M+x0r/v3073+uEChjSxUAufwr4a9UQqjPZW3v4NbebghtHHpAWuDB+Csf7I7+xlj51kGwBHwgAFxfX0MHuHew8hmoNjg2TGYjWNYAACAASURBVFuJOAQ+nzrz6Bc1YQ4kCoZayGVqfbk+MfHJ31nA668An1IM6dc7gStz453HP/x3t28Wo9gTg7kwaU9ht6cVuE0ZPCRYKmUKp5TiKykCNmZhTqAKNLe3ZxvVekmKrR1uO8ZnSNmDqdjoYSrQ8n8V7pFBBJK3S/JYBlqXYr1J5qq8RaroIgBrGAGv6C0/yv0A5Jwke098NQSg2ZAEZqtW4tmbr//2tddjUBFWakbDioHRkro5VWp/+/VxL5KPpmMRT+MvTpcaclTxiOlScTzO8xToXBw1CAB8990/+89Hj6DnjwB4RAgEd9cN7XS7+8c/keqvroMwAnsf7MOkaAh94RrRJqt8UbfmFQAPEHoB/sGVAiDUmalyvPd0pg2NreE2cqFQb+ezTHZwOl8aOtPWFy0DvUsWDF++Q9udX750zUS/3P0XjIY/r4Kl4R/+5T/dLMbDzQcPmhgMIpRSHEmS8bNJyJBh+qVkoJSuh8CecVwOBmHxl/FHq39TDD/qpdZPL8F3EicbkNXLYUBKRpRK0njFfYlSlK5o4pm3Fk6FrQ7oGk17nrcBKCEw5gDh28iHMgERwxz+8kIQ349GI5k3Xn/1RhQaah6Uiu2qAl9JRb9Tnfbr37565VrRr05NP0jC+hALcHyEST+biHGKfSkZaOyhH/n2t/8UCbh/3Hu0c3yEFhCEvX6b+0fr3UfHx/s/0QBkBoJ6sFPIrQPeHQ64hwiUSQdk8xQA+1pgNAB3d1UQTTHw3u7TADg0NrwUYgCu9XofuEzgc6Yvbd3vpZMu894NDH6vX564/jdQ+w2m/L4I9kTvvPmxlIfx850fffiXV9uRZKk5VdPxoExMlss+BKaglc98pKgSIiYwnNBjB3jdbYncH65/YwLyE8kzMmklDyfl3KQuPvNE1ooEqrnge8IWFr1C739JyRuCJhiedw+BLwKQt/yAThgceU8AJP+X5NpvBUdn2zuup9MKUV6+0L7p1+u1auR2uzk73YRWwETx6rWrr1zLpGqwTGRmqllh7HEyUChIKUJin1wwCqMcGTMA/wk94M+PYLHbT3/6EwbgT396CDw8erS+ufnIaoLWvYD7PTZ10MZH+6d3Kf9HW6kfaAAa9Fn8u3ULAUid0OWnAnB0OLSB7AMIwrzVpwHT6Vxp8Mz2+w0u+5gINMHw/peX70Dj843LEy//8od9tHvMNZBPoeCJUNfW41/86l8lRchtMo8//L23itFK/QHtAWSlAk27ir7N/g0RmBPfJ13E1A6j56XCwtqSVD/YXaa4C5q+GGQ2Ytn2JakOQ7DjBkSKlHGNR+A9kQGkN6BTkilpT6xDF/TMEkBP9jxi/mENBH9e7nvG+LeCi4srevPNtGy8BAt/vUg2lQinCtcKUPhQxGtGbr5+7erNdBPoN4VtgilPh8Am/jWd0hqAYhOFlOQCFQDfVRbw3Xf/FhB4dGQAiBdQ/YACySNDQOmJDtl5PXKA3VCXfV/AAZqz0PlJOLyiAAiL4fDcTwPg0Ojo2NpSCD6oPr25s9NzAHyOdJbR70Sw2DHRbwAn7t25wut+f0n7/T5WMgGwYdmbn66TOb833/zZr2BUwi8+Ng8CBf/H797MFKOpRO0kAnP2EbEml5IqMNwMU0yrEUgCEHZgVALjj+vFObSBNr9MMSPHMEQrltNeLxAh87pkpia9r5TOQtLaDzsvSWOumtaOH5PUCANbHkkndIrWvUmXIQ7Zr1TSvD+UCPxgHBiYKoWTv/W6h53R1djt16+Nx5s4RrqWg/LIdOktT0W2OO6AglsOdqXOwaDjJsEgDSEmbn/3d//pn979p3f/65/91d/+fOTiEaQA//5v/+vfAwd/SuXfY9gaTvb4IPwd9fa0kyMAggXEUQqSACQArtgAVNrrKkbyoQLg+jqsNPnO3t7Sk4GmzB+qi/zDGV07vXUHwOdGgwMvnmX0a/u/4A24uHcd+Xf9+sS9T6jzWTzfm+z8HpvCx2Pr8qlS0e8vfgDTUpV+phD4jhRH3n/v+us329lINFVFF1hCiFB0m8tJ2CqWj5J3yL8UP2gMGDY6E/OM92P3h8WPsPhIglclp3N8xgdysYMCYjGKFW5xts7DawPAknk5eT/cnY2tgDOwFgSSfyu0Fg72JpE+aA6AcfQBdr+om2nefE42UKGZgPF4Op1K/9aVbLU5NZW6+cp4NPEA8VfyxsdhXmC1/TpuCBeJ6KUeYu/khnVnXHJ/EhPHfT/yB/8/e+8b2/Z93/uuq1vFbm2Fk8wfBVIM/4Am6V7SHCmRCkNZEBu6GW/JklSmZuhyY2ZTyOUsj2oZnYHcDDneAguwc07IFqjB4rYNw+VkwaQ9kAD5nowxBMEQCkEPLgQP51zUPk8CWMPBTXJxgTzaud/Pn++fH6Wk20HkJoO+kijyR4pSUuTV9/vzdxwJKHzwq988/g0Bt+3te/fuIQA3BQCF/YV0b6u3g4NgEIA7Q7f5MNe+QxaYCXh7VdXC2BSgYB70xbXX6cH6KvAPFGB76FOr+06eQv5dGuLgXw82tvd6q/+ispmj8yU4x796ePLPVvOS2Df1BdZ/wPLLTHRk+Jn3pNG1yb8DIoH/MgC+duu9//HvEYACgf/5z9/kqfmv3Xrl7HA0U/BHZqawNwSyIUY6hDwvBdgIXhYpPnlDqQ0VddM6UIo/pcz49QxPLQSLUtAV00l9l58pwkZzICByME5PFdn6WumkpKulhj0rDOJkF67OhrIVAaoFceTKI97MRFlgAmAqVKwWQzBvNZ2mjUu8OIoRGCIx6Gr6JsX/T3jHmzQfBgEY8YMQLDfPj09MTc1OpvIwAotxx6QLKDPM4MNLQQ1GVIip0NSZu4zAb5za6e70H2z/UgAQwoC7W/0dBOCpkyc6rc6OBOCy5N9t7m6jPDANO22vwsi/g2KA60RILBt84omnVhmA60OnPi2p+8ipEy3sTEHz26MZ1bBt/QiA/0bO8a8dJv5UrYvq+TVdMAT/aOzB8Ll3JPAIg+iC8T59fQb0fv2PA30gFOt776NC9OP/D+Tfv//nv76YGP7hOz8Xl2+98lHUkSkIzekRCJzVCEQGJnGiXprJRUKQK+6AirxWIymrTpKSggYD6TphUPlmk37qUzpeHQ9Mp41HKADt9jmpB7PSgFMBQa0DLUq/0ChUsMGNCg6EwZVHPJtQshL+Ipj9V6rNVUoQ/itSE5zhgQmAgEBhhCcD1Xxy8WwchyQkQ2XcpARtwpPj5z3+bCRYn6s1rIA3GAqZrMNSFw4Q0kdQWeKATITAmXpa0E8wcKvb7e4I1bfZ7Qr1t7e5ubu7IzTg8vVTjzxy8sT1VgsnogoAUuqD6l5kSpfHPAuPu74GnMOcsGGBeRIqLAgeagkEggIcgsefXtZ38tRQG8qxeaE6tJ/0kILX/2WF00fnC36E+818Fr4+n2OU+xnXEjj1CnO/878wpl4ZrHtXu2F9zf6QeuEQgUYQ8NbPX3cPz88nvv3xP/8v//yfP54fyUTnMy/+1a1fv34RPTc03Dky082Z2WAxX640qEcsKfGWlABExqVZwVnJpKzpM0KASgmq3l+LCWlJDZm0c0wF+vh+keAmXyRfbgcj+XGmL2APQAcAzJvjTRmN4IJx6VGjQfiTXcD0z0eoT6Xy1O/byKd4IbvLpdbnkf9lERhyBsWvj/gC4l3jF8bPTlIGuFae9bs90ZFcqkIP00Eviz4OBKpCmJDLwKJODnOwUPyG770qVODd3e7mZndzp7PR7Qr8dfdwFPTWTm8ICu8eOdVrCSMMKnAZ2PcUE5BmnKIHXl9HEUgAxJywUoC3hc9tI++wA7jVhtfDzuDrnyH/oBQbAAixvyHszgMTLAjYOgLgv4Vz/GHs+00YX+Zl6vvNOBLDf/cPMtgnY37aA79rAO+AIuhfG8MQjPPex8Jd44zUP/+v//xxIiE8b6EwMvrRGUcBfqvPI/g3MuLw5Zqz3kAxDAiktUAEOcIEcYyyGVLaqTvi5jIJPQanuq+uUfuICT8M4sH3pJEIUSJQBhkt2XZCrwALTp5c+245z56zz2G6wBTM57kwsc6Hp3NZjGTKgAQ4kwvp3UbeFUDupaT9TWkHjBpQUCoVyQSqyanz4+Ojo858ba4215gad4/OD8/UsR4GKqTrKW9QcU5aX+2FFfgCkoNMQDifvH33vJB9XWBgt7Ox0QUKwqP+stBdO/1TJ4FIbURg77Y+yEBuACGNt7ZKAAQf3D5OALy9OkT8g1kLLVo9Ahhsfwr+TsJ4heuU/YAtnWB/rxP/4BwB8N/AEe738Iae8jHoZwNgYiTjK2Dp3/zv/QPIP0U/e6bjlnzqQBNsTIMZ2A38szf9MC/6//qv8Nz/+NgRhSFbQvSB9vN4PIWoA0+UEJguNRrlUp4b5CThiEX8SMKH7a3+IEmWhBEJyaT8eakikWvkOOGeBKDJRMp8IBXTkn8Wy07iIoOR/xSQeDzyHjZ+wOQF/FQNeAjAKq48+ilCsMR7iS2LiSzoK9wvWNhK9TkvJjXK4bjLHv+TJtilZOBUM17KT54fj41FJxtz0BYcc8fm3XmohXk2P4E54UrKGQhI1RdQR/pilQEJ6Vfh4+Af7gi/e08AUDCvi7cbgD88vVa7s7m5s3PqJPlgwcf19fWXZPcbnHXEnwTfmvi+hqPwVwXgTqH7BSkn2NeGEVvAPmJg59SByY/jp5aXT8A0BnS+vKf4rR5oQJpU3T4C4Jf9PJy+30HusRNOOLjyef7aR4w/QN+7MglC339D2xvg75//6dOmwbz30dnY//1P4iX/KD7++uMxOj6PB+UfwC8qKDji8GRnJr0hCxEox+Uxx6Tao3sMPvmAfTC5SkvJQIUwqf6S0gDzN21/JQHjSWYg3cIMGQYuvYOFxTSWXf2ZGz+qrARxQEOeimHC4Z+G6XXYn0I+WZrreDxdRtNanYhmZqpY4pIPuVwyC5wy5Z86AWfIyk9eHR2LDpeEbKy4cu5Rz2QZsiz1qfMXM04hJudKamsIKjxXSN7TstCl7zISg647OwJ7G5sQ99sQJhgRKPkn7rQ6/Z3l7g6MPT3Zg0uU88Bc71PghddlFlig7ybcrK22kYarq0Mnbq8D84aAfrx1rtVq88eJk/sV4COnlnvL3eVuj0N/WPz3J8tv3elJCdg6AuCX/Rx/SPt+Vcmzzn0MK/wlhn/wjoIciz3pfQ+EnxkANGYB7sMfhgPf++/6Bf8UE9bXB+Jv1JMh8RcFBAoGZvyLE7NBFyJQbbFUMlBG/JIaQcmkpKKUgpbUbZJbiBorreKHKh+iDe++83/KOxKvTFo17JTSzAp/5XKj3GgoDJLI+1uL+GdJf4x4ZG1Iiex03EXuF5RbI+TOzMRLtVp+JrCPeJqCqAIBZKkp96hvLFoVDjiedWeyecoKN9JN93Qc3jA85XUGeW6+DPix3HMZYJT6D04wkO5v0tnbQwpuIv8UACEzsiOAtLNzTMAJHnaIfwJvt5/gMVhEP+l98Z54fg2ywkM4WLBFFNQHDDCmQAZEIAzTh83CQnqi6wX5BxZ4p79zvcMOePUIgF/qc/xrXznMmc/2M1D7lxiJ0tSXkcTo69T4RrXP0v/+hO9rBh4AQ9P9ftowwFv0on+EkfkZtL6jo54C8w/xh8dRcDcnp4JxTAjL1RnMoLQlO9oshTqePXVZQpFdMVxjtZZkFEL4zuLgHgPQSIioe1gHU5QX8R0Ju/qdGYh63xvmN+DA3iP0uWECHRhkzAbnFQRlczLFFlNFKuWrh0pzMNfKNTEVsELZbMAVoryHzQQPCMFAcGqmGcnlS/X8ojubgjeqlBpA0jq2hZQnm16nEIHkbWUiRH0PmHekKvzkThfhx5/dTXVMAEJ9zM7JkydgbJYAoMz6YlXzOhZBS/gh/1RRYHsVNFxr/2lTDHAQgcdPnQD5h79wBxHI5X/Lb/V32AHDCJkjAH6Jz7GHtu48YfsGh3O/kPz4aD/+bv0nGQnkK+9pEprpENso6IMOp4R/DQb4v/+1Yx5if6Ojo76oDX+ZqBCiUcdIwQ1lgalwucEDAxhgjD5Lmt+0xc6XParBRqkL0fKSdOTiQdVGlzaPSpAM9B4nueAwraCn1CWpO6zyq9RqWORHZX6Q6WWll2f8UX0Mtuepfx76E1J1+KFGKnctB2nghZpr0unN5RadQW/QdTkdsDWEmPwLARkFsZzeqXA4OeGerl5agCkxd5+uY8UhVAdOXMw2QQPKYmfKcFAWBb+RNJRlMPB1Z0cTb09IQPsRaq8rZNfyzibMvzrRa7VwciABUBJQNoEI98v8ayMQ13j/ebt1XYOvY0MgHTXl9JGTJ4BwQm52+4KA4rf3OgKAuGAOFrIfAfDfwDl2aH2/v/lQ6R9Ovfr4HwYWXirUaRv8yo/PfmTbd06Xtfz7x/2zUO3twOK1f/131zKY+xhVyQ8MAAr+8QEVmJuYhIRwA2pi8sQPCbtkkqNwrMSS8r5EITEL2cfoxKwFlS3LZhASgOn9ByOFbIBR/BnslfzFw/JPbjzCdt+XXn75EvT5NkgDov21nzxP/rIQf8Viqiz8a3hy/PzZTLNYrVSs5kzQmXX7s7PJeqVWqaaCmn0hvmNwMBQKBp3iPZuxXL1Wq6Wfvnr1R5P5ar1kWfHnbtz1eKabk15n0MBfIKAkoAtlIdlfTBcHUoC/vU3kHnwjAu5q/oER7faWcS1mt9NaEh+CYcLzfmudK/+w641qnDG7QUFAlH9ogaFCBnYNix8D+C0NKkBUgaewFvDkqV6HbC4NoBEAFAQU9lect4QC5Rzw9dVvHQHwy3oOeePRwDHqX+DbPLnfzHzi917X+KOq5+cvSdnHpS+3fv3fCuKn/K8PWFyWf/98kPwzZgFKDfjRRaj88wn9NxZV9BP4y9CHZGDGk52Y8mIokGtikGUqvkdu1DLUmHrEhjfJ9dPyCtnntKxvsdlfhUNpjjFoSD+ftiRTk0bhs8x9IP8WiH7U6UutvjSKWob7+GcsmfxIJlUQMiUMc/HM+Pi4J+OfdVmhSGQy6M3mZq2GcMRgZi1bMxwyzyWLopmFKctqZtz5Uil49+rdiw737EQkNw6FfHfHxL/H5pRTjcsP8WdIJX7N4uhAIN3toPUl+iH/WATuSgAKBC4v90EB0i5zSGPAAJenYBlIe0ioMRwJuMqJ3dYSQ41bg7lAZgh2YLZWWvS1pAUg3544dfx3QP6RxoP5M7CKkwjYA/y9BXP4AY5CDQ6t/s1RL/CX8xz76kPE38AB9wvqLzqMfb+y5U1g710G2c+fV+WAz996c3x4XuBqZDj25s8Nxt0y5N/zv+G8duud0QTjz5dxaPuLEMzYT9SXnZh1hoqlBpYFyrrApBR8LKNMHl6WJpUkIAk+rRBxigxPhD7IAvNNkjUiD9xPS9iS4kzj76CIHm68rM1degk3ffCkAxz2MgfNvqrdg1mN7AM1S/8c1F6SqpeSZ8an/T4B/Ugw1MxOR2Zd4cbCJXgPaKCrBl22o6SgfihuJt3ZcDh4/uL5i9GRzOKF8bN3754X/HOIf4vNWSfvRyIRCHdcyvSyAWY6pne6va7UgHt7gyaYALjc66ECFBKOCNjm4hekXqvNy4BX28rc8gEluL5Ki0LW24hA5J98lXohnBOn3pJ1Lss7/S1x+iA6hQUXdnjnDrQgIxwby9eHLp04moj6ZTyHu+9330nY7jh47MFI4gfvAdFkuTNWu7wr4363FAB/9t9GhkcEryBa+I7BOpnb+KxNIHheu/XKR4moD/E3qkr/wPqS/VUELNA41kwmlp2cCqYuCwSWde2c4hlKKYag/GDSJKUfTlLag66l5dQ+yiajGkzq8F+SsGjxtSRlQOhtk+rXJJll1OEBs64WBPNw4v13cOA9qEGa91wd5B/ewW3I+O40BrVasrLjMV8m43MvOgNZ94wlTDH2uAXKUNLSnEqFFOn2oVCewNRsuBocv3pR/D9JwZ07f/Xq1btXL2ai0GXt1f2+mnUu5X+lL4brAoAQ5kP64RF3dpUK1GkQHIEPuzPF4UbfJ1D2CUOsALi21m4h5EwC4nzop7BbpA1PLmn+tRGfLCrFbae7jPle4B9tIBF/HYzM6vfv3OnfQQAul5cbvaO9IF/K87Ddr6x+xu8jhD/HSGKMVn5woA8jf+8a4w+ef14lQd776NtCNjqiAoQf20KBkNtQLyevyymSd/Xd137+0ZiQf4g/Kf+k/jPdL/CP2uMKMCRhdiqQCpcriMCwYShJRXGC1sIEMUs1Qh+F/yxs2rAYl2kShqqFLsniz5IiUKk/PeBUYlUrTVSAmOAVAIRJV7TyiMf9vfSyEIQ477ReskcAGaKXeQYqhgBh2kI+mfWJf2J3FpLfoWoFrG8t7Gxm69je656CipdgMGAAzwgIcp44FHSmrIDQf9HM6HRkIuI/e/XixcxYbHpxBsfkc/WLeBNAnYsCgNwQR8FBVINpEHhAOHbAe5u7u7vIQAZgh4KAwpMu91qt6zASodtZpbF+IOtanR6LvNXVNUBghxEoIbjKChB+Yh3d7xI7YLppt2V5IMAUJr0g/nju4M5yV1zfonMHYoGN5cqJg8unj84X+zzM0hc4ZuPvfMHjo41H0f/ynmac+HhXg08mg43zjx/5hkcAWYmLH79iPvXZ6o8Gn46D5gT8eQbcrwm/DMNvjBE45hdYCEGHsA2BLMSSrO0sST4m1GUWf/gUziyQr7EQP0kjCZLkvAjecKkMaUCLaSp5Sz/OY2byPO1UDbzngc8vvfTyy98xlr6xBtREhZNm+OHCp3hqMjs9LZxqEEf74aTTWtkVqQoQlifHxyNer3fKqicFvQZkoOoKgS8oHGxOu6ezQvI5vd7ZiUg2u9icgQCgjPgh9EK8/4O1n/0kWeFB0xtJwF085Im7KA87+NntXodkLgxH3Wo9QVvg1lfhMQBQfEDtM9yKSyus9AiAq6wAaSCMKQFbCn1tJqJA4A4oQHW6nfbNnVfffrB1Z+vOHUG/Rq/+qc3DR+cLfI49lI1H6iQSBgDnM55R4J+Qch+TmZXxP3H+063nVdyPwKgePI8qcDgB6HLMX+ORCZ92zCrp157/qx/CmjmQfx5KfkDRM0f/TAAK6ME6JqQf3hR8081ZbwgSwpW6kVYlRWZRUI6rkw29piUbXyU0Ul6X0sRSQJLoS6rUCNyj99MdH8rF8qEGjyqFAAmA31EAfOmplxZw8zlHLvkvkYxGj5025gumXEHvrNcZcllQx9ywvDjiFIr6GlPj055YthmkOTGAQJX8CBn5YPqWCgWnZidnof/XGRQMnBLHKcHHAUCXBh/lhDEJEuDXBBQAAXYEQELg5q4koDChnS70f/QQUL2dzd0dmOgHe92Af5stXgMCWd81SHhQqQzLQF6RRBMR0AhDnkRCkLGn+CeOUJsKgRh37L9w98YvH6ACbJQb1795JP++fOeRhyz/EsMmAAt+vwf4N3yNF14+ryN9cPOTW8hBeQ2zwFoX/r9PD8870AiPvvnzwZn3xtEAfO35X79+bZ7dryH/HAP6D7yv1n8+jw8+AYG5CfEfddrIhsgjySb5AvfSEjcG+xQOk6zECEMWYw8JigKQhh3I11uMP8xbsI1m/uWlAqzUFl7SAHyCxKAaeS8tMKk/4q+FuWgavYUQTGFmNxVPJcv1cjKSO5ut0mCYSmh62p9xjBVrC/iw6oIBV4YCDNmigykwwt4AhveCziAcaW+BdaT9UCyG5GN5XKQNDQBu9je7GwDAzV0pAtEC08p0yL+KB6AA+/3drZ2h2yDmxMPuZr8Fug/6gNEDA+/arS4jcIkU4G2pAHEuQss8bds3vAfGFyZQ7+Bftn3vxt27zzz3ySdbd94q99pHkwC/fOdh9f3S0fP++Gt4pODxjGUSFz+ismZKdPzcFHqmpTXEIF9455lEgrIhP3h9vwoc3BP82vM/f/PvYc+SD/EXVaUvXPus5d8YBf+YgYA/j2/U4xFuPSYQ6AxYJVCBZiwwqbWdJf2qRBfLOP6kAGBSabu0xZ40TRikeKBFfOJ3TCrVZy/mo98OWRBoAakBAZ9SFljc+w7zz0iCMH2JfxbtveP9S9ALDPQSt/m6FZr2T/vHJtIw3qUSyJ3xRx2TZcyJPAulzWE78sy7qAdJ5CHkMOlLStGGOdSAGP1zubikRuEwcEcDUIBvU/jg3fsMwN3NzY2uIiBqwG5XIE/wDyalXif/C5RcQ/mHSQ+ofjYRuARVMjIEKBlIKlAC77SdgO21FlRdL/d2IP64tb29/eBVQcDzZ375yYO3hv5FCzSPzhfrHP964TN49Xkfnfcw7s9nMld/gPt+FdtuPf8uS8DBoQd2/MH52evnhBGGrZnDz7wz8Go6xtisW+/9ODoicAb405XPjgHzW4AJWcr4+jxjiD7oloOcydgYJoRdVr1SYWepKwOl5VUek++z7rJk6Qo/l6YXUoscZz9IFVppRUhD7cHP2iadIv3ytPSyXq/DuHsBPUyCQBngUy8h/6gQUC7lxF+dlr+P14DQdmGIA/I6kHw9HBx3+z2ZCAxHqKSyOXfUnYSxpxVrcQau1cIBibuQTIFIL8xA4wRJSGpFiUAXs1OqPfOGrbANgLt9hJ4UgExADAB2eliNIp4E5O3C4pAHW9Du1hLXdrsg/bgLBApf1nDXeVvga0UgkOoADfyRe5b4u6IhSGmRdruFs/e7y+J3Pbh379V7b7/96qtv//LBJ32hNW+vP3WkAL9c55GvP7TGt+FhHHxvDj7Aa/j5Qyrme5flHyjBd7kGUMYDf/2mzPXeMm7xvPeL+eERgS/H/PDHr9yyJX6ft7vfn79+NUq5DyP3G5XRP+1+TfPrA1wS+0ZjdOPxxSJTXmccEsINqjG28palOYW6zlLoUkTklxjfmYr0jR8hA0kKEk7x/dRaEZZyef3JhYBYCShcMKx94zLolxdw5ZEx9TlJLfmNEgAAIABJREFUejTNI6WTVlINoMZMCG5DBx2Yzued/thYxhGETjYrm/UPe3G8S2Py6tVME0KDjRSCKmRPh9hCgSFNxZCEXkheVfSTkpDAx3dNC8zkEypQAXAPxgJ2+HS7u/fvY3oYCdiHBMd6a2d3t9taW22r08LrVPgH7JRZ4Nu27ehP3Nae1zj0Dn3uO9m6d/fVtx98srUDBYHdneUOvtWRAvwynUeOfSX68JIfCeNLX6OPZ3jlJYX/3n0XnDAE/1Qa+NY7Hw3/b2/KHLHNIMPDv3w9msBMBiwPls/o4pd35Zu8mCiMkZAj+UeRP0c0OhD9G/MR/UD7+c5CoxySj45ffI16piOTwUAxrFQgA5AtpgSWBl7SkjBLyhfRR1rdh6fUxFVL5UT4bST/1EQDS12RM1BL2ApMS49ehj44HE9f5qmnktLw7sWUZcVx8mrSStO6TVgFLPchwUok8RWIuEdj/kCjNhdu5vyReg33X9bqgVwMxrvM1YNBpxcJSPBySRQaVtiUhIqNSvlJDrIWNGEYgk5gmIJPExAIe32JQHFFENAAIL0Eb7e2trjVo9XfbK3i8AMTYzgpCxGIrXBMQEW/J3CRnNkYrPAHFrjfh/ELO9j7Qb8aJiNgyfXtS0c54C/Reah9v8beD5sGhOvia/4jyS2VAb6lWAfpXqHxEsN/+uanDnd574cXh0eikEu++gfv3TowHQI5Y8p98NwDBT+7/BvTxS+U+2D9FwME+um4Y57R3MSkM5CGhLDdCCsQagvM+o+AR1BTQEtaSv1ZMidsYZeIJWc9y64SS3Z9hHm6M36zLD3gCsbd47aPOaphgUZg6gIJGx44nSqWapVwMQWjFiyaw4Wb0PU+9BTuRQpOTU40XaVSvpnNhioY98tDDLCCYwIbzsisM1xrJLEsUENOsc7gXohVoIKdwqF8PZNP68TAHch9cNFfXyk/wbrdvV2oi9nYkAiEepguoRE5iABswWJziNsJcN1sIdA6K4gysr3rLQOAt28rI0x3II1iIBDxt4oWGPDXw8JAaH1DFnYgp7zKTcNH50txDnPf7wEnMZj9lShM8Hb0H/31Pz5P1heBprs+xM2b54dHgFjzI2pG4K19C0BeeXF4GDg2Mnz2I5UNeU19//Wb446Cjxxswcx92HO/GZ32AO/rOTvK5jcGn0w/t3tafPhj0xNTQVey1KhRNoTSrEk2q0mNOOBdmq8kDfVH7NPSkF+TVE9K6aflX55mPiPO6J5avS74R/1wDV55BOZXLv1Qthn+lHgYAVZOFrkHGNIfcd4GxwBMxdM84CVdyk/l3HkwwvVgNltbqNF8l9KsPxai6Vmacy59J8QCMDDwrI7/KcEYUJAMuULq6w5NP+0bChCigaD2dvc0AVc62AWCAMQ2YQZgu9UVxpSHH9CkGOoFYQKCzjMJaLhgUoEtShZL/q2yAgQBuNzjMYBUDQPmeujEqVPfPFKAX5bzUN2vFID0G22/N0EEBAb+6ZuyC4QGINwiygn5lxghjRZ1zGupuO/8/J2/BxGYyTiuibeyV/7d+qvH5zOg/gTFZOkfd/0anR9G6G8Msr4+gp9HwA/EX0ziTwBwOjc9Lb5HZryBFGRDaFqgTtASxC5rA8yFLlLxWTIbolGIkpFny0gBKYGo8EecC2sK5nnmfVgt/q2XcSKqOGXc+SGHYTH/0sUkjTaYa6TiKQoFou5j/BUlA8UdRJNVzc/6fSXB0/xM1hOHH8yXSklvxD2BI+9rc2UY4KLKArW403fYIBv4k68zgoAh/RTGAu90d9QAQMLfrpqCgJXRG3ukAVswCn+5K72xgCABsCPeoEMZEJBzbJeBZ5z85WkI6xKBT8hP6g1RPritTmuHQn69neVub4erobFW+sQpIQdPnDr2m/7LOzpfgHPs62MHcurzOfvIqsN/g08lhnknMD71bYlAGQ0U52fC/TqUQc04hj8LgW+eT4wIFZdJDH9MUpEw+K6w0Hb3i2XPGQcWvtjbfiX+UP+x8R3l2B/TT+BvOpfLipNz+3OTXkoIY2W0XL7BFNRumODGFyXf5HADloJK9iWTxsuU/svzxo9wtSQn3WsSSmVYKtVp5RF9sfoLy/1wyWRcuN+FOVxcGZxwFa1knCKAlP6VIcC40oHiq5ic9RXypbB3etHdBOQFh4d907lsSrxRQ7xRxZt1BoqpoJobHVLqT0tCZp1EIIX/6GUc86NYosakAGCHUyDAP84Dy3H4G4qAK7AMqdvVwUEBQIRWC3680zYUoEIgEfC2VIAagWqZMJ1VG/7AAvcF5oTvhaa4HeiL6y6BvRbvD3OxBBz7R70gX/hz6H2/A5hL7L/KSEyQCZZnePgHb6ocBwLs168/g/gTTMrwVALHsO91lQ0ZrPT72etnoSRm2GO44NduvT4+n8EqlphHrfzgyJ+t8M+UfyrzK3yvIf3I/uaQfxFxsu7pxVlnIJUHFahGL7NyY4pdJt6lWeSpL6UANSgtKfzUDyuaqm1vMPW0pBd+VH9KGEQC/hSXIVWrvPhNzgFUVC7G8yD/ylZloZacKJYrwslalPmI87e48aCYQgS6nJFcuJT0Z7O+vNCO9cWrZ/3uKRgaXU9W5iqpSKouvpW0q9UGWDJQKT59Ab9RAiU08GP01B2K7wHQWABu8mYkJODGHn4sQU0LVAJubu/e34VmEQAgznVB2KECFA9WOmiW2dbehIIYUoDizhoD0BYGpJkyJv3QAsNI/OX+8vUezIXuijfiBrplBCCco27gL/R55NhXD7n07yCZZ9wxMiAyCaJjgdcuvKdTvLd+9vEIrK2ErGx0fiQDydlCITMyco7nAA7WOcOP/OLbw9Hvqd7g18BCRzM+QbRYzDMmcx809MBe+jJW8OFeTEh9UKoY1R8kfZF/0vwy/pB/4izmcs1JaI8rMwJtIhC3AUsby8CzkuoSg075Xfh2OakcsaKiyvRWEWxlvdWSVn6EwyoVDCuPfgo+WbxQ4Y+Df+kkZnLr3hLsqaQOj7lGmoFXtAnAItyDrcDiIxD0AgCnY2PVS3M1l9+TyVq1hYVaXVBQv1GdRwWylbUjT6o++QwLwpB8Un6TClB8EgCpuA/510f+7TABOwKBeytLrS7sBFnu7mze393FdmFUgJ2OBCD29S6RBWYErqCsW6PZ0VICrt/W9TAsAG+v39YEJFuN2d/l/g5EAMUfsXazvdSSoxKEKOxvio8TRwT84p5jX/08Nx4lbH298uKA2EsoDzzwMlP9KRE4/OeIwFvgfodxay/MyR+BJx0FHyHQMXz1TSnx9kHwr37xjvHoZx8lHND3ERtVwT/HoAA0Cv8g6zsmi54x76vlH0T9TPwtNiMTcJrZXGQgISyPqfGUquPBVml9zXDLWvQpUspd57zvDVZ+NDjEB4ddLgcB+YWCgawQL8t6QauYCgO1GvHFJI43rcCqjrlyaDbN9EvZPLAL77hSxWLKFQim0mm/L+pLNWr1rC86VREgLIem0/hGzzYg7Vz2zui6FiXp+Mu81c8TFtkBu4xrlAWWAOwTAQXa+qwAe4zAlU6vv8mPQSDe372/hxYYEh5AvU6LB7x0bAcutWki6tramrbAt1UI8AAACgKutWjwX7+/DJMBt7qqwKaDo6JxUszOEQC/sOf417/yOed+ScXtu6TuJw5An/G6fQf+PKzl+/mbZ8H9QtduwTHPT0YL0IwmnPDIp7V9PK9LBF8T+HvzmfkCJT8w96sK/zI29ae8L4i/sx7o+xjlzIeO/IH449jfImq/ZhPwNzM5OdPMwrxUV7LKCeG8CUFLa7mkxTUx+7GnHTNBzzx5ue8N6vwaWOWCSV5ce8SzTmVOWH7yycv0B7wxuN9afioXnBPiLZ8vC2pV8pPZySJIPRf1w0n+pSgEKD7F1VTKFS+6JiO5bLoadvojYQgj5iemZ+GNLAvfyLrw4YRLZkK0qlOKTsf/7LJQPiev8atdBgB3t7e3ZRbY2IZEe4K7EoibulVkU5FPNbV1DA8sJ//BWiRhf20AfMJugW0AFLYZFCDNYAXgbS2rUhkG4KbgX+cIgF/U87nnfimOtw+ACfOuROA+GSizH/rQ/eHh33v91+/9ULpfT2be4GPG4wEnnMkkrn0kje4+Efga3773YmIE235HYz6z79fEXwabfsn+cvRPlr2YsT+En41/kSbhb3JqanZ2QohAb8CVlx3CeVMGMuc40/EXioMSg3xfEtIkH96qkc9Y5gx1znh46REQ8Kead1IK8mN+p78VirO+cGmukRJ6tVHLByaTMOuvHlw8c2bSFQikquFUSuaCTQbGMQwIT7hCzilnuFpcjMbFG9WDkVyuXrGCM2l4o/Ls3bt3m4FASOPMZX5TZHOZalAKP/3qkPowLfD29gNG4KZGIKZD6CElSxCAODSwvwJBwCUc7QIQXNEScIMJCEFBKJJeXwcJaAsC2hTgqs6BrFEMEJYg9UECCt4tYyeeuGnBbPwdnBTdaR0B8It5jn298Pnij44O8SXUlYT+Nvgr5VMJBqBBPg3C4asXYUq0z8fud1i/ZCQDLhWyIvMZe0KYe34l/V772XfPRin3S8mPqDyZjDH01Bh4AKvRZd3fqC30R+Z3Wppf+BLwQ/zNTsGyR+dUBFcnpaxSpcajsnQwUKk6jgTyA6Iet3+oMKC8zgzMq5UfNOwANh5hoxvOO52Tkw7UbwxzrSAJQnoT6kqplsvJZiSS889ORlyVhQVBw8iZ7LR/2mnh9kpLkC4tC6FTCL+4fiSccCiQyofT2eF4o5xeXMz6/bPZLKw8rzVC5+6ev+tzNye9OPBPUc68UYoPbgLG45DtGSZlSAOw2xf8e/vB9gMiIIs+pJ8SgD1WgHS6AnrtJViBdJPqXyT+WAIucYoEJiSsrWv+YS3g7ScM/XdbN9LBlqX2iRMwE3AZR+JDEWCnw8vgWstdHJa63Lt+pAC/kOf413730Pp+E7Y7hL1BXTh4Egc6YElAJN0YFO3tfxIGyKARLsyPvf5XNhX4mi59/vk7T/PM5xjOPYiqjZcG/aT7Lfhw3gsF/6jsBb2vX+Z9GX85zn2A+52ZnJmcnSX+BYOhwMQ0TP8MYXvcs4xAywSQhTXSpui7bCXVh2qJM+0xzrrCt6rWaeKzXnmEi98u8awX3nokDS9vwQzzO8C7pZPhel78+Vl/Juut1hYWwP3mpmMRZxhgOAc9bjIdnNaRwLgUgJANdrnEvcXheL2YO7c47StMT4EZruWbsPTjaqbgXwQCBkxJp5mm5Z9WgC4WgOZV9XM6Bri9fe/e2/fQCG+qvejmfvReTypA+Oh3ltYg+XsTbvbF/zpc3rwCJTKr62YM8AkmoI4AmgoQ1mmeOH7yBAIQB0NDQTStQrregeXo9PgIgF/Ec+xwp14N+tyEunzwqxPDpqr7lOMYM92vcaKF0VFM2GYS86//TDW+3XpHzkIQ7vcjh4P7fqX849CfPfiHYtKDWlO8kuTiPvM77c7ldOkLel8BQME/mPLpdKLscbki/tzErDMYSlfLtRquj5N1gRJybII19gziqfv0RS+kBEae9B/wD4ZdSQn41Esvfeell3HrG+eCcVIM4Q9/1mgaFjqzWramI9lYxpMU+JsrByI5t3/GEgYWEsPY2xuKkw9OGz0hTEAAIIQCUylvNl0vnpvOjY74UpD/LQfHgX8XHdGCOzLrlaOiTe4p9mnuSeFneF7FP/450wK/+iqMXmEC0tnQbriH25Pu8xO7WzvLnfbazZuyAsYUfxqAnS4qQMiCDDhglQVeBwXYkviDrmLBtkdOEgBxPzrQD5eF9Kg/BAKERwD84p1jX80chvvFkzBDfTLnOzysLsm7tqtG+YtJwgEizg9em5+Ha+IW4IZOOJrIXf4Z4++jRJTjgr/+i4KjQOE8D097Vg7YxJ/O/Xo8Z0epU8SP+HPrM83ww9jfYoRSv+R+p7xeb9AZQP4V44ue6QjMCkwlVU3MYFUMykG2vmyF0/IxpYwNGCa5rY4E4MDKoye+8xLMO33pEsx7pnl/1ImSV11ved2aIt47na9afv9oIRqkWGBucTaJPcOVejxYhvq+iSkh8YTOS+lS6LjWglgRCE974+GUe3QsMxycW5irpJ5G/EUdmViuOesM2Iv6bCekv+tIn6TiACDFu/RNAN67IT7eBhuM7NvY2OzudbUChE44BCC0wm0tL7+/fF0gsI1FKtgnh+Pz4WAQcAk2wAkAtsADUyGgFIBK/wH+7BZYfCDbjn8TlyIJ07uDxLuOy+K6sBSucQTAL+A5/vXDrXw22ZfQ5DOwZ75KJT9+g/4bOPPAPbwzjwzMwDpLKIuJJrDt4y9/8aP5TGHk4h/+5fO3/uEHmQI2ssVi3PfroHVvRu5jTE89oMI/6X5tVc9U95ID76tyHzMU/QP8OWHYMRVyxONWIDbqhnRwIBS3qo1KrSHX8V4m8Fmc7E1KCMovS2WGKQfC6o8PKUDe+faSHPiMS99efuo7QgI2aOcR0Y4sL1NXRyERs/FmTvwjxSu1undxMl6vofUtOSORKsQAZ2KzyJ44Ol2FPhcnhCEKCPfEK1Kppns05nM1KvXnYOOvwF/U56d/dFdIMc52x9B6mn3mXTsYxd0dZNYGAvDevXs3brwACIRJWLgl06YAu1oB7m5u9XrPCmHWasMo6CUGYHejC/DjcdBLS8ICd4W4u7mKIpABeNseA1yHGfoKgHCoyPmbKACh8LmHXcGd68u8F3P5LQHAo6mAX6xz7KuHFvyDY3O8Rl2gzQXLB5J6/3r4EQBRAo7Mw8MRQCC07I5loi++8+a5DDWwRc9/9ONrqP6ElVWlfxmZ+1DyT4988cmyP6j7U/MOuOyPC/9ygL9F6X4x+gfmVxyaZgx8SOabBV8stzgzFQy50pANqclRWRpE0v0yDA07bHwYaRNZBFMiBQiy72+MlR808Z4UIL7UMgWneKTeVLxfOuVyTs1OJOvJyER9Dq3v3EKtYU3CyqNKMDcdCQa9gXolLAget2VBVEAQ08Lie2BqZiYSrycnBP6uZsS/X9/04oQ3aOq8AQUoMae/m2wc+Al8aqdLAhAV4As34Ny7t41LkTb29jbEra6JEQjcYwW429/qvd979v1nl3swBRrNblfDEt50ZYmEYavVvokSUI2EuU210Ip/62YMULzsBP4X9U0UgMuwjU7gDwRgfwv3YgoFuHwEwC/Wecj7fodVKHD/MzLz+6+Wfwi/+Xm+kYcQCBCE7PZ8AXMXnoz4p3VkPHi/QOpPBgB18I8yH5J+ctypTPwq8ScTv9lsZJFzHzMCf0L9zQrvC/RD/KWwWi5thVOFzFgMVkp6A65UGtrjKuWSfUqCBpuBOslEzUYGIOZB8pQDhlmnLwP1eOPHd2jlxyUEoBr4Z3fcefmG9DvSwJZAvp6KzUJJdDk/lcbpVtAPEsjl/LHcRB6yGo2wK4V10C4jCQIfEAOECy5YXuTM113jd69eBfy5I83JIGArtA9q+x647H5Xa0bb60OhPuJqAwF479UXhAQEDbgtASg04B4jDW42CYCCgAKAvd77z/bK5Vd6LVSA1FCML9wADbiyBBIQxyLcRAKyBLx925YDGVSAQlF2cOvvyU+gDgYBeL2Dyg8B2IB2OMHEIwB+cc4jXzvcoX/mmxtBv8HnWSUqACZIA34qBeEJFHwUByQAEv1GTAY6Ch5gHlwbEff9fnEfJ2dlxP0xVfkHYw/s+44o+4Hz/nDcqfC+Z1H+uWXqY9wte36zOvU7M0H8g+Cfk3Y8UsgMN1rmq6PRMd9Zfy4iRKDwkRAKrFW4I1f7UZ0MsbjqTz7A5y6rBIhFms66HFZL315CAj7BFlit/KCJz/ZtIfTj/DsYskiyfCkemyzX66nmOc9oWq08yrkLmck6ysK5KuIIo34pnQ7BI/65inFqerNKqfGr4t/tmD8bgZkQoQM4NvAoZFyz3TPVIX/rC2ZtCKGnLDBLQFoSvIcKcJnxpwEoTh/N6LO9P1n+d8uU7gAudrvSCq8I/GEUEM7SzZs32yoNcvu2jX+r6zIGiHvlVldbXQzwHfsGSkAAIHxcRwAK/ffW8ltHCvCLdL72lUPu+x02Yn/q8f4bFfv7V2g/Bp4R+psnE2yckZGoML0jfKKFggPxhwg0Sv8yBv8KZt2fT8s/v6n+aOAB449zHxD8w+SHkH9OKn2RmKDZ8la+FHNkxnzn3bkIiMCQK25VEYFqWmBeE9BKqhigZGBS5kaSCo2qEIYkIBJQrj0X35/CSkAKAWINjG0sq6XuJnn9HE5/Tidd7pl6Nek+l/MXIkmcDZjOZqcTo3Ga+TxXnnGGAkXxGXdR6pdEoJ6WAFfFP3jalb3q8xHwNd7guUHJZ/JOYU6nPMxH8kUp7HuDSB8C8Ma9G3eBgAKAuCh9Q/Bvgzenb4iX7SkFuAtuVJjg5WffX36202YA9jcZgEIErgjqLckmkSXIlRgANOQfALBlEHB1rdUhE/zIMQFAVIBogpcRgEIBvvXWkQL84pzD3/drF4CfehI6PZL4F8X/CHzziXl9QaJvBL+PkBIU3+RxjIwo+KHvVduOombdH2k/YCCED8lCq2l/2vsy/3JZjv1B9K/JpS9eWfqH/7UDGIhb+WpdAPDi2NmYfzobmZhyiv+I01a1Uas1pEW1QclWH5hkASgtqyIYZDTCmoALLwsEfocOlAFiJTSEAPNcB2hkPvhukpmaVns3U1NOAUD/tHs06sb1Rvlm1l3wlmG+QWVhruJ0z6bLtXJSaFvhhcH1CgoKO5yW0UCXizpEUl7xb2VmcsqcZGU/qcELIfU9ZL9gPAhJBbgpOLe3ywrwBakA4eCe4E0CID4Unzw9UADwDVCAwo6+8kprEIACqh0hAIGAiMAlKJheQwKaCFwHBK5qAK5SEqTdOsH/cR0/eQIKX95a7ggILm8BAMtoga+3jgD4hTiHN/MZCvQGE7y2O0ZeRF7QCvA3HWadAuCg6kP4CdrJL6afwzg878WYemAE/2TP2xiOvIoZhX8Kf5j7xcxvRPIPMr8zmPvA4B/nPlyEPwRWGAEoftfFs2fPj+cWBQKDAeEXrTAgsGTsZbNYAbL2S6rUCPPPsgx7LEuhoROu3OBaaCgHfOnlBVp5JJd+5NW+OOgtUUcqTbl9HQagulzpfNoT8xTmZxcuLdQuR7LunLVwaa5ixecWakWP24IUSTjkohCgizAo5+VzIBAeu0KBoB4ESLhLpcxHxgkZz2m9NwhAxVIaBa0sMDDwngIgQU+6Xzj35RO7lJD9k/f/5JVnl1s3KQnS75MFRqiCAhQEhCkxAoVra1AzuLZqIpD03+rauqwD3AdAoQJPfuPEqZPL2AW89QAs8DLlno8A+AU4j3zt0Ba+YQXKmENSTpLOXvWi7K+qeBn+7Lif2fA7r3MeKg44oulnU34jdvbpgQcOveztgInPFPsDBei3V76oxC+YX555NSFL/yD5AeovgCtvgQ1F2l2OMq1e9Y0IAl68CgQEBKIzLKbzdYXAsIZUMqkpKFWfxdfS2sHmLS0BiYAL3AsM05hp7LOaj0o5kKRVt4pmgJEAiDuWcCVJGmDmEtRzjzobtbnqxHQOeuNqdedUZaFWXZytQ4Wf60IQciEUBeTiQFkiKHuEJb8E2FLqW0qxb5/+s5+Q8QIj+EcPQ32q6kMFSEHAezdevYe74ZiMBgA/uH9fxgC3+j0hAd8XQHpl+f3WzTYBcHOHWob7m7vdjRWokr55E5Mgq1QLvbomx2LRgQurbaEAb6oc8AAAxX9kx3/neK8DY2E0AK8PHQHwC3COH5r7nY/StJRRXzShkh4H5UIStkuf6X6NEpf5eSPxobK/hD78Iv03b6i/g/inFx7Z7C/2ffjG5MA/qnu2dX3Iwj/AHxf+0dQDHHvgheRv0JB/GP2ziFHVhssBACwICRgTBDx35mloDxYiMBmuy5oYe1UMs1DuvDR0m3nUNAQah8BLj2o0DMbAn5zAkC4vVEryvQB+vG6YTDAuHy4Wi66Ac2p2xlUqhSezkzDdtGJNLtYX5upeC0KBpakbZ4IMJoN4MCEGmIjZEVCAiLsU0S8lFV4q9dkEZNrZHus7rA55GYgCINZC3+Ohz7tYDkMABP598AEAkNDYh8KUP+k9u/z+K8sAQCYg5ks2ca5+ZwUkYBtWJq0R7NprkOUwALgKArBtS4IIR2wHoDgne51Or48AxK6Q5V7vxNFupN/2OX54C99GfFB/LCxkzD/2mQ5b2+IDSl8GQIjAk10e8zrip7yw3f3a5J898BdV454dJvxY/fm47m9MZn5l4Z9KfWj1R3XPi5Em5j4mJie57ZeSv5j7hdIXIAzzqVxfnB+BchuQgLGz/nH39JkLE9AclhI+WCCQpgXKbIXSfazP1ANphgl+XN2HK49w4wdvParQyiPVB0whQHjfdF6IxFqYxSS+H8rUtKQffksLAoZCwWQ9HJhebAgfXJ2KTJcuzZXz0Bpc9p7LncnNeqeC8VIJtS5pPxeOyGJHLD+gPwSzIi5543JJQejSz5jS8OBjDyKyBYZ50Nvb0gXLZjiaDYP6b4MA+MH9LsUDN3egNE9owGUqBbzJldBdfh4nKoALbtMySxZ8wgRLAtKoVGz+lfKP+Lfa7gwA8BTsZWcAkgTsHfHvt30+96lX6sA0KoE/KB4p6N7ig1IhhjjcD7x9R6k+lfndF/nTgT8TfoOhP21/za4P6X4LBEA17V6uuVTeV7d9ZDnzy6UvmPywlf5h6QtF6ShIV2+EHAKA1xzRi4KAMcHAceGDn378uVmnAIhAYFkhMDwoAVXgz1Je2JIA5Nwu7kKSk6DLAoM4D9Ucg2Bx0qPYgL62UFq/LYo/iw0wemB4hDRLVsMB/3SpUk5NLOZCUBANcxKSM+fO5Nxnp715GJraCKcQfGyBAWJx/DJ0IVEOo4OSeCgIUwYK9wPQ/sjOv9QdYyHc9jYxcNsGwF2xrNN6AAAgAElEQVQgGghAUoAIOIG4ndbQdcgDv7/8Sg/sLawH6SgA8kyZFVjmATuCDdO7Sp9kdm1ndfVAAD5y6oQQgAKADxCAb731liDg0VKQ3+45PPkHHbgwMR7yp1GQfzoEqLMfsipGVvwNy9oXCcGDYoEyADg/r0r+ONk7b2R85/dpPzv/oqT8uPZvoO0Nvjz4tzP87Pgj98sD/yJy3n1EzjylsQdBVn8umBkgEw0yR9EIj4q/2eG4JiQgaEBgoEDgmacvTHqDIVc8nS81arImRtngpMzSckLESI4oovEv4V0fpbo6JeJf3ng/EoBzNdcsVq3AH0nIS1vEviQ9FL9GCFjxT5G2nD53teTNLk5P1hZg2qAwwYtnsm6/ezJfgwWY0CaXFjqPO+QgNeziRAglQyTrpP01haCyw6kB2mn6DWRD5EMBQMjdStht8+FUx66SgJgRBgDuSsTttFqgAJ99X8gxmHi/1gYR2NEKEH6w01mCVuB1g4Co+miRuu2sSQDus8DHTwwNtXowr+tBH7civdVb3jkC4G/zHF7udxjw56N+s7ERI80xrLId8xmH/OUaer8h/ofRPqn/Elr92WJ/TEE7/ez8U+SzpX1Z/RWw7NnHuQ8PDzy1ZX517C8bkYV/xtgDJxQ+K/xh7sPi3AeeeqXuT1xzXBtRBAQfDCJQIPDx576HhdEWzIlRZYFG00bSuMckVFfyOOPF4sW/xsojM/qH/b8cARQCsFZ1N135UrnWqCaTVP6Stsj5kgtOsykuJoUQnGmWShPT2Vj5EsIutZibdmenLKRfpV6bg8WXWAYTV+1xKcoPA+mIhS5yxnFyvWx+XXEFPZsMVJRL2b6pl9BdUIDwQazbvc8A3N0zFeCm4h8pQGIcbO54v7f8ynKvhdquTSKwIxUgABAWg9yExIcmIBphg3wtHIPfVjngAwE4NNTrP9iGJAgIQIHBo1EIv73zyOH1/Y6A+x0jAnp8GQKdzfAmojDAz8EPEwjFf0nxM3EOA38Jo+pZg4+1n51/RvBP1btQ3M9W+Gxr+hXqz+MbVdPuTf7l4NPW9tFsUvJjxhj6J/mXLpLBlGvKq/VKdUL8fddG0ANnBAEvXsVIIPrgMxdenKJsCKrAZ3XjhlkXo6iXVHMT4FymUhj4RTj4+ae4+62EOy9N/8tvlQ4LDdeIp0ow52phoVbVKWCZA+Z6QEJgOp4KBavVZszvoeF+s9P+7GS6DJMSauW8E3pDGpMzcVRwcRX3w50hJP7wFgsE8d+N1IKG6eUUMYPRkIp8TA2okdkn/vUZgfd3BePub99HAO4qC4w10B8YChBHpUKjBtTCrGysgMpbXcNciADgjgwC0lAs8aTkn6x9abfbNyUAxfM4BIYl4LfWWwcB8Pry1vbbfSiCLh8B8Ld6jn/1sxMT//MnEeU5zMgRARLtgYeZfw5PDOrqYgV8IkEpYkLcAAH1A8W7xAD98AqnPBiCGoD7rK9DBv4AfIOxP/6zUbrK1G9s9KDYn9H1i6Uv1Pc7CVNfQABq+Sf0H+JJrWorV8LT1wT+4E+8BgiEP2fEEb127dpINHN1fPycQGAg5CpyQlhv0JTeVQOPiwFVGoQkoDHnHn9ltQoUrcqhg/hO1t/Cj4MAFE72EpjXRikfSqWFXmWXrdQfpUIQgkXBrWJ61j82miyVy66sfzEl58R4s+78wtxCxXt+gpmFW+LI+eKUGBcVBKICjBMhEXRxjgbGFQCVKuQb0xKnNAY1NlN3+rxlbZN3It1HCAIA9yQAN0kCogLcVfwjqbcDuzNXVjY2EIE8GbDLNTTdjiKgPDgAFYxwm1adwxePAdQxQDsAT564BApwp99/cEf47cbyW8IGHwHwt3SOf+2w3C+O35MgweGh0ENmqMDE8EhB8I+2qMUKI6bpVRA86Ejby8kPuqYDgAO2dz/8FAE/xfvK1Af8yWrVry3253bb8MehPyH+mjOIv1kufA7gpCcq/SM0SRiVyo2Gy3cNAIh/8nDiR1ef+eGP/59fvc/nj/7gxz+8cObM489NCQQmrTwh0N4coqxv0jTERsFMHkXj4AH22daP5CsL2NwrnLYV8E5EFpvBaqWepHw16T4KCWo/XIQJqK7g7ES+mne6m2VQjoKhMCZ1NoxzYs6PL05NOYNc8seW1yWzIikqilF2mKHoonwIPos/x/xTwUKXkfYwra+8ScXvkAjc2lUE3LsvPiT+0AJvQBbYACCMyceCv+6GYB8QsLPRvbkO1X68H522iazIdUZtvRaTVeAqiT96cm1VOuBvCQW42h4AIFngrWWovIFxgMvLR2uBfzvnkWNfOZSVH3Cg9A8VFAPQQ1MExqISgQmHLzYqj9/vic5/asxPXp6nGwk/M+qnDhlflfxwDHZ8EP6IgST/jKo/lfqA3MeYyn0MjrsH8zu9T/5B7csMJj9w6gH2vYUwC5BWlX9S/jUa1YmrQv3Nw9fw8I+e+YPXf/XGafu58v4ff/97j194/HuhVDGdxw7hsuoQtlgAsgVOshpMmiBE/sG2D/ytP4VP/HmefE8iMJ2Hvb8wzSXtbC6eOYOlPBZE8sLxFNXBKPTRHcyOwNWUKxQMV/Oz/ibsOGrkva4ajcuaq6Smx8/7pidS1Xq5XK+mqSwwRQowLr+hBaZsSJzFHZPRhfkTjhFqzrkGHvG1lHwOywFTO52dLVCAW4p5QMBdpQBRzwEA76sYoCyPXllZYQKK7ys3McUBRngFZgxurHT0zjipAm+vcxPIqtp2CeWBMgMCCnC1batyPnmiDQC8s7U8VOtVcArh8tE41N/KOf7Vw6p8HkYDPOrBAjptgtFQQjJkGLd0jMJAeRotgISJStwZyV/bsRX5md9YDA5WvBAA95vfqIMG3Q9U/amZB/jXjpmpX538kIV/NvlHwT/bxiNWf1j5zFiSYkywrBI4/+STP4JeFfEv48kfv/PGlcceFcijcxo+xHnssdNvvP9HP3666QUVmA+rhHA+PJAMsdlf+l3462g/Ei9JyrP+y+dlKFHY32SY8hbx7HTuzJlFccQ/VC4JvSO1ch4ak7H8RXIQByMQCotpQZ5QOpmf8kRKpXo6knPHUjQnplY8N3122I2j82ETXaWeCqiKaMoFc0bYxVMTaIJqnLxxnMScUn0cH+RMMccEFQv5OUXGwM5aG6rsdncVA/f46z4BEJPA95F/NgBubm4sEQC7G52lJUbgWnvtZmtpqSPwd1MyDs7NNQXAdSkCWR6uagSuvySE5IlvGoBjC3zngVCAFaH/oAzmCIC/hXP86797qCs/huczlEVVSPFhQcyopzAynMDJpFBgMsZLNTwxwZboAdQbYKCG3qAANIWf9L77pF9U9nvYa/4yZurDQ6kPhT+Z+52WuQ9j5gsNPYhMqKF/mPvF5C/+h8n8k5XPQoKV6o1GfubbT/7+k9fgn/ba3/87QT9gHqKPbhCAcCueeOP9Oy++OBVICdQYCWH7CBe7ByYCMiXz3BWS55Ag4k8PgE5DwqKSnz1zLifEn2DftN8fO+uslhFkjXyqqHMgUgKmZXUgRDaLRWcuUi/Fc+Nn3IVcEdx0Lb047Y+lK5QRhlEJc42ki2YjqNLouIuLoZXkY2ccp2/YUAeAJBRK6qWUCpT4UzhkXoa2VtbX2x1AoNKAm3YAwryYPeQfW2AJwM0NlIAAwZWlpSVxKzAHThi74NawPpAyvVwRjS5YpkRWCYE6/ieM8rcgm7Kxu6URyADcevCWcsBHAHz4B/p+Dyn6p898dEzxDz0l1NRhRfQYqD+ssRvzydnKwgaPaNJxRHCw9I8BmDCEH3lhe9bD4ThY/qnKl8zAol+j6Jn+RGnOZfBPul+3rnteNJIfct8vNX4EaNQJ4C+ZJiCx+BPut1Kfvfjh7z/55LfB+z7+qyuPPkbguyIpePoK0Q9l4BWhA9///uOPewOpomVRQph98L7+OBN/tOaISadlYDisfwya6ZL1cqXsPHPuzJnctHvcH8N/cDcpORyAmoxTQtgy8Ec2mL/irqC3XkqdGx8fHXHXgX/hp3OjTdgoDGTNeWawyFqG8mQhYJyqoV0uvgT0QkMMFYOqFkYlfxX4Uup6SmpEIxgIZ+v+ytrt9XZ3Cw7owF2ZACYLzANedrUCxGVxeLNBZ2UDcyGIwDVse1sD/nEDcPtmi7O+ayoTogg41GL6fWv1pdWX1tefWm/Br9pVYb6TJ65fH7ouALhc6z3LADyKAT7sc/zr/s8TfyPGm0V1UY0GICnAMc+YGimF5TE8Xw/VVqwwr0hnYm9YwU+W+83PG244MaLafXXKl6g3OPFAVr0MZj7knkv8O8Xf6DlrtH0Mtv1q9yv3fQj3K5MfHP2jJT8pDP4xj5h/pXql4coJ9ffkhz+6Njz8978S4u80Qu+0pOBp0oCn+RKHA79/4XFvSBjSPEzNp1FZedskZ6MIEC9jsoSFXp4zJxQVZFHImeR6PT915oWnz5wbHx2LjsXcucXcBGzAhD638qWFSqqYNo4sDFQpkWRSsCqQzqfcZ32ZxATMiQlP5DzNGkzdqgfPX72YiSZBAgKxKM0rS6NR3nFaGKsBU7JsME5l0+onUhqCWvxJ5Sdh6JIOeev+/b2bgkntnQeoAvu7BgK3d2lrEhb33d9WrXCbmAqGfSJ7AoB7+Ak+WHjiFdyEvkofCEO1GW7VVhG4ijFDrQC/hVPz1zdJacpa55MnYBogzIIBA9woL5d7nSMAPtxz/PMd+zJfGPXIWVcOuE841Ba4QBLQRxhEEtJDssAIwLGo5t9+DhLzSPxxKmQw/6EE4AE5X5J9OvVr878674tFz1L/4cSrfZXP09r9qr63pnS/U3rsi4sqn6nwmcVXtVpvVEoTfyb496MfXUtce/yP3yD1d9o0vlf4i3TgaQ4HCgROTHhD8bSsiZHlfJZ1sA7MK/7JghcmIF/jWQpWvW5FziyeixV8Y/6JSGRmcpa2XpZTi2Mz9Xowki4Cs6QBVllhCALSxSLIttAM9oFUanP1yay/Cba3kowsJvNNx0hY4LQ0BWNbQsg8GesjMYhMJNQh9ThbktL5EiX+UmSCOQCYkqFBJh+fVB/cbbct0NTa+WRrc3drq28kRHY7cnEcEHBP1bioOhdUf3t0MB2yt3V9lVSgIh32vsnHpgde1fZXCMC/AQx3xV+z12mdUABchnJDBGADI4C91tARAB/qOfaVzGfg7F99ohgm8wFSYeqVZzTmg77ikbFRbAJWHtjEHyPQ4xtFDTjqET/+WeE/BcB5pQIH0PeZoT/V7+HYV/dilj3rkS8Y+zs7IP/02AM586oJM/9o6sssrvuVwT859QV1GfW9YelfyQnu99vXrl1LfPgLML8y73FaWl4JQok++UAg8LsXXnSGIBZYr8zVGp82JwZ/I/teS35I3ys74FQAMRmuWovjfp/Qfs1qrRzwuqCkZa5iNXNZz9jkxNOPu0LJRj0eT8oECJVDmwAEn59KBb2zk0EhTZvZnCd/SfyBzth0XUhIVywYrtenslNBp6teLoZCLuId4k1uEGEqEhHjcqYqCb4UW2e6IrnHPJQqkCOGcPofYPHzZvv2E+sQCuz3d/tbOiKIK96kCtyg3R97CoArraUO9IlIBIqz/eHdrc66/ayB3GP+rQ9pC2wc0H/rq11w2nsrLQ3AYzt9KFYEAL6FfSBD7fYRAB/iOfbVz7X0byTmjmG1nGdsJAqLwn1ocDMFbAIBqEgLzHIQi2MAjZ4xTInIGcsFIwAoj1n/wqV/zEMDfuh95z+df3raywD9dNYXNapHjfujmVfmwGeJP951aS47n5AbP5B/1PgR15V/XPgC8q/SSJ/58Mkn/+xH164NX/vh+6cfPa1En1KBrPmuyCDgFU3G02+8/92nX3QKT2pV9ZyYfVMS4MhrbHw18PL2djo4yeSkO+bPZRerMN20DnNdaqXgBfEP6cvkmpEzzlINamIEYkwvLNtEiITFJI75CxTrVdd0LjZaFwDM50anS6glrdmJiTP+3CR0jVSqNBORS2FI53FRoBSE9Kwyulg9SJZZCT1uMpH+WGpDAiAO+tve3u2u3b69urK5tSkY2MecMIQEoZaPCUgLNHf3bAqw1dncxfUh0C4HX/eu3v3wha2lfQgk/N1u3znzyXXEn00BvrS++tR6C/C3u7Ei3rZ7jP/7O9nH4OTWg/4ydIH0ICJ4NAzmoZ1Hvva7n6v8G44KUHDEzIOKzwNxNBwhgEpP10JjXbSHqmFYBVKrGW/Z8B1gghl3CnkJFf6Thc+2OX/7/W/U4dD8M4v+Mhm2vTzuBXd9cNfvqN/GP1X5wmMP1JFjD6Dvd0pPvcLSP56wrEpf6kL+zVwV/BP4Swz/Bwz+aet7xdB6/M12n1/xxq++d2EqkComcYcw707K71OBtkeKhTQgBtl4WTlgcdKhKexdqUMhM3X2Rp6OvLrojmZi7qzzWejwWKiVwwJDALsk7QixyA4zCXFidCqeLJVS/lgUADhXKTabVmMOBiVMZLPTY7g8CQsOXSGXyoLIoyODfMsmmEQf+WNiXDwl0x9aC5opYdfOxgdY4iIQ2BHabGlvV/Cvvyk1oCxmRiO8tLSC4wP3YI4qAnCltbK5LbzxngYgrDG++/Zm+yACrnVejToyZ7ZaREA5F2YVMsAk/zahqmZlaWP3m6QBJQC3+stvNXA90hH/Htp55NjnGvyjE8V+CUSHKvfDAxneMaMOkG/5FR7JHA/PmhI2OjN/gA2mmN+8VIDMvgQs+iDoGfizkw+/MwL3eV/e8qb+Op9KfMQOmPmipx5w9G8igjP/Zmb0wkvV9wtD/yT+KPhXalTKgYuAP5B/P/ruG/9Rgs+W9FUpEPzQclB9e+yNP37x6ZkAVkbrOTHaCKPnpiSHuLls2eKAmoXmSSYRI8VUqV5qoP0tnsleuJCNZcYKsRmkVgNTuo28IBxZ36LKhQD/EIhFWIGZtvKpWCHjz0M1dK0Bt3ON4oXmojsHAwcXKigJG3nCGNfDxPVXStUCqgAhFkmrssE4O17VKaJCgPGUzJXs0KxnROD9jZsrH3ywtwkE3BQqUEBQFfJ1Wrjh4+YSLlGCxXGsAPvb4gfvSwd8/94NJOCHb++0OdynEh9r7Vbvk7sjY4WRq3eu22OAt1c76H4F/sBhb2zcv7+FCDyGyWnxhZ3H16/3Th3x72Gdz9n9yjOf8fhjOPOZ2UffdBW0hgxCB8sBqdrORyYY4OOBJeOAwH0AlMpvfl6mgrUD/lTvy8aXK/8yA+aX+n2VA8a/AAuzY2ris9sW+5tWsT+57XfA/Qax8Q3+kzTbfnkei3C/VgSCfyD/En/3/unHpKjTBDQEoAoHnpa5EaUQHzv9xp3nLlBZIGRDBAI5HaKIJmEooYffL/8tib68flYBULBDEK1YqufDdejpqNWDi+d8Y7HRxTRowkp1hvZ9QLcI10IXuSjGIhWINCziuIfUZCSXDZfDyRAMxhI/PPX4hWYk2EBn7fWnMMEsWEpajs1tPKVVoIsRyBqRFWGKIoUuChZKy6u+S1EID7oQv5ME3N7FqQd72B+MCFQAFPhrw4TTm4BAYYQNAL4NCPwANeAH95F/ePOgS41vtyX+cOhL75PxzJhv5MadFhbCUPxvtbW5uw3ud4Wmz1DRDRTDHP/mJ1sPQI3CPOjrvRMnj+J/D+kc/9rvjvwmlv1PnpGxGFSQYVKXyp3HqJd2zDwUA5QVgcRJDB6O8cR8OD6HKQINxcdVMCoZkkjMG/DDnjcDf1E56NShxJ/qeNMNb/TnQC5mn/xThX9U+oLL3uwj/2jmMy88cvK+X6PvTYb/UP7N/hklPxLDf/b9K489dkXpvys65yuxJy9oL6yfBAS+/4ePP4c1MWZCWKlAXR1zmTEoY4B5+ch+uLUtXa2jVReEetYZK3hiblj5Bvt/Xf7EaBzEYc1KqRhgOn3AXeqPc3pLdVc2E760MFcONZvN7AxMzxdvlL6R8IXKc5cuzYWDSCt2vSkJP7LFMJSQSmLUMymZD3bJPAknguMs+1Q6xJXqLuG85/vMwPsf4KEZMeJL8m9FILAF6y1h3dvKHoYCwRQjAHGMKiBQvMENUoDCCX9490HL1vnRJgQu//JswVO4+Gofx+GD/V3twRCu7T3oKt7EmCL/OSdOCht2auvBA2GBe60j+ffwziNfO7SZz3Cos002fHi0+NPfDUFISRCZGMakiGyJOxsbcwyUP+u6P3ngvs59OA6Qf6QBHZlB71ugqhefxJ/PZ+z5Heh6g+CfWfgn6QdTD5oy+Dclcx8y+CfxJ4N/pXKlETgv3C/kfoc//PEbjz3GVNPWVgm8Kxp6dvRdUY/gvPH9xy9QWWBdlQXaEh/yHJQgURZZH2opTuahV1gIwecWfaP+iRJ2coCMa3g9WadVLntfRaEVL8Jh5FlMPtUnHHeFUtV6POuzKo38hYkLucU44K+GejAYi3mL9UbghjdOzIoXVSgwpW5VQFAGAqlEmn65ln1SRMrgH/pll6u7tLKxIXt94RABIdWxIwhI7WorWOe81FqBVR9LUPoHz6MC7G5tb9+jOYL392C78N0nAYB4I1Rgh1SgMQNQEG/5l1cL4v/vz/XJAHce0CBCbCzBNPMeuGo83zh58jpUwQgE7iwf7UJ6WOfYYfb94nEUcOyzh92vzAAbW9XGOBHMBYEeyUofjRxVEDQTwlLuKQ3IF4w9b47BYwg/wp+t4ddQf2MemfWlgX9+W92fvfIlYtQ9U/BvRrlfLn2B/5zTPJyZ6Yelf/nInz1J7nf4B1z5bHO3yuQyB9VFJQKvSDjyU4+dfuW7j08EYU5MtVyZq5WVClQZXyPmRweeumw+wQMUeISC+CrG0wKB1fDMhYinSU1tde8UetZScDIUn3n6cVfAVaqn43FlgmlcQhGjgqQk4zjLP5UdS5fjEEsMYndIOTBbuYRvNONNNe/e8FIQL85ZX0nBYjFVZA7SZXoabLELq2a4Zc7FQUFmYZyAGMf/ERCAG3LeiwLgB/dhGHR/B/DXEq/o4Gv2NoT8W4KXbuxxHYwA4Ntvy0mq26++cEPRD+59eG9LqEC9/JwRONR/+2LGl3m72xIuGBC6/UABcBca8TCuCEmYTcj7Dl3f+WT7QX/rG0cG+KEcIf8+39zvgSc65pPTn/fZXwKghwGogoQ+HjmPoUAPiTFPLObTXSGq5WNf4++BoT8HR/8oAJgZSH3Yccz1N2x9AYFofQ+I/WkANiMTMveBjb8w8j7EC9+KuO4cYcPyr1QqC4b8GeV+rw1f+z7IP132Z5BPakCl9AwgauVnvObKr368OAvZECsMHcLlKo961tyzd4oYgUG+rMfo01wZKynMZzJfDTcj2Uwe0h5z1fGoIwSFgZfqs8HA4tNPz8RhCXoJ433K/yb5IXxZVC9oFZ1ZqxHKNXMTc5eE+qtfuDY8Ua9durRQmZ0N5O7emAkGXdLQGvovrrIiyv+6OBAoO4cRjrqNmBcQU1UMmuHukiQgqcAPJADvb0PLr8BfdwuXp8NzG0tLm7vCAe99sLexQUHAbp82iSAA3xYAfOHGDan/BAovfnhvh7nXaisMrq627pxxjLwNQ1O7ahj/hnDAOIVmE68AALutoetAwKHeTud6r7917HeOzmEfwN8hyb+RMT1O1UEw81GxCwosO/88uix6jAtiPNQSQtLRo4NxsdGMoQIF7gw1qBh4UOojGpU3+2uezZLnMTa+Hs9ZW+xPij/bzJdF0/3Kvl9j45FLuD4XLnyjLCypP2p8S+UE/p4E/P3ov7xx+jGZ3r2iYWebfyCRd/qKzQ5f0YhkBAqQ/uoPLkxCNsSiUVmlwWyIEHx5BUNGYJLvKggaJ0lFzckJf2w+XMO0R2mmEPMmy5WSdyIYzPmbGMyrWUFMBZPnlRkQdQk5WEwFrFLIPe2ZweKaWn1qLDoRr9fqzhcAgFenm5NB1oCSfUVDCSL8jNhgnIOFqbj8pFfij7tkqQwlhAGASEDpgz+4rwgoRGBr58G9e7tSGgo+3dtcW/kAO4C7WBqzufWABaA4v3z1xo0bL7zwwg3mHwYHW4y/IXFnSNw73W4/igh84e0NqK9Wy0g2VjZgR/v9+3t8qd8T6GsNta7jVOjrnZ2doxjgYZ9Hjn197JCSH4noqNvtodAiLH/zoPIzsFewWWCSfXxXFcso0QhVM75RyUBoJ5HH4fFElSGWS48Oln9KAWYG+t3E8ammN/ydyv2i/rMVvqipL6b4i8DUA73v1+h7w75f2fimGn9Lwv2GJ4T7Bfk3PPwffnX6UcUypeOUrDNgZ3JPGmIDjfq88b/+8PHZUKqYDJeehYSwNMKIOqr0+9vLVlJmQCwDhib35DhpcRBg3mzOHy7XIe2xUMtHFp3FUHNixulsYi53rh664MXtSLIeUFIvrRMilrDJ8WSq6fbMNKr0RuGZ3GwodOHu095UxD/qz844KXkR/7STMu+mUjpGmCLY8WX4xmlgKgXs3GQJKA67YEMECnUGmzLV1e1723tCAX5AAFwBfm0hqx6Ij91tUIDPAAGxGhB/rtum+c/AP/wckiqw3etvMP8oCCgYvAmp6Pv3aTtJv4XgG7qOGBzq9HZ2jqKAh3we+fpXDgl/wyO+GE60H3Pg9D+frHH+tOMx2Yjs83A5IN33EJV4NkIMsiFwRjIxt9tfkGmQEXv1s518NOvPEaV5fwb/8FeqXz2KLW+g/mJEP7PnbaDwT+07Yvhh8E+OPVC537gx9K9K0b9Gpew9/yTVvgx/iO73tDHtZcDunt7niG0P9NNKQ8LV9//oueaU6y8uQ0J4jheH8Mw/S5tdWzBQ3rfPz1JuGFRgIDgVrofD9drCpYWFSno2MBmZaTbBC88t1IqP3zjjxEifag1hQ0ypkSIBEGZGxwPeiVAjny/hrpGaNemduXv3jDPknZzA9e8ul8YbCkCM/xVt4IO4INx1kShUBFT001WA9D0oij0AACAASURBVBEXAJRzTQfDgPAIKPj7AkkfoD4U/Lu/cXMJZh+sLOE2dCgWlADbJQV445kXUARuizfYW1rj9O+QYJ8Qc20BwCFJQGGvN/U2um3w2dv6bCH/hpB/YIKXl7vdIwV4qAfc7+df+oxnvkCbMkaxkGUUm3p9jBmb8jM1oCagURCtAAhoGqVwIC4gHwXhl8FpqW6Ymi89sDn2ygRgVMX/BpZ8mH8P/i4Z+vNQ7uOgrjdj3RumPrjweVK5X1x4ybkP2iVpqegfNb49/X9Q49u1xN+//xjOPVAE02RTj03mnTZfekUh0RSO/MNv/NFzz3kxFEgJ4ZLgL9Zfm/yzwY4VoIz9qW+SgNjVJgBYpZqYRmoiOJPNRcI1apJ74YWnhYulf2zKBUMCREYBiyo8WIT+uFQwjsO7AIGV9IRTANAfEf/6QDlTEE+SzjhFviC/q1ek+I5MnKQM9UcJEwYgeeCVDVZ9jED2wnsrG7vbmytLS1yaAnFAGn7Vbnd2tra2hIR7QPgjBUgmWBBQvFGnzfgD3SfkH+g/rQHheqe7pQEofjd8B80p7m1h/oNOCwbid44AeLjn+FcLh1H5PAzu18P0o+OhNjib/kPsFPQDWQlokMh+xmg2DALQRyqwUBBsgl8g+BSDuKAtATJgfD+l5aNgMpgbULT5tZX9UeGfanuD4F9Wul9O/bL8C9LKD+771Z0fxD/hfquzH3LtSwIa3x4jfMnaF4k89V1TEIF3xXhGXjZ/REHxsStQFhh0xalDuPYshwLDBvKMvjd5BvUf54LxpGGMYT5fFSStlqvPNScDE9NT6H4boTM3nn7hhXM5GFINSdcitcfJmhiwxfo+bI9zpXgzSb0evNsMeMfPnp1uzor/63Cp9AeQrmjIPgN5KfNyirZsSidM6WE5Zp9pCAhsrS2RB17ZYwBua8cLDNy4uQbDTTekNtwDxSj4d1PA7Xqv3+9vAcK2dhGAyD9BwL8TADx3420j79EC/QciUAjA01IEPgoiUBGQrO+9G5hTuX+/3xOiD+3v9etC/fU6vSMAHuY5xH2/Iz6/PyYRiM0cYyjibPQbs9Nv/+HCaZkJ9skV6qMepQKZU6Mk0kYznP34rAyIY7DljQpf4BYQrdYcGT1vpvvN6YmnEn5Ncr8TkzOTuvQZR97z2Bfadyk3fkDfbz04zrUvwx9+l9yvgS8FNKkBDdoZ3JOe+IqZBDHpyS975bsXZkNCBOLIaFUZbeW13zXjfjoBoqWfDYjYxpyOJ8HHVyezM4L2VUh+VKyZM0L+nfMURnNCA6ZCrlKtnnal1KB8s0uODoUGsB0wcOPGTDAwOxFpTsK/OyP2B6kX0/lKM8yAJDjapGCc62OgjJBIivKPRiS01igIuDIAwPtIP5CBezfX1m9ubisoUk3gzZurL68+OgRFeuBiaXzgL1kB4sczf/p2p9PrcA4E3e9Q63Rr6HQLGQifeIN5FgQgyz96AADcudPviV8hQAgCsNM9SoIc2jnE0pcRD8AIB+axYPNIA2zqPlu3rQ2IxqFiGC4NpNpAPL5RnhQNRnuUq1Tcfk/G3PtmqL/ogcNOCwXb78X3RWbHmKoxs+1NVr4MLDuX285nzLEvcugfpE0tA3+U+61eUKV/P/7VlUcVy4zGNgNvintX9DN2QWj+iI2LfP2t707wvFToEFZlgcS7gaSHGRKkCkC1U5MjgXgRqCZU4Ew20gzCeNO5hvfGuReePnNXiHJQgKFAHibHVErpVFHvCklCfSA8lnUxeAQCq1PjNy7QstCQy8RfUQlAXDXHF8znxWeK78lAoCQhRwNlYhjWNH1CAFyRAPzg/rYiIH/d31tZW9GqcA/m38PE5/bLj/6ECbi1zQNUX2UJKFzwjRt/+kuh2nqIQFB/9AmBvTZ9EANbjMB7CEDJP3E2YQ7g1taOwN+yeCPxsdM/AuAhnWNfLRxW8mM46p52+8mhzmMLCPpfBqC8HYSdjsPZLKkdgDKPQhyUNXrcpAF6bdrtie7LASsAOkwAyqJnBWEj8yvgfVaWPduCfzr3wSOvIrTvg5IfMPbF2PhB8o/Ek1x3Do1vpdlrH/4+5H7nE3/6/Sv/URLNpt6u2O4ogXdF3ehP28/vf4mA4GOPXfnV9x6fCsSTNDUfEEihwE8ZF2jptIdlxAGTHAaEWxxwYOVnxP/tBOawJqbqnT53bizqiWUnAGL1BTxzlWoKyJXmFIipBvEBNQ2Hp85fdUdmppwBShqxziuiwiumixJ12g/jpeJ+8MnDdTEqKgjpkIBz9gEDcEUBEIYiyD4MCcI9VQgDApD4t7a6+pNHH/3JEFBqmwn44N4LMgQIUcC3hWoDBPYIgVeG0AcjApUzJpPc6j+4Z5N/21AE0+vjgMKdXq8r3qTb6R7VAR7OeeTw+n7hjBSgYNjvwfyKo0BT/Uy4SeElH0oIKfKZaQkP9whjeI6GJIx55Hg+HlAVYyMMZyxqy4FEefILGWDD+mZsv9QjZ+9rAzxQ+Mdtb/aZV6D9mhT8kwvfgir4F0/bN35Q4xuW/gn5Nz987Zc490AKOUPineZHUuapF6j7BiH1C8xLtjjhY6ff+NVzj3tdkA2BqflaBarOj/0oTJoOmFmYNO+n40Wn+PcRbNQrhMBmRtjf5ow3EMKx+XP1KqR363Ha/K4nBsYlBqE7BFmaDjSns5FZwT/MbxSLiL6iSvwW0QmLC2lSgkXJPgVDeeD+H8btp4gBQMG/qYlfCgDeNCyw4YEZfvi5fY8t8N7GhuAfDLhfe3T10Z+83F7oLfe3oAYGBOD2PeDeC4TAZ278Uqi26wKBQsGBAZZRQFSCGAdEKyxssaBgp4/4Q/7tbm50dwUAl2EMVr+/3Hu/RzmQbxwB8BDOI8cOLfkhz4jPH5PV1YloYUz7X4k9ST/jtqCssBEs9A18841RQBGmCupsBTOLmjViBcdBCtAu/2yGG6WlLfi3D3/jWv6p3EeTm36V+/UGnQFc+Iv7HNNpaX+V+21Uwk2ceX/t2nDi8T++8iiO/VN9v/sopq4Y+DOgqK6YP6ZedcV8DDUx35txumB7nNEhHFbLkfTJQ14YNZ9MfCSl+VXL1vlxPBXyeouNKiaEhdpLR7ITU85gsYGP8pHpPHbKuYq6P1gmQtgFY49c0krHA+L/Oyj2x64XfkASUCrAgXCges4ApQk9gmkcqg7FX+r0PvfiogTgiooBSg+8rRH4wQf3vn1vW/pfWvi2tjbU/kl7FcpT+lsPth+QBb73wr2/Awb+HaZBHnRaaF173W63h+JPnCviY4iKAk8DAq+0aUN6q7sl+Ycl1ps76IARgEIBduBTDYo+Op/fOfZVzyE1fpjHoctrElFScQVyvjhrKkMPfQWtA+1HXmLyeei+7A+RoUCGILJPzSpwu2NjDsW/KG/7MOWfXvRR4L5jPet+dFSuOvIbob/p3KD7lW1vEPybkRs/ZO4Xgn9y4r1ufBPu1/ntJzH3Oz/84esq+LefWCzxrpz+3w3QXVE8M19hY58hIfdT8bE3vv/ihBPmpUJZ4JxEoCoJzLO2G2gDMb4rF4wXBCYFXVIuC/MqUBY41whOOr2uEtb1VWcvZD0w9n6uQVjT/SBF6YJJBEK/SFzOf8HBgWn8jqIvnWb0Mf9Q+6W1FY6TVIxLNiprLH8AXi3wF/R+77nHL5x5mwC4YleAdO5r33vv7v/P3rsGN3XneZ8VICF5s7JW8kUryZLssbGUOraQLwKXZQYa8SROAGPASTo9Y1MFwjDF1HZNnCdRkqertd4q5G30NLYznmJcpMarpv0mbc/WQCav8MS40+AYnqktj6ufKsoUS7qBogp6ajaTF1u7+/9d/pcjySaZThq6m79t6ZyjI/kmffT93XNAQDR/kX7U32DjX7+BALyMedBLi1NTgoDaBBYAPEUAnM7npycIgRsBgBAMAV/gKOlAhUCJvzx85MkABgCeoyDIEwB+4+u5Z55yffv8i4bdbqkAXXFNGwNt6IODC85EERvJZDgbN2BYyEWyhSkUwukqBECf9gOycrOSmoDMQHvmc1I+ftBo+GIGf23iT/NP9fzjwjfM/GvdUs2VH7Ltgep7IH1/+/YJ67eq6cHmnR9A6l/2/Vms/NCCjXWgHYnlBu1g01YnoiCnqKjubeJRH4XZSVtba5sxIEwqcJ/UgAg+BpvOho5VKuDFeF9ykE4QjGpu24FNEvYd7Y5taa2orezGlJiqhoFdiXgLVLrtrsBYbJeNgCormqLKMFypmYzfLnIYdpHnsI3sXmQamcFdXYzCRo052u9S8rFRkRDuK6zf2urJ48czBxiAw3YfIPPPICAC8IYQgIw/aPAswFUm6EUAFAuqQaYymRSYwamfMQABXGC8inUtP4GGcJriIWJBKJjiIdx0ayK/dJG67+NnHppTi/thLOUJAL+NteGp4Nro+kYWxoGFJRpF+af8fx7KuROXcfoSKxz+8GoyDI2o4vGw5/PPr4Ttvjm9Rb5AX1BGRDxBt7aCDbsVoraJhNcKUwdAGfow4r9G0S/QT1e96ccwEv+o7qPdPu4Iur5A6nOrsn6V84/w18bdl5X1u6d793aQf2+B9+/HC2j9FiJPU69cjcA0TjBOY8RJ3tnPs0FS3g8eD6IhL2/dW9MsRCBEQ3pUhbDRBaHkYpsXzWDIG5S5gxDkieHwJLEqO1q21B1Cd+CObQd2NXR4q7qP7D9ydMu2GjkG1DCFlQTEB0HUNUrnYBedSAwjOcheQcRfG3gB2xqZhW2NXcr4ldIP3YQce2msqqqtmNx+fNeuwXp/oQK8wTawEQYxACg04AU53g1TnDcGNAAFAqdWMisZ+BQcRABOYBiEAAh28AQnBJaPIvkAfeXoCeSm+7Tyeb0lCDh9jqLJTwD4Ta8N67+ttgfmwixA5EnS5VTZf0mPdv2hCy4Z98Tj0V/cHB8/e7U3G49nsz86e/Lk2esfZmVblgIFKKPBMi8w6KE4iIyCYE6MYbu6k2wC27JfkkqQsppU5cVIwJBllH3ocR9y1jmvgW2FqS+1Fez8a27WTU/Z+N0HwY9DFZ0PNlPP++/8XbpMQUxRSgLPFHjG0rcz7RQqy20rXXDAHlgJlKdnX97aWtNViWmB+3v2mN0CUQdqn6D09xmRDwlBKQHp9jaI4+47FLMGWvZASkxPI/zNEtXd6Arcmxtsgco2RJM2fm2ZMG1tkoxo+nItcVeXLCFpbJSSsI0xKMFH9KNAMaCxq61RKkO8f2NjVQ3gb+uuwVSTfygzUQRAKQB/ZSzMTsb6kLszF6jP/QUM30KfFhjbAfybujM1Bfj7WSbzM4yGfIkAPAU+wFng37T4mKBQCOo/+AyACkT1Bys9oQQgmcGgCRF/+ScA/KbXc0+v+zabnvKKxgVE3DIJ2hh9qeiHQhAUXzwbvieYd/LkrZtXstlf3LwF2+Nn70WzMknFtrCZgu6SQEYwd8giH6B23oUQX764syD5xf7APm3+UjaNbdqHTPwrHPYrux5Qz9NWavuChb/YdgReuYiLHTL3BVL/ugYfcOaz4/0fgPWbThugKlBwrO/KlcpTRi5fyUNpY0vdxzi3BCQDgZG/eHFrRdXbsR3UNX/Pvn0Fg9R3MNgU/Aw7OBbjg4qOsAnRjB272zwJ76EeyArs3tdYFTvUgy3+JnPLoY5tgoCo4Cj5RV1L+nHXLJUm0yVN5S5JOAQe67pG6QzkUEmXTBAk9UcmMd3S2FxXUz3Zd3xXw2B9wh+JT80QAHUQhPm3QlEPCUCsTsPNG3PDwL9/ujBKBDwFAFy8jDbwnSlUf1MkAXOXJ1D/YRCE13Q+D/eDLoPYHGYjdYgZA/7lT53aeI6EH2hGvB69BsPZz2EhcP4JAL/JteGp8MPg9Q0sp2AIBmQhPyVIAKSobpC9fghCYFE4+4uz44J44uvk2c8BhePjsDN+9hfZcFynyqgVVDM0Ff9QAlo+OazDCtlaNkNaoNOe+yx9kTKVBpcgaMioezPoZ+Q9DyrnH/v+VOFHLba8x/ZNzdL4VXVvEPzoOdS6c+dmCn588Fr6dMBOJaYWM0txS26pK90aS4PPAKEiXlo+Trl5bxOBL/W1VFd1xXDKB46P22efG8KpgLECtx/LP+0F1Nvit97R3BEK7Tu6u3v/Gzgq7g2If9SllnPLHm/D9loKcajwL33ENABjEomNEpIUAZF0kzqR7WiCoSapDIF0sa+RNCPIv+q+vq2ZwfqmzkgwGb8zXAxAoB1mpGgRuIgtYeTe3IWP/+mfLuRnyG+Hs0OIf8IIvj01JSh4GxAIABRAG2EATisGjlL+8xgSEJOhUQBuhI4vE5KAcCmEIgBwFHKh89PTTwpBvrm1YX3wW059gQXOP7ZG3Zyz7DE4lqRFDr/eD389TswD7OEnfQECr4bDcWUDSwpS7EOawD7tBLQs04EH8i/BFmxHwh13FoV/PWRPG/2eUf0ZVR/U9EqHfhvU4thHi6r7rVbzLtHRz2zQXf+E9VvTRCOPeh1v/Z0sfEvbuaSkm0ktop6xq5dN7CnYGeAr4p75PdIjC3u3VdQ1VlKFcLfKiVnTEajAx2AsONjWWFe7/dAeaHPdQwM0N724NZfLLfcTAKsaleYzxF+buWkoQlMPsiBUXEQ/oIwLMyXxEjNe1JkHUf5t79u6NVVf7+8U//JQsACAhD+1FALJK6h4KOzgf7pwF3rCTMCsdEiAwRgIEFDwDw3hzM9ylzkLxlCAvKg1YHojR0EEALHx86lzyvsnNOC5U8JURgU4DcUg0//DE/33Ta1vse7XXFgDIsSYj/UfBy4IYBT08CTZ+nV+flbzj9knQQhG8dUsOuuwTV/yrbfiqAAN+5ealhrhC+UABISFaGIHdGwO2dL/JAGD3OsU7ynVn9dm/Bplb0bLU6PuV7a8r+WezxT7IP4p6/dod+Ug575Es8cXygMmowwwKfGmDOF04YmMzbSp7owb00Wbq/kJYc2+0tda09xVuUkGhJUZXGI0kt0PaLvBONgm9NY+8UD7dlR2CeXVJ9iH/IsH2wVtQR2zZGvjQAjNCrHzj+mlKMiqz8SjvJ3iIY10hLQgpNDI87saD9ZVVPQd35o5UO/3C/3nC3k9d84YALxRwD+NQBsAcQLw8PANTIueQ/4tLV5eXCQjGCXglJCAKykEoBkEwQXuwOmJ0bEA5UGPjQVGyzemISqcPsfhDxCAMAV9IynA6emfCAX4RP99Y2vD+uS37/xzgAD0JqA7C4pAqf6C0u3HAhA4lI1euWnDn8FAuAaj+NdXSAMKEzr7i6vZLDyWUoDi0T1yWCWlwegMFm/Cioc9IbZhQx6l/nT4N8hpz5abel7ZfH/K8yfpN8jW74Aq+7W3PWD8GYVvMvghtNChLdD0lCo/7tuCH6wBtVDT7QDThpUrTV/NRbmtRKQyhg3QyW9ih6A+AXJiXm+twcYuEA05unuTjIbsMMpCYjsU4lT8A01etonxUlrCXc1VbRAQ3tG8zds/tLzsh07Jgn+hgS1gARP3YgbkYtQvn7VeTEpD45jiXZdyILZJGchmMMWEwfjFWAmZ0KAP62r2buk7ntmVqvdHhjy+UCLkSyIAzxAAmX/LNgCS6w/mHsmcwF/JEcBycwk7wcCiYDAgMCPsYAHAc4U+QLKEr+WvTXOXBJCAo9zzjz1/iECcAowAXJxGATh/8YkA/GbWht+N/MPVG7SEBlQGMGYak9VLX6j+4tkrEPAg2J1k158Ng3D07NU4qcdw/Oat8bM/QkVIvQGpuZbPjGCg35E8gJQGHbeAZKGgNoC1+atiH0buoMCfXxq/JP7aVc8rwl+LTnxuVT3va/W8XzZ/VduX3cL63dNcLwf+Zg+OUPBDKrO0Al8Bs+SmcZZxJwOY6jR9unrUtHrMgg31ANAqa9uWukaBQMyJgXxmqQMNCahEnk0Eyk1DG1KEJCYQuEkAcGgosoz4w+YINVVm+RvxzbCH9S3qCHOwUWq7NolEqSEVAdsa5Q1dGpYHm5trqvuE/NuVOdDk93n63V54crg1AIdhIBEKwOXlzRJ/K5wSYwCQ6Dd3l1vn80xNBOCdRc6GwXU7dVkIuXPnRiaKTWCA4LVz0A8LqkF4nRLmNAMQM59HBABHLwIAIQYy/yQC8o2s555e9y31PC29nB6wgt0+Y+wRpJ7EJfwE/pI/wtgvo+7SpUumK5AV4PjZe6TX4uF7YCufvHX9w3BSdQn0cSq0Wyo51oDQhivcSynQcbfXiqsYSNIoOTGGi4g7RST/PuTISWHis7J+tyn1t716S0W1HnnEmc+AAdX0j3reP5A971Oz5adtrCs3YajBlk6bO+XGjXyhOGdCTS4b9uQ5NvaZ9xEI3Nu3parrTWEIH+3Z380q0KwQLsE8igSrLOlKnRZDh9u6Ys3bvcH+/qEhwF9iALyNin96xRTxyGY1OmV1sV1LBcR0c5f+7Opir6CEZ5f0A6oHrKqqnQTrd1eqyR9xezz45miFgoYJPDw8PLeE8d/c8mZi4KJcK8oEZv7Nzd21dY6m6DF1hsZ8GDCEPyWYlQLgNfyYgDjIqGp6KgF4DuUfmcAXVy5PYwxk/toTAH4D6+mnkg9D1je9wj5BQE5/kaJPwk/gL3pVyT/E3yeffCIQKCUgR4LP3ruSRYs1fvUm6kFEoGCnRxbDFdQCKyHnc+oi4LgsgEvq3gce7Coo+cfwMzv+efW4D8IfIpDKfltU3a+c+FbFFVxs/arM531CVO1p9cuBvzv/bqTMDqkSvj4pzdRSLJQ3mNhLq/umbcflfYsereCxaW9kYW/LlrquN3dsOqT6xKwVDYnFZCGwPKAu1RdM/93S0tAObySDLa0VNc26D4IcEcwD42xz04ld9muZPS35Jg1k2tEGsZaNXW9DfV6dwb9gEt/pvAzAC6wAYc3APCJBwBUYaKT5xzrwBvFvbq4QgNRJH066T8EQQODtqctQw6EsYPD9nZMbiMBrAoEbyf0HAnBkApyDKP5O0aU4mr98GU3g6fmLzzwh4G+7Njzj/l3kvhSsaNgHLkAPETAeN/JQwtkr1xF/pP4+E/j7ofj45JLpEDw5/usrUSdoxqAnefOkWuNnr2ff8pAHD+vhdFNAAiAi0J1UJSBq9Jsh/4LcQQb7Fcr72GMfSv4VhH7Z+gX8VevgBxZwcd0bpf7xxLcdB1TXvxep7YsKYPCXBpwioPT7aTNZQ1AdSZuGcMFN9vuk1VHbMvdHvrd3W0VzV+UODgjvVpnRRjq0hJ2JOwYeWb5vGufFYl2NVXU1tdXVFdW1tQJ/oPWAUTEmXmWM8Cf3u2Ix7opgoK9LK8A2ZQd3SQJiGiBDTxGRwx8Q/N2yt2/r1syBnL/TI/AXEv9yIQG9VhIBOKwAqBGYK+QfAlDavwDAxVIAhAVm8CQkRV/OFytA2MaEmGmBQMFA1fUeTeBrXPdLBBS3pU+duzYNQZBr8/Opp54g8Ldav6PYb+HiAjiATZKY96HAGeLP5bp61rB3b/1QLCIgIFAz8ObV3t4weu2SaABTXIQM436qXzP0H5i/IRnJ8HIJSNisAdGNT30KgDzsyCoue7OnvgxQ4VsLtfzDpn/VWv7h7IvCeedo/e56QG1feh3LC+WU+meSLG3AyTCDtUtP7hRSTGlCc9ekpXl20ffQt8j9QPnIS32ttVVtlZUyLdCWGS2Fnc0WrpSdYYw8wZg+IUY9mHEcbxeDTl20xXhaprKA21ZfEmys9aRFTF9dtj02jhsPVtVUT05tzaRS9X4r0h8MeS34p4tniHhmfHnBpgBhzRECV+R0Nu0JvCHNX1jzi0tLdxUACYGSgegMnJpCABbEgI0FAMwXANDg3ylUgOdI/01fuzaf83jWPf0Egf/R9ezTT/0OCj+KVxQJ6MRqt6TAn/P62VvXr0Sz8bgraqT+gZ778J8/+f4PP7n0CVLw0iX2C6IL8ObVbBa79mXj18/iDVIF3oMEGOqCoExZsHDMHi7uODYAxP4HSZ8nrnufcuRY38GW+tJhy3wZZPHHdW+trTr2W1tTU6PrfvFVr5x/VPjGfQ8g9oupfwpE5WkDRpJQ5enCAwwpk5P2tBYDgwqTNjTaQbnGCkBOzDZokgBj1PfLJgmbirpFx0z06WPaJo4pP6BgFQxj62qrJA8hDkXHTw0/aQ0X2sIxc4ftWuUUNI7aFu8fFNqzYrKv73gmVS+s336P+Df7fFA0Kf7l3pBPA5BtYETgPPFOtmiWXUp/ZfAPZlguzS/JYuEbBgDvUyjkzh0BQChgK+EClFZw/pr0AP7PG9OjCMBTpyYkAQUAyxmAP7l27WJT0uMOPfX0sw97pT9ZpdaGZzyPAn8OGgMcZvM3G72H+S5nBQKjVz43rF8wc6Phv/05akAWgZ/JgDAFPbKQDB2PR8lqlgy8dS/ukW1gjFRmMwvQC83xqQNWOOjtEAqADWDue2XGPkJeqpvT5q8NfzL4S+Jv+3aq+62pkc4/MOzwxW/r+rdjcHkzpf45tvLA3/JyIyWFhVvaDi2bYZteg1+KgyVPMR5QP54JWPtJtDt78PiWusa3uUnCUekKLE4IrJSOvlilLJV7k/Ng2kwqsoOOgViJ4o9EYKUGHoEu1mZXhCW0YZdWeMYxc3VBSTI2fgH+ZTICf/6IeL8T/JNvlJbX6ykEINvBc0vYCVBmBRoCUPFvBlMAIUsGIXjDRCCZwYuXMZ+lCICYCMgEnJYAhAUAPDVx6hSIP+kDlArwJxeX/B7w8qx75gkCv/4S1u+32fN59QXqzxEWnAH+CeuX0/0grPEj0/o9+4uoK+x09jqu/hzZBxAEOxhvZATedEJJXDyapYphKQGvJnk8JjVC4BQYXckRolwWQGA4GUKiJSzy/+nob0G/e9Xx3qb+gIDbBmToFzKfYWgF4I/m/Tarns+q6xV0/dvX8mAzW7/Hvgc971nFsYhTGk9u8CGp4zS4pE2cVsaxCTDjfONCMs/gXgH8g9IufwAAIABJREFUbI8gbysrn335+Pa6rhgODsEmCfs2ySYJRQQ0NCBtv4muQGkUq9yYmJwHGsOupwRBchoSCRUIbWqwzVSHWhCqOG9XMQS73o6B869Z4G/y+BTIv87IUBKcfxYVTOLTwxu8XGwCEwJ/ZfBvhZJgbhj8w/YJM0Iqrqi+MewIBAReJgZiKVx+VRMYEagBmEYT+BQtIOApOwAv+7HQ3Wd51294gsCvtZ793dT9lloCgL1xN+IvHo5eN5lny/W7mYxCr/qo759/+M732Q+o8mGkxXv28yvhcPaeigPDoXtZoeV8NGuJRKBFdSAhezzDC2mvbq906SECdf5zUcfnhIr9cuLfILc8NXJfKPGZMp/rlPyr1HUfaP3uqfPLwrfsl7NlAQM29uBFulyOwTRYVOAFNE9mVEmMKbYpMiqepe0XBgLtxwwAQqusH+w9Xg3RELNV1g7dMJVxVynNXIOJOi9GeQOZc5WGqxC5B0qRAh6MQ0lART06qu1ghUJNuxJeQ9B/VTU1k5OY+iys36GhIZ+Qf0FLSEB4i/RCFGRVAA5zWnRu8+Yc50Nr/TejFybOFDJwEaYECwpenFgTfxgGIfj9FyQgA1BlwWgA7vnJp5cv+4PkrA5Z654g8OusRyb/HNGoIxqHKZgeYf32Xj07bqa3GHFesc5+Ho9GXf/Q/c6777zzzvc/kRYw28ikAUHuffg5bRH+rsezGMglF6BbL53OrKDWgRktbNU2dHhhmHDQ4J8Ui0r8FQ38APkn+NfKqX8G/6jwjRmwySx829Swc/NmjP1GUxj7TUtEaUyZ5FHXUgem1X4hrEwKFq1S5nC68HjJu8uDAQgI91U0v005Mfu792CTBBohrDrEVJoOwEpiH8GOKCfpKM1iCUHUgm38EG2xNsMSrowphimjmK6QgnyizS9orJh8ACi/m9w7hZUfnZGgx6KGRKgCIdYF4S4E4AWbCczXM5wTuJJbhl6AZAEX4g/WvMwStC2sjluihlaFJjCU+cqD56T++y8bRzcyAEcEAIUhLIxhcXx6+gdYCfeTy5eXfRbOv4YAn0Dgw172TxYtgb9H4vwj8zeOGSqg/iDgMb76Ar/g3/6jwN9777xz4p13fkjq7yQjk2MhJ09KEtLn9SvZMFuyKg3Q4nLekG5mkFBcMwraGoQKdPsoYGLPffFj6UeiXXr/aOAHp74Q/qDud4ut7YFqemp0/Tvavbv1GNf9OnYupOXEI4mZQiGmTV37DSa0CsFW4Dcsec5aK60u9Z2MrZf+qqWiCmb1HvozTAuk3604KTBmmMHK4mX80TGgUoxapsI+EK+SNB+Diw1kLf3wEBCtkpUgXtrIFzMEIR+JtX2K0eDmOpB/wvpN+f2d/f0AviA+U0I+i+rDxXOEFeBwsQKUCIRB5csYEsbmB4X4m4ESusWVkghcnC+lALHdqT4Mk9LLtQ9wQmBvFByBExQE3og5MNPT1y4u3VgMeoR5ExH2FEB83TNPEPgV1nNP/y5a3pdcQv25kpQAmMxmDeu3JP6AapfeRf69884b7/yNDAAz/YiE2vN3khWhQCC0sqKBcG43m8A6Dxrm0Rl2rXbrQT+/9gTcgcb9qpPMeZcNg8r3pxofmF1fatn7B4VvKHGgcQDoP7Z+G5sE/qDnvSP7/mwgoMxM6cHjHbVnO0rgSysmKRAatEqbF/pWfWO64FZ1gj3yrJf9QYQKfO2v+mCA5qZ9lBOD5XE7dDgkZlwy80wCxiQQ2b5leSiPkSJsU/YvYTDWZuQBxthAbjNMYqZeV1sR//h2wF919eTUFDQ+6BTGrxWhN0c3loC48alhgQn88cecCFgEQMwJxOK4HAGwWP0RAKGJzMqdIgQKEYi0A8zNmwC0MXGjXqMT+WmBP2H9YiBk4hQpQEyCubx041d3/Wyw8OjDdU8/MYQftp5b73sUqX+woiz/0Pz9RYleB8UUPPnZ37yD628+OykDwDJoctLAn7EgExDzYNycz2LJgUgc1ShMam7v8HYMgmcPnHrt4g21QP4lzKYv3PCPWj5vk6l/2PPZlH9d9olvkPgMfQ82DTygnvdZx58vcPBDe/Ts1yrFRZ6jOachZ2zYr9ZakmiFj2DbLnwcDcxA+ezBXa11bULYQnmcDggzAFdJjak0gh+VCoTk9zMp2cYyUTGRPjXn5JWyhWkHhSADUYpC9hOKr+a6uoq9k5PHM5lUzu/r7xdPA58EIFamCx5aXq/ldV/+mBQgWL5nihGocgIXV+Uf9RFcXJzSBJRpgfMTeQbgnIE8ankAQ97ADib2vcEAzAvqjZ5CATgxwQoQBmIu4UCSTmj4ZsFzVvwWoGOfZEavvcD594jknyMadXkYf+Erv14FfydtGyclAj/7TJu/bAQrs9dIgGEEXk96bP4/fJaHQgX8k8IuJPSitwOjuu1ey+02PYWFRnKDmneJwY9tLZT7QhM/KqT6w7o3fIXLzBeyfqsPU+Zz1PHgpbRK/VPCzHTgSZyZmDKYVEqsrWXmKmwWHrcfLNoroir/wCOv9FXXdb29Y9PuPT09PX/GM4Tt1XExqfek3atAp3Uf3RxjUxdghd4/OKzkIToDyeyVGtFQfpWSdAQ6NpJZJlaif7DtoJB/tZOTIP8E/iKeZATfFN0+hh+GESAK4hUXAMAiBThjXLEhvHSX8MfHZ4YLAIgIZENYVYfM56Wrb54QiDDEmR+EwfzsxOhGsoAFAkfP5achDfAU4Q8AWA4tovOYbXg3Pz9E+YvUXySEgb6nnmRGr7qe3fBU/GGY+rZW1OGi4Icnnr1yr9j6PWnbNCPDAoGfnTwpiajsX+kBLCEBP0xK958ioKVaoYYM/EFeM+W/uBMCgB2Wz20mPxdm/ul5b7LpFcs/HHeu2x6o6IfR96D7aFfHg807H4D6e2tqVqf+FUBIgbDwqLFduAofwwTrf2wVfHPbBaxA+icvCwS2xTAgjCqQXIGMQOn8kyCUEJQ6UKo8xmGlIQxxEHobHWjD3UpScngzEy7GkhCSjOQWn89mdJuxcOiH4F9ma07wL+iJeC2sFLL42QHveoBAqAVWABwuZQLTgiYxgn9IPzoP8CchOCwB+Cs9TEnWh8zLLtBz6oPgh9kxs8DAc5wGA31RN6ICBAF4blQQcHSC/IKYbb0k1CQA0CKndQIs+BBUbz5B4GrrufXBR6X+qPyXjN8o9LmXgOPAhkFBvcMuP8baSWn/KtCV5t/Zq2FVzsHPb+UBVPIP2QYhYIsqkn3BYCjhBS2g5Z9semXKv0HIfDF7/mHsFys/NP6U8btjH3n/IPa7e9vOzZuPkfz7HnX9k1DRhq5WXOlyI0lZi0C1UZJwfAf7fR7OQfvtdtam1Zb+2fj6L97fVt0cq2QE7pEqEMFvJyBzr1IpQBRyGoEsFmMSYERMFRWOkUkLLQYRjOzxo40Y28DITmYhqcQ2BqfgH8g/of8Goen9EAQ8rKA76A5RxAt9fxBIFf92cWVTgCVsYEbgnBaFSMAZicwZyBiU6wb0RF00AQgtX9gEnpMb1PGUut5LAL6x8a83MgBPoQ9Q4G8Ub8rP370LxrS4bX4oiG/twvyFSDZ2WQr5QuueFIeUWI8u9cUBhW/QnQ+MXxptJBl36aOPLhmCb9y2OS5DHYRCaf3SbmkHIExPClMajKH9ZFWvmdbcQdqOAMhZgxKTmpFy2ptOfRkYwMznFom/7bLnn2p7gKqkEnJf2PsnrN89dYdp5Ec2+uD+COe+mKQqBF3auCpaaxEtvfbNBeshp2qaqh9X3SVQPvIXL7ZWVGFOTDfmxKi0QHMpxJmuPvL9qdskDxFylcpg1okxMY6EkE1MxnAluVnVYcSkxF+M7kfyD/GXyUDuS7/P6wW5FISyt6CF47IEABNerPtJuCPLFyUAh9cA4LAdf2oXBaBSgIjApUWzdfT0Rej4Atyboy8ygY2u96jyNgYEAMc2jgEAR4X4GxUyEMaNgF9wXjzOnMChuG1uKOijLpduBiH6e0Khdes3PFGBtvXs0085H5n8i/bGpfxzGtbvyUuXPjr6yVGZ3XzS/FLqT7v8NAiRgYp5l4z98ZvObBwHAtsM4CL3n1eZtgnIyWalaJ+XZFi/quyDjd9WyT8eeFlTC5nPzY3FXa/I+o0deLBz5zGM/W6dDcimp5IwclsCxg4auUqySqtE+wlfD4N6ycALPaz5wGkdlJErEBh5BQLC1CSBWmVRNEQ3iZYQVCRUWwb+2gwOVrKrj4GI1JRmrbSmY4Q/CcAY+wEVJFk3VsY+betqhtgvJL/U+0PQ90CwQqgmdzDIPkDQgPDfxrC/L7JyY16awIC/M6sScNjknryaIVt4Zs6GwEUtAu8K/F28eE2awWj9zknxxzJwI6bBjL0B4+FGAYCnyPwdHUEJODp/4+7M6CgSUChAlH7EPShqpuexkLOJJ5nR5nqEsV+wfqnwDTv96eCHkH/dn3wivgQCDc0nKSjBRzA8qWGonX+w8dmlH16yScDrH2b7VQsEXiF7YNcrTVsqAQmp5gc2+aeMX6PnHxm/ctwvt32p1fKvjfm3SeJvn7B+D20H+ffBW8L6PbwwYqb+rYqpApgVbT8sr8/+Tf7jS0tA2zG5X1Y++1pfay1EQ/bt6d6/v5vL43TLfIOD0s6NsSNQicJKqfmQYJVUOg07rBMVQCUX0cI1Hq+Nz0fHXyXzE3MFu6Dvy+RU3xSkPvcnfcL4hTwEyBoBWESQFhH4r0MMxL0sQDVvKMC18VdqsSVcgEC0gxmAgn/TAD5QgBNzc4w+qQARgGKN/fXYe2NlY6OkAEcnSABCo8DR/Nwo8y9/NxeH53lEfEArGwzleCGrEX6tJ2mBaj0n5N/DKPXtLWdS4C/piUPbFm39jo8L+Xf0k48EAo9+xEdN95+yd22CT7kE5aFLl6BhlonA8Vs3P/TIFAfo6ReyV/WytBMQ5MKOwXZ8A8XTjFNUz1Nj4JFh/bLxC/jDeb+U+Uwv6B3c9J5S/9rqwfp9662so/dllH/lSvZprkg5aEi3tCHvbADS3kKtyYpPW2Wtfspqt5jfyVScuGBwSN/2uq5KGBzCs5P0BE09OEQxrFJLQY50xFjwKWFokI6sWakOccwImMnGeTHmH6k/+aB0hPAH8m8w548MBYUNgEW/QvuJZwjYim7wFUcgC1BQ0DoMAYt5SoPBJa6/FgM5HgKXdgQuXb6DpXPzwL+LaPTmQfvNMPbw4hz1CgQDeOMbZX99/r0xBCCEgIF4bAJPTODMzFFIkbm7mKM3+BD3s/Z6QxgMEb8OREOe5MTAepSxXwcXviXjcWf2Rzr4QZi79MOj3d0fUYMDDT4t/5Bn4xJ843aTWGx/9hn0icFuMZc+Y/7B9fU45YdaNNCIC0BCchImxX59IQ7tdoRo7q9h/noN/umuB0bLU+x6RbHfGk59ae6S/nsl/4T1271JjfyI/gx73kucEPNKyjv9ubrSU+0DSz3Cf2hp8BqHJKfTgTK1bGdjk4S+LXUCPjA7CRC4m1WgLBDmroExCT6mnSKfusJz9G5MJr5wcXBMnd0mUUnE41tYMNJZn8Yam6tq9qL3L9Xkt4b6MVfEh24/qnXEt8iIeK/0ii0BwP5FDK6SAqQ0wFWN4LW4KKMhBgLvzs3fmbyzdGNe4O9a/pwWfBMzE4VrbOMbY2+MvXf+vfOnAYCj5hIAPHVuVCnA+fk7Qe70hvYLkM/nFirXEpIQ6C4Q+EdvCG9Y/2i6XuHqDScBf2D9XinAH/Lu0icfXdL8Y3tXRjxOFn6NK+GH69a/fPT97/9QSMDvX4JmgRKBJ//lqke6AENF4Q/Ma6bQh5VoHxxsp1hgwTkdHP2Qrj818KiltVXrv1qeeESpf/QarGTtR3W/u7er4MexV9JlgdWgpoTfb4Uwtb6BR7E9RED85CMLCwv/+38VFyNit8ywsQNCBUJOTKMMCOtugZVS9sWUAJSgY+5VUrSXCclQa6Pwh7oj2sJtUjPGYjLqy4jk02J8t0qgXyzWWIW5f5OZTK7JD+kilsyLxzdHLz452E4QHBQG5DJmrOS1D3BNF6Bx04xti2xgMoQV/+ZmBAKn7lwW+JtGATgqeTeHnxqJp8Y2CgKeF/x7HhUgGL+nJADTG8sVAM9NzM9PXB7COA4Y9BH4fYRRH1FABN7/savA555e9wjlnyvpocTn7IfXi/k3jnEQVn3jOtJrqkBtASslKA+dvZpN/PyHAoG0PmEC3rqeTNITmz5s/j9MbPG6PdQAWojABPmNJf8SXtnyWba8Z/3XghOPqOdV63Yp/yjzmQZeEv4qN22SfQ/2dHfvaKKBl7LwzYBL+qGYepifT64Sp/0WLsCSj5YeeS3TJH4NWG917ro/mw7o3wZj2gsvtlY0vy1++906IFzcL5WhZsCQJR9fVEqaSVEX01RUMMQDbTHF1BhHPugUSpThwl+Uf/X+iM8j+IYAjETcREC3xxei3GF6l7Ss4EoBAM/QGiYpaOrBUlyc0RszMjGQUgI5Y3pu7vIdiAFPT08gABUCbevc6NgbZYJ+55+HC+kDNCSgOGMYCAgKMD96OS5+qRD9UhZUM3MpO6Ie0nos7x9zTsyzTz/16GIfjt44OP/i8XjWcXXVul/t/bORT+o80xjWG4C/e9Fs2OX425+jEUwUFAi8dTNO9i+n/7H+s0KJhASgG+nHs+MgX8bIfaHcaKbfoKx7a2mhps/buOuBnHfOAy9LzftF67edej5nex2vLgTK5MwPk33KhZemPXn066zA173DqiutrhDRZP4GytILU/DvjEbBkiBr4juvjAROm3cVJ73YUtEYw8Eh+/f3HNIILNEnQapCjT6+1h8MQ0xuJioS5DDHqE1Zusw9dX/Ko+5qJO8fdH32dw4lfaEQdXym9FDw/1lBsIHBTgxGBBWFjPJJAH6sTGCJP3MRAxmJq6wZmRiI3NMlImJ74lx+mlA3WpqBo2Njb5x//vnzJ86fPy8VoFpCHZ47x3c8l58nAALJSdh6IZhD1j0XuITA7l//x5oZLazfR8g/SP0D/oWzMOVtdfix7NMS0ASgCT7D/B2/eQWniIQdjp+jBhSm8Pe///2P/vlq1sPzPIzqX3cyHHd7aZxbyEfqL8it/yyj8QGFh7X3T8Y+qOWftH23yOCHbeJRpTHvl3re1xyDwjeQf8uvjBiFb+oKr0uJNTvP0iU3C0/5hhgIK63BjDUf72eRfrzgXysu/AdHnldj7MoxJ+alvTxGHZskHN2tIsL4xyH0xSQAY7btytibBQTEG1lWxwh4bcxBbUHHGKPMP2H6Vn4KA5eaOfcvVd8UGkqC9w9KfNBZBv9xn0VwoBpxH/LQ8nbaAUisO0NxEB0NOWN8DTMISyNwWKZIFyzCHAU1JkYLGZgfPT8mtN97zwsJKBXghCbgqVPnphmA+fzF/OidpI8w7sbfBN/ssZ5TfHmxtgVEYGj9H6MKFNbvo8x8Bus3mYw7o05b7LeAfbQjMTcuYae+DBBq/o3zVMx4uNf783fefec/AwAF/37+D9m4h3Na3DL7xWsFwzADWFhBYP3i+DcanclewpBd/xXgr6HFmPixHeQfOf9g4lEdz7vkkR+q8Be8f5UQ+8WBv9HXqfDNrvK+ylorCGJbX/G0r78CgfSX/Y7s0HI4nEyGnWGP1T4wmLDQq1L/Wvq0zRVYPvLa8b11bbE3KSCsxsftMMLBrOtY3Wk7Vu2ztONtvSPPVifEYtIcVrfhNYx8Q/MX+151BpMW6iJSRW4yf0OkAwEcEYyPYSOEHA48n+AgCOLtDAGQiXdGGsIs/9aSgZwSOCyFYAECFdUYhGqdG0X334nzSEACYJpOHZ4RANx47horx3z+8rXRO3Gy67GEnUx6cenF1Ggc5wVX0Ofhjy4t8FFNPKIVTVLoN5ztLVH3a0CQMHfz17dOsqMPwyCMQUE5gKdy/UksEgWvh6ND//yf3333xAmBQIG/f/yHYFJGPyzLJ/WfL+zk2b/CVEjy5EuPHAJhz/3TZb8N7P2zJf5tp8Tn6lrD+YeZz/DiU6FfDH60HKN551HHj2nkRwGilMAqX2N9ZVdeeuSbdQTyEtbvKzlH73ImMyT+lTBG2WM1NB7q6TnU2AB5VU2vpcvKzNPLR17poxnCqAI5ILyJC+QM1MU08xh8GoaENHNHfhj7hk6kzEE2jaHyo44K315v8vt9/fg88MqyX2wbJZ4HQcgciVDtmNuKWJA1YkVWoGOVVoBnDP6RGDwzbD/EYnB1EThTQgEKQ3jC0HREQW0Nj53/ayH9Tpx/4TwpwFOYBkgEJADOEP8m8henUQHS270b85+FCgTJl4AGCZAT40UuYuD7jwuBGx5t3S/zzxldu+sVKbxb150yQ1pbu2jm9jqdV27eMgWgaRqfvXnoXQG/d999790T7/zwnxNhHIUk5/mS/88bSuL4yzgP/8XwL88991m20t+E9v1x5GMAml4NtLSo0Ids+idbPuPAS3ohb+LKt91g/dYdlsGPt16eLZNNn8vX9PKlSx/mY2uDMn1/JK3z9EqcULxb/IDqZ5M/bFn57JTD0Z/LpJIul9PlcvX29kYdUXfrJgG3Ta1B8Z/eulCgAtM/ONhXXSXsYBkQhoap8JcxcgJjUgaykrPRLWbHnryt6AaZRfgmcfJNPEsAsFk2PoDcl2AklMBngttHGVH0rhchB4mbk6HRFxgR+02LDMAz2geIpOP4xxnJRMM4Vigswp/6KIXAmdECBo5KGTiG+Hv+xMfPswJU/BtVCpCt5WsTE1+GCYAYCHFzNRwAL4JJgeLCbXGPX8iM/mNB4LNPr3tUIz8cEPwI+jw08PLzNZueEgNvXo32uqJRHO/LDj+44exVR69TCA9iIwPQZhGf/Oxv3n0X+uW/88L/9sPt4SSV9HL0w5KhDSH75Oxzln9BKf8ilqafVzf9a1D4a1HjPgh/AoC1FRUw7lIGP1jKsPrj1L/BB5z64vh7mfpXUOCmQRiQ+7bbv94qS99e+Gr3DBiXD1lC/gnrN7qcSnW6egX9nMEEBMXbvW6ny1vb/cb+TQ3gYXl/tsyMhgAC3z9e29wmoLf76H7ZLbCoQrjS0HjKzq1UAJR8I7+fUogxfQdp+b5JB97E+0Dh717ue9XkH4r7vB1C/HmDbkKDZckEeRgEAv3zhPVo+aAKGE1It3/x7tIEN0Qd1mHgM1IAGgckEk3TuOTikHARAm3s28gIHEUAQgz4xPMffwwAvEZtEMBqFvwTAJxmAObz8xcFAOPs8AkR1L3Y5zAYFHYwWMJWiBplealgeN0fR07MI637hZHnNPAoG75XMvVl3Jbncuu6IyqEnivqwCYxzDjkojPqjAsZyYMziyUgIvAdIf/e/X6j1+VRyX8Kf1j9m/B63R4EoIcav0j8+ShIZpi/KP+g6m2QYh/K96fVH018g7rfZpz3C69CrvvdR4Vv+7Yc3sltX368kC4zgh8l1mz6K8HoIatsdmWhMCf6t1zCnF1IORxDmVQk3NvrTHoHqmur9/Yd79tbXb2lpT3UUCfotqlFvM32vzhbXpgW+OL2iqo3hSEMOTEyLXCH3RdogFASrVISMSb5iNiLUVcEOMCqT13CapN3heAHVX5kMvVQ+eHDVz9FOzBSYEEwGAqB3dgBGuUfJsGAAAz5I5FI5+LSjCqFk7TT8BuW+8PSIh4+Y9DPjkCZFwO8K7SE5zA4PDo2OjoGX6NjG6G8Iy0QeA4UIMSAXwAATly7NnGO8qZJB24UChBdhdPTExKA9KaPvycWhaClb8kXAvk+4SaBfd8fgQp8dsMzyUcb/MDUF9uM89UoiOGM61cEAaNXsEP+STPkK6RhFsgVjsZJHsplbIMIfOcf/zacDMppRhzXDZnGrTcI/OPoL6sAyUhV+EEt70kADjRg7gskPnPLP4h9oPyrUwN/Y7aJl+j9697T1fQBW78PXpwtK8BbEaEWRrR8Cnx9fgVQzJWlF1buj6x93mo7vApNZ2H9TvYL6zeV6xfyz5Noqa2qOX54szDsd77aJ/4QrQOJjuaeIz2Ng70OR/hLWeEHSzx8YGRhb2st58RQkwR7z2jFPo09faRS2rkx0y3ISdCVhvyDK86D/rTt01hXVVXN5F6V+jck1JCb4r7kFcHeyT4aDWP5sCV0hDJI4AyvAGDIH+rMzF+wNUPQ5LNvDtu+pDFcahWbwYA/GCYyJ/GHHyQDQQFCBswL5396/vxY/trF/DlE4AhCEErhAID5aeibIAA4CW1GfG4y6sVzGQ16zvUGFSje4DFJEJ/sESDjH3pm9LPPrHuEdb+uJPr+4s5o9CHWr0qBAQQ6o1fPFpCNEOiMCusVBihd+fxswY1yfXZpy1txHfxw8z9bxzYE4NzJwtwXHf6wt32R0Q+a9qsz/7DjvcSfmfm3Y5Oed97dvaOBY78U/FDyb7UA8MKIGUV4yAoUbeDO6fTC/f92f6RIAgZsvj7zPoHVjWB8BPGQXy6D9Zvrd/b2hkMttY1VreDWFOvYg51NLeIPIhDYHut5o7vKJ/7tQ6+lT9vSAgMjL/W1UnncIWqSsIkIWFgjLJWcIp1SeErYVRpMZC7aT8VjGPyF6MfxVH3Cb3ncNOMoxO+JSiZhOoz4jIAhEMLJIAKHEStiQTVcU1NT6uKMDoKYhq9t2W+URnJJDVgyEAIYFAuy/mCNjuIGIBAUIISBT7zw/NioMHPz56bP4ZqgfoB5YQJTLvV8HhQgABCbOiDF3WTNo3sbewNCGoQFxXEh+AXhncD9h9wwVVi/8Ucn/8D5F4TYrwvrftf0/p1UOX8YzmDDV+W98BW09wvDA0bvrQLAWzevusis9VEKfEh2tVLJfVD4Ie1ft0r+U4Qk9x/jzzR+pfXLA4+E8Svr3jT+5MgP7Pq3u24npf71Ov78eyOBVShjqq0FYQOXIODXsIuhRu3+4n9bSP+HLeCibyYU5WSvYzmVWg67XOHQQHVVY/Wd4AX6AAAgAElEQVSrO83VNNDaum1bQ6JlX8/+PTUh8Yx7/aWRMrM4RPxYL/Vtr2urpK75+yEnZt8mOULYGKHJMhBVnTpg7Cs5KC/aTD7S0U/bYo3U9L4vsxXkH7a3DZEpQPqO0uESPkIg5sAANAQAIxgnFSZwZyTi76hP5XJTFyeGbWHgtdewcVKh+pPZMKW8gEjAufwoE3AjyMAxBOCJ8ycgCPLx+bFrF+eniX+noCc+dMO6eFFmUgMAJ+OY6YeOb7TzLXoVQHdUDIZAkxvICERpECJf4bo/VAQ++9z6dQ+D1Le3omEPx357r5RK/SuBwJMUBxYApFDvuLZ/JQNv3buSDUc/1KPPL8kOgLjO3suGWf5Z5Opm9af0X0iYvx4Of/ikOUTRD1kcotx/gzLxGcs+tmnrt9poed+sU1/0zI/de7qPNkPfA5R/b/09hwYekqAXSM+OpEsi0Din5D5fQpnG/aXFlf+OFnDBNyMBiHIvYDtoPIBxOt+7rGzkxSxbvy5nsH17bXPNViH/Ohl+x8TnB8fqt4o/UEuHe9u+I/sPbXdHHY5Xv1duU7Ony2cP9m2pYgTC+DieoFlpWzHJwgJbmPFm6D9l+fJWTN5FyD+BvwoaeVnf5A8K+Zeg5igWpgbDE0NYvAKB1DpP/PsTwAc35s8BHb1+v+WPiKtEKpVqWs5cnlMAfBj/eClTuACCsjrYzj7i3wQhcBgJOAbjMMc2boTsF6gE+akA4Cj0DkQCwlCQc5AQk89fm+Y8QARgWBDNK5N82JzHLURhBAce49xgznrw0nl/kDkxj3LikQNGfgRR/kWj12+tEvxQ7ON8P2bc9Su9HxpxDrspPH72Hs4QUft68zNxT7R+g4Q/Wfcr3vHl4F9h/Qr+QVgmqKK/EQ3IRHHfA/T9SeN3+3Z71xced95mpx9mPu9r2bkZg79CDi2kv5phK3SSIOBI+dp2cEBfBYx93Bq5D3Maby+YKTAl9WPA9jirLmH9fppykPzr7XWGBiqam7c0SeWnIXissx5i5A0diepD+/fv3uYUT4DjC+nTtuKQ9OzLW7dUxSAa8mdmk4RKW31cTEOvslJDjfcMVcjHY5UG//C6saqu5ktw/u1C+QcVYaEQ5QX7UBRBKqDbQxUfTEDinw+eMYIf3g6YFhPxJ5rqBQHrc7nM0tywAbaHL3lOkQZkDJoIlLXBtO7enTsD5u8YaMCNpACfP3H+44/Hpi9enL82TQAcwdFIeWEzq4xBBGAS3ZwRbAqIapeMIfit4K0+6OZehyEmI/s83d4/uOIQsH4fBqlvb2HdL8i/rGPV2G/BYvknbNhel9PlvGrauOPqAhFYyvqFul8Y/yFjGir44UuGwz4kYCJheTD4m8ToL8ZJyPvHQ4+M5D+p/gao5xUUvrHxS11fTPVH+FOFb7sP7ek+VCVEEgU/Dr8yQs6/h5uk4jRBwJGRdPlq9nJ5SQko9V969vLSncWV+7PpYg9jASuNg6sjMADBj6xjKJfJ9TtdYat9S11zza6dBesYXj4QCBwYaBhMdNQc3d+zaSAcdYT3/mV5UVrg9toqLI87Cq2ybF3zC8tDKrUUjOmj0utnOyKJCDdC34OKyerJKWH9wtAP8WL3SjcwG4SYA+KT5KMhwDAJk4smoEm+eO74E34/AjCVOgCG8MyaxFtrleCfXQHOaf5B06y7c8PoAYRYMCnAj//p/MaLly+iAmQTGBpgQRhEAfCaBGAE2QaOwEjEYgvHS+5P9P15KRpO85N82CVGQHLdH5YK3LD+ETr/HK6gxU3/rnyFeb9GzdvJ8XuOqMvpDDujjkI33ypRD7nOXs32s1Ur/tHS9rWC4pXrdMYtaHMeVMkvwjonE4FeGoRH6gvdoa3fBrDrlPHLsV9KfRH045Ef8LLbYRi/0PN+R73sexB9f/a0rvx4eF5y2cgsIjBQGDHmEwPGtm0PYHV/EeTf/WL7dzURuPqNcDxQNvLlA0c0N5Xq73W54h2tNV1VfYdt2OPtYyACPzjcBH+zdneirvtIz45BMD9e/oG9NgSaJPTVNkJmNAwO6dmjK4TNlBht0Oo99vpVsu/PQJ+6QXxB11OZ+Szw54O3PrebPP9IAbCDOSyKrU85XZg8hFaEE+WgIapf8I8AKCzpnL9zan74wsNQZ1uGCiyMhtgAiAScYycgdw2cGz5PrkBMg/n449Frly/OKwCC+pu7O4ft8k9NUOtUMIHzAEBMefFxdy9hDwsKYmSHoj38HmBJ9w/nBsH2H1BOzCOdeORwiX9B0OOBfJWHOf9OSvzxFyrAaBSq1cJRpzZ1HwI/sJu574HJNSH/4vBIUPrhcQvrV+JPTko3Yh/+hLew6RUHP1ol/qpR/1XwxKNGs+53k+KfsH43bVcDf6E6bBW+rLbSCoEPO1Prt0B5WWBkQeDv9sovF4B/q5q/yFBpPa9t/ZaV/yTjiC5nMn6M/Q7UNhcEPzp3GksQ8MGxw/Xwd+vwNrT1HOlu7hCGcOTgyGl7WuDIwt6+2q4YlcepVlmFhjDxTV8+bCEeP8W2V5D6DOovBMEP8v5ZCS95/7AeguCATxJLPgswSCyeFDgJDk70C2vAX1+PABSmNCAwN5m3IfAr43C4oEa4qCQEvYBz4hBYwDwxCZJiSAE+//HYtaV5gb956J8P/BPEuytOGN34XzaOSQGoTGB+AQi8o0/T7ZY9X/GmIPWAVcmCFoph9Am63X8gbfOfFfLvEbZ9cbjEc0gIwLBt5Iexbhn8OykTAHXO363rH0ZdAK1sr73wrQQFKf7x2fjZq/GkjH1Ykn/eUNxJdW+y9I0BGJT4c8vaD7PpvWx7NcBlvyr2USHbvnDmn4z9GoUfEPxoa9rJA3+/8/JXTGsJGFtl5enZUggMmLwrdOAJ6/f+4v3Ff7uN5m/BKsE6rf4CSkvaTxGk+nLZsSzUD6T+BTu21zTWbT0Mwm8zEe/wTvsCSfjgmB/Fc0eiZVPP/j11EBAW7wEoZ/W3HHlp75a6tzEaYiAQ+8QUZUYXOgQNL2BlpdaCuI0zPyqqZdurYBJiG15Ib0EjGLRgiJ8e2AIL5/6y/gHTl0aChDBaggJQAPCA+AMcAD+gIGBTLnV5wsDeBfyCj4ewcNhuBZdoCjOBiYAXLswAAHli0hJEhFEBjs4vLg0LiXcRAQj4A0/h6CmIk5Qj/GB4CAVB3G7OdXZzDCRCPLQ4MuLDZz3VwIR8NAwFWj/QjVAc8nuvAp9b73sYor7tFQ76ktkPH2b9MtjGOQKs7eBb14X8g5pdVzSrEbjqEvgLJ338po5YI79eEPsecOGvsn6DQRyCw6UfEn/eoso3rf506FfW/dK0c5X6p+Vfd3dlE/e8dzj+ftaeDfdVFzjzCIFSO61qpSqEzd5ZXFxZseMvYN+0+xXXVoCBsvSny45oairT73L1xhMttc3a+i3EHpvDEA/e+cGxw/gXbA8NbOo5sqfCLZ4NnS+NoBtAElyoVWiSADOE9+3p2S9zYiggbGZFF6yYvrY5AaUVLOQfWL9C/h3I+X0eX6IDAh/iJY+xz5CV6PDQWySlxPigOUDESghMRtwUJYFKYG8EzcJQAgCYQgmYwUgImMP+zst5BB6mR19QHHwYAs8UJQXaBSDlQsNjzigA/moREHj+47H5xRs3loQcHJ6Ym7+GIzTFuWPQGBXGxVEb/Xz+HALQ6aMZSFTsQS8I7P7qtiIo9Cj04ybPH3mMLBoDZqEWdv++Z0YL67f30cV+5eoNX1k785nyXajpi1SAhsg7e8/lCjvj4bDTcfVmCeWn12cQNQ4HsaYpRHEP5BpYv86w0H6y8wEFP3yo/qhHIGJSRn917h/hbxsHP6DplQAgln2w9QuZf11dct65pB+l/lXv5J73jh8vjJxenTClFjEpQCoQoyHyqDrBfMCA7TK9sHJnobALDAFSPq7toNoqhUFoepqNLk9N5cIulyvU0FpbVS2DH5tLYHCnJCBcHvPjX7Gjo3rf/v2HWoPCGNn6PSMgHIDHn32lr7qqDVpGU07MPkwL5H6pyiNoh+DqAAT80cDzvX19rw9C11NPKNFB7UAx6iHfHb00FsZNQs8LNSChBJrGmBEdgV74lt/y+i0AYFN9ExnBQgGmmkAK5g5nliYAVGcAgLRB2ywI16KfgUBbFJiDIDOI1eE5ScAbNwQCxyaWoC3hEmbGjE5wyBhzpUfBBTg2gY+Qn59fwjxAIepAwFJXa6wI5haHHO4Nof2Lw+JA9iL5fNI/SFnhv9dpgU8/lXz0+IP1C82/W+Om2TvOZR/ot9MZz4xBuuUk9USAvlWQRnPWQOOlkwW28Nmr2STGc8l6oeW1kigh41L9JWXunzR/I4b+65C5L+2y7wvm/knnX/WWClpm4Qe99GTdL8V+u5ul/Itm3x8pFcYovQrVGCACcgLVYc0s267BNOg9Zcq/YoEnrd3Cnypgu4JVhn0P+lOTU0PRXleyY6C1uhpS/0rRz4yFyP1jx5rg7zjYkag9eqRn00A86nDtnS4zESi+xSxGQ97cZKsQhjYxhhlst4h32KgnF1WCCOu3tmJy7+TU1kx9k+XzRDravZjuRql+nB6M8X6UP9gaDwRPMIS5cEIfAjAiIX+HAJ8PC+GEAgTVBxbwAUnBVCa3PHVxmOmHvLugzeDVjeHhgkBIcSB4bm74wscXoPJ4+C4REMC3uIRtWQGAG7E4bkxmSsMaEwpwFO56d+kGjEefmEyCjOVOCD4ICEvr1s1uQHQMWtT9VbCfnKDgF0RRgHaw7/e2YeqzG9Y/wqZ/xoIf4hc3x1fPfzmJ6X4CcVdViYjyAcp4MNb+ggMv6voFRUMM8Mnk51v3PDj214KAh0elPQvrNxw38Kf6/mGyq1vGSDD3xav4x/KP6z6k84+7HlRg0786cv5x2wPD+IXCNyGSuO9B32zga8o/XlKzBQJlAbvXT91ubppCzgy3yutAEQpLctDcgUhtKuzyT011QvAjMTAw0Dp47AMBts7NAMDD5P3rLAqCYCCEtxmBCUAgNUnofX+23J4WWP6Tl7dVN8ewT0zPfs6JQW9g5Q4uEdFasJCCBRBsFPJvL1V+NHVGPEOY9oRZL5j8B0zASDCmwgubF+xCNz4ZhMUIc3QjkPpH3YJCkActJGCTUIB+f05wL1MvCFifIVNYfOUy86TW1EIMsgosxcDCjOjiXGjyAX5MDzeMkZDFxUWiHytAahQjSQi9YMbG3hjDwDECUwAwk8TkPgQ/5DPCgDtq94UKUBwj/mHnIysUkrXPbioToV1g4e9l2/znHmndr7mIwj/6f0o5AUn+jZ+9GgVGuVwq1KsMYcm5Wzc/jIIGzGbNzGcadUkb4zc/TGI9m3grT0KfZx+m9EHs1yltX1B/0I1axn7JWViQ+9yhYh+q8kN1famggUc88NJoesV1v2D8Cuv3UHWnHPh77JX0818Tf5pmjMBAQB8tgpU6tloIo/DsVfeKtk8HZu9kXZ2ZKQHBXqfV3tLQsrvn0NYHD5Btm4s0YKEElIcPAwIH273tjd1Het4cjEYd2Zdny05LIYuIT3/v5dZa2TUfc2IwK3CTgb0dq0BP346FvzDybW/f1NZUh98KBiHxHYFHSXDoFoZ06ASYBhQmi5C5R54vioiQUWxx/MOPl01N9TkKgiAIU7xyuTv54QIEKpfghdVt4bUlIChARuCZGQG1xcUVxcClMdUpa4wrRaheeExP20QAMszcxi+IVb9urgkmscA8xBPQVoYByaFQiCpF4GWy7vcPgRueeoRN/8wVdUgZ+nmJJGiO9EZdxKdwttcofEMFOK6U3q3rvVln9EopLyBQ8Oy9bD8q91DIA33uwelneUMep1M1PY3TyKMkTj3ysd43sl9k8GNQWr8g/gZadOYf0s9seqoyn5X62wfWb0xZv473Hxb7LQUrg01l5WWm344vAgVFbPpu5QUENE408MhkLf3NNf/Sn+Zc4dSdqU5Xb2+yo2WgvabnxH964ciOww+IbIc3Hy6CnbqQJjBcfHC4A3qJJaz2HT1vHK2BaMh3XhmRIpB+xrKRhb7Wmi74Wx7qoYDwPqNPAkpBY4qIQUMDgJD7ApW/x7fuqm/qDHqCQsyBkgNbF/sBoHsYgsAhrALz4oveLXQg4ADyXogHcADS5bz+Tr+F9KNE6KYcU4/plwEpCAg8YwfgBRaBJg1Xw59dA84VAVA8xNyNxZWVFQQgBEFGZbt8LBEeGx4bpr4JYzJt5u7d/CgCEOCnXH5uhBs4fCzuhEOZMBQppnCgG13nPjKSfZjDJm7yrFv/e5UTs2F98lGmvtiWJqCzBALJug1TSRoMyYx+eN2o/R2XhjAeuXXvQxv+zLrf6x9K/EHAA6gHH/G403D+KdefbHwQCWn8GZVvYP62N5D4M9VfNfGvrkbNu1TqT/U9gKan23ZS6p8j+upC+de1fgukWCH8CrFnUK28nMDIzCsM9AbKJfj4QfU9SzoEy9LTmf7w8tRkLhx1xUMNAw3be068cOKE+Hpj3+EHDwrRp4zewsNkEHd2iDcWgcCBWM/+7kZLPD+bDuKbg/q20LthL3TNF39KmROD0RBqlvVmoRewhBbsoqbPfcd3DTb5I5GgJf6raMuGAGxedvZ1EP640MOLHf8gM4YsAYvmY8KVuFdnBExgXLkmSIAR+g8+0PxNvZ6hlUshAqUvkC5tnsBCBq4aB56TPkDGH17O3FjBhSJwcYnaoxoEFAv4N7H0KwnAOQAg/R74TAdPN5rCBDmchYfYU94+fHOgW/lemBbjhjIpnzu47pkNvy8qEGK/azLpd7sMR6Tz17ZoMEANRliSYRoMMgJVNGRcmcKMufFV0mCE9ZulrAayfkHz0ZfGH/n+6Bvx1COd+idWh879M91/ZuFHLeJP1r1hz1MI/dozn/fUHRYveEz923lw5HRp+RcouC4UYwHjDJNUts2AcbQAXvrM8qJKOvORTXxKQNIqg9S/3uXUZCoY7XX5BlsaBir3vwD8EwR84URP84+LCWjnnnGFaYGAwPbBDq+vdff+I4eqLfF8qP9eGhtDyO9aVjbyyt7qqhiPUVcIVFOExWVsh9J/hRCMNVbByEth/R6o93di11OEHI5AY69fyNvRnhBH0PuHagfpSGFgb4iy4ELQGDXS2QmGcyfmwKAB3JSrJ/s3JcQgaUAhAHGlKC1QS8AzamuVYEhBt3xTAkIeoFCAH3Mc5MLw3NLiSm5FMXCJK96QgMOjZ0bFQ41CzfDErxQAWQGGLOxrGIlYEX59RLA8XtxAGbBBGfX1Bdk5iFXCQEMf3U5wFKf/vqQFbngq/lgEP2jJUYn0I0WvmK2whFn7+ZVsOI5U8kCzfEBU0umStb/jMgpSYPYa0g/Wv1DmM7b1CBP/JAJtiX9BW+iXRyMZqS8q9jsI0863iU+u+5XOvwru+kItnzn1RZX9QuFbd1v9zs2bP/gOpf6VrVLDZlyVuEWdIVZZ4bkKWrZjTLOAibQSTA2UKw2obrU/Dl+XPZ9eyIVducmpZUj98zYMeKu7TxD+iIEnevaWEIEy/rHKcT9I7I6Qe9uhI0cODcBT4tUflBsTNOH3nX2lZQt0zd+nmiRwjTDZwJUlvIB8EBsfQOrfrsEOfwRyX0jfoWFLpW9C/XUkcCa4ZfFxOgM5CbVvsI0TkaxIpNPvtcD/F0ECQhYMKsAUJgQi9DQEIRpyebSQgNIWvlDCDC4QgMNs/+LVnAlAgT9hAC8vr0gELsl6D5SAw6PD2J91bOPYTAkAQkNUXvJ5D2yLCMqB0BNygOUetUOnzFm39Ii6aYSwOASV9b8PaYEbnln3+OAvaug/aQr/SKZEo/XL+PMlw73CzhJsQhmYdV4/yyqQVwnHn1xnr8fFHXXwQwHQwB8lPlPqH8+8tGjqJfPPq/Qfdz7gtlc87w2s31qj6V9jl8bfDtn079DRo/u2C/wdQ+/fj3/AM4FMDJWgTemFfFKxX3lMbhSxq4Q3Tx1Iy52APFhMT/sdAUPv9/cOpaZScWj70tDS0LrnDQN/iMD3eg5CEOTwKrQrPgSfnf6EIJDlrdmzv+dQq3injv7VD8pPaxxj4veXW2qb39yxY99ubJKAvkB4l2EZaAaDd2g5GOuqqpushcLfA01N7qDHSnRAFBcxB69g2HGH2ttxLCR0hIavkAU/DAMSxKAXc/8wEzACSdB++IH9HfVN/noBQFCB9U2pFMaBZRQkw55AsaYuTlwwl+EYLKkBlfgrLIYzTOCZebB7Bf9ymyUBlyDXeS5PBBweJQSCV5ABePcGm8BIsAglO7gtGvwO4PfJAdnwmvH5fNIIBt4FZSSI8qTpuA975vss3+OeFvhI5/0Wrai8lBu0yQ2c2frFYrRkLw7WDgshRzIw67xumrvjJgHHtQCEti8fUuqfeF57nIb5i3nPin+U+ifoB6UfbnLxqtRnr679YOtXl37oiR/GuPM2FfvV8u/QHmH9dj7YvBNzXx68OFKQ52EzRQPlrMWKARcwtuzFHwH+pPsR0+jsgLqVvwLqnIBqp88Q1FcBtasoSBfCEH3g6M9NpYYcva4k5L60Sev3xE81Af/Tey+vbQYfs13zpZBVAk3BUG33kZ5Yu1M8I17EgLD66SH15uW+Ws6JgYAwq0DwBuooiIyL4NensS4h/76snZw6LvjXGfH4QtjEii1c9GoJIzjR0I47VO+FBkACGAjlIF4MiIYs9AtH/HgfIQKFDOxgD6C/qd7/qh9CwfW5V1O7qCgE0UcaMJPJLWfmdUBYlYhcoPTAwmjIsIlAc5EJjAQcRvyBANysFKAAYB7XHE1DGp6YGR6G8o+JOZZ/N+7eIAVo0WBgwB10xQqCSRui+l9gYYRmwnMPbFSCYP6iyQvqEMapW9QqCYWDeKX6HudoCEw8WgtIv9MVNeMfUbkLmHPgQLhb168g/oSy9jijvHrDQXgTQl+gqv29ZNd/l9TFSch8TgI0IZQXVMEPpJ+Cn0p8Dsq6X1T6MvrBuX8m/hr0yA8p/yD1pbDlvZ52LlP/Dm/Gps8Ox+v2YUDlAb1hY83qK4DZfybUNKb0OeWGRrSjTJ9Zlh6RJwQKzrTflc85Xb6QcrlyU5lOZ2/UaQ02tA/sOUH8+6kBQXFk96sm547ZzV/e6NQ7fMIxIKDAU3uzQGCbVzw7hl4eOX1a/Wzwe6cX9vbVYDQEc2JUZvQmbQmbOTGxtsbGqi+/hOAveP+EigH5h//hBDV+Ac5ZIeAfOX5B4mExMLn9vNj8CmKjMANTbPm9OBjdH4lAALgTnYCv+uv99alX63NcFIcZMRKA6AuEnJipa6Yr8MIZTcKHaECp/lQU+GOBvyXm38rm5WIA5mEc0sQM9kDN56fz+XnA31weFGB+dAYBCOovQjXAboqF6BapmOccUTucBmhRX2y6QC8gBg1D4lyMiFjPPKaewGc3rA8+PvxzGAKQv4B9UULhlZtQskvqzxfvjerVG1cIdF09a6jASyUKP6DpKYaxIPjhMo1fQ/4ZbQ8imO6KXm7T+lX8k12fEX+2rle1wvzllvddbWz8quAHzjs/VMGpf72OH1O9axHnSiHHPGaHV1lB/wN9tnL2lQVGMEsmwMeMM5mYcEsaqkKkTJQpheQS5KixsU6XjXyZdQxlJrHvga+joaH+N1989N6JAgP4py+c6N4LCdGHd66+7HEQToo5tvMDYVYSAvf1HDla1dELFcJ/GTBLpcUv9hcvbqGu+TA7Sc5Rx4jwjk3S68cc7GpsrmpE/u2irn8JTH0mj56XRkDCZUNDAls84y3oFLTYC4gOQpSLkRClBWNJnN/rjxD8OrgULld/oJ4SoOXKSPnHJnGJtEC9CiTgsEFAUwCKBdCcWVpU0FsuBOD8PEpAXoJ/167l5+8K23dubl4AcH4in6I8QHrGQ3pEwpIg5K4I5BAkEmLdML02qEGMpKIbc8ZACgpzGSdMrH8szeDnnnE/Ps4/be8y/6Ik/vgSD8bR7epLuqL25UriG40gVjZ69V8KnX868fnk+L9cySZRyocw3Y8yX2TLKy3/mH7IP3QCRzj5JaH4Z3Q+kBMvSf5tp8oP3fO5rY1nLfLAIxh3Dm1fGnXq34tKzwQkjgIF1+XqZvsKGFcFnrri+wfK0rN3FsrLzPYqKAnlqWV4ftmILAsO2C+1GlUHyk6PfPrA4VrOTHVGe3vjwvpt2PbFn/7Jd//0ozdsCHzhhf1vYwzkoeVwpW4/thM8awKB4YYd+4901/hcAoGvpaFVFv/0QgWeHnlpL1QI0xz1np5u2TGVvIE7Kik9MBZra26uaz7I+PNHfJFQewf8ewUGQ+T784J6CYUatiUgIRDTAhGO6AZGCSi4Z0U6QQtGcFo6QtCb8IcwBTonRKD4yNXXYzlwfUqFgAmAqalMjoPBsJaX7WmBtuCwRuBwSQU4I0vhzhD+ZPC3BADnQQJOEASBf9fyQMA8KcCLP/nUTz2RIhADRuwlcP4T+sBJFFJlDNbAiNeHN4T2ccjyqewZyKImT2DQJ+MkAodPPX5msLB+w49R7osZ/XCw8evQjMPNXqcH3Ham/KPV60zCWxBUbGTj1426j89s+u/svbBM/ZPWb5j8f3Ej9CujHx7ybUBvXGX9er1a/anGfy06+Q/U3xYDf8069UWKPwp+dG8a4L4H0ejWhfLV2r4U8kaiSHFS7eKRNFNKqTTj/nj3kfuLtxcXRsrJ21gk5mgJktxZ0IXBAXWhdvWhsvLZTK9jOZNZDkd7w5b4mwz85rt/8l1Yf/rRe9INKPD33r7X0f132Aa2QtBp4Bk7ywqBkKMXat29f/+hCp94tmxdSOtugQEsaP507xbMidmE6eXdR/fI2SE7eHxIWxuovy+b70xO9oH1G/FB5QcGNjqIcgC4DjCD3d5tA5jvkgjRApcfi0F8QsCwEC/YzF4/wFFs+kOk/wQCc/VwWZ9rglCwtIFTrzMHMzYACgSmLhcjsKQP8EyhAAcIM0YAACAASURBVJxT7WDuoukrwLe8OQcuQAOAwL/8/By0fJEKUABw+lpe8C8/N4cA3FQXgee8tHCBeKo1llrEOYx9gAL0eHxQBuNG1mEUWNDOgyoRXj5gCrvhdRl86nHTgBue8TxG8i9q+PwcNgFYgMB4vBh/eEMYcQW5MWFIjGbZN37znkqEHr/ui2Pqn4r9htViAHrI95eEx6Gmz+jmoOQXP9DPr5NfDP1nFv5WQ+xDNT2Vdb8FIz/21DXt3LyZe97LVifGS9m+q4+Zx5luxm7ZbNr0IwbkOdJ4ha5/v7z9b79cGBkJqKoyeUq5AmdZYGHlvj0OUi5vkx90Y1lZ+pVlRzw1mQHrN5loaGiX+IP173+JCPypkIL7K3Y+EL+xWKv0g1lVBxL98LLT74WM5MSWPft79rV4HI7+rVQhzH7NsjLIidle0cxvOBBlBwTKbllC+wH96uq+rAH8Qeqz+E8DwOj9zeJkPwHADohxNGxpd1PWC8k/CJEkMPCB9/FiPxjIhg75of+V1+/vROdfExSBNKWasBROfMBFLgcuwIzSgOQCnJqS4eBcLnO5oEJY6T8NQd0TQY/H5F4waAbPSwLuhAs7AIGAeQnAGakA0QJGAH66qSbpCUZUgQe8ngQEfXAkyPktsCL8BWeBiYuvEPFqgU/8QjMNv4QKBEMKX5iPlxX8+GU+R809ScMoknDN1SuBKBAYwtC7MISzN0kF3rqXjWchS1oowZvc9QqCHzr1zxk25F+c8v5g+TyMP7dZ+aZz/+TE84Ft5P3bxvwz+h7gyA9d94uVH/vQ+u3uAucfpv5l3x+RWW2KVwo8cplhC4VDha+AhFygfGFWR4GVUqNrSFRZWFz85cq//fL2fegXSF3zA+ZpuCHs49n7K/fJBg4YX+oM+fAwQ3gZet4L69fVG/YKRbzriz/R/AMVuP+9F4T8O/L2B0L+Sfyt3hGrKCBi7mBOjBcmD3jdFXuO7N/XAo3bICemTHE6IMA+e/B4dVVXLPYmxDre5GyYHbFYTLwfVdXU1MDAy1bEXyd0PW2H4C8Uurm9lOfn7SDCud0tAECQghbn/YnXeiLEOMR7ie0OYSVbfnFHrP/lEpAm+Moh+gZfrScJuJUKQCgSnDHiwSnpCswVI7CoLq60D1CJQERgDum3TEkwt6UJPM8AnNEK8BoowHkDgOTzcWMkGJ18VsQnCAiOcIxwYCEo2bo8PgKufdLSdYMV5vOgB9BDh4QahPI4sfXMw6D0u1tg/a5Oo0eyorbrIvm36urtJQLCZW8SHRHin0HtVG/djL8ldvqT18/eOvsPWQ86KmThG9m+cWdcL7PjPac+h6yQmfoiaz9k5wPu+8y5f9WU/Fdj6/lMbV9k3Rv1vG89vJO7nv54QfY9MBxxijAFpFNXepPQSOosEChbmA2UldnPL5dYG1m4vLRI8m92YWFWDw4hfkpPYBkOB7lNTkCJVttD8Yb4TrOTTkf/1FQq3OtygfV74AtD/n33CyTgvx954b09xxl/myX7Dq8dCym1KC2w048BeKu9qvtIT2VDuNcRffEHsnUOpfJgTkx1zUHx5hN7u+3ttrbGxmaxqgT8Xqyd3LKlr6/1+PGtBzqaOiP9nkQ7Vrl5EzzU1GclIAwML3Ofd0srEE6Y3TTuCFxdPgyBoPYD+9filGjL74fm+eJCkC/hT3AhCBjCmAsNMhCwV5+SAEzJdEBj5Q6vXDQRqGpDSgDQLARRA0FwYwkRCB9KAHIUGJyA0P7ZDsC72Ej/7hwCkGQfBTFAuxHlfD6ZGWhxkxxLuvjcytPnxmo5ePF4AIUY/IAHsnyYS5Zc99i4AZ9b/zil/jmM5Jeo3Clp/5ba6aVPWlGnB56f8B/pT967ea+frFhf9srVK3FKZPGGZOZzYeaf6vlHop3+3Tr2IRv/Mf8GdfQDvX8Q+93C+FPzzuXAN45+bELnX3fNYTnw9zsvy9hvQFLFJJzmjm1Xna4ZSddlp2cXhCwrUzepslkIftyH6gDseR8oT88uQM9osL1VCIQZiqOBV26r5oD6Nvnt6CcoO12+cNiRzWUyna4oVH40tDdA8MOAH4vAf6/7c8k/7AdzWEvAVezeY2ttHfPDvyARGoj1HDnamBDv5J0HhYqWf5VAOaYF/tXWvS/WHTz4duPBg40Hm+terKmthVlve/v6+o63bKXCt/64p6MB+MdT/dCiRVOYnL4dNdsJdBgfToS4SRQbBHgfzIQOJUIRCCP7O/xcA5doaoIQSBNYvoKBr6ZyWA63NWUIwAzzjxAo9nMgApenLtqaJFzgOPAF7QQsoB/2OJ3jhgiIwLsUCpbBEAVAGQSRAOQo8Nw8KsD5TzfVCgMYLV5gGHr5MMfPTSLQTZ2Q3FT/5sMBstQeHc+mE1H/UdskYCBsQjARZjwm1z8MTL+b9dzjVPgBK2puUNrLVxOAgnjwEWUAukAFOik0H7Li4rHCQcxZCIbFaWEPPreDtsxnI/QbVx1PVeqfYfz6bcGPQSP1r0V6/yoqqs3MZ2p6GoMUNHb+kfUb64CBv9j09K9mzVbvmmsG4gzi2M8JMPk0vUCSldNk9ICJgwB4xoT8W1y8Dfgjy1YAMT8LU4TBb1YG58BpZdBc4P7S0sqKEQMh+KkfRT5o+UIKmj5nlsUfF6zfhpbf/Ol3S6wv/vV/xNgvrcNkAJduirVKawTzJJwfhyqwPeFtqOw+0t0IOTH+gyMBmUYEPkxQgcebdvXtffHFipoXa8TlZPVeoN/xqW1bdx2oh9jvUDwcbBf6rz2BU/3Q0QfNDUABhsggrqlIhLg2BGQftgEMRcgd6EWnMFaAJFD3wfw0qICrl0ZwDvJgiIBQDowMzByQvIOWMNgXRopAAUBEYG6qKDO62Ag2kgC1+pMikFUgZQPSmkcFOMdpMJgHKBTgNPoA51EBzuf3VbZ4BNIi7gj3PRJblOQs4efmHUjtC6FKCGKI1+NDoQcxD9R9MhcQAIj1+pAVmAyvexy8gML6fbzUnw576As751aBIWm+XqKgWoJ00NRPME8A0eX0iLfspEssp8sVD4YsW+Fb3Bb8lfN+2fr1WQXOP/D/GcEPOfF3G3n/KmTqS50Qf5j618apf7LyA63fQ9sh8xmt35+9lNbev4CxYcJLbSkYldttUnUQj5XhZPQ0YQ30XOD06bK0MHnvL90R/NPJLdgBWhBwFohZjjIwnaYT4bVzfyRtPnTRd4S+B3FHv3j9Qte/YMdAQ+4337V7/3D9yXe/UOpPKcBVyGbbXQOFcEunPwHsCrVs2n/kaIW3N+poWkjzBJUA/jplgf/1teOhA1uPC8k3OQm67/jxluNbM7sOIP46I9Dztr2lHf6tlpcUHZAM9Z4XU1qsRE1du5eGniIW6QY3eQrZLWjBQEDIjPL7oSQk5EXvH0ZB4KoeqoCRgCn+TMk06JT0BCqjWPbNMltlFWREG6UgEoAzhQBEOxjzoVfQHbh588pKXiZCUzXcxKgMgoACvAsAnJv5ciBI7HIHpQLASg6OfQDjEICWTG7B0jcfajzYAGcfVQ5gUAQDiSgm0ajyeeLBx8AG3rD+cYr90jLdf8y7hwrA3qiEX6/Gn4sQ6Eq6kwJ+tKBpqlOueJhtX6cR/EiS9UtvVEFfCflnS31WfU+3DeiJv0bsw1b5wQPfuPKtu7vKD86/78jUPwNhGnmKcAqA6jbDWlV3LJeIgpMDZTgLhMejwxKMW7jPVJvVVENfH/BPrGuzC7gu3r8MJwo7WQ8HISKb3058Yt8DRxSs314Mfgy0t2jr18a/f/3OTuX9wwjIarXAJdbqcWFQgfDP6AhZWw4d2b97S1I8dV7/XvnzgYAMCQUCp8tHXj7c2VT/6oFdgnq06gcF/QB/Qv45Xd5tg1jSjU1fEuTYC7FlC05Ab02sJUSNAL3tXCaC8EOJaMFY4Igwf4Xpi14/DAInBPoSWAKMnRDQAdiEIeAUtIVh1x/Rjz2BGeUUpEthB8s+MWaLmAIn4IxahRJwhlTg3RuSgLnllWsTE4p+o9gbUAPwLgMwEyZT1+cGbzkEPoIc27CQecRCgF8oRP49crj7sDSLij/Ad+gBIxmUhEWlcFhOKhgYjj/ygpANj1fs11Hg/ZPRYJkBWIhCY7tXfpnLRR8Kfrycesm0P9P4NWIf2vhFR4/mXyH9Wlq09budC39l3wPKfEb3H6Wfgfqjrn+D8OqFeefZrVTMyoRTwQjNGU2+8qIdBTx08vF9ZSII2Lbig5i2cPn+5ctLi/fvgPNvRD0+fVtEoODewjwQUnzdF6LhtsCfDZTq+6rrssDsVNYxNDXlj4s3mBAIYsPlZ65/FfJvM/LvsBKBioGHi7hWcqcYgxQNAVcgREO81Yf27z+03d3rcB3/C5niHQiw5X+waYjzUkCUwVoWhupQfzycdflaBlDVdZDCw0ViMIG+/qBv++46GRkGszeUgK6nKggcYQUIERSK/ib4e4DtqwAI6i+HXVHrqRbu9RQnAkrtR7spJQwBgbnLc4YdrDNhhh9uAhMEZ9AXyCHhlfzoKfL8cWNoVIB5yoO+C3mAd2fmsB00mMBANayAQs9eJOihbjDgFYTcCF9QyGBxO+X4QaNoDwlBgCCeCBSE+AmKQB82boLmJeH1jxaAwvqNr8GiR7HM9BeZ+uxYDXqKexjxlb4/5f9j+qkvgp8df06edEmzflkAsvGL+s+t5J+ufOtQyS8c+2ho4KFvHPyoNuRfI/Ovkgs/IAONC9+qwfv/AVi/b91H61eiS+ElYIuCBKQAMz7sULJf4f0FAUZmr127eH9+SSwBtaXFX67cvv1/oKiT98e0OXAVIgLFSYC+xV/evn37v9+34c/44eQ3LiuDgb/9QssMiT+6R1i/Db/5ooT6A+/fA8P7Z/Bv7UyY0jGQwluPPcBWWQJeVkcdzE7a5nQ4nHt5cEhAMjCwMHk42bncKT79ncA+WP39oP9cHdvaEyTuExjnSiQ4spFALSheww2xfe0WN79yYzdAsIchMdrLDQJRIPq9EoB+YV1DOxjFP2wGU9+UkhrQJgDVkYxCHwMQGJgyc2JWEYAq+cWGPmoPyIbwCuQF5ibGNkr08UgkwwSeI8mYiXt87O9zYxQYDV9sbMBHudWfR7w8MF3Gg00PVOEHYdCHjiRqVAfKEBNjxIlxZ/ipRwrA59YHHzfrN2riTwVA1ljMO479mvqP6Weyz1yq3Z8zbo/+6tgvvFGR+rN05QfbvrbCN8z9U9avMH9r1cSjKt3z2Vb6wfPOVe4LaT4FLoOBimTK7jSvNTLtoKQbOKICE+EWLv7yl4u3SdHdAaipDld4f4ADdNIjmQQ68P79+wsQGVY1wJp++geArn+BhZTDAX0PxB8drN+GwS9KOP+++ydf/OvOEvjbvFllA/42i8FItSGJUEdj9xs9sXbxFHK9PFL2vAysw9/idHphKhofGhrqHIK13D/U398fDmedveFtW9rRucsynzyAJAlB71meYEf1odoOsI+pQMRLCQHSK2iRBxBo6Q8hAa2Qv0kGgqkZYP2BV1+tfzWliuEyr2eM0G/KHgdOyWsKhyzL2UlnDC+gCgIPz9hToG36b2ZOtglE58dyZvQ8z4LjmXDDozP5vODfNaoFnhEPLBRg0BfB3peo9ty+CObwcXNAi8IaYPeK1wkMAYH+L0Fu+EKmMKhCUHuY/edBKQgMhDsGk+Kl9wgB+OxzzzxmqS9S8sltB+e+rEpAznjulbpP8U8IEZdLE7AUAMOG50/bvkbPUw97ONw0HTjEmRFg/aquf6rxwUALqb/W7VT5oQZeYvBDFn6olvfC+j26aZvEX9bx2ghn7hapK7mMY3ywjF7Qxj0C+m5qs5y4Bs0O0iMjI+fQxTcCYQ7lPSyT98DWgRgpCajcQbwnJdOV2xgrH/102ezLDxzLGRz4CyOPBgZ/891S3r//74t/fQvmIDHwChHIzsACEBbovTVDwnzCMYxAeEMNMUgLbI9Hoac2z0QhQQwJkJn+t/qRfLjign/iCeOprmmnzHYKAnu9nN4MA4G9Xp8VTHY0VB6qa8dGB9wo3yvdIrhJ75J+UoIy+NvEJvCrTVj+dgDjvq+mBPlezakE6FRKpcIYNOQlxWLu8NRF1TC1gIDKAVhMP/nBt0NSzNT5n54n/p1hAE4IAOa5F8IMtKABALpJAVrSER5khReENliUzhL0YIqfm4SfFeRcPzR33dLcBVBi9+AgygqMhiSdzuCjM4Efv9gvLOn3I/oVGr+lzF8V9MUtV680gQs9f84iBahbHhQ0vaJxb/g/xEa3Fg/9CDH/7LkvAzL6K71/OPPDqPtts8k/nnd+tHZoJ7W9EubvK2UFfQ+UnatM4GKzWJ1tXNl32OoDsCHVyk6LVVZ22micJx8nQJzDtBeZO2JmukhY0o8UYPMbp/F+utPhymUyy9j1T/w1tpXE3//1//4v//f/ufM7aOkW409qwD+HG/+n0mBbex0zzhEqUCAr5IEmCUfrEuJpfviVEfjN8XeDX/a0+LFz/WHxQSsMAIxGQzW1DeKOCdKAmBBN5W0AQGiKIACYaDm6uxrzYDpU2S/YwcLkhf5XYAZjhSTQ0G+UgYD4exW7IOwSCHw1BbFgbeVmMq9L1qnQhwFBCAezKbxMQ4QvaA+gkQZYMgDMCJT8m6GcmDvnPz5Ps+BQAQ6Pjs6MAv8gC2aGBCYCMIKGbuT/Z+7dY9s873zP6bQdTNECJIcSJYIUL6IupBzKtESKl5CmqJhqpEiyJMt0LDsxCccSrTS2Z1W2GZ9tsqBV5Cjw4Yw8dVoEg3ZH07Omi+ZsBt0mJ0CBcZHTrWsj2cEWqf4YDBzUTQsHwY5roLb/mXif3+V53uelKF9ms04fSxTvsmm+H36/v9vD/HNjOWAYm34hMQKzn33Y+eFDqkENjLgzNM2j1oMqaKwj89EuEuCWwf1CNgST7l/8tAD4hT+23O9m6ddY/tcoBNnxNqQ9pPzblPbQ+admPZsGnhpTX6BVW/WA+42h9y7e8leZX634BUtfEtrYl0Hu+9XNr5R/4yk44mnwy/cuN+zqw8mLVgM6zDOElLxjI/rwHq1W7QYEmxoHqO4l78ow4/NWGSgjBejls5RUoZlaEsb828FNWp89sBoR7rcGNUaw5VH0901zvx9//Mgjpx75wy+1EOAz2ikSkCi4pRV+Rp4xlcgcbQbHozszkA5xubAmxtMi3k7bD57ctmb89SEuevtvLKuw4G2wGloVn5uuzs60dMDiB8QDORVMSd5wOC7OBUqLDlB4WCzo54RJmsxyh582DemAQKJ/p5/CgLBk8uPJhaQwwCAED0Dyg8CHsq9Hwk6GBIl45JOxOBBvgrLA779qIJB7gRltTdMfr7+tCUC+4z8hAIXw+xYD8HWwwFAa/brcj+nltxfyMP6A5B12foCJdWIjB1pcyA2j1ONhByARnVz4DAB0tpDn9VEpNIb+KCIonHI+VHBHPyUAfuGPS/5pgT91jYVLYJovDvqx3pNlf8oBk/YzGKgrP7vMejSTf7LzF5JeLUb4T3mcTEYL/lWE+S1HqfM3S51voP9ov18ceT+uGj9k7hdn3peyR+FY/97zmP79gWz9kOqqVdHPqg5ZdnASPXziVaiTYk8uo6WN70UgtMpfwY/E30Py0KuIiZHAVumC5f30Jjn6dda1M/tXI8VqveoTr3U4VS4HY/NdEP5rYOCdj089ItapU//+k1/i/Bdd/5mywdQY9x8PBzIMrwsEAsj8/sTUnj2lgLtgsSRfPLmGs7JYBVq9F/ZuRFZDxVXA3yoA0B9oT7k4CAgiUhbCUC4EAdgibo1NTg0Eef8jnIaGaWLAoXiIkH87QQJ2dKTTHZxo3s7xP2gBnqPpLweeFDCb46q/Gk+EMdTf3RdvH/eGoQDlHISmAHybFKBGQHHnv/vx4xwEVAoQW0Pefv1luRXJ6z+r5antA0Qf+l0fFsWiO+qDBIdTMBE7RNw8+b7FzbkS9Lk+vC+00aOkwApAbIuDIU2hgi9a/nQs8Of+qHK/et7XouKAdLI1ASn1YQaf1H8m62vbHPozRl41EX+836+7hecehFX0z+BfReU+siz/tKH3mPsdVFP/dPmHM+9LnUevS/knDPA+Q5l4WZgZnWut6iavQR/TDa2aLMMlGSfFHQDOqgGM+YflIVYkrFVdj/LPyqBEx+iV7PS28nyBVvlw2PAXGt9g6p89lI5mg1uU/t15RC5A4D83TYQQ/yTHnt4CbJsvbuGNjwoEog11umNTR47MRPPi3bT0X1vXdCm75r0wIT6ABP5sCEB7S2dbGWHm4iLADOU5EIB+HPweh8RvemRxqjPFCWI/jGV1SVJ2pBF+HeDCt2c6tgs73gPqDy3wgbkDPQeE5kvSTpgL1aS4oEqfVf9HtY4pX7maxANrNC1QBQCNEpim8JP8kwSEe//tNgKgXATAn30onos3YBIKsJZvoSYQnIPg6xPGNozbTfjwCnS6eOoO+/W+EF/Yz0eRuG8Lij8IDJK2CGNiJG+LuLo7058GAP/Ixr4Yi9s/tJq/ratfVPbX1PTRyD8z/BCAMO5AK/wzb3gk9/xo4UVTTw36ZbDzQze/5SxOfcbkh9b41q/nflXjB5T+LQ5UjgL+jj4G+s9u+ceTa4oqXsk9A3Je/Sa+2irJpvyrcVRb1f10QOJcaGsrJzhavfIcnlHSU7aKcCLEMM+qtrC1VQ6YFu73wnrEslJF9xsKB8VL0RR/Qv49YqxTAoFf2YxAYywC37SFCmxeF7jFOoqhuLDPFVg8sqe3bLNY4rv/9zXKNmFOBJuX689H7AJ/ttVIxO72jDgAfWmwtC5KcmDNs58AKFAYglFZbpdncnoykcIbwtA6Ar8K8sTC+0LYjySgzP7yRkjbe4TkO3CgmjyQRPbxEGgu+VMlgPUGD9wEf4hAUIGv6iWAW6k/gqCh/0Auiu8fb6MYIPPvZfHn+x/+lgD4xrcgB/KyUIB9NMcAi5dRuIEzQvXna+mD+F9fCxkmnv8MWWCI/2Gug+KAbs4DIzCprsznjNvs7s62rOtTAOAXPpv/Y4r+Kfsr8RdplvxohF/B1PHBWQ/mn67+0POaBSCmfuMNux0ZE0/dnNAyil8Qfvqel1z4V6bULwT/uPNXm/mMcw+MsS+9qvHNs3OXwb9Vy/MXtkm0aNQyqCadrXHK0JOQlI/QLhiakKQfSjprKys6r6EmmXxU+kL6rxUZCii0EgLx4ZKSrXKtrZ38t2ci8Vq92mcr2H3pcrQca1r7wu5XZ+Ajf/jKjuvmZDBBb8eu6zeoUqZpe9yWaysSHt25E+kVTg/NHpker4Qslj7oEJYwb6WNQ5avQyywsBqxO8ttA9EwJIHhO83VMFjxAs1xoAdb4lAQ7Xan2hYnR4KudNgvawaBhmFiH0pA4YDT2+Eyyz/hgJ98cu7AgWRyCfiXrCbr9SrgUE5BrdWIhaoDhO2xGX21hSpWENZqG9X3XpdF0Hflnzn+R3b55b/98bZt32qVBHwVciC4G5KywOKZvy8UILGLUhgk+rCmD7OE1CSHAMSSaJ+sCwxzHMmJLb90bOHjKRDodsftdr9npL2SefgA/MJn/wjln176HLHco/OtYK73U2e1yucm3lff5tIc+tPEn0xVYUlTi5b8oNoX855HtCj6xzOfG+YemLc8mpyanhpcYfwVkX92y4R3TQMb+1d1fErGKU0nv71sSRX3Wr2KUYw+Jdbkk6INJuNrlThjHYiCr5WhR0Kw1UpXq201JYvhC7Y8gpn31Q3xmucz0Wy53DT5cfVOI/5IBf7hxlFTPzDjb9fNeeoUxvUACNxqHT3ah+l7Z6Z/9shsv1+8r0ITZzgLzq/d2knxbxEqsBCx9bn6SwNBToMg2PwgB7E0GuN9mUwqHILJGu58PBOYKvXn/Dgbi0ZnUfkNCEAhCTvwKw0/tkMH8NzC3JNC/h1YSiYP1ZNVAcH6MqHvAH5Vq0aqV/XCVQ30KQ7K6wQLO2rvvP3yqw35jw/5u5GBuv4TCPzWT8ECA/6oDObltz+k7TDfflVa4A9/0SGOhj5n0dknKNjX1yfLw+hIwfSukxK8CDoEJGV68UiiLSk4A0zTEcJ0b1vBUm6bGciV0w99IuAXPpO/G4ke+jLnP5T3vcuSPb+KfBEkn/1uob8Qz/pD9NnMmQ+nXJSicrP64+ifYX/VlkcVwp/Ufyr6J8e+DI5D8mPAmHo1I2fet5WP4nHN8m/VHrl+YZteAO1tlR7WqrQfF+IRH+WRq5iEd2g12MR4bEWe0VO1EtbwgtXrlY9Hq2tlyBE8uVpGYVE+dSvqQPUXsq5duF20rwgpUizYbeFgNirwh3NfGhnYjH+AwDvQE7Jrl5b7hXXjZtdVgdEbEoH3JuC9XDDcZSf8L4bz5ZHZI1OdMCThyX1ntq151b8MGln2bayKN53N5wzOCAKCqIP0LpXDQGUgXKBoXyrljLt9YYjhh6IDpdJ41iiRd2E5dEeHP838SyMA0ygA53rmhPw7IAC4tFyf+Pvk6NLyUr1arWPBi1ws/bSlAoM6Axd4UJZQgVfeexsFoAa7zfRrkH/omb/10y//9K0ff0v2gbz+M7kd+ttvyCzwe8/7KJcLgMv7KMGrAEgNvTjg1OnLIwAp6RFuIfChEabqGAwrgXoMw3PFbbaW4NBkW3e0nP78vYD1Ca8//+wf19hTFfaT0b978a+g0r7qhx0QaG75Rfo1ElDqv4a6F7nlB/W9If946ou0v2R+jS3fyuWgGvuSy/HUZ4j+aX2/jY0fAn+Ljp2Y/DgK/GMBmGzdZtVpxqrEKxmo0Ggg0uCl12tcVOzjC2RvrfIRFNgjfhEUrZxq8UpbTMG/VpSJVADDHKSnUH8P6KSorYaE/OsTnzvOdDlb9vxV0+gfVv8Z1FPn7lyFMTE3QQWyDwZSPX1zflhc3TVMt8BqIOAzjXC7v7VzJ3jYlnC2dIQ6pxs3/AAAIABJREFUhC1P/lerMSnLC4L2wt8ftVjszngxUSoNBnEPTBfMlgEEYncdKTwhCyupeAiBkM/HW7Ij01P9lZTb3+HH9kgQfxD0c1EnXBrrX2AvTDDAPQeSBxaSy8v15bN//YMfPHG2nkQhmMRciMbAqhb8U0XS8qoanVRrKhZYfU+r/sM5LsxACUKjCeR12j2dFeCXv/zTH78O5S8Cfy+//VsTAPHrWqTIKdyirw+bPrBIQlCwKH4Uwc7ipEC8GA5jwgNq/9AMu33ESzfHCNEqQ/I3Luxvqr13ZLw9EEtlHjYAP99yLyQ91GUKRsrSPwagCYb4U3KPhR+e50Zfc+ZjU8+HoQDjOv7iyvc6KcfPwT+t8Q0+0tWWbxXD/YL+4z2P5Ngrnvncz8mPkTap/nDD38X2DhiDIkRLEegXCgn+FSxja1aZ8mV0eZlTMiLnVcrLK1ULheYMKnolDPmybOKQtS0EMno+qnEhfciZAHlHPm+VkUKqhFHPyn8r4X6rxeLOhYWdIRj7Es2VE4vPPffNpoP/GhBI6+M7eEPXVZ6LhZi7/vSN+asM0a6uqzQx8N4K8D7XUcxWuMOxyT1Hpjxugbq5g61ra/LlbUUVeHuXJR8PrThmpnuzfgZeOlXhkhhUd0IKZtLllC8Uh+NYrGI427tYGuThMYKVPRwBFJeoACYFHcBCAc4dmIP8x9Ly2bPLT3zzH37wwgsTB4QTroMEPCB9cJ2NMAGvumBSfdUatcMxA2sL/KfWceUdJf5wjMuHNM5lswKE2J/MGn/rpz9962WDiK+///4777wP623KgQgJeC2CVXsk5xT/OLaHuV+Yk+DjAmdI9mKupIWKZXzGwQXaooW0YDxkK+SDk6Xe/nYAoOshA/Bzn/njCwBqzR+Ru8k/PdsrL8vsh2Z9Nze8mcuejXl/WuULNin2KfzxbDcp/zK85UeFWt94yyO2v1T5TLUv/bjfL2/4a6R+Jyenp2eiK3goHi2S/IMMsADgxJrVqgDDDCL5h6zCw1MVAyrFx9JOFfW1mmw0Mc+qlFyrEnit/BPlIGBOWWCqf+EKGH6gejA/N9IS7GJ8RZgv3PBXuN/owJHHH3/8ua/e2gqBkAY5peHvKjvlLnC7R2lXzKM3buqzA692SYtsBpm62Gh972WF0Qf7/T6/Z2rPnt5sXLzPzvLeSfRJAi/mhbHVgi20M7s4PekIgqHFkReZNNUEplOUCXOJN4Kf303xvLPYkm2b6W2vhMXnZNqVqeAE/AxulLW9J0PZDyDg3IFkMrmE/Hvx3LkTr5w/uJTEq+pLdQJftV6vswas1SgzrHhoxP3kAgByMqRWe+bKLz6U+Hubh1k14d/rXDCIwHv1rW+xGCQk0qisd955R81bePWdSBHGoaJ6w4Be3s1HC1fL0uZGWPridHKE0MfTnrVDSwpH8RR5cXymAm0zIwPj/e2e7ENXgF9y3YNGn+rakn+bUr5wlV3S0K71vdkaAGgz4Y/BR97XqPtzurnyBWd7y8Y35p9LNr6p2j/z2Cs19mWwvX+8Xw79M3If2Pg2Fdj5PToSKf2BEcDVQsSyFxWg1yqln9eriKUASPjzSi62sqaTQJPKkR9hNWhKgCN9R9E/xp2VQIj1gdLoysQv/iAlqJ6amCy+16w/r9qLGwu1FfE6h1zZWCUxDVscPScQeGQrBF6lQhiA4McfX1VXd3VJH3z96A3z6NQu1Id/0ygCd/yHJeHRXUdhV9uwO+9qX/zq7NfSkYIlcvbwmtx8BU7A2iehojExOTs1koXZB5AOdrlS5INTWO8nrkkFg5m43SbLSEMrianZEgyKxh5iKH3JpDt6IPOR6cANMLfPQQ2g0H+HlpfPLj97/FGxjgkrvIQBwAOQDa7LJUOBVZkRrtYMGWicYSmIDBTfHRtX3jPEn9SAEoBvK/yZlvmK19/mDdRf5xggABAi5H00uQAZBhHBYt5JdjZPvMOjBw8j1npODvrpEMRvXz5kt7tycGwMtA0NDnqilYcMwC988Y+sANqU/rVsqf9ktZ+ce2CsBvNrM1X+qVkHDYE/8L606P+wRY24VUOvmH8dFPxL055HUv5Fo7GsMfUvoIb+jcsNL/XGDxj7Mp5+HvTMUaH/nlf4s4MF3rtmNdQbK7VWowsO+cR5WMpi4DlSZVYDfK1qKVgxG5XDRb7isHvCLPNPARBFIQlC7gLBK71WVphenHswthrfqC1sxO2FuF+8FLHJ5x7HjX4RgVuqwC5G4MdXDf7RDYDAv7hxs6vhgRAKvNp1E4tlNAj+hwG4C178lRU8XtP9i3tm24I2i2XnxAWvVelr+Bw6eWHheUuo52uwR305HXbJXIgLw4AZLpAJpitCBNrxHQZGoiU1OFkaymawYpq3gYMRMFT8hxIQ8h/JJOi/Z88B/87tm1iuJ4Xp3Tt2AEr/6vVlQT8Ug4qBtGSVtLpQJeuL+OPaGMiG1Orv/awZ/7Tq50YCNq7XcUgCKkDwwC8LAMb7+nzuolOWrwDW8rxRogqc0yGElS7wnSfY+fAuRD7IjIgv8a4JlQchMyiOkfH2dsdDV4CfS9nuAqSHu2w2IwB46V07N75tUfnMChD/6BlgqfxY/WHiw0TAUJNhp5D4yPtk7gMTXdT1G4a5Lwb+OnjHN632OarNPcDKv4C59IV3fOOpf5z8mMwWH8Mj8DGxng8h/mwAwIIAoHVNJie8rV7OhxC5WBhaZUaYkxet7GfZ9xIsvZzkoEOZIClFoFcKQYQjl7iwJrQy+xh73AdHepTT0YoOUPq3fbW4Uas5xYvtTInXon+P3OYcACjOn7g133yBCjx1x8CfAh5IPWqfM62u4WF2wZ/Yuv78jRs34nAIVwZmj0y3uyK4d5J1Tf0r4d9/5ucLFktHbmBxarK/7Mc6GBeZYDQEaQiHBMVbouL3UXAF31O+TKBUGsz6w+Itg3mQdId47wj6peUIVAE7YYDHzj5x7lGhAB9/duJsMjmx/+AP/pcTx/YumBRgsjkBF4xV5fCgBCD9AQQ2V4Cva9nfu61XXxUy8Bpb4FcJgG5f0Vd0ii9QflTQAg2jLU6umtCVHh9SWP+M5KNymDAKQgFOezyTwInAuB3zYLcn+rAB+Hn//38l0IUHeurIxdOnL3I80ibOn75016lXmv3VRl7ZTavR9tqMnl+94SPvNLb6pTw9DfIJm6f+UQw8nUlrwT859pnwl9Bm3g9qG17K/d5A/U0uzi4G/EL+HSX8FTn9iwREBQi2Eo8/iteRNiOtxgi0epU59lLYj0qVvTJNwpFCBqP0xlZlX8kXM/AYc6ztKMlhJfzhJeOv4VUwRs4K+Ve12wT+NmyQ/ChHU9HSN6T6O4dC8PHH/6dvzG6BwK6rd+402yBkvtm+IfMg/24wuDTZd78KsNn9rh+9OS9gW7SBWgn27jky5WgRrqNj/0nIhrDbh5f9zL7rFvtKeWR6cSaAH4UYBsYUMFY8i3cETFpIZfzuAqrAeLwYL+Yr/aWptrKPCgHR+s714NhpHgF4YEn437N7zwP/vvzixNmz+w+/cv7c+RfO//AHyWq1vr4O+FtnE1zX0iFa4A8X10NL+MFoaTbCtdo7729WgM39b9MFnSWvq71HAIB5N6gF7JEXB82Kj6pbMGSe91HaNw/BdJSBHFXSJh5gJoQmYIXslnh2YHJS4A9Fwvhgt6OcecgA/FLlk8yBRC6dviipV7h4+uKl+0Zg5BIwTyDQbrHY6Sw8vDkCFfUi2vAXmfgw1b3oAOQtPmy69gP+wWeUT/5Hkfpzc9tHn1/Hn77lG0X/5NR7KH3Jofl16PIPS/94wyMa+geNb23l1cceuw74g+wHu1/gnx1Kby0TJ1vXOBGM/GJ91uplU6zkHfFIGlvEHos6r1SFhDjWc3x/4hspQCxxtpJWJGfNcT+vJK96rHxCCUCrde3M3pVCsVbrKIqXOlwR8m/yCDCPIoASgOLkza2SIfpqXjQjb4RqmBsqQ3yf1NPv1uQh128Kqg4Lq31DHLm+uDM6M7tnKtFig41DTq5x3hw/edZaz/zbdUsk4xlfnG6L4ihoQiA2B2NqGApjcBM6X4hjgYICfdHe6VJ/xrXdtT0txF9HTwXpJ+wv6L8nDxwSBNz7Auq/F/fuP/zC+XMvHT9+/qknJkD0AfuWhRBcJwqyD641wo975hh4HAvk7DBwsENHoAbAu2PPOAfrDQOAhXgRyvZW3GRr0eQi++AYimMpEHrivNOQgVg5iCwUoGyBGahwl5CtEE8FRmZoO/q2gZG28cHORPChA7D8CQIQhdvFS3ieeXafzy6ZJx5x8ZI6jwhsCsBmbR9Y+GeMelb8s9t4l6Nm0/7i9GmGOt1HZZta3bOJfqr0T+74Vo6qqc+c+zX1/codj7TOD3C/icLq87uefwyXFH8GAguWsydPWrfhNARDr0lFJxHHVpgZSQ0dMrDHwTor8wr1XSsLPAkzqzovyccLr7GS1uQQIyORf38rgxhL/yyFnQsLK+K19mXglSg9/mVg3nNAP44BCv59Y8tkcPPVpblhdV1X182nr5vt746Gn3ddkprGnR97Gmqsh7tAWs7fcIac+YIzB3sn5eLiUzt5uXWNJ5LhS7LmvbC+EYmEO0empgYSaT+9G2gqQhqn4VYqOC0wnXLhuy2E1iLkz41MzySCEDiGjTDlDiBzPU+OJg8kof7vBPHv2cPnXxL0e+mVw/sPbNQWDghzvHu5ikHAen15vb5e1RPCCyYdWNNO5K6ZC5wPwVjgO+/99n0DgVvov1fx20CfRkC56xwpQISd4FmRXa5kXR7i6Cgn3M44HVM+qA10crW0EIU+NQQBcr8tuYHJGYz+CZUwNDA+JABYzqQf7q5wX3J8YkkQBbGLNkIhrktbIfCSEXyMaMxrWBdtQDw9FsjYk9JP1sKYZp1umnhAgT9zw0fclPh18qyeFom/PhP/MtT4pjrfhP8tZ/Wxfx6532U7jbxvMvO0NDW92O23rT7P6Ht+tVjEEey+PEzfFP+IVSjGOHmmFQhIJkyV3skCF2urdL/MRvKr5JkhoWElw8oPleSkDmArE5LMrcQesZNVoSwHVCgkBNADJJWt29Yu1IuR4kZtJ4Sxw9AF/fuuW7PfUAFAib/n9tySWNt63fVGrgI8Kodm7dp1L2m31cKHUt74+tEbN4X4A2U5PIzBxdCqOEJbHItH9owExVt2dfcF2CzUyxFXeB0unI1YQjuzk7NTQ0Gc+QzNIUIGBlPAQ9iAE3MjKZc/DyKQ32kuT6lU6k6FOwQCcaW3V+DH6AEBwKWxY8C/R184QeLv2P6zB2rPJPc+9eLhw988cezZvcL6LoMVXqYOETphFQiFMSofjFfVJPm0nEhN6MDtC1IFbhaAr2r0w285TVDjn6YAI9goBWDzOYvAQJ86hOBogqig24n8o3g6FpZhy4iTMr+oCKH0L5TunwT5xzHytrahcYgBZh5yHeCXhtJbAOpBl12jlvSweGL4YFs+LnFYuIigxLOX1ONON1kX7U3ln/K+Gv+Mnl/d+obI/5L8MwEQ9rmU/31QrNmivG9D5TOrP5P9VfTjuS9G3xu5X630j93v4vRMtBBZpaK/4s6dmXRPWaxgMBosB4V76suH7AjAM6gBrdSawV6U0EWKjctSKCFCuGIDSwqPK1mkebZyAYvSfPwDJSPhkoN/Xi59YaWJ5riVhSX/BAKuWU/+29FIaKO2URQvtjstXgva8ggR+PjjSv09/kqT+N/dcddwaxflhZ/W1J9C4A7j8j3XDmPKtMDfdWix68IFzz88fFUgcBUEjKt/es/sSEW85x6bOMMI5I8CoXmXVy2hcq/4HGsP0k7oLiyFgXwIjgXiDqGUH3bCQxEorHU6UFqcSaRh/kHG2AXuQM+BpfUDzz6KCWCh/l46/8JTE8tLSwvLzx575dz5c+d++NJL584f2yv8LwUDq7TqpAKl+9VXTZN+UhRKEVh95z2JwNf19O+rBDyaokqTZEwisNECR+C4Ka4I/gkpJzRdEdIZADw6nPJUSpvXT2jnIyEP6YxPHHO2QiHjEfJvBJsD4KStDcpg2gPRzJ8+XAX4+YHxZjT7DyyScRcVxXQji3co5MH8IwIjbJAv2QmFp+Uj74VAVn0c/4sUZO2fPvHA1O+mcr6YnjNP+5MRWmzcxq4P2usg3OLn3K8c/rEJf0Fjy4+YnHnfKYf+Gfudm/E3mQAZu7r6fKi4MxXEBycSsZwjl8s5Ap5cLBot94RXAYBIwG0wpsnKcwqsXq9M3BKevAYQrRjWa2Vyeb1cymcle0wP9PLjmZ6KlV4Sf16CKMcArZwYkSwkEJPybIW9dIX7tW/UasL92vPoftXcA4VAWN+YvQ/328VF0HRp2EiBKBTyxnEc/7sH7/QESYNalJuMXH/65rxwv+J3YZ9dFyjBqwKBfpvQKJGW/ukjs0NpW8Ty2MThtTX6aCH5LBC4Q7x7K22zizP9QVeYByRksDYwTeNi4Hy6kgmLt2EcI4H5uC3dPrU4GYBZMKwCe3AQ4NLy0v4XQAAef+ncCy9OHDiwvL68tO+EMMIChycOHzsPovAJCUCBwGRVUbAhFMhxQMP4LrA4xAsYC7zyjqEAFf3w61XEIE1SlfNUJQUbFOCVQhEAWHRS3EgAkLnnLELQEyJK8SJdk6ee+jwNQMAyM9wPrsUpPh3iqf7JSZB/2B/FAOxvDyTK6YcMwC9FR8p35doDrE1OVtHwYtwSsXHK3GeLKMl3Wgb8LjYln1qXCpr8iygJaFS+yNhfY9UfGl9iX8M+R3rPB06paOGRL7Ls2e/vkBk/E/0g+atSv8aWHwGZ+5CVz7Lxo5fd7/RgBst67EV/JZjNeRwe8eBYLpvN5QT8Eg6HsNECgqNncdPyk61rUgQSitjQeq0ykGc1SvSojllG+VC0WNnS8j3JMLcahpdEjSEFW4m0/OQoLfn3UcjQSwRshdqXM2NFS1zIP3C//lQU8DdsFLHcOsHpj+e2TP+aIEdnpRzT7qPWjdXHrjPPqAhwhxlr2jJEoZ4rUTsswcOF/JuH2B/8OgHBYWg1Bhs8fPXjrzwNUiYfHJ89Mt3pF5/U2/edWeOXFF+xNeuZn9cslpXEwOTiVLcrbQRIKBJYSeHUwHQqmHL5bJgNwXddsdI+Pd0bTcMwrLQMAwoLvH5272FBwFcOH5w4u3v37bHlvYfPHRfr/It7d68v7z9x/KVHz+9dXz8LaRBsC1FVgSjw6no7cE3mPqQ+lMkQycBnhAhE/rH+k6JPke9VdWriHwHwxwxA+NeIL0h4iMOoGC864aIP6If9BMA87KcH+YtHl5vbRPAybHxpt4U9bTO9FCIa4SbRtoGh8XZHtpJ6yDHAz/vaS5+UCTbUHCzyvxKBly45ZZWdM95c552+KB/V5EYDgZJ7UgryyCsj/mf2v5vTHvg5pfDn89FwR6PprbHyRVU+y94PSv5m9doX2fc72G90flDhM9S+zID7LYfw7x/3B6M5wT+PR5zmsp5ELJtI5GIxjzgVCIyVk0v7YJO2MwI1KAIp4+GVsT8CmyQb6rbWVom6VkkwusTkY9yx1LOyo7N62d1Rolc+BRPRquHQytlhVH9rrT/viNjA/Ybsdmca5r/+fphm3ksR9+ZXMfnRkPztanJuWF7RRdUvw0398U1KgDRG/zZzT12gyzskLncZ5ET5hxMWEL2QcRE0BPzd+fjUqT985emQcGi+7OSePSWHS8j1Jy+fxIGpxssGG4dE/FFI5weCft4EJJVJ0RsFY4H4hnH5nYjAPL7d+mIzi5ND5Y4OrAOsQBsIlkHv3ffi+fMHJ8bGJsbOTpzdewLw9/gre5P1s2fHxp6FSwd3owRcVwCUC4KAuHW6yopws3BVyr8epl8P8G87ZEN+pgzwq5ryUxiU9GNPLDMg3zIpwCIKCHS9eSoig8QIXZdXk+SQhUg8jv3BaBjBRZu94AwOTc7MSP71kg8WDri9uzMbfOgWOBSe/AQJyNkPNrN0XqrAS5glgtcnvinpcXcBiPewKQAaNlgqQKn/DPkXkvpPTrzS1J+iHzQyyp0useg57G4J65UvGYrtNNS+lI3K55zAn0eWvrRz8A/sLzV+gPqjoaedcQsgPO4qEzUDAD3xFXM44JmyWXFZ+GG4KhcdncDNd096t5EKZNknJZvXyvXQXq/im5c1oKQYqxYvpTEZlRQO5HsbQJTHNj0a7ynDglakruo9hiEpByxQ+9JnEz5G/GOiMcKfmVxvftXkfptH/TQOds3fPHodmn/RSTdiUAUBJcT0bUJUWmTHLg707VK3Si5K8bcL5wtC7hflJhrgYcyFCPn3CA+nvm4TKiUfhCEJOadl1UIItMrXw4rbnlieryQGpmdxM7gMzsrC5uAMlQOmsUIwlco4xXsS3ntOoZjCsYHF0mB5OwBwbq7SA22/y2MTe/eO7d07IQi4e2xs3/lHQf49u7S0fnZsYmL/K2CPD569vY5NIVQTiMHAOs+OJvLB5khcBIg+uCblX43TIDIfLNa1nxnhP9MyLqqYYGMEUCrAOOwaKkQgQE6gr8gALGLZMx5gRRKDPnc+7nPmySOH/W6ce2BLdfaWZkZGyPcOQBFMGxw040OD7d2ecvphK8C4JT1ZytyLaw+wpKnVDLAk4SWuOhYaWUfgvemHCxFomnwakdG/QqP2k0nfxsSvnvbFZfCP9J8/7Ke9bXT1h9qvEsTJV7TnUVZteaR3fuCOR6bg38xMaVK436G0Bf7atpZgApSeR4ATniCaTWSF7fV4Ytmc+BK3xYQ0TOSy0eW/JwSurW2DQLzUXxST81Kql9IeZIu5YpnuxH6XhZ3EodVreDl5gZUgXcVsJF5K7FqtrYY2FO534nlLaGNjoyj4F67A7K/5qyikusxMu6W532bSz7jUBSE47PC4/vSNm1evak+l7g6EvXnUPBJQYm9HY6hPtcrR1TskLeGHgCyU/iH8UG92YRa4S01pPQX71BXhQA4nSnv2zMRCq5HI2cvebbosXvNeuL1qWQ0HJmcX23IucAxUFp12yTggGWGBwLyNa2KczlBLTjygvSw04HYBwLkkNsIJ0AkGnh07e/bsxDHBv0cf37e8e11cf/aJFyBBcn7/xPrufX89sUwVgXVZDlPlHIhhd2Xit7Zg5EDkRQ4E8rTAVzfzb/NS4nAzAMEBQ6gPFKA4WyTFh1E/wCF3lVKYMA6JRiwa9MXj0C4eGxG2CJwvu98B+T0w2B6IBR92Gczn4/ZIaqaUve+K5XsvLcRn4iCIwDwKZUSRWQVevGccUKxLduWCI3oMcFP4L2Qq+zN6Ppxx1Z2j6EeRvzDbX78hADMZDYCViin5i9E/6PsN8I5HsvFN9b318o4fpcXZUiIEwb9CPhXNCbvsEaAD7ZdzCC2YzQkHnIBAoLgCYIixwFh5bvfey7BbeatVikCp+EiySUgR3FoV1mBxBM8I61mN+8rzJvJZlb9TTGR7zDqTApFr1ssLIP86VsQrnc9A+/PNYbavhpu96+qSJ6rVFxh08y8QbtfBnpp74GSGBO5+47qpEFrJOybeDvNtMui3QwERB2wNDxP/hvF7mJY+pB8Q+N980MDq754+MjsQzEciz48dXpNKHF+WtZMXlgQC0+1Ts9P9URd0CKfB+sLIFygKBB2YdonTYCoct2FrCFjDeLp9cXqys0JZkAWoA1wWrBO0240gxJ64w2O3z66fPbT7xXM4IuHwvr1jB7/5gx/8YP8hloBVzQaTAZYhQKP2ZcEYmFBjOFJFjEBg/WeU6rgb+/DbpABlDBCTIHw4ySkiPkqA4BIqj3oLqBYQXkk3x9xDNnso4+idFMeG4J04SgB8A9gtAN9DBMA//cK9mPWJLgFAW8g1WBr5BG2wQuBFhppBQRKB/LpdukvQb4t1saCSIfaIhF9hU/KXRGCooemDW3hwqV1ZpPZrMcGPhr81pn7lzHsu/XMYtX+Dxo5Hvb29Gv9g6KkP/8ZgGIF2HpiWCjE/j1CCnmwMqJdAFyxUoLhFQFEYYU92dGkfqkCZDWETLMtS2NkyC9HfsgGWoORciJJ1Xs7ictJECRq5OEfslebZihU4ra38PGvWC0shrH2BfURdAn/Z3w/L5G/X5uJlbTXAkcUdcRDsLUs0wNROhcBh9QgSbMM8ElCqPEPXGfJvhwSiAUeVMrn+vRvzQmAi+hB+XZALAfdrDKk+RT741E/+cdXm9vky3YtHZnvTwnk8tvuCdZv8jKAX7nJ91RIKji8uLo5kYVBWUBCPcyDYGFKRLGzBIQn48VvMuwKl6an2OdwQbunQ0nJyfXlZ8A4k317hgB999NyzeyfWl6v7zgszLAzw4f37Jsb2/sMPXjj/0isH6zggq64sMIcClddV5lcDosRfjQOCPeL7Cmz0e7fF8UEkoYE/BCAfUeCB4xxdJ8PbWGBGDMxTWTQE/2y2gjsxWeLoH+yMo9Rf29CAEA/j7Y5PB4BxdzA6MtPuvhfXHmAZnR26AjyNPjgUlx8X+QejHyzqDSloy64CgA3212aedSrZxz+gHL3F6Plt8TfU/ZnVHwlAY/BBjvUfyr9ucL9y6os+8h53fCuDWLXYw6loNAbeVzjcrACeJydkYA7SIQJ7QvPFYuKGWILukYNL5dHdiMBWK4cCiVetSskpI8vXKEXXKsv6rOyBCZDyVq8CH+dJrFLc8AFOSQ8O/bPe3PZf9u20hFY2NpziJW5JR7PR399k/hkhQANaam2VCaGLUH/32C4ZpUOXelTOATRBlYfB3Lguna1BPHmyQz9DiV9jtv6u63/D0T/kL4CPTiT+TjH+iICP/OS/2UAFpgamjyx2pyOrq0f3nbFSKJA/M9ZOXq5GIn2Jr03vmepOt1AaGArm/eJNQyMzsDoG+uNCdnwf5n3OYnF7f2lqJDG3fS554EB9Kbm0tLR799l1YYYn9h6GmN+xJybO7n+K+Hfu8BPUkK8lAAAgAElEQVT7hT9er08ce+n4S+eOHawvMAHrqiwaCSi1noz+0Z7qUvmxCZYZYQgF8g6ad1+Kf2+88RYBsGYH6hVD2O0MhxceYkr+0YEWlyUwPv5HCxrGYVZusL13cgRzviMjWAMzAMcLNsLBn8FuT6zietgAFO/nvDuVtnlmJhP3wtqDLJuu/S5ykR9Kvovaa7V1C8iWC0KBBdr1w7zhkQ5AmfkwAoAUkfCx9dV63lD98W5H+oYfKvchkx+s/7h+z+Mwxl4NQuqXN3yT6g9L/2ZLMRskPwrOTNQjjC6wTfyMQsGLgJ2gnPC8iagHkh+QF6YYYMKB6RBPLpoc++vLF8gHSwSycKMCZytpQGPSqVceoniYar0f8rFeSTyruptUgsbd8DzBkXMsa2uX5ywW58bGCvqYcjYq5N9V5pRSgWbzqn50mS9q9xlWI6B57aIqZdPdCYSoAa/iOCxKdahUiKScFu3bIRkpy192wXjp4WGCH1XADFP0T7rfU/qEfsyG7LI53fl4eWTPnkVPS2TV8sz+k9vW+DWEl2rNeubfNiyrK57J6dmRLCU+Mq5UkN87rlQlTRHBVNDlFq+aAId4AxaLRWGEp74W7Vk6sLCQTC4lDy1DkmN9fWziIGQ9XjrxzcNQAfjo8Vee2r9v/+2J22Pr6wtPCCK+dPzciX0LDD9VGW1MhSEOyoEJCnbKBtMNGAvcqP3i7VehuQ2zvK++ehcc6gR8uVaIo7NaxVOdes64MV3TWcQ6GByyhL2mIWEahPzrnenFqr9eGI0u43+CgZgFgWEwuVjK/5AB+Dm3AGBLJeiOtHh6ez/JxmDVDifhhyDE6y59EgjUwn/m/K9c5tIXaX1xDoWp5bdFuV8j9+Fi/6JG3peNoaeq8VfL/Zq2O8fSvxlofOvMYPIj7qpEsegvIextAvIfAD8PuOBcztEprkU37HGwQc4hGwUOY8Hk2D8AAk82ItCrBKC0ZHzZq66XkCPRaAaccZs8nBUmFRLl0AQ4f2GsCMmPFSji8pfZ/XaxlyWuNKo7BbAtr4PJf49pW8GRgjsKhXr63bA2Gql184a2PTqrPAk+ST1OBHPsbwff6+mbV68Oc61hFz4llC4OI/4MApoR+AiUBbqd7ljv7J4pT8tqZPXAEyeVFCcEntz3TCTij05OTw85UtAXArkP4X4F+TrSNCIGSmOECgQExjFV6su7ywPT022J0Z6eJ3EE9PLy0u6zY2f37n/i2Llz5374vwr+nXvl8BNnd0/svX379li9uu/EuS8LPShU4bljE0k1KFoNCqwqwEktiNjrMaxxzYgF1kgkXvnF3wECCXKbEahnQNgACwBuCAsM9LOtQp1FfPOiY04oPif9xIJASH7EgwOlSZx71TtCsSLmHy3hn8b7Oz3ZTwGAdgHAcjRsK1j8gzPdn2Ao0J5nEXiayHfRqPS7+P8FgR98AL0hBX3os+Z/WQGawn957vogXa62+uhD/KnMh0sG/xpyHxVV+qwa37TSP6p90XO/vVj6UlqcHgnaIVhpc6cox5ETHhiSvTkM8yUSiEAYoQqaz+MR+hCp6EAPjO44l40mD038w4VGFdiwvFblib3q6NRuhUU1HLoYNE75HH61Kn3olf557eT+7RZbEXK/Nrs7E41Fc+R+kX7MFANZXV3S+LIvvrW5IJofAgC8TsCS6CIBaDyhTIrw3nAG2IzsB0tAeVkKyl38jQJQ+F8cfaAkILZ/fKwhT1syFPjvX3m6kPfF3TFMCLdEBAIv46ge7ZW7cHuXxZLpFnJ/MuD3p2BkJGAvlcHKUTjvojeTy4kqECxhPt6REx+PA4dGcSx+fXm5unt5fWzvvn37nnji4ItPHX7qxYNjS8u7b0+M3Z5Yr+8+eA788KPHwBi/dP7ZZJ2XCgPKbEhVOF9WfJKGkniUCFa3irtvLPwCBv0hBYmETWWgUoBvAQDtoP2QfxRigsUxQCxyo+ONDzs45FAx2iPhxEhpZgQBKMSf+NHL5BvBBMiAAODgIBRCP+wYICnAYMwl/pb2SKZ/ptt/L7Dd37JDtcsllQTBJRUgXHXJyM0+aChQENAWIfmnxp5K+MmeX9zoXP4Cp7F8WtlLWO72oZU9u/TgH7pfwl+2rOYe4NBnB7lfanzDYEabzP0K8TdZmpqd8uSxXDGeLmPqI+ZIxIT9LaPIi8WymPOF7o+AJwYM9DgE+wCJAXEOIozijgDOaBJCgbI3ZM1gmNdrleMMzBTTFSBfSTAz1J26TUOl6h9BA8wP8MLcg2VLIQ7yD6f+xbLY+TFsMrakrYxrtLPDs1//+iYCEodoxCl7YNJ/OKPP2FCuS2IQgoW72OiqxIb6KYWeRkTzova3q6oAEA31HYm7U9pPIyFy6tS/nPrDL23QHxf2LB7ZM1OOCAQmIRvCLyapwAtjq5bVTGJmdrqznGqhUVkp4YUzwj5UGIUwNr8CzSECgMV80de3sj03s1jqP7R9Lrl+qL6+XK8LCzwBJTGCeEtJmAa4vlt437H1A0L+QUDw+LGx+t5jLz16/EVE33ojANkCVxlxVTa+kPyQBllLlCASN+r/9DIREBDXFIFvKP7Ben1nAXuq0AKvssag44wvoOAr0lGHOBQHZaEQqvRPTva2cYx8hIKAqADxFCaHDA2Io8kTC2Y+85AB2AIxwGDCBTLVbrFlh0Ycn8A2mYU4TsyJIwIvnpbwk+lg/KaPCzx5QBF40cgAm7IfNjXzQJd/etcbTLzyqaq/FrP1bah8CcrKF+78APEXy3mk/JOlf+h+R9p6jcYPHPsynrJA9iPkCgI0AX0CcQEwwlmUfQnMIkM5jGBjQLAvR/jL5uAH2GVMtAAmc9ExSghDbwiFoQzgEa6spNV0OKofrOPMcs9rgp9X3iYttEwTQ+nf3p0Wof5WII0XDmZj2Pgh3S8VwXQRAnXsyTV86+vfEevrm2cCIgMhCXzje0w2zoBclU85Lyusu65e1YpgGkjHvneXFIfN+Ac3wwCELigzHKbnvPOxAbxTjQA8dYrTIY/84ZehuC8f8g8u7pntLTvtltWxC1AWyPMmYLVeGCsUipnu0lSpLVbGzTMF8oJYCAgbJlUoISL0oMuJIrBYXOkr9rk8vVOlzkM91UOwNdL6bqDdxO2J2+Jcff0sABBaQJanBP5+evz8UwfH4OITTx0UDnh94lDVsMHaduk1Ld0hvp6UtGM1qDzyAtvmZ679jFTgq2+okOBWABQa8PVahNSFkIB4nEEqhMyWdswBI+PkfcWt9kI8PdgLU08ReiNYASOLANvGQToMDInVP9jdCcNgPvPn92LWJ7oQgC3BRDoPmwfZI5Z4rHcgar8X4DaviFZJGLHh/BtIBpEINPIgF5l/8HUpTwDM5x/IB3MIUCZAbNoK6QkQWjShzCm3L0X914cTD4ztPlTqowMD2NT2FpTFL1T5nI1ljbkHAbnhJbrfAc39yrEvWaGBxd/RXYF8LnS6eWC34EQuEXBE+Vk8qAuRhg7phSEnnIMqmSyow4SHthjORUd3YzYEEbjWzAhr8DP5XNJ8huzTMWjclZ1zqzoHPwQC19Zan4XOD0p+QB1jNobRPwmwLkkqKdXmFRjx7PCb3+H1l7fMaJT6EDf95bDeUQrVGbczWYX823ndUH/MuV3S4epS0Lh6h7q3JCAisIv+9rQlicY7JQPxglKC/yIQ+PRK3BkvuNqhLDATt1iOTpzh/wOKF4hX6fI/FiKrqf5FIeqCfvEB6s8EgzQdJi2kHxTDVDCplvbHbSHon/UV+4rFDkfvYimQHK0vQUHg8rrA3u2Ja8tQFbMOF9eX6k+8gM1xxyaq65AMqcOOSMtjP/jmi3uXZAiwTlsmVQlpkoEc9KspC8wUrMkUCTKztrFR//7Lb7yhiUAVGNQI+BY54Ddev7KxKtBng9mVNmqwFxeEI6azKguiEiLAlHBgZHJyBFMfbYi+3hEul4XiP4oDDgkhMRgIOLJp12fuhaxPdn3uT222eDjoSREAhakUdn1mvLI16ZqvQt4Xkgi053EAhJMEoPS+F+XZ06o0BkOBeUoUOe8XgZeoCFrhz26in0n8xeNck5ln9+uUPR9i+c2bvbk6eLdfaX4reulflvc8gpnP2p4fQ6baP8r9Ti5OLybCBajZjmfKZJkFznD2AXSBQK5XiMFOhwOgFxAnAoaYBKa0CHIvywoQksaQIMnFDo39dWMo0GCVDjavFHRe7UZjeWVqWMGPHiqHLmDxC5QUivutbbvwj/lIaGOjKN7JIT908Sn3y3QiBUhzVeZVkoEJOPzm13/0HbUaZyMQOhGeN6DZ9/pf4JQCzU13YQX01atESANlUvVplGMJuUO/wVCDdAdSgfAbqPZFB51EoCYDuSLm1L/8+0922kLibZqCIQntECXv2HtG1mbyy3py/4LF0hcdLE1PdadwThbWAGZoSGoliPTDvJqflJN4Q664V7Ay2jOXPCR4twTM2w3sq6/DPPz19erYUxj9e2X/ev3a2LV1IGB9Yf+xF7754olXThys1yQCF/TRWDVV9iJOeoiJPTVt+ySp/7CRhGtiJAIbPbAm/8Sf199//4oN4IcEXBUumHyXTUpAKImxMQPFlcL9RlKDM5D87R2R+Y4Bcr7ogBGBkAEeGB8ab+90xFKuz94LWZ/sAgAKC2wAEOJqrvG2wQfaLTMSgtBaHjc1KsTdtPWJoM6li1us0zI5col8MHDK9+490Efr4qWC3v6rO2AZAVT0M+106eO9PrDsxd+o/ij4l+Hch8r9Yt9vlCr/jLFX3Yy/Ify/NEr/ZmDHt+mRCsA5YvMHgWYJwUwPxA09MTK5Hqh29ngCIPug7wMkHpQF4i0OuI8jB/jz4HwEjyOWwEEx0UMTqjAaVaBXSjvJMbrEA2M01WfWfKa4n3Gb1zilokIhbE4c3B7B5IeQfy2pbDabG77K+o/gNawbYQOKLOBu/aWCH/vgptMBwZjevHn0KM7om2dPPS/ztVepUnqHvnYpCyw13w4pAiXvTD/5AhDwsRs35aacjD2iHEs/ZuApXROeOvXx/I28DYYkBHtn9yx2uwqWyM5nT1jX6GXm1xP2TlpdqXxtenGmO+3CGalpWh1ghivQGAczA1MZd8iOYsnpdK/sDA5Nlb7WuZQEFVg/tE6L+FfHaujj5w6P1dflDVWYF/P4C98UwvClE/uMcmiKBBoEXFBSUKV/WQNKANaYg3AfTAjzMmtANsBvoQJ86/X33n+/Jlz8KklAG50wAG0sPrD5GQkojs+WRG9pBhrjZeAP/gyMUOwPBSAWkA21jY8PDnYmsin/QwbgFyQAoVHFLkWgJTUw03n/o6ILMOnL6WtpcYrDHs8jABX+xJkPNBF48aIsDwSeuVWWNu+8PxF4Ma7Xv2j8MzJTlIcCF652O3Kq4J/W9ebikX8y9idnvkDytxwsi2NeRv8QVJT86Fa1L1rpH+R+ZyZL09OTUfGCiL+gM50V0HOgvcV5qR4M6dEXktABeEvEPIEcohHTHgBAhCZmRQT5Ag4aNw3lg4xAmJGwzchFsms1g43VX0Psz7hx0xmr1IJeK81AXvO++KQlgvgL2eMuKN6+iZMDmH6a8+2al1dKqAH+lPvV1pvDeiyQn2YeK/wE/q6yp+6iwj9SlLwfuk40xt4uI/OhrjSUohl/dA344Odv3FFwMy1TDJD+4Pr4DkwLvJEPOZ2hQnlmz5HFgNtusTz5BJcFsuBeWzu5b8Oy2hedER+BnhTsHkwjAqFBLp0KBnswupJJV9IuJyIQfPBKsVgemVqccSSTdcyFLONmSPC1XsfhMCf21pB/1+Ck+iwy8fwTB+HnD4/tlyJwgQlIEDTVuyyw6aVT3lGO+4j53jsJgZs1oKQiA/Dt9z788J3VVUwDC/atGu4rDh1/0vqGMAwItS/loRKOfe7tpTwhlP8JA4zTX0gJUg4YqmAGO2Ei/kPeEkRaYEcQtvSz2aUKtNhiAzO5+wsFCskHzIONPy9dunjJxzsEXJL8A/z9+rvf/d1pRp9REUM4wwZhtKr5+wsFQhlMU/yZ/C8/p7K/sM0lDjwN415HYXPdszb1wIj9aeYXmUW5X8k/qn1R7pdKX6a6MxZhfwvxDIT64DECf4EA6L2ckHviOxBzQEcw9NFB1wdFATGxksMEMC4HARGmzaAKxIBgIhelhHCrzIYY7PKaWcarVV7X5DbTIljSKQ7/hLkHKxbbysaKkH+2cBC6+Kh2bpgDf8PMPy0MKB2wOL31Jss/MMHog3+EKvAvG3YIoZYMbPKA+J8sVcb8CLW/Hb3eQLJdBvV2yRSwwcEdBg/NDCQbDBJQbcuuFJ92TslCTIE8Ajt34rDAYdw4BCYalPbsmcy5hdlZeraVO4Tp5V1rPXN71RLpgJkHA1mXHzdRx0nR+M7qqVQE/1I0PL8FoJEv+gQAV9KxgcWn/mr3KKR+l4QKBCHIe8IdPPbsetXQf3uPvQT8e2F/vXr7RayJOTy2UDcSIepHzYgCPknDU1kdKqdcVd84WH+j+t7rSgMauRB2wOSB33rj7fc//PD9HQWI+jEtZAhKNl5JAELlcyjsmZmaAejBUTKCoSKoA5ReGPs/hrAEpl8oQHFY5cqpzzzcWQhSATqCTvg72w0fXBB/+4HovQujIzaBPxx16vQR8i4hATX3e/p338X1gXGNzAwj0BCBMln72j3oB1UwH5yOm+r/QkYFjFGKqUYe0NADbeKLDP51KPylyfym9dgf2l+a+RxDJ+sI8NRTHns1YOIf7nc+PZMKgT0PhSsxVH45RwLFnQBaDjvePI7OnIfUngejgOB1Y3gvxCCkikkeOrBOEEgIZjmLSjIXS+6+vKk3xGq9N+F4mQSft/Gnkotr21ovPxmxx1c2YIKRL51N5KDxTfpbHidK31L7Ifu40k7ov+9w9O9HfPIjeYVEIHtn+APjYATnZK8ui0sAI45JaKCYRkHtCrpVu9hMANK4hWG9ANqIAUr4EfrYHH9M/MPI580b+C51BRb3zM5E8xZLcfcFK09J4New9cLZ65ZQurO0WOrPAQDFmww+WeewPTjYE5zrSdMmSpANCRWLTt9K38rKzsBkabL/EBb4YQjwEP0AtBn4W0fZd/zR48IT1wUCoTzm/P4F6oeTGrAqVV1NU4BG/Z8ywbJ2pqqQWf/Zy8oFMwLf0AAICxTgh7UCiz97wS5+iiORjTDPXoIFAPGV+ydx7lUvtb8p6tH8Z8yB4BCEgZGBoQHMAifK6T97uElgAmALA9BGI1UYgZZ4d2kgdQ/+2Z0tLRBcMyHvkuF+L9oufvBduX4tEWiSgKcRgRyv8+Xzr91DBQoBWGhS/2eLa/IvrhU++2Twr4W3+9AL/2jmn6nwD4de8diDmDb01MH4G4SR97jnUUPj2/RkzgYtevZ8KpZDDSfUG9SxUIYDDC4oSaQcpENAFebIJsvrwR0HqNLGQ7O28Cw8RQBjhLlsdAwHppIKtG5ajSS8PzIaCRFYa9YLy5aIODxh95q4K5rIQecHlT53EQZlJYxUgfOKgXRuGBSglgHRFyOwS7pg4S9x5PP1ozdkEQzg7yrtg64BjBFnAE1eK7m3a9cWdYB023VsiMNBCFf1ATASfwxE4h9coeEPVKDQozaMq3Ti3kmwpc0y1MR4jdduDaomLasdncIMdKYysCd6EKbCVNLpHiECk8m5imwQ8ecBgc6VFWGEV1YSM7Ol7t1LS+R/D7ELXteifxMnjj9KExKOnwddWK2NHT6xd2HBPBxhgTtDTAhcMPngBQafoRqJjBtX/slQgY0RQAXA316JoP5bLcAfLMZF9tGhGMczhULEluqeKU32UvIDi//aZOJjYAgviFuGMA8iPPGQkBTt7d258kOuAmQAhoOBsi9O/wTSVYzA1NBM+92yIeB+W3zORslnLGFpf/1dbf3OCAWax19dvGTUK/vuTsCLIR7/Z+i/BvfLjb/K/VLwzy23OjLv9kaxv7RM/QL9BP9o6Cmlfk17fnDjL/IPcx+9Kvc76LLAqxZylVnMCQMrMIfulYYcIBIJjOCOsf7ZA4xLEPISBMIAQhHDhgmVPElAHlncMxY9NPHEZZUNaQCZ9cGWihsyAOHy2rYzMPdgYyeov1BLMJeIEf66KDIHg+S7eKpyl26D6Qr2tsO3TClg83pTGeEuyTnk2PW/wHHNsCDsBp0fjYV9TfG2y/Sj6f04B4y10PgrOBPcYH6N8OCpRz42828YNw5xh8S7KpQZnD4yPZQOFSx9WBNjfH6srZ28XI9EVsuDk1Mzg0GI+/X0ZNJAwVTP3KjwwRXxDf1GqUxL3B6Kw8aAgoIrqfbJxcnOZBKn36+jAza033p9AtpAfnr8/IuIwR++cDApkUc6kcVcVeZ3q1wUI057jORvrYbZD+JkjYSjRKa488b6//WyLgKVAHzLUIC/rUVsBAgblqIJCGpCBH2YuLol0TYzA+oApx5A5wdmQGgTOCqdGIEGOOwCbgNJMT44GEhkH3IE0FCAZXfcRn7ezlbYBgS0RdtmYsb+leYFCQ/cFN63db7XkH/NEHjaFAs0QnaX7pIQvrS5/c2c+zVNvHca+5yHVdubqfBZ4U+O/JNDr6LU9kv8k3MP+hX+eke0mc+lxdmZsg1K/2xu4X4JbVjI4qAylgRd40GN58DiGJSAHgdZXgQg7A0SEJcd2A/HN3R6KAOT9VDvXC6WHV3eqyWEm6PN+gA0VIcvnNlmffGAJRLf2CjmbTbI5ORytOdH1zCXEHch/nieKNJvmOVf1/C8vHqessA/+o6MAX7nq98wCPj1Wzw4Zlhw7nvXd0kBd30XbdcrJ79sXqYkB5vgZndr5CYUWXdhkJEHYnUNy1CgKf2hJUAa8Edr/qYTh94F22aPLLa7cOMQyIYYAYQ168mf11YtKx7IiMUg7QHbwVXSmZ6enlRPJSX+VHog7JKBmhgoGinGi319xeLoUOmpyUAS9wJWmeB1rImu730F3O/xExO7J57FUTEvHbtNG4XQmPx6VYlAiutRcA8RWFWuVwX/FCurhhdGAtaufZ8J+AYTUNGPAfj+8wXhe4UIBO8LH/h4wQAgdn5kOkuQ/CWZgKwj/Cn0URoYLw5AEWDbODaCfOlevPrEFytAT9QdV0Cx2yQH7YVIvDwz0jwbYvfBmH9yv1vIv034g0UJYS0GKNdFY1Spb6tsyEW7qgC0S/1H4Vez+6Wnwk2YKfexaatLNL80xlzV/aVgi0rY5oKnHiQSnJ/gqaeb5x5I91tKYONbAYjRidG9AKR9YfS9DOU5AGYJjOlhqUuik9IdxDngHZAvgAQMUDecEH/wNOLhOcqWCAGYyAU82dgSjYxu3bbt3F0Q+OBr29qF3TD1b2MlHrLH/VHxV4OxL1g+TGyT8/QYeaz8pCCcZxeMp8NaIcymdesWopSH3StO7aK+3fkbR7ewsju2NLn6Xcznd2GR4dVhSrnM8xh83AfE8MFGWgT51xR/w7iDphs/Y9Nte45MB4RBinT83BiSgKdrAoGWSN/SXy3OTrZXOlz4MdszNwcbIlUqo6Nzo+Is7qKU9tHbtwhbRPdV2qane3cfwiwIZEO4JPDa+vrEiZdgPNazu+u7r63vfvaV4y8dPlRXS0lBuZBz1aoRBFQNIETHhapGwgVOCqNTrm1c+5ksilYK8C1DAf72igVqYGgjsoJQgTaIAXI8ahWgESmEYeqpavxF3derkh8EvYE24XpxHKpQFINDA/2D7YOB8hcftgEWAPysLZQPpzYB0IgGRpydvUObd46zxzH5AfmPrfAnkx+NS4UCVS2MwpssWnFukQ2xNRTAYCm6boDz8bzxHCBO0f6G3eG+cNg88s/U9cupXza/2WyUC58pHNfJ9pca37DzY0TiD0v/FgfSuDWxzV8GgYexO8rkkrOFDIrwsoHORI6ACv43h2kOBxbJCB6KmwMY/hN3QxhSUBB6SMQzCFUZI/yRGY4lx/bTsEClAjcXPd//8lJfMfi37YVQfAXsL5T+5WDmPU/Oo4U/ZTxQZn+JhRQVNCKCcCoQ+KMfff07/+k/IfR+ZMQFf4ShQBoHo8s1aAi5cZOmZG2xdu3YSvbtkrc3Xr+L3C/thA60HsZ/QxcjEHMfEn6UAL7THH9QCHn15o2iDVq9sjN79pQ8TuGUDlwWCNQbDtfO7NtlCXV4JqcXexNplysNOyFV0uKNNhecC4oLc5Ue3EIpQx3CgoC+lZViJve1mdJIN+WAiX4UB6wvH8RxqceeGMMK6RefwG3iJP3kTiEKgFWZ5SUfbPDNCAHidVX9wgLXD3Jl9BtSASoJ+PZ7v71ij0RoGwreklZmTgkdEAGP9k9i7csI2l60Sqz7SPaRCR4Qsm9gYAhnoYL/HWx3/NnD59+ffOEzAMAKAdDUVmaTdYERS0t/71DDuFSb3w/JD8z+NsPfRbP7/d3vTKFALRtiVoEXL+XZuAr59tpHDfi7hK+9Kf/B9lfqP5P3lbnfMA18bjrxtKHypSwbPzT8BQJy6t845z7a5I5HuOPl9GypHIkU7BG7OwgWFqJ+ngB1+wYCjMEAcw+VIRTGQG1zLEFlL4FOrhQkBHZi6iNAoUDIomARjMcjcyVIzUQ0ObH/gpyU1SQbQmDb4vpNC/OYQv4lhfsVYkTgLySTHyz/mH5U/iJ9rzzfZWi/LkMBkgoE2n31f+YyGKYfnZ+9+fzqY7s2kQ6ytfeh8jYrwV361VofyC7YCfMqgZtJPkxnaR70qUfUF//cSv4xBGEb9VDeGYrnpo7s6S1DA8DSizwymluE11px45CO9qnp0ngw3QEOGKJ/PelKzygIwdG5SqVCrSI+rAosrrhBB5Z7Fxfb1nn8/bqWCNn/Auwg/MMT+xcEAasSf8oAqw3jFlR2Q8b6ajXmm5ECXqgaaWPywXQ7EnDjCs6JQQ9s+N+33vrp2+9fAeatFjD8Z1+FD32BPBtHzXCrCnfnDO15BP0BtJvsra0AACAASURBVPcHZkAo/qfXwFAH3MCAOBnvH+x2fP4hJ4BxCQCiBc62xG0s/CT++AQQWEi1T3aHdQAW4i0t7H9l+Utz/P0K8ffBBx/8zqQHf6eGIzSu14hebp/T5zaHAuMRM/0w6qB3YXM1oZN2Olfz7rWhL4b86zAA2BD84x0/VO6jUzb+Nsv9Tgr36whj5XM8FY1hvUsnJjgcFOXLQVEz1LYkGILiGXErEWAkZXpJEbLq6+xkD+zwsBdGB404xOIY8NAxD03KGtt/r0lZTdZWShFK/56xhMRBmBcfKkLL5rjxDf/MGzE/Cv/NKzJy9kOecn5X/Rw2d4QYIHzz1jxNuW/g2NYSz7j9bvE/8wL5h/ibZ/dOk/C7GIBqJL6BwFMf3xV/uLpu3ohDe1zYAWWBZXfEUjz0opeUuHqhz/zbiiWU6p6anur1CNRth0xwT09qdA62hRsN9gRHUQWKt6ETRyQIFQgdwp6R2cURmHag8Hdtfeza2NjEwadeOX783OMn9pI11raJM48IXODsBpvdKrV9VI066AV1E12hrl3g7PFGVTWHyBKYn/70rTfeuxJZhQXog0IYiAHSN6JQ6BNnuW0Sx17xUTKCaeABzgHTXnAjbUPU/ybOQjfVgHBW/YEvPuQCQF4AwDgowLDMAkv2yYuYDYnYsiMzibwZgT6fdJubCGhyv4J/vxPrg19vRmAzCl68hDNbYLNyX4uOwIuXbIhAo/hSLiX/YBMWJxb+QemzT+q/Rv51gAGmuW3Ghh/Bchajf9z4gWgKqLEvRvQP/m9nentl6V9bCsdTAzHI6+Y8nRToA7EWgF4OSHEEcp0EwE5ytyDzxHmBwQTKRIKjw9PZHUAekgh0UDkMbj8CqZEAdoqAJoRZ+omsqT2uOdfua3m9a9taD263FOAoxNI/YdAdv+eDvWveoB0OVFHhQGraIPoxBGlpGBQ+ePY7WiGgZOEtfA6eh3Vfq2lSpMl1pttxENbwMAtXilbyVui4JTq0oRitwZD8vbv8owUJ4RshmzMe8uOQhIrNYlkZu2CVHTqcV7oAG4eUx0uLi93ljKAfbIlZqaQEAINzc6PJ4CggEKbm+/M0QsXpdgoE9veWSuPrXBR4jQTgtTFx7vZT54+/dOI2VUlLBWiKAtZlaYv0wXS2psyvCYDMR4OBsotuY2PhF98XCpClH5z8+O/e29hYpQW5Dxsy0FZADEJiJFIopAbB/WJvPBmlNm3yC/BuvA3NrziUxvvBAkNF2fhQ+2D3lz4N+SfWn38WFGDKEwsbMUAzArkmJhJKzIxkTTbYHncrw2lGoEa6XyP8aH1gIiD74CYi8KK7CPkLmNzifs2MwIKuAE3ud/PYPwr+GZud66lfY+C9LHwOZvXSPwzGOXjLN4G//qEB1fkxo9zv4uxkLA8ffhFnitRfAgHngUSIJ0G1fJjqdXQCBT3MNECeIJ1HMLETLwU4GQK3YX2MR8lCah/GDYg9gEsop0ZTnIgBAZcAgSchG9IMgfcNReF+z4qXs7gi8Ge3QSGP5/c0NB7DZmr+c9dV4AMpKA4IqgCgdk7Bj0GICNRU4He+I8uhMQ1yDwQqxffgC8ZLX73Keg9VIMUBAYTDxq7Ad3hb4EfuS/7hQgTahBGOu8Znj8xiudjze//Ltm1WY+4ibhxisRTnOkvTpc4gSEBwwT3pucoc5ELmyuXRUZ6cDzUxsMFQccW3UlxJiAcMLslKGMHA2+tj67evrdfHnnpW1cfUNQ4a0wGlszVMblWlQ6pa5E8SsKrDj74IgbX6L77/t3/7LUiBfOtv/+69d65swIaoq6vUBQzNcHQwrrL5tYSyI1PQ+Cvtby93ABu+d6h/AEtfBsD9QvvbuDiqxsc7PyX59ycMQPcmACr28Skw3uLq7h0JagCMhAzi6AD8QIv3/eu7q5c+YPqBE26CwMaqaADdaxBcBIaJ73c/Utd/8MFHIQnAkGy/kf7XKcfeO/FxbtnzG97c92ZE/ypY+acm3tOGHzkPu99Ap5J/cuizyn7gjm+DfgvEQvKZKMTlUK7huJhOACDoNYrkiWfifpAAy8AA+Vq02KQL4T7iQgAZB7d1kg0mMQl/H9kSJ9uJcapMNHqWhgVat5qUdR9rbdvJ/Tst8eJGEbqZ/EHx7L+/hcnfYeLGsCqe+/gR7I4lHso1LEkI30bFIFGRlt4a/KO/VIWA+Libf3PfIvDB1i4aL93FSY9hNvDDTG7FQEQgMvDe8u+W9nP+5gq0XNqCI7Ozi/0uW8TSsf8YD6rgSTzek5cXLKurwZHSYmkwRgSsVOZ6kqNzo5XgaFJgsAdjgel0OM4JYSEC+zKCmZOd68ZCIXhblgfSiSYDMQioQ5CwZ5yvLyxog7Fk6E/ewZCANY4DIgM3alfe+cUvfvHOFbFqNSAg7QUnFoyEkVqEZpMEx2cw+dvbxhkQTAPj+D/Sf3AAUQoEDbAgH+iKwcHOT0v+/YkEYDqxBQDlQhFosaTHS8aYmIIUgL68ngdm9/srJNxHkUioIBFIBNQR+Jtfc4Pw5iUQyDE8t/LBH3xw+l2ZcTeZX5n9kK0fbuSfUfgn8Kfvd5TmtjeV+w1qyY9Ygje8lFNPWf61tamxf7L2BT4OsPGtTA29CSxeoaY5fAJBMX6mAJSxBLo7QesFUPhBbpmTvYKOQD6+1oGPZwsNw/LpuTAiiAXUnkSnI0Y6EZLJ2SzMSzVlQxQH7w+Ia62Xl8R/50rfinC/edSye3Hui6EBCXKIv1OICQVAosqwTJDMz8+rSsBhUo0yG6JU4NcV/jCPcrWxGGYTxx7wenkzFxXK2KRBaP77yn8X/hsxG3JP/JkX9IbA564tFJyZPTIV8AsjvH3/SbWBJr64ayf/7ZnVSF9wYGp6sjuYwi3Rg0HBveCCsMDB5GgFqmLgPekKx3lgqq9YXK2MLE61dZv4d02eWZcQlARcl/gzlcTUF+QlLnhR1TAq91FVwUDShjUmYEeNgoEbG7t2XEf+wdfGxopE4GpIDYMR/jASD2dHSjj3qpe7f0e4/W2I1Z+sARyQM/BBVAwNDQa+9KnJvz9hALakPR5/fgv0yR/kg4NtkwEn4i/k4xY4cxmM7n4/ugQJ/pBwiO/+GtknffCvjDv97qMtkiHvvuZ0tzAD0QcL/J3OGw4Y8Sejf5r3dcrOj5ZN+300zLsH6VdpTH7I0j9Htyz96x+n/0J9v3Pc8S3nLIh/mnC/WQcV/kG8LxCgGQgBCPA5PMgzD/riRICIB/bXI7x1JxIStF8A6CcQSLITkQiRQHErls1QaSAGEj04OhBaRFAFYml1LhE7NNEkG7Jm+iHPb0bitm0nx1YimPwQEgRK/3K/R5lDbFDjD7rufGwkChCBCifzDMAuKhCcp1wxe2IVDbzF06H1PUK6pGuWG37c19qlJ3m3Wtef5s4Pkn5yM/T5Lg5gQjnMsEyGkAq8M8yJkc2oa3otXH/zRn5VqMAw1MRMJkLiyDhwuXXbmtYfR9vHhVaypenpGY9wwAJ+PXNzPRAHnJurChW4lKzMpTEy4xZHGkzNF2/loj86MDXZdlsLA643rrqywdW6XhPNieG6cV4qvdqCRJ6yx3rRjFKAcgH4rixcwQXzUzdWirQhJngF22oIGz8K9lCsvVTipAcykGHXZl4qGtgGyk8cWf2OL34qyV+1/vyz4jPfnREAvKsCtHGi216I52ZGumHoqU/mQLZwv+Lcv15ahdepYP/X7377N98V6NuUDEYENqmJJgTKJAYgUADwo4tGBFBv/lB9vz5fC4g/4l+4pbHyDzd7MxrfVOlLVo68p5l/RC8K/rWrxjej9G+GZt63ZXAufx7jZR6s8kMKgnGmOhZhZhN4WWDQo0SduBpkXmengxgn7DL8ts5uFIbdVAgDtxIXAxwxDKAFxpggmmqekYVdJo5EbGkfDknwymGBknfGzzVrM/rhOOPt9lBxZQXC8C3BmMPze5n84FPSeUIhneIaOUMFdimCdXWxyqKcMHtgiT+JwDe//nUl/wwEdkFB3h++8s8PgMB7L9lTwkKvi9MfXV0qBdzF6WAJweGt6Lf1uiVEYNfNGzgB3h2Ymp2dyeUjkcjyhVaalIXxQDh7Ye+qZXV7Z+mpxd5oMJXeXgHzW5mbg2/YGxOqYmBT9ZQf5sSAERY+uOiKDZVKA52buCfpZ4oBMgYl9upcHaj74HrVSJEo8tWVKqQIYA3kn8ZAph+qQMG/FcyTxYuhOJth6AV2J8RR0Yuqj9veeNHATLLEJAMHaABqWz9E1sfbP1X5B+uzcQbgFgpQLVnpCDMSSjlDdWn4M/f9AgQ/Ep8Pqx/96tv/+X98+9u/+fUHDTFAXL8RoLy4FQJbaONKvzh5993ViFn/SQLmZe2gPvUg7Je7XWrqT008NfAXjAIAeb8jqf4cnVrnxyb5VxKf5L1BC/DP1hLEymcPNe8CBZFj7QEM4gH8oLAF8AVAg9PuAC4wwuJ8J8wXFCftAn3d3fCAbnh4J4lDQcZOeiJ4clSDUE6DA7ZwoCD+8kTOkcjGdk9o+4asaQBck+zTzqi1be3CP2Lpnw9G+Wai4ul+z3JHxcqQGXcM+DECH7lDKpAFoCkDwupP2U6Fu9mv7tHYJ+81D/uznfrDL+87Engf99t1Q22FSa3LpAL53zWv2V82+gy/+2DgLXUCixLCwgjbWzyLR2ZngnEoC3wKhyTIwbTWbdYL6wKBLkdpcbLfIxRgcC45uhBcEO43eSgZHYWMsCAjbqDkxPl6cdhCuOjKfW1qqhcRuEn/SfOr0U9CUCsLlABUMpBEoEqSyAtVyoMsmAUgaEBFwI0apkGQgMUQbn0UgkPSFxyCzjdxiAzA5L827vxVko+m/rWh8UUrPI4GeKi/+9NLfqj1ZwjAhMN1LwDSElY4YskMlWbKeVu+Qf41a/z49Ufv/vo33+Y/3/1dIyFx/QYnZQEAN7cAvyZTGYJkPpsEYEjPf6j2OZ/a7423+g2bJz6bh75Ugvpm58w/mkGgz7wfajOPvZrBsS8eNwT/CnlofKO0hsej4n5IOwdG9QTzutHdotHtRLRivgMJJzgpfhUCElCH2MTfLf7gGcwo4yMSnE3G35bABHMON9CEqGMMaqpz0d17cfc4bV6qVYrBTdKP2bjt5L7tWPrnBPcrtCyU/l3lyB/FyfDHnTtm+vG6c0eKKgmaeRkO7GLizGv467p15LnHn/uqNgyGFpahnMIdiO4SCXzg9TSNGGQo0/bCEm/zrAG7GH/GNQ++rgIC/QKB+VB6cPrIbBvUxOwc+9/WMBbolaFArIlZHQ2UFhcHoj3CBCfnRg/0VJPCA8PemMnRaHJpLoUJ4TyqQNxVN9QRmJxeHJLQu3bNACHFACUHq1UWgDr8lAWuS8UHC5IhXCmjRwRlGhgJuB030QQHXKsiAqsYAgQJuEISEDZEwinKfs9kqZc0Auo/OfoFjxuehkUiQl4Nu8CND3V3f+lTaP1oWH/OAPS48jTSxlwI3ZSAEAqcmRoKhkJ69E9WPivGyTPf/jbA7zff/vb/+PZm+Kk7f9Q0FXL69Efvyo3LXS6/m6bumPb+kP3DPqc29aCvSfAvg+ovrZvfIA99yRq7nSv7i8lfjmGYon/T0yMZzPvHofENGzs8NNcAa/scJPQAaxjaQ1mH3AOzi/Uv7cg6R2CwvXsQQo2dLATbuwl/3eJqRzc+gkwznkIhDM9KcGDCJYG1MVCzg0NTE4eWzmI2pFVHYHPy8fm1M9VCIY6lzyFnOiZ4Co2/7BpJG1Fw7GM5OL6Bgx9/fJUdMEf/5AVZdYxykFk3fOy5x2GdO6KNBIQkyMfUgQG/4Ce//I+mPDYvaitWLKfsNEY0SfA1mN6uBzfBRmTw6s2brhDUoVba9uyZbk/bLZa+/SflBxDXRp+8vLRqKY4OTAsVuFTZXp2bWxgdrQbnMAoYFZ44GQ1WYGv1sp8QKHS5s9jXk1icnmmHUKA+H0aKQK0aRklAyUCDhHDWUILGiNSqcr9Vbhiucf+wyQJXIQ5Yq5EC3CAXLL6gAtBZHoc9j3plrxumgdtGWAXKICDcAD2kbeO4CUjbUH//4Bc/96lG/3gZCjDUnHiNCyulI5ZEaXHoNU3+mYpfzAvgB19b3Epfv/kdbxm3SQW++xoSkDDWAn8FTH/oAUBYbh9nfltawptGXsFk3rTZ/ZZpuzcK/qntfh3Gjpf9tOGvwh/teDk9PVMB9xuxQ7wMFJqAXwLhhPjEmj8shAFnS+G9TjSzgDFkIqJNJZkRgHhOOF/i4DggsruTTDIEAbE9JEB9dblAIBFwyMpoh9B+MYQhTBuMJsf+GkdGW7eZa2LA/TbWyKytrV3eiMA4JohqZ6IJ6PyQh7SEAQT/BKC09Yg6kQicpzQwko/TGvNdMhMsnfD88K1vPC7Xc0eMPAjJPzmBRSDwEwwF8nbAXbQXJv8l5ykZotSgMsJdD0Y/WtIJw/yGuE18HNvSbbB3kr8QsRzdd2YbtAhblRE+eblmibgCI4uzM+3ROeGCq6M9lZ7q6NKh0eTS0lJS/Bndnnalgik/Ts3Px8UHe75YCUw+NdlvcE/Tfwg/TQnKGGBd6w6RCFQL52IpH8zlgLJWkLnXoXtgFIHEP3i7UBgwDnOv0t2LMPeFPC92/wIAe2UxDG0CAlPwkYYD47QLyFD/+Bf/COQfLABgiyvnuW8LTD/sFl93aer/1gl4NwQK/G3Bv+8qBGI2pIkGFOs1NrOZTNjWJAFCADRmvmDVs77XeVqL/lHhs5B++MVTX2Tln9zvfHBwEMvVB/TGX8r9dvosPPYlQWoMbWknpmgDGAqEDAY7204CGdCvG4noILY5At2Y+MDbhAoU8IMf4nz7YGd7P4Kwm9iJNYSBbkYonEdOU6E1jNWH/dWhLhASwrny0hj3hnBziJl6ayoUKH56L2+EdoqP83g8FA7CjsTzMvjHPpbl3ynTarDCKhsio2wyLcKQmediF3C/2npulkXgHa0FjZ7633/yz58YAWUjCO8y0tUls9Yy7KcJQDP+HpSGt3CCVxwKo/OwcUgp4LdFLAcOnqGNQ6QRtp75+UYk0pEVtrbU2TM3Wp0D4beQPJRMVpcOiT/lQ4dGwQcHXbh3Uqgo3uECN5XxqekRh4TftWvXGmSgGYBaNrgqQ4KmtVDbYAtM4KtKRywH6WvrysIC+t9aTRGwiP5XwMCXGylR7R/1fZDTheMFS6Fx9w8agQAVgOPjUP0CPSDtn1bn2+b1eacdAHhfClC3x0IEpoem//v/oRPwNNjgX33XlAmmkpcm+ONSmF8Zt/wGQoEgADeHAt99DQmImRq9/6NB/2nbHSn+dcjKP8If6z/BvnJWTT1IUOpX7vimbXnEO14S/6amp7+WKlgE/mDsC7V2wAhnqm8Rsq4bS5chmUEyr7sfEdbdOYhEA6h1MtggzgdnBPYGx4F7CF4hPAUJ+xGIqCG7sT6Qs8r4SzyUFobpqZQHxnlbOR66movFljEb0tq6pk/KamKItx3eWahVd4p3cj6TTdDUU1hGZrSLJkY1LqUB6QwgUDKTmKdOyP8CHd8E+WdC4Ddgr3TpfrVWXEDgVz5JAv7FjZtXOd1CyJuH0kAZ7uvqkoHOYRn6xPXmV9+8bz8sZTMgMB/K52HjkCOzkzFnwWJJPouhQNUgLBB4e0UgsH1ydmogV+mpCPRFq8n60tJosi6UYDIpCDiHWwm7fJQNgXBbsS/bu7g40om5kLrMiFxbZxmoJCC7YAlDIwoo/zDqBMqIeEYQkE5kL1xNicEqFMAIA7xA/AMPDPpPiKB4qr80SYKPql96Zd8b5EIg/sc1gAPURTpAow/6Bz+9zrfN6/NuBGBn+j4AaNMZaLdH7OmB6f9TQ6Bp/H0j8LSlygD/u3Yl+mAYFrhZAJ6GUKBgGonUxgLAPM4+kNmPPr3tTTa9Mf0IfhU18hQr/3BgqQr+tavS5zYDf5z7XZyejNnR/fpSMZps6kH3CxoQ+j7I5QbaMZ1LCk8ADmJ+wD5oKxnsBInXTTTsbMdaQ1B+gnuDfzUufvl4P/769sH2/kEUiywiu7FtBAt0AjA8EIYLOrA9LpFzdOK01RzYYaEDs1naOokSwtuMI8+sB9e27bN0VHfGQyFXVKjI398yNr+Q+IOZoU3pt+mqj+8MM/0IeBI3je73OfzDJPzGmxBblCNYDAj+y7/8P5+gBtyBGyHRAFYe4jDckAAxvDDfNnzrlcePP/6N6S2SIreGt1wCgau2fD7vy03u2TMZ80Usdh6SoPYNsXpP3n7GEtrpKc0uznjKo3MLowvCANeTUfFnKVrPCgiOJnFPzUwLlgWKj3mfYKCnVCq1SQ0IX/VrdZaCknhGWWBVlcRwMNDIAuPl2kZNFgDqkUAamVUznPCVWrUGIcAaC8CdFAO02SIF12CpRI2/bdj0Sx6YEDiiJkDzFiA0/QVqKob6A38k7hfXFz6DAAxk7g+A2gIE2mKlxaGPlALcYgDgXdZvtFM8A+1xDfD7AE8+ene1oOwvT0DlrY/kpke43RH5X9jxCGN/Jv6x/dX63njis4f2u6Sh9zCgm4N/Wu3f4nSp3Q97stN+59D0gW27PDQGJmBh7bOD/C9ZWFyDALJ2IeuEyxUABMZ2YpEh4m+wfXywe1z8GBzvH4fSKPEFNhhICMng9v+XvbeBbfO80gWR5gcJ5gIUhxJFXcmURIqmGEe0wh+JUiRT5OjPdMSQlKMkShSJSGSx9qhpp7JaudUUUHx3K8zAaxltJkWBDNYXi7jAzQzuZIAE2L2AsRjcXNRA0DuziBcz8B0gcjEI4EFVAxPlop1k3+ec877f+1Gy4/wsJm3zWiYpkqIs23r0nPM85zkElNCNRWcRpw57o4MUlp8jJuinzGhQw/nHeDZEtsdZ/T8HBLeavuk58qDX23EamfdO98+hPV311e/tzkfbGgAN+dMml5HKsmCfRkH+/b/+jw9NEqldBH+uNTAAcMdfWp+mrqNgXxdfGuFXf8ldDHi7FfmjrlR2P54EuuEQLHATe3FbQ0vTlXx3rLe37fEzogdLSMJW++UfbnoWTkfKS9W+IPIRNgY2Npj+nTw5P39yQEHg6UFERhMLhM1woaVl4Wx3vlhdC0MKvvieyxZjQZ8BQIE/bYY2WCjuwHNXHfTbsGZERARxymDqAJ4zCKjg7yrmxRtTheoUGfxY/+C5X8o/MGvQteybh/CLNWKIPoj8G1uf6879d3v72+6cAdadGU9/eGnpv0sPkDBMUz+bAt6ODgoLvC6/aTzOxf0AgNgE96f/7ac+r8E/KYA7GP+k+hXvs2z7HbaKXxP5Z6bedOazI31I6l+8T9xKWvsQ7Zesf70zED8kyspPQafpDM2pBWWyg+EvFNA1rII2BWTqtRUQBvy4WyFsnKlmEjUvYZ/6vMm1xJpCv7W1whreUwCIlDSmiQDUMDunrbTAdCYYItxLm/CtIMNi7iTyUikm5lURhLcsFki3z2x4+n2xnlQQ1a8lfphv+e291S+O7tXVHWoFjnDZO8LFb5dQrsqk+zAWvvr/aszT4MdK8L/83eengjwM/Hs4ujyh+GZlV7cBNQhqBshfuC6Ju954yfmjQq0ZudPDCzS3aY16y5h3uFBaLMUHZ3ye3HNbBgAZAs9c+c8eBYHJ6tJUIXV8/OAG3NAnL22cVEzwpKAgBecPtvbPQA0ZUxRwbOGAvzxXTLrh7733tCfatgYaRfiSIB6zQud9RQFPmMKXlBC9NqTOBwgIhCHmHzEfTCUwvM+tWPkW5eAXJnoaACkIJs8uGDih1Zv6juprpm+rQiD0RaJ/OPc0KgBMh4ZaPm4UpO6IMbrX0xqqAgJd8ff7IN47ztU7r7xiT8O98q4eD7mOKhhqyN5zAxj49phvvwEQHfy31/lsrH+ntfOlVss68CeZp2G97pyKX4m9ihrvM839lnNjHsSedgxmgzSRm9Hsj6d7qesXFn0DRW5cUT9VykaSgmAhqLuheJxqbLhfoDOTHV5drxVWV9fUmzqrCgDX4msEhAoPFRkM6JiEiCjBGdZBOB+LwmKCMhGSw7oR0NFsbv7oFbM6yfQCt7YaNAU8tPWoxxtrzQVzuvnn7oLdAv70sRuB/CYccMQ0AbXRRVWU08su7qfOf/of/+Ds4XhRKOCL6P/9bOfjMO2TnJ2HV1cEzAgCyakoo3tO9TviQH+dWqMg0HoSPWFkv2PNypEtELMhY4Px0nQlkWptqRXpL/0HRAS5FG66vNHbu3CwMFWq9tXGT1zCZvR5hXuXBuYvqV/zly4qCBxqHR4cog2aXvyH7+9f6PRXl5YCHyjYu8QdQEMCXZWw5oF6IuSStsGYOzfOMgKaVqDpCLpVkH8UAKTbqgQ+suCb8bUN5qfK5ShJHnk2PUelAjYnkbBuJhJwwaj/7//mkx97zv13t7W1psKDLf02sN358Xl8Q/ml6F9bAPiu6+q2B6SPZ4SdQvg6xuaY/BkS+HOQQEBg/6ZYoDn8lHJPZfbNxj8KPHVSX/S2X/L9se+Z/HPM/hztw6T+WeJHeapYKhZaFfz19va3diP3ABSQFlpSakKYPdA01xGBzY9q6TXq9wXQ4ksSAVQACLiLYMBO3Qf8U3inLguAvFV18nwFEFQwqO4HQir+SPU0hkQArFiyTqNyNH4XDnPlzWvjUA3nSA9JB4PZebM66VUuhDUR5HPoGY+voxbM5PZUv7gS/HvoH26Df/b5aHvbrn8FAqUInh3ZXTEQSPzvP/3zQwb7jJgiVuiPw7Q7PqMP7+zMF/VnBQTOGc+O64s1JHB29w0Nl+YsV27d83OPCNvDITcbN7GfoTtaWSzlg92py4f2xHNfeOuEp/fs8UJxaSpwelzVvZdOXprfmKedmNmLCgwvzY+fRhOntQOKK/3Uxx71ULUYDbhkEKcKJiLoNAI19rksgXKuLpw7twE3zLkNk4awwXZAVwkMWYRF4KtXiWbZTwAAIABJREFUzx1ZWPD19ncHyjT4GyW6x70+VkDyOgIB2OiMf9D4W19f8ovifXGdB+7qsQGQQO3WeLf3IAu2OzoVeHvvCqQ7gcBXTFSMEEC8XX9Fgx+FIPwcGHiDIPDGf9tk/NPhV2B/ba59v5162+VwHfx1p2jqTe8617GjBH8RSv0rJGTnh6X9VkuVaA15Z70zbd3gV1h0GSLw5M0fGF2TQbcQzMvJOArfNUX+cE29PMgbyUghrjgd2oAR2i+iEA50b5XOGo1LKhDMy/t0CqwLqz+fn1w04RD7YdgbE+TMfT9HEFJYFvhgGpwwFM6k52k25IxWQ8QCo4Hw0JmTnh5ssHN/Twsr0v2/fctd+zzkWGGc43igiQlCCCFkYQo4sTz3v7wola/AoDhg/vD21e8nxMbRnd9/yo1nf/TSrhPlWk8AgX+L9fCnzsRyZeS2Z9eyA9LvbRaEUQi3pKqLi0uJ2skzW3ZQIBfCF57a8WweON08XWrOzZ/YGMAiJEUEU/N80goFT4IEDrfKhDBVPf2nm4tLVZDAi5fMZIizRPOiPR53ySDghrlmLnji6sJVgNvGhsRiGf53TgshQgCl/3cOWQhj3l5PTzharUbzZW1/aTZVMEkhUZn5gPEvAZLIq9AV/CW+GNbnPeeeu+oBUGdO3fbYudG9vbl4/m+NCHJHwMdjwNecvNR3f81FsDrvvNtqvDA/p/qXi2B1rv3pa1b9y/oHr/xwqb+O8a+721j/cNJ62a/0/rT0SyuPXOKHrn6nIv2gfzNj3VlYTSBDSEYz80c/Jxdo816ABAxWNQjqAgrGCqriTaKiVVVxgfqAKHFxFOLlOUOjLKwzH12NAgIVCIIdokkI0AT++bkdyOFYRD61CsP4lwuSNTCTRhZ1GklZ7tVJThNQXRy6MN+C4V83j9nWhfB+Dpj9zl74MyAobmiBwMqKwN/00Z2dP/wXrp9F+sU7//p/fb7V7+jo0cryhOjOmgQur+x2dTmFvuvsvuF4tV3n6x+rhdh/hQyGFJWl/pv290RK00uZB5/Zktlgyxi91X7hiau9m4PJaLFYDqUGNuax6g3V78WL8+oXXY4PwcbaORYTCBwbW2hNF4qlaNKGPKcSdqGfOicMG2RVhH0wlzauxq4i9G/DngXerwv4j0YdPndWlb8duQSlPpPRjwgg419UdN8owx8NkAoFJBrYl/hC0j8699zdHe7uiDm45srEv6Mz4+lPJ+I/tkngu9c0Dtr9Pn1I+3j37c3Y21ZkNAGoon/XXvt2GzKwfn4D9e+NP9Ul8LU/vUYs8DXZfN4B/aOtpwe/hf8Na/sLR/450m+30/zT+z7Q/Ito/x3hH/2zWfSvWiyVCsNU/Yr1L5ilOOY0Nnvg5EgICYfY6kJ6bxKjHPEAalsAHoSNABe8q6riDaytwfq3liD8W1Vot4pPhU+IHSNorRxTWLiq6GAeT1AkMRAHoQyxn0aV2iCcIT0iBwM0DeJxlDTuJkU4HM7l0unUvB0WuLVlWWHAAR8dVBTwl3WVHJ8ulMEKAm9RA1vnQ138znbV3+CLWekGkhtwYiWK/NOdn/3hv774opF/qfr9fMWP0YFTDH/0xkddT0wucr9POxfNF9y1/cb6xD7wt/zGPn89e8/uiD0XssuCME0I15ZKwbYnLAsSr4+j3UkNFy6d9XiOhMqlpXw4dfIiKmBJgp4XEEyN14ZbFQpqW+DYWP/mQg3OaJ0WCFVY5kF0DWxEkPqZEH3rxNVNBJ4C+s4ZAkiJqW4APPGPG1QDqwr4rEKDzvBUlTeeS+6Vjr9C/y+R57mBZvuQ/4Um3z4Oh/7tzj135wbbbBXYd6fA5xzfTE8u/l8NwL17Yyz22rW9wOeA4fV3bvwU/6A/vWEh4LsK/969ocpawBkgUGjgNUJA/L6mft3g1R/W+G+d+mG8L4R+UIBTNa39OvCnjX/xpKN96MGPqMS+TGVjqvj19LYNZinrNJPD/C2pIMTAKO0FzM/PTj+othBwSeIAfQPVK0i/TyFiIL62ph5bK4DhqYo3iloi+kxxemV9fXn51eX19ZXFEhUYUS6G86uFJEA0icoZEIupEKwOCVKygughjIQZLYmgE4i7gul0dkBmQxq2tCCs6+CtQ01X5lMZCkBgBdP5duabtwhB0IfK34+E8bELRu/e0Pin4Y9Fkd2V5cpJ6fKNMgS+yO2/f/3Dz9X78vDDO+engWbLy8um8Sh4VhEA1HWwg4Jdu19f3gOBX7+N7e8WR/4et2mHsPpRnZ4KdQAAhf+RHGyq4SZ4YjaH4sVKMZoj9MNaYEBfjlAQV6lBUUMwH9e/MNbStnA2PbVUjDL+oQ4WFnhJ9wI3NP6JKZCRj+eBT5y4tHGugwGQpWDanq5lYLcX8B8F/q72+zwt6eaq4J8YYHTVolVDJwC6udnJP0h+wbwve84D/+6uHpcI8onxz4uP6fRHBQKvvU1+5bdvUwwr+kdSWb/3p+++a0HgtdfOipe5s+M1En9RAf/8xjVcX6O318Zk/AN50W165yVNvw1L7pXjfD7thL5kLecL6bZa+pUhHdv6R9VvMdmj4K+3t3+oJmVzUKAmQ5O4FGcfpBArmt1AIb2mXpL1C27zKdoXKEi9S1gYBxKy7pEvK8ZXXlr8yQsTjzhnYnKlUgUEEw9UFBBICnsg6SvqswSQmEpTx5Kbj5thsgHyEhFZLIKKPZhN2auT7LRA/PraM5l0Nv3L+jLYEKOPq4MRCGOrv9oMKBBo4JDu356dzTxvcG509Gf/oiHwcxU/6IyeL66I89qWdRFGMyLgJwTQKm+79ojAK5WRO/fB4OzaP0pUHdyj/pMPJ/0HvnfIaf9xUqC+2Drzf1zc7F3ozhdL1ebMyQHZBaegL0iYlrs4n1GFsPpPjVEoyoxWr9n2YGc2ulR8S+vA71H1e9EtB1tH6l8xvaAC3vw2amAqeTecxel7IrFOMAE8G5vxDgWmKPZPE0BAofY8N/MIMJv/8pz8R9cYKE1+Yatfc+65u9GqgT/d8fV6OoPNbwLbejdJtd/svXE7AIyNdbT0999458/+7BWNfzfGvk1yhkKyxthM7+bbN35+Q0EgNQBFBnktFhuz9v66hn9N5jNF3uuFRxb85Wh0Q5wvgn8FWflhfp5FOfS0lB/yoPz1NtaIV/k5hV4BIDb/hoIc7Bf00+wvtAo0/hTsqd+k7hYS8LPE17iSlYNylmwvEDyAtKWXbPDTZ/JrVSqMUQivrsIUgwGRECs2oRAny3CkqgZAMkdHAjQf5+dp4VwGTu9sbf7of5SwwFfdeakKEy88hVL5l7PuOthRhm8HgTwEZwDOKn2tm/yM2VlE3/++q8wd3fk7agX+y8eIH5/qjO48XV6ZoPafYNoyrDAjtBhpVuvADITypaob7qnl5elPCH97zvb73v6WzmDqsaatBp2QSrD3g3ZjjMZOgnOe3s1sX6lUTXLda50cXc4fHB4mFuijSngMzsBYplopUivwEgMgg6BWgy+6qmBdFPM5t+CdkRoYfcATTiL0CaMAHxBPtLq8iu5fMFqsMvjJhSmCmyn2lDJf8gn5XqJ2EgHhFyT35WPOA/feNca1r6++D+ite/fWkVm+mdjpyH9985VrPyWvyuZP9ymC5VwHBMZim2+/e/37f/b9718nCLzxdkebaBn4YadecXPsbca9a3Lx9lh/v65/Jf/Pin6xrC+O969bQl9M+UsxVWbhkaN9MIuXwbdKOQvxY2amZTDLy31zGQpd4QQs4mA0RBfmIRKYnmHqS7KZuSCmPrQC0evjihcWP0JD0n3Vpzq1aOBvcmVlZX35BU0DlytTih8ei0ZZFCYKCFdNPMJiC0QXNgayLRoleQizIiiBeXIuSCkPWCI8/k0ej2s4xBCox0EAge0XHs9ls4iCIf1ypMsVCTNyazVEe59HRgzYueGP0GVWmOB21/vPEs07L79xdh7+u3/91z0BMM/uufFpzujOzjdPcVdPQ9r07giFYY0Q2smfnL9OI4vAs6PpX70HcP/DNXLXPk9GVKC3v7+nNn9BKmACvR80aC5ofhadeeucx7OQKi+VogEYYOzkF9wMXpzPdmM4ZKgnxmbYsf6xhZbTgWplKiDdP3rie/ZcyMVLWgUWGUQVvwyBR2IMgFdN6bvBmYDnTjgIeGLjKmnAVxdivTODfVVM/uaj5uT10C9fYeQ3L4kIxgOYaP7C5L583Ln/gfu+UpcJuB/Gfczx+VpSiTdfeUfxtM2WG+4KeK8Ycu3ta68o8PubP7sOCPz5jcaORsG/Dv2ZfbGfutp/r4316/E3y/3n7v7Z+87N3FuWjM/E/0Iy95akvQQa//Q/rdC/eGcv6F+stTsr1W86GM5JaBZ8JoQxIVoCRzaaUICMfwFUrKr0LawaqCPw45ur7HtBfy9/LD/13KsCdz+pzBWrCneLc3OLk4yJE+ulqqqQj1EzcA2qCebkZMSOYhIweofQaYof9FNKFgIKw8hJyGERMfyAZI7JzTtb1KUVuKVnQ7YONV1+XP18+OXstkBfFxNA8/28vyn6w23BP7GUWGfWoX760e3Z9//clLkWBo7+7Gcue8v5hz+3Mzq68/BjJU3+MHy8ywKwVfvaOoi5tU1y8E+mP1b8tc9u5Ru7bnUZQsjIzdhCf89jl40E4qqD6abcc+GJ856ZA+locSmavDhPIKaoYMaigvPZ0xRtRDkxXh4EPdu9Wq1Gkx8AJ99j6HN4oKsCPrFh3DAwAcZ8vQKAOglQV8BaCTGO6KsLM709WUX/yuU8utPlqE58iXLRSyea7+NdSLoEprVvhcAXWfyoOwoCGz/hPMg+x+eL5ZrfvP7Ojds1AK/rq+vf/5vr31fw9/3v/9k7ry3o6rfH2n7p9W3+VCwwAMFrN17rp/GPRimABf905qlr9IMmP2r13T+Z+0gmpfptrmv+YfCteUhrv2kSFqB/pHkEI0hAQ/6XUDDCVSnCCzDAq8BvDcXvqtj7AHXsaSEYZAxcY/zLR6svCfdbrKpPi34gLqfKlWWhgesl3AsSiI8sEMEkKSTCjkBK0OcALtqqxHMtVKgrFgi3dI490n7F8eYfe8qEBZrxOIbCQ+3fC2ez2V9ape+2uQ3E2AuBtB/YhXqMLPrmiO4KggSOKPj79o4Dfz/bF7A+R+zTR7HAoyUWNn5Cs3AjElttQLBLsNCFdbMjlZc+yRRcl+y8+4abBVJIYL934QkMA2v7C/tgGpwL3QrcuvDEjmdzIR0tlaIRy9nCh/qB8+MHh1sHT3d2xNgYDTPEwlCkhMDUiy7eV98GdJzQAMADC/1jM70zVxkBmQBuSCI0I9+GoYFXz8ZmZoYhfuQl6U8TQIWHWgKmFiCC/3gfCM3BYftvX+CLk/tyJ+f+e+9us6Fsf4j7mOPz9Q6Hy2/afO+amwva4VjXFfqpEvhvXrnRCPEDUCbVLw5mgLwxXz+pIaCAeHv7p7L7V8/+agB0ol+09yVF8Kfn3nRWgWT+xXnjkRV6qhdeTgX7afAXg2/c9ksHtfePa07iXuEQk0lk+gXWMOjG9a4wP7L4CQ5yJSvvFgCL0ejSpMDckvhfylJ/TxWnBQInVpaAiFH6cJTTcRKEaboYgVphagZSLSybQ8QWTZ3KYNAsulNcMJOaP/ofaXUSs0BJSWASeOjrz/gBge9vCw3clt8i7kIQto+2/hmWZ8GeOZIJCPZ38w8MzTv/6aDuTrqEo/rNumvn4bXpyQlVzkoctPOnxrsffaTJIBfCBtH2swbd+vDCu5df/tYbu4ya25BDut4fU/99j1/hFUkW6xM92PEF0tlquvzBQu/mUETVH83Bx/ZgIJ3Uafpv3qFbgWgHpQvVpWapgfcDP1caDFTgsZgigL2bo+QElJlgOwnGGgQ52+/1dYbKRVLl2KoqpZKJwOLke3WlaikFfn2kf/Spgjge+b3fjOrXOg/ce1e/gR/fJy+B6fh6vbWkg4Dv3hjb7LjxrisT0IQfIC71b75//dprC22SY9AY408ak90fiH+Ojb0tCIg+4F+/1kHkz9X9GzLul24d+lyzq1/Cv7CL/vXViR965VF8GOIHpf4FKWmUZsuo6s0EZdERxztTJw5BB+xyLhRWmeYR88tH4XFeJWMzA+CqKX8BhhXGuMXq1KkpY4OW6OmlFekNTk6rR8uoOuil4aChShhmQ4qW5oxBJK0yOJuDkZB0mrRhrA/x8wLNK1cuiBpySKpgfQk1hARhVzKCgQtXK/AjB/00jerSjIruM53AWcK/r5rV558G+3DuAP9GsVGEnudWWnYOry4igJVwmv5gugQGsaVdwIa3dclll6uY/Ziz+42Xv/OyevsOQaDUwXBCb256Fx69oGUnBwPbrTvohsTENJzB4pBvH0+WStW8X+QPZn+Zi+/hOnfp4vhQ6xB5YtgXqCBwszE9VaxGL3JovsAeQeGGOGEuaQCEDnxYfZDCP48DgE4qgmWDwc3nz3p9/YP5YpF+Nhv4s8L/olQEs/ePlh6JBNLcjKUfv1H0T84D90or8LMcn6//tEDguzdaNiGIxNgYvY8r+vr1d98e6xD464zp4tdOPsU/9Ntig7l27TUT/iz4N2yrH2bwTa+7TMu6S535p9mfRN435x3xA/Qv2u0D+5vp6c5J7YuPzzGtYhYYYvcLB14FKMSUkYn4H/n7rGZx1AhnYpgnNIvmi8sTj0y8VD3F7ud89BjuJwycQjdwZVJDIFqBsB+sUjG9pj4TtRuRJBiHN5rip0FMtcFRZ2ZxXheyoqkV6M9kB06yGmJCEmwMJAjMvo/ePcsh+EbWyGapIUT/9AMO5RsRKlhfGr9/c2fP3vO9OHjHyDi6M7qPaKw+wc7N928qwlfHAEd3vnrzfd6OPjIivxnctj9EHtdDH364LX/4W0PcrU/X7O4uuN93vkOX6k2xQAX6iv6p0nFm4C/xd6tpXrsGO4f3GVQ0grCCwNiRSLFSbA67uF/wojbG1IYwIcztqhixwP4DmXxp6S3D/ywSaPp+8vvIQn9LW0zhn8f0AHUNrBBvg1t/QgGPqOed7qsWq/LjGRoH32qW/9V54Xyk+kY5AgbCbyKf/MLlvtzxuee+rzACfhoGGKNfmBBuSxfeVCTv7RkfAdgtLDHXr7/y7o9Z/FAo1qoHUmTxkYN//WMxVQeDAP74px20+6Mu+dQEH5D3r1vHvoj1OSO2OY784+Zfggc/nPK3rOCvGhwj61/HUIqna8lQQgia4X2UBDF+WvVLGS8876udfkC/VQbUqTIZqvnF+ZPQ/5pVAjr1lGqpUpLql3onq/yxx2APrFanKsvCAtcrVTIMkjma7ISIiYlw7AKl7/O2OfLF+Ck5kLcnkRUQtXsuTURQAWGaBeEzzgJNno9DMXyo/XtPYE76fYcFOqUhrgkCP/rIXfdacDcy4oY+PrOMgAaTPgP4qTP6rMK5f1+PqKMPU/g9PpXrkVGE4neZUT3ra8LXIqN4kLP3INudnS6H/mkS+DoVwu/fjHk9zz9F9M/xv1g4aO5z1cZ6cchCOlpdKjaHLiIXxj7kkal1D+GbhaKyvDwf19Eaaq5OJT64aCOgJn+CgpcunTh3NTbW0eFV/8E9IoJoBnjCMEAth5zriM30pKNLU5r84T+vTAo0CyBS8y/BMQjigcZVX3PiC259vv25526JB7xVG/AWd6sPivm4dPV6FYcKRt98B34/4N8YWWKk9L3uFMDvXGPxg1d+SPWr0c8AINq9YyCBN9pa2hpN9sGwlj+M+cWIHxb947EIe91bn4y9afGX684iiR80+NtK1S+Qz08b2CjxSqCPrM+0sI3XeKjaN8Lkj/t8QuNI0iBlg+hbmedLyqyhrfIzygxs9DH80eSPFjZa1GrIC+tz9GJlfhIQECQwwJ+fK3HaniTGQN5Q56eofxkPDmpXTCY1/hivTjJJWUwE1bfqoUNnvufPprO/dEHgCMsdBG7bH7H4YZe7crkf9snDdg18J+eWgKjwbEfhXBfj3Kh9P5ZgdmH44lkLAnH/rKjVuliXr+kjGcEjDIShUQDtdmfPo10jFW7+fcehgC+//N3X37g5s+mdefry1qEGQ/7a3USQS18XAOpe4IW3RmELjC6VppIZTvxT5z2mf7wZJHV6uHXo9HCnd8bn7ScWOBbrTCemiuXkB5r+uc1/6t6Nwx2x/pYe1L+KAM4sEP6d0KlYhIFc/hL+ne33eQdp4y/9LJcf4C4GyPSBTICs/wICE/lEX/KLsPLys5z7770bLLAe5z6eD8aodCUoVBAYGw5HFcV7u24sTpfBCP+79lpLG2sfw50iQcc0/pnoP3R6xzrw+7UOav91yqK4VpN7P2hZX6j7l02l05J6xd6/iAy+ydxbwhI/opJ5z9a/Xi+WBPkBF2FM1UZUDUx73IKUeh+J+NF8I0yl0QysUBKBl+QODPPSYO+pqvrNE74EX8/w1TE8I5o/Rp+aow/yq/zhBZGKo1QHnypaakipWj4lA3LoBa4Vkhg5TiYjEpvP2AyQpqAaLoaDtJsdq4P9NMCSy+WCmXRqnLbHnWFB+FBDg3YGAgKbvhdJMwQaIUTgjiFvu8vCP8MFRwy+WLBn3h0BCxRUujXb+3geODr672+SWWd7BK+ncY5oHhp7pNsyBHJRPCq7gfmPMWtcgCOUxq9jGDjRQcNb14h167ana+SNbwnmfUe/KSB8/eU3a5teH8QP3f1rdyheuygfph3Y/gPzDG2M3jrzi6seBWj54lI5ohHwvQ9sHLw4342Bp+5OfKf1izO643QAzbi+ECXlG1GY3jlx4MBCrL+xc8w7Q/jXu7nALUCCQDMMLLaYcwcWfL6etCpE8L90yimBo5KCyr5Z3vpLF4l8VOfe9/X9Rlifb39IDfHeEvNuYYaW7iH177xsjE6oOvjdG/WWmHeYAr57o6Olkdkfr7zkj7UXf+CHW4eefWtroe6fpX4I+6PJD7PxVxe/hH9+e+5N1p1LWqMpf8n6V4z0EP3rH0pnghFyOcvqNW6ohWkpUYYWdZAOQlPAiDYl6x/ZW7j2Be4VT1WLONVT6heEDIbCqXLZFBSEvaiH8xz+QuZBABwiEvIEyqdMK3BiujjFgnBUl8GU4RXiXXKkA9PeOaB9iKrgSAiyD40v09pMvz9H++PSuXlHDdG7k8wS9UNnjoXVX541G6IbZF2686exzqCdjX1OcWwNwgk100hmsE5bnc/X3b/vGd05/36XzOlJtUv37/w50zz+XDCfKMIpsCh8tcv+zQN+lMOqo1gVAmKxibvi3wt41r3qZXbf0PAn4Iebr3/nW//PmMdz9igthDNlLyCOjgOEDQ3OYw0NdidQ/SS6/MGox/tgKlGt5o9K6y8Im7MWRi6GLg4cRGr+cItXUoIVCfQuPDiUCitelgxdDF8EYm5gLPjiyQMPKjox1tbYEvMx/nlmNheuCvzp8lcWBqMD+GBspiObYPhj/YNHfZnsSds8L5NvJAInaOE56SB9v+H0T84D9ymyfCeszxwNXaYTCAjsTwECXce4ABX9axT61xOTVzD8zyl+afKjo6OFsu/b2tqc5p/MvrH2cZqTrxT2cfWb05HPiA0A/Uty+avRz6RelaX6xX+N3t7O7mA4w/O0YdaO/bTIl9Yg0YvxIB34X0ChTwGJL8zb8L+Cq1cFfor+qQv1RucU/apWbQhUcHmMROFVDsdalfkRqYVZlK7OOYJwdcp4Yng4JF4oUB1MijBtY49Qm9KMyUHE4ehWWv2Zo3Xq6gtJD8w/bsXE6IwsbgVufe0pBIeRGtJlE6KuLqGCIxpMBAusM2IhoM0CGQINmJ3f59btD7Ybgf7J5zDV7ujO87IAvUtAmUpkdSxYnHVgUNG/F180KTQ6kOYhqoO76lBun+M8+sa3BPyI+C2//PK6eudPXn7zxwpgBk7JKiSrzadx0On9tev3HZzUSIjFIb2e2IHQUqkYJTWEV4Hg7QMJxL908mBr6+BQY4vXx98u6ttGUc+FTgpFynanDw8dHBoicjjGUYJegj/gnyGAG5r5nZBGoLrvwIL61OGporRu+AjjYx2PU/Ax/ZYQ6zNlPivw+42yPt/+3H/PfV8xxmgHB2+NiFL8GvRjCPQ1ZprffMft/pNRuLEOwr/hYWfjm730w6AfJ5+2meTnHof9Cf450q9u/vG2c8psDsngLw1+JBj/9OAH9eFQ/fqp+vV1dKdBnvwZCRPg9iFjCJfSfrLA0DrziKpAA7ClFMjeHM3zy1HxWpxeX1+ZLs0Vi8A9ZoMghFB9SR7h/1WmqRdnVkdBgVJN51XtAQgsrQsELleqJJmIXLKKVAXQ2gijYCgQQW6+loIxHSyjz2HeFQJVJ8O+wEwmO//ElcuXz8AWKK5A0wzcarjw1HyqZpzRdaCgYU5jjoa+EdeNWXMhd4Ka3aYRaI/I7X334dGv3gT963IOhosVBH6VcM4uyQkcbyr65zwfD8MHgz/PR7J9xOAfNwJfFCnEuZAvfV8yOLv7DeF8RgJWAPj663/zt5u9vWefOLMl+X8NVgtQE0HT+9PMT88FtzsfQLbAH3p6z6ZD1VI1Gr7EACgIqGng/KXj1AJnFshFl3dzc2Zzkxrv6ncL4SIShPsV+Ztx8G/zLBNADXvGDYjgA+9wOF+tls1/03Je2//yvAkkL0HQ+Xxfs9kBgm+s5O/9RnpfbnHuv8dljJa3WyFgzKl9vaYaVgcZCdE3XdiH/W83xtj6p35asfWP8dMt/crajw7JvXclX1nih938E/FDZz5T6B/Bn6z7dc29ob87pX7IRhq5+m1N0aZJHp9A2aiFBB6vII0V7UBO/0vSAssCRf1htpebf6B6xTkCrYmJyUqxWFFnjvEPV+pxJoEimpBtGiMkCFGg/p4Mz0WPqdcEnaxW9MjcS5UpgUAOilldxdcludHqMiwjwiCqfqKAVMJDyCZAhB+GRgJzmUyq9sMneDZEbIHsh8HvQ4cI0nLiAAAgAElEQVTaLx9N1brZFtjVJe1A5nxdpkR0yJ6DgnzBYGPPBHehDt6+HQLe9ow+y9Wv9YpUWN+8KVWx+pSzvJ8dRz0yy2RxVv8xRvQvsr+8+JApgk0TUBDvViTQunN2t6Kx7+WXXzVA+Pq3fjTsmen/5mWTONGuzc4NQvfanfsxFKxBsMEBPnO2tpqunNj09A7Gy6Von5+yn/UyJLkOXrw0PnRaFcIU5hSD+QIox8env5+8NJ3Q28sVjofxjwkgi76cCs2F8LkjC77eoeYq6F+5bDFA5zRzK7CZzH+FBPcA880FhYXx3xr6J+d+ykgwx4V+dUAYsy6YAhoInPEOhn50HUnRsgfz+it/TeJHpyV+4F+r32vgb8yqfZH7IoNvpvxVuDnk1n4l94Wcz2kdXmVpv2z9a3asL8b6l+/2eWAMaDtNg2/ZtOwbBxEEhspkBVvs0PsLMd+i2d/AWiFB/I+7f8z2pqVzp1hbsaqg8IXJ5fX1xcpzc3NzqiyukvMlSuCnfq8l4wR7hQI1EwtrhcKqGaZDYoJilPoFJxaLCrKfcSwxFK+F7Gm9fYlyGUJ+tunosT3Kzw/yLqdcMJcLYntSMDV/9K0r4grUOTEGAptOhbprqhAmPVjTIE39RixA6TKU0MFBfWY1WnWxN+5Ztx9aUzxXQXx+782H0c0TOuegoPrzKBaoR/IcoLM/q7mPb/NXsf2RFcX6IjthBPoM5XOIX/0NBbO73yDeZzgg3fiT19/o9no8zz/VxN6/BgvRnOZffb9PX0ILUY81OffhnLly1eNZ6I4XS9U+qYM/4Bj8997zc2/wZG6wVX0bdMZmfD7sp+g1CKhucclrjofgz9M7owvgE9L0406gqocV/fPEavlitR718nkxQsvoG+Xd8yo4QsHmPlS/vx3dP9d54L67yBPjczDvliaYmFaBY6IHe3U17O2v9SUyCM2/Dgx85+0FSnEebh3ubNEfbCkfwL8Os/SNW39kfba1Dz35a/b9mrlfs+8tHLbm3mRBvQ49jbL6oeiff4wGf1uGsjkOVs5lNXNKcwQ+y6oEKX4OpseKoiQNf7D6Qd4VEj+o0DX4B/Fi3dyeUEC4UiqqMhjOAhkUXqX54WRybQ16MmMhtQKb2VGoChGAqjFGL5IaUibj4BpII62Xo2B/ikigAZEgbyihxAbJ78faTEUEEWmDPqDiueks1BBni/rWlujBBIFbZ049Vqudfp9jYujbX7BObgiyjNQj36x9pR8R2eLhPef8nhsPn7dLYboN/mfWzulX1EjlfFoNgvpS/ylNTqtGOcggUv3i7UMTA1F/uva5l61/lvL78vJ3Xv7ud771o9d6excevdCwJU0/UwIL/Ln7feaWYYG6IG7QH49z4a2/8MwMKxJYqiYJ9z74gCNQmQXiYn6clgj3jDH89WrQm6lHPw1/3s2Fs+IBdBQQuj4w5ovVEtUltJrLDk/ga8nBz0v9G83zwo8E7f8oJBK/6d6XW50HnFaghYL7He7hGf7HdJCvfQjNT/z1jXcVCXznxuaCiB+tjfRysTr8455tC8hfh4l9toJfbOufln5rED907IHM7Yr0K6FXbvoXZfFjKc7a78xwFhNjOV6yyy8QRgCCKhsRNKVKag6iJ0UZ6c+0vhfBVyTbQrUl4be6tDhdXSG8QwjJCytzFXfi308AkdLKy+uUBM6PRuhfgNJPwQHj3OqLsiA8tbToqCFlmh1GWiA5ECEJ075hzsqCFzBCmog4Y4IhMgNhmVOIFhrncmEYYtLBXO0k56VqCGxoEFs0hwXOq0IYOTHgX8YuTFjCxFAwxgWA+72DanVn5xaQZ/p95xnwzut7zW34/EwJ7ODvrMUHHcQdsfYxMX516Y/r0jBOa5+kAKZcGwff9x56zEDhG9L3E/RbJgh8/eU3VfXrO3il4ZBGOgftnBrYuqvBAKCgY4MbHwUAt7bOPKFYYH8qWilFkyEmgR+8955Iw1ILHxxSCDjYShC439HgR7tdYwstZw8cOMwjH7oFCAJ4oN/na/RXSzz5UTYqIc+/SekrM3BEAxH310yqYuK3SPzYc+6/9+5Gr+kB6sTAjz9OPYxbMzOt/nz8r3/+7rXX+jsQeg/4k+o35u13d/50+dvGsc89PXtzrzj1CsrvYLdJPdXaLw9+SOafQio998b5FfzPWqZ957UZ/Ofw9ZzGwAgi/8L+HM/PSrSoZC+HgrJFzs8TwLD/BTj+YJXmOspM/orTrz4yCcybWJ9eVGXvdGXuOZ1wJQfKyNSUbgLK8iN1iex7VVnHC8QDoYusUimMPzHV1iUtCL9aYTk578yGgAsGQknOJYxwToxiryEJTMVQS4hSA4M5hXuK/6FLgC85WztJCzSbBAIbTCWsILDhwhMp9Zf7yxEdkmBwggFBnz0sUN8vVxBmR236d36vzHGr23x2niWrc/0nIaSbNQJHl8475Yec+V+DgSO6gpfJPozCyRdm17r1OEgfRLfecArfZV3+vv7db/xtf2/v2cf15IdQOlPLOs4/V8+v3WGKe44AIQThC+8teHoPhKvFaj4O/kcl8AemITh/8WL65Phw5/DgcONYTIReAT73wYR7/8LCgw8eUOzv4DmH+h0HCB6JzXhb+6ra9ay7f3VdQLE/UwpCM08T9BUShd9W+sfngXvvatGwth8LjNk3rXf0fayIzHgHC/m//fFYf0sbmf909SvcT3x/SLsa0/DHOy97eEkIfQzBX6vgX7cOPkjRwl9t/QNs+d2DH8229svm9mpxaSnA9G9sMJulWbFMJkuXNDhBsyDio9EjICFey4udlyQ7xJMKoqLHyuxbLs5VSPxYnFufXJzGrO8Lk5Mrzz1XWVRnfXKC8WtFASBJbCSCCAKuKQYXSMTpJSn3SiJVWSiBanKqitkQfokX1p+bEk8M5GDCT0RR0871AFNU8sRESLMOsYGHEmKwMQQASEMu2KKZQVKWhAWanJgGmZE71PS9xxUE3vylAw1dWg/Bb2fKrA6ZLAWELDC/P3o7/cMFfj+jq5/RnT/T946OjlIjsIs53oj1GWy1RT6zLoc1Lo+Ymxa6bcMO/aE4pR2Mq3unHgx333jZQOC3WAD57stv/lh9RwycIvpnQ56wQSlu9W/BvR+40K6dUqItldg67Vcu7ngWBsLl6lQ0QghIpbAwQB6W26gNDbe29rR1jI0pssFaB/3uddAP7O/s2QePHDh3WFugxf6i6N+D3pnOYL6I2FMt/jJZ0AMDUe0dEw9Ms9l5+RuS+vxZDtSQmGAfrm41JEeIxrBmvyvvzPQO5qf6Wvs7ejqHO9ss65+ZemP214FfqH4be8zOD5N5b5zPuvytpZyNb7mgdP9c0q8ufu3qt1paSvQA/Tze1jSZnrPpTC6bSedEK8ixikxzZREaqyB3ncK+kJDLSCDOuVfRKFn/FNdjfFqemzP2vUce+XrpJVJBpouL9P7ENGrgKZSwOIVV2qGUxFQdlmdytCoUkcKqA4Hyhz5lwgJfQlIWxcissoUQlLEQwGwI6SG8SDjEjm2dmU+YbhISUANTXlaq9kOugxkCG/RwCIThQ1unjqq/5HFSQ3StKMWiKUftSrRrxIV+IxA/TBb+LUOez1NMoLs6Vvedt7CRnc32Dk7D7aTk1Z+e7xlx3SE8Tm7QNSb7uvSD8uU4QO/cdGNg127lW9993VFA/uTlN/7a4+s9cgyxfxaxMxSu3YCeYXsGCK2+oH664Y/WPYfaL1/0eDa7I9FSMf9B6OJFVxNQrk4eH27s7GlrbG3sUN9JMa8jCLMm3N/fcvbsEVX8HubQ0w1ehk4s8MCDiv5lsZ8zWpaxTWPVkm8aCX3h6KtmGSRFAlYi/hsW+/fpzj33fWVMiyC3L4H3UkBzfJ5+f7mabFWw1k8vQt0/I3yQ6iHSh9X6M3NvlIg7NOyKfamZ6pe0XwN/AXb+9RUSbu23rK1/0WyMCgWy/ik8SGfTWb1YzU+jcLSB3M/pz7QIE6GjnMIXCSR5vzkDIFZoFucWtfax8lxp8RFzlivTBIYTi5VJjY+iBEsNrMrptUQf1ifF2dWH9cFJ9gauSSeQReZT1SUtCE9SWCDJIcIjUQpjL0kyQLEPtEEOABhmAAwKnQX5g9UHaVlBIs3pdCp19JgLAk1cICaErzxWq9U4MrqLpuEMU9qv7rXOSBflQu3UVb+3PYKE+zxtdIdMzwKB2uAipW696tKlW4TIc/3ICfCyUc18AQ6mWxA4YvHFPSzwZT34+yff+j8be73wvhwysKcB0KCdsDq5S99NN+tQ0HqufKRA4Jkrl3oVBDYvlcqYdXtPKmE9KnyRgrAGhw60tbW19DS2tXV0jBGxQH8J31zqW+rBIw8eOHBO0b+D5845++DOkffFO9MWqRanKL6DEzw0ADZHo3oWhHlftBmwR0mo8YLCwOS/+22nf3LuuVuWZ/q4E3iLs6cI5uEQTQI9nYViNdcxw+LHfra/Nmw8Et+f1L4O/wP7G6LQPwk+sGKvdOaz3vdL1hfX1FtUBn+LpVKkw8OZ9zVCvxxRP5SJiull0sEQrQEOYxFwKBQgczS/doACWGgHUpwIIPQPvKQ1slFSv/R2DwBfiTHrJyUWhCdKc6QE65kOwjm08frWSFyORBD9nOTlwmu0QilKjhhmms4n+lpVsmTkVWjpEuK5kijPaWAP+BeidOigeKQhAWcyfnQ81deIL5uyU1MiCOvtcboQptmQC8fma901cQUqBNzWkNAltSIUEht7BG/AGd8f3dmLcfbVPocq39E9zxnFOMj7htrN6mafLne7RqgZiMdHKJSQ7vuI4g62ZwXpNPJpCNTI12XudjBP6KKhhAY+d7/FEyDf/ZM30r0+38G39OAvI1fTPiWwAJphee3uUlcG5eRxqzyWg8UhB3p7ezKr1aWpAHTg9wz/u2R2iFzaOHxguFVxBjgnqJZiMfFBdQ6g93fg8LmDJw6q35b2ew4rf9Mc+4cen44x4mY5V76yM0dXvmSBwXuJRPJ3gf7xuf+euztiXt/+fUABu/3udJ8Z33CyVE77PG7612J6fy0a/kD9LOPfsHrT3j+t/aZqWU3/nI1vOvQqvnffmwy+LSVaSfzo7cxmwmGIv7RSQxXBaPj5sxkFgMFwLhcO5/wRihpgT6Gqg5MRP5aAAJ8KJNSurpanyqeqZr3RS5WVCYV5ulQlRJym3t0L00IB12lSThCQEG4NQ21JxQGhLVPCDC0VZplZBuR41I6chusGaylN33BJkEBIM1BUAKKggHAtgtHyAnV/mByBGb1HGD80MCKsqv9xGo9TLFC3Agn9NAt8Kl1jQVhjggOAFP9ZN6fBCGhWIcnZWwGPsjZ8XjQRg3c7548+veN2DVIjcPMPblp+F6DXLCMfOaE1E5TH8e5HH5LdhcQORmt+wMCZIJsL9KxHDCo6pwup+W986+XvfPf1b/xtrNdz9uiZQ1sOVLU7N2zkM6WtwT0ieYYGmnsYBA0ltGjgmWPnPZ6z44FiqRx/TOifxQEJBS+dOHH84OED6rQ+2NMK4HvwCN47oO47d/jwicPAvoNkgZYG4JGYr38wWVziIc2yZL/oUVEpfKkGzmsy0Sw26OZE4Lda/NhzsDwuhg6g7xYAeCfH5/Nky0v50x70JWKm+DXKR5twvx7XxnOZe5Pmn/b+ifXZ0X5hhCP2l+TBj+Zm08PlPCpov9VMrFeqX6p5w1Q7h4I5eKCx7i0d9KdxA9EC5IjhPFWSQsgJiDEQ9sAg3FS96CkBPIgfuKr8sQOAjyyvrKyvr6yvVEoMky88JzowKRhIQQBkxbGlKQn2Bxpn1msySZRO4DGOS61WtLlw3RaE6YlwEmKFnKqG1Z+Tgrwi6m9FSGw4nM5xN5C2JcEzmU4rGpjJ5dSPEp4Q1mqINsSwIHz5idTp7hpK0G0aDRFbyojM+T6rgIlH0gQHyaZ886sG/9zgJ6C28+SjAzuunBgCwdGdp+fWp1fruaNCy5sm3k93+RwtxH2bDtwuevL3QyvJtUuoH30Jbthz7uiykN6An9wzSxD4o5rH1zt/pUm6f7qctUpdvm1K3PY6ZqjRTephQ/wcEHU4Iv45Lj9x1TOzEERMS8G0AA0PJC5I0X/HTxw8fPDg4cMH+O3gweFzBw8q6nfi+IkT4xuy+YijT896vW3+skk9jRoNhE2o+rsnz+0/WYLJbcDm337xY895QMelfqbjmQkulQodM8L/bN9LGwkfjbr3R7NyzsYjF/0z1j808pn9hZ2xX1p4RDq9aeSWZeMbix8zrSnYQ9I09ZZTrC9MKy8VIULPDwQpHFL35sgeHWYTDOsJaNKBYkn+abRcLU7xhqOJipS5i9OvWgj4yAsTE6/+ZGWl8tyigsL15ZJYAbUTUAFpgEpekkAi6lYgCV03EqesaR2ThbRBFkOqVTMbsr5UNqGqHKu1FufM6Ij6eMUCgwTY9DURhoPYQtNWXzntTFLYB0cgfo7UeDxOtscdYle01MKH2r/32ODgQU6YYiLEv8jjh/CVmy6JgiY/br/xd3TnsenllbWHNQnUosfo6Jpi0ROTpcecjx/ldOdZwzN1/asrYVt60aIIUk8f0kH+D9EedwE4d3HbZQNdl00E6zihdWN7dje46emNPXrGxF7pXxrvHNRz+noWy7NKXrlTMK/d4n7u5221X/57Vbi0+qNLFJXFlbA5OgtVln+oGvfSxsGD4+B8eDsI9sd7gOXy3JExn28wrvC0TG1m0T+0BZAZIEpfWv/GS9/YA9gX7/tdo3987idj9Cemf3WoOeMZDleXQp0xO/Ggo5G1D6l8O2XhkYl8FvFD+J8z90vGDgAgbfyISOR9s2vstyyDb7D++Tj1r8bdL05IwdojDH0AAgGoIRigaQRYZBHdA/RT8BRtAgmgCqZpNaSXiselRCboyToAlLNeqSxPLsMcyE1AqltXMf6WDCDeZY3q1kABKM5MkFaAFNb6ZMG6+KKn4ImxVidVpyRiBi8I9ZhzquPIzcdkSCgQ5tEQv1/GQ/CV59D/C2LdsfqSg+lsVgFhbZy2x2kW2OCkJGxhgeZR9bcvYYHbjCSAP45lgVt51uzKJOufYXDnrUtzFM2jlW2LTzxsA+Xo6DcXZZnl8vQ3zUOUbmojnCmEmcgR6NlVOO38oJm3h4QGggWaR+swzvlllb5d+vGREbMjnd+FthPrnYn9kCc/7DafA3ByrVmeJojmWQYoNfZZjK+dGoEGB53Hmi5cXPBsHo7Q+riLlghi4SBCoFMbxzc2Bi5ubAD1jtOburh0Qs+/0eTHgi82VJjS1hc7qU0oYFSDoaS+5DUGJgrJvt9a6/PHHFJDPjEE1p1eT2tfaco/5htzal8pfnXp606819Y/Tf+6tfclkxPxI2ysf31a/BAA5H9dSv0LtpAlqn+QnMBBdodgzAOWl2yOcgBzaTHC+KlfxoZADlagvUqhSFJ9LhIqCmtrGNctFucYjiYrWHa0vLjoTMNZR3cBX1gsYtdRmUUQWnhJq8+Ta0CsCEIWCLtQCdNyddKb15zMQW4FOrMhqqI+RStbtRying43Icw16AHSkLDB8Az3C0gGBgOmtU+qBgYJzI4PPPoWtQL1Ak1+Ywg8c0yxwNO5WdqbqYrgbTuYT2GgVKhYCY7g+odvc3YefnxxQnb2Fv0OVu48XV6fUHerX8uTE+vVb3KXUMNrl2F6UvMCmAzozToPcuiB5L48pEnghzL30aXL3y6jfQgplHvsGw7v09AIeI/FZg4/1WS6f1L3Njhg1iAAZjE4AbL2dl0LO/c7T2g3wNfQbr2ceULTlY1Nz+aBvmKpmghftMSQi3pDOnigAsGBjRP8i1Zdjm8wEpIAcnBj49y5A/0z3oyqfnX5W45q1leWG05sSJQBUDPARLzwu0j/5Nx/71f6Y58VAX0znsFyqdztoQqYN5336NLXDvxzFn44sQdm44d2PvuN85nmfq11l2WRfsHSlhI9M2z9q+F7HyvEwzT0QZAQDuvl6VifkeFlIOkctQR5KoQOEJDCpZMUWwBEmioWpb33yEplfXJlet0RgV1neY57gy/MVbkEXsuvShACsT9VtK5FMNYWQClMQg5m3DDyuyocUFyBU1NFOylrulquTk2hq7jGhTBpwoBAZGXhZ0M8xOjnFx8geX8UrKsKX9X/OVUZpxQGqnI4Ne5enWTiAht4PO7g8OBpVkO2wYPscPrR0Wclm35v9eumf6M7J0H/lpeBdArn5k4yzu3sHJ0W9ke/JidXyud3diQLfw/OWce5h2bh9C5jGwNp9A1bkLgRKCWwQ/XsWleTP7pPc0V5EPC+6ZuZOcor3zTbM2+6Em53mGCDfkq78zwNmLo+NmWx4F27fsjBQX5o68wz5zyes7lCcWmKW4HvGRzkEGjakLlxArXwuN6GKf2/gzoA+sDZGQ95X6ZY/GDcY8rXzPl/ZPprJvoXNd5nSr8K/K54X25xaDbkM0NgrzcztVQeahlrEfoH24sFf4J/xvhnYg8c65+xPnPoKXf/pPmndXwRP5ZK5ZSX5n57utMAPom+SnOV66fdSRyDIJKKAgaUjoBGPwcC4lY4QNvlkvFkgUWQMsbgSmJRXq5UKvvTP5z1uWnBSWKAGqviSZpYVpCXJAsLhntDATIF0mBIgYZFCgKAuhWIxOiKQOAEwgKrZfpvTC8JXYViEiKIzQ9TUAKq4CCH55uvlGafEaFDc4ScJFaj8ThOynJYICEgPDFPjA8O3iQ1RPLnHX1DcpjrBt/2np3ni+uEcYSAhHPFk2gkfnMO7yxbADgxuTJ1nnd+MLpZ7T+Ndy4FhA6P+mrmZ5NA8sQwqtFHC9p1OVWx0D55SD/HAUewXq8v9uSp9kOI/WtoMuimgU2zNQsRHZB0fjlQ5/xqd9qCDnNsd38G9c9xAbuTYqlCqVLtCwkFvKSuLokYIstAuB2ImndjYJxl34N8efhIv68zHMVMEo7EbmgAzNMVT47y3t+8TAAnqPz9jd559PkcKyPhUx9FAsdCS6XkcH9LW1td3N/e4vfHpvwF/zM7PzT9ozyUuMl8zhv8i9LOo6VSNRSTzPsc3M2Ef1m4/sI8/JGD9xlRASGCOqwADvIEMKZBQrwSjkbgQv5QADpFEgwwz9rKXImhbb1iewDr8a+iq9ZlmobjFiAAMBKC6yVANmbSL5IAQMU0SRcmOkeeQC0I86fFFnU9HjfxEnbMPUOVC4shNE1SUEUwITb5F0nHCXNYIP0OZkKK4ircS2UhpSNINhdMZ2qnv/mE3QqUrECxBV5+dHxw6PT7EDlkBdGzDz9PwPYsDWzcrI+/r2/+nT/6tQmmf68u0wHQrUefP7+2brE/hkH1yMT0L4n+jWhxo8vROWzkYzlkBDs/HPHDxkBnBYiMNncZ7sdvGhgFFEecvqBBQGjb3s2ZA4+7xA+NbQbUHDZXB3bmKYKU+mNcH6vZYbsDivJi8kqHGs68pVjgQhDTG8iJuaTA79J7gn5SA/MbLTsi2je+gfG3S1A/DnR4fYMJDL7VN//y1k3Jf+GqV9fAfX3x3+Hq1zn3G2P0ZziqjmhNVJbCPbE2M/DLOTHDrswXZ/BDT35I8EHG1n4J/pqlTxEV+NPel8Qw5x501oIhMgZD8CUJ2C8oGsxksTMjyFmoZIwOgSjmsBUJfmLs1cBYXAi7kZLkhGYGCAo4B/13YqVSESSUM7Gyvry+rL6JJx6ZXDSDbOsl8h2wb0WhWgRJCEn+IgI0DpyktMEIh/1FktwGFCaYN63AMlqBWhB+YWUJpT4JwuwKBHRCsA5FhAiSghMOCvqBOWdoJCQDcwxtTYIjBhNyqQEFgRf06iSNfuKMbj91dGjodO0wtr2Nuv0tgMBRs5y33uvMzx1YWp9g8jdJBJCp3uTkdAWiiIbEZVZCcDW92+U6s+4Lc4P42ix5Xxj5nC6gCwlffNGwQM32+FVGpOyVe5zy2BBARf8aYzOegcsifhhoc0DOubbBzsXhjB3GPrfASedm3ctf+OCqZ/PBlPrpGz0q7T9Cwku8EYl3YdJSzBN66g0m6A1Uv17PWCbP40hlwxOI92nmwJs/eOKDAFDm3/oCX9I/Offfe3fb58ACZ7rLpSl/W0ube9UvJ/5p9LOrXzT/sjkyv5C11/a+JPpM9SsQKAt/MxySoapfDLoxrgH5yPoS5NhnfOtjCI5QgBpkGS5/cxmeosBnCwT9kUA4EKIVc+i4UUcOo3DTE2R5/lrFMUFPrC/ie319fX1xcbpSqqxMvvACQBFR+Qqq8qtU2YKpAedCWG8EF2OooCrhEA+DsBpM7by4MUWTf2ZV1JCiKif503FY4DMohAGSib41zspScM1JWREa7wuSEZCoLangOWwOxpefAaummjiYS3UPHNWtQDFGG1vM1taZZ+YH1T/H4VHXfkr3Oe+6duzMT1cmJiYNzRPGt8wYKIgndTGD4HqFE66M38UGvj2Hgq405au71uehhyxboG720dFcz4ggzj0EfyPv39zs9x3mwV8Ls3SpqsFN450FWTb+0X2m9ceUT57kPJdfrEH/MiCqX2Cr6fLjm57N4UC1VIx+QBDIzb+LFzcYAWUnsDbFnGAd5KCqfju6A9WqxJwKCrL7BZfNDIMi/wr5SzTnSVhMfkn/nFOXGP3pjs/jSU9Vpro7eN3RsIN+xvfSrfkfO/+M94W7f2x9JvHXdj4b9rdUKQa4+o0NpZEKxU0/hXLYdUQNP1SGhIM8GoY6kCLl1Xt+zIPwZjjqoEXCoWQ8FGBYMkssAYBzz1XgBlx2KODkohlbq1QWX538ydcr019bXKwUnWHgNVGBMcWGBmAoRAZm6CG0+xfAFy6IUFzg4TjdCYyuymTflL06qcymmFW2RpMrEHIwcJWCYSjYP8wKdzhHbUBsTs+RJyZLW0NoNDCdqj19lEISDAQKCFJYICAwlU0dfH6UGR/IHdXBNiPcb9pt9PxTi5MT3OpblvXBTAwAACAASURBVD6g3Jo05E/jobpd2Z2d5cnf/bQP11Gwtf3hQ26se7H+yONIgmHOaJp7Xa5SWDNBqYaZ/t3c9Hn7f3jh0CENZfWIZsDMqlttALTv0xBpgM16kF/GDYL2BzIENly+BFtgsrpUzIfmL10yYvAlvR14AzXwhmw/p/j7Aw96vZ0Qf+nbQzPAsgOAnABYzkv2fTRBC9ETsvTjd9X7covzwH13uerg2Keqij0twaVK/nRLI++Ia3Vcfy74M2O/rH2AyHAwS0Qy79n7olsY5egUasRSJToI+PPMdKaC4QxtOkf4aYZCoSj/Kpc22y9hDSF8pPcpIwt8iYgiApcpaZ4xF25lxd7yvMNSAeAcuaFVGby4vv4quvfTemBjubLItHBiea44x/jHlSqpu4hDVSAH60uSrCu86w0OlmRBQSHNhNCEG82NrLElZlUnEcIV+JxrdRKjq7NzCRCIxGhM8QXDAamAaQwO7c80AaCCPT+MMFnKhVDXudT4Nx/VYYEcE+MsEYYaMtCdSp988qv1JPDZOvRzZn/p1ujOwLGViUmNeJMa/CaX9Zsmgup8neGPIXD2VgCoZQyy/tlYZ/wv7gpYHvtoV0PgiNMQdADPYn+4A96XTe/Mk89I989AW4MBQnM0WpleoL4hCKZL4HYXsDVowHO9jnnIgKL1mc9c3tj0LBwMRpeWon7WQC6JCmwc0SIFn8DluSOx3hg2/prQg6jte3YG4KLNYv4j33O+Gd9c8S+7f3vO/ffc/ZX+O0W9W+rGPs9woFQMDLZ1ivRhyl+98E2cz3rslzKbyd0bMfwvoVP/tPqLNPml0lI4RnO/LUM5SrTKUCp8jnOv1AsBTXPaFMLbkMALqSBWQJHhFiEwMRKmWRD4AVFQUnQzhGBVSXAeloQdTCqutzitDljfhDqLlT/WReq0AkqsC3bECs5xCUQKmN8AqkagB8NqQ3QQPcE4Eg6cuPw1hkBOS41GxRhd0a3A9RI2EXNaYN5AINYHw8ATwNdEf3lidszgEkkSGQV76m83m4MnGhfZVDZYO/kLIYGyN4QbgbhxqOG5x8e7s7lxKoRFBnl+D+jtc3ZGn54TrcMFgk5FLPRPVb+zfLoEBrtM0r0zACLUjfHPoJwBQqsP+KK0BVkR+Yf/8Obu7ohRfke0COI6XYKH2yOzN/v7Z46I90WASViaQ9zMbQNSLuZmyFuDAT/9nn4z75gVIQ5IOi/qfOSFKwO9nm9nE1gc8sElnobb0DRQ22DgA1T0b/zq2IxvOFReIu9zOS/fJoR9SEGQvecEgWgkJZo5AZ9sFX3JL7t/+x2oIZ+5Feid8XT0VZYCjT2tw3t7f90ceqBD/9ilgk4+x/5x6H1zwq1+SO5Bn5dT/4ZzxP6gAARZ+EAXjCzPCvoi6IVhHzo2IqVzbA/kdCxejYReYCiC9h8C5ykNKwK0YlcK+wyLjvwxMV1Sdd7k+vqKQsKKM7eGnUjFInnvj0XzgmNrsuU3QkQtRBZAdTNERuh4gbL3k6KN0BaQNUY/roTpP/HUqaIzG/LIS3MQiKNMMvFpCsgcDIkjkAOyYO/BBIwq8Un3wQ+FHG0FUChI89WYDMmka92PPeHsEBY5RCZEDm1dPjrYnc6NPz/qCB84z1rot58ODBZYXJ7Q3T7d8HP6foyFixr+6pgfL/mgvJcRA4Gofh+qQzuHBO69fvGf//JXv/rVr6+beFeH+zmyr7mlql9V3cycROxVuyCdwJSQO6eGde7XxM8Ivhog7fvN4/rD9GvI52losAik83l0r7FhC4Jwb2woUq1ONQfmL+oCmBuA0IEvbbAMfKRjxtOWiWJyCOUvjwlQu5y75nkpe/Oy9BwQqN7iX3pfbn/uv/fuFu9nPb5eT61cqmYUBZTAU5v81Rz4E+2Dh3LZ+1xwFv4Se6d/XtJ+m2s899vYjdgXfyjIxV+IjXAy7EGr03h/hvrmB+Bh8S9ppRH1MMw2ChnCsmXYT6uHUKcGkjKhFhWn9ZxGoOVKxdmFNDlpGnRzejcwE0A2N9M2uDWMAIcCCHbGFAgv+4UPsEC755IF1kpCJAMXdAlMe+XMgLATSTi5uEQkkKoaSc1XlbQikhySiq+fGKCCefJ8AwoVAwyGc8E0zcWlssSM1V95tjb+2P+mWaBtCyQIbPreY4O1dPb487oMNi3A/cmfOTs7j1aWHTHEdc0EcGV3xII/S++14HDEut7+8EONcXWdv4f2ufHPc//zVzi/fmdXR+0L4xtxYyC99Oz7N8f6Ywdo46/mZ4aa1YFcgwa5BgEpfqxJg5sBSQ1i8pwG57LBek8TP+t58nn0VUP7hQ+u9m4ujAf7VC2STwYuXpTydwDiL3sBD8P5N9OYTkzBgaWD7wUAy+z4E+mQoq5Y86UoGPT/4r91Ky8/1/N5uAJVHRzLFUvR7lbado7mX/dgd81knkr5G2TuFrZHPyj4gKR6cTEB/6qK/pH1z+PpHyQII98HgC5HC5Ay0HwBArL5TXEiygfwhzALTGUihaFmsulsKBTkcbgQp82DR4XicUKiNbTiymjFzT23uP7qC4+8sDL33D5e6PVSca54qjqlW3RSnIrAActLRGEUcb4IMUFVshY4IiYQIp9MYS1QkCp4Vd6wkIktMVKF670h01jIzhCYZ5KZhLeG0qJpXRLPtnD1D+WDUiX8sMCov5kUquGcKMS18ZNme5wVms84eOjMsYHT6m/oSZcefH6fW/V37Tz/+LQhew786fp3etfQv1m958jJADS+Fy1dMAQ6Ja7Gu4esVqCFg//l//6VPv/0yq7WgS0ANKCobij8G9v09g9cbjhkyk+GHuFmDfq0W0WxflI9jvHz9J3mI23G53q6BskfmHvb5c0AYkPT5Y3Nzc2FAwczZXTskkePXhQ/9IACv4PHD5yN+WbaerLN6v9Elb49SOxgqbdM9a6O/eM783rfL3eVEr9VG8///zgP3HfXfhD4iUQR30xvR7BYyqdaKfTUav052gfP/ZrUZ4Y/ST6Q/oUOPV2Kd9JKhBgy78Mkc+SgaGTCmADJ5aTsS1M9jGVqChjJH03BL/AYqkI4TMinyuNQPAn2hJhlP6XiB5CJRWlVqDPxeUkIoVMsLv5k2b0LablCW4GrepkH49+aCLxo8RFAIWqwECDnHnqA3AJMcjYCDcXR5JxAIGMg+aLJzz+l+GXxJ44gXK1OOb3ANSwNCZAnhgIRkJLlp5k/aimkM6ksbUzP5tRbOpVDRzCD+Tj1QKqbZ0PONDlJWSYjYevMUwODtdz8k8/vscS4HDDnnWqY79nZ/IOow/4c7MPlooY/m/N9jAis4Oqjj17ce9zwh/f++S/f/ZV1AIH04abqFTykSWN4X/q9MweeaThkwMpGs/Z2C+QaNLgZlNLP46cakDMf39TQbj1LXzqvYO633mvX99D79M6ZX4x6NhcWFnp6hlPYABjIjadyqe6Dw+Odbd6Yz+cbGwznixz6POUGwKi5ZvEjL610J/fqdzL35ROe+++5r/ETod2+d/pmehJLpb7TQxL43J2q1fS2c8p8JudLWHTYpME/Sqow8KcKwlJpKs3ab09K+n25nOI76WBYJt3gBvTjHp4EDtKAGOZBcrxFHBEJPDubo1lgZn6ojkMEgoVkiDa3FdagNByLCgWbW+LdwAoNp7+++NK6+mZ+AQH2JRY/sBK4fAysLJ9nARgUMILaN8InsEadQAyBBCIc7Ir0fTICJik6eo1iUlehHK9yaD73IbkOr+rZEIQFnqLUBcBtfo1SYmCuoZVxIfWFBXggOkh1PsyA8ESrvw31tw0ATOe4GZhOpeCMNmGBVkgC/Tq09dwT44MKQZ98mBHwlqs/3ObAndG1aUvztRqB65XtWfchfLNr4dkupwDWN3Hx0Yf1iLfn/MN/+Z+/qju/fmXXgJ68FJFAGfyNeR88+hxbnw0+tds1r+s+C/p0mSuoZT5Aszp+Il9YpXCDYXcaGoUIGmTUjzc58HvlXO+3v/0HZ8+eVTDY1tHZ0dLYRot8Yi2NLZ0pfzKvfh6Swa88pUGPCwRd+kadfUcO/Usk8oXfvdi/T3Xuv/eulk8CgfufXs9gvlIMDQ+y8yWrI59zet+5nyd/RfstyOhbs/lhFlUYU6wshWjfuSc2mA2GqOOPXWgKyLAUMkNp8OIj9IdoFo5twTACYig4neEeGeEkzZuQeIxkKd4KEqKiFKn1tMSX7dAEgc5Bx29urlSqrCw+B/grFk9p84HjUFmjUd8ANApsM1LwpOBQEcACXpu+RAqfhp0vRK3AOC0RZk+0kEA++BOUaTm7EV1eKk2h4xjVDUdMmEBjQS9Tkd0wJ2HB6oO/Xe4DIhs1g1Zghlh3Wt2jfgjl0t2nH3vC2Ruic7JEFW64fHS4lk7Xnq/ngADD/buBozvzFVfZa0DQqn61+YU3gNTNvs3aCOicj7QWfAsgJPFjz/mnN3X9Sy8yIrLwdtf7nd7+mQOnmmjw1wCgG6ga3EhmANBBSOcDzJMbGBRNiesCQAfXrBdp0HAol/o15GUv/8Xmt//gq6PPP//8kwNPPnmg80hHz3A33AzqB2pzmbgf4I9oQl4qXfquoW5fVG6wB7qZDwYLfpdzXz7hURD4OYzH9Xqy+VLVr51/2ayEngbZ+eKnQCrKY3HKXw1+evCteZB2AXqHVRXnj5DnDX6PLHiOoGiGol8UE8rADEw6CIpBDASL1OL3p3MKOuF/ztETCQFlJ1I4EKG4PhrSZTGWU6pwYEspMhg6VTHuLUP8zR8Tf8oqJRYQj02GyfMcifAkMML84uRdoQqZ8K9Am9jjZAok5EsIBIoaQl/+FMWlWuNxc/jjlPV0XCFA64PDNM9HGYhB/tFATmjMgAAEKQVH/c2lSQ9OBbNZBYaqnhr/IdSQC/Z4XIO0AgGBp7uz2fG9EMin3hW4c55l4MllW//AecmIH7OzrpwDc9MphUfqrvk4EOggoekHzv33/fAPZbChfdJU5Ni/Ta/3wFN68LfdXOhytsE+7XX3tzugZUGkA3HWh5lrecDhl+azWtBoXt95SJ0Lf7+58NWvXn3+/NNPPz0/MM92hUS+zP4WQr4p/gnMHBBmF0I+XHILicpevmQE/B1Mff4s5577vnInbb/bB8n4PGPpaimasax/LgCMmOA/E3tPP7iIW8H6V856yfrX0a3q2hxJuDT0CvoXzJKH0M8DYZmwQr8QjbzBW5gjNQTuQMZJ9YEBf4SCoMM0GaIQE8kqCkbCYGsoRZOqsKSkUjivq1NQX6cIA08JH5wTQlil8heCmyRBU3g9altMvEHnQHBBshBIJP1h/NelNKtAIc4p93HyQUMMLuilwcT/Cquchr9K1Q0aPLw6SUPg9BwnvgFvgZ/UW6RgmFyEtgHkeBEyBcFiLwq+eibKwVwqm1KlMEISUrlsrTY48Kg9G9LQIHKIujp0qOnKY0PdPBsiWOeUwrr7p2Fw5/zj05MTrH1o9BMzTMVF/xz386yRPup7gSMOAs6KIIydvwb7XCrIR9f/aT/8+/Wu1QCkF2XvS8umL3bysmz8teDIHGF8GvQchGy3IY7vampwH+F9NqDKk82HGtTkx35g/zn4sR+oOrjpB6oWVu9dOL+5MDr6/PkTTz458PRAVv20DwX64GKJ9ukmubGJEQDmm7nvl9e3m3nZUbNwwL4vJ98+6Xng7s9BEPb2toWWSs2pbo59yfHAgiV/mK1vFH5gYu/V93+xtJRsE+tf2h8MhKh2DofTMHwEWcullh+539AA40iFDHajUwACPhFFJgNyQ+SciUQoCCuM7UlhDGiEAMNUviJzJb7GCMjuG5o/gRGPuBhAUF1O0QY3XmIZJd0EYQVJMDsoHJj4iMhKzAimdwO8eRjjcQVq+7EFcI0p4KqRQfRQCH6zBYiIqPqknE2tzquVKjqB7LuG3BzGdidoPiHShlgDx04oBCGg9xdELgwSUjOg32SPTqt/h1qm1n2aW4ECgayFmFbg14+dbq2lU0/eej6Yz6imf5b1z3hfXLXv7Kyhfa5Z4PozUv/Ytk0CHTDE+NvuO7/eA3/v7ArwOW1AVL+tsX7PWUX/DCgZXGKwc5e0DZq0tdu39G33Iy44dZ6gK2HzTPN5rU9ufzB/UDuZptubmq7sfFv91Z8//+TAwMnjB0EeMrAQJAvxvjyGect5nn+L8tAv73aTbx5ywHBdLA3AxJfdv09xaDbk4wDudoco5MxMZ1+x2EyGNAJAv27YRTQBTIr9ResfUv3muz3wvviGs36FWzD7Ic6F+AynQPPCj4yCAQFBwtdskIzBOdoPp274qWbGIxkKio4EiDTCHxgOAZyoWmURV8GR/DciMZZ1NgV4U3JOaesL9eJWrR1uYHMFSnIgtKMpOKgsnAcYwYBwpEAdQOn8Uc+RNqGzGVo3AEkIWdU/Bp4h7DVJWStLMnunSKBCwFCY06FJ94EMQiIQpl8U19NtQPQdsplULpdSd4KFsxDVXetGUtZl8sRYealSCX/tLej24zYE7t2GNPrksZVJKn9dyscyxA+L/jnU77by7759wBErFcE5CEAAsdt9xQWBv36FrIAjlhEarzF7Ezu7Hr3ALNdBLVfZWY9M7Qag2g0jlA/VH24esx7QBW97g3PlPNl+4Qan/sXNJqZ+UEOaFAKe+d///KuKAZ47//TAyZMD6v+9X/0/6ivQREc0n6DUU2F/PPUhqQeCe7zzSNe/X3pfPu35rGoI9mX6PJ7BRKkakNG3oDHxCf7J2l87/UBVv5VqZgbNv96WQX/IHwkRggUp+wWzv+rdUI5CQHm8DVIHBT7TiiAifpkQmQMpK54AkfOTZSdcGKMgNIKi0AldQNraQSSMdvfiv1QZUx7sxVYw+AxXpYx/kuJCFesaBQECBbEJGBeEquQAhCkaYTCo8yO8HZj6gOoDFftLiAdm1UzErbElenVVTIE/mqqeQtWtx+NeogIc1BMhqRF/hGeBwXaZ6WISGFtCwPwoDidNC9OpCZjDBYTgdA0g2D04+MNfuGdDGjQEYkL46PhgKiXjcXXIJwXwDzEk4/T+HO/Ld/+DVfzOmqJX22DsWtgGuxEt3dYdagU63mfajCkl8u4rFv5d39Yqsr5E6t/7N33e2PFnOPRel6QG6hqc96Upx7DVrutaDXku7BLU4hvmNc1DBvcaNCjqD+TPIy/5A3Of+eO0s9G6qeny099WAHj+yacHjp+cz57MhcN9gUBzX4JZHWU7O/UvLpsNGDKVIOTDReHL6vfTnwfu3dcVeMeH4XOmvzu6VI5QUD03AKFeSvgpCyAO/EXLGHwLdJLz2duaoswTTrHyZzjNVJWtwUyERj0yqgDMUa2Luhcw6Cf8YyoUTKcpHo990jl2SfsZMihRxR8OMDrFiQUSFBEAwZfsZEwq7PtR2bhO6UEswuQEhAL2fdB8G1wwAfHAoAdIYjA3BGlHcJyEFpo7ptI3LiMkQv+0ECJH/jKqp1AHz/0xk8BFICCGQgprSfoSaKaZ4wCRi5/jFBwMwGEUJAWkQyQYql+4kNCJyIGN0zaC0wNPXLG2x23JcDCB4KH2y0cPKAg8Xj8ep8/oX3ztkQmH/bkK4fXndnX164LAW2DfvuRP308k8EOtf6jzUZcFlLvvaCegrn5NJ3GExY8xnyf2KG/81YilgcoQtlsdYWpu4LQ+wHlBeaZhi/KugUHrNfQjQgmlRObrpna8NTSdOfMWAPDcX5wYGJ+fV/+c4XQkGGpOxvtooxGJHgA+sr/gtgz98uibKpKBfbRPMZH8svr9LOeeTz8bEqON6TGg4MxYrlyNJrVlhS2AEWqNIfzPWvyG2Kulcm0G+NfbWgNQUcALQV+O9A0/jbwlechXJkOCFA1DEXnBYIjqwbD0xcJYp8bRoWFpG2JbsN/PoVLwqgQSqyRgMJ9bZSaG/06rer9CtCxRa8i/z+tsAno6AyAoHsKlqeFHRhiagEvStHEcNTBlZZH8u+oQPrY/rxHlW3PXwfzzQJXdBICSzTVZgQc2j51xlIpAX1pYfcWU8RWkJBiaA8YgMKZCspSKBWUEMhQZAtPUEAQEdh988vErlhrCOTFaFN5qOnV0uDtVO3grQfixyvqEgT+LAS5P/tHkyhsjsxYGdjkzIPvVwRrOblkiazWEdmI6XT6c3XfAAl95Z1fPf/Ch+bfZ9zs3vd5vnmqyrc8abBw40sRMAMn80lfWvbps1U+w3tdMr90FatZrOe8aQGw3KAjmZz5H+5kzl5/96vOggAPjJwcG/LkkXFt9BeRZibE5KmO/0vOj23lr4Ru4YCL/5eTbZz4P3NfIEPhJq+EYdQH5csbTG8wXy8lwWMe/WP0/Z/UR2B85n3H6u4NYBi6JVuBuKGch9CoqGOGZkDBzSsI83BOkT0B2kExNFXlDwxhJzsXVh4SwWZc0YIBmEGnQWDAZhBqimBuptBQ/72DQKoXxSaqk7rms6niqVXEyJ4kBBnh5JbX7MPMGpyGFASIDAfoIJWVRcCpJvRBQBAAZTvlFDR8E+NL/7alTHFK4rikgAJBkmzUK9aKof1I/qCsaJj+4KvlTKTRFczQGks5QJgxgD0wQHVkKi0l1H/77K+pcPqNXJ1meGEwInxoHBB7eXw3Z2fnhnO4BuoSQSURnOzKIpftaZ7buer9jUUPOh3b2YTKkKryb3d7d/fUru10uXKTyF96XzdiDWPmm8agO9CwG1i4gJijV3m6BlAWA+j39vAbzXME4c5fgH9p7DgA22B/XoHHvB/rTy2s1NTVdOHPpz6kEfnpgYLyWTin+F4/09aFbXo6ywdkYZhn5wAJBDa3U++a+37v34769vzwfez5LaD4zwBjtDWlMNxfLfQF8y/JKXm2AaRb+B+dLKZrpIfjzDWXDfp71D1PVDHRDqysc5NaeKgvwvZ7D0g+qAeEIpGj9DIkjKR+JKDidfgqQCWd4+ESCBIg80egcpVcFgE7JgrOvg0rhVS6H81G64PeYwBVkzSUZ/LC0KBnCzEeAIvGT1PqLYKtvkudc4pCKA2B/ef4Ea+IhpE8U1Y5q6QoSBDL1LJcJAUtsCVyfK5IQjGyZgABgjlm1KOI5Wo+Zxpv6K8JyEG4C0sr0LO9gSdNQCK4Gn/yrX1zhOrjdeGIaBAERGf2UhsD98vF3Rh+vOBBodQHpcAoCu5+t7h/fvpXmMXLLilixQAv+6MgzR3ZHbA9Nl3hf3m+b8Z197HK7pn8NAksa+xw4dCFj3Wk3z223QLS97okaSNudJ9Q97ABng/NS5rn66RoBL1x4a0eVwE8/vXH8+HgwpP7p/Mm+RLzQ3Jfso/8Xzc2O5gtdmErhfLOxPqvqN/57X3b/PpdzP1qBnxACqfzVJDBGCNjb21brm4piFzMlo2gHNBmgkXlVXFqK1tpo7re3sZtQD94X4n8ZMB00EcOUaUrGAEo9yIRCkimdQRwowwFs0FlszuzlAFXgJFkJWYMJUgBrKEBStELAiIRxJXh5rxVTRcUpoZGRfZmvcagLjfSi/k3y4kra+xGJhJO0bhMtQF6QVEhafhdL8l1bZdNLnmXlVRZE9OdVuFjmNqACwOcYAJcBgGWSgYlw0kaksPyAoNI/HfSnc8EspmAge8MHnSMLumJ8GI4j4AvBJZPNpbK1oaf/6sovpA4WY7TuAzaABDZcePzgUPet6uDRnSefWqnHPoOAP5k2EOgIIRq4jDps4xah2e6uBjbd7JNnbtcJJVrnpQ9zlA9cKfrXGPP6Dl5p0qH3tzwaFQ1ta3CAqu7CEEnrbgsV9Wl3mKNmg25gtD5Sfy7YX9qhBDc1NDW1n7lw4crO6PnzigAeHzitGDxsW4VkXyABEExQ5oGk3dN/H5DABAZAdJYSAPDL6vfzOw/c95U7T8qK8YX8MhzQp8DI0xYM9HFNST+kuPKlNle13JdrpLFfjyc2mAmBxsHXTBFXwSwpGKSBhCn8jnJP2VUD2hMG6wmEMxACAIDhcNbD+NeSCrONOkg9vzDYIIhgAG1IYoEghck4t+loSAM4pU3KDl6R+sGHR9jIOsi6L9IJkjTwAVQC9GGLUTwSSnICQoBel+rmQn51zWn3mTJGEUuhgebwnhLkpKoSuGIYYJUWEUO8oVQsbpDKtDNEcMWOMf5G43EcBUPeFxBB9XiWJ7J5J0EqVxvs/M+/+AWVwUYNMTExOJgQPnpg+DYQ+PAxrQbvPcuLu11mCoSvhAuO7KJL2OUcgbLtd379T7/edXYH34Ip7tdINLDZhZVvmzHf2NELh5yvRKDJAh0NUQ66Cfg595hytV1YoNylgaxdlmma1zFo50bJdn5d53PQO03mtWgWuInubwIECgCef3r84PhAuqb+USOhQiCZKOC7B2pws7oxxWEvCXb9SfHLtW9z4kvx9/M9d66GxDQAGhJINwCAhG49p9PBUCCuiB9nn5QxqhjJnlbo55nBE3oba3B0ZPw5cbJkyPCGCzj4KOA+FMqkI356FtXJiMJS/0cyQc5GUCiY6u2dmZmJDWUCYQlFIM8Ij4NwEFaYxehwEh5TyrLCkmBFUGnHOcEggCiOcjQvJpVVhBGgXwiYjHPGVYAdz+x/CVP3T92FOb8QpcOIx7CgYY8SFPJR3grHQ520/Ujja16epB49Rnmw6AGyH3qliCUQaAImMUkYkr4n/RSg3qcMApLnKEuFcJZdMDSIHeT6NxckY7q6q1YbPvD3vyAIvOyeDRFHIIZDmr43PzzUffrwXggkO+DOwJTFAt1nYnpE6F+X1e5T8Le4PLn+xkg9Am7vvmMcffXM0IHCWf0BI11d9VConra93fV+h7ffd/x7Rvww/EuDkoE4B7g0FhFW2U9sMLDY7jwuH9XOz9Xk0VE5rCsGP7mryWZ++jlN3CpsauemYVOTYoCXAYDnnjx+fGA8VaPFsX3xSFxxBlUE02ojon6MfkwH2UiLud/mZOD3voS/z/vcc9cdksCYgCCXv1oJSy1POQAAIABJREFU9vl8XJQC52IdrYggRn5dutba2OIl4Oul8tfTCg0D/Xze+SEjvjTzqq4DYDg08YDp3pA/lORRYNZBaRaYxOKc1+PzdmY5P0EC8RkC1UWA9mOG2I0YovQq2hBMoS6savDuSmNVhnmFAGxtjUZ/USkr8ofaN4IJYII+ilelET+wQJoFXpNlcCiWteAbXY1y3cIzH9FjupXN8Mc3opod8qamCqnAE9PUA4zS+EmcURwNAr+MBUIECdOelBxIYI7JoKJ/UH2RkJ/JqYss1kTVwAhzqfTpI3/xV78wJPBCU9PWq5Kab87WoTPPDAwPdh/cBwIJATcLK0b+cJ0/+uNdzfusceDZkTfW6eGVXZcoPDKyq53NOtnKMEOn9HVf1XNEAOD7SH0+8qjQv3bhYm4QNDhk7pfr9oZ290MawOQJTebVnGdppLTesT6p9RrmdeiG+YPQI/BCA/waiACeufzno88/+fTTTx8cOD7YnYPXM57oCxWa+2hpTiHPPgFKu4fgy/QPfFD9KhTu/RL/Pv9z/713dXAr8DYzwAR2hIHMAul4dRdQDsu8fBMdP5++G2+DJOeSrMnbPSjslHwuwWAAJS8FnAbDbKqJ9GEXZDhAfTDAT1DiEVq9PTWsDoYFEOGp6sUCNB8XVk9DHhaNI1MiYKDA8QVkCiQ9OJ5cLTD0FRKKuSHreZX129UEzfOyo5mirUD9kC2dpJ5cgJaAQA6OQFsGUMH5whvRSdoF/B1jU020TF7rKIcraAC0fvO69mpRNrGvz82xCoxFwRGyAoZoPRz1PbEeDvkHqHaDtBQZ6VgKCmk7Upo7gcH/j733i23jztJEkU6csbt71pRElSmRKYpVoUVGIKOYpFnmkM1QHiaxZCkSHcv/lQiOx3TsdPpuLCPWRaZfDAN+6bG82wMssBihMXtvY/bBgPOyWFwD12/7YAxuAAO7mCBAIzdzsemXTZCH5GH34f6+7/x+VUWKsmS7053p5rFFFotFSlGsT9855zvfsTkMYrWlDKiY980vvvitIKDkwUnWAiPhWJsYnjmQqmS6GsJ6OdKp2S7eZ2CQHO/k82EOiEffXg4BZMACA/gLQ+DLnQC3GfKZrBiDv82BxYH3b3VgeAisNp4J0C0MVAFEydN+uhoxEJkMP+8zuuANk6ELzLv5J/0ryf6AeqCHJIEK/24N31t/+6W/AgC+8eabJfXLOmapf23At/Hx6SkszpEu8JR0EH3p8779+/a7/ez3O4pdzz7V3E43JKtZoHRAfAbo459GQI2Di82RABcnq3TtswThYICFzq5KeeltwK4tH7tSJVSYt+BC7REjFPA6SqEtxyvWXWkZ20KSxDQfAQCVHrAj24gBV3ogxIldTdPPWf17EwbIDBbwB+pHEMzzWXR+BQOJfSz9OTGqYQCAsGtBLyRPv1Vpf7BmrbXVszJi4t+ok0EKLJ0X9ZfONPPamP/dlhBApsCKeToxDjdLDwQ1A5fOqJ5ej4msFxNyWI3kNTgHVyyiJ0JjBI+t9GJl7O0vvvjCcEBCoIzH+fghkpiJW8f2Kgh842YXCfzqpaPnunBPxz+0ghaIBDngt63Qdf9a1mUivv27LnsDutxvQLpNzvAse79f38hOYuNvZ/XPRNLHrQDsfELm3xraplPY4E8kOO56fdJ/Knxt6GLzEZFrhocDkE3qOTgpASIBXo3c++rtt//q1IFTb+x94xVMdWN6NKb+MemxgfE9qAIycSAEkgJS/pzvL/34DuOZp6PbKAUa/Z8kwEIKB3wA7MA/9WgolwgAMOoRs7jrR0GXonCKwmCALYaCIHsWUMIIMMLwpL0wa4uqzxExnCMOWYqFifIZLxcLaeTQMobSIAaCsMk+dgsMUOHZVSw2n6ZumQuIrsr4rtTwrop/C42srk6jxzstmy+nmfQ6WLSeLuhlmOCiaAFf9Wc/CGlG2rIgE8acrePEMSuBGvyMAIeXzi4snzPOqPNsgRAAsXEYTJNorr5Z6ntSwrSLJ+OA6HzYKAF6tEZAFuxxVxw4YINW0UiH68X2SuLt2woBTRq8oSGsA5bRtw6nqu32G2+HR0O+OqXtsDZA4IcyDRICQILht5dDwhm+poVE+OX/GppqM/H//vPnz3dRvpf9o/C9yZQV/RtQ+Pc+N/76fC1iUs+uSHYcaSzTsKXBzX/Q8ScSonE+EEZCT/vYZy4PwC8Z0b0PPjNs3sh/JfDv3moSAHjz5l8dOPDOO+12PVMq2sg11L+46cL+ccyD7Ns/JWpA4qFKhfcLAUz36d93GnCM3gYEIrQCpixlwKEgBTYIKHcKAMd8/GvWLbEv4NY3ded4+NkFkoEDct5NZt5k35vbTrmzU9gIxCE3lPvstIuRCPzKBAzaJdHFcBESZoFVuozamcoYqUikL4PKhznDC0NTh+K9vLYv5bYPeKbGrsamRfyXp7MViobcfM7Bj5gjb5MuTDP/ZTeYK4cpWQZwStEGHgtEvovL2mxrdpY32t1DMmRDBWF4aQaBXzt35syZZaoAkVGrBBtfOudbuB8A5I+bprwSJUElkD67wYkQmsEADkUMw7awrM9sV1/4xU0g4G9NHXBjN0QHNDGHqloTIxD41fHxDzcgn5z49luhfwb6eHvy23Pv/uvuSwGBveBPxX//duN4cDDsETx1kggI+qf+0b3y8+Rab/rXFSEATAYPk+En9KGGrmRwJgSOEdGvGDDUzwQo6L+qo7iYNLZacnY4otNf4X+RyH3FAH/xV6eOv/jGK8W6+ndsqd/JaSYc+/bvkdLfHoOAAoLY+Fv4cV/78l3Hzh1bC6OzWR//1B0Bc2hxcXJxkfCni33C/0IAqM6sQMhCN2f1w0ltM+YZ2MbF3nN6nSBHliWXDcutpEru7GyerQ7aooD+uDImbJcaFMmBH7HlwQ4xMkbsFHeQJtMXGvxSoRfHjQox9cHkNg3f5gLNoinqAyLm2SPZx82WND5FiyOm3fXzMgGHwiJOph31LxYAKJ0UkfXR7v4ilH3Ly+KwNQedM07ReGZcTzjpWqB6OG+sYFrYRXJR7LCwgJj7ltDNkWFgS7Yhiwcs5q65GdTmKHCd1A8tYXRFPA6ElGRzZiaeuPkSAPCfDAUUBLw1rDUxRhOI24mJ5MXXa5W21sR89dXrR17tpHM6fs1dIHr+zW9+PP8yh+c2xnv/W2/8+59+KyQMgHi7MPXTx58/z50fPznarX0JQKcD2jQ4JUPAFzBFtmP9qyJh2NOnNoCk/1To8mTonD5OBsCpX5Wk/EVuWP9bTa4JAN48dfzUG2/sbUsf0LPSmATZn57mrC+T3wD+oHye7kuffy+xa8fDl6j3aINkBQENBQyHD4Dq9BCUL3X4eNL2xTNrLGkEQ4zDPAdtEWIKABp1u5ZQP9yx5eV0naU/m9oZWZ4kW4KgkKZMhMdUycBR35nSngxoBbuUlMS4KB2pa8GRKQ4o+BTTgpIZFlcxUEFZfA5jP8JimuKZmLyM5USoX9BY4d4OKmr08NsVEfXRXnX2fKs1P7fMNcTGZ9VngWYwhDLBltA/WcU5S0dU2s/E0rLXiRavFr8xduD8YIsDGEWRNnfCoQHCuiClMF6xyCy5Xo2+8OJLL30sFDCEgLoUaFjgmv47sbY6czxX4WzIV7eXP+y0QzAPPvzWtH1PmsYHMerbd3vh36uvnXu5h7kf7O0/N3b5PXR/He2Rl6F9iWazuw/8PNLZv+kZPVDI3IWeESQzqbRJiQ2YmfeQc8ngTcx7mOf9d0z68GeuloQ4+PTDxL9hfMvvIwW+eeqNAwfeaBeL7UYMexz25dN59ID3TO0XyR92XcriI5X+xvq2f7+n2IluyObo54+ABCrA7QCgOo5zkNWz67ZeHSI2nxY3eijG58HoFIW8BpI/IFm1XCxlUu3C1HjawnIM3SGWMRLF8jxbholVJgyfBNgAul4ml42mHVFCx6gGxMuYBTt0SchzsXmMPvdpTLXlMSwsHWKs5U1zEk3loXR6ATTmWQSMicNgWjvd4Kqrev6XaCbbRs7MYd36q3BS/tsj8/DZP6MRkHs/xq/4imi85Nxr76nsd3lO1mNOiRAnpmA4Te7K5ciUhMMsRwx3cNdwQRvwbbRA9aCEKTEthiRa/np1u1174Re/eOml2x//pqMTIhCoUrE18QpEaAycWLt1+gDy4Gvpv+2o5vko+O6Rb09q4vd86EadePnbyz3EgpdB87rN/f4n/V16oF7nsS4JwvX06xvZ7LXTP9uM/gURArikfxwxGBQAXiSSDPVskz6AdQGgAcHgDXxwS/qPzWshczYYmfTJon6QRPqLb7oPgMdPHX/jlb2vZDAKUsg76fye/erf4H4IoZkEGx9NSF/25fval99jPGSFcDaQAHboABcXAYG7TQnQwGAIACerwSADdNAc3mXDFk3ONBV9Uhy0zAxIZiDertSizeKVhf1uGj/uaZvyYEBB2ngAonJocXWwQs5GbWBycfdKwWLnAvhX0FwQ/K9kpy1LwZreVxxz4WmaZ3kwzx0fADu4XEm/g/IXGP9JBVCv7OVGEGkAs5NyVWtaYHKvANCs+mBu++pr/3D5yBFuW1pemF3QokDpBtOEAYRR1rCLZpp+0nmKYFw7hikQmZoR6VBJ6oD89jUs/DKpo9tbogxQ80A0gtV5u1Gs5n7xV9gBdxscEAiIsbj7AQJqCAzjBxrCh/fGK7XYu6+++trG8t/fSvb7vLkNxj+ogL78WmewB4L49p87EPC//10n/J18vuf8x0kxPjj59VsD2bHX7z2k+Jf0bzpPyUEIyDTwdV3b8bLwe4UB0Uc0/w0NBkb8J0Lv62Mfa4DJVeDfME3JkkmkwMdPnXrljb17axlPijRufno/Vmzt37dv37RZe04s3FMo9Cfffr+xa8fTY5vkwSYF1oZY2bLoAP0uSFABFBVgwgBgs+5Y9ba/PYR2V1K0ww83rJ89yYk5zpHGUEhjLBuvxnOpRK69b3ZfHVuCHdsRXwCuy60TAG20fmWnersJRc5iJoauCL0R0lAYyAZzx3mlBBJIVQvxzcKzeXHuAqAVYiJ6mXZcf/o3hlejtYJlc1yJlJZlT2wkMwGmh+8sVg7PtczW83C8dg7QePGibLvhyAn7wePiR71wcUHvPmQGfBXZt4XNdrTFpxsM/RE96SAppueyHdwoWY26R2toWASi/wtvWC4MLgH/nvvFL9DR+PilL0JZsOCfQCBsYn4dgkCywMi9Q6lE3DMN4NAMsOwCMYnvSZ8KPq9FMJ11wFdVtuwLAV8OCWH+12bVvw3HtD39JpUdWHzu4mbal01DgKs30gXQlQxOJDX8GUQLkNCHQ/OseVvzbPBpNLHs6DlHNP3Dt5v/EWyCnDq+d+8bMPLBLlhb/YuCdmu6sF/B377907rzgb+FQl/78nuPXTueSpS7NdGm++FXAHFc7kiBO2WACgCjCQ2AY9Z0ulHkJFdD1vyypMVxNy44R/IrvJBqQDSCM9lmNBHNjeVyufz4VEx4n2CnI4rAkgJEJNQl9kiqQGL1tSgAxJs41MJggA2a6HTBrrUd7RkDebPCtYLjkuTR2TnGAh9m5xQ3xFnO0mkZDKTVBZoCFhxQSM4BT4sE0Mc/lf1uhL+/kK1HiupJHXDKCAKnRDQjzpdmC/u+fJ6fTXTQyOwt2fhpsX2Ebxarpmgh1ekPTTUMlyI19C+Xovp+tCupF577b38pAEgK+ImpA/5HHwED03wNLjQMXBv++aFUNOUc8at6AoIwwTJ5b9AFDm6AgN+2PjT496GhfxKfm1Lg3/3zt5vI/zZ2hZH9NssD1w6fXdtG9S8UYdwySKcBLhlGuWQHwPmHHYjng6O8i3m9AUzDCIUl+pBo3gGHgL9bq2v8RpsUWGXAe994o60oQSPWqFtIKQr7pqcL+6B6wcibyACn9qf7zd8/SOzc0SsPzgZ/DQfsbIJ0y2ASPgDae/aorA2jDA1YPXuS81LsKxmvKJvlDpioSGB7cqg8NpbI5cYG4s74uIN1cTCRQU+YNT9P5YkeJIXqcGVoN2byhoYGMgWXbWNHMUFbYR2XtLv5+lsVz6LADluTFEjmudcIUnzQPeAiWrwu0BEc0oH3PcxPCw5n4PJC/xxkzXnkybr+RwBU2W/r1xrwXv3wHApiARl89yx2bi4b032NgOPG7GNqXPofV2nbQOqpOasxAZTfF8Q95MD1EjeFwBsQSzK5KIlTInXsC8ae9Fx07IVrBw8eFE3L7TuffPSrXx1WcejQ4cNHjx07cfq+gcBIJwtkHjx8/8BYdqwQ9sP60NigPu/nvUEL2IR6/tsjApc/+/Zk13OAwP/vf33bfd5oADX4nQzuPv/85DfNgXL5lXvbaX6YMNwrwD8NfkkDgj5QRQyQRQyGGVCLGBTz0TKcSftwOGwu8c+bN/23SY2JsIAW+rfml1wBgL84fmrvG6+0M+o3F36Z5wvYCrIf5eh9UyoNnpJWcH/l5R8wsD9zIwSa+l82NAkSToFNAiwfKgVeFHXMmD21UFA/oUVmbHWObXha3mdZ8lNO/KP7KabjXLthtROLQ+Xm2MhYdKxZccfHYQhja4sAEUYzL0YNpb24e3ES8JdtttE0QReV7K9Af/m0U0plR/aW1IvSnBMpYG1mrMCREdb7CHVMdkEBMU5HdgjNC7fMucBGPVXCPjLawNBAz3Cm7Yyf/b52rnX2zNmzZ3967vJlLXSBzm9OANDUAK8YOczMOPZl0oEVmkR4btHJwZWNyJicbkgSbHNrKPUvDZYB0fk1+5CwIw4FQTRDKtVE8623Dn6g4qu/fOnOR8eO/fL9d07dfFvFEm7evnnqnfcPHebaEH82JASCaxOrJ94YKVf3n9MQKEMdJ4OxX1MBNGgVgNrL3x557dX//T993qOo9/K3//XbXufN07r1oa8A/RspZ39y4tbW9C/gXB0PDSb5yKRhKXxhODCvy5Fd/VxSvyaEiP45HxED4COEGoQECkb87Ff9mlnzmTYB8ObeN/Y+Vyl67ZWS+kWHJTP5/H4Fg0b5Ah+Rvu3fHzRgl9rNAv00uFcKvLszB4b2xa8BJrw9y+PYn4QpLgy46dk1mw7OYnoCzwN0e3UvBOymmMouDmWbYwlEaXxhGhOvlnijAh28ekMopOtVa9XKyspKJYMxORcpLIXEYpFacNs59dWm2up66KVdK8blwcC0mGZ2ZgQ3LYZaaB3jEQeAKalJkyvSBp8DJHltosAE+EOf/rUU+M0rBDxz5mxLL758tzWPMqBJgvU8iA+FeBOMIOdZdExrT1fxy8Z3xJPOD1BPxkG4hAX+WKW6ZdcVLNYhBSyC/TXq7Woq0czeUKEA8OY7h2cOnzp+4cLgejgGB9cHl26+/yVLgdTEGPwTaczE2q1j1Wwzs/xhmP6ZBoivgdERBjWVCJ/5T5s1eXuc3iwU/YuWy833f741/IUjBEebPB9cxBu/t8K53WHBwADSOl8Yet2GOiBughfqJ4dvmUoD0l9NAe9/9d9u3jz+4t5X9q7UHRv/XvHrjmKs/D5pA7MHHOs3P/7Q8UxoeVw2QEBhgQNhBqiT4KABvDvMAFUKXN+3vLDPw+BqnXoYABn97m1Zh2RJMuxSFIhCH+qFCi7b0cUhlQc1E9Ho2Fhpz9S0rJFzFQGihloROodv4DBRtdDZcLgVhDvi0GlWT5Rq5Ww5OzS2ohCwYdPeJe1yczoXaIIn+kpnav1ofS+ZaFqkNMBIyxH/F65Az0/LDDCWDM+dfc/Qv/mWIoAMddR6V07/bN5QQFhjTYn/lvbgv0r3LU7lxTC6jCE49fNA+mfpDaEsGmAPFPaCoA6AXxXYClJyOAXS4GgwtiW144ouZ28sAgBvHD907Nj7gwS8UFwYHRwdHVUH6ok7fy+W0b+WUiB+QDUETtw6+tzQUGXuw9daL2vid9IU+8z98x33Jk6e3HDqEePllz//JjVQHtqrV74Z/NlmIyRUl9N8zCdqfhdYo5/ZkyKniH80rTIX+ZzO1AGTwTnzaeTlSZpeySca5j3dT/3sVwLXsgb4ogLAVzKVosUlrsg9CjFKoKb30/x5X6zQX3n5h49dO8KqQJP4DhgFIFPhDgAMJ8DhLnAik18+P1uwrWIRAx2UQpPZNOCBikSWY/9kgfzLRWgo7hdXRoY0Ccw1U97U7DT6KJz8oLVCTF7IGWNbGqdptpNhEEij1LTdjmazbykATLTbxTo8B7V3IA0OkB8XYsL02PtwMH+c1k0QNpJREKSgGgU6CAYLHIGbvqJdXS6eOSv9j1ePKNA7qwHwTKv103MaFxUoakH0+IyvBRQnarrP5Ll9JE2UTdPOxhFzCEv+6+gFK35Y/JZxMrgBEghrbTmC/nmllhi5llX/MxT8XTh07Oj7653wNzpI9EMMEgMH75zA3pDOUiBxcCJy75eKhNn/18nn6VzQyfNCD09uxMDtRpce5mRQ/bvWbJYPdWe/2wXASIBM5lGPB4JI+j0BcGJYxaG14VUDnREfAP0ioaTSeG7YfBpzSVBrTIr2BfQP3E/f4NOhC/z2i5gDKRb31osNYYDsuqnfr3v27Fcx3R/8/Z6EsUvNBjmwzwJ9GYxP/7qU0EOJhGGAFWt2vjWX91AChKYP8mX8iDdshz5/MsqGyUjkxBiFs2juBNPjSnloIDsyMpLIJUZWYsvjTokMT9bF6YE4yYuZPTtkTo7IoBWQ1RX9y5bL2YHFaOaVOvfKWdoqBrYGABt5oLiX5Lv4x1ignhoEkKPABfwTpdU+FDMOF65PiwuWSoHPmBT4HwCA8xoAVQ78U90YPoc+CAbi0AeZmRLNC9CPU8lXNAbG5OuIFdC9ln64RTcEEQJiTJpe+B4XZNLzpVTkI44YevVKfKypgB7/N64dmDlxaml98EII/NTHqPwNQHB99M59YxOj4UbWZ6qf2OH7B0YG3vr6G4OAhgmGyn8h6HtcFAxC3uFzRf/KzeaKT/+2GcmND5OhB/qvAbBIUJTzQ2qAw7K7KBJJBhf775T08c4c+8Dnp8V8PqR90QBo2iD3DyoAPL5374uvVNorigrECnasAAFCDG1g7FLcH4v16d/3JkLCaJ0G+ynwgE6BOwdBAgooAIjjxEpmz/L51tweCykburweRzuofNHCPiAaTkLuobJj/FzLdH+jGEcpsDyi8uBEtJqeXeDUnCKCoH1pTNVREs2UmNyPHlkWoa1Ra0rlcmAoW8u0sVcXqbcLMOMudcl8XegBRfzisiWiSCFTaWpS0rGYTVbo0gVfrFWnp6mBxsY7Y2tKCmgAcH6+9dPW5fc0BTzDeTczEieyFyxgymNtJ4bv1Duy21wg7FIjid8LZh7OZquogeYQeyEyS62rqjbpcqaaSzTLA/iO3zh1YubA0nqAfj72BehnQFCxwPu+T0wHIKxNJO+/02wmvv7m5POB6k84XxchfIzo/SppfgxdO7pt6V8X8JlTyY4nTQobxJqf78t1SdbwAH//Fknw6nDH1YYLRjTYmcdJbX+lY9iwQNG+oJTAJhM/NN28/8Hbb/9i79691Vcy7WKmwd/fDa8wvW8//v+jFGL16d/3KXYaYbTJekMJMP4EfoDBEMhuXQNMSHtk91im2tijOOD8eNrjqjf9x2tI7uvQBLXEWS8XGj7W+LkAl7bHGQWBA6KJSYx5ywvTME+QrSJsocgacdoLWmlLzwzjvh0tZzV7XYy227CQpxUXe8MsEaLmx1qfW3Cw801YmGsqgGmkxAodRR6DbZgxjglDCX1FqwAhAvwHoXrvtsII6EsDX6XhARFwfMFsjbtCb2ouFY7BDiQmRlgW2y+WI6Mg6Akxv0W1lLmvh0nqOnQxcIYmCKrDeruaU/RvgL9x3j504vBSV+nPR0ENgUshCFz6CCxweEI7Rq8JPEAVOHHrxIsDY4mABYawqxeCbZUPdz35cvgU09+TX480m9k3f558pOYHwxCyTujTqWsXIBoCGIAsWNtwUrdBYN2yajDPT20jAZD6n8RgYjJUFAzRPyGAExOmDaz+3P/gJy++/eLeF59T+W8R7rXUfMFiyIntxz+uvvbl+xY7dzyVMAAotcCsGQZhF3hoUveBN+oA9fmRTGXFAgdsze5DzxY+fuJxR+gTlmM3HMdmGxgKFzvtKGpXsj0uvahnckICE9HcSMras1CAK6pLEBNdDAt/DTtGUwROmLhWu9ZUX+CNAalUpioVNEHIDdPSH6EwWrTSLkbjiHywlWYKLZVABa4F2mo57JfAHIEluwKNAKfGZ7HbrXXkPU0Bz56RGiBQ0NfGfHj2jNYCjrMTIhQQ3vvThWluHp7Oy+iJ408wOyYJtoh/JRpCcIe8ngWmuQ50lUWv0a7EoyMqy2fJ4ZTKfgX+whRwUJcAO5JgAuDg+vroR/eMMjqUGK6xIXxYAWv0G10K3Bbd2+SaLV8K+pctZ5ubup521QH93rWp5QGGUMYLoZ9/ZG55sGa6PiEOCAgzKTC8+/y9v3zKgFsnAAb1wKQGwoD+GeonADihuyAAQBUvvhiv1jOZYh2aV/WLFUnJvvx+x7P79O97GLt2PDUWpL9+DVDjn/qpW5zcbVLgIA8eGmEXeDcBUP3PTk/Nzc+3ZvfELI9mJpZ4Ithumo0PHCtoIq+DHRQ2DdtgOLL3J9McAgSiHdKsWVPjeTQA0BIV8bQCTxdZY1o3DdR7V2TXyQ1Y/Q8NlFOVYlFkNA1ZNkJRINkjiCP4HoqDMRQnY66MksRMd9jBSJwbc9kHieXJ2wBi6IIsz50529JVwFdf+/CcyoNJAlvvagC8jM4IRoKXF2ZnIYSh8lmsWCl/Fud+Dp2Qekr+LvpwEUZaFMC4FETDF1/x41Kj7sFhp15vtFPRMc3+Fo8fO/36Ug/252PgxkA35DZZYAQN4RD54g/trcPPlcdS35wMVrpJGFuYXrEVFZQwXRBeioXniXJ57HCn6f1W0VXK0wAWpKWGFGptPgfIAAAgAElEQVSEkovMXNpaCACHQ7G6unrvljH2i4QYZNJ/mAwdR4wLtOz94O+StQD7JkwPBJ/xv2R/8sJPnqvt3fsG9tqX1D/dkiL9+f0F9ZusVOpPfnxPY9ezP2hKETDrS6ClG9w9CTIZMEAC4KQGwEqmbrv7l1UevLCPNmggf+Q4Lnq+FEKjCIhT4FuiaLEtFrjg9Z6plaEKHBlJRBNj1djcgsMsGlzSI5gxV3TEYcuxVlJZDX+07S+P1fD7FhVDmQmOxVy34KLJy1mSgsj9qBzEChKLnQjpgmhDQcfOUwqIMRAuDwaP04NwZ8M+CH/x3ruXL18+0jp75PKH7772IXrDEMLMXSQFxCJ2bv8QR2px3UqnfbsZ7gIB88NX6skyAJFG2mmmvSV+Uxolkcc0Spl2fGykLMv53nr/xLHj62h+SJ9X8z7eyVEnBC5pBFQs8M7fBJbRnSwwcu/1a+VEXEPgye2BW2c85AX6KbielpvZ4xuaHw+DwzWBlQAEk0EWu/mrIkn9HxnKgIli5rX/BhMc91c57OGTSD8NNrioE2JzAe+N79WE4X4hDBQGCABM7a3ufa5SrVaKWHGvfmun1U+Eyk760r/vb0AYrWlfwACNDFCjXyADFEPUkUQIADMr6qPu7JltteauwOgUVX3p11IOw5odanIUNjfSTEdB02zueYTeLRMf4mxINBrN5drTC+NYiS56OXVdTEp/ddA/t1QTt9Yhop+6HclVMu26mKtCHSOzwpTcoXEiDlSUn7ANjMw65vCMa0tNLubGCg6cYxyIYWJ5o4PhJNyZ+b/+i65479XXfv3huXOKEOqioO6DoAkyDgaYlwUgnMTTDg2G/gH46QMIiHMbIobBN4xbJGyrTu2LhQpBqR6PJppZ+U6/cWLmwOCm9G8jA/RFMQKB9++ZhrCwFX2D8bg3JptjKAUGNHAbILg17PkzcJ+f/DrbHJjcjP5tctavWfKhVOs0iq36IhWdukbMsYIp4WTBG+l2hk5/SQFvfXkrmTQQqGt/YW1hJGIy36Q5FdK+TOj275ohgBoCI2vHbrzwwgup1HMrmXitVkQHH/a1mYr3ox27+sW/73Ps3PF0tDyk5X9BF3goxAA7QwHgkJxttkEBq5VMte05KhFWLDAGdkPdiksL/DR7wMAbAqOX1ttx0SZucIi4zlJgFpqYsYTK+UYaV2b3KVyUvcIcrQOUIr31VsaGNPPjx0C2GY2vtBsyXYG3FLaHzx9j9yQtn9o1MhiRPlNLKMN2DrvDbgH70sXBnKNw3IIEL6yzrcvv9TCDoS3Wu+9+KPaAc8sLpwmAV7iSBBwQZW9az2gfQPJQR6tfLEtcYPCbQsqmUA6J9k/MX0rUvmSZ/k7+5OjM4Zu6+TGqP7rxTxcCdSVwMIBBQODgJ+yG6MUhBgDRDVn72elXxkbGTDekC8aeJCT9VfSv2WweuJfsXf3rdXIt4g/Y6qclL/VxbLVjWjcUw6t+DdBApyCngU6kwP/nb+8lw+U9uSwZ8dPgpGZ/SR8Ph8PwNxFKgv079dl+/NRTP/jBc7lctZqqxVeqtWKmXX3qqWd3PNOHv+99QBht2B+wz9hh6fw3GAXRkyBhAGy3K5VKLZqK11bs8fnW+YWpGPW9TqkBTz9OwDlpKFoc9GmRARMb0zLy4dH4s1QqrowMDA2oPDiXSzXj1vh4ARyRrjJCk/AOxejA0A3BP8ZAeSQRz9Tpo6A+0mw0C9PCUiZU/fQAmvzRTWLO5aYxBUxZMkxSHZWv4oPbhTHEhm0gNIM+M3+29bPL//Duu6/1NoWRieCLNMe/MnVVM8D8NIbwUP2j4aAMsND2kKDnigm0RUcEyKDrHru/cECFIrDUrlRzI+UBfps/eGfmxKkPDg6i93FhNEC80MFoKBMWXWCYDYIEvgQIHNaW0eFEeGJi9eiLI+WogsBtRCcwboTJznERwJ/6HfXcsdWJhzR/N5DAtSCxNEH8M9W8bi2LBi51c8t0e9YM/uk5EM0e/w0y4C9ucSXIsCaN/hsEKbB5W0HXYWP7p0t+AfCZANom/3znrh07nn366aefUvE0YocCv61+9Prx/QgKo7MD2hBGT4JgKUhQA9wdqgEqAOSjZrudKbZXavFUPJWqVdrTy63W/Ow0N140xBeVo7u2Kw4xBCEK4mhpYFE6Y5e8NiCwMjI5lG0mVBaciNbc8dl8WjQvih6RMxarTc3+bgj8ZcuKMVZowSDprw+ArPtZMRG9YDVnWiMQvgBMlRAayclcKmDEM7DAfUgaAGe44ZI7zhFnW0dU1nv53Vdf7eKDrx6hFGZhQW8/4n726avw2M9L8U/b0NANH3VAT1BQj01jBQDqoZh4a7AMWKoX4wlF/4bYanrx6Iw0P3zw6whN+Hzs63wyhIE3D3M8Tkigjy1IhNfOHh0ZGol//c3n3e0QH9eefzRSqJsfJ79JlAd2v35vs8Hftd6HAjGREJBFIhFD44YpZcGZpH/jByQ/GpDMC4PaIfnf6r0vP1oVaaB5kc/8hiOG+SXlM/JJ7focEazrYH46CNXJP+cP0s5dJtTxFj90/fg+BSDQZL9mEmTRrwKGpYAAwAGfAWZWMplKLZXK5eK1asa7oiDw/PIUZdAiXUa2ycqf/LQr6gf7AfGuUjCoksK6bL1oFKvlRZUHwy0wmqgV9uyhkSmALW03ipWENH4Zi/CHGVP4lyl6nkyMYGccqR1XblrcGyKjcfSGERWOGKoSMAlJVMfwBjNzsav7iYFXp2QaeOHiLAzxz5xVAHjk3ffevXzu8pH51pG/flfxwZAt1rxQwIVx+h9wrVz+KhLgAk0ADQiTgdpSBxRJj0vlJBGQqzBLHH1TvwriiWaZOvTd16wTV4+L8jkEb2H+ZyZBeuFfaDgEDeG/CbbHrUUCrcjaRPLnh8aaCb8hvBkOPlJA+/JWM/vG6V7al575cETn5RoAw/CXjJh5XoOAw/q0fl6Ohm+x271mADAZgk3C3617939zP0kuKaCnU95hk1ADGE1qzHcMSZ8D8UsXA8TnG/7zrX7C+vE9D20TIwA4IDrADgJoAHBxJFo2ANiuZFQODAqYSykIrFWL460jigWmOeLgYsDLdj2PtlOK3Djil08TqliMY3M288GGng0ZWMyWE9FELjE2Wa6utFV6W1eAUEmVh3ZL32MR6kR12BxROBkv2sSTBsxUXU8Bpcd6Yxr1PWl+CNaJsJpdEIcptcNMWH1ZVMfQJ18lq9NXsRZOPA0wDCIbQc6cmfdNod+lIczc/FnFBy/rSeFz86SA2v8PWXQsn1fvRxdULf7DJ5H/eJBh0mKRRVochcMcCC21tfS5nJVv/fFjM+9/RfzrSf/8DDiUA/tn5UjjnyTCt7+857cyDeLwdiJy74AC3a8VBD45+unq39c3yuXm4Vsd2e+WQpi1iN9p6GrmBkwOODacNMzNVOoYq6saAf0c2Me/YcG/L1QGnIwMh8AvVAdMSkT8omDg+7IB9cIBqO0D4L/42LnjqTHdDs7KXmDdBTESGJ0CLzbHmhQI7i4XiygCVqu1eDyVS0WjuVRqpTA332rNzTogXJZsxUQ3AklwSTJfVw/0ssfrYvMROWCp3ihlogNDKrWNRqP4HIsDIyPkQgrzJPEFK2X2O5JI5KolV5vOQAGD0TkHQmum2BAAwhJQ8mLJxR0tk3bMejmRJvIVMJSGKT6XIokjKnYiXRQKaOp/rx05c/bMPNTQ8/Nnz/q2WGIKoxBziitFsJwpn5YBEFY8OZ6nPgeXPNHW0GI3hA0R2sg2Gh5tT+sr1XiurLPftw/PHHpxvUv1vCFGTR682bNBJrw+eudL0xAOAQzy4InV+6eyA10N4W3GxgxZ0b+Ugr8DFx9x8DfCTu6EYYD+yRD/W6WU5ZY+H1wht/RoDsqcIdbI/Pf+R1/8h+FhnzcaEGRbuCuSgfbFIN8mCEi47QPgH0HshCpQqwAHBhZNCtzdBl4sj40NERXLrAFmKpU4qoCKBKrbXN11Zlut+eU9MbQwGtoU2nFKDYVRQAJ2IKZdq4DNHCzfASgVByqVGnWV6i4OZUcSY+iBMg2XpDeAP5UmK/r3QjTerlvcImfpaqKrWyHANpvSF4f1PgN/VGAD6+hKKmeQkzMtllpgAV4I02LpgjbI7IJUATX+wRWQ8CemMEe0Lda5s2fn5lTGPIUFSFfFAaaQFktWaUvTC8vlbKDU/oB9Di2hXe5M9rhA2Su244kRLX1+65UTMwcudJq+bB69n5OzQSK8vn7zl2wIrwVb1HXDFWaBxwea0a+/+fyxc2AfBb/5eqSZ/cmxzSY/1kK3Henw2lrSRzCWAMNAFqKAX97zNXtyqxkdFhUJgk7o1/mvuQX+98kX97WWWjrL+h2S+l6nv4KMoeavUb5sRgL7KfAfTVAYLYoY4wazuzsHVgCYyBIVs4r/1YsZlQID/KKJFCEwUa1PL8wfmV/eb+lZjgbGQpwGtYEQpqRdoUWxfEEvCHJd5IANu1gv1avNxaGy4N+Q7APRXd9JukOj95EYi2caMm5CFgc0YXdD8JS1NrZDFCRSeOhSAOMIMYQWUBJSNk+kUxGLcbUm/QCZBHMv+uwsPRGM94ExBYQnzNlWS3tD/7qlAHB2YXaKQuhp7oDDbhI9A8KJZNdhVVQIoDS2WRC0ZDMI+r8K/uB7kJUW+4tHT78O6csFDr6NXjCANqpx7QKf6DBE7TUlPDgYnpFTj/SEcLgbolFmYuLWsbcXyy88pBvix8nwfYj96cHfZrnZfOded+9XNzZCn3JjSiyd3IACBqms0fIhlVUAGJ5oi4S44CrH1aTvEqJ/txT8ffmbL+4FEhd5X/Pi4ciwmQHhuw53DP72xj0TZID9hu8fR+x85ulccyDbYYbg45/IYBbLKjHlT6kCwHpRkbaqwr14PJFKpXIqC85Vaxl731yrNT+eh6TZ5vpbxdZQArMdY3LFkRBMxmHFkSvGCY1isViyi5XyUNkXI0rWu4hPiOpfdmRMAWC1La1USmA4ZafraqIbdO2YJf0ThnaSZgXQJfAVHMFLqgO5LI6TcTF0MDDNyyRYAHB57ozxgFYMMIDAVqt1TlPAy3DFQhdkCjuAp/Ns/xZi09y/JM1mfFLb1QDNb4Cl3bAkFUbvt5ZKGN+DD14/cfTUekDiNoSCv4MK8pZu375j4vbNpfWDBw+GcXA01CLpLgVG1rRJgo9JiubcOxQtN3OPVQoMTX6ofx/V+xvp31rPw65rbg3/Z7+REQDgsA+ASGX/wz/dS2r9StLv2ppQeSv73Ukj/xP0u//bL764f8tAHJTQJgP2SaAQQQHIQPuiMe6hABjpA+AfT+zcQcforhqgxr9JDYAjZQ2AxXaxmKlV4/FaPFdTDDAHKMzVVjLpcQWBcwvoAfOnvaCIIDseBEAxY5GuLGghSnA2VoLXi+2SXWrHs9Q6SxbOWxQCMTKXGIH4j+uX6LtFEgj+59BDmt1mz3ZNrs3n4ZFK4ketjJ22pDIo20LScItxAYHoAxcoYzFVwBmKAc/MH3lVlwDnz7bOaFMExQB/qoHxVQIgl8PRDAtL5gCq/E9LS/+ZfNPWjl5uQ75MzglC+2KXGplazmS/Qy9enXlnMFA+bwgFcktLNz/56FfXP/vsug45uLO0NGhmRvwEeDBMAwmB92/dCoTRBB65nRj++ZvlLLshYXD7nB+bg2JQBVT4N5JtvvBmt/ZlrePIPFrrSIYZq6u/NrgSMMSOZu6tf08t33AyhHsdNHAYeCdrkoF96sGXX35B+FsDuA2HXiCP8WDYyGH4Dmz+DkdCGNcL+YJn+wD4xxTwSMjqnUi7u/FPA+BIdlEAUKXAK5VqLk72p8BPkcEc7jNeeu58q3V+Ku9SAW07foJqsSnrCgVkd7aAVFn8XkqKA2IxWnVkQOBXCpHMgwdgmjCSy5TEW99yYD/tOrqlanuOYKGli34ig7HpBcgqnMOJZGihXcBdWlARd1glx9IkmsDAv6t+GRAAePZDQwFbpgaouKCxBdQAuMDdSMBP+uC7XEZCDxrP1dwPU9AgfhT8QQPt6BnnkvoWRkf04Nvbhy8eWloX05dRZr8XQgYwF9YPDt6888lnnwXYF4rPrn926cHtpfVQ70Qzv9HgcHB99Pb9QBMjP/RCtxRuXTxQHmh2Q+CmcTJ88DmrfwNv/PxRVr51RnI1oinghA+MwTSvtEB+8+VqJGmMCgBcfmHPIBgKfl8yfvtP//iPX3zy5f1boRG6SAB2IV8ErYpOCvzpHfNbYZ9c0meAf2QBVWDHXnQ/JgGAzZGRsZHs0GQ2AwLYLlZq1Wo0ByFMKgpJYAp31YxVwAKNuT2O7nwK3AkTY0PCEpCCKxX4GqHMQyekRCPQuGJE0geB8CVL79SxsVoJ70YTecfx/KTSlh1rPNSFReoCiTq8RqtS0hTCsA/MJW0u98tpzXIBMr6rYuysGODUgqKAKAJqCvjekfn5OU0AfacYpsDLF1UGPH7FOMFMo7dcwGdJk3b6CbAUAVkWUA9liK9RV/QvaujfjTePnTgV9nwO5C2Ig+s373y0Cfr5cenBg9GD/jsI/JnROFMKlPE4DYGGlhECb52uDpSvoRS4PQz04/OTX781kr127Kc9mx8dQBs87jpeW73FryloU4e6H8xn73/5hchgkn7FLiKpa0cqnFQgaGI1ybfyr5bOrz4R8cUwwgRDvi9Et20A4FpyuC97/qOKnc883TQ1wK4msNQAm81yeaiJJki93l6p1dD9YAbMcmAcEJiLt9N7ludbywv78m6JBihaBoPuqwLAGBEQ1M+BHR9n1NLIahslxQOLmQyKi7mxMYW2zbGRRAIrlOKK/lmWDBtDaChI5yKfVMl2nSjDBDhtgfrJ+wvgcStcWiAJKmRXJMrcp46aXSF/VaQwIIBX6YlFDjg3F2yCe+3DDy+fYxZ89rLRQr93eZ4ymCkIAaenr6h3oLeqSq0N+LEbY3Psg0AvKhiLy0Dsej2D6p8M/u6+cHQT2yuhbutvf7IF+Om49GB0vRNER/17aQiPfuS75ptq25qUAiduHb2WbV4DCdwGBBoOqLLfVLY5+Uo3/esCw7XgTGdeLPdrSS3m8xGwA/6If/dFx+xrAbWILxIxJFCQUMsBdS85GXpB0owD69doAMSh9r2SgbyH454fCgB/uNVPVD/+hcXOZ54dGzJJ8G5jBUMAhHdVE+s4mitthYDtSpWZb1zIHw9ABnO1aqVoT59RefDCfupPHCn/IfeUUpjFGQnmq6JgZgoLazwPzWVFLGuUGMZTNbxzLtem3arFdeKoqsFeviTeeiR/XMtuaYTxZAADEkSVd6ZjApXCNdNgoGwQxyynwAUhWAtMK5erMHVWSfD4lSm43cMWy18DwowXfjD+43ePzGsZ4Iz0gAuoAUIFzdWcRnIotBOJr/rvhGSHpv/oBrUrNR/+rh06ffS438bonH67oNjf7Y+2hX4SD5ZCr9bTcoEkxtfEJCPdW9TXJtZWDz03MJDy/VK3js+fP/l1ttzce6Kj+RGgXS9OuMkzCuZ09imP/fwXUuYvf/vF/dWkHt5ABHlv6LCDC3aG3/kwLzdAyPvh1VDxb9sAGFn7V1v9PPXjX1xAGD0kKbCGQN0EyZbLAMCBgXKmjhR4pRqvchoulxD+l1P8L47BkFq13di3PH9kfm4qj+lc3aQABOpMGPggSmWHdTgSOsUCG7ASUql1XDAQpDKn8JTPIWsEwDkunWekl8ASm9VApwGeMA1LOiI8jXkLWmK5nAomCiIHV8xTRuEAgDG6l8LJr8A2sNgC6irgmda5np4wf/HaX8MVa3mWbgjMna8WCjBClYSblqtgvpYUO9G38aiMVP/pDRqgtmvRRFN8DyZPHZ15f3R9MCja6eT3Aj/Wb376CPCHUCxwsCNCCDjqN4RXk0Ep0MAVzQIXt98QVtlvQv2b0IO/XTpmExtT366n9NGwb2OtHgdaFvQzvvyN4n++jCWEeb7FS1jiEobIpPE/8G+SIRyUV4a1L48Qa5E/68sA/xgDZoEDoQzYMMAyIjs0lM0gVcUsSC2Vi7LyR0G0gr94LhFnN6RSL+UXzrdac/uwKVMqgWmHEhVYF6Bip6iYYmsWd3WAOHFVUKnYLmaqFfXWcTaZU3BZo4MMbWKwfNOVwprMGFNswj4wi4BMO0kExXUPLWHtFSjX2tiJbkOwzO0hSIFjWKGkYPjqFabBtMafohQQCHi5lx0MuyJ6OTBKgCoFnlapdMFJ59Pqrwwck3iS3bpsfeDL5TJ0t1FqV+PRZpaSo93Xjp4+/Pb6BTPZFvQsGOs3Tv3q0eBPxaddCBgeDxYIvPM3oVKgzoPXyAKHL76ze+CtqJkNeZgbwufPf6NQfPK5mV6TH2u9IW9TTrgWSFnwEFSPqjyFfr/9zRdfYgjEIJdP5oTBCQAGABcxgBicSZrXCmCGEVI3f1fNNPJWsBfE2sQP+yXAP85QifDTPygPdRQBhwQAmyOJpxr1TLFeR7IqBcB4TsqAKSqjcUrd1TL1/bOtI63lKZfwhXmwtC26EEChrSfEkA7TPxRPsAwoXoM1BYKZTEZlvzHHA/8T11WZpWVWzeqaK5IXSwYtkP3Sigv9Bod+MK4rlqiKa4oEWhFOD474LrXQmAbGp1cgSEsr2Q0yI8aAtEQ497eXL3/42nuBH8y757Qd4EUzCQxHaVhr6Z4Ky4wW83CLuOyxWunSF0vhX0bRv2tvcfJt8sabJ469j+w3QL3R0O360qePDH+IBwECSh84hIHshgz+8u/1eJyRBQoKrcl4XPOtLRvC6P02m+WxYz/dzPelZy68eVIcARZJ+wIFOTQzRMqim7khBugDoE5lDf2LBGwwdMpvdQQAmPRT4k769wgAqH5X9AngH2/s3PXs00/9QKzZqcrLjoyM5X7w1NM7ntn1IyyAKYGlCe5JA1jlrDkooikKVKfilYqz58yR+fmFNDeE0KyZqzoAEIJlnNvAlIjFkV0Xg7Gler2dUSwQDZG6bBi2AY2crZOSH+TVVNFxoTpnzjz9BEuMzD8l8cX+cSqS2R22qYqJAUs5m4Jl6jEk4WyD5KevAACnrrITPKt9scD10P09chl2MK++do7L0ufmLjIBpgYQry0AS8UDGpvoLAKga2kbGD0KAmd+fONeaJZvqO/q7hu+7RWRqqODi5v1pU8e3vftug/i0/XO9+oKdEM+0aXACcxu+DuFAAGrx14sD7z19cMRENK/8tiB+5FH8H3ZOpLDt+79P/83pSz/9Nt//OK3XxL9pJ8RifjszQc4c2QwTzc4kuHj0CWhIHLq0Y9A+vcIEflXfQL4xx07n6HZ41Ni9vjsszueodHtzh+V6kCnaq3GKbhcTreA0QZRSXA0RVmggsdMxh5fbh2ZH48puEsXIFRJxzC5m6YrFAXDNg1aOJzrNww8BYK0y7Kh84OJsuUBCx29a0nyX6kL2q6sYUJXWSTPOkXWQkEyRFfP4fFz2PBo8CQnZ/INZTSmQQr7yACNGHBhWcWcKKDn5rQMsCXopw3xZR3IVYoAYQbtsOeS5hZM1zfisiUDFwj0KvHcmD/5MXP0+LoGqDBe+aqVR09/dXz2ICyMHt2IgOiG6NVJExMdGIZuyK2j1ybLia9PduTBsj9EbF8o/Vt84djPQpNva/5NV6xFOsbfOq7rUSFMrq4aJQv3WcrJ0PMB4/OpoI+A/ll93Pn64FJaIYRdnx85VvsiwD+F2KndHnfuNL/vdv6oUazDDaGaYqi8twY/BBQC42SBRD9kxLWMiwHh1tweQJ7NRix8ntOujAZjQ7kbk21tCihEEwg2SFhreJopkt3ZnP6AlSDgktgnDgPUBQrN4siJKxvIKbDm5BntWC3xqLLEEIHPaADUmXBBXAE5DyK+WCSB8MYC3uGGyDcnOzEvwgcBQyDT3IeZL8QKXLPpSqNHZDkCzTb/OqCr9Uw8NdbUGy8PHJt5P2x5H1Ks8Oz66EePi3/XO7PgXoEnaBaouyFhJFqbSN47fGGgnOjdEP5c0b9rzWb2l8HGXw1qnXfhHDgSCQ259Y6H2WZpDueDWwjyggw3lBKH630hgPSLg3iobf8eD/4mfthPgP9EY+ePrWKpVGxXKzWMwpkkWEhgAtkwpDFx8MJUpdhO71ckUEGgKwJoED5IY+x0QZHANDFR22VJPoweKtHLYeYo3QxESdJcaGAsXiHOUp5LboWxE9steS5bw8IG2fvVcjw6IUhpLs0OsKPVevjkafGEyUPNIuuRplQSPC62CLOK7c1pIFyeW2bMIv+FBPAq94HkFQBiIUjB4SZMElFAvENbCIW6JS6Q99qVavQtPW5z4dDM0SVd/PObHqOhYuD6Bw/Pf7eIzx74FFC/a0chUFjgB+KXqllgUK/DRMa9d94aGBj7JrRFPTT4m202axuaH502CxsAcLPY0i/QRNC+CMDP/5s0ACiPDNQFHoJymsjHB09C//oFwD/h2PkjrHYrFiu1msY/qflpPigOWSIMjNdquUzGLcweOTK/sEeBT8GxsbJcusGclHOJh+pIa0Zgau+KwEWWfnieEbXYTJA9NIOlusYhW20I4xBFPTI+BZO6Bkg2Rv89CxocS/igyw4I4LhQoDMg2iDAv1h+2giipxQIckvc7EXA3cXZ5dlldYRjoB8E0DIFDCNU7FUim3TFBZtNEEeLdOSr97wGpM/RMvFv9wfvzxx7h82PUb/7O+jnwYyDp54E/1R83OGqZUCvEwPXB+/8vV6g+WtpCPu56cTw//HKwGK2e3XS55+f/HqsXL526GEbfzue6TH7+1gRaoL4oJbsOm+eMyxQTpgrGYQ/CmweQ/ti4od/3i8A/qnGzh+78G/JQK+Xi9dEB52jEDqVyHFTSFxEfCCFiVStkpmexd6QqYIuyBH9yMUs8Y5H1yIm0x22LdiBdgXZE7XP0gNmXos7GX7DRnbLz5CJeAJ5tqA5dakAACAASURBVC0tjrRk3Q0r7dkyA4xLXYOZLvwAsSIYDDCWjxWm03l4O+up4ClQPEDgAiGPSe/F2X8HlfTCzJTKkmV8WDogdGP1F2E63E/s8dNxXll9Oi9TewHSZ/p7HT98+tDbekhtEIO/oyYPDhogg49dANRxSRPAAF27OeDoqB6PMxPCAYqsYW/I6okDi5PNjtVJiv5Fm9ls+36I/q113G2mB+yIJ0bDSAjSwgnuhgJh+CIfFDulz48caz/s1//+dAMpcB2zwHG4wcT1GEguVeNYnCKDuVxChMzqiE0RhZWlfXOtI2cWYoA58DsuK4/JyvKCwqlCmnPDKOmlqepTRzLapumeazxlUFdreKKoQ+MY0yQNW+bLPE6EsDjouplUtaq+qkq87E17tH0R/OVYLkuNrCG6osJRKTL2A9Pc+apYIyiIQyYsMY4dwFyEPg77A1ogQDp9FU740BLGXO4YYSqvLWkI6ZIQ2/WV1FizzOwXkx9Xl9ZNbhr8DQGWAqY7T4h/n4XLgDrT1pNxHQiooPaj+z4b6izaTQxfPLU4OWBc8z9H82NgIHv8vwSTH10Vv97I1uvso2FgkOn6tb5IJ/CZxzr39RNfzQjD169uP/vtdc1wv//7Jx0/tur1eqaYqckoHIleNKEHN6Lsh9RqUdYAaZSgzleKdnpuvnVkbiGPKh5SRctiVioG8rasUKNY2W+hWoJlsi1dj9Gx14uUttEg6YN6Oi1dEFGcoEuCA6eUNaYyu1PiOuPKRa4j7C8tKmwkrFyOhLngQn7atEJ0M4R5sEI+1gTH6ZUwNX5FBwqAmABOi7N0TJYQOzFLJlCIr/hvcTMriv+VuXNv8sbxY8feH10X/FmSGd1Rg3xmdlfFk3RAJB6E8c9QQOGBgwEXVGe+uvmr+34pMFzCUyd+dv+XP5lUiTDNr775emTx2punb61t6P12Vfu62eF28G6rK3wA9IEw2XlWw57fAImYop8PmIKWevC3B7RtJyL99PdPPHY06tTq1XS9D1AXNfPAoIXogCQEHDkkEq+m4tVKOj9+pjU/m3e8RlrwKI1VcUQ9QhHooWSQOMlElRMUDQIiYLHhakMBl0kvZYB4H0vX2nACzgOwwyplxVR6caDWEDh1XMFBpKgK/WKOVALRjiYJzAsDLOTzV3QifIXuMDPqzzhGPsD6WB2k/A8KQEX/YtMFjhQDRuG3ZdEGVTz60yz/uV5GfZNeeAv4t3vyJ6+fPnwTtldLoxdG1d8LS4ODSxcC5mdi6VcPR7eN2r8N8anB1VG/1jhq7nU6bAQ3vl9q5wrhCCyjh2/dP/RX1a8RlRffnLmnqOLDGF3QTNkO+HU9teHKUArb9bDrmQ2ngny3wwRh+EmaH+qb82d9+venHs/YdViYYjc6RoHB9XIqGY7mtBYwhXM5MsJajtNy6JFUK6XCtMqDsUXdIasTYxa6h7IvkmbP1LMp3nMxzmZz+WXDNr0Omzb4nnRAgGjggWlLFM7scKBrYrEh7DVhJ7i4GC8aQz5HanIuDbpcbtMUyTSGRBR/g59VrICp3ulCTLYkTRMEx/8dENDwPoFBFbCQ4SoQBoxnYoRyl3Q2xnE4KHIalVR0rMxtA1h4fuy4ZmGK/o0uDS6N+pW5wTAM3n5iAtjZBvEp36Amg/JYIyAWaH4pO4T1hHAoE8YPfjJoGnTg2qbYFs6k/VNbkbxe0QPofEYXPOdzQk0Rg7S38w3MzqMtcG6zSParf/3Y9aNSqdRuZyrMcSmBAfYR9ACBUXUUVYf0dEkZp6wUNDHO+HyrNT/lOqzsESQ4zIus1NMdDJpc0UBAeha259hmpUZaOrokVpbGF4E3W6xR5UrMh5TKk4r/jVW5k4OJMToqTLKhu8HGzjwpJ8AQHLAAVwQuCclPxzAYl5d+8JUrMwC/qSn2RtSNOYAABjMknH+LyQ4Q+hymXdHCkMXa2PlxDb1fBYDHD88cAuZc0NgzSNtTuJ8KCZQ/BKQnLQEibofwz5T/ArA1nRHzGQfv3Dfb4yb8up6+CXzyImGOF+m896M7Gw49DqPgI+FhMnyfDD9Mhh+bCzvP66z4ibQvKvr0rx8qflwvloqZYkVhHNNcmQeJQhBtfLF08gvcq0mtMJpS11cb08vzR47MjaexD9dh5wPTHazCuQqD2J6VVjG4HbsZHsAxJuNyuF7TOIvdjJJCMVplWVy2q11RkXc2JwfKGan+gYspmomOCjd1ov+r3iuWdgNxIL4ELAkBCZRcWPoh09iVNIWWL1GPxJDWWdiEXkiLjqbAtXNU4khXmyk7tM+lTAor36h9vvH6aez80CB0QbeAwzE4ajojvwMA/B//IwSAAng+GprPHJQFB6m8DswCu6t3HcuN1gyurYVRTEPdWvDatdBH8D4dL3jECNXygrQ26IpIzmv4oA+A8iiZFNP7x4W/vvi5H4xdjYwigGCAcZohsNEhM8AAQyCeOkRqXKvlNAOsSUmw1i4VsEX9/HieDV7HEm1LjC0JgJOQQd3w9TTVg88BEY61Qds0cUH7pqdEFOhSF+MSPmkZU0mk6mluICEmugrzoKJ2xaSf+mjMhgCu0hb2eeRjyFzzaGjkORpc4KCHSYVZFyTsXZm+giVwKmUGZKaxX8QR6Q5YoPRhZBTFbu99bqQs2pcbB2Zm3llaN6DjJ6Ojmp/5NTkC0+8AADu6IAb5DPeTzxy0QnQpUJsFamsUH3Y6kKo3bHWe7SCKm1613af8SPo3XSdDXZEQFGr2p08Mr4Z8Xx49+tW/fujY+eMSnJtrdEPQyhdRA+p5uHjKpL5imBqvURnIM9WMPX6eNjEF6PWAQgro4BQDnEunYVOg+7sY/nBlp4fFFZi6zifhwl1KoeRsDOt2Yw5nRlTyW/LkxYorKnDytPjPNvJq019muRHv7XgKGpnFKhDE0s5CDO1gxf84HCc+qdO6Pcz1l1dZ+wNEsnlSEADkoF2asj9LpIBWo1h7YUTWze9++9DM0ZvrAeD4jVkDhT4Xk+ceqQZ4qefh9ds9d2b66a8Pu4Z2Bt2Q5ITxS9W8zYj7OpLZ0HGIL257sqM7Nn1dN+RFdEKL88Fy8/BVpgboywL9lZeP2/xN/qt+9a8fOnY16nBDqMZzUv6je3NNcl5oYGrxBFUwCSbEtbjAom6RxDNFd3buyJHzs/ssW/Ja8jdHVl3adEvF+Kwlqj7myHqhLuTQQt4E00qWXVyYs+rgXDAeBIZ6uhKIt+RWJJFNwwRGyCAH78SthQ9sACBdUtMxt8BNmQUZDY6xFwIWOM2cmHkxb4CTcMHndjnaz9gyzwdhDwfxHKtYysTHgH/wfXl95sRxwtvSIDofqPuNjuoNSAERNHik7pc2oNyjh5/zbgaDgyEM1OcUBIbNAjUorXXmu50waHJbg5P+o+Ba8+ItqGQvCOwu7oW4nT42Ux9+OqyPsfpNb0UaTj4R/fvPaz/s418/gnjmqXamUqkYCxi6H4D+1Yw3DCdCcjnhfTIap6+tVVeq9bq9gG7IbD5GWqZQoyHgRyB0xPXApoW9OB40PG3lQvUf2yaAs5KdqcWWZ2Nwy7cNMFqSBts0yhI2yO6HKAk5rCFzycBc7K/keDLtAR1LOzrDIwZm+QUFfir5Zag79IjzyJDThQIwEYiZFsNB6aVAqIgVnOoztqvxVJPwt3jj+LETh24C1STJHVwKg45A32AIrXh4Zyt42zIejIbfb5MwJNR8RSgFvo88eNWMx4WxK0T0ug9CseYDoKkHPi4pjPSkfzrtDfWCDdkzeBigIO8f1/VZh4K/fvbbj3A8s1JZqdQMrkHvQuAjxrEvzPZInOVA8EMaRWNgTrLhXKZRWJ5rtWY5HscOBhwO0EFowN/FlUEy6JSF8bEk6NJEELkwYLNB0/tc3LYXzk+5JQFKVgNdDnxYku6yiKh9ETx/VwcGNRwqljkbjN6wU2AT5uo0jbLAAdEOodWBbH1D01eWX16djgEAMQEiXq5EY5o4OBaPvWKmxubH0NDk7mva9gqKF/VxYUnawD7s+RgYRqX1R8qBdXSKAx/0yIA7Q9NAPzEXEFxfH/3lfZ8uaWoXQjUdm7i7PAHWdUcydNtxOuCAhvUlQ1eGnyUqPqH2Za3f/OhHdzzzVKYqQmcd4gQtTeGc7Apmg4RdkFRUhoSrGhVhFujGzrdareXxmCf9DyaOwEGbAMXinbhGWzK2JiyLhggeUROmgtGU67Wt8eX9doN1N6kUIiNmL5j6P5vtFSGWRFrHrZfyZH5UYIswxoUrFoqAXNiejuUBichy03ngH3SCgD3MfAAe0/lpIGYsLT4MCmfTZJb4Y5fatVS0yeofbK9OvL9EaIHomfLnJWbAmg5KEroRnB5w7/kWeuiHxKXu3SAPjxAMKghc+oSlwPAO4Z7xECbYfSaUET9mBIlvCO/C+Nh5DMs/3AXal8eCwH7zox894pmnU1rnJ13fuMlzyQPj4pSvmGEiRev8eI3PS1MYXZF4tVLYN3fkyDycsiz6/EHg4rIkaMXchufqjofXKGHe16P0GUgpFsvij18bKTXalUx+eXyPJ5U/+Cc0PJinMgu2dBeEume+X9otxgcG7GkrRsVyWpsYuFY6cGaIOYW8A7d8LE1CA+SqeixlQsplCrCSjunlIvCBoUEXP43C3mIlLtLnxcndLx49fXRJqnxggOpmySTCfhOkZ5K6fnsrhNsitiaACFMLDPWDBY1vfnnP9AyC8biufHYDmnWe8F/2+I0Rie6qH+70kvRk6FzE1AMjQTqc1BJu+Q95ONT1imR/8q0fPWPXs08FmEf8izP1BSxGkfFqHijZMBddEgLRJalWqvFctV2xZltwjM5zwNfR6j50LCCEdjAGbHMeGN0MuyRJrqJ9sPdTQBhL23Y7WysWK6lmZXp5Sq7gRaIM9ARPuSeJEKiOYzGvsji5OFlLq2MXtgyOeHBhfk3hm1OkpxVdUtNw+SukVbaLkiA3frgAPWOjGqOGJs2mjaudCxX6FjM56f0uTn7wzszMO1/p5gd7DqNLgxr1DPnz/3TFhQdbQdxDY3v458doJwayG/Kre2IZbRZodtT2NonvKin26Z7AXtJPewPNn9/xDUDQNH8fs/mh6F8f/vqxSex85mnsgsuJ9pnGWHEtdjGlwVRNsFFnyaIWrAllTMWrtbZb2DPfas1NsQVsu3muOwIYKmSJcbuRJRijnuVMsK1NsajkU+mnPZatQZA4lirun9qnDV7oxOKJ4MV0RjxpLKeddmJoUYFTTSSAspLEoY+fYynM817BPiWMhnA+GWwwVpjGqAcfky+mBfaw+4P9Y6Kren9PfcZSOxNX+DeEnW+Lx6+eeB3SPxn9WOLSD9NvFQbYAXxdibBKgh+hDhhaEILDS+H9wNsJjc9hCBy8c+zeamAWuAmSrXXc9XzuIVdsK8IVvo5ENxkcBwgZXP3k2pd+9a8fm8bOXTueymlYY9M3qidBpPebo12gdITj0gFJ5QwYEhmrlWLbzc8qEji7J+0q7sR1Hg63ntO3FIwKPgPcjNlo0DQfQjubdUGqjTPZcmJMMc6EgsCp5f0WLrJNPgpdHkdL0nrAxLWrWXgkKAYYs+CTb+vCnfZkiNkrlYZsK4m5sbTOcKXo53CHEpdpokiY1ibT4mgtTRfX9orqS8kOUPvyk9dnTpzSsDII6uc3PgzQrQ8O9mZ/GpMeBQA749LHGwjgw3rB+opOAIRZ4J3/iPIZACSEcyEk2wTUHsEW66GRjBjKZx4F+OdPgYQAMXgJFIJPSP/W+r5X/dgikAfn9DJM7Q0oaChVQPJCgcSawJ5UC6s1eQBVTNwZP69Y4PlxdhLgdYB+CIp9xC5PlNBgftyz4ch2IXGyshuet9Icao4lEuqriCZiy+cL8I/h0nU6v9i6AsgM2LEyYhGjolKwXAIgvPsggymw+9vI5YrAV9pkWRhRYZUwX2ClLy3+XaKVYedEz75ZolysZzK5MdK/xd033jmBnR80PIDuxSS+Gu/WL7x0U8Xb6/5akI2NkIOjlx4TAXvg33aiAwEFAtc/uX/PuCBshl86Nd4U39ZCt5tH6Pkgm92E/HUSPz8xjoSx8knh78/60r9+bBk7n3n2B/EoB0HEAIalv5pAHtJd9jyCZnFNBohTuj6oALCWaeTH5460WrPTsh3dkqofhS/ww2I7g3vjHI5ziEe+K6mwuriYG8qWx7iRs1kpzM7GSp7oBQl9aXRnaXngxNxSdnIRoV6QSRMVzTScK4McXq1crtRLpJiENqqc9fbgGJLddEz6JOLBz+ZxjHhb8BrFanwMzY+hxcUbbx+aOczJj6XRJZPqjoa4381PBaruyLiGj4wdKLj+l49XB3zw6Pg3qm9ClcBBKQVye1ynWSBjLXz0UHTbCvokwgAYPm+GPnRjQ1/QAYX+TTISKKL72pd+/D5i1zNPQ/unCBjcrwh63BQX5xBITuufBQKNWT55IAaFAY7ReMWiTQxIoM2NlW4DGj+onW16YQnmcRwkHbO02FlhnLpE5c2NWnlgoDwCDIyO1KfmrtgllQnTOMYDhsWQLZOkpYvtTDuTabfbRdsyWmhL+5g6bqwUL2cHUsVinY4LqPkh25XiXwzJsMuBD+4+AjaiEqmV1ZZTgu9Lk/g3+daBmZkDHHwj/l0YxfCHjysKZn752fVLjOuXHiytGwQaDYERY/3gg20Y/3WHvxNz6+isQProF5BBOmUdE03MFpIYHU/Y8d1WJDvwL3RvUuInlD5P9OlfP7YdO3c8JZimpTCSDCMfpjdqNZ4SQ5haqEIYN4c4qNSqpdhsq9WaGy80GkAeh/0KSmJI5Ywkxm4I7XM5H4dVa416ybaL1ezQQHksQfvBzP7lKatuSz8FibPDvJqQZgtouY4nhT/RSLvcoOTYmZFsuTz0VuWVou4n0ziQNT4KZTjgCzyMcZQk7chKY/ZZ7HYt/sI1wN/Q5OTxqxdfF+mfr30ZHbyAvzr//eVnl0Lxsa/Y21gOvDD6qCTw0tK24a87CMKjftVSI2DglwpoeDjXewzw2/I1BDSf//k1PgOCydCx/5Ing7++7V8/Hil2PftUPIRpcXZ6ZWecCKHj1Aum+ExcAFEjJublatic5O5ZOK/y4Dw9/wg3hCDtDogZYY2BxEQPoyAF2EU3Go1iycukBoayzUQiAR8aa3Z2P3u/rkY4Ty/QBBg6mkG6It6ztXjPsuu1clbFUHMlowBQkmABQNnVyb5z2hKy6GoLLcx94MvBxt8EV74t7r5w6MSxm+sXfPSD9zOxb3BU1/mWProeBsBLDz7u5GxhFCQJ3H4p8NIjyl96hKGCYQgcveOXAh/qB93zZPf9FpHsuAsQL/yEyXTNE36aHKJ/j1v962tf+vHI8czTP0gF6zDjWEZUy8VrhuvF4xwCyckoHKuD8ZSZGUEDpRav1t3p8/Ot8wvTjkAPlSyOZ9Mq2nUK7LJaKN3BJZ+yQcuzGl69VKrXG6XM2OJQeQS2rKmRmjs7m2chT5ocSIY99Ie5aI4JK6eCxVjLhazQWxlT6DcwMDDUVFlyybO1LFtmhLHtKIbJubSZJyYEOtJxbpSKlfhYmc2PyRs3Z05j58eShg8BQUyABD2QpU/vXuqMB72cW3QcXP9YpkK2jksPBg9u+j7bDg1/PgAKBH7ir07avMW7oT/c0RzZJgB2h6n/hTsjAnlaBRjxUZIPHiX77XFRpF/968ejB1WBcWF2NIQh76uZih8FMXHtGS0f2KGeS4Aa6uZILWPlz7fOt2b3cwumpzWBXPMrdlagg9TGNGxJcKF2VuBXKqqbYiaq8uDmWDSRyyVW0gtTrCRyGsSsEnE4aid+fXoEmHwzbWdyoH8DNxQARiuZdrvUsGhpSqro5CEThNU9EZRGMo7YPuOCRrv9XG6sPETp8/Gjpw/fJNdbWloKQeCFjhbwx5c2xIPRwfUL9IfZGOuDS9tJhB/cVLl073cw7zOIrypMN3uKY0wzJoyBIbPAX2+nFPgIsfW7+WywI/kNzukznH3TO4+2hX8bY+3P+vDXj8eLHU+b0V/a4TPXrYkk2mTCAnyCgTn9lJyNp6rxarW+f3z+SGtutoBBN+z/EASMOVINxA3BT68DxuIQRxFAhX71et0rVcuLWQWBxNb2voU9sN73xARLwV5aXd4AADpaIu1ogHWLqfJAdgD8TyXSuVqmqFilx5FjvhhCGEsaHp4pGlq2uMqkLa+t6F9zgIO/H7x5QqR/MvEmez9GtRDaT4LV3x4IeOnjpfVNaeDBg4MfEwM3I4IqjR7d/OUS6zfvoPf84MHHD1VJC+wNSiPErwkSAg/f+24g8KHhl/56PBXifzISogd/Hxf/kn3614/Hjl3P/kADHICtUqMIMEfgy7EJ4qOh7ouQ/IlnAgCzmlppZ/JzR44cOT9F3wKvji1vLAl6EDJ7rifEUPTLHIxzS+pUqV0vAQLbqYHFgZEEEuFornhlbh/gkqb4eBe2TtjxMN75RDVvRcEX01+FYgPlXDUDQlnSCkKqnJ1CWqqJOJVGB9mih4NKxEvVeG5Eer+7jx87zeaHAT+TBmslYFjnMvrg0t1LnyrY+9QHwLufPhhdfwiBW18f/bhHU1i9hQG/h7E/TBf/6vr1u5fuqrj0YH3rVFm+3CDAIG/+zT3fKYvgsyHp/e5Dp8MdRcBkRJz/hrc/+dELIvuDv/14ooAqkCmvWEQLFNaqvCUAUiYoD/TssOzVpCiG8NjwYsvzcIym34tHayvFxViSs4lc0MagNQJUtOwSxNMlRQMBgqWSgkCVB49QFphKT83ut7B+BKjlyuIQWRzM9NllhziTU5mvhr+hoexIXAEgQFXw0eVkXjomZUMuoBNMtGGAb3mZeE6kf0OL1w7NHDu17nc+DPuTGRDEBc2tiIHrCsw2xIMtFCzrB9dHFQreuXPnAUPdfzyqwG990+w59FqFfz7W3t1Os6SjFSJf9/r6nb8xDeHu9m1vkeCmsY1LgtjQCTGFwBALNLZ/24K/XtHXvvTjiYMQCEAz4j/0PKq1lGmHwAwhRd4n5cGc4B8lgfLCaDU9PtdqzS8U0hhrE6984/LMcWA6JLBVYjVoFu01vHqdIFhq1FfGVB4LFpjKjVWd2YW8uKVKkANalNbY2Cjs1KtlQN8Nwb+BgWauulJseNId1i9irixKachqhE8yIS5Wc4kx3fw4dWLm/cF1QJ/88fnfqOSTprNg4GV9sAMC9fGD21gUtwma4fx6OD74QEHi1kjGWP803Hq+e7e79dwrRsMMUP5LFATqhvCvJ4L96A+LR0K6nhGAXrLzPnxe49/2mh89oi997sfvInY98zQrfzmRvjAbpkkg1C5coFSL0iKrVqvWOEAstqlgiuomqiAzU+T2uPkFMYdRTE/WxTFfFYUe8mPZ/uE14OznKeRrNNrFYqneKFZHFgfKCgEBrJn8MmZD7AZkK54sVGc5EXW8dKMyJtxPQaCCMcUER+KVtlZRC9BZsjZOj4o4nvSP4bRQqmdquZG3srLz4/DM4ZtS/NO5r0igly7IKIjGkyAJJihqCOzggg8eWsu7oD9wo++3Jn+M9QedrWcFgUubQaD+gkfDwkAfytdvfnLfuOZvBLcnh7vNQtcCQxQwbHzwxNqX/uBvP343sWvHU0L9KAek8k/boko3pAYjGG0io/PeWkr3j4GGCh0r3p5Zbk7an4b22WYPlp6pQubQHfG4OJi4CGMsRfMapWKRTLBYgyowGmUWXhxfyLsAS0qjG9g055BUWjaaH5r+KfgbyGabI6gANqTQ6Bj85foQ+MZwEpmHChpLmepzCe16+pZ9YuaAbn6MhrmfHK0P/qW6/csAX4KDAPvM0XUFgQc76nkd+LYp2G2FgusfX+pGwLvbm5nrKAXixPoSnbIeoonR8btAw2QX3UuGMJDPMg9+FO1Lj+hrX/rxOwxAoPYGRAUQDI8KGEzIpXKikaGJgixTz+UUFYwKBFaAhblaO1PcszzfmodTVom+9rIfBJ0IyYYdAKCYXFm6JWKXGugHqzzYa+eyQ5DE5OK5sWh9//I48JLZtLRQcFdaKQ+Z0h/oX7Y8MpaLV9TL2S0xa+jELoGTKUIKXTr1F9XXLJMfQ4svHj19CNmvSF+C5gf1f+rj9qe/UvHRnZvrAaJoGFxf2lgKvHvp4d2Qx4wNCEgIfEgePGqIYFcqzNmQj+6JzfITNoS38+KNHeCkrgkaLCT8PUn1r9/86MfvMnZKN4TDH6YXktODwAkRRafAz6JSFUxpK4Wc7FZS11dTlUZhz+x5BYELTkPRNg5zUAXt2JwKEbMXjLmJ2X2ammSvpCiggkC7kYkOqIQ2AYiN1tzlZfSVPeOZj6ZIJgfbKvxB9js0UB4ZGYumKm0MGXPLOm33NQrK1Jxjp2ktbZXalVSUG39V+nvtkF54PrpkUmA5vsDbwZsf+dqVTzv0J4KAgEAAE4HQoCG6Id3E74khEX2Xu9008NJD+y6jIoThYQcNXB+88+U9TQJDpcDeapWHxPZeYAAvdCZ00Kd//fjexc5nnq5xBwhKfdoQmlMfCo7iUd8mQRSCUhtMaa+EFF0VarVMaXp2TiXCsxBFNwhAgkUueZgW4iEztrQm2XUVBaQgRnHBRiUBVIvyk1SchamptF2g771Cv3q7WlapL4gfKJxiguWx6AvRRK1U4rCdrJ+zJQ+mb0xauCNFgPV2JZFokjtOZl85cRo7P3TxL6B/ug0yuPQRjQ/k4/ptY4vqp8GKOmpVYCcELqG1++So1xkfowHcAYAP64ZoCugrATshcOkOS4GRJyWBjxzJ4A7ISN+r1dW1x8W/Pv3rx3cRCgIhhskl2A8B5lVFIgNaWOMYnKKISFJTqYSwQBhMCwNkEzleb8eW5+mRAAmL9oixIMHzGjLpqw0TYuKeiqk2hZV11AJLddurjC0ir02ot20uxks45dqNYqaSAPdj15fwxwmSRDQ6Fs8w5DqdJwAAIABJREFUo9aNFlJFI8GmaaCH5rNdqsSjzSyT30mV/R4WgKD4bylogYzK8sv1Ox3GB9c/va19UEMQOHiwlzD6wceaBErjYxtouI1LFAsMQSCOHgaBpnkz2p0FEwPRENbrhrbhE9MxFbeNSG64jfg5b9J/OKx7v4/f/PhhH/768d3ErmefkqQ2JauDZShO1DFUAEbZBcnJ/jhJhAmW0Zren1mp1WN75o+0zo/nHahZyM3QnxWPQDE6oDiQ3i5iWeA1SpgQrnueVa9lh7JoCOeiIwO7JxeHRnIjzYEbk0M3bujKHxxSB7JNXKIS7zprf+i02LrtzOJiQ4bxmAR79UwmNabx7603Z469I80P1P+W5AZxwTBBqE+uX/LNry7d7enWtz76oLtAh+y0y9hlK3TbEOgnd70I6pteLPAhpUCBvg0ACBY4+hHH44AkW2Hb4wBgKPUN3crMhzweXn0i7ctEP/vtx3cXO595tkq4I+TlyPm0PBBoF5WNwWwE50QQmIMWRjYJQz2orq6U9qs8eH55Cmq+BuXMVCDbOj91BKpKQKsY12iixdtQQGXXFWWsR5ndJhIjWanYKcRD1U/w74bGvzF0jGttm8vk6LVgWwXxSbDSAor8dK7jZSrVlOw8mrzx4tWLh7jzwxT/Otq/SxekBHiJezoQn2oUfHBzA8qsd3ZDzPHHPc0NtgWE64NLSzdv4yvohsDeYNu1RXM0uJc8uFcETllbNoQfO5I9jgz8PTH962tf+vHdxjN0yorrOeC4jlQ8Sg00msJR8VOVbgn6wQr59N4kvmKl7kzNnp9vze5zSg3AnN1gNwTszGtopYoQQkeatpjaaMAkodho2HY7NzDUTIyVswOm5HdD7jC9odAwOxJFHh6vlkAmZfpYOh80pfHk0KOpjFuqqq87K4O/P3n94tGbcBeQ8CuAS7oDcoFweEHX3cIq5Ot3P+1l2jfaqyH8sXRDDIhtC/sQ6zc//eyz69cx8/Fxt7CQfZcOGojeSNiWsCOCQmAPFriuF2gOA1C+GwiMdAifg8MnNL2fSPYnP/rxncdObhBOyTiwIX98xOYwyZ54x9RU8pvjCIkIaBRhhFY6Vc20nYXZVuv8cpqO+Y6t14LIjIiAFUibE+PErpPGBQ27WG83Gp76k0E3RAPgosI+vRdkcXJoEdq/BL6QWqUE1LTowo/iH3seGLdTNNBj3VHRyUwlnnsrS9fTG+8cm3l/cFSDn+TAAS4YEBwkB1RwY/Jgf/S3m3Fd0LMhhKUHIW10gF8XQrdbIiEGfwXZAIFdPHL9ID7T3UuaCfL27kYWqEMD4CYkUL2bjMfpLerdUxpPEhvYX/jEE+Lf2g/7+NeP30dQFUihC8uBsiKdHZEUm7/si8gOpRyNA+msrzNnjIykUhXPXmgdOTJ/xS2VPFfbFKRtWCXQ1N5N0/IKyzlodoAHLnwC6416qeR6lYFFX+/HrSB6NwjGhhO5VCJXKZaArDCLccUuy3Ysr8E17HbJpo+05VXizH7VyyfXD58+fHPdcD+/99sxBUdEpIpEym4kgdcN5dqgP1GQdnCwIzs143Eavy6EBkG2itHrAeW820Prsr7euyG8mUfCaKcOphMD1welIYxG7HdAAnUhsBNYk+L6nHzc5m9/8q0fv7eAY7TU+3JxP2RzphHD1DAknMtph1R0Q7Rdakp8VCv2noX5VuvMVNomT4M/lR1rwLMFWz/cNHNVmv5xxzkyZdumKLBeUi+pjHFkbZLgN0kARPFvBB3iaLzt2Z6YJSD/VW8O0ocT7AErWFSYWm9Xte/B4u63Xj8N2ys//fUbwCaWRDQCAohUmENvgEAjiLnE+9tdueYgHV9C0GfiweA2cc+Pm52e00hwu67AZwpIoL4M43E9Q6biNofAlwKzwO1NCG87wrinvf+GQf9E+veY8Nf3fenH7zXQDclJ8lurwScrFY2SDhoMZPWP/eJaDvPAdEnI+Svm4tVqpbHnvELA5T10QEhj9M1RGNcAAQRG6bENTA1jjTmQyy41SvRIqNtesZJjHXBxSLhfFs6BiZz6MmordctSxDLGXofjcZemLTpApNJck+l41SgH3xT83dh79PQhsb3y8a/rr9zQ/gVegBcGff+rwP4KpcDb6xtZoPFICIEgC3SPhIBLG+beHnw8ukk3xFx5t1ce7Ot1NsuBNQLK9rjV76YbEvL9kwNt+/e48Pdn/aUf/fj9xs5nnhK1C8lflF0QbQQT5aHigLRQiOuBOTHO4vgIFTS1VK1t7VMQOD+bb9glEDzgHgbiKIPBhg8e0rmAeAjVIACwAWVgvZ3J4H1TY81mUzJfShGj1RIstzyxnbGk02wp6HShtfE0sfQU/RvROz8+ODRzFKbPS6EwWa/cGahQbGrJnB28sCRlt3A75Pp1zv2GA34vG9u0d7k3ZNsJsLrq47vdb3F3Y4lv3XxNPgreZUN4QyI8Oto7CQ5OAAK/g4Zwd+orXvhPqH3puz734/cfu3Y8/QNRvMRN6S9FnwQAoHR8U6YsmBJxtO6RSEc4Xqt6zj7uz5wt2OhMuCzR6R4IlHuuGPhxWzlWAgt2YTqkrhLYlTaJJI1ogH01dKErbRssEu1eqP/ol2ClacjvlbhJCWjYrqbGBP4Wbxw4ceJ1Tn6MLm2kgAJ2S4MaBQUJsRBJnRo0Q28dDeHrXbAEgOtyytKhILCzD/LQ2Fjj66F1QSnwQcd1hgVufMNN2sABAqIUeOx3CYE9W7+/C/rXT3/78YcICKNF+5yqagWgD3w5bQtIcaDUBZkDp3I+AFZTCr6K07Otc63Z8QIbta6tLQ5kkW/M4RiHw1XnsNBiNuuhF1yqr7SL0BYqHK3ibzyzog7bDdC9Bvsmtm4qK+xroBwIzQ1m36yigj9Z+Ls4+SKbH4NLHQBokt4gCdZYiDRZS6IHSZIEAkNpMPrDtzulehj6OLgJBG6aB1/Qf4NhEPLI7jx4I7Tha7obnhC+ex0KmQ0lQ0FAmeHbDAPX6ZfK8biJX2+57nKb4U99JIX/PSH8Rfr0rx9/sHjm2R9Ivktul+PUL4ke8c9vj+TYKuZhSiz1deocr7WLNkqB8+f3xLyGJxxPV/84D5xOo3/ryKpLskF0MTwLW0MylWo1XqtVKrVKVd1W420Fn17DTqMBLAVE+iDYZhdJA6TQy6QSpvlx482ZYwf8jb9L3RAYjg0ocUHmf8PETKjgdQWB6xuQzZ8Q7ohHsYnBKqUNqXRPrUsYKe+KdObuA9lQEuDgqPRBRkd7jcXpQFL9ye9wQnijpEYP/j6278tf97Uv/fgDxs4d2BsCmhcHGRS4yxmJdCpFpQxHQmSPEuWCOUMWMa0Wr2TsPcvnFQTucxQEujKnKwJobm2jg4sjD0gHAWjIgovtisK+Gm5UItxuZ+puDG0S45NFlxnb0T0QDwZcig0WV+IYfEP3ePKVYzOHCX8ifQlXAYmAARE0e5AM+dP4wKQYqNTZow2J/cLw5gujAzIYOGVtioMdTyx1uaASAjeMvWmyGGKBoh4MX+Pj3kOyYFEF/v/svXtQ02fe//202i5WW8uXFE1CKIHhEO7GgEIDbBIHQuwiZyIQJhrCNihBrGuDNmzrlgrqnWmLaWe8f9vhsV/R6bP+tib3wPKbu+Ois3/srF1630yETqWeOnbWqY7aYlfn1/k9ZZ7n+lzX9T3kBHjqvdt+35ADIWCw5eX7c7xCQ58saFng3YhrA7zPE8+flqJfSf/dWrzoUYwzPAtC76iNuPSRAtiT4flhAkK6LxBiZiMxgTAgnFOydtcma3td/RqEwMJUOrKGj0giHYLk1Ldk+jHkB4uKitZ2FOTsLDHkdOzcaTDmlOSQVmfS6oeNYinun0YozIRBO2iHzsgowHsPEmGELs8MvS8sw4W6PPlEMbBCCITFVBDhAcksRiCNhveRuV9xk7ObibUscCxmC3VcxWj3w70ukQhEr0kYDRnjU4HkeQr+it5G/FjhPywE1UO0J4Yg8IF1Rt/30ntp8k3Sf7+WPLYIDk1Hbg7vgCHLELSkKEw7AbElJJMitHuQHCQCj8DK1JK1a+DkpJr65/GiAhiNy6BdMKlkiTNefo/bl1MzVqZDpFtY0FFQ0IEo2JGzs6BoLay9Soe90mSepCg1vRTPwEEvdRGJrYuSC2DrH+Avb7mvuLLFo6BrryjjRAaQ0i8qEhY/QAupMcu8XeFgo8UOYTYkTCEmMhB2x7hHFJ0KxKfCRW7DZ/GamLEu3gdG9MRw8S9tixHwF41BCL6DQ3/ijNo7+MC2B6D7Xfv3rNT7IukfQglL8LpUcjQwDm2xFSSzckINhHTJEOxx2UGlEfoF0SM5ReurAYEr1meQnVjYAcIECMwEk5N/SXScSuaGcTUYGcHCjtKCQtI2iBmXSs6Kg5WD+KS5ZFr+gAXTHbIUuQbjL09XAYO/Cgd/5hHvAsljfATMW8AoFipoFElSgQg3+8KqIbjMK+4/ISiLnQqMe5pHLEXPGMdEoMLRRV0gpeA+flMWxhqJ4PE3nL8grMCbsgBWOBd4HyaQL4Lg7N89409qfZb0DyRAIGYengZR4ik5YvCUuA0QMoRGcoQmLhRD8ZbaQaXaYIDCsSE1s60BqiGZyTiKLQUHRw+Rg7gWxnjTCRmLcGMgnIhJToXLIHsPMgoL8WZ99I44WUq3KkD/Hxw3XNBhlFv0iU3Y/tVurAyyDJ/u48bfRA6Qy/2JJX6AZgMZGkyyzFTkVircrBzjQCQ2xslJ0Ku34GpIrP0v8ashor7AMfFrovZVIa4Dxy0IM9zpcc9GrIy+JwED7/PIy2ektX+S/pGUsHiRAY++kTCYNOfRdkB8rSYFYGIRYTCEnKSkJkfKwbNKOlY+X93QUFO2HrYYENuWTA4Nxudm4joIcXTpeKoNnyeCj9jEjCzNgGHfwiLRSXHpePIXRdSla3OM6hSMP/Sma66s8LMi3IXTzyGqgQjJwJhcIBYK35qj21RwvzPXzSLiV3Q1tys6FTin2KglgLgaEvU0BbcmhjpB6gKFOJg3fwx9nwOBigqhGvKOaJpjDjsYWTXhvgYXP+49+ycVPyT9wwl2JJDYVygC42ODoQ3GQGaH1eT8JKNRmyIj/lApUxuM5LxNpXFnx/rqTcgE1sMYSGo67YJOhble0hmYkZyJY11k6jLJyZbwCbJbH1GwENMSH78Op4DgqQ/ogU5PzclRpsDSU4S/5f2erc02OPODMk/BR75hAOQdoIPLBUbHwRwAFQJuYoAtgkpu4dyQ8CeGmIX1RINY6L8Rfw/q7qKeh6shHP66uJ4Y/vN8KjBSMUAI43F/EldD7jUSJpMfZO/q3ep/ocszUvFD0j+g8PmZyAPKlKTdWU26XaAiYqQLpNX4BCU1ng+hpREuKQgjxcaSohXZZGP0SnyYZTo5xTwTHx2CV8YU4bIGjouTSadfKq7zFpENp9D1B/jDw3ClqSRmzihQKmF5Qh4pflTa8a93ZOE3koEKhRiEAvoEDhKCkHwa5QkJbMNzgZAKjDrsN7oxeq6DfZlYU3MxC8LR2/AVtBoiEJAvHNOfSIDdnD0xgMDgN5+QZYG/u4eCMPV/99z6/L/wtbT3RdI/qpY8/ijsAKQFXy3nBbUpahLmagnsuK0IWvppJR0SVsIo29r1NVANKcPNK7gHBpr/0klfTCopZ0CDX2EyASAUPjIgzYc7/TJKM7iOGRQTQztNevLaHNL6B/zzV1VWOciRb7ztE3U/hwOQK4BE5f64O3wIzIsNdXVFUqmLUEnELzeOmGNOCLMLPBediTkb0hW9d5/htnfx/TAkMUhJSfN+cXpgIj+GgjBeFgjJu4XNhkRFwXjvyz1n/96Rtj5L+scVWZdKEoG46YVIqaRDcjgxCNsQyJGadHE0vuBHIBrOyXgejhCufr6U1nTx9hYIZmFldAYukSACrgUYwiYtyBem0mOCyXsqGQGhGxQ6jFo52Z2F7B9p/VNQHxfBwEgL6BBZQAeXEwwPhHn6cRCM1ekSE2ysd0Gr7OdU7PG4KBNIzw3hTWAXno8jqUBiYxXhFIxvBOGbDR/lEHj31RDO/s3HubiSel8k/UMLIVDJtb4oU9QUfFq6OUbN5wdp7KumrMRIVJO9BsqC9NXgAuvT02FFTEbR2iJ8sBEUfKHzBfcE4gsZcisipZIi5AlTYQ00DoPT8UhdcmmHQYuLH4h/PnvLxlp85gdZ6sKBLrICQulH+SdEwVSO8FtaRxBTKRQ1r7FvbEoRFZvG6x90LHw8jp4NHKaxWPtSFSIEktyhuCeG/iAKHn1zhcLom3k+4doCF2QCeZG9LxSe9yKp+CHpH15LHnsE70bV0iZAJekPlMlofzQpChtl2PURDwj5P2wD4VQRtbGkoGjliroG65YyvNAqnQS+OLRdW4hdXSmu/eIRX5L0S8Zr7osKwR3CKXK4XJyeurZErcXRb1PeclPtRlz8wENtIuxxhAsjocLBBb+izypi0E+cAORxEz3x0UVWAEaQjWVibcoSneaxEMVOBUbtiSE9MaJEoLggPEf5N1r8ssBn3vndXSDwWXrm0T1Hv//yjGT/JP0TCBqjtbgnUI1n3cgAnJKrfAiDwNAFY+SOEFHjhQoGwGWJwdhRsL56S3tDW9kaONQNRbfk4MzUQnx8XCrZbwrQA+bBx6V42wHOFIIdxEQs3anG9g/wl9fZsrGYdHoI9k/BAxB7OBaLAENBol6OiApFFPwoDcJSgBxtzDEmPkh4GzXZEStp2BWrfzC+QlzHM/8NYm/DJ22BYwSY+FYIuRVhXTBz0xA9fc5lgVEPkOMw73PyQ7J/kv5ZhOLgR0h0i2sdtCVGTSmHPyBMxH4Q+gdhgDhFSyoieGm0cW1qWVudta4mOxPWWUErDOyBKc0ognQfHgrBx11C3wusUS2CPTDcHvxUXBsuUKbA0lO8ON/VWAlrrxRuB58BFMW72IuFQqEpELoNwSYoUinhn6eIcoGYBQQIikgIsrFi0+hzQ5jYzTORmwvmEXwL8fcYo3Fw1PO48TiuEjIG4yvkNSko/hi+LjKHGNwY3UxTgVF7YmKawvuNfn8m7X2R9M8jhEAjqYUYlXRVNEkFktUwNEeI7xrIjhjMQ4OSfAE8fWdqYfaWhoaGmvWlMOiLrR00+RXSCRE8HAzNf8m4Dxq8YGkp7heE3sDSwg4j4C8Par9eT2WLncXZPyGkJQzEv/EAqzvnxQIEQdZOoRCZRT5MDodBVAhMaMNEe7uumCeWxztFPeqJccWyfK+L8B3GYhAQV0PoiDDGJCkI89jjODgfAXE1hB3+5k+/pvXceQLhZ5+5594XIqn3RdI/mZY8tkim5da/yMgSBBkgUEmOTIKIGE4RVlJAKo2kfRBbwxLojDaUFCbX1FmtW+pXwfHpONmHjR6JgZNxJQRi4sLS5KJScISIhrQ2klpAzjuH2u9yW3MlLn4wNP2nICUOdMWYZ9gpyr4+eEPCd0BfI1zNmIkRpKEyyQ2KOYCBwTunSNzErnHEdIGRusuCMGzKEo294Tg3OjZnuHiZSwKSayHk5mxgNPEixUCuk5wex21JiCtMP2T/7pl/v3lK4p+kfzYtefyRR2VqsgIQb4ZRy5R0XSC+aGkNxIgeN8ANZqDWaMQ8xHawpDQjG0xg2ZqidLB6yenpeHc+ol5mBgp915YWIa8HAAQOwoFvqfgpOSVk8gP4Z8qsbPGz1NTw7g/uIRMztQ/oh7D3HBa9gXuIhOdnZ/eFZliGhr9cHMw5QK4QwvWSRMMmxsQHTrtFz/2y0ZVj9MQYEfMcCpHEnvAnxQQg45jiEYgt4D70xh3VySUCGb4mHB+F8HzWj+JgTLZ3/uWdWI2BcObbr8ngxzP3euKvZP8k/ZMKqiHcQixqBonlo0UQrazEACd54FE4OCUET4yQijBuFcwpUXdk1zRYG7asLoL9ftD3V5qMD7jMgP6/wlIsqIEUAgNhpX5RclEOPvIDOp+h96XSM8Pyv8kczPBvcGjs/PU+AXpR6uu7fv5OCLeKiKLgyGoIw3mmaNiw5hhDbzG9nTlmQ0uMwY74IssChRxfdAhMnmZ2THEZQGwAyQdTlOLkJrwmEk/wZwa/+RPMxz3zLAIcIuA7AvqeRYHvMxh+94W/f/nZU/P9fyZJ0j+mEhYDAtVcF6BSy50kTLKAYAJpehAn/pT8OcPYDcKhR8aSnNTsTQiBbaszEdoKM/HWe+iKgWHfUoh2U9cW4ug3Ge+GSS3IyVGnWBLx4MdyVyPsPRB+jwUPh+zZGHi/+PgjCDx/fizEcs3TogRiWCaQoCV2NSTm3O9U9LxHrP5BcXS6ECkEtMXjH8O9JjB+Y7wHHNvXxTdGK3gCzhcLwzfLH/kEXCCEwoiCgD1MPgw/jn48/u6BglLvi6R/YuEBYa7pxYgDYSPtilHzZ4fgWrAR780yGjkGwqcMeECuYE32ljprXX06rL2Cg30zUtNTyZpnvOq5tLAoPaMIV4oRCHcqU/Qawr/+zsqNdvEvMV/HQL/eUxD7zo0/LMTAsRCs1+OcI00IKsIYGDMEpopd5o0FttjVkLsgIMO1IM5dRianqPPCNBwb476EB+D8wt/r3CfIBCLOYQxivUve3iVgfPbpdwj57v7cc2nyTdI/uxIeW0RWoeI6CEEe2Q1D2MefmIThZ6RzclpyhDAZkDPkJK+CgnDZ+tRSODhEWJZaWAg3RfjUt8KM1MLCDnVKGp37zYPJD1z7xb+qfOoPKMaE7lw/Px/6qPr6+ma7QmHVECKefwzNmJEIUhHJwnhl3hjVkNgIvJtqCPmm89tGM0GgwEFkCOl0sELBl4MF0kUDkaE/OwOrAjECI4TY9+tnEf3egeB4PvjF/PSzUu+LpH9+4U1ZNAjG7S9qOgTHB7tqbl80bo+hh6cTAGIiGgtK19S3wZqY56EaXET7ApOT1xYU4QIIPla9cG1JiTFNTvlnrm1pxGuvhNkPjmCIf18vmH+gvr47U4w4Dg4LgMOgEJM2cREY/czYs213g8AFii4LHCMHZyJ93QUPUzPLFUAYoR4SRwxHQMTAP4ngh4Ni6IAm8JsPgDEkrf2T9OMQdAVC8zO4OhkZ+QDoGWAdKu4PJO3P/A5VqIcAI420Wxq2p+5cW7C6pq5hS3XZmvTUjOSCQmQFUwF6yaVwUHBGQcHajhxtWhrpfclr0rVs7GRZamVEuAJ4sYh/C4l+BaE4+M4UxoMYf1xPDB9l83SJlQqMnFjr6oreW0B79SKeNtYVvez0/kVek4iBUyzPP3IR+b6IoFjMQ2DptTAAEvhBTpBswHrnXnJ///K0FP1K+tFo8aJHKeiE89PpPAhX8oBj041ci7SazsgpoXdGaYRx4hJD8oqytpotNW1lq1ZmphcVJheWrkwuSl2bUdBR1FFi2KlNsWgSSfbPW7E108GKf00ptyCCRfxbUPYvTH3n+xAhyHwIbQgMK4OI7nD0iJAjqjF6LMbqFto/GKMgPH9Ye/dSTJESCF4Pgx+gr5zcKgS4hyFPESb0ko98Qwj4f4vt3zOCA7x7AD4t9b5I+jEJ4mBKN9j+p+WOSCJNMtD8h+GnJewjoTAepYPmGCPhoMFgyClcX9/WVlOdvWLl+rL1HaVwPFxGjrFELdPKLPpEfOZH3nK2sdLDCPaFT9rhO8zMvruKfzn19c2OKWYY8TcMr4PwZGBoUjDSCMbY3xcTbKRKG/XMBxQHh70oNsRXTfihYO6Wz2jyP1vsQBh9l+YPPhEs4K9x9o8QEAbj7oWAP5OiX0k/Mi15/BFsAklLIJl/M5JgmBwdjLOCnAfkrCEOho1wkrA2TY6klysL0tesyshIX5O8JrV0Z06JoWRnGvqcXkOj37w8d8tGO219Jgea82lA4BU7df76fLCLqb6+vjtd5WbqiRxCCCyGAQcOMUR42sQ+zSh6PC5W/+ADSwWGU5k1k7K2GMMK8Tv9sSjTw35K7mdm2Np//45YQD4GFgzgvQBQyv5J+hFq8eM5hGsEcLArH3fAGLi+GCOuiChJCExuSYEYNmfJUoB/SJpEiyxNnpICKcUUrcViwfBLJFv/0JW7pdLPFX+JxI6NUczeZQJQJCgIK7jQGldVYpZDKDeYKMVcARirZS+8f3CMu4k6YeTupeCvqAB9ES6UBMGU32Ljx8QygujJju+uffIuAmBECExTgE/fHQDfkQ79kPTjFFRDZMTz4a4Y2h2jxCsRSNcLsYFK3BeophEyIaFaJoP1LonI5yVhJYouSUnU/eX5zI0bYfRN+C3levbI+z0bQKw+UUFYQVpqYoshpAjDDsZNdIKvayz2CkCyvEX8vLEYy07vT3MAlUa9FIeCC4zxozLske8+4R3gr3EMLBRB7tIASr0vkn68SnjsEa0MNqPCLgQl7ZHG5WE1OS5Ti/tg0AMGLWf/6LZomVaGA10Mu6YmgsEmfI94PwJAb+1WWHsvjtjCxHbdUwaQF6QCQz6uGhLjDwDR+JER3eVZE/NMy1hDb7RdOfKZMfoH711zAVD0SfrXyQgWUHCC8DR2z3fgAMN7YHAKkIbA81GP1ztPSPZP0o9ZSx5bhGBGGly0pB6M26GFLkHq+chQMIl/kTlE3EyDEBgsIHF81AhyHKT882+tYBlR/i8yXnOM3XsETIQRyHJ2yKGI0RVICIHREY0YlolC4FjsFYAxDhseu9vZkLkVD4AU2Vyqj6Ecj/lPCnom69r8DVcF/jWfAqQAfPou+CdNfkj60WvJ44/giRAeeELdA3hHxj9Ia4yaa4cxqrWylJQUC/AvEQW9TQR/iURAQMK/JLZqo4NLwfG/og7hDhOavY8ImAhmQzCFRN86XnN0BALJB7E2ZYlOLBfECmebi575IFKBVAv6RoqwjCD5sRQK/iN4itvxjSgEhiownwN8Z+EAlHpfJP0kBDsSyIZ8pbjYoaUVDyUHQqiKGA1GsicLcoAUgDjjB/jDBPRhABICmtmNVXgANB0pAAAgAElEQVSoP6YQogCA9xUCY+FU4IxZ+HPiRMM0VlRwHOEVa0cCX+YNp5IiMhWIXeD9x8ELYh8vwdUqeB5yPySyqmaXMA4XXgN551+eXugYiNT7IuknoiWLFz1KMKcmpRDSE6gmY3FcFKzmViMY8WlxspQ0OQdAEv6KDCDhXxNrr+8UABiDgw8GgEgoDp6aoYGwyGHG6I6m/KAg4YjCRtc44s390lSg6MkPqzE6UlGQ5E0f//PhH83s7QwHIHaAZDHWQjOAz0q9L5J+Okp47BEjF/xquawfPRPEoKWBcQlMypUYybpANQKgBYog1AKGA5AEwV6mYqOfuCiuBVAQaYO+izUIc4ukAvljhhWOuEURGi9GUIUVndEh9nZxzg2JNIF3tyzwAUr8c1F7a/a6mv8U7QBpABxuAOPRUMr+SfppaQlCIBmG05JjQXAkbDTSqJielE7WpMJnjbKUFFoDaeIcYBKNgPHJlwBAtqrFETtVz/3Shsau33cSkAqviREQGN5uE/6n0veIOFhUDRkjlzjVEFwQDo+Zxx5oQXgh8bCCuwovhqBX5/Vl1nzyp3dJFYQvAZMumIW1QT8rLb2X9FMTrEtVkx5ALcc/HPiqOQCq4WQQA00LqkkRRJMoFH9xQUQUAeexiqpd3GlCiphiQ10PDICwQ//OlMIshMFxSiE0bqSFVFJVINWQBW/KIstOIxj4gGZDFi784ikDuTwgw5q9Gza9HlYDoTnAZ8EALiAF+M6vJfsn6aeoxYsehUPUke+T8TVho1FLmqLB+BlJNURpQJ+SyZADpPEv6QNMJB5QaINhHRXkABCarle4HfDOC6rAU7PTD46AGIEzIgQquFg4goUc+vB9jiWMKLwVXWKDjeWrIfzVg2+Mnlf0ZfP4wwEwW2M9HasPmssBzgPAn0n2T9JPVNAVqKUVYK4BkGv+MwpVENwoLUsjVWCaAWzisoCkKEyKwIrajXaWz9XHEHJSd6YvPZgsIAgOVOK7AmlPIJ8NFBGQz5eJQQJXdCtVWIQbe+6XnmrJo5I8866OEJ5bC4mDqRRcMIwD4B5r9Sd/Ck8Ciifh5safdOaRpJ+yljz+CD4pmK5GMMA2aAGGUPzA0bBMq5bJ5XjhFW0DxA6QRMFNXB8g6/Bs7WS5LBVnUsIzVlNjN09cus9e6DABAkVdgbHwR/9ogYHcHUwQ0dBbGNhiIbBrLOKpY2MPY1ngPOL+doHfXl+mta7xk7B1gM/wDnBe/yet/ZP0E9eSxx+lW/HV+BQQLaxHgO2odCN+CQWhNiWF7Hyh/q+pSTQHTNsAHfa6SppAo9ThA08OQ4qp2fOHTzw4Dwjqe64rNIMXMBDqzbkjgdwNN1ziCWHq8eKPxwmYJM8WPVMh/qb3p3m+E/60GcW/3lUNdRiAkUXghYTAUuuzJElQDTEYuRygmo+DCQANOTgRCAery7kQGIe/wk4EfhLO6+hpt9bSPhgMGtGFQ09obPbmpUs354Pa3YhsyhJaYshN9KoEhiYDaY5SoEycThdSDQlDUXT/4EOuhswFQrPX5yqrq6+rq8Ih8P8TaxDknTmKIFLrnyRJ/xc+OQmqHgZYjG8Q+p+V5KgQQkSIgcVVYL4XOkkoA3sV1bu3WWtn8C+uABuG4yEQiWGn7syen740/SDDYIiD7+CN0QL0+EJIGAdJ9MtVaQTCiIbeKN72xUkFhm9TIF/xEKshcQFoNpt9PneNtbbHuqlKCIE5AD5LQ+D4JwI/LR15KUkSEUIgkM6AB98wAfFGrBKOhXBuUoqcToLQFTBJtCc6ic8Betkia/e29iqWzwPGEOPouoMQePPS/W5FCBdGIBPmAiPuhr0ICkLuDsMd10vKwLwJjLX6gGW4ukl4QfjhucBIodfLmpH9619lrWtls8UAFEXA3DKsePiTol9JkniRw+Og41k0ElyCPzTinamylJQ0ug6LWwVDB0EI/5bnLfey3jardffuSr84DObvUbGOfWOzs3eQC3zQCJzFRwiDHFw5mHwgXPPiw2EhEqbLAoUixz5c44hZEA7rCqQI/CFmQ7iXCvyzVbfX2L3ueisJgckyGIGAdBIkZhX4nd9IvS+SJIkFqUBlCtmXTzthDEotNEIbSnAbDDhAveAAk0TilmG5va01NXW7tzUUz4gQqFCEmUGGdQyP3UE6f2n6gRZD8BHCM17hzwpjXozxEHwjxoq4K5AD4VjXfOeGUP49uHND5hB+payb9fp86db2HpZxu+qtW6o+iWqCQQ7w2fglECn7J0lSpBIee/wRWIQK2UC8AsGAYmI1HoZDMXAKHAqiT+Rm4ZpoGpB3gBiAZlNqds+uut3d1aJ+QP4Ohx6GCXYBAs/fnH7QCITZENF0XJwImHshNAQmaUqMFkU42MZIHBxrU5ZDmA2hV2MPclPWHEL2z+e11bXXdbIOBxMXgNwyhGj8/Uza+ixJUgwtWQypQIQ8NdmAAOlAAxmGU6ekyC0WcvgHrnoIYTAHwOVet1vnal1pt7e0b2uvcLFMeAVYRB7eBE4/cBcoIBDEh79xUSjqqsN0UQg7EsaoHwQTGI2h8NPjxn4wBLJer8+9xmrtUbBwoJKr2rql4hPxIJzQBhjTAUqtz5IkxdOSxx7B9V8DCYG5qRC8DYZUgeH0o6YmLgQOrwK73TZEwFqT217Zva3u4MxMVB8gRx1GEZyiCJx+CKnAGUCg0BGjiLzHvw4FeYEELfSG7L8a48C2D65iEBCJVEO6hPEQem7IQ4yEzW4U/XbWdcPJAw4MwHrrpoo4RZBY/JPOPJIkKb4Sljz+yKP8Phi8IFCNkQjrsKARkIwC5+XRWTgSARMC+lgAoK3W7ja7W7d0d7e1zoi7osUUwmk0gsCb0w9wPwIIr4nBywId0fhzKKJNKcPHwGEI5IUAFwVA2j0T1jxDETgV85ClByGWNSP7p6sH+0fxp0AArKkIW4XwjFAEiYqApbV/kiTNo8WPP2qEk4BhCs5YQtoCtTwAE3EGkD8XiRRBSB3Ya3bbbDpdbafLbPbO1Nbs7q62hRdDCIIchDqsg7jA2QedCqSbskQtMWLvF8MH8olAHjS431nU5RIHgGF1ExIx4697OATEtV9fbUP3VscMPk8Y5EchcG34IIj4VPRw/klr/yRJmlcJixcpyVQIWRCoBBhqEQA1Gm4bQhNXAiFFEVIEAQdo09laO3Vu5FS8TGPd7vYePxvJQL47mXH4p7oIAh98YzR/bsjcKUAiDDTSsUNZQ/dfofgXWqKn4gKNDS8dE8f4cFKBGH+2+va6Cmr/HPk4B9heczDsSLhnRAYwbAOq1PsnSdKCRFOBZCsM3pSq1mrTLKQPmvN/3MFIBIDLcRHEZvPbajt1JgCg1+zvae9Gv65sjKIExx2aCpydnr55Dy4w/pfgaog4FUj+4Ki8ICeegJxIjQNpXxTOIuHmoHaRYJDYwK4HTUAIf33mzIbuNgfj4EVCYA9XBf614ACfjnKA0qEfkiQtVLAmhowEQ2egUanFXTAaYf8fFwQLVeA8HwDQZvO02kzYAprNM/7s9m2bPCzLRCGQywWCC6QF4btNBZ4/9Ls5VmvhTVkzYRujSWtMDDfIcL0w4sZAlpmamupCl9gNziLCmYWImUsazmEa70nY/tlruuvsrCNMrmoCQM4AvhtWBRYm4X4mTb5JkrRwJSx5/FFSCDFqlUaZOiUtTU/bAEkBJLwMIgJgbS0GIDaBXrazbXd3TZBDYFRKjmHdjhBXDbmrXamzN4///Oc/P35oLgSKjxAWKVZMTHsWRaUQRB0U4LILqenSU9T5Skj8wvG9CWf/zD3t7S0k+vULAPRXt2/qDGuDCauBvMMl/6ToV5Kku9PiRQbcB6M1alEALGyETuIj4Ca8FpqOgpAiCHaA7n6z14kBaPa6KxpoKpCnj4JaQJIJZBlHkE8FLjgOnj20/edYx+NTE6+JEXUFzinSro15cw/hK0bgPq4hBt7u4ZvEE7Z/69q66zpp74uIgK769hr7AcQ/fhLumQgAvvP0M09J0a8kSXetBIRAIz4oTg2jIHq+Cya8CMxZQB8BYG2ryAEiBLKOioZt3T1+Go5y4a8wp4F+xUXVkAUhcPYkwt/249fBBW6fjv88fIo6YxYQ6Ii6Q14C/0rCPeBdiFsoQ0vBD8wAsnjvi6m+25qhEGX/KANdGIBVXBGE24f67DNP4yNBkJ55Qhr8kCTp3gSHx+EDNLUp2hQCQJwCRMAjw3DcyZi4EdrsAAC2ttpcIgBCHKwra9/2YgUxgaIomGcgQk6Ia4yef0fC7HPXD4P9O3z+udnz+3/+8/1zMVOohkRRT/iQEZoDgTkR/FsoDtnQFLhAeL/vPdEcPlEEDoO/tXUIc6yCcE8UAOMQuMYW/NMT9DgQoREaKiDP/OwJqfFPkqT70JLHH4VCCBSB6amYuAACDCTuTyAgAqAdQmAPB0AnCYLR+4ytpntbm53sbY4wgSQQvptU4Mn9OPjdPn3++glEwuOxAUg5Ss4N8TICfMPYFymgTmRFeKFizYoprAe2GIY1A/76kf2r5aLfcP45/MgBbnAtXfLkk0898QSNgSH6fRax7wkU+kr4kyTpfgSzIUq1LC1NbiFJwCZ+ISB3LgjBIgqBXTgEJgDk2IffzV7Ws7V7d01xRCpQKEhADLmwxmhS/Jg+hCi4HYzgCTCCSPGNIzRGK1g2knUxm2HIa7ln4R/vQeHPbHZD8WOltT3bxkawj7sLIfAG0yKIchMSljz5FNWTTy6R2CdJ0oNQwuJFRkxAvSaJLIPhRA0gbgYkAAyiEBgA6PSKRBGY2bCtvdnPgwjQhx0gPxsC1ZA786YCp7f/fDucKnL+8P7t27cfPzR7fvoEvhf3a/pINUSUCuQlQFAcA9+jA3zQwvZv3dbuOg8rTH4I1/n43kYUHLsWSWk+SZIemvD5mXKSAiT4SxL4p+H2oiIAikJgnn5memNmXavat1mrYEeCAB8OgxQ9IWFHQlwE3qRHisz2ge2bPXQcfOD2+QvC3BHCccQVQmIEwIqoOw9JYutoxsXfTGt7iz+i9isOgiEEtvslAEqS9DCFEGiUiQiYlJdEW2EAgOS0uESzPxyAyAY6zRSC4AJZX3F1++6GCkY8GuIQSAhxMBPkUoHxxuPCHiXdgPsPn7x5Et3ZP0f2EMXBd6aYGF2BkSLdMLGqIUy8xx60FDD4AfhrrWvf1IkHf10OsfwYgn4JgJIk/UBKeOyRR1P0fAgs3ouPB0QStSq3zmYPC4E5H+jk04EzxTW7u2vsrLg5zyHCoELYkbCg2ZBpqIccB0c4exLdE3fE9EXexdWQKAI6eOpxdxhuMuS/LRxmSe+Lq9FqbXQIox/+iAIIFgGglO+TJOkha8niRY/K8MlwpBKcl0TWISTq9Xqtct3K1H7gHwGgqA3GzN2YIQ72MrWbtnWX+We40zu4G6EawnAIvD7fmpjZm9AFQ54Ed7dHE7NPdNNHlwUq5hXD8L0xfHv0nFrAU+5C8PeUl1db173VJmT/RBwkysd3syUASpL0wyhh8WOPL3rk0TS9BQ5JR9yz6OUWufzRRxYtW9pcWWu22cEB1tpc/W4Of07SDcO3RUMqsMfabd3lZ/nOFAd/o6C0cdAB4fk2ZZ1A0MMJwVnoDISWaPQlNyNPHe7jb7nZkHAbyPBXxP4xCtINTd4YZmF8W8hz5pTQ+0f2viD7p4jd+yL+uLK9TQKgJEk/mJYABRc9QrRo0aLHH1u8GPGvJ32DW2dHBAQAohDYScAnLgdzcbDPsdq6jUsFch2BDqErkIEJ4SDXGD3XIeonSBv07DTOBE4/dx4qItv3H5+ejXoq3xbIN0YL7lMUAnNMZBgBh3NR6wGKAJDFxQ9vekN3tmIm2v6F088BDlACoCRJP6wSEpYQJUC32eKljc0VBTttAMDoENhp9jqdxAuaaSTsZe3V3dtqWulsCGafwyFygQo+Dp4bgTgEPnwY14EP33yu7/DPSXMg7pOJEO8DEQJDYUnIaNFCCL0/D7hAC3nOXOLLv6T2m1XdvQW3PuPaR34sChIM+hVlEgAlSfpv1JJlSxsba7N0WVlumz2IHKDHDgB00gBY5P8I/0hXIFO7aXf71mLSFegQ5QAVnAtkhKX58c8NuXmY7ETYfhzqHzfRB/tvnp/ejtujefUJd2gukCzNj8m+cDER/YEPW2YU/ub1r2lob3HFyP5R7IkdILMLAdD1+Hz/kSRJkvQwlLBsaeaq1J06nXJC6aY5QLtJNArHYVDIBJpJKnAmo25bd7afdAXSSnBELtAVnLqDERi/MXr2/PShw4emz+OY9zoYQuQXYUL4UvjzwmvCGIFmZr6mGFEcfN8ebyEivS/raro3Ra79ixTPQDcCoM322Hz/mSRJkvQQtHhZ1ZqMtUalwRiQqQgAOwkAKfOcZp598JjZzL+bWUejdbe1h0sF0ijYQTKCmDwsvy41bjWEA9v04RM38ZQIpALRR4enn7subqPpC7sBBN6ZirksMFp3gb8FPi1KLL5g/rl6rA2NDNi/8Na/mPJjB2izL57vv5MkSZIevJZlVmSW7lSplIHAWcZvspEiiD1iG4xXHAubnQA/ohl7dvfuTbUKsrqeco8YQAcNhN2hroWsiek7/vOfH58lg8L7Sc7w/PGfbycbo0UhsOgroBrCxIqDwx4SGgQftnj7V1PMMjHoFzYHwkfCTE97tf0RqQ9akqQfXIuXZlSk5hgMOoS/8nKFDgAYJA5QlPzjd8I4heUIpCcQmUDWVt+9ra4VUoHE/hEECtfMAo8QhglhhLtZ8IDHyUN4XcLh+xqPw+QT1YIfHgbhb8OXh/42Gjzoj+GpF13/iFgGgwBYv0GKgCVJ+qG1ZFlyem3BTp1BqZaZ3A53ro44QD4ENjuFxB+543SSMoiT94AIgbWbdnfX22cYAXwK7i4BEEPj4Nk5N2UBAY9fugT9MIfII7PncXPMycjYuY9cSCpwbGq+agjXEP1QG2LokZd1yM7hfwsWLKaxPXupZAAlSfphlbB4aUVGYY5Npw4ETG6Fw6QWATBGCEwfMPNuUEAgk2nd1t4IcTBn/Bx8cyA8hOJg2hh9Z67GaDwVDAXhw9xT6N5AXCCm9V++Ekw5CNWQ8gXUg3Ee8GHyD+HPVd9d55lhSfIvfggcLqaqYYVkACVJ+mGF8FdRlGPQqXD06zDlatWqoEsMwHD68ddCBExygV4cB7c07IapV0bcCuNw8CxE8OGqIXOMx52/eenEiRMnb1LAXcdjwtMwLHKJJx5Rn6gW0vfc7ELODcEm8OEQkLQ+m1darbtsrBD+Rq4/EN+IHrZXPDXffyxJkiQ9SCUsW1pb21qiVIH9Kwf7p8412op1XA6QAJAk/6JaAUn+T8gDklTg1u5tm2oZbmO0Q9QaSArCjDvYNX8qcPY5bgTkPByaBFnB89P798fYkdAn3INqSDQCo0ohDwt/JPrtbOuu8YjwN5fC1mH5H5eaoCVJ+iG1GPCXYzCqsf1zm3JlapVh3dobBrEDdIYFwU5qBZ0C/AQEYhfoqdm2u8YGmwpo6Ovgo2HiAllH6AKPwOfmEYyIcOXgPp6Kz8UmJ54N8c3ZE0MaAh+GgH/LfWva23vgz48LPY53UQ9Im7AkSfohtWRZRW1rgQHcn/Ysxl+uSWXI6bgxocUALI4Kgb18/MsflunlAUiICAhsrOvurg4yJA7mOmKEagiChX+YX5o/R0vMc+TQpP2RRwbH/BI6GkKOEI4PQK4Q8qCF7Z8Xzjzq9M5LP1AEAW1SAUSSpB9QCY8trajtLFEh/mlzyxVuk0yWq1KVDA5OBGQpumJEQDsFID//wQXBXA6Qwx+XA+RCYZ9ipXVbe7MLpwId3FSIUBTBRwhPTZGC8FxdgVD93R5rPXSfGILhX49cYOxUoNAICPx7sBCEvS9en+r5dmsjy9KsJ7nw/S9ht1H+z1a7TOqBliTpBxOyfwdbdxpVWnXgrLu8HNk/mcmlKxmcUKq1aSm5GzAAi6MdICfaD0gu5EZUD2Ztu9q3NVSwM5wLJFZQ1BEDS/NJT8z0pTmW5p/YH10q6YtxT/QBSQV6F9ITMx/XFio8+OtLbWivtLFuHn0Oh0sRxj5OfAc0/4C/oGKkRTr2V5KkH0Zg/zzrsiD5F+h3l7v7c7UmlT+rpMSo1spS5E6zH/Gv2BMbgMQRmjkQ8i3RYhPIMvaa7u5NtSxLg196bBIPQYQNR2gBjdFRjOsT3+vj7gm9Mc9RBM7VE/Ng/R8pfujqrYj4NPtHqT+POAbabDKtYcPzHz0lVUEkSXr4SliytLa2uERl0gYCMrPbnYvw5/JnZRkQ/lJkMlm/m3HYO212AkBn+C4YMQXN/MVJo2DBB3pnOrfs3l0dFDHBwddEMIVYflPWfOtSw9Unun6OR1/4U/pm79AjhOPg78EREH5Wnzvd2r6L9TL0RyXvMWaAhbPghEG4oG58PMlU9N6WJxAAJQZKkvRwtWRZaWvnhhJlbgBan01Q/FDpbDaDUqmWydJykSNUuFyqglZbscgB8gx08g2AXuoDneHkE+JgR0XD7u4WG7cjgfOBAokgFUh6YsRrYgRnFw61iA/6whAYmRYk1ZD4LhCz6/4pyAL/fL6dNe01tV5W6PshWoALdASDwZmZt67Yina9ZH1q8ZNPPSYhUJKkh6eExUtLW4uzslQIf2f73e60tNxckyqrxKBE9i8tDeGv3OHS6VTKdcX2GFVg4vhwScTJOUBRIQTfcNMhLOvf1b67gWuMdvAVYTGGgrQxenquI4R5roU7PgGBvCvs48EIsyGOOOeGMAIE70+AvzzTqob2HhcZgKHQoy1AIuWTC8kH+vk7QRuiqOvLzwqKPUcqN3p21bQulRAoSdJDEop+C1vXZelUXPSLPF9KrhqKH1pZSlp/f3l5vsuF8KdUapUbOuMXQcJ46OXbACOcIHKBle2/aKggOxJiEFC8KWt6OmIBftzEoPBJ4SnRphHvSCg3x+sKnI9tCxD8vHm+4rruGhuNfjnyReJPUFjxw25XWSxs56q/rFiVjP5ZchV7Ov0jl59aIiFQkqSHoITHlnZu2FCiS5EFZClud38u9L6o1TJ1ABc/kP1D+FOpVEZlQCaTa4s9urkAyJWBeQvI98OIEDjjadu9u6aVmkDKQHEsDI3RUdUQnmUi08ff5T7RJ/J9YeKdIVRD4vZFz4e3+UTOPHKVWetWoejXTUs9hIJxFcY/m0Hd3+8q3NXS3NO8YuW6wdHUqsbO4ea/nVkk9cRIkvTAtWRpwTpdlkGbEpClubH9g95nRLsUi0WeBvxD0a8K2b+Adhx9bOm3e+y5Xq8mLgG9NAQWhcEcAIU4mK1o2NZeiUI9Wv7gpuJEjdEOsixwllRD4js/IT0opPzCuRj57L7ZMUdYKpAR3ZsPcXMK88/bieyfzouznA6FS8EBkCCQ9r/kO6JbYcD+6dC/Mlp71emWqqrmlip70D5RuLqmsmLtxYn8q8uknhhJkh6oEpat7txgyFKlIf45if1D/FOS2se4xQLFXxfGXyAlTS636PV6Tf+GVpspBvaEPmjaAUOtYNxqyLZuOD+TLwFHpQKRC7wTVg2J9HVhH0ffE1xin/jL8AGacY4Qvj8AQu03L6u6vc7DAtpdCt7h8peY8lMXGPTnJjbpDaktlaeRmotD+07+PRTaM5pd31hR7ArdvrBMioMlSXqAWrJ6fWaJTpsyHkjrp+Ev8A8Hv3J5fxoioArvhA6kUf7pNRqNqrhT540nPvzlCsNcHSQSgXZojG50sBR9jmgXKE4F9oURLjrEjXi8L/LzYZuyYGl+V3lkTwxzXzVgsvjAm9FgrXSxbhz+cpm/+OGvH7/R+0G/ucmnHp1cW5TZcvp0Y/Hw5ZN/nwoFXa6PL1a+vrXZE+r6+xNPSgiUJOmBaUlj2ZqcDQFk/3DvH+KfWquGzj/EPxT9QlegWmkMjMsAfxz/NIl6W2dxpAl0cj6QD3+Be85Y8OMR2LZ79ya72IqFF0MY1uHgz88UT7/1hROuj3/sufDwty/8IsImroZEtcQw97EYAds/U1t3XecM/jbuedgXqWAwH/29GS9OqjVypaeq1Xbg5Mmhqamgq1zhS/z4+ZqXNjVf+Psvtz3x5Hz/TSVJkjS/lixb9tiTT/xmU0d67cVRoB8W4E8mQ+GuE0W/JhMOfgMy5AbB/mkQABPhWpOYW1wRgUAuCqbL8b1e2gXtjc9Alqmt6d5d0ynmUBgCFfzS/FmuGhIRA4ttneihsCg4QtyXxKyG3MUhSWLRtX/r262roPfF7UbfqlzhJtk/3Pwcj4TU/wWHbSbnjLs1MyMrV663OF3nTvUevYDwl+ZlHN7y/LMTZ9pqVlVtevW130gIlCTpfpWweJFuYMPWl2oy0huPNVYdsZlSUmTAP4I/udPtdgP+EADHA+oUi95i0Wiw/cP8S+tILe0sjkoFhvGQNkOLAmBaBBHxkFVAKrDFDueEc8nASAT6g7QacolsyoryeZFk4677wj+Mfn5f5LpUfjX+3TIQF38LaqxtxV4zA/SD4gf5eeaq//KrUIN2lUzen5N+uqW54thmp08H9i8Y1AUSkzT9yvLbt2+f/fjKZ3+sqMqu+83x/ykhUJKk+1LCMk++aUNVc+e6xuZr164NNVcM+9NSkP2TySDadSL+0dpHIGV8PGBUWiDyxW8Ig8tLMicH5XLVuk5brJaYsCJw7CIID0CWdfS0/87aMzNDe4Yj+IfjUdG5ITG2YHHxMM+4iPxftAsUx8Ehb5gHpDth7g6AZtbrXZ5X1m6tYs24tcet4Bt7KAXnVHBYNz6uCVw8sxqKH99t9p07dejo8JTdGBhPTNTI1YrbU7dv5weufHVmVWNP/a9+98JuaURYkqR7VsJjS98fyh8+5wkOqOzHrn1TNfTdNyPnhlUyGv2i8Bda/3D0m5KWZrHIAoNGPcAPDKBGlpExKvjNcvsAACAASURBVNNY5Ja0rM7iGF2BfPmDlILNJBcYdlxSGANt9dbdDVVcM4ojCoKIRyFxNSQsmRcvzBUTMeyZYV/7XN/slJiAzD2sBjTj3pfkBmv1Boio3YwjRgOg+DpC/qBN1pSkMVy8ODFYumZFY3Ho9ydPjdzuGg4EBs76EADLb091dd0OMWffeuvimcnU9Or217qlaogkSfeoxYtcb331qefcsH3PnqELrj3Xrn1z7drnF7pu7ZTJafSLa7/KgBbjD5J/gZwOpR7jz1mSPqlM0judcrlcLyspWOdCv/4EfE4RDM0kD+iMmAn2xsAgO1NcvXv3Jg/MhojZJ26MFs7PDF8WKMYhTf9FFYBjM5L71OxUVBR8V8LRryq7uyHd52Vw+OsWvZcraAeMIg7+HEG7K295k3Zt5pHA+LjMsM4/curk5au39w1ljQd0+eXeRHfw869Hbn0bKmfZs29d+epiwYba6jfaX5LiYEmS7kEJy66G3MpBpaG1c0BrP3ny8nBw+Np/Xb3qV9hulZakWUj2D4e/45ANxKVfvcaiXFtgTEzKM6Zn5sj1cifyfwiBTrl2Q7HdzSFQIB/N/XG35rCB4CgCskztpm3dG0lBOGYkzDAOem4IFweL/V0c4omeIjZ9EU+YFa+Lvtu1MCwM/vqSG9rLXDT556bfiY9954x/g8N+/fLlmqzMluYjOcaAJa/4972npm6P7as1yvXjymCI9apaT07/3RMMoVdVXh546/+9cnHnusy2LZtqpMZoSZLuUglPLr1wO+SyqdQlg4Fxmcnze0Cg/dhVvyZRf7Y1o8PV76atf+Mp42mk9QUXfpMsg0U5ysIzk0oU/crRO7hFuFUVF9v6vWJhBDq9XBrQbOZ3IsQTy/rXWHe3Z/spixwcQXgOMvy61DvcEcIxk3vh6CMXMQSjWdl3R8EVg2n8u3AGmllofW6zNrRC6x8CGg5+3cT+8d6PIjCahP5gEOyfqqinpeX06e+OBVwH9vZeRvjbZxvvT3Pmh67eDilMN/7Hv1qrLoyhIFgRCimAgKOGwtXVNTVPSPtSJUm6CyUseeLw+bFQMOi3laj1ljST38VcOHVob/OegbN6Tf/AF57vUu0uk0kbUKN4LI10Puuh8AEUbEpZWVY2utwJ1s9C4OcEFlp0xa2xBoSd1AXOzT4qdsbR077NWqWgm7IUikgXyLDufGFNTEQqL5JtMRpkwj4r/qCvC8WuvAlcMPyI/fN5063WXV78HdxwhTOAcOV2lM+V+nPg3hf98jxLx6e7mluaEQBt6L/Fqau371y+Na7vP5t/G8tvCnz1/fufHrg+SwgYYgNXrlwZVK19vr66ZutjEgIlSVqonnzihf3nL1y+3Ni5Ob+834l+yYKO3OLmk72nhs7ZdZuPHbn21+++q7WbUmRp41znsx53v0Dvizb5zNrCjBw5ZP/ggq7ScChsydUVF7vC/J+4FMwhMJKD3MduikDWvrF7W4OHESLSiFCY7woUpQIjp0JEH/UJ73FpSIJgBd0Pw5C1+AsjINn6vG5Lew3ufUFCVwBB+mrL8SX+LgT/sN2UlNekmsysamxuPv3dHv8QtD6P/f1Ah97pLgf+Td250+XXpk28deXGl38+gf7pQn8boVD52QB6YNDQuqu+sjJ7sYRASZIWoiefan/5NeuB1081T25GTiL/rDtfoftWpR44crT35O+HDh479t2Zv17bU5jcakDwo/ijvX+apLSONWcGEy2DZ5JLLBZnmgUCYOIEEQn1uVmdXFcgnv6gd8NG4sLlFF1TsQrPpt3dWz0sXSTAU1AgIJ8KhMZocU8M8YARhAv3hBGf4x/oe27KB0Sjf8YCJ4KBf3mmnob2VSbWTcwfsn1APYiAYQcCvwgBFLX5AOxfU1PJ2oJbnoMVjc0VNs+p3qO3p77++66ARl8eAvPXNXt9+pQtVz4+PjFx4/v/85+n9gX9GIEzZxETR0tsGWUrdjUvWywVhCVJmk8JT/3b8d9sKXv9perRQP7tqdvISSgUpokbo8bcgWNDp3p7EQKPXNszEAh8XFrhUSVi9pHJN+CfceUfB9Edp96ydmWpUWNx4hQgAqEFbKDTqU+xd9pjzIbQXkBvtAGMIZZlaxu27a63zzAEfY7IaBjG44LCpixxzo+jGW/8xJ+JGQlzT+kb85pJ5u/u8JfXWtfd5vJyzs/NOBwMbYGhaUwHVwWJdID+YNCdl9dkSN/Vk7xu+OCRAcfl3lMXbt/5+9ZRjdfLhrD9O3/pF3/YstlttoyPy8c//ur//K1yZIogMD/k/PjKxRuqDStX9zQ3L5U2ZUmSNKcSnrT+bvuv2qobXjwzESgPTXVNTV1VuNWBs4OjOr/uSPPQgdd7e49WHdww/vHHE5uPjYx05uLcH4l/E9OSz0wGkvSQ8pMnBgpTS2UavTwtTe60EMnhTWXvtImOCjHTGJifBxF6AefAIevoadhmbfHzcTA3TyGYQMYRwgRE/ohsyhJDsC/ibtidyA/p8/r+DosR6BhIPACGBcZk7V+2ta6CRfYPoQ/bPlgBQ14xuXUo4uUAg0F/0vImeU5yYWvVqpaDNsWFUycv3+7ad+DWYJPTDfi7OnZ++pdv/uHPK+wOtxP9vVvGP77y1Zerqy5MBR3oLwC5QIiDJ0wFPbt2NTZKB2hKkjSHEp7qfuEXDdlbrO+VfiwzIQDeuvD1WFCl1A3sGSgPBu1HWg4MHd17aO+BioKJiT3Xrl0bGarIsoD3g/qvpuSPZzosGidX+bVMTGaUyPU4/CUIJNdpOg+XCuSiYC4VGBd4Ua0x0Bjdve3FCgW3JoYHoYiBQipwmhKvj78W+b+oFTKx1Xc+38cS9M07BoI/ibN/yXXd9cj+If+nwA4QLij+dUMBROGC8y+FLkCBgvnU/jUt1xgmk2tra4s7K7K3Hj156vPbd/6/ocHxJicOfz+/c/3EL978zz9/UBV0lJe7vU69fBwR7+LkqgMjQZcJvdCQonz8rbduGHS12WWNVdLSfEmS4inhySe6d++or68rG50ImEzl/mFPxc3pk1WqgdDVL84imgx7jnx3+pOhAwiBR88dO4YAeO3gyNDBLGcT8n9NxpXZo2l63PuS5iRJP/ngmdQSiH7TEAcJAlEYjGSrKlRh8jkFBArNMLEVyUCWtVd2b2s4yPIIjGgKJNWQiHND5rJ5kfCLfO7sTJKZB18cAxiOv7ystvZNxW4zA6EvABDukCUIvOLVgP1Bl6YpTz76aXLtkSPXjugUQ72/ef1C151bJeO+RC8UPz7/+vyl7W/+4ZWGP30yNOzPR36vHCHQMh6YuHHxyz/eCvpdJgTbUD5GYImtIrtlZWazlAqUJCmWljz1orWuOjt7V9FEQGsqdzmuXj13YMe/vj+pC6JQ63YoODw8fPBIbfM3jUNHe3t/f2DEgxh47NjwwYpWoz5JU7jmzCAEvBY5qXvgwod+fLSowEhMoAWzEUZD9LmZH34KjdFcLThuCWRusWxtzbZ/21osioNpKMwTEM4NCesKpFwTnGB4LjA2+uiDd2aazJhvCu4qvg/E2T/vqgZrj9vsJrVfBttAFAA7oOoLV4pyrgaiiJwC8dv9/UlNGkPRZCrm38Dw5ZNHP7+89egtFBT7fMC/sdnrJ17+w293vNt76OTl4c0DIeQJ890ajUU+PnHjypWLt4ZtOm2aGwrC3sBbN26o7D3V2c0jSyUESpIUqYQnqzdtaivLXj/61kQgt9zlyr899vXl6r99fzEHBZJff/751avFBZ2ec+c8yd+d/qb59UO9uCB87ItgMOjx6HRrPhzVJwLp0kj/cxrpgdYnBkYnO5x6J34gzYL4p2/Kyc4utKiKS+1mMQK5nQgRmouJLMtUWLd172JYEQAp+zgCMqFg5I6EPlEGkLvDUTG++vru+AgAmTnRB2IZsH+6tvYtxTNmjn0MDnvd5Q7+lTq4LCCPPu4maFcnNuX1F2YmFx1BANyTD70vt6fK3r+4vuKsD4e/Y+cv7Uf27+3e3sPHD+/1ZGUNfIH+mcov92r0+nGEwInRtcV2Xa4sF/nNULnzY0BgbdnWlqoqaTZEkqRwLXmipqZ6xfr0gomJgOqsy+/Pv/319Iv1Z768aNBlnbt5/TwgcLi4oBjZwM70058cqNyLEHig6tjmgYEvBuzra1YZkzR6C+134fpe4EZvCYxeHJRDZQT8n1NvXJU9GdA4LWmGta02dzj+ONpFLUWIWwxhbT0Nu9ub/fy61Mg4GEWdfnKE8HmyNF+gX9Q8sOijyFYZ+OTUch8tA8fZh8WlBnHrs6msvSHT7YXgl7eA8KbAITC3zIFzfAqR+0P2z2VpStKvq6qqqAX8+c+dOnn0wtTlv33/VpOxtXGE2D+Ev9++/S7C3/7tv6jL2FBSsvmLL0KIgKzXp9GMj0NXzLc7s1RqmRb9axCakSMEDhpqs7fuqmpcJk0IS5LEK2FZfXV1WXppx8TEhNKE8OcPTX196F//9uXFQaPKYKj41f4TgMCrV4fXrQMEFq3e2jJ09OShvUcPHLSdHaiqqTvtKbbpNXqOf5R+MAQit+jlgdFRowVsoFyjLy37y2iiHn9CtrMWL82n9Y/4UfDcLtBf2b3txVpSDYmRCwQocZuypi/hrsDogDfsETH8REnCO6E8nygEFlMvXLj427qlu8buNWPzx9BrXAZW0E0I5fiVltPQV8FDUOEPQvSbpC3MbKz47rtrRzYHL/eeGrl94cP3v/rY55vJvzry+edfX7+0/c3/3PH2u4cO79/+wpuvbsnIGRzM2bNnID8/VF5u9iYmJo6Py9B/zhy7TqUFBEIq8OO3Rgc3ZG6t7ml8XnKBkiRRPbm0pbJszVojsgxGkwvxLxiauvzSv/6fix1ZcNClKvnPf3h5/6Xrs8gE7rHn5CAEFpeu+u6bltd7D+3d2lyx9TcvVuzZc+6WR5WkgV4X3gDidKATRkXSBkcHtSg0W27Y9ZfJNFwQgaSgJWVdbSfXFcj3A96dWDPLdNbs3lbTOcMyHALDhZCkoCcnCV2BfRR04bFv/CJw33NdM3les9joxQEgwt9yb323tRSyfwwXABMG8mVgzECHWxHm/Ij9C7qSmpb7SpIbq4B/e5gLuPW55f3v30r0efMh+v36/M3jL//hlR3E/iH+7fggdacyMNiB/PjZ8nwFioN9GkRAhMDBnA0b/GdlWkgF5rMIgTeM9p5Nbat7eqSCsCRJSIuXDR1oXlloSEHRrxq7v+DUhaG2j96/MaDz61Qqk6u1bcdv3wQEggsc3pOTYx8e9hy59s3pjXt7e1+v2bR1z55je/bsOVjhUev1XLsfKXsgBlqQ99NrZAiBFsvz763KabIAEiEniJ6rNxZ7cDWEKwJHtcIsAIiQCqzr7m4Lcn3R0WEwbMriz88M35HQJ1RDROFxFP/67txm87wsRp5ijgwg7n3JrLNW27x07o1cGK4HBs5BL8f4ozsQFApx9OtH9i/J57p1sGqkqgLZP/vvofdl32fffzXuw7Xf2113rp/Y/ec/73i79xDg7+XXXt2xZXWnQRmYuDFRohs4exZ5y3x4GUkoEA5MDA5++63LBKnAUGjGiwvCnl01bT1rpGqIJEkJi4eGhjJLDfLA4CCJfoNTUyPNK858OThgs9n8LphGbdnyxm//AAjEcfDVnTs3IAQeO3btr5VbX3zppa0t64/s2YwY6Kmqsufq9RD0Oin/8DYEi9OCEVi64sPSpkRYnYUJiefoNJas2lqdUBAWgy3eXixzNBZnmMaGbZAKFFZWRSHQIVqaz1eBxbSbqwjSd2cqlIRTgCQBGGMUhDS/eH15hur2ulafV2z+GLcwBUxfkZuSj5ZCHPiu3+9Oykvq//bWrZGRqqGR4SAc+nF16n9/9tVbPsq/O33T+9/8w44PWk4dPr79hRfefO2VHXX1meuMAeXEjQ7k4VUqMIHI7qE4WIMiYcTFAoJAWJLAepEJnNClVte19TRKcbCkn7iWLBsaqqotSUH4MxL8hab2NT+/KqNgZ5ZNZ/Pn56OHzh3d++7bOxACXzgxjRG4J8tgCwbtm49trG7ZuPdQ7+uVjUDAY8cOVlVk4UORaAxMY13ok16uXvXemdESfSIeHZZb+EKJM3dnaquOwM9r5vfCzHFQXCyxrA3Oz6xiZoQ1MZEI5M8Nuc43RvMJQD4cfu458R2uWtI32xVifbwBjFEBwX8A9L74MhusPTrS++IWCEhbAdHzTBR+5cT/Ocqp+VMo/EGdJg9Fv0VrDbbhcyNHgsOnYPJt6P3vr4z7kvDkW9fs9RO/IL0vvb/6HbZ/b9R9sLrWpk1JCUxMKNG7UoVMYH4ohFOBEAlPTIx+aw/qtP1uPCGsh2qIvaINIbBHQqCkn7ASli0dGjq4LjeA4lMU6gb9wWBwal/Pp58Wrdtg0+lswVAIHhs5dehQLyDwzZe3/5IgcLMBIbB2xeq/tG3d+Hpv796tLemtXyACHjs30qkCAOI4GA5Jgoten2hJLVuxNnFwMjlHgxFIvSG6SknrVxekdrpoJSQMe15zzBg4FhpZli1u6+6GqTMCvBhxMByiTsbjwg+P6wunXl/4FVhFxL+Q10sNIHWA4fhTkOJHXmtbe12xl/JPweUA8X14Y8oJ/riuP1r4wB/5Nyj1eXmB0dHRiXGZv9PuHzl58vJU14fvf/+W3ofxd/sO7X3BxY9fvLLjFWT/tnxwuqpTp5XLxz8OTATgdCqEwPyzIQcioA/OZ0EmECHwW7/JpHUzofx81oLi4Bz7rk1bshuXSgiU9BNVwuKlQyMV6/o1g6MdYP8Q/a5OXRj646eThXZ7VpbO7w9dvRq02YLNv9q///jh3pfefgXFwdtJKjCoK1lflq4rOPPRlsqNmw71vrh1dcax//qvY18MH6xd56SpQJLmA/9nXN/26XiTPklfuH5NSRIlJHGBKSkpco2ytqKznyuFzE26+GJnPDXbdrfZ2XgmEJYFhu1IiMr6xYqI8cmYoZAZl4Dxd1EoIuaBMQ5Zr9dnXmO19vi8gv3je6BxAhAfBaJQcKsQ6BUt/vp1lsRAx+DoxY6cwYmA1jV86uTRqal9f/v+Chf9ds1O/5K0Ph8+vv+Fl19+842y7LYPPjjdUlGs06ahv+ZxImUgoBo4m+8I5QMCExP1EAePjn5rO2vSksbo8bdu3FDbWxq2rFjVI23KkvRTVAKKfis6VRb16GiJyYTxd/XCSOPK5KLWYvuGLB0i4tVjx/Zszire1f7yC9v3Hz/U+zZC4Mu0GvJN2coOlT/on/zsb20bAYGvV3537NgXX3wRHL7VaZNhxhEM6hNzk+s/zUnEMEwyZNSvMKDfSYuTq5XgYLl/Q23mOq4aAgpPAM6RDhSJZR1wfma9nyIwBgT5TVm4GiLGX+wMIIp++54bw/zzUv/H4y+sJ5CF6Ld1U3v1Bs7+8QEwIaDCDUXfcsxBBbZ85Q6+CUbhCPqdSXlJhsz6srUlO0cHc4OXYe1f13vvQ/bPTAZ/YfLtt69A7x8UP9589ZUdW8oyV53+YFfGBpU2zaLRaxItUPuVjU+oMQLRKwUEJmk0sCoLuUCby5SLuwJxY7SxtvLFLSsyl0pHJ0n6qSnhyaUjQxXr0mQ5o6M6F7F/FxD/0o8cKy62rwP/FwweO3JsT1ZWzvo3XsMEPHwIpwJffgHFwX//ZOSqX4ee5bdf/GxLW+XW3l+hOPg7RMBjQYTAWwaZRq93Wpx6i0aTs7ptMk0DeT8ohlg66mtW7lyu53OA+E0uzy1Or7WJCAi6OwdoJo3R7butPUJjdDQBuaX5eDaEtAX2cVYvwhJi/M12Td0OeSEBKP42gvmj2T9fnmq11Qqtz2LvJ7rAIhg6BUymQQT3RwZ/fe6CydHSsuzMQoMOih9TUwfe+/6Kxeclkx/E/r390iHofXkZih9v1NV8kL0mY82HGTkmWZoeSh5JiYngA9WBQMCICIgQWD7j1YAJHJ8I3Ljxrd1m+tbEKEIszIa8NaGr2NTQtqpRWhYo6aelJZD861TKS0oLUPSLkDWMot9zVWsyju0pLi7eYINySNB+7NjozqyBzRlbdrz6pgiBb778i0vTs5AKDOqMuqB/4Mv3P6pu+T10BVZW7Nm8Z/OAK+vWrRK9BhFQn6jNrP7juIYuQ9ADAvNSazat1y+3cP7PmYbHhy1pxRUeUg2JPht9wWJZpqX7F9aKGb4xOtIHMoybpgLxhPD5OMVfYF9f3yyKfm/fJvk/DoB8GZgvBptZZP9SG7or3SL752a4+BcKIAzdhOUop56Pf2noAZvfmZfHBlMnL46ODq7Nrtl49OSpEWT/vr8SQH8ysX99J15487c7XurFrc8vv/bqK29s+eCDD7Lrqz+cLJ3sSJHL9YlEeAxEBgw0DgxgBOLGaMs4DoRLi20uLdRi8llwgROu9DprdaZUEJb0E1LCsuYDQx5jmrKwcB0k/4avAv7A/nmGhzuL19nAENrt9g4UHet0ttT6uh2vvEYRCNWQP//5tf2XSDVkQGk06lwTX37UduDA64d6925srt08oMoNBDoK1xpRHJxUmr1itElD4Icu0BGjX65dU1eTkYgj5DQKwJS0tDRfUdnqWnd0HeSuRKoh2zbVcqnAGJ3R/LrUO+evXycMFDfF9GHrB7m/O12IfiEzrX+IvgOXCcT2z+31+XTZ7XW1YvzxEKQFYEpAkgQUmgCh+KszaZq8QU9t6ejF0RujAdvRQ7/Ze27qf6PoV86aIft39Q5e+/dbKH5A9g/bv5oPPjhdn/3ehx9+Ojl6wyAHA0iVpMeBMCKgDsfBCtas4VKBF0dvdfpdblYRUuCuwLcCtuyGhuqMNRICJf1EtHjpgaERuzatI7nD4PIPD2P7NzTU+N0RdLe1024D/AVttp05394o0dlsrc9/UPfGK2ACEQJPHO79oOaVP7z5Am2M3qxSql0K/+hnf9tYiVtiWlauTQkEJiYmRgtLnNrM7MlAoh43xJCVWE7c/ZeXU9ZQn6PB/TBkgWBaSr+66LOLBVUjtDF6oYm/aJGN0d2Vdi5ojTUcwhWE78yeB/URw0fe8QeIfmNTU4h/CgTh8CMxOQ9IvhPiX543uaF7l8sXRT+uBQaXgxky/0bKwOQeQDDo1zcluT1Vx/agf3BGBw3DR3tPHWipzH4f2T8zPvQDel/A/r3be+gEtX876pD9q65/D/Hvj5OTg4hrykQU/iYB/pISkzQ4F6jFcTA0RjNmXyIuCE8gBCYjBJJFWTMahMCJwNpqa11Z5lLp6CRJPwEtWYbwVyxL2ZlelAXuD+Hv6oV9Q43Xjhy7cNDTWmxH9Cu22202Q8m3g98qEQA7q05/sOWNHa+8+hpC4P5Dvb29b+8ABB6fPj/79dWrmwf6kaGxXfzsozaCwI0rRwPKwcFAoGRVzQplIsac0wnoc8IMCG6R0VgM9VtWG5Lg8Ey5s78/RZ9buOLMoFxuso9U2MNd4L2YQEdFHUKgfybMt4kEViwISxLGxrpwRjAs/EXs65qaCoVCCH/oT2fD7B9teuHygPjMo5rumoII+8dwIbACzwKjZ0MVxMHQY5DwHqxy9CJspsQmp63iyObBG6M3bgzaD5w8ORScKvvyzF86mRk8+SbqffnldsH+If+H+PfHTyfX5ihlstEzo+qmJoAfCM8Cozh4PBBQDqhwHFzuAwZaYFHMxVulNrIrsBzi4Lc+DnS2tdetTl8qFYQl/ciV8NTSo0OeLLmhNLXD5EL4u3Dh6oURsH/HPOcOHgT+DQP/7DadUalWKpVGXVZxRQsi4BZkAl977dXu/wmpwF5xYzSihNbh9+/88rP/qK7c+u6hvVt3JQ8GJsYn2xqqc9SwIwHXQ+QWPe2Mhg3RTmfS2rbsdFmSHucB9YOTZyYDKTJZbq7JU+GxUQLeNfuoWNiRYN3W0KgQHSEchcBQaGqqC2kKhG7HkLoAfVO3EfpAZky/CIoKxWCENrM3r/95a0OjOSr6JfiDEJhsQy3HJWMHX/0gJWm/s8lnKvbsGTAM7rkxaDj3e8j+DX321ZXxwsyKYTr59jKyf29D9u8F0vq8BeMP828S8c+olMn1gYujo/LlSQICx7lUoFKpgm2p+eACk/CqrBuTRSgOdiEElpd7vVANMWXWWbc8v0qqhkj6UWvJsqNHqzrlzsLMQp3Jj+gH2jfU8t2RIwdHKipaixESOzuDwD+V0mhEAFSpdOtqe7LRb9yWuh07/uON12gc/O7br/z2Dy9vx2tibgf9arVO5x/88m9bNm6EHQkbG1sHTne3rxmfWLvOBKMhYACdcmcaV/lFF6cvMXnXipwkaAd0lv7lywkn4h8CYG6/y1NVawrbj3X3YtkZe/3ubS964k7HEQSGMP144mGRD/IVCKNMFP7Cvh5OPNch+7fOF4t/XA+0uxxvg3a4FeRAYNoIqGCCNldik1fX2bl5QFkyOIjsX2/vgeBI/ftfTbBmr+ng0Dew9Xk/zf7tp/avDvHvdHU1sX+Tox0GVW6uRa9pmrg4mZOYh/HXBFcaPe4KDMB/RRcg0I0DYb0eTOAkbIzG+xlmzCgOvvKxtszaXp0uVUMk/XiV8FjlgWaPUZ6zMmODCuPv6oWuEeT+vjtysKKqorYVlj57iocBfy6XSqVSowsCYNGq7PpqRMC27C3IBeJqyGGYDXnlD/yOhKBfqdT5baO4K/D1XhQHV9fVjAYGBnL2eIpNUPmAvTByJ9f7BziU6xPVhStT1Zq0nDNfjgbSKP9yc1NydbVVeE1MBAMXnBVkzSQVuLV72yYPQVic8TiFIxgKE/4Ey8AbMxf+oKvajPCX3V6X7uZanwX0cTMg9CwQPARXzs3AgdwKv11nafI57MWbzw6oAoGSDVV7e0+dG6782/c3VKwbel+ufv719V++TLN/GH+vUvwh+/ch8G+0IydLZTLlOvWaxKRxhMBBTROmH3aBGIEkEFZBT0z5A1cmkwAAIABJREFUDDRGQ5UYIfDTW56gH/xpOTuDqyHrdlkbyhqrpKOTJP04tXjpgQNV6+TK1sxWnS44TN3fgcZr146MwO5Nz/Ct4VuezmLEP53L5TIhBJqAgDtLP/3wPUTA+uy2Oi4VuB3i4Hd34B0J0+dhU1ZQBbtkdBc/+6j6wMa9L+2t6SkaLZkYGBzYfMxTnKuBoJc7LN3Cn5pucaoLBnMyzkxO6C1pKWkYgCatFl1tqDgYkQpcsFiWv+OofXFbd2UwvgtUEMSFhI8E7MX/IgW1f3m+1rrualt08Zfr/uPngN0KF8NwqwDhnXH4IftnDg7bB5DODmR5jvaePDBc9d77Xw0i9pLs3/VL7a9A6zMpfrz56itvYP5R/H1auBbxT6cyuZ1Or8aHYl/9IFRDllMLCEURCy0IYwTilhgoCONqyCQQ0IReXnn5jA8QOA5zfJVV6yUXKOnHp4SnWo42t6o0azOTs1y24QvnEP4+v3z09Gk43G2oqsLjuXWrdnjYM1xsswH/XCqXCaRSGQo+/eOH7723Iru6pmYLRuCbHAJxHPzCL6f7kAkMBU0mv9+lu/j+R1s3btyL4uCe5EHVQMnAwJ4jB+3yRPB8cnJinNNC+CdPS9P4iv5yZhAyg2m5spQURMD+XKLOCtwYPSfr5hA1gf4e67b2FsUMQCvmeNy9CfHP61uuq+6u64zEH938Qksg1P3BEDBUQsoZBZki0dlVmqQk//BwEPB3NtA5tPfQqQsXmt///ooWfaHQ+vxG9ie9h49vh+LvKzT7V/0esX+lBR07s9A/ViaT04nPpk9MbBofnSzNXZ7Hm8AkC28CldATU86YfUka3BgNCBy2udS5rCKUj1OBbwUK6rrrdlVIm7Ik/ci0ZNnSowcqclIMGZmtNlg1cuHc5/suHzh9+q/XqoaaG6sqDt66dbDWg/wf7oJ2+V0EfwBAY07pp+99iBhY3dbWBgh85RWuMRoGhGFHwonrszgOVpkcCtPkR3/5S0vl73t7925cVZSF7c3wuXPBfieciMSlAfHxSOg668yZUadMrUUATEkDCvIAzFW1IgRGpwHdMWgXV4DA7Pbd1qq5/dxdiiw+8GZardkx7B/XAI2jXzz5hjuhcfHE4cADIS6bLTfR50b/3OSfRTJtGDp1aO+B4aGP3r8SQF8D4S/e+/Lmb1/5VW/vyd/sJ63PdTUffFDP4a+wYN3ODZh//f0UgL5EX1JTYO3kaG5TEh8IJ+FyiDowHlBCW6BDUQ590YDAAKQCbyEXCH835eY0KAgb1ze0b1mfLiFQ0o9JS5YdODpUa0zJyUy12eznRkbOfT6y73ILwt83Q83NPVUVt0ZuHfR4hiH+9WMCugQCqg0ZKz7FJvA9RECoB7+xg6YCT0SkAq+6TKraXZk3vnr/o8qW1w8der0yswAiPJd/+Nywv1/vtKRZMAIhHkbv2qIVZyb08hStUqkl/jBNjhEoy9XmmvqzahtbTd67q4W4yYULg3FjtJAKfCAmkPS+bKju3tLp87pjGUA+AUi7oHH6z0HGQdCX+zcYNXlOv8fjP3sWkV6Hot9Dp0bOVX705SgMC4eu3u66Mwtr/16xvnTo8P79/9b+21dp8beeK34U5GzIQvgD/wf/tOi9GhQFQ3ib1zRx8ctBeZ6IgPxsCE4F5jOwKxBPjEBLDEIg1IMVIdarRybwY0NZe3vbykwJgZJ+LEpYtvTAUHqW3pCaUYzxN3IB2b+jp/+K+HegBfm/kVsjBwGAncVBxD8bzQES9TsLnn9+siD50w8/FCEQx8G0GvLS23Rd6iwi4MGy5wtMLtWNL//WVln5em/v79en2l1n0bcDBLq8iRZoCSRlEI2vY8VnN8j5cSlqpTqXRMgpgD9aDjHZqjKL3fcRCINYVuHZtHv31uKZiFPU71HAv+W+ldaGRpPXTfhnphdKQGEGmCCPtkGTJmq3P2jTjo9nHRxBfzFnTRbnhgOnevceuHDgo/cvZqGXh4/8pUde4q3P0PvyHx9t2VLzQfXGetr7V1iQk5WF/zvBfyJMQLx2B4+D+DQTkxcHfcubwggIpQ+CQIeC9Xo1SdxsyK3aYT/MKisYMhvycU59t7UsY6WUCpT0o9DiZUNDQ61KdWEGiX5HkPvD/PsG4a+lBfEPAAgGEPm/IHoTO8B+Y/qKNTuzikuLkAn8IyJgdTWJg0k1hAwIW6Easv3EpfN/v/xJc7DcZHK5jFeQCTxwdC+Kgxs9NpeJItDo00AkDEYwyZj+lzMTODPoTEHxr1qtRUFwSpostx8BENFPq83VpmjXpddmhS3JuqsQGAsaoxut29qr/fFnQxYqOvlWWmPFrc9xuv8Y0S2uAjsgDYiTf+6gTaf3uWp3ZR85e3bgbK7tIByzPDKy8bMvL7ocDgeKfqeg9fll0vpMJt9e3VGzoiy7mhv9KFrbsS4L+T8VlKpMbhMcNq9BJhAjEJTkRNFtiU8UCEM1RDYeQFK58smaGBgNseCuwMlaux9cIFNOx+Nu1VkbdmVIywIl/fNrybLGoYOlJXpDMtg/D7J/nwP+Nv4V8a+ysrJnqGqoqgr419lpt9uDwaBNBEB3f8GKsgK3y7ahuLM0GeLgD8UIfE2ohsCOhBdO3DwJjdHBfPSl7MSVLz+qHIJUYGVVJ2yccZ0trmjuRHEwkkWvL6r/y2Aexl9aGnqk35miNihT0Mey3JQUbP9wS4w8tzO11RS+JSYuA1nhrlv8McvOsD3tv7A2Ou4zFQitz768/ue7G1bmRUW/EQSkWxBoFYQA0O0I2uR5evtQVet3lc9vPmvyHDh5aO+BkUpk/3QOWEF2+/bYc9PQ+/L2u/jQj5dx9u/f//2Dsv+fvTcBajpP8///s9Oz0z3dM7MIw9Eh/AgUZw8GFYSwEAoQJEIOwhUqYIgkhgQ5EwUawjVBhlIh3TuktfJDQIbmaBMryr+gtEH/FCOKLnKtB4pdWFqN1Xh0q7U62737/zyfz/cbsLvn2HumKo/IJa2CnRfv53o/27YGUNW/wqT9lEwH/KmxAiQikAjBiCCn0OnlxUXW+kgMQiCeiWFZWBbGDTALBI8ExMoIvB4X+aUNdkM2AQKhFJjlKtaJMnc51uMc8Vceb7x9mudayGJ6uYZR8g/jD+TfVG5KTnvPl+0U/ziYf+gnBUCQf8xtbpExBgWbLZFKObK4eSQCIQ/m4zxYVI4QWGH3SKg8c7Sm/+wXv3xx6/nqLDeYa3A5/Pnx0fZ2hMD6bCEHCOjNCttcrQkOiohwitp2cd5CtkDI8bj8fE8PVoyZAcYIkAQT/rmgMLDCU4R/dh68zsCuDTgEFShN0enFdsfo/0jgzbfQVi+RMs2/lYLdtyH4rfRXTYzwqXqgWiLhOjkbU3OExh1bZLwA99ShhrGhnvZj9+8NQ+sJ8Q9s/5Ltrs/ro899/IDN6MsPvd/9+6H6B416LNLVBnU+RUCsAklDxDnUsjw3TyEwy94NcZnGMzFIBW6ZJVOBuBsCDWErXo97d8dTsh5Xna6T+/EcuyGO+CuOt97p6BAKo1iBfpFJFP96DvbmXgH+pSD+Zbe3t/egFHidf1Yj3QVWcJlx8W5mgwFOZUokEmlGYazXPBGBxxABBSp6QbgUlwKPjEwcxV6B0BCeVcBAi2Xt69HenvZmlONlCzO4weixF+j7iXtGhMdw/MUZPPti90TN90Zq0JsRFcVA76MbwS4hLp4e3ijfTNFmIATaB6HV3yMC/5Qs7OraJMzT6wRCQOB3L8f9GQH8w6PPSt+EPyz/1seg6UYIjUE1Ilx+aJU2J0eL+LPlhiK1qKSsub0nZQTJP7aCbVxdhYvnZ4nrcyeefaFn//r60tICzs3PL8YF+pPmBzWmxFUHG4IpCWgXgrga6Ow0szw37I27IYSDUAskBLTgbsiOLtw2wQvCa18iBO4GhTy7oyoREJiUpkwP8HF/5y0HAh3xVxlvvsNb6nANC2F5+exns6VLS3dA/g0VnUfpb24u6L/2nvYve4j+s0lJBowFIEhAQ+CugLh8AxcqemxEQKkkI7Aw3GtxEROQ5MGq9cHozuZmPBi9c8/dL755vPDcyjWod6ifPvj8ei5CYGfDUKos2kXR1naD7Zvp43bR/PP1M+owGG3w9vTEczDRhYEsSINDCAI9nWIC0vM6jFqelt1a9SdQZ4/v/wikAmWiYn2RlXgk/DshSMk/P7HyQBWefTF8F3y0/KPfQZwAYRpw06auTcYMQ1arMTPlRBvgbwsnG6wjinJ7ryP5x2aD/IPF352HzkDzg/i+1JLZlz7c/Ni+zXc40s83ScFmMu1NKqTTgw2GdQIm4jQYhgIRAkMtc3Nh+T93plUg5ZSFa4EM7g4YfgHPfKdp0g1ZumPdjf6ms4iMuCEcKNClx3v5OHZDHPFXGG++8fZSR0dclEtYZCybKZHeuXNnCWW/RX3nL1/pLcrNRfhDAOyx8w9+IgVIA5DpF+8enR/MJQBkS4xsiX/G/sIwex4sR6GiS4HFJtO6Y/TZm7dRHvx8dguwwPLg+H3ohnQ2p/A0EkTAp3u3ikXuiio4jok98729vT1hCtATWiGeHi7m8EIXD9IFDk709hGJqyU39rbtzZZnsv+MNJhiX1fChgog/Wtdm7qMu9KLlQeMf+hy0h8OPPrcGi1XqsKrEgxAPyIBNwrBTev0IyOAdBsEnhsligjnBOEn1RqEP8UOSSqUR7NPt6dUu0sVRrZ1dXUByb89uPkBo887K+yjz/Tsi1d44P5CL3cvNncjALkgAcmUpYcHdYUqMQIT0Kl1enh+0R9EIJUF4wFAPBiN8mCEwE3YK9CZIHB+8Q5BYNeWHXgwetpLrBNVCx3dEEf81cWbKPvVeoWzGF7h/kymBDbfYPYFst8rQ0W5KSntOKj6n01jAyOsvfDUZkX84xyIDwsxcAn/ULrFhvD3z0gKi42k82AyGC1urKwpL68lZ0M+pAejbz9+jhC424BQcfjz4/J26IbUZwo1bW2pBcoAr7ntsmBQKmCPle+Rb/DOD0YA9IBVEE/v6OG4aOgGB+fnR6UpBcIbbW1tSdl5ZaYimbrKTjn1BqGHX4ean5oinvp1FdgFEKR2QyQBumIxb/c6Av8sJYjln8E3XVnNJc3fhNdmX+wEpEFIjqCr7Xfhdlul3KAqSXWAqxH4p5CB/OttXzmYKuX4uXtJ6OofzL58SLs+Y9N72Pwl/IuMLfSXsJmFc+4cLoIXjT9cLDUYgslyDWYglQUjCGZl4VKgc2jWOgKDaBXIZIJHDb6cFITvhiwvfrlkMyIEvrtjx1MD5MGM7ek6Oc+xG+KIv6548523bVphZFRIrGsUypckNtvqHYS/oT6U/V4pQvxrp/QfD/EPPFE16CckwFajVSJRJG1N82LSAgPhD2lAlHdhBPpnFIbHubpTCOT38ftUKrmI5MHQDTlCEAh58K3ns7NIKnGDZz4/noYROJTtyzcVyNBvGbnVTcZtJSYJKAEO9vAweEKQvJcxPBzj6RHEjk/PExoR/9iuRSV1prKGMlXYv3dBeGMnBL/dtUmapisu+G43ZPf32keTANfT0CSRXgA3jww0915Xf+vFP/oVqvSHwmhjR7S+ezptTgKlN25SNhhGtLev9GglUokkLDVzidw8Ir4vezbKP0r/zXvFwuwf/Fswh+f8AtUbFCAg0JNcFvAm50iBfxEYa07OzgiBsazQn68T0G4WiBC4A6nAHXQ3ZObBvcXqJessbpbD3ZAHCIFblTq5r+vbP3Ig0BF/LfHG21qtzDWOsT88NobJZEsQ/oB/KPsF+fc6/xAA4YeNY7VJsRW+UeEX71bIpbuM4IeAGagAAkok/v5IBXr5QCKMGJjG75PzBaQUWLFzg1fgnrtgl4oRyEV58OfXUw721Dc0C+RushsKhXFHm3v8rqQqpwhSuSJnQTw9YAsEnrzNZoYhXJDOt20x3rjB2ZZXVldWUlIyeX+OJzWsq0C6v/EHYLcx1n8NJbNalV5fpP2DdqnfDrz5ZtiaLt6WQGSfIUGdn0AVAb+nGYKX4KgpGCz/pBKWU5U0dVekYsuWGzuM2hRYlW7vXUnVAP+s1tUnK5TvCx59Ll3ffEP8o+RfWFIGNfrHVZvn5ubZBjsAybwQ+RpCWynCA2fB1Fy0k1PozPzycD49GO1ENuFcpvGGMFdBTQU64b1hQGDqHRt8M9iEwOgBpcBCgTI9wNXPkQc74q8j3nwHJbWuXvtZYXGBLIQ/OHi572Bv7vnLl6eQ/CvKbW/vxQA8DfpPq72zBPxbRQCEToiRk8b3RbqPOCIwuWAJQwAIgRBIEmFAICyHyPlp4BVIbcfhqUD7EfVfPsalQESKKsuDr0dX2gUFDc3ZQplEYTQadzRt47uzW4GABpK7eXobPGETGMlAQ0REdLxYwNtttba1CQPy6upKmpsn73+9XCjs4SmICOzqeo14XRt52PXamxsLgvg/7NrEEycr09Ydo/9YFoxt/36eJNIJJK0JBpxcU6D7fhcYAkC880vCKmVXtXZlxvv471Zs2bFJCtW/+pze3naZBKy30T/PrRe/6qyroUaf7bMvwD+k/oB/keGFsPfLpL4p3QAEhjMN6B8HnmBcCADo6e3h7TGdmIieIqaDqCQYyBbqtLY8Nxwa6kwnwnCeHhrCLlAKVGzZTQ1GQ4sEEPilzWrchKcC8/FuSKxYJ/KL83N0QxzxVxBvvC3lRLoGMgrDokH+GaG8fnAF8AfZLx/Jv972FBh/Se2AsKEnm63JZh0AFSiRbk5zDwRjKwWRgPjJzj8Fm8qDORqZl8+5c3z+sQCUB/cJ7AgstdvEUI7RC4BAdUL+zPJoWmbPleaG5pxULXRa2m7INqf5MDEADcBAbxdPgwGGAF288128xGJxHsrK25pQuljX0NxcMvn1A7PRaP3s4cpp4/duhtAFwO/8AomujZXALmN1gV7H57z7R6yy1vHXyuYrVa5VVflqovsSvrsCR8/+qTfsAOMfu63S4KAubdp2maINqTcJr7ehszklu7fXfT9bkoHxh31fjo6M5uHmB1X9Q+kvH3Y/4OpRHJJ/bGrymYQhZHj+XCybWJbheUk4KzWNe+q4CJgIF0lJJwQRMCt02rw8Z3ayt0PI9AukwhYW64YC8mCEQGKcMPNgGWZijNjz66ka74a4i3QqPy8fhwp0xF94vPUjmUTm6hoTUxjLYAazJXuttgUk/6ZA/uUS/gH+sntSTwMAlzqWlmy4Cthks1mlEmEA3wv0GX64MYkCRE92AEIxEBLhDCmHE7Y54Bg0hKEZghEIdqk77XappBR4G6tAdcIOmdvcWmzqExiMHsrhoUQbvLNkF7fHclsT8RCgh6dnMFIxLp6eHkH7A9IFPG1Kh9XakdKMgDHeLP7o6zV8rXj11rNHz6rZrRsRt8H6YAPxXiNgl/3XuygGGlNFunQ+z9hF348jz3YbX8NfQlVVaJWXWMdXVJH5QzUegDF8j/yzk3B9BhD9KVJ2UCvb7+IcuL5wFdocmIrM6R1qj0PfSaL9V0H+fXF3JxgfNNc3dG8cfU7Dvn+Li5GxYRnU6DNNQPRbcRnDc+5hCihR0ADELRCQf4nTERsaIbAe7IQQuDY3zAhdd8raUAq8wbyxA+k9PBMDCFx7EIcQaNy9CZsF4t0Qy4F0ZYCrl2M3xBF/0fGjH0glrj6FIfvjonDxDimMOwdXUhD+LoP8S4PqXwrRfyj/PY0IqAX8DeBGiEQaL3dHlIE9KzxryyRVwA0KEGfDGIHGpPi0xflFejWE9kjAuyGkFAg2MSfv3n4BZ0Os2W6RFsvh5ZdPnsBUYG6qUKrACPTa6i6tikiEBRCDJ3kQO4X6iMUHODCWqM0eauhsqB9vbrz/IAquFa/eevzoiy/OJo8UhuKxwPU0eMP8C/UmrffsCLS/1UVU4G4tX6krydU+pa8II/YZN7SFu6D2F/rzJLlOFPe67dX3dEHUdAcEz/9hCCYkSDNlrU5PbW5zZm8kdA0SHpxPTsnpra/mKHYrjE1E/rVUnKkph+z3pE5XewjkH8Kf3fggktj+sel/AiIB4XuTef7i4v4EA5MbggDoQTVBEukuMA1ASgWiRHh6GEqBtAqk+sHTBIE3oBsCNjHO8E5qN2QW58HkbsglzwBlenycz9s//VP/DzrCEf878eZb7/wNO8zHKyY6LDAa3OxRfmWz3ukB/LXnonzqQHt7bwql/3hI+50G/XdHu6S1gRWMdLM8IBKhTYINYdhMIv9eAyBVDQQZ6BewNZwj8/Jd3w3pE4jsCGzpbmgoKSf3M5EIfJJbvR9BycWytjz1BE8F9gICjW1tbRm+2zdnoMQNZXD4RHBifqxKLHCVfsXhaDPBUKZ5qFmEV8WMs6urK88e3TyLgHH0SLuVzoNh6mVdA9pfvFYC3PDM/hIh8KnxgLwgTyDokNC6z7gbA3ATosEm9IlyqyR8ZTo/AWb/CPL+oPaz94Dp+Re1wnonN69aGrnoGsPleuYHC5GabShK6R1K4UmMu+HTWX2Mbf/O2F2fK0dGcPMDRl8Q/5D8C0fyT7KOv/VvRUwmKwS6If6wNujiQiqAHtT5+Y0EdKKbIc7OM8vzhR7rIzFB1OEQGIxW3NgBdqlVTsQ5wbI2DAgEkwTohgQBAiMF6eJtm+XvOPrBjvhLjDd/pPHPiPSLZQXGYvkH1b9bPVdeDpy4fP5KkfxYfDvOfhH+MlNTU09DLC0t3UEItIEVTGSafJu/BBZCaP6BAAze2Ahe74YUuqW5stkZnLA4V9IMoZyyaMfo0lJ8Oan86KFDpWe/ePRsZRWXAtWMmQeLKe1PkBCqT0nVSoGAbWGb412Z+Yl4IMYjgrW9pKBamqQJ0whzipBeGhoXj9xbY+4m8u/ZFzf3QL744/e7O3P307shVGXPTjbyTvVG4NHbc124Fggfi7eLq1qfSrTVRei7gm1jIwT9aRKOVpPEZgrFSn5SaxXBXgJ+YdhYA6Q7HesvN+HND7W6S2GzLVh76kXnAnG3wj+zHj7rlN7czYUKKyTzz/HNI7z5Ri/+1jSmuQXQqx9U81fC/h7+IQAymAyWZXjxXFyMwRMBENFvmpJ/YHKAX6LXIggBg+AwsFNokHl5PjrCbhboRE5luthVIBKBVbQ0pE8nEY+ECETAS+FiXaPqbQcAHfEXGG/8rT8zzC8uxhxrjmGQ7setW0+unD9/+cRAJuLfAcAfeqS/hj8EwA48CiM7IHdDObDUigC4V+LPZlL5LyuYS/DHZDMVpC6ouMHeLD8XyJT4S/wzwsIjFxftU4EIgY32UiDYpaYjEXiorvuLx3gweodaHYzy4DlQgdAJ5WkkN9rabrAK3dwiuU6JHh5BEZEqcQpHyklKkmXmQrlsvHnkOJZ/QPPHtylglGCbeOU2Q2sCHV0U9NZfbByUwUmvmgjDLqpSWIUjoaqrCy50GO0XQeAjcbcHfQHY8fzwhKr8Df2Odf333SnodRGoruoSZtogs7amiIuEhlauDGZfiqZ6ezPDYfKFND+g+odHn+nZl/JGFX/7tnjS/PXxgubv98k/hD82E/0rMwCBc3PhXA9PMJWISEycjkgMwh3gCKcI/CKCzoJJOwTuhsxHZ22YiYmw58EsJnfHph1dVWQ9zhP7pWqtxt0ol8dOWZcOX4oaVep/gpLgtxylQEf8RcVbf/sDSZKvXxijMCyGwQD8WRdurTxB+Lt8vu9AZNy29naEwBzIfjMp/gEBO5agEaLVuqfx/TKk+CQwEoCwcMCkJqGDmVSQDXwUXK+ANF+mguTKGUlhdq/ANP6GPJhCYFn55OTRCjwVCN0QQ77Bc+bw8rbs9vZx6Aakatg3mC7cNl61e6xHUGh0mrgg02qVSji8HJL9iieh+QHAQPLvV9goqhJu5OJdsRo5vRtih2DXa2+tvxMjUE20INT/iARsbW2tej1aIbJa84NxfxWp34QEA5X5Jqjz/2Drg0YgKQCqu7o6huqLUrKls7OzbVp5Xq57Kow+p6Ss9Gj8JVj+3br14lf2i+ct9NEPnP66uS+C75VXeFiSP+17dWMD/HCFlhkTg/iHCBgSszy3WGhI9PAmqW8iFn5BWAUGRVA/6SwYo214eTlmg1MW1Q2BPJjF3YECfWWciQrEebDCkJ/QhU8nPbi4d9hHpVP+7Gdvv/1TBwId8RcTb77xAwUzzt01JCrMzGLh7BdG/8D34PIUn88/ti0paRuefU4l8q8H869jaekEIqBWmCJwS5JqOCgAgCA6SAUQEmAWJFvkQYct2P3d5NsZIJFgKBBsYhACyVQg9kjAMzHrjtEN9YIj5HLS7cewG6LOT0jwhFLglXbohhRlp3KCg5ltu61+B4RsH1FJzm4j4p82uwicAsbHRo5/HrXbSPD3zRdnSyvWb+SCYNLlZdrPhnStA1Btf1O94T34XYhNasI/9DBvRbzLej1Cs0IhDLj5HcxVk4zXsNH64PsgSAs/6iOMPc3dDQVlej4CYNO7T7VFJXV1zTntK+1ahsRI5N9jvPhLfF/so88qUv6LX1xc9PENQ9+KJMSZB77t4Cci/nBER+PLzQxGSJVleW4uBsp/HiT9BcUHLyKCKPpFrPdCkAr8+fTy8nD+a16B2CTBcxpsYgCBT8kV9URAYHRMxldGuBL6NHDq2uWBwOFFVX+p/IBI9DNHKuyIv4x464d/o5D6+UQxCs2MEJL9wuYH7v3mFvE/+aS9/dyXYRrsfQrR03M6FfCHJCDvdIe2uijAFeBnIwD0pwqAwZQARPiLiUZBOsO+/PhYnAxDK8QIPjH+SZpwL193shoCBOxbt4mp6+xseJ8ajP7imxf7kAh8F+GINbM2JxgijtHZPKlii/WzLbbtIqVAC3iQ8lLqSxqax5vLP/rcDPJvdeHWs0df3GwhuxLd9JFIJJhEAn6qYr0bgp9Tek/dRd6npsAHGOwCHdcFpEqgFSDovdANgQDYGpSPTJwFAAAgAElEQVSP/QgNwWr0pDYY6ATY8P0E3LThJ35eeF3cPN5gqqw8tsO6pW03V21MLaorSGnvSGKTZH7f4xe37fIPZv8O4c03VV+fHPEvwG3zPIpY2poWGz+/Jv8w/6JjojEALS7eHmvLc/MMwjyEvwgnjDv81rcSYRxZzii7NSeumwU60TeEkQjEpUCU8cIH4lnBtfCvpIiAWyKnzl+Ggoo5hldgUspVI471OEf8JcRbP/qhgh2+OZIVVRiN5R/mH5F/V4r4xxD/qqsPtPtpMrS81A6Evh6MQd7ppYenT3d0pKYJdmk00AahBSAFQGoGkAkIjIn2j4r2ZzNj3VRzKA+WUARUGLEKzODEhm/0CoTdECBgbWWx3S4VX04iefC7CeoQy8zwxaIr2C41J5NnNG5pyk0X50BxzEjk34Xx5smvP/fHwNj3GJq/0Pw4UtIA+WLFodqj5eUiFQqBIEXI/ENu0V20UUICeQ4FQETBTXQKjBGYlbURgKGQ/xqww0qwgasm4s/eA/7TOXCC2mjjzR0XlejKGxvdWqskqUkGrnHv3sySsgDMP6T+bj2+/cWenYco+beTVP+I7SmMPu9yR9lv7Px8uITIv92UAlSQQXSgn3802z8mmoklIIvl4pk4vTa3NZzRitjnBATEi8BO+FkEVAODXu8HOzkHzSwvzyRunAqMgOW4aW+LJeQGVoHEKcsJH9AMkxolL6emps4jADa1HTZLc3RK1cXNPm87dkMc8b8db/yQy9W4+7EZZrOFieWf7c7pldxrkP0WyY99cu5AdXv1gc0o9dUmZXSs4+80QmEqj3dAECBD+NNoNRoMQCr/xSVAJIMQAFlEAUZFs6PdBWlmLpuMSYNHjAK/DnkwIHDR7hjNxwhUiez3MwkCwSPh0+fPn29BXAlhrA379GDH6KGUTC0v3cTHlqw+2bnNnSXN4+Mj9yn8wezfzbuldPMDgEF8QhH95HI5Xy6Il71+OY5Kf4kU7CLaD2tBxCeqV0EUIJaAWa8TEPEP+6vghQsDkM9ARp/t8RoEX5d/6io1HMDb0tFYPjIiatz+c/+i/nQ/xe69bK4xO72g2rgbZ7+38egz1DIp2z8k/yD7xc2PzT6RMjhPHzXvF076H7sp+WfEX262PyzjgAJkwPcmxD8XTw+U/K5dPxfuEWpv+RIhGOFE1QMx/kgvBH8AUoHLy9GtoVlZTnYGUrshiIG4FoiPqONa4Eyh8PK18+enrp0/sbDypM3c5B8YLxLHc6xax26II/5X462//RtulG9mGMtsjmYB/1DCuNRzpY9U/45h/lWf25zKEwqFHR0ajobXQ7JgxL+e1I5qOX8Xwh8EABDxj5q5xQiEyxxceJBBBhzNcuXLfRjo4SchyTAIEvyAZJNmSGzc/CKZieGn8fvQA1pl74bgBWGsAm/efgGlwC0osWSa15Zf9vQOwXCcoCSPt0OqkTaFNyrLGpqHxktG7z1ALCezL4/ugl6qTKd8Qkm7QNWnAvwdOxbAVxVVJ33XM19tH39REwJ2qUkFEDQg+rV1AH5bAGJ/KeC/gUutvlH4+44JKsVAugCYUGW9dcu229qT1zgy0tjYGKCtN5X2l9RnSpnMthvCvpJ6HvSyb+6pqD263vygNt/kpPe72RfzD2m/6OE5P409+aXVH6IfIJAAEHdBXMBK1iOxdXp5bs6c5UwAiOUexh7KfxOdqL6IE/0CEmGLeXnYM5QGoLOzvSPsYgkxoC+SIaIVVKDzNJKAJ1D2e/7aS9np8UcHZ2eNbTPTMQfS06tXnwz9zDEZ7Yj/rXjzjR8yFWFum6Mt5ijIfhUIf3dOt1/B+OuTwxGd6nPnNvvxOoQnTmi1Hac7tBzt6dMPT/fgdggvQODG03ZosScCFoD+/pABE/zhImAwMwQRMAY92KJ2qT4pZCDtQS+KUEshbIqBuB/s60e5xAjk8Rs8Elo22qX+EtulwkhMzPDw/Msr7b3NJcojTV1GSdL+qEB5ua6uuXnk+HIUPfoH8g/ppfIP7auyOF8U9BH+HQtIk+flFfE22KV22XVgFz35QqZggHzqrk2wo0YkIGmDAPh+ThPQmTjSgARUc8HQ8I+nv/bRF/RKlXHl0bNbq0tDYhHwT1xeMD5elqwsqCuTx4bE7I8yu+aVDD3DvZxyevT5EN38pfjn5xopk0pJ+Y+LEOibweWuV//asBsFCED/aGgDgzzHAtAj0SMiKMuyfH2OEeRMp7tUM4SgMIJKhLECxNouK8tClQLX5wKDpnHdz9uDmeFvwIOSrRHmNXMwd+/D85dPRPaOje9bWLDObnG5dMlZKNDlnb59U+/ohjjifyfe+CGbud9veyDKfpEYQI8QlP3e6YG935eXEf4Q/6rPHVj05Qm1gD/EOZT1ntZqhSj3Tc1M5eUI+K5CxMYOIfpFmYaTlJGBO8BsBdmCQxQI4YZwWQz0OGO4q0aHY6KjooCA/vSunALSZcw/f8ouNc7VHdbj5AFIBPb1nYJuSC19P/MIQeAevCA8O4sIGIyEa2B2XvrH1367t6vLdRvLiXFxYqRRWX59TbHbuBsv/t4ko38bjKJIvojp98knW7e7BfAFAgFCoL0bQo36qXEWrKbEoJrqAEP+u2l9DOb1JghKh1sx/YJxBxwDUG2gGyDfXwCku78JCXP6lrtfPBovaCwvF4kaxX3z1+/nNetKSpTlorzM2CizOSYqNa/zLOX6TI0+l+Pmrxzvfpzz8/EK10jXm7/cmOU5rwzuRv0HAMQCMDoGvk+FBLu4YDMd4gNtuXfdl4HSWiz1cPUv0Rm9gOlApwjSH6HAiEuBThiBoetn1J1wRzgisXBznHe+GkZiDGHzZhiw4bZx2seasznmma92L8wmVLlcmo7OLKlrGDxU85OfOhDoiP/xePMdmYIduc2XwTBbWGT2z3bnVvbUFJZ/0Pyobq+uXnQVCjUa6HJ0IAAuLcEJJBmvJ5WXnSvfKuQh/iEAdmAASjPwEpyRKECEgBAUrBAWkxUcmybfGhUThWJ/4H5/f0JAxD94YpPOJDwwM5I0Mq/Ic8cC3D7BAKS7IcQulfZIoLohOA82sLeL00/97re/bdvEU/YLNKyLE69GR8pF2dYtswu31psfRzq7qXYBzhcFFP/O7XJ33xx/TA4EzMvRGr41FYh9otWEf+gnyD+cAK+nwLgLshGAoa0GLAABf/jm5PdCb519NP66qtRu2P9hDKm/kfL0krzspfbcOXlZjS5d/GFZc0l9ShjLHBMiqRZVQivbTnNxngD4xyfyTyjD/CP4uwGbv4Vz864SAGA0rf5oAYj+zTH/PD3hrl5iPr4H1zozNxeZH0rSYKL1EkktEEGQSoTtVcIgvB43bA4iTllZxC0wwjnQZ9twooenpyFBneH68uEA0zMxyClpqHkoNTzQPO3y1Ve7N80+n7VcOuxaVKarVHbXORDoiP/xeOf64v5tmwNZgWb0SGCwjUbbnaWenMvr2S/Cn7uPUCvjNDVxZABAwB/Sfpk8jXAbXxCA5B8OoVCI+Qcz0Hjwlk2kRUgwC86Tcz0N21TywhDg3/79AMF1EcgG+hGLGKxOMqQZGZuPnfOhLycBAsl2XEUpfUGYskv9FBCYUChQHrn2u99dO2/rLSstHfwwZaJx4hVCYEn96dlbz8a+uLmHND867bMvuFtKyb9z7r6+Qp9dn0DvWaDKE2RKgggCYd4FUEfTD+fC8I4ujC1oBNMS8LUeCAEgDMEQBUgAaCBjMBvcrzbwj6r+tdrG31dWnqlJHxlFABSJ65cOjo+v3BpPn/y1GCXC3WVlJc05EoOFdWMgRVxCzb7UlItFeQJ5kVwO6e82P/heJV2ffiHBGJ47p4EM2B9rP4I/XAJkMELgiDwAMNF+Dy7LY3hubjjU2Z7swkAMjMI406txFAQJIJ2yImaWly0b8uAs57iAxRkYgfHIZ8/PQULxsMk7YWl8vOer4cgk1vSlGQYDAfD5bPClB4f9SkzKkpOleD/EEY74H4x3Fi+6ucag7JcF6g83f3NA/V1OScP4O3du0Z2n1WqaOE2kzwH2VwDA7OxMbVjANpT9YvzxgH8yTpKUtkEgChDhLwQg6O0SJpf7MliQ/iICIgbuj8IqhCYgE/OPSQ3oxgXEu4a7uq9fEEYikAxG79xgE7Oz5SY2yspNR/j77e/OX55AfDD1l5RVHr8/OTkxMYEYMv5o7OYecApIb+jckC/i7BcD49w2Hy+hTIsIGI9XkQUqVV+mP7UbgpVfF138w91fBK8uKP/BditVA0QS8NtN4FbDegbMxYMw3wGfel34kUhI0JSdPNtZpmtUjY6OjqhGSsaejY+t3Pq0+f7x5QfHR8aaG37RiTTsID+axW7byysqGUxGNNehTBmlvwKM863uPCFYUqzzbwvOg40KZvTwvbkwfyZGH4qo6CjEP1wAhOt5nsGwRZ2fmE82QYKcs6AbEp2YhbLeIGoYJigRP1H8i1hviTg5taKPXxsedqHcUrOcLH6bzRHoP55ODDYvDw+fuDw19bBtFX061oWvAgubbmRFXLpk2bKwb9/s06pL//Ivw/FiXbq+4lDlTxwNYUf8D8Vbb7z1/7zxtuu2yLjhNUswnn2x3rnTg/j38OXlgADo/Z5brD73pVCrReqPQ/hng72306k9mUgCJiXJZMJUIgBREizDHWBsg0ATEBogiH8uEVG7BPFmFxZ6yPlH4djvHwi3uZEKYePhaDY2DoRgczPc09wzJBxZpO+G7bg+yisQ26V2km7IoZ1nv7j97ELZx1MwX3F5qhEljWX6ssmv7y3PTUw2TtwfHc1r7mw5hHcluukbuZRPMvDvk3OLfq5eMvQ31xACItqiRFjVx1O83gyhJmA2wVE4NX2vYxOtAKu+MwjdSifAXDWWgH+w9UsgiGf/uIuVKMdvGUxXqUAAivR77naOPdv3+NHogxjpU/O9xs6GZqxhk0V++9sGPhvoqU+H7FcEc4wCAeJfwAHMP7hK8JoANMKoJZtpnp/ziZWACIzC+o8dzWQi3Q/8cwkO9vbMR/yzW8A4OWdZlu/NRzsTFYgVIN0UpkUgPRmNh/2cnafXls3eMBid5eQSXugdilNhVtiy2XJpZmBu3nZrfPz07EJHIIvRdqPKOWJa8fz5wsLsu11VYJe6HJCuLK+sVDryYEf8z8RbP/zBD34WHx8bu2vz8L1CNow+W++czkb4e3h5KiAAsaEa8OcrBPmH+WfT2gZIFwQJwExOoDA1VSiDDLgD8Q/lvxqKf7B8ReQcEy7zhnhkeQn44S4uDAYeBQT8RQUGBu7HqTB6JFKJMAGgoksWcDEW7mdyYiO9/KjtODm1HUc5RmMRSNmllh357bVr15Bqza1vmGisM+nKr8+P9372mbx8YvTV6MUAgfIobRS1k559geyX1Mt8veIwtxEB/TZvxSm3QC7Iy0sRrotAsvuRgDNfeEZd6thEd0G+PQdDmiAGioAgAeE//KN1QHVClZGPBa4O/f0mEP/Si5HYPXvz0aPOvqbZWevs7POX4sHubvRJJBf3DxacaPtsdXXfSp4Yqn8CPMp4LH5rJuIfBwBIDtODYSyBH/FnZJjnL/plcKOp7DcGWvMs6noyfRd4nYBBTs4zy/eGQwBkZPYl0QkrP+fEoAh6V9jeDcYdYdgNCQrNcvYMSSS5cCLz4eWHe5HYm76xhOTf7PM754ZDPL2ZbQlVCfnWx7c/1RjBL7E1//C//MtymlgpRkrfkQc74r8/3nznB/lcXvqBsJe7Xu5lRM7PW61Q/cu+/PLhy2w3lPye+/LLxcUvoZ5ul3827erAQEcHLxXJP2FguF8mWMIIha64AEjrP6k9CcZjMEgC5gemybfHRISwGIiAMTAMHeWPkuCoqMD9kA/DcggV0LEMiw/wiVFQ5zNlca4+515DIK0Cacdo/ZGPf/c7xL8r9fUNnQ1Xxssm74+0L6yMj6/01Jc1vnp1/NWrUVW6fpCefaHxh4t/iz6RpGwpxQT0cd/lRuXcApUgPoy+nKQmTWBcEaQoSHm+fP8qSBZWgFx7qLl/lH1k9YMnEEOnR4kojzSdWIfS24qdFcUnTQU9CwsLz2dRttiu7NfXHioeHOxvKdWLfD9bXbhzOrdALCgqKkI8T0nJzuR1aLUaGxGAVLCNbKzI0TMJgt7w3JyvP4ON6IfbHyxuCNnXWz+MTjsBYmkXihC47J3lRCqBzk5kJDBivT2MX64T0GlmbTgmyDkoC2/IBbFPXIZhquFLlrArzfWnV/dl33vgcsOg/uwzJPwMskZlvXYLLPU8fVqFCHh4mC9O56fl8R0HNB3x3xxvvN0zaysqS5FwI8Pa2GzNdh+pdel05ksk/15mH0D4WwT++QqFGg7mnwbsTgdsS6sdJ1J5mZmuYYE8wJ8fzAGiVNVXKJMh/uEWiHQD/xAADSxX+bHwCO9gDEAGA6+D4DIgVoJRgEP/aKoSqGB78ePDuNQFYYk0SSMjXoHH7Otx9m4IIDA9HeHvd+enrjQ3NGDX55Hjnz/4/J8PLhwc73z06Gx/5cSrV68uXpSn9++kZ1+o4t8nwD/XOBmHAjYCoFYo9HPfdYCyJUR5ZaaU7IaoofVLGh+bSPuXGtqj2sDfSYHJGAyXZqD6Oynwptdf7UqQVKM/r7FS2ZgnQiFW9g8Ovldce+hMTXH60MrBTxECP/10pVd0prJSpzP1l6JkfqduahUR0MbLFYuK+Py0lJSczFR8n1S6EYD0lg0EFP6Y0cNz58KJAQKTwQwh8g+Fd7CdgPmkF4yZFzq9dm/OnJiF+UaV/IKcpp0S7RoQv5MO59CImeVhlhMA0Mmw9yU2Ejq/bE5tbu4dWM2+/vlhj/wbO2bB1mwTd+3rr48H3nm8D72+6WlX0OHD/3I4Li1dFJAmP/a2oxToiP++eOtHy/f82stKMhUKq8TlBoe33Vdi/Uqb+vLlw4dTmdvPLc5j/LlC9tvUlITYIMMScBXlvy9TM/3CzHFIBYIlFq4ACmO9fIQcSgDSCbACDAC5wUFxfIFPiDc0g1GABKTTYNwOppJgQkCFWhYw6hUDVSsmscwHYRYOpUBMQLichJ2yKBF4ti79t//0u1fnpwr6W852dzaPl3z09WHvqvy10bFnjx+B3UFFbTkiYJ9KparEzQ/sFIB7H9goFKAN8yJ7jeDhCgT0cd+2nSKgQJVX5MMmdql4BbhrEzggbKJISOXAXXYBCArw53QG3GpY5x9G4B/Z/02oUgsD5HyBsqZcpPpYNKFq1MO8z2CdTl+p05c1j688fvzp45Vnz670TY6MKE0foOR4Z3Jysi6vw7pqs9l4gnRRWk5OSk7P6aUlm41jg8PMFP8k6wGzf9D4YMQMX1+MDQ4h1T+XYMqywRCc7+2RTwWlAYFszs4ew/fmzaGh9GIIMYoBCJL1YOrjWmkEOieiPNjj5z+PkGD5hxA4kNQ7NtRha7/49YNL+fnqLc8hFt7Ntxx+cHjmk5IvXiAR2LXjaVf+pcOHD4cHiAW7qt3edqzHOeK/Kd780Q//ZnpZVFakMSrUPeM9Ek4qB88tF3q5v8zMRGRw/RIFwp+Ww0kC/SdD/BvQntBC+pv6UmhGH5ia6uNH808oC4vzcZVRCTDVBMH+pwb/rQJ+IcJfCIuFnhhAQCZjAwKpgJnAaFbSZvnFQrtjCdOOQGyURbohcDxOoMJ5cPJgifjaeaT/BMpkoGF3Z5loru3pli1bZlevdHZ2DiJMVBQPVja+mpg4hbhZqStXyfGVNMonOZyWfxgTUqIBeT7bdn0Sf4xWgfFe3CpcB0QA3JSAux9ddA9EjYuAJAXOWh8ExIZYQWQGJnhdAv7BGmBCVZI7+uNElZCeI/kH/APC9euLlaIjSlN3w/g3tx89uj12c+zK+amLI5V6ffEhqAPW1dWJTjQN2GzazLyC+pzs9p7Tp5furB+nN1qtG+EnIb3f6BhGjHl+bjEQs8/FhVaAKAX2zvcgCpCGIFn+dXKCbkhMln0FmBil0g0ReyuEJmCW8/SMOZrJPHEZx8u2jvHxFdudA8c/PzytvrEF5N++F7cPGj0Spy/NzDz46EznygLSgF077Kb5ojRfnp/jdJIj/lvirXdWZ5+6lxRkciVMzxBtc8P4aau1jeWd6OQUMuzq4774JQ6ojiWR9BfFwIB2oOMED/FPWBgd58fj+fj5+GD++Xqh9BeR0tVHSPMP74EgAnINrgKVV6t3cDCLS41DQ97FYMZQOjB6HYD+0YzINHmcCwhHYpIA/tF4QVjKiY2jLwgjBPL75NgpS3nk1LVr185fPtLfn5xcsbMiuT89+/nCLIqFfSsl/f21Z2qLBwcHW5J1E4DAUyjDrBSAS/wxyPC9wjV2/BnZbRLJXinO9BEC/bbt2ooRyJfL85SiSMoGv4u2Kd1EbpVTCjDh24PQIAUBgK/VAP9QGxiav5rqT859kl5TrsL4Eyn1SN0lH6rV11aKP/z4yGDLyc6ze072n6xrOXvhyZMnUxOVR3U1Naa6OtNgbY3b3gH0T2OzZhaUFMF+NgagjQAQX6jHzjz+/hkZZPaZjL4wgs1z1+cYnqT/QZZWIAO2K0BaBVK2gM6hM8tzw0HY/B4/0QC08w8Ftr4KwhowK5Tls3WbZuDEw8uXT1hXxobuLBw89vWD6SqCv+cvvrjbz4+hzLMe/P4j+cGF2XeJaT5GoI9KtJkjFDqcshzxXx5v/uzRreeruQU5mgwJ08UlxMJpHxsb6tE2BTuj/5enLeZYry+/nP/SC+TR3iQkixAWOJwBjW0A6z/fsOhCL5B9PjwfHx/0wlUI/IMGSJivjwyUlIRe8zUkxau2R+VD7ssMwRHMCoF5Q5wIx0Tjfog5ygwEjGYGusnnArlM0g5WUAgkIjApiRMOpUCyIAxH1PtE6Uc+/u1vf3tt6pSppf+9QX1x7dGao/KDUC17jvg33lxzSK/Tm0ywKrGzthwh8NSpPhWijBz6O+6+XrF4ZBFpP2MbaRRI8OcqQwT09UV5cDxOuvN0NY252aQUiCuBm+iDRa81Qb61CoJS4KDX9N/3NkFw7yMhQSpMdXUtUlY2jowA/lSCRp2+uKZGr68p/7is4cOPi3cWm1DCX1s72N/f+Wzl8ZMnryYr08uVZXX6msqrc+bhwKamAamRk11QktKxtHSHJiCY4mAASjIypAh9+/3374fxFzb2ZuSGDM+5eTEhUQ+mXLsM9jbIhjSYzndbI9aW5wITs5xpnUcqfxGUe6DdJ4vsxlUZtSdeBgiymwYG2k6Pj/fMLuQg+ReRcANnv59+c3fPoatz0/nB3omJ3tPTDz6/d93PZsXXBCjTfPM2lcBPqpU5rqg74r82fvqz7puPe4rqO6RSNhOBSWFskyyNNzRfeSn0T3QOigiJMRfGIf0n4yTt3euPmYCiSYO7vzyelzk6Dr1wBf4h+Ll6Ifkn1MqIC1ZGuK+QgzMu3M9gugtUsSwDbNqHcFkhuNwOqTDuhcQwaBWIB3IZ/r7y0WH8Dvhv2dTZJKaCQlNGUlg4bRgNvgWIf6cQ/85PiZJLoVxmQplu+UTvyu2Dtz799NbK+HiDsrK83ITAiLPJYmXjxCmUB8tFOp3IzTcyLjw8KcMf1F8bkn9GYxsoTSuGvVYmFEa68tw3b/3k3DGxvlJ+rCiP7+cPCCQu0F32IqB6kz0HJvzLskvArCAud0MN8Hvhh/mn0PBkSal5unTVyEjjiEilyrt4/H55ZY1OV1l+4UJZd8OH/cUfmGqO1lYqB7s/6L756OajK0gEjqjEOoS/q0fnpgMP5GqamvZK2jh8WJyzEQICA8ltFvTFQ/IvIwPjDwltJgYgkxvMGJ7bXsg0cA14XxsnwRv5tz4SSNoczh5r9+bNQVQ3xIm0hYNoy2h7K6QV8W+T9OHDhwMDAXm5HM7KeO/q89PHjj+4FJSA5d+n33xxtuLM1evmG1u27EB/hgdcEF6en//yq91YBO542ooR6CY6IMvgCB2lQEf818WbP9NVVAyOD/EkUttnVqSvUJ5ks0oLM+s7G4ZyXKMMIea1BzPm4UhZkr8/4h+HiqYBrVbYwROGMcJcXXm+viAAQfx5xUXKkP7T2m0A47ziMjABFWoZX+xuCCZecyHUsBmSgEzQgAwWxcBojMCYkMIA1ZwFJ8TQDmFSLjGwu4oEGtSw/GkEIgYGCNLTT11D8u/y1I8rMOAGi2tGL167PDQ29uybR49uPxrr7j5yakJUXlOsP3ToUHL/oBIprImJCdWoXKRXFmmiwpIkdPEPGgXwcq+UyF30CcXFRfr6+PoWIfn3ySf8oj6VqM+PeCSoqTEYfLRy06YNRcDW1lBqECaLboJs4N/3579VaqlQy5amKHV5fbC2oioqKqq///vff30fZevlRz5sODv4i7MnT+4xHSkvP9JwsmVPSwt6NnYlM9UNfQDwr2absddkSskU7mcxYiyFghJBKiIghUCbjeZfBlaARP9RPrUIgQbG8ty5MHUCUoEGLlaAHvl2CNIrIaTFgX9kRSzfWza3Ztn5RxOQdowOigAEVilOwDDBwxNt0bzesfGl5wvHjn9+KavVQLJfMLG+et/Hdsc6u2XHjh047ZhZW4Mbwl/hLymYx0yjPDiKL4jPkGiEDhXoiP+i+OlPTIM1yoKh1Ngk6+rCqhWpK+tXw0JtUxMvt6Ghoaja1X9mbcaC8uAwDXrMEP5RU4BCoVATbY4TIs3H80U/AH/CuHCEC41MoyE2WIiASeFesZDE+m9VpQUSH2ik+SD9dYGNYFCA8A4GkYEoDaY9ssAkJpAQkBoLhFIgm0hAioCxkb6Li9sC8o58fA34d/6IXl9cnAzLbZX3515evtxw0tS5Z0/3nu7ulv6PT10oEJXXFuv1ep3JhBJKAODEyOioKl1XkoqYZ2UbJeSJhHQDACO9IsMzC/TloxdHR+UCQd+1iUaVDykF0j0QexPErgCzNnRBwIK0ymQAACAASURBVA7Qzj/F9xMwIYGt7Ujini4wldUX9fWNquTuuZ3N7aqPEAGPT5SXp5ed3Nk/2NLSUnqyoQA8rP++tLT05Hv9H4w/mRIj/B09erRWP9TbbDKNj4/Xz81YZmYs2wQluUs2uFIKN+o1UhuHVoDoR5R/FNsOQDDqNlTNLM/N7Vejb02e3vYcmC4EIgDmrytATMHQmbXl4RBnquFBcZFiH9UNDlJLTzwE/P3jQNvCyni7bXbpk88fOAW1qnHz45svTlacmbyY2jv+ZGBv25bZWfCMjpiedpmB3/or47vkW0orUoGXLnkFCLaxIRF2lAId8Z+PN3+iP2kqE4mKsiPNbav79i3YJGz/jK9mln1t1hOZOUUNcFoj3BIBVw8thbFhSQSA0iYbBwSgMNBSGOlF+IeeQP4JQf7JcJME3wKRorzSPywuLoMtE4j8mCE414JhW2YwywW7wgRzgX8oKyYzgdAOYTDC+Kp5M2wJ7w8MxASkpgKpQ45GaigwI4mjiQ2L5IuPnDp//tr58/80Ja5BgCuuram5+urlwydPLvTvLO6vSN55qHYwOfnDC80fFpzCyWRdWU1N5eTICCjA0YnRPoFSOaT5SiHBM3LQA0FPEulGAso0nHZljcrNLWB0VFBUVtDXl64TywvV1FRgl30VxJ4CV60PAuImiB2Aiu/PgWG1hMOTSSQ9ZXWd4+MXTvWJClZWGjpX9o1V/vr3v//98YnG9LLkQx/0l+78+51wIL4TipngifjBBw314pryyqNHa4pNYnHDeJlprLO7v2Zi2GI2B/tnigtytHCl1KZFCMT/gElScJcg9gfkOCkxaURPhnzzvYvzTEOwi4sh2OCdvyELRhIwMTFinYCYdlkwGD2cSPxe8IoctsaiD8cFtVYpBl6+PPHwxIkTA+zT4yD/3O99fim0tXULJf9Kz1y977eCJPqVE3vb2maBgE74snrIDGJgIEodqG8pTkgFWnzS+DIJR+vohjjiPxtv/Uy3c2d/gUoQ7z4cwzTaDh68dcsmiTLvbwsr5NgyA1Kqc+C0Rm9q4LRToodBIYkNBwQi/dfEQfiTBVrM4XHCSKQAXb18ofiH9B/QT0bjjwzBgBVqYPhmsRuU/nC1iYXdYFxg3iIEvRN+ggakaoGMkP0Boq1RZDJmP90SthMQXLWgoYybIWAXmClKP3X+2sQ1GDB7NSFKr6mtKZ+cfPXw1rNnz8b6kwf1lUfPlCsRJbo7G7obLpwSNTam6xD+Pro6olKplKLRiYm+vqFmU1mutYtNflcjJQAzpEkooBXMkWrz9KID1VNgxVWdO1hXXw97quXHkrqqcBpMBmLefX0ZbmMPJDSf+9oY4LcJiH4XtkzobzxdUNfZOdZ84cKpU0pT981HY8/GlOUj93//0a8n7t9vVJpOllZUgBVs99n+nRUVh2AAvOVsQ3rlVcT1Gn1zdo6qsayurLOlv7+4WOc2jJJJy/7sEoRAG9xp1iICaqQc9JnhGZgoNnRAmArKpRG3aYINIWtz5+ZjIjw8vb09MP48AH755FmifSKQXnlzdkIINHuTbgiVBFPHg9FrXU0Pcfa7PNBmGx/rmX3ec/zzwzPhUlL9++XNlkNnJud6xrpPtvTn+UYx29o+IxoQX05yQTJwJiYkmN6ucUIq0OIqPxAn1QoduyGO+E/FT39SWVurEwv424fNLCbbqP2y59ntWxL/vU1WSZtE47r5GD+lPbe5s7k+J9JssbS1Gb8KjEVo5GiabJoTWk6UJRClu+EoORS6QngR9acl8g+awDgFhoeahGGJ8wuLRvlvDFaAIcGkBeyCfnKhH8IiAER0ZLi4+PDl8yw8Hg3sM+MsOCqauMQY2TgLpo84ShSaIvB9uXbt2uW+H3/86tXkJNT5yicv/uOT8budnWcHT7ZAuUxc1tJytqWlu+VkQx6sV1SWI/5dHeHnlSWnqyZOnTo1PoY0U0GmgsukdyTgr47oRzRvBidHXHas+supqSlVAcox+0vGG+qUsKkv2szGlUDaC2FjDRBRz94EycoiAAyha4Df4R9XqtWwbSllprpfvP9+w4ULJUqTydTd2V2XXi4e3X5R1PgRFoH6Q7W1tRWHkktLk2uR2oUB8GRT+dWrV4/quxtS7vQ29/aWKHV6fT8Q0FQSEDXNYFn25hbUZ2oph25yogDPAEbj7RyorgIACQOxCkR5cHh+BCX/No7CwETgeh2QVP6cspzWlkkp0IneEQ6iRKBi4PI/Xb58ee6h2dgzPn5ndl/8cST/QpkDqwvP97344m7ymaujmb3Yk1Yv94tioP/P2rZs2dFFJmimXeCUCIMVYjDggmurcyJ0Q7bzN3M0rr6OUqAj/sPx5s9+Uq4sb1TJL87PWBD/rKsdmb3dg0VNe62rq7M7dks1Qr+Lo/L27CE4MVkdaWa07VVwYwJjNbj8p/W3mMNkVHsg0gv9iIzDzQ+ZVmsHIMIH0YAMi5kZE+kehyQezoCp9i82BmSFsLjgjcrFQpBpiOKLtscEr2+HmMl2nP+6CKROi8BLtY8Yyb9Xr16dn+orKR0skU+C51VjeeXEy+azLYMtpSdLS00NH15o6C79+9KW0pbiZFNen6gc4Q/x76h4aKistKy+uezjCx+ijLKzu6x5aYeCop9/RkYGxT8pWzqkFLcfPLiSMgWy7NGjuoYGXWWjWKlML7864meoSvh+O4Qs59cASAtAheLbAjABqn/aJMVSs8n0i1/85he/KCszDQ4OlpUpdTU16R9+2Hxlpbfk6ke/n/z1ZGO5Tt+vrymuqCjWmQbr6tAHKBuv/vpqZY2+YQUx5snBZwWqxkpdTXFx8eDge+81VE97Wm7c6KgvEfAIAjWURSP+kkIBEPhHDrWQZT30WoRleW4xusoj3zsfe2K9FutZsBPlCuOUNY0QGBJq74Q4kV/Mb4PR53+8/E8vZ2zY+ODg/c8PO7U+Bfm38Pybm3uQ/LuI5B82cS2/OF84YzFHRTMVOxAB8R4JPixsYYW4BBug1kCXAgur0/wCI919HQ1hR/zH4g0+HrHlu82tIfwh/bd662C26upH1wdsd27duvUc5a8ardAdIzC3oaG5Nycy6gYTUYsRVRgmE3KizUnAOcQ/pAFRhIdD60OGj8DBI4w6BYyDbTHvB5/TMHe3MDgvDOlWCAsIyOSSWWjgIQv6Iwa2n+hieAiL7gdTQ9GBRAPSBGRi1YIwIhMc+fj8+fOw+VZSUpdc15w+eR8Q2JiuLCnr7wdZQcpl3S07cbms+4MPShC2GiehXaosaR6qL67rHCzWl73/CyS7Osc665qXjEYJ0n5AP+Af+iGRtpeIj3158GBPT5pYh7jU3WkyKcvFaS+n6pWVKEbmuV04D1ZTg4C0JSplh5AFKXBWfjApslEJ8EYCJiQotEKOxDZU1935/vu/+Y3J9Hf65ORivRKJzMbJ8uZn4w1IoZ4sPooYeH9CrNMPKnVIvStNLSdPmnQlH09MIv032D32aGz81spY/Uv07zZRrteb6gZP7ilNVvrGcNus1p76kiIhJiDZ9iOSmlQAAYDkrxZMKUEPhMDr92LyExM90M/XAZi/oRVCz0E7wx2QYYuTM00/9N58xcDDy5fRE4w+j/feeX7w2PHPp1urZqnm75gSyb/sceLJeLRy5NyweYaFcl5LCBeb5uPTSSgT9vZ0CWEBAtGXNaG1NQgQGOsWEB7r5eXqQKAj/v3x1s8C+sAwKd59eAa7nloXHj/qPTB6fO7EQMfK7ce3bq2ukkav38WR3OyUeigFZmuY3p7eHt4hMYGFMVGcJqo7EA4RFhsGok+jxQ5YWir/5YAClMQg/uGHGzPGK35XeHA+kn3ckGA8BRPCBP4BAtFbLIMhLk3lx/Kk+sHURExUFF0JpFohTNwNVqglWwuOXLt8HrLfRtNgd5kpXTz59ecXEQEbRSJxWR3iHy6XJXd3n6zYCeWynS0n/66svFJXV1J5tFLUmJ7e0KyrG0Sk0el+/Jvf/MP7Y//6qLus12ZkZxD+JUH2K+kYKhMdOAcCcAj4BwsXOl26CsmylysNOpQHX/1ozh9EHDUMTXJgchaETAJmYQC+NgZI8y+BVP+0Qqk0uwEQ9v4//MNvivu733tPX1NTo0sXqeSjI2O3H3WSPearH90flaMkH/2x5WKxqbRlUFfS/HHj1au64uSWszcfPXs2Vn/6Tg4/PkCQrqurw0Pf/59edaJt7+rqnd6CgpwOjQ3/80hx/RR/McmMOZMe07bvwXnM3Ls3zKgC/iVuyH/Jz4iNCCSzzvgqumeWsxMFwGDpiZcvgX8P92pB/i20//PXSP4lzJLR55sthyavb+shlty1R8tFAa5my/RXXzGAgMFwPzOhCgqMSAYmek67uLh4o79IFfnS4lJg/LbwsPC4tx0NYUf8O+ONt9MC+AJ5gJvrjAVOHhmts4/vmvjb516eEAp5QzfhuNDq6qoGz/PNXRTkQimwoT4lk9Ma5JGYFeK+uRDQgAQg+sGJDUP4A/7hoEqAHFoB+seYA/0lpOAUw4raLg9IagWNQcqAXJiCxgRE72pl7hKNFnqEUL0QAGDM+oawP24GR9OtEEWVME+Jsl/ofaDHOnBJN3n/esCJHR196Y0jExOigs5ke7msH72Cy2XFlZOTv7561NRcdEBQJhaVmfQ1Ot1gf79e94vf/MP//fD2L391s66s3cr0x/xL0nAk1t4SccDigfZ9B4caGn5sMqG8U1/ZWN6Y1js+NtbcUHdSn46odLlD0VqV0KX+VgqMCJhFCcDWfKKuqCzYLgATEloTCoUaJP9M3be/eXbht//3N3iSu65MhzRqQZ6KfyBnqPMuOVxXrK8pV+WVHwUHGKUoT5es15WVNB9prEQpMZxHuXu3e+zgnZWh3t7c3KKCdN2hiork/sH+Un1a22erC+hTKMnL1GjojT/qThXmH5yqpxUg3oQLDvZO9Fi7d33Ys5WYwbymAL9NQIxAfBLYHAGJsFNrK6tQ9hBHE6d3bPzO8zvHvn5wyalqB735VnHm6shSz0p3aenOQ7WVjaK+bWEMF2+Xr9YYMy4hLlwQgaAC8bJdhIenp6eHJ1KGVHkVBqNnfLa7BwbGRTq6IY74d8Sbb7yz7cBWvjxgqw/IP8CfzdZTdvX+3EvXE64IgILi5D03sQq0YZidODcqyIV+cEN9bqZ/omekm09YdCFCHm73csI4YSCVCjnoNQJBGVUCRCIwA+EviRTc4dHGYATHBggCovIh/w1xwU2QELwKAg75Pir5osU7GEYCSbf4NZsYSgMSBCoUHD5ufrx61Vd/RGky1SmVuvLjc0vj4ysLC+NlSAVOjojSdXrTe3pdTUVFbY3pg/8DViqT938N2a9pbKj5wwspgkplOkozdTXF/aa6D/7uH3777Jtf/upRibKkRxqVhD7FpCR/XkFJXvW2A19+2VvXcra7u6ykrrhmclSuin+Z++wZkmWIS8VXf3/8/NBQdTSIwK7XLFEJ/tALDMCNQc8BJiQ85fXykqztStPYr755Nn7h/feSUbJeitCmq+vuLsmT5/asjNeVtiRXoKR4cLCl36Q7dObXV8uV+hqUB5+pHawbu6CEnkcy0rjJyabOcRQrKytDQ/WCxsmjNXqwCixNTn/5GdKAd3qKCgQ8KYdjP9NCB65McCkFiGeg0cv8iOnh5XvDHkERVBYcEbH+3N4McVrfeMsKQnlwDIJWkOfa8JrZPHDixEBTz/hYu23hn49/fri1qmoL9j345d2WQ0dHLrZ3dg/WKaFt3yjom+IlMbw9El08LS7T0xb4VrGDRmAQOA56IAAymFz0tcWlwAiUB5t9tsXt53jFve3ohjjiz4y33nk71X0rP2D79vkZFxZ186NHPvn18gCSf8K4SNdjV88cKj37BUbgACeJY5O6XhyV5+aCu2h9SqFffJxnokuMOSyMA8NxHBBKGUkcqSYpENxTNFpIhaF0hh5lEsQ/KdyEAwEYg2cAgz29+AKvGG9gnwuNQFaIp3dUvOgTc5AhhAxGM7FDAjNmXQPupwgIU9Fcto/oxx//0/lXr6Y+LqszfYAeRcqjk8fXGHf2PRsbe/aooVs3OXn/1VR9nb7fpKysra1Rmlr6B01lgvsf/fpqJZTLOhvGV+pFI+KG5iMIgMq67pMn9+zUX3n84ptf/uu/lZjqO/z3hxXu16SUiHN72tt72guKwZu+s6Fbf3QyfqtcntlzpfMuSt+wvUzN5LX6ssrJRQZ2SEhYt0SlZqGxMwzdBGHZU+AEdUJ+1eynj8oKeupNdWPfvLiN+NePjRwOnalRdna39JfVX3nSM9Zdl1xRDD4OLZDSFh86c/XqpEqkrMEeYHdv17W0nHzPpC8u1ifrTYNl4+PPAIL19fVF/AmkDXeCVWCxsm8AIdBmy6wXp2ilNADJcDmIQKgCBlMKkJKAwQbPxCDL8vV5c2Ji4oYseF0Jks3gIHoAEMz/wATfJcgyvLx8eObSzN69Wiz/eq5//cCptQuP/u0jm2+j2UOd6NtHReXoqEiE+Dd1IoPhmRhBbqh7eHu7uNzgqhMQAnEpMGgaycBpC4OhUAMC0TsBgdOBrpsLo2Lj4hylQEf8WfHG2x1LvPi0Xe5zw6T5Aa7PqVsvzi0PyBD/Yjky1wOqyjNnKhACH6NE2MYBBGp8L47Ic4tQHjyUmevr7WSxuLBiAsNQ7lsIg87+CHL+0iRNUhKIPw6dAktionEbGHuOIOUWw8Q7BwaGuyAt0tvDBZyXEAEtiH9BLHeRfNgFLFKhJRKCMIFFIHFLXReB0dAKYQaHyZVHziP8ne9Ttpzs/qCuTll59f7xBzdu2A5++nisu/ts6c7ayslXU9lD6TV6XSNKWMWDpcm6kvrciY9+DUTYc3Zs/NFYHp9fhlhYoNSVNXSehRRzsOHZixff/Ou/jdUpi2RMdmpBiQDRr+d0rw56KKWlJwdRCjqVmV3U17MyhrgziFLMZLBjrisZPHPmzEQSXhBeb4LAJEwrJMDoyfAtN0AgYGuV9dMX/7oyXqIb+9cXL24/u4AUHgK1vrhWeaSsuz9Zf+TClZWVusEypJL0/e8NgjhM1isrj06qBHwRBmDLzbvwN+s3mfphC6a/v24MYrz5AorcAH4jnIpK7i821eX1vdxrs1lt2SLRAQ5udhuxAsSu2+DUSNt1EQTiHx75+d4z4HzVGhRB1/8iIuhaoN0ehmTC2ADQ2Wl6bc41dnht7fDhwxZuz/h4z+o+7HvVugO7/n36K9h8m7zY23CWukca4LMZ8W+bzB8ACF0PJDgRAj2gEAndkFaiLxMRGy0zDAYXfX2xCHSKuHR4JszPNzBDI3OYBTriT8db7/BOd2SmxC/6ouwX409q6+Dx/Hzm4wZOyMDsT6PtyK4vOIIeNHBlF2qBNinU+4Rzo3I5X17fXNJctDUW/Y9oYTGiCgPDgH9I4En3Iw2YgeuCHCqk/tGBZAwG2y6xY2KoLRAmNzh6O39zoKcnTEIjBLp4V8XKRRejvbEXEzkZF8IlIhBqgRsqgUBDZrSbWPnxZWj+iouJTagSpbb31rZsmX2+Mn6TyLJaBL6p3PpylANCJ0Gs11emFwxdOTV5tBgo0nK3u7uhNzs3vb/lZGdzQ12dPhnKZcX9JwGBL5AIrCtJyS0Q9670tB/saR4EXVZRcai2slyQm9PT07vS3lxXV7wTaS7sRo/y4P5DZ87UnMqUgDyxC8BW7ASYFQqvqdfxx8JuWPlVrdrc3k9ffPriYD3w79mz5mQo5PXrdDU/fr9ucLC41tQwNvbo2SCim0mp1PcPFldUIACmF4iVjXKBuDa9sjYZvZNafi7WAQBbBjvv3u0+e3MM8W+oNyU3baLxam2tyVRXpiuuHGhqarLaOlIKBNVSPPFtXE+CFfTfjqYfeunhCYaA3mv37i2zWiPyCQODXteAERF2AJJmSCtj+WKa2/DhtTULkn+9dxZ6LiL5l/UUF//2vfhiT8WZydHs8c6TLfRFgqlU4bb4rXHRIRiAzs5waTMx0SMx0duT29W1wxBBSoFQC7QgBKI8mOozIQIenol1DY/KCJM5dkMc8cfjzR+9vWTryAnYNudlxtmv1SrVCH19fb3CY2NjkW6z2WzajtTe8YYPjxzBJybv3iYqEBgouzgiiI+vLylrKCjaFoUIaGFGZ+Br5nhjLImTgUtLSZh+Gk5GzP4wDVk7JQIwJoZBCIieuYQGusf7uXi6wPExF4+YrY2j5lCUFZOLwVxojnCpVgg0QxjEJgs9xcTEsOJUIP/On7/cp0zGuqy4snxi6oQVbxY8a0AEgNL/oGmwxdRcV3vm6lFdcU26rubomTOmsSERogikmFBQq2tozxHXIAXX2dmQXnmmVq/vhxTTNP4Cq0CxSVm/chBFuw4lv/2D+tozRycniopy25+AFXOJSVdcW6sfHDT14/aETne0UnTqSlE8m/CPMsTC6g+rQcMG/Qf8q6oyptTVlQyt7Hvxaf2jZwh/Jn1yMvHpL+k82V+sr1F2n0XRDfgtVip1tRVI5OlNf1dWpj9UI5CLTUfKa5SViHrFh2pR/quDLDh552D/Thh57EYq8EoviqkceWOlsqSu/1Dt1eXhZYTAVasttyCPp4CFP9JRp+qANAEpO8BgT28PFPn5rREIgcNVERiA5Ef+eisE3gYAtpLhv2Dz8vLynEoUb2GfHhvvoUafq2jX07vJh66OkNHnCjhIhbNffnV4uG9ctKdHIjZPwI2PICfEQA8Dd38gCws+Z9i2i0j0RirQzN69ifbdJggMYybJHCrQEX8s3njbatWkpri7+w5bQoj8k2pkXl6RcYh/YYhatjuwMJo61Hm2G5+YPITy4Ju4IWzN8JcI0+I3j6qKigrKOlEq6WqxhDCYCrYkA3tr+kubpFD2k3DI5kRStLmQgy+CJEn9M+DeL+25hCgIi2/e3oW+foWwDucREadSLVoSXVDu6wL3uIkChN4wZiCTdsqKhovdrKiAdOXH2PX048HB90CWnbk6oZo6vbDwHFz/Ouv0Fcn6Yqj8w7HI/opDZ642ipU6lCOfOdRys6EfFOMH7yUXY1E01H6qvBbmhc92flheqdMVQ7UsGefBL178W0lRO8z+FelJillzdHL0VF9fbu6zZ4/GHt1uNpn0NYhHyS39uD+hFIt15ZefFBQXyRRAP1ICpJ6AgRtSYATA/CpGdYlpsMyUrDv46adDYyvPhkr0tcnAsqNHPuzsTy7WpR8pQ59EaS2IO/QmzDzXDtb9uK7MVFyLYCsoQABMH/l1OUZgsd40iCD9/yYjGVuMjwN0dt58NH4FRW9OgLxRV1tz9ejVtRnzthN7mwb2tmlTCoq0YK1jxHOA9l4wpQGhDxJsAEd8IKBHfpBlbXkxKr8qiHbEooqBEflVWBIGEQK2tlaxT8w/XH6wvHxuF/pW2ru6cHAUZl/+f/beParpO93/Xd2d1ulvztlTK94KWMElNwdTFUWuLrFAEAghAQmLpIDhK5eYkMAXA80VSkQWg1DWJuDiFxvMYEwKuLj8FhxqImVlpELqtbsFbz3Moqu6FOiUcY167G+f5/l8E7Sz917n3zMzfrBeUAlg8+L9/jzP836qr3lv/+Af5FIL0/sHHwUuZJkMxoWrN7q64vwimUwFJmIQh0kSY7dviSsoKK0+0Fh9iMwbhyZunLpyJav/3XfQCMPndTUgsCuiMogVlZ/05isCvjr/9Xnrjdf6+ytr1m8J3NTlyyw878+LYrr49kVERNXlDdwabM/IyEjT2QASXgQ2kGrI/f6oLcEb8iq3gg+WcAwmuYGzfv+VcGxHZglw1C2P9AvnEebBqYqt8hjhJLwBjPZcAfqSF2bq12dzeNf+El+fjSE7uZe6Nm7G68AwrImEMXeDYWHhZDbOE5BAsgLjAuICQf6dx9grkH/lVus2oxTs1Cjy7+bRCxcWwZfSIMs0oP8Iy6SAitoei6hzxOUeqjg8xk4mWYFWKRhj8JjO5eW2tZ+Ac2T3mseblSo1aRvUaGXOORCBDmH38W4hxQQIVqjc85cmz+OyuYV7Y2bUZRoaVJlGjY8itRmNcrpJdfGBRHp2YnSLf+P7jcwhl4Dkx1Jvp3F8fP2B6viyUZVNrgWbq5y7cMFpmHZO63iUSioFTzgut7LV9Kq2NtIioqQbbJ9YrTbQmqtUGoqv1ag73e5OAKCczzfgkLASNC7TzLN2mxVbetRIwN6x3nvLBIAt2S08Ffydoc7hsK20KPDcyZMnv63PEIkSkj5s/bD1hQZcAaC3GdBvYz0iEEiXmNh39093Y6sbI6sZ/qEc9N4LVqMGxDvA6vi6M2fu3v1/7t7tEnSD/COp9182/sj0vlxA+dfpWm8nvX94n8AtBvkH/Ev47PMbw1e6fP3QSZPlmWuQgmt89ids8EksKKgvYKZACBYjEzGcaKD/w3cOMFetuEO4q2xfrCApae8rBL46/9V547W81rzAhA2btoSA+RVgODoGy0dFkFNSBV61Mi0l5UxGxgaOijx9zLhicgi37N6+vbiUk50Vl5UUVbnhUnFhusQgl4s5xyICEsPhWdMqyKrKIt43j7S+RGXFxpYwoSPAPyZ6roqUQBBnmIAfQEod4X6bY0N8t3KLd6/e6EOiEeA/ogF9iARc0YCMEYYXv5BCStFz/vzVy5d7cElGeYNUdeL09cuXHwwOzi6iLGvDdkAlEM1qVROWUXyqdjKNIy3uUajYWho9c4WV3aQEcmGc8syMaaz3IwVYT6vZIFIoO9HUGkFF2o4/fuywd3d389RNwDewba7RyclJcN7TDvCXDVI16K1VzVojrVI1SWkjyDL2kNv99OlV48S8i5cZGF3//m8bPebXa4G9g7bV1fHtqbriWoUR5J6K7r551Dk+ff7qeR6Xw1ereONym1RFfWQymRuSm4aUzXL412goB+MOorBWoZF2nug4MaSxWBYcYoOz4VAQDAAAIABJREFU49mzZx3zShV8PPBnrPgnjVqjBtcJg3o0gw0GANrlnTgsrJamWORsucjecqZvyicxch1HnJtXCirwP5ngeM9N4OYCv831nmHgjaEMAkMjPcbXWxBmkAjkaqzPwtQX0H+PupjW5+xvfvj9ocYPXrQ+D7mCWxzY00hu/1D+TRL8fX1jX0hcQEB0rN8azwG999u47Z9Hvx+J9ZB6Mi7YyMyGRIZG9j0a3jvQ+u47hIuHSFhg1/4qf1ZVxCsEvjr/6bz1Zl5rUeWe7Vs37e4K8BeQzRCCoCxP0ElJVZAAxGBGypYze8vyA9MVqgqCQJNeplAOVSQfnlmeW7pzvz8oOiuqLOPz0eLCTI7MpDcIsyMSN4cVtbbmYegVU/DAwdnYEIZ+UVgYCfJsniBj9+h/A0jrMwIw3McvvG/X+r5EphpM+Ee+8/E2xxACelSgb7jvHq5iAvl38Sq4VTZxvx3P75776qvLS3MLMyjLtFYrlgtoVQV7G9hTjQ0EobLnAUfa89SlRGkoxeUaapr0/pWzjWw2AOOTNlB5UqPcMH5WATySa60VatqyuOiwDHZ3c5opjVqtck0AdZ8sXZ52Oszw7K1QUtbet80mQA0NCKThR7W7o8M9f3pCOzLPFRcXp6cfLCnABhiSBg0QDMUdGwX11dVFA7ceXL54dTJXSKkxwI8e/AsA8OL58xMK10Qxl4J3gFI0m3p7exsqmjoVPH1veUwDwg1kHsVXqfBx3Gog9M/LBqfTjUlZzzpqKVoK5h3+XEx5r3ktqERckofb4h1Oi5hWAf6AfxqDXm/VGhwmevRRn49fqP9OjigQ9N8LAsYX/YKAfmGbAYIrp/HK3bvDYRj3x1z8efQfArE6NLSade4M4G/4+7tdeS0O5+DN45/98OjuvqIPmOLH7TH4cCaOOcntX5PKc/s3GczsoyoJiQ0Hy+3bFcfsT8ctUrs37Z06tHoK6yHA4XpMxQIErlkdCQycuvJo+M+VH77rUYG4N+RRV1Z0QOy+fbtfXQW+Or84b7wmaM1L2blpy6YQf5B/A7gZQgAAZExqSBWa18rKjE3rcClkRgIXhBDOFXh88FAFbWKuAvOCqgCBN76ZLyZdgQZd+pa4xPiiHTtIdh7jebNiuzzuFwXgCv8QgHGMBAzwxKGC6PPz6evr8yOel1SEmRfmHtAnnAnICiDGOSCsYD+HXzv6dOL8xcuXi4FjGmnTUMfpP9V9991XX/37knMMZZnKhnNtWrmcVjVZjbRWa5TCU3/iMsqy+RGuqkJqAzmHvDICQiustk41fpymtvc+0VCUvs2gq1UqwUN3upXTS4vOlsHBwQkFl0upVcW4zGxpadlBZFlTJ19ubRjrxeT9VRpaAYzsPPGsw92ZPj9i4HINAMBiEU8xMbo/ztenmsRiwXO0oD48bjjTIEdZdvHyE4kcsaRu0nTfvGkB/TfhcrtcEz0cGUVTGPbcUI7yrw3nmGOwB3Hb26tW0apO5YkO1HK2uQuPl50GEc0eQgS6XApauo1MviWXW81m7dsa9PMNh+/NOOBxlETbcgt5MoNWbxqzSjW117um/KbWhOzkFWYgAVsD/kYCMiMhmAdY/yIPpnHjIxCBiaGRL1phqlECFgD+SqPOnHswfPfu98PRt+yOOab1eXV9RPt9T+o9fDjBLU6P/MN1zIC/TMK/GzdKomN9w+GNhfr5dvmGktJ5ZMh+30MkaxpM78aNGzejD0YEklk7gsAblf1EBDZ6rgKvRCfFxSZF7Xv91WzIq+M9v/7Vb5JaBZsStu7fVIKxL3n9ra394FWP5JFx3hAi/3DF76a9u3fnw8+yC3HROF4j4aLxj5onRjsrkpmWmPtHon+KDgm5+80IR4jTcQZRemBA9YEPPrh2f4AgMC+oK6LMe/uHHdLe1WNBrFj/uBf8QwT6bJ66cqUPONcX7sOAzwtAIgEDAsLCAjwnPL4gOoFq7nn6FDzT5ctPe+wydYXa/fybB9/hWXI6MBy0QqWw9X6yzYpjcRQjy0js3/zpp3LxSMvI6GQx3rEpKC3Y17Vm27YGGzH5yWNjY73vNfP5fJlI0sMHLLmHOqeX5iwt3d3tI0pF7QSX0jRPAv8ch4ksAy554mVAlhlphUKjPgFW1K1WSzhig9gwLq6dGC0sLOarpaA2DTp7cHBmand2Tg+3c6gpmRRop6dlUpXS3QmfZyMA0H52YmJ9bScQsLaZJxJjnl85yr828ME4x0zm3HrfWwvyT6WCv2Qzm4RLx50GScLt2zPWoROujmcdLqWxoYLJCmxoMHtVYIOZJkH5tIafa7ELOXyKMmq2wdcBFXfrlampqcSuY+L0vfEfegSgP1GApeQb3gESBbh5JRCwoCB0ChDYVQA4xxfUgdVogatL+3HoI+TR8HBf3pzDeQfk3/Pvv2wE+3v//uzsz9j74p7IBfwx8q+Wy1nB39c3dgP//PFyIBQs7sauEN/IQ6vrff1WH0IxiARMDJ1K3AhSFDeGMgiE1yaiCvzp5rueevAhRGBfVpAvKylk96vZkFeHOb9+47UkVtmG7Vt27+tD/gkGBgZY8SxP2HFSFpF/ZQOVlWAddu+LiqpsTztWSLbsMk86ve5qswoocZhBYF1QXKygP+r6aDFHIgIEinU1+fU/7vjuu/v3+/NaWdEhEV79B28bBGCVVwDGBjH6j7kAxBtAn74rV3z8MBEBVaBH+4UxBAwnBPQE5oeFFyQGcqlm3GcO8u/y06ejFouO6lRMPvjqq+/uzy7PACXgaTWkkNnKe7FnxGqjqVqFRkO7OjpOuEdGR8VG/Rxn/pvrl2pVKrC/1nKrscGKwfI8rPSQtpG1bWeba0UyvtJ9AgCovrgEdtE5eJynUDAE1I5Pg/stB1nWSYEsA1+Kusz2ydpVlErdCQAC/knHxw0GQ5uoWTExUVzI4fEpKfsLospiYpBJa2lsXS4/fM+kB52pxkZmqVWbNnDTWTt6o4qrAuWJj8YxyExWglmwiw1WKRlpBqWqod0nOjoBuRrzjCMnrUWY2pKL08sOE+jPZx2AQKVGagWPj5UeUIFGFcg+hn9So33ObrB0W4qLXUqKNkqltFZvz+6b6ttcWiYRHYsq9SLw5X7AsDAmFv/lPKzQ0Km7f7p7pTE0FGsgkcw0SOOHA+3n6upCuqKvtA7iyt+bqfM4+fYp3v7dvHD7tq1pyDVqcTDBByj/gH/BmcHBgL+vb0RUAf/8w8LIW1+9ek1fV5dvQWLomkNriBv2iMBI0pFT7xWB+EokYMTN1g8+ZVTgIdyiju1WrKSy/a/CAl8dOG+9HiXw37IzcNP+LtL7IujHxRBZ/uEstKxJQQJ4BQYY5JfhdC8mwLSn5Qh7irmMCEw26s1mfZsCuwI9A8L9YJj6+1PWj45IJCK9CURTTdS33yEBr2Xsr3qBvyhm74QHf9gHCAQM8PXoP5/NuK/Ch2kEhNNHtnGTNUnIPz8mJSsgnERlFcRmgvy7/PTi5OST7Mme+dOj56fn5nRare6rr76avX3v8NhhtIuglxpAljWwbWw2zeMpVeAWOzqG1CKDXm6VjYtdp58DAhVqjYZdYcXuZYCSvq2ZZhBo1o+Pc/kaFQ7LDTWpnTe79YbBxwsaFRBQwa+t5Rvl5sPljPwzmTGNmbkpNRtpt1ulUqItNfecb5O1nc3Ejea1XD6vmMOjbWiZ4c+ye/FKYdUqFIENvTTe/lmNGqltzNTu399yrCQg2mDSUnwAYO3Z8zoxDfg2YbNIMltj/MQInp6NKEP3a9V+JHc42qPyy7acsi8vLi/+7uFhNbkLnB9RakAAk2FifM/g64CR7nR3SqVGh9PhXDr+H5zPA6+fBlDS2rUfmcZ6i4en+uKrd6TpRNlFRR/+7T0gcwuIN5deE8zIwFC8CqyvJqGn2AK4urq/8kxd3ZHYPt+Aflx6hL0vP3zZ6Nn59vjhGO1yjaY6TWPlL93+ZWYG4z7SG/tLqmLjcBIZHiWSCRcM7Rvu8nt/DcM/jwiMBAZiQHV9KdMDzTRGAwJLonBvCOODSUEYdw5WRUW8ugp8dd56M0nA2ndw+7p1JX3h2PqMNrUsquxcZVKfb1USul8M7sMBtixyIzhQ2U4AKOGIAIGdylopuQrUN/8CgayffooqW3eJqECCwNzK7659N5CbWtnv3RoH9jdo5f6PpLiQIjABIOAP1R/IP0/VA6GH8edhYZ57QB+mBIJIDPcrKNrOp86D7ru0J+dMpV3vzE0fmTh/FSNCaWp8bhllWcVQpwL1UnlMMiCw95O3sWmOwmu5ITUtNzjkWp3DrFHOnz49gaHKUqkNp0UwINBkkjWTkdqGMZOcBqlEA2Nwa4hjzrm8bLZJNUolv1nhqp1o5mutFXgrh00c7KYm0GVITo3S3XGiU2qmjPcePswJnJQcy7HoQEgq+AouV8QR8SipSqORghsmNQm9HDSnlClKsK1Grdasb/dn4Wco2qCXieWYMq1o5o2McGkpTpgAMLRmYJmG5hW73G7AH9bnz65qq4RPdf5npyzTS4u/AxU4pnaTaoiLlpJ2aDJSgmUgWgXMZIMgdCw/XtY9GcjeP3x9RMGXmeCrRnITDQiM37GjP9uuC1yphHgR6BmJW9mMhLFYTPUj8sqjuyWbPdHP1a2VIP+OnIzz9RV0O52DN8nkWySTe3Xz8cf32E1DxSlpTkb+KTH4oAfxd+qzz76+sW5fSFUsCWIIQwBGNpJ2msaNV4a7ClYA6Fk9jAhEScr4YGY4BBfIDe/7ibTEEB889eXvr/jGBfgHRezb/aog/E993nrj9VhW1rqDgft3RzODvwJsVga5h5GlcX1xQQJkFfw6KktAihhlZR4A9vRwirnc0REVuVKC562sWQnSpZz44Nl+QexPSVGVgZdGOBKdARCok6R8dyY3Z+DazZsDTDNgUt5LAjAoNoiZA/H19AD6MPIPQcfc/BEE+vl47wJJRkIAWRyyuSCfQ529ePnp5SdPeuzddpNjFszsvGvi6lWdSCQzmnCgnjSLgA8muozclmlBLkkpl1utorRaucMg05sx9Q/zop9eElPGBpIPWJEMODGbmsHENiWXj8HfOdEJskxF0TYNvGWzTaXSWKU0RSlcLlfzyAgf3oYcr7GS2VKN0Yg5MxrXCaBsJ6g/vWNhoTurLCq/RmJ3yHg8fnNtrVjEKS4W0VIr/tlkpj0ZWHZ2ghQypL3mVasAZf6sWPgk+UvaZCYTQ0DF/EQPh69kJ1eolBTV0NAgpUX2864TbqnVbHLo29qaa1rz4CvZnxPE43OLiz//7uPbM6ohtxuIr1SqPATEvHybTQPOnHnkBYdj8Nr97lsDA096uHyayXHYJt8T++2Oa9f6W0TB+WiAX/bBuB2dAWC9RwAy0x/gVP2uDA93Ra5Z3Rj6Tn87LjPy9fUtqrQ47HduHv/r8++nGpncK8/K3xG8MZZLKypQ/vUg/zy3f/sjCP+KGABWowRsxJnixtUbr5TEJb6/QkCP6U3ENZ2kHuyphjAqMCKv9cNPPV2Ba0AFXvH1CY9LSip5NR73T3zeevNfYv3379qyf9MwqCl/f0w6xos/LHjkl4H99SXtygz+vDvACQAzCws5Ik7m+nQF0xtMugKbAYE4Hffw58X7949kRf+UVJaxZ3REpNPpTSZxboqw8tr9+/dv3hnoJ5uEsP4h8NY/wACTZhaGf2E+iD9v5Zf5AX/i10eAGO5NyQL957PaL4FPXb38708vP7jONRpNDodzmTc/ev0bV+3Z5vOpFrvcbPXKPzC/FYwsa7BRro4TQ1KzjKIwNh6OTQMs0NBU7fz806tXxUbSE6NWk9sy00dyStUkVbrcJ064m2wG8K24O1Plxtw9KVtq1FIKhVLR8fybszR6ZzL5ZrS997ZUw+t5+qyjU6223pvRnz3b1g5fYcp2/VUkFusMMrCzzdyRkfM5dplGqoFHIAhkS2XTl+c73OiYzWvX/tu/9bDiWfClIixIIoPPJBAQjtLtKhZRKvj0qxVcfkWylK+zT18FAJpnZvQfrf23bTbxkw9bjxRly2zyluNLS4uPf/fxQ/gAOzux4RlHQ9hSdecQMBb3f1orQO2yrYfNjuNHj3ffuQnfCUFODqk1tt7ecit3+McPrl27NiDUCfNK41dUoFcCegC4shwuMTEydLWPr08ihuA3NvbfunXu5JW+vr7w1m6Ho7v/6F9P//BlQXU1I/9w5e/QSAKZfJMqapWe0Y/MTMAfVj88/INHI4wli5RQAoIVXhPeFRIXuoLAlbtAvAksPeBpiVlDvDHeBQqY6bhGTzXkCvxvFBtSUvL6q6vAf87z1huvxbKStm7YtD8izgfwV9QqEJDcKsK//CicA0kKCUnCzDvsi2a0IAIwJSc4vbAwc2dCYTGX1IOZKzKTnhkQ7r3H+OCg6KwyRGCxTic2GECNpbZf6wcE3r9zJy+viozArRSAcYjNl2mDDggPR/kX9qLn76XSr08f0s+P3AFiX2D9xkAuyD/cqnM5s1ZjtdrkMt7I6F2hoeUJhzfx9OL03JwYC74fka06FVLNNrwtU1O1WJTolGpB64FU0xpxakOD42Xyj7RgZ89fPS+GX4Mu8/T7oMU8O08cs9Fg+GjtKnDQYJhBaSppyrjNZrZqKADg6ct2voqN1/gUZW1osNL27Mvwt1Q24JKjrflsKukHyt8qkhsMDoNBzOcrXPNPlwbnHFqQlUpEIFsjty9dPP2sUwPu+6O1bzdzhCks/ziWf7ZOLMy26x2AQK2Wr6iV25rcbux7pmh4t/U6JwCw468LC+P/c9XZXLHRaJNllOmMRtG6ANbS0uzs7OPf3V6YGbOSfhwXqEDV0FBFRYMZZLHNZpOy2YBEa69jbm7x6NHjxy2W1PWn55W0DV02u3ZPEIrAa+0WXU30iglGKDFzwWiDVwCIizE3x8WFA6j6Hg0PV1YO1B0J8u3r87/lJPLvm9Pf91Uf8ORezZDgA4uBFOmbVLXrE3p6hJOZoP6I/AP7G8TyZ2DrEZnelcMkZ7CvpMt39QsCEgRGJuKIcEH9AU9BmDTFTF3BgvCH3rjUNVOIwAC/AEBgxKu81H/G86vXWaygvdu37N4fDboK5J9AgDMZdXVR+Qz/8vqjBiqjkrqGQ3AKpJ+MsAEaiQIMPpWecDCBA4dBYFMFg8C2NkXni6vAI7GAwMp1l0aKc3Pscq3cwMmtBALeAQIO5AUF5WXlMQqQxfJHAHorIIz79dhezwnzFD+wLTDcUwQBRViflUlRPbhV7MG0jo+yzEifeP6nJ9/dn3M653RAwKvTllOZOqOUkWVq2tj79nsamls88ezZCZW017T2EyNFa4xWDQ0sUgEeAQgNakXt+ctLcw4b20gxeC8v18gsT58/O9Gp7p0xmfTjbVrlxKUNw103nirWtjGmV0O7n89f1PGUSjVbo+DxpMlSWcudB5efP+swziwstLX9T41UlpLXWsTKENlssvNt4zqnw8BXdIwuOR3Li06tVKXAFkMA3/h5V4dSjvz7t57hqmxJbpl/WapMnM2K0snsDodeq6WotfcON3V0uHo4cqlG5gQsOnRXJ0YWnON/OMvPfjeHr8WIGBtVXPLTnzNyJXZA4LJz4fbHD+9psC+wwwX/UKDXZ+4B4RpsGJUlxeq43rm8vLg4Z7FMT3dnXJ93Yf0nWUpxM/NPfgsEvNat464TlCIBP2RMMBMM+MIEgwcO3Rgbgq2AYFYP7E3gTOa3suJ84wZaHM7um9j796XH/aL8Sx5yTwQzwQc4+aY4/+TMwVTg36nPP79xY19JSJCA5c+oTZw8Jm+/OhRePBkzaxKxGrL60EsExGs/rIZgOeSlasjqqakrXT+1vst4Y6Ya8sg3vCA8OiQk4s1XCPwnO2+9mcUqiti+a9PekDjEH8q/oKykOgx1KQP85YHiGyDJVSFdw8NZUfALeKkcQP61p2QfS/h8ZybyTydhEOgdK9B7BoSZq8C6I7FJUXn5O6+vFxlEYrlWJuKkRfUDAQfuDJZhCCoBIAtbAL0DbWGk94VRfx7d5+fnE+aVgASBvgHMz0I37+JRokkQfw+WxvUfGdeuojVuslP2zl/+MuswOUw2xcT5wtHJBxaUZclNJPa0wSp3Wnpcz56p2A3k8lJL0TZsi+Fzm7UfaXsPo1CkJy4vzV64bZJqlAosdktpnqUFAUirkxsOzzj1Zur8ZE5K3ZH7s06jSYtp9GAhVa6JcXnnUKeS1qiBZbTeOdf94PrzZ/MLC4a25tpapc0qFaflCbU2Y+2l6z3j40670zEyXzzucB6/cOGCE8Soyj3UZB0zNStcfL1J/lHzBp/fHooMyhWmipvTo+JzxLoaoQxEoFz7tun2TIX7hKtn2s6n5pYB+HoT+Gnd+bPNFE8i0YCcY5OZPWVmaq6IspWvtWAI4OOPP35oVgMCT+BVQHnvPczXKmdje7gNZ6dNCw9NpofLwL/JpZT2wEtoxTVGucyu4106iSKwv0XMCazHnhhSCCn1IJBoQFIIqV4TvTciAJ3qmmpB9pMzgVxeblB8a7fTMXf/5tw83v4xsaePvfLPYW7AG1fS+wf2d8v+rZ95bv9wTwxz/8eUQBjAFnhGjZnxusQrwyF+h16uhqA8BCO8eSN2Bb7cE9N3JVrQGn/g5atAv8SNvoDA115dBf4znV+/8bpAkLflYGD+7ujw8IB4HNetyqpKOpJUx6SVguIrI3H3SRjWHI0TbgMYhYX8u3UrLXvPrprM9PRCRGAhpxgQ6PXBYybPgLAnKKsuWpBxMDBq1yhXpDPI5HKZSJjWP3D/3P3KwVsDRACSvTtxHvwFhJM11xh68JIF9vN5cfywQOwbFwBYPLSbQ1HCJcDfA5FtzGzG1D7l6e+v+H1w8v7i48XlhbHD5RUaxcRpYAQ27WCKAE/Dtonnjs9dnT/hZjOtINhaomJraGWtTm/uNeN1GBssYfPl2dkLPy9oNbRCJe10uynD+MV5N6XFwL3DYBtNTktL98DNo8cXPrFKO5uapDartYFtdIw1DQ11nhXTUpVhbg4U3uSl5/Mix/j42WaXy8XHSTy5zUiPPJ+/NMlpG7c7nSKeTDadNjt79OjROb5K0eluKr83896/UZRca6RF2WUBuDCzTCja82OGTizJFWvZ5TaDSfu2/vbH5iF3bXObjgBwbloi08rF4lUAa0osEWEaNNtqY7Op4FQxzY5hi1vAJH8FRvh3D8d6pW6XGlyvFVw/GPYKqRX5h58Pk/lw79jhe87p6ctLg7duPdj6zbxbKZPp5Rqpsutb4oMH0kXC/NJS7zUgQJBkA3pWBDf6bNm1eyMuPW98pzJnT90RVkhCcU27xeEcvHM8/RvsffmAyb3Clb+drnQ7czmBxd/inp70zODgg7t33/h6f0RJFW6l8+CPZM+UFrw4ng5DROBUSER0oheBnpiY1WQ2pIBcBjZ6RSAWhKNjWWRvCLyOuQr0KdjsG5JU9fobrwrC/yznrTdjBaz8mu2b9pX0+YX5I/6CqkJCQo6QqL6IpLz+PGZ1ZRSG1WOOSxwriAHgrVvtt9JyarJzclODhemFEuDfCwRWrCCwExujZxCBt7ITNmUNVG76DBEolsvlYlFqRn/duXPnAKUDAhYpAXv5h+73SgCp8TIiMIwIQC8AvQUQogLD/fdQ9PklEGoPLjfDAx82OxxUbc85fIr+5S+LMzMzOJLLtloBgeNyJWglSqPh8TXy/3j8+EL35QmNDVCHss2q1fJdapVipMdhtpX3SpukUqsNnpMa4Z2bFx4/dhilUmXHMzfbbGiWknRpI0HHYb2lZenO0Tlnb69VStNSMJHossfwWa04b5nj644evT84bfhINjoiMjQ3UzIRV0HxbeVsq5FiNymLMzkyK9uqM+jlooQnT4A2c3N3dFKucqji8O3bH71thD8VU26Ti47lCxIPNVZVFeTKRDlCuTU5xpbQ7jR99Afn72aoTqWCK5FrAX/TwsxCrlwr5tAxyRpKzuPX1mrYajUt3CLi22Ji6GN707Lbn1z+7v7iwu3bD+/10uCPjbgriTnAP3YFINCmbgK/32tyOJdnBweXlpbaN30zwhWDPVe5H/WdJCLw2oBOnJ5V+nJDIJaDS8kt4L6De+Lex5u66v7uyTMnjwTF1f+Y1aIzWAaO5s4//31jNbPz7fHHJPiAyL+VyTfMvcoM/izh4P6uEsBfENlI4u24iScac6XSUhCZyLjg1asb3+/rGo4OfckEM7eEIAIxqGGlIIxhgVNTfbGs1g891ZD3sTP6il+kj39VSfRrr3zwP8X5NVP82LVub0kX9v4VsUD+If5CkpKi4CULW6ErB9D+ZjE5ViD/8vxbMQwQ8DeYnZOT3dLSkpuaCQSEw+lBBP7iKlCPA8Jkbcjy9JNbR/KSfhqo3HpphKvTGeRaPciYjLq6c2fOtQ8OlvmzWAz//H0D+oB/nu5mBn/EBr+s/7wy0McvsYRDiXH47EGOwfyJlF1RUaFUjATfIvj7y/EFm1WDsky6DbCkAVl2osM1wdVqNI7//fjChaO5fGuvbZtNym5ig/azyYoVirM9EmODtalJowEyNJAlGeLZm0cfP16mlK4TJ4bKx0xSJjwAw/es7HKtfXrxwqJT38DWaLSUxqYh4atWo1HdOXF1eo7S3bx5/8yD9SJ0/vLkZJov46SL+HxaytZIpVRhqk5rjYmRCx16UXpwcMLktN3gbBEbxTy+3PG/l+12i8WiM+jsFvhUd9+6BdrbLkuVaI3lMTGiFMFPeZXNa8cXZoyaTtdEscxkGBcVptvTOT2pOYFbRNYYkLA2WQa3nB7dm1TI08RIM/cnZWSc0Vmt03POheXbv/v4oQkks+P06RMEgdtsGAKLMyJWWkVaHmfMM7dnl/DcKrtRrFIrlerOvjXDxel5O67t+LE1hSPKETCzIR8weMIdTgUF0Xt27g/D9L/VRWmTT84WybwgAAAgAElEQVQdOXLS35dVaTE40wYGT4E6fyH/xthD7pFMkvrszb3C4m8w9r4Ewpfmrugg1suIrYdHIJuYEH6JaIMTyYxJJEkZDAUExoUeWtO4Zo0nGhpbEBNxOq6+4NOXELg6cuOUb2xrqzco6xCphiRu9IkNCYl4VRD+xz+/fuv12LjY3du37t3f1dcXEID6LygkAuAXgqvbkqoE/Qz/yjCogOFfVCUY4NbWfkxD7c7Jze7ubslBAqamZp4qJBAs7CEIVKmYnLmVrMB7C8s4IFyX9FMULlEfESMC5Tgbko/rwM6lZKfkFWH/M6YAYvGD6YIhHYAeAr444TgdR1pg/DZvrEqneJbLl5eeCHHhz9tazdCJ09+sH7xz89pfjh497jQ3SDWrVBqaYZltBp5trgmhhdI9fvz46GyLBrMDbEabVarGaFTZ9Hib0zluK5dq1PBLMimBZJRZuo9eeCxTTLjcTVYTzRAOgGdjg0oyOpdvL9xeMDVYsYxMa3Cwli3dZpTTKsXVi0tyQ8vgk+uXLgUXgjPlaJJj2LRcLONxeWCONcW5IrExOUbKCUzJSRX2CCUisQzUsUxm0IkkklPwmU0F8M3NzQH94Pvjx7sH8ehk2mRbOnxp6q/ksL9oc5jNWoXLNcF3GD6S6yQWmTHzXP+ZtH0p8mQ2bV64KbC0BDUGavgymzx4v6Duiaw8xio3OBcXcbHTAvBvoQOrIUrUf9Zyq20bmHirlq9qwmG8w/CPNwf86x68ZeGrVKpOtSo2Q8bWiHLqfvzxxwOtNVxJCqseEfUBuQoEOhWERezZ6o/hB9UFZTWTZ+qAfwGsshan3nLreOo3fxr2qf70GtP7N3MY5F/PivxjRj/SMfYU+LduP3iPqq4ubH9G/hV9iw/AJIXhbWPBZiIBE1c8MCIw0rckJKzx0EsycDXjg+EPexujPeZ4qi8utij+gHcrFTZG90UmhseGVL325luvVOA/9HnrzZBY/6TAg3t3D1/p8/GLx9m3rIh9w6AAk+C/qiBBf97AQH5l5Qv5R+Y/ygZuDfS3DgzWHMvp7gb64cnNzU0IPnUqnTCwh/NSNYRBoNLtUnnXhiQBAqPyr49yAYEABJm48GB+Xd3Jb+MCc7IF/iQC8MqVOE8OTIDn8i/MewtI6r4+4X5+4RiSH+4X6rudJ7aIx5eWnnCZgWTKffqHcw8ePBg8Oju7uGgxYEOLUSu1aZqYdRgatXviYk631v74wmyLiFlghMvVaJL6J1+YuWd6OKOx2jQ05mg12NQ4hAHkkNr/ctTBvzShVFNcGpRfBZuNiMTCgdE0dm+sodeWXM4mjTQYrqXRyuQ2dlPn/NPLbYa28eLCU8LMycn1T7buzQQEgsyyZadazaNborRsa0wyL+PPf85Iy+XI5FjVJUNurvn508x5/pz88A2er7/ehTw8fnywe647rTstZYM0JtkoNzgcJjlPMcI3cMR6k96AivJJ68knXMAxu6Lhz2D/wqoPsqWUXGzU9PSwY9haPk+m656Fz9Fj54zDYXB3MLMhiHS2Fb4olDdo5c0UQSBGMjinu291i2l1Z6dKzZZK5Ea2jaZ562N/W/DBB625IklG6aelINJKyRLPgvCIwNjG6uqC0OrW7ZlPAH8sf1Zeml3vHLw5B/LPL3pfnXfyDXe+5TrJzjcy+QbyryeYtD5//vWmfNzJ2doa2xUdB4D9Nv6l41lJt5FkLzB1ECxvkKjpNbG7Q8LfP0Q6or3FEMAd+uD60pWkLE9ntK9vfL13M9Wh1b///ZdTjYkBsdHRr72aDfkHPr9+A+Sf/7qtgbuHu/p8wuI3JsYL8hj+VVUh/liCvCi86isr84b3kem3yoEBvPwbqKzJ7Qb5hwetWUsOIDAhOPNUOiAQ/g8GAr7ISDDrJYW1pCXmIarAOlCYef3nro8Wi9AHm2SczEBWfDwr70xuQqAgHm//4jzBLsxdnxd/YQz/fJglwfjd5sgSztlxzJ56sCTSsNkVyRVDHc+/P/nVV18t4TIOlGW9OOSlpVW461wttW7DrUhPHwxq7Udnl8h2SEQZsIzSSNnlVi2AzAosAxcIopFWVwAxNSRYfmjizk1n81MXXiAa5UYr/FVyWwZcNRrhO7Wabqqwvr3NZiTBf0atVqNWqZQdp5/KRDqZXKwTymycM3VnarZkcDEY2toSn2uJiM/Y1gseXbI9WCSTUzRFKTvBv4+MjqafSvhs/Z7smlSL0+4wgFw2GMQiEcc+mTrXPTiQAezbCp/5ue4WOV8sE3MkBrneIebLwSo7nQaZ1pYcYxUJaSsNZj25cz9xjvm8bWw2Jcbf08jEIp1dx0lFBDodAEBVJ4bUdNTyKXYy08BNKvmraObr2L0F55xdRmM9RS2lKfjCZUOxS/MCfeJ37PixTCgS5pWWlpJqcGmpf1x0fTVKs3cqcybPHDkp8PcPyrAYDC13jp86/cPvq6tL+8/d+svRRdL67ApeCT4grc94/eeRf8A/XMbUWlQUFxfrv3LL6AUgyaDx+GAmaIEsGgkNbTzkE1JSsnkNoaG3FhJKjDAOh3gSoxkEJk719YWHgTAMRRH4/hrwwV8mhiYGRAMCX1VD/lHPW2+Cqcjaugvc75W+MKx+xBfE53n4VxUdy2Ix426VZVF12PrnQWBZ5UA7AHBwMDehxsM/i8VCEJgDDDyWcAoOMcIvRGByuVnnJFeBzNqQxdm6OnTX/VsujWBBWK+F5+/OkKCyjHPnnmQmRPShHSddgKTIEe7tA3yp/cXHh3QA+m0O2MU7e5Hwb1IkM0qlTUMnnp2++8G3BICOsXszY2ZjeTkbuzcAW+De4Kn7nlbOr734ldxyZ1Ao01SQaVi1ijYaQSsls40VAFGV1LZNarXhcjQV/F2tXMtWu0+MPniga37aMSKT0SqbjWzWsLIrpFYQiEbV0JCC7v3E2vueraEX3hTmSKnVmGA6Mj/P1wXrZHq9yBaTTOXWnXtSrNUgdk9VF7FYrPaxw1bc1U7T5ILRPVJcmNrSDW532em0OJ0OubHXBh4d95aQ09trvndP71g+3n7mSdr1nRbL3BwKcSFnVGxYcOgNTqfd0m0Ry7W2mBhceFKRHENtQfMIL1EykLsUV0yztTrJuEXYM9nDES7NzjkdOs7MPevQiQ5QnQB4awMJ1Uq2ms16OYPAhnszeho/gaomNr+Yy6MwixXebxtdvPfb+vgPdrTbxdksIGAptsOEhwFkwP62dk+C/DvJ8i+K6naaDIN3LKPPv+/78VO8/bsze+H24Yoh5egxZudbE7P0CN6nzEzS+7dpHyP/WgkBgamxhIBF5Jt/PJOGUU9yYTy1kGpMnSEyEMgHCPQPXdNI1m96HC8ZjyOZNUxLzBqPOQYE+mxOjHxpNqQvNBJnQ0JehQX+Q5633njNvyho3c51u/fhnBkp/kZFBQXEdXWB+Y2O9Wd5Ikux+kvYR345QPr/7twazEk9lkbwZ/EcvJ7v7s7Oqak5dgqdMKhABoGoumiqocEbl5qM1RDMCiTllcBRUg1BH8zZsyn/zJlzZ3YW7iyL9wsPYHJQfTwIXNF9DASZ1yRu3MttPr908fLSgyeTIv1aUFDujudPvvru2nffPViac44BLlQqjbRCSgPEVmlBlq3i88TgMuVy3oTccqZb6FzWAwLhab0K3K9x7TarzapSDXUCy3q34WYNuXyVUkmD/HOf6Djhun5dzJ//q0NuMOjBA6s0Giu7XAPA623Q4iSbHH4Gf6m83EpTfIw9Bf410Q7HX2W6VIvdDioQ6xZyiRG4lByTrNngL2DFs9LMNtR9ChdYXhdXZ7fbHTqdRCgUgd4TifG9xQWWJLiKDd+VYyc2nobesXuO8eknd69fGrUDBFtyhSIgoMNpFwrnZrstIrkU3n0N+P/goFKsIOAXOdYuLl+aLOXLNLa26cnJSYkuncNpsYC21GFftJbn7mAyEsD3ozBuwEr+RxQisFeugo9HLTXKhEL9Wfi3dSnkcvisSdV0T37pAUBghkSULfgUF3qGhYENPlD9YWUq4379+9PsDn33ne7C0z9cqf7RU/y4PcPv7HR95m199hR/Mz2Tv+t2R2D+kIBVhCn8rdhnE1cVhPQjB1cGkgSMsLDNHvyBBsSwQdIdTaaEN4ZExBWQHQMvRCDeBfrh+7fSFUh6YnB3a5jXCK/ByOgvQ0N9okOqot981Rb4D3d+9fq/FMXvC9yFtd++MPhfqrU1L6osH8wwmM/Y2DgmCIbktGR58JeXN5DH8O/Wre7chBzAXzeDPzupUjIA7M7OrqlBFQhGuAdVYK1CUTuifLE2pHMlK/B+XlJSVGXlLrwKNGDXmih916a6rccmnxxMzU6q9wkLCPdbaXXxDPz6hXtnf+E1fpFVCdyzTPbyklCs1xt0CtfpH+pA/H33l6PLC457h8sr1Aq+bZtm23tGq027igLVAqwVEQTKZPaUWy2G5Z8X+KAMsULCNvZabQ1Wiq+gZGZms4b1EzmfyyOLNTrcuFBJLOM6HJQY7KgcF4tLk5PJRrlys75ZrDc3lDeUs60AXOCfCnAxpFZX0IaFBYfdMj0JsgwQaCuP+UJj1bBjYuiE2KKishwJj6YUtRMTIyNcsUEvl8sxaBX4J5SIdCIgrVyrNdpA/4HOZOO+YUQgmxws6ZT36qdbzly/fj1YKLTMtaTqDM6WycmenunuFpnRht0tVOHub4tIeClCoyi+NJBix3yxiq/9RHse+CdhHkgk0i3/fPv27Rmp+8SJZ89OKPgaqVWDxezyXkDgKpR+tBKD8qX6ObvT3tIzcgmTsuCTADr5Pb0kv/HAOz+2pumEKfEFYcgXsJT9OaT3JTYgq91i0Du7B4WjP3y/8dMDLwUfjN4IdI55bv9qizmAv3RS/P386727S7KyAH8rGfw78IOIDonGejDL37s0Ohw14OaCFwd9MBIQtF7k6tWxERG+mIH/gn+hq0lj9Ob60peqIUDAL9F4eNOz1uBsyJWpNaEBsdEhr64C/8HOr994DYQHuN/dXVfAXpLWZ+Dfvn0lJcOPfv9lXwD+GqvASUlZ3trHAGl+HsD7v5Sc1NwX6s9ODhIQAAiqMC0NEHgsmFwFpks4xcUJwbWAAXKPbvplVuAAPMbAQMZno1zkCSJw/Zb0Y2fOnTtTE5ziv9Ej+rwAxBTA8AAfogrxVxsPbeLKLl6+uLQ02421A4POoMDbv+8QgEdv3xsbO4ypp+I2QC/IMmuDTc7n8cFoGuViMamz6g3d3W3O5dv/4aCkIObIkoyGGGBZW5upNyYG3mPrtm1aGc+TYDrURIm4YlBYBgregAFD+EAlST/BqMBkwLueVDHx4uwTm5FWq1U4X9aUTOsMDod9CaBkOX7cIpJJrZQMh205EQfiM1JlWhtV23OxR2wym7H4AadZJtbp7E6H3gSvw10fDYziw/fIewCF+EMy/MRmNMkM9paUu39CIdidm2u3AAITxEablmJ/8QU/Df6tWbjPFxuJWSzQnHkcmmZrZBT4V3GhRJieLpFwgICW5cWfP/4Ys+hxcZJLQdtsNHZ6Y7uPjaZpjUbVqZJaMcdm7viccE/eta4/zSuVlNZkHmtIVu7xrX7ngx8HcsWZEQX1yL9PbwVfrwP++cZF5ej0esvgnG7+h75qcL/XVnKvXHtanE4j7nx7If8+w9u/wL37ojz4KyIEbC1qJY02rK6uIPw4vAT0RDC8RMACkIDVkY2RGxNBDTYWVO2OCCMIbHxxExi5EpLgReDUVCK2BQaEe1/XuBoRmLgmMiA2JPbVVeA/0Pn1G6+z/OPyt6/bh7XfMFxThHIvogSsb3R016Pvv/99AIsktGAdmOHfCv7ab1Wm5eZmt/wCfzqCQCIB0wbT4GQfZFQgIHDn9sxivAr0rg1hugLRB5PZkLwkeKPr1o/wxBiUZTiWXhgYVQZG+MlkQoY/0/QczjCvz3P3x7hiv8SNERzx9OWLwL8H3UKDyaBziuZPf3/lgx0AwNk5xxhosYohN7MkAzdiSivYNJcLnpyIQAM+nl6kEyvOjjuXF2QUBVZxmxVRVm41YVRgMpOR9/ZaDEpWugF/bLZcYgCYGURUbS1XzKOamykpGy+vSAqYecwKP2kCr9jQa5OqOtVsmwoAedh06pQQAJU6md6TOtcts2r+F+YqFG8qEmSLKZqqHZ2cNpitoBylRr5MhkXg95B7DQR5/81BGOJLOZttM4JmhBe5zD75ZE+wBL8Y6SxCyiqlC3lsTU9ZPUJv5QgERaw0mUwM7pji8+GLAScVxSYgkCNsmcWkrI9nxobcSldHh0uhpFVkV0g5W2PUSDEOR4rd7TMLy8vOwWsDg/395y7W8mVasrfDKE+I+/GDd98dsOgy8wB/Azk1ezH2xTcpW6LX61pahKN/evTtpz++ew3d7+9I6/OlXL251wrKUs3kvmQGB5PY08BNu7HxgPViCzvi70NyGcgKCumKBv4VMfxjisEvE5CMx4UmTuFPMO0gLHp3FSCwmmmR8fRFEwRu9KhA4B/+ZihBYHxpqTcsELsCp0ITA+Liwn7zr68Q+I9x3nozyN8/ZN3BdcPgfon8KwL+RQD/AH/RmMMHCOwKysKrQMK/lwF4Z6A9JzcnzVv7IPTT6Zw6Jzzt5ggBAYApaWkbdm3fidWQ9Rt2pr88HYdlRT3xweVjKz4Y3u4uEpSl04M95RzLyAcReO5J5sH8sM1hntu+8JXKLykF+4X6buC2TV+e/iM2P9vh+eU0KE4///3GT3fgUollhxnv1DsVhH/IMgw81lBiEQcIyEcEGsbh8SQSHbe2eVxnaG4z6I3b8HmM2zF7x3qxl5o0cjdYpZ3uIcKywzOGHCCgKFVCga+nKL54XCymQCPhIG0TG0staqmGVg5VsNH9DqnZRo1t7J7+s8+3Zqe1CIWTCZlirVVLffHFF/KDsVnZIormF+fmWDCYFbWcTSvHnR4o+P5b8v3tIdkF4OZlMj6l1ertkzvXj+I/itxm5AVv51EyWWq+P1APtBRSsBX0X5RQLpdkJ4hkRHAajTzh5OSkMFUiM4qXFklY4EOTSkWBE3YBAlUgcyukzIgI2F81fi7HzCbH3M2bt7rv3L95P6e4tnOookKKRRruum8/2HHtw1t2UbagMjf73Mnovr643akGvcHSYhk5/UPfp4z8m8XJt6bOkZ34seMu49HR4mJsffEUf2/sj/gb/oH9bfUeFiu6KyTIowH/CwKStXPAP88vqqtDw0v2xda/j0Xe1Z6eQILAjRv96usPVIfhgnUSI706dGpqKiA+nhCQSENSDVmTGM/62vWvr24C/wEOuN+4gIBNG7bsB/nHFH9ZhH8h0bHRsXEBvjgLEvL9D99fiYsNwhtosrrSi79b7WnHclaKHwz9CP90Xgk4ONie0p6SkrIVCPjZZ19/vR6rIT3FXK5CofJ2BTJXgUxW4Oz9/jzwwXkDG0a56RJ4UprE4vSafBSB5/akH0wK3ezD3P75rPyHxY/f7i4Un794cXppaelMDsg/y7LD9fz7PnK5dHRx2XHvcHLTUKeiDdPoK7C82JRMDPi0HWkMItBo1Bvg3ZfoZGJuc3Pz+LgTLKcN8wErKthWwjLwsPAO49TXiaEmMJq2h7edGSmphadO6Qx8mqb4PK5YrOO6lGp48mtw9k+qpG1v43YhXMUG9rfCagakGbampGRkbE8vTBXy2VZjJjeZLY4QZHMoqnb9LezSLsc1bmhmrb2/YF/yfzr/HQNRWSMCjTazfjz3+iWR3iAT56TlgLaTaWW5An/8lySnqDRbphXnZufkVKbo5DSfL9fa5KLJnJweudWW3n9ubpGoQIdpxgiqFxCoBOerUYP6hY/RCB8oG0UuW6rVzx2fnb1z9OiF490Jp5+5NUYcGEym13/74453r72brRNlnvv2SFbsVMguHco/i270+ff+n366w9v6XAHyr8Xb+qyqvbT1YKqQ8A/wt3dfUhZO/r6k/4gDJvgjMGdFh5TE+hd5omHiv/2bDMLQxESCvoJqLwV9AYFe/DEAJAzcuLGxOmK//4uuwNVTRATGf+qthuBsyNT77+8bGfkfryTg3/359a9ej471jdi1dVMJtv6FxQPuBFko/6qiAX9xAf5FrSgXYkEEProSh7uQcCNcWRlz+XcrrSY3p9vDPw/+DOTodOi8iAK8NYgRMSkpgRu+vrE1gVwFFhZyONwVFYjPVpKRkNwwc9vTGC2IOpa55xJWQ7A6IZJsL8OC8JaE4BpWmN9KEcSHFEHA/voGi4qvXkT7OzhoNxgsczrF/A9fFrwD6uLm4uLCw3sNmHoq02MwFRuzTGmlqonde89hcE5P94AKBO9n1OpBt8KzUy+urT2LRthJQv+2STWg/aS08ZP3jGqpSqEcGgKWge+DP2nPqMzY+tkpjpzGRmVFbbNMPH+6R2wES0vRapWSj4MoNu3Zno5nbnUFxkevXaXVYaRi2ZbPT/GMVpvcUsmh+DKOiM/nJnQvYPmz/As0u/8F+NjMLV/yF/DdFziOV+75jS/+Mw8RglpSLTHK7Wk3LnHB5epyytJyU3UyuSxbwKy1ErDyRSD/cnJys6Pys3OEYuzmk8mNcpHMaBRnB/hn5FiWlmYXF5y3QQYaKdeJ0/MuMtcNih1sOu71BCMMbthmA8m/OHt8bs5iWTpz97RLianSbCm/58nJD3Z88GlrrkiUm1fEysDbCbvFPvLND13vvIPu9ya2PrOb3CM7X+p9Ke6Z3LBuVwLT+8cUf5F+/r8AoBd/5ER3lVTFkd/Bppv4em8QawFJyvdgzyMByfdxwxEBjUxPTONqRu7hS8SlrVWkK7DaWw0B8Rge4F/qGZlrxJiY74eHv675DQDwrVc9MX/P5603X4v1Z+0/uCWiC9frgvvFbpeQiGFwv7GxcX0BpBoiCAqJ9o8DBF6JW2mAwewDlH/Y+gf8m/Pwz6kzOA34jWhAlICDabfaycnI2Lt33a6dzHQImY4rZgaEk/9mQBirIXV7E9bvL1v3GXYFykg1JHhdUlT+ubozl3IGWv38PN3PTB7WZt9NxaKcpYt/xNHUbifIiznR/PPvv6y+xsi/mZnDJPS+DZe/JSdLaYDdR0hceBLfW3A6p0GR8vhGG9DIAAg06PUGUTMQ0K7jXDWYQerQKrWK1tp6e60aWc9TF+g/NqjV3y20NedEVbanBG5NoMBaynH7EY87//zSkkErlVI8ACKXTmbbTNOXnz575pb2mu+ZzGuN27S5pIXoIN9mk+sGB7tzjwllcqr42OAcpu+x4eWLF/Qj3MM9bci7LwB1Xuh5sEdwiL+Fvwk/i3kJg+iGbVKbVmyfG3xyiQtsk1TmZ+emiuRaUUoQEJCVVSPTinLhq1hGXkpqak5amoSnpeRmo9Fo09K1+e2puRIxr216zjm3tPgzNsUoOp53uODLVkX54RkbuRPV2my0xggoNywvLywvzlmmQYb3l/xp/oQbQ3C0Yk7umZD4D75ltQt54pQWncmks1hEo396VPTOuwz/bs80NLldCS0O3DJS0aRS4M7Lnp709Xv37vp817r9ZUkk+MALP/i/9FtCwF/wDwAZ2zVMBoSZ5ujSlSzqgkiE4AGPGPT+WNBYHx0R4hfaGNrorYZgivT+Szf6QgsKSgsOrBAQ22SmQAqsILDg0enrJV3YE/2r3+S8ugr8+z2/el3gX7R7+9YzWPzwQfyB/ksKCenqAvz5+gYAEQXAvypsA/T3BxX4qEvA9D8j/wZSamqyB5F/lhX7a1g55BbQwnjg9vbK9sqM/fs3gRE++NlnnrZAMh2nVP7iKhCYRFpicvbsDamCx8ABYYNIT7ICc8uCSvLr6m7UtFTGR/oxxQ849aGxmbzzlx88eLA0e/+WxeFsOS6afwbyr5SYq2WQf7iKUtGM8g9TT1V8rdVDXDKP7EQRWMxDsaepFQMCdTg4Jm5u5hYXX3Q6KJVUo1AqeJS13Errli4/7egYYo/NPHy4oH9PltGaV1kZlZ9uNMoBm3z4cxiZP603giqi+fAGaKlG63BePA0AtJnhvLdKZmPbQIHlCbVWrSj71mBLWrtQxONO3nGaCeTYL9c6ksmOSoQeoR0ZQv7PJxlffslFLwWBUPAw8JXJbpnsaTba5Kl5+TWpEpB9hRnx8RkiuUyYm5ualpSRK0zNyU7LKMuQ8GmtkY3eNpkG/sk1yTGylm7Lv39FYvPlCleHW6pmJzeMGfExselbo8W0VJv+4cw908yCZfry5aXBgbq7P3S4O2mtVi/Wqkd8v/02RFCUL5TJ9Cj/iuf/FPIhwR/T+9LkHs1hcq+amNyryZ50sL8JW4d3b9od4b388ycrR+I9+q9oBX/9DP/gVayQkiACQKICmYVMBYkFXjWI7CstKK33MrA6rKskejPe7DEMXLMm5Pr1LmKEN4bVv9gbggWSKR/wwe8SI7zjzDejudlnIqJf+01aSo4k+NVd4N/neevNfxHEZ63bjvKP6X0B/AUlAf6Af3G+AeHxReh+q4LAJPtju4SgavjRo6q8fsK/gfbsmpo0wN/cS/7X8NLRrQDw1q0BwN/u/IyMjJQtW3d9/pl3NgR8cG2tslP1y6zAw/duL88t3e/Py0oawMx8rohkAchEhQfzQyLK6s5tSM2prN/MlID9NvpuEDVfvfjHyw8q6wayDQ7noEX07Pn3U+/g5dL9xeWHM2PJTZ2M/PP6K4qd/CKS4fDM7WVCQFrK5qcXivUOBoFiMa+29rxBb1QBAWkel5aqablz+uLTZx2qsXv3HCa5zLhNnl7Wykrj2axyEI4OvZxP0S7XWVMvLhdRAQKxfVhq1o9PdHSokH9a7dUHIhz65YptNvGxdSm5qbm5Eh6vsNuOqe8Ed+Ur0o8oPKLv4DekuKdDikMqml8eUo7AyHo224M/vD9EJHoYaDUZDFhL1o+fl8Oj5uRlpwol4INTQXiK4PFzM6LSUkH/ZRq6E40AACAASURBVKdk5EcJWBkcOUXjG+Rnpoq08IZk2dnduRe/ImGBtx0yRSfm3RixDMJW43ukxfehvEGLPUMNZieoxQeDoOLPgQ9WiHVyjVqluBL+bZcgvr61WyTTCUUj3wy37niXaX3++V5DRafrUqp+JfcKgw9S05mdv+v2De8rCVrBHzP14bHArF/oPwGZj2NFlyQJvC64lMSwbsQoLvgWht/Vlx5Y0YWkHBIQUhJb0MiowDWRw9fvTh1azRSESTmEFITJfPBG7IsGFXigNO/JpdTU3MnJM7F5ZXntuUIJ519f+eC/v/PWG6+xWHH7NmwN6boC9jcc9V9cENZ6Cf584RWtmEgKXhjTqFgscm1eMvyohAjASpB/aSj/AICe4q/hF/wzGEgZhACwvXLT/nzMy6/MyNi0Zev2z70qEDMSaleqIYBAGR98sNp0j1wF9guykqIq130zOiLWieVkNmRrUlL+uZMlByU5gnpchu6XGFIoO3vxD3+4uLQ00G7XO+aO212YKoz4Ozq7vHD7HuN+9aYx7E7B0VJuMd/TgsMUX9gkl8suqlWpi3NbLKZeM14FmgCBPEWbyQoowz3gGqnbrbaaDVcnOk6YzSaTVnZs9zE5uOYaidGqtdz8y3GdXO+Qa2nFKv1MAz6VV8mlbA0GBzTMOJpdSrCVRkqS282RYsMy26oVVsWmIP7EMk72nOkX9Et+6TDsI9ij8eBw8N8c8noPCj2KEL1yOdsDQfhQtUZreXmDySK2lVtFZWXggyUyrdYr/1JB/uWkpWRU4q1gfH0Kh6LVdGaeSGuMSeZvyDuTUrmVEt/HIInHP99eMNnAu4+4VPgu4XI7mxV+ZFs1KnUyPoZp5vaF2dmlpdmBk3e/GaE0KqVK2TfVF1JUXSoYOLJBJB65cfJdIv+Ogvw7jMEHOU6S+lyh9qz8ZZYefb1l/76SkpKuEOJr/ZlxX8/cB6uVRUrZgiDBSj2HqQhXlUQJij4s+pC44IAAH+zAxlNP+IffyM89Vri6Ma5kn2/BGrzbi3w03PfbNSttgT5h3u1xTKcMiMC+vnhBSk1wbkvq5JNzglsPUvJSJDpJ4fotr/aG/L2dX72exfIP2bJ1b8iVvnAy+VbkH0RyT7Hzpc+X9EILkH+4jgMEINMAk5dUNzxcEhXVnn0wO4XYX0/11+mln2zFAuvsZBoEAJixaW8laMayyrLKyvyMdVs2fP65l4CFxZ7NSdg4Bwhsa64ddTFdgTgdF5RVVVVy49IoV0cQKBZlbon2j/cPOjOZniZILIj0reGOn7/6h+nppcFKi0E/N2spxpWyWFu8eWFxYWHmcAXIP5me3P55r9c5XKU3kqENFzVhRP+y03m11lWY2uLotbJNRATq9TKxA56gTdJVeodG7TrRMZR8eOajZpdLawJ2pKexwjL0vVacrpDKLNMtEp7cqJXLte8BdcsrVNRZp1yzilLjqN/Ds80K2gZmkZuaVsNjsysqyo0tgrLs7DTgnyh3zoEjJuwX2o9UOtDYEvgx6EPS8V8cHnNevIKAkKEg22OJSc2EMBDAhLeL5WaHXV5eLk8T5Nfk5Eokx2pyc8qisoVof1NSMsrysNbA8q9nZYuL18UfpClbMj8iOr8yQyKNsQrv35mdvXDh8c8LWrNZdvr5vFKlgsfDu9P34DurrVmJy0EbzGP3Hi5iVODgQOum2k7gn8rdF79dktsef3LgpP/uGpGk/UOm94UJPlhvN/1N7ClT/F23H9xvEMu3q6uK9VLoAeEfaWBkefiHCGwVrDTFZCEC3y06cMC/JDqgtJQE83siCVcgyKhC0ha4Ma6kJCAU92heCT1E7vzIcAiuEEbx+HI1JNIn4mAL0G9y8kndgMWZdiY/eq9IXrypJOnMb16FBf4dHSL/gvbtCozowtZnHIoCxFVVhVRFR3fF+vYFMFtAgqoY+Yf6LyhIkHekn+wFHt6XsX1rSnv3S/wj5Q88+hUEeurAQMAt6zIqKwcqcW3IuTIg4CZEoEcE9mA1pBazAj0tMQahiMnMJwisC4qNFQjKNoxyxeCDATsi0Z6QzbFJ4IMLg8uK9nNk41cvXp2eHmzHXKXZRex9+TLS0/uyMIO3f0o+U/xlkkW4HE56erGnD/vFPPJhvAo8f/5irkXfAMDREgQa5HLxzFiFmm5zLspVtS53U/nMQ/PbFF9us1LgyFMzivJkVrbNBpwCPymi2DFG4F/b8u2HY2pQneN6q/isUt378PbCH5sVFN+YHMPm63JTMlVDKrrGPyOnPSNVJ+a0OM3lZKTXK/7InR+57JMi+jzg8xCPx8UjFnNF8Cnhkh+43BUYMnIQKYhC8AtihtmMFS7/go19NWanzFquTc3mpNbU1GQfTJek5QrR/qalYMwUuW1DrSUQlJYGS2kZJRfnltXwY2LYWpmumxBw0WHU6+Udz56Dw4WHslkbrMZeKyBczwcCIgLLx2aWEYB3ukXKTpVKpe6MmsOo25z2PFylmiERpZLcl4djyST3itSmvKn3k6lk9oPsvCS3f/7+gECWN2CfOGD/Ik8P98v6b4WARUERu7OKPmXlB5YElDJmmPxXXxpf6pWDnpcDBIEFcSXR4VN9m1e/OExYIM6UMBPCpEiyxvfG59jyD/JvoFvncLa3l8V9GZKpFa1rvT8793+8qob8nRzc+eHvn7Th4P6QPk/rH97+VZHBj2hG/jHqLxozqJB/rCA0HKAAByoH8jI2bNibkfaL7j/n39hfsMNeAKalpaS0t2OGVlQlWZ1ZhggM3PXZig/u8TZGJyfb9HrCJEBgOeODj7CKWvujKnGDsMhAsgKLj0XkRZ07d27DpEQmvkrk34N8ix7k35zr+Q9fMjt1Liw77o2VM70vJiZYicg/Tk9Penqht/5MpvHazjIInFlwzgGMGlBuaWyAQOzDNogoleLs9KJDyp1wq8c+vu14z2jkk1x5nkiSnndgK91UwaaCczk8a0wylSCR8f74fy9+/JBW0s0Xx23nz7s6HR/f/vc/NtcWZuRn0jExVqMxNyJ41f9lqWwXVAoNBuGcmRlj84q/cq/tXWGfh3oiEdBO5DnFHO8pFnHgl/CbgEWuF4MEgsQNoxP23AaWE5nZYHJqy61GGQKw5phEqxWlpm1NywD5l5cUVIXAiSeCKb40Ad8Dns3KL48p1/JEIrFOeAee6HqjTa8TK90nnnXM1/IpmkRlNZTHNJj1MtLSTm4znHNz3ToMS+hUqdUU7mTS2Q1yUWBf9Kat6zZwxJZFvJ1wu9ZbTJ7alIJM/gYHI//Izktv7wuwDxAYG+8NPWAEIPNFmTkswQr9PAgMCcpI2BkNwIv/ML70A4adhH/e74kXBgaiDa5ujIweHvZ7nymGNK6MxyUmbvTzYYaYCQG7vr4R65+RnXPmSLtTbxAG7s67tmPHt+9HS8TCO4vLM9p//T//v556r87/D86v3iwTsPK2bNhSwkx+gMGNI+a3C4AX2xcQQHAYhFoQM6EJ/8iXWwHZflmZsmFLe3vg1rS07peGPwx/e3QIQLswNwfERRoCcCDKe8rywQcHbvAgsLAwvQc78QBJKoVCCioQC7RKz9oQ3CAMD1xWFohBWSKyNkQsyU6Kyq/bUMw9/4erVwF/Z7J1+vHZRd3889+vbvyUyD/nzL2GCrz9kzHul+gL5F9henrmKYaAL/dhu4fKDwMBLYbeBhvYOgCI2eQErMv0Mk3nxMXLBmmzwq2a+d3C+EeUrHCnmB3D1vApmygj72t3Z2EO+PPkGFvh1sC0wPVn/zD788cmWll78bzx/IRbsfDx4sVVvD1nnmREbOHYYmxWmaAo5/9l792Dmrz3ff85Z11s91pr79paL0Wo4HARl3IUUIKAA9aQmJCEhOyQSWLEhxgk5iEhkYghN5aROhShzibFYdIFcmgMAh2QNTC2yXI7jLbodnvbrVK1Q8dO6VR0W+2MXadrn9/n8/0+Cdju/cfv7Nv6wy+giBcw5Hk97/fn6u/lJUoHGM9MdJBgaQH9SmP0i8k+1Hk6WYx9Eh1iz2SCV5Opqor8XMWhUKejEJQTCMaEIK0XpAjEippwlIUvQqtWq0XaMh3cVExCXHSv4WvQAFMAgiko4pfZS0vNcoW5VGDxeC5eNJm0Yq036LUE/Aw8lI5L77wz6bMq7OZB0ltTF+qB3yOLQrE7LhplHQ4rpricsio54/XiGK+AoSov7ykYArUuEsToXzup+46NPb1QVl5+PB0HHyzdWsMHvsUqn/cmFuTnJ8YKYUgLMyUgSsSsyix0vgsJWFS5qSS7sggXkyADq/fiWFaMDO4s2rmXuGJgIBGB20gw8MCadRkZhVw2BPTemnkEriJzYgCSe3nLhdWHtmem1RSrwemIludqrl957cprICOXavse39xd3/RXv3keCvxLP9j4m5XIy04lQ59x7gvyL5/WvhQmDA0VEf5hEzDgD2dCJxYmcgDEEhjb+mxh5/R0r6pRNc+/6I8IyPipBR4QqdXtKtCASEBbLcGfhiMgIDCeDKEz88cnfK1cg/AxblYgbRDW5GfwbLblE+Ng/XBmPqPTSmvLZRee/vF/X3z4cNrW5/XP7Hs8DvJvzTay8wjcL5V/bV5uqRjoCxQYwL/y4yXpZVXzkcf4SIZ60C0RVlCKowLdBgMnAnEd77173zMu+OPubz6LntUtO/FQlQKusE4QDlmkQsl4dpYyHK7bYkkpThHWSu1bBGcf/26OtU5+f8597p1J+dxvH5wVbLGLvhZLi6vcIVd4bjihqDKxSOhhmRnvYGhe/v19aenfc+IvTj8wuEA1OGQWFgKQ4A+ONv4SO/hbRAwyzDwDBXEGUgTCv+/2eAJrWXC+pOlXZ3EzyopKTUVFJXGcnNdMTDxU2eASAIkVikCAufjw4oWPLzABDHNa/LIqcafIZ7VOvnNv0mcJ19W30o5BeCgP2unQ/KCi69KlSw5Hk12k9fTLLBav2x0IhF3WdCnPNmLrbDRaJ85fJOq8takLk7/l/eXw3eHcLz8tvvVoZzWOvU9MKEjDNqVqfEriE7KgAF6xP6QDTAK+xhm4s1pTks7P4vMqX3sNJ1LHy2d2kpdqaoOLaDpkG5cPXpPcnZF8hPBvzZEFKnDFiiUgFn+/rbp2uWp0ZM+nq/KXYyvLqRvS4esjwztf3rnhypV/vtwwwDiddovlr56LwL/o88LPfwZPmYrVH+DQU6x9IfqvIB9LXzDdMZRZFMNfwlDyEnjWJXISsLID+Ve7fNPSzs7O0VHwvyKtiADwR/hj5wWgliyvAAk4KuQkoIZ7AwTmJa2OI7Cs3NRftrHEN6/KfjQrUJNWwauVIgJ1dFYgI6+y1V7448WH74X9/kjfrce6d776aPMBkvx9PDd3s4U0/h4MxvVFHH/HSxoa0suQuPKFCCR12C6DJdDkstrDAYvC7rIHgl57E5DzzXff8dknJ93gkr2lWwzK5pNK4XpFyCyou2nDy6ySX2IPh8PykhyesXRLXYCNzEW8rO+ezzI5aQ3O/TlqCYS2bAmo+t8OBVoEra3XikBmiXWsJ9oTd7/zKV9CP4I+wB6G+xjqgGUEgRzrAF3acu2C0w+v+Bv9hIKoBVEIYkzQReOBHAG3tIQCBoNn4CASUKsVpcP3SMK6GWFWYoUGmUNjgLSrdm/FDjl8UQbWHbC8//EFQKXbjW9sX1+0r10l0nVdevPSO/esBicpiamro109Budpgd0KJvlSV5Nb2x6NXOwdYH1WuxtnBbpcFpFtGEsCJBJP7Nvjk5Gdl+Vk7N/qvFwesb+c/90JX09WWiJOvsrgtB/gD+hXQFFIukKq50Xgzkpl+dLqnR3V/NzaSsAfod6GnfhzNf0BJOFO9MLYL7KX1EZjq+/m5JoMnJe6hg7LQvyt2UzHxBzISoIbvrL36cmK1TjIofyDa7UjvEePvj1UVP3kyZMrn3757sT5Mn9PS8j8XAX+BR+cepqVlZuyvObyEO18i/Ovu6BwKGGoiNT+5RcU4AjmdevoPiLynOsAAmqS1mdLbcA/LIBp79NWmUwkARz1/+RgDBAuy74+UTv1wJ0gAFECYiMJvGEoEBCYeoNLCKcvy16GDcILkMTS7jhuVmBFGvwl6XlcIulnLaxdlpa29enDf/qn9+yugP9wdBw7PzD5gZ1vIP9aT3fh3IO4/JOR4F8ZfKpTm9bvaCgv4xDobCLDTejOdodVEVj7+sFjhlBLD45GcYXMjsnJSZ9iclLulsmDcHB6X4gRCtlQ2FUqKDWnZGFuXKhwLVoUrgvJA1vqwgqdDsNdXlauYK0KC+pIHWNwlW4JhUMunJAw3g0Xd7Gc9fh7UP7Fgn/wgvSzI/0wnidD8KEDpnkPHNBnwnENphjzROTlR8dkKotpQYZjoB2HTdNKaSICwxaW9WgPvs7gdiXQ6CogGfhgaRHc+rJozV1iIu2rrd7LM9rNdjsrN7iPseGw3W0AHdfjjT6ORqJw+5M7ui6986d743I71sK0ltI2ZIsdvK8D9J+zKeAfiEQP73vsmbh6ddxBssaBt3vYdD2v06ZUpTNhQWzuVTnyj069x83TsfAfKreixDTgH7xfUFPDJ8wD+BUWJsIr3p6r8U92xGcj7NSv31hbTYRgVo6el7iXWN/qGADjOpDsKiE2+NCubaTmb82u/Iz8JdgbsibWGbcYc7+bt6ctvSHsVaqFJ0+o/N7IgGiHvrl27M61nG9XHLpy/fr1K78f+j9ffXJe6w+V1psNz3uE/1IPyL/KxPwb64n8yySdb4WFlH+F6H650mewwkNkARvSLwHusonIv8pKXvb6pFobp/9I9TNcZp5/JQNCCAgXKvXACECaBhmhCpAeXhyBp06dWnbjg3JMh6Aq64oPyjpGBmXtvktnBe6v4I/YVi8bl3kYxaI/yAoK7l/9+J/+6GNZg91y76uPjhD5d+vB3Bxt/OU63zh9AfzrpxfYB8uXL29ILy+LLWpaGAo85g0TFrpKW9wKmcHs9J07ByLOojO5Q1585msZFtdVutwCs12wZYugKk2j4fM1QsPf/e+PTYGwYEudhZF4Lj5UXTCx+BcsbotOq56JmoyMvRRrlUu3CDwanMMid8r8YH8FcfyVxqwvxvxA7wG9fDTrqzMa531v/FD4oYgjIOR+SWxtmZZCUEf+FQWOPCS1MRwD6wa9oCTbD76uU6sJAJVKpZZxW0RpRURcYZY13nS7q8ikcAnkRnkg/BKu/EBFGXYHI3OPI16vH9SpAyTgvUmrgewPoNVFYYPF4eiCYx4MRiLRD797rNuUK+0Ye3fS5fYe7DlTV2pmxDyb7cQJYbrcYcXaP6BfjH/6Wm7sfexL2JvFTysinR/VWfljNRWJicA/eJJibIagmjsk/VFdqdyUF4dhddrWYj7grwNfOmj/CNGLlIZFe2lNzN5DnAw8sqogI3/XkTUUgHRY6uLFq/ira1Yl8Dqf5okH/F6PVq3qHB4+efL+W2+9tXLDk5Fvh1/bduCVqbe+eneiyoo77J6LwL/I8+Iv/2dWYVbx+qU1JPdbhPPTyJ00v3Ah/tLyAX9LcAA9FsAkUAcM/NOkbpLW2myd05R/tP3No8OhVbif59kuEOAfDgU0aUXqdhUJAto6aRBQwwGQp+GDE84tzlu6evn6GzdOce1xC2JzdFZgbFwqFkbvr4C/l21UKOz2P8gKC/VPP/7j9zJ/JAII1A6/RvD3eI42/lpR/sWSHzhZqayMw1/K6qUpO0rQd/cTBCrivjuIE0zhE+8Ovmo22xWGJsc48u/SpPbwNBsY8BgUAzO9fQxrqKsLYOlLqX0ZyYzzNBV6tUhrcTPuUMgO+Ht44YJKiDPvvEFG+/TpBdFM3wBjDljsIBkN6yurKyv3pgsU7GAs+VH398T72g0GEH/oc1HxUd1n1M1H/IBtfYC4PqSc6Jkf+kTciYEQIUh0oE7HUBlIooHYU4IIbAn6PaJ2i0XSCF+3CAkoBgRaLKIKKvfJsFRkyqFEIcuatIxOEaobBALa7Varwx52uRRg871BNwv3OZ8Dh/ePW+G7YiffObOD7HHqahLAo7r7JqDS/3BkenT4yuxTebgn0IKsD4dZZXPzyWZNZ5lEUgb3pnIy9295Sp4eniPDlRRmG4gC5PGzCN3wK0ss7B7bmpFWWJiVGJuAOg9r0HwdtdlJFRR+w2RaDCAwT4O/Qf7FGBg5uL5RxFXGcEYYsyFLCmoKDiH7uPbgxdsTp3ttiSu2bz96Qk3meKnUyukRjSbtU7iOEvd99oDfsWHbgSOvbP7o//zw7gfp4GNkkvLn7XF/cefFv0rXF9SkpOZcjpf+Af8KAYAJhQkJyUsyMfmB2d/CIeyzTUb7m0yfYbgcXZ+drefhAIRpyr94ASAiMOaBmRgAPWQwjGlA2xdTgFKpLRYGpATk44jpWn1ucdLya9fmC6MltCSGlOkN0sKK0611XFWgpjBNKTcssv+d3a7bMwqf6OIyBGAErnD/zJMnH87LP2+stpZbqhjzVylLk/KkSakbT3FD+rlFTViCA8RF/tXX15NZgS6n3eBD/k0sf9S+jzF4WIeV8cwcbmew9DkgENjTa+lIFfKfsYlYpv3i6+FQ6OyFCx9faO/tlDbqWI+yvU+VcjXd4w6HXeHQWsVGPrnLHJGHcHlGPPqH+LOTwB/HP7kP4AfCr4oTfYRrIg5/fRzsYh/o4yBI0hqiOAP7ORmIVpggEKFN6wLrgh5TLxBQ20h0I5YBArFJKLAIswqVhDbVe/laC6sV2tQKbFIZhP+D1Wj02c1NXT7GfSboP+YFPaStAt0OCMSxinZXk9nZRWblO5vILngBPKrB6O3bvaO3b+27rjKEzK31ODumpS5czjvaPDI8LDZVlZeQpZfrU5KklH9AwKNUsVXzhHpicTu4Ia6JBd1bczISQP7RADXtj+Ma5Cr1STXVlH7DlHQ7O6o1xVINNzpr/sDHSb/IgooYLh2yeV3G/sTti9EIL178yuKVGnjCi0/s+TQfbmnBKD7MJaO3Nfn5ez799NN1RceDHtuVJ1c2HFhz5JWP3vrqq0+upZb0S8qO//p5YfRf2Pk53Jt2JOXkX8aVb0Uc/hIKyUFFyBW/oPxbkrkOkAhPr2SOf9WVqZuScF9HTP8tmH/ggWvW439GAWKsiiuDQQWoJKWAGPautdFEMJ6Kioo0Po+vybt67RqGAoFI5WRUltE4PysQRSCpLSOzAmdn9VUK4J/LYLH4990e8EZvz7AIQEZusLuj2PhL5J+CTj2tp531EoI/Ult7Y2lesb5Wr1+9ftOp2OfDuVyxAdUh0sOLI5xDLuu5c4bXFzkmPxAOCE+M+t0G63iZycNE2VDYDNItZMzr0FRo+FTN8nh8vlR18eBaVhcKrWUAKqpOW61eWpvXYBpQNbSFXAyWlHgq6SxSAGBdmGY/aO7DTMYJYrmLUUaPEfBXVsa52nmR1y5Sw9uPT0wBLqAfFxHUclYYEUhigaQuEAjY49H29rnZdBUhoFoF3yKhymOxeKQ4AYOc6r1i1q1TSqUSgrLS+lBIoe0zGR1NjsmzXktodzAS9SMCRX06hQEQOGkFAnbBDcvcY7GDyAubm1qbmszhHu/M4Ye3bh0+/KB9/LTD4XQFQri9xCx7enR4ZGRY02CSlHxw6gPgH7G/w6gAaWHfhixho5RrfMNXkhpOLKgZGysgFVqx4mgKwerKmpqsH5MODy8vVzOv/uIHjfDOeG30ofgI1c3J+fuTiQJ8ZU1iJ+66efh180kRDnIA3Feli6dra/I/f/Kko3rloR/+NJl6+7t9TzYcwFIZ8MFf3OnOXVYGd9vnhdF/MeeFF1584cVfNi9PX67fSucedFTD7ROEH8FfwrpMkvzNIqUvOGYKd1AmJieDDEwkZfd5O1JqNaj/pqcX9r8NRMkEBLJAZ56AntghFridKkAhUYC22traeBQwLa2iopK/9Nq1rcVJq1NuLKiJMS4o04tlQ+oHcWiBTKFgFAa318/IdTOHH9+Kjk+eV0e9LElOeiNk7gt2fpyJ1dZi8iMm/1JX5+WSz6+Xrk7dsYxDIFeHTQdzmZ2ut92L7E1N1nG0v45F7yv7otHpfd8FXQadaUDnbzv2ekBnLi01qCsqSUJbEyturK3gad0WZaUkYHYF2LLV8F8FNOZmnzrOBEJm2VJDqd2ik1Ynkp7CvVWlpO+Xwx/G/uRyoJ+R459RUlVm0lLiUfAB99TtsV/Du2ogIRw1/Yg6hsJYbJCGBykETZwTVpCMMBmtAOQd9LePegLyRpUoLgKlYjVOB9STms/KLKkH5J9Y2mAIgfYj4xbC0cfRvoE263v9lsGAuT7UE4zMRf2Rgb4+E6OwTt67Nw56new3CAowFhgIu+zwaIQD0ZmZBw9motGB/nNglgNhcz2IXpddrj0BBBzZY1Obym8kLZVitTzyDw4FoE0pxnxGFoUfTuRNy8LJRN1jYzVZRYm4bDOzKHaqwc5UP8s5EIJ4OjQ5efpna6XjCKzeiX0iRaRJLjZB9cCuhIKCVSABX/72ETzfVQ+/tolxyjjcT6omNnbqc7c2f/5k3/XZ6lWrLn/11dg1f/C761c2vPHGtgM4MfrL+/m52cuWZac8V4F/GeeFX/zsZ7/42bq8p/z8PGPDHnKvJPld5F9CAkEimXqKUpDMmYK767pk3DBIBGBFyo5cnIBgGyH5D45/3PaPKBkCgz4YHTC8eHBzmYc6YFMfjbETCUgQqNfHAAiXWGVl7rVrNeiDc5OWYoMwLYyOGVNAUn28RqUVLqsIu8i+iEXYanVynwKkn+/dCZPtdtQC51V3wO1u6iKlz5z885Gd2v20uuKDlKTiHB5Rnjy9LSmVluAAAQkCKXGb7IbAYM/rdofvHEb/Jif726ORvtsfzgUHw0BdP8McO+YNWsxmgygtqyJW1UMZWCE1WViTqjY5W+4ymxWNGro8oHaZIhywVOVUMIzaY3Fr3AX6DwAAIABJREFUcR69RpO1yUX1Xx1xv4g/VH+6efxpOe6B5GvHn9rb1chANYIPSUh+g/6Sg2QfFxAkGHwmR2wiO44YmhGmCEQCRttH5XajWKWeR6BQKWLcFnUtVhjjqECVUCzB2vTBQCAUCrX0RCLR6MWz3ujFQKnL7nS6woM9mA3x9/VpBwCB9+5d6kL9fPMu+STmcChgwGbhgJ8smIvcjD78+OP0CYcZpaEr4GZZiYqnAQRWSkWSHXpqEDQEgECtjmFhdh6WtpCm3yykH/yIvXHwml+Ts58oQCTgIQJAeNairV1IP0pAeOuo0CfVVnYs8MYxBBIfTOqiSX8wJwLXbE/IX7crcfrw4dHe9qcnbO3+oNek1UomziuRfydnr1//8M8fDmeuWjF1+fJbP1yyHL5+5Q0k4BFQgV++NZSQm7I8VSp9rgL/As6Lv1wytXlzYXFxVn7OntXp7aPDezF8guxL4PCHpicrLQHd75Jk4N863C24bl0mRlgKlm7K20+64JB/8QDgAFWAUdIF7PHjwloPlX+IQaoATWiBVRwApQBAqX5eAvLzs7am3NjKp2WBuaAC50Vgfyw2F5sViGNbugxof90W8Fwmf9Dff8w+OW4Ufh2NzMx4vBb3q6++6na77Xb3wsZfmvxA+bf8Wt5WHvY6oADj1UqTVi9fTyKP5XRbJyGuw6oI17WYrT6Kv+/TPd7IzL7HfkO4LmQOWCzH/GSsQr2dYRlVRRYvfviVGhXrZpA4SvHxcSuIJUa8szqrWiNyhw1yWaNUqVUpVUgXEa+oUpP21FfPRf9A/imQfjH8jRurysqRZGqkHkEfElAdf8XTrl7wMZF6gQKkeRDKwHk3TAgoWygCS5GAvepFzmVSpUqtxj9KkyEqE+tmG/dLPW4W/i8lDOmmC4WxYKdld09P5PFnQbC+AayQdttdArg/IQI9fSKPAWyww+5sEvQE8HPUtwLnDG6zK9wS9gbvBu/ede++G30ICJy4dNqOZcNuHG+hFRPRp5GWmVIBhrXgiSn/hm1CfQUSi3PkaZSA8fVvhd05+YR/h0C+wc/rkotosXM83hfTf5wKlEprOR4+Q0BSFriXzs9CCNJkyIE1m7NswkfX9432njg5OhDEYKdJMrFMKAX8nZzFKf53B4b37l2Bc7K+/NM7E0DAK0jAA0c2gwp8ayiZnwefMO/5CuH/5vPCL0afrJlaWVOsH5GO3alpXrpM1C6uTE4oIACkW5BI8hfUH+FfbNcGHLyt5i7Pzski0BgZWZAAjm2/JFXQ1PHqdH4dkX8M54MHBrQLAEgIaNMjAEngbOz+2LVrGWmIwhgCU2JVgQSBMl+8RuVMz0GDVa4A/Wfx+6NRj9frH/DI7v3wwyeq6/see72RSDAceOmll3AIfHi+9Jm6X26tRG4Ov4LrHdVocCbD0rgIpKITPp3PJzcLnNZxov/Gz4v8/oGZBxEW4/6CJqcCKwHJVC2XC0vpxKAlebUjuCk+azXYRRNwR2VTmcqmp7XukCCgs1XvYMNu67nzE0Z1LU8Mj4Qa6SLiV1auLvdh0LGUyj8ZNngQ+2s0Vpk4/CHl1O3t3E/0UAK2t6tjv839giMgFwvs+2l9IPHBMlIS43KZOQKGo72esDVVCtSjoUD4bmUrGxskFosORwWqVGXOJjMOrzGHzC4zTZXfPDM42IMjr112d8DubBWEe8AHR/ys3WzB1SgBu8ECHhcHIbpchkAAP50Z/ngLTs4PeWdmZh4+PDdptVoNrP/YQS9OupVWVGqAc9llIqGGLpsZxqajWg0wTIPvzSOQpEG4BHBy91hGFpl7urcoEwea00AgSZ0s4N/8GZHaNPFfPINA0h1SRIfEkGzImjXbOmxidXvn7du2E31+HOMK8q9E3CndWnty9vY+nOLfdXx4wxvwd1ZNffTlDz/ceDRy5crLgMBtFIGXpzKbT9p4+ueTsv5bz89/+cO7o9dHxMLh6+1VG7c2p+5YrRea+qTJycT9Av8wv5ZWkI/vr0TwDZFRy5lLMtcVZRalrd6Ul0D4hwJw+pkECG6/pNleD20F8egkOobmgsksBBMCsH0hAKV6vT6H2py0nBvXLg8VpoEjraAIzMnNowg8dfx4PBuCVYF44bnl8kV2u4X1u8/cjHgjA1F28quPjvzz/asDM1F/sOfM7tLWwEuvv/pqj8XgEnBjhRF/pLjiRkpS7taaCm5qEpWAZC5X6gfcSAaaEDbiVFTf5OQlTGqeVw5Ezj6cifTY+y+U+bq6HFbdWbYl1NoK5i08GAoZWItEmMbH8u5KvtriZkQgozp5QlBT0b7r1z3uljo7aw7brd9/P9EP6kosFQMCVSqPJcCIs3iqE/cw5kjlH23lNWLeF70vmlyCNxXHPRV9V6Ui73LgU8+/xVRgTAhq58thFjBQwmlAIgKpBuzrZQVVPKlUCCpQhDmTdLVqx/odIp2F0TaoGsQlDuBYE/yHQwF3AG9GpWFBvaA0YOl5O+yyu8IB9MGBQM9cBBBXGvluLui2sJYAlgvakZDuQCDwutkccDucrQ5ruKdn8Gbk5megAr8fH/cpLOxZv9fCSMqUvKzK4eHXNDtMItswIaBmRFMBH0L+cRETOvUqa14BJhYdSuge6yYGOHPVPP9oRQwh4E9OrVQaQ+C8DuTWrL9BE8IUgAeKbOJOm61RJNaIPSD/RCKTcSK7U1o8dvLz2X3f/fau4PSlCeHIlQ0b3nhj767tYHvv3BkDgfnyy9vI9Jg1H+EW9cw9zc21ml+9+ByB/03nxV/+T/jWnO9TS0cOD/h1VSJhXk3znqPNSlNJbvIQDgJE/FWmIf7olo2hZLpmHC1wJsi/vPwirgsYHXDvTwQgOVEPRR6qQBIHJDFBDxZwqOMAlAoBf7m5eh4QEPC3+urWtP1jb11Ow1wIHxBIamK4wmiuRqUqtjZE4GZA/7lZPxtGPTgXjXrHr+7559+/ceXzh96gN7ib1BGvfWnRq26v12txuhQL8PdBKg7WpPKvg6x42jPM4+Fw1qUpsfnUJB9cJlG4HKTypcsx8bQ9evbirceRgMuoVl/o91nPSTx+b7h0cK3LTpKYArucZbX6NJ6mcrnOTeSfslaqwqCn2uQxSTzuulJzIGCud4Je9PT2MiGXLBV+WwV0sXjE5dKlk62lLpB/tL0X079GSRURfzHFp0LkIfTo+zEEqtTwC7WKwx8VgIR+cSPMmeEfHQlHQM4GIwF72lUhh7TWNk/AclFJQ2Njgwh+UK/mb5zEmqTwYEvLYE+P2xUSCMJmZ2uT3dIz2PPqIheufjI4DAZDOGAGALLffTdH8GexgDsGi4yzAt09b/cMBtqsVoU33HJmcHfPmbuPHz78+ur5iXGFwuuneWSVNAsQePSoVGVSgeiaHtF0IAjhTRMvnCIIJADEQu3EIrIDHRC4v2gVju4rWnAIAOPUG6GvRFgCAjtH4r+zoFZmA1cWWESSwduGO8WjnSdPNneKxQNev0mkrZrYKLTljuU0o/v9ZnfrpclzF3o7hzds2HBlwxtAwMtw7o99W/na77f9nuyUWzP10eWpNUWa2hHeieehwP+W88LPf/XktSOJKVUbMxKunapiLYzOpLbt39M9tCQjvWp5xuZVOPU5Kw1nIMR2jNNFG0BGICB/9Y6My5e7E9E08ngjtk5xPAAY4x8nAf3UB/sxG0L0H0OTIFoyDEHFKUC99IRev7U2h8fn5924OpZWwa8Yu3+/e39aGtYE8rEwWp+UtHp5HIH9WBYIPtghb2tTKFi/3x2GK7deMNgTkD+9gufJvgeRwUFzKzAyHA6H1rotYIcjrMFp7b9woZzulF0N7peTf1hO0UGjgDyQgGRC/6ZTFIHl5UZHk5WY30uOstGBSPTWd3N3A077QN/FhxfPvv++B4z2YF1dSyjgEuD8OoGdhYdUzasVgWNE3SatxQn3KhwtLzbBA+EWCEKCUrNgS73dM3pYB8wxbBWjucW2C0uDsN/XZFaA/DNR/WeUSMrKKf/UXOxPFX+lLKSHgBH+lEqtVsXVoOjZWOC/ikBcxSdX0Ho9SsA6by/bVF5Rq5cKxYSA2jJtORBwx44d4IQZ7YRjEm5BLqxoBvfrxlCg3eC0W4KDQMRXA66A262QK+x0Jn8dezjqBf5ZgH9kxbDdFaoLBVoGd7eED7IM29OCc1lDawU90YedX3999ZN74wqLNzqABlMtrt2zZ0/zHo3UBAhEXgEFRzAiiH6hmRe3waRKOyYBgXqZhWMZCSj/MhfyjxIwzsARzljjG88mjRFwYTCQtMkVUQ24qxrD3Z2dX5+0qQB/7SrtgGQitfPR1rEclH+f3W05fcnnORvFka8b4Fm4Ye/mzVNTSy5nXL7fXbBz77Zt3G51VIGr9thstuK8Xz9Xgf/l5zd/fevJkyvTJpN+aGjo/lefTOjgevUMqHOmNq9YsX3rhbLUrEOJWVm0C2QlMb5D6IApCXcVJS1LKSzq/vLL+wmYt6wd6VwQARyIHU+cgCCQiP8lItDDKUARWuBYHYxUXwwWWM/LyMn+YGw/EE/Dr+CPfXn/fj6oQNSB8FzfupVkQz6IQalMIvPJ5IsWLbLKdWwo1BMOu5pOdzVNim7v2/cEO3+DPT1mM4bUwy24VMN9LIJH4XRaq5adojtleaS1Pi2LzAvBsTY42BVgK8W5hCnZ6zdtLDl+vKRM0eTgcr8TwvZI9OGHv7sZckxOGjDmPxOd+yxC5wpiNYi5vh6TF26LQmFhGDdThvKPJ0UKKZV0trJUpGMs5laBQdZ1aUI8suHz5i/fvXTasZGHIlClZSQMc+H9qi6zBVO0VYR/iD+a+QC4tS+kXm8vfSf2xh3gn4q8cmehC+YI+AwDy7DzJTYnxixAF1zn7zM79BW1tTahUNkAfwWbThCBDQ1aicViPY3BVJ+B8DIcMg+2hF71spaDg3VbtrT0BF9/O2BQKOxgk0mbn8UTCLtR/gXww3L4JPWtgcHBli2lLT1eLy49Ka2vaxl86XXv48O3Z2+fXA0I9Fn8fRcBgVqVkMi0jg6hpEw4cnt0urOTIJDHDRHSxABIm5WLErnyv8x1Q2M1aSQRHGPg3uqFEnDk2YOhwE5bnIDzRpgQEGzwrr2aztFOW+f0yWbhgDcIcBYKSzZ2duaNdX9Okh+7W7smZWcjweCAGBPLQMA3cPP6FFGBl7vXZW47AAw8cmTxK4vfeuvy4kN8aVJxXtIvnqvA/9Lz4l/bb/751q0+bWPlEsxuXB67+skEY/F6dJLGgsVTR48eTRGVixMTMfexbtVKDP4NLUmmQnBJZuahmh1Xa8isBFyHmYVBs87peARwHoAxF2yiZYAM4ydTmzwLkyAEgDQACIfPW3r1Wk0GTZ7y+RUZY19+CWpQAwDkCJi3NJULBR5PLzf65G2LDIsUrM4uqGvZPegOuKyTk9+3zzyY+XDfrZmBQEvIFXbbAwFarGt2ewkBZZNOp2zTtRt5xTn8igpy5XRwL5wCrEUTLF26OmX58vWbNpXInM7Je/cQf5Nlqmhk5tafvzkDhriszBfePchgmLEnTFrrXO5wy2AAiGtQGMz1cpOF9YjUWpUNV+4Suy/EXA8vrVJ4cW3IWpUyeU8VncPzuLfxvKB0nGdTNQIly1tKmad3ztvNFg+O8wP3W1VOQn/qdirxiNttB/QB/HpV//ZRkx8WnGcg+GxZtCkOQIATzsnCMCAr2JFF7gdgg0XlorKyMhOWIJLMsbXpdJPT4YC/4RI0OV1hOu8lGCYDBrF1JmgJuEiiREAUMYsFSW5unE2bwu56uweTRqWloZ6eQXinFSdGw78Qffxg3+3Z2ROoAn1sdAZVoEjZWbsHqLRTbBKZlKOjuExmuhNHiXOFA5R/HR2EgEVFiTHBl5mcn5GRWLQ3kyPg3iKuGobzvwsReJv8iIuZ4ypweJ6AJB1cPTI6Tdo2T4j8Qa+nDAR6aloaL7emeZbIv/rTDt9ZeEK0hHQ7ijPyK5pnhze8cYCsUB+agqtpKDnz0IEDJBJ4BFTgR1OLE2vy8q5de54N+a88L/61s3T3zTl/n224IwueGJ92zE4/vXq+youjpCQpRwuam5vHsqvUPJL7XUm8L6f+cA548tLz1wppFWB1AYi0/RoeCQG2P2uBYwQ0Uf6hAmRRBEoknAXWkmEjKIqAgHpAYC1Pn32jGPHHx1cgYFpaBjC2G2OBGj4vpzYnNxf7gykCyyWytjbDokUKhjG04lQ7c8DlmDj3jx/3zUWxtOxxNCwIo+xwhcJN4INBlxETHJGNj1tdhvKcmhou9YtXDpbUEgBWEgWIAEQbnLJaqpQ3Oe7dQwC+eUnO+KMPH3x2N9Q16WPOenSuejPLhgX1Zldrfb3THggPgoqxgCe3C1pbfUqRSNWoVvKlSvI/RakLVxeKziyeJ5iXqHZ6grgtDYzgmeCMr7TUqPaI4AFRbKkLS65dlRhcAR0oM0lVWTmn/lT0BaGH9GvnENhLMdj7Ixqq6VusPmaBFox1BoueqYkGAvrI1GjQgKQeMOgJ6fDx4AEBUxsb0tNJ3SBOUyjTiuTmJuxps4PYRVNrpj3ag6F6PJgUPhN2OckupnqzggEA4voV0tSC59hBEM31TbhGGPdANbWaXSSt33Lm5tzjx4f3zc6eBAR+YpT7Z2Yuog9WSnlIrZFatUQrHhXjQkE6SXIkTsCYVkO5Fl8Ucmhd91h+4qG4C47lQZ5VgLc5/M3Cm01qWxAKpADsIBKwshPFp62Z/xTlH+rziRKlNC25oHn2OpF/pyeZs6TTqMn4wZ373d3NJz/fQAoAF68BFTi1krRSEQTipqU1U+CDNydszSveqn++N+S/6rz415aAs7U+7JFWzM4+gTtUx/D169fbH127OqGzuBGB0u7umu6h/EatsgB37CL8OPzBN6+ouORGwcpMEmfBqPOeO3fG+LbpeQesHdDGg4CeAcCfh/EwpBCavPp1iEQUgASAyvXiFOFSogBra1efv1bDyyH44xMCVoBAA6P9ZQ0QkAQCc2pzsSowBRiYrpO3tS1qU7AenQKb+etbXc5LE0+//vji3TPem3fhBMMtoZALLs9wKIBNqOGABXfP+pnx8Xsyh0suxHV2WUQ3dMRDgCQNTOQouGCp1NZpCjjP3bv3zjuTk5fevFRmknvn7pqdjnP9umCP37PoDy+5DU6nw/X2HzCfSccfh1nW2drUddqnVCkb1SbWpFLSZI+UFntrcKBnYlrRiD/cUorLOMjSo1BU3lpqloNfVoXqQm6L7sLVKiCRQlLWX4Vdgxz+etHztisJApWEeRz06E9K1b921KqF+IuFA2ldYAyBeDnLZFhfpLCiBkQCtkQCFpumFjsEMRII3hf+bBnBX7rKf7cnDGLX6Vz7UjgAjwIOD8OJXmazqwkHH7SEnF1NOArQpWDwieX39oQwsQ30O3s2EulpqW912u1rSQ1Nvd3+0uuLDBSBuIDgwYfXZ2ebT9z54vwEIvAsIlAl1BBs8S6Y1L3i3kcYirORLnINmRGzgIAxC0xf13V3FyRzBNy7kIBx/NGDP5NfxxDYMbxAA+7tGOk9PDr69YnmE2qUf/CAVaWLO3O3jjV//uTJd5+dqT99yXcWY8Gl9U3Wqhv3wfJmNO85+imdmr9m8ZrtU9unplaBithG08FHXtmMCFxTWJMDbv45Av9Lzm8M4Z5XFzmt5dfGNLP79l3Hovrr17+98cG17PP9RrnbwsoZUfGnU9vXrNjarhImb1+ybiXJ/RL5dyht+aa8dSuLsNcSty8gMHLuFBdzCnDeA5toEsREOn8ZrgIGnvp+7NUw4eWmjU1bEnIWeOmNq8U8GtXJ4dfkZNTkIAH5Ffu7v7zfjfngDB4/B31wbnFeXqqWkSsw+8F4TIwh4La7nM6uS+e//oeHF70tpQFzayjU6grXC3Az2WAIB9kbFCxuZmMZljEen6iq0tkNJl5RNYc+ejCZWMHjAIi7imvFrEvx/fcEgAbHpUtlKpEnGHZaZZIB7+CgF+72gwHWalW4Q4NhszmMY+tbnS5XU5Oz63SrVYn+02SxMFqxkPKvljS0agCABYVpntfDpRR/AhxDEIoyTaX2KrW6KhQi+00+uWq02F0GxiSik/nQ/FLg4Y/kqGLSTwmM7SUvcAgIlT9i4UIIcid9Hn9kdLTEyBFQQQgoKN3SY3U1ariHQy9dvbwRQ4HlpBixMfrNzaDb7cQdxwG40QAJnfCXQAwHXgrYwfrCR7qamgQC4J8bk/TBMPyWXYH880eI/HMa3D3hsNvehO+FB3ssFoMTN77svgsi8MG+67PDI2N3vvhkXB6dmfFjvlUpxQzw8FFpObxPjXDntG0EZ6mhBpyP1y1YFEcQmNzdnR8LA8YAGCMgij8KPwpBikBbXAXGADg8Mgr86zxxUqz1whejNRmrNnXato6B/d334Xd/DraetiLkyRRrx/hxBOD9y937j376xht7iQZcvGbNihXbp1YAAg9t+z3ZKPfKK1MfvTW1ZlUh3O6b/8cvn4cC/7PPC39lF4A3cRuz74ylDQ8/Gr09O1xdkJNTc+1q8W1VmbFKQnYL6dTVf/PK9s2JQq2It3kVwG8dDf7tSkq/OrQqmQyLrqYABMFkk167mqrkksDaPlOfllOAJhPdiO7x69D1+An/8GhFDVoTXtWNSmUKBWBe6tViUgYIP2TU4MnIgFc+vAACh5ILKjAQyEeDXFubI5a0tbVZQU0AYhm3hWENDod18vw/PHzwGKvOQPCdPm2196xdGwiEAC5hsjvyGIMrwFm5XIZ7100eNsCqX6sm7aQd3FjXykqSb+Eu+dpardtQdf777yfffPOeMWBQWMsALSKF0+Hz+Afrw8fmbu6uGwyCrISn/aALt9e1NjlBCnXBpz/dqsBGMpFWwuBceXDVtNtZo6nAroW0xGWlLSD/WmjfLy4/ckclzlKzTGUShPB7oKsquVrFuu12hYfAL+53lUA+fOPeURLq4RveTuKH/uLfQOBPI4FwQZN0M06b4QgIErDOfbpKo4/FaLFFZkdDg1rdoBZp1QM3g+Bpwy4sagahB/9xlwG72OyAsh6XyxUCU+usFxhwZ6nfbzHgvFMEIMi/ubu7S7FgBltnQm4FmaxPIoiAwC6CwJufzQECZ2dnNQSB/uhjrDjWqpX6PXuaNUcrU8tMKnEvInB6mizVAgJ2dFTGCVi0EIF4CjMyEmM2OC4BR4ZH4uRbcAgE9Z0LE8I7O2yjIDlHhSdtKg9p/ZDcO5/dqd+ac3L2OpY+uyY/mXiPyr/WLodv4oNrl4eGMPFRmFj9Bu0CwRFam9eQbUrJRWTKKnzwbwGBHw0tXlVYkVaheY7A/9zzwm98rvr60hCz7M797oTEytqlwlsPHnQU5IyN3ckZvt2bjgt0dBaLl2F02QUrhvbsOanUqvkrt68k6i+zpuRqzbpDmUVYZ1VNHDDpArF1doo3bmzg5mBp++L4ozkQLANkdET+MX4PLQo0qZfvIADckYqRsaTi1dnXamr1oP9yeMA+fgbHQEAgQBBUYMGSdQUV+wGHYIQ1Ui24X+sihRyeh/DlMh64vMbvTXz8Dxfn7sI19fZg2OKzWplAy5lwSzhEOmqxIIPIP9wgjDNqPNHoXCTgZsVkECZHP+A5P86/Wp6QMehE6d9/f25y0uhhQ6yHZcpAtKp92KplNr96F57uW3BWIBmV5bL6Jru6kH+I39bWUgPFTLnWhNV9QpJdQV+P+3rSsqqZLS2xjR946gIWhcdkBWLowmHkH0iy8vQSSVvAYFWYqM4jkk9JqNcrhld44XDXqxQrY+8v4B99t/HHBHzGB8ckIFZDG43wSjYnGexmeOC2hLt8tXppnjSvmBPFwuWNjY2qRvh7A97g3M2bPaDhzCFzkxmo7yTrmgwtdS0gh0tDoT/AQ8GyiD+vRe6zBoCIBuAfmcoNoi9IGhPNBlDyjNwuII2NwYOAQMyG3P0GVOCH+65fH6YIjDyeIQgUKU/u2bMHvlury8pUvTQYiKmLkRiqqrl5pj8mYFFBdwbNjVQXPasAf3quAwFnNXERCH925NGjR7c7O0/UKgdA/sHDNfHJVal+69hWTH78+WZL6yXrxd6ZYEsd6TOXVS27VpNMU79DqBfe2Lt3F0l8rFm8ePPUZsyHJFMEkqrAoctT2w/hesWs//E8Ifyfd37zawZu7E32qjt37hcmJlZqbCeU0buRYZ7t5Mk9WZXTo+KNVThkk2GDDIYCM7pPNu+RqrXirO0rgX8Fq89fG1qVidPwi7DclArAYQ0AcHRa3Hg+Xc3VQZMooInyL0Y8HTbDIQGpBjSZROIkpQoUYCoKwNUpV/MQO6j/aniEegsOH7m3P3lVchqfV8FP0yh1CsCftY0xqbVYKguXl/Xeu3dO/sPDYEso3DK4u67F4n+P8YZJaVkY+Od0sG1sm8GOIU7WYmHRkkcjc8GenoB7YHpndRZHv0qc4cyv5W3FjLRNxMhN7e1l/d+fOydng94Ayhhff4lWbrYb2wJr4fIl4f7SwZ4QWV0rM57zAf5Ot4bMOKuhzq0mNhMPdrmp9ZUku00BWKQPl4ZKtyw4LcBnk8nnrHfZQywZco8IPN/fZrc7rDotCe8B+IBsSD4x+UHMmV7AoVisxHbdnx5EIfzVRvqmVjX+SAXOm2BMOJOya7kMCOgCApbWNVmLQfkhAvGegKFAIf6javDOA5HgzZv4GA6GgYBNp7twmpWBVQjofGtBSODi5F/QzZokPrvZaWg7G43gUhanwRI8M1gHesmlYNEeGMjYxZYzQdLbfZqEAiOPHxAENo/duXpeBgiMRnDmsrD5KA4E3L/DpFWJR0EGTt+mCIwNS+3Y+RMfDAwqAh9ckFi0MA3yb/APD/4WDxEIf2zn8Ahv/7ffDttsUoz+DeDgg6sneGCcMPkB8o8kf+GRYANNOGTcWFaSklOwbtUUIHBoamolVmI4qiNGAAAgAElEQVTT7XEkFrgdDiJwXYyAR14BVA5tz4QrqiDtZ88Twv9J5zf9DHZ86jbdGbuM8m149taoaPKdd/lSZS844Wb9o85OZbpRpjOBacOJ5lpp4p49aYV6kUi66pU1uaeyu1eRcmhSARMDoKa21kaqAFXpZenqWAwQo3ye2CEIxPI/v85Px0ST7RVKPU9IU6Mp2ddya9FxwnMqJ4dALwctcA4RghlE9/H5BetWFuxPy+KJGOAfvHhEeDf29Pktjsl3vxj7/POHZ0OCtWtbWkq31J0J+r1n4B24pNauddmtPgXLgvc12AF+uOwRvqRIJAhPWbh8LX3De0n6FwsOQQDW5OTo9TlpnYxBBqq2XfuP3/eDW7Ycs7AWg3XiQr9bYFX3PvQHWnCqQlNTKwb+W5vgvm8sN1qdTaD+BKCA6ltaLCoOM/gTThTdUZ2FzX0UgNotdSHkXmlsGv2WFrdOYhzQOerBszMEgACl/v5+nz1gt1p1IqCckrO84H3FsaNE+C14/6ccRHbGzXCsNlA0nw7mRKCpCgCo4xCIBCRT+q1J+iRpUpK0mCaqsCQmRSxWkZY6T+TmzbuD4fDgYKil/jTuebO7nLSXpFTQEgpg6QuLyQ94PpmMVof1mD+CG+mbnIssRP4B/0hUkGHkhia69g8RqMAZZ4DAOfTB16/Dk3Psyy/G5X5AoBf4oxLu+fRoR2IirxwTwsQHI7CGh+OzAn8aCcSTmZBfsz8xZoGpAPwx+KYXEhBrYkD/jdj4CUNLMhN5Si75a5xYPsIDmzIL/Pvtzd0g/94jYyYFjolxnxX4tz4vo3DdqhVAwCVTUytWrAQCfrqXrFEnq9W3L94+BQhcF/PB/+uVNVP3AYFFZLLhL59nQ/4Tzs//ijRVycqujt0vwGXRw7MPHqtK3v3hTo20fQYXa5zMzZWClz0+bpQgAjEMJdJXJyYPZQlVquLsjdfWrViCo2DWJRdxKWBSM1LLm6aTsHpF5VVlIiIBEX+xTmAdHQwNNpgh81HxFyZciiRSifm1QgBgamqS3qanAKzJwagfCf+hAY7bYGRgRcG6dQWNMl8bHFZnUqo8gL/HXsXkva/uHP18diZ67O21cFXV001GQSwyo+8ePPYe1neAAVYYAH5n/ZagF76iYHjt2jAg0G1p15A9snyMMiKDeXxbHyuvQv7N9PV7GK8fXbZBwbCer3s9FpOy9+FMFCQStvdj5K+JrpaTO51ODP+11teFA2EOgJSAjSqRh7XoUtOyKisq9lfATxZ0mBz9YpNI4eqSSEy+pnqBXaeT0DUfpqpzPlyqYbD6JKoFvFtIwGfeQfyJ/zUtGENgw0/TIaTPg+5LopvjZAw2ceCMVHsqDwiIHjhXz4lAKe0NwcaUKPjZwVA4fPcmJkFPd5EE8ha487Ts7mFR/rFer9vscgcsA5732o55I3c5+dcD8g8rJ7EsBqtDGYXBye2jBwSyVpx0W7cbjTAicHiYDypwAhBIhg+I1PqsxMSE5MKk9CoRiQRSYg3HZgV2xHZ7xNjHWeLMhJqaAtIOl9Wh4fg3Eiff9O1pODEGEgIO12LZX03+0NBUQQrgzwvPXaPxVOqjET6f1L4Q+Sc76+V2zFjTU0rKLyxL1VckZq7aHj+4QRh88BucCgQduH0zIJCUxBw4kLh1F4YC37o/taoIzEjW81Dgf/h58dfL4MqC2/sHY935BH/D++buyrOz74xl5BSrI7hjd/bkydylwk7h+olxY5WElMSwuvWF21euWpNWLivPPUCyIUV0FD7u3+KKRkbiq5DatVVVuJsCrtoBEx39jMDTEer5Y+97JEQA4ngRpb5Aunx9ijTGPx4/h0t8ZBAI0jhgnID8/TUN8jacy8KYVMI+nMcSZa33fvjy6IbZ6+iPcBwViLHW1vpQC+6YNGOdWenuuzf9Z9+TkTVCIGzcbBRccxCZtnbt2pd6gjd7AqwQh2ruJ+gFDcoXexTGklPt7YcHotiQ6ge9aLBa5X3RSCT62Ps6q1XN9FUZDeZQKKAA1ee0ygB/LnPbuXfefBP4J2gZDLgDDEEOTtSj+W6yX02fVZlWWZFWpFyLpcaluO9XQBGI+zh6PHAX0UqsTa12BmcmIgFFZUYf7hVyORw+iegZ9P3bh2DyGQo2wosK44GNauKDG4kKVKcvJGA/JockHrI7k+EkYHg5X6/PzdMX014dGglcKhTjoCx1Gft2T7AnHH7p7u8+240PPdwJmkqRf/CYYz7NG+yBr9wdCLsHBuDBu4t/yH6QW8mHMxYVdNI/HUlIymBw3QEO+ybZkDM35+aID74ynDF254t71sjjPvDBAx72+KHCwsKitPVlnnZEICHWtyPzadsObtNbLBjICcJ1GAqkClATV4CUezEE3n60QAUO16qXFed3D13OEZFBQwMeHHzw6NHWkyD/vvvzTUHrJVr6TJK/Vp+sPE+/fKPSlpaYuXL7ZrI+E/dnbiYI3EuNMF0pMrV9atXKJSsObNufx9tGffD9yysOFcGXvud5KPA/9vz8V9qy8jKJsaS4u/sogAueJdcf29/8JClvbCxjf84Ow266WOPkieIkaWfnpolxDAWSpIEpadXf5EjkIqVIWLAZ66AXGmA6OwX4J+aqYERliECSBTbRTjgdeaHFgCQU6OGkjUikUvWKU8a6a6R0FgzJkdbwa5B/+ys4CIIN5gBYk1GwXy1rA+/rk+tEnSpPZODhjN96790fujdcuX5r5jFcXi2lrae77Lizw1xaCmYs8LrB3kQvo+hZoxEQiAW5btpkCghk3W+/Ggx+9tk3PQFPZ3VBBv2kBTYTq9NuBP61sz3BYBCe9Ra7dXLCaNTOPEDjPNgSYvoazl/QKpoEYVYO1g4eLkuTnfn43T/96c1WcH+7QVzCY0Zk1zwBcbkQK+JVY/mhB5e+AfsE9KBnFOA0+qiopFwrkjiaXHIJt+pNJCqTWQ3hcNhldyhkJrW4U/gT4I0u/EUq9xZzxOs5BYgQJHHAeBgwPiwrXVROooD9Ek4GEiCBBNxiVlZgeBbpx4nAYvh2JQmFwtWNOnu4DcwfPCQH5373zSBGAnB/QB26V78b+dcTCtsDAfDIbk+U1L60OhVkbiK4X7PTENN/eG9k2kB0OumAH7qKtIurCiShwNkre7rv38GE8Eyfn7U3WQ/tSUs7WsmryZaYVFigQjXbt7FkSNwHEwZ+Gk+KZCYX5O/PiuVACPs42Tf9ExGI/2LzyY1Vy3IyUk1sEIzAWZ0xXfzoUe7Jk7Ho36X3zkaI/GvqcpAdC+WpNTVJeZWJh3bt2ryZ7E9avIZsEF4JVw8gkJS/ECOMhYGbE64VZ3GhwMVTH12+vOQQJuXSfvZ8WOB/2Pn5r5VqdUN6VVlKd34BidsNj4z2yd/54U4uqJ38An6q73Q9ReBJ4oM7U5ZNGOEawAgOy6Rvksk3TiUWi9TCzJWZ65JjNdC4DJi0jXV2ijkFKOpDG1xFC6FNIPU4+mEdjF+HnXCxAKCWLhzLzk7R5+fX0kJorP/j1F9cAmZQCwwQzM9fXdbW9l5bm09mUqL8m5mJyieJ/Lty/UPQf3fx8uqyL3K/HQ4onE1NDkMg/LablpZhRP1sfz/GtrAnCyenerCY1cO++mrws9/97rOg26LlFe6HT5xfoWYUEnUD+N8BWpsRjXod1on0KmOVqG+Odv2WCtzyiQsiv8FststB/Unk9iYnM/DH7wGA9S27B8NrXQoRWlExJSCteRTjzD8Lo67MyrJZcOsRJqjNLjhmM1nIsQWn0fepl21SqmUOl0EGCOwjwQJ1mUxhD4eQgQa5TKsC/BDU/ZiEQnGKGH9LSF4QgTQ5gmcHZaAKk7jzuZB4cxyVgKYqkwTn1aAIJCa41NyYholxYGAu5R+tEJfqk8rkdrtEKfIcO+Z3v+qd+93NEPZ9YO9bXRhvM6zf0hNqCgQCuCfF7Q0OktLnmPyj0w45+YdxEgYQ2Gawx5Y/9wSPKRxd8VDgh/tmnwxXdo998e64329xOi5NvgJPwsSjmor8nBKTtpeEAgkCnynfixfFxJvj4CQX7E/jciBE+I0S6o2Sl2kOiaMUgJ0nP2/ek1S+bL0Hb5gekH/LRoF/J2jnm6C1y/e+nzwj6Ji1qvL0CyUl2bkFhYmZZIA0akCyQhMQuJ1DIBcKXIN7RXaNXbuzbu/vf7+NSwh/9NZlsoIxMbHiOQL/Y84Lv/gVxoREZRtrLheQVWXDcKPrLZu4OnZSX8vPL0yslJ6fPE0QSEKBW4uLbZ0px8dlEqxgY1mdXKb/26GhoYTVWhHvUCbu25oXgEQBds4rQHTAdE8tFkGb0O+SHDB5oqMLxo+bcKwxEKFxRzZYKXFtYdpWaYx/Cw+Hv+6MsYyM/JoSedu593w+mU5t6434+w4/YCbvffXl5X++8mTf4cfRm0T+ORR4nbUEQJU5fIoQXcUNCKzHzUmPL1583+hTsJagFxAYiXowpKPzeueAgP/yfy0uS7smf3+azaSQpTeIwM+z5lK6hz3g9PUrlVXG/r4ZL+Y36rH5P+TSecKhOoHZZdBJDObTl067LO9N/ulPpwF/4bDd2Cgmc24wWsbF2gCBqYBAi1snzGoPC+q2kN0XWKFoN8zP4asLDoiLx67lbZKBPpJRrSxq7+0V6RQurJoOu8Bm6sqBgZ3PoE5MmSgUks8qJO/AS2rcCa+PeWG0wY1ohKkSBAKW0KLoclNZVX8/6EBSFc2ZYHNqFqnAJAykByVgLd8UDisaper0cpNpYxV7LDJ3E80wQDDUcpdVGAysF5yvC+Sf2emqF7gt4dL6006Dl46NaKXRP1qRhKbAQ30w00ZWkXKbT+nGF+zbJKHAJ1eGj3Z3X7U2OScvdV36mzV6UePWrLSMwgM8kSeGwDgDYyqQILCITEiYH4mwLiFNQ5MghHz0B0ymjB5G9tGPwb8F+AMAasRabqWNMV346FEe4O/Wd999s7v+tFUGToLIP7pjpjy9ZNmpDz64kZu8csmhXZt3bT6whuwQxkMRuCTzEPpgGgn8X0N3vrh/ZFVy9c6Xf881h2xGBK4sSsSimJ89z4b8uw/grxOuCpW2IQm0HhALaz9He8XK7Kt5W/U2nqYyq2PYpmZ8+EzDHbuAwJyanNpO6fqJcZnRKLeQsrnGQszb52eLGvZnJlMFWElqYHgjNlSAhH9qyr8BrQk3Ng5grsNE+eent3nyZCeNpFpRQ0PDsh3LAc1YB7M/YT9ZCJLDr8mYZyD3XndNd0Z3d4qkzXfuvXNynVYsHvBHHx6OWu/98NXlN65ceXJrJhq9eaYOLy8MrreA+5XLgJRycymdGG2xO4kPBgT2G30yd2gw6FUYvBjeC7Ief2Tus9/+7nf/N2JwMcpKtVxedgr5NxAIrwVrStbHGftF4vaBgfa+AVZQ52qCazzU0lInAIEIug3n3bnsl948XToYNLx5KYxe1VcSG3SIVSNxBDaSWxEuF2LQASP/gHLkGOYJOBgdbR4bq8m5asSBqISAfe2IQBP2/IVCoBlxpr9J1NvZ2UlhR0DIgY/8Kv4ekYGpoLXJC1KwUbkDAKhubKR1gQ1Y1owmGABItmVyAPRIdHKDPSQwJGWlVaSlkU5EXm2cgjy9OxRwM+lGyXHVo3atCR9GklYfDJ+5+VuP1apQuANY+wzIXhQwh3vcoJHt3PcHeAFKluH4Rz9nLFjMtBmczqZ4KBCXP9e3xEKBgMBOnd0B59Klv1WBPWFUvMJVu3ZlJaV72kfj2ZDhkeF5BhINSDZkZnKDUYsOrSpKzOcjAKcXnlFyDk+TvDJIwNnZzz/HSjAtPE88feoBXX/j9COpdHr2+q0Hn91sOd3lw9JnrvbPZ+wvKy9Z1nDq1I1rxTn5yZmrMlH/HcH1wXSXOoYCt69YtfIQVxLzt4vHvrgz9bdr4NLK6tj5MhmUdeSVVwgCVyECs/jPE8L/zvPir/GbCfxbP9adn6ahhU+jvUrl06VJJ/Q2cq/UjEzPRDDiQnbsPsYdu3xAoE14fsIoM1aRfDBjWp0wlTw0lNNQnlKwLr4PnY4CJAIQECii/BsAApqq4G0gpgK52B/NgHBhLVFJCUoSMW0E4RUmVJABMPyMZ0UgIWBGYW66rO3cuXM+nUfV2e6PXLz12D/57g9fJm7AqX+Pwf7uLm3tcrQdpPKiySF73yjplzm4eFLw4CI7rs88881c9Oz7RoNZ0BL0eg1uP2ZDvHBnn5sDAv7LnNxu8Stkx4mWZcODuOtWAKrSZwTW9M5ggQ/DNrWaA0AgXN0IAq6uNBSwMAoX47t0qbXu5s2/sztB9bgMxhIlN+caEEhsMEUgiQSqtIwFbCERgGQ0Cjm4m5cScMugd6Z5z1hBwtgnRgazwVo6CFUpVpnk4EpDApBZLqfdITeWK4WdUmHsiIULTwq8CFM5I7ycvFIrrKKhwEYuE4IQRP5hFLCczHvhMKiTKQxhgWIrrkStoN3Y81XiFcJQncvldjO6gXYRDkjQRbCwCBhoufvN3PuT53z4PwqAJGwJWF59e/eg22BYdBCTBWgXnTH5p8OC7wHy+XSxuyQmhJvi3zp8YsL7Z+6iD75+vc/tssN/3dHl6LMEQMmznoaMNUUdiYVLTdr2+XxwfJpBDIEoAGOTAVcOJWd1ANZ5MQU4GnPAHAIxpDgN/EMBWKtEp+CPRk07ssWjj4TC6Vu3cOwpqf1Dv8HtmEH7m76sYdkHN67l1uQnJmauXLUSFOCRNaT4jxrhzdsRgSsP7SI2OOHOF5fXvAJonJq63J3WsZPzwTgsEAi4iris59mQf8954Rfi0U6bTSxqzO3uPqqp5fCHI1ienjih19MxkLXTvZEgDTqfbi3l1oyD9dRoUicmJnQSrJtjWNaUO/XpUEKmTSRamli0IAUyQnMgZHOECCNWA+QJDS5X6xmYLwaksUAdBSDgb9lGYsnEwpSlJAVSkYB1zgSB9OyP4687P5viT2ZSS+HpOHD7w+j4uz+89dEbV548AfzN3TyD7rft2MGe3Vj7ArdjXHgJYo9bGzLY4z1ISstIn/3Z95y4j7bHy9rdXkBgEDSun4jAfwEVeLwR+TdgR/EIBHReOvd+v1bUPgOUfTwX8VqsuLp27VqcfSIwGyxAAFMfa9b2n3M0AV9ffdVud4yXyAzysmyp7ZGUIhAjgSTpKqKRT7GSMQcEKABx5RuhAK7kIJNI60hJ4GC0t1mT9emuy19MGEnOSITDsFQq+Je0MrcZrTCBIBj9KpEShKCNOOKFh5pjIY0TpopBBFINiMHAOAGRzA1cSSDmQUCbk2EvHAHlCpdAnpNFdw7hjxU4pAKVIC9rqVlgNgcCwH+/Lr0BfHB6GeP1Bv0Bt9/rPzc5eQ++YQ5DIFQqcONtqS7s9QZjO6nsBjaGPy7XjWXzsWwIiMBYTQwi8FibgRRGo4Kf8bvsdmw77rJaLRaL1+t2B+y6pEOv7dz5cpHYZGrvjVcFLkTgwqLAzCVDQyQNXFkJ/5sRzgHHGIirvaiSnEX993mz0uQPBv3+qJ8xquBRFou/vvXgwWd34X7rYzj5R2ugytLTwf9uurG6eGtOWhr67V0rVqzajhqQKMA1i7dTHwwI3HVo24FtIP+IEcaPcgh8mUPgkc2Xh4a2ZyaizPjZcwT+v54Xf905PT3SqWpcDfKvQkNS/tOj2BCgfCqW5tXy4APTNh7PpmJbcMEkLcHffXcOfXBzxdaS9OWrz4/LZBJG4bawrKwkZygx6+gesVqtr6ZF0GQbEt0HrEKB00dqYAZIZ71Jq1abPLQcRkfrYWhwEAGYvmyjSrV+fWpqasrqJNJkoM8pWJe8H7veKhB9+QSA5L3CvDI5rqI8Z9SKO0V+f/uHj9l7X3351qcbrlzf9yAauXm3pf50l5WNRZfwdowT79PLZLjPkoTUEYHWeDakjezfho8pDCQUiN1xkbnf/va3/zLHiLCaxyTHtGydwOy4N3HhH//xgrpv7mZPD7Y9WNreU9jt2F3cKjCH3IzF7Ox/yLgu/HHiTcc33xx7NeD0HT+Vkl0uA03XiKPlbJwIVCppygGHIIpVbnNgSynp0EP+ka1sdAaLgCNgS090dERz9NNP71+dMJrI3BY1manVKxQ3loEOJAwMuZxOg0NmLGvEJRVSROACDHJuGAODqYSBYgJBsMGYD2kkrSHUAzc0kFwI7Qh5BoB2lwT3XqXRU0l2FJBTsb/EgNbfFQ4oJCBq1Ur4fuq8EU8gAJL63JtvTk4CAYGgcK/BjkGMpXLRP5B/cf6h/qOlo8R00+NhGDmGAuvr6+oGz9C9f6ScKWgJv21fZLc7rUYdI2fhSekOBMAIi2wvv7bz25c1DSZTL2kNmV4oAxcS8FBi4eUEEsPpqATzAzTn7G8nFwZEAvYS+zs7/HnzCTWRfxEvY0yHuzz+iZkHf76J0T8sfR6cXzFYfiE9HVcsJBXn7N+flkUCjrt2rVi1YvuaWB4EXfAriLvtIAS7r35x/wiZCEPTxFOXL9doOl7jjPCRNfDrqRVk3lLi896Q/6fzwi9+ZYNboVi9PjcjP4vi7/Yo8E/9FERI6tKtAK/R0U49r9nWqBDQHbvHMOhceubmZ49vzZ6QpG+tqMVQoFFnpD5Ynl1QdHTP5yeVWlVlIhKQ7AMm/KOrJ5B/A1gEaCIyUK3SDiD/8KntiRUA4lTh9AZMiu5YvxwAuFSaRAtseRUJ6worcAQWVYD793fv359RkLFeRvFnUneC/Osb/XDO9+5Xb30K8u/6hw+iQXS/px1W+nREd4XPR+RfSbmErM9sooPqgsfAB5MWq8jZ9wCBYCV7/KzDwGJBoJvV+XvAB3/jBwDOgMbAAVutp9+8V3Lhwh//+MeLkTMtLS1mQTgUPsuwBquzXhAgM9/DgtOXzn1stH9870/vyOciB19VVIk8ppTU1I06g1kutekpAYkIbFQRAIIIVHrC9jAIQLNBLufWfsjgS7UquL2UVARGZkZPnrzTffn+F59UaQk828mAUzS6KmAgbqNsIcUxmC2RiJRSClsaeSQemP7AJUMwEqjk0iG0KJCaYACgCAiYHteA2jgAGbldUVUTA2AWh8E0MqSnIksoAT9uDoQDFp36xAn4utQ+g8VvsXgYnUk2SQh4Dl00HXtaOkhr/5xAfTaGPwnOhdT2iSgByYJOTgcybaSCicuGHMO7V2nYguv9/uBytvV7vKxOJhs3wLfPi1v42kde+3Z457fFJR4RPh25ukA8GlIcTQm4Nyt3rJDU8WdVkz7OkVq+xtbZifjrnI8CwmUzOzw7PLxHaWKChH/yfpy/Ix69dWvm8Hd361q7rMew9q+US/72lwH+0k8tA/5txQWDWQhAskBk+4pVqzYfwGLAxVw6BLO/r0zVXL0zdGDXNtoIR8sCL1++n0EJSCZGrxm6fHnlSrLkLv+XzxH4//v8/FfTVP5Ja/ZnVXLqb/Sh6sKFp3gNLNVj+haulZwMvn6HzEnzbl54phEEfvPZWZO4uSIfPII0ewI3kjG0MFp49FMwBrPtptQKbhg+/KuY6FS1q3HlIndoVMdjUqu1HgQfKS3jrivwCqQEFzEM/FuaVExKYHAGan7ykkKQfVQC5sMpKEg1Kt4/9/25/rIGobDPG+39cE727ldfXkb3++GDx5G7u+sQfywJxpBkHNqR8pL04+klJWXzG4RLaTyJIHD33UjkPZ+jSSBwe3U+K0VgwNwU/PNvP4uIZg73WexmV8B1+tK97z/++OuvP754NhoED1fvdIbWvhQEvci22ZtcbnBfgtY3//TOvU989nf/9M4lNnLsbH+jljGppLyGQNheak/SY4k3YSARgSqKQLXI7bLUbRGEUAAi/7AJlxLQQG0wiQTWDQb7Hj794quvvrz/5RfnG8gcQFpOSGYLChtNckMgPIixSkAxDlo2ipRk5Ko0HhYUc8lgoThFKF6QEd6BuRCCQGQgne8SK4aZ14A6ndzAAACJ+8W941QEggrEgGBFWmWS0Q34c7kCL0me1opFJqPPgPt8TR4/I/P5fIDAe4BAF47FrxeQdcBN9gXRP5z3APdMwr8YASkCGZINsTqb5rMhBqfBAPz7O9cfAmcv+r0DfVX9qh3jcpyzexDcddCvf/nl4W8T9ekSEYexaQ6BMQLuLVqdfiMhM5MM882qxnVeQEDNfv5IZywZQhww/j0UjiT5wfr9XoVM1Nuuwvafx4/n7lqsl6xtfk7+dVl9MmM/ud+e+uDG0ryt2OpN+IfDk4CAK1ZgzA/BRwtfsPbllcJrV4c2/3/svX9Qk3e69//9nu8+X8/O7jNbtxWxLdTCQPxxhFZQwVodaIuJ+Z2QhgxJIcY0mjR3EhKJGPKra0odlsXSJcXpiRvMgzEUdYTuwGDJcR0GzqrbVeu4Sq0dHDu106Vul+6c1unuea7r+tx3wD3nec7z/LvbW2u7ri0hue/X5339el+bmpubWTXk4aXIwE3nT7z/9t5DL6FRFiJw6aZ/ff/8eZCszxYUPPtdQfj/7vr+DyV4rsl2lNj37m3k+z3hw703PT2tx9U8oLjswL+8mlWbSyvz5Z6+9k4aRU9QKrAlnZigOHjVqjq7vWgKVCB1BVo4zqgE/n18aVhqyCttQAD29sowNsNVPfQEpQQEoicgxMHSMElARZgHINws/HSYrgwD4DxlDbaXMQ/o+i0nntzMsn97AX+PVday6HdgQOPQhWOzN17jJo98+j5EvyD/5uc/x8GqEX8Xa63F6ArvR4VctLz2nXeWt4lw0QXujsulAruWUBwMCMTvM4CjwRAnhyJc0BnwcNk/fzjRDQCMRDif0zk5Nf3rX//63r35iUQCJ0xGtO6OjiTgBv641ef3xUH+vXX//utvfTvpf+stjzUUC8sdFov++Ge/DofQIcpaZW9iZVNGQGQPItDgSMcxAg5aMQCmg0FBXqSavxKBgMCz07ePfPvtpx99dHtKVNs/LKPhErWZtjUAACAASURBVMbAXqVkhzrMhYCA6D8fcruRgfJWnUSpXEAgz0HUgCVsVo4vBaMGxCAYr1aqgzDjBvbxUSEEO2Esit0NzL+rtHRLOa8CQaWX1pFvrcwSCsJpEcq40QXIMWCyxt3ZbNjtjplMUdwhgLlbiIPTmaC4peWB4gdzewD8wcHJfqFzk0cgikBhNgQ/unjQGnrojYd+6ftlJjERAf6l9MP9vRVmlQY0IHz+O10+Q+NzL730x10S42Cqnyq5iybkIAze07BDVHRgzbp161gbA7axnoRnw97YUAdPiJc9IhQ938XaIBY/EsBXbXSsTNcN58+9WUw3t3RGa1NZfvKNsn8C/0ryNlTWlRL/CmglMWhA+GvlipWPr2wmBUh/PbXy3SvvLn1xNeYCm5v52i/hEW1hNjccejRnkvDCiRMnVqx57NnHCr4bj/u/uf7xez+gnQl6Wc3u0tJGUGmg/m4M37tnMExjJgkekd4vMWDKK9y2aktpdXGtjTZMLrhx+Nt33vrwwy/uAgLrKhubrkyNqhQOJgItxuOXPv746ZMy4/Kmhmrvaa9OqmddgItFBOk/JgL1Rocg/oh/5MIpADCvkJyWaLUD5Zb2PnvixGYQgMC/Z5/codKoTp0C+Tc9rfWFYv2vTWhY9HvpqxtfwN14y9Uy0qflEslxXv5hNmYAbsj1Z+Bqa1XLzQICWXdtIuL2YZsZTmod6/L4rWiOoPL4AH9R/5Ls/FzCODycmshOxNxBq+Mz4N/s/K1xnLDDLGPC5epAf5m4WxvV+MQjr9+/f//iiP/OpGfSb/W5FbUihUmqO2oIZWirhoaGW+xkIMCQhCoQDgvOaaUSCI5BUFFITl6koJk8HlyaKxaGgwGB7mPf3Dly5M61y3nAQLN0uFci0/PrRIFqvb0StFnIZMbH0dgh4QYKakxGg8y7wEC+N5AVQ4QBOapAEUn1VA4mAAqfnpwvhAAATVquqaFRICAikABYytsmeqvtbYA3RGAEDrrBbDYRx+172GAU4TQ8Ac/Bm5WOo02sYIgvyD8Kf6WGFJ6dKSqhORbiYByP83gYAl1OX3ztL3/5y2BQjB/jxPz87Mxwtz3vzNQAEBBb8cTiOKd/6RcvvbSiVOdg43F4CQg89LSydnkprkcq2FrwJEpA1sh/shqiZIiGyRgVYiaQf9hEc0gpjSXcEP26rdH1EvLfnqVm0xY4b2PwbeaKv3C7qbH8AeHvBtqwhZuZqOWQ8AdCcOULLyACDy6l3r8frbvy0YkXH0YgvrBixcoDB/Ywc2gsB2/CVOCqhkM//gWPwKUvnHj/xIp1JFm/a4z+P72+B/JvBoSZTgkfSCMFqcM3kFHT0gtwm3XrZF8Of9nr9TbVVFW9C4TcXbhDLoSK2DfHWWx8V+D8DUTgqlX1jXlTozYTxMEJRKD+5d8dunTpZr+0rala0tpK/uy4q1HKNCD6K2EWEEcK8IdeT9ENHO94qyD+1FJDa1ubrkRWnFuIRBsxQVjsXbUZjr0tiL8NCq3qnE3hME7/yzffKFRWwO+d2z99/3cMf1T86OzzdOVaa/0evB0dcrVoeVl+/tX8sjaRmpaawzcXyKUCMZgaIQROnO2KIoMsIbiTJyf9XRfOJlxxU3c33OCAQGswdOHX97LJjg78Ov4uLjHuAiR1pNeuhVcSaO9D+QfvE6bgPD6r6kxVSWtrrUjNZZzY0eK0FVez0L66uomvhVAxROaAh5kygBzPP0COmXdjjlItxMmGg8ktKx3vik7iRqZo69dXbr/zb929vd5eVILM+gAZSAMmoWSGGJggJWgyYoNMLhnIA7CE/6HLXcJgCFZCQAGKmEs0HwRDHGoLxSWl1dX1OQTS9XJ9/cusIwZN/kVWsRhkWSx7NoafRcZndUey2UgixJnOCQiM+sgrUNB/KgWbh0yB9IPbBk5lnCKSUif9ggg0UUEYPjux0xdaEgT8OdnhMJ5MzL82293tVebLZAZFtK+z05l5Y6gj7du458c//uMf68sUg93YmvUa3xt9svHVkpJtaOOG7TAFbJipgXZaV+POE0LgDEZKR19Gr1+7wYTFjxinjcrR6ld/D9sAsPjR14XZ5o6M1g/yT2MzD8ix/CvamF9cZa/DzSSHyg+xegtIQHY93vzCphdWPrICo+CDa6ouv730RTYNvBTIuGKN0Bb4MMlArAeDCuTrwbg35P33z69chwQs+K4g/H9ygfyT9MIPnaxpd2lDdS/L7PbfM+D5msJ+Crg1hiVKb9OGym3vVq4q3VtXk1+LKyb9fdh91ZF083OYrnE2IFy3t+HkSe8ZJCC2xHAcp5Bc+uqrV155pVtqWF8mk9F+HuzTkKYMvIpg6o+vekj1ein+HdAE/5caHrLaVlwSWVJE/EMCVrI1cPX1e0uBfSdOPLauFOSf7ZzK5ujWff3NN3eAnyqrb/SjP/zh0iWIfrNzrPgBWEqyVtQARiOnBgbM8sOijSV5V4qvFFW0imirOSKQj4MJgUv8GPCP35qbOHtMpdEGAx6QcJMX/TEu5Iq7I5Zjp85ms4Nuny/eQ+KCZCZ1/BOYht5Ytj840uK8+NZFeJM6QqG41eeRF2748o9fftlm1oL8wwKvurqOxx9JpRwCZRKuXZsWBCCTQUYjvkgbRcG0mNLJqtAMgeK1Pg8C2u83r79y+9o1tV6GiQcdmb6w5j/4uKVhbn/8jbXJh0gHMiEIb+9RXgbizyJqh6FUoC4fRSD9RAayUjCpQDi+5LkQWAEhraR+wcWQLwQ3sj2luK4eZ+IUTsrTTUxEtD6xKwOBuCYBkQS3nwsPIALP3Tk3avPw+0BI/vH8o92otO+OVhhTLEzJwFwYHMY8ZBDC39Cyn8PB4EynIZLubE/HY9nZ2Xs37/bCvb1j6s7rfT5cyAI60Fz9ix//8cknKw2OFENg/2uY03u1qqqcGqIpOqVxdn6UiRh4GhGIXYFHXy59bN2zSjhQQP6hz24tKof+WUH+ebp6yPigJTCqhs9LMUD9Bu/ADae0s9VMh/h8I2pA+IFGwisP4GrMlSs3vXhwc96VdS9S4Zdi3tWbVqw4cKB5zx42C8w2h8DdT43R+wCCoBoBgefPP44O7AVbvisI/5fX937Qy/CnrK4H+ccndvu7U8YLeGsZiX/9sl6vvbpuL2ba4IZukuinB6hkGuhsD2YWRtE7aDTk41cP4c1RBHEwHMluQuDgzUsfvPLKa2aFVMfS+5igz1lsGnOVRKYkHIaSNiNWP3DaQCSV1pIArCiRSHgFaOcFIPAPALhq82Pnt8lBzp07p3B0e/WDprEjuEjJobFy/V9d+uCLeaH3pQuLH3w2hqJfs1x9+PA7JXlVGzbU5JXgCmEQgYTAhVQgPJuUCnSNgwjkfMGMFvBy8eKkRxvjnFxPvM8TPXYq7PZZwhZfBqjHZGZySEyrG9FgK9MO8BPD31pct64bLXGfaqO9sWDztj/WWOJBKw7QKorsTYL+Y0NkFAUDApW6YJ8WntS0VQiA6R3jCUjLybVW3lPPxYwCn3GJM1YPTj/4PaNTV69cuXqmtXv45oyXFCULholyxrM9y9Y+9MYbyYdCWBbRqOStkkUVEUlRERAQs4E61hbIRCASsLVNGAjBkRBAIH1uYYVKG5c1Un6ikTaI8vEv7idoJAIqmyo0Tn56N2kxedo7nRrbgEgD99DZsz2RmIMh8NyYLeoPWkFuW1SmnNUXpv7Yone29NOA00Qp2ropqEDFKWvAT/xbQr0/maCz3RfPYJidmoUA5bXX+vs/O3r5zqQffRnFLU6N7tE/PPrSk+u2yUEFsrt9+HRdUzVxCfG39cmtWxeGmfDCPQWnTx+qlg2//PLLW9ZUtprcbtR/Vs9YKyZ37t3je+39XQvNBlZFW4mUWhpE75SVFCrt1Q+sJUGxuXUd6j+IgXEsGHsAD1Rdfvcgjz/GQMwErlzZzM/BHWQdMecBgQW7HuXNAgGBJ94///jWXaRav5sN+d9e3/+hZLh3GJ4LyYbd9Y3em9TaCfRLXbhATEqlZvGegMDJ3siMOTeXNtTblfpa5ATco35PuwAJar7aef3zL7AxGntGvfmHeQQCAS2Dp4fD4VR/v1SqY6l5gYApKoQ4HkCgw9i2nuQfPmG10tbW9W07KpgbNAuB7ZXUA713L76kZx+rE6k0Kghnjal+ry4W6R42KnDCRK6C6Eo4jC/6tYuLH2jEYQb5B/y7mrdhW+Xu3RvyrtIGYRCBA2bGd4ZAEIH7+Tg44fN74vG4x38xatNoNVzc6vePWsKnunwehXEwG7YExZ0BbQ9NcIkx2YX/CTFGvxfhX8/Eb/3kc51ELSq02+2N5aUKXzqEe3CtarROIXsbQQI2sVWboLxN7R7sgYlrNTTlwQNQLucJiFEwv51cvIBAYGDQhwgEUE+OHs6/crXMOPvn1yBkgw+buaOCDlT2SrqN4UjioYeAgclQCHUgHlELCAQVWISpQBqO44dD2nR8IUQ4weCUUsvp4DJpQ3FdnZ19J3WNuM+kvhEBuBdUIM4HNxXLQ5m0sxPOhnRHKHvWFO0LqMyOlCPgRBeJLPrHD4yyMHgs6vNpTQv4wxE/7O1hGz/ZZaA8CmVFkYEK9FhE/j3x8yVx9ItwOePpOC5QwuGM+fk//enGvXv3Pjv+s3ev3bk40kKt2VqH8qUfP/nkI0/mSR3YYjjb7/XOoK9pOQlAUGW40iG304u/Tp7uPfq11GDfVVpiJhvXmNYTVfejPr03Twdu58J5S8lMk8MokRhAAa6vgE8V+XfyUMOhnzECUgNfwZNrEIHkioAEXHXmyomnMBXIJoGZCqQtIc0H+GoIK4dsIgRu3UMicB9tjzt/4hFq3yn4h+96Yv6XFxY/hodB/hUpK/c2NHpZV+dsCtTfBXSpHzSmursBgSAAUa+XYmIHexzqmspEarhsELx4+tgUkjCHuZ3i4BvHX12FCNw4pgIEkkuMW8Vx/a+8AgQ0SimXzmw2Gf6IgJhMh59GcjaWiyg7yOLf1ta2HWU6ki1KwQlmFc2AoCJ9bEuxQqNQqBTGbqkqm52IzH4waxmrhW8AJ3y1yxJoKgzyj5IxVPxg2T/Gv3feuVpcU7kbx7YEAh4GuA8oeInLV0N69qPETUNwCdIqHdfYTPA9aUMQDg8YYolYrKvrtxcuDM4abV1O5xNsgsHpiz/0RCjY7o/eoezf9o7r1yHuk8HLx4VvdTIuneakwe1Bc7FdWQXfVnUOgCQCvVh3apL4AhwKQB8JQMY/hkAs2AAC2W5erQ8LyeJfUS6QMfBXYmfgIl0jfVHFjoqrxtTc3OyNGZD8MkEG9sLXkBkcMUwJZlh7jEZlNsj43kCZpITNyOnyZflMAZbxADS0GWoNUvIHFAlJDIfGTQDkqzmMgSAFG+vqGvEfq5tKNGIQxHFaiZeGNyMMsu/CYDZr8VwMxJPX5+az6F8qZwgcG9OixY1g84UCENu7u/UL+DPkEsly3Amv0Ab66Dj4+RK23L4lmEmH4uJ0eig58fn1uc+vz9+795vf3L176NUrt9+62OeLh5a5OQuadgA+ni2Sh4GAwzP9M1jXAAKiAmQCcJdg6Uv9/I0nZ4Y/O35cKXJI2kwcy/55Bqi14d7s7Bzt8Fzca0rlKwhs7HXFFW3Ye0S7iQUDBlwxQwAseHIdrdImAK67MvUuwY8AmBOCNCG3YsXjzc1C2o+EIRAPXugeHosYCGMcTLvIvhuP+19cKP+w+FFStWH33kbvzOnTw/2z3bOpC8YLxhR2GFDPPQrAXm81nealDVvwJqirqag9XCvXaNVyppMwFUhDSNgS4xKm4+rqTp9WQhwMoSGuFnJw3PAHr/TDCSw1GmR8FMySSKwSrDbK1SzDZZTXUmCspmcd9d9GbIKWFLFxWQQgG4Hbu3fvlnWVco0JcIa0dkTjyWw2dVg1Ona0N6XRqgByNi7p6uzze3j518JaURF/ZpR/Z64WV23bjSmrOnsVRsFIQD4OjmKes3M7SwX2WAMBD7VqXPT1hCPumImL+/yTqsHuwVgikQiFjv32wuC/macHQ06EUEu7z5rpGEo7tQPfHLl/f6QFpwbnenoGm7DXr6nRHg6mg5ZeSdBaRoZRNWTv0JhDINYLAIB2dbs/TlNwGiyE5vinJkt6PhGowVqI1ccHwr/iyyEgA38lxpVziMCREb/GXKE7c80SG5x97eZpnNLSCcPASonMgB9SEhlI3TFmgw7kJ7ZGF1EqEB0S8vnO6DJ9m46fDG4FBopE+GpQAUJwTwBkVSo7360J7MNfSpEcrVY8TtLxeDrTQXNrWbSMzU4kONW5cx7fUHJufp62uU2dQwLeGRv1B7UOI8Mf+9ZJAbKF7zkRSB2lcrXa4gtMTmJ3pG+JL5MWo99gEGibBqXnErvb0+M7OxLzWKnDubVXPzoCf5YW/1kUskO/ePSll9Zt1ikccF8CAE/TviQMfbEMvIsHIC8CG04P3zt6/PjJrdVSODsiJP+w94/4B/JvvKMl4O+JJMZdgvwj/unz2/TKOrukF12jTzYKFlwNP8NcAWgLkJuoAJsBgKsPVq6/uuXgQTQIZOXgnAikWbhNK0gF7hMCYYAiqMAnC3YxBK6G33sBt4uwV/5dQfg/ub7/334gQXcQWVFVZV29nXf36QfkAQBR/g0S/zA1PNx7mk4sWgsOt0D9huKrZxQajejKFZGNR6DgSklx8K0PIQ4+/mrdKhCBJZgKtFgsEYiDOQc6Ad67123EUSgkoJACJACq1TgRjP9UKzXy62SZ/msry4cAmGrASIomssKqL927d/OWzRUKjcMxYMTu2HAsYtG4tXeOXJs6m+0fdpwFSQmXwuP3aUn+tTwg/9SH0YqoGPhPKfv6arsyr6hkBxOBhEDsNhYG7TNBH/bqToJUSUQS+88OWqweq+32kTFTDC1+hzrEvlMX5LbfZmPWgJhue23a5Yqb+n/9zbf373d2XP/8w4n9b4SkdY24lVHPpTNWX2gwFQbSKAsLq5iureaHZ0kDAgLtSk0fE4AYnRIAc6EnhcGLRCAikMqe7OIZuF1MC4hG2kfaITg3GXVXx0wTWcfsazMzvP+fUBfROyzuBMT3oVBIq9HQvJyEjYYUFWEeEONgGSlAkoCsFEIvhQ2EGMOZDBeKS+pyPlj2BVHbCO+uzuRDvxwx5QbYm5q4dSs5kU3uDJkcJlW0z5lJzM0PxmKDg9qAf3Lyzp07o1qf1cIfizn+GWjnsZ6WfxqYDgRtaNQE/ZN3Jj0eOAxCOPKC+0bWro1nxE4cQbH624G+49cn5v70yleIwJ9tvnxkUtMDwQlnCUslLz366NZ1B9QKx2A39jYDnsp3UQkY+Vewi5laIgDLG7/Wf3381erG8qpWB7ljcNrRAb0OXhrIP5w1EncGsPjBp1vQx8YUDhvbcDeeXlJdavcKDlx4IVKxUbJ0Cwbca6gMcrD8yuV3N63et2nfaoIZ8W9RHLyadQUeONDM98RgzyAiEAi4R2gLhMD4/OPr6IV/Vw35D9f3ftArmcF7W7ltd0OdF3tf+mf7+2Xd0kFa0cbjL4UNUr29tJ+2saGBHYKlq949o9KazxyWT92+PKZaaInJTcfxRlmv7sWR4qIxFW7VxWqI220cHgYN2A8IfACAUl4GEvhQU8gxscT0X1sbzqKWyIokeYWFyqqqmm1NldW4/hd7n6scnAkkQqq/O4UevOFBxeiRTz756GczgxPZ2WzMohaZ5aLDKl96ofjB8IfqD+VfYY29GrUtcL2xsakJEFixAwlICBxQqIQBYXHAGqXiRx9uSk5MxNxalYkLv/zx0QF3gsU6251WlerY2Yi/zx9wBjU2rdjJzX5w8zMA4Ou3Pv/JRM+SJcFMxqRsaLADK0IcPOYWSaNOL5Ow+WammBqZDrRX4z6NRkPAE2JTcCpeAGL9E65p5A7WQqghhhBoxVQgywU+AMFnXGKkIHr/d4qDkfnhiuVjmphp/jU0ssP2PtYg4/X2thlxEWg8ibGwRqXAJmm0iAEAIitLKAlYRj9YQzQrBYukajq43B1xUzwuqadNIDkI8hnBam+TRYwrgTvb42lnKESDa2IQZ+lEJL49Hg5HekznLo4E44m5L2bdwUBL3yQR8M6ox6cN071BIbCUCIjkIxmIO5uwJKLXD1oDnlEU6Lh4PhOPW1EJBtPpTMYZX5Z5KBmy+NkW9fFbc+/duIFx8B9OfHQHZ0MiQDGcjtuzZ099o1caTg1jJ0xDOa8AmYziJWB5uV3/Nci/xtJ6mYKtSuA8o23oGXKP5B82m7JJc+bjRSbWYYdxh8iB1hYy2emG8pz/1smTVFWh5afPQgiMAyEgAN+duvz+QUoE7gO9x2LgpQ9crBzS3LynmbXEUCCMq5MKcKEcHwkTAtkr3/JdKnDxBdGvpBfLH8oNlfWN9l4yKJjFPeXTBim2JPP4I/030+u1nwbJjvyjm2BrqVxr24glU/nhyx9dBp0U5VuHc5ZsLA6+cRezQHlTy99RWWK0YxdUoFQmIzMs7HYRtAz+5LdNqNUUUqEcxCMfRAZEXAjAoqK8PGVhVc2Gpkoqgewt3fxs3Q4ywEv1pyLXMYEeDtvufPvJ+U0/O/nBjSxar3f4FCI1AE+lDeYGf7H2K2f8y8+r2kD821LOlhbbm5SFRfk71pMIPAwi0GzDxuh2CJwv+v1+gKHVBzExljC1CofFajp56W5/DNRGZwsoG3jafMcmMp0jfX5cgRR0z773wd27qABHf/JhZP/Pu86d02YybqMUOzUUA2cHZXUH1pQr9W0yIbPZSGkzQiCl0Ro0IxrsgREE4EIPCDs7KPOFBMS9bOQTKCDwV7g+JIfAZ7DkCfFwu7OzxRm/NTc/K9uoVnCx+dnhmzMyHb8nCbN+eiPmbEPJZaADoyADJTSUQg0xVAvJ1y0AkCaDsRCsRgKaEkmLyelmChC3tij5v3vxO7MrD52Drw+qLDSEJeCQL9jZ6RQHAk5fKL72oVgslIg5bNFJvz95PYINfAhAus5FrSACpWwfHRCQ1X8RfvgL04K67pjPTwLdE9WGQMZarW6rLx5fEnSmxRAFwwEVj3Fsf2ZHxzjNLd29dOnHzb/H1UnZcAT3BfY3PLfnF3v+cEhpHOzHgTisgtBSa/j5GPxgx78E5N/x0w31eSJTJOGOhS3aUbVuWLeDev8it3a2tPex3heXMMlnMpmMrVgBluJmYgi0Th8qpwiY+Een3qq9paVEW/REeDZ/6t3H9wH+4C8UgatJBjINiKh7OEdAnA3Zg3qPCMirwDVbkYrMI2ETxMFoyg4A/4fvZkOEC4sfErTlU1Yh/9Chb/gG1n6NF3CvInYlpwaFBCD+SS+FwLwALCgoUWlrK7FggJSYunxZbRNcBChZxlEqsIN5BZ6szp8qqZZM2VQWjvItnNWkl5EfqtEh5Z9jtVrAn1RdWysS4QNFJBRh/wsb5SopKs4rzKtS1mzYUFmJRYvSLVvy5BakQne3IwgneyJ7Iay58+lPTzz3/KW76PqX2Il7ZDmzfMCmstm0Tid24i8Uf89cvZJXBdF0PaZfFvy6lJLikrL1i1OBKqsz4AHx1xcIBOOhJzLB9k5nOmgyGm1a081X3oOY14n7zdHLziXOXN8JAFzCxUIB7WuvvHL37mcAwLf+MhfZ79O4o9FR91A6non7nNv9xyxKDKjWHNgrARGoBFQQ/+qYJmCBoyTgd5ORFghABQnAbpYB4wNhrIUI5WBQgX8lA13b/xMGogt9Gu3yZl/TTalisfn+/pkcA6nyAbEwMRBjYayIFFG+EB1iKAxmEpCvhLSSOSAeWQARi8nitMjqcuoPR5uVDIHVSovjHG7B87uH8KQcSobiwbXpILxad4iyJ/GhxGDYhj3QZJXvCkxO+oMe7OiOdnW5ubBRQCDxHxGoX+CflPNZIfaNeiaJfyBgQ3GrG95oa1DcEswM7XQ9k8k5Rnd0JOfmv/jgKyDgo3se+f21UVN2EI/PwZSsYc/WXbue/pls0NB7aFd5AXlD565dQERvv/7o8buvNuzWhWPuRMwS03hG18uG4f3j5V/niKeLd/FvD5KNa9gEr92hwM9OTw4xGGAfYvFvYzXpY5qIYwA8sHXb5ctv72sWrk2gAjehJQJTgQ8jAoWCCEPggeZmfjYEi8Tnzz/yyBqIjfcJZoH4G/TqH/uuMZpd3/8BHkPD8Mxt21bf4KXWZ1b7xZHcsEJhNqYW8n8yiIC93oUIuHmv2Wfb3bChMK+EECg3Qxwsz6UCt2NLDEdGWR23Ppz/4p60trKBUoFRjYVEoMbtVuhK9IbpaTgUpThUVSuqFfAnwqQSAhDb5WtFra0GeMyIf7LiPAQg8G9bJe6C21u+rVZjU8sd0v6UO43+ITsnYtGxoqeffvqrr766MZsYSqaZGX2GA/yZ1bVmq9OqUA/Imfxj2T97dR2vbA+RYRfuLAEEluSXrefjYLnaFmj3U/Kvr13sAvmQ2B/3BwLa8GDK+NsLN16bzXJutKkPxjMurH6kx8Xt/mPhVIS7+cEHd3/z62+OfHtkLLY/HfRpFRatJhsTPxMEObrdJz1UXo+VpcceX9mIjZhMAcIPZCABsLHB3BfNkBHqYgGoX9xFxBDIcoFMBzIEolXWr/4qFH4GW3/RIzqTTg/t3Hlr7s9/ull2eBQe/ddu9go9glQa0RkRgsueeCju09oM5BOYz6Lg3EX9gKgBpayVHQiiCIcyJlm9MNHMmhnh8nq99iYH56dd6OTcB29Txpnp6HhjP8dFki7XzmTiCXEa/gsDqqAziAAUBzXujBip5lmyZMl+ODoHU8wagi1O5lUg+d3IHKH4smUh/LMaDvDnBnz7tJw7DkLb1x5k+QnXUILP0NDqpPn59z746itA4C/W/P72qCmFK4TD4VRv+YE1v/vdHw7pHfq6rUIn4DochsNA+FCv4etXj7/6cikcveiKFuY8k2rZsET2jyE8rwAAIABJREFU9WfY/IJL7PxC63Mnv8TEYnIYjCaFEWcK9PxOTpy223Xo5Gl4p1Aev1rPAAiCc09D2dS2fUQ1JgGbV2/atI/tCmENMQg6HoE4DEdx8HPCeBzrCwQEsgWaxEAIjB/B0ZBdBU9+VxAm2ytsd5FIqpq21YH8g4+DNT6D/GO1D4fCNiBl8o8B0OtlAhBIUVDQplUVbW2otm+oKSzi++bGLl++PLYwPbHYKGsuO3v37vHq6tOne9ePjXIcIhCzzoodbdIBo9RoliPkUEbg4yxqbcOqokhEv4hqMf9H/NPpJEXFWCqoqdnGlqGXluYrVAq1HO6qcDyzdq2zc+T110fN/R9cugT8e+W1LOd0BrAImIHD2Klh/0GNL6BRi3j8lWD2r7qunhe2AgCJgMpiQiBJXG0gwGq/FycD+ORC+Bb3ePzu2ER2fh5/JhLLugA7gaCzBeNgcdAX9Jz67WzMPUPy78hbd0bNUev2Z9IZrUrBuc+aVYHt2522Goi5EYD1pVuePLC1WqKTeKtZEpDNW+GRo/T4NQtN0DQSjQ99Pz33+gUEOngE4hYnoR6CGAEIUl34QQpCEDiUGcokM+O3bl2f+wLN88PheWKgnm1Jx8qIwYGxcDKZiWtttYRA/L8qaDaEAZAVQthUsDwWiZkUpkzIJKtb2AaizF1eu7LNPzIy0hfw+wLwRnWCmk6zewVtolwdO5OZtctiYU3A6czAK28RQ8iaSYfcWqt/yc9//uYyCDe5QZr+kAoIJLcvva4/ZQll3ogvi4PeAugh/tzAHjyW/B6tG22osCG9RTxEe0PQx7eF7FK/eAUJeOml5058cmQ0NpsKx2LZVL933SO/AwSe1ht1OAxSsHXdmoI1jIAzsq+PAv/Kq9vC+HLgQPeMbZRI8oo/uzE7P3cd19wtyD+0cUUfrzBuvcY8jYE9UDwAb0KIDcEXCGSslJeW4rMFsM3bmL9534GtzXsEBfgCisBNm/hcIAuDMeIVgl5sC1zRzBeE2YTwCy+cf/yRR1a8wFQgxM/nz594HL6BrWu+mxD+f76H8g/0n1JZVbm3ER1ub2Ln8wXjhQu0m82I0a/Cdk6NiWXsmAUBeNor1EB2rbL55HW70BuX6gXYNYKUEF2+PWWz0XRcZ4sLbutID9xonZ3BxBy2xNytrgSsFJ8ZVXExbIlxc26LXC+dNup1aoWR9dQaDEz+SWm6gOFvOREQc4AVkiIJ8m/DhibUf3u37BZpTKDODvcbrGJ4nuO+vov3j0zLQHQh/mazsVigPRAMhnxpXMrm5BwICpHZ0+5TwEs+cya/uHCDnY1sCbUd2tvOPNyVhcXFRfnwzZ0x+9r9d4h//qgmSEVMCKVtp6K+ZHJi7nry+ucT4x3JrmNdnC+AXc9OZzATcrZHf/svZ7mZu5/9C8i/O6OjUdVyufOZZ5whaybEGe3H2v1tDbsaSnMFwGfXNBfYEYB11SwEJgY2HhKNRENsCs5k4isgDH/9DIIsEEb9xRBoIhGoYclAYiBfEXE9CEH4iIaGEIHJZPJWYm7+teG2w+Hs/PAMIZBnoExnjLmBHxBIas2tMmwezAcJKBgFsmVJrYyA6vAEyDeFJs2ZJHW5VSBVSrYRDluXvPb8QEsnIDDg8YAKhF+t1DuQTKbhdfGNVBE3cBH51xnwwV0SIhOxoM/38zfffDMCzLGk+N5rA/m9ogTU9Q9q42vhiseBf7hbk8Od9BzHWa2ermNYjAAYBTHwFxyjPX7mGI1rQxCBTz//3Nu372iysxdwi3pK0vD4ASDg071StXIXmiGs2UoQLJ/pPwpneX2pxGiJJN0WE8k/SV7e0aM3vpiboFmjxaMfaOMas4TxdAkPGlFQMALOzLANmr3e8lK7kkZCWINFwdaG/Kl31xxAX4QDZA+4cG3aRARk/EMFmCMgBsI4O5IbEF69+vym8ytXPg5c3LePrVbHasg6FtD/fa9O+v4PZb2k/5oKq+pKq9nk22y3EVv/0I2KLahMGVOOc2PLdcO4U7u3l1eAJxt2laqtphqaCsdyAbavFfOtwxAHX5syYxzcx1KBicT+ruhoX2fHdbjPbtw9XV25oakp7/KYhiEQ7lKNVFZj33B5WoHVkDaDSL28jaeftLZVtHz5cuz/Q/ztaKMaMDxJLP6tW7Vl1Q6VCl01ur9U4CYjV9rneevbjz777LOZmzdufPHF/OxExI3Rk9MZxyYWQEjIgu01hw+PeoKa2qIreYU121jtrYGU7aHyckEBYt4Krry84ryi9ar2vjvfvkXxLxra+3DDUcCjsYRPWV3iUNo1JG7JOLenuZ6Im9PixjafVhsXtwM0vznFff31N0eO3LkzqVUf/2xa96Uj+IwLHm69LhbRbybewhcvZUOze588oJRKWBGYEFiHzcP26AgTgNqcAOxG9un6dWyJul7IBGITuVnBD4TxELQyHRgUdCBTgoIOfAYZSJ4woGjjibnZmatjoyCAhhcYqMP2wAiGk8GgRwUqsAhtUtlgHFlkYTNgKyh4gxx3oDlwEthiyqsXAKh84GrSxXE4cMSPYXDQGlVpaUqmoyPdQhXqFlfHeCZISz/FTo0NXr7bbXXHaZwNCdgTiUy4QzEBgSQCUf5xgL9f/tLpDHEWkH8EPmCPRuPxRI/1IJaARUueyKyFz257DoHMNB9OZ4bAR59f8/7tMVN2NgWBfKrbu2XF755//vmne42Gpq0HqDlv5VavXvdqdWX9lkqphQslsPgxOdYG+Cs8evfGPPleYa+94DNp1Wp5+Ye7HTCj3s2HVMx4a2YGHqxee2lpNQKQDuGt5RLRVRCBe7YyADbvWYTAfTwDWU/gw8K1VOiMbubbAvnf27Tp/IqVK1aufAEReJAh8JFHyHXhd//w/3//71QF8tEv8K+wpqm+0e5F+Qf6T2qcNg6guRrjH3pudBvGxq5dllAGkABY3dhQUKjS1KIxpEAKvMXziio2sr65qWvXIA72CC0xQ4nwqS7BJQYboyt3w4MtOazCVGCIWmJMGyor1AMDOPvbVouuz9JaLIZgb8Xy9a2tLADGJpgKXIYEEXBNDc2APFslV5kvrxfV6rsVvnbcxDby+pFP33/5N7/5Tf+N+c/nsp/PucdBlZlUHgioMO2fzsAXDDvUh8euTakCPkXRqkreTYYnILvqG/lBXHp2a5RGa8Bz59v791+/ePGiJ5R2ujGrFIiquFAkFtruzATbW+BZDorT6DAX6VlitcZD1mB7e9/I5FtvneO+vvwN8G80+EzcYT/+mU5vSYud4paxrU29jQ0U/CIB60kCltcbOA4BmOMfSu71ff4Qa4JGGwQWATN7P6SgIAF5BPKBMEFQZdHwDEQdCK9woT3wgWAYPqZx5F8cVN7E4GzRmTGF0djfr2M+qhQKG8Iaq8fqC/ijWA4p4ZOAFbw/IALQIJWHI8A/s8mScVssynrhPRQQSCJQItGFOsTiQKAPRCA2AgIiAIVBcYszEIzHcb8vJg9oU7DbFO7hbCRjEYDi4JIlb775zz09MbRzDhsNAgD1uu5wKP7GWsCf08fx8s9H8k8bjVpiE4lxV0u7HwL5oY60W1idlBTmNrezhlVA4FeXnt5zAqshqRSOonRLdj/ZDAj8wyGdVL+7+cAjjxxoUOoK33773b11JXJq67cg/3QSwN9xkH+87xXf+5fz8TINSh0mxB+VFAUFKFzYfOltLC+to/RS+a6msrJt/CISXgKiCMxBcNM+AiDfF710gYCUCnxhZTM/G8IAuHopmmfBlauGYEH4kQPNB7buKvg7NQuklW8AvBll8dG6BsLfDOJvenqagiiq/Q6m+M9Kr586cjsPzykvFqoaG8rlVvPu5xbGgexeSnMXFpdUsFTg4XdABKKLgB9vtHgE3VK7aHfcdbjP7t59tb7h5GnJ1FgUVKCbpQLN75jNA4BAk7ytDG7oVnbV5thHV1kFyI5iVgEBANbvbdNYBqZu3y4qMoS5eCYYGHn9/rcfffyzjwGA92aTHbeS6Ux8u9hyyoJHfXvQ5/dY43E06Tdh78thszao1W3Zgtm3+gaBgIfgr5cbG3PiBaCvtAT95+7cuX///lv+vj5NdiIudlo9fu3Zs4mhUGIovTZj9Y/4Pb6htWvHE5mhpBsH0jIQveEjHr0TdQ9MffPNuXOauPiZ7SH9y4500ApSzCUqLy1tpGJvnSD/tqxRWkKclHKAQMD6RobAhmifijlBsyk44h/Sjxik5xOB3UIvETIQ95RjKIwrcxdkIJaFMRrOxcMLFETLwqEMIjAYDLkHu4s/mjIPdsv0OQRKJG2KKNrf+D1R845itjedTcWxRpg2gzmcjXBw/5isGfjCyjp2OBIC4UcVQRB33YXgHAIV2NneKcYV78GAVqP1AS188WTSHQJOIwbhvAplJyJnUxcskUiXD37H6XxofyKZXNKDBDRprFzYwFdCdCD/4vE30PdPa6EWA4CgD/iniUaPnY3NXd+5HWJpLpHs6NgutnaRV2BLrllLMDDiVeDzzSc+AQ08TwjU1Wxufm7P83/4w2m9Ov/JFQdO678+/u7v339/dysZHFligL/lMklh4fG77wH/dlLxt2dx7x9eRqPCEiYBKPRU8NcwjWPTYKe9tKAcPury8hKUf7iTfUED7jmALtELOnDTvn18IHxwQQQ+nOsKXAEisJnRTmiTWblyRTOrhqwmBD5SUQf/7XUH/r///ncnAv/xhz8YJq8DSfHRyvpqL7N87jcA/qQQAA8aHdT6YmT4A4XRr8u/duSjJi8IQG91Q0OFVpW/tWCBf4AK3OGDIpBHoPqw6BoiELsC+zwBMT8g3NfZCffZHE4goaGuVyIaVeFUCCFQq1DLB2xaDegbfRuWQ5Zj4m85VRjRc6RtR1kZTsGVFDMvfABxnk1jGxgQLb+aJzW5l0HkOfn6t5d/8/HHlz7+zY1sdmLI5RL7rQ85nft73JGeY11+vy/k1jDRyVnMosO4fo7zWSTlzLGdfrALvyvWwwvfsV1q9WlOfTP51v37dwLwHGrms9lI3OnzaLlERxp72TrSPceOWSJJkFHptLPFFdeaNBAgA/46W3wxSygdMp0akEodHOdzPeMCFWaFcL1FYy+lDB+bj0UCbimoc7jdYYPESx0RNHWIECyXjPjdz1APDF8CBv5B+EsRMH5AlAfEdrgFAtKSNgVzyMMBHA3HGEh1YWcuJfgrgGBuZpiZFmbi8Ed8PqtFX3R1SjHYLRXxDITnVCePspY8lRzC4hLkXwU/FKxvkyoGZwfR3VphSrsVFlNxLgeIErAKEIgKUKIzSCFCzXRgSnY7WlS1B/rafRoNJg3gdzHxNxQP9gEckU/Z2dlBSwijVV/QyrqKW3w9PV3YUwcIdOB3rO+2+ILxEALQJ2T/QvA3jTaqOnU2O/E5yL/AEqEoEdTCecDsUhf1q9IK4Q///B4S8NCjz73/0TUbIDAci0ll1c+uaX7u+T8839gmVSp1R49vq3x7dxlb9RDTeM6pdZKqKpR/89fHO2jJYIQVf3Mu/mF52MTiX14BprpneQTqmEMtDsXhw1VQ3qBsLatkrjDCNjpyiBYwyOcBWTGERODBh5cuRuBS3J2EfqlsNoQG5lafXwEMxF5BVg158YU8eXHBrq0H9ugmJ//7fwWMv63rH7//Qwnt8etVFldh6x+zvepG/k3TswOfkDD80c26C/plkqtHbn9U4/XaGyVmTW09WqIdyqECO/wZAguLi69uZCXTqWtTY4DAUZt/YUuhh7nEzFMqsLr69Ez+2CiIQGyJsXBujRn5Z5QrHNK29ci/5cvXL5Z/ZTgFh02AeVWg/0qVrSoLDv4adDqpBQMi0+iRT99F8Xf3q/c+n5gj11MNN5R8YigBD5DlWFc0avXBTathCaKwAzcRz8fiIamdspnMtC73XbHwDb7hcDxkOXXqm29ef+uOJZ3h3JbBbHY+qw0EtO40RL8ul+sZrPVgztuFAHGKM5wm2M7416kdDHMZXMATm72ZClu49DPOoFjc0hIwV5fXY48Lfila61n6bKnOErJIsRWQTQOzKgi8JnOfBn1gfNQD6FDTXhQkIFoZMB2of4CAi43FhGUZGqEmwpQgZQRZYfhXru2uxVURkM0AwEDApxEVXRkzA0mNUqrAy3RFkrIxnMqYjEYVrbIiwB9KwDLGv3BsfnYQ/StMoYwpbDFhCMyPgtSgAmQXANBgiqdd2IXj2o4ysL2vry9ANv9aJ1DemU5n3vhlOzov7kwm5uazqXA8TdW0EISw6C0RDIW6NBaVzWzzWC1Gg36Qg4PJ9xCEz12sw5SzhkLJjDUatYXPZkGWtbCJtA6aAPfBv6rSLDY549hiV9x9yheEH33+wPu3r5lSs6lYJKxT1q9rhkD4D7/zGh2646+u2lylBvkHt5JFGx1rlTXVVB2n7N9Olv0jn8kWvvhhCpscZoY/PgI2Iv5mZ3Hcitp3GAB7vae9p6sPlTdtLCrfxQNwF0rAPWtoMTujIMsBNm9aCIQJgQsEJARiHLwC/vxzCyJwKaUCm5kKPLhlo3rD6hXr9jQYo2OXf/hfIeNv6gL5R8UPwF9eNU1+wMXk3zSWEaXdKeHCYj1VGft1suEZ7+Xbn75b3yDSqvJ2LeTKSnlUIP6IgCACy4iAhw9PAQHl8lxLzHiStZ9uF1KB9m1eb2/ZWFQLCKRTW6NV1KKfEiCwdePG5cs3rt+Ywx/qv4qSnACs26IzWRQQMqfg1Tk4dyx81nLn209PUPR790/Xx8fHyYy+J9LRMT7UERd3uDUqG0Tl1qAb1BDNvaN9c3b+w0QobtEf2tpAZYj60gbSXNWsCGyvq5ZycXcPCLxzk5NRi1scCnMhLnwhOxsDSMTTzgw+VJROYo8XaIo33oAoslMcRP61j06Zw5w1lsiIxdbB14YdoYwVp/OD5qpynLhrrBNMDxrrC3Y7Qm6HnhYXNbGRw0ZWcvf6L3Ku7ek0AFCBETCfAOzHQRr0NiUl0c8TkNlKCDKQCMhKIhYhH8gSgj5WZBBSgq7FOtCF5YZAIOD3KEpqbo/Bv29W85FwScnGMSAgLls2VxSX6FgVZIduhzEcm5iIOaQgPC1pDveUK+vpbaxuyl0sBNYbDA43W8/ZQS6lIxffutjnDGpNFqpWAxnhFEGvwO3iofFkdtZkhd9LJmIxaxDe0mAmnhxKW4+pgIDmUa3bZAJdC99RPG7lFuRfJu302FD+oR8VTqQl+RHIgFZFiQENb96RSwXS4j8sCH9FqcDn9r3/6R3TLBaEB2V7y9c8dfC55tXl6x3G4t072JIH+E9MHtZJvqypOX7zi/m5XPaPH7VE9QfkM8tz/BNygKgByV6O9W7rCIAzwL9GZVtR6dZd/C46QQKyXODWA7QtaaEkTKWQ1cwk6+FcKpDFweiX+vjjB57jEYimCav5TGDzwR+VyNeveXHpiz/66M7k1Ecf/T0BECc/aBtbb3FxE+CPltr3s+wf60Dp5gEo7b6nR0dv0Bm6YRmVQIov3749plpOZh6NuVixkY+A0bEECViVV1RSRqMhIvlhioMFlxg6a/GoddH6TFSBdoiDl49pNLEY7lA3ud02kUiOA7oK+cYdeLXtwAgY/rajIj+/hNd/NfbqQrlKAU9aqru/Vx+ORMLZmOrIp79/8vmPP/4NnMWJId6MvicCERPmttY64xbbgBm7tK2hSA81IcZikYm5uYlEMhlyx3SHytnKnvpS8qsjrNfVyUyhJ/bD1fPPXR4tUNNn5ayeqGpgkItz4VjoDdzcSJ1l6aEhFDMAe1z9G8A1yePOdk1rt/7yQI87lMYH28nFQFsBcsTcjr3lrLwByo8Q2Li5zsC5TUY27CIhlziKfzErKR+ZjD8jToNIsrEMIHtsMHsEEEQFgdEUnwjMrVhZxEA06GMQRArCSWPNVUUeSAm6cilBYqAfZ/6i8itXacmzupWPhHXLx+4cuXMO9JUIzqT8ClCBbQYHyuKIQ6oGARiMk3lfTT3xT2iFaWqqahKSgHq9QxtMr12bTsM7l24Zuf86aEBnwErWVa6hDNFR3NkZcKYzyQj1BMYzGET4+4IhQpnYoyKfrLFRD7xK5J+VYyOWgD83HDjtftXZ2EQC8efXClgCWebRmGihMpwG2gf7VVk15DqJQEwFPnf+p5+OqRGBsW5veduZxw80r9tdVatQK0j+cdrRsY2yL7+sUfLyb6QvSsVfkn8ejYreBLlabnSw4HdQCIGFq5vcHPQybDGb6T1t95bVFjUe2oVt14f+in9AwD1rciqQ+McTkPdGePgBAlJX4EqIgxkCVzP/wPMvnH/hhRdXmeV5GBw/2j9253Lhlct/R80wWPyYATXXe7TwqL2R4Q/5pwf66Q1sRRsmKPCjoX1FICtQZwAwh9EK+srtIx+tK6Ve6EY+BmZaSVCALNABFXgGEIgr1qam2GhIX27HrmCUBcHGjePVIAK9xVMQB1tMuEHYHdKaa0VAwGmForYsv6yN9tAC/8oqUP4VFRUX51UpK5vKbCr0BUn1D0sM4UgslY2NHvnk/C+ev3Tp7o0vvpjDPBGa3kcSSbSjwraKZft7zg7IFTYc6PW5IzEaXwIEJpKZTDKZiIcGvQ2le1etqqPFjWz8rK4p5Q7tX7b/5z9f1tWlwa7FSMhq9ViPTU+b4prU7PzEhE9MrWXt7UA1ZyD4xjKrv70z0HfxIihdV8jYn40NfzAbiWP9WezsDK7NmLTbt1vVlQWljXybM2UBG+tLa0wk/2gDpo4BEPiHb3G53cN6YHwaDd8Dw/MPm9Npbq0ftwvQhhU9Gw82SA0pqeArQQgcCPPBMNZEOMoICpMiQaa7tgt90jkhmEYrVf/FqOjKbRDqGpsIV6KD4pPJpsaOXJsajUbNy/NLdBU7WkXhsxMAQOCfXA4ql3YXKbbVVVfS3SEEwnB7VFEZmNa9q9ChZS28/dc7tneOjASsSwLtYozFO8YzmFfNxDPBeDoz1JEMn+3CjcsYB4cn/b5gy3Z4u60q+DQRgVG/HyNgDrO7HE7uhZLJuLPdHz07kUjs3A4H4YL/ow+3npAgPgU/LRqrj1Z6EQI5rNOhRwLcmpQKvPT8vn/95NNr3Tf7BydSYad/c/OBdZsr1SqFOcZxFk10VCTD4i/2/s3dYtk/xlk0GkLMmsJykTochk+BnywYFEbr2d9wzw5EWfDxoRsdaIG2JnJG2LW1YJcQBgvXHoLgmsVtgRAE8z2BiL+Df5UJZNUQWqB5UDDNP7966eN5itotT+07uO90SjV15cqVj678t/8KG38r1z9+T0K1j5mjecX2OnsvK8HjyiP9NDx2rW24xKWbP5n6u/upAELLwOAxk1CzUvW7tz/9/d76RRLwJBb6mATEec+mGkx35xUX5x8+vH79YbX6MDUFanLTcclIF0UbdJvduHu8us572o4uMSa+K9CnNaNpwbQD4uD8/B1tbWzitAJXoQP+CpXbqovMKht6Ps8Oe4cHAX/zWdW3n/50zfNPX/rqqxtfzH+YM72HSAkjrE4s8t2KnL0wQJYGtqjVCjFzOJYADkaeWPvGG8nE9evJ0KD92VW76+oqef7VNci4eCKy/803f/7QEgu+uFgs5LN6bCb4kvdi8Au8UeYo7nZ8I+5r72z3a+NDSXc86J9E/rW0WFPZicF7781fH8/44QTAGmc849Y6fabCreX1jTz7qNmlvE5K8k+vwy1DBMCF93jr8r5JvgkaImAmAHX41Mh4/g0zIcjCYJ6A3TQqZuQNFnMby+nZR3t5CzCQy6UEgwspwe2uBesEkIFpkIEXJ6Oi4o8ANFqFoY2Vn0vKpo7cvjamGrs2dlikHpNPX5jPZsPkySAEwCY5ectWshOSqUAshOBPSW+eweLmNHHn2ofeSP7kekdLe1+f3xMgLQr8o47OTAZ/opFYNhvZ/0TIB69wKOY457k4MtLeHoxzCoctigDEeB5HP8hhAz7bobTTF/AfA/6NY1SKy/+Y/2PAo8UsKp8TCJtMxyxdVmGlVyIS0VA1xIXVkD+9gn3Re5o3AQKPvHZzMO60ajav3vRYmUpe0XVswOhQRcfaSoryMPv3Bfb+jVyk3j8XWzKoUdkU4VOO1lo5+Snh9DKv/+gnazJDY1dSGv3UY9YmktlP8qs4CxgCt7J+vRwC1zyIQKyFbMqJwIcX1YP5agitFt6TQyBEvavktjz4V5564cvwufWIvytX/176ob9HvS8zM715xVV11b0zw/zOD8M0xU5tOh3bUYkj9t0Y/lKdipmDyKhVCffBVX706SdvLwTBwsgYC4J5x4+mqqodte/kVzAjlanLteYHXeV5w2iWCvRW1xer5eunRvGhxA4Vq1WlFqkhJnc41G35ZTsqQP0R/tADobCpuqbWBmewGeRfb293LDY4O2+68+0nJw7w+Ju7fkuMQU+Edh6J4UkJ4j7Llo5bc3PZCwM0LotruAGBaH4UNrnfeOiJxPXPfzLh5rob9+5eVbe7blVddV2p1+FOzs31vPnPbz4Uj0RwtXEoZI1Gow79hYnExERyKG5JdY9NUTYrhKu+opoMWnz2/PYOuj4HVOHIRPbG/EQk43JOjk32BXyhJ8bhFfngG3U0lTfw074g9BrKi0xujnWBU1uHTNJUnTtiyuujIxYXK4HYFgSgTtB/wzKBf/18Qww5BPDDcblImIcg2cWbeAhqNKgEF6cEFxlo5RiIRJ88N3Xl6qjH55HjVlLKBU5N3b5tVt2eGrs2JZei/d0gfCW13GHJWGl/UVi9qr6arByAfpULcXATmjhKHFzIbWw1cvH02ieuf3g9DaLpop8AKHbG09sRI7gzE+JglyuTGB9PDg0tAQJmQrHBATSjoBY/LtgeHYVXBfyDix/9cCdBi1s9wD+04+Pd6BF/7SDL8C1UoLUPU8O0RV1YITzOj6534mwI5mioKXDf0n/95LbJF9BYTI/9aFWrYvmTR3+8K2tpAAAgAElEQVS+BBA4VltSnHelEIu/JP88mtgi+UdfRrS+1swsrAdTRkOKeisGF19sKIQBUNbaKhHWsaMF69atu/5jIhAvFgYLKnA1LwIXdwQuCoRXgAhccYBNCC9d+tTDFQr55oc3bXp495Ttm8uXS67glpg//sPfw7oQNH2m4kdTUXFdg5dXf2hdi1mItjJ8inj86fVUnqIGGB6AEqYAkXHVNbcRgQspQApxqAbsxQinRtlkr1ouyq8qqbjK6sGHr15ZLsTBLS7XEG4QplQg8wo8WmYTwROxnKbjMDcHCLQtX1+7fHp6QCHPL8oH+vHyL09Zs63EplEMmOXG7n5vL8i/7lnH5Lef/utzzwP+PrjBNp7jJl5hB4PVl0ku278Eb2sQndkLF6YxxWhTad2hSHYQTSzDpmVPJCY+/MlPPr8Vskga3l61exV6cui4zMSH89lj/+PNtaBbkxPZs6GgFaVNGGNfeB4hKHUrxqbuZTmfM6hRRaM2U1AstmYv/Mtb91/vGxWBwMzOz0VUKl9Lu1n3tc0XD9GD6IxDsMZJGxvqcZgKroI6qdsdlqL6o8xdq17GL8qha1c+64FhNgg8/3jhx3b2Dg/T/8ATjCHQwJzy+Fwgv3B+sQ40scIwQZDTaLWcIARzwfCiFkFC4OTk6JmqKU8goKrFXAlCsG3q8mXOYrJNjcFbksqqDVJcZ2DKBNkGN0XtKlSAKKfRA2shCm6qLpXBUeeQoZA1ah9a1jP34bgzGAz0BcRpZyaO5HN2OrEbMCNugReTCXa6Olwdif1PvIG7g2NhW9Rv5cKWEPy56BgCMK6N+nHg1urRciFne59Hc5bcmBcXJXw8/hTojUsEJBl4ynLsPyCQH4+78QFmAg8+dUnR58F3a3ObyZgarMxb4ula0nVqoLWw5uhC9s8UEYofDH9hdX6FnDYXGGnRA3xshhSv/vhyCO025gnYJtJ5vQIAG07SepCCv4qC+evAgTV7DvxVQwzi74F+mId5SxiMgx8/wBD4o71mW/GPfrR0abM3eu5y/sYzgMCKq93lD2/62zfI+h6r/Q73KvOa6uwzi/Gn0+8oy5fIIBbGljJ9P8un99P8r0BAtAlmBPTCzfzRp5/+fgsLgHNdgLi2AvN/cIPb80UbC7EjpqSMWmLM8tqiK6JFbqkLu+NufT5/ISyXNAILvPkiaonBaggX0so3Tk1N/3paEW4tKcLyR1FeHoS/TVVqk2JALT/c3d3r7Y5lL9yYVR359qfnfwHy74P3vvjiw8/HccSKY6b32ykshS+3bH+XL0BNiB9mL4C2lCtUmCtyEwLRyDIyMfdPP/nJXyas1kHvls319ZuVCis39+f57Nmzy3CjTsc4aMB4KOG2mFSm8MStRBxTSuJ0xnoO5GCgrz1oVQ0o3IFAeyh79tTr9+/UGmNnL8D/NeQ2DkTb/dJ791IcLWZEU4aOjMbCWXQNDci/ggIZBIPGVpR/OP4npfXzaM3F9F95uY2MANOsB4a1wPQz/g0PS4ZlkmEhFJahCqQwmMpZ/MpclICpB1SgY9HuNBPRihO6BHNC8AE7aZeLEDiWnz8aaLcqWqkPERi4Y73JbZmakhvvpQYh4kYvVEU8CNGoJWYyOcpWEf7I2bpSKIZsAAbWK7UhzqGUGE3GNolywNIDejoTRItUTAiOvgVvJ1y+zFBHmopHGZ+P9askh5JutztiCTvGJj3xoDNkdXoO2zRaX5yLXpy8CDoQNGAQEGSZID8WHMiFqJR2n/oh+mX8g/dQLefHBcMQqJpMXR4fXxAeF5yy4HSem3vvA0Dgo7OcFhspu7pMsUgsFmuTLvEgAbs0ct0M6/3r81io96+FFX9tilNhc1vROxCmYOzLH0CplEHfzeOPCOjASVM2FaIH1Y9ZQB6Ah9iOEFrkkZOAewQFuOeBKBgR2JwbDPmPYfDS89gFjbMhBypstVt+9PDDLz5Zdm6qAgKrq5fPwAUAXLr6hf/3b9oaQRj87W3Ky6tr9LJ9v7jxnAW/+RIJSyNRw4uMf4r6Kc3ez54tnoCAOZwF2f0JiMByQQA2MfzVsDlPu3K5usiuVBbmFeaVVPBNgfIdNSVmlUZoicHu0x7Kt+y8NZGdvXnXa6+zeyXrx0Z5oyyL1qo5PDX9zfS00eTYAcEv8i+vSqlTqOSiKdFhA2X/sv2vZUdz8g/4x8s/dtdTLiaqibuoCdFt5UXgfPbeNEhAbRJ+D+JgQCClAlEC/uQv/661uqVNW+x6bTDylz9/OH+h54k0oUAcjPvcyaGQCo72WAIQ1tnZIkbbvwwXSreMjAScTm0o2D7S6UxGjk2OtQ1Gzt6bzUIwFo8ZBzxR/ex8Nhb/VXotRHVDaZdLbAUR6JA07NpSUG3kQP5hHx31r+BUg0zpXSQAlZ6LbhczAsQeGAIgfyrhpyIZpk8PDjD4uIQouNuwaE9QKvcUYtrpAl8VdijCCqqGEgS5XDTMhOBiGUgIFJMhn6hC7mkPakDsGciaoqJWMTA1pQgPGtEO1ah2OHwgVHH0H1hdVEcX7+1vr67kNaC3odUZD8UtBv1gGOJ+qdpxNkIzeJlgPJmYn7x/H0JclH8dLpczk16b7ghpqVQxNNQxFOI4rQUIOKAJBuHFtvu7FSYH5+bQouci6EK31e/pouJvy+KWZBb9Mv2nljLrMCEVeApUIEPgogFhOJ0xQHnvg5spNPw2HTvWpQ2DfkMZR85cVp+1yySdpd6/KDM+oK8TVdnMAwp1SYnaLDcK1XgpddcCAuHfBvSFw2HHolUT8CHpyZjkZi8fAgsrkgqeLFgUBvMI/OtE4D4hEYgicHFHIE/A1YjATQer5Jr8gwcPvrhvw9jUR6s2FJVdvXrmTMWZ9fpyCpdX/u0iUGj9G/YWFh1v9Pby8g/xh+FvBYS3w3y672uMpvr5ESvGv4VnrbcX/dyoRbfhbUDg+0IXdBPvGoDjPDXrzRt3V6FdPZWDi/LJLxpUYH5lmQICRc8CAnE6biRIqcC7M9gYbc+7fW1UE+OreT6VaHr666NFcpO6ovAKdr/kmVVjU1NTtRtLmnpTkdi9V+ZHj3z6rwefuwTy7xWQfxSLeHJzmGj6bFP5hD5sQmBLx/XP52cvDMijQezKgTh4IhuO4DKviQ//6Sd/+cu//5s/6O6Oxd0Q/s7PX9i/dggoJ8YAyh0ZEju1uI+cCwVbxPEMPLE4zCBOu7Z3BqxcqN1n7evELscLstRE9h4246Sd8XRocPrChdnB7ERyHAdFMvE0Nps4fZyJczuaCnRcyIKDFkL42wZ0g2OkurGU13+75H3RDCuB2Hj+EQCHe3vRngKXdUiGJUwBskwgSwTqWR7QwIJgqdH4HyLhxSlBJgSFTmmIKSkYpqqwmE8Gpn2eyXNjIqnK3xmwwX+4lcx58ne0SpGGrbQRLhzMYGqOiwEA1TW0sr6O1ZTsZGyNFvl2e7l6u9NqjcctJRKHRSEVqR2mUDwUysS1mUzk7MXX799/62JfkPY6BdO4wSDuXuJj2+ldQxA8dJnCsRDgb4nf3+mexTTGYNh/8fXXgYB+q7brLOj/DqEl2bVdyMqR/MP9L8x817jQIBnGVKBGy4x8hfiEVUPms25/VKtF/ecwK8Kpmd4Uh0upon5/NNr15jFHLHDR39PD51sIf4oBhbmsptZsVvP4o48Ai4uDrBpC+o9N21Mp2CA16mky+ObM6ZnTpxt5k3y2KBidsXJTccK1RxgN4UXgalYMYQg8mONfzi519aanXijTKlYfbN731KO6samq3W+vejfvKuq/2o27N1Gj9OpNK/9GqyHf+yHznZhRFldVN/by9MvJvxJJ75dfUkiFIk9CApDgp5PxkwY8AZF/ylyHbvm7tz/9ZEsDjcyibR7tM1M2lahriyur4J+QgaAC84ry+flgc22xslZwS+WrIVoPBMId47xn/u5VuzcUTo2hgGCG0VbFldLK4h0ihUNaVbOharlNMfXN1NQ7FUp7f3YiNfxaeOzbn658Dosfr3wx/+Hn6MHLFlB3CBt/BwYUHmbRj8GNO9eEmL1g80NoFYLf80UmIAROcKYJEIH/BASEL27l0N8PNJsYVyDFM+2BLoiYnc4gdzabPctZ0fQZCJhh2hCCNy0c6wGtCYSKa+K17iyE5n/6cDyNMw3iZGxwYu7DuQnWiIEWdy0tLc6glfqxcUGew4A9Ifyzgu0tyL+6OoF/1R7aheT0YQZQbuRbYAB5pMnZNqscAEkC0qJR/MnskukJTLFImH6QFFwEwbCQElQ9UBUJLl4qwhC45Ny5b8bUA572dhU+3a165lGGIbcIAmB1GOJfLfEvZnK07m7KAVBY8GSnFXENGzHIjvuC7rDeaK41qtefMauWwBHjxvyov3MEEdgXCIhbnGit/YwLjyor2aeiv1qkx6KFCNnq9/eNtLuz2VhsMBvz9dHi4zt+nxX1P2ixhVW8wCXGP7PAP1Yh4tOhChBkirAJh0MeSNGMtGzfGdF4Rm2arq6usGEwbDQrjA5tVBOJWPAoh0D4zX8+NTCm4OUfbZlByq4vvCoyo6XbwoXdFUZKAAICKQOItWG0nEuRPyoBcPjmTW8OgAIB0YZr154FAmJJmK+D5EohFAevRgQKe4P5xmgegEtf3KZQFa9e3dz8i9OGsamS/KtXdr/99rtXKtaLSp5l5RJUipv+JqshP4TgCPnnLZI11fHRL+GPmUgW9c58yas81BO9Mhb5Iv4EY2AZKwLjwHaTku3rwSLwKkwF4rAThcC0z1FZa96xYUNhYZUS8QcchLgVx4N5EdhWUyxXRaOePv4+C8VY92nHrc8/nL9x99W6zaWNTfkUB7OWmLimIm9jrUg9oHDoihUqNci/w+uLQP7FYv1M/u37Mcg/wN/cHN/7gmPo/N3IVl6q2G394LbOuezZaF97IB5HYegGERjDnQ4AKlCB/z5htczOp+DB8rWw1Y1BPxzxuFosHpmYmMu6n7B6/NiVlnaiwRZIM6vPkeoWuy9EA+2WfpB/s+99eGtInMFUvnhnIpZI3rqFXp8t7cElENK9ASQFTGTEPoWFMxnQUop3NcFO4yJcCiK4szaU71rfdxF7YDJUApEvlED4rCxpwF6shQwT/2R8M4xQDe42sHW5yMAUxGI8AY00smZcYGDYtEgHUqO0j3dSXYzAh7q++WZszKxpF2vlZEpIFrYGA+0uVSsyGSsufuYinMWk+PpVpQBAxsBcQ0x1da3zGVB3mLsT6VoNkvyypiKVzx3jMlaTamy0HQj4FpZ6gxkqG213peFzcmPLHg5rJNzxoA9CUP/FEVBnkWx2cDDmtmr9CMCLk36/L07F38R/Iv8OyynJiiMzeCDg94/0t4VBBZ6yaDyBwEK/Ktya7VYaH1J1aVP92Wx3r8F2507UQVNwpjDXFfV0gQgckMZYwEHFjwGzuWjbGblcVCvwrxXtCgGAyD+gXthhNBhZChAlICYHc+YwaJFPV/UiBu7ahXEwInDPQj0EEbhmUUcgxcGCCBQYSEEw/PLUynyNedWPHl666SWZQr2xouzM1JmrNZVv7y4sq3nkKT5Qpl9f+Ie/NaPo7zHbK5B/JU319gX8MflXViKZkfBJvt6j+Cih4OPDXh5/uXwTCkAv7usR2jca6xCBZIiKV03TDoWoBgfecWMbIbCwEBlYVHKVWSqbzRuV+WZcnIRMEgcz44IzeQcbEH710KGTp3srxkZxc1IIqyFxTl4rGpieNls0A9duX766Pr+pyRCbSN384t+OfPvTFc2Y/bsxPzEx3rEdb3rK+bj4XIxiYECulpttGr9AXDZKALHNretzZ495/P6gOJ2McVZ3hMXBFkAgEDARnh8ctPi0Pnz6IbDpiiXRicq6ZGgIx+oyGbemy+oLtLgwVR+Pu30tnZ5fGzLcqUl/wMfFZt/78+cQLovT6XYIqjpD7oyzvT2ICXJf6Ikhl2s85NZyWicEaev1Ujxm9MzSpBXdDiW8yq7n167UR4UmaGAKJpUY/3p7h3GXlQBB0IP0MfXzo8GEPz4XuKgYwmJhQOCgEA3npGDYgQxkTYIoAxdcBHHJupALdHXsP4UTjsd84qBKbgQ1heuApbQLRM6lfdSHvCzCcSbTwPEmHoCl9YC/3Xx3JWrA6rrSDQqfmN7TOCdtUuZV60whiILdIY1tuc6rtPWN9L1+/3WIg3GhL87Z4P4B9zLqZ3INBQNWrcff1+ePhjmL1g3K0Qohgw+OpddJBvoBgm52EPL4MxH+zIfVhD99bhG10Sj0RppMLBXoWUgFWv3R0dFR4B8OTU7M3/xg2Hznk9/fnrLBIbF/IpsY8qEI/Odj02UKTzvtmMY7rmxD8WHEXxvFV/q2NpaPkOKZM4i5Vweuf+C7AuHrM3vA2f7+BYtolgdsEDQgxcEFPPye57OBOBe3EAXv4+vBq3PDcSQCaTzkRz/aoNIUbnrq4adWex1TbRvLLm+E0HdH2Q6Jve7JpTmRyF+b/qa88r//Qxka7gzf9CrzmqpzvS989AtPWy+vHeAfjlIwtfgiL0wegFQGUbIiMLuwAFL/7qeffvJuIwHQni+HD7+qEKsVDIKFVfgLbtUWVuweVqhLajYSAgP+gJgFpmwQndoObtw9CY8JTsep2HQcZwn5NPL1apvKNjA1dfvKlZomCRU/Ulj82PT809T7MnFrpwtzPvy8J618Yzvf1GqRmh/GE4IbN7P+uDWX7QEEtoudydj/5O79o5q6833vdc6ZM84851kPw7IivRZaYQFSb4EjIGAVHugIiUASEgJySSbGuA2SJuzAlpQmOz88RnRRxNIh4uqJJ5CLMSlnXAJdsOwkw2LxQHvkTIv1Wmurd9FlV9tVfxxxpqM9nXufz+f73TvBnrnr+fNp7xek/iiCSfZrv9+fn1qrjQX6gQ+2mAOf/PkTtyty+TIrMWNe0jE8PzfrDJl5zjLo6+jokIAsCTkHLazFau8z+wB/TnPf5NL84/d81pnb81oVb3n4yS38VInEbLdxZt7J2MDO+YAkPtrEVRO2WDj4JieHNw7hA4z8Q6lAu4BxLWZRWSPdvJx/KHXY6nyxJkQEoF5wwHUYAZTG6YdPHHkexectEQfE1h7kX6IqcE0oECloIpeleICB8YCgUpkokhadMCLwWcPC8rUZBdNnZrRkY1UtvMPfpGdDPiyutgzi0wYC8KQOrrDqxsbGwwkZiCqQSMDGw+kKM24P5UI+rfR8AxN2Op04qmJlIhYbGWpWDE8eP3789JLdzpvDZl5ClmwFXsXGDTNvVVmBf3aVAes4XUoGcGdxkgEOtuGl40soAzmzMI2ZFKWg+5XV1zfkVAn8o4+LoAFpShyNsEsLCLRRqz0e5jyKadyuogKfAKr+2Ipp29TRXVN3lg2gOq/f6q1xMIx17vHYovECGA0S/TPlZBXnnTmTQxd44TXWTJt7BNjiIeDDbAjl30AwPh+QasBPEwSM22BCwF8dIP73o3gY8MmKQDEZkis0h4j8271docfkb8Gu1JzlN9tT8/KW33lrW09Pt7pr81r0Yfscrlx65n+fbMhP/g4f1fsTXfKs4sayG9/DXypZB4cGWSrt6jrfRcLpUqGyjFxIdNaIuChxiAIwTkA6xmQKfXCXXFfRLatKr0wBzZeSQrkHP8E935gLkWZkFQoLJvUbKytz9B4glL1vTXccqjIcyPblkcbq6vau1DPTOEmDlsQ4jUqVEdzvxsIeeTWRfyvas1+8VvLSL0nuF+tQsd9J5RYL/unNGLcYnTlTlVOvT6xsF6YfYXgHiDs7249re8H8euAa8roMPrOdiX0CALx8+YLX6wOM2ZfmjV6Wt/PrXiVl/p0Oq2/89Q1+v99tgauR9zlB3i2dPr50+7HTevvbeTIKDySKOcxLOiRc/6uB8TCrsnmYcNhHEiC0ISuMC8onJxekagF/Pc0tZNwU8K+4GHd9Zu/NRgF4YGZJEXoxRGtg9GIEEJ6foYQFhp9MkIWV+IPI95HEjEDaHEwpSH3w2nQIOU+Y4UREUJwi+H0E9roXlz+7re13dIYs+Mn1DfDpDVoeR6DibDPLIDpg0/mT7XWg9RobheZCwQfTcph2XVljdbdKgjcZX5hlzRIf7m5jnWzsj/di0djIgMHeN3kajLCVM4d8nLmTjnAO+EBzsyD/wB+zbhTtLoN1fs7jAUe8zgc3mJBjiYjAeRD3tCaP1iTDzQNp3UJ5hEEC4N8AeSBM8WwIIvACKYyG14qEUSjJcikV0Hf/9Vgs5rr/wQcvvTl18MsGJ2bEOvGG5lNuXJjzvPHGhcUq3Bu4vfjKW2dA/e0hteJ5aly1jEMqatcA0EQSwJqWAXzYxfGAIgBRA/4lAh4of54sZVpTFfg8+OBDa2wwRgKxHobGAgUCNiVtUagyk5LWFyRVLMxcbTucv6U0q3Dbxo05OZk7j5Y/vy+3IK4BcwUI5j71v8fydHC/OG5xpKsrq7SsjCY/JuL4K8yAK2fiwQia29Gu85jiJVUVgpsSgupZogCUCp0gOBL6ooA/Osek7eZnX9xsKzTqM4vTU+REAKL0Q/eL9EunU4BTMjJS6YiE+oZmqUxllHnit1pcnymEAnFW4EW4TNrlhWRQFvaGGFQcr6ja/s7GrI2M0xuNjKy4sPPj39D9Iv6+vlWDyQ/sd+qlfUgeoxG8COLvrbfeQgLK1q6qi4cCL12PDoIl5rAvDlQiQyrIVLOxh27X+xcuuKJRC+ewe3DuG8dsCAQCRGba3K93gBEevwRaEoQID1fcceDf8PQ0E7JaVSACTEbOgZMPJDWSV/23ejGCT8qye3kclQDfH3b9Ly1NTvb16esAfOJwZxJklWOdXBECMDsbV0OkzM8LyzBRAMYjgCT3Edd/N4gHnog/aySNL86HGaChQJINEVVgojY6Qj88kRRJMJCkRBhWRKAwMKYjMLvts7PTSpsjFDaQT9DIVGYnlhMCAfstuABI++jIyWo1xjLpqa7eksiFtAuDxooAgTUS3kyqg5yM0/m6k7F47957GHW7tXoFuOBvj89brRzO5qKZrBBWRzsx+oezAv1e76DFM6c3abVGD0CJdHw47ASA8/h8c4A/LUl+oPzrFoZoUwYOYPVJUJMYmENahGUXXDgnxu6wTSuUSg/wD+CMKTVfwBJZ+fQ3f3/yy4sfjhh4p23YxvgujXd02D3wLb7x6zfOLW7szqzciOpvD5kYkVqYSjCIfpsAsIHebDQmOnG9Rd1M+EfHDgsemGRCyKq4J1Mh5S/8M27xOCAQkDYGH/1eazD1wbm5Yk1MclPS7hwmpy2pqalgxzszVXkZGeltm3YBAnuq9hSVNCXve/7orszseK5Y/LTckqd+/Anhn/2fZELI/Rtd0ixda5dAvzj/MqQUf3WUa0Nd4FTl5LKS1q01wqgBs9SUgHICwK72rjUKEF/NFTc/W5BtqyxOwV6N9PTSURL6Qy0Yh6A8BSckpBICnjEqFfVjMqNHLIkREDhJZwWCD26t3lLWlbkACAQfzCpVYY5XNWSmZhWCuvIHgyj/9v3TB6T0+eHX1xONv2LKj+BPWHie153TUI9fThFPP8OXwwg3mf8WnT0H2LIYXC4Fh+ict83OxkwtFy5ckMWi0aiKtBeo+i2B3nGc9WuzWvwhMvUvFPKxCvic4dPffrvU18e53D4J6/Ua4GvXaqxmHH4g8ZG1EFhuQ9jMMzbb5CQug3QQ/nXWyJrpSh/sq4AHOB3wtxaA4HvOLNEaGBSA9bQGUD0itmbT84DAkIj3OAJJALdZqAlEu5cAoHg039eCprUQTMxNSKyWQxXYQYpixgf33PzutoIJgXIzwP9m8ZH2NwLAQXgzGDTnzx/MrpOTZQNxBgozJjAZIrTEpch4iaSjN7wVN7j54DFlrApt9G4Mxzs2NEzDneU4oAwb9Uh6QmLGTXG+t0m9yn7s3mVnxxZNBoNxcYwJ+C9hfZFvq3l4/jhBoN3OKGRC7hfA1C3sEMCHZoS0TIMeDgrwF9uDXbILY/BSsWLsD/jH+sKA58mlYTOnjQRHPv3yyy9fPraitdmUtn4VFirWdNqxKhAQeG6sKqXwTFVPXh6ubs3KyiAXjnqgWRxQ1tBAGBjRCNE/zcDIAJ2KMCD0g4gm+FOxHFAg4IHyzZtwkdEuuCWKncGJWhg4L+3b97SYDs6NFwUWNFUYFRm5SeuTcivOzGwsLEy9mnq1uHrnzrK69M3r1yfvLsl9rie4uj5hgakKhLP7x54Q/snf1ZGH8+KQOqUskfygM5PgagPZQKpnqawbwgkdoD+GKAG/f7LiCpAgsL09EQnUgZnZ260wTt1pI+IP59UjBCn+0tOFTWAYD8SiwLx33jnjUepzhI5cQZVhScxgPzNM6u9JSUzrli3tuqwFuAtrDYw5JGsAEZh5c9lkUnA+69l3S14Ral/uXr9Eal/64xu4aO4X/A5deJ6VtR0kIOZC1n45jDyuoyMw/d5z58DraC08B/ibt9lmgzFvdHYRr35XLIKThplzgxtIaoX2lXa8+CJS9PVnWQvX17d0+vQSyDrG63WaXV6/2eEZy9HyvJWXmF+/tR8MORY9+gMgTft4pXEOrkrHZKeEB/kHf2AiLRtqwfxi+ldXUQRvbVsaiQBMK5qnNTBYBF1PI4D0KRl64khFAor8qxMudGFAjFAZjVWBtCQmGBSCgUFRBVIEfr9EUEub5eII7BAICDZ46ouzHk6mDIXA3IdxOB5tKeknCyC1GefPl2er5agAs+P4qxZfNVQDYuA4Q4VzD3rDPqeFAYmJG5Jc7HjAHfO6vZrmnGkbGloUgbgkxDHpkJhDYbi3YHV6pyQcCLgBIDIFLm/VmsPmPuyzCfVK7EvHqQ+221V6eK2dOVMFvrRF4F8damQiAcnY87j8pUbYVG+w28BDgGlQKM29vePjTg5zzlgzf//jDz/8eOVhzOKZnvaoWB6r4c12Fb6y1r1xzqiQbVF44xAAACAASURBVMvKSsWLJUMq3JDU6hahwrO2AZdcUxVIS5FA/jWrB9YuCRmZWOuCE/x74Z93kvlYB9J2ZueL/MNUcLmYCTkqEFBIhZRgY0hSUo5KtjOpoCDp+aszC9vz8vKw8O9BlrSrNT+5gKzNXP3mmwNJ8ToYAkH6IRcQ+CMOBf7s/5IS2g1IMzJ0ZTcE8TeyIsg/ir+RCbyOMK5HK/wo/obq/gMBCf/EsgsiArGsFTN8WNvamCkzbqwovfnFzanSFNKvkU7eSDoknR5SEoPNcemZeqVxWxX2YurRmCqF3XEJY4pNmJgQbj1cXSbfZlSqfKFwSCYtzFEwxndwqJCBUY6Qjb8fP6TtnqTz4xIdwmazktwvcb/wZOP4hCzc1CSIQLEfuVcMBWLd8nXv7AUlB5feHG78tUU+HfHGJn4bU/XPGV0ullGqOCdu1EHOsv5AQNKJUEMr7XNMLnWG7MN9fQyoBYOFY31muFBVjJkz1rpYc28Hzgd09PWFekN9kw6bSlFfr4DfmJys6Q1JwPFfMqmF1AfNfcDDWVSG244rtmTvyM7flVb+1qTSh2MQVIIAbBabQNYYYBGBNH4rpbOxhCImIQZFIEjr0WhpNA0HakiL3JMRwSfssIymhWl1IDXCQmU02ODRz/VM1cEWnHtAXK9AQPJx8cjokX2NcQAerqYILBNcMLxs2nWV8ILQc2Ysi+w0h1gXDqOye4wuvzMMd6gY+GCvpkWjsA4PAwJt8NUdIJolEng5AHMRdjgj0OkFDzmmwaIlm93G4aR9UmZuE0KB83ZOoc8hSVn6eIzU0Te1AEBc/roWgSYtA/IPXiuKOeAfSl4zF+YU/euc4LgffvLHP39y1x/oH3uv1gjfkw0nWftYMM8eD1gMbt0/XtgoJV5KACBwtqe7Cle7NpBkeXwwRb2G5oGDzc1CNwiZEE3DgDfWuuBTp9L+eWc+zQYjAvPzBQQeOpoYlr9mYVKJwMAT61OUiryCpPUFJ+Q5IP8Qfu/k7dnT3d3TVb6vZH1T0/rc1Qer6kdpgv0V/a9IwNynf7QJ4Z//H8oB0uqrydlYjMkPwf2S4heQfzfA/U7gFnsplX9DIv7IdVT3PQBmkeuKSkCiAdvFTAi8lPcWVSn1usNF8pSbX3w+VVwqCD8sARQkYHpKKR5UgaPFhQrltpTtZ0hJjF4/JgNw2GxP1qjUYIMwqMDf7G3MkCmZrfBqH3ddJLVerBajxyYDG3kZ5N/du6Td09q/pg9JSeUfdb+pmemlxbp0arxBAwoIdCSSLzYqOt0sbw9fYjwkfeh+eOzhvT9GVVaFx3OOWQdf0sAGkLOMxR3AaS59uLkRPi9kB/U33LE/bObcbq/W4PRhgApXCnFji6AsDDyO3/TxaN767DZQFfVaFU8/Gb5+6Nb1S5q6ZiH1q+vS0Qe1iJwt2dk70tKeb5wfVooC0FSfQwCIU7CwCvp7B585LGMXnjysYhfDXSNCSQztDRmI704ih0wNDIoV0nExeFkggkmQgUI+hBKwg9jgSIuT7z6oNunHTAa317D2mM6P1u3c19iMFvhw42EyZ3YN/3DjJzZLFlpC44AyrJYMwd/gsdpVLo1hfJzvA3EXfQgIdGlq65W2YaIC6RKP3nAIR+v6fGRvZthnceFY71g0aun3eKwcjk/oxKpxDwLw+O2z80t2xkSTsiQyJ9weMFEOAAQpHCH/bNz/Siio5YanZ/DerDCocHVB36Sds6tmDeecveOWwLjfH3aaJf2Ll11a4/wwo/J4PAaW9WoKtxttNpCBb5xbzIojECucejaS1dZwErEH4oRReWImeABQHCRD8hNxwLUaMD9tV/ZeIRNCuuLSdu49QKOAh+jaYMwH74tHAl+hccATadsY2Y6kpvVNB6RjC2B+rxIE9nTX7ikufwlJWfD06upLJ44sZu1OFtknemARhj/W9rif/92MyoVPb117XW0Lcb8rYu2fug6XgJBRSoi/812i+usidTDirSt+HRG9QR0wZSQSsKyL8q/1VJZCkQp2BiNX6Z8BAiuRfqX4AxMi6aOEhqWlo4jAMp1e1ZCSknqVJkMIAdcY0/h6GtxR+PDel0M5CotvqznsCwRW/vDp5eAHH8Z4xgWaxWhVuVcE9yvKP6HzDeSfhiY/3nknMz29sqK9rDgzQUCSDRG+XAfW+zMk+RIG92vlx8NW4F/Yx0ajd6PWaYvbq7RZ58bwPm3h++z9r5KvU2MGyK0j4//mvz29BHY2zIfG/W6ve9zHqBgE4DrWec50OWIyeviQ71lnv8o+abdih6iFTuai5by3fAFfbZ3gfru6sPYPp+eBAwYLfDh7x860tJe2xwcBavWJGkA43xeAtCNkaM3Ni/6PQmOIMCyajgoU5qWKKjBIMsO1a5rlaHkMtcMueBfyIWsQSG1weCu37YgaHnKZIaEAccKMafSgRvP87my1lKybbyQ/hMEw1TR6DA64soHv6Ahhow2otkv+qNd1bnAwFmQ7JGEQ0uEQtm27vS7cYU8I6DA7cGc62f4sgT8HU+yDRz52NxZFVfbquQsgwsAhOxw852MNxvml46dPf/fdWTDChlqhrJXQb4S0DKIeaAkKHIr/u5Wcdfr2zDTIPy2uGeRB4nFWhcVtMHCdDpXdEeJtznVm9+VZ9+zi4pzVA5yUmQxer6Z72wxIQtzZeaG2rqsLA+oAwD09Pd0bEX5IQHLbaVnMaRAigUFUn/A2oB6hE/JHRr6nAQGB+Zso/ogEPCUgkPjgX5YnlsYBAeMHJGDuiaRKhTKjpCC54ER1S872jCtXrmRcTQX+VVWl7Hrm+fJDh/aVrD4YGFrfdDRt85r4X+IIldE/yoTwz396pG3ZaJH1EPcLj/la/klxB5x0gvBPTsN/DygA6WUUR2DiSMUzhAwkUcAyIlf2yvVKfVm1DsegVsorK698Bj6YILCSUFCgH5zKysriim0KY14FDokppMmQerII06hQPolAoV3tskwVvuXf4Av4LUrXystf/ubDgfppD6OU4SoIoyV6vbczXvos9CHBtUj131vvXE1NKS2uIFqjNPMqaUUBG1wPCEw045EvxwyDOfXgqjN72KLiwmGfj2MYq17jcjvZQZVn7n0QnfVjg77wOB2wwDm3hp8N85xi7vS3x3Eigg/j8k7feAgD+Rb2F74NzvEQbzDNzCzIOHNoXKW0WvF7M3C8c7Cfzoref+l64PXXLc11NPeLU8aQf5gsBQK2tR3esRMAeGB6UhHCbeggANfUAFKxh9iTk2ctQUEcjEAYSCvY6VLzZqHuY00skDaDBeMqUECg6M/iR3TCuENDIaZDeHMN2a5uXscyGwGAMgCglypAMgXZ4Hp0sm5QXvJ0dYuUWuDsxrgDJqe1tVWnKzSaUUxKeF84ROdVuKP+gN/LdEpCuJXJDD44iqFAV4NJhTO2ed7RaQ6DAESxzzs4xsf5Qh2+wKVA4JIv3PvsBVBlCtCJHC6+gmdCNjN/Ggn43W2PlZGp45X9dSRIQPLAtbWUgBoCIk1QpmI8M9duT3uMWgPr9GG5NWdjDF7W6R50gteF27NV6Qz4A/Duj7lkczN6o8JgqquLuL0mEIFWm/UNQOBYi5QE1SkAu7ur4ODSeFLtWZvTQB9nGn+kBniCDGGPa8AbmAomLnhvdqvIv1O/EkXgGh+Mg/LJysy12eDcghfqlYq2pOT1TeUZORtTgX6ZpB9he3dhccn65KO4c33101bd2KJuUyLyF8+ArG0o+RFmQ37y011l509uWfa4Rm7gwzmg0TSL9pfIPzLgRTqaCP6RuF5XQgB+zwZL4wyUo10maRAwbK179ygVmfnt7RU45Ki4tLK0uPjmF19MVaSXXknHYQhx/lWWVuqKKmWehrJ2tMjYHyxMiSEq0PgEk2hVoMRvYF4PB65fh1eWCcyRd+WY6fZt46NmC6/StzTk1MssPMo/f2IKh5j8eAvk31XEXxHYr+zG1jJdesbVd8SvN6Y3PpF88YFwnJvDgLnVAC6W4ezD87dvT8tcLoOF9fsDPuuFsfqZ392PkU2WOFXJKentNRtW3nt8+tslHBw3jmskObBLYOYYg8XNkpSvhJmbeTwQYXkzozAajXq9ymx2es/NHf/2eGfv/luX4NMMzTT6h/hrB1QTo9jYVtS2hQrA8pThYZwDw6sUxngKOD6YYkiEn8hAoYZJbAoRY4GJpXHCGRCCgS3CsBjBByMG4wT8/uAE9MEK2iPHmTv70BeqlApWlYcArAcACuoPj6vlpM6gPvHCPnktxgCzBQIKSRCiAtu7urbZJWYzGQ9m5nFHb0evz7l/fDxgYTHIireVvs5Q2I2dvl7OLHHarDywzYkjY8w4LQv45+O4mk7AokTiMPvMYRDhg7MX5uatZNitwc1668/cPv3ttyACZzyMRRO/q2OzJ62EgX8/ARBhUTCoZaxG/czMnALkn9PH4j/XalUaDO5AmPUHnIGAReExeAO9ly51AIhZg6yqp7beeGZPrSkYBFIPyPOmrdgdBypwD0jArKy8vJ6ejRvJflfcGg/PIOi/uBUOUgiSMzIxEozvysRVFaQi+jfZZTQVspcKQCEOSERgYz5ujIM3Mhzw6NHEvqTcghSFqjAJ+Jfbtm3h6pUrV68A/3A6XV5lCaY81uc+t3l1NSkp6dHYEfiFEPNbkwZ54vzI2uN+9rd/tWnzlvNHjhwc7XZFBkjwrwUQSKJ/Q8QOkyqKUUK8NfyTdwHc6J1L+oQBJgScIBYYf+D/i/1wezMUqo3VjeKwczDBoPKKSwGBNwF4pcKpJBmRyqLiKqU+q02H3XGkPzg+IoH6YEV8d9w4GZQ1DDfarVvDWOplgpfW2Jhn+vb0xvOXo8EVr89nwpKCM1qV3bnG/YrRP8q/yuIiuPb2Zu89iHYLmEu/XtwHi33vvTzjwezvkp33+191D/Zz89PXMh5tm1EoBw1eLOPr5Pr1M48vxyzwKWY7mB5O0umMHDv23x5/e3oSa6t7x31hn4UxS8zwfcDF4kRlIwGtwlxwsWG4OgHZDQbOMdwX9iMAlyT7sZCQNdHsR5dcRwdMICayD1dvgXN4x45daWn5xmFPqCYk4ZRaAYCkBhohJ1rgB3gPi6tAafwOlriBEQSS7rh4e8gAscL0rUXIChMGrq2SjscEheoYeJawINPRN4y5BY8LdLHBqc/akmdCAOKKDMI/mdbUfL7MYDr63PNPiwBcowDph9au9rRtdofDzNt/7Qu97vSRNeXmMHzgVc6tb2NyNRQy82af0+mOsTxoTrdbBcxz+nxObt060lSDP/eZ3/4FZ3fYGW789dcvwe0qOiubm5u2MqzbFXG5La6ca6cBgI9vL8DzKWuWiv2CZGgYKQ/CShiyB1YTdBlUHoXMODcH+g+XyymV/QxON1BYwh1mZyhwqWMcR0fipLVeEKxv+7RjLbX1DZmlMwqDNjgy4HVHJs4/msOSGFSBamlKal7e9u3bNm7bRnQgPNaLtQ05a+KvtXH+AfxGJsgQ9oGECb64t11IhZz6jagCEwvj0rJb84VQoFgMQ2OABbvqGeMWjP6VZ761sHzlymfIvwegR7N2rG/C/uCm3aur1YuL58t0L6ynddNi4uM/0A9P7jN/86Mh4M9+8jd/vWnzpi03z58/clCXZwIEEvGnMdXi5TbxAPiH0zMp/6Rx/CHWMBcyJPAP37Mw/UsuOGEWAi3VoAqwtb1KpczcK9T1FxMNiAisLCbdcRXFVPmlV6bjh6JMmXJjRUVlKfYIp5DbUWoqFWVnUJSNYdEBduxSH+y0ehjevNXnx1lVFtar0dSfhft4zo1PV6J+92wgbKmvra8/I1PyvfHSZ3S/DTT6d/VKemUZVtLt3XsSAIgErEzPpF+voQFssF4oQgSlMTwML1jgn82B9Xpet9M61qOu++pR8+Ks3+8mUk7C2+YvzLq54SUbb+YUSp733vvtsff+9TH8WlLTWdMZAsvGKm2k7crChsb5PockFB4PdYT92PkhQbnC24ePT9Zc8vcvfTu8H5SOz9CjLiT80xH+UVoDKbZsARu8Y8fOXbvKdTaxBsYoI1NMaBewVGyC6yLv8qE1PpjMiMGi6AQChXoYkhARhSAdEyO8oQwkzcJBzRpl8j0dqFUyuPppGG4WS0s2a79WNqZl9T15OwplpnqTYRDsL9V/uDfXpc1OPvr8c9IWWgiNCKxuFLtB4Getcukry0vHhx32dYFebHFzMm/3mcO8bXLS1h8ef30r7wBvHArzvJPBpBIBIMsyODOLVa3zmXnO6QyM+wLhX7w+7lThFGi4DfX2hnsDXvjGxoxzgEBvJAK3ztp3rn139jEQcKFeqTTVDYm3BOFxoAQkOaAI2HuVUonRP5zEgZlv7CeXyRSMuY97NtRbg9ufvWTrB11uM3i5paEqPX17zsyMURYZmQh6Y8FR3Vseq3UdIPC/LhZmFOJiw+179uBeV5TdOQ04i6FWCEFQ2R0UNyQB90ZW4h0hEzfaW7vIbASxGiZfBKCIwPzqvWkkDniIpkJIIuTES5kKLuepptwT+6rzFpazQP5dvXo1JQOgX/pCU9P69esLkjevvlTQdNBUm78vWaybxjfsHjnxFwCYnPz0X/1IbPDPf/rXm/C8efP8kfM9Y4vn5RFvBGuMmtUNJvXQDYI/Uf6BSO8S1B8VgPQIBMz6XjZYSoZvEgPcBe43T8X07CXwI6eogla2FsMpuokILK7EwB8piCnS5Sjri9pocQyWx6AKjItA0QdjpTLdHRdWKjmQf05cZx6NzgY1rukv7iQnv/uFKXY54vVjvavZos/BQhoVj9E/JYn+CbUvIPlLK8pIHR0esrakHRc1CdNZQQRiFSLmn3EPxdKk3WYDVRGSYF3ZOGOiJVn3V6LhXqzWM4e3hnolXPRW59LxJY8KdJ7z4W9/+/F7713YGsKLU9IJFizUG9J6bNY5GeDa0WkGceLDUYE1WDosCbMGxqFSYHbn1tcbuGHfeCjEG7vV9I5Cs7/VZDZ+dvZhcnYcxghgWs4kbkMPgQMGm9mwtgkkbn27aBnn2iPEcevWPn3qEaEoZiQ+KYYMzBIPbicT7DB1w7RVhPyWCZQRw0scw/MefVXPniq9FsS6w2bnOVNWbfPOVNkYABAUIHG/wL8jR0zatKaSfc9tbgYAltEymMY4/7KzdaaWFtbVcPrb04BAM2lx8znD4Cl9YDj72V749bM+MgEh7ONCZjqm32KxoORjVSyYYPh9LtwhCYdCYAACbosFizNBlm0NhVivSTM2pp8BI2yJoTF1DaQuPJ57fPvxwoLeYtHUSUX8YZMg6RMkIdCIAfNXiECZ1o3NzAaLyqoglYFGFbfO30sqOvEVQja5k/2Zd2OX1aN1OVUbN+J8CFlw5MZKzB1snVqw2tate+PXb7zfk5lRiPtsCvOAgc3NVTk53SQXDAgUArHiElrBBw+hChQkIOBvbTJYlIDIv3hCOL8xO+0o0YCHBAl4Il/PK3Yk5eaeOJSZs+dKSgoY4KtXsjLUaunOJuRf0/rV1dXm5n3P67aA9qNblYT1mvE66O8nRHBQ1o+BgCD/Nm/evAkU4JtTFWpNwyNQgQdbtAb0v2ppj0ajxuQH1tDCNSMlyQ8Rf7oukX9y0UTVCdeQlOKvjgae8DN0jTq9SlaK7ldAYEVZUdEaAlZgd9wU/KyyuBS8aKFRtqetspRUx5QiBsm46MyMrNS8bXEExo2phFOpkCB+1tdX07v/+sMVr3b51L+99MoHH3zl8ru9t1CVmUM+JTBTf8ZodXBC6V8Oyf1mZZYWE57k559aS0CdPCUDl3XSAdVwFDaHDdTf0qSDN4fGA886edxdaYiQfdUrK7FLcO3Zh3H5eW9HhyRwq3dyyaYIujjvH/8I/PudVUIi975xukTD7Hp/cHA25mWdYMlwvDF2r0rMnC/MGVxBiznomrM5xr/+ZMOzDAcy0qgyNPSgoCbZ3zKwv3v3CgjMzt6RnQ0AfKFaNewVa2AwBUL4R2J8CQSidhd+Fk9jkRRJnVATKKpAXBcyQrxws7BAmIxDE7LCwgolwZ0FKQbh4nQBBmzc8LANbe/MDDzAVwtbTAZnWIK7ihiTpqVabRrTAACp/ZWZ6i5KDYayptySfSWNJtoKRwKAh7cQBIIUlJp4Rb3Wolo6jXNP7bgIGEcqhntBXw0OusO9L77Yeymw1Wx29JlJtA/411ljYXHuBMvSICDPMHyn+fVxnBXYG/CTJm0MaIQDGwYjl03YBzQzbWXdsRVQgZFmRODt248fLxqVLpIPbsY5LS1UA5ITUXJvv41fQaH14sx9A0DfY8SZ0WOLszhhDTsY4RuSdEjsgH6Ojku9e29l5f7iYg6Y3IWFazOmgRs3grHYSFnmjM2+7o1/fP/xwraMjKys1NRU3Jyc07Ctu6pWAGAL/eottUFqg6kXHsAt3YSA8MTSXHCCgL+JE3BNSUx2YzbuTCcicN/Rkt2ZStX2Zwr25b5SXbixEPiXggmQjIw8te6FAlB/gMDVb1abdIumibLnjwp103go9HITscDkJ+3w7h+BBvzJ3+xC/MHZ1VbaYloYPQLnZFplgyHSDFfOjbqW+lpxu9GQNGF/MRtC19VQAIoIjAeTpKTDaohmgbu6yhr3qFSFjWUkc0n1X1kRzjuvIPUwxRXFxRU3bxIfXFxZWVTRoNhYXFQppITT6ZxUnJIgBQIKIxLWIlCpgqsBm5x84Hw6O3l3gNVc/OCDD/7+gz+8HGTDPsdknwRrA0OMVo+fquA4RQOcHMH9FreLo1QOkHckILZeyUF1ptJ8MDphBT9snfOg+x02k72wrI+z2X0AseDl+/fvB70hCThXdGC4qrZG4gv3DXveX1lhg789dh/458AUZm84JDGbQzUgSaN3/f7rd90Bp1XF8XxofKu5r0/C40xDZmzEGxr43YX5Yd9d/4ZnObun6p099QalTL9H10X9b2s24k9A4A54AwF4NMdhFWpgZHpTQ6IIOo6/LgpA4b/kyIeESOCajDA5I6QIboQa4pFmcV7WQHx7iCAFiQzE3wpGvCxntw9jLclp0lk2Nz195szMtFKFnWk41/pFzmRqbsFBCgSAMq1WI704YmEXC1BZJMtddQhAVLUY3MQET3Z2ejCm5bSaiMzT17eEE69sdnOfA+eSkbokfwBbPGijjQ/+YBgnEpr7zBzuSQD5h3dG+C17/zr+7cB4B+mzCV3C5aedmETrHff7Y7HLJo2mAXzptIqNrqxEol5NXcbM7dvghN9b1FpcA3XqnicBGHSpgH/gwVU4apq1aLVehvFoZVilcPlyNLq/ps9mXfeLrVjR6bAxzldZUqtgc976+i4SEON8y8vXAIErn07EohGpLs9j8ywuzvWfa0jNgBtvalZhd0N3T093S3ctvtEZgbQduTYoQpAiEFTgygQd204AKBLw1BORQJGA5WmN1fnPEwA+vy93p55TbilILsl9Pn1hW2Hq1SulD0ox6ViYdziX8q9k9Zv8E0knvpKCLDhQDgjcXRLvHz4RrwNM/g/BwNzdf/UDjwP+7G93vEDxt2lTflZDzvLUkfPAv5NpH+3MlLkwyzRSJ63Vt1DFIETzhgT7S3Z16agITJemiOxL+CgpufCQgF1lGQquAYhCq6HbyXtFO1bvwof2igrkX0XR1E2sCoRfbVfoi4sE5UfrAUlaBOcESrE5TvDBRJWNGT0eJWc2hwN3o77xcCDM2Zfm7cOKkZdf/vAPH3z48r2YhYc7sR1VGThMs0J/5k8zMzMeO2PMqcoB/mWlVLZX4zYNRB8RgKfy9woArKwUEAhf7y0955ifxuTvks1qw7IOMFxmKxbS+qOxhw8ffhLzY+M9x3A8juGU4PRozm793f0RVvPx/d9xHMObwQtJQo5QKIRTAsLh/eNgbcMS37l+FmcFhsCmMU6n09w5OfeVK/zee7dPL7H+Vzes8+hNpneuZl7V8xKfukxHFqCvpR9535W2+YDVrkgIQFIDqKZTYIaGhFwUZR+VgRjCpQQkKZI68QkUNWAd1X9kTkKz2CZMjXBigQgVJRoXNveC9nUyjH34OCg1OKdPz897FB4lqQZUMaDEJB0vWsAn4yQpBKBLK6sdGqrVGhbTTmA/akGtBidbZzceJroWiwHz2+s5p9vFuSLahWZDqLNvctK2NOzAfW24uKAmND6ODrNPGEfF23ke+OhwAP7IoH0wyk6nj7fb+gcHXw301vQ5QCb2ATpx+SmuZu7swPbuGHba1nZXzaAKjK3cD7qjQWnmAhJwebkZENii7iEIJABsbo6onL8A/pl5pdbi9nsNBq+FIeuD9YC/GO68pD2QIafVbrcp2fHxgP/Vfs+0jRTt31u5f79nY15qZsryZwv6yMqnI4DAkaIry29NgxW2zi2kZkqleTk54II34vRYYF+3MCOVlKbTQKCgALEcEDfXCmHAtaNh4iIwP6EAybIQrIjBkuhX9mUxzJ7ypn25L7X2dBeC8Lxy5UHKgwfAv+KnMPgH/Fv95rm08+cPHixPSsptbG/Nx/LB3fHlwsliEfQaGRgn4HM//f9C0P+v5yc/pezbtQs+pKUs35yaKmo7uCvto5MHjxyp3G6KIALr5IX1uH1viNSzCBIC8UdW1SQkYNwGrwkj0d8ZKuuqVylTQP6hdyMEpE0hRUVlKASxkRXfK4oAgV98/nlpvT6vqJjgj+aDSXUgaRHBMQlSJGCegMAz9TKlR8WT5K9TQkJDDGP1LM0trqysfPzyhx+vxOCVaUNV5jOj6FIxPpW+4czMmWkbrzyTV3gV3G97K+Uftb+nUP9RD4wmuBJDj1fh6yn54fnb89j5Nq9QgqTow+4Ou/L9c7bQuNPt9wdu+X3AHp5bhz2wiFzOBzjgPL97jx1773dzvhDtTZWYw5IaSZ+kpjNs7uvotNvDobB7EKQKY3eYnetYCy/pG568/XiOf3z222+Z31MCSgAAIABJREFU69cHZ8daXK5aeVGpDKzwpYHDCEAS/xMAKBjgXWlHsxw2tgawTObAaHKoAJSSDdqC/vv+wZUt9A/F3uC1PpjwT0wJr62LEVZoAhNHBjQRMKcMVpk4WVC012/5WSeIQFSBt6fJLl1SCoNzApGAPmydAOOLSzC1prqyZpdrrCUfM4v7ko/KWqTUAgtnZ3aWcuvbOPXU4GqpA9mF+ysncce5A+fb27FlsANT6XZaEMBj9zEPf8ZiTtZiYcNhH9xRnBzTPxjF5kTcNL8VHDLYBHh6fOtwuWVNB67Zil3WgMpazFkAFQg++H4s6mqWL187iwh8pDFYTHAz6aFBgJGgwel7FgDI27QuN+snQ9hUOH1WP7Z4+fLd65dq+ob7cbx0b4jxWK0eBYN7EtyzESUW0df0Xv/k3v37zVlZWZkp6VeWF/SakRsDsWhQvjNFr7LZ5q3zMwuZPd3deYWYDOmmhxhgwX2Tvpy4AMQAtLCihxLwxsWLaxFICQjkS2hAWg549ESRjFMUvbKv5MSBoebm1IyMjKtXMoB/D9TSHXTsadNTq6u7C04cuV+9vqCpqaCgvLqsNe35fbt3i/P0E29xR5w4JT9kE/zzv/1rwfwSAG7a9ObUlZtTb6Ztzj948Mj5UTjw0hwZwtaPQn29lCR8BfxR+1tMLDAlYPraZkYRf0IvXGuGksspa9W1iwAUxwMWEQaSNi7EHza0AgI//2yhaEsxJkNI9iO9tLiSJEGwGAab5eQp0syswlQBgQqFB3fxhANuFitJavo4zjl9+/F79+8+fHjv3m//+DDqd67rV3js5jDc+DnW5+N4n+LMzMy1s9McJ0upKG7DSfJ0kiiN/51C/mXj2BoSo8T+5Mz0FobMcDm9tLQ0Zxp0skpscrVbOdarHZR08s7QeKiP5/s6zTjtmV2Hjq9fCR7M6WT6L/TLHp+ddrtxViDvMIcQgOaw2TxutoOcYcLjrwcCASeZFcg5wcQNLy1NHv/uNjN/+viS8+u7Xo3MkHP+X79SK3mJedJxJltH0tVr+IekyN+5qzzN6MBlmBJxEjStAayTTvxF/iV+PUSqlRKzHeP8o4XRdOHViFgfLR5cf4V1IBxns9ltv37jjXXr2FfdcAKBMA9ySE8mSWtMMi1dnET2kIdrfDg9wCAzacEB18vlWlYjbU4rIH4qSa5VS3U4Dlr4V21u1NslOMuKn58ZODYRdLuCEaYTVGAf3n54O2fjwMX2cU7nBo6xg+vFcYvgghkl68MdWWzIzDvRB4P8I1Xwdo51BsbDOL0PXgsgy9w4LhUQeOn63VgkiEYeGDjjUUUfjqx4va669GUk4ONHjy5YDBp1IS4zUY9EGKDqs79++22PzOv3uw1Y9WwxWJQy2eXLwYdf39rfJ+4W7jSrFFjSidGPMJh1YZg5fLk/3/v4q0ePAIDFlTcRgRM3gtHYwN69PQrrPLbjzSykDtXt2ZOXtx1cMMkIC/knuPE0P0lAXBzXHG8JwXrAi5+uJaC4Li6hAeH8EgD4ipzhG46eAP7tVffUZUilWRmZVwj/Sjc3EYKB/Fs9eHJfmTwNS2TWFxQkNeWXtWcfPZqYoRUviPkL9YC5z/xgJeDP/vavxOAf4g9/bN5ZNvXmrp0nj5w/P5q+vDx6vq2yxRWsw0i5vFufk4KrfOX4PkrDf1QBxhkopoK/JwC7pFrOWNna3kV2e1EFSJY9kCAg/qetiIhAAkBBBU5NAQHTi0tLr2BRjCgBUQSOwjsWBWI2JG9jvULJhM2sEm/CDDaITg5ztvlrj766HL3kJ+8BZ2+o/5x2UGnjec+Mh+PDTgvLcwr9zNlr8Eu2pYzS72ScgXsJAVuxALcCIS+vLC6qM3C2ucfffYuz5vQuy+DsrMUHtOo/t2Grc9AfetvH2RyTNs73ujm8wRfCqwrkn5PFPn9AIMtMn7097b0LCJTwdrJA1xzu3drbK6Ywx3GZrY8F6cqFzLioZ7LPOj2j5JVWXyAayanX1qq/+up90Fhg3PoWWgGAh0VGEAjmZ+MUhLSjcs5meTE+CJAAsG6kbmhCrIARqHcxAUE5vGGSikpAUQE+2R0nVgXSt2Y6H6q5RaNVMnb78PDw0uQSfMSR8r/+NZCfYZVaExYJY0VMhBZEK0CmWwkBfTUqGU4/kOFqkx7dgNMiLRsqLyAjOZteMpmk0vbqw4IC3JWvHnwbJBsQ9vbylXci946BTIp6VWHstp0cJkaXYUD9MYgyLHTBLUiOPruK7Mdicc4EkEplsRi80VuXOvoAemT+N/gAzqpSYUoq4Ie7Fe4NwYEasRVS+r9tcYEg8FjQ642oMwkCl5cfjRm0QfynBy0gddkNz77dr3VZAH9ag+XVDX5WiT3llx8+xJ2X8d2aDrvHqB8b0+NCONxWIuwNIQjEEUZfjUrlui134KZfP/DpxOVobKSxbJt++vbMzNnvPltOkRbm5REE9pAp+XECEifcQrbGgQWu1dSKE/LjJhgI+P35WE+44APlhw4VGeHKxCrANPmeQvDcKRkpKVcyMgrV8h0l68m2zKdXV59u+mhUmr+b1MIUYEa4IDetsTVtLQGp+ssVnXACgrklJT/UasCf//SvX9i8abNogQUNuGvn4TffnAL1t7y8PFUxdXDXZnnQNUCyH5n1+h4drnIbIulf3dojpoK/j0ApduzXqlRVU3em2rvodsP2xEwEuvKmqLqtqK2taEsbfGhDKYgEpNmQ4spiUQbSKTFECKbISUkMyPVtegVD9mK7tVUNFieu/LIBqJZH71+eHQeL4wiNgxmSSNYZvG7DOeu0XsWplCq8Njiembl27a0FvcrpkoI1QOpR+uULm3URgNiuUqnTFbX3sLwHZAAGtmZMBtYbibl9nJVhLIPOcZ9/fPwSMTrKdeFLvlA4DGBjVDiNyefEsVAYiWcVCoMhCscJCrATBGAIA5IdPjd2DGBWsiO0NexUGpVg8I4fx7F/yoiXDUeCbrYns3BPTkOLhg1J+M4XXwxpS9uJAjxM4JefTQGYn481MPUOHARo5hGA9Q05YgqEpjq6hMFkF4UPQ2t1oFwk4FCdEAsU8UcnfNNgoJr+qqXWJKPwmyQHCIiuFGyoTaXUksJAnFuCras4xxMEnwJ74qxogs0hWR1WwGD6V911qkuadrLrQFMyKa0t0BmapfJ2Wt6Tn50mdwWe3bAOPstzrbSrvSh14H/8cSXmZg0yFSEgfMFhO8/AA68Kg8E0YwByHWhqFHnYX2hxhnkfx4A1xZXn2ATJsHTpEa/sV/YblGZx9ylBYM3+63cfXl4ZgH/mto2LC9PzqtjKSCTqDWZd+QwQuLx8c9FokbU0yxgbjqHesM4gc3nhuzF4VU74axmFcezy5YefXMfo3yBds4WT1hT6hsXFBqNxxgq4dgYukbYlLG8i08w/nngkHT1y8M07dz67duYYhgJjQ3t1Z6aBf3A+W5ZmFebBG3BQ3dwjFiBhImqEGGGkX1DTQI0waV4dOSbmQYRMyMU1kcAEAn9V/k/lhQyTk3bipX2HslMKM/GSepCSmYL80z3TtP4EADD3udXVfUn7Th7JL6DZEBIUXF+QlFueX47dc+JJFmXg9ythfqilMKTzAwTgru8BcFPagSOjo9IskH9TRUdOvvDMC2lH1K5Ic1fXg6HWLL0sq7WdNnXQ054gYNdaBSgmQeBuDu5XrytLwfnPrTpdgn7VZW1tZNdDW3Vb25a2LUXIv6IiZCARgZ9/fmcK+VdZShlI6gBL04VZWcQNp3cblVwItNSt6zGSU1T0A3bmH3/11b2HMX8YrI/N0WezOX/Bbxh0+936xQuMjXNaFAY24LQofbzyzMxYvUbGsLWnXjlwipJPxB84YAQgCMBRXXWXjFHpxx4/nj/97XdVLrfbFQGOcUqF1c6woQ5fGMtpnx009A9igW4ohD4YDKCHwRCgBfu9WKcf9Mg//uNgNAafib1cZhyL+SJZ1+iHC+XFmt7erc9usDCOTjL2tLNT1TyyYmFXYixvfWc1q/CqAnCKDp+rwupJMi8lIQCxehG74NpVdoO4DFMmFEHjMsz/VQRwaO1PhUCgqAEn1tQEogQkz+dQXXOtyYBt2HaH3Wwn4ThCwb5JO4O6jxZFazTCuBRhc4iLRgFBdvGhMGOCF4y6pa5rtL31UFNScvuRfesp/06caHHBXbSsmvybnn+phyPlKqx17r3/fnFo6GKZfOBhzOvSWtwuE0OIOzxst/O8SqHlsSoG5z7bHcNYD8WyfnjIOQfvQ/55o9cxKWEj+COt2aQDRcmJq1b9rzLEmCICH67UNfds21hVBQi0xI4NRNze2hQMBV5buLlcpbQobSBlAbUGk5b1e5u7tYOvsk7c/gz8i31y/VLnpE0ljBqig3YbchZzqgrfmsaafYfPeekS3Z+JocBbKALv3zh/5OTm34MKfGvg2KcTsVhQU5Xx2XfffUsQeBWIhEWBeXlCCqYFrXAz4g4JWBusbdBQHTiQmJB/IwHAeFF0IhtM+Pdv1QpeUfrKoaOvHJBnXblSSvj3AIxVT8bO3PXIMWz9yP3oI538YAm2gjSh/EvGgfkFSUlydZqoAJPFSpi49FvDwdySH6IHxs6PzZs3i+lf9L8CAfPzb3z13v1Hy8ulU1OHd73wTNpOsMOPNC5THV4k7Tl6PfHBFH5Ez1EAkoJAYZpPXAJi0YyeUfboMMSEIw+2tOvEmaig/ciUIzhAwC1bUP9RBdiW8MF3UATS5hCSCBEnJeDMaLmuUK9ktpq3hsP+KODPbRhbWDB65mcWvvoqdj3gD/8iMO5TWG3K/tClwKXxAOt14a4GDwO+VKEEUYahK4spEvufd6OsZeDAARB/WFZH1V9jdisAsB1DgGWttUqV9kz92Ptz87cXNF6vC+SfEy4CFRBQ5ZOYn8WVRR3jAWGhtiSEKyiUBiyFdTp9G5xur8vlNZhchnXr+s/NbvCxFp9ZEuol1Rg1IfjegIekrXXcx+PUv3FHX59dNjBRN+JivU402sbKbgvYwHA4xBnl7aBJy2i3bJyA+WjfAYCLDjoJmsFVIH+hCJqeduFHnH1DCf6taYxbE8wl97I6da1J4bEyiBw+jIXFfJjrxQ0oHLKvtrlZ3JmmIfKP9gO78A2bgpVKBvMkjEWpOfXfT548kHbySE9PUlJrXdlL65OpjmiSG1pEAOZvyjDwpF6F85gGXv74xo0bXUOfrkTh0awdiIAz1Vt5sxkoOGzjwAJzGFfAbVN2Bls/yLoj1mm1Ddus57xR3H7qsInLT4FLKtqAouKE/QqX/IMWqx17FMEH311ZUat7tlV1bwcjrIytBF1eV3Pm1WtEBS7rbTZUsiqty+B3WgymYK3X7/eZHTYjyL+7tzo6h60GsluY9ppP6/VVG6u2Z+zRCxWrDsYJIhBDgbhgYf/1Tx6u3P/4y98cOPDC719DBL78qZd1B1t3ff7Fd+R8sZyBZdgAQNIagpHAHkpAIgJbulvEUODAilgP/X0ErrXBNBFyqHwjx9WXv3ToaHljxvLUFTilD/AUpurKm0iHR8kzq5tzk54+P9rYhOFAlH/JZG9wQVK+yak5sE9cpiQyL5ELSSRCSkqe++kPbjDMz3+6c230TwTg5tXV/COj7713f/FRYWn1wZMfladlbynCXMjoIxP44PahobL0HGMVjqVEABICllEVSCuipfInrhxpV56Sq9d1SZGEXXIceVAd13+464vQrxoXPwABq8lbm5ARmSoqIiKwApMhJCFCyUcwmCJPr0zvVqi4rSFM/kZaTKAJNDLD9GeffTb6r195sescVFlHAA0mCKz94+MGBe9TGvV67BxxWrSAQCAiG3bOPrx797rf6XQN5aflk74ychobW3FwK/ZbyDUqZe2ARnbhv86NNUfcriCoMs7qga+uUij6N7wuFJYBygJk5EhfH5gqdtBlGjOqsKLFF2a9sy4XYMBrsXG/Xtc/G/NafBKQB46+zj5JL1ZjAETwQsSusUls8FdqIt6BGyNeJ8fhIBUermm4wDtCLmlbZXplMQLwsGCBaSkgmve0tGxGFICkC6S7pUe9BoBPCL7EScQDSTUM0YB1og6soyWgYHo14Hkxtc1jHgcJCG/j4TCgxqVpIQMEa+mcLKENDlf4mFwRgj+XwaBiMeXqZFUgyPSnPvxwtUu9RaetLZGr25PXnyDz2EvWH9W64MWiQwecdrghHHqdd/RNLk3XrqwcO/YpziOaiF7yse7IwEhzJBoLmvz7OydxsQHDk0XE6GYtVP5h9A++Htzw+on86+izW/vd4voXBLZWC9+XEhPvffGRQqACUZV9jSrwvrqnu3vPnoXbKuXKyMCsO6JOBxV47drNBasVVx7ItHgT1WotTnfMxZjtNs/l2N2vUf6RPTNx+aevr9q4sTBjT05D/RjOFIKvxzM+gkCPVUTgvY+//OCDX7700buvfb5sYg0jK7HYxN7fUwR+8cXNZexEyRMRiFsz6dYW7AEGGMYzIQMDCQLSZZkiAIWi6MTa9CIZr0x/5VD5obSK1Ct3pu5cuVmaQviXsjO5ieCrZHX1qdGDaentRwuSCf9IThj4l5QrNzhN7UfFjZrJYiAwkQkRDzypJc/9zQ8MgKTzY9MTZyfgbydA8L/8qe6r++/db27Oe1C962h5/paiitKUrKyU0fb2VJOrGWealmXWy/Iaq2kwr4wUtOhIKqQr3hIsCsAuqYwxZsDvycnWWrmOTH1pbBX0X5HQ5k7OFuGgGwYROFUh+GDSHVdZeaWS5ITThXEJ6cXFqSD/+K18OBDwDtR63S4sQ/PcBtE4+ijilDh+jeX+NUIX5os1Ida/4W3eMFZfT6e6wFUrAzQCAkNs1O3HFCwbuXgobS/pqchuJZPoysp0ZY2NLUqVrGEgGLlw4b1HLSA8Vh76nTaPAi5pm9LlxURfDWly6pT09kqwLMYOV1FvIOqNRWRGmgX2PYsi0AXe2cBw1nPnYrGoV8UD9baasWq7j+Oe3QAXIsYs0Ux2+iKgcAZGHkYRGOgbuXVOFvwv06DTyXFcYRH2ipFEAZWsJHiZdqA8y2xl4R/Lq7ANuCEHlAKNAEpp0wdCDuvX29fqP1oSTf98SETgUB0VgqgI61pM2HKNSzoBf/BmJidk9rEGk6aFRuZpp8KapUkmcW0mtsg6sThQpVTi8g/4Fxk/+vC3q7XSDLWltqUlv4lcJ3DpnEiSWtQAwPbG7PxyuUrSMQ4ac/j4NXjwI5qVYxMTn95o9nWEgW/elZGJgZg7EoyG+kABWvtxCGlNDRlSi5RlnQEnj8NPDbILg16cgDtppzlZEpWDb4XwT4abjBCBws4XNKZ22q529+HKyIh6z7Y9hcvXbitjxyaC0WhwqHv+9ndfzBD5h0uvLFotPKH+QIjRT1vPzT78hNb+DWKWhW4ZVMDzkFO17Wrqnm3bN+aQKW641KuPY8VQIMmGYCjw4w+BgK+s/3290njm2IefBqOxiQO/JwT893///GYGaUnMw/a4PJoOaR5AEajGEdXIPo1ggsVMcFwDXvyPNvjAoZe2cVzV3pfKf3moMT3z5tTUnampKcRfXVbFM+tpJmN19emCpI9GR/NzBfCJ+Es6qnFa1PnlzxMFWJJcIpS+5MZ/JCfHFWDJDw6AP/vJT//6e/jbJZ6Sp//0f3ffv69WZ8JjUbolv624FDMNKaPYHLdlj0uj7mrXlRXtkdVnVJfpBC8r6EGdqADFOtoheY5S1aAjTCQZEhSNU5998fmbjYSA7UhACj/Cv8MCAeENP7S1AQOnbgICb5JIILbHXaHBwNLS4pQcTH6Q7EewLujFIehaxe2zn1f/Zmhbt9b5C1GVjQcCYXjN22xmMjraNTaGvSNkl5vXJPO63V4DF3b6fYGA/5bfrbl4YK+wigIHceKwqToZCJYztXAJLj6qi3hdK/eiIP8UMoNK6VEaZt23cOo91vsBF/A1D1f6qyrrZJ9k3B+NxSIuBCXjA6EEztkEBHRbrFbwwTGX8ZyFxxVJdgfOf8YMpll14dww8M9hdWEvKujMkJm08atU7KuBSyGJKiMbt+VVVuraEw6YhCsFAu4ympUhQQAKYxAIAKViCXQiBdLevtYFD8U5SMfXSieoI1a31OMACPCRmOS104OQ5wEBgu5rbhF74WoTswGFwJ8B+U/YZ1AIm5Is8MG4qSn38Fh6vYaNDB1dn3wiNxf3MiYnZWs17dI6eVl2Wn4OjwNMO+zW6Y3NA5r6Mw2Rh7HgsYkWe58Zvbc/ujIxEox5IyYrANBmtZpxnV5vnH84n9EXDoW1Jpr8neTI9r8OQf4h/4SdllqDOFeSzBZ0q+i471soAkfUqXvyClOXZ+aVdwGBXgvnmP/uu8cMo0T5h20sFoZhfSGH3TrWcjl2fX8NrX2hW+bIllV9fU7OnoyswtTCPRtzGjQaikD0wYhAEgoko3wRgR/+4e//PkOvv/La8rXaYx9iKHDiV6ACv/ji3wGBlRSAqYWFwECxDEktJfxLdAYPiDPyCQEnbvwHAhIA/ie5glNllJf/qnyvLmO0aArPnQdX4KJP3yGE83Y/9dTupIK0g9VHCfhOkCAF4d8JqYE1dR0of/75eBZYiAOK9nfNj9yS3bt/WAD8Oa19iWc/EvwDFVhy0PTgT39qzniw+uDqg0xsA8vMysoEwXHkIFxqaW21roi8rL2rVbfRWF+RXSaUNMMbArBSqIPJpBpwKMOI8ao4/ggAde2tNz/74k4bGmHB+8KPxsYtjVsOH6YMbCPRQPIf9MJtiMybFaXFN0EBkpQIVgXuMarWmbH1wx+baPZ6gxMjEcX02S/e/ODDl4Mu0+9m/ftr6AR6swRU2bDHY8fdcbfuRi9fXmyon6kfG/MwTovLZPL63S6LL/T6hg3+rz+JBtgRkIDViVNWq2JkDQ04+LL5xoA7Gjx2L8rZ4HWtUFk92kH3dcws2m0qeM37wD45bCp2/JJQ6VVzCdurLpu0WiVj7g1xFi/O5wfkWmy2foNRcRn+KomEw+oIVaijN+SM3f9vc98en7TWR9yDoDOjrN1hDodCKgPrdgf2A8Z5S0+RDh6EYp0wBmGvGLKkADyawVnjNTDIP7I3qY4KuYT7bSfLCRIqUOgIJj+law6QhHXNtWDYcOChbQkQM0wYOAz6lrMqZZpmMh2AzIcRtqfTir/4XhBgA2lAc6rIuCsF2ZHUrwTJozIotfknXjlysEyjqd2b1JRMAZicXHDUZGhvr5N2NR7OlPESzBRNzi/UjdTWdp/JMUWvuw2RgRbPkgPHHQACYyM3RuCOpLE6bHCIKAWZHMaEuxPHb4fNoQ6JwYsNuSD/3H46ANeBOWGFyD9MT19YqwKF2ByqMuwNWZmoUxcWZo0u3543BIOsY9gGALyt1JoMTiL/VIzF7UP3a5x9eDfq6yODxqn8wwloMlyrWVWYkpGZmZJRiCOeG+oRgUIoEF4rfhGBvaQk5uWgtuWVpHfffe2zhYGXAYHRlYuH7gACP//3f3/tzco6dRac1CyQgaQaUy1NryMteQSBOKObVEivkFzwxMQxHJCa6AuOZ4NP/accnq9/6aVfHTiwN+XR+fMVQL87YIEBf225TVS7PbX6TEHBR0fOpxUIYb9ksjApeX3SPhNrUR8qT8tPWwPA5FwxDRL/L4ViydNPP/fMDwmAP/mbTXH7S4v/RPWHv5ReUKeVr37zzTcpDx7o2rvqulqlGSmVU23VB7OBgI07DqdoXLWAu6KylAbFxrZsOqgNc6VggYuJAEwR8CevVyl6QP5lCgaYEhBneFaAD76zBT0wwV81Cf5lA/8Qf29uiR/ihXHQ+9Tnn5OqwCsVJBJYWZSuV/bzbyP/oiN1wWhk4saAdhrc78kPXl6JzM7G7voZ+yTWjvF2u6TTrjA6X9+Ata6k1PXy4iKu2dIrlDj6SIMpXZMqHN7gvvsP//BJ1OkaOplNwdx2OBvkH/YLayKRAWmdyxs8dizqnJ83omrweGZno1juD/qNhYusN6SK1/sHyGzCyb7eW3exuWDMqATS2YwKRKALEYil/nMXYnexZI1XGo1Y3uz8+uHv/p+z356e1ngHZ4OxqJ+1eMBsOoaVLue4LwSXlBkVTUp1ezEmkhpF7Zeo3z5wQOZQhF/EQYAKLVkGrCZzEOrWAPBiF2FfPOwn/ART+GKAsF0ubc6pn1Z4cGujjR5k37B92KZS6DUtajoXQJiUL8g/Aj9hHL6BsM/JWJRk2KkB1J/SoOxXWvoZHkcwqow7T+TuKzmanX+iIB5BSm5qqrU0t8qlXWX5eXYzdsxMHj/bPTIw0NLTXavxcpPzM0aXS+aZpE3dYR8bnJgY8Pp4iR2+Q0wAM6C/MfrnxB0rYQdIcrPbHcbaF7dblH+g3sgALhlWJwpbLY1apXLNzhcQ6bRSGZ6+hyMTUmkqMGdhGr93q23+7NlpdL8s/B0g5g1eJ2ezzkViD6/vd1gVijVbVuksirGNhamZKXJdcXrGO1Vn8JWnGSMIJMo/kQ0h08wfxmYnPvjgg5f+5d3XPv/szMDLn47EYgO/ef73d177/PPXXnt3h7w5A6ckZKWm4hMgLZaqWwYGakUJWIseeGVtLvgvueBTp+RGXik/8KtfHchvHx09P4oG+MoDeL9StAmTv/BcPLP6VC7w73wryr9cij9idJOaUgwWTfuBA/mtXWVp+3bH+Zf8F9wv5d8zzz31wwHgz7H2hZb+EeLtSryTU1ZRkpSky3vwX755UHZxVNp+8uRBXeXUFI4azs4+fPDNqakjam2krqwaLFimUZZRfbiRbusSLTDZkinNkMoLFZxeTvBHoCinMUDMlcDVi6JuqhEccCNxv4g+nOaUvQMJSBBYLcQDi0CeV1RgScznUxVTOCShsqIyz6jo/wXaX39EOhCLDlycCCpmQP6d+vDYimt2FruQ4GLpBzXgU3GO4Wmjczywge3Hferp3eHQAAAgAElEQVQY376Mgzhy6mVaA8u6XRqNARCo5cIbvJ/853/4H/9TxdZ2ZR9G/O5or1WpTLXgW0watVTjja789qHbNn9toR6uF492Frs9OyeHOZYlFxevVHgURqPKTAZU0zIHCZl9dNlk9Jg7lTm1JjYAIhB9sIGxWc9FAw6wb2Yzo3CaHY7w9bvvv3/2dkPE671/PxYIhcZZ8Eq2eY/WZcChqXRzY4ezQYeNwNVCIzApWxQAWN5FUyAhjm5D736iC0TMgKD0a6cqsCtxxPk+0qyeetm0B461fx3W39nQ+JIiZ5WsqjlVmIlC4n5E+rWsTXyg6SXsc6qUysS2Dy0QkDAQ7gN2q0KLAETPe+JE7gnSSg8/BW0hZTWtujppe1n5wuSkg+ds8wstcDk396iDLpdy6fTMQo7M5ZoFwYSTxMDjOqMxC28212A7iM/HRi24iQPTRbwvHDZzVrv5WRZuhTZh+bMQ/SPz92UyUaqiBLygPUezIcLuU/TBqMouXY89vDcxhFM4eiw8GO15m3VagXxH+We1eQwW7Lq8EIHXQgfIP4PLG0jsmcG16lV577xTmCnXtbcX0y1beD9dHBu7gKN8QY6qfAJxccfMLf9d9MF/+OCXRxGB194aIKHAkdbNv38Nzrvv/vNhdZY0A57SDHgadEUZzbQVu0XQgJSDK2RCtGCDb6ydjIAEPLW3heP1e3E0TOPo6FfnR6embt65c/POzQdX7pSsp3ejp1efWn/iwMEjabkkHIgQRPzlrk/aoWEx+ndgb7u6eSj/6D5xIJZYBZ0s/ILQMDm55LmnNm966gcDwJ/95K82vbCm8mXNIVkQ/O+mtCzjtpOrq988GLp48OTBndW6iqI2HLYJtpSECrZs2eYyDYFI2rtzu0KfmY8TA8pQ2snJAjcBgXpGQXK/Uql8rQWm1TPtZa04/fTN7Mbqw0LgDwCIvfxbdqwVgcQMT00VTQklMVNkZlaKDKNvSqfP760bikSDQ58OgPv9/Pf/BvIPLg98KWJQzhCB12KItXr0HqWvlwa46avs64f377+3mKM3Gvx+uJMDAkGUuQy+re4/AwH/x584trZ1JyBfbWBltTmoa1qGRrzuy5/eu84vzSxntcgUCq0rBpwlKy/h4tqP3sqmkOGeH4VNGJrvHjwHl6oERWfw8ph1SV9bG7HwITdFoNeicl/vxa5+lTMkMYM87ez1uy/k1EbdwXt/vDveIZF0+PRGj+eCyRWNBjp6t4bJDoyaGomhub2xEQAoeN+4AjxwQOMQBwFiGzAqQCoACf/iJTCoAMk5H8cfKWySS3uqGozTirlz5/rP9eMRFaDHeGZj3ZBcmoAfbUioFbVfLbIPuRAOk3gfOQryjtuOtMQDK/p5icQxDDJJpT2QjCPY9xFbheIC+Se3mFpb63Ap+qGZpeNLk5Oe5pFgsLu7p/nhdSfc4RaWM1OrtO6ot99jQxWIGwVw16+kJsxznC8avatcWgIEIv98oV6+3xIIjIexBY5WJ3VS/NEBhIR/KFiFxeakW5kRpotf8vst/RSBt64Dk250yU2cnQpij8zi9FlANKoYqxb4Z/XI3ofXwv5OEv27FHDyErpoAflXVXj1nbdSU3S4zqlMl05mCuXgbF0NLnRA6vUxqgCW4GBhtN0+TkKBX/7hg79/5RWCwDMjH34ai8YmTpW/8M//gmd3mRBjr3yzOK+FPhlEhq8NBAotIUJB4FoR+JtTcgXIv3/CQGD76PnzwD/EH9DvwZ1/IZptffLTq6vJSQUnh/YK+EvIvxNyi1PTCu63rK5F09KVdlRMAouFf/FUMI0G7n5h146iHc+98AMpg/kJ6fxI2F/R9+4UHPCunXgO7yk9kXQi/a1vvlk9md1WUVxZXFxGlFgF3CrOT50/kn2yVOMaKMtu3ZtfmWOs1+1tFZIgOioApXJdj0JZRZMfaH+RgWIMUC4QsKwNfXB24+EtRABiRceOHTvgxxYCwR0iAAkCsSKGFEZPVbQVVylw0opSa/AOSAfg7vjlRGT67BevffTBh8eCrsvkpdgHVg1e83B9mK1GvUKhYOir2k1rXbHqAAk4o4S7L4vFMBqXxe0FOgXu/vk/AwGVnLcuW2dSKesxaq2prZsIRmfv//YhuzQ/s106VCu7MOsV5B9ZLkLr/T2y+obFhnqjh3op/HoGogIvgQ+OjBkbaoMuC2Pn3NEo8cEW99e3sGLWACqGYewYBYrURqKulXufXB/HUYE1vMYEfj5Gt9dJzFhe3Skx806LSboFCCgG/06J/KtWccqOmpBQA5NoAxYBOCTyrz2RAqHRwKG6woWqnPoxmR50MVlUBBAEAajyKPT67h4yKDA+B+ZJ9mko+1Q4boAMBBVlnwLeEDYCAA0Kqx3+VSCTlFqlKR+zg/tyxYOxJZ3F0L63Sy1tb209emZy6dvTS8OG4EB3d/dAzDc8P7O8nJUhzdquDdzyu71waxl2AOc4ngAQfG8o5HTP4krLpSWcucpLOn3uW/C4hUDO0do/Kv/oAhLUfzRfI641p4WKKnHBAo5tiZfp3VsZUNrtDOIP5KvBYFFqjQaVVeGCT/DMjcVidy91kOgfclZi93hs5A6kr99W+M627amZWEqAgzUqhB0zDfUkEihTePC14iAJYbdFofCQOPXXf7738R8QgSXvvvvaF4jAiRjc5tOOPv0v/y9z7x7U5L3v+//2b1/ca2bPsBwR4XCpwHDtBqyAXBpgoIuQSG4kRGBIDqQhhpImJPJAtCE3N5E6lNK6S4rj0AVyMCZl1RHt6NENdTkcaCunq1DHqkXX6NTRTm+72tNtO2uf3+/z+XyfJ+Da+/z2X/vXPlBAK7fkeV7P+3N7f2oTPvwwJ68Np6uKOuN2HxD8qWk0bh1/LBP47xWD32ltMJnkzVgKbj158o9R/p29desjXHKJRd3Yh7U5MR8eLEvew5c9cnjDgx3JFrtR1lyZDM8S3FylrQTAEl7trecBo4HwdlFnSnxKalLiX/9HaPr/5firv0xcP6J5PyEATq5gACyH11cHDhhSEh7+8ENRF/CvCq0Lis8WVwH+ioqyAYAFmfEWiyyztbU5M86g2s18Q9sEZ9S2UoNJkdImjR7KjUUQnn9lZeJj9+7f+6icxF92OfEPANiLCKS3vDbEcjAqQIyF7937KkWhxu5XUH86JZ4XN9emzJ/D1/kYs3/TVx59iQU/p4ONO+1bWNx56tSpabODPN/grD5iN+FJjTOY3y5Nm+GKnPD5PPa5CNZnA3pPePyzv//7//3/zNnt3oBdnwX8m9Y1jU7Oz1258c0ct/z5SqF0dvLKlfk5MvvAfn9huRLOO2UtLaGwdESvIt+RIyBWsPgyP39lZCQSeMmDo7DBOa8X/TMD46F+x4lL38xbjSfgR/RNjQQCU9/86/Xnu7GpTVLnjszPzX05xwSmi7Nan+7HyVe10R48V9TYytc/ChCBAMHkF3ZbNcIyTIXBAgEqawKUbdR/iD3Bj7YH37Uptbt3Li7Cj74EOAB1iv06IOYwytO1NFE/oCxqBi/AT+h20VkUlO/jTPYNGy6Reaj/KPQVCKiGRwUA6MIOFF1BTnvJfpZAorfEP1lBj0zW09oofsGwb9/ym28un+H0LQfqvZrlN6+tpGfggrJ8cz/atly6dALYQZbPeNi9XrcEbmWO5eWXXwYCOk3uIev4bXjc6uBJj/b+gfyj8JcBkEc4AyAgUOE9xQrC2JJOeVybg/xLb1+f87g3beI2oRQmaQvyz4mZCbX/8ik0fnl+HzsVGGcdhiyzWaEwNBQW1tQcyIhr6yrrpXStuKqa3+2KiwYRgWa/YwznlkE5BrwUoQwRcVkc/FzC++/fu3t+6tDpEayGVA7UJiQABWsTlcpesTR/NznT8CJwhPXCRNZrwSwKxrG46GTwO6Mqt0b2GiYCW08/eAAARP4BAG999VEJ60UvefgwJybm05Pi7VtYN18Oz7gd1PvX0wHyT9qkq2+SlhVU8sPAfLzL/jmv/gCmedkpGTvzs2t/GQD81XrvyxOpP3wVIQFFiYQ/xFBvSvzeHTEDKT/88ENVJ+4ixCpv8dmTt6qqDmZj58XevWVab0SKHSO9aSr97i4MglkOsK0rX6NOW8dfXDQFiH4JGwHYmE1xMCCQzIyZAGRHL7wIcfCx7LOdzCih89jqeZPJCXf+8PjcyOhUIHLzwaQC8fcMyL/IlStXPoPo9wzzYMNzHqLSxVsrS9MGFTV3sbOaJpC64T777bfTflc/sHTcZ7IHQMagpZsnPPfZv/5vQKBJL8+Cq8PSIpXN+yKz//S1ZvnzxcdS4N+3oMng2ho643LwDQ9Y8cN5T1pjfdTAdtUNsTg4gAVhiLvn5iNT3okLQTXuR3OPI2V8dh/6K/zhznz4xB/8Tk4fmYvc+F9fXghZJSEJtvCYvOMXZkDy7UOBGfSEQzMTm1DEcJJ9rrjmxtb1ELgD9F9ls9ll5Htg9AqLTqgBjwqLkBB/WAPp4a14unqkGdqGaUTft99+O3Jl6sqULoKdK4Ayr6UJezplbCekYIfP6CeUezHfF0T20WIjo23jkl/inhrEN1ZAUAXChxo0oOp3qW1A1szN/HWFcfDhHIx/jcrmLikKwMzMdgV6+pxZfrm/3+SNmM99vpJC51B1en7WAjaNTMxdOoJmYwDAoX0up8bm5TibRqN2Lp9ZXkavWhcXvFDHutNn2PZT7H3h18+R/tPxLv7wixiIgF58cwIR2N/PDwizXat1oeDWrZveAP7h0iMb/moOlH8q1bk/XIF77vPsnKNTAbesatSKmppp+c6rF2v68tNSMP5tJneNTHFRMb9jRi43RBGI/Z96/TgWhCn1yBCIKvA3+3PefwULwrMP7gACy14YAAKWbO6tyUpjt6UDgEC+J5ApQJ1AwCkIgp8UgSAA5Zy7vhVrwa09gL+DJw9CUHfrq1WQfyUszVf7MDZhR8zhvQcrNwt9LCUlFBjHZCo8RimcaM09TXAGyHrKmpNxFrhECHoxjcukIHtNKq9Oy99ZWF5bG/tLAOATrc98zUO0MQkIfyIBSBQSNTYm97TsrAAR+BBzfNTqDCHw2YN7M8v3Av/27n21rT6ia8sUl2Vmy1WKNPR5Rg1Ylm5QU+tfHL1uzAAS/orbirr4SRCxuLH3q/v3vjpWjum/KPxI/8Eblgvk84HYGn0su1Dvd1rR1nR8ahTLY2s3p1j0+/0/3fHiqXhBMsS34Q+SKnM6zNfu3lqRK+BGy088UfMpxcFfP7pyCv6aw1ZCjcnmBS0z7tPbgiwOnmuoaWiob9GO1gfm7/zT//I533xrJQ0N1+7M+yYu0GphzYaKn98M/KvBNQ9Zcjbx5BpinWW+gBGRC7IlYpR0h1FbaTg3m46ze6z9y5ffuxQ88ePCgsMVnD+E0S/JP9CQErstDCEjF+wfcgc3UaQ96AkAR7DBJx1iqsZo/wsy8AWpiZqgrSARN0bAvBO0UALp6cL14sq4jF0H4OJfQhdrOnDHhUWBzSENfYXYBxPF35Paj1ST16jBgQvOBNBRD/OHjSC4zkCmAOm9Hh8S3M3mMqn0wEldcg7N0fMykOdfq1QrawNhmzmgGCTViy4LLpN6cfX4cYA4LqSR9Sn8VDGdcI+54Fzol/Rr9Co/+mypNfDQcmNj6Na4vEw+MS7rPom1u5uXf8Y/41897vckAsoNFp6BEAljy7eQCvTZICh2m7YiADk/tT7D3UXt8INiPHduGvj32fV13yvGP7XZrFfU5BdmvH10J/KvDfiHCv3VAiRgVXV6BnMXl8undQ3YFeh3unC0buLCBZ+Pb4ymVCBDIF8QXlu7Mzc/2QwITIqzNBzb06jUsmcnP5+6kUZGaEmTIAHZsuCRqDUCEPAdmd6taXoH+Xe65+A7aPtO/S8o/3LYeo/Yh9v3xOx4de/e9iezfzkxe6RGu66nMrmgSwonQRPwrxXbYDbOwjHdx6cBS1I74+LzC0tFJSUJvwQA/tVfJD5Z/NgQA0fpx/CDaqxRrIQH99OYmPbvHv5QtPcg8q8LGLR3L/y/7IN07N0rtXhHmhvLxCKIS+VFYuRf2wG1Oa1LiHzj+PxfNAhmArCsiLVAZ6Pt+Vf37n1UgdjNZOw9JmAwWgo5xrKBolKzGheLua1ho3Z0yjc/e/oOyr/fPfP9J3fmT13BLnxe/l1gfVhOv98sb1i8e38ly6wWFggPUucVdel9+dn8KTjZXVaIg9Umky9iADoZvZowIPAfvjY0NEwb62cjvsjaP31tWnhrBeTfTZxQQvlHGW/SmRT9+s3m6WmgH27W3Jk1zTYWR9d1zl3CxUb7ggGja6ifXBFwkt4e8AbC8EO+/ObnJ9yX33xzQa5ycuMX+skqWtLvcv33X4/bXWfG/Kbw6+7QhIfS+EOczYTOn2f605rJwZUmgEkCVlYaXIrws1ZWArHIdS1sGVx0FzDl/1rFrT2y+N01DXJdZP7ON998c+PbGzduzM5OTqFrVX3fgXTye2Sd7Nr1gu+69LNgfx9G8iaHw+GnVhncaesYJhAaiYL4nxrbnvHQ4+JR8zm/Hw0KFegMaNS3JGPncwlvqLkjRmq3SV9rHtVqR1txx0m75fo/3O6WWIcAgcsvLzvkytHZm2s3b4KYHfEeOUF7RpeX+63ohWX0+gLTKpPHpLbZwyE3cPDMMksFArrgL0B1st6/Dfhj/IOD32mik+O6K+EAUeaIVkM8bi741FNvvOvmcOYNJ9+McFopvPpz5iU2+Ts0RqdCdzfdcjWYf1UYLl4tTLv4dnyakvgXdVlrLCurqk5J57dNw5OgkyMCzf6xfdgYPSM0RmOpjlKB3z+zv+RDTAVa7nyCZoE3K0uqGzIGNn+4ObZNppXyK6vYrmJSgFPrEnBEMIehhemn601uCxaCT58ePVlQmfzqQTFWNW/dWv2o5DDb7hEbWwvy7+DBZBbKbtnMx7abcfLXJsXib08TPHTa0R5genKlAMBo00s0DN4uqoor3J2WnbQ5p/aXAMBf8b3PidHuFxb6rtOvApN/iECsR4jbpMrMvNTKnILHxxMe/vDwIQCQrPvEvcAl8UEx8K/14OkHD7SRgFQMCMwuNKuz2nBGf3e+ksJfJet/IZNopZR111IFpIj8nztZByA28x776t5XH4mY7CvPPLYXfoJyTAGW9x7LZi8IQVF2g8b/MmDCYbcp0g8EApNrs5bzd+999JuPvz805f3D/GdodTnmXO93BfypFHIKSu/eXVzfoT5IcbDGianAL7+ev3J5YQziYF9A7TQF4Oq0+2xGe3j8s68NcGpyQU9g8sVHpuXPV+KOj87O3nk0P3cdJz/GNDbUgaQtHGq4wi3TuqxtOy9evBi/e1tWVgOt6xRiqQvjgRPDzjGnyfPUU8N628zEhA2n27BRDS7S5ZffXOA+f9OphivQzwH5KKvFDb80MTNjw82NL4UGZwB6aPrpcnJuN8qioaEMCIFZDPwaAbBjoNjhxB6YMApACzYBMivoWSH8BR3fI22CK84SiczPo1Us4A/phzsVR+Df0l1KKo3CT8uzj196pLNYcO0th7LP4XRgg/QC3yXocEQ5iMizReGHx/CJU6dAAuoxzYb1VsoI9m6hVbQoA7fEVOrs3tHmViXwrwtYkZm53zIxfptSd3VDb/4EKFOPzK6trd0clWojvnHU8P7Ly8uYU/QEfD5fJBIYDwY1apPL7d5q9wX7z7yMqcBll9sa4jj0ChSKv0/wT3CWYjlNeZSAXhzYFRDo5n6Nrs8uNcT76PqMjs9wmpwzT1+Zosk36gPgewyx98+sUEzXxO862rd7dbUwrovFvwXoPlAAUXCjGEVgyioiEHOBuoYlBdwf6OTsdwrjcQyBn31DucDfPFfy4Suv3Hrr7UOfTM7PTbX1lm/O+bC29sOS1C6m8DFFgbTDJSERBCBjIHXDkAIEBN7Uqt1qLfkD3pw9uTc5MTWv4tgxAODqsbzN7EYUG1uyZceeT1sza/nsn1DN3ZOTYbfr2joqC7pk9RZdkxTkX3NysjAJshkbmdabADFqzqtKj8/PqKqA6LnklwDAXz0R/0a134YmaBGrf2DqrTe7Syntiq3NS6woTzl4OCYmFeJgCFqz0bkKEEhzGgcPnnzn4IMHD26OeEdGG8Vd4qoatTm/rUhZ3cb8EPC/OGWcUioVJoEFBYhfhp9+EzdiCaQcEVghikbAfDQMUpCHH6i/8gyz4/M//fTTmw51RDYbOTJ9/PSIGaPfZz5+EYu/j77EU3FMcwTlX52w8RzdAPrefjvr7cW7d8/jRt/1iScbnmVwkmEcvDDmctttAZXDCfoPR9uN6mDYY1hamgZMeSLzEP1CDHYc+Dc/9/Xt5+vonEevy24KefzmU7RbuGZn/tX4tIzCndjsOk1Cgv9+WH05May2BeGDgNo6OOPR+P2ctX9sAedrcbJe4wjaL8Olo1DDZ0gk+6wv0dd/yWfEzY3d3W74h2f6Ua26xpZxWFiCAMQsINWAyeC8YUwdFkogWOI8QBGwlK9+SNHNwOLVey/h6pJvAH934OWbO3fQP0TG9v2N8vTTCvgTol5kn9FGtQ6Nw4/7kB0LDseygyHQQf85GAZRCsJBWUH6wKhCH0QEH76yamtQU7CZlnED//bEiC0eS09z6ygomp5WFEqZ7bqZpyYmbt9GrLwMAIQA0Tu5dnN2VDoZmHl+wgcUurzw8hiOG46PB+AYnwmFTfB4D8N9aeL57v5l0I1UDbFyaCYBskyQf1H+TbElk2yvE/6ODQICpxXkWYBPnsTNbX393Xff3aRi8i/g04OylitA/i09evT1hX3R4i+maemcUxjkhfFvH605kJ+RspqW3gXP0WuvFnS8Sou20GVIXAQIXGUIxHZUOEv5VOCQSzPBGqP58TghDv5NO6nAvrXTs/PzI6crk2qBgLUlJckYB7Nt7bigAPel6xgDhTwgm4ublVlMJvnN02trp+FmeHBvpkgEBEw8dqzqrKiW+AeB6sOcHTv2tHfkbhYmf2nj2+YtMeUWj1FWgMVfJv+6UP4lJ+euC8Bo4YNygdvLq9MK8+OytxMWfwEA/Nu/3pD829D1vB4Ci0gFovzLzoboV1lQEksuMamp7XsK2vKSAIGZaA2FHBQXZZ8VnwQCnnzw4I9//OPslLelK7OoSlxs0CjaWnlLGBb1IvzQSHU02gWDCpBC4E4mAHsbCXHHvnrlI4GAoigKs1GQAv56K7MVGv9buGHn3Ln4Nux9uSmLv3b/3kcvYO9LhBIxeCqq1+Uf23jekIUA3Lazb/Ha3bsGlZ9qbk/EwZgK/MNlBxqbwo3fwdkCXrjS7Xqb1W1emoZAzuR2+68W9YzevHnnDso/1vsSnSvAcSdcLWyQN9TkZ8SlxKVn5Nfwa9QZAoU4OHAEUDZ44XrANLTPrVaBMHHgkBnEcHp7yBawmxYWzGaDgqO16zjK/Oyz3TPjPra5kfP7ATqYLu9fHhsaGqoblMGlxNv4YwUk+bkitdPIpuCiVvgQ/vacPt0j1bbAtW00AijmL/HaD0J5OHCpNgJyVFgJvDHrx6sjHT/XgcIP26ORfQtOB8DFIdBPEIK8EvQzHbjeCa3fcCi8FosnrKrYUlLSDi85MTFSm13XVdAM+k9GkRUAsFL70usXLsxcuPD8YN0yAnB4k8keme1qUzapJSE7/CKnLr/5Zj91nI/Pz/ls1n2SkEmjOmHz2XEOrZ9zYxy8sAz3Fzda9kTlH6X/+PiX7TRhvyr8EZ4zWjGooH91yqyCh5uzb90K+s+vJ+MDRSAY9E6N9B01TC/deUTZP8cRvskmKv8MNVcvHj1ag/bKyrazq+nK5tfYkwQIxEIItn51FrF6cP5Og9mQ1SC3UDUEa8AuzTgWX45oHFHH6AdUEK798P17969Wr1Fj9GtAHtrIUVsh005OyliiYoQIuJ4IvMPaYUYmZ7VGt7rpNM7FSdF6tTe79+HDh83JQMDYHPgi8NWSHtbu2LED151jLzQZH5QQzmJilEa7pS05GeWfTtciU5Y1E/+ScwUzmCe6/yCQ7oyLL4yvrqDiyS8CgL/6iw2mpwL4ROupQKH8gZWHxi6ptGz79lT8f6l5SXmpvW0Fe3bUYjVEXEQTWI3YEg0S8ODpkw++eHDjwYNvI94WGg3JN6sblF0sjmKtf/BudL0GIqQAy8oED5hGnH+jyPcrAYHH1qUghcW95aLeGo3/8z/9CQTg+cW0Jtb7cv7+K6+8/8z3OPkmFD80QvEDVRliCaG0bVf+7sLC/L6srJW7K4hAPg6OlviwUfnKKbjha2x6i0UF77xem91uM3qsnAoXWahNnHHk9NohxN9tVvA7siHkMZvlFgvw7+jbwL/S4mqq8tH+TPgBnkgFIspADt4e38RxGs7qdjicy2Njbps3YgwGfCaA4YJf4w4bzVy/ZIbt066buTCDi5dcDrNcfg5+9LEzddgNKHn+eepCIgAye9/ndrvUQaEJ2qLrO9CEMGvSKcxUh7BBpDg3h9B7ROibj0yNQCxDrYBR+hH6tEz3YcoPF5djdx9JKBVNhyAA8aC3pPqc7CP+T+yPG8dAnsAfKtMWY8iuiTuMfsObt+xottj1slaIf2WMfx0IwIICqXdiZgYIeOHCmZ+WMbY+As+JRdkm05tsgSMBIwjAM2T/IglOTARsLpysxQndYBg+sgaDE6F+XCsAMnDMhYUXnn+EP4F/9WzF5HqOExAo5xEINzUIqE32l7a+scmk8qL8A/2HvmaR+palpSt3vr4OJ52T77FmxV/CX8PVq/Dk9+2Ol+FEdZn47OpqV/NrTKeTum1sRJ3RWVVcmhK3y2B4Gzuj5cwjgcbjOBupQCN5MgySTQx2BT63v/b9V96/e75pjVYIN1cKO4kapfis8b8FEXBDGMxMoi0ajWVydnJ2Vvb4+MmDcPE9LHqIR0EefIn29tr27XkJIP8Os7Z0Vh870FQAACAASURBVPzgsRaTbbEbtc0FINBR/jVJeflHAXBCtA+aXkjwxfaWZhTGp2Qn8eUQDIH/758ZgH9DYm7j8NvGgzKAfA2kV1yd3pZcEktJwrzY2Ni81ArRpzl72ttjHwIBGzFph2WQzoNlB8tOnvziwYMbX9y4sTbltUixq6yoRq3OV7YJRQ+Kg0fXI+BS1gPTJRSBs2kOpJdyfiJA4Ee/w59hAwARfxWJxSrT5R/RHfytt75T4v1v7Y4Bot/ffdp5cDLivXLl62jxY0JQZST/DIaGozW74jPSQZXtgqh08e6tRbMK2++pRYVutHCfHaq7/eWj+VOg1uACsiiAhAFCIPrJcSAB1SqHO+hl8o96DFnrXx0zO4IrpcEilwP/LsbHlbaVlbWVxmVAcFPTh1U+2ljMt8TMzEhQmw4NQRwc7B9zPx/mnMC/cNAXCNh9Jodf7Xf2WznztMWr5iT70GBraKi7u86KXieqaR1oRrimcTghZL1w+4K0mYrAJP86qAfGaQzVhUJog2BpoLBVj1uIhjcdwQP5d2n+Ejryz0ciU1plDzwLPUphA0i05CGUOywKPa/7sOxpVpmJf0hApgHZ4XwSf/QH9Ub4baAfUhm+MH5ZbCZp6apMaB/IBPnn7Skg/kl7yujaQlfazORkrW0GEXg7DALQoQEC+jxBTUM9Ctkjev1lpzUcksDDtOyyTowH/AvLY36FJaI34do9e3AGPRYRf1QQ7ufUG+SfTscWuKMAJEs9oc7T10ddTHjI5XoO5J/ds3XrG8Mk/4zGuXFPeMLnC0RGvhXkH/mrsoyLQ4X8k++MuyiXZ/XtzkABAI9xa2v22VulrdSr/moHyVs6euH8L9qtaKCeGKEzGkQnnJC8TYxv2M9XQz77Bpe7ftz+u999+Mq9u4uH1man5iI3mwcSaj8EAm1JKEIFOIm/TAszBozAwfPvztTkiIpTj8xOMv4dBP5lPxQD/d552FyJ+IMj4WECyL8tOSVMxjHjAyRbzIDSjsYvEP3KWiy6Fq2yi+5RxL/c7e0sB0jtL0wClqQWpcfHp1UlsiESzAciAH9eS/y/FRqg1+XfRgAmRhOA5eWNXT2i2u3wNxWpIP+Qf3BUiF5NPhyDKvChiNpVRJmNONrz4PSDmzce3KA8+pR3Cl1iyqoNGtXurrZoGCxIQaAfv0O4izWhkQBECxiagSPYYRz8u/UqMDtiextM/h9/fOstwN9q8cjc3MjaIR0Ovn368SeT21aWrqAD5Ybel31C9Av8O3r07V3xuEWkNK7w7SzQZIu3QARidmcMo6fujdNx81dOXT6H2mna4DfZMQ7Gep877FGrcJ+32+4T5J99/ILQ+wKnPIa/8qPIv6vp1cVl4lYgIPb7b6OhT7nBIFRf6urQKtDtgu89GHIvLDhdocGg0xoaDAXtPo/Jb/CO2zWcc+Hy5VOXvHps9g4/7Xbh3m5gjgKuR6vrXeYV2H0h6JmYAADy+i+ZMoBSx4K9GwUg/NwqWj0EIavtCDsgZpzDakEgMKWVKakHmln/SXnrRi1PP/Q0ZXXeYBA+n/hl1pOPNrye4yF4zuHgq7+05w3eYl0E2KdSqVnjC08/eCEIYlNivUXv9RqHPSabrAtUtt2OG4FtHmNLa0FzGeo/ZVkrXlsdzJa7IDezxTMzE55xjyEAUQPCT8XZMOOnj+g5SXco9LQbF1yGZ5636/Unhk9ZvJGAZgz9yMKgDeusDhwMeRnrIWP9JqPFwOOvnilATP01MVdRvtR9oKWvBggIz1qDQd0/5sC1SluHVWR7ajZ6ZjzBUGhiYjwycucRut7zOy9R/rlY9As8iz8qz2L8k6IABAC+01p+drW6kYlAALyoAke44ZlryzKkVa9eZRXhrCx5w3TUJkZjvyDYxOD+zC8/u3EDM4HPtYMKvP/W0UM0G3K6srbkw5IPIYaN7YInb3ISYU69MBFCYIQJQIvGZJnEarBW+8VJ4F+2mNTfiw//a3tCe/t2xF/SFgx/mZbje18oDRhToPCA/EvuYL1/TSDR1/Vf5YCgAHP4esnmnITy0oz4+NJyJv9YY/XPD8BfZSPmNuBP6P9LZK2AlP4TkfRqTGvbk4AiMTE1NymPbUzKIxV4eEf7wENAYEEm8EpU0AgYO3kSEHiDP76NRJp6uoBvhSq1IaOr5wkEboh/owuRSAL20hyIALv1OFg4EmPj1Sbzjz/++Plb1+4Wz0bmIpOHpgxv3X2Fel8ilqUrj64PRttQmfxz+IFKFryLoypLqcaF69XpV6nzKmvl1k4D2dsJA0/Y6AVQgUjj0ZVphRlT5HAWamwBNr5ld7tNHNraQ1CFBT+HLTpXwHpfIM6WA2iJf0XAP3TRry5Nj9+F3w8tgOUgAtUO3FMmcZqCwa02k8vlpM3CLusmJ1yo5OJu905ZAnCheRCBJ/TmxWmNNRQKo6cNYHZaoQkHh/8bfA5tLrs9EXzd1tYsBMDJtN9Vx6lwGSb59XEuEG42Rj8fk3/APu/UJJuE27D6Y73ZhQk/yvdh0GsXqqY40bZ+IP/OqYmCKC/XDxDKKrM++il68oAh9gH8dEg+jV1vgbCwrKD9sNym7GnxGnF2RCcta27tgShONtrV3Ey1UlKA8Jtl6NFlIhQ04e4BeAUEHrHZApewgdKNVoGhYNDN0aJ1T2De55ufn/ON2/2XFzg3bj+1uj1G88LCmZeRgU6XS23hZ1dYA3QLWgjgZqGmjceBvr6amposhcm1vABo54DSNg/IP0UADQbDEqu1222ZmsOKm+OJ4i+Ofsj70i7COda38wDTfz14pmOzUmP22dI2MfGvQgQAwQ8KMuRZxdlFQjUEb5doFsib5rtsnmg1hKbxbjzAVOAzv2lPIKestU9G5uenepJqP8zBasjmZCkSkLoBSQEyEQgI1KlNat0kjgY3Pf7iIPAPgt/v4OWTh8ntCdu3Dwxsj01K2IG7PnL4ppctOXxcG3NYawP5V4CTv5j900q7xJmZxD8SgKAAha3ADH8lqVUg/9KrUvmuQPr7XwAA/xr4xgAoVDw2NAGyFhheAJZnWux9yUnAPQh/c1PpyItNSkpKLK8YaD8cs+XhDz+kFuA/FGWKu06fPr22tsbwd+Pbb694I9oupbKos1CtyVK29bAW6CdbANue4J/ggopfkCiIcfD7v6sQmgFFqZ0Gk3rxRzxWqtso+j2k+PxP997/7fff84O/M86F5SfaUNflH0Wl1VVFnZ3iomq+9coACLyogAsZRWAUgTQdRwiET4Qr1mB2mGxeuIIxFRiyoqFzOMi5qMkm2mPIsoz0fQB/aXHAPwhKG8lGvzouQ+hzkAsqcAwkRXjwQtiN/MNGXU/A9lTQNTTkCktABc4FjMaXxuH3AMV3+fNrXzQZOatb46co2+gOzd354IM3f3oZs0JwzNi1mVhdxPAXNBOcj5UWk01SRzsiNWojr/uOBGw+n90X8EbqtcrTra09wtaP0dGN7KMigJzpPtygK9Cf0cwMAfDGQ31OrYIw9xyZmyL5jCoV9besH7zwU6BbdD0y1abXNSjstr7DMXDskRm1Hc3NrXCXxKIvtr80NWFunf02WCrNbE4WN5jctquFEbudAAgC0682njAacbWA3VonwZsQBzcUTygkAS1/e2Li+tz4hfDw9LTeP9YPj7JJY7cH9NwZpgJBcXNGNsJSz2tAfrsujz4teruiED6wu8XodsEtyuE0qfVeuCtB/OybCAeDVonV6RpyBgIhvvVZyP5h8XfakJWR3mBoyOo7oKVVOMoeMgxuhRdxY292dWmxKJnRAwFSVi9P78iEs6WquHSVbwuUN+gadLxpfj+nQQQewa79M/skc1//KxuPe+a32BRz99okbxMTux0AmLN5z45MKYXBRMAIf0xNKdQaBf7VSNPS45MHyzqLqjD4/eE7wF9tQkJS0kBCbAJtukRYkd8fm9Ch0Q8s/nYkF2D2z4LZv7JmkrDJeMfNzU1qT6iNVkHwJam8Or6wsFRUu3nzhsQgAlD0MwOwvDxbtGH2Q0R6EOHH5/5EQg2kPLPQGDRm5NVup+A3EfEXG5sUi2GwKO8wPFAoAhNF2Kki6i07zZaurN2YvUGzBFPeiLRNWVpW3aBR9/X0sC5Aof6hXE8ACpMgAv4yy6MikOLgxGPHEIGJFbs0mvMrK4i/1TaZd25q9lDk3N17r3z4z1j8EHpfPl+c9tGiL+pIVrHsn+HoeV7/FYHOFIu7SuNABBICF++uYFcgmhFBOMns37D+hi4x84hAVAqKcw41EMlmHzcaTaGw56lf/xo3c4dnZvgiM0W/IDIZ/+LTS4uLyhppoUgjmoMp49J4AhICqTHaoVa7uyWo/ygvFZoYH/cFtvY71G5c5mOy2Y+wjRVDLsfnn09HbGFabQRq1uS2jv/9o/fee/On5e7B52cgLtRLqQmQCiAkAHM7vrVhmRYE0gkbCaUjNkCfLeDV1WulgtdzdNfHk41+uE7PjrbN+AVsRl+A1thR14pKfwpXej+JQIQg7rhUo9SjxjlqcOHhR5+q0MGXhVjaeGJYbzmgTM6J2Vyh1Bnt+poD9YBFIB/KV1zU3Vw2CuCh/B/SDwsFuOakSWEyyVc7ywtkXg+28SEA/cNA20jE6+q3hqySIRdugAuG0AgaH8CQJOypCx0BeXji8vKYG8JWi96DXUN8GLwMstjCjFv5CggmAaME5DuKAV4jGmyhh1uWQ0/yD2J6uDGEwvCtnMObNr00rnEuP1H8xeyf3pAft1NuyFrnX1tP9GTH8z27s7q0CDOcuLggWWbZ2VlZ8CrmAjurquN4BGYxqyyzmfLU66b5CwuuQd4x+vuP/wsGwvfuXjv0yU2aDclNINBsaW+V4e8zNYLjcIx/OqPGqCOXrAOPj58sE3cWFYH4e/jDiw9fqAX6JeUOpKLt357D/EA2yTg22xaTI7PZdWUFHc1dshaUf6O4pqCApx8vAGtLhEk4+LzEorT4wrSiPJZIzOG7Yn4JAPyb8s7Ocr4Fmj+YCOQBKFoHYHZZmsLusbQlbCf8pQL+gIV8AjEvIefwjhisBwu4LFtbe7C2dhMHCQiBI17vCE38pqk0ikIciEN7LDx6NkbARXwRRCxmNoD4jYU5YFH2sa8++ggAWJFXquD0K3fvruB+YuXUnHdybeRfrt1/5f2BZz558Y730jzf+zJ8xBiYiGJpmucfYQn4h6uD4CyDuDQlPYPOMvlR3OsVnVZjLTEO1hLz5aMrV+DTgYDThnN+VSBgxNlPNZAvCAQMetySqNcbJf/kpDOvZqQA/8Ritp6DCNijVKZnXCUACi0xcJmo3dax5THmrtyPusXnm9FMm01WCbA7YJ/whGilHDYInhjHj61uTqXy9PdLJq77jmxaXpYMDg7OzJga4NEEAL62HgDnVk7aQ6YTGh/wLwDiz3YE53l1QBZldNebUOzY0OuCnYHk3xfU2DQo6ByAUHwxBvReQQGyQ4UQBO6d09NHZKmsJ/jp9Rv4Bx9b5AAXHZDwhB73ZgzrtW29O2J2JHcp5cEQZ9ORSytm0/HA8DfKPwqAUQAOZAWD5owiNKE82NOiNsFP56CxE40eLuexM7hCCv1ukX9uN5olYhnY7XGHxud940dOnQL1ZrIHPBIXhJACAJ1Op8moEwjIM3CkiVQgij8Z4U+KvlcgvBcc1PtiB/7htmmTyz0zaDUGfAAlo1+93vvHZ/906RkNBnlWDfKPAAj8KztZRnbpXW1FRUXZ2cfOllb3osat7OqbTicWYkmksbMIRSAgMIvi4GgqsL/f5LsACAxkLS6QMRdDIIjA9toPX7n/VtMapQJvFuQmsFa+yi50RxWqIJEpi9qkp0pIy06Qf6A3iqq/++7hiy9+0pHbvh0JlhdbC/Lv8IcYyeIoyOYc3t1lzw6xDou/HST/sPkFe5/56LeS8Jebm5CQwHshbEb5lxIfHx/Xu50PfzcLXdElJbU/MwD/9m+yi6o618NeFvQy8gn+LywDWN6Lq45kFo/H0rg5lgXCsXmMf4kUDyeACtxBCKSJ4fJWFIEvrh2anZy8A0Hwt9/qvN6mHkCgOF9lMqS3KdM38I8WrDETfRYBswpwb2ZvdvnG49jZjz766HcVWZxm6fHjxZUfV84WTQYCd9YmLRj9Jv0We/8uXfnsS7Jjoeh3kIM7pkuIfuUo/xYvxqelVBd19vayFW+gykrj0liHiqHm2LH4aayGjEUdMI9omFEW2pdi/4yu78CuBrMtEID4zdtks1rdT70e9NhNbkk/LzPlvP67eHU1BXd0kEMznNDNtEsJCLhh4gnNP+QKjbsf5MgZzNN57BBQ7ZOEQ27vlMXsXHb69b7xkBUubeZ66vZd7677fXfYrnFL3P2gVGcmtnLLy/0zMyG3OgMtJ5gATGb8q6x8YeSlcFATuHJqOADiL6BH2+b15fRPso9FvfUU86KvsppC1mGsa4ACRN0YCAgZQLMAQGQg/olGOgxoJY/jswhBwh/qPkQfKkoQfkZFfVpZZUzM4YIu7bTRZrS0aHVeS1/Kc/t7qDuniWRpG9wjkYY0WYXVHGICYPE5Uzdnk1dXFhw8+cUXXzwG6WjXUJehxjZ1aOSnn5bPoJkyh0s/QuHw60+HPKCTHKbwRHhwwjMzHtCbL1/2h0NWp9PVf+bM8piLjcY5TZzJW98i0I/e8EXgpkm2PK/J5qKUI5xMTP4BBTkTzv5x3fs49JrsnvAFqDtTKIRh9q8wpQbxV3OA5x/aK7KtYfiuqggtNXszRZ3VVaLKjnxDTeZzLBRGBGJbIMXBzC5VLl+aXjKwvSHoGO2bD6w3Rv8rdgV+/8xvcT7u/rUmMs2P9CTn5taC0mpvH+jRtggEtOg1Kgt+UH+g8PjBg9nYeQPx7+nTp2MZwAbykmox+qWUH4W/OZhOxN6XGK3dU9+ajPKvnsm/1sYCofqRm5tHn789IdoGWJJYHF8Yn16UtyH7x+cGUQGW/7wA/Luq0riU7I1DH0z9rQNQQA/aO5eJ21qMHqM2OSGP+MfjrzIvLykpNTEv5/CeHZsxDq4gApa3AgBffPHQIRynurL0wQdLFm9EBgTsaoM4uIF3iKGESA/boYlxAS2Dw6VmvUwArkfAPAI/en9VpTE8/uCD994D/kkjmP2bOk+9Lx9//P2hK1ewDYFvyaNIxHn+HOt9EZJyF6+ml1ZVZRP/UGjAt2zDHr1dEJfGp1zduYItMWqHc70xmk4y5pkPCGwAgGjrA+MT800t2BUIKo3bhL0xnNutRu0nb+Czf6txKWhRj0oTV1O+2kxL74iAcRmFu7fxCMwyu1hn2hlcUzJzYeIlD1DVqrk0H7GcuqxSeIODaOuJVp7oehq6/XydNWjzRjRWT1iC0/HjmxxOThLSQGi4W1kmblyvgOTiPbnHNjM+PheAH1WvsNAYHNsIPPmE6ON3GLF5XjjQv4XwdUKt9mNR12bz+Y4wACLXFOaNBz8qRk7yXmafQtoPax1Z6JFaD5RT2ENBo66p7QXM98Ucbu1SwjfUtUjbml843J6zJbkNyayVNTXRICsoL5qs6ojyr6AZaOh+1uoOqvq6/vg/P/jg210X3/bOjQcBYGpN2H5n6s030SvQHeTwsQqF0O7F47OpbSCaQSD/OhSyGxVylRu3l7jG0AUwaMUUrNP5xhu4pt5Lbc9T0Ti4hfFvEnfnWTxuTxDHnFXkeq9WoeMz5gc4DTfE+a5fgKeme4JaOjHk0JD8s/Sl5zcYGmpQ/vH6T0nVJogEkIPFRTwAM5NFnY3KrIY4eNKSK5OTWc5TxNoCsXfg4ts1iEBd/ZKOmeYPOS3eCfRkGF5ABFJj9PfUGP0cxMH3r428eBpdQXo6creXlAABSwqULVN89k/tJR3YcuDxydZG7L0ue/jwk4efdAwAvOCcyUsl/GHMyxdzS2ppInhzTDn5/iU3tyqp9290Q/GXD39zc5OSEhJq+U/c3psSn59RWr5diH5Z/YPe/hIAWByfn58OQXAFC3kreALy2T9+9IJ8YHAIGG5a0nqb3aKsrY3lJ+hSUytzY/ElL7GiEgi4Y0McDCIQ+Hdo8tDIyMjSlfeW3tMpvFPSHmVPWZrZZC7sovwf8Q/PCLgpFgkVEDHuAekl6ysWArMvCD9dosjAWdXKLz5478cPVqqbAqDz76D8e2XgNx9//8mNK48effn8uvzDU3HMf/7aIo5+GFhNtnAV03/Zjbjici8SkFa8tUEYXFi4evbiUYPh7ZVbclW0RYW5xDjPnCHDaCCgPCtfNnlnzhOcoiy+3WjkJG6bzx6wmziryZDVQPxDzsI3aisCIO1tzsRmf7T8QP8c1MFK0JzxgMCst7Oy1G4XuZScOePqF8bsXU63PUDdyZe8gXBdGHVG0I0tHBIJCEGX49RSky10ZNjVP3gdAGgyuTlDRpZao8pKb+QFYDLhD14HqnSewbAd8Ufdxi14UeNVjQScjLoa1OsszLMe/fvWnVuGjcNqNdYagIAUAhsxr+fFGHcj/chBXsHgZ/EKlQ9LPSCtaQmEn1cvGR4etthAmVmDan1DWZ9FJ+tqLajEbrOByo6OyvY97V0ymXK0JWhvkVHgSa21HQRAFgA3NzZ3cM9K6iTu4IkPvoB76tvXLl69qMd+bLtHEgzo+8+8/BMgsN/NufftC4XYTnofLj96Fh7Y11+3Bo0KNW4ndY0BADmv1xOyqzWc613ujTee2hr0GCPCEjsiIGYBkX/SUa2R+/Xrr/8aZ0eY/FPB062xwVOOsyibfLcHh4b27auTCA0HapJ/hrSUAw1Hs2oONB3Q8gBkxhMoA5Vt1dXFEIEB/5qphBpvyCqrTP40GQlIBSwgIJylYvQKTAMCvo3T6w26JZ0OW0gXzjn74VxBY0nh7IyaBbaXIAIPMZuYdzpygV+17TkDjV2jI1M6vVpFcbBu28pxVH9FxcVU+32YmpuL37syL2kz8G9zbQk7NrMoOqdk847NMhrNKWhG22fdCI2+8eFvbvSIjd2ekLCd3LAw+1cYzf5F0390UA4w7+cF4P/1d0U1ioas+N5UXgAKib/yinJRtAGGcnC9YmlLi1YKNy2pzu6xlG3PS0xOTmQ1YXiBt3mJ5aJKiIO3oEUCP7/bu3Zo7dB3AMB63RIAcGmpnnaoK3u64lUmc0YXrgFp66G3fFqYBuEyAX+NbBHIeicM/kSpFbtMpvomDad4/MEXbdp5Kn58/ieQf78B+XfjxjePvrzdTa1/Pn796hhFpSsriw18USKDihK0N20vW53WyhaXKFOqz1bvysKSm2Fxhe8K3GCURbtwcG3IlaWlppbAhFfhngBdhdNxRnXQ6rH7gBuafqta/jacq1cRf8WY0mzE9N+rLICDgFuMiZ+eFGVcXEZGRiGc1gqIfqn2ccbp11gJcWG30+/nwhPw9X1z1+fGB7vDQY8HBKZraAgXBns8Vufl977Qu/9weWHMPT4OAHSYjx6Vpl3NUpuC+jLWVUb3ZLotH94dknhsPAB5XRMVfVqqdcBVHQwHg7iraEOzshrxZxsexlYT5J8tcAT1Hy5yV2w4cIUQCj6mAZF9aCraIpNlNNUbN3HWsPZg6+Pw79USVcyAWNtisdltli64cHIH6GCRenIHiMCCnsmILRxS6+shNO/h+ZeMrwWvIQBbWzu0pjoc6+M8tqVdhVev3vruq/fTaY+91ahXaaz7AIEvj51xua1Ph4Sd9ONhjEpxyOf1rXYOfSbGxshMy+hVc3Y7IJ9799033nhjq8cTtOn4IWeWBoTHZ1I2KovY3U8//e7TT3NqXv7hzku10aYx+U8YA+PYb+/ELVXWuqjvFeBvW2mGBQR+PeNfBnPfYfPXSmUpbnOtIgBigJDcltVQnNrYlUn8g4cjOZnpXqqGFFXHsa5AQCBoQMu0YeeiQ5gj8pFpPt8YjbMhHz+3n9oC39Y+WMMt6u90VIIkw+nq/UVytdoy5Y14p/oWb+Eai2Lc+Hv69MOHr7HvmZwcu3kLXMXtJOIo7mWjdSV7YhotHr0U7q4g/+r50Q8h+7eBf7mx24GAKAC3l2fkF2ZUixI2881/mzceBMC/+NV/xKj/1OPvOrehRc+28tRENvS7XvlAE5gNoxe9YhmNu2DyQqv32OoLtqOJTKxw5OaBJBT1VrTviInJQQQms+hVfBM04KGR+ix5w3tor5nVgC0xePdrwMXArbQzDoOBtjK0ly7iB4FxBTnaL5SvB8GZ5RV5nWZO//iLL74wc6qPerDWPztieOtP9z4aeObj75F/0eKHMPnh5KNfrO++TT0pgKX1xblYms1sxFXEEI1UnS3NyGepOcPRa7cElxjhLGMnGaUCv51ssRhNuF5sYpyvhmjcYbsvYMSRDc6cf/XqakpKcVeXuKxRWM9BAqZ5b6aYtqRAEJySnp6WcfWAET1fcCzhTL9ab+LcVgkgzj1sPDHs7h6cCM/MDM4E0cs+jJepm4PYzWQPhvcNLfy4qOL+sPDmMmB4/CWzzqvPKk5ZfVvFhSZGWUtCLguBK3O3V9q6UQB62bArT0DW4EHso0KvB/itVqNZ1UbfPrVaBcJNzRPQhwIQ9R+zCGVvySkPXZMVTPdZdFmYJGhqmT4FAXT493Uhm0x50/4st+n3GqVUa4m0SJvb97/wQi6S74XcSr5UA8fAjkoZ/ABut1pzbudoKz/NwhdAiH9iiLhKFdzvQQdbgyZV1ndnv/rqd10KLjgRMDqBORGbWzL08vKbwEA38I+2n0pmZkL7hmg/PTyRGP4iAPsdKlxEbNOAJg2G3S4OAbh13BO0G6fYuJ9wp5BJR4ye4Lvvvmu1cvo+Pfb+Ifk0w0Z4WPynLs1fp6VHw57Xg5x7aMgF91w1tT5npPfpdHLcDk83G0y3Us0J8z4pKSmlAgDhTp/cu1u+Kzs1MbU8W5yJQTDeEKj1kQZEGhuFasjRGlKBLYU7WWN0dHrdj2fnzHW0iWFdgVgQIh3EzgAAIABJREFUvl8z+8nNyPzUaEFyUntJ++aEOIVJrQX+ofxD/K2WIv9A/7W+lsv4l7p9C8m/7bXEPcIfGRvElAjyjxV/qVjF9/5R8DsQjYFzWSN0alF8fmF6Zx5zxucTf+sCEAGYmv0zAzA7RYVm4FlFeUIUjOjj5d+GxmO4CylbIMip1yoBU0qdzaOPK0nKy41NYvjLpdbARBCBiYdjYnZgSwx8CZJvPbMAwBFsaAf+NSxt2yY3RkbbUpRlxfBk5ItbhRowmWHhQuBsFgBnkgAU+JcJX3lgJ2dagsDngw8ea7eleH1Tay9C9Hv//U9/w/D3r7z84/0Ior4HmJZbvHv/7goFpSD/xPzecHY0YnqzqPjs2ZS49LT4fFafBREYRSAbDRk/oqbWU7jNfn0n3RuSgGDi3DMTKALtHqPKFHL7Aupz5xbG+u0HqoqrqorEYvgtyJWKERAlIJVB4FCW4iXQpjP1L//000+o/8aCbrcN26utLgdaAhq37ut39/eDqnD37wtzoVAQtAral9g8cGEPLbz1Jz/3+U9vOsO3b/t0Ov2U7PFsbw1ndUtuyyp4ADK45B6WhbppUzdzO2F+nxj06ryEPg7ZhweZVW1UgEa1Sg0B8LCfTwLaWAaQr+wi+lh114sfs5D3AMS8u2qmvfi9WrQHWhosBl39tN4WAoF2ql7aI+7Yv+NwVPZtPAZe2J855VWp9JzLfP5ahmy0kY0yrxdAWuEoK2vuUCqszz77LMTBJvnqh8/Jg4OhIE6nWKYCdhsEtNahZYqD+/s5LujCnfRWl9vNcWThwuRfv+mUJWA0+9Uak91kgqic49yb/vEfX3rJbvdwdi+JQHiMWgiAEXvwqTeQfxqF0ReIKNRG9Fg14vrTU1cu8UuP0AE3rHG4BOMDRV/p7gZ5fV9fTVaTgD+ef9gBQQAsLqYacHl2QVWWPCU5uQIBVA6nZ3L06GDVECoIV2M15CIGwoWyer4gTCEK9mudULNqCO8Y/f0zL+wv+fCV+9cOvPhgEhujk5MH9uRtU5s08ZU9uohu6fFx5N937HjY3EGNiAXJqdj7sgeghweSi94BCGM6LB6jNnOj/GttFnr/qPYxIPBvIDcJHRnK03btjk9B+cdSfzl/JgAJgD+7AizfacY7oWoniEC+9FG+/iJoQECRuEfahM2iEAcrqzAV6DF25SZgxJ9L8o/PCYJu/DRnR8yOJEBgBbPyEyu/G0ECwnG+YXEl7uyKwQhXQk9bWYYZEMiA0BWtAaMGbEQErtvgY3NhRWq1BuQf4m/x8cmeiC8ie+fOubfu39v+wjPff//JjW9A/qHtFe96ut6SInSkrNy9fwuTf+JGoF/jXtJ/hD9sUK46e7ZaSam5jPxdDIGoGhvMwnQcnwpkRlmPZPUciDJ30O4JW8PjvoDXaEejrJBH7T937pzf6Q5IMzPxG+1F1YcIpBWV8B2pGRr4V62sLi6VGt0ux8s/UemynwvY3VYgHMcNn9j0dNg3Hn46FOKcTicXfvppuMJBhdo5h8YUtMKV3b9P8/nnC6aXl7nwhdvz9ZGA7ouTf/zA5Ob2SX7/+/yCZr4riwFwwEgCUM+2ndWT0TH59wU53BRu5/FHALRtxJ/RqFKr/H7in1+jIWnIN7TwFlYs5sWSL6C1SapUHl9qqF9qaXkM98nWvXv3Hmzt6pG2AB8tB5Rlyfv3Y74Pj9wn2Ueiof21ESMa7iscjm3He5RS2WxPsxD/Mv2M/GvFnvKCDLUEwmCPx2RsceD9iYZC9BGvD1iuNln3Db0MBHRZ3aCbNWzJbnDrVrjDmBwOWuHumZ/zXRppURwJQChrcnHcr4PB18PBl4CAaElrtwg1EK1MZwsGtwIA0QADs3+G3To1p7HhI2M+NT+PHQdjDhv1vljZ+mfqfUlLz5IfrUHn7cJdB5j7rJS5iuERF5dSWloMArAI7vGZ4j5DfiM5PSCDEss7ewswHq0UGEgIzM5GqyxA4LZdabsa5GiSoFhXgRO+6ArhaCqQ3ALv3z3wCSLwTmtjhkqjMRTVtg807lz64vjxW6spRL9DPzxkErugILUEJ99Q9CUkMPDx5Ywd7S3o+8fLv/omrbJMCH/x2SPybQiD20tqE0sLd+and6bS5O+T6BMOLIL85c8NwMTebXK5WWNSG1JEqRVC6zOVP0QbFCDOAmNfQj0ugpRh54rWYre3NOYkgP5jcyFkqvA7EIHZovY9MdgV+LC8ohz7lkWd3438ywhSZXFxpfrs2Vsr59V6bU+XsqwsS80p4sRl63Mg5AeNg3C0CFPYBZIpSs3OMmlI/i19cLxnJBAYWZu9ev/+vffbUf69iNk/vvdF6EMQJj+wJkvzaKu37t2/RYuGo+KPQmC4u54921mFDdnKUiBgfCHffS9fXFlkXYFsNGRmwkfrwJxqdcA+1D/mCk7MhMJWt2ecPBJsepvbrQEAms0at6elrANTjHuJf7idA9ONmRgBl1W1VbeVVhe16ewuh2NhGQi47HLt4wLzcx6QInD52TyDg8GZEES/Lw0P27aGBmdCobCkm7wC3RKK6/aZ1OccJpd1ZmZ86kB+va7lcdO022py76uT2JWsLTU5lZ2bA23B7iCVdC3YyS3sJkf4aeDFju4ONgGCvG99wBhgAFT58cVPvdpGYY0l039Cq58XS8v5Umna4+NLS9MmHI+Av9GmpdO2OJwU0HYlD+QcpmIHyANWanyBZ18HH6e3D8BNDWSqNyJfvDg5OyuFz54aURYw/r1G/GtsxUXTmMAoaNylkdSZVJz76X0AgH24TwnHTnCVgEcDCDzz008vOzGh4DH6nSDKgjMz4bDbA88fiG30CpybvzMyEvHhtA8gcJj2N0u44SPDmAgwmYw6XPDZpG2ymNwe5N8bw5T9g8fAprco1FjkPXWF33mp4c02XCCYVWhcNr0zpbBBnlXDFKQsPp810vD0k6bFIQAxAAYAZmamZDUoiXGZLHkL15CYeh9JAG5AYGNnVSlOlKGpDFVDaDZkzDXE56ltwxtTgd9//Fx7OzplXZz8ZG1kfqpBrTbEp8bklLTHHv/ii+Orq+kMf9+9U8Af2Pq84zBCLwEi4BL0q0pg2T+xDid/CwoE45eeMjyp8cerZOj7lN59yviXVLI9O2Pn7oxiUQLL/OX8exD8ZeQARbGdGenpWSpAYE0njXUwBlaUP5EChGhW3NWllCEBcfZF2dbVozV6bNKBnNioozRriqY4uD0mJoYsEirQt69c1HXg6L+gDlvNrrp69+7dxUWzMaIV9/SIixtMmqyu5rLoJAivANk+OCH/l3w4XcPJKfr94PFBacQ3P3to6txb995//0M+/CUDXpb9mxHc+DY0JF+8Glda3Hn23v17X4kae3sbowCEjzrPHjvWyVQZHnHpGWw911GDQb5ya0UwwGTZlpds588vnzHZJyY2+R3ukEQS5gBZHhKBgEB72K1Ge705u9so+00HKUD+EGogZUVtbcXVxdlKr8eE/SXLyy8vcGF7MHjkUmDOB/rOBTFZnSQ8ONhNy+PI/nQQQDtk9RjVtPQD+IfrHu2emednbBkPOzMO7N4tN4XdNPmgKhbBDQMuo2S+C2bA0h2iFhiIUmmeF/N9SD4GPrtvAwCf2NtBhqXM6kWl5hcYCfQj2Qd/tjT0yZR4a2xp2vX4vU3vcucUNlzwEQpJrDaLpUVZVvBCyWGq9KLsG6CrpVKIzjuQfyRSczpabPYjqCoN+W1l35Fd8UgkoG8pe4HXf63NOE1dVgZvUFt3NBo4jdotmQn3D505M2aCBx+nTwIBexA3kzveBACaTJzLzeH+JSPXPQhq0D4MD/cZDBovzD16dGfK6wnPgK7XwO+Pgzag6TcNEwEBivoRLcg/DY57P/Xrd4f1Xpr8xSahmQlLn8J/6r0rX399QUK2p/w9Fzv/KPuXlrZNnoXFXxoggfA3Qys0XWZkZKSlkQBkGUCReKdhVy/NuKwTMDW1V0ztPxsOBGRjb1Vaehx1BWZlNch5mxg07WD3Z1+0GkJdgeiUNYA2MX2H1nRqjbHptecOv7C9JCfv7PHV+LSMNALgw1cL6ORsLkDflz057VjDJd1XkoD9fLU4+Wu315eh/NOy3r8yFv128MVfXvsRC+HJrK3NK87fthuzf5t5/m3+txqQ+gB/dgAWiVJjMdatrlGZTKqdnYkVUQPA9UPECAgXL5zp2C2hq9cCAcuU9Ta7XpkUm1qRuPGoSBQd6+xsPxwTsx27Amm7ZXn2dwcAf8XV6RevXbt77dri4nmzSjfa1dYlzldp1H1FYn4dGd8Fk03ZPx6AosQiFfxwJP9Wjo9Ozc2PrE2e+/xP9z5q//TTPz5R/PBFXU9ZR7Kc78hLK62uEvf2HvvqHi5d781uxPUmFAEj/7JpeXE1T8CUuLSM+F07aThOnrWysijEwXjhjF+JHDFpjOMzF67PXeJwFS+nMaqdiEA98wp0B22Bua+/HA96vKMdBU/yjyJgXGPX2VVvC3rghAVJsmDWu61wfW0aPnEJRKDbzXnCT4fx94CzOgzaAq6tOsnMRNjNgcIDAYilzTqbCkg2Y28QwbXysCheEcTZhzq3ehs8bCJRQWIyP5lUOVBp7HYj37C9j2MrevnDY/eNsxDY9+/hT08AZBYuUeEH4SzPQBznlR0//vjxklYmPd7WHPPpH/7775f/9PjxY4yxgZHagoH9h3PaB9oZ/0D7VQ6wTBHfoBONgAcGpEZPELeP6qcLR2/2NFbJpqamcN7ObNG2RuPfVjpDAIGN4tbWxoIMEIHdg4M4Qu200qyjxeuBWwa2JinMOOLLufvH4IaiUqBjTn8o7NnkPNPPKu0TE+Pzj7wmqyQET4PPzqFXYBjuOiETFn2w9VHjbfHiSInn19wm6v2jhSYez0zI7ZjedYDk38alR/24/spgmJbvTt/V0JBV00fFDzTRlskeS9MzCIHAP9zhGVdKLTBVnb1xDTUpomhIklnAD5WlihrF1MvUwUrClAtMLig+W8WvTuKdspb4VGA/P71+xBg1zUcR+P0zv/nt/pJX7h3Vq1QNU/NTN6ccV2O2JN1aTYuPZ+m/0/z52VqAvX+H2xF+FPfink3q/tvRqAf5h8YH0hYm/4TsX0cyG/3gJ+DY26TtCZ0Zu3ZnVOPkL4+69emPXxoAq0SJ6G2VlCCKk6tNGkWciBBYLnpS/+FMLsmXNiXZp6P/jRJbYix2j04cmwrQiy7WrPgdfonOqgLQ0zgd1ytCZ+dMUVF8RvF3GAhfowMQqNK3KLvaxOLdas6cgdooOgeHg3DZ5QL+KvI1pmnA3wrgr002PxeZnY3g5Eft/o8//vjGgxvffHl9kPW+kB/B0PpAGt+Rt7rK5tFA8on4ZXN44AkH+CtnbTBwlJaWKktT4pTpIAILd1GfstxAnvnMiGOfxA3Sb5xU2bOD17/2uRC1mA7XODk0I7bh9m83XFJff317YiJon3pnAwKpuUdcVNRWVNSptHCgw8bHX/rHYQfQx2TyBmwO//CJIy95hk1u69NkpTS0b9++0IUQ+l7190sghrNivmdQIsGTfSrOYOL0yo7m5DyR+CLu/LF2z9h3dqItdzkCMDWZxZa5HUaI/QTweSbsE+sERPHns9mfkH+BdeAZjX9GP+HAE0CqPH78i8fHjy8NB4MauHfW7nj1xO9/v3ytRVffIhUXoLlBjpDyY+8o/B1gMTDVDIVjoBlvB3bk1tLszdnZntPvtEpbFEYaLFHUS/HuIfCvDN/Sh9s4WhAqsYbtRmxm9psb5seDoRlfIOADPahQkHfimTGXy2oy0cxMaGKT2xp6OiQZGjpjlYQnAl61E7FHXU4uuIOA1q6DOFg9rFadO+fA5CCExxw3rFDYqPcFg+AJyZDz8qkrd+48ui0RHMAFrzUDRBw1aXFvy9H4gNV+WbvlrEy6khEPKCQBmIL8g/NNnF20W56fyfsAZooIgCJEIESXqaJscQHriKnEmnByR0dmcfExUWN2UelqfBSBDawxmiGQqiHMKWu9GvLPv+01QPR7de2dyYDGubAKAEzfnR9/QMBfayM+tsmbY1D+JSUkJPD8Y+McewZI/uHOS5B/9S3M9r6AReaVgu5jAjAP3iTUJlbv3laYkp3HS7+cf0f9MQJiDvBnBuBfVZUnpsbir5yUmp1m1nDqrCo+Dt4g/pgbTHk5IyDEwS06uhOgjZ9Wb7cdEG1OpYE4ygHyxqrHOsXtQEDsCuzNJBFYXpQ28i8YCZ/nCbh43uhtwgaYYoOGM6QUtBIBO3kFyK+CS0woVZkUj7/4YGlpcaVtFKLfyTUsfrzyYTu1Pt/45puvJ/aRA6Uv6vuC8o9NZID6u7q6isYHLOzdW1COCCwHGGUD0s/eOpYNQWlRWRWEpcrqUizPKeEGnQ53SL4aggPCuwzklrrgd9F9lm75dd3P3x4Pcn4/rvrBlbEYB9swFagOh3Dl9sxEMByYfK2DwQ8be9DlH75XZlm9nQv++vXX8cJDTYHNGBrHwuL0Kc7pBxR6rOTf4HaBWukGyecOmiDMkVgp+IVwWNL9/OBUlzI+A/uqm9vL9GG30f1sndWYXoSFRQAgRcD8nbkgYDfabAQ9j2diHP4j+I3Tq4/aF5kC/DMBKOjA6EF/wvQeRHLHTx4/eezV5NT2zblipXZpSaGazvrxxLvDu7Kxva89Z3+7oPt49OVu+DDaMkFJyvb9UiPH2e2bTP7pyTt37kzOjqKb0GihHD3yDXKLpb6NFUDoYJFCq1IFMtkKatgqsRq9uBVANd3kez4cqgMKXGII1HMIwOFhE+5JB1g+fzssAcUY5NxuNxbxIVQedsDHYYge9X4T565Dr0C3RqUaVgEBVQ7gH+f26LFYbgMpbIdbVtDaP+afvjL/5fWgxhldtMWvP4WgtDBl91Fct8BP18jWj8crK/GAv/Q4rAAXF7cVd/amN2SV8sU4ISRBEKIrAsS/qSKxuIDdJ1AJVpYdP1uBsMQVwsLekIYsTAWy2RChZdU4vG6aj9UQmd6k2vXVvbuTOufC4iICEOuzyL93WtlR9jB2D/X+JfD8Q/mXwLJ/Fo9Nxnr/+OwfjX50EJr54LeSqfrcvMrc9trsjG27MPvHy7z/E/4QgCUJsX/5t/8Ro/5Tj78uRgBC0J+wfXteYtE2lUnDx8Hl/+bAwJG18VIqkNWD20rTIQ42ZqRuT1yPgz8igy34ErFbAIHUFUjWBuXi7wB/SMDzizwCzUaLrKurqzFNZVJnFTWLhRiYBCBOgOSJsjSmLIx+f/xxFYsfkdk7aHv10fbfPEPJv2+u3w6jQRG58XWznR988Zfxb3UVoNDZKJxn8PYYpgILQI2dXT2L/MOjraoYguCU0lI4OeNS0hGBafGFlG2RYxy8zay6/Pl5xxB1HVwI1ZFAkzwPp9sps4rKo2qHyY5tIhgHgyALg7CAw+OVdfDndWMvbnvq7GyUGT2ereigECQoAXhMHpNfNewdaTo1fOLUpfmAjevv5zZ5ghxaYDoBli8NYy2z/8wQEhC+dijU1EWemmXNzTp7KKwfNdW5s8qKiqsJgBWJVJ+jM7O9IODRgPLzIP4mEH/jHkH/8fiz/zsBMPLuCfZht4uuXnv84KsHT558de/jad2BtGSaacspG9W2WKaX4l/t2J+T075+DKwDcMPBEIhxL/39/sZ6tcmksZscl6dHpqYAgDfRTO3mzVFpfgMQsEFnUVj6lM0MgGxksqurj+uGxyEIYAt1PwWaTz88fOlKfbgbc4/wyM/NB9BWVe8HZeg4ccLl9gStksELF+qoYhwMhd3wr8L2S3OBI/AoWyWScECvwiLqkNUaNKnhKUUCakD9cRrM/mGGEZ6liTDG2/5TuGqhe8ihsATI94/3vTLIG/rS02vkR3HuF3N/Mq0wcTgJL9r4wviM+Iw4vMNiCbiouE++O1vUuLEli1QgEpD5fyU3YksMSxOIiqqPVSZTshAbo5ldKiKwQafbGAfP4Go8wcz3s2++X6tXqxVxtZvfX/UvfL5y8Wh1zJbYtN0ZyD8xf08pe7gfe/8AAgmsh5lhsLZkS2UL+v41F7T2aFHZk+1z1PlgXfrlVuaxp7S2onr3TpB/qSX85Nv/mX+kAFP/5j9C1H/u8VcAwMRYHN0DBCZtT63KAgQqMsqpHvzEgX3JWDxoFGMaiyGwHhHYQ6Mh+uqEVEr/CXPFImyIKa+ohRvLjlqySMDKhkhA4FGGwJXF837jSE9ZV6OoUM2p8oGRzAsB/bCw9TkV5d8tbH5574PjNyM+r4zk3/v79/Py7zNyPT21tMQ7UPL40yH+aO4X1V8nnGTNVPFlaqwcU4Hl4tXVs2g/Dqqzq6qtDe7J1aV4pAAEUQTGAQIvMgQaFlfuXrt73m/iU4GgxaxuzjVEA8KXTl3GTJlapTZBHEye+UY9BMKvPzVx/cvrM55IT3I53AAyGzN78dc6PcUFfT4sLELUhwOoRhtc/A5F05U539y8b8Jz4pRXMa0KhkIzE3aNc8yp1mAZ2Ko5xVxPuwdBxLxuYm1Djc1Kdchq152+aVdXlRdhZr0TvhWPP3aH7iAA0jE+Pr4hBUjxLzuGsQnmz1Wf8A7AqLDoDkiVJ4F8S6fadgD0SpqrWyy447ep/kpLy7cyZQH85Y7Dm3kn9Sj/+BA4VwiDeQYySUj/Cm4HZB7tnx65E/F6LX2Ts7On4eqcHR093VNjiUR0FotCb9EC7WmGFufIlAorj7JwiNmWBXzw4Fn66yRYLwqDTJ+bA7obFQYVnBEn3NzwJld/MCiRQNTcH5ZYg24rbuAbvzAxfiE47LRarZ6A5ZR/YcyFZvd2m7vfb76sAvlnUinU6PuiD9g5+0TICqi7fGn+6+vM9tQ3Ph5aX3o0nZVRXdjQUNO3WytjSyn/bNhaG78CATC6gKBFhlLeUAr4a9zYlCpiOpDVQvBJTMxuzKRCeXZxUeoL2K7SQcMhaJKQxghICJRTNYQfpcTxOKEa8kiv1rd8/M+H/3nW618s3Lnt6HcxW1Lh0f3uu57WHjaWV5a6A566kqQkZAAEvrVIwQT0EizQB43SjuRmlv3Trmf/1p2vBP2HPExIyI7ftiutCF3vheLv5n/bAbgBgD+zHyoAUBQFIMT822NFcQaNSSMvrkj8cw1IRVk4xNg316WU4uwo9oNL24qVB/R2e18maMiKjc5aogo0L83dQyLwh4dYAYBAWKwlDQgEXCQCYipwBC/l6m0mzhyXmRl1gykXpfYaTOqllQ/Q9up4z+RcYGTt0FH0Pfjn3378PfHvS/Q9cKqP+HwBT9166zM6DLDel1JQf9lM/TULr3DSZX91//6tW9mNJDexMIshcDUDILYoH4+jIz2DT7YYGlbv3Tqv4lOB+7BxbKt9E8fOsa8vTZvN51Q0H+Cx42iIz6sDgr2+de6zf/jMF7RPtYrQ2QYfw0yZLTjum/O99I8cAO4p4B82omlUauPI7LfzEFxf6LYOq879+N4lu1USsmERVqWR1FmDgf/2P978aZki4JlQKBTsw6pos7jeAxSwHZq01MuUKcqU0uq2Tpys59ugKdr8r/MeE1VAJoTXJxhoJ/rZhp8Qf9GQ14Z2LfAkHzy4V/Tqq69W5lRzIb02ec+Oze1lWovN5pXJpGUF7TExh3Mo7N2/UQAi+gZ4DrJ3RMJc9vc5hw8fbm+tt5k0aptGY14amYp4FYajWVNTI7Ojyu+k38lmR3sysigOVigU9bI2MfYK9EiVDSY3iLa6fVY3vFCP5jigDMJYF5t9C4X2dYfH5wGKuMCq3+F3m4aRDsA5vHVZrVzQ7YJ4N+juD810z/iGISYO2n2XLpkXFjibNxBED7LL/ssmzqTSGzUamnyDm0gIs8vT84+u88VfiDkkTseYi/X+TW9Lqd6dxdseUMVDJpNuwF++VgsCECKLFGVpdVf1Nnl8F+iJ1szGaHSSiXEwEFAkwixgAfUmp1aUNxZUFnSeLa/s4A9qjBYXYUuM4BWI9WBSgWPRaghzjJ4I6CNolPWOTq3Ytqumvt4QF3O4FuUf+kDSVB5VP3KSkH9AvtpaegdI2JOrtdl1PdHiL/leZUaNXzb0/vEDRwmp1bt2xZf2bij+/n8eQNqfuQ2QAJjKA7CWZGBi9i4z1oOLEjcgkIaBcSM5JrLYPGublMXB9f8vd+8e1NadpYv2PD1d5w/iso3hggiPAgS5WIwB8zCCghmDZD2RkEGDdEEROyKotZFgg4z1TluNKQ7BoQcZFxcfEQ5Wi5C4bJhC5TTEl6Lg5phJtx03zsueaxcuJ5U4mbTnZmIfz8xd6/fbAtJTd6bzV6fODwzEDjYg7W9/31rf+hYQgx6VVGa2m3XiVLIxbidgWiyumBCmlAIEppJSIIm5F5a9gSQwFuMh8MjaomZWjmuF0yycVlHT24gQ2NubUylOUmsVxPp8406ddNY/O/XRyD9fePBm219tT76RLHoSQD7ABVzw9LRYZkhyGjZ/b91KA6FRh88rTKOqFPGjb72oRO/cefBggSAg4F91cTUSwDgAqtKwTpNGIZAPrjq/tnl/DTPz4Qnvdmm9c3OTp+wMvzsO01JBNmlIq9Ue1I34MTA9Ep38+H//6b9+7uXMuhbUNr2VPQaGW3r0aGl09EAE1MpVIBcMg+4yjdZ379Ejf/hFoLE2zvHkneWgFziLRglXltbm5rxL//2/Y+zzAHoCIxwX8hp1Z5uzWNBxPqud1dfl9xQVSRPLSvhs8vyCAvrkPJ3evuzFXiZC4KT3AODfAXhBEMS5h1EKf9vq10jxL46DSpmq85WXXgHoezWv9FWieFMyzSGvr9Zg9VnlLe0Ex/LytonfMfI2GXdKnKaQ15ZOgfB0HBXxLXxSm6hVddzqoxxUY9GPzPowrDHXYF1UWkeuAE0ak165cmWsv4Hs61UYGUcSKcCMNaqx+25zu16LeLwe3DAvCUUlkQG72W6bn4cJ3XOGAAAgAElEQVSrfqBLMmQLef3wM0SkdDo4x8qG88y8242hOsDdQ1EP58FhOqeEmIgPvIZxCmzQOrO4yrAh4HlA9FYCyEztQbKCntH67R7XuGMl3vwd9fOGK0fMQnf+Hq7J7Ovro6kHckyX3Q4dixPAInm2FHvAWTWdmQ25ifDka2lpRGmwUwbE4BF4ACvR90LtL1X5Kc2NCx0CNA0J4giIT+NyhED67GxAFjgzo+RJIO2GmOGp6lSazB98/OVPvlKurszUHkQLh67qr05+/fV2/ndnBhn9wHF+bAYQKUgKgIXFRrimQfHysc9y9P7Fg6+20a9q+yU5XZh98FBWccqxOPDt+/8xQNODkyCpf2AFTCRwAXy/6Yj7RPinp2d0HFbDnS+pokC8i/+RNzidgQBIuyFZvCXmkDStTJVFpuPSydK47U2b2BCpnKioysPpONTBaIkRVlQkvhHjSSCcG4durS1qrWONHb2VWfAv1wpFgFHA/4QWTk3g7513Fzqn/Usjn9xTXnj4xcv/jVqfP/z4gxfr49a/gfoh59ubazGLUoHru6j1D7P4sPhHIg9EfLONSFEhVv8WHjx8uNArRAAsxu0gSAFrsAaIFBDgj6AgYGA2dQWeV4AOXiMZCY6AJgTKiwRlgQ7GKKLH1381o9Zq7OGw3dLv82Mp0G9kbOFHgID/usR4zGMCsVgk17q0gH8AgAfQi9E1EAKSYQ9H7Rp1wAzo57UNwbUNus4z7A/h+jcbp1EChxkakoRHL555Ov/iiwB/0dDKisMbClmNtqgnZG2aNSQWVJ3OE6h0hxJrWssJAawqIMlsqDQFPjtouRAVwYB9uF/Ee+AAoYHDceiL61+e+JmNVkOTtFN0+/Yrr9xu21eYcPuVhARBzuAxsQouZCtrlEnbUTeRqKTdspc/yYTytbXF3+18ALfDwryqZqkeo2c83R4WCLNGvT417fMpyKoUU2xzM2aZHZEDBH59RQ4QeChXYTBoPN31imZAQKnoxAXEMteeSbgbhAHc3d0Ygjo/r2XD4b91jQ+hywVQDr5Bzu2W1EucTo5Z3djApKx5D87EwQ84dCD62tycXUNWC12dG5gbHdbi9lNDQ8DtdpI9pAFlriEUZYAE4+Sv38uBvLh0/TGdfON3XsKX4VQrGhRKZW5aYm1uX/+hbcOfdHe+9iHyKylbKs2Eu1R12XFFEtzoWwD/GntzvnsqsQZYKRIDDRQLSLsBrqKKZgp9VWQykM/GbiwvJxBIwgJzFfG9IWR8nXRDjEpFwyrOhiwFVg6urazMrK9f9+mlqsZWYsoeG5OqmnHyNy8d093T3yQOaIoD+0432e2GzubmRtV3vX9x/OOFLz9tmZ9emlF2+GBSSUVqKY9v/xkBhCdO8h//gQngj/60mAJgMg7/0Q5QenKqOM2kYbSmrEpCAmkmFR9QSgCwopEEKbdSV6ChQa8DVq9qstrt1g66NpMaonkmWDGRI9h7gh8QRhJYIe7IPk9H4wgC3rj1dkxtlnUK63I6Dmo59SGhOCcnpUatmUHwe+fdz16X+/zTV67IYhce/N9tf0nhj1qfyeQHOuVci7GAZu3OjYOgfUnxLwnZEEl9aaaDuHGzVWNjxcKdhYUKkNkLDx8+mEBnCgJgNdXAaRT+EPr4d9s6GKfj7q8piTnOGR8QHuZcVAcDC1xRa0GrzrJeuz8YDE4CsfNQEvhvLGe3dvZYGYcZ8G95aTQUjaK9ZQjgbxLre+oZq88ekgwAn/FEoziUEEUjDAdaz+NhcODzxfCB8TOuyFzUo1X4QDUyc5FoFGhMfcQsK88X51RmJCf3SnWgE4FAVPHqF1/aBL4DTOiF6GvPE97n3YPkz0utLwTrvtP7gN/DgV5pa+dLrwpuV7XlWA4h7cvP/BYAUKU3yvR6naoVwC9hX97Jk+iTOEkAsJTC3m4A/O45jYsS9w7uO92JBhdimbTKAkB3GdZoQvpnVeD+M+Vi7O07d+7HYgrZFFyl2dg/GJMW+RibTVLf0FzeU2416i48fXpm3hUagIdgYM7rjcLZ43A6zPbIwNUDe1xkO3wUuJ4HPgk+zeXUejjtOCDg0zMbLhz77QLKODfXNTBJV//h3xMeHb2oMSt9LEemhTfOBCyzslkf68Wdc2azg2EYDD4gNWdnPGuSLNpSW0y5tQezjp9vOHyIRM1K+am3sW36d1x36FBRUZI8E//oddWh3OM1WMIlALhL/zbzCAjPVnElPGPF2MwSVU5MFGD3gwfAbQRsxnzd4pJE6goklUDDjIkvBQINDptNuVaLEzSK3bLW39dnmAEInFHqpbrtDNyv8xMKCwePgfzdT4EvNZXK372dSkr/OuPev/KW7dj7bSMnBUAAxNT01I5stD5nHMuLdz/+81O6/8//sD3gH/3oxx29FACPxTUwgcH9wiTQwZqD1STbFA151JaHjw7lUZQExvvBsv6kLJUqsdbsZZsqM+Ic8E3iiBG/B39JR13+IEmJ+Qa9NHWNFRU1h9GjvHb+DQDAt2/ceHvNovFJm+HZUKNkGEsZEMdsGdK/37zz7uuqaX9w5KMRy4WH/7X0v/1lvPlBqn9x74sjtkiqfzfu3KDFPwz9I1EsAAcE/7bhr64R6J9QWNdRXtzRe+fhwy8qhMUIgSWkCogO/bK0RIKC6Ieh/ZDspPh03Ob9GwqMwItnEYX9dgYz8wdIWupKYNESinqxjk5GQ/xmjWfu0b/8FCDQzrGsU0Mj/ryRgbm5EIq4PXZ7VGJzYUBl0B5yd8OlTGNPu3Gow6MNLntD5mvDLhDad5/jnFw0IuGUtdl6ACquW+JB3wbXL6oSkPtSxrECDNRrBAlMnqXUeNcmMHu5116A8xxKX2YPY9dS3WvWkDfoYyRtbHxjbZK2vvQSKN7bIG73FiYIGeXpfFG51cNZR776ViUtF+QB+BXuzTuZd5KgX1sp+Ygi4LHfQb1k8gv/MG/f3jZBs0qPO0YI+DXpDapm9dGj9d0uy8g0iNwGon4B/24udCzc31xTGEYASjLxOv1oFtsXknqFSDoitbLs6lM4Z8Y9dPt51BbFtMOLZjIzMxc+8HfYq7dxWPED/Ovu4uxsJGQMDGFGwtMzbhfj6baFIqAaujBP1OGaH+IjVa4ZtR63cwOn5ead+ivT16YvfzQ7fHF4dNSM6lLtw5Xn8+O7lx7R3L/ctLS3G2pB/VLlSwFwjIc/nv0VJWXjRkxpq6pPkVTeLOxspQhIYY9sTMjhARAZINyw4QXgr+I9hMGMgpScdloFFOzE46CxvoTGi9fSZojBquQL1Tazwhr0j7JO52rsyPG+PrhQ1y0rFos+jn5T0t/mAf7tPQbwhU4QvPRTCfzlpeLSt7FmuN/Q2GfVd4OvquIckJBAQVVqckbNwYNJNRX78/bu+z2Kf+Tk5R37Q1cAkQEKeQAsjcMfquHk9ALhcVIKFBIIJEMZvZjIB3em+O2qUVhXzJNAhUGmB8WSli1jvWx2RirthKRQHCQ8cGLhpdODhSeoK7CRdEPKiK4EBEQMRFOgRQM/c3js0yy49CZzHeHvN7/5rHMEQ++vkObHX/01aX58+fHnd+vnNxy8EKkfj8XiuS9r9+/cQutfGTr/KPWjhzy/Ghtbcqpv3unA0l8xIGBxRwfo4DsdiH9UA98kHJDgH75JRD2ciLMh1BJzXmHahIvTBNcDPx2HQVlkBPPqB48ev/t6zOW2hUJhEJ0sbhD2sj6t5yro4J/+6yOt1ri09Hh5mSxuHJjj1S/gYMh+DVDR7/VyLg/wvxewri/xMKC7rl1/7A9dv37J4YrcnTzwHOg3xtZl05gOpenN2icHufr6UF8zzsyL6WNSUFrVKVW1iDAKizceIwBy3AvkvObdsx18gNEHNP+FrwEqQfM2im6/+upLt/OP5VCDS0KCPOo1j546NapsaqzKbxs8gVty8gjtI5CHg/L7Bk8W5pH/aPv3J+/kicKEE4PtndImnCXz4joSeK6Ul+vsEqUUABAg0ObVYPEP6MpibBPwT9jYWLxw8/7medmIXJ4tVU1PRiQEAJU9cnlPa5PBOYQJEk/HQewNzY9j8NUAhtGDEjhaf3Rg7rnnnnMPgThFAghYGA36WI8GuB3NSMAdSJ7n5rq6Sa1sctI+zDixc/Di3SU/5x5H+Ts/P754RPrRp7945f17do4ZNl+amblk1jrtNPdqdJIarsYdWpJ7pdBlvaF448jhfpp4JaXqckf/Av3TJSVly7NJIvQhRW0ZyKdiYW8nBgrE+R/9gHIMfBHAG/TjTrwpFqAObs/IF4vav4uA8KSGG3pxCergw321ubg0BEuBuEU9YGpQR7quhj2OrbXj/X1wla5fX39nZsXSRHlpk+7rY4UE/oj8JRQoneBfXkK52WuW79A/+a7mb7zxm0/bwBjZUNWW2nGo9ngi8b4QaPuPkS9+Sv/w+PejH+8CwB0CSEuBNbmog5MqUkgLGF5wRpjuiiO9KpKS38mPhigMfU1yAAqMSFDW5NOA1RReDJOz0FHZdqKwcP833/y2EdFHWNFxi0JgLqDf5ts4GqIxj/SIcsQVoIM11m8/A/z77Bdjs37f1Cc/i6H35a//8p926N/2+i13IKYm+LdOspjvP7hz52ZNR0cdPqmIn4A+VcgTTdSRht6/uvIOYXF1Mb52oA5e6AABTCRwDdYAy3aUMA5tppUBC8xMiu9yAx28mauMK42u7ZSYrruP7l2/FHA6OU8kPKklEIhBWUYmGv74pz/96SOWwJ9ZS1ah2zjG4Q+TvJcwWquBVHjRd+aSDLzgcdtwvMFuc13/Kui9/s7K6gYzeeBUyOWM3XqD6ar3aDW5UkPTYafHWFPFV8spxU1J31vV2UIYYBUxm7Slt1X5MO8zSkYtCNhpv4OBLGv0WfUAm6/evv1q5+22gryEE1WIfydx/uJbg+G6Xt5ykrR5KfgB5yNgd+wYvssbbLYaywZPlO7CP54IluI45AlRuVRmRfCzo7hukqo6y5ub5QYfIzEaNYhYR+vr3Q4L0D9TbPP+rVsL6BgCUl5zZzNmnR6Ryn2cG+GvWyIJfvKLK1cuX5n21mPs6TlcIOp0rAY8ku76gXA4HMWiArkpvRZyudwuDpOw3BwQcR+jNtsZB2dzUyEM5LGbuMojc/DwAQQiCxy4GiVrScfH5x0Kq2LzYNNHHy7bsWioAfwDFshqGde4dvfOS8Q/kyw76TymPt84ckjHi984ANLy3yFdkQ7QLzsTVyH2yYr4lSB1WMTLoRXqHSAkBJAcRMCJCTFth4iI+MwQ8BK4vZ3PyUIILC+pKctMOt6PQYEKq4FAoKUhdxFhXeLcfPsw6F+MALq+/qtffQuiDbd8NklbBhMKT5TSODvC/9Ixyj49fV9+P2s3qOCLU+no0rdWzN/ZTn7Jr4p3P4hBW5DfllFz+GBSceV+Cny/J/ztzfsB4B8BQDIJQuO/+DogeZu6vzLbpGU0DcVAAnGOI4dE0gMAkocJ/zuHbLpVYT+YpMRgKVDaZPSyfSmpxBHD90IoGFZ0dIhxPopYYhABeyuqi0gh8LxijfZDAAJ9usbKN3uVHMOY1z/7jNC/kU9+ZtoC9bub/g1t16HrnbFYAIMPDIpcav27cefBF2TjB3VTEQCks2giwcItIBiE/gH4IfHDQErQwQ86qrEFchM0cMnNMqwFohgmmX3kv8oA3HnTAZxNUgoEqIsHRmMUESBy6O7ny5cuAjLaJFE763B6gz4jjoaYPdEPPv7p58HZ5WXWwzEcEBOMqg56IzYX5xidG3hxTgKiLMSydoYBuRvFwQh7yOYeWvn7a3veXTl3bsM+eeqAx9L/bWbZLQXXFYl6MqtUpsBBUT79BgUCrE1U9FamDuqMqnipBh3H6W35Vlap2SF+O/CHSTBmQ7+856VX02/fvj3Y1mK194lO4AhbQk6fwafvKb8sGBxE298groZtI8W+Uh7cCOc7uTdBZY1KzLIWIIHUAoMlwby2PNyfM9guJZrXi5rXgNOTKPpaQFH7g7Mam9Vs9nYhBNbbhtysz7R561ZZTbUw59WXMKS2uPrmjTWTbFoLXA6oXHe3zeO/97N7P/sZcOVopGtogwQpjju1GnwYuiMDODPjco2TDgA3Pm4DtHN5OK03xGDeIdxbGJxr654/h5+HW0GiNo8knieKpUAP2cq8Me+06Jdnb91fM1h9DCbK4D7l4eHRi4CBaobjsybpzkur0nokE54UpPubXXQkKXFn0R7P/4pQ/pI4fGma6nhDrrQVvSe4GLiuN6eus66ZAmAzolmOKIfSDIJ/gooK+AguOPgtaompKsgg/miSE7O7FNhZk5hZ1F/bgIuTGgwzFovpsAVv0O5FuLLe6MPF9tdnrl/61euDCSI5Rn193Ya2zWMFBakFhACmpxIZnHwsodPnZXXlLY2dGH8Hyq6ns5FXvwVVcfMLrQOSyK7T6b3Zh4+ndcTp3+97Sv/kD2wBJAcBMGU/P/t3jMBg8vZJLegowqCs2urKSuyEVNIGVTwiEE9vr7Cus7VMqutHBMzV67LSVNkNZi97qAIHhHlfND8fLO4trhbAbQdTYhrrgKIJsRRIIRA9MWtAAhssGmUNqN8ZDTxd1TopTn78bDr27AGqX+p9IRt/nYFRKkSA/gUcaiWwP2z+Yu+3rKR64cGDL+gWHQp/InKXrRR03KDwV9cB2rcDK38dxXWog+88fLYAIhhI4AKIYEIFbyIEJhI9TBAQ2WAW6Ya8ATALOhgHhJ2872ouHB6Nxaj5fvnapcA46GB7EEiiPRhEC+24Mzr3waPg8rVrZi9eUED7AtdGvR63Z8+w/8BAV1e3iwm9doDMaDAuN7I1r23ozLn5rScrztiFpxtc2M9Gj0qMuq+kabVaG+eRHEzpLUb+IIrTBfw2xYJWn9fcSaQKuVGTWQurxqA0s7swkLVrEZKQ95Xffuml222npaLChPYRq1bCmqeapZjnrFO1NrcNDg7ug5e9hPvtnvEgQAcoN5gjM5s5D8hovWgwDxGx9CR8wmCboE6lNxKXIfA+skuBVLxa8E0TDv4GNZxR6QNximxYcrR73KHOFBbD//XW2bNvnX2JzH10LJzXYBHfBhA4RHZdssuzLBOKAnRxEqKDzwGb4xiny2VD+xB3wI5Dg24S+WwDSMOlbVqt1h7itFomxHHDbIh83lYAaHokxPBhepPoceECFP8cs8uP733660+n1asxk8XhYEIhBhvmWAscNWtdJPWeev9mFLlJb5+ng78Icdk3biSR1FNkgQB/RbokXVER4X9yaaIqszZXh0uRenq2C4C9+J7CH+YgVOLTVCRGASyunBCnVGIpEGmHGIcbkW+lCkTxmCxEwHY+KAKISGL28YO52EcHVpqrt4IOdjlib8TWYrHzMtn6+vr1d759FasabXW6/sZ9aH0uyCiAV7TBAfxR+Vult9ut0pZGHO4hk7895UgcRDu93yreYFpF2h/JGVlofRan/r7Ej568P/qzP3T/gxwKgOlUAgP4lRL2FwfB1FSigxl1UYUYdS+5FeVUkrFgSgR7hUjjW2tUmbp+Q4OhQdafnaVSZVtZr1FVkMojIN8MwY+FNZXphYQEfoODYULQwVm5ZFmlKRYngZZDWP1795JazWjZ4NQnTf984eF7p1+m8PfhY6p+43VoZ8wSoOqX4t+tmzdx4dHEFw8evEfzM2imOCCgICf78C0hqF/AXjhCYQcFwU4EwoWHzx7ewTrgws2ahZuAgCU1pBtSRhQwgUAsCqIlBiEQzuYmugLjvqsB/3XfMOmG3P3g0fKlFYeTY/w+Y8DJsEGzc9zp9XsjEdZ37eLFJT8HosqxcmnUDlf0gQPopsUkmz2RueejV8Mh+x4cvw9Fcb3PufkzzxY9zjMbLg8AoD1SfzRk1VkiUQlAxmFxXTlxUPAIiFePQNTE2n2qZqqX+Nt1W5XVjLH3JO6UxRaExoy7KFUvAeu7/Y+NracT2lSdJxKaDaxP4zECUhpUbenJg9gf3DtIwszhALC1YccDOSAwPdL8KD3RJrWyRiPDGTWs33y8qhDYYmG6oFHabzAi7SM7L1HztlDwK+/s6eyUG+H7ZxivY2XGgAnOjMcGMnjo3NMzGn35W5cvf/oWnpfeailvbtFrN56eGQL5awM5i5+1urW5uspFIzYPEx2oxw1IT1fh58kEMPbUafeCnvW6OM0KIBlgWyTkPcBqNMOnoh6G1QxrQ897/f5o/fzTpxdWLmo9kijwbWqbm4t4vGyArGaxLy0t3fvJP71/z7gaU840NFguYgSCNxwCEjh6bdZgwZ2UDn7n5ZGkN1D9Uu8zcLzErBs3AAGvEA8gwb+koqQk1L9SqUqX24crwXADBJ1nbsHaWnMdeYuPI6n/AdxhNLRIDOoX72zxmHYBxbz89Hz6gYCUAtvPkmUpiICtqqzsQ2/UKpD+6WQypcO5eB4VSywG38e6Xrb+en5hISnsZqQg/TudklKQQfCPlAEBBkv3tmLsM3xxJP0Ym7+du6t/PP3jUywAjdNThUkHD5UJC45tS9//0PvHn33pPwj6B+fH1UI6CYL5/7QOCIfvCGFVoABHQzitoiwlpYLPSsVCLc8AcUC4t446YrL79QaFwdB3KFMlzcTREINwb0bcEhjXwikVxcXNoIP3AQR+/SqFwOJD5y0AfzHAQAqBJPXvs9dLdCzn0cwaNp89eO/lv45PfmDo/Qa1PnfVA8EPOOA+DOgXzz0ACYXGAsHEgwcPUqoI/yNQLTpZY8qtrqwDzVFHoI9CoLADTTCYS4k6eKG4pKy6bIHgXw2JhrnJd0TgQ3wtS8vKvoW55IcO5q5tbsaUfCq5hPHypUBqifnVpYADSFbQZwloQ64NeOPHoCvu4qWLwaUlNuTSYnKnA2M4w7jEDjdKdMFlOBC1RRlHQMNJ3KRc372xqo5EtNoQiGkAsVDkaBd6X2yAgIk5oKFyaH4SmsIA9QZbjV5W39OCO+Hik0qn89tOGzRWJWl12O1a1meV6V7vfOmVl15tk4+dTBA0lScM9nQmJMh9ZqVVw5nNsVyDvhMbvQT80OQM3O8kn25wso32OhAH9yY0y1j4+7Bt7/PZPR6l6mSdtF9pps0OxL6ecn7ang6w4UogA3avOc65sXXzIIkYZTVcff3R7qdPn606zVO/fv/9y5cvAw6+9dLtMTO3+uzpGbcEfr6M7QVOu7p1f0F459k5uCEAlmH7H+Ts1iUN43IxuB1dGx2Ym/Nwsw1PVs8hbs7NheEuNBqORL0MYzbaR9lweE7S7d54em41sBJgMCGajo/ZOPiSh50bG6tc5OoHj6bvfbkcVMqmfWbj+rfXrUHv3FyUY4ZHr8kOr1vNWqeLUZtMypncpOPnz+due59p5H1mdhJxQJPub1JRdlKmPDtTLlVlyxp08DOg42ck1aaF2GBEgpw6nLBAdgFYUykg7j9x5ZspCIh8SjvZ10NdgYL96fz6jvY4AjbTrIjO1prEPoXS0nD8oEymHt/YWiMFm4aZGcvKjCZkbB6sOraPIGBhYWEbcD+AP9zhll4AKJiemn4iD5u/KvibVJT+SVvr4jvPd9ofO/iXXlqQdrA2s7gy9XuAH54//mHQPzg/rtkNgMeO8UI4ncIfwcH9wiIllgJLxGKEwJyK+EsFBUKcEK7DpWpZSVgKNMj6dFmJafJas53tE+2PO6Lf5IuBKZUVxdUpeykENuZQX3RJv8lkAfzjWeANwL8V69j08nW9QhviYhNtcfijg7+OYd6E71hcwZVvDfHiH/Z+ce6NRpUBCfwig0bp5uSIi02W2gpEXMBcgL2OYiGlgMIOZIAYzbsAEPhwYQEdgQCARAYTAgjIl4avZRQCSVBMUtLxXJwNAQhEHRwgKTHUFTg+VD9w99HStUtqwECz0sy5HCjBTl1bnjIABA5fHF1aXrKHQnZGOzx6amAA6Z9zmJ2c6zqKveHXnvOyRsaN+IeDvxojGwn5gl6vdWp21mpmI/USiUcikTCKSriE0ETWKyIVJHie5ljh6UvTOtrjUVhk4LbfiAwQpKgCV6J/K339F7/Ql7cNSpuaEwRTnYVt0p6Tch9CmcHssDT046IkfXnhPiJ789qA/H1X+tK3eYPteniMzb7ZWXjsfBgk7+GIvqaal2AfDbHq7MGpDqyISQ32FyRDwOWcqw8Xmqs3Y2aEQLsW9CwA4JOZgNY4dZmAJWDgNKNdf/gMaPAQhut4Wc1K7GYv0KWFtZVVLXsK8E8i2QAGeFHj2BgHAWsxaWz1kqh2dnrmybmn88TdF7UHQfTWS0KMwwww5g3hAF2IQwUbCAxrATkdWicobEBUFM+rjlB9N3yWf2kyiIGEaotpZNqinPV60EgenrPXNlwCHcwyLqfGpOgrqj3fgKNvdOqNWF+w+JeZmZ1NJn+R+2VnSzOB/WX2KWqB/qmI/CXhv/ytgWyxz8lpoYUMMYEbMTY/Umhlg0CfmIIjrfYKMvJ5CKRjIWfPEgTEn3VZg9KkOJ79Rm2DZnx1k3ptrVYrIOCM9uhRj7X5tkiwF0u6eberUjLyCxD/9hfgXu/U1PRSldlubuqsK++R40aUJrmqsy4n7n3mRz+qqnaaH+n7i5MOF9VUFJT+nrhHzr69qT8U+gfnL+IASFbg8YcaAqkvEJ3h+zsOquEmXyTEfIP4fBwfVgVIiCOuQKxaVSppEnUFNoEOlhaBDjZLMwpSUuKuwBS+G9JRUtyGA8Lf/M3XjTkYD1BZkXYe5MSiCU4MAfCd9RWnPTj9yUdvb6o9HvXYr//pfZC/H39+tX5+3qnlTfiuxZjDAerXgOr3DRr7UtxRgZqQdMqqxAiBKZjFIqrMtFiyUtCEjaeYhz6eBXYWd3QA7hUvLNwHHbwAGIgAWFJTAhqYeqNrEsv4U1NDBuQyk4oO0m7IZswS21zbvZ7LRVbTPFpGCNRonU6tBgDwtVNfTS1fu/dVyKO9eC9QxqYAACAASURBVHE0uMS5OI4lQcJoq2UncXEjH7t/ioRz4pb0bpfy7bUGTuuzh2wuuBKnrV4P48HAJlNrDhbRgUDQAjrin4rQP7i8gALSpyy8kCm06n68oaP9FcNK9eWnRXpdW0JPkyChakRa1d7S2TLCkjD6ZZ9xemQEl4b4fE3tgwQBT1LEi3udeTAs3ZvXYsW+rs/ns+ikfYsaDav1hjycUS9tRdMYT0rKe3rGaDcA9/zqrLit/AWPa/XJjZdA4r6UZTKakS4azc5zAIDvTlm1WkNrHZYCm9iQ8hev/k9kgEPAjSdZo+/6lU8vX+756JNPvrpmZsMDOO7hOfN0VcttnNlwOl0ui8Vjs3GsbxYAcAO9RPCjCk16bfPzoFkt5nA4Mhcdcnuir4F6sDlwoGeY4dwc58GBxmiI+zsGOLbNDRJjbm5uaXraoFQapu/JAs5pmTrAhtFxwKiHh08BAmq5cfXhovMKDD4g+Mf3fvGdXJ4NN8miItC+mP4nzQJM1NU26FQqWv+Dx4jEuvKnkVjsRLSUQco2KZUTQPdwFKTyVSB/VAWLsBEi4plffmp6FVmWsk0Byc6ATJPF0pBVk3RICQQbNNX5fz6vQPyzKtdbO5SSo12hppGvU5P3Fba9Wgn8j8DfflIFBPgT6OyE/nWis02G898tOTv4RwoqBRQDyW/lH0tJO3gwUZiS/J9B3ndP3g+H/sH5i2raBEnm+R9fCjy2uxKYnJpamUbSUrNwawhVvhhbEQfB3t4KQECsBEqzMSKhQSY7niTNyuxXsl5r8bH9WAKkCEg9gQCBnZVthWSH+tc5OcDJeit7MxVKE3LAmdjajSfvrL27HmB899549l8rarUc5/vkfZ7+Ee8L4t+QYzGA9G+moSFe/LuJneUcmqVGH7eUBw8fTrQ3C6pNmreFZAyPxMwQ6QvvFuiH2BDpWAAKCOfhs4cLgIYL1BZYghhIWSD2iF+HX6rtdghpCG9ubt65s0aG0IfoCCaxxAx1IQT6tBjTCchg38Mtv//rTz/79T/9rF/rGb447AWpyYXgkuIJ7dW5iKR7iGRtDUQ986B979q6hxZ1I6rXj2vpMjiXxsCS0Q+JRJPU20IlFFw8xEHRXNVosNsNeI1JdfLOHMG2ExoBMKNFJ5PNrK8bDeUZnQZVwv4+aWGhVN/T2SPtEVUNFpb7sFXh8wV9Zo6dnZ6WyWZng6xPehqtL8Tyt8P+aB84L+FlHZl38QXVCt3U1JXjsUWcg2YYrVHXTBIQkfj1UN5HN3DKVTIGSdlAlHOsv/7pp5ffeuutT66hGxtXbRgXz209eferqXs+jbqpLqXT6tE2vfWLX/zPZ+fGPZj8Msf6lj/+5YefYFLg48nwpGZ+3u0JReciNg7bGhtOM+sBLLNJuiKTy7MOWySKsaduWyQU9YCydazMeAci0foIMjncly7xaFE0Dw9rOZyi665/8aqdAQUd9XIuJyeJRO2zBsO769P37n01s7pqkumNnATwlNOYL+45NeofZdWxgEZx/FB/P5n7HeP17xht/iZlJSYS+JPi8EeaVG/ow4dmbAwQsJMo4BYeAJtx2BZ+XMTUQhmeeKISLhUBsoUcsYCUnUSVxBxI3lJFmn86lSeAuDEZOODZ9ro+k0VRBM9cqdq5ugXq5J9jcFGRRViNGQXpBdXG+qNe6b79KfvTC1Kw/UEWeheQ1bal++D+aW5qLS9vxaVH+iZpKyYf8P8WH3ZFYZBCcHoyqf5VFGxP/v5+/pdjPyD69yPKAGkeIA+AvBuGegIJDKaTZogwG3WwIg0eE1IDzOFzKxD+cIelkFYCgQT262UN+BPMzsqSy4x2VtaRGieBOxNyFR3lr/7jIIXAShxKq6gs7jcRBmg6f+PJkxvr7767rnHE3gMhlqbQcuy1Lz+/KuG9L2QGyaEOgOaZobEHbxP6h/DH45+APp9EogkggRO3LMqySkr/OuhrB/2QqGFkggQEqwEAO+48e3Z/gbDAkrKFMuINRHcgVgRL+LAEHBch7nu0cd/44s7mdmA0D4F7GFIK/IAZ32DCIS3Zq6sN3nv/0/c/WUhSakAqOiwANxrO1u0mC3XmgM14XB6PC8uJro1z5zbcAwNe2cjy0pX3v5xEWNHAbYCBixPgz2MqbiznB6magQI24qyLDtSLDJSWHO7eelUzyc+s4mP42vaJzD5ZX3mTISdBpFMl5Fhl8KlNus4Wwel9hQkiVLLBIFC5a6yX404Fp2cB/3A42KDau21u2SWA807uHeyx2vfYcRGyJVc+NTIyNSU/aAkwuDjOzlrlQCN6cBCCxz6SDD8mVXpIgvPQxqJh6pc/+cknoHK/nLRrzUayS8BoVK+88+69e/emjWarXsNZ4I9fv/NkFXP7PO75cY09fPcxfNLlj6aWBugWOCaEUGbzzgFnC1zzoWcPQGrgg4+9koGBOYw9DUUi8NlqzAq87qmXRCQY0xjCbFQAQIy9ByGsceG+zK67fgYfvigTCh2A/y8y6bv+GL6Y4NLjd999srW1OL24gZDLmpWXLo6OBo1WtcPFWWjuCxW/eORXCN0t0iWBbMjE0Y8sqSqpL7cILo04A+ykBLB8mwDyJQweAyuEE4h/uCQT2yEgf3EurpI/YmqIAfJXlY+uQB7/4J20AVRUVnNjp0yzuhXbxKq6BVN0TEZbRNmbsP9YVR9goXTwNN1hVlCA62zpu9S9Imz+qjrLWwn9I+q3ke6ow7Hyqqpt7x9tvyD9O3w4qyMl/fdCvfjZl/fHf/4DMP/tOtsAWLpLAvNAmLz7pKeTlBjN4Q5xZbwCSDe2If7l4LBwY11nZ2tZYqaOBGXl6nEtWLaB9bI6jMuP2wIpBUxJEbZ23saZKtDBOWRriDiltdaEOxXO41jIwfX1b7+1mH2f/OP/9utfy61ab7hraH5cO4ozmHANOQMBh0XRMMMP/gL8LQD84dwH7xQV8O6Xs2cXHj7cupVfKcQw0l2QN0H/Y0I4QQCxY6KjuLO6o7q4F3TwswegiIkzuvomFgPpkEhZPC8L/wAQEF2Bby8sHFRgKZBuEEYI3LGVRYH9adjJsF2NZkCHPfiTy188OLI8PW23OVcu+WaVpgDu/+B9ZYw3fMDO2VyOVZJ6ZWOnppdmr/zk8eRcyM6qNcBVMMBZImHMcuy8803EFlzrJCoHNWrAISx0rhr0Pc1EtZDE0bZ0AMBGtikhQSc7nSAYkYtamqxwBTbj4r4TJwpP9PjsuAcoCGf0wIHJyXAYuCvAH0lFyM2h5hfeAVOahxFWCYXtTeyeYXbYrlUrmq5Mjej1TSNTV+S5iwEyVWfXWnVkIVwc+wAgelp0TCSKzsb5p5tAq372MwTAK0tXw36yCo7El5rNl94FCJwymDmH7tdvvbJw44kNKWOIcTi0IUSykamPeq6MaLvrQUiH7MOIdxIJZ+fGV1d+dX06aPOGbPVXPw9jzgRmBUYjeELXgn7/o0dR/F0Jrv3AvaKeEOalajHXgsOtf94ggwFbQy7OBtxR0jUwF3z0+aPlpeDVyeufvf7t5rkN4/RiwMEC6Futl4xK4/Cp4WHOpZXRqV/e/CePm/+SipIya0oSM3H4t09xGOBPOhZXwLQFskMAaQkDnrxIrio7FiaIeAEMTCGLgsViSgAreRQUicnTHJ7hCIGi9rPw0t5enmtRNhQ1tp+9bHWubq6hRyFmMuGcitIcrT/qMSR0sqwqQadsqEjOIO2PVKz+EQBMPtZqtht1reWdvPVZ2lPemJMT734UFOTvzP2S30lNB/pXVPI9vS/79pb+0Q+K/v2IAKA4I14DTOabwMl8HXB7MASHZNL3i2swLdVSVJFSWUFlcA7NScWcBHhTR1feqvC5r0cLJU4GZfdbWbtSmo5bQyq3e8F4KoU1FafhGvwtQGAzrg2pSKlIRAvT+Vtra4f69U16/WfrZvYeVv8e+9Val4tfP9PV7QL4CygVDes8/SOR9xT/4vBHAZCkAArvYAR+vP6HqLfAi+AFIcAgIuHEBJHD1fCbxQvw/z97+AWSQDgLBP3olBz/Dt63knnh7LdvLtwiidEghNESE5+OQwjkxnFQANgfCzrRbzdbAsMzb8eaXrl9GadBojbHikUZm3nH7pHwMf7a8BzoObvvna2n5+a7OaPVvzRy5d5SeCAaCk2SlAIsfUq0BqPdSCGQB0BRjs7sNct00kwdLcHqOkkcDBXA6W2n0083G60Cqay8uWdkZKyzpbEKJ3OxuTtYKNIHcQJ4mB0dXQLsC1+9Ojfw4t0PlnHdpVJpNCt1or2DRALj/51Q2HY6B/ScTzuMGaqBFRlwpBH9SFMTsMCRqUO5FhKsoMFRX3m8NTo21tPTUq6wAaZEQ+Mbq2sj09PwfwMGfjISIblNo6wGf0a4T8X4K5DBUyNG3a//4ZU7T1ZsWMeTuBxabygasbkWDY+nfvYvwMW6u7q6Ii9wnHtoCNsX5sDq6qVfXQ9GLzpcNoBZRLJxzmaL2oAxd4UwKzA6Fx2iWYGSeknUw6EJnPXYxoECAgCOa8zeqM0GRJOzeaISyRD8q/ZQNBy2+22Sa199+OFnN7bOBe41NQBU+/1WXa1yeM+e4T2jjMtl1PWoKAJeofI3G70vRPyqSqprVPLa3EyUv6qxHfjbkcDN2wcXR7dX9ZZ0iAn+0V8EBMXb9G9bDBMEbMeBH0BA+LTmbLhyGlpFgrNyzWpsc23tfOw8cAkcWjcYfGY2crSese9pTUi4nXm++BjBvVRcZ0voX6mAeP86y3vi9K+nLidO/zBXMv92PPqAXFmpx8RpR46kCb8n/du794/+7IdF//Ck7QLAYzvSt5R2QNKTd2qB6an7KzJxNERRRq0wtBcsRGhBAIRTV1yMeW2qLDkgIBxAwEx5NtHBxWRx0vYhvuiK4mrRSdwa8jff1GFDuEIsFtYCAt7avFHdNDLS1N8/c9GiDl5//PldidOi0TJ2SpacGBKqVBhyt5sfNcVCYQ6d++U98uRjbP82NgorJtDhUiHcJX07KO4h8uEr+a/exsYOXNkBsAg6+OFCMUXAkmpCAmtISbCEfowgmJZ2c2Ehi86GNJzfRQK7sZMRdTk1oHtB/dqDQT9rtFosMllsy3Tv/V//bHlp8oM5iSsQ21r7zeMlzibBUBGNNtLVZWPvffWb1afnxgPWoD84fe/xkj0Kakzi0Rj9JPSm2+1hlVaWVaQ1N/L4J2i1gurUSZN0/bitqkHWpCrP2ca/ttPJ6W3tOgyzl3c2NjdXnUYaV0pmePMK21qtCFij2JbBJSZzuIoTzsAHj2aNPqXSajUarZlVg3v3ngDmJ2hV6axGMz9PN6wNPNHfmyZgBggINHBkSq5T0i1KGtaol5KiF17yLc0qI+YWDNicq7GmEZnMcD53+fGjpXtWG52jCQ5rNWSTEZAyi2VdN2WV/sPrN544sODZPTTvRPyz2WwOk2/Jappcmlmdnx8CQRuJepxOTsvaT7HqldWVSxdDFx1OnJsjSOaxvQCg6ZbUe+BzB2wuj4fcnrq6JBLg3XazzysZco1j5J8zoDR7QwzjdDr3cKFQREJ811qnS+JhvM8/N/n48aMvP/ts89yWcqTp+ozPFwz6rNbhPaf27Bm1My5Hg7Rnp/yXTQAwO5sGv6hKsmoJ/VMh/pEKIADg5e0CxjYBxNrNWVFzdUlFioCqTP5KQRjEamAlkcI5cRQU8UeACNjeqrCYFEfqqtpbrIFVTFon+KcE+JtZ/+TDdYBApiuy/jo8M+SdAHoFlP4R/EtNzlf57Gb4I6R/MhryXrdN/4iSKKD1PwFuZhJUJaP3L6mksuD7jX7kAf37AXU/4ue/UABMJw2Q0h39G9fA26ZAIoP3VxBLTG5ZCvHWkfpfBbK/3gphDlLAjnISWamSw9WIEKgHEpBZJDN72b6M1O3dwdtMsKKmLqOQ7o6rexXn7cQpJbWmt29OiPXTer1VvRJbX59h72LuS8BqUjPR+AymcmZdlptby1f/qPeF8j9RvAJIZysJMvfmfIG5VxW8AKbVP576TcQxkD8TyA0reu88e3h/YaKaPwh6CxT84lQwrWThverMpHhQlmlHB2M3ROJaVLMIf1wkPDkZnJ2d7TtuZBp0euvy48fTjz94sau72+bcWvnVst+54XR7HBalxub23/vlh1/95tzTc2uzAH/TgEmTLAdX87hT47NHoljUxwx41gCQZ2hpx0Rokaif9RqbMkntFfEPzVuNlcS2dZoPIs1PPwsXZ35C4Yl9+/j0Pnis2/YWNsvo6o/Ra48+uNqF2IeECwdqh64uT/t8PsyiN5qtnXltIqnMCiARYs18XiCrifUDlZs2yEamZ2dHdEWHjvc36a5I1xbVfKwWlgKJUm8uN3k8uL5o/tyWfgrwDx652cmrXMBidM7XHz3aNTcZNGsIBPqDrK3eeeNby7cLT1aI6nWNbzi8gH84umaZCZzbvHBm1ap0bpyZJy6XEKc1+8hKZsvKioMLLC4tnpnHYPA9nigOx3GhIVuIc6J5YG7uNdC2yCgjxIgdhWeSaxzuUloLurbNGvWwfU8INxq/wJ3yeA7YtQ6ng41enZy7Ohm+u/zZ669vxrbO47Z0n38yaNUTEghMmHFp9D3x7APcepmdlJ2J1hdAPbmstqaxlZe/AH+t1AEDv1q+SwDh9t3eXpxYIojDH75QBCRlQPoS18FiIoPpaW+rLLKolbklVVX/xxX16oXNzQvoqTWRzc2Kb7/97MP3P/rW6DWkJAxK1dby5FSEv1QggRkZ+/e/mbq3SobVv/LyHhxoxUyTzp3gv+29Hzz3Q0J4TJx48EhZb8ax70f/fiijH797/kxYSRhgKe8C3A1/x5K3HTEUAIEFplSjJUZ9qIOQQKp9qQbu7W0U0nx5jMlKRAjMleXq+1EI9+NoSGbBLgSMR0Z3dOS0JRQWpn7zzTdisgY4pTKxRpwhXF+/filgOni8r+9IrZJxYQKRn1VqGBsNvQfxC1fRG8T6XAKQRZ4/7Tz+xckfQrOQSt/eiQcAgUBWsf4XZ3884v0uAk5gSTBn4SGWAhd4JVxykwIfAOFNYpGpWXhvooYsjyviIxJi2xDoJrsyg0CSRhmbpOvFyeXlx3K8cxj0I/pp/+SS1wbwF41G3I5rfs/8/IaTszEaDxf85S9/+eFv3tnalPmC176aXpqLRObYgAv3PcI1bovYbC4uBCyt3mM0oGOrGb5bqRKwsChT3k9mEQ2yJhy8wDisfAqAdB1v6sstjYUn0Kgab2WUlu47PeYzA3j4gqNLH9zFLXfddP8mZnyOO5lldIH4SA3JZyX7IFmfoUknQ/wDvFLP6Kbggunr00/7WI11pEmXlKSTT30kPxKz0MWarF2TSXyA7UmebpvHM75x4YIeTTb6EZmBHd/YuhBTaznM7kMdHNQENOagPwq3D3dsLfDkyTATCnm1jMPBeEGdwk1gzymfcnHzzp0LW9ag3ePZ2IAbTSTEcV78JnAfqUWtXfy3f1nErEA3rnqLdNXbwqEXXpgLBRwO1j/QNReR2LDTXm9jGFzuNo6xB1pQtejGVptH7QB/HhuIa280FL76/KhZzU7ODQAtfi4kmbz30SuvLNxfbKj1Ga0Kn9/vk/UpcTaEHR3mGEvTmEqO8x7kZPL4J9Xn9qtUncJyoH9EALciAezBvSaogN/aJYDh+ducllaM3hYCPpT6bV8sKcgAiR+GYCAdmyMMUPBymsKkVByqO/3yW4bA1rP7F7D9gfBnMZrOj8gOHv72syuzFw2JLYVt1bcqkgvycfy3IONN5H8F6aWtRqR/uN4RGQtGVbTg1BSPfxk7tj8KzNj8PZzdkVJwbBvZfi8g/CF5/75z/pQHQCKB4df/ILU/in4U/v7H7m5IemqqmGwNMWWBDgYCSFJi6JLdXmEdYqCQVgIBAXX6PlmurK8/W5qpw7lQa11qwQ4A8u8r68or8wr5wGgsLqLpKaVx/fqw2qSX6fv6+g4fzl3houHwQBdnAfBF69/6ei7iH1G/1bu8L6QpJuABkLRWGnlY6yV7kL7YRrn4byPgVcArSHn0yUwIt8GwAnXwFwv0lC2gGC7hvTElZTUT7y2UlMFtfSctVaEACFwzWdSce8OhZRgtC4zpwHM225DbPt3fr1eqHYr+kXvLrMfm3Jh3eUjqaSg8gGMgZrvHzTwG/PvqN795sj4bDF7/6rE/KrFFurQzAcfFGSso1DmsoTEeCWYFejQGK9nWpaP0T46hvQYFFh3k0ta6HBG17RMKiIEIVc09ogQs+/H4lwwcsLjWSKwvwaVHdwco7cMJfycSbDhq9ew9mcmiNGIevVeiterlreVnMxmGBfgLamK1U1Mj+r5avWzaaF7cMimnp+TSRKl86soV6XGFMejzYYKzkhhiREeAFbtdq0/Wm6anZfqmr64vmx3nnt2/c0Npf+7v0IKCOthstKg1uJ+tnjsfCwSA/oXs7PCwlrED/rnGHaPhA0u+3MTq4qza2SVAqOGNcwCBEZwbxE1UvqDd71Ma/+3x6pkzT59iwxb3nwOHhOdNaBTNA11HuwYkkb/DDBgb3EjhxjI+7p7XkswysxrwD22MHM4UuzlPaGBgbnKJJGxhUffA3z4fvPLpW3W1tTe2FjEt2+DzB2ebZJcuAssfHt3DaKxA/4ow8i9Tmk2cfyqpvLYhWwXUEBRlZ7wBzEvg8t0VwLMIf6K6zLJKfn6dnJRtEkgJIZkHEdFfOfEdwoIq0WGL0qRILKhqv2xd3dqM4x9W/xreOC8bkdWuKw/4cvLKZbpmcX5yfgZ6/0gX+M2M1ORUWv0jS85kePfEPHH6FaRQKymVvjz85SenlB0+nvY96d8+9P798Kp/9Pz4v1RsAyBCIB+LtSsbi7cExj9OTy0gpUBtQ1plJaF/QiHCoJBywF4ctSBrxrEZcrxJL6vV63U6ebauFiBQJkzN2OWIIWFZKZXl1SLM5f7tN19XV4qFAFwTlXWW4RUDsgUAwL6DB2tjDhtRvxYLjiavy2pzc/m5X7oDrZ13hZ5tjxf/CPnr3fH9IQt8SNJPd7G/3l6APvqK/ewJqonJH8FnVHyBpUAhugIXqksIEaRnYeK9iYWaGnhSk8DozFu3tuNSN2Ou8VWt1g6XLYNl/0m7w7m1ubWyPjLSsLL+bdN00M5wWgfHcFGyhFsSGZp3mJcfs9pf/uT9D9/9zbsNAHbT9x5/fjeCBfx6xno9GFxeptZvmy3CgZIcAgVnN1qVwHrsZr0UO00NOIWIbSc53MIxvIOOwfGryKtEnT3JQABL25IxqCoZFz7cxPwVgL/g8gcv1g8R3udyOVdBR2pxwRm2D63TI7UKpdVgDEmOalowk/3lhu5uD+szWnKnsOtx/FDT9CzA3+b9tcVF64gcNxnJrwAE6hRKO3z1R9X04egfn4fjnB4Z0ev7+qcfTWoWty7cqWlNtIIsfe5v0ZXSFWExGGEIv2fv11YtFw2FtBrtsN1u93qA/q1cDEeu3mUP15QU1xzRzM1FovaLq2c25oecGrjZ2P3LvllsTwRnrzPdJCRh3u2GWw/GnqLEHiVIVg8QGH3+gAv+bBzUL3xVQ07DrJ/I+tHnX4t6OCc2ssYZe4iULCcnw12EF9e/GF66tnxvZFb36kt37iMEzsoQAg1NIISHf/5/ngKg1ph0cnkSjn0g/CUC/WsoAt6Hr9Ke5pxyngCStcadNBRiuwJ4VtBYk1iB8NceB0Ae/vj3fBKCWCAmTZAceuBhTrJoTA1FvVVVLbLAFmiQC5trsRlEP7Uiq7Hk5ttvjBjsIUNHQkKVzNwkaEvfXwDwB/wP2F9+8jGVGe6frZ2tYzpSriKTvzk8/GUIeO9fviB+kvd3HDqSJUz5fs1feN79gbef/0fnL/58hwFuj8PxBPA7xUB+ZQhujNpfUHwYdfDB4soK0v4gQpjgSW9dI9kzVAwQmKbKzAYdjIXVfh08MQ7hAuEkQcFOTmAKHxfYUSLEUmDeN9983VtRienTwrTDMwaZDF4B6wBcYrHF8aEhlzOQexCkpNZS+/Ybb9+8WdZB2J9AROPR2nn5y+OfkAeyDr7t0QGkDkuBOYTlIccjIa+AfhT/JuIFwd4JCpqglR8gBE4g/cPXYloRRPzDORESlYppqVnZRRQCa02rziGHGvBvj1brxmso6r22dh/w76vZ6XsjX304vTz5HP4ZF0IkQzeaJ+IJvHPv/31k/8mHX737zroBIGn63vLdAQlGwHfVM7NYCZwMIUdzezjbCyHXuMupNZsZm6bPaLbq0Pnc12AwNBhkfU3wY1a1djZiJD7NgyYgmN/ePNa8bx+/uCg5uQ0e48Iyd7ebAfG4PBl1IxtyMk6gfk/WZ1ZAioLIa8ARgumRpiaF3TYkOaptaW9RiV5uwEkyxqK7MoVNKt3UtM8Su4Dzufc3Y1bZFN8I+OijES1G+B01/lWnwphYdciNAOgO+Wf7+vum/R5Qv/eBurcmWtBuEn7NhjLYznpp7OnR0CxqUbsW4W/Sa+fgYb94yQ9KdCiQVAOXa9Li/JAkEvZfuwQQuKrWarVeXIA0O+3zWWUyjaSrex7nqOeH3B7MC8JFzuGrUaS4tEH1PGCc0+EE/HNprFYgj0of4N9zz4c4Z8B4UYvr3zy4+k8SHYggK3aR3X8fLM1OAwk8K5oACLQYfdMjsqA/OKJbv/jzn/989NSoxhHoJ9gH6CdVqbJlffIeFWl+jPWoelowXRkZIADg5d/pAYvOijrKqsWCuKiNH9oFJgQQkRAjEshLJU0iEYlOV+eqlQ2HawTtZ680rPK7tmdippWVFUttXXtzY3nxLYvX2Co9kibVoWTISi3F5kcK0MCC/DYxXJBWOVIVEnygk3by5hc+/KBgl/yF38tIFqcd/q71+fc6Pzjv33fPn/6ReIcBIgTyTpjkbSK47YZJ3xbC+8VpDXDjNSVVwCNBcKaOEq5eYQ4tBZZXJKjsAgAAIABJREFUExKYKdfRZkh/kVSa2aQEwt1aSlfHkU4wTwTFHdUdeScKTyR/8ze/FcBfMlGZfExqmEVPh0yGM7ex2ObmotOlAfV7PBf+ZU3uTXQtE/HLtz3w8DG5OfwXRXGsjuIf+YWlwC/EwDHJapJeOtUH+FdJERDBkOhhooUJCURLzATFPwRAIIML700U01FhFZ+UgDoYExLeUHLjTo+N0wDGAULhbIdLuflsc+3d648+mP3448f/8mjy6twe9TDLuDjXOFaqQOeFbMPvfrhs/6e/fzfAGINBQMqlOYlNEpFgtcruD1+dA5jsRoea1zsH1+8w6FNzyD3kLJLqsNParyc/J4A/xD8AQJDAgvxdp6q9fCz/BAjgZCR/baX7EhLyEsok9SAD2WW/ZxyRT6PRBAIz6+uy9fUZkIM++Nnnwl870jTrBU6GANhj5GSdDdhEGHL6RnRN6H2ZNgL9Qwe6cAEg8LxhegpjUHqky2EbSXA2dlo9Xer+PvcQIuDQkMesH/E5zzwD+KupLu5MjJEw+rnXXvAMdXtcbsJ5u+tDLAAaRvDZ7eE5D+NwrFy6tnQXx4BMWSVAoaQzgfH57hfv4rTh6oplMeDgQOp6l5an8Y4JhLWrfnx+4yk2QzD2tHsnK9CNSDsQIdW/cZfLofT5Af6svlHvc89PehlHYAY4sR330TMc/N/wjbtccK/Chen1V5cePb735Yfvv3X27MSdCzGLcXZkyhD0zzbpLv3856dGfQZTwGGSk44v3IWONxxX9cCHYzj8QdRvi6gR5O9lmgOzuwcCz9iSmxOi+BF85/ASOP4B6QdjIpMIH+MitVrRUCSsqjo7Ao8Dev/WcJYK8M+UhnKo+Wy5me0/kVDY0qTXy5vQLVCXl4o93YKM/XmdPtAPqlZqfSbe5xZMo6H/bkFBAajlgvw4/ImqUo9VFB3OFKakf7/m7968H2r1jz9/8Wd/XLALAPE1DoG7eyDbs3HHaCkQdLBCo9Uos4SV/LLLeCsERTBphRS3gkjMIvYMhMBDqIP1RrjplO90Q97kHTHiyo4S0eBgIVkgXNFbkJqXkNCuQl5jaDAtIvzBoxtbdTlMtbmH3zZpOUaTJQTcEmM4Wvt2PhqBP/QU7CKAO2+J8F24g4hWMYEhDHHxS6wFCIIUASsmKqhMhpfeiQUCgbQdUkzhrzpuDSxLwy1yuDskMzM7s0/rBgmlBeRjlErWCxA37ljb2lp7/bPP/C/OBSfDH0SiXri+0RaN2c974H/GoGRvNPqrS+xn7zxZZFyMD0hiRILTX0O418HuxWkRLNlHEf6wIuX14Z7M8Y3xIyr8h/vJhno9JpIA/NWUEAAUp+Tn7+clcJVA1NNyYl8ev7Qj73SSVnYyocYG+lti8zCBwKLaaAT8s8ysG4D1rQMEKtVGH2Jqn4kU5YCV2fVWRmL2mSX/F5mw9Rj1U1PTpsWt+/dvdtSRcitCoMk6fe/K2DQnoQn29XarkbGZMcIBK4xDrqEhzqyO3b8DT4zWupZXXq8NjPMQiN5km8tmq+/2wA8HWNiwVmufDA/YXA71pevLn1/tGhp3qg1SDIr56KtrFzGB+0WyhmVmJmZh0PFMINAgCwatRjZaPzR/BhOjPR7PCzYbCYbmDhxgcFzHjeoX/t1xy6wfXc3WoDcEDNKvVVuss0G/PcQ5Ahf9B7wM5x5yMczz4clRLcYk2F78/OPHX375KbBA8RcP71MIhE+Y1TVdv2g1zFy6qHUgBGLzN7cvMU7/4vO/PT3NosbyHloC3EX/RM0dNzu2bS3/Dv/49wKKfwIcjcuhA3HFJo1ScbBM3C76SLkaIxdIbGZmZcaysnK4saoKDdI6u0+qevVYDmjwTp1OrgcWaChPxxVwx0QGO2uQ9/Qg/UP5q2oF+kcG8cRIPfPzM6ryMzK26V9BsjjrSFFJZer3hb8faPN31/mLPxHvaoLsJCKUUriLW6J/96RmdBxXaxl1bU1FDuF8jULSD+YZIKhg7AbDM12azVtiQAfL5f0Gs9fclJOeIabgR5Uwtrl6S8oFeWRx0m/TSWpZ6f5WHeKfBQCQ5O9tbm45nYEGEL9vawACFSVV8T2pNCGXRj9jEH5jDl/7E1Ipu+v0VmA/+D0idynY8TnXlZUTAIITlRNxXJwQVtCmyIM4BFL8K9nljaYLlFSYFShVMC6ng8FNHnbLDKh9tSMQu7C18tmnH354PdrtYjlbxO3a4xryjrKhU8O4Dp0ZBrLF4golD6e9ceHCokbj5OxhgAIQg90uJ2d7Lco4550ae+S156KhEGnVujm71z2/sTHvzlXJGGVfLgZ3kDw6pH81dBGyGFVOnAAKWsYEhXvhocX276BIp60P6VtuujGH1IZbHZUgATVqoH8Gq0lhQgRcj6HG08vUHopkIEuNVq3HGGSRASICugGpDbH79+/gjxR+fPiDXrh5P2aaHjHbhtwUNm3eoM/O+cz2qAS/cFzgcWbDacmu6xkb63nr8uWxJqWDLmWLjJ+Zl0jcNpsHvju71j7Malj75JxkyIWb2OKbKK9Nf3QZztTjJf/FYcfGfBdmL05fX7esuru6yGxIcHoaWFnQ4Mdp8XNPz61yHkkkynBDbqc2HA7b99jcjpUALv2Yd1hn/ejns456ybYAs2VmdjnoD3k4h/qafzIc1mqAGmuYgYHw5KR5JjY+NNR1FyHww0/feqs95YsHAIG+6akR+FsMOl3TDHZDAAHVtVJVf62uB75F3GzM7x4n53J5s6huOweruZGWAHuLFyao+iX1v7iPX8CXAQXYgqANYYp/hC4IqkRFao0i95Cw6uWWJozjgJfYWuwJ3A1WZrJEL/91e/vLLQazvqqtdb0Jg12ac1RyuRynHnWVwHFUPi/Qv05qfabBL80E/wjiYvJ0frz7AV8Vev+KjmT1ZiR/T/wr/ZMfovfvd86P/yQlfQcAd0/EJW8PgpD2R/IxXBy/jYAF4rJcjVZrPNRbic3fRtS/2Aiuw6mzug5AwOLOzhIV0cFNslqig7Ozs4klRpWeusMBaUskRSwsEb4JfD0vGfFvX0rF/nRFNGpRWxQK4njevLAJGDHOmW7d/KI4V8Nx2sOCkzz+tbfHe7/E/LytgDu2xe/OqSAQiIlDlVT0EgAEAohWqwrxNhnkURAQ8Au0xEwQ9fteRwlRw2SL5uslmI0AR1XSK2UB/gCWOc6uNPhYs0mpNm0+23ry9x9++Xh5ae7vTnnhWg9oQ8+HopOTc1f9SHO4EMCkWo0Ok5AtsLUFAKjRMh4Xwk6XhBs+FX4xYh92aPy4ANfm4oaAyCAsujfOAAB2W2VmCYPre6VFxHerqmktgS+ruDgHvpWMbQEsEI31FO4DAGxLb9s3KJ01a2xajdo0VE/AzQM/R7PZolxH/IOby8Ha9XV907c31ixWH+PGvWqgSiUee3BWw+GGE+ytSpBS2RjLjYWOhcaKHKxB4H4ygMA7a0bgTfDnHgnuLg95geoGMUvKI7ENYacZQMnN5F6+/Mknn3w0dmXk2uiwwzlP2hbz+A9xrB3ASKvVaDDxUTI0jvj3wd2BoXEMwZhcmvroo7GP7i2FgZVdHF6d7x744PNHj7+6vnpmvrteErGFmODstAxZ2ezkQD38pavDds5m4xxOPisw4mGvP1k9tzE/HvAF/T6lyepjQyGOY7RqpXV2dskfcjkDxmtL4YEujwb99mpGUt81tzTtYzHiAv+9fwEEBBLYLiJD4L7pJtmy3zci7SeuQI3D4Tjf36/C6EPifNnhf53werlFVFkX7wAj/J0VFd/sEBMLf/O/o3/0ZMBrhkBMp4NxNrhSLBDkVSuB/tWWpFS93GkKrN1Yo/yPp3+nq6qqXh7UsdZWYBQteh0ZymkV5UjhvYG1G7Ny+ux2g7y1R0UmFpqw+0Grf2ICvMD8MP0+/hWI8kszEo8UFYv3/69V/ds+f/on++MSmDRB+FzUbQN0cjwaMHlXHRBt0QUVWaiDTUUduG1S2NjbiGboRtTAjY3kHXHEqBKluiaqg3E2RKdXsnZfzXdt0aQWWCmsqcw7gezvRGrFhFjK1ddrDiuVDedNihiujwMA3IytOjVJE2+mlBEdfFxQRQMxdsFfb1z/EtibiL+Lv8HghS+A1D14D1APYY6UVcirOG65rxDHY79IR6SClALvTHwBPLC6uHihGMdDFshIMB0Prm5VOMYd2PvgOI0CL62G3LW1+8+e3fzsq6W7Yf9cNDwXZjUB82h0LvxCJGSTRLxwfeG6cmAeRjNr99ujHm3AMazRmLVYqpJ0207h2PNA2E/Tv7o4h2NjfNzpdLnHz2CFv1tiUaptGl+QNffjmL2qFQ4S02JcXyUWFOQXbBPA5oS9eUgABzuUdrvPbNNYLD40IyL+4dIfrakJ8M/QV5SdKcUAA51cmrbmcJGt4rhaEiQiCNNAgITR24hAl2ycGVdnVTS2YII9HmxsirK08MW5AcpsHvgCIxznWN1adXEcibDHKHkAwJUDnKbpk0+uXJE3LU+GJ/17XM6VCzj+Vy8B+geYycJ9gPWHI263E/Dv0V1+EW94bsA7K1eNyQ2YHQs/l4sB57wEdPDje9dXzp2Bn0jEw2jNQezWBoOzwdAGAUAG1yOBvNV44Hvx+pevP7nwdMOhDBL6NxtkOQ4Xnlushtllv5djAurg0l1suTMY+Txj0WKzCNNu/ayDrD+9+/GXX34ILPAv2yvvPAQIVE6PTPuWZkd0MwiB8KXHYrGkHqJ+d7E/ioFwGkWNddsdEFHjwsIEFm1EAIUUAEkzj0eeFIp/IoClN6kxkBK0KnEu3MFqk4RV7Uj/1m6Q6t/MzBOAv4as9tNV7VUvl/vMsrY63bfSsR7c2oNZjKCD8dG1sqyZBfoH6heIiQxjelrrGnOad+CXrHrjwQ9e8lOLi44kfu/mxw8t+OU/OD/+84L0eBd4VyJMfCg4eacUuEMAk8lwXEYHGQ1RlFVUIgKiBwagr5G0hXH5ZR3q4Faig/npuONyIIQyYOKynIKU7xzMzq8Y+0UKLhAW/PbrGlPkaEQhLijpzz1/3mQCBFyLXbiAbX4nZ62rahMlKbUejwV0cPuu4h91P3/3EAzEih5IWrLkeKJS/AVaYlLEoHpTkPYRCSzm+9IVBBJBDvO9YfxM0kB+772FBYJ/WA9c4EfkyspKqqVGIA4aux2ugBnsDVplPt8m/gv/8Nm1uW7uwMCLA0dx3AGTbHAi1jM0hNdXgAs9/5x9FIdu/X4zG/XAlTis1nAOF1Cz58Nz9bwXI9KFK9TVltiiw+mmWYHd3R7jusLCaYKgL50KBL/Wzk5SnSxGiAcNDAi4H30MovKe0hN7S9uO5VUlsUDGWNZpMQA+cIBsHngTsbnGOWuTDoSQ9Ouvv5Y2TY006VSHtChZUclGMUKFY5yrF7Y2PBFUzZhB0A1QNs4YOhH9Ll9+69dvAS1q6WNcZ4Di8QA45HKubt2/c2Fr1enyvBDyghDGz/p/lj8IMb4pqVSqN88NXA1zav06AuCQx273khx9tdns90bd444VMqIyT+gfTkFyM3CxymecfObEtYugg7uvfv7xo+voiRn6/8h716A2z3Pvd7drtW4/0UwJhoIogkEipIKGgw1UwIbWIAE6Q4FBCijiiQiKhASyVUfnBBV7KMb1Gst4XFEwlRXJEI+BDBq7YIZhiToQxzgOtR07a+PBY3viw/KimQRvZ2Zf1/08Aidt9zt+9/7QtLfNwQeQAOn3/K/T/+q0A8lcvun11REnIFD7eJ/F4cUWRLveLtdCHGz3TXtm5x4fmcJrlE4EyHMpTAOWealfOTIzDfwzSZ2z9Mih1Q348/vFUpN7yhpdfEVU4CtXEIF37hx8qbUYq99a3fBwyDM9UlN3qm+bQiGdcs/Pc4VE/B1mpB/Dv9Pthe1wlWDVVjApwIrSSVZ2A63+cIoTX6K/yGGz6DCUxeaxo1BMZOepFeLt28t4Ja1d4fnw8jLgjxvxb4AAnMuq/Tngr6RVIhY3x8S0CPe2gzBoB9ah+hM2ZbcLa4T1Kg1m/4RCeEriD504H5C9H3S/TQlrs/aLBeGk4uSq+NLElF3PPdMB+fePH/1Gz/e+8210BGQaYXYm0Bpws/KxVRRO2fU0DQGBbH4+Vwo/9e15xagCyUEQkpoIyQbmAQILJNgVSIvAxvgaYXo9pgLTY1MI+Ta1YHEin7+7/W3WrmxOySNDR6W0lM3K3t9lsEvJzpBwGKLglZVlQKCi/uD+bn45RJGUqOJXJZv44xR9nX1YzY1aHhSRAi+8Btgl3nsCRGMh6EgAzKf1X/GmCuTzi7ZKwxAHX/gT9tDsjg6H5BHLQGyGmWzmuiH6NYD+26aqHnF5Qo0jHsP84M3JW7fLFo16MzGwwWfsNHHyEgRGfRBzAfakCsfzP/iBwzirE6nFOqXOiHMuZjulklr0gdGOTjK1MAqBG+6gdWtFXC3wb2ACgkubjdJ4Rhp1JoUDt8zZtTVNtYVo7o8AzCMApA1/MxGADdgE/dMYjhhAgIJnngvKxwuhnx3CVQCgDXSlQon4SwcCPhoefpQlxgWdE71ogQcvAbuZfD2Djyd69fZtDm+gsnPf4ycbc5RmGPjX3o4u9ge7NF73Bjo4dwqCDq8d2wpXbuS1591cmwd1jK43AghLj3y0/pNPh+wKXWpZjtRW2aNQvv46APDxEkU5cHGnCy4IKg1pfjk1c58swIougLGZRKnYCO0my/iIjYJ7fmkCdxDMzpqWMLCdUg319PhmVkdG4DokUitGBZ0TNrPBYNbbbbgkZMilca+p4d9C8P0eOjPqlU7Nz899MDIyQ/CnnZ1Bk1rsCHeL1TKlUqfeLrZsbk5Cl5+Jzo4zn/4EEPjhxZdeaj127+YKiMDh/tC0Z6SmUasAneyGTzlV3t6+mf87zcTATA90Q2s2BwB4sKn0GJ/EvtgIg7/RxZJGIPxOJPgjBqmAo0RWJovWfwn8Kjk8FNL57MymvXMg/8hSbb8fy7/+AmBfa8mvGqp1BfCRnKZaNqZAGpoKu/AJWFN3OJtFWrTRnQHC38ZGlH9R55dNhfnUyU7Z1RYP8o+d8gy2zz987psk/+jz79/99pYr9M6ETW9UYN1OBnbMy66Up+JgnCzMIHGwOL4N14NUkBi4IoOzG5OCHDIblweBcAHEwcQlhgtxcE1qavpendGoS07gRQG4aZfKfzuPz+H/sETlUJWX7Upic+0/6zCK1DQBI8A/IGBknlLV/P7nKQVqudmukHFeI3vfOJxaZjDv6xqwLWp4gO3OpOp7rGjsT3+6jZuTSACcyCfU25zQA1WIAOSTrhjSG3Nh7NgxUgxpY4ZD8khfdGleW7yWsmDdknL0KRudLmd/f8gpBeVz4OCbcRF1H0aynWhEIhgdGgUlh+VODGw9IZAXwIUfOLxe14wO2+48mC6zm+akGo8CF9di34ZN0FGJgxBuqVokN9v0Azg5ESC+e6GRkfC8CW/bbDY6hRx+W15pM9yjPLSVgG8rm8cjqZzCRklMzE8P1msgpsVe37kduWo5Lqv0etEfAD675dScxSxXAvySHz2qeSQ8Snn7TvzOsoQ3heZQeuv8ymRDU8MksIxyDKF/IQSzT5bP1+NI3ju1mNrvUhqoxbvLTx4/BgCODg0Z5W7twnHy9L+7qJEbhl7pgBh04MiRj859+ZNPzwTsCnWV2mqXDr/++vj5wcf7FA6Uf0Z0WQ3pNJTFdGJ25sqZyt4BRR/tnN0JEbEsNS8veYfWNGCLIlDjtgz0YpceRMSAMr8GxHPAOw0IhDjYqZyGz2DddsgzY7SRLc5nfB6/kxR/QyGjIBDwqtR+Iv+wC0brn5mm5Z8JpKRaxpXJtufK5Jh26CUdhASBpCvw048JAg+2tk7euBnR6gCBTrjfonKtAgdp5ufnw1lPIRDDXxIBMwXgVoBS3iTDP+a0MjLw6ycROciGZwn+oSShVC2Vbd8eV1xS0iWb21heXj4bicj8MplaPbejgvDvzzXK6sSYmIrGmqYUen8Hq6EJ4mAQfxKhEgff4BeEv42N9WRbH86V8DHO/trB6kcKPy43Pi8x6RnD353fkOzf0+ff/433tAqMxsLRRkB8tStaDHkqFE7Blph0sZySq9OKOBk0/zAfSA/iMgVhkgqUpEZTgXVolLXHaTSKMhIAOmw2m1GCyCA2Dj4W5cgqCuUOpUTxs58FjCqdUj0XZvbGwSVveTliModOv/arXWliuVmvyH0tm4Oh99fBl7FpeUBGPOi0Hh9X3F0YG7uQOHbr9u0LjFM/OWNP/YFMnx+Dt8C/CxcuoIrkAwKf3Cs6tgnAydK29mo5IgiPuG5k2lM93u/UrD259epL73x4dXgkNDuNVg5W0B+AMgFEY14K7edGP5memVn0a5FDDm9waDrEFekgLjN4IYxzH/Jo5CYrhKtBuxXbRxS491gFYu9d28QETnIZjEZ4uoXPTkKA6VaYFNSPf+tTZvDbsE87CsDEEmaPTYPOqKurPjTkeMOMqixyuEaYFtFqVNhuZ6BsvRP75j9YeHjKYlUJORWgIWukdu/M6rm5fUdAAfb0BIIgh86/jZHunTuLJ6SKIBoq6637nizfHb9ebaDEZfzdTUKNw/Prv7wPANxn1YPeDSo0nvXVq9fGr12/vn7F51Ho4X7rg17bwKmPFr98660rrwhsJoViz+uvv35deG7eYiT8MwQD3qARtLG7T4Mjep0DjAcaMcFwT51MzqgtyxJJ3YRJgECMg91LE72or2dPnVqoNqBDIMTt0zMjgECXLqQYWEKWeoJms62z58p0yOPz6JRKIF4AtLhXpaweWZ9xDZlNbn9oGl0qcOOvW4r845ZnpXPFWqk0uvsP3W6jCPz443VMBR78BarACMbBSqcHIvvyOZN7fm4OVGA4rb2QUYA0/go3V4E0tLLaSPYv+yBNv4PRGc6/whCLzQYqMv0wJSD/pDk56cXdJQ17xR+c/6JqR075wgIA0O+PxMWiSnytdkQXt3//Tw8IJd07u7EfHpv5ALjwHGyvMzg09UQD0viT4Hp21H/Ff327EP6mJLRl5SQXPWvx4x9k5++znu9/59uxm6YwCVuuMAlb7YBbnYBPHSBgYmkOiH85aYkhGpCkAQF/tdgiDX/RnkdSgWkkDuaSlhhQgZgKrOe3sJF9bEYF0s6pxVx/2w9jmnEIS+DQ6JQPr437EYD00iTyas5E1Te0tOzOkoIAkkpAA+4uohtXNsEX5R9t+hLt+sMCBxAN+TaGxY0L7EQ6/ce8SuRvUTCxqBjVH8o/chKxJebYscm2tjwsCudlZElNuHYWix/V/c7pUM34iGpq8PZv/vzSxasPF9HJyzy/ZKEcP/Di888G72H23jTQKzhzBQkI0Z5BYQyOjvqcOiWWTzwGu83SJ5eurXBNtkCPF131ce+x2BF0zP5hGzzXeym50WFwhrQRiC8Ljy+H59zoKt0jsOytKCL73ukQmMXCXn4cZ+rSGahAD8njz298MYxFjsNZOtwThz0n1qXHRzbOP3z4UGumRE0lu6vNdtf6g8X/nNu3JMBnvcBqMsysXr9zGn5dnTYa3UtLEMYHvQHb3PnDV1//tU6hkLVXG13rf3z96kfLa0t2b0DfC8LN4POt/3p8/Nq1YVdPwPuGZcBq9uL8n77vDx+sf/nWp1eCdtXq6x++fv3uOTcWP4wGl8uLBqaUWH1K45m+cqazd6APs38dHZ0kKJ0Kny2o5ZSmnlRrt5zHoqlARODMSMiBiVO0yvLN4FYj0HpqdMqanbX3zVlsjhm0MQD+uYIBtIbpGPU0rm7Kv/tnUP4NEPwh/7IuV5XLRH6xlrm56OIrTAVWvnLl44+xGnLwpdbse7duRsT+keERjydUVyebM83NzYXX1qYiEjoBeJqh3+YyzKa8tmI2q2ELgNGDm36jACJ5ODYrEbeEsHj4F915aqlYtqM0saWkSyQ+d34Htiwt+CPwEl6ehGAXomVJdR0rpvvVu3drmcFveASw0TewoaEZoi6VkixnqW/E4gfxfcbul+Kt2JdufUEYZ+7iJ+8A+fesrc/PxX6Dsn9fORAHx0an4aJFEPoNDT5MAUZp+DQGk2LZRXEQByu0VW3FHIaAtbgtbjcWQkhjdF5zfnOZJBlNi5l6cCqocPiJOCWZsU/lAZlIOC+DnbK72v+FMeBwVi88vHrtbnw5iYEjGxsRJu8xZVYJS1piy9Ryyk6J81jZX00AMoVfBl3HmJE37PtDRZc4Rmg3duvJ7VtjPGDvBULgra6cqHk1Rr8XSM8gfpJinI67haN0k0DB/HK3aUqKxY9tquGR6Zn+w/1O99rtWxf++6V3gH/r96+80jsxHw4bhkaDBhMuCAH5NOTzoIoQ9HxC+ni1UrnCCzpLIXUqyYy9x2g3m+afDC6Xy+16LA3Dc1OksQd86+f/c/7xPpsczZ+cTpUS4svDXaffvruglTtGcVbOrqnK2J1HiiAoGXj0YszMltZ6Azx9e0Yd8rmFh+P96NI8Phxyoq+LCxBo2gcArH949eqIwi7dKzY7Zh48WD13zmSD6Bdi9gmT0eibXkU3+tfXfUZj3/wSoIzs1VA0Xvv1678eVpmMDmJlczfixgVGQbPFonjDGxzVrP56eHy43wGK7MUfUwqKzD9X6vtO/GFx/a23Pv10GPXfgl9BYSOewUgcnHsAgLoQyL8OpvjbE/VAm5o6eTafw4EYWKYWR5cQYG5uetZtAiShqvZ4AZbA50BHh9dFRKDHKbea5k6dsLvn5t06kH9isc7pCuqDAbKCRV4943I4TG7xImb/NuWfX1a9Jz01h7unvFrk9/vR5Qf3FVSiR4LLgAgE4jLVkJdebuUXbBf56TjYM1K31y+dw4BlbW1th4TJ/kUnQOhVLiD/cHUfOpZvwY/0AWZvcoiuQ2AA3EpjqSQ7VavmcnOLklIactX+L87j3gj6+BcuAVChK2ZIAAAgAElEQVSzWeyKOllzTEwMa/wuq6UFNwK2dNN2VlgY0Rg1uupG2qm7vganJptQ/vGZ7pcoAsl9yGYlpbTl5sQV8Z6192/XP37v89893/v3f/t2Ej0PsqX/SOSLr59K/TFeqVsiEBCIqUCFOj2DD6EoxMEYkdaiP0wtRsW0UWBzGRJwb305iYNzU9OEgECHrnkXLwoeGj4YwWVIxNUH9scUGgzK6x/e/WKHTElWPIMI/GADFeCNt99edpudXd0tSXFaBaWnuLvZXycgbXYaJSCGv9j7h4qObr6GG+MlItF47KfvwOYdGRsbA/yNkRoJn6YofAL8AD5ozWPxUosbtILGuO1Efb9neuTw+IgG5N+FzJfeuf4Q+PcpahiLwmUwOHp6FFK3262V68lT1qNxQyD1ShSBCn2lfk4tVc2EqtEJ1eOwLz1Z8zuNQb3eTmlFMjGlt135cv0/zz1+PC/2vPHGrFPlcc0M45rd69evrlar55d6e/V24Ie0AO4ZjsgksrAGAhKw+1ftqqGhbWYrorh+FU5NTQ3wz+dwOdH3WQNysm9u4/zdh+NXrzea9HpA2eriuVNmQQ/u07BZKQeASTHy619fv15vBAUEEkihMAs6sB/QLB6+/uH168OGVcDfw/MbFtRfHQFK0eeFO6OXi0bg9kJIexCBXjOKNoFe76W2/e4PMx//5GOg6hd+OQ5iGBQGB34BaEbv0M3cx9ZnlH9Y/ABVRvA3dfRsWgVnd0VZPOqyzSUE5PuJLTG9gqDBYO61DQzYkLMCAY6G9GvgSxjYN++2m6ZkIZR/Op0GLjFw/2wD1l6rxmk0UyaxbmaayD8afyKZbE96Wer2nD179nBlakAgRuUm62bm8ZAC4+DKM9FUYI2savLGchirIXAJG6nJwnm0tUFAoCwLx38Z/DETcG1tx8gakNYS1hb6on3QTx3203/IbMkQSct35BRkJnR3+bXb3377+Pnz5xbOIf+4y8d4xfzsEhbIv/0/7S48Lsl+oaWb3uCSRC6C3TtZOPpRH91QhcWPdrr6W4zAS9yqgGST7B8voTh5e3pG7LPi74VvrPyjz/e/862khF3MivSdCfSmYBqBJP+3K4q/975KwJRYXmJblRjiYFEyh4mDKzJ2Y2sggJBDT8fRJjFpNfH1jcx0XKowvhENoxNTvgIe1ICJtWmSAz9tq9tb7TT403JER49+fjYtNzwX3oATWYY49Isvzoctiuqm2MzdOXLKbKfii4sz6ObnNsbsmXl1jKT+sNf52LF79yD83fJjSGTzLmBxY+yvCQh68ALDSvz//GJmVI6PgfOxxDKRwgzP9D703a0PeZz94yD/MPr9xUXg3ypuseudsJjQyb7HbjHJ8f+JpRYmdeXR0HHw/fURQKDFZtnTKFMZfaFqGYmDzQMmjU9Aps7McjnuyRz1TX9wam0KM/izsx7jb0fPhITXDl+7/ms0pb/5ZN8ACTArzbIK3KeIiVXi5NvSnWvu6Dkz5DMPrK3srVbiAqPx8cN1Tq8XnshkFxIGwm5E4Pj16+POmT/+8eG5D9xm9BsNeCnKTHr/FKH19fUH60ZBYPQM0xJHFgsZVCPDpz88Hfr11bsPP5ij9PReDcrhRWMD65TO5/Hcn5bjF10JBPQOTFitFDa72M0nFmdmqq/tcOOaNqOhzwBECmKTTWUn5XGdgW8dbssbJQuwQJVJp7Tqo+VZyQDA2mZQZlwZRKZS9G4hy/jgK0EEWhUOh9fcZyLzKoKA3W6cNlitSwMDS/v2mbRY/NWJdCEDZUb+Bcxuymx0GeQmt3/x/id09k8hl4rVIpGsKjkta29VVdXePeVckQjUHd4cyTxWMtUQ8i3oIXHww8Zq4cESzuSNk2odiYOdjXWN4bm1jbWVlZVwJJ04oG4CsILBHwbALBqBmwBk9F/r3+BfSa5IlJOVzO/OzK7z+xdqvjhOCAgA9JcXEMNAVmFjdWFMzC/fXviiBH0gMf4ljpDAwl8JQf41omM/s6VF0lzYRMLf4ugtMAqQjsRjY9viq8r4z1r8eC7pH27rxzOf73/32+iPith7bysE3op6mdj3q5nAFEAgj11cVo5bQ3Ly4DKdgT0wKAFxOI7svmQQKInWg8n8fo1QmKs0OFRx7FiaOQz/cPSnpIhTpxRmx/DFXqNS+fnJy20N2QVcJGBkeXLyxhfLWAyZolTC7G5WGVdB2e3aguKiLfVHO/sx0x7H+MXHio9h9IuFjUTGlAvLHom8JCTaWLQQ8xQBkX/FWwcJSn+yW7efLGtNZspBbdum8Neg/BsfH5FODd4a+++LFz+8+vAhyD/BxMDmFruBcIS7gLEU7g0ha0OmNXIT1i/vry8uKuf2ze+tHnEa9EanTqlDyBnt3jOYy/LKTTabHZQOPMtnT2H/7izwzxsICDo0aD2FvizVe+qywvNLdoxKO+0qSTZ+FWw2D9cC88ut2DUX8Lo3LtXUy2RHT/avrg7X5IrtgcDoKLqcopUeRKDujY27d++eHlm9ev78httOGGKDr9CLizWsctcnPsMnPsoGCq1niASBNj22cRvsVv+b12bPv393wxokxvUDlm3eoWBA32sziQ32+akBq0YO8rMTVGDQa7FQBo3GGOicOLJx7pR6ZXC+V+81YjLS7oWwVWCx2PRGl7mX9P4x8g/5pwVZxs1JL6vlNNQ2x1WVcwFLwCQ3XZ7AVKDn0Am3W4Mty4cMeuy5rhSYzSjzgH9exdKSyOkykNZnXDIK/9AhUKgMvqEhl0blnLlC5J/V4pai/tPJ0vLT91TF16TXZFXt4R49KqMRSEQgVkPg5uhUYCemAtcXR67jbMiBjEkch6b7sPuzImEgYDi8shbeLmkqZExQm2rzjhVx6DGQbGK8nLmFwOyvFoFLNl+xSjJ3gxAtzynjtZQ0i+b8jfXVC+fvHj9+HDSgf0cGzS2Jsq5BWPFCc107Lk7P7MbwN7M7ATD4K1ajwaisOSzBVVU1aFaIa+tR/7FYxYlP977Q94KVkliWk972TL0v5Pzj+v49y/n37347ZReNQGY/CFMCTvgq+6JQjGrBpCQ2P00GcbB0RxuHpAIhAt6dUUtemB5BsjtTIkmtqdtcGyIhu+NUzbwkmj+0/oP3W/h7jIaazP3HF+pVDvnlDD48PkpayyIbyzdu3AD4bSxjQTgyRzmF3bHsOEwF6sWldBzMABDfFtGNf+RcwOpHYjGd7BsjQfAYoGJs7Dc4GpL5Ff6NAf9oKhL9x08sgrdMIYVVGrbaKSOOfvQt1M1Mh8avkeLHhddeAvxdffjg0086cJcF3cBWiW184ZXIwkK5WmoasDJL1D0409/b8cn0esg/51/A7kHKaoQIikGgt6fSrlCF6hVmDWXt7Tgz7fT4XM7FGdcQWfbT6x5eHVl/0H/y7NksuJDg4rKJXpvV7DDo0vk8FpkDYUm0Zj0Ebr371nLh0V+XlVW1MH3fM9JfL7IMYIxrpoxkIRzEwQrL2vLd4/5zH23M2QT2oF3fazWbgX/Y+mwy2Jfm1/YNKHCeQxAY8hkOydHKweUV2HqXbhw/sbD8ZB/EoHb0J93mDfT0CKzmbSdU8rWVyJF5ucH4Lq6L7+gIUiaTQUMJbLaJI4+PuKcGj7p7e202C0AJbqij0qYw/hg7aEy0/GPw50b8HZVxq9KaEYB5cbl7uFwlCrOnyxO+abrT/BWfaxso5oEJm1mvJ7anE8ErTp3LpYHoF8vslIKi7IJOq8bj6+no8XlmZnw9DGelWjF82qz81PI9Weno6pyatZcsfYGYGxDI7Dygb85Hj/FVDvnuYxx85+LLB7Mz7gECnaugAl2hekDgRjhy497NwfCOdno7AMq/7C0fBBp5mUzRgfGhejoMZvqRu4uz1OU7ynOLUrqzs6a01f39I4twzn9x/PgXOfn0sEhhfSPrlzElwsZ2dhJWvtAHDQOA7pb9+yW49E3SdVhIpnwkXc3tTU1kaopFxuu+kv9D/PHycrPyi59F/mHr33MJ38ji79843/vOt3jROHjr7VOqj/776F8kbaIR42B6NCStlsTBJP+XQRYHEwa2AQDbiUVCKvwskIB7aEsnp9FY3baL5g8tzpJaJBgcN9YrNbl//mW6Rr6n5LXWkpLXft5UgMpvI7KRs7FAemI2FIrqdt5Yca5UTukpWQaPTzu5MKZ/NP+wy+8YqX4kJvLH+LT2S2QsGdhs9gXscOF1J5I/kn8qjvKPuU80QrE9OrHo8pRJbobodBulqldOz4yMDyula6T2+5frVx+ufvzpK529uPF86Awdw5lMUvX2yErkpEwsNVkGmEZebOGwMK4mjY0jM74hyqQwe11OEbbEeAwOCBQ3Hh5W2BdPWGxej9Pg8oRmpn1YKgD+DWhDOu30lZm9ufHx6biPIvL4yJLVrNAYzLZwImYAu3drKaOCMusnjjy5dBjjn5qaeie1FA7rRnRzJmtvr96xDe1EIRDWeAOVE4M3l/0fbKxNWXsFerud4R8wleozLh0ZXF5xG7cFMbkG0tHlkculBm+nTd+7NBhxh5883oeOV1YKNaOgEt758Y9dHm0kN3671uUzBl/cNtDb2ylw4IZj7IXsxUE18ec6Re/ExNKS1U52mndaDICwHqPnBMo/oFIv3ZJH+Hd0T3xyG1pdVCSn7y3nYpeeSEQC02g1xEXUdmXP0NA2u9m0NGBFc3+If22KEaWTln/YN65wu01m20Cfyxgg4bPvk55KckMEf+ry5LLL3D1Z8bjTQyhMz63afhI1ICIQFLybSQVGuwItJqvgzKdfAgKJCuTfu7ccVitJNSRUlxuJ3Lxx6+bK4FoknSxIyZssatjaBMKoPrLbDX99vQeQwV9mS2m5ujw3Kzkx4bVm7pQa+YcAPLe4sPDFJT6P5O8k9cKWmJj97cczyLJfuvCBdpAt+7MbDQYljqYQ/oH6ay+s4NDZv691P5O7k5lQXJCVlsFLeEb5903s/fu7B1OBu5gE4NbsB/06ZZOBXyuFkFQgOzG/HEdDyktBBNKyj5SEK2o50Z0hdCpQKKQXCFfvrUmTxNU0ahyGOl7UIiGRncDCZS11ZFyRFRPTXKdzqJp+9Rr8VH/++4ZlphyMwfDy8o7lsMnQ381LaIMI3K5XpKYUM2O8RYzDFQIwcewYndEj6g4ByNjR0Lxjt5CWmG42/ZfsRMRflH+kYkLPCsOn4rWJ3CaF3KDQC8zb65yu0PD4qngNFOTPQf6NP3z44Esi//oMtI9zL8msq7ncPWdvDq6IxE+riGnSwiFAl5F+pe+VUUqKNloOj04nUhEEmufOv61xnD/lttoNLpcTx/XtyL/e3gEI16bW9i1RuvqHENU8qhmu+WJlbd6t0tg7Oy1t3aAAW5rN2DMI0u7G8Wvj4zXC8dVVpWpt8OZKWBwKqdwDA5iAc3i9Ro/HLBCQ5ub5+bU1jRkdos2Y/tPbJizbHG/4HO5IfFyu2DfkFQiAVBCa+wCBdpsN9OW+J4Mm6xHQnxNH9k1YkX/Yv+IIjH7iUlelp1apIS4NBN7owx5uu1yBLZEoSpf2aTyhEQTgkSNHJmxW4LG1D6dmOoBkvjNbxV/EH+6gP5uWX0EAWBqXexb+gsvFVKAamBT9fg4FKonvKXxnD71hJQdudMCtHAkB/pROl4OiKCxzSOUKA2N7Wjn6VO+fSCTbUXrpJBcuKmSPOQYr8Vk5RAQCG3UEgXAFs3Uy1RCx3x1tjL569cOL77S28o/diITFI6vVTpenui7+0uXBlfDK4OAa93BTYd6x2qgNwib+iAjksYv/VgsgloJLukvi1bKcqrSipF2tQrVW3c/wb3Hxg9lzb5Lev5LsxsbamJiYEkkZn6Q/0MmA4C+zJQZ0hLOuub3rMFnVjL4v2Puyxb8o/ogK5bAyEzLi41H+PWv1459F/jHn+9/9dtJWO8zOr/UCbp1dKV/5i5TYJHZRMpmO21HK2c0gMKOC9svH1kCcGminG6MJAmVoxihMltThoh8hG70Ci9lJbKHRoaoX1tQ1Z3c1Nsb7dYX7m3UGXdPPX8OSFit/exiLIQsLKAKXI+cjWoVGCHKuQKsABMqTMValvf3gBWd9E4uP3buwVefgR/EHb6O9L7xY9H9G7I2xx/B/s58SgMU0A7FoUrtnCnv/cPhDHFEZPP3jw7rw4O0/xf4ek3+LWPzojBY/OjrpwqJYxC3fs+fkjrM3VyIi7eZzCFNXiEBMBc6EzJ0CSmUMUgqTw+hx6nBA2GD0UhEptbF2ZN5msztniLNKoLNzAm5AI51auXnzyVpYd3/96rhQODw8PF6zI2xCvAAASzisnYUKK/zJvVzWdW388OHDVz++ojo6OHhjcvKsyDM96wT9iZvZvcHfegEggkrBvsdHptbm5R7bhG0ArUBxGZHJOBoMjuq1uWlx6WKIbQOCF/UgEAOBIUeQRpltXkoJKKkZ174dWRqwIzT7DgUhDDbL4lOF8VyTDaNtHw6SWaxk7VJvb2VQKRkZOX3aiY3Yjx8vDaAf4PNDPbi7tyPIXDmw929KTfh38uTZ9LI8eOY2AAELcCs9iUxlsq1UIDBJT2Zd4HvbMxq0v/uuFY0QTCKPxykWK3UedH1BQenXeTwuh9dsMkGQbBMwlygt3JBoe1n+WW753ni0lpWQbA2KwKycci4QUK3WqYGA2mhjdM8QfJ4+dPSqZGZDTl+8ePEg59gluMKM9EMc7Kyuyw2H1yKDgytr4ZOlfFwS9U6Uf4jAg3QPNCCweBOAiSVP4a+kO08kyqnakcfuLulSatVHt/i3uHi3OJb8T0m1pCQm5oVCSS3tG8gjHw6nu6VBadBUHy5E46t60gDaVbGbQ/OvmPXUofGXXZJSnJYL8u8Zol9yXvj2N7f35e+c7zGjIUy4y7yNtgQi9lL+WgEmkL5odka8GF1i0jIwDsbYt5aWgXQqMKOQBMLN9DwiiEAZGpJJ4qrEBoeyOYUNaqyC2DUK64RNTTWNjfWN/rqDMfvzqzWautYWNPvpzk6ThVEBLkQWsClw+fyC2xDqShwrQpNCvV1UyitGCwMCweJjiezSy5c2+TfG9PuNRf+AxMN3uumuwKSxC/fujeHewEQ2m0kLFo/RtWA2u0xtgjBIDvyT1zc6NeLyeiXg7zd/+v2PQP6tPnjw6SeVGP0afHQMRzL4fr+Mm5MDz+Gs3OWVlbD6qVzSEF2/7A26PH0TNgVEog6NHMNSp04NItAAIpCyDD4+4rabbXajw2oPBnCjBRBm2hNZnrxxE+Sc6ZP7w4eFaTXDw9fGNb3Y3WHJ6K4zKFltFEGAbrir6/D44fEZ477BmzdvTGZkFHBdV+57PLN9FohvHdh9gvMTlbYluTPkeeMQOjgPWO12+4BF0TfUE+jpHFCnxiWnq63YCRd4MWi36wV6fRRlTo9Dr9EZsAA8sW8J4Gk5dGhotLJzws1NTZbE5WhNE70CHP/ri/IPrguG4Q/Hx9+5OuNFAi4NIAD1ox29tIMzbn5C33q3FPiHAET+JeeT5242pyKPEPAkIaBS5t/MzXXaLWavsa/PAhxE/sE9tGhxwEYn1jmNXrsZJ3VP6UIzWAkxyTWHnv+BmbJh67MbVwuJuLllcSfL92bFo7mYpAsjleZoHFyOy0/Var+O3ByG3b12RzBaDSGN0euoAj+8eLAhYxJUoK6fVEPq684CAkk5eOVyVwMC8J2vKkAkYDaLl0iA1Mp6uihR0sJPV8vKq5KLkloahOIp4N8InNBiCPn3dmYSAI9dWFPHiYn5Kau9mcPCSzSLTRqb4WmS0l3jBPnXVdguYfgnYZwPSMqRtSU6mTGUTF5bfG5p8TPYnpLk3ze69+/vnu99j26JiTbBMGJwC3fvRe0Bo3+XQmcDk2LZxaU70C2VW8bn08UPkgLcjaEwaMC2PFSBzfnNjEWCErsCUyWSmkaVw9CYGPMcTuzUwb+1t3bV47KW9ibhePIX6X/e32hwNu/vJtmNjKqw3x8pxzao5cjCwvnzp/oM1Q1sdsYeTAWauUlJtJkB/GLzy8PLxZvw22x4pl+xycE/sMd4f7qNHgn36OwfeyyKP2ZOJDGBf3bKTdu+uWU1IZdzeLw6PPjk1thrRP49BPn3Su8EPb9A5N+ABeSf3y/icnOyLp89m5u7d0dkJSJT0yqCbolBEWixKIy+NyiNxg6yQiNXUGaHAWQLWfdImZeOmOS4scxqp+wCIJwJbuDKJ674MhxMvnFjcN+Ap18YlyY5HPLZcftGp7lZKK2kqusoEFEAModz/PS14ZDiyJMbuEggY3fedkXPmU+mPZ4+gLmd9q+v/FmlXFjtGRlfPNTbix72Npt1QOHyBXsqe5fmy9NADXFNE2T6IuhFmUejDL0CZ+SU02M02yCKnsAFSLYgTgsPmLT1EkBvnQ67HnFA2D4AoS4iziaXmuTrDx6s+oJ2M72eSND7LvDKajYHcBsKUWUm6ZQ4qv+yUuPy21AAZpMguCAuPTeHEYEivx+/n6YBq80ix05FlxnU67vvvgvBthviXpcOs39ePUn/aSH4nyHyzz076zsTcOD2Xzr6FZWXTZ5F/qWnCskWt2b8TYvA+Cpya0dBBYrolhh4BFiiXYG0R8IrRARiIPxOdtG9S2FtqL8fbn2kJv1seCUcPgmB8NF0XOf8tQiY+CC0trLYiMCnKyDszF8mgyjNKY9LSfl9OzccPvr550A/OIuLs4vC7BTQfyW8uGrJTpB/XZJCXJmED3O6sFGS+Ryr2kiyf7T8w97nrsIKskYCBCDddJ24Sb8GTslOdnJWWlHsM45+/PC5f6bs31cOGQ2JdgUyEnBT6jHwS/kbqUAQgfwCkgrcDnEwMx23G+siGbWkP6atIhoHb7rE7K2Dp1gNxsHVTvyxCWsONxD5h8sKslkN6XUH4DInUTqVtd3Eq7G4rFyEU0ARiIMXkIDnTvVp6rLZ7IKjUsqsp7LYxOXlGP/YZCR8ic0uZpCHge8Yqf3SgpC9eYCFKbG4Cu5CCt1IwmZm9Ji6DJsdF3a7TyA0TNo91Z7pxfHhkanBW7dvHfjRRcDf6vqnrwhI8YNxL4EQDgIu1H/cPbmpaanwOytnz0l0ryQIZOJg1EYaj2/0zJWZWXNnwKuQoleg2YFNehqXwYNzsiZAAx5rrw3x5zvTozfFF7Qda8sonbzx5Mi8uH/8cL1RT6yiezuDOqXKLnd6vDZc9gZKyOzsD0nXBm+0ZVRk7OZzKnK1FpuAbum19urJMo5KgWP1+uGR61fXHQJmSaZtYsk62oMuBOLGw4eJgzMaQnX0BKxL8E5vgPYKRLNAA0VsafR6YOfSviUc++sD+TN+7dr46oznUJ8bbm9g374JZGaQ0ng8Wqnc5TLa8VAm2wRab+khfgWFG8S2R4vFNDWFqgzpdzIrPq0gP6+CFi/wqqI0Pzk1PouoQC4w0K/2IwLdbjkl6BgdRfn37rtE/pHWZ6XT1yNAHwi3WIdlJAfgT4Xdhh02k9RNsowikSw3//LJ8pwsOvwl+g8eogwCU0EEMgjE6rMfF0+6rV+ziek58ymjAt9p4By7txzWjaxiNaS6jivVggYEtR6JxH+9BkIfYuqbSKtAxCBEv7wUTo5aFp+VlpGSdKBOTfinC4VGZoCBi9XtsSlsNqukNquuLSYm5lWhhMMmm4OBZ3wy2ZbJq9EYnfWHu9D3lJF/7YVNZPTj6ZMd7f3L5OXFp+cXP2vx4x935+//D4eMhpBOmIRdm/h7qiHmPUYg/lVqMCmJjIZQcm18G4dov4pauhRMAmIyHpfXXopOWYhAXADXWA8isKBGZHQYxTXCmpr27K5GlH/NTdgw2p2SfbjrwKsH9leEQvEcukVqd5qM0YAbCzgUdP5cnyIkSUwaS9XKFXqBtJSdSHz9bi4nZqKAi8o+Jvc3RnTfGMn1kVWpbF5s0titW/duP7mVmMkmBIRwIkpAdubuHClohRMn+kD+kdbnh/3atdv3/nzs1s38aw8frtOtz9H5BSws0qZyIhn35MnLyQVl+WVxuEV4Oxr40tNc0ZaYaQ/OfL1yZX12oFevkGKt2Gx1uGgEujwGL0SyIGu8IJesRpcLDWYs4fj83ZwiTm1h2+TNlRVZf0gP+gsrDZ1o/Ok0a5wuL4k49WazzUZJIzdutKEb08GDDYXCBalpqVfwypB3oBddT0FzBexe38zqzOr0kB44JuiF4Jkk9bAl2TPTf2382ni/81AfhXd54MjjJRtaPwsEwd+asbJgocxeM4SV5srOzonHj5/Mw930Ta8OD9cMj/g+wcZhq+XIY/go+CCDB7CkDKGONpnMdru5z2DHnSFkSYm+J0hZLGT0AyJOOvuXmxpXkE/G9snWHiRgHhGB9E76ozKmMVqqlSoEuIQd8KfvtbnVTmJ76vQoBJV6XPrpD9G2pybp7LTvTEdlrxU7/4B/Sv/2uPyTR1H+kaVuxF+2vbkdMYgEjAMRmLuDuTXQnGqdXyt3w48PLwevwBWM9kjo+OTTdaIC38H1cZNnIQ7GlhiPc0/8CiHgzZW1SDPm/w5mP10FYUywWkvgAcvwj5eZWSZSb99elc/bVVKYswZRNNA3BPAbCc2M1GTvjOWxeeyyPckg/355QNgOD1Ks0vGzs/k4CJkYWwTyT4dbP8jkL8i/w12FTbUNdPPLJvtYtADkZJckJSbnYqXlmeTfD78xts//u+f73/lWSgoj/xgZGK2HfJV5m6MhSdgVnYD14Lws0hKTzKG7AmuxFoIvOCZcSwrCeSgCk4U1e0k9uLEuraxZUq9sjJPUNGe31zGb6nHLLfZ1lrTXYak/+1EoJEG3Mw6fn7GMW9I3zuGhhyKlhuqmFF7GDjlF6e3qtl2JxXxAHO1zRfe+YKxLAl8kH5u9JQHHeCktN27fvtCdhBb4Y91jbKYgTBCYwItTu+e0p+bm5tz+vSPTnpGH/TqQf7/p/u8fXYyLRB5+/OkZAW3dHpV/JPvnB5+pnYUAACAASURBVG0BT+LLaWV5eXnN+YSABIEoAuXMQCuIQNL023EG4jdKjl6BiBSzF/uUVeiYarTb3iVWMiarPjAKoaZJ6k8tPHjw1XfeKWwCBN4QGW1LS8A0iCPNIMpcBoUcAj0K/rsexePAksWdzm84ffoOcTC9NjI7C8/fTts+4kUvCOh7AwGv2Wt0GS0Ws14PzCS70rFbz0L5fK7QOKJs2udCi2XLGqAMu1oEnZUBB6VQuAHmCsrr9RoMXsAKAPCjE46hIV9ouKZm2BnsQd/TE+fRKgv0n8vlOuQMhTxyYNw8iOk+4/PwLSME1OvtVruekoMqI7KM5l98WnJ+e2EFApCPznV8nDUqbC+LS6UzgagCuVygklqkVkAUjfyz9Vq1tPFByOWSgnAdWJqfQ98rI2BaemrWxfheubHIAj+i9MnL5UeZ5j/GXhsn2ACCEAfjBmhJWnp8/A5acorgh4qN0dKtK9hTdqmIwDsQCB/kHJtcDqtHGnF5XGP85SgCwzuaW1ujEpDF8I8GYGsJbUtfwitpyd6hluVWpfK7f3UwKzw4uHL05FERuniFZmb6m3hJmZm8nbvj44tB/rUcqKUNPPBbA79YxYm82HSNUdUolER9r2ogEi4sJPzjf6Xyi3eAz2GlJOWlx5c+s+/Vczu/+aMf/6vz/e9+KyWBGYmLhsC7mLA35W+QEP86BTCIcXAZ3RJTQJulQviLHlnIv2h9mAmEU2vqG3G1LaYpyFFWC9GwQtjVhOuf6S233d3ZEmHbC7VNOx+F+ttZHDT3251cvuBf8CMAFxcWEYFig6qek8S7BHSBOLi8OBbVG7H7I2HsGC3/2CAAscwxRoq+bB6iMLP73s2bt1pi2bwkMh3XQrbX0X0x7MzCcuncKcTf3By3Go2PhqvVg7d/M/aLly7euXb14eLM9OiW/MMUFohFWv7JSAtHQWlhRW1he34c7s88WV4eIfVgqRvi4F6cLdCjV+BErwDHulR+PyaZLBSFcbAKjtOgoax2u8VEGU3zA70YZ3tGyI60d+7cuXO6QaiyLj3GTZCVQa/dG/QaqfnwlIVyADEpCtSjGf51ySTqunPnwzunT5++3j8NolNBi7JOAKDX1inQm6ltDqOjD57VgFqHHQLhTvj3/+sDF7DMUz9c1+8cGj0z5KBU59HAtLcT+3H0ZvQAlQKx5X3bjG84hs50oPH9k4/Oz7iGHM46oXCv2FrZEfDNvP8+AlBAQkZcyU5Z3OHycn+fw+Mhfn/odW2zY5XEanaT2gd8446ePXs5HeRfYSHTvAFP8mIMgmuxpT4uLf3yWZqBXC53obxcZAKAvkvKH7jz0hNS6kZ8owaxdm5+fk6HtqdGs8U9NztL255ij7VaFJbJthcUoPzLpbN/yYwApA9x2yb14Li01NycnHIuNgUCAXXipywZzkTj4MozTDUECNhQfO9G5GhdDcbByr24OhUJCAhMbwIZzkjAzVJEa9T1AH1fupO56u056W287lZJhGxFhK8SbhOuHCD/UmJjAYGSurgXYmL2s17lkAIdUI3sN4SHemyhEuRfHfG9ivIPwt+mBqwh8YtZ0UoLnf3L5rAS+HG56Hr/bOHvD/+pev/+/vk+xMEJTABMXmgd+DfbYr6CwVgeP5krpxTarDY+qQdX7Oag+sNXu5nZkIp22jQfLlRKpagafmjo1qjxGpXCwyD/cFUBmebGzs6klsK45m645v1P/0g/v7hoNxZ647Yv+D/4YHERfi8qq7nlXK1CLMnctTNNLZfbBYpU9hgOShIMRiNgNgmAeQR9dOwL4QSpAY/9CmkYm/IrTAWOxbKZFplYVpzWrfUT/oH883j6h1dDa7dvjf33Ly7+hRQ/Ph1dWps39R3yRVufSfLPL6OTWGdTgX+1RAnnx+ES9ZNHudvPRltiSAuHHkLcbSYyIOxDoyz0TjCZKK8DB3ZVuErT4LBY7GYHNfhkDTiIK4JOo0UfnmGHHkQZ6iuBXS8IeKmlfbd/c2twzQ2qDESd3oZ4XDlFGYY//PD66dNd4yEviDKvG/1Ll0DFGSlcj25S/Hh06JOhNyAwVRiHhkYFNABXf3Lf6NA0CtP3qAIdgaH76w8QgBP4tA8EHQ7DCa1WDEIrNOvwYVqt02YfODL40UcPHqz7HJr6/Hi/yWqe/vIzBOA+m6CyEmc1hnwGy8C8urF6fTo45AqiT7bXq9fbSO0FjkXKJcm/s2cx+9ce5R88VTF5jzoGh4oKkkEE5iICT5Zzy/eUaxHd9nfh81hw56VTqdPNuIJmCEHhR0GyfyD/5jblH/JPBOQsv9SWXn50+454wF+cRLKJv8LCQkLBt3HbCsFgHPpYoqQnqUBA4JYlw+gmAjuYVOCdi++8nF00eWwyt78fl8eN1KVevnzz5qUbN26uRFJB99EEZG0d2gqfDfzj71Bz03dklXZ3H6wKow/6CnYi4iiLs7FiZ1IsLzOJUxfPh6dCd0Mtk6FOLKb32vATWUINNpEJyczpU/jDxW/FfNSYiYmb+o+fzUpKakuPz2M/I/7+JeQffbAlBhTfTpLvS6EjYOZlsy4Mb97bwiFdD0arwIxctRzi4FQ+NkYz7TD0QQYyfYHNzQW4PrMaVGBjXU1qfbVOY3SoJPSmPhZpbO/uxu72THZtfkb3/v07mz4/+qiIj4KyKC994YPFc9gZv7hYXV0OcJFrlIXvvcffji0xAmle7FhxcVEif4wug4yRvB8GwKD7xmJpCMID6t7t2/dSMtm8WF5s7FhsyxguThrLRGDyktq4UrFsAQG4sb0aW59XV7H3pZse/MXel57eCbdfrNn07iTZPxGDv8tpBZjBL2KSV2mXiWopP7mywiUtMQPYBGyifsDYbQY+uT8zc+oEIlBBOUAwkVENo9FjMNus71oGnzy54XeMjvr6r3W1v33n2p3DTu+2/7z7+PER4F8QHQUsS09uF79Wcm85IjWAehuCkHng8eON91enjaqa001dXTU6c2WPt/rtydso5QRBuA1c6UMFBB0dPaOGvkNkqKxSgJ2BHz388q0rQ16FOD5ebdY77r/12dWPNh7v60XjF0HQ+/wbMyGdDo2nfN6AF3e/vejw6u0n7l69+tnH03a7dI9Y4fv4rZ/88f33B3GniABCXXtQMORyu+f8jSO+TxwBrx1En3e0p0egnyAr1OFYTeocxF9qXHJzM/Jv96u7o3u7yfqr2sLC0vyy5Li41HQagXtlClx3rrfb9FapzuPS6EQ6J+jxIFwrPLqFkRna90p7ivheRXv/4IJ5drIAPn4HI//o8LcLCUgemcTJj6hAsuZDWC3b81Q1RIeN0SZiNk28Ag1PO0bfuXOwIoPPn7yxnNP/kHQFpqZdunnp5g1sXtojacAB4M0NSCx6uytEv5ndvDiIfnPj84p53V3lg09uovyTEdUp1qUWJwD/YnmSuuaduDxbwmEKdCDqiMFHIi+Dln+Iv2qaf5J2TP8R2hZHm5/p4gdEzCUJxcm5yUXPbPzy3Lf+JeQfOd/D+eAUpgyy2RQdzfptlUGeLgeT95N4PBIHU/LyMszcEALuphGIfdKciuh0CHHKAhGIW77htRIQaGisRTfbEswBQhjMogMETvPhpu5fxuyCOLi0aDeZ+y1bOLf4AfJvET4c5ZVW7qxrSEkqE8kV2BLTlkA/Nvh02x/29zHdL7FsLH/w2N1jZA6ER6JhHkTHQEGcjrvFGwMdGCd2i7ncyMKpuYW9IY9nZHhVt3bz1p9afk8P/n585UznBBZ/XQavoJPIPymJfpkc1uXLBaXYw8vnE+VSWpacdpmIQC7GwejuaRoYMMmpALN5p1fwyifTM85TWrdbrjDbEU9AQJUB3lB20HJPnrz95hcKr6PxcHvh22++XW3wTl99fwMiYOJXF7QPmCLHDxw82Hrwv77waDSOUaLKlo5sfARI8hl1wop2oYyyK+reefXG/w0A1AtIO+KQUUPZsC14Qg4CzdHT2SsIBG1L8+ff/+NPPv70jNesUEvNBGVXz81PYOUYgnaIgkd9IdKb5hoKBnoQZcHR0Y4OQd/Dq1f/+Nn9oYDX4XvrJ599dufunE0QCATtWJUOBHocmjmxsj8U7Ana7Q6zl/KiV6AAJzfgLGEforYK6FeQD/grJN2kqAD5fBb84ryKWroQd0DhYnoIhC+fzRJTA0tLA6TxUYu00emUHp8jCDcJ4kwH/PN5zSapeJb2vSIjdmI1yL/Lk2k5J3dkxaempkHwWyDBSU26AoIisLkwetqbuwrba2Sy9NTcqpP0bAgaZemeHhB+2i4Vp+NO10KoW3RscnnHAnYFupz1wrhLeACBkR2lra3ZtPDbVIDwCO9uqa0Sl8fnphWltGTHhQef3B7ExinkrVpdnpeUFBublMAR1mXHxLzQ1F+Dq4xIuQ7RBhDkFaeqjJpqwr9G3HoE/GtGJ2oO7fxM977gr+LsYjL6EduWml6a+GzGBz987gWQf/98vX//L+f73/02XCM26x+EeGRbZsp7JB+YQu8N3sRfSlJKCv4ZLleJ+RAHU9KcNj6nlu6LxrGQCjoZiFKQkYFMHKxUyvDnVgdPbEMdGnpvLalikatWoVDC+vObB1549PnJNrQ+OHasSLKwSEfB8MHk8gxxcA2r5YepYrncLDDnsBPo3j/+2BitAenAF7UeD96koPyDgBdUIS9aHWHzEsh03E6Qf8AztSgcyanCfPbwsG7qye0//fkXPyLy78tPPxEg/kj0a7UsRVv/4PlBBrhAxGD+j4O5l2w6dstPjkvLxVkGLrbEiFAFut30CloGgZ2vXJkOLSIC4cml19vRscCpcvkMGoXlyOMnBW8ePFgll+9t4h8QaoK+j79EAB4h8WWHnlIcWr/+zjsHD168uu4zyq1YXPB6R23u9++8/tlP7g+ZtcI6OVX90i8OvH3jyZJ9yGvX9/Z6hwIOl8ptAfjMuc4E9OYl9NcK9ADJ7t65igbOQ3q99/5bP/kS+EdhL6DdrrdBuB3o8YbICXYE9AK71/u8F51kBALzLCDws8/uu+6/9eVnV68uoMFWx6id8qIMDAi8ntnF1VVPoEPvDXqB8l7sKRR4DW6CwCU4E5SyC40kC5vgusmppecXMGfGJwqwIiMvDzcA5JeVJRc018mtS/uwodpqNcEPSQfRLyI5GNBbrZWdFvgD9r5oZz3oe9UbnXyTlVfll50t35sL8g+Lv8mSsuboISWQ9i0AFhY2NO8R5eY1C9PSc3fsIW3YpCXGT6cCaZef6PI4TAX+8Tr2Rb/z8kE+IDACCCQeCcK0S8tAQJCB4R2FJYz4a43yrwTlnygtKz6f19JdwF2jm2dEfrFarRaL0pJ2xcbGJrAl9RKIfvd39RfSW3UyyToJAGDJLo7OYVDW4SJMXHpE5B/hH7P5iMWK2t/zadvnBD7Iv8SUZy1+vMD7Zvv+/W8cjIOTdkbtsXYxqcAUZkkIweJXAIgvWA5OSollZ6QSt9T43XyshmQQAO6GNxzMCdL74wrz0CiGdonZU1+3t0YorMPFSc07oxuaE5n8Nzz4myU1b7fExPzPo5FHGcT9hd9WQ4aDQiHQgDQB3VJd13s7i3ZI0SVGHv8eM9fGNEIT+YcH8Nd94dbtW++9R/KCGBZjXwxpAuyOBTBG1FKVU6XSatX19Wj4OzwiXrt9D4sffwH+rX98BYsfxLwJw1/rVDgM0a9ShrUPwB+EvySGg8cfXnQ5dAGzuSAuLTWL6IiTpCVGC8fNDAi7PFJc9DOEHgmYCrRYJ5bcBocPCKgxGDwa09LgJMROv3jbLxXXKY1D019igm1jyYoOzr0TA5Q3cGb1+ofvXLy4/onXYUQkB4N456iFO3/87MuPfXaLQlpz8aUDByZXrPicNeKC4mAw6HAqtfPzWp2jIxD0Umgahd4Cgm3nHq4+QAROA8oeXH14yo7rOoNeNL/CFe5e58z09PqMHo3og2jrp0eUmSmDZvHh1QefPQD8vX/+FA4bg/Kyo+u9oFLQMer6ZGb9/pCgI+i12xVmrP9io4/DozKB/lvadwRoZpHX4cUR9R8xVaNHGMhDANMnbXm4AQUg2JZXrbDMzwMAQQLKsfdFKVsI4QxfIKA3meDy5DFQlEl7avZ+tPgrR+MDWXkcyL+cqlxa/UkkBXSujyEg8o/Z4lELEWSTsLpagls+yGzI3j3lJAzW6fy0NaGFNHXizw9Tgb2dwen7aBZ4/cOLF19uLT52Y3l7NUkFhuokaaAB7124cCMSScWOrtbWzT2YJd2ccvX2uPjU3UndtfFkC9jKSZxADk9NTeXkpYD8i00qSkvlAP9ea2rnJ8HDFOJhjH8xrGWza7D4W0MG7Tf5B19ExVOLz4sZIVHMyL+0tmfn365/MflHHyICd32l9e+9aNIvmhj8ak0kKSUJCZjES2zboYU4WFaGLQzMEnXEH4fsDuHgRnXaLRB/dFV1dXsbiUtMncpobMxmCAj6jb70Iy4lcUUv/DQm5tGjzyWEgEVF7fWzyL9QSKcTHf386FH1lFzV37DzvUmuQqHQ69Vt5GLJzP6i2GPHjhENOAaUu/Ae1oVp6RedgoOT1NIWttularFKpZLV9aP86w9NDd76089/cfHiX65evYq9LxMTW70vIP/CK5GIjPAPo99LyWUoImrp7it89tbS++KT41Ixc3US/heKQLi+S6PTcYzBMRkQ1om17vmlea3BG/AR91KIsxUKWdtrPzr48gGhigL599lnn71//gTQB1QZllCDgY5A6Nr1Dz+87uwJOIx9ChNlxuEyQa959s7rfwQR6NMBHQ+8eWPDiiiD/+P1vghc8nrIhJUn2IGrgL1eM04Iw7tGzR/Or3725Vug5B48PKehvQL1gNtgEESrwDt9ZWjoig9g2AHkDAoEQSspI2sMXvvswwczq1ffP3cCYlG9oNdmB2gC/3BJnlfvMAIrcTe71+jwWvVmswKX1bmcUtPAviOPjyxZLBaFqBlzx5xXSQTMIVVMGoC072NhW1tbRpFEZTHNEQBOWNBEQqfWhZwqOfAY9KlUum2bz9jXB/Jv5sor2PtH5B/gT7R98lIudj6npsUh/wq29B8EwsgN5F9hBSjQpiZORZ16b2ETWfJBd0bvLSeZQNCauqg7a3RzEojApSlrzxXGIwEIyBq7d2M5Z7Ef10b3p8VNTl5g8ycvnQ1HClCXRfFXwisTydLTU7H3r122hvyLyPz+ObVWOxW+DBdkwB+vdm/eCzExLU1d2ZmxmL2GyAX5B0Ewr1hEHEQY/u2th3e3+EcEYCJ5zefjIzGblVKcHF/Aj33m6se/RvH3b5zvffdbSSmb3YAJXy2D/M2CMIbCoBGTYhNLt0spSo4uMRgD47YkoB8nA3t5UQhmZDDlEGGaUFjTiCvrJZIuSb3KYaznJ8F1i8PnF3Hofhp45Fe0px0/sD8m5ocQBzcXFXEyivj85noMxXQhHUm+hcNTYbmqpvW5lDKRXE4J7OrEnbFkCCSRIR07FosfIP/uxSaN8UhZZDM5CNdUiIH58VNaFaU3q1Q6kH+uUP/D0NQa9r5A9Pvh1QcPPia+L27avKmSriv6RfCwJTVMkH+XyvLzCukRViJh8bnL5DwL4uJzc04y1ZBI5KhoKmq6Dgg8pEGvuTMgAmcXT83N6ZyAiKDDhS72gAiDUVHOefllCK6U9z/77I9XH54zEyt6kG1mHGzr7BXDfXvwwIDFVaPBQJkH0MAZgmPD4vDrn322fu3ifwH++uxo4NxpI/7IQLoe3/T6+v0rrp6OAAozUGYDE1YL5Xje2HfiPz96+GB99epHp2wCfUBv652w6wFlAUKyoKBnVG+juQjM6QSmUYAyB/w3y/nzoYd3TxHDBbPFAncOCdlpQ9MCKwDO/oPfPv+8w3sm4N0G991sBMYbHEaVdv7x48dH5v+jT6GQ76nAnzo8RF5FBvJp+cfBxauv4uMgY3dtncJy4ne/m18CASjFNUgQ/cL3yyGXUsGOSrPK6Tsz6jukmp1F36tN13si/y7T+CO1j4IyCQ2/ruPNZflwUAQS/jXVvtrQIBRx25twpQfRgIjA3CwUgcQslSDw6WqIZ6GcdoxGBH744Tsv/+LPfy6evLG80F8/4nQ5G9Pzi9oK4uLiLp8Mn2xmlRAFmNndksEVV6WnxxXvamnYEY7goyOi9ov9c3NTU5FjCZmZmUkJ/BphJkS/hXVdvEw24R+LRDasxJSSOoORLv5uyT+c/iD9Bxw+bX6PArAYI6kGVjevLT4tg/3Mox87v/Uvir//gx4NSYkij2mJib6/yb9okZgAMCmBTgUm8YrTZNgSk1uRjaUPjHwxACYvdBxcQWsjiRCkH46G4N4qSY3S4HBK2Lxs8sAn+MNf8NAvO17x55ifxrAe9WcVkrnfYo5khBAwJMb021EgoFuu7Gp5oThXqpDbBfKqpAQi9IgDIPYAjmWO3bt160ISaYqJpXsC8QU1IoQHZVy0yBRL7fbwXiUpfojXBm8R19MPr15lih8KzP5ttj6L1Tj4i4HL2cuXgX+leXBXdxP+0V0HKF4IAfML0lLjq4gIPHoWP0D0tMEx7jobsAk+wThYqdR5fBBavhh0MPVgg5ESpye2HvzFr9dxF8cphR7Y06k3O+xeO4SivRYPcGz6U5fVqg96sSnaBCjT27FP2e6/88f1mv969YuNE4AllIz232LpGCPUoMMHt+MlHc6C4G+DADKTCVWZ0dj3h3PnZ8+f35gfmIDbseLQG36QzdYJUs5mE1jMwaC+kwjKgN5OgZajBLaBiaUNv8oPN+T1Uoo+iLTt+qC+A1OS3h87KKncEDwz9HwQJavX2yc3WczoTQhfn8YZPvJ4n+k/+gweg0KcXptdS5+o+isqAgByMIfCKeqqVig0J343N7+0ZCLyj9g+OxxIQIXNpnC6RpFJnhlfT8emv6pMJMu6dOns9izAXzKNv63sX1lyGRKwmfaxBwA2ZDfVy3IhCCa2powIlKSm0iJQhnGwjkkF0o3R0yMzLvye93a8cuU+qQdffOlHrayiyRvxdf2N6JHQKGwuSE279OjR5ZORrMLXuoFM3bw0kSw1Pq0tdudrku3Iv0iEmBAC/8KX2C2ZmbwUXkF6OwQ+2cK62hQeyeLwsKDBZrN4CbvRQWRT/hG3dQnJ/2HfRRE2QOMjsJiFnm74gMzkl6WWFT9z8fdfpPfv7x50S03BdSFf8cHajH/fS0j56roQOhUIHEyKZWfEkzg4jk/cUlH+7ablH3lF5kPongNJTT09GoIIrHOCrm/jcaKu0hVtGPxA7JOfLDnwS+wK/D8/f8RCp1J+YkVNaBpiYDUh4MmjK1MkDn5hZ1u5XA5xsLTth7FsuhJMENh9AfGXycODBZEtALIzu1vPTmkBf2KpVCmLqIzOhyD/Bm//JvP32PvCyL8lXFzmY8ybcPJDhEMJR0+i9d8llH9tIFFwSRGGv0wM/CpZJE625GEXGx0HE6Osp7wC0TBaHo2DR5ygMPUBXCzk8DAIBDDk/f73I+so//SAPdpJwE68Aq1So35pbd8ApTDjdJkDNKMCwkkAWRBE2d27i7kHvtAa3njeqFCYzGZvINAjEFj1vTaH3aq3WimrDTQeRsFBr5lSaFQqUHNGw4lT7rmNx/uWjixN2MxmtKUBAAL1AkG7ZWCgzzg6+qKgktQ/gmh7imi19u57vOY2OADCwD+FGfWpHrf2BoeGRoMujwfY9MoZQCYw1WzUaODLJxPQOP0nCs9b/mObZ3raoJCL2rF8RFoIogDETQsZnFc5DYd1CsX0NChAi4XIP5Ey5FEoAIBw1xUg9jSu0UriezpE257SK39l3ILJyydPZqWnxZHGl/wt/DUXAAwBgM15eTT/ajkNQhk3v4EsNKILwu3tJA6uydq7F42yiFOWX4fTjRaLrbNXYRyNzobgdBxZn/mXiy+/3Jp478aNL+r7GzGXXCMpi0t9BOdyJJKW/VpJC5+rzklLKyjatTO7LhzZvuPsSWLCir2nkWMtKdgMm12Thr1/nDoJKwE7FmJjMzFZAxow84U4lQOzf3FY/G2sp+UfHf7C9woegpxiPlkAR+fRs5OSMPvHTnjW7N8L//ZPaPzybOf73/lWbJR3ZCSEDoafaor5WjCcQiMwBeNgJhVYxEGn/IyMWpIFxCi4CBhIysGk/CahjbJwFlgoqamGZzxEQgjANwuRgGTxUVtbXmmy8EDL/pif/8+jz/P46AGYWFxYH3KKnWIxXOaPrtwcHFybc6vqWDt35YsUCnj+idtSYskkCL5c+M2te2PdPOwIxPY/Mg9Cz8exk3iS8JTWLxarpOLGOrhm+7lY/MCVR4i/q/TOoyXTIdq7Mzr4uxAtfly+eRutB1D8cbA7HzMvB4jnGoKcxPplOGOKXWyEgOgVKGMMjmmzOVz3SBA4PePUdwqsEHx6HWa0sHeqPMA0g0FWKzp1bmPNqkeAWLCGEAAQ26zbDJYjT27eXFMYfxwAABK7ArkC8wAgyiZWlk9FFuRGh/GQRt6noNCLvgNrsb/9sRf98qihIa83iH8pCNhBASIBAYFGg0Y+f+SIZR/EpkvoWoC+qEDBF0d7HHK53DPU09HTI4CYuLMzQMnNetsA+r7AdwiXvlGUHB0U5ehPKOjUv4iNMqNDuPIX4dQz+ls71SeXGwCBJgtl9IRwMZRTrf3df7ju3ycI1HU1cPAnn4GPF8AfEvBVeBoXNkpNJs+0BwAoV9GtzyG4KaORMpukKk2fwYAG2bbeXkGgg+nPxJ1v3KzSS2dPVsWn0n1/xwF7pdGxj4LjSMD8/DxsvyYDeM3lovQKmn/vNNFhMJGBWAwha5Nor0BAIDxaFKapKeuWTcxSL2mMBhX4l4s/eplUQyaFtApU4qDuIxqB29MacrXctIK4ttiWkjJueHvW2R3lXL9/A/kXXubtTIrNzCwp21uxPyam+7iQk9RNOrViMQpms9i8lArns1nxqAAAIABJREFUX8s/jOEr6GdYEY7IZTO/OJxiXhI/OTW/OOXZJn+f+2fZ+vH/9WAcnLBVCWHU4C6mE5rowE0EkkIwVkNS6K0hZVxcIJyVh30MGXQYXEQAuBtzgqQhBq68QMC6RtoiAX+qe3UGh6quiHQNEgJW5GW05VXktWXkp73Zsn//T3c9+vxRG6jAY/xEvqRajOOzYrE6HFkZXFkJh6VKCeunY+kQB5v19u3Fu5B0iYnAv99ciEXsEf0XizWRaAawuzZnagqv6SqtqK4Rs3+r/TcHb//pzy/R8u9LevB3c/IN9+kQ3xem9pF+qWDy1u1bk3yStiIT7rQARAKSUL+0NL8ARASOmNLDcXurlnE0RCqNunuSOBhdVLwuj3nCZrIKgl54ZuMWD5IKNBiM0rm5jSdHKDNwhbJYcK2kbcD8221vPK9Yu9F2I2Ic+vGLgiBoPFw7rtFQtFnCkcE5qQGYqNFoFArK6A2gbAO5ByrzeYPccOjFnjOjgSDaw+BaYrmpz6Bx4vpMo0ZuosxLQED0L6WlHIjHn3UMuTyHgGU/+1lHz4voadVpx1WUxCxLr3AAfoF9mM1zT7kHBizWd38b6MF0YY/DC9+6TsyaDQ0dOnFKKod7pJKaKMoQIgjUKXXT99eBgBoFZajvqi0k2d+MDFz8CYfDb+hCRwXF9MfTJ05onK7pEG5WVpjkBgVFubV++BxGL6XVyuHagBUYi4Vk/7iy8mSUf1XpqXESJu/XjO3O7aV5+fllBXCQf0QANlVwMlKV3FIaf01NbyIA32QIeFiC3SZVuDoTvQJJHKxS55SbMJMb3ZyEdqmjdDXk4sWXX2plHZucLPvi4XA/aYnp6iIEfJQuE6vL0+JKExNadueGIzvi43dsxxlPEIDhyGRCCjw6u/nJcYkxMT999biElZKJ/MukLTwAf5lCFT35S49+4OIjtLNB73syd8UhTfh8/I3vZGfy2lLjMiCS+1/x7unzQ8z+/cvLP/p87zv/lhS7lf2LNkAzA8IJf+PQKjAhhcfOSFWjmXIyn4/uMBW4NZMRgXRHYB48zgvpcjAtAvFyVteoMjrEElYR2si058GrPNx/CU+Itvw8/v7/h723D2rzvtZFp7vdpf2L+FgWsJEIggFhcgTeRrKBChhozYeFPpCgQJE2VmRZRKqEBMIK1neuVZqhhNQnEDyUHhyKKRiHsY0Hjl0I18OFJmacmHocx6k915543E7sZCdO3TST7nvXWr/3FaQfp/U+3Xv/Uf8wH7GxCejV8z7PWs96FsaBAwSWSJTK4pJUZYbGYtLYNDYz2QhWVubnTGOvPr91eCfo4GC1IStxNxpdAP9wGISm4XAWjl1M+JqyL3Meh/HNIKX3NoKw6j/2wfeK0CzzInpfAP9wby0b/KXJNx+jf1I293v+yvp6oaIs596duzeG97OoSRq93C/mAZBz8RYWCoWZoIOvnD+PO2j3nt+UlhoPjB7yWUe2bUvQRSd6pgdDwNEM+hhZYlAHR9/7bNnqx6xAnwf0rt/XF5rYNj1tKajsaqsI9UxPVk+w9oLLHfKjw6438PIySNoQAKILcMkdCuLWpMDgBHwnILxxKQcW8n7oDfT6h/weMmMDN8PlcZGYBkC0Y+3lzz4740cuR+YaatowLoeNmB8+6WUZXL29HR1BA6A0CG0X0j+dbe5CtK/vEA6mAEr2dkxO9tJ6ECRJ1xaWZmwEgcACra4YQWDYqJp6ABwwFgMItDRnF2/GP6Xk1X6Tx7NsWLh/P2ZiwQfGKYuhD3AdZ9wuTkXcIa8vallaCkcBAv0smhv0at4s0L+decnCNA7/cNoDALAMb0rl5Qh/ZYB/dLMttleoM+qzW754EABPAQIOoN24AR0xdWiJGdeYdxVKLZuaWZG4Mfr/eveddz4BFvhPpZJL92aFDR9iQ3iqQUsQ+HG3WZqZkdGWvvuZspX5pILk5L2YckT4l5a7RyQQpKe0Zn68IzHx2abOeoDDXFS/iIJ44X672OF2G9nk70bzA+dn+KopwV4x93F+aTrRv0cOPtgi+Puu/n3hfP2rX5KlcHC3BxOiN1Tvn2gGizgRjKZAmaRtLysFgo6hvUnZ3GQITYoABWzDAWGKCuQgsLsBrjKjxe1y2Lty5EVtcjmt/+WOXGF/4V8BAz/+7W9baUFqqqQtSQMcECBw/ijOUQIJtIVVLbvfKDfrKTO/HHRw7klUvqzohx9JGAEEMZwuPzE3bx4fN5vN0gJjLIaTb98FtDw8fOP2levv3HqXp38jo9zeWrQ+r65K67jeL4bXgUzPVt67ffdOKkf+uMnzbCATyGHx2QZPtjQhQmBWVnJyXvdBHH49wUHgEFcKBBZocY1On1uIWUBZOa16HUASIBI856kbgiYXxBsMC8SoVDfAZHtgLrOlqT7Ph1tsJ0YPJeCqoiBOWaDbGOkf6Ge4GbhwH6V/yBc8+wStYGtvH8VSGZCy6p7RUAKmVdnG5+dwIs8VDk8hwjismHq6hkwyEARZ2YFrNSamp0F797Jn/TTQP5zodfYG3YjRcELYFbHBLWJmKRY5V92BiS2ArtVOEO3bErwIFz03EQIBA7HkqI/qEQJjCIFji8gBF5Csmhq6MABjmOt4HTNFl5ejc+H79xdJMjuMUyaXARAUh+yMU4sLGAVxfCl281zIbI5yzQ+pNGl9/QrAXwE2f3n2V4QAiA+IAihguaKsTN4mb8PmQWWWI6mcis9/gH9FRQSAAzUMAisqcEeToyIzyxgGHRzPSIhDIOngd7Ab8swzpSeVs7M1jR9SYnSD1m5vMKvzhBnC8qzKrssrQP+yCrop2mh8ZnxXzr4UnP3I1raKgf7tb2mSpQvYwSIgHFFpAwW/cJO/3Qh/jP3R2D2PgDz81efnSuTCwkdferRlz5f/Hr1/f/585asUkYD49sZm3Hvjj/GPZeWn86MhAlychKMhcmU2ImA980SjHuY1LiGgtqYBdLBRjdNxgIGog10HK+tBI7flMDHEvZOnaQ/s25GIOriSEFAmK5MCBJrN8/OUpHF1Zd6mN10XJ6ZesZElRp0DwlxwklJhaDZYxn4B/onEaUfn1IBmZo0avS8xVf+tY2U/+IHkWyB/My+vXmTVP/0RtriRZYrAvXoVmx9k/UP4Q6aSnV2qvHf37jCiXyrXAgEC2IIImNOGegsEV1paJkCgUJjFLd85f3tl3qzDAWHuKbRA+rL93MiC4Uxv0Kozz1+4AH/u4rohFr2LElRoA9DQIZzh7ej1qbVNTU0Zc0O95MqIuL3OAGalEikzAUbEYi403bncVq+v7/ihJ6d7OhC/OiYAybCfE+gFLIwsWWbgG5u/EMXd6TFssONiycn2aj8b2A3AZ2JEtbOqyukPBgGIezHVgUVFB62uEHpw4G1w0Ep74cOxhWvnqnqHfO7QNqCy/iGPe3R0mzsBMwbbaTneuM1mAh6ISWEEgVjWGxtDBFyw6H1WRyut5UP86zQalpeX53TwJ0hOLRh7qgdyDOipGzeOTS0A/bNGTRh80O7UqaUanc6srpNWFNwA+peXnCUUcq4/6vU+B/iHDwe8liH9g9sXVs/sKnUyjWuCFt6Ef6wMCAhIEEjrxrsPSqUVyWkHNRqH2TEO38MXWKDvzAYEAgl8plQCQviVDwkCVQUqU12mMCtTUbhSt7JyOTkrq6CR8O/N8ZXyw9uR70kqW+sp96pFjKNwIH6B/oklAoFEsKcSY59rudwrqhghsHP0T5n9h0csUJZnYu7VI1b/tv/D393ox186X/vKlyXpfDRMSjwrZhMOpm/oYUpHSBdhJRD7wcWZZrTEJNcDBOZgYD61Q2iZOq5T5/wwwtqG7m4VzgeDEM5r6G52uEOmmvxs3gmzcRQNtQfgChE9/O1HxTK2xU2oRgQ8Oj9/dP4qLeUdtzg6t2+5lKTH6Tjr3vQdIhlnfiZbIMYGSk6mP1sknRuvW62rM6t3NYxFIsb+W1ONN35w6fC33vrFL371zjsPFkax+dF3hI/9Y4O/8BekR+PwV5+Tg3ddXLyVeufu7eFSMbWBORMvoTzQWCo4pSEHhJOWmZWHCxiPViAEUilwiBlrmb7sADYIT2k9NprnQaAjBHJZgXra4uYHbhsIIpKd8dmaB1588cWB8SjKL5xbG8LRMmegIwAMKWxC+POA3AQJbfAcByTvqer10xRtdVU1YJo3ARgMkMCFxamL4xg4j11VgkAj7uu0eHH7B4al+oLByUlnEFSs3xp6cpvbGsBNlMgzO4JuN8O/waB3kABwPLxw/2YP3DAMbvjZjbqi8JMDvnoO8NmKhKn95vv3ly7OaOAWhYs3bPrY4sUpLAWqxhYJAvUGn17VcjhVqZS9WGvxLM/Nzf12YcFE5UK1espE695wbHEMc/8GvUD/FnHNXIdPNze3UoHD2Tsx9R7wLwPkL6N/RVzRuRUBUDGr4OAPUzbqa417sVbdgvfkPxTB9SCC7QSBNbVIAhu7C8ozpGYN9kLGNYiAG5amI0c8XEYCNkNAB/+3Z3JLAAI/7T/WD0LdlifMKhCWf5wj37WSnJWRVdDAsi3HP+0CxSQQHc7WFqXA1Z3/3IFSBn+ogSW5Aolsz76azbl/zYz+caO/GJpDlSVe/tZXZssEbZlpQP8eTf5uBfr3uPr3xwf7waINTyC85Sww6V9sDHMHd4aIaEYOILBtl8ZgNaiFyuIcWpfJliYR+PFzIVotyzNTsfHg7ryG5jqT2+3Q4vzcxinG9Uc5NbWt+xITv42WGC7CvniXGico5/FcvfzKK5+adeHGF7ekyNV6gx50cMH2dERAjEQ9SckwcE2l52fMz9dVrKqBLOSR9fnYLVXyvR+cZBvP3/ng3ZsTay8vR12RkWl+byPtPIJz9DziX7mcRbcrS5Qsu0Q8fPf2DWUpBQ+RmRFwXl6EI1zIOMq15do0PICEGcABN6bjmKuM8AtjBwDicNsjZgUapSvz84wkUVigxWLw46KkoHdobQgZ6ZHFW7989dVXr48t0VxxFS7hBfpXNWHVW9wWIEwuoEn49/T6viMxwAhc4p4QClk9fvjr1tDoNqzeB6qngZQBBAIAeicHMVgrPIWsLGYJTVRh6t/LPzkSCk5MWn1+v8cwjc3coHsmClDbEfBimwUlNuJfEFvk4cX7156mhVF462gP6m06mw3nnwHZRwACabfau8ACNXq9xmEcV2t0VAoEEjg2NrW4CAgY01ut+uZ8Sel1hwvgT6cHKKfqn1GtDusujDscyDNVYxT7bAD6tzBKOy+x93FUellad2J2feeJnTj4m6YlAlgk53wtrSh9kf2B+qXySld24cG6LBrcYZpkMwQWtZxqKepk+DcwcBp7IbXC8mQVTgfzGLg58Dvi2pyR8MlbbwEJlJXMzhZ+2uBwmeHRLysv+vjjyo8LkrJACTQ2E/6tzspQLqWLFdqmHZh7ZWc5gAIRDXAiDO6pdLgsxoYB7UbwlbbTTqO/G+q3i72ij1IsUiqECqXgUeXv37v378+fr3/1SyKkeW/w/Q9qAadwQ8F/WA0kLwylJIhEIkkbGw1RYCUQKR2K4RxKyEImiBclRpHjNlNAQAdBIJw6S8itKmY9ZO50kSaqrKlpwm7IRw+/0yWSiEtKJOnyvWbbPE6ErNyYXT+/slI3bwkf279jS6bNgJn5tmLMFSfXCxFBuLYU8+9dvXy5YlW6uqthKhIzHrt1q+Hez3++779x8Pf+0x1n1ubqNBR8R9U/an5Iyft35YpQUdbGKs9Kihsi919p6Y3bt2+IKcmYXZG4FwpnWJFzAAfUFmoLC7EgSLvOyBh9/qpaw2cFVhErS8DRkInRERpXW01KWpGqTYCAAABh0MEWWoAZXPvs5WVPQmRkYfF7p06d+t7iwsiRPuB173322ctnsCUbdrljQJhceh22yQEBl5YAlbgl7tOjbviCHr1+sIfPZKg6d23xwcWLwCQDuCgd13Vi8FUkFg61dwAA/j+LC96g04pRDvqJKgoLvHjh5ZfP+A2If0dcR9xePwjjobXlmaXF92+2g/rt43b++nR4d4pSvxtHX/oSfIgQN99/sLhk05mmxsZUdbaoIfZgDBFOZUQIjC0A+/SaBhrRa6IzLdB3j91io8Oks40bHRobql/K/QPEXaDcK0rmVkuldXWZZfJkXHmO3r/COP0j/MPSXzkTv9xdtatgPKkNDdhE2BkCVvICuKXo1ZZTwAAHCAAHcOdyWWtDc/NBKUbEUEOYi0vlXZ2RGJeRQDr4k7f++ZlnDqenXrph1mS2KbRTYzWquSuvtiSfL9jb3UwFwNXLyu0pOPqWnVYuS0zc0TJQROpXgCVAcgAK0lMycPRDyzd/efrHL/7N32h8dCH+5ecK5JlpxemPCH9b/35y//4dB3WwiPP+cY7AdM4jmML9x2YATOdTYoAEypRparil2/a2MWM0OznceznHAYU1WdQLUTvUoIO7uxtUDpfbUtBVzCMgpaKiM0xpr6nNBgjc8/A7D4tlYmWqTJZafgJ00vzK+uzllasrcOZtoIMPby85r0NjtLdOuV1wkuGfRCJIUebNz1/Gs5K0txltCrfG+tOGT6Y8A/j3S4C/d29W957xYPXPjb0AFnqPCyn44h/wh5x4bB2DQPQ/lw7fIB2s5IQI4B++zMrLFK+Ua9F2gcNXmO9JrkAyEl5ewQ20VAqEL+QdPISk7EzH9E3UpRdXG/N2JWlAw6IODsfQpIfN16HPPn/tzZh79Fzk2C/tnWMj0+dGt1mPv4lRWb29VosFPg/kLwCmSaN2hE2WpUUUpTwqTVh1OoQyZzzh+EzvxLV3HwApW14bAorpA2CLLI5NhWPwrwS/DwwwMkKDvwbNuC7Y6xy8//sHP1n+7PseN9G/yMhI0D/kW1tbvoD0D8dmcFt8TzvG8XkIlGxsgJYFSXmRMGEpcGnJpglPjfWr1HMe1+ItBoHIAmNAA10YwT9nWqDiH9E/ozEMj8MUQM746tgtbumRBr+1dm4xVV1Fkkqa1VZ45Ure3mQhpR5oWfXvuSIk46z8N1tWRvCHe6NaAS/xsWpiDxh/VWLtj+p/RT8tes5uHzg1MHAd8O96Z2tNwzEMX1YRBKIjBn7Z/qgb0suVAn8BOviZ52XCil1p5WmVnRdjLt9Q0qmi5L1ZjSracrP6nIyav7IyhfLbiYnbnxtoyoX/zk1PF5AFRpAr2l3pcFuMtdoBCr5qpOof9n5BSTU1cQBI1xu+1rfUi9OVhUJ5SfruR6v+bd0ie0z//neHRkMI8t7gSB83JPIn7DDYB0YeSEQQIxLyMC3VnIGMrkhOl1kOCg78ABeGtCpoKSH1QoAEqo3N3Y2NB1EHa8qLOVNE/ChLirXNNdk7EneUYinwEsVjFCfPz19Zv7LChDBZYnSNRTveKNPoMTPfUJCewlUC03MLj86tXD5/HgAwuRGNqv23xvIuXXr7W996661fkfUZ6Z/nCOZeVQfh5u6J6szjUtb8OM/PvWVTbDsFndOEJ0v9TR2++/mNYjHavbu6yMhd2TbLWGC5go2eUkckM4MngSeu3F5hzyDMCgxNczP2gWogZYsXP1xtbMg7qrO63K5IGDMSANqABAID/H8vvns/MulqfLVywBiCJ5574eJrPwYADBhMHP1zAe/WOFSO8BKiEopSF9Uzq5wGG9BOjQ5bEsTKjkSHcCD53QcXUdiuLfuGPJaRkYUpEqaxuZe/3zcy0dvr9AYDXp0+GMAk1wdver7vIfl7ZGR6YsLpW4YzQ0DbMRRPzEbfpEZakVShiXr8TCfS94do0UMT0OMajQMh0DxniC0S6ZwiEvgAa4G68G/h9xbJmTOF9C9K9M88vtoP+OcOWTH4YOFmDxd7qqmr6D7Yvd525cSJgvUrBVmkfhVc5rMcrjOg4Sh/Z+U0t9iVk91Sa0zC2zLhB+V2IPoVVVL3o4Ve7fZX0QoD+DdwHcC05tixhmMNjd3NzXA7ZMNxFzExelNWYOTIcT4ulUUkVHbXZRRmKoYz+1Ue3wXdwVdPJRfIa5pXAQF/3XU4JVeQe7heWyNKTPx2blGlODcXtG86DoSg+hVtl2Va3JbGGi03+stNfnCDvxQaEe+AAPsrUubK2oTCYlnKI3n/tmzd/tj79xcPQqAoJe6L5shf+h8hYDqPgvGkLAFAIOhgQ10h6uDKto1bLQAEWuXKW7luMO7OhKsKZ0MK9h40WkIhY1lq1yYAxDzwVElxVvMrb2Mp8Du/tb9NG4/2DKcVHEUaOBeHQL2lYX/it8vNBszM16ftEJ2UnRTty941N78rLwnO5QZjLDIG6vfY7M9Pvv2tf/6E5O/7NzuA/llinPXZ997VC9hWBPzj4a+tjYnfLxy2+CF///57n9++UYIVT/jWcoD/sVNWxsNfK3JALZBAbtNP3QlgohoWFajzVrP1mXqMS715bWHq1ocfHss6Mefx+q0uHBCOud2umGGNApz/+7sLbktzS1GFxzm48O5vPkAAXEbndBjYEZbboraDqqmLS/dxifsZ3OJJJpiAT4eTp2rGymhUI3Y8unam4+lrDx4sHY8ilNlc09UTQAKNpIN1EdTPwUMLI8FqJzkXr7271MfRv9Hq6on2YHT5QhTg732if/GFKYB/c2bpwYMVals06hviIJAPkmo/Rw1hM0Fg83zUY5kam4qg1J1avP/uv91f+O3/92//9mAxTv+i0XHjFNK/xlu3GP0LLy1wqffwswP8a+7OvLR+4sTe5OSMzPUryVp7WZldXkT4h70oRdks0D/cmJyDxuF8bZ1aKGPYQY2ELm4KnVAwfk5hE2Tg+vXrra1AAo/RQRJ4UEWWGIeDmw2J4gZoBoERrhtCpcBjjiRhRoZC9vMbc2vL46s6VUtncl5rm6KgLqkt5TAAXXqp/aMmzP3LbxGLAPVECH+UWC5I317vCLlUNcwpwVmf0c/Iw1++Upkfd77ANyXeU1yYIZftebTmx5Yt2wWPm79/+YAO/tIGAv4pH0wcALERwo3GYUyMQFCSJkVLTJK8mMe++JUml7eW4WwS7o1r6KbNcQ5Hnap7796Gg2iJ2dulZACoZMtgsPkra2tosJMOfviwS4BhkQKJfKdtDiGQR8CVOZ2jdl9i6k6dXoe747p2iwSSzPn5pIKCXatJuwq6w/DEOnbrWOGln8u+9dYnn/yCp38Y+0cbz4lZzMO/VFFxsIJTv2j8o9Ahfs3N/jj8MUWivHP37j2Ot8rbylACMwhUcKecVDCu3uGWnZ1fvzwPnExn03m4oKwIH5T14NatDz8tWHlveW1NFxkdCVNWoMuyvPy7DzHz7/6IV99stoYW3v39b2699rsfL1uA+YVjC0DKJj3RqBmghKp/Z/ieBM0y29R1q6tSs26jgblw5DitKbl2f2npuM027hhsh3/BHVlksxrh+zc7AtYji+/eHxwMTVa3P/3+fVcIx04wHhqzAoO2mZkYNX+HGNByoRGAf0crDh48KOXnn3sJcUcifYS+xAIvOpAFGlV1Fzzu8NhYDCDQOBVZ/P27sfv/9vsHMZ0pRtZn3fIFon+rH966hSvPif5dO7cRe1onrciYnb2C+foZmcLCwsL1yxmtRXZqf+ADoJhVYLAqyV8s4OZ8qt6ZU8LRKHzkaFo9DoCEgZUtcpwHPnX9+kAnwl8tj4C4gbwbS4FMCCMEbkqMhp8n5wq89u5is7AwuUy579nOKc8FuPHoVEWdBUk7M+UKrXJ3OtA8Uf1A5+HEHVvfbspH9Qv0Lxfdz1gHTDmMO38bBljztzHe/GjhY2OVccsBAmClUiTD6p/gUb0vW0SP6d9fd77G5oPjAQlvMALIZHH6ZirILIEbzmiBJCeLRkOyKkFn5NCQB/A/ORYBcY8kzsymaVEGd2NWvtqhlqq68xrymjWukEaI87+4/pytg0EIlCi1jQ37dyQmCh7+Vl6CHFAmSBWqEQLNDAGRBOp0Y0Xb35itAAj0VluTBPnn31spKNi762BSXm0/sz4fa7tE9O8djv6B+rXENq28BMaxcvVq0onzlHqFT59iDP2LL7lhHRCCvyZCQGUJ6ODbsxTjL8dZZkDAWSpAlRH/IxMuckD0BHIQeOXGebXGDErKx6bjRnE6bugMItIDIIGN8++9955pdGLCxRYnRSyuvou/+u5vfv/f748MBoJuxL+fHVsdt7m2Ef2bxEQFwFPNxUVy5J2Ju7mpoAlYsbqadJQh4AbkeoZQly4uLl00xiZZ7Ck6ZMilF/P6PD957cG7o6FYgrN6FPTnoBXo32QVxp62t3s14YWRmwS03LpkHJvxzCH+JR082I0ISM0ezkQ9wkPg09feh6+nAQgEjmeOelykg13egPvBg9j93y+GNR6PxagaA/png9uiBtXvg8UIrvydWVq42cPvJQX8W60QXlIU7CrIyhQK0wrLy1rlN25kCvHy+indgBD/5Hz3oz6/XDoupOhuQhFeRvLdkKJKrm1S1Np56tSp6wNE/wABj+EKZJTBwAIbm1VS6dGj1AuJlwLx5/k0/Dwt1JnvudZYVpapffGf/rXfpbeNg+K3qH7amby6upqnTN8tyhWkyyprsrcC/XuhSYx9D1FKOopfxL/Du5VG5v3jdv7izvNWO87tMfgrEYuVJTwA1lfW54tKFJny1JRHy/3b+nec+/fvOF//xy8LiAVuSon5EzMheGhzMNYBRWw4DnQwjoZohHCflYM+pAtN3gZXqN2OqWzl5WlpXCmQfNFq48GGvIZknI5ztKYqGQVk8EenRNsIt07QwQ8ffiyjeUmBuEYzZ5szxyFwft7man7x+S1Csx4h0Dt3dT2zYedq994spH/NgH/rCH//RKmnlPsyhJNvjP5x3hcQvxVXf3z19vq6Aot/XcUlPO/jEZDRP9BRTVhKwj7Nvbt37xACUpgDxjkQB4SDCIhzWGQKzCAdTK7A9fVdarN5Lurjs+YWjuhYVuADgMDV8RWpq2cIejf7AAAgAElEQVTCGXTTdJwbqKvlyEWMov/9/YWFBwB/3zumgluF2xK+//4oZgVWOU3jiIU3e7hhvp52zs0NWlGKFYCKo+Z4th1C4NLx41wmw+JUpAfn3dong5N8KTCs91147c0PR9wzfT6vyz2IQyYjEwHnRDUgdpU3vDDKvC+8zsZlHEjLKnbl5e3de7CiTg1P/ni/O75WAyDw5v3FpTCDwDpN1BCbCrudfn/C4gJawC8uxVxWfdgS1TkI/lZvjaH3xRfVLC3efHpT7pVUund2NisPtC9aXwpZyEsbQGC5ndof8IL3Ia6jpqzsduztEjflc/iHUpLGKGihFa+B7a2tnfaWTvupAa2iE+Hv9LHThH+1uAe5loQwBmVRMVBNpkbO2N7z9ChtvlqbL1O02b/7s+++Y0L6pzGZZlwHD7ySNz7+aT4aZUXpXR99hCvP3z6QjzHQInhqUe0Pq3/7kl1A/7Sb6F9nJ7c3mXYGlIhxdQqDPxwGEcnKMstLRI+ae/W4+fuI5+tf/Yc/7nv8KQzEcARKCWRMUCSTFNPiJF1FeXExQiAig5zwD5GhtRV332iFNRlZyAJVdQ5shjQkN3QbcTQkR1KMg/HEAVNZOKSkuEZr35e4YwdAYBEiLMZlHJybw1zdebZldX5+Tjd17F92SJJtBp3B6dTnaX+9utqQR+sLb03N3zgpe/u/UfMD6V8vMJjjm6zPNpp8k1acOH/1xz++janE2PuNgx//nsO/bFZKwgK7EiHwBgeBs+wbnS3jZXA5TuKnpQnTcDpubxIrBe5av5xUxyCCc5UdWbqwvAaIdA10cPPq1Eg7ruLA/ZmWOhU2OdxLH77zM4DA3//mNx/0jzlwYs4SBqQLBieqqtudlikgskz9crPMvdycbMXOpKSdO3dW1Jltf5RNeKbj6dHIoqEDPhtn34AFog52hN3ewNCF114/5L6w7PMH2ejHhBPD8oHzdAAkTuC6ZGyz9FTxu9g0gEs7C7KSkwv2JtXVOTDynQKVe7kUlT4DlgJ7zmEODkAgln7HL0RdOPDsH1xaijkcS/A2HDZYvXqj0WEeB/n7YCGCOy81i3H6x4JfKjJzyvPyMoS8869MjuK3Un5jHWg7NqFmSfwODw/n1Hcp0+rUwlSyrCOSMO+mMp8l8dI2Gx4B7ZQKCEB4nfE/UsAcDTxGJPDgwTgEGvluSC8Xl7qSWVaes+66+f4iCHg4Ns3McXdBygsZOztzU9IB/sR2YQtW/144gPQP4Y95YED9bqlUuVwqjv41YvWP9T5o6xYu+kD+t6n/IU5XlmPu1aM2fx97/x794NaQTTj3J7Bv059ys8HY2UIIzFLTaEibEiSwHH1y5IMpwzIgsEAtTs1qM7Nq93YfxG6IUZW0d29ed4XGHTLVSkpYFTCVY4CYeN9WW4t7E7758DsfvS1LLZHIUgTldTYd+QI5HbxiszhOPZ8ox36w1RnUvCLUNsYi4WPHbjmu3vn5YS70HuhfT288+KCD977wg2/ritu3b8/mF2fnc7i3nxYccksHsYiE7K++GPgfNhiLi/OH79y9O0tz/Qh/bWW02UdOgwjlHAKmsUrgLkYCT1y5sX6UL5VxOngpuoyWGNDB/eHRdkzuGwwGXQ0DDkqJcblnPvzZBw9+9r1bMzqTKxSyxBYimEUPrKyq3WlaZNZnz0ZPgqGSNGkv6HkMeKpTmzcbeSOL6Kg+Uz3odgcDZ3C4BMPvB0OxxSlXwB8489mPVwye915e8w35vQb3oNOJsYTA1pxPjYawiY0bA+LVP6BlZrVUuhM5WWZyEpbLaK0GHwFBEGjAZkEVYPz9paVxjRkeb6Mr6PfBZ3iPHJkaW1z60ZGlmaWpsMFn0IBsvwX4NzII//bU/Wvn4qn3mPu3c3b2yok8rP21luOFBDdVVv0rm72xLgQInJ2l5kfOcH1OsTLP3J0j4dpWqfm0NwNBhdPA9SySkgaHCf7kTP4C+tVyBJArBLJiYHcFC83H2PzxTQ3hkcacwsy29eWO9tHohTfV8CfRCzMz7obdu1NT9+wB/EtpqmndjqNv+fmoeUVsgJTOnucbOO8fzQgQ/aPmRxfhnxgT/3DXZVy3o/evUJm+Z/ujqF/c+va4+vfvOF/7R5yO486eeEzWH4MfvuUMgSwuS1KSk4WWGE1BZXYlq06TQwG9MASBhdpCys9LbqBuSJ1RdRDng1VhkAPa1FRggLQVMJV7Iymx1/z67R2JiR8DBKZSxku6WFin0ZiPzh3ldbB53tTfeWJeo4djDQaNxthi/+lj/ev3Lgme+de33mKxf0/3nlmLHsFSWRWX+0Lql3lfMsvbuoZvAATGhS+/35Up4PiNGEOvc4YxySS7C3XwPWAcDAJn4Ukol2MdECQwwh/80gLhxZ3fuzhLzPqNK2Y+KIum4xY4CLy2MGapxqxAwCNdnckdM6EQDgY8+jc/vDi2+ponEAy5wrHIYNCJ+vdMoLeXkbI1Rv+q+Ix4DXa0dyVnZWUVwH1FisJ0UybDzZHYEpqkDaOjTyb0+Sn2dMLrDYW8AYyF+f5nny0vv7zsW1tbG0LDtHcC+x/uQ0+emw65+uJlRi6NHvDv6NGkgkxgZIWZ57mNt+NmXKvBf3/UDeEgELfEm43hQZp2BgAcO31r7NWm02H9zMzM1JjN5zc4+gH+QtZl2/hU5Bx6X4Z4+KtYn10/caIgI43bdlSGsS/y5+DKwrE3gMAbCkQ/ZiXN1tapC1MxNpSxvxL+UQQEVOIjiLYYDgEBAFvLZjsHTtcA/nEdEB7+uFogTsfR5qSjcLGOG8fNMwSBHQGdtlBY2dl/3Dfk0b32+qpaMzNzHCDQ3bBPtGePCI6sVZu/JXHH8+J8CfZC0jn6B68pu4scbosKvX9M/tbWDGxYX1j9GSOfefmbnSpSFqblPPrK8y2Cx7l//76DOjj9z1b/4ic+GkwsMB0fYUmJYqfOYNBLC7uyMRQLERCIEYiUVjKJtJZjgmhNZkYDg0AKymrI61ZZQAe3pW/QPw4CZSWZn7bmJiZu/fg7Dz/OTQcIFKUX7zJrzHNH446YcY3JtpKRKdUZ9DZDcGIwfPr02NW7P9io/r1/s+fMGZ8+zpXi9A/x78qVNIW8rUspvvH553eGN1Z3siWHPPpR0jWOY+ZwHLBLWQwk8AYiICpgbITgrzJigBRHl6ZN4yqBeSfoHDx/ZT2JIhLYgDDo4IUl3fLamepQzOUHgR6oHrSY3YO0VEMPEDT0XlRvGf/dj5cDgaAVRKkft7FVOYf8wclBt3WIgqyZoCdIR/xTS5MwIFmYmbX3oFRqZBC4AUmgg3WWI5OYmGUIUGCM1xp0ogs60Dv08rLJ5Bn0ff9ltpkXsLaqI4Q/s/bRCFZO27mFUYR/oEuPnjifkdbaalekZZ0noTiu5hCXixCgURQf65diP9hA9A+OR/3LT9469a9vfc9kiAICjr+m8fj9rgW31XPBdpGNfuDXmdMAyZTuKps9j3tJ0xj5a5VTxCm8weQDJH83bqzPcpNEyspk9d4cvJEi/pXkl5TkA5KUiIlRKbkHE6UwdUE67UWzZZ0DA6drefkLh39PIIgHrtTugwcpMpozRnt80fNyeVn5GBBWPyD26mpSsxEA8PhxTzRtH2KcKLceyzeJO/bls+ADRv9ABYty96Q3WNyOxhpG/9D6TJn31PtFnOa3vnG7E7Mx+AWrf39983frlse5f/+n5ytfxt1x3EDIXzrx2ZAU0sFppIN3teVn45AmTczKy9iYOkKgQstSlBtofzCSwIYGuBTUrpCrYXd6HP8kYglZAGU5n35aiTb6hw8ffrwbWaBIUFaBQal0cDbEPL+CxaFkjdpk0MET2iK9ffcHud/653/6JG59xp1HzL5L1b9xNVb/pBvel+JscWnpHYDAZw9v0EBcYccKMV055FaED4q7eM9iV7HyxudUCqQ2CIM/fGHpCPAqRBn8ihA30J44fyKv+6C04Ma61KbbsFSMjiwhBPoMIyNeq8drdbkHB72GKChQ3GM0BJyMsgIDTmcAV3sAKZtoD3r6tk1PD/ZF+8iRXLVZlNYdBVWaCRxUm1kAFBBHx9TmTcIUg7kiIxNYEzzi7e31D/Vi7CmRso6RRhU2zq3f/+xl2kwZ8Dt7g6P4BZDMxe8dRDTNZspMLBDiHBogYPJ5tmScWOAGBBIJJFcgkMCI1+n1D2Fn2px59Wr/L371yS19VGPWjP/uzTdnZkxWf9ALD8zFBS713kMrf6XS8uF1zKYVppUrWu0AgHI738aVo/EFxO/svRvAAbGEDOpAXYbbMvKVRP0ARRAC4zm2tI2OW8qF/+M5OXIt5iAAAh77o9NA3ZA4BGJUVp0aPVwac5JCXpijiLb39PijGNoLaqLZ+ObM8T7dzny0uaTkdmrzQf1uz1dKaGKUJufRApiyJ7He4f6D6l985RG39BcRO14AFO9Rpv17Uu8f5/79nx3QwZtLgTQj9+fqgemcJ5A+kElSc7IwqcCW19ZVKbfL7VggayVkoCVdCnIFoiuGogLrVCiD4TJrdLjcJi3bjipB/BNzUbm59pqB/aSDHz6k/FxReiroYJt5jsPAlfkVkGLNxob+sAVooDXonU/d9623PmHNj3PVvSAVY3H6R4Ga5HBgG9/kAH/FOPe2/1+G737++bBk0wJ3fC7lU/cXKMbw5omVYvQCKodvYCkwhzfDyHESS1GGFJBqgEQB4X1mZlZyQcHe7oq6ivPrV+pwOm5zKRBI2eD0zZFw0lyg2um16vVepx83YgTXvj9ntHjW/ACAZ50Ac/4AKGUvwF57+zQGOMe9L0T/UJSCKs1IU9jtrYWZBSdo7TcuPLNxpUCs3uNfQuo3PTroxaEUTpT6rbd+8aux67/8wLD2GSLgMrDUwCT1PCgrkDYG+JgnxUy7WgCWhOWUOI8ckCw/+NXMbMOujw8C46bxqqafOvvSWfhCQYOqdqrxztWpRZNu3hSJmXQXgATOLC1Z9F6/KzbSw7l5WOp9Acaeni9A+gdcU46lP9bFxXrDLCv+Yfdjtkyek12/U50H9K9Eicq3hDZQi9kHfDef38dZX99SVJQz3GbvZElYm6TvpoMAeJpyYrjAVAbx3YVtheWKjGhvh9Nz4YLNZjIdPz6zurr65ow0R1LZIhOJ6muQ/iW+3ZQv2kPZSQz+4PmxR9DtcjsaBjqx+Ru3/lHvt4nbN0OgzaFfvVKQKhcqHrn69/e68/dver72j7g9M4XjgX+MeqKN95wMThFxpQ4uLVWdSVsyiwADyxjyKVoBCgEigAYCCOKEMEXm4xL1jJqaxnDIbayUcet8xWzLEXyULrbXVO7DtNSHv/2I1qim7ylONms06nkzvKxcvgoAmGYLWiNTx2ptBpqOq+WaHxj754taIlz/coh2Hq1S94NZ/9D7oiTVsX//M//z3t3P7156hkM/kFBKRgG7WIlpeLh4WFlSjHF2w8XYBWaWmGFAwJy2WbJEz2IYE+OAWAdEBigkJEQpDEJKLV2f3UkDwhxEYCkwBqqvZ+HWlBVImSdq8J+xYvz84KTrWP/Sg2NTVsDF/+UMBIb8Q/7e4KGbT1fRthHOzc01P8y0RvTEXsQ/XMpSmHmFSo+Mlm1iZdMslQYhMOQEoUsFQJ9u2fLge7dOL+o9tjncTf4yCuEAxp4CEeyt5nmmzjZnViP+VZzISxYW2iliChEwM/kKQaDajCG0rP+MKdHtXCRDIBh86exZf8AXPv2zxVuvvvChy+OxqYzY3DbFYqgflxZj1uqJjZ2XwP6o+kf0j9/uVlRZTy5mNvmB+EfGl67h4Vl5Z51UIUvNpq1BqZjeXYJLTLGWkp9KEKjcKOdimONwJa4EYQyQef8A9Pr5X4SAaI4euH6ahUbvJSGclCmXFxa2CW2+gH/OPBed0+ksIH6Pz4yvFm5JTBRV2rvk2uwdSP+axKB4c/F5QtU/eCrtrje6LSoAPUb/GmoH0PvSwrM/jgDCZYdEFYNfBMrCtDYZVf+2/iXMi5/H3r+/zaGowPT//VwIOyIuIyaFmxIWSIoLpToDpsRkVzL4A+BrxWJgK9zEW2lvDc7HsYwEqVHajDvUa7JUFreru2SLLJWYn4DWfGBmbq6yXFv5/I7E3R9/56OP9wHLFOTmtqEOtmnm5i+vXwEALFd7fF5Tf/PtFR3AR9DpOvYrpH9Vm1Kfe1nsn5of/F0n/OvilMfb++E8k3vv889vlJaKqXaEzUOQViy2C8APXtCmAy9KFukJoFiClpicrhzeD4ieXABA4IDa9VeExAS1r6RhPyQzeRcikvrE+nqF7QuB0YB/1R7PxLmRBK/H4DsztKzvg+ON/Oytf/npq5981xz1Y1Qztk8DwR9O93SgOW9ik/cFSZmZ4V8WsjIcdEUEPH+i4igpt/FNpcDqQMA/mIADyRPBs4hJAadP57CY5j2x+7HoHIZT6T2ggz9bo1pgaPApygqkQAKq/h0l/peXJSxsBTxqOfBcC25IFmYQAh7F9fDj5jjppO8vFAT4e+ksqG3X4q37D777yScfjAzOr2hM4bDJfejIwmjQgAg4NWaDv8F5XzCalOhfVoawXEG7fYsoy4XGi8oUNPeGvd9hqk3gxrRCuTgfrVRifskubXEGHExFIsjPMxKzAvgbpuXAjAHWNlDTt/9Yfz97QxAIDBDBj05NTU1WXveJirw0tHzW14x7/MtztjmAv6juuOW4bWZG2oU938QdudoipH+H8/NzBSLG/8gDLRBt3dOA9A/gj6p/DeT9K+JTXzieCuK9RMlYan6upC0N6N9uwL+tfz3+bXnc/P1bHdLBe1LiS+P+3OFKgCwmCyu9IhnrBxs0u+T1lfYyOyIgjcS1KuTo4ZJj8RwRMINF5qtUqkYKxEUdnJUuYkHhxADZmg9JcZpC/PyOHTgdl5ouk8GdVZaGOnj+siKtYkWoba3zeJZ9nrl7byg0er3OEJxcYPTPcPwI0T/umTW+quLpX6GiLaerOBtnfIkAliIElkpufH53FiCwBMUU8D8utXAYgxpKhocxphWxkVPBmGSI03HKLrIDco7ocgwJZG6YctYPwbxAYdYuLJWppXmgg822eGD09PSEN+oL9FYDraNwe6sn2gcUUL9w6xdv/eJ7R+dvrxiApIEmRWsekjIAJCewMg7+sPmhxqJc0t7kTEAlynuyEwKy2py0blzNrylBIB188tARgzeA+AcMMODFOKqx5nBoMmQxTsVGIhbQ3Z999hkQQV/QOTHxFC6r47/SUcK/XQUZ8JVwXSPL1rPbcUPylfMcAuKxReOB2BPI/s4Ggj7v6LWFhVvffedBZCIo7V5d1UQWpxZuPt3TEbQen3ntw9pPAVeCXp1ZPS5dTVq/t37+fEFWZmF5GSptsu8h/lXS5CEW/wD/hnMwKjQ7W5kqSU3F1Vw4xR1voxEAgh5OxVLgfiaCydQ5PJzD2sDAAFmZ7xgQwH7EP3zDndOnTw9sQsDMLLi9KMrkbWUNNt/Q8njdvMZisRzv0x2f6UvQ5KSL9mzfgRCI8PfCC2L0vpDupeqfKGVLKzZ/azqZ/G1G+kc/wXpSvzwB5OdW6rPFuUpFeRtLvX8k+HtM//52ByMSOJBL2eiHbB6LEzEA5EGQc8XQ1pACnI4zZ7RRMjQdBWlg7A2z/YXYEcYRYbY7Dvth2gaHO+SwpwhkAtz0y1YdSaj10VZIvqqPHz6Up5Om2C3JUKuzFJl15hOFnfajvjl4yvWNndrxbI3JoNNZJ56uIqMI0b/4ykspWp8p+EBRhoO/ePEB7om5yh989Mww6OBhMZ/bThwDd1go0aYNTyUxm9dTgiKGA3+iHEZLTDGwkVluLpjgr3wWaGB5IesJayk1mlufeVSaNZultsWDlpy2Ob/TiumlE0GfR+8KTXr1pnBMP+de/M3Yym3HVOevHIahM72B/+U86/cHQ6HJySCSQqqVxdUv1sqEaYh/hEocKyMIRJ8eB4FDvqh+smd6ZDKI+AesLOiORUZiY/1TI9MTk9iADrtHIpHpM9+nWiDWHSesUY8nOjfHVf+OntiZl5XJr+s+0HKAALeotTwtk4uAUOP/kppZcEBrB7wIgE6/xwtoePP9Bw8WYoZgUL2z+fqn+mAsAozWORiadK++8vqbM0sWb8CvW02quDK7fmVXMnZ0AHIQ/wApgP9h4BAWUWZZ9W+YwV92ycmTJUog5l2AG+K4kUpMr0wHi+NTPflYysAioJ2XwKiAjzU29m8+HABeH7h+HfEPLYOdhYVlZWnyrrQK/dDa3Liqe6faZDmCZF0X/Ea7NaMkVYaFmsTEb7/w3IH0FOr9somQlHTR7n1E/3j4w+Zv50bqH7dxBpvVnEzPl8na0spKUh6V/QH9ezz68bc8X/nqPxAE8uD3R/moFAyTwuekpsTTUmUSpQJHQ/R1abghTo48sAyuZTubDylqbS2irbraTFodpzLWqbAlptU2gg5uzgehm4vbskgCEyFML2lTZKO3ACCwHp1WsvT0Lm2jymHSnNB2dh4F+gcIqLeMvfXWr5pNOiwFBgys+YErLLD6t8rwj1a+zWLvl6zP+zcm31jyX+m9u5/fHsY17V1svIAV/1JJ/rLnF46sED4OU2Xw3h02HYcDISDOypECKgrL18vLX0EIRBBMAxAUZiTvpaUhdUmZ6zsBAqNRn/8M/H9bkZT1+QM+Dz6f+txuUywScazqQqOW1ed+emvx1rExC7A3J2KW1zkJlNHr59UvD395yRlpzFDR1HSgBe865VwyF0FgHWvQUlZge/sE4R/u/cA+xQKmIkzg/nWrJbYUXgDK3BFYAx28trwGzDNomNPNbajfvcmAf+VoXUOobYojYGscAdE4XIdC2BYFhE04GzzrPGt1uXGy7ox3ZDQSBoop/fT0O7+s8xisIK4HcTWdM2qb+dHxpSUX/BikCpC/BckZwsJyGvsg/MtuqSfzM4nfstk2vPsg54Nb0UmifHhbyqlXirnHSMxMpTwAMvwDiLlUUtzE/o87eQqIBcDNAIhCmBCQ4O/UwKnOU3a7XKGQl7XVlxsNvuW5OVPYLE0yho/j41WQqW//RrUu46POZ7757cR9zz0nTqGieBz+9myv3Ez/sPsxwLwvTXzvF4+Sx7/8UkFxeXkbef8eCf+2P27+/q3P12iBcMqfLATyVBAbICkpG+kIrBQoS+3KVAMJtO1UVMpbAf/szBiN7hi7HFsiBIDaNFYKrDPWNTeSP0BlCVlq83eD0EUQlNHiQIFMJBIo7dr87WiJ+c7DVBEKYZHAjguET2hrCtVWvX4u6jF4ouFb73xwDX3R+uDE9Ln40o/xug3vy/qsHCff6NLjPM8yGgBhz5L9yjuff34DC305RPOw1scy+jmjNlFA4ogH6BOKsR98b3i4rWyWioA4FjcLKAgIqEhD/OMGRISZyWxAWH00r1BYgSRpeX7O59OHps+NDAZ9BH8GV2wpsi0SdjgswaA1Bjr41uLC4uLIILAxJG1BZ/uEVe/xIKUl+ct6skj/SFNlH2jiVLACWRlrhjAI1Njg6LyAdMGnEAB7e6vQHLOwEIn5zvRWg/42uUYiIxNVVR1Br3+NnaGhAMpSJrN5oG39aetzQDazmzYQ0F4OKv8KN/9cVwePp1rn9Xu92P71GUKjk08N+ofWvBODkZhmbv7T67/83q1+jcfgDRoMkz3t7VUB3wVsJyyZDP45dXfylYzMNAWWTHDJav0BoEoH4IuUEfzh4bry2cphxD9e95YU5yhLGAQyIiiOFwPF+fvz95cMXypRNjEApDh87QB2gdGRggjYvJkCnmYc8BTyv1N2eXlauVyp7HRYEf/mdBaLyVyRtDrTN649vFtWMPiNb4QavrmvdN/h5w6wanjKPpS/uEx7u6TG4gqz6l8DOl9rBrS084ODP/Yad913KXMlbYVlShl5//56/Nu6ffs/PK7+/e0PXwrclBH9BwDIPhZxNJArBuIK9dTiZFqclCfPQQi0l3EQaAf6h6ZALWuG4HJqtjaE6eABlStkKtu9R4Iu+txciYwC1GQCkSi75qdvg8h49uHDh2/vQ3RMl7UaTeas2TekITduro3OXYhaR25WnZnT6BAC+dwXm1m6quLZX7lcjtppg/iJ3y6VMALIxt+axBLQwTf2K4cZviH2lbDutIzVmKhFUlKMGMggcvgOjYYAB5xVcIZAMkUrytmiRmqNkCWGC8pSJ5dlSs1Xz9s8Hp3O295e7Y+6+qwAgEHMUwk7wiZ0k/i87sVb7/QvXLvZUwUy2Xv27FODVq/TixvakP3Vceo3K5M2BBURAWxp4kmZolyYyX29Oim8qOvqzFaAPyecQMA5iVDX6wcBGtOvrZ1ZW9ZNhb0TwTNngoOTwMqcQ5wrMBDwaOAfAWwryMpIo69EfQnAPm7dOLZoWxWF6+tXrpzndHeF2Yq7MwGy/R6DExvC1oSEhMHJkDvieP3D0+/cun//4ur4/LJ3W4K/twP5p0GHCBi2mKIBr0YrL2vFmQ+gfzn1B6h1AfKXgz82+YspQjz9ix+EQEYA+WYIVwtEnFFeupSK0T7Z9bQXuHVDA39RAfMMEDUwCOBT6LpOK+8S76/V+xH+5uDacrn0uvEKb9D4P58/vD1RbnKFX0jcfTgXnyvpbHFYLnZBRHt2ZDtCluZOeyvX/K2pwdirymyu+8H1P8Sc/aU+W5JSXC7MEZD376+Hvy3o/XsMf/8h5+ugg0XUDPnzs8HIAnkzoIiEMbyRSUrKdrEFwm1FAH92apTijJwdba2sL0IQiNeGChcIY3WkVdvocLvr7HuoDyzIFXAAiNtl7Fr726wU+BHbKr2nqyBpNl1gDOH2bj3cmm3jusHAkGdqSqPT6azODtynw+ceYPEPg1+6NikPnHt7EVkgJiGgVyw/m4W+fH53uASeZkqWUYNxDEA6xRwEcu1gfA4iAAIC3rt79/Ys+mFoPh8blYR98KaV3keMI2QAACAASURBVOIOdQpJYK457AffuLGu1tlsGpuXHIoWbP4Gq2h4bMGl0XmWl5fXPEuRhcXIdFVHhzfssgICehNAAAesNoyr47YYZ2VmChn+0UhBUzaKU1pK1dpamJl1ntPBUumq1OYNOAGUAP+cExOTk9QFmZx0R0y2C8sXNI6psCsQDHrdIdqXHlh7mRAQIDCow9CwgkxUpa20h7yIdTCp4ljJ8KS1vHBdeAUx8MQJqc5/BvAbtLY3asXBuw6/dzAUmpgYHB1dfPDuB/cXRm8urb5++erykNc7xOZbLCYL2kpmjsOPwdBcX1/ZIm8ryqHlQPW4SnUWmx+48I3QrxjvT5cY/vGlP4LAri7lJkQUc1gIbwD+cMSiKbuJAJDvA59mFBAIYPMmCOTKgPA5uG64DCjZ2y3Neh+Pf8TW9RYs/zU8u1+jzyrVqjIE+0gNHWb4R8vD9uQ2WFyOhk57J+ae8tbnyvp475eRP3F+CeN/+TIJVf8eNfd06+PRj/+4gzpYBA8JPxnyJ0aD+ZBUEc2EsDcp6QJJqhLTUg26JEUlQCAxB8YBAf2KyNqKrhguFwgHhKkfrK0BEuiqFafL0A+TK4gfkUiprXluCwVGP0wV5EpOnhQIUmXpEkfIbYDLEuCkbtVoi/qDIyMjNiSBVqfXtgr4V5HE6N+6nLwvKH337y9lY7/I+XAIHQ6lvhTjyEfJvc8/v6NUIgFE9kdd6Vzc5ZpbKiFBTEIYaSBfJ7x3B3Tw7Cw/FTerKONTUtk7GpFL08a3hhy9Mjt7AlWsFQDbigtx+374FKYddPjdg5b+8Qtzc8vLF2KRydHBM2eG9LHR6Z6g1XfW+wQioF9XJz3K7NwgFiklxV7Ex2kCBNIzHBEwTZhB2YTwFSvqrIEA0T/Av6r29olpqxW3YmIMTXhm5uLFxYWIy+PxBQcHnWiZcQZ933+Z+sFrfr+1DmAWJzI4/lfUUllf38RtWOO+Gn6XmIOTceWEITC05sGROo/NNVnt7D0z5AWMm6yunuiZjtwcjYQmndWHXvv1Kz/99MKaz9DniepdQOI1Febo8eM/OnLEHQxYavY31Wd35bxQz2Y30GcJ5G8W+1LYe4Jbz6VN6nfTUdZ3laClXoymUoZ++IvDP/zx1BNmYxz0wGlWA+xv7GciuHmDAtYeu379OlC3QvQd5v/LqfAX4a/PEja5rFXfqLZYJlefT5Q1mMq3w9Ng3z6Cv9xcfKZs73K4Xc3a1nj1j8X+ZbPUK7ZvhjyLXPkPvX+ZbY+68vyx9+8//HzlyxJB+p91w5Ddk3og6VxCTDrRfyCBMklXpllvMNh2KerRA8iWGMrtCviora2SCygnW2BtA1limhtrtIXaWiPo4IzDKRK2PZCPEhKIZMqaV/KfT9yx++HDj5T7TqbiMiSZRJPQ1weiRKOW1jmQ+nmcPe3VHjWWAr1BvXTnTq73O0vWZ2J+NPALKPjC/nxxdv7+VLgFv5iPc7/FNPOLPufP7945KUMBLCHwywUyihiYi2N6RDawNVLCGsJ47oEOnsV4LJbRqeAhkDvMG6PlMhIQAneWKQp0uJHSbQhZXSEiZcHAkNXrUY2NGccvXKhzjE6PTkycte2yTGOlzGn1BgNBv983BDLxBI3JZqYVKjhOVvRcJRbWD9QjMStiuyIVhWmZWWhUPn/CFvQP+f0If0EgmmhvTnhycBC+6OjoyMLC4n1gZaN9tnGbJzgxiRvqgBpaloEErq0tIwt07ZXLFUT/iP9VVh7IbgEudYDWrD3HHkfaTlRWrvb6fXgCPp3G9WTICh8GJ384OTHh9AIntwKceoAbHlrAqNpfv37Bo3f1mWwWlyuMo3t9/+NHAIEGv1dtL1G+yqUXkMdydjaH7jUUH1kcp3/0VsK3f8XiUokyp7gEsC+V9gWyyu2lSye5gZBs0sA8AA6gE7oR28CNmxkgwCG1QTrLyssUaYVdpS82WmmPcRTUb58L4C/qOH191WixeKuqw5++Ui/uPCURpKTsy90HTAHT8EEDbc3tdrmMtZ2tnQz+GjD3pYhr/VLPraSExj+UzP+SL5KUZShSKffqr+x+sM96nPv3H342LRD+E4dFwqTzc3EMAdOpBQYsUL5XA/LUnFlZL7ezNa5y8nbhBpFKbjLTThCILLBO1VzLW2KMrVvi3C/OAlPsNZ35LCXm4eH0k3DJn0zpBv3osmjqpGqNyQQAqIt6qzv8c1IbIKAh6LXtvII7PxSzNPmGsgOpXymh4IvovkrFezBWh9jgL5GMYTFaYu7lppIzW8ZjIIBgKeA6h4BcO4RE2bCSSoE5XEYqgz+GgWwUEFmgthBlcHIB25y0c1edFfDPYE0wGIJV7T09k1ar12r1zIwtLo699uZrq+Hp9gmn1awJESmrqg5aAT6cCC9+v16amYnwx20HQlhiu2TrieJQ6lMrhfRnZlxZP2jw+3HKF1RvyDtR7azuDQQHJwEAO5zTPZPnzo2MjIaqJw6NO5ZmPH5n0Os1GNzb3Bb9MjBAHA9ZA8jtbMJlpxz+YbzUJgJIGIhZLU21FsB0j29tyOfRhN0hN4aVeSefmoATTAgG3S7gexbv5MjIzfsP3n/w4a9fv/renMHlMp+oc7ldJrMNEXBpyeLxRxtbgAW2xOnf7CyVG9CTVFJ86eTJEh4AeexjL4CAqfBJEu7gn5wEsMyncRAEmqamTQB4mqbhjm10QTgYxNGQ6510H2tT/sv1MMLfe3M6Dv8Meukrp99553Sjxu3qfnZfg0lVK9mdwgxjIhoASdmzpd7htjQPxKt/tdT84Hq/+fH6H7m0lfh7gq40YY7gUazP+Hlbdwu++hj//uPPV76aipaYPwmCXCZWevyksH4IKmOBLBUtMVarrkJRzG2ksduZtzWHi6jEJw6yQCwFYkoMkMDy1prmcMjVnLsddwny6IeVQEG6uLWm6HlWCqzcJ0uVCeRp8vE+E9BHswnwDy36c7Y5oH51u6Q6g07nDRpOUPEcq3slYgr+2/+2WPw2a/w2NcHvpSrxIsS4l5ycHK75Icm9d/fzO5dy6XkEzA/+R2TYl8klgzYHgPBcLKFBEVLCoINvDOdgRqCCI4F0GAPUkgwGlViYlpG8F0jZeVPQF40a+hLgxUuVsoDV7Y1eePO1xWuRxQe3HjxY6Pm/q3VSvdc5GTxzptfpnHS7XN6hACFgIKjRymlOAn+gDJY4CYxlfgp9wiQyBXzNNpU14B8aAgAM+K0hAD6/3z/4Q6ScAIi9vcEAYF5wMNB7aCkWWVq64MMVwhaTyx1ymaJr38da4DJArqG5KZs9hOhL7oo3QNimSfrt+qZ+a8DaB6RvyGdzoK7V6SxWzJ1xTvZMhAafGBkdPWKxxEZ7zt08Nz06PRj+9U9fuXz1vWXbXpVZY3G7Yw6zru9Hx49bwi6/1zawv6Qljn9M/KInXYn0j8sPF0uoRJvK/H4geSVieHjgtlQik+FIOVX/TgIsAgDCPS6fEHADAGkYBDkg3wnZAMDTnfK2srLCrv37j0WXL6D81XHy12BSNRRc/vT6L/rdrsbDiYmtdcKUPdT82JPCBuBStu9A719tZyfgH8U+1wx02uHnBXfZ/A3vC3XdOPonk2cqSh7J+8Lw73Hz9z/nfO0rX04VfTEhZnNiAnMDpvON4PR0AdA/UsIygaRYWKe3GnQ7y7LriyrlNNjUVo+71OPLuhgCkg4mXzSywBqjxe1qEKeIBNQOiR+RSNmaicNH2z/GBcI5mR/JEreUVYzjonC9C2uBOrxaPX6DOivLrAMFbnXqMoZLMGlDzOEfn/qM12IqqGKlsomm29jcGxz01qZKTt4BCDwpYq5sxD6GgGwbOzZC0BOIeoy1g7Ebcgd0MJYCkQOygx8i+yP8I2e0MDNTKBR2ow3OEDUYEhLcCZMTVCnz+pZ/d/n1i6M9IEwXRs+FOpwamzeYsM0JpMznsQKhslhc1iGfz/vSS2cDIRWDHiKA8udymLW2CWUj08B2Mp9X1rqc/rMAgGeG/Fbr4GDICqCLmadAyia3JST8MOT1wD8+OPrEkyOR0ZGYyXYh6vMC+AEEAoLNrWElED7BO+iqrac4KUbc4Q2/Z5etG2/Jvx4LWuH78fp8OnU4MuKy2Uxur9ftRuLaERycmH4asxxwAJoI71NB18VXnpPP3rh7ew4ksNoRjsTCRrWt7/jx4z9Z6vP6kHUCn27DwV/q/OJB7wtDP0A7Ss6ggh+zvPBRGvCwiJGqSwD+AAZLmNMJwaaJASDrgrBAhAbEv80I2NjfUNOKRD6n6cXrGs/y/DzAX1TfZ+iDy0mnPvHb/uaDBXUJlqzKGmPDc9mS7fsY/cul+L+UPdvtJow9LeJH32q1bPCX3Nj85C9df/kU/ieW5QjTcmjp0V+Df/QpW/EzRY+rf/9p5+u0QPgPjmjTez4YK4VtCxEhAuJ70MFtyRocDcmqpIZeURu8R/zrqudBsIiDQNYNUR1koyFGt9uh2JfCk0AOCGUiSWXNKy+ADk55+J2P0oq3ogVfednWZ0H4A/zTmQAAxy/4/bq9hVk2A07HeSvk6RJ20eHU29vc1UcvL4jF2U31Odwh/VtCc2+pksOpd0AHS/ZhPyaXdLCADIqcukpNBZwEBogkcJh80znDN+7cmW1jvRA0bsgZGAIBLHylvFBRCESQdqlrjWgUseKWcJ3jyJNPeIEzeaxrF1779a9fX3L2AiUbDAasnjk9tk8nB4PBYKgP2BSQMovF4PH5zr700kvBYLi2qZ7j1QSAbLgef8hFbGWuXV5pbzY44ZOdQ2fODCH+uQ19fSGvl1oS1ROTT26bng716Y9EJp8+N90zOjE9YrFpxgECkQTSMk7N8stra76EUGgw6HYMNGVzqXxF3IIhhoDPtbS80NLgClrdbgBAj8YYG4mY4J4ED7s7BN+nNxBIeHICE7ZGIxE0aHZ04I6hI0sf/uqns/dO3vgx+osddY5YJOY4KJ3pO/6jH/3kiMvqUrUWt7Gx303VPzHX3GBwl0okMJWqfmI+TEgmUWYDBEpOnjzJzNAl+Zi1gmXADSvgQDwPgXVCGP6p4F2DVtHWVq6ob3q1Ue8h/qeLRoEAGgx6h7DsCiKgadClTUz8ZrOr9nDibo4CUPMjZYsYm7+1nUWYfICpz1ptJ8s94C85Hv3yMas1uyRXUiZk9I/Dv78Iglvp5fHk73/uQUtM+p4vyuD0L3iiOUcMNxlMU2u4DwEtMUmgg/XSQiWmpbZxK4S7QALXd3WxUiDwlXItJuUyHYz94M5G0MGqph3pDAFRhlJIAkBg2qevgPhIFHz8bOKOxOcPp6ZuF1qDCQa93gI80GKbr1AZgQRa1WVlUgqM9up3Pf/N/fHDX4LwJMLrsLiLh7/47MfJVKyySw5funP37qVnD+NGQ8Q/RgERAvkyIPMFYimQILBr9s6dG7OzLCiarD8MAMvL03AwBA2Q9rKSGhcmL3tBHRoslnAMgMJjMPiWL3z4wW8eXDwS9CIp8y2PTyU89URoumdiMmT1eQfdFg3qUotG7/EFX3rpfyQMBkNTRZKuSiqqIqUG8Guqp/U/yABxfZC4MwwQug0AMDDkMQD9Mxj63LiCJBgIOKuqgxPT05hcFYuMTgAn63nqqepBiw3zTS9gSGEYvmAkMmVe9p99aXAQk/vdqhYxw1e4jRXxe3YBUQ7kn3JYvd5QxP3SS9HmschIzKF2uLzWPhfgnyHaZz00in6eqqqJ0dHqXtDiuGHj5v37ix/+NOfVJuUsQCD8JIwqgMCwqnv8eB82Q2Iur75BqWQD2cVAy1OB/kn45i+fmyZmuMf6HlyUmgR4H+hgwD8JT7deJMRp4hkgA0A2EIy2lw3+p+pvKJeXp5W1dbVcd3DwB+B3PNrX59Fl7d+fXym8cjQUOthg1BY1ONwuY37iFrj+BUz+7k7E0Y9GbSvf/eDpX3bTZvInFrPqX312rqi4UNgl4IJftv41FJBB5GP69599vvaVr/6D4AsAmM4DINcE2fAEYhgkLYQhISyQYUqM1aqTKkChyZnwrWT419XF62C+FIgNYewH43Scye1qzkVnwaY6oEwgSulKq219PnEH8MAdu0uVynqN8xvecZAoeqBIJulBqcM2N7fs8+trJELsBxusXp3wcGkpY4Bof6HQODHLvSrm0G+YFQBT4YnDnmMnJTIBBWVxCMgAkA0rx8uATAgrOR3chTr4xmxbG6EfFbDKWBMYF1vgYEhb65jVD1IR8MKqt+DSj+4Mc59hee611y+O3Lw5giGkoD0rVt3To5MTg85qEMBufdQDstRi0xmQlFm8gIAvhUYHB139RfzOW7b2op7hX2VRG2jVlkZDcHBk5CWayHCHQP0aDF4Mwx8Emep3/nCyp7qKsvtG0PuHHz355JHw+LjZDBAYhS/FFghPafq8T5196gncXgJfEG5ioEzlbbj+lAPAphePubzBQZDuob7x/jCuQTfGrDTe7PVETZbICMbz+J2BQGCi2unzJSQk4ADK0zcXP7h1651fvpo/PHv16pzOElY1T8UiUyopdUOOTDk8VlMtbU9FT6aSN78gBKLyLSUQ5EGPmDmL0oCPZSdl8MhISlEQE95QwyGbM4sXFbXaiQLWnK7lNyH1MytMo5C69pVFA8aoh4p/uj798b5onydapzhcuv/FF5tUblNr4mGtEa7ShrDLZczeTd5nxL/cbqR/mLYAV3IDNj86mUOpKT+fn/3g8Q9+t0SWqgD6l07Vv78O/BhN3P049++/4HztK1+Sif6oF0LJF/xESApTwVxHmPq36SwoK5MtTioCCGzjn7HsOVu5sa+L7wcbqR/caq9BS0y5YA/pYL4YCO/fSClqaCzanZi4VVTyUWWa4Rvt+jTZzpk+fZ/FcXBnnckyh9fuss/aLBYl68gSY1XnHMbkA7b1COsvLH6X23Y+nMPwTwkEEPkfyCdqAX9TdOfu5/dOHuZtiWy/dW68E4L1eCU1hIeJBVI35M5sDhPC+CpXsI1J8EZRNvtcjSXoN4BSTEgA+oeNUn2fKfny1d+tvn4xUl01OTF6rqd9dPHT/pGeb/RMTzwV7HV6fQaXRUeVOQ2SMkvYpE946aVtTw4OBr2m2uyurvqiSvxBttTXH6CbSWWOvCgnu9NhdU5MjoaeeOklAwBtyKB3Ieoi/Hn6+hIOYQZzb29Hx8S5adCk+BFOxy1dBATEid45j9UdvmjEBcIqTcLZs088uW10Mhi01IDIRgBEKxO5mSqbOqeswUk8oXD/GJA4o2rKZfVYLC6DzxN9c3Hh2tOY9nfoyaDXFwj4ABYPHcIFu2f8I++/++CDd9751YF85b3bP57Tmab6VeFIxKGqO973kzdXu1/r81vrijCgNrUE4I/zIKGqJbGLSIKtDoZ/MgkZ5HGQEu5cb+wR5Ndj4HepeD9281NZJEIT08B2PhEBc/EZB2R+6AYt5tu2tXQ2OKLLX8A/XXIpqQi7w9Usfn5Hrr2zvgjwrdESctWI9+DzYM/WIqJ/djt5/1jsKd4fWO+Xhz5O/wIAinOLCwsZ/ePh7y+BIMu9f+z9+y86X//ql0TxUiChHgWkso8IDEXxoWAuHgE5IJLAEvlOlpbalF3f1lbJ85YcKltl18cRkEqBvA62oyXG7cjZuieXqwPKODKYntrqWK3fLSlJffjb4DeCFTJR7haxLmhp7q7QgA7Wz82xZoil9tmc83oDdkP0BeJvcpcgDSBR6l9xVxdPAOmUMIsZ01H4Iks/iaXAZw/LmA5HBsjYRmp8FJ9FaBUX8yTyzp07wzgZIqeNIQqaDV7Hjuxwq8ozZHC5+wD/9CYX+UQsLs/c5ZLhT1fD1kDwCdx1VBVxLGGrgFLptyV4olFktgiB7vC42RQBhuUwbHti8qmnAHOsUwP7s9vqMS+Kfow58CunKEeZfczid1YjAD6Z0Af0z613uVB0u71BXBMau3YOF/B6gZVV4xbMQNCLMX5P37xPEIgxMraowRpbnBrDfAajLuGH27aNjIYAczXa7LaiNmCAOSi8c5RNja7BUOiJQeeEW9W/CIxRpQq7gd0C/nmimjcX7+NmZs+RI6PTk1jAjJpc0+dGIoc88/NDHT03338XEfDV/NRL925ftVnCYwiBsbHmutXXV978yfEjXn/04Iu5qcXDl3j4Q8MLMzoT/pWiVVPG8T8ya8J/iN5Il5Xmyoor6wECxak86yIJHBfBzAt4mm0Dpk5IA+6aK2trsQP9I/gD+Uvqty+6Ii8t3b//mcMNFo19u72hUdVc07K/SVujrVFZ3GHt7q17tmLwi7GhE/CP6F9NDdK/lvqmbNb9iAMgN/orFkkUmXHv319CPnYI/3Z/6fHWo/+qgzqYz8wX8QNyCIKiuBMwhSsEMhKYwmGhSCYrTqvA0ZCKckC8nA3hVo/mNZBu9VQK1IIQ5rohLCKhptnithzM3oM5qSJGAkU0KZd+oDELUGh3onHQ3Sx+443na/Xt7W7juAXATq+3mKgdDCRwquVZIWb1IwHNLC3l9AduzUbM6ireRP+GWe7pyZNUReLKSQLB4Ut37969tE9E7JNm8+j5hhQxPhnChaXyOHrnDo6GzJZhViA6YWaRASrkGRZgXyBE+xL6TBaX263T6SzR6NzKp68UNX1qch8apeWdHp9zerqaSFlVz82RSPi4TueymEw6g9XqYr2CsMPiHnzqqR8+GQIdbGxRdrXUVzJ7Ef1Yu7IHHFZcJeecGA25gP7Rvk2rF7DX6vN5LLGFayhKrQmhQasv2Bvw+kIhEOUAgWyR0UWjWS2t0+iwEzw1NoU62GE5dGgkMjLi9noNKruSr5sWZw+EraCztz35w0FLwzGgi/39U66QFRBbH41eePPiA9rNQptJ2ycMuqhOo3G3t/ecW1A5aG3I0zff//0HgICvlgpK/n/23j+o7fvM951u2037F/VawbCSqASDJHRGVmpLBnQkdMUeSLCQ0A8USYMUUGRZinStSAZZcbERykjH9bgEj7t28TDs2mFwYmKcccwZGPvAyTAMPo0Zt7CMm9R17iSTTJOJHa/Xc9fuzpztfZ7n8/lKOO3Z9v5x5/aHPzi2jAGhIL2+7+fX+7l9cz4azE16J4vFYsC7a4kC4eRANlhvminLP6p64CUKfpZyjZQuR2pmnIFvWK5/7z00EJer1fLubi18UPmnjggkZ/w4JyDtxmRBsKfDojNb9O09J70l+Ye9L+dGRpaqpGgb+VI8EfYXKioUXqsHDiCwp6MD3SyTAV1FF/b+dfX30tIH9H1h8k/gnxACIwAVuIlaraqpUYkaG/5fTf5u3dIg+foT/P3/eGg6jofBm00RvgJA5hTIh0R4V6DGBCSKRBwH2/mSVnjJ4r7C7kw3tfDS+zAV2MG6Aq1Wmg8GBEKU0VItFwCoAZzCV5NtkcGzvOBJBipdA10F63P/+bmhcDCcciMAEYEuLAgvDyY/+ue+WjulAiNOVZ+UioJaI3N3HjeoBN1mHDeZhA4LdsSYStKIJIVXaDREJhLJ2YsMxaiGM5JUoJi1RXMGAhfuEAJjMT4dBwhsMuusqYEsBKGRyFPhaDiVCtqjQIlPbj5682TnvXuf3Vv88Mj+y6tz8+ljiC4QZeRm/yIQ6d23HazC444MFRNKGxApEAhH/tN3np6YWDh1OHkWxR926JEmazf4/Kl9+2jF+flUEuRfEleeD0SSEJNm8+dOLNz98NljhyLomXgm5QJV5k6duXBm4vsRtCk8whA4FQiEgqkJCNIXJycpFQjgHV6A48oOJL0KSp1mDL7R1OHI8PDw009/PzA6uZDzHpwspk4NUUdSCPD3xYdkzo2rqZ7dv88VnZqyhdL79z87VJw4c2IE14aACrx168t7n332vf/yEkNgYtSLgbS1NTryox/96FzSlXXs7pELwS8JQPbTkfI2dTkV6ekXPD1m3ntPRu8ACaiRiDMZk1RaIqCPzcOVCyG4Gh2dUT3ezl64WlnMiuZ3rAx/UQdr/UuPrMxi9FsodIZzvdqO7i7PyZ449rh4+rXaeEdHP1ZDEslUoqM/jtk/j2B80OMr9f5pywtX8VvQFjTmOr284Q/N/vEAeevWhq998/e9RJ+c/2/P72yJKR8+FSehUnA1dsOI0Cxagj194thOaompzdCYEzXEoD8LIpD+o85oQiBLBR6k7YGd+OTqRbtV1hSjYRYJ+OSv9sO/PG8Jnj/18sunkrnA9XvWEeQfvALDRQqEl5cjxV/8o3ED13ZiQ6K0gDklBcPfeKn2YSSTAxMTGByAzI1mBiPuGUDgHUlBhFkmunP5psMQaBSzxmhKBhrG78BRqWIcgOZZXYdjIPLUUwNwXMFgKhW224Ph/Nz8GrwOz967vnj3iwX35cuftL779ACa4A8MfHfo6acGB5FIXyy++64d1AhElcnIUCpnxXJpMTCdTCWHF+5+kcxGcpd8WP5oR1GWMZ4MDgzuO3weEHgKhB+Tf0MR+MOdXl56+8QCgPbYGFsXfyTiAKXmiDxH6yxH3IOXQXW+/8WD69evOUP2ofNnJlKpYUQgaLtAorhwFwjoTg8OBDvQN1H7i5w7nYR3TaRy/umFhdxBS1du6PyFIRzOnrp+/RaXf3w3QdYBwbXSmR/M5gefg/ubwLUhl489e+V9ioM/O75HOosIZHHwAsTBIAJHRhxRuyt/oLugxooHj39ZBhCVn1xdZh8+PWbew5IsCUL2uymjoGYYLIMoiIDdrIu7/5LQC9N51tPZZcaNS7p4Sf4R/yD8fcpRq31pz56WQk8g5zlaUfAEunwt2p5muk539mp98c6TXf5gMujtAqay3j+e/VP4SrYvUj4CR/Gvr0WjqmwySNr+UP7xEvHWJ8XfP4rzDbZAuHxkfFeShP6UlOWgjHoC8f1YDUG3VEurUA9WqagUjKt3qRiCv2VYU0wva4mx4nwwppJZPbi7EVti1LwWQSCcEVk87X1/5wkGDxrpJQAAIABJREFUIi8PBROT1z/44PPPp5B/yWISgEHFkLm0O3Dp71Q4mAy/Qk1yDY9XDRx+2P1iFJO/EjaWUXBL4gLuYoblHCUybIm5I5EQ/NjOEky6q0sikNeEmQjEr3sDCDgei5nJxlMX97uz7uRTTz319wMue/L7yRzwzzX3yc3K5njHvevXF794/8VjqzfXHg1fQVE2lk0nL5w58/2nngIViJm5xetT6POVJEE3jGk20GQdVgTg3btF+NKBfl8mA/IvY+wZTQ0ODpw6df7U4YiL4Q8/CZXxcn7p3cW7Hz537HI2ySyzn3NH0ZXGjQuLUQTiTnOMg289uHfNHo0898aFiaSAQBCBObg70IDpNNxhXOrzJrOuIvBvOBmwFpFYk7mgLXh+H266vHb9wS3K/iURtC/v339oLB21KVuVzuj8zTTbIDwxnMRqCE8FfvbZxeNS8ezHK6HotNU/uTBcnDwwlR9xhKZG4B6j9dICPIHkUjYAQvJPTuwj/qkpPQs/r/eob4pHxNS+JNdyCyBWevApWCFYaAakfuiOXh1aV7THO61Bnv2D/92U/pt6E6PflpaOXCLeI21pPtuvVrfs0fp60OcAQt3mPVqIpju9Hf3NmL7xsOoH2f75fELvs5a135MA1GrVYnOlRdzW2MjJ9vvot4VnCZ/4/v2xHLRIeEz1VbNueN4YI9tkjlDNO6JZa4xGY2xSYhx8QGfisyAsDFYoMhgEdytYNaTUGM22hvTCJXYo6ZE3SIRCMDNLlYskIl1nLml9raEumQy8A/h7/ZE3EMWcH7zuXUwEfjKXdY++8EplCISJa8Bts0jEJADJXQkJaDCYaL6AAism/nhSiQlAKru8cuNXEAf3Mf0noqZoIR3I+qLJI8ZIgTDLBCICZ3Wx2dnZjDc4uDxvDwP/RqJc/rkc8zdnVT39KP8evH9l/7HVOe/kR8NHgOQOEGXuI7Q4KRXBnUZAJEDgkgOtU85MEAL908Xi9GQuOXwXmeQejIz2mAwZxfHO8GA2HRkaGjqVcrHsH9ZALpyPgNJ7G/D3PsTZWTffrX5sMG+fstlCDr49k4uy/S8DkeAO84P7njt1ZmI4lSpO8lRgDqPgMMTNA8lAcCAdxr8uTJ+dHl4AKoMmTaXc0eW56NS9j27BPY1lXaXdBNm8I6Rs3bajanYt/9j6TIbAW4TA43vk4tm1FVSBGAcvBqp2n57LoxBLZ6OV/6VPXYp+pewapebuuRosUGlmZuA5VuqaYv+mbtFIMxmWfWN7d7ltYnOcJCAisL8ZB3/bm1H+5Xn1g+LfNOaN92j3FNr9uVhFRTzgP1loLKixuAwisLcLoueO/q5AJ/YDCcVf1vvXvQl/0hJ/kcAt6kxlpaG6kcs/jr//iIL0UVu3PvH9++M5uDXk8XG4xwBYHosTQCiSVYvIIkEjztTj1hB7lcrQrgL8UfkS3nDNA3ZGIwF7y9NxVr41hFxiukQyUSkPCISa0WgkbfCs7Kko+MPBYNH75uve0YdvXd0WBbWHBHQ5CIBzeXf4nb8R76KWGLdjt0FuEmztWeuLmJz/hNKHmlbT4dcXlY+k7xXchlmQEH4xFGZaVK75bQ3IEMjiYLgRt2YHIiNLSyArgrnkRDJot4cdcyvrr17s6X907x5IpSPHLi+vWCdA/rkHBqLo4Jw/xog0nIoALV6+gmHpVDTvPvzceQhLU9PxrgASCbCEIhBU2UD4rM/UY41k02k3fEAKix84O4Ly78Jzh/NLS2+/e/cLkH88J8ctsyEoBVEmLDKidZYsM/fF3etv58cGDx+GODgZERCYS0wTAtNz2Ww6n1tYXCguWkex98U/WUxhnXhfdmXt0b3/devD5y6PpWkz6cts6eUc8m+7fnY77WzPHuKq88QJjIP3v/g+qcCLx1vUxtsfQyA8PToKjJ/s3LaUTufT587l08unmwtqNf8ZSekihUtkSAHiD2MGwl+JqDRAzlo21dgvqDEaaAEles/7hHboS828Hbq/HXS6TpVp7gxEGf8cYZB/WPx16lsAWdo9noC3+2hFn8fa1UCWL2o1fDWfr7n/JOAPopP+eLz/ZCdvfuELCoThN4KfietPrVyNvX/yRqx+/CHSjx0gYNuT0Y8/pvOtb//1X/GWGCH8reatMERDHv5yDlIWkG2JxpYYHA0ZcCkt8LRESwQqgagyFAZnhFIIELASnlEHKA5m03G5VNKpgOefSMRXZ2ooGq3W+LzXkkmP2hAeCiL/NswKsxKiXSIgPp/n4S3tnm4u6JxEQLdNZxJz/OHom4El/yj0nWGRlZp9/RL9GAJncDQE43mUfiQ18BWGL0dxiYFGIcBma0Pu3LhxMpzNYv4vPR+yhydQ/tkd+fm13p6Ll05+fu/LB1+Q/DtYBFH28rODtl12+9TUlGOwTKSBMYiDISy9fj3qyB4CAk7YDyYWJ7FnLgcisPjg33/zmwVXNjL9Ti6ShscHkXLShWFvMpxMPp0aOv/cvuzS2zmQfy/uvzyGOTlhX3J+zqaEE2I7zanxBkRZGneawx0uvn0unR3cB3Fw0ZVOLk5Owx0WAwmgHiLQHc4t/GZxITA6jb2C/unU0MSpNw4PZrNv3zv7X+9S9m+YLabn5tzO1h2147NVB5w2QuAgQ+CEoDqvAAG//BwR2GK4/fEKisCOSWyrmV9aTi+dOxfNr36y01igcWxpeUZbJBhHAv/wSUbjOmoBgcjAFqlULTZlFKYSAQUzh0uIwLguprfU6HzN74D8y3P553KB6nTsNOC4rtbnT8QrCvGOUY+xoa9PVugDDmNdBeJgX0cwlUxgoqaD+NexWf6RANwj1fIZOAx/WySGphqVhPD3lfTf77otdAdu3dL2pPj7x3a+8fW/+q1qCLXElMgnEfphIDCh8WARjYlo5MYmTAW6WvVGEH0q6oJB+UepQFU7H47D3XEe2pxk9VM1pAbjYL+xjY+GsCwdfNXGxq5wyttXkQnYU0P2qzHcLtMSc7rIKXWOBcFz0bl0ZPJioyVEM8Mum1mOGg20nwHNlaj5GRXgjIbiW7yDGc49+oMP9xUAgRAHP2bSQBvsuGO+mPjH42AmMvVvRbJuKn+4ozhfi8VfkH918YsXf/nOvXtf3sKc3Nwu68QFYsWhrHK2csfUVJStjmNEoo6RI4RAx9ihfZHENAhDiIADiMBEsLj44Natuwvh7EDaEQyHi0XSfUDBcHIodebM+X2DWcfbxQW+L1kQZbjyd24eDaNbnWUi0R2OEAIvYAEaEHho3/mJYjAdSS5e3yQCF5IL079ZmPaOLkwUA/5AMRKZOP/cYVB6b2PxN59Po9BE0B4Sdv62Vs3eWd9etb1ViRuL+R1SKpAh8FlE4D1SgVLD7ZsrrfV+Kz7CACJw6dzS29HlH8zVavvQoYI7lKm53tNA9PveeyT/6LS0MALiR0rV2DjdIgcEllphmJfNJVxQjo4LFrOvp9PqyC/R0wXp5xpJ55VmkyGTMRo8Cb+kokLqvx7vA/xVw29wB3gn0sJxayppt/px4QdbetRP7rQ+NBgn8bdHkICk/6QFsaVWJ2/c1Pr8e85WVv14Yvv8x3jYaMhj/Ns8HSwrRcA8EyhhbdGEQEMlbQ3ZGYNLbIaPcWUoDu5mRsBMBCICeRzc2WXBxUmpYH1fI9nlz4ioL6Z6i/FAMpkLePyuYJc2kAxXvQTPupYWaW3Ije4IDIEoA+ciwbPHZ3ZEcYGw27XTKMIJA975Uq7+amao41pDW605+/iBu5VUQxx8BxAoYTVpShViECwYFJvYaJyBRcJibacDQlLkX2QkGMbsH9p2ray93tNz6ReIvy9AKi3P+4tsjR3tcWo1j9c77bTSXEDgiBvj0itf3H3w03x67rQDixPuFKgj3hWYXLj173cXiu5gcSEH/BPk39DQxJk3Dh8eTI9g9u/FY5tKshSUzoVOK1uVrQeUpQXCKMquTJRTgXfffXspO3h4aLgYzKexMRoRGB4YKC4sFBcWFydR/mFNJgl6+xTIv7z9pw9wM/PY/O5rw8JqKpR/Nltr3bh5o6q21nNACQTE3XHpscHSAxS6Alkq8KWCaW3NvBJNBKx4h4Ft80t4ppaWl21dLY0SNTW/CNk+LFbNbMKfWi1Rs2IZ6j94KlAbjFxsZGHpJgnY067Djb+x7p7OUD6/FKXaB/Ivn45WZYzdKpVRf8Da9Yy2vcPr3QPoQ/xBDFwo4H+FrlwqbAXw0XIlilOQf1z+SVnDFSv9UvGjRZJpwuJvw5Y/tPiLEnDr1oYnxd8/0vNtvj2zBEAqe1AY/DgAJSWLBIqE4YZct92OoyFNRiNNxbXTSAh2wxAAVc0CAnE+2E8XWewKpNGQ9i3VDFIQhhaOgvwLWz0eayLXW1HRnAgPBfb8Hbqe9kl35dPcIGsJ+Tc/l3fn+vvGldgpGHE5mzQzFPjywzKAlPnTcOH3VQDieWXmDo+DWWO0nBVCpCX+saZAWiki9wXS2TSO8j71VDiYQvlnd8zNr71+8WLzyXv3PvqSZf/WRicEUYZayamsV8TecnAi7X+2XJzAcun1tZX04KF9b0BYGnHnrE57EsLEXLh4FwiYWljI5XLh5KkhzAEmI24QZSD/0ufeXXj/Cs/+le/Jgfw78NZbBw60Op1soe/gpuJEltVn76IIzKaSxYQ9n3UXp6dzQ/Al3y0uFoenvZM4l9JqzWXTweGhgcHlpSmQfyQ0TwAsz2OZhS2mt00B1tfr65qaauoPtuKuOttUlAJvVn0ZPpEUAm9siTnedbBSO85SgYjAnLJ1/te//vXS0q+jcIHowX4AannmZ1P0y6Ao4fV7+CipWo5OqWxDEmbhNgGwOxMzmy0qsa/fHwX8RaMO7H3O47HpjJifUdQHPM9UVMRz072vyPok1X1ofCBRywrqQkOfF33/OlgfoacTs380+uHTUvlDy4eOaOxSq+iWyuT6Wr2cG7/8vqKH0PkHv574/v0Rn29sno6rrmaLsbg1DOuLkZXygdwiRkQtMSK5ycym4yxGhYLmgZkOpBZBFU6c8nIwtpb6D/gBgVXUEpMDBGZkrBoia0T7jYCn09Pp83V6u4JJr7YjmPRrC3DhLxR0O+byeYdjqSwC865A/0wNWSS43CEd6D1OwBkpb37BFw69iGZK366E4nfBm1rSdwMRSIKQ1UMwLSVYswulEFwoovU40riy0/1U2mEtDqWCIP/m5m+uv+q7dOkeyj8sya7O+4d5To6t/FW2vnX6rVpVpRP3+WZxh+XLR66cEcqldx88uI6ibN+poXAQiDQdcGKfMmBv4dbdJIiy8CksfuDkW8Q9fGofftHwAut9wdZnVvyle7JDWHpg9+5duw4cUDptAVognH0MgUAkQCDEwRDQusOJwNRSOpkcgM/Onns3Fw5YixMk/9xpV244EgHSXV9EpI+h0Lxy5LksfLksPiTbNWvV7PrV2hq9uddSt2ubEgjopKXtpVTgmWEeeL+IqcDrnv49e6Tjsxs3Q3MJ1oNjVa78Gs/bdofjgK+gFix6SvKP44/GxkGfkQJkFWIaCWYIFFNOjyNQEQP9p1dpezpCy4A/+HbOnRtxIADtdfREVMSt/i5PT4PU09mNtY9CH1pz0B7Evr5e8v3rOtmJzTAdHSz7h7b7PlJ/guuklq89l6Pvn0H22OTb76IgMo//+aT370/gfOubX5fzwocwHCeTCSXhai4BS8UQCe2MBnChZaAmw0ZDtusUVAwhW3dmkMD34bBycFetx3PQX6oHd1jDuDipDVDUKKqFmNgLl+B+XzNciv1ha1/FUW8umevqw2aFQmF2HpeC55ccUcTf3CdYDz7rm9mIuqkevEMnIWsXeSkE5t0v7LzH1ISMJzCFd0skNz791ac3CoJPDa9MiksAFEMULJY3O93AP2BHeiSYyxVzFP2C/Hvz0sVfEP9AKq3O7ZgUSrLZfB6g5Gw9gKb5u3p120OoAlmYCHEpEml1eQCb9H66lM6ic7PdsZxOTgdwSANTgQvJxcXcUvbQ4ZQr7I6kR1JDh7H8gJNv+y+DKKOcHNzTGIa/cFfA2oM7q6q27z6ARLIlQnaBSLjNEok0RqLs7uI5+EbcjkRAGR04PLacXs6OnEtYsQyd8E+GAXw5UJtpJv9Kk28Q0adX5h0Ou80Z2KGf3bi60aTHbpGmqqtvnVZi8dnGUoGHDm1qibl87OUPbz346JefXTqOCLz98fy8fXqS7sp6GjTgr3/902u2uVCltoDhLeVqgX/0UyCfCuLez4FVLaxKr2lBAqr5NAgQkPmiAgB9mZjebNZltJe8dvzfEXUAAEfy5/IjeaVFAf+c6e60dvRVaEHcxQsSKQKQGNsnkfU1tPiTyUBHP9V+PZ0nT1I6Efm3qfeFqUAjDqBI1SZzjU7exvn3FQG49fEbAgDxw574/v3Rn29982tyYT6Y22OxhuiSPVbpVAuBsAjloUguVtXb3QPuUJ1Wm2HYw3GQ7m4V4C/TXvJK5YEwIJDFwZ2B1FCu95m+Z9rRkQ3w16n19eN1OB6HOCQR7JLmwgnfUWzXKojXMbnDVSAyEOPgd46O73KQRUK0VnNUUzJA4HMe8nKJg2k/0aYQmF5rMgnuQdIUSHJwcwQx74bB36VSTcvZYJbol047gsmhiVy9xemYW2nSNV/6JWX/MCe3uuItUk2CyT/QZE4QZbuuXr3a6vT26rZBTIZNc6w4cebEtbU0Tk5AHAyaLBJJhXOgySJhEIHDgMBcOJzLvb30g9WxwUgq7U6mhgZQ/hXfv3Jkk/zD6Dc9h+uFMQDeXltbW1+1nSQgSLKQ3VEiEqYC3VkWeGMqEHRRIDeUXV5OZ1cvpxG6wCSUf0sJ4F86v3Qde/+OXU6D/Lsg9P5ts+xyTk3tvLP+1lsblfpmHPnu5SuLlUobicB8Odd5glTn4STEwawrkBB4cz7HJpIT21AE/uTNV+vn5k7HX2mTtAABZ268R+FAiX+0wkokYWUQFIAthMoSkUzwXMMZNZ3Z3GRRSV/oj87N2UP20JzLde5c/tzISLSOlqsYm63+9oqKir2eTtolrWGljwLgr7GiOZcKe/ubgX9ev99zkgbfuhn+sOWF3Rnv/YPLeovMUNOE8u8PGv2gD6Devy3Vf/3tJ/z7oz8QB8tL4o8pQWaEIHgEyigypvE4Mo3mmTUZtsRQHOysMVL5o11BOUCEYaZb8EoFBjZRk6mfWmLqeEtMwudPgvwD4RfXxjs8uHqh2eeLW3Pxioqj1mBwt/SlFhxhMuyKYhzscESjLBJeyrsSJ7c2UUuMyxXdBa8S8QzzP4CXygwf9+X844lAGQMgKzzjC60wc+fTT29wo1Y5dVCLNx1pPESppPwyyDo0cw4Go6H1yvX1S5ew9vvRgy9exN6X7dMTFzbJvymbTancVlVfv3Pn9lan82BvpZIXJ7ArcGi6iJm5Qzgd9+Ddt8/l3e5gImFfSruwQxkRGEwmzy3hOjdAII6/If7QjerYmJuJMup9QfkXwvXqp1t3VaFDf109LqujqHSKI1BQnclyKvD6VDQyOIY7i1dX80C+Ys7mnAb5Zw8kINKPTi0y44O0cE8szm6ta6q3zALxNmr0tBa3u11fSSuLUQY6bag6qTGaq84T+bm5Q/tfLCFQOnPn9tp81D4ZIAQqV9beXF/bdQ0uZcoekOCAP0r/ldSfSCQq32DNgFiwVZN9DAtIaQmMyoz2FEZtjze6DADMBR3hcPjcCLw5ISCJZ3wo/woVFVqrvxdkI9BMjNUULLAUGlqsyaS1i1qf/V6vFy68Pe0+ofel1PrMCYiu9yY9yb+GP4h/W7hIfFL8/dM53/z6X4lKqUCuAtmInISbIhAIq9lt8s1i03ESkdhMbqnb4GmnEIw9CYOKDHfJMrMFwvW8JYaPhoRTqVTY2tnh6fD5uigFHe/xaaUt2ub+vdpHXl+HPddF7i8thdiOEgEZA8+lk6PaRj2mAh3YFSiSEMJmNAxwKAPpNaSWlJKAAglF7N8xip/5FBBY4HtCBBFIA3UarcexjGVLjL/R9wrw55ibW5t5T9wD/Pvowd33qfXZu1AuyWJOjkGpFpFUtUN5OuSsb661EQLHDh3KJs9TNSTL2oYX3307n09DWOqcz7uTuUSimBoODyeT6R//G241HxsYiOTD7y588SHJP6DSkRKVgH/zIdvp029t21lbQ3vbq0iTIQKnsDiB1ZD9HIEjI9infOT9uw/eHRhcXc0uQxxuOzsZCCScgZw7H7UGQtE5jH6p+FuOs7OY/ZuamnLGboD8u1oL8W87jmHs7WnXN9VtCAQMOKeihEA+i7Lov84GhDEV+MEvL+7Z8zd7DLevzocSk5NkTnhg4+b8r+FKAT/L7UbgH/yQmDYvtcWohWII3RR8vNWcSogkqckA+k9n0Ozpt+Hk20N7MBh2hM8B/t6uN2gz8J32Wv3dFRXPNCescY1JYaT1gSapHFBa6IsnhoKeeHtzF16Uvd5O3HmEuT9FGX4CbbH6K9UYmsryr5TkE1i36c/SbYbJJ75/fzoHt2eKBAlYXc3d8Xk9RKgFcwISAPnmJDhyVW3IHYlEq1RaBU//daNhTEaFbgm8FkItMTwOFlKBwYQHYuNmbX8nzR81I/8w373nzWven1dUKCaLzt5CC2Wjm2xEQEd0zgFvc0CmdLHzH9sqWSrQ1WpolJAEFIbfuM7DFxQF7ZszgAIC4X03Pv3VHVGBj8Nxh0C5XNTWY8PBC7iXpSUu/xw4+dHb4zO91o+9L1gond8J8u/lUp+wnYmyt3bVVzZZLDV1G7hAOGTtiFeRJluey+5/9sgR3qTHXGJ+al/CDJvTFs2nuX9zIhFO/+Df/u3ffpDNDg4kSf7xnBxabZHQdETn8Y5On27dsR34B/9v9RYiIABJ6QygCATJnH18Og6I9OFhCH9XLw9m5zyj2INonXal86FAwBaamrp2/RZl//Jc/lGaEb1fbAdmZ+ErbwD/aDEucqK7WWepqQURePqt0/DdO50hlgo89uyzbwwXF3gqsOQV+L2/fUExC9SzUxw8nFC+Nf/J/NJUwBlyvDXb8jxrSBKphX5orgV5dpY7eWuoIVAq5XbgBp1OX6MSF457Qp8A/pB/QdR/I+eu6agrq8eT6GqoqHip09oF4MN2URP9Ds+vo3v8qRTIv2aIOvy49A35pxA6/8oApL8Y0fdPbK6MiauFybf/nf7bKkS9vPXvifz7EzsQB2uYK7SEb0yvpqpHtdAOLZEJRqmIP9YdTdUQjVi3g1pi6owKHvzyvhjaGKKj6WB9F3UFbhaBHR1dHd6Onn60ZutC8yEtA6Ba3v2oq1nb5fkXa8LbTc97saGKx8EsEnYAnFzTHX3jSmwJdLvsu+RtMuxoIfptroOIeOsizwBKRI/9m+zOryAOFnEA0ptcfdwTBfH3a+pccyRpwRAWP2p6Ll76xaN3fvlLypStKkc3yz+7PYROzKcpVWZuBkSgSDp92mY7WKNvtS/Nr+SFculEkrXEXHn/wfWpKXvIFrA6bfBwMA622xOJnGv5Bz9YBVaNDQ5d4SXZC5vkH3xGCPH31q6q2hpLrw43yAGQmCajOFjoCuSzKBNJd3rs0D7AH37RrN07PZzw+xOY/QsE4BOu+a8/uIvF3zQNmaDxASF9yjllq5pF+bdRx/mHTSivIQH1FrhDLjuxHGKnck82P7CpB+fFD78AAn7w2c9+9sIew+zayhxPBQZaT8/DUVqdK6HT/S/1YVhamgdh3CvxjxWGNdQOw8sgUqPKbDHrVOqXupysOSBYBPyFR0ZG7DtxNNPnM++29lZUVPSe9XZz8mFvO/whbil05FJBT3NPT3+HF/nXyZ56Cq0w71E+JqlWYZSLQP6pyPhly1fF3+NKcOtW/s9064nv35/eocVJQhgs49VgSWlxOvOILnnFYB2YsRKgItftoOk4vZY5A9J0cDtpQZWwQL3UFcgRSEtEgqmEp4N1YBH/KN+jLhS6vIFmeArffzjdBc97eO5KVLuWGAGDjihCcCnqdlt9z8T4dFzUImlD9ceaoEsIROnHvL0Y/h4HoGimegYQOCPhGhA1ZKE/ml+inrWlpSDhD+5sfgXxx4oftxbSl1fndi7y3pdB6n2xYU3iNGqlOkssBtzXWSo3CBA22852y/ouR5pNq/HpON6njL5VSiCg1TrlSCeL09PAvyIgMLIKcfCPV+ETxoSSLM3jOuZCdEdwV1d3VtU19cb5duHepspaBiS4QxCBLBU4yKshw6kBhr/V1SgtPVLW6W3pPITfSuU1zGgyoVkcnhCyfxT92nbpZ0HmXa2ttJiJf1p2fLgf0LK+scFTgUqshwBzV+bH9m+uhuDwC1OBx/cQAjEOzuHgces8aMBtj661zkdb49VteCnlyHsMgjwY5oYJbH5NmtGZ9ZaYvODrnGPGLyT/wq4R17ZuLVXfOv1N8NyRd3i7qluwqVMqNhloLbFYo7WmktZ4T3P/SZB/bIdrL/FP+jj8KAI2GkwisblGp/mK8cH/5ggCcCsr/v6+l9uT80d3vv3Nr8vLFWCmBmWsEMIygMRB9m8ipgQlwnicsQ4XCEe3Z7TCXDAzDGSHWcT0WjYhEDcOeryJ5FDS3wv/3s1mj1rYkJK6oPD4u175+c8V9x8q43Ix7hUz6ZWOPPLvnCMYnUMbqKV88OwLsqYQNUa7Q7q2NnzlaDjjNBx5ZOsq4mHwjBAJc5EBH3Tj00/vADgphBZVa0cdy9iuhgqQRb8g/25umC9exMmPew+++PDI5eWP184OXzny8su8TzjKqfQW5sosOhWWCogQSCTlaae/01hn5y0xrB5MGukyaiRCoDIAx+6KIAJzw8liIpgGAlIqcPDUkNBlg95g9tA84Q/4V1dZo+9t5osukYB1WJsgAoawTZm3xGAj9oXDnH9p2yjt703Yp9bWWhO200oq6JDFQriI/TxsxNhhx/C3dnaD5B/ozGYIaKJYAAAgAElEQVTSf6+xwoDP192uM1ua1tcZAomAU9uqnHm6wzLj2Qj0Rx98cOniCy9oM+trKxAHkzmhdWPbysqvr13zt9pDHm1jW7VE4F8JgeVUID4j5OoWDY6EGGMo/0wydby1xL8wnqS9lhbU9HR4OhTAv/5rj7QiqZRWDtN4o9Ek19Rg718cbU+9Vsa/Xr70t8w/LjS1WoVJI1LVNGUkbY2/d/SD5Qa3cAJukfz1N37fi+3J+WM8IAJF5ek4CXNHoNIvmw2m1hg2MMIKJMhAioY1ctVO6ouuJFsY6oemJWcMgAICm6grEAl4wEsjIolgKpXrxA5/I3v6EQKx8zXu8bz+83+ukI9OH4xBHKMymAx1IQfgD6PgaHR+KRSNQhx8smVmu4MMo127TY0yQf2VdZ6Ml4DpTVJ6cTH8gVqUiH746Q9vYEO0SPZSf2juk5vUsLsUTQ4h/8LR+Zu39/ouXnrnLPa+XMHW547RyQmsFAyO8eIHS8oBLGqbzM04EYjJT0slxaUYIfordUpeDHlsXpes+65fxyaWRKKYdLvD07lcMZXMJcKrPyYRmB3cRzUJxj/grI0JTcISZhfa97b34DL1uL6ppq6KCHjaiQQsz+s+R/wD+eewovFBIDCdsyeU22c3lMp7H33Eev/yxc3FX6xnb7PMXj19dWOdcbZbsVdYDoTr2TLtqMNqQAVi0+M2pbK1rqY1ull1nigPv5AIvPjCcQU6ZbFUYPjAwRUg4E9+4j17LXq6TtPYBj8iXvIQLlClrhi2yQ9dY+QZ3NIX0/RpO6LLvD2+6KB1qso4PeWaO6z3n6+o6FO80yyXkN+CXOBfQXUglQwA8yD6tRL/umj0V6FVPKb9xKzUYpSS/JNXf2X04yscZLJPkH/sA5+MfvzpHjYdx0ohfDJYxneDbDrVEkYV3l5HIaZGjouTBtw2vcKYYaUQbpTPIRgDBDKPBGy+wqcg/Ge1BoKpoURvQbgEy1vUGn4pjnd2/HyP16odfbjdZMqoDEa5cWeU5wFBAIaidnvUlUrEK2a20QhoJFqlaWADbhoy/RPxdh0ZA6CsBEB6nWkErfjee//zh5/eaNEUjntdc/M3/+EmIHAJ7QhY8eP1vcePXzqJxd9bHz577PJy7ejEhQupyKFjOCaB9MOKLOLvan2dRUdSSaHYS4kyQNJ2SgWGWs36EiD2l1OBx54FQDxA/+ZELjyUhIdUzCECi7mgixC4ms0ewjibJn8ZZlGV1dZY9CBeml/FopNPQYOxvTwOxm/GRvVgXpzIIvyyq8vK0eJEMYEQhKAbILmmf/2/wmNChxmQfyXfK8KfsmZ2Ax5SFXI2Tv0vQgSMdPDhBQ73pTTVQCD81rZd9bNVzqnHenBYY/RqKQ6+CAh8wWdeX5nPTXq88I1MW0EE/uQnP3nkdc459TJaTsmrH/jDEgrAQlEEUaYA/Jl14rZCv9PB+RcsRh1hV9LepaWQo8nvbQH596qnX81mjdRCf7umpSs8FPR0oQ+qn1sUsaW/Pu1Xol88WpNGEqurMbQ1Nn5l9Pe3lODWcucfHdGT4u+f8vkWuqUSAGWyMgAfwx+fC5Gx/Bq12eHfNHJDjRNHQ3ajRQIVhNnvJQbqeC6wA6fjaEIYzkFvIJxKWhWF8gWYnxZfpz/n91U8c//06RqxETSgWKzbFs0TAc8RBMkqcPT4Vr0SzWPcLruurVpEuUAR7SCRaCQzm5qhy7VgNW+5oEFUkWTmzp0fii7ZADKYn1+ZR/nnwt6X+auvX2Th70dkfLC64l2knFx2fp5cAlhKDvGHNQkdocKAuOhuxuJEJS+G2G3bzXU2R7k4IUxOoEZCr8Apu2vADZcDW3FhMVdMou1C+gcQBP8A4+DDkXwoKvAPQFvZZNFj+q+npxtfwd18WWRvTY1QmzjttNlwWs09OMjUXzbqJ/lnnR46HJ70b9umnLp275f/ncwcHMXSjB0lNG227bPrVyHMrq20YJqxHXuEaUaMHwUZ4MJFzWy21NTu3LBYNjAOvkY9OKwxmuLgE3nW9ENdgZcu/u0Lx/fObqysV45OkjNXKyHw8893hea3tbfBU46QR0+rcj8MuwH8k6r0TZYmlbxxT30Ifa/m56LRMFyiwsnw7mbkX3f7Tm/8KMi/eGdvG34iikqpWK6RS6WydiXJP8KfkluVx9H4ZfPSyzL+WmRifSVl//5j4ysGP6Hyu/VJ8ffP4Hz7m18Tqr+kAiUsFVham8laYphvNLqk0g51ElkQB1eFaDQkYyx3BeJ0CFsiwhuj+WiI1+896GVWRInkULBS2sJVoJgy0uRE1Ovv/DlENLL70wczxnGDQTwjbgrlmQSMRufsNBriyp3se28dTVQdbtcOQ5uMSUAWBcvojY/CScqhsZrrwJn3ZrB0LJqZ3YVNhljxmA+5UkNJcqJZefQq4O+X73xA2T+Qf1dHeUfeofTK2krUDphBKq1c3aiqFEqlCjQu3utDTxwQgZVEwNOhkLJOtx0kUj69yU9ZcBAAETjlyKbhlem3nzqzCCIQR0Mc6ewPUAWuDh4asMPXUBJoN2rhnvRxMkOBF7DPt7e0L7xXj2EwlSZYbSKybxD0HwAwa/PTyvPri6l9keL0qPceZjRvve9eXsXevytHeJkF8TflXB+n7B/cD8pMhLqPj0lo97wmMJD2uDfrzDWW2fUNngp0TpUGhPn4X8kr8IMPfvlPF//2eGb8xqdoFkhWYIHWlbVHP3n0+ec7lkKdx/vwMgo/EtDq6k1NgOx2i0mn1zdBRNrXrVwm37/oXDToCDpA/mH7QXNPt8V6UFtR8Xz/aIcWvg7jH9n9SNVqS5gmf7sw+kVrjs4u9L1nwpZBT16iHxbjQP5VGoXoV8Df1sfxt3WLwL4tpQ7BJ75/fw7n238tGGWxPsBqnvorV4CFojBDHxVZqTVQJI9hKtAdqtSW5oIZCEuL47hjfkdnPejAg/RkhJgYEYiNz1qj1GQ0si4sKaZu4h29GNT0PZze3q7BQTWNqS404ogG8QAEHyIC3Yn+vpnKKJaDI+6dpq3ceJr5wsxIOP9km7sBWZsg4g/fJ/vHkyF6WYXgVzA5lAw7qPel96JQ/OWtz3xKFliRzoeazLtsrPpxdWO9xmJuxj3JCpPpNeNrbHkPpeYq65kmOx1SWvTCdNyxzanA/S9+cev69Z8uzW076B2ddB06NQwIDA9jKjDL+qJXx/a5bdtQ/e0E+ac3U/G3p+fVHgAt9wZ4Fe+tF1sQ66klRrmt1bGPy7+x6MFp3FhuXZyIpNOR4YXF0Xc+YI9pfu0aIB19/8bS+XzU5pxS7hxH+bexDpjFJGM75v/oXhB8x7Xa17gIxLRgt848O65nfYitSppJfswutVzxvvXgA1CB4pkZ6SyrhgQQ8spta2uP1j4HFWiz1e052kY9VhgDl0ogIkKZVKe3NFkM1X0v1M6h7x9c/IKIP4criLan3fBt1h+Ib6mo8HkDCvrxSyQF/jUkbYrEUNIK0e9JD+tBwApcLwvsfSbT5qiDHZnJUhvTPK7+Nnc8fwWBJQHY8LUnxY8/i1OKg7n6k7HKByt7bAqEqSOwmpWDeUAsNzXhaIhrl86E3dBsMo675mcU7ZsRiNvj+Oakjk5rEJ6j7QWpwmjEDDS9xgxGiHvbuzp6+gCB//JwsuvnckCgVK3Y8bYD6BdkAxpw0umw/+JRLMPgaEiopq1tBrkHgk8yIyrNgtAwHCuRsJERQf5JGnu8IP/m825X1G4vtz7z3pcPIPpFO5b5R5PDJTcqB3ykrUrXtI2KH0gLM4t/Tcw/HYQZQYkRkHeohHb3Yq2A+UgxM9FhIQ6+e/2n135y9uxHk+FsNjKxsDidSwICc67lH2MxZHXs0EB050ZVVV1Nk16nY/zrocWN3BsF34UaUN9UU1mPLSoH3Iez6eU0fOqyEou/Cf/k8PnDrqhj4MKV4Ukq/l7G3r9i8RRvZ4yGnE5n6/rsOuIPBS1G2XsJEz09ewUE8kygFDcU+WKxcUMzCM96Cr2VpAIpFSjEwcD4fLrkFdgzs+elF/b4VOsrIUBggqbjdgECIRB+1BpSNr3UgD0FaglTfSKBg3KD3mJpMpva+i7tmJtzkPEVw5/LVik2wFVWW+m5L8bi73WvqY1lDfFzsadA1mcJpoIeWllN4S/rfomzxKbCWMafmAlAkH+VNca2cvLvdwXAW8tVXyH8bXhS/P3zOWiRUBqM45vimE9CGX+8FEKRMBs5Q1yKRIY6jIPtVRkTI6CCjccpMjQgjI2BaBhNkbAHFyfhFbmjw2MNp8KeFikGJZiZwUjSYMAV3r0ddb5nqCvwYW+1HJ6lhULcGg5j/1fQwYbj8ml30NP3zKyTpuNcSuPzqAIk/D8mCOgWAnAGp0XoxnsS9Qy8UgpdIfoq83N52w6Uf8C/T+ar0PQek38PaD/k6s2zC+VCaRQrvzZ4yYJausrwF6MdoUatidUJkICMSV2VpcxcyLazuXLK8di8LmuJwVTgRx+dnVwYTkaj+ezhiQUcDRkOJ4LLP/7xv4EGBFHl9gMH9HHE36sMgD0+n6AAaU9QXGfG0kRTZWWNbQBlahY+cc7DXO8Xhw9n3cO5oPu5/ZHJxQ+Z8QHIvzcGlscOYfbPprw2tWt29iprfe6lJGN7997uvYryfQkAlIJwkhoz4yZtT3s71nvKLTFOlgocO3SMt8ScSI+tUqT/S+yLfuGFF45rYxs3o6wrEFOBa2s/ARFYe3q+1dfQxobNiX6UpZDI5Dp83AZZw0snQ0v5aBRXkjrCYeCfY1eG8s3dtQd6t1ZUHD3p7a+WlRsI0f+loYC9f13xeBddbr1M/gmFHQW2Rz+uANVyS61OtMn44Hf3vwhsLOm/J75/f15nU1+0sCiElYIlPBfIMcgLItUcMohDuaqKFghXUjaM8Y92xsFR4f5v5pQFaKDFSQEl1uQ6Ow8mkqlgh1Gq8CnYAf7hAm9VTF//6LWjIALvT46qMKWtKUi7AmFkILeM/mQuv5wOnnxF1GQHEehyu7YZ22Si3z4zpVvkwo6ZQsnPL1qBffPzn8zh0o9iMWFntlel1mda+jH/aJp8r9iCNOSfk4ofG+M3ZoF/gD/6lk1GwAJrFWF5Oax8Y3m2SlCBzg7dzs2jGoJ1H5ZLF0eLFy4kpxI5R3oQ4uBpiIMBgY786g9Ws6vZscHD4ZPd3c0U/77aDPqSMeliT0kCgmbTwf0193Qk4fuEMzaW90/SJvbJhaGBvCM1lAq7BseSRfdlnLE7MUFN1tmb84AVm1K5wzK+waJfbJDr6eneuxfTmRDOt9OmDAGAJJWkxvEbUl8P/FjbY2a9pRIuBVe5CGRegWOb4uBVuL8FHBD+Pz+7ePwFNAv8+OZcYpIcoxOtIAI/f/Xn2qbW+aruvupqCFslwjCITK7S69GMoLEQd2LhA/GH9AP8OS1SSrVYDnZKKyq2xr390moUfwURHy+WtPV1JVO5zub2XrzY+v1s6yXgrz2DxSoDAFBK9j+MgVq5RBKrbTK1NWwpwe0x6j3Gv63l1ucnvn9/hucbX/8rZg5dLZREeE8gyUGhH5ABUcJGQnhPjMZkZltDLCZqiWFFYdKAGcqdC32BXawvOoBxSSc8RXOpVCAulRJLMox+KgP+qtn1urbimQrtw4f3pQWpXFMoaDtySdABwZJpfj7tGu15xrQzSi0x9jpNg6D+hMoH4e899q6ZmRvv4W6Q6j21IcQfnNOY/UvlajdCcyvo+nfpF++88yXufNt/efmmMPlG47h2zj9M/m3EZsSz5hjPiRlJGb2m1b7GAdj8JpIeJNk6r07YbDsslgMhqoYMchOVE2RZ8OyLE7nwof3uBJoPLq8ODhWnp4Ph1HDQ7oAw+fIqtsRErHFfu+7V5lfbAX97kYA9rATC7ovi4ObuHn9qcOCppwYHx7IhL7reBwLTyYGIO1wcOn8qeO4pgG5+efkct1g4NJbNr3x8c0XZWjsO8g/ieb1eR7UPTDHu5VoWc4F8VZrWhIkz6fj4jMlH48HUFKNvwuEQIQ62RUtrQ9impuVPPjn0cmmD8B6peHwWB4TZVoDAttpXb7z26puv7wqFmrSN1WrqskITU4lJZ7FYzIbqLXs6Qgx/yL9zrrAruF0lx1xke8cOM1weFZ3+5oIMBKOkUKqf9Cn8aPzS09Pb6fXz3ud+uEDgpCY8v+ACbTTiQxHLWcu0ptqkr4xpGjj/NjHvdzW/COzD8PdJ8ffP8OD2TBHvBxRCYdKDLBco4SGxpCQFSx0nIg22xAxEHNtVYjSM7sZgONONm5MAge3cJwYjYT4ZQoFwbacnEB5Ken0txD/C3zj8MowbTDGP5014lj/zLw8f6o8W5JoWdV+zNZwMu8gegREw7w57WyoMrW5SgbZYRSMLgcs2+TwklszcuEE0lG31KZcZ/uZX7EnM/oUdV+/crmH8w94Xan2umixvoiQvZgF/6zVNTWajyDSe4fzDEVJqpBVW98TJrsBCmTlWn7U5d8ZqnKwxurw7Dhk36BoeOJxMJCeK06Gl5exAqshaYnJ21+rq5VWUdIeTnVpjpr0dE4w9F3s2nXZGP1W79FLu8MDIj340MHgof8AKfLGBCByKpN3u5PCFlyPvLi5cuTBRPPfu8MQmK8OptY/XZsn3j/RsM2VuFXv37vUJJBe6AdnjQ/ln4vEwyXxsjV5nsyGtLBUYLUX6F65MWDumspch0n//iy+//OCfjh/f07JHqlpfmbcHApQKbK2fnX0EcfCj1mhrzT838LRLgzym15stMfmWoz3KOXSBZYNvYbjG2Zs0Um1Goe0/eBDLZJ05j7pNjf0LpebBxme6wkMo/1j4S70vtPejm11f8WCLtFSIgqurY7U18k3Zv/8g/N2Mvy2yJ/Lvz/N8+5tfEzMRKEi/Tfwr5QOrqcOYd5rwljuNJlOFi5NCO7EvOiPUQjIZNieHCAQhGO8VhuMCLBfo8QbgBe8xwueoGABp+5vBJDfpOigObrv/8KECt+q0UBycLG9OciwBAoOdfY2VNgd3iamWMQCWBkQYB2/c+J+Mfy94IfpdWYFfIP/QoAurKiuvS+U+7H35EntfQP6tTC5s2g9pp4Y8rMhuMFjo2hXyGROL2k0USGn59kbkXzPGwHoQgZZKHgiDClTuNNc7N1sWUJiYTYfPnJkovnvi/JWFaTtKqAi65eeSyWIiCoDM/n02lTo1EO70Zbqp7iugj0lqHLhpV2V8XveAOwwAHMyGcPUmut6nIm5X0JF3H95/6MTd918E2Tm8wNYrEdLRk0a5/sM7t69erWuy6NpjlLhF86u9/GHodLp2lQpznEatEZemjN8Qm7RCRpBEYDcEwpa62nI1xIbVEJYKPL9YHEZzQt4VSBYJf/u9PdrZ9flQIkGpQBYHw/Eo599qlrXBpbat0WCh7F91X0vV3Bz8jwsx/RceGQl6jWoEsKL+oH5LRUXBO9rR14aJaXJXxTKKrM0XIN+/Zsw1U/QL6g+TfxniHwMgSkBMAwLWW6pNTXU6kn8cf48rvvKtrY+fJ71/f8anlAqUSd6TlaaEZRyHTP+RSSofORM0IPxFrtuN03HKJiOmAgmAmHXpxkVyvD863ttPS0O8JAIhEAYE+oFEiRoDE4CIQIORnJo18t7OTpYKfHhfLFG3tIBAqLWHcXkmh+CS45zbNRk/Wt0UIosE14aokVKBM4JRIBL6Bsg/Kv6qm9HkeWXl5srN0yD/UhhPz8+v6S9duqjY++YHD0D+HQP555k8c6HUJxdF12fOv/UazP3hOlCFUYPbuxVaE5ukUlAKsLmHZK5OZ0YC9jZ1lXOBtm0W3fapTcNj6CAQDg+fR5eYdw8/dyoHUJqK5rORVI5SgbmEI5sdeerp1NCpw0OTcS1h6dWe8qANXVDa9yr6pyMDqWTyqR/9vcM6ic4D8Hskm4f/S3BvAwMnJj58GWdRzkwISKc9Ts4dlvH1jY9vY4mZrXdRCPWVdsY/nUqFvDApjPDLAPzTkoUUKUAgoQ9Tve0QB1duXCUEOpkKRGeuQ1nXqSNHQOaGqe+RdQViNaRFa5hdm48mJtEQNufcsZ0I+Hqn09bpK7RVa1RNen1TTN5QaFYuz2EP5Gk7hr/hkXAi3qfGEbe4d6eoouL5Zm+n9HkyMuqTEf8kkra23nAq2Ak/gZMC/ljriw9TzAYBgCgBtSYxXLgkIpB/4lL0uyn799UbXPYJIvCJ79+f9fkWLhDmcTCtDeGTcRKOP0k190fAAgiZpEooK1gtwwXCShwN2dFuIkGhwguvgmtBgYDYEFMviECr1+PZ6bWGUymnzsRTgGjjITahXanG1DF5thue74DAXk0ftnjJFDsdrjTgD+dDcDHYOYiDJ49XVFc5ItgSY9dvbZAx6afBLhjZKzdu37mB63gkW457ovOIv5s3V2y48w0hOn9zHTf+/uLzzz77gPX+bZsU1oOnWfGX84+pP1JF9JISi+Q0dIorxIyUFmtHAL7ajFVbM9V89L1dNXW11DMHGmlHk6rG5iBAcKMszMk9+59f/vCL4b8/HE44gYBomZ8aBgTiRuLtStdT3/3ud7576tTh5OhFLWt8YdzjANyr8HnDA4cHhlKpp340NTo9XJxE1/tIPmp3uPJT9vCJ4StHjh0CTbb/jZL8C6GpX21s9urV9fXbn96epYsV76/xUWQNBNfRzwKLBgA9wN8MPkRFiYEofvl8nL7msVQgtn7fnBvk5Z6iK7vKugJxOu74Cy17tCpAoJ175lu3MRF40uN0Nkkz+qYmi95Y/XxLJy5DePjw9IHdBwLBcHIk7NGq5Sap3NhxMAbyr+Wdd9qr21jBTk34q26rIOMXkH/9TP6x2kc3L7DhhVgBOOcENGq16mo59v41lFqfvyoBSwx8PPpF+feEf3/eh7ulygSLLBb/CtNxzCqBNcDw9ZkkuhCJGrGqnsXB5JbajcvThaJIN02HUEdMBxsMsSoxDj6IK5QSEAcfUAEC8TJtZEalUjQ87faO9vdVVBy9f/9hO0Y7Gona7Jxzg75B92YioMMFcfALz8cgxKQ4ONNQzV2wsCfw9scf3yhIWjTVaHwA+FtD/pH8A/x9cnPd0kPFjw8+unV3eGBsdd7PfK/K8o/4B/hbb9LFqKTDXvsKCKGA+EaFlsXCih4Wl2IQjDKQaiHAwKaaSiFKrDWM652bROCFM0MgNI8de/bFDycmTkxduwasdRICi7lgsIhWMa7Id7/zne8+PXRqKPzO8W6UZuYYoYkyCj3a/sTQqVPnD5+Hf0f5txiwTocjaYcdwt/8VGJx8f0Xnz2UzQ4cPjR4qCz/nM4d+nH4ntabenW3P/3VbYMWH5AP05jdjH+6GLsUESxI/lF5X0FrKgUKUiawO4bFEG6V1dqKoyE71pXpQYz0UQQWwy6Kgz+89b++pB3qLXt8Kv3KfGiSIfDALiYCT+46XQXRr0WlaXwl3oqDHw9DD3OJgN/rt4cTvWoZDm7oPFj8PXrxnZOaNmZkXsDnoFpd3Xa0PpfKeeLNmP1D4yva+tbTw382xhICUdTC4zWpRbHKJlOjUPzdrP8ex18p/GU3nvj+/UUc3J4pFEFkbBKkWrIJgLxBmnKA1UItBIWhSCM27KTFSTVaLUsBKngOkAXF3Xx1HN8f7CQEwjmAoyF1UjRyo0VF6NWHc03VjT2ejtcqMBU46pHK1BqRpFGmD7ncALu8w0VDciA6XLmTr1TElC5qidktbeQt0IUbH398+yiOB1f7tuU/+Rjpd3XFFibfF8fcP3w824ODvx/c+/LLL668fBk+YJQXP8ayfOcRV3/rFh2Jv9LB1m2pRiM20iBwBicBOf7grRcRCLFwLyhBswUD4d1XN2ZnryrrVXVOR7ka8sZzx44NDh5CBN5dIKMsZatzHhGY6+iCKDGYCyaf+vvvPj0xMXFqKNfVDcqMsQm7K9sVvs7kqVPf+c5/+0/nUwmUfwl/IJfK5nGZ8Zx9qmR7+v0zp4bSg4fGxlj2T9lapbJgQG+Jt/f4MrguSsp5pmin4Fen4/xToLEoyD+T0VhGSQn5WjYhjNuKatYpED7gdO7W653lvscLZ4YXzo1kVwmBWBD+2fcAgdrx2zfn7ZMB3hiNCOzw79arVDHxli0vddqXl4F/uPgDTsLqr29pFOGWzPvb0fb0pV+807OljTWsYvNgtURd3aD1g/zr74lz+ceND3pItYLeQ/xlGP7gASkU8mpNU52ujVV9iW7/UfNfefD3SfH3L+XgaIhkk0Eq7w1kWrD8i7qPWVQsEvwHNEb9Ntwagm6pCtYU3cMSgopuYXVcaTrYGnAGnFb/AUBgAFOBerm4xD/yxNSoZdK4t/O1ZyoqtP/68L4Ynu6AQG2tHXtfHK4RB5okBOEV5wpcfKbawjYI25tkjWiNgN5/N/rgz7a/6w998g+/+vjjj9fWlNz2dG7u5m3V3os9l04Kk2+r856zkxPkkYdSCffwKin5dxWjX2p7Lh2+P0Irl5tYgknVrmNm2AyDcYZAMyBQr2+qrKudvTF79fTp0weadLtCfDpu/7P7Dw8ODD0VQQReef/uIkOg0hbNR/2TuQROxwECR77//eGFu3eHT0UmezMxnSqGCMyoFNqTucipiaef/u5/O5XDnZcs+wfyD/k3dR34d2X/MfLXv3JkCIhEBR2b89qu2Vmg1QY8JNboMo422VKhtKvj+m+c67/x8RnmLyUAkCNQoKACH7mOrLKuXm3dVjdb6wxNTbEBYaEx+lzJI+GDzz772R6cgJy9vRJN8AHhA2tvPgoqMb9gqdH6DmB96+HcXJCM75Nha3ehoGkRt8QO3ldXVGzpv9e/p5G3q6rVlI9u7OsIpxKdfOkbm/xA+dfj8+GIkZG+ZwOvgcAvrUamqtObGrdsadjyWOy7uQ2mjL+t5QE42ZPRj7+YA3GwBnjGCiDcH7VcB2Z/Z50wrCrMzPfQ10MjNwV7gKIAACAASURBVNTa0C21SmVEAciUXze/WeoIrGTl4EDAaQsoDxzcfvBAKJxKeg0SzP6hsZuw0U0iUngDj7QVFa/8y8OH7QWZGpe+KRB1rjxSEDeHIAGDZ48fndkAVQjvVMYaEco//CFWhav7erzR+Y8//tWvfvXxmi2MvldRCH/X3ty79+LF/tc///LLux++fOzysnNy4syZ1MBzx8aYSYqS8Q/75Fjfs5bNqyiYoyaVfhUmsQkYgBWcWIyo10wghEifg1CHzrD68fEmXg/erqsR4mAArXvou0+XtlmiW+o1nK/ddjA8lBrGejAZZZ04AQC8uzA04DrYzYtFGWOPJ3lqaGJi+OnvPpVgtqeTueGhEVcQ+DfFlh7tJ9d7tHIdoIwByj+c/N24ulHTZNa1K2jnrlY7/umv7gAmMt2qmFk3q0PCYisS1kvHZwT+GVDqGujhCwzUsgwbmiHq9Pqauo318dldSqUVAmE2IHxMKPewLfGsK/BnxwGBWsPsx9gSg3Fwztbq3AFgV8U6TitDc59QiZ+3vwQ9ChwT0Wj7Pc3Pw0XQO8oKxtV9MomaGhTaGhTo+9dP2T9vKfvH+IcyHSDI8E3ffCajlYj1dTpJwybECbzbrP22lAofggBseDL68Rd10C213AK4aSROiIApMOb2y6wkLKOQRKKRZ+pC7ojbXotPOTYYwsVgpuSYTztDPAcPYDHE6VQe9Oz2HIQ4OLyzTSQG/smBgCJ+JI3t1kDXUZqOu2rso4k3mc7pwvY/nBEIomG0I+8unv2bCuP2KMXBuzRb2tg4XNtLHdGllbW1NeDfCuKP975cugjn1c8/f8CKH/NW1vuSnl/K56n2y81Y1pvMbOqNl0AhiCKbUGAHxvYqQCCDEoonBj1SgDQUQoMhOuPMeA1rGEHjqqpYnZLahkFnui+wLR40GoIIvHdNubPuYPjMxNBQChujh1Nhuz18YvHBv9+6m4wcDndIxeMQnor7cwORhbsLC9//fs4/iSXVA9PDQ/A5mBOYunb9QXm9Ekb06aidPSQm/0DRxlRsNAwpfnzPOMTBBmC4zjxL+tLAd2rMzMjFRpMRFw2xLBpl0vgn4i92G1tiYmbz+I1ZVg25puSbk8rDL/k0VUMoDsZUYItW0YQIxFRgrlZliGUMr7756usrgu+fI4i+fwFtI44cVfd4OvoqKp4/eb2zjRc/qlH+yQqyxqNdIP86mnn2D7eeE/58rImbrfpleQrSqxD+qiot8oaGLYLzQYl7j/OPab9y9Ptk9OMv73wDEMg6Ysr8EwDIbkv43iSWAZQI7YEajVi/IxqJuJxN9PJg7KMJYRqM4ytDaHfmQb8SEBhQth7cXk+jIXZ9Hy5u06j5rkv8r7GtxuvFrSHa+/9Hlwat8NV9mp12XBIXJhEYZY3R0//0yhbyCoQ4uE6DqUBZ4eK2pV+v0bkaCg8Nuez26NzKmh5t/z777IMPvkSTgNVl5/TwFTb6kd+x7qTol8s/SwxbX4QFGUYtTkXgLR9VfoEaBpOYTfBR/MjWdgi1EHikuszMuE6P5RC+ycimrNTVhxDZeYd7H5+cGOFGWXcnX3/9kd11CkLHVCpZxJaYZDgRTi4+uPXvv/mNayCSi4sNRp/XNeAGWbgwXJykyTdrIJcaOnXhvNsB+JvEcRbM/lHrMxZ08tT5d621jkaZawHp7d186YeCUK64DSrQENPFNvHPNDNDi/OkRvTpYVUEjkFSgZhbo6W9aHwBovHGzGx5QFgp7Otke1EmiugVeFnoCgQEviQ1jt9emYc42N9kMGZiNZZXX33z/1op8S/sCuc6pVjQkrTc79Q9U1HRbbX2b6F+wWraWl1dkMkapJT9a46T/PMK8s/nE4ZY2A9N4J/CJBFbamKyhvLo22+xr/TXTQDc8qT37y/yfPsbzCeLFX6rSyGwhK3Q5O0w1dwfiycBaYEwtsSgW2p0l86o6GYQFLKAPApuauqqrK3f6TnoP6CkAeGD2z0ejx9dYqQiDYbBnIA4Iy9pMHUEOluwJeZfH7ar0UeuUN19wJWkbemOoIteN+l0ePTiMzPrDhKBNhW8UlpOMvkHp5Wyfw7ceYS+Vxd/+csP0CMKjQ8+sW02PmjVVbYq3yIr5nULll05/7B71iTdzD8I23RAvvEZcQZCOJUursMA2Izxb7yZE3D8xjiazJNdKt8r5NxltuwIRecBgqCRXn6Zrc8cu3zs5Q/vfvTR9WtT0exzb5xPAQKLi9O5IkTD9mARROC/3y26B5LeHpB/2eLCrVt3F3KjKP+s1sTwUGrojecO56MU/b64eeflYDY/51S2tip3MPlXo9epaMrDyCCB3S/dqvFPP/0Ux3DGsfphMMG5AfKPpmYhCMbkH2Nfhss+lgQEAFIgnME5uZilZn297JHA9pSM/S6vwM8+O/69v2lpMUIcnKgB4J6cnAzYo+tvvrmCDmX2OUfU4Uo62xvbMMZQ3L8vr6g42j/pMTUi/fqIf/i8bGwE+ZfrjDf3nuTyr6u/v7m9R5hhJps1Klvzb1cuMzQ1Gdu2lPC3VZB7j+Fvc+MLu9X4pPj7F3m+xVpiCHzVfEWwMBJHgTBVSWhmWLCgElKBIk2m1gaKJVqbMSoE/MErpTQXjAtDagCBnu27D0AgbMVysKej02MNDyU90j4SgUwBQrSjhtja5w2cLCACH97X9bXh3GhbM46GuGhWik3ILafD77xQoaknjwRXa8ynnFt5tPZoba1uF/W+2CH8vbmmY8XfDz54QEs/PlnJcYd4GpOYCjnrVJaNt66ur6+bqfir5aZ4+Ip6jUVV8GhUQsEAsGGcwchUpTPHMQ6mTCA9zLhqZpx8VlD16i1NtDsOEbgdEGgLhaJpAgSWS4dHsmNj6YEr6BU4lR88tO/U0MRwBONgMsoKhosPbj1YeIgIjGRdC79B/llHi9j7Fyimnk6lDu8bTE/9j+vk5D+WPsfkHy09ijpbt7Vua7qzjr1/Fu7jpWBUF0Z7Vao7n356Z5x1ygHyMPuHsCcE8jSggjRgJmMQKGg0sr4Y/GgjTcfVrNMEIPMKnJqKlvseAYHnCPIMgT/72Z6Wl7SVVeZMTNVzNjc8MJZdm0UAovMt/Oyi9epGeGo1yiu9PSD9e0YDzY1tffAU7OujDmhZX9vz0gBcLeOK5t4OvvStH+VfN/ZpltSflAEQjxRtnzOyhi1bSs4v5WbnzQgUAl8h//dE/v3lnm8JqUBiYKkvkAlB3iwtIeBJBASy2jAuEI7tosVJNUZEYMbAnaJJGenZ1riautr6+ipqibFy844ObyKVynUVqtUaDV8SpiavEJks7vf3Pl9R0fCvD++bGlEZtrV02JNJCIMhECb+gQh0T5986XmD04Ge+Q77/NrngL+1ncpgaigZxlB57fVXMfxl8u/IsdXl+VCRev+EyTcIFm27Yjdm19f1ZhW82o3Ca4kN0jNrvEwMCwazZtUsCEDMys3MjPM8oE5nNpOFaby53XAj1gvyT1dG4Dq3ymqtM1dus4UcQECukSaSoZvLFCU+uP52fmzw8KnzZ4aTboiDE8FkMkwI/F8gAl3ZdPjub27dvTvpZ75X06mhoTPnBwYH0/b/cf3WpuXqQu+fs3XHjnqUfxt1OMzCjaE4yPGaBN/zLDwQRKAJg18m//DBStmKDXgv1lCpmySDVW8hpmRJgZkZEy0OUcXMrB58dRsfEC6lAjEOXiiOLLPteLdwNOR7vqY6cywmnrVOBrPZpeja7O0VdP9D4xelqq8Nnlptmfv34aK3tWPSo24D6Sdrw8CXkoANfV3BZKKD9f55KfvXxfDnU7CtbzwDiHlbfLxyScZiMVY3luTf7yTfls3ij3HySfbvL/qgVSC1OfOyh6wEwGr+O4XAMr6GTcYxCGpRpDFZyCVmV0yKPYHkD4gAhFCxVw9vFogKKytr6zrrIRBGEWj1eju7AIEQBwcUjRKqBKuZVxz+1qbuCPi16JYKCOxD6soajAeDKRchMM/yR8tp1+TFivcsTpqOc2x7/VFt5e4QRr/ke7Uzjvi7hPj7gsk/8r3av5/th+S9L29dnTXdUPHkH38d8WViKJoyGawX0BlnVVmDyigGBDIA8m46s2pmJtYbx782sx6ZuJl5qCACnbvNhlpn2UHgyMToaPgpjBJffP/u4ttojrDvjfPD4XQkidNxqVTQHkwuPvi/7y4ki8i/xdHRBcz+TRZTQ6nzbwxCpPs2yr+Xj43lT5zAyd/9fOmRze/dbqHsXw3Ivxgbj2CPCQN5wFYMs3+xjGEcEDguZcVfwTSPCIilECPrJoE3FTWVMAICL2dmhNFogGkMHuLGpgHhklcgWxtybiR7+fKzL36IIvAXtRZQnhr5rDK/ujzljF4FAOKQI1y4aguNfRJJY/X9+3H4cUv919sb+jD07evD6SME4TOFANv5W5J/J0FpdzMLL8a/EgDx+ttSrdFXqiBq/i3+PVb82NT0J8i/J8Xfv/QDcbCc5/tKEyGCOYJEIvjo82ZAGRWCqT8QpKDY0EQLhHe3m4xkDtjeHovFdXEzehn3WvQYB3fVdNWx8TiEIFl4dOCAsN8kk2AlhK3zIIHZ1qbw5HAR2NZ/uf+wXVSNUOxrP5BkqUDE3yefLC+n08mPLr6ipcVJrki0vtYG+EgGg9G5+Zs1Paz68eWtW7ged3k+wT2iSP6xyQ/ajmvRg6gzlumnLb2m4HGoYjoBf+MqA2bNxg2ZccPMjXEgiZk0oN4cuzEzjllBHesQbGYQJCe9ncwnZmcsthvHZzEO3n84dQZTgSPZY5gou7v4U0Dg4X2nhouOtDtJu+OGc8FkePrB3eGFu7cWcyD/itPWyelUJJU6tQ/wt3S9VPydEHyv6DFZ/XUk/6j4284GWaQU0+Mt+I6RfrOY/DNKAYF3ZjbhD1OAggakNCDgL8MmazEgNhgV4pn3ZkxG/B/EEajSmZnOJRF4rewVCJH+BNql8nrPZBfE3aa+V/acDaeXpuanwq23GQAdrbG+NrWkr6/5YJMcBH9X4KS0oa/QV41vIhmTf51JkH89PYL821z8EOSflJvVYv+SSKRCi+lSfLuJeZtuCQ1/ZQ7izt8n/PuLP9/466+JJHwgRFJuBxRYSMlAvilJwvHInWIgDqbREFsls0jAfZkQtVCHMJuXtXQ1ddVUdnR0dvJAGDfYdHVYk0PBDk0j2tkTAYm0MllbWzwQ6IKoqA1EoKKBGm/UNaFkEmGXxjUfgMB82p07a1U6QUo4XBEHa30Ozs3NrzWT/PtMKH7MKXM8U0a+V9QpQmt4K7H1D3cyMdt0k7BHjKAB/OPyb3Z8dpxahqnLFgNhEoEgD82x8Rs3Yog+TkBdrJnNiqCFM6+GvPVWTayJbRDOLqefo3LpiRGMGF/GlphoPjs4MDScs+dRBeaCw8PugQFHcHGhuFDMhYLFos06mUPTq1MDY9k8Vj9o5fkJ7P0TXO+Rf9dqxs3cyYbZvnBhRPoPUA4wj6nQhMeo0JrEN+788IZIWrZNFvNFk9RRjK3EioyK+QrQbK14Bo9Yq31NqDRgRtFSwzeVKEubk8aOca/AMNsKcLd/3Ki4+LN/vmiL5Keu2aPRpHK9cgXi31CtqKG6r3BU2+XRg/zb6/H2NCL6qvtYtqW6uu15nzWV9Pf2lCd/+/sh+lWw4i/zKIPfcQrEiEnOlmqxriYmK4++fQV9wl8eYx+eJ6MfTw473/i6WCPbtC5YACFyj9mnMgKK6H0UBzOPGIiDdTga4lKapdQIHQMkxM1AQDNEwWY4EAlTVyA3ykKTmI6u3t7ORCqV6H6+WqShbTml/sPqlo5coAsDo38dvd+3BfdJ9GmqwhEkIK0PQ7/ofHr5JggtGhhxuVM0+Ta/Zmk/frEHm1++RFRcXr4ZKPtelXv/uEUeZsrErBJgFGtNQkVRARKWyz8E4Ph4hk/MGkgcQTSogseki924Ma4rn+bmZsHBCiJhQGAdholXrx7Y1RSrCjny8/NpWpx05AqEie40SKQj79968PZSOhsBAibs+WyqOF08NegaCkddyWQxGMwFw47QtDviKg4PDWTTSz/9au8fPSZaea4f11VWNjUR/hRC+8trpP8ygHLdbGz8/2Hv3WPaPtN9X82aS2f+8mLz24DHP7NtELbx0S/OSUwMHtts6LETF7CNjWOQ7WLXUDt41YGAQ7PTAB45kxNlSLJTUQUx6eSyYDqkDkqKhNWsdiorgmmmogMLZZp20qNGidqqmWZnuvZKIq0lnfd53vdnm3RGZ511mxnJL1cTErAdf/x9bt+HupDBkWX41Xv3Vi2iAqQAJDQxm8WraWRDtfCB3EAwLPzLDEhjuU5EYBMTgcwrsCNcNB13hsTBp68tx8zyH/3dzX+4kvq/78zOZqMLc6e8DTXTKVersT6kSIeOJr3t5HnuqDdgF8TeP9qMIK2XYPG3yT/Qmy/+wsZzbH020dovehiKvw8nNVY3mKT1m/nHwPfE6Ec5/Ui/T/qd75X4Vzp4vvvtbyqLFgbTcjAnmqSygoiC+o9Cco5nGhCsAmkq0LVNr6LDcPqmZogRCf4a9APYFAhdgU5nO0Hggba2ADylky8dGB9MBDQKujOWRd/QBlav8sV7fsNSgbCqhJfWx9QRT1EcnHItrd26dWu9NUoZ6Ipmlyua/CdPXv6M9r5A6/PKYSb/EBUddPIXp2Sb9YQTaH9nzmSU6PpM5R8oJqL+mkX6gf4Dj02zSEBaDZmZgWD4iQPwE7uAmhuqa+vqqqq271dXVrfsWFtbGmJ7haAlBhujd0Eq8J05UH+R+UDU5RnrH3UnXpl7fyEYSczNRcYdwQjwb7C/n0SQbPLNc2qi+DrNdnS21iyur9+CTCX6MxIByAxcwdFKo1mMLWryGDebzDLofcmsrt7LKMGPAtdH0igYwmAzIpAZS0HgDzYxhKimmR//eNVMuZNkKhAgX4RAR1Eq8MxE56LJdG/p9Y8/emfoWjaXW8otzM2dchpmLobrQvWhkCKkrPVC32dvPNBbDpO/+QZowj9dPJHoGRblH06+YfS7yb8/P9+sk2vNLdUa/omdl5sguDn8Fd+Xir+lU3yoVSDou+vIQGm+KKLg6deZV5ZojsDl3wmmGjoakiQIxDiwV4/iD8ZlB6hxCnZGw3BImxoQSIKaXieJgxN2GUEclIMVPJ1NlkoNZV1t89AVWP/g4cPfh6RQDDHoOzwejIOXQAamltYIAVvDkUQkDHn1odnzJ0+e9F+mrc8733jv2vKFiTfFPjkXmqSQ8JdOfmhstPhx8jjRSZmMIMvzz4ZbiDaHvyZGBtzqBEzMEIAsYiqQgo8mAmPMxCrGEAim0bVVz7R2dlTGVneIu+PE1WoQJe4Er8B3crABKh5w9B/yuCcn/+fk3DveC4mnJgndFmajHs8g4G/27d8B0wvZP4zoZwn/tlU3Xr1atU7C2hlapmDKCOQfzu+RK6EhL6YZuBozMPpBcCfIVldXlQyBVARiP6DMLIpAxN9Mvvhhmrl79x5Ryzq5mAsEn5gKqgLVreqVto5ZikBIBZ7xJU1Jf5ZAfiyVm80SAuYIAU8NbzWoVAR/IWta5XVC06d33Csvh5ZTK+3Agqe/kD0I8q/I9w+zf+IiYznt1szzz5TmjI0NeeOX4raXTdqvTJz+yJ+S71/pPHG+xdxSxRCYDYjwRW2BcBSsGMJTz2hsjJbFtkBLDIyG2PTUKaWhV987QKfGxKVJEAhjQVhN42CnN54YdDTWG3i68RWpCyrAwPUG4jAdl37w8IH5KPwYq1Ab9QxBGOx2uVIk4L11a21oZGww2NkKa0Nc4ZqTJz/7jMm/95Z73qZS6SAzPujsnFaj70uzHqfEKCaOQwIwcx0QCL0vGj3I1sWGW0wAaozG47hoVibPx8FE/WWuQ0/MEwIwJhr5MS97sE1trCUSsLOjY0tL3WajrDMJmij74IuvfjWbW3IFEyP97sTk5OR/m3v0ydtvX7kyHgnOxmdnZ1Oj/S4i/754cyfsvKS9L/Q6Ef51qjcWYelRdYP+HpFopnw7N3a/aED/gVpFFWuWyQj+kH9yuUUpwBYBaMUskoDkE5S6Jpr0BJsYaIyGJwHwTL179y6JnJFCQJ4kQWDLOiJwfyuMx7FU4L5jnmqT8vK5dyZHT48Sdoej0bm5uWu53FxvWQiOtV5wHujaKpH4e3q6rND4HDIoFFot/M8zSHSBQSL/mjZn//yqbuZUiIUq+CVMdFRZrpA1Nxq5J1eelxfeFzJ/+cIHvCtN/pbO1w+6pYrcK3TEsPCU7U0qGguhBy4KShoHRyubk+AKSB79REsREA6woQlcGSL6xMD2TKgHExHoHR8cbLMZMA+I7ltSaoVkDR2I9wzD1pD//t8fSK3ozGWqdA0NpdyEgCQEXicAJHzwkOh3TQ2zIa6OK5/d/OiLN3cde+/O2vzE2ecK8g/w11oY/AV3PHmfro/uwyUh4fXrSjlsLYkR1VrI/tHwl20Zk4kpspnVVRCBxhlMFRb4F9M0EcGFRlZ0VE4PS4Rrt1ycnibis7Zhe2GpxpGi6biPP3p73pHqPzjkIvh7atJx5e9//eHw//qHc+Fo0DH7i8ezrtH+hCj/JorkX5jgrxKsSq9CRaepa4aIwFUTTY2ZYV0VTLDQQ+iHLrSrGZlY/dVaLMrMKuGhVglOVEqljKlAExIQXLJmVs0kGEYAolOCyYxthIyAOpz/0Te3YNfPttbWfBw8tKyRzXSeOXt25OBQGPAXmYMzNBQ1YauLocz/4IGcyL/h++1aMH6xGqyhNE+zf6F22PlL/sNQ3z9ffvI3H/2SN8zYmnDZqoXTtDQYDV+3vS98zli4ufhRxn+zVPwtnT9wYDSEJv4YBUUA8lIxJMZ9cRxXHAPTJermapyO227roqMgMDbRxA6DwkDeLLAtgHHwwIATugJ75Aq6N5HnGQClVoncN+6lO9T/sQlbsa3lGoLAFNrEuNYbb9WurOSGRlPLzX2NneCelXgbLPLeuLZ8YtPKX7H3hfCvoWjutw8fUDI50UVyJZcxE/4B+dYL/CPUMJvFMilVR2aCDZgMNmFLjEjAZuw0IUfDZCD1dW7S61tq2frMbS0N28Aoa+i0WCuYOMUc5d/6H+T3JJHu5GSkdv12z9/8+td/33PjRnNb0PH48cLCwlz/2V3oe3XmdVb8deHWj86r6xvkWtVVt6Dxi44g8J5STgUa2jfM4LUw45GZoJZLI156AIGZDCcoBTSnzdeFIeEpI5TPmLAbRsXiYfITzGY0FxQbkEGAwd6QiuLNSQ61TWueWdr3g727Di4B/kD+zS3MTU6mnkkbSKRrkD44ZyN3al+7t1sSIv+hCP8UaVoELpPHifwbsKH8g50y9ikRf7RFSc46YOR0RlmnUDZXa6x52+dylurLc69MhF/55vi3JP9K54+e733HzItuWApxQgTVoJR+gRerwJw4HYxFEYIopQYWJ7nDFZoucI1vphkyyj/RUJQh0OcDm5iedhIHD2NLjFNLucrROWTIiRsMTb62dhIH89ASY8WWGKElPISpQFdFQ3UdTGPlUokTl57ueuRwuT2JM7veeC+3/+3inW8datr7wgZ/k9Tsjz6UYIEiVEGImjCRELG4+Ev4h+AQjxldAzLgHmpEeyyCQA12S4P8QwkIDXdNuCleo2G29k36lhpxg/AzjdVqMRXIpuPcgMDnzhKVOufpH021DbfP3/r0wCefxG9szF/47YfzrugsIeAC+Tsj+ewfSNrZjs7Z5TWQf9vrqpubcZqZCD+UaCL/Ysg/GHuDlwxinlxhpYXSj7xqBXLlr1MEKmlsDPIRruwqmEQbjdgOSPkHRWGzeebevXvASbMYCHdpYg0t+a7Ajo66mNHUGD14bN9LQ7lcNov4m8vNDaVWNN0PbLzB2uV7IEgkRz+8PyzUh6DtifCPx/nf+rQdi79M/qHzwQDBH0trUmxD/g/DX3I3CnyyUW8q8I8mATfRj6YCqforIJAv+f6Vzh8/6JbKlqbnQ18aFuctU6lHKsemQ+icCLTEmEgc7PG4Wls0mqaBZtYkZ2N7LpAILBK2UxFI4mBnL6QCBxOBAbBGgr5o2gxhJS8GwRkPDBMEKh4+fCAL4RiyeXvUQw4B4PmqhTlXzrEQ8Tjs/89nv70A27WHRiffeQuXHonyT42+f6xNGPHHHknkjeDvegbTfzYbIdpMofpB0AHgIIfIo3yOjPCPhMJGI11vMpOZiS2Cwx4cDdWAYiqQmjqT69vbiFtDgIDqupaqDhicOEhbYmg9+KWRobk59xwYHv7NJ29f6Xu+LRWMPrr02wtvf3LuwkTEQSTgwkLq4M9e3yuucYfir3rtNsi/qprqZpjzZVQ3AQJlOvjlKMTNKGLR+AVG38h1EZB95IAjo8CRG4AXwJxWKTB1CFcW+IcegUZV0StUkgGBGdo8iRR6XqXR6HF/JrR+tzbGNKqWcGr00OkUVD5y0bkgEDDlWq+X7LY8aPE7vU2Q/Tt3ThcKaUMo/xTQACi1brW10exfL6t+2KfA9hSjX1b2ZcVfAKBOZVHI9I0aTgx/y8T6R2H2g30mKsCS/Cudf+GB6Tgc/eCLjbIU9BIv5gX5gk00SwUSDac0V6td/R7XFn2S2g/rC4t+4PiZDISCMEMgEYEDw97xsUSbrgzXj1CbatYToe0Zj+N03MOHLQYrVEoMym0uT7+r1jlc+5OXJ12u6ELu2tA7n3z1xZklGDNNnAFUoPyLwoI0tZpm/1r06HmPDyaTjj6cuOsZIiggn9+Eox2rM2L0azbLqPzDSikrEawC/1hHDEyLaDIZ88wiEpCwr1mDmUBgHxwbakHIA1bXVm2AVWBHuLO2oSrMbKRoHPzKiMdF4sNJl2P+k09+99U//MM/fLJ059Vs/Obf//qTtybe/t3ZMUd4YW7u/Vn3C+LkG1yn5dvr0NBdW93SjAuOQADqoPRrvEuieLVmagAAIABJREFU1Bm6fpTF8BR/hH5ayP0ptRbyQl4FAQhIEHj9OnSjY02YptgI/rDJWKwIs7ow7l0z6cw0mM4jEHKnuEX94nRdjPwm7Z2zQwdHl+haUxSALtfyzNGjWwn4VOfOvUjkX3vAXh/C7B8Jikn8S07ZUWdiDEY/mPzz2u3Q+0cnP+CYxd5nGGbWqXRahaa6QWkohL9irq84/5fHX9HhSsXf0vn/PN9DBObbYIoqIOwF+mGo7hOzgRSFgiDT1GAcXKdR0bRfUxH/qCpCuxhMBbbRVCDEwT2RwUidwYpxME0/hrAeTJRB3EceNuX/ePXhQBkWQwwNnR739l7da3Mvvzw5iT0WnsGPnzv2XjgQdbsjr2D2DyJFaH0Rix/AP3GKihwTIQLHKZnvS7O+uQXYl8lQ4SSqPzDvx+yYUmm+B2CgrSJYDDbOxGLwFxabY8102hYBCJZ7NlzrQeshA+CZL7qlhvfXNFaCUyBLBf5shDBici6Xcw1+8LvfffU3f/83F8LZR48qZwMXvvzRJ7/7+Lm9u0YiwZWVR49WoqMvHYLJt0515/LaLSK4NqpqYeslOvzBNevTHScwMs0QBFL8GVn6D3mFS6gEi9ICRoywi0CgDegEgXBXKllTjAwpT/NsJloPgTlABKCR7RGBf1EwUwLSOLgrFmvcsaNaYzQ3bFFHR09fA9MXAvY50IGTI2GNTG4J7SYIJBCUDLT5bLtD0lCIyD9cS0NIWN7VORjp6fXbBpzgeo/RLy3+6tjomxgAAwF1Kjkva4ANS4Wlb2V/6JQXAMg+Kcm/0vkXne9++5vMMFqaHwtmkTBrCVTkM4GsG0ZsjxFkLZUQB6sbkl1sPMyWF4Fd+Blti4EVwj09Yhw8YIfRkAGrlKUUFVItbck5arAHArZy2hIjo9UQ4ZlotdLQ+xMCwByRGNEoQeBLp4fmwGHe5fLAgiC68lLdehV3HkGeTMeCKR2msOSyDCdH/BHltsi6n6HHD+sGIv7klH8W2eKte2Y2NmGmkig5o5mJQUGY8BPBBzJQQySgnmpAVIBQCm52VhMRKKYCtzSsh8Ud6rsIpkmMmFtwHNx55M0vvvzRV/PxwAkYGXzUNjHx9gdH9u164ZWxseD29ZX3F+ZSBw+5w0TRLt9aJ//W1ZoKwj+4cTWwwfi47ng30bJgdn/v00+p6YtOpjPrKNAg+IWg1wIQhA9aAY14OC1uGL2uECgCgX/oEyPDSgPTgDMUgJSAKqICldd5JROBuu7jhIENlVUxIjjJL+Z56T1oVne55iJQ+hhKvfCDXRFnzGix1O/eCqMf7/jS9QR/IYNBynrf6+udsPMXJn/tRbbPheiX/ihUgVj+UPLG6gaZwSBGv/mwNy/+yovhlz9lhm+Usn+l8y87kAqElphCM6BCLA9LxUqINF8MkVIO0uk4pakBR0NaG0xd4ogYDYBt4gLhpnxBmLXEkDjY2R4fHAsky7ExGmZDtBgJ81qr1hlf+SGNgyu0IZzHUwqctHGSiKfJn0zORSAQTo0eeuXNIz8DB2mX2xXt6KDybwN6/2LkoUvTSMfpw5bgT5D3wbAs9PMVF3/BKcAso4ubCDigaKBNL96+tSqXs445cWLCqJnRLGo0qzAbQpcZ0UowO+RaaproFQWzVJGA4Y7tLRsd0ehS/6GDk5NDQ25XznF4ZNe+fcfe6D8zOH/iAgwLnrtyJX7olYNvnB555fXXj+x9JToLmcAFz0sj0crbt6D3BfGnb7J1oXUVLcuy5fMzZkBgRkmuBYt+kX94tErgn5aFv2hGy4EMvA57nwXl6r0MzQXCFWXjccYZBkBx9Tj0QusEBQe35HFAlMVYt61akzSbm9c7+09fyxH9F4wA/sirq7HatfMHOx11FxtCobLd/vttXfUg/yD6hRMiGr8rPhjxFSZ/vXTpUTH/xMFl+I1UcqmsodGoYL4vZfmot3yzDKRfLhV/S+dfe2BxEjXKoj0x1B+fmWQV2SPgYBwNgnGdOixO0tR0wGhIXUxHe4Op/KNbQ7q6RNtAmgpk88HDvQPDB4JjEa+yjBddAqnsJA8Sne9XXi26pT5sCOFEnlbgG3KpFBGBJAyeBOq5UoeO7N15bCjrAAQ61K2tdOVlA0AJywT5CBi2YfT1ded9/9ZvifwzgvsJ8k+Gq+vIu/Tq3dt3M1o6NgaHRGGQC0QCEskHtjIajH0BfjEYBUH5p2Gjwb2UgBssDO7oUNfe2h7uPzgCgBhKBSNnX/+fr4ycfu/a6EHHhRMnenyPvFd+9KOeoVEPuQlfASvXnYfcwYU5gsC50ZHp1g2M6VsaAH82HIfI4y9GiJwkEnYVUoEWvJ4Z1LGCHKSfVhA5iJlAAW9mLQc45K5LeWiO5tiUMGQ9EfVmEwuB84c60MsFIgJJ3N3XZ2mo2tKsMSrNxhbHyOjSnSzRf+4IwZ97cq61N2QIqft3/qB/i6yeT3f72g3QDWhl/FOQ6NdQC1s//IR/bOdvXv7JRfnHRnVoA4yFi7U0yKzFS38LyCvg72unnv9mSf6Vzv+vg33RFEL5IjBVg3RdMP0zACByT0wGcugSs4OOhphUOB1GCUg9A+kSdSaO8qlALxGBA/a2xGBwoEyKTqk8bUeEB4q1fqAtDhYJ1n98+FAJmUJBkBqzoyNPvQznKRJspVy53OhL+w6O5lrBK9Adnb56FXyvYrFkMgmLjvownwQPJuh96WO+f4R7zev53hcTdAxnMtcBfri6U8k9fe+fPr33tJY2ijAJyAZnjaweTISWMTYDACwUQcj5ISUgDAPCYFxNFbPM71DX7YgeHILs3+Sco3/X3iNvjnmeGnIP5QLzX524f//m55989cnKbOra0NjgyLF9O3ftemEkESFh/vsL7sjQIVdVQ2NLczMEv9S5FJe3Af9w4S+4Hsi1M59+eneV4g/DX6oBtbiKFPUflIG1jICwoIrij3yNAlAsfZvNxjwBRRAicskTCrmX5X0WXe226phGJsjldtfo0FIWtre45+agtPPCoZ7/tUdrkDQlPHGphIS9Ol25NRSyWusNIdrubt0qx9EPEv5Osd4/J/W9Ksr+McsekO4quULZUq1RFPW+/IH8nyj7ykryr3T+Tee7OB3H/F+KguF8GhDfcwWvVFoSgSOYWrYBAlt7oclEJGCXH/KAsEaTycBCNaStB+LggfZAYjA+ILXS2TheLAdL6+XOQMB/VCKRQSrQyvNCS11sPTc64nmZQPCppyYJ/6KzrqGD/alwZWsUzAKjF6ubC7XfPvpgEmAQNtOH1Y8YRL/Ni+LkGyb/cG9x5vp1EH9gV7hKSJJJa2mRQIkW8jQMBnVkxFQgIlAGKUEIgyn7iAIkb00aXKPZC17RMBtch4HwxU7PwZTLTQgxtxA8tJOcYyNjY67c+794+3dvffXR//7yq7c/+ODtd99dJoAfO3j6jYOHXhlLwBLJOY9rYW5opD8woIF+G7rKvRv5R37moog/M/6O9+6S6wldznK6gwryfriNnuk/pgHJB4yDV++tQhlfa5GTF9r7I6cikM3AFOlAuEVVx1U6SyYjb2h9piFmVFr2+OdHRwn+oPabmiSvqTn3z3fu/bm371LwlR557w5VWhqCybcQyL8Qtnpay6T2RCI+BfLP7oM4oH1qGF2fab5WBB/W7MkrATsXqygq/opzHn+IgCIG6TeWbJ9L51916GiINA8+Cj3IA3KsHKwQzWHy7TAUgoLSWBsGt9Qt1CqfERBDYbpHDtwDIQ6Gxmg0yvK1Qx+YNzg46NMZFIyArBxMwia571ftOpiOe/jwgTLpfGDeKsmsDY2OjD711MtPzc3lojlH1JE6OOJS76hS44BwawNkrI4XOslkFtm9e6sy4B9dE9m82JLH3wx5uOOiNCKbrl+HkrY2A+m0tFZLm4XlAqBFyaQRhMKMCJoZLCBraEzMIKjRUP69BgaxDQ0NLdXV1es16+tVjpGDJPJ1TU66FsbHfrZr17E3To8cTGVXVt4/++bZiQ8+eOvNMz9/7sy7n3/+6PG10yOe0dFUYowQcDzsdoFqnBs9FGlXGSGsR/kHShZ+Jpv7xQoOdHhfh8Xx5G6Qg5CVU/0ncLT9hTbDaGlHjJZPm8mtAnlXWEeOApAWfxgDoRoM43F0UBi7ooG6x+XpmZrWuuaYSbA8OxwZvZaD6Jf8irnJFHT2BBNju36wNxIZObBVsrtWDT5YCsz+gfu9FYofKib/mjATgkvfmrqZ8Qu25Ij3G7qfqiwKczORfwXngz+mAJ88ZSXjl9L51x50iSm0A0LwK6VeMRii0mJwAX+4PRgvCkpZrMrh6fd0VBDiQSYQ8KeCQBjXqTMs5hEYCEAqsLdpYLgnMha0p+sRpQqaK0IEWm09AedWiWQ3iYMfPNhNWBhKL2aHJoeeeop2nEWXwg4SB3s6t1dUq11uD6GvPI386+vDx9IeiGctlH9PGF/lBz/kWAAhIpDjCULu8WlBqWS9wqgClXR01ixWQ0x5BJrE4Je2wNiYd35vg17f0NwADGxsbLZHDo0ODUHIHg2Mj/312Ojo6dH+odTsysq77/xs38H+l37284MjIy+98qv7X97//N3caL+HhL+uwbHDJ9qC7hSUFuYmR/rjw5bjKnZwZV2MjX6wa0GiX0HIAAHTFpr2w+iX09I2GKCfxcJC4HQG2pt5yAVyCin5FqIZC92PMhnVgMVGMXR/nDzd2FpJNLagTT/b5hnNZbNLUcI/Aj+i/8avnOuJB90jP9ibcBqPvjg1YORCoTStfoAlQii0W2JPDI7bm/z+YVr8tU8N56NfHc36URFIu59B/tU2Kw355pcnKr9F6Nvc/VJm/UZp8rd0/tUHLBJYG6CCL1qaxADIisHYAlNskUC7AvWVLuoSA3qP6j8b+VxcJAwWqnQ+zk7tUn04HecMJBLjvWkFx4MKlErT0C5LhKhB0duzMiyRSJQPfr+V4E8uN8Ya3btGnsJ2OkLAYNSFsxbuLYsz6x24QLjCAvD7Dc1s3f3009U9tGIQWxQP7Rmm5IBUn5ICQ5Cu/vjuahoqB5R/rF+YERCG4+guDdEmBjwSRABqQJM1NenpBhHwUAV/sOZYU8/gyCRUf4dSHfHDg4MJl2vS40ktrPzq7bffnjh0aNAzdHA01X927JUPfvfW7766//ly9po7kXin0zc/MREJRtyTOFw7Oepp6wZRpKJLP7Ajp2h8D/AHvyeYnxLw0T3MDICQ9NMWMoBa7Srgj4dt9SRMJmpe4JQCy73JZGLAz0wRTXkAqmTGZ9RVeqOZ4y1TrtFrWSb/5iZTQ0OuSvuVH/2IIHDQ3Zou1zzy2uX16TQ0v4SoJYzVUGaLJyKY/cOdv2LvCytp98lZ1YPKP+h9UZhbGiH7J648L5r4KMLf1+Wf4RvfLoW/pfNvOd9lW0N4ujozD8O8azR2BWI7IM8ygawiwgtsgfCWGKYC8UDqnmlArAizaggrCINLzAAaRvd0WXkshoAGTKdJLMxLy5X2gE8FDbWS3SGdanF9/9jeQx1ZyKfhOeVyuaK51Gh/m40zPRMlItB9oMvC1ATEhD99VqejKbM8/YrlH6o/1ijCZVataQ7Rp9SyCqpWm2egXCyUYig8A6/UKEtD8VcwzIIwGI5N5Yy/MjqJAHQFLkyAlXXQ5U5dm1351Vtnz7x19r+dPTvoSqUig69/fPa5s68cOfurz8+vrWWvedqmeqKRxOBhx3gECgwLCwv9I0G7zgLepDTkpr3PtIGb8E8O8k5Q8gLk9rg877DBiKMfaAicVq7eBfmHF/BaQ5MRUYFKWn1ASSxCkNZDEIJmU6O6tcVo5CyWkz4q/3KUf0TdOvZv2b6+duVHFxKRbnJPdW0ZsBqkaS2yTwH0M5SH7JFBMfvXUyh+iJMf7NDSPQhCTohVtCg3+f6VF2GPkpAl/jZB8K9KO39L5998vvUd2KHOYl5F/o25w/AMhnx+JoSpQagHK5NgkeBx1Kp0KpoF7BK929HBWCUWhGlXoGiZ7+wJDkbatVvhoSnOJEPbmNWq8o37dBJJSK57sGUjuusHngaFcWUhB3XHnxC2RFyupVwuNRKZ2mM1bnF53P2uGnkaFc2P75FQGFWTqP+oZZSJwY881jOUf1paLSBAQy0lUIAAGJVMB1IPUTn0poF6ZLlAU+b6KqUfvDXF9PkdcvpmvbHb6x71zM3BbznbNn6G8CxKotpUdq1q5dTru145+/Ozzx05e3h8YeLs3r3PHfk//vqFFxInXmtqWLt966rr1LjDEUyAf77bhfPBk/0kDpaTqFsfo96F6PhslrPRDxB02OwnVne1tNpBW/9EAKafhicFHhYP0KQg+QizIRADy+h0MAU9ol5mEkWgWdC0hrc3aMit8f3L42B8AKO/5C5IEbZHL148sb/nwPnKsYRddfy8zXJcHpKCDz4ufYPot17SDdm/ASz++ujO33zrM4i/Pjl7zoK9VfJulVIqa2lM8mLrS7nY/FdogdnEvbwDQkn+lc6/z6FWgTTyleZ7YehlysN8DYSn7lh0mTqHcfAzGAdXJFUUgZgEVOH+Wvo5dovAaAithiACh+1tRCPU1CugK5DXUs8kRKChNxC3nzx+3PLg4eDOFzrkUssev+OFkcnUyy//hJxJEIHR3JAnPlxvbe6Iut2ujmqY/1fKT57E5heRf7FFdH3OD77JWbJPS+GhJRfAKxDmxYR8+zANjwUl64thFWFWD9EkTSwOhihYX3xixuFA/1AKmv8mg22Bw2cSDgdRdQR/67Wf/2rw2MGxn/9s7869r585PHH2yM59+2CByF9Pzl+5/LzSOnPjWsodGe8IH544PB4PQksMOU95Im1NtAUxSfDHRt/M0MpNkI2OB+SDIFAEIt446rtIFzJz2jR39+49Jd3Lp4VvpZCHIj6UQYCj4rWUi6VvHJCT1XZ0VseSSqXu5Alc+pZ1zdHqBwnt9Zr1qxdPnIiMRWzkeaon4txaFuIVaQI++I8C0e9WL936QXv/mPzzs+QfRSASUEebX+QKQQOjHwX+FUe9T0bAxb0vfEn+lc6/0/nut78psCldwB9XDECedsFI83lAyj46HQd6ogEXJ7XGVKj/uhgAk6gC8XMoCPcOO4tSgcMDw14SBwe66hXw6GQSkLbESOp6/BZeIelNeLbpQn0nL/f/4AcjqaGXJwkCJ3/ykzkiA6OzuVHPib7dhoZOt9vjVtv2WCzY+wfAKES/Rsj+yfLRrxzyfUqAA0a+QDqoByP/IDzEyTEkIYbBYmO0OS+PkpqkmS5Rx8qEnq0OaYpputojo0MQ/k7OBSChN94RJ/Hs0vJ6i/3R5+9MPvU/zh7Zd2zfvp0/O3sW5kJegvWZH7z11ief/eZkt2bx1o2lVGI8QMA5cfhCPAhxMLDeE2lPmujCI0o/GeIPpt2o54sSiQbOf5y4hp6hEFbxrd79dDUtBsRYFMFIGavFuDVEbsEpYnEIkF5Ps9KsdjyjMcs4Wd9wfOhaNpvNYf4hlSLyr2IPuZ1bNqYHx3pee6TReeOJREBVD5UP8kymgPrvUSj++gag+OHN+750F+Rf/phZ+KswN1ZrDOWblB6rfpQXwe9rp7T0rXT+Pc/3vvMNDva28uKmEJ6a97Hwl1ZFKPoUrByCOFRAV2Bjh2fE46jSYNo+mUwi+WgqsAvLIX6xJQY3CINFgrPX6RsfTLTJFQp8iPI8OidBAbreIvCcIbnf3hV+Jfha/IUf7HrF7XBMPjUJCCQQPBVxVFatpUaDV542yLZgS8wW054+4B8sCirwz0Q7/+jDHPN/WpoxA9lHfm/ykcvgbB5dYUzIwDEhqBQYAc1MBDKbBCOM06EKBH8EujtEY2wKeIawPJqKtl0gFAt0EowtZdcae52f3//VO2+/9fq+YwcPvnTs2Au79r7w0kuHRkZPv7HvuY8/+PLmzZsf+lWqmds37rgiBIHxwxPjF+Yjk0jAucnE+BRBMGOwmbU+KynPBOZ5gAi8znFFBATLCQGWBKeZGCz8CUsUcuSfAst8aAkXxClADITNteHW2phZkMm6va5ruWXKv9xcjsi/yq49ffI+iy0w5rBJrL09F3ztvuBgxCs/GlIQFU9C4d2hdqLsRfkHtn8F/vWJAOyj+g9W9sm1Qqy6WVZfRvWfWAEpZAHFYnBe+okq0VqSf6Xz73ugHszn/QF5EX6FgrDYE5NPBjIlyPNK2Boy4u5shFEqZF9eCYof85lArIb4MBWIcbBdDgPARD/wbGeIFDdpmtp8lq2m1lfGdv7g54lIPHCihyCQyMCfvPzyXLxny4HWDtdo/wX/i1aN2kUQ6KhTyVVolCx6/s1Q+adkvi9KahhA839KAWhHUSFc59m8BJVRGBKz1kAWHbK+QGyKmTGuZqAxGiotFIExmz3YDxnKoclUoGf88MR8WxvIv7Xq5t6pz+9/wpYeeZ4aGRk9REA4NDL2XwfBLfWFw2/97qtP7t+85DeZFm+/uuQKzve0jU9MzAfGE1AMWdmx4En0+JUw+Ctjxle0WGOhplcFTQfZzDwBya0ngPzT8pvgp6U1Eip9ucwqZkQxG6Bl2UCZjI+1RrdpNDJy9QfiKZB/TP8R/uWqiGTsszzdFBxs7Toq0Tmnmqba7eD0M15jKcfJ3922NjR+wZ3nOPk21ZTP/iEAdSz8pf0vRP61VNDRDzHtly90FMe+m9iH8q+09ah0/t0PpAIx6hUrwWxPkoJRkKlBsSdQBCESURnb4eofcbc269ASoYv1wySZAszXgwkCaTWEILAXDaMHgwMhKXlgKrQYc4fAIUHL8eZmeXrrD53DwRcOEfxd+NG5tfPbo6MwHPeTX/kevR8JOqKO3Eiip+/F+uZKsFGNtsiMMzMi/WjTiJkFvyB0tEqlKJkg8UejXQ6wAfzl8FMOCwoUgcxLmbXLEblipu4BM7A5iTNDbZbE23obkX/9Q6DYJoeivhNEwfX0XDhMot8avX748/v3P4Gdl2+8N3Rq4uzPx9z9B08Pucdwd1wqe+eNnW9+8NGXNz/77JJOZl68fWeJiECKwLage3ZL5ezc3FMjEV83r8TeP1CxNH2JRQ2O5vQo2gQCtAwNdzltmr/36V0hrS0qiBQQqGV+WZnV1VW4skqIpsFNWiYThJqooyFp5mVKXV0x/uYmh1LLsqfJN6YtvkS8O9Rr9wZ8TpvFP9U+ZQ8kxsZ7j9ZL6+vrBnHyd2AYrIDyOy9V+cmPQhCM0x9ansg/oZD9K1Z5Rez7eggsLcm/0vmPON9jLTEKUQIqWGMM9YdhTTE4DsfC4XyPtGCmLTHbY5gBtOFUsEosiHTRpcKFOBhHo5zOYTSMbusyoBcgA6AUdojwUnmTd6W3fmtLfCz4yY/OPTr/6Nz+bOrllxfeXfnF386digSDDkc01T/+4U/rlY1Rj9vjaoWyb1HrS55/Am1+QexR3SQWPuj0BAkIIRXIibJQiZGwkjUGsqZhOSsSsKZA1hJj7G6PDi2FZxdIxLrSMz5x+ILvxHzQlV1riQ2cJ/yji+zozssjP49AF53rEOyOG+9RD51+49iRjz/6iiDwsk4pN91ay5I4+IQvQCg6P08IP/kywWr/4LjdAgqPilgLzL3htMcTbBMI0DKYUU0T/K2mtWkReUUU5FgOABsGsX4Ct4FcS7SdXEgnw9HWZqOSU1qGp5fuPMadlyj/JlPRdcuePsK/gXikZ7dE0tTW5iVPZcPdugG73dkeTyTamraqAoPY+ze8qfevmzX+bcIfyj8eev/yK8//aPLva/wrFX9L5z/qfJeOhqAbDMsHwqcczQgyOVgkAXkqATmYnlMa66I4GmIk4o82AWIiEAPi7ieMsigCiUTopW6pFisPO5PIj0nDTySPU14hd7Y1SSRG6BqMnz/vPXHi4cbGysLK4wXIj52C+dlgNDrkmfenpbHtLuiLrpsxUfyZZKz6QfeiYasfRwuiHA2DOSadaPMIl0HjKDEFyOFgrRb3qrHJWXhnzjPQOJO5Dkt5jbaAZzSXyy7Pzi2g/LvguzDuWlpe12h6z1+5+eWXH328D3dewtKjXYdc0WjUET24b+euifm3YHfc6WP7jnzw0Vc3b3526eT395jWb2QhDu6ZJ/8SiYM9ky/DaIjH7TULYFBF1FoBeAi1QsMzAu3HqzyRf3c/vXs9reVF4uXbA8WPHPsDniN/gcbEMDKnrXVFK/RmjrPo7NE72eXlLOAvB9MfQ2pjGsJfiz0xbpM/b+n1OpsGpsjdaB/WdZM4eAramnogn0Gzfz7M/hXwV5T+A3dXzABqYeevrLj3r9Dwl08AUhw+wb+S/Cud/8DzLXRLxSiYNehh+EuzgVAIZkUQ6IvGNw6FIGBLqcHpuM4GMFWywYZy1IFdMFsKxWA/dsQMs7UhPcUtMUEnb4DuGqQffXhzCoWg8z/zSHeUf6Z/MO67enWjS9fXtSOF/TBzc6eoCnQNJU74BWVsm8vjcYcblWLRghZ/YfQNIz6q8LDyAdO/NPdFHfOQfxme4pFa6AmUkxYsnrABYWyNhlwgeujNmDLXlSavC4q/qVwu3EPw99aFEyfGI0vLazGjfvjDmze/hEV27w3N4dKjffteGorOzs6uOIZeOr00QteGwPrMfc9BHEwQ+GyffOYWIDDeRuLgw/MXxhOTk3OpObfDEenxU0EHBOQsHJv2LaIfvOMzP16FIeEMeToq/kNeW1CC9ErSv8Mrrq/+MpPB54Pd+qin1WiEvSKX46nHy1D9iCIAU6nZagHazdO2eMK+W7J1qseu0nUT0jmn2tvbB3Tdw3an3Tc+GPTR3r+i3hfR+GBT+QP5ZzU1NhqlhehXtD6gLCx8XnTwQqn4Wzr/wee73/6mkhPbAZk5FhZGyBdF2ScVe2HEnkCKQEGmV4Nb6jM2nYpl/5CAfhyPY16BA+gVyEQgzsiDW+pgR7IcQ2yxcU3L86GtvfGEVy5J13mDY+6NxaTuZJ9xrSqlAAAgAElEQVRFXrvwsohAQsCgYzY1FPTKM5nGDhgN2ZHklUA/EYC0+0+LtIMIl6MhsCBQMUSzgfhHGfzZ+H24SEMLtlIYCBMCsn8ONSCdkCMENB1wQ+8LtMf5LkDx48SFYDS73Kgx6j/87c0v//mLN/e9MZrCnZd7YZFTKqxWr7SGo9nsKN2hPjExOfTeG8d2vfkFSwXKTYuAwPHAfmiJmY8HJ1OpyWg0l/I42r+fFlDGaouGP4qBxkE7EcHfj6+LzyJEBhaU4KaImWPw1ypoH2FI+ozbVWOSkbuyrz2ae7xMw1/ylkqlKpNQJdGmvfMBW+g3oe6pJtyhDggEAtq7+mzDw01On90mNr/Q1ud8+NtXQKCOZf8ETWODcnP2j+q+8j+Iv3w60Fry/Sud//ADcTCqPikDIIS4qAQ5sTCSXxZXeKNINFZAS0y4NqnDXkA6HuIXHRLyPlnDzCgLU4Hkki84mPCm66nbFi1WSOu1bST47fEdCPR0ba1L9O+X98GxHF+ZQwKSc2qORMHRaMoz7sxkMhXRfo/HUaPkGK/Q9R7zfxx2vgg8FYAC6yFB1GH1l0KQv44/H7EI34Tzs/liCAUg65eD7popoj5TWCBoOzF+5jCErsHo8npMZTv/+f2bJPo9cuwNIv8mcI8x7HyLdrSurFRuaaiE7B8g8M0zE6c85MK+Ix9/BAi8dFKuBAQuuYgIjE9MHI7Hgx4PYCiXcgeGnwZyWVgmkNFP1LBIReDfqoGaOPJMFVISitzM809Lryl5miE3XFnMNdKpMZJrHfJ3pKKPs4x/JPwdytXKlGa5PBSLx9slklD7gWEdsxXU+f29IALt/oE2u5+crianF5tfoPgh2p4W1T3oB/LVtLmhupD9y2u+svJyEYCbyJe/VP9X3ynJv9L5Tzg4GiKl9Q/6AcfjcFcS6wik08HXxXaYfE5QMG4Pkzg4XMHiXmqS0OWn83HUK7AoFYg+wcMwHRcZTLQrQ/nHaSgEyyR64Jtge2bavj8x6OzbQwj4mz0/XJl8+eVJJCCoQBJZpjxxmywzs+Ho97gdtXK6CAgIKNDuP44JO/qwhzaYfPwrFD7hM9c52g4oakDWFC1jcTDlH3wU/HF3CqwBhibDvgsTE+NtPQHHUnatt9v/GuLvi+dE+UfxB5tM1JWVVYurW6IpujaEIZCmAikCPztpsZgX15azDoyDJ+YPxBOp1DUgYMoV77KkEV8C03AM1/QzLfT+raL4I298Qe7lqyF5/DH4wU0tCLw1U9nvqjMKCj7dZ48u/OJdqv9Q/uW2aZTgVC9vj/vkEkn60Ra9BfhnwRHs7m7/wPCwE1qfh/2F0Y/h3ia/irneFzU/97HeFyL/WvQywybOFbJ/eRYWI5C+l5Z2/pbOf9LBBcI0DyjNf6QO+lKxGYa55VP0USbityqbYTTEta2ZDgQjAZOsJxouMxHIpuPoorDh4V47uKX2pkMoT/iQrieRCNid7fambnvPVG9Vg6QpniAqKG2xQByce5kGwj/BTGB4Njrk8nZbpbEOGA1pjbFdaBgAKwUti3Y5VumgzCjSTnmM4GgIGslzWiVtG1SKCCyIQJmgszuGUq7UXC7l2uYbJ1KtrSfuWlqutnX7h5F/WPw9dfiMKP9g6Zu6ckf1zOL6YmUYEIjrM0kcfObUJKQCd338BU0FnpTLZ1puZJcc8cD+C4cPj8cjbrqINzcUfND9Iqz6zbAcn/i7w52QBvmXwVtPgfwDCvJ5FOJfSKfJa1oMm6kWTtc3uEbCMRlnVaSbWlO5d99dW1teZvzLrhP5ZzIpe3sCLRJJmf6RVwcVY/JPobs+TN+cdAbHEnG4C3HrB2b/8kuPitSfjqk/i8LU0JhUFJZeis1/+TLIH0j/weWS/Cud/8xD4mAlrXxIxV5ABdN/UjSKRg3IDALzIhCmSXjBXNGBLTEYBwMB/SraHU014R9siRkecHrHBwd7dOU8icSOOoODQd9Uu3e4z9/u9XrbfL+RSORbIoMH5EdBSlhk2+fEVGAkMu4IdxAROH5lTxmv74R6cJXSSnuZWQ6QRrkCBMG8wNHBD1FEMTVFL1wnCGRtMugUQ19ATMrEI1fW+wMESoA/Iv98bx+ej3cGHC4i/7pUTVOEf1998dxO6H2ZOPMm4O80yD9HWK2uW7y3frVy7datVlifOXrwJUwFgggcGn1j396Pv/jn+4DAPqV5puVqNnqg2heHVOB8kBJwwZVyONPlJArmRPzRYJbcRU+DPyCOVmtpBpBnL0wCppkSTOM+Fo7pbIv26NHWkf4qo2CVWvfULF3L/eLx4+W1tbXHyL+1GaXMbJLx3vgBg0Ry1H6gF6ohkB6waGn7YNrSkxgk6pcoPx/KPxr96kTXU1H6ib3P4PvX2CyzFnb+FoGuSPt9rfelvOT7Vzr/uQcs8zncEowasLA0BKJiFHubE4D0M6yGcIKxBuPg2qRJRfthsAaior2BNhoGiwjMWyQMoEuMT64IqWDI1D4F8s/pxY6y84+c9vM65f5IxIsPKsvTiysiAt8JIgGjrsj8cNqqqAu7PO5wDc8x9QYSUED9hxUPHifexDQYx4JCuED+4HomQxCYYRYJAm0ipG6pMhoIk599sp0oOCREVA2Tb+c03rgrS+RfV9fwfZb9Oz3kOnzmTSh+QPbP5Zjt6KismFnc2F5Vd2Db2nqN2gHrM0+/xKohBIEsFXgTEdhnnlm/tR51BALj4JHgcLlyjx8/XsjlovO/1abhl6ZFbKYCFVKUfwBAHiofCDuqALEOwgJiGgyLfwlOqMI94ogpifzTNs3mFlbID3n8PkNgdo0j/JuR6TsDvZLdlvOP7F24Vo5aTlsEi0VI95I7rI08QWEyY3Pxl3X/UfO/fO+fqQWWvhU5H5TT7r8ncn9PnlLvX+n8Cc63vinD/mQqAXm6RhgqwAqEnQINEgrwK4qIeU6zA1xiWvVoC4MrzujKpLxTIG5VQ4sEr6+thy7MHnAGEmMOpzMyFvQOT9kHdH6vz2efGvbr5F32lfMSiaQ3kAj0gv7QPm1tyUGrMNGA74yTKDg8O7swmTinqt9tqoKWGLUGFhlztIEYcUYLvgKTfWL8W/QeCgIZ2hTIiek/Rj+5khrKKC2Wgc5UagEqpNdmey6cOTMeCLRVrK/VDPhVAx8S/H2J2b9JVvw4htm/2dmO2R3NM9UbNbW1NVv2d6rXbq2xDcL7CAJhNOTUEA4IkzgYqiE6mSyzupFdio7H4+NQDXG4crOPAYK5iO9SOsTyehwLbTM//vGPrWn6Rah+KCgBaZqCh9CXLyjAfD6QC5m2HOrfInBSRdpij+beX3k8+/7C3y4s5JZvrC2vzfCQ7DRWB3xaicS8suLENIAcZohhB4nFkpZ7E4m41263t7cTKU+eqPK+L3KRfvSFGf/xQrKiuPjLuvzKyope88wrhmHJ9690/iQHtoZgS4w4H8wGQzgaDisKA8J5hwSeZgR5ztyiJnGwawe2xCD8AIVYEFapwDfVz4yyCi0xYBUILTGDiTa7s93Z3W33QU69qZtICK3Fbx/W/eZ42hyP7DfVpwWiAk1rcy//ZO5vwUN0YWHWEZ1dWPBE2vfsvq5XExHo2GKyShFlVOGxRsCv8a9QSc3jD2J5DkNgNg8iF1OKIUt79Br5aRCSrlw4fObwfCAedGUXlXLNwNSVm5D9A/lHe/+I/Ds9hPJvtrNmpqWqrqKlpbF6+4HW6c7ltVvbAIEoAncyETj6xrGd2BJz83mzTKlLtqxll4IEgdQoy034R15no+Pn+sqlnFjIJZ8Q/rEhEFR7CspBuB8UNBXIiAcJwLTYZ6k1SFo8L3Q0QK73Rb86N7sC/CMAhPD3zo1FpSCTKRUDbW1Oe7e1aWVHEso/cjn66RMIWhRHm4JjEZ9zyk6ewggE0fdAVH+o/PLOV6z6QeVfUe+fWPoQLxWhrxh/9X9Vkn+l86c53/3ed+gCYeaMquCZNwLTegpKQEWRCuSpeTRRX6YacEsN1yRZ4GtTFdphupJJm59VQ+z29nxf9PCw0zc+7h12EtoNtIOqaPJ3Q8hLHrHyXvvwUYmkviYYsPelZTqVyaifBduAOVwtvhANr7z77lxifjhkFRo7XG4SBysZAZUCzQGCsOO5J45AX1D+ZcSLsEdDmReBFoykCUkvqyEZt5BbyM32oO9VIB7NLp9vunRSrrp//8t//oAVf8++fgTlHwmTHR0dnZUtixtXN6obwDq/YgN2CKtJmKkmCBxiqUCsB9M4+Iuvbn6GXYE64/paNuqYj2McPB7J5R5nH8/ORqNtwxapVozhecXqL6VY9Uiz2kYaX7R5GwseZSAiMF8d5uv5zpGRbWZBoQj9l/ZZ4N/s+48X3ke0P74xoyWKVyu3B54xSNJ274Fqk0llMpnlbLM84Z8cRj/ayf3V7kV7n4GilZeFw0q/5FgEyP4Vih/louCjb380AC7jv1nK/pXOn+58D91SC/uSIBKW0vk4doqAyEQgxMXkezhjDbjEdFRDR4zfb+sqAJDWRiAQ7u3NpwIhiQ6Lk3oHhtvbdU6fFzvKiP5jW86k8l5ncnf90a0P5uNOWVLTtDhDdObcJPSsEQbO7jj/+bvvLngSbd2GrYrGsMfj6oyBcTULgGkMzG/SgDT3x6JfCklB/BLHdoXAHiHcvJaWT0UJ/kAi5dQ9hwcPB9oCjqXlul4S+X34+Wef/d1HH++k8o9m/0j064oS/KmrFtcvXtyo6G2KxWz65nVCwIvTnZ1rt9c6o4VUIMTBk9feeGPfK2999SW2xPT16TTrNwCB8xgHByOu7OPHrY8as8G2S1aexe3XM+RXhagX0n1puDtAAypA7MFnvJSgkXxgtRCWIEyXEfkXNVr50J60v8cV7ezsnCXxLwEgIeDy4lFU2E09bUmJRJL02o0ysMs36cxmkwkKQUJoYHws4h0eHp4Cn1sf5P66xNLvJuN7BkALb2qoNtbXF2Eur/5oA+Af4Z+htPO3dP60h8TBAkf7YKS0D0Z0hqHUk0oRePSFEpAtE1ZwMnRLdVXqdd1+ujiJ4o92BapYNQTcUovi4IGmXjsM1tuJIISYiuo/C7Ze2JznLbslEvOB8bbmGT0uflvLplLQtbuy5fznv5glD+OoJ3Kur6wePPM90R1Gq4JjDKRqTyiEwTwzdiDw+yW6qeDX2bgIfx0zgWgcqlVqOT59OYC1iMe5aAcYH4x3tsWXsjcqmmy24Sv3P/nqn79663Qh+wfFX1c0TPDXur5+lfIP8gAafQMSsFVN4uDby5gKPA0tMSwVeO3OtZfeZKnASyf7TDO3bmej4/Px4MREJD4eia41L64vZ5cc57rT8NtnrtMrAZRL0wowz7NqLwUg1eg0QhZPvVI94tlmJvdp+qft4aXw9HRnx+zswvvA9sdrJkSkvD1gT0skVruvF93yUQOSIzfLeJ0XJn8J/+z4xGUf9n995weCsI/KPy0Xq9YX2z7nsSeqv83V3/zH0uhH6fzpz/e+81fULVXBDBIUCjoILMU0O06H5DdmIhVpSpA89JSmCqgHO6psOpUfwmA/WMUUImGYFtm8NYSEU+Rh1RYZS8SdKtx7jgDErguVSa6zDTxvORoKJU/Eq5qb0ft0EdvWVtbWVkC/QDHE5Y4702VSvdrtcYcrlCRAZOFvvhea8k9UgplfrmbEL7P+OPhGSJ6hApQrBU7aZw9iFYJAIgCTagE1kX+v3mqw2Qam0Pjl412jN7KRUzj5Rvg3xPi3DLy7Cvyj6U+NvrmxDkXgtHr59o1llgo8BnHw2TPxLcvvgUvMFygCCQEtxsVby1gMOUxC7vFIcMfGdHY6G43Gp/qkfOa6AunH8Vj2kEITYBrlXhpByKfTtB0wTeNirJSEDI2uQ1G90hqy7unevrQ0PT3d0TG78JjcenO52WYFgtLmi+skkt02rzeJXojUEZEwUKVUtMQHIz4Y42734ZPWMHQ+s9pHYfatT0z/ybVE/iUVm/gn5v7oCFzh4qZTVvL9K50/i4NuqQpkoKLYJJU6xOTjYDEIVoggJK9CsiYM03GNKlMXGwuxsX4YeLWJ2zPzlvk9XiRhPDGW8OksVEwocfKgS2WWy7W6XvvAb45KJL+/EK+5h/5X3Mzy4+XaZczOLczOZmdnc6nEhctH68v0HS6Pu6OBl+ZLIbwgro+kAARVuIr4w8BXgIKBaJzKcdfB8x+Sf1y6KeDKri0TAOaikP2bJ78h+cIiuQa9j2jrMxR/L3zy1pHC6Ecnwd+NjY2LF6/WVDcT/uHOcVUy1txYUYcE7AQEZsNRMQ5+/a0Lb01MpigCaWP0r//P7+ua15aXgiQOJtglIjAS7ghns9moq01Tdh2MD6CkAYwDwcdpaRc0bFphNSpKQrEKnFYYjna+MPKMVGFI79kzlb0zDfyLx8nzBol+Fx7htImCr+jwbpVIQt62XmiFht0qJhWhoFFl4uQHBgfj7VCwIvcXGP9hnuLryT9UgdT3r6JZWRz+FgTfH2h+KdRAFKXib+n8mRw6GoK8K2yQwxERyjxekTdFYGNyYos0J8hi26IkDm5toPVgrIdgWRgnRGhXIFOBFIEoBL2+QGIw4lQyBMpNxqSKakESB1crdc6+tPdhICYD+ytlhgTCwL85JCCcqDvi6zPUKxsdJA7exuLgfIzL3iEBf0n4x4tfgW9CQNJGaIHDzKDAW9qjqezyjRuEsh3Q+xdvC4xHl6v9J7sHzn9I5N8XH+86djo1N3H27ODgCPg+p1xhwr/pG7dR/tW2NOi72FpcQkDbQGN17QZD4I21G53YFfjSsYOeV15//cxEBKfjnmPTcb/+9cmTtsZliIPnD9NUYBAAmM2GWw/4Q4yA2P3HUxtALPamFVoxS6vlxNpHWsspyho8I45mqOHvuVQF/Hs4PR2Phx0L0dzcSi+WSaSqni02iUTS5PWqOFiebpYB+uDouIpxSE9A0oKmbdudAzax8bnI9qWvjxZAwPa5AYxf6ssKgGO5v6/jr+hSqfhbOn9OB+JgZpRKO6OlzCUQmmSQe4p8AUREINOBdIGwJ1ql18GKJMgG2rAzOum3wcKQri4/RWBhcZLX2263w2hIwIaz9ybonJFb5JgJVHU11PqcIAL/cX57UgabLznTOoxmQIF2Njc7Gw47HC73+FS6vt64w+V2hWuUVmp6mh/95bBnWwouevQSq4cIdBAO+cehW6pSsPg7c9HZ2cfLy7lw5zhM/gbiwezya5dOXrpsh+j3i+eOvTeaOnX47JG9ew+mloZA/nWoCdxuE8pd3VhvaEb+sYqAqqupt6Gxoor8GcTBlSQO7iAicCibPbiTTsedQqOsN6lR1m8vPXuyu3ntRpaIQEAgtMRECf86KrPRuF1nlXKFXmeof6RRAVKVrhDbYrSsAmKQdo6M7FBaraG05XLgzp0b5Ddoi8fjjtmoa+GA3Ar5Q94ebw9JJBZfW68gyDCXx5bEq5S6A4nBoLfCaW/P2/lAbC+2vuQBSB3woX4VE3v/ygrwE+sexY0wTxzDN0rZv9L5szqIQFoIoV6ByD5eVIS82CDDsRwgfQNqCkpjLU0FJoGAgEC/jSUBaXMgCkMRgT6YLQBLdXCJGWuzpeVELBpNcqhHkEcV4Ye+uaKuSSqRbE1eePjAjGNqGdNabhJUIIGggxAw7Ii63PGBUJlV0+ryeBzNvHVzA4yWt764eu8eyj+aFBSbojENSEfhAInXlVeiS0RU5sK5aABNWgj+otD7cunyFWh9/ujNfW+cTtHs375jLx2MbqyFHbPq1rVbG4i/xjz/jiMCwS5R39xSvYEiUE0QuHZDPdu63jF6EFOB0BV4qqgr8LeXTp48+XzzreVocP4CIHA+Hgl2VF7NZpcfO8btz8J6UezxY0NvAD2s0yswJoY7jDEwdFTvPtSR5KxW6x5/ZfbVVwn/HhL953A4gnMrPwylYZDEtn+/jNy0qrY6uZYuUKcbkk0msxJ61Hvaayn+yPMUOl+htpU/GQDDVywKU2OjyVq086hMjHD/kP4rKMBS8bd0/gzPt78pCFIptQnElkAOW6Mx1cSSgAW/VJ59RHcmWCBM4mC3uhpHQiATSONg2hgNILSJyUDoqiXhla/dSXDYlhgLelWyZNJEH1o6XVcspm9u0FdvqVAREbj1wcOLLVIBmtMsr63QmVlCwHB4OhteWnIHfZfqDfXVYXe/a1sM4mCuoABDiruf3l0VE4FijRhsYNgcHIc9g7+5vH8pRZA663BFAyD/AtD7t6O3yX/5wyui8cG1uXfOFEY/wjX6us7WW4x/Lc36mCYJAKSU0Km6ydOAXt/QCAjEgnDr2tqtxW2uvEvM2bMThyeH8i4x4JFw8vjzi2vLEAdDS0yPNx4NZ28sLy+HHW0f/tTAEEcNagkEFawPWsG8YfCPFSGhtb9/O6ewSg3PTi3fIfy7QROAhH/xOjn0FqYt9h47kX/1P7Q7DVpcGgcIlJnlMrNgIvIv7rVX1NBMxQGi/3oHmmwqVdHeD/FukveB8Utss+9fmdj8IiKw/A+qv1Lxt3T+PM93YXumFLkmzgVDtwsWQyj4FCz7h/KPNZrgnwnmBnRL3RYzM6NAjITFinAymVeBYBfY3hMI9Hjt9t7huvjgmKNXC6Z0wA5VF8Ffsx76Xypqen8jkUiUD+YPKHlwr9daKrIiAR2OjmlCwKVUcOpFQ5msxkH0Z61g5fIijwtlPv2nuwrKREErcpFVi5WsYMxL/8s5Rza75HZ1uNydsK4j0HbBsbRc03Tp8uUrVzD7t/fY6cl38ranEP06Op4hv+LGNMFfTTWRf5quJBNJGAWrVM+ruvTNBOON6wSBlZXq1orF9fWrdDqu0BKTN4y+f/Ozy5cuneyOQSqQEHB+/u15aIlZBgKuhMd9Jw1W7AGEW1qLBMRBONoeqBWjY4nRNeLQGKwhhfXktuyr/3Qb8Dc9DfmCYEATgvA3JG87YCQ3at/wa3IFPA1AyoGaQCitDcGxSJvdXtPuxTTtAS/lH3nyMpnlmw+0v1gUsoaWpKK+IPTEii+r+v4R/EHxtyT/SufP84hdgQrWD80zyyyOIQ+HQFgpJN8XiBjklMYKTAVuiam6aSrQBl0xKgIHWh5FcQgisLfXSR5jAUwx1dbth1RgU9pi1nWTUJgop4bmxcWGRb0+1lDxw/RWydbfP5yvNSm0SrnAmeqyk6kcLt8gBFy+A+wan9KWGUzboi6Xo0aw0nqHls+A/FPwmzQh7RBkjdNYJdkzDBXX6ex0qj/cNn6GRL9tYbD9I9Hvh1dufgKTb7D04/CZs0d2QvEXWp/DndD8VzUDwx8VjQ1NTTabRkUFoPy4DiDOrqqeILClomb71Y3FxavTrTXr22YpAl+iRllQDXnv2K7XaVcgIPCS/taNpahv+ARNBUbCFwkC15Zzjvbnn8YBYY46wmAJmFZEFLQkrFAYhI5DnhqhPpQO9dmzdz4l5/ZFov/C4bijw6kz8FqpQl7T5jRIJOlLH3ZD5yW5ZWB7OmzGs6RV4E/rra2FlW8BTNPakX9JcsAyUIbhMmK+D4sfgr5RrzQ8ib+vTf2WPfmxJP9K58/5fPubMiyC8MwvWiHaBFLU0Xwga4rOF0XoJ7LYMw5Pv7ujkTkk+KkG7FIVDsTBUA+BGmMAs+w1djt0BXpVFpWtieCvpbGxpQFboJNGTbX9+XoSr/3+4cPedAg6VtKqlYVJFznBICHg9I1s9k7K3eYPlUljF9397m166NsmClB59+6PpSERfNRaBeDHo/RTKlH+pU96wcE+Oz3tcsXPzR8m/As4ssu1A5cufXiF8O8rcL1/LzWHvlc7j1Hfq9lOtVrdenH6anNmEcJfG26HIgLwOE0BHqcETELlBxFYvXhv8erF1unOqpbGVge0xBx8ad8+0SjrPTTK+ggJePLZvq7FtVstHeMkDh48HB8POqbXlte2kdA4/KGlngbBNBVIm6AhpqX5CWlZg2MkHOOJ/nvav+XOq8C/u7cJATsehh3bNKEQ+SZDU7vPLJHs9k8N9BVc98FXW85pneODwZ52WqVSY/UXyh9E/yWTmiTOh6BEl5tppceiMDezyd+CymM1EFEGFuofZfnScHn5N0ryr3T+rM93v/0NJZcfi8Nyo0KsBYOkUkj5gvwTc4EcnS0zM7dUPbbEoJH6ZgCqaCDci10WgUBHAOqMzvZAYixYK9c0twD+1tcJ/2Appclsttnbm0jIdvTBw6tNR9NgfZVu7nS7IygCCbpu3FjO3hly+U5KDNJqh9vj2qEsBz/RzGpGwTQfnaDFF1oF5rgM8E/x9G8D0WxnZ6c66okExifenhruCYL88/sv2+/fvP8VNT5wH544e6Rgewr4I/y7ePXqhl6WmdHHNPTq0UY58mYm8HtepYpR+OubYzMzLZgKnJ5W18Wq6XQcSwXidBy0xHzwhSgCheumq9lokE3HOYKOyrU18DCd7fEfNUD1Q7sHFqczW2iYjoMnqfKybf2eWsFqtRp+as++Cvy7DWf96nS4o4IzSHltSNF+wlkukch95/y8lu5dEgQLbCGWG17sAfmHvS+s+cVuryb8I/dCkrySe4LxD69mt1zL6Stw52/9k/gry6cCv6YB4VNDyfevdP7sD1okUAJiSYR2QEMbjJTGvgpWDS5QkBIRLBJoHLwjpsJFcUhAVT4GVtGSCOwcgzGDzgCmAp1YDx6MV+hbGqvXGyD+1cwA/sA0xelr+yFB4O8fPHygS0PoGlLWdkTcrqALEZi9sUxkYCo4ZTHUy2odHk+4VonL7XjUfDxHGwS1omOMwAoivEK3JZxVq5cvTrvcjjhk/074nFfXqgeamujSjy/e3PXGe5D9e5MaHxD8zXZ2ivhbr6luGVApMzMQ/h5XdUPpgzbB6ApXlbwQ/pFQvmaD9sRUVse2d2xOBUaGsCsQ68E3n1cKlm79+lUcED6cSATjjsjslnVkYB/IWYIAACAASURBVLzn0h5yZ6S1HPY8Y10kja1K0vpY1BPWSA1Wa/rScvYG4u/GjRu3b6/dvlgVM1gJOA3JA95ucjv+8JxXJ0Xpx7EZaq0l7YS9l/ZhVvzt8baD/OuF2J7oPw25L4xEA4L4Y5O/ChNm/+qL1F+5KPfKygvsYyXhfEBcX/L9K52/iPOtb8oEnq4Nof2AMPxBe2KwJVChoH2ACEIuz0DyJgga0S1VBQ4JAMGCCDRRMtj8A0477QkkCAS90X4gEBkb7GwhGhCiXyo6MDef7mrvOZ+WSLZ2PXzYQqJXTps2mGochIDRpehSmBAQzlLqwkCoXmKudLvdnTFANKYCxZgX84DMNBWKIIQeA613spWVy5VhtxvUFol+x13Lq9eV/uHz7TdF29M5lH/7RN+rzhV1qxrwV7Xe2KxvGhjoknNmk5FeN8J4Qj+diV1VogJVSc2MOQmFn8YKFIEEgQdizVvYgPC+nYDAiVNzqdE3jmEc/NnzRAM++/2+5PryUhALwmCUFWmt2lhbe3c56jj3rFWhVUBXDPQGptPwppDWc1s87ur6ehL+7nFmXyXC71PA341XyZPD2iJfTp7FrBbnM87dEsmLl64MGBRstATXgwpahQWyf+1ikyYWP5zO3mai/5Iauh8eCWgSfa+g+BsTipYe5ePe8nKx9U+MfYvICLbPJfyVzl/GgdEQDg0S2EAIRxuLxTGRAvGo9MP5OIpEQRZ7Jurpd6v1Kh31iNkcBKtgc0gTELDd6zsABCQPui3eLfsdibHIM4szzYuxGY0J+AfZKVj54ff2QOfu0aaHV2P1MBmhUGi2Rd1BR56At1+9sxQ51711t2Km09Pv2mI0GJibiog8bb4RWpnJ8GXdB7LZ5eXlHZUujyMu9r4s1zTJOVnv5ze//Op3sPNy7p3DZ17fu5fKP5eD4E9N8HeR4K+6pRmKH7ZkUidwMqMIPQJAc0EDdidnZoyQDG1q6m2pWGdtgeo6W4vaAUZZOB23VzTKOrb3gy//7ubN3/6WIPCkTn8LEYhGWXGXQ00I+Plra9HA8E/rpQA9Xou2qCGF1CDRhD2dGoNBanjxUs8doB/B36uQG1ha2jBBQ7u13ua1y2H048PL2AwDe0ZYYlTx4jAb/YClHzj6Bvjr1ZPrp6ECkLw3qowqE43x5WlzS/HOXzHsLQS/m06ehaXRj9L5izrfw1SglKYA873QbGsSx2bjFHQkRMHTj6wpRjA3qjEOpqlA2xMAVMFe9YEBJ10aQggYj7ft37+tslJN4mBH7cwM0Rzi5ksB9kTycmdbT9NuyVbrw4cPzFYeJJyysYPEwEtQw4AZNvKYz7niPovBqqwgms6xXWlAIguiWZaWegViHVixZ6o1e4NEldvIt8Zx6RHsfKsa9v9+4PzlS5+h/HvvGrM93Ud9r8KzEP2qL17d2GhsaY41AdmTRqNKJxcy5iTG9iqQuHkJqNLMzJgw5elvahpoaGxcRxWo7txvt9V0OPKpQNYS89611NmPaVPgpZN9uiKPhMh4MOLYvvhD1cx6Ntx2+UUr9gFCDYQPpQ3cNrerQgn8e7Z9ehkzf7dfJTfHnTvZ6XXeSu4ug2D31hL8dbX7/AqpFvsHGf/4+r62xGCgnTqW4QYriH4HBoB+5KioBCQERAlIXi3KGBR/N8m/snz7c7nYCvNEHFyOxd9S9q90/pIOLBBWMAQq2CQc9kazNCCvEKNfsRWGFUPIBXN1p3ukP1qb1HWjTbR/MwNZU3QvjlwF4uE4dJZUbtuhDo4NBjQyM4t/ZWxsVzBo23t8aUgFEgSmYa+RNsTVdiw5lsJLeQIu51LxqXT91votDreno4WHrkCIgDOUgAJdG0z4d+lEGPZirK2lPOMXDk+Mk0A8ml1r9Hf7X3t05ebN//3VxLE3rqXeeYu2PjPfK4h+Ifu3UdHQTEsfz7Mro5NlZKakhl4wifwzzqD+w2cAvLYNLY21tBrSsV+vIXFwtBiBjh03ToujIegSA/sz0SgrQgSqIxKpjMXWq3ZUZsO+X7+owOhXm1aEDDKHp8O0u95gMPjV2du3b0HxAwTgq6/e2DBvDZF7zmr0emUSye6BNljNDHUUqVgDTtc3jY9FfMOYkcW1H7DJntCP0J3Ev0byQvkHpCehvs7CyRpajND7UlT9KP/Dke+mU1r6Vjp/eYfEwX9FrQJpMZhjxQ/Ug1QEou7DwSyeZ+3RNDGojFVBHNzhhPWywEAsg1AMYlTsb8LZOLv3QGtnRzwcjneqK3dsfyaQGEsckHNKEgCjBLRoBYsAjW9ddt8wiYO3/v7BwwGiYQTy8NdULS1FkYCAwLUby8tR1/zlp8utM1Uuj7vTaLDyYgxMPaMhE2i1DAc6EX/ZfpR/YHt658YtTXd30/nPb9786KOPf3btTnZygu28HKXGB6z4QQc/bJokxd9xFeT+upKyzAwUS1XgJwUBsFE1s0rwB2Y4dFUo9P7oGxoaN5hRllffInrmH9u398ibb5/4VWToPRIHIwLBLdXy7EnV+o2lKMbBE8F4MFi5cdXr3a7Oxu0WQ0jLp6VSg6LOHa3gQyFr/bP2bHYN8XcbngxevXNjkTdIybcoq3fo66H42z5gxXK+gvkGcrzB0gbbqYB/sLjFh+Uo7H2G1nWNMYn8wzKwEcJ8Hez8jSlZ8bcsX+QQCZifCGFULFRF6kvyr3T+Eg/0RQu4M5jl/9j6EAVX1AmNhRC2QpOjFwgTBVlDq6vfgy0xOA3iJ6zooqMhqiTTRUQD1mwhBOzsCDsIZFq3VNX44onBcWdaocQcoMWC3gUw8qq1tff0goXng4dXuwQcAuMaLi4tIQCzywSBN2Dl7fgJf32ZoTns9jhqZQY0jM6wxmfyD/Ehf3t4+RZUVV39wfhhsD0NRO/cXjTJYeflzS//+QPo/Zv13hdXnqdS2PvSitWPjfUGvR4kEdN+dPK3Sx9LylZnNABACIGNRg3hH6xGgd0AXSqxLRzG4zAVWDk9vb+2uRZcYlJQA37BM3H27MQpN6QCwSsQROCzz36/r1u/sexg03HjDpejs6ruwMqObLRneI9BqrCWadTuTo01JLW+6G8lDL8F+b/ba7dfhRSg0UrCX2tI5YPev6M/3NYuT2vR44Jqv7RWGnJC9m94YBi9GtH4AOSf34/jiyoRgBpEO5GAcu3m0Y+iGFgMhUXBt1kClnz/Sucv9nyXbQ3hmUu0Ij8WJyo+Bfu80BLDPufMLZ24QFgDqcBunAjuShIkJGE0jobBvY21dSSwa1V3xOMkDt6/pcbubHcMjsW7jgpmGa79pSsiIWGl6I0HBkgcLH/w8IHWAIpOqm2ZzhNw+QbqOvfh9nSZwdDYQRDYCFvuhPwLJ/2/psLZNRIp3gL5R32vwtnl146f1HVf/hCLvzuPYevz/8ve+8e2cabnojeJEzh/8aoeSGI5I8zIEEUOMKKORZri7HBYaUFmaVGifpCmeCmFVClbNHVXqyxDJUJ6pChgulfY29hYQNs1hBqNDaepVXuRVICFNXq2EAz6brc3rXQMud0e3YMaXmSDk9sepUBkAfeP+73v982Qsp3N9pxtd5OdV7JE/bAkO8mT53nf533e199c+CbSv5sIf4T+3QL6B+KX0lj0xb01SlAu4nIVCi7tOnA+AERVLax/rCLGk4/hDmCELgcGvKEQQiChgUO93evH+6dgGrK08RrRwT/4o9ffQWP0t2hKzI0XJycJBNLA6EUIjB4fn2pvTaYePuyfSmeWl8OtUxMhu5/g32+3buyQP9Muwh/Mf6u7bqR/SjwFf2Hn3k95/HjziuEfjNIn07OzlP6lkP7FVkoIf85R5lkiwpf8s4J/Xir5p0XoX6EHh7+HvX8m+h1CvbrHDWEr98+qL24dPfKcQ6FzEDMo1QRAcMRQzSvSwCz6QaMVyLna0BLTohIdDPwPENCJT0RZJQIBb9bXfby561QTIVhD/f39QxCaH4/O5Rdm0h4OOSBAINvkkHOjybEUjDNDBALp9/errRsmAqKyrW4MTq+Eww1S2xSMoiGqgTemHzfOX73zcIuAxODIIhw9GuqbJoD4xoULF2787L+g9w+Gv2++Tujf1165ufTKS4MQ+tyO8HertdtHqB7Cn8au4YLTBdDPReif5vjgAxgVqKvr66vAnRLkOZFwEXzEi6ERJ7LAUA+bhlxs7+oJdV2d2tiqgivwG2CJef07S0ZQ1j9hK3DSU4CzIYtGUNZ4f5LwtVjHxFis2D7QFPT7c+Hl95qqhP4hAMKfbae6fd0NsWbhRCzqIX9bN36y4gA8hIYuxmZxfIXSv3iJmv+Q/pWKePfNWVdqGQbB5B9XOcgHfT417PfXVt+M8S97sx7zag+h+2fhn1Vf5ILVEN7OEmLY2psxB2EtP5aWakxDKAjCJ0iuE3g1JOTB/7ISxs048FeABIZVsePNzadOnpybax8DS0wqGS/FY/0zs+NxWXEIFAAV4yBaLpAag6jA5b39/U/s4Hi2i65biID9Bgck6jaf9uTcblf7yMhUa1A04E9fmb76o48efrRdfWl4bPH1N/vbgf5dzhD4e+9nSP++8e3vvZT/Szh6ROjfS9WtqamJ9iaT/oUKEedj8Efwr+B1weRaDV7/4ANNW/34Y5X5R1x0lkqgEFuBmBUW8Hp7aFzq2sXe5pBve/3EknE77s9MS8z/w1qBCIEsK3AGIDA/3gd3elubBob7feFj/lxucmWourv7MeDfLhLArXUR4M4uBtIR8P69VxolctieI0+iTM/L+RVG/0pofsH7VKVAwMQ/NskhyhdpYKIs8Wp3QTq0+cacL8dqG2+HivUH3Vbun1Vf+DIPJ2EnEAo3QpgaRiy0G2rYWBPmMCuQ5xyhE3BAuAMPCGdoNgK4RlwRrzeb9cHub2NrazOhgfNz4Ivu65uHoKzk2MzsdE9YlhQJoU+nnXtZlCPp1BvLtk6RkEDNjbAru05uTFQvVg0OSCBwKf/2hWN+sdA+PDLV6HADRlfe67u69RGpraUzY9fg6BF4/7pKNzKZ9372s7//p3/5b9/65p/fzr/5F+bRo6WmUMuJ9rkmbP61+GrwBwAI8w9Et/WCyxwTCBJEEKpooIuYAAhC2HW2jOwXWp9GTszaXG/rda15ou58Jlhi8qwV+C9/T2/HIQvE7bj86/nFgfwirOwODHao3b7c6VeLvRtb68j/dgn9I/i3rQD8hXNabE+E3L/SDT4MeGjPwR1h+IfodmfzC+OpUrFEY+8h9i8bQPXrGWXLLB4AQZWeeC477FoPzf1zU+hjCGc8aGioY331j63hr1Vfjjry3NMSi0WwG1ZoUxHziHXmRIQ3b4YgCVSCx/GAcJvTyMwnVMhFY/96erp7enpaWlrix4+3JpNwP3hoDC8Ix6Op8dmZtDMMAEgQUDEQULZXLv9zCXTw6P7v7El+lNvy9tDGRH+7AYF3204SHfy+7vbz3RPDw+0+3h6+8P7YHYJ+ly9fHRnGzbexsYGJ6uVi5pMIwb9/Au/fnxP692b9yfOJuZbVli6w/m33FArk5z5Lo/HI0yhVv+SJPJcJ/YN9EE1dJ/i3uqoiAWT0jz6IgI7ElpoLpiGh7u3tW3ebfevHT+AIyLDEYErMd5bggvDv/p1hiZmcdFJLDJ2GjE+n+iZ6Q2pP/8CpzPH2KkU/3Jfb2dlZtxO4E/1iPJ7ptNn0QMlD0S8nVuD/WQQAOz1pHP4G8OgbDH9XigB/mYSHbvMBBppuRmdZUziXr1AX/NJghl3Vg50JfyYjbAg/8+zn/YtllVVfiDp65BkFDYFoCoT/lBj4UbrH82xDmGeDEXMqTD5PcXUQHTzc6w16aDogoUEuyP0j7K+lu8fX4+tuIYh3PNqGEAg62IhIyMcqPFxxg0mIAYFcLhiPFSEt9dP9/YQfN3/92t3+iSFAQAgPIIyytbqZv3KjIdxwvWtwZKoj+OL5oYcE/964PDwyjan3Vwj928omnM4M0L9/+G+/+81D3r8lFnzQUfhg+9Z2t48AHWhCSIbHPChC/wrA/oD+qQz+gqu7H3/gIDp4ddWYnzIEjLhw9gMMMEHYYSRS8PpatntW1+/Cbkj70NBVMEabgdFv0u04hEBGAl27RAcTCARX4PjwQJuSiMeSJ4ju3yLyd3t3m+4L7+yqbqB7DU66+nF2pciHeSp/ZZyBVPwNkfGFfKoYCcTR+wfDj2IGxK+H5p4C/mFCPsO/oB27f270/uGuhwl7DYz9HaJ/NSy06J9VX6J6/tlnJI5ZAnEkjLAH4pc6oEVzOMJzRh8QPwdagd6mwZEzg71e1L/QCnN5YRzQ0tLdTTigL5vtiffE442wGpLq6+trx658NDkNrUBdJPTPSG/CVBdedsYfniUQyO/tz5dFsPtVOFfXUP/FtaamE1tbza1tW20PqwOL50dz7rDaMTUyNd10+TKhfwNnxq9h7OnY+M1qS0RVEz+D7h/LvaK5f3jyHI5+tLf3Nq2d7AmurgPYqUz9vkUgYnSU8L/COoU3taw54bCktr77cRCS5REC2SJtwSSBOPiB5iftgHoLqx946W4IQGA/ywr89gsvfOuP//iPvvPO0vdMVyD4oukRddiOyy/kT3h7TkCwdrSjur27vr5N4K+ZPFU7VkV3WMzl9HgyQ/52KpeB/onkHXY2Aq7k3M6+2ZmxeBHpH1ifV0ol7P3hmi82N7WgRzP3WTROcflcClv9aKAA2HDMRL7Hu3/GUER8zur+WfWlKrgawgJiRN4YiLDVOOaCodAHcviv6PvopFjktRawxEw0J/C/LEKBCsD/thH+fD5MSc1m44T2xdjpONTBsdTi7ExfICdLBgJydCTM68Vk3NOJELgXbIDNrhzvPdF/sbep6eRWR9fWVltzx52r+WvRyYZj56KDg4NXH15+9+EUDH/ZyfOtYkJVz2L37+9+95t/fXsQYp+/QWNPpwZM63NzSwgcLqtwNFeg14AI/pXLBcL+CLqtngX/M8BfYXdXE5A6adfhN8BgxKSAhAFGKAC6ympZBYK4Giz0NOIF4bVegMCrE1PGNARTYsAVCJYYBoE4DaneHB8fn25c6bs2PjYPANi0DfjX2tZ8t+vWyRbBDfbAXCIa1Qk/PhtdkbH7R/gfL4ucXa74c8Xx2fFkKVBk3b/oCsw+KPzRVV/yhDtvGv6/yiMGCz7NX0s+MACQid16NniI/1n0z6ovX+H1TOaHofiH5hfqDeTYSghGUZnzYLTEQIyWw9U1MHJmZMgX1MqJSCGE2actLS0E/kLegBcPZwICRqNJhMB2aE5F47E+wng6KsdkFmFH8+4hG5nQHLhugdtxbj/5PmJYaent7z1x8uSpkycJBG6d+Oijv8lfee+3Yv0nJ4aHB0/0j4zT1PuxqY1qY2ZULbPh77cI/ftLpH/fpLHPQP/u0Nlvd6hQUAmiqUHKjybp9LcAmTUugougfjWn4NneXRWEIJwXggvjlATWaWCjIQimEgKXrvVVlejgUE8j7oY0AQu8OoFxqUZQ1nfegbMhL/zg7/7hX+gNdWwF3pyaDxavvT67mH/5ZmO8q3r58vHjbc3NXV1NXRm7Pyza/TlC/8hfS+69lQTr/gH/43OyyHeeg+5fnPxVQ/ILsOxS0cA/8+pRkChgGueQ8Mi8y1dQ2NE3Y9vjcdJ3zIBA80NW7p9VX8p6/shTT6OYEllQlkH9zMho4x2mIKZgyMHhpJNgiekNaU4XAcBQyNdNBXCo6PV6AzUIhJQYTCahOngMLjXmCPhhrBVyQABA0Z+IJovLnbZjn+7dKqPPNxxWj/f2zs/NzfU2nTixdfny//3Rnb8Z728/efny3MDg4PD44utvXusbm7hZbS5mnM43EP7g6BHLvYLhL029b+/tRfxr8YUKiXLCSWTtdQIO96j5BfGvsArbvpiFFdTX7+9+gOghBOmByWDwMARS8AMhTT62ukvwDy6HRkK+HnAF3kIS2D5EF4R/75vfZEFZL33v0HacnDjV3nP9+OLitTcXXntps9HXtvbwo4dJgn8dHXGPO0ygLpyJxSH2WQhkOD+lf9C2qFTI31dDPD+bTxYp/UunUtE4Vb81/PPQzFMmfx18MBTSjJu/pvytAWBD3cv6soJfrPrSFkQkYOePxiEY2Qh2uh9HrS+HgJCxQLTE9LRTS0zZ5Q0R4udD/UvIIOJfhEJglkIgKLS+eSCB0ApcmI7wIuV/rEQgO4Hkw7eWbTZxb/9uMAw/jD/s6iL6eY4QuJO7b7xx+aMf/ejqxtZHly9ffjg9MDCYX+xLjw3crF7OjDoz77Lu37eR/oH379tG6nNTb28TeF+2fd4IW/yQrl930JNHZRh+rK8TjauuYhigoG5vrUsSfpigCMwPwBWDOth1GARVQgC1j3d3V5FhEQiE1Pzt7busFdje308XhM3A6JdeqXMFBk6ccuXWqzcH3jzzvdsbA92FxrWHsVgy2THflnnVDeYXvYgJ2q9eyAjM+4K+pYqYC7uFNHT/AoHSCu3+gfelrvuH5TEBcFSTFZXQP/PkL514mHPgR53PdRL4aevqh1Vf4jryDIFA8FMgE+QoAnJsGmIgHl8XFoMqGD9PUlsHRl4e6W9UnYUQKy8K4AgGBgANLGWpDp7HdGIkgbH0+MLMnOAWWYgJ4B9+h4rwxkdFnfwX7yE6ONeAxmglmx4autjbtVu4/PBHd+78853q1lbr5Wjv2JtvEhY4PT1RbX3DCfTvZ5T+fe+lQZP+wfC3f6j9TtMc9b748ODl6FsIEdevXyf8D2jc+moB0IzmhDoEX/XuKt4WAgRhKhi2KBgE1oq84Rxd3f3pxyxDFWJx8HYSIiAlgVcxK9BMickvwXYctcS8faJHCuvO1eODr93eqG6M7xVa1pIE/1LzPYIfvC/LkWRUJPTvwnsX+BzAXziM4yoIje7M5hfyySz5+42maO4LLr4h/6PIjSwwSPWvh9A/zecLGt4/s+Fnel8aDNwzcNB8bdE/q77cBVGBCm4HGz5A6Aiap0IMzVvDQ8YCyQNFCp2cGjkz2O5zFQpeX8hgfxDBZGBgtoQ6mE1D8HQc0cH52fGYnjP4H4yC8bvbg8U4TDxPf7K/7w3b4bvYPdG59uZQqDV958d3/jl9p9q6tdW+uPjm64v97QME4Fq0oJp5A7x//y8Of/NvspPnOPwdIuJ3bg66f7j5C75tAn+TnslJwUFIIABawbXuQvmracGgVLi7tStJDoZ/tIvmBBmsrqoO0MEmBoJBWt398KerHmfCDMahN4RpXGovTkPQFfg9mAeDDn7zD0Ze+d63v/aDv/uHH7epL/6HF+Xfem/6zO1qtXp1PE4YYDL2dioWCcP/jNzSXhI2f3M33vMw+KM5ZuTRstCXnxmLFgn8seCXFYC/w+2/IHpgRoEBeio0+IW1/BqYAcbgfZ/VBiTlt4JfrPrS19Fnn1LY6WCRaV6ON3JRDeVbk8CMBvIYpCUVegfPnBk/5VVdBS+tQIHCn0EC6yFwrg9P9NBWYECumLNgIIAiF7aHPfHSW502m3tvf0/IQcyTvcF5vC2aTI/1Xbnz4x/fqW5vbw8Nz8xcGyPsr2lgZOK4dpbSv2/9+V/XVj/ozbf29qa5pltA/7oB/srU+TwpTBIA9HiA0xEABGW7Snie6nA4uqtbH3yVHtdlJBA4IB2FqE5qiTExUF398MOPBdiEKdcCEhPlQsHl22ZH1FkvcOmV19AS84M/ev3N/NLtP//2n/ynd//z3//9f/7bG28vEfpX3dgYePN4aG8t+XayJDfApps/kdyD4e+9925U/Ab9g1Yt4F88v7AYBfUbpd6/eBG9fx7Edpjs0OW+oJPGWQuy1tMT9LuN3D9DBh97bNr7yBvup5+14M+q34A68tzToGoxMZ/nWSwgZxpimDA2yF8dCSSfoOJqyMBxV9nlLXiLXjDFUAhkNLCIw5B4K5F3dBiSjOFqyMzMWMIvGhyQIKAMrciwkoiX7hEIDBIIdPjtQALlzNtXSI39+Mc/HuslXC768M7g+PTAxpYr1Ds4OBb9+39C79/tpfxfEPr3wgu/hyfPr7bfweYfDH99EHsF535JTd4j8Cc4nWcTKGtd0P7TVgnGSa5qdVvSIbtQMtpoCIQUAmGZ1kEtMeiKWf34pz9d1WBRLkEDtUZx3QzaihGvkRjNEHAQg7Je+Ma3aGb+7bXtPLYCN/7w/7i0Q/jf99/JFyPNF+eiCXtYzNnDUjQZOWazLd+7MVkB73MYI3ygCRhehtWPPuj+0eFvMmpYnyn2GfwPLdBA/3SlAKsftatHDWz6YUw9zFWQwxORhrC1+WvVb0gdPfLU0woIXw4HIjjkoOqXhQXSNygKivQxnZLwnOSiV0NaCAmMBLyFSD38ZTAnkDpi2mgrEDlLPB5L52fzbYJbpMMQ/MI8HnGXApfLmJb6O4QFog4WPaUrFAKvniBatvnhR6mp4eGujNOjxvsHx6/8y99B6j10/4zcP/C+3GGpp+R3eNH6TOcDQAA9aF9OuFaB08HRJtC/xy/eUiW4XAKHw2EMAhyQASAjgaqpg8urP/3pxyqkQETK6AlUVScEq0L+QCRRNoKyzFYg6mA4IPzHf/SdO6veDWgF/sXwgwcbDx48OPibzXe+4/R3t7dIYdzzSMSSfvIXcO7CpGwXc2LYj94/u72S8+eyhvcvmkLzSwm8zzXx62Hi3SPQQH8HF/T1aPVXP47VDX8bjtVQ0QA+4wVvBb9Y9ZtTRzEiAZvstBkIGlgU2SqwIYY5M0e6NgwBHXxyCrbjfEGV8L+Iy0vRL2FwQAMBGQSmqS86CzfUx1vtuACMHFCu8BUMa1V82dFlm8326f6nAb+Iy8mTK+evXbny4+kT6+ve5pPNDx/emcqnA/f+689+9v618Te/DvTvdaB/FP6mhtrTd5rM3Bdgf6pGudEkrL6VKYsjT8Hr10H/BuX1tYl1jjX/sAALBYdRDANVVfsAzyUj/wAAIABJREFUMJPQv//Twe6sAQISQFwtR0YTrgREsJSdiQJYYtAV2IvpYAPm+czXozf+8R0IjP7TP3iwReTv0u3bBwfff+et0zm9AvjnluJ489I9ekHPIfELw/CXwJ+YW9b7Zmf6Vuq9f2j9G6XSvq40HP96ZLHQUuDch1LvmQQ2G4BP6gHCzd/P+1fGKqu+RHUULTF2YzmOClwMSWCq1whIMFQwK3yEh5POTHUVtIRB/hIGAGZMFRxFXzSea4R5cDYem56dHXOFRdgG4eA0LgcACJcunNmi0Nlp++TT/T05jH5seTR25dq16ab10PrJpuau5ujDjaXBt7H7N7IxuLSER4++id6/qav9vXNz9OD5to/in8cTRPiD1d9RRC6w/rlWy6qDu379evDWxlq5Ipj4J0kKEkEBOSB5zRDQgMCPf/pxsH4kjGtxeFlExVz9hNNV8DEd3NSEOngCz2f+3mC873XCAodf+euNg2r1YOPq1SkCgZs/vNeQA5ezPVdIxuFgyr1RTwW9L347EnMYDB+LA/3LHvb+Jdjs1wRA+Knp8q8ggvcvbHj/6oa7JgA+uazcP6t+84pGJFDyRyEQZyJibTnOHAZTHDSUMKTEuJoHzpwZ6e9WIR2gRv/oa8MVHW8EFkggcK4vPQ8RCVHQwSkBDkNybDGOBywURSlReiPXabN98r/tf6KEQXbbldKVa4tr3T1qR/uJ6t2trYPq4PB/+hfs/vUP5F//AQQf/B54//rv3DkxPwfy926Lz1sA9cvaf5B+AJu/q+uUAa4CXgnS9dXqVIugG+gHmTVweERCJKQXTYQgwUBQygQBy6sffPDIehypNwpldfQsJoSN4r0AzEigEIiuQBiG3L61evNr3/izH/zx11+B0NerV69ufn/z6uZLL2296g8TAAyHo+ch96/B85YApucc4J8oi+CKXtbnZ2bH4plAFvAvlUrGwPsyyrx/kwwCAf6CCICaIrsezf07xiIP6qcgj5dF/6z6zaxnn5JEGhSI23HsfJxIQ1J5zMkSTT1MgREOiPC1VuCQT8OAGCxXxFDBgWKxaAjhVgwuSRMIjJdQB89EdT9+JURADCIkD5RMyem32Y598jv7CdTJvF2P9W+ElHDb0PzJ6sHB1tZHd6Ze/8G3//r2d978i/xA/uvfppu/V4ea0ifnTe+LC87gIvzBCi6s/rpcsPjmWlXB4BIUdLVpsD0osP4ZARBFlwQ8vQQYKEGSNR51Yr1AiItZfXQ1JOJKBM6WVyOqhgBIk0gJBIYoCyQIeAcWhLvUwtK3QQf/3k0Cf0NXv0+K4N/m5kBcbwjnwvZIcu+rNltn5a0g+QeQw+EvpB6IdnuDO56fnY4FMoESHL3E1HtI/fM4H5G/SAA9Zbr6YXr/TOh7wuj3kbKGv1b9xtbzzz0l4bkk0W56XkyDIE5ExNpM5JAQ5pVgN1hipjoKmjNh4J+TSWE0xJgQiGGBwGGIhivFIC017rZzRjgCHQnLMu/JBt46betc/vTTvVX0RYt2b48Utj+8miL4V9062fUweWfqlVdGXv/jP/vWy1Pk0dLgQH97b++JO6fu3sXNXzSoaEGANx3xD3c/vC66+Us+QPCve2LquF43QRV0WWElIQWkqAIimM2DoaP4wSFXIIHAsy5nObCKc2AEwFEwBha8PXA87hbOQk74tMYpuKH+7Zc2trZuVQH/NjcPNjerXiVQyoqdUjxaAO/f2beEsEgFsJirVCoEAk8LOPzNZIp49DIVW1kp4skPzyH5ixVE+scVjM1fBmzG7IN5AD8D/mD4a+GfVb+xBashgH5sGMLRhBhT8vK8YZVhyGggICGHSrB1YuTlkYlGQMCEK+GKsPtB6ArMsP3gbgKBaImhHrZstpRcnJ3tExoYANJnkYfBcCJbhH6YtLcf5/AycNhPfj38GwJ/7RAVc7Lj4Y+unvn6n8Hqx2tTA7j5NjeH3j/0vqA/xZh+eCY9kGPKmn+qE2YfQUnqXWovVwR0DpOSdIHFdWF6v0L0sMQYIB2FGAhYXmWuQAMEV9fJH7XsAsgdxQjSUbghBxCIJLC997imJa8ODAy+9r3bYP3bAAAk5G9zY8sP6y/RZHQ+DoEQb717lnA+PhcOhwkXB/aXg9WP2cVkEehfitG/4qObb4Jg9P80j8Pu8Pno8PfzCN/hso6+WfUbXpASo+DtTJ7KYHo9jtliGPEzCaAJgdQX7WqFw0lDLU6nOQ2JUPxjWrguIwGnIYQEZrPR9PjsTEqr8EY+AkdVMCdKkShAYOcn+/s+zs7hRblj2w+qVaBUd+7caZp/+NHDqVe+9gJs/k61T01N9zadhJtHLSFm/Qsy+MPgUwQqLDS+BB1S9+BUG1G8Djr/1eFwE17vJD8EaGAJXiGyUACEfqAGEcuq6iofXhAu0Nsh7Mgmq7OwGxLaJhB4N+Twpcfmepde++ub1Y2rE5ubUxv9V7+/uVFdDx9bPt1pawjEoft377++K1RyFUjCguQXNEEve8Zg8zeTKVH6l1yhm2+Y+WyQP/Yawq+C9Oibv/7oW83m8jn07/P+/bDKqi954QFhmoeFwle0G0pY5A0JDJBHj2hynGmJIZ+neOFw0nCTF3ICQQUHIpnAISxkWYFUB8M8OF7KZkEHL8ZFP88IoExEMA97IHYtGk0cs9ncn+zvFXIivMvZ2nVyaIhIyvY7fXdOPHz37Bsnll77+itLU1NDJwgE9uPib6gAoc81egTBf2qZgNU60b6rq0GBwESQd/UOtqs6a/ExCFQEGRIL4X6nLMiAhhLlVhIFQaIwkQJCXcdlElaQEghnN8rmcrCT3o0HEtijObrXeuf6X/oebP5epep36urGmTND3asO+d5yp81G4G/5rctvyDkoyL3HxV/7MTj6tgjBL5B7mgLaXDO/eOrEL1oByffUec3rU2s3f481PAH0Gg69Zm9Z9M8qq/4XXA1BB4zdDnMPKnxFYx/EnP4aSpgKZBxT2KEV2E908ECb6km46tkfFFzVrfkCoZmPlph4sVhKgiXGabPThEBadBIdicbfAl/cp/t70mk/H48VbZWW9qHe9qGxvlR0dXV3e+vO1TP/8cxE01xvsmNieOpWD6Sblin+GRDoGXWqJgH0AJe77vcNDjZSfgfop6MHWpLgdhNtAXJIAYkOhvfXLIEEAp04C1FXg/VZgXAz04l2GCdbCkEIdDq9PV5J3SbAPP7a9wh73Zig+Le5tDTxH7/ywvDJgircg5G3zf3G5clcrlJBBOQrwADDnRUIfikFMkXD+xev5Z4Kh8ujEVaI9I+ro3/1M+BHqp4RNrit7p9VVmEdffaZp9lqBjubdGj4UfvFbDGMFdLH5eaJ4TPDE8ddzkTBBEC8KI6HNCN0JJylLJDlRReL8fnFmZk+D0TiY04qiGDgn/awVIzG0BJDINDV1qoSpOgsNEOzL5kthFqbmqq9d+4MvvzacN/8fPPdpqnB/hY1SJQghQd0t9DgP9qrU1Uifj0O2dW/NKRWqNGPLoAA/9N1WUfUI6ULMrXECAJbDUEKSAAwyAISVtVHUmLgSnIdAKrOs4nRiFd1qIQEnhp+Bbt/mwOAf4CATa748J985Wvj/UMv3hP87rMR6P4hAcyBDCbq12+P5meg+1eMwzY1BB+Y5pdH0E8TgpDmyquY++d+NOXKxLzP0L9W7p9VVtUKUmJ4DrxoMAURWTy+yfco+DFzNEe3RbCAKSqFDrwa0qPWtQITZXpH2JlAWwy6o6NRTIlJp5PxbDEQT+cX8lE5TBFQBHegTF7a7X5PNBlggdHxTltnZ05Sgj1jffHC+vYpSLuvVk/+6M5Lr7080Ly9vd7TOzx4IgE4hc4XXYfN3zK9bLTq0laDQYcnKEgtS4Ntsun9A/zTJR2LQB9IYEmHGQg81GWEUckhCUwqB9leyOojWYHsdGYZtTB1RWeKXoeiFVzluTOvHBxsEPzbRPSb+oOJy/cmOyvRkRe+8vW2YzndUyoJKH3hRaViz4XtfrcwNjvTV8oEiisAfxj7bAQfgK7XDYTH8FMIPpBY9+8wzj1B/z6iiy3vn1VWHSpYDRFpPCr1xNC8GIMG0mtxlPzRW+o1CCTw1D58ZmSqI+IplxEDy5EIqEE8KV5OUAw04lJhO47o4GwRW4HTWbdfpvZqQEJkoHbRGY0F3DZbWD5NhKIuqKuFgW8sJHrursEF9qH29urWnTubt18bPkXwRwu1D483e2Rq/ZsUJnH4C/EtcPAcZrmOijo0fMtFocNB2Z8CylcGAqjLkqzDDARP1yEY0vGIhDywDgGpEFbBFViXlkpPJZE/raqWE96QKhEAForTrywR+HsAc18AwO8vvfC16Rt/eyE3OnZmosVtc+cqOgS/hP2sBWgXw6eXo+OzizEc/oL8Nbx/o2bvz+wAwvUP8l0w9lk0gw/qNfAT5a/x0Br+WmXVo3X0yDNPA+0zUmJEgwAa6yB18QgcfS8bCIMvunkADgg3EwgkcBcpUwVMXoEyLDsjdD+k1gqEkJhSluhgwng8fvjSIjYDRQ79cHYlkEwGiPa1HRMFZ8A79/I3/nRMv9ve3gcA2N8/VK0eHBy8c+bMdFEjcHCc6OD4pI4IOIon3Gjon6oFHVpQqLRODYL3z2OwP3yC/Teid8kvnT7JBAzZBSdCDw9FxOAwhNFAtUwXhGs62JUA2AfLja8QVN5yei4kh1+5SeTvZq1G/uSFbyz0XUgtzPRLDYrD787l/OGw388mIOQtm6dvZmaslMkUV2KpFJ48h/D/UafR/KuDvyAwQN2BN38fpX91WFfXDqzHP+vqh1VWPaGOPguWGBwDwyQY+oAibwx+RQP0eLPqIdBR6BiA1ZAetMS4qCUQuBgBwAjOR9EVUyoRFojnM1NoiYnDdlxMqGBIIL7gEQDDfj3aF6sA/XN82jH1wgv5UZsyWWqfaB8a6h/qn9iAOvjh0msjb1/QJ3OOrqnhseI5nV49YrMPCD0lyCWp7UvtXEWolaQj/kmgeakIhuEvEkGcB0sAgDpwRN1EQNoKZKshYIw+vBkSwdNJ3rISLDs9mbGXYfi7MbWJrT9S/WOL+ZE/+coLC98dCUJL8+5fuf1+An9uP8M/uxtWPxZx9SOKqx/RlZIR+sz4nyHgCRw6CPxxjhAcfXvE+/dZlpdaWZu/Vln1GfX8c08pBPzsPN0O4RgNFI0pMKODh35RCOQkzQerIYMnQh4neKJBDJedTjM8NMEgEFuBdB4Mpy1KUUhL9VXsgH0yJCPwaAfhxVwi+c8ZQZLdn0x97bsdSnjyxXf/8mt/Mt13sb9/YuLm5iYBwM0ffv+Vl8dLuliRC+3Dw/OjOpr/APxg+AFOZklpHR5oYd0/BBKAPAJyIIJBAOP4Az2AMABBU6AkozAm74OOIk3KAhAEBDQg0FGzxLBxi6tQdkhEB4/GBl/ahOEvjj7e2dxcOuj939/vmx7If/eFr807jh1TnEGNUD+/H/gfeQ3075gwNjOTJpBHb55j7h8OP9iPret1GOjxBHUZbv4+Sv8OP6xhojn5PWYdfbPKqp9TR488F1QwJZCdSmLnMw8xP+Mtro4Fcpwiqa39wyMjE60RtZwoAw2EFqBTNWCQLskVEQEpBFIdnJqemenzgusPzTAim0fzfjkxKnHyckMrQY/5cxeS3/3KV/7j4Fgf4B8phMCDH26+PAvXh3Whe2J4oE0NljH2gBTAnyC7epeatHr6J1A0IQRPYg1ACUYfVAJTP44O7yGPcSpMk7LoTFjAiBjmiXFcJyDrUg0WWPCqDq2Q8GT6XkL6d/Uqwb93cPej7fjbv//759PjC/m4zXa957iWe5XAn9vtBugDGDzWQL1/mUxpxRj+BgK13JdDq28QfarzwVDd6sdh7DPcLo88pG9b9M8qq35ewWoIB31AO/NC4ysGeKLZCDSGIwb+ATVUFLUZdHB/I3iHE64yQUAjQTlBHpIXEXMakmIkMJ4t4nZcctIN3yCHp4CAA8IQBrqCeuDd097xPx3Pf+MrX5/JD1y5MjR1kxYi4J07S6/Nvv3bFUGXmwfPTLQEVbr6AXts+qtdg1OhBrOdVweB0O0T2MFihepeAEQ0xOBQGN8LoChA1xBXR9AVowUhVYGxQAzJwlsjhYJDWveujr6ffwm8fxtXmfVlc+Pi+fmu460r5/OzczabLbjViL6/HAHAcA4ZoNsGqx/pItA/6v2rnTyfpPyvHv/Ik6wUul2c/1Du32H8q3urngtaw1+rrPq8QksMAiCqYM7AOnY03RyJ1OggA0BoBYZOTBEd3OTTnGVYEEaDCJXBsDYLyTEsJoEeTqJRgaVoX352PCqHRXa3GGWwKMN+SDhRzHXa/uri7De+8vLwwPSVf/zHu1sXKQBObV7dqFabDr7/0suL708KHqnQMTjc672uYe6Bw6G4hqaaJP4x+BOY/UU3SB/sAyPWIQCCDMYeIOIjUEUaG+2oJQVSCMTNYHzhLaiSM1LQMmNLmwew+TtF4I/g39LmyVu3Lp5Pd7VO/a/jIduxsFSIVOjg10/pX87dsAz0L5aB1TeqfleKNedfPfmT6Ak4idd8kPtXl3r/ZAR8FB2t7p9VVv0i9TzMg+3UBCNiQALH2XFQa7YB64uCJKKjomjd/XA1pKus4aIYYYBYMBGGe2oJGpdlWmJQB0NKDKyGBMJhO43p5zGkC93RiuJ3C8cLkYnvnpno+8ff//3mwuXkxQ0AwI2BqzANqR788A9eW7gSEDSN67k4ONWmOoJod95emgrl9MP8T2L4B5MQGR6BDCbwB6CHsIhjYIRBgEj8EIVAlpIg1AlhOBXnQvwLCmVX2bkyjkePcPYxBfTvak/Ztb22tnZl9k/vhG02fm4xnmvImUUA0N0Jsc9A/zKlWJp6/6jz2WhZwjOFQbrpwivl7trRt0eq/uaH+S72ssGif1ZZ9QsV6mADhZDe0SvCiHWGH7DmEQRyaDBFTlIbh0bOjEy0Qu8P10Ei6Ik2fkWoJyZeB4FUBxMI7HOeDjMGCMgqyhV4paxur3baOj0DC29e6dj2Jc/vr91auzk1dXNig42DD/7mnZdnz49KwaDknTgz1UoAzqEXJtog2oBlPUsC8xHDSwA87PvBIghsgCg4EJEFYw7CIrJk6pRRJEGmCEiDAtEXCAAIw5ayi9A/zeXSRsdeenD/0g5zPkO1amDKXt0e/O544f/6q1wxNQ3GR9syw79wzt95GnL/oqOjsPoGgTlA/zIG/atJX0BAXP7VRbz522Dk/tUgroaA5nvrP0DonzX8sMqqX7CoJQZ90bTsSPXMFTlkfgiDbEOEMxwx4ArswMNJPqeGNmhAQCcjgpQE4opwyZyGGJaY8YV8s9SAs2Do//H0iXwXuXLalpOk5PjCVDR2fn//rldrXJuYuEiY4BRMQw4Ofkh08Hhs8nqQWz05ODyUJcxP0xSKHg72C2EQGBWhfoh4IHyRBCLs1XUAqSpGZwyFQ0mXqHWGRjALHoaA5LmgOiTy0BOdWLp5CfHv+yz4yqdjfkHr8PD8aZtNa0klV5KLhO45OxkBdNuchP6lAgT/MPeUWp8N+YvoXGd+gXfKEub+1dG/Q1Pgzxh9HLNWP6yy6l9Zzz/3NL2bRPGOpiQYXM+cgRh+aHM1BN8X9PXCasgpl1Z2wl4wBUGYCoM3GkMDoRPYfUgHZ9lqiA3ATxTtHIM/KLvQEfATFti+8N3xW7e6C6NvTTobL9Jx8BKgDZLAM9MZ0cHxrqaR4RM6pxjZpgb6AagImPkiU31L/S4GANKWIJhhEABljInWGSDCOBjagcZyiCGDCy5NCa6uqqPpm7erO5fA+/wODH9v39xSJz2jnslz6YVx2Gf2dsUTpVg0mhqfHY8towGwYbmUn10k9G+Urr4x+GORz/BjmexPQAKow81fNXwo+KquarcvH/uI1f2zyqp/bR157mlJREMM07tGQEydKZoz1thqYAi9Q0VrbB8cGZlqBh1cjsAzVcLAAAEFISSBCuEaBJaKxRgRiWMRMWyQQA4zYsJyjCDjaINbux7pXxhuIxgBa7+uVpyGDA4yCDx455WR8xmCfIpvaHjwoUbvfAgUByUTAXXEMxqBiqCHXBB2gWX2TJ8UTmYeQVICYqMZGC1gYr5A8E+SwHIdHbj9oLoDm7/vbFLvy3rQ85bT4+nOfyfpttmuPyTqNjCaWYnGYeCzGK8QCZsYm80D/QusxFLs5G/t4ptMrX86dcF4KP3z9rhq9O8JOFdnfzE/Sh66n7Hon1VW/asL5sEKBhQYFzOZIOZMP4xoUkHDI80gUXI149WQbqfmpNkweDsOHped9I3aNCRNU2JK2WI8RUTivOCGb4QxMQT+3Im+2dmxZDJbloiU7M7PTjvPYfCB4r24jxxwaWnz9uaDA5gH59+e5Ihg7R4c7g/xdjx8LjAh6UBAQfczTHkB0lACG4EIAHGKfI+lc+G7cCKCH5ZQK9N5CDNGB8sFTQqqq8HA3CCDP3Q+k1/VVYjqE4S5mWmvzeYvnJwncj+2MuopRqMrybGZmTFnJQvdPwJ5JVh9q9E/2v3Dn6s2/qD0D71/j62+NRyrG34cwj72ccWif1ZZ9T9Uzz/3FI/34uipJBqDypBOZK9qUpg3ZTHBL8Xha4LVkLkCXK1wwXYc4mDC6XJSLhgxXIGGJSYJJDDel19YjC+7DVHtt7XlZ8eTBCXioxHRdkyszI/MJF8lECjIueDxicFBgoAEA29v3iQkcPOlM9PvfVXWK8HmweEmbZkgn0NiNFBgayC6xIzPMOPVkRNiD1ChY18gg/gaeSBrDOLnw/Kcjs5Agn9SsEzon6Y5+JWJ2xvVHVz9pfC3se0g6lirRMZnkkT9Ki2tPUVYg45FS05PNhaNJ6dn89MzeaP7BzffVnDzg80+cDhtDkE8kwQBK0oB6N+hm+fHfpFqsFY/rLLqf7TggDCqWvQnc6wnyM6p44CYDkNE2gg0ZDFMR4gO7kYdfKoAlhiVDoFpRhZ9GHHSXiBkBbLA6JVsMRslDGncy9vh64gNxenZmb5oPBYNZGLpZPytnM3mmc7nA0CQ9EpOuztB8I/UbYI9Nx8ABL60eEPm+Vy5d3CwQ5JproFuDBNk/H105wOIoE7tf3TyKyv3FJ3Cn874n06N0hJjiYrxlRyaK6jArl2ib+nmzs7OxhSd/C5tHmwRyIcYwr7x6YLN1umKZxOjiUgR1qBj0aInQXT/Smp8xhj+UvpXxNgrELwUpPXa+GMSvM9qj8+8+ftZUPcETLS8f1ZZ9T9VR4884+CoK8+IxUcwNEkfHYkw+mcMRRgLLLf2Q1pqC7oCKQEEDYytQPTFlKEXCAvClAVCSgyBRByWan6et8tRIhST5MNFTyCZSiZj2eDycqctNDCbTlT0ewSeuMIa4h9BQCKDH1wiEPjKTNJT0fWcd4joYEVk3E9GD4yMWyCU/bG5xz3qeDZ2QmTFWIpjLUCkfwrlgoLM5LSqOpSgIEzGJ5Y2KP6h/L29dLUnqBG4D2bHpqNw8/KNnogHd2ECxdIKoYErmclMCVzPxdFR2PxN0e5fjf5RVQ4DENS/aH6RCt0F5fDN30PAV+/7q/8U6+qHVVb9z9aRZ5+SAPTsIrsah4H5TO6ybqBoQiDtBiJ7IyTQ4UVLTK/PYzhhIgkcjBgLcgkzKStGSSDVwan8wkyzbosQrZgm/HBldDRKkSIQ0ZTcaZs7lp9JTr6qoyOl5+ISdgKRAhIEPLj9Sn7lt3J6RW6cGmxXX61QWUlf6qzvB+CHEpi8vlcDP53aYdAHg3ZB6o5WjKhAAkz3BEErOzjFIVQyvYObW4B/Gwb/2yrAerCmpvLpis1WyUbfVZ1OREBnJlBaIX/MlUByDJNeKP1jsX+Af2z4i6rc9ACy4W/Q/njuFQW8Y3Wjj/pX1vDXKqt+OQXzYGZOthvwxxujYToZNkbDHGfKY3yoBIkOhrRUL5yppHeDI4lyzRVorMeZgdGQllqilpg0XAcnmFHyFJNgFkSiNKrpDadPd/Jz+emorAPb0gq3NpboetwDKCCBS9OlSkWuODqmJjq0ikzHv3T1g/qdmQFGpnoYvTCcIjPkk2kHkCpg2gbkFOwdIj4R/OMlSZmMb9w+qBL8q24yANzY1iAcJhgfGmi02WyJWHMBzvbicc3RRCYRKJVKycWZfIwFvxj4Rzc/YO1XpuMPgRFAWP0A799nrX48WvXzYcv7Z5VVv6TC65lIADEli8fcaDMsgTMemzKYCWHUwVojbse1qQwAmQjGtFTWDMSsQNTBMA9ORYEFRhdnF2aA/kUznij0ybBNNommEMm9bLN90pcfKmiQRxCUqQ4m+HebIiCBwJHzowQBT2tNg1OXKxRXYP5BF4B1Bnx0xEHxj9pfYCZMFbJCLYHs3bg7jMzRowbtvOSQRueWNqtbW9WDg40DpIA3t1YhHkEtzy3O+202f0u60aEB11U1IxVsdDQ1u5BH63cUU+/h6AcMf5H9CfQnM9t/iIhA//yfJX8PV/1nWN0/q6z65RVbDSGYhpHRdliJE1H/miEJlA3SEC2jFYjYKBW6ICWmvQfGwZEIboMw8GNRgXUQmKZpqQQXSqm+WLYUDXhKyRTbEWPZoJ6gww6nJRPX8nMgOVXVoXWvLTECeBsR8GDzpfG3X7STHzc0NDwUIHRQYdIXV+AEQwabaGhQP6qGdap6mSVQodEwOApWVYnTBf7cysTmwY+2tuDyx8GDjc2bN6shB+Twaz19Y0VC/1abu7yaisdCNJTBYGYpTs/MTKeB+SVp98/wPgvm9JfhH4w+PDpe/XhS7HN9PSp9oazcP6us+qUWXA1R6NRDtMMGHJsCM0cgZwhhZpeu9QN5TtF6hmAefMLrNHzQkUQN/zKJDIsKPKSDyXuKpWhfLA74VzJdIrSCeu50p829d23i+KqG4fdq10YNARECb98eK50jbFU4PjXYpYnU94xl9AGZ0GVrPZqkAAAgAElEQVQAiKRPRps008fkbQ4tgjQahjx0qBqnCELlQmrq4ADY3wEQQPINb96FMELXaqFtIk3oH9fd1KKqcDBEdapwPFhTCbAlZ2bH00koQ/0GmPcPGSADwFr3j9d8Pk38fPr3qPmvwW7RP6us+uXW0SMEAnmjjAGwyJgfZyrfGvjxhh7mOa0bDicNNCdwP9hpnM10JsyIBDQFslZgGldDsoFSPDnz3Xy6lC1G6vEPQMKjSW44mdk20B+qeDTN45GDdzduEvS7fRsQ8BJC4NKVGzlRzimtg1OtYo6tfUhMaFIErA1F6LRXYQvANQGMUxD8GNA/WRC4cz+ZHrzzo60f4W2Sgw3y7arrUlB1qdd7+qed5MdyNfXiNAQPlBCGShBQ0APg6ImBITBGIDBGe5q1g7+m/8/Av4pSaClw7nr8O4RzT2J+WG6r+2eVVb/8OvrsU/R2XA3wsPdnrwNEQ/fibLj2aZzDRXTwyPBQo+ZxsnEwAz/0RFNbdLFozoMxJSaaTE/PzM5OZ0edCXocPAjYAGbkoFooO9ydp23q3GJK02HO4JBDazUOeOnSQXVnYyn/jxcqFdFdaB/sD8kVmIBg3CnbAjEVMPXBEHnMyXQ+LDMzDFXA+JukoBYER2DlxeTUxtbDKvn6yADJ97q/Kjk0LeiZn04eI6jceKKtFpdfXsX4VM/8zOxiEjdfCPhF4/GisfnL+n9M++oG/ZPVHsj9+zz293hZ3T+rrPq3KbwaQi2BbD3YdEXzdA2u5oc+xAJFTnGETk6NjAye9CIJrEfAhMEBH1kNgZd9Y9MzC/mUR4Aemsdp8CNNdXl93V55udPWuXdluiXoCBIAkoLbRAf/IYG/P7xEqgoD2pHFn9wDEtgzMXgiWGFGaEW/pzPFSbDuHjy4RxHxuqmKWT+QvpvIZ0FVFR7QNzB9s7q7Vd0CANwB/Lu/rkjk+wcL7WMBm+10sKvLZ1wKcVECqDoKY7MzYzFYCEnB1h/c/HCaB8/hO9yjRh247ClMegSec3V7uYafr36f5H22hr9WWfVvV0cgJcaO19tgCALgZzdnv1xtEMLTAQkDRSzF0dMLlpiTLo9hCoyUTSFMPYGRCAhh1grEkXAqmZomOjgqyJDETOEvSPCv4F0Pdbeo4rINWoEX45IOV+A47e4DA/8OLl26f3B/6+bIdLFS0StS98RAWzAno4SWjS6gTI2A99iMl5fA7Md6gHQjDj9LJt9T4smHoPu3Ua1ukTqoHsD3uLSryHh+rmOikfwwXLLXh7hH76a7VtVy2RGcIzx2nsJfOh0D9peAi5cU/mi7kUE7nfPIWk/IcTj370lil7kA63zQFv2zyqp/04J5MEIgwh4qYjYONv3RvNEJNBuCKIWJDm6dGD4z0n8cVkOcTiJ8nWUjHyaBSVnmNITeUIdxaSwWSy8uzE575SBig4PQv0IhFFpfD617QwWHe/m0TZrbn4tUJAjCrxR2Hvzhg0sPAAJ37u+uf3z/wdJ43w3C/exS10B/Y67CJq1G569uEAy/JvW6sQgdmMCbwaAiEj5YCbTf3DgxR7jl/fv3Dy6B+l2XFYfDoQfmel02my1yqqNgnkpyFZABSt39CzNjSXYSNJ2KZgn+OZ0MABkM489Elz90CH4p8J8x/Kj3+j1aFv2zyqp/63r+2acwLJVngQhgC8S3eBP1jI4gX0NE7AkqUoHo4DOD7SHNWA2BxZAEvZlElTBNjIa01FQSxwVRDJFamJmHpGfK/tZDIV/It+6Fe0SqsgyuwP1rSYdOmJheUXYvQQ8QwOmnH+/u7OxcIhD4k3MVuZIrDA32es5RGYx1jw4/GBZSTzQLY6EIiDZBnUArR/gg/2Js4ubFi3Pt7dUqIODOg0u7eoUAlyS3TcdO22zHonONqlpDP/Jc1hzzM7NTc63HW5nNMRYP1OBPYI3IOveLXtG6ezT/IflbT/M+WxNb9M8qq/4d6nlYDYHbwSKTvaKxHEIVMPO/GCZpQxGDNlaCoTlqidGYBxDUb9nYDgZEBAjE7TgoghlwOak1NjazMJMUJM3pcnm9oXUCgF5vAWzHLpcmLnfacsUrYz5YVSMA4tgG+Du4v7t9f6e6trP24NLtpcWfTBII1HvapzoAAlmx9Tjd8KAQLOIYLaTIhEsgDoHAoMDLpYmNjf21833t7XdgBHJpZ2uVq4B/OdI3HyH0z5luK+BlTqMiLqeWHZjNjxEUT84TVd8Od6CKEafh/aOoi8DL5C/SP9cT6d8Tka/2Tov+WWXVv1Mdecah0KU4ka4Hm5MQvJ5EtTHtDYoGBrKUBE4jOnhkeKA1YewDQyoC0kAnNQZGjONxhAimxsYIaWqLxuOp6dmF6WxQLXgJ/Vsn8IcQ43SWy66ykOu02XJ7++ddPAESpVJZ3dq4dH/37g7c6F0jJHDnwe18+r1zlXs5R+vARMtkRTdxD4fKlAoaSphZUqj1D64iASieuxDdeLCzjwSwvTpxsLGx87FcIYhbmezua3HbbEJ3skXTIChfNWcgwfI87PTFwOKN+Jdsi1MCyNSv0W008p91Tg35tF9g9YO1/2pl5f5ZZdW/Wx0lOpizo/C1i2J9SIIxEjFkcL1XGl8rLC213Rf0MB+MExeD6yISAhQCs/FkeoxAIJDAeDydX5gdS6gogIH9kc9XETPJQ4UIUJt062JSz0kEAjl5fevuGsBftbqxs3PxEujgwfMv5nQiME8MtEeWK4zzGRxQN5SvwQepMpU5An+yLImvlno3Lu2sXVybu9jePtR/dWpzaxVX7NyFvjlIvY/3JZ0CPRbiZPCncqGBhZn+ZBt2NNv75lJE/8aLcCTFlL+60QLE4pRQi+tx6/NnWv7MclurH1ZZ9e9YEBWoAPiB5LWj9DV4IGODNUZooiE+gpSYUBNYYk54PU5G/RJ0LwQBkE2E0RkdTab7kAQCBCb7Z2Zner0EAQH+1HIZliw0SFtRE075WKets7i/v0dEJIFAXuhZu3kTz8btsNoYHH//xYpeyRVOTJx0VvRaCfokAz7TjayzDCwJMxAqN5IbDxD/9tfaLw71Twxc3bZXULsmh47bbbbK5VSjJMHFOMDAsqquqqpDnZuZHZin8NfXd2cu2dbanUX8M4KfKQAa7mfw/vVo4c+Av8ce15XV/bPKqn/vev65IEQF8rgcx8bAdt7AQGqJxgGxsTPHsXEw+bjDB6shU80uzUnp3+Eqw0gYIRAcMUAC08lkW1vz/MDsd/ON1GFMGCDin1ODhpqzFD9LdGjD3v6+C/bZJLmiNV9ECNwx6+bItfcmIUi1u3+iEXQwQt49ffIeICCBQYG9SzATmcEVWNFL7Tcv7eys7aytrV28eLF/oL9LdYsEvyqR3rmIzdY5GY96RDwb7BDYwaSg4CX0b6wt2kowvH2oLz2fjDXGfUVvoOzUgkHBSGcVWPdvEoJfuguP0b/Hhx8Nh9+0Vj+ssupXUkcxKhBEsN0YhNjZdhxvemDYFLimjjl8Q1FbJ0bOjPR3Q1ZUGRDvcKFTGufBMSSBY319Tac6Ok62jy/MTvsUtexEh7GqeTQPnKoUhEDy4VsQQb93LRnJVSRFrsjqrZs3L+7UVfWlmfM3iPyteBon2rM6WmImCfhNEvybnCT4d0+oQ0DFATMJ+asXkjcfAP5hAf61FySRk/WcHuuLE9Q9fbaUkBS8lgT4h65sBVY/xtOx1rZkH1G/gH9tjS3ZrNcVKauaBoeamNimzT8MfqE3f5/sfXnkua4s+meVVb+aev7ZpxWOoB9eUAcNbGcymKNZMYYrptYQpIwQGKLDdWKQ6OBen+Z8pMxDwgnkgIQE9o0NjU2P9TadOnXqxFB+diYdgaPjIIGDxi4tqfjDyx5Cx5zn9/cEO6x08HLooiGC72/d39raqm4sjb99gQBfpXzi6nwG5sGgficpCmImHzUJCnAIGHOxzsX7b14C08stxgCHmp1Exiuy25fs0wjkCqMBQcGTcQ44mQleHYcYWpydGUu2tnbMzxH5O5fqiB1v6cmGCgXoDRIKSI91Mu/LpEeQgwUf2/x9HP9+XlnBL1ZZ9aurI889JVHmh0lZMBChg2GGd8wpY7JBkZFAPJ8ZwsNJHa6gM/EoAwQchBj9Iibmp+ba+6en+4d657va2jqmZ7470xUMgpcuiGISS5JznmgqmiMQGNnfzxKSKSucX+qpblQRAHfuAwJu7WyMjK9UZL1SKfb2twkVQD6kf0gBKQQCNNErILLsmb/94D7WrVuEBV7cP1EI2zlO4eVoewuBv3MrJQ9IbvhtxglixZGamZ1ORqOtHXjybh6yD+LZbKCA+yGqZgAghT/M/evuCT5x9vvzjM/W6odVVv2K6yimpdrtyPNwKMJCAnnjNe37icaWMBPCMDmRtOOggydaWWy8WZpBBdEVHW9smycI2D/RP9Y339FMNPH47MJAVhI0YH8OgiAETiRdIqAWSKbeOA06eH9PFStAAsXgXdYGvE8RcLc6OHLlvXNEBzu624d8AIGCTvEPOeAkDIQdDgUOKvHnSv0Pdu6zIhxwf25PtSOkB1JJQv8633u7JBCgZU4+xEBeLC4u4OZvDOhfexrN3AT+Amw9DvK7KPpRBki+Hdz8/UW8L4/oX2v4a5VVv+p6Hi0xuBRsF42NEGz6sVkIY341KcwsgXZIS8WIhF6fYEDgaA0Gy+UyuxkSbes60ds+1D/Wj8201mTf+OxMX0RGxGFqEkNLOaGYLFY6bZ38/v5eELbXOF5ev8VUMCDgLnkiJPD8hXOCcu+t5v5T2XNM/hLsuzd5Dwic4viA04kGrox23KT49yHg3/39tbWQDPfqRE80HT1mszVk3g7AAXcOTscxSpfzdOVnF1MwtcZQh3Qyehzon5fBn2u1rGoOgwFOCh7M/VPDPx//Gh55jcU/Y9E/q6z6lRezxOBMGCCQXlLHOpSdRcHPlMOwQcdJrhOgg0+4PI/An7PsdJVdkUAg5PN1N7Y2d5ya6xsbIyRwLhWLRpOwHZcUKnD0V5Ic0LqDo76ywusr0RLRwbZPwBJjByFbsRMIZAh4fxdBcGPkzbf/u58IYeFUf3L0q5OsCSjAA0G6/gHcSecmV65u7mwh+ftw50P4AttBP/wB7MV0WiHfYrIYkAnNJH8+zIvWFUGvvBoZX5hJxUsQ5kVX30D9Fr2BCAAgBUE6BcHyCBWp8CTvX3092Qdo0T+rrPr1qKNHnnNgF5AaovEBPahOQa8Gf4whijUsVByYljrRVvbUwx/4ogkERrxeLwHAlsbG1raO+TSFwFQSdivGZmYXGyuAIorMdjfwfpGYWImV3Dbb8t7+ftGN+7w5R8talSEgFcLVqaVr/+W/E9SreE/MNeoM/HAM4nBIguxQKi+mbh6Qz0T8+/DD+5cu3Q8pIoE6Xoim4p02m/5eaRTRj+CfgjfjFFnU5+GUU6kUj7Fs6xjAX5HCX40BapoDupc09w9XPx69+ftEyldfVvfPKqt+beooRAXSGTAeEbZTEOQNGwyNzWL0TzQ4IM1IkNTmCbwa4mEs0ADCcoIwQC9hgD09LfGWOAQkEFQZGxsDXhWNpogOTieI9gRPCfMUwy1fUS7GUk4CUcLe/p5QkQlLE8Ou46wReIki4MPq0syVUUBAydfU7KQi+B7gn4TX0j0rQxtVin8f3v/wEuBfsMLBUpwnnRSI+i2eXxEgL4YIYBoZTfhkDg65p+OlEtK/NBw6jpeyAH+RBHMvulTXKnQBwQvoEeDqx+PdvycbYQ6/bXn/rLLq16mef/YpdjgOkc9ux9CsmvCt8wLW+CCdhvCOAm7H9YZYK5AOhVVnwlUA/CMA2JPtiXdDRkwaY1IhMToaj6YBAjUI+YMQF0xwBjVKvm4gGdeJSJX39hv1HHyE58pbOzuXdgAAAQG3CQscnnn7xa+C6O3u6PacY/RP0Iks1S/Mbe48/AgBkNC/Dwn8rQLScTkh2l48Tehf6rwTvh/yP4lmZ+WE1CzQvyzSvzT+iCWYfUTKEUJnCQKedQH6lZmDUVC4crfX8XNuXh7SvnWf0/D0c5b6tcqqX6868szTioirIeyAMH1MAa+2IEdpIJsPU0MMb6SlnqKtQLobDOsgRAEDAoayvmzW1x09HkMWCL5ouh03NrMwHpVFCVuAmCwKDTmZE4V4rFix2To/2d/35SoAUKKjGyCQIeDDrYeXtzZHrr3/IoyA1cbjIX0SzH9ECevcb68MHcCnbO2iZr5E8M8BMMrnil1A/2zOWFzg4ftwsnE2jq9A8Es6nkX5myYkdYVQwUAggGEPKri9DRGs4pmQIKF/Ppf4WUfffs5A2Ap+scqqX8PCiASEPuqJtiMG2o3YGI46AlH31kwxHNXBnNYCOri/RfOwm5mJRAJagCEobygLq8EsKxUgsA8vJxEInJ6dHcu4eYGIUA5PV1JdyouJaGyUYJX70/19RC9ZrDBLzP37Ozuggi9fri6NXLtBSKBwz7vd7RQcwAKVe397fvPB1keG/v3/CPytw2FNReRj533LkPsXjRBFj/in0CtLsvhqcmZhOlksxmF1BejfSqlUjGRqDsdyuczOhKhwKlivBHtCDr/78fbf43r38Fthq/tnlVW/lvU8247D9WCKf9QXzfKxjCYgfc1GIQiMBFAKeDipv4e6ADEZkEhggoDerNdbNE6GQLI8skDosRESiDq4z1nBaD2O3ToHFihKmWi8QuSqY29/T8KPV+TCrTVqi97CRiC2Avtu4BTYVYCu3OTki+8PbBBw3KXzD+j+7V6voL6OpJKgq997OyuIKIjh+1DIzcXzs+NA/6Iof+HoZakYiNSNtVUnHopTIcNQVT26VAiVf97w98mjXxj+PmvJX6us+jWtI885wA6DGMhTMyBzxYiGLbDWCTR9gbA7Z+ccXtyOO+n1EODAc3Gogb3eADyTJ8jI6kYEhF4gpsQAIvbNLORjQhjjq8wD5wTteMl7PCAwS4wkYrCB4qPz4AM6Cnl4+eHG8JvvXzhHgG9SF4QLkzdSEwdbl7cN9Xv/0tY6B4ZCXuhORo4RRjm6EuB4FL8cp9AjSn5PcnZ2OgqXjJMpBOYVOHqeQeQDUa+BBoYbwS48FueUZC3kdfwCuX+PFWd5/6yy6te5nn1G4tECI1IaSC/HmWvCNeirQSBdECYwGWzshwPCjR4B4hDKBAILQAIpANLLmYQEtjAS2EfPZ5awFbiYXa7IFJQUAwFlMdgdSxASeHpvfz+zDCYWTnS0VFk2AiLgRw+3NmeuvXdv8sUL/+FF4bd+MkHo3y54BdH+vHNp20F+m8K7I6moTLBUzyR0kTb/sED9ns4uLuTTJSJ/o9D9S8aihP0FEP7gmJ3moZwWolLLQANVWSn41M+mf4feeWj5o8Gif1ZZ9WteqIOx84e341ARQ1yMyGQv9v9EuiPCBiIc25fjlXLzxPCZ4f5GNALSKyEE+yKggBEDA9kiDcxnEAh0C6KjiQ4eS1AElCUGfxWZfM9yPHoW0lKJDvbYYXDB8667a1UDAQECt6o3h6+8d25SmLwxv1Hdvvxwd5fxv5376/CFOF6KRbMESHOZiEdm1mcKgRwX1udmkP7F8ap7OhaNZwH/Mgh/mkfQoK0JEliFEEOXGpRV3+PD38/xwWBZ3j+rrPoCFK6G8Az68HgIlcCm/uXttWEwI4LGdpxSODV15sxwUwhsMOxYZsRAv0AAL6jTXmAMzgxhKzCOgdGzM0kPziZkhk48QJeoZ5M/0TuJDoZWoB2gK1cp3DqEgJcbq8P5ty+8uDLxYOfy5YfM/nx/Z2f7eg7xLpIE+tepBzISL8tm/488tIeLhP6lSoFSPAazX0r/MpnEKBy+xKgaxgDR/ELwT5Zcvs9c/ah1/hqOPcL+rO6fVVZ9Qero86CDaSoMKGA7TkWMqEBTCXP1ECiyGYkS9A1BWmpXmRCnsivhAhZYAOQDMCRPBQyLBhaYpNfTU6iDY2P5hfFszi+zwUSFlxm2elbefw+Gt5/8zn6oAvqV54UeAoHVLbzwC3V5a2Pk2vmNHQKGW2z8sbNzd12CqUpYiqUiBEErNwIe5HycbGhg/picQvoXKK0kTfwj5G8U777BVMUT9HicGnQBVbgY5+CA/j168/cw9j2xGjiL/lll1Relnn/2GUURqQKmMVl12MdWQcQa/at1A8kvRWvsh7TUxjJOg6ETSMkfskF6PRgzEmo6GEyB0eT0zMx0fJkzKSCAFUFVuZJYKXkIhPk/3d9Tc/juitZya21tDRGQIN7lj7a3Nza2Lsd3txj/29nadvAwVK4UkzHdZlu+UAro+FuR/oEG5u3++CJ4/4rFFRz+pmIrQP9GSQH780A8oEBkMCm4X1Iua5KD0D8erC/1vua6X59V/qee/by/cqussurXp55/7ikJeR+IYMA/kTpiKChST6DIiXXoh5oYV0N4rWuA6OChHno3KRLx1qNfIEARsJSNm9MQgMBSPDm+MDsv5Az8owhIVDERqitFiEjgiQ6+V0EEzLla1y7eWrt1C/zOW5ePvzF0y9vSsru7vb1NEHBn2xnmcbs3msyS3+jPlEbtCH8chT/yw/vl1OzCYpz8MFGgf2h+yWQo+lEAxCcigVEDl1WJ00JeCdSv6f07PPD4TPpnt+ifVVZ9wer5556mmtcuMh74yOiXrw1D2DlNjmPtwmDoJK6GFAA6IqwCxssAGwmzVmCazYPjpWhffnY8KYdlsyhhkytCpARXQ04n9vf3cLAh5yRv10UCgLeq9+8TFnj5anV9GwrW5G75dIA/jve2dePwN5EQeAUBEIfM5Kv67cXxWej+Fc3VD/C+OE38w3RADWYggH9qwqNIhZAKN38PWZ8fAb2GJxBBv9X9s8qqL14xXzRKYBaOAKZoDpdEDOInGvZoHlUxHQfbecWBlpiJVlWjjkAKfxnkgJkAYuAjrUBIXonHpmdmp7P+HNPBSNfwW4meYmmyAQ8n7SUqwAJlu9Byau3Wzq1bkJO1W93Z3Qb+19zV0VbAHTe7J54uEuns9mSw+ydzLP2Fk/mcnobuXyCAq2/nU8koLL4B/Rtl8EfYH2TkB1m8q0fXQqHHvH8NtQeHmoD1n2LRP6us+mIWRCQo7HQ6Q0IEPdHcAmHIZ2pgpoMhMp8GRg91B51linx1hR3BQDFboiQQBsLoi84WcTuuL7gsmvMKni0I855SAObBtr39W5ob5sV8ONiyBiTw1v2trZ0dYIB7rV3NIUnUBaHCRWKxV21gfjmLqVrkx1KYBBbdWaB/xQh2/4D+RQn8Zejo10OjTgXUv0ENA64JgLp6yvZj/3rrs9vq/lll1Re2jjwDOrgGgFQS03uaDPbYdjBfMwhydEFYKZycOnNmsMkLrUAGgfVAiNtxpVLdNCQJ4fMraQJO87Kfo14V5lohz6KSCCQwLZWwQL1CwTHSShBwbecuAUDAv+PN3WVOhhsjQjyaIJ+77CHopSgc3fylX8ouEPo3BvTPGP7Gs4FMgjpf6JkmB4w/PEFmghYqqrfg8De4H1v8NepJrBAeixb9s8qqL3DB1RDeCEagC3FI/+wm5eOMcAR6L441Azn4DY6eIUICB5rBEkOEcIb8YkgYoM/QCSwBCYzRpKxUMl4qZqOQlpoNmxu7HBPDHO+IvPvWMqTEfLqfwPAYXhRCJ5EEVgkA7t3d80oi5GvxzmQcun+vjo6i948Nf1FQ5wKLCzPpbKBYitLhbzReNOgfDj4w8Jm88gThSLDTKcuFHhfXUE//Hhn7mpa/wwDpfvq5z/v7tcoqq36t63m6Hce8gCIdDNemIzxzyMAgxFDCxn6wqMB23MjIxHEViFTikAzOmEIYpyGwh8F0cDYbG5tZmC7m7MYoBPuBSDCld98ViA4+RluBqJI98VNrt+5u7Gzv7e1pmHAgBqMpoH/HdI9ujlKYkvbrfbMLYzD8XYHcU9j8zRZh+uvxaIh6BgMEB0wQ6J+s9Xglvzn8qJ8A/1w9bHn/rLLqy1BHnnsajdF4OpO3U1sgxUAek/NrHkHenIkgCRR5qdA8MHJmsLeHxmQlHpXBiIBFNg2p6eB4anF2Ji3kavNgGbU3+arObEa3ddoICdy7l8P8BH207datjbXt7QgcA5bkSrY16obu36QHgvYlRTF9NaK7e3ohnyrW6N/KShGGv0b3zzxUjHvAKtHPmPtXN/xoqMe9hkce1CGi5f2zyqovRxEdrCh2Nvyw06xAdAfagehRT6CBfUwZ0wEJHNyUfJiW2uXSjIwYhoEZ1gnEgXDJ2I6jpsBiEXTweDwnUuFKERBmzrLoKJZGO1lKDAT96XpF9zZPVHtWyYclidMp/TstexD/lFrEDO+X07ML09GMYX7B4W8kwbwvQq08AIDkB/ZUCP1zfI735Ynlt+ifVVZ9Weros09JPM1JtdOoLDudhEBLEEkg9cBQnVqXHwisTevG7biOCKhgeIrQfqDRDgzQtMASQKARkVDKlhACA7Iom9MQ8oXBw8IJkaKwbLOJn+ztO/WKAvdEJre3JYKOCidF9rwVoH8Exij8GfRPFu3Z8dlx6P7FWe4fbP46wfwiHGJ/AvpfNGdQl7w9EPxSv/rxBPSzvH9WWfUlr+efQ0sM0jDwBTJ3tB1DszgzPp9aow0yiHho5xV6OGmou2z2ATOJGhUMRDIBaorBrMA+mhddKpVS47Oz6UhO5IxhCHw9YHLcaClz77TNxu3t75VzHCAgupxlMdjS5gT40z1wIlip8UdC/4LpWRz+FuMs9hlj/1jsQa33B7dFAP6g+xd60tWPJxLAQwzR6v5ZZdWXrI4ewQPCHGYDYj4gBqeKjAbWuQF5E/zwFazOSYUmSEud9wqJMnpiEgljIIyM0LQFRuk8GPOiS9loGg4IVzp5ztwOpk4+Xo6864Q+H7QChRxQPUlSRH8gGRfJez0Zp0Ohn0mjrzgubCuOL8yki5FiNpqiC8hs8xfgb5LBH9w8d5DSVAJ/CjlExNsAABdVSURBVKV/j6feH6oG84X5Hov+WWXVl6+OgisQc1LREo3J0VQXs1iYmvLFhZB6XzQX7GknEDjVFaGdQKqFMwlatBdIk7LY/UywxGRLpdhYfnY8WhE5I8WFMTqOFxIBj/t0J7gCi+RtRVJkT7QNun+vejIe4IMGWoJ09nvGZmdg9SNLj17CqIUFH1DwE3Qmfgn9CwadHqGi+kKP0r9fpPl37OnnrJvnVln1Zaznn31KYZYYO0NCGIXY2diXjYOZLdAkghxOTrjgcTyc1Agx8wh6aA1MsODUw5aYFJ0HR+PFbGx6dmEsIYpGRALHeoKy7CkG3iI6OAw6mEhjPZKMczZb51dHRxVeUkz+R16H7YT+5VOBTKAUS+GcBWa/6H0x8U/XgQEiAQwS+qe7fOWwsfrxyLD35+Gg/2lr+GuVVV/WguuZ1BJoZ1mBHN2Qo6fTRYP6GashtYEwzzsKHQNEBzf5PGiJiSAIJiga0vBUAwFj1BWId5NoYHTa4xbrAJDSQMEZKNshJYboYE2IxsAh2KCPesD4AgQQe4AyJ3Zq9d0/pH/FOvjTCdwpkqBLSACDQc0p8Bj7fOyR7t8vQAC556yjl1ZZ9eWto0eegsBo5gikE2EWkkW3QmosUOQMAsgjO+SUoA908MAp0MERJn+dESebDEeM9ThzO462AktR0MGxSg7W3xSD/2FJiYhn2dbZ+cnv7EWjsCYnah4Jdt4UMP/RGUjYHcfN30AR6R94rYs090qAa+oCRLBKCoFBCTuAmurRHQWfy/5o7PMvsAdsDX+tsurLXkeffUbCvh5in53BH7ME4gYInYeYJJBnbUEig7lgyxCshrSVnWUnzkOMK8IUBB/LCoRhRRYsMbOz0wHwRStspYNaYzheiETg2qUtMYqrH6oDPgXYn6RI+Dmi0Ed+bzyTKUX///bOrqeJvV3jaWlJOTINE11Np2ZG49g2GWu0PIVmCsGkTdigVSlVUwwYNZKuxJDwzME+0RNO9gdwf6j9qfb/fvlPZ0BFeFxriVw/6etiLbNOrtwv133fO5JYc/GPbX/vKPOli5yhVP9qtV7Uo9GPNb+82MjK30mxO62GWPwCwFWArobwKEhFf7gQ6IkJJhkIdmfjcY5mxUYi/fjhk+fbz5/djIJ4FLP0iTtQXdKUB9sokEqBbFfR0ZDNgIPAZjoIdJ1oNKqQMfratX6tqmeFHZ+aIobjfQ7/9iYrQ63+Dan4p7ZnFj8TAIY+p7+1VhT0mn57ndY+nw74zggAG3mEfwBcBUqFuaoj8yD68GQsRM8l2TSYGyZO4pDhLklYXSJLzId77YiCv2AyCmKpBmo3ZLAys8TYPNhI4Mbmx8PXd2odV6M/dUdTA7g7aDXuX7vv9UxkytfV6Yniv+P9lu79m2rzd3hkw79VI39NnhMhDw17YHpBsErhX69TzurfN32AqbfuHKp/AFwVaDqOvYBaC/RMguuJMYa90jbvtdLn2lqgefjLPB33R8CLsgI2xchPSgFTC6P5hPoRSeCnz3vcDBF3n8e2aLp7OZr4jbCqC1949RUFh97/7L399HprOpgOt7T5Ic4/7nys8prAVTrCpBaYiMK/m/XKV44enUUjB+8LAFcIGg3hSiBfTNJdqSx8HPjpaJybRvfou45fv0MHhJ9dj1qJIWYireB0N8Ro4FaqFHhE21I//jnat4ZoVwTQKKATdau+Tn3II2w6/dYu7f2bqvePmx8vWy9J6t69k9JfuNqsNTn8owrg6nF3fS0qfyX7PQvc/AXgilEqzPccXhLo2Vqgx3sCpfBHLQ8+FUJiqAGhq80Q1wnXbjx9//7DgwOTB8fxSOeDTUocDzQOVAlMbYmh+eDNt5/e7tT6rq0DOrrpzw113XNSHqw0huZ3XwyPjnTyd4OyX7vwWfSvaV78mi/L740SHtyse9+WvxNfp8aDUf0D4OrBpUDNgLUZLBooy7IkBWYN9JJhOUc+u2Fvjafj7tX5dhw/rD2Q2iFyRp1HQ1KlQCNmJg/+eMvrcIeDeiDJfFzikebux360e/hxdziZHkn4t/HlaIWKf+9qSeeXV2Xp/G9Ua1L1r/qNk+ffo4zwD4ArSakkoyEVqQaKL7Diuanqn6vGaIkBdVGMXA3p3qY8+M1NHg0RWyBZY6gnoumwrkigfvArXZEwpH7w4eO144rRP1JAlT2Xr4fYBkllf+P1p9c7e3L0iDvJKyvqfeEdqXwdLlz17f4Dqv5l9/59V/NS7+H9A+DqwisSeB6YbDE8IndKATX/dZ3Uq1dxnLB+7yltS233AnLEBCqA6o5J8uBkNORVMhry6eOrZofUj2JAV4JA+iCr/473j18dytE3vvm7s/FlmsgfBX+igSYBtrufV/fj6+u9rPyVzzS+EP05hH8AXGFMHhzymtTZ6Ux2BNJUiMR6KoB2ebSnewNpOm7tAR1O+u+DgNVvwHNx6owe8bYscgUeHc0kcIskcGvz9eHHrd6+7IluSm9FVwY6zf7x7Y+Hn3emvPePVXM6mSTyJwtSQ+r+6vRva7VZW1qO3R+L/jI0EP4BcMVZKM6FjuxIqNjjcRXPhn6etIZ1RI7bw9ImcXhVYLQsB4RHXAqMSfz4j7ykmiFbO1oK3KADwhu7ZInZ329S9Nn0vOMKu2Mo1y4Hm4eHu8PJZI8PjbzYOGL949ZvjV0vLH+rNY3/eqvNeH29V77A5K+L8A8AsDCf56UwIn4pUwy3gG3dL307RHvClYoTxree0AHhpV5rpIMh/NoVIbTjcTwfPNuWuveFDwiPrnkkgeavlpZIxWtc23j76fPWCqW/L/jkr+w9qCXND6n/1ZRW9ThcW2bv33njv3KuCP0DAEgp0EvawdQWkWYwVwM9vRusFUBH7NCONEM8L6w/+LD9/umNpSgItBHC4sd1QTVGcy2QJZBLgVvDvaPhq9d8OIkM2C4LoHtcWQx2Dz9uHqXCv2Tyg8WvKc5n38pfrXZcX16qXkD+4P0DAFhKRdqWKstSXRFCXZslU3KU/Dp6QVgt0eKRoQZKdekRXQ25E5MExqN0ITAeTQbsiFnJdkOGR9OV4ebHT683mjwd13Sbrtv3hib8G77kvX8c/h1J+PcuaX6s2sGPao1ksVk9WK73v5v9fr0Z0oH3DwAwY6HI/WBXY0C+oKSjca6eU+c30imxC6M5D3bD6NYbI4GPr/foFC/vCIwTXyAdEJnY6bit2QHh6cp04086IHy/T/8VZ/9+7a4J/6YvX67QzV89+kHev6T4xxKYhH+tZjM24d+pvX8/AJq/AIAMpQJNx6kfkI2B5IqhTrDtiTjpYqA4A0kHSRKrB/9FefCjtV4k8d9ADgnHIzsonLHEsLllz4SFO58/fdxtNczf2NnfovX5k9FkuvGCt8hMZ+mvWF9YA5PqX+3YN+Hfj3r/0nRQ/QMAnIRHQyrihvbsnphkP4zDabF6AWV1qmTBPB7nhW2ejvuXjIaMtA6oBNIPtg1h3ZlvgsDB9NXb/327c9zptDY/HW5OWhL+bdrqX60m+ifBX1PzXzFEd9fXwvH5w79yH9U/AMBXWCjmZNqX72VqX9hTX6DLRUCHtwNqaOgmIkgHhG8+3n6//eZ2HEgp0M7IkRuGVyakJfDV5q7kwVQKPHw9HL49/LwxeTnhtc8vdr6kvX9c+pPdf/b2Ua3pt5fr7vnlD94/AMA3oRUJcj5dBoPJGE1i5zgzO3QyEeLK6vxkW2r93oft7ad31wNiFgca7QtGyfG4PfHEGAXk/c5GAnc+Hxp2j2z1T7x/E9l8oAEgq5/RPz6C1FoNg6WlC03+VlD9AwB8m8J83vdsG1j7IdrzqMjUMJtgJAPWCFCm4zxXp+Nu0LbUTAJsfdEcBYon5sWrXZLA4d5ktLL1+c8tPvomt5SS6l9K/pLwz3zfDNvXu/0LmF8Q/gEAvk+pSNtSVf3EDENv1AXoyXIsPhRnGyNiE+RSYXX9LlliHgZRYKuAZI0OkuNJ1hU4pDUvRgJpy/0omE5Ho+nGjkSFlP4GXP+bWf+s94++Paajb+dXv8Wyh+ofAOAsFubzMgMnEuhpUTA5EcejcZ6b9IYTFSRLDI+GPH+2HLExejCLBM2bCQeBg8QY/WJzc5f7wYNgMNx5xXpo8t9BYIc/aO5tVc7+ClFtNfz+3r9vUs7PI/wDAJwNSaCYXWRPjMc9EbkdpwZAKf3ZZrB+prMi/sFDuqF+t00782OSwEAn5OiY5mCyoieEJQ/WU2/DjRcmHny1s/WFesMmYtQKYC1pexA9k/52l9v+Rap/GP0AAPwgCwW6nil94Ir4ozkI9BJXjIR/0gDRFTFcGzS/1FujPPjJw0ErSGqBIoKsgBNrirH9YCOB3BShZTFH05WVySilgJZWrRXVmrX2+sFFJn87ueJZ/8sAAGDh65m6Ml8awnZbKj1mN0RECTUPthIY3X7M21KjyO4HNLFgLEI4UGvMYMVaYkzqS+Hfi43h3tTo3yDmqmHE216qVTr4a9SvFbysHXdvrlUbFzC/9Odw9QgAcA5KekC4wmvyK7YtYoM+x5b/ZGW0bswiCaTf8uM/nmxvP3+2HARqigniWMNBFkIjg9QOOcrejpuqVJKX0AR8Pb53Wev1jPwFvVV/bTn2LiB/aP4CAM5NqTBHUSCnv1IP5PlgjfVcx0aAjmvvBzsaBJp40W8/IFfgv9q9iJ3Rsd0TQzoYSyxICmgkkDe/GP3bmw4CclAbuvTU6tWiXi+KWvShttq9oPfPg/cPAHABFoo5xxFftKsLEiqyKWumdo7NgtUfbSUw7C09e/7+/ZM73ZYuSCUNNIHgiOUwjgcigZQHb21s7Jn0dzAK0kRB1KJmMmlhs3bRvX9Y/AIAuCB6QJgFkLvBPB4igZ/n6Jmk044YSY3jO29MHvz4JpkCY85rA34VnRNvNDeESf1WBgOre8zLlBSa8G+9zeHfWXp3kvx84az/RQAA+BYmD+b5YDYF8uEkuRTiyjIYR9Jfx7VbAuUfyWKZsH6PXIGP2pzFcl4bW1EjITQKWFd39EDDPxPyRYnwcfZs9K/VXo77Jpr7Uf0b62sjj+YvAOA/oVRIrobY+eCKl1hg1B7NG1NdK4baEObDSTdMHvzhTlwLgnocdONEAWM+pxmP9JT6gFu/QSsKOOtlxZSmSc2vL7fPvfePNLA/h/APAPCfUTJ5cOjaJYG8J8u1m7H0QlKqBujaiqAjoyG9W2yJuW10LSYRTASQtXBAn3VeLqb4j5FgUcO/3sFSvX+B7kcnj71/AICfAFliWP9cnY5TJ+CJ2p/rzN7JfDCdmotuPXn/7+1Ha62XJHuibfwsHkHukEhd0GhfL4pmKXAwaoXd9TX/1NG3sylXUP0DAPwcSoWcr3qn48Fu4gYUc6Cja1MTKdQg0Ks4fvsBb0uNWxTmdW0AGGhFUGNCqv6JALa0+jeKWr32UrdyXvkbj6n6h+YvAOBnoXmwXA12KACUgFBFUcfkXNdaA11bCqQB4Wj9GV8NiXoU9lnYDaMfu1z7I/WjBDjqUrbc8k34dyHvXwXVPwDAT8XkwT6nwCx+Inue7sm31hjHTUJDEUMuFBrN7F1/s/3v7WdrvcjW97J0tQDY5QSYLDKBXz1Y73XOJX/S/sXoBwDgp0OjIQ5vRdBlWPJBsmA3cQPK2nzxSRsBDGVbqlP/w+TBT2/IaMhp/euyAPKHOK6PRq1aff3gIt4/hH8AgL+EhWKOh+Mk+GNrjLzaeE/yYMmCZ6Mh1AypeOESb4mhPDgTBUbJS6J/g6DmHyx3K+cK/yQAxOIrAMBfxUKRVgXKeWC7FNVNGaHVCzN7o/BAcW+JDydd71VJ69KzHqqAJIyD0QE1f5fazsWqf5A/AMBfhsmDtQIot0P4eqabtEBOjsWlJdBzundoS8zd5d5qkgh3Y677qT2GVybUorW1budck79j/mnkEP4BAP5KKA/WbancEvbsmkAv6QArnnXDCHxp/eARHU66e7Pnt1qtJPrrqgCS+q322stt/zzqZ8HoBwDgL2dhPufLZJxkwo72hCXjtedDUq3gJAg0/0p17d6bp8+fvnl084Am34IgkPUI5IiJaqvV7tL6QbV/AflD8xcA8LegC6NZ9ioVUjy1xzhuJgYU3ZtpII+GONHanbtPPjx98+DO0kHM1ugueaCroR/Vl5bbUeXc1b8xqn8AgL+NUiHHx+FsB5j3RtvE17WOwEwGLHgVwvPjtVs3Hj16eHup3o2q1aofhqHfrbeX6lWv0ymXG2dJnjBW698YzV8AwN/IQjHnO5IGUxBolS9xv7iqgFkNDB2v3+80Oo2yeeqHPkkfrw/0HPoQev1Op9H4kfBvPHu7WEb1DwDw97Iwn3P5XBzvSvW4xOfY+yC6MDrbCTYCGBq17KcbvOYdKZ5kvY1Gg+K/H9A/YqwhYAM3fwEAfzcmD646HAXqRBylvJ7OxNkY0Pk/x0kHgUYsTQh4IsW9TyySFDZEHH9QApkOwj8AwD/AQpEOCLtsBuRmcDIGLKMgInnaBwlDJ+Q+iElzTcTH4dv4vmU8XpQw8KwGyHjR2v740clh7x8A4J+BSoGu+AFp91ViiHY1DMxmwaGkwFTnS3V6uZxXTvNN9bO/nbzto/kBAPjnKMz5oTSBpRdywgXjOqkUOBUBNspfwX75rRR4bJ/HHD6i+gcA+IcpFedCV+6FeLwXyxqhM7W/JAL0uNNrtS4b+Vm+oXwnKKP6BwD4x6E8OJTeL+0/TZLgrAAa9TNPJlIUq8ss2pthmyBfCQBPSyDCPwDAL0FhLs9RIHd5xQCtKphSQNoNSL+QFcA0SRc4I3njkxLI77D3DwDwi2DyYJ+9MLQZZmaDTmfBFAGaH48EsGPtLiciQPsmFejZdm/2UxnhHwDg14FKgSGPA2svxP5JB4GhNkEkAORb59TxSIWAKozZkI8aHqkvxmUXzV8AwC9Fga5nunYnloSB3kz+OAA8YYMRqUsU0I6ElNNql34RA2AHk78AgF+Ownw11G0ISRKchIBshA7TESDHf4uLp7PgVOg3e06eMPkLAPgVSQ4Iz5rAszqglgB1EkT0L5MAZ0bh7KYXUcCxBn+LuPkLAPhlKczn/FDaH8mO1FQJ0HaBy1boJNorZ8lEgOO0EOLoGwDgF6ZUmDN5sE6CuKnoz+UaoFOhEFC6HYscA56uAEoJcJwNAkUoUf0DAPzSkCUmdLNGaBMUhqFrVNBJj8JZWUsEcBYCZqfe9HMe4R8A4FenRKMhUgn0Uulv6CRd4Eyme2ogTr8/Ef+V81j8AgC4BBTm8671RGfKgGKEzmyDSZUAUzbAVP93kQuBaP4CAC4HpRJNx6U8MNYHKE2Q8gkBXEzJX7YHYnWwg/APAHB5oDw4Hf/JQlTn9D7A8skc2LpgUikwmr8AgMvFwnzez6S/vpsIYJLqZvQvGxgmoPkLALh8cB6c2ocaWgFMJj5OOKGTCHDRzr2NsfcPAHBJKZIrUMWPR0FSEWB5ZoUup7HyJ1lwOYfRDwDA5WShmAudxAntZlLgJMXNksl+Ef4BAC4xNBri6EboE6NwonGn9uIvLiZdEFT/AACXG5VA8kGLD7CcaoJ8LwKszEH+AACXHMqD+STIV5ogX58EofCvgfAPAPA7wJaY0z7A8teSYMmAF1H9AwD8JpQK810TBeo+QFmJv2gl8FQAuLjYQPMXAPD7UCrmqlkbjJW/0wqI5i8A4PeitDCf8x0jgOnrlxIAZhQQox8AgN+QUmEu51e0C5w0gU8KYCM/j/APAPD7USrO5d3OqZHftATm51D9AwD8npQK83mnYrLgjP7Z4K9j5A/ZLwDgd6VkJNCEgV6FAkGrgI1Gp1/x8rliAfIHAPjNKRTnc7l8PnQ8Igzz+VxuvlhA7gsAuAqUSguFYnFeKJrID+IHAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAACXif8HvOqpyWIHvywAAAAASUVORK5CYII=
- data:image/jpeg;base64,/9j/4AAQSkZJRgABAQAAAQABAAD/2wBDAAoHBwkHBgoJCAkLCwoMDxkQDw4ODx4WFxIZJCAmJSMgIyIoLTkwKCo2KyIjMkQyNjs9QEBAJjBGS0U+Sjk/QD3/2wBDAQsLCw8NDx0QEB09KSMpPT09PT09PT09PT09PT09PT09PT09PT09PT09PT09PT09PT09PT09PT09PT09PT09PT3/wgARCAGQAZADAREAAhEBAxEB/8QAGwABAQADAQEBAAAAAAAAAAAAAAMBAgQFBgf/xAAZAQEBAQEBAQAAAAAAAAAAAAAAAQIDBAX/2gAMAwEAAhADEAAAAP2YAAAAAAAAEyRM0NDAANjY3KFSgAAAAAAAAAAAAAAABMgQMFjcobGTYGpg1JmhEyXLlAAAAAAAAAAAAAAROYmXLlDIAAAAAMEyBzlTpLAAAAAAAAAAAA0OQkdJ0GwAAAAAAAANTnOYqdZuAAAAAAAAAAc5xnSdJsAAAAAAAAAADU5jmOw6AAAAAAAAAanISO0qAAAAAAAAAAAACRxFTrNgAAAAAADU4TJ2mwAAAAAAAAAAAAANTiMHcbAAAAAAGpwFDsMgAAAAAAAAAAAAAAwcZM7zYAAAAA1OE3O0AAAAAAGELhMhRkAAAAAAHEaHcbAAAAA4jU7jIAAAAAAMHlvP87fLu19FPT6LvkAAAAAAGDhNjtAAAAOY5j0DYAAAAAAA57j4R8zJRq6/Yvo2mgAAAAAANTzzpOkAAA0POO8qAAAAAAAap4N83zDxVWi1a+iez1Z32AAAAAAAJHAeibgAA4Tc6wAAAAADFSZ+ceTwnlkzRatUWrVV6nT1Xf0p22MqAAAAAByGh3AAETiPRNgAAAAADyL5/jXg5nPco1RatUWrVVq1RrqmvXenqbAAAAAA1POO0sADgKnUAAAAADWz595vj3zsJk3WjVFq1RatVWrVWqrZv05263TIAAAAAOUkd4BM889I2AAAAAB4N8vxb52EGTdaNUWrVFq1VatVaqtmqzXpO3Q2AAAAANTzT0CgOQwdgAAAABhOG8/z58qbOQZN1o1RatUWrVVq1Vqq2arNWb9B13XIAAAABxmTrB5p2lQAAAADVPgL8vzHnNZQZN1o1RatUWrVVq1Vqq2arNVb6Wut0yAAAAASOI9ImcB6RkAAAAA8S8PhHydlLlBk3WjVFq1RatVWrVWqrZqs1Vq7XU6UUAAAADB5p3kiR3AAAAAAgz595cDl5zj5zlysE3KNUWrVFq1VatVaqtmqzVWrtXbu0AAAAAOEqTNzqAAAAABiiILJjwHn+PeHgmOm67WuxqltWqrVqrVVs1Waq1dqzd2sgAAAAHKaGh1FgAAAAAYTgvPwnn8F5PEnGTOsqay3ma62vc3eu6qtWqtVWzVZqrV2qt3a2AAAAAInKaHeUAAAABqnzd8nyrw8jG6brsoybrRqi1aotWqrVqrVVs1Waq1dqrd12UAAAACZwGD0TcAAAAGD88vyPHcLLsFyDJutGqLVqi1aqtWqtVWzVZqrV2qt3XZQAAAANDzgemZAAAABrZ+cvkeW4Wa2C5Bk3WjVFq1RatVWrVWqrZqs1Vq7VW7rsoAAAAGDzAemZAAAABrZ+cPkeY4Wa2C5Bk3WjVFq1RatVWrVWqrZqs1Vq7VW7rsoAAAAGDzAeibgAAAAwfnV+R5Lz2a2C5Bk3WjVFq1RatVWrVWqrZqs1Vq7VW7rsoAAAAGh5xk7ygAAAAMHw9+b848VmtguQZN1o1RatUWrVVq1Vqq2arNVau1Vu67KAAAABM4Dc6iwAAAAMWfMPJ8W+ZZdlLkGTdaNUWrVFq1VatVaqtmqzV2+hqzVGsgAAAAETlNzc6gAAAAYs4XP8zfGquwXIMm60aotWqLVqq0a2O929F26ZuhlQAAAAABymhQkdwAAAABg/N78fictlGQZN1o1RaKNTVNlu11N+u9PqztdsZAAAAAAOEqVOA9IyAAAAAfOXyfGPm7BcgybrRrdRsbLstVs3droa6Z073Xsb3ayAAAAAYPNO8oeadpUAAAAAmz+dX5PI5jIMm60aotWqLVqq1aq1VbNVmqtdDfY3lQAAAAJHEekDkMHYAAAAAap5V4fBvmYTIMm60aotWqLVqq1aq1VbNVmqteg7UXIAAAABxmTrBM889I2AAAAAB8pfD8s8WUGTdaNUWrVFq1VatVaqtmqzfc69jYAAAAA1PNPQKAHAVOoAAAAAGtz8i8fzjxEybrRqi1aotWqrVqrVVs13zt3uuQAAAAAcpI7wAROI9E2AAAAABg+avk+VeDVndaNUWrVFq1VatVWzfqu/fOoAAAAAGp5x2lgADhNzrAAAAAAMJwufy18XlOGxRatUWrVVs16Lv6072ayAAAAAAchodwAANDzjvKgAAAAAAwczHgXyeC8tWqLVr23p9eeizWQAAAAAASOA9E3AAAOY5j0DYAAAAAAwCNx8G+blKNXa+xfQrNZQoAAAAAGp550nSAAAAcRqdxkAAAAAAGteY4fOPJRr6Ken0XfIAAAAAAMHCbHaAAAADU4Tc7QAAAAAAYsRgyFGQAAAAAAcRodxsAAAAAanAUOwyAAAAAAAAAAAAAADBxkzvNgAAAAADU4TJ2mwAAAAAAAAAAAAANTiMHcbAAAAAAAGpyEjtKgAAAAAAAAAAAAkcRU6zYAAAAAAAAHOcZ0nSbAAAAAAAAAAA1OY5jsOgAAAAAAAAAA0OQkdJ0GwAAAAAAAANTnOYqdZuAAAAAAAAAAACJzEjoLlDIAAAAAMEyBAodJYAAAAAAAAAAAAAEyBAwWNyhsZNgamDUmaETJcuUAAAAAAAAAAAAAAAAJkiZoamoAMm5uUKlAAAAAAAAAf//EADgQAAICAQEFBQYEBgMBAQAAAAECAAMEEQUSMUFRISIwMkAGEyBhcZEQUmKBFCNCUKGxFTNyc5L/2gAIAQEAAT8A9E1yJxYRstBwBMbMfkoEOTaf6p71/wA7feEluJJmh6TQ9ICV4Eie9s/O33gybfzRcxxxUGLmKeIIi3I/Bh/YntSvzNHzPyL941zvxYxanfgpi4jniQIuGvNiYMasDy6wVIvBRNxfyj8dxeaiGpDxUQ41ZHl0hw15MRGxHHAgxqnTipiXOnBjEzPzr9olqP5W9bZelXE6npHynfh3RFRnPYCYmGT5zp9IlCJwWAeM9CPxWPhkeQ6/WMjVntBErynTj3hK70t4HQ9PUu61jVjLcpn1C90RK3sPdGsrxFXtc6wAKNANPRlQwII1lmIralDpHres94aSrKZOxu8Ili2DVT6a7KCdi9phLWN26kyrE52faBQo0A0HpyoYaEaiW4nOv7QFq27NQZTlB+xuw+jJABJl2SX1VOwSuprT2cOsqpWodnHr6u2lbR28essqao9vDrKckp3X7RAQRqPQMwRSSeyW3m09F6SjGNnebsWKoUaKNB61lDAhhqJfjGvVl7VlN5qPVekVg66g9njMwRSWOgl1xubovISjH3u8/Dp/Yb8fd1ZOHSU3Gluq8xFYOuqnUeIToNTL7ja36RwmNRvd9uHL0Y9BkUburrw5yi41N+k8YDqNR4eTdvncXgJjUe8O83lHodq7YTA7id+48BLdp5eQT7y9tOg7BMbaeXj6blzadD2zZm1FzhuN3bRxHocij3Z3l8pmNduHcbgfCybtxd0cTKqja+nLnFUKug4egyrxjYtlzcEUmWXPkXPbYdWY6mLFlFjU2q6HRlOsx7RfQlg4MNfQFQykHhLajU5HLlMW7fXdPEeA7itCxhJscnmZTUKk058/QFgoJJAntBn474D0V3oz6jsUxYsWLNj5dK4aVPYofU9hMBBHYfQXVCxCOfKAmt9eYiOLEDD48q3ffdHATEq4uf28e6+rHrL2uEUczM/2uUEphJr+tpkbRyswk33Ow6cosWLFixZRlXUeSxgOkxtrhu7eun6hEdbF3kYEePlVf1j95i27j7p4H4r7Pd1k8zwlaGxwvWKoUADgPG2tt6jZqlBpZfyQTN2jkZ9pe9yei8hBFixYsWLFixZj3vQ2qN+0xstLxp5X6eMyhgQeBjoa3K9JRZ7yvXmOPw5Vm/YRyExK9ELnn423faEYWuNiHev5vySM7O7O7FmJ1JPP8BFixYsWLFixYsQ6HUTFyved1/N/vxsuvVN8cpi2blmnI/Ba/u6maIpscDrANBoOXi+0G2xgVmig65Dj/wDIjMWYsx1J4/iIsWLFixYsWLFixJjX+8G63mHikBgQYylHI6Sp9+oN+OY/BP3mGmrM/Txdq7RTZmC1zceCjqZdfZkXNbaxZ2OpPwCLFixYsWLFixYsWVsVOolbh018XMTRg/WYb8U/f8bW37WMoTcpA8TWbf2n/wAjntuHWmrupB8AixYsWLFixYsWLFiyl9G+R8W9N+kiUtuWqfwtbcqYytd+xR8/F9pdpHA2WVRtLbu4h/2YIPgEWLFixYsWLFixYsWLK23k8Wxdyxh85S2/UpmW2lYHUzEXW0noPFtoqv0FtaPpw3l1l3s3s68H+QEPVDpL/Y2ltTRe69A0v9ks5PI1dkt2TnY//ZjWD9tYVKkgggwRYsWLFixYsWLFixYsqOh8XLXS3XqJhtrWR0MzG1sUdBMNdEY9fQ3XVUVl7rERBxZiAJtL2l2DUGS3cyTzVE1m0tv4l5P8Hs5avmXP+om2Svnq1+hle2sRvMzJ9RKM3Gu093fWxPAb3bFixYsWLFixYsWJB4mYuqAzDbSxh1EyTre0xhpQPn42btjBwNRk5VSEctdW+0zPbzDTUYlFt56khFmX7ZbUyeyp0oXoiy/Ivyn377rbG6uxJgqdvKjGDFvbhW0OzMpuFf3YT/gclx5qh9SYnsva/nyUT6LrMb2cyKD3Nq3onHdQaTFosp8+Tbd/7CjT7ARYsWLFixYsWLF4eJkjWg/KYx0vWW9tr/UyoaVKPl4ntL7RX7IvqoxkQs67xZ5kbX2hn/8AfmW6dEO6P8QY9fTWLRWP6BBWg4IsH4CLFixYsWLFixYsWLFixOHiWjWph8pV2Wp9RD3mJ6xPIPp4ntlcX2+yckRQJXBB8AixYsWLFixYsWLFixYsXxH8jfSDutr0g4+L7WnX2kv+i/6lcEHwCLFixYsWLFixYsWLFixfFPEwcfF9rRp7SX/Rf9SuCD4BFixYsWLFixYsWLFixYviniYRusR0ieQfTxPa9CvtFYTwZVlcEHwCLFixYsWLFixYsWLFixfEfyN9IBvNp1lv/a/1MqOtSn5eJ7dUsM/Gu5NXp+4Mrgg+ARYsWLFixYsWLFixYsWJw8S06VMflKu21PqJkjS9pjHWgfLxPbfG97s2m/nU/wDgyuCD4BFixYsWLFixYsWLK0ZuAJiUv00i16cTANPEyTpS3zmMNb1mYulinqJhtqjDp4m18T+O2Vk0cSyd36jtH+YkEHwCLFixYsWLBBci8WEwscZahktT6c4mzUXzMzRMepeCD0GY2iATDXWxj0Ey11rB6GYjaWkdR4u3cE4G2b0A0Rjvp9DBB8AixYsDBeJAn8TWvFtfpDngeVPvP461uBC/SCx38zEyuUsUOqkg/KYu1bU7Le+P8ynLqvHdPb0PoMttbdOgmGulZPUy1d+phK23LFPz8X2t2d/E4C5KDV6OP/nnBB8AixZuhhz/AGMGLX0P3n8HWeZEGAh4M0XZ3Sz/ABFwCODiJhv1WJjOsrqfpK1YSi917CdR84lgfxrG37GPzlK7lSj8LV3LWEoffqB8SxFsrKOAQw0IM2ts9tmZ70HycUPUQfAIsWLFixYsWLFixYsqXfbTxb33KWMpXftUfjmJwf8AaYb6MydfF2/sn/k8LuD+dX2pCpQlWGhHH4BFixYsWLFixYsWLElNe4vi5j6sE6TDTi/7fjam/UyxGKOD0gIYajxfabYnHNxl/wDqo/38AixYsWLFixYsWLFmLR/Ww+nik6DU8ozGxyesqTcrC/BlV7lmvIzEs1QoeXje0OwPcl8vDT+VxsT8vzH4iLFixYsWLFixYsxMbXR3HZyHjZdmibg5zFr37NeQ+G+v3lZHMcJW5rcN0isGAI4HxtsezC363YICPzTkZbU9NhS1CjjiDBFixYsWLFixZWpc6KNTMXA3O9b2np4zMFBJ4CO5sct1lFfuqwOZ4/FlVbj7w4GYlvFD+3j5+ysbaKaXp3uTDiJn+y+VikvR/PT/ADCjIxV1KkciIsWLFixYiljoo1Mxtl22dtncX/Moxa8cdwePlW/0D95i1b77x4D43QWIVMINbkcxKbBYmvPn6DIwcfLGl9KP9RNsbBxsTEfIx98Ead3iIsWLFmzNl1X4y2275117JTjVUDStFX0F1gqQnnygBsfTmZWgrQKPAyad9d4cRKrDU+vLnFYMuo4egyqBk41lLcHUiW0vj3PVYNGU6GLFlFTXWqiDVmOkx6RRQlQ4INPQFgqknhLbDY5PLlMWncXePE+Fk07h314GY1/uzut5T6Ha2x0z++miXDgZbsvLxyfeUNp1HaJjbNy8jyUtp1PZNmbLXBG+x3rTxPoci/3h3V8omNTvnfbgPDI1Ghl9Jqb9J4TGv3e43Dl6MegyL97VF4c5RSbW/SOMA0Gg8RlDqQw1EupNTfp5GUZG73X4df7Dfkb2qpw6ymk3N+nmYqhF0UaDxmUOpBHZLqDUeq9ZRkGvut2rFYMNVOo9azBQSx0EvyDZqq9iymg2novWKoRdAOz0BAIIMuximrJ2iV2tUezh0lVy2js49PV23LUO3j0llrWnt4dJTjF+8/YIAANB6O7FD9q9hhDVt26gyrL5WfeBgw1B1HpywUak6CW5fKv7wBrG7NSZTihO1u0+metbBowluKyale8Ilj1nunSV5at2ONIGDDUHX0ZIUak6SzLVdQg1j2PYe8dZVis/a3dEStaxoo9TZQlvEaHrHxXTh3hFdqz2EiJmEeca/SJej8G8dr0Ti0fMJ8g0+sZ2c9pJleK78e6JXQlXAanr616kfzLHw/yN941LpxUxbXTgxi5bjiAYuYvNSIMmsjzaQWo3BhA68mH47682ENqLxYQ5NYHm1hzF5KTGy3PAARrXfixiUu/BTEw/zt9olSJ5V/sTUo/FRGxEPAkRsNxwYGHGt/LPdWfkb7QgrxBE1PWanrAC3AEwVP8Akb7QY1p/pi4bniwEXEQcSTFpROCj0f8A/8QAGhEAAgIDAAAAAAAAAAAAAAAAABEBElCQoP/aAAgBAgEBPwDf6xjgePRUqVI5kf/EACoRAAIBAgUDAwUBAQAAAAAAAAABAgMRBBIxQFAhMEEQEyAiM0JRgCNx/9oACAEDAQE/AP6o0NeQqVcp702KrJFOpm46UsqJScpesZNMi8y4y5XqL4IpT4nUlJRKmJy6DrOfzjNkaomnw1Wuok6rmf8AS3zXpFuJGd+DRXr5eiGxdxEZcFXr5FZF7O79F3EIi+AqzUESlcXfQhPfeLlepmdtihEXvq88segpZn1OhY6bBC3rjF6k8PAeGj4HhZeCVBotbvoXAtxWpOrRWpOrB6IixC7aFvpVoxJYuPglipeBzb8mos36EhC7aFu2YjEZHYlXnM6eSxbYoW7Ri3erY0Oj2aFu3oYr7m1Qt29DFfc2qFvMUv8ATaoW8xi+raoW8xcbw76EaCdxCEhLd+CpG8e/cuQWYVOxlXAYiGSYv32bmczmcTERdiNQUxb/ABMM0bi7NjKZD2xUxQFESEKW/ksyKsMj2a32hWpKaHsULgMRR/JGuvfRFcC0V8P+S78VwlahdfSODhr6L5peijcjC3DSpKWpPDNGW3zSZGlcULcRYlBMq0EvginSuKNuMlHMiSs/VRuyKyovxtSlmPZmhUpMp08vIamn9U//2Q==
- data:image/webp;base64,UklGRjwiAABXRUJQVlA4WAoAAAAwAAAAfwAAfwAASUNDUEgMAAAAAAxITGlubwIQAABtbnRyUkdCIFhZWiAHzgACAAkABgAxAABhY3NwTVNGVAAAAABJRUMgc1JHQgAAAAAAAAAAAAAAAQAA9tYAAQAAAADTLUhQICAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAABFjcHJ0AAABUAAAADNkZXNjAAABhAAAAGx3dHB0AAAB8AAAABRia3B0AAACBAAAABRyWFlaAAACGAAAABRnWFlaAAACLAAAABRiWFlaAAACQAAAABRkbW5kAAACVAAAAHBkbWRkAAACxAAAAIh2dWVkAAADTAAAAIZ2aWV3AAAD1AAAACRsdW1pAAAD+AAAABRtZWFzAAAEDAAAACR0ZWNoAAAEMAAAAAxyVFJDAAAEPAAACAxnVFJDAAAEPAAACAxiVFJDAAAEPAAACAx0ZXh0AAAAAENvcHlyaWdodCAoYykgMTk5OCBIZXdsZXR0LVBhY2thcmQgQ29tcGFueQAAZGVzYwAAAAAAAAASc1JHQiBJRUM2MTk2Ni0yLjEAAAAAAAAAAAAAABJzUkdCIElFQzYxOTY2LTIuMQAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAWFlaIAAAAAAAAPNRAAEAAAABFsxYWVogAAAAAAAAAAAAAAAAAAAAAFhZWiAAAAAAAABvogAAOPUAAAOQWFlaIAAAAAAAAGKZAAC3hQAAGNpYWVogAAAAAAAAJKAAAA+EAAC2z2Rlc2MAAAAAAAAAFklFQyBodHRwOi8vd3d3LmllYy5jaAAAAAAAAAAAAAAAFklFQyBodHRwOi8vd3d3LmllYy5jaAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAABkZXNjAAAAAAAAAC5JRUMgNjE5NjYtMi4xIERlZmF1bHQgUkdCIGNvbG91ciBzcGFjZSAtIHNSR0IAAAAAAAAAAAAAAC5JRUMgNjE5NjYtMi4xIERlZmF1bHQgUkdCIGNvbG91ciBzcGFjZSAtIHNSR0IAAAAAAAAAAAAAAAAAAAAAAAAAAAAAZGVzYwAAAAAAAAAsUmVmZXJlbmNlIFZpZXdpbmcgQ29uZGl0aW9uIGluIElFQzYxOTY2LTIuMQAAAAAAAAAAAAAALFJlZmVyZW5jZSBWaWV3aW5nIENvbmRpdGlvbiBpbiBJRUM2MTk2Ni0yLjEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAHZpZXcAAAAAABOk/gAUXy4AEM8UAAPtzAAEEwsAA1yeAAAAAVhZWiAAAAAAAEwJVgBQAAAAVx/nbWVhcwAAAAAAAAABAAAAAAAAAAAAAAAAAAAAAAAAAo8AAAACc2lnIAAAAABDUlQgY3VydgAAAAAAAAQAAAAABQAKAA8AFAAZAB4AIwAoAC0AMgA3ADsAQABFAEoATwBUAFkAXgBjAGgAbQByAHcAfACBAIYAiwCQAJUAmgCfAKQAqQCuALIAtwC8AMEAxgDLANAA1QDbAOAA5QDrAPAA9gD7AQEBBwENARMBGQEfASUBKwEyATgBPgFFAUwBUgFZAWABZwFuAXUBfAGDAYsBkgGaAaEBqQGxAbkBwQHJAdEB2QHhAekB8gH6AgMCDAIUAh0CJgIvAjgCQQJLAlQCXQJnAnECegKEAo4CmAKiAqwCtgLBAssC1QLgAusC9QMAAwsDFgMhAy0DOANDA08DWgNmA3IDfgOKA5YDogOuA7oDxwPTA+AD7AP5BAYEEwQgBC0EOwRIBFUEYwRxBH4EjASaBKgEtgTEBNME4QTwBP4FDQUcBSsFOgVJBVgFZwV3BYYFlgWmBbUFxQXVBeUF9gYGBhYGJwY3BkgGWQZqBnsGjAadBq8GwAbRBuMG9QcHBxkHKwc9B08HYQd0B4YHmQesB78H0gflB/gICwgfCDIIRghaCG4IggiWCKoIvgjSCOcI+wkQCSUJOglPCWQJeQmPCaQJugnPCeUJ+woRCicKPQpUCmoKgQqYCq4KxQrcCvMLCwsiCzkLUQtpC4ALmAuwC8gL4Qv5DBIMKgxDDFwMdQyODKcMwAzZDPMNDQ0mDUANWg10DY4NqQ3DDd4N+A4TDi4OSQ5kDn8Omw62DtIO7g8JDyUPQQ9eD3oPlg+zD88P7BAJECYQQxBhEH4QmxC5ENcQ9RETETERTxFtEYwRqhHJEegSBxImEkUSZBKEEqMSwxLjEwMTIxNDE2MTgxOkE8UT5RQGFCcUSRRqFIsUrRTOFPAVEhU0FVYVeBWbFb0V4BYDFiYWSRZsFo8WshbWFvoXHRdBF2UXiReuF9IX9xgbGEAYZRiKGK8Y1Rj6GSAZRRlrGZEZtxndGgQaKhpRGncanhrFGuwbFBs7G2MbihuyG9ocAhwqHFIcexyjHMwc9R0eHUcdcB2ZHcMd7B4WHkAeah6UHr4e6R8THz4faR+UH78f6iAVIEEgbCCYIMQg8CEcIUghdSGhIc4h+yInIlUigiKvIt0jCiM4I2YjlCPCI/AkHyRNJHwkqyTaJQklOCVoJZclxyX3JicmVyaHJrcm6CcYJ0kneierJ9woDSg/KHEooijUKQYpOClrKZ0p0CoCKjUqaCqbKs8rAis2K2krnSvRLAUsOSxuLKIs1y0MLUEtdi2rLeEuFi5MLoIuty7uLyQvWi+RL8cv/jA1MGwwpDDbMRIxSjGCMbox8jIqMmMymzLUMw0zRjN/M7gz8TQrNGU0njTYNRM1TTWHNcI1/TY3NnI2rjbpNyQ3YDecN9c4FDhQOIw4yDkFOUI5fzm8Ofk6Njp0OrI67zstO2s7qjvoPCc8ZTykPOM9Ij1hPaE94D4gPmA+oD7gPyE/YT+iP+JAI0BkQKZA50EpQWpBrEHuQjBCckK1QvdDOkN9Q8BEA0RHRIpEzkUSRVVFmkXeRiJGZ0arRvBHNUd7R8BIBUhLSJFI10kdSWNJqUnwSjdKfUrESwxLU0uaS+JMKkxyTLpNAk1KTZNN3E4lTm5Ot08AT0lPk0/dUCdQcVC7UQZRUFGbUeZSMVJ8UsdTE1NfU6pT9lRCVI9U21UoVXVVwlYPVlxWqVb3V0RXklfgWC9YfVjLWRpZaVm4WgdaVlqmWvVbRVuVW+VcNVyGXNZdJ114XcleGl5sXr1fD19hX7NgBWBXYKpg/GFPYaJh9WJJYpxi8GNDY5dj62RAZJRk6WU9ZZJl52Y9ZpJm6Gc9Z5Nn6Wg/aJZo7GlDaZpp8WpIap9q92tPa6dr/2xXbK9tCG1gbbluEm5rbsRvHm94b9FwK3CGcOBxOnGVcfByS3KmcwFzXXO4dBR0cHTMdSh1hXXhdj52m3b4d1Z3s3gReG54zHkqeYl553pGeqV7BHtje8J8IXyBfOF9QX2hfgF+Yn7CfyN/hH/lgEeAqIEKgWuBzYIwgpKC9INXg7qEHYSAhOOFR4Wrhg6GcobXhzuHn4gEiGmIzokziZmJ/opkisqLMIuWi/yMY4zKjTGNmI3/jmaOzo82j56QBpBukNaRP5GokhGSepLjk02TtpQglIqU9JVflcmWNJaflwqXdZfgmEyYuJkkmZCZ/JpomtWbQpuvnByciZz3nWSd0p5Anq6fHZ+Ln/qgaaDYoUehtqImopajBqN2o+akVqTHpTilqaYapoum/adup+CoUqjEqTepqaocqo+rAqt1q+msXKzQrUStuK4trqGvFq+LsACwdbDqsWCx1rJLssKzOLOutCW0nLUTtYq2AbZ5tvC3aLfguFm40blKucK6O7q1uy67p7whvJu9Fb2Pvgq+hL7/v3q/9cBwwOzBZ8Hjwl/C28NYw9TEUcTOxUvFyMZGxsPHQce/yD3IvMk6ybnKOMq3yzbLtsw1zLXNNc21zjbOts83z7jQOdC60TzRvtI/0sHTRNPG1EnUy9VO1dHWVdbY11zX4Nhk2OjZbNnx2nba+9uA3AXcit0Q3ZbeHN6i3ynfr+A24L3hROHM4lPi2+Nj4+vkc+T85YTmDeaW5x/nqegy6LzpRunQ6lvq5etw6/vshu0R7ZzuKO6070DvzPBY8OXxcvH/8ozzGfOn9DT0wvVQ9d72bfb794r4Gfio+Tj5x/pX+uf7d/wH/Jj9Kf26/kv+3P9t//9WUDhMeBUAAC9/wB8QCQeRJClSNBz9tH/Ds7/gIKL/E4BZYV7YW6Mkt1tm7mumD0oTYMtMTWTKQJb+TgkcpUniGc9Ug1kEYiQLRpEkKcq4F/MJOP/SzsbyKmDbSJKi0gXA8G99/uExmIraNpKTfo32rAbC9H8C0Kuw5CXLmp1Ts8RlLlaKBlaP3gXDVqMCIMOZxxprrDnvt3rY5fyjZwYATv06iH9g30+weigddRHooi7/XVFNuxQTizIMAIbatm0Y+/+z0+scEROAoZQxapTwOGNP9CPZtmrbtm15HWOszRiDHe1tW2Le8g4Airy3yNre0mIYbbRs1muptVHvusRIkhRJ8jxQ7s16n5kFe90OxIAPCZFsu7bSc7CQM+6+FsJ18v6XwJdA8vMWBUiSTdtW7nufbdu2bdu2bdu2bdu2jW/bNg4g2rYSVLo6VoJJV6R03hdQsrZtjabcz/clJam/3d1lAUzZQ28JdxgxsjlLYd7u7k05JUm+55wkyBIoRrat2lZ6rINDkO6aMVl8A+6UEEmSI0keNX9Y75/NQ9Nc9CaV27aWbcvc1/1+mhSX6CSqE6kaIblkJ7k7RP8J7p7cXZNDojGe+9oM3DZStAyZWd6DJyCAu0/LuQJUQjkURnqkBPyAb/EKD/EEHjAt52qAemiBnBMj8BZO4CYuPRiWc3XBcozctARvYjzOPhCWczXDEBTYZQ1uYRSePgiWc2VHc5TfbRF6YOdDAEPQ/YhNOICO94/lXAMxALHHzMJO9LhzLOcqhVWofNgy2oK+94zlXBmwBq2PGkYCQTAKy+8Wy7kSow/mIMkhXQgEEAAgIRO+vlOgGjYj8zEZqQWAgiuoe5dYzlUFo3efkZHuAKCoBgSdsP/+sJwrLeqj9hl8AwBEAEDBe8h/d0B3jNjlZtt8RzqUXgCy47P7wnKuzmiFJHtqlKEDIGJQBWVUJbIY4+4Jy7mKYBoqnsd3sUsEAPQZst8PlstDAqxHjxPcDAYZERBAsSvKCHeD5fLQD5ORbZ9MECDMwDeJmfFNhnko/94LlstDFaxHkUGWAoNsnNrDUAOZ60JEVAOi6H1guXwriOWoDwAkQznsZiMlgywCApR7wHL5lhhDMZ/AVKacw3dAoEyKyB1guXzvgmWZtAqBUtxk5/ENpNh1B0XefmtsjURtYhCLAsotJZZSZ5USNFQDghZVFmkIxFDA3B+vL/5y+ZH9WzcmffBcv0/x2fKx/v6QeJ9NbDafU+jLhL408T6HL8iXJ/jKVVG3Bf4LPPHp/0DDLr4JbPFdpN0ucik++ftnynbHJ/98vuDefxM/HmZiM95rR29W2bSUbay9ljVrapKpMHhtPt/xqx7Z0SclK3qdWtRhsVgsdiwuyHSooagGQMphcEMRwJX44u/vF3z+1bebgsw6IWtB+hk9Rq4lOzNbBZXG9ozq1VzLsllMH7P1YOVu56U6Var/z1E1PBf+PwkNiyAWy4zvOtZVGlQZCYjdNbkQP/357eS67vr2s290keZga2CpW1NJMJz40FDIlSQgW8IxUnfHbmw0nrRcX8bp0Z1DzyV7PmCnEyE7+S66UAwgicvwyx9fDyu592dfj1WoeK1kKHFY8KIwFSC+sDAIALTjQwCxsxO7ypRM8CFe/vu7PB9k4oK449IGW25WZXU4UgCgjYvww++/gmou+/3Nl6vjRWBWwdfCMAgBcShsmJIAwKJwABAgCAoiL0N513Jnv/rg/pYl9khiYWGp00tsyIAUWTUg5hqVn39/brmwJB5xYza+wlpcBIIBaBBeEBQDq0ACLITAKwqFQo0QCuiXg70Z3/9xe7/K/xo6Fndc9vM9jIeABrgAv/r+XOXVRq5qlWFxrdKWqzQMDKBgeIWGwmDoYHFAEQiLb2hUhNBImkKVGHt6+HTpf3jhBWEZZEqdZ4OfkXkIOB+//vGc+lWT32ZksGIl5CuwAIFBIAaQ+IaBIQADIVgwPtUOCqJo6hQhFIpsxBh2QiV3uEcZSJMu28P3KCOigTkbv391G7W2mSFJYu0eeiNYu9MqILxwMIAKJkFCMACmKXcBYfiBKaJEUMioCBJJI+eyjI9vvfpY1q+HOwgCEARBqpsNutUVyiHj7LM/nFvDt0wNFUWIJNHVrPFm2AsACjsYChtHGA5AYSBs/IQhAF8YNGwEJYKMoCIIIQSVENtkk147OXyNUiQI4sKCICPNVVYN6K2anPve+fubW9b1v5WhZbAiCUMiCNaguBhADcLGHYVDMDCAwNEABMYCWLhRKCRKFI2QoKKiiDJJTl+9lhQulSAdu833EH4gAOM8/OP9Y9K3/5u/0hfxEiGcCNYIgsQKlSASFwZwKAwABEAYTRZxERQWRKKiIEJIaYxC0eATfISTXVwQxB2E5X8EIMoL79SW//342GLNuiRjEMJpght6PSAkCndcglhkgA8AGIKj2QIIYVEwGlkhgAgJESCDKEIImwhpUfa5lE6nepvvyDAFEuQs/O/zY/U1K0PxIISrLM2KRJAALkASoEiOwgWjBeMggGDBEBoIcAFqKAECJUAhKFGoqBEUofwVT7Ie61FXGhGEZXAzUiJflaUw5Lyw+97fp8KrjV3pHvRWiZtu0YOATAmpSqgE13AwBHVx44B6uEkBSWqyVGnauBCS5tIT1AQQCoUWJQqJQiiVP2+N6j6lLiw4bTHsDT/iDLz+fUq8MHidBSFgQmhNEHSIp6u87ASfu37hZSf6vOO1RT97uVvL3DYbtm3oNmttS1JcMS17rQFI7paQxF0zzejatyV3m90sg8iC17I9ETEULRSigRQiCkko9x/j7dWjnpQO8q/7jNShrn0oAM0YJ1ymr98vdm6xDnY4m6Q4tGSVeJULBfBaN691LGP5gDHGZUyX2pqxWbOtQlUzMRKpS+KtewSCJ8W0paEpohIZWW12GEXNXdhr9tDdMrqSVUqsyxJlcQENiJESQrGt8erV3H9VSkPaKSxXGWHKumAQQcpRpK/fz4Kr4ByglJpc+Ei4K/836395WXl/8zdm8Vbe4AOZTpbJRrCoE5GVICpAQAA0BLBGTJAwUkkoS4UkkQ6ru+kh52ApYg/zcMkZi0oCRiEIgkJKXu7+f2V1b6VyEBxApjJQigE1/Bw9pq/f98CD4kIOPg5PG17wb7ZbX8WTlsetz894y1gkdVM6lLz0kd+JDgDA4gJcMA0HiQBioE+DthMJddnKuiREGWYeZZ5LT1t21OJKHQmhNKqHD68Y4908fKdyQRDvVJor3wQggBLvuihyCP724308LuIj+wAf+v+V5TG5fzPVMk3fxpwBhjGM6AChHS9wuMMGuFg6Y2UCEUCvd9gBDmABLi7AUsWiJLqPvm2p00OroytJkgmhKB6qKy/XLJzoYgfBqRF/K+pWd0zHAfjn97Opu3jnpA/Hh7O5d/VRywsyzWLpNbkzQBSHg6XJYVxcGC4uAGNxp027tCUxorPX9MeBOBiNcWEAl63MlXFSauS17FEKbAvo38mPVxG7jlySIJbqZzO+h6XnoTr/+vEYv9/jD65T7jUPah1nLGJN+hiVXBwWNw7A4rAAB0gCgMUBXDoEwwU4IFGPLhZMZ0LavrlYHELuFKXuOq0s5YDlCHESyuAp0xNr7OxJLQgCY+SDyBjxa4+7Vf74/tPRl72ueXFd8RLPmhUK6SNKKG4soMMzXNywOEBncI52k3VG6aIxek50exxIU9V2IIUEPQuvyvNg9HZz3tudfc8ztee1dffJsA470uvgPZ+2RGf1rNYc7UldEORI1N1X+e1/t/ih8+Zej41rRy2DGEaUJBiLo5Nq9XQ0MVza+e2QlnaflZoYksYFdIimwkDoPo17roOXALwPP8G/8B/8Cd/Ae3K7D3y2o/d83Nb6ZnutxS5JQRCozzrwXaZhaUv2qXzn8/8Wy1ody5ICEJQ5lagdBIHo/hUkAoBETB/qMt4xkCiKECR6P4GIBI1fn5y+ODx9hOf/3bF7z/cFS/Vxtl0Rd9wBIEPkAwIJwpBhZQ5E2cZ3P/8v+DrjQo9IG0GiP2q5SgP9iXoOROVAFCt6e1jDpjNQyOkcBPi/1QY7s/ADTAG/YmcN3T962l4+T8MO0vnlUA8RZrixUgxgtosffP5Tc9m5liFIliDQ9OfqqHyXqwA0wUAHBGkCGGQBpKkdiLZuqt74cPMx4LddvZ2ePbfWCTt23Kl8b+1I1DXJZvHjz7/7v7GBQHZkEUFMIbcPNBOIjAQkypPFQGIkYULH0OBW3/Q0TMAV2JHgm/zxZProhhcEGbyMIUHVDci4CbRV/PLz72qv6yZAxIhkgUQ/W1GeVXT98peGxMAaAImgDHMxodcwAaTExDTne9qMybAv9Z/u1x0vFjt7+CZVFcQcT/No5e8etbJEirOXh0oDkQQM9wxArGBmDglpignFvjQE6zjj8QfsBHylpw9SB0EgEECq7uZ20LzAP+/ocGibpUT0LCImUqdZIMqECoZuEzFBmV9lGkQ0ARQ+RNDYF63HHdifwr/Pm+mJe7RBpCGoK7AmQd0UaCi6HFO8w4YXgMhVIj2014lMgnKD1YAIaod9os+7GK7C2zIPewAOgPd9Q+m0tXMbLAGJKZ5Z2GTCbCJDlPkNKaWhCCoFMUE5r3cbL1JDsBbgELKikYluPdQelQBgK+5+U4nfW3ltZvMqqHcLlPJs3c2D6orlJJGRBiKBplMUbUtbjHfgICRWqTLCKBAQhvQeE1ANiMzfO0+r2dPQETC9bekwSDMJNwkSJGAFU9x9Eo4rBXhMg/EY4CgikflQg7KxAzcvnqnXJFcEIhATBw9EUKZ4wKQEEEkwhYZAY1njhtoKH6mhOAdwHBzKoEZADO4WwGQaRmZ4UcEsDUGCqW+ZMshVfWhOynWMEjNxAPkrbFhtIv6DM5AI9vENEJDN987zZBQNQZCYhZwh2pTn7HxEbkgYgSh3CEjakTAY3wGcAoqQrc98MuhCmQLT4lkJ28gyyPv9x17WgOIF5T0QiEhQOQBcecsiXAY4Can46YBh57Gw3SQoXljDDtFMVZ75Dckm+pGbNCYxURvM0QRBpN5IPlpZgdUAp4GSwO5Vb5FMVV7q60xGMbSAYAgx9Xqc7omggWEIGE2SGZgJcCJSkZT6ttkZ+WBa/aSXjeJGD3flZAhsQ6NABJWMhEF01xDtj/sSgFNBCIkhogSayK1eEGZcBjJbzZ45S41h5FoEgzoJEgFTcrkNtDDo9coIgJMRSQEdOzYeS6PN926bS6iGBDWeiNloB2J6BYk2wg8yCi/gdCiRzSeNwNCPAhsFwo27jWp1otfAP2jCNNwHYassATgZY3yp9y2HWpMCsOO794lRWctuKEMsVkBxwKorBgLC+TAK4AroSNnD9zgNt7778OYTp8LE8d0y3g8SE2l4mCzBEbgGEVKCblVNkEE0LMC2vvsxqfFNSD8725AG+CFZigUAF0Ek9q166z22v/ufyNgmdYPRRkNDGwkotxOjExpYmqwBuAxRlKMM9b6FJ0S21z2NAo1f23hCQxttFK67rHQnwnlZCHAhKIakIVCWOhGm1JSvD1EFDNm0svFB4/fbsWFsXU6Tr8JIHIJLkUqa4CguPvBNumqkthYB2bHuNV+3Wd0m3NBQY2+Rht+TyWEj/oNrEcVEZjIQ2yvQ7QIAIRxr7DTvS97h9hDeCdeSWfgW4GKo6MAzETu+fyAQiV2W4hP0RjFUC8UkaxDIx+GNcANvwR0kEtnaaQmg9pgoIg64/5SiQKShSoc1BwQtagwMGoKUB0AkMt/lIYXv8ePzEc4ASJ9e1YJdv0WIPMJFCpT4UsMv0/kedhzKe+chDhBs7rvFkGEaAnmMYpBV1QCqalUWj1BQBEgAW8v+yTb8Y1RHSdMBY9jVkPFBlXEaPkJjFW/fT26GCACEPACiSGT++48d/4R8ACjK4OLQZSPfANUdmzxE3K1Rt+4zpkA1IIYIwhDj+uLd+w/VwuCoAP2eHMKqw8XczwC2pmFrrsW79++LY21UOQIRJbwT1Tn+3iGDLkQG3YAMEcC4Eu/dv0vTaInKtzOSiJDw+OB7Z6jZGX4a4EKYpmw0NAS3PxJEyP/vvuY9GHf38V2sUK6UvP/wtnmzPkgCDNxkSkAiAVU5+N0z0t0QVFmToMoaAnJZ8cHDm8LNmqISNAAwpS4gQYh3CElY2cf34IeJa/Dhw+sA3dAb2mCgoT5PcMvy/yFQwgj0w86NR2jjEqBHowkAA9BzRKmZYg4hSlwLhsxCPoxTgYlcgI8eXpVmPVih3r4ZaLhlAWUPQwm/H4KKTPje9fOPZsjZ+PjxZVqMbarW29dowRgkCEhXoX+OxR1yRz97+fhRgFasDlNrm+kdNDC1TgBiD95oF99Qh6EFMKei0RCj26Su7gbQ6wAaal1AgoNxbx/fpMyFjFPPPn1UAX2RF6CZntsoTRkDGOjH3uCMIiBFd2vzr0Gch08fJUALtGgAGHJDyeWMBEoAh4vphivUpgHUQ2CcBpYU7RiAtin3BmMmJEGviwA5uu8GBPZtesKJYRff414DNDNO9qGu51p39ONVIQA19G3t/jEElOA0YAD+gxrrNuqgAYa64BBCpL53NvgGqMugJqcBtW+1bdQOjZqNkomop8ohqLjKQPew9J7vwJ2nGQoM/j4RNvS6hq5S8sHv/vLOm8kYMsoI2JCzgAAf1gwAgwPUDsonHYmIyMHvvk2+N7bBzjpFnkYro9a2UeOtUSU2vTYSiAiCY/tukc0Nx1G3qGacBBxHwMZM/X2sgwYCtS78cXTdX319zve4FcWc+N0fJ3HklobMFGEDMNDbiEhA/x1CKjaluhnZu/N45vq1o+Q2igoYXSVSThFzCPQfmYXdPaGP4sCJadX3kZSGiUoDdL0uESRykL3U1ykH+CYgwl9wZoreTf0ySMYMte7o4NGLSNln3r35R+/AqUl9zB6PAb/UMVDrjhobvdrJ90gVbsO5CQGmD6cTFUECOHqh3tm76TkAe04GZiFglXCrdgglB0oESoNDwJ+0SfrBbOdxc5DwLd6EkxPuozoCjMHHTAMYNfQT6MIIRLHHbE1NwpeIP5Vt4Zp/ZtCyaEP0e6AUZx/bpCB6DPiRNmKSEokjEsmyB3gbF+GShGi0E7PwtAR8UusA8OqgndEKNB9kO4A2cFXCdJRBW7oZ/p2sY1JwE98eBH5DI+TcaxDGwIUJR1ADOUJ7ORP9G+L3mJeCN9HqsJH4CtkQ3gfMgGsTvsEhNEWOqClqRbmjVPgt9RCj8dcJRiIOvtgDjAcAuLoCm080EQ+3Axxeoi88WML/2IKdCM2AO1iLt+HxEm5iGiagMtIhOeIjjF/xE97A8S2TAFBTQUlOAAAAOEJJTQPtAAAAAAAQAEgAAAABAAIASAAAAAEAAjhCSU0EKAAAAAAADAAAAAI/8AAAAAAAADhCSU0EQwAAAAAADVBiZVcBEAAFAQAAAAAA
- /blog
- data:image/png;base64,iVBORw0KGgoAAAANSUhEUgAAAIAAAACACAMAAAD04JH5AAAC7lBMVEUAAAAtuvv4qz41r/ulCf6OMP70nk73qEI5pvpAnPvqjGPhdnoNCxvFOr1+QPzBLc9zUPszMWXxl1byokW4F+jLbomwC/JsW/tccPm3INjKR6zTU6T7sD1tSexHkfojdqv2qEAsPHcSHDT6q0D3pUTsl1A0pPDQV5j5q0Erqugqj873qTxWX+BEed19P/wiXY/sjl77rj3IQ7F3FJV3NlH7rUDsj18tn+EvoOfQXI/4qUBRSsM7ieGTIPctltplONCrBP4vgcfFQ6rym1F0UPzZc3Mtis88ketcLbklbqVjQte1MbUqt/I7nvbWZYllXvZJi/ncbn9HWMO2JcyeGfxVePc6VKtWObmHFL+6J8zrklVCOprnimHkfXG4M7CBHNmVGbM9RKBAL468WXrLbWuIKvCcA+YoruWWDOXDQax9Q/7ddXUuY6eINP9aafDRanRVGpr4qjyjC/R+IN7QVpmRE9KpEfWXJqI2JneUKZClRHwAAAD///8CAgP8/PwEBAUKCAowtfkPDg+1tbWnp6f/s0H29vY/qv9Thv9pZ/79qEr9sD98S///uEBImf9efv/e3t6JiYnhbYkwMDAsLCwwwP9jcf90Xf8uyf83uv85s/+YGfxTfPeTJ/6tB/3j4+PqhW1UVFT/sEgbEQ0xu//w8O/hZJvzhnj+pVVFo/9Pk/9MifoOHDIgHx8JDhssGxKEN/26urrSR7rtkVyiF/9fX1/6nF0UNVRDQkKcIf+4Bv/EJeHQ0NDPOczbVazXYpDteoYeCCc9JxSJPv/o6OgperisrKx/f38nP3nig2UVJUUfU4BODXlzc3P+mGslCz/KhzuwczhWOBu9E/VHCGGMUUBNKCqGWSfDw8OoQIgmIFpISEg3NzdkRRotlNZvFrmbmpuRkZF0J2qeUFszB1FMGkVAPz/elz1xRykOEic3GiQygMmhoaFVHps1LHvZjEmTYiqaaCk3WKsbSHG/gTN4O+0XQ2WpXFWgZTkpKSnVP9c7AAAAe3RSTlMA/v7+/v78/P7+/v0I/f7+/SX+/v0L/v39+/7++h39STw2Erx2G/39zsiGJ/3oPf7CpEL+/uXit5iKif769dHHxq6qn4+OY0j9/fr57+jo1dPT0saurJ+djHlmXko2Kf7+/v7+/vHc2sq/uK58b2piUlH+18quiFpWQkFO9K+bAAAMIElEQVR42r1bZ1gUVxQdl7KLNAURAQUM0kkwsWFLokZN7D1qrIkmGlt6W4ZZ1GWlK0gvIh1UBEJHEBAsFBU1WGONsccS0/7lvt2PfduYfcvueH74fQ77OOede957M7MXqjdwX7li29Spw0dn9O3b92fA6OFThi1f4epuQb0C9N82ddN88zxABqCvVIKNTUVFfr6p1/Bxy30pLmH309j5c2IaGhrMEU6dAgUyD5AGG1PT/PwwU68pru4UJ7B4a+yc3NwYAGJvkHpwSoaK0xUAUAAICwsbNe5Lw9P3H/uNZ27uUYBUwro7v9zv6mo6LENT17n7Fzuf2oAFpqa2tmGZfK9xvgad/E+TnZzqPT09j4KGT+6M7MoSCdVAi7LOgYqwzDBbW35mJv9NVztD8X+/sbTeycnTySk39zKQyxkV0X0RRJyFKvBt+WKxm2Eq8eNGy1JHR0dw4PLIh2jmmE0NtFRD07N7UAVbnjjczVVv+lWTLUstgb/e8fZDISs7QP4B0blO20w+HyS8qWcWls2ss7S0LC11vN0o1A1Nz2wzw/m8yFHD9HF/YR3ir5t5ezuylwi4Foef24p5/HBxr+tgsdQaYFlnCbPH/LpJ4IuhDoPH9W7lL6x1QApGNGJ2nTU0vRSH88Ij3Xx7sfYcah0cHGpn3sXB640C+v69SB4k4Uud7R8wAOhrYfr64nAnmCAO160Mr317fgDA4QKL+8Qu0Bd5Yt7gyDftdCj/hpoBAwecX6Ol+uRJuIcUeBGfkkM/rRk4cOD5ESJMryeyXqIgePkSzl/Kn95OY369TWCei5ECd0J+4/T0gWTlJy/DxfBwMgWvbagxNk43/g0GGRa/IgVuWpNosSEd+L/C/AZVAGtBm4Bvgd+YE34aFMBa0LIfLC0rAwGY38AKInmDxayn4xcpZSllxu2c8KMt/SLsB4NdWTaAidUpKWVPgJ8rdIp54lG+PS6ArxH/De7oaaHorJhlKSytTkupXl2EB3Cg4LAtLIVhPQRgYlpaSsoZTgqAFZwT88IhBhoLkJaWVs1VALGC55E8sZcmAR+mmZhUQwC4BoqBpiIMXW9ikjaxkTMDsAVNPF64hpXwjgkAFYB7PBPz1LfkH4qLTUxWM8JXgax7EESVHFq8cwwU/CbkFvhQ4IvdlAV8ZHWs+Nj7NMlwRsjoWyfmLBxLrioGWFkVE2wBBsrIuUy+cgq+sLKyAgNI+K/dLNm5X18h9MtM3mBfxSUQITWAgL88JxDwmNGPH1kgVrBg6F8RVhHvE80/JzAoKCgwcKfmO2aaJt6N4OndHW+CEYArJLbuDAT2QPhnJ6Ph4wyhBBh6P4yfOUx+CrwT0S9iBtFTwKVAGYI0e7Cd+DE+C16iuMnXYL9+/SL+IBpZAtQ9Kti+58iRx7Gk22EYn+/aXYEEUPCAaA12SAXIq6AE0XF0PecEWUCbwmy7a9B/RoJ9v/FkpdveDMzKHuAFgvIJPz1OVEwRvEzzspMdAwn29gkkFQDsCZGxa0riDsWAap/LxUzbMNlWsAQEEFZgD6ZX9+ASXMCXtZ/K8EpVWgOLuaH2CeMZIRF/EIuCW8oBJamBm3QX8gvFFSDjD1JQQONNKkhBAaP91/2bHzbKDi1C+1B7e627EI35NXuAUhgURO4BHMrwbt0VLcLQ0FC/Iq0OKM6/ZLfm1ViuGlBWZMEXDBACiwXxoaHjdfJ/BxOruBpvdjMx4IFSDtjBPDXNnwK7wIL4QaFrsVoCfthv9yp6UC6k8WGJP6dtP6A7TfPd7CCDIEBbBpX4RSgQsfvwld2HsIKqHPIk3s83He1OfTQoPj6+lU0ArTp/GuxTUnAV/t9dhSpSD+CmIN/GdCW1ORoUsD8PqvPDcFwFLEB6/fccshzAVmRjk7+CWgIC/ETE9ZfPSV4FKEGWwkQZlSrQLA+qT23yl8sEMMT5w1SgQHZ3kFOlZDSj5MEeliJkna2oGEYtiB4U/YKtUifU5o/PxhP7QkJKrqkOwQpgZ7rWswKms8JmCghIjV7Lwl8VpMKPgcL43yF8D6ReBTSIJd5SAa/vSo0+2bMAEZxxGvxX0aHuQXNgN/7rWcC/p22GywT0ZBMDBnTzH9HI39O4qzBOhg48TFXmL6d/lgrYBQK0JiBnLzk/KMD3zzfZBPQdzSoAcBz9HhxncgF7ugc+ZhXQFwQcYBFAywX8TusigMbKb+olADt5QsjoYsD+kO4MlGsTUHigkCgDseQ1gD1KvgpC4Ltm9gyAgLaeZ1KFZiLbcDWlkFZdh2rnxC0W3XfyMkZTk0DAC6J9YF+shirQsXsZFQn4pMRHtWb8k5cxnJoU5Vz4gmbZCfFOjD3ADyO7Q0L2deAdEs9fhpCrLPyMVMCSKOcoP4alnLcUFah40CH7SYnCNBlF/0P2swUna11GxiZqc4Fz1ASGLdHoiQdXgVaMWghck+6Sh9ROaQDiZ5va4XUZeVOpaQVRUc6sNyTbSzRXgZE/qobIFdAq82c95x+am+ctp1yco6KiWtmfSJU9YBQEIGAPcP60+w8/62owz1tB9Z9QYBb1p5AmViD3AGYbEqSkAK7s0zp/jJHQj7SSeu1tEPABu1bVKjB4m1JSQJI/DPpOQ8N8eE80SWJW8AhfJqoCjQOqqGAvQf4wmE/MGzZRFOUDAiYU6aJgdywOqJICkvxhZMWYN0wFAS4eBWZmldgvgio0X1UWhkHsP6ALWrK2oTc0syVmkjY0gNyD5kPql9F18vnDyDsxMXPcKcDbIKAFDyDyoAMxYAW6zB9HIDdmPoWwWSIQmLG+osFU+Ixj8FdxWAFB/vA2BH1xY2Uvao0EAsmfcJFMAb490exBMwk/jBqZezRmJeKHnSBZIEELkagKsnfF+HFDLQeXCN8WX849OseOksInSSDxOEikgJG9p+vA19SqEIROYO14mOuZK6sAWohGArwOtKDq5o7j5axL5DHR3ePIes/ctygZLLyTBMmPRMS9SVoCWkIiIMvTqf4b+XfIPslGguRKMgtoBvFpC6gW0PRdaJEci/tWPJKNkltY+EmXCAA2KaIIgoBVlByTkoyMjFqF+imQvS1vriL57N1Sx/rJFIZLsBFYINTTA7p8Z8mtQyS/hb4MAiCCGGPikAUwlmNgA0rBACULgo2S9EgB/lKT6GOXoU8VDFC2ABQQLgT9DaizLN1IUaoWBCddB/2cA9bLTBAABihjUiIoaHslFtyus6ybrN7AMCs7OBhOBO4VnLG2tLZcRanBJ7FPMOSQYwFwnq2xtq5bps4Pp3JccHBcG+dNLCNqra0Xyk4BtRyCguBWjtt4LqBmYZxAtSJkXy/CCjjgb4Ru4VpcANUigIK4Fi75RWsGONTiAqivhDhQ4M+hBSOgXdhhFdUjXPrE9emT3cZZO187ald+i2KBT1wfUMDNlgwBrIFu4WUUKwISQUAwKOCCPx34v9PW1OrNmYIL0Cxcs0h7Wy83CmjEb1zzLklj82dSBfDSxKCNze3pxsA/hCJVAGvBoK3dI4wxP6mCDwy3JxbdAP50Un5Q4I0UxF0/aKD2/jOry1KI+HESxySiPdHjb4P8gUN7Shl06y6yo3SARUAcKMhOgjLoi8Yb1UBf9h2lI6bNgpMpOO7633r+kUv7etQsPPENSmcM9UYKkpJbUBJ6Xf0baYDqRVB+3WHhA0cT3Kwb+T8Q9u4PnRqfmADSJm6hegkX78RseGhL8vAvQoXQmf4vKf8ibH8vTJiViB4bkz38D0p/Lyk7mP/ECrWpmqzfQumFIWOys40AyR4fVMrOdC3k0g+IrrwP9FbFx4rfw9XvfR2C4eFdIEkWXPc/KJJzqAKrE535eAb0J0KTqNXn4L4BMM07KSkZvcuTSB75VxbJ2TCwpqIrwJ4QAQ2KEZheb1hMHwM5EAiQBrMJLW2VRYy6CbTowZWPx/slJKDmQFDwHtAbEP0DvI2S0CtVswL0Hc+EFv+Tla2tB2Vobb1ycu14v1AAaowDCZ9vwbU3nA0Bs5MlYAEgClBYWLgrVYbo6Oh4QCgCODAXJs8NhrgEzJ4tkRQUmDkDDhw4sAshOjp1EIJUgT2w21FcYui0gDHzoA7IAqmEVOiAQIgfNHfxe1vBee5hMWT69Gk+i+fNcy6UmpA6b/HirVunv9Er8v8B0aBKsXnCNVYAAAAASUVORK5CYII=
- https://www.gelato.network/blog/nft-lending-management
- data:image/png;base64,iVBORw0KGgoAAAANSUhEUgAAAMAAAADACAMAAABlApw1AAAC/VBMVEUAAAA01ts72uAoythM3ecny9goytcgyNUiydY61OAxzttO3egmy9gwz9lP3edN3egjyNVL2+Us0d4iydZJ2uUpy9kiydYiydZO3ehM3OZH2uQ51OBF2eRD1+JQ3ulL2+ZE2eRO3ectzts91eE61OA20t8mytgkx9ZG2ucgyNUv0N1P3egiydYkytdJ3egpy9c61eBG2eU61eBB1+Mkydcny9gpzNkgydUozdkx0N0iydZO3ehN3echyNY10t5O3eg/1uIsztpM3OYiydZN3OghyNYx0N0+1uFQ3ukw0NxQ3ugkytZE2eRL3ObRiE9jMAFN3OY+1eElytciytZJ2+VB1+Iny9hF2OQ3098pzdk71OBD1+NO3ej+3JAgyNZL2+Yz0d4x0N0szdofx9VQ3uk51N8uz9tA1+JH2eU91eAuzds20t851OBH2uUv0N1G2eViNAYxz91mMgNkMQE10t/NhUzLg0v92o7Qh05gOxBhNwtfPxVtOAhqNgZK2eR2QA9zPQxeQhn72Iy8d0C4dD2HTRvTiVDPhk3FfkZ7QxJwOgrCfUSaXCeARxXal1udXipdRh9oNAVXbVP61YnAekKVWCSKTx320ojcnF7WkFXIgEhZWzvzxn5SemWzcDn1zYToxHziqGehYi0ww8usajVWVTSpaDKlZC9I1d9IzdRKuLdKpJ9SjX+ofUFcSiWPUyBD0ds/ytIrxtFJx8wuv8fnsG5YZ0tRX0NXTyyEShgxu8A0srRBkohSk4ZTgW62cjuwbTdcVDJ2RRI6z9kxtLg5paM6n5ySYyxdTipvPQxJwcQ4qqpOrKhAl4/50YfwwHrruHRLc11aYUOBURxK0ttFg3XSq2bKomDGnVxYc1tAztY8yNA/wsdKvb5Bs7NLsrBIqaZKn5dRmY9PiHhHfWzfoWJSb1fUi1FPZ02yhUiLXCWFVSA8ubxQoZk+m5VDiXu5j1ChdDl8ShdNl4zuyYHjvXbas24wydVLkIRpOQq/lVWabDPdt3F+ThnKllgmi7cgAAAATnRSTlMABhAfIE39+++PDp9eFfquVT8L2VM34KuEXzG/Sf3y8e7goIFxYUEvG/TtycSCKCjy4OCfmW3u5+DPztO/uqxo0LySj3Jn+ezn3th3xLQlAAEDAAAZWUlEQVR42tSVwWqEMBCGE8lpwyZYPMRFsngTAvsCCoJ4EKGQB5hj3v8ZmqZMD4tS1xp1P2NmRkfyD8kg2R5aPdIiaxWXptTaOafHWkrV5sUtISeHssILb0btZhik6lNyUi6FasZBuz8RpssqciooS5UR7hVqXpCTcLm1ndFuBTJn5HCumZw58uAW0ORHNja9PJQZRNAKE9phviAADDU/qqtplfERnL88QU5ww+y+b4yxnN+BBYTAU+bkAFgrB0BQKhqUhkGIEB9iyeiVfOduoKyvtYBXcTDPniXQW98IWMcZSmC9+ZH/niV85EZDLMqeRCZJ+ZN8Ox3MJ1m0kxllRmJSdbWwfjXrRwB8hC6gDW8xKczohPFMyAY0NuI5SjIjnteelLPs6VxitN9CpYYFuiCMNeDnkTaBplIsFvE/4mxCWwu7I11CNuXBhd2XctNjlH4Kuzf3fEP9tbAHoMg2XNXdHoPcpBEYf0n/6RrhixbreWkjiMJUei8tHqxQam+FnqRXodBzazws7KEHr3sJhkhEE7MaosSfqEE8VPQgokkMWggIPUTNTSSnkEsOwWLP+R/63jezvnTd6ETbj8nM5M333vvezuxu9D09PUdHqNEHPUZMYAXIICaxwUPPtDsmGNF7gQEQxPhvKnj5YVTAQgR+I3QGAJJlXVji2DnHu/6n6e//YI3+P4wYcN72P+38uBzEQhPAJBP5Zvkpwb4WrLIgo1DQY/L6Ca8v6LcIWifmIttLCAKa1gUmD0CbEdCDcJSv0OWyIPGjK+gfcr1MCITeJ0FE6Nz4+AoQDyFKGDWTyHpVvj/2FD3/6lrBkOACn+DOkKsQvCq1qAEVPPLnj2UOFzAnm7NRwfNHvb+M4+dKhdZNuVhuVa/q7oPq680qk2+OCnnjGga7ruBZn6l+N3d9VjtOxCOhyNT6duOofj8932pUUkyOJy5rxaZrWkFPl/o/Kf1h9Jh0up7X2VQk5IF01aqdd8HNt7bj7exUo5SzjPCiy/+dDIaVbhr8lcCme7d0NhXyYapRcoklPrd09/o07mevl/OKIfElo9OWvK+738+s0wkzHGoW9RZNOBTNHQd2mjaznv5ocjo5rq9rtuASXWkhphbjuIWKZowTOaodE2d1IjtEBohIsGDhQUVgAa+7OEBDtkMe8JQyOCK06w8t5WoRpX5x7WJubvdgflpVcFpScrgG1IuKm5UQsHSyfz53frGyGFXscj2Mi4P43CkfTk0DSuDB/FH0qg8ZkdfREyVdqsEVyhWhYPokHRsGMumV2XHWtJMDnfy0DOqvamDPriwMK8TOfyaxB8U64kM26LoUdqcGG3WmN/Kz3kF21w2AvwZkIaRbXYeiQ8jXoi5muIJ4C3sIpo5iN7Bbi7sZYS+sLbHtsuqGvUzScJhQkRfjs+Eb7ItLdMEYogjCDB7zWVz/A9IvyKgKKk1yHBvTyXlexf07k55sZ08cRnHTlJy/E3BSePEMIqCg12gDPo4B5IQINBWQzb5dK0f4+F9AiSCzO8OaGnlyJi4jTOyrCt+8q2kfe3KNK4jf2F5OADus81APO48DJrdB7xsm69S2rXqo1iZvLYd7cktfUUFsjzUlfuXg6JGLcd6t/YyfvbzIG1arK+GSGanQ9AIwZHKAKCeaQH+R77AUIizpfPgOvs9wZad5z5F1lGqoduIOOba2QQupgi88Q3QIHvz/e89H2xDfdkSSDwdJPkTVdvYNvy+SmwHkTS43/tsw60DPQ0+gAdsQpW2+A/bkBAmWV/lYZG3Bm1Oudj6IHNsKMfmHYdoXD/wN+cU2xfUxv5N2ISLwWKxftVWbIsPG/nAQDrmAbZBN8PL+J5BtjHKCn4oLgZrSs3wsim1kFrnagRzlaqumeQfv/Q00YBvjD61WE9pEFIRRvCiICHrQGhCq4Emr3kW8eNuSQ6Ck5xACORRLwsZGjNhSm6a0liSHSHoopa1NaROEggfTSi+lePJmUvtjwZOeevHozvf2dWKzE7Jr8yV9O++92Z1vdmfm7YtWnxOnmCOn+ATCYlHrlqcp3HLOym8oYxKltg13y/wvPvSdSFTdNmMRC+tHwxk5cuDzNs62TscikJw3HXVjSUr5H46FolHGpVrn8Y37SoUaHKmrv/jj8ffT5EBecGC4F2GhlUuvKNyygjJeJz71sw2YpROZeuNAt1xCNVWtbjfowAA66L1fIwdWBU4xtb76lO7i4XN6WnFBOUUOLC9qB7QxajURfEmgz81zYgb0y1BXUexFBxhjFBbVsrL//htRzJjiE4AD2gjAjBnHnj0U3qIv9buACqERQ0BOLcZKd/sd9Takp5WEAz4Xxp0fwRU8gHZRRhKPxQRW80Rq5YPSXZqiIoQiKlWh3h9ujJ8XSlC/GxSfC+sAsE5LWeI7NH2lBK15cSnhkS+/3dhGIWouQQE1i4MSBGBuGayGBVbZFCVByVIM9Jfx3j0x2uphvfoi2XGEQyG68MQXsGAZBJTM3WbxN5XGF3MCq/EJ1Eao16ok51umy9YSX5+8FmhoweER3L2P2bYAxaUt2qFMCqwKI0SrCnW1c8tIOQzNdx/atgzcanLgmk/Udp74gNKyKkR2fBUvE1CvQHNByuExaJYFu8JgV1MEPQ64RRF79HFnWqM53Fcobq/w1rMZM2nKlkO31i+fTOGnAbc4wpZeyuJJbO3LCDZky4yznjmLenXg1vqJSnrmvC/gFkvPKQnmBQfAawuRvSfWK8QaeTq05MKwUxrfRQS5Q3mKi4uwrZzaJsV9qqKp10K5Qgps1Vybv/3vKswRFOaW4TiEbWJaeMOZS2KvTnoHvS3eRYeTnO1tQEjjM92+QDgcVjStoy2yRMCcPY/j8gDFkEBsg4gN7dG5R62yfX6QZo/CNmABlnHUf9QASsBkYwzdeRxuG/AG2HtFtoWVYD1NublPesvYTwoO5HvxztF0fe7h4EDjVmMN6vFj1I9G/THQ99MQGhxJYwf1/WPMOTRS2CiS9mGLDXH8JcptxTaNttk8m2X4G2Oo208ALw2WpKFwrTiAXzvlfX3ioGyhCj8L8ptcb7HMJmAFspK4w8ANfcoxdLHLLwP6jogcUSF9uyA5QB4MWUiQNOLogDkJrYOIbFymwGvZ1Qd+T9hdwdtETHCAITpQ+IgiuuvJPK9lt3r8nlD5KteXLIKbkS+ImTKwVvFk/sHxZv5RxO8JkT9E7Znzr3N51EeNt5mYk9LsC1ot/ni0f/Z4GfZ7xHeQyzkvsbmRBmTeOL90D2Iv4NH8bV1EkQJeEBnCIuu8GJtxRsyUa23vdM2LbU6CM0gBb/iJGHpteMQCiihqkBc8tlPgvN8rKlWOIQ8wUYMGShUvHnAS3On6Nywi8uUww/RL0wgh7Ne9IJ7G6VPTpVrT9ZkONQKN63Dg+mNSihDxiADMQIl1KvtfE/Y/c2c8PwFVqQYSa3s1m2lEhr+J4S17MxaJBIN6DAINYIwHuAehtv9zyC6QL3NxwyOyq3q5e1X8RfT05dFqe9yHBG5qQGXx7R5riBQtUMPQvDGpTrQ1K0ef1d0fTOVmwN8bChv5pP0U1vY3lXXY1Ey0aYJmjlF0u9SbXFBPM1hHySeEnap9+5O5YdD3jsJM/pnyYOWwwnbQCoAWlHrgwCPdbYkIHzf31e0fTOfHjf+HOZNPq6ewtrvZQINFGShDXUF3qB+tqNwdmYsbp4L43MRbPIR3pZo7LlSGLjwIukKlqMInPVkwjVPCaDaTtMNoU7bs8Gyu0DLwNBiMts+/Pq1u/+q4aZwizPWJZ3ChuBN0Aaqj93qCUXIAbkRtEUP4AhAwtvMT4Z/MFIxTRnb1BTY37AFzCv1LiAWqo1etOdKJMkhdg0VS0fxnY8Zpw3wzaXsQskyF2CZzC1pSCFPUUPuQ1jF08aFJ9TnuAdTHVH0N8fNyfdToBBbSiKLDimKEFgebGURw0x4+onUsCl2AVdkZQF2rXhyk6jk2YxodQWwhNYgNziYsgyw7AA+YHRS6aD8JUTnGX4LS5oezeZjA/Qf/jiA+n8LbXQnWG2kA3NfkHpADTDra7EDjXSip/yK3ETM6htE51KKt+nFAK9Pc8jMhmRzo1n12OtrXFwr19bE3GK7jd6wXs6NGB2FmkMnFCnHvg2kBoEbvEueJbIgIW4coDoQQfSCisSaWVf0vGB1FQf3cfgBOoKXIHXfRQT9qUYMDDEwI/d0t4j+RNTqM7Bh+bNzpawtwoC3UsQKgAHUY68+wIp+2A395uZqYJoIoXEVMNJp40ItHjJr0ojFq5GLChcRLucphE9rEHmrS2NK6WEtQwFq1FklVqFZrAeVg8GBs/MH4g38xRutPVA7GaCICSgRMEP/jvDczvGrZWVTaj+3M2/F19/vmzczOzm49vR0C0Om35R01u7ARDU2vgBvYg/erpp/+rVvN+re5J61KHrsxRQFLpiTgFY5AHQpSxw/tOtzU6J8C/cbI4cORq35jhwg0op0vp1PA5rdwCb4YNr4EReCmpLquiWJk5Nm2g9+KcgXGK6ZXbmQTgL9cWivhQiYdwINsAO3gEBQ8ZRj43VBpwKu2rcakheNyKK5lGCrw40Pmk0PIejNnAJskRGRXwVwICzExAHP+HDBchkY0BCsE9oZNRsm90nNHo3EIvHgtAPLZkEQhJQELBXOpk4RQRPhdzCEIgOJhL0eTOgRYuQiv8XKMfw/vxpIOcYcsSxZM5pbJiLAU/4kngIlvDeFdcIfy4iOx/4iyB9eRpyKiEWxDL5CA3EgF7PpQDQhYsQlLkLBUIEtk9houYs1QYYpnqtQyFGisJc/a48YXMzhg4CUwkZCNHyH7AtzQFK3c6CMBYEmTFQv3K1hhxh0TVpklgjxQigf4Et5TUKJ4fv9ZMqaUgPtLYHF6FQqSzH08NjxqbA81PVavQe9uqiDUdqo6QRtIlWgzntLh4+NHUIliTEQLTIBvo6CJi6OlPh9Utg/I+6qqNm5miY+lUMxMhs0H1F1gd6SC0KycbzdlC2gyuZYdveEDSuwPKhKlwD4jCxnbrSrGlTkkiVQJvuysfRsQa1RHgATU/LMAQie+K9JeZRc8DAguBwFzqBT8c2EfCsAA32AsoK06qwmdUgnobCbP6k5jv44gTuiAEPGQGZXOxNXp8ioT3Npi+LoJouYUjULwkwIFjmePQtegRPWqxS0TYlYLoNhqJuADjdqKyYtAnXLBNywvxPQKkeJNhdsmxPjy+qINZgLuq143QVr7idYuv3IqlOV5MWwm4L4JMf6AY1apmYDLZgL8bRNN29thU6JjorsEO/0mAgIkYPJ+yh8xzSxhhXZRDqZCgBHCF2XHPOw3mU3vqlYGgN5UQAF2pAMJMKeUm8vE61rl0skuXckAiwsIK6cIe5CXd3+D2Q1jw0X0rN6jnHLsEwJwzEEWxNAOKZZaOOZZ7WpgJ/4YVk+TD+0IBvc0HdxtvogbqQsG6yIHa9QCsBOreZUKAYs3mAjAYbTH7F4r3NAwtUceNeCpFhriAu6pec2ZeN/JY3dP5uAWpS8DMGr/tBUO8cG7cCHrzmGEfwBIiy0Cc8p/d8KNe2KKU4nq3n5boVATHfyCUwlRj5hiLkzOr0gKKLZKXZDxzeN2ox/aOJnrStkKhtQozJmuj8P5iTWj5LELMKuU3pkr5SIlYf6BduXh38BFoXeZuK1AiI/dgTMOuARntuHHDdUKGXIssUygxI5uHraxnH8FbLeIzFu88MQKFoLU2Ec441NZhUAEbU5KtKZiErCgnDFmxaLa7eDFPszgIbxcAfiUKFAIosneL3DCW1iRbgwDGJBDykvtFsKKDVjXXBtyRgvEeiAE9/DRzKCethUC8Yf6KL4AMgQ8gBBykpu01lsIM0vsTnSS/RsBgeP5pZNwwDstsaitAEjFWrAFnW+XI5AQIbo0h32phTBjqdXjdLrZB1IPNzxuJ4SOGc5x/LVGzzMt2Rey5RutMf05/ucUwy5GBSlBCvWJFCEDlkWWLCwqdeaCy0DzAyyuN3e16InWfCuIJrTkN3zUd8uVQ8lNVpklG/PXO5W4dAEO+WRM0xN5akXEX9ef9fAWZMQGlWALIiy1qhU8xblml65piWg+YxBNalpy1ItTUZeKkBVvhwlFpSYhCGAvOKFpWh5bUagvwU7AA3DhkpKQuIoRVqNel8vl5AZusohhACfxXTFN05N9tvwglHqgs+PfwRuGYaQCIEZgiLJlfwpYZBXsXUKGCwy0EPd24h37V6ZAq0/HQ3mgz8Z/jfHvRf4XzslTE4C9sDbk/pZyvTPLLxdnH+EvZt5/10FBZvo7Qqg1o2sMY++Bf+Ap1R0ZKAAxj5jTpYCU8swhMgca93BK2jya1ACJvmmeXPenksg/OVqLS+vdnIcDUqIjLQoAYUUZEOVkHcBamPJ748N8NWqkHhXEHk5nX+5vzfDD1o98wVnE5XGsOVmH8Ce44Ie6MGHGGqsDiKMnh7RcuI2f5AtXz+s1LiEdnaYohKLpmMb5P+drfI/aBQcef5Fhgh+6Cv82kjqyIWuAdj9gP/Y+eaZrCD2Zjk/L2J9O6JL/E+R/5uZvTHhKkngAcrGmnL4xGc6+CaCCH6BASoiGQv839ETTMHYK/j1ebED3HWpgAHIxv8yhRvujCkSPbEXYF/ri/0G/LxOjQ/XerUD+w2dVLCgAub1grYmCc7wbVPd8JQVaLMHC8E89l7WdB3Sclq89FYg350wDYICiskqHBFgyp8Lu81tQQXCwRadT6w8yqXj/X4kI9cdTmQf1Oh3jRBev/y3ns/lXUiaNyhKLIeatrax0wIYAf9whOEABoPnbdwgCgWlojYemOuq0pjPQ8gn1z97xNdPAQLc8I7IFiEyQWVdkLGBuWeVkcFDCYiBWod+PtGgIikPiIRNhesPYmnqY4OwJLSMfxbOnge7ZdE6ysrDGokAxfFuNX8Scv2vbQBTH5YaYEFwIKU32LlmSNYSspVOHggMHGbr0LzB0MLIH1xo6lkAGBzpYwXiUB6FgYXsKsoUxoTXGif8Ap/gH5BeOIU0D1Z0sf12opZOWfHL43uku732f9CRBLrihTzKoK7ItA0iHNIm5V+IrE591CgeMlDo9/+wN7KVgR3Bj9b13BqWm6PyFX5FRR7NI2R8/T44vj46OvllY3eXxiaV8zuIxrX5Gsp3zDL8oMFzuY0+0bvLDhOGN/NEFSTq0kOJuS/70Tx1vB2eqZ/A3ggcr294Z5M706UbdUx+FFABZuZtu7uhVj8uPO9iF0NanfW9Kv0RsNprnciaI+EO5Y2LTEuXjRkTw5OXuPge5Sj6Gve2hcuH3OsTlC2WIXe9EsYbT71FA3EVE3Fyp5evkzP9tpFqPnVGcX/3vxxZ98Dgkr7W5kQhvAeFJRDMgtBHWqEUNwjqgtXXrKoDPKbPfGcujjBSP/1e2JGVG8vhCGVDtQNSvc1YMhuMfNp2ZzKKA3FlYn/HhRtjo5hMQYr8dWuZt/6ZzPr6XR9nMhOxIvh+fd26UW7P1hdUNEIsVI0y4eCtwsrED9e6oRgUpIIuHeur0rtUaDgamaQ4Gg2Hr6e40VX9wtAOxd1UKEz52Xgi8RLYJN+FGs4DvkvZDTNS7DcLN9oLAzfIWTwaopEozn4z5VJ/MNys4+RzgBuC+DfhRjat2Mc2dQ6LQa9cMlfhhS/DFwmaY+CKsaqXGWbeop8VEbE4msURCTOvF7lW5lFOJP9YFn7z+N4Mo4UPVjFql2+wV83m9cJBOJy3S6YOCnv9e7DXblaqhwS+3f9zA/IRWdpnbKMX+pGNq2vGowQ7ZMxiTqHU1tJJRblSrNUa12igbJS2n4jetNnWPKASNuWXQfm1B8E1o8VV0CrKASSY9EnJGxJ6d1QdRk8ZMgCFcYYw3sC9WkAEATBa0Ij5UQIk9IlCKPOYBB0sbQiBWI8jAKxOYHKthckGgP1AVIVxwiNtRr7mIEBxk8GwsQX8AQu/Wos8H6j84y5HZDPacDxxBv4eZ2QWYtq09xwk6LObXz8/iZng2Lmyrd8KyH9ogxYJ+UrDIXoHDkI1VCGX1eP4HJ/S3OTJYcRAGwvCkQRJEQRTNGygBxYsiCJ6kp97Wey++/ztsHUdmISy0VG0/TTqZSTP/H/NBTdiTGlAHksxSWddfmfx1cMatVGGhm+o1zeez/ncQRaO4Jw5uRTNDttyiu8sFjbIVc4GdaDO3nauAr5xrTvg8PxXshvDK6Wx0ADsi6mE6l0zCvsRtMp3IeIG9EXmppme5T2+hPTiCuupQHKmjgHDiO+c4cFec5GiQcAy+11vUjdJxLA9NOHOBcbziRgq3M/AURLdwHPLWq/sCNWXQAxVIGP1gkv0+YKf04F/Jk7nAkYi0satetrC159UyOElwnV6OmSyHo/G9Qd+PYdY3OIM4OMZCV/lwDkIG5k0L88zxiholnEgYmUzNm5r1nWccmFmfGSNc005kiRisd5WEk/HTsdckb9POBpYELShCM+yRTGFJJbcYPkBcXEu7SmX4mh8vJ7nuBMoEPnwIEeZjotXsyHsam7Q1fJb6atjDa9jM5AI+j59em6F71YMumyCGL0H48mEiedqDypqo+Br1bENGlSmTTqt/hdsu64fRC+FrEWEaXavGlH2SddaqVbbVXdKXpqnaKP2+i3cRcSjrIs09L1rwvDxPi1qGAnbnF57vyCFg7EkbAAAAAElFTkSuQmCC
- data:image/webp;base64,UklGRgQzAABXRUJQVlA4WAoAAAAwAAAAfwAAfwAASUNDUEgMAAAAAAxITGlubwIQAABtbnRyUkdCIFhZWiAHzgACAAkABgAxAABhY3NwTVNGVAAAAABJRUMgc1JHQgAAAAAAAAAAAAAAAQAA9tYAAQAAAADTLUhQICAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAABFjcHJ0AAABUAAAADNkZXNjAAABhAAAAGx3dHB0AAAB8AAAABRia3B0AAACBAAAABRyWFlaAAACGAAAABRnWFlaAAACLAAAABRiWFlaAAACQAAAABRkbW5kAAACVAAAAHBkbWRkAAACxAAAAIh2dWVkAAADTAAAAIZ2aWV3AAAD1AAAACRsdW1pAAAD+AAAABRtZWFzAAAEDAAAACR0ZWNoAAAEMAAAAAxyVFJDAAAEPAAACAxnVFJDAAAEPAAACAxiVFJDAAAEPAAACAx0ZXh0AAAAAENvcHlyaWdodCAoYykgMTk5OCBIZXdsZXR0LVBhY2thcmQgQ29tcGFueQAAZGVzYwAAAAAAAAASc1JHQiBJRUM2MTk2Ni0yLjEAAAAAAAAAAAAAABJzUkdCIElFQzYxOTY2LTIuMQAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAWFlaIAAAAAAAAPNRAAEAAAABFsxYWVogAAAAAAAAAAAAAAAAAAAAAFhZWiAAAAAAAABvogAAOPUAAAOQWFlaIAAAAAAAAGKZAAC3hQAAGNpYWVogAAAAAAAAJKAAAA+EAAC2z2Rlc2MAAAAAAAAAFklFQyBodHRwOi8vd3d3LmllYy5jaAAAAAAAAAAAAAAAFklFQyBodHRwOi8vd3d3LmllYy5jaAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAABkZXNjAAAAAAAAAC5JRUMgNjE5NjYtMi4xIERlZmF1bHQgUkdCIGNvbG91ciBzcGFjZSAtIHNSR0IAAAAAAAAAAAAAAC5JRUMgNjE5NjYtMi4xIERlZmF1bHQgUkdCIGNvbG91ciBzcGFjZSAtIHNSR0IAAAAAAAAAAAAAAAAAAAAAAAAAAAAAZGVzYwAAAAAAAAAsUmVmZXJlbmNlIFZpZXdpbmcgQ29uZGl0aW9uIGluIElFQzYxOTY2LTIuMQAAAAAAAAAAAAAALFJlZmVyZW5jZSBWaWV3aW5nIENvbmRpdGlvbiBpbiBJRUM2MTk2Ni0yLjEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAHZpZXcAAAAAABOk/gAUXy4AEM8UAAPtzAAEEwsAA1yeAAAAAVhZWiAAAAAAAEwJVgBQAAAAVx/nbWVhcwAAAAAAAAABAAAAAAAAAAAAAAAAAAAAAAAAAo8AAAACc2lnIAAAAABDUlQgY3VydgAAAAAAAAQAAAAABQAKAA8AFAAZAB4AIwAoAC0AMgA3ADsAQABFAEoATwBUAFkAXgBjAGgAbQByAHcAfACBAIYAiwCQAJUAmgCfAKQAqQCuALIAtwC8AMEAxgDLANAA1QDbAOAA5QDrAPAA9gD7AQEBBwENARMBGQEfASUBKwEyATgBPgFFAUwBUgFZAWABZwFuAXUBfAGDAYsBkgGaAaEBqQGxAbkBwQHJAdEB2QHhAekB8gH6AgMCDAIUAh0CJgIvAjgCQQJLAlQCXQJnAnECegKEAo4CmAKiAqwCtgLBAssC1QLgAusC9QMAAwsDFgMhAy0DOANDA08DWgNmA3IDfgOKA5YDogOuA7oDxwPTA+AD7AP5BAYEEwQgBC0EOwRIBFUEYwRxBH4EjASaBKgEtgTEBNME4QTwBP4FDQUcBSsFOgVJBVgFZwV3BYYFlgWmBbUFxQXVBeUF9gYGBhYGJwY3BkgGWQZqBnsGjAadBq8GwAbRBuMG9QcHBxkHKwc9B08HYQd0B4YHmQesB78H0gflB/gICwgfCDIIRghaCG4IggiWCKoIvgjSCOcI+wkQCSUJOglPCWQJeQmPCaQJugnPCeUJ+woRCicKPQpUCmoKgQqYCq4KxQrcCvMLCwsiCzkLUQtpC4ALmAuwC8gL4Qv5DBIMKgxDDFwMdQyODKcMwAzZDPMNDQ0mDUANWg10DY4NqQ3DDd4N+A4TDi4OSQ5kDn8Omw62DtIO7g8JDyUPQQ9eD3oPlg+zD88P7BAJECYQQxBhEH4QmxC5ENcQ9RETETERTxFtEYwRqhHJEegSBxImEkUSZBKEEqMSwxLjEwMTIxNDE2MTgxOkE8UT5RQGFCcUSRRqFIsUrRTOFPAVEhU0FVYVeBWbFb0V4BYDFiYWSRZsFo8WshbWFvoXHRdBF2UXiReuF9IX9xgbGEAYZRiKGK8Y1Rj6GSAZRRlrGZEZtxndGgQaKhpRGncanhrFGuwbFBs7G2MbihuyG9ocAhwqHFIcexyjHMwc9R0eHUcdcB2ZHcMd7B4WHkAeah6UHr4e6R8THz4faR+UH78f6iAVIEEgbCCYIMQg8CEcIUghdSGhIc4h+yInIlUigiKvIt0jCiM4I2YjlCPCI/AkHyRNJHwkqyTaJQklOCVoJZclxyX3JicmVyaHJrcm6CcYJ0kneierJ9woDSg/KHEooijUKQYpOClrKZ0p0CoCKjUqaCqbKs8rAis2K2krnSvRLAUsOSxuLKIs1y0MLUEtdi2rLeEuFi5MLoIuty7uLyQvWi+RL8cv/jA1MGwwpDDbMRIxSjGCMbox8jIqMmMymzLUMw0zRjN/M7gz8TQrNGU0njTYNRM1TTWHNcI1/TY3NnI2rjbpNyQ3YDecN9c4FDhQOIw4yDkFOUI5fzm8Ofk6Njp0OrI67zstO2s7qjvoPCc8ZTykPOM9Ij1hPaE94D4gPmA+oD7gPyE/YT+iP+JAI0BkQKZA50EpQWpBrEHuQjBCckK1QvdDOkN9Q8BEA0RHRIpEzkUSRVVFmkXeRiJGZ0arRvBHNUd7R8BIBUhLSJFI10kdSWNJqUnwSjdKfUrESwxLU0uaS+JMKkxyTLpNAk1KTZNN3E4lTm5Ot08AT0lPk0/dUCdQcVC7UQZRUFGbUeZSMVJ8UsdTE1NfU6pT9lRCVI9U21UoVXVVwlYPVlxWqVb3V0RXklfgWC9YfVjLWRpZaVm4WgdaVlqmWvVbRVuVW+VcNVyGXNZdJ114XcleGl5sXr1fD19hX7NgBWBXYKpg/GFPYaJh9WJJYpxi8GNDY5dj62RAZJRk6WU9ZZJl52Y9ZpJm6Gc9Z5Nn6Wg/aJZo7GlDaZpp8WpIap9q92tPa6dr/2xXbK9tCG1gbbluEm5rbsRvHm94b9FwK3CGcOBxOnGVcfByS3KmcwFzXXO4dBR0cHTMdSh1hXXhdj52m3b4d1Z3s3gReG54zHkqeYl553pGeqV7BHtje8J8IXyBfOF9QX2hfgF+Yn7CfyN/hH/lgEeAqIEKgWuBzYIwgpKC9INXg7qEHYSAhOOFR4Wrhg6GcobXhzuHn4gEiGmIzokziZmJ/opkisqLMIuWi/yMY4zKjTGNmI3/jmaOzo82j56QBpBukNaRP5GokhGSepLjk02TtpQglIqU9JVflcmWNJaflwqXdZfgmEyYuJkkmZCZ/JpomtWbQpuvnByciZz3nWSd0p5Anq6fHZ+Ln/qgaaDYoUehtqImopajBqN2o+akVqTHpTilqaYapoum/adup+CoUqjEqTepqaocqo+rAqt1q+msXKzQrUStuK4trqGvFq+LsACwdbDqsWCx1rJLssKzOLOutCW0nLUTtYq2AbZ5tvC3aLfguFm40blKucK6O7q1uy67p7whvJu9Fb2Pvgq+hL7/v3q/9cBwwOzBZ8Hjwl/C28NYw9TEUcTOxUvFyMZGxsPHQce/yD3IvMk6ybnKOMq3yzbLtsw1zLXNNc21zjbOts83z7jQOdC60TzRvtI/0sHTRNPG1EnUy9VO1dHWVdbY11zX4Nhk2OjZbNnx2nba+9uA3AXcit0Q3ZbeHN6i3ynfr+A24L3hROHM4lPi2+Nj4+vkc+T85YTmDeaW5x/nqegy6LzpRunQ6lvq5etw6/vshu0R7ZzuKO6070DvzPBY8OXxcvH/8ozzGfOn9DT0wvVQ9d72bfb794r4Gfio+Tj5x/pX+uf7d/wH/Jj9Kf26/kv+3P9t//9WUDhMPyYAAC9/wB8Q6lDQto1U8+e97w5ARExAXtVBQfl/UpcX4dS2bTvZ+5z8NaWKfxFxkvKNvUdOmyhJlTotkn4y6DEFstAQQzihpabEQmSgjPIJxAxtSkzSogGB8YEhtFE/gQwaSZLSPftw6MID/h0gAVeRZLtqfNPNlxz/EIALNCAQSPw5J5igCcAz//96u3G+v9//f865usK1xdJKXjGtHF/JMrPMzIyyzMzM9vLKTGKZ2RaYrmTrgsjS1a7wSivJzExCy/srdHXXo4yeQsb1tqE7EwZ3W4fpKZwwqgtzqdRbhjRzw8yc1E7LOeGK41mqwlFKT7pP6M643Y7KMDslnjCz6oy7bB7Cvwszp+LUKVOeMFfubxi61P8wM9ODyCPIme0CrsLkrUJl0v1DC3VSMT+C5AGcmbthxi5OuZOSk38VZnCeAHNS8g203irMnNQpT2ihClVbubzlzrahO7PQhZkZulR4wsxcecC2bdkSbf+O44wrbhoVW8cOwkSfkRvs7u5eOihbp42Zx+7u7u7uYARbUlJCxc6RW3dfAgAojW1tWxUUReEOgQRPCMHirt3pdJa7Hnd3dxvAmYNO4YziPHLlz+0zjtP/CQAI4OKPAMrvqutWMguACAgosONEM4KMwA7EPBFsSm3hAKsI0IqzzZgnwcqKkkxMAjelUA2qohJSBogYEGGmZKY0YqYphTUOkI79wT4hhnFLqOBkupFpINCUOguBBHjbT7CoJfDJngYOESYzbEohw0gCBqbZ+1Xjx2fKpCcC9WSrh0QqMXtkYnRo23La3gbops/b/PtZ/H/9jy3jV7H8njyqg/noq3wcmQlELYhAygFjRnI3qmTMVv14yLFliVhWnbz83cAR0gZ4GctHRhgxTYqQYJo+RFS/o+IV/qvdSzuk7fFmnuP6R4jh5ZTNuu+oSU/jLF03mZA0bPooU+9e+6acEMVyGuDDUtm96IVoFEt7mLhGBCcRRxLsp+njzH00L3x9qEUtli+cMhTgpzs46qhLJvA+36HJSJMmiUvJIMKypIgpkADBoZWEYrpzN0venyBrj3xV12r64+1hZsznuvaTUf7yK75croKPNfIuU8wLuZenk1DuhUzAtCgRVUuHvQuBd50N5rDSs0t3Q0Ik8W5iVp7K/lGKoM1Qk2OBh34vNtG8iUUiWZLga45eCWRC2u53LwXeDjtxMuzv6TKu3Rznghxbw1r57/e8djly1ChlnTxOpdI7cb5YzFWVSJAZkEFIoEpUycPY3DryuEF1fKZE6uv5L6/njzUWiR+PM7ueeMF6RVzni1m0UWrc2ZBC4Ov9jxyAE0MGxwS1NP6CQwEVgAKoQChjQAIQA8XZyPHtRwltToolQUEFoOqq7ManqeWSYRJFQGs+ikcT2S+z9Mt7krneNd+epmjiAjoJlUmkHV8wQnF8R9eYAEyjAPS/DwQRqyNUIhCG/Ry9icjaoihsgYXIdFksViecFihEksEisoZcQC64AJgDMA0lIRsUkZViVfTofnybwU6aAC11vShJ7ZQMBSASicK2G3Srp53qoCiXMS2RV6+NfdddNgOPk7yzN0kqpbELGw6JjcMxE5LNMsmaCEiCkM1JCjBSmEHbonpGGQKD+IFxwhrdVLV73OaIrKMTKeG60+l0uRxWwCGxzGyaWegHmoieYGTEDXOE+WXRp82CD+NCN/yCt4JzPueFYpJCd/zFYvWCt7Ipdsz7DV/EL2E7iWTO5DsbCZOJJ6mQhRxI5a+O9f+pT2KzIk4r4nu18OtV8KkNsK/2Zpb7aN1VL9co1Gy9rTpYl/gwTxkiZWneLvOkqpHbxAnwJtw8qAerIT69yqdVJ61lNewSuAIkeEYCCZmZnJEBJxGpS5p7yboRqARmG+HNOtiPu8CP7+lNu68pmZX6pgU+iaFPcuibHPqmhN6JRYmkuHSy6Z2czXF7OsT/q5TBfSIdmzMiTQQvQZ/dZgI368BbHr3l0V0B3QteAekKKJbHeEWk6yMWGAss1sVwosVNFB/ZythtZHs3Jd0LklR3Zr/wUOD1Gngw0z5rgKEgQTkQvxQbtyzooB2cYmNU5dPDlbAqlrrcCAeBpvNeTrLCVob6Ufttw3F/v2+7wftCFy+lkuyJN7dqY75mwTFWGQ2SMiViuGRIiaQ5pmgj8UQOGajco57AcpozxnSr5d2td8u9bZd9Xufa/UBgVOVD7vv8UOLloVT+odSr45uWebUq+eq22MsXPh9vNkAhMBGY5l5fRi2tQBJ0E4EblOHGVQKbDnsa7p5y60Wl2EWl2MWk1osqcYrh2CVwrOJRG1XTLPWtwaJ6vi+3Avvqz+Zpa7XMjQQDwwzrChyXw6arHjJaLzIbbNAfZljyt3Gn/WrUqF/03vFrMYz8tkeeUgisuhmezHXu8aDTxtknxee9+NNVPyMeJg+L9pp27KpziT7HDgRm88XUVmJHJu0WmQFJU/uRSImceFux3W7WDYg0IhPTbmovi6hwxnBdZBlDGiL7CKd5mqcZFELkEanJytr9dQ68H5QCd2W/PElVs4WjNwkpmAeOSAWylE5Hh6Iq0K1mgExt+PkDgfUKr9bu3iIYU1AU68y7RgJPJ1rWRpbgS9lr/yHwz2VT/rvA1j8NNuprvXf70HvntxkCa4w2Jav633P00t/ze/UganGl2qunE66aJynVTLVkKjAca1nLEj7zyegLhpvdxemcISnuvh8TnXcKt/VMvdmcCJPNu6bfFlcp6M8Zu6+P3KOuC2KkqggP0WF2tRjlr1Rg65//2uingTNQFFkPUAeOrP/TI5R3kkGRg/57kvhtOQvcBGRRTPMG1hQM87cnkO9+3yyEK2xiwEizzbxjLfAoSzugzrfj7zvv9f6/dxR6RMCD/bZsgDcxHdRvVMn70Ft3N31jf4Klnx1l+YtpVu0HmOrXw66NChqRYfIVq70ZCSyPLcxWTRoxO3IzOMQq5a/xcdIAuzaqeuCCIQX1qQ4sKhf05r0zroNZ2w074IxIIm4AWWADqZxs0gozwCVwjZwY/Y94i4k3Dc1RFZa0Spp/VL1jkPBK4DZTCAZTmAxWJmgJCiHiiIStfk6S0HkEn0RPoGgj0NONRJBtiifwvJ1WMpG1Wvr/7dx/n0+h8bH9nLo47fnsSO+kiVPp61et3baoa2OU84xL1FmtYDbirFAlEjM2DwW2VXIK2U03m0zMiA2f83YlMO97dAVJoztXMc3+WdXv8bxx1YaYZw71wAm5SAhEgRNwcEEkAqQATtAnN66HOn7ZhBHDNccM5sVA4OThJCClM6GYCDiJaIcZ4O7i1chEWbrp6wjshvzF1C2xq4jPOcbyFCtl/L/AP9sKmgAGzTQGg0/rCLxs9+cW+ojeF1j3lXjFneGmFovefhW+RGY41bkVJJNzDT87FJhOuy0M2tqabUYm4M90amxXDCbPJQam2T+t6krmjWtqY5bZ2VFI0BGMZFNh061c272Y62aKukvW6L2MRJ3mgJMCgWaQqUNbqKzgg0MmJ8Gty8Rwgp20Wc9/8S7PfnG20+XUm3bxyjlM61wBpgiSVus0xCHH7raO2a/eLv/1Mebb/PedU9caIwyNJ8G7fG81r2nyc9Fxi6bPYbcOrYc+tsDjPiJThTxZhBSOmx++5yE52qqnXI7/i9toHqpy5zoxBdynvyuZN64+kUwhgUY2NkkK3fePa746lsqsfVMWU23ctFbcZpIP+U6kC/Yb4na8laFyTbKkUINukPC61aXjW9wI2AedOBOYbQS6DsB/jjtzB6448iJI4Z9tjGnhmDERl7iyLPCs7fZMcr/Jzt10eATZTSZJB8IgRHPMwvaaBedl3x6jeViwHnKQ8aXAi7xHnjHiuUJkGa9kS1QmXRP5CqgyOoc+yYnAOH2zCm6CZ0wOFhysTL1/5u+KX6A2FplCOiA3wSB4W79RuQC3JsBO593/iAa3SLZo3WVFrjYej7UoAyeZKxYrqlQwaHjWysMpwcyJNg8wrnyjDSE0gLo+brrqkZs/hGsBSasHG6PKcyIhckdb3F4ba/jd+q/y9/4BlSkmOBCcCdMErVfC6+LdWp8fZu0hpK3YmWRz0WrMv/rQmYQql0CWxNJtH2u7mrAEhmP9kcMqE1QARTl4FVd/3riyLppMTh+SoGWW333AEX2BRzWwXgvjWvmrjPVbRCKXSJKMNWUDZ2Msxp83sd4yt3DY6AYNT1t5OBUQk4j/SV6nO+SkvN/hxgDh/XTOrmZSSrBMlCVr/8F2A0QqarnsZsqDqbt7vPOuAxsiEHhGcGuZiLX1MmLRx9un/H6BtmeqTcQAwH64Apwo8552TgWGC92I7ZZQYlkFgINXcRXzxhV1UXg4I7WZgWmulQTlWx5NmjTO0qPZNHElz2ww1LfbEYP8bguUPQ5OrJLWyFS3ukHDu62+CkwiTqybAlan6nRGkUI0hRhzRIgJzvPu5i7SNe0FrfTjaYddycADf1jl4b+AMQwcY1pmIBOSVdv195laxb0M8Cp9y0tmZQaS0LIlZ2o/XNFGAkSye8l24csPU9bRiXij1LmgiKWAqrgG88YVdVF+o/K4nKWnI3JcgGaSssGkSIqcODdD88ubbpemQ19xJ/ps0ODxncQ2Jz7i1TmpoSQASZO4RUJ6JRL0mL8lAtUi1+qMYUFNHFPXByOO/sNUi/4ISdKB+w0yWaYAKZpMTlP0ee7oyyFiUgcu8zKJwTXLRLsLYCdtEqkGoo1alm0NAR78SC3roMrkDHHYD9zRwICozUnYcWeyOFKImNGNWh13zkZgXiY1iVoo4oT+6NlgWw+n4JAFlgRDUmJEb85MhknsZCxJJDNFmMFLRD3q6HNdgU7ZPGc5dNLWp3po8eW+e3zAfgLHmeZCYoKVBbh7SbCSEP8mz6lqWeTMEADG0M1iFZy3QasmTQfZDcRwDYhpIskg2ca9npOxGEFCe4DNf04izFj9n48giZhDkg3ZOdqiQqA/4eqhHgorg1ZthUpmWWFuawbFqKrmAmwmzUimKbMU5FzwUSYgrY80Uxs7fcVrhoAK+2DoVzNCnMDn73Mbc64zr2rhyC2iMAE50bLB9jzwGKuIdmRu2EyDHa/2I15JHWTkKUlZDZqCqffPqrry+eLKOig9QiOngRD3Ut0N0w4okXa7ycIGW5Z1R3nU8jmr9X8E8X3lw/TKDLb1CJUVphky3AfOEOQOPb4ZYLjVz0h3oIh2tjG9OBVjl5sNiGXGAD2NqetAaYik4wGNu+HEdBf2kQCb6fCMbyp/7XKL15ikJEJqwdj3Mxw9Y0em4LdwCYOdfUY1y/93cvcCcKoBZAqN8aTka5gE06a/m31y3f8wa8BR3qDh8eARedJA3e5msDJhRpQl++ykVX89M23QhYOHk7eft4Eo9D9hLXBtAHVDhHURvp//m1PaOgkT6BKuWE0WPF4GqQDJPnuDTdZESI/iJ6zywy31psVsXmGSPph12gOBwCFLmAsjY2aoZ41dFOut5xpVLrCuGHpAmcJCzUDYIIBlwIiRwKwh1AZw6qEt4FV4tU1Q1ScG78SJ2NtsbG+E4/hzbUvfyaCVh1NWmv0iuh8zXA9eFYDKANUAPlFAGG5afiyDBGSKSF0lLY+JAJjjWs+qbiJGEs0dd3b/tmheyk0Jh5WI0SfbPLzRai9WnwnJlMNJ6UWuhgL2Qhk5M2AAVV2DlnVRZQoNFAOhJ7X2MsKsDfoT/6MSgB/A4wwWPcIbc0kjY22nIeq5L/iWH4fbxPdzSaHv0TOB7lqAq4NfG3RdsAKzrvvVnBiD1MhNQ7qqQVUsN4C8OooENXxsosHOaXYUR1zsaWgkBKbwwxGhPa5tBLS/nfXI2gyMtOgs4K4PXPRRJhkIThW3UdVVzBs3qIuiLWcMN0JcaehvVFcg3QDc+uDWBy8g1sO8naZNGFk8c2AtY6XgsqfZ6dox5uDhlJRbJ6mhm665X/Kp0L32QrH9gndGRWMvQ/+9JIduJMrIMtMs0jcu6qOZbGu7TP525uMDkDI5Y4kgCZkYBeK1jQKaCJKmmITOBLU766AWQMVSXMkSiABJJtg5w+662pdsnvvmCc18KphwRb67He1/Lp/bK/cels5wuWaxg4L79Hf15o2r6mDs4fQhEyKlMgadN6sWj3k765XZbJdWs13ZLXjrtq+ozC4zZlrat95Vc3PbwX7L9SsHD6eKUw9hJBq8Mfko+96GFE/SVkPJbpE7CsXoC4K7SFqnbH+ALfAwtdMk0g1SZz60ZGBGMBBcE6MQZNMgmw1V5766Xgf7vX2GPjk2c6h462A915lJmffLmOU6c1/abnt4gXmJJ/P0daOCqZOK7zPJohCm4D5v4XC1sczk9KAwZg0Ga9C0w24LIWqpII24ggqRlGN3W+AuS4cJeh0Ob6MwjSViDCwQyy3CVeA4ueS4yXAHgezjrvU5Wf5DTVJFqbRXqxS8MvogB/cGkmQZMYF4UuZOmBdzSEtvU3oCl777dBfN1fzeaSZilbfmhMwznuyvjDmRRWQkCRykqB6mrRYxM4n0f5dUzDe4hQPwdyXzxtW/k8nZhsaEaDAVWWPNpXFiZclfEWdsYMAlQawqegNMy2VUJDnGQlyhG3Rcr5WHU3BdkUSgWQQnLBORBfMDX0yeCvdkoxFFZJOS5o6pBeYDRaYaI5ygnFEXr0o8G5EDQlL+hwSCHDTz5YxEHJ12awu8n3BeX/P/HpR9q/8c3jpYm+7ccgU0sW0KIOLN4TEctP83tcyn9IcC4yTmGHNm0ixZ3A+9BplAEnpUwlFJOJZkOp7/Jo+TtesAElEoUaWAQcd2Bc4ZgiW4NF1TFFV3AkGxK7UWvNn/51yHsr/htuHOKnYdJgrcVshe7KKshcB+rMU21MS2wLMFj45tRktdqSAu8zq1Q1OV6U7tVkMWzY05FrM4SfJc02oUh1ChICz3wVQBYMq9i6qI57tX18UiY7ALlwIoKhHSARwhRZDvdT8S2O9570S7iq2+VEmDYSf1BRZpg2UnXFaLy2nW1Ti+kUej0agrBiujFLjkOZ5bzbIb9cLMZp2p/KM6XxYNcO1vSq4jqDFIVpHMd3Uj8I09bR67rHHLOGshLv26Y4cCZeoDm7XQxCosBckSGpi8HGJ4qzWwL/kucEJRkWPnYKVPyeLx1eumDu5CQ6MqXHFL5+02G0y8wmyIQmC3uz190jJenZjIYgv0HrV+o0rvbd+EXvHcxDsn9s6J7sorOyqe3Vsyu1oyM/fKCdbB5vQFmpofegNFjYksAAgzSHyaMX2tOQ6PBD5V48th1DlB+voKCXKa4fYjxPbjeujo5jp9fMp1v1y66DEBOEHZVos/G/+tb2rllTjwSh17ZY+LpmV1Md7bu11Ub87CSOMsvqGdG2rxB5VAxzszKp6W+GQlvlnJEqndDdAvE5fv4fBUoNrLc9vnSeKb1b3xG/fN6pXI6vhmhd5ZxZJp6VJ52TpY/+dmFXLXvQ9qnNgkm7Gqn3PzMcbfMCuV97js03XJJ/uSCfuHLxm/L5mwKxl/8Im/lEq+lko8LPFwututTq9DU5O3DyJxewBMUCYbRdHAGtJBk6DA5fvauN8Ys5rvn/tl3RWJnXk+ufV7+WoVfGyIl5W+XIadnhuI4PqZp+1GCB7NoyJ3HpbIPPtk7Yqn33mnX0tn3xS7e+i5j8+J/QhigbHMBLmKq2i/mbL49WPJ7KN35t4rfeeVvi2Rsykee+26fe5WzJj20MNyGbuST0/eySef5NPF+CTfeKdui6fviqefvdLPPpnbwveHk64Ku+3Wk82W0wrGsAnAbEYDMwI4ZLij0XAiNeSQIYBDEoxkAgAgpo6DS9XIlEwQkQmKqr0NLMdY/SzvxU6plGCR++medxUjzN602dwHHJKWmIdIRRzmJhmJwHYEi81md9kldrlAsgacGWKxmUlQIUSdSEd4uD3cBpXYfVRHZGRkeGRkZJAdcJEbRxbVRPAAeVNkKy2ILAsCaYmIIEWTyTeiSIyOkzO7uczClgARrTqCQgCdSYWZGpPEnRl3BbhDJWXuuKlu1hTAIZFAFmaWwkiLOKWn/RsrGrWQKXFDAGlADNB4lQQnCSIzMpDIiWCTbHZrECYXjKKYQ0xEuGAZ84w1iTiJMDnwI0nE2zWQpLkUFAChWzPmDkoKkcRMyFfJDWKSoJmVEcs15jbDLfGo520gihPPTdkkkZHYKyZm750JzBkR04wZxoAJwJhwYsigX+hePv/mmEDfLZG4zUkd9KAH/SNJ0xfLCf3BTpzonXYKZoIhgUjQP0qC2Y/MzEmRJpKAYU1E9haFJBIgbmklc6i8qwaqfetDkBSYlPbJiOO+UHJrhyesKGZ24iQBnaOaJNwejT++41OJ6a0QeEXbPoKYeS/GVHMEcrPNHvNwjGkEsmWj2OSb5RA8Ovs1Ppzrodh2+D8bR/DWEZKkydDciHN221erh8NqGNVGN9ug+ZERyDDO4BYfjphTA6NqumaxNm/OGBHjwEREhCqM0LGfD4w2Z7kennfYVJhgiS/wrIP+NYzEmwQrKYEMwdpGBUNgs0DcXQetvGVfhnlvDc2Na96STJm0whXPBN0SjW0JYooE3pIrZmdSAmnp2m+RMfv3gVBu76v3efizUJu3DKAlALRE41u2vFdtMOqfWYUPTx2az6NRA5yi+JmPGsWmOAkaMSoff78eHnAfAYVvj/PEDZ2NaQ5ougYwAo0JtK4ExgJABYhhAAE3bxyaX6tuMPysYil8JHfVHq2M9SCLXB9bSSmcGIy+phR4mbmJi/NeLKmZ/UjPFdr8vcwkEdMwFJEZ6mt9D22PPafstQdJE2Q6VJIs2dQOm2otT+Lhjp7xZ6vdxrZHmJEpjG2/iT785Okwv3WztLKJJUhEbXnqx7e9ZTMygMRQhaUDJ5t9tDXWP/Muu4txy4s6DApcNbGwwwsgQQXcSSMhc2Ong8ZONC9B5Uxzhvil9hupHo20LE6lA6cVs6Ts+lVFDCPOaCoUvH4vp95Nf/f0h5tZ6XqW/9kC92OtzwEsmjQocDrDSdzNWXCSJJNx2XrpoVfPX+0dDzfEcn08WhuTLUrd3XfUpqWTmyQb6PxDODMP5RpnzVbg+n4NsN1ufaxXx935PHPNVw+66CAdkknR6A6PUyLyUFxK3B04iYzBxoXLfbw//TUwXhfP62LRAOfcu0uTn0IkRzVU0oZM+Ku76N2r+e2NwFRgfvrl40/RfPRfk5gyFjaLJR+2rY9zXYwE4jznb+0RUb1hxBn1jZAQIZMVPvXORuBB/IqKuX5BUTr1RKYcoWDRxEH+MwVspNU/ciMQGrTnXanAwu/JuM8+6a5Ky4lK6on9o0HGB8t8Xf3/kFF9lWnqIThxjLCVJKnhWs97oZO1rTHAyHDcGWXnrYME/m4iP6frEMs35/7uehzga5JUZEZbyQKYiNXUqQ7sDrBEXNNJj0H8KmGin8R0Ad64M+t/XvbTNV7JFphkwjDN2qxV9xPK7lvqA0faLz3q75kzMtvc2T9nG9bpupPf+5i4NlbTrauAQ7pPq+h6/VKqTLxOwq71vCj2+Gb6/XlDhK1XtmwRqrJo0iDfmQJ2MjwTAQPJ1slWLe9u2L9ch8MFgDSefOVC4HO9RXkhBukYBNjeRUKo9qMYZrbh1NGoNve5xf8nLGW0MDINbkBu8vY9rU0Edn2HdyMBaLakgVZdHMtm3sgO3cUEJCIZ67oCVSeDFJhnTfJXeF2HW2sVVEVuWpq1x4F8XVySVXBdOFcOxESN4kA2JKtjPfFm3UQkiDTaNhqxMVMyCUzUyhiqbzHWsmkQSIEeh+ljzvC66WgD6uy3Z/Vwbq2Ix4niAqiqo8KH7USLY3BmNI9Gxngzx5lbpaQitOYNDzTWgmkLg4DPJgv2Adpt65z3sL8GupXbYl/9wuxjspRNbCB9I/NnRpzqggyWs9Si4L1VjVcjIp3IzNJFe7+kwX6iKpbA4/baRiASVvy4XOhGopOgaeNAzKL3QatBJq0065jzu7Me2z2q2lm/aNg/7qA82reAmHvlKw5Z8Fp35c8TBBmKW0XuXASer4OewKvdbtyRwEqMct6+JpnnvjuX2AzV/2U1wcLMsX1XXZx6eFYXT9bFbUeNHdgLJ4wLJyxuWxaQTM5ItDpP4k2VtxurddehraW/HwT2W/z/IBGpZvG83i2bunER0yZF0G6nSuBDp200WJd6vst3fDrLiaxc7uFR0XEP+yjtN+qB2VQSqid8WgXX8yOjtwHRGniZpKyncC9icpNtJHT/T692t7oCPOP7+c8MoJDklWi2tQbOk28MiBhnji3ZW3TeJzC4W0NHx2/Rz6hSUwv+O/LN2YcQG0fTUOnVcNzlnuYqHL/Zy6tTjBKK/6dRoRu5S5vp9LpcfvFEFpJAd7eolXAYaXEJTmx//ep8B6djLk/GnsPn3VYMMTknQ1dHmFWtjQcx3IjCJL8fe+V3lyWvhZqzn/C5QHhHA05yVMfiD07VX/WsZmZQqMLh1yztNXUErOKxbVIWseB07m7F5C2GntwKiEkOcYqqy+BZd2NrBcv/t5hmiY/b/huv7KpEfKlh8rXT5XBszZPWmEYaKr6ejLfchWuRezcz7W1QLKNXMnVvR95za/9PM2bxLiaA0vbPxmY9DfFhNIgVAN6dlInBJqUbYJWojAimOMlBMGRkZ1+JawZw97NXgb+Kqxe1dIxkNdIzHSAqtG9NQqaFw1dbOmmWrAVHIJtg/RRB3Y6NBEb14Q89IQR+qsDZAVSmEBKUtZfFm677+bDVwGSsWR0riMiC/yYV8mtiHeMtPq6CS6JiHL5YRcXX43FWuIqr4PVz3l17eD3LisavrMhzelnt85hbRP9UdNrSe+KeegUweklunia5QSL/tj8qSCoB1In+WK3kOsgaYEvJ4JTozK6Hy2SHJtDyXXxZ6MS9JTzXvrQOhkYP1yWxwMjoYaqIYMQZw8ewIGubduk3wz3u6Qs8ytbL6aBxa0Oc5ri8KJ6+mWC2A3gm9AucG0BhkkZML3c1vBt7Tm4nMma7PtoIp2T+HpHbZQdDYDvS7Nqh5b+w9M67RhJDYkZFxVeTcVZ4cC4cc8534IzimalnwsKCPKdWVT+Wr6yTorSY3mQ1HIacYCtc4WnX367+ui54f+J511ksXi2TG3jlnZdKHq30vjPj+asZX61p2O2B6YZ4ErUQQrqQWQcNKkQv2dpsis0RJKJJ64c4V0UajDSjqPD9KQnW0k031//bkBzGnlcuBa5f4HX9RradYjmPJlmeA0Uf9wucGjvBBMUZBRV9MK+SvyUytYTeql/W6UDVXa8Edp73Fm4egkK2WhvTqVeUNnKgX1NdFd/V4670FK1wzF3uw3eqT0rfM2Fj0/KeXPh/zJlJ66SQSiR45p9Lp0xc6KRluAHOj/M6d1Ttw7SHbuMFTlYCaZ/jW6p6tK+2Kskre60G/9XQAeeY82yBS5zyhkVSIbfB5QahYi8YcWZR4ccLrmQ1az95RWxiOWT0MXgw4OTZ25v9sZh0kU8E4PWwk+dcGRmqS4Kg867pRfQ/3oXLvZQy0YpqnjvVkJN9WRsWTLI+FlhnqG6AWyxnoBO1Kn9Mx1wbKFjg4TXXoZNSMqlcLGVttuW9OPT/3P9Dl+0NHf0M639BV/1dlx67lDXO7HqWA8MRp1exijmqw+9Z7v9qZLBM5cM3lVhmhmBZ/MK88vs5WYqR4EdJpC7nWs55ewKdCcIY4KB6xXCzThU+flZHe06wOrIk5WRoOp69Ip6MN7MDFHwyzn8jBpxciZKJLbmPjh8na5fAqgKAOswMV6AZfXVFpLmxJpvg4jTUyNmMOqMPzH7vmuvUUS2dnRRJGWiY8XC9N4y5V+iw/pFMqqvgrdmB2uqYWNGoq8NhSX1ERS8NZS0QU/d63QDabB79f/ej206lx16tA3k09LCJNuMU6ugLNit/PyWuZccrWw44ylsXfmJ/3WZi7uRAmtTAuxl2xfGLd+KVC0tlL+c9OdTg+nPJklTMfvV6gJl2dtLWCez4wLaad+e8M32Z6fetSWGZGKPhSwZFUjLf1rIfx1NtS+OViBOWbZV9vJt93zm8ekbpl9GPX66MV8YrdGtY60vDbKUFYzHCwBjuxfgKSfVd7GmZk656StQBkZ0hJJjjaCVwmOvSkRs6SECJ0aOStJJUqxwp60nfP3i4Z7aVyO76vage9chNRNqoWfv3NsbL+rhdHY+/rHTeramQpbwTWSwpngST7/D4AtfFoz/bYsx5bd15wAPenkTIQjKacFW/Pp7uHd/dq2tdLKm/+rf6KGt/uM82LLLrRqKPmwsh4s3vbYbjvbdYA59eBy8ELqP9mdomXVUKjNfB4zXwROD1VGuHsD2NxPSWd65Kktr94rouzmda7dXcK3FY6+NK4NWGeDxyZG05d6MBwzgRd5vNtaO3EV6VfzMRSLxSTgZ3jDS1LYHbXgc54Mw2EVmNUZDn67hZOvw4a9A/+KHGRcn8O2HMQbiWz5YbyEhcbB+7r4g4+xR+6Gixx+6+u59pFLyFJEOaCjUw427JKmL7JQNOyqbb1ZlpYzzlDr/P6CCKm0sEZYZumt/mBiSBmQG5UNyJjeGn9j2ylX0Kl22K2WP/NFoh113w3JZ6HxQPOUUfIlrpa6AbtUjiJjQTU2f9rUbCTNMGtuyWBFWCoad3ptvdmeZAlmPrYPARYdQinmNrk0OWlPzVjl1Vbm+I+TyXwB7XjKfdNtllLdmsF7hcr46DgVWmRYMATcTn0RBgM1LMAcPCDmYBAK2ZenzEAKFcgpPYFAG/EpeQBHim0OZvyAiaiEKjqomhDgAug+BvEdrnH50Y3+LREXDzsB3I4JkhmpP+JK6NddogDkFA5nbRvob6faC8CBdUE7FkX1ISUkjCqlI9+Nnm+Dclk+TuLgw5XhPYL3JlGNniNImZps87cSJB0YvJng9P9fGyBpbV3xbroj5K/iMT0h4RMgkoE3tNTZ/3IgllgkZiYrlbfXeLJ/7Hy3GwN8bCQbshicv+9JJQZUaMUNOHdFjJjkmWcGh2G4yCZpIM1jhPd6d62m8kWMFNhixAktrhJcmmSNLmiJx2//VYrgGzLx+grvgjAFBTQUlOAAAAOEJJTQPtAAAAAAAQAEgAAAABAAIASAAAAAEAAjhCSU0EKAAAAAAADAAAAAI/8AAAAAAAADhCSU0EQwAAAAAADVBiZVcBEAAFAQAAAAAA
- https://www.gelato.network/blog
📊 Detalhamento da Pontuação de Risco
Total Risk Score
100/100
Contributing Factors
Active Phishing Kit
Detected kit types: OTP Stealer, Card Stealer, Banking, Personal Info
Credential Harvesting
Credential harvesting detected with 1 form(s) capturing sensitive data
Code Obfuscation
JavaScript code obfuscated using 131092 technique(s) to evade detection
🔬 Análise Integral de Ameaças
Tipo de Ameaça
Banking Credential Harvester
Alvo
Gelato users
Método de Ataque
credential harvesting forms + obfuscated JavaScript
Canal de Exfiltração
Form submission (backend endpoint not detected - likely JavaScript-based)
Avaliação de Risco
CRITICAL - Automated credential harvesting with Form submission (backend endpoint not detected - likely JavaScript-based)
⚠️ Indicators of Compromise
- Kit types: OTP Stealer, Card Stealer, Banking, Personal Info
- 131092 obfuscation techniques
🏢 Análise de Falsificação de Marca
Impersonated Brand
Gelato
Official Website
N/A
Fake Service
Banking/payment service
⚔️ Metodologia de Ataque
Primary Method: Two-Factor Authentication Bypass
Victim is prompted for 2FA code after entering credentials. The code is intercepted and used by attacker to access victim's account in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 131092 techniques to evade detection by security scanners and make reverse engineering more difficult.
🌐 Indicadores de Compromisso de Infraestrutura
Domain Information
Domain
gelato.pages.dev
Registered
Unknown
Registrar
Unknown
Status
Hosting platform (subdomain)
Hosting Information
Provider
Unknown
ASN
🤖 AI-Extracted Threat Intelligence

"Nunca pensei que aconteceria comigo"
Isso dizem os 2,3 milhões de vítimas a cada ano. Não espere para ser uma estatística.