
Phishing Analysis
Detailed analysis of captured phishing page
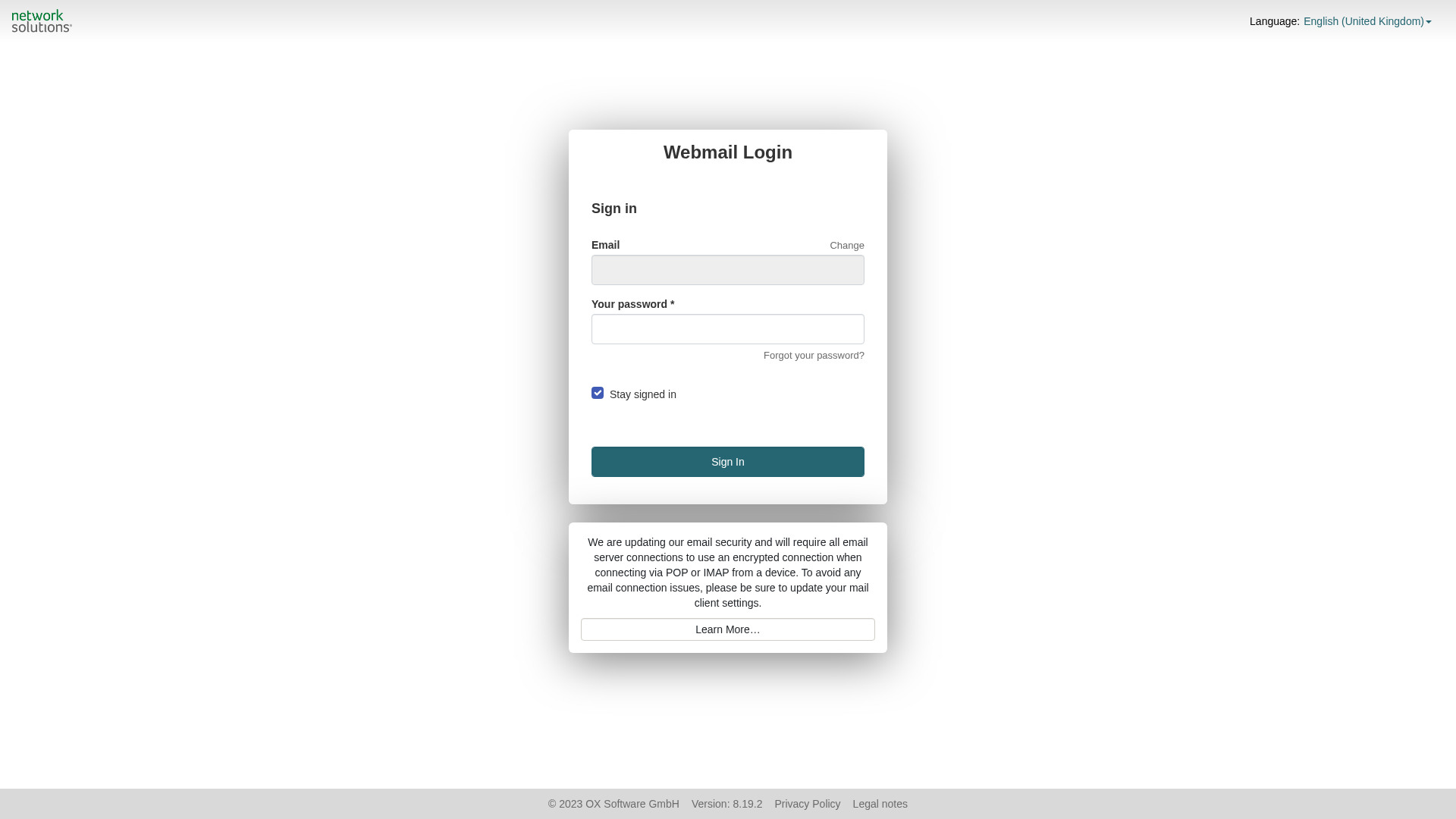
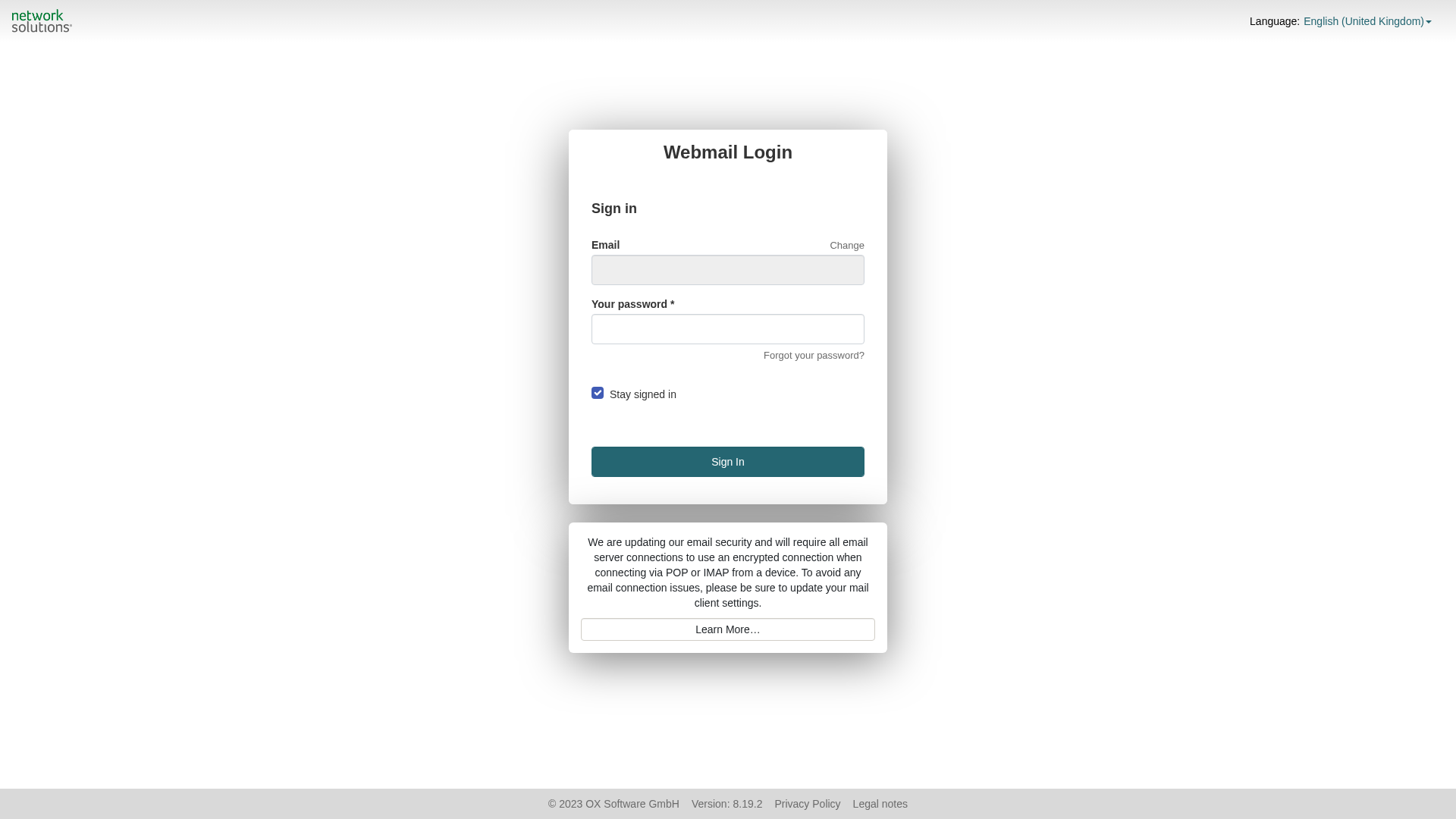
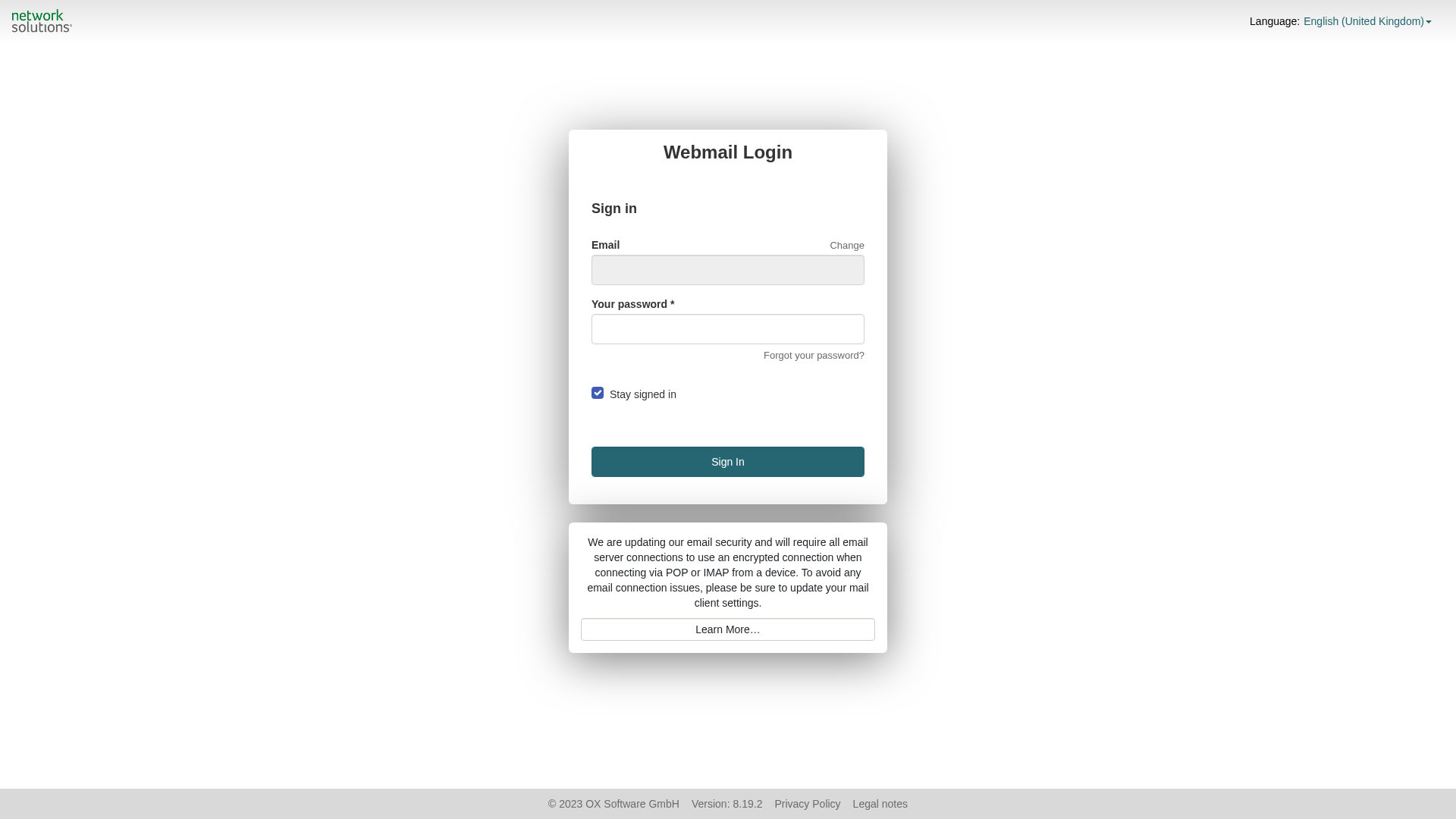
Captura Visual
Informações de Detecção
http://www.is.gd/DrUbjB
Detected Brand
Network Solutions
Country
International
Confidence
100%
HTTP Status
200
Report ID
d024070f-303…
Analyzed
2026-03-16 19:38
Final URL (after redirects)
https://bafkreihpec5h3lagmctlyyobawh3wffvtpk44srberrpyspxntqteq53qq.ipfs.dweb.link/
Hashes de Conteúdo (Similaridade HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T174B2EEB76028A95B52521FC477D0AE29B943E10ACC82B1FCD6F781D958F0E93BC4D61E |
|
CONTENT
ssdeep
|
192:unyglHKGUMCLS/Qxt4bWygT/3KTCAYWeWQv8SZuzUxojlXYGYql+K:unXNbUMs6UtMPCvNaefZuzblX3h1 |
Hashes Visuais (Similaridade de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
f3d84c6656d85872 |
|
VISUAL
aHash
|
66e7e7efe7e7e700 |
|
VISUAL
dHash
|
8c0c16164d4d0c4c |
|
VISUAL
wHash
|
00e7c3c3e7e7e700 |
|
VISUAL
colorHash
|
070000001c0 |
|
VISUAL
cropResistant
|
8c0c16164d4d0c4c |
Análise de Código
Risk Score
89/100
Threat Level
HIGH
⚠️ Phishing Confirmed
🎣 Credential Harvester
🎣 OTP Stealer
🎣 Banking
🎣 Personal Info
🔬 Threat Analysis Report
• Ameaça: Phishing de Credenciais
• Alvo: Usuários do Network Solutions
• Método: Imitação do login do webmail
• Exfil: Desconhecido, mas provavelmente um banco de dados
• Indicadores: Incompatibilidade de domínio, formulário presente
• Risco: Alto
🔒 Obfuscation Detected
- fromCharCode
- hex_escape
- unicode_escape
🎯 Kit Endpoints
- login-page-configuration
- login-page-configuration-custom
- https://www.networksolutions.com/mail-admin/forgot-password?user=solomon.chika1%40gmail.com
📡 API Calls Detected
- defaultcache
- GET
📊 Detalhamento da Pontuação de Risco
Total Risk Score
90/100
Contributing Factors
Domain Mismatch
The domain is a URL shortener and unrelated to the brand.
Forms
The presence of a login form suggests credential harvesting.
Obfuscation
Obfuscated Javascript code is detected, attempting to hide malicious logic
Credential Harvesting
The website tries to phish for user's credentials
🔬 Análise Integral de Ameaças
Tipo de Ameaça
Banking Credential Harvester
Alvo
Network Solutions users (International)
Método de Ataque
Brand impersonation + credential harvesting forms + obfuscated JavaScript
Canal de Exfiltração
Form submission (backend endpoint not detected - likely JavaScript-based)
Avaliação de Risco
CRITICAL - Automated credential harvesting with Form submission (backend endpoint not detected - likely JavaScript-based)
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Banking, Personal Info
- 6 obfuscation techniques
🏢 Análise de Falsificação de Marca
Impersonated Brand
Network Solutions
Fake Service
Webmail
Fraudulent Claims
⚔️ Metodologia de Ataque
Primary Method: Credential Harvesting
The website presents a fake login form to steal user credentials. The attacker creates a web page that looks like a legitimate service, and tricks users into entering their login details.
🌐 Indicadores de Compromisso de Infraestrutura
Domain Information
Domain
is.gd
Registered
2007-09-12
Registrar
Namecheap
Status
Active
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Network Solutions
http://bafkreieblbaolujlruolakxfo26mvcjncldvoqjcgcpmbyberkaj...
Mar 29, 2026
Network Solutions
https://eu.orbitor.dev/ipfs/bafkreihxkhc3zqivf7yc4ii5no5a7wu...
Mar 29, 2026
Network Solutions
https://tourmaline-chaja-24f4f7.netlify.app/
Mar 20, 2026
Network Solutions
http://apac.orbitor.dev/ipfs/bafkreihxkhc3zqivf7yc4ii5no5a7w...
Mar 20, 2026
Network Solutions
http://latam.orbitor.dev/ipfs/bafkreihxkhc3zqivf7yc4ii5no5a7...
Mar 20, 2026
Scan History for www.is.gd
Found 10 other scans for this domain

"Nunca pensei que aconteceria comigo"
Isso dizem os 2,3 milhões de vítimas a cada ano. Não espere para ser uma estatística.