Phishing Analysis
Detailed analysis of captured phishing page
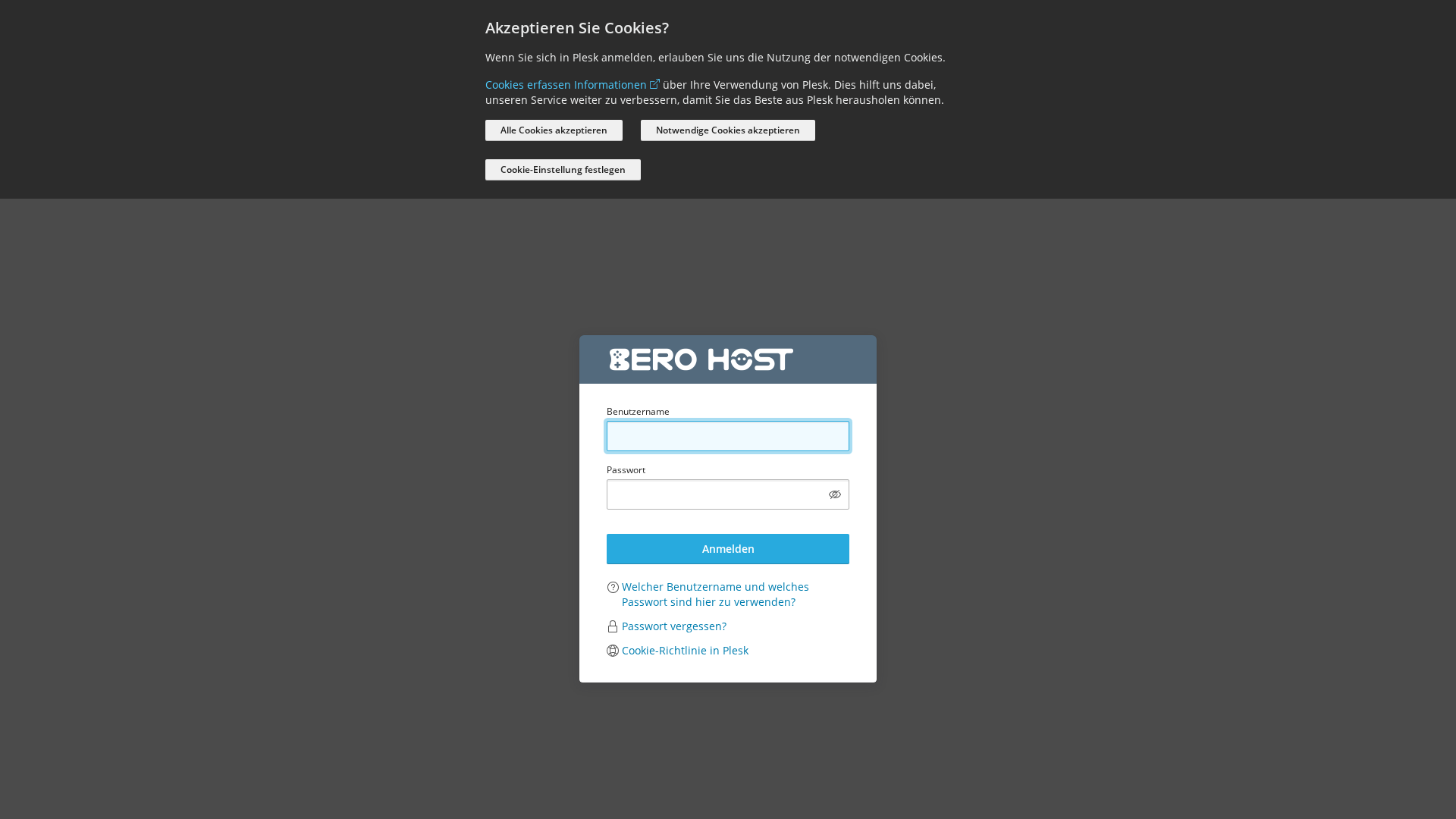
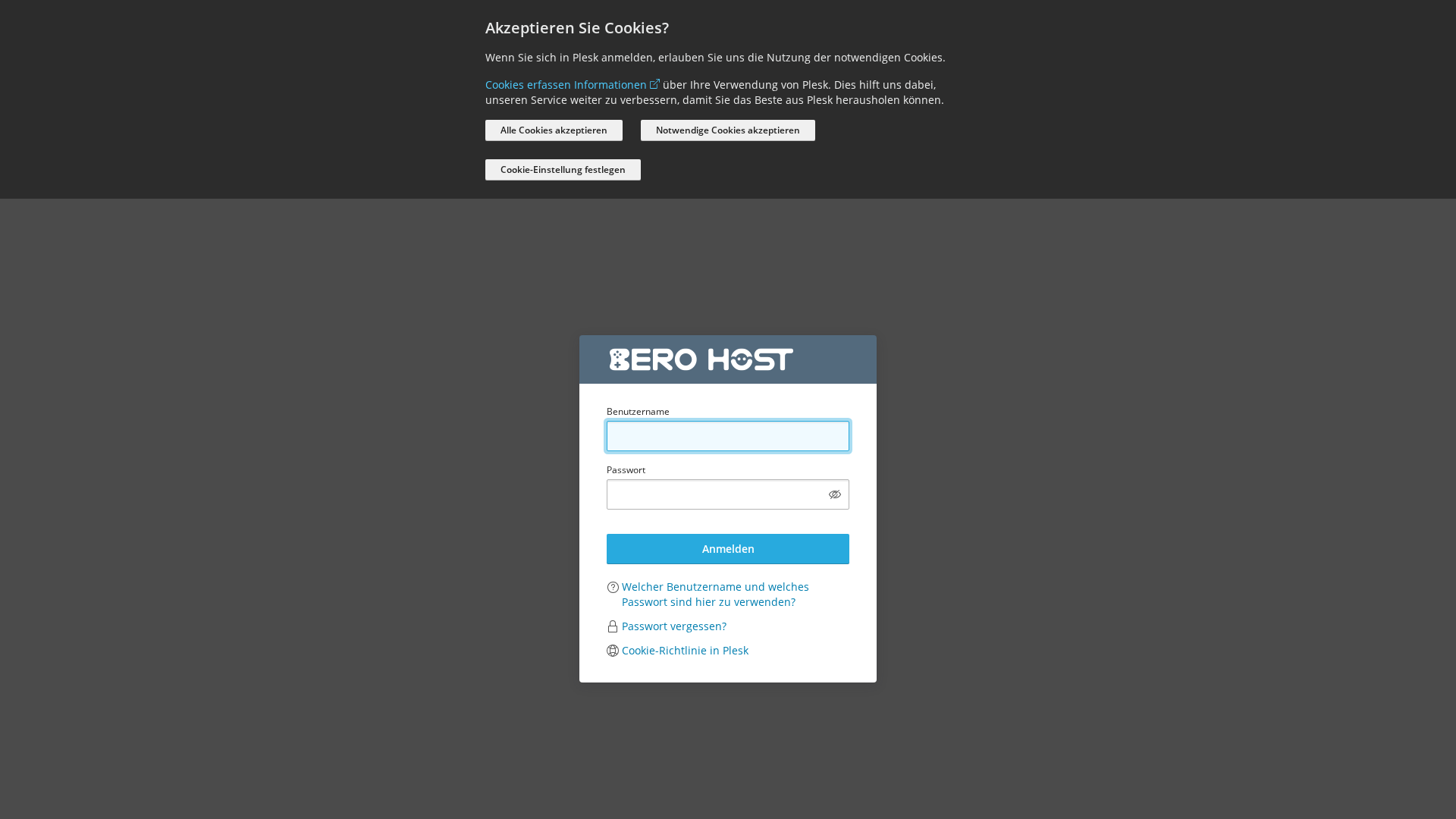
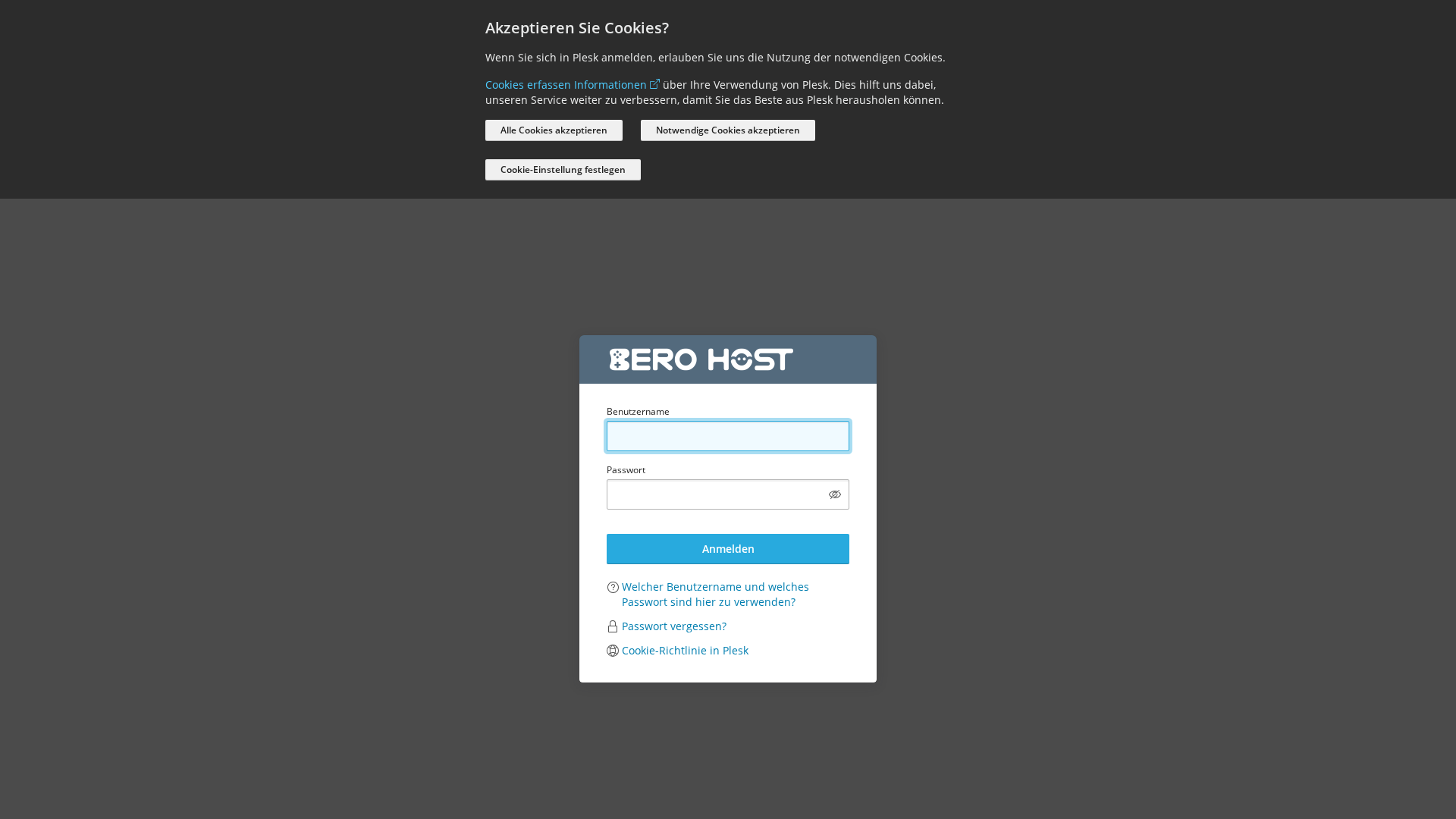
Captura Visual
Informações de Detecção
Hashes de Conteúdo (Similaridade HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T14AF10E32944CEC3B23231FD17592BB14E2D6C76ECA421A10D6B9439E0FEBED2E446657 |
|
CONTENT
ssdeep
|
192:8HEJikYMzvUAZ6C3CYEQctxdUAKe8I+jKkrAr+jg1rA+j3rrALdv:+EJikp8AIe7/AKe8I+jKkrAijg1rA+j+ |
Hashes Visuais (Similaridade de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
cc666699333133b3 |
|
VISUAL
aHash
|
0010001818181800 |
|
VISUAL
dHash
|
70624cb2b2b2b24c |
|
VISUAL
wHash
|
001020381c1c1c1c |
|
VISUAL
colorHash
|
070060000c0 |
|
VISUAL
cropResistant
|
98a6b2803336b8b8,70624cb2b2b2b24c |
Análise de Código
🔬 Threat Analysis Report
• Ameaça: Phishing
• Alvo: Usuários do Plesk
• Método: Imitação via página de login
• Exfil: Dados do formulário (nome de usuário, senha)
• Indicadores: Domínio suspeito, ofuscação de JavaScript, envio de formulário.
• Risco: ALTO
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- document.write
- hex_escape
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- ${(0,m.default)(`/admin/report/download/file/${encodeURIComponent(n.file)}`)}
- /login_up.php?modals[cookie-policy-preferences]=true
- log-in
- https://support.plesk.com/hc/en-us/articles/12377667582743-How-to-log-in-to-Plesk-
- /logout.php
📡 API Calls Detected
- GET
- /modules/notifier/index.php/notifications
- /admin/copilot/gen-answer
- https://o447951.ingest.sentry.io/api/4509632503087104/envelope/?sentry_version=7&sentry_key=c1dfb07d783ad5325c245c1fd3725390&sentry_client=sentry.javascript.browser%2F1.33.7
📊 Detalhamento da Pontuação de Risco
Contributing Factors
🔬 Análise Integral de Ameaças
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 110 obfuscation techniques
🏢 Análise de Falsificação de Marca
⚔️ Metodologia de Ataque
Primary Method: Credential Harvesting
The attackers are attempting to steal login credentials through a fake login form that mimics Plesk's login page. Users are tricked into entering their username and password, which are then captured by the attackers.
Secondary Method: JavaScript Obfuscation
The attacker used JavaScript obfuscation to hide and potentially execute malicious code such as keyloggers or information exfiltration code.
🌐 Indicadores de Compromisso de Infraestrutura
Domain Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)