
Phishing Analysis
Detailed analysis of captured phishing page
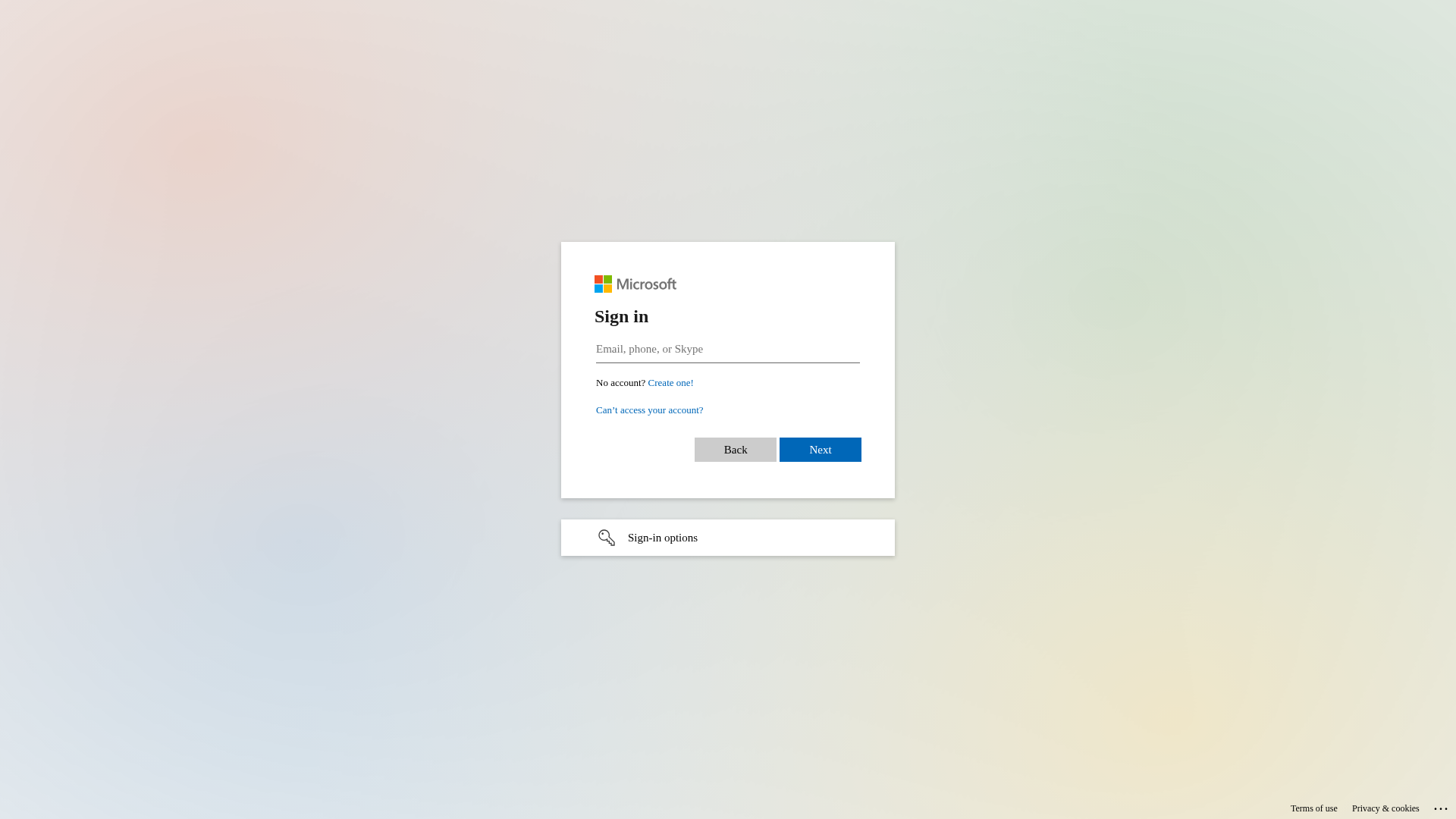
Captura Visual
No screenshot available
Informações de Detecção
https://auth.properties/PLGLhAll4w08P-0
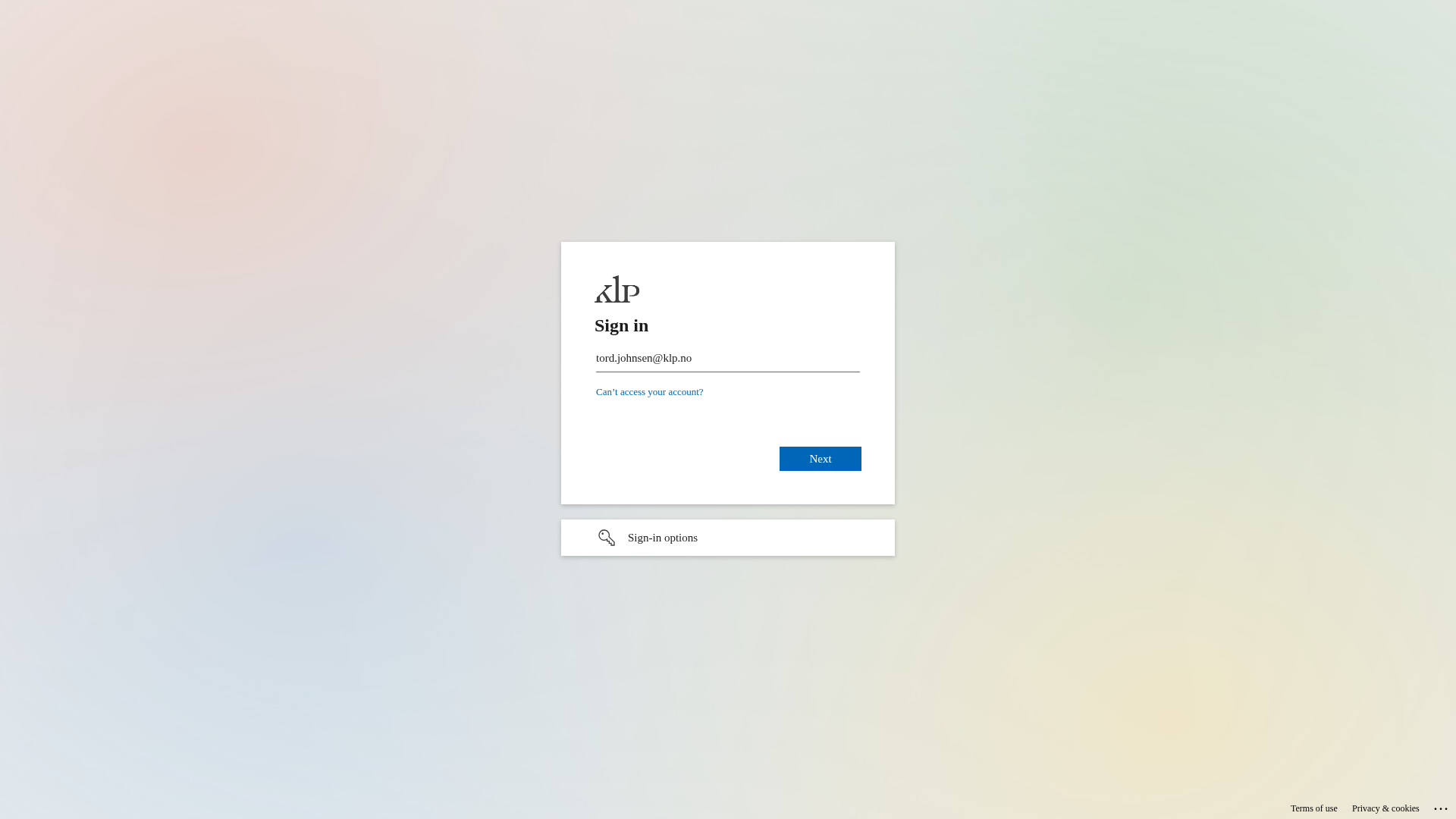
Detected Brand
KLP (likely)
Country
International
Confidence
100%
HTTP Status
200
Report ID
e3659a8c-8b2…
Analyzed
2026-03-19 05:43
Hashes de Conteúdo (Similaridade HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T14DD1DD7060509D3B42C3C7D8B3BA6B4F3794C246EA87565A67F8C35C0EE3E56CC1A226 |
|
CONTENT
ssdeep
|
96:DIpkCGTHRPy9OkrwkMEs39TbJG9KjsWsjO40U2gs0sjOpOVJQ6Q6ynQjNsjO+:ZsOk899TbJG9aGJOVJQyyQja |
Hashes Visuais (Similaridade de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
9c497326cc99d966 |
|
VISUAL
aHash
|
18001818191f0f9f |
|
VISUAL
dHash
|
7161713331727d38 |
|
VISUAL
wHash
|
191818181f1f1fff |
|
VISUAL
colorHash
|
070000001c0 |
|
VISUAL
cropResistant
|
7161713331727d38 |
Análise de Código
Risk Score
70/100
Threat Level
BAJO
🎣 Credential Harvester
🎣 OTP Stealer
🎣 Personal Info
🔬 Threat Analysis Report
• Ameaça: Falsificação
• Alvo: Usuários KLP
• Método: Tentando roubar credenciais.
• Exfil: Desconhecido
• Indicadores: Página de login.
• Risco: Baixo
🎯 Kit Endpoints
- https://login.microsoftonline.com/common/oauth2/authorize?client_id=00000001-0000-cff1-ce00-758486212919&response_mode=form_post&response_type=code+id_token&scope=openid&msafed=1&msaredir=1&client-request-id=d98292e6-fa3f-ce32-3763-21bc5137cc6d&protectedtoken=true&domain_hint=klp.no&nonce=818112778954.ec82d3ed-b372-7cd6-3e42-fcfc13352e79&state=cGVybmlsbGUuYnJpa3NkYWxAa2xwLm5v#
- https://passwordreset.microsoftonline.com/?ru=https://login.microsoftonline.com/common/oauth2/authorize?client_id=00000001-0000-cff1-ce00-588007067520&response_mode=form_post&response_type=code+id_token&scope=openid&msafed=1&msaredir=1&client-request-id=d98292e6-fa3f-ce32-5054-21bc5137cc6d&protectedtoken=true&domain_hint=klp.no&nonce=610319169527.ec82d3ed-b372-7cd6-3e42-fcfc13352e79&state=cGVybmlsbGUuYnJpa3NkYWxAa2xwLm5v#
- https://login.microsoftonline.com/common/oauth2/authorize?client_id=00000001-0000-cff1-ce00-385887996790&response_mode=form_post&response_type=code+id_token&scope=openid&msafed=1&msaredir=1&client-request-id=d98292e6-fa3f-ce32-4723-21bc5137cc6d&protectedtoken=true&domain_hint=klp.no&nonce=468105755024.ec82d3ed-b372-7cd6-3e42-fcfc13352e79&state=cGVybmlsbGUuYnJpa3NkYWxAa2xwLm5v#
- https://login.microsoftonline.com/common/login#
📊 Detalhamento da Pontuação de Risco
Total Risk Score
25/100
Contributing Factors
Impersonation
Appears to be a login page for a known brand
Unknown Domain
Without domain, not possible to check for suspicious indicators.
🔬 Análise Integral de Ameaças
Tipo de Ameaça
Two-Factor Authentication Stealer
Alvo
KLP (likely) users (International)
Método de Ataque
Brand impersonation
Canal de Exfiltração
Unknown
Avaliação de Risco
HIGH - Automated credential harvesting with Unknown
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Personal Info
🏢 Análise de Falsificação de Marca
Impersonated Brand
KLP
Official Website
klp.no
Fake Service
Sign in page.
⚔️ Metodologia de Ataque
Primary Method: Credential Harvesting
The attacker aims to steal user credentials (email and password) by tricking users into entering their information on a fake login page.
🌐 Indicadores de Compromisso de Infraestrutura
Domain Information
Domain
None
Registered
None
Registrar
None
Status
None
🤖 AI-Extracted Threat Intelligence
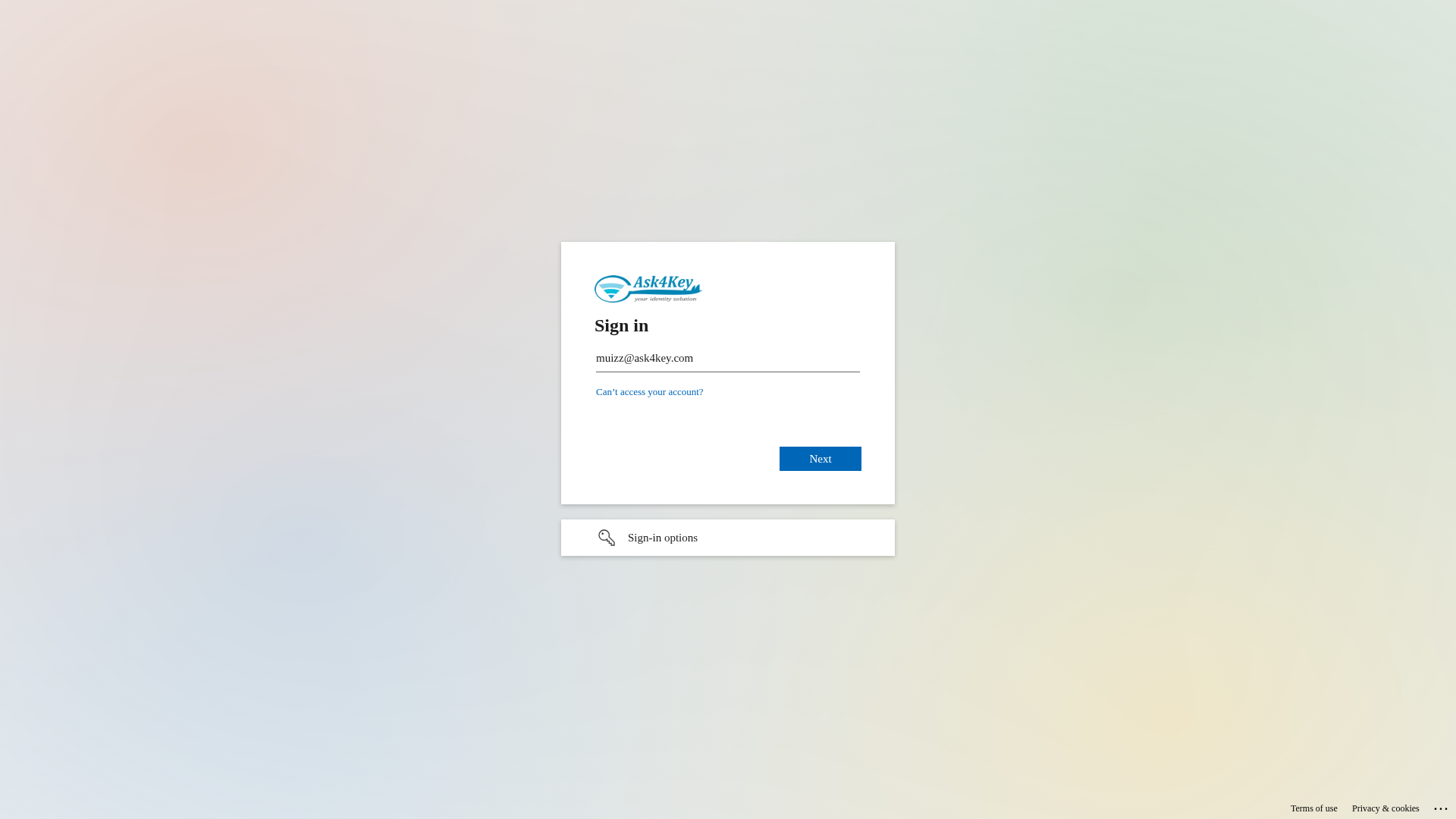
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
KLP (Norwegian pension company)
https://sso-auth.com/jFpa4GFJOqDj
Abr 08, 2026
Microsoft/Office 365 (impersonated)
https://sso-security.com/szfxOkBlNOxSHzCY?=userid&messageid=...
Abr 08, 2026
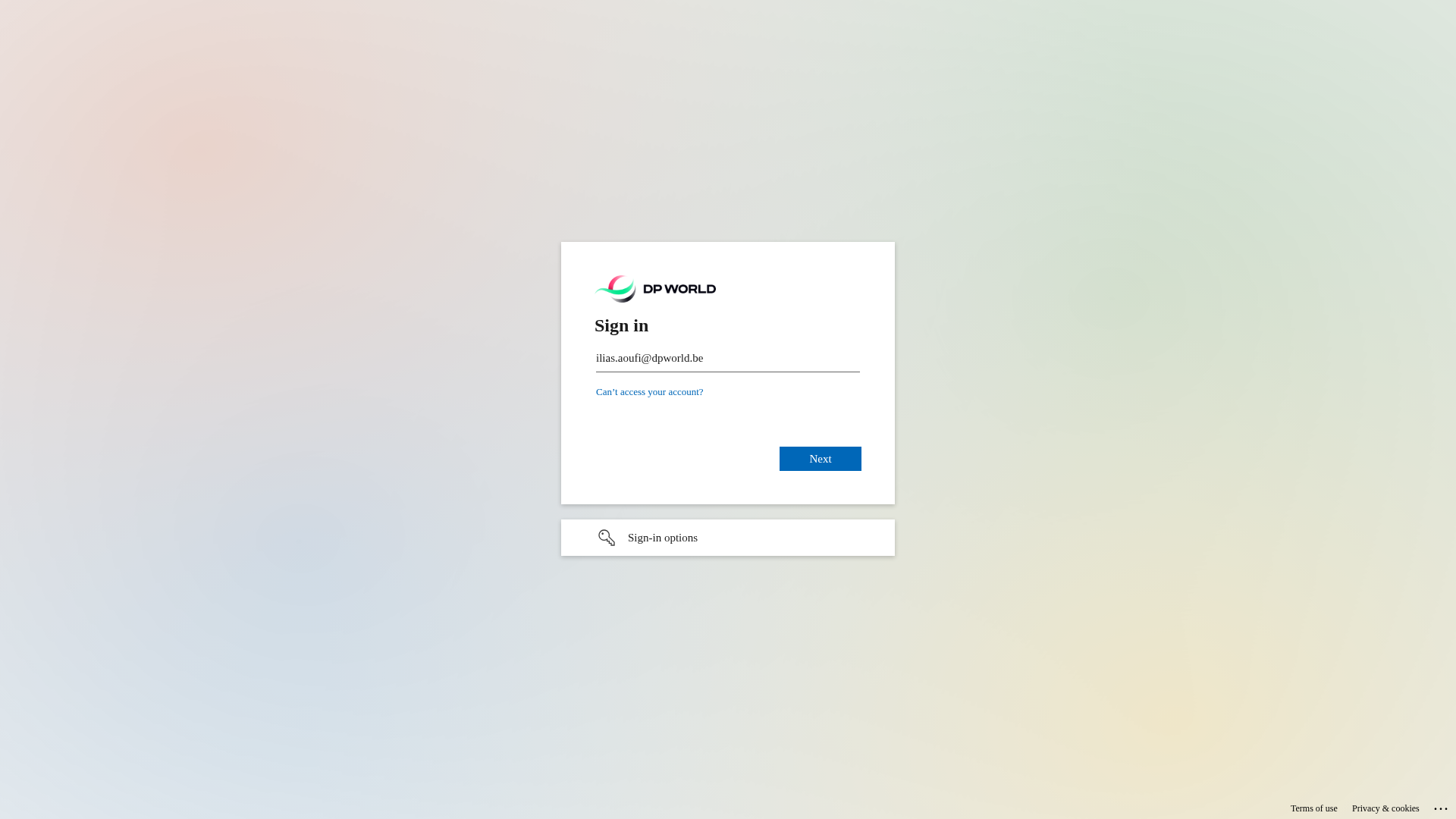
DP World
https://auth.properties/TAKkunrvccF5
Abr 07, 2026
Microsoft
https://notifyhubss.net/e0df002ddw68f44a87e92784420q0782dbe3...
Abr 07, 2026
Microsoft
https://notifyhubss.net/e0204ed4cw27574283e9e0e1917q4fd0d12d...
Abr 07, 2026
Scan History for auth.properties
Found 10 other scans for this domain
-
https://auth.properties/qdUWGEce6AeYbtI
https://auth.properties/11rW4wS9oz4
https://auth.properties/gj3hNm5WGG0P
https://auth.properties/oeadTJxslK7K4sSvEA
https://auth.properties/jgyWcAFwqnQ
https://auth.properties/xGsHR_GoayJtyg
https://auth.properties/TAKkunrvccF5
https://auth.properties/YFIF0_lAoxI
https://auth.properties/oT7Om3GHmc0FKO_2oQ
https://auth.properties/l_waqLRYr1qBDC0wSw

"Nunca pensei que aconteceria comigo"
Isso dizem os 2,3 milhões de vítimas a cada ano. Não espere para ser uma estatística.