
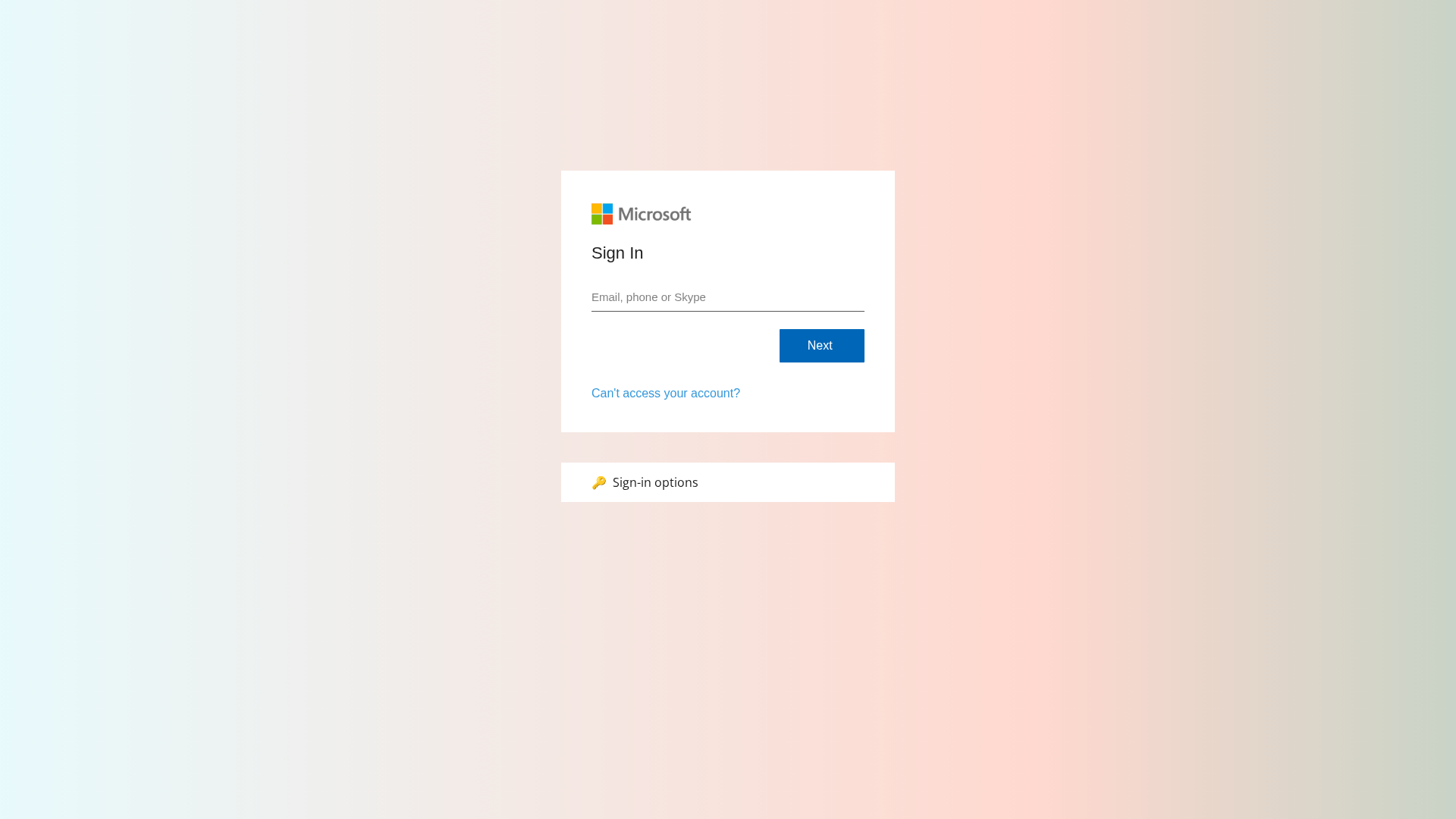
Phishing Analysis
Detailed analysis of captured phishing page
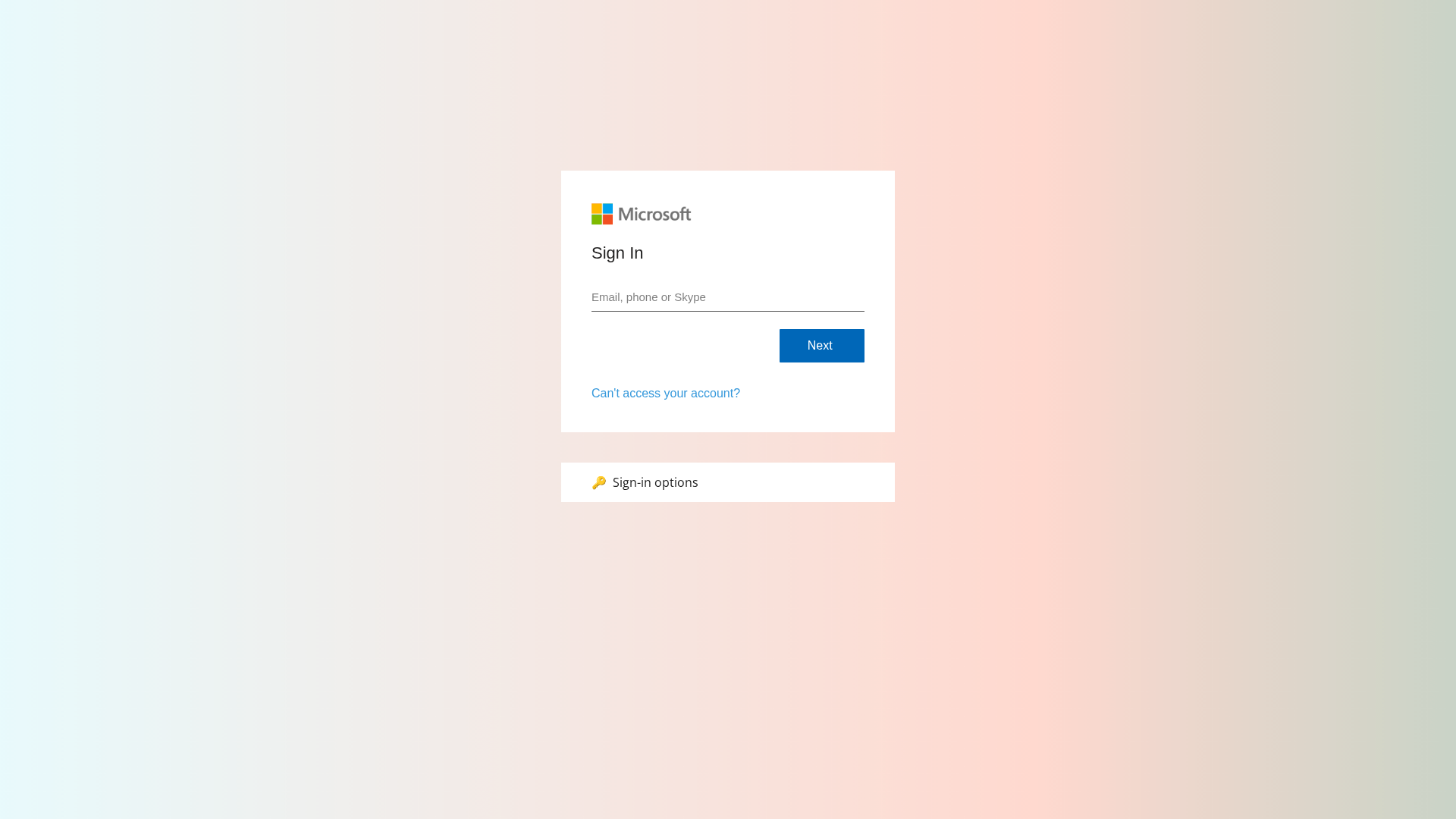
Captura Visual
Informações de Detecção
Hashes de Conteúdo (Similaridade HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T113F1CE31E244C91B7251C9A4F6B1BB9A3B459385D70B0B70F6F0A23ABDC9CB04D942ED |
|
CONTENT
ssdeep
|
96:XNo9+uvTBSTST8FKF1fiPhevO9dShcFSTqM8V8+hucyBF+uuuup:XN6rQeQmfiPovO9dt0z8FvyM |
Hashes Visuais (Similaridade de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
dd88333366669999 |
|
VISUAL
aHash
|
f0f8f8f0f8f0f0f0 |
|
VISUAL
dHash
|
0010302430000000 |
|
VISUAL
wHash
|
e0f8f8f0f8e0f0e0 |
|
VISUAL
colorHash
|
07000000180 |
|
VISUAL
cropResistant
|
0010302430000000 |
Análise de Código
🔬 Threat Analysis Report
• Ameaça: Phishing
• Alvo: Usuários do Microsoft
• Método: Imitação por meio de uma página de login falsa.
• Exfil: Dados do envio do formulário.
• Indicadores: Incompatibilidade de domínio, JavaScript ofuscado, formulário detectado.
• Risco: Alto
🔒 Obfuscation Detected
- fromCharCode
- unicode_escape
- base64_strings
🎯 Kit Endpoints
- https://a#б
- https://тест
- https://a@b
- https://a
- https://itsuppports.com/js/usecure.bundle.js?v=fbaff749-4ed9-4292-b9a1-20c3648c09f1
- https://a/c%20d?a=1&c=3
- https://x
📊 Detalhamento da Pontuação de Risco
Contributing Factors
🔬 Análise Integral de Ameaças
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, Banking
- 21 obfuscation techniques
🏢 Análise de Falsificação de Marca
⚔️ Metodologia de Ataque
Primary Method: Credential Harvesting
The attacker creates a fake login page that mimics a legitimate service (Microsoft). Users are tricked into entering their credentials, which are then captured by the attacker.
Secondary Method: JavaScript Obfuscation
The JavaScript code on the page is obfuscated to hide its malicious intent from analysis and security tools. This code is likely used to handle form submission and data exfiltration.
🌐 Indicadores de Compromisso de Infraestrutura
🦠 Malicious Files
🔬 JavaScript Deep Analysis
🔗 API Endpoints Detected
🔐 Obfuscation Detected
- : Heavy
🤖 AI-Extracted Threat Intelligence
🎯 Malicious Files Identified
usecure.bundle.js?v=fbaff749-4ed9-4292-b9a1-20c3648c09f1Similar Websites
Pages with identical visual appearance (based on perceptual hash)
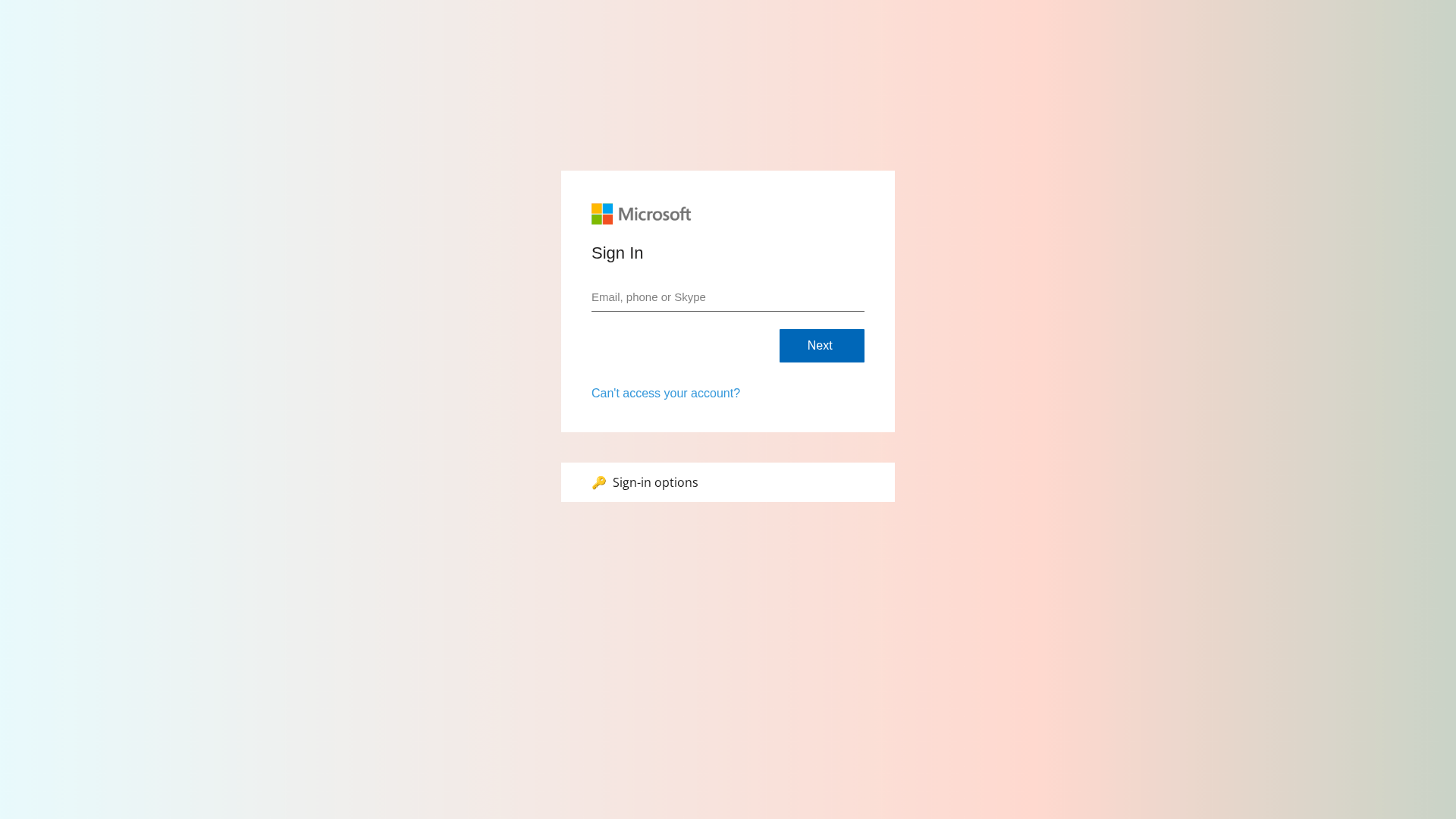
Scan History for itsuppports.com
Found 4 other scans for this domain
