Phishing Analysis
Detailed analysis of captured phishing page
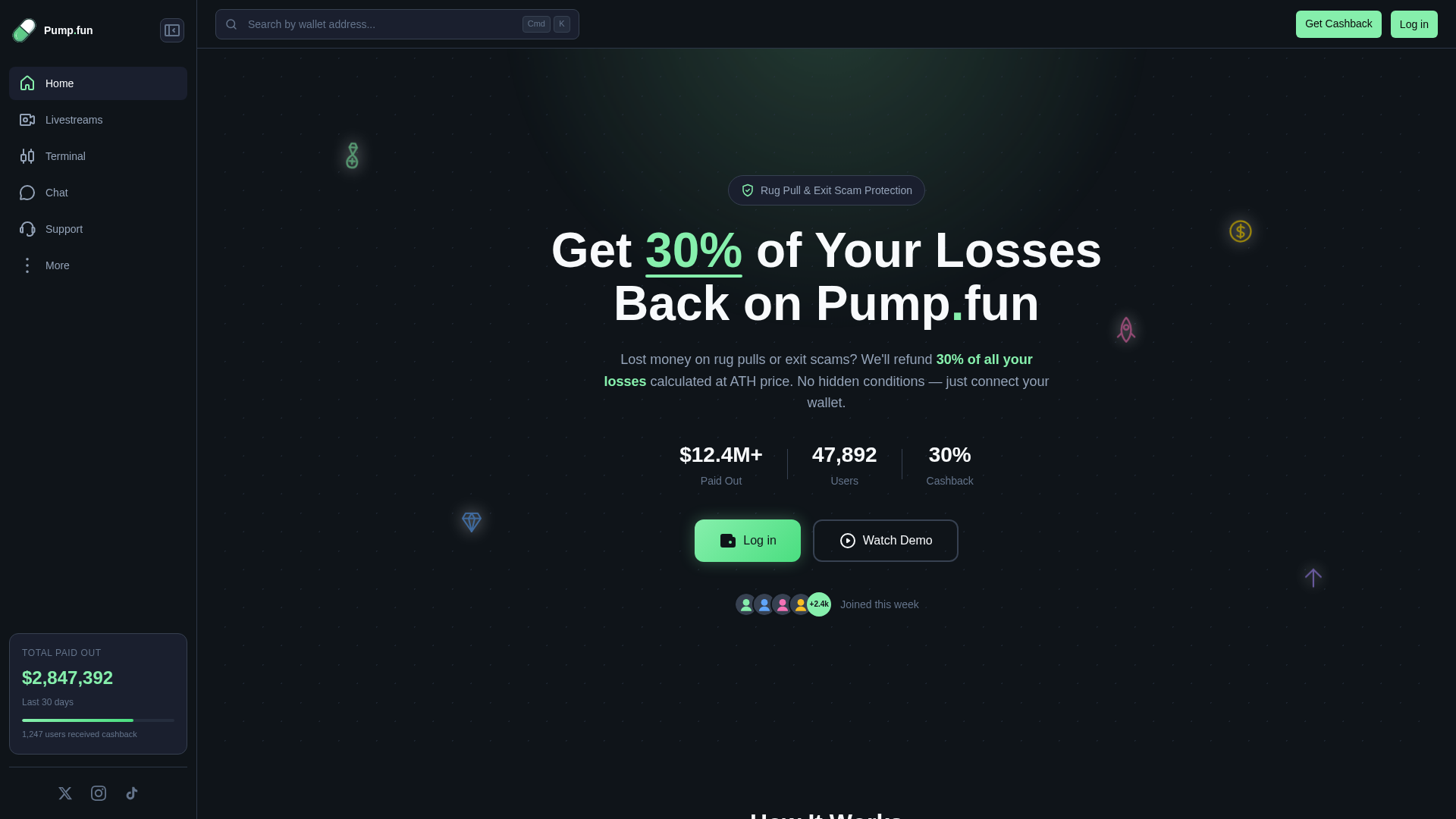
Captura Visual
Informações de Detecção
Hashes de Conteúdo (Similaridade HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T16FB2B7A453446D3DB05383E8CB36337A32BA52D6E70A0218C5F843B8AA55DDEED375D8 |
|
CONTENT
ssdeep
|
384:usnQsR+scVhNSz6btp6KnP0iDhTk4Pyx5eFy:uVF1pf0iDC4oeFy |
Hashes Visuais (Similaridade de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
999a6f6922ba88ae |
|
VISUAL
aHash
|
9d0c1c1c08188080 |
|
VISUAL
dHash
|
7978313950d22810 |
|
VISUAL
wHash
|
fddc9e1e1c3d8088 |
|
VISUAL
colorHash
|
38038000000 |
|
VISUAL
cropResistant
|
7978313950d22810 |
Análise de Código
📊 Detalhamento da Pontuação de Risco
Contributing Factors
🔬 Análise Integral de Ameaças
⚠️ Indicators of Compromise
- Kit types: OTP Stealer
🏢 Análise de Falsificação de Marca
⚔️ Metodologia de Ataque
Primary Method: Two-Factor Authentication Bypass
Victim is prompted for 2FA code after entering credentials. The code is intercepted and used by attacker to access victim's account in real-time.
Secondary Method: Standard Phishing Techniques
Uses typical phishing tactics including brand impersonation, urgency tactics, and social engineering to trick victims into providing sensitive information.
🌐 Indicadores de Compromisso de Infraestrutura
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for cashback-pump.com
Found 2 other scans for this domain