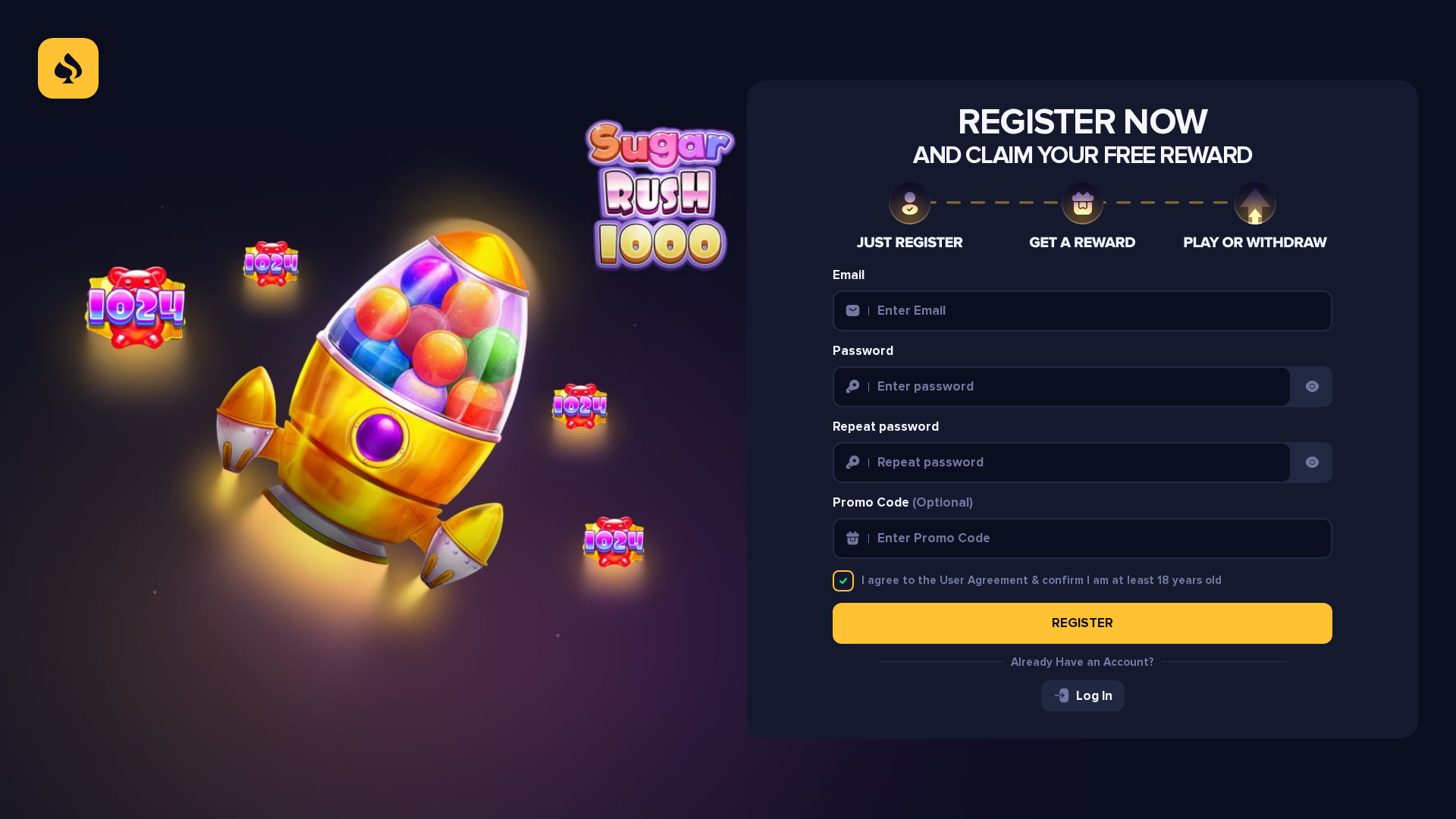
Phishing Analysis
Detailed analysis of captured phishing page
Captura Visual
No screenshot available
Informações de Detecção
Hashes de Conteúdo (Similaridade HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T179E229B4A230D335B1C24BD8DA6425287A5FE1DCD7C695B4E388AF11B0D6CECD9260CB |
|
CONTENT
ssdeep
|
384:4r/jMJgubTPRhiXkdvNTDhPhLxeAxeDWNW1Tp34PxeeJEmuW3AsV6QRWOMd:4r/jMJguZhhPhleMeDGCSPxeeWmHtzW |
Hashes Visuais (Similaridade de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
c31e3cb163f34b48 |
|
VISUAL
aHash
|
801670e060766e00 |
|
VISUAL
dHash
|
0c34e6cbc3ccccc1 |
|
VISUAL
wHash
|
8016f2e070feff60 |
|
VISUAL
colorHash
|
38200448000 |
|
VISUAL
cropResistant
|
1230929aa6e2eaea,8e9ab365666a4c74,2d1cdcc7e3f8fdf9,80100c4c4c081000,0c34e6cbc3ccccc1 |
Análise de Código
🔬 Threat Analysis Report
• Ameaça: Phishing de roubo de credenciais
• Alvo: Usuários desavisados
• Método: Formulário de registro enganoso.
• Exfil: wss://gambler-work.com/api/ws
• Indicadores: Domínio recente, ofuscação Javascript, envio de formulário.
• Risco: Alto
🔒 Obfuscation Detected
- atob
- eval
- fromCharCode
- unescape
- base64_strings
🎯 Kit Endpoints
- http://developers.facebook.com/policy/].
- https://crypto.sardine.ai/buy
- https://betza-game.com/_next/static/chunks/4bd1b696-ad7506e6ce5b48e8.js
- https://react.dev/link/hydration-mismatch
- https://betza-game.com/_next/static/chunks/58211-d9d578b8de9e3293.js
- https://qa.meldcrypto.com/
- https://connect.facebook.net/en_US/fbevents.js
- https://betza-game.com/_next/static/chunks/53331-ed5951db58e70abe.js
- http://localhost:3001
- https://betza-game.com/_next/static/chunks/53069-c3a95b8ce62cca48.js
- https://betza-game.com/_next/static/chunks/49080-aa8410705e183b35.js
- https://gambler-work.com/api
- https://gambler-work.com/payser
- https://react.dev/errors/
- https://guarda.com/buy/
- https://www.facebook.com/privacy_sandbox/topics/registration/
- https://betza-game.com/_next/static/chunks/92148-6f19ac7166461fa8.js
- https://www.facebook.com/tr/
- https://betza-game.com/_next/static/chunks/app/layout-2344be9881d79b44.js
- https://ramp.network/buy
- https://exchange.mercuryo.io/
- https://changelly.com/buy-crypto
- https://openocean.banxa.com/
- https://www.moonpay.com/buy/btc
- https://nextjs.org/docs/messages/react-hydration-error
- https://betza-game.com/_next/static/chunks/app/(auth)/layout-2f72bfb00bd0ee9b.js
- https://changenow.io/buy/bitcoin
- https://global.transak.com/
- https://betza-game.com/_next/static/chunks/34230-e87c8d35c9fa1ab6.js
- https://betza-game.com/_next/static/chunks/63712-08d55a4030f898f7.js
📡 API Calls Detected
- POST
- GET
📊 Detalhamento da Pontuação de Risco
Contributing Factors
🔬 Análise Integral de Ameaças
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 116 obfuscation techniques
🏢 Análise de Falsificação de Marca
Fraudulent Claims
⚔️ Metodologia de Ataque
Primary Method: Credential Harvesting
The website presents a registration form designed to steal user credentials. The Javascript code likely attempts to intercept the entered data and send it to the attackers.
Secondary Method: Social Engineering
The site uses social engineering tactics like offering a 'free reward' to entice users to enter their information.
🌐 Indicadores de Compromisso de Infraestrutura
🦠 Malicious Files
🔬 JavaScript Deep Analysis
🔗 API Endpoints Detected
🔐 Obfuscation Detected
- : Moderate
- : Moderate
- : Moderate
- : None
- : Light
- : Light
- : Light
- : Light
- : Light
- : Light
- : None
- : Light
- : Light
- : Light
- : Light
- : Light
- : Light
- : Light
- : Light
🤖 AI-Extracted Threat Intelligence
🎯 Malicious Files Identified
fbevents.jsSimilar Websites
Pages with identical visual appearance (based on perceptual hash)