Phishing Analysis
Detailed analysis of captured phishing page
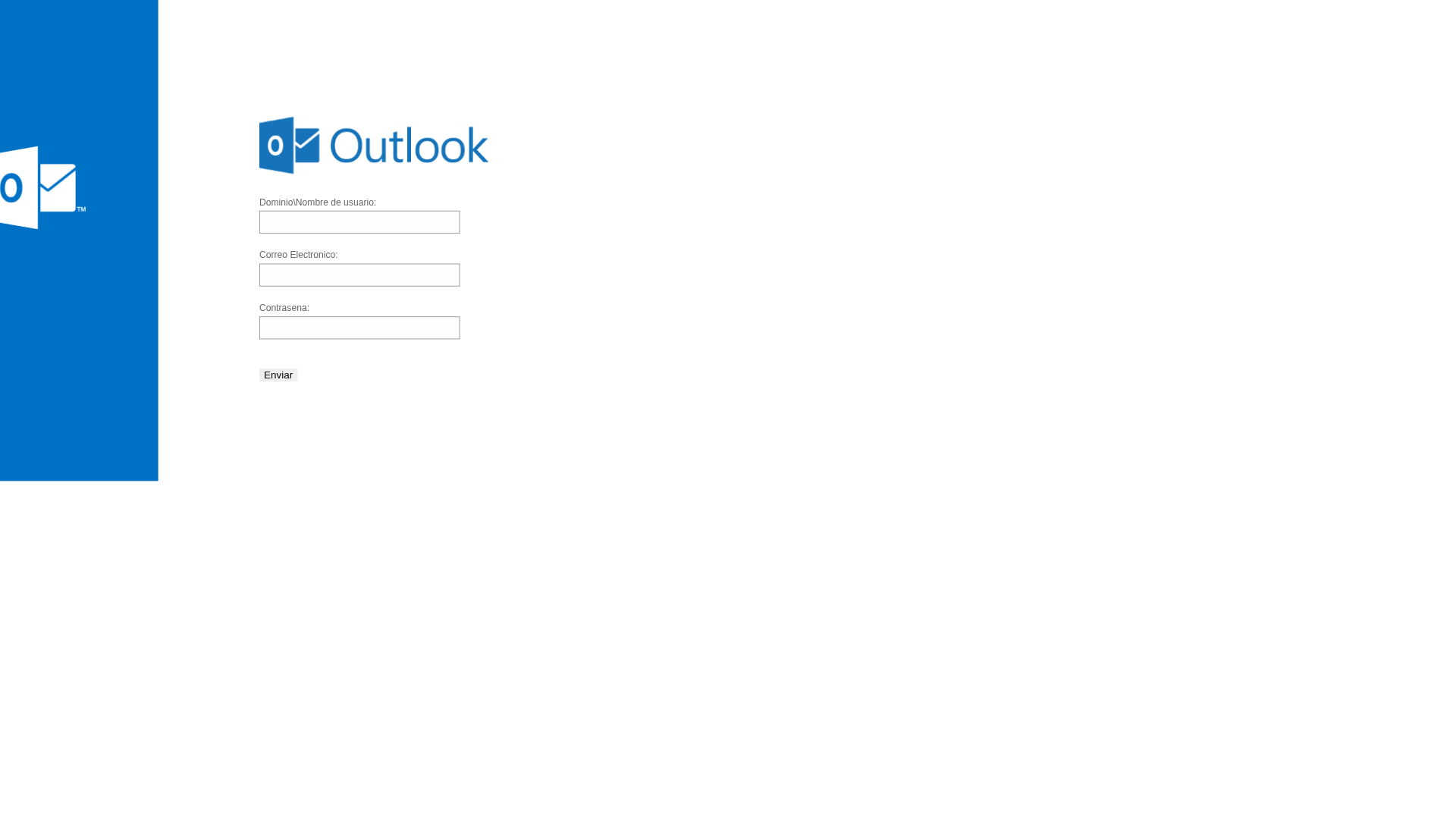
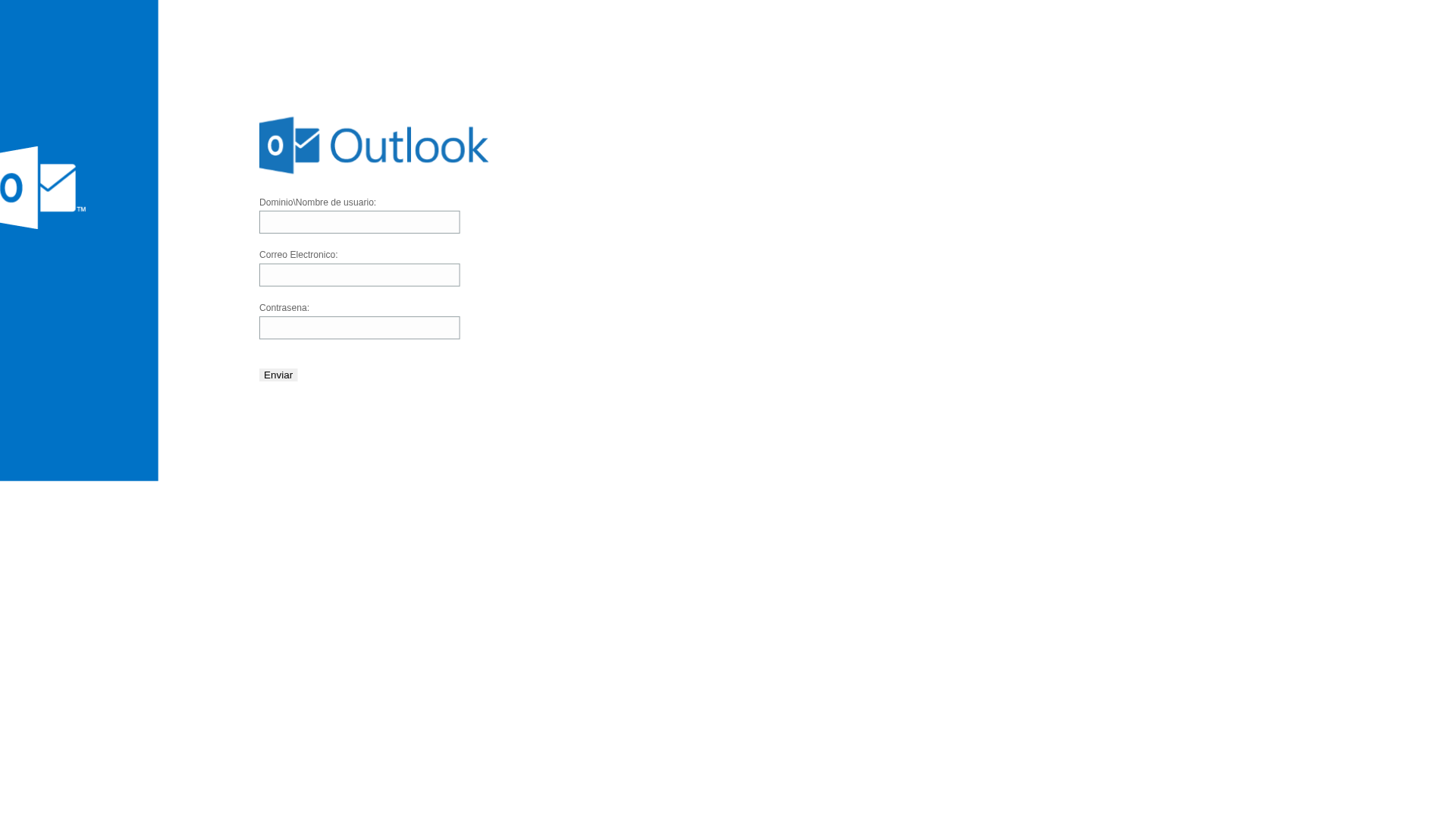
Captura Visual
Informações de Detecção
Hashes de Conteúdo (Similaridade HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T18CC132219008DC2F4222F1F4EA61794EF1DAE701D74A15CDA2F487AD1FEADE0CE57668 |
|
CONTENT
ssdeep
|
96:zKL+cafLrBw5Rgd+JR+sGMdSFxuPeNfz0m:4+cafLrBw5Cd+JR+wwCeVzF |
Hashes Visuais (Similaridade de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
8000ffff0080fff3 |
|
VISUAL
aHash
|
7f1f7f7f7fffffff |
|
VISUAL
dHash
|
d0f0f0d0d0008000 |
|
VISUAL
wHash
|
7010101070f0f0f0 |
|
VISUAL
colorHash
|
070000001c0 |
|
VISUAL
cropResistant
|
d0f0f0d0d0008000,8058848418600000 |
Análise de Código
🔐 Credential Harvesting Forms
📡 API Calls Detected
- /udata/custom/isGlobalRecaptchaEnabled.json
- /udata/system/captcha/
📤 Form Action Targets
- https://submit-form.com/jJ89K1TLB
📊 Detalhamento da Pontuação de Risco
Contributing Factors
🔬 Análise Integral de Ameaças
⚠️ Indicators of Compromise
- Kit types: Credential Harvester, OTP Stealer, Personal Info
🏢 Análise de Falsificação de Marca
⚔️ Metodologia de Ataque
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: Client-Side Form Interception
JavaScript intercepts form submissions before they reach the fake backend. This allows real-time credential harvesting and validation without server round-trips.
🌐 Indicadores de Compromisso de Infraestrutura
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)