Phishing Analysis
Detailed analysis of captured phishing page
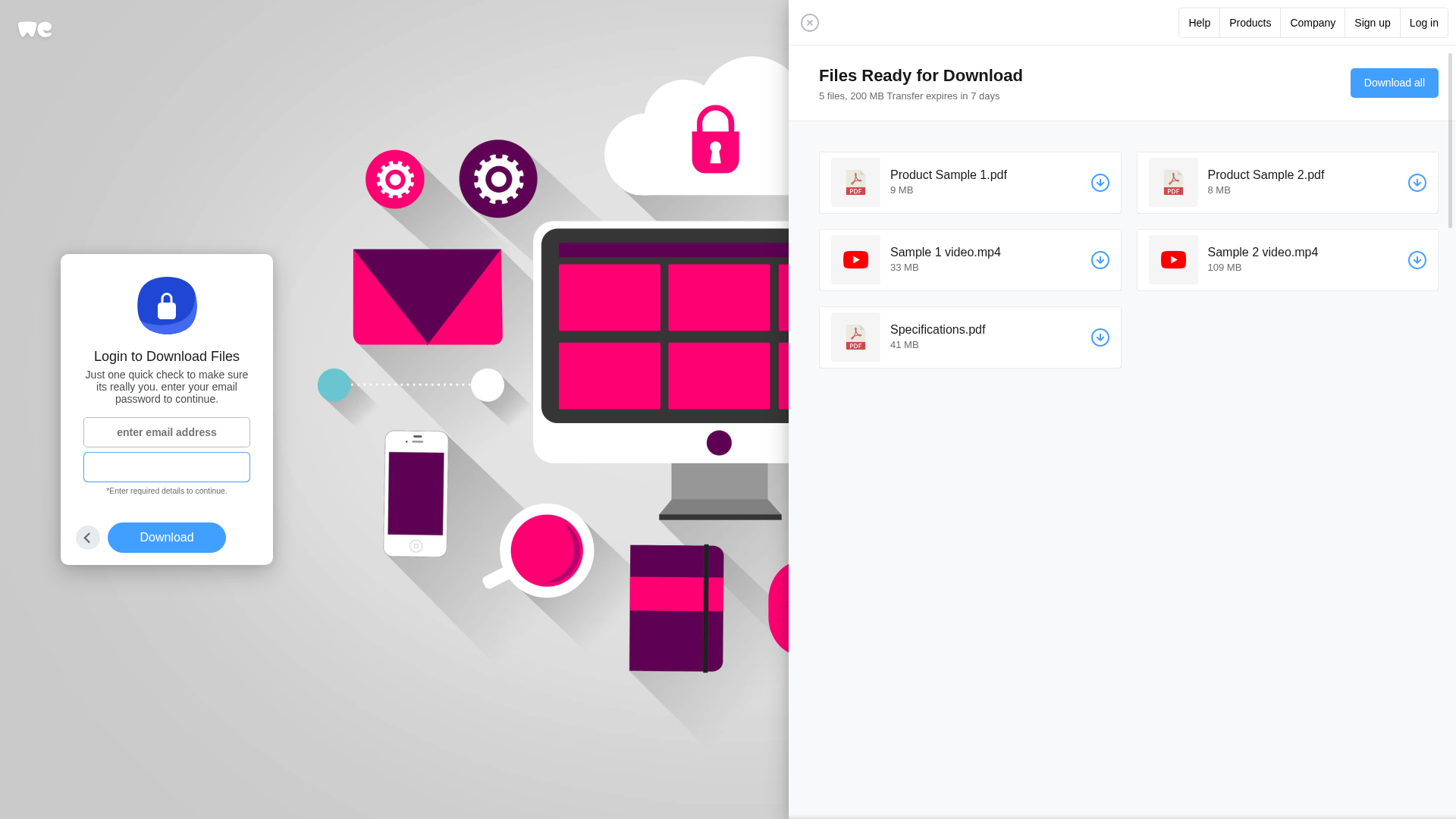
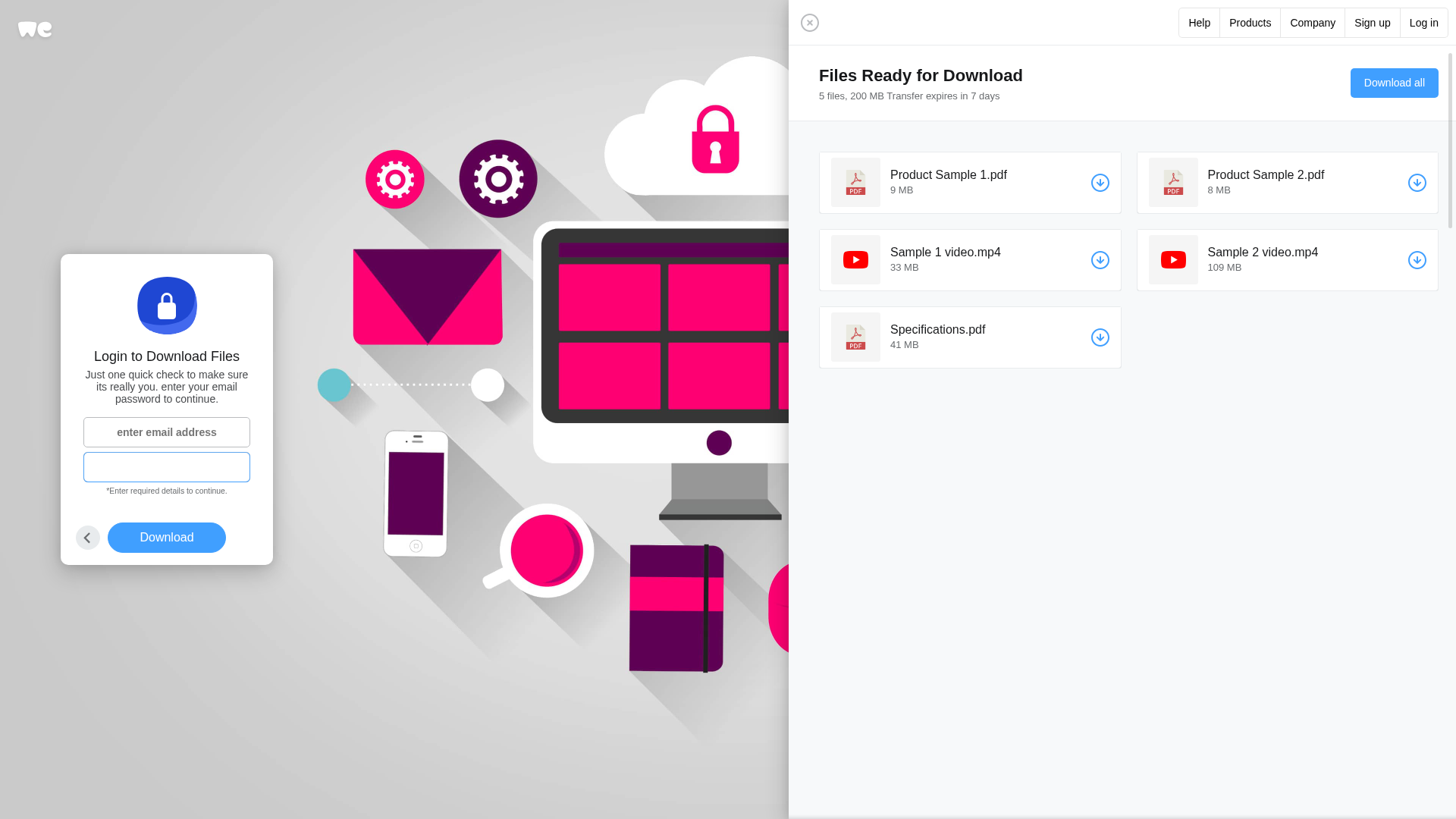
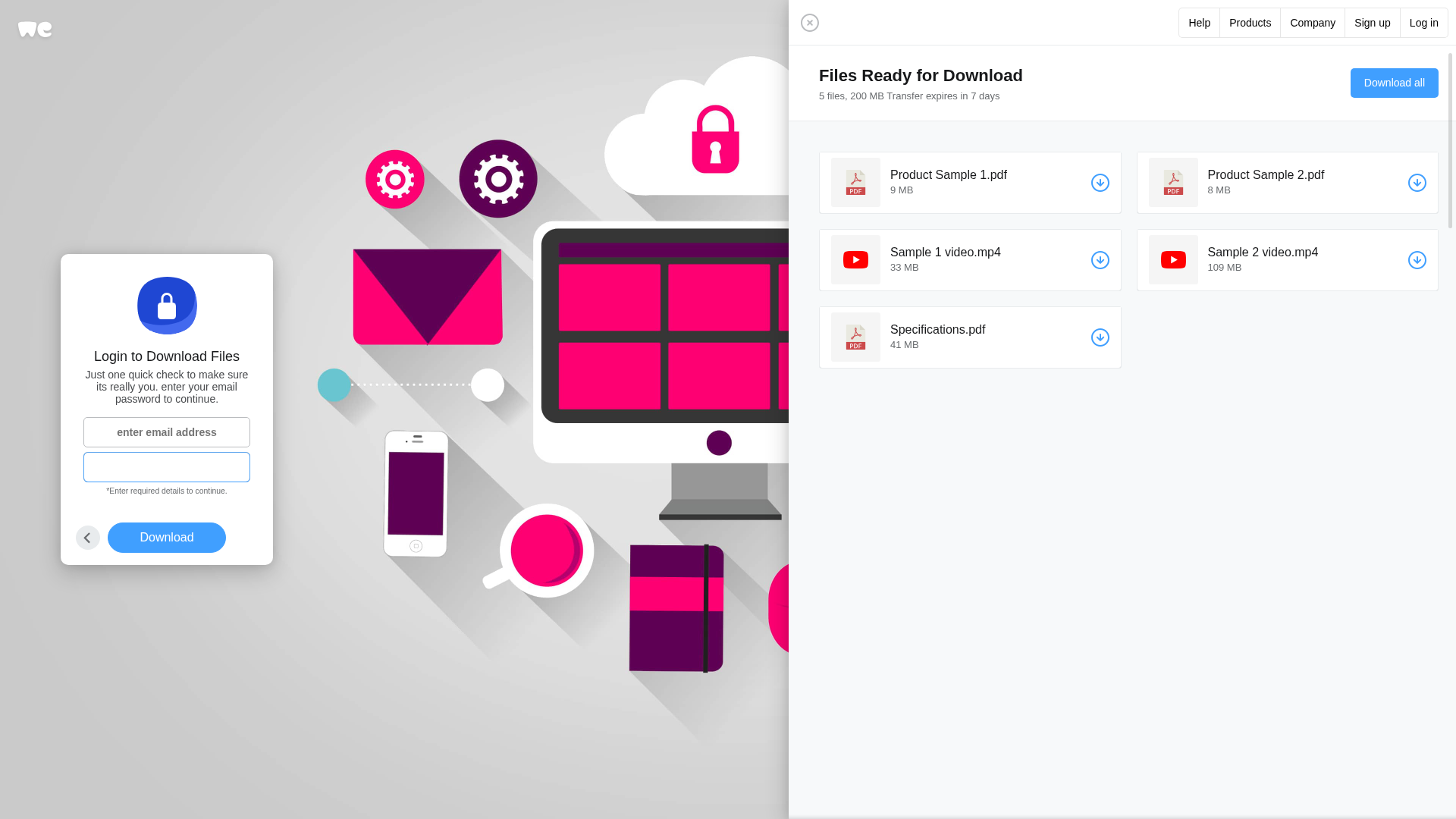
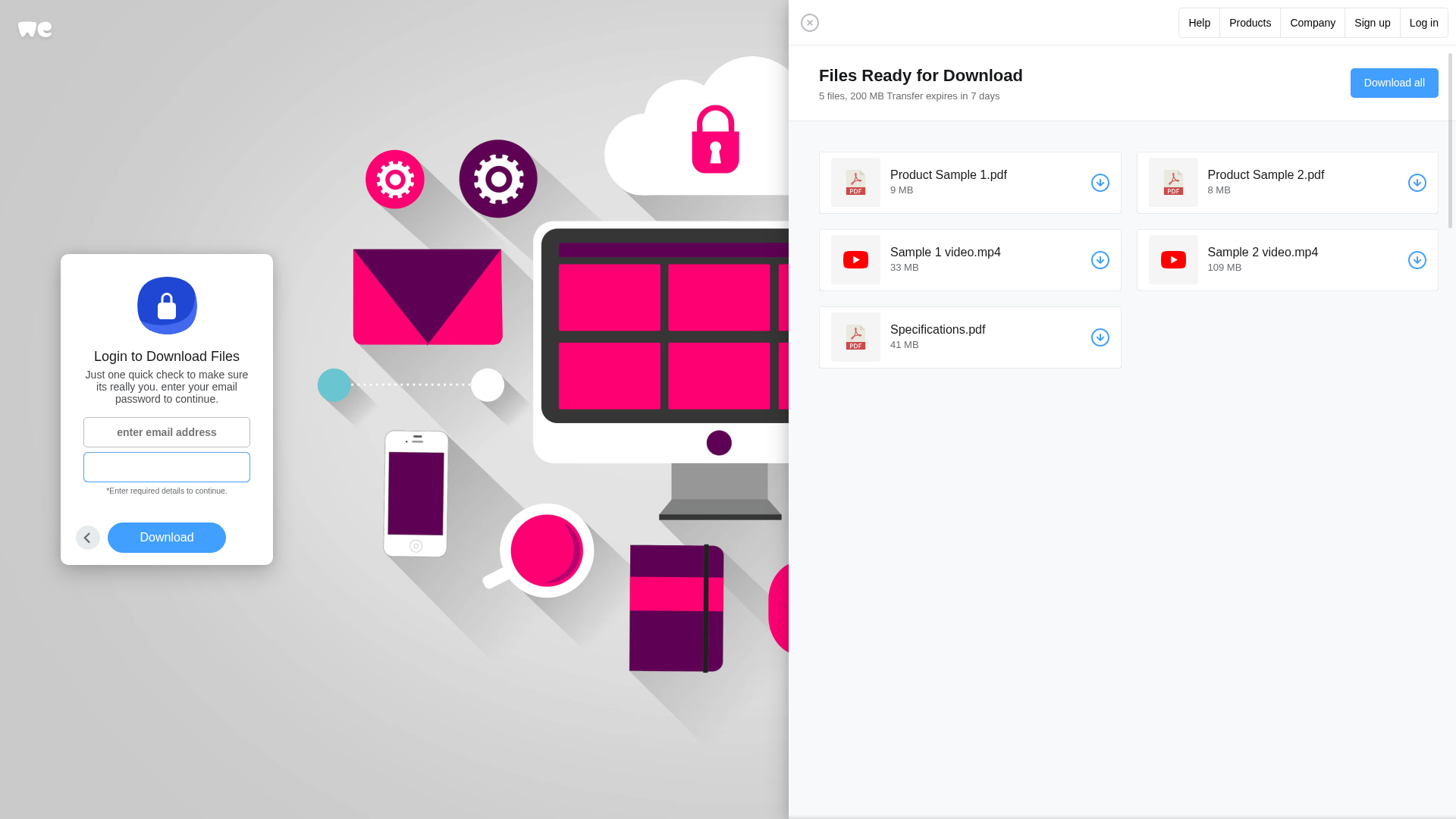
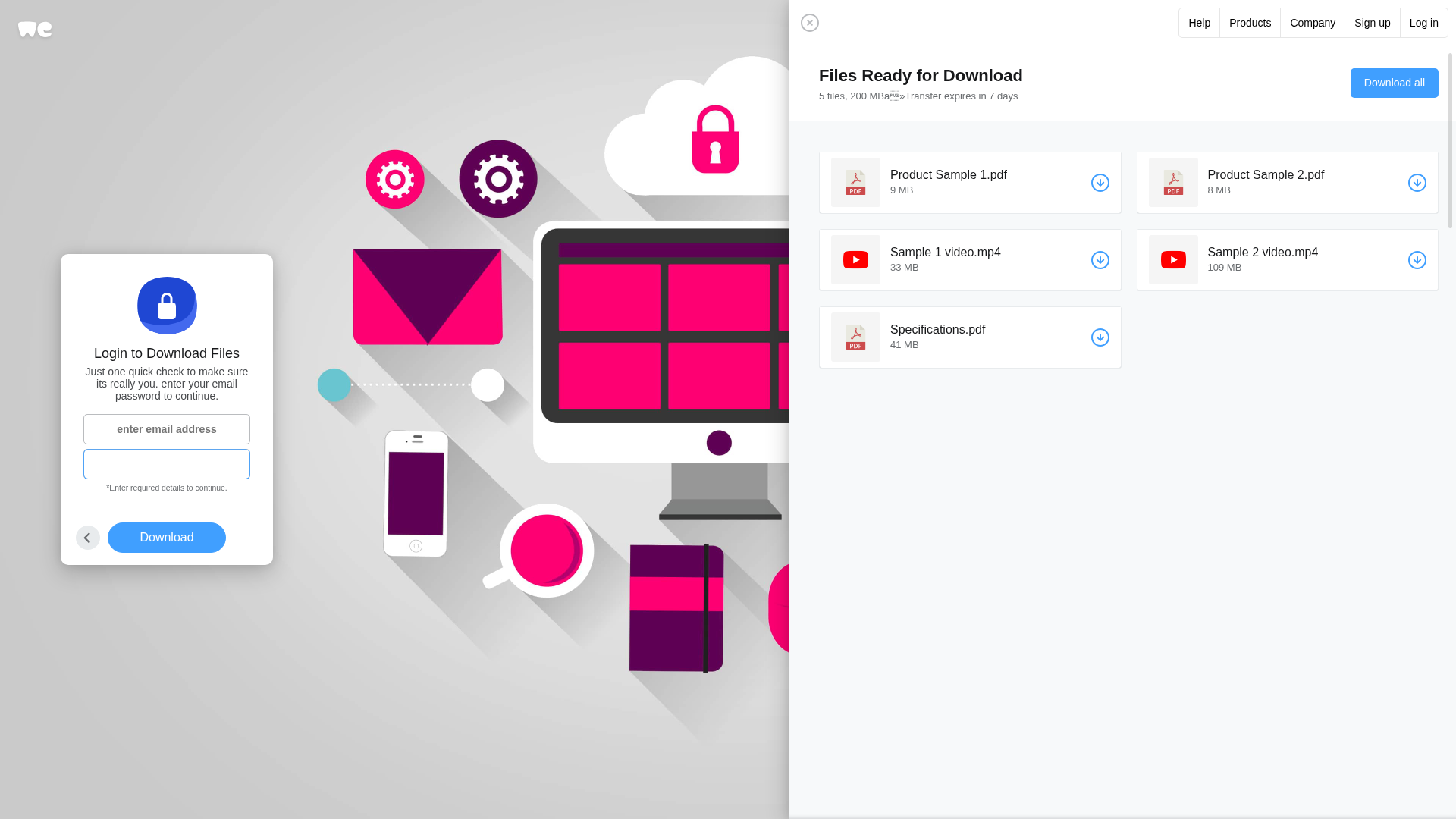
Captura Visual
Informações de Detecção
Hashes de Conteúdo (Similaridade HTML)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1C7A2C6F34910A47A42078BF5D7E1BB5C20AFD15FDA170500A7FE46E923C3DE2E91A45A |
|
CONTENT
ssdeep
|
384:ORW0+7WTPDqW8DCYjQIQSK8Qx8GyJWW8wjgF1lf4Bh:ORH08PDfg9rNe8GuPdgJ4T |
Hashes Visuais (Similaridade de Captura)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
b31ccdc7cc3330cc |
|
VISUAL
aHash
|
1f1f07c7cf072f0f |
|
VISUAL
dHash
|
febc9d8cac8acafc |
|
VISUAL
wHash
|
0f1f0707cf070f0f |
|
VISUAL
colorHash
|
07000000006 |
|
VISUAL
cropResistant
|
febc9d8cac8acafc,50888a8a8a8a8a8a,45012b13960e4d6d |
Análise de Código
🔒 Obfuscation Detected
- fromCharCode
- unescape
🎯 Kit Endpoints
- https://wetransfer.com/log-in
- #logo-path
🔑 Telegram Bot Tokens (1)
- 7955745927:AAGW...brUjU4Ug
📊 Detalhamento da Pontuação de Risco
Contributing Factors
🔬 Análise Integral de Ameaças
⚠️ Indicators of Compromise
- 1 Telegram bot token(s)
- Kit types: Credential Harvester, OTP Stealer, Card Stealer, Banking, Personal Info
- 6 obfuscation techniques
🏢 Análise de Falsificação de Marca
⚔️ Metodologia de Ataque
Primary Method: Credential Harvesting
Victim enters username and password into fake login form. Credentials are captured via JavaScript and exfiltrated to attacker's server in real-time.
Secondary Method: JavaScript Obfuscation
Malicious code is obfuscated using 6 techniques to evade detection by security scanners and make reverse engineering more difficult.
📡 Infraestrutura de Comando e Controle Telegram
💬 Message Templates (3)
| ID | Portuguese | English | Trigger |
|---|---|---|---|
🌐 Indicadores de Compromisso de Infraestrutura
Domain Information
Hosting Information
🤖 AI-Extracted Threat Intelligence
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Scan History for ipfs.io
Found 10 other scans for this domain
-
https://bafybeifucnntp2tzvo2smmgd2nrz2anlih4bapzou...
https://bafybeidainj73npe2kepzldqmuwzes5stwbgtu2pb...
https://bafybeidzv5orafwm4qq7m5wdptagbyyaksssolxhe...
https://bafybeiby3jwvxj44lno5pu2qjn5ezh5mlm4fkoy4q...
https://bafybeiaz6xbudbilnb4a52kkl2ffapf7oim253s7i...
https://bafybeieqilhn5yjrdt2cs46bglcamzimrcgbfuvq3...
https://bafkreidpy5pr2m6yvnk6v7ry7tu5lydi2rkd5reft...
https://bafybeih4lunv4ykv3qnx3n4c2c3d3gl5vlonz34ui...
http://ipfs.io/ipfs/bafybeibo7ht7ythkoucqnhcd4lzr5...
https://bafybeicfvmv4fni2inofzgesr4hc754scsn2zsohf...