
Phishing Analysis
Detailed analysis of captured phishing page
63
Risk Score
Medium Risk
Threat Level: ALTO
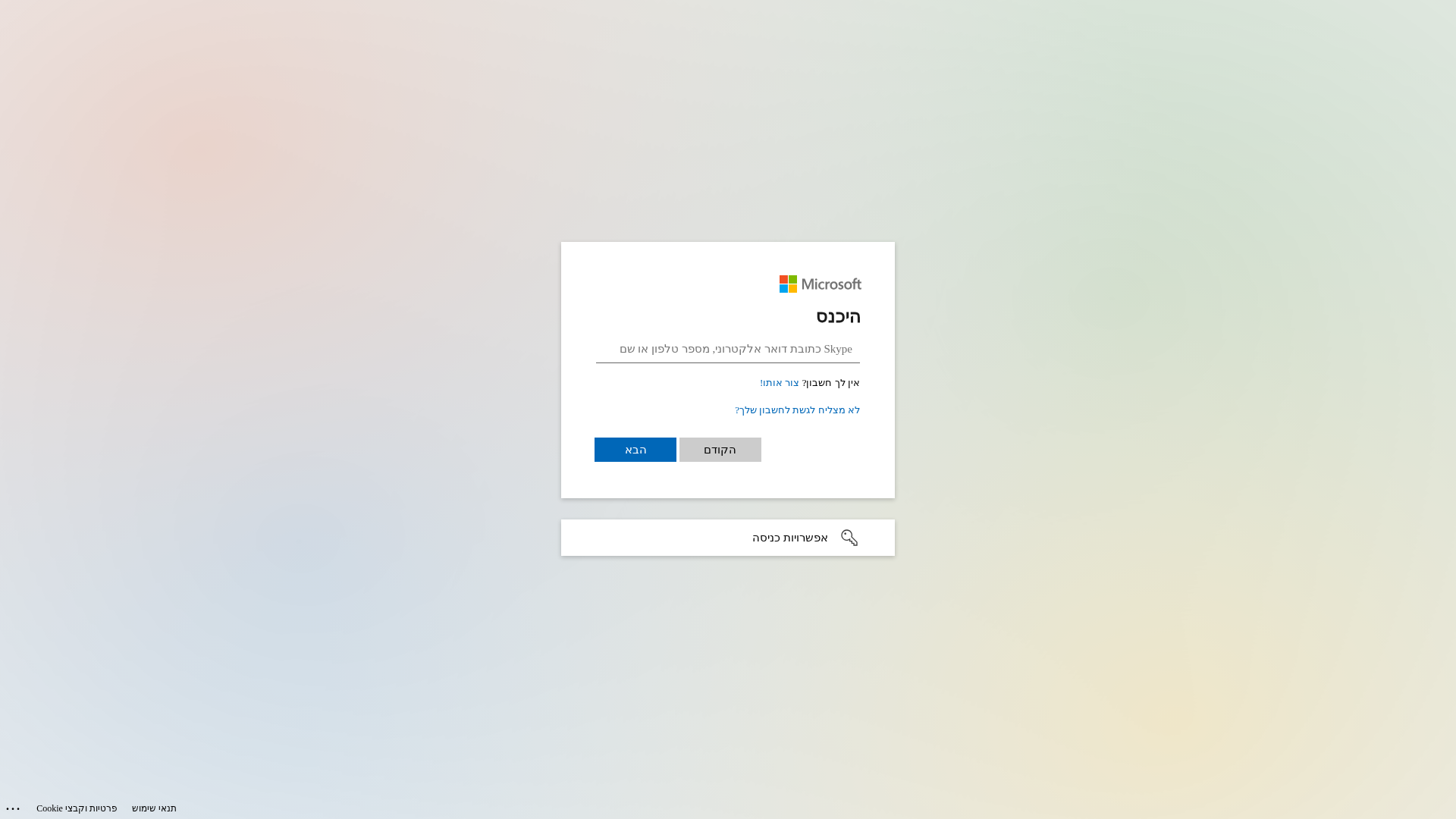
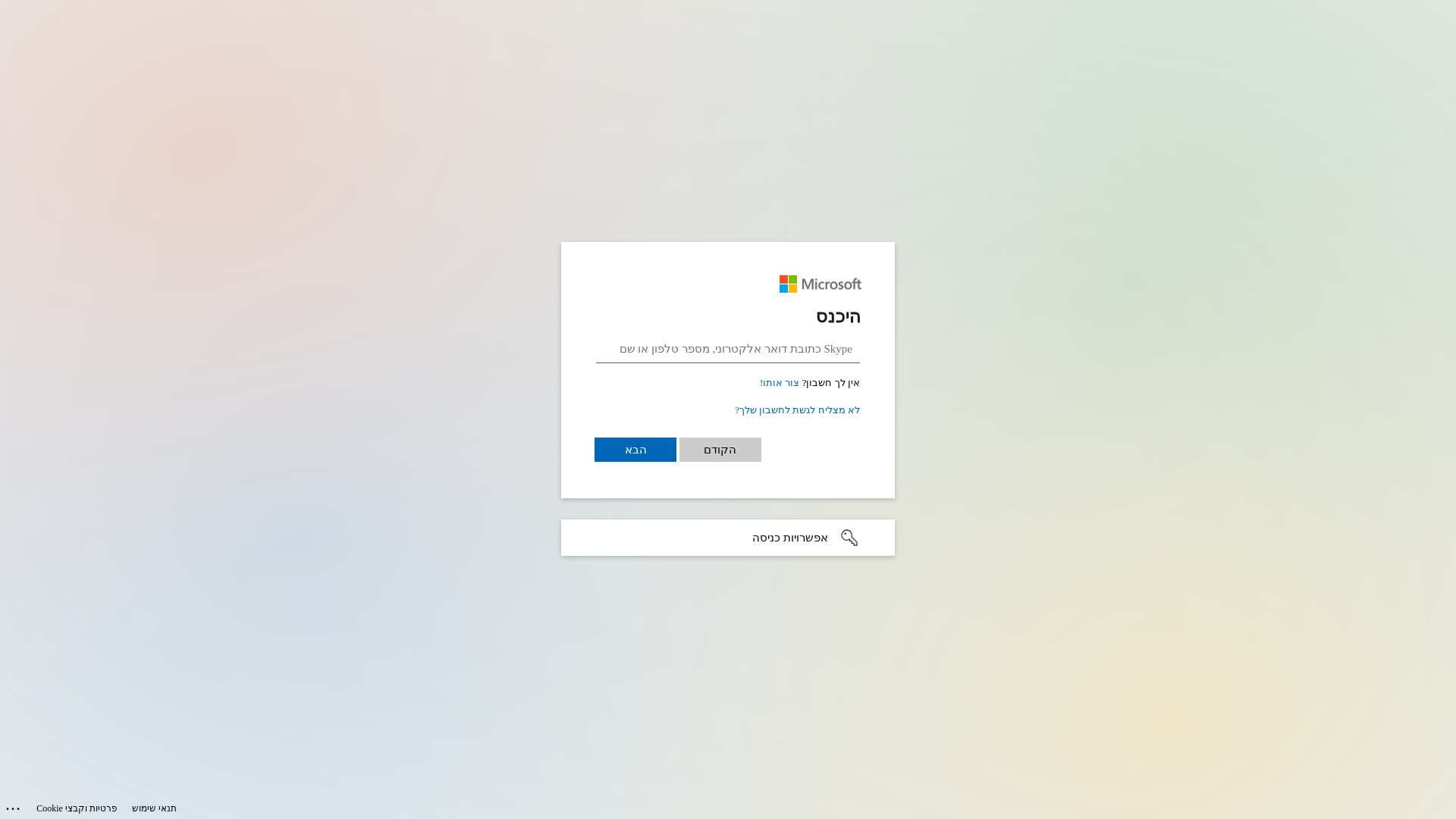
• Impersonating: Microsoft
- • Threat: Credential harvesting phishing kit
- • Target: Microsoft users
- • Method: Fake login form stealing credentials
- • Exfil: Data exfiltration likely using atob obfuscation
- • Indicators: Unrelated domain, Microsoft branding, login form, obfuscated JS
- • Risk: HIGH - Immediate credential theft
⚠ Risk Factors
- Brand impersonation of Microsoft on non-official domain
- Contains 1 credential harvesting form(s)
- Credential harvesting indicators detected
Visual Capture
Detection Info
https://notifyhubss.net/164393ca05179d4e85g99238f18084a1d1cf.html
Detected Brand
Microsoft
Country
International
Confidence
95%
HTTP Status
200
Report ID
caf8b460-07c…
Analyzed
2026-01-11 13:08
Content Hashes (HTML Similarity)
Used to detect similar phishing pages based on HTML content
| Algorithm | Hash Value |
|---|---|
|
CONTENT
TLSH
|
T1DBD1317060C09D3712D3D6D8B7B5A71B3785C301DE8B66AA97E4C38D4EEBDA1CC19291 |
|
CONTENT
ssdeep
|
96:6W9GQbeu0nPK/AmvUAK5KndPsb+vNR1j7fEAE9Nlt8dSsTioS4n7B5Q2GAMFJf:zBbMb8Rh7S9NAVnl5NEnf |
Visual Hashes (Screenshot Similarity)
Used to detect visually similar phishing pages based on screenshots
| Algorithm | Hash Value |
|---|---|
|
VISUAL
pHash
|
9d486633d9cccc33 |
|
VISUAL
aHash
|
180018181d1f0f1f |
|
VISUAL
dHash
|
716131337b327d79 |
|
VISUAL
wHash
|
191818181f1f1fff |
|
VISUAL
colorHash
|
07000000180 |
|
VISUAL
cropResistant
|
716131337b327d79 |
Code Analysis
Risk Score
63/100
Threat Level
ALTO
⚠️ Phishing Confirmed
🎣 Credential Harvester
🔬 Threat Analysis Report
• Threat: Credential harvesting phishing kit
• Target: Microsoft users
• Method: Fake login form stealing credentials
• Exfil: Data exfiltration likely using atob obfuscation
• Indicators: Unrelated domain, Microsoft branding, login form, obfuscated JS
• Risk: HIGH - Immediate credential theft
🔒 Obfuscation Detected
- atob
Similar Websites
Pages with identical visual appearance (based on perceptual hash)
Microsoft
https://notifyhubss.net/13a6a40855506d481cgb8da4fca0007cae1b...
Jan 11, 2026
Microsoft
https://notifyhubss.net/k949b93007b44a44ec1934c2bbax6adb6612...
Jan 11, 2026
No screenshot
Microsoft
https://netfimarketing.com/t17b96992t0e77403fab4c69635se7606...
Jan 11, 2026
Microsoft
https://datagivers.com/57bb55786e18614f266bf44132fq0f5eb969....
Jan 10, 2026
Microsoft
https://datagivers.com/f89269ef6kb0f94aefz89226951sc5989905....
Jan 10, 2026
Scan History for notifyhubss.net
Found 10 other scans for this domain
-
https://notifyhubss.net/13a6a40855506d481cgb8da4fc...
https://notifyhubss.net/k949b93007b44a44ec1934c2bb...
https://notifyhubss.net/k70bd5a53738d94bcc194a13f9...
https://notifyhubss.net/k269d5d807202f4f3c1871811f...
https://notifyhubss.net/z6970aeb1r6d3846b908b29592...
https://notifyhubss.net/k418e7afb7b9b64a5e1a206268...
https://notifyhubss.net/k46fc05327515c4988192f157b...
https://notifyhubss.net/k750ec9a97a85d4ded1ab493a0...
http://notifyhubss.net/za4e6325dr863b470d0b6570bc0...
https://notifyhubss.net/z33388c39r46f4410f0ad3df30...